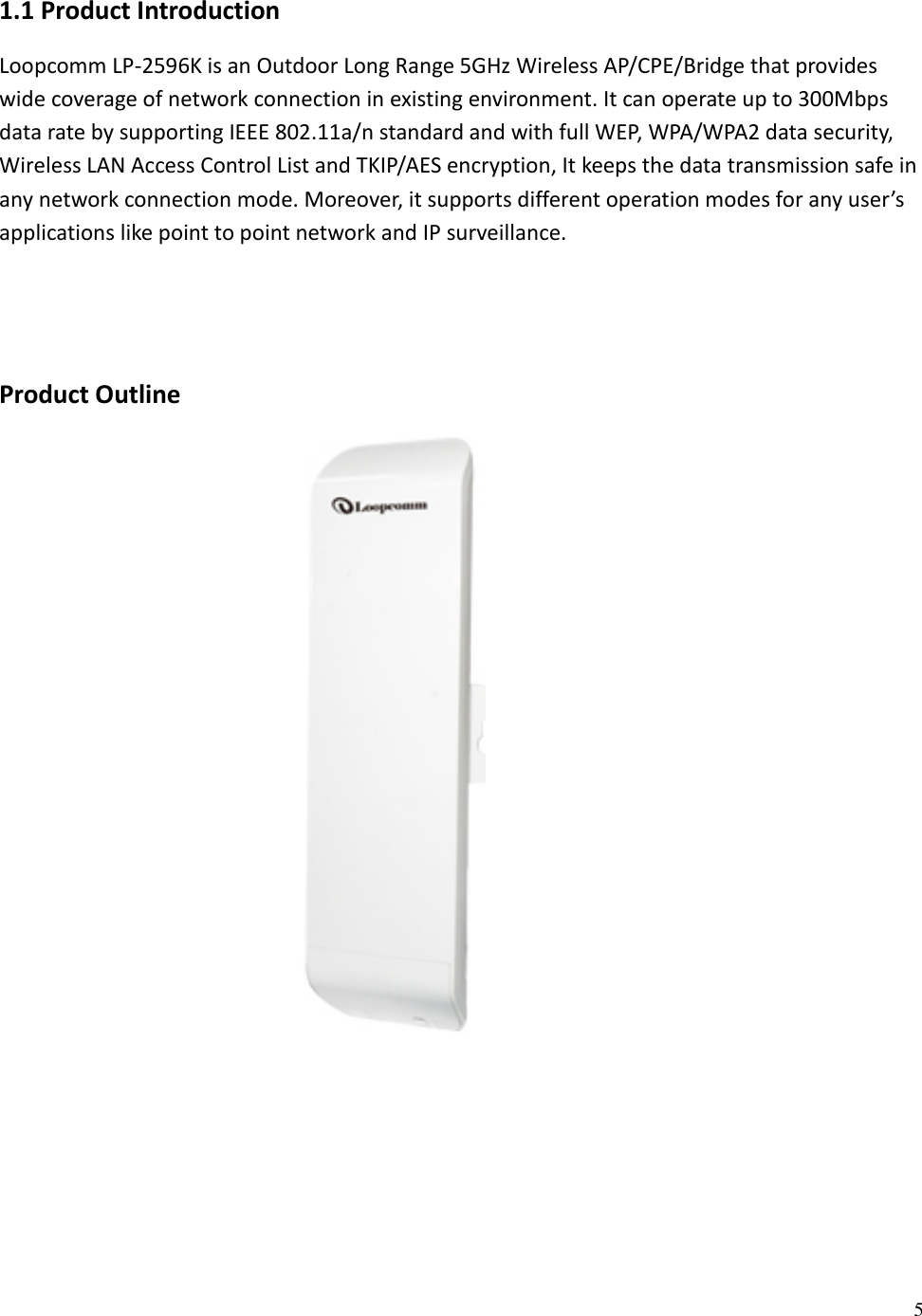
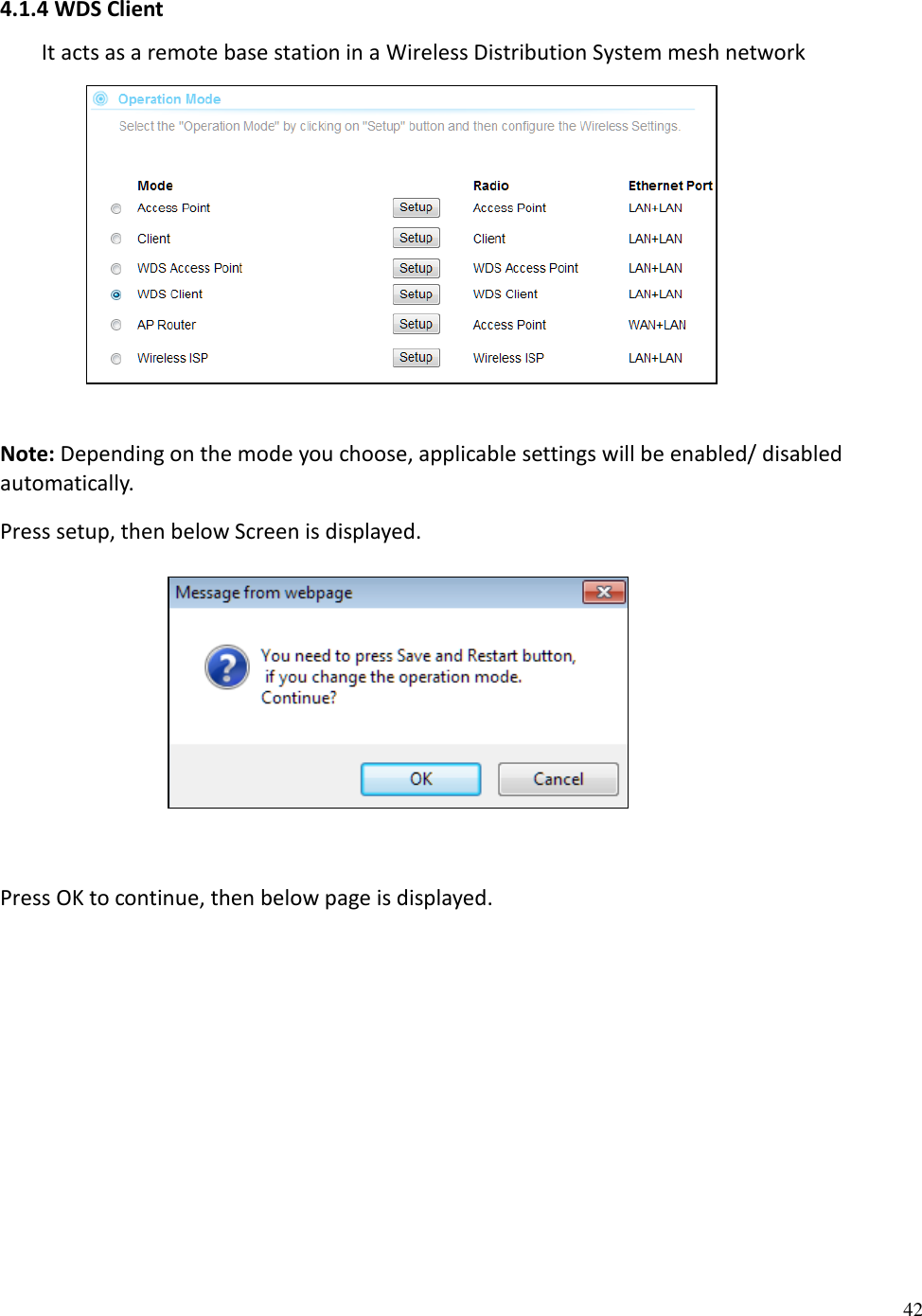
