Configuring VRealize Automation 7.0 V Realize 70 Configuration
User Manual: Pdf vRealize Automation - 7.0 - Configuring User Guide for VMware vRealize Software, Free Instruction Manual
Open the PDF directly: View PDF ![]() .
.
Page Count: 430 [warning: Documents this large are best viewed by clicking the View PDF Link!]
- Configuring vRealize Automation
- Contents
- Configuring vRealize Automation
- Updated Information
- External Preparations for Provisioning
- Preparing Your Environment for vRealize Automation Management
- Checklist for Preparing NSX Network and Security Configuration
- Preparing Your vCloud Director Environment for vRealize Automation
- Preparing Your vCloud Air Environment for vRealize Automation
- Preparing Your Amazon AWS Environment
- Preparing Red Hat OpenStack Network and Security Features
- Preparing Your SCVMM Environment
- Preparing for Machine Provisioning
- Choosing a Machine Provisioning Method to Prepare
- Checklist for Running Visual Basic Scripts During Provisioning
- Using vRealize Automation Guest Agent in Provisioning
- Checklist for Preparing to Provision by Cloning
- Preparing for vCloud Air and vCloud Director Provisioning
- Preparing for Linux Kickstart Provisioning
- Preparing for SCCM Provisioning
- Preparing for WIM Provisioning
- Preparing for Virtual Machine Image Provisioning
- Preparing for Amazon Machine Image Provisioning
- Scenario: Prepare vSphere Resources for Machine Provisioning in Rainpole
- Preparing for Software Provisioning
- Preparing Your Environment for vRealize Automation Management
- Configuring Tenant Settings
- Choosing Directories Management Configuration Options
- Directories Management Overview
- Using Directories Management to Create an Active Directory Link
- Configure a Link to Active Directory
- Configure Directories Management for High Availability
- Configure a Bi Directional Trust Relationship Between vRealize Automation and Active Directory
- Configure SAML Federation Between Directories Management and SSO2
- Add Users or Groups to an Active Directory Connection
- Select Attributes to Sync with Directory
- Add Memory to Directories Management
- Create a Domain Host Lookup File to Override DNS Service Location (SRV) Lookup
- Managing User Attributes that Sync from Active Directory
- Managing Connectors
- Join a Connector Machine to a Domain
- About Domain Controller Selection
- Managing Access Policies
- Integrating Alternative User Authentication Products with Directories Management
- Configuring SecurID for Directories Management
- Configuring RADIUS for Directories Management
- Configuring a Certificate or Smart Card Adapter for Use with Directories Management
- Configuring a Third-Party Identity Provider Instance to Authenticate Users
- Managing Authentication Methods to Apply to Users
- Configuring Kerberos for Directories Management
- Scenario: Configure an Active Directory Link for a Highly Available vRealize Automation
- Scenario: Configure Smart Card Authentication for vRealize Automation
- Configuring Groups and User Roles
- Scenario: Configure the Default Tenant for Rainpole
- Scenario: Create Local User Accounts for Rainpole
- Scenario: Connect Your Corporate Active Directory to vRealize Automation for Rainpole
- Scenario: Configure Branding for the Default Tenant for Rainpole
- Scenario: Create a Custom Group for Your Rainpole Architects
- Scenario: Assign IaaS Administrator Privileges to Your Custom Group of Rainpole Architects
- Create Additional Tenants
- Configuring Custom Branding
- Checklist for Configuring Notifications
- Configuring Global Email Servers for Notifications
- Add a Tenant-Specific Outbound Email Server
- Add a Tenant-Specific Inbound Email Server
- Override a System Default Outbound Email Server
- Override a System Default Inbound Email Server
- Revert to System Default Email Servers
- Configure Notifications
- Configuring Templates for Automatic IaaS Emails
- Subscribe to Notifications
- Create a Custom RDP File to Support RDP Connections for Provisioned Machines
- Scenario: Add Datacenter Locations for Cross Region Deployments
- Configuring vRealize Orchestrator and Plug-Ins
- Choosing Directories Management Configuration Options
- Configuring Resources
- Checklist for Configuring IaaS Resources
- Store User Credentials
- Choosing an Endpoint Scenario
- Create an Amazon Endpoint
- Create an OpenStack Endpoint
- Create a vCloud Air Endpoint
- Create a vCloud Director Endpoint
- Create a vRealize Orchestrator Endpoint
- Create a NetApp ONTAP Endpoint
- Create a Hyper-V (SCVMM) Endpoint
- Create a Standalone Endpoint for Hyper-V
- Create a KVM (RHEV) Endpoint
- Create a vSphere Endpoint
