HPE Security Fortify Static Code Analyzer Performance Guide SCA Perf 17.10
HPE_SCA_Perf_Guide_17.10
User Manual:
Open the PDF directly: View PDF ![]() .
.
Page Count: 32
HPE Security
Fortify Static Code Analyzer
Software Version: 17.10
Performance Guide
Document Release Date: April 2017
Software Release Date: April 2017
Legal Notices
Warranty
The only warranties for Hewlett Packard Enterprise Development products and services are set forth in the express warranty
statements accompanying such products and services. Nothing herein should be construed as constituting an additional
warranty. HPE shall not be liable for technical or editorial errors or omissions contained herein.
The information contained herein is subject to change without notice.
Restricted Rights Legend
Confidential computer software. Valid license from HPE required for possession, use or copying. Consistent with FAR 12.211
and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items
are licensed to the U.S. Government under vendor's standard commercial license.
The software is restricted to use solely for the purpose of scanning software for security vulnerabilities that is (i) owned by
you; (ii) for which you have a valid license to use; or (iii) with the explicit consent of the owner of the software to be scanned,
and may not be used for any other purpose.
You shall not install or use the software on any third party or shared (hosted) server without explicit consent from the third
party.
Copyright Notice
© Copyright 2003 - 2017 Hewlett Packard Enterprise Development LP
Trademark Notices
Adobe® is a trademark of Adobe Systems Incorporated.
Microsoft® and Windows® are U.S. registered trademarks of Microsoft Corporation.
Documentation Updates
The title page of this document contains the following identifying information:
lSoftware Version number
lDocument Release Date, which changes each time the document is updated
lSoftware Release Date, which indicates the release date of this version of the software
To check for recent updates or to verify that you are using the most recent edition of a document, go to:
https://www.protect724.hpe.com/community/fortify/fortify-product-documentation
You will receive updated or new editions if you subscribe to the appropriate product support service. Contact your HPE sales
representative for details.
Performance Guide
HPE Security Fortify Static Code Analyzer (17.10) Page 2 of 32
Contents
Preface 5
Contacting HPESecurity Fortify Support 5
For More Information 5
About the Documentation Set 5
Change Log 6
Chapter 1: Introduction 7
Hardware Recommendations 7
Sample Scans 8
Related Documents 8
All Products 8
HPE Security Fortify Software Security Center 9
HPE Security Fortify Static Code Analyzer 11
Chapter 2: Performance Improvement Tips 12
Hardware Considerations 12
Tuning Options 12
Mobile Build Sessions 13
Memory Tuning 14
Java Heap Exhaustion 15
Native Heap Exhaustion 16
Stack Overflow 16
Parallel Processing 17
Chapter 3: Scan Quality and Performance 18
Breaking Down Codebases 18
Limiters 18
Quick Scan 19
Using Quick Scan and Full Scan 19
Limiting Analyzers and Languages 19
Disabling Analyzers 20
Disabling Languages 20
Scanning Complex Functions 21
Chapter 4: Optimizing FPRFiles 22
Performance Guide
HPE Security Fortify Static Code Analyzer (17.10) Page 3 of 32
Filters 22
Filter Files 22
Scan-Time Filters 23
Excluding Source Code from the FPR 23
Reducing the FPRFile Size 24
Opening Large FPRFiles 25
Chapter 5: Monitoring Long Running Scans 27
Using the SCAState Utility 27
Using JMX Tools 27
JConsole 27
Java VisualVM 28
Chapter 6: Troubleshooting 29
Function too Complex to Analyze Message 29
Dataflow Analyzer Limiters 29
Control Flow and Null Pointer Analyzer Limiters 30
Send Documentation Feedback 32
Performance Guide
HPE Security Fortify Static Code Analyzer (17.10) Page 4 of 32
Preface
Contacting HPESecurity Fortify Support
If you have questions or comments about using this product, contact HPESecurityFortify Technical
Support using one of the following options.
To Manage Your Support Cases, Acquire Licenses, and Manage Your Account
https://support.fortify.com
To Email Support
fortifytechsupport@hpe.com
To Call Support
1.844.260.7219
For More Information
For more information about HPE Security software products: http://www.hpe.com/software/fortify
About the Documentation Set
The HPE Security Fortify Software documentation set contains installation, user, and deployment
guides for all HPE Security Fortify Software products and components. In addition, you will find
technical notes and release notes that describe new features, known issues, and last-minute updates.
You can access the latest versions of these documents from the following HPE Security user community
website:
https://www.protect724.hpe.com/community/fortify/fortify-product-documentation
You will need to register for an account.
Performance Guide
Preface
HPE Security Fortify Static Code Analyzer (17.10) Page 5 of 32
Change Log
The following table lists changes made to this document. Revisions to this document are published
between software releases only if the changes made affect product functionality.
Software Release /
Document Version Changes
17.10 Updated:
l"Sample Scans" on page8 - Data updated for the current release
l"Tuning Options" on page12 - Added the new parallel processing option
lReplaced "CPUs, Parallel Processing, and Multithreading" with "Parallel
Processing" on page17 to describe the new parallel processing
implementation
16.20 Updated:
l"Sample Scans" on page8 - With data for the current release
lMinor edits
Removed:
l"Java Permanent Generation Exhaustion"
l"Keeping Tainted Information in Memory"
l"HPROF and JHAT"
16.10 Updated:Minor edits
Performance Guide
Change Log
HPE Security Fortify Static Code Analyzer (17.10) Page 6 of 32
Chapter 1: Introduction
This document provides guidelines and tips to optimize memory usage and performance when scanning
different types of codebases with HPESecurityFortify Static Code Analyzer (Fortify Static Code
Analyzer).
Hardware Recommendations
The variety of source code makes accurate predictions of memory usage and scan times impossible. The
factors that affect memory usage and performance consists of many different factors such as:
lCode type
lSize of the codebase
lAncillary languages used (such as JSP, JavaScript, HTML)
lNumber of vulnerabilities
