LINKSYS WPC4400N Wireless-N Business Notebook Adapter User Manual wpc4400N
LINKSYS LLC Wireless-N Business Notebook Adapter wpc4400N
LINKSYS >
Contents
- 1. Manual 1
- 2. Manual 2
Manual 2
39
Chapter 5: Using the Wireless Network Monitor
Administration
Wireless-N Business Notebook Adapter
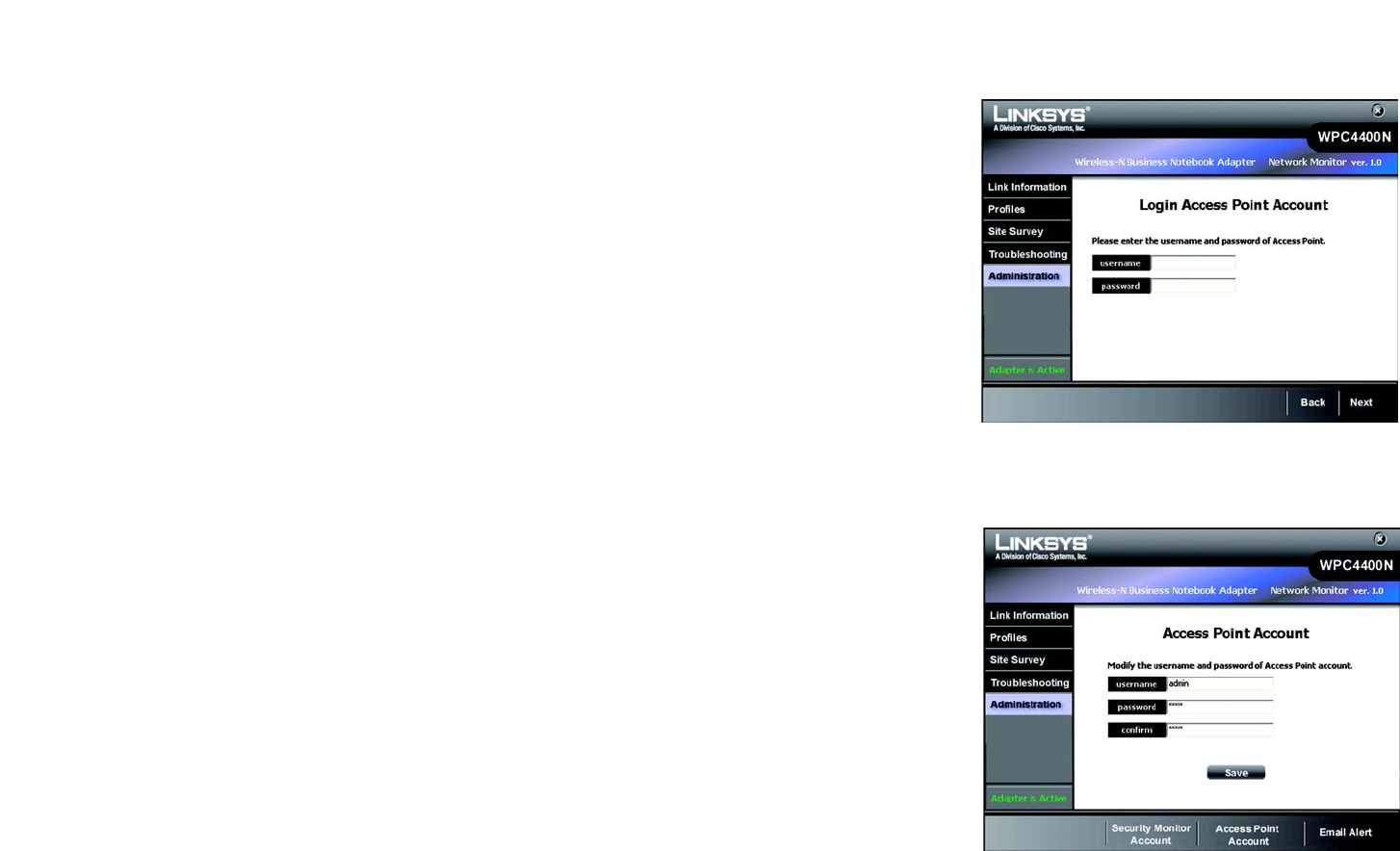
Log in as the Access Point's administrator:
Enter the Access Point's administrative account and password and retype the password in the confirm field
(default account name is admin and password is admin). Click Next to continue to the administrative options.
Access Point Account
This will let you modify your Access Point’s username and password.
Figure 5-41: Administration - Login Access Point
Account
Figure 5-42: Administration - Modify Access Point
Account
40
Chapter 5: Using the Wireless Network Monitor
Administration
Wireless-N Business Notebook Adapter
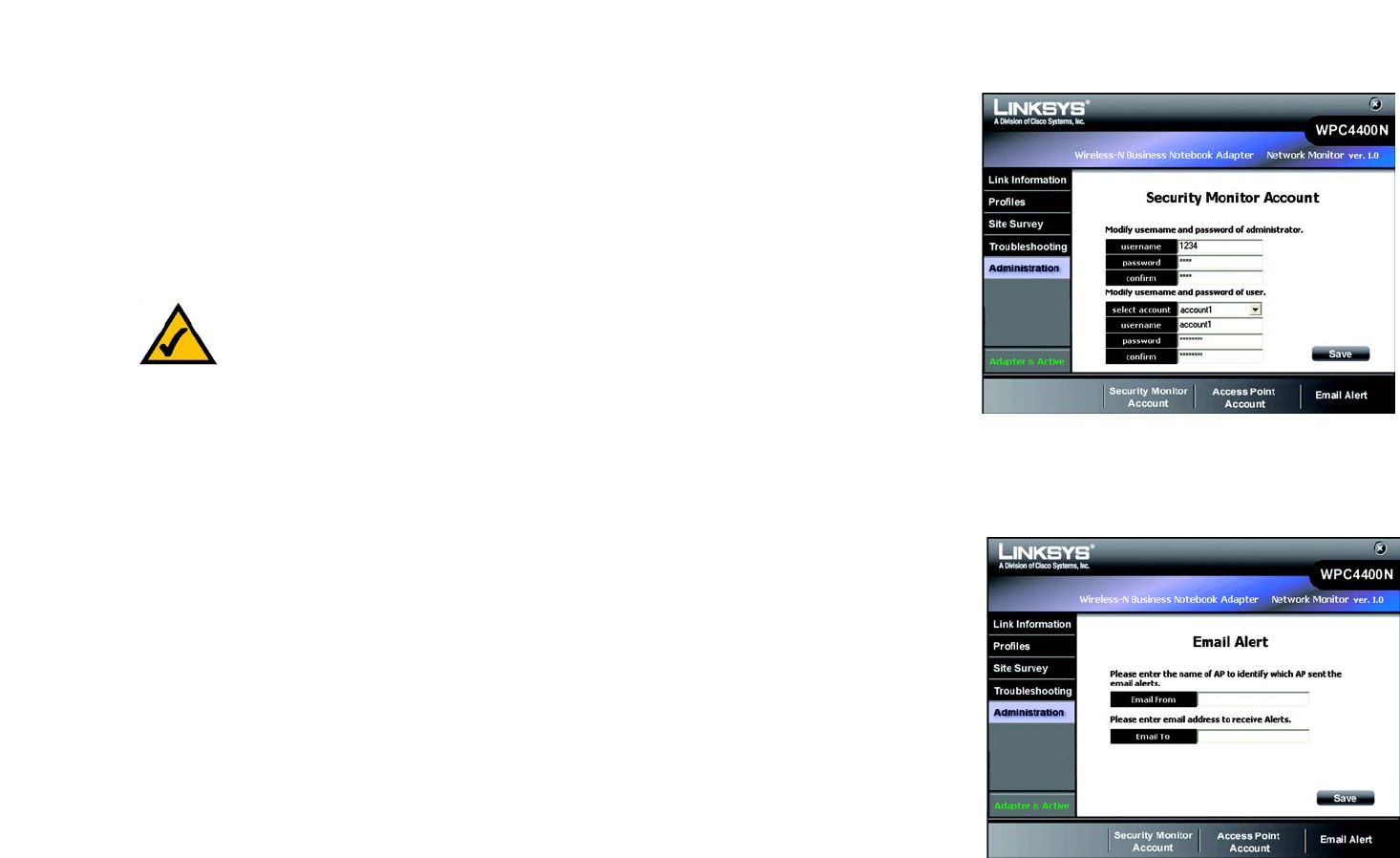
Security Monitor Account
The Security Monitor Account screen provides you with the function to create and modify your Security Monitor
account. The Security Monitor account gives access to the administrative functions of the Wireless Network
Monitor.
Please enter the administrator’s username and password for modifying the Security Monitor account.
Select an account from the drop-down menu to create or modify the username and password. There are a total of
five accounts available. Click Save to save your existing changes.
Email Alert
This will let you enter the Access Point's name that will send alert messages via email and the email addresses
for receiving instant alert messages.
The username and password for the Security Monitor administrator
account may or may not be the same as the Access Point's administrator
account.
Figure 5-43: Administration - Security Monitor
Account
Figure 5-44: Administration - Email Alert
41
Chapter 6: The Administrative Functions in the Wireless Network Monitor
Accessing the Wireless Network Monitor
Wireless-N Business Notebook Adapter
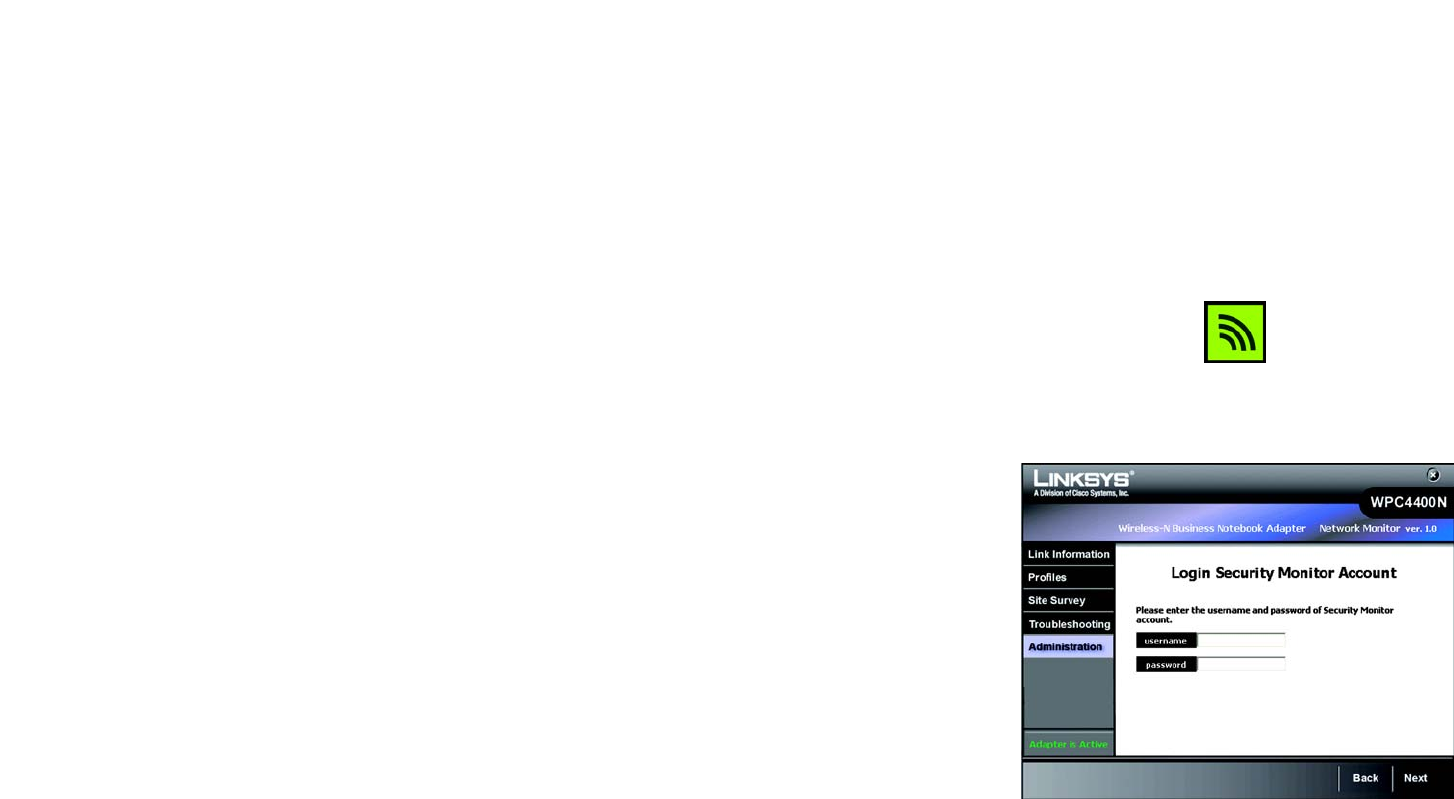
Chapter 6: The Administrative Functions in the Wireless
Network Monitor
Use the administration functions in the Wireless Network Monitor to classify your wireless networks into different
groups and monitor the activities and resources within your networks. The following functions under
Classification and Security Monitor screens are only enabled after an administrator or privileged user enters a
valid username and password.
Accessing the Wireless Network Monitor
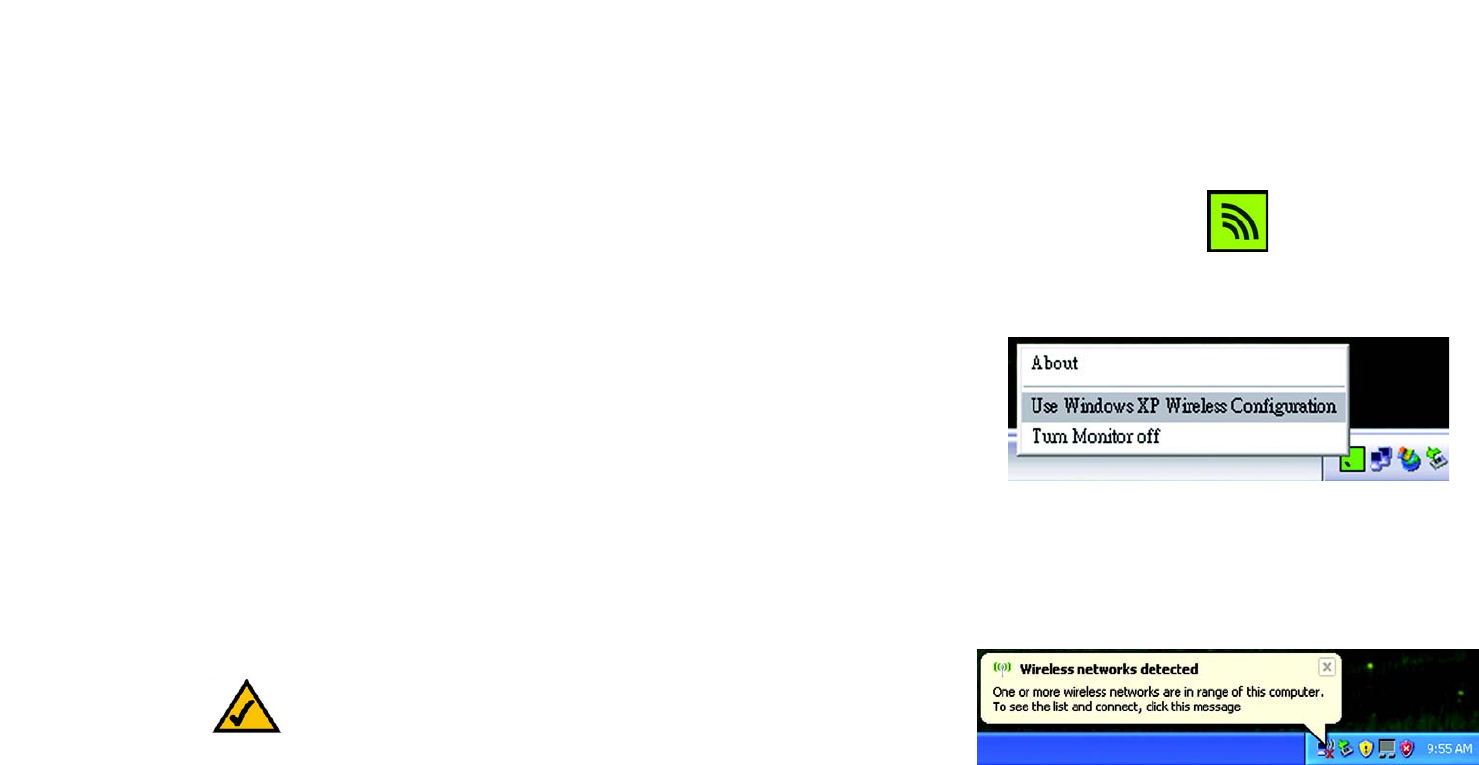
After installing the Adapter, the Wireless Network Monitor icon will appear in the system tray of your computer. If
the Wireless Network Monitor is enabled, then the icon will be green. If the Wireless Network Monitor is disabled
or the Adapter is not connected, then the icon will be gray.
Using the Administrative Functions in the Wireless Network Monitor
The Administration tab will give you the access to the administrative tasks of the account information and other
functions, such as classification and monitoring of your wireless networks.The Classification and Security
Monitor function will be provided after login as the Security Monitor account at the Administration screen. To
configure the trusted/untrusted wireless networks, click the Classification tab. To view the summarized report
of the monitored wireless activities and alert messages, click the Security Monitor.
Figure 6-1: Wireless Network Monitor Icon
Figure 6-2: Administration - Login Security Monitor
Account
42
Chapter 6: The Administrative Functions in the Wireless Network Monitor
Classification
Wireless-N Business Notebook Adapter
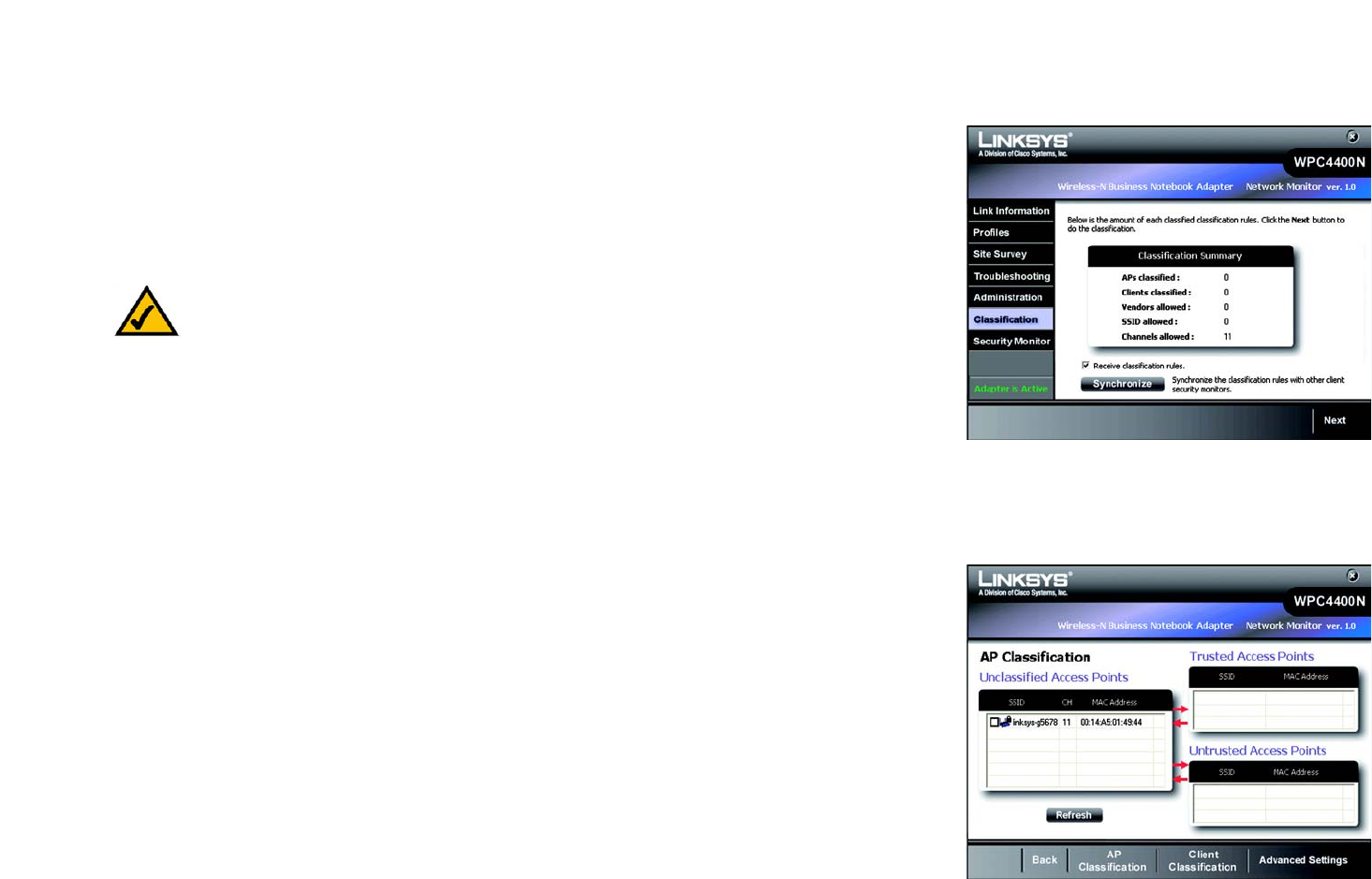
Classification
The Classification screen displays a summary of classified networks. The table shows the number of classified
clients in your networks. It also shows the number of classified Access Points based on their Vendor, Network’s
SSID, and Channel. You may uncheck the Receive classification rules to disable this station from receiving the
network's current classification rules. The default condition is checked, so each station always receives
classification rules in synchronization with other stations in the network. You may also click the Synchronize
button to send out the classification rules to other users within your monitored wireless networks. Click Next to
configure your trusted networks.
AP Classification
The AP Classification Screen lets you classify the existing Access Points as Trusted or Untrusted. A Trusted device
is one that has been identified by the system administrator to be known and legitimate. An Untrusted device is
one that is known and not legitimate. This device could be a malicious device or simply a neighborhood device
not part of the network. Remaining devices that have not been classified can be considered Unclassified or
Unknown.
The left table lists the available unclassified wireless networks with their SSID, channels and MAC Addresses.
The top right table lists the Access Points that have been classified as Trusted. The lower right table lists the
Access Points that have been classified as Untrusted.
You may check any items from the Unclassified Access Points table and click the arrow to classify your
selections into Trusted Access Points or Untrusted Access Points.
You may click Refresh to refresh the list or Back to go to the previous screen.
NOTE: You will have to log in with a valid Security Monitor account to view this screen and all
remaining screens in Chapter 6.
Figure 6-3: Classification
Figure 6-4: AP Classification
43
Chapter 6: The Administrative Functions in the Wireless Network Monitor
Classification
Wireless-N Business Notebook Adapter
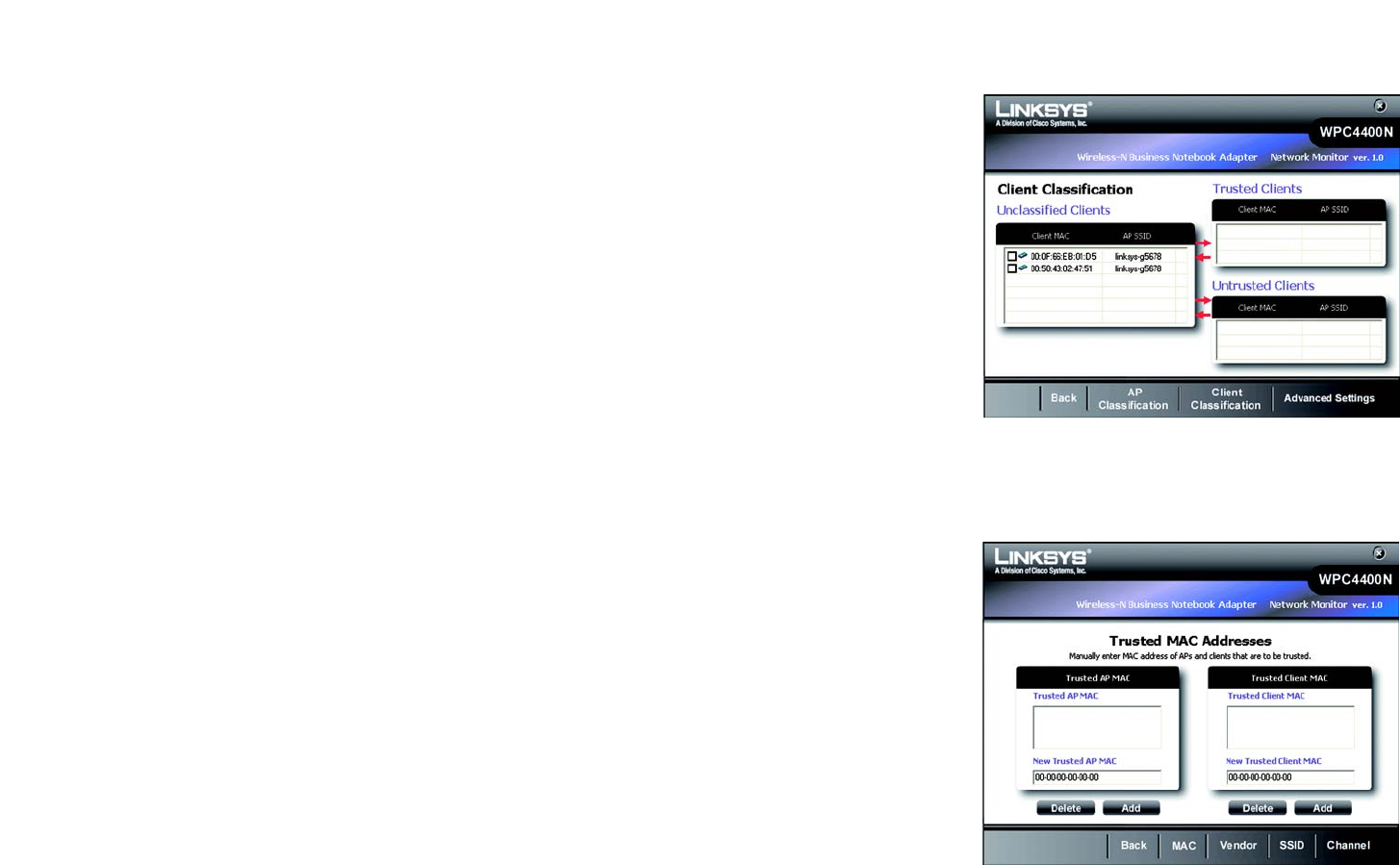
Client Classification
The Client Classification Screen lets you classify the existing wireless clients into trusted networks and untrusted
networks. New Client information is received from Linksys Business Series Access Points. New Clients start off
as Unclassified until the System Administrator classifies them. A Trusted Client is one that has been identified by
the System Administrator to be known and legitimate. An Untrusted Client is one that is known and not legitimate.
This client could be a malicious client or simply a neighborhood client not part of the network. Remaining clients
that have not been classified can be considered Unclassified or Unknown.
The left table lists the available unclassified clients with their associated Access Point's SSID. The top right table
lists the clients that have been classified as Trusted. The lower right table lists the clients that have been
classified as Untrusted.
You may check any items from the Unclassified Clients table and click the arrow to classify your selections into
Trusted Clients or Untrusted Clients.
You may click Refresh to refresh the list.
Advanced Settings
Click Advanced Settings for classifying your wireless networks with more options, such as Mac Address,
