LINKSYS WRE54GV3 Wireless-G Range Expander User Manual Book
LINKSYS LLC Wireless-G Range Expander Book
LINKSYS >
Manual

A Division of Cisco Systems, Inc.
®
Model No.
Range Expander
Wireless-G
WRE54G
User Guide
WIRELESS
GHz
2.4
802.11g
Wireless-G Range Expander
Copyright and Trademarks
Specifications are subject to change without notice. Linksys is a registered trademark or trademark of Cisco
Systems, Inc. and/or its affiliates in the U.S. and certain other countries. Copyright © 2005 Cisco Systems, Inc. All
rights reserved. Other brands and product names are trademarks or registered trademarks of their respective
holders.
How to Use this User Guide
The user guide to the Wireless-G Range Expander has been designed to make understanding networking with the
Range Expander easier than ever. Look for the following items when reading this User Guide:
In addition to these symbols, there are definitions for technical terms that are presented like this:
Also, each figure (diagram, screenshot, or other image) is provided with a figure number and description, like
this:
Figure numbers and descriptions can also be found in the “List of Figures” section.
This exclamation point means there is a caution or
warning and is something that could damage your
property or the Range Expander.
word: definition.
This checkmark means there is a note of interest and
is something you should pay special attention to while
using the Range Expander.
This question mark provides you with a reminder about
something you might need to do while using the Range Expander.
Figure 0-1: Sample Figure Description
WRE54G_V2-UG-50114NC JL
WARNING: This product contains chemicals, including lead, known
to the State of California to cause cancer, and birth defects or other
reproductive harm. Wash hands after handling.

Wireless-G Range Expander
Table of Contents
Chapter 1: Introduction 1
Welcome 1
What’s in this User Guide? 2
Chapter 2: Planning Your Wireless Network 4
Network Topology 4
Roaming 4
Network Layout 5
Chapter 3: Getting to Know the Wireless-G Range Expander 6
The Front Panel 6
The Side Panel 6
The Recess for the Power Plate 7
Chapter 4: Connecting the Wireless-G Range Expander 8
Overview 8
Connection to a Wired Network for Setup 8
Connection to a Wireless Network for Setup 9
Connection for Auto Configuration 9
Chapter 5: Setting Up the Wireless-G Range Expander 10
Overview 10
Running the Setup Wizard 10
Moving the Range Expander 16
Chapter 6: Configuring the Wireless-G Range Expander 17
Overview 17
Accessing the Web-based Utility 17
The Setup Tab 18
Appendix A: Troubleshooting 23
Common Problems and Solutions 23
Frequently Asked Questions 23
Appendix B: Wireless Security 27
Security Precautions 27
Security Threats Facing Wireless Networks 27
Appendix C: Upgrading Firmware 30

Wireless-G Range Expander
Appendix D: Windows Help 31
Appendix E: Glossary 32
Appendix F: Specifications 36
Appendix G: Warranty Information 37
Appendix H: Regulatory Information 38
Appendix I: Contact Information 40

Wireless-G Range Expander
List of Figures
Figure 3-1: Front Panel 6
Figure 3-1: Front Panel with Ethernet Network Cable Connected 6
Figure 3-2: Recess for the Power Plate 7
Figure 4-1: Connecting the Ethernet Network Cable 8
Figure 4-2: Using the Power Plate with Cord 8
Figure 4-3: Using the Power Plate with Plug 8
Figure 4-4: Using the Power Plate with Cord 9
Figure 4-5: Using the Power Plate with Plug 9
Figure 5-1: Setup Wizard’s Welcome Screen 10
Figure 5-2: Check Your Wireless Network 10
Figure 5-3: Confirm Wireless Network Settings 11
Figure 5-4: Wireless Network Not Found 11
Figure 5-5: Choose the Access Point 11
Figure 5-6: Configure Wireless Settings Manually 11
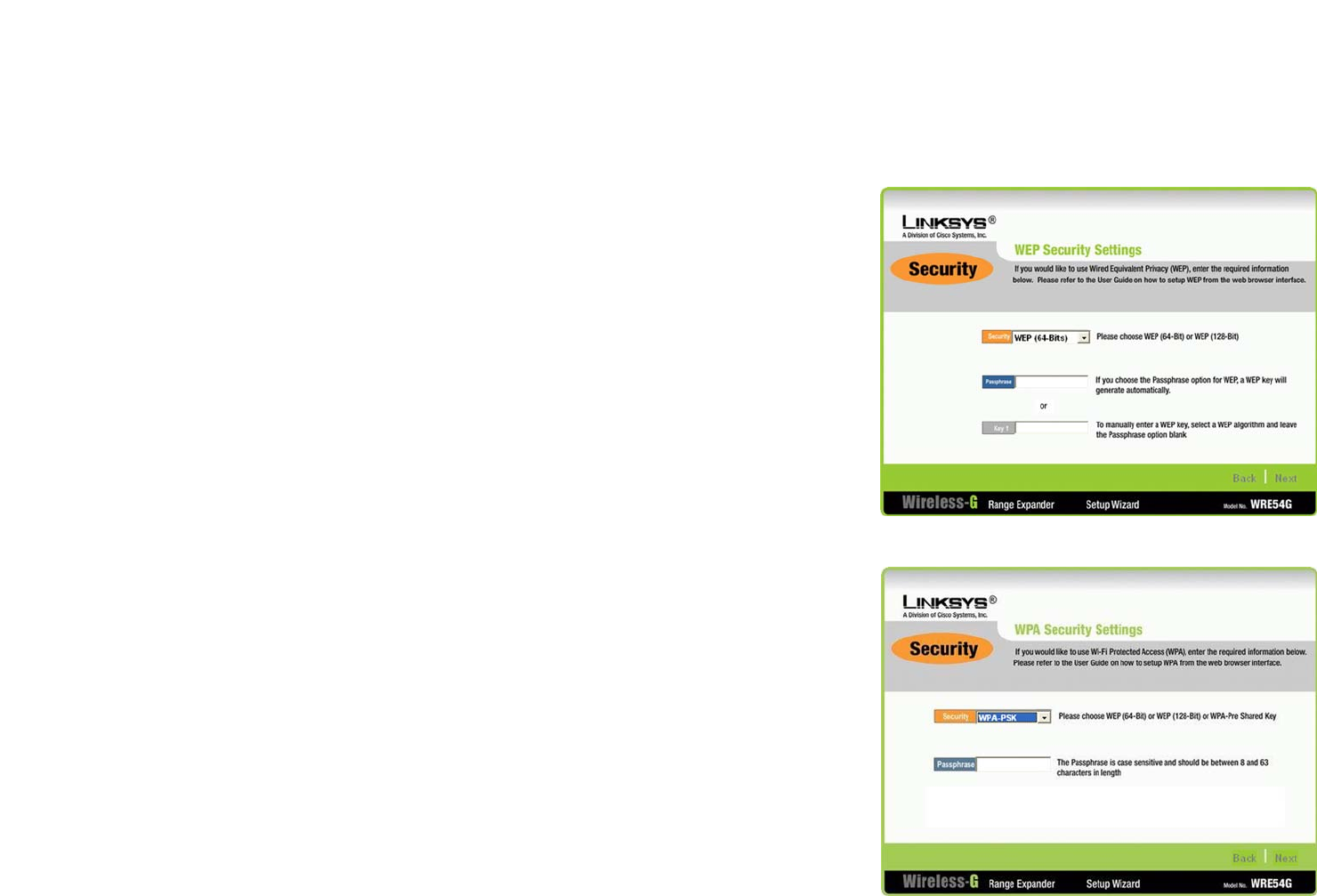
Figure 5-7: WEP Security Settings 12
Figure 5-8: WPA Security Settings 12
Figure 5-9: Choose the Range Expander 13
Figure 5-10: Enter the Password 13
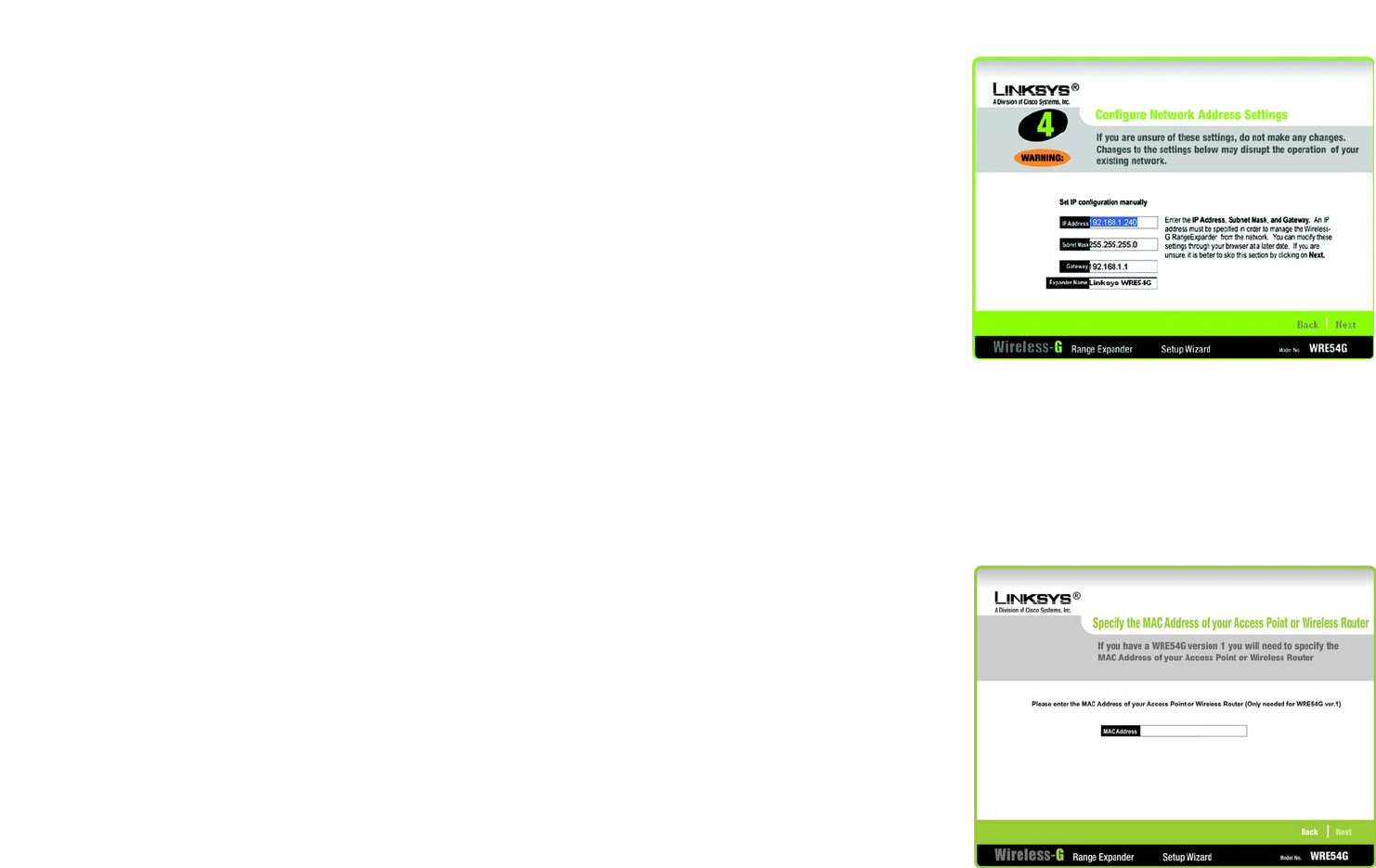
Figure 5-11: Configure Network Address Settings 14
Figure 5-12: MAC Address of Access Point or Wireless Router
(WRE54G v1 Only) 14
Figure 5-13: Confirmation Screen 15
Figure 5-14: Congratulations Screen 15
Figure 5-15: Using the Power Plate with Cord 16
Figure 5-16: Using the Power Plate with Plug 16
Figure 6-1: Login Screen 17
Figure 6-2: Setup Tab - Basic Setup 18
Figure 6-3: WPA Security 19

Wireless-G Range Expander
Figure 6-4: WEP Security 19
Figure 6-5: Setup Tab - Password 21
Figure 6-6: File Download 21
Figure 6-7: Setup Tab - Help 22
Figure 6-8: Firmware Upgrade 22
Figure C-1: Upgrade Firmware 30

