GF20 8172 15_Systems_Management_Bibliography_Aug80 15 Systems Management Bibliography Aug80
GF20-8172-15_Systems_Management_Bibliography_Aug80 GF20-8172-15_Systems_Management_Bibliography_Aug80
User Manual: GF20-8172-15_Systems_Management_Bibliography_Aug80
Open the PDF directly: View PDF ![]() .
.
Page Count: 19
Systems Management
OF20-8172-15
OENL-OO
Systems Management Bibliography
This bibliography lists
and
categorizes selected IBM
publications
on
the
management
of
data
processing,
including audidability,
data
security, systems management,
and
generally useful application development techniques
and
includes texts, manuals, briefs, bulletins,
and
papers as
well as certain forms, templates, bibliographies,
and
indexes.
In
most cases, the publications
are
applicable
to
various IBM
data
processing systems; publications applicable to a specific
data
processing system
can
be
found
in
that
system's
bibliography.
---
----
--
-.--
-
----
-
-.
---
---
----
-----
-~-
..
-
Preface
This bibliography lists
and
categorizes selected
IBM
publications
on
the management
of
data
processing
including auditability,
data
security, systems man-
agement
and
generally useful application develop-
ment
techniques.
In
most cases the publications
are applicable to various
IBM
data
processing sys-
tems
and
include texts, manuals, briefs, bulletins,
and
papers as well as certain forms, templates, bi-
bliographies,
and
indexes.
Systems management briefs
and
systems
man-
agement
manuals
are two types
of
publications
found
in
this bibliography.
The
briefs describe a
technique
or
procedure that helped make a partic-
ular
data
processing installation more effective.
The
manuals discuss in more detail -
and
usually
without reference to a particular installation -
data
processing techniques
and
procedures
and
other
subjects concerning the management
of
data
pro-
cessing.
Organization
This special bibliography has two parts:
•
Part
1 lists
the
publications
in
six different cate-
gories; a publication may
appear
in more
than
one category.
•
Part
2 contains
an
abstract
of
each publication
in
order
number
sequence so
that
its usefulness
to
an
installation
can
be determined.
Part
2
also shows
the
type
of
publication, the
number
of
pages
and
the
availability
under
SLSS
(System Library Subscription Service).
Sixteenth
Edition (August 1980)
This
is
a major revision of, and supersedes,
GF20-8172-14.
Publications are not stocked at the address given below; re-
quests for
IBM
publications should be made to your
IBM
rep-
resentative
or
to the
IBM
branch office serving your locality.
A form for readers' comments is provided at the back
of
this
bibliography.
If
the form has been removed, comments may be
addressed
to:
IBM
Corporation, Technical Publications,
Department
824,
1133
Westchester Avenue, White Plains, New
York
10604.
IBM
may use or distribute any
of
the information
you supply in any way it believes appropriate without incurring
any obligation whatever. You may,
of
course, continue to use
the information you supply.
Note: Order numbers are
in
sequence
by
the second
character.
The
first character is
the
use key, which
governs
the
availability
of
the document. Use key
G means
that
the item is available to customers,
through the
IBM
representative, without charge for
quantities
that
meet
normal
requirements. Use key
S means
that
the item is for sale
through
IBM
branch
offices.
Bill
of
Forms
An
order
number
in the form
OfGBOF-1234
is a Bill
Of
Forms - a single
order
number
for a package
of
separately available documents.
Flags on
Order
Numbers
Maximum
case: **GC20-0001-5#
A double asterisk preceding the
order
number
indicates either a change in the publication (such
as a new edition)
or
a new item.
When
more
than
one edition
of
a publication is
current, the order-number suffix is followed
by
a
number
sign
(#).
Preface
Part
1.
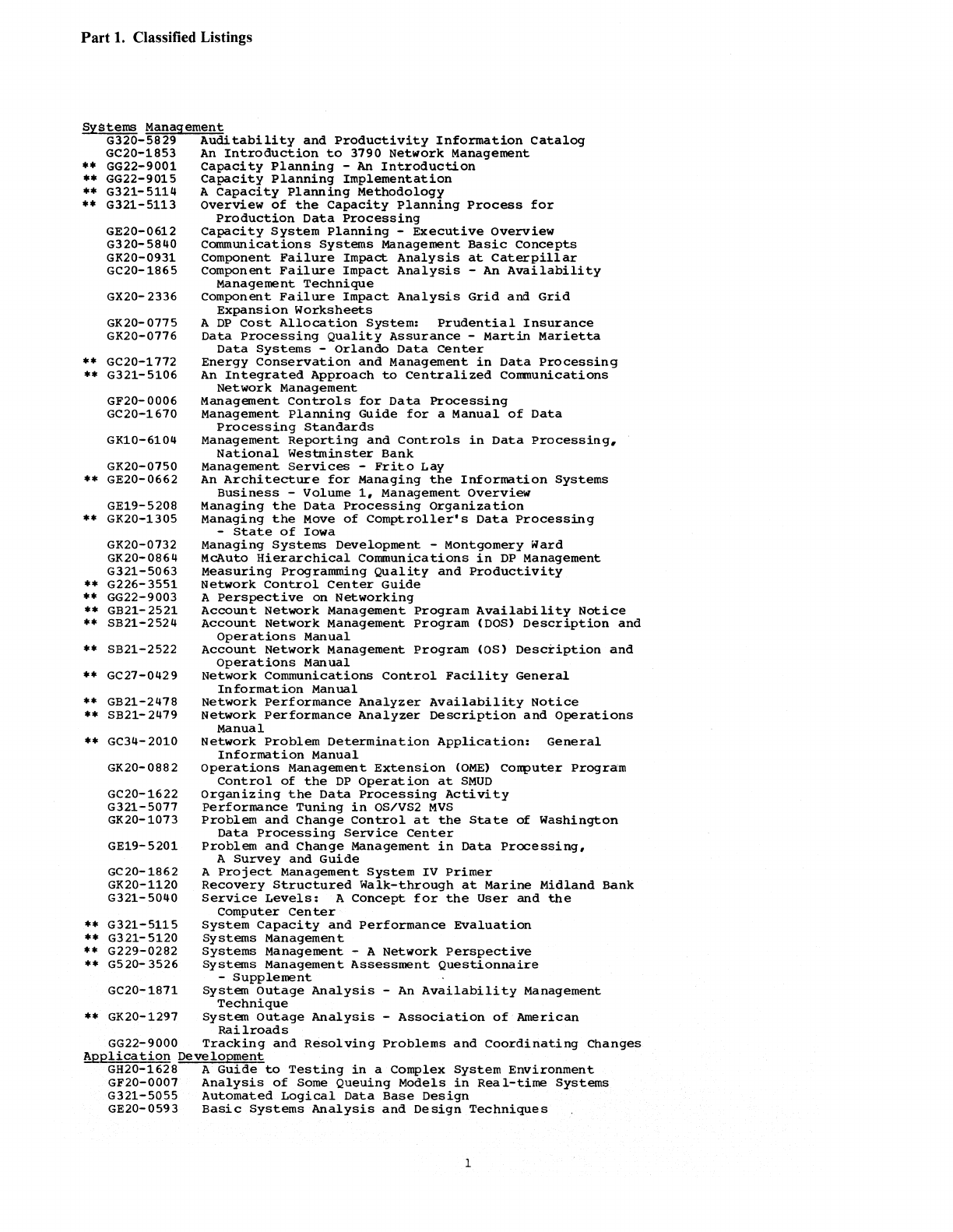
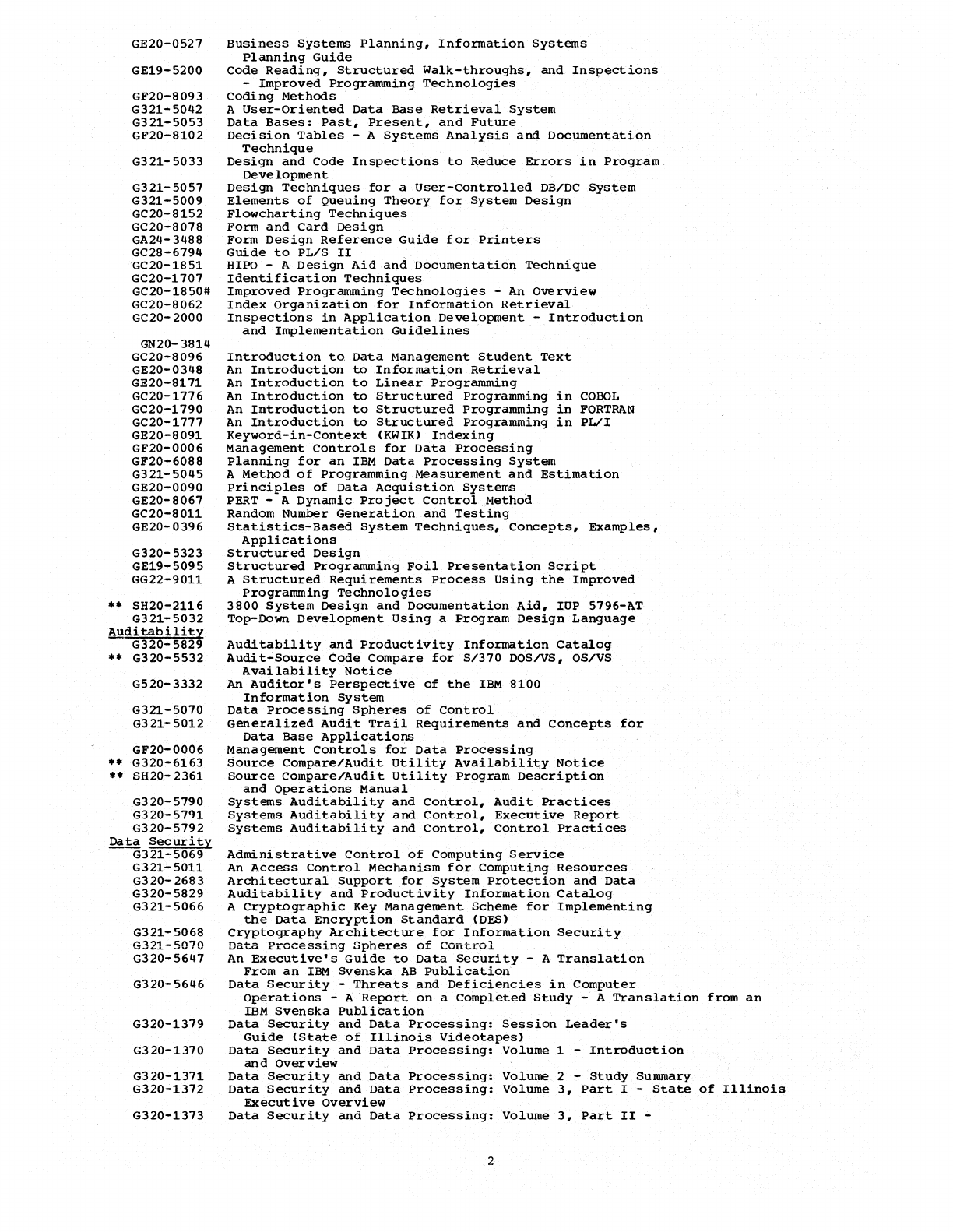
Classified Listings
Systems
Management
G320-5829
Auditability
and
Productivity
Information
Catalog
GC20-1853
An
Introduction
to
3190
Network
Management
••
GG22-9001
Capacity
Planning
-
An
Introduction
••
GG22-9015
Capacity
Planning
Implementation
••
G321-5114 A
Capacity
Planning
Methodology
••
G321-5113
overview
of
the
Capacity
Planning
Process
for
GE20-0612
G320-5840
GK20-0931
GC20-1865
GX20- 2336
GK20-0115
GK20-0116
..
GC20-1112
••
G321-5106
GF20-0006
GC20-1610
GKlO-6104
GK20-0150
••
GE20-0662
GE19-5208
••
GK20-1305
GK20-0132
GK20-0864
G321-5063
••
G226-3551
••
GG22-9003
••
GB21-2521
••
SB21-2524
••
SB21-2522
••
GC21-0429
••
GB21-2418
••
SB21-2419
••
GC34-2010
GK20-0882
GC20-1622
G321-5011
GK20-1013
GE19-5201
GC20-1862
GK20-1120
G321-5040
••
G321-5115
••
G321-5120
••
G229-0282
••
G520-3526
GC20-1811
••
GK20-1291
Production
Data
Processing
Capacity
System
Planning
-
Executive
Overview
Communications
Systems
Management
Basic
Concepts
Component
Failure
Impact
Analysis
at
Caterpillar
Component
Failure
Impact
Analysis
-
An
Availability
Management
Technique
Component
Failure
Impact
Analysis
Grid
and
Grid
Expansion
Worksheets
A
DP
Cost
Allocation
System:
Prudential
Insurance
Data
Processing
Quality
Assurance
-
Martin
Marietta
Data
Systems
-
Orlando
Data
center
Energy
Conservation
and
Management
in
Data
Processing
An
Integrated
Approach
to
Centralized
Communications
Network
Management
Management
Controls
for
Data
Processing
Management
Planning
Guide
for
a
Manual
of
Data
Processing
Standards
Management
Reporting
and
Controls
in
Data
Processing,
National
Westminster
Bank
Management
Services
-
Frito
Lay
An
Architecture
for
Managing
the
Information
Systems
Business
-Volume
1,
Management
Overview
Managing
the
Data
Processing
Organization
Managing
the
Move
of
Comptroller's
Data
Processing
-
State
of
Iowa
Managing
Systems
Development
-Montgomery Ward
McAuto
Hierarchical
Communications
in
DP
Management
Measuring
Programming
Quality
and
Productivity
Network
Control
Center
Guide
A
perspective
on
Networking
Account
Network
Management
Program
Availability
Notice
Account
Network
Management
Program
(DOS)
Description
and
Operations
Manual
Account
Network
Management
Program
(OS)
Description
and
Operations
Manual
Network
Communications
Control
Facility
General
Information
Manual
Network
performance
Analyzer
Availability
Notice
Network
Performance
Analyzer
Description
and
Operations
Manual
Network
Problem
Determination
Application:
General
Information
Manual
Operations
Management
Extension
(OME)
Computer
Program
Control
of
the
DP
Operation
at
SMUD
Organizing
the
Data
Processing
Activity
Performance
Tuning
in
OS/VS2
MVS
Problem
and
Change
Control
at
the
State
of
Washington
Data
Processing
Service
Center
Problem
and
Change
Management
in
Data
Processing,
A
Survey
and
Guide
A
Project
Management
System
IV
Primer
Recovery
Structured
Walk-through
at
Marine
Midland
Bank
Service
Levels:
A
Concept
for
the
User
and
the
Computer
Center
System
capacity
and
Performance
Evaluation
Systems
Management
Systems
Management - A
Network
Perspective
Systems
Management
Assessment
Questionnaire
-
Supplement
system
outage
Analysis
-
An
Availability
Management
Technique
System
Outage
Analysis
-
Association
of
American
Railroads
GG22-9000
Tracking
and
Resolving
Problems
and
coordinating
Changes
Application
Development
GH20-1628 A
Guide
to
Testing
in
a Complex
System
Environment
GF20-0001
Analysis
of
Some
Queuing
Models
in
Real-time
Systems
G321-5055
Automated
Logical
Data
Base
Design
GE20-0593
Basic
Systems
Analysis
and
Design
Techniques
1
GE20-0527
GE19-5200
GF20-8093
G321-5042
G321-5053
GF20-8102
G321-5033
G321-5057
G321-5009
GC20-8152
GC20-8078
GA24-3488
GC28-6794
GC20-1851
GC20-1707
GC20-1850#
GC20-8062
GC20-
2000
GN20-
3814
GC20-8096
GE20-0348
GE20-8171
GC20-1776
GC20-1790
GC20-1777
GE20-8091
GF20-0006
GF20-6088
G321-5045
GE20-0090
GE20-8067
GC20-8011
GE20-0396
G320-
5323
GE19-5095
GG22-9011
..
SH20-2116
G321-5032
Auditability
G320-5829
••
G320-5532
G520-3332
G321-5070
G321-5012
GF20-0006
••
G320-6163
••
SH20-
2361
G320-5790
G320-5791
G320-5792
Data
Security
G321-5069
G321-5011
G320-2683
G320-5829
G321-5066
G321-5068
G321-5070
G320-5647
G320-5646
G320-1379
G320-1370
G320-1371
G320-1372
G320-1373
Business
Systems
Planning,
Information
Systems
Planning
Guide
Code
Reading,
Structured
Walk-throughs,
and
Inspections
-
Improved
Programming
Technologies
Coding
Methods
A
User-Oriented
Data
Base
Retrieval
System
Data
Bases:
Past,
Present,
and
Future
Decision
Tables
- A
Systems
Analysis
and
Documentation
Technique
Design
and
Code
Inspections
to
Reduce
Errors
in
Program.