lType of vulnerabilities (analyzer used)
lComplexity of the codebase
The information in this guide is based on general guidelines to provide a set of “best guess”
recommendations for hardware requirements. HPE Security developed these guidelines through results
from real-world application scans . It is important to note that there might be cases where your
codebase scan requires more than these guidelines imply. To improve these guidelines, HPE welcomes
your feedback on how your project requirements map to our guidelines.
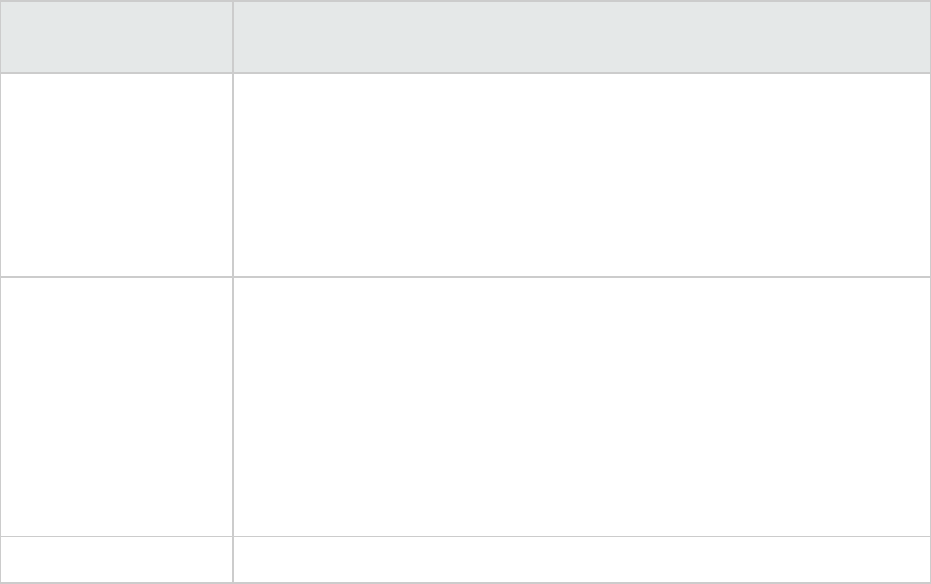
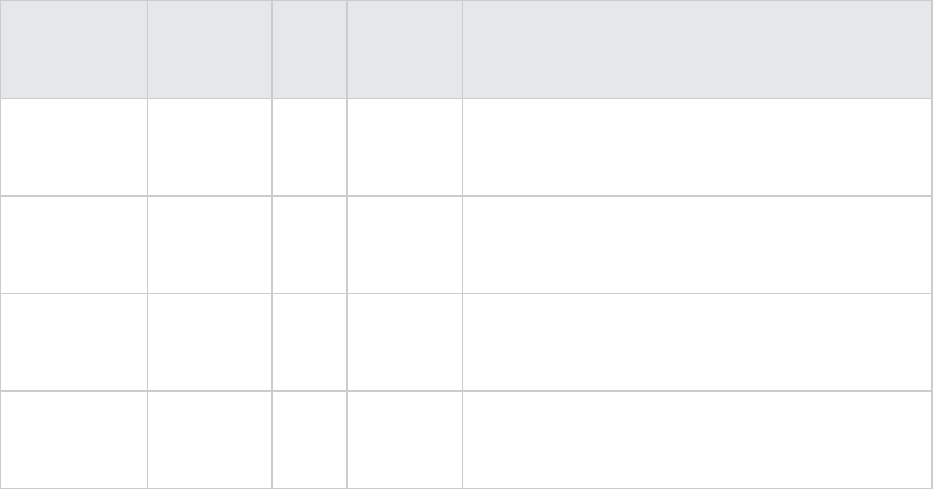
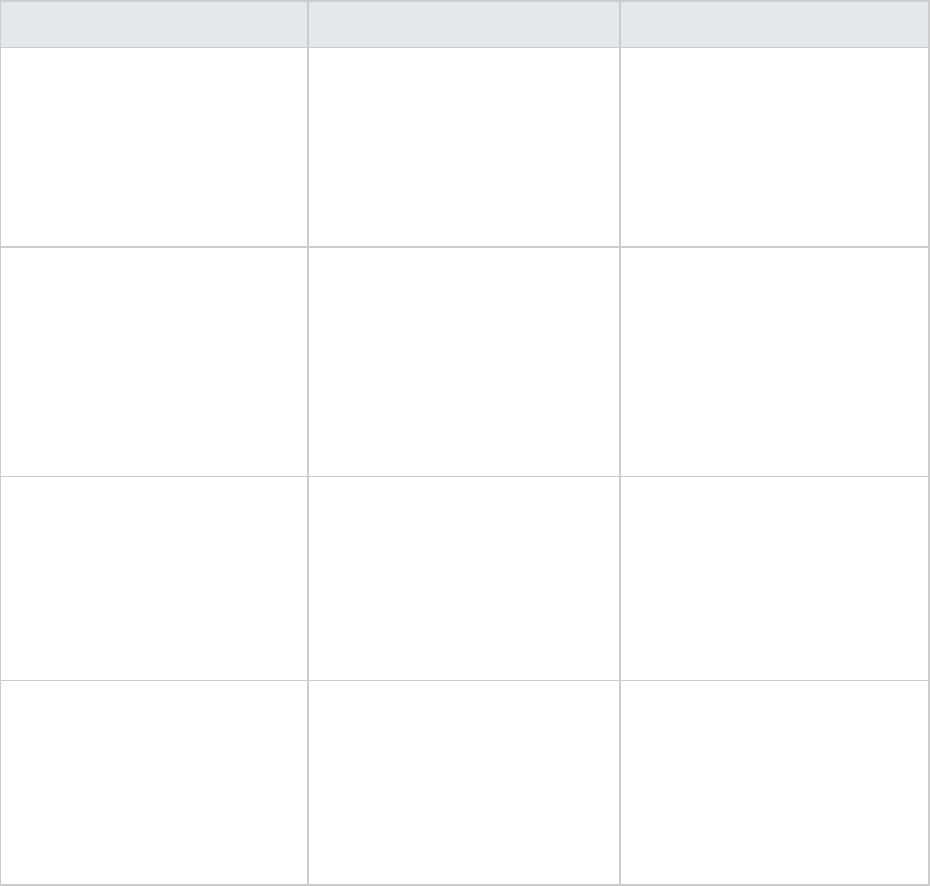
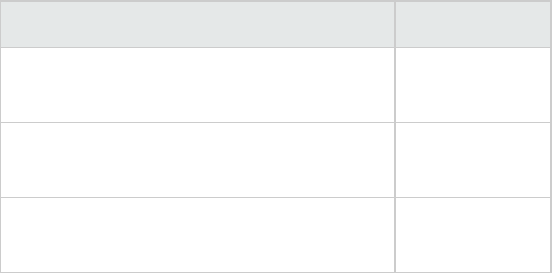
The following table provides recommendations based on the complexity of the application.
Application
Complexity CPUCores
RAM
(GB)
Average
Scan
Time Description
Simple 4 16 1 hour A standalone system that runs on a server or
desktop such as a batch job or a command-line
utility.
Medium 8 32 5 hours A standalone system that works with complex
computer models such as a tax calculation system
or a scheduling system.
Complex 16 128 4 days A three-tiered business system with transactional
data processing such as a financial system or a
commercial website.
Very
Complex
32 256 7+ days A system that delivers content such as an
application server, database server, or content
management system.
HPE Security Fortify Static Code Analyzer (17.10) Page 7 of 32
Note: JavaScript scans increases the analysis time significantly. If the total lines of code in an
application consists of more than 20% JavaScript, use the next highest recommendation.
Sample Scans
These sample scans were performed using Fortify Static Code Analyzer version 17.10 on a dedicated
Linux virtual machine with four CPUs and 32GB of RAM. The following table shows the scan times you
can expect for several common open-source projects.
Project Name/Language Scan Time (Min:Sec) Total Issues(2016R4) LOC
Apache-HTTPd (C/C++) 13:10 2,205 32,562
Azureus 2 (Java) 38:46 10,722 96,644
WebGoat 5.0 (Java) 03:28 1,556 9,580
WordPress (Java) 04:06 774 10,438
CakePHP (PHP) 04:57 1,861 51,479
phpBB 3 (PHP) 05:12 1,416 40,454
Related Documents
This topic describes documents that provide information about HPE Security Fortify Static Code
Analyzer.
Note: The Protect724 site location is https://www.protect724.hpe.com/community/fortify/fortify-
product-documentation.
All Products
The following documents provide general information for all products.
Document / File Name Description Location
HPE Security Fortify Software
System Requirements
HPE_Sys_Reqs_<version>.pdf
This document provides the
details about the environments
and products supported for this
version of HPE Security Fortify
Software.
Included with product
download and on the
Protect724 site
HPE Security Fortify Software
Release Notes
HPE_FortifySW_RN_
This document provides an
overview of the changes made
to HPE Security Fortify
Included on the Protect724 site
Performance Guide
Chapter 1: Introduction
HPE Security Fortify Static Code Analyzer (17.10) Page 8 of 32
Document / File Name Description Location
<version>.txt Software for this release and
important information not
included elsewhere in the
product documentation.
What’s New in HPE Security
Fortify Software <version>
HPE_Whats_New_
<version>.pdf
This document describes the
new features in HPE Security
Fortify Software products.
Included on the Protect724 site
HPE Security Fortify Open
Source and Third-Party
License Agreements
HPE_OpenSrc_<version>.pdf
This document provides open
source and third-party software
license agreements for software
components used in HPE
Security Fortify Software.
Included with product
download and on the
Protect724 site
HPE Security Fortify Glossary
HPE_Glossary.pdf
This document provides
definitions for HPE Security
Fortify Software terms.
Included with product
download and on the
Protect724 site
HPE Security Fortify Software Security Center
The following documents provide information about HPE Security Fortify Software Security Center.
Document / File Name Description Location
HPE Security Fortify Software
Security Center User Guide
HPE_SSC_Guide_<version>.pdf
HPE_SSC_Help_<version>
This document provides Fortify
Software Security Center users
with detailed information about
how to deploy and use Fortify
Software Security Center. It
provides all of the information
you need to acquire, install,
configure, and use Fortify
Software Security Center.
It is intended for use by system
and instance administrators,
database administrators
(DBAs), enterprise security
leads, development team
managers, and developers.
Fortify Software Security
Center provides security team
leads with a high-level overview
of the history and current status
of a project.
Included with product
download and on the
Protect724 site
Performance Guide
Chapter 1: Introduction
HPE Security Fortify Static Code Analyzer (17.10) Page 9 of 32
Document / File Name Description Location
HP Fortify Software Security
Center User Guide: Legacy
User Interface
HP_Fortify_SSC_User_Guide_
Legacy.pdf
PDFonly; no help file
This document is the user guide
for HP Software Security Center
version 4.30. The legacy (4.30)
user interface is available from
the current Fortify Software
Security Center user interface.
Specific areas of functionality
are available only in the 4.30
interface.
Included with product
download and on the
Protect724 site
HPE Security Fortify Software
Security Center Process
Designer Guide: Legacy User
Interface
HPE_SSC_Proc_Design_Guide_
Legacy_<version>.pdf
HPE_SSC_Proc_Design_Help_
<version>
This document provides
information about how to start
the Process Designer, configure
its connection to your Fortify
Software Security Center
instance, and then use it to work
with Fortify Software Security
Center process templates, which
are used only in the Fortify
Software Security Center legacy
(version 4.30) user interface.
Included with product
download and on the
Protect724 site
HP Fortify Software Security
Center Installation and
Configuration Guide: Legacy
User Interface
HP_Fortify_SSC_Install_and_
Config_Guide_Legacy.pdf
PDFonly; no help file
This document provides system
and database administrators
with complete instructions on
how to configure Fortify
Software Security Center server
software using the legacy
(v4.30) user interface.
