ZYXEL 11AXAP24 802.11ax (WiFi 6) Dual-Radio Unified Pro Access Point Datasheet
File info: application/pdf · 161 pages · 3.82MB
User’s Guide
Users Manual-2
ZyXEL Communications Corporation 11AXAP24 802.11ax (WiFi 6) Dual-Radio Unified Pro Access Point I8811AXAP24 I8811AXAP24 11axap24
Extracted Text
Chapter 13 AP Profile
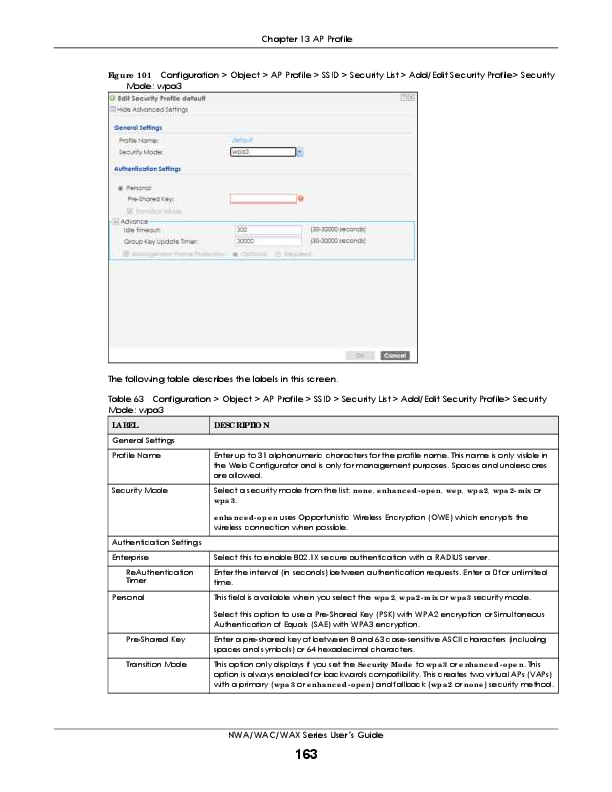
Fig ure 101 Configuration > Object > AP Profile > SSID > Security List > Add/Edit Security Profile> Security Mode: wpa3
The following table describes the labels in this screen.
Table 63 Configuration > Object > AP Profile > SSID > Security List > Add/Edit Security Profile> Security Mode: wpa3
LA BEL
DESC RIPTIO N
General Settings Profile Name
Security Mode
Enter up to 31 alphanumeric characters for the profile name. This name is only visible in the Web Configurator and is only for management purposes. Spaces and underscores are allowed.
Select a security mode from the list: no ne , e nha nc e d- o pe n, we p, wpa 2, wpa 2- m ix or wpa 3.
Authentication Settings Enterprise
ReAuthentication Timer Personal
e nha nc e d- o pe n uses Opportunistic Wireless Encryption (OWE) which encrypts the wireless connection when possible.
Select this to enable 802.1X secure authentication with a RADIUS server. Enter the interval (in seconds) between authentication requests. Enter a 0 for unlimited time. This field is available when you select the wpa 2, wpa 2- m ix or wpa 3 security mode.
Pre-Shared Key Transition Mode
Select this option to use a Pre-Shared Key (PSK) with WPA2 encryption or Simultaneous Authentication of Equals (SAE) with WPA3 encryption.
Enter a pre-shared key of between 8 and 63 case-sensitive ASCII characters (including spaces and symbols) or 64 hexadecimal characters.
This option only displays if you set the Se c urity Mo de to wpa 3 or e nha nc e d- o pe n. This option is always enabled for backwards compatibility. This creates two virtual APs (VAPs) with a primary (wpa 3 or e nha nc e d- o pe n) and fallback (wpa 2 or no ne ) security method.
NWA/WAC/WAX Series User's Guide
163
Chapter 13 AP Profile
Table 63 Configuration > Object > AP Profile > SSID > Security List > Add/Edit Security Profile> Security Mode: wpa3 (continued)
LA BEL
DESC RIPTIO N
Advance
Note: Click on the Sho w Adva nc e d Se tting s button to show the fields describe below.
Idle Timeout
Enter the idle interval (in seconds) that a client can be idle before authentication is discontinued.
Group Key Update Timer
Enter the interval (in seconds) at which the AP updates the group WPA2 encryption key.
Pre-Authentication
Select Ena b le to allow pre-authentication. Otherwise, select Disa b le .
Management Frame Protection
This field is available only when you select wpa 2 in the Se c urity Mo de field and set C iphe r Type to a e s.
Data frames in 802.11 WLANs can be encrypted and authenticated with WEP, WPA or WPA2. But 802.11 management frames, such as beacon/probe response, association request, association response, de-authentication and disassociation are always unauthenticated and unencrypted. IEEE 802.11w Protected Management Frames allows APs to use the existing security mechanisms (encryption and authentication methods defined in IEEE 802.11i WPA/WPA2) to protect management frames. This helps prevent wireless DoS attacks.
Select the check box to enable management frame protection (MFP) to add security to 802.11 management frames. This option is always enabled if you select e nha nc e d- o pe n or WPA3 as the Se c urity Mo de .
If O ptio na l is selected, WiFi clients will not be not required to support MFP. Management frames will be encrypted if the clients support MFP.
If Re quire d is selected, WiFi clients must support MFP in order to join the Zyxel Device's WiFi network.
Radius Settings
Primary / Secondary
Select this to have the Zyxel Device use the specified RADIUS server.
Radius Server Activate
Radius Server IP Address
Enter the IP address of the RADIUS server to be used for authentication.
Radius Server Port Enter the port number of the RADIUS server to be used for authentication.
Radius Server Secret Enter the shared secret password of the RADIUS server to be used for authentication.
Primary / Secondary Accounting Server Activate
Select the check box to enable user accounting through an external authentication server.
Accounting Server Enter the IP address of the external accounting server in dotted decimal notation. IP Address
Accounting Server Port
Enter the port number of the external accounting server. The default port number is 1813. You need not change this value unless your network administrator instructs you to do so with additional information.
Accounting Share Secret
Enter a password (up to 128 alphanumeric characters) as the key to be shared between the external accounting server and the Zyxel Device. The key must be the same on the external accounting server and your Zyxel Device. The key is not sent over the network.
Accounting Interim Update
This field is available only when you enable user accounting through an external authentication server.
Interim Update Interval General Server Settings
Select this to have the Zyxel Device send subscriber status updates to the accounting server at the interval you specify.
Specify the time interval for how often the Zyxel Device is to send a subscriber status update to the accounting server.
NWA/WAC/WAX Series User's Guide
164
Chapter 13 AP Profile
Table 63 Configuration > Object > AP Profile > SSID > Security List > Add/Edit Security Profile> Security Mode: wpa3 (continued)
LA BEL
DESC RIPTIO N
NAS IP Address
If the RADIUS server requires the Zyxel Device to provide the NAS (Network Access Server) IP address attribute, enter it here.
NAS Identifier
If the RADIUS server requires the Zyxel Device to provide the NAS (Network Access Server) identifier attribute, enter it here. The NAS identifier is to identify the source of access request. It could be the NAS's fully qualified domain name.
OK
Click O K to save your changes back to the Zyxel Device.
Cancel
Click C a nc e l to exit this screen without saving your changes.
13.5 MAC Filte r List
This screen allows you to create and manage security configurations that can be used by your SSIDs. To access this screen click C o nfig ura tio n > O b je c t > AP Pro file > SSID > MAC Filte r List. Note: You can have a maximum of 32 MAC filtering profiles on the Zyxel Device. Fig ure 102 Configuration > Object > AP Profile > SSID > MAC Filter List
The following table describes the labels in this screen.
Table 64 Configuration > Object > AP Profile > SSID > MAC Filter List
LA BEL
DESC RIPTIO N
Add
Click this to add a new MAC filtering profile.
Edit
Click this to edit the selected MAC filtering profile.
Remove
Click this to remove the selected MAC filtering profile.
Object Reference
Click this to view which other objects are linked to the selected MAC filtering profile (for example, SSID profile).
#
This field is a sequential value, and it is not associated with a specific user.
Profile Name
This field indicates the name assigned to the MAC filtering profile.
Filter Action
This field indicates this profile's filter action (if any).
13.5.1 Add/ Edit MAC Filte r Pro file
This screen allows you to create a new MAC filtering profile or edit an existing one. To access this screen, click the Add button or select a MAC filter profile from the list and click the Edit button.
Note: Each MAC filtering profile can include a maximum of 512 MAC addresses. NWA/WAC/WAX Series User's Guide
165
Chapter 13 AP Profile Fig ure 103 Configuration > Object > AP Profile > SSID > MAC Filter List > Add/Edit MAC Filter Profile
The following table describes the labels in this screen.
Table 65 Configuration > Object > AP Profile > SSID > MAC Filter List > Add/Edit MAC Filter Profile
LA BEL
DESC RIPTIO N
Profile Name
Enter up to 31 alphanumeric characters for the profile name. This name is only visible in the Web Configurator and is only for management purposes. Spaces and underscores are allowed.
Filter Action
Select a llo w to permit the wireless client with the MAC addresses in this profile to connect to the network through the associated SSID; select de ny to block the wireless clients with the specified MAC addresses.
Add
Click this to add a MAC address to the profile's list.
Edit
Click this to edit the selected MAC address in the profile's list.
Remove
Click this to remove the selected MAC address from the profile's list.
#
This field is a sequential value, and it is not associated with a specific user.
MAC
This field specifies a MAC address associated with this profile. You can click the MAC address to make it editable.
Description
This field displays a description for the MAC address associated with this profile. You can click the description to make it editable. Enter up to 60 characters, spaces and underscores allowed.
OK
Click O K to save your changes back to the Zyxel Device.
Cancel
Click C a nc e l to exit this screen without saving your changes.
13.6 La ye r- 2 Iso la tio n List
Layer-2 isolation is used to prevent wireless clients associated with your Zyxel Device from communicating with other wireless clients, APs, computers or routers in a network. In the following example, layer-2 isolation is enabled on the Zyxel Device to allow a guest wireless client (A) to access the main network router (B). The router provides access to the Internet and the network
NWA/WAC/WAX Series User's Guide
166
Chapter 13 AP Profile
printer (C ) while preventing the client from accessing other computers and servers on the network. The client can communicate with other wireless clients only if Intra-BSS Traffic blocking is disabled. Note: Intra-BSS Traffic Blocking is activated when you enable layer-2 isolation. Fig ure 104 Layer-2 Isolation Application
MAC addresses that are not listed in the layer-2 isolation table are blocked from communicating with the Zyxel Device's wireless clients except for broadcast packets. Layer-2 isolation does not check the traffic between wireless clients that are associated with the same AP. Intra-BSS traffic allows wireless clients associated with the same AP to communicate with each other.
This screen allows you to specify devices you want the users on your wireless networks to access. To access this screen click C o nfig ura tio n > O b je c t > AP Pro file > SSID > La ye r- 2 Iso la tio n List.
Fig ure 105 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List
The following table describes the labels in this screen.
Table 66 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List
LA BEL
DESC RIPTIO N
Add
Click this to add a new layer-2 isolation profile.
Edit
Click this to edit the selected layer-2 isolation profile.
Remove
Click this to remove the selected layer-2 isolation profile.
Object Reference
Click this to view which other objects are linked to the selected layer-2 isolation profile (for example, SSID profile).
#
This field is a sequential value, and it is not associated with a specific user.
Profile Name
This field indicates the name assigned to the layer-2 isolation profile.
NWA/WAC/WAX Series User's Guide
167
Chapter 13 AP Profile
13.6.1 Add/ Edit La ye r- 2 Iso la tio n Pro file
This screen allows you to create a new layer-2 isolation profile or edit an existing one. To access this screen, click the Add button or select a layer-2 isolation profile from the list and click the Edit button.
Note: You need to know the MAC address of each wireless client, AP, computer or router that you want to allow to communicate with the Zyxel Device's wireless clients.
Fig ure 106 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List > Add/Edit Layer-2 Isolation Profile
The following table describes the labels in this screen.
Table 67 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List > Add/Edit Layer-2 Isolation Profile
LA BEL
DESC RIPTIO N
Profile Name
Enter up to 31 alphanumeric characters for the profile name. This name is only visible in the Web Configurator and is only for management purposes. Spaces and underscores are allowed.
Add
Click this to add a MAC address to the profile's list.
Edit
Click this to edit the selected MAC address in the profile's list.
Remove
Click this to remove the selected MAC address from the profile's list.
#
This field is a sequential value, and it is not associated with a specific user.
MAC
This field specifies a MAC address associated with this profile. You can click the MAC address to make it editable.
Description
This field displays a description for the MAC address associated with this profile. You can click the description to make it editable. Enter up to 60 characters, spaces and underscores allowed.
OK
Click O K to save your changes back to the Zyxel Device.
Cancel
Click C a nc e l to exit this screen without saving your changes.
NWA/WAC/WAX Series User's Guide
168
C HA PTER 1 4 MO N Pro file
14.1 O ve rvie w
This screen allows you to set up monitor mode configurations that allow your Zyxel Device to scan for other wireless devices in the vicinity. Once detected, you can use the Wire le ss > MO N Mo de screen (Section 10.3 on page 116) to classify them as either rogue or friendly. Not all Zyxel Devices support monitor mode and rogue APs detection.
14.1.1 Wha t Yo u C a n Do in this C ha pte r
The MO N Pro file screen (Section 14.2 on page 169) creates preset monitor mode configurations that can be used by the Zyxel Device.
14.2 MO N Pro file
This screen allows you to create monitor mode configurations that can be used by the APs. To access this screen, log into the Web Configurator, and click C o nfig ura tio n > O b je c t > MO N Pro file . Fig ure 107 Configuration > Object > MON Profile
The following table describes the labels in this screen.
Table 68 Configuration > Object > MON Profile
LA BEL
DESC RIPTIO N
Add
Click this to add a new monitor mode profile.
Edit
Click this to edit the selected monitor mode profile.
Remove
Click this to remove the selected monitor mode profile.
Activate
To turn on an entry, select it and click Ac tiva te .
Inactivate
To turn off an entry, select it and click Ina c tiva te .
NWA/WAC/WAX Series User's Guide
169
Chapter 14 MON Profile
Table 68 Configuration > Object > MON Profile (continued)
LA BEL
DESC RIPTIO N
Object Reference
Click this to view which other objects are linked to the selected monitor mode profile (for example, an AP management profile).
#
This field is a sequential value, and it is not associated with a specific profile.
Status
This field shows whether or not the entry is activated.
Profile Name
This field indicates the name assigned to the monitor profile.
14.2.1 Add/ Edit MO N Pro file
This screen allows you to create a new monitor mode profile or edit an existing one. To access this screen, click the Add button or select and existing monitor mode profile and click the Edit button. See Section 1.2.3 on page 17 for more information about MON Mode.
Fig ure 108 Configuration > Object > MON Profile > Add/Edit MON Profile
NWA/WAC/WAX Series User's Guide
170
Chapter 14 MON Profile
The following table describes the labels in this screen.
Table 69 Configuration > Object > MON Profile > Add/Edit MON Profile
LA BEL
DESC RIPTIO N
Activate Profile Name Channel dwell time
Scan Channel Mode
Select this to activate this monitor mode profile.
This field indicates the name assigned to the monitor mode profile.
Enter the interval (in milliseconds) before the Zyxel Device switches to another channel for monitoring.
Select a uto to have the Zyxel Device switch to the next sequential channel once the C ha nne l dwe ll tim e expires.
Set Scan Channel List (2.4 GHz)
Select m a nua l to set specific channels through which to cycle sequentially when the C ha nne l dwe ll tim e expires. Selecting this options makes the Sc a n C ha nne l List options available.
Select one or more than one channel to have the Zyxel Device using this profile scan the channel(s) when Sc a n C ha nne l Mo de is set to m a nua l.
Set Scan Channel List (5 GHz)
These channels are limited to the 2.4 GHz range (802.11 b/g/n/ax).
Select one or more than one channel to have the Zyxel Device using this profile scan the channel(s) when Sc a n C ha nne l Mo de is set to m a nua l.
OK Cancel
These channels are limited to the 5 GHz range (802.11 a/n/ac/ax). Not all Zyxel Devices support both 2.4 GHz and 5 GHz frequency bands.
Click O K to save your changes back to the Zyxel Device.
Click C a nc e l to exit this screen without saving your changes.
NWA/WAC/WAX Series User's Guide
171
C HA PTER 1 5 WDS Pro file
15.1 O ve rvie w
This chapter shows you how to configure WDS (Wireless Distribution System) profiles for the Zyxel Device to form a WDS with other APs.
15.1.1 Wha t Yo u C a n Do in this C ha pte r
The WDS Pro file screen (Section 15.2 on page 172) creates preset WDS configurations that can be used by the Zyxel Device.
15.2 WDS Pro file
This screen allows you to manage and create WDS profiles that can be used by the APs. To access this screen, click C o nfig ura tio n > O b je c t > WDS Pro file . Fig ure 109 Configuration > Object > WDS Profile
The following table describes the labels in this screen.
Table 70 Configuration > Object > WDS Profile
LA BEL
DESC RIPTIO N
Add
Click this to add a new profile.
Edit
Click this to edit the selected profile.
Remove
Click this to remove the selected profile.
#
This field is a sequential value, and it is not associated with a specific profile.
Profile Name
This field indicates the name assigned to the profile.
WDS SSID
This field shows the SSID specified in this WDS profile.
NWA/WAC/WAX Series User's Guide
172
Chapter 15 WDS Profile
15.2.1 Add/ Edit WDS Pro file
This screen allows you to create a new WDS profile or edit an existing one. To access this screen, click the Add button or select and existing profile and click the Edit button. Fig ure 110 Configuration > Object > WDS Profile > Add/Edit WDS Profile
The following table describes the labels in this screen.
Table 71 Configuration > Object > WDS Profile > Add/Edit WDS Profile
LA BEL
DESC RIPTIO N
Profile Name WDS SSID
Pre-Shared Key
Enter up to 31 alphanumeric characters for the profile name.
Enter the SSID with which you want the Zyxel Device to connect to a root AP or repeater to form a WDS.
Enter a pre-shared key of between 8 and 63 case-sensitive ASCII characters (including spaces and symbols) or 64 hexadecimal characters.
OK Cancel
The key is used to encrypt the traffic between the APs. Click O K to save your changes back to the Zyxel Device. Click C a nc e l to exit this screen without saving your changes.
NWA/WAC/WAX Series User's Guide
173
C HA PTER 1 6 C e rtific a te s
16.1 O ve rvie w
The Zyxel Device can use certificates (also called digital IDs) to authenticate users. Certificates are based on public-private key pairs. A certificate contains the certificate owner's identity and public key. Certificates provide a way to exchange public keys for use in authentication.
16.1.1 Wha t Yo u C a n Do in this C ha pte r
� The My C e rtific a te s screens (Section 16.2 on page 177) generate and export self-signed certificates or certification requests and import the Zyxel Device's CA-signed certificates.
� The Truste d C e rtific a te s screens (Section 16.3 on page 184) save CA certificates and trusted remote host certificates to the Zyxel Device. The Zyxel Device trusts any valid certificate that you have imported as a trusted certificate. It also trusts any valid certificate signed by any of the certificates that you have imported as a trusted certificate.
16.1.2 Wha t Yo u Ne e d to Kno w
The following terms and concepts may help as you read this chapter.
When using public-key cryptology for authentication, each host has two keys. One key is public and can be made openly available. The other key is private and must be kept secure.
These keys work like a handwritten signature (in fact, certificates are often referred to as "digital signatures"). Only you can write your signature exactly as it should look. When people know what your signature looks like, they can verify whether something was signed by you, or by someone else. In the same way, your private key "writes" your digital signature and your public key allows people to verify whether data was signed by you, or by someone else.
This process works as follows:
1 Tim wants to send a message to Jenny. He needs her to be sure that it comes from him, and that the message content has not been altered by anyone else along the way. Tim generates a public key pair (one public key and one private key).
2 Tim keeps the private key and makes the public key openly available. This means that anyone who receives a message seeming to come from Tim can read it and verify whether it is really from him or not.
3 Tim uses his private key to sign the message and sends it to Jenny.
4 Jenny receives the message and uses Tim's public key to verify it. Jenny knows that the message is from Tim, and that although other people may have been able to read the message, no-one can have altered it (because they cannot re-sign the message with Tim's private key).
NWA/WAC/WAX Series User's Guide
174
Chapter 16 Certificates
5 Additionally, Jenny uses her own private key to sign a message and Tim uses Jenny's public key to verify the message.
The Zyxel Device uses certificates based on public-key cryptology to authenticate users attempting to establish a connection, not to encrypt the data that you send after establishing a connection. The method used to secure the data that you send through an established connection depends on the type of connection.
The certification authority uses its private key to sign certificates. Anyone can then use the certification authority's public key to verify the certificates.
A certification path is the hierarchy of certification authority certificates that validate a certificate. The Zyxel Device does not trust a certificate if any certificate on its path has expired or been revoked.
Certification authorities maintain directory servers with databases of valid and revoked certificates. A directory of certificates that have been revoked before the scheduled expiration is called a CRL (Certificate Revocation List). The Zyxel Device can check a peer's certificate against a directory server's list of revoked certificates. The framework of servers, software, procedures and policies that handles keys is called PKI (public-key infrastructure).
Adva nta g e s o f C e rtific a te s
Certificates offer the following benefits.
� The Zyxel Device only has to store the certificates of the certification authorities that you decide to trust, no matter how many devices you need to authenticate.
� Key distribution is simple and very secure since you can freely distribute public keys and you never need to transmit private keys.
Se lf- sig ne d C e rtific a te s
You can have the Zyxel Device act as a certification authority and sign its own certificates.
Fa c to ry De fa ult C e rtific a te
The Zyxel Device generates its own unique self-signed certificate when you first turn it on. This certificate is referred to in the GUI as the factory default certificate.
C e rtific a te File Fo rm a ts
Any certificate that you want to import has to be in one of these file formats:
� Binary X.509: This is an ITU-T recommendation that defines the formats for X.509 certificates. � PEM (Base-64) encoded X.509: This Privacy Enhanced Mail format uses lowercase letters, uppercase
letters and numerals to convert a binary X.509 certificate into a printable form. � Binary PKCS#7: This is a standard that defines the general syntax for data (including digital signatures)
that may be encrypted. A PKCS #7 file is used to transfer a public key certificate. The private key is not included. The Zyxel Device currently allows the importation of a PKS#7 file that contains a single certificate. � PEM (Base-64) encoded PKCS#7: This Privacy Enhanced Mail (PEM) format uses lowercase letters, uppercase letters and numerals to convert a binary PKCS#7 certificate into a printable form.
NWA/WAC/WAX Series User's Guide
175
Chapter 16 Certificates � Binary PKCS#12: This is a format for transferring public key and private key certificates.The private key
in a PKCS #12 file is within a password-encrypted envelope. The file's password is not connected to your certificate's public or private passwords. Exporting a PKCS #12 file creates this and you must provide it to decrypt the contents when you import the file into the Zyxel Device. Note: Be careful not to convert a binary file to text during the transfer process. It is easy for this
to occur since many programs use text files by default.
16.1.3 Ve rifying a C e rtific a te
Before you import a trusted certificate into the Zyxel Device, you should verify that you have the correct certificate. You can do this using the certificate's fingerprint. A certificate's fingerprint is a message digest calculated using the MD5 or SHA1 algorithm. The following procedure describes how to check a certificate's fingerprint to verify that you have the actual certificate. 1 Browse to where you have the certificate saved on your computer. 2 Make sure that the certificate has a ".cer" or ".crt" file name extension.
3 Double-click the certificate's icon to open the C e rtific a te window. Click the De ta ils tab and scroll down to the Thum b print Alg o rithm and Thum b print fields.
4 Use a secure method to verify that the certificate owner has the same information in the Thum bprint Alg o rithm and Thum b print fields. The secure method may vary based on your situation. Possible examples would be over the telephone or through an HTTPS connection. NWA/WAC/WAX Series User's Guide
176
Chapter 16 Certificates
16.2 My C e rtific a te s
Click C o nfig ura tio n > O b je c t > C e rtific a te > My C e rtific a te s to open this screen. This is the Zyxel Device's summary list of certificates and certification requests. Fig ure 111 Configuration > Object > Certificate > My Certificates
The following table describes the labels in this screen.
Table 72 Configuration > Object > Certificate > My Certificates
LA BEL
DESC RIPTIO N
PKI Storage Space in Use Add Edit Remove
Object Reference
# Name Type
This bar displays the percentage of the Zyxel Device's PKI storage space that is currently in use. When the storage space is almost full, you should consider deleting expired or unnecessary certificates before adding more certificates.
Click this to go to the screen where you can have the Zyxel Device generate a certificate or a certification request.
Double-click an entry or select it and click Edit to open a screen with an in-depth list of information about the certificate.
The Zyxel Device keeps all of your certificates unless you specifically delete them. Uploading a new firmware or default configuration file does not delete your certificates. To remove an entry, select it and click Re m o ve . The Zyxel Device confirms you want to remove it before doing so. Subsequent certificates move up by one when you take this action.
You cannot delete certificates that any of the Zyxel Device's features are configured to use. Select an entry and click O b je c t Re fe re nc e to open a screen that shows which settings use the entry.
This field displays the certificate index number. The certificates are listed in alphabetical order.
This field displays the name used to identify this certificate. It is recommended that you give each certificate a unique name.
This field displays what kind of certificate this is.
REQ represents a certification request and is not yet a valid certificate. Send a certification request to a certification authority, which then issues a certificate. Use the My C e rtific a te Im po rt screen to import the certificate and replace the request.
SELF represents a self-signed certificate.
Subject
C ERTrepresents a certificate issued by a certification authority.
This field displays identifying information about the certificate's owner, such as CN (Common Name), OU (Organizational Unit or department), O (Organization or company) and C (Country). It is recommended that each certificate have unique subject information.
NWA/WAC/WAX Series User's Guide
177
Chapter 16 Certificates
Table 72 Configuration > Object > Certificate > My Certificates (continued)
LA BEL
DESC RIPTIO N
Issuer
This field displays identifying information about the certificate's issuing certification authority, such as a common name, organizational unit or department, organization or company and country. With self-signed certificates, this is the same information as in the Subje c t field.
Valid From
This field displays the date that the certificate becomes applicable.
Valid To
This field displays the date that the certificate expires. The text displays in red and includes an Expired! message if the certificate has expired.
Import
Click Im po rt to open a screen where you can save a certificate to the Zyxel Device.
Refresh
Click Re fre sh to display the current validity status of the certificates.
16.2.1 Add My C e rtific a te s
Click C o nfig ura tio n > O b je c t > C e rtific a te > My C e rtific a te s and then the Add icon to open the Add My C e rtific a te s screen. Use this screen to have the Zyxel Device create a self-signed certificate, enroll a certificate with a certification authority or generate a certification request.
Fig ure 112 Configuration > Object > Certificate > My Certificates > Add
NWA/WAC/WAX Series User's Guide
178
Chapter 16 Certificates
The following table describes the labels in this screen.
Table 73 Configuration > Object > Certificate > My Certificates > Add
LA BEL
DESC RIPTIO N
Name Subject Information
Type a name to identify this certificate. You can use up to 31 alphanumeric and ;`~!@#$%^&()_+[]{}',.=- characters.
Use these fields to record information that identifies the owner of the certificate. You do not have to fill in every field, although you must specify a Ho st IP Addre ss, Ho st Do m a in Na m e , or E- Ma il. The certification authority may add fields (such as a serial number) to the subject information when it issues a certificate. It is recommended that each certificate have unique subject information.
Select a radio button to identify the certificate's owner by IP address, domain name or email address. Type the IP address (in dotted decimal notation), domain name or e-mail address in the field provided. The domain name or e-mail address is for identification purposes only and can be any string.
A domain name can be up to 255 characters. You can use alphanumeric characters, the hyphen and periods.
Organizational Unit
Organization Town (City) State (Province) Country Key Type
An e-mail address can be up to 63 characters. You can use alphanumeric characters, the hyphen, the @ symbol, periods and the underscore.
Identify the organizational unit or department to which the certificate owner belongs. You can use up to 31 characters. You can use alphanumeric characters, the hyphen and the underscore.
Identify the company or group to which the certificate owner belongs. You can use up to 31 characters. You can use alphanumeric characters, the hyphen and the underscore.
Identify the town or city where the certificate owner is located. You can use up to 31 characters. You can use alphanumeric characters, the hyphen and the underscore.
Identify the state or province where the certificate owner is located. You can use up to 31 characters. You can use alphanumeric characters, the hyphen and the underscore.
Identify the nation where the certificate owner is located. You can use up to 31 characters. You can use alphanumeric characters, the hyphen and the underscore.
The Zyxel Device uses the RSA (Rivest, Shamir and Adleman) public-key encryption algorithm. SHA1 (Secure Hash Algorithm) and SHA2 are hash algorithms used to authenticate packet data. SHA2-256 or SHA2-512 are part of the SHA2 set of cryptographic functions and they are considered even more secure than SHA1.
Key Length Extended Key Usage
Select a key type from RSA- SHA256 and RSA- SHA512.
Select a number from the drop-down list box to determine how many bits the key should use (1024 to 2048). The longer the key, the more secure it is. A longer key also uses more PKI storage space.
Select Se rve r Authe ntic a tio n to allow a web server to send clients the certificate to authenticate itself.
Create a self-signed certificate
Create a certification request and save it locally for later manual enrollment
Select C lie nt Authe ntic a tio n to use the certificate's key to authenticate clients to the secure gateway.
These radio buttons deal with how and when the certificate is to be generated.
Select this to have the Zyxel Device generate the certificate and act as the Certification Authority (CA) itself. This way you do not need to apply to a certification authority for certificates.
Select this to have the Zyxel Device generate and store a request for a certificate. Use the My C e rtific a te Edit screen to view the certification request and copy it to send to the certification authority.
Copy the certification request from the My C e rtific a te Edit screen and then send it to the certification authority.
NWA/WAC/WAX Series User's Guide
179
Chapter 16 Certificates
Table 73 Configuration > Object > Certificate > My Certificates > Add (continued)
LA BEL
DESC RIPTIO N
Create a certification request and enroll for a certificate immediately online
Select this to have the Zyxel Device generate a request for a certificate and apply to a certification authority for a certificate.
You must have the certification authority's certificate already imported in the Truste d C e rtific a te s screen.
Enrollment Protocol
When you select this option, you must select the certification authority's enrollment protocol and the certification authority's certificate from the drop-down list boxes and enter the certification authority's server address. You also need to fill in the Re fe re nc e Num b e r and Ke y if the certification authority requires them.
This field applies when you select C re a te a c e rtific a tio n re q ue st a nd e nro ll fo r a c e rtific a te im m e dia te ly o nline . Select the certification authority's enrollment protocol from the dropdown list box.