Development
Design
Techniques
for
a
User-controlled
DB/DC
System
Elements
of
Queuing
Theory
for
System
Design
Flowcharting
Techniques
Form
and
Card
Design
Form
Design
Reference
Guide
for
Printers
Guide
to
PL/S
II
HlPO - A
Design
Aid
and
Documentation
Technique
Identification
Techniques
Improved
Programming
Technologies
-An
Overview
Index
Organization
for
Information
Retrieval
Inspections
in
Application
Development
-
Introduction
and
Implementation
Guidelines
Introduction
to
Data
Management
Student
Text
An
Introduction
to
Information
Retrieval
An
Introduction
to
Linear
Programming
An
Introduction
to
Structured
Programming
in
COBOL
An
Introduction
to
Structured
Programming
in
FORTRAN
An
Introduction
to
Structured
Programming
in
PL/I
Keyword-in-Context
(KWIK)
Indexing
Management
Controls
for
Data
Processing
Planning
for
an
IBM
Data
Processing
System
A
Method
of
Programming
Measurement
and
Estimation
Principles
of
Data
Acquistion
Systems
PERT - A
Dynamic
Project
Control
Method
Random
Number
Generation
and
Testing
statistics-Based
System
Techniques,
Concepts,
Examples,
Applications
Stru,ctured
Design
Structured
Programming
Foil
Presentation
Script
A
Structured
Requirements
Process
Using
the
Improved
Programming
Technologies
3800
System
Design
and
Documentation
Aid,
IUP
5796-AT
Top-Down
Development
USing
a
Program
Design
Language
Auditability
and
Productivity
Information
Catalog
Audit-Source
Code
compare
for
S/370
DOS/vS,
OS/VS
Availability
Notice
An
Auditor's
perspective
of
the
IBM
8100
Information
System
Data
Processing
Spheres
of
Control
Generalized
Audit
Trail
Requirements
and
Concepts
for
Data
Base
Applications
Management
Controls
for
Data
Processing
Source
Compare/Audit
Utility
Availability
Notice
Source
ComparelAudit
Utility
Program
Description
and
operations
Manual
Systems
Auditability
and
Control,
Audit
Practices
Systems
Auditability
and
Control,
Executive
Report
Systems
Auditability
and
Control,
Control
Practices
Administrative
control
of
Computing
Service
An
Access
Control
Mechanism
for
Computing
Resources
Architectural
support
for
System
Protection
and
Data
Auditability
and
Productivity
Information
Catalog
A
Cryptographic
Key
Management
Scheme
for
Implementing
the
Data
Encryption
Standard
(DES)
cryptography
Architecture
for
Information
Security
Data
Processing
Spheres
of
Control
An
Executive's
Guide
to
Data
Security
- A
Translation
From
an
IBM
Svenska
AB
Publication
Data
Security
-
Threats
and
Deficiencies
in
Computer
Operations
- A
Report
on
a
Completed
Study
- A
Translation
from
an
IBM
Svenska
Publication
Data
Security
and
Data
Processing:
Session
Leader's
Guide
(State
of
Illinois
Videotapes)
Data
Security
and
Data
Processing:
Volume
1 -
Introduction
and
Overview
Data
Security
and
Data
Processing:
Volume
2 -
Study
Summary
Data
Security
and
Data
Processing:
Volume
3,
Part
I -
State
of
Illinois
Executive
Overview
Data
Security
and
Data
Processing:
Volume
3,
Part
II
-
2
G320-1374
G320-1375
G320-1376
G320-5649
G520-2882
GC22-9062
G321-5012
G321-5067
G321-5010
GC22-9063
G520-2965
G520-2838
GA27-2865
GF20-0006
G320-5650
G320- 5522
GC28-0942
GBOF-1200
GC28-0722
G520-2881
G520-2169
G520- 2700
G520- 2741
G520-2797
State
of
Illinois
Study
Results
Data
Security
and
Data
Processing:
Volume 4 -
Massachusetts
Institute
of
Technology
Study
Results
Data
Security
and
Data
Processing:
volume
5 -
TRW
Systems,
Inc.,
Study
Results
Data
Security
and
Data
Processing:
Volume 6 -
Evaluations
and
Installation
Experiences:
Resource
Security
System
Data
Security
Controls
and
Procedures
- A
Philosophy
for
DP
Installations
Data
Security
Seminars:
IBM
Education
Course
X8851
Brochure
Data
Security
Through
Cryptography
Generalized
Audit
Trail
Requirements
and
Concepts
for
Data
Base
Applications
Generation,
Distribution,
and
Installation
of
Cryptographic
Keys
Hierarchical
Approach
to
Computer
System
Integrity
IBM
Cryptographic
Subsystem
Concepts
and
Facilities
IBM
Data
Security
Forum:
Denver,
Colorado,
September
1974
IBM
Data
Security
Symposium,
April
1973
IBM
3845/3846
Data
Encryption
Device
-
General
Information
Manual
Management
Controls
for
Data
Processing
Management Memorandum:
Security
Features
of
IBM
System/370
Operating
System
Integrity
in
OS/VS2
OS/vSl
and
Os/VS2
MVS
Cryptographic
Facility
-
General
Information
Manual
Report
of
IBM
Joint
Data
Security
Studies
RACF
General
Information
Manual
Security
•••
The
Right
Thing
for
Your
Computer,
The
Best
Thing
for
Your
Information
The
Considerations
of
Data
Security
in
a
Computer
Environment
The
Considerations
of
Physical
Security
in
a
Computer
Environment
The
Fire
After
the
Fire
42
Suggestions
for
Improving
Security
in
Data
Processing
Operations
Fo~
and
Templates
GX20-2336 Component
Failure
Impact
Analysis
Grid
and
Grid
Expansion
Worksheets
GX28-1630
Decision
Table
Worksheet
GX20-8020
Flowcharting
Template
GX20-8047
Hexadecimal
and
Decimal
Integer
Conversion
Table
GX20-1971
HlPO
Template
GX20-1970
HlPO
Worksheet
GX20-1702
Proportional
Record
Layout
Form
GX20-1818
150/10/8
Print
Chart
••
GX20-2353
Systems
Management
Assessment
Questionnaire
Bibliographies
~
Indexes
GC20-1764
Atlas
of
Applications:
Volume I -
An
Alphabetic
GC20-1768
GC20-1783
GC20-1141
G321-5036
GC20-8071
Bibliography
of
Quantitative
Methods
Applied
to
Business,
Industry,
Science,
and
Engineering
(1961
to
1972)
Atlas
of
Applications:
Volume
II
-
Bibliography
of
Quantitative
Methods
in
Business,
Industry,
Science,
and
Engineering
(1972
to
1974)
Atlas
of
Applications:
Volume
III
-
Bibliography
of
Quantitative
Methods
in
Business,
Industry,
Science,
and
Engineering
Management
Science
at
Work - A
Bibliography
Covering
All
Enterprises,
All
Functions,
and
All
Techniques
Selected
Readings:
Data
Base
Systems
10,000
Division
Codes
for
Proper
Names
3
Part
2. Abstracts
GA24-3488
FORM
DESIGN
REFERENCE
GUIDE
FOR
PRINTERS
This
publICation
conta~nform~
te
considered
by
personnel
designing,
ordering,
or
using
forms
for
the
system
printers
listed
below.
Tnis
manual
has
two
sections:
general
forms-design
information
a~plicable
to
system
printers,
and
specific
information
(Appendix)
for
particular
printers.
The
general
information
relates
to
items
such
as
form
length,
~~dth,
weight,
fastenings,
and
other
forms-related
items
that
must
be
considered
and/or
met when
forms
are
designed
for
system
printers..
The
specifications
are
not
intended
to
be
restrictive,
tut
to
permit
the
customer
to
purchase
continuous
forms
from
the
manufacturers
of
his
choice.
For
detailed
information
on
forms
feeding
and
operating
procedures,
see
the
appropriate
component
description
and
operating
procedures
manuals
for
the
particular
printer
er
system
..
companion
publications
useful
in
designing
forms
are:
o
OCR
Input
Preparation
Guide,
Order
No. GC20-1686
o
Print
Chart
(Six
Lines'
per
Inch),
GX20-1816
o
Print
Chart
(Eight
Lines
per
Inch),
GX20-1818
Another
publication
which
is
not
an
IBM
publication
but
nay
be
helpful
in
designing
forms
and
for
comparison
purposes
is
International
Standard
ISO,
2784,.. DiIl'>E!nsions
in
this
manual
are
to
this
standard..
IBM
printers
included
are:
1132
3211 3618
1403
3213 3713
1qOq 3215 3715
1q43
3284 3717
2203 3286 3791
Line
Printer
Feature
2213 3288 3792
Line
Printer
Feature
2222 3610 5203
3203
3612
5213
3210
Manual.
32
pages
GA27-2865
1m!
38q5
DATA
ENCRYPTION
DEVICE,
1m!
3846
!lATA
ENCRYPTION
DEVICE,
~
INFORMATION
~his
manual
describes
the
IEM
38q5
and
38q6
Data
Encryption
Device
in
sufficient
detail
to
enable
propsective
users
to
decide
whether
to
use
this
type
of
data
protection.
Physical
planning
diagrams
and
specifications
are
included,
as
are
general
guidelines
for
the
selection
and
distribution
of
key-variables.
Manual,
8
1/2
x
11
inches,
44
pgs,
10/77
GBOF-1200
REPORT
OF
IBM
~
DATA
SECURITY
STUDIES
Over
two
years
ago,
IBM
announced
that
it
was
initiating
a program
in
long
range
data
security
research,
technology
and
documentation.
Part
of
that
program
involved
a two
year
joint
study
with
three
IBM
customers:
The
State
of
Illinois;
TRW
Systems,
Inc.;
and
Massachusetts
Institute
of
Technology.
An
IBM
installation
at
our
Federal
Systems
Division
in
Gaithersburg,
~d,.
served
as
a
fourth
study
site,.
Each
focused
on
a
particular
aspect
of
data
security.
The.
groups
coapleted
their
work
this
spring,
and
the
results
are
included
in
this
BOF:
Data
Security
and
Data
Processing
.••
Volume
1,
Introduction
and
Overview
(G320-1370)
Volume
2,
Study
Summary
(G320-1371)
Volume
3,
Part
1,
State
of
Illinois:
Executive
overview
(G320-1372)
Volume
q,
Study
Results;
Massachusetts
Institute
of
Technology
(G320-1374)
Volume
5,
Study
Results:
TRW
Systems,
Inc.
(G320-1375)
Volume
6,
Evaluations
and
Study
Experiences:
Resource
Security
System
(G320-1376)
Volume
1,
for
executive,
contains
an
introduction
to
the
data
security
and
privacy
issues
and
an
overview
of
the
findings
of
the
data
security
studies.
Valune
2,
a
more
detailed
summary
of
the
data
security
study
is
for
management
and
will
be
of
special
interest
to
those
charged
with
implementation,.
Volume
3,
Part
1,
an
executive
overview
primarily
concerning
.privacy
was
prepared
by
the
State
of
Illinois
stt;d
,
team
.•
The
remaining
volumes
provide
a number
of
detailed
technical
papers
that
may
be
of
interest
to
various
other
people
within
customer
accounts.
A
complete
set
of
nine
State
of
Illinois
Videotapes
on
security
and
privacy
for
use
by
agencies
within
the
State
are
additionally
available.
~'hese
tapes
will,
however
be
applicable
to
a
more
general
audience
--
not
just
to
those
involved
with
state
gove,rmrent.
A
complete
set
of
tapes
is
being
sent
to
each
region.
The
tapes
may
be
loaned
to
branch
offices
for
loan
to
customers
for
short
periods
of
time
13-5
days).
Customers
may
wish
to
borrow
individual
tapes
to
show them
to
an
employee
group
or
to
determine
whether
they
are
interested
in
purchasing
them.
GB21
A
Session
Leader's
Guide,
form
no.
G320-1379,
will
te
distrituted
with
the
tapes.
It
is
alsc
availatle
separately
from
Mechanicsburg
for
those
who would
like
to
understand
the
ccntents
of
the
tapes
tefore
ordering
them.
1.
iihose
Right
to
Know
2.
Fellow
that
Card
3.
Implerrenting
the
Information
Privacy
and
Security
4.
5.
6.
7.
8.
9.
Program
Admiriistering
the
Information
Frivacy
and
Security
Prograro
Eesigning
Privacy
and
Security
Into
Infcrmation
Systems
Software
Security
and
Tern,inal
Access
Ccntrol
Concepts
Physical
Plant
Security
Contingency
Planning
and Backup
Systems
~hat
Every
Executive
Should
Kno~
About
Privacy
In
Information
Systems
Customer
purchase
orders
should
te
sent
directly
to:
S/T
VIJ:EOCASSETTJ;:
Duplicating
Corp.
500 Willow
Tree
Noad
Leonia,
New
Jersey
07605
Tel.
(201)
9Q7-6Q50
or
N.Y.C.
Nes.
1,
5,
6,
8
cr
9
(212)
239-
4653
21.95
23.30
U-MAtIC 3/Q
inch
Ncs.
2,
3,
4
or
7
Play
tack
Machine
Required:
SONY
VIDEOCASSEtTE,
or
equivalent.
Bill
of
Material
NOT
AVAILABLE
UNDER
ELSS
GB21-2Q78
NETWORK
PERFORMNCE
~
~
JlQ§!L
FDP
5798-CZ!!...
NEtWORK
PERFORMANCE
ANALYZER
=
CONTROlLE!!...
!!l!
~~
NOTICE
This
Availability
Notice
contains
complete
ordering
inforIraticn
for
the
Frogram
and
all
its
related
documentation,
for
management and
data
proceSSing
personnel
who
are
prospective
users
of
the
program and
others
who
require
inforn.ation
concerning
it
..
Written
in
ALC,
the
Network
Performance
Analyzer
(NPA)
collects
comrounicaticns
network
operating
data
fer
analysis.
NPA
data
nay
be
helpful
in
highlighting
the
causes
of
performance
degradation,
such
as
excessive
traffic
at
certain
periods,
or
insufficient
line
capacity.
It
Ray
also
aid
in
isolating
performance
problems
induced
ty
high
line
or
cluster
error
rates
caused
by
temforary
errors,
0%
wide
fluctuations
in
.message
rates.
With
NPA
data,
networks
may
be
tuned
for
greater
efficiency,
and
potentially
improved
response
tines.
Elements
such
as
polling
rates,
network
paraIl'.eters,
and
line
loading,
may
be
modified
and
performance
improved.
~uning
nay
also
free
up
capacity.
NPA
inforK.ation
nay
also
be
helpful
in
capacity
planning.
Information
sucb
as
3705
utilization,
message
flow
rates,
and
line
usage
rates,
may
help
deterIl'.ine
hOll!
Kuch
unused
capacity
exists
for
network
growth.
The
data
tray
ce
displayed
online
as
collected,
or
reviewed
later
at
a
tenrinal.
Data
of
particular
interest
nay
be
monitored
on
er
offline
fer
exceptions
to
user
defined
limits.
~he
capability
of
displaying
realtime
information
may
be
es~ecially
valuable
during
periods
of
poor
performance..
The
data
gathered
is
also
available
for
forItatting
into
rer:orts
for
study,
and
compariscn
with
previous
feriods,.
This
allows
modification
of
systens
parameters,
and
otservance
of
sutsequent
results.
NPA
consists
of
a
host
application
prograrr and
one
or
nore
reodified
NCP
frograms.
It
runs
under
VS1
or
MVS,
with
VTAM
and/or
TCAM.
NFA
can
coexist
with
subsysteIrs
such'as
eles,
IMS.
or
TSO,
tut
operates
independently
of
them.
Flyer,
8
112
x
11.inches,
4
pages,
6/79
SB21-2479
4
~
PERFORIIANCE
ANALYZER
~
HOS~,
l!lR 5798-CZR,
~
EERFORMANCE
~
=
CONTROLLER,
FCP
~~
DESCRIPTION/OPERATIONS
This
Program
Descriftion/operations
Manual
provides
t~e
user
with
sufficient
information
to
understand,
install
and
successfull~
use
the
program.
Fer
further
information
about
this
publication,
see
abstract
for
GB21-2478.
Manual,
8
112
x
11
inches,
139
pages,
6/79
GB21-2521
ACCOUNT
NnWORR
I;ANAGEMENT
~~
FOP
5798-DA2
(OS/VS/CICS),
FDP
5798-DAT, (DOSIVS/CICS),
~OTICE
This
Availability
Notice
contains
complete
ordering
information
for
the
Frogram and
all
its
related
documentatiGn,
for
management and
data
proceSSing
personnel
who
are
prospective
users
of
the
program
and
others
who
require
inforn:ation
concerning
it.
This
FOP,
wLitten
in
ALC,
is
specifically
designed
to
automate
the
core
elements
of
systems
ulanagellent
with
an
integrated
set
of
interactive
application
programs
and
batch
report
programs
as
fellows:
The
problerr
management
application
provides
~reformatted
screens
to
ensure
consistent
protlem
reporting,
assignment
and
resolution
of
system
or
network
incidents.
It
has
create,
update,
display,
and
browse
functions,
allo~in9
nultiFle
aSSignments
on
problems
and
permits
extensive
comments.
All
fields
except
the
comments
are
editable
and
searchatle.
History
files
can
be
created
for
batch
reporting.
GB21
The
change
management
application
provides
preformatted
screens
to
enable
planned,
coordinated
change
activities
including.
equipment
installation
or
relocation;
new
application
programs;
PUT
and
engineering
changes,
and
feature
changes.
It
likewise,
has
create,
update,
display
and browse
functions
and
includes
an
approver/reviewer
facility.
All
fields
are
editable
and
searchable.