Included with product
download and on the
Protect724 site
HPE Security Fortify Software
Security Center Process
Designer Guide: Legacy User
Interface
HPE_SSC_Proc_Design_Guide_
Legacy_<version>.pdf
HPE_SSC_Proc_Design_Help_
<version>
This legacy document provides
information about how to start
the Process Designer, configure
its connection to your Fortify
Software Security Center
instance, and then use it to work
with Fortify Software Security
Center process templates.
Included with product
download and on the
Protect724 site
Performance Guide
Chapter 1: Introduction
HPE Security Fortify Static Code Analyzer (17.10) Page 10 of 32
HPE Security Fortify Static Code Analyzer
The following documents provide information about Static Code Analyzer.
Document / File Name Description Location
HPE Security Fortify Static
Code Analyzer User Guide
HPE_SCA_Guide_
<version>.pdf
HPE_SCA_Help_<version>
This document describes how
to use Fortify Static Code
Analyzer to scan code on many
of the major programming
platforms. It is intended for
people responsible for security
audits and secure coding.
Included with product
download and on the
Protect724 site
HPE Security Fortify Static
Code Analyzer Installation
Guide
HPE_SCA_Install_
<version>.pdf
HPE_SCA_Install_Help_
<version>
This document contains
installation instructions for
Fortify Static Code Analyzer
and Applications.
Included with product
download and on the
Protect724 site
HPE Security Fortify Static
Code Analyzer Performance
Guide
HPE_SCA_Perf_Guide_
<version>.pdf
PDF only; no help file
This document provides
guidelines for selecting
hardware to scan different
types of codebases and offers
tips for optimizing memory
usage and performance.
Included with product
download and on the
Protect724 site
HPE Security Fortify Static
Code Analyzer Custom Rules
Guide
HPE_SCA_Cust_Rules_Guide_
<version>.zip
PDF only; no help file
This document provides the
information that you need to
create custom rules for Fortify
Static Code Analyzer. This
guide includes examples that
apply rule-writing concepts to
real-world security issues.
Included with product
download
Performance Guide
Chapter 1: Introduction
HPE Security Fortify Static Code Analyzer (17.10) Page 11 of 32
Chapter 2: Performance Improvement Tips
This section contains different methods of tuning the HPESecurityFortify Static Code Analyzer to
maximize its functionality.
This section contains the following topics:
Hardware Considerations 12
Tuning Options 12
Mobile Build Sessions 13
Memory Tuning 14
Parallel Processing 17
Hardware Considerations
The system requirements are documented in the HPESecurityFortify Software System Requirements
document. However, for large and complex applications, Fortify Static Code Analyzer requires more
capable hardware. This includes:
lDisk I/O—Fortify Static Code Analyzer is I/O intensive so the faster the hard drive, the more savings
on the I/O transaction. HPE recommends a 7,200 RPM drive, although a 10,000 RPM drive (such as
the WD Raptor) or an SSD drive is better.
lMemory—See "Memory Tuning" on page14 for more information about how to determine the
amount of memory required for optimal performance.
lCPU—HPE recommends a 2.1 GHz processor or faster.
Tuning Options
Fortify Static Code Analyzer can take a long time to process complex projects. The time is spent in
different phases:
lTranslation
lAnalysis
The Fortify Static Code Analyzer analysis results can be large and therefore cause a long time to audit
and upload to HPESecurityFortify Software Security Center (Fortify Software Security Center). This is
referred to as the following phase:
lAudit/upload
HPE Security Fortify Static Code Analyzer (17.10) Page 12 of 32
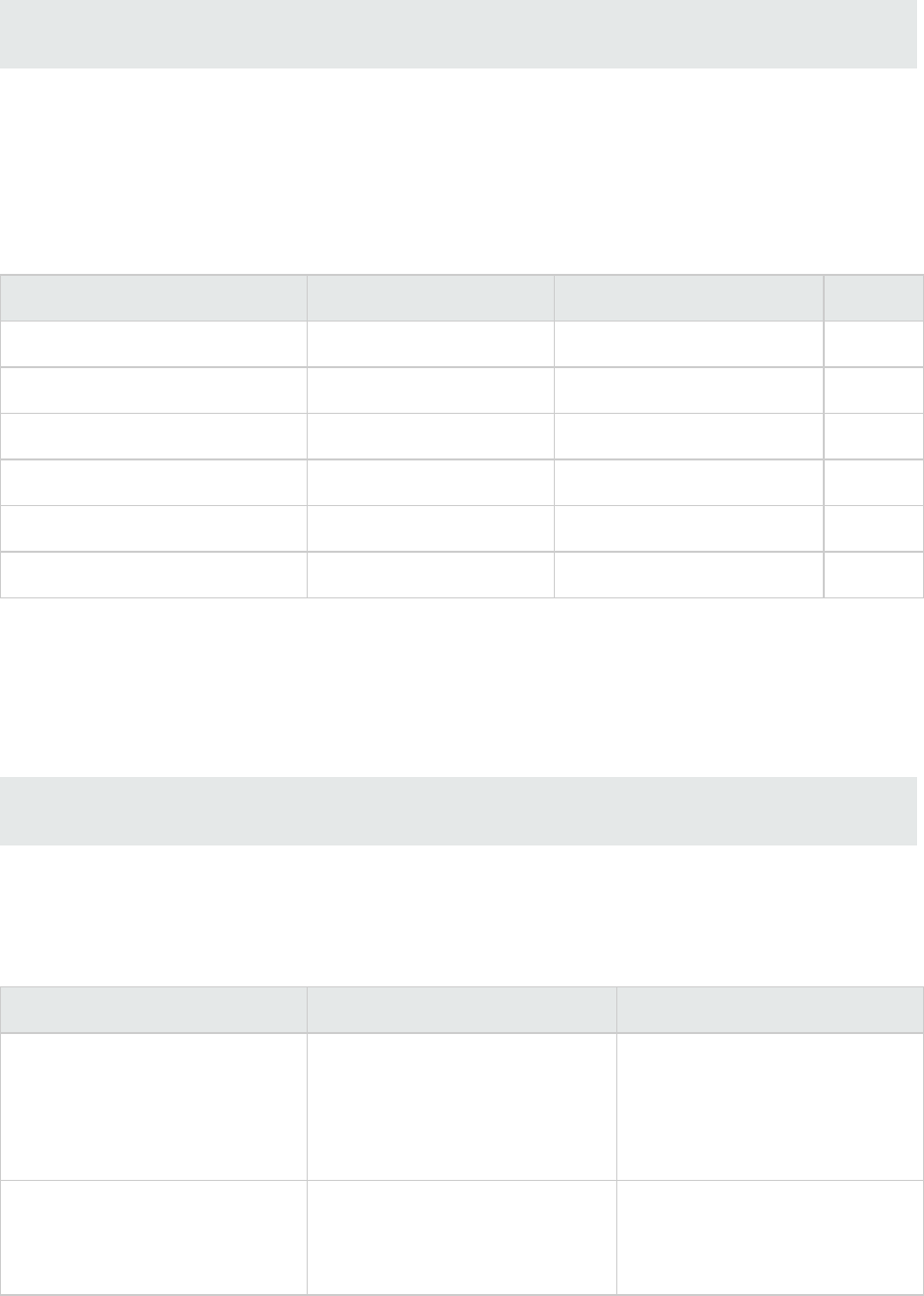
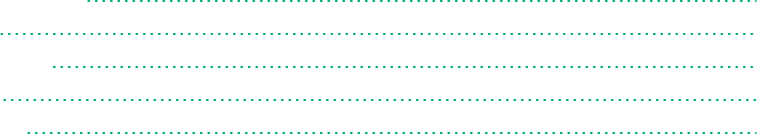
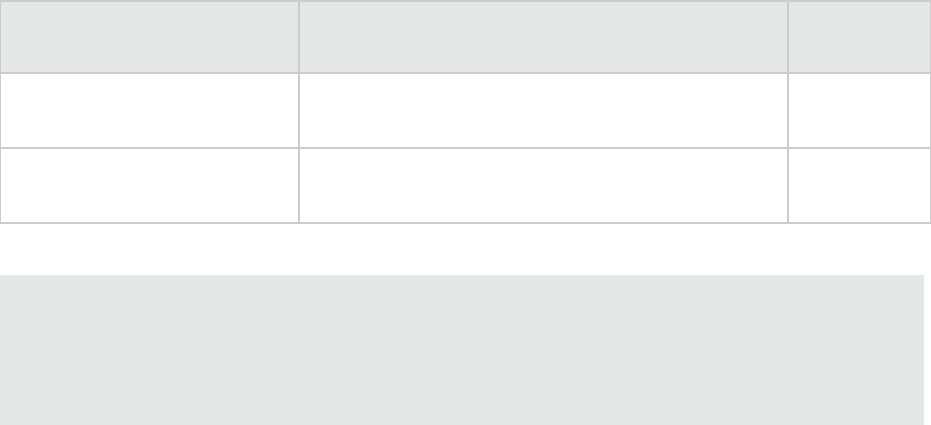
The following table provides tips on how to improve performance in the different time-consuming
phases.