Sim ple C e rtific a te Enro llm e nt Pro to c o l (SC EP) is a TCP-based enrollment protocol that was developed by VeriSign and Cisco.
CA Server Address
C e rtific a te Ma na g e m e nt Pro to c o l (C MP) is a TCP-based enrollment protocol that was developed by the Public Key Infrastructure X.509 working group of the Internet Engineering Task Force (IETF) and is specified in RFC 2510.
This field applies when you select C re a te a c e rtific a tio n re q ue st a nd e nro ll fo r a c e rtific a te im m e dia te ly o nline . Enter the IP address (or URL) of the certification authority server.
CA Certificate
For a URL, you can use up to 511 of the following characters. a-zA-Z0-9'()+,/:.=?;!*#@$_%-
This field applies when you select C re a te a c e rtific a tio n re q ue st a nd e nro ll fo r a c e rtific a te im m e dia te ly o nline . Select the certification authority's certificate from the C A C e rtific a te drop-down list box.
Request Authentication
You must have the certification authority's certificate already imported in the Truste d C e rtific a te s screen. Click Truste d C As to go to the Truste d C e rtific a te s screen where you can view (and manage) the Zyxel Device's list of certificates of trusted certification authorities.
When you select C re a te a c e rtific a tio n re q ue st a nd e nro ll fo r a c e rtific a te im m e dia te ly o nline , the certification authority may want you to include a reference number and key to identify you when you send a certification request.
Fill in both the Re fe re nc e Num b e r and the Ke y fields if your certification authority uses the CMP enrollment protocol. Just the Ke y field displays if your certification authority uses the SCEP enrollment protocol.
For the reference number, use 0 to 99999999.
OK Cancel
For the key, use up to 31 of the following characters. a-zA-Z0-9;|`~!@#$%^&*()_+\{}':,./ <>=-
Click O K to begin certificate or certification request generation.
Click C a nc e l to quit and return to the My C e rtific a te s screen.
If you configured the Add My C e rtific a te s screen to have the Zyxel Device enroll a certificate and the certificate enrollment is not successful, you see a screen with a Re turn button that takes you back to the Add My C e rtific a te s screen. Click Re turn and check your information in the Add My C e rtific a te s screen. Make sure that the certification authority information is correct and that your Internet connection is working properly if you want the Zyxel Device to enroll a certificate online.
16.2.2 Edit My C e rtific a te s
Click C o nfig ura tio n > O b je c t > C e rtific a te > My C e rtific a te s and then the Edit icon to open the My C e rtific a te Edit screen. You can use this screen to view in-depth certificate information and change the certificate's name.
NWA/WAC/WAX Series User's Guide
180
Chapter 16 Certificates Fig ure 113 Configuration > Object > Certificate > My Certificates > Edit
NWA/WAC/WAX Series User's Guide
181
Chapter 16 Certificates
The following table describes the labels in this screen.
Table 74 Configuration > Object > Certificate > My Certificates > Edit
LA BEL
DESC RIPTIO N
Name Certification Path
This field displays the identifying name of this certificate. You can use up to 31 alphanumeric and ;`~!@#$%^&()_+[]{}',.=- characters.
This field displays for a certificate, not a certification request.
Click the Re fre sh button to have this read-only text box display the hierarchy of certification authorities that validate the certificate (and the certificate itself).
Refresh Certificate Information Type
Version Serial Number Subject Issuer
If the issuing certification authority is one that you have imported as a trusted certification authority, it may be the only certification authority in the list (along with the certificate itself). If the certificate is a self-signed certificate, the certificate itself is the only one in the list. The Zyxel Device does not trust the certificate and displays "Not trusted" in this field if any certificate on the path has expired or been revoked.
Click Re fre sh to display the certification path.
These read-only fields display detailed information about the certificate.
This field displays general information about the certificate. CA-signed means that a Certification Authority signed the certificate. Self-signed means that the certificate's owner signed the certificate (not a certification authority). "X.509" means that this certificate was created and signed according to the ITU-T X.509 recommendation that defines the formats for public-key certificates.
This field displays the X.509 version number.
This field displays the certificate's identification number given by the certification authority or generated by the Zyxel Device.
This field displays information that identifies the owner of the certificate, such as Common Name (CN), Organizational Unit (OU), Organization (O), State (ST), and Country (C).
This field displays identifying information about the certificate's issuing certification authority, such as Common Name, Organizational Unit, Organization and Country.
With self-signed certificates, this is the same as the Sub je c t Na m e field.
"none" displays for a certification request.
Signature Algorithm This field displays the type of algorithm that was used to sign the certificate.
Valid From
This field displays the date that the certificate becomes applicable. "none" displays for a certification request.
Valid To
This field displays the date that the certificate expires. The text displays in red and includes an Expired! message if the certificate has expired. "none" displays for a certification request.
Key Algorithm
This field displays the type of algorithm that was used to generate the certificate's key pair (the Zyxel Device uses RSA encryption) and the length of the key set in bits (1024 bits for example).
Subject Alternative Name
This field displays the certificate owner`s IP address (IP), domain name (DNS) or e-mail address (EMAIL).
Key Usage
This field displays for what functions the certificate's key can be used. For example, "DigitalSignature" means that the key can be used to sign certificates and "KeyEncipherment" means that the key can be used to encrypt text.
Extended Key Usage This field displays for what EKU (Extended Key Usage) functions the certificate's key can be used.
Basic Constraint
This field displays general information about the certificate. For example, Subject Type=CA means that this is a certification authority's certificate and "Path Length Constraint=1" means that there can only be one certification authority in the certificate's path. This field does not display for a certification request.
NWA/WAC/WAX Series User's Guide
182
Chapter 16 Certificates
Table 74 Configuration > Object > Certificate > My Certificates > Edit
LA BEL
DESC RIPTIO N
MD5 Fingerprint
This is the certificate's message digest that the Zyxel Device calculated using the MD5 algorithm.
SHA1 Fingerprint
This is the certificate's message digest that the Zyxel Device calculated using the SHA1 algorithm.
Certificate in PEM (Base-64) Encoded Format
This read-only text box displays the certificate or certification request in Privacy Enhanced Mail (PEM) format. PEM uses lowercase letters, uppercase letters and numerals to convert a binary certificate into a printable form.
You can copy and paste a certification request into a certification authority's web page, an e-mail that you send to the certification authority or a text editor and save the file on a management computer for later manual enrollment.
Export Certificate Only
Password
Export Certificate with Private Key
OK Cancel
You can copy and paste a certificate into an e-mail to send to friends or colleagues or you can copy and paste a certificate into a text editor and save the file on a management computer for later distribution (via floppy disk for example).
Use this button to save a copy of the certificate without its private key. Click this button and then Sa ve in the File Do wnlo a d screen. The Sa ve As screen opens, browse to the location that you want to use and click Sa ve .
If you want to export the certificate with its private key, create a password and type it here. Make sure you keep this password in a safe place. You will need to use it if you import the certificate to another device.
Use this button to save a copy of the certificate with its private key. Type the certificate's password and click this button. Click Sa ve in the File Do wnlo a d screen. The Sa ve As screen opens, browse to the location that you want to use and click Sa ve .
Click O K to save your changes back to the Zyxel Device. You can only change the name.
Click C a nc e l to quit and return to the My C e rtific a te s screen.
16.2.3 Im po rt C e rtific a te s
Click C o nfig ura tio n > O b je c t > C e rtific a te > My C e rtific a te s > Im po rt to open the My C e rtific a te Im po rt screen. Follow the instructions in this screen to save an existing certificate to the Zyxel Device.
Note: You can import a certificate that matches a corresponding certification request that was generated by the Zyxel Device. You can also import a certificate in PKCS#12 format, including the certificate's public and private keys.
The certificate you import replaces the corresponding request in the My C e rtific a te s screen.
You must remove any spaces in the certificate's filename before you can import it.
NWA/WAC/WAX Series User's Guide
183
Chapter 16 Certificates Fig ure 114 Configuration > Object > Certificate > My Certificates > Import
The following table describes the labels in this screen.
Table 75 Configuration > Object > Certificate > My Certificates > Import
LA BEL
DESC RIPTIO N
File Path
Type in the location of the file you want to upload in this field or click Bro wse to find it.
Browse Password
OK Cancel
You cannot import a certificate with the same name as a certificate that is already in the Zyxel Device.
Click Bro wse to find the certificate file you want to upload.
This field only applies when you import a binary PKCS#12 format file. Type the file's password that was created when the PKCS #12 file was exported.
Click O K to save the certificate on the Zyxel Device.
Click C a nc e l to quit and return to the My C e rtific a te s screen.
16.3 Truste d C e rtific a te s
Click C o nfig ura tio n > O b je c t > C e rtific a te > Truste d C e rtific a te s to open the Truste d C e rtific a te s screen. This screen displays a summary list of certificates that you have set the Zyxel Device to accept as trusted. The Zyxel Device also accepts any valid certificate signed by a certificate on this list as being trustworthy; thus you do not need to import any certificate that is signed by one of these certificates.
NWA/WAC/WAX Series User's Guide
184
Chapter 16 Certificates Fig ure 115 Configuration > Object > Certificate > Trusted Certificates
The following table describes the labels in this screen.
Table 76 Configuration > Object > Certificate > Trusted Certificates
LA BEL
DESC RIPTIO N
PKI Storage Space This bar displays the percentage of the Zyxel Device's PKI storage space that is currently in use.
in Use
When the storage space is almost full, you should consider deleting expired or unnecessary
certificates before adding more certificates.
Edit
Double-click an entry or select it and click Edit to open a screen with an in-depth list of
information about the certificate.
Remove
The Zyxel Device keeps all of your certificates unless you specifically delete them. Uploading a new firmware or default configuration file does not delete your certificates. To remove an entry, select it and click Re m o ve . The Zyxel Device confirms you want to remove it before doing so. Subsequent certificates move up by one when you take this action.
Object Reference
You cannot delete certificates that any of the Zyxel Device's features are configured to use. Select an entry and click O b je c t Re fe re nc e to open a screen that shows which settings use the entry.
#
This field displays the certificate index number. The certificates are listed in alphabetical order.
Name
This field displays the name used to identify this certificate.
Subject
This field displays identifying information about the certificate's owner, such as CN (Common Name), OU (Organizational Unit or department), O (Organization or company) and C (Country). It is recommended that each certificate have unique subject information.
Issuer
This field displays identifying information about the certificate's issuing certification authority, such as a common name, organizational unit or department, organization or company and country. With self-signed certificates, this is the same information as in the Subje c t field.
Valid From
This field displays the date that the certificate becomes applicable.
Valid To
This field displays the date that the certificate expires. The text displays in red and includes an Expired! message if the certificate has expired.
Import
Click Im po rt to open a screen where you can save the certificate of a certification authority that you trust, from your computer to the Zyxel Device.
Refresh
Click this button to display the current validity status of the certificates.
16.3.1 Edit Truste d C e rtific a te s
Click C o nfig ura tio n > O b je c t > C e rtific a te > Truste d C e rtific a te s and then a certificate's Edit icon to open the Truste d C e rtific a te s Edit screen. Use this screen to view in-depth information about the certificate, change the certificate's name and set whether or not you want the Zyxel Device to check a certification authority's list of revoked certificates before trusting a certificate issued by the certification
NWA/WAC/WAX Series User's Guide
185
Chapter 16 Certificates authority. Fig ure 116 Configuration > Object > Certificate > Trusted Certificates > Edit
NWA/WAC/WAX Series User's Guide
186
Chapter 16 Certificates
The following table describes the labels in this screen.
Table 77 Configuration > Object > Certificate > Trusted Certificates > Edit
LA BEL
DESC RIPTIO N
Name Certification Path
This field displays the identifying name of this certificate. You can change the name. You can use up to 31 alphanumeric and ;`~!@#$%^&()_+[]{}',.=- characters.
Click the Re fre sh button to have this read-only text box display the end entity's certificate and a list of certification authority certificates that shows the hierarchy of certification authorities that validate the end entity's certificate. If the issuing certification authority is one that you have imported as a trusted certificate, it may be the only certification authority in the list (along with the end entity's own certificate). The Zyxel Device does not trust the end entity's certificate and displays "Not trusted" in this field if any certificate on the path has expired or been revoked.
Refresh
Enable X.509v3 CRL Distribution Points and OCSP checking
Click Re fre sh to display the certification path.
Select this check box to have the Zyxel Device check incoming certificates that are signed by this certificate against a Certificate Revocation List (CRL) or an OCSP server. You also need to configure the OSCP or LDAP server details.
OCSP Server
Select this check box if the directory server uses OCSP (Online Certificate Status Protocol).
URL ID
Password
Type the protocol, IP address and pathname of the OCSP server.
The Zyxel Device may need to authenticate itself in order to assess the OCSP server. Type the login name (up to 31 ASCII characters) from the entity maintaining the server (usually a certification authority).
Type the password (up to 31 ASCII characters) from the entity maintaining the OCSP server (usually a certification authority).
LDAP Server
Select this check box if the directory server uses LDAP (Lightweight Directory Access Protocol). LDAP is a protocol over TCP that specifies how clients access directories of certificates and lists of revoked certificates.
Address Port
ID
Type the IP address (in dotted decimal notation) of the directory server.
Use this field to specify the LDAP server port number. You must use the same server port number that the directory server uses. 389 is the default server port number for LDAP.
The Zyxel Device may need to authenticate itself in order to assess the CRL directory server. Type the login name (up to 31 ASCII characters) from the entity maintaining the server (usually a certification authority).
Password
Type the password (up to 31 ASCII characters) from the entity maintaining the CRL directory server (usually a certification authority).
Certificate Information
These read-only fields display detailed information about the certificate.
Type
This field displays general information about the certificate. CA-signed means that a Certification Authority signed the certificate. Self-signed means that the certificate's owner signed the certificate (not a certification authority). X.509 means that this certificate was created and signed according to the ITU-T X.509 recommendation that defines the formats for public-key certificates.
Version Serial Number
This field displays the X.509 version number. This field displays the certificate's identification number given by the certification authority.
Subject
This field displays information that identifies the owner of the certificate, such as Common Name (CN), Organizational Unit (OU), Organization (O) and Country (C).
Issuer
This field displays identifying information about the certificate's issuing certification authority, such as Common Name, Organizational Unit, Organization and Country.
Signature Algorithm
With self-signed certificates, this is the same information as in the Sub je c t Na m e field.
This field displays the type of algorithm that was used to sign the certificate. Some certification authorities use rsa-pkcs1-sha1 (RSA public-private key encryption algorithm and the SHA1 hash algorithm). Other certification authorities may use rsa-pkcs1-md5 (RSA public-private key encryption algorithm and the MD5 hash algorithm).
NWA/WAC/WAX Series User's Guide
187
Chapter 16 Certificates
Table 77 Configuration > Object > Certificate > Trusted Certificates > Edit (continued)
LA BEL
DESC RIPTIO N
Valid From
This field displays the date that the certificate becomes applicable. The text displays in red and includes a Not Yet Valid! message if the certificate has not yet become applicable.
Valid To
This field displays the date that the certificate expires. The text displays in red and includes an Expiring! or Expired! message if the certificate is about to expire or has already expired.
Key Algorithm
This field displays the type of algorithm that was used to generate the certificate's key pair (the Zyxel Device uses RSA encryption) and the length of the key set in bits (1024 bits for example).
Subject Alternative Name
This field displays the certificate's owner`s IP address (IP), domain name (DNS) or e-mail address (EMAIL).
Key Usage
This field displays for what functions the certificate's key can be used. For example, "DigitalSignature" means that the key can be used to sign certificates and "KeyEncipherment" means that the key can be used to encrypt text.
Basic Constraint
This field displays general information about the certificate. For example, Subject Type=CA means that this is a certification authority's certificate and "Path Length Constraint=1" means that there can only be one certification authority in the certificate's path.
MD5 Fingerprint
This is the certificate's message digest that the Zyxel Device calculated using the MD5 algorithm. You can use this value to verify with the certification authority (over the phone for example) that this is actually their certificate.
SHA1 Fingerprint
This is the certificate's message digest that the Zyxel Device calculated using the SHA1 algorithm. You can use this value to verify with the certification authority (over the phone for example) that this is actually their certificate.
Certificate
This read-only text box displays the certificate or certification request in Privacy Enhanced Mail (PEM) format. PEM uses lowercase letters, uppercase letters and numerals to convert a binary certificate into a printable form.
Export Certificate
OK Cancel
You can copy and paste the certificate into an e-mail to send to friends or colleagues or you can copy and paste the certificate into a text editor and save the file on a management computer for later distribution (via floppy disk for example).
Click this button and then Sa ve in the File Do wnlo a d screen. The Sa ve As screen opens, browse to the location that you want to use and click Sa ve .
Click O K to save your changes back to the Zyxel Device. You can only change the name.
Click C a nc e l to quit and return to the Truste d C e rtific a te s screen.
16.3.2 Im po rt Truste d C e rtific a te s
Click C o nfig ura tio n > O b je c t > C e rtific a te > Truste d C e rtific a te s > Im po rt to open the Im po rt Truste d C e rtific a te s screen. Follow the instructions in this screen to save a trusted certificate to the Zyxel Device.
Note: You must remove any spaces from the certificate's filename before you can import the certificate.
NWA/WAC/WAX Series User's Guide
188
Chapter 16 Certificates Fig ure 117 Configuration > Object > Certificate > Trusted Certificates > Import
The following table describes the labels in this screen.
Table 78 Configuration > Object > Certificate > Trusted Certificates > Import
LA BEL
DESC RIPTIO N
File Path
Type in the location of the file you want to upload in this field or click Bro wse to find it.
Browse OK Cancel
You cannot import a certificate with the same name as a certificate that is already in the Zyxel Device. Click Bro wse to find the certificate file you want to upload. Click O K to save the certificate on the Zyxel Device. Click C a nc e l to quit and return to the previous screen.
16.4 Te c hnic a l Re fe re nc e
The following section contains additional technical information about the features described in this chapter.
O C SP
OCSP (Online Certificate Status Protocol) allows an application or device to check whether a certificate is valid. With OCSP the Zyxel Device checks the status of individual certificates instead of downloading a Certificate Revocation List (CRL). OCSP has two main advantages over a CRL. The first is real-time status information. The second is a reduction in network traffic since the Zyxel Device only gets information on the certificates that it needs to verify, not a huge list. When the Zyxel Device requests certificate status information, the OCSP server returns a "expired", "current" or "unknown" response.
NWA/WAC/WAX Series User's Guide
189
C HA PTER 1 7 Syste m
17.1 O ve rvie w
Use the system screens to configure general Zyxel Device settings.
17.1.1 Wha t Yo u C a n Do in this C ha pte r
� The Ho st Na me screen (Section 17.2 on page 190) configures a unique name for the Zyxel Device in your network.
� The Po we r Mo de screen (Section 17.3 on page 191) configures the Zyxel Device's power settings. � The Da te / Tim e screen (Section 17.4 on page 192) configures the date and time for the Zyxel Device. � The WWW screens (Section 17.5 on page 195) configure settings for HTTP or HTTPS access to the Zyxel
Device. � The SSH screen (Section 17.6 on page 203) configures SSH (Secure SHell) for securely accessing the
Zyxel Device's command line interface. � The Te lne t screen (Section 17.7 on page 207) configures Telnet for accessing the Zyxel Device's
command line interface. � The FTP screen (Section 17.8 on page 208) specifies FTP server settings. You can upload and
download the Zyxel Device's firmware and configuration files using FTP. Please also see Chapter 19 on page 225 for more information about firmware and configuration files. � The SNMP screens (Section 17.9 on page 209) configure the Zyxel Device's SNMP settings, including profiles that define allowed SNMPv3 access.
17.2 Ho st Na m e
A host name is the unique name by which a device is known on a network. Click C o nfig ura tio n > Syste m > Ho st Na m e to open this screen. Fig ure 118 Configuration > System > Host Name
NWA/WAC/WAX Series User's Guide
190
Chapter 17 System
The following table describes the labels in this screen.
Table 79 Configuration > System > Host Name
LA BEL
DESC RIPTIO N
System Name
Choose a descriptive name to identify your Zyxel Device device. This name can be up to 64 alphanumeric characters long. Spaces are not allowed, but dashes (-) underscores (_) and periods (.) are accepted.
System Location
Specify the name of the place where the Zyxel Device is located. You can enter up to 60 alphanumeric and '()' ,:;?! +-*/= #$%@ characters. Spaces and underscores are allowed. The name should start with a letter.
Domain Name
Enter the domain name (if you know it) here. This name is propagated to DHCP clients connected to interfaces with the DHCP server enabled. This name can be up to 254 alphanumeric characters long. Spaces are not allowed, but dashes "-" are accepted.
Apply
Click Apply to save your changes back to the Zyxel Device.
Reset
Click Re se t to return the screen to its last-saved settings.
17.3 Po we r Mo de
Use this screen to configure the Zyxel Device's power settings. Click C o nfig ura tio n > Syste m > Po we r Mo de to open this screen.
Fig ure 119 Configuration > System > Power Mode
The following table describes the labels in this screen.
Table 80 Configuration > System > Power Mode
LA BEL
DESC RIPTIO N
Force override Select this check box if you are using a PoE injector that does not support PoE negotiation.
the power mode Otherwise, the Zyxel Device cannot draw full power from the power sourcing equipment.
to full power
Enable this power mode to improve the Zyxel Device's performance in this situation.
Note: Ensure that the power sourcing equipment can supply enough power to the AP to avoid abnormal system reboots.
Apply Reset
Note: Only enable this if you are using a passive PoE injector that is not IEEE 802.3at/bt compliant but can still provide full power.
Click Apply to save your changes back to the Zyxel Device.
Click Re se t to return the screen to its last-saved settings.
NWA/WAC/WAX Series User's Guide
191
Chapter 17 System
17.4 Da te a nd Tim e
For effective scheduling and logging, the Zyxel Device system time must be accurate. The Zyxel Device has a software mechanism to set the time manually or get the current time and date from an external server.
To change your Zyxel Device's time based on your local time zone and date, click C o nfig ura tio n > Syste m > Da te / Tim e . The screen displays as shown. You can manually set the Zyxel Device's time and date or have the Zyxel Device get the date and time from a time server.
Fig ure 120 Configuration > System > Date/Time
The following table describes the labels in this screen.
Table 81 Configuration > System > Date/Time
LA BEL
DESC RIPTIO N
Current Time and Date
Current Time
This field displays the present time of your Zyxel Device.
Current Date
This field displays the present date of your Zyxel Device.
Time and Date Setup
Manual
Select this radio button to enter the time and date manually. If you configure a new time and date, time zone and daylight saving at the same time, the time zone and daylight saving will affect the new time and date you entered. When you enter the time settings manually, the Zyxel Device uses the new setting once you click Apply.
New Time (hh:mm:ss)
This field displays the last updated time from the time server or the last time configured manually. When you set Tim e a nd Da te Se tup to Ma nua l, enter the new time in this field and then click A p p ly .
NWA/WAC/WAX Series User's Guide
192
Chapter 17 System
Table 81 Configuration > System > Date/Time (continued)
LA BEL
DESC RIPTIO N
New Date (yyyy-mm-dd)
This field displays the last updated date from the time server or the last date configured manually. When you set Tim e a nd Da te Se tup to Ma nua l, enter the new date in this field and then click A p p ly .
Get from Time Server
Select this radio button to have the Zyxel Device get the time and date from the time server you specify below. The Zyxel Device requests time and date settings from the time server under the following circumstances.
Time Server Address
Sync. Now
Time Zone Setup Time Zone
Enable Daylight Saving
� When the Zyxel Device starts up. � When you click Apply or Sync . No w in this screen. � 24-hour intervals after starting up.
Enter the IP address or URL of your time server. Check with your ISP/network administrator if you are unsure of this information.
Click this button to have the Zyxel Device get the time and date from a time server (see the Tim e Se rve r Addre ss field). This also saves your changes (except the daylight saving settings).
Choose the time zone of your location. This will set the time difference between your time zone and Greenwich Mean Time (GMT).
Daylight saving is a period from late spring to fall when many countries set their clocks ahead of normal local time by one hour to give more daytime light in the evening.
Start Date
Select this option if you use Daylight Saving Time.
Configure the day and time when Daylight Saving Time starts if you selected Ena b le Da ylig ht Sa ving . The a t field uses the 24 hour format. Here are a couple of examples:
Daylight Saving Time starts in most parts of the United States on the second Sunday of March. Each time zone in the United States starts using Daylight Saving Time at 2 A.M. local time. So in the United States you would select Se c o nd, Sunda y, Ma rc h and type 2 in the a t field.
End Date
Daylight Saving Time starts in the European Union on the last Sunday of March. All of the time zones in the European Union start using Daylight Saving Time at the same moment (1 A.M. GMT or UTC). So in the European Union you would select La st, Sunda y, Ma rc h. The time you type in the a t field depends on your time zone. In Germany for instance, you would type 2 because Germany's time zone is one hour ahead of GMT or UTC (GMT+1).
Configure the day and time when Daylight Saving Time ends if you selected Ena b le Da ylig ht Sa ving . The a t field uses the 24 hour format. Here are a couple of examples:
Daylight Saving Time ends in the United States on the first Sunday of November. Each time zone in the United States stops using Daylight Saving Time at 2 A.M. local time. So in the United States you would select First, Sunda y, No ve m b e r and type 2 in the a t field.
Offset
Daylight Saving Time ends in the European Union on the last Sunday of October. All of the time zones in the European Union stop using Daylight Saving Time at the same moment (1 A.M. GMT or UTC). So in the European Union you would select La st, Sunda y, O c to b e r. The time you type in the a t field depends on your time zone. In Germany for instance, you would type 2 because Germany's time zone is one hour ahead of GMT or UTC (GMT+1).
Specify how much the clock changes when daylight saving begins and ends.
Enter a number from 1 to 5.5 (by 0.5 increments).
Apply Reset
For example, if you set this field to 3.5, a log occurred at 6 P.M. in local official time will appear as if it had occurred at 10:30 P.M.
Click Apply to save your changes back to the Zyxel Device.
Click Re se t to return the screen to its last-saved settings.
NWA/WAC/WAX Series User's Guide
193
Chapter 17 System
17.4.1 Pre - de fine d NTP Tim e Se rve rs List
When you turn on the Zyxel Device for the first time, the date and time start at 2003-01-01 00:00:00. The Zyxel Device then attempts to synchronize with one of the following pre-defined list of Network Time Protocol (NTP) time servers. The Zyxel Device continues to use the following pre-defined list of NTP time servers if you do not specify a time server or it cannot synchronize with the time server you specified. Table 82 Default Time Servers
0.pool.ntp.org 1.pool.ntp.org 2.pool.ntp.org
When the Zyxel Device uses the pre-defined list of NTP time servers, it randomly selects one server and tries to synchronize with it. If the synchronization fails, then the Zyxel Device goes through the rest of the list in order from the first one tried until either it is successful or all the pre-defined NTP time servers have been tried.
17.4.2 Tim e Se rve r Sync hro niza tio n
Click the Sync . No w button to get the time and date from the time server you specified in the Tim e Se rve r Addre ss field. When the Lo a ding message appears, you may have to wait up to one minute. Fig ure 121 Loading
The C urre nt Tim e and C urre nt Da te fields will display the appropriate settings if the synchronization is successful. If the synchronization was not successful, a log displays in the Vie w Lo g screen. Try re-configuring the Da te / Tim e screen. To manually set the Zyxel Device date and time:
1 Click Syste m > Da te / Tim e . 2 Select Ma nua l under Tim e a nd Da te Se tup. 3 Enter the Zyxel Device's time in the Ne w Tim e field. 4 Enter the Zyxel Device's date in the Ne w Da te field. 5 Under Tim e Zo ne Se tup, select your Tim e Zo ne from the list. 6 As an option you can select the Ena b le Da ylig ht Sa ving check box to adjust the Zyxel Device clock for
daylight savings. 7 Click Apply.
NWA/WAC/WAX Series User's Guide
194
Chapter 17 System To get the Zyxel Device date and time from a time server: 1 Click Syste m > Da te / Tim e . 2 Select G e t fro m Tim e Se rve r under Tim e a nd Da te Se tup. 3 Under Tim e Zo ne Se tup, select your Tim e Zo ne from the list. 4 Under Tim e a nd Da te Se tup, enter a Tim e Se rve r Addre ss. 5 Click Apply.
17.5 WWW O ve rvie w
The following figure shows secure and insecure management of the Zyxel Device coming in from the WAN. HTTPS and SSH access are secure. HTTP, Telnet, and FTP management access are not secure. Fig ure 122 Secure and Insecure Service Access From the WAN
17.5.1 Se rvic e Ac c e ss Lim ita tio ns
A service cannot be used to access the Zyxel Device when you have disabled that service in the corresponding screen.
17.5.2 Syste m Tim e o ut
There is a lease timeout for administrators. The Zyxel Device automatically logs you out if the management session remains idle for longer than this timeout period. The management session does not time out when a statistics screen is polling. Each user is also forced to log in the Zyxel Device for authentication again when the reauthentication time expires. You can change the timeout settings in the Use r screens.
NWA/WAC/WAX Series User's Guide
195
Chapter 17 System
17.5.3 HTTPS
You can set the Zyxel Device to use HTTP or HTTPS (HTTPS adds security) for Web Configurator sessions. HTTPS (HyperText Transfer Protocol over Secure Socket Layer, or HTTP over SSL) is a web protocol that encrypts and decrypts web pages. Secure Socket Layer (SSL) is an application-level protocol that enables secure transactions of data by ensuring confidentiality (an unauthorized party cannot read the transferred data), authentication (one party can identify the other party) and data integrity (you know if data has been changed). It relies upon certificates, public keys, and private keys (see Chapter 16 on page 174 for more information). HTTPS on the Zyxel Device is used so that you can securely access the Zyxel Device using the Web Configurator. The SSL protocol specifies that the HTTPS server (the Zyxel Device) must always authenticate itself to the HTTPS client (the computer which requests the HTTPS connection with the Zyxel Device), whereas the HTTPS client only should authenticate itself when the HTTPS server requires it to do so (select Authe ntic a te C lie nt C e rtific a te s in the WWW screen). Authe ntic a te C lie nt C e rtific a te s is optional and if selected means the HTTPS client must send the Zyxel Device a certificate. You must apply for a certificate for the browser from a CA that is a trusted CA on the Zyxel Device. Please refer to the following figure.
1 HTTPS connection requests from an SSL-aware web browser go to port 443 (by default) on the Zyxel Device's web server.
2 HTTP connection requests from a web browser go to port 80 (by default) on the Zyxel Device's web server. Fig ure 123 HTTP/HTTPS Implementation
Note: If you disable HTTP in the WWW screen, then the Zyxel Device blocks all HTTP connection attempts.
