Edgecore Networks SMCWTVA100 Intel WiDi Adapter User Manual Manual
Edgecore Networks Corporation Intel WiDi Adapter Manual
Manual

IEEE
802.11a/
b/g/n
WLAN
11n Dual Band Dongle
USER’S GUIDE
VERSION 1.0
© All rights reserved.
All trade names are registered trademarks of respective manufacturers listed.
This manual may not be copied in any media or form withou
t
the written consent of original maker.
SMC
SMCWTVA100
Intel WiDi adapter(具無線功能)

1. Introduction .........................................................……...... 1
2. Wireless LAN Basics ................................................……...... 3
3. IP ADDRESS ..........................................................………….. 4
4. Install Driver/Utility ...............................................………….. 5
4.1 Windows XP/Vista/7................................................... 5
5. Wireless Network Configuration ............................................ 7
5.1 Utility Icon .............................................................. 7
5.2 Client Mode (Default Setting)........................................ 7
6. Technical Specifications ................................................ .. . 14
7. Troubleshooting .............................................................. 16
8. Glossary ....................................................................... 17

1
Thank you for your purchase of the WLAN Adapter. Featuring wireless
technology, this wireless networking solution has been designed for both
large and small businesses, and it is scalable so that you can easily add
more users and new network features depending on your business scale.
FEATURES
Support Microsoft XP(32bit/64bit) / Vista(32bit/64bit) / 7(32bit/64bit)
Operating distance of up to 300 meters in free space.
300/270/240/180/120/90/60/54/48/36/30/24/22/18/12/11/6/5.5/2/1
Mbps selectable Data Rate according to client adapter default
antennas.
64/128-bit WEP , WPA, WPA2, WPS
2.400GHz ~ 2.4835GHz unlicensed ISM Frequency Band. Modulation
Method. 5GHz UNII, Midband, ISM bands.
IEEE 802.11b : DSSS (Direct Sequence Spread Spectrum).
IEEE 802.11a/g n : OFDM (Orthogonal Frequency Division
Multiplexing).
Easy operation and setting up.
SYSTEM REQUIREMENTS
Windows System : XP(32bit/64bit) / Vista(32bit/64bit) / 7(32bit/64bit).PCs
must have a device driver installed. It allows you to communicate with
WLAN 11n USB Client Adapter.
2
BEFORE YOU START
1. Confirm Box Contents
WLAN 11n USB Client Adapter
Quick Start Guide
Driver CD
CONNECTING YOUR WLAN 11n USB Client Adapter TO PC
Quick Start Guide
Connect your WLAN 11n USB Client Adapter to your PC. Install driver.
GETTING TO KNOW WIRELESS LAN ADAPTER
LED Status
ON – Adapter connects to remote.
BLINKING - WLAN Adapter is active.
3
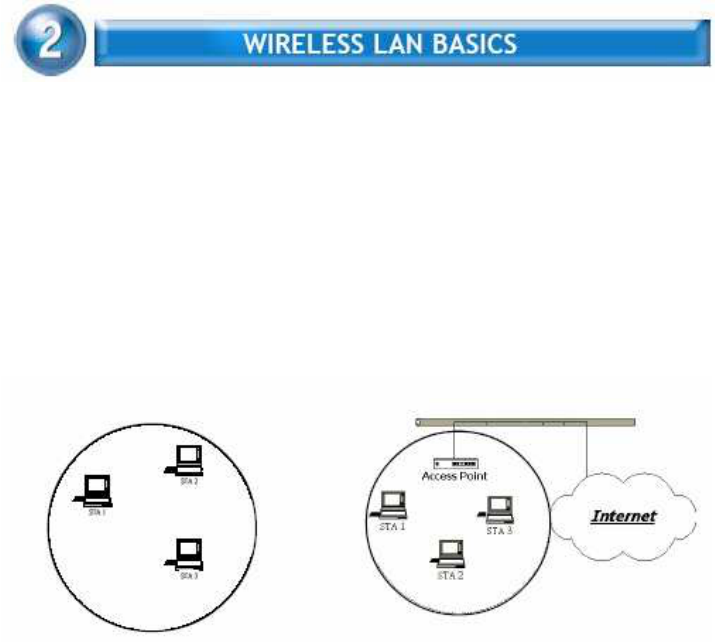
Wireless LAN network defined by IEEE 802.11a/b/g standard committee
could be configured as :
Ad Hoc wireless LAN.
Infrastructure wireless LAN.
Ad Hoc network is a group of PCs installed with wireless LAN cards, this group
of PCs is called a BSS (Basic Service Set). PCs in this group can use their
wireless LAN cards to communicate with each other, but can not
connect to the Internet.
Ad Hoc Wireless Network Infrastructure Wireless Network
The most obvious difference between Infrastructure wireless network and Ad
Hoc wireless network is that the PCs in Infrastructure wireless network can
access the resource in the Internet through Access Point.
Depending on your requirement, you can easily set up your PC’s network to be
a “Ad Hoc” or “Infrastructure” wireless network. Generally speaking, if in your
network, there is an Access Point in it, we recommend you to set your
network as an “Infrastructure”, so it can connect to the Internet.

4
To use the WLAN 11n USB Client Adapter with a computing device, the WLAN
Adapter must be equipped with a proper Interface. All drivers and supporting
software for the WLAN Adapter must be installed and configured first.
Ask your system administrator for the following information, which
you may need to provide during driver installation :
Your Wireless Client Name.
Your Wireless SSID.
Your computer’s unique client name and workgroup name. For your
network account, your user name and password.
Your IP address, gateway address, and subnet mask if you’re not
using a DHCP client.
Any computer on a network is identified by a unique network address. There
are two methods to assign a network address to a computer on a TCP/IP
network :
Static IP addressing.
Dynamic IP addressing (DHCP Client).
In network with static IP addressing, the network administrator manually
assigns an IP address to each computer. Once a static IP address is assigned,
a computer uses the same IP address every time it reboots and logs on to the
network. You may manually change the IP address in the
Network Properties
dialog box.
