Intel LEN3945ABG Intel PRO/Wireless 3945ABG Network Connection User Manual Contents
Intel Mobile Communications Intel PRO/Wireless 3945ABG Network Connection Contents
Intel >
Contents
- 1. Users Manual
- 2. Users manual I
- 3. Users manual II
- 4. User Manual
Users Manual
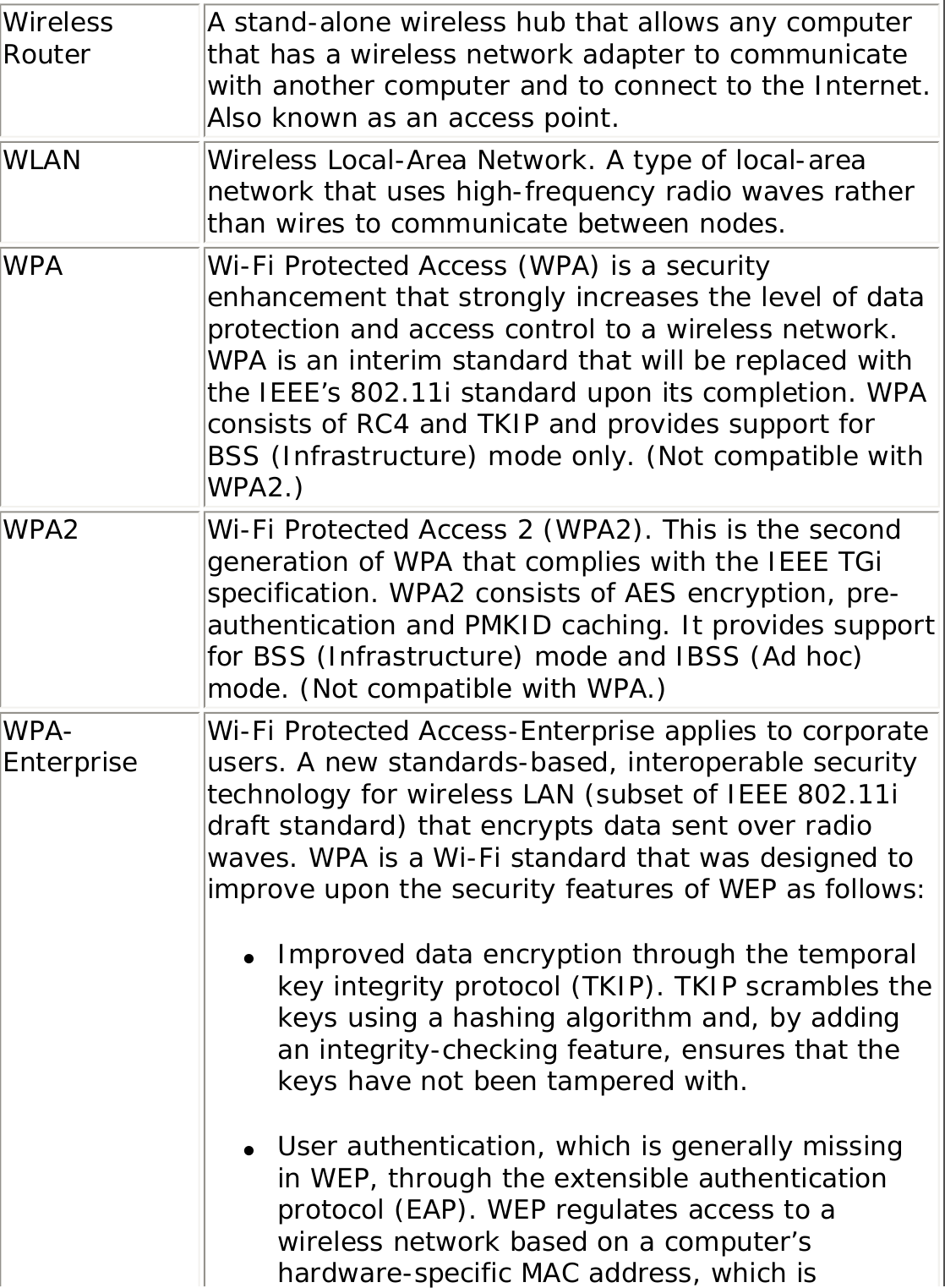
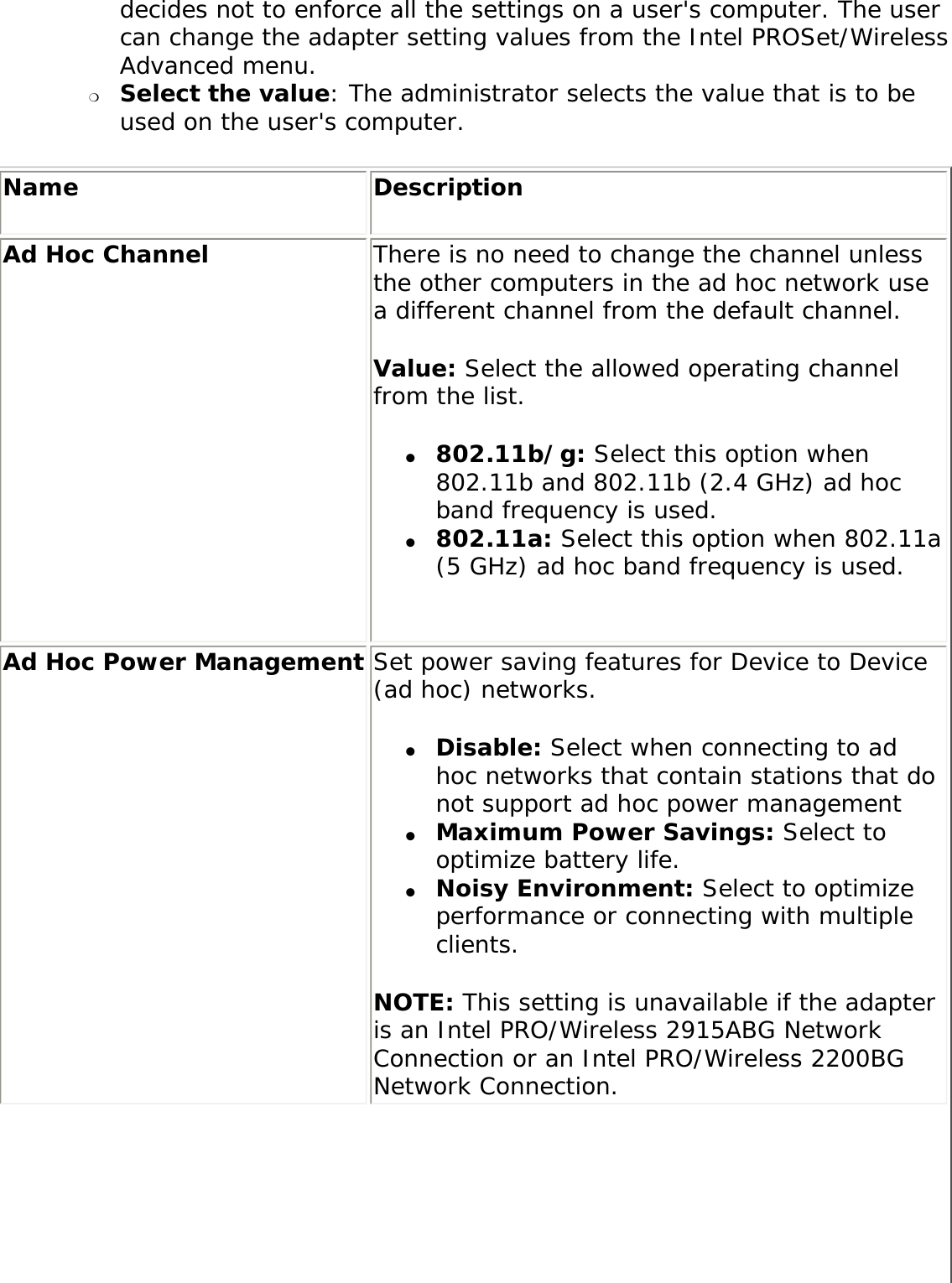
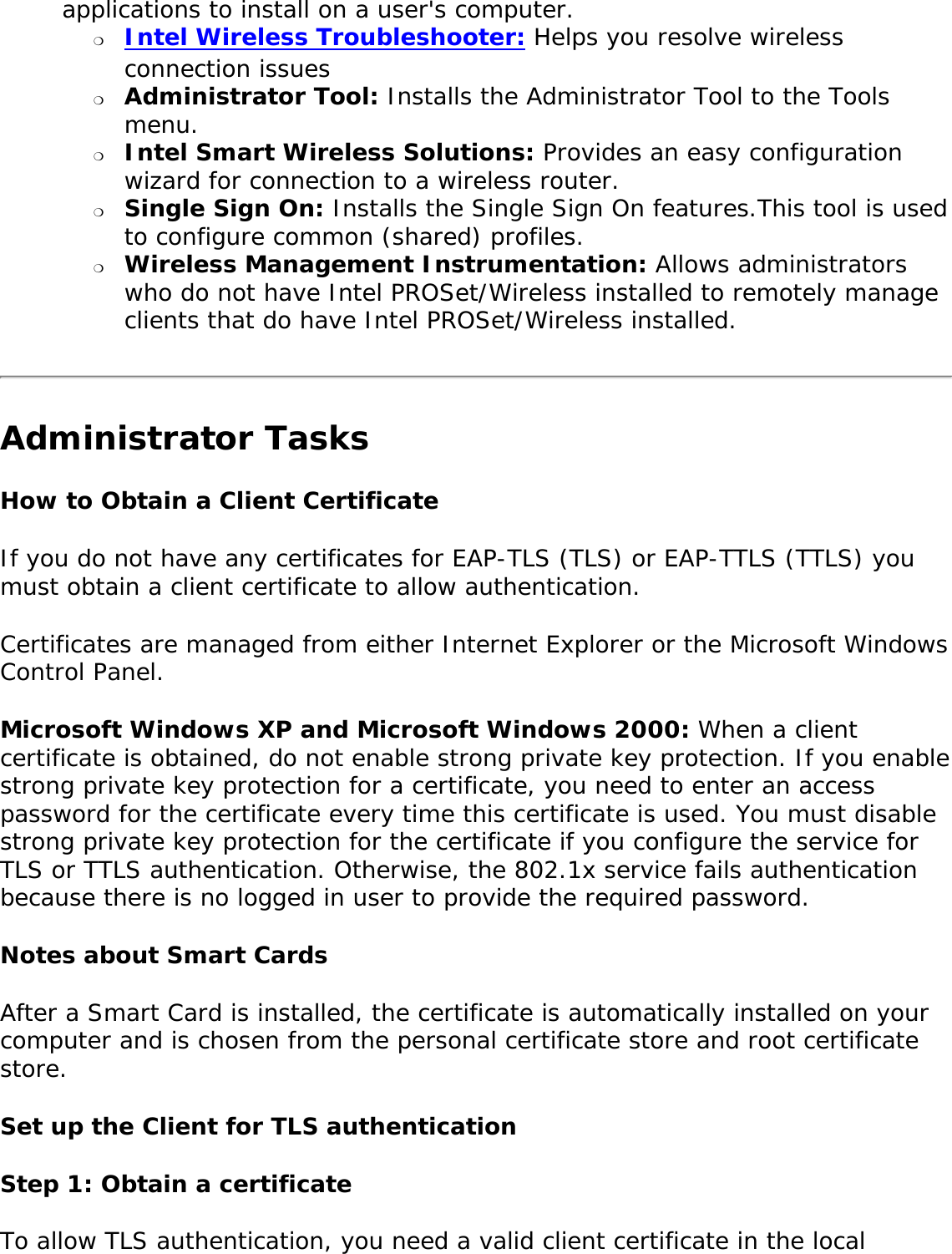
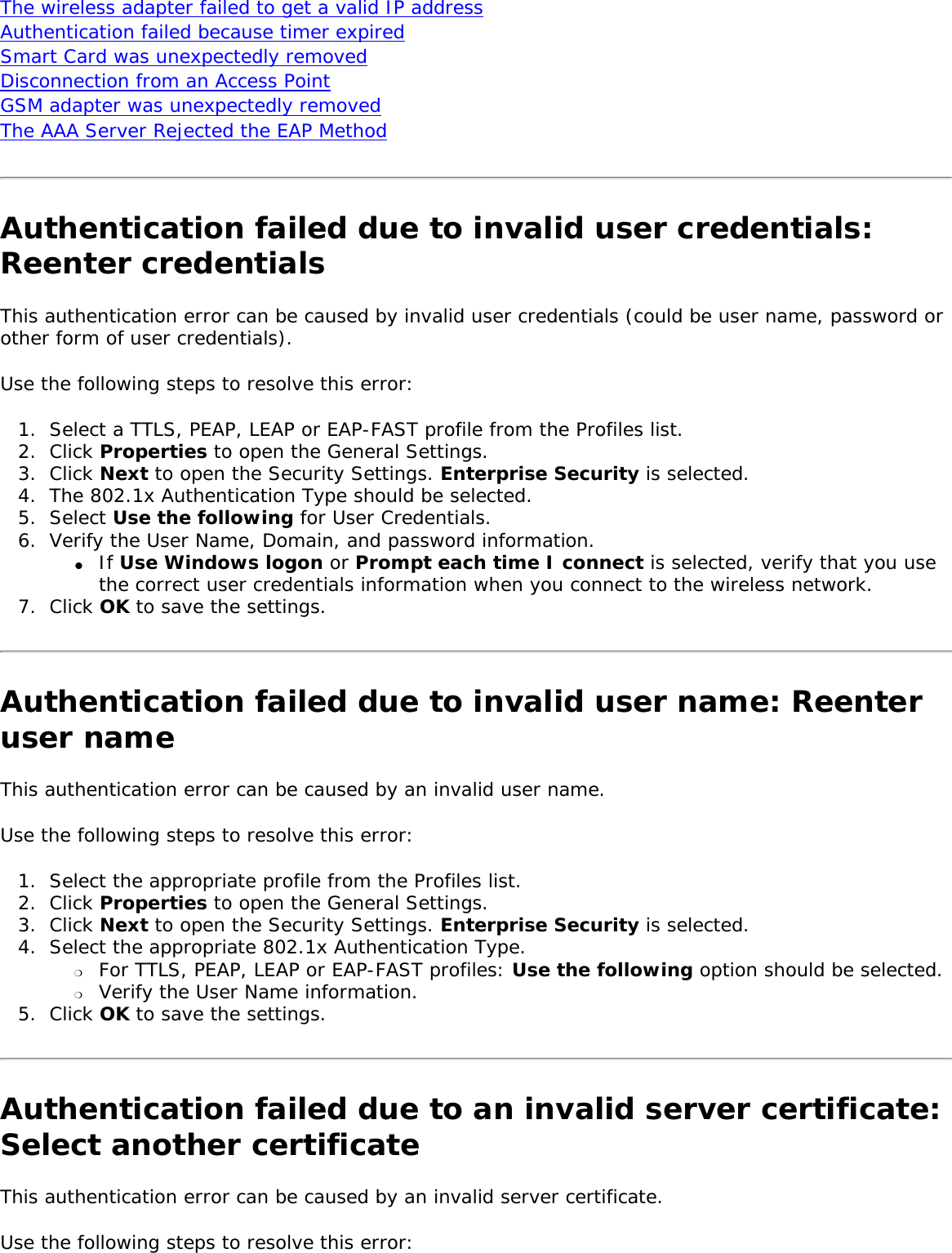
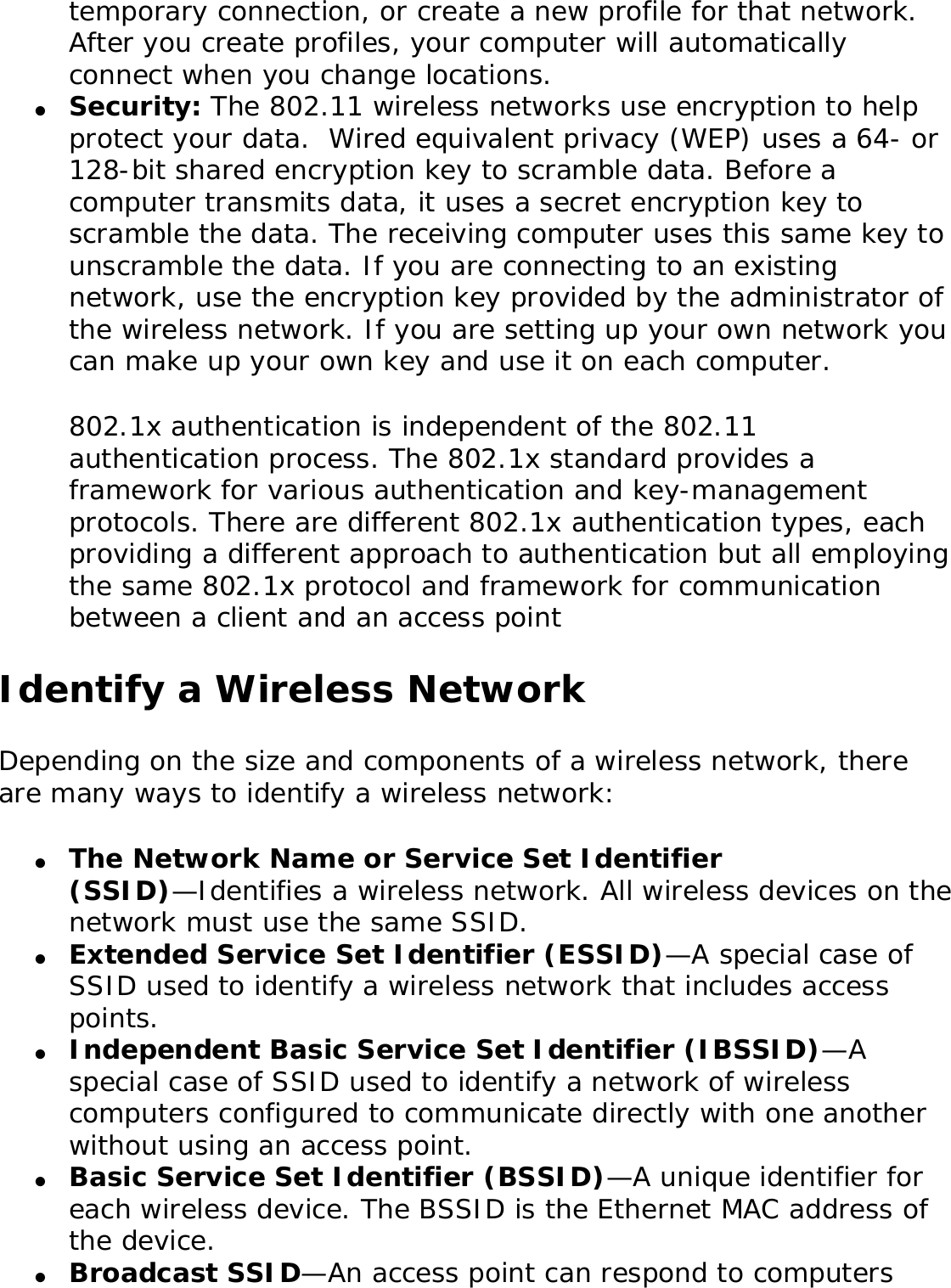
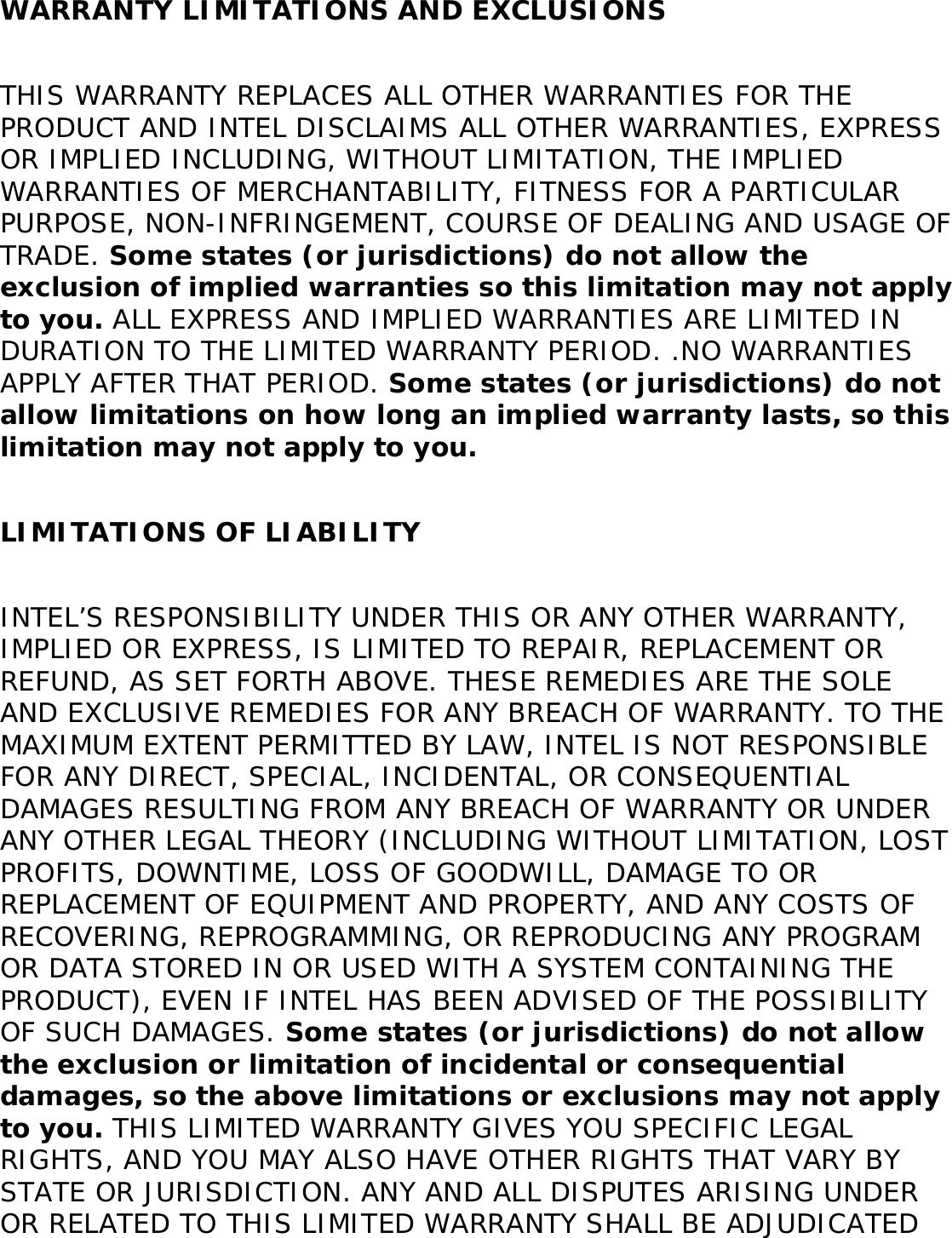
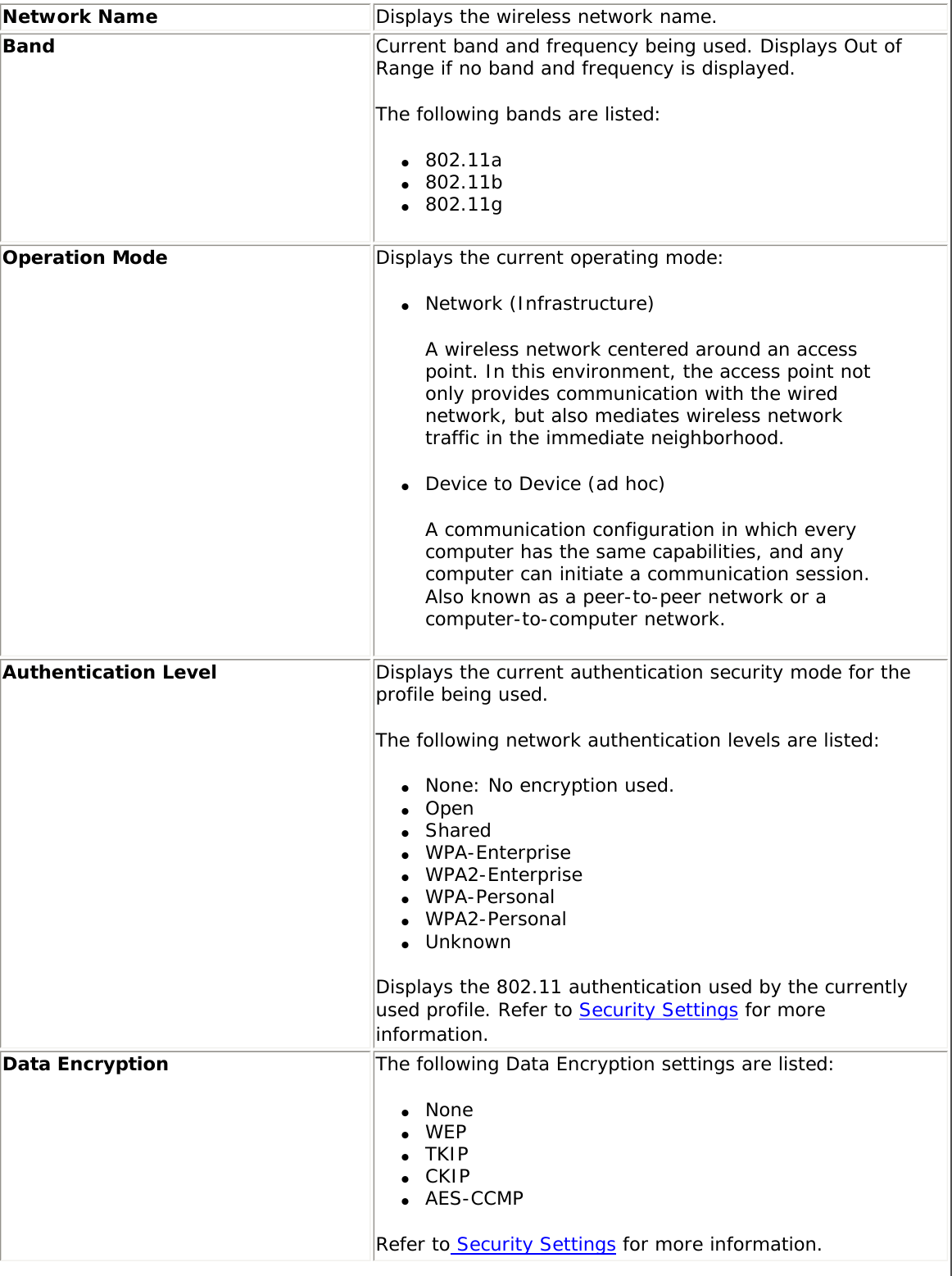
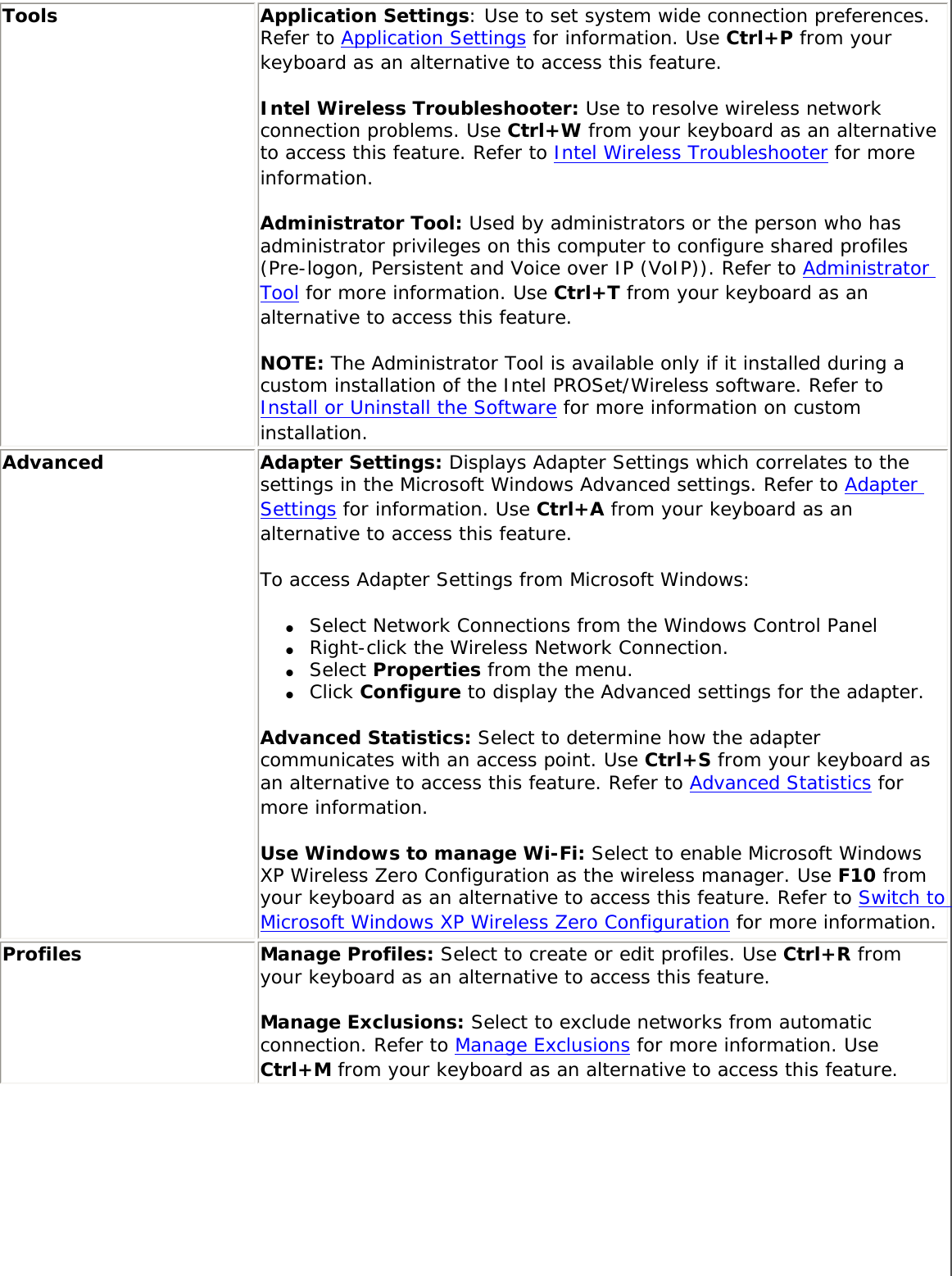
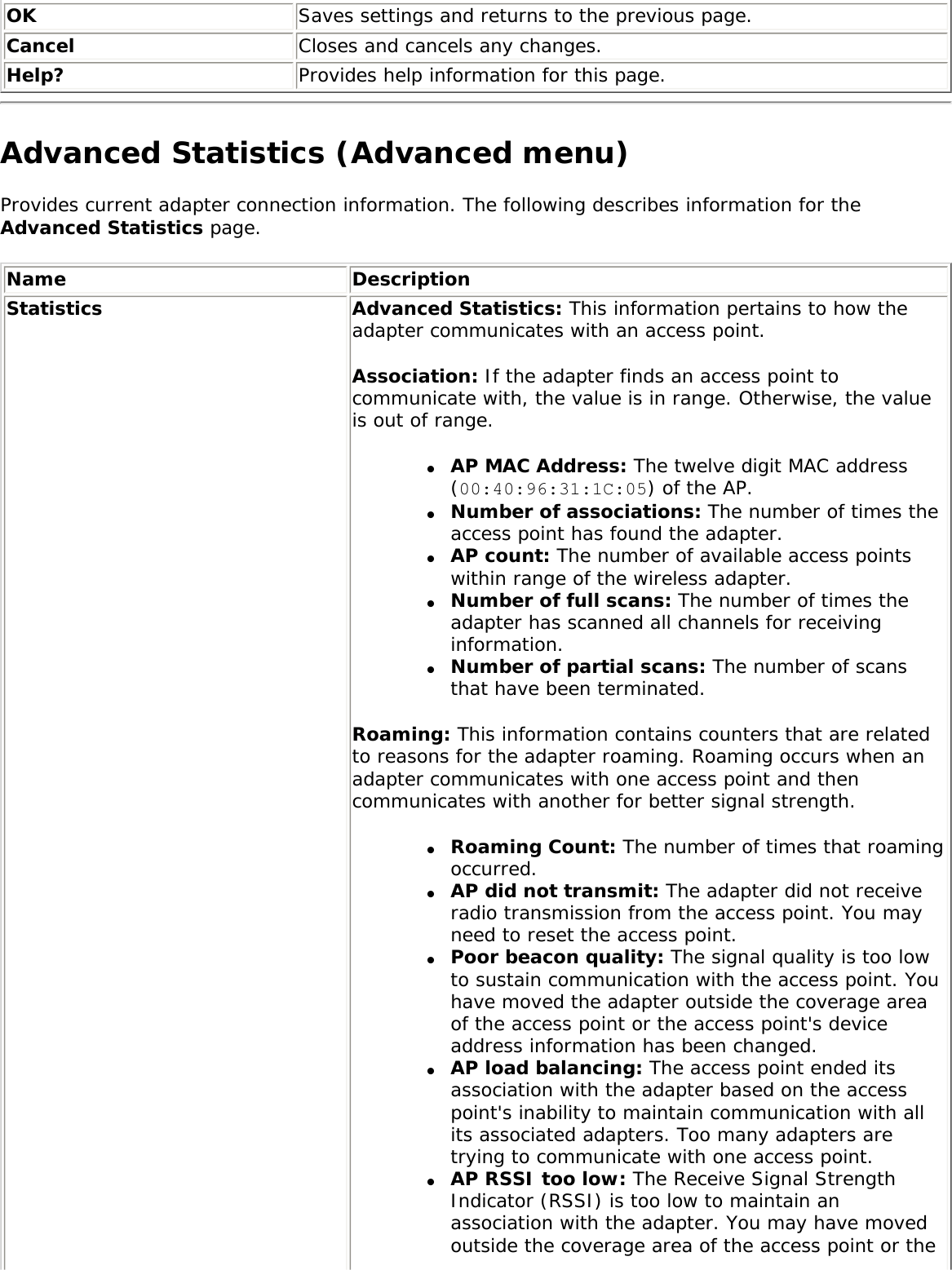
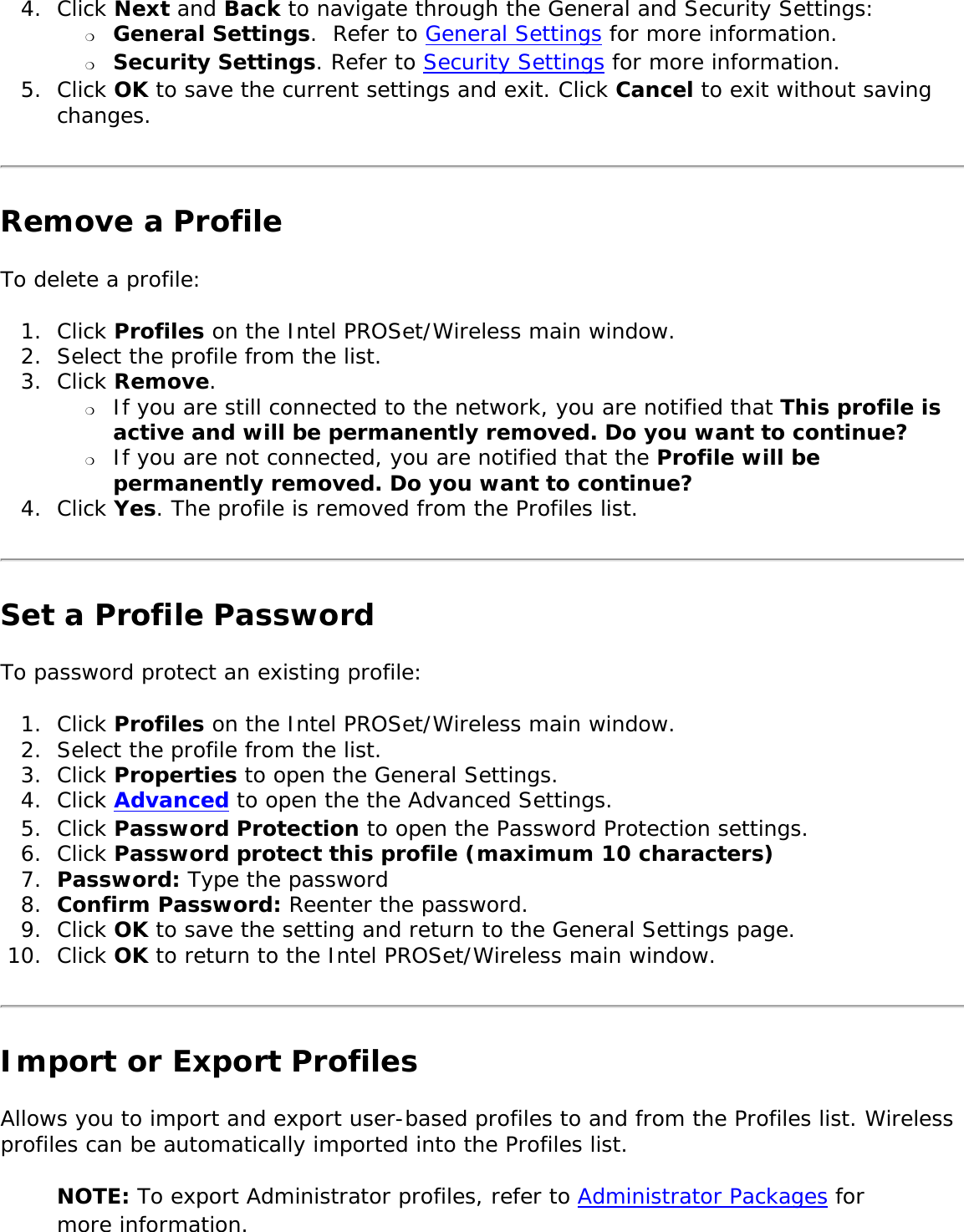
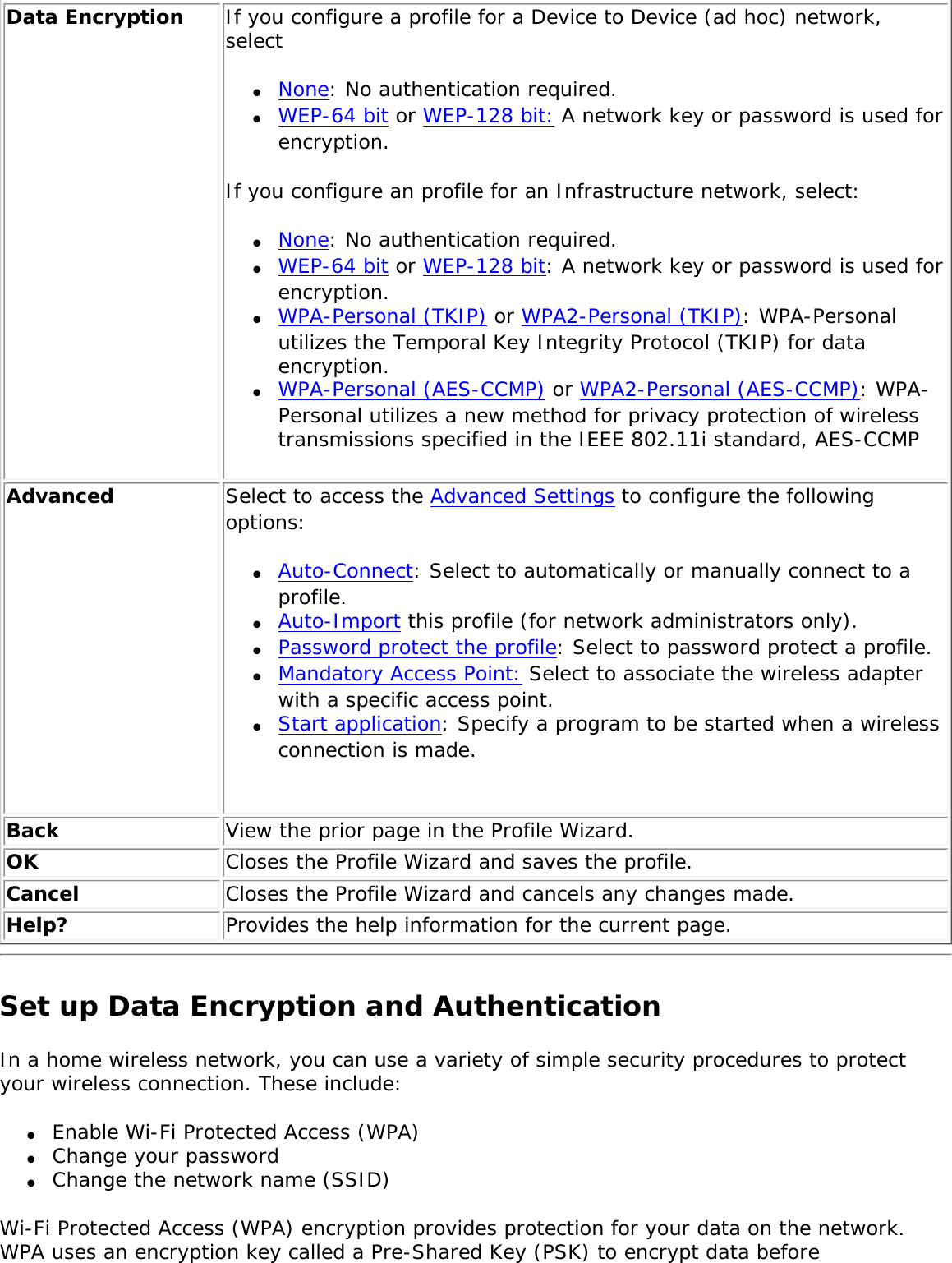
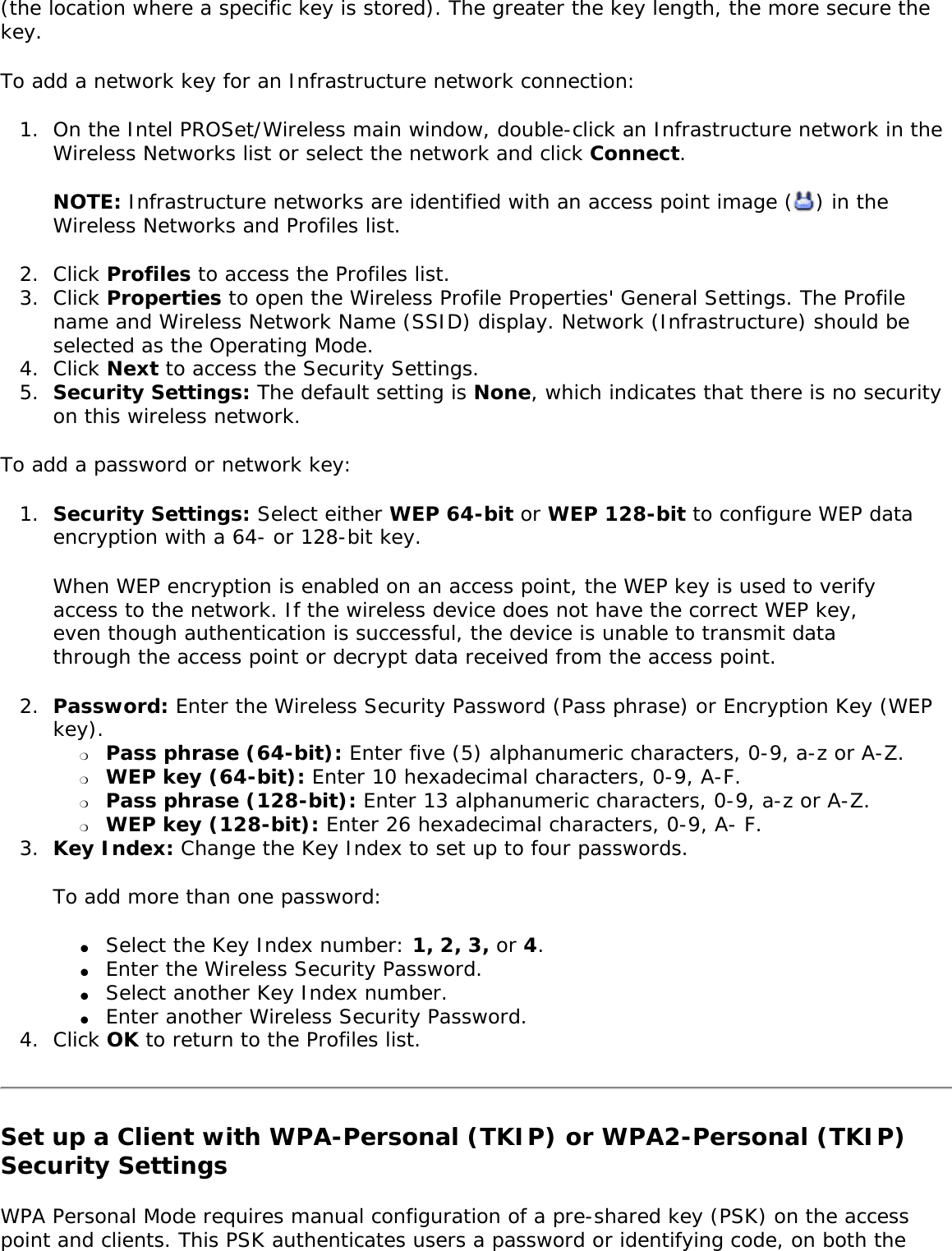
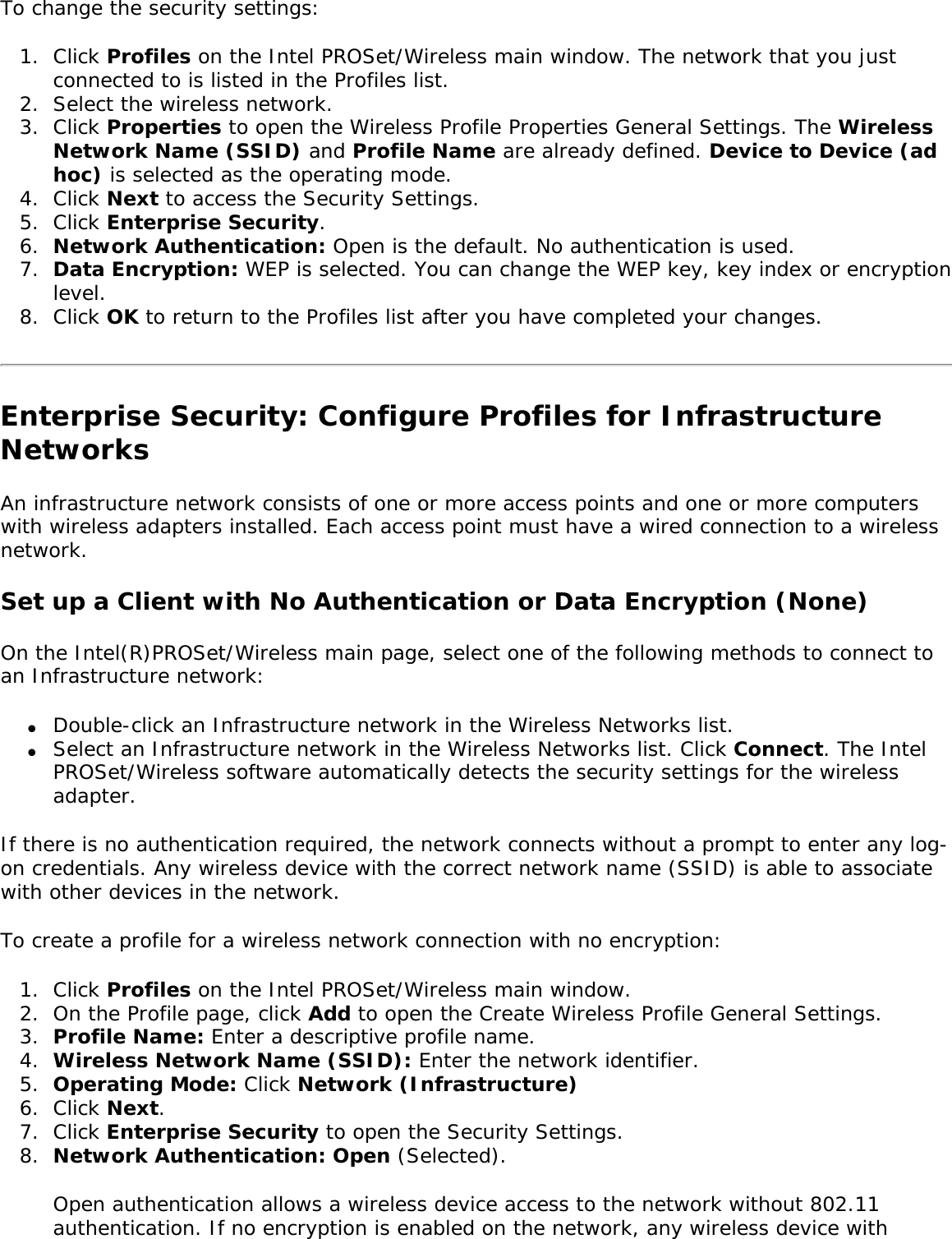
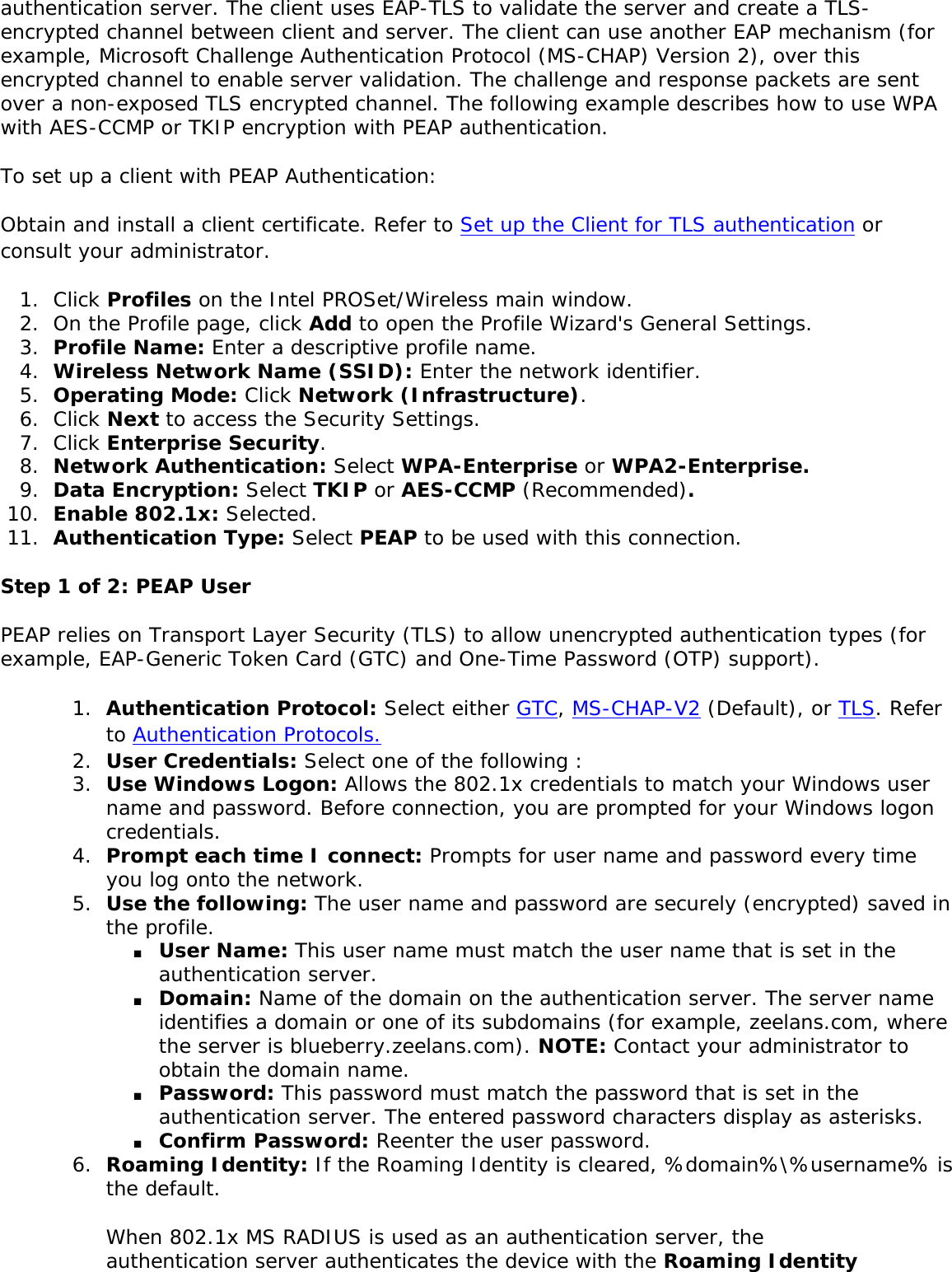
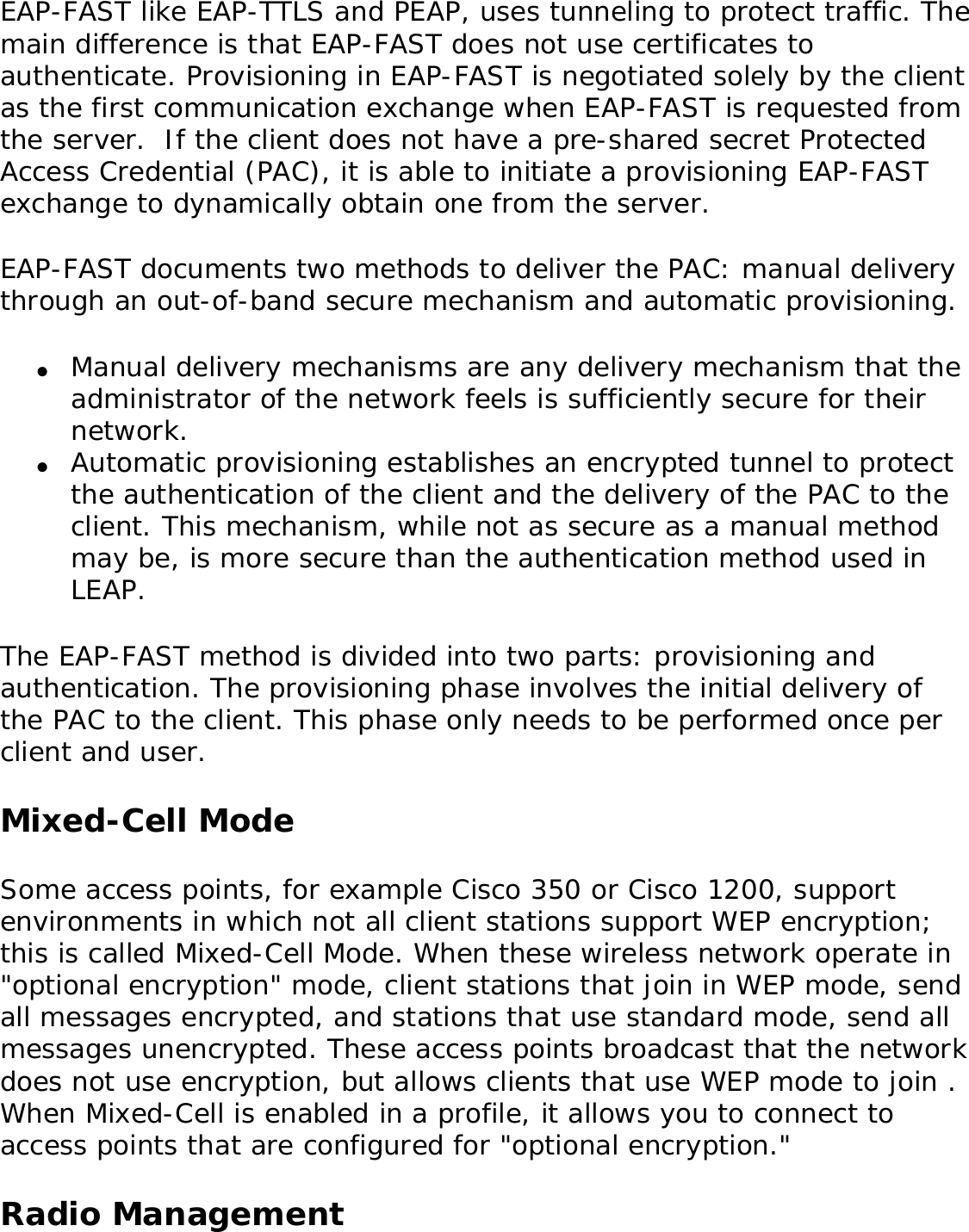
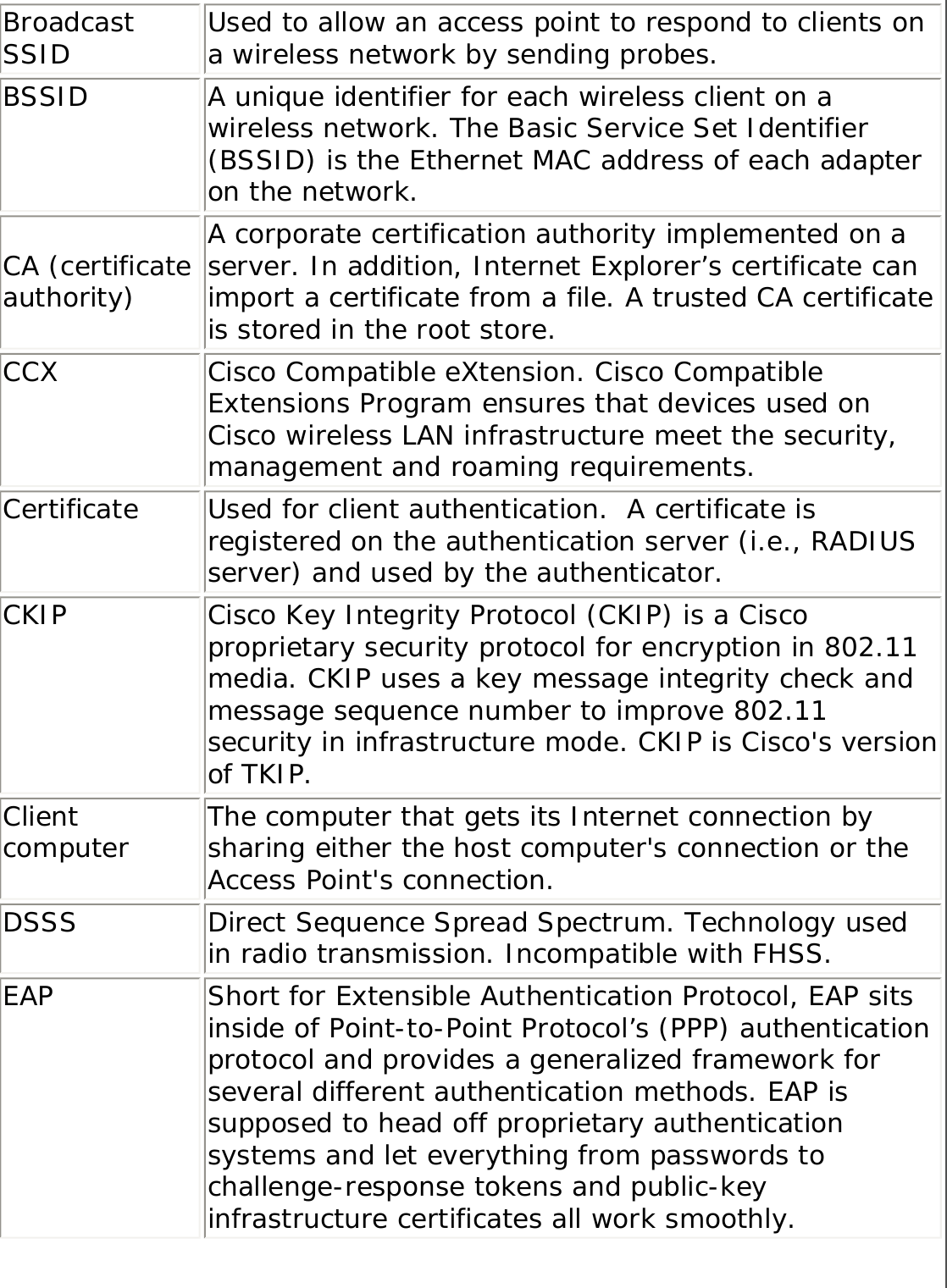
![Wireless NetworksThe Wireless Networks list displays a list of wireless networks within range of the adapter. Name Description The signal strength of the wireless network access point or computer (Device to Device [ad hoc] mode). The signal strength icon bars indicate that the wireless network or computer is available for connection but is still not is associated with an access point or computer (Device to Device [ad hoc] mode).Network Name Network Name (SSID): The name of the network that the adapter is connected to. The Network Name SSID must be the same as the SSID of the access point.Status Notification that the adapter is connecting to the wireless network. Once connected, the status is changed to Connected. Profiles: Identifies a network in the Wireless Networks list that is connected and has a profile in the profiles