17.5.4 C o nfig uring WWW Se rvic e C o ntro l
Click C o nfig ura tio n > Syste m > WWW to open the WWW screen. Use this screen to specify HTTP or HTTPS settings.
NWA/WAC/WAX Series User's Guide
196
Chapter 17 System Fig ure 124 Configuration > System > WWW > Service Control
The following table describes the labels in this screen.
Table 83 Configuration > System > WWW > Service Control
LA BEL
DESC RIPTIO N
HTTPS
Enable
Select the check box to allow or disallow the computer with the IP address that matches the IP address(es) in the Se rvic e C o ntro l table to access the Zyxel Device Web Configurator using secure HTTPs connections.
Server Port
The HTTPS server listens on port 443 by default. If you change the HTTPS server port to a different number on the Zyxel Device, for example 8443, then you must notify people who need to access the Zyxel Device Web Configurator to use "https://Zyxel Device IP Address:8443" as the URL.
Authenticate Client Certificates
Select Authe ntic a te C lie nt C e rtific a te s (optional) to require the SSL client to authenticate itself to the Zyxel Device by sending the Zyxel Device a certificate. To do that the SSL client must have a CA-signed certificate from a CA that has been imported as a trusted CA on the Zyxel Device.
Server Certificate
Select a certificate the HTTPS server (the Zyxel Device) uses to authenticate itself to the HTTPS client. You must have certificates already configured in the My C e rtific a te s screen.
Redirect HTTP to HTTPS To allow only secure Web Configurator access, select this to redirect all HTTP connection requests to the HTTPS server.
HTTP
Enable
Select the check box to allow or disallow the computer with the IP address that matches the IP address(es) in the Se rvic e C o ntro l table to access the Zyxel Device Web Configurator using HTTP connections.
Server Port
You may change the server port number for a service if needed, however you must use the same port number in order to use that service to access the Zyxel Device.
Apply
Click Apply to save your changes back to the Zyxel Device.
Reset
Click Re se t to return the screen to its last-saved settings.
17.5.5 HTTPS Exa m ple
If you have not changed the default HTTPS port on the Zyxel Device, then in your browser enter "https:// Zyxel Device IP Address/" as the web site address where "Zyxel Device IP Address" is the IP address or domain name of the Zyxel Device you wish to access.
NWA/WAC/WAX Series User's Guide
197
Chapter 17 System
17.5.5.1 G o o g le C hro m e Wa rning Me ssa g e s
When you attempt to access the Zyxel Device HTTPS server, you will see the error message shown in the following screen. Fig ure 125 Security Alert Dialog Box (Google Chrome)
Select Adva nc e d > Pro c e e d to 192.168.1.2 (unsa fe ) to proceed to the Web Configurator login screen.
17.5.5.2 Mo zilla Fire fo x Wa rning Me ssa g e s
When you attempt to access the Zyxel Device HTTPS server, a Warning screen appears as shown in the following screen. Click Le a rn Mo re ... if you want to verify more information about the certificate from the Zyxel Device. Click Adva nc e d > Ac c e pt the Risk a nd C o ntinue .
NWA/WAC/WAX Series User's Guide
198
Chapter 17 System Fig ure 126 Security Certificate 1 (Firefox)
17.5.5.3 Avo iding Bro wse r Wa rning Me ssa g e s
Here are the main reasons your browser displays warnings about the Zyxel Device's HTTPS server certificate and what you can do to avoid seeing the warnings: � The issuing certificate authority of the Zyxel Device's HTTPS server certificate is not one of the browser's
trusted certificate authorities. The issuing certificate authority of the Zyxel Device's factory default certificate is the Zyxel Device itself since the certificate is a self-signed certificate. � For the browser to trust a self-signed certificate, import the self-signed certificate into your operating system as a trusted certificate. � To have the browser trust the certificates issued by a certificate authority, import the certificate authority's certificate into your operating system as a trusted certificate. Refer to Appendix A on page 267 for details.
17.5.5.4 Enro lling a nd Im po rting SSL C lie nt C e rtific a te s
The SSL client needs a certificate if Authe ntic a te C lie nt C e rtific a te s is selected on the Zyxel Device. You must have imported at least one trusted CA to the Zyxel Device in order for the Authe ntic a te C lie nt C e rtific a te s to be active (see the Certificates chapter for details). Apply for a certificate from a Certification Authority (CA) that is trusted by the Zyxel Device (see the Zyxel Device's Truste d C e rtific a te s Web Configurator screen).
NWA/WAC/WAX Series User's Guide
199
Chapter 17 System Fig ure 127 Trusted Certificates
The CA sends you a package containing the CA's trusted certificate(s), your personal certificate(s) and a password to install the personal certificate(s).
17.5.5.5 Insta lling a Pe rso na l C e rtific a te
You need a password in advance. The CA may issue the password or you may have to specify it during the enrollment. Double-click the personal certificate given to you by the CA to produce a screen similar to the one shown next. 1 Click Ne xt to begin the wizard.
2 The file name and path of the certificate you double-clicked should automatically appear in the File na m e text box. Click Bro wse if you wish to import a different certificate.
NWA/WAC/WAX Series User's Guide
200
Chapter 17 System
3 Enter the password given to you by the CA.
4 Have the wizard determine where the certificate should be saved on your computer or select Pla c e a ll c e rtific a te s in the fo llo wing sto re and choose a different location. NWA/WAC/WAX Series User's Guide
201
Chapter 17 System
5 Click Finish to complete the wizard and begin the import process.
6 You should see the following screen when the certificate is correctly installed on your computer.
17.5.5.6 Using a C e rtific a te Whe n Ac c e ssing the Zyxe l De vic e
To access the Zyxel Device via HTTPS: NWA/WAC/WAX Series User's Guide
202
Chapter 17 System 1 Enter `https://Zyxel Device IP Address/' in your browser's web address field.
2 When Authe ntic a te C lie nt C e rtific a te s is selected on the Zyxel Device, the following screen asks you to select a personal certificate to send to the Zyxel Device. This screen displays even if you only have a single certificate as in the example.
3 You next see the Web Configurator login screen.
17.6 SSH
You can use SSH (Secure SHell) to securely access the Zyxel Device's command line interface. SSH is a secure communication protocol that combines authentication and data encryption to provide secure encrypted communication between two hosts over an unsecured network. In the following figure, computer B on the Internet uses SSH to securely connect to the Zyxel Device (A) for a management session. Fig ure 128 SSH Communication Over the WAN Example
NWA/WAC/WAX Series User's Guide
203
Chapter 17 System
17.6.1 Ho w SSH Wo rks
The following figure is an example of how a secure connection is established between two remote hosts using SSH v1. Fig ure 129 How SSH v1 Works Example
1 Host Identification The SSH client sends a connection request to the SSH server. The server identifies itself with a host key. The client encrypts a randomly generated session key with the host key and server key and sends the result back to the server. The client automatically saves any new server public keys. In subsequent connections, the server public key is checked against the saved version on the client computer.
2 Encryption Method Once the identification is verified, both the client and server must agree on the type of encryption method to use.
3 Authentication and Data Transmission After the identification is verified and data encryption activated, a secure tunnel is established between the client and the server. The client then sends its authentication information (user name and password) to the server to log in to the server.
NWA/WAC/WAX Series User's Guide
204
Chapter 17 System
17.6.2 SSH Im ple m e nta tio n o n the Zyxe l De vic e
Your Zyxel Device supports SSH versions 1 and 2 using RSA authentication and four encryption methods (AES, 3DES, Archfour, and Blowfish). The SSH server is implemented on the Zyxel Device for management using port 22 (by default).
17.6.3 Re q uire m e nts fo r Using SSH
You must install an SSH client program on a client computer (Windows or Linux operating system) that is used to connect to the Zyxel Device over SSH.
17.6.4 C o nfig uring SSH
Click C o nfig ura tio n > Syste m > SSH to open the following screen. Use this screen to configure your Zyxel Device's Secure Shell settings.
Note: It is recommended that you disable Telnet and FTP when you configure SSH for secure connections.
Fig ure 130 Configuration > System > SSH
The following table describes the labels in this screen.
Table 84 Configuration > System > SSH
LA BEL
DESC RIPTIO N
Enable
Select the check box to allow or disallow the computer with the IP address that matches the IP address(es) in the Se rvic e C o ntro l table to access the Zyxel Device CLI using this service.
Note: The Zyxel Device uses only SSH version 2 protocol.
Version 1
Select the check box to have the Zyxel Device use both SSH version 1 and version 2 protocols. If you clear the check box, the Zyxel Device uses only SSH version 2 protocol.
Server Port
You may change the server port number for a service if needed, however you must use the same port number in order to use that service for remote management.
Server Certificate
Select the certificate whose corresponding private key is to be used to identify the Zyxel Device for SSH connections. You must have certificates already configured in the My C e rtific a te s screen.
Apply
Click Apply to save your changes back to the Zyxel Device.
Reset
Click Re se t to return the screen to its last-saved settings.
NWA/WAC/WAX Series User's Guide
205
Chapter 17 System
17.6.5 Exa m ple s o f Se c ure Te lne t Using SSH
This section shows two examples using a command interface and a graphical interface SSH client program to remotely access the Zyxel Device. The configuration and connection steps are similar for most SSH client programs. Refer to your SSH client program user's guide.
17.6.5.1 Exa m ple 1: Mic ro so ft Windo ws
This section describes how to access the Zyxel Device using the Secure Shell Client program. 1 Launch the SSH client and specify the connection information (IP address, port number) for the Zyxel
Device. 2 Configure the SSH client to accept connection using SSH version 2. 3 A window displays prompting you to store the host key in you computer. Click Ye s to continue.
Fig ure 131 SSH Example 1: Store Host Key
Enter the password to log in to the Zyxel Device. The CLI screen displays next.
17.6.5.2 Exa m ple 2: Linux
This section describes how to access the Zyxel Device using the OpenSSH client program that comes with most Linux distributions. 1 Test whether the SSH service is available on the Zyxel Device.
Enter "telnet 192.168.1.2 22" at a terminal prompt and press [ENTER]. The computer attempts to connect to port 22 on the Zyxel Device (using the default IP address of 192.168.1.2). A message displays indicating the SSH protocol version supported by the Zyxel Device.
NWA/WAC/WAX Series User's Guide
206
Chapter 17 System
Fig ure 132 SSH Example 2: Test $ telnet 192.168.1.2 22 Trying 192.168.1.2... Connected to 192.168.1.2. Escape character is '^]'. SSH-1.5-1.0.0
2 Enter "ssh �2 192.168.1.2". This command forces your computer to connect to the Zyxel Device using SSH version 1. If this is the first time you are connecting to the Zyxel Device using SSH, a message displays prompting you to save the host information of the Zyxel Device. Type "yes" and press [ENTER]. Then enter the password to log in to the Zyxel Device. Fig ure 133 SSH Example 2: Log in $ ssh �2 192.168.1.2 The authenticity of host '192.168.1.2 (192.168.1.2)' can't be established. RSA1 key fingerprint is 21:6c:07:25:7e:f4:75:80:ec:af:bd:d4:3d:80:53:d1. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '192.168.1.2' (RSA1) to the list of known hosts. Administrator@192.168.1.2's password:
3 The CLI screen displays next.
17.7 Te lne t
You can use Telnet to access the Zyxel Device's command line interface. Click C o nfig ura tio n > Syste m > TELNETto configure your Zyxel Device for remote Telnet access. Use this screen to enable or disable Telnet and set the server port number.
Fig ure 134 Configuration > System > TELNET
The following table describes the labels in this screen.
Table 85 Configuration > System > TELNET
LA BEL
DESC RIPTIO N
Enable
Select the check box to allow or disallow the computer with the IP address that matches the IP address(es) in the Se rvic e C o ntro l table to access the Zyxel Device CLI using this service.
Server Port
You may change the server port number for a service if needed, however you must use the same port number in order to use that service for remote management.
NWA/WAC/WAX Series User's Guide
207
Chapter 17 System
Table 85 Configuration > System > TELNET (continued)
LA BEL
DESC RIPTIO N
Apply
Click Apply to save your changes back to the Zyxel Device.
Reset
Click Re se t to return the screen to its last-saved settings.
17.8 FTP
You can upload and download the Zyxel Device's firmware and configuration files using FTP. To use this feature, your computer must have an FTP client. See Chapter 19 on page 225 for more information about firmware and configuration files.
To change your Zyxel Device's FTP settings, click C o nfig ura tio n > Syste m > FTP tab. The screen appears as shown. Use this screen to specify FTP settings.
Fig ure 135 Configuration > System > FTP
The following table describes the labels in this screen.
Table 86 Configuration > System > FTP
LA BEL
DESC RIPTIO N
Enable TLS required
Select the check box to allow or disallow the computer with the IP address that matches the IP address(es) in the Se rvic e C o ntro l table to access the Zyxel Device using this service.
Select the check box to use FTP over TLS (Transport Layer Security) to encrypt communication.
This implements TLS as a security mechanism to secure FTP clients and/or servers.
Server Port
You may change the server port number for a service if needed, however you must use the same port number in order to use that service for remote management.
Server Certificate Select the certificate whose corresponding private key is to be used to identify the Zyxel Device for FTP connections. You must have certificates already configured in the My C e rtific a te s screen.
Apply
Click Apply to save your changes back to the Zyxel Device.
Reset
Click Re se t to return the screen to its last-saved settings.
NWA/WAC/WAX Series User's Guide
208
Chapter 17 System
17.9 SNMP
Simple Network Management Protocol is a protocol used for exchanging management information between network devices. Your Zyxel Device supports SNMP agent functionality, which allows a manager station to manage and monitor the Zyxel Device through the network. The Zyxel Device supports SNMP version one (SNMPv1), version two (SNMPv2c), and version three (SNMPv3). The next figure illustrates an SNMP management operation. Fig ure 136 SNMP Management Model
An SNMP managed network consists of two main types of component: agents and a manager. An agent is a management software module that resides in a managed device (the Zyxel Device). An agent translates the local management information from the managed device into a form compatible with SNMP. The manager is the console through which network administrators perform network management functions. It executes applications that control and monitor managed devices. The managed devices contain object variables/managed objects that define each piece of information to be collected about a device. Examples of variables include such as number of packets received, node port status etc. A Management Information Base (MIB) is a collection of managed objects. SNMP allows a manager and agents to communicate for the purpose of accessing these objects. SNMP itself is a simple request/response protocol based on the manager/agent model. The manager issues a request and the agent returns responses using the following protocol operations: � Get - Allows the manager to retrieve an object variable from the agent. � GetNext - Allows the manager to retrieve the next object variable from a table or list within an agent.
In SNMPv1, when a manager wants to retrieve all elements of a table from an agent, it initiates a Get operation, followed by a series of GetNext operations. � Set - Allows the manager to set values for object variables within an agent.
NWA/WAC/WAX Series User's Guide
209
Chapter 17 System
� Trap - Used by the agent to inform the manager of some events.
17.9.1 Suppo rte d MIBs
The Zyxel Device supports MIB II that is defined in RFC-1213 and RFC-1215. The Zyxel Device also supports private MIBs (ZYXEL-ES-CAPWAP.MIB, ZYXEL-ES-COMMON.MIB, ZYXEL-ES-ZyXELAPMgmt.MIB, ZYXEL-ESPROWLAN.MIB, ZYXEL-ES-RFMGMT.MIB, ZYXEL-ES-SMI.MIB, and ZYXEL-ES-WIRELESS.MIB) to collect information about CPU and memory usage and VPN total throughput. The focus of the MIBs is to let administrators collect statistical data and monitor status and performance. You can download the Zyxel Device's MIBs from www.zyxel.com.
17.9.2 SNMP Tra ps
The Zyxel Device will send traps to the SNMP manager when any one of the following events occurs.
Table 87 SNMP Traps
O BJEC TLABEL linkDown linkUp authenticationFailure
O BJEC TID 1.3.6.1.6.3.1.1.5.3 1.3.6.1.6.3.1.1.5.4 1.3.6.1.6.3.1.1.5.5
DESC RIPTIO N
This trap is sent when the Ethernet link is down. This trap is sent when the Ethernet link is up. This trap is sent when an SNMP request comes from nonauthenticated hosts.
17.9.3 C o nfig uring SNMP
To change your Zyxel Device's SNMP settings, click C o nfig ura tio n > Syste m > SNMP tab. The screen appears as shown. Use this screen to configure your SNMP settings. You can also configure user profiles that define allowed SNMPv3 access.
Fig ure 137 Configuration > System > SNMP
NWA/WAC/WAX Series User's Guide
210
Chapter 17 System
The following table describes the labels in this screen.
Table 88 Configuration > System > SNMP
LA BEL
DESC RIPTIO N
Enable
Select the check box to allow or disallow users to access the Zyxel Device using SNMP.
Server Port
You may change the server port number for a service if needed, however you must use the same port number in order to use that service for remote management.
Trap
Community
Type the trap community, which is the password sent with each trap to the SNMP manager. The default is public and allows all requests.
Destination
Type the IP address of the station to send your SNMP traps to.
Trap Wireless Event
Select this to have the Zyxel Device send a trap to the SNMP manager when a wireless client is connected to or disconnected from the Zyxel Device.
SNMPv2c
Select this to allow SNMP managers using SNMPv2c to access the Zyxel Device.
Get Community
Enter the G e t C o m m unity, which is the password for the incoming Get and GetNext requests from the management station. The default is public and allows all requests.
Set Community
Enter the Se t c o m m unity, which is the password for incoming Set requests from the management station. The default is private and allows all requests.
SNMPv3
Select this to allow SNMP managers using SNMPv3 to access the Zyxel Device.
Add
Click this to create a new entry. Select an entry and click Add to create a new entry after the selected entry.
Edit
Double-click an entry or select it and click Edit to be able to modify the entry's settings.
Remove
To remove an entry, select it and click Re m o ve . The Zyxel Device confirms you want to remove it before doing so. Note that subsequent entries move up by one when you take this action.
#
This the index number of an SNMPv3 user profile.
User Name
This is the name of the user for which this SNMPv3 user profile is configured.
Authentication
This field displays the type of authentication the SNMPv3 user must use to connect to the Zyxel Device using this SNMPv3 user profile.
Privacy
This field displays the type of encryption the SNMPv3 user must use to connect to the Zyxel Device using this SNMPv3 user profile.
Privilege
This field displays whether the SNMPv3 user can have read-only or read and write access to the Zyxel Device using this SNMPv3 user profile.
Apply
Click Apply to save your changes back to the Zyxel Device.
Reset
Click Re se t to return the screen to its last-saved settings.
17.9.4 Adding o r Editing a n SNMPv3 Use r Pro file
This screen allows you to add or edit an SNMPv3 user profile. To access this screen, click the C o nfig ura tio n > Syste m > SNMP screen's Add button or select a SNMPv3 user profile from the list and click the Edit button.
NWA/WAC/WAX Series User's Guide
211
Chapter 17 System Fig ure 138 Configuration > System > SNMP > Add
The following table describes the labels in this screen.
Table 89 Configuration > System > SNMP
LA BEL
DESC RIPTIO N
User Name Authentication
Select the user name of the user account for which this SNMPv3 user profile is configured.
Select the type of authentication the SNMPv3 user must use to connect to the Zyxel Device using this SNMPv3 user profile.
Select MD5 to require the SNMPv3 user's password be encrypted by MD5 for authentication.
Privacy
Select SHA to require the SNMPv3 user's password be encrypted by SHA for authentication.
Select the type of encryption the SNMPv3 user must use to connect to the Zyxel Device using this SNMPv3 user profile.
Select NO NE to not encrypt the SNMPv3 communications.
Select DES to use DES to encrypt the SNMPv3 communications.
Privilege
OK Cancel
Select AES to use AES to encrypt the SNMPv3 communications.
Select whether the SNMPv3 user can have read-only or read and write access to the Zyxel Device using this SNMPv3 user profile. Click O K to save your changes back to the Zyxel Device. Click C a nc e l to exit this screen without saving your changes.
NWA/WAC/WAX Series User's Guide
212
C HA PTER 1 8 Lo g a nd Re po rt
18.1 O ve rvie w
Use the system screens to configure daily reporting and log settings.
18.1.1 Wha t Yo u C a n Do In this C ha pte r
� The Em a il Da ily Re po rt screen (Section 18.2 on page 213) configures how and where to send daily reports and what reports to send.
� The Lo g Se tting screens (Section 18.3 on page 215) specify which logs are e-mailed, where they are emailed, and how often they are e-mailed.
18.2 Em a il Da ily Re po rt
Use this screen to start or stop data collection and view various statistics about traffic passing through your Zyxel Device. Note: Data collection may decrease the Zyxel Device's traffic throughput rate. Click C o nfig ura tio n > Lo g & Re po rt > Em a il Da ily Re po rt to display the following screen. Configure this screen to have the Zyxel Device e-mail you system statistics every day.
NWA/WAC/WAX Series User's Guide
213
Chapter 18 Log and Report Fig ure 139 Configuration > Log & Report > Email Daily Report
The following table describes the labels in this screen.
Table 90 Configuration > Log & Report > Email Daily Report
LA BEL
DESC RIPTIO N
Enable Email Daily Report
Select this to send reports by e-mail every day.
Mail Server
Type the name or IP address of the outgoing SMTP server.
NWA/WAC/WAX Series User's Guide
214
Chapter 18 Log and Report
Table 90 Configuration > Log & Report > Email Daily Report (continued)
LA BEL
DESC RIPTIO N
SSL/TLS Encryption
Select SSL/ TLS to use Secure Sockets Layer (SSL) or Transport Layer Security (TLS) if you want encrypted communications between the mail server and the Zyxel Device.
Select STARTTLS to upgrade a plain text connection to a secure connection using SSL/TLS.
Mail Server Port Mail Subject
Mail From
Mail To SMTP Authentication User Name
Password
Send Report Now Time for sending report Report Items
Reset All Counters Apply Reset
Select No to not encrypt the communications. Enter the same port number here as is on the mail server for mail traffic. Type the subject line for the outgoing e-mail. Select Appe nd syste m na m e to add the Zyxel Device's system name to the subject. Select Appe nd da te tim e to add the Zyxel Device's system date and time to the subject. Type the e-mail address from which the outgoing e-mail is delivered. This address is used in replies. Type the e-mail address (or addresses) to which the outgoing e-mail is delivered. Select this check box if it is necessary to provide a user name and password to the SMTP server.
This box is effective when you select the SMTP Authe ntic a tio n check box. Type the user name to provide to the SMTP server when the log is e-mailed. This box is effective when you select the SMTP Authe ntic a tio n check box. Type the password to provide to the SMTP server when the log is e-mailed. Click this button to have the Zyxel Device send the daily e-mail report immediately.
Select the time of day (hours and minutes) when the log is e-mailed. Use 24-hour notation.
Select the information to include in the report. Select Re se t c o unte rs a fte r se nding re po rt suc c e ssfully if you only want to see statistics for a 24 hour period. Click this to discard all report data and start all of the counters over at zero.
Click Apply to save your changes back to the Zyxel Device. Click Re se t to return the screen to its last-saved settings.
18.3 Lo g Se tting
These screens control log messages and alerts. A log message stores the information for viewing (for example, in the Mo nito r > Vie w Lo g screen) or regular e-mailing later, and an alert is e-mailed immediately. Usually, alerts are used for events that require more serious attention, such as system errors and attacks.
The Zyxel Device provides a system log and supports e-mail profiles and remote syslog servers. The system log is available on the Vie w Lo g screen, the e-mail profiles are used to mail log messages to the specified destinations, and the other four logs are stored on specified syslog servers.
The Lo g Se tting tab also controls what information is saved in each log. For the system log, you can also specify which log messages are e-mailed, where they are e-mailed, and how often they are e-mailed.
For alerts, the Lo g Se tting screen controls which events generate alerts and where alerts are e-mailed.
The Lo g Se tting screen provides a summary of all the settings. You can use the Edit Lo g Se tting screen to maintain the detailed settings (such as log categories, e-mail addresses, server names, etc.) for any log. Alternatively, if you want to edit what events is included in each log, you can also use the Ac tive Lo g
NWA/WAC/WAX Series User's Guide
215
Chapter 18 Log and Report
Summ a ry screen to edit this information for all logs at the same time.
18.3.1 Lo g Se tting Sc re e n
To access this screen, click C o nfig ura tio n > Lo g & Re po rt > Lo g Se tting . Fig ure 140 Configuration > Log & Report > Log Setting
The following table describes the labels in this screen.
Table 91 Configuration > Log & Report > Log Setting
LA BEL
DESC RIPTIO N
Edit
Double-click an entry or select it and click Edit to open a screen where you can modify the
entry's settings.
Activate
To turn on an entry, select it and click Ac tiva te .
Inactivate
To turn off an entry, select it and click Ina c tiva te .
#
This field is a sequential value, and it is not associated with a specific log.
Status
This field shows whether the log is active or not.
Name
This field displays the name of the log (system log or one of the remote servers).
NWA/WAC/WAX Series User's Guide
216
Chapter 18 Log and Report
Table 91 Configuration > Log & Report > Log Setting (continued)
LA BEL
DESC RIPTIO N
Log Format
This field displays the format of the log.
Inte rna l - system log; you can view the log on the Vie w Lo g tab.
VRPT/ Syslo g - Zyxel's Vantage Report, syslog-compatible format.
Summary
Active Log Summary
Apply
C EF/ Syslo g - Common Event Format, syslog-compatible format. This field is a summary of the settings for each log. Click this button to open the Ac tive Lo g Sum m a ry screen.
Click this button to save your changes (activate and deactivate logs) and make them take effect.
18.3.2 Edit Syste m Lo g Se tting s
This screen controls the detailed settings for each log in the system log (which includes the e-mail profiles). Select a system log entry in the Lo g Se tting screen and click the Edit icon.
NWA/WAC/WAX Series User's Guide
217
Chapter 18 Log and Report Fig ure 141 Configuration > Log & Report > Log Setting > Edit System Log Setting
NWA/WAC/WAX Series User's Guide
218
Chapter 18 Log and Report
The following table describes the labels in this screen.
Table 92 Configuration > Log & Report > Log Setting > Edit System Log Setting
LA BEL
DESC RIPTIO N
E-Mail Server 1/2 Active
Mail Server SSL/TLS Encryption
Select this to send log messages and alerts according to the information in this section. You specify what kinds of log messages are included in log information and what kinds of log messages are included in alerts in the Ac tive Lo g a nd Ale rt section.
Type the name or IP address of the outgoing SMTP server.
Select SSL/ TLS to use Secure Sockets Layer (SSL) or Transport Layer Security (TLS) if you want encrypted communications between the mail server and the Zyxel Device.
Select STARTTLS to upgrade a plain text connection to a secure connection using SSL/TLS.
Select No to not encrypt the communications.
Mail Server Port
Enter the same port number here as is on the mail server for mail traffic.
Mail Subject
Type the subject line for the outgoing e-mail. Select Appe nd syste m na m e to add the Zyxel Device's system name to the subject. Select Appe nd da te tim e to add the Zyxel Device's system date and time to the subject.
Send From
Type the e-mail address from which the outgoing e-mail is delivered. This address is used in replies.
Send Log To
Type the e-mail address to which the outgoing e-mail is delivered.
Send Alerts To
Type the e-mail address to which alerts are delivered.
Sending Log
Select how often log information is e-mailed. Choices are: Whe n Full, Ho urly a nd Whe n Full, Da ily a nd Whe n Full, and We e kly a nd Whe n Full.
Day for Sending Log This field is available if the log is e-mailed weekly. Select the day of the week the log is emailed.
Time for Sending Log
This field is available if the log is e-mailed weekly or daily. Select the time of day (hours and minutes) when the log is e-mailed. Use 24-hour notation.
SMTP Authentication
Select this check box if it is necessary to provide a user name and password to the SMTP server.
User Name
This box is effective when you select the SMTP Authe ntic a tio n check box. Type the user name to provide to the SMTP server when the log is e-mailed.
Password
This box is effective when you select the SMTP Authe ntic a tio n check box. Type the password to provide to the SMTP server when the log is e-mailed.
Active Log and Alert
System log
Use the Syste m Lo g drop-down list to change the log settings for all of the log categories.
disa b le a ll lo g s (red X) - do not log any information for any category for the system log or e-mail any logs to e-mail server 1 or 2.
e na b le no rm a l lo g s (green check mark) - create log messages and alerts for all categories for the system log. If e-mail server 1 or 2 also has normal logs enabled, the Zyxel Device will e-mail logs to them.
e na b le no rm a l lo g s a nd de b ug lo g s (yellow check mark) - create log messages, alerts, and debugging information for all categories. The Zyxel Device does not e-mail debugging information, even if this setting is selected.
NWA/WAC/WAX Series User's Guide
219
Chapter 18 Log and Report
Table 92 Configuration > Log & Report > Log Setting > Edit System Log Setting (continued)
LA BEL
DESC RIPTIO N
E-mail Server 1
Use the E- Ma il Se rve r 1 drop-down list to change the settings for e-mailing logs to e-mail server 1 for all log categories.
Using the Syste m Lo g drop-down list to disable all logs overrides your e-mail server 1 settings.
e na b le no rm a l lo g s (green check mark) - e-mail log messages for all categories to e-mail server 1.
E-mail Server 2
e na b le a le rt lo g s (red exclamation point) - e-mail alerts for all categories to e-mail server 1.
Use the E- Ma il Se rve r 2 drop-down list to change the settings for e-mailing logs to e-mail server 2 for all log categories.
Using the Syste m Lo g drop-down list to disable all logs overrides your e-mail server 2 settings.
e na b le no rm a l lo g s (green check mark) - e-mail log messages for all categories to e-mail server 2.
# Log Category
System log
e na b le a le rt lo g s (red exclamation point) - e-mail alerts for all categories to e-mail server 2.
This field is a sequential value, and it is not associated with a specific address.
This field displays each category of messages. It is the same value used in the Displa y and C a te g o ry fields in the Vie w Lo g tab. The De fa ult category includes debugging messages generated by open source software.
Select which events you want to log by Lo g C a te g o ry. There are three choices:
disa b le a ll lo g s (red X) - do not log any information from this category
e na b le no rm a l lo g s (green check mark) - create log messages and alerts from this category
E-mail Server 1
E-mail Server 2
Log Consolidation Active
Log Consolidation Interval OK Cancel
e na b le no rm a l lo g s a nd de b ug lo g s (yellow check mark) - create log messages, alerts, and debugging information from this category; the Zyxel Device does not e-mail debugging information, however, even if this setting is selected.
Select whether each category of events should be included in the log messages when it is e-mailed (green check mark) and/or in alerts (red exclamation point) for the e-mail settings specified in E- Ma il Se rve r 1. The Zyxel Device does not e-mail debugging information, even if it is recorded in the Syste m lo g .
Select whether each category of events should be included in log messages when it is emailed (green check mark) and/or in alerts (red exclamation point) for the e-mail settings specified in E- Ma il Se rve r 2. The Zyxel Device does not e-mail debugging information, even if it is recorded in the Syste m lo g .