Phase
Options / Property
Name Description More Information
Translation -export-build-
session
-import-build-
session
Translate (and scan)on
different machines
"Mobile Build Sessions" below
Analysis -Xmx<size>M
-Xmx<size>G
Allocate additional RAM "Memory Tuning" on the next
page
Analysis -Xss<size>M
-Xss<size>G
Stack size allocation "Memory Tuning" on the next
page
Analysis -mt Enable parallel analysis mode
to reduce scan time
"Parallel Processing" on
page17
Analysis com.fortify.sca.
ThreadCount
Number of threads used in
multithreaded operations
HPESecurity Fortify Static
Code Analyzer User Guide
Analysis -bin Scan the files related to the
given binary (for C/C++)
"Breaking Down Codebases"
on page18
Analysis -quick Quick scan "Quick Scan" on page19
Analysis
Audit/upload
-filter
<filename>
Apply a filter using a filter
file
"Filters" on page22
Analysis
Audit/upload
-disable-source-
bundling
Exclude source files in the
FPR file
"Excluding Source Code from
the FPR" on page23
Mobile Build Sessions
With a Fortify Static Code Analyzer mobile build session (MBS), you can translate a project on one
machine and analyze it on a different machine with better hardware. With an MBS, you can perform the
translation on the original computer and then move the build session to a better equipped computer to
perform the scan. The developers can run translations on their own computers and use only one
powerful computer to run large scans.
Performance Guide
Chapter 2: Performance Improvement Tips
HPE Security Fortify Static Code Analyzer (17.10) Page 13 of 32
HPE strongly recommends that you move MBS files with the Fortify Static Code Analyzer export and
import options.
sourceanalyzer -b <build_id> -export-build-session my-session.mbs
sourceanalyzer -import-build-session my-session.mbs
Below is an example of the steps required to use an MBS. This example runs the translation on
MachineT and the scan on MachineS.
1. Machine T: Translate the source files.
sourceanalyzer -b <build_id> <SourceFiles>
2. Machine T: Package and save an MBSto a file called build-session.mbs.
sourceanalyzer -b <build_id> -export-build-session build-session.mbs
3. Transfer build-session.mbs from Machine T to Machine S.
4. Machine S: Import the MBS into the Fortify Static Code Analyzer project root directory on the scan
machine.
sourceanalyzer -import-build-session build-session.mbs
5. Machine S: Perform a scan with the same build ID that was used in the translation.
sourceanalyzer -b <build_id> -scan -f myResults.fpr
You cannot merge multiple mobile build sessions into a single build session. Each exported build session
must use a unique build ID and you must import it under that unique build ID. However, after all of the
build IDs are on the same sourceanalyzer installation, you can scan multiple build IDs in one scan with
the -b option.
For example, assuming all the build IDs were imported to the local machine using mobile build sessions,
you can use the following command to scan:
sourceanalyzer -b BuildID_1 -b BuildID_2 -b BuildID_3 -scan -f myResults.fpr
Note: The resulting FPR (myResults.fpr) covers the same files as if they were all translated into
one build ID. However, there are rare instances where dataflow between the files is lost if they are
not translated together.
Memory Tuning
As discussed in "Hardware Recommendations" on page7, the amount of physical RAM required for a
scan depends on the complexity of the code itself. By default Fortify Static Code Analyzer automatically
allocates the memory it uses based on the physical memory available on the system. This is generally
sufficient.
Performance Guide
Chapter 2: Performance Improvement Tips
HPE Security Fortify Static Code Analyzer (17.10) Page 14 of 32
As described in the HPESecurity Fortify Static Code Analyzer User Guide, you can adjust the Java heap
size with the -Xmx command-line option. Heap sizes between 32GB and 48GB are not advised due to
internal JVM implementations. Heap sizes in this range perform worse than at 32 GB. Heap sizes smaller
than 32GB are optimized by the JVM. If your scan requires more than 32GB, then you probably need
much more than 48GB such as 64GB or higher. As a guideline, assuming no other memory intensive
processes are running, do not allocate more than 2/3 of the available memory.
This section describes suggestions for what you can do if you encounter OutOfMemory errors during
the analysis.
Note: You can set the memory allocation options discussed in this section to run for all scans by
setting the SCA_VM_OPTS environment variable.
Java Heap Exhaustion
Java heap exhaustion is the most common memory problem during Fortify Static Code Analyzer scans
and is the result of allocating too little heap space to the Java virtual machine that Fortify Static Code
Analyzer uses for scanning the project. IdentifyJava heap exhaustion from the following symptom.
Symptom
One or more of these messages appears in the Fortify Static Code Analyzer log file and in the
command-line output:
There is not enough memory available to complete analysis. For details on
making more memory available, please consult the user manual.
java.lang.OutOfMemoryError: Java heap space
java.lang.OutOfMemoryError: GC overhead limit exceeded
Resolution
To resolve a Java heap exhaustion problem, allocate more heap space to the Fortify Static Code
Analyzer Java virtual machine when you start the scan. To increase the heap size, use the -Xmx
command-line option when you run the Fortify Static Code Analyzer scan. For example, -Xmx1G makes
1 GB available. Before you use this parameter, determine the maximum allowable value for Java heap
space. The maximum value depends on the available physical memory.
HPE recommends that the value of -Xmx not exceed either 90% of the total physical memory or the total
physical memory minus 1.5GB to allow for the operating system. If the system is dedicated to running
Fortify Static Code Analyzer, you do not need to change it. However, if the system resources are shared
with other memory-intensive processes, subtract an allowance for those other processes.
Note: You do not need to account for other resident but not active processes (while Fortify Static
Code Analyzer is running)that the operating system might swap to disk. Allocating more physical
memory to Fortify Static Code Analyzer than is available in the environment might cause
“thrashing” which typically slows down the scan along with everything else on the system.
Performance Guide
Chapter 2: Performance Improvement Tips
HPE Security Fortify Static Code Analyzer (17.10) Page 15 of 32
Native Heap Exhaustion
Native heap exhaustion is a rare scenario in which the Java virtual machine is able to allocate the Java
memory regions on startup, but is left with so few resources for its native operations (such as garbage
collection) that it eventually encounters a fatal memory allocation failure that immediately terminates
the process.
Symptom
You can identify native heap exhaustion by abnormal termination of the Fortify Static Code Analyzer
process and the following output on the command line:
# A fatal error has been detected by the Java Runtime Environment:
#
# java.lang.OutOfMemoryError: requested ... bytes for GrET ...
Because this is a fatal Java virtual machine error, it is usually accompanied by an error log created in the
working directory with the file namehs_err_pidNNN.log.
Resolution
Because the problem is a result of overcrowding within the process, the resolution is to reduce the
amount of memory used for the Java memory regions (Java heap). Reducing this value should reduce
the crowding problem and allow the scan to complete successfully.
Stack Overflow
Each thread in a Java application has its own stack. The stack holds return addresses, function/method
call arguments, and so on. If a thread tends to process large structures with recursive algorithms, it
might need a large stack for all those return addresses. With the JVM, you can set that size with the
-Xss option.
Symptoms
This message typically appears in the Fortify Static Code Analyzer log file, but might also appear in the
command-line output:
java.lang.StackOverflowError
Resolution
The default stack size is 16 MB. To increase the stack size, pass the -Xss option to the
sourceanalyzer command. For example, -Xss32M increases the stack to 32 MB.
Performance Guide
Chapter 2: Performance Improvement Tips
HPE Security Fortify Static Code Analyzer (17.10) Page 16 of 32
Parallel Processing
Fortify Static Code Analyzer uses parallel processing in the scan phase to reduce scan times by
harnessing all CPU cores available on your system. By default, parallel processing occurs during:
lPre-analysis—Construction of the analysis model used by the security analyzers
lGlobal dataflow analysis—Interprocedural taint propagation to identify dataflow issues
lPost-analysis—Issue filtering and rendering to the FPR file
You can optionally enable parallel processing (parallel analysis mode) for all security analyzers for faster
performance of what is commonly the most time-consuming portion of the analysis phase.
For more information on how to use parallel analysis mode, see the HPESecurity Fortify Static Code
Analyzer User Guide.
Performance Guide
Chapter 2: Performance Improvement Tips
HPE Security Fortify Static Code Analyzer (17.10) Page 17 of 32
Chapter 3: Scan Quality and Performance
This section contains the following topics:
Breaking Down Codebases 18
Limiters 18
Limiting Analyzers and Languages 19
Scanning Complex Functions 21
Breaking Down Codebases
It is more efficient to break down large projects into independent modules. For example, if you have a
portal application that consists of several modules that are independent of each other or have very little
interactions, you can translate and scan the modules separately. The caveat to this is that you might lose
dataflow if some interactions exist.
For C/C++, you might reduce the scan time by using the –bin option with the –scan option. You need
to pass the binary file as the parameter (such as -bin <filename>.exe -scan or -bin
<filename>.dll -scan), and Fortify Static Code Analyzer finds the related files associated with the
binary and scans them. This is useful if you have several binaries in a makefile.