list. The wireless network uses Network (infrastructure) mode. The wireless network uses Device to Device (ad hoc) mode.The wireless network uses Security encryption.The band frequency being used by the wireless network (802.11a, 802.11b, 802.11g).The wireless network is on the exclusion list. Connection to a network or an access point that is on this list is not automatic. Connect (Disconnect) Click to connect to a wireless network. Once connected, the button changes to Disconnect.Properties Provides detailed information about the connected network and its access points. See Network Properties for information. Refresh Refreshes the list of available networks. If any new networks are available within the adapter range, the list is updated to show the new network name. Wireless On (Wireless Off) Switch the radio off and on. Refer to Wireless Off (On) for more information.Close Closes the Intel PROSet/Wireless main window.Help? Provides help information for this page. Network PropertiesClick the Properties button on the Intel PROSet/Wireless main window to display the security settings for the wireless adapter. You can also add profiles to be excluded from automatic connection. If network exclusion is enabled (see Application Settings) then the Network Properties also indicates if the network is excluded from automatic connection. Network Properties details Name Description](https://usermanual.wiki/Intel/LEN3945ABG.Users-Manual/User-Guide-598567-Page-11.png)
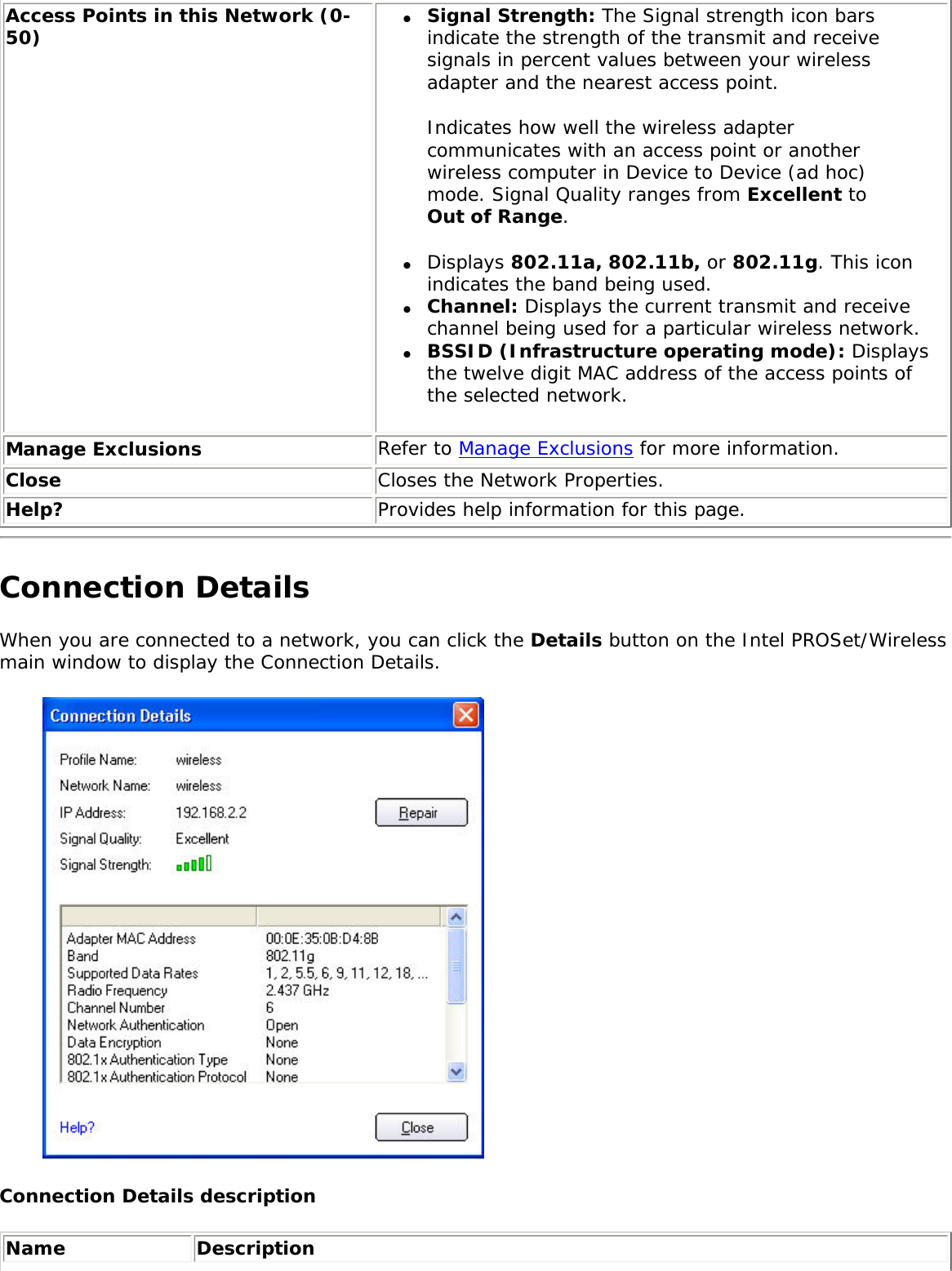
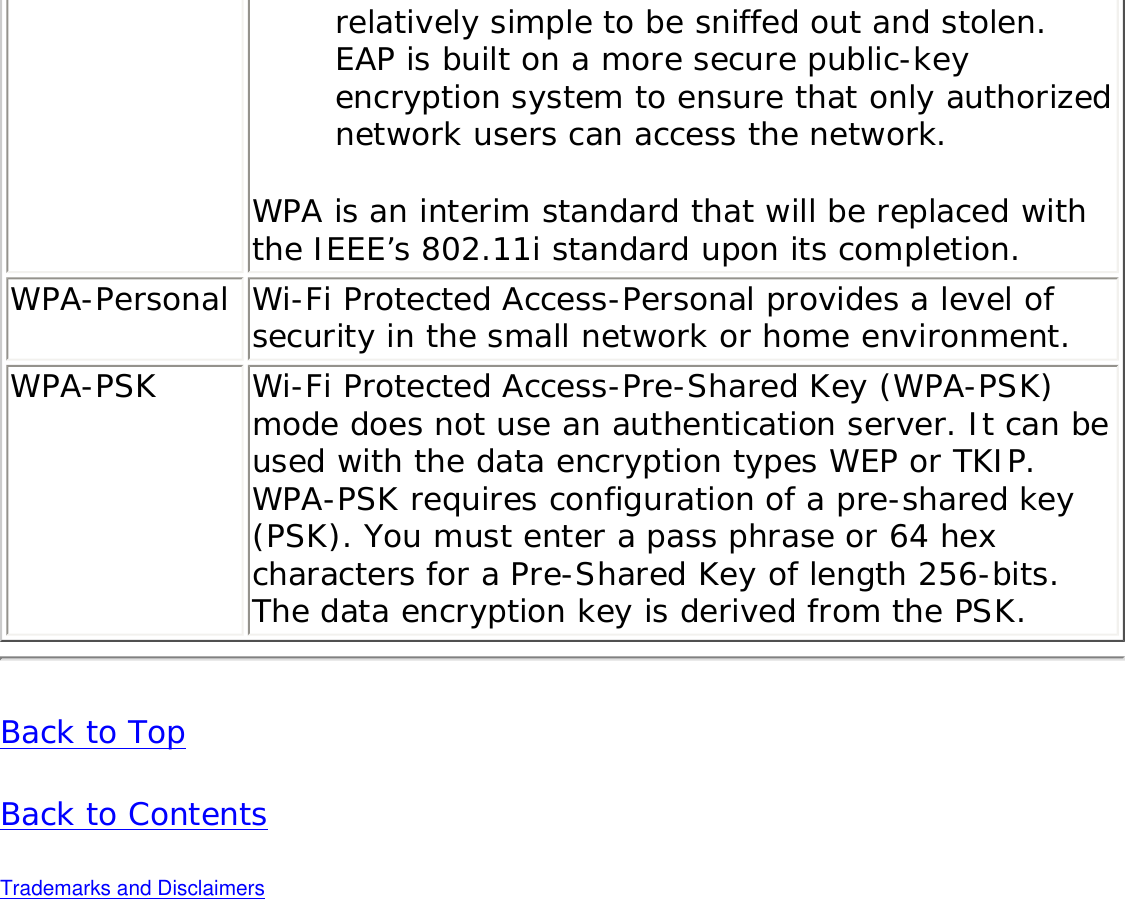
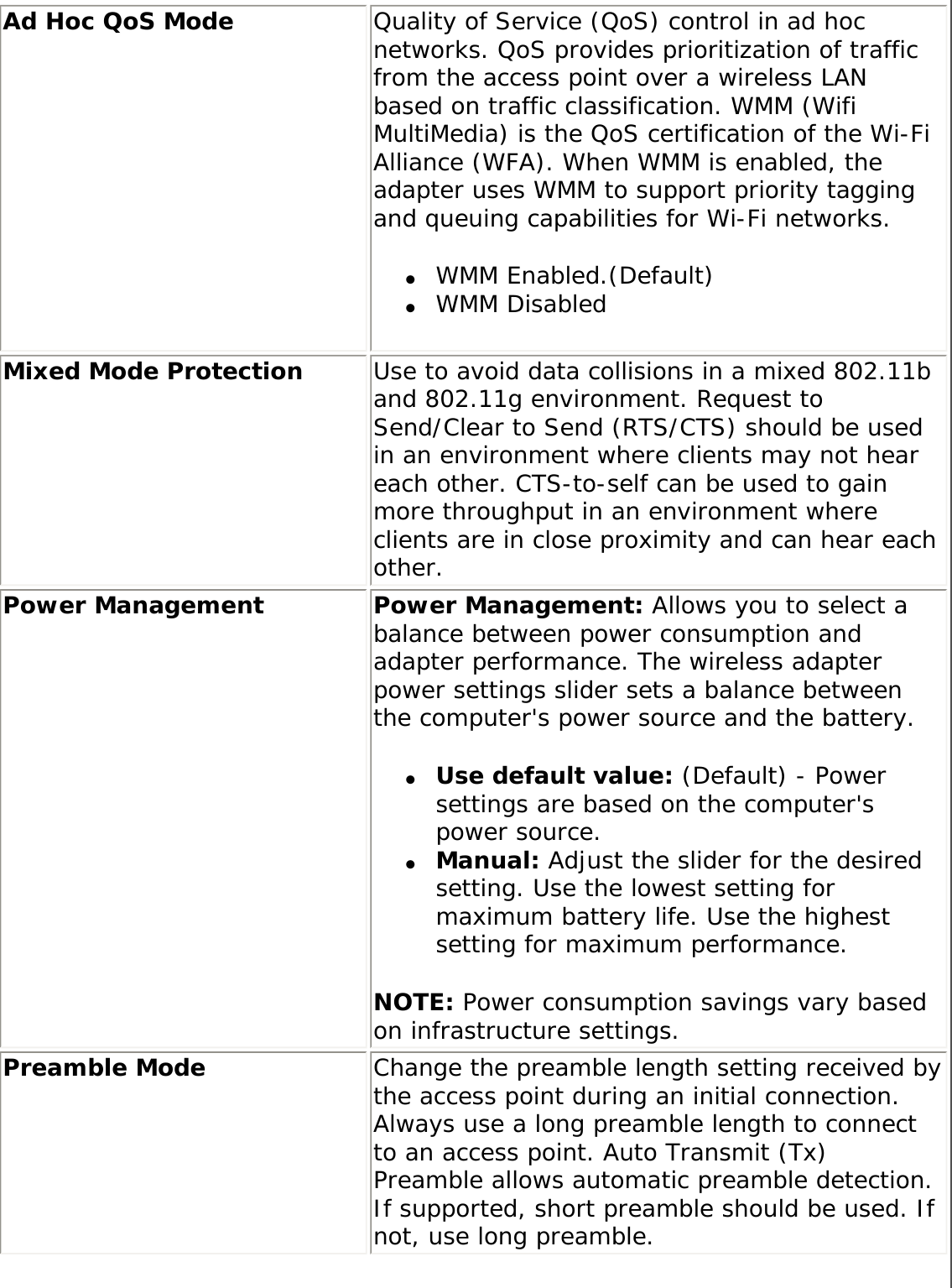
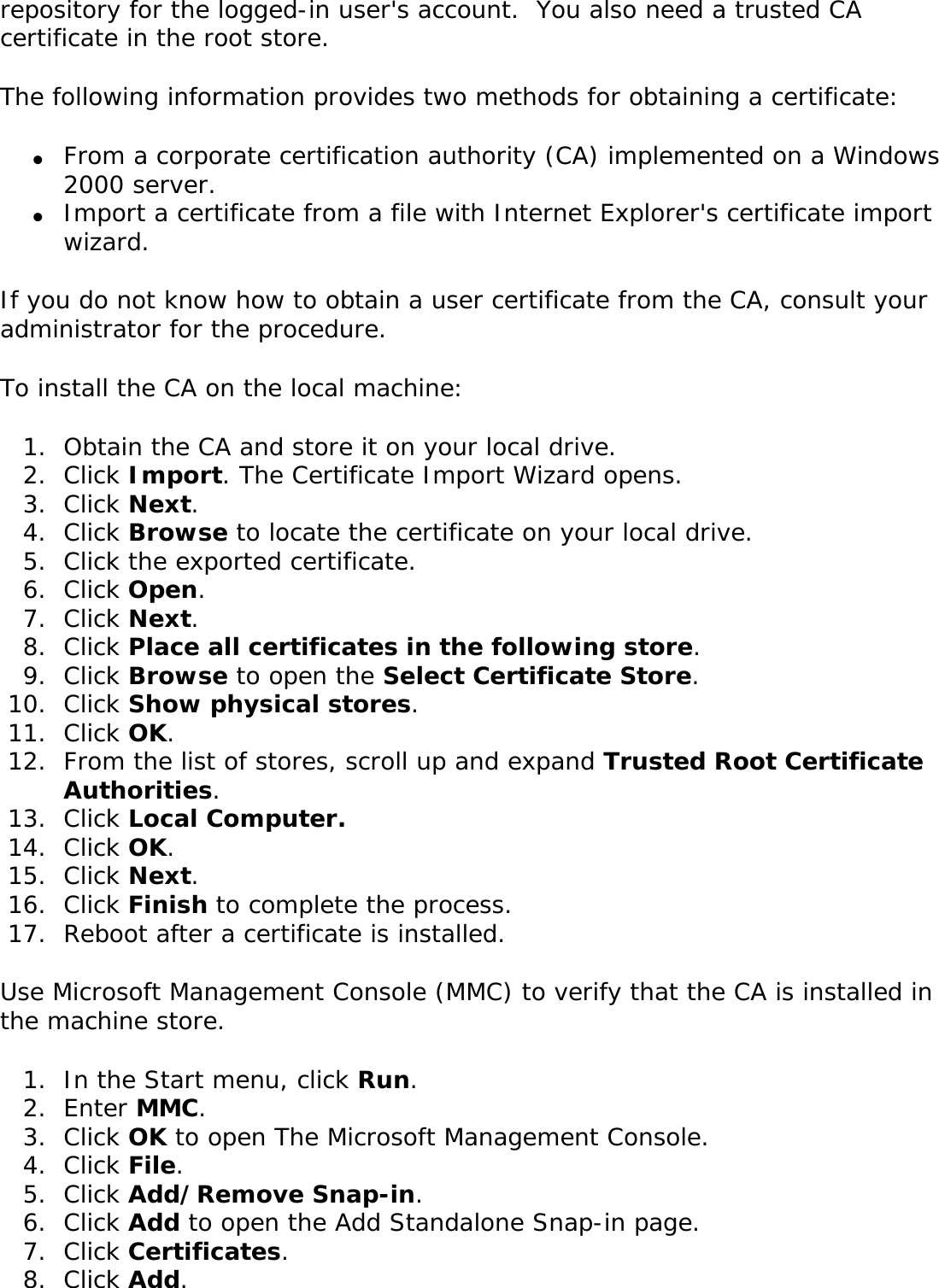
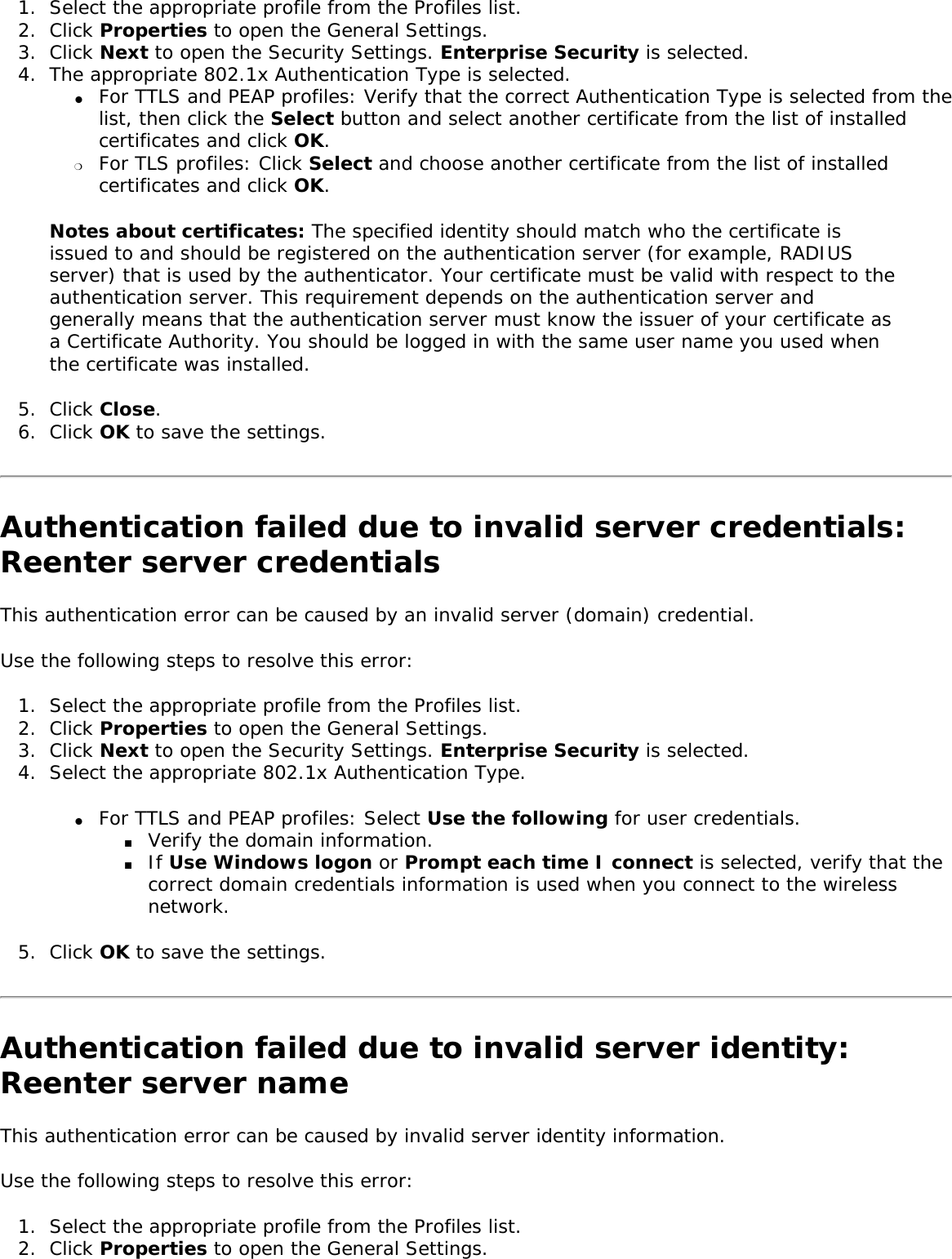
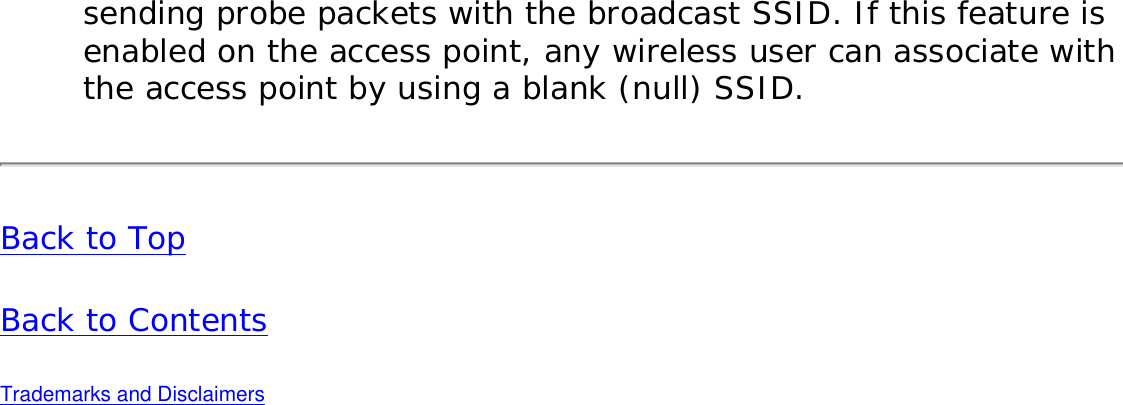
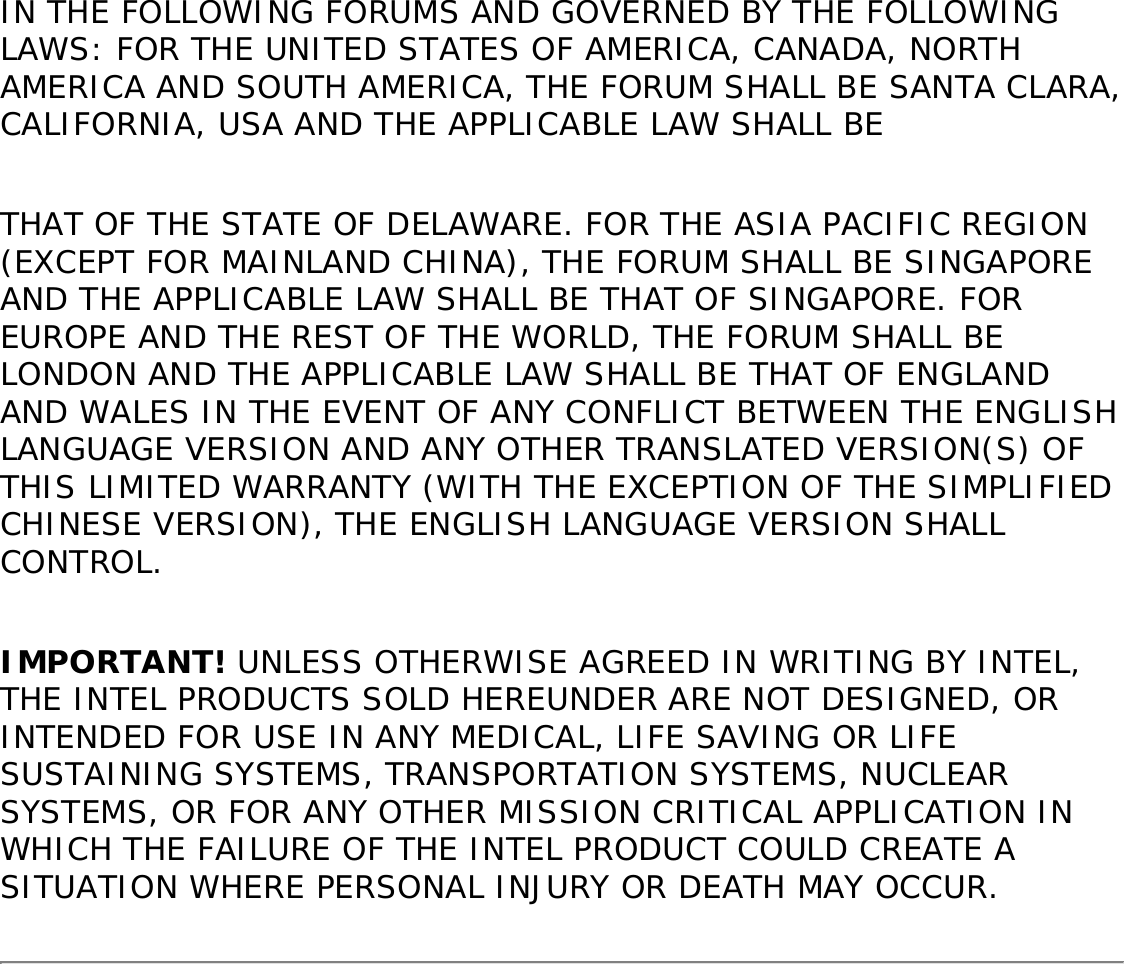