Network using static IP address is easy to set up and do not
require additional network management software
.
In network with dynamic IP addressing, a DHCP server in the network
dynamically assigns IP addresses to all clients every time they log on to the
network. Network using dynamic IP address requires setting up and running a
DHCP Server.
5
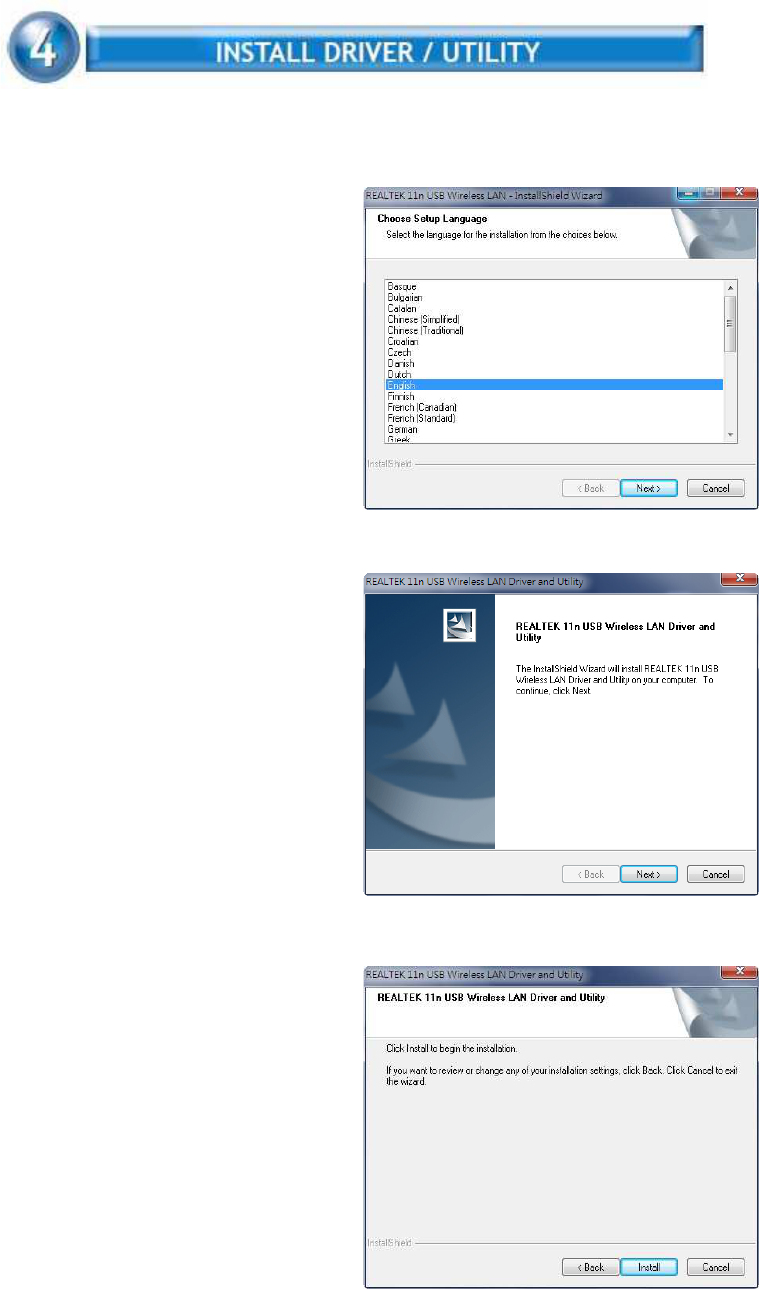
The installation & driver CD will automatically activate the autorun installation
program after you insert the disk into your CD drive.
Step 1 :
Insert the installation CD into your
CD-ROM. Choose the Setup
Language and click Next button.
Step 2 :
Installation descriptions shown. Click
Next to continue.
Click Install to begin the installation
6
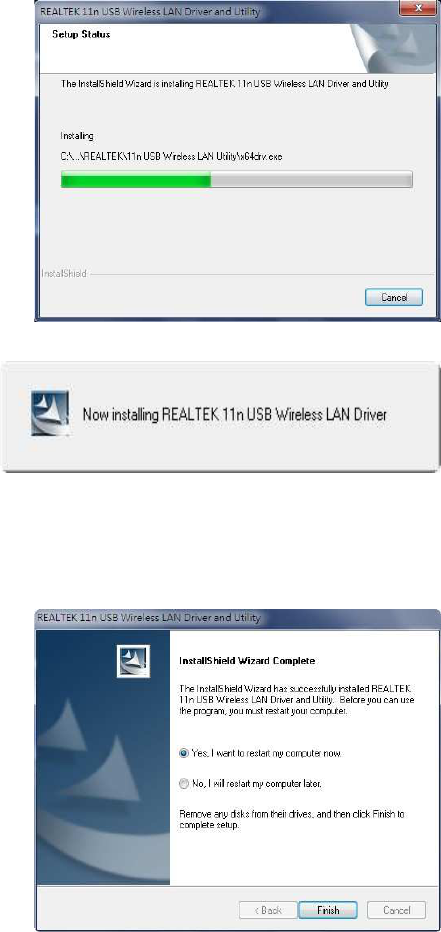
Installing & configuring WLAN utility
Installing Drivers.
