D Link IR636LA1 Wireless N600 Dual Band Gigabit Cloud Router / Cloud Router 2000 User Manual 2
D Link Corporation Wireless N600 Dual Band Gigabit Cloud Router / Cloud Router 2000 2
D Link >
Contents
- 1. User Manual
- 2. User Manual 1
- 3. User Manual 2
User Manual 2
83D-Link DIR-826L User Manual
Section 3 - Conguration
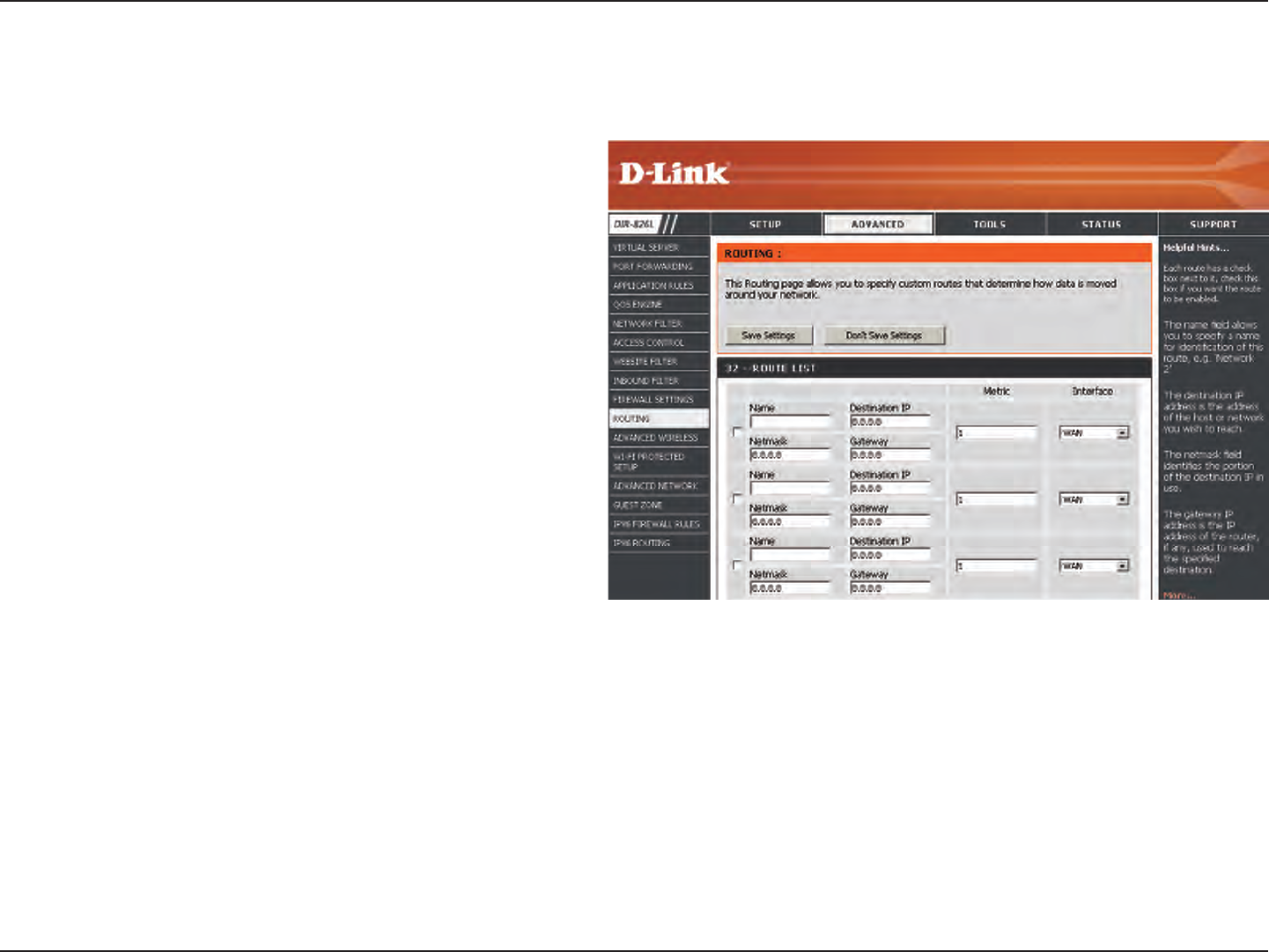
Enter a name for your route.
Enter the IP address of packets that will take this
route.
Enter the netmask of the route, please note
that the octets must match your destination IP
address.
Enter your next hop gateway to be taken if this
route is used.
The route metric is a value from 1 to 16 that
indicates the cost of using this route. A value 1 is
the lowest cost and 15 is the highest cost.
Select the interface that the IP packet must use to
transit out of the router when this route is used.
Name:
Destination IP:
Netmask:
Gateway:
Metric:
Interface:
Routing
The Routing option is an advanced method of customizing specic routes of data through your network.
84D-Link DIR-826L User Manual
Section 3 - Conguration
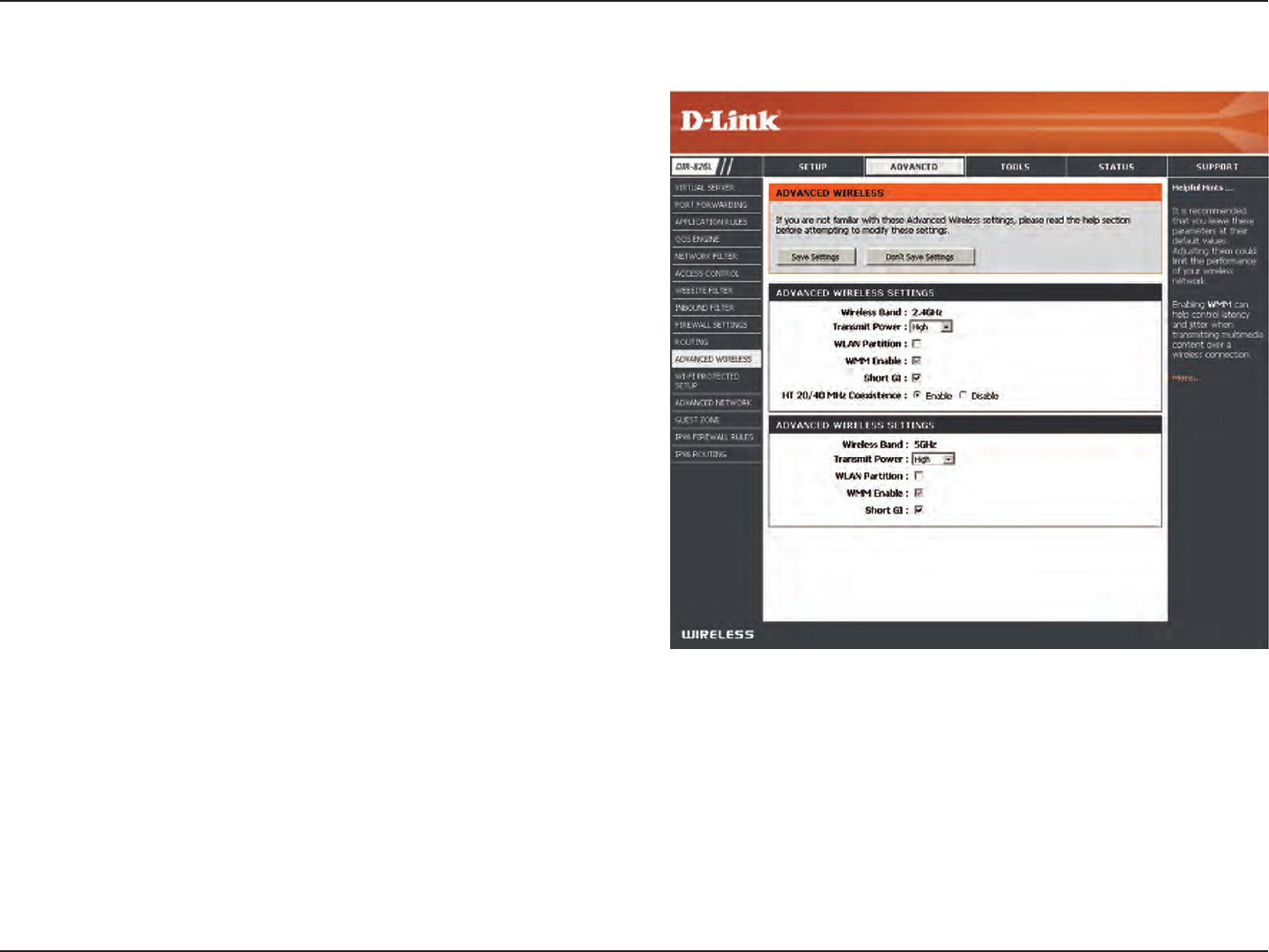
Advanced Wireless
Set the transmit power of the antennas.
This enables 802.11d operation. 802.11d is a wireless
specication developed to allow implementation of
wireless networks in countries that cannot use the
802.11 standard. This feature should only be enabled
if you are in a country that requires it.
WMM is QoS for your wireless network. This will improve
the quality of video and voice applications for your
wireless clients.
Check this box to reduce the guard interval time
therefore increasing the data capacity. However, it’s less
reliable and may create higher data loss.
Enable this option to reduce interference from
other wireless networks in your area. If the channel
width is operating at 40MHz and there is another
wireless network’s channel over-lapping and causing
interference, the router will automatically change to
20MHz.
Transmit Power:
WLAN Partition:
WMM Enable:
Short GI:
HT20/40 Coexistence:
85D-Link DIR-826L User Manual
Section 3 - Conguration
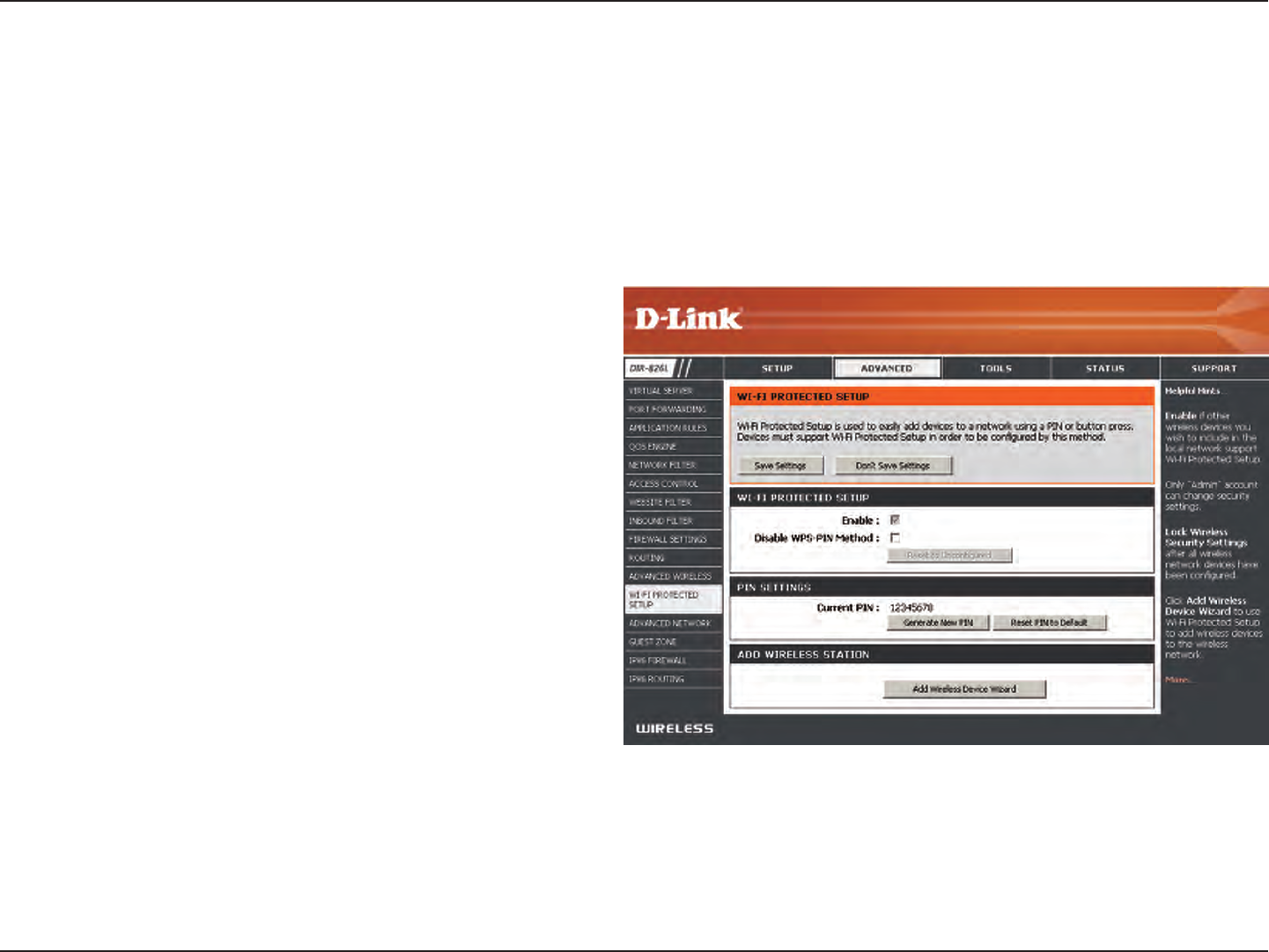
Wi-Fi Protected Setup (WPS)
Enable the Wi-Fi Protected Setup feature.
Note: if this option is unchecked, the WPS button on the
side of the router will be disabled.
Check to disable the WPS PIN method of securing your
network. This will not aect the Push-Button method.
A PIN is a unique number that can be used to add
the router to an existing network or to create a new
network. Only the Administrator (“admin” account) can
change or reset the PIN.
Shows the current PIN.
Restore the default PIN of the router.
Create a random number that is a valid PIN. This
becomes the router’s PIN. You can then copy this PIN to
the user interface of the wireless client.
Enable:
Disable WPS-PIN
Method:
PIN Settings:
Current PIN:
Reset PIN to
Default:
Generate New
PIN:
Wi-Fi Protected Setup (WPS) System is a simplied method for securing your wireless network during the “Initial setup” as well
as the “Add New Device” processes. The Wi-Fi Alliance (WFA) has certied it across dierent products as well as manufactures.
The process is just as easy as pressing a button for the Push-Button Method or correctly entering the 8-digit code for the Pin
Code Method. The time reduction in setup and ease of use are quite benecial, while the highest wireless Security setting of
WPA2 is automatically used.
86D-Link DIR-826L User Manual
Section 3 - Conguration
This Wizard helps you add wireless devices to the wireless network.
The wizard will either display the wireless network settings to guide you through manual conguration, prompt you to enter the
PIN for the device, or ask you to press the conguration button on the device. If the device supports Wi-Fi Protected Setup and has a
conguration button, you can add it to the network by pressing the conguration button on the device and then the on the router
within 60 seconds. The status LED on the router will ash three times if the device has been successfully added to the network.
There are several ways to add a wireless device to your network. A “registrar” controls access to the wireless network. A registrar
only allows devices onto the wireless network if you have entered the PIN, or pressed a special Wi-Fi Protected Setup button on the
device. The router acts as a registrar for the network, although other devices may act as a registrar as well.
Click to start the wizard and skip to page 44.
Add Wireless
Station:
Add Wireless
Device Wizard:
You can also simply press the WPS button on the side of the router, and then press the WPS
button on your wireless client to automatically connect without logging into the router.
Refer to page 109 for more information.
WPS Button
WPS Button
87D-Link DIR-826L User Manual
Section 3 - Conguration
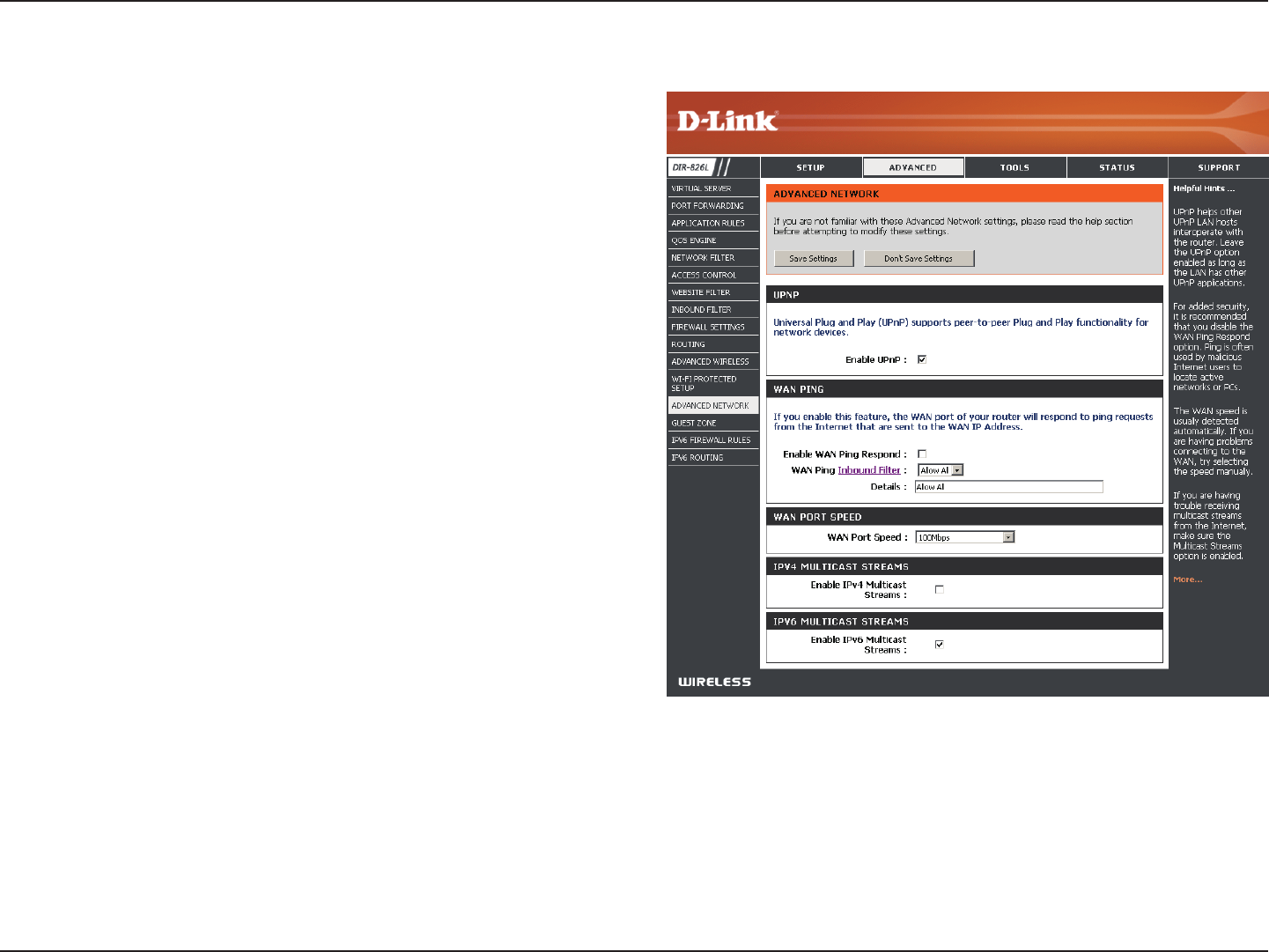
To use the Universal Plug and Play (UPnP™) feature click on
Enabled. UPnP provides compatibility with networking
equipment, software and peripherals.
Checking the box will allow the DIR-826L to respond
to pings. Unchecking the box may provide some extra
security from hackers.
Select from the drop-down menu if you would like to apply
the Inbound Filter to the WAN ping. Refer to the Inbound
Filters section for more information.
You may set the port speed of the Internet port to 10Mbps,
100Mbps, 1000Mbps, or Auto (recommended).
Check the box to allow multicast trac to pass through
the router from the Internet (IPv4).
Check the box to allow multicast trac to pass through
the router from the Internet (IPv6).
Enable UPnP:
WAN Ping:
WAN Ping Inbound
Filter:
WAN Port Speed:
Enable IPV4
Multicast Streams:
Enable IPV6
Multicast Streams:
Advanced Network Settings
88D-Link DIR-826L User Manual
Section 3 - Conguration
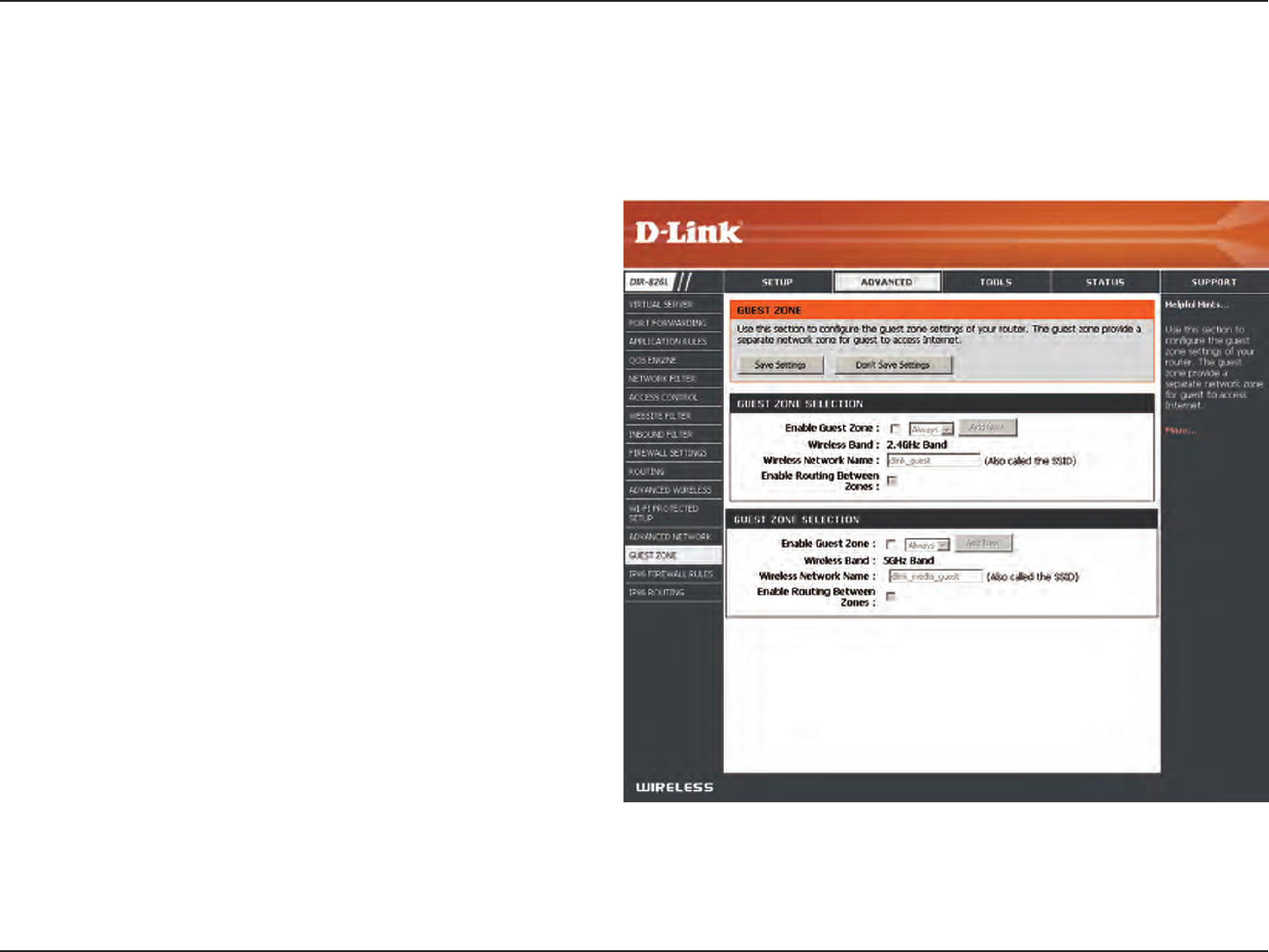
Guest Zone
Check to enable the Guest Zone feature.
The schedule of time when the Guest Zone will be
active. The schedule may be set to Always, which will
allow the particular service to always be enabled. You
can create your own times in the Tools > Schedules
section or click Add New.
Enter a wireless network name (SSID) that is dierent
from your main wireless network.
Check to allow network connectivity between the
dierent zones created.
Select the type of security or encryption you would
like to enable for the guest zone.
Enable Guest
Zone:
Schedule:
Wireless
Network Name:
Enable Routing
Between Zones:
Security Mode:
The Guest Zone feature will allow you to create temporary zones that can be used by guests to access the Internet. These zones
will be separate from your main wireless network. You may congure dierent zones for the 2.4GHz and 5GHz wireless bands.
89D-Link DIR-826L User Manual
Section 3 - Conguration
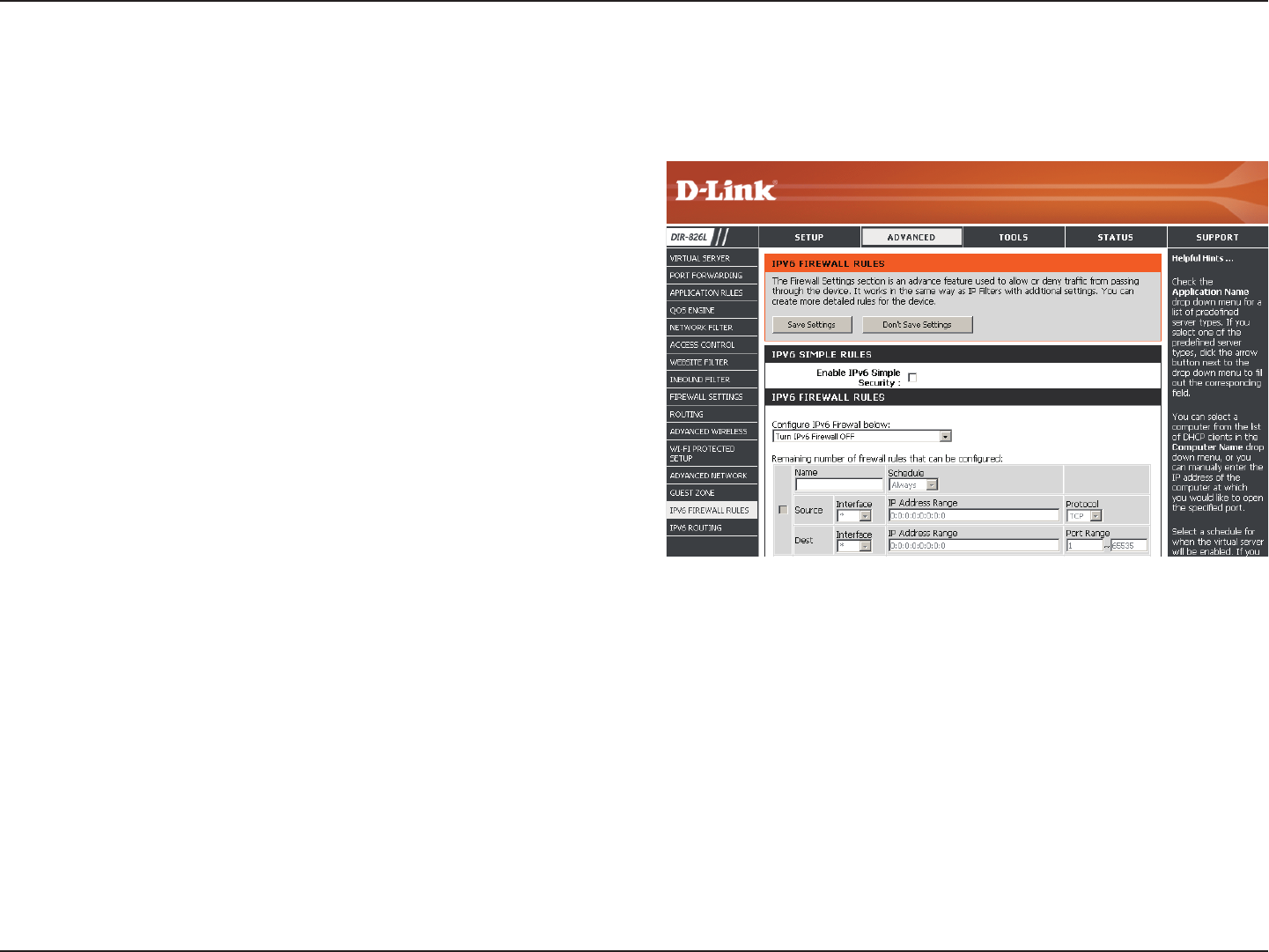
IPv6 Firewall
The DIR-826L’s IPv6 Firewall feature allows you to congure which kind of IPv6 trac is allowed to pass through the device.
The DIR-826L’s IPv6 Firewall functions in a similar way to the IP Filters feature.
Check the box to enable the IPv6 rewall simple security.
Select an action from the drop-down menu.
Enter a name to identify the IPv6 rewall rule.
Use the drop-down menu to select the time schedule that
the IPv6 Firewall Rule will be enabled on. The schedule may
be set to Always, which will allow the particular service to
always be enabled. You can create your own times in the
Tools > Schedules section.
Use the Source drop-down menu to specify the interface
that connects to the source IPv6 addresses of the rewall
rule.
Enter the source IPv6 address range in the adjacent IP Address Range eld.
Use the Dest drop-down menu to specify the interface that connects to the destination IP addresses of the rewall rule.
Select the protocol of the rewall port (All, TCP, UDP, or ICMP).
Enter the rst port of the range that will be used for the rewall rule in the rst box and enter the last port in the eld in the second
box.