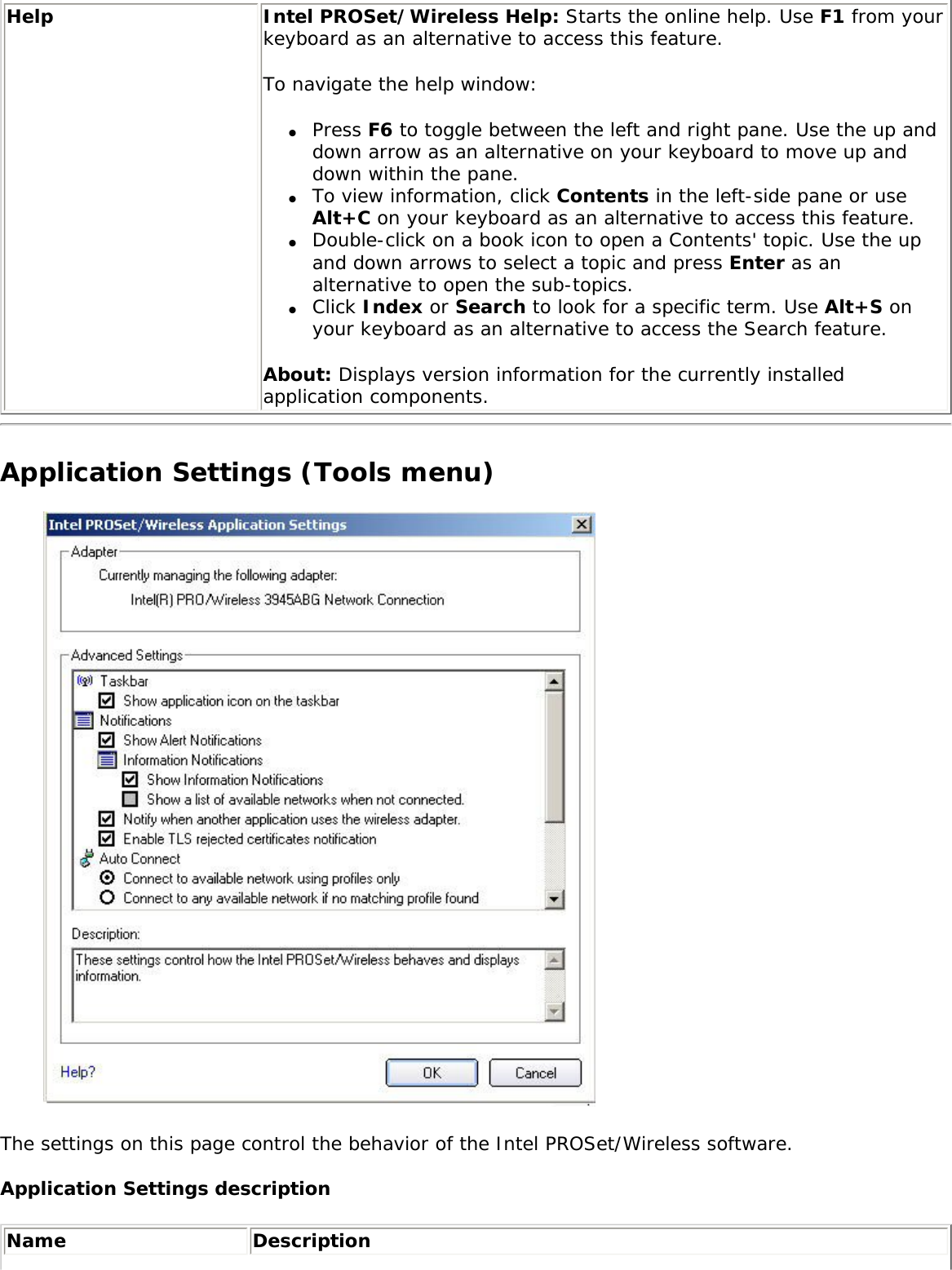
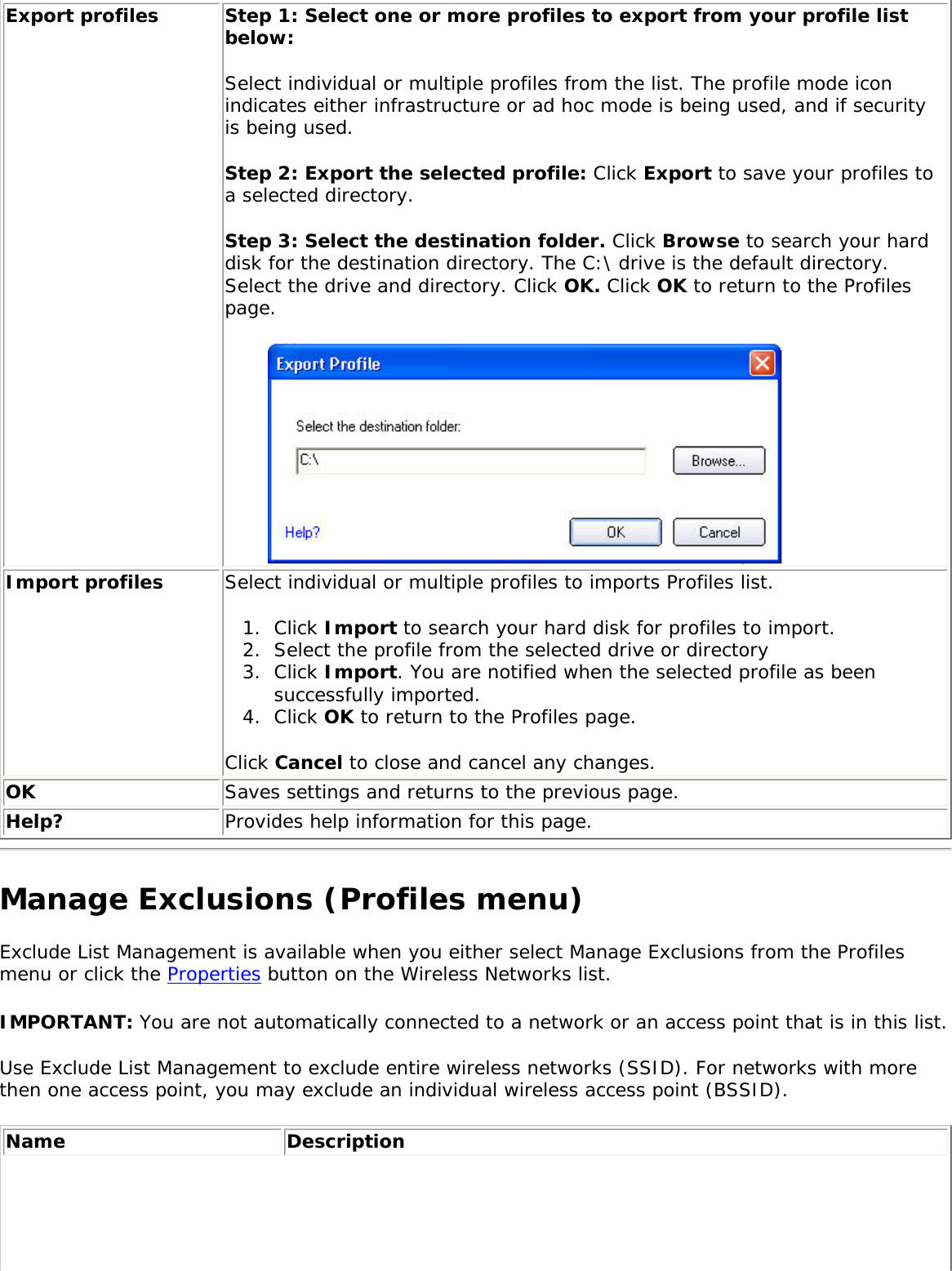
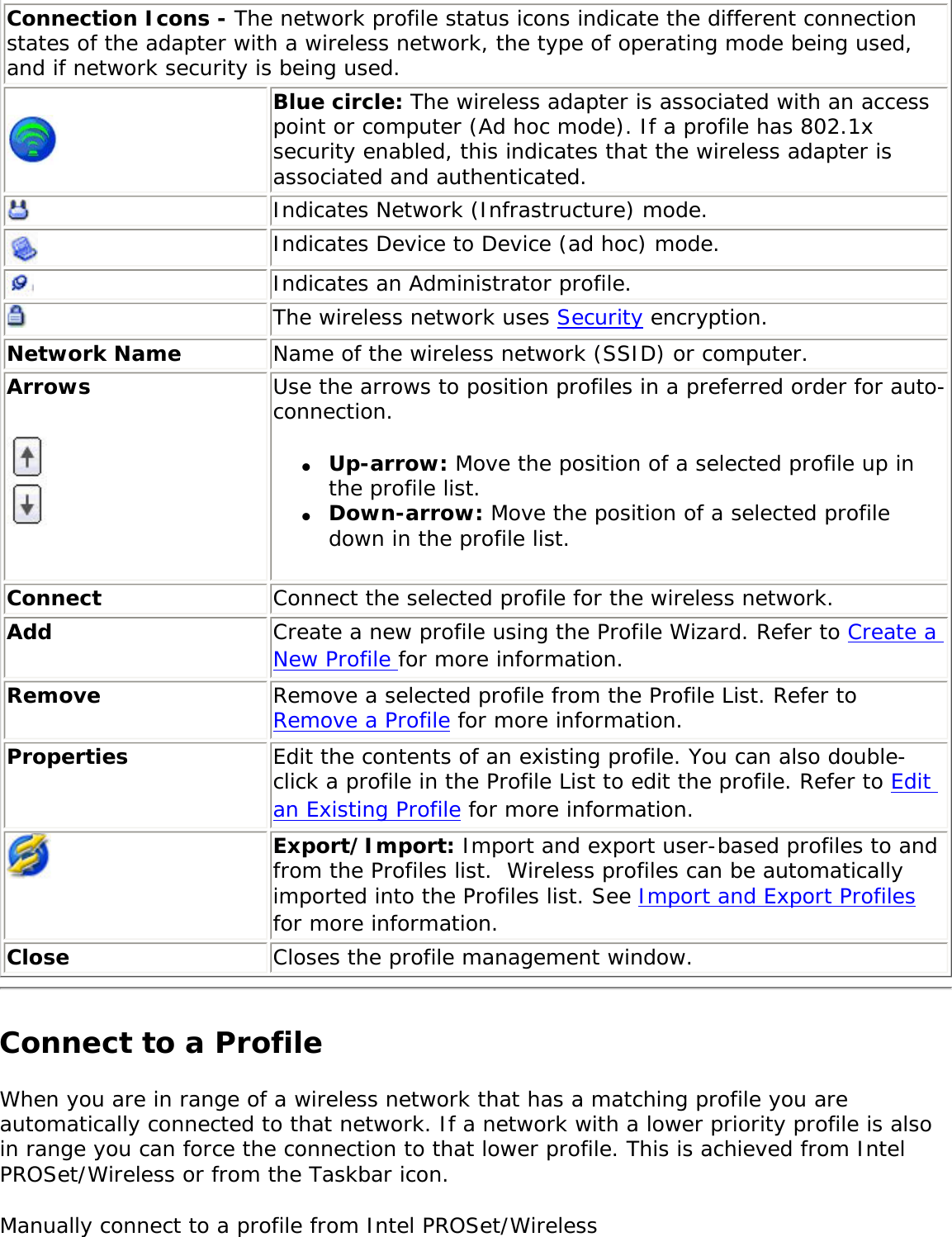
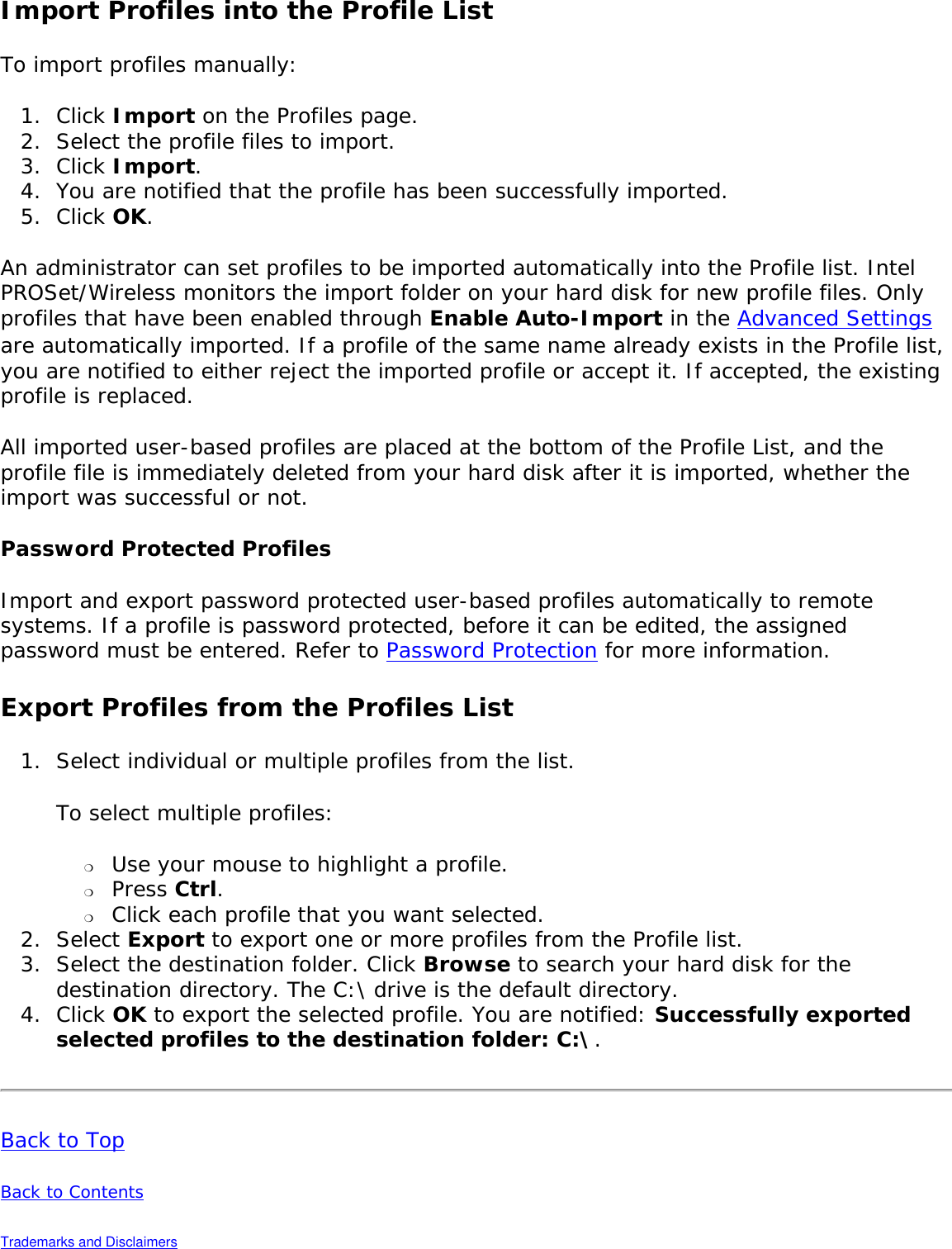
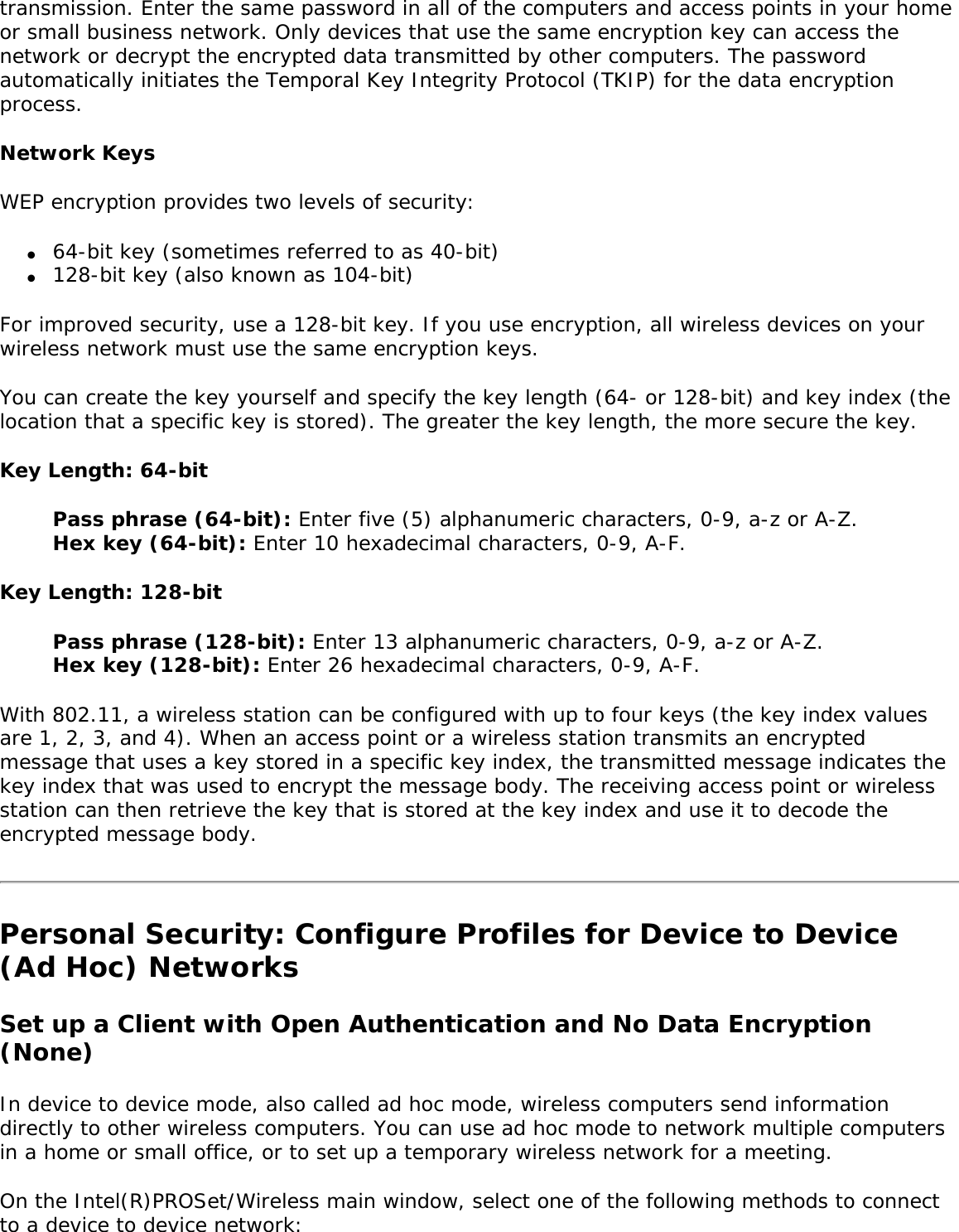
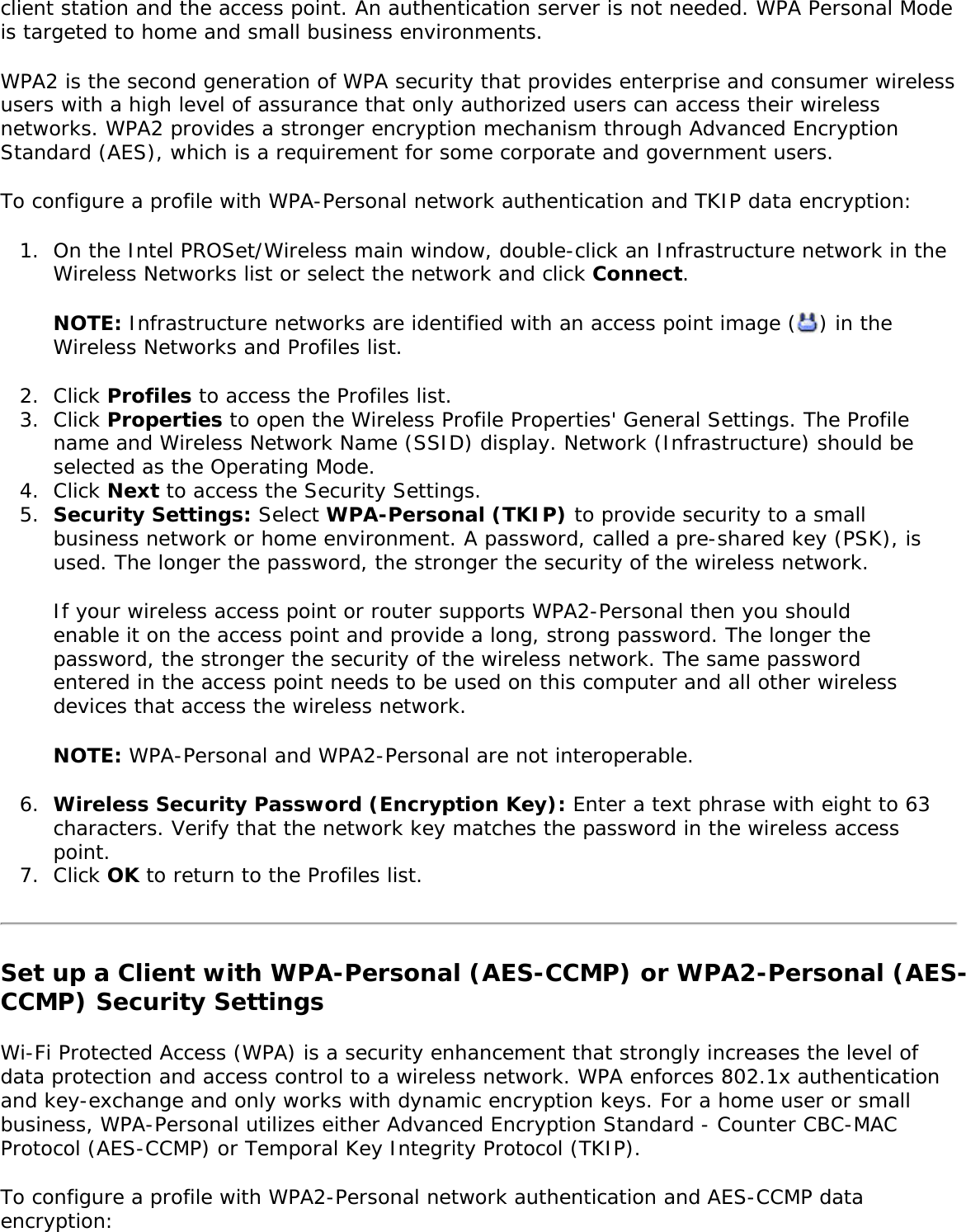
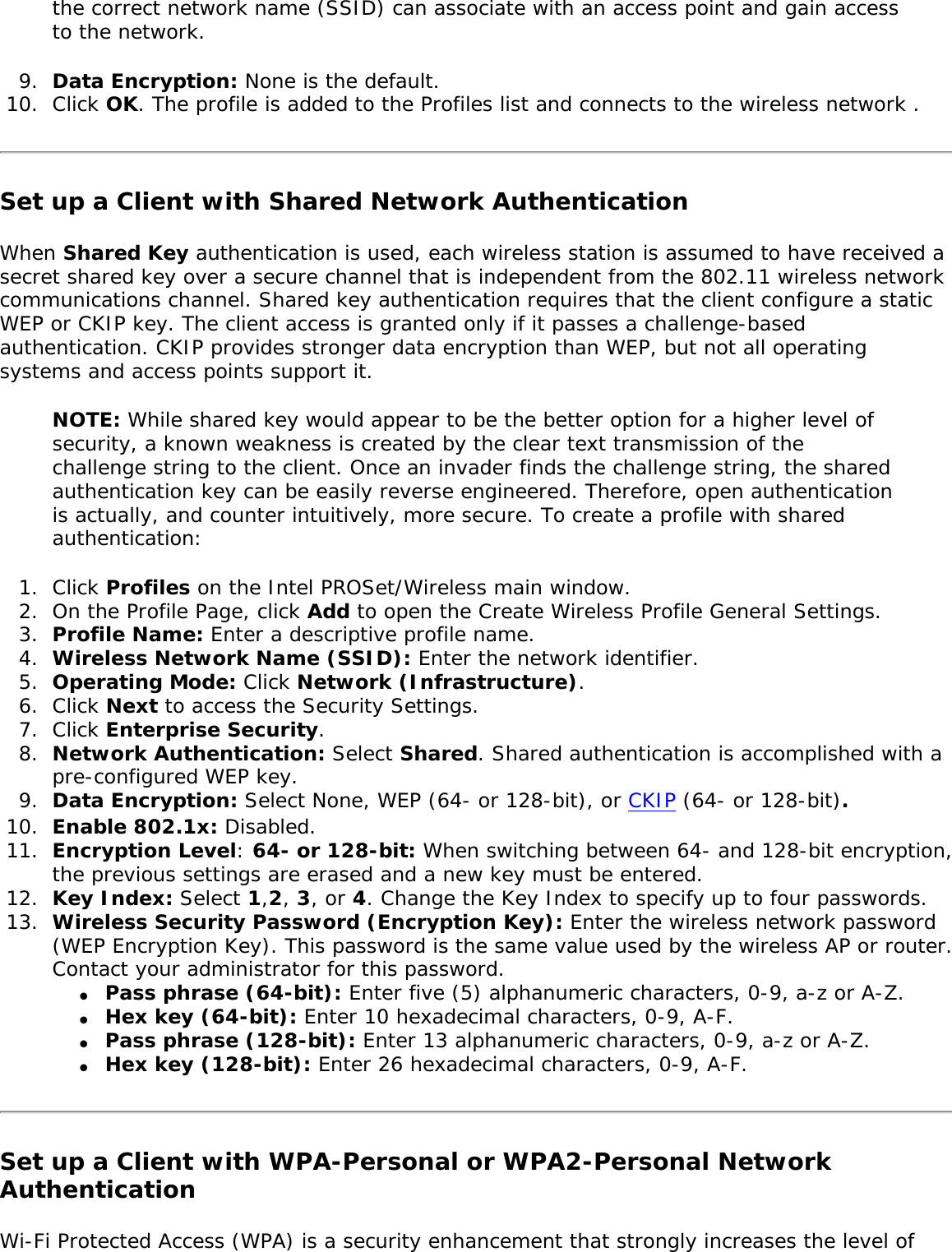
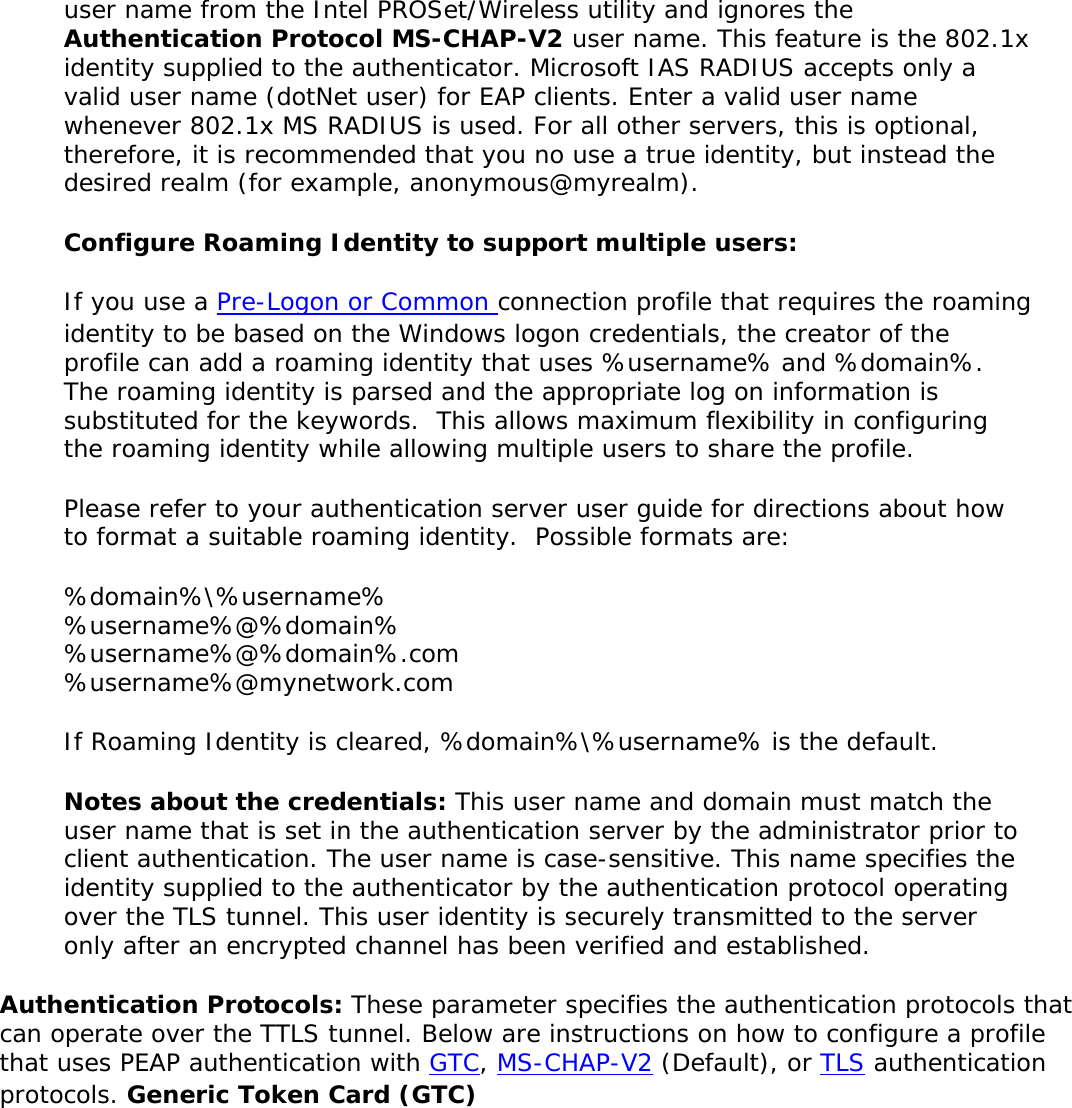
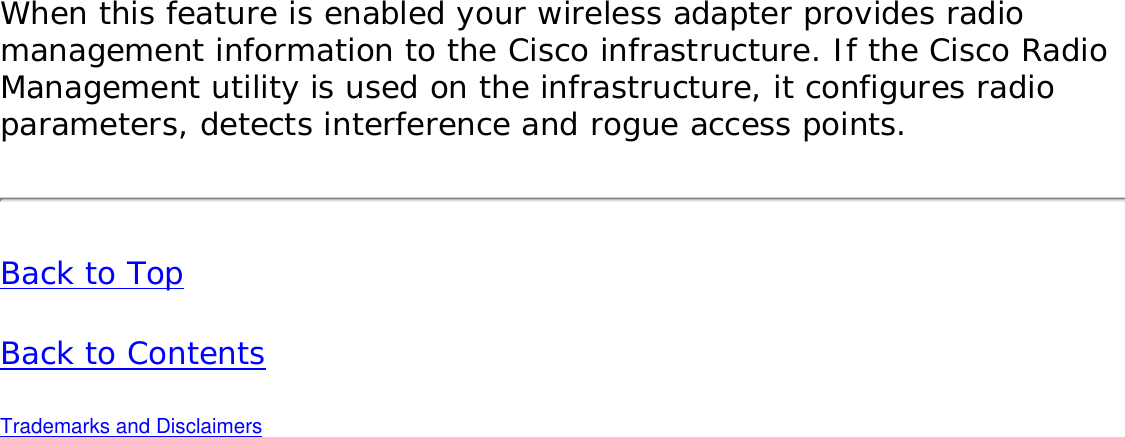
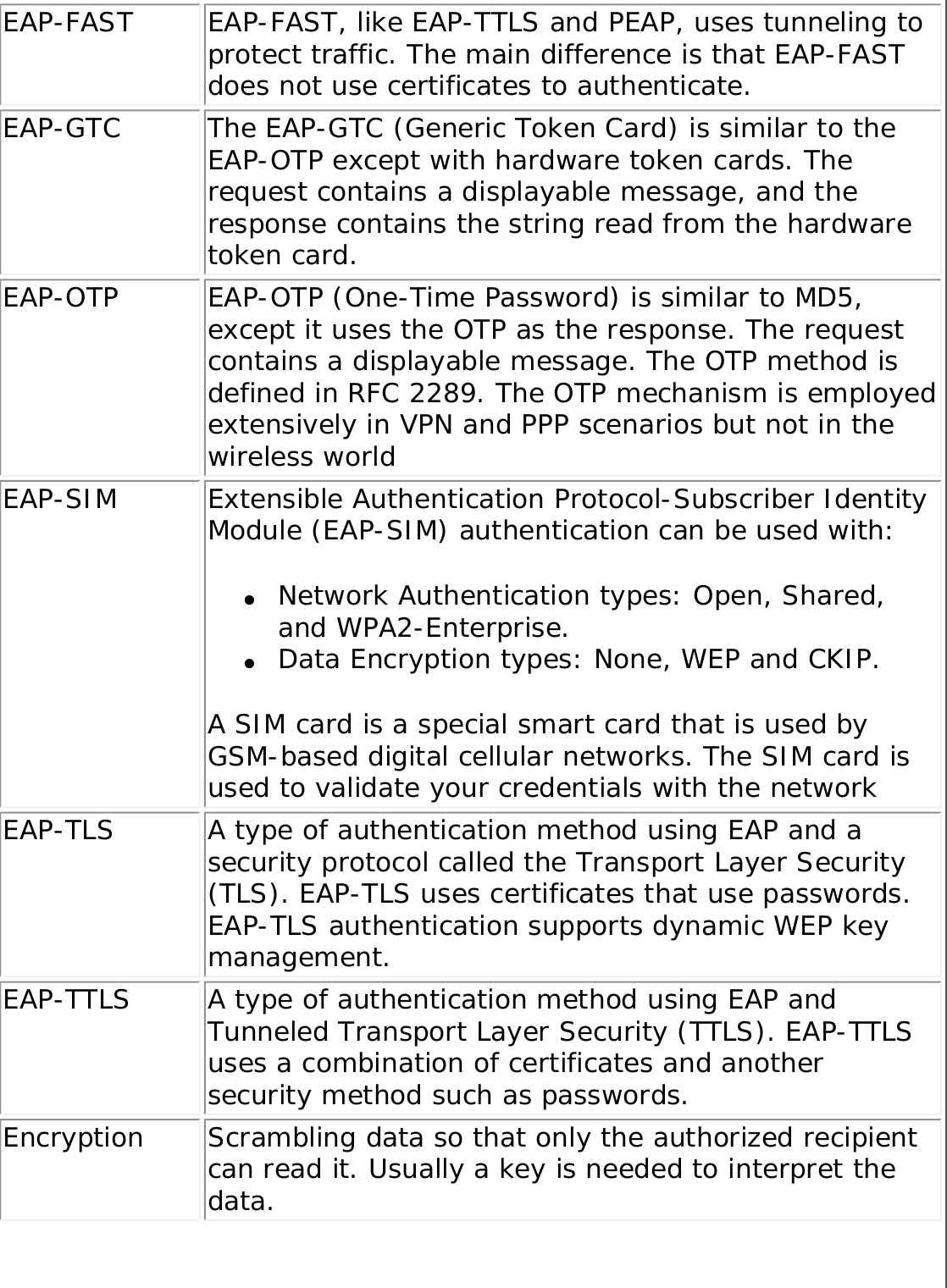
![802.1x Authentication ProtocolDisplays None, GTC, MS-CHAP-V2 or TLS. Refer to Security Settings for more information.CCX Version Version of the Cisco Compatible Extensions on this wireless connection.Current TX Power Cisco Compatible Extensions Power Levels.Supported Power Levels 1.0, 5.0, 20.0, 31.6, 50.1 mWAccess Point MAC Address The Media Access Control (MAC) address for the associated access point.Mandatory Access Point Displays None, if not enabled. If enabled, from the Mandatory Access Point setting, the access point MAC address is displayed. This option directs the wireless adapter to connect to an access point that uses a specific MAC address (48-bit 12 hexadecimal digits, for example, 00:06:25:0E:9D:84).Repair Renews the IP Address. If you have trouble accessing the network, verify if the IP address is valid. If it is 0.0.0.0 or 169.x.x.x, then it is probably not valid. If your network is setup for automatic network address assignment, then click Repair and request a new IP address.Close Closes the page.Help? Provides help information for this page.Profile Management The Profiles List displays the current user profiles in the order that they are to be applied. Use the up and down arrows to arrange profiles in a specific order to automatically connect to a wireless network. Use the Connect button to connect to