55801a 5580 OPNAVINST 5580.1
User Manual: 5580
Open the PDF directly: View PDF ![]() .
.
Page Count: 130 [warning: Documents this large are best viewed by clicking the View PDF Link!]

OPNAVINST 5580.1A CH-2
N09N3
28 Jan 02
OPNAV INSTRUCTION 5580.1A CHANGE TRANSMITTAL 2
From: Chief of Naval Operations
To: All Ships and Stations (less Marine Corps field addressees
not having Navy personnel attached)
Subj: NAVY LAW ENFORCEMENT MANUAL
Encl: (1) Revised Table of Contents
(2) New Appendix E
1. Purpose. To issue Navy security department staffing requirements.
2. Action
a. Remove Table of Contents and replace with enclosure (1) of this change
transmittal.
b. Add enclosure (2) after Appendix D.
DAVID L. BRANT
Special Assistant for Naval
Investigative Matters and
Security
Distribution:
SNDL Parts 1 and 2
DEPARTMENT OF THE NAVY
OFFICE OF THE CHIEF OF NAVAL OPERATIONS
2000 NAVY PENTAGON
WASHINGTON, DC 20350-2000

OPNAVINST 5580.1A CH-1
N09N3
20 July 2001
OPNAV INSTRUCTION 5580.1A CHANGE TRANSMITTAL 1
From: Chief of Naval Operations
To: All Ships and Stations (less Marine Corps field addressees
not having Navy personnel attached)
Subj: NAVY LAW ENFORCEMENT MANUAL
Encl: Revised pages 3-3 and D-1
1. Purpose. To institute within the Department of Navy revisions to incident report (IR)
policy.
2. Action. Remove pages 3-3, D-1 and replace with enclosure (1) of this change transmittal.
DAVID L. BRANT
By direction
Distribution:
SNDL Parts 1 and 2
DEPARTMENT OF THE NAVY
OFFICE OF THE CHIEF OF NAVAL OPERATIONS
2000 NAVY PENTAGON
WASHINGTON, DC 20350-2000

OPNAVINST 5580.1A
N09N3
26 JULY 2000
OPNAV INSTRUCTION 5580.1A
From: Chief of Naval Operations
To: All Ships and Stations (less Marine Corps field
addressees not having Navy personnel assigned)
Subj: NAVY LAW ENFORCEMENT MANUAL
Ref: (a) SECNAVINST 5511.36A
Encl: (1) Navy Law Enforcement Manual
1. Purpose. To detail procedures, provides guidance, and sets
forth standards for military and civilian Navy personnel
performing law enforcement duties; this instruction is not
intended to create any rights, substantive or procedural; it does
not place limits on the lawful prerogatives of Navy law
enforcement personnel.
This instruction is a substantial revision and should be read
in its entirety.
2. Cancellation. OPNAVINST 5580.1.
3. Discussion
a. The commanding officer is responsible for the good order
and discipline of the command. Law enforcement personnel
assigned to the command's security department must have
standardized policies and procedures in order to enforce the law,
maintain good order and discipline, investigate offenses,
safeguard the rights of all persons, and provide service to the
community.
b. The language used is intended to separate recommended
measures from required actions. Words which are directive in
nature, e.g., will, shall, must, etc., indicate that the measure
is mandatory.
DEPARTMENT OF THE NAVY
OFFICE OF THE CHIEF OF NAVAL OPERATIONS
2000 NAVY PENTAGON
WASHINGTON, DC 20350-2000
IN REPLY REFER TO

OPNAVINST 5580.1A
26 JUL 2000
2
c. The requirements in this instruction apply to Navy law
enforcement personnel of host activities providing law
enforcement services to their activity, to include tenant
activities. Navy law enforcement personnel are composed of
officer and enlisted active duty/reserve military members and
civilian personnel, either permanently assigned or on temporary
additional duty.
d. The provisions of this instruction do not apply to the
Naval Criminal Investigative Service.
4. Responsibilities
a. The commanding officer of each ship and station shall
implement the law enforcement policies and procedures contained
in enclosure (1), as directed by reference (a), and Section 797
of Title 50 U. S. Code.
b. Echelon 2 commanders are responsible for inspecting
subordinate commands for compliance with this Manual.
5. Reports and Forms
a. The reports contained in enclosure (1) are exempt from
reports control per SECNAVINST 5214.2.B.
b. Forms to be used by Navy security detachments/
departments are listed in Appendix B. These are the only forms
authorized for use.
DAVID L. BRANT
Special Assistant for Naval
Investigative Matters and
Security
Distribution:
SNDL Parts 1 and 2
OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
Navy
Law Enforcement Manual

i
OPNAVINST 5580.1A CH-2
28 Jan 2002
TABLE OF CONTENTS
CHAPTER 1 THE SECURITY DEPARTMENT
CHAPTER 2 LEGAL ASPECTS
CHAPTER 3 INCIDENT REPORTS
CHAPTER 4 USE OF FORCE AND WEAPONS POLICIES
CHAPTER 5 INVESTIGATIONS
CHAPTER 6 EVIDENCE CUSTODY PROCEDURES
CHAPTER 7 COMMUNICATIONS
CHAPTER 8 EMERGENCY VEHICLE POLICIES
CHAPTER 9 TRAFFIC, VISITOR CONTROL, AND IMPOUNDING VEHICLES
CHAPTER 10 CRIME PREVENTION
CHAPTER 11 JUVENILES
CHAPTER 12 PUBLIC AFFAIRS
CHAPTER 13 BLOODBORNE PATHOGENS
CHAPTER 14 DOMESTIC VIOLENCE
APPENDIX A TABLE OF REFERENCES
APPENDIX B FORMS
APPENDIX C NAVY UNIFORM REPORT WRITING SYSTEM
APPENDIX D TABLE OF OFFENSES
APPENDIX E SECURITY MANNING (ASHORE)

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
CHAPTER 1
THE SECURITY DEPARTMENT
0101. Mission of the Security Department
0102. Organization of the Security Department
0103. Facilities
0104. Standard Operating Procedures
0105. Law Enforcement Functions
0106. Afloat Law Enforcement
0107. Dissemination of Information
0108. Employment Outside of Security Department
0109. Training
OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
1-1
CHAPTER 1
THE SECURITY DEPARTMENT
0101. MISSION OF THE SECURITY DEPARTMENT. The security department fulfills not
only a law enforcement requirement but is responsible for physical security and loss prevention
as well.
a. The objectives of law enforcement are:
(1) The protection of life and property
(2) The enforcement of laws and regulations
(3) The preservation of good order and discipline
b. By attaining these objectives, the security department will maintain a safe environment
for command personnel, protect government property, and allow the command to perform its
assigned mission.
c. Physical security and loss prevention matters are issued by reference (b).
0102. ORGANIZATION OF THE SECURITY DEPARTMENT
a. The commanding officer has the responsibility for the safety and security of the
command. On installations with multiple commands, host/tenant agreements will define the
specific responsibilities of law enforcement between the commands.
b. Law enforcement for an installation is the responsibility of the host/regional command.
Commanding officers of tenant activities will retain those internal physical security
responsibilities unique to their commands. Security officer duties are specified in references (b)
and (c).
c. Commands/regions having a law enforcement and physical security mission will
consolidate those functions in a single security department. The security department will be
under the supervision of a security officer who will generally (though not in all cases) report to
the regional commander or commanding officer as appropriate. The security officer is the
principal staff officer to the command for law enforcement and physical security matters. For
security departments having a total combined strength (military and civilian, including contract
security personnel) of 100 or more persons an assistant security officer/operations officer should
be considered for assignment to run the

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
1-2
department's day to day operation. This allows the security officer to be available for command
duties, program review and coordination with other base elements.
0103. FACILITIES
a. Due to its universal recognition, the word "Police" will appear on the exterior of the
building to direct the public to the police desk.
b. Law enforcement related facilities should be located in an area of the installation that
allows for free access by command personnel and others in need of assistance. Individuals with
complaints or questions will be met at a "police desk" in a public area of the building. Access to
the remainder of the security department facilities will be controlled.
c. In addition to the normal office spaces, the law enforcement facility should contain the
following: A reception and waiting area; a police desk; communications area; interview rooms;
conference and training area; secure stowage for evidence, weapons, and other valuable property;
and a separate entry for employees and for individuals in custody.
0104. STANDARD OPERATING PROCEDURES (SOPS). Each security department will have
written SOPS which will address department procedures and implementation of this instruction.
Mandatory SOPS are specified in this manual as the subject is addressed.
0105. LAW ENFORCEMENT FUNCTIONS. The following are normal law enforcement
functions of a security department:
a. Management. Plan, direct, and administer the security department; apply policies and
directives prescribed by higher authority; provide advice and assistance to the commanding
officer; review, verify, and approve reports; review and endorse incoming and outgoing
correspondence; maintain liaison with other law enforcement authorities and military activities
within the geographic area of responsibility; supervise law enforcement personnel; investigate
accidents and incidents involving security personnel; establish and maintain command security
education and awareness training programs; maintain crime prevention programs.
b. Administration. Process security department correspondence; maintain security files
and records system documents; establish personnel recall rosters; maintain training records,
equipment, supplies, and forms.
c. Patrol. Maintain protective presence to deter crime; respond to calls for assistance,
alarms, and reports of criminal activity; enforce laws, regulations, and directives in areas of
command jurisdiction; apprehend and process suspects, enforce traffic regulations; investigate
traffic accidents; provide timely response to non-criminal service requests; provide escorts;
provide information and assistance to persons in need.
d. Investigations. It is Department of the Navy (DON) policy to maintain cooperative
OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
1-3
working relationships between the Naval Criminal Investigative Service (NCIS) and naval
commands/activities in the investigation and prosecution of crimes. Prompt referral of
investigations and regular communications are keys to maintaining good working relationships.
The security officer, together with the NCIS representative providing service to the command,
will establish a case review process.
(1) The command investigator should seek to participate jointly with NCIS, when
NCIS has assumed investigative responsibility, and when related to command business.
(2) All cases investigated by the security department will be documented with an
Incident Report (IR).
(3) Liaison with other military and civilian law enforcement agencies by the local
command will be per reference (d).
(4) Where the regionalization effort has been implemented, the investigative
responsibility will fall upon the Regional Supervisory Investigator (RSI) with coordination
between the RSI and the Regional Security Officer (RSO). In those instances where conflict
between this instruction and the regionalization process should surface, the RSO and RSI must
submit the issue to commanding officer for the region for resolution. Chief of Naval Operations
(CNO) (N09N) must also be apprised of the issue for continuity of policy. Examples might be
the storage of evidence, access to evidence lockers, chain of custody of evidence or carrying of
weapons by regional investigators.
e. Special Operations. Conduct specialized law enforcement programs required by
location/mission of the command, e.g., wildlife protection, animal control.
0106. AFLOAT LAW ENFORCEMENT
a. This instruction shall apply to masters-at-arms/security personnel aboard ship, except
where it is evident that the policies and functions are not applicable to afloat commands. It
should be noted, however, that some requirements may apply periodically, e.g., juvenile
procedures may apply aboard during Visit Ship, family cruises, stowaways, etc.
b. A security officer (ODC 649X)/security technician (ODC 749X), when assigned, will
report to the commanding officer via the executive officer, as discussed
OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
1-4
under reference (c). For ships without a security officer/technician, the Chief Master-at-Arms
(CMAA) may be designated as the security officer.
0107. DISSEMINATION OF INFORMATION. Personnel shall treat the business of the
security department as "For Official Use Only." Information regarding official business shall be
shared only with those for whom it is intended under established security department procedures.
The security officer will publish an SOP regarding removal, copying, sharing of official records,
and other security department information.
0108. EMPLOYMENT OUTSIDE OF SECURITY DEPARTMENT. Personnel may engage in
off-duty employment provided the following conditions are met and the off-duty employment is
not otherwise in conflict with prevailing personnel regulations and directives:
a. Such employment shall not interfere with the individual's duties as a member of the
security department.
b. The security officer shall approve the outside employment in writing, prior to such
employment.
c. The employment must have no hint of conflict of interest, either financially or by
authority. Employment as a private investigator or bail bondsmen is prohibited. Employment as
a private guard or watchman is allowed, providing there is no conflict with Navy law
enforcement duties.
d. Members of the security department may serve as regular/reserve civilian law
enforcement officers so long as such service is in a personal capacity not involving the exercise
of military authority, and does not interfere with their regular duties.
0109. TRAINING
a. The training organization, Phase I, Phase II and in-service training are specified under
reference (b). This training is mandatory and personnel will not be authorized to perform law
enforcement duties without its satisfactory completion. Roll call is also a good forum for
updating policy or conducting awareness training.
b. To ensure adequacy of training, each security department should have an active field
training officer program. In addition, security officers will review training records quarterly to
ensure all personnel have received required training and immediately schedule personnel who are
delinquent.
Enclosure (1)
1-5
OPNAVINST 5580.1A
26 JULY 2000
c. In addition to training specified in reference (b), law enforcement personnel will
receive training in:
(1) crime prevention
(2) community policing.
d. Training available through the various agencies in the local civilian communities
should be explored for use.
e. All security department personnel who operate emergency vehicles will receive the
Department of Transportation Emergency Vehicle Operator Course (DOT EVOC), from a
certified instructor, at least once every 3 years. The DOT EVOC curriculum is available from the
Naval Safety Center; Code 42; 375 A Street; Norfolk, VA 23511-4399.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
CHAPTER 2
LEGAL ASPECTS
0201. General
0202. Jurisdiction and Authority
0203. Article 31, Uniform Code of Military Justice/Miranda Rights
0204. Search and Seizure
0205. Lineups
0206. Medical Records
0207. Financial Records

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
2-1
CHAPTER 2
LEGAL ASPECTS
0201. GENERAL
a. The legal aspects of law enforcement are a result of statutes, regulations, and court
decisions. Criminal law is in a constant state of change. Every year, military and civilian courts
at all levels render decisions which affect police procedures and policies. Within the Department
of the Navy, the Office of the Judge Advocate General (JAG) is responsible for reviewing laws,
regulations, and court decisions and establishing policies and procedures. Staff Judge Advocates
(SJA), Navy Legal Service Offices (NLSOs), and command legal officers will provide specific
guidance to security officers on legal matters.
b. Security officers and security department training officers will continually monitor
changes to procedures and revise Phase I and Phase II training lesson plans accordingly. In
addition, security officers will use roll call training to publish changes as they occur.
0202. JURISDICTION AND AUTHORITY. The jurisdiction and authority of Navy law
enforcement specialists is limited. The security officer will prepare Standard Operating
Procedures (SOPs) defining the law enforcement jurisdiction of the security department.
Included will be persons subject to the authority of the security department, geographic
boundaries of jurisdiction, including level, i.e., exclusive, concurrent, or proprietary, and any
agreements or understandings with local law enforcement or host nations.
a. Off-base apprehensions. When authorized by a commanding officer or his/her
designee in support of a military purpose, Navy law enforcement personnel may apprehend a
military member off-base. A suspected military member in civilian attire should first be
identified by a civilian law enforcement officer to avoid the unlawful apprehension or detention
of a civilian.
b. Naval Criminal Investigative Service (NCIS) jurisdiction includes major criminal
offenses and counterintelligence cases. A major criminal offense has been defined as any offense
punishable by death or imprisonment for a term exceeding 1 year. An incident in either of these
matters requires immediate notification of an NCIS agent before any substantive investigative
steps are taken by the command, including interrogations or searches of property unless such
steps are necessary to protect life or property or to prevent the destruction of evidence.
(1) In instances where an immediate response by NCIS is not feasible (e.g., vessels
underway without assigned agents) commanding officers may conduct such

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
2-2
preliminary investigations as circumstances dictate, preparatory to a later full investigation by
NCIS. NCIS should be immediately notified to facilitate guidance to the command.
(2) NCIS may decline the investigation of some cases. If this should occur, the
requesting command will document that the case was declined by NCIS on the IR including the
time/date notified, agent notified, and the time/date declined, and the agent declining.
c. NCIS is responsible for liaison with all Federal law enforcement, security, and
intelligence agencies, and the primary liaison with State and local agencies in matters of criminal
investigation and counterintelligence.
0203. ARTICLE 31, UNIFORM CODE OF MILITARY JUSTICE (UCMJ)/MIRANDA
RIGHTS. General guidance on the use of Article 31, UCMJ and Miranda Rights is to be
provided in Phase I and Phase II security department training. However, actual application of
these rights will be continually monitored by security officers, training officers, and field training
officers. The following special provisions apply:
a. Persons under the influence of alcohol/drugs will not be questioned about a criminal
matter, except in matters of extreme emergency. Any waiver of rights made by such a person
will be questionable. Other information (e.g., personal data) may still be obtained.
b. Juveniles. See Chapter 11 regarding juveniles.
c. Foreign Nationals. In a foreign country where the United States maintains military
facilities, a citizen of that country, or another foreign country, may commit an offense against the
property of the United States, or against the person or property of members assigned to military
forces located at that activity. These suspects are not subject to the laws of the United States.
Therefore, if they are interrogated as criminal suspects, they should be warned or advised in
accordance with the procedures that control such advice in the country where the base is located.
Status of Forces Agreements may also apply. Specific guidance will be obtained from the local
SJA.
d. Non-English Speaking Persons and Foreign Visitors. Generally speaking, all people
within the United States, whether citizens or not, are subject to the laws of this country.
Therefore, with the exception of diplomatic personnel, these individuals should be afforded the
same treatment as that given to all U. S. citizens. Any person, whether non-English speaking U.
S. citizen or foreign visitors, will not be questioned until their level of understanding of their
rights can be fully ascertained. If there is any question, contact the SJA for guidance.
e. Prior Admissions/Cleansing Warnings. Occasionally a situation will occur where a
suspect has made incriminating statements to a command representative, or to other police
personnel, without a proper Article 31 warning beforehand. When it is suspected that an existing
criminal admission was improperly obtained from a suspect, the suspect must be advised that the

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
2-3
previous admission cannot be used against him/her in a trial by court-martial or other court of
law. A "cleansing warning" must be provided to the suspect, (e.g., "I advise you that any prior
admissions or other improperly obtained evidence which incriminated you cannot be used against
you in a trial by court-martial or other court of law."), as appropriate. This statement will be
acknowledged at the bottom of the appropriate rights advisement form. Prior questionable
admissions made by a suspect must be completely documented to include particulars about
previous warnings. This information will be included in the ROI and any documents pertaining
to the report.
0204. SEARCH AND SEIZURE. General information on searches and seizures is found in
reference (e). Up-to-date information may be obtained from the SJA or the servicing NLSO.
The following are additional guidelines:
a. Command Authorized Searches (probable cause search authorizations)
(1) Prior to issuance of a command authorized search, the Affidavit for Search
Authorization (OPNAV 5580/10) will be completed and signed, under oath.
(2) The Command Authorization for Search and Seizure (OPNAV 5580/9) will be
prepared for the commanding officer's signature.
(3) In conducting the search, the individual(s) having proprietary interest over the
premises should be present. A copy of the signed OPNAV 5580/9 must be given to the
individual, and he/she will be given sufficient time to read it. If the individual is also the suspect
of the offense, then no questions will be asked without appropriate self-incrimination warnings
(this does not include requests for identification). After serving the authorization, it is
permissible to ask the individuals present to open locked doors, lockers, etc., providing they are
cooperative and not a risk to the safety of security personnel or likely to damage or conceal
evidence. If individuals are not cooperative, or refuse to open locks, the locks may be forced
open by police in such a manner as to cause the least amount of damage to the property.
(4) Occasionally, a search authorization may be served on an unoccupied premise,
vehicle, shipping container, etc. In such situations, a command representative should be present
to witness the search. A copy of the authorization will be left with the representative to be
delivered to the suspect. Another copy, plus a receipt for property seized, will be left at the
premises. It is the security personnel’s responsibility to secure the unoccupied premise after the
search to prevent theft and vandalism.
(5) Following the search, a receipt for the property seized must be completed and
provided to the individual with proprietary interest in the property, along with a copy of the
authorization. A signed receipt must then be returned to the commanding officer authorizing the
search. The original of the search authorization and affidavit will be retained by the security
department conducting the search.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
2-4
b. Permissive Search Authorizations
(1) A Permissive Authorization for Search and Seizure (OPNAV 5580/16) will be
completed prior to the search. Oral consent authorization may be made in emergency situations,
but only with sufficient witnesses present to testify that permission for the search was given
voluntarily.
(2) A subject should be advised that the permission to search is voluntary. There should
be no further statement made to the individual to imply that if they do not consent, a search
warrant will be obtained and the search conducted regardless. Security personnel should record
the exact words of a subject and of the person giving the advice in their field notes.
(3) A subject may withdraw consent at any time. If, during the course of a search, a
subject states he or she does not want the search to continue, then it must be terminated. Any
evidence uncovered to that point may be used to substantiate probable cause, and the matter
presented to the commanding officer for a search authorization, if appropriate.
(4) At the completion of the search, a receipt will be given to the subject for any property
seized. There is no requirement to provide a copy of the permission authorization form to the
subject, although there is no objection to doing so if the subject requests it. The original form
will be kept by the security department conducting the search.
c. The last page listing only blocks 1 through block 16 of the Evidence/Property Custody
Document (OPNAV 5580/22) will be used as a receipt for property seized.
0205. LINEUPS
a. For the results of a lineup to be admissible in court, the suspect must be viewed with
other individuals of the same sex and race, and with other similar physical characteristics and
clothing. For lineups of objects (e.g., weapons, photos, etc.) similar rules apply. Lineups, when
conducted, will be photographed for later verification that requirements regarding similarity were
adhered to.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
2-5
b. A suspect does not have the right to refuse to participate in a lineup. However, the
suspect does have the right to consult with legal counsel and have legal counsel present during a
lineup. The Lineup-Acknowledgment and Waiver of Rights form (OPNAV 5580/5) will be used
for a suspect who chooses not to consult with a lawyer or have one present at the lineup. This
form is not used when the suspect requests a lawyer.
0206. MEDICAL RECORDS
a. Records of medical treatment obtained at U. S. Naval medical facilities are the property
of the U. S. government, and may be obtained by security personnel for investigative purposes if
the subject completes the Authority to Release Medical Information and Records (OPNAV
5580/14).
b. In the event the Navy law enforcement officer/investigator cannot get a voluntary
waiver from the person whose medical records are sought, it may become necessary to seek a
subpoena from a local judicial officer for access to the information held by a non-Department of
Defense health care provider.
c. Whenever medical records from naval facilities are requested by local law enforcement
officers/investigators, the request must be in writing from that agency.
0207. FINANCIAL RECORDS. A Customer Consent and Authorization for Access to
Financial Information form (OPNAV 5580/13) will be completed to gain access to records of
banks, credit unions, and other financial institutions. Consultation with the local SJA should be
made to ensure compliance with the Right to Financial Privacy Act of 1978.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
CHAPTER 3
INCIDENT REPORTS (IRs)
0301. Definitions
0302. Reporting Requirements
0303. Dissemination
0304. IR Retention
0305. Case Categories to be Forwarded to NCISHQ (Code 28C)
0306. Hate/Bias Crime Reporting
0307. Victim and Witness Assistance Program

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
3-1
CHAPTER 3
INCIDENT REPORTS
0301. DEFINITIONS
a. Criminal complaint - a notification from any source which reports or alleges that a
violation of law or regulation has occurred.
b. Significant incident - any matter which involves police services and requires more than
a simple notification. Examples of significant incidents are: fatal or personal injury accidents,
other serious injuries, deaths, medical emergencies which required a police response, etc.
c. National Incident-Based Reporting System (NIBRS) - a computerized system of
capturing law enforcement statistics through law enforcement department's input. System is
maintained and regulated by the Department of Justice (DOJ).
d. Defense Incident-Based Reporting System (DIBRS) - a computerized system of law
enforcement data collection which, in addition to complying with NIBRS, collects additional
data pertaining to Department of Defense related statistics, e.g., offenses occurring on or off
installation, military related offenses, victim and witness information, etc. System is maintained
and regulated by the Department of Defense (DOD).
e. Hate Crime - A criminal offense committed against a person or property which is
motivated, in whole or in part, by the offender's bias against a race, religion, ethnic/national
origin group, or sexual orientation group. Even if the offender was mistaken in his/her
perception that the victim was a member of the group he or she was acting against, the offense is
still a hate crime because the offender was motivated, in whole or in part, by bias against the
group.
0302. REPORTING REQUIREMENTS
a. Criminal complaints/activities and significant incidents will be reported by OPNAV
5580/1, the Incident Report (IR). This form, whether hard copy or electronically produced, is the
only format acceptable for DIBRS crime and incident reporting.
b. Security officers will direct the preparation of an IR for every criminal complaint or
significant incident which is brought to the attention of the security department. Complaints
against members of the security department, on or off duty, will also be documented on an IR.
c. Non-significant incidents, e.g., unsecured doors and windows with no unlawful entry,
alarms with no malicious involvement, routine money or personnel escorts, ambulance/fire
department runs when no police assistance is required, and stray animal calls, will not be
reported via DIBRS. These incidents may be recorded on a locally prepared form or the desk

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
3-2
journal or communications log and retained locally.
d. Matters in the following categories will be reported on the documents indicated, and
will not be reported by IR:
(1) Non-significant incidents: DoN Desk Journal (OPNAV 5580/19)
(2) Contact with individuals under suspicious circumstances, but with no immediate
indication of criminal activity: Field Interview Card (OPNAV 5580/21)
(3) Impounding abandoned motor vehicles, or voluntary storage of motor vehicles:
Vehicle Report (OPNAV 5580/12)
e. An Incident Number will be assigned to each IR prepared by the security department.
These numbers will be structured in the following manner:
(1) The first two digits will represent the year, i.e., 00 = 2000, 01 = 2001, etc.
(2) The next five digits represent the Unit Identification Code (UIC) of the reporting
security department.
(3) The last five digits represent the sequential number assigned by the security
department case control log. In some instances the sequential number may be generated by the
on-board computer. For example, an incident number of 000021500013 would represent the
13th reportable incident (00013) recorded by NAS Dallas (UIC-00215) in the year 2000 (00).
0303. DISSEMINATION.
a. The original IR and exhibit(s), if any, that report on investigations under jurisdiction of
NCIS shall be forwarded to the NCIS office to which the incident was referred and assumed. If
NCIS does not assume jurisdiction, the investigation will be completed by the security
department and all original documentation forwarded to NCIS Headquarters upon completion.
b. Continue to send the original paper report of the IR to NCISHQ, until the responsible
security departments is capable of electronic transmission of reports. Regardless of the capability
of the security department to electronically transmit IRs, all IRs reporting violations referenced in
section 0305 shall be mailed to NCISHQ if exhibit(s) is/are included.
c. Copies may be provided to other commands, Staff Judge Advocates, family advocacy
personnel, installation housing officers, etc., as appropriate. They may also be disseminated
outside the Department of the Navy providing that security officers comply with the provisions
of SECNAVINST 5211.5D.