- Create a vSphere Endpoint with Network and Security Integration
- Create a Xen Pool Endpoint
- Create a XenServer Endpoint
- Preparing an Endpoint CSV File for Import
- Import a List of Endpoints
- Troubleshooting Attached vSphere Endpoint Cannot be Found
- Troubleshooting Locate the vCloud Air Management URL for an Organization Virtual Data Center
- Create a Fabric Group
- Configure Machine Prefixes
- Managing Key Pairs
- Creating a Network Profile
- Configuring Reservations and Reservation Policies
- Reservations
- Choosing a Reservation Scenario
- Creating Cloud Category Reservations
- Creating Virtual Category Reservations
- Edit a Reservation to Assign a Network Profile
- Reservation Policies
- Storage Reservation Policies
- Reservations
- Scenario: Configure IaaS Resources for Rainpole
- Scenario: Apply a Location to a Compute Resource for Cross Region Deployments
- Configuring XaaS Resources
- Installing Additional Plug-Ins on the Default vRealize Orchestrator Server
- Checklist for Configuring IaaS Resources
- Providing On-Demand Services to Users
- Designing Blueprints
- Exporting and Importing Blueprints
- Building Your Design Library
- Designing Machine Blueprints
- Space-Efficient Storage for Virtual Provisioning
- Configure a Machine Blueprint
- Machine Blueprint Settings
- Adding Network and Security Properties to a Machine Component
- Scenario: Create a vSphere CentOS Blueprint for Cloning in Rainpole
- Scenario: Turn Your Rainpole Machine into a Base for Delivering Software Components
- Add RDP Connection Support to Your Windows Machine Blueprints
- Scenario: Add Active Directory Cleanup to Your CentOS Blueprint
- Scenario: Allow Requesters to Specify Machine Host Name
- Scenario: Enable Users to Select Datacenter Locations for Cross Region Deployments
- Designing Machine Blueprints with NSX Networking and Security
- New Blueprint and Blueprint Properties Settings with NSX
- Configuring Network and Security Component Settings
- Associating Network and Security Components
- Designing Software Components
- Creating XaaS Blueprints and Resource Actions
- vRealize Orchestrator Integration in vRealize Automation
- List of vRealize Orchestrator Plug-Ins
- Creating Custom Resources
- Creating XaaS Blueprints and Resource Actions
- Mapping Other Resources to Work with XaaS Resource Actions
- Designing Forms for XaaS Blueprints and Actions
- XaaS Examples and Scenarios
- Create an XaaS Blueprint and Action for Creating and Modifying a User
- Create a Test User as a Custom Resource
- Create an XaaS Blueprint for Creating a User
- Publish the Create a User Blueprint as a Catalog Item
- Create a Resource Action to Change a User Password
- Publish the Change a Password Resource Action
- Create a Catalog Service for Creating a Test User
- Associate the Catalog Item with the Create a Test User Service
- Entitle the Service and the Resource Action to a Consumer
- Create and Publish an XaaS Action to Migrate a Virtual Machine
- Create an XaaS Action to Migrate a Virtual Machine With vMotion
- Create and Publish an XaaS Action to Take a Snapshot
- Create and Publish an XaaS Action to Start an Amazon Virtual Machine
- Create an XaaS Blueprint and Action for Creating and Modifying a User
- Troubleshooting Incorrect Accents and Special Characters in XaaS Blueprints
- Publishing a Blueprint
- Designing Machine Blueprints
- Assembling Application Blueprints
- Managing the Service Catalog
- Checklist for Configuring the Service Catalog
- Creating a Service
- Working with Catalog Items and Actions
- Creating an Entitlement
- Working with Approval Policies
- Examples of Approval Policies Based on the Virtual Machine Policy Type
- Example of Actions with Approval Policies Applied in a Composite Deployment
- Example of an Approval Policy in Multiple Entitlements
- Processing Approval Policies in the Service Catalog
- Create an Approval Policy
- Modify an Approval Policy
- Deactivate an Approval Policy
- Delete an Approval Policy
- Scenario: Configure the Catalog for Rainpole Architects to Test Blueprints
- Scenario: Test Your Rainpole CentOS Machine
- Scenario: Make the CentOS with MySQL Application Blueprint Available in the Service Catalog
- Scenario: Create and Apply CentOS with MySQL Approval Policies

Configuring vRealize
Automation
vRealize Automation 7.0
Configuring vRealize Automation
VMware, Inc. 2
You can find the most up-to-date technical documentation on the VMware website at:
https://docs.vmware.com/
If you have comments about this documentation, submit your feedback to
docfeedback@vmware.com
Copyright © 2015–2018 VMware, Inc. All rights reserved. Copyright and trademark information.
VMware, Inc.
3401 Hillview Ave.
Palo Alto, CA 94304
www.vmware.com
Contents
Configuring vRealize Automation 7
Updated Information 8
1External Preparations for Provisioning 9
Preparing Your Environment for vRealize Automation Management 9
Checklist for Preparing NSX Network and Security Configuration 10
Preparing Your vCloud Director Environment for vRealize Automation 13
Preparing Your vCloud Air Environment for vRealize Automation 14
Preparing Your Amazon AWS Environment 14
Preparing Red Hat OpenStack Network and Security Features 20
Preparing Your SCVMM Environment 20
Preparing for Machine Provisioning 21
Choosing a Machine Provisioning Method to Prepare 21
Checklist for Running Visual Basic Scripts During Provisioning 24
Using vRealize Automation Guest Agent in Provisioning 25
Checklist for Preparing to Provision by Cloning 30
Preparing for vCloud Air and vCloud Director Provisioning 44
Preparing for Linux Kickstart Provisioning 45
Preparing for SCCM Provisioning 48
Preparing for WIM Provisioning 49
Preparing for Virtual Machine Image Provisioning 59
Preparing for Amazon Machine Image Provisioning 59
Scenario: Prepare vSphere Resources for Machine Provisioning in Rainpole 62
Preparing for Software Provisioning 64
Preparing to Provision Machines with Software 65
Scenario: Prepare a vSphere CentOS Template for Clone Machine and Software Component
Blueprints 70
Scenario: Prepare for Importing the Dukes Bank for vSphere Sample Application Blueprint 74
2Configuring Tenant Settings 79
Choosing Directories Management Configuration Options 80
Directories Management Overview 81
Using Directories Management to Create an Active Directory Link 84
Managing User Attributes that Sync from Active Directory 97
Managing Connectors 98
Join a Connector Machine to a Domain 99
About Domain Controller Selection 99
VMware, Inc. 3
Managing Access Policies 103
Integrating Alternative User Authentication Products with Directories Management 108
Scenario: Configure an Active Directory Link for a Highly Available vRealize Automation 127
Scenario: Configure Smart Card Authentication for vRealize Automation 130
Generate a Connector Activation Token 131
Deploy the Connector OVA File 131
Configure Connector Settings 132
Apply Public Certificate Authority 133
Create a Workspace Identity Provider 135
Configure Certificate Authentication and Configure Default Access Policy Rules 136
Configuring Groups and User Roles 136
Assign Roles to Directory Users or Groups 136
Create a Custom Group 137
Create a Business Group 138
Troubleshooting Slow Performance When Displaying Group Members 140
Scenario: Configure the Default Tenant for Rainpole 141
Scenario: Create Local User Accounts for Rainpole 142
Scenario: Connect Your Corporate Active Directory to vRealize Automation for Rainpole 143
Scenario: Configure Branding for the Default Tenant for Rainpole 144
Scenario: Create a Custom Group for Your Rainpole Architects 145
Scenario: Assign IaaS Administrator Privileges to Your Custom Group of Rainpole Architects 146
Create Additional Tenants 147
Specify Tenant Information 147
Configure Local Users 148
Appoint Administrators 149
Configuring Custom Branding 149
Custom Branding for Tenant Login Page 149
Custom Branding for Tenant Applications 150
Checklist for Configuring Notifications 151
Configuring Global Email Servers for Notifications 154
Add a Tenant-Specific Outbound Email Server 156
Add a Tenant-Specific Inbound Email Server 157
Override a System Default Outbound Email Server 158
Override a System Default Inbound Email Server 159
Revert to System Default Email Servers 160
Configure Notifications 160