a wireless network. Once connected, a profile is created in the Profiles list. You can also add, edit, and remove profiles from the Profiles 'list. Different profiles can be configured for each wireless network. Profile settings can include, the network name (SSID), operating mode, and security settings. See Profile Management for more information. Profiles list Name DescriptionProfile Name Network settings that allow your wireless adapter to connect to a network access point (infrastructure mode) or computer (Device to Device [ad hoc]) mode which does not use an access point. Refer to Set up Profiles for more information.Network Name Name of the wireless network (SSID) or computer.Connection Icons: The network profile status icons indicate the different connection states of the adapter with a wireless network, the type of operating mode being used, and whether network security is being used. Blue circle: The wireless adapter is associated with an access point or computer (Device to Device [ad hoc] mode). If a profile has 802.1x security enabled, this indicates that the wireless adapter is associated and authenticated.](https://usermanual.wiki/Intel/LEN3945ABG.Users-Manual/User-Guide-598567-Page-15.png)
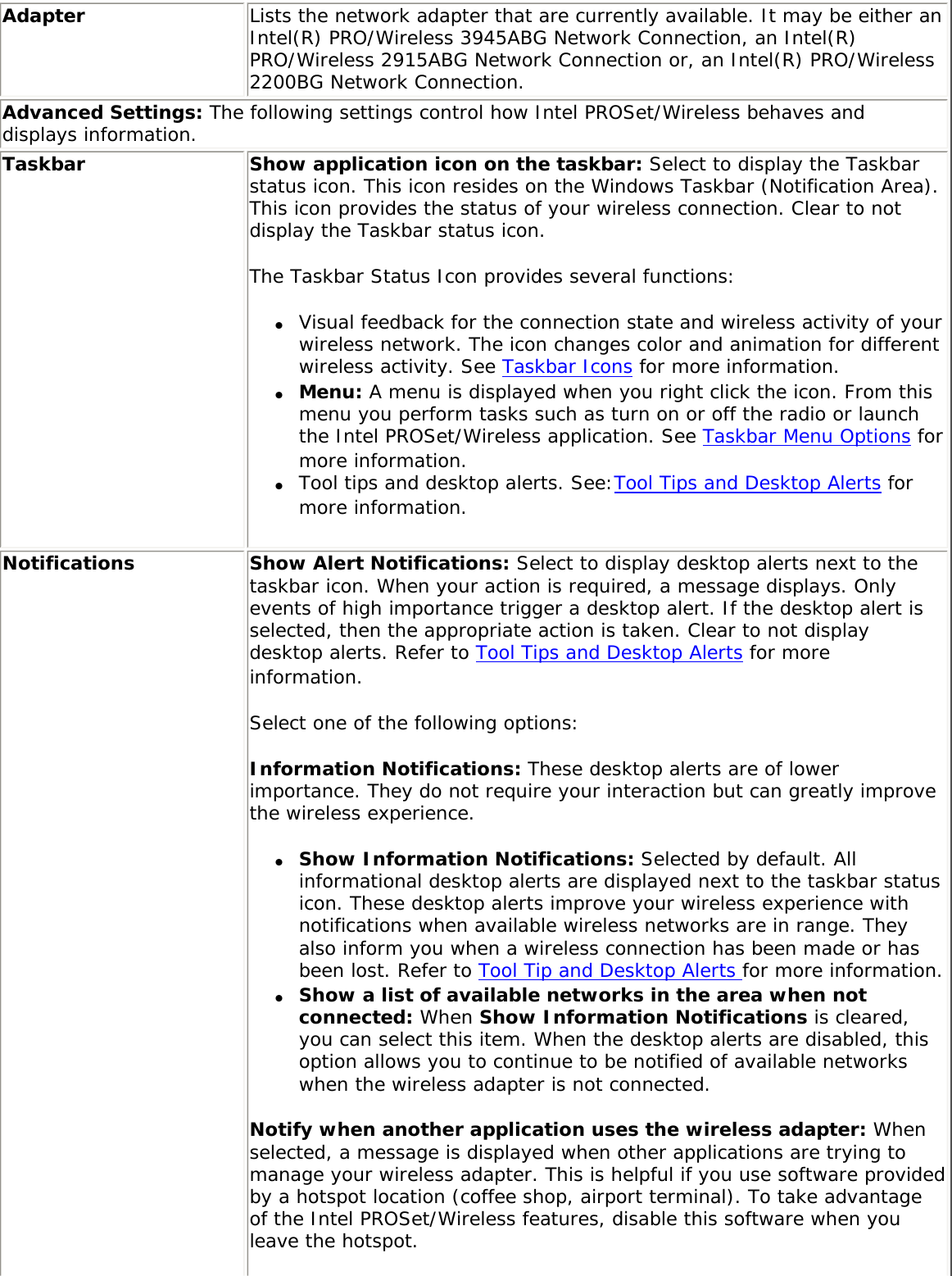
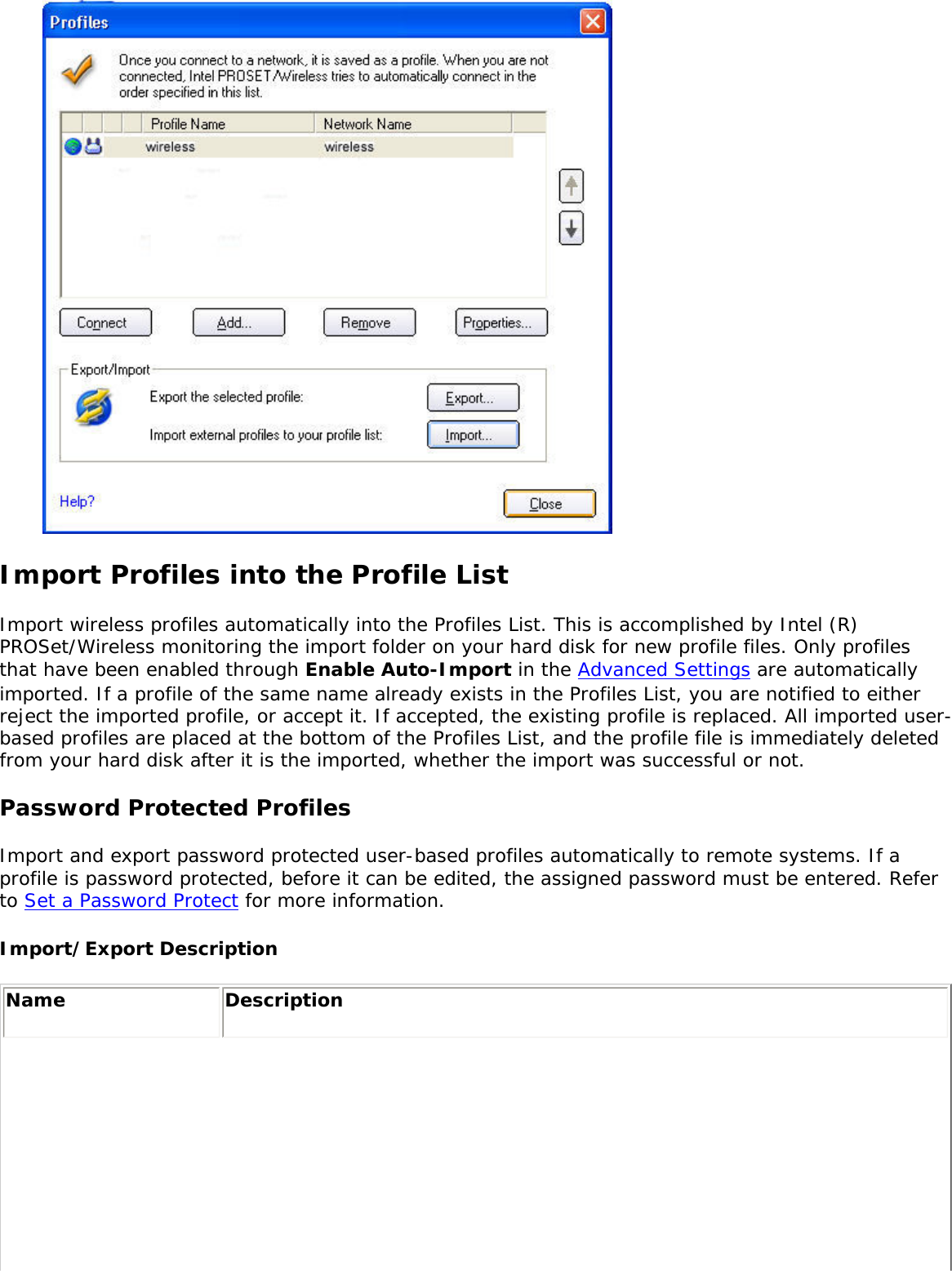
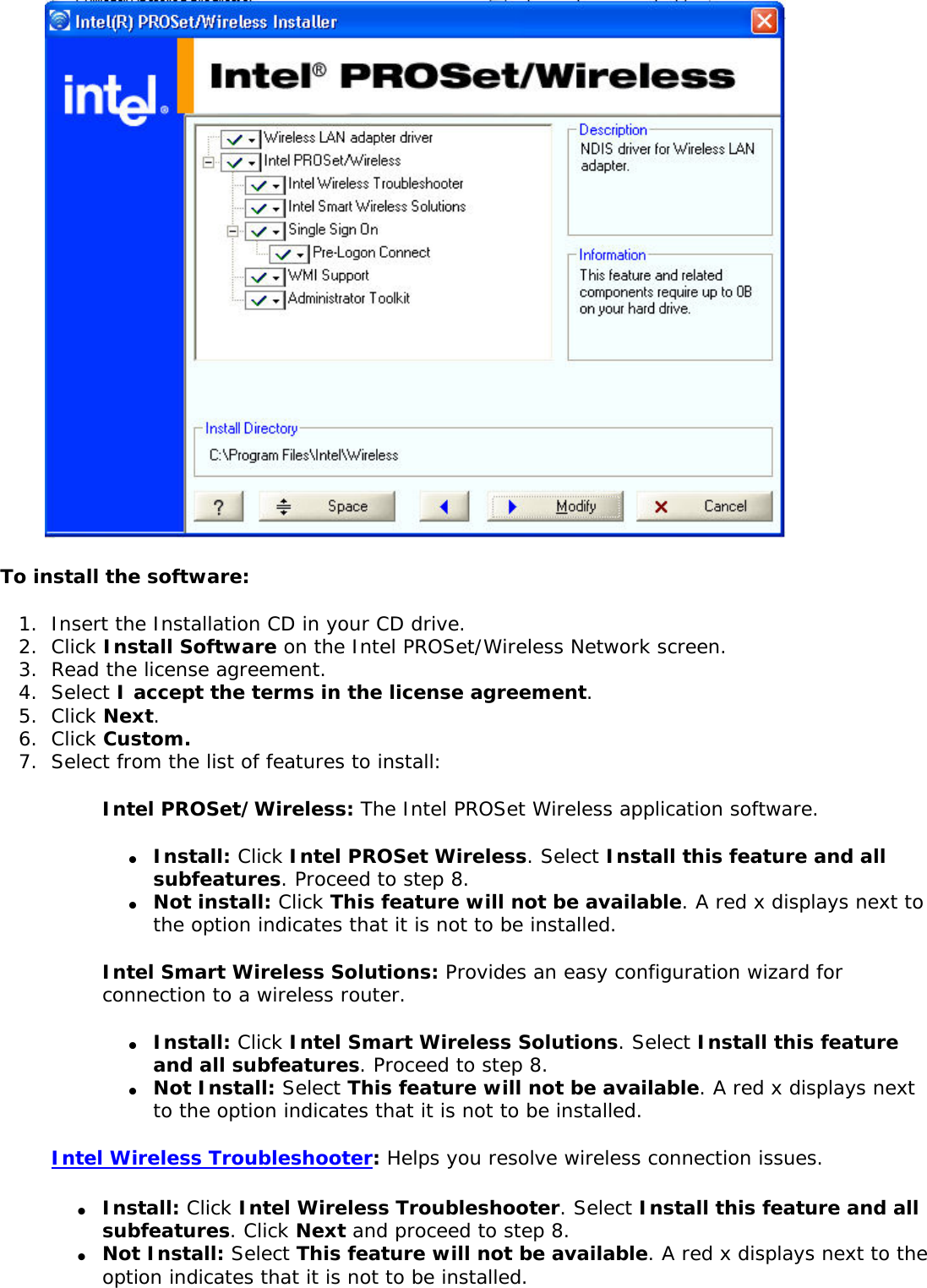
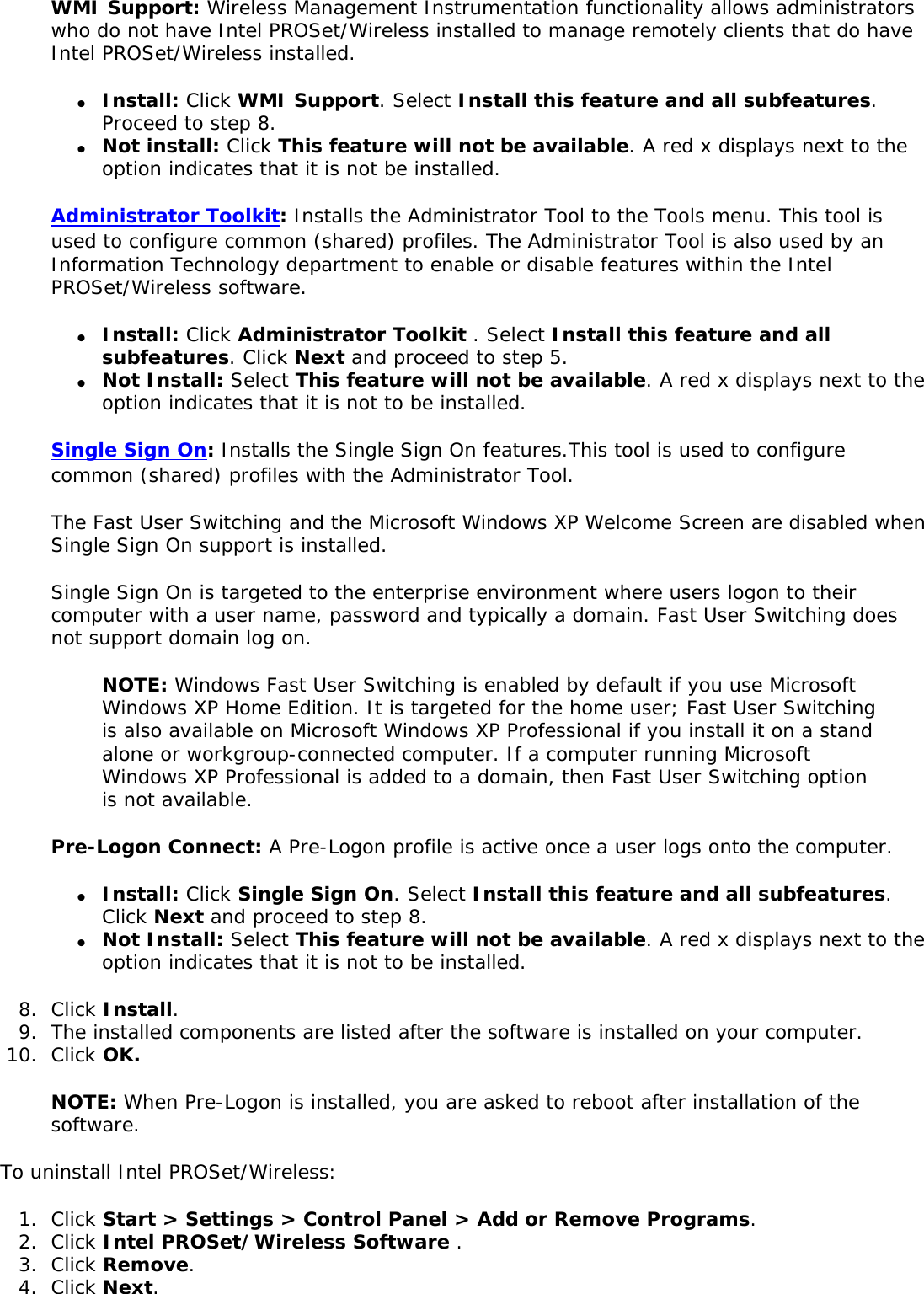
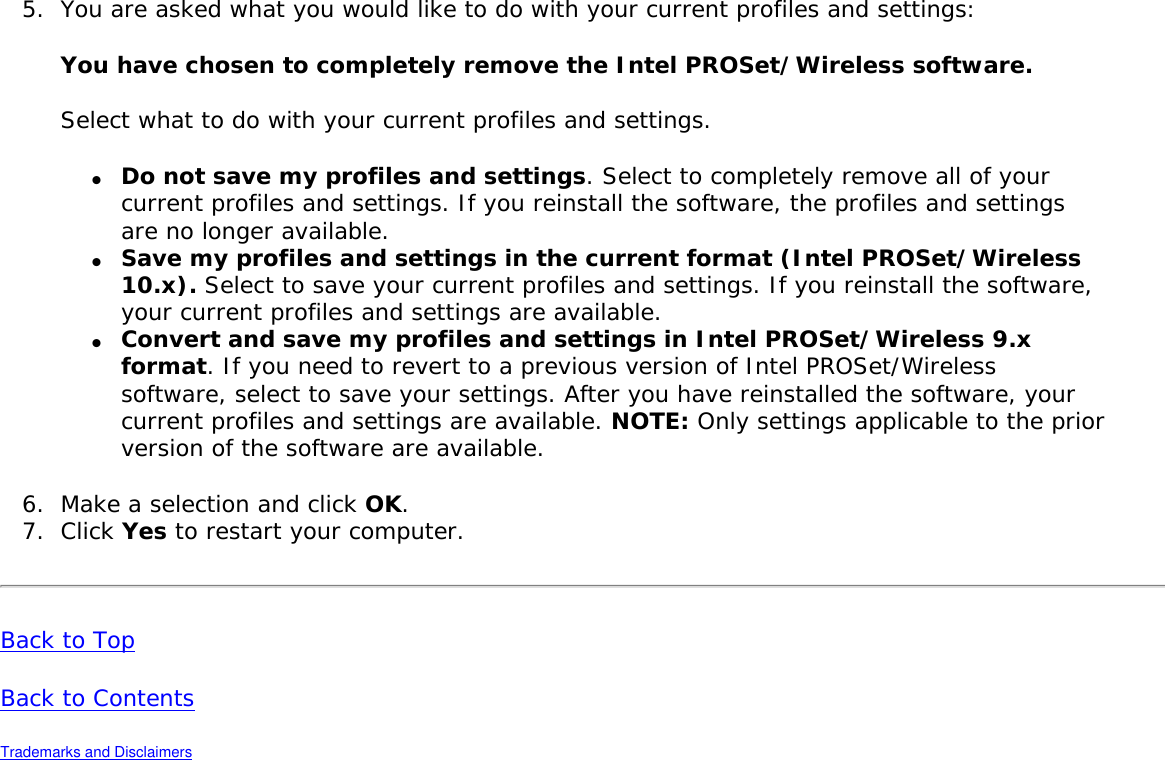
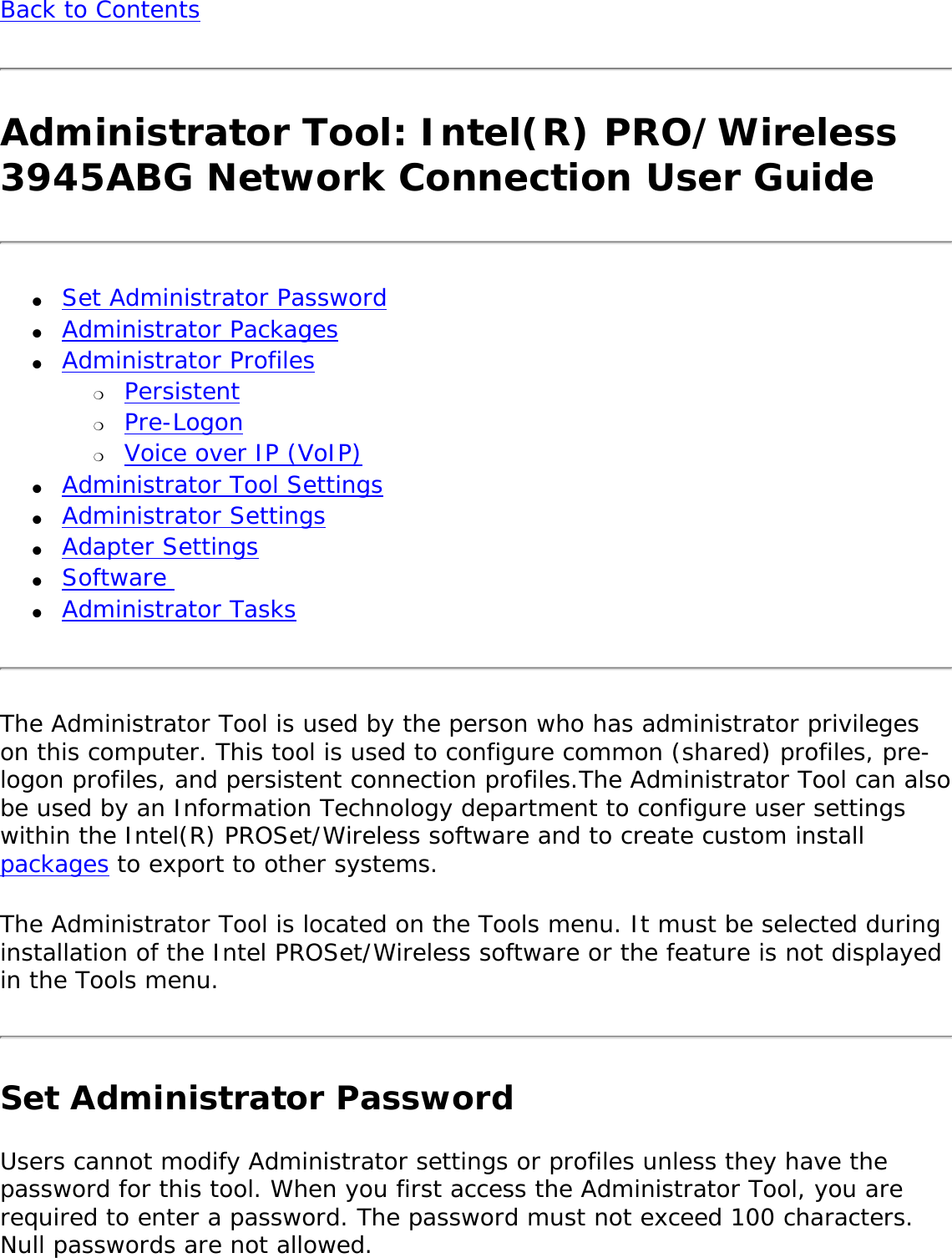
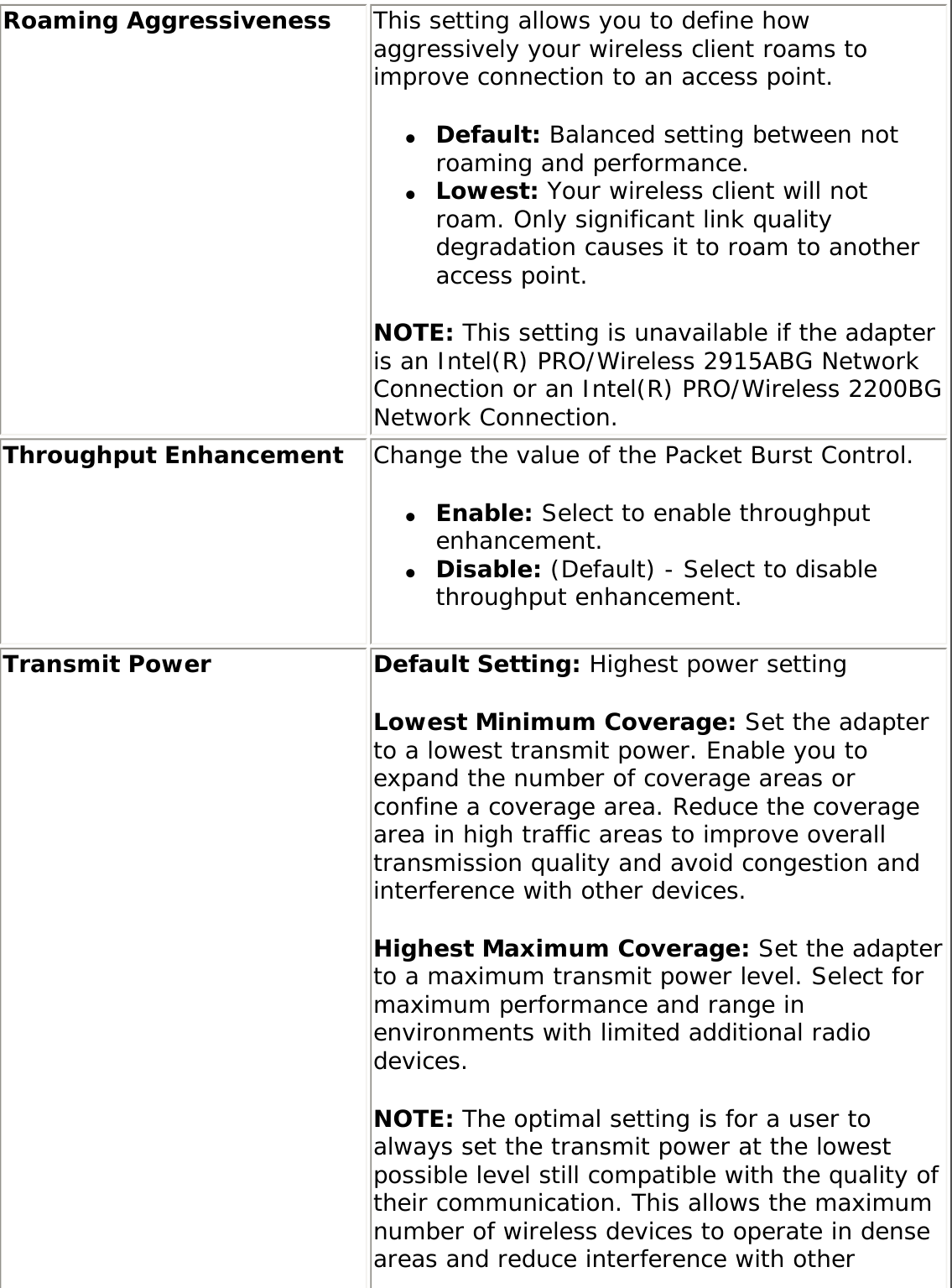
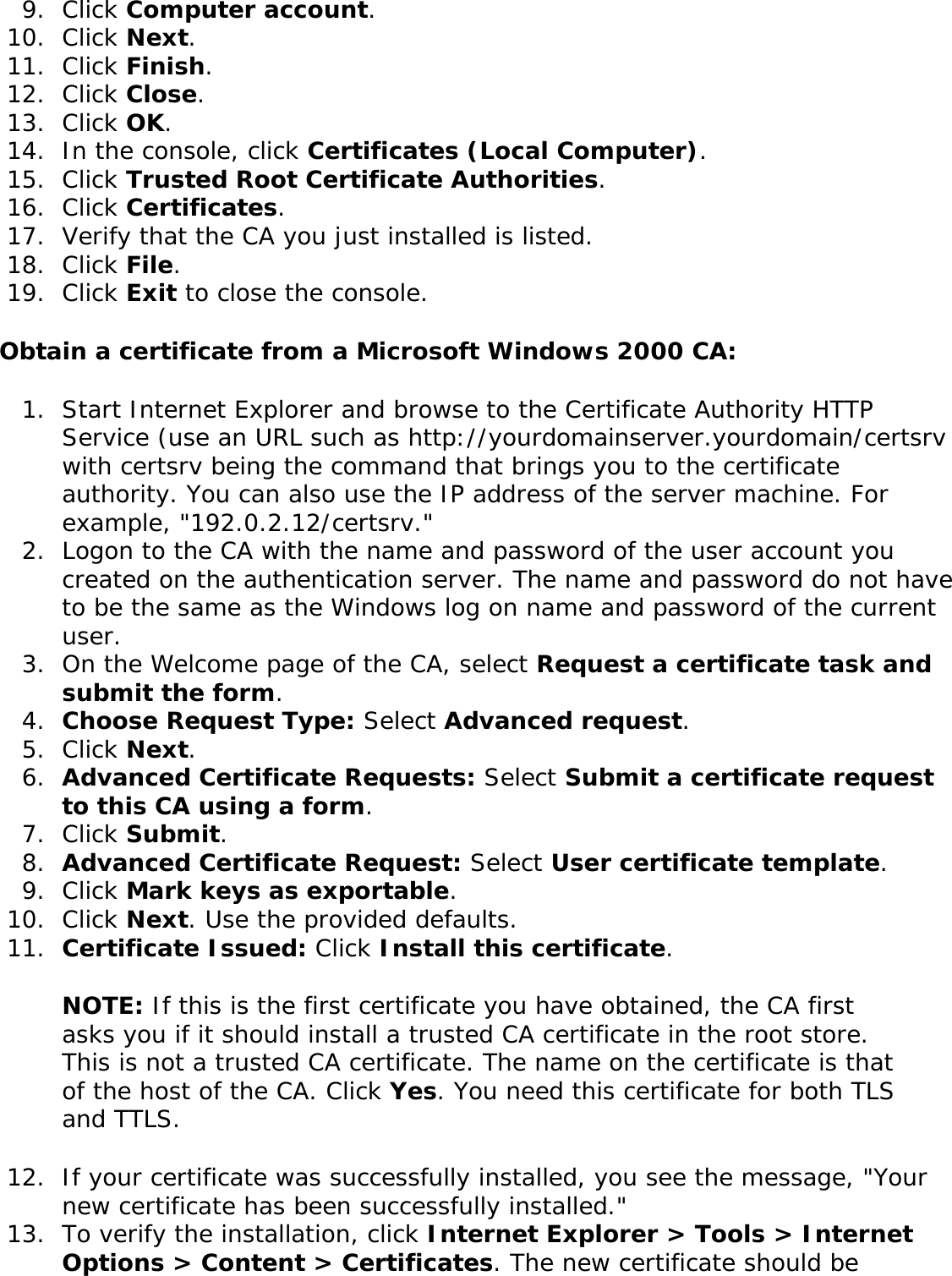
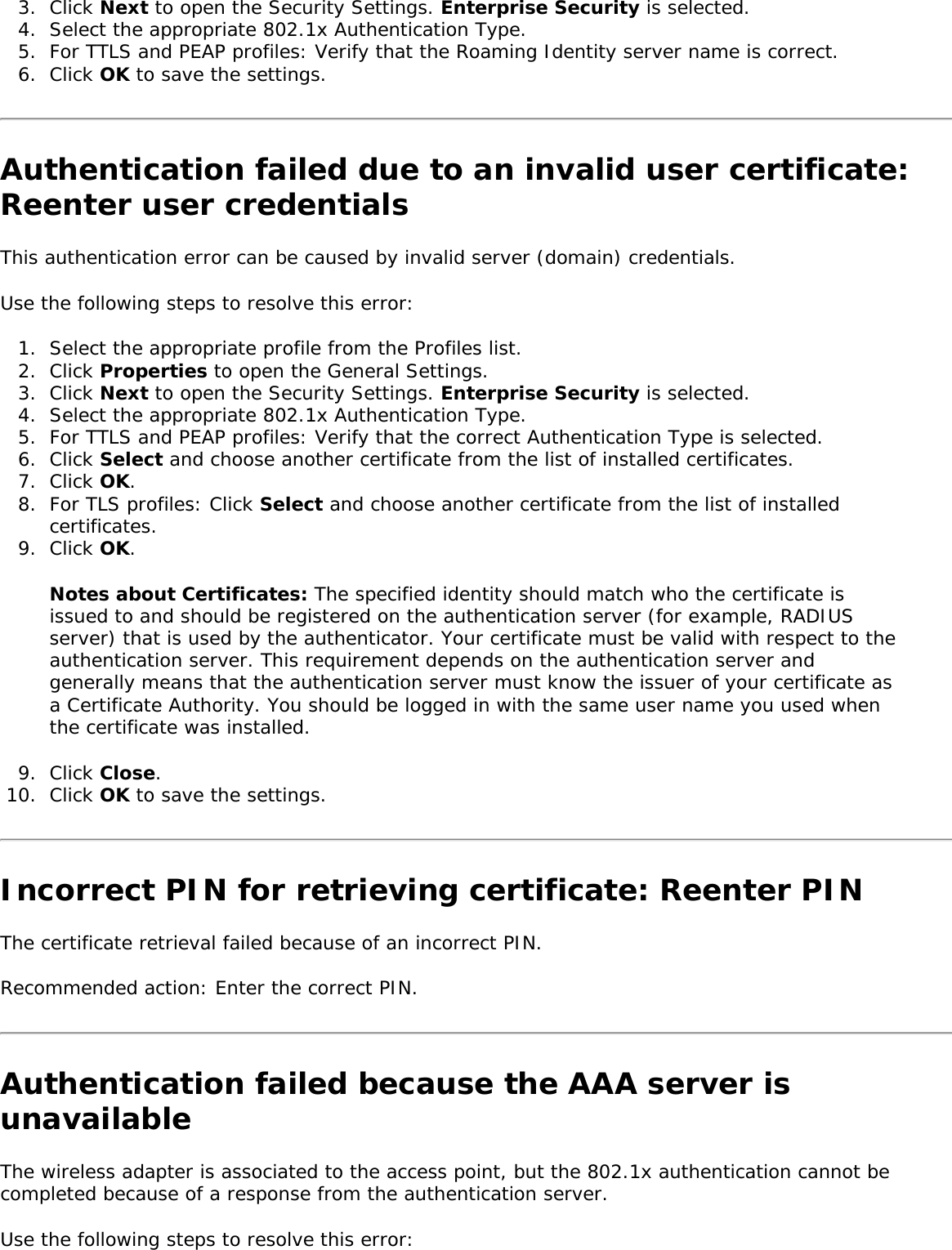
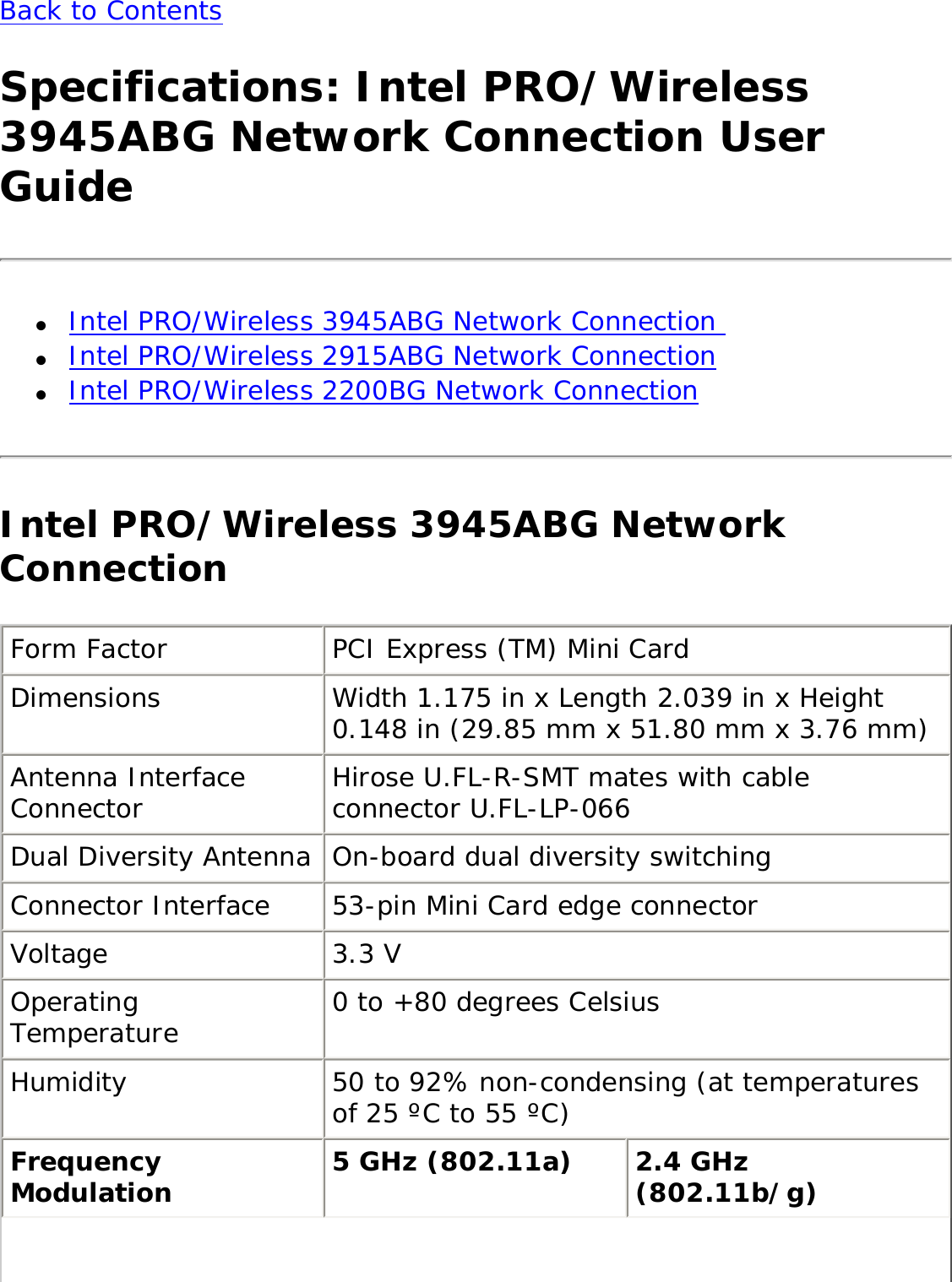
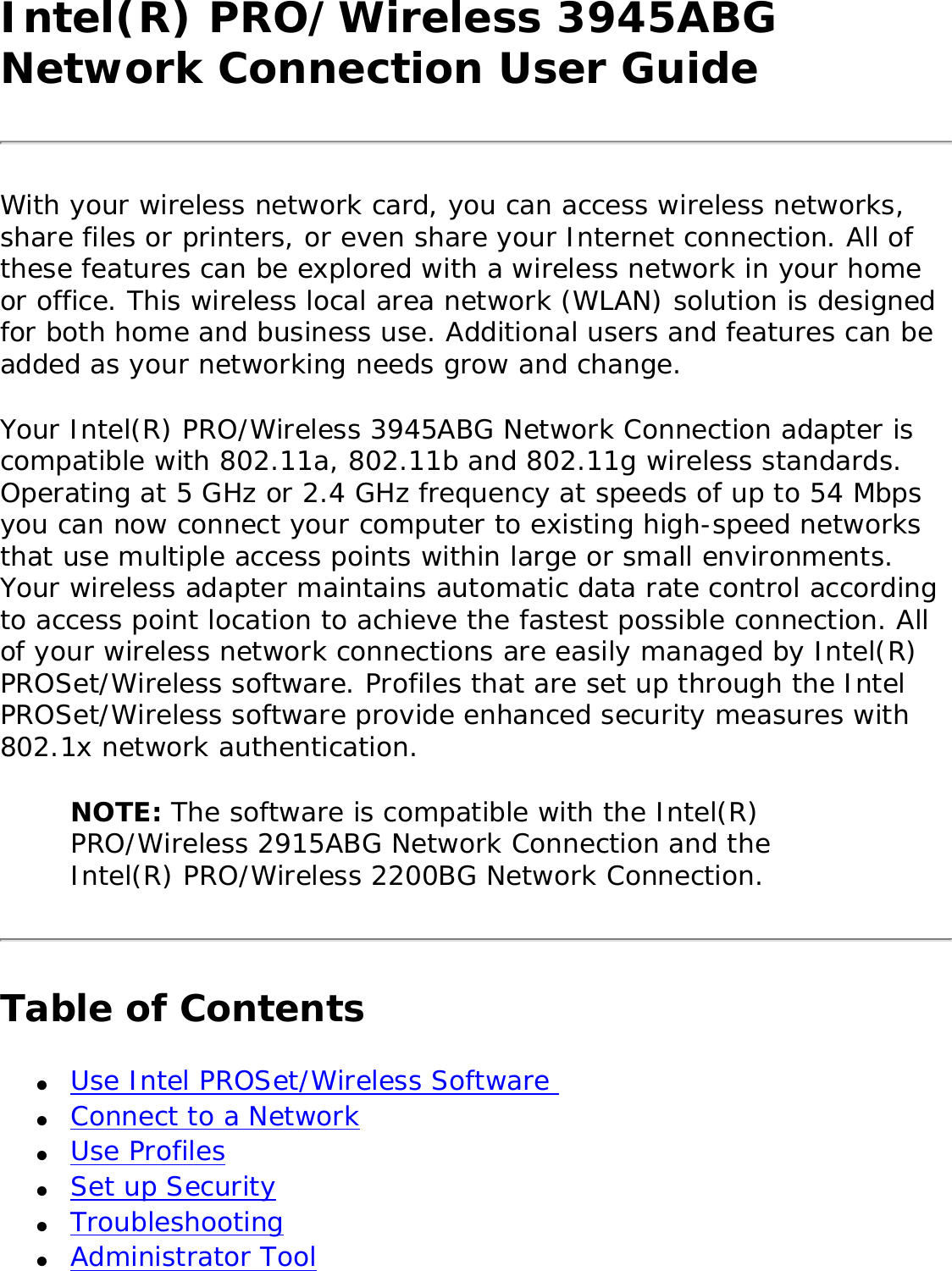
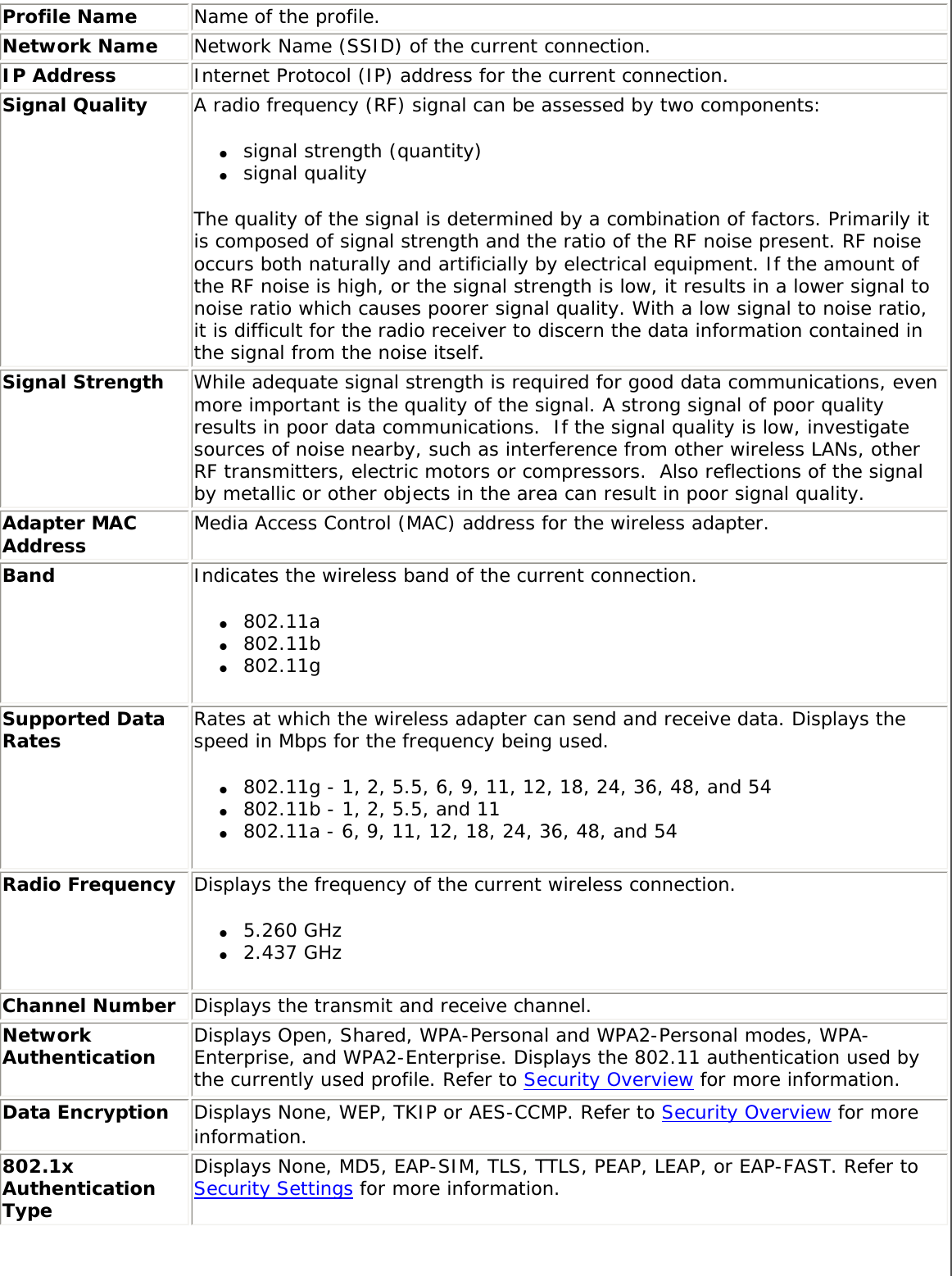
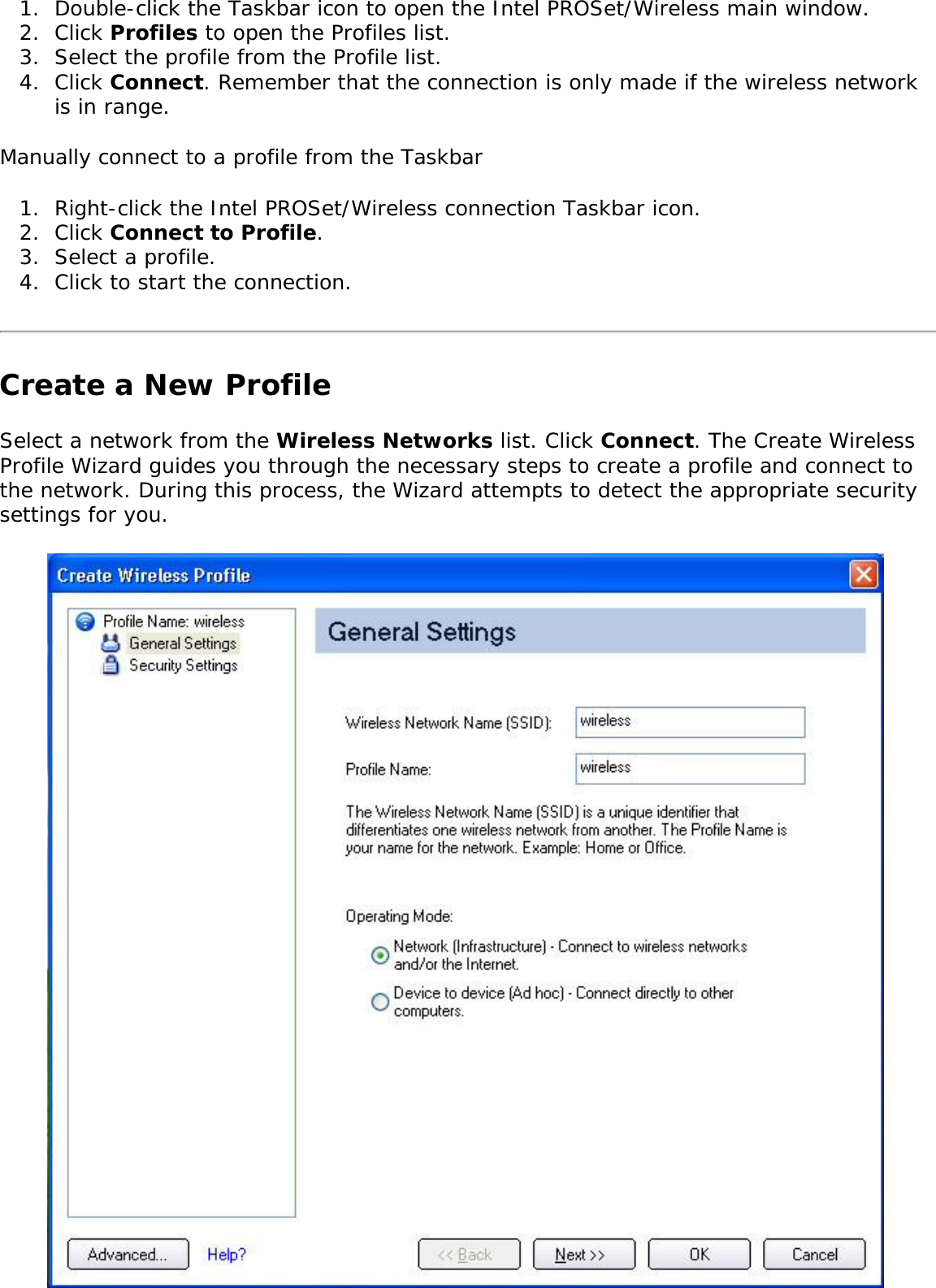