OPNAVINST 5580.1A CH-1
20 July 2001
3-3
0304. IR RETENTION
a. Copies of IRs will be retained by the initiating security department for a period
of 2 years from the date of the incident. Retention of IRs beyond 2 years may be
authorized by the security officer or the regional security officer on a case-by-case basis.
Any retention of an IR beyond the 2-year limitation must contain a written explanation
for the retention, signed by the security officer. IRs stored or archived electronically may
be retained for 5 years if the security department has sufficient capacity.
b. The NCIS serves as the centralized repository for law enforcement reports
within the DON and as such they maintain reports for periods up to 50 years. Incidents
that have been adjudicated or otherwise investigated to the fullest with no apprehension
or identification of subjects require that original reports and exhibits be forward to
NCISHQ for storage. A report is not to be forwarded until the incident is closed.
Reports forwarded to NCISHQ must be complete and contain all exhibits.
c. Disposition guidance for IRs is contained in SECNAVINST 5212.5D, SSIC
5580, paragraph 1.
0305. CASE CATEGORIES TO BE FORWARDED TO NCISHQ (CODE 23C).
Original IRs and exhibits that report violations which fall within the case categories and
punitive Articles of the UCMJ specified in Appendix D will be forwarded to NCISHQ.
a. Hard copy reports will include exhibits and disposition of the case. Do not attach
command cover sheets. Reports must be legible to ensure clarity during optical imaging.
IRs will be mailed to:
NAVAL CRIMINAL INVESTIGATIVE SERVICE HEADQUARTERS
(CODE 23C)
716 SICARD STREET SE, SUITE 2000
WASHINGTON NAVY YARD DC 20388-5380.
0306. HATE/BIAS CRIME REPORTING. Police officers conducting an investigation
which indicates that the offense was committed as a result of hate or bias must report
same in the appropriate area of the IR. All hate crimes will be referred to and assumed
by NCIS.
0307. VICTIM AND WITNESS ASSISTANCE PROGRAM. The Navy's
Victim/Witness Assistance Program requires police officers and investigators to advise
crime victims of their rights. These rights are enumerated in references (m) and (n).
a. Ensure that a Form DD 2701, Initial Information for Victims and Witnesses of Crime,
is issued appropriately.
OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
3-4
b. Victims/witnesses referred to base investigations or NCIS should have the current
telephone number, recommended point of contact and other relevant information completed, in
the spaces provided on the form.
c. Indicate on the IR that a DD 2701 was given to the victim or witness. Also indicate
total number of DD 2701s issued in the reported incident when there are multiple victims or
witnesses.
d. Police officers and investigators should follow local instructions as regards who might
be eligible for victim/witness compensation. Not all victims and witnesses will be eligible since
state boards set limits on the type of crime, extent of loss and other rules regarding
compensation.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
CHAPTER 4
USE OF FORCE AND WEAPONS POLICIES
0401. General
0402. Use of Force
0403. Methods of Force
0404. Arming Law Enforcement Personnel
0405. Weapons Policies
0406. Prisoner Handling
0407. Detention Cells
OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
4-1
CHAPTER 4
USE OF FORCE AND WEAPONS POLICIES
0401. GENERAL
a. There are varying degrees of force that may be justified in a law enforcement situation
depending upon its gravity. The escalation of force must be consistent with the need for the least
amount of force required to resolve the situation.
b. Law enforcement/security personnel may only use that level of force necessary to
control/stop unlawful resistance, and to prevent the commission of a serious offense involving
violence and threatening death or serious bodily harm.
c. Use of force guidelines are applicable in overseas areas to the extent that they satisfy
applicable provisions of international agreements or arrangements relating to law enforcement
and security matters.
0402. USE OF FORCE. Use of force policies are set forth in reference (g). All Navy law
enforcement personnel will have a working knowledge of those policies. Briefings on use of
force polices will be given quarterly, acknowledged by signature, and entered in individual
training records.
0403. METHODS OF FORCE. Commanding officers must ensure that Naval Security Forces
are provided standard law enforcement equipment and trained in its use to ensure that the
minimum force necessary is applied. The minimum amount of necessary force will be used in all
situations. These methods/means are listed from the least severe to the most severe on the
following continuum:
a. Verbal commands. Issued in order to have persons comply with requests in non-
threatening situations. This might include asking disputants to separate or asking a subject to
produce documents under legitimate circumstances, e.g., drivers license during a routine traffic
stop.
b. Physical apprehension and restraint techniques, e.g., come-along holds, take-downs.
c. Handcuffs. To be used for safe custody, for a limited period of time, and for the
protection of law enforcement personnel as well as the detainee.
d. Riot Control Agents (RCA) (CS and Oleoresin Capsicum (OC)). RCAs may be used
to subdue, in self-defense, or protection of a third party, if circumstances warrant their use.
(1) If RCAs are used, personnel will receive medical attention as soon as possible. A
person who has been sprayed will not be released until he/she has been advised of the safety

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
4-2
measures to be taken, or until medical treatment has been received.
(2) Use of OC Pepper Spray is authorized for use and complies with reference (g).
Because it is environmentally safe, biodegradable, and produces rapid physiological reaction in
low concentrations, OC spray is now preferred.
(3) Law enforcement personnel will not be issued chemical agents until they have been
trained in their use and knowledgeable of safety precautions involved with chemical agents,
including necessary medical treatment following its use. Because of the variety or products
available, training will be tailored according to manufacturer's recommendations.
e. Police Batons. Police batons may be issued at command discretion provided
appropriate training has been provided and documented. Commands should include
manufacturers' prescribed training for the side-handled police baton and collapsible baton. It is
permissible to provide local training for the standard police baton. Collapsible batons are now
preferred for shipboard environment.
f. Military Working Dogs.
g. Other DoD-approved non-lethal weapons may be used.
h. Firearms. No firearms shall be drawn and readied for use unless actual force would be
authorized under the circumstances and per established guidelines.
0404. ARMING LAW ENFORCEMENT PERSONNEL. The authority to arm law
enforcement and security personnel is vested in the commanding officer by U. S. Navy
Regulations, 10 U.S.C. 1585, and reference (h). In exercising this authority, the commanding
officer will be guided by the following:
a. No person shall be armed unless qualified in the use of the firearm assigned.
Qualification includes satisfying all the firing requirements of reference (h) and receiving a use
of force briefing quarterly.
b. Personnel who fail to achieve/maintain the required proficiency may be assigned to
duties which do not require the carrying of firearms.
c. Qualified personnel will be issued an Authorization to Carry Firearms form (OPNAV
5512/2), which must be in their possession while carrying a firearm.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
4-3
0405. WEAPONS POLICIES
a. Personal weapons are not authorized to be carried by duty personnel. Only
government-owned weapons are permitted to be carried.
b. Weapons will not be carried off-duty. Weapons will be issued for use on duty and will
be stored in an approved security container at security headquarters when not required for duty.
c. Weapons may be carried off-base by security personnel when in a duty status, such as
transporting prisoners, travel between activities, etc. Security supervisors must insure
compliance with applicable Federal and local statutes/Status of Forces Agreements.
d. Only ammunition obtained through the Navy supply system may be used in
government-owned weapons. Special ammunition, such as bird-shot, wad-cutters, etc., is strictly
prohibited for law enforcement and physical security uses, but may be used by Game Wardens
and for training.
e. The carrying of unloaded weapons by on-duty personnel is prohibited, except for safety
reasons while on the firing range or while participating in training exercises.
f. When weapons are stored, weapons storage facilities will meet the requirements of
reference (i).
g. Fully loaded weapons will be carried, per reference (h). The decision to load weapons
on board ships continues to rest with commanding officers based on their evaluation of current
conditions.
h. Shotguns, when carried in a vehicle must be secured in an approved shotgun locking
mount, or locked and secured in the patrol vehicle's trunk.
0406. PRISONER HANDLING
a. Personnel will use the minimum force necessary to apprehend, detain, transport, and
process violators.
b. Persons apprehended will be searched and restrained. When restraining any subject
with handcuffs or other devices, the hands will be behind the back unless approved "travel
cuffs/waist chains" are used. Handcuffs will be double-locked.
c. When transporting prisoners in vehicles:
(1) Prisoners will be secured in the vehicle by use of seat belts. Offenders will not be
handcuffed to any part of the vehicle.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
4-4
(2) Law enforcement personnel will not engage in vehicle pursuits, high speed, or
erratic driving.
(3) Law enforcement personnel will inspect the prisoner compartments of vehicles for
contraband and weapons prior to and after each use, and will search prisoners prior to placing
them into a vehicle for transport.
(4) When prisoners or suspects are to be transported by a person of the opposite sex,
the driver will notify the dispatcher of the vehicle's mileage before starting the transport, and a
record of the time and mileage will be recorded in the Desk Journal. Upon arrival at the
destination, the dispatcher will again be notified of the ending mileage, and the time and mileage
will be recorded in the Desk Journal. When possible, another patrol officer should ride in the
transporting vehicle or follow in a vehicle directly behind.
0407. DETENTION CELLS. The operation of detention cells is the responsibility of the
security officer. When a detention cell is available, the following standards will apply:
a. Detention cells must be certified per reference (j), which specifies the requirements for
processing of detainees and prisoners.
b. Standard operating procedures will be prepared.
c. Only designated personnel will be allowed into the detention cell area. Personnel
working in the area will not be armed with any weapon, including firearms, riot control agents,
batons, or other such devices unless in the performance of duties such as during prisoner
disturbance.

Enclosure (1)
OPNAVINST 5580.1A
26 JUL 2000
CHAPTER 5
INVESTIGATIONS
0501. Program
0502. The Command Investigator
0503. Credentials
0504. Controlled Substance Investigations
0505. Interviews and Interrogations
0506. Reports of Investigations
0507. Informants
0508. Fingerprinting Criminal Suspects
OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
5-1
CHAPTER 5
INVESTIGATIONS
0501. PROGRAM
a. NCIS is responsible for facilitating, managing and establishing policy for the Navy’s
law enforcement/investigative programs. NCIS will assign special agents as Regional
Supervisory Investigators (RSI) or Regional Investigations Coordinators (RIC) by region to
provide oversight of the investigative program. This oversight will include, but is not limited to,
the training given to command investigators, case review, investigation standardization,
investigator screening and/or selection process. RSI personnel will work in concert with
appropriate area security directors and/or regional security officers. This team relationship is
essential to streamlining investigative operations, professionally accrediting personnel and
incorporating base investigators into NCIS tier 3 and some tier 2 cases. The goal of this program
is to ensure the Navy operates with a single operational standard.
b. Where appropriate, all NCIS procedures will become standard operating procedures
for the investigative units. Command investigators will be limited to those investigations
involving the ship, station or region to which assigned and not assumed by the NCIS after
referral. All other investigations must be approved by the security officer and/or the RSI/RIC.
0502. THE COMMAND INVESTIGATOR.
a. Command investigators selections must be based on demonstrated professional
capabilities, experience and knowledge of legal matters. One of the primary responsibilities of
the RSI is to establish and maintain an effective criminal investigative program. This is best
achieved through implementing NCIS standard operational procedures and a robust in-service
training program.
b. The primary course of instruction for training all non-agent investigative personnel
(civilian and military) is via the Army Inter-service Training Review Organization (ITRO)
Military Police Investigator course located at Fort Leonard Wood, Mo. The other recognized
course of instruction for civilian personnel is via the Federal Law Enforcement Training Center
(FLETC), Glynco, GA. Commands, not NCIS, are responsible for this initial training.
c. For in-service training NCIS has developed a 5-day Crime Scene Course of Instruction
(COI) and a one week Basic Investigator COI. This in-service training is a substitute for ITRO
training courses, but is an additional required course of instruction.
0503. CREDENTIALS.
a. NCIS provides command investigator credentials for all base investigators. Command
investigator credentials (OPNAV 5580/26) are issued by the RSI/RIC. Credentials will be
serially numbered, and contain the name, description of the bearer (i.e., height, weight, color hair
and eyes, sex, and date of birth), a color photograph, and signature of the investigator. Although

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
5-2
OPNAV 5580/26 does not have blocks for the description and signature block, these items may
be typed on the reverse. Credentials will be issued for a period not to exceed 24 months.
b. Credentials will be strictly controlled by serial number. Logs will fully identify the
person to whom issued and will record the disposal/destruction of expired credentials. Unused
credentials will be securely stored, and will be inventoried annually.
c. Once credentials are issued to an investigator, that person assumes responsibility for its
safeguarding. If credentials are lost, the investigator must report this loss immediately to his/her
supervisor. Credentials will automatically expire upon transfer from the investigations unit, at
which time the badge will be collected and the credentials destroyed.
d. Commands that are not regionalized and require their own investigators will
coordinate their investigative efforts with the nearest NCIS office and/or security department.
All investigative entities will use applicable NCIS criminal procedures for reports, training, and
other investigative protocols.
e. Investigators are often tasked to work off base. Civilian clothing may be authorized
for military command investigators. Liabilities associated with working off base vary by
location. The local status of forces agreement and applicable laws contain relevant guidance and
should be reviewed prior to establishing local SOP/Memorandum of Agreement.
0504. CONTROLLED SUBSTANCE INVESTIGATIONS. Controlled purchases of drugs will
be controlled by special agents of the NCIS. Command personnel may assist in drug purchases
to the extent requested by NCIS, with the approval of the commanding officer.
0505. INTERVIEWS AND INTERROGATIONS. An Interview/Interrogation Log (OPNAV
5580/7) will be initiated and filled out legibly in ink for every interview/interrogation. The log
will be kept in the case file.
0506. REPORTS OF INVESTIGATION (ROI). All cases investigated by the command
investigators will be documented with a formal ROI. The format and all supporting documents
will be completed using the current NCIS directives.
0507. COOPERATING WITNESSES
a. The use of cooperating witnesses (CW) can be beneficial in successfully completing an
investigation. However, use of CWs is to be on a limited case-by-case basis and will be
documented by current NCIS procedures and with the approval of the security officer and the
area’s senior NCIS agent (Judge Advocate General review). Prior to using an individual who is a
military member, authorization will be received from the individual's commanding officer.
Command authorization is not necessary for civilian employees of the Navy. The authorization
will be documented. Only NCIS-trained/certified investigative personnel will handle CWs.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
5-3
b. The reliability of a source is an important element in determining probable cause for
certain actions that may be taken as a result of information provided. In most instances, the
information provided by a source will be sufficient confirmation of the source's integrity or
truthfulness before a judicial proceeding. An investigator must always be able to attest to the
reliability of the sources of information.
c. Informant records will be established, maintained and securely stored at the security
department. These files are to be the responsibility of the investigations supervisor. Access to
this file will be limited to the security officer, investigations supervisor, and the investigator
involved in handling the informant. Others may be granted access only on a strict need-to-know
basis.
0508. FINGERPRINTING CRIMINAL SUSPECTS.
a. All military criminal investigative organizations must submit criminal history data, per
DODINST 5505.11 of 1 December 1998, to the Federal Bureau Investigation (FBI) Identification
Division. The required submissions pertain to all military service members investigated by the
military criminal investigative organization for commission of any offense listed below and also
in Appendix D of this instruction and who are the subjects of any resultant judicial or non-
judicial military proceeding. Judicial and non-judicial proceeding is defined as a court-martial or
a non-judicial hearing conducted in accordance with Article 15, UCMJ. Offenses that require
submissions are identified in Appendix D.
b. Offender criminal history data records required under this policy will be initiated by
preparation and submission of a standard suspect fingerprint card, FBI Form FD 249, to the
NCIS Regional Forensic Laboratory (NCISRFL) as described in subparagraph (1) below. The
block on the FD 249 for the contributor’s ORI and address shall read USNIS0000, NIS, WASH,
DC. Correct any FD 249 which has a preprinted contributor’s ORI number and address different
from above by typing a label with the NCIS ORI number and affixing it over the incorrect
address. The card must be filled out in strict accordance with the instruction and be typed or
clearly printed. Ensure the block entitled “Local Identification/Reference” is completed with the
Incident Number. Submission is required even if charges are reduced to a lesser offense.
Submission of the fingerprint cards will not be delayed by pending judicial or non-judicial
military proceedings. The fingerprint cards should be submitted upon notification the suspect
will be administered judicial or non-judicial punishment by command. Further requirements are
addressed in the following sub paragraphs:
(1) The NCISRFL will be responsible for ensuring the print quality is sufficient for
acceptance by the FBI for filing. Therefore, two fingerprint cards will be forwarded to the
servicing NCISRFL. One card will be input by the NCISRFL into the appropriate regional
automated fingerprint record system and one will be forwarded by the NCISRFL to the FBI. If
the fingerprints are of insufficient quality, the cards will be returned to the submitting security
department to be redone. The NCISRFL will not check for accuracy of information on the cards,
only the quality of record prints.
Enclosure (1)
5-4
OPNAVINST 5580.1A
26 JUL 2000
(2) The FBI replaced the FD 249 fingerprint card (Rev. 12-29-82) with a revised card
(Rev. 12-1-94). Security departments are to used the latest version card and ensure it has the
NCIS ORI in the Contributor’s address block. The revised cards can be obtained from the local
NCIS office. The Final Disposition Form was also revised from R-80 to R-84. The Final
Disposition Form is to be completed and forwarded to the FBI by the security department..
c. If the investigation is referred to and accepted by any other law enforcement agency,
including NCIS, that agency will be responsible for submitting the fingerprint cards (FBI Form
FD 249) and the Final Disposition Report (FBI/DOJ R-84).
d. The policy of the Navy is to obtain at least two record fingerprint cards and the right
four finger impressions on the green Final Disposition report, FBI,/DOJ R-84, at the time of
interrogation for offenses, per paragraph a. Fingerprints obtained during the interrogation
process are maintained in the investigative case file until the command notifies the case
responsible investigator that action is pending against the suspect. Once a non-judicial
punishment hearing has been held or court-martial charges have been preferred, the two clearest
fingerprint cards will be completed and forwarded to the servicing NCISRFL as noted above. If
the interrogation is requested from another Navy law enforcement department, the security
department will obtain the necessary fingerprint and disposition cards and forward them to the
department receiving or who has received the subject for court-martial or non-judicial
punishment.
e. At the conclusion of the judicial or non-judicial military proceeding, the security
department will report disposition information by means of the Final Disposition Report sent to
the servicing NCISRFL as noted above. Disposition information will be filed on the record
fingerprint cards if the disposition is known at the time of the submission. Fingerprint cards,
disposition forms, and pre-addressed envelopes will be provided at no cost by the FBI via
NCISHQ supply department. Security departments should secure the training assistance of NCIS
or local police identification units if personnel are not familiar with the process of "rolling"
fingerprints on cards.

Enclosure (1)
OPNAVINST 5580.1A
26 JUL 2000
CHAPTER 6
EVIDENCE CUSTODY PROCEDURES
0601. General
0602. Responsibilities
0603. Evidence Records
0604. Evidence Lockers
0605. Evidence Submissions
0606. Evidence Inventory
0607. Transfer and Shipment of Evidence
0608. Disposal of Evidence
0609. Evidence Disposal Guidelines

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
6-1
CHAPTER 6
EVIDENCE CUSTODY PROCEDURES
0601. GENERAL
a. It is all Navy law enforcement personnel’s responsibility of to take every precaution to
preserve the integrity of evidence in its original condition. This means that personnel must enter
evidence into the custodial system as soon as possible after its collection, seizure, or surrender.
b. Host activities shall receive and store evidence received from its tenant activities.
Tenant activities shall not operate their own evidence lockers unless they have the capacity to do
so, i.e., suitable storage containers and a formal agreement with the host activity. Whenever
practical the security evidence locker will be combined with the NCIS evidence facility.
c. Whenever a requirement calls for a "disinterested party," that party shall not be
assigned to the security/legal departments of any command/tenant activity. The disinterested
party will be identified by name, grade/rank/rate, and billet title.
0602. RESPONSIBILITIES
a. The security officer will establish an evidence custody system consisting of:
(1) An Evidence Custodian, designated in writing
(2) An Alternate Evidence Custodian, designated in writing
(3) An evidence locker/room meeting the security construction and locking
requirements of this chapter, and
(4) A bound Evidence Log (OPNAV 5580/24), an Active Evidence Custody File, and
a Final Evidence Disposition File.
b. Conduct a complete evidence inventory on relief of the security officer, evidence
custodian, alternate evidence custodian, or, in any event, at least semi-annually. In addition, an
inventory will be conducted whenever a discrepancy is noted.
c. The evidence custodian (or the alternate evidence custodian in the absence of the
primary) will ensure that:

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
6-2
(1) Evidence is inventoried, tagged, packaged, and marked prior to storage, and that
evidence custody documents are properly completed by the person delivering the evidence prior
to its acceptance.
(2) That evidence logs and records are properly maintained.
(3) Evidence is disposed of following current Navy and command policies.
0603. EVIDENCE RECORDS
a. Evidence custody records will be composed of a bound evidence log (OPNAV
5580/24), an active evidence custody file, and a final evidence disposition file.
b. The evidence log shall be maintained for a period of 5 years from the date of the last
entry. The active evidence custody record shall be maintained as long as there is evidence in
custody which has not been officially disposed of. The final evidence disposition file shall be
maintained for a period of 5 years after the close of the calendar year covered by the file.
c. Each custody document received by the custodian will be reflected on a separate log
book line. The log shall also contain dated entries of all inventories, all changes of security
officer, evidence custodian, or alternate, and all changes of lock combinations. Each entry
indicating a receipt of evidence by the custodian shall be assigned an evidence log number
consisting of two groups of numbers separated by a dash (-); the first set of numbers will be a
three digit chronological number of the document for that calendar year, and the second group
consisting of the last two digits of that year (e.g., 001-96 for the first evidence custody document
for the calendar year 1996). Each entry will be made in black ink on the next blank line and no
empty lines will be permitted. In the event an error is made in the entry, the entry will be ruled
out with a single line and initialed by the custodian. Erasures or "white out" entries are not
authorized.
d. The Active Evidence Custody File shall consist of copies of each Evidence/Property
Custody Document (ECD) (OPNAV 5580/22) relating to evidence which has been received by
the custodian and which has not been disposed of. This record shall be maintained in one or
more loose leaf notebooks, and filed by Evidence Log Number with newer entries being placed
on top. This file represents all evidence for which the evidence custodian is responsible.
e. A Final Evidence Disposition File will be maintained on all ECDs relating to evidence
which has been disposed of. This file will be kept in the same manner as for the Active Evidence
Custody File. When ready for filing, the evidence custodian will complete the final disposition
section. The duplicate copies of ECDs will be destroyed. In the event the original ECD is
forwarded with the evidence during the final disposition action, the copy in the Active Evidence
Custody Record shall be completed as if it were the original and transferred to the Final Evidence
Disposition File.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
6-3
f. The required evidence custody records shall be stored in the evidence locker to prevent
unauthorized access to the files.
g. Only approved OPNAV evidence logs and forms are to be used for evidence custody.
If evidence is received from a non-Navy source, an OPNAV evidence custody document will be
initiated and the original evidence document will be attached to it.
0604. EVIDENCE LOCKERS.
a. Evidence lockers will be used to safely secure all items of evidence. Lockers will meet
the construction and locking criteria specified for “Q” and “R” coded items in reference (b); CAT
IV arms, ammunition, and explosives; and classified material in reference (i), specifically:
(1) If only small items of evidence are held they may be stored in GSA-approved
security containers. However, if the container weighs less than 750 pounds it will be secured to
the floor/wall. Since GSA-approved containers are not allowed to be physically modified in any
fashion, containers of less than 750 pounds can be made to meet the weight criteria by adding
weight to the inside of the container, or by using straps across the container with the straps bolted
to the floor/wall. If straps are used, bolts will be modified to make them non-removable.
(2) Larger items or amounts of evidence will be stored in a vault or strongroom
meeting the construction requirements of reference (i).
b. Only GSA Group 1 or Group 1R three tumbler combination locks are approved as
locking devices. For evidence stowage, electromagnetic locks are not required. Specifically
prohibited are key-operated locks and cipher locks.
c. Temporary evidence stowage containers. Construction and lock requirements do not
extend to temporary evidence lockers (drop boxes) provided the drop box is constructed so that
evidence cannot be removed without destroying the box or lock; that the box is within the
continual sight of the security dispatcher or a security supervisor; the key to the drop box is
stored in the regular evidence locker; and that the evidence is not held in this temporary storage
for more than 24 hours.
d. All evidence received by a Navy component having an evidence locker shall be stored
therein with exceptions of evidence too bulky for storage, evidence of a classified nature that
requires special handling (e.g., Sensitive Compartmented Information and Communications
Security), perishable items such as food, human/animal parts, items of an unstable
chemical/flammable nature, and explosives. These types of evidence may be stored elsewhere,
with the prior authorization of the security officer, where restricted physical access to the
evidence can be maintained. In any event all such items, unless of an especially bulky nature,
shall be wrapped or placed in containers and sealed so that any unauthorized access to the
evidence can be detected. Personnel maintaining temporary custody of these items will be
briefed on the requirements for secure storage and the probable requirement for them to testify as