History
files
can
te
created
for
batch
reports.
The
network
configuration
application
provides
an
online
data
base
of
network
components
and
the
ability
to
create,
update
and
display
records
containing
component
details.
Detail
may
include:
component
name,
id
characteristics,
location,
phone
numbers,
vendor
information,
etc.
The
configuration
file
supports
display
of
the
physical
connectivity
of
components.
The
batch
report
facility
provides
a
network
map, component
detail
listings
and
change
activity.
Flyer.
8
1/2.x
11
inches.
4
pages,
8/79
SB21-2522
ACCOUNT
NETWORK
MANAGEMENT
PROGRAMS
OS/VS/CICS.
FOP
5798=IiAQ.
DESCg];PTIO~OPERA~
This
Program
DescriptionJo~erations
Manual
provides
the
user
with
sufficient
information
to
understand,
install
and
successfully
use
the
program.
For
further
information
about
this
program,
see
abstract
for
GB21-2521.
Manual,
8
1/2
x
11
inches,
360
pages,
8/79
SB21-2524
ACCOUNT
MANAGEMENT
NETWORK
PROGRAMS,
DOS/VS/CICS. T-DP
5798-DAT, DESCRIPTION/OPERATIONS
This
Program
Description/Operations
Manual
provides
the
user
with
sufficient
information
to
understand,·
install
and
successfully
use
the
program.
For
information
regarding
this
program,
see
abstract
for
GB21-2521.
Manual,
8
1/2
x
11
inches,
354
pages,
8/79
GC20-1622
o,RGANIZING
THE
DATA
PROCESSING
ACTIVITY
This
text
is-designed
to
help
the
organizational
planner
develop
the
data
proceSSing
structure
best
suited
to
his
own
needs
and
environment.
It
is
directed
primarily
to
data
proceSSing
managers,
the
executives
to
whom
they
report,
and
others
responsible
for
organizational
and
personnel
t;:lanning,.. The
major
topics
discussed
are:
concepts
applicable
to
organizing
the
data
processing
activity,
t;:ossible
locations
of
the
data
processing
activity
within
the
larger
organization,
data
proceSSing
functions,
grouping
of
functions
into
an
organizational
structure,
and
grouping
of
functions
into
job
families
and
job
fositions,..
The
Appendix
provides
some
typical
job
descriptions.
Manual,
128
pages
SLSS -
ORDER
NO,.
SUBSCRIPTION
ONLY
GC20-1707
IDENTIFICATION
TECHNIQUES
~is
manual
ext;:lains
and
compares
a
survey
of
several
tyt;:es
of
coding
techniques
for
individuals
and
non-individuals.
An
afproach
to
improving
coding
methods
involving
a
statistical
approach
is
outlined.
The
publication
is
baSically
a
state-of-the-art
description
of
the
identification
teChniques.
Data
ProceSSing
Techniques
Manual, 50
pages
SLSS -
ORDER
NO.
SUBSCRIPTION
ONLY
GC20-1741
MANAGEMENT
SCIENCE
AT
WORK
A
BIBLIOGRAPHY
COVERING
ALL
ENTERPRISES.
ALL
FUNCTIONS.
AND
ALL
TECHNIQ~
-
A
great
number
of
problems
in
industry,
in
science
r and
in
engineering
can
be
solved
by
the
systematic
methods
of
mathenatics,
statistics,
and
operations
research-
management
science~
This
manual
is
a
specially
organized
three-way
index
to
almost
5000
journal
articles
and
conference
papers
which
have
mentioned
the
application
of
analytic
methods
to
various
business,
industrial,
and
scientific
protlems.
Manual,
Special
Bibliography,
112
pages
SLSS -
ORDER
NO,.
SUBSCRIPTION
ONLY
GC20-1764
ATLAS
OF
APPLICAtIONS
(I)
AN
ALPHABETIC
BIBLIOGRAPHY
OF
QijANt·ITATIVE
~
APPUED
1Q
EUSINESS.
INDUSTRY,
SCIENCE,
~ND
ENGINEERING
(1961
TO
1972)
~his
manual
is
a
collection
of
references
to
applications
of
quantitative
methods
in
business,
industry,
engineering,
and
science.
The
quantitative
method
may
be
from
mathematics,
statistiCS,
operations
research,
or
management
science.
The
data
on
which
the
alphabetic
index
is
based
is
a
collection
of
8,300
references
to
journal
articles
or
to
papers
given
at
conferences.
Some
350
journals
and
periodicals
were
scanned,
covering
the
years
1961
to
1972
Manual,
293
pages
SLSS -
ORDER
NO.
SUBSCRIPTION
ONLY
GC20
GC20-1768
BIBLICGRAPHY
OF
INDUSTRY,
SCIE~
ANI:
volume
to
Atlas
of
Applications
(GC20-1764).
The
older
manual
was
based
on
8,300
references
covering
the
years
1961
to
1972
and
gathered
frorr
350
journals.
Like
the
elder
manual,
Atlas
of
Applications
•••
Volume
II
is
a
collection
of
references
to
applications
of
quantitative
n,ethods
in
business,
industry,
engineering,
and
science.
The
quantitative
method
may
be
fran
mathematiCS,
statistics,
operations
research,
or
managea,ent
science.
The
data
on
which
the
alphatetic
index
is
based
is
a
collection
of
3,000
references
to
journal
articles
or
to
fafers
given
at
conferences.
~he
journals
and
periodicals
scanned
cover
the
years
1972
to
1974.
SpeCial
Eitliography,
200
pages
SLSS -
ORDER
NO.
SUBSCRIPtION
ONLY
GC20-1772
ENERGY
CONSERVATIo,N
~ND
M~NAGE~ENt
IN
L~TA
PROCESSING
This
manual
examines
several
aspects
oreIiergy
conservation
and management
that
nay
te
of
value
to
installations
using
IBM
data
proceSSing
equipment,
and
fresents
sane
considerations
involved
in
developing
and
implen,enting
plans
for
ccntrolling
ccnsumftion
and
minimizing
the
impact
of
energy
shortages
on
data
processing
operations.
Manual
SLSS -
ORI:ER
NO.
SUEECRIPtION
ONLY
GC20-1776
AN
INtRODUCT
ION
TC
STRUCTURED
PROGRAMMING
IN
COECL
This
text,
intended-for
progranmers,
descrIEes-and
illustrates
the
use
cf
structured
programT,ing. 'Ihe
technique
and
its
sU~t;:crting
practices
are
generally
descrited
in
one
chapter.
A
reference
chapter
illustrates
the
imt;:lenentation
of
the
technique
in
COBOt
and
is
followed
by
a
chapter
presenting
two
sarr.t;:le
frograrrs.
A
knowledge
of
COBOL
is
assurred.
Manual
GC20-1777
AN
INtRODUCTION
TO
SlRtCTURED
PRCGRAMMING
IN
PL/I
This
text,
intend€d~r
progranrners,
descrTEes-aDd
illustrates
the
use
of
structured
prograrrming. The
technique
and
its
supporting
practices
are
generally
described
in
one
chaFter.
A
reference
chapter
illustrates
the
implen.entation
of
the
technique
in
PL/I
and
is
followed
by
a
cha~ter
.,resenting
two
saIr~le
prograIrs.
A
knowledge
of
PL/I
is
assurred.
Manual
GC20-1783
5
ATLAS
o,F
APPLICATICNS
VOLUME
III,
BIBLIOGRAPHY
Q!:
.Il2t!'!UtAtIVE
MET~
.!!:!
BUSINESS,
INDUSTRY,
SCIENCE,
~~§INEERING
This
nanual
is
a
fellow-on
volume
to
Atlas
of
Applications
(GC20-1764)
and
Atlas
of
Applications
Voluroe
II
(GC20-1768).
The
older
manuals
were
~ased
on
11,300
references
covering
the
years
1961
to
1974
and
gathered
from
350
jcurnals.
Like
the
older
rranuals,
Atlas
of
Applications
Volmt",e
III
is
a
collection
of
references
to
applications
of
quantitative
rrethods
in
business,
industry,
engineering,
and
science.
The
quantitative
method
may
be
frOIr
mathen.atics,
statistics,
operations
research,
er
managenent
science.
The
data
on
which
the
alphabetic
index
is
tased
is
a
collection
of
2,500
references
to
journal
articles
or
to
papers
given
at
conferences.
The
jcurnals
and
periodicals
scanned
for
this
volume
were
Irastly
1975
issues.
Eitliography,
185
.,ages,
3/76
SLSS -
ORDER
NO.
SUBSCRIPTION
ONLY
GC20-1790
AN
INtRODtCTION
TO
SlRUCTURED
PROGRA~MING
IN
FORtRAN
This
text,
intended
fer
programmers,
describe~
illustrates
the
use
of
structured
pragranrring.
'Ihe
technique
and
its
supporting
practices
are
generally
described
in
one
chafter.
A
second
chapter
illustrates
the
implementation
of
the
technique
in
FOR'IRAN
and
is
followed
by
a
chapter
presenting
two
sample
prograres.
A
knowledge
of
FORTRAN
is
assumed.
Manual.
8
1/2
x
11
inches,
48
pgs.,
7/77
GC20-1850
IMPROVED
PROGRAMMING
tECHNCLOGIES
-
~N
OVERVIEW
~u"ent
is
intended
to
briefly-descrite-8ix
recently
forttalized
techniques
designed
to
improve
the
~rogram
devel-
opment
process:
structured
pragran,n:ing,
toP-d9wn
frcgram
development,
chief
programmer
teams,
HIPC
(Hierarchy
plus
Input-Process-output),
and
structured
walk-throughs.
Manual
SLSS -
ORI:ER
NO.
SUBSCRIPtIo,N
ONLY
GC20-1851
HIPo,
::
~
J:ESIGN
H12
liND
~!~!!Q!i
1ECHNIQUE
The
purpose
of
this
manual
is
to
describe
a
deSign
aid
and
docuIrentation
technique
called
HIPC -
Hierarchy
~lus
Input-
GC20
Process-output.
The manual
is
intended
fcr
systems
analysts
and
programmers
and
describes
ho.
to
use
HlPO
as
a
design
aid
and
documentation
technique
throughout
~e
development
cycae.
Manual
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GC20-1853
AN
INTRODUCTION
TO
3790
NETWORR
MANAGEMENT
ibis
text
is
intendedi10r
IBM
systems
engineers
·and
for
data
processing
installation
management
personnel
responsible
for
installing
3790
net.orks
.•
Manual,
qO
pgs,
q/77
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GC20-1862
A
PROJECT
MANAGEMENT
SYSTE~
IV
PRIMER
this
prirrer
is
intend~
use-as-a-learning
tool
by
the
person
who
will
be
responsible
for
creating
input
data
to
PMS
IV
from
project
data
(CPM
diagrams,
task
lists,
dependency
lists,
etc;).
It
assumes
only
a
limited
knowledge
of
data
processing
concepts,
and
is
written
for
those
already
familiar
with
net.ork
planning,
resource
allocation.
and
cost
management
concepts
since
these
are
summarized
only
briefly
here.
The
primer
illustrates
the
basic
concepts
of
PMS
IV
through
the
development
of
a
sarrple
problem
throughout
the
various
chapters.
Readers
needing
to
use
the
other
features
()f
PMS
IV
(listed
in
an
appendix)
are
directed
to
the
PMS
IV
program
description
and
operations
publications
.•
Manual
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GC20-1865
,_,~~-=
~
~~
=
~
AVAILABILITY
Impact
Analysis
(CFIA)
is
a
technique
to
raise
the
level
of
system
availability
by
ways
to
shorten
recovery
times
when a
system
component
fails.
~is
manual
describes
the
steps
involved
in
setting
up
and
using
CFIA
as
part
of
an
effort
to
improve
system
availability.
Manual,
32
pages,
5/78
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GC20-1871
mIm!
~
ANALYSIS.
~
AVAILABILITY
MANAGEMENT
TECHNI2Y!
System
Outage
"Analysis
is
a
technique
designed
to
assist
in
data
processing
managerrent
in
increasing
system
availability
by
reducing
the
number
of
outages
and
their
impact.on
system
availability.
This
manllal
describes
the
steps
involved
in
~is
manual
describes
the
steps
involved
in
using
BOA
as
part
of
an
effort
to
improve
system
availability.
Manual,
8
1/2
x 11
inches,
qO
pages,
12/78
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GC20-2000
INSP
TIONS
IN
APPLICATION
DEVELOPMENT
=
INTRODUCTION
~
IMP
ON
GUIDELINES
Appl
development
inspections
is
a
disciplined
technique
for
technical
prcject
review
held
at
the
end
of
various
application
development
phases
to
improve
program
quality
and
project
manageability
and
to
increase
productivity.
This
manllal
is
designed
to
provide
enough
information
to
the
manager
of
the
data
processing
activity
and"his
technical
staff
to
answer
the
question.
·Should
this
activity
uSe
inspections?·
The
manual
also
provides
guidance
in
preparing
for
and
performaing
inspections.
A
case
stUdy
is
included.
This
description
of
the
inspections
technique
is
~ade
available
by
IBM
with
the
objective
of
~roviding
information
that
may
assist
others
in
improving
their
own
application
development
procedures.
It
does
not
require
the
use
of
lEN
products
or
services.
However,
IBM
DP
Services
will,
subject
to
the
local
availability
of
ap~ropriate
resources,
respond
to
requests
for
assistance
in,implementing
inspections.
Manual,
8
1/2
x 11
inches,
6q
pgs,
7/77
SLSS
-
ORDER
NO..
SUBSCRIPTION
ONLY
GC20-8011
RANDOM
NUMBER
GENERATlON
AND
TESTING
Random
sattpling,
simulation
studies,
and
MOnte
Carlo
methods
have
been
in
use
for
sany
years.
Papers
describing
various
aspects
of
these
topics
have
appeared
in
technical
journals
and
textbooks
available
to
a
relatively
small
percentage
of
computer
users.
Meanwhile.
applications
requiring
random numbers
are
becoming
more
imPortant
and'more
cosmon
in
bUSiness
and
industry
as
well
as
purely
scientific
areas.
";rherefore,.
this
manual
has
been
prepared
which
gives
the
mathematical
development
of
the
power
residue
method,
outlines
computer
techniques
for
implementing
it
and
also
offers
brief
corrments
on
otber
methods.
An
appendix
provides
programming
illustrations
for
binary
and
decimal
com~uters.
DP
Techniques
Manual,
12
pages
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GC27
GC20-8062
INDEX
OaGANIZATION
!SH
INlORMATION
!!lS!!]!!
Methods
of
indexing
vary
with
the
nature
of
the
naterial
to
be
indexed
and
the
ways
in
.hicb
this
material
.ill
be
used.
This
beok
presents,
in
sittplified
form,
the
basic
principles
behind
organizing
indexes
of
various
types.
It
is
written
to
help
systems
personnel
understand
the
proble~s
they
will
encounter
in
crganizing
infcrmation
for
eventual
retrieval.
StreSSing
that
an
indexing
systes
shculd
always
be
developed
in
the
light
of
the
particular
retrieval
prcblem,
and
that
the
specific
eqUipment
to
te
used
is
a
secondary
conSideration,
the
book
covers
name
indexing,
special
indexing
!including
auto-encoding
and
the
I<iiIC
index),
and
indicative
and
inforl<ative
indexing.
Manual,
56
pages
SL55 -ORCla
NO.
SUBSCRIFTION
ONLY
GC20-8071
10,000
DIVISION £f£!.
lOR
PROfER
!11!~
This
manual
contains
a
four-digit
code
based
on
the
name
frequenciES
found
ty
the
University
of
Cregon.
DP
Techniques
Manual,
23
pages
5LSS
-
OaC~R
NO.
SUBSCRIFTION
ONlY
GC20-8078
FORM
ANC
CARD
DESIGN
ThIS
Ranuar-is-aIVIded
into
two
sections,
thE
first
devoted
to
forrr
deSign
and
the
second
to
card
design.
Its
use
presuppOSES a knowledge
of
IBM
data
prOCEssing
equipmEnt.
It
can
be
used
as
a
guide
for
individual
study
cr
a
text
for
class
study..
DP
Techniques
Manual,
16
pages
5LSS -
ORDER
NO.
SUBSCRIPTION
ONLY
GC20-8096
INTRODUCTION
TO
DATA
~ANAGEMENT
STUDENT
tEXT
This
~ubiicatTOn-rs-an
introduct~thEicencepts
of
data
management and
information
processing.
It
is
intended
to
address
both
programmer and
nen-prograrrJier.
Topics
presented
are
Data
~anagement
and
Infornation,
lields
and
Records,
Cata
Storage
DeVices,
Data
Crganizaticn,
FUDcti~ns
of
Data
Management, and
concepts
of
a
Cata
Base
Systerr.
Manual,
8-1/2
x
ii,
60
pages
SLSS
-
OaCER
NO.
SUBECaIPTION
ONlY
GC20-8152
FLOWCBARTING
TECBNI<;IlE5
Adhel'ence
to
standard
techniques
fcr
:the
~reparation
of
flowcharts
of
data
prOCESSing
syste~s
and
procedures
greatly
increases
the
effectiveness
of
ccmmunication
between
the
programmer-analyst
and
the
many
groups
with
.ton
he
deals.