Vendor, SSID and Channel.
Trusted MAC Addresses
The MAC Addresses Screen provides information and function for configuring the existing wireless networks as
trusted networks with MAC Access control of the Access Points and the clients.
The tables list the entry of MAC addresses of your trusted or allowed wireless Access Points and the clients.
Enter the 12-digit hexadecimal numbers in the field and click Delete or Add to delete or add the entry. You may
click the Vendor tab to configure the trusted AP vendor list or SSID to configure the trusted SSID list, Channel to
configure the trusted channel, Back to go to the previous screen.
The Trusted AP with the MAC Address that you have entered will be shown with its associated SSID and MAC
Address in the AP Classification screen. However, it will be shown with an N/A SSID if it is not listed under the
Unclassified Access Points.
Figure 6-5: Client Classification
Figure 6-6: Trusted Mac Address
44
Chapter 6: The Administrative Functions in the Wireless Network Monitor
Classification
Wireless-N Business Notebook Adapter
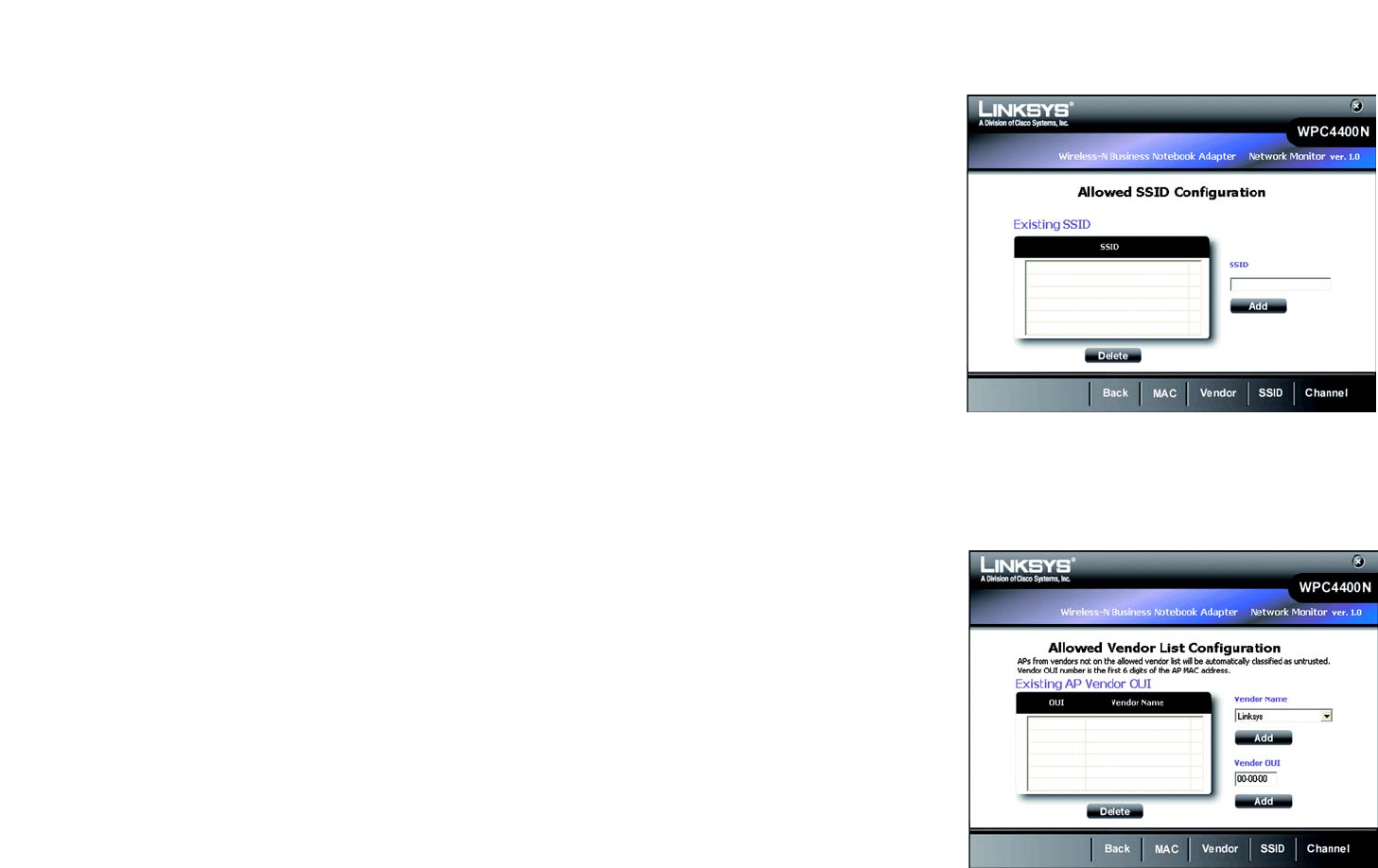
Allowed SSID Configuration
The Existing SSID table shows the SSID of your trusted or allowed AP’s SSID. You may check any item and click
delete to delete it from the list.
SSID - This is the unique name of the wireless network. It is a 32-character unique identifier attached to the
header of packets sent over a WLAN that acts a password when a mobile device tries to connect to the Access
Point.
You may enter the SSID of your trusted/allowed wireless networks in the field and click Add to add it into your
list.
Allowed Vendor List Configuration
The Existing AP Vendor OUI lists the OUI and Vendor Name of your trusted or allowed Vendor’s name. You may
check any item and click delete to delete it from the list.
OUI - The Organization Unique Identification is the three-octet used to generate LAN MAC Addresses for
hardware manufacturers.
Vendor Name - This is the name of your desired vendors.
You may select from the drop-down list for available vendor’s names and click Add to add your desired vendors.
You may also enter the Company’s OUI and click Add to incorporate your vendor’s OUI in the list. APs from
vendors not on the allowed vendor list will be automatically classified as untrusted. Vendor OUI number is the
first 6 digits of the AP's MAC address.
Figure 6-7: Allowed SSID Configuration
Figure 6-8: Allowed AP Vendor list Configuration
45
Chapter 6: The Administrative Functions in the Wireless Network Monitor
Classification
Wireless-N Business Notebook Adapter
Allowed Channel Configuration
The Trusted Channel Configuration shows the available channels for using in your wireless networks. You may
check the channels or click Check All to check all of the channels and click Save to save your choice.
Unclassified APs on unchecked channels will be automatically classified as untrusted.
Figure 6-9: Allowed Channel Configuration
46
Chapter 6: The Administrative Functions in the Wireless Network Monitor
Security Monitor
Wireless-N Business Notebook Adapter
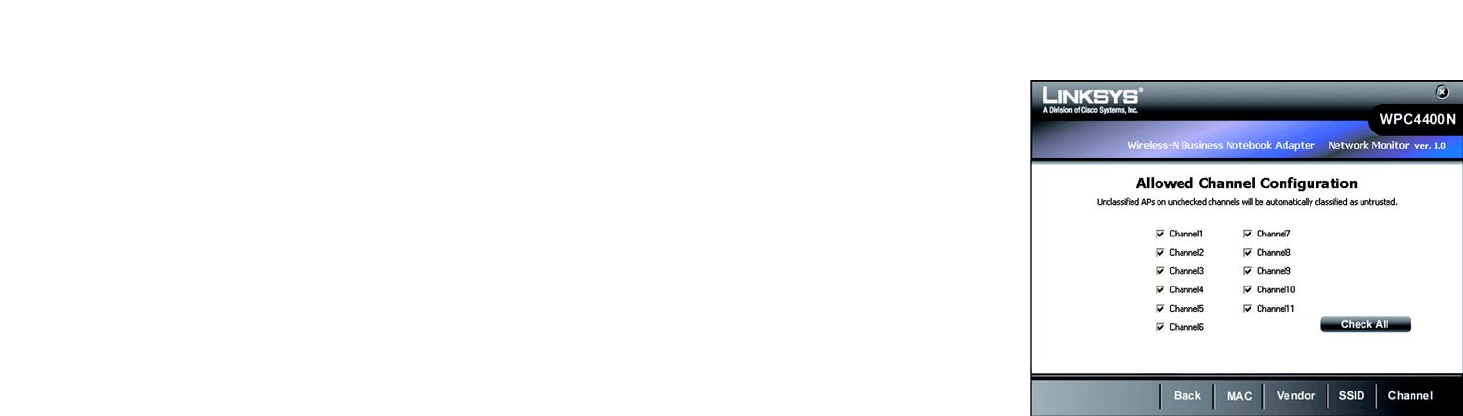
Security Monitor
The Security Monitor screen displays the statistics of your wireless network and alerts you of network activity.
You may click Channel Usage, AP Inventory, Client Inventory, or Alert to proceed with more security Monitor
functions.
Channel Usage
The Channel Usage screen provides statistics of the distribution on your channel’s usages. The histogram shows
the number of Access Points in each channel. Click the radio buttons to show the specified period of time for data
calculated. You may select on 24 hours for data within the last 24 hours, 7 days for data within the last 7 days or
select days for a range of days.
You may click AP Inventory to view the statistics of the distribution on your AP’s classifications or Client
Inventory to view the distribution of the client’s classifications on your wireless networks.
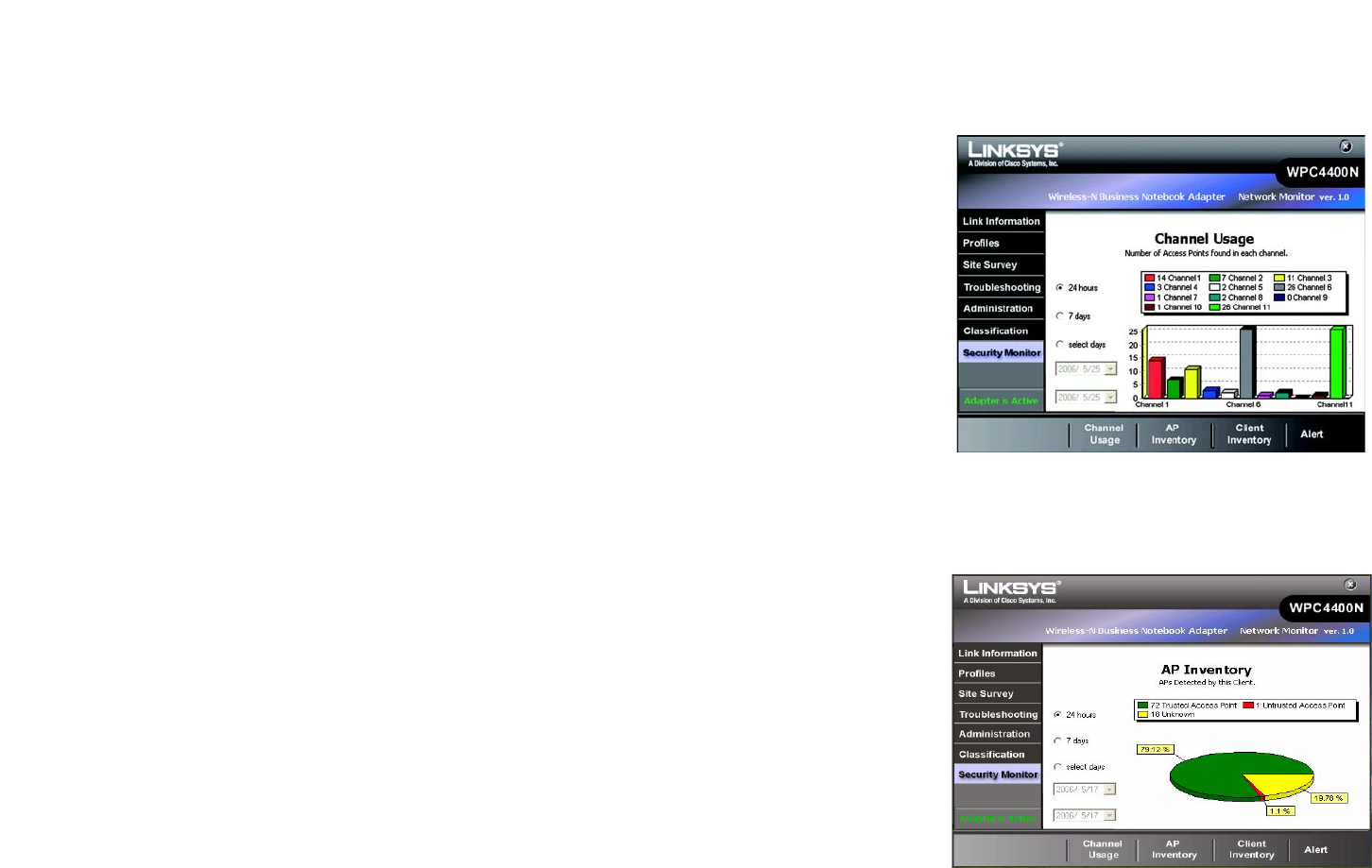
AP Inventory
The AP Inventory screen provides statistics of the distribution grouped by your AP’s classification of your wireless
networks. The pie chart shows the percentage and number of each classification type. Click the radio buttons to
show the specified period of time for data calculated. You may select on 24 hours for data within the last 24
hours, 7 days for data within the last 7 days or select days for a range of days.
Figure 6-10: Security Monitor - Channel Usage
Figure 6-11: Security Monitor - AP Inventory
47
Chapter 6: The Administrative Functions in the Wireless Network Monitor
Security Monitor
Wireless-N Business Notebook Adapter
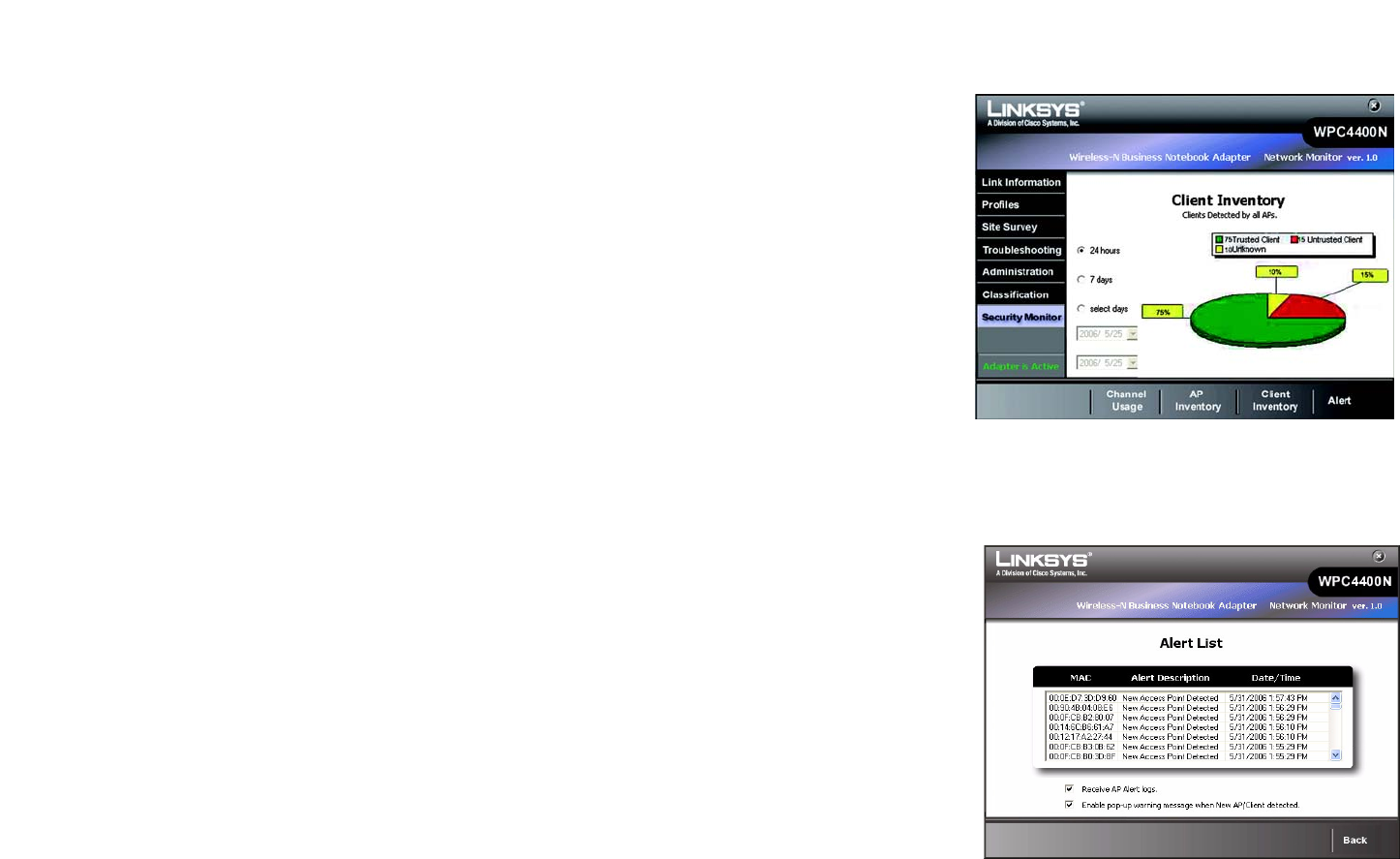
Client Inventory
The Client Inventory screen provides statistics of Trusted, Untrusted, and Unknown Clients. The pie chart shows
the percentage and number of each wireless client’s classification. Click the radio buttons to show the specified
period of time for the data calculated. You may select on 24 hours for data within the last 24 hours, 7 days for
data within the last 7 days or select days for a range of days.
Alert List
The Alert List screen shows the list of the alert activities within your monitored wireless networks. It requires an
username and password to access this screen. Please refer to section "Administration"on page 38 for more
information.
MAC Address - This shows the MAC Address of the wireless client that performed the action.
Alert Description - This shows brief descriptions of the alert activities. The alert system will alert you when new
Access Point or wireless clients have been detected.
Date/Time - This indicates the date/time that an alert activity happened.
You may click any item to view a more detailed information for each event. You may also click Back to go to the
previous screen or Exit to go to the main menu.
Figure 6-12: Security Monitor - Client Inventory
Figure 6-13: Security Monitor - Alert List
48
Chapter 6: The Administrative Functions in the Wireless Network Monitor
Security Monitor
Wireless-N Business Notebook Adapter
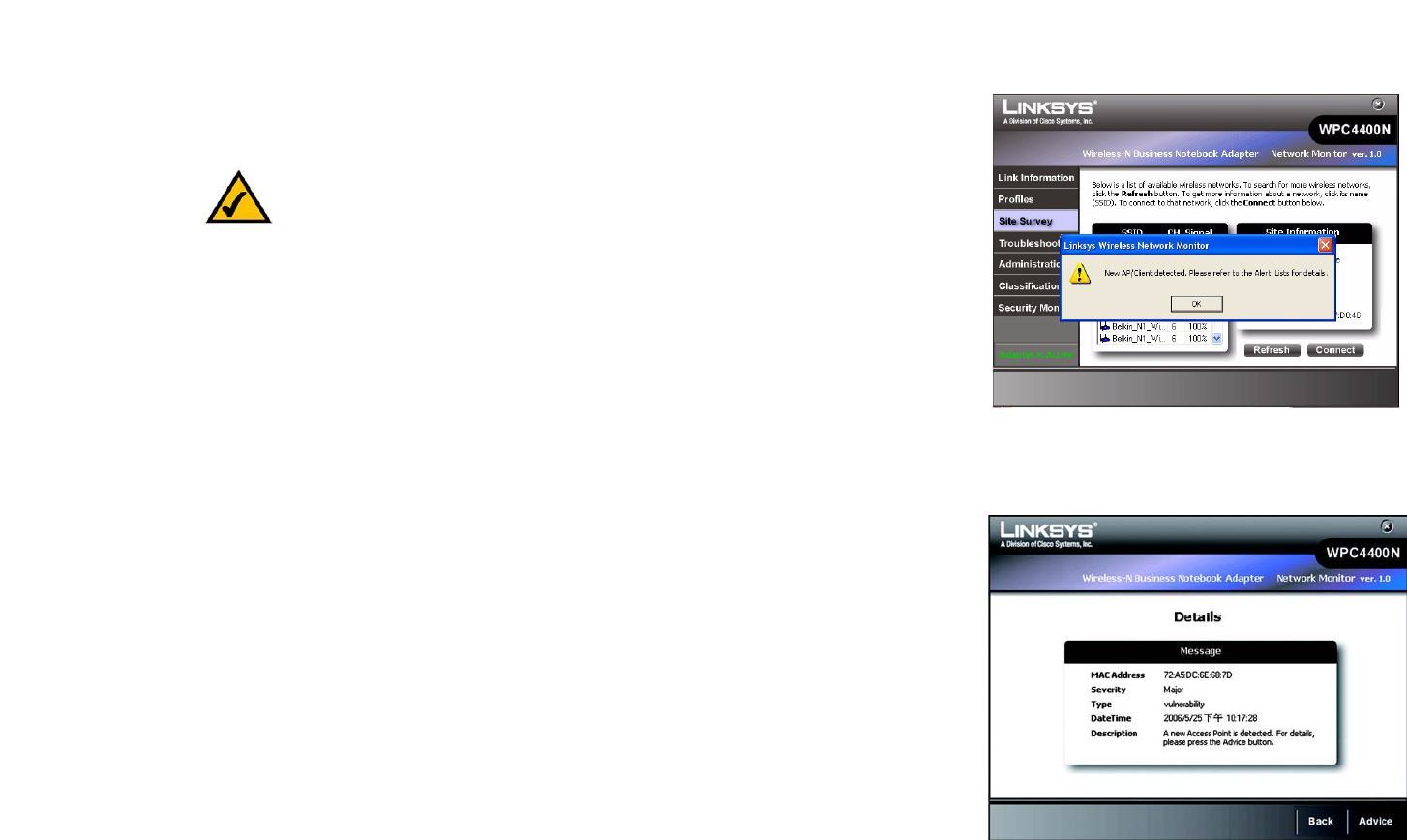
Alert Information
The alert information screen shows the detailed message of each alert event.
Message - This indicates the description of the event.
MAC Address - This shows the MAC Address of the wireless client or Access Point that performed the action.
Severity - This shows the level of the security severity of the action.
Type - This show the type of the networking activity that was performed.
DateTime - This shows the Date/Time of the alert.
Description - This shows the detailed description of the event.
You may click the Advice button to view the advice message, Back to go back to the previous screen, or Exit to
go back to the main menu.
You will be alerted when an Access Point is detected.
Figure 6-14: Security Monitor - POP-UP Alert
Figure 6-15: Alert Information

