LINKSYS WPC54GV3 Wireless-G Notebook Adapter User Manual WPC54GS UG 40220NC
LINKSYS LLC Wireless-G Notebook Adapter WPC54GS UG 40220NC
LINKSYS >
Contents
- 1. Users Manual 1
- 2. Users Manual 2
- 3. Users Manual 3
- 4. Users Manual 4
- 5. Users Manual 5
Users Manual 4
23
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Wireless-G Notebook Adapter with SpeedBooster
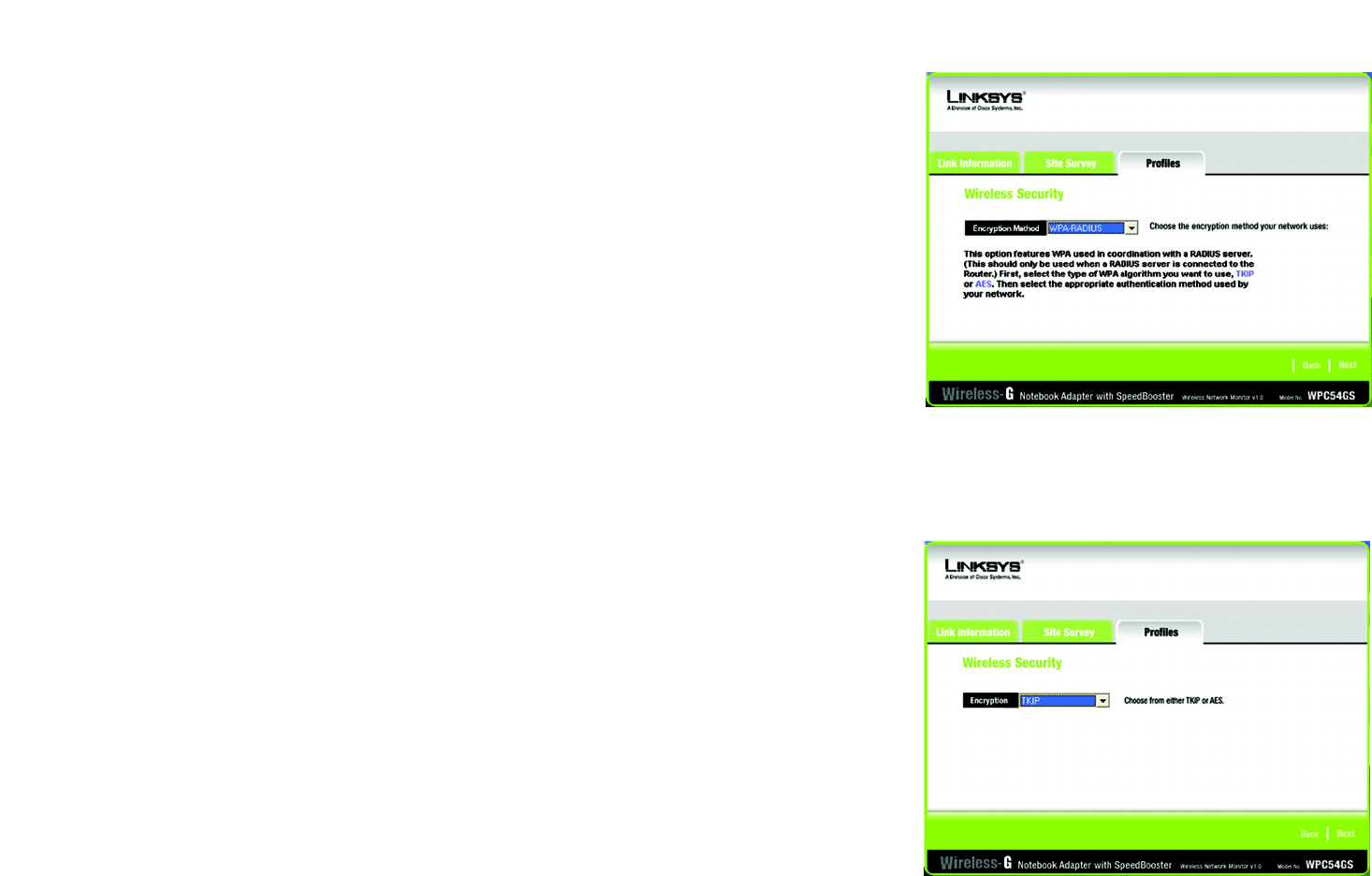
WPA RADIUS features WPA used in coordination with a RADIUS server. (This should only be used when a
RADIUS server is connected to the Router.) WPA Radius offers two encryption methods, TKIP and AES, with
dynamic encryption keys. It offers five authentication methods: EAP-TLS, EAP-TTLS, EAP-MD5, EAP-PEAP, and
LEAP.