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
6-4
to their custody. Further, they will execute the ECD upon receipt and release of the evidence.
The original ECD may be left with the evidence unless the storage conditions might cause its
destruction. In this case, a copy may be substituted and the original maintained in the evidence
locker.
e. Access to the evidence locker:
(1) Access to the evidence locker will be strictly limited to the evidence custodian.
The and alternate evidence custodian . The security officer will be provided the combination to
the locker in a sealed Security Container Information envelope (SF 700). Should the security
officer gain access to the evidence locker by removing the combination from the envelope, the
combination will be changed and a new SF 700 will be provided to the security officer. The
reason for the entry by the security officer will be recorded in the bound evidence log on the day
it occurs.
(2) Persons other than the evidence custodian, security officer, and alternate evidence
custodian may be granted access for official purposes (e.g., assistance visits/inspections).
Approved visitors will be entered in a log showing the date of the visit, time, identity of the
visitor, office or official capacity of the visitor, and reason for the entry into the locker.
f. In no event will lost and found, supply/cleaning gear, or any other non-evidentiary
items be placed in the evidence locker.
0605. EVIDENCE SUBMISSION
a. When any person submits evidence to the evidence custodian, it shall be properly
tagged, and if appropriate, placed in a suitable container. The original and two copies of the
ECD will be securely attached to the evidence or its container. The original and copies of the
ECD and the interleaved carbon paper will be separated only by the custodian accepting the
evidence. The original and all copies of the ECD shall be signed by the evidence custodian in the
appropriate block acknowledging receipt of the evidence. The original ECD shall remain
physically attached to the evidence, the first copy shall be placed in the Active Evidence Custody
File and the second shall be returned to the person submitting the evidence. When the evidence
is turned into a temporary depository (drop box) the ECD shall be signed by the person
depositing the item in the "Released by" column, and shall enter the name or number of the
depository in the "Received by" column. When the seizing person is also the evidence custodian,
he/she will also complete the "released by" column on the ECD to show release by the seizing
person and receipt into the evidence custody system. When any evidence is checked out of the
evidence locker for whatever purpose prior to its final disposition, a copy of the ECD shall be
maintained in the evidence locker in the Active Evidence Custody File. In the event that the
original is lost or destroyed, a copy may be used in its place.
b. All evidence being submitted shall be carefully examined and counted/weighed by the
accepting custodian. Any items entered which are later found not having evidentiary value

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
6-5
should be promptly returned or disposed of following the directions of the commanding officer,
security officer, or legal officer. If there is any doubt as to the value of the evidence, advice
should be sought from the servicing Navy Legal Service Office.
c. When pills/capsules are entered into the evidence locker, they will be both counted and
weighed.
0606. EVIDENCE INVENTORY
a. When evidence is first received into custody the receiving party must first inventory
the evidence personally. Subsequently, when evidence is transferred between parties, the
evidence must be verified.
b. The contents of each evidence locker shall be inventoried semi-annually. An inventory
shall also take place on the occasion of the relief of the evidence custodian/alternate evidence
custodian, or the security officer, and upon loss or suspected loss of evidence or when a breach of
security is known/suspected. If the inventory required for the replacement of the evidence
custodian/alternate occurs within 2 months of the regularly scheduled semi-annual inventory, it
may be substituted for that inventory.
c. Inventories shall be accomplished by the evidence custodian, the security officer, and a
disinterested third party. Additionally, if the inventory is required by the relief of the custodian,
it shall be conducted by the incumbent and the relieving custodian.
d. The inventory required by this instruction shall, at a minimum consist of a
reconciliation of the Evidence Log against the Active Evidence Custody Record and a visual
accounting of each item for which there is a log entry without final disposition and an ECD in the
Final Evidence Disposition File. The only exception to this sighting requirement shall be
evidence which has been temporarily transferred to another activity. Evidence which is stored
outside the command evidence locker because of its bulk, classification/other special nature, and
shall be sighted at each inventory, as it is not considered to have been temporarily transferred.
e. When the inventory is completed, an entry shall be made in the evidence log reflecting
the reason for the inventory, who inventory was conducted by, and the results. Participating
individuals will sign the log above their name and billet title. If the inventory was because of the
relief of a participant, the log entry shall also reflect that all combinations were changed. Any
discrepancies found shall be immediately reported, in writing, by the security officer to the
commanding officer. The security officer shall then cause the discrepancy to be fully
investigated and will make a final report on the discrepancy, its suspected cause, and actions
taken or recommended.
f. At commands with large amounts of active evidence, the signing of the Evidence Log
by both the incoming and outgoing evidence custodians attesting to the fact that they have
completed a visual sighting of each item and have found no discrepancies will complete the

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
6-6
transfer of evidence. This negates the need to record the transfer of evidence between evidence
custodians on each and every active ECD within the system. However, where holdings are small,
completing the ECD is still the preferred method of transferring evidence.
g. Sometime prior to the semi-annual inventory of evidence, the evidence custodian will
review the Active Evidence Custody File with the security officer in order to identify what
evidence may be logically considered for disposal.
h. During inspections, the inspector(s) may conduct a review of evidence custody
procedures by reviewing selected items of evidence, the associated documentation, and a sample
number of final disposal actions. This will not be considered as a substitute for required
inventories.
0607. TRANSFER AND SHIPMENT OF EVIDENCE
a. Temporary Transfer. When it is necessary to transfer evidence to another agency on a
temporary basis the original ECD will accompany the evidence. The evidence custodian, prior to
the release of the evidence, will sign the original and duplicate ECD. The duplicate will be
retained in the Active Evidence Custody File. Those persons handling the evidence prior to its
return to the evidence custodian will complete the appropriate blocks in the accompanying
original ECD. A receipt must be obtained from the receiving agency. In the event that only part
of the evidence will be temporarily transferred, the original ECD will accompany that part with
appropriate notations in the item column to the left of the transferring signature. A duplicate of
the original ECD will be reproduced and attached to the balance of the evidence maintained in
the evidence locker. Upon return of the original ECD, the duplicate may be destroyed.
b. Permanent Transfer. In the event that it is necessary to transfer evidence permanently
to another agency, the original ECD will accompany the evidence and will be signed out of the
evidence locker by the custodian. The duplicate copy in the Active Evidence Custody Record
will be executed by the evidence custodian, and the final disposition portion will be completed
by the agency representative receiving the evidence. The appropriate disposition entry will also
be made in the bound evidence log. The duplicate copy will then be filed in the Final Evidence
Disposition File. In the event that the receiving agency does not accept all the evidence listed on
the ECD, the original form will be retained with the balance of the evidence in the evidence
locker. The agency representative shall receipt for that portion of the evidence taken by an
appropriate entry on the form, and shall be provided a copy of the original form. The final
disposition of the evidence will not be entered in the bound evidence log until all evidence listed
in the ECD has been disposed of.
c. Transfer to other naval commands. When evidence is transferred to another naval
command, the original ECD will be transmitted with the evidence. In the event that only part of
the evidence is transferred, the original will be forwarded and a copy attached to the balance. If it
is known prior to transfer that part of the evidence will not be needed, the original ECD will be
retained and a copy forwarded with the evidence. The command receiving the evidence will

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
6-7
continue to use the custody document attached to the evidence. The item(s) of evidence will be
logged the same as any others including the assignment of a new evidence log number. The entry
in the bound evidence log will show the new number followed by the log number (in
parentheses) of the originating component, [e.g., 085-94 (244-95)]. The new number will also
be placed on the ECD just above the original number. The receiving component will then
reproduce a copy of the ECD and place it in its Active Evidence Custody File. The component
which transferred the evidence (if all its evidence was in fact transferred) will remove its copy of
the ECD from its active file, appropriately annotate the disposition portion, and place the
document in the Final Evidence Disposition File.
d. Transfer by mail. Whenever possible, transferred evidence will be hand delivered.
Evidence which is to be mailed must, in all cases, be registered and a return receipt requested.
The registered mail receipt and the return receipt will be stapled to the ECD in the Active
Evidence Custody File. If the transfer is permanent, the receipts will become a permanent part of
the system by inclusion in the final disposition file with the document. When evidence is
prepared for mailing, it will be double-wrapped with the inner wrapping marked to indicate the
presence of evidence. The package must be specifically addressed to the evidence custodian.
0608. DISPOSAL OF EVIDENCE.
a. Approval for the disposal of evidence shall be requested in writing to the commanding
officer. Authority, if given, will be indicated by endorsement.
b. Evidence which was used in any courts-martial action shall not normally be disposed
of until the trial and subsequent appeals have been completed. Authorization for disposal must
be obtained from the trial counsel handling the trial, or the judge advocate of the next senior in
command if on appeal. If the evidence was used in federal, state, or other civilian court, the
authorization must be obtained from the appropriate prosecuting attorney prior to disposal.
When authorization for disposal is received, the evidence custodian shall complete the final
disposition section of the ECD by recording the name and title of the person authorizing the
disposal.
c. Any evidence which was used in any administrative process shall not be released until
all appeals or reviews of the initial action are completed. Prior to disposal of such evidence,
authorization shall be obtained from the judge advocate or command legal officer of the
command which has cognizance over the person against whom the action was taken. In the event
of their absence, their counterparts at the next senior command should be contacted. When
authorization is received, the evidence custodian shall complete the final disposition section
of the ECD indicating the name and title of the person authorizing the disposal.
d. Any evidence which is entered in the evidence system and which is not used in judicial
or administrative action may be disposed of after a period of 6 months, or sooner if it becomes
obvious that it has no evidentiary value whatsoever, or if early disposal is directed by the

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
6-8
commanding officer or staff judge advocate. Extreme care must be taken in early disposal since
the original incident may later indicate that the evidence should have been retained.
e. In significant unresolved cases evidence should be retained until expiration of the
statute of limitations. Such disposal may be authorized by the security officer after consulting
with the requestor and the staff judge advocate. In such cases, the evidence custodian will
complete the final disposition section of the ECD showing the security officer as the authorizing
official.
f. Active evidence belonging to ships, stations, or units scheduled for decommissioning
or closure will be transferred to the nearest active evidence locker, as specified by the area
commander/coordinator, type commander, or Echelon 2 commander. Prior to the transfer, all
evidence which can be reasonably disposed of will be cleared from the locker and appropriate
ECD entries made.
0609. EVIDENCE DISPOSAL GUIDELINES
a. Evidence which is the personal property of an individual shall, whenever possible, be
returned to that person, with the exception of contraband/other unlawful items. When personal
property is returned to the owner or his/her authorized representative, the individual receiving the
property shall be required to sign in the disposition section of the original ECD (or copy, if the
original is absent). If the owner/representative presents a property receipt when making the
claim, the receipt shall be obtained and destroyed. In the event that the owner refuses to accept
all the property seized, this shall be noted on the ECD, and other appropriate disposal shall be
made of the property. In the event certain personal property, the possession of which is not
generally unlawful but is prohibited by command or installation orders, is entered into the
evidence custody system, the property shall be returned to the command having control over the
individual from whom it was obtained when it has served its purpose. It shall be necessary for
that command to receipt for the property and make a determination as to its disposition.
b. When evidence has been received which is the custodial responsibility of the authority
requesting the investigation, it shall be returned to the requestor's representative and that person
shall be required to receipt for it in the final disposition section of the ECD.
c. All U. S. government property which cannot be identified as belonging to a particular
activity or command shall be submitted to the activity supply department or the nearest Navy
supply activity. In addition to any documentation required by the receiving activity, the activity's
representative shall receipt for the material in the final disposition section of the ECD. In the
event that the activity declines to receipt for the property on the ECD, a suitable receipting
document shall be obtained and attached to the ECD.
d. U. S. government currency/negotiable instruments, which cannot be returned to a
rightful owner shall be turned in to the U. S. Treasury via the activity disbursing officer.
Enclosure (1)
6-9
e. Final disposition on government owned weapons will be in accordance with and
comply with reference (i).
f. Evidence which cannot be returned to the owner/entered into the Navy supply system
for disposal, such as drugs, illegal firearms, or other contraband, shall be destroyed. Such
destruction shall be accomplished by or in the presence of the evidence custodian/alternate and a
disinterested party, both of whom shall sign the final disposition section of the ECD.
g. Under no circumstance will any evidence be converted for use by a Navy component
or for the personal use of any individual within/without the Department of the Navy. Releasing
controlled substance evidence for use as training aids to Navy drug detector dog teams or for the
purpose of "controlled burns" or making a training aid display boards is not authorized.

Enclosure (1)
OPNAVINST 5580.1A
26 JUL 2000
CHAPTER 7
COMMUNICATIONS
0701. General
0702. Radio Communications
0703. Wire and Oral Communication Intercepts
0704. Standard Navy 10-Code and Response Codes

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
7-1
CHAPTER 7
COMMUNICATIONS
0701. GENERAL. General communications requirements are contained in reference (b).
0702. RADIO COMMUNICATIONS.
a. Radio will be the primary means of communications between the dispatcher and field
personnel.
b. Access to the security department communications areas will be strictly controlled and
protected to the maximum extent possible.
c. The role of the dispatcher is an important one. Without a trained, qualified dispatcher,
police communications can be crippled. Security department dispatchers will be specifically
trained in their duties, with formal commercial or police training highly recommended.
d. Communications policies:
(1) Security departments must have radio communication practices that are standard
from base to base, and are compatible with most other law enforcement agencies. Personnel
transferring within the security field will not be required to learn a new radio code with each
transfer.
(2) All security departments will use plain language transmissions, with an abbreviated
10-Code. The codes specified in section 7-4 will be the standard 10-Code for the security
department.
(3) The standard phonetic alphabet will be used for clarity and standardization.
0703. WIRE AND ORAL COMMUNICATION INTERCEPTS.
a. Recording an interview or interrogation electronically is acceptable and encouraged,
provided the subject is aware of the recording. If the interview or interrogation is to be recorded,
ensure the subject openly acknowledges the recording. This can be done in writing or verbally
on the recording itself.
b. The Naval Criminal Investigative Service is designated as the only Department of the
Navy (DON) component authorized to conduct communication interceptions for law
enforcement purposes. No other DON command may conduct such intercepts.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
7-2
0704. STANDARD 10-CODE AND RESPONSE CODES
a. Standard 10-Code:
10-4 Acknowledged
10-6 Busy on assignment
10-7 Out of service
10-8 In service
10-9 Repeat
10-15 Prisoner in custody
10-19 Return to station
10-20 What is your location?
10-28 Registration or drivers license check
10-29 Check for wanted
10-38 Traffic stop
999 Need help - emergency.
b. Response Codes:
Code 1 - Routine response
Code 2 - Urgent response, without siren and lights
Code 3 - Emergency response, with siren and lights
Code 4 - No further assistance required.

Enclosure (1)
OPNAVINST 5580.1A
26 JUL 2000
CHAPTER 8
EMERGENCY VEHICLE POLICIES
0801. Authorized Emergency Vehicle Policies
0802. Inspection of Vehicles
0803. Emergency Response Policies
0804. Bicycle Patrols

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
8-1
CHAPTER 8
EMERGENCY VEHICLE POLICIES
0801. AUTHORIZED EMERGENCY VEHICLE (AEV) POLICIES
a. A security department vehicle shall be considered an AEV when it is equipped with
approved warning lights and an approved siren.
b. AEVs operated on naval installations in the United States will conform to the
emergency lighting requirements of the local state code. As a general policy, emergency lighting
on AEVs will be mounted on the roof of the vehicle with any additional operational lights
mounted on fenders, grills, etc. Security officers may authorize certain vehicles to have lights
inside of the vehicle on the dashboard or rear deck.
c. Vehicles operated on Navy installations in foreign countries will use flashing red or
red/blue combination lights as determined by local requirements.
d. AEVs will have a siren installed in conformance with local laws and codes. The siren
control shall be installed near/in combination with the vehicle's radio, and shall be placed in a
location which allows the driver to safely reach it while driving and wearing a seat belt.
Exceptions may be made only for unmarked vehicles where concealment of the radio and siren is
required.
e. AEVs will be equipped with seat and shoulder belts which must be used whenever the
vehicle is in motion.
f. In addition to the AEV equipment required by reference (b), each AEV will carry a fire
extinguisher, first aid kit, and highway warning signals (flares/reflective warning devices).
0802. INSPECTION OF VEHICLES
a. All AEVs will be maintained in a peak, safe operating condition. Each AEV shall be
inspected at 6-month intervals. Inspections shall be done by qualified personnel who will, at a
minimum, check the following:
(1) Steering system - For any worn or loose parts and for proper adjustment.
(2) Brakes - For adequate lining and adjustment.
(3) Tires - For wear and alignment. (Retreaded tires will not be used).
(4) Seat belts - For proper operation and wear.
(5) Shock absorbers - For wear and alignment.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
8-2
(6) All driving/running lights - Operating properly.
(7) Emergency lights and sirens - Functioning properly.
b. AEVs will be checked prior to the start of each patrol using a checklist developed by
the security officer. In the event items of a safety nature (such as defrosters, wipers, brakes, etc.)
are not functioning properly, the vehicle shall not be used as an AEV until repairs have been
accomplished.
c. The security department shall maintain a record of each semi-annual safety inspection
on each AEV. These records shall include the date of the inspection, agency performing the
inspection, and results. In the event unsafe conditions are found, a record of the corrective
action, by whom accomplished, and date accomplished will be recorded.
0803. EMERGENCY RESPONSE POLICIES.
a. Definition. Emergency response is the rapid movement of police personnel in reaction
to a serious incident. AEV response generally involves the following factors:
(1) The use of flashing/steady burning warning lights on the moving police vehicle.
(2) The use of an audible siren on the moving police vehicle.
(3) Operation of the police vehicle in excess of the posted speed limit. Emergency
vehicle response is necessary in only two types of situations: (1) where there is a need to have
police personnel at the scene of a serious incident faster than they could arrive without
emergency response, and (2) when it is necessary to pursue an individual suspected of violating
the law. Emergency vehicle response will be authorized only in those situations set forth in this
section, and only when the safety of everyone involved has been considered.
b. Emergency equipment may be used in certain non-emergency situations, e.g., traffic
stops, to warn of hazards, accidents, disabled vehicles, funeral escorts, traffic escorts, etc.
c. The use of an emergency vehicle to lead a non-emergency vehicle on the roadway
under emergency conditions is prohibited. This situation often occurs when a motorist is
transporting a sick or injured person and seeks police assistance. Police personnel should either
call for medical assistance at the scene, transport the person in the police vehicle, or provide a
non-emergency escort, as appropriate.
d. Emergency vehicle operation:
(1) The person initiating the emergency movement of the AEV will immediately
broadcast that fact as soon as possible, and indicate the location, direction of travel, description
of the vehicle and occupants, reason for the pursuit, changes of location and direction of travel
during the pursuit, and location at the time the pursuit is terminated.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
8-3
(2) The patrol or shift supervisor may alter or terminate the emergency response of a
patrol unit.
(3) Police personnel may violate traffic laws while operating AEVs when it is
absolutely necessary, and when emergency lights and siren are engaged. Any driver of an AEV
becoming involved in an accident while violating the law, even under emergency conditions, may
be held accountable.
(4) Security department personnel operating unmarked vehicles may engage in pursuit
only when the fleeing vehicle represents an immediate and direct threat to life or property.
Whenever a marked vehicle becomes available to take over the pursuit, the unmarked vehicle
will withdraw.
(5) Unless otherwise directed by the shift or patrol supervisor, no more than two patrol
vehicles will become actively involved in a pursuit. Other patrolmen should be alert to the
pursuit progress and locations.
(6) Patrolmen will not attempt to halt a suspect vehicle in a pursuit by striking the
suspect's vehicle with the patrol vehicle.
(7) Navy law enforcement personnel are not authorized to engage in high speed pursuit
off-base. In situations where a suspect refuses to stop on-base, personnel should alert the gate(s)
via radio. Also have the dispatcher notify civilian law enforcement authorities, giving them a
description of the vehicle and the nature of charges suspected. It is permissible, in instances of
serious crimes committed on-base, for Navy law enforcement personnel to continue following
the subject vehicle off-base providing they comply with all traffic laws and regulations and,
furthermore, there is a command policy authorizing personnel to do so. Policies will be specified
in a standard operating procedure (SOP); the SOP will be reviewed and approved by a judge
advocate general.
0804. BICYCLE PATROLS. Bicycles may be used at the discretion of the command. If
bicycles are used, the following minimum standards will apply:
a. Bicycles will be of the mountain/off-road or hybrid type. The bicycle will be clearly
marked "Police" in a prominent fashion. The bicycles will be equipped with quick-release clips
on the wheels and seat post.
b. Bicycle equipment will include safety gear required for new bicycles (brakes and
reflectors), and will include front and rear lights (to be used during all periods of reduced
lighting), a rear rack, and a rack bag and/or panniers to carry administrative items, baton,
flashlight(s), and foul weather gear. Equipment to be carried will include:
(1) First aid kit.
(2) Bicycle repair kit (to include tools of the types and sizes necessary for that
OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
8-4
particular bicycle), a tire patching kit and/or one spare tube, tire pump, and a tire air gauge.
(3) At least one water bottle rack with water bottle.
(4) If pedal foot retainers are attached, they will be of the clipless variety.
c. Personnel assigned as bicycle patrolmen will be:
(1) Experienced in on and off-road bicycling, and capable of handling equipment
repairs which could be expected to occur. Formal training will be provided, if locally available.
(2) Physically capable of riding the bicycle in the type terrain present at the command.
Because of conditioning required, persons not qualifying in the past Physical Readiness Test will
not be assigned as bicycle patrolmen until minimum physical standards are achieved.
(3) Equipped with an American Standard Testing Methods/American National
Standards Institute-approved bicycle helmet, shatter-resistant bicycle glasses (clear and shaded
lenses), padded gloves (regular or finger less), and padded shorts (or padded long-pants for
colder weather). Other shorts/pants may be issued to be worn over the padded shorts, if desired.
Footwear may be of the "gym-shoe" variety or of the "hiking boot" type to protect against ankle
injuries.
(4) Patrolmen will be issued a portable radio capable of being carried on the belt.

Enclosure (1)
OPNAVINST 5580.1A
26 JUL 2000
CHAPTER 9
TRAFFIC, VISITOR CONTROL AND IMPOUNDING VEHICLES
0901. General
0902. Radar Policies
0903. Issuance of Traffic Tickets
0904. Intoxicated Drivers
0905. Traffic Accidents
0906. Decals and Visitor Passes
0907. Impounded Vehicles
OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
9-1
CHAPTER 9
TRAFFIC, VISITOR CONTROL, AND IMPOUNDING VEHICLES
0901. GENERAL. Development of traffic policies will be geared toward efficiency, safety, and
service to the public. The primary purpose of these policies will be to regulate traffic flow,
reduce traffic accidents, and make streets safer for drivers and pedestrians.
0902. RADAR POLICIES
a. Each RADAR unit will be tested at least annually at a precision measurement agency or
laboratory. Records of the maintenance, calibration, and repair of RADAR units will be retained
for 2 years.
b. An external test for accuracy of each unit's operation must be conducted before the unit
is placed in operation. If a test is conducted after each violation, it should be recorded on the file
copy of the traffic ticket (serial number of the tuning fork and results of the test). Damaged
tuning forks which do not give an accurate frequency reading must be replaced.
c. Operators must demonstrate proficiency with RADAR equipment. Training programs
must take into consideration local, legal, and certification requirements. In addition, hands-on
training in the field and a reasonable period of practice will be conducted under the guidance of a
field training officer before an operator is allowed to issue a traffic ticket.
0903. ISSUANCE OF TRAFFIC TICKETS
a. Each security officer will develop standard operating procedures (SOPs) regarding
traffic control and the issuance of traffic tickets. The SOPs will include use of RADAR, traffic
stop procedures, issuance of traffic tickets, distribution of the tickets, and traffic court appearance
requirements. Only U. S. Armed Forces/U. S. magistrate tickets (DD 1408 and 1805) will be
issued.
b. Only the U. S. Magistrate or commanding officer of the installation (depending on the
type ticket issued) will negate military or U. S. magistrate traffic tickets. If the security officer
decides that a traffic ticket should be negated due to gross administrative errors, the reason for
voiding the ticket will be written on the back of the ticket.
0904. INTOXICATED DRIVERS
a. Standardized field sobriety tests and other procedures for processing suspected
intoxicated drivers will be developed by the security officer and be published via SOP.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
9-2
Observations of law enforcement personnel will be recorded on the Alcohol Influence Report
(DD 1920).
b. The blood alcohol content (BAC) will be determined via blood, breath, or urine test.
The BAC required to prove intoxication will be based on host state or country requirements.
Each command will develop a SOP regarding driver refusal to be tested under "implied consent"
laws.
c. A person being tested does not have the right to have an attorney present before stating
whether he/she will submit to a test, or during the actual test.
d. Police personnel will ensure that the vehicle operated by the intoxicated driver is
properly secured at the scene of the apprehension, turned over to a sober driver with the
authorization of the owner, or towed from the scene and impounded.
0905. TRAFFIC ACCIDENTS
a. The DoN Traffic Accident Report (OPNAV 5580/1A) shall be completed in
accordance with reference (k). This includes all fatal, personal injury or property damage
accidents involving government vehicles. The same rule applies for privately owned vehicle
accidents except the combined property damage must be $1,000.00 or more before an accident
report is required.
b. Photographs should be taken at the scene of all reportable accidents and they are
required whenever a government vehicle or government property is involved.
c. Public Works Departments will provide the damage estimate on government owned
property and vehicles.
0906. DECALS AND VISITOR PASSES
a. General procedures for the issuance of Department of Defense (DoD) decals are listed
under reference (o). In issuing a DoD decal, the following documents will be checked:
(1) DoD identification card (active duty, retired, dependent, reserve, or civilian).
(2) Certificate of state registration.
(3) Valid state driver's license.
b. When visitors who do not have a DoD decal come aboard the base they must receive a
visitor's pass. In order to obtain such a pass, they will:
(1) Show a valid driver's license and vehicle registration certificate/rental vehicle
agreement.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
9-3
(2) Fill out a log which will include name, home address, destination, make and model
of vehicle, license plate number, sponsor, time of arrival, and estimated time of departure.
c. A "barred list" will be prepared by the security officer and will be checked prior to the
issuance of a decal or visitor pass.
d. DoD decals and visitors passes will be strictly controlled and accounted for by serial
number. Unused decals and passes will be securely stored to prevent theft.
0907. IMPOUNDED VEHICLES
a. Command policies for the impoundment of vehicles must be clearly defined by
command directive and publicized so that operators of motor vehicles on base are informed of
the policy.
b. Security officers will prepare a SOP specifying the impoundment procedures to be
used by the security department. Included will be the procedures to be followed prior to
impoundment (e.g., notification of owner), procedures used for the actual impoundment (method
of transportation, stowage, and inventories), required documentation, protection of the vehicle
while impounded, and release/disposal of the vehicle.
c. When vehicles are impounded because of the death of the owner, close coordination
with the Staff Judge Advocate and the supply officer are required.