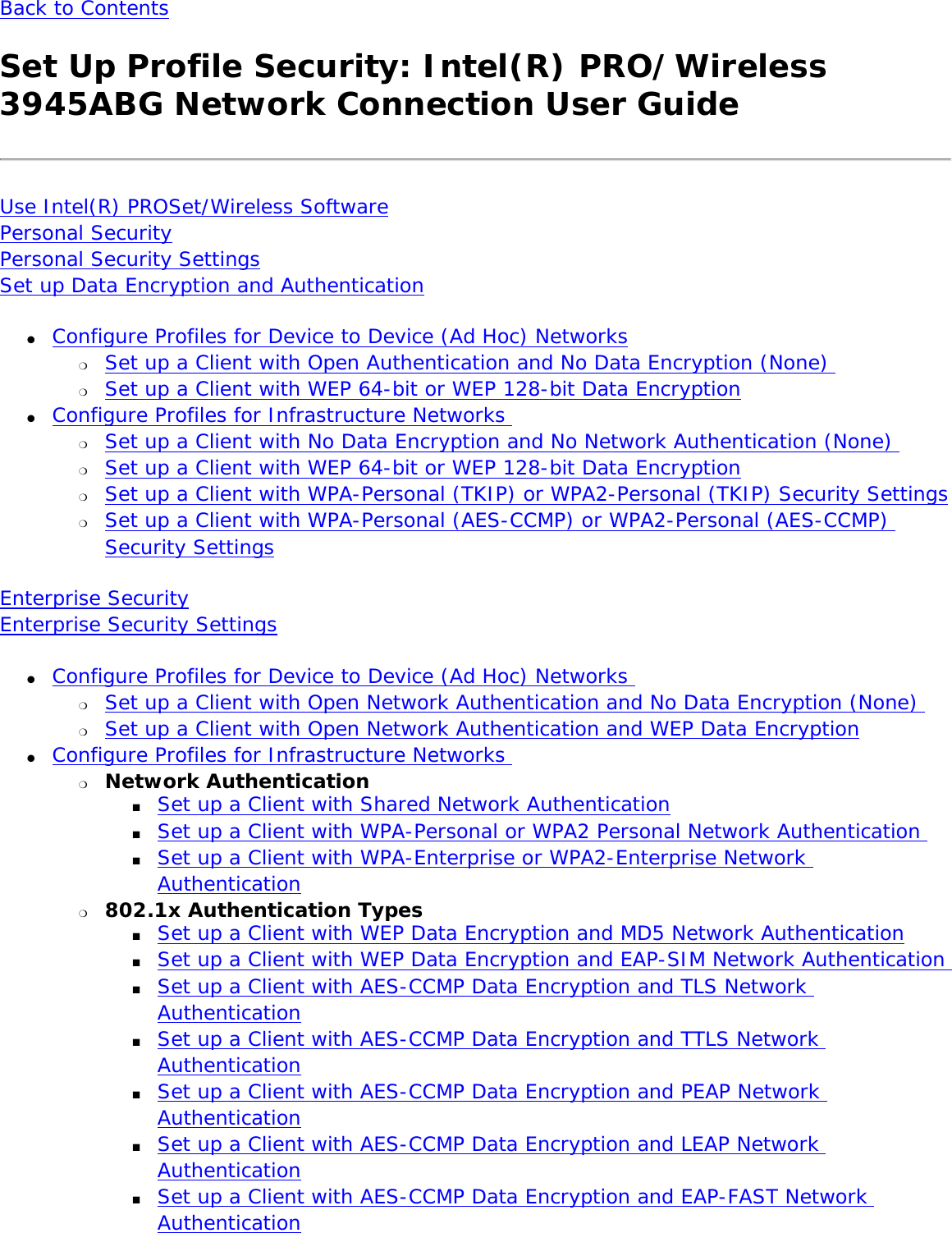
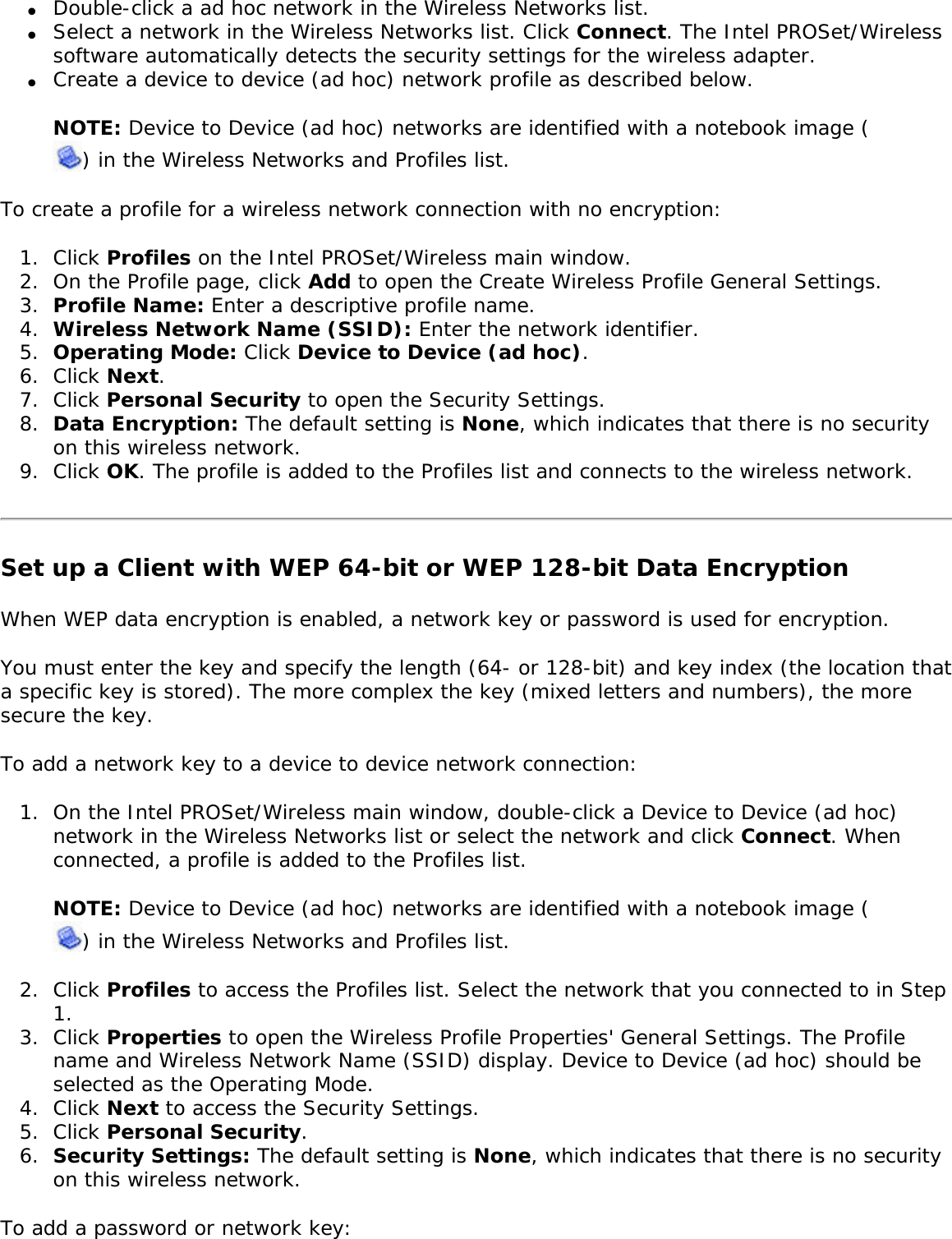
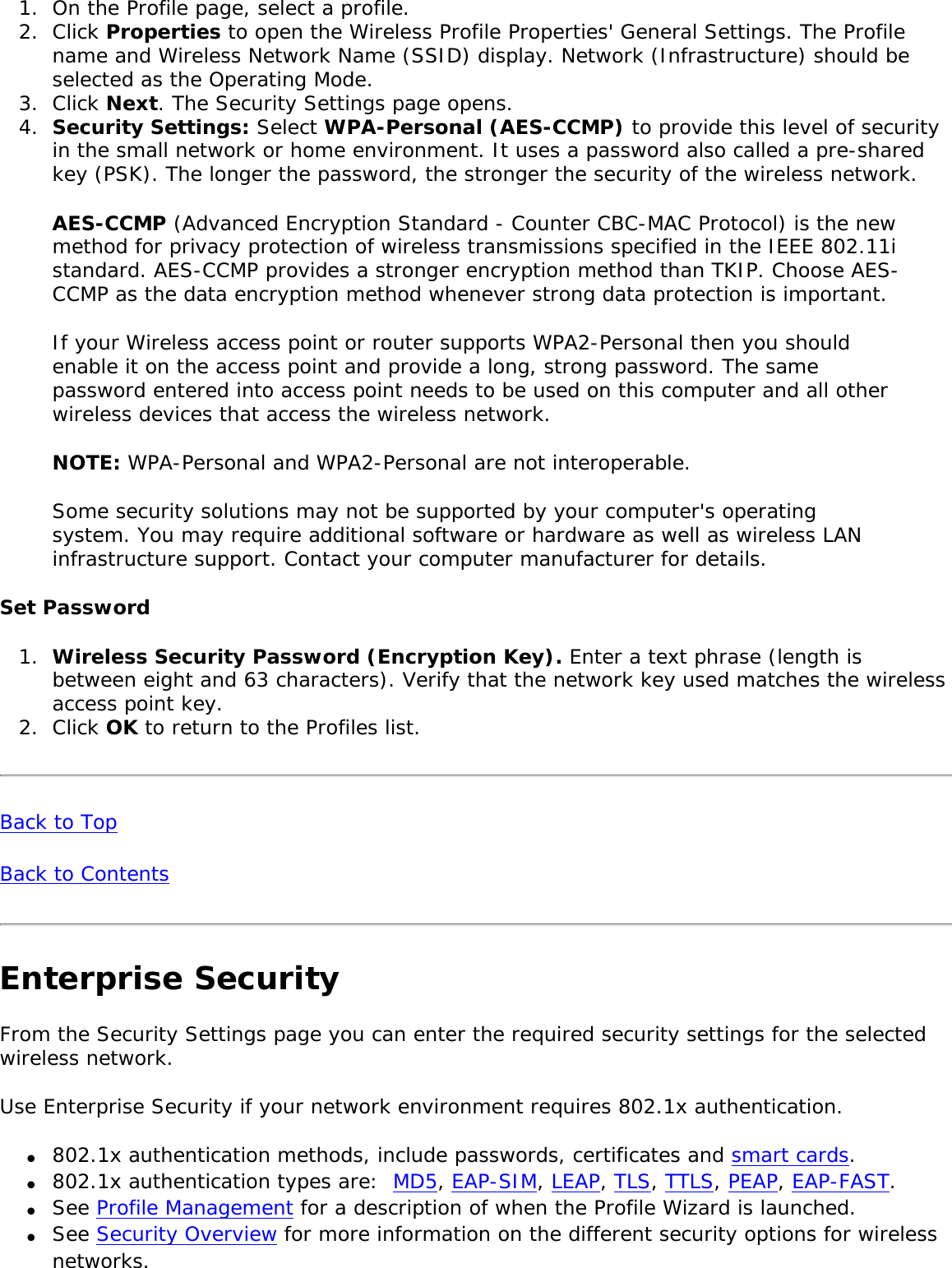
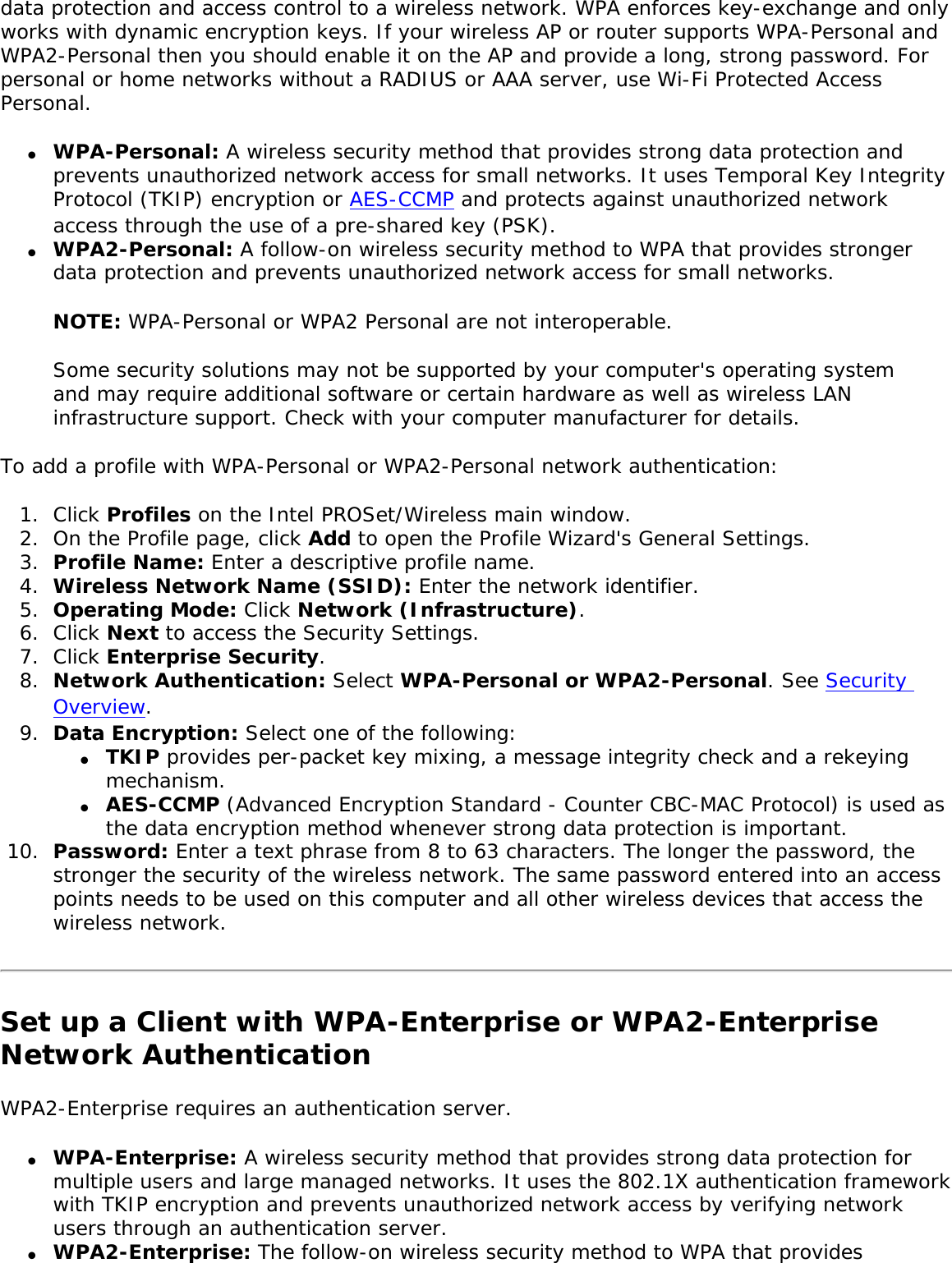
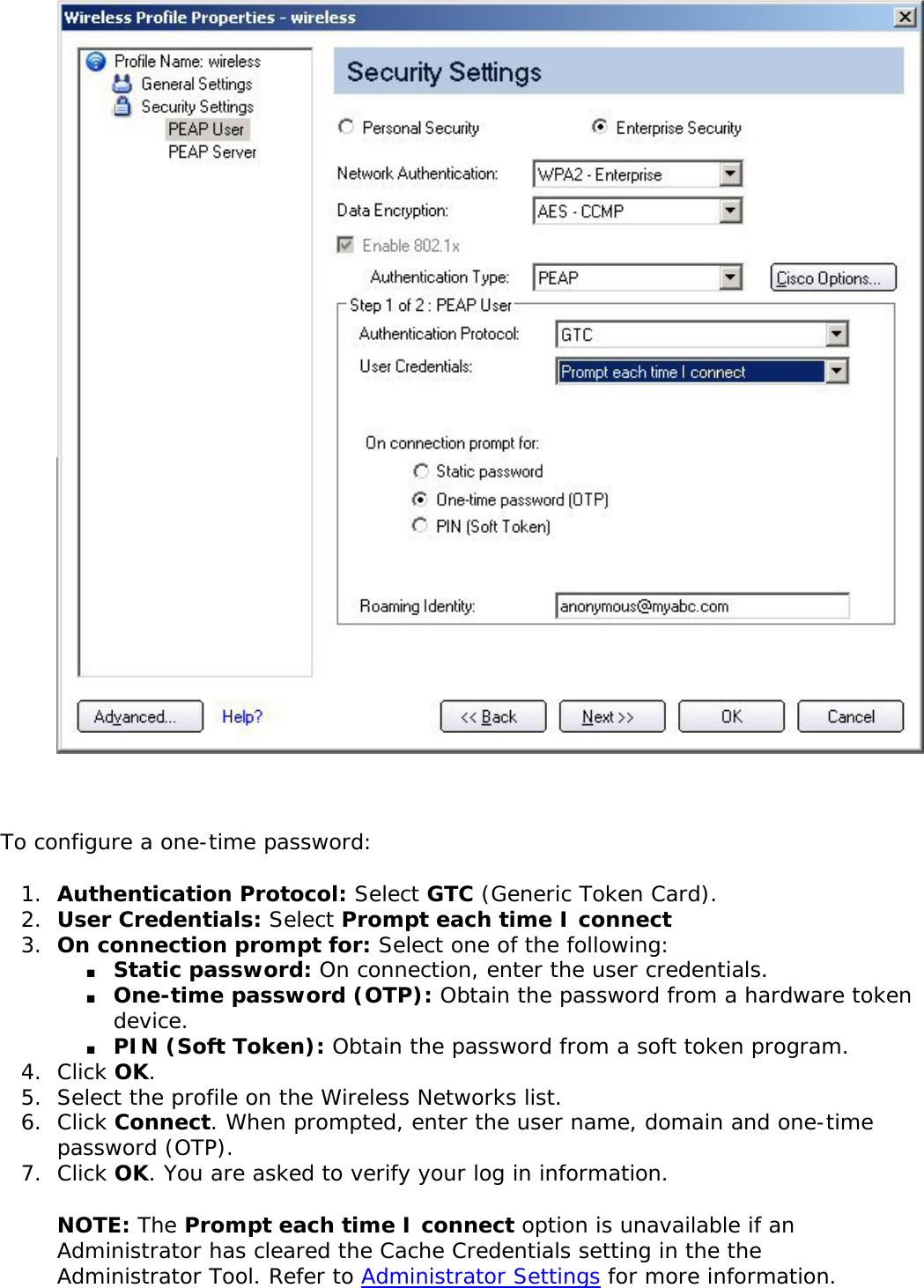
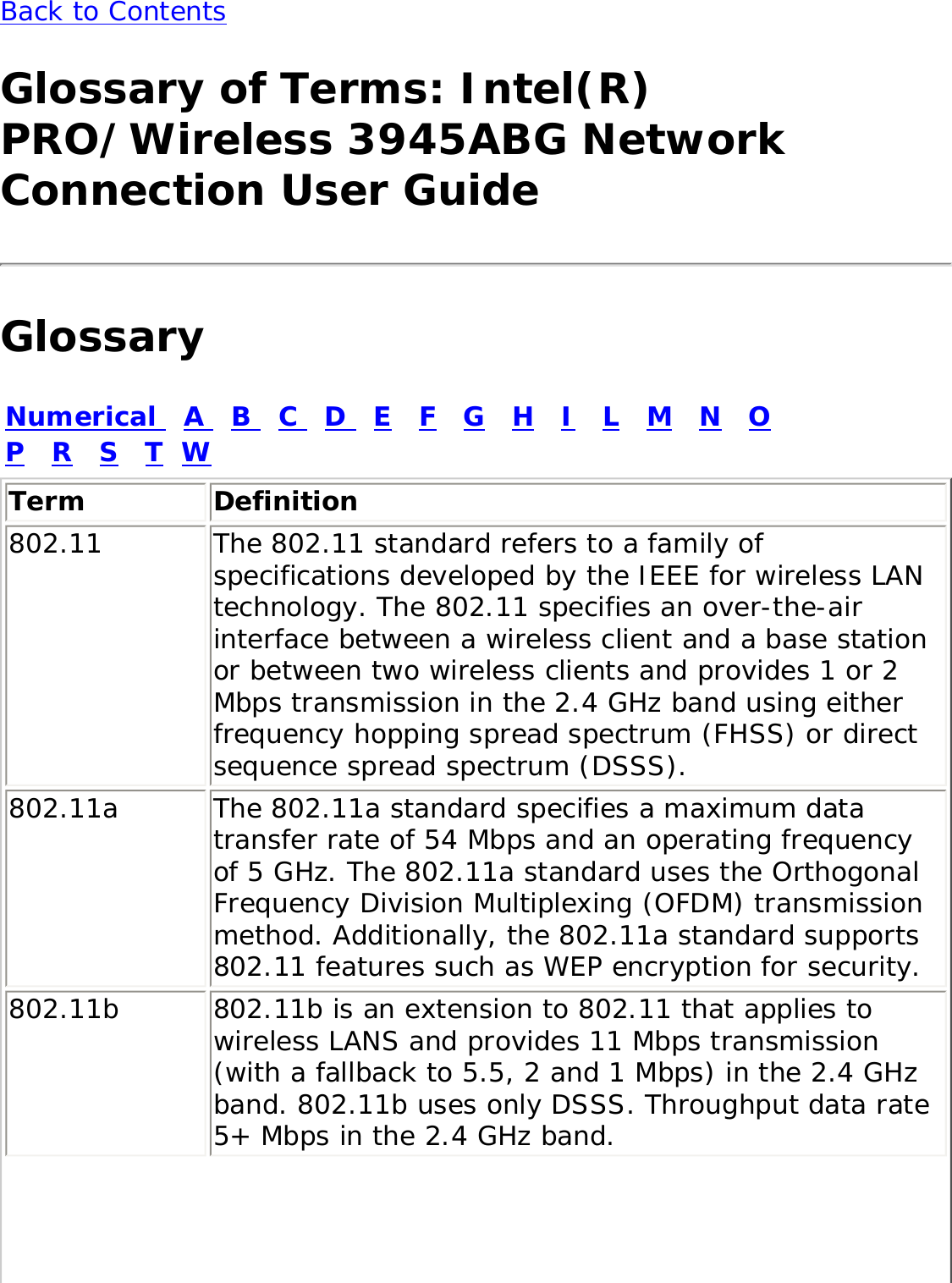
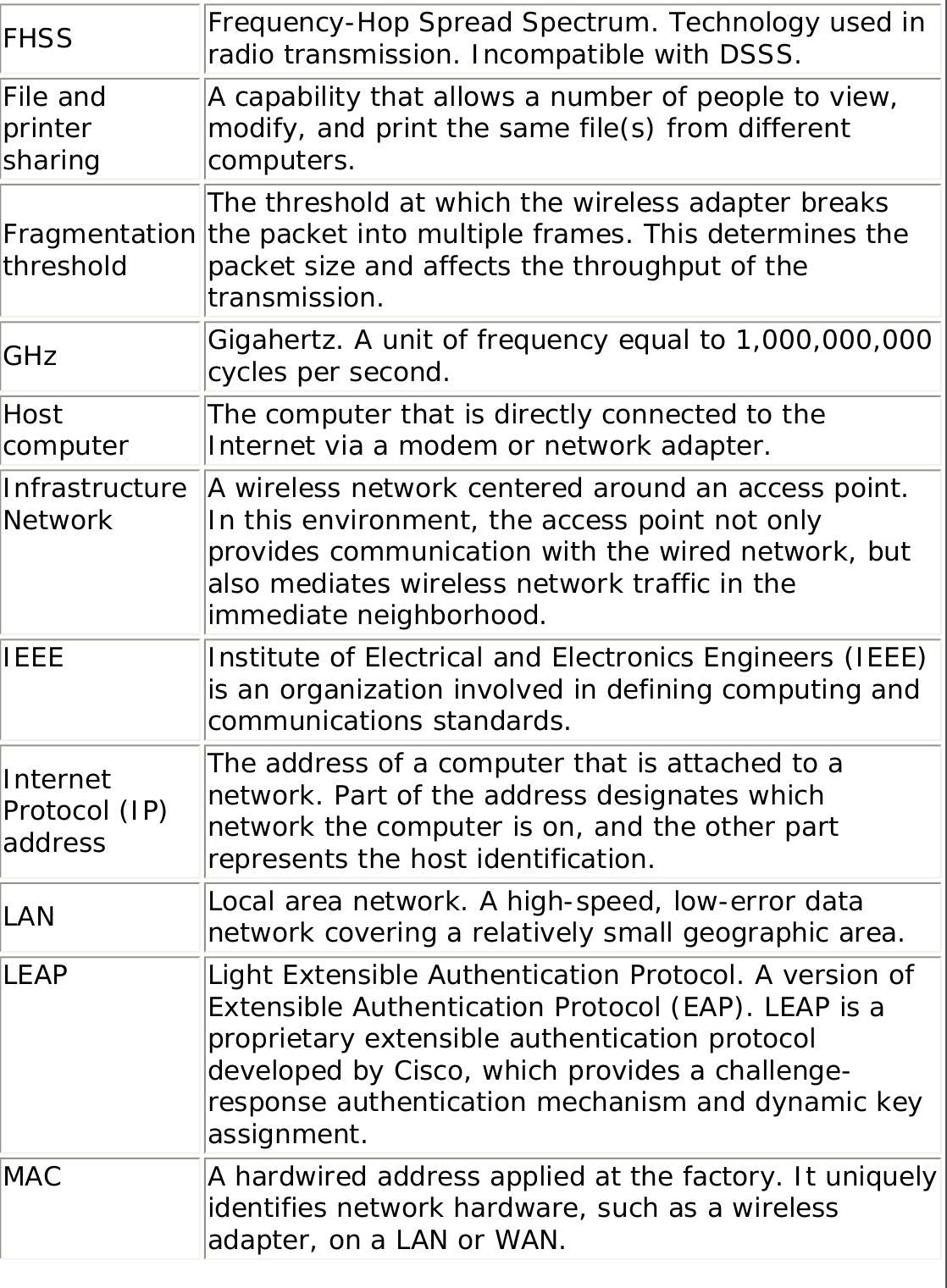
![Profile List Priority Arrows● Use the up-arrow to move the position of a selected profile up in the profiles list.● Use the down-arrow to move the position of a selected profile down in the profiles list.Profiles List Icons The network profile status icons indicate if the adapter is associated with a network, the type of operating mode being used, and if security encryption is enabled. These icons display next to the profile name in the profile list. Name DescriptionProfile Name Profiles are network settings that allow your wireless adapter to connect to a network access point (Infrastructure mode) or computer (device-to-device [Ad hoc] mode) which does not use an access point. Network Name Name of the wireless network (SSID) or computer.](https://usermanual.wiki/Intel/LEN3945ABG.Users-Manual/User-Guide-598567-Page-37.png)
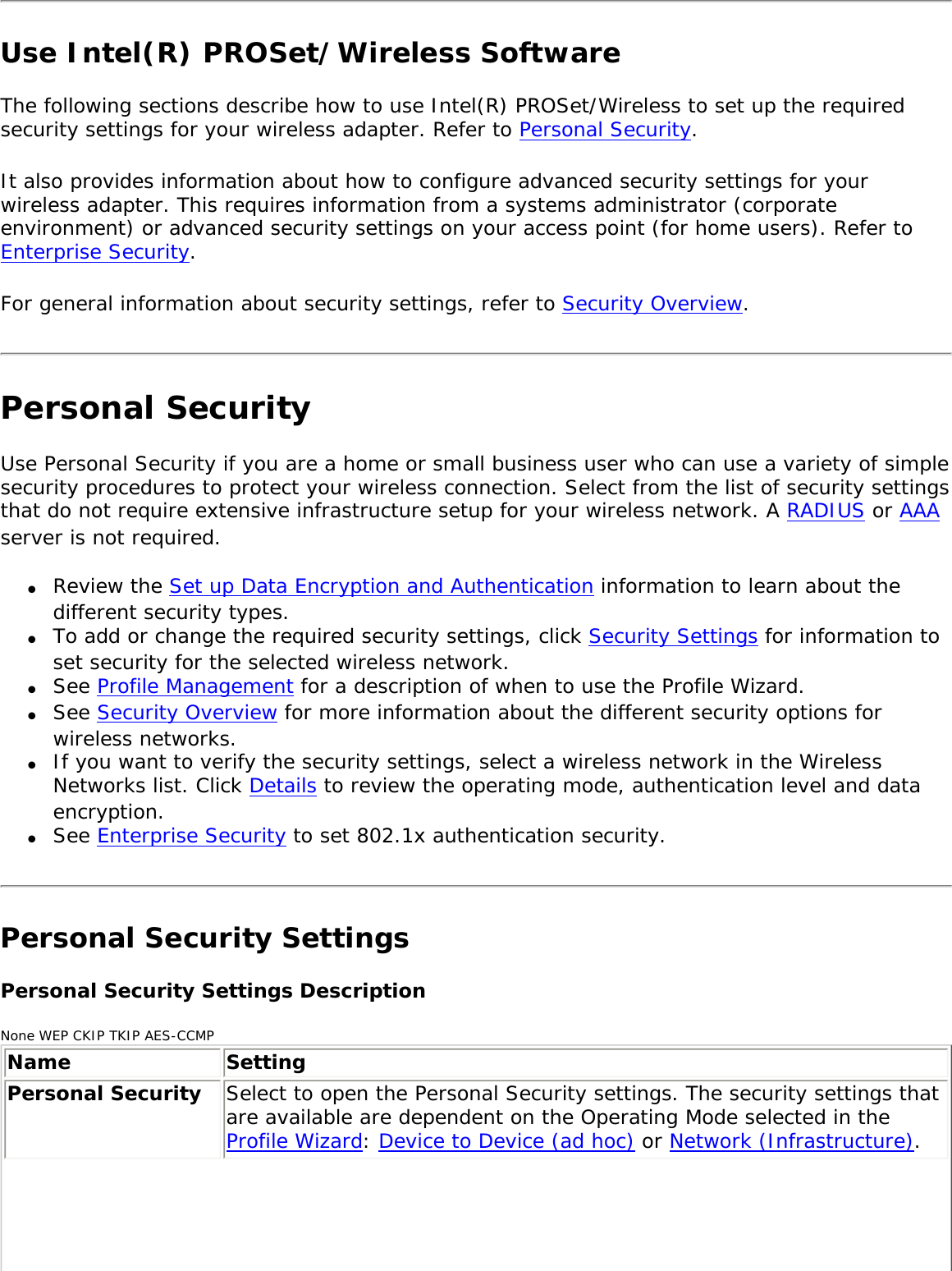
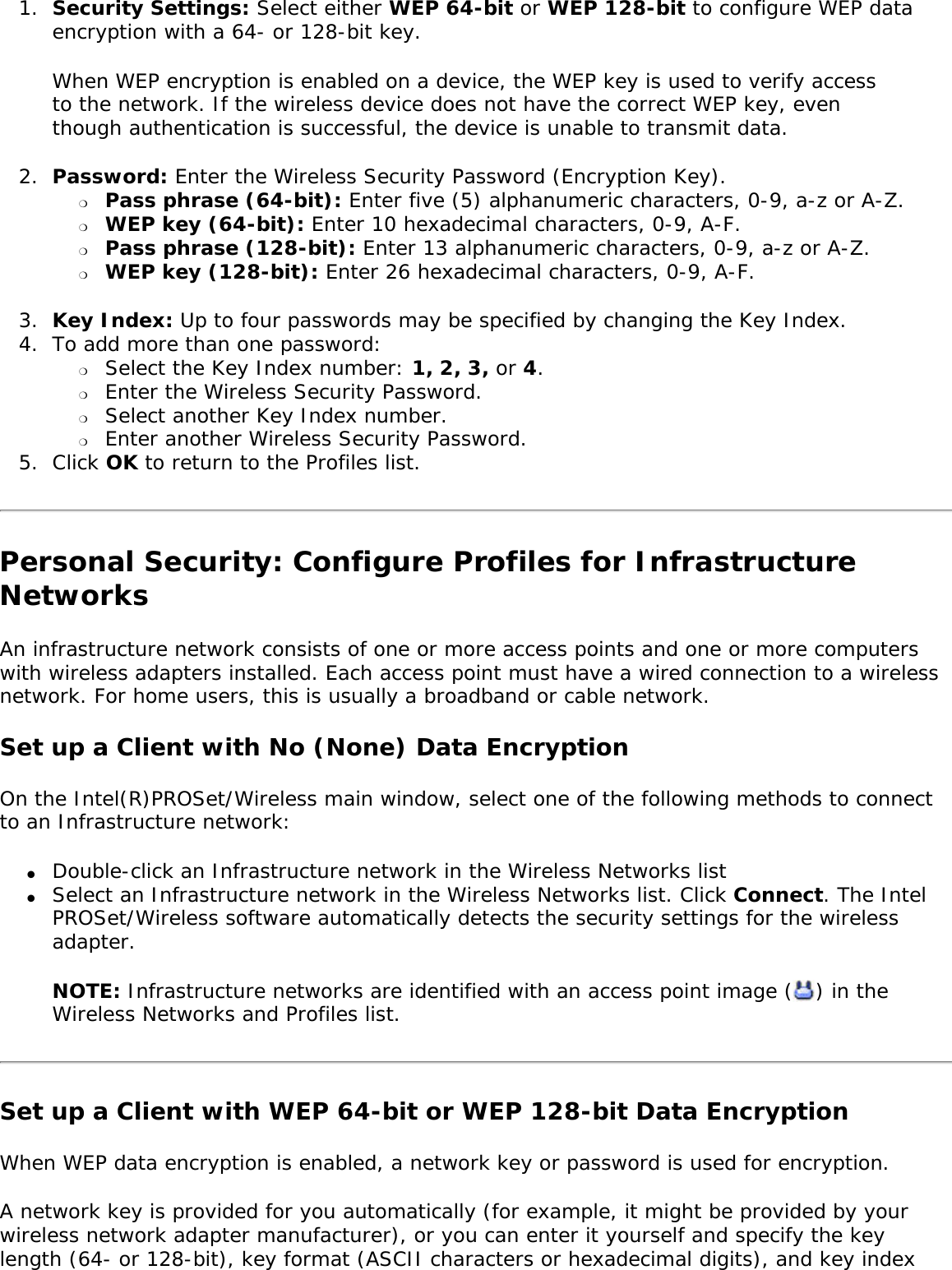
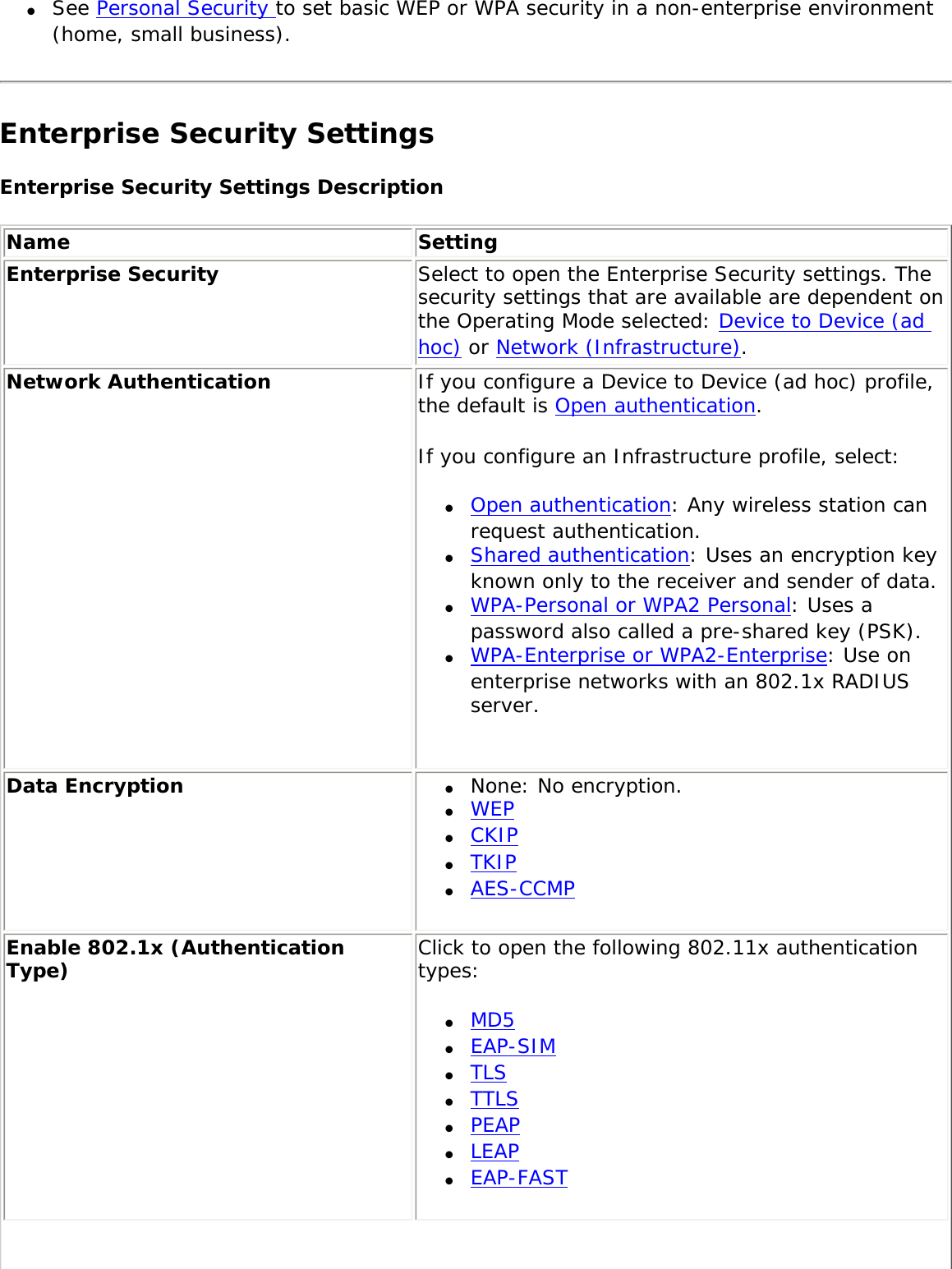
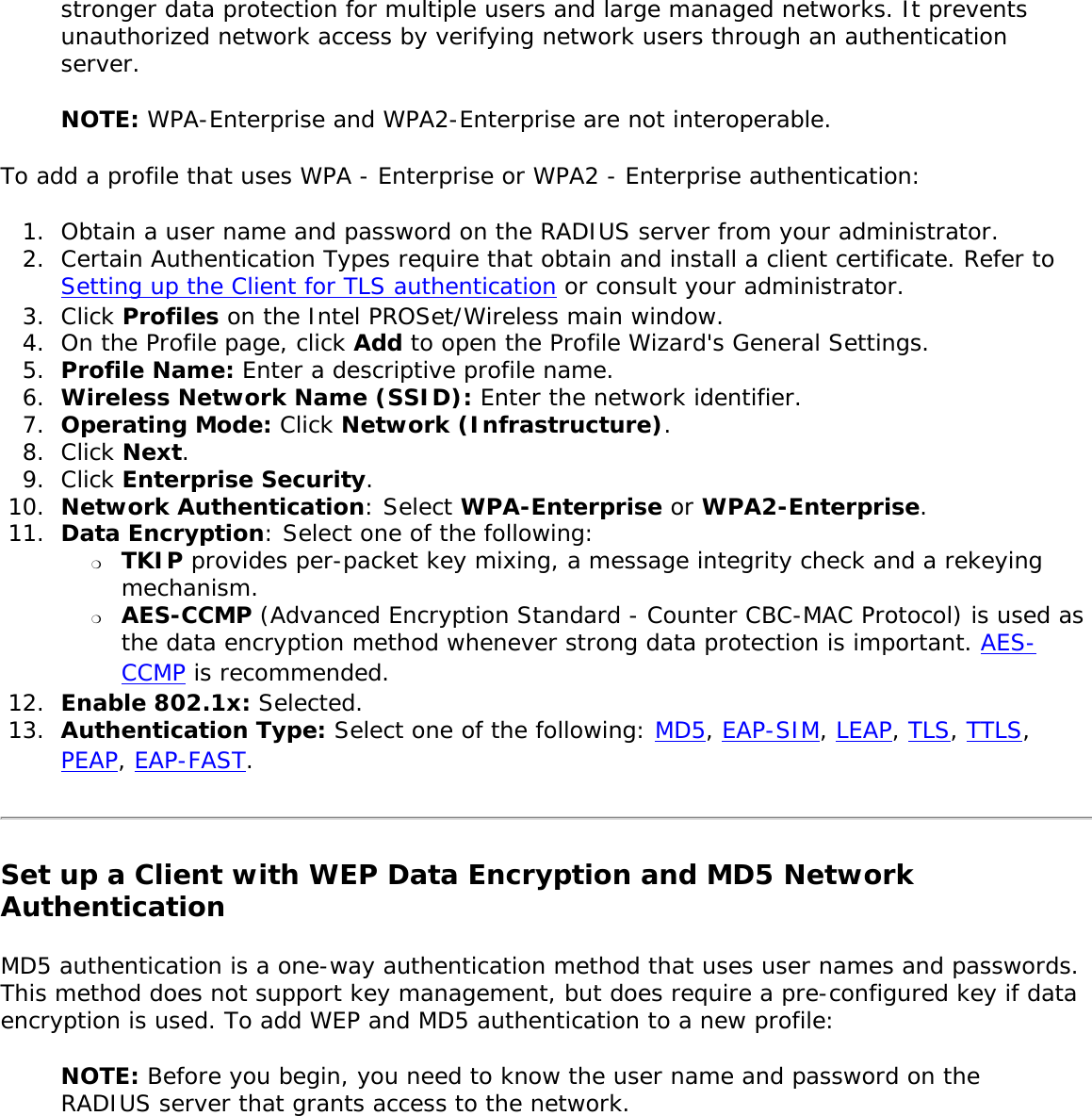
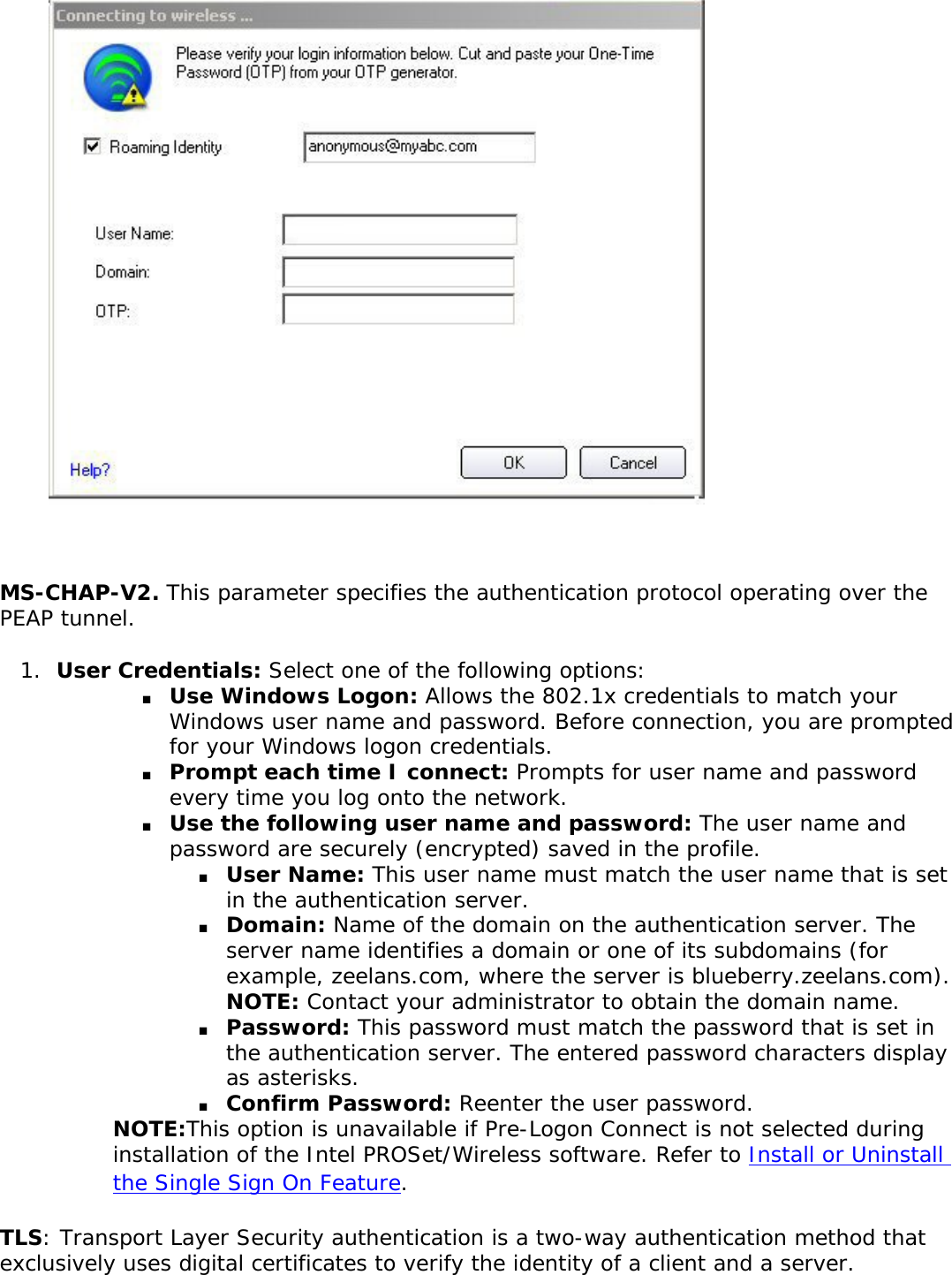
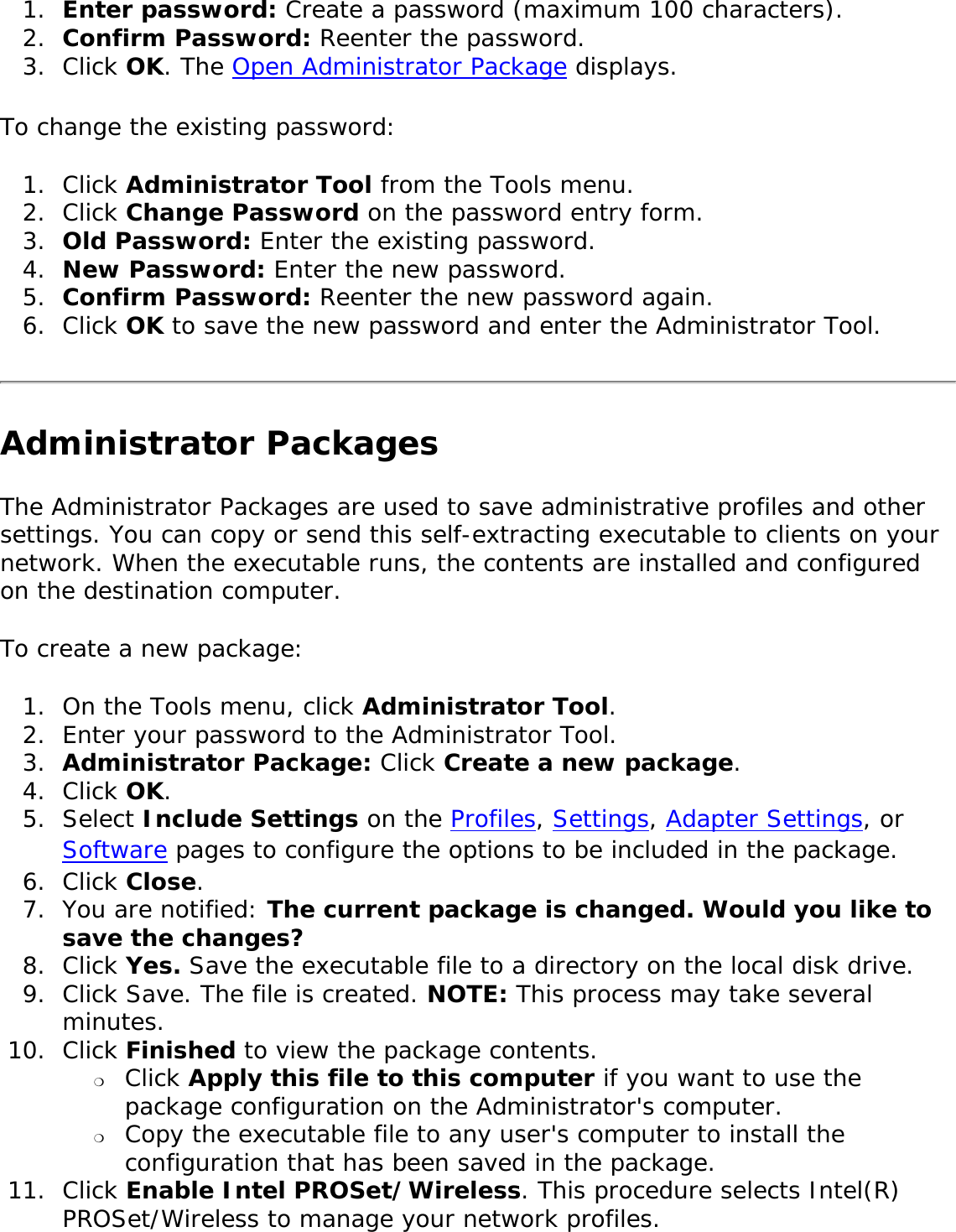
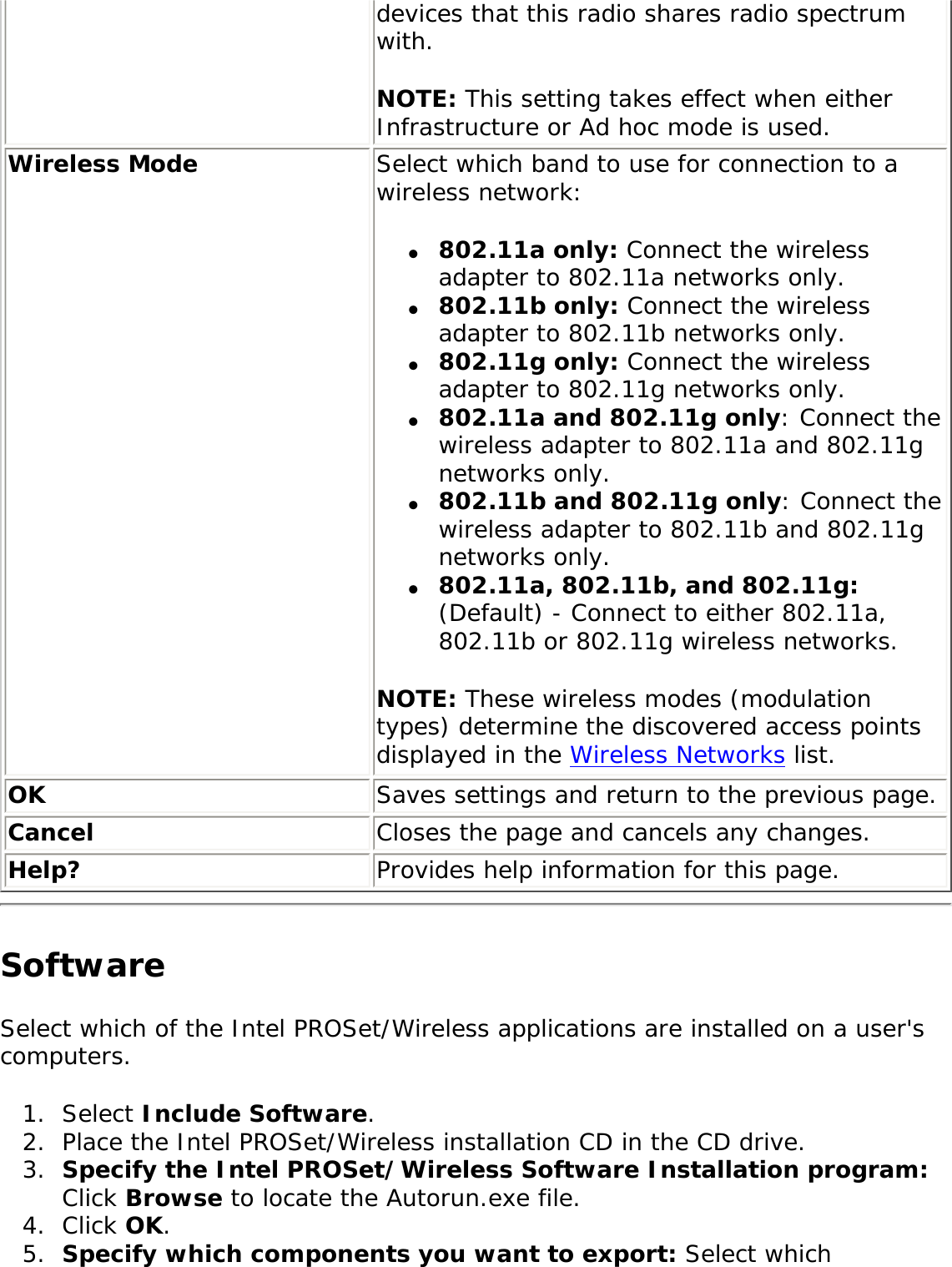
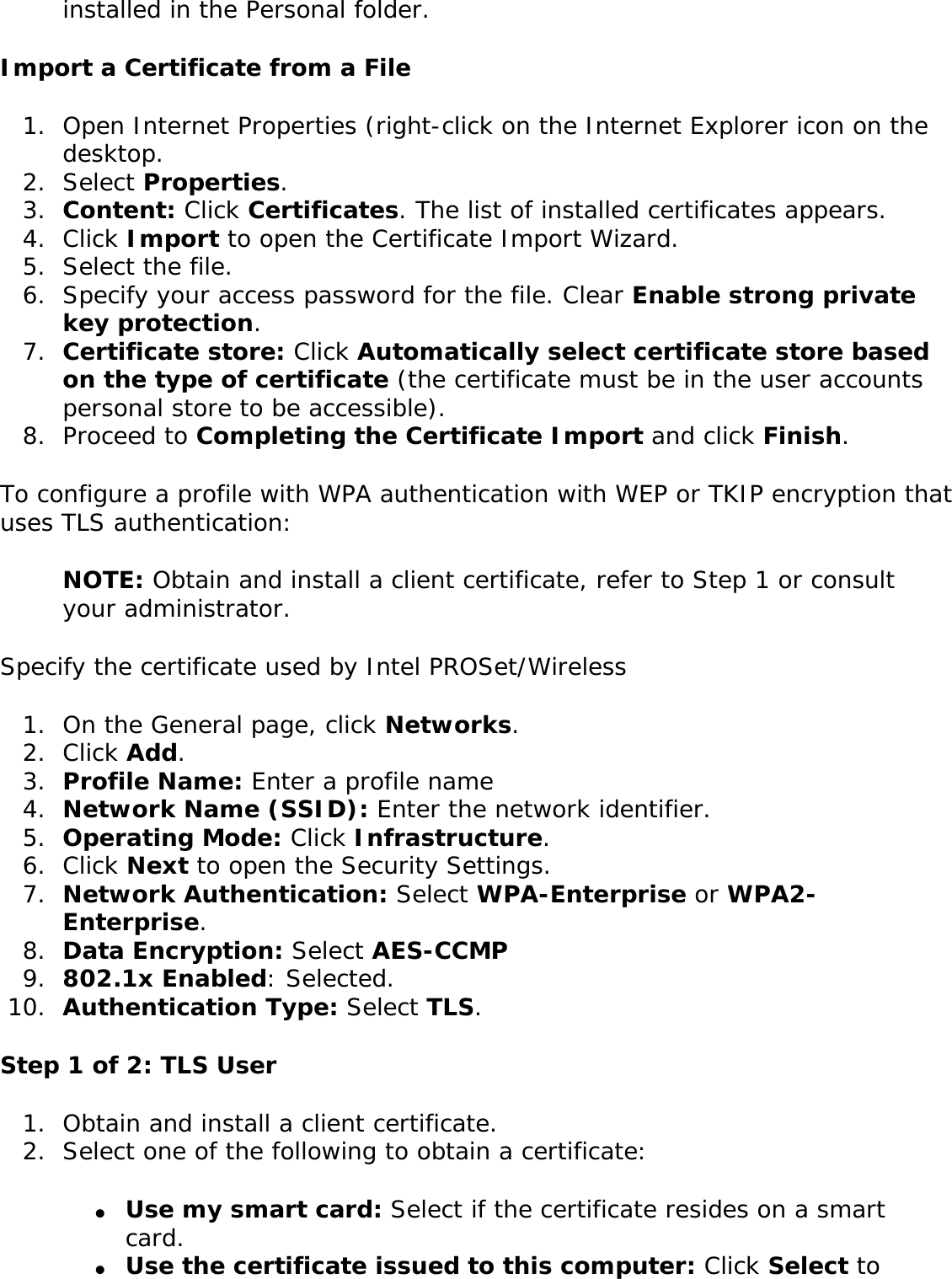
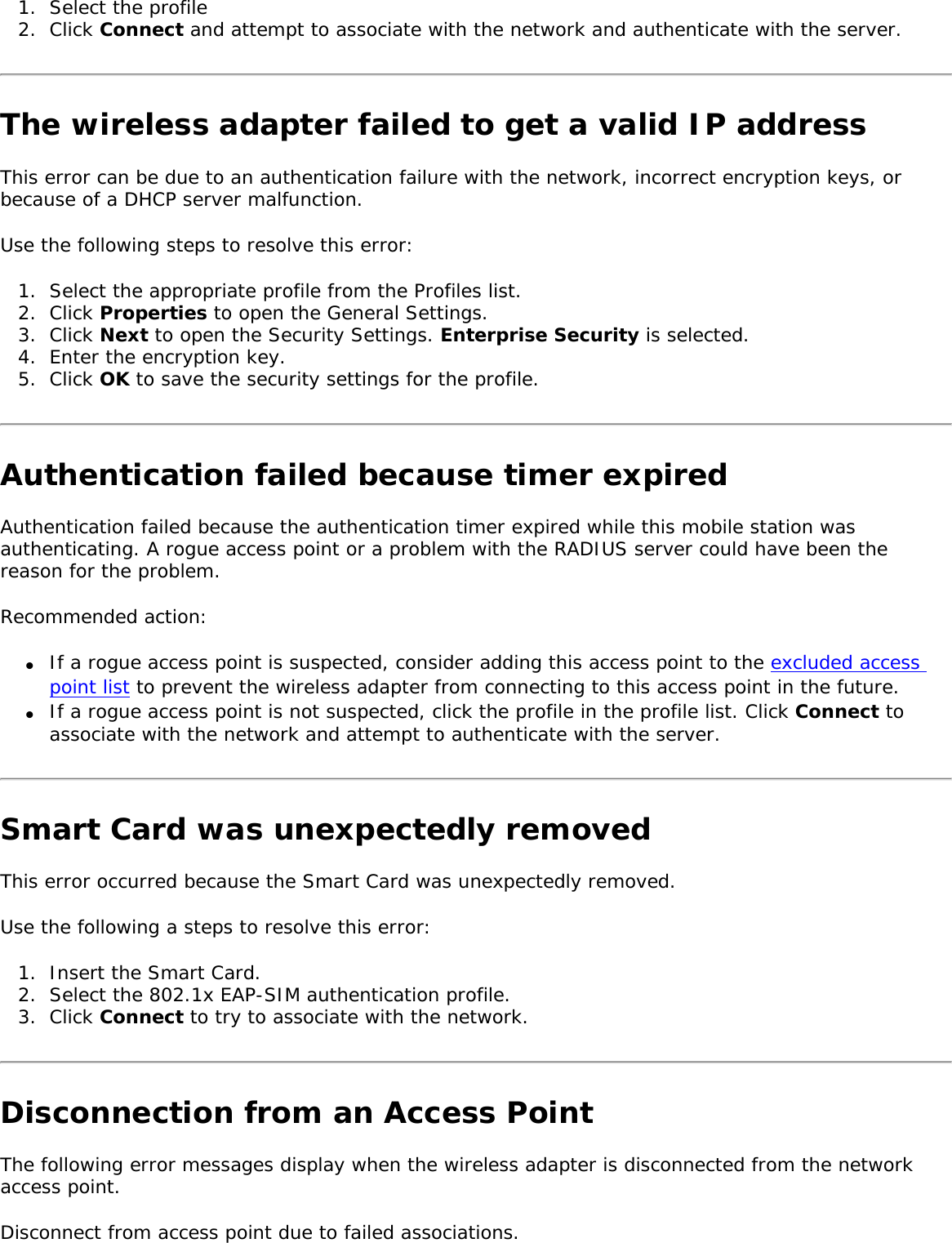
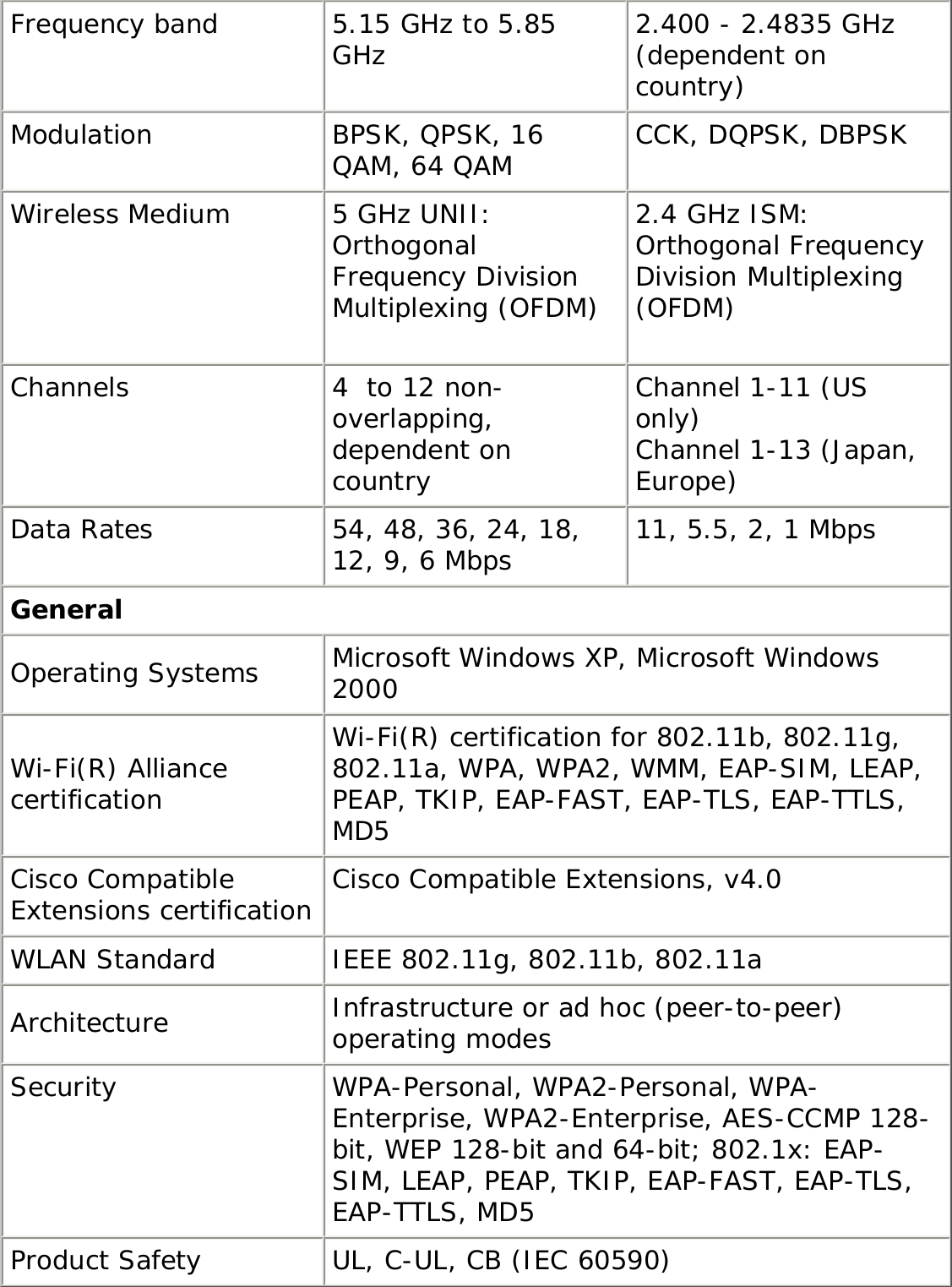
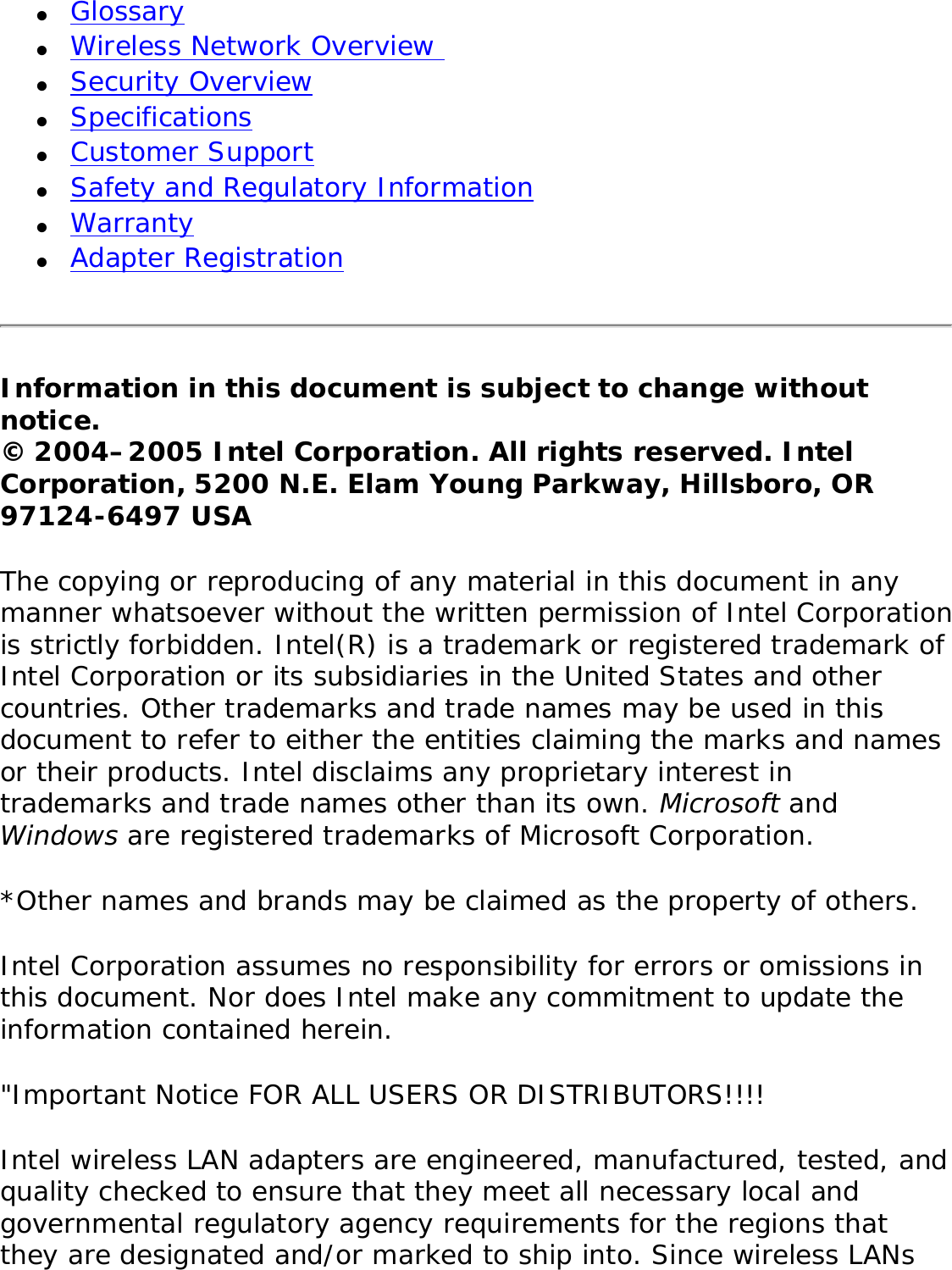
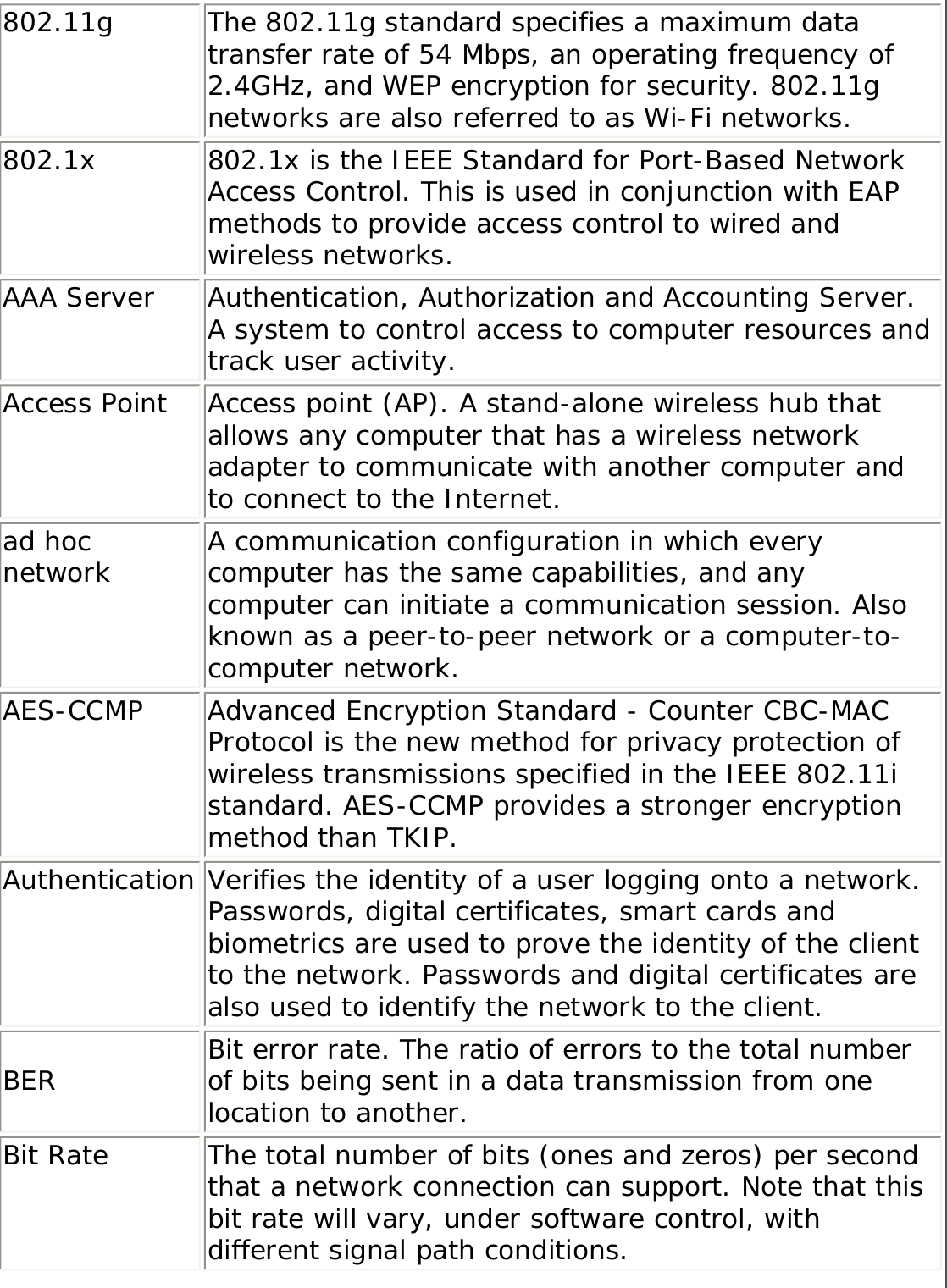
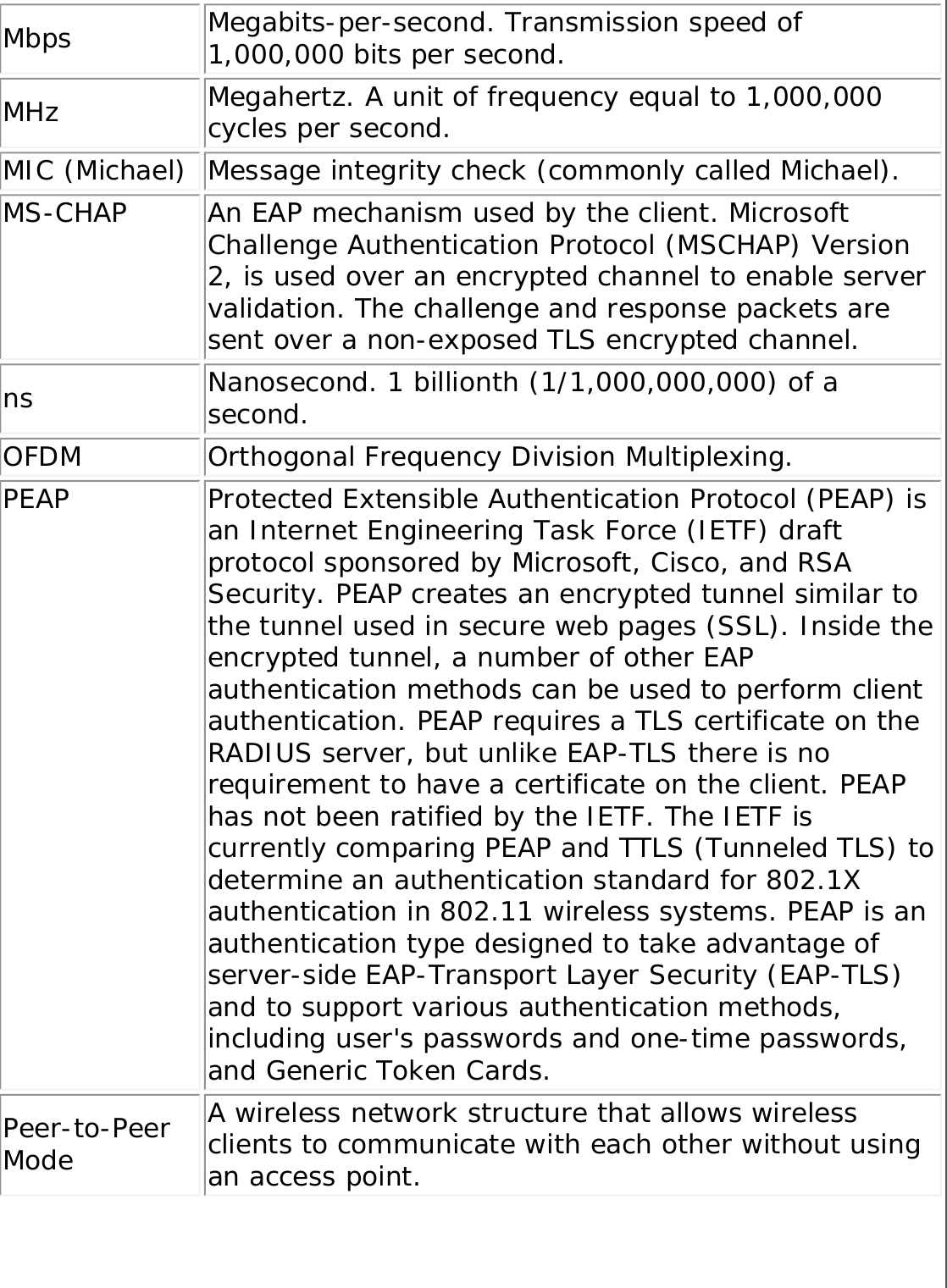