Click the Next button to continue and the screen in Figure 6-19 appears. Click the Back button to return to
the previous screen.
Select the type of algorithm, TKIP or AES, for the Encryption Type.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-17: WPA RADIUS Settings
Figure 6-18: Encryption Type
24
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Wireless-G Notebook Adapter with SpeedBooster
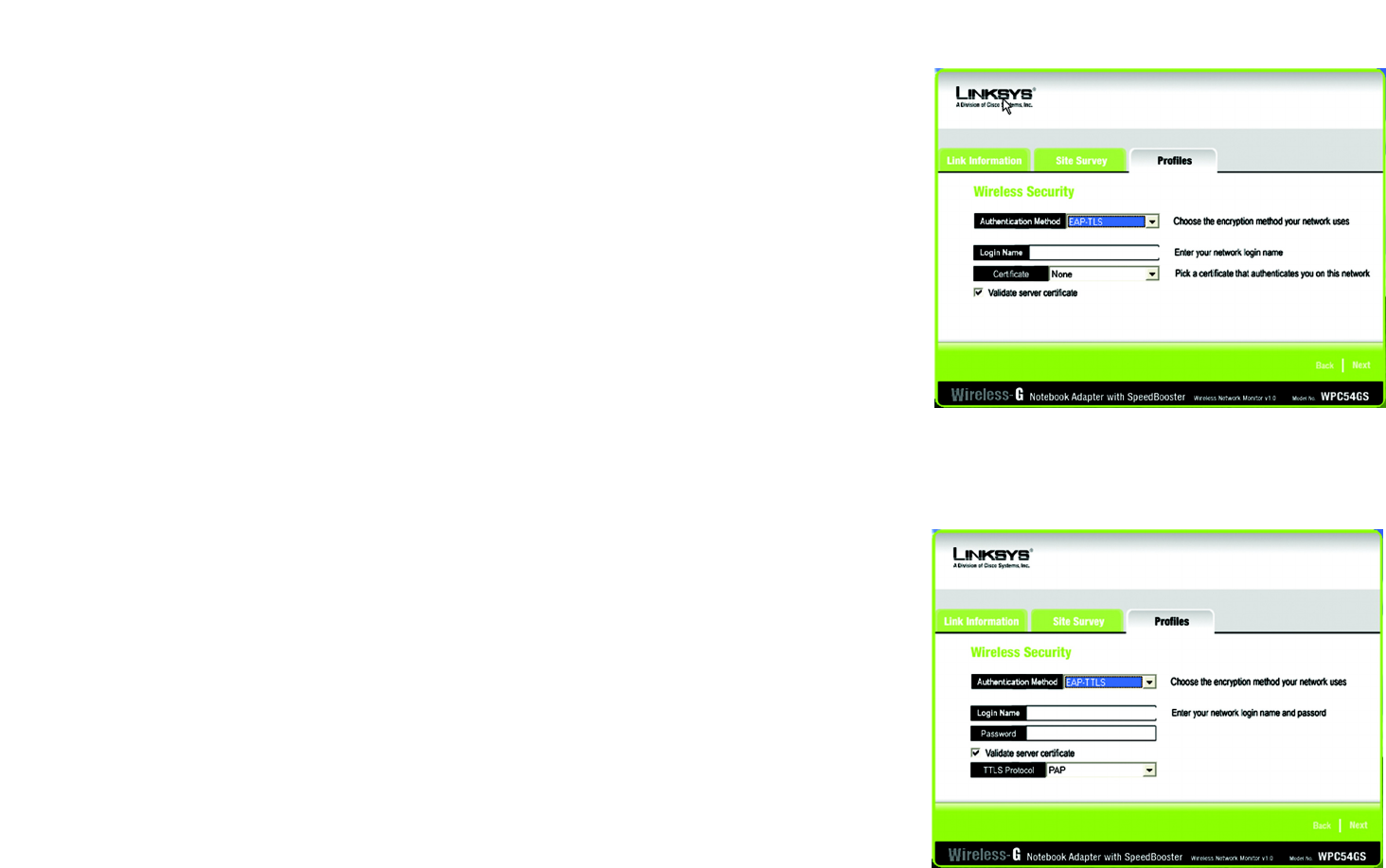
Figure 6-19: EAP-TLS Authentication
Figure 6-20: EAP-TTLS Authentication
The screen in Figure 6-20 appears next. Select the Authentication Method from the drop-down menu. The
options are described below.