Step 3 :
Click Finish to complete installation
7
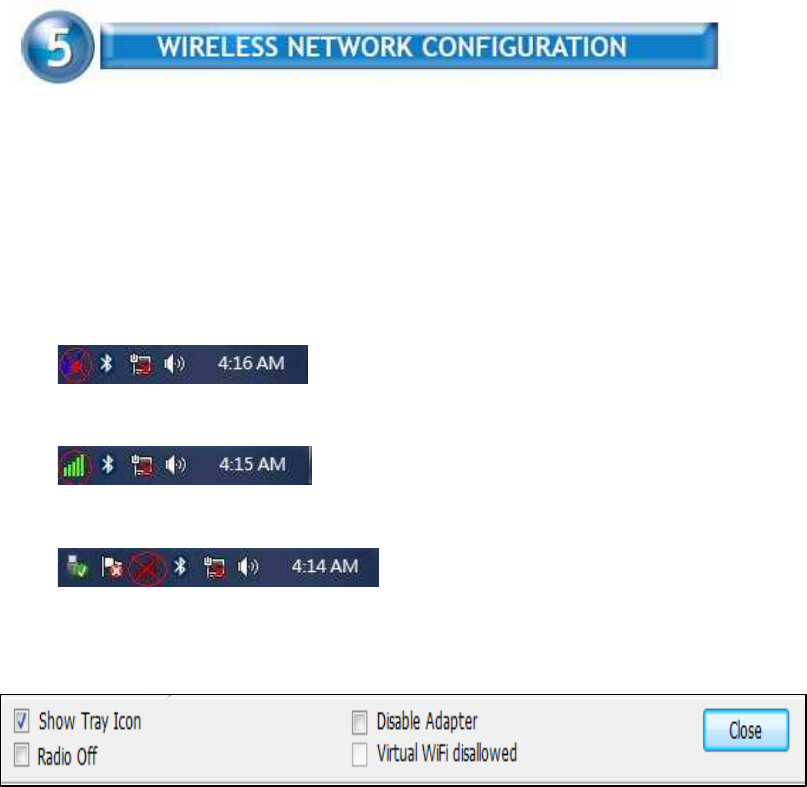
WLAN 11n USB Client Adapter uses its own management software. All
functions controlled by users are provided by this application. When you insert
the WLAN Adapter into your laptop or desktop, a icon should appear in the
Windows System Tray automatically.
5.1 Utility Icon
▓
Client mode utility running but no WLAN Adapter plugged
▓
Client mode utility running and WLAN Adapter scan available network.
▓
Client mode utility running and WLAN Adapter can not scan any AP
5.2 Client Mode (Default Setting)
Wireless Device Control :
▓
Show Tray Icon – Show icon or not show icon in system tray.
▓
Radio Off – Stop wireless signal.
▓
Disable Adapter – Stop wireless device.
▓
Virtual WiFi disallowed – Soft AP off
8
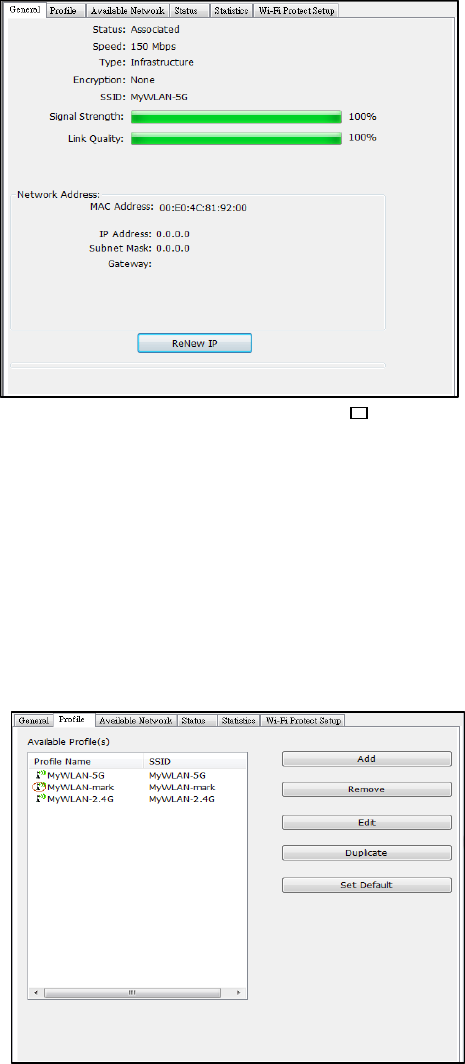
5.2.1 GENERAL SETTING
Once device is set,
double click on that
icon and the
configuration window
will pop up as shown.
It shows the current
connected network.
The signal strength
and link quality are
displayed also.
The bar graph
displays the quality and strength of the link between the node and its
Access Point. Link Quality is a measurement of receiving and
transmitting performances over the radio.
Network Address displays current MAC Address, IP Address,
Subnet. and Gateway.
Click Renew IP button to refresh IP address leased from wireless
AP.
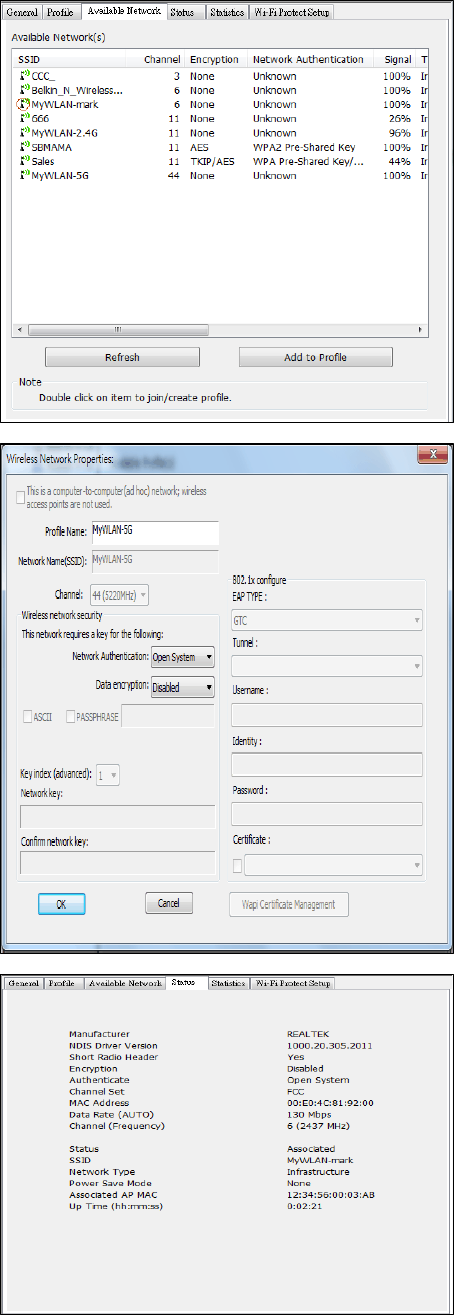
5.2.2 PROFILE SETTING
In profile tab, you can
Add,Remove,Edit,
Duplicate and Set
Default to manipulate
profile content
manually. Strongly
recommend to use
profile after you do
Available Network.