The
manual
descrites
in
detail
the
preparation
of
system
and
progran
flowcharts.
The
symbols
USEd
are
these
provided
by
the
IBM
Flowcharting
Template
(GX20-8020). A
flo.chart
worksheet
(GX2D-8021)
is
a means
of
standardizing
documentation.
It
provides
space
for
drawing
program
flOWCharts
and
contains
an
area
for
identificaticn
ef
the
job,
including
ap~lication,
procedure,
date,
and
pagination.
Manual,
38
pages
SLBS -
OaDER
NO.
SUESCRIPTION
ONLY
GC22-9062
DATA
SECURITY
THROUGB
CRYPTOGRAPHY
PreVention
of
unauthorized
physical
and
logical
acoess
to
confidential
information
has
been
the
traditional
ttethod
of
protecting
the
secrecy
cf
computer
data.
Cryptography
prQVides
such
protection
in
situations
.here
the
traditional
rrethod
is
not
effective
or
possible.
Cryptography
preserves
the
secrecy
of
computer
data
that
could
te
aCCEssed
ty
tbe
unauthorized
by
concealing
the
infornation
using
a~rocess
in
which
intelligible
data
is
transformEd
into
non-intelligible
data.
This
nanual
descrii:es
the
sale
of
cryptography
in
data
security.
Manual,
8
1/2
x
11
inches,
40
pages,
10/71
GC22-9063
lEN
CRYPTOGRAPHIC
!1!!ESY5TE!!
CONCEPTS
~
JACILIT!!§
~~
The
IE~
Cryptograpbic
suEsystem
is
an
integrated
hard.are-
software
i~plesentaticn
of
end-to-end
cry~to9rapby
for
protecting
data.
It
consists
of
the
follo.iog
separate
products.
1.
IBM
Programmed
Cryptographic
Facility,
Frogram
Froduct
2.
IBM
Advanced
CosBunications
Function
for
Virtual
Telecosmunications
Access
Methcd
(ACP/VTAM).
Encrypt/Decrypt
Feature
3.
gncrypt/Deorypt
leature
(or
RPC>
for
the
IBM
3276
Display
Station·
.and
tbe
IBM
3776 !Models 1 alld 2)
Corrs.unication
Teninal'
.
This
.anual
descri.bes
the
cryptographic
Subsystelli
and
the
Cryptographic
concepts
and
techniques
errplcyed.
Manual,
8
U2
x
11
inches,
q8
pgs,
10/77
GC27-0q29
RR
GOMMUNICATIO~S
£2!!!~
FjlCI:LITY
H.£
~
573~-XX6
A
INfORMATION
.:
.
~
T
manual
is
an
overvie.
of
the
prograrr
product
Net.ork
Cott·nunicstionS
Contrcl
Pacility
(NCCF).
It
is
directEd
to
6
GC27
customer
executives,
systen
administrators,
system
analysts,
system
programmers,
application
prograroners,
and
terminal
operators
who
are
operating
with
DOS/vS
or
OS/VS
systeIr.s.
Manual,
8
1/2
x
11
inches,
40
pages,
10/78
GC28-0722
OS/VS2
MVS
RESOURCE
ACCESS
CONTROL
FACILITY
(RACF)
-
GENERAL
INFoRMATIoN
MANUAL
-
PROG
PROD
5740::xxa-
---
-
---
This
publication
contains
overview
a~planning
information
for
Version
1,
Release
3
of
the
Resource
Access
Control
Facility
(RACF)
progran
prcduct
(5740-XXH).
It
is
intended
for
the
use
af
installation
managers
and
personnel
responsible
for
systeIr
data
security..
It
is
assumed
that
the
reader
is
fa~iliar
with
OS/VS2 (MVS).
RACF
is
a
program
product
that
provides
access
control
by
identifying
and
verifying
system
users,
authorizing
access
to
system
resources
and
logging
detected
unauthorized
attempts
to
enter
the
systeIl'-
and
detected
accesses
to
frotected
resourceS4
Manual~
8
1/2
x 11
inches~
56
pgs~
3/78
GC28-0942
Os/VS1
and
OS/VS2
MVS
PROGRAMMED
CRYPTOGR~PHIC
FACILITY
GENERALlNF~oN:-PRoG
PROD
5740-XY5
----
The
Progranmed
'cryptographic
Facility
Program
Product
provides
OS/VS2
MVS
installation
with
the
capability
to
protect
sensitive
data
through
the
use
of
cryptography.
This
publication
is
intended
for
installation
managers
and
system
programmers
responsible
for
planning
the
software
data
security strategy
fer
their
installation.
Chapter
1
introduces
the
general
sutject
of
cryptography
and
provides
an
overview
of
the
Programrred
Cryptographic
Facility.
Cha~ter
2
identifies
system
requirements.
Chapter
3
descrites
each
cerr~onent
of
the
facility
and
describes
how
they
work
together
to
provide
a
cryptographic
capability.
Chapter
4
defines
the
functicns
available
tc
the
user
and
chapter
5
identifies
planning,
security,
and
operating
considerations.
Manual,
8
1/2
x
11
inches,
48
pgs,
10/77
GC28-6794
GUIDE
TO
PL/S
II
~he
piIS
~ompiler
is
a
proprietary
program
used
by
IBM
to
develop
other
r;::rograrr.s
that
are
made
generally
available.
This
provides
general
inforn:ation
on
understanding
and
interpreting
PL/S
II
listings.
The
book
also
provides
some
guidelines
on
how
to
modify
compiler
generated
assembler
code.
Readers
wi
11
be
ex{:erienced
systerr.s
progranm:ers
who
need
to
understand
and
possitle
modify
cf:erating
system
modules.
They
should
know
the
basic
assembler
language
such
as
PIlI.
Manual,
56
pages
SLSS -
ORDER
NC.
SUBSCRIPTION
ONLY
GC3Q-2010
NETWORK
PROBLEM
DETERMINATION
APPLICATION
(NPDA)
GENERAL
INFORMATION
PROGRAM
NUMBER
5735-XX-8--
~his
document
provides
introductory-information
about
the
IBM
Network
Problem
Determination
Application
(NPDA)
Program
Product~
which
allo~s
a
user
to
record~
retrieve
and
exaRine
communication
network
error
data
in
an
interactive
environment.
The
docunent
frovides
a
general
description
of
NPDA
as
well
as
initial
planning
information
needed
for
installation.
Ma~ual~
8
1/2
x
11
inches~
18
pages~
10/78
GE19-5095
STRUCTURED
PROGRAMMING
FOIL
PRESENTATION
SCRIPT
This
presentation
---eiPlares-
one
of
the
IR,proved
Prograrrrring
T"echnologies
known
as
Structured
Prograrrming..
A
comparison
is
wade
with
traditional
programming
followed
by
a
discussicn
of
the
varicus
structure
types
and
consideration
of
some
typical
prograrrroing
situations.
The
presentation
was
developed
in
1975
by
the
Improved
Prograrrming
~echnologies
SUfFort
Group
en
assignn'.ent
at
the
~orld
Trade
Systems
Center
in
Zoetermeer~
Netherlands.
Manual~
96
pages~
12/75
SLSS -
ORDER
NO.
SUBSCRIPTION
ONLY
GE19-5200
£Ql2.!!;
READING,
STRUCTURED
WALK-THROUGHS
~
INSPECTIONS-
IMPROVED
PRCGRAMMING
TECHNOLOGIES
This
document
addresses
itself
to
the
discovery
of
errors
and
suggests
how
three
sUfforting
techniques
within
the
Improved
Programming
Technclogies
help
to
approach
the
ultirrate
goal:
error-free
software.
The
three
techniques
described
here
are:
code
reading,
structured
walk-throughs,
and
inspections.
Their
use
within
IBM
has
offered
Significant
benefits.
~'he
intent
of
this
dOcuIr.ent
is
to
suggest
how
they
might
be
of
value,
either
individually
or
collectively,
within
other
data
proceSSing
organizations.
Manual,
10
3/8
x 8
1/4
inches,
56
pages,
3/76
SLSS -
ORDER
NO.
SUBSCRIPTION
ONLY
GE20
GE19-5201
~
ANt
CHANGE
~~Nl\GEMENT
1B
flAU
f!!Qill.§!.!!§
=
~
AND
GUIDE
A-rack
of
coordination
and
control
in
dealing
with
data
processing
prctlems
can
be
costly~
in
terns
not
cnly
cf
resources
wasted
tut
also
of
user
dissatisfacticn.
This
rranual
presents
an
a~Frcach
to
reducing
such
costs
-
the
introduction
of
systematic
problem
handling
to
sfeed
prcblero
solving~
ease
corrrrunicaticns~
and
enatle
as
rrany
protlems
as
possible
to
be
trated
as
routine.
Prctlerrs
are
eften
caused
ty
changes
to
prograns
cr
equipnent~
so
{:roblem
incidence~
and
thus
costs~
can
te
reduced
when
control
of
the
installation
of
changes
is
improved.
Manual~
84
pages~
2/79
SLSS -
ORDER
NO.
SUB~CRIF~ION
ONLY
GE19-5208
MANAGING
~HE
DATA
PRCCESSING
ORGANIZATICN
This
tookis
cfferea-as-aDaidtoeffective
nanagenent
of
the
data
Frocessing
crganization.
It
gives
an
overview
of
sorr,e
im{:ortant
management
principles
and
sho\lis
hc~
these
princifles
can
be
apflied
to
data
proceSSing
to
ensuxe
its
economic
use.
ErrJ;hasis
is
on
nanagerr,ent
net
hods
of
irr.proving
overall
productivity
and
quality
in
data
processing,
rather
than
cn
prograrrrring
and
software
engineering
techniques.
The
took
covers
all
the
rrajcr
elenents
cf
a
Ir,anagenent
systerr
for
the
data
processing
organizaticn
and
includes
chapters
dealing
with
evaluation
and
selection
of
applications~
long
range
planning,
short
range
planning~
prcject
managen:ent~
operations
nanagErrent~
and
managerrent
reforting.
It
is
directed
primarily
tc
data
processing
managers
~
tut
«,ay
alsc
l:e
cf
interest
to
senior
rranage~ent
to
whom
data
processing
managers
report,
to
users
of
conputer
services~
and
to
others
with
an
interest
in
good
data
~rocessing
managerrent.
Manual,
146
pages,
11/76
SLSS -ORtER
NO..
SUB
fCRIFUON
ONLY
GE20-0090
PRINCIPLES
Q!
DATA
ACCUISITION
§X§!.!l!:!.§
For
IBM
custorrers
whc
require
a
tasic
understanding
of
the
fUnctions
of
data
acquisition
systems~
this
nanual
t:rcvides
an
introductory
descripticn
of
their
operation
and
use
in
a
system
environll\€nt.
This
manual
acquaints
the
reader
with
many
of
the
various
items
of
hardware
conncnly
encountered
in
data
acquisition
systems
~
the
rr,eans
of
connecting
then
in
a
systen.
conf
iguraticn
and
the
central
processing
unit~
featUres
and
programming
capatilities
necessary
for
efficient
operation.
~anual~
27
pages
SLSS -CRtER
NC.
SUESCRIFTION
ONLY
GE20-0348
7
AN
IN~ROtUCTION
TC
INFORMA~ION
RE~RIEVAL
This
manual
uses~he~anguage
of~he-ncnspecialist
to
fresent
ways
in
which
digital
computers
can
te
used
in
inforrraticn
storage
and
retrieval
systems..
Indexing
nethods~
file
organization~
and
search
strategies
are
discussed~
and
a
,erief
titliography
is
included.
The
Il',anual
is
intended
as
a
first
reader
for
those
interested
in
the
broad
aspects
of
data
tanks
and
nechanized
libraries.
Manual~
38
pages
SLSS -ORtER
NO.
SUB~CRIP~ION
ONLY
GE20-0396
.§TATIS~ICS-BASED
SYStE~
~ECHNIQUES
CONCEPtS,
~~MPLESL
APPLICATICNS -
APFLICA~ION
MANUAL
This
is
an
intrOductcry-rev~anual
cn
sixteen
techniques
for
analyzing
and
improving
systems~
whether
business,
industrial
~
scientific
~
or
engineering.
There
are
questions
and
answers~
short
examples~
tasie
concepts~
and
an
applicaticn
bibliografhy
for
each
method.
The
Ir.anual
is
to
serve
as
an
awareness
tool;
difficult
topics
such
as
confidence
lireits
estimation
procedures~
and
analysis
of
variance
are
deen~hasized.
The
techniques
covered
are
Eayes
and
cluster
analysis~
continuous
sinulation,
correlation
and
decision
analysis~
discrete
simulation~
discrinination
and
econometric
analysis
evolutionary
operation~
eXFerimental
design~
eXfonential
srrccthing;
factor,
Markov~
qu€ue~
regression~
and
tirre
series
analysis.
Manual~
53
pages
SLSS -
ORtER
NO.
SUE
SCRIPTION
CNLY
GE20-0527
BUSINESS
SYSTEM§
!~!.!!~
INFOBMA~ION
SYS~E~
!~~~~1~§
G~
Business
Systems
Flar.ning
(BSP)
is
a
structured
a~proach
to
help
an
organizaticn
establish
an
infcrn,aticn
systems
plan
that
can
satisfy
its
near
and
long
tern
infcrmation
needs.
~his
guide
cffers
assistance
to
ESP
study
teams
by
explaining
the
approach
and
presenting
guidelines
for
conducting
a
BSP
stuoy.
It
can
also
be
used
for
general
reference
on
tte
sutject
of
planning
for
inforrration
systens.
The
guide
covers
BSP
principles,
concepts,
and
study
overview,
then
devctes
a
chapter
to
each
of
the
n.ajor
activities
of
a ESF
study,
and
includes
a
final
chapter
to
acquaint
the
reader
with
follow
on
projects.
~anual~
92
pages
SLSS -
ORDER
~C.
SUESCRIPTION
CNLY
GE20
GE20-0593
BASIC
SYSTEMS
ANALYSIS
~~
DESIGN
TECHNIQUES
This
application
manual~
intended
to
assist
the
beginning
applications
analyst
in
learning
the
basics
of
systems
analysis
and
design,
and
will
also
help
the
artalystto
decide
how
to
proceed
into
the
"whats,
hows.
and
whys"
involved
in
such
things
as
test
plans,
doc~ents
of
understanding,
testing.
tracking
mechanisms,
etc.
A
numter
of
topics
are
addressed,
mostly
from
the
"what
to
do"
and
"how
to
do
it"
point
of
view.
The
section
"Major
Events
in
Designing
and
Im~lementing
a System"
should
help
a newcomer
to
systems
analysis
to
have
an
idea
as
to
where
to
begin
and
the
questions
to
ask.
Manual,
45
pages,
8/78
GE20-0612
CAPACITY
rum
PLANNING:
EXECUTIVE
OVERVIEW
The
objective
of
Capacity
System
Planning
is
to
translate
business
~lans
into
the
data
processing
capacity
needed
to
support
those
plans.
To
accomplish
this,
significant
milestones
based
on
business
plans
are
set
up
over
a numl:er
of
years
into
the
future,
and
the
data
processing
growth
plan
is
used
to
determine
how
much
data
processing
capacity
will
be
required
at
each
milestone.
This
overview
descril:es
what
that
effort
involves
and
what
results
it
can
produce.
Manual,
7
1/4
x 11
inches,
12
pages,
7/78
GE20-0662
AN
ARCHITECTURE
FOR
~
INFORMATION
~
BUSINESS,
~
1
MAN
~
The
purpose
of
this
ment
is
to
build
an
understandirtg
of
the
architecture,processes,
and
data
elements
that
comprise
the
Information
Systems
business.
From
this
understanding
the
reader
may
begin
to
implem~nt
effective
control
and
efficiency
in
the
management
of
data
processing.
The
document
gives
an
overview
of
SOme
fundamental
management
~rinciples,
and
suggests
how
these
can
be
applied
to
the
data
processing
organization
within
the
framework
of
the
Information
Systems
Architecture.
Manual,
8
1/2
x 11
inches,
49
pages,
01/80
GE20-8067
n!!!
:::
~
~
PROJECT
CONTROL
mllQ!2
Designed
to
acquaint
the
reader
with
the
PERT
technique.
It
is
divided
into
these
sections
-
(1)
the
technique
-
its
advantages
and
implementation,
(2)
the
network
development,
(3)
the
computer
program -
data
preparation,
and
(4)
description
of
PERT
in
operation,
including
sample
calculations.
tp
Application
Manual,28
pages
SLSS-
ORDER
NO.
SUBSCRIPTION
ONn
GE20-8091
KEY~ORD-IN-CONTEXT
(RWIC)
INDEXING
.
KWIC
indexes
constitute
a
new
approach
to
the
problem
of
how
to
furnish
information
promptly
about
new
literature.
This
manual
presents
the
principles
and
.advantages
of
RWIC
indexing
and
gives
essential
details
about
the
parts
of
an
overall
RWIC
index
--
the
KWIC
index
proper,
reference
code,
bibliography
and
author
index.
An
extensive
list
of
recommendations
is
included
for
preparing
master
~achinable
records.
This
involves
reserving
particular
card
columns
for
specific
items
and
includes
suggested
punctuation
substitutions
and
other
special
indications.
The manual
also
gives
instructions
for
~achine
printout,
mounting
copy
for
reproduction,
and·
binding.