EAP-TLS
Enter the Login name of your wireless network in the Login Name field. From the Certificate drop-down menu,
select the certificate you have installed to authenticate you on your wireless network. Select Validate server
cerificate to make sure that the certificate for the server is valid.
Click the Next button to continue. Click the Back button to return to the previous screen.
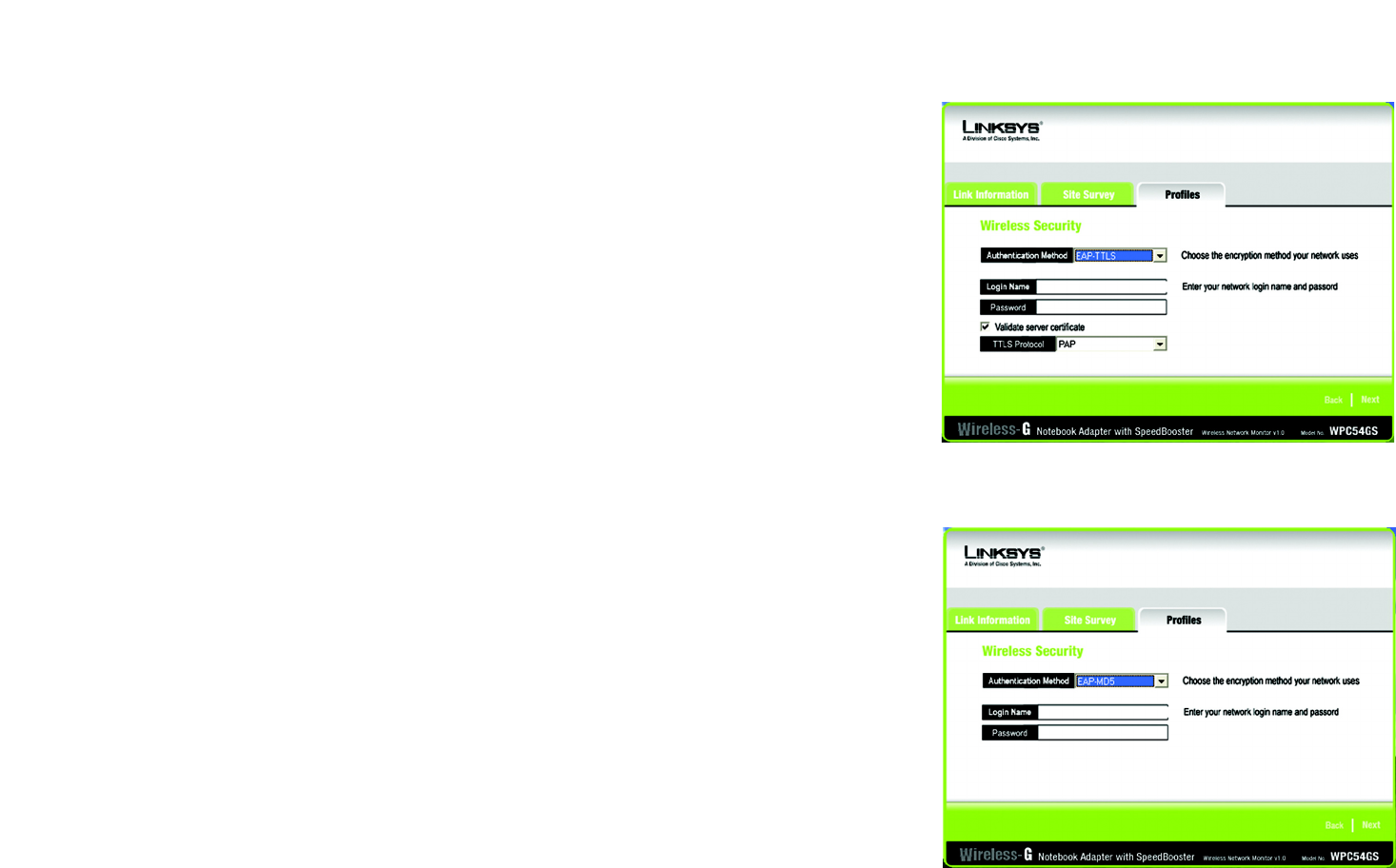
EAP-TTLS
Enter the Login name of your wireless network in the Login Name field. Enter the password of your wireless
network in the Password field. Select Validate server cerificate to make sure that the certificate for the
server is valid. Select the TTLS Protocol from the drop-down menu.