1
Chapter 1: Introduction
Welcome
Wireless-G Range Expander
Chapter 1: Introduction
Welcome
Thank you for choosing the Wireless-G Range Expander. This Range Expander will allow you to expand your
network beyond the range of your current access point or wireless router.
How does the Range Expander do this? Once on your network, the Range Expander repeats the signal to all
devices within its range. By placing the Range Expander at the furthest edge of your access point or wireless
router’s signal, it could conceivably double the area of your network.
But what does all of this mean?
Networks are useful tools for sharing computer resources. You can access one printer from different computers
and access data located on another computer's hard drive. Networks are even used for playing multiplayer video
games. So, networks are not only useful in homes and offices, they can also be fun.
PCs equipped with wireless cards and adapters can communicate without cumbersome cables. By sharing the
same wireless settings, within their transmission radius, they form a wireless network. While access points and
wireless routers bridge wireless networks and wired networks, the Range Expander can then take that signal for
networks that use the 802.11b and 802.11g standards and extend it beyond its current range.
Use the instructions in this Guide to help you connect the Range Expander, set it up, and configure it to expand
the range of your Wireless-G and Wireless-B networks. These instructions should be all you need to get the most
out of the Range Expander. 802.11g: an IEEE wireless networking standard that specifies
a maximum data transfer rate of 54Mbps, an operating
frequency of 2.4GHz, and backward compatibility with
802.11b devices.
802.11b: an IEEE wireless networking standard that
specifies a maximum data transfer rate of 11Mbps and an
operating frequency of 2.4GHz.
access point: a device that allows wireless-equipped
computers and other devices to communicate with a wired
network. Also used to expand the range of a wireless network.
adapter: a device that adds network functionality to your PC.
network: a series of computers or devices connected for the
purpose of data sharing, storage, and/or transmission
between users.
router: a networking device that connects multiple networks
together.

2
Chapter 1: Introduction
What’s in this User Guide?
Wireless-G Range Expander
What’s in this User Guide?
This user guide covers the steps for setting up and using the Wireless-G Range Expander.
• Chapter 1: Introduction
This chapter describes the Range Expander’s applications and this User Guide.
• Chapter 2: Planning Your Wireless Network
This chapter discusses a few of the basics about wireless networking.
• Chapter 3: Getting to Know the Wireless-G Range Expander
This chapter describes the physical features of the Range Expander.
• Chapter 4: Connecting the Wireless-G Range Expander
This chapter describes the steps for connecting the Range Expander to your wired or wireless network.
• Chapter 5: Setting up the Wireless-G Range Expander
This chapter instructs you on how to use the Range Expander’s Setup Wizard and configure the Range
Expander.
• Chapter 6: Configuring the Wireless-G Range Expander
This chapter shows you how to configure the Range Expander using the Web Utility.
• Appendix A: Troubleshooting
This appendix describes some potential problems and solutions, as well as frequently asked questions,
regarding installation and use of the Range Expander.
• Appendix B: Wireless Security
This appendix discusses security issues regarding wireless networking and measures you can take to help
protect your wireless network.
• Appendix C: Windows Help
This appendix describes how you can use Windows Help for instructions about networking, such as installing
the TCP/IP protocol.
• Appendix D: Glossary
This appendix gives a brief glossary of terms frequently used in networking.
• Appendix E: Specifications
This appendix provides the Range Expander’s technical specifications.

3
Chapter 1: Introduction
What’s in this User Guide?
Wireless-G Range Expander
• Appendix F: Warranty Information
This appendix supplies the Range Expander’s warranty information.
• Appendix G: Regulatory Information
This appendix supplies the Range Expander’s regulatory information.
• Appendix H: Contact Information
This appendix provides contact information for a variety of Linksys resources, including Technical Support.

4
Chapter 2: Planning Your Wireless Network
Network Topology
Wireless-G Range Expander
Chapter 2: Planning Your Wireless Network
Network Topology
A wireless network is a group of computers, each equipped with one wireless adapter. Computers in a wireless
network must be configured to share the same radio channel. Several PCs equipped with wireless cards or
adapters can communicate with one another to form an ad-hoc network.
Linksys wireless adapters also provide users access to a wired network when using an access point or wireless
router. An integrated wireless and wired network is called an infrastructure network. Each wireless PC in an
infrastructure network can talk to any computer in a wired network infrastructure via the access point or wireless
router.
An infrastructure configuration extends the accessibility of a wireless PC to a wired network, and can double the
effective wireless transmission range for two wireless adapter PCs. Since an access point is able to forward data
within a network, the effective transmission range in an infrastructure network can be doubled.
Roaming
Infrastructure mode also supports roaming capabilities for mobile users. Roaming means that you can move your
wireless PC within your network and the access points will pick up the wireless PC's signal, providing that they
both share the same channel and SSID.
Should you consider roaming, choose a feasible radio channel and optimum access point position. Proper access
point positioning combined with a clear radio signal will greatly enhance performance.
infrastructure: a wireless network that is bridged to a wired
network via an access point.
ad-hoc: a group of wireless devices communicating
directly with each other (peer-to-peer) without the use of
an access point.
roaming: the ability to take a wireless device from one access
point's range to another without losing the connection.
SSID: your wireless network's name.

5
Chapter 2: Planning Your Wireless Network
Network Layout
Wireless-G Range Expander
Network Layout
Linksys Wireless-B and Wireless-G access points and routers have been designed for use with 802.11b and
802.11g products. Products using the 802.11g and 802.11b standards can communicate with each other.
Access points and wireless routers are compatible with 802.11g and 802.11b adapters, such as the Notebook
Adapters for your laptop computers, PCI Adapters for your desktop PCs, and USB Adapters for when you want to
enjoy USB connectivity. Wireless products will also communicate with the wireless PrintServer.
When you wish to connect your wired network with your wireless network, network ports on access points and
wireless routers can be connected to any of Linksys's switches or routers.
With these, and many other, Linksys products, your networking options are limitless. Go to the Linksys website at
www.linksys.com for more information about wireless products.
6
Chapter 3: Getting to Know the Wireless-G Range Expander
The Front Panel
Wireless-G Range Expander
Chapter 3: Getting to Know the Wireless-G Range Expander
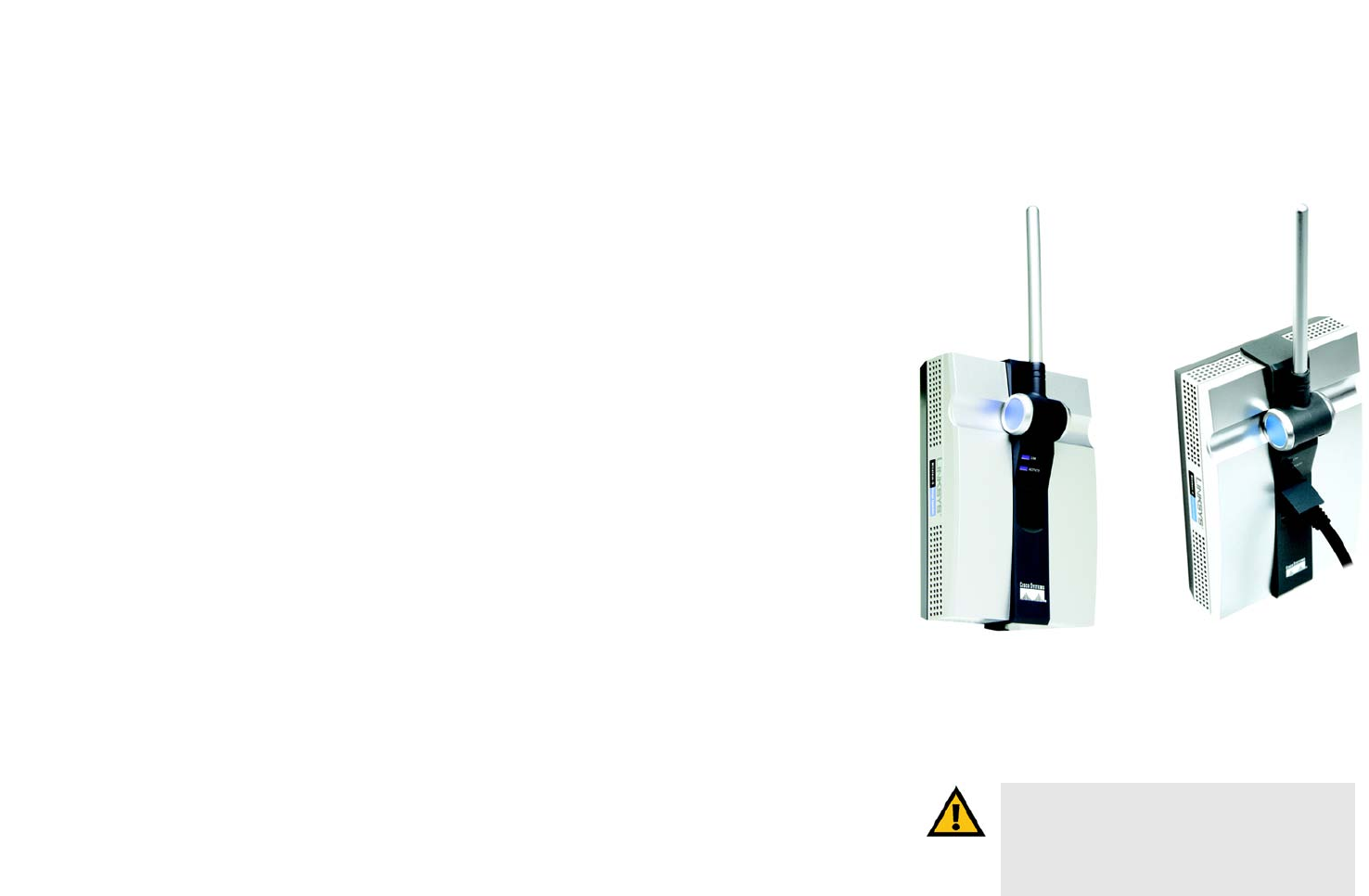
The Front Panel
The Range Expander's adjustable antenna, LEDs, and Ethernet network port are located on the front panel.
Antenna
Make sure the antenna is positioned straight up into the air, no matter how the Range Expander is positioned.
LEDs
LINK Blue/Red. The LINK LED lights up when the Range Expander is powered on. This LED will light
up blue when the Range Expander has connected to an access point or wireless router. It will
light up red when the Range Expander is not connect to any access point or wireless router.
ACTIVITY Blue. The ACTIVITY LED lights up when the Range Expander is powered on. It will flash when
there is wireless network activity.
Ethernet Network Port
The Ethernet network port is located underneath the lid below the Range Expander’s LEDs. This port is used if
you connect the Range Expander to a wired network for setup. The Ethernet network port has two small LEDs
that light up green when the Range Expander is connected to a wired network.
The Side Panel
On the Range Expander's side panel, you will find the Reset and Auto configuration buttons.
Reset Button There are two ways to reset the Range Expander's factory defaults. Either press the Reset
Button, for approximately ten seconds, or restore the defaults from the Password tab in the
Range Expander's Web-based Utility.
Auto configuration The Auto configuration button can be used to easily connect the Range Expander to the
nearest wireless network, via an access point or wireless router. Simply connect the power
and press the Auto configuration button. Your wireless network must have security
disabled for this feature to function.
IMPORTANT: Resetting the Range Expander will
erase all of your wireless settings, including
security settings, and replace them with the
factory defaults. Do not reset the Range Expander
if you want to retain these settings.
Figure 3-1: Front Panel Figure 3-1: Front Panel with
Ethernet Network Cable Connected

7
Chapter 3: Getting to Know the Wireless-G Range Expander
The Recess for the Power Plate
Wireless-G Range Expander
The Recess for the Power Plate
The back of the Range Expander has a two-pronged recess where its power plates can be connected. Two power
plates come with the Range Expander, one with two prongs for direct connection to a power outlet, and another
with a cord to reach a power outlet.
Either of these power plate can be slid into the recess and is fully connected when the orange tab snaps into
place. To remove the power plate, slide the tab to the right and slide out the power plate. Always unplug the
Range Expander from the power outlet before removing the power plate.
Figure 3-2: Recess for the Power Plate