The following table lists useful Fortify Static Code Analyzer command-line options for breaking down
codebases.
Option Description
-bin Specifies a subset of source files to scan. Only the source files that were
linked in the named binary at build time are included in the scan. You can
used this option multiple times to specify the inclusion of multiple binaries in
the scan.
-show-binaries Displays all objects that were created but not used in the production of any
other binaries. If fully integrated into the build, it lists all of the binaries
produced.
-show-build-tree When used with the -bin option, displays all files used to create the binary
and all files used to create those files in a tree layout. If the -bin option is not
present, the tree is displayed for each binary.
Limiters
The depth of the Fortify Static Code Analyzer analysis sometimes depends on the available resources.
Fortify Static Code Analyzer uses a complexity metric to trade off these resources with the number of
HPE Security Fortify Static Code Analyzer (17.10) Page 18 of 32
vulnerabilities that it can find. Sometimes, this means giving up on a particular function when it does not
look like Fortify Static Code Analyzer has enough resources available.
Fortify Static Code Analyzer enables the user to control the “cutoff” point by using Fortify Static Code
Analyzer limiter properties. The different analyzers have different limiters. You can run a predefined set
of these limiters using a Quick Scan. See the quick scan properties in the HPESecurity Fortify Static
Code Analyzer User Guide for description of the full set of limiters.
Quick Scan
Quick Scan Mode provides a way to quickly scan your projects for major defects. Although the Quick
Scan is significantly faster, it does not provide a robust result set. To enable quick scan, use -quick
option with -scan option.
With Quick Scan Mode enabled, Fortify Static Code Analyzer applies the properties from the <sca_
install_dir>/Core/config/fortify-sca-quickscan.properties file, in addition to the
standard <sca_install_dir>/Core/config/fortify-sca.properties file. By default, this scan
searches for high‐confidence, high‐severity issues. You can alter the limiters Fortify Static Code
Analyzer uses by editing the fortify-sca-quickscan.properties file. If you modify fortify-
sca.properties, it also affects quick scan behavior. HPE recommends that you do performance
tuning in quick scan mode, and leave the full scan in the default settings to produce a highly accurate
scan.
Using Quick Scan and Full Scan
lRun periodic full scans—A periodic full scan is important as it might find issues that Quick Scan
does not detect. Run a full scan at least once per software iteration. If possible, run a full scan
periodically when it will not interrupt workflow, such as on a weekend.
lCompare Quick Scan With a Full Scan—To evaluate the accuracy impact of a Quick Scan, perform
a Quick Scan and a full scan on the same code base, then load the Quick Scan results in Audit
Workbench and merge it into the full scan. Group the issues by New Issue to produce a list of issues
found in the full scan but not found in the Quick Scan.
lQuick Scans and Fortify Software Security Center Server—To avoid overwriting the results of a
full scan, by default Fortify Software Security Center does not accept FPR files scanned using Quick
Scan. However, you can configure Fortify Software Security Center so that FPRfiles scanned with
Quick Scan are not blocked for an application version. For more information, see the
HPESecurityFortify Software Security Center User Guide.
Limiting Analyzers and Languages
Occasionally, you might find that a significant amount of the scan time is spent either running one
particular analyzer or analyzing a particular language. It is also possible that this particular analyzer or
language is not of great interest to your security requirements. You can limit the specific analyzers that
run and the specific languages that are translated.
Performance Guide
Chapter 3: Scan Quality and Performance
HPE Security Fortify Static Code Analyzer (17.10) Page 19 of 32
Disabling Analyzers
To disable specific analyzers, include the -analyzers option to Fortify Static Code Analyzer at scan
time with a colon- or comma-separated list of analyzers you want to enable. The full list of analyzers is:
buffer, content, configuration, controlflow, dataflow, findbugs, nullptr, semantic, and
structural.
For example, to run a scan using only the Dataflow, Control Flow, and Buffer analyzers, use the
following scan command:
sourceanalyzer -b <build_id> -analyzers dataflow:controlflow:buffer -scan
-f myResults.fpr
You can also do the same thing by setting com.fortify.sca.DefaultAnalyzers in the Fortify
Static Code Analyzer property file <sca_install_dir>/Core/config/fortify-
sca.properties. For example, to achieve the equivalent of the previous scan command, set the
following in the properties file:
com.fortify.sca.DefaultAnalyzers=dataflow:controlflow:buffer
Disabling Languages
To disable specific languages, include the -disable-language option in the translation phase. This is
followed by a colon-separated list of languages that you want to disable. The full list of language
options is:
abap, actionscript, any_sql, asp, c, cfml, cpp, csharp, cobol, html, java,
javascript, jsp, objc, objcpp, php, plsql, python, ruby, swift, tsql, vb,
vb6, vbscript
For example, to run a scan that excludes all SQL and HTML files, use the following command to perform
the translation:
sourceanalyzer -b <BuildID> <TranslationFiles>
-disable-languages any_sql:html
You can also disable languages by setting the com.fortify.sca.DISabledLanguages property in
the Fortify Static Code Analyzer properties file <sca_install_
dir>/Core/config/fortify-sca.properties. For example, to achieve the equivalent of the
previous translation command, set the following in the properties file:
com.fortify.sca.DISabledLanguages=any_sql:html
Performance Guide
Chapter 3: Scan Quality and Performance
HPE Security Fortify Static Code Analyzer (17.10) Page 20 of 32
Scanning Complex Functions
During a scan Fortify Static Code Analyzer, the Dataflow Analyzer might encounter a function for
which it cannot complete the analysis and reports the following message:
Function <name> is too complex for <analyzer> analysis and will be skipped
(<identifier>)
To see a discussion of a resolution for this issue, see "Function too Complex to Analyze Message" on
page29.
Performance Guide
Chapter 3: Scan Quality and Performance
HPE Security Fortify Static Code Analyzer (17.10) Page 21 of 32
Chapter 4: Optimizing FPRFiles
This chapter describes how to handle performance issues related to the audit results (FPR) file. This
includes reducing the scan time, reducing FPRfile size, and tips for opening large FPR files.
This section contains the following topics:
Filters 22
Excluding Source Code from the FPR 23
Reducing the FPRFile Size 24
Opening Large FPRFiles 25
Filters
Filters are usually part of the issue template and determine how the results from Fortify Static Code
Analyzer are shown. For example, you can have a filter to put SQL Injection issues found into a separate
folder called “SQL Injections”, or you might have a filter so that issues with a confidence below a certain
threshold are hidden. Along with filters, filter sets enable you to have a selection of filters used at any
one time. This enables you to more easily customize your view and allows you to define a different view
for developers, auditors, and managers so that they can more easily see the most important or relevant
information for them.
Each FPR has an issue template associated with it, and in Fortify Software Security Center these are
specified on an application version basis. For further information about issue templates and customizing
them, see the HPESecurityFortify Audit Workbench User Guide.
Filter Files
Filter files are flat files that you can specify along with a scan using -filter option. Use a filter file to
blacklist specified categories, instance IDs, and rule IDs. If you determine that a certain category of
issues or rules are not relevant for a particular scan, you can stop Fortify Static Code Analyzer from
flagging these types of issues and adding them to FPR. You can use a filter file to reduce both the scan
time and the size of the results file.
For example, if you are scanning a simple program that just reads a specified file, you might not want to
see path manipulation issues, since these are likely planned as part of the functionality. To do filter out
path manipulation issues, a file that contains a single line:
Path Manipulation
Save this file as filter.txt. Use the -filter option for the scan as shown in the following example:
sourceanalyzer -b <build_id> -scan -f myResults.fpr -filter filter.txt
The myResults.fpr does not include any issues with the category Path Manipulation.
For more information about filter files, see the HPESecurity Fortify Static Code Analyzer User Guide.
HPE Security Fortify Static Code Analyzer (17.10) Page 22 of 32
Scan-Time Filters
An alternate way to filter at scan-time is to use filter sets to reduce the number of issues based on
conditions you specify with filters in an issue template. A scan-time filter can dramatically reduce the size
of an FPR.
To do this, use Audit Workbench to create a filter and a filter set and then run the Fortify Software
Security Center scan with the filter set. For more detailed instructions about how to create filters and
filter sets in Audit Workbench, see HPESecurityFortify Audit Workbench User Guide. The following
example describes the basic steps for how to create and use a scan-time filter:
1. In this example, suppose you use the OWASP Top 10 2013 and you only want to see issues
categorized within this standard. Create a filter in Audit Workbench such as:
If [OWASP Top 10 2013] does not contain A Then hide issue
This filter looks through the issues and if an issue does not map to an OWASP Top 10 2013
category with ‘A’ in the name, then it hides it. Because all OWASP Top 10 2013 categories start
with ‘A’ (A1, A2, …, A10), then any category without the letter ‘A’ is not in the OWASP Top 10
2013. The filter hides the issues from view in Audit Workbench, but they are still in the FPR.
2. In Audit Workbench, create a new filter set called OWASP_Filter_Set that contains the previous
filter, and then export the issue template to a file called IssueTemplate.xml.