Click the Next button to continue. Click the Back button to return to the previous screen.
25
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Wireless-G Notebook Adapter with SpeedBooster
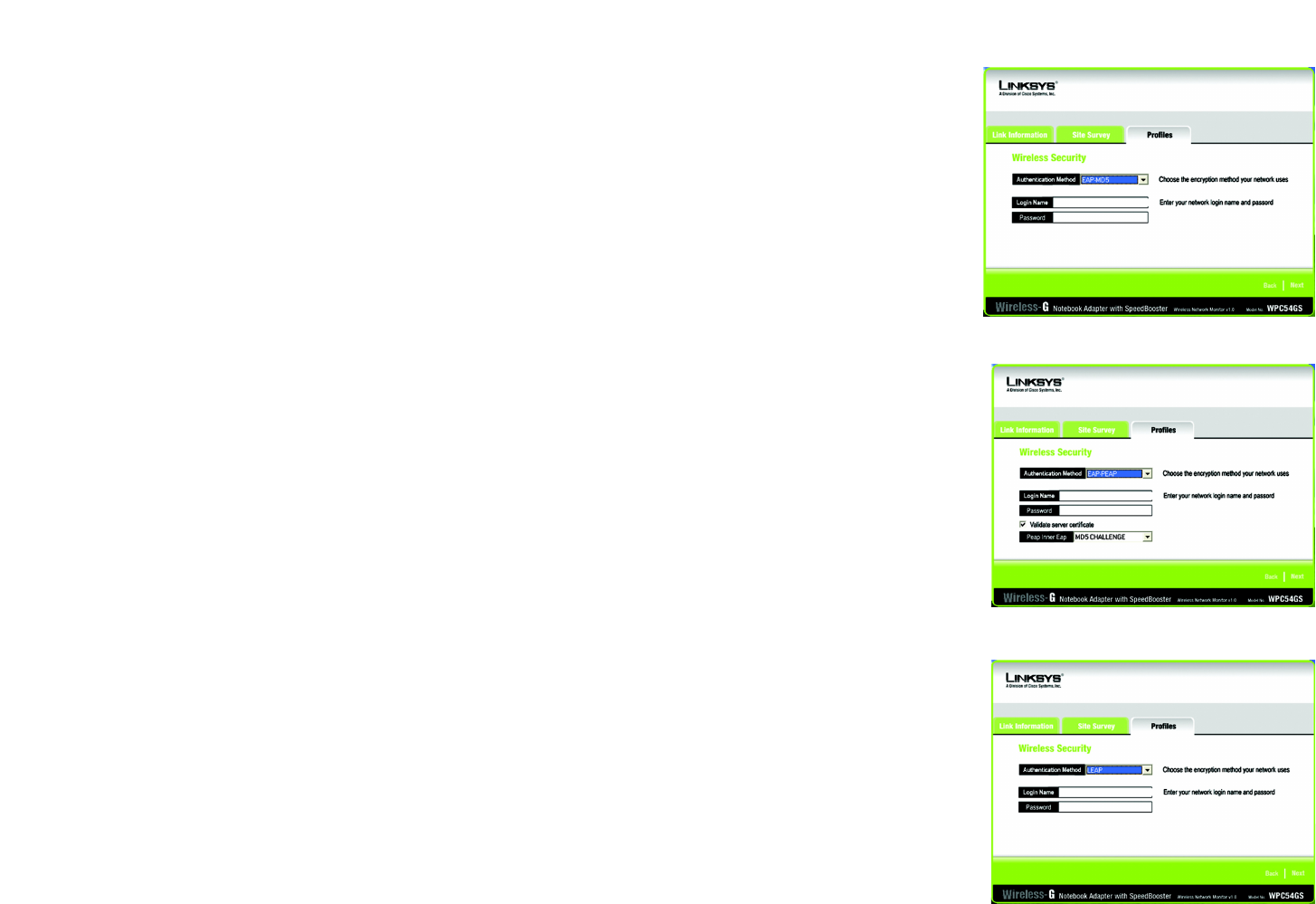
EAP-MD5
Enter the Login name of your wireless network in the Login Name field. Enter the password of your wireless
network in the Password field.
Click the Next button to continue. Click the Back button to return to the previous screen.