8
Chapter 4: Connecting the Wireless-G Range Expander
Overview
Wireless-G Range Expander
Chapter 4: Connecting the Wireless-G Range Expander
Overview
Linksys recommends that you connect the Range Expander to your wired network for setup. Proceed to the
“Connection to a Wired Network for Setup” section.
If you want to configure the Range Expander using your wireless network, proceed to the “Connection to a
Wireless Network for Setup” section if you have security enabled. Proceed to the “Connection for Auto
Configuration” section if you have security disabled.
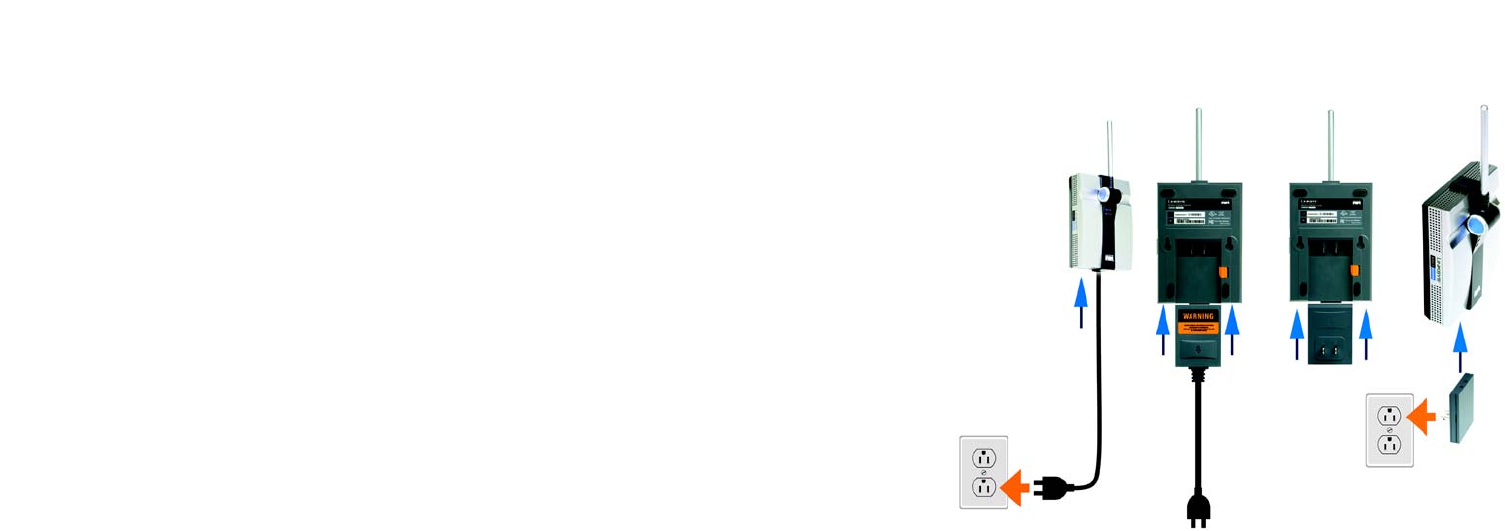
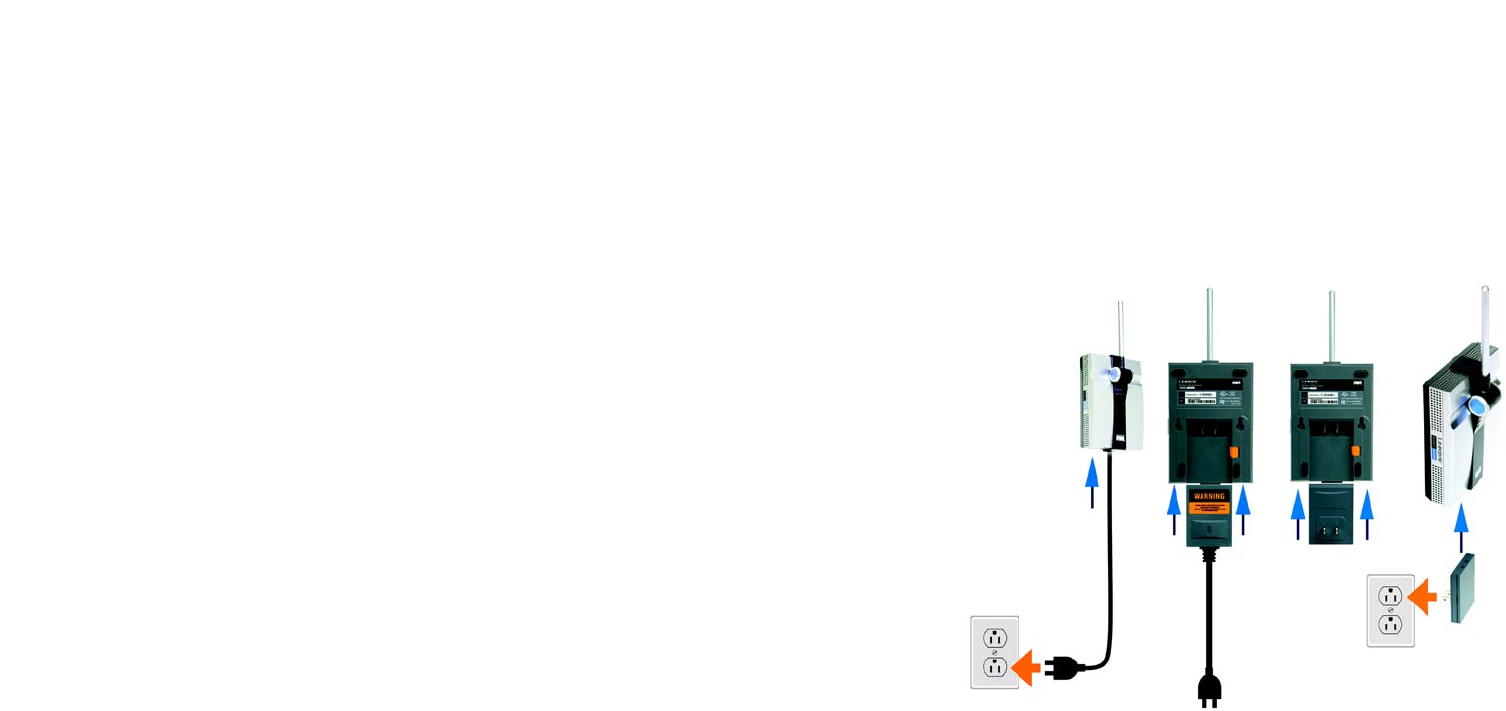
Connection to a Wired Network for Setup
1. Flip up the lid covering the Ethernet network port on the Range Expander’s front panel.
2. Connect the included Ethernet network cable to the Ethernet network port of the Range Expander.
Connect the other end of the network cable to an Ethernet network port on your network router.
3. Connect the appropriate power plate and connect it to a power outlet, preferably a surge protector.
Proceed to “Chapter 5: Setting Up the Wireless-G Range Expander.”
Figure 4-2: Using the Power Plate
with Cord
Figure 4-3: Using the
Power Plate with Plug
Figure 4-1: Connecting the
Ethernet Network Cable
NOTE: The Auto configuration button can be used to set up the Range Expander if you have security
disabled on your wireless network. Proceed to the “Connection for Auto Configuration” section.
NOTE: The Auto configuration button can be used to set up the Range Expander if you have security
disabled on your wireless network. Proceed to the “Connection for Auto Configuration” section.
NOTE TO ADVANCED USERS:If you want to use the Web-based Utility to configure the Range
Expander, then connect the Range Expander to your network. Open the web browser of a networked
computer, and enter the Range Expander’s IP address, 192.168.1.240. Configure your network’s
SSID, channel, and security settings on the Basic Setup screen. For more information, proceed to
“Chapter 6: Configuring the Wireless-G Range Expander.”
9
Chapter 4: Connecting the Wireless-G Range Expander
Connection to a Wireless Network for Setup
Wireless-G Range Expander
Connection to a Wireless Network for Setup
Linksys recommends that you have the Range Expander in the same room as your access point or wireless
router during setup.
Connect the appropriate power plate and connect it to a power outlet, preferably a surge protector.
Proceed to “Chapter 5: Setting Up the Wireless-G Range Expander.”
Connection for Auto Configuration
Linksys recommends that you have the Range Expander in the same room as your access point or wireless
router during setup.
1. Connect the appropriate power plate and connect it to a power outlet, preferably a surge protector.
2. Press the Range Expander’s Auto configuration button for five seconds. The Range Expander will then
automatically detect your wireless network and configure itself with those settings.
4. To move the Range Expander, unplug the power plate from the power outlet.
5. Locate an optimum location for the Range Expander. The best placement is usually at the edge of your
wireless network.
6. Fix the direction of the antenna. Try to place it in a position that will best cover your wireless network.
Normally, the higher you place the Range Expander’s antenna, the better its performance will be. Its receiving
sensitivity can be enhanced by proper Proper positioning of the antenna should enhance its receiving
sensitivity.
3. Connect the power plate to a power outlet, preferably a surge protector.
Congratulations! The installation of the Wireless-G Range Expander is complete.
Figure 4-4: Using the Power Plate
with Cord
Figure 4-5: Using the
Power Plate with Plug