Enable Checkbox:
Congure IPv6
Firewall:
Name:
Schedule:
Source:
IP Address Range:
Dest:
Protocol:
Port Range:
90D-Link DIR-826L User Manual
Section 3 - Conguration
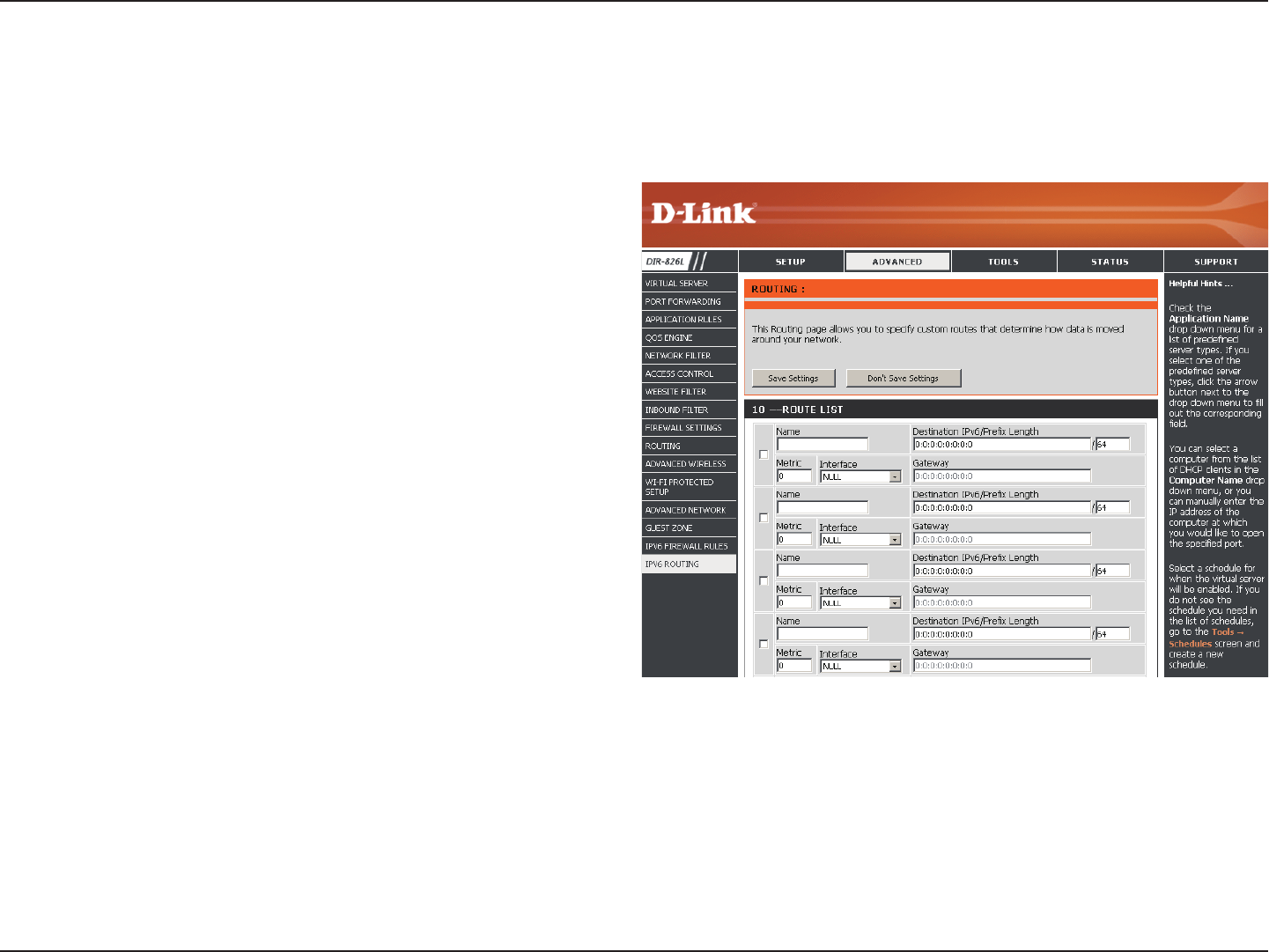
IPv6 Routing
Check the box next to the route you wish to enable.
Enter a specic name to identify this route.
This is the IP address of the router used to reach the
specied destination or enter the IPv6 address prex
length of the packets that will take this route.
Enter the metric value for this rule here.
Use the drop-down menu to specify if the IP packet
must use the WAN or LAN interface to transit out of
the Router.
Enter the next hop that will be taken if this route is used.
Route List:
Name:
Destination IP/
Prex Length:
Metric:
Interface:
Gateway:
This page allows you to specify custom routes that determine how data is moved around your network.
91D-Link DIR-826L User Manual
Section 3 - Conguration
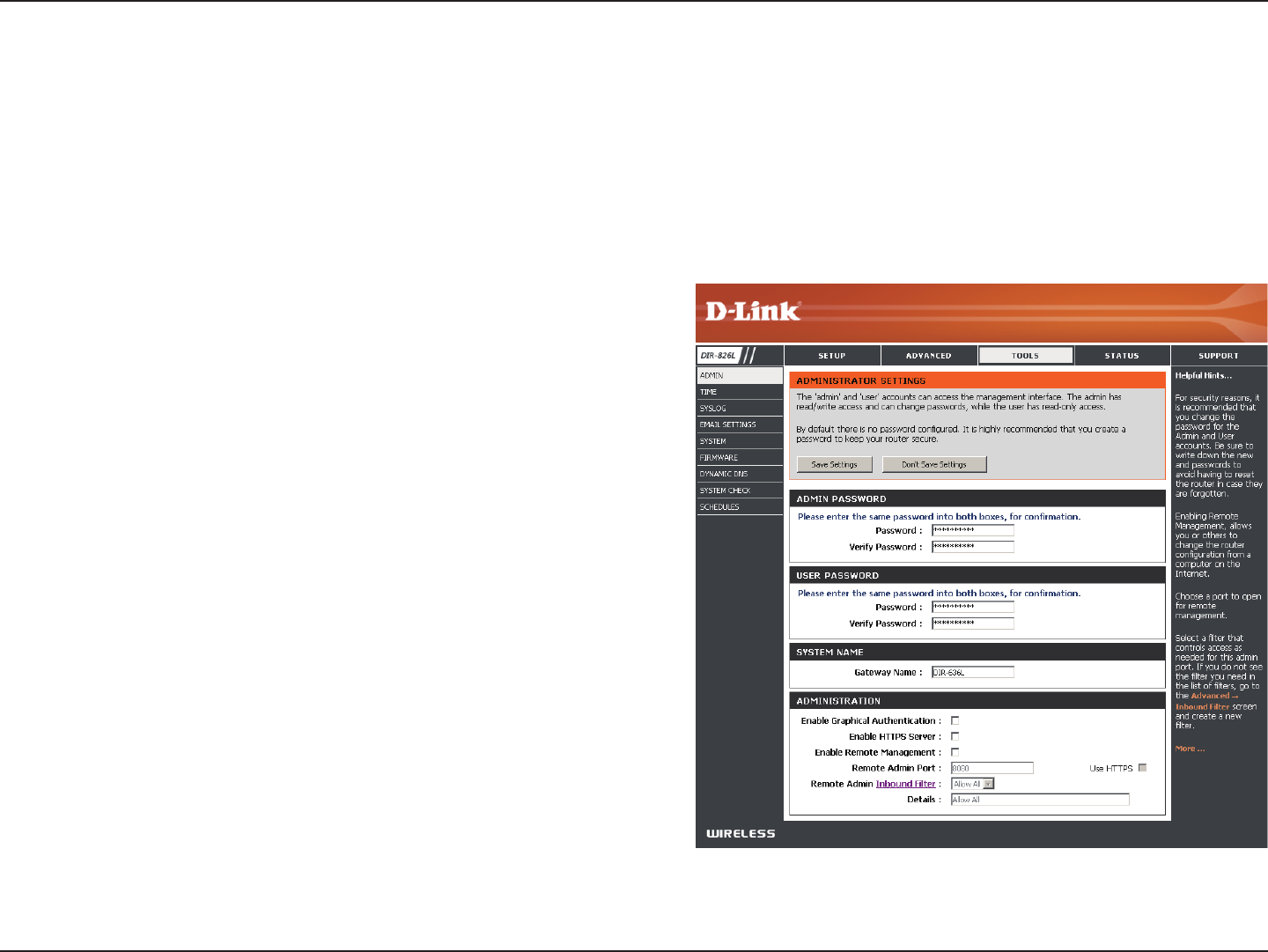
Admin
This page will allow you to change the Administrator and User passwords. You can also enable Remote Management. There are
two accounts that can access the management interface through the web browser. The accounts are admin and user. Admin
has read/write access while user has read-only access. User can only view the settings but cannot make any changes. Only the
admin account has the ability to change both admin and user account passwords.
Tools
Enter a new password for the Administrator Login Name. The administrator
can make changes to the settings.
Enter the new password for the User login. If you login as the User, you cannot
change the settings (you can only view them).
Enter a name for your router.
Enables a challenge-response test to require users to type letters or numbers
from a distorted image displayed on the screen to prevent online hackers and
unauthorized users from gaining access to your router’s network settings.
Check to enable HTTPS to connect to the router securely. This means to connect
to the router, you must enter https://192.168.0.1 (for example) instead of
http://192.168.0.1.
Remote management allows the DIR-826L to be congured from the Internet
by a web browser. A username/password is still required to access the Web
Management interface.
The port number used to access the DIR-826L is used in the URL. Example:
http://x.x.x.x:8080 whereas x.x.x.x is the Internet IP address of the DIR-826L
and 8080 is the port used for the Web Management interface.
If you have enabled HTTPS Server, you must enter https:// as part of the URL
to access the router remotely.
This section will list any rules that are created. You may click the Edit icon to
change the settings or enable/disable the rule, or click the Delete icon to
remove the rule. Details will display the current status.
Admin Password:
User Password:
System Name:
Enable Graphical
Authentication:
Enable HTTPS
Server:
Enable Remote
Management:
Remote Admin Port:
Remote Admin
Inbound Filter:
92D-Link DIR-826L User Manual
Section 3 - Conguration
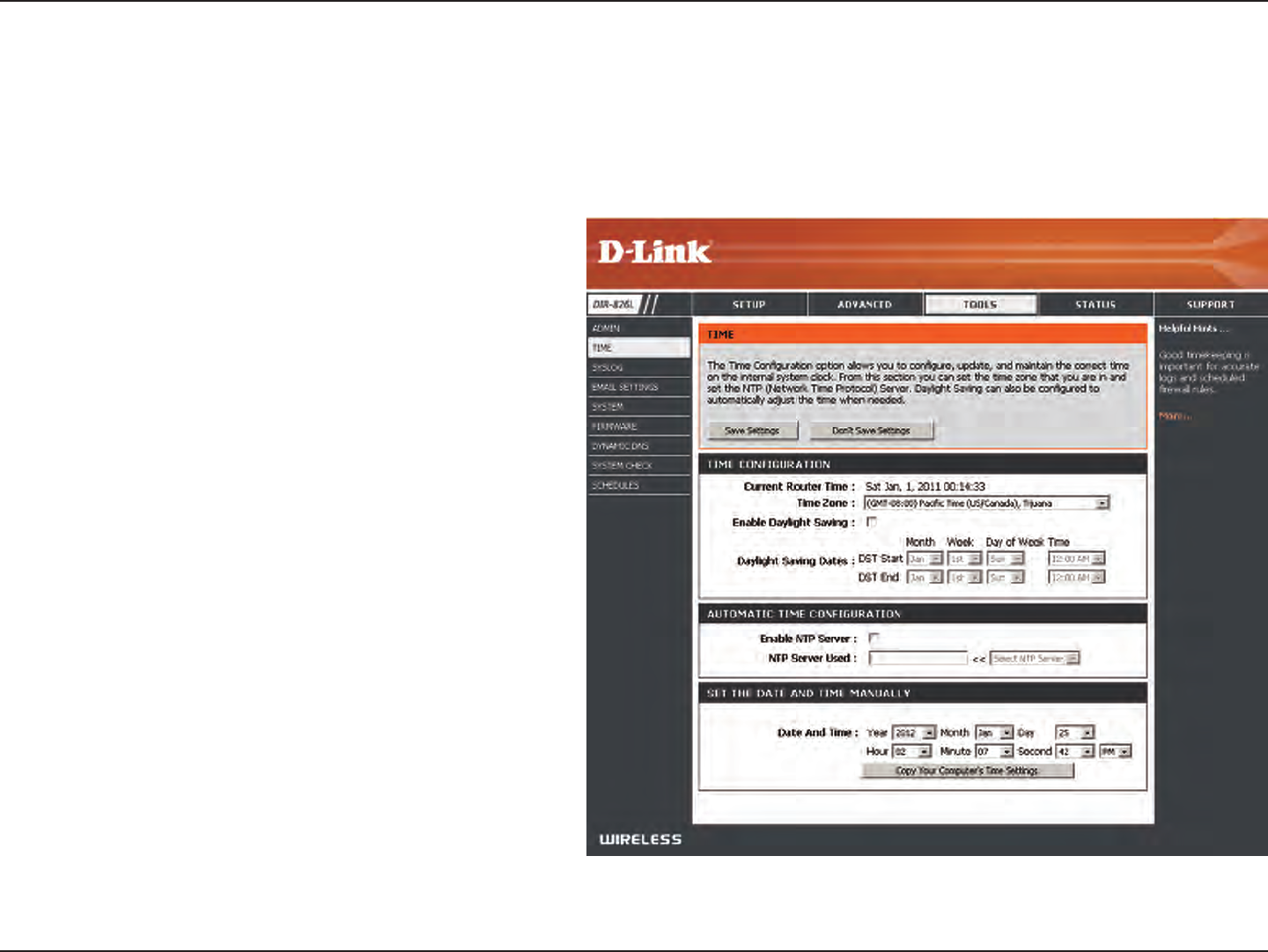
Time
Displays the current date and time of the router.
Select your Time Zone from the drop-down
menu.
To select Daylight Saving time manually, select
enabled or disabled, and enter a start date and
an end date for daylight saving time.
NTP is short for Network Time Protocol. A NTP
server will synch the time and date with your
router. This will only connect to a server on the
Internet, not a local server. Check the box to
enable this feature.
Enter the IP address of a NTP server or select one
from the drop-down menu.
To manually input the time, enter the values
in these elds for the Year, Month, Day, Hour,
Minute, and Second and then click Set Time.
You can also click Copy Your Computer’s Time
Settings to synch the date and time with the
computer you are currently on.
Time:
Time Zone:
Enable Daylight
Saving:
Enable NTP Server:
NTP Server Used:
Manual:
The Time Conguration option allows you to congure, update, and maintain the correct time on the internal system clock.
From this section you can set the time zone that you are in and set the Time Server. Daylight Saving can also be congured to
automatically adjust the time when needed.
93D-Link DIR-826L User Manual
Section 3 - Conguration
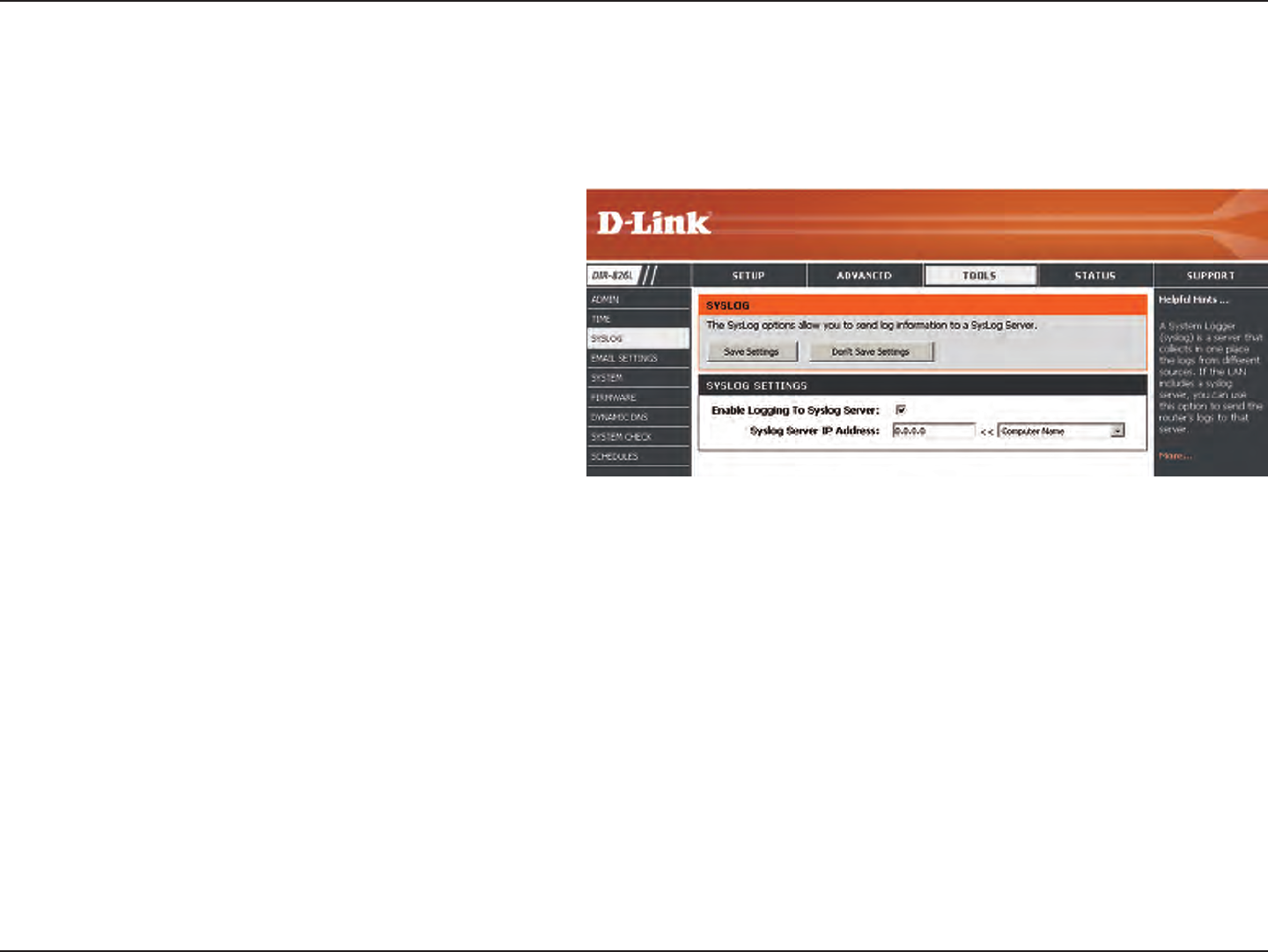
SysLog
The Broadband Router keeps a running log of events and activities occurring on the Router. You may send these logs to a
SysLog server on your network.
Enable Logging to
SysLog Server:
SysLog Server IP
Address:
Check this box to send the router logs to a SysLog
Server.
The address of the SysLog server that will be
used to send the logs. You may also select your
computer from the drop-down menu (only if
receiving an IP address from the router via DHCP).
94D-Link DIR-826L User Manual
Section 3 - Conguration
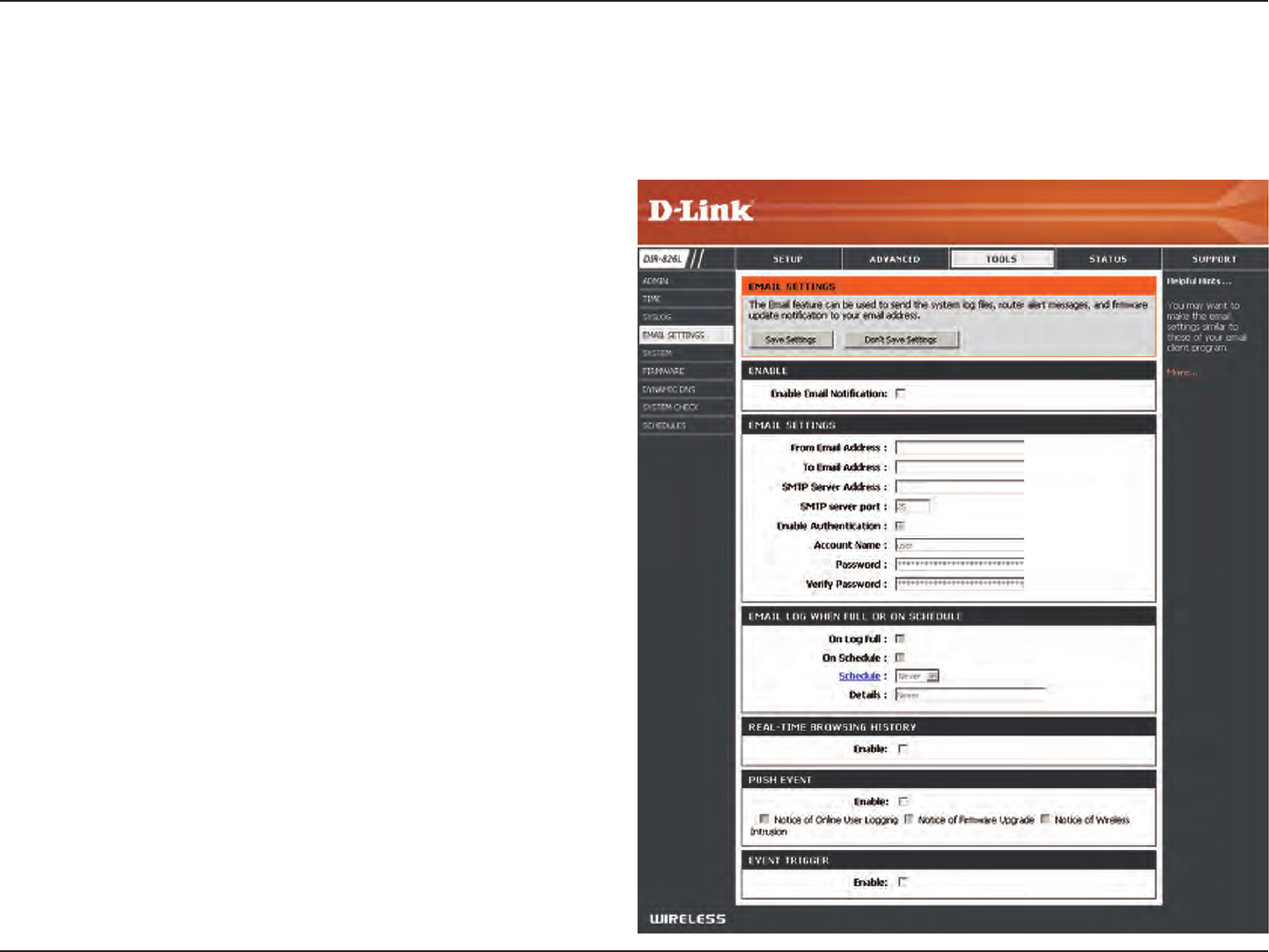
Email Settings
The Email feature can be used to send the system log les, router alert messages, and rmware update notication to your
email address.
Enable Email
Notication:
From Email Address:
To Email Address:
SMTP Server Address:
SMTP Server Port:
Enable Authentication:
Account Name:
Password:
On Log Full:
On Schedule:
Schedule:
Real-Time Browsing
History:
Push Event:
Event Trigger:
When this option is enabled, router activity logs are emailed to a
designated email address.
This email address will appear as the sender when you receive a log
le or rmware upgrade notication via email.
Enter the email address where you want the email sent.
Enter the SMTP server address for sending email.
Enter the SMTP port used on the server.
Check this box if your SMTP server requires authentication.
Enter your account for sending email.
Enter the password associated with the account. Re-type the
password associated with the account.
When this option is selected, logs will be sent via email to your
account when the log is full.
Selecting this option will send the logs via email according to
schedule.
This option is enabled when On Schedule is selected. You can select
a schedule from the list of dened schedules. To create a schedule,
go to Tools > Schedules.
Check to enable browsing history (for mydlink Lite app).
Check to enable and select which alerts to be sent to your mobile
device (for mydlink Lite app).
Check to enable event triggering (for mydlink Lite app).
95D-Link DIR-826L User Manual
Section 3 - Conguration
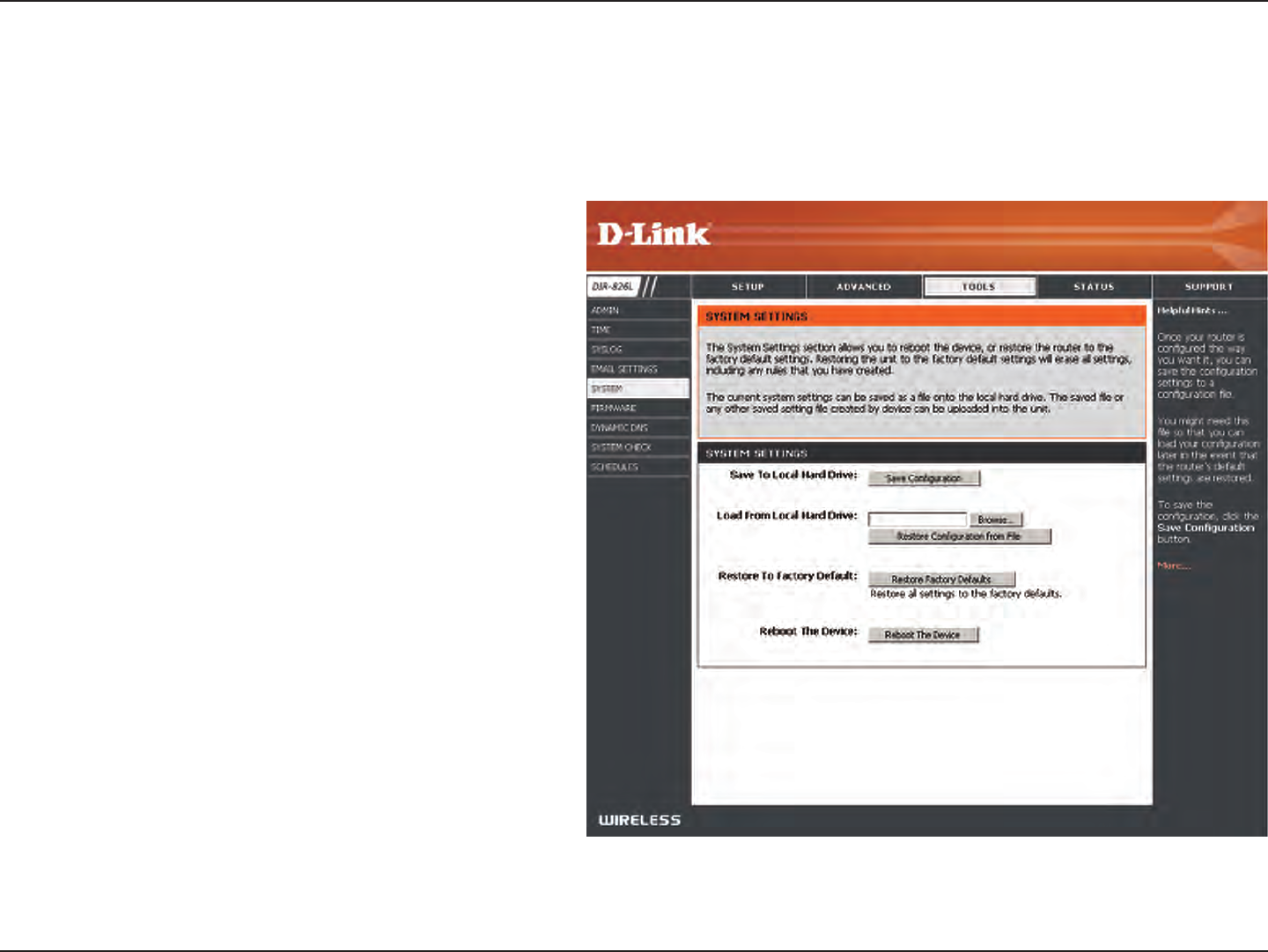
Use this option to save the current router
conguration settings to a le on the hard disk of
the computer you are using. First, click the Save
button. A le dialog will appear, allowing you to
select a location and le name for the settings.
Use this option to load previously saved router
conguration settings. First, use the Browse option
to find a previously saved file of configuration
settings. Then, click the Load button to transfer
those settings to the router.
This option will restore all conguration settings
back to the settings that were in effect at the
time the router was shipped from the factory.
Any settings that have not been saved will be
lost, including any rules that you have created. If
you want to save the current router conguration
settings, use the Save button above.
Click to reboot the router.
Save Settings to
Local Hard Drive:
Load Settings
from Local Hard
Drive:
Restore to
Factory Default
Settings:
Reboot Device:
System
This section allows you to manage the router’s conguration settings, reboot the router, and restore the router to the factory
default settings. Restoring the unit to the factory default settings will erase all settings, including any rules that you’ve created.
96D-Link DIR-826L User Manual
Section 3 - Conguration
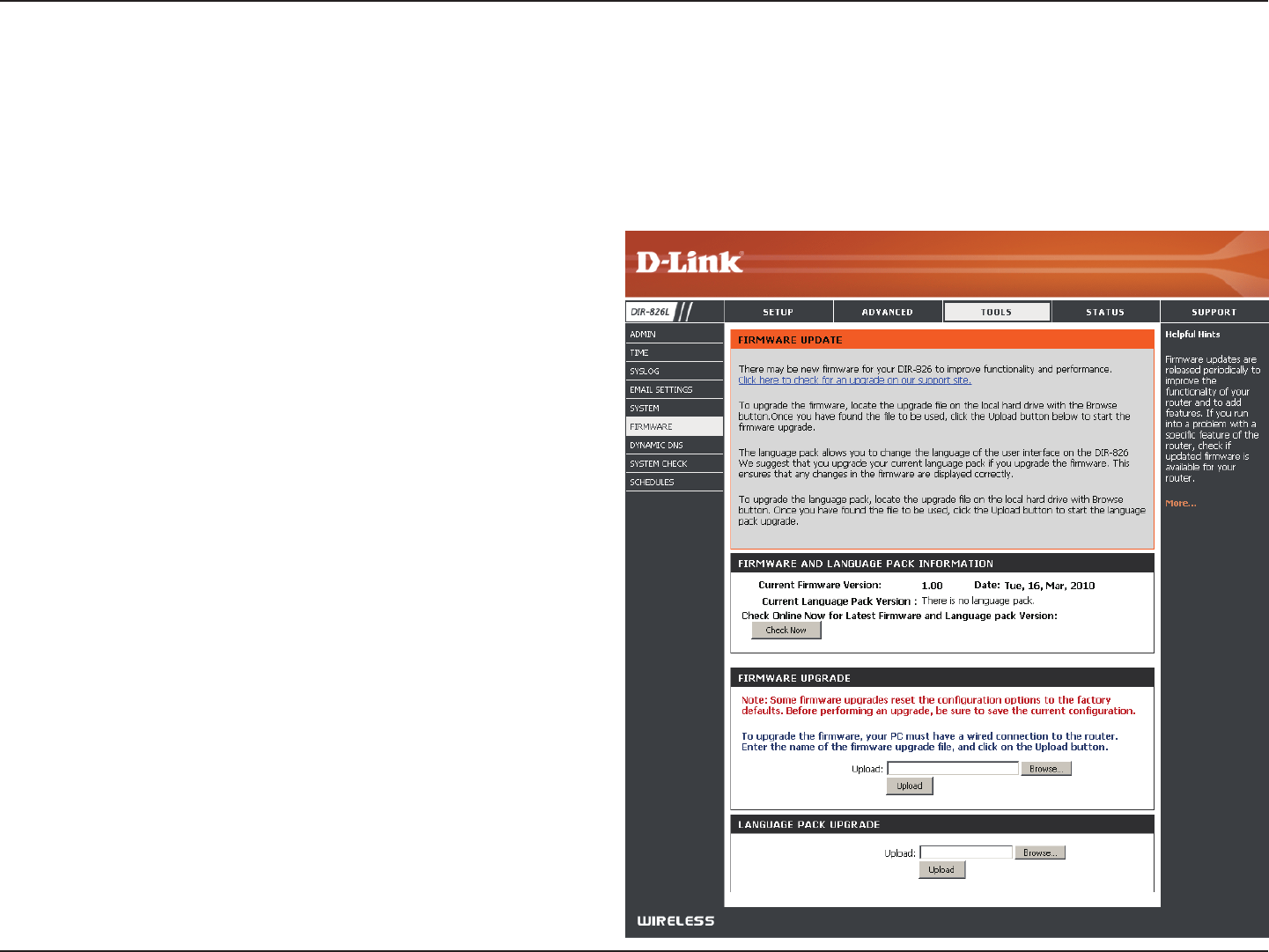
Firmware
Browse:
Upload:
After you have downloaded the new rmware, click
Browse to locate the rmware update on your hard
drive. Click Upload to complete the rmware upgrade.