Enclosure (1)
OPNAVINST 5580.1A
26 JUL 2000
CHAPTER 10
CRIME PREVENTION
1001. General
1002. Responsibilities
1003. Surveys

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
10-1
CHAPTER 10
CRIME PREVENTION
1001. GENERAL
a. Crime prevention is the anticipation, recognition, and appraisal of a crime risk and the
initiation of some action to remove or reduce it. Crime prevention is a pro-active method to
reduce criminal opportunities, protect potential victims, and prevent property loss.
b. The Navy Crime Prevention Program is directed at the quality of life in the Navy. It
presents military personnel, civilian employees, and dependents with programs designed to
reduce their chances of becoming the victim of a crime.
1002. RESPONSIBILITIES
a. The security officer of the host activity will establish a crime prevention program at
the installation, providing assistance to tenant activities, if requested. This includes:
(1) Designating a Crime Prevention Coordinator within the security department.
(2) Publishing standard operating procedures for crime prevention.
(3) Maintaining an active liaison with NCIS, local law enforcement agencies, and
other organizations to provide for an exchange of crime prevention-related information.
(4) Offering crime prevention services. This includes crime prevention briefings and
surveys.
(5) Participation in crime prevention campaigns to highlight specific crime problems
for intensified public awareness efforts. When possible, Navy campaigns should coincide with
national crime prevention campaigns.
(6) Making crime prevention practices a part of the daily operations of the security
department, involving all members of the department.
(7) Using all available records and information, develop and maintain trends and
analysis information.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
10-2
b. The Naval Criminal Investigative Service, Law Enforcement and Physical Security
Assistance Teams, Atlantic and Pacific (LEPSAT LANT/LEPSAT PAC), have personnel trained
in crime prevention who can provide assistance in developing or improving security department
crime prevention programs. On-site crime prevention training and assistance can be obtained by
contacting:
c. Officer in Charge, NAVCRIMINVSERV LEPS ASST TEAM, ATLANTIC, Norfolk,
VA; commercial 757-462-7893 or DSN 253-7893, or
d. Officer in Charge, NAVCRIMINVSERV LEPS ASST TEAM, PACIFIC, San Diego,
CA; commercial 619-545-9427 or DSN 735- 9427
1003. SURVEYS. Crime prevention surveys will be conducted for living quarters (both
residential and barracks), at non-appropriated fund/retail activities, and at Morale, Welfare and
Recreational facilities on request. These surveys are designed to assess the vulnerability of the
location as a target for crime and to provide recommendations to reduce the vulnerability. The
security department should keep a record of all crime prevention surveys conducted and follow-
up to see if recommendations made have been completed.

Enclosure (1)
OPNAVINST 5580.1A
26 JUL 2000
CHAPTER 11
JUVENILE MATTERS
1101. General
1102. General Procedures
1103. Records

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
11-1
CHAPTER 11
JUVENILES
1101. GENERAL
a. The age limits for classifying persons as juveniles vary according to the laws of the
particular state. Federal law defines a juvenile as "any person who has not attained his 18th
birthday."
b. Active duty military personnel under the age of 18 are subject to the Uniform Code of
Military Justice and are not affected by juvenile laws.
c. The security officer of each installation will become familiar with host State juvenile
statutes and prepare standard operating procedures defining actions to be taken with juvenile
offenders aboard installation property.
1102. GENERAL PROCEDURES
a. Whenever a juvenile is taken into custody for an offense or other act of delinquency,
the juvenile must be provided with the appropriate constitutional warning against self-
incrimination. This warning must be provided in language which the juvenile understands.
b. The parent(s), guardian, or custodian must be notified that the juvenile is in custody,
the exact nature of the alleged offense, and the juvenile's rights against self-incrimination. This
notification must be made immediately after the juvenile is taken into custody and the
identification of the responsible adult is obtained. The time of the custody, the time of the
notification, and the identity and relationship of the person notified must be reported in the
Incident Report (IR). This notification is the responsibility of the detaining agency and must be
made even if the matter is referred to the Naval Criminal Investigative Service (NCIS) or other
agency. As Department of the Navy (DON) policy, the parent, guardian, or custodian must be
given a reasonable opportunity to be present during any interrogation of the juvenile. If the adult
cannot be present for any reason, the reason for the absence will be indicated in the IR.
c. Fingerprints or photographs of a juvenile may be taken. These records must be
safeguarded under 18 U.S.C. 5038, et. seq. Some states prohibit fingerprinting/ photographing of
juvenile offenders without a written order of a judge/magistrate. The staff judge advocate should
be consulted for establishing local policy.
d. Federal law and DON policy requires that a juvenile in custody be taken before a local
magistrate at the first opportunity, and that a juvenile shall not be detained for longer than a
reasonable period of time before being brought before a magistrate. As a practical matter,
juveniles detained by Navy law enforcement personnel for minor offenses are normally released
to the custody of their parents.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
11-2
e. In many instances, a minor offense can be disposed of without delay. Serious offenses,
or offenses involving repeat offenders, may require administrative or judicial action.
(1) Offenses under the jurisdiction of NCIS will be referred to NCIS at the earliest
possible time. Juveniles detained on offenses under NCIS jurisdiction will be turned over to
them at their request, provided there is no unreasonable delay.
(2) Within U. S. jurisdiction, juvenile offenders will be referred to local police juvenile
authorities. Security officers will establish liaison with local police to develop working
agreements for the referral of juveniles.
f. There are no special requirements concerning the interview of a juvenile as a witness.
During the on-scene phase of any incident, juveniles may be interviewed in the same manner as
any other witness. As a matter of policy, however, in-depth or follow-up interviews of juveniles
will not be conducted without first advising a parent, guardian, or custodian of the nature of the
situation and the need to interview the juvenile.
1103. RECORDS
a. The age of an offender has no effect on the need for detailed and accurate records of
any incident or complaint. An IR will be prepared on each situation which fits the criteria for
that form.
b. Security departments will establish a separate file for the retention of records
concerning juvenile offenders. This file will be in a distinctly different location from adult files
to lessen the chance that a juvenile record will be placed in the adult IR files, and will preferably
be kept locked to prevent unauthorized disclosure. Access to this file will be restricted to
individuals specified by the security officer as having a need-to-know. Provided local state law
does not object, juvenile records may be released to:
(1) The judge of a juvenile court having jurisdiction over the offender.
(2) An attorney representing the juvenile and parents.
(3) A government attorney involved in the adjudication of the matter.
(4) Another court of law, in response to a specific inquiry.
(5) Another law enforcement agency, if the request is related to an investigation of a
crime or a position within that agency.
OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
11-3
(6) The director of a juvenile treatment facility or agency to which the juvenile has
been committed by the court, providing that the request is made in writing.
(7) An agency which is considering the juvenile for a position immediately and
directly affecting national security.
c. Neither the name or a photograph of any juvenile may be made public by any medium
of public information in connection with any juvenile delinquency proceeding.
d. Juvenile courts in the various states may impose additional requirements or restrictions
on security departments concerning juvenile records. These requirements may include the
sealing of records. Any such requests will be coordinated with the Staff Judge Advocate.

Enclosure (1)
OPNAVINST 5580.1A
26 JUL 2000
CHAPTER 12
PUBLIC AFFAIRS
1201. General
1202. Media Personnel Entering Closed Areas
1203. Exclusion of the Media from Certain Areas
1204. Briefing Rooms

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
12-1
CHAPTER 12
PUBLIC AFFAIRS
1201. GENERAL
a. Since security department personnel are regularly involved in events at which
members of the media are present, they will be trained in dealing with the media.
b. If contacted by the media, security department personnel will be courteous and brief
and refer the person making the inquiry to the Public Affairs Officer (PAO). It is the role of the
PAO to handle all matters with the media, and is the only person authorized to release
information to the media.
1202. MEDIA PERSONNEL ENTERING CLOSED AREAS. Duly authorized representatives
of the media, i.e., news services, newspaper, radio/television stations or networks, may enter an
area closed because of a menace to public health or safety, with the authorization of the on-scene
commander. Authorization for such entry will be based initially on the severity of the hazard
and/or authorization granted by competent authority. The decision to assume the risk of danger
remains with the media individual involved, and it is not the responsibility of security department
personnel to provide for the safety of these members of the media who voluntarily choose to
subject themselves to danger. Security department personnel, however, do have a moral and
professional obligation to protect and preserve human life and will cause the revocation of
authorization and removal of such media personnel when warranted.
1203. EXCLUSION OF THE MEDIA FROM CERTAIN AREAS. Media personnel do not
have, as a matter of right, special access to sensitive/secured areas of a military installation,
including designated Restricted Areas. The media may be permitted, by the commanding officer
or designated authority, into areas which have been secured from the general public. Generally,
they will not be allowed into areas secured to preserve evidence/where their presence may
jeopardize law enforcement operations. In addition, the media may be excluded from areas in
which classified information/equipment may be compromised.
1204. MEDIA BRIEFING ROOMS. During events which may generate above normal media
interest, special areas will be designated as media briefing rooms. Here members of the media
may be segregated and briefed by the designated PAO as events unfold. Media briefing rooms
will not be situated where they could interfere with operations.

Enclosure (1)
OPNAVINST 5580.1A
26 JUL 2000
CHAPTER 13
BLOODBORNE PATHOGENS (BBP)
1301. General
1302. Applicability
1303. Responsibility
1304. Recommended BBP Protective Equipment
1305. Hepatitis B Virus Vaccine Declination Letter

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
13-1
CHAPTER 13
BLOODBORNE PATHOGENS
1301. GENERAL
a. This chapter introduces Navy law enforcement and physical security personnel to the
threat of infection from bloodborne pathogens (BBPs). Complete guidance of this topic should
be obtained through knowledge of, and adherence to 29 CFR 1910.1030, Occupational Exposure
to Bloodborne Pathogens; reference (l); local instructions; the installation safety officer, and
medical department.
b. There is a tendency to think of BBPs in terms of Human Immunodeficiency Virus
(HIV) and Hepatitis B Virus (HBV), but other infectious diseases, e.g., malaria/syphilis could be
present in human blood. In addition to blood, law enforcement/security personnel should protect
themselves against exposure to other blood products, human tissue, body organs, and bodily
fluids.
c. The gravity of this subject can not be understated since exposure, without taking
preventive measures/seeking immediate treatment, can be fatal.
1302. APPLICABILITY. This chapter applies to all law enforcement/security personnel,
military and civilian, who engage in any one or more of the following activities:
a. Patrol
b. Investigations
c. Evidence collection/processing/custodians
d. Field supervision, including security officers/chiefs of police who might be called to
crime scenes
e. Brig duty
f. Urinalysis coordination
g. Other duty exposing law enforcement/security personnel to human blood, body fluids
or tissues.

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
13-2
1303. RESPONSIBILILTY
a. Security Officer. The security officer shall coordinate all issues involving BBPs with
the activity safety officer. These issues should include but not be limited to:
(1) Provide input for the Exposure Control Plan
(2) Ensure law enforcement/security personnel are trained in risk reduction from
exposure to BBPs.
(3) Ensure all law enforcement/security personnel are offered HBV vaccine (at no
charge to civilian employees), and if declined they are aware that they may receive the vaccine at
any time in the future. In the event an individual declines after being offered the HBV vaccine,
the declination must be in writing and filed per reference (l)/prevailing instruction from the
installation safety officer.
(4) Establish procedures for immediate medical attention for security personnel
exposed to BBPs or those thought to have been exposed to BBPs.
b. All Law Enforcement/Security Personnel. Personnel who perform the tasks identified
in paragraph 13-2 may be exposed to BBPs. These tasks (and many too numerous to list) could
place law enforcement/security personnel at risk, but as first responders, they would encounter a
host of situations conducive to BBP exposure. At an absolute minimum, personnel must:
(1) Be aware of the risks incurred when exposed to BBPs.
(2) Receive or have been offered but declined, the HBV vaccine.
(3) Have issued to them/immediately available, sufficient protective equipment, and
properly instructed in its use. Not all protective equipment is necessary under every
circumstance. The risk level for exposure will dictate the level of protection necessary, e.g., in a
pat-down search of a person a pair of latex/surgical type gloves may be required. If blood, urine
or feces is apparent at the scene, gloves and other protective equipment may be necessary before
conducting a body search.
(4) Be cautious in the handling and storage of evidence/contraband which may be
infectious. Of great concern is being stuck by hypodermic needles. This may occur from:
(a) Search of persons

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
13-3
(b) Search of vehicles, including police vehicles after transporting personnel
placed in custody
(c) Search of premises, including lockers, closets, and other areas
(d) Recovery of lost/stolen property or during inventory of containers, e.g.,
suitcases, foot lockers, vehicle trunks, etc.
(e) Handling of stored evidence or while preparing evidence for shipment.
c. Extreme caution should be exercised when apprehending suspects who might
intentionally inflict injury in order to infect the apprehending officer. This may occur by biting,
scratching/attempting to throw or smear blood, saliva or bodily fluids on the apprehending
officer.
1304. RECOMMENDED BBP PROTECTIVE EQUIPMENT
a. Latex gloves
b. Face mask - Fluid resistant
c. Safety glasses - Clear with side guards and impact resistant
d. Contamination control coveralls - With attached hood and boots
e. Biohazard waste bags - Red color labeled "Infectious Waste" with international
biohazard symbol, and
f. Hand wipes - Antimicrobial.
1305. HBV VACCINE DECLINATION LETTER. A sample HBV declination may be found on
page 13-4.
OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
13-4
-SAMPLE-
HEPATITIS B VACCINE
DECLINATION
I understand that due to my occupational exposure to blood or other potentially infectious
materials I may be at risk of acquiring Hepatitis B Virus (HBV) infection. I have been given the
opportunity to be vaccinated with Hepatitis B vaccine, at no cost to me. However, I decline the
Hepatitis B vaccination at this time. I understand that by declining this vaccine, I continue to be
at risk of acquiring HBV, a serious disease. If in the future I continue to have occupational
exposure to blood or other potentially infectious materials and want to be vaccinated with
Hepatitis B vaccine, I can receive the vaccination series at no charge to me.
Printed Name _______________________________________
Date __________________________
Signature ______________________________________
SSN ___________________________________________

Enclosure (1)
CHAPTER 14
DOMESTIC VIOLENCE REPORTING
1401. General
1402. Security Department Response to Domestic Violence Calls
1403. Patrol Response
1404. Domestic Violence Unit
1405. Reporting Responsibilities
1406. Military Protective Order

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
14-1
CHAPTER 14
DOMESTIC VIOLENCE
1401. GENERAL
a. The role of law enforcement in domestic incidents has become a coordinated
community response that includes police, medical, family advocacy and the command or civilian
court system. Standard Operating Procedures should be published, by each law enforcement
agency, detailing the response to the scene and subsequent coordination with the Staff Judge
Advocate, Family Advocacy Officer, Family Service Center and the Naval Criminal Investigative
Service. The security department’s role in the response is as follows:
(1) Receive, report and identify domestic violence on and off the installation
(2) Complete an on-scene investigation and initiate follow-up investigation
(3) Write a thorough report
(4) Make appropriate notifications
(5) Aid in the issuance of Military Protective Orders (MPOs)
(6) Enforce and track civilian and MPOs.
1402. SECURITY RESPONSE TO DOMESTIC VIOLENCE CALLS
a. Dispatcher - Upon receipt of a report of domestic violence the dispatcher must collect
the pertinent data of who, what, when, where, why and how and also determine if a weapon is
involved or available. The first priority is to determine if there are any injuries and appropriate
medical services are dispatched if injuries are reported. Dispatchers should keep the calling party
on the line to give patrol responders current updates on the situation. Additionally, the dispatcher
should check available data bases to see if there has been previous trouble at that location and if
there is a weapon or weapons registered at the location of the complaint.
b. Time and resources available, the dispatcher should check with local law enforcement
agencies to determine if they have a record of domestic violence at the location of the event or
persons involved.
c. In all instances, the watch commander should be apprised of the disturbance call and a
backup to the assigned unit should be automatically dispatched to the scene.
1403. PATROL RESPONSE. Patrol personnel have to be vigilant when responding to domestic
violence calls. The potential for danger is heightened by some common factors generally

OPNAVINST 5580.1A
26 JUL 2000
Enclosure (1)
14-2
associated with domestic violence situations. Some of these factors may be extreme anger,
alcohol or drug involvement, mutual combat between disputants, weapons use or availability of
weapons at the scene and the law enforcement officers perceived encroachment or involvement
in “personal matters”. Patrol officers must, therefore, rely on their training in domestic
intervention and conflict resolution. Enclosure (5) to reference (p) entitled GUIDANCE FOR
LAW ENFORCEMENT AND OTHER FIRST RESPONDERS IN SPOUSE ABUSE CASES
addresses the basic responsibilities for first responders.
1404. DOMESTIC VIOLENCE UNIT. Wherever there is an established Domestic Violence
Unit (DVU) policies and procedures contained in the MOU or MOA will be adhered to. DVUs
are composed of personnel specially trained and readily available to handle domestic violence
incidents. Where DVUs exist, they may be the primary or first responders to a domestic
complaint and patrol personnel might be called upon to simply assist or back up the DVU until
the situation calmed. This may also apply whenever there is an agreement with civil authorities
having concurrent jurisdiction with Navy law enforcement on properties located within or
outside the installation proper.
1405. REPORTING RESPONSIBILITIES. In addition to a copy of the incident report going to
the command, a copy must also be forwarded to the Family Advocacy Program staff. Whenever
there are injuries reported, the responding unit(s) should fully describe the injuries and secure
photographic evidence of the injuries. If the NCIS or the DVU is not available or does not
assume responsibility for following up this investigation, the law enforcement department should
also secure a medical report (if one is available) for inclusion as an exhibit to this investigation.
1406. MILITARY PROTECTIVE ORDER. Where warranted, a Military Protective Order
(MPO) should be procured from the command.
A-1
APPENDIX A
TABLE OF REFERENCES
(a) SECNAVINST 5530.4C, Subj: Naval Security Forces Ashore and Afloat
(b) OPNAVINST 5530.14C, Subj: Navy Physical Security Manual
(c) OPNAVINST 3120.32C, Subj: Standard Organization and Regulations of the U.S. Navy
(d) SECNAVINST 5520.3B, Subj: Criminal and Security Investigations and Related
Activities Within The Department of the Navy
(e) Manual for Courts-Martial, United States 1998
(f) SECNAVINST 5211.5D, Subj: Department of the Navy Privacy Act Program
(g) SECNAVINST 5500.29B, Subj: Use of Deadly Force and the Carrying of Firearms by
Personnel of the Department of the Navy in Conjunction With Law Enforcement, Security
Duties, and Personal Protection
(h) OPNAVINST 3591.1C, Subj: Small Arms Training and Qualification
(i) OPNAVINST 5530.13B, Subj: Department of the Navy Physical Security Instruction for
Conventional Arms, Ammunition, and Explosives (AA&E)
(j) SECNAVINST 1640.9B, Subj: Department of the Navy Corrections Manual
(k) OPNAVINST 11200.5C, Subj: Motor Vehicle Traffic Supervision
(l) OPNAVINST 5100.23E, Subj: Navy Occupational Safety and Health (NAVOSH)
Program Manual
(m) SECNAVINST 5800.11A, Subj: Victim and Witness Assistance Program
(n) OPNAVINST 5800.7, Subj: Victim and Witness Assistance Program
(o) OPNAVINST 5560.10B, Subj: Standard Procedures for Registration and
Marking of Non-Government Owned Motor Vehicles
(p) OPNAVINST 1752.2A, Subj: Family Advocacy Program
OPNAVINST 5580.1A
26 JUL 2000
B-1
APPENDIX B
FORMS
The Standard Subject Identification Code (SSIC) for all OPNAV 5527 forms has been changed
from 5527 to 5580. Use of OPNAV 5527 forms will continue until existing stocks are
exhausted. When ordering forms, cite the OPNAV 5527 form stock number as cited below.
OPNAV 5580 forms will be issued automatically as stocks of the old forms are exhausted.
OPNAV 5512/2 (6-81) - Authorization to Carry Firearms S/N 0107-LF-055-1400
OPNAV 5527/1 (6-98) - DoN Incident Report S/N 0107-LF-114-9600
OPNAV 5527/1A(2-83) - DoN Traffic Accident Report S/N 0107-LF-055-2707
OPNAV 5527/1B (6-98)- DoN Incident Report/Addendum- S/N 0107-LF-114-9700
Narrative
OPNAV 5527/1C (6-98) - DoN Incident Report/Addendum- S/N 0107-LF-114-9800
Complainant/Witness/Sponsor
OPNAV 5527/1D (6-98) - DoN Incident Report/Addendum- S/N 0107-LF-114-9900
Victim
OPNAV 5527/1E (6-98)- DoN Incident Report/Addendum- S/N 0107-LF-115-0000
Suspect/Arrestee
OPNAV 5527/1F (6-98)- DoN Incident Report/Addendum- S/N 0107-LF-115-0100
Offense
OPNAV 5527/1G (6-98)- DoN Incident Report/Addendum- S/N 0107-LF-115-0200
Property
OPNAV 5527/2 (12-82)- DoN Voluntary Statement S/N 0107-LF-055-2710
OPNAV 5527/3 (12-82) - DoN Military Suspect's S/N 0107-LF-055-2715
Acknowledgment and Waiver
of Rights
OPNAVINST 5580.1A
26 JUL 2000
B-2
OPNAV 5527/4 (12-82) - DoN Civilian Suspect's S/N 0107-LF-055-2720
Acknowledgment and Waiver
of Rights
OPNAV 5527/5 (12-82) - DoN Lineup-Acknowledgment S/N 0107-LF-055-2725
and Waiver of Rights
OPNAV 5527/6 (12-82) - DoN Investigative Notes S/N 0107-LF-055-2730
OPNAV 5527/7 (12-82) - DoN Interview/Interrogation S/N 0107-LF-055-2735
Log
OPNAV 5527/8 (12-82) - DoN Telephonic Threat S/N 0107-LF-055-2740
Complaint
OPNAV 5527/9 (12-82) - DoN Command Authorization S/N 0107-LF-055-2745
for Search and Seizure
OPNAV 5527/10 (12-82) - DoN Affidavit for Search S/N 0107-LF-055-2750
Authorization
OPNAV 5527/11 (12-82) - DoN Complaint of Stolen S/N 0107-LF-055-2755
Motor Vehicle
OPNAV 5527/12 (12-82) - DoN Vehicle Report S/N 0107-LF-055-2760
OPNAV 5527/13 (12-82) - DoN Customer Consent and S/N 0107-LF-055-2765
Authorization for Access to
Financial Information
OPNAV 5527/14 (12-82) - DoN Authority to Release S/N 0107-LF-055-2770
Medical Information and Records
OPNAV 5527/15 (12-82) - DoN Forensic Examination S/N 0107-LF-055-2775
Request
OPNAV 5527/16 (12-82) - DoN Permissive Authorization S/N 0107-LF-055-2780
for Search and Seizure
OPNAV 5527/17A (12-82) - DoN Evidence Tag (Index) S/N 0107-LF-055-2785
OPNAV 5527/17B (12-82) - DoN Evidence Tag (Adhesive) S/N 0107-LF-055-2787
OPNAV 5527/18 (12-82) - DoN Investigative Notes S/N 0107-LF-055-2790

OPNAVINST 5580.1A
26 JUL 2000
B-3
Envelope
OPNAV 5527/19 (12-82) - DoN Desk Journal S/N 0107-LF-055-2795
OPNAV 5527/20 (12-82) - DoN Field Test Results S/N 0107-LF-055-2800
OPNAV 5527/21 (12-82) - DoN Field Interview Card S/N 0107-LF-055-2805
OPNAV 5527/22 (12-82) - DoN Evidence/Property S/N 0107-LF-055-2810
Custody Document
OPNAV 5527/23 (1-83) - DoN Evidence Tape S/N 0107-LF-055-2815
OPNAV 5527/24 (2-83) - DoN Evidence Log S/N 0107-LF-055-2820
OPNAV 5527/25 (2-83) - DoN Law Enforcement S/N 0107-LF-055-2825
Communications Log
OPNAV 5527/26 (3/83) - DoN Command Investigator S/N 0107-LF-007-1200
ID Card
OPNAV 5527/27 (3-83) - DoN Fingerprint Card S/N 0107-LF-055-2835
(Major Case Prints)
OPNAV 5560/1 (7-78) - Non-Government Vehicle S/N 0107-LF-055-6005
Registration
DD 1408 (12-87) - Armed Forces Traffic Ticket S/N 0102-LF-001-4080
DD 1805 (9-98) - Violation Notice S/N 0102-LF-001-8053
DD 1920 (8-73) - Alcohol Influence Report S/N 0102-LF-068-4800
DD 2220 (11-79) - DoD Registered Vehicle Decal S/N 0102-LF-002-2205.

OPNAVINST 5580.1A
26 JUL 2000
-1
APPENDIX C
NAVY UNIFORM CRIME REPORTING SYSTEM
1. Purpose
The law enforcement agencies nationwide have periodically reviewed uniformed crime reporting
resulting in the Uniform Crime Reporting Act of 1988 and the development of the National Incident-Based
Reporting System (NIBRS). The revised OPNAV 5580/1 represents the Navy and Marine Corps
collection platform for NIBRS data. The Department of Justice receives statistical data based on NIBRS
guidelines, compiles the data, and publishes a "National Crime Report." Law enforcement agencies and
other organizations having legitimate interest use the Nation Crime Report for planning and policy.
Naval Security Force (NSF) and Marine Corps Military Police (MP) personnel use this form as a
means of collecting information, compiling it in a systematic fashion, and articulating the facts and
circumstances of criminal and significant incidents. The nature of our society requires reporting only facts
with direct bearing on the incident in question excluding personal opinions, biases, and vague statements (I
think... or I believe...). The form helps eliminate the sometimes ambiguous nature of the who, what,
where, why, and how approach to preliminary/initial investigation. This guidebook is a block by block
"How to.." instruction to assist the first responder in collecting and articulating the appropriate information
and to insure consistent language required by NIBRS is used Navy/Marine Corps wide. Sections which
are not-applicable or unknown should be left blank on the form.
2. Incident Report (OPNAV 5580/1)
The revised Incident Report (IR) OPNAV 55801/1 consists of four basic pages broken into Eleven
(11) Sections: Administrative, Complainant, Offense, Property, Victim, Witness/Sponsor, Suspect
/Arrestee, Additional Police Officers, Narrative, Reporting and Approving Official, and Administrative
Disposition. The IR also consists of a series of OPNAV 5580/1 forms considered addenda:
*OPNAV 5580/1A: Traffic Accident Report
OPNAV 5580/1B: Narrative
OPNAV 5580/1C: Witness/Complainant/Sponsor
OPNAV 5580/1D: Victim
OPNAV 5580/1E: Suspect/Arrestee
OPNAV 5580/1F: Offense
OPNAV 5580/1G: Property and Narcotics information
*OPNAV 5580/1H: Domestic Violence / Dispute Report
(*) Currently being revised but not available at this time.
a. ADMINISTRATIVE SECTION - This section is to be used for the recording of information
that is applicable to the entire report (e.g., incident number, date of incident). An incident is defined as
one or more offenses committed by the same offender (or group of offenders acting in concert at the same
time and place. Although multiple offender, victim, etc. sections can be submitted for each report, only
one Administrative Section should be completed for each Incident Report.