Select this to activate log consolidation. Log consolidation aggregates multiple log messages that arrive within the specified Lo g C o nso lida tio n Inte rva l. In the Vie w Lo g tab, the text "[count=x]", where x is the number of original log messages, is appended at the end of the Me ssa g e field, when multiple log messages were aggregated.
Type how often, in seconds, to consolidate log information. If the same log message appears multiple times, it is aggregated into one log message with the text "[count=x]", where x is the number of original log messages, appended at the end of the Me ssa g e field.
Click this to save your changes and return to the previous screen.
Click this to return to the previous screen without saving your changes.
NWA/WAC/WAX Series User's Guide
220
Chapter 18 Log and Report
18.3.3 Edit Re m o te Se rve r
This screen controls the settings for each log in the remote server (syslog). Select a remote server entry in the Lo g Se tting screen and click the Edit icon. Fig ure 142 Configuration > Log & Report > Log Setting > Edit Remote Server
NWA/WAC/WAX Series User's Guide
221
Chapter 18 Log and Report
The following table describes the labels in this screen.
Table 93 Configuration > Log & Report > Log Setting > Edit Remote Server
LA BEL
DESC RIPTIO N
Log Settings for Remote Server
Active
Select this check box to send log information according to the information in this section. You specify what kinds of messages are included in log information in the Ac tive Lo g section.
Log Format This field displays the format of the log information. It is read-only.
VRPT/ Syslo g - Zyxel's Vantage Report, syslog-compatible format.
Server Address Log Facility
Active Log Selection
C EF/ Syslo g - Common Event Format, syslog-compatible format. Type the server name or the IP address of the syslog server to which to send log information.
Select a log facility. The log facility allows you to log the messages to different files in the syslog server. Please see the documentation for your syslog program for more information.
Use the Se le c tio n drop-down list to change the log settings for all of the log categories.
disa b le a ll lo g s (red X) - do not send the remote server logs for any log category.
e na b le no rm a l lo g s (green check mark) - send the remote server log messages and alerts for all log categories.
e na b le no rm a l lo g s a nd de b ug lo g s (yellow check mark) - send the remote server log messages, alerts, and debugging information for all log categories.
#
This field is a sequential value, and it is not associated with a specific address.
Log Category This field displays each category of messages. It is the same value used in the Displa y and C a te g o ry fields in the Vie w Lo g tab. The De fa ult category includes debugging messages generated by open source software.
Selection
Select what information you want to log from each Lo g C a te g o ry (except All Lo g s; see below). Choices are:
disa b le a ll lo g s (red X) - do not log any information from this category
e na b le no rm a l lo g s (green checkmark) - log regular information and alerts from this category
OK Cancel
e na b le no rm a l lo g s a nd de b ug lo g s (yellow check mark) - log regular information, alerts, and debugging information from this category
Click this to save your changes and return to the previous screen.
Click this to return to the previous screen without saving your changes.
18.3.4 Ac tive Lo g Sum m a ry
This screen allows you to view and to edit what information is included in the system log, e-mail profiles, and remote servers at the same time. It does not let you change other log settings (for example, where and how often log information is e-mailed or remote server names). To access this screen, go to the Lo g Se tting screen, and click the Ac tive Lo g Sum m a ry button.
NWA/WAC/WAX Series User's Guide
222
Chapter 18 Log and Report Fig ure 143 Active Log Summary
This screen provides a different view and a different way of indicating which messages are included in each log and each alert. (The De fa ult category includes debugging messages generated by open source software.)
The following table describes the fields in this screen.
Table 94 Configuration > Log & Report > Log Setting > Active Log Summary
LA BEL
DESC RIPTIO N
Active Log Summary
System log
If the Zyxel Device is set to controller mode, the AC section controls logs generated by the controller and the AP section controls logs generated by the managed APs.
Use the Syste m Lo g drop-down list to change the log settings for all of the log categories.
disa b le a ll lo g s (red X) - do not log any information for any category for the system log or e-mail any logs to e-mail server 1 or 2.
e na b le no rm a l lo g s (green check mark) - create log messages and alerts for all categories for the system log. If e-mail server 1 or 2 also has normal logs enabled, the Zyxel Device will e-mail logs to them.
e na b le no rm a l lo g s a nd de b ug lo g s (yellow check mark) - create log messages, alerts, and debugging information for all categories. The Zyxel Device does not e-mail debugging information, even if this setting is selected.
NWA/WAC/WAX Series User's Guide
223
Chapter 18 Log and Report
Table 94 Configuration > Log & Report > Log Setting > Active Log Summary (continued)
LA BEL
DESC RIPTIO N
E-mail Server 1
Use the E- Ma il Se rve r 1 drop-down list to change the settings for e-mailing logs to e-mail server 1 for all log categories.
Using the Syste m Lo g drop-down list to disable all logs overrides your e-mail server 1 settings.
e na b le no rm a l lo g s (green check mark) - e-mail log messages for all categories to e-mail server 1.
E-mail Server 2
e na b le a le rt lo g s (red exclamation point) - e-mail alerts for all categories to e-mail server 1.
Use the E- Ma il Se rve r 2 drop-down list to change the settings for e-mailing logs to e-mail server 2 for all log categories.
Using the Syste m Lo g drop-down list to disable all logs overrides your e-mail server 2 settings.
e na b le no rm a l lo g s (green check mark) - e-mail log messages for all categories to e-mail server 2.
Remote Server 1~4
e na b le a le rt lo g s (red exclamation point) - e-mail alerts for all categories to e-mail server 2.
For each remote server, use the Se le c tio n drop-down list to change the log settings for all of the log categories.
disa b le a ll lo g s (red X) - do not send the remote server logs for any log category.
e na b le no rm a l lo g s (green check mark) - send the remote server log messages and alerts for all log categories.
# Log Category
System log
e na b le no rm a l lo g s a nd de b ug lo g s (yellow check mark) - send the remote server log messages, alerts, and debugging information for all log categories.
This field is a sequential value, and it is not associated with a specific address.
This field displays each category of messages. It is the same value used in the Displa y and C a te g o ry fields in the Vie w Lo g tab. The De fa ult category includes debugging messages generated by open source software.
Select which events you want to log by Lo g C a te g o ry. There are three choices:
disa b le a ll lo g s (red X) - do not log any information from this category
e na b le no rm a l lo g s (green checkmark) - create log messages and alerts from this category
E-mail Server 1 Email
E-mail Server 2 Email
Remote Server 1~4 Syslog
e na b le no rm a l lo g s a nd de b ug lo g s (yellow check mark) - create log messages, alerts, and debugging information from this category; the Zyxel Device does not e-mail debugging information, however, even if this setting is selected.
Select whether each category of events should be included in the log messages when it is emailed (green check mark) and/or in alerts (red exclamation point) for the e-mail settings specified in E- Ma il Se rve r 1. The Zyxel Device does not e-mail debugging information, even if it is recorded in the Syste m lo g .
Select whether each category of events should be included in log messages when it is emailed (green check mark) and/or in alerts (red exclamation point) for the e-mail settings specified in E- Ma il Se rve r 2. The Zyxel Device does not e-mail debugging information, even if it is recorded in the Syste m lo g .
For each remote server, select what information you want to log from each Lo g C a te g o ry (except All Lo g s; see below). Choices are:
disa b le a ll lo g s (red X) - do not log any information from this category
e na b le no rm a l lo g s (green checkmark) - log regular information and alerts from this category
OK Cancel
e na b le no rm a l lo g s a nd de b ug lo g s (yellow check mark) - log regular information, alerts, and debugging information from this category
Click this to save your changes and return to the previous screen.
Click this to return to the previous screen without saving your changes.
NWA/WAC/WAX Series User's Guide
224
C HA PTER 1 9 File Ma na g e r
19.1 O ve rvie w
Configuration files define the Zyxel Device's settings. Shell scripts are files of commands that you can store on the Zyxel Device and run when you need them. You can apply a configuration file or run a shell script without the Zyxel Device restarting. You can store multiple configuration files and shell script files on the Zyxel Device. You can edit configuration files or shell scripts in a text editor and upload them to the Zyxel Device. Configuration files use a .conf extension and shell scripts use a .zysh extension.
19.1.1 Wha t Yo u C a n Do in this C ha pte r
� The C o nfig ura tio n File screen (Section 19.2 on page 226) stores and names configuration files. You can also download and upload configuration files.
� The Firm wa re Pa c ka g e screen (Section 19.3 on page 231) checks your current firmware version and uploads firmware to the Zyxel Device.
� The She ll Sc ript screen (Section 19.4 on page 233) stores, names, downloads, uploads and runs shell script files.
19.1.2 Wha t yo u Ne e d to Kno w
The following terms and concepts may help as you read this chapter.
C o nfig ura tio n File s a nd She ll Sc ripts
When you apply a configuration file, the Zyxel Device uses the factory default settings for any features that the configuration file does not include. When you run a shell script, the Zyxel Device only applies the commands that it contains. Other settings do not change.
These files have the same syntax, which is also identical to the way you run CLI commands manually. An example is shown below. Fig ure 144 Configuration File / Shell Script: Example # enter configuration mode configure terminal # change administrator password username admin password 4321 user-type admin #configure default radio profile, change 2GHz channel to 11 & Tx output power # to 50% wlan-radio-profile default 2g-channel 11 output-power 50% exit write
NWA/WAC/WAX Series User's Guide
225
Chapter 19 File Manager
While configuration files and shell scripts have the same syntax, the Zyxel Device applies configuration files differently than it runs shell scripts. This is explained below.
Table 95 Configuration Files and Shell Scripts in the Zyxel Device
Configuration Files (.conf)
Shell Scripts (.zysh)
� Resets to default configuration. � Goes into CLI C o nfig ura tio n mode. � Runs the commands in the configuration file.
� Goes into CLI Privile g e mode. � Runs the commands in the shell script.
You have to run the aforementioned example as a shell script because the first command is run in Privile g e mode. If you remove the first command, you have to run the example as a configuration file because the rest of the commands are executed in C o nfig ura tio n mode.
C o m m e nts in C o nfig ura tio n File s o r She ll Sc ripts
In a configuration file or shell script, use "#" or "!" as the first character of a command line to have the Zyxel Device treat the line as a comment.
Your configuration files or shell scripts can use "exit" or a command line consisting of a single "!" to have the Zyxel Device exit sub command mode.
Note: "exit" or "!'" must follow sub commands if it is to make the Zyxel Device exit sub command mode.
In the following example lines 1 and 2 are comments. Line 7 exits sub command mode.
! this is from Joe # on 2010/12/05 wlan-ssid-profile default ssid Joe-AP qos wmm security default !
Erro rs in C o nfig ura tio n File s o r She ll Sc ripts
When you apply a configuration file or run a shell script, the Zyxel Device processes the file line-by-line. The Zyxel Device checks the first line and applies the line if no errors are detected. Then it continues with the next line. If the Zyxel Device finds an error, it stops applying the configuration file or shell script and generates a log.
You can change the way a configuration file or shell script is applied. Include setenv stop-on-error off in the configuration file or shell script. The Zyxel Device ignores any errors in the configuration file or shell script and applies all of the valid commands. The Zyxel Device still generates a log for any errors.
19.2 C o nfig ura tio n File
Click Ma inte na nc e > File Ma na g e r > C o nfig ura tio n File to open this screen. Use the C o nfig ura tio n File screen to store, run, and name configuration files. You can also download configuration files from the Zyxel Device to your computer and upload configuration files from your computer to the Zyxel Device.
NWA/WAC/WAX Series User's Guide
226
Chapter 19 File Manager Once your Zyxel Device is configured and functioning properly, it is highly recommended that you back up your configuration file before making further configuration changes. The backup configuration file will be useful in case you need to return to your previous settings.
C o nfig ura tio n File Flo w a t Re sta rt
� If there is not a sta rtup- c o nfig .c o nf when you restart the Zyxel Device (whether through a management interface or by physically turning the power off and back on), the Zyxel Device uses the syste m - de fa ult.c o nf configuration file with the Zyxel Device's default settings.
� If there is a sta rtup- c o nfig .c o nf, the Zyxel Device checks it for errors and applies it. If there are no errors, the Zyxel Device uses it and copies it to the la stg o o d.c o nf configuration file as a back up file. If there is an error, the Zyxel Device generates a log and copies the sta rtup- c o nfig .c o nf configuration file to the sta rtup- c o nfig - b a d.c o nf configuration file and tries the existing la stg o o d.c o nf configuration file. If there isn't a la stg o o d.c o nf configuration file or it also has an error, the Zyxel Device applies the syste m - de fa ult.c o nf configuration file.
� You can change the way the sta rtup- c o nfig .c o nf file is applied. Include the setenv-startup stopon-error off command. The Zyxel Device ignores any errors in the sta rtup- c o nfig .c o nf file and applies all of the valid commands. The Zyxel Device still generates a log for any errors.
Fig ure 145 Maintenance > File Manager > Configuration File
Do no t turn o ff the Zyxe l De vic e while c o nfig ura tio n file uplo a d is in pro g re ss.
NWA/WAC/WAX Series User's Guide
227
Chapter 19 File Manager
The following table describes the labels in this screen.
Table 96 Maintenance > File Manager > Configuration File
LA BEL
DESC RIPTIO N
Rename
Use this button to change the label of a configuration file on the Zyxel Device. You can only rename manually saved configuration files. You cannot rename the la stg o o d.c o nf, syste m de fa ult.c o nf and sta rtup- c o nfig .c o nf files.
You cannot rename a configuration file to the name of another configuration file in the Zyxel Device.
Click a configuration file's row to select it and click Re na m e to open the Re na m e File screen.
Remove
Download Copy
Specify the new name for the configuration file. Use up to 25 characters (including a-zA-Z09;`~!@#$%^&()_+[]{}',.=-).
Click O K to save the duplicate or click C a nc e l to close the screen without saving a duplicate of the configuration file.
Click a configuration file's row to select it and click Re m o ve to delete it from the Zyxel Device. You can only delete manually saved configuration files. You cannot delete the syste m de fa ult.c o nf, sta rtup- c o nfig .c o nf and la stg o o d.c o nf files.
A pop-up window asks you to confirm that you want to delete the configuration file. Click O K to delete the configuration file or click C a nc e l to close the screen without deleting the configuration file.
Click a configuration file's row to select it and click Do wnlo a d to save the configuration to your computer.
Use this button to save a duplicate of a configuration file on the Zyxel Device.
Click a configuration file's row to select it and click C o py to open the C o py File screen.
Specify a name for the duplicate configuration file. Use up to 25 characters (including a-zA-Z09;`~!@#$%^&()_+[]{}',.=-).
Click O K to save the duplicate or click C a nc e l to close the screen without saving a duplicate of the configuration file.
NWA/WAC/WAX Series User's Guide
228
Chapter 19 File Manager
Table 96 Maintenance > File Manager > Configuration File (continued)
LA BEL
DESC RIPTIO N
Apply
Use this button to have the Zyxel Device use a specific configuration file.
Click a configuration file's row to select it and click Apply to have the Zyxel Device use that configuration file. The Zyxel Device does not have to restart in order to use a different configuration file, although you will need to wait for a few minutes while the system reconfigures.
The following screen gives you options for what the Zyxel Device is to do if it encounters an error in the configuration file.
# File Name
Size
Im m e dia te ly sto p a pplying the c o nfig ura tio n file - this is not recommended because it would leave the rest of the configuration blank. If the interfaces were not configured before the first error, the console port may be the only way to access the Zyxel Device.
Im m e dia te ly sto p a pplying the c o nfig ura tio n file a nd ro ll b a c k to the pre vio us c o nfig ura tio n this gets the Zyxel Device started with a fully valid configuration file as quickly as possible.
Ig no re e rro rs a nd finish a pplying the c o nfig ura tio n file - this applies the valid parts of the configuration file and generates error logs for all of the configuration file's errors. This lets the Zyxel Device apply most of your configuration and you can refer to the logs for what to fix.
Ig no re e rro rs a nd finish a pplying the c o nfig ura tio n file a nd the n ro ll b a c k to the pre vio us
c o nfig ura tio n - this applies the valid parts of the configuration file, generates error logs for all of the configuration file's errors, and starts the Zyxel Device with a fully valid configuration file.
Click O K to have the Zyxel Device start applying the configuration file or click C a nc e l to close the screen.
This column displays the number for each configuration file entry. This field is a sequential value, and it is not associated with a specific address. The total number of configuration files that you can save depends on the sizes of the configuration files and the available flash storage space.
This column displays the label that identifies a configuration file.
You cannot delete the following configuration files or change their file names.
The syste m - de fa ult.c o nf file contains the Zyxel Device's default settings. Select this file and click Apply to reset all of the Zyxel Device settings to the factory defaults. This configuration file is included when you upload a firmware package.
The sta rtup- c o nfig .c o nf file is the configuration file that the Zyxel Device is currently using. If you make and save changes during your management session, the changes are applied to this configuration file. The Zyxel Device applies configuration changes made in the Web Configurator to the configuration file when you click Apply or O K. It applies configuration changes made via commands when you use the write command.
The la stg o o d.c o nf is the most recently used (valid) configuration file that was saved when the Zyxel Device last restarted. If you upload and apply a configuration file with an error, you can apply lastgood.conf to return to a valid configuration.
This column displays the size (in KB) of a configuration file.
NWA/WAC/WAX Series User's Guide
229
Chapter 19 File Manager
Table 96 Maintenance > File Manager > Configuration File (continued)
LA BEL
DESC RIPTIO N
Last Modified
This column displays the date and time that the individual configuration files were last changed or saved.
Upload
The bottom part of the screen allows you to upload a new or previously saved configuration file
Configuration File from your computer to your Zyxel Device.
You cannot upload a configuration file named syste m - de fa ult.c o nf or la stg o o d.c o nf.
File Path Browse...
Upload
If you upload sta rtup- c o nfig .c o nf, it will replace the current configuration and immediately apply the new settings.
Type in the location of the file you want to upload in this field or click Bro wse ... to find it.
Click Bro wse ... to find the .conf file you want to upload. The configuration file must use a ".conf" filename extension. You will receive an error message if you try to upload a fie of a different format. Remember that you must decompress compressed (.zip) files before you can upload them.
Click Uplo a d to begin the upload process. This process may take up to two minutes.
19.2.1 Exa m ple o f C o nfig ura tio n File Do wnlo a d Using FTP
The following example gets a configuration file named startup-config.conf from the Zyxel Device and saves it on the computer.
1 Connect your computer to the Zyxel Device.
2 The FTP server IP address of the Zyxel Device in standalone mode is 192.168.1.2, so set your computer to use a static IP address from 192.168.1.3 ~192.168.1.254.
3 Use an FTP client on your computer to connect to the Zyxel Device. For example, in the Windows command prompt, type ftp 192.168.1.2. Keep the console session connected in order to see when the firmware recovery finishes.
4 Enter your user name when prompted.
5 Enter your password as requested.
6 Use "cd" to change to the directory that contains the files you want to download.
7 Use "dir" or "ls" if you need to display a list of the files in the directory.
8 Use "get" to download files. Transfer the configuration file on the Zyxel Device to your computer. Type get followed by the name of the configuration file. This examples uses get startup-config.conf.
NWA/WAC/WAX Series User's Guide
230
Chapter 19 File Manager
C:\>ftp 192.168.1.2 Connected to 192.168.1.2. 220---------- Welcome to Pure-FTPd [privsep] [TLS] ---------220-You are user number 1 of 5 allowed. 220-Local time is now 21:28. Server port: 21. 220-This is a private system - No anonymous login 220 You will be disconnected after 600 minutes of inactivity. User (192.168.1.2:(none)): admin 331 User admin OK. Password required Password: 230 OK. Current restricted directory is / ftp> cd conf 250 OK. Current directory is /conf ftp> ls 200 PORT command successful 150 Connecting to port 5001 lastgood.conf startup-config.conf system-default.conf 226 3 matches total ftp: 57 bytes received in 0.33Seconds 0.17Kbytes/sec. ftp> get startup-config.conf 200 PORT command successful 150 Connecting to port 5002 226-File successfully transferred 226 0.002 seconds (measured here), 1.66 Mbytes per second ftp: 2928 bytes received in 0.02Seconds 183.00Kbytes/sec. ftp>
9 Wait for the file transfer to complete.
10 Enter "quit" to exit the ftp prompt.
19.3 Firm wa re Pa c ka g e
Click Ma inte na nc e > File Ma na g e r > Firm wa re Pa c ka g e to open this screen. Use the Firm wa re Pa c ka g e screen to check your current firmware version and upload firmware to the Zyxel Device.
Note: The Web Configurator is the recommended method for uploading firmware. You only need to use the command line interface if you need to recover the firmware. See the CLI Reference Guide for how to determine if you need to recover the firmware and how to recover it.
Find the firmware package at www.zyxel.com in a file that (usually) uses a .bin extension.
The firm wa re upda te c a n ta ke up to five m inute s. Do no t turn o ff o r re se t the Zyxe l De vic e while the firm wa re upda te is in pro g re ss!
NWA/WAC/WAX Series User's Guide
231
Chapter 19 File Manager Fig ure 146 Maintenance > File Manager > Firmware Package
The following table describes the labels in this screen.
Table 97 Maintenance > File Manager > Firmware Package
LA BEL
DESC RIPTIO N
Boot Module
This is the version of the boot module that is currently on the Zyxel Device.
Current Version This is the firmware version and the date created.
Released Date This is the date that the version of the firmware was created.
File Path
Type in the location of the file you want to upload in this field or click Bro wse ... to find it.
Browse...
Click Bro wse ... to find the .bin file you want to upload. Remember that you must decompress compressed (.zip) files before you can upload them.
Upload
Click Uplo a d to begin the upload process. This process may take up to two minutes.
After you see the Firm wa re Uplo a d in Pro c e ss screen, wait two minutes before logging into the Zyxel Device again.
Note: The Zyxel Device automatically reboots after a successful upload.
The Zyxel Device automatically restarts causing a temporary network disconnect. In some operating systems, you may see the following icon on your desktop.
Fig ure 147 Network Temporarily Disconnected
After five minutes, log in again and check your new firmware version in the Da shbo a rd screen.
19.3.1 Exa m ple o f Firm wa re Uplo a d Using FTP
This procedure requires the Zyxel Device's firmware. Download the firmware package from www.zyxel.com and unzip it. The firmware file uses a .bin extension, for example, "600ABFH0C0.bin". Do the following after you have obtained the firmware file.
1 Connect your computer to the Zyxel Device. 2 The FTP server IP address of the Zyxel Device in standalone mode is 192.168.1.2, so set your computer to
use a static IP address from 192.168.1.3 ~192.168.1.254.
NWA/WAC/WAX Series User's Guide
232
Chapter 19 File Manager
3 Use an FTP client on your computer to connect to the Zyxel Device. For example, in the Windows command prompt, type ftp 192.168.1.2. Keep the console session connected in order to see when the firmware recovery finishes.
4 Enter your user name when prompted.
5 Enter your password as requested.
6 Enter "hash" for FTP to print a `#' character for every 1024 bytes of data you upload so that you can watch the file transfer progress.
7 Enter "bin" to set the transfer mode to binary.
8 Transfer the firmware file from your computer to the Zyxel Device. Type put followed by the path and name of the firmware file. This examples uses put C:\ftproot\Zyxel Device_FW\600ABFH0C0.bin.
C:\>ftp 192.168.1.2 Connected to 192.168.1.2. 220---------- Welcome to Pure-FTPd [privsep] [TLS] ---------220-You are user number 1 of 5 allowed. 220-Local time is now 21:28. Server port: 21. 220-This is a private system - No anonymous login 220 You will be disconnected after 600 minutes of inactivity. User (192.168.1.2:(none)): admin 331 User admin OK. Password required Password: 230 OK. Current restricted directory is / ftp> hash Hash mark printing On ftp: (2048 bytes/hash mark) . ftp> bin 200 TYPE is now 8-bit binary ftp> put C:\ftproot\Zyxel Device_FW\600ABFH0C0.bin
Note: The Zyxel Device will not upgrade the firmware if the firmware file you upload is incompatible with the Zyxel Device.
9 Wait for the file transfer to complete.
10 Enter "quit" to exit the ftp prompt.
19.4 She ll Sc ript
Use shell script files to have the Zyxel Device use commands that you specify. Use a text editor to create the shell script files. They must use a ".zysh" filename extension.
Click Ma inte na nc e > File Ma na g e r > She ll Sc ript to open this screen. Use the She ll Sc ript screen to store, name, download, upload and run shell script files. You can store multiple shell script files on the Zyxel Device at the same time.
Note: You should include write commands in your scripts. If you do not use the write command, the changes will be lost when the Zyxel Device restarts. You could use multiple write commands in a long script.
NWA/WAC/WAX Series User's Guide
233
Chapter 19 File Manager Fig ure 148 Maintenance > File Manager > Shell Script
Each field is described in the following table.
Table 98 Maintenance > File Manager > Shell Script
LA BEL
DESC RIPTIO N
Rename
Use this button to change the label of a shell script file on the Zyxel Device.
You cannot rename a shell script to the name of another shell script in the Zyxel Device.
Click a shell script's row to select it and click Re na m e to open the Re na m e File screen.
Specify the new name for the shell script file. Use up to 25 characters (including a-zA-Z09;`~!@#$%^&()_+[]{}',.=-).
Remove
Click O K to save the duplicate or click C a nc e l to close the screen without saving a duplicate of the configuration file.
Click a shell script file's row to select it and click De le te to delete the shell script file from the Zyxel Device.
Download Copy
A pop-up window asks you to confirm that you want to delete the shell script file. Click O K to delete the shell script file or click C a nc e l to close the screen without deleting the shell script file.
Click a shell script file's row to select it and click Do wnlo a d to save the configuration to your computer.
Use this button to save a duplicate of a shell script file on the Zyxel Device.
Click a shell script file's row to select it and click C o py to open the C o py File screen.
Specify a name for the duplicate file. Use up to 25 characters (including a-zA-Z09;`~!@#$%^&()_+[]{}',.=-).
Apply
Click O K to save the duplicate or click C a nc e l to close the screen without saving a duplicate of the configuration file.
Use this button to have the Zyxel Device use a specific shell script file.
#
File Name
Size
Last Modified
Upload Shell Script
File Path
Click a shell script file's row to select it and click Apply to have the Zyxel Device use that shell script file. You may need to wait awhile for the Zyxel Device to finish applying the commands.
This column displays the number for each shell script file entry.
This column displays the label that identifies a shell script file.
This column displays the size (in KB) of a shell script file.
This column displays the date and time that the individual shell script files were last changed or saved.
The bottom part of the screen allows you to upload a new or previously saved shell script file from your computer to your Zyxel Device.
Type in the location of the file you want to upload in this field or click Bro wse ... to find it.
NWA/WAC/WAX Series User's Guide
234
Chapter 19 File Manager
Table 98 Maintenance > File Manager > Shell Script (continued)
LA BEL
DESC RIPTIO N
Browse...
Click Bro wse ... to find the .zysh file you want to upload.
Upload
Click Uplo a d to begin the upload process. This process may take up to several minutes.
NWA/WAC/WAX Series User's Guide
235
C HA PTER 2 0 Dia g no stic s
20.1 O ve rvie w
Use the diagnostics screen for troubleshooting.
20.1.1 Wha t Yo u C a n Do in this C ha pte r
The Dia g no stic s screen (Section 20.2 on page 236) generates a file containing the Zyxel Device's configuration and diagnostic information if you need to provide it to customer support during troubleshooting.
20.2 Dia g no stic s
This screen provides an easy way for you to generate a file containing the Zyxel Device's configuration and diagnostic information. You may need to generate this file and send it to customer support during troubleshooting. All categories of settings and shell script files stored on the Zyxel Device will be included in the diagnostic file. Click Ma inte na nc e > Dia g no stic s> Dia g no stic s to open the Dia g no stic s screen. Click C o lle c t No w to have the Zyxel Device create a new diagnostic file. Fig ure 149 Maintenance > Diagnostics> Diagnostics
The De bug Info rm a tio n C e nte r screen then displays showing whether the collection is in progress, was successful, or has failed. When the data collection is done, click Do wnlo a d to save the most recent diagnostic file to a computer.
NWA/WAC/WAX Series User's Guide
236
Chapter 20 Diagnostics Fig ure 150 Maintenance > Diagnostics: Debug Information Collector
20.3 Re m o te C a pture
Use this screen to capture network traffic going through the Zyxel Device connected to the Zyxel gateway or ZyWALL, and output the captured packets to a packet analyzer (also known as network or protocol analyzer) such as Wireshark.
Click Ma inte na nc e > Dia g no stic s> Re m o te C a pture to open the Re m o te C a pture screen.
Fig ure 151 Maintenance > Diagnostics> Remote Capture
The following table describes the labels in this screen.
Table 99 Maintenance > Diagnostics> Remote Capture
LA BEL
DESC RIPTIO N
Server Port
Enter the number of the server port you want the packet analyzer to connect to in order to capture traffic going through the Zyxel Device. The default port number is 2002.
Start
Click this button to allow the packet analyzer to start capturing traffic going through the Zyxel Device.
Stop
Click this button to stop the packet analyzer from capturing traffic going through the Zyxel Device.
NWA/WAC/WAX Series User's Guide
237
C HA PTER 2 1 LEDs
21.1 O ve rvie w
The LEDs of your Zyxel Device can be controlled such that they stay lit (ON) or OFF after the Zyxel Device is ready. There are two features that control the LEDs of your Zyxel Device - Lo c a to r and Suppre ssio n (see Section 1.4 on page 20).
21.1.1 Wha t Yo u C a n Do in this C ha pte r
� The Suppre ssio n screen (Section 21.2 on page 238) allows you to set how you want the LEDs to behave after the Zyxel Device is ready.
� The Lo c a to r screen (Section 21.3 on page 239) allows users to see the actual location of the Zyxel Device between several devices in the network.
21.2 Suppre ssio n Sc re e n
The LED Suppression feature allows you to control how the LEDs of your Zyxel Device behave after it's ready. The default LED suppression setting of your AP is different depending on your Zyxel Device model. You can go to the Ma inte na nc e > LEDs > Suppre ssio n screen to see the default LED behavior and change the LED suppression setting. After you make changes in the suppression screen, it will be stored as the default when the Zyxel Device is restarted. See (Section 3.3 on page 38) for information on default values for different models. Note: When the Zyxel Device is booting or performing firmware upgrade, the LEDs will light up
regardless of the setting in LED suppression. To access this screen, click Ma inte na nc e > LEDs > Suppre ssio n.
NWA/WAC/WAX Series User's Guide
238
Chapter 21 LEDs Fig ure 152 Maintenance > LEDs > Suppression
The following table describes fields in the above screen.
Table 100 Maintenance > LED > Suppression
LA BEL
DESC RIPTIO N
Suppression On
If the Suppre ssio n O n check box is checked, the LEDs of your Zyxel Device will turn off after it's ready.