CP
Techniques
Manual,
24
pages
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GE20-8171
AN
INTRODUCTION
:!2
..
~
I?ROGRAI!MING
~
This
manual
is
a
primer
on
what
can
be
accottplished
on a
computer
with
linear
programming
systems.
~h~
presentation
covers
the
entire
scope
of
linear
programming
application:
problett
formulation,
computer
operations,
interpretation
of
results,
and
additional
information
that
can
be
obtained
through
the
use
of
complete
linear
progra~ming
system
for
a
computer.
The mahual assumes no
mathematical
background
l:eyond
high
school
algebra.
'
The
first
chapter
deals
with
concepts
and
examples
of
linear
programming," The
second
chapter
deals
with
deriving
additionalinforttation
about
a
solution.
The
third
chapter
completely
describee·a
larger
example
of
linear
programming
in
oil
refinery
scheduling.'
The
fourth
cha~ter
is
a
descriptiOn
of
the
sittplex
method
of
linear
programming_
A
detailed
glossary
of
linear
programming
terms
is
included.
Manual,
67
pages
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GF20-0006
MANAGEMENT·CONTROLS
FOR
DAT}!
PROCESSING
This
manual,
written-Ey
PrICe
Waterhouse'
CO.,
discusses
external
and
internal
controls
necessary
for
data
proceSSing
systems,
the
responsibilities
for
these
ccntrols,'
and
the
impact
of
these
controls
on
the
audltability
of
the
sYstems.
Both
batch··
and
online
versions
of
an
application
system
'
il~ustratin9
oontr~l
~rocedures
are
also
included,
as
is
an
audit/review
questionnaire
that
can be
used
as
a
guide
when
conducting
an
audit
or
review
of
data
processing
department
controls.
'
Mallual, 95
pages
SLSS
-
ORDER·NO.
SUBSCRIPTION
ONLY
GH20
GI'20-0007
}!NALYSIS
OF
SOliE
QUEUING
MODELS
!!!
REAL-TIME.~
This
manual
presents
asic
theory
which
descril:es
relationships
among
the
principal
elements
in
a
queuing
situation.
Several
queuing
models
are
discussed,
and
the
theory
is
applied
to
32
short
examples
of
problems
encounterEd
in
real-timE
systems
I
numerical
solutions
are
given
for
these
prctlems.
The manual
concerns
single
server
and
multi-server
queues,
machine
interference,
networks
of
queues,
and
combinations
of
random
variables
encountered
in
queuing
analysis.
Manual,
75
pages
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GF20-8093
~
!!ruQ!l2
Specifj.c
,.ethods
of
alphabetic
and
numerical
coding
are
discussed,
also
the
way
in
which
they
may
be
developed
and
applied.
The
~anual
lists
and
describes
the
characteristics
that
should
be
included
in
the
ccnstruction
of
adequate
codes.
Manual,
20
pages
SLSS
-
ORCER
NO.
SUBSCRIPTION
ONLY
GF20·8102
~
TABLES
:::
~
g~
~
M!!:
OOCUMENT}!TION
TECHNI
UE
The
aS1C
concepts
of
decision
tal:les
and a minimum
set
of
conventions
for
their
use
in
systems
analysiS,
procedure
design,
and
documentation
are
described.
The
purpose
of
such
tablES
is
to
pro~ide
information
in
a
cOllcise
format
that
is
easy
to
read
and
understand.
The
tabular
approach
is
used
to
express
complex
decision
logic
in
a
,.anner
that
encourages
the
analyst
to
reduce
a
problem
to
its
Simplest
fortt
by
arranging
and
~resenting
logical
alternatives
under
various
conditions.
The
resultant
tables
present
a
system's
logiC
in
a
concise
manner
that
is
easy
to
visualize
and
grasp.
~hile
the
ccncepts
in
the
test
are
presented
on
a
level
fcr
co~·prehension
by
students
in
basic
ccmputer
courses,
the
techniques
are
applicable
at
all
levels
of
sophistication
by
everyone
in
a
data
processing
environment.
Manual,
8
1/2
x 11
inches,
20
pgs,
4/78
SLSS
-
ORDER
NO..
SUBSCRIPTION
ONLY
GG22-9000
ll!!
SlfS'IEM/370
TRACKING!m1
RESOLVING
PROBLEMS
~·COORCINAmg
CHANGES
This
is
One
of
a
series
of
Techn1cal
Bulletins
distributed
by
the
Poughkeepsie
Systems
center;
This
report
is
intended
to
assist
the
DP
manager
in
the
development
arid'
imple~entation
of
fortt,al
~roblem
managett,ent and
change
control
procedures
within
the
DP
function,.
It
is
directed
primarily
to
DP
managers
and
to
the
executives
to
whott
they
report.
It
describes
functions
that
can
be
integrated
as
a
single
unit
into
the
existing
CP
organization.
.
Technical
Bulletin,
61
pages
SLSS
-
ORCER
NO.
SUBSCRIPTION
ONLY
GG22-9001
~
INTRODUCTION
!Q
CAPACITY
PL}!N~
This
tulletin
in
intended
an
as
introduction
to
the
concepts
and methodol09ll
of
capacity
planning·and
how
ca~acity
planning
can
be
a
·u~eful
management
tool
in
the
complex
data
processing
~nvironment.
Specific
topics
covered.include
definitions
of
terms,
performance
~easuremertt,
~ethod
implementation
and
~erforRance
prediction'
An
atpendix
contains
visuals
for
a
capacity
planning
~resentation.
Technical
Bulletin
~anual,
8
1/2
x 11
inches,
136
pages,
2/17
GG22-9003
A
PERSPECTIVE
ON
NETWCRRING
This
Technical-SulIe~for
IB~
ana
custo~er
~erscnnel.
Its
purpos~
is
to
~rcv~de
some
insight
into
the
issues
and
ccm~lexities
of
networking.
It
also
aiscusses
hcw
these
interact
with
various
implementaticn
configuraticns.
Manual,
8·
1/2
x 11
inches,
48
pgs,
5/77
GG22-9015
...
.
CAPACITY
FLANNING
IMILEMENTATION
TECHNICAL
BULLETIN
This
iechnical
Bulletin
is
intended
for
aata-proeessing
people
(technical
andm<inagErial)
engaged
in
cc~~uter
capacity
planning
activities.
The
purpose
of
this
bulletin
is
to
discuss
"state-of-the-art"
teChniques
for
im~leKentin9
a
capacity
planning
gograll.
The
~rocess
is
concerned
with
understandirtg
and
quantifying
user
service
objectives,
'WOrkload
charactQrizaticn,
resource
ccn.sUlr.~tion.
ltcnitoxing
and
re(:orting
conpute"r
oE=era"t;ion
on a
continuing
tas~s.
As
pOinted
out
in
the
discussion,c
user
satisfacticn
is
the.
most
critical
factor
in
the
capacity
planning
process.
Manu·al,8
1.(2 x 11
inches,
160
pages
1/19
GH20~1628
.,
.
A
GUIDE
TO
TESTING
i~
A·CCMPLEX
SYSTEM
ENVIRONMENT
This
dociiiieiitdeScrites
the
methods,
techniques
and
~z09rams
necessary
to
test
in
a complex
environment.
It
also
gives
a
description
of
the
various
testing
en~lron,.ents
and
cf
the
testingR.ethods
to
be
u'!edin
each
envircn~ent.
.
It
is
intended
toth
as
an
introduction·
to
testing
for
executives·and
managErs,
and
as
an
in-depth
treatise·for
those
res~cnsible
for
setting
up
and
executing
the
tests.
Manual,
90
pages
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
SH20
SR20-2116
~R~/~I~
QOCU~ENTATION
~£L
!YE
5796-ATY,
The 3800
Design
and
Documentation
Aid,
5796-ATY,
developed
by The
Firestcne
Tire
and
Rutter
Company,
Akron,
Ohio,
provides
OS/VS
COBOL
and
3800
Printer
data
processing
organizations
with
the
ability
to
standardize
and
easily
maintain
installation
documentation.
Using
the
Hierarchy
plus
Input-Process-Output
(RIPO)
technique,
standardized
documentation
for
installation
management
activities
is
produced
on
the
3800
Printer
in
the
forn
of
Visual
Table
of
Contents
(VTOC's)
and
EIPO
diagrams.
Commands
are
in
80-
character
images
which
are
submitted
either
through
cards
or
TBO.
The
program
is
a
series
of
modules
written
in
OS/VS
COBOL.
Manual
SH20-2361
SOURCE
COMPARE/AUDIT
UTILI'IY,
ill
2196-N.h
DESCRIPTION/OPERATIONS
This
Program
Description/Operations
Manual
~rovides
the
user
with
sufficient
inforRaticn
to
understand#
install
and
successfully
use
the
program.
Manual,
8
1/2
x 11
inches,
88
pages,
9/79
GK10-6104
~ANAGE~ENT
ING
AND
CONTROLS
IN
DATA
PROCESSING
NATIONAL
WE
ER
BANK--------
--
----
!his
publicat
~s
intended
to
describe
the
teChniques
and
procedures
used
by
the
National
West~inster
Bank
for
rranagerr.ent
reForting
and
controlling
of
their
data
processing
installation..
Erief,
8
1/2
x 11
inches,
12
pgs,
3/77
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GK20- 0732
~AGING
SYSTEMS
DEVELOP~NT
MONTGO~ERY
WARD
~TION
MANAGEMENT
BRIEF
This
brief
describes
Montgomery
ward"s
system
of
project
managenent
for
system
develoFment.
A cammon
approach
is
adopted
for
the
conversion
of
a
control
program,
the
installation
cf
a
new
cpu,
or
any
data
frocessing
project.
Procedures
em~loyed
are
of
interest
crOSS-industry
to
data
processing
Ranagement.
Brief,
28
pages
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GK20-0750
MANAGEMENT
SERVICES
FRITO
LAY
INSTALLATION
MANAGE~ENT
BRIEF
~tline
for
interactive
communications
between
the
DP
staff,
called
ManageR:ent
Services,
and
executive
manageIrent
within
Frito
Lay
is
described.
A
project
accountatility
control
technique
is
the
basis
for
executive
management's
awareness
of
the
activities
of
management
services
and
for
management
services
understanding
of
Frito
Lay"s
business
objectives,.
Of
interest
tc
installations
whose
mission
is
the
solution
of
l:usiness
problems.
Manual,
16
pages
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GK20- 0775
A
DP
COST
ALLOCATION
SYSTE~:
PRUDENTIAL
INSURANCE
lhis
brief
covers
Prudential"
s
system
of
taIling
for
data
processing
services
on
a
cost
basis
to
the
company's
line
areas
when
productive
work
is
performed
or
new
projects
are
deve
loped..
'Ihe
automated
jot
accounting
system
used
in
controlling
cost
uses
data
derived
from
the
SMF
featUre
of
OS/~FT
cr
Os/MVT
.•
Brief
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GK20-0776
~ATA
PROCESSING
QUALITY
ASSURANCE
=
~B1!~
MARIETTA
~
SYSTEMS
ORLANDO
~ATA
CENTER
'Ihis
brief
describes
t"ileincreased
efficiency
of
data
processing
services
at
Martin
Marietta
Data
Systems
Orlando
Data
Center
resulting
from
a
quality
assurance
department.
'Iheir
procedure
entails
the
certification
of
all
programs;
audit
of
system
development
projects;
reporting
and
control
over
operations
~roblerrs;
and
~iroonthly
review
of
DP
concerns
by
IBM
and
Martin
Marietta
personnel.
Erief
SLSS
-
ORDER
NO,.
SUBSCRIPTION
ONLY
GK20-0864
MCAUTO
HIERARCHICAL
CO~~UNICATIONS
1B
QE
MANAGEMENT
~
computer
inventory
of
more
than
$171
million,
MCAUTO's
installation
is
very
complex.
By
tringing
together
a
cross
section
of
functional
departments
and
management
leve'ls
at
SCheduled
and
structured
meetings,
the
installation
is
able
to
avoid
most
problems
and
to
resolve
those
that.do
occur
with
m.inimal
impact
On
productivity
.•
Trial-and-error
approaches
are
largely
replaced
by
teamwork.
Continuing
equipment
changes
necessitate
continuing
a
ttention
without
cOItlTlunications
barriers.
A
valuable
tOol
used
by
the
managers
in
planning
the
logistics
of
equipment
changes
is
.a
ma.gnetic
layout
of
the
machine
room,
scaled
to
GX20
size·.
MCAUTO"S
ideas
fcr
communication
Ray
have
apFlicatility
in
even
a
modest
cCltIuter
installation.
Brief
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
G1I20-0882
~~:~:~~C~i
~~~A~:M~~iRi~i~~Si~NS~~E)
£Q~!!
fBQgB!~
The
cperations
Management
ExtensIOn
is
a
set
of
ccmFuter
progralr.s
to
in,prcve
ccntrel
of
the
computer
installation.
The
Jot
CrEation
FrcgraR
expands
"shorthand"
statements
into
error-free
test
JCl,.
Job
transfer
edits,
rearranges
and
catalogs
JCL
into
its
production
format
and
autoRatically
updates
the
procedure
litrary.
Jot
Setup
processes
the
~onthly
Activity
Schecluler
file
and
the
OM·!
tape
library
file
tc
update
the
jcl:
streaRs
fer
execution
and
procluce
a
series
of
operations
control
reports.
Job
!~ecution
is
a
continuously
running
"monitor"
that
allows
the
o~eratcr
to
initiate
the
track
jcl:s
from
the
ccnsole.
The
Operating
Systerr.
is
unaltered;
OM!
is
sirrply
an
extension
of
OS.
OME
is
applicable
to
RCSt
jcts
in
a scheclulEcl,
tatch,
production
env
ironment.
Brief,
16
pages'
covers
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GK20-0931
COMPONENT
~£;
g!~£:!
ANALYSI§
m
~lLAR,
INSTALLAlION
~ANAGEI(ENT
BRIEF
This
brief
descrites~w~component
Failure
Inpact
Analysis
technique
is
used
at
Caterpillar
to
assess
current
backup
and
recovery
~rccedures
and
to
consider
alternative
capability
and
procedures
.•
Manual
SLSS
-
O!l~ER
NO.
SUESenplION
ONLY
GK20-1073
PROELE~
AND
CHANGE
ceNTROL
AT
THE
STATE
OF
l\ASEINGTON
i'iATii"FROCEssIiiGSi!RVICE CENTER---
---
--
----------
This
trief
descrites
the
probleft
and
change
control
procedures
at
the
State
of
Washingtcn
tata
Processing
Service
CEnter.
Theee
procedures
are
designed
tc:
Ensure
that
protlems
are
resolved
and
not
fcrgotten
FacilitatE
effective
utilization
of
~roblen:-solving
resources
Ensure
the
orderly
a~~licaticn
of
change
RedUCE
protlems
introduced
through
change
Involve
management
in
setting
problerr
and
change
priorities
Brief,
8
1/2
x
11
inches,
12
pgs,
8/77
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
GK20-1120
RECOVERY
STRUCTURED
l\AlK~HROUGH
AT
I(ARINE
~I~LAN~
BANK
This
trief
descrites
and
discusses
the
use-of~e
technique
in
identifying
and
highlighting
actions
that
could
in'I'reve
system
availabilitj.
Brief
GK20-1297
SYSTE~
OUTAGE
ANALYSIS
-
ASSOCIATION
OF
AMERICAN
RAILROADS
This
brief
discusses
System
outageAnaIy~=-an
availal:ility
managemEnt
technique
and
the
Systen
Outage
Analysis
study
conducted
ty
the
Association
of
ARerican
Railroads.
Brief,
8
1/2
x
11
inches,
12
pages,
11/79
GK20-1305
~~~~~I~;
i~:/OVE
OF
CCMP~ROLIERS
DATA
FFOCESSI~!l
ll1YISION,
This
trIef
descrites
tne
move
of
a
complex
installation
consisting
of
three
interconnected
SysteID/370
I(odel
158's
controlling
a
netwcrK
cf
over
300
terminals.
~he
systems
were
relocated
in
five
days
with
a
mini~um
disrufticn
of
service.
The
installation/s
Public
Safety
Network
was
interrupted
for
only
one
hour
and
17
minutes.
Applicaticn
trief
GX20-1702
PROPORUONAL
RECORD
lAYOUT
FORI(
The
front
side-or-thIS-roim-consists
ef
the
Propcrtional
Record
Laycut
Porn.
It
is
suitable
for
card,
tafe,
and
disk
recorcls.
Positional
markings
are
00-99
and
01-100
in
decimal
nctaticn,
and
00-63
and
01-64
in
hexadecimal
notation,.
The
tack
sidE
of
the
form
is
the
record
fermat
forn.
This
form
permits
record
layouts
to
be
prepared
without
the
space
limitations
of
positional
narkings.
Space
is
also
~rovided
for
reference
data.
~hese
are
general-
purpose
forms
and
may
te
used
for
all
systems.
Padded
Forro,
25
sheets,
11 x
6-1/2
NOT
AVAILABLE
UNDER
SLSS
GX20-1818
150/10/8
PRINT
CH~RT
The
~x-rs--c~is
~rinted
in
green
ink
and
~rovides
150
printing
positions
(at
10
positions
per
inch
horizontally)
for
a
Irinter
carriage
space-setting
of
8
lines
per
inch.