49
Chapter 6: The Administrative Functions in the Wireless Network Monitor
Security Monitor
Wireless-N Business Notebook Adapter
Advice
The Advice screen shows the advice message of each alert event. You may adjust your wireless network settings
according to the advice to better protect your networks.
Figure 6-16: Security Monitor - Advice

50
Appendix A: Troubleshooting
Common Problems and Solutions
Wireless-N Business Notebook Adapter
Appendix A: Troubleshooting
This appendix consists of two parts: “Common Problems and Solutions” and “Frequently Asked Questions.” This
appendix provides solutions to problems that may occur during the installation and operation of the Wireless-N
Business Notebook Adapter. Read the description below to solve your problems. If you can't find an answer here,
check the Linksys website at www.linksys.com.
Common Problems and Solutions
1. My computer does not recognize the Wireless-N Business Notebook Adapter.
Make sure that the Wireless-N Business Notebook Adapter is properly inserted into the PC Card slot.
2. The Wireless-N Business Notebook Adapter does not work properly.
Reinsert the Wireless-N Business Notebook Adapter into the notebook's PCMCIA slot. If the wizard for finding
new hardware doesn't start automatically, troubleshoot with the following steps:
Right-click on My Computer, and select Properties. Select the Hardware tab and click on the Device
Manager, then click on the Network Adapter. You will find the Wireless-N Business Notebook Adapter if it is
installed successfully. If you see a yellow exclamation mark, the resources may be conflicting and you must
follow the steps below:
• Uninstall the driver software from your PC.
• Restart your PC and repeat the hardware and software installation as specified in this User Guide.
3. I cannot communicate with the other computers linked via Ethernet in the Infrastructure
configuration.
Make sure that the notebook or desktop is powered on.
Make sure that the Wireless-N Business Notebook Adapter is configured with the same SSID and WEP
settings as the other computers in the Infrastructure configuration.