10
Chapter 5: Setting Up the Wireless-G Range Expander
Overview
Wireless-G Range Expander
Chapter 5: Setting Up the Wireless-G Range Expander
Overview
The first part of this chapter explains how to configure the Range Expander. The remainder of the chapter
describes how to move the Range Expander to its final location.
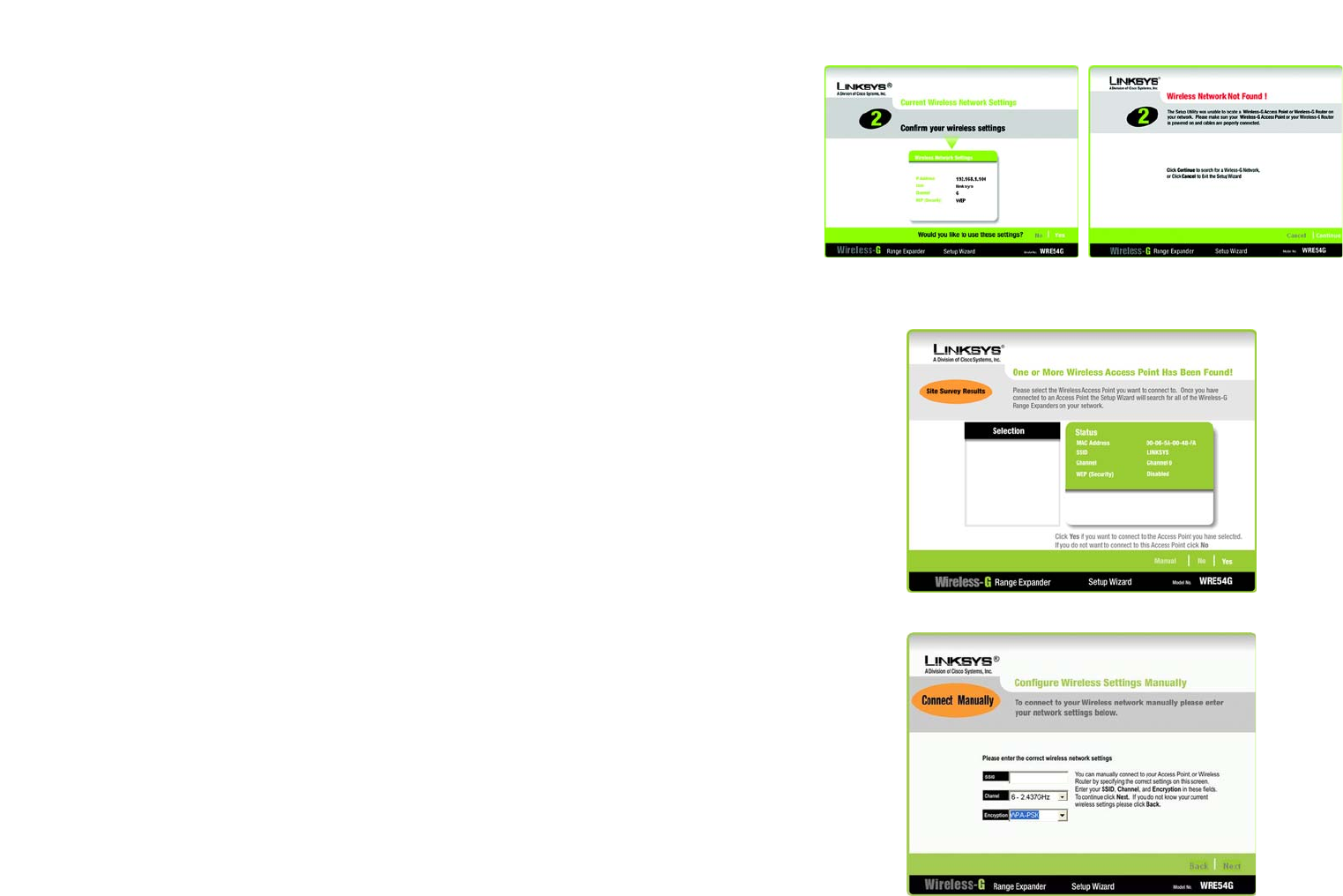
Running the Setup Wizard
Now that you've placed the Range Expander within your wireless network, you are ready to begin setting it up.
This Setup Wizard will take you through all the steps necessary to configure the Range Expander.
1. Insert the Setup Wizard CD into your PC's CD-ROM drive. The Setup Wizard should run automatically, and the
Welcome screen should appear. If it does not, click the Start button and choose Run. In the field that
appears, enter D:\setup.exe (if “D” is the letter of your CD-ROM drive).
2. Click the Setup button to continue this Setup Wizard. Clicking the User Guide button opened this Guide. To
exit this Setup Wizard, click the Exit button.
3. Make sure your access point or wireless router is working properly before you continue with the Setup
Wizard. Click Next to continue or Exit to exit the Setup Wizard.
Figure 5-1: Setup Wizard’s Welcome Screen
NOTE: You won’t need to use the Setup Wizard, if
you set up the Range Expander using the Auto
configuration button. The Auto configuration button
can be used to quickly set up the Range Expander if
you have security disabled on your wireless network.
Figure 5-2: Check Your Wireless Network
11
Chapter 5: Setting Up the Wireless-G Range Expander
Running the Setup Wizard
Wireless-G Range Expander
4. The Setup Wizard will run a search for your wireless network. If found, you will be asked to confirm the
settings. If the settings are correct, click Continue and proceed to step 7. If you’d like to choose a
different wireless network, proceed to step 5.
If no wireless network is found, a screen will notify you when no access point is detected on your
network. Click Continue to survey your network for any access points or wireless routers, and proceed
to step 5. You can click Cancel to exit the Setup Wizard.
5. The site survey results will display all available access points and wireless routers in your network. Select the
one you want and then click Yes to continue. Then proceed to step 6.
You can click No to return to the Welcome screen of the Setup Wizard.
If you want to manually enter settings, click Manual. The Configure Wireless Settings Manually screen will
appear. Enter the SSID of your network. Then select the channel setting of your network.
If your network uses WEP encryption, select WEP from the Encryption drop-down menu. Click Next to
continue and proceed to step 6. If your network uses WPA security, select WPA. Click Next to continue and
proceed to step 6.
If it does not use wireless security, select Disabled. Click Next to continue and proceed to step 7.
Figure 5-3: Confirm Wireless
Network Settings Figure 5-4: Wireless Network
Not Found
Figure 5-5: Choose the Access Point
Figure 5-6: Configure Wireless Settings Manually
12
Chapter 5: Setting Up the Wireless-G Range Expander
Running the Setup Wizard
Wireless-G Range Expander
6. If security is disabled, then proceed to step 7. If security is enabled, the appropriate Security Settings screen
will appear. Enter the WEP or WPA settings. Then click Next to continue or Exit to exit the Setup Wizard.
WEP
On the WEP Security Settings screen, select the level of WEP encryption, WEP (64-bits) or WEP (128-Bits).
Then enter the passphrase or the WEP key. The passphrase can consist of no more than 16 alphanumeric
characters.
If you enter the WEP key in the Key 1 field, it must have 10 hexadecimal characters for 64-bit encryption or 26
hexadecimal characters for 128-bit encryption. Hexadecimal characters are the letters “A” through “F” and
the numbers “0” through “9”. All devices in your wireless network must use the same WEP key.
WPA
On the WPA Security Settings screen, enter the passphrase or pre-shared key in the Passphrase field. The
passphrase or pre-shared key must have between 8 to 63 characters in length.
Figure 5-7: WEP Security Settings
Figure 5-8: WPA Security Settings
wep: a method of encrypting network data transmitted
on a wireless network for greater security.
wpa: a wireless security protocol using TKIP (Temporal
Key Integrity Protocol) encryption, which can be used in
conjunction with a RADIUS server.

13
Chapter 5: Setting Up the Wireless-G Range Expander
Running the Setup Wizard
Wireless-G Range Expander
7. Now that the Setup Wizard has found an access point or wireless router with which to communicate, it will
now search for the Range Expander. Select the one you want. Then, click Yes to continue, or click No to return
to the Welcome screen of the Setup Wizard.
8. You will be asked to enter its password. Enter the default password, admin. Then, click Enter to continue. To
exit this Setup Wizard, click Exit.
Figure 5-9: Choose the Range Expander
Figure 5-10: Enter the Password
14
Chapter 5: Setting Up the Wireless-G Range Expander
Running the Setup Wizard
Wireless-G Range Expander
9. The Configure Network Address Settings screen will appear. Enter an IP Address and appropriate Subnet
Mask for the Range Expander. Then enter the IP Address of your network gateway, as well as a descriptive
name for the Range Expander. Then, click Next to continue or Back to return to the previous screen.
• IP Address. This IP address must be unique to your network. (The default IP address is 192.168.1.240.) If
you are not sure about what to do, keep the default IP address.
• Subnet Mask. The Range Expander's Subnet Mask must be the same as your network’s Subnet Mask.
• Gateway. This IP address should be the IP address of the gateway device that permits communication
between the Internet and the local network (this is usually your network router). If you are not sure about
what to enter, keep the default Gateway IP address.
• Expander Name. You can assign the Range Expander any name up to 32 characters in length, such as its
location (garage, downstairs, living room).
10. If you have the WRE54G v2, proceed to step 11.
If you have the WRE54G v1, enter the MAC address of your access point or wireless router. You can find the
MAC address on a label located on the bottom panel of the access point or wireless router. Then, click Next to
continue or Back to return to the previous screen.
Figure 5-11: Configure Network Address Settings
Figure 5-12: MAC Address of Access Point or
Wireless Router (WRE54G v1 Only)
gateway: a device that interconnects networks with
different, incompatible communications protocols.
ip address: the address used to identify a computer or device
on a network.
subnet mask: an address code that determines the
size of the network.
mac address: the unique address that a
manufacturer assigns to each networking device.

15
Chapter 5: Setting Up the Wireless-G Range Expander
Running the Setup Wizard
Wireless-G Range Expander
11. You should now review the settings you've chosen. If these settings are correct, click Yes to save these
settings. If you wish to change any of the settings, click No. You will exit the Setup Wizard and can start it
again to change your settings.
12. The configuration performed with the Setup Wizard is complete. Click Online Registration to register the
Range Expander, or click Exit to exit the Setup Wizard.
To configure another Range Expander in your network, run this Setup Wizard again.
Proceed to the next section, “Moving the Range Expander.”
Figure 5-13: Confirmation Screen
Figure 5-14: Congratulations Screen
16
Chapter 5: Setting Up the Wireless-G Range Expander
Moving the Range Expander
Wireless-G Range Expander
Moving the Range Expander
1. If necessary, disconnect the Ethernet network cable from your network router and the Range Expander.
2. Unplug the power plate from the power outlet.
3. Locate an optimum location for the Range Expander. The best placement is usually at the edge of your
wireless network.
4. Fix the direction of the antenna. Try to place it in a position that will best cover your wireless network.
Normally, the higher you place the Range Expander’s antenna, the better the performance will be. Proper
positioning of the antenna can enhance its receiving sensitivity.
5. Connect the power plate to a power outlet, preferably a surge protector.
Congratulations! The installation of the Wireless-G Range Expander is complete.
If you want to make any advanced configuration changes, proceed to “Chapter 6: Configuring the
Wireless-G Range Expander.”
Figure 5-15: Using the Power Plate
with Cord
Figure 5-16: Using the
Power Plate with Plug

17
Chapter 5: Configuring the Wireless-G Range Expander
Overview
Wireless-G Range Expander
Chapter 6: Configuring the Wireless-G Range Expander
Overview
The Range Expander has been designed to be functional right out of the box, setting it up with the Auto
configuration button or the Setup Wizard. However, if you'd like to change these settings, the Range Expander
can be configured through your web browser and Web-based Utility. This chapter describes the Web-based
Utility and its different features.
Accessing the Web-based Utility
Open your web browser and enter the IP address you entered in the Setup Wizard. (If you kept the Range
Expander’s default IP address or used the Auto configuration button, the default IP address is 192.168.1.240.)
Press the Enter key and the login screen will appear. Leave the User Name field blank. The first time you open the
Web-based Utility, enter the default password admin. You can set a new password from the Password tab.
Note: The Range Expander is designed to function
properly after using the Auto configuration button or
Setup Wizard. This chapter is provided solely for
those who wish to perform more advanced
configuration or monitoring.
Figure 6-1: Login Screen
browser: an application program that provides a way to look
at and interact with all the information on the World Wide Web.