Configuring Templates for Automatic IaaS Emails 161
Subscribe to Notifications 165
Create a Custom RDP File to Support RDP Connections for Provisioned Machines 165
Scenario: Add Datacenter Locations for Cross Region Deployments 166
Configuring vRealize Orchestrator and Plug-Ins 167
Configure the Default Workflow Folder for a Tenant 167
Configuring vRealize Automation
VMware, Inc. 4
Configure an External vRealize Orchestrator Server 168
Log in to the vRealize Orchestrator Configuration Interface 169
Log in to the vRealize Orchestrator Client 169
3Configuring Resources 171
Checklist for Configuring IaaS Resources 171
Store User Credentials 172
Choosing an Endpoint Scenario 174
Create a Fabric Group 190
Configure Machine Prefixes 191
Managing Key Pairs 192
Creating a Network Profile 194
Configuring Reservations and Reservation Policies 204
Scenario: Configure IaaS Resources for Rainpole 239
Scenario: Apply a Location to a Compute Resource for Cross Region Deployments 243
Configuring XaaS Resources 244
Configure the Active Directory Plug-In as an Endpoint 244
Configure the HTTP-REST Plug-In as an Endpoint 246
Configure the PowerShell Plug-In as an Endpoint 248
Configure the SOAP Plug-In as an Endpoint 249
Configure the vCenter Server Plug-In as an Endpoint 251
Installing Additional Plug-Ins on the Default vRealize Orchestrator Server 252
4Providing On-Demand Services to Users 253
Designing Blueprints 253
Exporting and Importing Blueprints 255
Scenario: Importing the Dukes Bank for vSphere Sample Application and Configuring for Your
Environment 256
Scenario: Test the Dukes Bank Sample Application 260
Building Your Design Library 261
Designing Machine Blueprints 263
Designing Machine Blueprints with NSX Networking and Security 299
Designing Software Components 313
Creating XaaS Blueprints and Resource Actions 329
Publishing a Blueprint 376
Assembling Application Blueprints 377
Understanding Nested Blueprint Behavior 377
Selecting a Machine Blueprint that Supports Software Components 379
Binding Properties to Other Properties in a Blueprint 380
Controlling the Build Order of Blueprint Components 381
Scenario: Assemble and Test a Blueprint to Deliver MySQL on Rainpole Linked Clone
Machines 381
Configuring vRealize Automation
VMware, Inc. 5
Managing the Service Catalog 385
Checklist for Configuring the Service Catalog 386
Creating a Service 387
Working with Catalog Items and Actions 389
Creating an Entitlement 392
Working with Approval Policies 398
Scenario: Configure the Catalog for Rainpole Architects to Test Blueprints 417
Scenario: Test Your Rainpole CentOS Machine 420
Scenario: Make the CentOS with MySQL Application Blueprint Available in the Service Catalog 421
Scenario: Create and Apply CentOS with MySQL Approval Policies 425
Configuring vRealize Automation
VMware, Inc. 6
Configuring vRealize Automation
Configuring vRealize Automation provides information about configuring vRealize Automation and your
external environments to prepare for vRealize Automation provisioning and catalog management.
For information about supported integrations, see https://www.vmware.com/pdf/vrealize-automation-70-
support-matrix.pdf.
Intended Audience
This information is intended for IT professionals who are responsible for configuring vRealize Automation
environment, and for infrastructure administrators who are responsible for preparing elements in their
existing infrastructure for use in vRealize Automation provisioning. The information is written for
experienced Windows and Linux system administrators who are familiar with virtual machine technology
and datacenter operations.