51
Appendix A: Troubleshooting
Frequently Asked Questions
Wireless-N Business Notebook Adapter
Frequently Asked Questions
Can I run an application from a remote computer over the wireless network?
This will depend on whether or not the application is designed to be used over a network. Consult the
application’s user guide to determine if it supports operation over a network.
How will the Wireless networking technology help with my business?
Keeping your business connected in the internet and managing networking in your office without wires give you
the freedom to create a dynamic office environment that changes and grows as your business needs. The Linksys
Wirelees–N Business Notebook Adapter will not only let you communicate sensitive data in a wireless setting but
also give you the security and management options within your monitored networks. We designed our wireless
products to be simple to set up with the advances of the latest data encryption methods and Security Monitor
functions. It is aimed to benefit your business from its full wireless networking while stayed protected.
What is 802.11n standard?
802.11n builds upon previous 802.11 standards by adding MIMO (multiple-input multiple-output). MIMO uses
multiple transmitter and receiver antennas to allow for increased data throughput and increased operating
ranges. The real data throughput is estimated to be 540Mbps which is 10 times faster than 802.11a
What is the 802.11b standard?
It is one of the standards for wireless networks. The 802.11b standard allows wireless networking hardware from
different manufacturers to communicate, provided that the hardware complies with the 802.11b standard. The
802.11b standard states a maximum data transfer rate of 11Mbps and an operating frequency of 2.4GHz.
What is the IEEE 802.11g standard?
It is one of the IEEE standards for wireless networks. The 802.11g standard allows wireless networking hardware
from different manufacturers to communicate, provided that the hardware complies with the 802.11g standard.
The 802.11g standard states a maximum data transfer rate of 54Mbps and an operating frequency of 2.4GHz.
What 802.11b features are supported?
The product supports the following 802.11b functions:
• CSMA/CA plus Acknowledge protocol
• Multi-Channel Roaming
• Automatic Rate Selection
• RTS/CTS feature
• Fragmentation
• Power Management