18
Chapter 5: Configuring the Wireless-G Range Expander
The Setup Tab
Wireless-G Range Expander
The Setup Tab
Basic Setup
The first screen that appears displays the Basic Setup screen. This allows you to change the Range Expander's
general settings. Change these settings as described here and click Save Settings to apply your changes, or
click Cancel Changes to cancel your changes. If you require more information, click Help.
•Firmware. This will display the Range Expander's current firmware version. Firmware can be upgraded from
the Help tab.
•Name. You may assign any name to the Range Expander. Unique, memorable names are helpful, especially if
you are employing multiple Range Expanders on the same network. Verify this is the name you wish to use
and click Save Settings to set it.
Wireless
The selections under this heading allow you to configure the Range Expander’s connection to your wireless
network.
•IP Address. The IP address must be unique to your network. We suggest you use the default IP address of
192.168.1.240.
•Subnet Mask. The Subnet Mask must be the same as that set on your wireless network.
•Gateway. If you have assigned a static IP address to the access point, then enter the IP address of your
network’s Gateway (usually your network router) in the Gateway field.
•Mode. Select Mixed and both Wireless-G and Wireless-B computers will be allowed on the network, but the
speed will be reduced. Select G-Only for maximum speed if your network only has Wireless-G products. The
final selection, B-Only, allows only Wireless-B products on the network.
•SSID. The SSID is the name shared among all devices in a wireless network. It is case-sensitive and must not
exceed 32 alphanumeric characters, which may be any keyboard character. Make sure this setting is the
same for all devices in your wireless network. For added security, you should change the SSID from the
default name, linksys, to a unique name.
•SSID Broadcast. This allows the SSID to be broadcast on your network. You may want to enable this function
while configuring your network, but make sure that you disable it when you are finished. With this enabled,
someone could easily obtain the SSID information with site survey software and gain unauthorized access to
Figure 6-2: Setup Tab - Basic Setup
firmware: the programming code that runs a
networking device
19
Chapter 5: Configuring the Wireless-G Range Expander
The Setup Tab
Wireless-G Range Expander
your network. Click Enable to broadcast the SSID to all wireless devices in range. Click Disable to increase
network security and prevent the SSID from being seen during a site survey.
•Channel. Select the appropriate channel from the list provided to correspond with your network settings. All
devices in your wireless network must use the same channel to function correctly.
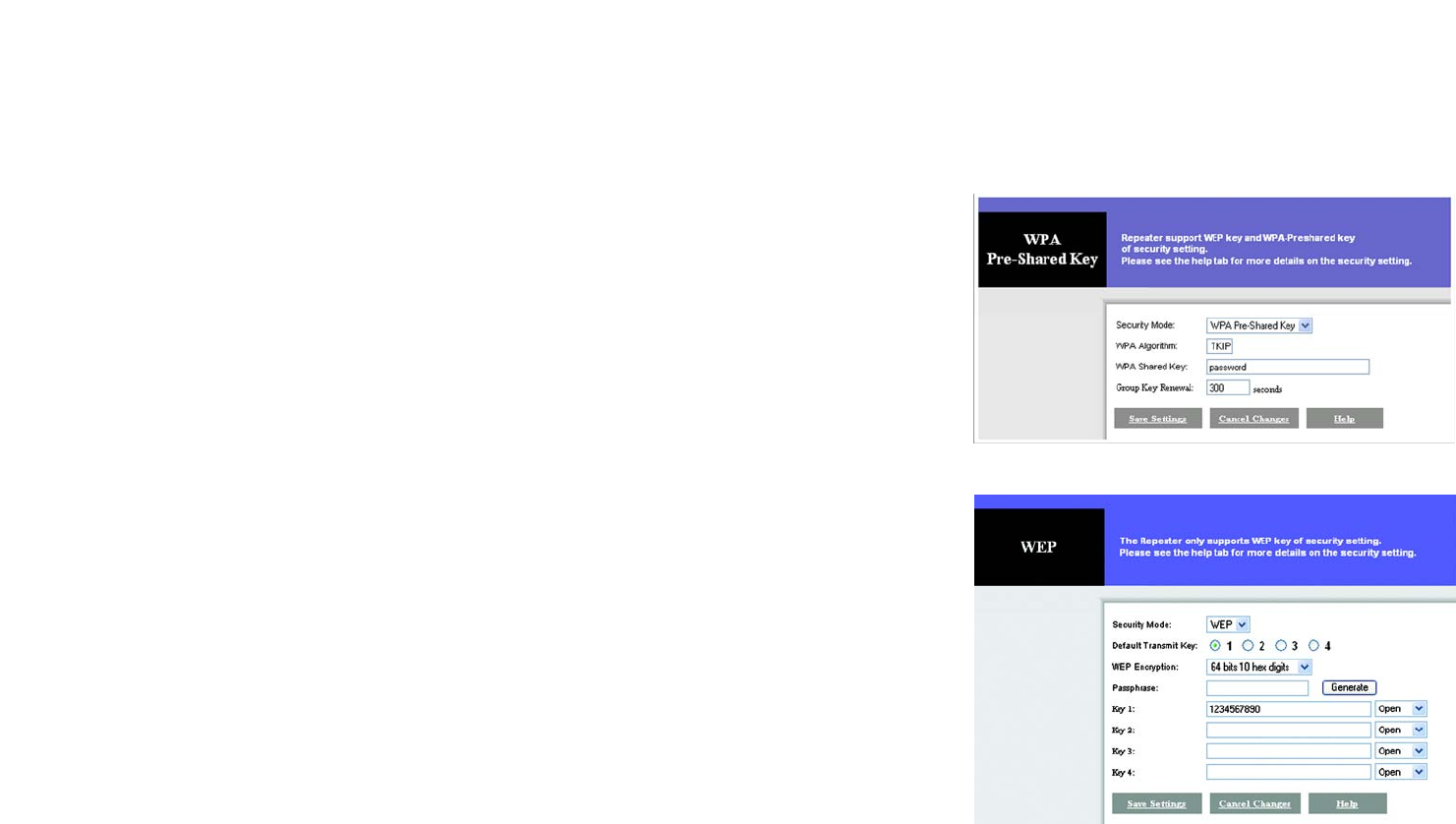
•Wireless Security. To disable wireless security, select the Disable radio button. To enable wireless security,
select the Enable radio button. Then to change the security settings to match your network, click the Edit
Security Settings button. A new window will appear. Configure the appropriate WEP or WPA settings.
WPA
Security Mode. If your network uses WPA security, then select WPA Pre-Shared Key.
WPA Algorithm. TKIP is automatically selected.
WPA Shared Key. Enter the pre-shared key (also called passphrase) for your network. It must have between
8 to 63 characters in length.
Group Key Renewal. You can specify how often you want the dynamic encryption keys to change. Enter the
number of seconds in the field provided.
Click the Save Settings button to save these changes, or click the Cancel Changes button to undo your
changes. If you require more information, click Help.
WEP
Security Mode. If your network uses WPA security, then select WEP.
Default Transmit Key. Select the key you want to use as the Range Expander’s default WEP key.
WEP Encryption. Select the level of WEP encryption you wish to use, 64-bit 10 hex digits or 128-bit 26 hex
digits. Higher encryption levels offer higher levels of security, but due to the complexity of the encryption,
they may decrease network performance.
Passphrase. Instead of manually entering WEP keys, you can enter a Passphrase. This Passphrase is used to
generate one or more WEP keys. It is case-sensitive and should not have more than 16 alphanumeric
characters. (This Passphrase function is compatible with Linksys wireless products only. If you want to
communicate with non-Linksys wireless products, enter the WEP key manually on the non-Linksys wireless
products.) After you enter the Passphrase, click the Generate button to create WEP keys.
Figure 6-4: WEP Security
encryption: encoding data transmitted in a network
passphrase: used much like a password, a passphrase
simplifies the WEP encryption process by automatically
generating the WEP encryption keys for Linksys products.
Figure 6-3: WPA Security

20
Chapter 5: Configuring the Wireless-G Range Expander
The Setup Tab
Wireless-G Range Expander
Keys 1-4. WEP keys enable you to create an encryption scheme for wireless transmissions. If you are not
using a Passphrase, then manually enter a set of values. (Do not leave a key field blank, and do not enter all
zeroes. These are not valid key values.)
If you are using 64-bit WEP encryption, then the key must be exactly 10 hexadecimal characters in length. If
you are using 128-bit WEP encryption, then the key must be exactly 26 hexadecimal characters in length.
Valid hexadecimal characters are “0”-“9” and “A”-“F”.
For each WEP key, select the authentication method you want to use, Open key or Shared key. For Open key
authentication, the sender and recipient do not share a WEP key for authentication. For Shared key
authentication, both the sender and recipient share a WEP key for authentication.
Click the Save Settings button to save these changes, or click the Cancel Changes button to undo your
changes. If you require more information, click Help.
When you have finished making your changes on the Basic Setup screen, click the Save Settings button to save
these changes, or click the Cancel Changes button to undo your changes. If you require additional information,
click the Help button.
21
Chapter 5: Configuring the Wireless-G Range Expander
The Setup Tab
Wireless-G Range Expander
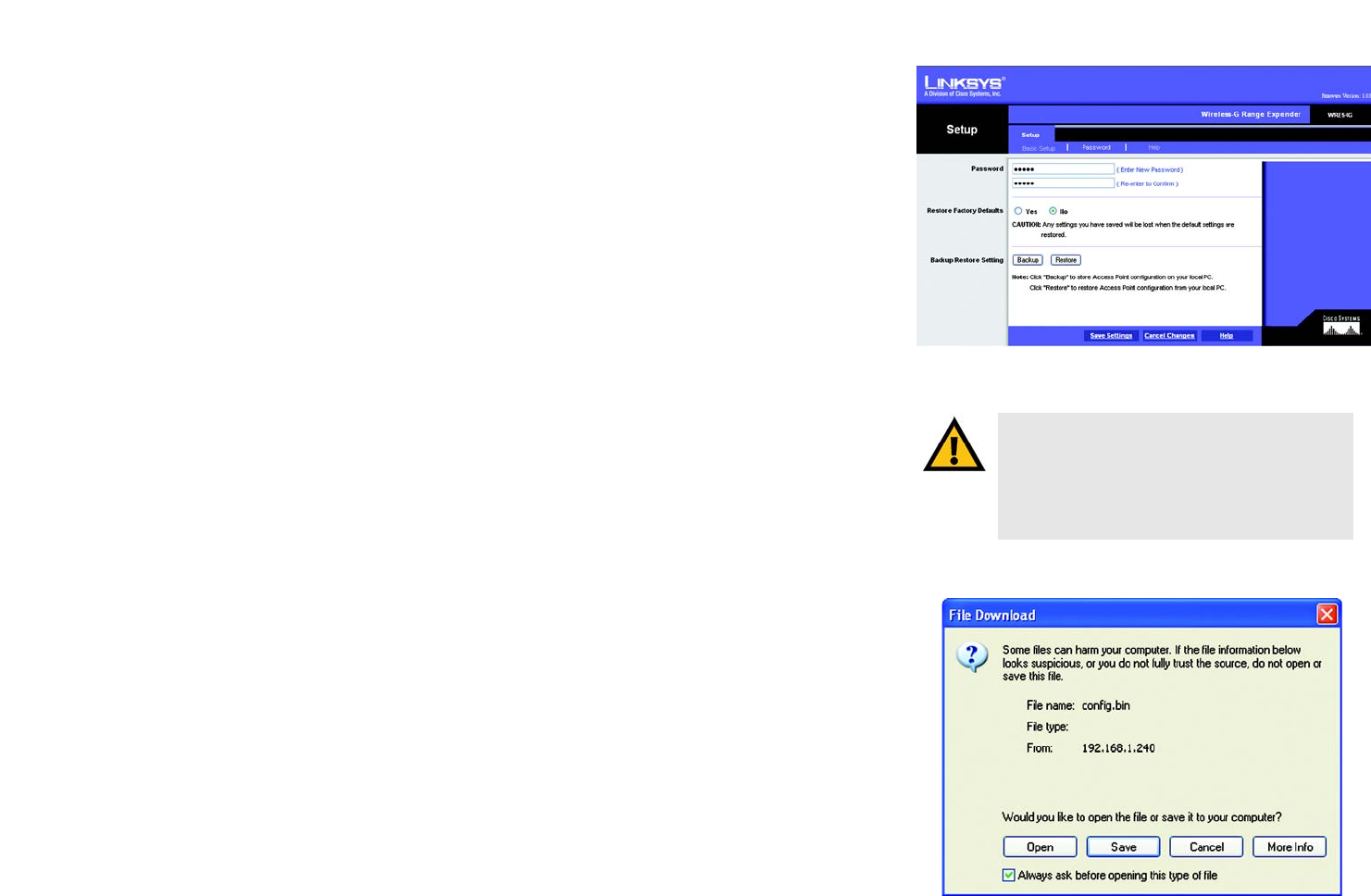
Password
The Password screen allows you to change the Range Expander's password or restore factory defaults. You can
also back up or restore the Range Expander’s configuration file.
•Password. This password protects access to the Web-based Utility. Enter the new password in the Password
field. Then enter it again in the next field to confirm it.
•Restore Factory Defaults. To restore the Range Expander's factory default settings, click the Yes radio
button. Then, click the Save Settings button. Otherwise, keep the default, No.
•Backup/Restore Setting. To back up the configuration file of the Range Expander, click the Backup button.
The File Download screen will appear. Click the Save button and follow the on-screen instructions to back up
the file on your PC.
To restore the back-up configuration file, click the Restore button and follow the on-screen instructions.
Click the Save Settings button to apply your changes, or click the Cancel Changes button to cancel your
changes. If you require additional information, click the Help button.
IMPORTANT: Restoring the Range Expander's
factory default settings will erase all of your
Wireless and WEP settings, and replace them with
the factory defaults. Do not reset the Range
Expander if you want to retain these settings.
Figure 6-5: Setup Tab - Password
Figure 6-6: File Download
download: to receive a file transmitted over a network
22
Chapter 5: Configuring the Wireless-G Range Expander
The Setup Tab
Wireless-G Range Expander
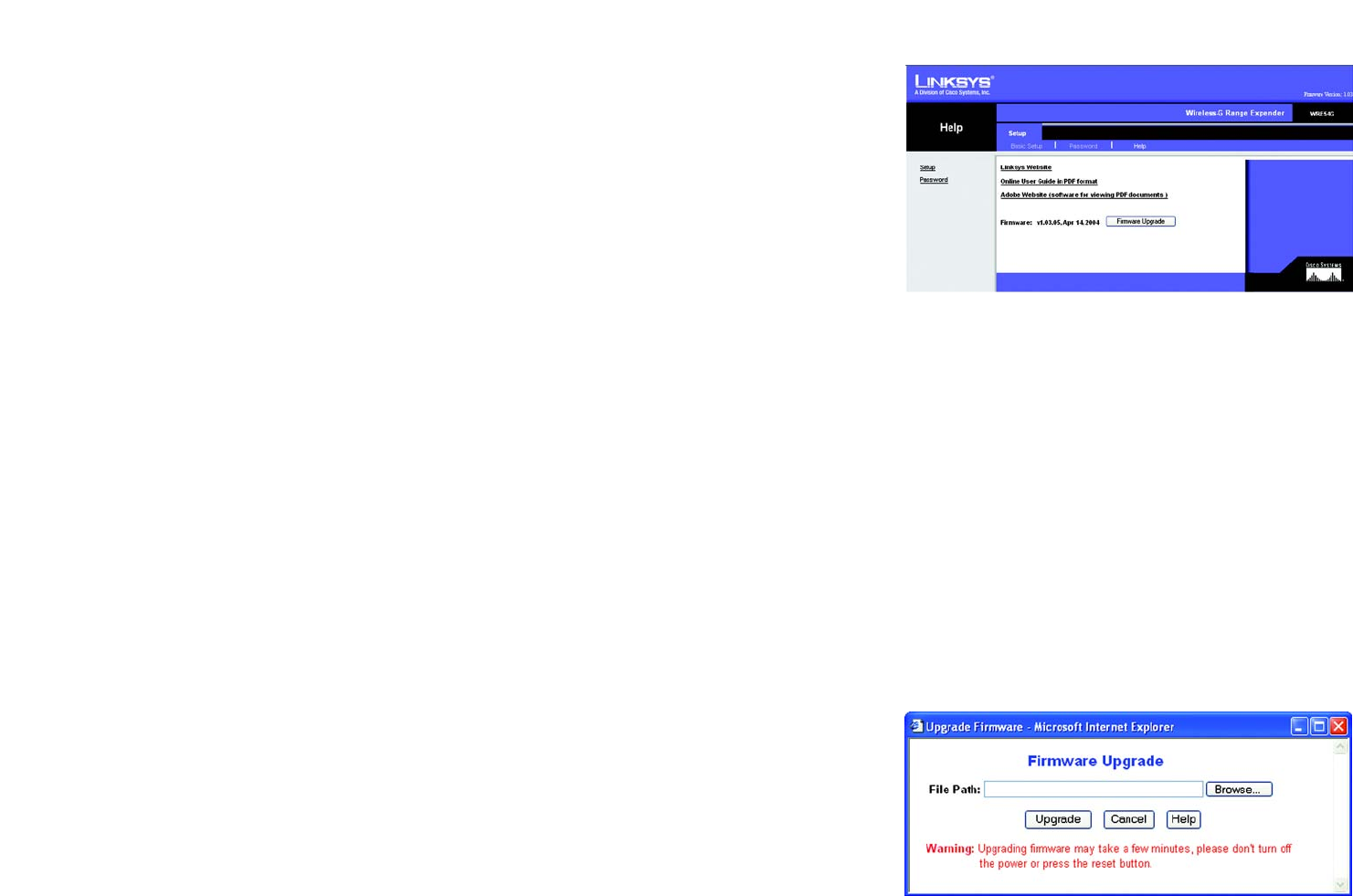
Help
The Help screen offers a variety of resources. If you want help information about the Setup and Password tabs in
this Web-based Utility, click the Help tab. You can also access the Linksys website, online User Guide for the
Range Expander, or the Adobe website (to download the free Adobe Reader program). You can also upgrade the
Range Expander’s firmware using this screen.
The links to the help information for the Setup and Password tabs are listed on the left-hand side of the screen.
Linksys Website. Click the Linksys Website link to connect to the Linksys homepage for extensive help and
product information. (This is available only if you have an active Internet connection.)
Online User Guide in PDF Format. For an online user guide in PDF format, click this link. If you do not have the
Adobe Reader installed on your computer, click the Adobe Website link or go to the Setup Wizard CD-ROM to
download this software. (To access the Adobe website, you will need an active Internet connection.) To download
from the CD-ROM, click the Start button and select Run. Type D:\Acrobat (if “D” is the letter of your CD-ROM
drive).
Adobe Website. Click the Adobe Website link or go to the Setup Wizard CD-ROM to download this software. (To
access the Adobe website, you will need an active Internet connection.)
Firmware Upgrade. The version number and date of the Range Expander’s current firmware is displayed here.
New firmware versions are posted at www.linksys.com and can be downloaded for free. If the Range Expander is
not experiencing difficulties, then there is no need to download a more recent firmware version, unless that
version has a new feature that you want to use. Loading new firmware does not always enhance the speed or
quality of your Internet connection.
To upgrade the Range Expander’s firmware:
1. Go to the Linksys website, www.linksys.com and proceed to the product page for the Range Expander.
2. Download the firmware upgrade file, and extract it on your computer.
3. Click the Upgrade Firmware button on the Help screen.
4. Enter the location of the firmware upgrade file in the File Path field, or click the Browse button to find the
extracted firmware upgrade file.
5. Click the Upgrade button, and follow the on-screen instructions. If you want to cancel the firmware upgrade,
click the Cancel button. If you need more information, click the Help button.
Figure 6-7: Setup Tab - Help
Figure 6-8: Firmware Upgrade
upgrade: to replace existing software or firmware with
a newer version.