Apply Reset
If the check box is unchecked, the LEDs will stay lit after the Zyxel Device is ready. Click Apply to save your changes back to the Zyxel Device. Click Re se t to return the screen to its last-saved settings.
21.3 Lo c a to r Sc re e n
The Locator feature identifies the location of your Zyxel Device among several devices in the network. You can run this feature and set a timer in this screen.
To run the locator feature, enter a number of minutes and click Turn O n button to have the Zyxel Device find its location. The Locator LED will start to blink for the number of minutes set in the Lo c a to r screen. The default setting is 10 minutes. While the locator is running, the turn on button will gray out and return after it's finished. If you make changes to the time default setting, it will be stored as the default when the Zyxel Device restarts.
Note: The Locator feature is not affected by the Suppression setting.
To access this screen, click Ma inte na nc e > LEDs > Lo c a to r.
NWA/WAC/WAX Series User's Guide
239
Chapter 21 LEDs Fig ure 153 Maintenance > LEDs > Locator
The following table describes fields in the above screen.
Table 101 Maintenance > LED > Locator
LA BEL
DESC RIPTIO N
Turn On Turn Off
Click Turn O n button to activate the locator. The Locator function will show the actual location of the Zyxel Device between several devices in the network.
Otherwise, click Turn O ff to disable the locator feature.
Automatically Extinguish After
Enter a time interval between 1 and 60 minutes to stop the locator LED from blinking. Default is 10 minutes.
Apply
Click Apply to save changes in this screen.
Refresh
Click Re fre sh to update the information in this screen.
NWA/WAC/WAX Series User's Guide
240
C HA PTER 2 2 Ante nna Switc h
22.1 O ve rvie w
Use this screen to adjust coverage depending on the orientation of the antenna.
22.1.1 Wha t Yo u Ne e d To Kno w
Positioning the antennas properly increases the range and coverage area of a wireless LAN. On the Zyxel Device that comes with internal antennas and also has an antenna switch, you can adjust coverage depending on the antenna orientation for the Zyxel Device radios using the web configurator, the command line interface (CLI) or a physical switch. Check Section 1.4 on page 20 to see if your Zyxel Device has an antenna switch. Fig ure 154 WAC Physical Antenna Switch
Note: With the physical antenna switch, you apply the same antenna orientation settings to both radios. You can set the radios to have different settings while using the Web Configurator or the command line interface.
Note: The antenna switch in the Web Configurator has priority over the physical antenna switch after you Ena b le So ftwa re C o ntro l in the Ma inte na nc e > Ante nna screen. By default, software control is disabled.
22.2 Ante nna Switc h Sc re e n
To access this screen, click Ma inte na nc e > Ante nna . The screen varies depending on whether the Zyxel Device has a physical antenna switch or allows you to change antenna orientation settings on a per-radio basis or on a per-AP basis.
NWA/WAC/WAX Series User's Guide
241
Chapter 22 Antenna Switch Fig ure 155 Maintenance > Antenna > Antenna Switch (Per Radio)
Fig ure 156 Maintenance > Antenna > Antenna Switch (Per AP)
If the Zyxel Device has a physical antenna switch, select the Ena b le So ftwa re C o ntro l option to use the Web Configurator to adjust coverage depending on each radio's antenna orientation for better coverage. Select Wa ll if you mount the Zyxel Device to a wall. Select C e iling if the Zyxel Device is mounted on a ceiling. You can switch from Wa ll to C e iling if there are still wireless dead zones, and vice versa. Click Apply to save your changes or click Re se t to return the screen to its last-saved settings.
NWA/WAC/WAX Series User's Guide
242
C HA PTER 2 3 Re b o o t
23.1 O ve rvie w
Use this screen to restart the Zyxel Device.
23.1.1 Wha t Yo u Ne e d To Kno w
If you applied changes in the Web Configurator, these were saved automatically and do not change when you reboot. If you made changes in the CLI, however, you have to use the write command to save the configuration before you reboot. Otherwise, the changes are lost when you reboot. Reboot is different to reset; reset returns the Zyxel Device to its default configuration.
23.2 Re b o o t
This screen allows remote users can restart the Zyxel Device. To access this screen, click Ma inte na nc e > Re b o o t. Fig ure 157 Maintenance > Reboot
Click the Re bo o t button to restart the Zyxel Device. Wait a few minutes until the login screen appears. If the login screen does not appear, type the IP address of the Zyxel Device in your Web browser. You can also use the CLI command reboot to restart the Zyxel Device.
NWA/WAC/WAX Series User's Guide
243
C HA PTER 2 4 Shutdo wn
24.1 O ve rvie w
Use this screen to shut down the Zyxel Device.
Alwa ys use Ma inte na nc e > Shutdo wn > Shutdo wn o r the shutdown
c o m m a nd b e fo re yo u turn o ff the Zyxe l De vic e o r re m o ve the po we r. No t do ing so c a n c a use the firm wa re to b e c o m e c o rrupt.
24.1.1 Wha t Yo u Ne e d To Kno w
Shutdown writes all cached data to the local storage and stops the system processes. Shutdown is different to reset; reset returns the Zyxel Device to its default configuration.
24.2 Shutdo wn
To access this screen, click Ma inte na nc e > Shutdo wn. Fig ure 158 Maintenance > Shutdown
Click the Shutdo wn button to shut down the Zyxel Device. Wait for the Zyxel Device to shut down before you manually turn off or remove the power. It does not turn off the power. You can also use the CLI command shutdown to shut down the Zyxel Device.
NWA/WAC/WAX Series User's Guide
244
PA RT II
Lo c a l C o nfig ura tio n in C lo ud Mo de
245
C HA PTER 2 5 C lo ud Mo de
25.1 O ve rvie w
The Zyxel Device is managed and provisioned automatically by the NCC (Ne b ula Co ntro l Ce nte r) when it is connected to the Internet and has been registered in the NCC. If you need to change the Zyxel Device's VLAN setting or manually set its IP address, access its simplified web configurator (see Chapter 4 on page 56). You can check the NCC's Ac c e ss Po int > Mo nito r > Ac c e ss Po ints screen or the connected gateway for the Zyxel Device's current LAN IP address. Alternatively, disconnect the gateway or disable its DHCP server function and use the Zyxel Device's default static LAN IP address (192.168.1.2). Fig ure 159 Cloud Mode Application
25.2 C lo ud Mo de We b C o nfig ura to r Sc re e ns
When your Zyxel Device is managed through NCC, you can access only the following screens through the Web Configurator:
� Da shb o a rd � C o nfig ura tio n > Ne two rk > IP Se tting � C o nfig ura tio n > Ne two rk > VLAN
NWA/WAC/WAX Series User's Guide
246
Chapter 25 Cloud Mode
� Ma inte na nc e > She ll Sc ript � Ma inte na nc e > Dia g no stic s � Ma inte na nc e > Lo g
These screens also have fewer options than those in standalone Zyxel Devices. The rest of the Zyxel Device's features must be configured through the NCC.
25.3 Da shb o a rd
This screen displays general AP information, and client information in widgets that you can re-arrange to suit your needs. You can also collapse, refresh, and close individual widgets. Fig ure 160 Dashboard
The following table describes the labels in this screen.
Table 102 Dashboard
LA BEL
DESC RIPTIO N
AP Information
MAC Address
This field displays the MAC address of the Zyxel Device.
Serial Number
This field displays the serial number of the Zyxel Device.
Product Model This field displays the model name of the Zyxel Device.
2.4G Channel Information
This field displays the channel number the Zyxel Device is using and its output power in the 2.4 GHz spectrum. This shows No t a c tiva te d if the wireless LAN is disabled.
5G Channel Information
This field displays the channel number the Zyxel Device is using and its output power in the 5 GHz spectrum. This shows No t a c tiva te d if the wireless LAN is disabled.
Use Proxy to Access NCC
This displays whether the NAP uses a proxy server to access the NCC (Nebula Control Center).
NWA/WAC/WAX Series User's Guide
247
Chapter 25 Cloud Mode
Table 102 Dashboard (continued)
LA BEL
DESC RIPTIO N
Cloud Control Status This field displays:
� The Zyxel Device Internet connection status. � The connection status between the Zyxel Device and NCC. � The Zyxel Device registration status on NCC.
Mouse over the circles to display detailed information.
To pass your Zyxel Device management to NCC, first make sure your Zyxel Device is connected to the Internet. Then go to NCC and register your Zyxel Device.
1. Inte rne t
Green - The Zyxel Device is connected to the Internet.
Orange - The Zyxel Device is not connected to the Internet.
2. Ne b ula
Green - The Zyxel Device is connected to NCC.
Orange - The Zyxel Device is not connected to NCC.
3. Re g istra tio n
Green - The Zyxel Device is registered on NCC.
Nebula Discovery
Gray - The Zyxel Device is not registered on NCC.
Slide the switch to the right to enable NCC discovery on the Zyxel Device. The Zyxel Device will connect to NCC and change to the NCC management mode if it:
� is connected to the Internet. � has been registered on NCC.
Note: The switch is always on and cannot be disabled when the Zyxel Device is in Cloud mode.
If the Zyxel Device cannot connect to the Internet or to NCC, move the mouse over the status circle to check the error message.
NWA/WAC/WAX Series User's Guide
248
C HA PTER 2 6 Ne two rk
26.1 O ve rvie w
This chapter describes how you can configure the management IP address and VLAN settings of your Zyxel Device in cloud mode. See Section 9.1 on page 97 for information about IP addresses. Note: Make sure your VLAN settings allow the Zyxel Device to connect to the Internet so you
could manage it with NCC.
26.1.1 Wha t Yo u C a n Do in this C ha pte r
� The IP Se tting screen (Section 26.2 on page 249) configures the Zyxel Device's LAN IP address. � The VLAN screen (Section 26.3 on page 251) configures the Zyxel Device's VLAN settings.
26.2 IP Se tting
Use this screen to configure the IP address for your Zyxel Device. To access this screen, click C o nfig ura tio n > Ne two rk > IP Se tting .
NWA/WAC/WAX Series User's Guide
249
Chapter 26 Network Fig ure 161 Configuration > Network > IP Setting
Each field is described in the following table.
Table 103 Configuration > Network > IP Setting
LA BEL
DESC RIPTIO N
IP Address Assignment
Get Automatically
Select this to make the interface a DHCP client and automatically get the IP address, subnet mask, and gateway address from a DHCP server.
Use Fixed IP Address
Select this if you want to specify the IP address, subnet mask, and gateway manually.
IP Address
Enter the IP address for this interface.
Subnet Mask
Enter the subnet mask of this interface in dot decimal notation. The subnet mask indicates what part of the IP address is the same for all computers in the network.
Gateway
Enter the IP address of the gateway. The Zyxel Device sends packets to the gateway when it does not know how to route the packet to its destination. The gateway should be on the same network as the interface.
DNS Server IP Address
Enter the IP address of the DNS server.
Use Proxy to Access If the Zyxel Device is behind a proxy server, you need to select this option and configure the
Internet
proxy server settings so that the Zyxel Device can access the NCC through the proxy server.
Proxy Server
Enter the IP address of the proxy server.
Proxy Port
Enter service port number used by the proxy server.
Authentication
Select this option if the proxy server requires authentication before it grants access to the Internet.
User Name
Enter your proxy user name.
Password
Enter your proxy password.
Apply
Click Apply to save your changes back to the Zyxel Device.
Reset
Click Re se t to return the screen to its last-saved settings.
NWA/WAC/WAX Series User's Guide
250
Chapter 26 Network
26.3 VLAN
This section discusses how to configure the Zyxel Device's VLAN settings. See Section 9.3 on page 101 for more information about VLAN. Use this screen to configure the VLAN settings for your Zyxel Device. To access this screen, click C o nfig ura tio n > Ne two rk > VLAN. Fig ure 162 Configuration > Network > VLAN
Each field is described in the following table.
Table 104 Configuration > Network > VLAN
LA BEL
DESC RIPTIO N
VLAN Settings
Management VLAN ID
Enter a VLAN ID for the Zyxel Device.
Untagged/ Tagged
Set whether the Zyxel Device adds the VLAN ID to outbound traffic transmitted through its Ethernet port.
Apply
Click Apply to save your changes back to the Zyxel Device.
Reset
Click Re se t to return the screen to its last-saved settings.
NWA/WAC/WAX Series User's Guide
251
C HA PTER 2 7 Ma inte na nc e
27.1 O ve rvie w
When the Zyxel Device is set to work in cloud mode, the Ma inte na nc e screens let you mange shell script files on the Zyxel Device, generate a diagnostic file, or view log messages. See Chapter 19 on page 225 for information about shell scripts.
27.1.1 Wha t Yo u C a n Do in this C ha pte r
� The She ll Sc ript screen (Section 27.2 on page 252) stores, names, downloads, and uploads shell script files.
� The Dia g no stic s screen (Section 27.3 on page 253) generates a file containing the Zyxel Device's configuration and diagnostic information if you need to provide it to customer support during troubleshooting.
� The Lo g > Vie w Lo g screen (Section 27.4 on page 254) displays the Zyxel Device's current log messages when it is disconnected from the NCC.
27.2 She ll Sc ript
Use shell script files to have the Zyxel Device use commands that you specify. Use a text editor to create the shell script files. They must use a ".zysh" filename extension. Click Ma inte na nc e > She ll Sc ript to open this screen. Use the She ll Sc ript screen to store, name, download, and upload shell script files. You can store multiple shell script files on the Zyxel Device at the same time. Fig ure 163 Maintenance > Shell Script
NWA/WAC/WAX Series User's Guide
252
Chapter 27 Maintenance
Each field is described in the following table.
Table 105 Maintenance > Shell Script
LA BEL
DESC RIPTIO N
Rename
Use this button to change the label of a shell script file on the Zyxel Device.
You cannot rename a shell script to the name of another shell script in the Zyxel Device.
Click a shell script's row to select it and click Re na m e to open the Re na m e File screen.
Specify the new name for the shell script file. Use up to 25 characters (including a-zA-Z09;`~!@#$%^&()_+[]{}',.=-).
Remove
Click O K to save the duplicate or click C a nc e l to close the screen without saving a duplicate of the configuration file.
Click a shell script file's row to select it and click De le te to delete the shell script file from the Zyxel Device.
Download Copy
A pop-up window asks you to confirm that you want to delete the shell script file. Click O K to delete the shell script file or click C a nc e l to close the screen without deleting the shell script file.
Click a shell script file's row to select it and click Do wnlo a d to save the configuration to your computer.
Use this button to save a duplicate of a shell script file on the Zyxel Device.
Click a shell script file's row to select it and click C o py to open the C o py File screen.
Specify a name for the duplicate file. Use up to 25 characters (including a-zA-Z09;`~!@#$%^&()_+[]{}',.=-).
# File Name Size Last Modified Upload Shell Script File Browse... Upload
Click O K to save the duplicate or click C a nc e l to close the screen without saving a duplicate of the configuration file.
This column displays the number for each shell script file entry.
This column displays the label that identifies a shell script file.
This column displays the size (in KB) of a shell script file.
This column displays the date and time that the individual shell script files were last changed or saved.
The bottom part of the screen allows you to upload a new or previously saved shell script file from your computer to your Zyxel Device. Type in the location of the file you want to upload in this field or click Bro wse ... to find it. Click Bro wse ... to find the .zysh file you want to upload. Click Uplo a d to begin the upload process. This process may take up to several minutes.
27.3 Dia g no stic s
This screen provides an easy way for you to generate a file containing the Zyxel Device's configuration and diagnostic information. You may need to generate this file and send it to customer support during troubleshooting. All categories of settings and shell script files stored on the Zyxel Device will be included in the diagnostic file.
Click Ma inte na nc e > Dia g no stic s to open the Dia g no stic s screen. Click C o lle c t No w to have the Zyxel Device create a new diagnostic file.
NWA/WAC/WAX Series User's Guide
253
Chapter 27 Maintenance Fig ure 164 Maintenance > Diagnostics
The De bug Info rm a tio n C e nte r screen then displays showing whether the collection is in progress, was successful, or has failed. When the data collection is done, click Do wnlo a d to save the most recent diagnostic file to a computer. Fig ure 165 Maintenance > Diagnostics: Debug Information Collector
27.4 Vie w Lo g
The NCC periodically gathers log files from the devices being managed by it. Before the NCC pulls logs from the Zyxel Device or when the Zyxel Device is disconnected from the NCC, you can use this screen to view its current log messages. To access this screen, click Ma inte na nc e > Lo g . Note: When a log reaches the maximum number of log messages, new log messages
automatically overwrite existing log messages, starting with the oldest existing log message first. Events that generate an alert (as well as a log message) display in red. Regular logs display in black. Click a column's heading cell to sort the table entries by that column's criteria. Click the heading cell again to reverse the sort order.
NWA/WAC/WAX Series User's Guide
254
Chapter 27 Maintenance Fig ure 166 Maintenance > Log > View Log
The following table describes the labels in this screen.
Table 106 Maintenance > Log > View Log
LA BEL
DESC RIPTIO N
Show Filter / Hide Filter
Click this button to show or hide the filter settings.
If the filter settings are hidden, the Displa y, Em a il Lo g No w, Re fre sh, and C le a r Lo g fields are available.
Display Priority
Source Address Destination Address Source Interface Destination Interface Protocol Keyword
Search
If the filter settings are shown, the Displa y, Prio rity, So urc e Addre ss, De stina tio n Addre ss, So urc e Inte rfa c e , De stina tio n Inte rfa c e , Pro to c o l, Ke ywo rd, and Se a rc h fields are available.
Select the category of log message(s) you want to view. You can also view All Lo g s at one time, or you can view the De b ug Lo g .
This displays when you show the filter. Select the priority of log messages to display. The log displays the log messages with this priority or higher. Choices are: a ny, e m e rg , a le rt, c rit, e rro r, wa rn, no tic e , and info , from highest priority to lowest priority. This field is read-only if the C a te g o ry is De b ug Lo g .
This displays when you show the filter. Type the source IP address of the incoming packet that generated the log message. Do not include the port in this filter.
This displays when you show the filter. Type the IP address of the destination of the incoming packet when the log message was generated. Do not include the port in this filter.
This displays when you show the filter. Select the source interface of the packet that generated the log message.
This displays when you show the filter. Select the destination interface of the packet that generated the log message.
This displays when you show the filter. Select a service protocol whose log messages you would like to see.
This displays when you show the filter. Type a keyword to look for in the Me ssa g e , So urc e , De stina tio n and No te fields. If a match is found in any field, the log message is displayed. You can use up to 63 alphanumeric characters and the underscore, as well as punctuation marks ()' ,:;?! +-*/= #$% @ ; the period, double quotes, and brackets are not allowed.
This displays when you show the filter. Click this button to update the log using the current filter settings.
NWA/WAC/WAX Series User's Guide
255
Chapter 27 Maintenance
Table 106 Maintenance > Log > View Log (continued)
LA BEL
DESC RIPTIO N
Refresh
Click this to update the list of logs.
Clear Log
Click this button to clear the whole log, regardless of what is currently displayed on the screen.
#
This field is a sequential value, and it is not associated with a specific log message.
Time
This field displays the time the log message was recorded.
Priority
This field displays the priority of the log message. It has the same range of values as the Prio rity field above.
Category
This field displays the log that generated the log message. It is the same value used in the Displa y and (other) C a te g o ry fields.
Message
This field displays the reason the log message was generated. The text "[count=x]", where x is a number, appears at the end of the Me ssa g e field if log consolidation is turned on and multiple entries were aggregated to generate into this one.
Source
This field displays the source IP address and the port number in the event that generated the log message.
Source Interface This field displays the source interface of the packet that generated the log message.
Destination
This field displays the destination IP address and the port number of the event that generated the log message.
Destination Interface
This field displays the destination interface of the packet that generated the log message.
Protocol
This field displays the service protocol in the event that generated the log message.
Note
This field displays any additional information about the log message.
NWA/WAC/WAX Series User's Guide
256
PA RT III
Appe ndic e s a nd Tro ub le sho o ting
257
C HA PTER 2 8 Tro ub le sho o ting
28.1 O ve rvie w
This chapter offers some suggestions to solve problems you might encounter. The potential problems are divided into the following categories. � Power, Hardware Connections, and LED � Zyxel Device Management, Access, and Login � Internet Access � WiFi Network � Resetting the Zyxel Device
28.2 Po we r, Ha rdwa re C o nne c tio ns, a nd LED
The Zyxel Device does not turn on. The LED is not on.
1 Make sure you are using the power adapter included with the Zyxel Device or a PoE power injector/ switch.
2 Make sure the power adapter or PoE power injector/switch is connected to the Zyxel Device and plugged in to an appropriate power source. Make sure the power source is turned on.
3 Disconnect and re-connect the power adapter or PoE power injector/switch. 4 Inspect your cables for damage. Contact the vendor to replace any damaged cables. 5 If none of these steps work, you may have faulty hardware and should contact your Zyxel Device
vendor.
The LED does not behave as expected.
1 Make sure you understand the normal behavior of the LED. See Section 3.3 on page 38. 2 Check the hardware connections. See the Quick Start Guide. 3 Inspect your cables for damage. Contact the vendor to replace any damaged cables.
NWA/WAC/WAX Series User's Guide
258
Chapter 28 Troubleshooting
4 Disconnect and re-connect the power adapter or PoE power injector to the Zyxel Device. 5 If the problem continues, contact the vendor.
28.3 Zyxe l De vic e Ma na g e m e nt, Ac c e ss, a nd Lo g in
I forgot the IP address for the Zyxel Device.
1 The default in-band IP address in standalone mode is http:/ / DHC P- a ssig ne d IP (when connecting to a DHCP server) or 192.168.1.2.
2 If you changed the IP address and have forgotten it, you have to reset the Zyxel Device to its factory defaults. See Section 28.6 on page 266.
3 If your Zyxel Device is a DHCP client, you can find your IP address from the DHCP server. This information is only available from the DHCP server which allocates IP addresses on your network. Find this information directly from the DHCP server or contact your system administrator for more information.
4 If the NCC has managed the Zyxel Device, you can also check the NCC's AP > Mo nito r > Ac c e ss Po int screen for the Zyxel Device's current LAN IP address.
I cannot see or access the Lo g in screen in the Web Configurator.
1 Make sure you are using the correct IP address. � The default IP address (in standalone mode) is 192.168.1.2. � If you changed the IP address, use the new IP address. � If you changed the IP address and have forgotten it, see the troubleshooting suggestions for I forgot the IP address for the Zyxel Device.
2 Check the hardware connections, and make sure the LED is behaving as expected. See the Quick Start Guide and Section 3.3 on page 38.
3 Make sure your Internet browser does not block pop-up windows and has JavaScripts and Java enabled.
4 Make sure your computer is in the same subnet as the Zyxel Device. (If you know that there are routers between your computer and the Zyxel Device, skip this step.) � If there is a DHCP server on your network, make sure your computer is using a dynamic IP address. � If there is no DHCP server on your network, make sure your computer's IP address is in the same subnet as the Zyxel Device.
5 Reset the Zyxel Device to its factory defaults, and try to access the Zyxel Device with the default IP address. See Section 28.6 on page 266.
NWA/WAC/WAX Series User's Guide
259
Chapter 28 Troubleshooting
6 If the problem continues, contact the network administrator or vendor, or try one of the advanced suggestions.
Adva nc e d Sug g e stio ns
� Try to access the Zyxel Device using another service, such as Telnet. If you can access the Zyxel Device, check the remote management settings to find out why the Zyxel Device does not respond to HTTP.
� If your computer is connected wirelessly, use a computer that is connected to a LAN/ETHERNETport.
I forgot the password.
1 The default password is 1234. If the Zyxel Device is connected to the NCC and registered, check the NCC for the password.
2 If this does not work, you have to reset the Zyxel Device to its factory defaults. See Section 28.6 on page 266.
I can see the Lo g in screen, but I cannot log in to the Zyxel Device.
1 Make sure you have entered the user name and password correctly. The default password is 1234. This fields are case-sensitive, so make sure [Caps Lock] is not on.
2 You cannot log in to the Web Configurator while someone is using Telnet to access the Zyxel Device. Log out of the Zyxel Device in the other session, or ask the person who is logged in to log out.
3 Disconnect and re-connect the power adapter or PoE power injector to the Zyxel Device. 4 If this does not work, you have to reset the Zyxel Device to its factory defaults. See Section 28.6 on page
266.
I cannot use FTP to upload / download the configuration file. / I cannot use FTP to upload new firmware.
See the troubleshooting suggestions for I cannot see or access the Login screen in the Web Configurator. Ignore the suggestions about your browser.
I cannot access the Zyxel Device directly anymore after switching to NCC management.
� Check the Zyxel Device IP address and login credentials using the NCC and use them to access the Zyxel Device. Note that the built-in Web Configurator will have limited functionality when managed through NCC.
NWA/WAC/WAX Series User's Guide
260
Chapter 28 Troubleshooting
I enabled NC C Disc o ve ry, but the Zyxel Device is still in standalone mode.
Make sure your Zyxel Device is registered to the NCC.
The Zyxel Device is already registered with NCC, but it is still in standalone mode; it cannot connect to the NCC.
1 Make sure that NCC Discovery is enabled (see Section 9.6 on page 107). 2 Check your network's firewall/security settings. Make sure the following TCP ports are allowed: 443, 4335,
and 6667. 3 Make sure your Zyxel Device can access the Internet. 4 Check your network's VLAN settings (see Section 9.3 on page 101). You may have to change the
Management VLAN settings of the Zyxel Device to allow it to connect to the Internet and access the NCC. Note: Changing the management VLAN and IP address settings on the Zyxel Device also
pushes these changes to the NCC. Do this only if your device cannot otherwise connect to the NCC. 5 Make sure your Zyxel Device does not have to go through network authentication such as a captive portal, If your network uses a captive portal, the network administrator may have to create a new VLAN without this requirement. Change your Zyxel Device's management VLAN settings as necessary.
I want to switch from NCC to AC management, but I could not find the AC Disc o ve ry menu in the Zyxel Device Web Configurator.
1 Unregister the Zyxel Device from the NCC. 2 Reset your Zyxel Device to the factory defaults. 3 Make sure that your Zyxel Device is in the same subnet as the AC, and enable AC Disc o ve ry in
C o nfig ura tio n > Ne two rk > AC Disc o ve ry.
The Zyxel Device cannot discover the AC.
1 Make sure your Zyxel Device is not registered to NCC. 2 Enable AC Disc o ve ry in C o nfig ura tio n > Ne two rk > AC Disc o ve ry.
NWA/WAC/WAX Series User's Guide
261
Chapter 28 Troubleshooting
3 Make sure that the Zyxel Device and the AC are both in the same subnet. 4 If you have to set them up in different subnets, see AC management and IP Subnets on page 99.
I accidentally pressed the Nebula button in the NXC's Web Configurator. How do I undo it?
1 If the Zyxel Device is not registered with the NCC, register it first. 2 Unregister the Zyxel Device from the NCC. 3 Reset the Zyxel Device to the factory defaults.
Some features I set using the NCC do not work as expected.
1 Make sure your Zyxel Device can access the Internet. 2 Check your network's firewall/security settings. Make sure the following ports are allowed:
� TCP: 443, 4335, and 6667 � UDP: 123 3 After changing your Zyxel Device settings using the NCC, wait 1-2 minutes for the changes to take effect.
I can only see newer logs. Older logs are missing.
When a log reaches the maximum number of log messages (see Section 1.4 on page 20), new log messages automatically overwrite the oldest log messages.
The commands in my configuration file or shell script are not working properly.
� In a configuration file or shell script, use "#" or "!" as the first character of a command line to have the Zyxel Device treat the line as a comment.
� Your configuration files or shell scripts can use "exit" or a command line consisting of a single "!" to have the Zyxel Device exit sub command mode.
� Include write commands in your scripts. Otherwise the changes will be lost when the Zyxel Device restarts. You could use multiple write commands in a long script.
Note: "exit" or "!'" must follow sub commands if it is to make the Zyxel Device exit sub command mode.
NWA/WAC/WAX Series User's Guide
262
Chapter 28 Troubleshooting
I cannot upload the firmware uploaded using FTP.
The Web Configurator is the recommended method for uploading firmware in standalone mode. For managed Zyxel Devices, using the NCC or AC is recommended. You only need to use FTP if you need to recover the firmware. See the CLI Reference Guide for how to determine if you need to recover the firmware and how to recover it.
28.4 Inte rne t Ac c e ss
Clients cannot access the Internet through the Zyxel Device.
1 Check the Zyxel Device's hardware connections, and make sure the LEDs are behaving as expected (refer to Section 3.3 on page 38). See the Quick Start Guide and Section 28.1 on page 258.
2 Make sure the Zyxel Device is connected to a broadband modem or router with Internet access and your computer is set to obtain an dynamic IP address.
3 If clients are trying to access the Internet wirelessly, make sure the wireless settings on the wireless clients are the same as the settings on the Zyxel Device.
4 Disconnect all the cables from your Zyxel Device, and follow the directions in the Quick Start Guide again.
5 Reboot the client and reconnect to the Zyxel Device. 6 If the problem continues, contact your ISP.
The Internet connection is slow or intermittent.
1 There might be a lot of traffic on the network. Look at the LEDs, and check Section 3.3 on page 38. If the Zyxel Device is sending or receiving a lot of information, try closing some programs that use the Internet, especially peer-to-peer applications.
2 Check the signal strength using the NCC, AC, Zyxel Device Web Configurator, or the client device itself. If the signal is weak, try moving the client closer to the Zyxel Device (if possible), and look around to see if there are any devices that might be interfering with the wireless network (microwaves, other wireless networks, and so on).
3 Reboot the Zyxel Device using the Web Configurator/CLI or the NCC or AC. 4 Check the settings for QoS. If it is disabled, activate it. When enabled, raise or lower the priority for some
applications.
NWA/WAC/WAX Series User's Guide
263
Chapter 28 Troubleshooting
5 If the problem continues, contact the network administrator or vendor.
28.5 WiFi Ne two rk
The WiFi connection is slow or intermittent.
The following factors may cause interference: � Obstacles: walls, ceilings, furniture, and so on. � Building Materials: metal doors, aluminum studs. � Electrical devices: microwaves, monitors, electric motors, cordless phones, and other wireless devices. To optimize the speed and quality of your WiFi connection, you can: � Move your WiFi device closer to the Zyxel Device if the signal strength is low. � Reduce wireless interference that may be caused by other wireless networks or surrounding wireless
electronics such as cordless phones. � Place the Zyxel Device where there are minimum obstacles (such as walls and ceilings) between the
Zyxel Device and the wireless client. Avoid placing the Zyxel Device inside any type of box that might block WiFi signals.
I cannot access the Zyxel Device or ping any computer from the WLAN.