OPNAVINST 5580.1A
26 JUL 2000
-2
(1) Incident Number - This 12 character (alpha/numeric) number is assigned to each Incident
Report to identify it uniquely. The Incident Number shall begin with the last two (2) digits of the year
followed by the five (5) digit Unit Identification Code (UIC) or Reporting Unit Code (RUC) of the
Installation Security Department or Provost Marshal Office followed by the five (5) digit sequential
number.
Example (1): “970021500013" (“97"=year, ”00215"=UIC NAS Dallas and “00013" 13th
report of the year).
Example(2): “980014600013" ("98"=year, "00146"=RUC MCAS Cherry Point, PMO and
"00013" 13th report of the year).
(2) Originating Agency Identifier or ORI Number - This number appears on the electronic IR,
not on the 5580/1, and is generated as a site-defined default, entered by the system administrator. Only IRs
generated CONUS need an ORI. It is, in essence, the ORI number of the nearest civilian law enforcement
department, using their 7-digit ORI with a two letter suffix, DN (for Department of the Navy). The ORI
used on electronically generated IRs is separate from the ORI used on fingerprint cards which is a Navy-
specific number.
(3) Report Type - Check the appropriate block to indicate the type of report being submitted.
Authorized entries: (select one)
Initial Report - Self-explanatory.
Supplemental - Select if report being submitted is to add and/or change information to a
previously submitted report. The Incident Number will remain the same as the Incident Number assigned
to the Initial Report.
(4) Date Received - Enter the Year, Month, Day (YYYY/MM/DD) the incident was first brought
to the attention of the military police.
Example: If the incident was reported to the military police on July 04, 1994, the entry should
be "1994/07/04".
(5) Time Received - Enter the local military time the report was received by the security
department.
Example: Format for time is HHMM “1330".
(6) Incident Received - Check the appropriate block designating how the incident was received
by the security department/provost marshals office not how the individual patrolman/MP was notified of
the incident.
Authorized entries: (select one)
In Person - Walk-ins to MP/Security Desk, PMO, NCIS or CID
By Telephone - Telephone located at Security Department, PMO, NCIS or CID
OPNAVINST 5580.1A
26 JUL 2000
-3
By Radio - Patrolman, or MP on patrol reports incident to Security Department/PMO
Dispatcher
By Alarm - Self-explanatory
By Crime Stop Call/911 - Self-explanatory
Other - Message, Letter, Computer, E-mail, CB, etc.
b. COMPLAINANT SECTION - This section is used for the recording of information describing
the complainant for an incident/offense only when the complainant is not the victim or witness. If there
is no complainant leave section blank. Additional Complainants should be listed on the “Incident Report
Addendum - Complainant/Witness/Sponsor” (OPNAV 5580/1C).
(1) Last Name, First, Middle - Enter individual’s full name. If no middle name enter “NMN” or
if initial only, enter the initial in quotation marks, i.e., “L.” Include Jr., Sr., II, III, etc.
(2) SSN/Alien Registration Number - Enter the individual’s social security number. In the case
of foreign nationals, local policy may direct that the employee’s service number or host country
identification number may be entered. If individual does not have a SSN or other identifying number,
leave blank. DO NOT HYPHENATE THESE NUMBERS.
(3) Grade/Rank - For military personnel (including foreign military members) enter the
individual’s rank or grade (not MOS, Navy rating, or job speciality). For government civilian
employees enter the individual’s pay grade, i.e., GS-12, GM-13, WG-7, etc. If the individual’s status is a
civilian with no government affiliation, military retiree or foreign national, leave blank.
Example 1: The individual in the Navy is a rated GMG2, “E-5" should be entered vice GMG2.
If the individual is a Staff Sergeant in the U.S. Air Force, enter “E-5”.
Example 2: Individual is a Police Officer for Department of the Navy, if the individual is a
“GS-5", GS-5 should be entered, not private or corporal.
(4) Branch of Service - Select the individual’s branch of service. If the individual is a service
member from a foreign country, select Other and enter the individual’s branch of service as reflected on
passport or identification card, if available. If individual has no service affiliation leave blank.
Authorized entries: (select one)
Army - U.S. Army
Navy - U.S. Navy
Air Force - U.S. Air Force
Marine Corps - U.S. Marine Corps
Coast Guard - U.S. Coast Guard

OPNAVINST 5580.1A
26 JUL 2000
-4
Other: - National Guard, RN - British Royal Navy, RAF - British Royal Air Force, SARAF -
Saudi Arabian Royal Air Force, etc.
(5) Status - Select the individual’s personnel status. Complete this section for all individuals.
Authorized entries: (select one)
Regular (Active) - Military service member. Self-explanatory
Reserve - Military service member. Self-explanatory
Retired - Military service members only. Self-explanatory
National Guard - Self - explanatory
Family Member - Military service member, i.e., Spouse, Son, Daughter, etc.
Civilian Employee - Individual employed by the U.S. Government
Civilian - No government affiliation or foreign nationals
(6) Duty Station/Employer (include Department/Command/Division/Unit, etc) - Enter the
name of the individual’s duty station or employer, including department/command/division/unit, etc. if
active duty military or government employee. If the individual is TAD/TDY from his/her permanent
duty station, enter their permanent duty station in this block. If the individual is not active duty or a
government employee, enter the individual’s current employer, i.e., McDonalds Restaurant. If
unemployed or employer unknown, leave blank.
Example: If the individual is permanently assigned to the USS George Washington (CVN-73)
TAD to Naval Station Norfolk for training, “USS GEORGE WASHINGTON (CVN-73)/Air
Department/V-1 Division” will be entered in this block.
(7) UIC/RUC (Unit Identification Code/Reporting Unit Code) - If active duty military or
government employee, enter the individual’s permanent duty station unit identification code. If the
individual does not have a UIC/RUC leave blank, e.g., civilian with no affiliation to the government.
(8) Work Phone - Enter the individual’s work phone number. If unknown, leave blank.
(9) Address - Enter the individual’s (military) duty station address or (civilian’s) home address.
If unknown, leave blank.
(10) City - Self-explanatory. If unknown, leave blank.
(11) State - Self - explanatory. If unknown, leave blank.
(12) Zip Code - Self-explanatory. If unknown, leave blank.
c. OFFENSE SECTION - This section is used for the recording of information describing each
offense committed in an incident and/or complaint. Only one Offense Section is to be submitted for each

OPNAVINST 5580.1A
26 JUL 2000
-5
Offense Description being reported.
(1) Date(s) of Incident - Enter the Year, Month, Day (YYYY/MM/DD) when the incident
occurred or started, or the beginning of the time period in which it occurred (as appropriate). If the
"Incident Date" is unknown, enter an approximate date the incident occurred.
Example (1): If a robbery occurred on July 2, 1989, the entry should be "1989/07/02".
Example (2): If a kidnaping started on November 1, 1989, and ended on November 16, 1989,
the entry should be From: "1989/11/01" To: “1989/11/16".
(2) Time of Incident - Enter the time (24-hour clock) when the incident occurred or started, or
the beginning of the time period in which it occurred (as appropriate). If the "Time of Incident" is
unknown, enter an approximate time the incident occurred.
Example (1): If a robbery occurred on at 9:00 a.m., the entry should be "0900".
Example (2): If the time of the incident are unknown but the time of the incident was between
10:00 a.m. and 1:00 p.m., the entry should be From: ''1000" To: “1300''.
(3) Offense Status - Used to indicate whether each offense in the incident was completed or
merely attempted. If there was more than one occurrence of the same offense within an incident and one
was completed, then "Completed" will be selected. Enter only one per offense.
Example: It should be noted that "Attempted Murder" is to be reported as Aggravated Assault,
and all Assault Offenses should be marked as "Completed."
Example: During the same incident, Suspect/Arrestee -01 raped Victim -01 and
Suspect/Arrestee -02 attempted to rape Victim-02, but left the scene before the act was consummated.
Since one rape was completed, “Completed” should be selected for offense #1 “Forcible Rape”.
(4) Offense Data.
OPNAVINST 5580.1A
26 JUL 2000
-6
(a) Statutory Basis - Enter the code that describes the legal statutory basis for the offense an
individual is suspected of committing. In situations were more than one statutory basis may apply select
the statutory basis with jurisdiction over the offense.
Authorized entries: (enter only one)
U - UCMJ - Uniform Code of Military Justice
F - Federal - Federal U.S. Code
S - State - State Laws, i.e., Traffic Laws, etc.
L - Local - Local Laws, i.e., Traffic Laws, Curfew Violations, etc.
X - Foreign - Foreign Laws, i.e., violations of Status of Forces Agreement, Customs
Violations, etc.
Example: If the suspect is suspected of Unauthorized Absence, “U” should be entered as
no other agency provides a statutory basis for this offense.
(b) Offense Description - Offense blocks are used to identify and describe the types of offenses
involved in the incident (e.g., Arson, Prostitution, etc.). ALWAYS enter the MOST SEVERE
OFFENSE FIRST. After the offenses have been classified, the Table of Offenses, located in Appendix
D, is to be used to enter the appropriate Offense Description. Care should be taken to identify all of the
offenses involved in a particular criminal incident.
Example: Generally "Traffic Offenses" are excluded from this offense category. The
vehicle related offenses of "Hit and Run," (of a person) and "Vehicular Manslaughter" are, however,
included; but "Driving Under the Influence" is not as it is a separate offense.
Example (1): In the same incident, the Suspect/Arrestee assaulted two persons by
threatening them with a handgun. Only one Offense block should be identified as Aggravated Assault.
Example (2): Care must also be taken to ensure that each offense which is reported is a
separate, distinct crime and not just a part (element) of another offense. For example, every robbery
include some type of assault; but, because the assault is an element of the crime of Robbery, only
“Robbery” is reported. However, if during a robbery the victim was forced to engage in sexual relations,
both “Robbery” and “Forcible Rape” are reported, as forced sexual intercourse is not an element of the
crime of Robbery.
(c) Location/Address - Enter the appropriate location of the incident. The location/address
should be entered in the same format each time that location is used.
Example (1): “Desert Dome, Bldg.. 34, Petty Officers Club, ASU SWA”
Example (2): “3430 Bay View Court, Virginia Beach, Va”
OPNAVINST 5580.1A
26 JUL 2000
-7
(d) On Board Military Installation - If the incident occurred while on government owned/leased
property, i.e., base, station, leased government building, military aircraft, or military ship, enter “YES”,
otherwise enter “NO”.
Example (1): A burglary takes place in base housing located on government leased property,
“YES” should be entered.
Example (2): An individual is arrested by civilian authorities for reckless driving while
operating a government-owned pick-up truck in downtown San Diego. Since this incident did not take
place on a government installation, enter “NO”.
(5) Weather Conditions - The weather conditions at the time of the offense should be entered. If
the weather conditions are unknown at the time of the offense, select Unknown.
Authorized entries: (select most applicable)
Clear - sunny, clear sky
Cloudy - include partly cloudy skies
Rain - self-explanatory
Foggy - smokey
Ice - self-explanatory
Snow - self-explanatory
Unknown - self-explanatory
Other - sleet, hail, etc.
Example: If the weather at the time the offense took place was rainy and foggy both “Rain”
and “Foggy” should be selected.
(6) Lighting - Select the lighting conditions at the time the offense took place. If lighting
conditions are not known at the time of the offense, select Unknown.
Authorized entries: (select only one)
Daylight - self-explanatory
Dusk - time between daylight and dark
Dawn - time between dark and daylight
Dark (Lighted) - use of artificial light, street light, etc.
OPNAVINST 5580.1A
26 JUL 2000
-8
Dark (Not Lighted) - self-explanatory
Unknown - self-explanatory
(7) Offender(s) Used - Indicate whether any of the offenders in the incident were suspected of
consuming alcohol or using drugs/ narcotics during or shortly before the incident; or of using a computer,
computer terminal, or other computer equipment to perpetrate the crime. Up to three (3) entries can be
made.
While there is no requirement to indicate the offender(s) was suspected of using alcohol,
computer equipment, or drugs/narcotics, if the reporting officer did not indicate otherwise, Not Applicable
is to be selected.
Authorized entries: (enter up to 3)
Alcohol
Computer Equipment
Drugs/Narcotics
Not Applicable
Example (1): Witnesses to an assault reported that the victim and offender were in a bar
drinking beer when an argument broke out and the offender attacked the victim with a knife. “Alcohol”
should be selected.
Example (2): A rape victim advised that her attacker bragged that he had been "free basing"
cocaine just prior to the incident. “Drugs/Narcotics” should be selected.
Example (3): A medical supply warehouse was burglarized and large quantities of Methadone,
Morphine, Benzedrine, and Valium were stolen. “Drugs/Narcotics” should not be entered because, while
the drugs were the object of the crime, there was no indication that the offenders used drugs or narcotics
before or during the incident.
Example (4): A computer "hacker" used his personal computer and a telephone modem to gain
access to a company's computer and steal proprietary data. “Computer Equipment” should be selected.
Example (5): A private residence was burglarized and a personal computer was stolen, along
with other items. “Computer Equipment” should not be entered because, while the computer was one of
the fruits of the crime, it was not used to commit the crime.
(8) Type Weapon/Force Used - Check the box listing the type(s) of weapon(s) or force used by
the offender(s) in committing the crime. Up to three (3) types of weapons/force can be entered for each of
the offenses.
If the weapon was a fully "automatic" firearm, an "A" is to be placed in the appropriate box,
Automatic Rifle. A fully "Automatic Firearm" is defined as any firearm which shoots, or is designed to

OPNAVINST 5580.1A
26 JUL 2000
-9
shoot, more than one shot at a time by a single pull of the trigger without manual reloading.
Authorized entries:
Firearm (type not stated)
Handgun
Rifle
Shotgun
Other Firearm
Knife/Cutting Tool (e.g., ax, ice pick, screwdriver, switchblade, etc.)
Blunt Object (e.g., club, hammer, etc.)
Motor Vehicle (when used as a weapon)
Bodily Force (i.e., hands, feet, teeth, etc.)
Poison (includes gas)
Explosives
Fire/Incendiary Device
Drugs/Narcotics/Sleeping Pills
Other
Unknown
None
Example (1): Three robbers held up a bank. One was armed with a revolver, the second had a
sawed-off shotgun, and the third had an automatic machine gun. All of the following should be selected:
“Handgun”; “Shotgun”; and “Automatic Other Firearm”.
Example (2): If a bottle was used in the commission of a murder, select “Blunt Object”, if the
victim was beaten; or “Knife/Cutting Tool”, if the victim was cut or stabbed.
(9) Location of Offense - Enter the incident number from the Incident Data box in the
appropriate box indicating the type of location/premises where each offense took place. Only one location
can be entered for each offense.

OPNAVINST 5580.1A
26 JUL 2000
-10
(a) U.S. & Possessions/Outside U.S. & Possessions - Select the global location where the
offense took place.
Authorized entries: (select only one)
U.S. & Possessions - continental United States, Alaska, Hawaii, Puerto Rico, Guam, U.S.
Virgin Islands, etc.
Outside U.S. & Possessions - all areas not part of the United States or its possessions, i.e.,
Europe, South America, Southeast Asia, etc.
Example: An assault and larceny take place at Naval Station Pearl Harbor, the “U.S. &
Possessions” block should be selected. The assault (offense #1) started in a bar, continued into an
adjoining parking lot, and ended in the street. As the bar was the location where the offense was initiated
and best describes the circumstances of the crime, number “1" should be entered into the Bar/Night Club
box. A larceny of a radio (offense #2) from a vehicle parked in the parking lot outside the bar, number
“2" should be entered in the box next to Motor Pool/Parking Lot/Garage as it best describes the location
of the vehicle when the radio was taken.
(10) Type of Criminal Activity - This section is to be used to provide additional information on
the criminal activity of the offender(s) in incidents involving. The following offenses:
Counterfeiting/ Forgery
Stolen Property Offenses
Drugs/Narcotics Violations
Drug Equipment Violations
Gambling Equipment Violations
Pornography/Obscene Material
Weapon Law Violations
Up to three (3) types of activity can be entered for each of the offenses listed above.
Authorized entries:
Buying/Receiving
Cultivating/Manufacturing/Publishing (i.e., production of any type)
Distributing/Selling
Exploiting Children
Operating/Promoting/Assisting
Possessing/Concealing
Transporting/Transmitting/Importing
Using/Consuming

OPNAVINST 5580.1A
26 JUL 2000
-11
Destruction/Vandalism
Harassment/Stalking
Other: (Specify)
Example: The offenders published and sold pornographic photographs of children.
Because up to three types of activity can be entered, “Cultivating/Manufacturing/
Publishing”, “Distributing/Selling”, and “Exploiting Children” should be selected.
(11) Vehicle Description - Enter a description of the vehicle involved in the incident. If a
vehicle was involved in the commission of a crime but details concerning the vehicle are unknown enter
only that information which is known in the Vehicle Description section.
(a) Vehicle Status - Select the status of the vehicle as related to the offense reported.
Authorized entries (select only one)
Suspect - description of the suspect vehicle used to commit the offense
Stolen - description of the stolen vehicle
Recovered - description of vehicle recovered after being previously reported stolen
Target - description of vehicle that is the subject of the crime Example may be the vehicle
that was vandalized or in which the victim was sitting.
(b) Year - Enter the year (YYYY) the vehicle was manufactured
(c) Make - Enter the manufacturer of the vehicle, i.e., Chevrolets, Ford, Nissan, Toyota, etc.
(d) Model - Enter the model of the vehicle related to the offense, i.e., Maxima, S-10, F-250,
Corvette, Camry, etc.
(e) Style - Select the body style of the vehicle relate to the incident
Authorized entries: (select only one)
Sedan - (2DR/4DR) - circle either two or four door
Pickup - self-explanatory
Motorcycle - self-explanatory
R/V/Camper - All Recreation vehicles
Tractor Trailer - includes all tractors, either with or without trailer
OPNAVINST 5580.1A
26 JUL 2000
-12
Van - includes all passenger and/or cargo type vans
Boat - includes all boats with or without engines
Other - All-train vehicles (ATV), bicycle, airplane, etc.
(f) Color - Enter the predominant color of the vehicle, i.e., red, green, black, etc.
Authorized entries:
BLU = Blue
BRN = Brown
GRN = Green
BLK = Black
WHT = White
GRY = Gray
YEL = Yellow
RED = Red
PUR = Purple
SIL = Silver
GOL = Gold
TAN = Tan
ORG = Orange
(g) License Plate Number - Self-explanatory
(h) State - Enter the two letter abbreviation of the state where the vehicle is registered.
Example: If the vehicle was registered in the state of Texas, enter “TX”.
(i) Vehicle Identification Number (VIN) - This number is normally located on the vehicle
registration, title, or on the vehicle body, i.e., door jam, drivers side dashboard, etc.
(j) Owner’s Name - Enter the name of the owner of the vehicle. If unknown, leave blank.
Example: It is discovered during a traffic stop that the driver (John Adam Doe) is
operating a stolen vehicle, the registered owner of the vehicle is determined to be Jack Abraham Smith,
enter “Jack Abraham Smith” in this block.
(k) Other Identifying Marks - Enter other identifying characteristics of the vehicle, i.e.,
missing rear bumper, dent left rear door, DoD decal number, etc.
(12) Burglary/B&E Only
(a) Method of Entry - Complete this section only if the offense is Burglary/B&E. It is used
to indicate whether "Force" or "No Force" was used by the burglar(s) to enter the structure. Check only
one entry.
OPNAVINST 5580.1A
26 JUL 2000
-13
Authorized entries: (enter only one)
Force - A forced entry is where force of any degree, or a mechanical contrivance of any
kind (including a passkey or skeleton key), was used to unlawfully enter a building or other structure.
No Force - An unforced entry is one where the unlawful entry was achieved without force
through an unlocked door or window.
NOTE: If both forced and unforced entries were involved in the crime, the entry should be reported as
having been accomplished through "Force".
Example: Investigation of a burglary complaint
disclosed that the offender(s) entered the building through an unlocked street door and then forced a locked
door to an office and stole a typewriter. Since one door was forced, “Force” should be entered.
(b) Number of Premises Entered - This block is to be used only if the crime is
Burglary/B&E and the "Hotel Rule" is applicable. In such cases, the number of structures (premises)
entered is to be reported.
Hotel Rule is applied to only temporary lodgings. It states: If a number of dwelling units
under a single manager are burglarized and the offenses are most likely to be reported to the police by the
manager rather than the individual tenants, the burglary should be scored as one offense.
Hotel Rule has been expanded to include rental storage facilities, i.e., "Mini-Storage" and
"Self-Storage" buildings. Therefore, this data element is to be used if the offense is Burglary/B&E and
either BOQ/CBQ/Lodge/Hotel or Rental Storage Facility is entered into Location of Offense. The total
number (up to 99) of individual rooms, units, suites, storage compartments, etc., entered is to be reported
in this section.
Example (1): A "Self-Storage" building was burglarized and 11 rented storage
compartments were forcibly entered. The owner/manager of the building reported the incident to the
police. Burglary/B&E should be entered into Offense Description and Rental/Storage Facility should be
entered into Location of Offense and the number "11" (for 11 compartments) should be entered into
Number of Premises Entered.
Example (2): A private residence was burglarized. Burglary/B&E should be entered into
Offense Description and Quarters/Barracks/Berthing/Residence/Home should be entered into Location of
Offense. However, because the "Location of Offense" was not BOQ/BEQ/Navy Lodge/Hotel or
Rental/Storage Facility, no entry should be made into Number of Premises Entered. It should be left blank.
(c) Method of Entry - Select the method of entry used to gain access to the premises. Up to
three methods of entry may be selected.
(d) Condition of Premise - Enter the occupancy status of the premises.
Authorized entries: (select only one)
OPNAVINST 5580.1A
26 JUL 2000
-14
Occupied - premises rented, mortgaged, assigned barracks rooms, etc. and person was
physically occupying the structure when the incident occurred.
Unoccupied - premises rented, mortgaged, assigned barracks rooms, etc., but no person
was physically occupying the structure when the incident occurred.
Vacant (Temp. Unoccupied) - premises for sale, vacant hotel rooms, unassigned barracks
rooms, rental/storage facility, etc.
Vacant - premises that do not qualify as one of the above.
(e) Tools Used - Select the suspected tools used to gain access to a premises.
Authorized entries: (select up to 3)
Bar/Pipe - self-explanatory
Bodily Force - foot, fist, any part of the body
Bolt Cutters - self-explanatory
Chopping Tool - ax, hatchet, machete, etc.
Explosive - dynamite, home made bomb, etc.
Gripping Tool - pipe wrench, pliers, etc.
Hammer - claw hammer, sledge hammer, etc.
Pry Bar - crow bar, etc.
Saw/Drill - circular saw, hack saw, hand drill, electric drill, etc.
Wire - coat hanger, etc.
Screwdriver - self-explanatory
Missile - rock, brick, anything thrown to gain access to premises.
Unknown - self-explanatory
Other - slim jim, lock picks, glass cutter, file, etc.
Example: Small metal filings are observed on the
floor below a broken padlock to a storage facility, the lock appears to have been cut with a hack saw, the
“Saw/Drill” box should be selected.
(13) Bias Motivation - If an offense being reported is the result of expressed hate or bias due
to the victim’s race, sexual orientation, religion or ethnicity, the appropriate box indicating the type of bias
OPNAVINST 5580.1A
26 JUL 2000
-15
or hate should be selected. The incident must have occurred as a result of hate or bias. If the incident
was not a result of hate or bias motivation “NONE” should be marked.
All offenses considered to be a result of hate or bias will be reported to the Naval
Criminal Investigative Service (NCIS).
Example: If a white male assaults a black male because of a dispute over a parking place,
there in no hate or bias crime, even if the white male harbors a hatred for black people. If, however, the
white male assaulted the black male solely because of his hatred or bias (not as a result of the parking
space dispute) then a hate or bias crime has been committed and the “Anti-Black” block should be
selected.
d. PROPERTY SECTION - The Property Section is used for the recording of information
describing property that is lost, stolen, recovered, seized, etc. as a result of an incident. Property
information should be submitted only for crimes against property and/or Kidnaping/Abduction. A
Property Section must be submitted for each Type of Property Loss, Etc. (e.g., Burned,
Counterfeited/Forged, etc.). Additional Property should be listed on the “Incident Report Addendum -
Property” (OPNAV 5580/1G). Refer to paragraph i. NARRATIVE SECTION regarding evidence
submissions when submitting Incident Reports.
Kidnaping/Abduction
Robbery
Arson
Extortion/Blackmail
Burglary/B&E
Pocket-Picking
Purse-Snatching
Shoplifting
Theft From Building
Theft From Coin-Operated Machine or Device
Theft From Motor Vehicle
Theft of Motor Vehicle Parts or Accessories
All Other Larceny
Motor Vehicle Theft
Counterfeiting/Forgery
False Pretenses/Swindle/Confidence Game
Credit Card/Automatic Teller Machine Fraud
Impersonation
Welfare Fraud
Wire Fraud
Embezzlement
Stolen Property Offenses (Receiving, etc.)
Destruction/Damage/Vandalism of Property
Drug/Narcotic Violations
Drug Equipment Violations
Betting/Wagering
Operating/Promoting/Assisting Gambling
OPNAVINST 5580.1A
26 JUL 2000
-16
Gambling Equipment Violations
Sports Tampering
Bribery
(1) Property Description Code - Used to enter descriptions of the property which was burned,
counterfeited, destroyed/damaged/vandalized, etc., as a result of the incident.
Up to 10 items of property may be entered into the Property Section. Property descriptions
codes can be entered for each Property Section (i.e., each type of property loss/etc.) involved in the
incident. If more than 10 types of property are involved, the nine most valuable specifically coded types of
property are to be entered and the remaining types of property are to be combined and entered as "77" =
Other. Additional property should be documented on the “Incident Report Addendum - Property”
(OPNAV 5580/1G).
Authorized entries: (enter up to 10 per Property Section)
01 = Aircraft (airplanes, dirigibles, gliders, etc.)
02 = Alcohol (alcoholic beverages, e.g., beer, wine, liquor, etc.)
03 = Automobiles (sedans, coupes, station wagons, convertibles, taxicabs, and other similar
motor vehicles which serve the primary purpose of transporting people)
04 = Bicycles (includes tandem bicycles, unicycles, and tricycles)
05 = Buses (motor vehicles which are specifically designed, but not necessarily used, to
transport groups of people on a commercial basis)
06 = Clothes/Furs (wearing apparel for human use, including accessories such as belts, shoes,
scarves, ties, etc.)
07 = Computer Hardware/Software (computers, computer peripherals [e.g., tape and disk
drives, printers, etc.], and storage media [e.g., magnetic tapes, magnetic and optical disks, etc.])
08 = Consumable Goods (expendable items used by humans for nutrition, enjoyment, or
hygiene, e.g., food, beverages, grooming products, cigarettes, gasoline, firewood, etc.)
09 = Credit/Debit Cards (includes Automatic Teller Machine cards)
10 = Drugs/Narcotics
11 = Drug/Narcotic Equipment
12 = Farm Equipment (tractors, combines, etc.)
13 = Firearms (weapons that fire a shot by force of an explosion, i.e., handguns, rifles,
shotguns, etc., but not "BB," pellet, or gas-powered guns)
14 = Gambling Equipment (gambling paraphernalia)
15 = Heavy Construction/Industrial Equipment (cranes, bulldozers, steamrollers, oil-drilling
rigs, etc.)
16 = Household Goods (beds, chairs, desks, sofas, tables, refrigerators, stoves, washer/dryers,
air conditioning and heating equipment, etc.)
17 = Jewelry/Precious Metals (bracelets, necklaces, rings, watches, etc., and gold, silver,
platinum, etc.)
18 = Livestock (living farm-type animals, e.g., cattle, chickens, hogs, horses, sheep, etc., but
not household pets, such as dogs and cats)
19 = Merchandise (items held for sale)
20 = Money (legal tender, i.e., coins and paper currency)
21 = Negotiable Instruments (any document, other than currency, which is payable without
restriction, e.g., endorsed checks, endorsed money orders, and endorsed traveler's checks; "bearer" checks