23
Appendix A: Troubleshooting
Common Problems and Solutions
Wireless-G Range Expander
Appendix A: Troubleshooting
This appendix consists of two parts: “Common Problems and Solutions” and “Frequently Asked Questions.” This
appendix provides solutions to problems that may occur during the installation and operation of the Wireless-G
Range Expander. Read the description below to solve your problems. If you can't find an answer here, check the
Linksys website at www.linksys.com.
Common Problems and Solutions
1. The Wireless-G Range Expander will not connect to my Wireless-G network.
Go through this checklist:
• Verify that your PC can communicate with your wireless network.
• Press the Range Expander’s reset button (with a pin or a pen) for five seconds. This should reset the
Range Expander’s settings back to their defaults.
• Disconnect the Range Expander’s power for 30 seconds. Then, connect the power again.
• Press the Auto configuration button on the side of the Range Expander. As long as it is within range of an
access point or wireless router that has WEP encryption disabled, it should communicate with that access
point or wireless router.
2. The Setup Wizard does not detect the Range Expander.
Go through this checklist:
• Press the Range Expander’s reset button (with a pin or a pen) for five seconds. This should reset the
Range Expander’s settings back to their defaults.
• Disconnect the Range Expander’s power for 30 seconds. Then, connect the power again.
Frequently Asked Questions
Can I run an application from a remote computer over the wireless network?
This will depend on whether or not the application is designed to be used over a network. Consult the
application’s user guide to determine if it supports operation over a network.
Can I play multiplayer games with other users of the wireless network?
Yes, as long as the game supports multiple players over a network. Refer to the game’s user guide for more
information.

24
Appendix A: Troubleshooting
Frequently Asked Questions
Wireless-G Range Expander
What is the IEEE 802.11b standard?
It is one of the IEEE standards for wireless networks. The 802.11b standard allows wireless networking hardware
from different manufacturers to communicate, provided that the hardware complies with the 802.11b standard.
The 802.11b standard states a maximum data transfer rate of 11Mbps and an operating frequency of 2.4GHz.
What is the IEEE 802.11g standard?
It is one of the IEEE standards for wireless networks. The 802.11g standard allows wireless networking hardware
from different manufacturers to communicate, provided that the hardware complies with the 802.11g standard.
The 802.11g standard states a maximum data transfer rate of 54Mbps and an operating frequency of 2.4GHz.
What IEEE 802.11b features are supported?
The product supports the following IEEE 802.11 functions:
•CSMA/CA plus Acknowledge protocol
•Multi-Channel Roaming
•Automatic Rate Selection
•RTS/CTS feature
•Fragmentation
•Power Management
What IEEE 802.11g features are supported?
The product supports the following IEEE 802.11g functions:
• CSMA/CA plus Acknowledge protocol
• OFDM protocol
• Multi-Channel Roaming
• Automatic Rate Selection
• RTS/CTS feature
• Fragmentation
• Power Management
What is Ad-hoc?
An Ad-hoc wireless network is a group of computers, each with a wireless adapter, connected as an independent
wireless network. An Ad-hoc wireless network is applicable at a departmental scale for a branch or SOHO
operation.
What is Infrastructure?
An integrated wireless and wired network is called an Infrastructure configuration. Infrastructure is applicable to
enterprise scale for wireless access to a central database, or wireless application for mobile workers.

25
Appendix A: Troubleshooting
Frequently Asked Questions
Wireless-G Range Expander
What is Roaming?
Roaming is the ability of a portable computer to communicate continuously while it and its user are moving freely
throughout an area greater than that covered by a single access point. Before using the roaming function, the
user must make sure that the workstation is set to the same channel number used by the access point of the
dedicated coverage area.
To achieve true seamless connectivity, the wireless network must incorporate a number of different functions.
Each node, for example, must always acknowledge receipt of each message. Each node must maintain contact
with the wireless network even when not actually transmitting data. Achieving these functions simultaneously
requires a dynamic RF networking technology that links nodes. In such a system, the user’s end node undertakes
a search for the best possible access to the system. First, it evaluates such factors as signal strength and quality,
as well as the message load currently being carried in the network. Based on that information, the node next
selects the right access point and registers its address. Communications between end node and host computer
can then be transmitted up and down the backbone.
As the user moves on, the end node’s RF transmitter regularly checks the system to determine whether it is in
touch with the original access point or whether it should seek a new one. When a node no longer receives
acknowledgment from its original access point, it undertakes a new search. Upon finding a new access point, it
then re-registers, and the communication process continues.
What is ISM band?
The FCC and their counterparts outside of the U.S. have set aside bandwidth for unlicensed use in the ISM
(Industrial, Scientific and Medical) band. Spectrum in the vicinity of 2.4 GHz, in particular, is being made available
worldwide. This presents a truly revolutionary opportunity to place convenient high speed wireless capabilities in
the hands of users around the globe.
What is Spread Spectrum?
Spread Spectrum technology is a wideband radio frequency technique developed by the military for use in
reliable, secure, mission-critical communications systems. It is designed to trade off bandwidth efficiency for
reliability, integrity, and security. In other words, more bandwidth is consumed than in the case of narrowband
transmission, but the trade-off produces a signal that is, in effect, louder and thus easier to detect, provided that
the receiver knows the parameters of the spread-spectrum signal being broadcast. If a receiver is not tuned to
the right frequency, a spread-spectrum signal looks like background noise. There are two main alternatives,
Direct Sequence Spread Spectrum (DSSS) and Frequency Hopping Spread Spectrum (FHSS).
What is DSSS? What is FHSS? And what are their differences?
Frequency Hopping Spread Spectrum (FHSS) uses a narrowband carrier that changes frequency in a pattern that
is known to both transmitter and receiver. Properly synchronized, the net effect is to maintain a single logical
channel. To an unintended receiver, FHSS appears to be short-duration impulse noise. Direct Sequence Spread
Spectrum (DSSS) generates a redundant bit pattern for each bit to be transmitted. This bit pattern is called a chip