1 Make sure the wireless LAN (wireless radio) is enabled on the Zyxel Device. 2 Make sure the radio or at least one of the Zyxel Device's radios is operating in AP mode. 3 Make sure the wireless adapter (installed on your computer) is working properly. 4 Make sure the wireless adapter (installed on your computer) is IEEE 802.11 compatible and supports the
same wireless standard as the Zyxel Device's active radio. 5 Make sure your computer (with a wireless adapter installed) is within the transmission range of the Zyxel
Device. 6 Check that both the Zyxel Device and your computer are using the same wireless and wireless security
settings.
Hackers have accessed my WEP-encrypted wireless LAN.
NWA/WAC/WAX Series User's Guide
264
Chapter 28 Troubleshooting
WEP is extremely insecure. Its encryption can be broken by an attacker, using widely-available software. It is strongly recommended that you use a more effective security mechanism. Use the strongest security mechanism that all the wireless devices in your network support. WPA2 or WPA2-PSK is recommended.
The wireless security is not following the re-authentication timer setting I specified.
If a RADIUS server authenticates wireless stations, the re-authentication timer on the RADIUS server has priority. Change the RADIUS server's configuration if you need to use a different re-authentication timer setting.
I cannot import a certificate into the Zyxel Device.
1 For My C e rtific a te s, you can import a certificate that matches a corresponding certification request that was generated by the Zyxel Device. You can also import a certificate in PKCS#12 format, including the certificate's public and private keys.
2 You must remove any spaces from the certificate's filename before you can import the certificate. 3 Any certificate that you want to import has to be in one of these file formats:
� Binary X.509: This is an ITU-T recommendation that defines the formats for X.509 certificates. � PEM (Base-64) encoded X.509: This Privacy Enhanced Mail format uses lowercase letters, uppercase
letters and numerals to convert a binary X.509 certificate into a printable form. � Binary PKCS#7: This is a standard that defines the general syntax for data (including digital signatures)
that may be encrypted. A PKCS #7 file is used to transfer a public key certificate. The private key is not included. The Zyxel Device currently allows the importation of a PKS#7 file that contains a single certificate. � PEM (Base-64) encoded PKCS#7: This Privacy Enhanced Mail (PEM) format uses lowercase letters, uppercase letters and numerals to convert a binary PKCS#7 certificate into a printable form. � Binary PKCS#12: This is a format for transferring public key and private key certificates.The private key in a PKCS #12 file is within a password-encrypted envelope. The file's password is not connected to your certificate's public or private passwords. Exporting a PKCS #12 file creates this and you must provide it to decrypt the contents when you import the file into the Zyxel Device.
Note: Be careful not to convert a binary file to text during the transfer process. It is easy for this to occur since many programs use text files by default.
Wireless clients are not being load balanced among my Zyxel Devices.
� Make sure that all the Zyxel Devices used by the wireless clients in question share the same SSID, security, and radio settings.
� Make sure that all the Zyxel Devices are in the same broadcast domain. � Make sure that the wireless clients are in range of the other Zyxel Devices; if they are only in range of a
single Zyxel Device, then load balancing may not be as effective.
NWA/WAC/WAX Series User's Guide
265
Chapter 28 Troubleshooting
In the Mo nito r > Wire le ss > AP Info rm a tio n > Ra dio List screen, there is no load balancing indicator associated with any Zyxel Devices assigned to the load balancing task.
� Check that the AP profile which contains the load balancing settings is correctly assigned to the Zyxel Devices in question.
� The load balancing task may have been terminated because further load balancing on the Zyxel Devices in question is no longer required.
28.6 Re se tting the Zyxe l De vic e
If you cannot access the Zyxel Device by any method, try restarting it by turning the power off and then on again. If you still cannot access the Zyxel Device by any method or you forget the administrator password(s), you can reset the Zyxel Device to its factory-default settings. Any configuration files or shell scripts that you saved on the Zyxel Device should still be available afterwards. Use the following procedure to reset the Zyxel Device to its factory-default settings. This overwrites the settings in the startup-config.conf file with the settings in the system-default.conf file. Note: This procedure removes the current configuration. 1 Make sure the Power LED is on and not blinking. 2 Press the RESETbutton and hold it until the Power LED begins to blink. (This usually takes about ten seconds.) 3 Release the RESETbutton, and wait for the Zyxel Device to restart. You should be able to access the Zyxel Device in standalone mode using the default settings.
28.7 G e tting Mo re Tro ub le sho o ting He lp
Search for support information for your model at www.zyxel.com for more troubleshooting suggestions.
NWA/WAC/WAX Series User's Guide
266
A PPEN DIX A
Im po rting C e rtific a te s
This appendix shows you how to import public key certificates into your web browser. Public key certificates are used by web browsers to ensure that a secure web site is legitimate. When a certificate authority such as VeriSign, Comodo, or Network Solutions, to name a few, receives a certificate request from a website operator, they confirm that the web domain and contact information in the request match those on public record with a domain name registrar. If they match, then the certificate is issued to the website operator, who then places it on the site to be issued to all visiting web browsers to let them know that the site is legitimate. Many Zyxel products, such as the Zyxel Device, issue their own public key certificates. These can be used by web browsers on a LAN or WAN to verify that they are in fact connecting to the legitimate device and not one masquerading as it. However, because the certificates were not issued by one of the several organizations officially recognized by the most common web browsers, you will need to import the Zyxel-created certificate into your web browser and flag that certificate as a trusted authority. Note: You can see if you are browsing on a secure website if the URL in your web browser's
address bar begins with https:// or there is a sealed padlock icon ( ) somewhere in the main browser window (not all browsers show the padlock in the same location). G o o g le C hro m e The following example uses Google Chrome on Windows 7. You first have to store the certificate in your computer and then install it as a Trusted Root CA, as shown in the following tutorials.
NWA/WAC/WAX Series User's Guide
267
Appendix A Importing Certificates
Expo rt a C e rtific a te
1 If your device's Web Configurator is set to use SSL certification, then upon browsing with it for the first time, you are presented with a certification error.
NWA/WAC/WAX Series User's Guide
268
Appendix A Importing Certificates 2 Click Adva nc e d > Pro c e e d to x.x.x.x (unsa fe ).
3 In the Addre ss Ba r, click No t Se c ure > C e rtific a te (Inva lid).
NWA/WAC/WAX Series User's Guide
269
Appendix A Importing Certificates 4 In the C e rtific a te dialog box, click De ta ils > C o py to File .
5 In the C e rtific a te Expo rt Wiza rd, click Ne xt.
NWA/WAC/WAX Series User's Guide
270
Appendix A Importing Certificates 6 Select the format and settings you want to use and then click Ne xt.
7 Type a filename and specify a folder to save the certificate in. Click Ne xt.
NWA/WAC/WAX Series User's Guide
271
Appendix A Importing Certificates 8 In the C o m ple ting the C e rtific a te Expo rt Wiza rd screen, click Finish.
9 Finally, click O K when presented with the successful certificate export message.
Im po rt a C e rtific a te
After storing the certificate in your computer (see Export a Certificate), you need to install it as a trusted root certification authority using the following steps:
NWA/WAC/WAX Series User's Guide
272
Appendix A Importing Certificates 1 Open your web browser, click the menu icon, and click Se tting s.
NWA/WAC/WAX Series User's Guide
273
Appendix A Importing Certificates 2 Scroll down and click Adva nc e d to expand the menu. Under Priva c y a nd se c urity, click Ma na g e
c e rtific a te s.
NWA/WAC/WAX Series User's Guide
274
Appendix A Importing Certificates 3 In the C e rtific a te s pop-up screen, click Truste d Ro o t C e rtific a tio n Autho ritie s. Click Im po rt to start the
C e rtific a te Im po rt Wiza rd.
4 Click Ne xt when the wizard pops up, and then on the following screen click Bro wse .
NWA/WAC/WAX Series User's Guide
275
Appendix A Importing Certificates 5 Select the certificate file you want to import and click O pe n.
6 Click Ne xt.
NWA/WAC/WAX Series User's Guide
276
Appendix A Importing Certificates 7 Confirm the settings displayed and click Finish.
8 If presented with a security warning, click Ye s.
NWA/WAC/WAX Series User's Guide
277
Appendix A Importing Certificates 9 Finally, click O K when you are notified of the successful import.
Insta ll a Sta nd- Alo ne C e rtific a te File
Rather than installing a public key certificate using web browser settings, you can install a stand-alone certificate file if one has been issued to you. 1 Double-click the public key certificate file. 2 Click Insta ll C e rtific a te .
NWA/WAC/WAX Series User's Guide
278
Appendix A Importing Certificates 3 Click Ne xt on the first wizard screen, click Pla c e a ll c e rtific a te s in the fo llo wing sto re , and click Bro wse .
4 Select Truste d Ro o t C e rtific a te Autho ritie s > O K, and then click Ne xt.
NWA/WAC/WAX Series User's Guide
279
Appendix A Importing Certificates 5 Confirm the information shown on the final wizard screen and click Finish.
6 If presented with a security warning, click Ye s.
NWA/WAC/WAX Series User's Guide
280
Appendix A Importing Certificates 7 Finally, click O K when you are notified of the successful import.
Re m o ve a C e rtific a te in G o o g le C hro m e
This section shows you how to remove a public key certificate in Google Chrome on Windows 7. 1 Open your web browser, click the menu icon, and click Se tting s.
NWA/WAC/WAX Series User's Guide
281
Appendix A Importing Certificates 2 Scroll down and click Adva nc e d to expand the menu. Under Priva c y a nd se c urity, click Ma na g e
c e rtific a te s.
3 In the Certificates pop-up screen, click Truste d Ro o t C e rtific a tio n Autho ritie s.
NWA/WAC/WAX Series User's Guide
282
Appendix A Importing Certificates 4 Select the certificate you want to remove and click Re m o ve . 5 Click Ye s when you see the following warning message.
6 Confirm the details displayed in the warning message and click Ye s.
Fire fo x
The following example uses Mozilla Firefox on Windows 7. You first have to store the certificate in your computer and then install it as a Trusted Root CA, as shown in the following tutorials.
NWA/WAC/WAX Series User's Guide
283
Appendix A Importing Certificates
Expo rt a C e rtific a te
1 If your device's Web Configurator is set to use SSL certification, then the first time you browse to it you are presented with a certification error. Click Adva nc e d.
2 Click Vie w C e rtific a te .
NWA/WAC/WAX Series User's Guide
284
3 Click De ta ils > Expo rt.
Appendix A Importing Certificates
4 Type a filename and click Sa ve .
Im po rt a C e rtific a te
After storing the certificate in your computer, you need to import it in trusted root certification authorities using the following steps:
NWA/WAC/WAX Series User's Guide
285
Appendix A Importing Certificates 1 Open Fire fo x and click To o ls > O ptio ns.
NWA/WAC/WAX Series User's Guide
286
Appendix A Importing Certificates 2 In the O ptio ns page, click Priva c y & Se c urity, scroll to the bottom of the page, and then click Vie w
C e rtific a te s.
3 In the C e rtific a te Ma na g e r, click Autho ritie s > Im po rt.
NWA/WAC/WAX Series User's Guide
287
Appendix A Importing Certificates 4 Use the Se le c t File dialog box to locate the certificate and then click O pe n.
5 Select Trust this C A to ide ntify we b site s and click O K.
Re m o ving a C e rtific a te in Fire fo x
This section shows you how to remove a public key certificate in Firefox.
NWA/WAC/WAX Series User's Guide
288
Appendix A Importing Certificates 1 Open Fire fo x and click To o ls > O ptio ns.
2 In the O ptio ns page, click Priva c y & Se c urity, scroll to the bottom of the page, and then click Vie w C e rtific a te s.
NWA/WAC/WAX Series User's Guide
289
Appendix A Importing Certificates 3 In the C e rtific a te Ma na g e r, click Autho ritie s and select the certificate you want to remove. Click De le te
o r Distrust.
.
4 In the following dialog box, click O K.
5 The next time you go to the web site that issued the public key certificate you just removed, a certification error appears. NWA/WAC/WAX Series User's Guide
290
A PPEN DIX B
IPv6
O ve rvie w
IPv6 (Internet Protocol version 6), is designed to enhance IP address size and features. The increase in IPv6 address size to 128 bits (from the 32-bit IPv4 address) allows up to 3.4 x 1038 IP addresses.
IPv6 Addre ssing
The 128-bit IPv6 address is written as eight 16-bit hexadecimal blocks separated by colons (:). This is an example IPv6 address 2001:0db8:1a2b:0015:0000:0000:1a2f:0000.
IPv6 addresses can be abbreviated in two ways:
� Leading zeros in a block can be omitted. So 2001:0db8:1a2b:0015:0000:0000:1a2f:0000 can be written as 2001:db8:1a2b:15:0:0:1a2f:0.
� Any number of consecutive blocks of zeros can be replaced by a double colon. A double colon can only appear once in an IPv6 address. So 2001:0db8:0000:0000:1a2f:0000:0000:0015 can be written as 2001:0db8::1a2f:0000:0000:0015, 2001:0db8:0000:0000:1a2f::0015, 2001:db8::1a2f:0:0:15 or 2001:db8:0:0:1a2f::15.
Pre fix a nd Pre fix Le ng th
Similar to an IPv4 subnet mask, IPv6 uses an address prefix to represent the network address. An IPv6 prefix length specifies how many most significant bits (start from the left) in the address compose the network address. The prefix length is written as "/x" where x is a number. For example,
2001:db8:1a2b:15::1a2f:0/32
means that the first 32 bits (2001:db8) is the subnet prefix.
Link- lo c a l Addre ss
A link-local address uniquely identifies a device on the local network (the LAN). It is similar to a "private IP address" in IPv4. You can have the same link-local address on multiple interfaces on a device. A linklocal unicast address has a predefined prefix of fe80::/10. The link-local unicast address format is as follows.
Table 107 Link-local Unicast Address Format
1111 1110 10 10 bits
0 54 bits
Interface ID 64 bits
G lo b a l Addre ss
A global address uniquely identifies a device on the Internet. It is similar to a "public IP address" in IPv4. A global unicast address starts with a 2 or 3.
NWA/WAC/WAX Series User's Guide
291
Appendix B IPv6
Unspe c ifie d Addre ss
An unspecified address (0:0:0:0:0:0:0:0 or ::) is used as the source address when a device does not have its own address. It is similar to "0.0.0.0" in IPv4.
Lo o pb a c k Addre ss
A loopback address (0:0:0:0:0:0:0:1 or ::1) allows a host to send packets to itself. It is similar to "127.0.0.1" in IPv4.
Multic a st Addre ss
In IPv6, multicast addresses provide the same functionality as IPv4 broadcast addresses. Broadcasting is not supported in IPv6. A multicast address allows a host to send packets to all hosts in a multicast group.
Multicast scope allows you to determine the size of the multicast group. A multicast address has a predefined prefix of ff00::/8. The following table describes some of the predefined multicast addresses.
Table 108 Predefined Multicast Address
MULTIC ASTADDRESS
DESC RIPTIO N
FF01:0:0:0:0:0:0:1 FF01:0:0:0:0:0:0:2
All hosts on a local node. All routers on a local node.
FF02:0:0:0:0:0:0:1 FF02:0:0:0:0:0:0:2 FF05:0:0:0:0:0:0:2
All hosts on a local connected link. All routers on a local connected link. All routers on a local site.
FF05:0:0:0:0:0:1:3
All DHCP severs on a local site.
The following table describes the multicast addresses which are reserved and can not be assigned to a multicast group.
Table 109 Reserved Multicast Address
MULTIC ASTADDRESS FF00:0:0:0:0:0:0:0 FF01:0:0:0:0:0:0:0 FF02:0:0:0:0:0:0:0 FF03:0:0:0:0:0:0:0 FF04:0:0:0:0:0:0:0 FF05:0:0:0:0:0:0:0 FF06:0:0:0:0:0:0:0 FF07:0:0:0:0:0:0:0 FF08:0:0:0:0:0:0:0 FF09:0:0:0:0:0:0:0 FF0A:0:0:0:0:0:0:0 FF0B:0:0:0:0:0:0:0 FF0C:0:0:0:0:0:0:0 FF0D:0:0:0:0:0:0:0 FF0E:0:0:0:0:0:0:0 FF0F:0:0:0:0:0:0:0
NWA/WAC/WAX Series User's Guide
292
Appendix B IPv6
Sub ne t Ma sking
Both an IPv6 address and IPv6 subnet mask compose of 128-bit binary digits, which are divided into eight 16-bit blocks and written in hexadecimal notation. Hexadecimal uses four bits for each character (1 ~ 10, A ~ F). Each block's 16 bits are then represented by four hexadecimal characters. For example, FFFF:FFFF:FFFF:FFFF:FC00:0000:0000:0000.
Inte rfa c e ID
In IPv6, an interface ID is a 64-bit identifier. It identifies a physical interface (for example, an Ethernet port) or a virtual interface (for example, the management IP address for a VLAN). One interface should have a unique interface ID.
EUI- 64
The EUI-64 (Extended Unique Identifier) defined by the IEEE (Institute of Electrical and Electronics Engineers) is an interface ID format designed to adapt with IPv6. It is derived from the 48-bit (6-byte) Ethernet MAC address as shown next. EUI-64 inserts the hex digits fffe between the third and fourth bytes of the MAC address and complements the seventh bit of the first byte of the MAC address. See the following example.
Table 110
MAC
00 : 13 : 49 : 12 : 34 : 56
Table 111
EUI- 64
02 : 13 : 49 : FF : FE : 12 : 34 : 56
Sta te le ss Auto c o nfig ura tio n
With stateless autoconfiguration in IPv6, addresses can be uniquely and automatically generated. Unlike DHCPv6 (Dynamic Host Configuration Protocol version six) which is used in IPv6 stateful autoconfiguration, the owner and status of addresses don't need to be maintained by a DHCP server. Every IPv6 device is able to generate its own and unique IP address automatically when IPv6 is initiated on its interface. It combines the prefix and the interface ID (generated from its own Ethernet MAC address, see Interface ID and EUI-64) to form a complete IPv6 address.
When IPv6 is enabled on a device, its interface automatically generates a link-local address (beginning with fe80).
When the interface is connected to a network with a router and the Zyxel Device is set to automatically obtain an IPv6 network prefix from the router for the interface, it generates 1another address which combines its interface ID and global and subnet information advertised from the router. This is a routable global IP address.
DHC Pv6
The Dynamic Host Configuration Protocol for IPv6 (DHCPv6, RFC 3315) is a server-client protocol that allows a DHCP server to assign and pass IPv6 network addresses, prefixes and other configuration information to DHCP clients. DHCPv6 servers and clients exchange DHCP messages using UDP.
1. In IPv6, all network interfaces can be associated with several addresses.
NWA/WAC/WAX Series User's Guide
293
Appendix B IPv6
Each DHCP client and server has a unique DHCP Unique IDentifier (DUID), which is used for identification when they are exchanging DHCPv6 messages. The DUID is generated from the MAC address, time, vendor assigned ID and/or the vendor's private enterprise number registered with the IANA. It should not change over time even after you reboot the device.
Ide ntity Asso c ia tio n
An Identity Association (IA) is a collection of addresses assigned to a DHCP client, through which the server and client can manage a set of related IP addresses. Each IA must be associated with exactly one interface. The DHCP client uses the IA assigned to an interface to obtain configuration from a DHCP server for that interface. Each IA consists of a unique IAID and associated IP information. The IA type is the type of address in the IA. Each IA holds one type of address. IA_NA means an identity association for non-temporary addresses and IA_TA is an identity association for temporary addresses. An IA_NA option contains the T1 and T2 fields, but an IA_TA option does not. The DHCPv6 server uses T1 and T2 to control the time at which the client contacts with the server to extend the lifetimes on any addresses in the IA_NA before the lifetimes expire. After T1, the client sends the server (S1) (from which the addresses in the IA_NA were obtained) a Renew message. If the time T2 is reached and the server does not respond, the client sends a Rebind message to any available server (S2). For an IA_TA, the client may send a Renew or Rebind message at the client's discretion.
T2 T1
Renew to S1
Renew to S1
Renew to S1
Renew to S1
Renew to S1
Renew to S1
Rebind to S2
Rebind to S2
DHC P Re la y Ag e nt
A DHCP relay agent is on the same network as the DHCP clients and helps forward messages between the DHCP server and clients. When a client cannot use its link-local address and a well-known multicast address to locate a DHCP server on its network, it then needs a DHCP relay agent to send a message to a DHCP server that is not attached to the same network.
The DHCP relay agent can add the remote identification (remote-ID) option and the interface-ID option to the Relay-Forward DHCPv6 messages. The remote-ID option carries a user-defined string, such as the system name. The interface-ID option provides slot number, port information and the VLAN ID to the DHCPv6 server. The remote-ID option (if any) is stripped from the Relay-Reply messages before the relay agent sends the packets to the clients. The DHCP server copies the interface-ID option from the RelayForward message into the Relay-Reply message and sends it to the relay agent. The interface-ID should not change even after the relay agent restarts.
Pre fix De le g a tio n
Prefix delegation enables an IPv6 router to use the IPv6 prefix (network address) received from the ISP (or a connected uplink router) for its LAN. The Zyxel Device uses the received IPv6 prefix (for example, 2001:db2::/48) to generate its LAN IP address. Through sending Router Advertisements (RAs) regularly by multicast, the Zyxel Device passes the IPv6 prefix information to its LAN hosts. The hosts then can use the prefix to generate their IPv6 addresses.
NWA/WAC/WAX Series User's Guide
294
Appendix B IPv6
IC MPv6
Internet Control Message Protocol for IPv6 (ICMPv6 or ICMP for IPv6) is defined in RFC 4443. ICMPv6 has a preceding Next Header value of 58, which is different from the value used to identify ICMP for IPv4. ICMPv6 is an integral part of IPv6. IPv6 nodes use ICMPv6 to report errors encountered in packet processing and perform other diagnostic functions, such as "ping".
Ne ig hb o r Disc o ve ry Pro to c o l (NDP)
The Neighbor Discovery Protocol (NDP) is a protocol used to discover other IPv6 devices and track neighbor's reachability in a network. An IPv6 device uses the following ICMPv6 messages types:
� Neighbor solicitation: A request from a host to determine a neighbor's link-layer address (MAC address) and detect if the neighbor is still reachable. A neighbor being "reachable" means it responds to a neighbor solicitation message (from the host) with a neighbor advertisement message.
� Neighbor advertisement: A response from a node to announce its link-layer address. � Router solicitation: A request from a host to locate a router that can act as the default router and
forward packets. � Router advertisement: A response to a router solicitation or a periodical multicast advertisement from
a router to advertise its presence and other parameters.
IPv6 C a c he
An IPv6 host is required to have a neighbor cache, destination cache, prefix list and default router list. The Zyxel Device maintains and updates its IPv6 caches constantly using the information from response messages. In IPv6, the Zyxel Device configures a link-local address automatically, and then sends a neighbor solicitation message to check if the address is unique. If there is an address to be resolved or verified, the Zyxel Device also sends out a neighbor solicitation message. When the Zyxel Device receives a neighbor advertisement in response, it stores the neighbor's link-layer address in the neighbor cache. When the Zyxel Device uses a router solicitation message to query for a router and receives a router advertisement message, it adds the router's information to the neighbor cache, prefix list and destination cache. The Zyxel Device creates an entry in the default router list cache if the router can be used as a default router.
When the Zyxel Device needs to send a packet, it first consults the destination cache to determine the next hop. If there is no matching entry in the destination cache, the Zyxel Device uses the prefix list to determine whether the destination address is on-link and can be reached directly without passing through a router. If the address is onlink, the address is considered as the next hop. Otherwise, the Zyxel Device determines the next-hop from the default router list or routing table. Once the next hop IP address is known, the Zyxel Device looks into the neighbor cache to get the link-layer address and sends the packet when the neighbor is reachable. If the Zyxel Device cannot find an entry in the neighbor cache or the state for the neighbor is not reachable, it starts the address resolution process. This helps reduce the number of IPv6 solicitation and advertisement messages.
Multic a st Liste ne r Disc o ve ry
The Multicast Listener Discovery (MLD) protocol (defined in RFC 2710) is derived from IPv4's Internet Group Management Protocol version 2 (IGMPv2). MLD uses ICMPv6 message types, rather than IGMP message types. MLDv1 is equivalent to IGMPv2 and MLDv2 is equivalent to IGMPv3.
MLD allows an IPv6 switch or router to discover the presence of MLD listeners who wish to receive
NWA/WAC/WAX Series User's Guide
295
Appendix B IPv6
multicast packets and the IP addresses of multicast groups the hosts want to join on its network.
MLD snooping and MLD proxy are analogous to IGMP snooping and IGMP proxy in IPv4.
MLD filtering controls which multicast groups a port can join.
MLD Me ssa g e s
A multicast router or switch periodically sends general queries to MLD hosts to update the multicast forwarding table. When an MLD host wants to join a multicast group, it sends an MLD Report message for that address.
An MLD Done message is equivalent to an IGMP Leave message. When an MLD host wants to leave a multicast group, it can send a Done message to the router or switch. The router or switch then sends a group-specific query to the port on which the Done message is received to determine if other devices connected to this port should remain in the group.
Exa m ple - Ena b ling IPv6 o n Windo ws XP/ 2003/ Vista
By default, Windows XP and Windows 2003 support IPv6. This example shows you how to use the ipv6 install command on Windows XP/2003 to enable IPv6. This also displays how to use the ipconfig command to see auto-generated IP addresses.
C:\>ipv6 install Installing... Succeeded.
C:\>ipconfig
Windows IP Configuration
Ethernet adapter Local Area Connection:
Connection-specific DNS Suffix . : IP Address. . . . . . . . . . . . : 10.1.1.46 Subnet Mask . . . . . . . . . . . : 255.255.255.0 IP Address. . . . . . . . . . . . : fe80::2d0:59ff:feb8:103c%4 Default Gateway . . . . . . . . . : 10.1.1.254
IPv6 is installed and enabled by default in Windows Vista. Use the ipconfig command to check your automatic configured IPv6 address as well. You should see at least one IPv6 address available for the interface on your computer.
Exa m ple - Ena b ling DHC Pv6 o n Windo ws XP
Windows XP does not support DHCPv6. If your network uses DHCPv6 for IP address assignment, you have to additionally install a DHCPv6 client software on your Windows XP. (Note: If you use static IP addresses or Router Advertisement for IPv6 address assignment in your network, ignore this section.)
This example uses Dibbler as the DHCPv6 client. To enable DHCPv6 client on your computer:
NWA/WAC/WAX Series User's Guide
296
Appendix B IPv6 1 Install Dibbler and select the DHCPv6 client option on your computer. 2 After the installation is complete, select Sta rt > All Pro g ra m s > Dib b le r- DHC Pv6 > C lie nt Insta ll a s se rvic e . 3 Select Sta rt > C o ntro l Pa ne l > Adm inistra tive To o ls > Se rvic e s. 4 Double click Dib ble r - a DHC Pv6 c lie nt.
5 Click Sta rt and then O K.
6 Now your computer can obtain an IPv6 address from a DHCPv6 server.
Exa m ple - Ena b ling IPv6 o n Windo ws 7
Windows 7 supports IPv6 by default. DHCPv6 is also enabled when you enable IPv6 on a Windows 7 computer. To enable IPv6 in Windows 7:
NWA/WAC/WAX Series User's Guide
297
Appendix B IPv6 1 Select C o ntro l Pa ne l > Ne two rk a nd Sha ring C e nte r > Lo c a l Are a C o nne c tio n. 2 Select the Inte rne t Pro to c o l Ve rsio n 6 (TC P/ IPv6) checkbox to enable it. 3 Click O K to save the change.
4 Click C lo se to exit the Lo c a l Are a C o nne c tio n Sta tus screen. 5 Select Sta rt > All Pro g ra m s > Ac c e sso rie s > C o m m a nd Pro m pt. 6 Use the ipconfig command to check your dynamic IPv6 address. This example shows a global address
(2001:b021:2d::1000) obtained from a DHCP server. C:\>ipconfig Windows IP Configuration Ethernet adapter Local Area Connection:
Connection-specific DNS Suffix . : IPv6 Address. . . . . . . . . . . : 2001:b021:2d::1000 Link-local IPv6 Address . . . . . : fe80::25d8:dcab:c80a:5189%11 IPv4 Address. . . . . . . . . . . : 172.16.100.61 Subnet Mask . . . . . . . . . . . : 255.255.255.0 Default Gateway . . . . . . . . . : fe80::213:49ff:feaa:7125%11
172.16.100.254
NWA/WAC/WAX Series User's Guide
298
A PPEN DIX C
C usto m e r Suppo rt
In the event of problems that cannot be solved by using this manual, you should contact your vendor. If you cannot contact your vendor, then contact a Zyxel office for the region in which you bought the device.
For Zyxel Communications offices, see http s://se rvic e -p ro vide r.zyxe l.c o m/g lo b a l/e n/c o nta c t-us for the latest information.
For Zyxel Networks offices, see http s://www.zyxe l.c o m/inde x.shtml for the latest information.
Please have the following information ready when you contact an office.
Re q uire d Info rm a tio n
� Product model and serial number. � Warranty Information. � Date that you received your device. � Brief description of the problem and the steps you took to solve it.
C o rpo ra te He a dq ua rte rs (Wo rldwide )
Ta iwa n
� Zyxel Communications Corporation � https://www.zyxel.com
A sia
C hina
� Zyxel Communications (Shanghai) Corp. Zyxel Communications (Beijing) Corp. Zyxel Communications (Tianjin) Corp.