9
5.2.3 AVAILABLE
NETWOEK SETTING
Click Available
Network tab and it will
show all available
networks that radio
can reaches. Select
proper SSID & BSSID
you want to connect.
Click Refresh button
to force and rescan
available
networks currently.
Select one of SSIDs,
and click Add to
Profile to create
profile that
can be configured
more wireless
parameters.
In this page, you can
edit your profile name,
configure wireless
security like WEP,
WPA, WPA2,
802.1x …etc. After
finishing setup, click
OK button to save
configuration
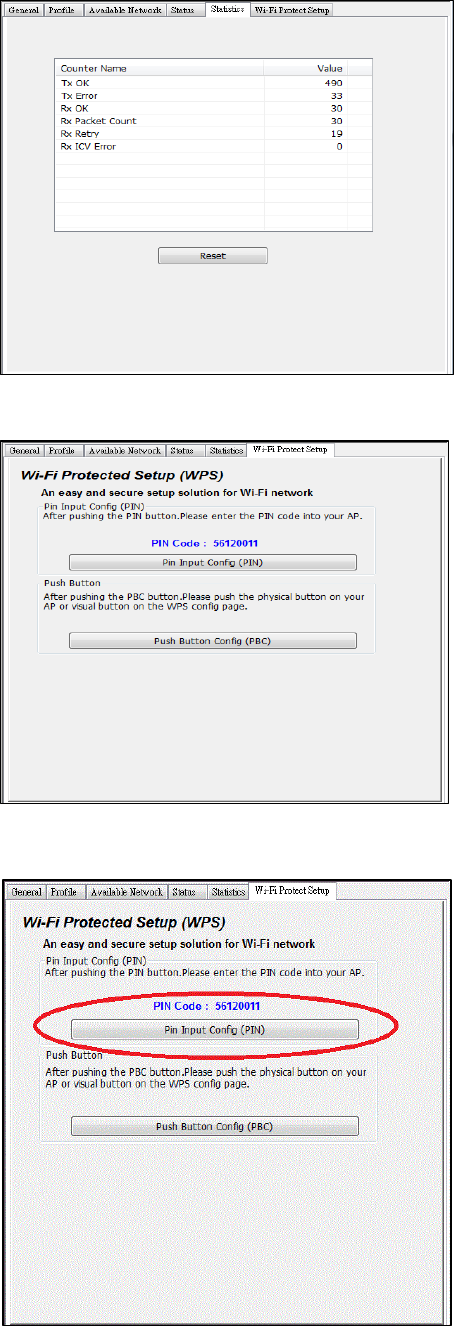
5.2.4 Status
Status page tab,
shows all wireless,
networking and device
driver version in
details.
10
5.2.5 Statistics
Statistics page tab will
show real-time TX/RX
relative counters to
check or evaluate the
wireless performance.
Click Reset button to
set counter to
zero.
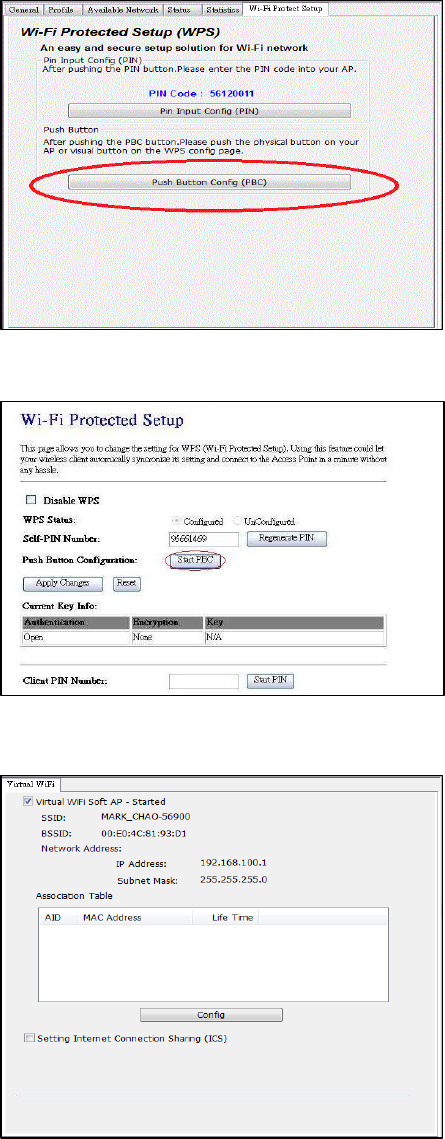
5.2.6 Wi-Fi Protected
Setup
An easy and secure
setup solution for Wi-
Fi network. you can
choose PIN Code or
Push Button method to
connect to an AP.
▓
Pin method:
Step 1 :
Push the PIN button.