OPNAVINST 5580.1A
26 JUL 2000
-17
and bonds; etc.)
22 = Non-negotiable Instruments (documents requiring further action to become negotiable,
e.g., unendorsed checks, unendorsed money orders, etc.; food stamps; stocks and bonds; etc.)
23 = Office-type Equipment (typewriters, adding machines, calculators, cash registers, copying
machines, etc.) For Computer Equipment, refer to code “07".
24 = Other Motor Vehicles (any other motor vehicles, e.g., motorcycles, motor scooters, trail
bikes, mopeds, snowmobiles, golf carts, etc.)
25 = Purses/Handbags/Wallets
26 = Radios/TVS/VCRs (includes radios, televisions, videotape recorders, high fidelity and
stereo equipment, compact disk players, etc.)
27 = Recordings-Audio/Visual (phonograph records, compact disks, tape recordings, cassettes,
etc.)
28 = Recreational Vehicles (motor vehicles which are specifically designed, but not necessarily
used, to transport people and also provide them temporary lodging for recreational purposes)
29 = Structures-Single Occupancy Dwellings (houses, townhouses, duplexes, mobile homes, or
other private dwellings which are occupied by a single person, family, house mates, or other group)
30 = Structures-Other Dwellings (any other residential dwellings not meeting the definition of
"Single Occupancy Dwellings," e.g., apartments, tenements, flats, boarding houses, dormitories, as well as
temporary living quarters, such as hotels, motels, inns, etc.)
31 = Structures-Other Commercial/Business (stores, office buildings, restaurants, etc.)
32 = Structures-Industrial/Manufacturing (factories, plants, assembly lines, etc.)
33 = Structures-Public/Community (colleges, hospitals, jails, libraries, meeting halls, passenger
terminals, religious buildings, schools, sports arenas, etc.)
34 = Structures-Storage (barns, garages, storehouses, warehouses, etc.)
35 = Structures-Other (any other structures not fitting the other "Structures" descriptions, e.g.,
outbuildings, monuments, buildings under construction, etc.)
36 = Tools (hand tools and power tools)
37 = Trucks (motor vehicles which are specifically designed, but not necessarily used, to transport
cargo on a commercial basis)
OPNAVINST 5580.1A
26 JUL 2000
-18
38 = Vehicle Parts/Accessories (motor vehicle batteries, engines, transmissions, heaters,
hubcaps, tires, manufacturers' emblems, license plates, side view mirrors, radios, antennas, tape decks, etc.)
39 = Watercraft (motorboats, sailboats, houseboats, etc.)
77 = Other (all other property not fitting the above specific descriptions, including intangibles)
88 = Pending Inventory (property description unknown until an inventory is conducted)
99 = Special Category to be used by the National Uniform Crime Report Program to compile
statistics on certain designated types of property, e.g., "CB" radios, which are the object of theft fads)
Example (1): The following property was stolen as the result of a burglary: (1) a $10,000
stamp collection; (2) jewelry worth $5,000; (3) an $1,800 personal computer; (4) clothes worth $1,500; (5)
silverware worth $800; (6) a $650 TV; (7) a $450 VCR; (8) a $400 microwave oven; (9) $350 in cash;
(10) a $250 typewriter; (11) a $150 shotgun; (12) a $100 bicycle; (13) two credit cards (no value); and (14)
10 blank personal checks (no value).
Item (1), the stamp collection, was the most expensive property; however, because it does
not fit into any of the specifically coded property descriptions, it should be included in "77" = Other.
Items (2) through (12) then become the nine most valuable coded properties as follows: the jewelry and
silverware should be entered as code "17"; the personal computer as "07"; the clothes as "06"; the TV
and VCR as "26"; the microwave oven as "16"; the cash as "20"; the typewriter as "23"; the shotgun as
"13"; and the bicycle as "04". Items (13) and (14), i.e., the two credit cards and 10 blank bank checks,
should be combined with Item (1), the stamp collection, and entered as "77".
Example (2): If a house was destroyed by arson and the homeowners are away on an
overseas trip making it impossible to determine the property loss until they return, enter "88" = Pending
Inventory. [Note: An updated Property Section with entries describing the type(s) of burned property
should be submitted when the results of the inventory are subsequently learned.]
(2) Type Property Loss/Etc. - This section is to be used to describe the type(s) of property loss,
recovery, seizure, etc., which occurred in an incident.
Authorized entries: (enter one per Property Section)
1 = None
2 = Burned (includes damage caused in fighting the fire)
3 = Counterfeited/Forged
4 = Destroyed/Damaged/Vandalized
5 = Recovered (to impound property which was previously stolen)
6 = Seized/Impound (to impound property which was not previously stolen)
7 = Stolen (includes bribed, defrauded, embezzled, extorted, ransomed, robbed, etc.)
8 = Unknown
9 = Lost& Found - includes property which was turned in as lost & found.

OPNAVINST 5580.1A
26 JUL 2000
-19
Example (1): For Arson, the entries might be “1" = None (an attempt with no property
burned), “2" = Burned (property burned), or “8" = Unknown (not known whether property burned).
Example (2): For Burglary, the entries might be "1" = None (an attempted burglary, or
the structure was entered but no property was taken), "7" = Stolen (property was taken), "5" = Recovered
(stolen property was recovered), "8" = Unknown (it is not known whether property was taken).
Example (3): If the same incident involved both Arson and Burglary, the choices of
property loss/etc. codes shown in Examples (1) and (2) would be applicable, depending on the
circumstances.
(3) Quantity (QTY) - Self-explanatory
If several items of property have the same description they may be listed on the same property
line. The quantity of these similar items should be entered. If unknown, leave blank.
Example: Two victims had their bicycles stolen at the same time and place - one was worth
$300 and the other $150. "04" = Bicycles should be entered into Property Description Code, “7" = Stolen
is entered in to the Type Code and their total value "450" ($300 + $150 = $450) into Value.
(4) Description - Enter a brief description of item
Example: Computer; Video Camera, Wedding Ring, Dining Table, etc.
(5) Make/Model - List the make/model of the item
Example: IBM Select III, Canon AE-1, Seiko, Motorola, etc.
(6) Size - Enter the approximate size of item
Example: Ring - “10", Shoe - “12D”, Clothing - “Small”, etc.
(7) Serial # - Self-explanatory
If unknown, leave blank
(8) Color - Enter the most predominant color
If unknown, leave blank
(9) Value - Used to enter the total dollar values of the property which was burned (includes damage
caused in fighting the fire), counterfeited, destroyed/damaged/vandalized, recovered, seized, stolen, etc., as
a result of the incident.
The value should be reported in whole dollars. The value entered for each property description
should be the total value of the property loss/etc. for all of the victims in the incident. If the value is
unknown, enter one dollar ($1.00) which means unknown, i.e., "1" = Unknown.
OPNAVINST 5580.1A
26 JUL 2000
-20
If drugs or narcotics were seized in a drug case, no value is to be entered, but the estimated
quantity of the drugs/narcotics is to be reported. Therefore, when the offense is Drug/Narcotic Violations,
"6" = Seized/Impounded was entered into Type of Loss, Etc., and "10" = Drugs/Narcotics was entered into
Property Description Code, no value is to be entered the Drug Type, Est. Quantity, and Measurement are
to be used instead.
However, when drugs or narcotics are involved in other types of crime (e.g., they were stolen
through burglary, robbery, theft, etc., or destroyed by arson) their value is to be entered and Drug Type,
Est. Quantity, and Measurement are to be left blank.
Example (1): In Example (1) given under the Property Description Code (4.,a.) above,
the values for each specifically coded property should be entered as follows: “5,800" for code "17" (the
jewelry and silverware); “1,800" for code "07" (the personal computer); “1,500" for code "06" (the
clothes); “1,100" for code "26" (the TV and VCR); “400" for code "16" (the microwave oven); “350" for
code "20" (the cash); “250" for code "23" (the typewriter); “150" for code "13" (the shotgun); “100" for
code "04" (the bicycle); and “10,000" for code "77" (the stamp collection, the two credit cards, and the ten
blank checks).
Example (2): In Example (1) given for Property Description Code, above, since a
determination of the property loss must await an inventory, "1" ($1.00) = Unknown should be entered into
Value. [Note: An updated Property Section with appropriate property loss values should be submitted after
the results of the inventory are learned.]
(10) Secured/Unsecured - Used to identify if property was secured or unsecured. If unknown,
leave blank.
Authorized entries: (select only one)
S = Secured
U = Unsecured
(11) Owner - Enter the owner of the property code for all property.
Authorized entries: (select only one)
A = Federal Government
B = State Government
C = City Government
D = County Government
E = Foreign Government
F = Private or Personnel Owner
Example: Property is seized as evidence from a suspect listed as Suspect-02, which
belongs to Victim-01, the “F” code should be entered as the property belongs to a private or personal
owner.
(12) Disposition of Property - Used to describe the disposition of the property held by the
security department or provost marshall.
OPNAVINST 5580.1A
26 JUL 2000
-21
Authorized entries: (select only one)
E = Evidence - self-explanatory
S = Safekeeping - property listed as lost and found
R = Return to Owner - property listed as stolen or recovered and not required as
evidence
(13) #Veh. Recovered - Enter only if incident involves a stolen auto(s) and enter only the
number of vehicles recovered in this report.
OPNAVINST 5580.1A
26 JUL 2000
-22
(14) Date Recovered - If previously stolen property is recovered, the Year, Month and Day
(YYYY/MM/DD) of recovery is to be entered into this block. Accordingly, this block is to be used only if
"5" - Recovered is entered into Type Property Loss/Etc.).
If there is more than one date of recovery for the same Property Description Code, enter
the earliest date. If the recovery date is unknown, enter the date of the report.
Example: On March 28, 1989, three cars were
stolen from a used car lot. One of the cars was recovered on July 1, 1989. On July 24, 1989, a second car
was recovered. The date entered should be "1989/07/01".
(15) Suspected Drug Involvement - Complete these blocks only if one of the offenses in an
incident was Drug/Narcotic Violations, "6" = Seized was entered into type Property Loss/Etc., and "10"
= Drugs/Narcotics was entered into Property Description Code. Do not complete when drugs or narcotics
were burned, stolen, etc., in connection with other offenses, such as Arson, Burglary/B&E,
Larceny/Theft, etc.
Up to three types of drugs/narcotics can be entered. If more than three are involved, the
two most important (as determined by the reporting agency taking into account the quantity, value, and
toxicity of the drugs/narcotics) are to be reported under their applicable drug types and the remaining
drugs/narcotics are to be entered as a single "X" = Over 3 Drug Types entry.
(a) Drug Type - Enter the suspected types of drugs or narcotics that were seized in a
drug case. Therefore, it is used only if one of the offenses in the incident was Drug/Narcotic Violations,
"6" = Seized was entered into Type Property Loss/Etc., and "10" = Drugs/Narcotics was entered into
Property Description Code.
Authorized entries: (enter up to 3)
A = "Crack" Cocaine
B = Cocaine (all forms except “Crack")
C = Hashish
D = Heroin
E = Marijuana
F = Morphine
G = Opium
H = Other Narcotics: Codeine; Demerol; Dihydromorphinone or Dilaudid;
Hydrocodone or Percodan; Methadone; etc.
I = LSD
J = PCP
K = Other Hallucinogens: BMDA or "White Acid"; DMT; MDA; MDMA;
Mescaline or Peyote; Psilocybin; STP; etc.
L = Amphetamines/Methamphetamine
M = Other Stimulants: Adipex, Fastine, and Ionamin (Derivatives of
Phentermine); Benzedrine; Didrex; Methylphenidate or Ritalin; Phenmetrazine or Preludin; Tenuate; etc.
N = Barbiturates
O = Other Depressants: Glutethimide or Doriden; Methaqualone or Quaalude;
Pentazocine or Talwin; etc.
P = Other Drugs: Antidepressants (Elavil, Triavil, Tofranil, etc.); Aromatic

OPNAVINST 5580.1A
26 JUL 2000
-23
Hydrocarbons; Propoxyphene or Darvon; Tranquilizers (Chlordiazepoxide or Librium, Diazepam or
Valium, etc.); etc.
U = Unknown Type Drug
X = Over 3 Drug Types
Example: In a drug case, the following drugs were seized: (1) 1.5 kilograms of
"Crack"; (2) 2.125 pounds of Marijuana; (3) 2.0 liquid ounces of Morphine; and (4) 500 Valium capsules.
The "Crack" was entered as "A" and the Marijuana as "E". The Morphine and Valium were coded as a
single "X" entry because more than three types of drugs were seized.
(b) Estimated Drug Quantity - Used to indicate the quantity of drugs or narcotics
seized in a drug case.
Enter the number of whole pounds, ounces, grams, etc., and three more
characters are available to enter the decimal amount. A decimal point must be entered to separate the
whole and decimal amounts.
Example: In the example given above, the entries should be "1.5" for the
"Crack" and "2.125" for the Marijuana. No "quantity" entries should be made for the Morphine or
Valium because it is entered beyond the three drug types. If within the three drug types, the quantity
would be entered.
(c) Measurement - Enter the type of measurement used in quantifying drugs or
narcotics seized in a drug case.
Authorized entries: (enter up to 3)
WEIGHT CAPACITY UNITS
GM = Gram
ML = Milliliter
DU = Dosage Units/Items*
KG = Kilogram
LT = Liter
NP = Number of Plants**
OZ = Ounce
FO = Fluid Ounce
LB = Pound
GL = Gallon
*Number of capsules, pills, tablets, etc.
**E.g., Marijuana plants (bushes), etc.
Example: In the example give above, the
entries should be "KG" for the "Crack" and "LB" for the Marijuana. No entries should be made for the
Morphine or Valium.

OPNAVINST 5580.1A
26 JUL 2000
-24
d. VICTIM SECTION - is to be used for the recording of information describing the victim(s) of
an offense. A victim section should be completed for each victim associated with an offense. Additional
victims should be listed on the “Incident Report Addendum - Victim” (OPNAV 5580/1D).
(1) Victim Number (Sequence)- Each victim in an incident is to be assigned a sequence
number from "001" to "999." A separate "Victim Section" is to be submitted for each numbered victim.
Example: If there were three victims in the incident, three Victim Sections should be
submitted -- one with Victim Number "001", another with "002", and the last with "003". Victims 002
and 003 will be listed on the “Incident Report Addendum - Victim” form.
(2) DD 2701 Issued - Select either Yes or No, if the Victim/Witness Assistance Rights
Pamphlet (Form DD 2701) is issued to victim.
(3) Victim Related to Offense #: - Select the appropriate boxes to indicate specific offense(s)
associated with this victim. More than one box may be selected if victim is related to additional offenses.
Up to 10 offenses boxes may be selected per victim.
Example: Victim 001 is related to Offense No. 1, Simple Assault, however not related to
Offense No. 2, only box number “1" should be selected. However, if Victim 001 is related to both
offenses, both boxes “1" and “2" should be selected.
(4) Victim Related to Suspect# - Select the appropriate boxes to indicate the victims
association with which suspect(s) number. More than one box may be selected if victim is related to
additional suspect. Up to 10 suspect number boxes may be selected per victim.
Example: Victim 001 is related to Suspect No. 1, Simple Assault, however not related to
Suspect No. 2, only box number “1" should be selected. However, if Victim 001 is related to both
suspects, boxes “1" and “2" should be selected.
(5) Last Name, First, Middle - Refer to Complainant Section
(6) SSN/Alien Registration Number - Refer to Complainant Section
(7) Grade/Rank - Refer to Complainant Section
(8) Branch of Service - Refer to Complainant Section
(9) Status - Refer to Complainant Section
(10) Duty Station/Employer (include Department/Command/Division/Unit, etc.) - Refer to
Complainant Section
(11) UIC/RUC (Unit Identification Code/Reporting Unit Code) - Refer to Complainant
Section
(12) Work Phone - Refer to Complainant Section
(13) Address - Refer to Complainant Section

OPNAVINST 5580.1A
26 JUL 2000
-25
(14) City - Refer to Complainant Section
(15) State - Refer to Complainant Section
(16) Zip Code - Refer to Complainant Section
(17) DOB (Date of Birth) - If the victim was a person (i.e., “I” = Individual was entered into
Type of Victim), enter the individual’s date of birth, (Year, Month, Day) (YYYY, MM, DD). If unknown,
enter “UNK”.
Example: If the victim was born on April 11, 1965, the entry should be “1965/04/11".
(18) POB (Place of Birth) - If the victim was a person (i.e., Individual was selected in the
Type of Victim block), enter the victim’s place of birth (City, State or City, Country). If unknown, leave
blank.
Example 1: If the victim was born in San Antonio, Texas, the entry should be “San
Antonio, TX”.
Example 2: If the victim was born in Naples, Italy, the entry should be “Naples, Italy”.
(19) Sex - If the victim was a person (i.e., Individual was select in the Type of Victim block),
select the box that indicated the victim’s sex.
Authorized entries: (enter only one)
Male
Female
Unknown
Example: If the victim was a male, select “Male”.
OPNAVINST 5580.1A
26 JUL 2000
-26
(20) Race - If the victim was a person (i.e., Individual was selected in the Type of victim
block), select the box that indicates the victim’s race.
Authorized entries: (enter only one)
White
Black
American Indian/Alaskan Native
Asian/Pacific Islander
Unknown
Example: If the victim was a white person, select “White”.
(21) Ethnicity - If the victim was a person (i.e., Individual was selected in the Type of Victim
block), select the appropriate box that indicates the victim’s ethnic origin.
Authorized entries: (enter only one)
Hispanic Origin
Not of Hispanic Origin
Unknown
Example: If the victim was not of Hispanic origin, select “Not of Hispanic
Origin”.
(22) Resident Status - If the victim was a person (i.e., Individual was selected in the Type of
Victim block), select the appropriate box indicating the victim’s residency status.
A "Resident" is a person who maintains his/her permanent home for legal purposes in
the locality (i.e., town, city, or community) where the crime took place. [Note: State and county law
enforcement agencies should base their determinations of residency on the town, city, or community where
the crime occurred rather than their broader geographical jurisdictions.]
Authorized entries: (enter only one)
Resident
Nonresident
Unknown
Example (1): If the victim was robbed on Naval Base San Diego, California,
where he is assigned to the Admin Department, select “Resident”.
Example (2): If the victim was a business (i.e., Business was selected in the
Type of Victim block), leave block blank.
OPNAVINST 5580.1A
26 JUL 2000
-27
(23) Type of Victim - Select the appropriate block to indicate the type of victim. Select only
one entry per victim.
Authorized entries: (enter only one)
Individual
Business
Financial Institution
Government
Religious Organization
Society/Public
Other
Unknown
Example: During a credit union robbery, the offender pointed a gun at a teller
and demanded and received money. The robber also pistol whipped a customer who stood in his way as he
made his getaway from the credit union. There were three (3) victims, i.e., the credit union (Financial
Institution), the teller (Individual), and the pistol-whipped customer (Individual). Therefore, their codes
should be entered into their respective Victim Sections.
(24) Aggravated Assault Circumstances - Select the appropriate box(es) that describes the
circumstances of either an aggravated assault or a homicide. Complete this box only if an Aggravated
Assault.
Authorized entries: (enter up to 2)
Argument
Assault on Law Enforcement Officer(s)
Drug Dealing
Gangland
Juvenile Gang
Lovers' Quarrel/Domestic
Other Felony Involved
Other Circumstances
Unknown Circumstances
Example: Two rival juvenile street gangs rumble over "turf" rights to sell drugs
and one of the gang members was beaten and stabbed with a knife. Possible selections are “Argument”,
“Drug Dealing”, and “Juvenile Gang”. While all three would apply, there is a limit of two entries.
Therefore, the two most descriptive codes should be used. In this case, “Drug Dealing” and “Juvenile
Gang”.
(25) Injury Type - Select the box(es) that describe the type(s) of bodily injury suffered by a
person (i.e., "I" = Individual was entered into Type of Victim) who was the victim of one or more of the
following offenses:
Kidnaping/Abduction
Forcible Rape
Forcible Sodomy
Sexual Assault With An Object
Forcible Fondling

OPNAVINST 5580.1A
26 JUL 2000
-28
Robbery
Aggravated Assault
Simple Assault
Extortion/Blackmail
Authorized entries: (enter up to 5)
None
Broken Bones
Possible Internal Injury
Severe Laceration
Minor Injury
Major Injury
Loss of Teeth
Unconsciousness
Example (1): The offender assaulted the victim with a tire iron, breaking the
victim's arm and opening up a cut about 3 inches long and 1-inch deep on his back. The entries should be
Apparent Broken Bones and Severe Laceration.
Example (2): The victim, a respected religious figure, is blackmailed regarding
his sexual activities. As he suffered no physical injury, the entry should be None.
(26) Relationship(s) of Victim to Suspect(s) -This section is used to report the relationship
between the victim and the suspect who committed a "Crime Against Person". Therefore, this section is to
be used only if one or more of the following offenses:
Murder and Non-negligent Manslaughter
Negligent Homicide
Justifiable Homicide
Kidnaping/Abduction
Forcible Rape
Forcible Sodomy
Sexual Assault With An Object
Forcible Fondling
Robbery
Aggravated Assault
Simple Assault
Intimidation
Incest
Statutory Rape
This section is to be used to indicate the victim's relationship with up to 10 suspects
involved in the incident. If multiple suspects are involved in a offense the Suspect/Arrestee Number
should be entered into the box next to the Relationship of Victim to Suspect.
Authorized entries: (enter up to 10)
WITHIN FAMILY:
Victim Was Spouse
Victim Was Common-Law Spouse
Victim Was Parent
Victim Was Sibling (brother or sister)
OPNAVINST 5580.1A
26 JUL 2000
-29
Victim Was Child
Victim Was Grandparent
Victim Was Grandchild
Victim Was In-law
Victim Was Stepparent
Victim Was Stepchild
Victim Was Step Sibling (stepbrother or stepsister)
Victim Was Other Family Member
OUTSIDE FAMILY BUT KNOWN TO VICTIM:
Victim was Acquaintance
Victim was Friend
Victim was Neighbor
Victim was Babysittee (the baby)
Victim was Boyfriend/Girlfriend
Victim was Child of Boyfriend or Girlfriend
Homosexual Relationship
Victim was Ex-Spouse
Victim was Employee
Victim was Employer
Victim was Otherwise Known
NOT KNOWN BY VICTIM:
Relationship Unknown
Victim was Stranger
Example (1): An employee assaulted his employer (a person) with his
fists. Victim Was Employer should be selected.
Example (2): Two unknown suspects rob a male and female couple.
Victim Was Stranger should be entered to indicate the relationship of each victim to each
offender.
Example (3): The victim is assaulted by two suspects, Suspect #1 is the
victim’s brother and Suspect #2 was the victim’s friend. In the box next to Sibling, enter “01",
in the box next to Friend, enter “02"
f. WITNESS/SPONSOR SECTION - This section is used for the recording of
information describing a witness(es) or sponsor(s) of an incident/offense only when the
witness(es)/sponsor(s) is not the victim or complainant. A witness/sponsor section should be
completed for each witness or sponsor associated with an offense. If there is no witness(es) or
sponsor(s) leave section blank. Additional witnesses/sponsors will be listed on the “Incident
Report Addendum- Complainant/Witness/Sponsor” (OPNAV 5580/1C).
(1) Type/Sequence Number - Select either Witness or Sponsor to identify the
individual as related to the incident report. Each witness or sponsor in an incident is to be

OPNAVINST 5580.1A
26 JUL 2000
-30
assigned a sequence number from "01" to "99." This number will be entered in the dashed box.
A separate "Witness/Sponsor Section" is to be submitted for each numbered witness.
(2) DD 2701 Issued - Refer to Victim Section
(3) Last Name, First, Middle - Refer to Complainant Section
(4) SSN/Alien Registration Number - Refer to Complainant Section
(5) Grade/Rank - Refer to Complainant Section
(6) Branch of Service - Refer to Complainant Section
(7) Status - Refer to Complainant Section
(8) Duty Station/Employer (include Department/Command/Division/Unit, etc.) -
Refer to Complainant Section
(9) UIC/RUC (Unit Identification Code/Reporting Unit Code) - Refer to
Complainant Section
(10) Work Phone - Refer to Complainant Section
(11) Address - Refer to Complainant Section
(12) City - Refer to Complainant Section
(13) State - Refer to Complainant Section
(14) Zip Code - Refer to Complainant Section
g. SUSPECT/ARRESTEE SECTION - This section is used for the recording of
information describing suspects and arrestees of an incident/offense. When an arrest is made,
Suspect and Arrestee information must be completed. As much of the information is the same
for both Suspect and Arrestee, these sections have been merged into one. Additional
Suspects/Arrestees should be listed on the “Incident Report Addendum - Suspect/Arrestee”
(OPNAV 5580/1E).
(1) Suspect/Arrestee Situations.
(a) Incident Report - No Arrest - If an incident/offense is reported but no
arrest is completed complete all information in the Suspect/Arrestee Section with the exception
of the Arrestee Only section (i.e., shaded area located on page 4 of the IR or the Suspect/Arrestee
Addendum Sheet). The following additional blocks must be completed: Sex, Race, DOB. If
additional suspects are involved complete additional Suspect/Arrestee Sections. If suspect is
unknown, an “Suspect/Arrestee Sequence Number” must be entered in the Suspect/Arrestee #:
block (e.g., 01) and the value for “Unknown”checked or entered in the Sex, Race, and DOB
blocks. If the exact number of suspects is unknown, “00" must be entered into the
Suspect/Arrestee #: block.
(b) On-View Arrest - If an arrest is made on view before an incident report is
submitted complete all information in the Suspect/Arrestee Section for all Arrestees.