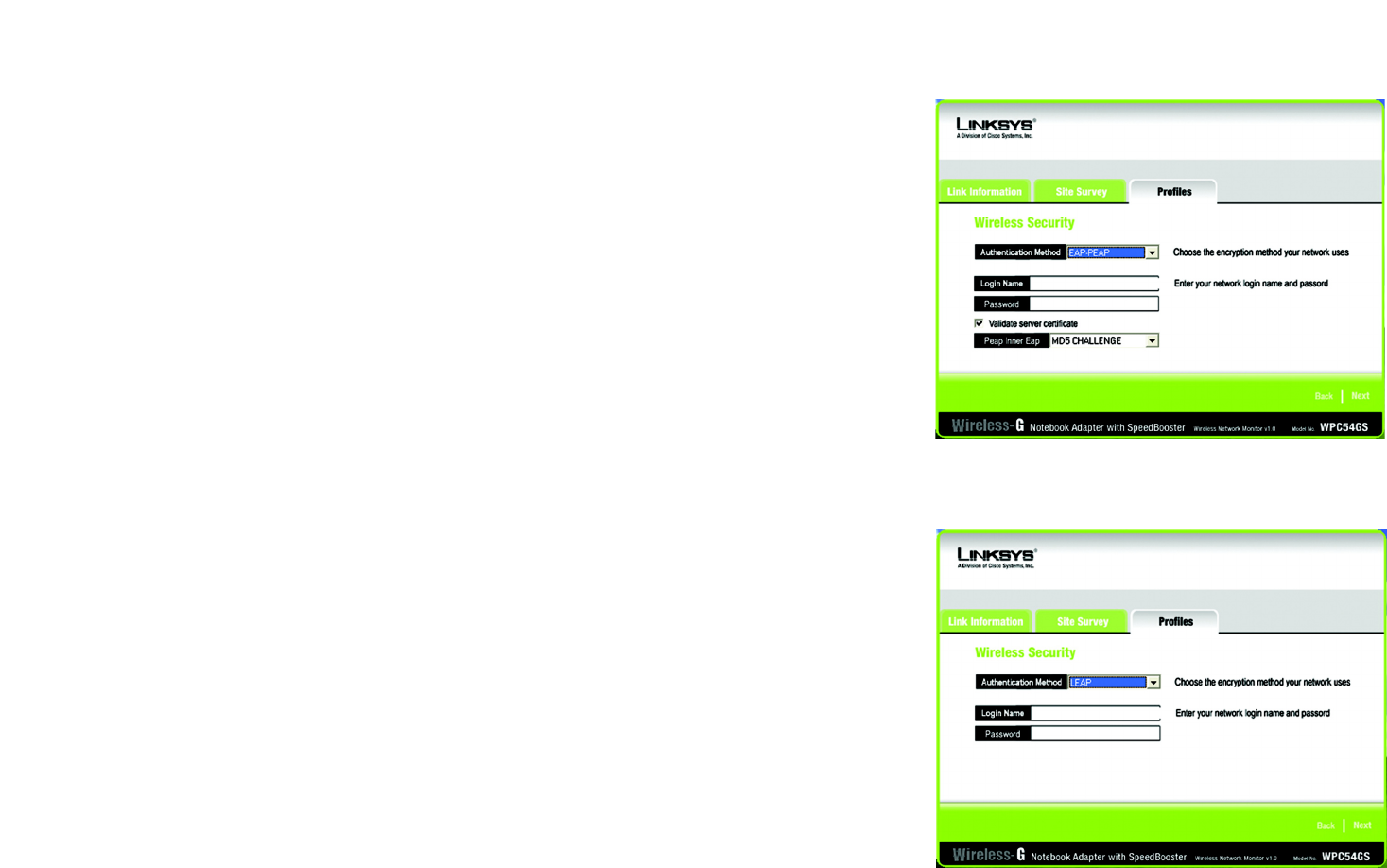
EAP-PEAP
Enter the Login name of your wireless network in the Login Name field. Enter the password of your wireless
network in the Password field. Select Validate server cerificate to make sure that the certificate for the
server is valid. Then, select the Peap Inner EAP from the drop-down menu.
Click the Next button to continue. Click the Back button to return to the previous screen.