This
form
replaces
GX20-1778
which
allowed
for
a
~rinting
span
of
144
characters.
Frinter
charts
requiring
iSO-character
spans
(3211
with
18
additional
print
positions)
Ray
te
prepared
using
this
chart.
This
chart
may
te
reproduced
using
most
standard
office
cOFying
roachiiles.
The'grid
and
otller
preprinted
inforKation
n:ay
te
"droFPEd-out"
using
a
green
filter.
Padded
Form,
11 x
18,
25
sheets
GX20
NOT
AVAILABLE
UNDER
SLSS
GX20-1970
HIPO
WORRSHEET
This
worksheet
is
used
for
drawing
HIPO
diagrams.
Padded
Form,
11 x
16-1/2
inches,
25
sheets
per
pad
NOT
AVAILABLE
UNDER
SISS
GX20-1971
HIPO
TEMPLATE
Thls
plastic
template
plrovides
cutout
shapes
used
in
drawing
HIPO
diagrams.
It
is
enclcsed
in
an
envelo~e
outlining
the
definitions
of
the
syn:b~::>ls.
The
sYIllbols,
and
their
use
in
the
preparation
of
HIPO
diagrams
are
further
descriQed
in
HIPO
- A
Design
Aid
and
Documentation
Technique.
GC20-1851. The
HlPO
Worksheet,
GX20-1970,
also
may
be
used
in
the
preparation
of
HI
PO
diagrams.
Template,
10
to
a
set
NOT
AVAILABLE
UNDER
SLSS
GX20-2336
COMPONENT
FAILURE
IMPAc~r
ANALYSIS
FORMS:
COMPONEN'I
FAILURE
~
ANALYSIS
GRID
ANQ
GRIt
EXPANSION~WORRSHEET
This
padded
form
is
used
in
performing
a
component
failure
impact
analysis
ICFIA).
Its
use
is
illustrated
in
the
manual
Component
Failure
Impact
Analysis
-
An
Availability
Manage"ent
'Iechnique
(GC20-1865).
padded
form,
11 x 16
inches,
2
pgs,
3/79
GX20-2353
SYSTEMS
MANAGEMENT
ASSESSMEN'I
QUESTIONNAIRE
The
Systems
Management
Assessment
Questionnaire
is
a
set
of
yes/no
questions
to
evaluate
the
implementation
of
the
Systems
Management
disciplines:
Change Management
Performance
Managment
Problem
Management
Capacity
Management
Processing
Management
Audit/Security
Management
Recovery
Management Management
Re~ortin9
There
is
also
a
sutjective
evaluation
for
each
discipline
regarding
the
extent
to
which
the
items
in
that
category
are
effectively
utilized.
In
addition,
there
are
questions
on
which
tools
and
aids
are
utilized
for
Systems
Management.
This
questionnaire
'~as
prepared
jointly
bY
the
nata
Processing
and
Field
Engineering
Divisions.
Foldout
reference
card,
3
1/2
x 8
1/2
inches,
14
panels,
10/79
GX20~8020
FLOWCHARTING
TEMPLATE
This
plastiC
template
p:rovides
cut-out
shapes
for
drawing
standard
symbols
used
frequently
in
flowcharting
computer
systems
and
programs.
It
is
enclosed
in
an
envelope
outlining
definitions
of
symtols
and
use
of
the
template.
More
details
are
given
in
the
Data
Processing
Techniques
manual
on
FLOWCHARTING
TECHNIQUES
(GC20-8152).
Template,
10
to
a
set
NOT
AVAILABLE
UNDER
stss
GX20-8047
HEXADECIMAL
!
~
!mill
CONVERSION
!!ill
Tables
showing
hexadeci:mal
and
decirral
integer
and
fraction
conversions,
examples
cf
arithmetic
ste~s
in
the
conversions,
and a
powers
of
16
table.
Reference
Card,
4
pages,
3-1/4
x
7-3/8
NOT
AVAILABLE
UNDER
SLSS
G320
and
de
not
necessarily
represent
IEM'·
s
vie~s
or
q;:inions.
Manual
SLSS -
ORDER
NO.
SUESCBIPTION
CNLY
G320-1371
!lill
SECURITY
M!!1
DA'IA
FROCllSSIN§
VOLUME
l ::
.§1yg
.§.!i!!!!l\!l1
In
May
of
1972,
IEM
announced
the
'formation
of
fcur
stlldy
sites
for
the
purpose
of
gaining
more
infornation
abcut
rata
security
and
identifying
user
requirerr,ents
in
this
vital
sucject.
This
manual
summarizes
the
results
of
the
findings
of
the
four
study
sites.
As
stated
at
the
cut
set
of
the
projEct,
these
publicaticns
report
independent
findings
of
the
study
sites,
and
do
not
necessarily
represent
IEM·S
vie~s
or
cfiniansr
~anual,
27
pa
ges
SLSS
-
OR~ER
NO.
SUBSCRIP'IION
ONLY
G320-1372
~ATA
SECURITY
,
DATA
FROCESSING:
VOLUME
3
PART
1
STATE<iFILLINOlSEXECUTIVE
OVERV~
-
--
-
In
May-r9~~anncuncEO
t~tion
of
four
study
sites
for
the
pur~ose
of
gaining
more
inforrration
about
data
security
and
identifying
user
requirerrents
in
this
vital
area.
This
rranual
(one
cf
a
series
of
6 vClumES)
documents
an
overview
of
the
findings
of
the
Management
Infarrraticn
Division
of
the
State
of
Illinois.
It
is
reprinted
with
the
permission
of
the
State
of
Illinois.
As
stated
at
the
outset
of
the
project,
these
publicaticns
report
independent
findings
of
the
,study
sites
and do
not
necessarily
re~resent
IEN·S
vie~s
or
opinions
..
Manual,
43
pages
SLSS
-
OR~ER
NO.
SUBSCRIP'IION
ONLY
G320-1373
DATA
SECURITY!
!lill
aOCESSING:
VCLUME
1
~!l!
l
STATE
OF
ILLINOIS
STUJ:Y
RESULTS
In
May-r972,
IEM
announc~formation
of
four
study
sites
for
the
pur~ose
of
gaining
more
inforrraticn
atcut
data
security
and
identifying
user
requirenents
in
this
vital
area.
This
~anual
(one
of
a
series
of
6
vclumes)
doculIIents an
overvie",
of
_the
findings
of
the
Management
Inforrration
Divisicn
of
the
State
of
Illinois.
It
is
reprinted
with
the
permission
of
the
State
of
Illinois.
As
stated
at
the
outset
of
the
project,
these
puclications
report
independent
findings
of
the
study
sites
and
do
not
necessarily
re~resent
IEM's
views
or
c{:inions,.
Manual
SLSS
-
ORDER
NO.
SUBSCRIP'IION
ONLY
G320-1374
DATA
~
! !1!1!
!!l~§l
~
!!...
~!l§~~
INSTI'IUTE
OF
'IECHNOLOGY
STUDY
RESOl'IS
In
May
197~
~nncuncea-tEe~crmation
of
four
study
sites
for
the
purpose
of
gaining
lIIo~e
infornation
atout
data
security
and
identifying
user
requirerrents
in
this
vital
area.
This
rranual
(one
of
a
series
of
6
volumes)
documents
an
overview
of
the
findings
of
the
Massachusetts
Institute
of
'Iechnology.
These
pul:lications
report
findings
of
the
study
sites
and
do
not
necessarily
represent
IE~'s
views
or
opinions.
Manual,
300
pages
SLSS
-
ORDER
NO.
SOESCRIP'IION
ONLY
G320-1375
DATA
.§!£..!113ITY
!
DATA
FFOCESSING:
velUME
2L
!!l!!
'§XS·IE~.§
!li£L
.§.'!.QQX
RESULTS
In
May
1972,
IBM
announced
the
forrr,ation
of
four
study
sites
for
the
pur~ose
of
gaining
more
infornatiqD
atcut
data
security
and
identifying
user
requirerrents
in
this
vital
area..
This
manual
(one
of
a
SEries
of
,6
volumes)
documents
an
overview
of
the
findings
of
lR~
Systems,
Inc.
As
stated
at
the
outset
of
the
Froject,
these
publicaticns
report
inde~endent
findings
of
the
study
sites
and
do
not
necessarily
represent
IBM's
views
or
opinions.
Manual
SLSS
-
ORDER
NO.
SUEECFIPTION
CNLY
<3320-1376
DATA
SECUllITY
AND
DA'IAPROCESSING
VOLUME
6
EVALUl\TIONS
AND
INStA~EXPERlEiCES:RESOURCE-SECUllITY-SYSTE~--
---
In
May
of
1972,
IE~
anncun~the-fcrmition
~r
study
sites
for
the
purpcse
of
gaining
ncre
infornaticn
atout
data
security
and
identifying
user
requirements
in
this
vital
SUbject.
1his
rranua! _dccurrents
the
study
findings
of
the
IEM
Federal
Systems
~ivision
Study
site.
It
is
cne
cf
a
series
of
6
volumes_
As
stated
at
the
outset
of
the
~roject,
these
pu1::licaticns
report
independent
findings
of
the
study
sites,
and
dc
net
necessarily
re~resent
IE~·S
views
or
epinicns.
Manual,
122
pages
SLSS
-
ORJ:ER
NO.
SUEECRIP'IION
ONLY
G320-1379
DATA
SECURITY
AND
DA'IA
PROCESSING
SESSI~RTS"GUILE(STATE
OF-ILLINOIS
VIDEOTl\PES)
In
May
of
197~IEM
anno'unced
the-fornatIon-of-fcur-study
G320
sites
for
the
purpose
of
gaining
more
information
about
data
security
and
identifying
user
requirements
in
this
vital
,subject.
This
session
leader"s
guide
is
intended
to
be
used
in
conjunction
with
a
set
of
9
videotapes
Frepared
by
one
of
the
study
sites,
the
State
of
Illinois.
The
guide
itself
was
also
prepared
at
this
study
site.
Details
about
the
availatility
of
the
videotapes
have
been
sent
to
DP
branch
Offices.
As
stated
at
the
outset
of
the
project,
this
guide
and
the
videotapes
report
independent
findings
of
the
study
site
and
do
not
necessarily
represent
IEM's
views
or
opinions.
Information
on
the
purchase
of
copies
of
one
or
Rore
of
the
tapes,
the
tYfe
of
playback
equifment
required,
and
prices
and
terms,
etc.,
may
be
directly
obtained
from.
S/~
Videocassette
Duplicating
Corporation
500
Willow
Tree
Road
leonia,
New
Jersey
07605
(201)
9Q7-6q50
NYC.
(212)
239-Q653
or
fron
your
local
IBM
Data
ProcEssing
Division
Marketing
Representative,.
Manual,
15
pages
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
G320-2683
ARCHITECTURAL
SUPPORT
FOR
SYSTEM
PROTECTION
ANC
DATA
EASE
SECUR~Os:AN~SCIENTIFIC
CENTER
A
set
of
~tUra1
erteiiSIOns
to
a
nach:r;;e-ot
the
type
of
IBM
Systew/370
is
Froposed.
The
proposal
involves
hardware/software
interaction
to
constrain
the
execution
time
behavior
of
application
and
higher
authcrity
prograrrs.
The
extensions
consist
of
the
addition
of
a
new
state
to
the
previous
supervisor
and
problem
states,
enforcement
of
disciplined
transition
between
states,
hardware
distinction
of
five
information
types
and a
mechanisn
to
ensure
correct
I/O
data
transfers.
Application
of
the
extensions
to
a
shared
database
system
shows
that
the
protection
of
the
operating
system
is
enhanced
significantly.
with
respect
to
errors
or
deliberate
attacks,
and
that
a
bigh
level
of
protection
against
unauthorized
access,
can
be
oetained
for
the
database
itself,
without
excessive
cost.
Report,
8
1/2
x
11
incbes,
31
pgs,
12/76
G320-5323
STRUCTURED
DESIGN
-
REPRIN~ED
FROM
IBM
SYSTEMS
JOURNAL
consideratiOiiSaiid-techniques
are
proposeathat
--redUCe
the
complexity
of
programs
by
dividing
them
into
functional
modules.
This
can make
it
possible
to
create
complex
systems
from
Simple,
independent,
reusable
modules.
Debugging
and
modifying
programs,
reconfiguring
I/O
devices,
and
managing
large
programming
projects
can
all
b~
greatly
simplified.
And,
as
the
mcdule
library
grows,
increasingly
sophisticated
programs
can
be
implemented
using
less
and
less
new
code.
Paper,
25
pages
NOT
AVAILABLE
UNDER
SLSS
G320-5522
OPERATING
~
INTEGRITY
~
~
~
W.S,.
MCPHEE,
REPRINTED
FROM
IBM
SYSTEMS
JOURNAL
System
integrity
is-a-EaSIc
requirement
for
operating
system
security.
Presented
are
types
of
systen
integrity
problems
and
their
general
solutions,.
Techniques
used
in
Os/VS2
Release
2
to
solve
these
problems
are
highlighted.
paper,
23
pages
NOT
AVAILABLE
UNDER
SlSS
G320-5532
AUDI~
SOURCE
COMPARE
!l2§
AND
OS/VS, IUP 5796-PDF,
PDM
NO~ICE
Audit
-
Source
Ccde
CORpare
for
5/370
DOS/vS
or
OS/VS
is
a
pair
of
IUP"
5
which
analyze
the
differences
between
two
versions
of
a
~rC9ran's
source
code.
The
variations
detected
by
this
audit/contrcl
tool
are
higblighted
on
a
message
listing
which,
in
turn,
tecomes
a
vehicle
the
user
can
use
to
verify
the
only
authorized
changes
are
made
to
an
installation's
sensitive
programs~
Audit-Source
Code
Compare
has
been
used
by
the
IBM
Corporate
Infor~ation
S¥stems
Department
audit-control
groups
as
a
tool
as
assure
that
only
authorized
changes
are
made
to
the
installation's
programs,.
This
frograrr
may
I:e
executed
under
any
5/370
cos/vs,
VSl
or
VS2
system.
~his
Availability
Notice
contains
corrplete
ordering
information
for
the
Prograrr
and
all
its
related
documen-
tation.
for
management and
data
processing
personnel
who
are
Frospective
users
of
the
program
and
others
who
require
information
concerning
it.
Release
Notice
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
~~jf.:~~~~~~~~
COMPUTER
.
.!
=~LATICN
identify
the
types
of
hazards
prevalent
in
today" s
data
"rocessing
operations
and
to
develop
aFproaches
to
protect
against
these
hazards.
The
initial
results
from
the
first
phase
of
this
study
are
contained
in
An
Executive's
GUide
to
Data
Security
--
A
~ranslation
from
an
IBN
Svenska
Publication
(G320-56Q
7)
and
in
this
volu",".
The
Executive
Guide
introduces
the
study
and
presents
an
approach
to
data
security.
~is
volurre
provides
the
detailed
results
of
observations
made
in
nine
data
prOCessing
installations,.
Hazards
identified
during
the
study
are
classified
into
generic
categories
which
fcrrr
G320
the
I:asis
of
subsequent
phases
of
the
study.
Manual
SLSS
-
CRtER
NO.
SUESCFIP~ION
ONLY
G320-56Q7
AN
EXECUTIVE'S
GUI~
1£
tA~A
~Y~l!
= B
1R~§!!lIC~
!!Q~
iN
IBM
SVENS~A
AB
FUELICA~ION
X-data
~y-StUdY-to
1dentify
the
tYfes
cf
hazards
prevalent
in
today's
data
processing
operations
and
to
develcf
a"Froaches
tc
frotect
against
these
haz'ards
was
jointly
Flanned
by
the
Swedish
office
for
Adrrinistrative
Development
(STA~C)
and
IBM
Svenska
AE.
It
has
I:een
carried
out
I:y
staff
from
StatEkonsult
AB
(A
state-owned
ccnsulting
company),
which
was
commissioned
by
S~A~C
to
undertake
the
study,
and
IBM.
The
initial
results
frorr,
the
first
fhase
of
this
study
are
contained
in
Data
Security
--
Threats
and
Deficiencies
in
Ccrr"uter
Operaticns
--
A
Report
cn
a
Completed
Study
--
A
~ranslation
frorr
an
IBM
Svenska
AB
Publicaticn
(G320-56Q6)
and
in
this
volurre.
~his
volurre
introduces
the
study
and
fresents
an
aFproach
to
data
security
in
terms
of
its
basic
elerrents.
~he
study
report
provides
the
detailed
results
of
observaticns
Rade
in
nine
data
precessing
installations.
Hazards
identified
during
the
study
are
classified
into
generic
categories
which
form
the
I:asis
cf
subsequent
phases
of
the
study.
Manual
SLSS
-OFtER
NO.
SUESCRIP~ION
ONLY
G320-56Q9
DATA
FCR
DPIN
This
caticn
is
addressed
to
information
systems
nanagement and
presents
measures
that
IE~
and
others
have
found
useful
for
lirriting
risk
in
data
processing
installations.
While
it
is
hOFed
that
these
rreasures
will
be
of
interest,
they
are
pro~ided
for
inforuation
~ur~osEs
only,
IBM
nakes
no
guarantee
or
representation
with
respect
to
theix
a"plicability
to
a
specific
data
proceSSing
installation.