OPNAVINST 5580.1A
26 JUL 2000
-31
(c) Arrest after Report - If arrest is made after the incident report has been
submitted submit a supplemental report and complete only those blocks not completed on the
initial report. The same case number will be used for all supplemental reports. Complete all
information in the Suspect/Arrestee Section not listed in the initial incident report (i.e., Arrestee
Only section, name, grade/rank, etc.).
(2) Section Completion.
(a) Suspect/Arrestee - Select the appropriate box(es) to identify the individual
listed in this section as either a suspect or an arrestee. If the individual is a suspect and is also
arrested both blocks should be checked. See explanations above for various situations.
Example: An individual is observed by security patrolman breaking into
a parked vehicle, the suspect is arrested by the patrolman, both the Suspect and Arrestee blocks
should be checked.
(b) Type/Sequence Number - Select either Suspect or Arrestee to identify the
individual as related to the incident report. Each suspect/arrestee in the incident is to be assigned
a sequence number from "01" to "99." A separate "Suspect/Arrestee Section" is to be submitted
for each numbered offender. If nothing is known about the suspect(s), enter "00" and leave the
remaining information in this section blank.
Example (1): A corpse was found in an abandoned warehouse. There
were no witnesses to the crime or suspects. A single “Suspect/Arrestee section” should be
submitted with "00" entered into Suspect/Arrestee #: and the rest of the section is left blank.
Example (2): Two offenders were seen fleeing the scene of a burglary,
but because they were wearing ski masks, their age, sex and race could not be determined. Two
“Suspect/Arrestee sections” should be submitted -- one with Suspect/Arrestee #: "01" and the
other with "02". "Unknown" should be selected or entered into Sex, Race, and DOB blocks.
(c) Suspect/Arrestee Related to Offense # - Fill in the appropriate boxes to
indicate specific offense(s) associated with the suspect or arrestee. More than one box may be
selected if suspect/arrestee is related to additional offenses. Up to 10 offense boxes may be
selected per suspect/arrestee.
Example: Suspect 01 is related to Offense No. 1, Simple Assault, however not
related to Offense No. 2, only box number “1" should be selected. However, if Suspect 01 is
related to both offenses, boxes “1" and “2" should be selected.
(d) Involvement - Select the appropriate box to indicate the suspect/arrestee
involvement in the commission of the offense.
Authorized entries: (select only one)
Principal - selected if the suspect/arrestee acted alone in the
commission of the offense

OPNAVINST 5580.1A
26 JUL 2000
-32
Conspirator - selected if the suspect’s/arrestee’s only involvement was
as a conspirator in this crime
Accessory - selected if the suspect/arrestee is not considered the chief
actor in the offense, nor was he present at its performance, but he is considered as contributing or
aiding in the commission of the offense
Solicitor - select if the suspect/arrestee solicited or advised another
person or persons to commit a offense
(e) Last Name, First, Middle - Refer to Complainant Section
(f) SSN/Alien Registration Number - Refer to Complainant Section
(g) Grade/Rank - Refer to Complainant Section
(h) Branch of Service - Refer to Complainant Section
(i) Status - Refer to Complainant Section
(j) Duty Station/Employer (include Department/Command/Division/Unit,
etc.) - Refer to Complainant Section
(k) UIC/RUC (Unit Identification Code/Reporting Unit Code) - Refer to
Complainant Section
(l) Work Phone - Refer to Complainant Section
(m) Address - Refer to Complainant Section
(n) City - Refer to Complainant Section
(o) State - Refer to Complainant Section
(p) Zip Code - Refer to Complainant Section
(q) Hair Color - Enter the predominant natural hair color. The color observed
should be checked against the color shown on the individual’s identification card or drivers
license. If the hair has been dyed, make an appropriate entry, such as “brown-dyed red”. If the
person is completely bald (be alert for wigs and toupees), enter “Bald”. In the case of partial
baldness, the color of the hair is entered and a remark is made in the Identifying Marks block on
the extent of baldness.
(r) Eye Color - Enter the color of the iris of the eye. It is incorrect to enter the
condition, such as “bloodshot”. If unknown, leave blank.
Authorized entries:
BRN - Brown
BLU - Blue
HAZ - Hazel
GRN - Green
GRY - Gray
OPNAVINST 5580.1A
26 JUL 2000
-33
(s) Height - Enter the Suspect’s/Arrestee’s height in feet and inches (e.g., 6'2").
If unknown, leave blank
(t) Weight - Enter the Suspect’s/Arrestee’s weight in pounds (e.g., 180). If
unknown, leave blank
(u) DOB (Date of Birth) -Refer to Victim Section
(v) POB (Place of Birth) - Refer to Victim Section
(w) Alias (AKA) - Enter known alias used by Suspect/Arrestee. If none or
unknown leave blank
Example: Individual’s real name is “Joseph Doe” however he has also
gone by the name “John Doe”. “JOHN DOE” should be entered in the Alias block.
(x) Sex - Refer to Victim Section
(y) Race - Refer to Victim Section
(z) Ethnicity - Refer to Victim Section
(aa) Resident Status - Refer to Victim Section
(bb) Description - Select all appropriate box(es) as they apply to the description
of the suspect/arrestee
(cc) Identifying Marks - Enter any identifying marks, such as partial baldness,
scars and tattoos together with their location on the body and a brief description. Give a word
description rather than a diagram or picture. If there are no identifying marks leave blank.
Example (1): Partially bald, 2" diameter back of head
Example (2): Tattoo, Heart, right bicep
Example (3): Scar, 3" left inner wrist
(dd) Type of Arrest - Indicate how the Arrestee was arrested.
Authorized entries: (enter only one)
On-View (taken into custody without a warrant or previous incident
report)
Summoned/Cited (not taken into custody)
Taken Into Custody (based on warrant and/or previously submitted
incident report)
OPNAVINST 5580.1A
26 JUL 2000
-34
Example (1): The subject was arrested while in the act of
soliciting for prostitution on a street corner. The entry should be “On-View Arrest”.
Example (2): The suspect was served with a traffic
summons to appear in court. The entry should be “Summoned/Cited”.
Example (3): The subject was taken into custody as the
result of a complaint being filed. The entry should be “Taken Into Custody”.
(ee) Date Arrested - Enter the Year, Month, Day (YYYY/MM/DD) when the
arrest took place.
Example: If the subject was arrested on July 23, 1989, the
entry should be "1989/07/23".
(ff) Multiple Clearance - Indicate whether or not the arrest of the Arrestee
resulted in the clearance of more than one previously reported incident/offense within the
jurisdiction served by the security department. If so, it is important to indicate that there was
only one Arrestee responsible for the Multiple clearances of previously reported incident/offense.
This is done by entering Multiple into all but one of the Arrestee Only
section used to update the affected Incident Reports, and by entering Count Arrestee into the
remaining Arrestee Only sections. If the arrest did not result in multiple clearances, enter Not
Applicable.
Authorized entries: (enter one per Arrestee Only Section)
Multiple
Count Arrestee
Not Applicable
Example (1): After the suspect’s arrest for robbery, it was
learned that he was also responsible for five additional robberies within the jurisdiction of Naval
Base Norfolk. One Arrestee Only section was marked “Count Arrestee”. The other Five
robberies the suspect was responsible for are marked “Multiple”.
Example (2): If the suspect's arrest did not clear
additional incidents, the entry should be “Not Applicable”.
(gg) Arrestee Was Armed With - Indicate whether the Arrestee was armed
with a commonly known weapon at the time of his/her arrest. Up to two entries may be made.
If the weapon was an "automatic" firearm, an "A" will be entered into
the block next to the appropriate weapon. Refer to the “Offense Section” for definition of
"Automatic Firearm".
Authorized entries: (enter up to 2)
Unarmed
Handgun
Rifle
Shotgun
Lethal Cutting Instrument (e.g., switchblade knife, martial arts "stars,"
etc.)
Club/Blackjack/Brass Knuckles

OPNAVINST 5580.1A
26 JUL 2000
-35
Other
Example (l): When the suspect was Arrested, he had in his possession a .357 Magnum handgun and a
penknife. The entry should be “Handgun”. Because a small pocket knife is not generally
considered to be a "weapon," it does not qualify for reporting.
Example (2): The suspect resisted arrest using a liquor bottle and a chair as weapons before being subdued.
The entry should be “Unarmed”. Although the subject used items as weapons, they were not
commonly known weapons. This information should be entered into the Narrative Section of the
Incident Report.
(hh) Disposition of Juvenile- Complete this block only if the arrestee was 17
years of age or younger at the time of the arrest.
Authorized entries: (enter only one)
Handled Within Department (e.g., released to parents, released with
warning etc.)
Referred to Other Authority (e.g., turned over to juvenile court,
probation department, welfare agency, other police agency, criminal or adult court, etc.)
Example (1): The suspect, age 13, who was arrested for
vandalizing a school, was released to his parents with a warning. “Handled Within Department”
would be selected.
Example (2): The suspect, age 17, who was arrested for
murder, was turned over to civilian authorities to be tried as an adult. “Referred to Other
Authorities” would be selected..
h. SECURITY POLICE SECTION - This section is used for the recording of
information describing the responding/reporting security police officer’s/ Military Polices to the
incident/offense. List additional security police personnel in the Narrative Section of Incident
Report.
(1) Last Name, First, Middle - Refer to Complainant Section
(2) Grade/Rank - Refer to Complaint Section
(3) Duty Station/Employer (include Department/Command/Division/Unit, etc.) -
Refer to Complainant Section
(4) Badge #: - Enter the individual security police officer’s badge number, if
assigned. If no badge number is assigned leave blank.
i. NARRATIVE SECTION - This section is for the recording of additional information
not listed elsewhere in the Incident Report. This section should list the chronology of events
including the specific elements of the offenses reported in the Offense Section of the same
Incident Report. Use “Incident Report Addendum - Narrative Section” (OPNAV 5580/1B) if
additional space is needed. Also note any evidence that was collected in this investigation with a
brief description of articles that are listed on the Evidence/ Property Custody Receipt (OPNAV
5580/22).
Example: The victim was unconscious face down in the grass with her head to the
north and her feet towards the south. The contents of her purse were dumped on the ground,
approximately 15' west of her left shoulder.
OPNAVINST 5580.1A
26 JUL 2000
-36
Evidence Example: Item (1) One 12" X 12" Blue Bandana
(1) Enclosure(s).
(a) Enclosure #: - Enter the enclosure number of attached supporting
documents (i.e., 01).
(b) Description - Enter a brief description of attached supporting documents,
(i.e., statements, photographs, sketches, etc.).
Example: (01) Statement of Williamson (witness)
(02) Rough Sketch of Crime Scene
j. REPORTING/APPROVING OFFICIALS - This section is used to record information
concerning the individual preparing and approving the Incident Report.
(1) Reporting Official - Enter the typed or printed name, rank, title and signature of
the individual who prepared the Incident Report.
Example: John A. Adams, E-5, Patrolman
(2) Approving Official - Enter the typed or printed name, rank, title, and signature of
the supervisor who reviewed and approved the contents of the Incident Report.
Example: John A. Adams, E-8, Asst. Security Officer
k. ADMINISTRATIVE DISPOSITION SECTION - This section is used to record
administrative information concerning the distribution and referral of Incident Reports to other
departments or commands for further investigation, administrative processing (i.e., non-judicial
punishment, Article 15) or judicial proceedings (i.e., Court-Martial, civilian judicial system).
This section should only be completed by the security department Admin Division or the
Approving Official.
(1) Incident Status - Select the block that best describes the status of the incident
Authorized entries: (enter one only)
Unfounded
Cleared by Arrest
Cleared Exceptionally - if selected, the Cleared Exceptionally section must be
completed.

OPNAVINST 5580.1A
26 JUL 2000
-37
(2) Cleared Exceptionally - It is used to indicate whether or not the incident was
cleared exceptionally. If not, Not Applicable is to be entered. In a multiple-offense incident, the
exceptional clearance of one offense, clears the entire incident. An incident cannot be cleared
exceptionally if it was previously or at the same time cleared by an arrest, i.e., if an Arrestee
Section was or is being submitted. In order to clear an offense by exceptional means, the
following four conditions must be met: (1) the investigation must have clearly and definitely
established the identity of at least one offender; (2) sufficient probable cause must have been
developed to support the arrest, charging, and prosecution of the offender; (3) the exact location
of the offender must be known so that an arrest could be made; and (4) there must be a reason
outside the control of law enforcement which prevents the arrest, i.e., one of the authorized
entries below with the exception of Not Applicable below:
Authorized entries: (enter only one)
Death of Offender
Prosecution Declined (by the prosecutor for other than lack of probable cause)
Extradition Denied
Victim Refused to Cooperate (in the prosecution)
Juvenile/No Custody (the handling of a juvenile without taking him/her into
custody, but rather by oral or written notice given to the parents or legal guardian in a case
involving a minor offense)
Not Applicable (not cleared exceptionally)
Example (1): If an incident was not cleared by either an arrest or
exceptional means by the time an initial Incident Report was submitted, then “Not Applicable”
should be entered.
Example (2): If, after an Incident Report was submitted, an offender
was arrested, the previously submitted report should be updated with an Arrestee Section. The
incident will be automatically cleared when the Arrestee Section is received at the FBI . This
data element should still contain “Not Applicable”.
Example (3): Suppose an Incident Report was submitted and the
offender was later arrested, but the victim refused to testify and there were no other witnesses.
The previously submitted Incident Report should be updated, by submitting a Supplemental
Incident Report, to change the contents of this block from “Not Applicable” to “Cleared
Exceptionally” and check the block “Victim Refused to Cooperate”.
(3) Date Cleared - If an incident was cleared by exceptional means (i.e., a entry other
than Not Applicable was entered into the Cleared Exceptionally block), the Year, Month, Day
(YYYY/MM/DD) when the incident was cleared is to be entered.
Example: The incident was cleared on May 27, 1989. It was entered
into the computer system on April 6, 1989. The date “1989/05/27" should be entered.
(4) Referred To/Assumed By: - Select the appropriate box that describes the
organization the Incident Report was referred to and/or assumed by. If known, enter the
organization’s Case #:. If unknown, leave blank.
Authorized entries: (select only one)
NCIS - Naval Criminal Investigative Service
OPNAVINST 5580.1A
26 JUL 2000
-38
INVESTIGATIONS - Security Department’s/Provost Marshall Offices
investigations division (i.e., command investigations, Military Police Investigator).
LOCAL POLICE - Local police (i.e., local, state, sheriff). Include Foreign local
police organizations.
Other (Specify) - Army CID, Air Force OSI, Marine Corps CID, FBI, ATF, U.S.
Customs Service, etc.
(5) Distribution: - Select the appropriate box(es) that identify the
organizations/departments, etc. the Incident Report was distributed.
Authorized entries: (select all that apply)
Commanding Officer/Officer-in-charge
Legal Officer/Staff Judge Advocate
Family Advocacy
Equal Opportunity
Medical/Mental Health
Drug & Alcohol (DAPA)
Other
OPNAVINST 5580.1A CH-1
20 July 2001
D-1
APPENDIX D
TABLE OF OFFENSES
1. Offenses
The following table lists offenses to be captured by NIBRS and categorized for reporting
crimes and offenses consistently nationwide. State statutes are very specific in defining elements
of crimes so that persons facing prosecution know the exact charges levied against them. This
list of offenses for NIBRS to be utilized with this OPNAV 5580/1 form are generic enough not
to exclude varying state statutes relating to the same type of "crime," yet narrow enough to elicit
consistent responses nationwide.
Accordingly, the common-law definitions found in Blacks Law Dictionaries, as well as those
used in the Uniform Crime Reporting Handbook, the NCIC Uniform Offense Classifications, and
the Marine Corps Law Enforcement Manual, MCO P5580.2A (Notal) provided the definitions
for these guidelines. Since most State statutes are based on the common-law definitions, even
though they may vary as to specifics, most should fit into the corresponding NIBRS offense
classifications.
If a State statute for an offense includes additional offenses not included in this list, the
nonconforming offenses will be reported according to their State or local classification. For
example, some States have "Larceny" statutes which are so broadly worded that they include the
crime of "Embezzlement." If an embezzlement is perpetrated within such a State, it should be
reported to NIBRS as Embezzlement, not Larceny.
The original IR and exhibits, if exhibits are part of the IR, which report incidents that fall
under case categories listed in paragraph 3 involving any of the enumerated UCMJ punitive
Articles listed in paragraph 4, will be forwarded to NCISHQ.
Additionally, an offence involving any of the UCMJ Articles listed in paragraph 4 requires
that two sets of linked fingerprints be taken of the offender, and that the prints be forwarded to
NCIS per SECNAVINST 5580.1.
OPNAVINST 5580.1A
26 JUL 2000
D-2
2. Table of Offenses
-A-
Arson
Assault
Assault, Intimidation
Assault, Simple Assault
Assault, Aggravated Assault
Assault, Simple Assault (Constructive)
-B-
Breaking and Entering
Breaking and Entering
Bribery
-C-
Counterfeiting
Curfew
-D-
Destruction
Disorderly Conduct
Driving Under the Influence
Drug equipment/paraphernalia
Drug/Narcotic Offenses
Drunkenness
-E-
Embezzlement
Extortion/Blackmail
-F-
Family Offenses, Nonviolent
Forgery
Fraud
Fraud, Welfare Fraud
Fraud, Wire Fraud
Fraud, Bad Checks
Fraud, False Pretenses
Fraud, Confidence scams
Fraud, credit card/ATM Fraud
Fraud, Impersonation
-G-
Gambling
Gambling Equipment Violations
Gambling, Betting/Wagering
Gambling, Operating/Promoting/Assisting
Gambling, Sports Tampering
-H-
Homicide
Homicide, Murder (non-negligent Manslaughter)
Homicide, Negligent Manslaughter
Homicide, Justifiable
-K-
Kidnaping/Abduction
-L-
Liquor Law Violations
Loitering
-P-
Property Damage
-T-
Theft
Theft, Larceny
Theft, Theft from a coin operated machine or device
Theft, shop-lifting
Theft, Burglary
Theft, Theft from Motor Vehicle
Theft, Pocket-picking
Theft, Purse snatch
Theft, Theft of Motor Vehicle Parts and Accessories
Theft, Theft from a building (non-burglary)
Theft, Motor Vehicle Theft
Trespass of Real Property
-V-
Vagrancy
Vandalism
OPNAVINST 5580.1A
26 JUL 2000
D-3
Prostitution
Prostitution, Assisting or Promoting
-R-
Receipt of Stolen Property
Robbery
Runaway
-S-
Sex Offense, Sodomy
Sex Offense, Incest
Sex Offense, Rape
Sex Offenses, Pornography (Obscene Material)
Sex Offense, Forcible
Sex Offense, Forcible Fondling
Sex Offense, Sexual Assault with an object
Sex Offense, Non-forcible
Sex Offense, Statutory Rape
Sex Offenses, Voyeurism (Peeping Tom)
-W-
Weapon Law Violations
3. Case Categories
OFFENSE OFFENSE
Forgery Communication Incidents
Bad Check Domestic Assaults
Arson Assault
Counterfeiting Deaths (all)
Burglary/Housebreaking Kidnapping
Unlawful/Forced Entry Child Abuse
Larceny Attempted Suicide
Destruction of Property Controlled Substance Violation
Vehicle Theft Robbery
False Official Statement Drunk Driving
Hit and Run Sex Crimes
4. List of UCMJ violations requiring submission of fingerprint cards:
Article 78 - Accessory after the fact (for crimes listed below)
Article 80 - Attempts (to commit crimes listed below)
Article 81 - Conspiracy (to commit crimes listed below)
Article 82 - Solicitation
Article 90 - Assaulting a superior officer
Article 91 - Striking or assaulting warrant, noncommissioned or petty officer
OPNAVINST 5580.1A
26 JUL 2000
D-4
Article 94 - Mutiny or sedition
Article 95 - Resistance, breach of arrest, and escape
Article 106 - Spying
Article 106a - Espionage
Article 107 - False official Statement(s)
Article 108 - Military property of the United States; sale, loss, damage, destruction, or
wrongful disposition
Article 109 - Willfully destroying or damaging private property
Article 111 - Drunk driving
Article 112a - Wrongful use, possession, etc., of controlled substances
Article 116 - Riot
Article 118 - Murder
Article 119 - Manslaughter
Article 120 - Rape and carnal knowledge
Article 121 - Larceny and wrongful appropriation
Article 122 - Robbery
Article 123 - Forgery
Article 123a - Bad checks ($100.00 or more only)
Article 124 - Maiming
OPNAVINST 5580.1A
26 JUL 2000
D-5
Article 125 - Sodomy
Article 126 - Arson
Article 127 - Extortion
Article 128 - Assault
Article 129 - Burglary
Article 130 - Housebreaking
Article 131 - Perjury
Article 132 - Frauds against the United States
The following offenses under UCMJ Article 134 listed in the Manual for Court-Martial
- Assault (Indecent)
- Assault (With intent to commit murder, voluntary manslaughter rape, robbery,
sodomy, arson, burglary, or housebreaking
- Assaulting a federal officer in performance of duties
- Bribery and graft
- Burning with intent to defraud
- Computer related and associated crimes
- False pretenses, obtaining services under (value of more than $100.00)
- False swearing
- Firearm discharge. Willfully, under such circumstances as to endanger human life
- Fleeing the scene of an accident
- Homicide, negligent
- False impersonation with intent to defraud
- Indecent acts or liberties with a child
- Indecent exposure
- Indecent language (communicating to any child under the age of 16 years)
- Indecent acts with another
- Kidnapping
- Mails. Taking, opening, secreting, destroying or stealing
- Misprision of serious offense
- Obstructing justice
- Pandering and prostitution
- Perjury
- Public record. Altering, concealing, removing, mutilating,
- Obliterating, or destroying
- Seizure. Destruction, removal, or disposal of property to prevent
- Soliciting another to commit an offense for crimes listed herein
- Stolen property. Knowingly receiving, buying, or concealing (Value more than
$100.00)
- Testify. Wrongful refusal
- Threat or hoax. Bomb
- Threat, communicating
- Weapon. Concealed or carrying
- Any offense under 18 U.S.C. charged as a violation of Article 134, which has a
maximum punishment of more than one year.

OPNAVINST 5580.1A CH-2
28 Jan 2002
E-1
APPENDIX E
SECURITY MANNING (ASHORE)
1. Staffing Standards
a. The following procedures will be used to determine Navy security department staffing requirements.
This security staffing process enables installations, claimants and resource sponsors to identify minimum
staffing functions and capabilities as well as prioritize posting requirements. The process also enables the
staff to identify the specific impact reductions have on capabilities. Staffing positions not addressed by this
chapter will be assessed by normal frequency, task and function criteria.
b. The following criterion were used to develop these objective measures:
(1) Security mission.
(2) Desired outcomes.
(3) Measurable indicators.
(4) Objective, valid and reliable data.
(5) Able to address multiple purposes.
c. Where feasible Navy security units should be organized into a regional force structure. Staffing
standards, when applied within a regional framework, have proven to be the most cost effective and efficient
security force structure. They provide the following capabilities and enhancements:
(1) Common procedures and equipment for all units in the area.
(2) Increased ability to prioritize critical situations and provide coordinated, flexible command and
control for all security forces.
(3) Realized savings affiliated with regional security systems.
(4) Increased security, inherent with a regional reinforcement capability.
(5) Enhanced training achieved by a consolidated antiterrorism (AT) planning, exercises and training
program.
d. This is an outcome based staffing process and is designed to provide end-strength that addresses the
following situations:
(1) Identify staffing requirements for all posts from FPCONs NORMAL through DELTA.
(2) Identify posts where technology can augment staffing requirements.
(3) Identify the “C” (readiness rating) for every post and link them to protected assets.
(4) Link the analysis process with other assessment tools to identify crime trends, vulnerabilities and
program effectiveness.