Once you have a rmware update on your computer,
use this option to browse for the le and then upload
the information into the access point.
You can upgrade the rmware of the access point here. Make sure the rmware you want to use is on the local hard drive of
the computer. Click on Browse to locate the rmware le to be used for the update. Please check the D-Link support website
for rmware updates at http://support.dlink.com. You can download rmware upgrades to your hard drive from this site.
After you have downloaded the new language pack,
click Browse to locate the language pack le on your
hard drive. Click Upload to complete the language
pack upgrade.
Language Pack
You can change the language of the web UI by uploading
available language packs.
Browse:
97D-Link DIR-826L User Manual
Section 3 - Conguration
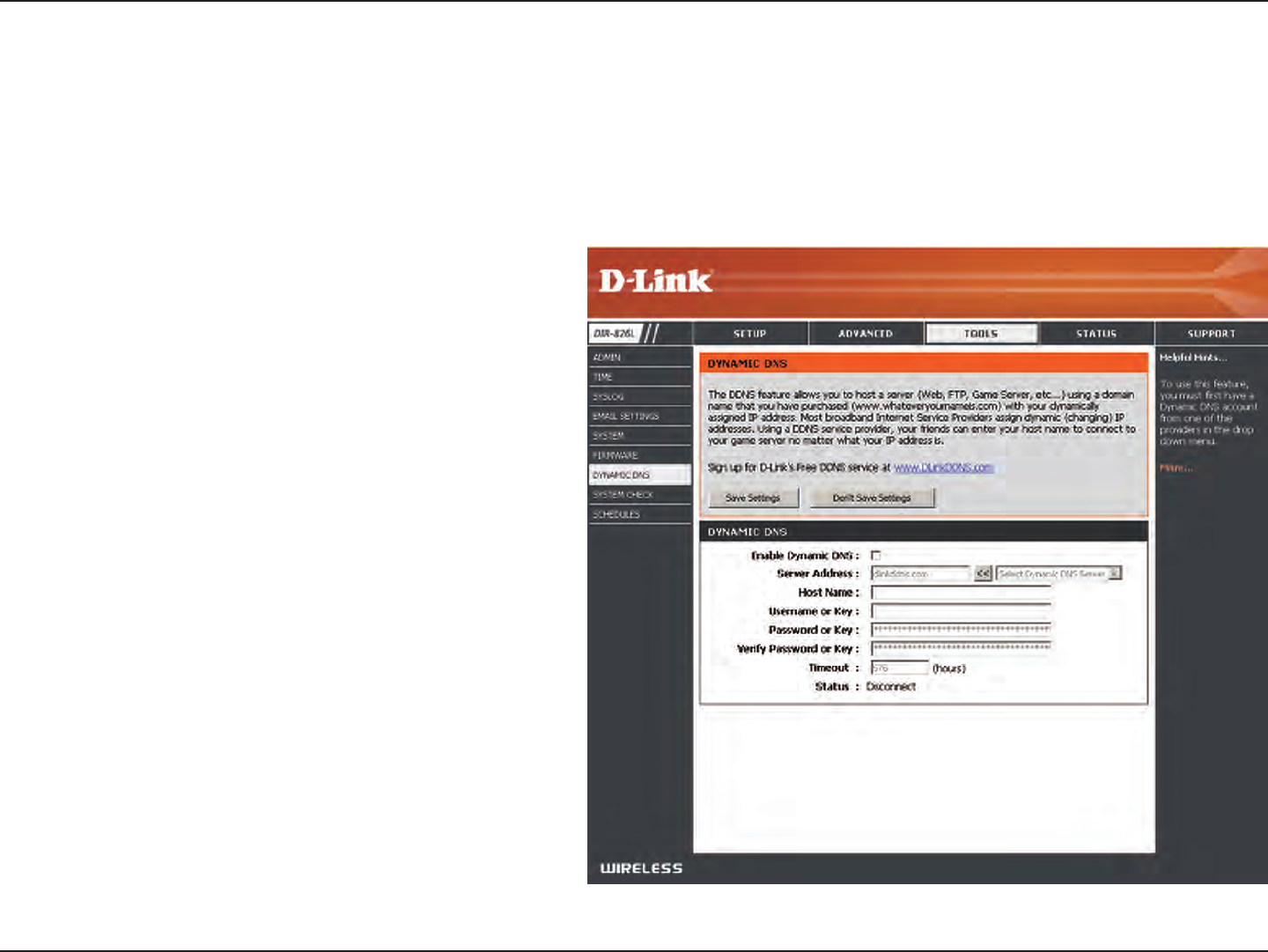
Dynamic Domain Name System is a method of
keeping a domain name linked to a changing IP
Address. Check the box to enable DDNS.
Select your DDNS provider from the drop-down
menu or enter the DDNS server address.
Enter the Host Name that you registered with
your DDNS service provider.
Enter the Username or key for your DDNS
account.
Enter the Password or key for your DDNS account.
Enter a timeout time (in hours).
Displays the current connection status.
Enable
Dynamic DNS:
Server
Address:
Host Name:
Username or
Key:
Password or
Key:
Timeout:
Status:
Dynamic DNS
The DDNS feature allows you to host a server (Web, FTP, Game Server, etc…) using a domain name that you have purchased
(www.whateveryournameis.com) with your dynamically assigned IP address. Most broadband Internet Service Providers assign
dynamic (changing) IP addresses. Using a DDNS service provider, your friends can enter in your domain name to connect to
your server no matter what your IP address is.
98D-Link DIR-826L User Manual
Section 3 - Conguration
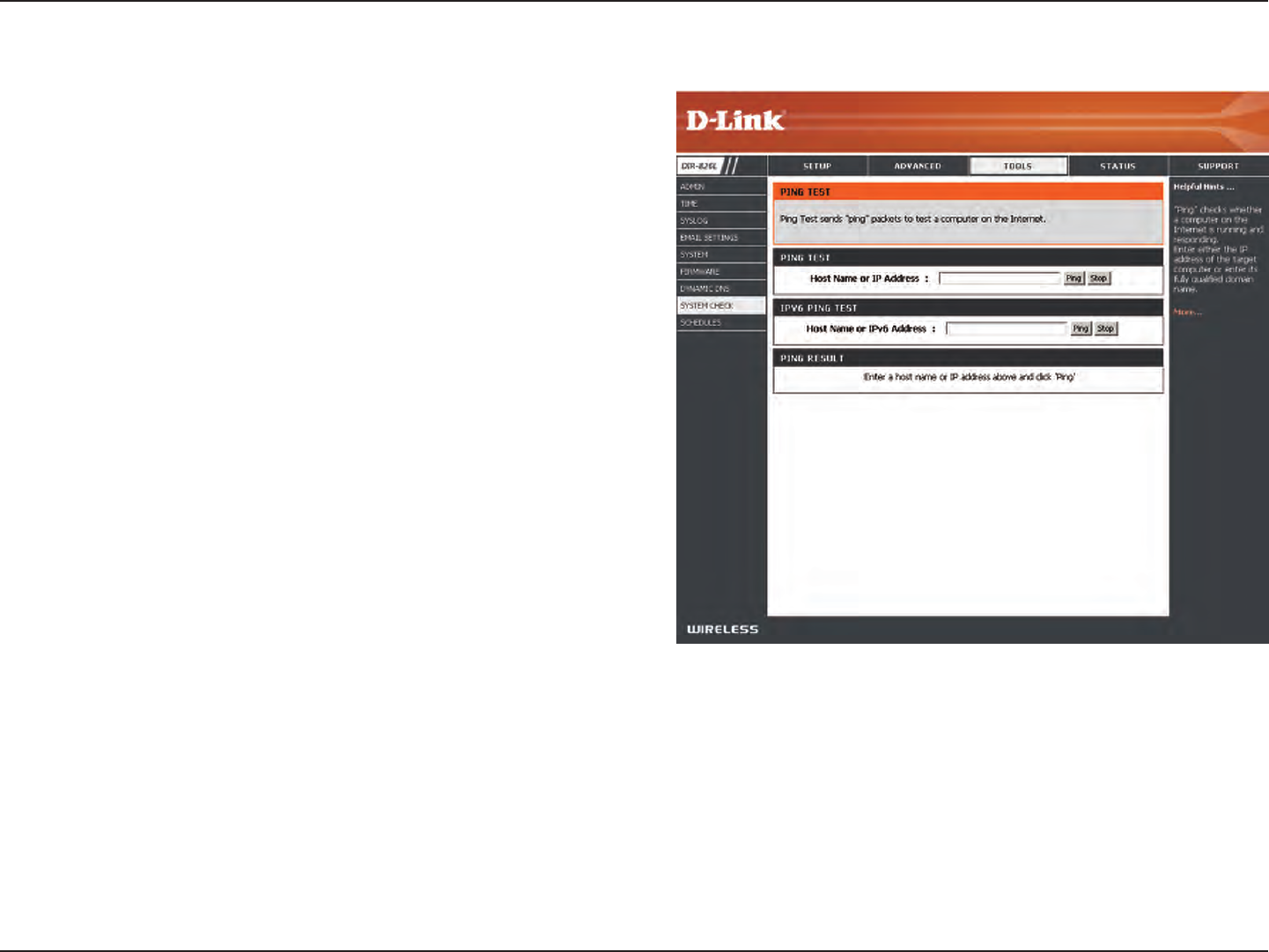
The Ping Test is used to send Ping packets to test if a
computer is on the Internet. Enter the IP address that you
wish to Ping and click Ping.
Enter the IPv6 address that you wish to Ping and click Ping.
The results of your ping attempts will be displayed here.
System Check
Ping Test:
IPv6 Ping Test:
Ping Results:
99D-Link DIR-826L User Manual
Section 3 - Conguration
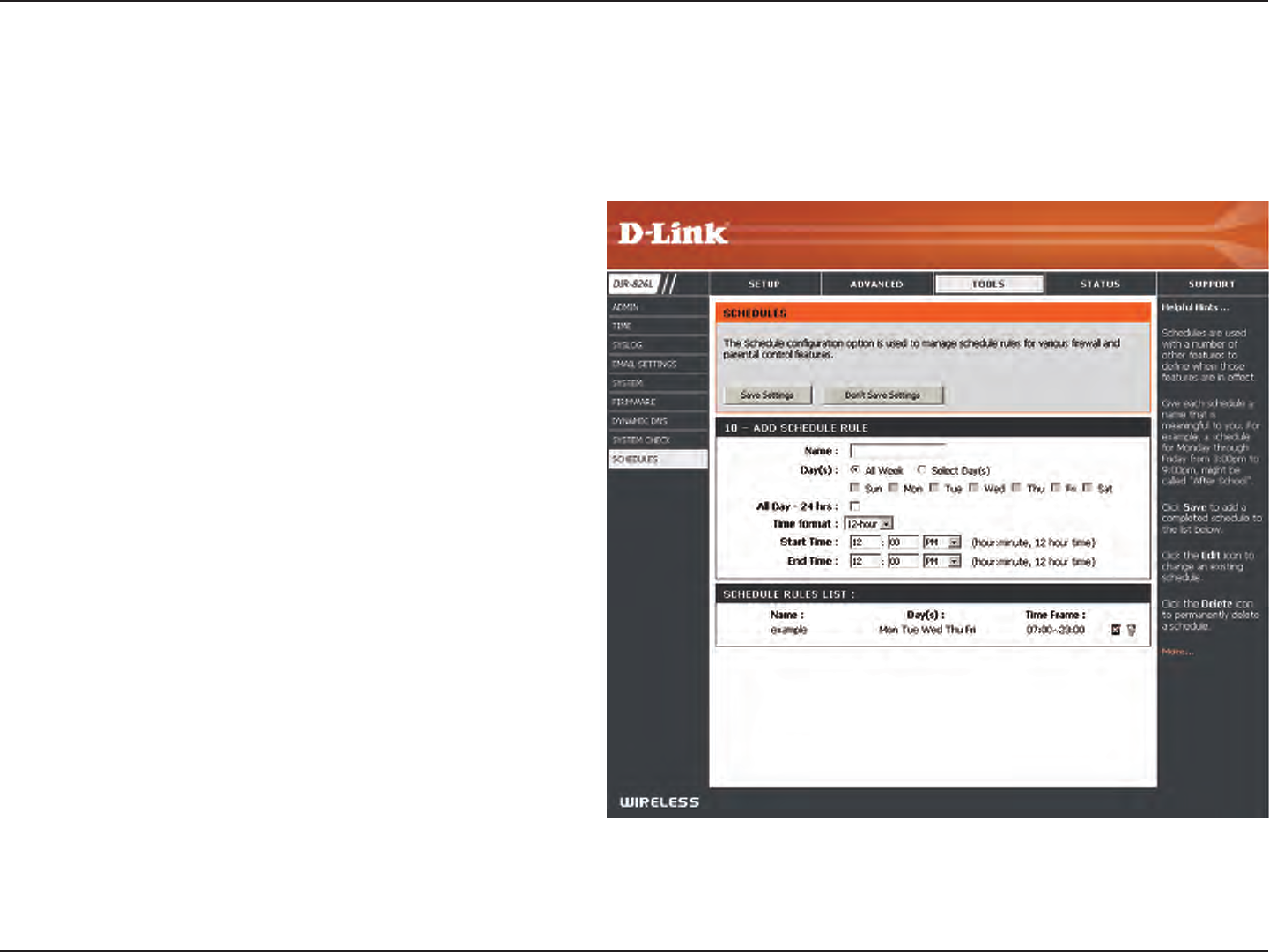
Enter a name for your new schedule.
Select a day, a range of days, or All Week to include
every day.
Check All Day - 24hrs or enter a start and end
time for your schedule.
You must click Save Settings at the top for your
schedules to go into eect.
The list of schedules will be listed here. Click the
Edit icon to make changes or click the Delete icon
to remove the schedule.
Name:
Days:
Time:
Save:
Schedule Rules
List:
Schedules
Schedules can be created for use with enforcing rules. For example, if you want to restrict web access to Mon-Fri from 3pm to
8pm, you could create a schedule selecting Mon, Tue, Wed, Thu, and Fri and enter a Start Time of 3pm and End Time of 8pm.
100D-Link DIR-826L User Manual
Section 3 - Conguration
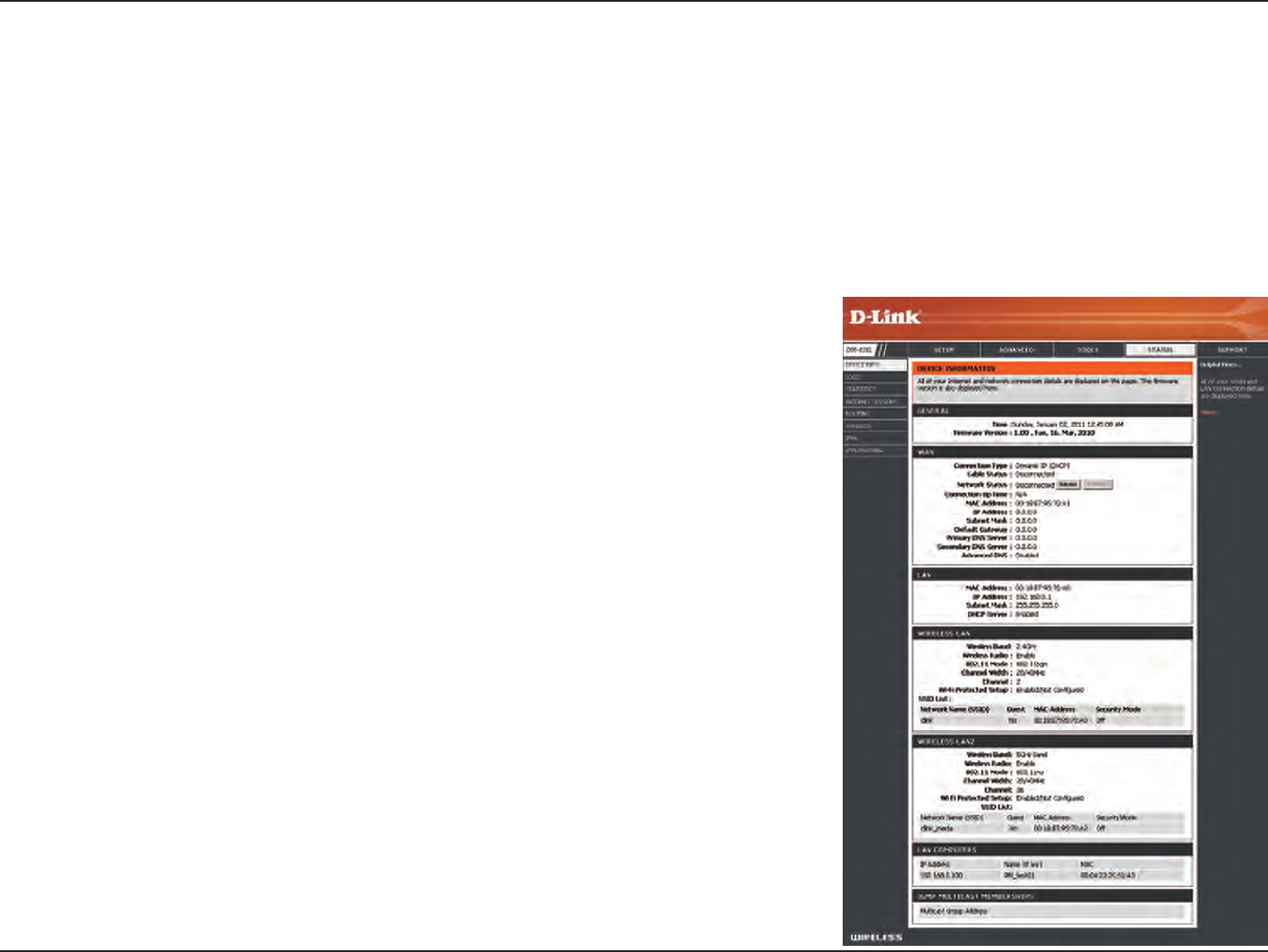
This page displays the current information for the DIR-826L. It will display the LAN, WAN (Internet), and Wireless information.
If your Internet connection is set up for a Dynamic IP address then a Release button and a Renew button will be displayed.
Use Release to disconnect from your ISP and use Renew to connect to your ISP.
If your Internet connection is set up for PPPoE, a Connect button and a Disconnect button will be displayed. Use Disconnect
to drop the PPPoE connection and use Connect to establish the PPPoE connection.
Displays the router’s time and rmware version.
Displays the MAC address and the public IP settings
Displays the MAC address and the private (local) IP settings for the router.
Displays the 2.4GHz wireless MAC address and your wireless settings such as
SSID and Channel.
Displays the 5GHz wireless MAC address and your wireless settings such as
SSID and Channel.
Displays computers and devices that are connected to the router via Ethernet
and that are receiving an IP address assigned by the router (DHCP).
General:
WAN:
LAN:
Wireless LAN1:
Wireless LAN2:
LAN Computers:
Device Info
Status
101D-Link DIR-826L User Manual
Section 3 - Conguration
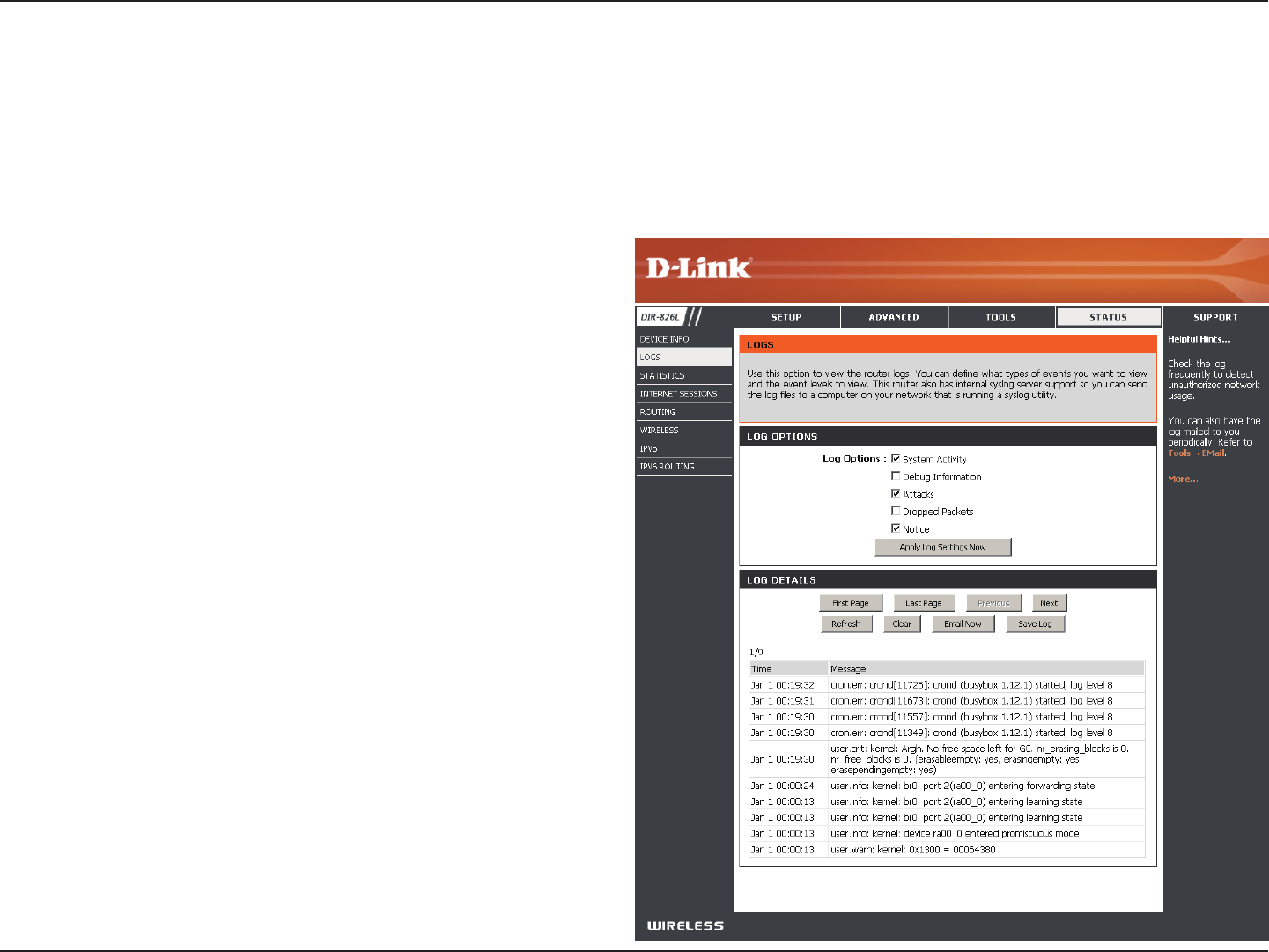
Logs
Log Options:
Refresh:
First Page:
Last Page:
Previous:
Next:
Clear:
Email Now:
Save Log:
You can select the types of messages that you want
to display from the log. System Activity, Debug
Information, Attacks, Dropped Packets, and Notice
messages can be selected. Click Apply Log Settings
Now to activate your settings.
Updates the log details on the screen so it displays any
recent activity.
Click to go to the rst page.
Click to go to the last page.
Click to go back one page.
Click to go to the next page.
Clears all of the log contents.
This option will send a copy of the router log to your
email address congured in the Tools > Email Settings
screen.
This option will save the router log to a le on your
computer.
The router automatically logs (records) events of possible interest in it’s internal memory. If there isn’t enough internal memory
for all events, logs of older events are deleted but logs of the latest events are retained. The Logs option allows you to view
the router logs. You can dene what types of events you want to view and the level of the events to view. This router also has
external Syslog Server support so you can send the log les to a computer on your network that is running a Syslog utility.
102D-Link DIR-826L User Manual
Section 3 - Conguration
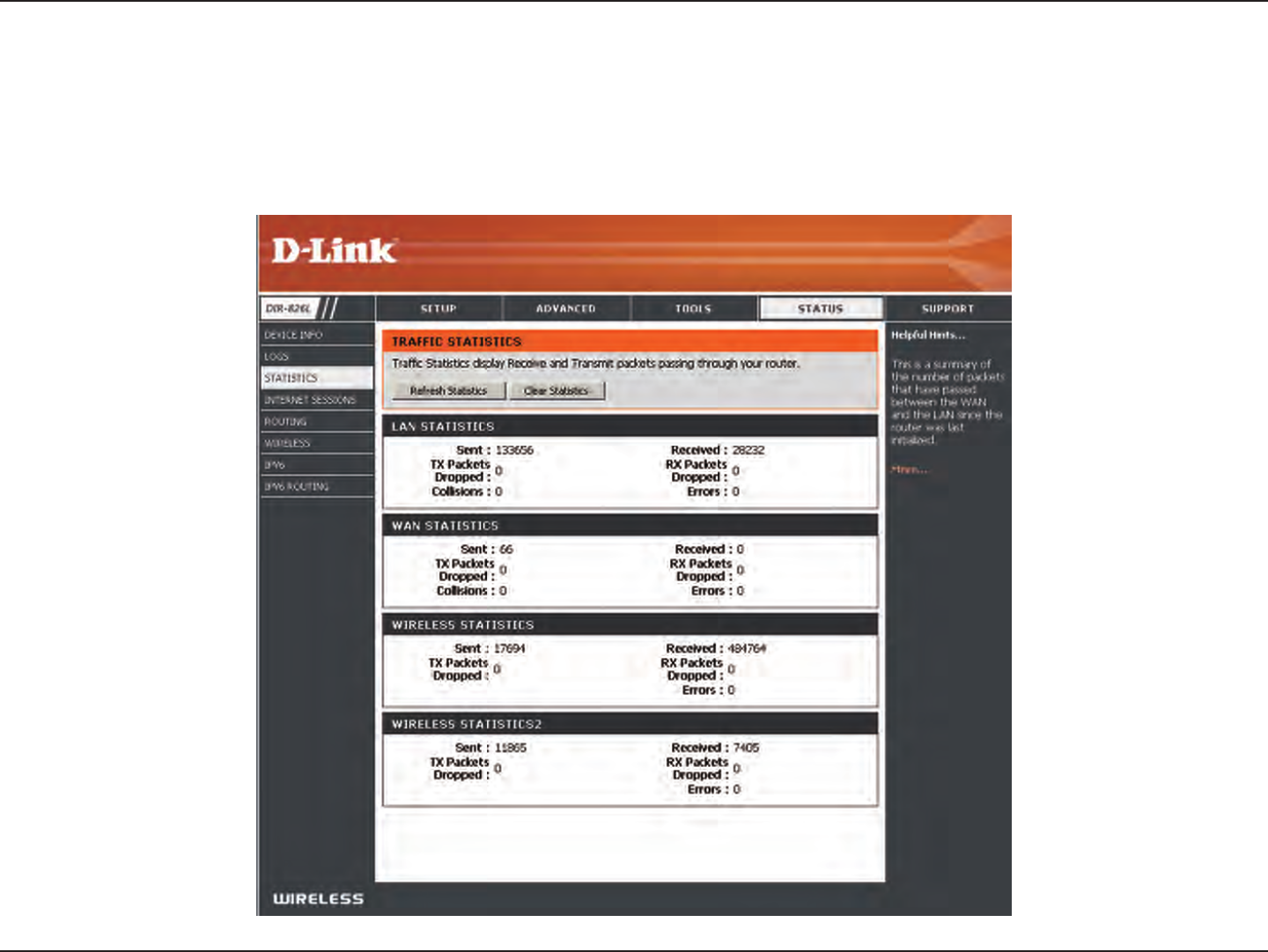
Statistics
The screen below displays the Trac Statistics. Here you can view the amount of packets that pass through the DIR-826L on both
the WAN, LAN ports and the wireless segments. The trac counter will reset if the device is rebooted.