LEAP
Enter the Login name of your wireless network in the Login Name field. Enter the password of your wireless
network in the Password field.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-21: EAP-MD5 Authentication
Figure 6-22: EAP-PEAP Authentication
Figure 6-23: EAP-LEAP Authentication
26
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Wireless-G Notebook Adapter with SpeedBooster
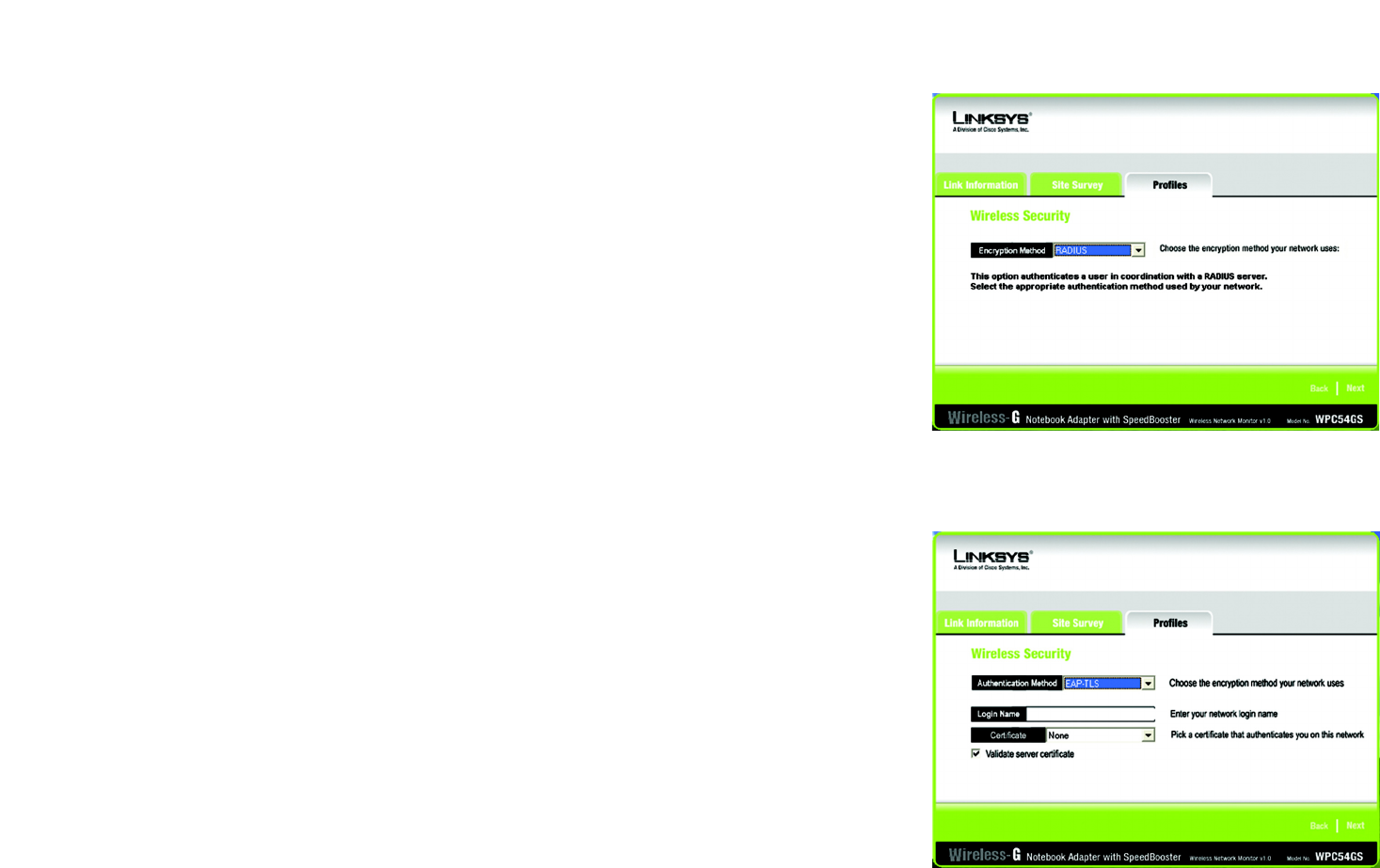
RADIUS
RADIUS features WPA used in coordination with a RADIUS server. (This should only be used when a RADIUS
server is connected to the Router.) It offers five authentication methods: EAP-TLS, EAP-TTLS, EAP-MD5, EAP-
PEAP, and LEAP.
Click the Next button to continue and the screen in Figure 6-19 appears. Click the Back button to return to
the previous screen.
The screen in Figure 6-26 appears next. Select the Authentication Method from the drop-down menu. The
options are described below.
EAP-TLS
Enter the Login name of your wireless network in the Login Name field. From the Certificate drop-down menu,
select the certificate you have installed to authenticate you on your wireless network. Select Validate server
cerificate to make sure that the certificate for the server is valid.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-25: EAP-TLS Authentication
Figure 6-24: RADIUS Settings
27
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Wireless-G Notebook Adapter with SpeedBooster
EAP-TTLS
Enter the Login name of your wireless network in the Login Name field. Enter the password of your wireless
network in the Password field. Select Validate server cerificate to make sure that the certificate for the
server is valid. Select the TTLS Protocol from the drop-down menu.