OPNAVINST 5580.1A CH-2
28 Jan 2002
E-2
2. Staffing Rules
a. The following rules will be applied when determining the operational staffing requirements:
(1) Reimbursable posts must be dedicated to their assigned assets and will not be calculated into the
base (host) response forces.
(2) Patrols assigned to special assets (i.e. airfields) will not be used for response outside of their asset
protection zone.
(3) All patrols will have a 10-minute backup or will be assigned a second person when required to
operate outside of the 10-minute back up zone.
(4) No more than 50 percent of on base patrols will be used for off base response. Patrols assigned to
leave the base cannot respond outside a 10-minute radius if they are providing back-up response to the on
base patrols.
(5) Patrols assigned to housing areas will be determined by workload and the 5-minute response time
requirement.
(6) Additional staffing positions (billets) will only be authorized for the watch sections with 10 or
more personnel assigned. Watch section Supervisor staffing will be made in accordance with the following
matrix:
NUMBER OF
PERSONNEL per
WATCH SECTION
Additional supervisory billets
per Watch Section
LESS THAN 10 0
10-19 1
20-29 2
30 plus 3
3. Security Patrols
a. Security patrols are single person mobile patrol units assigned to a specific asset protection zone.
Installations vary by size, population, workload and mission, therefore the number of patrol units required to
support the force protection mission is determined by measuring the following indicators: workload,
performance (required response times) and minimum capabilities. Each of these indicators measures a
different aspect of a unit’s patrol requirement. The largest indicator will be used as the staffing requirement
because it is deemed to support the minimum staffing requirement for the unit.
(1) The first measurement is patrol workload. The patrol workload is determined by averaging the
number of calls for service per shift. To determine the calls for service analyze at least one year of
applicable data, (i.e. desk logs, communication logs and police report logs). A call for service is defined as
any activity directing the unit to support the security mission. It includes such activities as responding to
alarms, crimes in progress, security checks and gates inspections/ relief etc. It does not include traffic
enforcement, field interviews and other self-directed activities. These activities are accounted for during the
non-directed periods. This standard assumes the following:
OPNAVINST 5580.1A CH-2
28 Jan 2002
E-3
(a) A unit will be involved in productive patrol related activity for 6.5 hours of an 8-hour shift.
(b) 2/3’s of the productive time (6.5 hours) a unit will be engaged in directed activity (calls for
service) and the average call for service is 30 minutes.
(c) 1/3 of productive time is available to patrol their assigned sectors and conduct self-directed
operations.
(d) Average time to complete a police report is 60 minutes. Therefore, each report equals two
calls for service.
(e) Based on these assumptions, one fully trained and qualified officer can handle an average of 8
calls for service per shift. Additional officers will be added based on the following matrix:
AVERAGE SHIFT CALLS
FOR SERVICE
NUMBER OF REQUIRED
PATROLS
0-8 1
9-16 2
17-24 3
25-32 4
33-40 5
41-48 6
49-56 7
(2) The second indicator identifies the required patrols by determining patrol zones based on response
time. All patrol zones in populated areas of the base will be established to provide an average response time
of 5 minutes to emergent situations. The average response time is calculated by determining the distance a
vehicle can travel while on base, with lights and siren (code three) which is 10 mph plus the posted speed
limit or if off base, the normal speed limit.
(3) To construct a patrol zone, determine the distance a patrol unit can respond within the given speed
limit in 5 minutes. With a compass identify the number of zones required to protect the base. Response
zones for non-populated areas will be established to provide response to the asset in the area (i.e. 15 minutes
for AA&E assets). In non-populated areas with no governing response requirements, periodic patrols of the
area (i.e. twice daily) will be established.
(a) The following chart illustrates patrol zones by speed and distance:
MILES PER HOUR DISTANCE
30 2.5
40 3.5
50 4.0
60 5.0
(b) All units require a 10-minute back up. Using the same process ensure all zones in populated areas
have at least one backup patrol unit within 10 minutes. When identifying the back up zones, remember some
zones i.e. controlled industrial area (CIA) or flight lines are dedicated to meet specific asset protection
requirements. Patrols zones designated to specific asset protection will not be used to meet the requirement
for backup response outside of their own zones. Otherwise, they would not be available to meet the initial
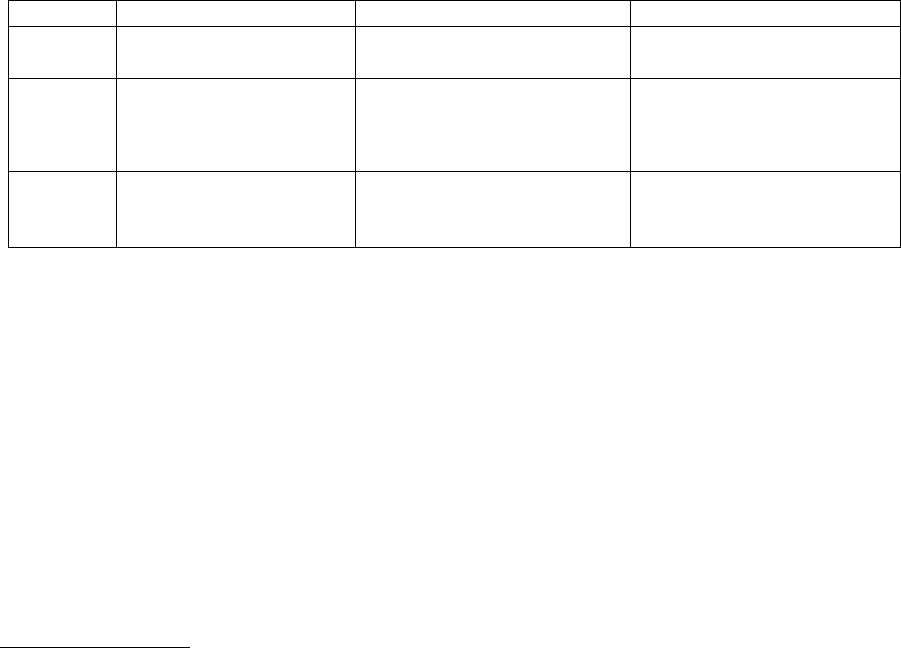
OPNAVINST 5580.1A CH-2
28 Jan 2002
E-4
and backup response requirements for assigned assets (see Annex A for examples of asset protection and
their response requirements).
(3) Minimum capabilities staffing indicators establish patrols by identifying minimum patrol
requirements based on the type/level of installation. If there were no crime, no incidents, or calls for service,
we would still need a security force to protect the installation, facility, center, and/or asset. The following
matrix categorizes installations by level and establishes a minimum patrol capability for each category based
on their ability to handle a prerequisite number of calls for service:
LEVEL TYPE CRITERIA MINIMUM STAFFING
ONE No homeported fleet ships,
aircraft or housing
Must be able to handle a
single call for service
Two patrols
TWO An installation with
homeported fleet ships,
aircraft, and/or housing
areas.
Must be able to handle two
simultaneous calls for
service
Four patrols
THREE Defined by fleet
CINC’s, Major
Claimants
High threat or critical
location
Developed on
an individual
basis
(4) The patrol assessment process. The following process is used to identify the installation’s
minimum patrol requirements:
(a) Identify the number of patrols based on workload (calls for service and police reports) per
shift.
(b) Identify the number of patrols based on response times (initial and backup).
(c) Identify the number of patrols based on type/level of the assets category.
(d) Compare subparagraphs (a) through (c) and use the largest number as the minimum number of
patrols required to protect the installation.
4. Gate Staffing Process
a. Every installation with a gate and perimeter fencing or barrier will have at least one primary external
vehicle access control point automatically validated for 24 hours a day 7 days per week. Any secondary
external vehicle access control points will be validated by a workload. Vehicle gates in operation with a
usage of 15 or less vehicles per hour will not be validated.
b. Pedestrian access control points should be kept to a minimum and will validated by workload. Note:
It is often more cost effective to automate low usage access control points.
c. External access points with high volume traffic (vehicular and foot) may require multiple sentries to
handle the workload. Each post will be individually assessed and validated to support the workload and
security requirements of the post.
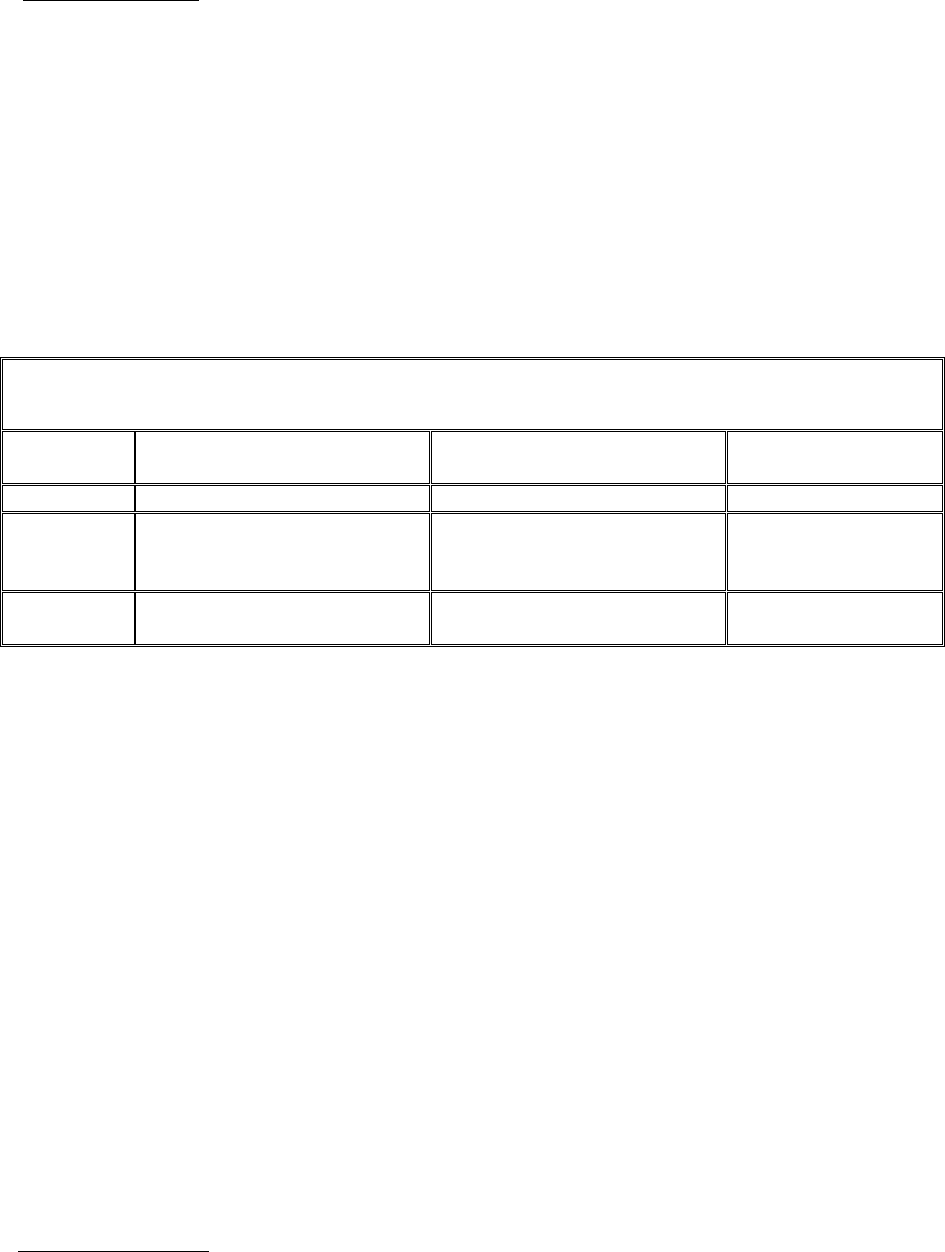
OPNAVINST 5580.1A CH-2
28 Jan 2002
E-5
5. Patrol Boat Staffing
a. Patrol boats will be assigned to installations required to protect afloat assets. The number of patrol
boats assigned and the personnel required to man them will be based on type of assets to be protected and
waterfront area to be patrolled.
b. The primary mission of the security waterborne patrol is to deter unauthorized entry into the waterside
restricted areas and engage intruders prior to them accessing Navy assets in the port. For the purpose of
calculating the number of boats required, a waterborne patrol zone will normally be about 2 nautical miles,
which facilitates an approximate response time of 5 minutes to any asset within the zone. Additional
missions such as providing escorts to vessels in and out of the port area or patrolling waterfront properties
where no afloat assets exist will be assessed and validated by the claimant separately.
c. The guidelines for determining hours of operations for the harbor patrol boats are as follows:
WATER ASSET VALUE/RISK MATRIX – STAFFING GUIDELINES
ASSET
PRIORITY
FPCONs NORMAL/
ALPHA
FPCON BRAVO FPCONs
CHARLIE/DELTA
A 1 boat; continuous patrols 2 boats; continuous patrols Same as BRAVO
B and C 1 boat; frequent random
patrols
2 boats; 1 continuous patrol -
second frequent random
patrols
2 boats; continuous
patrols
D 1 boat; frequent random
patrols
1 boat; continuous patrols Same as BRAVO
A boat crew will consist of two personnel, at a minimum, and be able to sustain operations 24 hours per day
7 days per week.
d. Crew calculation:
(1) One boat: 7 days a week 24 hours a day (plus ½ hour extra each shift change) = 178.5 hours.
Times 2 personnel = 357 hours or 11 people.
(2) Two boats: 7 days a week 24 hours a day (plus ½ hour extra each shift change) = 178.5 hrs.
Times four personnel = 714 hours or 23 people.
Note 1: Claimants and/or fleet CINC’s may validate additional patrol requirements at the installation to
address local force protection issues.
Note 2: Random hours of operation will be established by local policy.
Note 3: Staffing above the baseline plus one will be accomplished by auxiliary security force (ASF)
and/or other trained base personnel.
Note 4: This staffing does not include maintenance support requirements.
6. Investigation Staffing
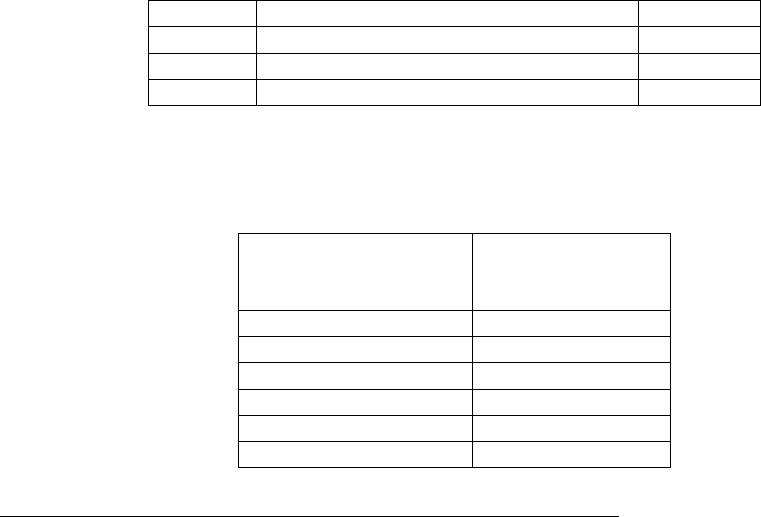
OPNAVINST 5580.1A CH-2
28 Jan 2002
E-6
a. The number of investigators will be determined by conducting an assessment of the annual case
workload per base. Each investigative report will be assigned a value based on the work required to
complete the case. The total number of points are divided by 15, which is the (threshold) number of points
required to justify one full time investigator. Small commands with insubstantial workload should train
backup investigators.
b. Case evaluation will be based on the complexity (number of leads/ amount of work) required to
complete the case. For example, a simple case is a case with less than four leads and can usually be
accomplished in a few days. Intermediate cases require a moderate amount of work (four to seven leads,
interviews etc.) to accomplish. Complex cases require significant work to accomplish. They may require
numerous hours of surveillance or other operational actions to complete the case. The security officer or
designated representative will evaluate and assign a case workload number to every completed investigation
based on the formula listed below. Note - Investigations that required more than one investigator may
receive case credit up to five points depending on their participation. The following formula will be used to
determine case workload points:
TIER TYPE OF CASE POINTS
One Complex 5
Two Intermediate (4-7 leads) 3
Three Simple (1-3 leads) 1
c. Based on the above formula, one investigator can handle investigations where the workload required
to complete the case is equal to or less than a monthly average of 15 caseload points. Additional
investigators will be added based on the following matrix:
AVERAGE
MONTHLY
CASELOAD POINTS
INVESTIGATOR
END-STRENGTH
0-15 1
16-30 2
31-45 3
46-60 4
61-75 5
76-91 6
7. Military Working Dog (MWD) Staff, Handlers and Support Personnel
a. The validation of MWD teams will be based on the classification of the base or installation.
(1) Level One bases will not be staffed with MWD teams. Claimants may authorize an exception
based on local threat and/or criminal activity.
(2) Level Two bases will be staffed with six personnel to support six MWD teams. The senior
handler will also be assigned to supervise the kennels.
(3) Level Three bases are located in high threat or critical locations that require increased force
protection. Bases will be individually assessed and staffed based on the force protection requirements.

OPNAVINST 5580.1A CH-2
28 Jan 2002
E-7
(4) In addition, in areas where the Navy has formed regional security force structures all of the MWD
teams from the local bases will be consolidated into the regional kennel. Regional kennels with 24 or more
MWD teams will be staffed with two kennel masters and one training supervisor. All other regional kennels
will be staffed with a single kennel master and a single training supervisor.
(5) Units that are tasked to support FAST will be staffed with five additional MWD teams.
8. Administrative/Support Staffing
a. The staffing for administrative and support staff (i.e. pass and ID and armory, etc.) requirements are so
divergent that trained staffing personnel will validate each location.
b. Security training sections will be staffed with a minimum of two personnel. Those security
departments with more than 100 personnel will have 1 trainer per every 50 validated personnel assigned to
the security department.
9. Auxiliary Security Force (ASF) Manning
a. The number of personnel assigned to the ASF is determined by first establishing the security force
manning requirements for FPCONs NORMAL through DELTA using the process outlined in this chapter.
b. ASF staffing requirements are determined by identifying the difference between current security force
manning levels (set to meet the designated FPCON) and the remaining security force manpower
requirements up to FPCON DELTA.
c. Limited additional ASF staffing requirements may be established to support other security related
functions (e.g., command posts). ASF posts will not be established for the sole purpose of providing fixed
guard services at locations that do not specifically require them. The ISIC will approve all ASF posting
requirements.
10. Force Protection Condition (FPCON) Staffing
a. The FPCON staffing process identifies personnel requirements based on DoD force protection
conditions (FPCONs). Specific capabilities and workload have been established for each applicable
measure. Baseline plus one staffing is the staffing required to elevate one level above the installations
“normal” FPCON condition without using ASF. This section will be used to identify a unit’s baseline plus
one staffing requirements.
(1) FPCON ALPHA workload standards. Specific measures (by number) for FPCON ALPHA have
been established. Specific workload has been assigned to the applicable measures and will be used to
determine the number of personnel required to support FPCON ALPHA.
(a) Measure 4: Limit access points - establish a mobile vehicle inspection team (two searchers and
supervisor). These three personnel should provide a minimum of 40 hours of coverage and be directed to
perform inspections on a random basis varying times and locations.
(b) Measure 5: Limit access points - post armed sentries at all installation access control points.
Note - some CONUS locations may have a waiver from their fleet CINC or major claimant and will only be
required to establish access control posts at higher FPCONs. Waivered installations will be staffed with full
time positions to support this requirement.
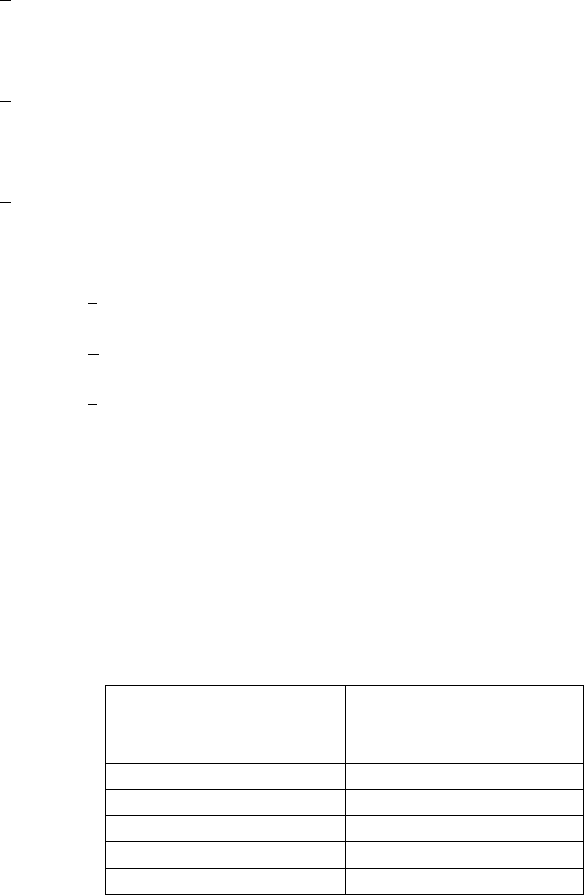
OPNAVINST 5580.1A CH-2
28 Jan 2002
E-8
(c) Measure 9: “Mutual” antiterrorism measures - in various locations, especially OCONUS, joint
posts have been established with local forces. These posts foster good relations and enhance security for
U.S. personnel. Any post authorized by local agreement and sanctioned by the claimant will be validated
and staffed.
(2) FPCON ALPHA and normal uses the same minimum patrol activity workload standards as
discussed earlier in this chapter.
(3) FPCON BRAVO workload standards. Specific measures (by number) for FPCON BRAVO have
been established. Specific workload has been assigned to the applicable measures and will be used to
determine the number of personnel required to support BRAVO.
(a) Measure 19: Provide protection to:
1. Domestic accommodations (off Base Housing) of which the minimum criteria will be 50
units with a defined U.S. perimeter. Minimum staffing is one patrol with one 10-minute backup plus an
access control post.
2. Overseas schools - provide one mobile sentry 1 hour prior to the opening and during hours
of operations to include “after school” events plus 30 minutes. At locations outside of the 10-minute
response radius a secondary post will be established.
3. Other soft targets - In addition to base patrols; surveillance detection teams will be
deployed to provide at least 80 hours of coverage per week. This staffing will vary based on the area of
coverage, location, threat, support of other law enforcement and NCIS assets.
a. Level One bases will be staffed with 4-8 personnel.
b. Level Two bases will be staffed with 6-12 personnel.
c. Level Three bases will be staffed with 8-16 personnel.
Note: This position will normally be assigned to the investigations division
and coordinate with the local NCIS office.
(b) Measure 22: Establish two person vehicle inspection teams for every other gate. This will
provide 50 percent coverage at all external access control points. Inspection teams will be validated to
provide 24 hour coverage as required to support gate operations.
(c) Measure 23: Increase patrols/Patrol staffing. Use the table below to re-assess patrol workload
to ensure that only one-half of their patrol time is dedicated to directed work and the remaining patrol time is
available to provide deterrent patrols. The following matrix will be utilized:
AVERAGE CALLS
FOR
SERVICE PER SHIFT
NUMBER OF
PATROLS
REQUIRED
0-6 1
7-12 2
13-18 3
19-24 4
25-30 5

OPNAVINST 5580.1A CH-2
28 Jan 2002
E-9
31-36 6
37-42 7
(d) Measure 25: Provide one protective escort for each person listed on the High-Risk Billet
(HRB) list. Billets are normally assigned to investigations.
(4) FPCONs CHARLIE and DELTA workload standards. Specific measures (by number) for
FPCONs Charlie and Delta have been established and issued by higher authority. Specific workload has
been assigned to the applicable measures and will be used to determine the number of personnel required to
support CHARLIE and DELTA.
(a) Measure 33: Strictly enforce entry control (post a sentry at all gates and randomly search
vehicles - provides a two person search team at every gate and/or provide staff to operate any security
equipment.
(b) Measure 36: Increase patrolling/staff. Use the table below to re-assess patrol workload to
ensure that only one-third of their patrol time is dedicated to directed work and the remaining patrol time is
available to provide deterrent patrols. The following matrix will be utilized:
AVERAGE CALLS
FOR
SERVICE PER SHIFT
NUMBER OF
PATROLS
REQUIRED
0-4 1
5-8 2
9-12 3
13-16 4
17-20 5
21-24 6
25-28 7
(c) Measure 37: Special attention will be given to vulnerable points. In addition to base patrols;
surveillance detection teams will be deployed to provide continuous coverage. This staffing will vary based
on the area of coverage, location, threat, support of other law enforcement and NCIS assets.
1. Level One bases will be staffed with 6-12 personnel.
2. Level Two bases will be staffed with 8-12 personnel.
3. Level Three bases will be staffed with 12-24 personnel.
Note: This position will normally be assigned to the investigations division
and coordinate with the local NCIS office.
(d) Measure 42: Requires augmentation as necessary. The minimum augmentation for Navy
bases is defined as follows:
1. Level One bases will establish a 3 person reaction force manned 24/7 X five section
duty, requires 15 personnel.
OPNAVINST 5580.1A CH-2
28 Jan 2002
E-10
2. Level Two bases will establish a 5-person reaction force manned 24/7 X five section
duty, requires 25 personnel.
3. Level Three bases will establish a 10-person reaction team manned 24/7 X five section
duty, requires 50 personnel.
Note - this is a response and containment force, not a “SWAT” team. Their mission is to respond and engage
the situation so the other patrols can remain in their assigned areas.
EXAMPLES OF ASSET RESPONSE REQUIREMENTS
(Annex A)
Reference Asset Response time
(min)
Comments
(One responder,
unless indicated)
OPNAVINST
5530.14C
Non-alert Aircraft 5 Page 3-6,
2 people
OPNAVINST
5530.14C
Priority A assets and
life-
Threatening
5 Page 8-2&3
subparagraph I
DOD C5210.41-M
4-1994
Nuclear weapons Controlled
DOD C5210.41-M
4-1994
C4I Controlled
NAVSEAINST
9210.22C
Reactors/Special
Nuclear Material
Classified
OPNAVINST
5530.13B
AA&E 15 Page 3-5
Executive Order
12958
Classified Top
Secret
15
Executive Order
12958
Classified Secret 30
DCID 1/21
Storage
SCIFs-Open
5 U.S. Citizen
DCID 1/21
Storage
SCIFs-Closed OCONUS
15 CONUS
U.S. Citizen
OPNAVINST 5580.1A CH-2
28 Jan 2002
E-11
SECURITY STAFFING FORMULA (Annex)
1. The Navy Manpower Analysis Center (NAVMAC) conducted a detailed study of the security function
and developed the following guidelines for determining manpower requirements:
a. Standard workweek: 40.00 hours (routine is 8 hours per day, 5 days per week, excluding meal hours).
b. Productive workweek: 31.66 hours.
c. Analysis of duty hours:
(1) Total hours available weekly less non-available time:
(a) Training (1.47)
(b) Mandatory refresher training (1.72)
(c) Diversions (1.00)
(d) Leave (2.62)
(e) Holidays (1.53) (8.34)
(2) Total hours available for productive work: 31.66
d. One Post Manpower Requirement:
(1) 25 1/2 hours a day 7 days a week: 178.50 hours.
(2) Weekly manpower requirements: 5.64 personnel.
(3) Rounding rule (5.361 to 6.432): 6.00 personnel.
e. The security workday is 25.5 hours and workweek (WWH) 178.5 hours. This workday/week takes in
account turnover/relief requirements.
f. End-strength is determined by adding all of the weekly hours that personnel are assigned to fixed or
mobile posts and dividing the total weekly work hours by 31.66.
(1) The security staffing formula works as follows:
Post # of Per Hrs Total Hours Days/ Week Total Hours/Wk
1 1 24 25.5 7 178.5
2 1 24 25.5 7 178.5
3 1 10 11.0 5 55.0
4 2 16 34.0 7 238.0
5 1 24 25.5 5 127.5
6 2 24 51.0 7 357.0
* Per the formula above: validated weekly post hours (WWH) equals 1134.5. Divided by 31.66 (total hours
available for productive work – above) equals 35.8 (round to 36) billets/personnel.