103D-Link DIR-826L User Manual
Section 3 - Conguration
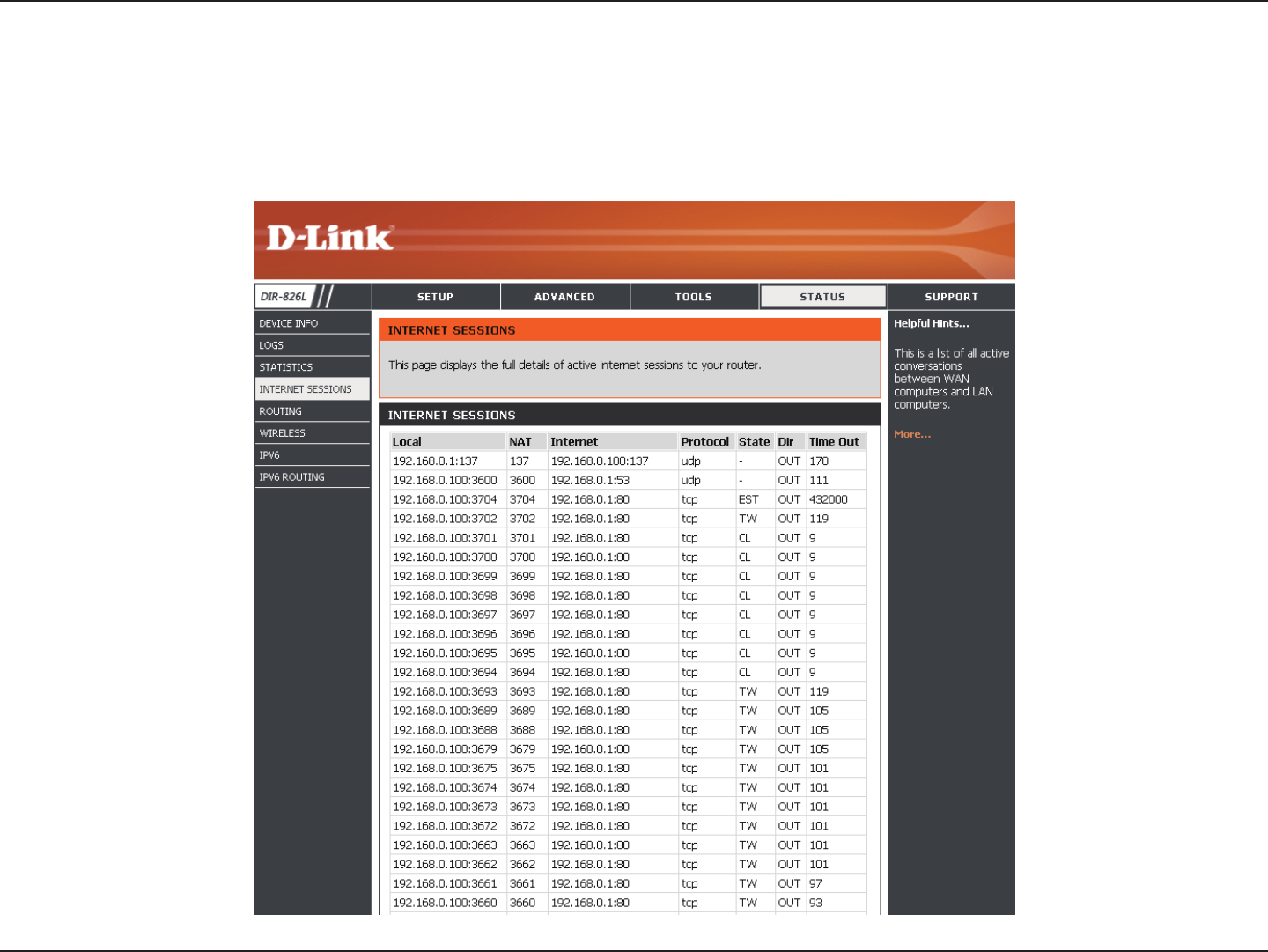
Internet Sessions
The Internet Sessions page displays full details of active Internet sessions through your router. An Internet session is a
conversation between a program or application on a LAN-side computer and a program or application on a WAN-side computer.
104D-Link DIR-826L User Manual
Section 3 - Conguration
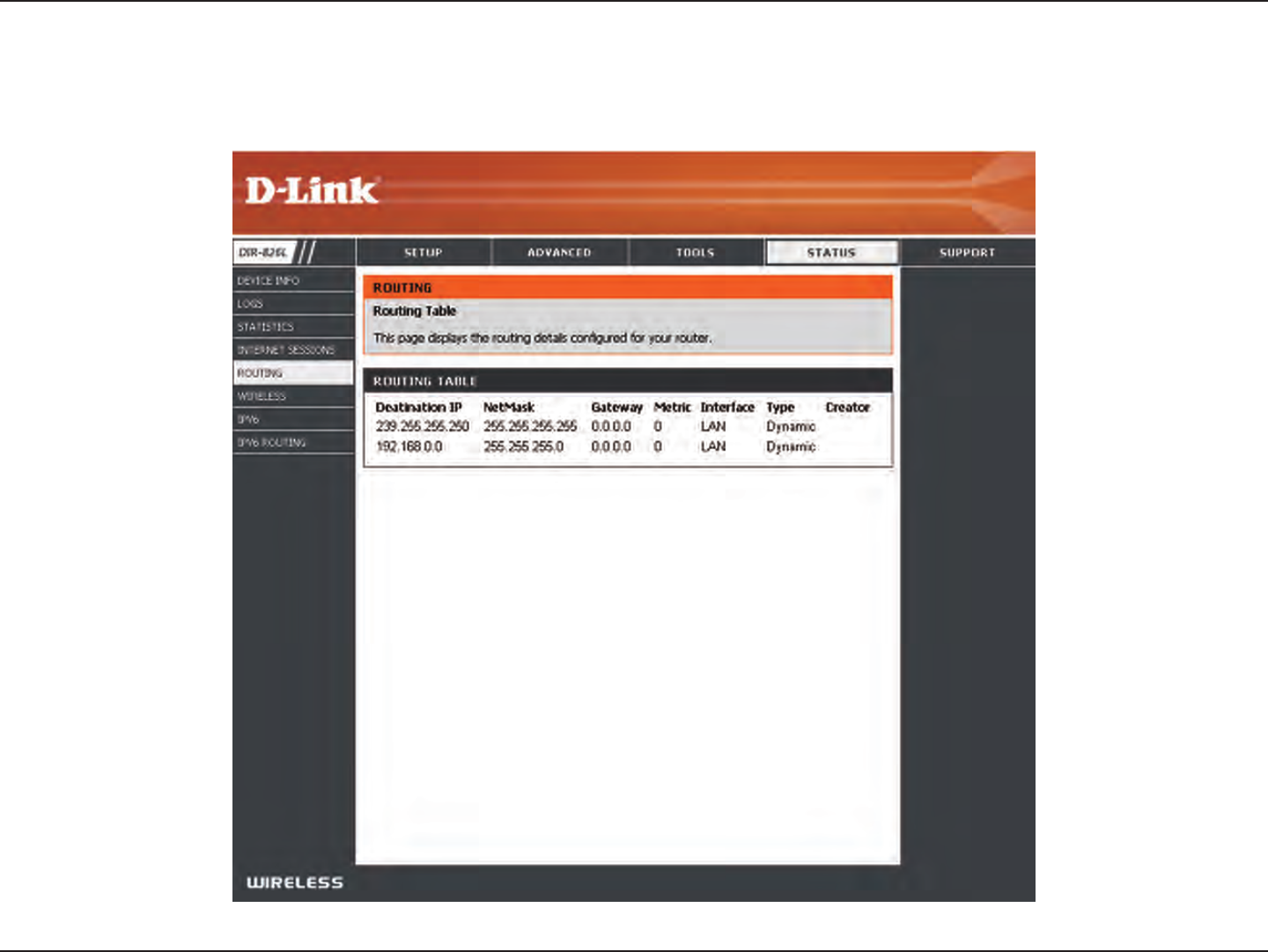
Routing
This page will display your current routing table.
105D-Link DIR-826L User Manual
Section 3 - Conguration
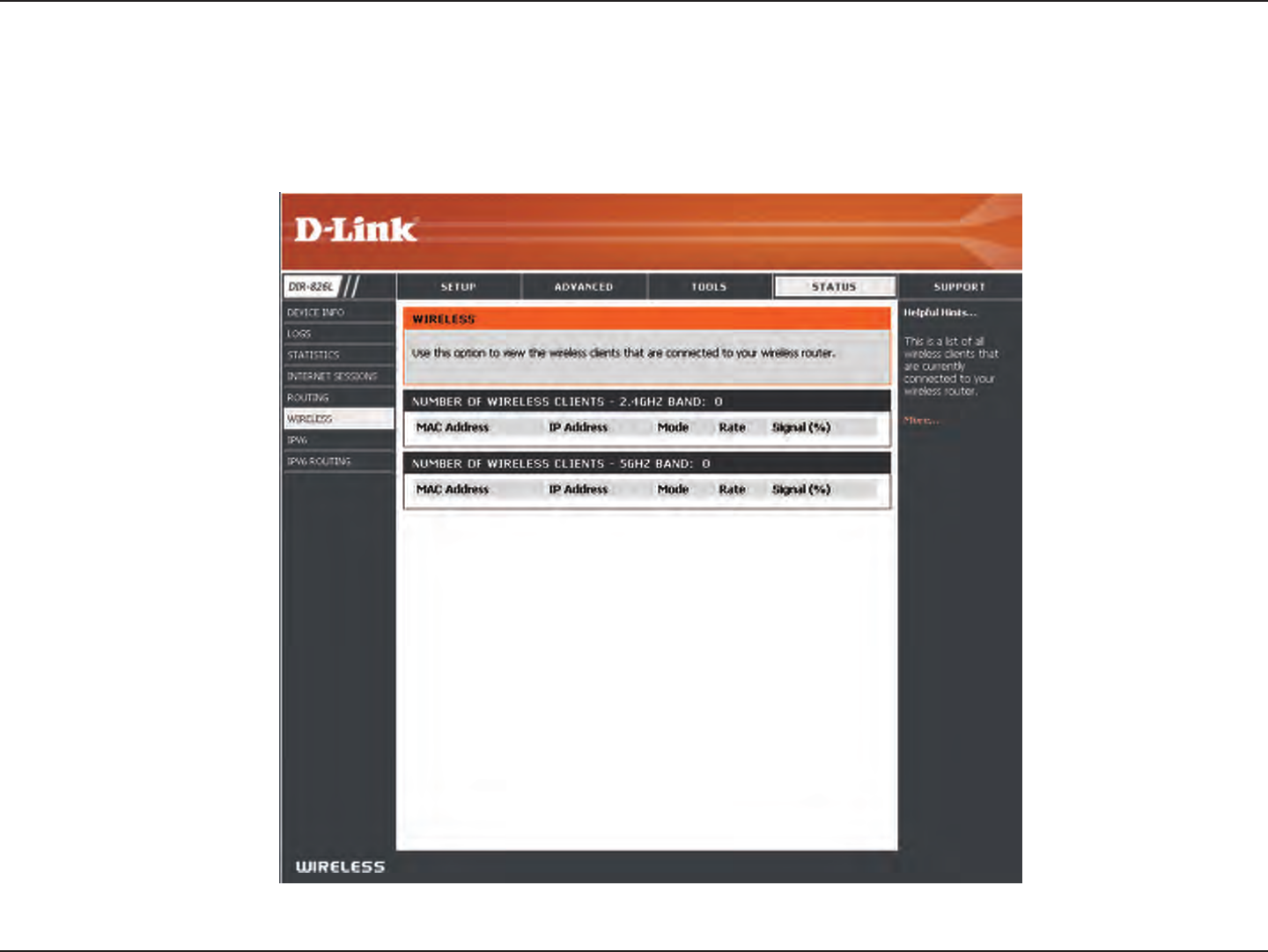
The wireless client table displays a list of current connected wireless clients. This table also displays the connection time and
MAC address of the connected wireless clients.
Wireless
106D-Link DIR-826L User Manual
Section 3 - Conguration
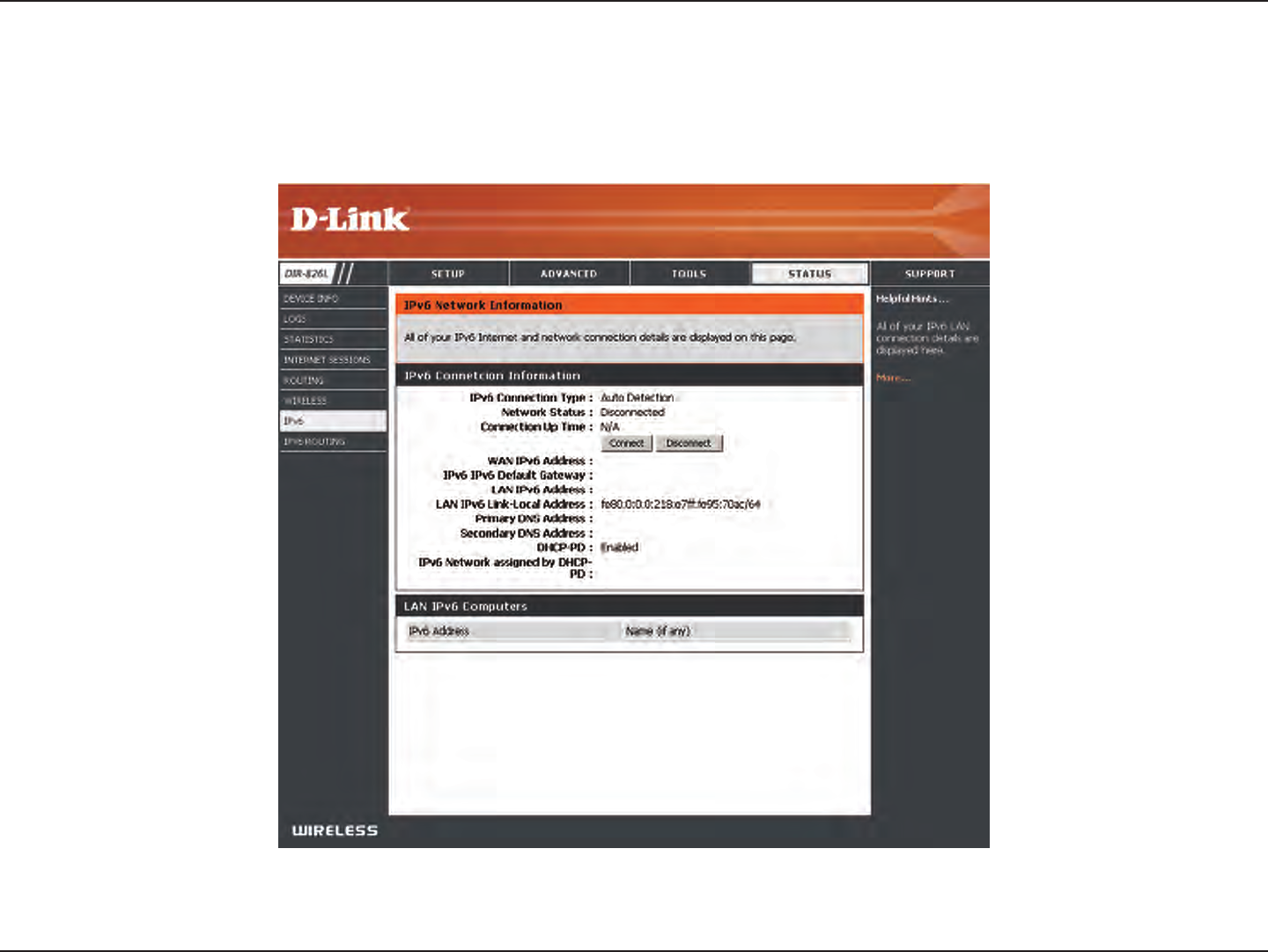
IPv6
The IPv6 page displays a summary of the Router’s IPv6 settings and lists the IPv6 address and host name of any IPv6 clients.
107D-Link DIR-826L User Manual
Section 3 - Conguration
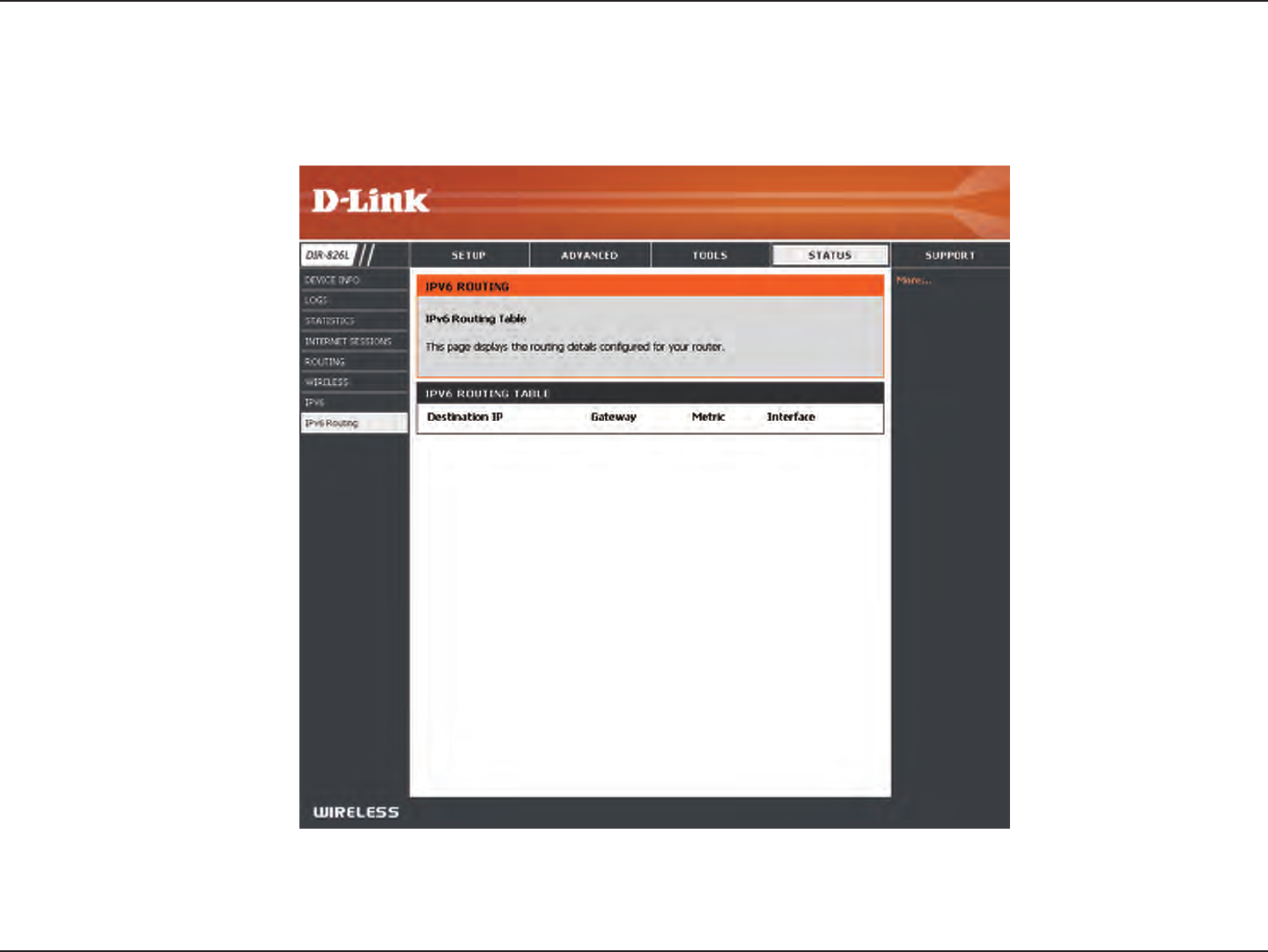
IPV6 Routing
This page displays the IPV6 routing details congured for your router.
108D-Link DIR-826L User Manual
Section 3 - Conguration
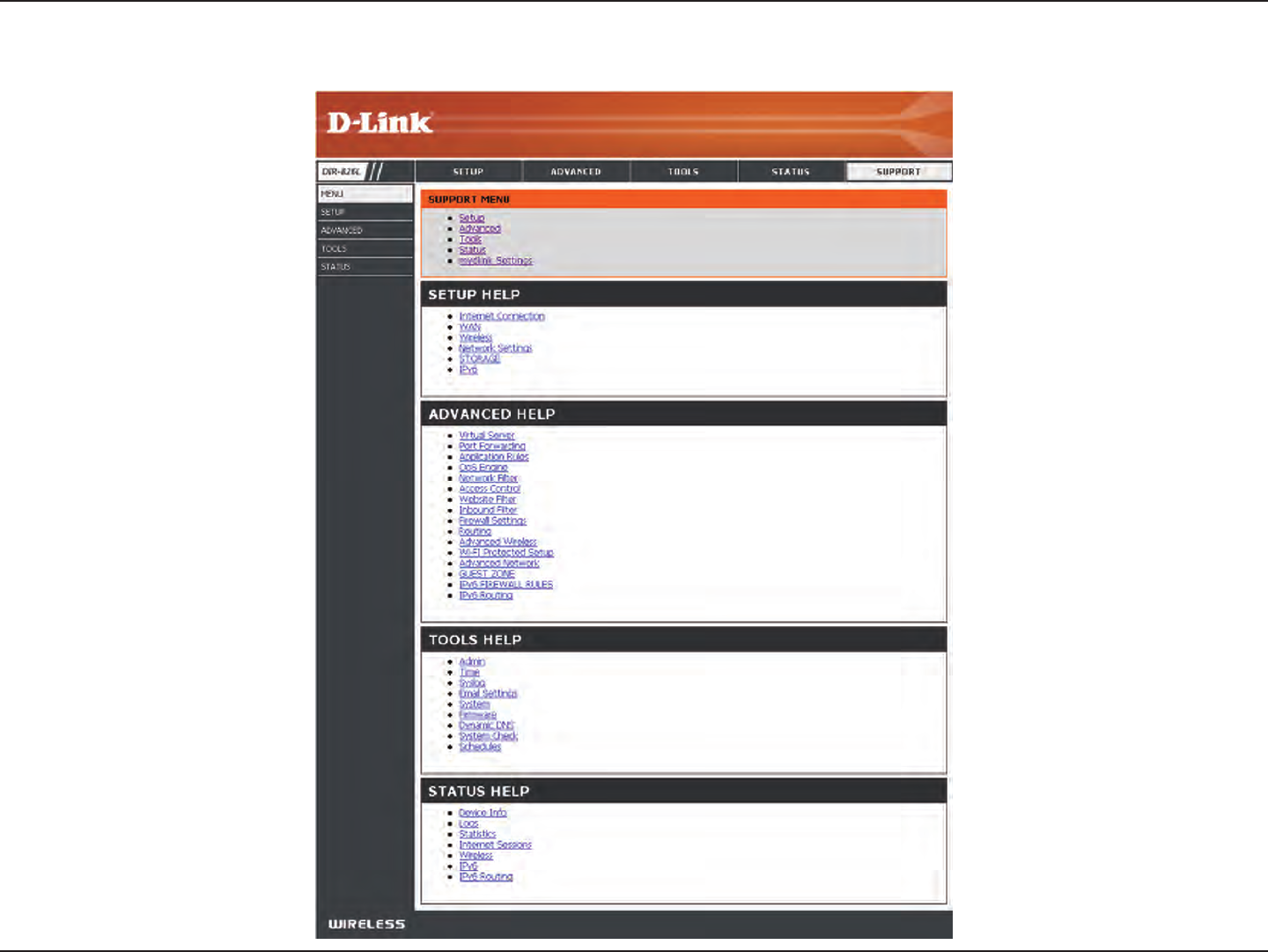
Support
109D-Link DIR-826L User Manual
Section 4 - Security
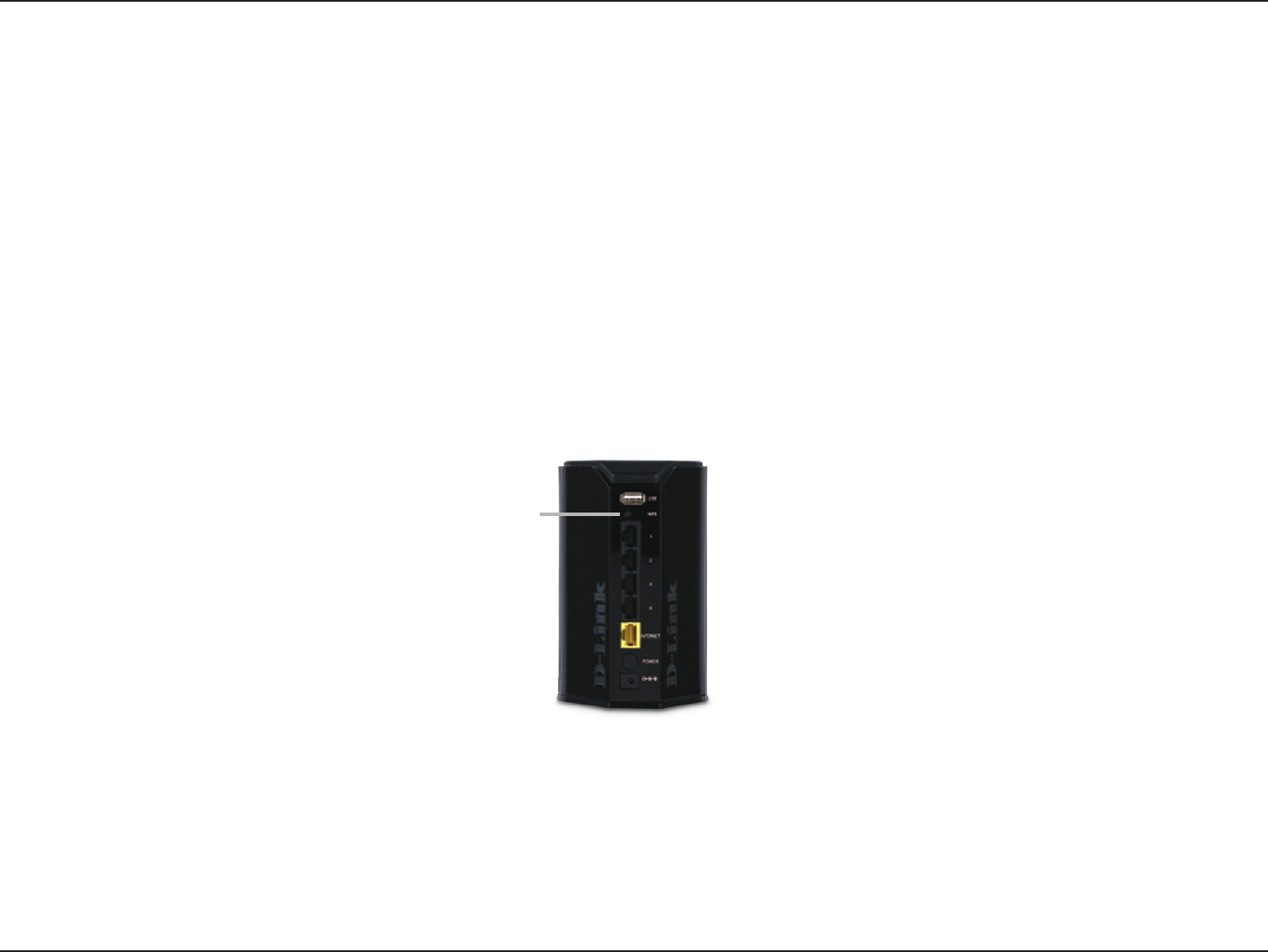
Connect a Wireless Client to your Router
WPS Button
Step 2 - Within 2 minutes, press the WPS button on your wireless client (or launch the software utility and start the WPS
process).
The easiest and most secure way to connect your wireless devices to the router is WPS (Wi-Fi Protected Setup). Most wireless
devices such as wireless adapters, media players, Blu-ray DVD players, wireless printers and cameras will have a WPS button
(or a software utility with WPS) that you can press to connect to the DIR-826L router. Please refer to your user manual for the
wireless device you want to connect to make sure you understand how to enable WPS. Once you know, follow the steps below:
Step 1 - Press the WPS button on the DIR-826L for about 1 second. The Internet LED on the front will start to blink.
Step 3 - Allow up to 1 minute to congure. Once the Internet light stops blinking, you will be connected and your wireless
connection will be secure with WPA2.