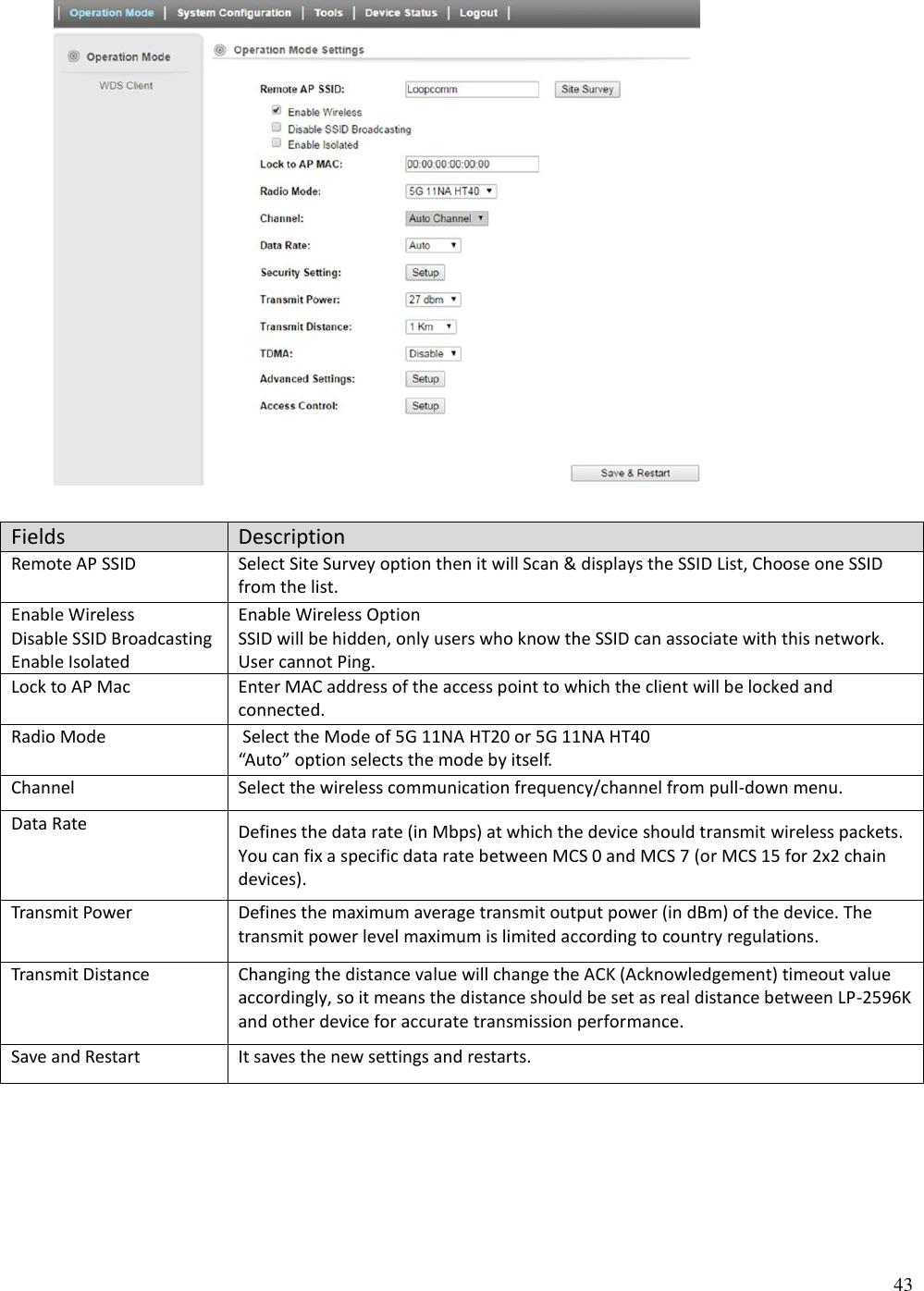
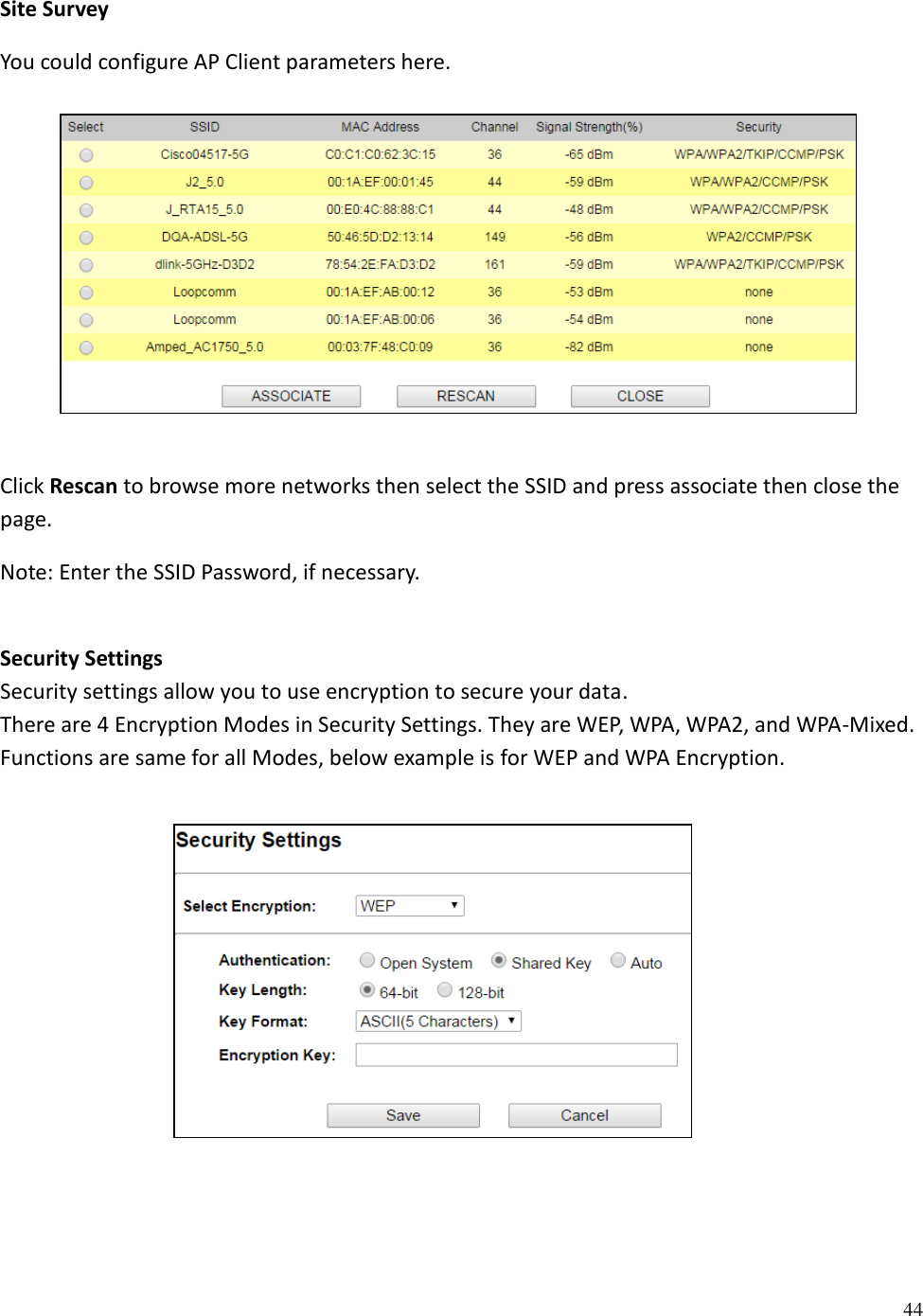