![only if it passes a challenge-based authentication.802.1x AuthenticationHow 802.1x Authentication Works802.1x Features Overview802.1x authentication is independent of the 802.11 authentication process. The 802.1x standard provides a framework for various authentication and key-management protocols. There are different 802.1x authentication types, each provides a different approach to authentication but all employ the same 802.1x protocol and framework for communication between a client and an access point. In most protocols, upon the completion of the 802.1x authentication process, the supplicant receives a key that it uses for data encryption. Refer to How 802.1x authentication works for more information. With 802.1x authentication, an authentication method is used between the client and a Remote Authentication Dial-In User Service (RADIUS) server connected to the access point. The authentication process uses credentials, such as a user's password that are not transmitted over the wireless network. Most 802.1x types support dynamic per-user, per-session keys to strengthen the static key security. 802.1x benefits from the use of an existing authentication protocol known as the Extensible Authentication Protocol (EAP). 802.1x authentication for wireless LANs has three main components: ● The authenticator (the access point)● The supplicant (the client software)● The authentication server (a Remote Authentication Dial-In User Service server [RADIUS])802.1x authentication security initiates an authorization request from the wireless client to the access point, which authenticates the client to an Extensible Authentication Protocol (EAP) compliant RADIUS server.](https://usermanual.wiki/Intel/LEN3945ABG.Users-Manual/User-Guide-598567-Page-89.png)