Click the Next button to continue. Click the Back button to return to the previous screen.
EAP-MD5
Enter the Login name of your wireless network in the Login Name field. Enter the password of your wireless
network in the Password field.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-26: EAP-TTLS Authentication
Figure 6-27: EAP-MD5 Authentication
28
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Wireless-G Notebook Adapter with SpeedBooster
EAP-PEAP
Enter the Login name of your wireless network in the Login Name field. Enter the password of your wireless
network in the Password field. Select Validate server cerificate to make sure that the certificate for the
server is valid. Then, select the Peap Inner EAP from the drop-down menu.
Click the Next button to continue. Click the Back button to return to the previous screen.
LEAP
Enter the Login name of your wireless network in the Login Name field. Enter the password of your wireless
network in the Password field.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-28: EAP-PEAP Authentication
Figure 6-29: LEAP Authentication
29
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Wireless-G Notebook Adapter with SpeedBooster
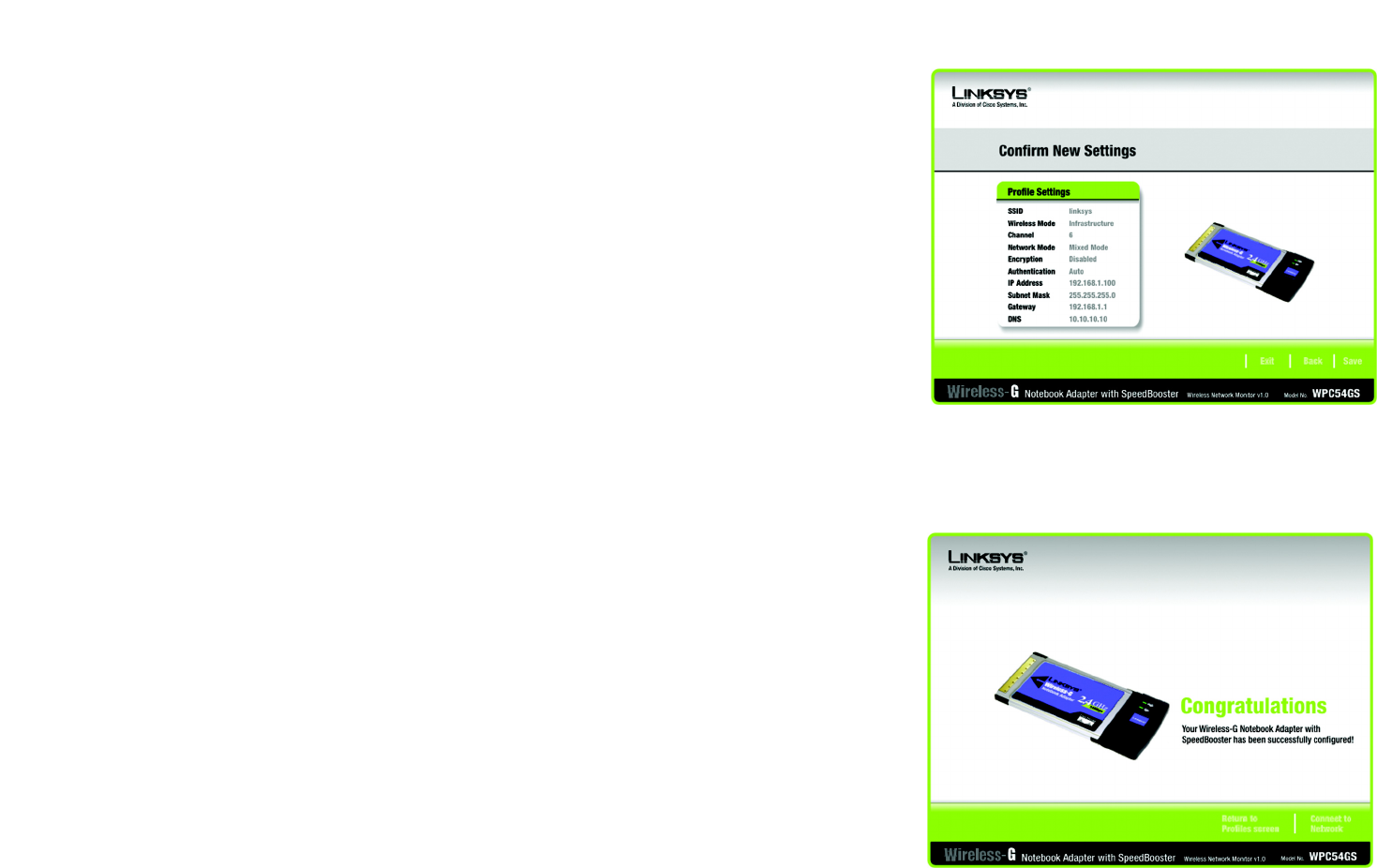
7. The Confirm New Settings screen will appear next showing the new settings. To save the new settings, click
the Save button. To edit the new settings, click the Back button. To exit the Wireless Network Monitor, click
Exit.