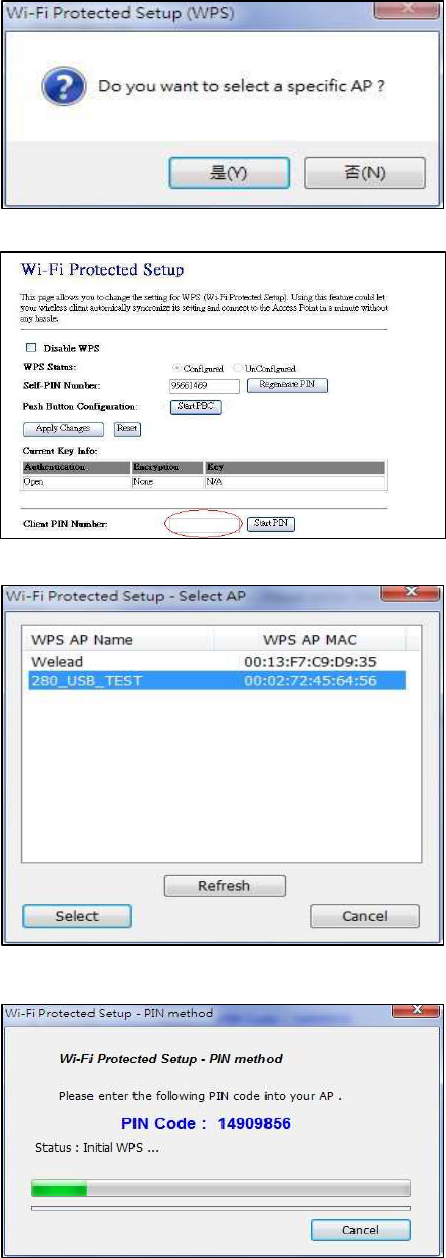
11
Step 2 :
Select a specific AP
Step 3 :
Enter the PIN code
into your AP.
Step 4 :
Select AP that you
want to configure.
Step 5:
Wait for configuring
your wireless AP to be
the security setting.
12
▓
PBC method:
Step 1 :
Push the PBC button.
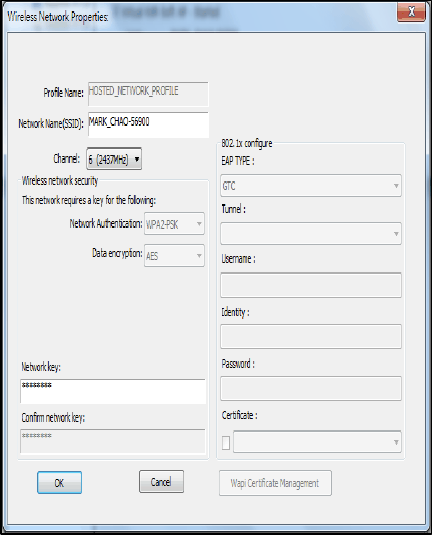
Step 2 :
Push the physical
button on our AP or
visual button on he
WPS config page.
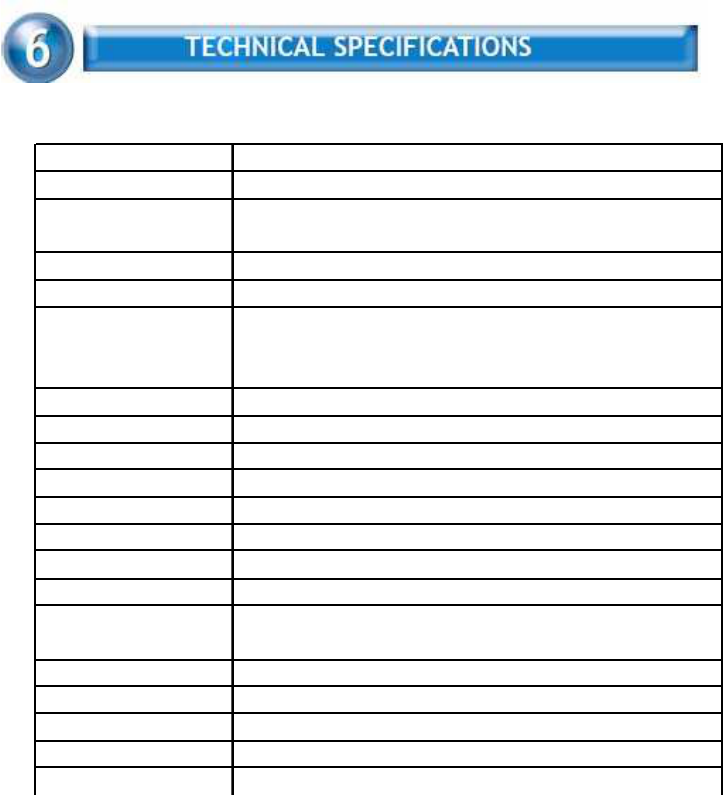
5.2.6 Virtual WiFi(Soft AP)
Setup
Click to Enable Virtual
WiFi. Push config
button to set.
13
Enter Soft AP SSID and
Security Key.