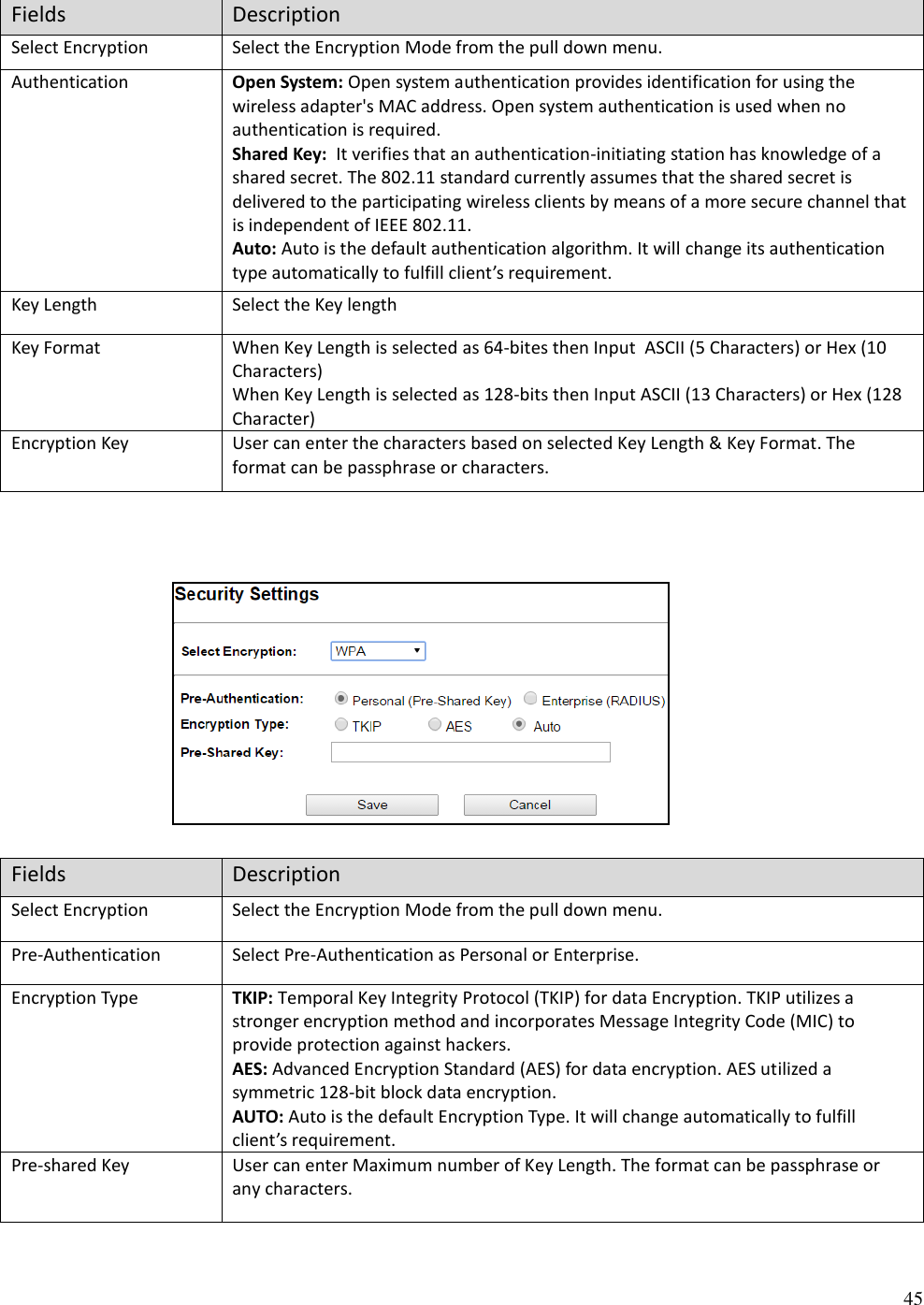
Loopcomm Technology LP2596K 802.11A/N 5GHZ OUTDOOR AP/CPE/BRIDGE User Manual LP 2596K Injector 20141016 no DFS
Loopcomm Technology,.Inc. 802.11A/N 5GHZ OUTDOOR AP/CPE/BRIDGE LP 2596K Injector 20141016 no DFS
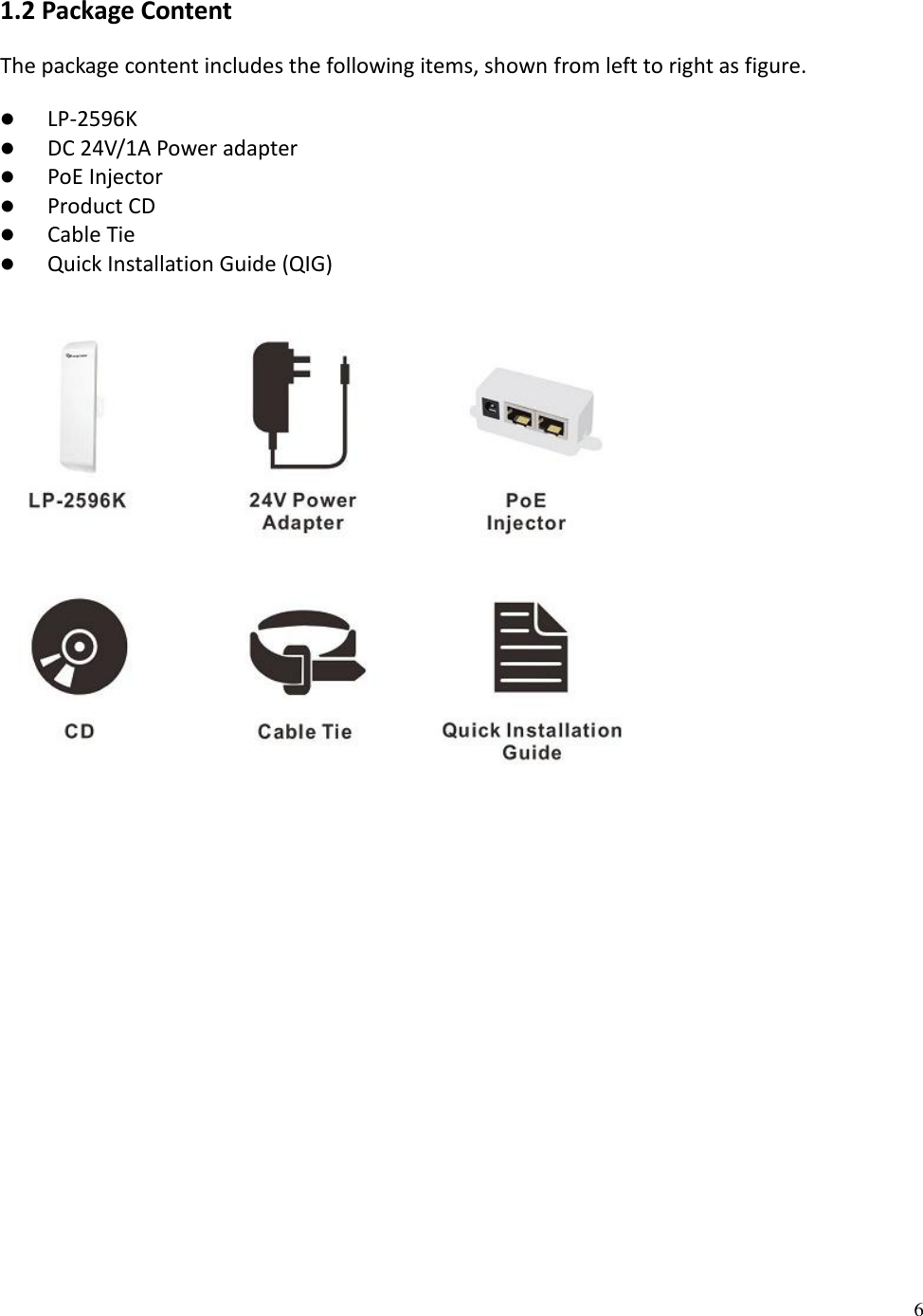
LP- 2596K User Manual Injector 20141016(no DFS)