![● PAP: Password Authentication Protocol is a two way handshake protocol designed for use with PPP. Authentication Protocol Password Authentication Protocol is a plain text password used on older SLIP systems. It is not secure. ● CHAP: Challenge Handshake Authentication Protocol is a three way handshake protocol which is considered more secure than PAP (Password Authentication Protocol). ● MS-CHAP (MD4): Uses a Microsoft version of RSA Message Digest 4 challenge and reply protocol. This only works on Microsoft systems and enables data encryption. This authentication method causes all data to be encrypted.PEAPPEAP is a new Extensible Authentication Protocol (EAP) IEEE 802.1x authentication type designed to take advantage of server-side EAP-Transport Layer Security (EAP-TLS) and to support various authentication methods, including users' passwords and one-time passwords, and Generic Token Cards. Cisco FeaturesCisco LEAP Cisco LEAP (Cisco Light EAP) is a server and client 802.1x authentication through a user-supplied logon password. When a wireless access point communicates with a Cisco LEAP-enabled RADIUS (Cisco Secure Access Control Server [ACS]), Cisco LEAP provides access control through mutual authentication between client wireless adapters and the wireless networks and provides dynamic, individual user encryption keys to help protect the privacy of transmitted data. Cisco Rogue Access Point Security FeatureThe Cisco Rogue Access Point feature provides security protection from an introduction of a rogue access point that could mimic a legitimate access point on a network in order to extract information about user](https://usermanual.wiki/Intel/LEN3945ABG.Users-Manual/User-Guide-598567-Page-94.png)
