LINKSYS WMP54GSV11 Wireless-G PCI Card with SpeedBooster User Manual Book
LINKSYS LLC Wireless-G PCI Card with SpeedBooster Book
LINKSYS >
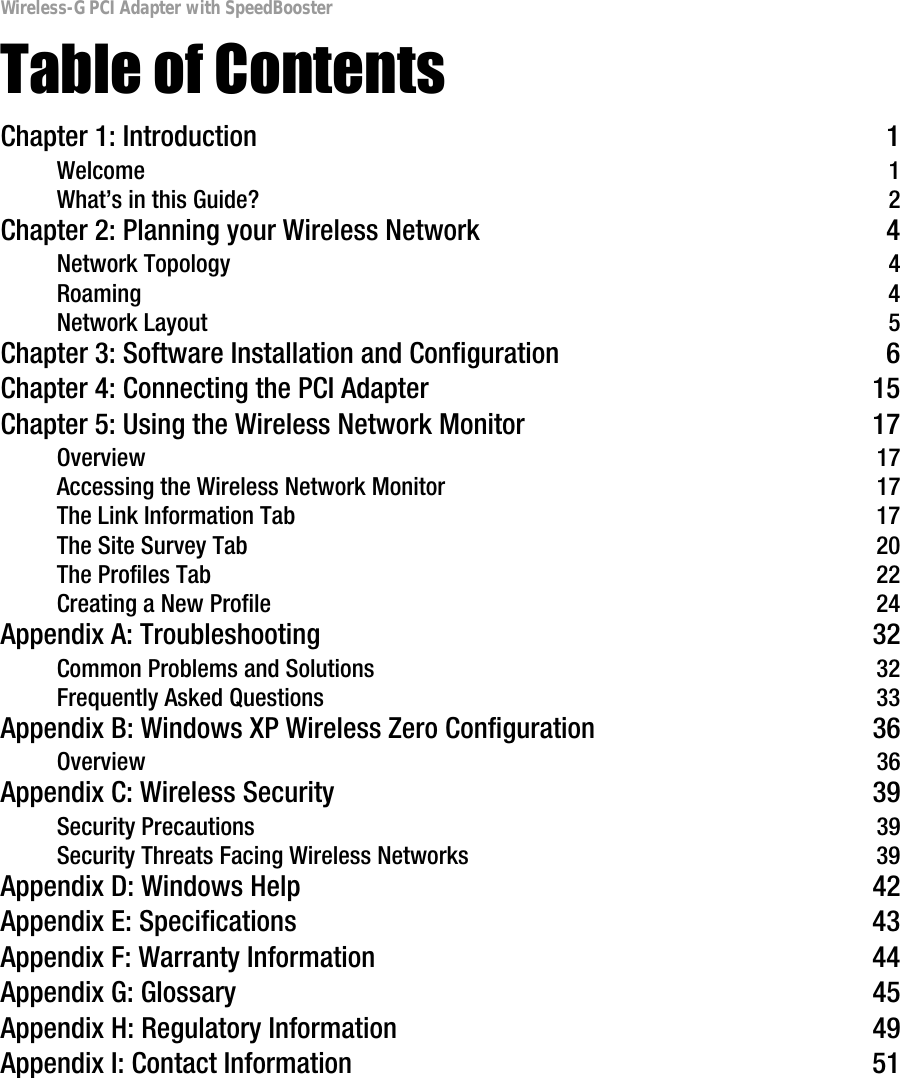
Contents
- 1. Users Manual 1
- 2. Users Manual 2
- 3. Users Manual 3
- 4. Users Manual 4
Users Manual 1