26
Appendix A: Troubleshooting
Frequently Asked Questions
Wireless-G Range Expander
(or chipping code). The longer the chip, the greater the probability that the original data can be recovered. Even if
one or more bits in the chip are damaged during transmission, statistical techniques embedded in the radio can
recover the original data without the need for retransmission. To an unintended receiver, DSSS appears as low
power wideband noise and is rejected (ignored) by most narrowband receivers.
Would the information be intercepted while transmitting on air?
Wireless networks feature two-fold protection. On the hardware side, as with Direct Sequence Spread Spectrum
technology, it has the inherent security feature of scrambling. On the software side, the wireless series offers the
encryption function (WEP) to enhance security and access control. Users can set it up depending upon their
needs.
Can Linksys Wireless products support file and printer sharing?
Linksys Wireless products can work with Netware, Windows NT/2000, or other operating systems to support
printer or file sharing.
What is WEP?
WEP is Wired Equivalent Privacy, a data privacy mechanism based on a 40-bit shared-key algorithm, as described
in the IEEE 802.11 standard.
What is a MAC Address?
The Media Access Control (MAC) address is a unique number assigned by the manufacturer to any networking
device, such as a network adapter, that allows the network to identify it at the hardware level. For all practical
purposes, this number is usually permanent. Unlike IP addresses, which can change every time a computer logs
on to the network, the MAC address of a device stays the same, making it a valuable identifier for the network.
How do I avoid interference?
Using multiple access points on the same channel and in close proximity to one another will generate
interference. When employing multiple access points, be sure to operate each one on a different channel
(frequency).
How do I reset the Range Expander?
Press the Reset button on the back of the Range Expander for about ten seconds. This will reset the unit to its
default settings.
How do I resolve issues with signal loss?
There is no way to know the exact range of your wireless network without testing. Every obstacle placed between
points in a network will create signal loss. Leaded glass, metal, concrete floors, water and walls will inhibit the
signal and reduce range. Start with your access point and your wireless PC in the same room and move it away
in small increments to determine the maximum range in your environment. You may also try using different
channels, as this may eliminate interference affecting only one channel.
27
Appendix B: Wireless Security
Security Precautions
Wireless-G Range Expander
Appendix B: Wireless Security
Linksys wants to make wireless networking as safe and easy for you as possible. The current generation of
Linksys products provide several network security features, but they require specific action on your part for
implementation. So, keep the following in mind whenever you are setting up or using your wireless network.
Security Precautions
The following is a complete list of security precautions to take (as shown in this User Guide) (at least steps 1
through 5 should be followed):
1. Change the default SSID.
2. Disable SSID Broadcast.
3. Change the default password for the Administrator account.
4. Enable MAC Address Filtering.
5. Change the SSID periodically.
6. Use the highest encryption algorithm possible. Use WPA if it is available. Please note that this may reduce
your network performance.
7. Change the WEP encryption keys periodically.
To ensure network security, steps one through five should be followed, at least.
Security Threats Facing Wireless Networks
Wireless networks are easy to find. Hackers know that in order to join a wireless network, wireless networking
products first listen for “beacon messages”. These messages can be easily decrypted and contain much of the
network’s information, such as the network’s SSID (Service Set Identifier). Here are the steps you can take:
Change the administrator’s password regularly. With every wireless networking device you use, keep in mind
that network settings (SSID, WEP keys, etc.) are stored in its firmware. Your network administrator is the only
person who can change network settings. If a hacker gets a hold of the administrator’s password, he, too, can
change those settings. So, make it harder for a hacker to get that information. Change the administrator’s
password regularly.
NOTE: Some of these security features are
available only through the network router or
access point. Refer to the router or access
point’s documentation for more information.
28
Appendix B: Wireless Security
Security Threats Facing Wireless Networks
Wireless-G Range Expander
SSID. There are several things to keep in mind about the SSID:
1. Disable Broadcast
2. Make it unique
3. Change it often
Most wireless networking devices will give you the option of broadcasting the SSID. While this option may be
more convenient, it allows anyone to log into your wireless network. This includes hackers. So, don’t broadcast
the SSID.
Wireless networking products come with a default SSID set by the factory. (The Linksys default SSID is “linksys”.)
Hackers know these defaults and can check these against your network. Change your SSID to something unique
and not something related to your company or the networking products you use.
Change your SSID regularly so that any hackers who have gained access to your wireless network will have to
start from the beginning in trying to break in.
MAC Addresses. Enable MAC Address filtering. MAC Address filtering will allow you to provide access to only
those wireless nodes with certain MAC Addresses. This makes it harder for a hacker to access your network with
a random MAC Address.
WEP Encryption. Wired Equivalent Privacy (WEP) is often looked upon as a cure-all for wireless security
concerns. This is overstating WEP’s ability. Again, this can only provide enough security to make a hacker’s job
more difficult.
There are several ways that WEP can be maximized:
1. Use the highest level of encryption possible
2. Use “Shared Key” authentication
3. Change your WEP key regularly
WPA. Wi-Fi Protected Access (WPA) is the newest and best available standard in Wi-Fi security. Two modes are
available: Pre-Shared Key and RADIUS. Pre-Shared Key gives you a choice of two encryption methods: TKIP
(Temporal Key Integrity Protocol), which utilizes a stronger encryption method and incorporates Message
Integrity Code (MIC) to provide protection against hackers, and AES (Advanced Encryption System), which utilizes
a symmetric 128-Bit block data encryption. RADIUS (Remote Authentication Dial-In User Service) utilizes a
RADIUS server for authentication and the use of dynamic TKIP, AES, or WEP.
IMPORTANT: Always remember that each
device in your wireless network MUST use
the same encryption method and encryption
key or your wireless network will not function
properly.

29
Appendix B: Wireless Security
Security Threats Facing Wireless Networks
Wireless-G Range Expander
WPA Pre-Shared Key. If you do not have a RADIUS server, select the type of algorithm, TKIP or AES, enter a
password in the Pre-Shared key field of 8-64 characters, and enter a Group Key Renewal period time between
0 and 99,999 seconds, which instructs the Router or other device how often it should change the encryption
keys.
WPA RADIUS. WPA used in coordination with a RADIUS server. (This should only be used when a RADIUS
server is connected to the Router or other device.) First, select the type of WPA algorithm, TKIP or AES. Enter
the RADIUS server’s IP Address and port number, along with a key shared between the device and the server.
Last, enter a Group Key Renewal period, which instructs the device how often it should change the encryption
keys.
RADIUS. WEP used in coordination with a RADIUS server. (This should only be used when a RADIUS server is
connected to the Router or other device.) First, enter the RADIUS server’s IP Address and port number, along
with a key shared between the device and the server. Then, select a WEP key and a level of WEP encryption,
and either generate a WEP key through the Passphrase or enter the WEP key manually.
Implementing encryption may have a negative impact on your network’s performance, but if you are transmitting
sensitive data over your network, encryption should be used.
These security recommendations should help keep your mind at ease while you are enjoying the most flexible
and convenient technology Linksys has to offer.

30
Appendix C: Upgrading Firmware
Wireless-G Range Expander
Appendix C: Upgrading Firmware
The Range Expander's firmware is upgraded through the Web-Utility's Help tab. Follow these instructions:
1. Go to the Linksys website, www.linksys.com and proceed to the product page for the Range Expander.
2. Download the firmware upgrade file, and extract it on your computer.
3. Click the Upgrade Firmware button on the Help screen.
4. Enter the location of the firmware upgrade file in the File Path field, or click the Browse button to find the
extracted firmware upgrade file.
5. Click the Upgrade button, and follow the on-screen instructions. If you want to cancel the firmware upgrade,
click the Cancel button. If you need more information, click the Help button.
Figure C-1: Upgrade Firmware

31
Appendix D: Windows Help
Wireless-G Range Expander
Appendix D: Windows Help
Almost all wireless products require Microsoft Windows. Windows is the most used operating system in the world
and comes with many features that help make networking easier. These features can be accessed through
Windows Help and are described in this appendix.
TCP/IP
Before a computer can communicate within a network, TCP/IP must be enabled. TCP/IP is a set of instructions, or
protocol, all PCs follow to communicate over a network. This is true for wireless networks as well. Your PCs will
not be able to utilize wireless networking without having TCP/IP enabled. Windows Help provides complete
instructions on enabling TCP/IP.
Shared Resources
If you wish to share printers, folder, or files over your network, Windows Help provides complete instructions on
utilizing shared resources.
Network Neighborhood/My Network Places
Other PCs on your network will appear under Network Neighborhood or My Network Places (depending upon the
version of Windows you're running). Windows Help provides complete instructions on adding PCs to your
network.

32
Appendix E: Glossary
Wireless-G Range Expander
Appendix E: Glossary
802.11b - A wireless networking standard that specifies a maximum data transfer rate of 11Mbps and an
operating frequency of 2.4GHz.
802.11g - A wireless networking standard that specifies a maximum data transfer rate of 54Mbps, an operating
frequency of 2.4GHz, and backward compatibility with 802.11b devices.
Access Point - A device that allows wireless-equipped computers and other devices to communicate with a
wired network. Also used to expand the range of a wireless network.
Adapter - A device that adds network functionality to your PC.
Ad-hoc - A group of wireless devices communicating directly with each other (peer-to-peer) without the use of
an access point.
AES (Advanced Encryption Standard) - A security method that uses symmetric 128-bit block data encryption.
Backbone - The part of a network that connects most of the systems and networks together, and handles the
most data.
Bandwidth - The transmission capacity of a given device or network.
Bit - A binary digit.
Bridge - A device that connects different networks.
Browser - An application program that provides a way to look at and interact with all the information on the
World Wide Web.
Byte - A unit of data that is usually eight bits long
Cable Modem - A device that connects a computer to the cable television network, which in turn connects to the
Internet.
CSMA/CA (Carrier Sense Multiple Access/Collision Avoidance) - A method of data transfer that is used to prevent
data collisions.
CTS (Clear To Send) - A signal sent by a wireless device, signifying that it is ready to receive data.

33
Appendix E: Glossary
Wireless-G Range Expander
Download - To receive a file transmitted over a network.
DSL (Digital Subscriber Line) - An always-on broadband connection over traditional phone lines.
DSSS (Direct-Sequence Spread-Spectrum) - Frequency transmission with a redundant bit pattern resulting in a
lower probability of information being lost in transit.
Dynamic IP Address - A temporary IP address assigned by a DHCP server.
Encryption - Encoding data transmitted in a network.
Ethernet - A networking protocol that specifies how data is placed on and retrieved from a common transmission
medium.
Finger - A program that tells you the name associated with an e-mail address.
Firewall - A set of related programs located at a network gateway server that protects the resources of a
network from users from other networks.
Firmware - The programming code that runs a networking device.
Fragmentation -Breaking a packet into smaller units when transmitting over a network medium that cannot
support the original size of the packet.
Gateway - A device that interconnects networks with different, incompatible communications protocols.
Hardware - The physical aspect of computers, telecommunications, and other information technology devices.
HTTP (HyperText Transport Protocol) - The communications protocol used to connect to servers on the World
Wide Web.
Infrastructure - A wireless network that is bridged to a wired network via an access point.
IP (Internet Protocol) - A protocol used to send data over a network.
IP Address - The address used to identify a computer or device on a network.
ISM band - Radio bandwidth utilized in wireless transmissions.
ISP (Internet Service Provider) - A company that provides access to the Internet.
LAN - The computers and networking products that make up your local network.

34
Appendix E: Glossary
Wireless-G Range Expander
MAC (Media Access Control) Address - The unique address that a manufacturer assigns to each networking
device.
Mbps (MegaBits Per Second) - One million bits per second; a unit of measurement for data transmission.
mIRC - An Internet Relay Chat program that runs under Windows.
Multicasting - Sending data to a group of destinations at once.
Network - A series of computers or devices connected for the purpose of data sharing, storage, and/or
transmission between users.
Node - A network junction or connection point, typically a computer or work station.
Packet - A unit of data sent over a network.
Passphrase - Used much like a password, a passphrase simplifies the WEP encryption process by automatically
generating the WEP encryption keys for Linksys products.
Port - The connection point on a computer or networking device used for plugging in cables or adapters.
RADIUS (Remote Authentication Dial-In User Service) - A protocol that uses an authentication server to control
network access.
RJ-45 (Registered Jack-45) - An Ethernet connector that holds up to eight wires.
Roaming - The ability to take a wireless device from one access point's range to another without losing the
connection.
Router - A networking device that connects multiple networks together.
RTS (Request To Send) - A networking method of coordinating large packets through the RTS Threshold setting.
Server - Any computer whose function in a network is to provide user access to files, printing, communications,
and other services.
Software - Instructions for the computer. A series of instructions that performs a particular task is called a
“program”.
SOHO (Small Office/Home Office) - Market segment of professionals who work at home or in small offices.
Spread Spectrum - Wideband radio frequency technique used for more reliable and secure data transmission.