![TTLS Tunneled Transport Layer Security. These settings define the protocol and the credentials used to authenticate a user. In TTLS, the client uses EAP-TLS to validate the server and create a TLS-encrypted channel between the client and server. The client can use another authentication protocol, typically password-based protocols, such as MD5 Challenge over this encrypted channel to enable server validation. The challenge and response packets are sent over a non-exposed TLS encrypted channel. TTLS implementations today support all methods defined by EAP, as well as several older methods (CHAP, PAP, MS-CHAP and MS-CHAPv2). TTLS can easily be extended to work with new protocols by defining new attributes to support new protocols.WEP Wired Equivalent Privacy. Wired Equivalent Privacy, 64- and 128-bit (64-bit is sometimes referred to as 40-bit). This is a low-level encryption technique designed to give the user about the same amount of privacy that he would expect from a LAN. WEP is a security protocol for wireless local area networks (WLANs) defined in the 802.11b standard. WEP is designed to provide the same level of security as that of a wired LAN. WEP aims to provide security by data over radio waves so that it is protected as it is transmitted from one end point to another.WEP Key Either a pass phrase or hexadecimal key.The pass phrase must be 5 ASCII characters for 64-bit WEP or 13 ASCII characters for 128-bit WEP. For pass phrases, 0-9, a-z, A-Z, and ~!@#$%^&*()_+|`-={}|[]\:";'<>?,./ are all valid characters.The hex key must be 10 hexadecimal characters (0-9, A-F) for 64-bit WEP or 26 hexadecimal characters (0-9, A-F) for 128-bit WEP.Wi-Fi Wireless Fidelity. Is meant to be used generically when referring of any type to 802.11 network, whether 802.11b, 802.11a, or dual-band.](https://usermanual.wiki/Intel/LEN3945ABG.Users-Manual/User-Guide-598567-Page-106.png)