Manual
SLSS
-
ORDER
NO.
SUBSCFIP~ION
ONLY
G320-5650
MANAGEMENT
MEMORANDUM.
SECURITY
FEA~URES
Of
IBM
SYS~EM/370
A
management·oriented
report
on
hardware-aDd
scftwai-e-----
features
of
System/370.
Designed
to
highlight
featuxes
that
can
hel~
installation
management
in
chOOSing
features
that
night
be
useful
in
their
data
precessing
environment.
Also
contains
an
AFpendix
of
selected
IBM
publications
cn
physical
and
data
security.
ERCCHURE,
29
PAGES,
6/76
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
G320-5790
SYSTEMS
AtCI!ABIlI!Y
.! CCNnOl.&
AUDl1
FFAC'IIg§
This
rranual
is
part
cf
a
study
by
the
institute
cf
internal
auditcrs.
It
presents
infor~aticn
on
auditing
in
the
data
processing
environment.
including
audit
tools
,
techniques.
Manual,
8
1/2
x
11
inches,
226
pgs,
5/77
SLSS
-
ORDER
NO.
SUBSCRIF~ION
ONLY
G320-5791
~
AtDI~ABIlI~Y
.!
CONTROL.
EXECUTIVE
E!!QR!
This
is
an
Executive
Summary
of
the
Institute
cf
Intexnal
Auditcrs
froject
to
study
audit
and
control
procedures
for
data
~rocessing
installations.
~opics
include
Project
~ethodclogy,
tiscussicn
of
Conclusions
and
Cost
Implications
of
Systems
Audital:ility
and
Control.
Manual,
8
1/2
x 11
inches,
2q
pgs,
5/77
SLSS
-
ORDER
NO,.
SUBSCRIPtION
ONLY
G320-5792
SYSTEMS
AUI:ITABILITY .!
CONTROL.
fQ!!~ROL
f!!Bf11glJ
The
control
practices
report
is
part
of
a
study
I:y
the
Institute
cf
Internal
Auditors.
It
presents
infcr~ation
relating
to
control
techniques
applical:le
to
comfuter
I:ased
information
systems,
computer
service
center·o~eraticns.
and
the
system
devel0Fment
process.
It
alsc
frovides
an
overview
cf
Data
Precessing
Centrel
Practices.
Manual,
8
1/2
x
11
inches,
156
pgs,
5/77
SLSS
-
ORDER
NO.
SOBSCRIP~ION
ONLY
G320-5829
AUDITABILI~Y
AND
PRC[UC~IVI~l
INFCRNATICN
CATALOG
11
This
catalcg
frovides
a
quick
reference
tc-ZEN
prograrrs
that
can
enhance
the
productivity
of
Fers9nnel
auditing,
designing.
de~ele~ing.
testing.
er
dccuuenting
System/370
progra
..
s
and
systens.
The
Frograrrs
descriptions
in
tbe
catalcg
are
in
alphatetic
sequence
ty
sutcategory
within
the
following
cat'egor
iee.
• CICS
IMS
OS
tOS
VM/370
Fr09rams
tbat,
are
not
listed
in
the
atove
categories
tut
that
perform
audit
functicns
cr
are
used
as
audit
aids.
Catalog,
8
1/2
x 11
inches,
364
Fgs,
9/77
G320
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
G320-5840
COMMUNICATIONS
SYSTEMS
NANAGEMINt
~
CCNCEPTS
This
preli~inary
publicaticn
on
comuunication
systems
management
concepts
is
primarily
intended
to
assist
the
executive
1:0
whOll1
the
information
pr9cessing
function
reports
in
evaluating
the
degree
to
which
an
existing
or
1'1anned
cOlnrunication
systems
management
function
meets
the
organization"s
goals.
It
may
also
be
of
interest
to
managers
with
communication
systems
management
responsibilities
and
to
IBM
rel'resentatives.
Manual,
24
pages,
7/78
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
G320-6163
~
CCMPARE/AUDIT
UTILITY lYi 5796-PLZ,
NOTICE
The Sour,ce
Compare/Audit
Utility
accepts
text
inl'ut
from two
files
and
produces
various
print,
update
and
summary
files
detailing
source
line
matches,
insertions,
deletions,
and
reformats.
Input
files
can
be
sequential
data
sets,
Os/VS
I'8rtitiOned
data
sets
or
partitioned
data
set
members. The
SOurce
Compare/Audit
Utility
features
speed"
capability,
Simplicity
of
use,
and
accuracy
through
a
unique
algorithm
which
is
able
to
resynchronize
the
comparison
despite
a
large
number
of
source
level
differences.
.
Release
notice,
8
1/2
x 11
inches,
8
pages,
10/79
G321-5010
HIERARCBlCAL
APPROACH
TO
COMiUTER
SYSTE~
INTEGRITY
SYSTEMS
JOURNAL
REPRIN~
Security-rs-an-important
factor
if
the
programs
of
independent
and
1'0ssibly
errcr-prone
or
malicious
users'are
to
coexist
on
the
same
computer
system.
In
this
paper,
we
show
that
a
hierarchically
structured
operating
systeu,
such
as
produced
bY
a
virtual
machine
system,
that
combines
a
virtual
sachine
monitor
with
several
independent
ol'erating
systems
(VMM/oS),
provides
substantially
better
software
security
than
a
conventiOnal
two-level
uultiprogramming
operating
system
al'proach.
This
added'protection
is
derived
from
redundant
security
using
independent
mechanisms
that
are
inherent
in
the
design
of
most
VMM/OS
systems.
Such
a
system
can
be
obtained
by
exploiting
existing
software
resources.
Journal
Reprint,
7x10
inches,
20
pages
NOT
AVAILABLE
ONDER
SLSS
G321~5011
AN
~
~
MECHANISM
FOR
COMPUTING
RESOURCES
SYS'lEMS
~ ~
The
architecture
of
an
access
control
mechanism
for
the
resources
of
an
0S/360
or
VS/370
cosputer
system
is
I'resented.
The
use
of
this
operating
system
corrponent
for
data
l:ase
security
and
integrity
in
a
research
and
engineering
environment
is
described.
The
techniques
described
make
possible
ccntrolled
access
to,
the
system"s
I'rocesdng
l'ower,
contrclled
access
to
the
database,
decentralized
authorization
resI=Onsibility,
measuring
dataset
usage,
and
event
recording
for
automatic
dataset
migratiOn,
archiving,
and
staging.
Journal
Reprint,
7 x 10
inches,
20
pages
NOT
AVAILABLE
UNDER
SLSS
G321-5012
GENERALIZE
!!!l1
~
!Q!!
DATA
~,A
P,U
REPRINT
~iscus~ed
1.
It
is
defined
he~e
to
l:e a
generalized
recording,
of
"who
did
what
to
WhOlt"
when,
and
in
what
sequence."
This
information
is
to
be
used
to
satisfy
system
integrity,
reCOVery,
auditing,
and
security
reqUirements
of
advancements
of
advanced
integrated
data
base/data
communications
systems.
This
l'aper
hypothesizes
What
information
must
ce
retained
in
the
audit
trail
to
~ermit
recovery
and
audit
later
in
time
and
a
schene
of
organizing
the
contents
of
the
audit
trail
so
as
to
provide
the
required
functions
at
Ilinimum
overhead.
Introduced
are
the
concepts
of
,types
of
audit
required,
CB/DC
audit
assumptions,
tiree
domain
addressing,
time'
sequen¢es
required
to
support
'versions
of
data,
what
constitutes.an
audit
trail,
and
implementation
considerations.
Journal
Reprint,
7 x 10
inches,
20
pages
NOT
AVAILABLE
UNDER
SLSS
G321~5032
'tOP-DOWN
DEVELOPMENT
USING
!
~'
DESIGN
LANGUAGE
SYSTEM
JOURNAL
REPRINT
"
Discussed
is
a
program
design
language
-a'
fo~
of
I'seudocode
-
that'has
ceen
developed
and'
used
to
organize,
teach,
document,
and
develop
software
s1stems.
An
exau,ple
of
top-down
program
design'illustrates
the
key
steps
in
using
the
language:
deterll,ining
the
requirements,
abstracting
the
functions,
expanding
the
functions,
and
verifying
the
functions.
Syntax
and
conventions
of
the
language
are
given
in
an
appendix.
~~r~~!I~:~~~n~ND~Rx
si:~s
inches,
20
pages
G321
G321-5036
SILECTEC
~EADINGS:
[ATA
EASE
SystlMS
SYS7E~S
JCURNAl
REiRINT
--
----
This
short
paper
was
chosen
for
l'uclication
cy
the
editors,
who
hope
that
the
connents
and
references
"ill
I::e
hel~ful
to
readers
who
desire
to
strengthen
their
background
in
the
literature
of
data
l:as,e
systems.
Beginning
with
early
data
case
ccnCEl'ts,
this
l'aper
cites
a
selection
of
key
references
of
hierarchical,
network,
and
relaticnal
data
cases.
The
authcrs
of
this
selection
are
R.
Ashany,
Asscciated
Editor
cf
the
IBM
Journal
cf
Research
and
Developmen-t, and
leict.ael
Adall'owicz,
Associate
Professor,
Polytechnic
Institute
of
New
York,
Brooklyn,
New
York.
Journal
Reprint,
7"
x
10',
20
pgs
NOT
AVAILABLE
UNDER
SlSS
G321-5040
§i!!Yill
LEVELS:
!
~
!Q!l
II!
!!§j!!
Mil:
11!l!
f!l!l!!!!:ll:!l
CENTER
service
levels
rel'resent
an
important
concept
that
can
be
applied
toward
the
solution
of
difficult
protlells
surrounding
communications
between
users
and
prcviders
of
data
I'rocessing
services.
In
this
paper,
this
ccncel't
is
descril:ed
in
terms
of
the
architecture
which
defines
the
scol'e
and
structure
of
service
information.
The l'ap,er
further
translates
tte
architecture,
into
data
~rccessing
terrr,inology
by
presenting
the
data-l:ase
structure
anel
data
elell,entsrelated
to
eervice
levels.
The
paper
also
addresses
the
1'0st-procEssing
of
the
data
base,
a
ste~
essential
to
I'roperly
cCllllunicating
serviCE-level
inforlfation
.•
Journal
Rel'rint,
7 x 10
inches,
20
pages
G321-5042
A
USER
ORIEIITEC
DATA
BASE
REtRIEVAL
SYSTE~
DiScUssed
is
an
eXl'eriiDEiital,
specialized
data
Case
system
develo~ed
for
users
who
do
not
require
the
sophisticated
resources
of
the
large
data
base
systems
l:ut
do
require
many
of
the
cal'al:ilities
they
provide.
~ata
reanil'ulation
and
retrieval
within
a
data
base
are
made
availatle
for
the
non
prograllmer
user.
'the
function
and
design
attricutes
of
the
systeu
are
descrited
including
the
reasons
for
tasing
the
systell
on
APL
functicns.
'
Journal
Rel'rint,
1 x
10
inches,
22
pgs,
3/77
13321-5045
!
METHCD
CP
PROGRA~~ING
Ml!ASURl!MEN't
Mil:
ESTIMAT1£~
Isprcveu,ents
in
I'rogramming
technology
have
l'aralleled
improvements
in
con~uting
system
architecture
and
materials.
Along
with
increaSing
knowledge
cf
the
systen
and I'rogram
develcpment
processes,
there
has
l:een
SOll,e
notacle
research
into
~ro9ralnr.ing
~roject
measurement,
estill'aticn,
and
planning.
Discussed
is
a method
of
prograllning
I'roject
productivity
estiuaticn.
Also
presented
are
preliminary
results
of
reSEarch
into
methods
of
measuring
and
estirr,ating
programming
project
duration,
staff
size,
and
cOlfl'utez
cost.
Journal
Re~rint,
7 x
10
inches,
3/77
G321-5053
£ill
BASES:
PAST,
!Bl!§l!~
lli
!!!1.!1!ll! =
~~
JOURNAL
REPRIN't
A
broad
~f
cClllfercial
and
research
data
l:ase
systess
are
analyzed.
Connon
characteristics
are
discussed.,
~hese
systeus,
which
have
roots
in
older
filing
systerr.s
and
in
punched
card
systems,
are
grouped
into
the
three
categories
of
hierarchic,
network
and
single-level
Ilodels.
Alsc
presented
is
work on
the
standardization
of
data
base
systems.
Besearch
tcward
the
disccv~ry
of
new
cCDmona~ities
is
also
discussed.
~his
paper
is
cased
on
an
extensive
published
literature.
Rel'rint,
7 x 10
inches,
49
pgs,
8/77
G32i-5055
AUTCMA'IED
~
~
EASE
DESIGN
=
~
!!Q!!~
!lliPRINT
This
~al'er
~escrices
the
design
effort
for
an
integrated
data
tase
and
then
develops
teChniques
for
autorrating
sigrrifi~ant
porticns
cf
the
laber.
'these
techniques
have
been
inccrl'orated
in
a
program
to
provide
an
effective
data
case
design
tool
(Data
Base
Design
Aid)
in
current
use.
't'he
precesses
invoived
with
this
aid
are
discussed.
Rel'rint;
1 x 10
inches,
35
pgs,
8/11
G321-5051
DESIGN
'tECHN
l£E !
]§!!l
CONTRCLLEC
~
§!§~
-
SYS'tEMS
J
UFFINT
, , ,
The
flexil:il
usefulness
of
an
integrated
data
case
12
can
be
lind
ted
by
ccnstzaints
inhe.r~nt
in
the
data
.l:asE
RanageHent
systeu.
Cne such
system,
IBM's
Inforuaticn
Management System
(I~S),
has
teen
e.tended
in
terms
cf
data
dndel'endence,
access
control,
data
integrity
and
user
cOInrunicatioh
cy'
a
9~,ouP
of
techniques
integrated
into
an
IMS
a~l'lieation
call.id
the
Product
Developrrent
Ccnlllunication
and
ccntrol
(PDCC)
system.
This
l'a,er
descrites
the
IMS
extensions
provided
ty
PDCC
and
discusses
the
system'~
implementation.
Ptcc
is
the
protcty~e
cf
the
I~S
Al'l'lications
Develol'ment
Pacility,
an
IBM
Installed
~ser
Program.
Journal
re~rint,
7 x
10
inches,
18
lOgs,
11/17
G321-5063
~:~:~N~E~:~
CUALITY
AND
PROI:UCnVITI. =
§X§lm
DISCUSSed
is
.e,
unit-of~m~~sure
situation
in
~rc9ranaing.
An
analysiS
of
c.orrmon
units
of;'
measure
'for
assessing
~ro9ram
quality
and
prograunei
I'roductivity
reveals
that
somE
stahdardueasuresare,
intrinSically
paradoxical.
LinES
of
code
~er
I'r09raUner~~onth
and
cost
per
dEfect
are
in
this
category.
Presented
here
are
attem~tstc
gc
beycnd
such
paradoxical
units
as
tb.se.
Also
discussed
is
the
usefulness
of
separating
quality
me~surements
~nto
measUres
of
defect
renoval
efficiency
and defe<;:.t
preventicn,
and
the'
usefulness
of
separating
l'roductiVity
rreasurell,ents,
into
work
units
and
ccst
units.
Reprint,
1 x 10
inches
G321-5066
G321
A
CRYPTOGRAPHIC
~EY
MANAGEMENT
SCHEME
F~
IMPLEMENTING
THE
tATA
ENCRYPTION
S'fiiNDARD
(J:ES)
---
- -
J:ata
being
transmitted
through
a
communications
network
can
be
protected
by
cryptography.
In
a
data
processing
environment,
cryptography
is
implemented
by an
algorithm
which
utilizes
a
secret
key,
or
sequence
of
bits.
Any
key-controlled
cryptographic
algorithm,
such
as
the
Data
Encrypticn
Standard
(DES),
requires
a
protocol
for
the
manageDent
of
its
cryptographic
keys.
The
complexity
of
the
key management
protocol
ultimately
depends
on
the
level
of
functional
capability
provided
by
the
cryptosystem.
This
paper
describes
a
key
management scheme
that
provides
the
support
necessary
to
protect
comDunications
between
individual
end
users
(end-to-end
encryption)
and
that
also
can
be
used
to
protect
data
stored
or
transported
on
removable
media.
Journal
reprint,
1 x 10
inches,
20
pages
G321-5061
GENERATION,
DIST'RIBUTION,
AND
INSTAlIATION Q!:
CRYPTOGRAPHIC
KEYS
A key
controlled
cryptosystem
requires
a mechanism
for
the
safe
and
secure
generation.
distribution,
and
installaticn
of
its
cryptographic
keys.
This
paper
discusses
key
generation,.
distribution.
and
installation
procedures
for
the
key management scheme
presented
in
preceding'paper
G321-5066.
Journal
reprint.
7 x
10
inches.
12
pages
G321-5068
CRYPTOGRAPHY
ARCHITECTURE
FOR
INFORMATION
SECURITY
Information
being
transferred
from
paint
to
point
over
a
public
corrmunications
carrier
or
stored
on
portable
media
can
be
protected,
by
the
use
of
cryptography;
from
accidental
or
intentional
disclosure~
Control
functions
are
required
to
insure
synchronization
of
the
process.
In
a
communications
enviromr.ent,.
the
control
functions
become
logically
part
0 f
the
network
architecture.