52
Appendix A: Troubleshooting
Frequently Asked Questions
Wireless-N Business Notebook Adapter
What IEEE 802.11g features are supported?
The product supports the following IEEE 802.11g functions:
• CSMA/CA plus Acknowledge protocol
• OFDM protocol
• Multi-Channel Roaming
• Automatic Rate Selection
• RTS/CTS feature
• Fragmentation
• Power Management
What is ad-hoc mode?
When a wireless network is set to ad-hoc mode, the wireless-equipped computers are configured to
communicate directly with each other. This type of network will not communicate with any wired network.
What is infrastructure mode?
When a wireless network is set to infrastructure mode, the wireless network is configured to communicate with a
wired network through a wireless access point.
What is roaming?
Roaming is the ability of a portable computer user to communicate continuously while moving freely throughout
an area greater than that covered by a single access point. Before using the roaming function, the workstation
must make sure that it is the same channel number with the access point of dedicated coverage area.
To achieve true seamless connectivity, the wireless LAN must incorporate a number of different functions. Each
node and access point, for example, must always acknowledge receipt of each message. Each node must
maintain contact with the wireless network even when not actually transmitting data. Achieving these functions
simultaneously requires a dynamic RF networking technology that links access points and nodes. In such a
system, the user’s end node undertakes a search for the best possible access to the system. First, it evaluates
such factors as signal strength and quality, as well as the message load currently being carried by each access
point and the distance of each access point to the wired backbone. Based on that information, the node next
selects the right access point and registers its address. Communications between end node and host computer
can then be transmitted up and down the backbone.
As the user moves on, the end node’s RF transmitter regularly checks the system to determine whether it is in
touch with the original access point or whether it should seek a new one. When a node no longer receives
acknowledgment from its original access point, it undertakes a new search. Upon finding a new access point, it
then re-registers, and the communication process continues.