WPS Button
110D-Link DIR-826L User Manual
Section 4 - Security
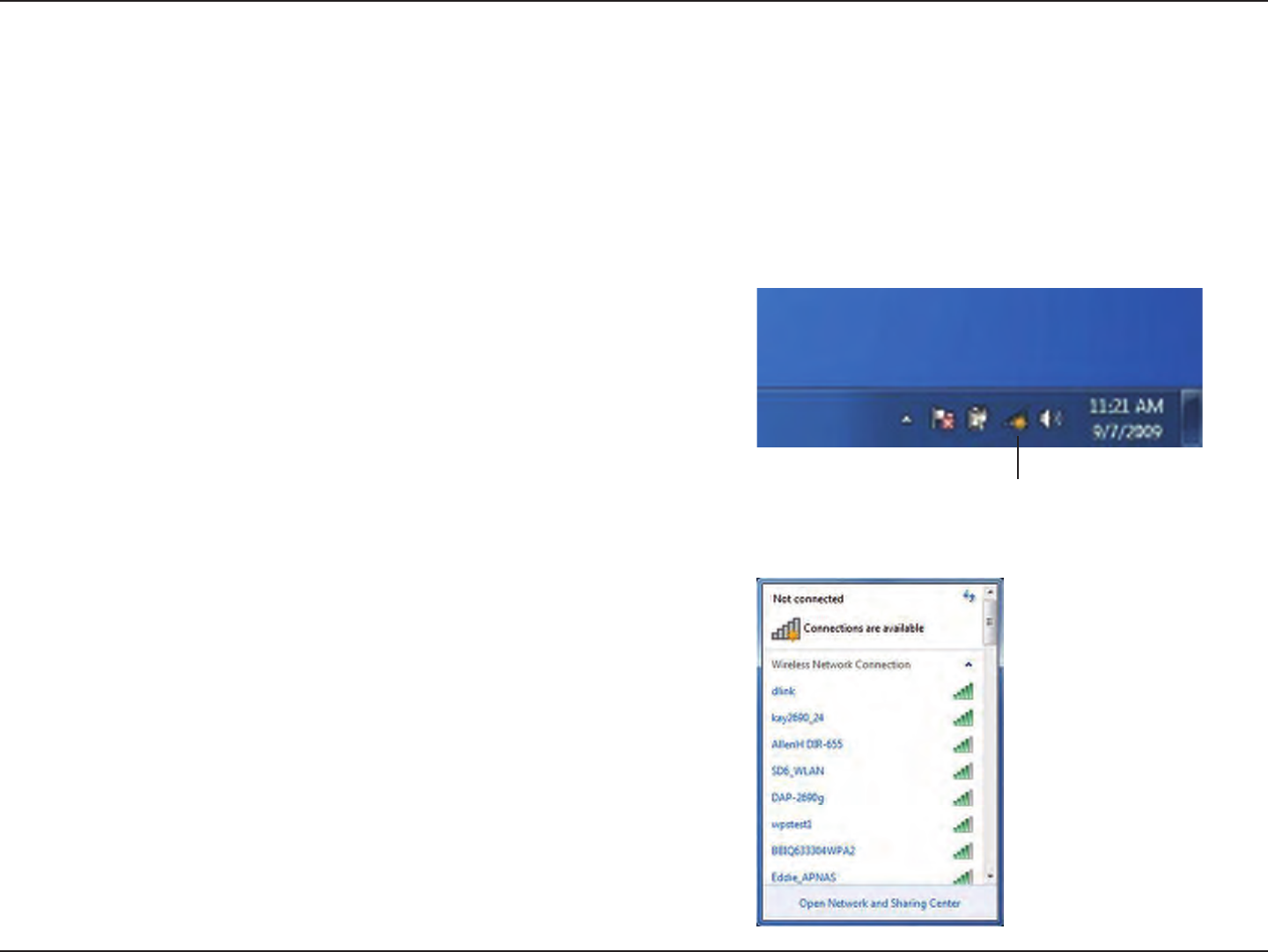
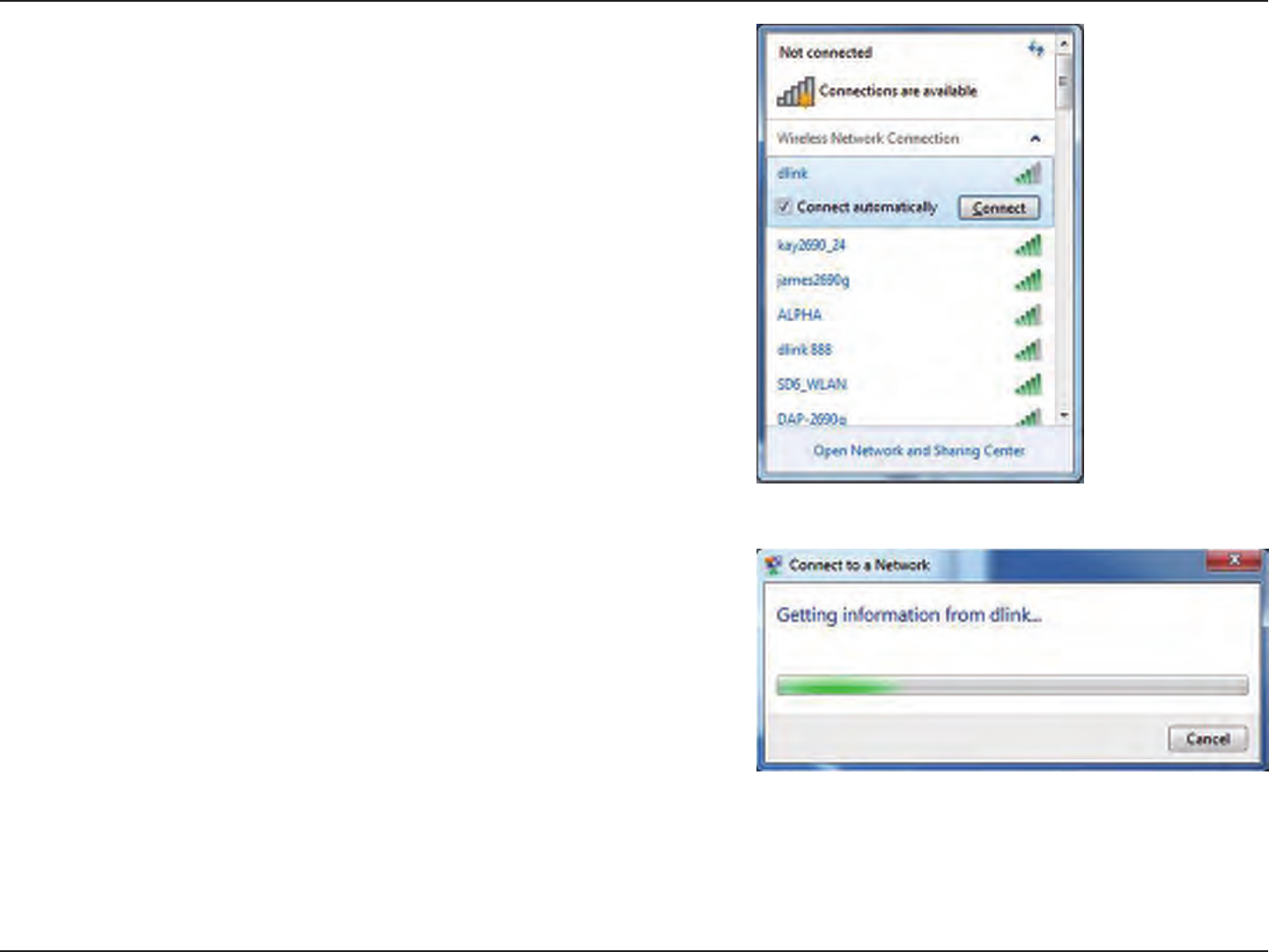
Windows® 7
It is recommended to enable wireless security (WPA/WPA2) on your wireless router or access point before conguring your
wireless adapter. If you are joining an existing network, you will need to know the security key or passphrase being used.
1. Click on the wireless icon in your system tray (lower-right corner).
2. The utility will display any available wireless networks in your area.
Wireless Icon
WPA/WPA2
111D-Link DIR-826L User Manual
Section 4 - Security
3. Highlight the wireless network (SSID) you would like to connect to
and click the Connect button.
If you get a good signal but cannot access the Internet, check your
TCP/IP settings for your wireless adapter. Refer to the Networking
Basics section in this manual for more information.
4. The following window appears while your computer tries to
connect to the router.
112D-Link DIR-826L User Manual
Section 4 - Security
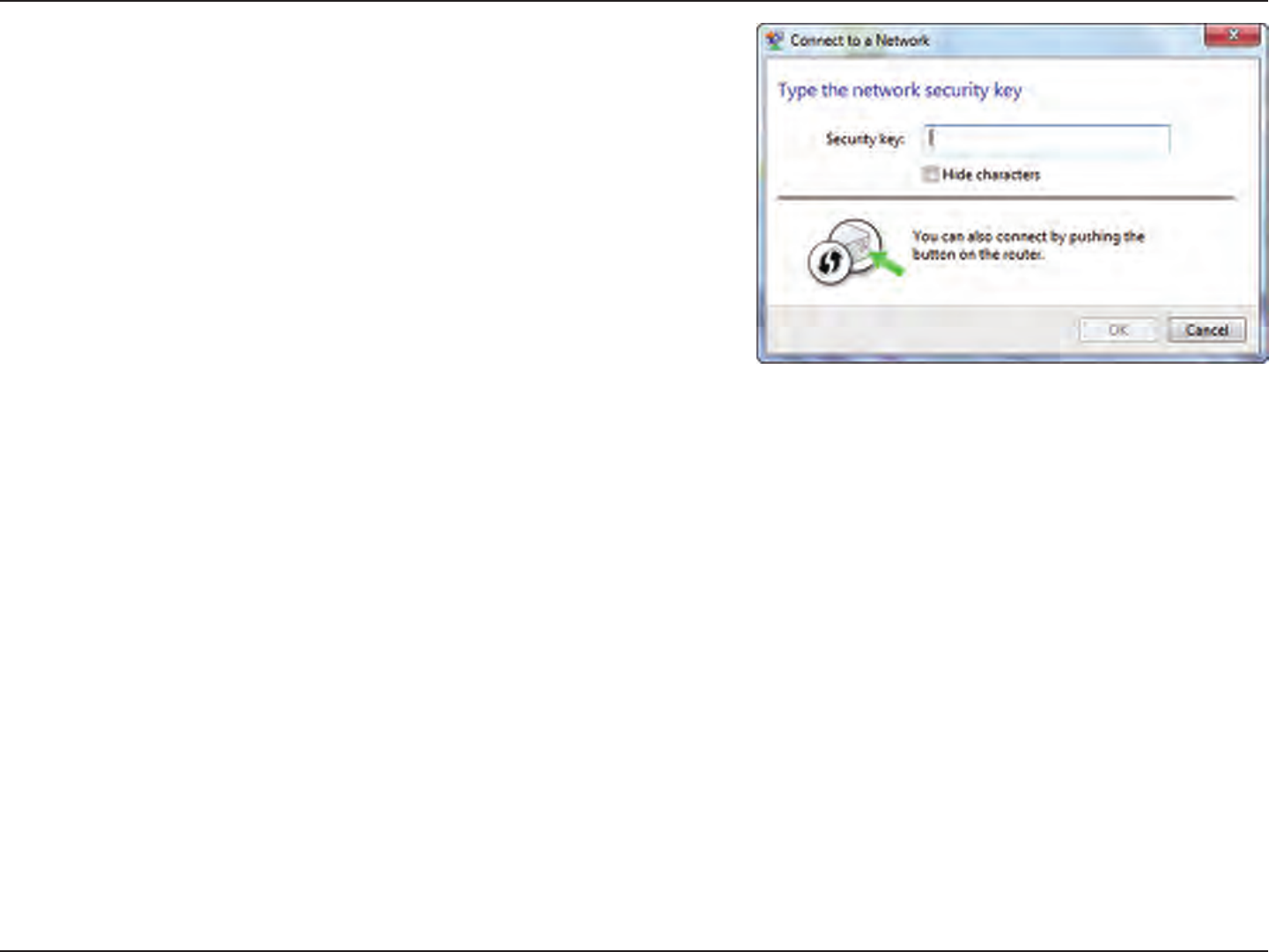
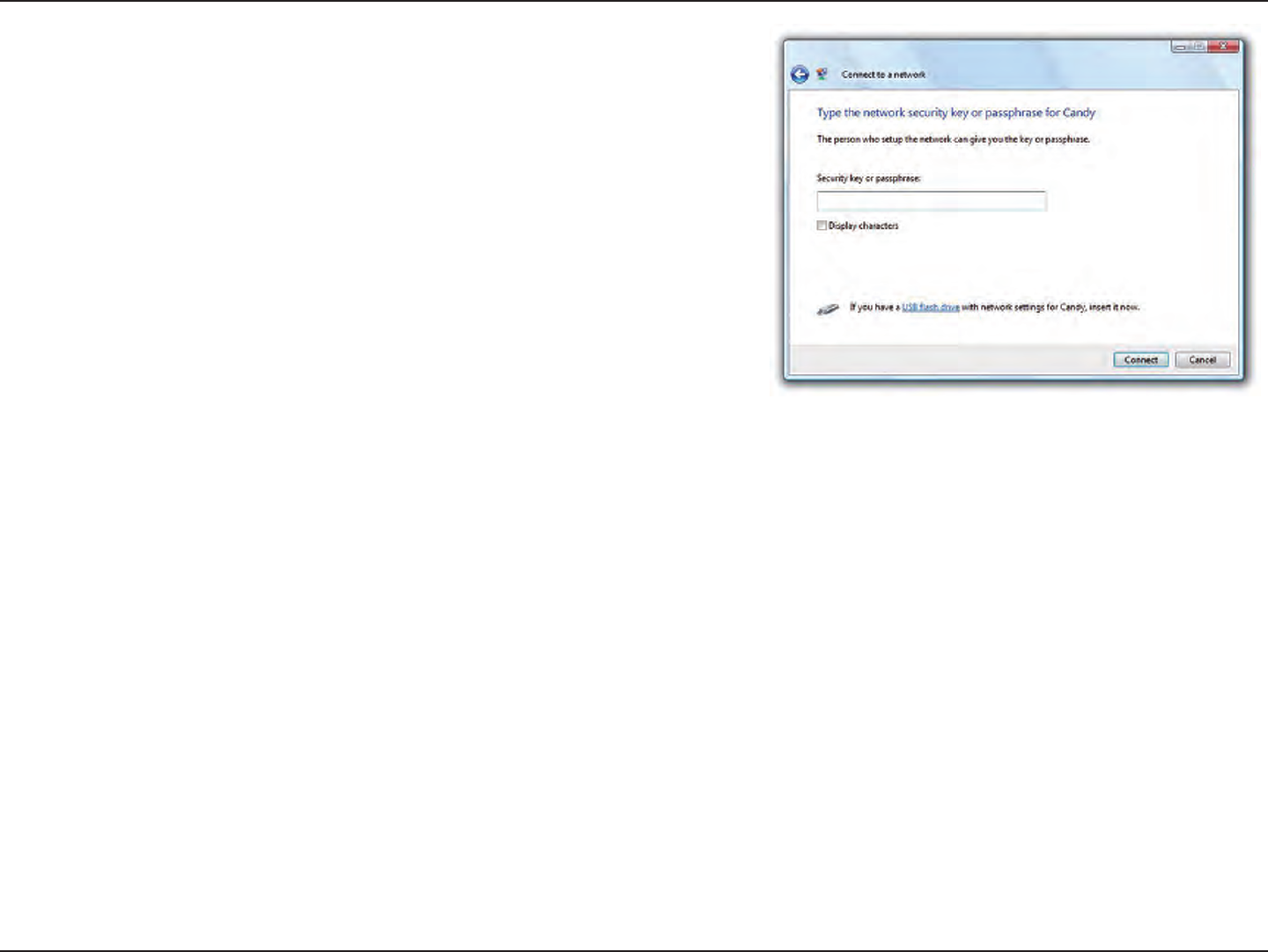
5. Enter the same security key or passphrase that is on your router and
click Connect. You can also connect by pushing the WPS button on
the router.
It may take 20-30 seconds to connect to the wireless network. If the
connection fails, please verify that the security settings are correct. The
key or passphrase must be exactly the same as on the wireless router.
113D-Link DIR-826L User Manual
Section 4 - Security
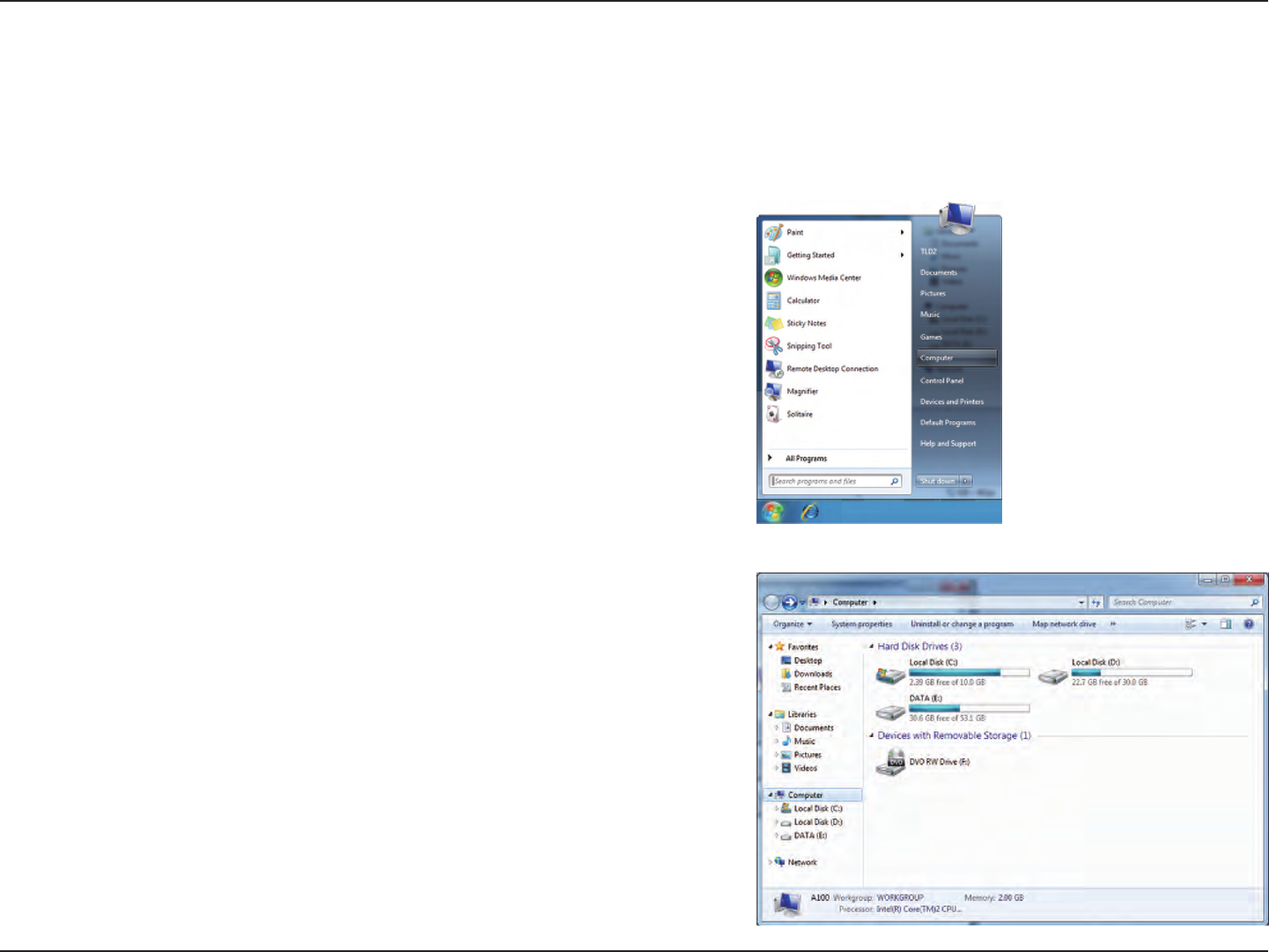
WPS
The WPS feature of the DIR-826L can be congured using Windows® 7. Carry out the following steps to use Windows® 7 to
congure the WPS feature:
1. Click the Start button and select Computer from the Start menu.
2. Click Network on the left side.
114D-Link DIR-826L User Manual
Section 4 - Security
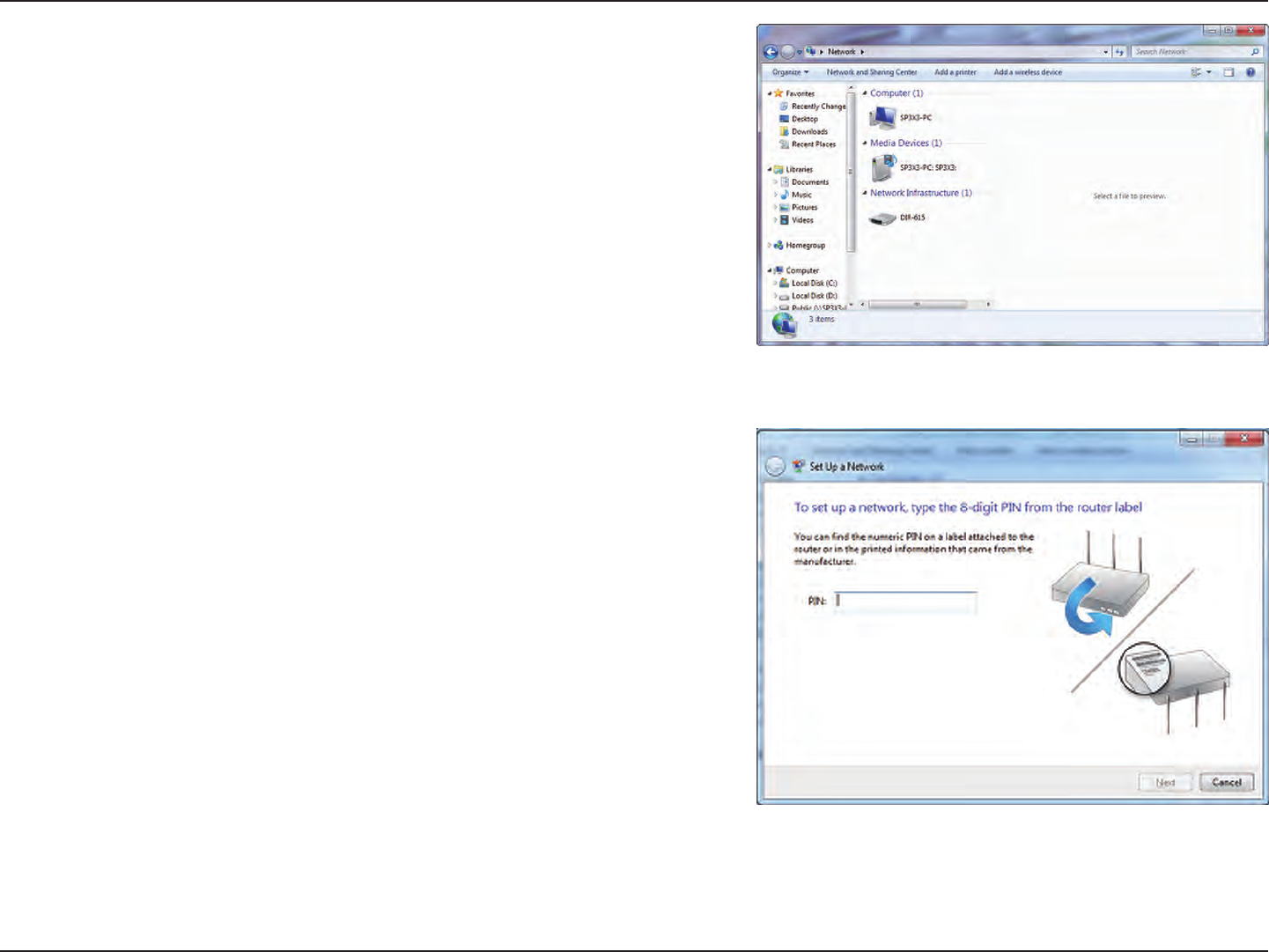
3. Double-click the DIR-826L.
4. Input the WPS PIN number (displayed in the WPS window on the
Router’s LCD screen or in the Setup > Wireless Setup menu in
the Router’s Web UI) and click Next.
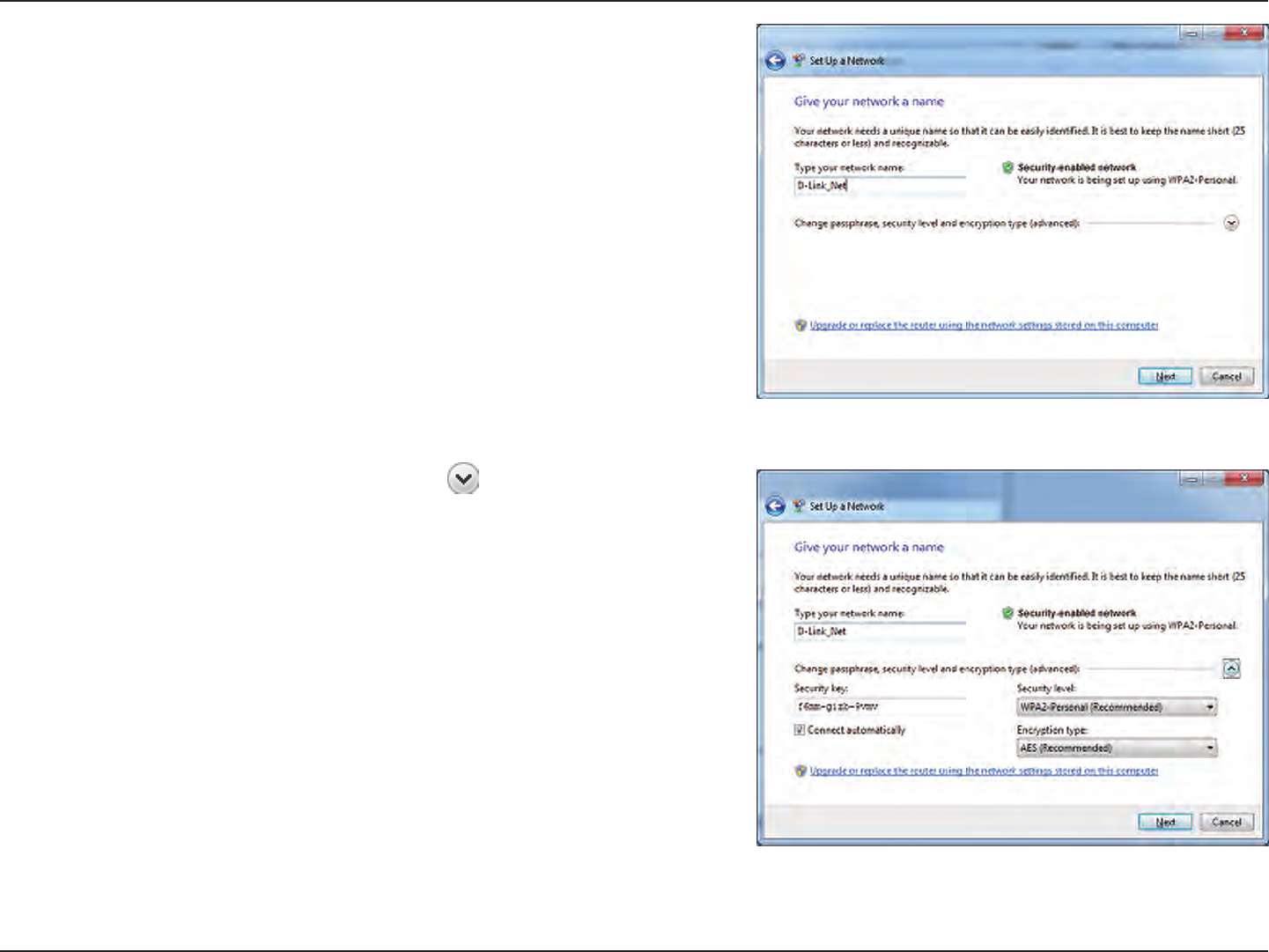
115D-Link DIR-826L User Manual
Section 4 - Security
5. Type a name to identify the network.
6. To congure advanced settings, click the icon.
Click Next to continue.
116D-Link DIR-826L User Manual
Section 4 - Security
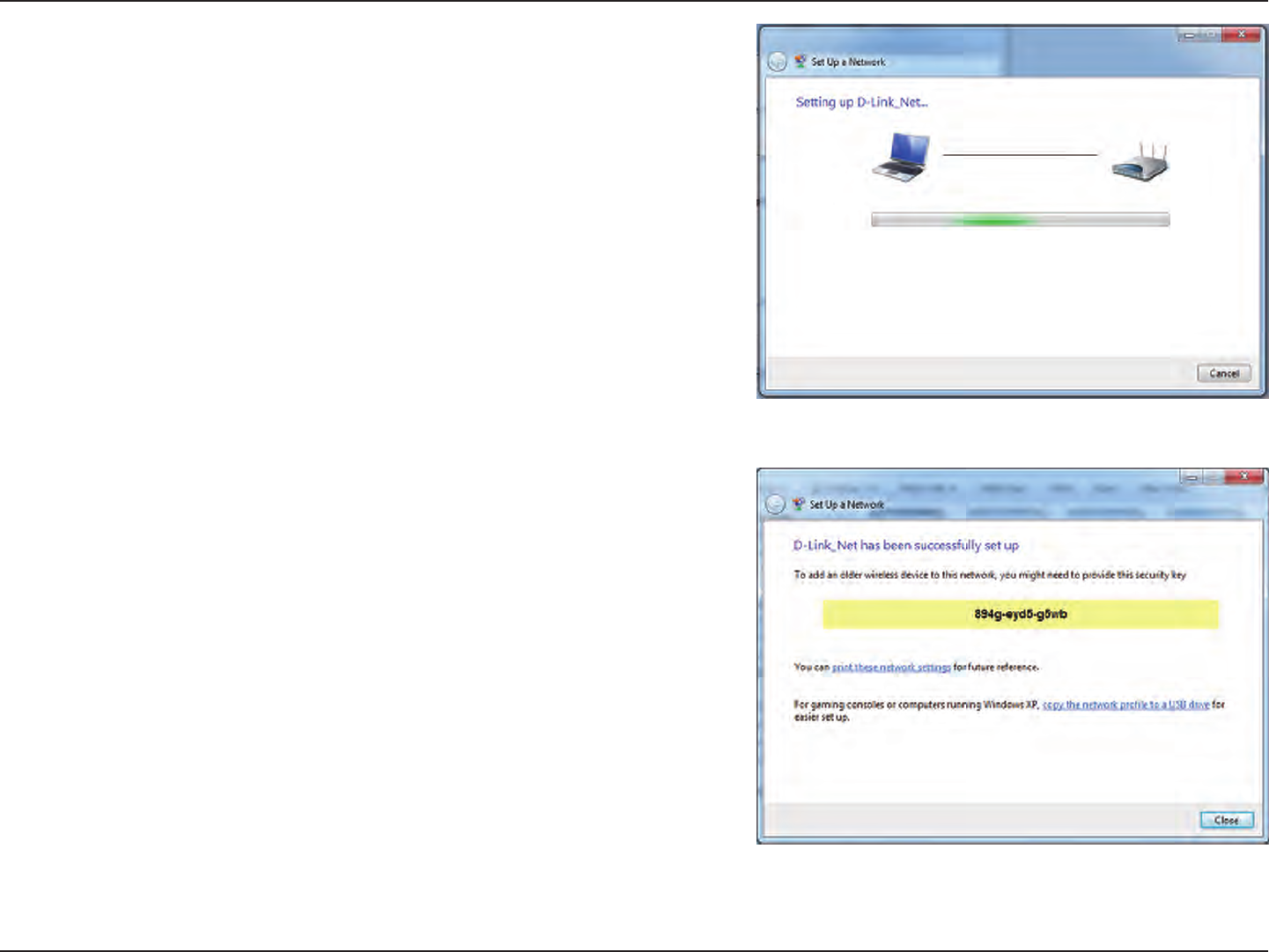
7. The following window appears while the Router is being
congured.
Wait for the conguration to complete.
8. The following window informs you that WPS on the router has
been setup successfully.
Make a note of the security key as you may need to provide this
security key if adding an older wireless device to the network in
the future.