3. You can then specify this filter at scan-time with the following command:
sourceanalyzer -b <build_id> -scan -f myScanTimeFilterResults.fpr
-project-template IssueTemplate.xml -Dcom.fortify.sca.FilterSet=OWASP_
Filter_set
In the previous example, the inclusion of the -Dcom.fortify.sca.FilterSet property tells Fortify
Static Code Analyzer to use the OWASP_Filter_Set filter set from the issue template
IssueTemplate.xml. Any filters that hide issues from view are removed and are not written to the
FPR. Therefore, you can reduce the visible number of issues, make the scan very targeted, and reduce
the size of the resulting FPR file.
Note: Although scan-time filters can reduce the size of the FPR, they do not usually reduce the
scan time. Fortify Static Code Analyzer examinesscan-time filters after it calculates the issues to
determine whether or not to write them to the FPR file. The filters in a filter file determine the rule
types that Fortify Static Code Analyzer loads.
Excluding Source Code from the FPR
You can reduce the scan time and the size of the FPRfile by excluding the source code information
from the FPR, especially with large source files or codebases. You generally do not get a scan time
reduction for small source files.
Performance Guide
Chapter 4: Optimizing FPRFiles
HPE Security Fortify Static Code Analyzer (17.10) Page 23 of 32
There are two ways to prevent Fortify Static Code Analyzer from including source code in the FPR. You
can set the property in the <sca_install_dir>/Core/config/fortify-sca.properties file or
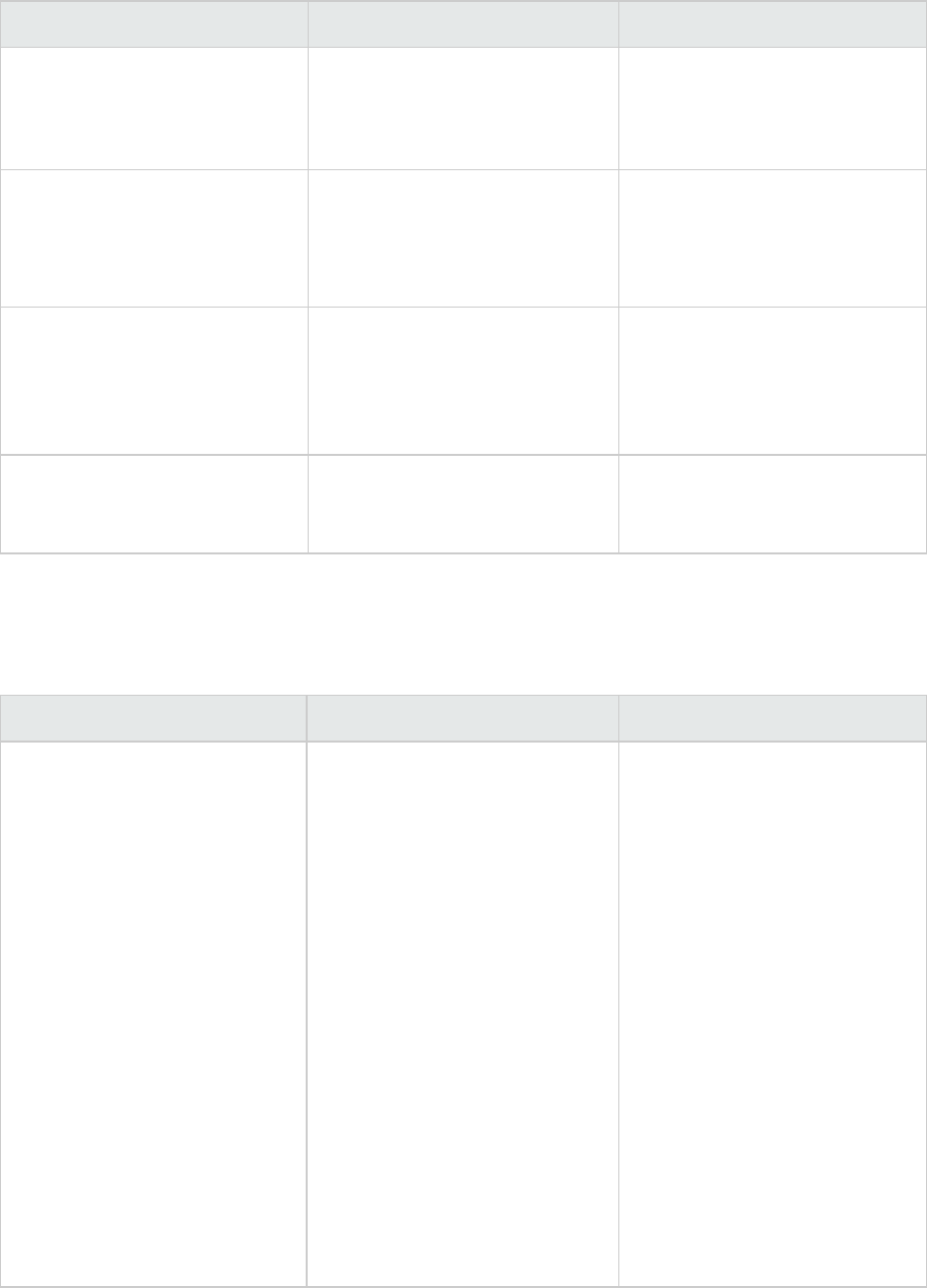
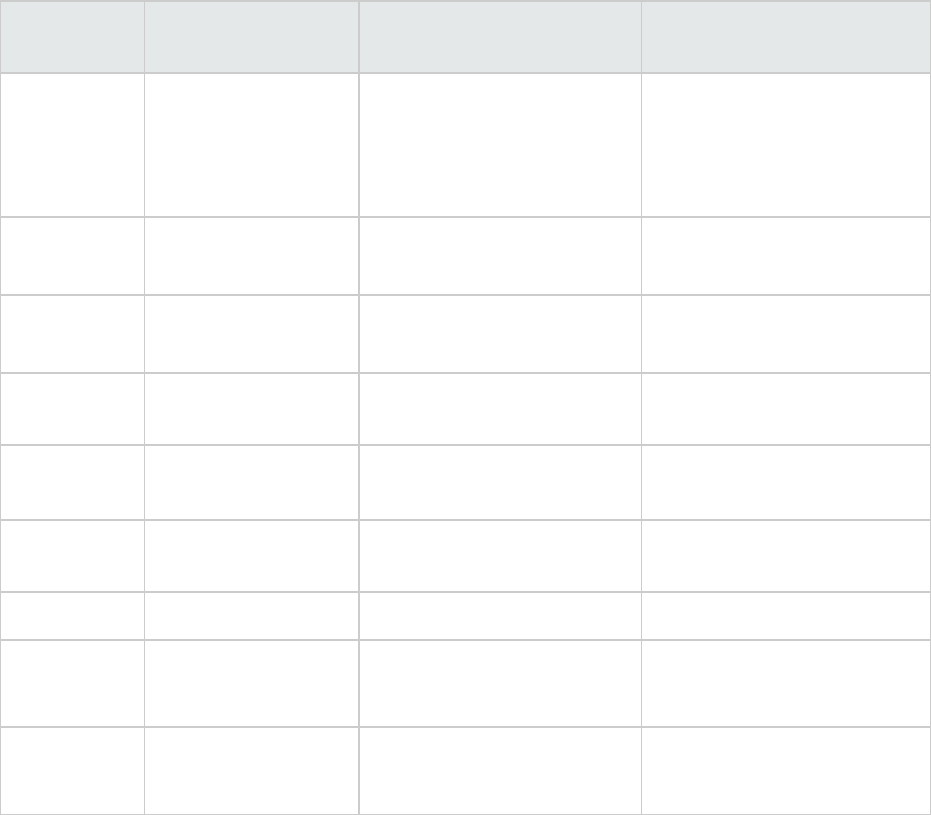
specify an option on the command line. The following table describes these settings.
Property Name Description
com.fortify.sca.
FPRDisableSourceBundling=true
Command-line Option:
-disable-source-bundling
Disable source code inclusion in the FPR
com.fortify.sca.
FVDLDisableSnippets=true
Command-line Option:
–fvdl-no-snippets
Exclude code snippets from the FPR
The following command-line example uses both options:
sourceanalyzer -b <build_id> -disable-source-bundling
-fvdl-no-snippets -scan -f mySourcelessResults.fpr
Reducing the FPRFile Size
There are a few ways to reduce the size of FPR files. The quickest way to do this without affecting
results is to exclude the source code from the FPR as described in "Excluding Source Code from the
FPR" on the previous page.
There are a few other options and properties that you can use to select what is excluded from the FPR.
You can set these properties in the Fortify Static Code Analyzer properties file: <sca_install_
dir>/Core/config/fortify-sca.properties or specify them during the scan phase with
-D<Propertyname>=true. Most of these options have an equivalent command-line option.
Property Name Description
com.fortify.sca.