� https://www.zyxel.com/cn/zh/
Ind ia
� Zyxel Technology India Pvt Ltd � https://www.zyxel.com/in/en/
Ka za khsta n
� Zyxel Kazakhstan � https://www.zyxel.kz
NWA/WAC/WAX Series User's Guide
299
Appendix C Customer Support
Ko re a
� Zyxel Korea Corp. � http://www.zyxel.kr
Ma la ysia
� Zyxel Malaysia Sdn Bhd. � http://www.zyxel.com.my
Pa kista n
� Zyxel Pakistan (Pvt.) Ltd. � http://www.zyxel.com.pk
Philippine s
� Zyxel Philippines � http://www.zyxel.com.ph
Sing a po re
� Zyxel Singapore Pte Ltd. � http://www.zyxel.com.sg
Ta iwa n
� Zyxel Communications Corporation � https://www.zyxel.com/tw/zh/
Tha ila nd
� Zyxel Thailand Co., Ltd � https://www.zyxel.com/th/th/
Vie tna m
� Zyxel Communications Corporation-Vietnam Office � https://www.zyxel.com/vn/vi
Euro pe
Be la rus
� Zyxel BY � https://www.zyxel.by
Bulg a ria
� Zyxel � https://www.zyxel.com/bg/bg/
NWA/WAC/WAX Series User's Guide
300
Appendix C Customer Support
C ze c h Re pub lic
� Zyxel Communications Czech s.r.o � https://www.zyxel.com/cz/cs/
De nm a rk
� Zyxel Communications A/S � https://www.zyxel.com/dk/da/
Finla nd
� Zyxel Communications � https://www.zyxel.com/fi/fi/
Fra nc e
� Zyxel France � https://www.zyxel.fr
G e rm a ny
� Zyxel Deutschland GmbH � https://www.zyxel.com/de/de/
Hung a ry
� Zyxel Hungary & SEE � https://www.zyxel.com/hu/hu/
Ita ly
� Zyxel Communications Italy � https://www.zyxel.com/it/it/
Ne the rla nds
� Zyxel Benelux � https://www.zyxel.com/nl/nl/
No rwa y
� Zyxel Communications � https://www.zyxel.com/no/no/
Po la nd
� Zyxel Communications Poland � https://www.zyxel.com/pl/pl/
Ro m a nia
� Zyxel Romania
NWA/WAC/WAX Series User's Guide
301
Appendix C Customer Support
� https://www.zyxel.com/ro/ro
Russia
� Zyxel Russia � https://www.zyxel.com/ru/ru/
Slo va kia
� Zyxel Communications Czech s.r.o. organizacna zlozka � https://www.zyxel.com/sk/sk/
Spa in
� Zyxel Communications ES Ltd � https://www.zyxel.com/es/es/
Swe de n
� Zyxel Communications � https://www.zyxel.com/se/sv/
Switze rla nd
� Studerus AG � https://www.zyxel.ch/de � https://www.zyxel.ch/fr
Turke y
� Zyxel Turkey A.S. � https://www.zyxel.com/tr/tr/
UK
� Zyxel Communications UK Ltd. � https://www.zyxel.com/uk/en/
Ukra ine
� Zyxel Ukraine � http://www.ua.zyxel.com
So uth Am e ric a
Arg e ntina
� Zyxel Communications Corporation � https://www.zyxel.com/co/es/
NWA/WAC/WAX Series User's Guide
302
Appendix C Customer Support
Bra zil
� Zyxel Communications Brasil Ltda. � https://www.zyxel.com/br/pt/
C o lo m b ia
� Zyxel Communications Corporation � https://www.zyxel.com/co/es/
Ec ua do r
� Zyxel Communications Corporation � https://www.zyxel.com/co/es/
So uth Am e ric a
� Zyxel Communications Corporation � https://www.zyxel.com/co/es/
Middle Ea st Isra e l
� Zyxel Communications Corporation � http://il.zyxel.com/
No rth Am e ric a USA
� Zyxel Communications, Inc. - North America Headquarters � https://www.zyxel.com/us/en/
NWA/WAC/WAX Series User's Guide
303
A PPEN DIX D
Le g a l Info rm a tio n
C o pyrig ht
Copyright � 2022 by Zyxel and/or its affiliates The contents of this publication may not be reproduced in any part or as a whole, transcribed, stored in a retrieval system, translated into any language, or transmitted in any form or by any means, electronic, mechanical, magnetic, optical, chemical, photocopying, manual, or otherwise, without the prior written permission of Zyxel and/or its affiliates. Published by Zyxel and/or its affiliates. All rights reserved.
Disc la im e rs
Zyxel does not assume any liability arising out of the application or use of any products, or software described herein. Neither does it convey any license under its patent rights nor the patent rights of others. Zyxel further reserves the right to make changes in any products described herein without notice. This publication is subject to change without notice. Your use of the Zyxel Device is subject to the terms and conditions of any related service providers.
Tra de m a rks
Trademarks mentioned in this publication are used for identification purposes only and may be properties of their respective owners.
Re g ula to ry No tic e a nd Sta te m e nt
UNITED STATES o f AMERIC A
The following information applies if you use the product within USA area.
FC C EMC Sta te m e nt
� This device complies with part 15 of the FCC Rules. Operation is subject to the following two conditions: (1) This device may not cause harmful interference, and (2) this device must accept any interference received, including interference that may cause undesired operation.
� Changes or modifications not expressly approved by the party responsible for compliance could void the user's authority to operate the device.
� This product has been tested and complies with the specifications for a Class B digital device, pursuant to Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This device generates, uses, and can radiate radio frequency energy and, if not installed and used according to the instructions, may cause harmful interference to radio communications. However, there is no guarantee that interference will not occur in a particular installation.
� If this device does cause harmful interference to radio or television reception, which is found by turning the device off and on, the user is encouraged to try to correct the interference by one or more of the following measures: � Reorient or relocate the receiving antenna � Increase the separation between the devices � Connect the equipment to an outlet other than the receiver's � Consult a dealer or an experienced radio/TV technician for assistance
FCC Caution: Any changes or modifications not expressly approved by the party responsible for compliance could void the user's authority to operate this equipment.
FC C Ra dia tio n Expo sure Sta te m e nt
� This device complies with FCC RF radiation exposure limits set forth for an uncontrolled environment. � This transmitter must be at least 20 cm from the user and must not be co-located or operating in conjunction with any other antenna or
transmitter. This transmitter must be at least 30 cm (WAC6553D-E) from the user and must not be co-located or operating in conjunction with any other antenna or transmitter. � Country Code selection feature to be disabled for products marketed to the US/CANADA. � Operation of this device is restricted to indoor use only, except for relevant user's manual mention that this device can be installed into the external environment. (WAC6553D-E is a device for outdoor use.)
NWA/WAC/WAX Series User's Guide
304
Appendix D Legal Information
BRA ZIL
The following applies if you use the product within Brazil.
Este equipamento opera em car�ter secund�rio, isto �, n�o tem direito a prote��o contra interfer�ncia prejudicial, mesmo de esta�es do mesmo tipo, e n�o pode causar interfer�ncia a sistemas operando em car�ter prim�rio.
C ANA DA
The following information applies if you use the product within Canada area.
Inno va tio n, Sc ie nc e a nd Ec o no m ic De ve lo pm e nt C a na da IC ES Sta te m e nt
CAN ICES-3 (B)/NMB-3(B)
Inno va tio n, Sc ie nc e a nd Ec o no m ic De ve lo pm e nt C a na da RSS- G EN & RSS- 247 Sta te m e nt
� This device contains licence-exempt transmitter(s)/receiver(s) that comply with Innovation, Science and Economic Development Canada's licence-exempt RSS(s). Operation is subject to the following two conditions: (1) this device may not cause interference, and (2) this device must accept any interference, including interference that may cause undesired operation of the device.
� This radio transmitter 2468C-11ACAP22W(WAC500H), 2468C-11ACAP22(WAC500 and NWA1123ACv3), 2468C-WAC5302DS(WAC5302D-Sv2), (2468C-NWA5123AC (NWA1123-AC v2), 2468C-NWA5123ACHD (NWA1123-AC HD), 2468C-WAC5302DS (NWA1302-AC), 2468C-NWA5123AC (NWA5123-AC), 2468C-NWA5123ACHD (NWA5123-AC HD), 2468C-WAC6502DE (WAC6502D-S, WAC6502D-E), 2468C-WAC6503DS (WAC6503D-S), 2468C-WAC6552DS (WAC6552D-S), 2468C-WAC6553DE (WAC6553D-E), 2468C-WAC6303DS (WAC6303D-S), 2468CWAC6103DI (WAC6103D-I), 2468C-WAC5302DS (WAC5302D-S), 2468C-WAX650S (WAX650S), 2486C-11AXAP24 (NWA210AX, WAX610D and WAX630S) and 2468C-11AXAP22 (NWA110AX and WAX510D)) has been approved by Innovation, Science and Economic Development Canada to operate with the antenna types listed below with the maximum permissible gain and required antenna impedance for each antenna type indicated. Antenna types not included in this list that have a gain greater than the maximum gain indicated for any type listed, are strictly prohibited for use with this device.
NWA/WAC/WAX Series User's Guide
305
Appendix D Legal Information
Ante nna Info rm a tio n
ANTENNA MO DEL NWA1123-ACv2
NWA1123-AC HD
NWA1302-AC WAC5302D-Sv2 NWA5123-AC
NWA5123-AC HD
WAC6502D-E WAC6502D-S WAC6503D-S WAC6553D-E WAC6103D-I
NO .
TYPE
1
PIFA
2
PIFA
3
PIFA
C O NNEC TO R UFL UFL UFL
4
PIFA
UFL
1
PIFA
I-PEX
2
PIFA
I-PEX
3
Monopole
I-PEX
4
Monopole
I-PEX
5
Monopole
I-PEX
1
Loop
2
Loop
3
PIFA
I-PEX I-PEX I-PEX
1
PIFA
U.FL
2
PIFA
U.FL
3
PIFA
U.FL
4
PIFA
U.FL
1
PIFA
I-PEX
2
PIFA
I-PEX
3
Monopole
I-PEX
4
Monopole
I-PEX
5
Monopole
I-PEX
Dipole
Dipole
Dipole
Dipole
1
PIFA
2
PIFA
3
PIFA
4
Dipole
5
Loop
RSMA IPEX IPEX N type U.FL U.FL U.FL U.FL U.FL
6
Loop
U.FL
7
Loop
U.FL
8
Dipole
U.FL
2.4 G G AIN (dBi) 3.08 3.07
3 (2400-2483.5 MHz) 3 (2400-2483.5 MHz)
5.82 (2400-2483.5 MHz) 5.02 (2400-2483.5 MHz)
3.08 (2400-2483.5 MHz) 3.07 (2400-2483.5 MHz)
3 (2400-2483.5 MHz) 3 (2400-2483.5 MHz)
5 4 4 4.5 3.28 3.37 3.15 4.33
5G G AIN (dBi)
4.06 (5150~5250 MHz) 3.79 (5725~5850 MHz) 3.99 (5150~5250 MHz) 3.78 (5725~5850 MHz)
4 (5150-5250 MHz) 4 (5725-5850 MHz) 4 (5150-5250 MHz) 4 (5725-5850 MHz) 4 (5150-5250 MHz) 4 (5725-5850 MHz)
5 (5150-5250 MHz) 5 (5250-5350 MHz) 5 (5470-5725 MHz) 5 (5725-5850 MHz)
4.06 (5150-5250 MHz) 3.91 (5725-5850 MHz) 3.99 (5150-5250 MHz) 3.79 (5725-5850 MHz)
4 (5150-5250 MHz) 4 (5725-5850 MHz) 4 (5150-5250 MHz) 4 (5725-5850 MHz) 4 (5150-5250 MHz) 4 (5725-5850 MHz) 7 6 6 7
4.38 (5150-5250 MHz) 4.23 (5725-5850 MHz) 4.31 (5150-5250 MHz) 4.22 (5725-5850 MHz) 4.38 (5150-5250 MHz) 4.36 (5725-5850 MHz) 5.12 (5150-5250 MHz) 5.20 (5725-5850 MHz)
REM A RK
Ceiling Mounted: Antenna 1, 2, 3 Wall Mounted: Antenna 1, 2, 4 Ceiling Mounted: Antenna 5, 6, 7 Wall Mounted: Antenna 5, 6, 8
NWA/WAC/WAX Series User's Guide
306
Appendix D Legal Information
ANTENNA MO DEL WAC5302D-S
WAC6303D-S WAC6552D-S SECTX-DB r2.0 WAX630S WAX650S WAX510D NWA110AX
NWA210AX WAX610D
WAC500H WAC500 NWA1123ACv3
NO .
TYPE
1
Loop
2
Loop
3
PIFA
1
Direction
2
Direction
1
Direction
PIFA
Direction
1
Dipole
2
PIFA
3
Dipole
4
Dipole
1
Dipole
2
PIFA
3
PIFA
4
Dipole
5
Dipole
6
Dipole
1
PIFA
2
PIFA
1
PIFA
2
PIFA
C O NNEC TO R I-PEX I-PEX I-PEX
U.FL U.FL I-PEX U.FL
U.FL
I-PEX I-PEX I-PEX I-PEX I-PEX
I-PEX I-PEX
I-PEX
I-PEX
I-PEX
N/A N/A N/A N/A
2.4 G G AIN (dBi) 5.82 (2400-2483.5 MHz) 5.02 (2400-2483.5 MHz)
1.12 (2400-2483.5 MHz) 0.8 (2400-2483.5 MHz) 0.92 0 (2400-2483.5 MHz) 0 (2400-2483.5 MHz) 0 (2400-2483.5 MHz) 0 (2400-2483.5 MHz) 0 (2400-2483.5 MHz)
5.08dBi 5.56dBi 6.06dBi
0dBi 0dBi 0dBi 0dBi
5G G AIN (dBi)
5 (5150-5250 MHz) 5 (5250-5350 MHz) 5 (5470-5725 MHz) 5 (5725-5850 MHz)
1.29 (5150-5250 MHz) 1.07 (5725-5850 MHz)
4.22 (5150-5250 MHz)
5.34 (5725-5850 MHz)
1.32 (5150-5250 MHz) 1.39 (5250-5350 MHz) 0.44 (5470-5725 MHz) 1.63 (5725-5850 MHz)
3.51 (5150-5250 MHz) 4.22 (5250-5350 MHz) 4.61 (5470-5725 MHz) 4.68 (5725-5850 MHz)
4.5 (5150-5350MHz) 5.2 (5470-5725MHz) 5.5 (5725-5850MHz)
4.5 (5150-5350MHz) 5.2 (5470-5725MHz) 5.5 (5725-5850MHz)
4.5 (5150-5350MHz) 5.2 (5470-5725MHz) 5.5 (5725-5850MHz)
4.5 (5150-5350MHz) 5.2 (5470-5725MHz) 5.5 (5725-5850MHz)
U-NII-1:7.8dBi U-NII-2A:7.7dBi U-NII-2C:6.8dBi U-NII-3:7.2dBi
U-NII-1:7.5dBi U-NII-2A:6.8dBi U-NII-2C:6.5dBi U-NII-3:7.6dBi
U-NII-1:8.19dBi U-NII-2A:7.7dBi U-NII-2C:7.14dBi U-NII-3:7.6dBi
U-NII-1:6.8dBi U-NII-2A:7.5dBi U-NII-2C:5.81dBi U-NII-3:6.99dBi
U-NII-1:8.3dBi U-NII-2A:7.8dBi U-NII-2C:7.1dBi U-NII-3:7.98dBi
2.5dBi
2.5dBi
0dBi
0dBi
REM A RK
Wall Mount Ceiling Mount
If the product with 5G wireless function operating in 5150-5250 MHz and 5725-5850 MHz, the following attention must be paid, � The device for operation in the band 5150-5250 MHz is only for indoor use to reduce the potential for harmful interference to co-channel
mobile satellite systems. � For devices with detachable antenna(s), the maximum antenna gain permitted for devices in the band 5725-5850 MHz shall be such that the
equipment still complies with the e.i.r.p. limits specified for point-to-point and non-point-to-point operation as appropriate; and � Where applicable, antenna type(s), antenna model(s), and the worst-case tilt angle(s) necessary to remain compliant with the e.i.r.p.
elevation mask requirement set forth in Section 6.2.2.3 of RSS 247 shall be clearly indicated. If the product with 5G wireless function operating in 5250-5350 MHz and 5470-5725 MHz, the following attention must be paid. � For devices with detachable antenna(s), the maximum antenna gain permitted for devices in the bands 5250-5350 MHz and 5470-5725 MHz
shall be such that the equipment still complies with the e.i.r.p. limit.
NWA/WAC/WAX Series User's Guide
307
Appendix D Legal Information
� L'�metteur/r�cepteur exempt de licence contenu dans le pr�sent appareil est conforme aux CNR d'Innovation, Sciences et D�veloppement �conomique Canada applicables aux appareils radio exempts de licence. L'exploitation est autoris�e aux deux conditions suivantes : (1) l'appareil ne doit pas produire de brouillage; (2) L'appareil doit accepter tout brouillage radio�lectrique subi, m�me si le brouillage est susceptible d'en compromettre le fonctionnement.
� Le pr�sent �metteur radio 2468C-11ACAP22W (WAC500H), 2468C-11ACAP22 (WAC500 et NWA1123ACv3), 2468C-WAC5302DS (WAC5302D-Sv2), (2468C-NWA5123AC (NWA1123-AC v2), 2468C-NWA5123ACHD (NWA1123-AC HD), 2468C-WAC5302DS (NWA1302-AC), 2468C-NWA5123AC (NWA5123-AC), 2468C-NWA5123ACHD (NWA5123-AC HD), 2468C-WAC6502DE (WAC6502D-S, WAC6502D-E), 2468CWAC6503DS (WAC6503D-S), 2468C-WAC6552DS (WAC6552D-S), 2468C-WAC6553DE (WAC6553D-E), 2468C-WAC6303DS (WAC6303D-S), 2468C-WAC6103DI (WAC6103D-I), 2468C-WAC5302DS (WAC5302D-S), 2468C-WAX650S (WAX650S), 2468C-11AXAP22 (NWA110AX et WAX510D) and 2468C-11AXAP24 (NWA210AX, WAX610D et WAX630S)) a �t� approuv� par Innovation, Sciences et D�veloppement �conomique Canada pour fonctionner avec les types d'antenne �num�r�s ci dessous et ayant un gain admissible maximal. Les types d'antenne non inclus dans cette liste, et dont le gain est sup�rieur au gain maximal indiqu� pour tout type figurant sur la liste, sont strictement interdits pour l'exploitation de l'�metteur.
NWA/WAC/WAX Series User's Guide
308
Appendix D Legal Information
Informations Antenne
MO D�LE D'ANTENNE NWA1123-ACv2
NWA1123-AC HD
NWA1302-AC WAC5302D-Sv2 NWA5123-AC
NWA5123-AC HD
WAC6502D-E WAC6502D-S WAC6503D-S WAC6553D-E WAC6103D-I
NB.
TYPE
C O NNEC TEUR
2.4 G G AIN (dBi)
5G G AIN (dBi)
REMARQ UE
1
PIFA
UFL
3.08
2
PIFA
UFL
3.07
3
PIFA
UFL
4.06 (5150~5250 MHz) 3.79 (5725~5850 MHz)
4
PIFA
UFL
3.99 (5150~5250 MHz) 3.78 (5725~5850 MHz)
1
PIFA
I-PEX
3 (2400-2483.5 MHz)
2
PIFA
I-PEX
3 (2400-2483.5 MHz)
3
Monopole
I-PEX
4 (5150-5250 MHz) 4 (5725-5850 MHz)
4
Monopole
I-PEX
4 (5150-5250 MHz) 4 (5725-5850 MHz)
5
Monopole
I-PEX
4 (5150-5250 MHz) 4 (5725-5850 MHz)
1
Loop
I-PEX
5.82 (2400-2483.5 MHz)
2
Loop
I-PEX
5.02 (2400-2483.5 MHz)
3
PIFA
I-PEX
5 (5150-5250 MHz) 5 (5250-5350 MHz) 5 (5470-5725 MHz) 5 (5725-5850 MHz)
1
PIFA
U.FL
3.08 (2400-2483.5 MHz)
2
PIFA
U.FL
3.07 (2400-2483.5 MHz)
3
PIFA
U.FL
4.06 (5150-5250 MHz) 3.91 (5725-5850 MHz)
4
PIFA
U.FL
3.99 (5150-5250 MHz) 3.79 (5725-5850 MHz)
1
PIFA
I-PEX
3 (2400-2483.5 MHz)
2
PIFA
I-PEX
3 (2400-2483.5 MHz)
3
Monopole
I-PEX
4 (5150-5250 MHz) 4 (5725-5850 MHz)
4
Monopole
I-PEX
4 (5150-5250 MHz) 4 (5725-5850 MHz)
5
Monopole
I-PEX
4 (5150-5250 MHz) 4 (5725-5850 MHz)
Dipole
RSMA
5
7
Dipole
IPEX
4
6
Dipole
IPEX
4
6
Dipole
N type
4.5
7
1
PIFA
U.FL
3.28
2
PIFA
U.FL
3.37
3
PIFA
U.FL
3.15
Ceiling Mounted: Antenna 1, 2, 3
Wall Mounted: Antenna 1, 2, 4
4
Dipole
U.FL
4.33
5
Loop
U.FL
6
Loop
U.FL
4.38 (5150-5250 MHz) 4.23 (5725-5850 MHz)
4.31 (5150-5250 MHz) 4.22 (5725-5850 MHz)
Ceiling Mounted: Antenna 5, 6, 7
Wall Mounted: Antenna 5, 6, 8
7
Loop
U.FL
4.38 (5150-5250 MHz) 4.36 (5725-5850 MHz)
8
Dipole
U.FL
5.12 (5150-5250 MHz) 5.20 (5725-5850 MHz)
NWA/WAC/WAX Series User's Guide
309
Appendix D Legal Information
MO D�LE D'ANTENNE WAC5302D-S
WAC6303D-S WAC6552D-S SECTX-DB r2.0 WAX630S WAX650S WAX510D NWA110AX
NWA210AX WAX610D
WAC500H WAC500 NWA1123ACv3
NB.
TYPE
1
Loop
2
Loop
3
PIFA
1
Direction
2
Direction
1
Direction
PIFA
Direction
1
Dipole
2
PIFA
3
Dipole
4
Dipole
1
Dipole
2
PIFA
3
PIFA
4
Dipole
5
Dipole
6
Dipole
1
PIFA
2
PIFA
1
PIFA
2
PIFA
C O NNEC TEUR I-PEX I-PEX I-PEX
U.FL U.FL I-PEX U.FL
U.FL
I-PEX I-PEX I-PEX I-PEX I-PEX
I-PEX I-PEX
I-PEX
I-PEX
I-PEX
N/A N/A N/A N/A
2.4 G G AIN (dBi) 5.82 (2400-2483.5 MHz) 5.02 (2400-2483.5 MHz)
1.12 (2400-2483.5 MHz) 0.8 (2400-2483.5 MHz) 0.92 0 (2400-2483.5 MHz) 0 (2400-2483.5 MHz) 0 (2400-2483.5 MHz) 0 (2400-2483.5 MHz) 0 (2400-2483.5 MHz)
5.08dBi 5.56dBi
6.06dBi
0dBi 0dBi 0dBi 0dBi
5G G AIN (dBi)
5 (5150-5250 MHz) 5 (5250-5350 MHz) 5 (5470-5725 MHz) 5 (5725-5850 MHz)
1.29 (5150-5250 MHz) 1.07 (5725-5850 MHz)
4.22 (5150-5250 MHz) 5.34 (5725-5850 MHz)
1.32 (5150-5250 MHz) 1.39 (5250-5350 MHz) 0.44 (5470-5725 MHz) 1.63 (5725-5850 MHz)
3.51 (5150-5250 MHz) 4.22 (5250-5350 MHz) 4.61 (5470-5725 MHz) 4.68 (5725-5850 MHz)
4.5 (5150-5350MHz) 5.2 (5470-5725MHz) 5.5 (5725-5850MHz)
4.5 (5150-5350MHz) 5.2 (5470-5725MHz) 5.5 (5725-5850MHz)
4.5 (5150-5350MHz) 5.2 (5470-5725MHz) 5.5 (5725-5850MHz)
4.5 (5150-5350MHz) 5.2 (5470-5725MHz) 5.5 (5725-5850MHz)
U-NII-1:7.8dBi U-NII-2A:7.7dBi U-NII-2C:6.8dBi U-NII-3:7.2dBi
U-NII-1:7.5dBi U-NII-2A:6.8dBi U-NII-2C:6.5dBi U-NII-3:7.6dBi
U-NII-1:8.19dBi U-NII-2A:7.7dBi U-NII-2C:7.14dBi U-NII-3:7.6dBi
U-NII-1:6.8dBi U-NII-2A:7.5dBi U-NII-2C:5.81dBi U-NII-3:6.99dBi
U-NII-1:8.3dBi U-NII-2A:7.8dBi U-NII-2C:7.1dBi U-NII-3:7.98dBi
2.5dBi
2.5dBi
0dBi
0dBi
REMARQ UE
Wall Mount Ceiling Mount WAC500H WAC500 NWA1123ACv3
NWA/WAC/WAX Series User's Guide
310
Appendix D Legal Information
Lorsque la fonction sans fil 5G fonctionnant en 5150-5250 MHz and 5725-5850 MHz est activ�e pour ce produit, il est n�cessaire de porter une attention particuli�re aux choses suivantes � Les dispositifs fonctionnant dans la bande de 5 150 � 5 250 MHz sont r�serv�s uniquement pour une utilisation � l'int�rieur afin de r�duire les
risques de brouillage pr�judiciable aux syst�mes de satellites mobiles utilisant les m�mes canaux; � Pour les dispositifs munis d'antennes amovibles, le gain maximal d'antenne permis (pour les dispositifs utilisant la bande de 5 725 � 5 850 MHz)
doit �tre conforme � la limite de la p.i.r.e. sp�cifi�e pour l'exploitation point � point et l'exploitation non point � point, selon le cas; � Lorsqu'il y a lieu, les types d'antennes (s'il y en a plusieurs), les num�ros de mod�le de l'antenne et les pires angles d'inclinaison n�cessaires
pour rester conforme � l'exigence de la p.i.r.e. applicable au masque d'�l�vation, �nonc�e � la section 6.2.2.3 du CNR-247, doivent �tre clairement indiqu�s. Lorsque la fonction sans fil 5G fonctionnant en 5250-5350 MHz et 5470-5725 MHz est activ�e pour ce produit, il est n�cessaire de porter une attention particuli�re aux choses suivantes. � Pour les dispositifs munis d'antennes amovibles, le gain maximal d'antenne permis pour les dispositifs utilisant les bandes de 5 250 � 5 350 MHz et de 5 470 � 5 725 MHz doit �tre conforme � la limite de la p.i.r.e.
Industry C a na da ra dia tio n e xpo sure sta te m e nt
This equipment complies with ISED radiation exposure limits set forth for an uncontrolled environment. This equipment should be installed and operated with a minimum distance of 20 cm between the radiator and your body. This equipment complies with ISED radiation exposure limits set forth for an uncontrolled environment. This equipment should be installed and operated with a minimum distance of 22cm (NWA1123-AC HD, NWA5123-AC HD) between the radiator and your body. This equipment complies with ISED radiation exposure limits set forth for an uncontrolled environment. This equipment should be installed and operated with a minimum distance of 30 cm (WAC6553D-E) between the radiator and your body.
D� c la ra tio n d'e xpo sitio n a ux ra dia tio ns:
Cet �quipement est conforme aux limites d'exposition aux rayonnements ISED �tablies pour un environnement non contr�l�.Cet �quipement doit �tre install� et utilis� avec un minimum de 20 cm de distance entre la source de rayonnement et votre corps. Cet �quipement est conforme aux limites d'exposition aux rayonnements ISED �tablies pour un environnement non contr�l�.Cet �quipement doit �tre install� et utilis� avec un minimum de 22 cm (NWA1123-AC HD, NWA5123-AC HD) de distance entre la source de rayonnement et votre corps. Cet �quipement est conforme aux limites d'exposition aux rayonnements ISED �tablies pour un environnement non contr�l�.Cet �quipement doit �tre install� et utilis� avec un minimum de 30 cm (WAC6553D-E) de distance entre la source de rayonnement et votre corps.
C a utio n:
(i) the device for operation in the band 5150-5250 MHz is only for indoor use to reduce the potential for harmful interference to co-channel mobile satellite systems; (ii) the maximum antenna gain permitted for devices in the bands 5250-5350 MHz and 5470-5725 MHz shall comply with the e.i.r.p. limit; and (iii) the maximum antenna gain permitted for devices in the band 5725-5825 MHz shall comply with the e.i.r.p. limits specified for point-to-point and non point-to-point operation as appropriate. (iv) Users should also be advised that high-power radars are allocated as primary users (i.e. priority users) of the bands 5250-5350 MHz and 56505850 MHz and that these radars could cause interference and/or damage to LE-LAN devices. (v) WAC6553D-E is an outdoor device and only uses 5G Band 4 (5725-5850 MHz).
Ave rtisse m e nt:
(i) les dispositifs fonctionnant dans la bande 5150-5250 MHz sont r�serv�s uniquement pour une utilisation � l'int�rieur afin de r�duire les risques de brouillage pr�judiciable aux syst�mes de satellites mobiles utilisant les m�mes canaux; (ii) le gain maximal d'antenne permis pour les dispositifs utilisant les bandes 5250-5350 MHz et 5 470-5 725 MHz doit se conformer � la limite de p.i.r.e.; (iii) le gain maximal d'antenne permis (pour les dispositifs utilisant la bande 5725-5825 MHz) doit se conformer � la limite de p.i.r.e. sp�cifi�e pour l'exploitation point � point et non point � point, selon le cas. (iv) De plus, les utilisateurs devraient aussi �tre avis�s que les utilisateurs de radars de haute puissance sont d�sign�s utilisateurs principaux (c.-�d., qu'ils ont la priorit�) pour les bandes 5250-5350 MHz et 5650-5850 MHz et que ces radars pourraient causer du brouillage et/ou des dommages aux dispositifs LAN-EL. (v) WAC6553D-E est un appareil exterieur et seulement utilise 5G Bane 4 (5725-5850 MHz).
EURO PEAN UNIO N a nd UNITED KING DO M
The following information applies if you use the product within the European Union and United Kingdom.
De c la ra tio n o f C o nfo rm ity with Re g a rd to EU Dire c tive 2014/ 53/ EU (Ra dio Eq uipm e nt Dire c tive , RED) a nd UK re g ula tio n
� Compliance information for wireless products relevant to the EU, United Kingdom and other Countries following the EU Directive 2014/53/EU (RED) and UK regulation. And this product may be used in all EU countries (and other countries following the EU Directive 2014/53/EU) and United Kingdom without any limitation except for the countries mentioned below table:
NWA/WAC/WAX Series User's Guide
311
Appendix D Legal Information
� In the majority of the EU and other European countries, the 5GHz bands have been made available for the use of wireless local area networks (LANs). Later in this document you will find an overview of countries in which additional restrictions or requirements or both are applicable. The requirements for any country may evolve. Zyxel recommends that you check with the local authorities for the latest status of their national regulations for the 5GHz wireless LANs.