VMware Technical Publications Glossary
VMware Technical Publications provides a glossary of terms that might be unfamiliar to you. For
definitions of terms as they are used in VMware technical documentation, go to
http://www.vmware.com/support/pubs.
VMware, Inc. 7
Updated Information
This Configuring vRealize Automation is updated with each release of the product or when necessary.
This table provides the update history of Configuring vRealize Automation.
Revision Description
001836-06 nUpdated Prepare a Windows Reference Machine to Support Software.
nUpdated Prepare a Linux Reference Machine to Support Software.
001836-05 Added note to Specify Tenant Information to indicate that tenant URLs must use only lowercase characters.
001836-04 Minor updates in reservation and endpoint sections.
001836-03 Added information about mapping dependencies between blueprint components. See Controlling the Build Order of
Blueprint Components.
001836-02 nAdded Scenario: Configure Smart Card Authentication for vRealize Automation.
nAdded Join a Connector Machine to a Domain.
001836-01 nUpdated the following topics to document a reservation policy limitation:
nCreate a vCloud Air Endpoint
nCreate a vCloud Director Endpoint
nReservation Policies
nUpdated Understanding Nested Blueprint Behavior to include information about on-demand load balancer and on-
demand network settings in an inner blueprint.
nUpdated Amazon Machine Component Settings to add information about EBS volumes in machine deployments.
nUpdated Constraints and Values in the Form Designer with additional information regarding constraint values.
001836-00 Initial release.
VMware, Inc. 8

External Preparations for
Provisioning 1
You may need to create or prepare some elements outside of vRealize Automation to support catalog
item provisioning. For example, if you want to provide a catalog item for provisioning a clone machine,
you need to create a template on your hypervisor to clone from.
This chapter includes the following topics:
nPreparing Your Environment for vRealize Automation Management
nPreparing for Machine Provisioning
nPreparing for Software Provisioning
Preparing Your Environment for vRealize Automation
Management
Depending on your integration platform, you might have to make some configuration changes before you
can bring your environment under vRealize Automation management, or before you can leverage certain
features.
Table 1‑1. Preparing Your Environment for vRealize Automation Integration
Environment Preparations
NSX
If you want to leverage NSX to manage
networking and security features of machines
provisioned with vRealize Automation, prepare
your NSX instance for integration. See
Checklist for Preparing NSX Network and
Security Configuration.
vCloud Director Install and configure your vCloud Director
instance, set up your vSphere and cloud
resources, and identify or create appropriate
credentials to provide vRealize Automation with
access to your vCloud Director environment.
See Preparing Your vCloud Director
Environment for vRealize Automation.
VMware, Inc. 9
Table 1‑1. Preparing Your Environment for vRealize Automation Integration (Continued)
Environment Preparations
vCloud Air Register for your vCloud Air account, set up
your vCloud Air environment, and identify or
create appropriate credentials to provide
vRealize Automation with access to your
environment. See Preparing for vCloud Air and
vCloud Director Provisioning.
Amazon AWS Prepare elements and user roles in your
Amazon AWS environment for use in
vRealize Automation, and understand how
Amazon AWS features map to
vRealize Automation features. See Preparing
Your Amazon AWS Environment.
Red Hat OpenStack If you want to leverage Red Hat OpenStack to
manage networking and security features of
machines provisioned with
vRealize Automation, prepare your
Red Hat OpenStack instance for integration.
See Preparing Red Hat OpenStack Network
and Security Features.
SCVMM Configure storage, networking, and understand
template and hardware profile naming
restrictions. See Preparing Your SCVMM
Environment.
All other environments You do not need to make changes to your
environment. You can begin preparing for
machine provisioning by creating templates,
boot environments, or machine images. See
Preparing for Machine Provisioning.
Checklist for Preparing NSX Network and Security Configuration
Before you can use NSX network and security options in vRealize Automation, you must configure the
external NSX network and security environment that you intend to use.
Much of the vRealize Automation support for network and security configuration that you specify in
blueprints and reservations is configured externally and made available to vRealize Automation after data
collection is run on the compute resources.
For more information about the available network and configuration options that you can configure for
vRealize Automation, see Configuring Network and Security Component Settings.