9. Click Close to complete WPS setup.
117D-Link DIR-826L User Manual
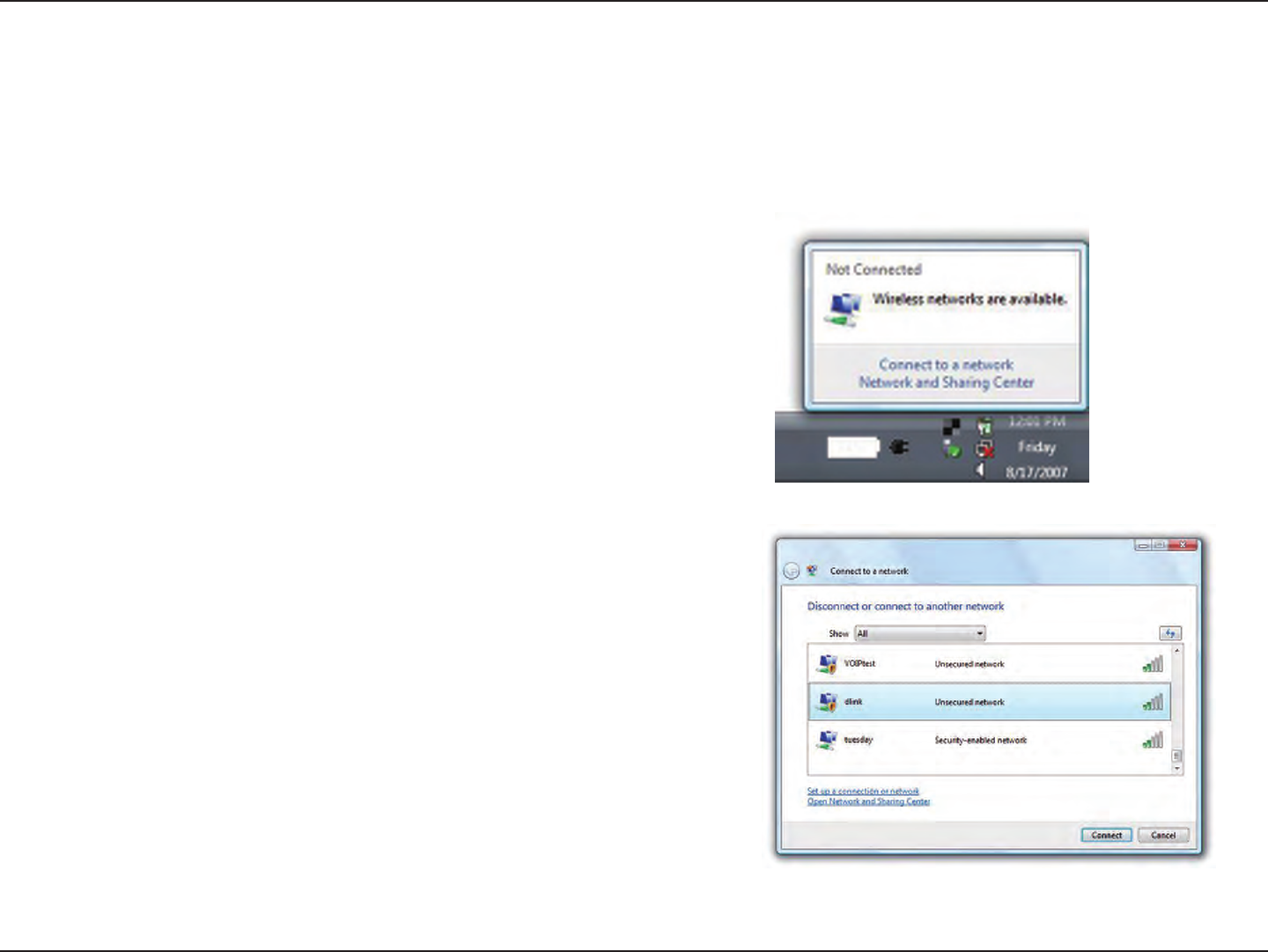
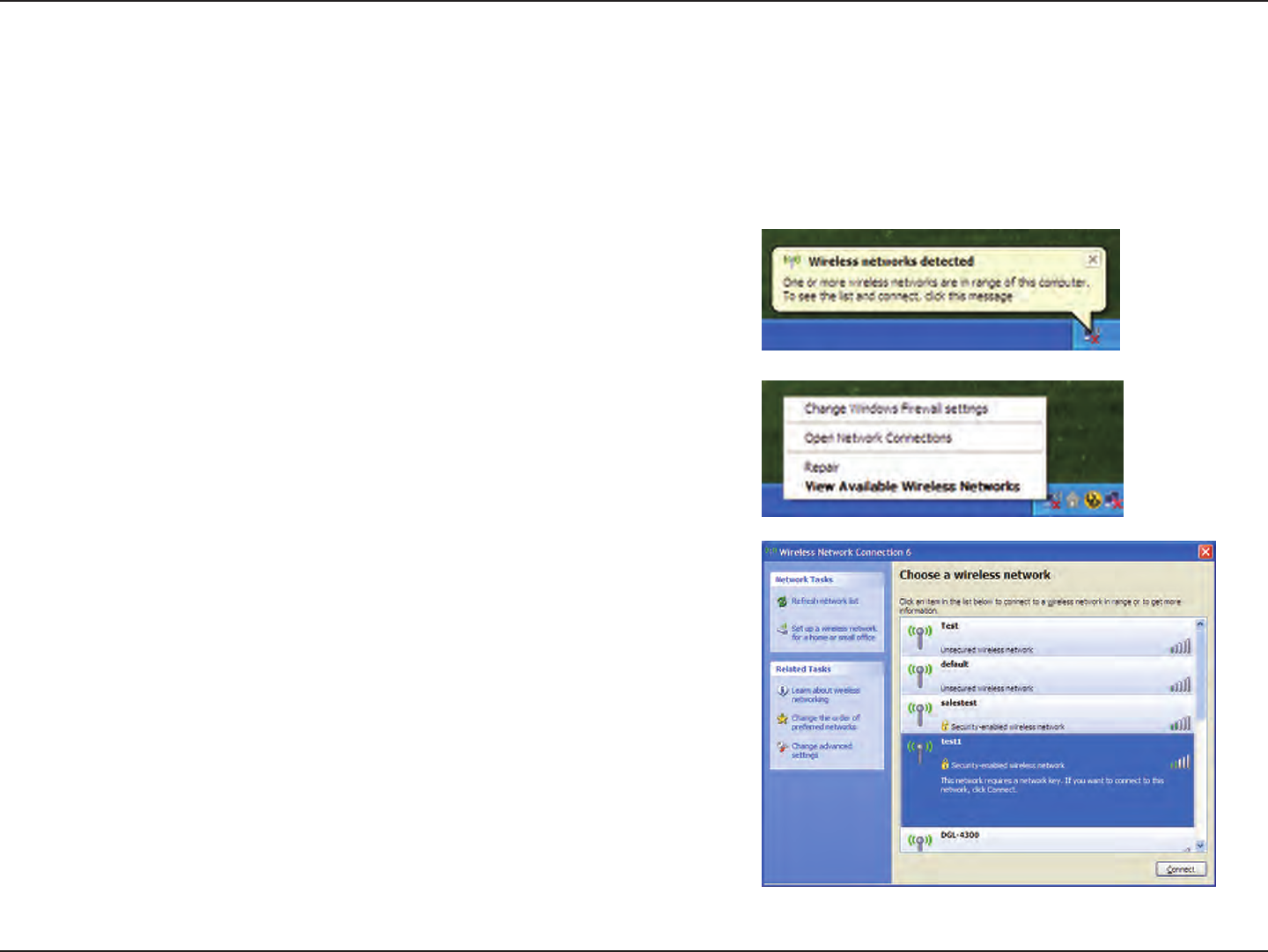
Section 5 - Connecting to a Wireless Network
Windows Vista®
Windows Vista® users may use the built-in wireless utility. If you are using another company’s utility, please refer to the user
manual of your wireless adapter for help with connecting to a wireless network. Most utilities will have a “site survey” option
similar to the Windows Vista® utility as seen below.
Right-click on the wireless computer icon in your system tray (lower-right
corner next to the time). Select Connect to a network.
If you receive the Wireless Networks Detected bubble, click on the
center of the bubble to access the utility.
or
The utility will display any available wireless networks in your area. Click
on a network (displayed using the SSID) and click the Connect button.
If you get a good signal but cannot access the Internet, check you TCP/
IP settings for your wireless adapter. Refer to the Networking Basics
section in this manual for more information.
118D-Link DIR-826L User Manual
Section 5 - Connecting to a Wireless Network
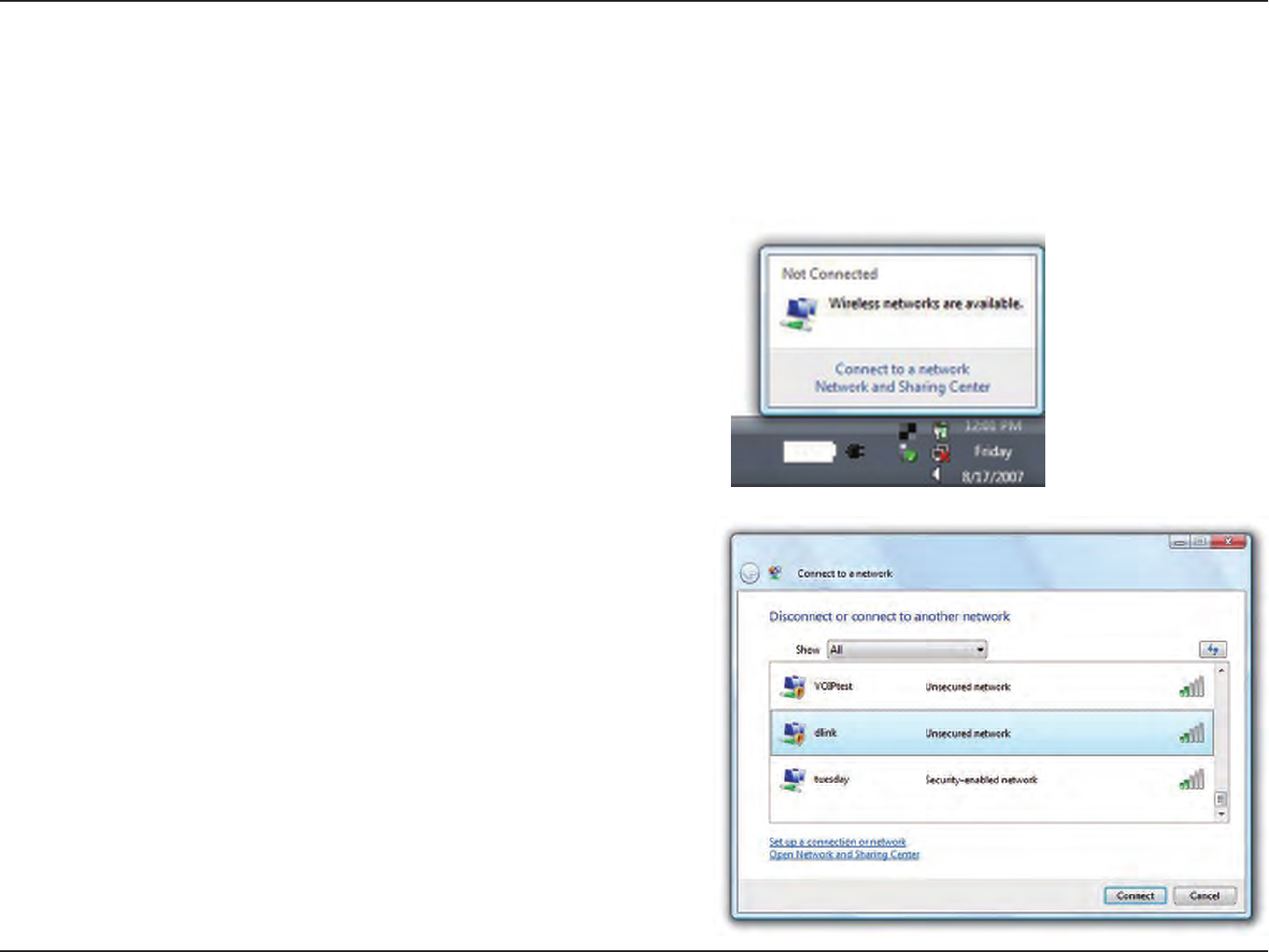
WPA/WPA2
It is recommended to enable wireless security (WPA/WPA2) on your wireless router or access point before conguring your
wireless adapter. If you are joining an existing network, you will need to know the security key or passphrase being used.
2. Highlight the wireless network (SSID) you would like to connect
to and click Connect.
1. Open the Windows Vista® Wireless Utility by right-clicking on the
wireless computer icon in your system tray (lower right corner of
screen). Select Connect to a network.
119D-Link DIR-826L User Manual
Section 5 - Connecting to a Wireless Network
3. Enter the same security key or passphrase that is on your router and
click Connect.
It may take 20-30 seconds to connect to the wireless network. If the
connection fails, please verify that the security settings are correct. The
key or passphrase must be exactly the same as on the wireless router.
120D-Link DIR-826L User Manual
Section 5 - Connecting to a Wireless Network
WPS/WCN 2.0
The router supports Wi-Fi protection, referred to as WCN 2.0 in Windows Vista®. The following instructions for setting this up
depends on whether you are using Windows Vista® to congure the router or third party software.
When you rst set up the router, Wi-Fi protection is disabled and uncongured. To enjoy the benets of Wi-Fi protection, the
router must be both enabled and congured. There are three basic methods to accomplish this: use Windows Vista’s built-in
support for WCN 2.0, use software provided by a third party, or manually congure.
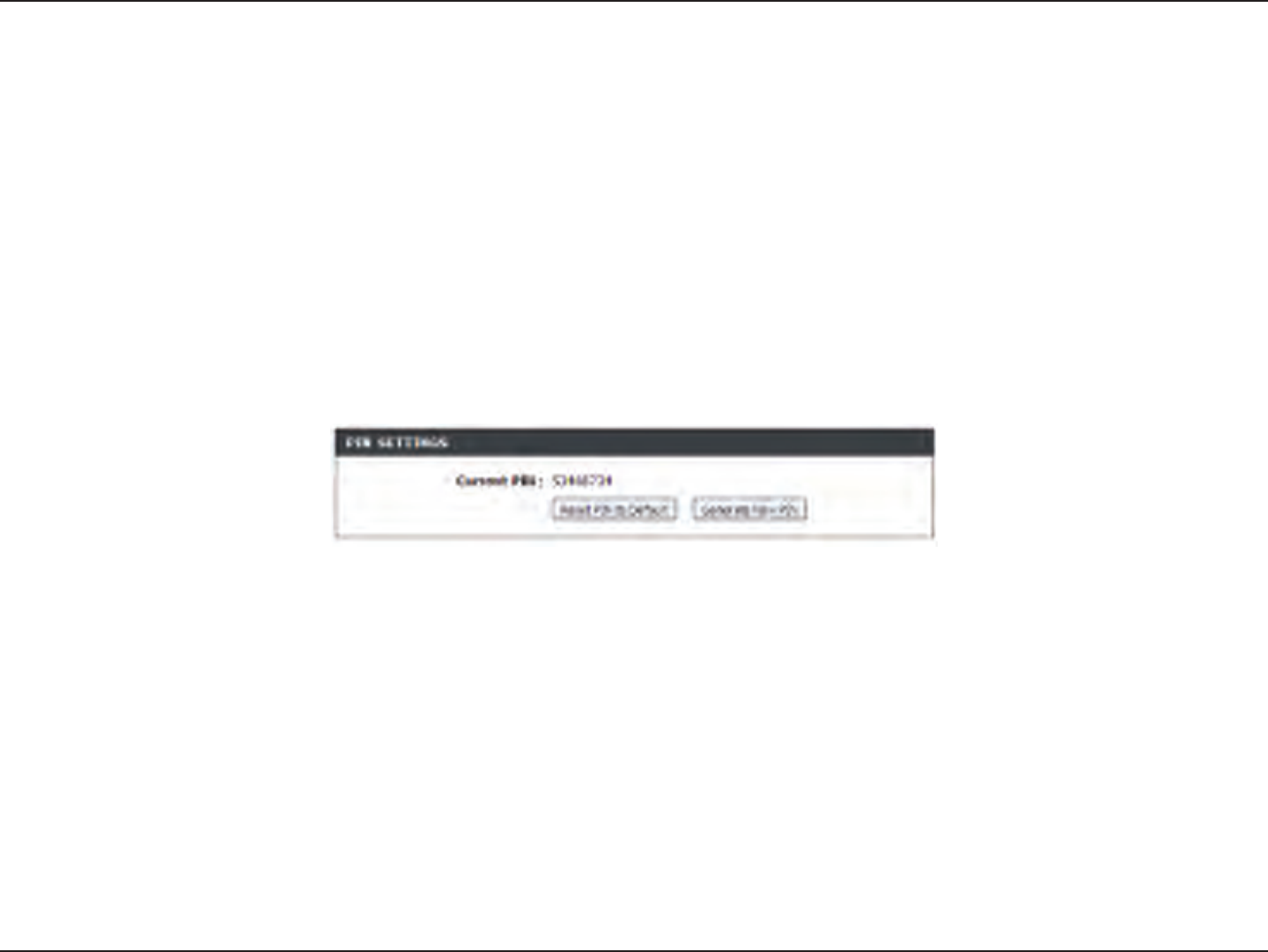
If you are running Windows Vista®, log into the router and click the Enable checkbox in the Basic > Wireless section. Use the
Current PIN that is displayed on the Advanced > Wi-Fi Protected Setup section or choose to click the Generate New PIN
button or Reset PIN to Default button.
If you are using third party software to set up Wi-Fi Protection, carefully follow the directions. When you are nished, proceed
to the next section to set up the newly-congured router.
121D-Link DIR-826L User Manual
Section 5 - Connecting to a Wireless Network
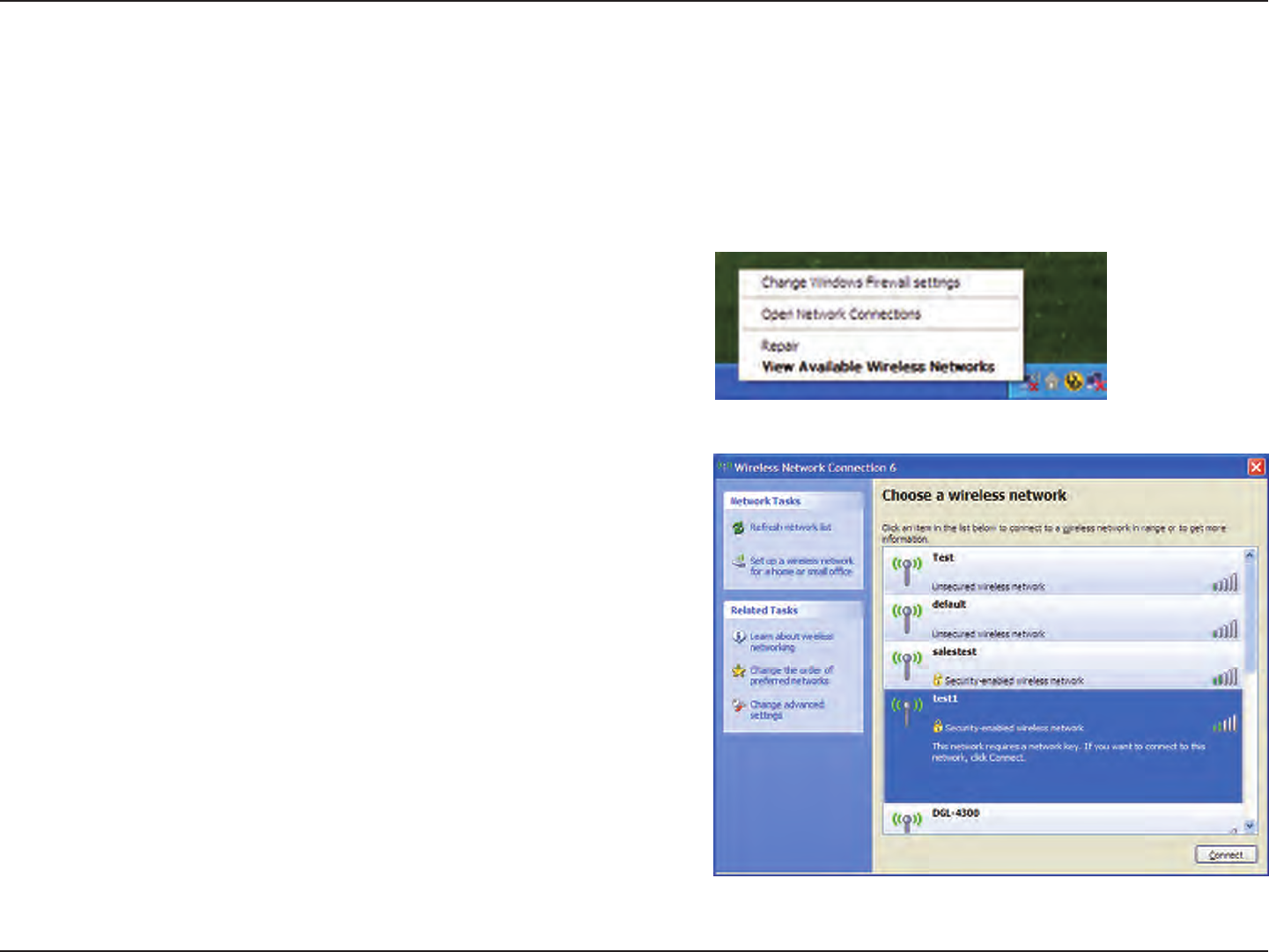
Windows® XP
Windows® XP users may use the built-in wireless utility (Zero Conguration Utility). The following instructions are for Service
Pack 2 users. If you are using another company’s utility, please refer to the user manual of your wireless adapter for help with
connecting to a wireless network. Most utilities will have a “site survey” option similar to the Windows® XP utility as seen below.
Right-click on the wireless computer icon in your system tray (lower-right
corner next to the time). Select View Available Wireless Networks.
If you receive the Wireless Networks Detected bubble, click on the
center of the bubble to access the utility.
or
The utility will display any available wireless networks in your area.
Click on a network (displayed using the SSID) and click the Connect
button.
If you get a good signal but cannot access the Internet, check you
TCP/IP settings for your wireless adapter. Refer to the Networking
Basics section in this manual for more information.
122D-Link DIR-826L User Manual
Section 5 - Connecting to a Wireless Network
It is recommended to enable WPA on your wireless router or access point before conguring your wireless adapter. If you are
joining an existing network, you will need to know the WPA key being used.
2. Highlight the wireless network (SSID) you would like to
connect to and click Connect.
1. Open the Windows® XP Wireless Utility by right-clicking on the
wireless computer icon in your system tray (lower-right corner
of screen). Select View Available Wireless Networks.
WPA/WPA2
123D-Link DIR-826L User Manual
Section 5 - Connecting to a Wireless Network
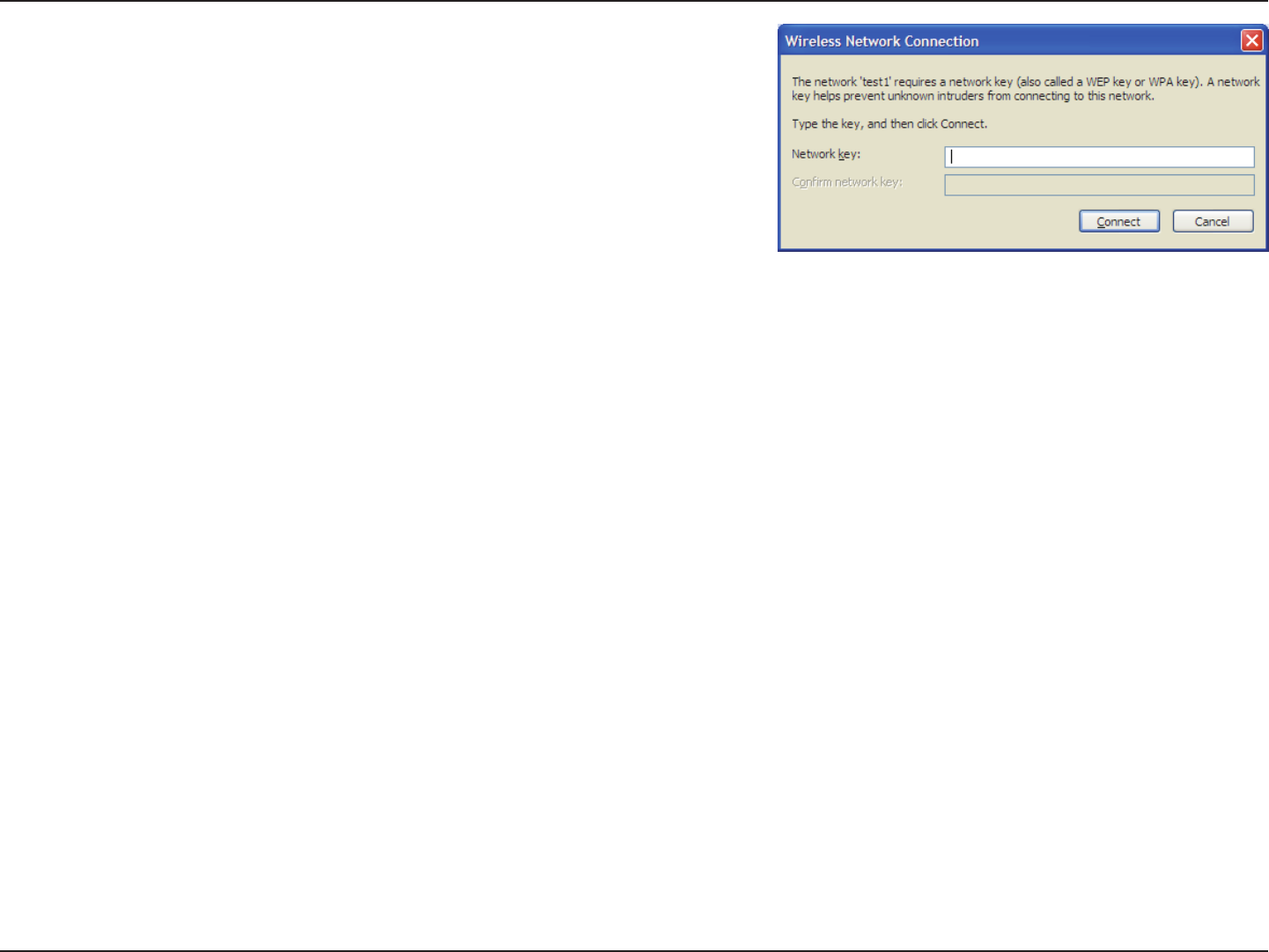
3. The Wireless Network Connection box will appear. Enter the WPA-PSK
passphrase and click Connect.
It may take 20-30 seconds to connect to the wireless network. If the
connection fails, please verify that the WPA-PSK settings are correct. The
WPA-PSK passphrase must be exactly the same as on the wireless router.
124D-Link DIR-826L User Manual
Section 6 - Troubleshooting
Troubleshooting
This chapter provides solutions to problems that can occur during the installation and operation of the DIR-826L. Read the
following descriptions if you are having problems. The examples below are illustrated in Windows® XP. If you have a dierent
operating system, the screenshots on your computer will look similar to the following examples.
1. Why can’t I access the web-based conguration utility?
When entering the IP address of the D-Link router (192.168.0.1 for example), you are not connecting to a website nor do you
have to be connected to the Internet. The device has the utility built-in to a ROM chip in the device itself. Your computer must
be on the same IP subnet to connect to the web-based utility.
• Make sure you have an updated Java-enabled web browser. We recommend the following:
- Microsoft Internet Explorer® 7 and higher
- Mozilla Firefox 3.5 and higher
- Google™ Chrome 8 and higher
- Apple Safari 4 and higher
• Verify physical connectivity by checking for solid link lights on the device. If you do not get a solid link light, try using a
dierent cable or connect to a dierent port on the device if possible. If the computer is turned o, the link light may not be
on.
• Disable any Internet security software running on the computer. Software rewalls such as Zone Alarm, Black Ice, Sygate,
Norton Personal Firewall, and Windows® XP rewall may block access to the conguration pages. Check the help les included
with your rewall software for more information on disabling or conguring it.
125D-Link DIR-826L User Manual
Section 6 - Troubleshooting
• Congure your Internet settings:
• Go to Start > Settings > Control Panel. Double-click the Internet Options Icon. From the Security tab, click
the button to restore the settings to their defaults.
• Click the Connection tab and set the dial-up option to Never Dial a Connection. Click the LAN Settings button.
Make sure nothing is checked. Click OK.
• Go to the Advanced tab and click the button to restore these settings to their defaults. Click OK three times.
• Close your web browser (if open) and open it.
• Access the web management. Open your web browser and enter the IP address of your D-Link router in the address bar. This
should open the login page for your web management.
• If you still cannot access the conguration, unplug the power to the router for 10 seconds and plug back in. Wait about 30
seconds and try accessing the conguration. If you have multiple computers, try connecting using a dierent computer.
2. What can I do if I forgot my password?
If you forgot your password, you must reset your router. Unfortunately this process will change all your settings back to the
factory defaults.
To reset the router, locate the reset button (hole) on the rear panel of the unit. With the router powered on, use a paperclip
to hold the button down for 10 seconds. Release the button and the router will go through its reboot process. Wait about 30
seconds to access the router. The default IP address is 192.168.0.1. When logging in, the username is admin and leave the
password box empty.
126D-Link DIR-826L User Manual
Section 6 - Troubleshooting
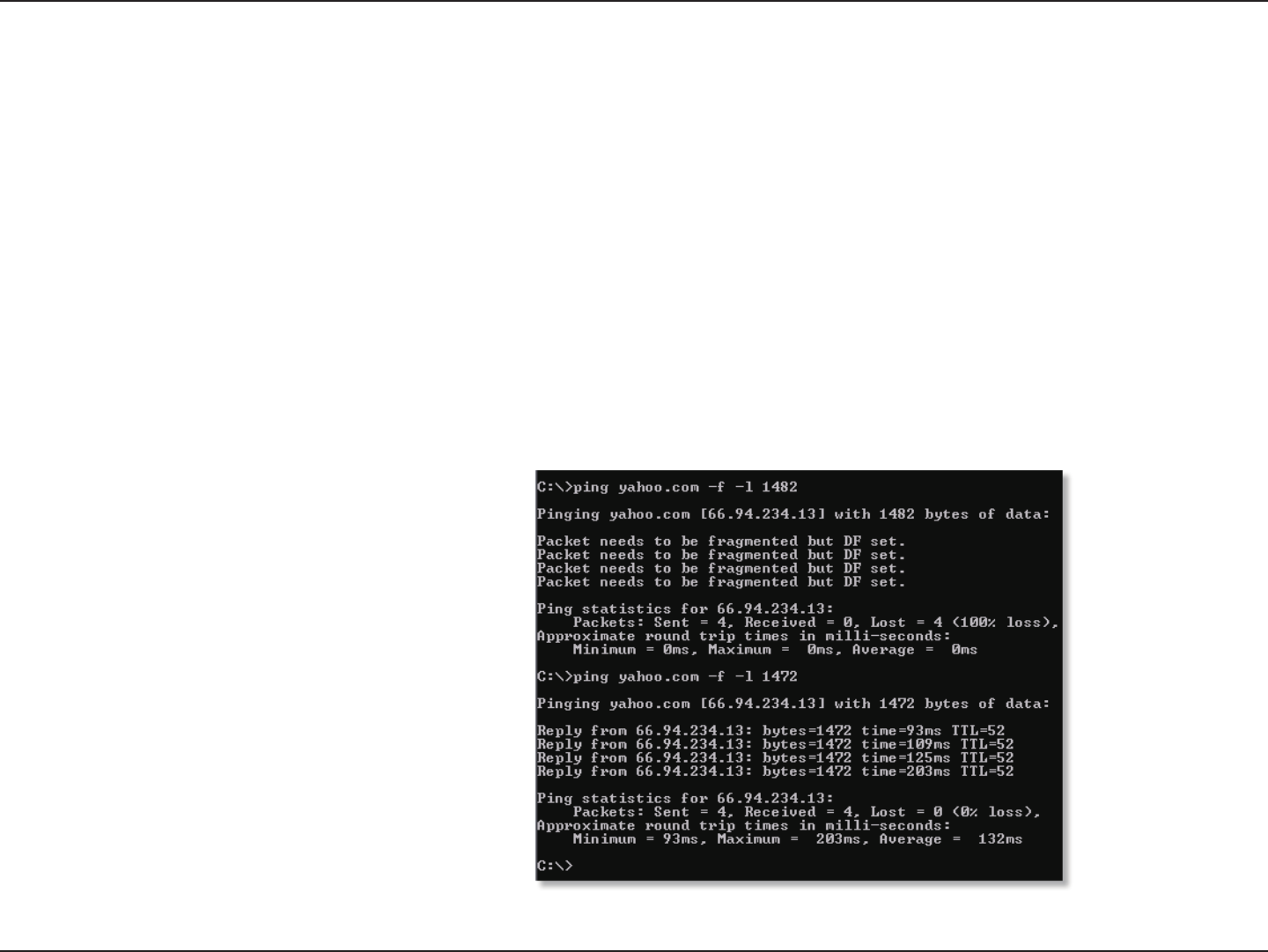
3. Why can’t I connect to certain sites or send and receive emails when connecting through my router?
If you are having a problem sending or receiving email, or connecting to secure sites such as eBay, banking sites, and Hotmail,
we suggest lowering the MTU in increments of ten (Ex. 1492, 1482, 1472, etc).