14
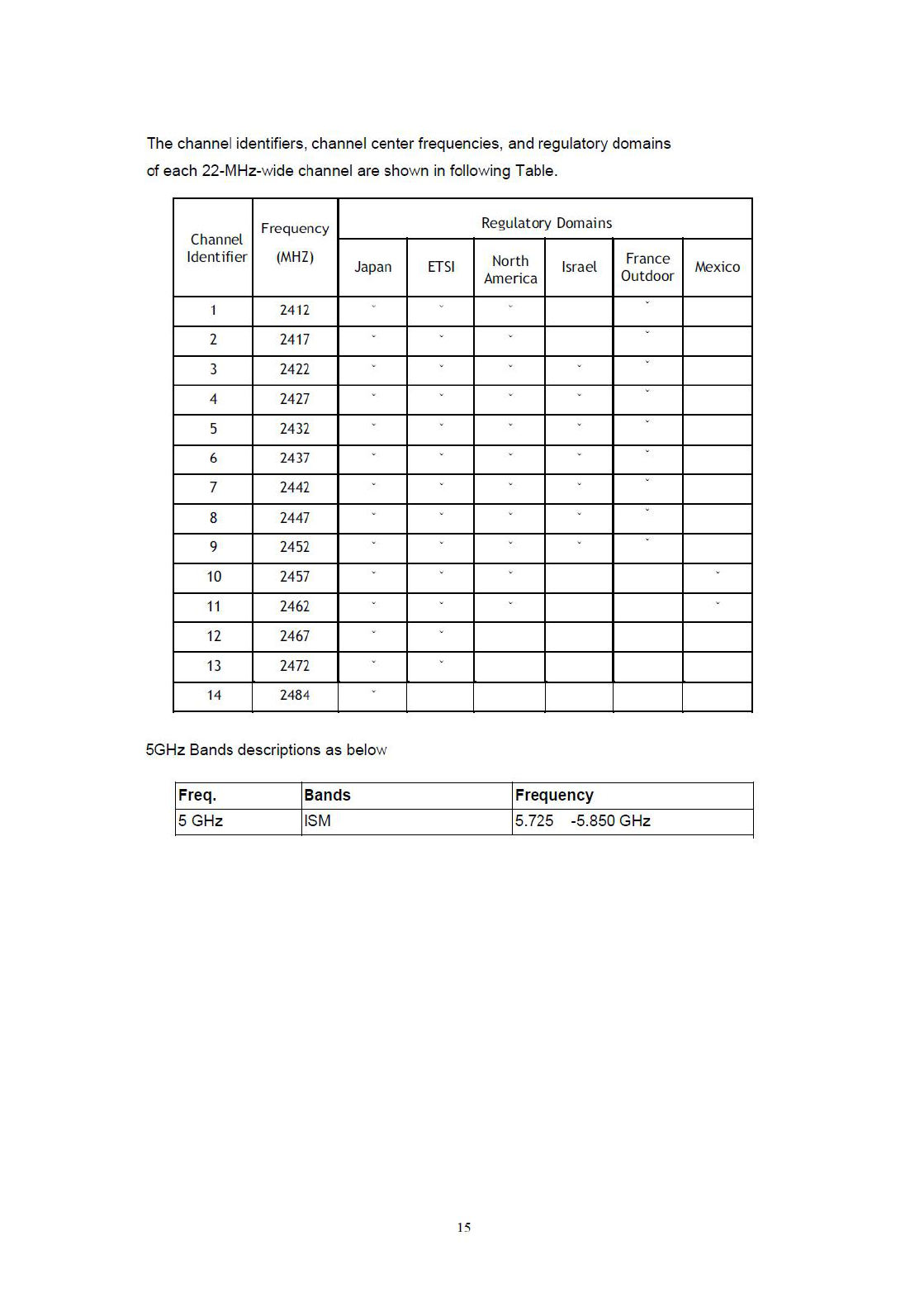
Product Name WLAN 11n Dual Band Dongle
Standard 802.11a/b/g/n
Data Transfer Rate 1,2,5.5,6,11,12,18,22,24,30,36,48,54,60,90,120,180,240,270 and
maximum of 300Mbps
Modulation Method BPSK/QPSK/16-QAM/64-QAM
Frequency Band 2.4GHz and 5GHz ISM Band
Spread Spectrum IEEE 802.11b: DSSS (Direct Sequence Spread Spectrum)
IEEE 802.11a/g/n: OFDM (Orthogonal Frequency Division
Multiplexing)
RF Output Power <13dBm@11n/11a,< 17dBm@11b,< 15dBm@11g
Operation Mode Ad hoc, Infrastructure, Soft AP
Receiver Sensitivity 11Mbps -80dBm@8%,54Mbps -70dBm@10%,300Mbps -64dBm@10%
Operation Range Indoor@Up to 100 meters,Outdoor@Up to 280 meters
LED Power
OS Support Win XP / Vista / Windows 7
Security 64 bit/128 bit WEP, TKIP, AES
Interface USB 2.0
Power Consumption Transmit: around 420 mA
Receive: around 280 mA
Operating Temperature 0 – 50° C ambient temperature
Storage Temperature -10 ~ 70°C ambient temperature
Humidity 5 to 90 % maximum (non-condensing)
Dimension 59x24x10.3mm

16
Symptom :
The LED is off.
Remedy :
Make sure the PC Card is inserted properly. Otherwise contact your vendor.
Symptom :
The LED is always on not blinking.
Remedy :
Make sure that you have installed the driver from attached CD. Otherwise
contact your vendor.
Symptom :
The LED is blinking but the PC Card icon does not appear in your icon tray.
Remedy :
Make sure that you have installed the Utility from the attached CD.
Symptom :
The PC Card is linking, but can’t share files with others.
Remedy :
Make sure the file and printer sharing function is enabled. You can
enable the function by checking the icon of My Computer -> Control
Panel -> Network -> file and printer sharing -> I want to be able to give
others to access to my files.
Symptom :
Slow or poor performance under AP mode
Remedy :
Try to select another channel for the communicating group or move your
device closer to the Access Point.

17
IEEE 802.11 Standard
The IEEE 802.11 Wireless LAN standards subcommittee, which is formulating
a standard for the industry.
Access Point
An internetworking device that seamlessly connects wired and wireless
networks together.
Ad Hoc
An Ad Hoc wireless LAN is a group of computers, each with a WLAN
adapter, connected as an independent wireless LAN. Ad Hoc wireless LAN
is applicable at a departmental scale for a branch or SOHO operation.
BSSID
A specific Ad Hoc LAN is called a Basic Service Set (BSS). Computers in a
BSS must be configured with the same BSSID.
DHCP
Dynamic Host Configuration Protocol - a method in which IP addresses are
assigned by server dynamically to clients on the network. DHCP is used for
Dynamic IP Addressing and requires a dedicated DHCP server on the
network.
Direct Sequence Spread Spectrum
This is the method the wireless cards use to transmit data over the frequency
spectrum. The other method is frequency hopping. Direct sequence
spreads the data over one frequency range (channel) while frequency
hopping jumps from one narrow frequency band to another many
times per second.
ESSID
An Infrastructure configuration could also support roaming capability for
mobile workers. More than one BSS can be configured as an Extended
Service Set (ESS). Users within an ESS could roam freely between BSSs
while served as a continuous connection to the network wireless stations
and Access Points within an ESS must be configured with the same ESSID
and the same radio channel.
Ethernet
Ethernet is a 10/100Mbps network that runs over dedicated home/office
wiring. Users must be wired to the network at all times to gain access.