53
Appendix A: Troubleshooting
Frequently Asked Questions
Wireless-N Business Notebook Adapter
What is ISM band?
The FCC and their counterparts outside of the U.S. have set aside bandwidth for unlicensed use in the ISM
(Industrial, Scientific and Medical) band. Spectrum in the vicinity of 2.4 GHz, in particular, is being made available
worldwide. This presents a truly revolutionary opportunity to place convenient high-speed wireless capabilities in
the hands of users around the globe.
What is Spread Spectrum?
Spread Spectrum technology is a wideband radio frequency technique developed by the military for use in
reliable, secure, mission-critical communications systems. It is designed to trade off bandwidth efficiency for
reliability, integrity, and security. In other words, more bandwidth is consumed than in the case of narrowband
transmission, but the trade-off produces a signal that is, in effect, louder and thus easier to detect, provided that
the receiver knows the parameters of the spread-spectrum signal being broadcast. If a receiver is not tuned to
the right frequency, a spread-spectrum signal looks like background noise. There are two main alternatives,
Direct Sequence Spread Spectrum (DSSS) and Frequency Hopping Spread Spectrum (FHSS).
What is DSSS? What is FHSS? And what are their differences?
Frequency-Hopping Spread-Spectrum (FHSS) uses a narrowband carrier that changes frequency in a pattern that
is known to both transmitter and receiver. Properly synchronized, the net effect is to maintain a single logical
channel. To an unintended receiver, FHSS appears to be short-duration impulse noise. Direct-Sequence Spread-
Spectrum (DSSS) generates a redundant bit pattern for each bit to be transmitted. This bit pattern is called a chip
(or chipping code). The longer the chip, the greater the probability that the original data can be recovered. Even if
one or more bits in the chip are damaged during transmission, statistical techniques embedded in the radio can
recover the original data without the need for retransmission. To an unintended receiver, DSSS appears as low
power wideband noise and is rejected (ignored) by most narrowband receivers.
What is WEP?
WEP is Wired Equivalent Privacy, a data privacy mechanism based on a shared key algorithm, as described in the
802.11 standard.
What is WPA?
WPA is Wi-Fi Protected Access, a wireless security protocol that can be used in conjunction with a RADIUS server.
What is RADIUS?
RADIUS is Remote Authentication Dial-In User Service, which uses an authentication server to control network
access.
54
Appendix B:
Windows XP Wireless Zero Configuration
Wireless-N Business Notebook Adapter
Appendix B: Windows XP Wireless Zero Configuration
Windows XP Wireless Zero Configuration
If your computer is running Windows XP, then this choice will be available. If you want to use Windows XP
Wireless Zero Configuration to control the Adapter, instead of using the Wireless Network Monitor, then right-
click on the Wireless Network Monitor and select Use Windows XP Wireless Configuration.
If you want to switch back to the Wireless Network Monitor, right-click the Wireless Network Monitor icon, and
select Use Linksys Wireless Network Monitor.
1. After installing the Adapter, the Windows XP Wireless Zero Configuration icon will appear in your computer’s
system tray. Double-click the icon.
Figure B-1: Wireless Network Monitor Icon
Figure B-2: Windows XP - Use Windows XP
Wireless Configuration
NOTE: For more information about Wireless Zero Configuration, refer
to Windows Help.
Figure B-3: Windows XP Wireless Zero Configuration Icon
55
Appendix B:
Windows XP Wireless Zero Configuration
Wireless-N Business Notebook Adapter
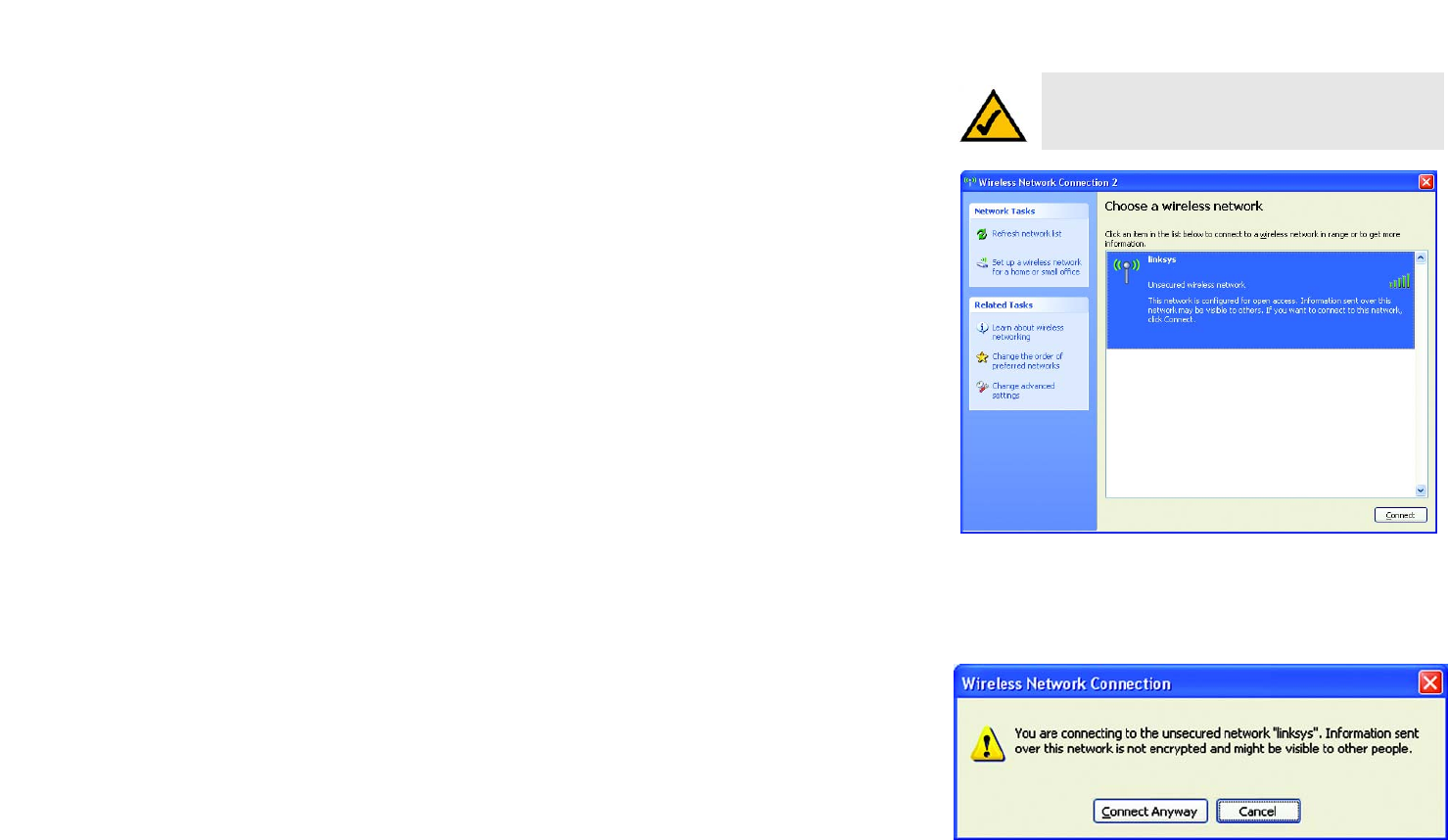
2. The screen that appears will show any available wireless network. Select the network you want. Click the
Connect button.
If your network does not have wireless security enabled, go to step 3.
If your network does have wireless security enabled, go to step 4.
3. If your network does not have wireless security enabled, click the Connect Anyway button to connect the
Adapter to your network.
NOTE: Steps 2 and 3 are the instructions and
screenshots for Windows XP with Service Pack 2
installed.
Figure B-4: Available Wireless Network
Figure B-5: No Wireless Security
56
Appendix B:
Windows XP Wireless Zero Configuration
Wireless-N Business Notebook Adapter
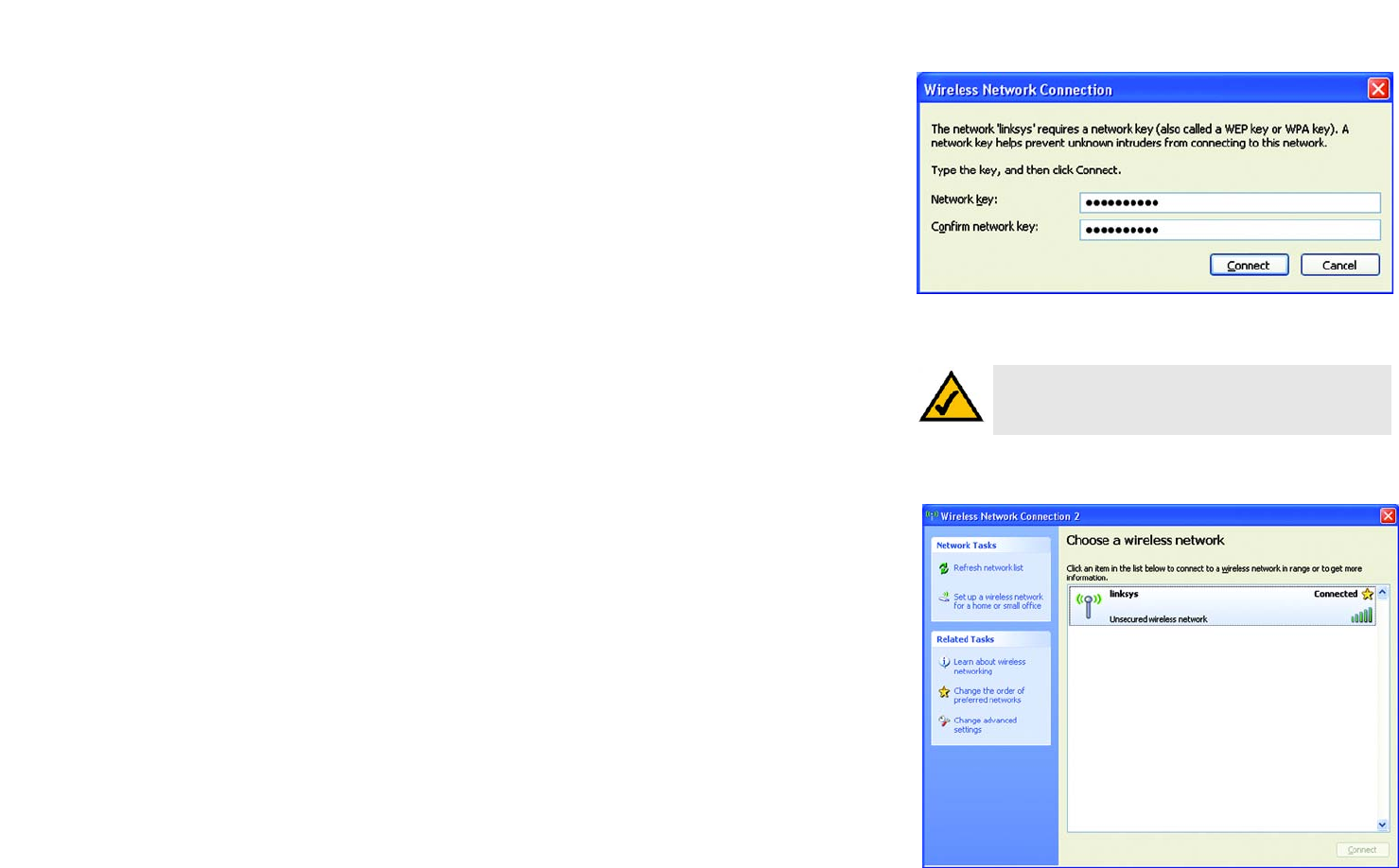
4. If your network uses wireless security WEP, enter the WEP Key used into the Network Key and Confirm
network key fields. If your network uses wireless security WPA Personal, enter the Passphrase used into
the Network Key and Confirm network key fields. Click the Connect button.
5. Your wireless network will appear as Connected when your connection is active.
For more information about wireless networking on a Windows XP computer, click the Start button, select Help,
and choose Support. Enter the keyword wireless in the field provided, and press the Enter key.
The installation of the Windows XP Wireless Configuration is complete.
NOTE: Windows XP Wireless Zero Configuration does
not support the use of a passphrase. Enter the exact
WEP key used by your access point.
Figure B-6: Network Connection - Wireless Security