IBM's
SysteRs
Network
Architecture
(SNA)
has
been
extended
to
allow
the
use
of
cryptography
when
sensitive
inforRation
is
being
processed.
Architectural
similarities
for
the
file
environment
are
discussed,.
Journal
reprint,
7 x
10
inches,
13
pages
G321-5069
ADMINISTRATIVE
CONTROL
OF
COMPUTING
SERVICE
The
complexity
of
necess:ary
administrative-controls
for
computer
service
exceeds
the
capabilities
of
clerical
Itethods.
This
paper
presents
a
practical
method
for
describing
the
external
administrative
environment
in
a
data
base
which
can
be
used
by
the
operating
system
for
dynamic
enforcement
of
limits.
An
attempt
is
made
to
address
consistently
the
different
forms
of
data
processing
that
may
be
concurrent
in
a
single
installation;
included
are
general
purpose
time
sharing,
transaction
oriented
computing,
and
scientific
computing.
Described
is
the
architecture
of
an
operating
system
component
that
could
be
regarded
as
the
interface
between
administrative
security
mechanisItS and
the
security
features
of
the
system
software
.•
Journal
reprint,
1 x 10
inches,
28
pages,
5/18
G321-5010
DATA
PROCESSING
~
OF
CONTROL
The
IBM
System
Journal
is
published
quarterly
by
IBM.
This
voluRe
contains
the
following:
There
has
long
been
a
need
for
better
definition
of
the
audit
and
control
aspects
of
data
processing
applications.
~his
paper
attempts
to
satisfy
that
need
and
thereby
provide
a framework
fer
imprOVing
communication
between
systems
analysts
and
computer
scientists.
It
introduces
the
concept
of
spheres
of
control,
which
are
logical
boundaries
that
exist
in
all
data
processing
systems,
whether
manual
or
automated.
The
paper
descrites
their
essential
properties
and
protrays
them
as
they
relate
to
each
other
in
the
batch,
on-line,
and
in-line
processing
environuents.
Included
are
spheres
of
control
that
define
process
bounding
for
such
purposes
as
recovery,
auditing,
process
commitment, and
algorithm
(procedure)replacement
.•
Journal
reprint,
1 x 10
inches,
20
pages
G321-5011
PERFORMANCE
~UNING
IN
OS/vS2
MVS
-
SYSTEMS
JOURNAL
REPRINT
A
procedure
of
observation
and"CorreCtICilispresented"fCr
the
coarse
tuning
of
an
MVS
system
by
analyzing
it
into
its
software
and
hardware
components
and
increasing
their
efficiency
successively.
The method
involves
adjustments
to
swapping,
the
input/output
load,
the
CPU
load,
main
storage,
and
the
system
resources
manager.
Also
discussed
are
performance
measures
necessary
to
characterize
a
systen,
tools
to
tune
a
systen,
and
various
aspects
of
data
gathering
and
the
effects
of
adjustments
on
system
parameters.
~wo
illustrative
case
histories
are
also
given.
Reprint,
1 x
10
inches,
24
pages,
8/18
G321-5106
AN
INTEGRATED
APPROACE
TO
CENTRALIZED
COMMUNlCA~'IONS
NETWORK
MANAGEMENT
--
~technological
advances
have
increased
the
size
and
number
of
tele~rocessing
networks
as
well
as
broadened
their
scope
and
ccmplexity.
This
added
size
and
complexity
has
magnified
the
need
for
communications
network
management.
One
approach
to
communications
network
nanagement
is
to
provide
centralized
control
which
is
integrated
into
the
SysteroNetwork
Architecture
user
network.
This
approach
is
described
in
this
paper
by
focusing
on
twc
program
products
that
provide
centralized
o~erator
control
and
problem
determination
capa:~:dlities
for
a
network,.
Journal
reprint,
7 x
10,
23
pages,
11/79
G520
G321-5113
2Y!!!Yll!!
jl!'
m
£llifll!
fLANNING
PROCESS
1m!
mml£llm!
DATA
~overview
of
techniques
availacle
to
address
capacity
planning
in
the
production
data
~rocessing
envircnment
is
presented..
The
production
data
~rocessing
system
is
briefly
described
and
its
capacity
is
quantified.
The
measurement
tools,
reports,
and
data
required
to
implenent
a
capacity
planning
program
are
discussed.
Modeling
and
prediction
are
placed
in
perspective
with
the
overall
objectives
of
the
capacity
plaaning
process.
Personnel
(managerial
and
technical)
and
organization
considerations
are
also
discussed
.•
Journal
reprint
1 x 10
inches,
24
pages,
2/80
G321-511Q
A
CAPACITY
PLANNING
~E1HODOLOGY
13
Di~is
a
ca~aclty
planning
procedure
called
USAGE.
Various
cusiness
elements
to
be
individually
measured
and
tracked
are
presented.
Outlined
are
methods
for
estiD,ating
worklcad
growth.
Se~aratE
linits
of
capacity
for
on-line
worklcad
and
catch
wcrkload
deD.and
are
discussed.
A
simple
graphics
presentation
procedure
is
included
to
ccmmunicate
the
results
of
the
study
to
those
who
need
the
infornation
for
making
cusiness
decisions.
G321-5115
SYSTEM
ill!£!ll
A!<D
IEBFOI<MANCE
~ALUAT1Q!!
The
perfornance
of
MVS
(Multiple
Virtual
Storage)
systems
can
be
predicted
fcr
changes
in
workload
and
enviroM,ent
by
an
IEM
marketing
aid
informally
called
SCAPE
(for
System
Capacity
and PerformanCE
Evaluation).
written
in
FOI<1RAN,
the
programs
use
sim~le
queuing
formulas
with
enpirical
nodifications.
ResponSE
times
fcr
complex
worklcads
IIMS,
CICS,
150,
and
batch)
through
the
CFU
and
auxiliary
storage
are
expressed
as
functions
of
application
lcads
and
other
parameters
that
define
the
systelt's
environn.ent.
SCAPI!
can
predict
the
effect
on
performance
'of
different
CIU
models,
larger
~eaory,
additional
channels,
additional
direct-access
storage,
larger
block
sizes,
and
alternate
wcrklcad
projections
..
Journal
reprint
1 x 10
inches,
22
pages,
2/80
G321-5120
SYS~EMS
MANAGE~ENT
Effective
systems
management
is
dependent
cn
two
factors
-
visitility
of
the
data
required
for
systeDs
DanageD.ent
and
a
structllred,
disciplined
manageD.ent
system
to
effectively
utilize
this
inforDaticn.
Discussed
in
this
paper
are
two
programs
to
assist
in
dealing
with
these
factors.
1hese
host
programs
use
VSAH
data
loases
and
are
accessed
via
CIVS/VS
or
IMS/vS.
~he
prograD.s
provide
applications
to
assist
in
problem
management,
change
ltanagen.ent,
netwcrk
configuration,
and
Frotlem
detera.ination.
These
functional
application
tools
are
described
in
terms
of
their
content
and
their
relationships
with
the
overall
systems
managemeat
tasks.
Journal
reprint,
1 x
10
inches,
20
pages,
2/80
G520·2169
T
NSIJ:ERATIONS
Of
tA~A
SECURITY
IN
A
COMPUTEI<
NM!NT
--
--
- -
----
rochure
is
a
guide
to
provide
general
D,anagement,
systems
deSigners
and
operations
manageu:ent
with
various
data
security
considerations
in
crder
to
assess
and
minimize
potential
probleDs.
It
does
net,
however,
attem~t
to
cover
highly
classified
systems
within
the
governnent
-
those
with
stringent
requirenents
peculiar
to
data
invclving
the
nation's
security.
The
crochure
discusses
considerations
of
data
security
necessary
when
conputing
systems
store
and
process
either
proprietary
data
or
personal
information
on
individuals.
While
it
does
not
cover
the
much
broader
social
issue
of
privacy,
it
does
proceed
with
a
recognition
that
the
protection
of
individual
privacy
places
special
responsibilities
cn
these
who
determine
how
systems
are
to
he
used
.•
The
addition
of
remotely
located
terminal
devices
significantly
increases
the
potential
probleDs
and
the
resulting
concern
for
data
security.
Problens
range
from
preventing
the
curious
intruder
from
browsing
through
personnel
rosters,
customer
lists,
operating
statements,
etc.,
to
preventing
the
malicious
intruder
froD.
altering
payroll
rEcords,
cbtaining
secret
financial
data
or
illegally
obtaining
copies
of
new
product
specificaticns.
Booklet,
6" x
9",
44
pages
SLSS
-
ORDER
NO.
SUBECIlIPTION
ONl·Y
G520-2100
~I~g:~i~iRA1ION§
Q!
FBYSICAl
SECURITY
~
!
~
Protective
measures
designed
to
secure
a
ccm~uter
installation
and
its
vital
records
against
fire,
unauthoriZEd
access
and
other
hazards
are
discussed
in
general
terms,
are
detailed
in
sample
checklists,
and
exenplified
in
the
AAS
case
study.
Manual,
Q3
pages
SLSS
-
ORDER
NO.
SUBECRIPUON
ONLY
G520-2141
THE
FIRE
AND
AF~ER
~BE
FIRE
BrochUre
describes
the
FID-fire
ef
1912,
and
IE~'s
recovery
efforts
to
get
the
facility
back
into
operation
in
the
shortest
possible
tine
span.
The
otject
lesson
cf
this
narrative
is
that
nc
ene
is
inDune
to
mishap
and,
therefore,
should
have
a
recovery
plan
in
place.
Erochure,
12
pages,
11/18
G520
G520-2797
~
SUGGESTIONS
FOR
IMPROVING
SECURITY
ltl
DATA
PROCESSING
OPERATIONS
Suggestions
on
how
to
overcome
some
of
the
problems
of
physical
security
and
data
security
rr~st
commonly
encountered.
It
is
not
a
checklist,
but
a
collection
of
observation$
and comments by
peofle
experienced
in
operating
dat~
processing
installations.
References
are
included
to
other
IBM
pul:lications
on
security.
6 x 9
Booklet,
20
pages
SLSS
-
ORDER
NO.
SUBSCHIPTION
ONLY
G520-2838
1.!l!!
DATA
SECURITY
SYMPOSIUM,
~
1973
Reprint
of
27
papers
presented
at
the
April,
1973
symposium
cn,
data
security
held
in
Beston,
Massachusetts
..
Compilation,
264
pages
SLSS
-
ORDER
NO.
SUBSCRIPTIQN
ONLY
G520-2881
SECURITY,
ru
.!l!§.!l!
THING
FOR
1Q!lli
£OMPUtER,
THE
BEST
THING
POR
YOUR
INFORMATION
Offers-SUggestions
and
examples
to
belp
management
improve
the
physical
and
data
security
of
data
proceSSing
operations.
A
brief
list
of
pertinent
publications
is
included.
polder,
14
pages
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
G520-2882
DATA
SECURITY
SEMINARS.
IBM
EDUCATION
COURSE
X8851
BROCHURE
DeSCribes
an
IBM
Education-course
on
physiCal-ana-dit-a----
security
being
given
for
one
day
in
IBM
locations.
IBM
specialists
in
data
security
prograIts
and
p~ocedures
conduct
detailed
sessions
of
interest
to
executives
and
other
personnel
charged
with
maintaining
security
in
a
computer
environment.
Erochure,
8
pages
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
G520-2965
1.!l!!
~
ill!1.!!1TI!Q.!!.!!!!..!.
DENVER,
COLORADO,
SEPTEMBER
1974
This
publication
reprints,
without
changes
and
without
com-
ment,
the
36
papers
given
at
the
data
security
forum
held
September
10-12,
1974
in
Denver,
Colorado.
The
appendix
summarizes
the
results
of
the
data
security
survey.
Compilation,
536
pages,
soft
cover
SLSS
-
ORDER
NO.
SUBSCRIPTION
ONLY
G520-3332
AUDITORS
PERSPECTIVE
8100
~gn
and
implementation
of
distributed
data
~rocessing
systems
pose
s~ecial
challenges
in
the
area
of
audit
and
control.
This
publication
describes
six
requirements
of
concern
to
auditors
and managers and
explains
how
the
features
of
the
8100
systelT
and
associated
programs
address
the
requirements,.
Manual,
24
pages,
9/78
G520-3526
SYSTEM
MANAGEMENT
ASSESSMENt·
QUESTIONNAIRE
~~
This
document
is
a
supplement
to
the
Systems
Management
Assessment
Questionnaire.
It
is
intended
to
clarify
and
expand
upon
the
questions
and
the
subject
matter
in
the
questionnaire.
This
document
is
divided
into
eight
sections
representing
the
SystemsManagement
disciplines.
Change
ManageR.ent,
Problem
Managenent,
Processing
Manasement,
Recovery
Management,
Performance
ManagelTent,
Capacity
Management,
Audit/Security
Management,
~anagement
Reporting
Each
section
should
be
used
in
conjunction
with
the
corresponding
Systems
Management
diSCipline
in
the
questionnaire.
Booklet,
3
1/2
x 8
1/2
inches,
16
pages,
10/79
14
..:
E
ai
0
E
....
Q,
en
's
:E
0-'"
Q)iii
CI
Q)
c:
en
.;:::;
0
......
~
8.
==
ca
ca
...
E]
"0
E
~
E
E
6,
o
...
;~
ca
...
.r:.
0
.~
'-
~
0
en
Q)
E
.~
.!!
.c;;
..0
c:
e
~
Q,
Q)
~
5
:J
~
~
f!
c:
Q,
~ ~
en
:J
Q)
Q)
o.lQ
ca
Q)
enS:
Systems Management Bibliography
GF20-B172-15
READER'S
COMMENT
FORM
This manual
is
part
of
a library
that
serves
as
a reference source for systems analysts, programmers, and
operators
of
IBM
systems. This form may be used
to
communicate your views about this publication.
They will be sent
to
the author's department for whatever review and action,
if
any,
is
deemed appropriate.
Comments may be written
in
your own language;
use
of
English
is
not
required.
IBM
may use or distribute any
of
the information you supply in any way
it
believes appropriate with-
out incurring any obligation whatever. You may,
of
course, continue
to
use the information
you
supply.
Note:
Copies
of
IBM
publications
are
not stocked at
the
location
to
which
this
form
is
addressed.
Please
direct
any
requests
for
copies
of
publications,
or
for
assistance
in
using
your
IBM
system,
to
your
IBM
representative
or
to
the
IBM
branch
office
serving
your
locality.
Possible topics for comment are:
Clarity Accuracy Completeness Organization Coding Retrieval Legibility
If
you
wish a reply,
give
your name and mailing address:
What
is
your occupation?
__________________________
_
Number
of
latest Newsletter associated with this publication:
_____________
_
Thank
you
for your cooperation.
No
postage stamp necessary
if
mailed
in
the U.S.A. (Elsewhere, an
IBM
office or representative will be happy
to
forward your comments
or
you
may mail directly
to
the address
in the Edition Notice on the back
of
the title page.)
GF20·8172·15
Reader's Comment Form
Fold
and
tape
Please Do Not Staple
Fold
and
tape
•••••••••
0.1
•••••••••••••••••••
I
••••
I
•••••••••••
I
•••
I
•••••••••••••••••••
II
~
••
11
••••••••
0.1
••••••••
II
••••••
II
II
I
•••••••
11
••••
10
••••
I
••
II
•••••••
I
•••••
II'
II.
II
•••
0.1
I
•••
II II
•••••••
1
•••
1
•••
1
•••••
II
••
1
•••••
1
••
_
••••
111111
Business
Reply Mail
No
postage stamp necessary if mailed
in
the
U.S.A.
Fold
and
tape
==-=
=®
--
----
-
~--
-
.......
----
---
----
--...--
..
-
-~-.-
Postage
will
be paid by:
International Business Machines Corporation
Department
824
1133 Westchester Avenue
White Plains, New
York
10604
Please Do
Not
Staple
International
Business
Machines
Corporation
Data
Processing
Division
1133
Westchester
Avenue.
White
Plains. N.Y. 10604
IBM
World
Trade
Americas/Fer
East
Corporation
Town
of
Mount
Pleasant.
Route
9,
North
Tarrytown,
N.Y., U.S.A. 10591
IBM
World
Trade
Europe/Middre
East/Afri~a
Corporation
360
Hamilton
Avenue.
WhitePtains.
N.Y
.•
U.S.A.
10601.,
First
Class
Permit 40
Armonk
New
York
Fold
and
tape
I
n
5.'
o
...
6'
g:
):I
0'
:l
II>
C
:l
I
I
I
I
I
I
-n
CD
,2
?
G')
m
2
§

GF20-8172-15
==-=
=®
-
---.-.
-
~--
-
-.
-~-
---
----
------
---...
-,.-
International
Business
Machines
Corporation
Data
Processing
Division
1133
Westchester
Avenue.
White
Plains. N.Y.
10604
IBM
World
Trade
Americas/Far
East
Corporation
Towr.
of
Mount
Pleasant.
Route
9.
North
Tarrytown.
N.Y
..
U.S.A. 10591
IBM
World
Trade
Europe/Middle
East/Africa
Corporation
360
Hamilton
Avenue.
White
Plains.
N.Y
.•
U.S.A. 10601
-
."
c;-
z
?
G>
m
Z
r-
8