Gateway
A gateway is a hardware and software device that connects two dissimilar
18
systems, such as a LAN and a mainframe. In Internet terminology, a gateway
is another name for a router. Generally a gateway is used as a funnel
for all traffic to the Internet.
IEEE
Institute of Electrical and Electronics Engineers
Infrastructure
An integrated wireless and wired LAN is called an Infrastructure
configuration. Infrastructure is applicable to enterprise scale for wireless
access to central database, or wireless application for mobile workers.
ISM Band
The FCC and their counterparts outside of the U.S. have set aside bandwidth
for unlicensed use in the so-called ISM (Industrial, Scientific and
Medical) band. Spectrum in the vicinity of 2.4 GHz, in particular, is being
made available worldwide. This presents a truly revolutionary opportunity
to place convenient high-speed wireless capabilities in the hands of users
around the globe.
Local Area Network (LAN)
A LAN is a group of computers, each equipped with the appropriate network
adapter card connected by cable/air, that share applications, data,
and peripherals. All connections are made via cable or wireless media,
but a LAN does not use telephone services. It typically spans a single
building or campus.
Network
A network is a system of computers that is connected. Data, files, and
messages can be transmitted over this network. Networks may be local or
wide area networks.
Protocol
A protocol is a standardized set of rules that specify how a conversation
is to take place, including the format, timing, sequencing and/ or error
checking.
SSID
A Network ID unique to a network. Only clients and Access Points that
share the same SSID are able to communicate with each other. This string
is case-sensitive.
Static IP Addressing
A method of assigning IP addresses to clients on the network. In networks
with Static IP address, the network administrator manually assigns an IP
address to each computer. Once a Static IP address is assigned, a computer
19
uses the same IP address every time it reboots and logs on to the
network, unless it is manually changed.
Temporal Key Integrity Protocol (TKIP)
The Temporal Key Integrity Protocol, pronounced tee-kip, is part of the
IEEE 802.11i encryption standard for wireless LANs. TKIP is the next
generation of WEP, the Wired Equivalency Protocol, which is used to
secure 802.11 wireless LANs. TKIP provides per-packet key mixing, a
message integrity check and a re-keying mechanism, thus fixing the
flaws of WEP.
Transmission Control Protocol / Internet Protocol (TCP/IP)
TCP/IP is the protocol suite developed by the Advanced Research
Projects Agency (ARPA). It is widely used in corporate Internet works,
because of its superior design for WANs. TCP governs how packet is
sequenced for transmission the network. The term “TCP/IP” is often
used generically to refer to the entire suite of related protocols.
Transmit / Receive
The wireless throughput in Bytes per second averaged over two seconds.
Wi-Fi Alliance
The Wi-Fi Alliance is a nonprofit international association formed in 1999
to certify interoperability of wireless Local Area Network products based
on IEEE 802.11 specification. The goal of the Wi-Fi Alliance’s members is
to enhance the user experience through product interoperability. The
organization is formerly known as WECA.
Wi-Fi Protected Access (WPA)
The Wi-Fi Alliance put together WPA as a data encryption method for
802.11 wireless LANs. WPA is an industry-supported, pre-standard version
of 802.11i utilizing the Temporal Key Integrity Protocol (TKIP),
which fixes the problems of WEP, including using dynamic keys.
Wide Area Network (WAN)
A WAN consists of multiple LANs that are tied together via telephone
services and / or fiber optic cabling. WANs may span a city, a state, a
country, or even the world.
Wired Equivalent Privacy (WEP)
Now widely recognized as flawed, WEP was a data encryption method
used to protect the transmission between 802.11 wireless clients and
APs. However, it used the same key among all communicating devices.
WEP’s problems are well-known, including an insufficient key length and
no automated method for distributing the keys. WEP can be easily
20
cracked in a couple of hours with off-the-shelf tools.
Wireless LAN (WLAN)
A wireless LAN does not use cable to transmit signals, but rather uses
radio or infrared to transmit packets through the air. Radio Frequency
(RF) and infrared are the commonly used types of wireless transmission.
Most wireless LANs use spread spectrum technology. It offers limited
bandwidth, usually under 11Mbps, and users share the bandwidth with
other devices in the spectrum; however, users can operate a spread
spectrum device without licensing from the Federal Communications
Commission (FCC).
Fragment Threshold
The proposed protocol uses the frame fragmentation mechanism defined in
IEEE 802.11 to achieve parallel transmissions. A large data frame is
fragmented into several fragments each of size equal to fragment threshold.
By tuning the fragment threshold value, we can get varying fragment sizes.
The determination of an efficient fragment threshold is an important issue in
this scheme. If the fragment threshold is small, the overlap part of the master
and parallel transmissions is large. This means the spatial reuse ratio of
parallel transmissions is high. In contrast, with a large fragment threshold, the
overlap is small and the spatial reuse ratio is low. However high fragment
threshold leads to low fragment overhead. Hence there is a trade-off between
spatial re-use and fragment overhead.
Fragment threshold is the maximum packet size used for fragmentation.
Packets larger than the size programmed in this field will be fragmented If you
find that your corrupted packets or asymmetric packet reception (all send
packets, for example). You may want to try lowering your fragmentation
threshold. This will cause packets to be broken into smaller fragments. These
small fragments, if corrupted, can be resent faster than a larger fragment.
Fragmentation increases overhead, so you'll want to keep this value as close
to the maximum value as possible.
RTS (Request To Send) Threshold
The RTS threshold is the packet size at which packet transmission is governed
by the RTS/CTS transaction. The IEEE 802.11-1997 standard allows for short
packets to be transmitted without RTS/CTS transactions. Each station can
have a different RTS threshold. RTS/CTS is used when the data packet size
exceeds the defined RTS threshold. With the CSMA/CA transmission
21
mechanism, the transmitting station sends out an RTS packet to the receiving
station, and waits for the receiving station to send back a CTS (Clear to Send)
packet before sending the actual packet data. This setting is useful for
networks with many clients. With many clients, and a high network load, there
will be many more collisions. By lowering the RTS threshold, there may be
fewer collisions, and performance should improve. Basically, with a faster RTS
threshold, the system can recover from problems faster. RTS packets
consume valuable bandwidth, however, so setting this value too low will limit
performance.