FPRDisableMetatable
=true
Command-line Option:
-disable-metatable
This disables the metatable inside the FPR. Audit
Workbench uses the metatable to map information in
Functions view.
com.fortify.sca.
FVDLDisableDescriptions
=true
Command-line Option:
-fvdl-no-description
This excludes descriptions from theFPR. If you do
not use custom descriptions, descriptions listed in the
HPE Security Fortify Taxonomy
(https://vulncat.hpefod.com) are used.
Performance Guide
Chapter 4: Optimizing FPRFiles
HPE Security Fortify Static Code Analyzer (17.10) Page 24 of 32
Property Name Description
com.fortify.sca.
FVDLDisableEngineData
=true
Command-line Option:
-fvdl-no-enginedata
This excludes engine data from the FPR. This is
useful if your FPR contains a large number of
warnings when you open the file in Audit Workbench.
The caveat of this option is that you need to merge
the FPR with the current audit project locally before
you upload it to Fortify Software Security Center.
Because the FPR does not contain the Fortify Static
Code Analyzer version, Fortify Software Security
Center is unable to merge it on the server.
com.fortify.sca.
FVDLDisableProgramData
=true
Command-line Option:
-fvdl-no-progdata
This excludes the program data section from the
FPR. This removes the Taint Sources information
from the Functions view in Audit Workbench. This
property typically only has a minimal effect on the
overall size of the FPR file.
Opening Large FPRFiles
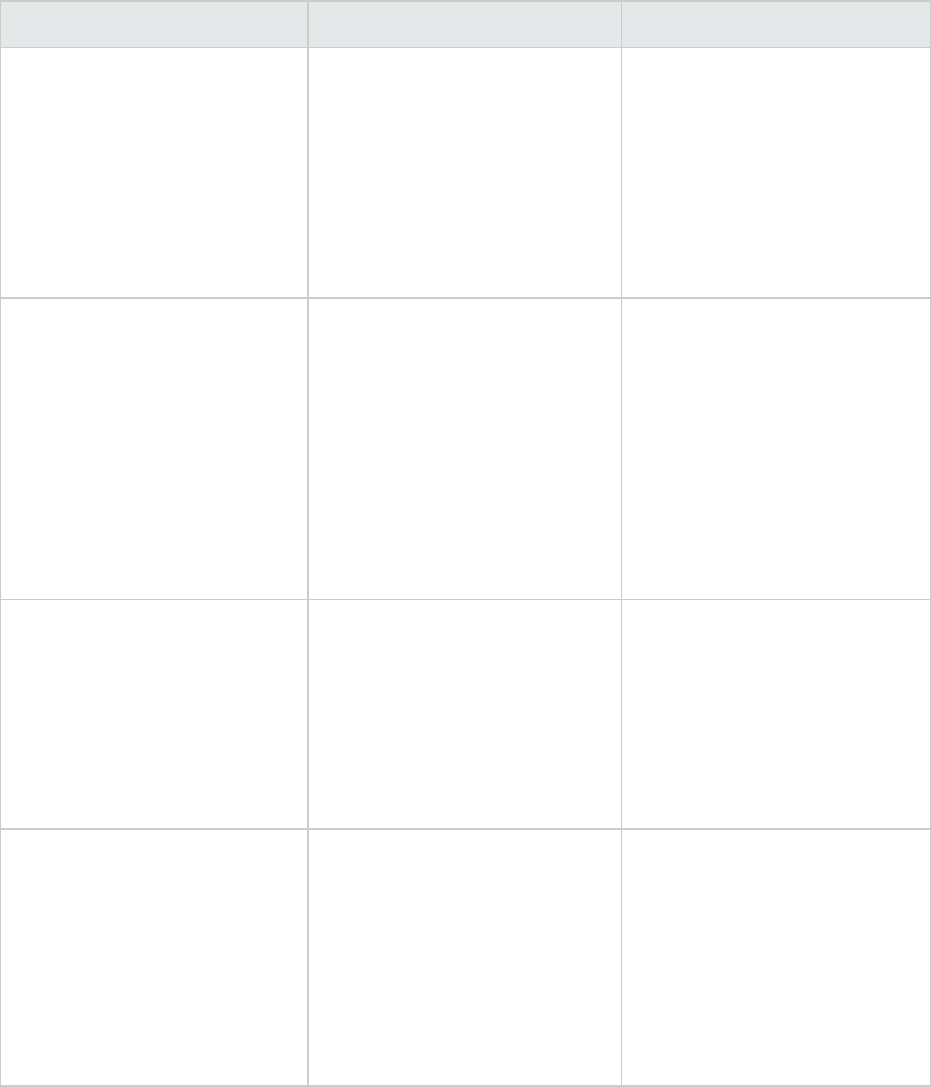
To reduce the time required to open a large FPR file, there are some properties that you can set in the
<sca_install_dir>/Core/config/fortify.properties configuration file. For more
information about these properties, see the HPESecurity Fortify Static Code Analyzer Tools Property
Reference Guide. The following table describes these properties.
Property Name Description
com.fortify.
model.DisableProgramInfo=true
This disables use of the code navigation
features in Audit Workbench.
com.fortify.
model.IssueCutOffStartIndex
=<num> (inclusive)
com.fortify.
model.IssueCutOffEndIndex
=<num> (exclusive)
The IssueCutOffStartIndex property is
inclusive and IssueCutOffEndIndex is
exclusive so that you can specify a subset of
issues you want to see. For example, to see the
first 100 issues, you can specify the following:
com.fortify.model.
IssueCutOffStartIndex=0
com.fortify.model.
IssueCutOffEndIndex=101
Because the IssueCutOffStartIndex is 0 by
default, you do not need to specify this
property.
Performance Guide
Chapter 4: Optimizing FPRFiles
HPE Security Fortify Static Code Analyzer (17.10) Page 25 of 32
Property Name Description
com.fortify.
model.IssueCutOffByCategoryStartIndex=
<num> (inclusive)
com.fortify.
model.IssueCutOffByCategoryEndIndex=
<num> (exclusive)
These are similar to the previous cutoff
properties except these are specified for each
category. For example. if you want to see the
first five issues for every category you would
specify the following:
com.fortify.model.
IssueCutOffByCategoryEndIndex=6
com.fortify.
RestrictIssueLoading=true
This restricts the data that is held in memory,
but it might cause poor performance.
com.fortify.
model.MinimalLoad=true
This minimizes the data loaded in the FPR. This
also restricts usage of the Functions view and
might prevent Audit Workbench from loading
the source from the FPR.
com.fortify.
model.MaxEngineErrorCount=
<num>
This property limits the number of Fortify Static
Code Analyzer reported errors that are loaded
with the FPR. For projects with a large number
of scan warnings, this can reduce both load
time in Audit Workbench and the amount of
memory required to open the FPR.
Performance Guide
Chapter 4: Optimizing FPRFiles
HPE Security Fortify Static Code Analyzer (17.10) Page 26 of 32
Chapter 5: Monitoring Long Running Scans
When you run Fortify Static Code Analyzer, large and complex scans can often take a long time to
complete. During the scan it is not always clear what is happening. While HPE recommends that you
provide your debug logs to the HPESecurityFortify Technical Support team, there are a couple of ways
to see what Fortify Static Code Analyzer is doing and how it is performing in real-time.
This section contains the following topics:
Using the SCAState Utility 27
Using JMX Tools 27
Using the SCAState Utility
The SCAState command-line utility enables you to see up-to-date state analysis information during the
analysis phase. The SCAState utility is located in the <sca_install_dir>/bin directory. In addition
to a live view of the analysis, it also provides a set of timers and counters that show where Fortify Static
Code Analyzer spends its time during the scan. For more information about how to use the SCAState
utility, see the HPESecurity Fortify Static Code Analyzer User Guide.
Using JMX Tools
You can use a variety of tools to monitor Fortify Static Code Analyzer with JMX. These tools have
advantages and disadvantages, however the GUI-based tools can provide a way to track Fortify Static
Code Analyzer performance over time.
Note: These are third-party tools and HPESecurity does not provide or support them .
JConsole
JConsole is an interactive monitoring tool that complies with the JMX specification. The disadvantage of
JConsole is that you cannot save the output.
To use JConsole, you must first set some additional JVM parameters. Set the following environment
variable:
export SCA_VM_OPTS="-Dcom.sun.management.jmxremote
-Dcom.sun.management.jmxremote.port=9090
-Dcom.sun.management.jmxremote.ssl=false
-Dcom.sun.management.jmxremote.authenticate=false"
For more information about these parameters, see the full Oracle documentation available at:
http://docs.oracle.com/javase/8/docs/technotes/guides/management/jconsole.html.
HPE Security Fortify Static Code Analyzer (17.10) Page 27 of 32
After the JMX parameters are set, start a Fortify Static Code Analyzer scan. During the scan, start
JConsole to monitor Fortify Static Code Analyzer locally or remotely with the following command:
jconsole <host_name>:9090
Java VisualVM
Java VisualVM offers the same capabilities as JConsole. It also provides more detailed information on
the JVM and enables you to save the monitor information to an application snapshot file. You can store
these files and open them later with Java VisualVM.