35
Appendix E: Glossary
Wireless-G Range Expander
SSID (Service Set IDentifier) - Your wireless network's name.
Static IP Address - A fixed address assigned to a computer or device that is connected to a network.
Static Routing - Forwarding data in a network via a fixed path.
Subnet Mask - An address code that determines the size of the network.
Switch - 1. A data switch that connects computing devices to host computers, allowing a large number of
devices to share a limited number of ports. 2. A device for making, breaking, or changing the connections in an
electrical circuit.
TCP (Transmission Control Protocol) - A network protocol for transmitting data that requires acknowledgement
from the recipient of data sent.
TCP/IP (Transmission Control Protocol/Internet Protocol) - A set of instructions PCs use to communicate over a
network.
Telnet - A user command and TCP/IP protocol used for accessing remote PCs.
Throughput - The amount of data moved successfully from one node to another in a given time period.
Topology - The physical layout of a network.
TX Rate - Transmission Rate.
Upgrade - To replace existing software or firmware with a newer version.
Upload - To transmit a file over a network.
URL (Uniform Resource Locator) - The address of a file located on the Internet.
WEP (Wired Equivalent Privacy) - A method of encrypting network data transmitted on a wireless network for
greater security.
WLAN (Wireless Local Area Network) - A group of computers and associated devices that communicate with
each other wirelessly.
WPA (Wi-Fi Protected Access) - a wireless security protocol using TKIP (Temporal Key Integrity Protocol)
encryption, which can be used in conjunction with a RADIUS server.

36
Appendix F: Specifications
Wireless-G Range Expander
Appendix F: Specifications
Standards IEEE 802.11g, IEEE 802.11b
Port Ethernet
Buttons Auto configuration/Mode, Reset
LEDs Blue/Red-LINK, Blue-ACTIVITY
Transmit Power 802.11g: Typ. 13±1 1dBm @ Normal Temp Range
802.11b: Typ: 15±1 1dBm @ Normal Temp Range
Security features WEP
WEP key bits 64/128
Dimensions (W x H x D) 3.18" x 8.27" x 1.77" (80.7 mm x 210 mm x 45 mm)
Power Input: 115-230V AC 0.2A, Output: 3.3V DC 1.5A
Certification FCC, CE, UL
Operating Temp. 0ºC to 40ºC (32ºF to 150ºF)
Storage Temp. 0ºC to 70ºC (-40ºF to 185ºF)
Operating Humidity 10% to 85%, Non-Condensing
Storage Humidity 5% to 90% Non-Condensing

37
Appendix G: Warranty Information
Wireless-G Range Expander
Appendix G: Warranty Information
LIMITED WARRANTY
Linksys warrants to You that, for a period of three years (the “Warranty Period”), your Linksys Product will be substantially
free of defects in materials and workmanship under normal use. Your exclusive remedy and Linksys' entire liability under
this warranty will be for Linksys at its option to repair or replace the Product or refund Your purchase price less any
rebates. This limited warranty extends only to the original purchaser.
If the Product proves defective during the Warranty Period call Linksys Technical Support in order to obtain a Return
Authorization Number, if applicable. BE SURE TO HAVE YOUR PROOF OF PURCHASE ON HAND WHEN CALLING. If You are
requested to return the Product, mark the Return Authorization Number clearly on the outside of the package and include a
copy of your original proof of purchase. RETURN REQUESTS CANNOT BE PROCESSED WITHOUT PROOF OF PURCHASE. You
are responsible for shipping defective Products to Linksys. Linksys pays for UPS Ground shipping from Linksys back to You
only. Customers located outside of the United States of America and Canada are responsible for all shipping and handling
charges.
ALL IMPLIED WARRANTIES AND CONDITIONS OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE ARE LIMITED
TO THE DURATION OF THE WARRANTY PERIOD. ALL OTHER EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND
WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF NON-INFRINGEMENT, ARE DISCLAIMED. Some jurisdictions do not
allow limitations on how long an implied warranty lasts, so the above limitation may not apply to You. This warranty gives
You specific legal rights, and You may also have other rights which vary by jurisdiction.
This warranty does not apply if the Product (a) has been altered, except by Linksys, (b) has not been installed, operated,
repaired, or maintained in accordance with instructions supplied by Linksys, or (c) has been subjected to abnormal
physical or electrical stress, misuse, negligence, or accident. In addition, due to the continual development of new
techniques for intruding upon and attacking networks, Linksys does not warrant that the Product will be free of
vulnerability to intrusion or attack.
TO THE EXTENT NOT PROHIBITED BY LAW, IN NO EVENT WILL LINKSYS BE LIABLE FOR ANY LOST DATA, REVENUE OR PROFIT,
OR FOR SPECIAL, INDIRECT, CONSEQUENTIAL, INCIDENTAL OR PUNITIVE DAMAGES, REGARDLESS OF THE THEORY OF
LIABILITY (INCLUDING NEGLIGENCE), ARISING OUT OF OR RELATED TO THE USE OF OR INABILITY TO USE THE PRODUCT
(INCLUDING ANY SOFTWARE), EVEN IF LINKSYS HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. IN NO EVENT
WILL LINKSYS’ LIABILITY EXCEED THE AMOUNT PAID BY YOU FOR THE PRODUCT. The foregoing limitations will apply even
if any warranty or remedy provided under this Agreement fails of its essential purpose. Some jurisdictions do not allow the
exclusion or limitation of incidental or consequential damages, so the above limitation or exclusion may not apply to You.
Please direct all inquiries to: Linksys, P.O. Box 18558, Irvine, CA 92623.

38
Appendix H: Regulatory Information
Wireless-G Range Expander
Appendix H: Regulatory Information
FCC STATEMENT
This product has been tested and complies with the specifications for a Class B digital device, pursuant to Part 15 of the
FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential
installation. This equipment generates, uses, and can radiate radio frequency energy and, if not installed and used
according to the instructions, may cause harmful interference to radio communications. However, there is no guarantee
that interference will not occur in a particular installation. If this equipment does cause harmful interference to radio or
television reception, which is found by turning the equipment off and on, the user is encouraged to try to correct the
interference by one or more of the following measures:
Reorient or relocate the receiving antenna
Increase the separation between the equipment or devices
Connect the equipment to an outlet other than the receiver's
Consult a dealer or an experienced radio/TV technician for assistance
FCC Radiation Exposure Statement
This equipment complies with FCC radiation exposure limits set forth for an uncontrolled environment. This equipment
should be installed and operated with minimum distance 20cm between the radiator and your body.
INDUSTRY CANADA (CANADA)
This Class B digital apparatus complies with Canadian ICES-003, RSS210.
Cet appareil numérique de la classe B est conforme à la norme NMB-003 du Canada.
The use of this device in a system operating either partially or completely outdoors may require the user to obtain a license
for the system according to the Canadian regulations.
EC DECLARATION OF CONFORMITY (EUROPE)
Linksys declares that this product conforms to the specifications listed below, following the provisions of the European
R&TTE directive 1999/5/EC:
EN 301 489-1, 301 489-17 General EMC requirements for Radio equipment.

39
Appendix H: Regulatory Information
Wireless-G Range Expander
EN 609 50 Safety
EN 300-328-1, EN 300-328-2 Technical requirements for Radio equipment.
Caution: This equipment is intended to be used in all EU and EFTA countries. Outdoor use may be restricted to certain
frequencies and/or may require a license for operation. Contact local Authority for procedure to follow.
Note: Combinations of power levels and antennas resulting in a radiated power level of above 100 mW equivalent isotropic
radiated power (EIRP) are considered as not compliant with the above mentioned directive and are not allowed for use
within the European community and countries that have adopted the European R&TTE directive 1999/5/EC.
For more details on legal combinations of power levels and antennas, contact Linksys Corporate Compliance.
Linksys vakuuttaa täten että dieses produkt tyyppinen laite on direktiivin 1999/5/EY oleellisten vaatimusten ja sitä
koskevien näiden direktiivien muiden ehtojen mukainen.
Linksys déclare que le produit est conforme aux conditions essentielles et aux dispositions relatives à la
directive 1999/5/EC.
Belgique:
Dans le cas d'une utilisation privée, à l'extérieur d'un bâtiment, au-dessus d'un espace public, aucun enregistrement n'est
nécessaire pour une distance de moins de 300m. Pour une distance supérieure à 300m un enregistrement auprès de l'IBPT
est requise. Pour une utilisation publique à l'extérieur de bâtiments, une licence de l'IBPT est requise. Pour les
enregistrements et licences, veuillez contacter l'IBPT.
France:
2.4 GHz Bande : les canaux 10, 11, 12, 13 (2457, 2462, 2467, et 2472 MHz respectivement) sont complétement libres
d'utilisation en France (en utilisation intérieur). Pour ce qui est des autres canaux, ils peuvent être soumis à autorisation
selon le départment. L'utilisation en extérieur est soumis à autorisation préalable et très restreint.
Vous pouvez contacter l'Autorité de Régulation des Télécommunications (http://www.art-telecom.fr) pour de plus amples
renseignements.
SAFETY NOTICES
Caution: To reduce the risk of fire, use only No.26 AWG or larger telecommunication line cord.
Do not use this product near water, for example, in a wet basement or near a swimming pool.
Avoid using this product during an electrical storm. There may be a remote risk of electric shock from lightning.

40
Appendix I: Contact Information
Wireless-G Range Expander
Appendix I: Contact Information
Need to contact Linksys?
Visit us online for information on the latest products and updates
to your existing products at: http://www.linksys.com or
ftp.linksys.com
Can't find information about a product you want to buy
on the web? Do you want to know more about networking
with Linksys products? Give our advice line a call at: 800-546-5797 (LINKSYS)
Or fax your request in to: 949-823-3002
If you experience problems with any Linksys product,
you can call us at: 800-326-7114
Don't wish to call? You can e-mail us at: support@linksys.com
If any Linksys product proves defective during its warranty period,
you can call the Linksys Return Merchandise Authorization
department for obtaining a Return Authorization Number at: 949-823-3000
(Details on Warranty and RMA issues can be found in the Warranty
Information section in this Guide.)
Federal Communication Commission Interference Statement
This equipment has been tested and found to comply with the limits for a
Class B digital device, pursuant to Part 15 of the FCC Rules. These limits
are designed to provide reasonable protection against harmful interference in
a residential installation. This equipment generates, uses and can radiate
radio frequency energy and, if not installed and used in accordance with the
instructions, may cause harmful interference to radio communications.
However, there is no guarantee that interference will not occur in a particular
installation. If this equipment does cause harmful interference to radio or
television reception, which can be determined by turning the equipment off
and on, the user is encouraged to try to correct the interference by one of the
following measures:
- Reorient or relocate the receiving antenna.
- Increase the separation between the equipment and receiver.
- Connect the equipment into an outlet on a circuit different from that
to which the receiver is connected.
- Consult the dealer or an experienced radio/TV technician for help.
This device complies with Part 15 of the FCC Rules. Operation is subject to
the following two conditions: (1) This device may not cause harmful
interference, and (2) this device must accept any interference received,
including interference that may cause undesired operation.
FCC Caution: Any changes or modifications not expressly approved by the
party responsible for compliance could void the user's authority to operate this
equipment.
IMPORTANT NOTE:
FCC Radiation Exposure Statement:
This equipment complies with FCC radiation exposure limits set forth for an
uncontrolled environment. This equipment should be installed and operated
with minimum distance 20cm between the radiator & your body.
This transmitter must not be co-located or operating in conjunction with any
other antenna or transmitter.
Linksys declares that WRE54G ver. 3 (FCC ID: Q87-WRE54GV3 ) is limited
in CH1~CH11 for 2.4 GHz by specified firmware controlled in U.S.A.
IC statement
Operation is subject to the following two conditions:
1) This device may not cause interference and
2) This device must accept any interference, including interference that may
cause undesired operation of the device.
IMPORTANT NOTE:
IC Radiation Exposure Statement:
This equipment complies with IC radiation exposure limits set forth for an
uncontrolled environment. End users must follow the specific operating
instructions for satisfying RF exposure compliance. This equipment should be
installed and operated with minimum distance 20cm between the radiator &
your body.
This transmitter must not be co-located or operating in conjunction with any
other antenna or transmitter.
Règlement d’Industry Canada
Les conditions de fonctionnement sont sujettes à deux conditions:
1) Ce périphérique ne doit pas causer d’interférence et.
2) Ce périphérique doit accepter toute interférence, y compris les interférences
pouvant perturber le bon fonctionnement de ce périphérique.