Configuring vRealize Automation
VMware, Inc. 10
Table 1‑2. Preparing NSX Networking and Security Checklist
Task Location Details
Install and
configure the NSX
plug-in.
Install the NSX plug-in in vRealize Orchestrator. See Install the NSX Plug-In on vRealize
Orchestrator and the NSX Administration
Guide.
Configure NSX
network settings,
including gateway
and transport zone
settings.
Configure network settings in NSX. See the NSX Administration Guide.
Create NSX
security policies,
tags, and groups.
Configure security settings in NSX. See the NSX Administration Guide.
Configure NSX
load balancer
settings.
Configure an NSX load balancer to work with
vRealize Automation.
See the NSX Administration Guide.
If using NSX 6.2, also see Custom
Properties for Networking in Custom
Properties Reference.
Install the NSX Plug-In on vRealize Orchestrator
Installing the NSX plug-in requires that you download the vRealize Orchestrator installer file, use the
vRealize Orchestrator Configuration interface to upload the plug-in file, and install the plug-in on a
vRealize Orchestrator server.
Note If you are using an embedded vRealize Orchestrator that contains an installed NSX plug-in, you do
not need to perform these steps as the NSX plug-in is already installed.
For general plug-in update and troubleshooting information, see vRealize Orchestrator documentation at
https://www.vmware.com/support/pubs/orchestrator_pubs.html.
Prerequisites
nVerify that you are running a supported vRealize Orchestrator instance.
For information about setting up vRealize Orchestrator, see Installing and Configuring VMware
vRealize Orchestrator.
nVerify that you have credentials for an account with permission to install vRealize Orchestrator plug-
ins and to authenticate through vCenter Single Sign-On.
nVerify that you installed the correct version NSX plug-in. See vRealize Automation Support Matrix for
version information.
nVerify that you installed vRealize Orchestrator client and that you can log in with Administrator
credentials.
Configuring vRealize Automation
VMware, Inc. 11
Procedure
1Download the plug-in file to a location accessible from the vRealize Orchestrator server.
The plug-in installer file name format, with appropriate version values, is o11nplugin-
nsx-1.n.n.vmoapp. Plug-in installation files for the VMware NSX ™ networking and security product
is available from the VMware product download site at http://vmware.com/web/vmware/downloads.
The vCloud Networking and Security plug-in is also available at this site.
2Open a browser and start the vRealize Orchestrator configuration interface.
An example of the URL format is https://orchestrator_server.com:8283.
3Click Plug-Ins in the left pane and scroll down to the Install new plug-in section.
4In the Plug-In file text box, browse to the plug-in installer file and click Upload and install.
The file must be in .vmoapp format.
5At the prompt, accept the license agreement in the Install a plug-in pane.
6In the Enabled plug-ins installation status section, confirm that the correct NSX plug-in name is
specified. See vRealize Automation Support Matrix for version information.
The status Plug-in will be installed at next server startup, appears.
7Restart the vRealize Orchestrator server service.
8Restart the vRealize Orchestrator configuration interface.
9Click Plug-Ins and verify that the status changed to Installation OK.
10 Start the vRealize Orchestrator client application, log in, and use the Workflow tab to navigate
through the library to the NSX folder.
You can browse through the workflows that the NSX plug-in provides.
What to do next
Create a vRealize Orchestrator endpoint in vRealize Automation to use this endpoint for running
workflows. See Create a vRealize Orchestrator Endpoint.
Run a vRealize Orchestrator and NSX Security Workflow
Before you use the NSX security policy features from vRealize Automation, an administrator must run the
Enable security policy support for overlapping subnets workflow in vRealize Orchestrator.
Security policy support for the overlapping subnets workflow is applicable to an NSX 6.1 and later
endpoint. Run this workflow only once to enable this support.
Prerequisites
nVerify that a vSphere endpoint is registered with an NSX endpoint. See Create a vSphere Endpoint.
nLog in to the vRealize Orchestrator client as an administrator.
nverify that the vRO work flow Create NSX endpoint has been run.
Configuring vRealize Automation
VMware, Inc. 12
Procedure
1Click the Workflow tab and select NSX > NSX workflows for VCAC.