As with JConsole, before you can use Java VisualVM, you must set the same JVM parameters as
described in "JConsole" on the previous page.
After the JVM parameters are set, start the scan. You can then start Java VisualVM to monitor the scan
either locally or remotely with the following command:
jvisualvm <host_name>:9090
For more information about Java VisualVM, see the full Oracle documentation available at:
http://docs.oracle.com/javase/8/docs/technotes/guides/visualvm/.
Performance Guide
Chapter 5: Monitoring Long Running Scans
HPE Security Fortify Static Code Analyzer (17.10) Page 28 of 32
Chapter 6: Troubleshooting
Function too Complex to Analyze Message
During a Fortify Static Code Analyzer scan, an analyzer might encounter a function for which it cannot
complete the analysis and reports the following message:
Function <name> is too complex for <analyzer> analysis and will be skipped
(<identifier>)
where:
l<name> is the name of the source code function
l<analyzer> is the name of the analyzer
l<identifier> is the type of complexity which is one of the following:
ll: Too many distinct locations
lm: Out of memory
ls: Stack size too small
lt: Analysis taking too much time
The depth of analysis Fortify Static Code Analyzer performs sometimes depends on the available
resources. Fortify Static Code Analyzer uses a complexity metric to tradeoff these resources against the
number of vulnerabilities that it can find. Sometimes, this means giving up on a particular function when
Fortify Static Code Analyzer does not have enough resources available. This is normally when you see
the "Function too complex" messages.
When you see this message, it does not necessarily mean that the function in the program was
completely ignored. For example, the Dataflow Analyzer typically visits a function many times before
completing the analysis, and might not run into this complexity limit in the previous visits. In this case,
the results include anything learned from the previous visits.
You can control the "give up" point using Fortify Static Code Analyzer properties called limiters.
Different analyzers have different limiters.
Dataflow Analyzer Limiters
There are three types of complexity identifiers for the Dataflow Analyzer:
ll: Too many distinct locations
lm: Out of memory
ls: Stack size too small
HPE Security Fortify Static Code Analyzer (17.10) Page 29 of 32
To resolve the issue identified by s, increase the stack size for by setting -Xssto a value greater than
16MB.
To resolve the complexity identifier of m, increase the physical memory for Fortify Static Code Analyzer.
To resolve the complexity identifier of l, you can adjust the following limiters in the Fortify Static Code
Analyzer property file <sca_install_dir>/Core/config/fortify-sca.properties or on the
command line.
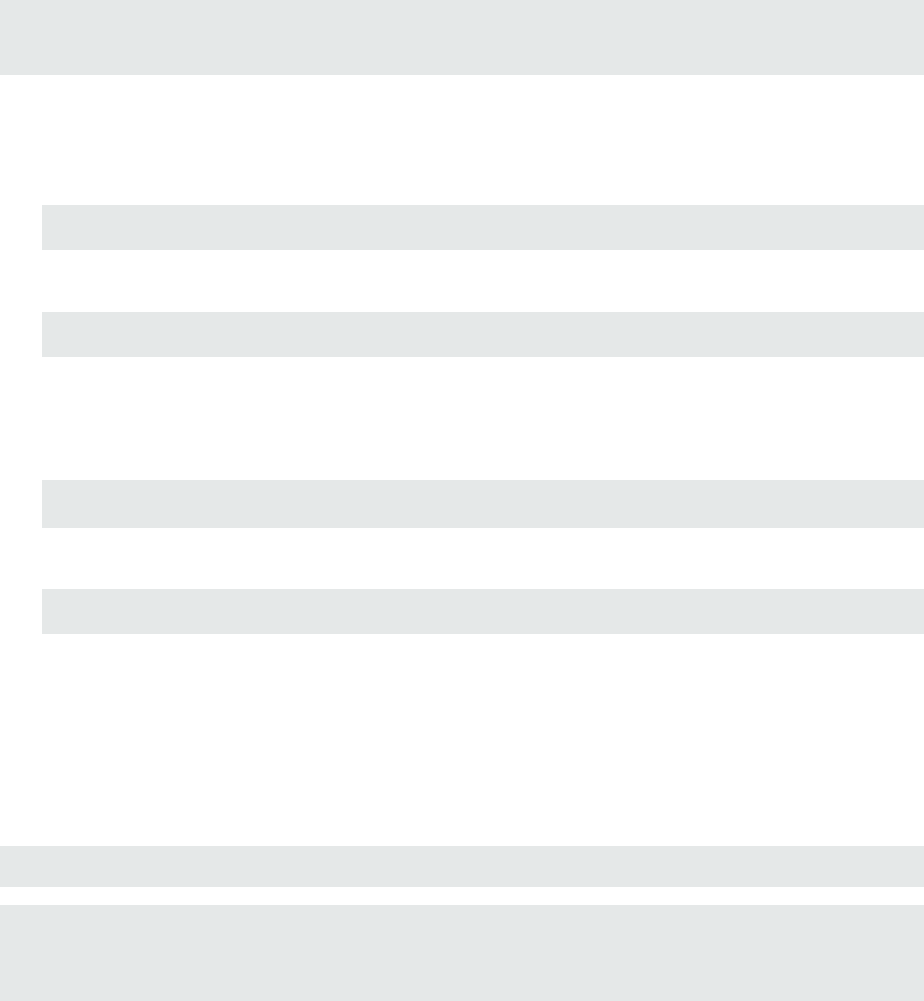
Property Name Default Value
com.fortify.sca.
limiters.MaxTaintDefForVar
1000
com.fortify.sca.
limiters.MaxTaintDefForVarAbort
4000
com.fortify.sca.
limiters.MaxFieldDepth
4
The MaxTaintDefForVar limiter is a dimensionless value expressing the complexity of a function,
while MaxTaintDefForVarAbort is the upper bound for it. Use the MaxFieldDepth limiter to
measure the precision when the Dataflow Analyzer analyzes any given object. Fortify Static Code
Analyzer always tries to analyze objects at the highest precision possible.
If a given function exceeds theMaxTaintDefForVar limit at a given level of precision, the Dataflow
Analyzer analyzes that function with a lower level of precision (by reducing theMaxFieldDepth
limiter).When you reduce the precision, it reduces the complexity of the analysis. When the precision
cannot be reduced any further, Fortify Static Code Analyzer then proceeds with analysis at the lowest
precision level until either it finishes or the complexity exceeds theMaxTaintDefForVarAbort limiter.
In other words, Fortify Static Code Analyzer tries harder at the lowest precision level than at higher
precision levels, to get at least some results from the function. If Fortify Static Code Analyzer reaches
theMaxTaintDefForVarAbort limiter, it gives up on the function entirely and you get the "Function
too complex" warning.
Control Flow and Null Pointer Analyzer Limiters
There are two types of complexity identifiers for both Control Flow and Null Pointer analyzers:
lm: Out of memory
lt: Analysis taking too much time
Due to the way that the Dataflow Analyzer handles function complexity, it does not take an indefinite
amount of time. Control Flow and Null Pointer analyzers, however, can take a very long time when
analyzing very complex functions. Therefore, Fortify Static Code Analyzer provides a way to abort the
analysis when this happens, and then you get the "Function too complex" message with a complexity
identifier of t.
Performance Guide
Chapter 6: Troubleshooting
HPE Security Fortify Static Code Analyzer (17.10) Page 30 of 32
To change the maximum amount of time these analyzers spend analyzing functions, you can adjust the
following property values in the Fortify Static Code Analyzer property file <sca_install_
dir>/Core/config/fortify-sca.properties or on the command line.
Property Name Description
Default
Value
com.fortify.sca.
CtrlflowMaxFunctionTime
Sets the time limit (in milliseconds) for Control Flow
analysis on a single function.
600000
(10minutes)
com.fortify.sca.
NullPtrMaxFunctionTime
Sets the time limit (in milliseconds) for Null Pointer
analysis on a single function.
300000
(5minutes)
To resolve the complexity identifier of m, increase the physical memory for Fortify Static Code Analyzer.
Note: If you increase these limiters or time settings, it makes the analysis of complex functions take
longer. It is hard to characterize the exact performance implications of a particular value for the
limiters/time, because it depends on the specific function in question. If you never want see the
"Function too complex" warning, you can set the limiters/time to an extremely high value , however
it can cause unacceptable scan time.
Performance Guide
Chapter 6: Troubleshooting
HPE Security Fortify Static Code Analyzer (17.10) Page 31 of 32
Send Documentation Feedback
If you have comments about this document, you can contact the documentation team by email. If an
email client is configured on this computer, click the link above and an email window opens with the
following information in the subject line:
Feedback on Performance Guide (HPE Security Fortify Static Code Analyzer 17.10)
Just add your feedback to the email and click send.
If no email client is available, copy the information above to a new message in a web mail client, and send
your feedback to HPFortifyTechPubs@hpe.com.
We appreciate your feedback!
HPE Security Fortify Static Code Analyzer (17.10) Page 32 of 32