57
Appendix C: Wireless Security
Security Precautions
Wireless-N Business Notebook Adapter
Appendix C: Wireless Security
Linksys wants to make wireless networking as safe and easy for you as possible. The current generation of
Linksys products provide several network security features, but they require specific action on your part for
implementation. So, keep the following in mind whenever you are setting up or using your wireless network.
Security Precautions
The following is a complete list of security precautions to take (at least steps 1 through 5 should be followed):
1. Change the default SSID.
2. Disable SSID Broadcast.
3. Change the default password for the Administrator account.
4. Enable MAC Address Filtering.
5. Change the SSID periodically.
6. Use the highest encryption algorithm possible. Use WPA if it is available. Please note that this may reduce
your network performance.
7. Change the WEP encryption keys periodically.
Security Threats Facing Wireless Networks
Wireless networks are easy to find. Hackers know that in order to join a wireless network, wireless networking
products first listen for “beacon messages”. These messages can be easily decrypted and contain much of the
network’s information, such as the network’s SSID (Service Set Identifier). Here are the steps you can take:
Change the administrator’s password regularly. With every wireless networking device you use, keep in mind
that network settings (SSID, WEP keys, etc.) are stored in its firmware. Your network administrator is the only
person who can change network settings. If a hacker gets a hold of the administrator’s password, he, too, can
change those settings. So, make it harder for a hacker to get that information. Change the administrator’s
password regularly.
SSID. There are several things to keep in mind about the SSID:
Note: Some of these security features are
available only through the network router or
access point. Refer to the router or access
point’s documentation for more information.
58
Appendix C: Wireless Security
Security Threats Facing Wireless Networks
Wireless-N Business Notebook Adapter
1. Disable Broadcast
2. Make it unique
3. Change it often
Most wireless networking devices will give you the option of broadcasting the SSID. While this option may be
more convenient, it allows anyone to log into your wireless network. This includes hackers. So, don’t broadcast
the SSID.
Wireless networking products come with a default SSID set by the factory. (The Linksys default SSID is “linksys”.)
Hackers know these defaults and can check these against your network. Change your SSID to something unique
and not something related to your company or the networking products you use.
Change your SSID regularly so that any hackers who have gained access to your wireless network will have to
start from the beginning in trying to break in.
MAC Addresses. Enable MAC Address filtering. MAC Address filtering will allow you to provide access to only
those wireless nodes with certain MAC Addresses. This makes it harder for a hacker to access your network with
a random MAC Address.
WEP Encryption. Wired Equivalent Privacy (WEP) is often looked upon as a cure-all for wireless security
concerns. This is overstating WEP’s ability. Again, this can only provide enough security to make a hacker’s job
more difficult.
There are several ways that WEP can be maximized:
1. Use the highest level of encryption possible
2. Use “Shared Key” authentication
3. Change your WEP key regularly
WPA. Wi-Fi Protected Access (WPA) is the newest and best available standard in Wi-Fi security. Three modes are
available: WPA-Personal, WPA Enterprise, and Radius. WPA-Personal gives you a choice of two encryption
methods: TKIP (Temporal Key Integrity Protocol), which utilizes a stronger encryption method and incorporates
Message Integrity Code (MIC) to provide protection against hackers, and AES (Advanced Encryption System),
which utilizes a symmetric 128-Bit block data encryption. WPA Enterprise offers two encryption methods, TKIP
and AES, with dynamic encryption keys. RADIUS (Remote Authentication Dial-In User Service) utilizes a RADIUS
server for authentication.
Important: Always remember that each
device in your wireless network MUST use
the same encryption method and encryption
key or your wireless network will not function
properly.

59
Appendix C: Wireless Security
Security Threats Facing Wireless Networks
Wireless-N Business Notebook Adapter
WPA-Personal. If you do not have a RADIUS server, Select the type of algorithm, TKIP or AES, and enter a
password in the Passphrase field of 8-63 characters.
WPA Enterprise. WPA used in coordination with a RADIUS server. (This should only be used when a RADIUS
server is connected to the Router or other device.) WPA Enterprise offers two encryption methods, TKIP and
AES, with dynamic encryption keys.
WPA2. WPA2 is a wireless security standard that defines stronger encryption, authentication and key
management than WPA.
RADIUS. WEP used in coordination with a RADIUS server. (This should only be used when a RADIUS server is
connected to the Router or other device.)
Implementing encryption may have a negative impact on your network’s performance, but if you are transmitting
sensitive data over your network, encryption should be used.
These security recommendations should help keep your mind at ease while you are enjoying the most flexible
and convenient technology Linksys has to offer.

60
Appendix D: Windows Help
Wireless-N Business Notebook Adapter
Appendix D: Windows Help
All wireless products require Microsoft Windows. Windows is the most used operating system in the world and
comes with many features that help make networking easier. These features can be accessed through Windows
Help and are described in this appendix.
TCP/IP
Before a computer can communicate with an access point or wireless router, TCP/IP must be enabled. TCP/IP is a
set of instructions, or protocol, all PCs follow to communicate over a network. This is true for wireless networks
as well. Your PCs will not be able to utilize wireless networking without having TCP/IP enabled. Windows Help
provides complete instructions on enabling TCP/IP.
Shared Resources
If you wish to share printers, folder, or files over your network, Windows Help provides complete instructions on
utilizing shared resources.
Network Neighborhood/My Network Places
Other PCs on your network will appear under Network Neighborhood or My Network Places (depending upon the
version of Windows you're running). Windows Help provides complete instructions on adding PCs to your
network.

61
Appendix E: Glossary
Wireless-N Business Notebook Adapter
Appendix E: Glossary
This glossary contains some basic networking terms you may come across when using this product. For more
advanced terms, see the complete Linksys glossary at http://www.linksys.com/glossary.
Access Point - A device that allows wireless-equipped computers and other devices to communicate with a
wired network. Also used to expand the range of a wireless network.
Ad-hoc - A group of wireless devices communicating directly with each other (peer-to-peer) without the use of
an access point.
AES (Advanced Encryption Standard) - A security method that uses symmetric 128-bit block data encryption.
Bandwidth - The transmission capacity of a given device or network.
Bit - A binary digit.
Boot - To start a device and cause it to start executing instructions.
Broadband - An always-on, fast Internet connection.
Browser - An application program that provides a way to look at and interact with all the information on the
World Wide Web.
Byte - A unit of data that is usually eight bits long
Cable Modem - A device that connects a computer to the cable television network, which in turn connects to the
Internet.
Daisy Chain - A method used to connect devices in a series, one after the other.
DDNS (Dynamic Domain Name System) - Allows the hosting of a website, FTP server, or e-mail server with a
fixed domain name (e.g., www.xyz.com) and a dynamic IP address.
Default Gateway - A device that forwards Internet traffic from your local area network.
DHCP (Dynamic Host Configuration Protocol) - A networking protocol that allows administrators to assign
temporary IP addresses to network computers by "leasing" an IP address to a user for a limited amount of time,
instead of assigning permanent IP addresses.

62
Appendix E: Glossary
Wireless-N Business Notebook Adapter
DMZ (Demilitarized Zone) - Removes the Router's firewall protection from one PC, allowing it to be "seen" from
the Internet.
DNS (Domain Name Server) - The IP address of your ISP's server, which translates the names of websites into IP
addresses.
Domain - A specific name for a network of computers.
DOS (Denial of Service) - A network security term which defines a type of attack designed to prevent legitimate
users from using wireless service by flooding with useless/malicious traffic.
Download - To receive a file transmitted over a network.
DSL (Digital Subscriber Line) - An always-on broadband connection over traditional phone lines.
Dynamic IP Address - A temporary IP address assigned by a DHCP server.
EAP (Extensible Authentication Protocol) - A general authentication protocol used to control network access.
Many specific authentication methods work within this framework.
Encryption - Encoding data transmitted in a network.
Ethernet - IEEE standard network protocol that specifies how data is placed on and retrieved from a common
transmission medium.
Firewall - A set of related programs located at a network gateway server that protects the resources of a
network from users from other networks.
Firmware - The programming code that runs a networking device.
FTP (File Transfer Protocol) - A protocol used to transfer files over a TCP/IP network.
Full Duplex - The ability of a networking device to receive and transmit data simultaneously.
Gateway - A device that interconnects networks with different, incompatible communications protocols.
Half Duplex - Data transmission that can occur in two directions over a single line, but only one direction at a
time.
HTTP (HyperText Transport Protocol) - The communications protocol used to connect to servers on the World
Wide Web.
Infrastructure - A wireless network that is bridged to a wired network via an access point.

63
Appendix E: Glossary
Wireless-N Business Notebook Adapter
Intrusion attack - A type of internet attacks in which an attacker tries to gain or access the information
transimitted through the networks.
IP (Internet Protocol) - A protocol used to send data over a network.
IP Address - The address used to identify a computer or device on a network.
IPCONFIG - A Windows 2000 and XP utility that displays the IP address for a particular networking device.
IPSec (Internet Protocol Security) - A VPN protocol used to implement secure exchange of packets at the IP layer.
ISP (Internet Service Provider) - A company that provides access to the Internet.
LAN - The computers and networking products that make up your local network.
MAC (Media Access Control) Address - The unique address that a manufacturer assigns to each networking
device.
Mbps (MegaBits Per Second) - One million bits per second; a unit of measurement for data transmission.
NAT (Network Address Translation) - NAT technology translates IP addresses of a local area network to a different
IP address for the Internet.
Network - A series of computers or devices connected for the purpose of data sharing, storage, and/or
transmission between users.
Packet - A unit of data sent over a network.
Passphrase - Used much like a password, a passphrase simplifies the WEP encryption process by automatically
generating the WEP encryption keys for Linksys products.
Ping (Packet INternet Groper) - An Internet utility used to determine whether a particular IP address is online.
POP3 (Post Office Protocol 3) - A standard mail server commonly used on the Internet.
Port - The connection point on a computer or networking device used for plugging in cables or adapters.
Power over Ethernet (PoE) - A technology enabling an Ethernet network cable to deliver both data and power.
PPPoE (Point to Point Protocol over Ethernet) - A type of broadband connection that provides authentication
(username and password) in addition to data transport.