To nd the proper MTU Size, you’ll have to do a special ping of the destination you’re trying to go to. A destination could be
another computer, or a URL.
• Click on Start and then click Run.
• Windows® 95, 98, and Me users type in command (Windows® NT, 2000, XP, Vista®, and 7 users type in cmd) and
press Enter (or click OK).
• Once the window opens, you’ll need to do a special ping. Use the following syntax:
ping [url] [-f] [-l] [MTU value]
Example: ping yahoo.com -f -l 1472
127D-Link DIR-826L User Manual
Section 6 - Troubleshooting
You should start at 1472 and work your way down by 10 each time. Once you get a reply, go up by 2 until you get a fragmented
packet. Take that value and add 28 to the value to account for the various TCP/IP headers. For example, lets say that 1452 was the
proper value, the actual MTU size would be 1480, which is the optimum for the network we’re working with (1452+28=1480).
Once you nd your MTU, you can now congure your router with the proper MTU size.
To change the MTU rate on your router follow the steps below:
• Open your browser, enter the IP address of your router (192.168.0.1) and click OK.
• Enter your username (admin) and password (blank by default). Click OK to enter the web conguration page
for the device.
• Click on Setup and then click Manual Congure.
• To change the MTU enter the number in the MTU eld and click Save Settings to save your settings.
• Test your email. If changing the MTU does not resolve the problem, continue changing the MTU in increments
of ten.
128D-Link DIR-826L User Manual
Appendix A - Wireless Basics
D-Link wireless products are based on industry standards to provide easy-to-use and compatible high-speed wireless
connectivity within your home, business or public access wireless networks. Strictly adhering to the IEEE standard, the D-Link
wireless family of products will allow you to securely access the data you want, when and where you want it. You will be able
to enjoy the freedom that wireless networking delivers.
A wireless local area network (WLAN) is a cellular computer network that transmits and receives data with radio signals instead of
wires. Wireless LANs are used increasingly in both home and oce environments, and public areas such as airports, coee shops
and universities. Innovative ways to utilize WLAN technology are helping people to work and communicate more eciently.
Increased mobility and the absence of cabling and other xed infrastructure have proven to be benecial for many users.
Wireless users can use the same applications they use on a wired network. Wireless adapter cards used on laptop and desktop
systems support the same protocols as Ethernet adapter cards.
Under many circumstances, it may be desirable for mobile network devices to link to a conventional Ethernet LAN in order to
use servers, printers or an Internet connection supplied through the wired LAN. A Wireless Router is a device used to provide
this link.
Wireless Basics
129D-Link DIR-826L User Manual
Appendix A - Wireless Basics
What is Wireless?
Wireless or Wi-Fi technology is another way of connecting your computer to the network without using wires. Wi-Fi uses radio
frequency to connect wirelessly, so you have the freedom to connect computers anywhere in your home or oce network.
Why D-Link Wireless?
D-Link is the worldwide leader and award winning designer, developer, and manufacturer of networking products. D-Link
delivers the performance you need at a price you can aord. D-Link has all the products you need to build your network.
How does wireless work?
Wireless works similar to how cordless phone work, through radio signals to transmit data from one point A to point B. But
wireless technology has restrictions as to how you can access the network. You must be within the wireless network range area
to be able to connect your computer. There are two dierent types of wireless networks Wireless Local Area Network (WLAN),
and Wireless Personal Area Network (WPAN).
Wireless Local Area Network (WLAN)
In a wireless local area network, a device called an Access Point (AP) connects computers to the network. The access point has
a small antenna attached to it, which allows it to transmit data back and forth over radio signals. With an indoor access point
as seen in the picture, the signal can travel up to 300 feet. With an outdoor access point the signal can reach out up to 30 miles
to serve places like manufacturing plants, industrial locations, college and high school campuses, airports, golf courses, and
many other outdoor venues.
130D-Link DIR-826L User Manual
Appendix A - Wireless Basics
Wireless Personal Area Network (WPAN)
Bluetooth is the industry standard wireless technology used for WPAN. Bluetooth devices in WPAN operate in a range up to
30 feet away.
Compared to WLAN the speed and wireless operation range are both less than WLAN, but in return it doesn’t use nearly as
much power which makes it ideal for personal devices, such as mobile phones, PDAs, headphones, laptops, speakers, and other
devices that operate on batteries.
Who uses wireless?
Wireless technology as become so popular in recent years that almost everyone is using it, whether it’s for home, oce, business,
D-Link has a wireless solution for it.
Home
• Gives everyone at home broadband access
• Surf the web, check email, instant message, etc.
• Gets rid of the cables around the house
• Simple and easy to use
Small Oce and Home Oce
• Stay on top of everything at home as you would at oce
• Remotely access your oce network from home
• Share Internet connection and printer with multiple computers
• No need to dedicate oce space
131D-Link DIR-826L User Manual
Appendix A - Wireless Basics
Where is wireless used?
Wireless technology is expanding everywhere not just at home or oce. People like the freedom of mobility and it’s becoming
so popular that more and more public facilities now provide wireless access to attract people. The wireless connection in public
places is usually called “hotspots”.
Using a D-Link Cardbus Adapter with your laptop, you can access the hotspot to connect to Internet from remote locations
like: Airports, Hotels, Coee Shops, Libraries, Restaurants, and Convention Centers.
Wireless network is easy to setup, but if you’re installing it for the rst time it could be quite a task not knowing where to start.
That’s why we’ve put together a few setup steps and tips to help you through the process of setting up a wireless network.
Tips
Here are a few things to keep in mind, when you install a wireless network.
Centralize your router or Access Point
Make sure you place the router/access point in a centralized location within your network for the best performance. Try to
place the router/access point as high as possible in the room, so the signal gets dispersed throughout your home. If you have
a two-story home, you may need a repeater to boost the signal to extend the range.
Eliminate Interference
Place home appliances such as cordless telephones, microwaves, and televisions as far away as possible from the router/
access point. This would signicantly reduce any interference that the appliances might cause since they operate on same
frequency.
132D-Link DIR-826L User Manual
Appendix A - Wireless Basics
Security
Don’t let you next-door neighbors or intruders connect to your wireless network. Secure your wireless network by turning on
the WPA or WEP security feature on the router. Refer to product manual for detail information on how to set it up.
There are basically two modes of networking:
• Infrastructure – All wireless clients will connect to an access point or wireless router.
• Ad-Hoc – Directly connecting to another computer, for peer-to-peer communication, using wireless network
adapters on each computer, such as two or more DIR-826L wireless network Cardbus adapters.
An Infrastructure network contains an Access Point or wireless router. All the wireless devices, or clients, will connect to the
wireless router or access point.
An Ad-Hoc network contains only clients, such as laptops with wireless cardbus adapters. All the adapters must be in Ad-Hoc
mode to communicate.
Wireless Modes
133D-Link DIR-826L User Manual
Appendix B - Networking Basics
Networking Basics
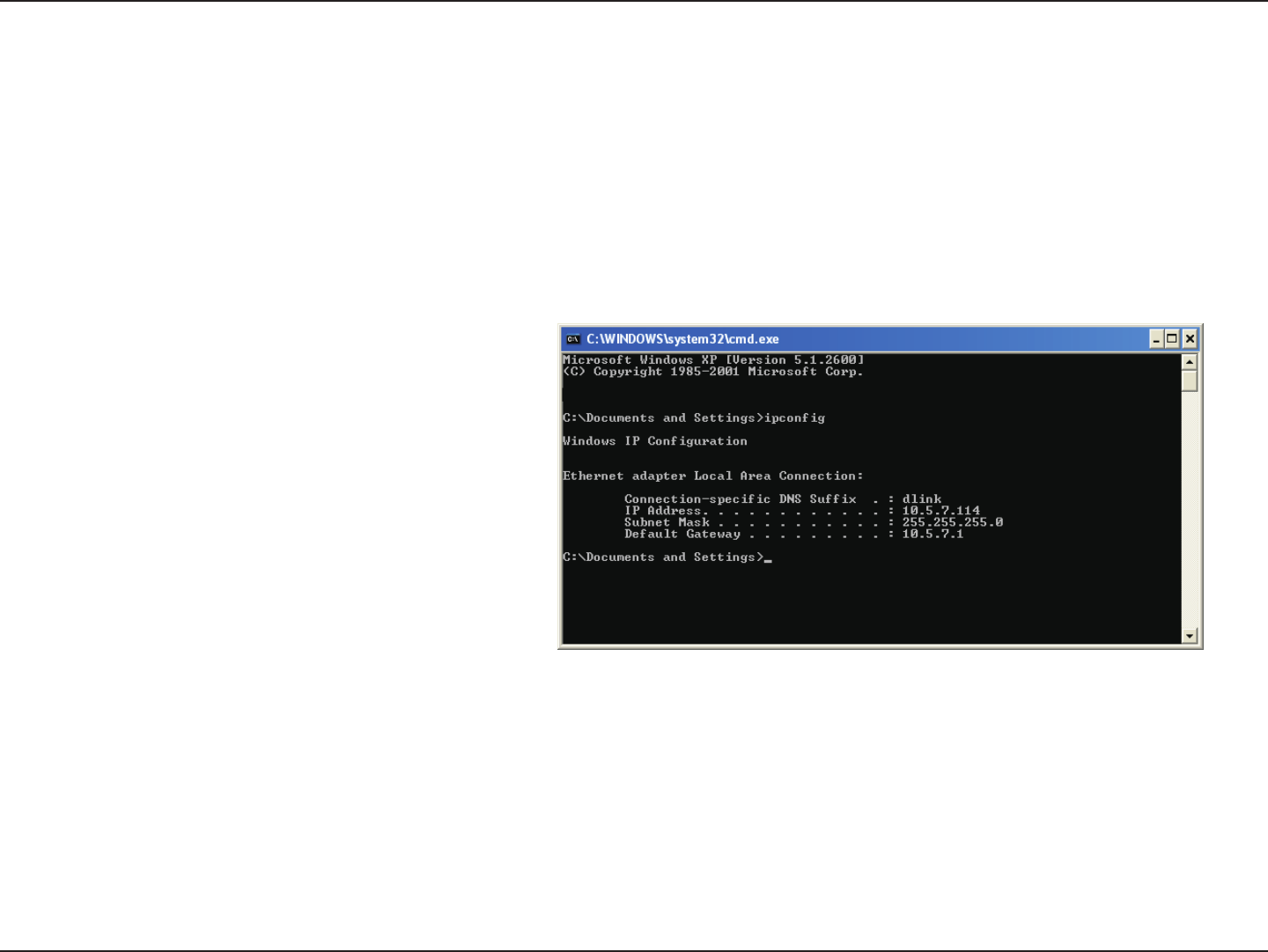
Check your IP address
After you install your new D-Link adapter, by default, the TCP/IP settings should be set to obtain an IP address from a DHCP
server (i.e. wireless router) automatically. To verify your IP address, please follow the steps below.
Click on Start > Run. In the run box type cmd and click OK. (Windows® 7/Vista® users type cmd in the Start Search box.)
At the prompt, type ipcong and press Enter.
This will display the IP address, subnet mask, and the
default gateway of your adapter.
If the address is 0.0.0.0, check your adapter installation,
security settings, and the settings on your router.
Some rewall software programs may block a DHCP
request on newly installed adapters.
134D-Link DIR-826L User Manual
Appendix B - Networking Basics
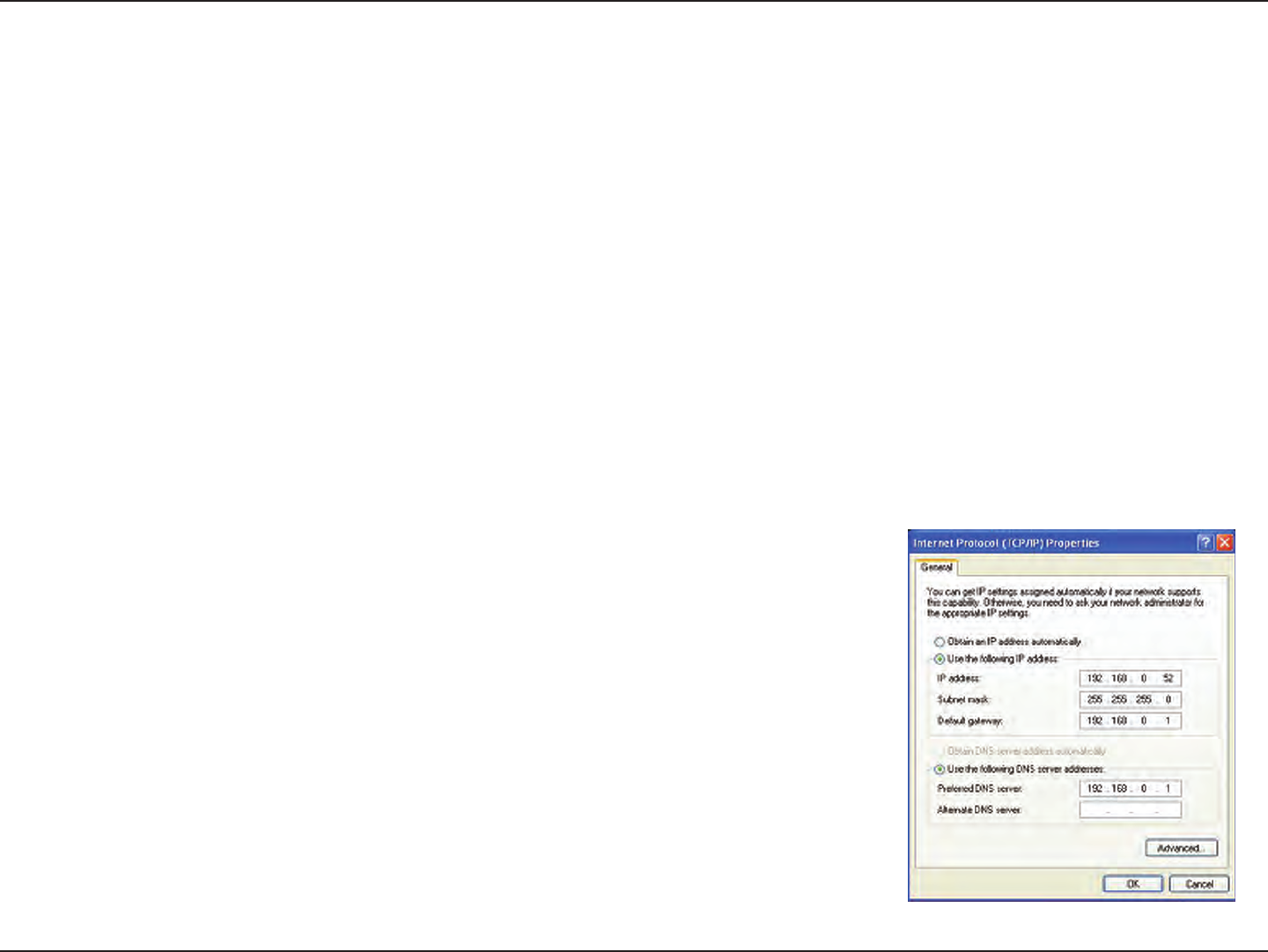
Statically Assign an IP address
If you are not using a DHCP capable gateway/router, or you need to assign a static IP address, please follow the steps below:
Step 1
Windows® 7 - Click on Start > Control Panel > Network and Internet > Network and Sharing Center.
Windows Vista® - Click on Start > Control Panel > Network and Internet > Network and Sharing Center > Manage Network
Connections.
Windows® XP - Click on Start > Control Panel > Network Connections.
Windows® 2000 - From the desktop, right-click My Network Places > Properties.
Step 2
Right-click on the Local Area Connection which represents your network adapter and select Properties.
Step 3
Highlight Internet Protocol (TCP/IP) and click Properties.
Step 4
Click Use the following IP address and enter an IP address that is on the same subnet
as your network or the LAN IP address on your router.
Example: If the router´s LAN IP address is 192.168.0.1, make your IP address 192.168.0.X
where X is a number between 2 and 99. Make sure that the number you choose is not
in use on the network. Set the Default Gateway the same as the LAN IP address of your
router (I.E. 192.168.0.1).
Set Primary DNS the same as the LAN IP address of your router (192.168.0.1). The
Secondary DNS is not needed or you may enter a DNS server from your ISP.
Step 5
Click OK twice to save your settings.
135D-Link DIR-826L User Manual
Appendix C - Technical Specications
Technical Specications
Standards
• IEEE 802.11n
• IEEE 802.11g
• IEEE 802.11a
• IEEE 802.3
• IEEE 802.3u
• IEEE 802.3ab
Security
• WPA™ - Personal/Enterprise
• WPA2™ - Personal/Enterprise
Wireless Signal Rates1
IEEE 802.11n 2.4GHz(HT20/40):
• 144.4Mbps (300) · 130Mbps (270)
• 115.6Mbps (240) · 86.7Mbps (180)
• 72.2Mbps (150) · 65Mbps (135)
• 57.8Mbps (120) · 43.3Mbps (90)
• 28.9Mbps (60) · 21.7Mbps (45)
•14.4Mbps (30) · 7.2Mbps (15)
IEEE 802.11n 5GHz(HT20/40):
• 144.4Mbps (300) · 130Mbps (270)
• 115.6Mbps (240) · 86.7Mbps (180)
• 72.2Mbps (150) · 65Mbps (135)
• 57.8Mbps (120) · 43.3Mbps (90)
• 28.9Mbps (60) · 21.7Mbps (45)
•14.4Mbps (30) · 7.2Mbps (15)
IEEE 802.11g:
• 54Mbps • 48Mbps • 36Mbps
• 24Mbps • 18Mbps • 12Mbps
• 11Mbps • 9Mbps • 6Mbps
• 5.5Mbps • 2Mbps • 1Mbps
Frequency Range2 (North America)
• 2.412GHz to 2.462GHz (802.11g/n)
• 5.15GHz to 5.825GHz (802.11a/n)3
Operating Temperature
• 32°F to 104°F ( 0°C to 40°C)
Humidity
• 95% maximum (non-condensing)
Safety & Emissions
• FCC
• IC
Dimensions
• L = 4.37 inches
• W = 3.66 inches
• H = 5.71 inches
Warranty
• 1 Year
1 Maximum wireless signal rate derived from IEEE Standard 802.11a, 802.11g, and 802.11n specications. Actual data throughput will vary. Network conditions and environmental factors, including
volume of network trac, building materials and construction, and network overhead, lower actual data throughput rate. Environmental factors will adversely aect wireless signal range.
2 Frequency Range varies depending on country’s regulation
3 The DIR-826L does not include 5.25-5.35GHz & 5.47-5.725GHz in some regions.
136D-Link DIR-826L User Manual
Appendix D - Contacting Technical Support
Contacting Technical Support
U.S. and Canadian customers can contact D-Link technical support through our web site or by phone.
Before you contact technical support, please have the following ready:
• Model number of the product (e.g. DIR-826L)
• Hardware Revision (located on the label on the bottom of the router (e.g. rev A1))
• Serial Number (s/n number located on the label on the bottom of the router).
You can nd software updates and user documentation on the D-Link website as well as frequently asked questions and
answers to technical issues.
For customers within the United States:
Phone Support:
(877) 453-5465
Internet Support:
http://support.dlink.com
For customers within Canada:
Phone Support:
(800) 361-5265
Internet Support:
http://support.dlink.ca
137D-Link DIR-826L User Manual
Appendix E - GNU General Public License
GPL Code Statement
This D-Link product includes software code developed by third parties, including software code subject to the GNU General Public License (“GPL”)
or GNU Lesser General Public License (“LGPL”). As applicable, the terms of the GPL and LGPL, and information on obtaining access to the GPL
code and LGPL code used in this product, are available to you at:
http://tsd.dlink.com.tw/GPL.asp
The GPL code and LGPL code used in this product is distributed WITHOUT ANY WARRANTY and is subject to the copyrights of one or more
authors. For details, see the GPL code and the LGPL code for this product and the terms of the GPL and LGPL.
WRITTEN OFFER FOR GPL AND LGPL SOURCE CODE
Where such specic license terms entitle you to the source code of such software, D-Link will provide upon written request via email and/or
traditional paper mail the applicable GPL and LGPLsource code files via CD-ROM for a nominal cost to cover shipping and media charges as
allowed under the GPL and LGPL.
Please direct all inquiries to:
Email: GPLCODE@DLink.com
Snail Mail:
Attn: GPLSOURCE REQUEST
D-Link Systems, Inc.
17595 Mt. Herrmann Street
Fountain Valley, CA 92708
GNU GENERAL PUBLIC LICENSE
Version 3, 29 June 2007
Copyright (C) 2007 Free Software Foundation, Inc. <http://fsf.org/> Everyone is permitted to copy and distribute verbatim copies of this license
document, but changing it is not allowed.
138D-Link DIR-826L User Manual
Appendix E - GNU General Public License
Preamble
The GNU General Public License is a free, copyleft license for software and other kinds of works.
The licenses for most software and other practical works are designed to take away your freedom to share and change the works. By contrast, the
GNU General Public License is intended to guarantee your freedom to share and change all versions of a program--to make sure it remains free
software for all its users. We, the Free Software Foundation, use the GNU General Public License for most of our software; it applies also to any other
work released this way by its authors. You can apply it to your programs, too.
When we speak of free software, we are referring to freedom, not price. Our General Public Licenses are designed to make sure that you have the
freedom to distribute copies of free software (and charge for them if you wish), that you receive source code or can get it if you want it, that you
can change the software or use pieces of it in new free programs, and that you know you can do these things.
To protect your rights, we need to prevent others from denying you these rights or asking you to surrender the rights. Therefore, you have certain
responsibilities if you distribute copies of the software, or if you modify it: responsibilities to respect the freedom of others.
For example, if you distribute copies of such a program, whether gratis or for a fee, you must pass on to the recipients the same freedoms that you
received. You must make sure that they, too, receive or can get the source code. And you must show them these terms so they know their rights.
Developers that use the GNU GPL protect your rights with two steps:
(1) assert copyright on the software, and (2) oer you this License giving you legal permission to copy, distribute and/or modify it.
For the developers’ and authors’ protection, the GPL clearly explains that there is no warranty for this free software. For both users’ and authors’
sake, the GPL requires that modied versions be marked as changed, so that their problems will not be attributed erroneously to authors of
previous versions.
Some devices are designed to deny users access to install or run modied versions of the software inside them, although the manufacturer can
do so. This is fundamentally incompatible with the aim of protecting users’ freedom to change the software. The systematic pattern of such abuse
occurs in the area of products for individuals to use, which is precisely where it is most unacceptable. Therefore, we have designed this version of
the GPL to prohibit the practice for those products. If such problems arise substantially in other domains, we stand ready to extend this provision
to those domains in future versions of the GPL, as needed to protect the freedom of users.
Finally, every program is threatened constantly by software patents. States should not allow patents to restrict development and use of software
on general-purpose computers, but in those that do, we wish to avoid the special danger that patents applied to a free program could make it
eectively proprietary. To prevent this, the GPL assures that patents cannot be used to render the program non-free.
The precise terms and conditions for copying, distribution and modication follow.
139D-Link DIR-826L User Manual
Appendix E - GNU General Public License
TERMS AND CONDITIONS
0. Denitions.
“This License” refers to version 3 of the GNU General Public License.
“Copyright” also means copyright-like laws that apply to other kinds of works, such as semiconductor masks.
“The Program” refers to any copyrightable work licensed under this License. Each licensee is addressed as “you”. “Licensees” and “recipients” may
be individuals or organizations.
To “modify” a work means to copy from or adapt all or part of the work in a fashion requiring copyright permission, other than the making of an
exact copy. The resulting work is called a “modied version” of the earlier work or a work “based on” the earlier work.
A “covered work” means either the unmodied Program or a work based on the Program.
To “propagate” a work means to do anything with it that, without permission, would make you directly or secondarily liable for infringement under
applicable copyright law, except executing it on a computer or modifying a private copy. Propagation includes copying, distribution (with or
without modication), making available to the public, and in some countries other activities as well.
To “convey” a work means any kind of propagation that enables other parties to make or receive copies. Mere interaction with a user through a
computer network, with no transfer of a copy, is not conveying.
An interactive user interface displays “Appropriate Legal Notices” to the extent that it includes a convenient and prominently visible feature that
(1) displays an appropriate copyright notice, and (2) tells the user that there is no warranty for the work (except to the extent that warranties are
provided), that licensees may convey the work under this License, and how to view a copy of this License. If the interface presents a list of user
commands or options, such as a menu, a prominent item in the list meets this criterion.
1. Source Code.
The “source code” for a work means the preferred form of the work for making modications to it. “Object code” means any non-source form of a
work.
A “Standard Interface” means an interface that either is an ocial standard dened by a recognized standards body, or, in the case of interfaces
specied for a particular programming language, one that is widely used among developers working in that language.
140D-Link DIR-826L User Manual
Appendix E - GNU General Public License
The “System Libraries” of an executable work include anything, other than the work as a whole, that (a) is included in the normal form of packaging
a Major Component, but which is not part of that Major Component, and (b) serves only to enable use of the work with that Major Component,
or to implement a Standard Interface for which an implementation is available to the public in source code form. A “Major Component”, in this
context, means a major essential component (kernel, window system, and so on) of the specic operating system (if any) on which the executable
work runs, or a compiler used to produce the work, or an object code interpreter used to run it.
The “Corresponding Source” for a work in object code form means all the source code needed to generate, install, and (for an executable work)
run the object code and to modify the work, including scripts to control those activities. However, it does not include the work’s System Libraries,
or general-purpose tools or generally available free programs which are used unmodied in performing those activities but which are not part of
the work. For example, Corresponding Source includes interface denition les associated with source les for the work, and the source code for
shared libraries and dynamically linked subprograms that the work is specically designed to require, such as by intimate data communication or
control ow between those subprograms and other parts of the work.
The Corresponding Source need not include anything that users can regenerate automatically from other parts of the Corresponding Source.
The Corresponding Source for a work in source code form is that same work.
2. Basic Permissions.
All rights granted under this License are granted for the term of copyright on the Program, and are irrevocable provided the stated conditions
are met. This License explicitly arms your unlimited permission to run the unmodied Program. The output from running a covered work is
covered by this License only if the output, given its content, constitutes a covered work. This License acknowledges your rights of fair use or other
equivalent, as provided by copyright law.
You may make, run and propagate covered works that you do not convey, without conditions so long as your license otherwise remains in force.
You may convey covered works to others for the sole purpose of having them make modications exclusively for you, or provide you with facilities
for running those works, provided that you comply with the terms of this License in conveying all material for which you do not control copyright.
Those thus making or running the covered works for you must do so exclusively on your behalf, under your direction and control, on terms that
prohibit them from making any copies of your copyrighted material outside their relationship with you.
Conveying under any other circumstances is permitted solely under the conditions stated below. Sublicensing is not allowed; section 10 makes it
unnecessary.
141D-Link DIR-826L User Manual
Appendix E - GNU General Public License
3. Protecting Users’ Legal Rights From Anti-Circumvention Law.
No covered work shall be deemed part of an eective technological measure under any applicable law fullling obligations under article 11 of the
WIPO copyright treaty adopted on 20 December 1996, or similar laws prohibiting or restricting circumvention of such measures.
When you convey a covered work, you waive any legal power to forbid circumvention of technological measures to the extent such circumvention
is eected by exercising rights under this License with respect to the covered work, and you disclaim any intention to limit operation or modication
of the work as a means of enforcing, against the work’s users, your or third parties’ legal rights to forbid circumvention of technological measures.
4. Conveying Verbatim Copies.
You may convey verbatim copies of the Program’s source code as you receive it, in any medium, provided that you conspicuously and appropriately
publish on each copy an appropriate copyright notice; keep intact all notices stating that this License and any non-permissive terms added in
accord with section 7 apply to the code; keep intact all notices of the absence of any warranty; and give all recipients a copy of this License along
with the Program.
You may charge any price or no price for each copy that you convey, and you may oer support or warranty protection for a fee.
5. Conveying Modied Source Versions.
You may convey a work based on the Program, or the modications to produce it from the Program, in the form of source code under the terms of
section 4, provided that you also meet all of these conditions:
a) The work must carry prominent notices stating that you modied it, and giving a relevant date.
b) The work must carry prominent notices stating that it is released under this License and any conditions added under section 7.
This requirement modies the requirement in section 4 to “keep intact all notices”.
c) You must license the entire work, as a whole, under this License to anyone who comes into possession of a copy. This License
will therefore apply, along with any applicable section 7 additional terms, to the whole of the work, and all its parts, regardless
of how they are packaged. This License gives no permission to license the work in any other way, but it does not invalidate such
permission if you have separately received it.
d) If the work has interactive user interfaces, each must display Appropriate Legal Notices; however, if the Program has interactive
interfaces that do not display Appropriate Legal Notices, your work need not make them do so.
142D-Link DIR-826L User Manual
Appendix E - GNU General Public License
A compilation of a covered work with other separate and independent works, which are not by their nature extensions of the covered work, and
which are not combined with it such as to form a larger program, in or on a volume of a storage or distribution medium, is called an “aggregate”
if the compilation and its resulting copyright are not used to limit the access or legal rights of the compilation’s users beyond what the individual
works permit. Inclusion of a covered work in an aggregate does not cause this License to apply to the other parts of the aggregate.