Beacon Interval
In addition to data frames that carry information from higher layers, 802.11
includes management and control frames that support data transfer. The
beacon frame, which is a type of management frame, provides the "heartbeat"
of a wireless LAN, enabling stations to establish and maintain communications
in an orderly fashion. Beacon Interval represents the amount of time between
beacon transmissions. Before a station enters power save mode, the station
needs the beacon interval to know when to wake up to receive the beacon
(and learn whether there are buffered frames at the access point).
Preamble Type
There are two preamble types defined in IEEE 802.11 specification. A long
preamble basically gives the decoder more time to process the preamble. All
802.11 devices support a long preamble. The short preamble is designed to
improve efficiency (for example, for VoIP systems). The difference between the
two is in the Synchronization field. The long preamble is 128 bits, and theshort
is 56 bits.
WPA2
It is the second generation of WPA. WPA2 is based on the final IEEE 802.11i
amendment to the 802.11 standard.
Temporal Key Integrity Protocol (TKIP)
The Temporal Key Integrity Protocol, pronounced tee-kip, is part of the IEEE
802.11i encryption standard for wireless LANs. TKIP is the next generation of
WEP, the Wired Equivalency Protocol, which is used to secure 802.11 wireless
LANs. TKIP provides per-packet key mixing, a message integrity check and a
re-keying mechanism, thus fixing the flaws of WEP.
22
802.1x Authentication
802.1x is a framework for authenticated MAC-level access control, defines
Extensible Authentication Protocol (EAP) over LANs (WAPOL). The standard
encapsulates and leverages much of EAP, which was defined for dial-up
authentication with Point-to-Point Protocol in RFC 2284.
Beyond encapsulating EAP packets, the 802.1x standard also defines EAPOL
messages that convey the shared key information critical for wireless security.
Advanced Encryption Standard (AES)
Security issues are a major concern for wireless LANs, AES is the U.S.
government’s next-generation cryptography algorithm, which will replace DES
and 3DES.
Federal Communication Commission Statement (FCC, U.S.)
This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant
to Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful
interference in a residential installation. This equipment generates, uses and can radiate radio frequency
energy and, if not installed and used in accordance with the instructions, may cause harmful interference
to radio communications. However, there is no guarantee that interference will not occur in a particular
installation. If this equipment does
cause harmful interference to radio or television reception, which can be determined by turning the
equipment off and on, the user is encouraged to try to correct the interference by one of the following
measures:
- Reorient or relocate the receiving antenna.
- Increase the separation between the equipment and receiver.
- Connect the equipment into an outlet on a circuit different from that to which the receiver is connected.
- Consult the dealer or an experienced radio/TV technician for help.
This device complies with Part 15 of the FCC Rules. Operation is subject to the following two conditions:
(1) This device may not cause harmful interference, and (2) this device must accept any interference
received, including interference that may cause undesired operation.
FCC Caution:
Any changes or modifications not expressly approved by the party responsible for compliance could void
the user's authority to operate this equipment.
IMPORTANT NOTES
FCC Radiation Exposure Statement:
This equipment complies with FCC radiation exposure limits set forth for an uncontrolled environment.
This equipment should be installed and operated with minimum distance 20cm between the radiator &
your body.
Co-location warning:
This transmitter must not be co-located or operating in conjunction with any other antenna or transmitter.
Limited Channels fixed for use in the US:
IEEE 802.11b or 802.11g or 802.11n(HT20) operation of this product in the U.S. is firmware-limited to
Channel 1 through 11.
IEEE 802.11n(HT40) operation of this product in the U.S. is firmware-limited to Channel 3 through 9.
IEEE 802.11an(HT20) DTS band operation of this product in the U.S. is firmware-limited to Channel
5745.0 through 5825.0 MHz.
IEEE 802.11an(HT40) DTS band operation of this product in the U.S. is firmware-limited to Channel
5755.0 through 5795.0 MHz.
IEEE 802.11an(HT20) UNII band operation of this product in the U.S. is firmware-limited to Channel
5180.0 through 5240.0 MHz.
IEEE 802.11an(HT40) UNII band operation of this product in the U.S. is firmware-limited to Channel
5190.0 through 5230.0 MHz.
OEM integration instructions:
This device is intended only for OEM integrators under the following conditions:
The antenna must be installed such that 20 cm is maintained between the antenna and users, and the
transmitter module may not be co-located with any other transmitter or antenna. The module shall be only
used with the external antenna(s) that has been originally tested and certified with this module.
As long as 3 conditions above are met, further transmitter test will not be required. However, the OEM
integrator is still responsible for testing their end-product for any additional compliance requirements
required with this module installed (for example, digital device emissions, PC peripheral requirements,
etc.).
Validity of using the module certification:
In the event that these conditions cannot be met (for example certain laptop configurations or co-location
with another transmitter), then the FCC authorization for this module in combination with the host
equipment is no longer considered valid and the FCC ID of the module cannot be used on the final
product. In these circumstances, the OEM integrator will be responsible for re-evaluating the end product
(including the transmitter) and obtaining a separate FCC authorization.
Custom design antennas may be used, however the OEM installer must following the FCC 15.21
requirements and verify if new FCC approval will be necessary.
End product labeling:
This transmitter module is authorized only for use in device where the antenna may be installed such that
20 cm may be maintained between the antenna and users. The final end product must be labeled in a
visible area with the following:
“Contains FCC ID: YZKSMCWTVA100”.
Information that must be placed in the end user manual:
The OEM integrator has to be aware not to provide information to the end user regarding how to install or
remove this RF module in the user's manual of the end product which integrates this module. The end
user manual shall include all required regulatory information/warning as show in this manual.