8. The Congratulations screen will appear next. Click Activate new settings now to implement the new
settings immediately and return to the Link Information screen. Click Activate new settings later to keep
the current settings active and return to the Profiles screen.
You have successfully created a connection profile.
Figure 6-30: TKIP Settings
Figure 6-31: EAP-TLS Authentication

30
Appendix A: Troubleshooting
Common Problems and Solutions
Wireless-G Notebook Adapter with SpeedBooster
Appendix A: Troubleshooting
This appendix consists of two parts: “Common Problems and Solutions” and “Frequently Asked Questions.” This
appendix provides solutions to problems that may occur during the installation and operation of the Wireless-G
Notebook Adapter. Read the description below to solve your problems. If you can't find an answer here, check the
Linksys website at www.linksys.com.
Common Problems and Solutions
1. My computer does not recognize the Wireless-G Notebook Adapter.
Make sure that the Wireless-G Notebook Adapter is properly inserted into the PC Card slot.
2. The Wireless-G Notebook Adapter does not work properly.
Reinsert the Wireless-G Notebook Adapter into the notebook or desktop’s USB port.
For Windows 98SE or Me, right-click on My Computer, and select Properties. Select the Device Manager
tab, and click on the Network Adapter. You will find the Wireless-G Notebook Adapter if it is installed
successfully. If you see a yellow exclamation mark, the resources may be conflicting and you must follow the
steps below:
• Uninstall the driver software from your PC.
• Restart your PC and repeat the hardware and software installation as specified in this User Guide.
3. I cannot communicate with the other computers linked via Ethernet in the Infrastructure
configuration.
Make sure that the notebook or desktop is powered on.
Make sure that the Wireless-G Notebook Adapter is configured with the same SSID and WEP settings as the
other computers in the Infrastructure configuration.

31
Appendix A: Troubleshooting
Frequently Asked Questions
Wireless-G Notebook Adapter with SpeedBooster
Frequently Asked Questions
Can I run an application from a remote computer over the wireless network?
This will depend on whether or not the application is designed to be used over a network. Consult the
application’s user guide to determine if it supports operation over a network.
Can I play computer games with other members of the wireless network?
Yes, as long as the game supports multiple players over a LAN (local area network). Refer to the game’s user
guide for more information.
What is the IEEE 802.11b standard?
It is one of the IEEE standards for wireless networks. The 802.11b standard allows wireless networking hardware
from different manufacturers to communicate, provided that the hardware complies with the 802.11b standard.
The 802.11b standard states a maximum data transfer rate of 11Mbps and an operating frequency of 2.4GHz.
What IEEE 802.11b features are supported?
The product supports the following IEEE 802.11b functions:
• CSMA/CA plus Acknowledge protocol
• Multi-Channel Roaming
• Automatic Rate Selection
• RTS/CTS feature
• Fragmentation
• Power Management
What is ad-hoc mode?
When a wireless network is set to ad-hoc mode, the wireless-equipped computers are configured to
communicate directly with each other. The ad-hoc wireless network will not communicate with any wired
network.
What is infrastructure mode?
When a wireless network is set to infrastructure mode, the wireless network is configured to communicate with
a wired network through a wireless access point.
What is roaming?
Roaming is the ability of a portable computer user to communicate continuously while moving freely throughout
an area greater than that covered by a single access point. Before using the roaming function, the workstation
must make sure that it is the same channel number with the access point of dedicated coverage area.
To achieve true seamless connectivity, the wireless LAN must incorporate a number of different functions. Each
node and access point, for example, must always acknowledge receipt of each message. Each node must
fragmentation: breaking a packet into smaller units
when transmitting over a network medium that cannot
support the original size of the packet.
mbps: one million bits per second; a unit of
measurement for data transmission.