64
Appendix E: Glossary
Wireless-N Business Notebook Adapter
PPTP (Point-to-Point Tunneling Protocol) - A VPN protocol that allows the Point to Point Protocol (PPP) to be
tunneled through an IP network. This protocol is also used as a type of broadband connection in Europe.
QoS (Quality of Service) - A mechanism which gives priorities to certain types of traffic to ensure the throughput;
for example, the streaming multimedia.
RADIUS (Remote Authentication Dial-In User Service) - A protocol that uses an authentication server to control
network access.
RJ-45 (Registered Jack-45) - An Ethernet connector that holds up to eight wires.
Roaming - The ability to take a wireless device from one access point's range to another without losing the
connection.
Router - A networking device that connects multiple networks together.
Server - Any computer whose function in a network is to provide user access to files, printing, communications,
and other services.
SMTP (Simple Mail Transfer Protocol) - The standard e-mail protocol on the Internet.
SNMP (Simple Network Management Protocol) - A widely used network monitoring and control protocol.
SPI (Stateful Packet Inspection) Firewall - A technology that inspects incoming packets of information before
allowing them to enter the network.
SSID (Service Set IDentifier) -It consists of 32 alphanumeric characters to identify a group fo wireless network
devices uniquely.
Static IP Address - A fixed address assigned to a computer or device that is connected to a network.
Static Routing - Forwarding data in a network via a fixed path.
Subnet Mask - An address code that determines the size of the network.
Switch - 1. A data switch that connects computing devices to host computers, allowing a large number of
devices to share a limited number of ports. 2. A device for making, breaking, or changing the connections in an
electrical circuit.
TCP (Transmission Control Protocol) - A network protocol for transmitting data that requires acknowledgement
from the recipient of data sent.

65
Appendix E: Glossary
Wireless-N Business Notebook Adapter
TCP/IP (Transmission Control Protocol/Internet Protocol) - A set of instructions PCs use to communicate over a
network.
Telnet - A user command and TCP/IP protocol used for accessing remote PCs.
TFTP (Trivial File Transfer Protocol) - A version of the TCP/IP FTP protocol that has no directory or password
capability.
Throughput - The amount of data moved successfully from one node to another in a given time period.
TKIP (Temporal Key Integrity Protocol) - a wireless encryption protocol that provides dynamic encryption keys for
each packet transmitted.
Topology - The physical layout of a network.
TX Rate - Transmission Rate.
Upgrade - To replace existing software or firmware with a newer version.
Upload - To transmit a file over a network.
URL (Uniform Resource Locator) - The address of a file located on the Internet.
VPN (Virtual Private Network) - A security measure to protect data as it leaves one network and goes to another
over the Internet.
WAN (Wide Area Network)- The Internet.
WEP (Wired Equivalent Privacy) - A method of encrypting network data transmitted on a wireless network for
greater security.
WLAN (Wireless Local Area Network) - A group of computers and associated devices that communicate with
each other wirelessly.
WPA (Wi-Fi Protected Access) - a wireless security protocol using TKIP (Temporal Key Integrity Protocol)
encryption, which can be used in conjunction with a RADIUS server.

66
Appendix F: Specifications
Wireless-N Business Notebook Adapter
Appendix F: Specifications
Standards IEEE 802.11g, IEEE 802.11b, draft IEEE 802.11n
Channels 802.11b/802.11g/Wireless-N (20MHz)
11 Channels (USA, Canada)
13 Channels (Europe)
LEDs Wireless, Activity
Protocols 802.11b: CCK (11 Mbps), DQPSK (2 Mbps), DBPSK (1 Mbps);
802.11g: OFDM
Wireless-N: BPSK, QPSK, 16-QAM, 64-QAM
Transmitted Power 802.11g:
802.11b:
Receive Sensitivity 54Mbps @ -70dBm (Typical)
Wireless-N @ -70dBm (Typical)
Security Features WEP, WPA
WEP Key Bits 64, 128 Bit
Dimensions 4.76" x 0.59" x 2.13"(121 mm x 15 mm x 54 mm)
Unit Weight 1.76 oz. (0.05 kg.)
Certifications FCC, Wi-Fi
Operating Temp. 32ºF to 149ºF (0ºC to 65ºC)
Storage Temp. -4ºF to 185ºF (-20ºC to 85ºC)
23 ± 1 dBm (Typical)
22 ± 1 dBm (Typical)

67
Appendix F: Specifications
Wireless-N Business Notebook Adapter
Operating Humidity 90% Maximum, Non-Condensing
Storage Humidity 90% Maximum, Non-Condensing

68
Appendix G: Warranty Information
Wireless-N Business Notebook Adapter
Appendix G: Warranty Information
LIMITED WARRANTY
Linksys warrants to You that, for a period of three years (the “Warranty Period”), your Linksys Product will be substantially
free of defects in materials and workmanship under normal use. Your exclusive remedy and Linksys' entire liability under
this warranty will be for Linksys at its option to repair or replace the Product or refund Your purchase price less any
rebates. This limited warranty extends only to the original purchaser.
If the Product proves defective during the Warranty Period call Linksys Technical Support in order to obtain a Return
Authorization Number, if applicable. BE SURE TO HAVE YOUR PROOF OF PURCHASE ON HAND WHEN CALLING. If You are
requested to return the Product, mark the Return Authorization Number clearly on the outside of the package and include a
copy of your original proof of purchase. RETURN REQUESTS CANNOT BE PROCESSED WITHOUT PROOF OF PURCHASE. You
are responsible for shipping defective Products to Linksys. Linksys pays for UPS Ground shipping from Linksys back to You
only. Customers located outside of the United States of America and Canada are responsible for all shipping and handling
charges.
ALL IMPLIED WARRANTIES AND CONDITIONS OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE ARE LIMITED
TO THE DURATION OF THE WARRANTY PERIOD. ALL OTHER EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND
WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF NON-INFRINGEMENT, ARE DISCLAIMED. Some jurisdictions do not
allow limitations on how long an implied warranty lasts, so the above limitation may not apply to You. This warranty gives
You specific legal rights, and You may also have other rights which vary by jurisdiction.
This warranty does not apply if the Product (a) has been altered, except by Linksys, (b) has not been installed, operated,
repaired, or maintained in accordance with instructions supplied by Linksys, or (c) has been subjected to abnormal
physical or electrical stress, misuse, negligence, or accident. In addition, due to the continual development of new
techniques for intruding upon and attacking networks, Linksys does not warrant that the Product will be free of
vulnerability to intrusion or attack.
TO THE EXTENT NOT PROHIBITED BY LAW, IN NO EVENT WILL LINKSYS BE LIABLE FOR ANY LOST DATA, REVENUE OR PROFIT,
OR FOR SPECIAL, INDIRECT, CONSEQUENTIAL, INCIDENTAL OR PUNITIVE DAMAGES, REGARDLESS OF THE THEORY OF
LIABILITY (INCLUDING NEGLIGENCE), ARISING OUT OF OR RELATED TO THE USE OF OR INABILITY TO USE THE PRODUCT
(INCLUDING ANY SOFTWARE), EVEN IF LINKSYS HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. IN NO EVENT
WILL LINKSYS’ LIABILITY EXCEED THE AMOUNT PAID BY YOU FOR THE PRODUCT. The foregoing limitations will apply even
if any warranty or remedy provided under this Agreement fails of its essential purpose. Some jurisdictions do not allow the
exclusion or limitation of incidental or consequential damages, so the above limitation or exclusion may not apply to You.
Please direct all inquiries to: Linksys, P.O. Box 18558, Irvine, CA 92623.

69
Appendix H: Regulatory Information
Wireless-N Business Notebook Adapter
Appendix H: Regulatory Information
Federal Communication Commission Interference Statement
This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to Part 15 of the FCC
Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This
equipment generates, uses and can radiate radio frequency energy and, if not installed and used in accordance with the
instructions, may cause harmful interference to radio communications. However, there is no guarantee that interference will not
occur in a particular installation. If this equipment does cause harmful interference to radio or television reception, which can be
determined by turning the equipment off and on, the user is encouraged to try to correct the interference by one of the following
measures:
- Reorient or relocate the receiving antenna.
- Increase the separation between the equipment and receiver.
- Connect the equipment into an outlet on a circuit different from that
to which the receiver is connected.
- Consult the dealer or an experienced radio/TV technician for help.
FCC Caution: Any changes or modifications not expressly approved by the party responsible for compliance could void the user's
authority to operate this equipment.
This device complies with Part 15 of the FCC Rules. Operation is subject to the following two conditions: (1) This device may not
cause harmful interference, and (2) this device must accept any interference received, including interference that may cause
undesired operation.
IMPORTANT NOTE:
FCC Radiation Exposure Statement:
This equipment complies with FCC radiation exposure limits set forth for an uncontrolled environment.
End users must follow the specific operating instructions for satisfying RF exposure compliance.
This transmitter must not be co-located or operating in conjunction with any other antenna or transmitter.
This equipment has been SAR-evaluated for use in laptops (notebooks) with side slot configuration.
Linksys declares that WPC4400N ( FCC ID: Q87-WPC4400N ) is limited in CH1~CH11 for 2.4 GHz by specified firmware
controlled in U.S.A.
IC statement
This Class B digital apparatus complies with Canadian ICES-003.
Cet appareil numérique de la classe B est conforme à la norme NMB-003 du Canada.
Operation is subject to the following two conditions:
1) This device may not cause interference and
2) This device must accept any interference, including interference that may cause undesired operation of the device.
IMPORTANT NOTE:
IC Radiation Exposure Statement:
This equipment complies with IC radiation exposure limits set forth for an uncontrolled environment. End users must follow the
specific operating instructions for satisfying RF exposure compliance. To maintain compliance with IC RF exposure compliance
requirements, please follow operation instruction as documented in this manual.
This transmitter must not be co-located or operating in conjunction with any other antenna or transmitter.
To maintain compliance with FCC RF exposure compliance requirements, please follow operation instruction as documented in this manual.
SAR compliance has been established in typical laptop computer(s) with CardBus slot, and product could be used in typical laptop
computer with CardBus slot. Other application like handheld PC or similar device has not been verified and may not compliance with
related RF exposure rule and such use shall be prohibited.
Règlement d’Industry Canada
Les conditions de fonctionnement sont sujettes à deux conditions:
1) Ce périphérique ne doit pas causer d’interférence et.
2) Ce périphérique doit accepter toute interférence, y compris les interférences pouvant perturber le bon fonctionnement de ce
périphérique.
70
Appendix H: Regulatory Information
Wireless-N Business Notebook Adapter
User Information for Consumer Products Covered by EU Directive 2002/96/EC on Waste Electric and Electronic
Equipment (WEEE)
This document contains important information for users with regards to the proper disposal and recycling of Linksys
products. Consumers are required to comply with this notice for all electronic products bearing the following symbol:
71
Appendix H: Regulatory Information
Wireless-N Business Notebook Adapter
72
Appendix H: Regulatory Information
Wireless-N Business Notebook Adapter
73
Appendix H: Regulatory Information
Wireless-N Business Notebook Adapter
74
Appendix H: Regulatory Information
Wireless-N Business Notebook Adapter
For more information, visit www.linksys.com.

75
Appendix I: Contact Information
Wireless-N Business Notebook Adapter
Appendix I: Contact Information
Need to contact Linksys?
Visit us online for information on the latest products and updates
to your existing products at: http://www.linksys.com or
ftp.linksys.com
Can't find information about a product you want to buy
on the web? Do you want to know more about networking
with Linksys products? Give our advice line a call at: 800-546-5797 (LINKSYS)
Or fax your request in to: 949-823-3002
If you experience problems with any Linksys product,
you can call us at: 800-326-7114
Don't wish to call? You can e-mail us at: support@linksys.com
If any Linksys product proves defective during its warranty period,
you can call the Linksys Return Merchandise Authorization
department for obtaining a Return Authorization Number at: 949-823-3000
(Details on Warranty and RMA issues can be found in the Warranty
Information section in this Guide.)