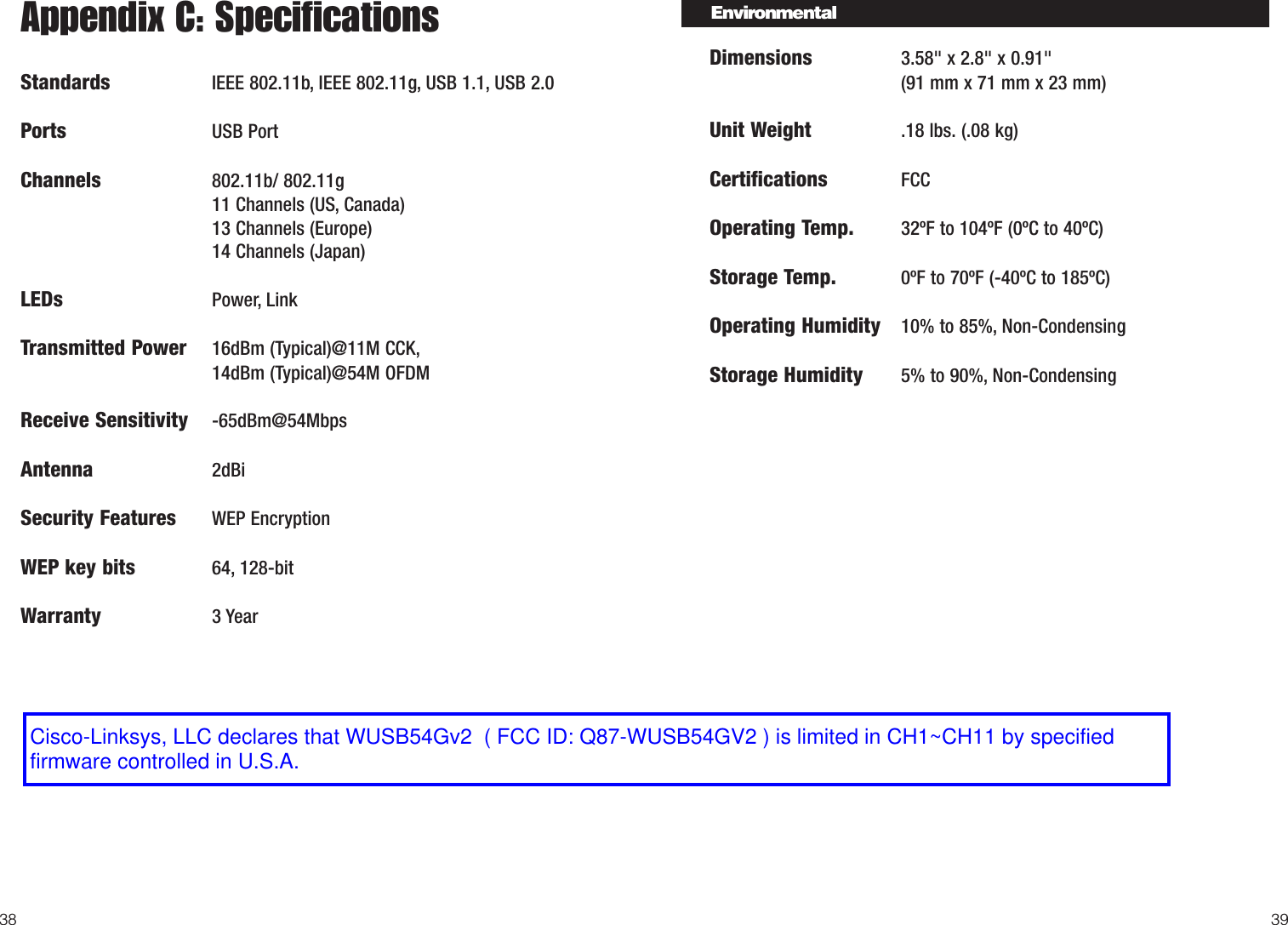
LINKSYS WUSB54GV2 Wireless-G USB Network Adapter User Manual Wusb54G ug Rev A
LINKSYS LLC Wireless-G USB Network Adapter Wusb54G ug Rev A
LINKSYS >
Contents
- 1. Users Manual Part 1
- 2. User Manual Part 2
- 3. Users Manual Part 3
Users Manual Part 3