6. Conveying Non-Source Forms.
You may convey a covered work in object code form under the terms of sections 4 and 5, provided that you also convey the machine-readable
Corresponding Source under the terms of this License, in one of these ways:
a) Convey the object code in, or embodied in, a physical product (including a physical distribution medium), accompanied by the
Corresponding Source xed on a durable physical medium customarily used for software interchange.
b) Convey the object code in, or embodied in, a physical product (including a physical distribution medium), accompanied by a
written oer, valid for at least three years and valid for as long as you oer spare parts or customer support for that product
model, to give anyone who possesses the object code either (1) a copy of the Corresponding Source for all the software in the
product that is covered by this License, on a durable physical medium customarily used for software interchange, for a price no
more than your reasonable cost of physically performing this conveying of source, or (2) access to copy the Corresponding Source
from a network server at no charge.
c) Convey individual copies of the object code with a copy of the written oer to provide the Corresponding Source. This alternative
is allowed only occasionally and noncommercially, and only if you received the object code with such an oer, in accord with
subsection 6b.
d) Convey the object code by oering access from a designated place (gratis or for a charge), and oer equivalent access to the
Corresponding Source in the same way through the same place at no further charge. You need not require recipients to copy the
Corresponding Source along with the object code. If the place to copy the object code is a network server, the Corresponding
Source may be on a dierent server (operated by you or a third party) that supports equivalent copying facilities, provided you
maintain clear directions next to the object code saying where to nd the Corresponding Source. Regardless of what server hosts
the Corresponding Source, you remain obligated to ensure that it is available for as long as needed to satisfy these requirements.
e) Convey the object code using peer-to-peer transmission, provided you inform other peers where the object code and
Corresponding Source of the work are being oered to the general public at no charge under subsection 6d.
A separable portion of the object code, whose source code is excluded from the Corresponding Source as a System Library, need not be
included in conveying the object code work.
143D-Link DIR-826L User Manual
Appendix E - GNU General Public License
A “User Product” is either (1) a “consumer product”, which means any tangible personal property which is normally used for personal, family, or
household purposes, or (2) anything designed or sold for incorporation into a dwelling. In determining whether a product is a consumer product,
doubtful cases shall be resolved in favor of coverage. For a particular product received by a particular user, “normally used” refers to a typical
or common use of that class of product, regardless of the status of the particular user or of the way in which the particular user actually uses,
or expects or is expected to use, the product. A product is a consumer product regardless of whether the product has substantial commercial,
industrial or non-consumer uses, unless such uses represent the only signicant mode of use of the product.
“Installation Information” for a User Product means any methods, procedures, authorization keys, or other information required to install and
execute modied versions of a covered work in that User Product from a modied version of its Corresponding Source. The information must
suce to ensure that the continued functioning of the modied object code is in no case prevented or interfered with solely because modication
has been made.
If you convey an object code work under this section in, or with, or specically for use in, a User Product, and the conveying occurs as part of a
transaction in which the right of possession and use of the User Product is transferred to the recipient in perpetuity or for a xed term (regardless of
how the transaction is characterized), the Corresponding Source conveyed under this section must be accompanied by the Installation Information.
But this requirement does not apply if neither you nor any third party retains the ability to install modied object code on the User Product (for
example, the work has been installed in ROM).
The requirement to provide Installation Information does not include a requirement to continue to provide support service, warranty, or updates
for a work that has been modied or installed by the recipient, or for the User Product in which it has been modied or installed. Access to a
network may be denied when the modication itself materially and adversely aects the operation of the network or violates the rules and
protocols for communication across the network.
Corresponding Source conveyed, and Installation Information provided, in accord with this section must be in a format that is publicly documented
(and with an implementation available to the public in source code form), and must require no special password or key for unpacking, reading or
copying.
7. Additional Terms.
“Additional permissions” are terms that supplement the terms of this License by making exceptions from one or more of its conditions. Additional
permissions that are applicable to the entire Program shall be treated as though they were included in this License, to the extent that they are valid
under applicable law. If additional permissions apply only to part of the Program, that part may be used separately under those permissions, but
the entire Program remains governed by this License without regard to the additional permissions.
144D-Link DIR-826L User Manual
Appendix E - GNU General Public License
When you convey a copy of a covered work, you may at your option remove any additional permissions from that copy, or from any part of it.
(Additional permissions may be written to require their own removal in certain cases when you modify the work). You may place additional
permissions on material, added by you to a covered work, for which you have or can give appropriate copyright permission.
Notwithstanding any other provision of this License, for material you add to a covered work, you may (if authorized by the copyright holders of
that material) supplement the terms of this License with terms:
a) Disclaiming warranty or limiting liability dierently from the terms of sections 15 and 16 of this License; or
b) Requiring preservation of specied reasonable legal notices or author attributions in that material or in the Appropriate Legal
Notices displayed by works containing it; or
c) Prohibiting misrepresentation of the origin of that material, or requiring that modied versions of such material be marked in
reasonable ways as dierent from the original version; or
d) Limiting the use for publicity purposes of names of licensors or authors of the material; or
e) Declining to grant rights under trademark law for use of some trade names, trademarks, or service marks; or
f) Requiring indemnication of licensors and authors of that material by anyone who conveys the material (or modied versions of
it) with contractual assumptions of liability to the recipient, for any liability that these contractual assumptions directly impose
on those licensors and authors.
All other non-permissive additional terms are considered “further restrictions” within the meaning of section 10. If the Program as you received
it, or any part of it, contains a notice stating that it is governed by this License along with a term that is a further restriction, you may remove that
term. If a license document contains a further restriction but permits relicensing or conveying under this License, you may add to a covered work
material governed by the terms of that license document, provided that the further restriction does not survive such relicensing or conveying.
If you add terms to a covered work in accord with this section, you must place, in the relevant source les, a statement of the additional terms that
apply to those les, or a notice indicating where to nd the applicable terms.
Additional terms, permissive or non-permissive, may be stated in the form of a separately written license, or stated as exceptions; the above
requirements apply either way.
145D-Link DIR-826L User Manual
Appendix E - GNU General Public License
8. Termination.
You may not propagate or modify a covered work except as expressly provided under this License. Any attempt otherwise to propagate or modify
it is void, and will automatically terminate your rights under this License (including any patent licenses granted under the third paragraph of
section 11).
However, if you cease all violation of this License, then your license from a particular copyright holder is reinstated (a) provisionally, unless and until
the copyright holder explicitly and nally terminates your license, and (b) permanently, if the copyright holder fails to notify you of the violation
by some reasonable means prior to 60 days after the cessation.
Moreover, your license from a particular copyright holder is reinstated permanently if the copyright holder noties you of the violation by some
reasonable means, this is the rst time you have received notice of violation of this License (for any work) from that copyright holder, and you cure
the violation prior to 30 days after your receipt of the notice.
Termination of your rights under this section does not terminate the licenses of parties who have received copies or rights from you under this
License. If your rights have been terminated and not permanently reinstated, you do not qualify to receive new licenses for the same material
under section 10.
9. Acceptance Not Required for Having Copies.
You are not required to accept this License in order to receive or run a copy of the Program. Ancillary propagation of a covered work occurring
solely as a consequence of using peer-to-peer transmission to receive a copy likewise does not require acceptance. However, nothing other than
this License grants you permission to propagate or modify any covered work. These actions infringe copyright if you do not accept this License.
Therefore, by modifying or propagating a covered work, you indicate your acceptance of this License to do so.
10. Automatic Licensing of Downstream Recipients.
Each time you convey a covered work, the recipient automatically receives a license from the original licensors, to run, modify and propagate that
work, subject to this License. You are not responsible for enforcing compliance by third parties with this License.
An “entity transaction” is a transaction transferring control of an organization, or substantially all assets of one, or subdividing an organization, or
merging organizations. If propagation of a covered work results from an entity transaction, each party to that transaction who receives a copy of
the work also receives whatever licenses to the work the party’s predecessor in interest had or could give under the previous paragraph, plus a
right to possession of the Corresponding Source of the work from the predecessor in interest, if the predecessor has it or can get it with reasonable
eorts.
146D-Link DIR-826L User Manual
Appendix E - GNU General Public License
You may not impose any further restrictions on the exercise of the rights granted or armed under this License. For example, you may not impose
a license fee, royalty, or other charge for exercise of rights granted under this License, and you may not initiate litigation (including a cross-claim
or counterclaim in a lawsuit) alleging that any patent claim is infringed by making, using, selling, oering for sale, or importing the Program or any
portion of it.
11. Patents.
A “contributor” is a copyright holder who authorizes use under this License of the Program or a work on which the Program is based. The work thus
licensed is called the contributor’s “contributor version”.
A contributor’s “essential patent claims” are all patent claims owned or controlled by the contributor, whether already acquired or hereafter acquired,
that would be infringed by some manner, permitted by this License, of making, using, or selling its contributor version, but do not include claims
that would be infringed only as a consequence of further modication of the contributor version. For purposes of this denition, “control” includes
the right to grant patent sublicenses in a manner consistent with the requirements of this License.
Each contributor grants you a non-exclusive, worldwide, royalty-free patent license under the contributor’s essential patent claims, to make, use,
sell, oer for sale, import and otherwise run, modify and propagate the contents of its contributor version.
In the following three paragraphs, a “patent license” is any express agreement or commitment, however denominated, not to enforce a patent
(such as an express permission to practice a patent or covenant not to sue for patent infringement). To “grant” such a patent license to a party
means to make such an agreement or commitment not to enforce a patent against the party.
If you convey a covered work, knowingly relying on a patent license, and the Corresponding Source of the work is not available for anyone to
copy, free of charge and under the terms of this License, through a publicly available network server or other readily accessible means, then you
must either (1) cause the Corresponding Source to be so available, or (2) arrange to deprive yourself of the benet of the patent license for this
particular work, or (3) arrange, in a manner consistent with the requirements of this License, to extend the patent license to downstream recipients.
“Knowingly relying” means you have actual knowledge that, but for the patent license, your conveying the covered work in a country, or your
recipient’s use of the covered work in a country, would infringe one or more identiable patents in that country that you have reason to believe
are valid.
If, pursuant to or in connection with a single transaction or arrangement, you convey, or propagate by procuring conveyance of, a covered work,
and grant a patent license to some of the parties receiving the covered work authorizing them to use, propagate, modify or convey a specic copy
of the covered work, then the patent license you grant is automatically extended to all recipients of the covered work and works based on it.
147D-Link DIR-826L User Manual
Appendix E - GNU General Public License
A patent license is “discriminatory” if it does not include within the scope of its coverage, prohibits the exercise of, or is conditioned on the non-
exercise of one or more of the rights that are specically granted under this License. You may not convey a covered work if you are a party to an
arrangement with a third party that is in the business of distributing software, under which you make payment to the third party based on the
extent of your activity of conveying the work, and under which the third party grants, to any of the parties who would receive the covered work
from you, a discriminatory patent license (a) in connection with copies of the covered work conveyed by you (or copies made from those copies), or
(b) primarily for and in connection with specic products or compilations that contain the covered work, unless you entered into that arrangement,
or that patent license was granted, prior to 28 March 2007.
Nothing in this License shall be construed as excluding or limiting any implied license or other defenses to infringement that may otherwise be
available to you under applicable patent law.
12. No Surrender of Others’ Freedom.
If conditions are imposed on you (whether by court order, agreement or otherwise) that contradict the conditions of this License, they do not
excuse you from the conditions of this License. If you cannot convey a covered work so as to satisfy simultaneously your obligations under this
License and any other pertinent obligations, then as a consequence you may not convey it at all. For example, if you agree to terms that obligate
you to collect a royalty for further conveying from those to whom you convey the Program, the only way you could satisfy both those terms and
this License would be to refrain entirely from conveying the Program.
13. Use with the GNU Aero General Public License.
Notwithstanding any other provision of this License, you have permission to link or combine any covered work with a work licensed under version
3 of the GNU Aero General Public License into a single combined work, and to convey the resulting work. The terms of this License will continue
to apply to the part which is the covered work, but the special requirements of the GNU Aero General Public License, section 13, concerning
interaction through a network will apply to the combination as such.
14. Revised Versions of this License.
The Free Software Foundation may publish revised and/or new versions of the GNU General Public License from time to time. Such new versions
will be similar in spirit to the present version, but may dier in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Program species that a certain numbered version of the GNU General Public License
“or any later version” applies to it, you have the option of following the terms and conditions either of that numbered version or of any later version
published by the Free Software Foundation. If the Program does not specify a version number of the GNU General Public License, you may choose
any version ever published by the Free Software Foundation. If the Program species that a proxy can decide which future versions of the GNU
General Public License can be used, that proxy’s public statement of acceptance of a version permanently authorizes you to choose that version
for the Program.
148D-Link DIR-826L User Manual
Appendix E - GNU General Public License
Later license versions may give you additional or dierent permissions. However, no additional obligations are imposed on any author or copyright
holder as a result of your choosing to follow a later version.
15. Disclaimer of Warranty.
THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING
THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM “AS IS” WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR
IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE
ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME
THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
16. Limitation of Liability.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO
MODIFIES AND/OR CONVEYS THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL,
INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO
LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO
OPERATE WITH ANY OTHER PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
17. Interpretation of Sections 15 and 16.
If the disclaimer of warranty and limitation of liability provided above cannot be given local legal eect according to their terms, reviewing courts
shall apply local law that most closely approximates an absolute waiver of all civil liability in connection with the Program, unless a warranty or
assumption of liability accompanies a copy of the Program in return for a fee.
149D-Link DIR-826L User Manual
Appendix F - Warranty
Warranty
Subject to the terms and conditions set forth herein, D-Link Systems, Inc. (“D-Link”) provides this Limited Warranty:
• Only to the person or entity that originally purchased the product from D-Link or its authorized reseller or distributor, and
• Only for products purchased and delivered within the fty states of the United States, the District of Columbia, U.S. Possessions
or Protectorates, U.S. Military Installations, or addresses with an APO or FPO.
Limited Warranty:
D-Link warrants that the hardware portion of the D-Link product described below (“Hardware”) will be free from material defects in workmanship
and materials under normal use from the date of original retail purchase of the product, for the period set forth below (“Warranty Period”), except
as otherwise stated herein.
• Hardware (excluding power supplies and fans): One (1) year
• Power supplies and fans: One (1) year
• Spare parts and spare kits: Ninety (90) days
The customer’s sole and exclusive remedy and the entire liability of D-Link and its suppliers under this Limited Warranty will be, at
D-Link’s option, to repair or replace the defective Hardware during the Warranty Period at no charge to the original owner or to refund the actual
purchase price paid. Any repair or replacement will be rendered by D-Link at an Authorized D-Link Service Oce. The replacement hardware
need not be new or have an identical make, model or part. D-Link may, at its option, replace the defective Hardware or any part thereof with any
reconditioned product that D-Link reasonably determines is substantially equivalent (or superior) in all material respects to the defective Hardware.
Repaired or replacement hardware will be warranted for the remainder of the original Warranty Period or ninety (90) days, whichever is longer,
and is subject to the same limitations and exclusions. If a material defect is incapable of correction, or if D-Link determines that it is not practical
to repair or replace the defective Hardware, the actual price paid by the original purchaser for the defective Hardware will be refunded by D-Link
upon return to D-Link of the defective Hardware. All Hardware or part thereof that is replaced by D-Link, or for which the purchase price is refunded,
shall become the property of D-Link upon replacement or refund.
150D-Link DIR-826L User Manual
Appendix F - Warranty
Limited Software Warranty:
D-Link warrants that the software portion of the product (“Software”) will substantially conform to D-Link’s then current functional specications
for the Software, as set forth in the applicable documentation, from the date of original retail purchase of the Software for a period of ninety (90)
days (“Software Warranty Period”), provided that the Software is properly installed on approved hardware and operated as contemplated in its
documentation. D-Link further warrants that, during the Software Warranty Period, the magnetic media on which D-Link delivers the Software will be
free of physical defects. The customer’s sole and exclusive remedy and the entire liability of D-Link and its suppliers under this Limited Warranty will
be, at D-Link’s option, to replace the non-conforming Software (or defective media) with software that substantially conforms to D-Link’s functional
specications for the Software or to refund the portion of the actual purchase price paid that is attributable to the Software. Except as otherwise
agreed by D-Link in writing, the replacement Software is provided only to the original licensee, and is subject to the terms and conditions of the
license granted by D-Link for the Software. Replacement Software will be warranted for the remainder of the original Warranty Period and is subject
to the same limitations and exclusions. If a material non-conformance is incapable of correction, or if D-Link determines in its sole discretion that it
is not practical to replace the non-conforming Software, the price paid by the original licensee for the non-conforming Software will be refunded by
D-Link; provided that the non-conforming Software (and all copies thereof) is rst returned to D-Link. The license granted respecting any Software
for which a refund is given automatically terminates.
Non-Applicability of Warranty:
The Limited Warranty provided hereunder for Hardware and Software portions of D-Link’s products will not be applied to and does not cover any
refurbished product and any product purchased through the inventory clearance or liquidation sale or other sales in which D-Link, the sellers, or
the liquidators expressly disclaim their warranty obligation pertaining to the product and in that case, the product is being sold “As-Is” without
any warranty whatsoever including, without limitation, the Limited Warranty as described herein, notwithstanding anything stated herein to the
contrary.
Submitting A Claim (USA):
The customer shall return the product to the original purchase point based on its return policy. In case the return policy period has expired and
the product is within warranty, the customer shall submit a claim to D-Link as outlined below:
• The customer must submit with the product as part of the claim a written description of the Hardware defect or Software
nonconformance in sucient detail to allow DLink to conrm the same, along with proof of purchase of the product (such as a
copy of the dated purchase invoice for the product) if the product is not registered.
• The customer must obtain a Case ID Number from D-Link Technical Support at 1-877-453-5465, who will attempt to assist the
customer in resolving any suspected defects with the product. If the product is considered defective, the customer must obtain a
Return Material Authorization (“RMA”) number by completing the RMA form and entering the assigned Case ID Number at https://
rma.dlink.com/.
151D-Link DIR-826L User Manual
Appendix F - Warranty
• After an RMA number is issued, the defective product must be packaged securely in the original or other suitable shipping package
to ensure that it will not be damaged in transit, and the RMA number must be prominently marked on the outside of the package.
Do not include any manuals or accessories in the shipping package. D-Link will only replace the defective portion of the product
and will not ship back any accessories.
• The customer is responsible for all in-bound shipping charges to D-Link. No Cash on Delivery (“COD”) is allowed. Products sent COD
will either be rejected by D-Link or become the property of D-Link. Products shall be fully insured by the customer and shipped
to D-Link Systems, Inc., 17595 Mt. Herrmann, Fountain Valley, CA 92708. D-Link will not be held responsible for any packages that
are lost in transit to D-Link. The repaired or replaced packages will be shipped to the customer via UPS Ground or any common
carrier selected by D-Link. Return shipping charges shall be prepaid by D-Link if you use an address in the United States, otherwise
we will ship the product to you freight collect. Expedited shipping is available upon request and provided shipping charges are
prepaid by the customer. D-Link may reject or return any product that is not packaged and shipped in strict compliance with the
foregoing requirements, or for which an RMA number is not visible from the outside of the package. The product owner agrees to
pay D-Link’s reasonable handling and return shipping charges for any product that is not packaged and shipped in accordance
with the foregoing requirements, or that is determined by D-Link not to be defective or non-conforming.
Submitting A Claim (Canada):
The customer shall return the product to the original purchase point based on its return policy. In case the return policy period has expired and
the product is within warranty, the customer shall submit a claim to D-Link as outlined below:
• Customers need to provide their receipt (proof of purchase) even if the product is registered. Without a receipt, no warranty service will
be done. The registration is not considered a proof of purchase.
• The customer must submit with the product as part of the claim a written description of the Hardware defect or Software nonconformance
in sucient detail to allow D-Link to conrm the same, along with proof of purchase of the product (such as a copy of the dated purchase
invoice for the product) if the product is not registered.
• The customer must obtain a Case ID Number from D-Link Technical Support at 1-800-361-5265, who will attempt to assist the customer
in resolving any suspected defects with the product. If the product is considered defective, the customer must obtain a Return Material
Authorization (“RMA”) number by completing the RMA form and entering the assigned Case ID Number at https://rma.dlink.ca/.
• After an RMA number is issued, the defective product must be packaged securely in the original or other suitable shipping package to
ensure that it will not be damaged in transit, and the RMA number must be prominently marked on the outside of the package. Do not
include any manuals or accessories in the shipping package. D-Link will only replace the defective portion of the product and will not ship
back any accessories.
152D-Link DIR-826L User Manual
Appendix F - Warranty
• The customer is responsible for all in-bound shipping charges to D-Link. No Cash on Delivery (“COD”) is allowed. Products sent COD will
be rejected by D-Link. Products shall be fully insured by the customer and shipped to D-Link Networks, Inc., 2525 Meadowvale Boulevard
Mississauga, Ontario, L5N 5S2 Canada. D-Link will not be held responsible for any packages that are lost in transit to D-Link. The repaired
or replaced packages will be shipped to the customer via Purolator Canada or any common carrier selected by D-Link. Return shipping
charges shall be prepaid by D-Link if you use an address in Canada, otherwise we will ship the product to you freight collect. Expedited
shipping is available upon request and provided shipping charges are prepaid by the customer. D-Link may reject or return any product
that is not packaged and shipped in strict compliance with the foregoing requirements, or for which an RMA number is not visible from
the outside of the package. The product owner agrees to pay D-Link’s reasonable handling and return shipping charges for any product
that is not packaged and shipped in accordance with the foregoing requirements, or that is determined by D-Link not to be defective or
non-conforming.
• RMA phone number: 1-800-361-5265 Hours of Operation: Monday-Friday, 9:00AM – 9:00PM EST
What Is Not Covered:
The Limited Warranty provided herein by D-Link does not cover:
Products that, in D-Link’s judgment, have been subjected to abuse, accident, alteration, modication, tampering, negligence, misuse, faulty installation,
lack of reasonable care, repair or service in any way that is not contemplated in the documentation for the product, or if the model or serial number
has been altered, tampered with, defaced or removed; Initial installation, installation and removal of the product for repair, and shipping costs;
Operational adjustments covered in the operating manual for the product, and normal maintenance; Damage that occurs in shipment, due to act
of God, failures due to power surge, and cosmetic damage; Any hardware, software, rmware or other products or services provided by anyone
other than D-Link; and Products that have been purchased from inventory clearance or liquidation sales or other sales in which D-Link, the sellers,
or the liquidators expressly disclaim their warranty obligation pertaining to the product.
While necessary maintenance or repairs on your Product can be performed by any company, we recommend that you use only an Authorized D-Link
Service Oce. Improper or incorrectly performed maintenance or repair voids this Limited Warranty.
Disclaimer of Other Warranties:
EXCEPT FOR THE LIMITED WARRANTY SPECIFIED HEREIN, THE PRODUCT IS PROVIDED “AS-IS” WITHOUT ANY WARRANTY OF ANY KIND WHATSOEVER
INCLUDING, WITHOUT LIMITATION, ANY WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT.
IF ANY IMPLIED WARRANTY CANNOT BE DISCLAIMED IN ANY TERRITORY WHERE A PRODUCT IS SOLD, THE DURATION OF SUCH IMPLIED WARRANTY
SHALL BE LIMITED TO THE DURATION OF THE APPLICABLE WARRANTY PERIOD SET FORTH ABOVE. EXCEPT AS EXPRESSLY COVERED UNDER THE
LIMITED WARRANTY PROVIDED HEREIN, THE ENTIRE RISK AS TO THE QUALITY, SELECTION AND PERFORMANCE OF THE PRODUCT IS WITH THE
PURCHASER OF THE PRODUCT.
153D-Link DIR-826L User Manual
Appendix F - Warranty
Limitation of Liability:
TO THE MAXIMUM EXTENT PERMITTED BY LAW, D-LINK IS NOT LIABLE UNDER ANY CONTRACT, NEGLIGENCE, STRICT LIABILITY OR OTHER LEGAL
OR EQUITABLE THEORY FOR ANY LOSS OF USE OF THE PRODUCT, INCONVENIENCE OR DAMAGES OF ANY CHARACTER, WHETHER DIRECT, SPECIAL,
INCIDENTAL OR CONSEQUENTIAL (INCLUDING, BUT NOT LIMITED TO, DAMAGES FOR LOSS OF GOODWILL, LOSS OF REVENUE OR PROFIT, WORK
STOPPAGE, COMPUTER FAILURE OR MALFUNCTION, FAILURE OF OTHER EQUIPMENT OR COMPUTER PROGRAMS TO WHICH D-LINK’S PRODUCT
IS CONNECTED WITH, LOSS OF INFORMATION OR DATA CONTAINED IN, STORED ON, OR INTEGRATED WITH ANY PRODUCT RETURNED TO D-LINK
FOR WARRANTY SERVICE) RESULTING FROM THE USE OF THE PRODUCT, RELATING TO WARRANTY SERVICE, OR ARISING OUT OF ANY BREACH OF
THIS LIMITED WARRANTY, EVEN IF D-LINK HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. THE SOLE REMEDY FOR A BREACH OF
THE FOREGOING LIMITED WARRANTY IS REPAIR, REPLACEMENT OR REFUND OF THE DEFECTIVE OR NONCONFORMING PRODUCT. THE MAXIMUM
LIABILITY OF D-LINK UNDER THIS WARRANTY IS LIMITED TO THE PURCHASE PRICE OF THE PRODUCT COVERED BY THE WARRANTY. THE FOREGOING
EXPRESS WRITTEN WARRANTIES AND REMEDIES ARE EXCLUSIVE AND ARE IN LIEU OF ANY OTHER WARRANTIES OR REMEDIES, EXPRESS, IMPLIED
OR STATUTORY.
Governing Law:
This Limited Warranty shall be governed by the laws of the State of California. Some states do not allow exclusion or limitation of incidental or
consequential damages, or limitations on how long an implied warranty lasts, so the foregoing limitations and exclusions may not apply. This
Limited Warranty provides specic legal rights and you may also have other rights which vary from state to state.
Trademarks:
D-Link is a registered trademark of D-Link Corporation/D-Link Systems, Inc. Other trademarks or registered trademarks are the property of their
respective owners.
Copyright Statement:
No part of this publication or documentation accompanying this product may be reproduced in any form or by any means or used to make any
derivative such as translation, transformation, or adaptation without permission from D-Link Corporation/D-Link Systems, Inc., as stipulated by the
United States Copyright Act of 1976 and any amendments thereto. Contents are subject to change without prior notice.
Copyright ©2012 by D-Link Corporation/D-Link Systems, Inc. All rights reserved.
CE Mark Warning:
This is a Class B product. In a domestic environment, this product may cause radio interference, in which case the user may be required to take
adequate measures.
154D-Link DIR-826L User Manual
Appendix F - Warranty
Federal Communication Commission Interference Statement
This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to Part 15 of the FCC Rules. These limits are
designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses and can radiate
radio frequency energy and, if not installed and used in accordance with the instructions, may cause harmful interference to radio communications.
However, there is no guarantee that interference will not occur in a particular installation. If this equipment does cause harmful interference to radio
or television reception, which can be determined by turning the equipment o and on, the user is encouraged to try to correct the interference by
one of the following measures:
- Reorient or relocate the receiving antenna.
- Increase the separation between the equipment and receiver.
- Connect the equipment into an outlet on a circuit dierent from that to which the receiver is connected.
- Consult the dealer or an experienced radio/TV technician for help.
FCC Caution: Any changes or modications not expressly approved by the party responsible for compliance could void the user’s authority to
operate this equipment.
This device complies with Part 15 of the FCC Rules. Operation is subject to the following two conditions: (1) This device may not cause harmful
interference, and (2) this device must accept any interference received, including interference that may cause undesired operation.
Operations in the 5.15-5.25GHz band are restricted to indoor usage only.
IMPORTANT NOTICE:
FCC Radiation Exposure Statement:
This equipment complies with FCC radiation exposure limits set forth for an uncontrolled environment. This equipment should be installed and
operated with minimum distance 20cm between the radiator & your body.
This transmitter must not be co-located or operating in conjunction with any other antenna or transmitter.
The availability of some specic channels and/or operational frequency bands are country dependent and are rmware programmed at the factory
to match the intended destination. The rmware setting is not accessible by the end user.
Note: The country code selection is for non-US model only and is not available to all US model. Per FCC regulation, all WiFi product marketed in US
must xed to US operation channels only.
155D-Link DIR-826L User Manual
Appendix F - Warranty
Industry Canada statement:
This device complies with RSS-210 of the Industry Canada Rules. Operation is subject to the following two conditions:
(1) This device may not cause harmful interference, and
(2) this device must accept any interference received, including interference that may cause undesired operation.
IMPORTANT NOTE:
Radiation Exposure Statement:
This equipment complies with IC radiation exposure limits set forth for an uncontrolled environment. This equipment should be installed
and operated with minimum distance 20cm between the radiator & your body.
(i) the device for operation in the band 5150-5250 MHz is only for indoor use to reduce the potential for harmful interference to co-channel
mobile satellite systems;
(ii) high-power radars are allocated as primary users (i.e. priority users) of the bands 5250-5350 MHz and 5650-5850 MHz and that these
radars could cause interference and/or damage to LE-LAN devices.
Ce dispositif est conforme à la norme CNR-210 d’Industrie Canada applicable aux appareils radio exempts de licence. Son fonctionnement
est sujet aux deux conditions suivantes: (1) le dispositif ne doit pas produire de brouillage préjudiciable, et (2) ce dispositif doit accepter
tout brouillage reçu, y compris un brouillage susceptible de provoquer un fonctionnement indésirable.
NOTE IMPORTANTE:
Déclaration d’exposition aux radiations:
Cet équipement est conforme aux limites d’exposition aux rayonnements IC établies pour un environnement non contrôlé. Cet équipement
doit être installé et utilisé avec un minimum de 22cm de distance entre la source de rayonnement et votre corps.
les dispositifs fonctionnant dans la bande 5 150-5 250 MHz sont réservés uniquement pour une utilisation à l’intérieur an de réduire les
risques de brouillage préjudiciable aux systèmes de satellites mobiles utilisant les mêmes canaux;
De plus, les utilisateurs devraient aussi être avisés que les utilisateurs de radars de haute puissance sont désignés utilisateurs principaux
(c.-à-d., qu’ils ont la priorité) pour les bandes 5 250-5 350 MHz et 5 650-5 850 MHz et que ces radars pourraient causer du brouillage et/
ou des dommages aux dispositifs LAN-EL.
20cm
156D-Link DIR-826L User Manual
Appendix G - Registration
Version 1.0
February 27, 2012
Product registration is entirely voluntary and failure to complete or return this form will not diminish your warranty rights.
Registration