� If this device for operation in the band 5150-5350 MHz, it is for indoor use only. � This equipment should be installed and operated with a minimum distance of 20 cm between the radio equipment and your body. � The maximum RF power operating for each band as follows: NWA1123- AC v2 a nd NWA5123- AC
� The band 2,400 MHz to 2,483.5 MHz is 97.95 mW, � The band 5,150 MHz to 5,350 MHz is 199.07 mW, � The band 5,470 MHz to 5,725 MHz is 743.02 mW. WAC 6503D- S � The band 2,400 MHz to 2,483.5 MHz is 99.54 mW, � The band 5,150 MHz to 5,350 MHz is 183.65 mW, � The band 5,470 MHz to 5,725 MHz is 941.89 mW. WAC 6502D- E a nd WAC 6502D- S � The band 2,400 MHz to 2,483.5 MHz is 94.19 mW, � The band 5,150 MHz to 5,350 MHz is 194.98 mW, � The band 5,470 MHz to 5,725 MHz is 986.28 mW. WAC 6553D- E � The band 2,400 MHz to 2,483.5 MHz is 92.26 mW, � The band 5,150 MHz to 5,350 MHz is 198.61 mW, � The band 5,470 MHz to 5,725 MHz is 995.41 mW. NWA1123- AC PRO a nd WAC 6103D- I � The band 2,400 MHz to 2,483.5 MHz is 92.68 mW, � The band 5,150 MHz to 5,350 MHz is 192.75 mW, � The band 5,470 MHz to 5,725 MHz is 966.05 mW. NWA1302- AC , WAC 5301D- Sv2 a nd WAC 5302D- S � The band 2,400 MHz to 2,483.5 MHz is 93.33 mW, � The band 5,150 MHz to 5,350 MHz is 192.31 mW, � The band 5,470 MHz to 5,725 MHz is 391.74 mW. NWA1123- AC HD a nd NWA5123- AC HD � The band 2,400 MHz to 2,483.5 MHz is 97.274 mW, � The band 5,150 MHz to 5,350 MHz is 198.61 mW, � The band 5,470 MHz to 5,725 MHz is 995.40 mW. WAC 6303D- S � The band 2,400 MHz to 2,483.5 MHz is 194.09 mW, � The band 5,150 MHz to 5,350 MHz is 198.61 mW, � The band 5,470 MHz to 5,725 MHz is 995.41 mW. WAC 6552D- S � The band 2,400 MHz to 2,483.5 MHz is 93.11 mW, � The band 5,150 MHz to 5,350 MHz is 198.61 mW, � The band 5,470 MHz to 5,725 MHz is 914.11 mW. WAC500H � The band 2,400 MHz to 2,483.5 MHz is 87.7 mW, � The band 5,150 MHz to 5,350 MHz is 174.58 mW, � The band 5,470 MHz to 5,725 MHz is 443.61 mW. WAC 500 a nd NWA1123AC v3 � The band 2,400 MHz to 2,483.5 MHz is 88.5 mW, � The band 5,150 MHz to 5,350 MHz is 181.55 mW, � The band 5,470 MHz to 5,725 MHz is 195.43 mW. WAX630S � The band 2400 MHz to 2483.5 MHz is 19.56 mW, � The band 5150 MHz to 5350 MHz is 175.39 mW, � The band 5470 MHz to 5725 MHz is 826.04 mW. WAX650S � The band 2,400 MHz to 2,483.5 MHz is 91.2 mW, � The band 5,150 MHz to 5,350 MHz is 177.01 mW, � The band 5,470 MHz to 5,725 MHz is 899.5 mW. WAX510D a nd NWA110AX � The band 2,400 MHz to 2,483.5 MHz is 85.31 mW, � The band 5,150 MHz to 5,350 MHz is 172.19 mW, � The band 5,470 MHz to 5,725 MHz is 651.63 mW. WAX610D a nd NWA210AX � The band 2,400 MHz to 2,483.5 MHz is 92.47 mW. � The band 5,150 MHz to 5,350 MHz is 177.01 mW.
NWA/WAC/WAX Series User's Guide
312
Appendix D Legal Information
� The band 5,470 MHz to 5,725 MHz is 889.2 mW.
(Bulgarian)
Zyxel , 2014/53/C.
Na tio na l Re stric tio ns
� The Belgian Institute for Postal Services and Telecommunications (BIPT) must be notified of any outdoor wireless link having a range exceeding 300 meters. Please check http://www.bipt.be for more details.
� Draadloze verbindingen voor buitengebruik en met een reikwijdte van meer dan 300 meter dienen aangemeld te worden bij het Belgisch Instituut voor postdiensten en telecommunicatie (BIPT). Zie http://www.bipt.be voor meer gegevens.
� Les liaisons sans fil pour une utilisation en ext�rieur d'une distance sup�rieure � 300 m�tres doivent �tre notifi�es � l'Institut Belge des services Postaux et des T�l�communications (IBPT). Visitez http://www.ibpt.be pour de plus amples d�tails.
Espa�ol (Spanish)
Por medio de la presente Zyxel declara que el equipo cumple con los requisitos esenciales y cualesquiera otras disposiciones aplicables o exigibles de la Directiva 2014/53/UE.
Cestina (Czech)
Zyxel t�mto prohlasuje, ze tento za�zen� je ve shod se z�kladn�mi pozadavky a dals�mi p�slusn�mi ustanoven�mi smrnice 2014/53/EU.
Dansk (Danish)
Undertegnede Zyxel erkl�rer herved, at f�lgende udstyr udstyr overholder de v�sentlige krav og �vrige relevante krav i direktiv 2014/53/EU.
Na tio na l Re stric tio ns
� In Denmark, the band 5150 - 5350 MHz is also allowed for outdoor usage. � I Danmark m� frekvensb�ndet 5150 - 5350 ogs� anvendes udend�rs.
Deutsch (German)
Hiermit erkl�rt Zyxel, dass sich das Ger�t Ausstattung in �bereinstimmung mit den grundlegenden Anforderungen und den �brigen einschl�gigen Bestimmungen der Richtlinie 2014/53/EU befindet.
Eesti keel (Estonian)
K�esolevaga kinnitab Zyxel seadme seadmed vastavust direktiivi 2014/53/EU p�hin�uetele ja nimetatud direktiivist tulenevatele teistele asjakohastele s�tetele.
(Greek)
Zyxel 2014/53/EU.
English
Hereby, Zyxel declares that this device is in compliance with the essential requirements and other relevant provisions of Directive 2014/53/EU.
Fran�ais (French)
Par la pr�sente Zyxel d�clare que l'appareil �quipements est conforme aux exigences essentielles et aux autres dispositions pertinentes de la directive 2014/53/EU.
Hrvatski (Croatian)
Zyxel ovime izjavljuje da je radijska oprema tipa u skladu s Direktivom 2014/53/EU.
�slenska (Icelandic)
H�r me� l�sir, Zyxel �v� yfir a� �essi b�na�ur er � samr�mi vi� grunnkr�fur og �nnur vi�eigandi �kv��i tilskipunar 2014/53/ EU.
Italiano (Italian)
Con la presente Zyxel dichiara che questo attrezzatura � conforme ai requisiti essenziali ed alle altre disposizioni pertinenti stabilite dalla direttiva 2014/53/EU.
Na tio na l Re stric tio ns
� This product meets the National Radio Interface and the requirements specified in the National Frequency Allocation Table for Italy. Unless this wireless LAN product is operating within the boundaries of the owner's property, its use requires a "general authorization." Please check http://www.sviluppoeconomico.gov.it/ for more details.
� Questo prodotto � conforme alla specifiche di Interfaccia Radio Nazionali e rispetta il Piano Nazionale di ripartizione delle frequenze in Italia. Se non viene installato all 'interno del proprio fondo, l'utilizzo di prodotti Wireless LAN richiede una "Autorizzazione Generale". Consultare http://www.sviluppoeconomico.gov.it/ per maggiori dettagli.
Latviesu valoda Ar so Zyxel deklar, ka iekrtas atbilst Direktvas 2014/53/EU btiskajm prasbm un citiem ar to saisttajiem noteikumiem.
(Latvian)
Na tio na l Re stric tio ns
� The outdoor usage of the 2.4 GHz band requires an authorization from the Electronic Communications Office. Please check http://www.esd.lv for more details.
� 2.4 GHz frekven�u joslas izmanto�anai �rpus telp�m nepiecie�ama at�auja no Elektronisko sakaru direkcijas. Vair�k inform�cijas: http://www.esd.lv.
Lietuvi kalba (Lithuanian)
Siuo Zyxel deklaruoja, kad sis ranga atitinka esminius reikalavimus ir kitas 2014/53/EU Direktyvos nuostatas.
Magyar (Hungarian)
Alul�rott, Zyxel nyilatkozom, hogy a berendez�s megfelel a vonatkoz� alapvet� k�vetelm�nyeknek �s az 2014/53/EU ir�nyelv egy�b el��r�sainak.
Malti (Maltese) Hawnhekk, Zyxel, jiddikjara li dan tagmir jikkonforma mal-tiijiet essenzjali u ma provvedimenti orajn relevanti li hemm fid-Dirrettiva 2014/53/EU.
Nederlands (Dutch)
Hierbij verklaart Zyxel dat het toestel uitrusting in overeenstemming is met de essenti�le eisen en de andere relevante bepalingen van richtlijn 2014/53/EU.
Polski (Polish)
Niniejszym Zyxel owiadcza, e sprzt jest zgodny z zasadniczymi wymogami oraz pozostalymi stosownymi postanowieniami Dyrektywy 2014/53/EU.
Portugu�s (Portuguese)
Zyxel declara que este equipamento est� conforme com os requisitos essenciais e outras disposi�es da Directiva 2014/53/ EU.
NWA/WAC/WAX Series User's Guide
313
Appendix D Legal Information
Rom�n (Romanian)
Slovencina (Slovak)
Slovenscina (Slovene)
Suomi (Finnish)
Svenska (Swedish)
Norsk (Norwegian)
Prin prezenta, Zyxel declar c acest echipament este �n conformitate cu cerinele eseniale i alte prevederi relevante ale Directivei 2014/53/EU. Zyxel t�mto vyhlasuje, ze zariadenia spa z�kladn� poziadavky a vsetky pr�slusn� ustanovenia Smernice 2014/53/EU.
Zyxel izjavlja, da je ta oprema v skladu z bistvenimi zahtevami in ostalimi relevantnimi dolocili direktive 2014/53/EU.
Zyxel vakuuttaa t�ten ett� laitteet tyyppinen laite on direktiivin 2014/53/EU oleellisten vaatimusten ja sit� koskevien direktiivin muiden ehtojen mukainen. H�rmed intygar Zyxel att denna utrustning st�r I �verensst�mmelse med de v�sentliga egenskapskrav och �vriga relevanta best�mmelser som framg�r av direktiv 2014/53/EU. Erkl�rer herved Zyxel at dette utstyret er I samsvar med de grunnleggende kravene og andre relevante bestemmelser I direktiv 2014/53/EU.
No te s: 1. Although Norway, Switzerland and Liechtenstein are not EU member states, the EU Directive 2014/53/EU has also been implemented in those countries. 2. The regulatory limits for maximum output power are specified in EIRP. The EIRP level (in dBm) of a device can be calculated by adding the gain of the antenna used (specified in dBi) to the output power available at the connector (specified in dBm).
List o f na tio na l c o de s
COUNTRY Austria Belgium Bulgaria Croatia Cyprus Czech Republic Denmark Estonia Finland France Germany Greece Hungary Iceland Ireland Italy Latvia
ISO 3166 2 LETTER CODE AT BE BG HR CY CR DK EE FI FR DE GR HU IS IE IT LV
COUNTRY Liechtenstein Lithuania Luxembourg Malta Netherlands Norway Poland Portugal Romania Serbia Slovakia Slovenia Spain Sweden Switzerland Turkey United Kingdom
ISO 3166 2 LETTER CODE LI LT LU MT NL NO PL PT RO RS SK SI ES SE CH TR GB
Pro fe ssio na l insta lla tio n instruc tio n (WAC 6553D- E)
Please be advised that due to the unique function supplied by this product, the device is intended for use with our interactive entertainment software and licensed third-party only. The product will be distributed through controlled distribution channel and installed by trained professional and will not be sold directly to the general public through retail store.
1 Installation personal This product is designed for specific application and needs to be installed by a qualified personal who has RF and related rule knowledge. The general user shall not attempt to install or change the setting.
2 Installation location The product shall be installed at a location where the radiating antenna can be kept 30 cm from nearby person in normal operation condition to meet regulatory RF exposure requirement.
3 External antenna Use only the antennas which have been approved by Zyxel Communications Corporation. The non-approved antenna(s) may produce unwanted spurious or excessive RF transmitting power which may lead to the violation of FCC/IC limit and is prohibited.
4 Installation procedure Please refer to user's manual for the detail.
5 Warning Please carefully select the installation position and make sure that the final output power does not exceed the limit set force in relevant rules. The violation of the rule could lead to serious federal penalty.
NWA/WAC/WAX Series User's Guide
314
Appendix D Legal Information
Instruc tio ns d'insta lla tio n pro fe ssio nne lle (WAC 6553D- E)
Veuillez noter que l'appareil etant dedie a une fonction unique, il doit etre utilise avec notre logiciel proprietaire de divertissement interactif . Ce produit sera propose par un reseau de distribution controle et installe par des professionels; il ne sera pas propose au grand public par le reseau de la grande distribution. 1 Installation Ce produit est destine a un usage specifique et doit etre installe par un personnel qualifie maitrisant les radiofrequences et les regles s'y rapportant. L'installation et les reglages ne doivent pas etre modifies par l'utilisateur final. 2 Emplacement d'installation En usage normal, afin de respecter les exigences reglementaires concernant l'exposition aux radiofrequences, ce produit doit etre installe de facon a respecter une distance de 30 cm entre l'antenne emettrice et les personnes. 3 Antenn externe. Utiliser uniiquement les antennes approuvees par le fabricant. L'utilisation d'autres antennes peut conduire a un niveau de rayonnement essentiel ou non essentiel depassant les niveaux limites definis par FCC/IC, ce qui est interdit. 4 Procedure d'installation Consulter le manuel d'utilisation. 5 Avertissement Choisir avec soin la position d'installation et s'assurer que la puissance de sortie ne depasse pas les limites en vigueur. La violation de cette regle peut conduire a de serieuses penalites federales.
Sa fe ty Wa rning s
� Do not use this product near water, for example, in a wet basement or near a swimming pool. � Do not expose your device to dampness, dust or corrosive liquids. � Do not store things on the device. � Do not obstruct the device ventilation slots as insufficient airflow may harm your device. For example, do not place the device in an
enclosed space such as a box or on a very soft surface such as a bed or sofa. � Do not install, use, or service this device during a thunderstorm. There is a remote risk of electric shock from lightning. � Connect ONLY suitable accessories to the device. � Do not open the Zyxel Device. Opening or removing covers can expose you to dangerous high voltage points or other risks. ONLY qualified
service personnel should service or disassemble this device. Please contact your vendor for further information. � Make sure to connect the cables to the correct ports. � Place connecting cables carefully so that no one will step on them or stumble over them. � Always disconnect all cables from this device before servicing or disassembling. � Do not remove the plug and connect it to a power outlet by itself; always attach the plug to the power adaptor first before connecting it to
a power outlet. � Do not allow anything to rest on the power adaptor or cord and do NOT place the product where anyone can walk on the power adaptor
or cord. � Please use the provided or designated connection cables/power cables/adaptors. Connect it to the right supply voltage (for example, 110V
AC in North America or 230V AC in Europe). If the power adaptor or cord is damaged, it might cause electrocution. Remove it from the device and the power source, repairing the power adapter or cord is prohibited. Contact your local vendor to order a new one. � Do not use the device outside, and make sure all the connections are indoors. There is a remote risk of electric shock from lightning. � CAUTION: Risk of explosion if battery is replaced by an incorrect type, dispose of used batteries according to the instruction. Dispose them at the applicable collection point for the recycling of electrical and electronic devices. For detailed information about recycling of this product, please contact your local city office, your household waste disposal service or the store where you purchased the product. � This device (WAC6553D-E, WAC6552D-S) must be grounded by qualified service personnel. Never defeat the ground conductor or operate the device in the absence of a suitably installed ground conductor. Contact the qualified service personnel if you are uncertain that suitable grounding is available. � The following warning statements apply, where the disconnect device is not incorporated in the device or where the plug on the power supply cord is intended to serve as the disconnect device, � For permanently connected devices, a readily accessible disconnect device shall be incorporated external to the device; � For pluggable devices, the socket-outlet shall be installed near the device and shall be easily accessible. � Do not use a power adapter that has a power cable longer than 3 meters.
Enviro nm e nt sta te m e nt
ErP (Ene rg y- re la te d Pro duc ts) (NWA1123AC v3, WAC 500, WAC 500H, WAC 5302D- Sv2, NWA1123- AC v2, NWA1123- AC HD, NWA5123- AC , NWA5123- AC HD, WAC 6502D- E, WAC 6502D- S, WAC 6503D- S, WAX510D, NWA110AX, WAX610D, NWA210AX, a nd WAX630S)
Zyxel products put on the EU and United Kingdom market in compliance with the requirement of the European Parliament and the Council published Directive 2009/125/EC and UK regulation establishing a framework for the setting of ecodesign requirements for energy-related products (recast), so called as "ErP Directive (Energy-related Products directive) as well as ecodesign requirement laid down in applicable implementing measures, power consumption has satisfied regulation requirements which are: Network standby power consumption < 8W, and/or Off mode power consumption < 0.5W, and/or Standby mode power consumption < 0.5W. For wireless setting, please refer to the chapter about wireless settings for more detail.
Dispo sa l a nd Re c yc ling Info rm a tio n
The symbol below means that according to local regulations your product and/or its battery shall be disposed of separately from domestic waste. If this product is end of life, take it to a recycling station designated by local authorities. At the time of disposal, the separate collection of your product and/or its battery will help save natural resources and ensure that the environment is sustainable development.
NWA/WAC/WAX Series User's Guide
315
Appendix D Legal Information
Die folgende Symbol bedeutet, dass Ihr Produkt und/oder seine Batterie gem�� den �rtlichen Bestimmungen getrennt vom Hausm�ll entsorgt werden muss. Wenden Sie sich an eine Recyclingstation, wenn dieses Produkt das Ende seiner Lebensdauer erreicht hat. Zum Zeitpunkt der Entsorgung wird die getrennte Sammlung von Produkt und/oder seiner Batterie dazu beitragen, nat�rliche Ressourcen zu sparen und die Umwelt und die menschliche Gesundheit zu sch�tzen.
El s�mbolo de abajo indica que seg�n las regulaciones locales, su producto y/o su bater�a deber�n depositarse como basura separada de la dom�stica. Cuando este producto alcance el final de su vida �til, ll�velo a un punto limpio. Cuando llegue el momento de desechar el producto, la recogida por separado �ste y/o su bater�a ayudar� a salvar los recursos naturales y a proteger la salud humana y medioambiental.
Le symbole ci-dessous signifie que selon les r�glementations locales votre produit et/ou sa batterie doivent �tre �limin�s s�par�ment des ordures m�nag�res. Lorsque ce produit atteint sa fin de vie, amenez-le � un centre de recyclage. Au moment de la mise au rebut, la collecte s�par�e de votre produit et/ou de sa batterie aidera � �conomiser les ressources naturelles et prot�ger l'environnement et la sant� humaine.
Il simbolo sotto significa che secondo i regolamenti locali il vostro prodotto e/o batteria deve essere smaltito separatamente dai rifiuti domestici. Quando questo prodotto raggiunge la fine della vita di servizio portarlo a una stazione di riciclaggio. Al momento dello smaltimento, la raccolta separata del vostro prodotto e/o della sua batteria aiuta a risparmiare risorse naturali e a proteggere l'ambiente e la salute umana.
Symbolen inneb�r att enligt lokal lagstiftning ska produkten och/eller dess batteri kastas separat fr�n hush�llsavfallet. N�r den h�r produkten n�r slutet av sin livsl�ngd ska du ta den till en �tervinningsstation. Vid tiden f�r kasseringen bidrar du till en b�ttre milj� och m�nsklig h�lsa genom att g�ra dig av med den p� ett �tervinningsst�lle.
� �
� �
- :
� � - � - � � � � � � � � � ( : / 110V AC 230V AC) � �
NWA/WAC/WAX Series User's Guide
316
Appendix D Legal Information
� � � � � :
Ab o ut the Sym b o ls
Various symbols are used in this product to ensure correct usage, to prevent danger to the user and others, and to prevent property damage. The meaning of these symbols are described below. It is important that you read these descriptions thoroughly and fully understand the contents.
Expla na tio n o f the Sym b o ls
SYMBOL
EXPLANATION Alternating current (AC): AC is an electric current in which the flow of electric charge periodically reverses direction.
Direct current (DC): DC if the unidirectional flow or movement of electric charge carriers.
Earth; ground: A wiring terminal intended for connection of a Protective Earthing Conductor.
Class II equipment:
The method of protection against electric shock in the case of class II equipment is either double insulation or reinforced insulation.
Vie wing C e rtific a tio ns
Go to http://www.zyxel.com to view this product's documentation and certifications.
Zyxe l Lim ite d Wa rra nty
Zyxel warrants to the original end user (purchaser) that this product is free from any defects in material or workmanship for a specific period (the Warranty Period) from the date of purchase. The Warranty Period varies by region. Check with your vendor and/or the authorized Zyxel local distributor for details about the Warranty Period of this product. During the warranty period, and upon proof of purchase, should the product have indications of failure due to faulty workmanship and/or materials, Zyxel will, at its discretion, repair or replace the defective products or components without charge for either parts or labor, and to whatever extent it shall deem necessary to restore the product or components to proper operating condition. Any replacement will consist of a new or re-manufactured functionally equivalent product of equal or higher value, and will be solely at the discretion of Zyxel. This warranty shall not apply if the product has been modified, misused, tampered with, damaged by an act of God, or subjected to abnormal working conditions.
No te
Repair or replacement, as provided under this warranty, is the exclusive remedy of the purchaser. This warranty is in lieu of all other warranties, express or implied, including any implied warranty of merchantability or fitness for a particular use or purpose. Zyxel shall in no event be held liable for indirect or consequential damages of any kind to the purchaser. To obtain the services of this warranty, contact your vendor. You may also refer to the warranty policy for the region in which you bought the device at http://www.zyxel.com/web/support_warranty_info.php.
Re g istra tio n
Register your product online at www.zyxel.com to receive e-mail notices of firmware upgrades and related information.
O pe n So urc e Lic e nse s
This product contains in part some free software distributed under GPL license terms and/or GPL like licenses. To request the source code covered under these licenses, please go to: https://www.zyxel.com/form/gpl_oss_software_notice.shtml
NWA/WAC/WAX Series User's Guide
317
Index
Inde x
Symbols
Numbers
802.11k 21, 23, 24, 25 802.11r 21, 23, 24, 25 802.11v 21, 23, 24, 25
A
BLE, see Bluetooth Low Energy
BLE. See Bluetooth Low Energy
advertisements 127 advertising settings 128 BLE 126 Bluetooth Low Energy 21, 23, 24, 25, 126 Bluetooth Smart 126 iBeacon 126 iBeacon ID 126 major 126 minor 126 UUID 126 UUID format 128
boot module 232
BSS 18
AC. See AP Controller access 56 access privileges 18 access users 129
see also users 129 admin users 129
multiple logins 134 see also users 129 alerts 215, 219, 220, 222, 223, 224 antenna switch 241 AP Controller 21, 22, 24, 25, 29 applications MBSSID 18 Repeater 16 Assisted Roaming, see 802.11k/v Assisted Roaming. See 802.11k/v
B
backing up configuration files 227 Basic Service Set
see BSS Bluetooth
C
CA and certificates 175
CA (Certificate Authority), see certificates
CAPWAP 97 CEF (Common Event Format) 217, 222 Certificate Authority (CA)
see certificates
Certificate Management Protocol (CMP) 180 Certificate Revocation List (CRL) 175
vs OCSP 189 certificates 174
advantages of 175 and CA 175 and FTP 208 and HTTPS 196 and SSH 205 and WWW 197 certification path 175, 182, 187 expired 175 factory-default 175 file formats 175 fingerprints 183, 188 importing 178
NWA/WAC/WAX Series User's Guide
318
Index
not used for encryption 175 revoked 175 self-signed 175, 179 serial number 182, 187 storage space 177, 185 thumbprint algorithms 176 thumbprints 176 used for authentication 175 verifying fingerprints 176
certification requests 179, 180
certifications viewing 317
channel 19
CLI 36, 61 button 61 messages 61 popup window 61 Reference Guide 2
cold start 68
commands 36 sent by Web Configurator 61
Common Event Format (CEF) 217, 222
comparison table 20, 22, 23
configuration information 236, 253
configuration files 225 at restart 227 backing up 227 downloading 228 downloading with FTP 208 editing 225 how applied 226 lastgood.conf 227, 229 managing 226 startup-config.conf 229 startup-config-bad.conf 227 syntax 225 system-default.conf 229 uploading 230 uploading with FTP 208 use without restart 225
contact information 299
cookies 56
copyright 304
CPU usage 71, 74
current date/time 71, 192 daylight savings 193
setting manually 194 time server 195 customer support 299
D
date 192 daylight savings 193 DCS 110 DHCP 191
and domain name 191 diagnostics 236, 253 disclaimer 304 domain name 191 dual radios 19 dual-radio application 19 dynamic channel selection 110
E
e-mail daily statistics report 213
encryption 16 ESSID 264 Extended Service Set IDentification 136
F
Fast Roaming, see 802.11r Fast Roaming. See 802.11r FCC interference statement 304 file extensions
configuration files 225 shell scripts 225 file manager 225 Firefox 56 firmware and restart 231 boot module, see boot module current version 71, 232 getting updated 231
NWA/WAC/WAX Series User's Guide
319
Index
uploading 231, 232 uploading with FTP 208 flash usage 71 FTP 36, 208 and certificates 208 with Transport Layer Security (TLS) 208
G
EUI-64 293 global address 291 interface ID 293 link-local address 291 Neighbor Discovery Protocol 291 ping 291 prefix 291 prefix length 291 stateless autoconfiguration 293 unspecified address 292
Guide
CLI Reference 2
J
H
HTTP over SSL, see HTTPS redirect to HTTPS 197 vs HTTPS 196
HTTPS 196 and certificates 196 authenticating clients 196 avoiding warning messages 199 example 197 vs HTTP 196 with Internet Explorer 198 with Netscape Navigator 198
HyperText Transfer Protocol over Secure Socket Layer, see HTTPS
I
interface status 73
interfaces as DHCP servers 191
interference 19 Internet Explorer 56 Internet Protocol version 6, see IPv6 IP Address 97, 249
gateway IP address 97 IP subnet 97 IPv6 291
addressing 291
Java permissions 56
JavaScripts 56
K
key pairs 174
L
lastgood.conf 227, 229 layer-2 isolation 166
example 166 MAC 167 LED suppression 238 LEDs 38 Blinking 46, 48, 50, 52, 54 load balancing 110 Locator LED 239 log messages categories 220, 222, 223, 224 debugging 94 regular 94 types of 94 logout Web Configurator 60 logs e-mail profiles 215 e-mailing log messages 96, 219 formats 217
NWA/WAC/WAX Series User's Guide
320
Index
log consolidation 220 settings 215 syslog servers 215 system 215 types of 215
overview 13, 68, 246
P
M
MAC address range 70
Management Information Base (MIB) 209, 210 Management Mode
CAPWAP and DHCP 98 management mode 27 Management, NCC 28 Management, Standalone 27 managing the device
good habits 36 using FTP, see FTP MBSSID 18 memory usage 71, 75 messages CLI 61 mode, default 27 model name 70 My Certificates, see also certificates 177
N
NCC, see Nebula Control Center Nebula Control Center 28 Netscape Navigator 56 Network Time Protocol (NTP) 194
O
objects certificates 174 users, account user 129
Online Certificate Status Protocol (OCSP) 189 vs CRL 189
pop-up windows 56 power off 69 power on 68 product registration 317 Public-Key Infrastructure (PKI) 175 public-private key pairs 174
R
radio 19 Radio Frequency monitor 14 reboot 68, 243
vs reset 243 Reference Guide, CLI 2 registration
product 317 remote management
FTP, see FTP Telnet 207 WWW, see WWW reports daily 213 daily e-mail 213 reset 266 vs reboot 243 vs shutdown 244 RESET button 69, 266 restart 243 RF interference 19 RF monitor, see Radio Frequency Monitor RFC 2510 (Certificate Management Protocol or
CMP) 180 Rivest, Shamir and Adleman public-key algorithm
(RSA) 179 RSA 179, 187, 188 RSSI threshold 143
NWA/WAC/WAX Series User's Guide
321
Index
S
SCEP (Simple Certificate Enrollment Protocol) 180
screen resolution 56
Secure Socket Layer, see SSL
serial number 70
service control and users 195 limitations 195 timeouts 195
Service Set 136
Service Set Identifier see SSID
shell scripts 225 downloading 234, 253 editing 233, 252 how applied 226 managing 233, 252 syntax 225 uploading 235, 253
shutdown 69, 244 vs reset 244
Simple Certificate Enrollment Protocol (SCEP) 180
Simple Network Management Protocol, see SNMP
SNMP 209 agents 209 Get 209 GetNext 209 Manager 209 managers 209 MIB 209, 210 network components 209 Set 209 Trap 210 traps 210 versions 209
SSH 203 and certificates 205 client requirements 205 encryption methods 205 for secure Telnet 206 how connection is established 204 versions 205 with Linux 206 with Microsoft Windows 206
SSID 18
SSID profile
pre-configured 18 SSID profiles 18 SSL 196 starting the device 68 startup-config.conf 229
if errors 227 missing at restart 227 present at restart 227 startup-config-bad.conf 227 station 110 statistics daily e-mail report 213 status 247 stopping the device 68 supported browsers 56 syslog 217, 222 syslog servers, see also logs system log, see logs system name 70, 191 system uptime 71 system-default.conf 229
T
Telnet 207 with SSH 206
time 192 time servers (default) 194 trademarks 304 Transport Layer Security (TLS) 208 troubleshooting 236, 253 Trusted Certificates, see also certificates 184
U
upgrading firmware 231
uploading configuration files 230 firmware 231 shell scripts 233, 252
usage
NWA/WAC/WAX Series User's Guide
322
CPU 71, 74 flash 71 memory 71, 75 onboard flash 71 user authentication 129 user name rules 130 user objects 129 users 129 access, see also access users admin (type) 129 admin, see also admin users and service control 195 currently logged in 71 default lease time 133, 135 default reauthentication time 134, 135 lease time 132 limited-admin (type) 129 lockout 134 reauthentication time 132 types of 129 user (type) 129 user names 130
V
Vantage Report (VRPT) 217, 222 Virtual Local Area Network 102 VLAN 102
introduction 102 VRPT (Vantage Report) 217, 222
Index
wireless client 110 Wireless Distribution System (WDS) 16 wireless LAN 264 wireless network
example 109 overview 109 wireless profile 136 layer-2 isolation 136 MAC filtering 136 radio 136 security 136 SSID 136 wireless security 18, 264 wireless station 110 Wizard Setup 76 WLAN interface 19 WPA2 137 WWW 196 and certificates 197 see also HTTP, HTTPS 196
Z
ZDP 31 ZON Utility 31
W
warm start 68 warranty 317
note 317 WDS 16 Web Configurator 35, 56
access 56 requirements 56 supported browsers 56 WEP (Wired Equivalent Privacy) 137 wireless channel 264
NWA/WAC/WAX Series User's Guide
323