2Run the Create NSX endpoint workflow and respond to prompts.
3Run the Enable security policy support for overlapping subnets workflow.
4Select the NSX endpoint as the input parameter for the workflow.
Use the IP address you specified when you created the vSphere endpoint to register an NSX
instance.
After you run this workflow, the distributed firewall rules defined in the security policy are applied only on
the vNICs of the security group members to which this security policy is applied.
What to do next
Apply the applicable security features for the blueprint.
Preparing Your vCloud Director Environment for
vRealize Automation
Before you can integrate vCloud Director with vRealize Automation, you must install and configure your
vCloud Director instance, set up your vSphere and cloud resources, and identify or create appropriate
credentials to provide vRealize Automation with access to your vCloud Director environment.
Configure Your Environment
Configure your vSphere resources and cloud resources, including virtual datacenters and networks. For
more information, see the vCloud Director documentation.
Required Credentials for Integration
Create or identify either organization administrator or system administrator credentials that your
vRealize Automation IaaS administrators can use to bring your vCloud Director environment under
vRealize Automation management as an endpoint.
User Role Considerations
vCloud Director user roles in an organization do not need to correspond with roles in vRealize Automation
business groups. If the user account does not exist in vCloud Director, vCloud Director performs a lookup
in the associated LDAP or Active Directory and creates the user account if the user exists in the identity
store. If it cannot create the user account, it logs a warning but does not fail the provisioning process. The
provisioned machine is then assigned to the account that was used to configure the vCloud Director
endpoint.
For related information about vCloud Director user management, see the vCloud Director documentation.
Configuring vRealize Automation
VMware, Inc. 13
Preparing Your vCloud Air Environment for vRealize Automation
Before you integrate vCloud Air with vRealize Automation, you must register for your vCloud Air account,
set up your vCloud Air environment, and identify or create appropriate credentials to provide
vRealize Automation with access to your environment.
Configure Your Environment
Configure your environment as instructed in the vCloud Air documentation.
Required Credentials for Integration
Create or identify either virtual infrastructure administrator or account administrator credentials that your
vRealize Automation IaaS administrators can use to bring your vCloud Air environment under
vRealize Automation management as an endpoint.
User Role Considerations
vCloud Air user roles in an organization do not need to correspond with roles in vRealize Automation
business groups. For related information about vCloud Air user management, see the vCloud Air
documentation.
Preparing Your Amazon AWS Environment
Prepare elements and user roles in your Amazon AWS environment, prepare Amazon AWS to
communicate with the guest agent and Software bootstrap agent, and understand how Amazon AWS
features map to vRealize Automation features.
Amazon AWS User Roles and Credentials Required for vRealize Automation
You must configure credentials in Amazon AWS with the permissions required for vRealize Automation to
manage your environment.
You must have certain Amazon access rights to successfully provision machines by using
vRealize Automation.
nRole and Permission Authorization in Amazon Web Services
The Power User role in AWS provides an AWS Directory Service user or group with full access to
AWS services and resources.
You do not need any AWS credentials to create an AWS endpoint in vRealize Automation. However,
the AWS user who creates an Amazon machine image is expected by vRealize Automation to have
the Power User role.
nAuthentication Credentials in Amazon Web Services
Configuring vRealize Automation
VMware, Inc. 14
The AWS Power User role does not allow management of AWS Identity and Access Management
(IAM) users and groups. For management of IAM users and groups, you must be configured with
AWS Full Access Administrator credentials.
vRealize Automation requires access keys for endpoint credentials and does not support user names
and passwords. To obtain the access key needed to create the Amazon endpoint, the Power User
must either request a key from a user who has AWS Full Access Administrator credentials or be
additionally configured with the AWS Full Access Administrator policy.
For information about enabling policies and roles, see the AWS Identity and Access Management (IAM)
section of Amazon Web Services product documentation.
Allow Amazon AWS to Communicate with the Software Bootstrap Agent and
Guest Agent
If you intend to provision application blueprints that contain Software, or if you want the ability to further
customize provisioned machines by using the guest agent, you must enable connectivity between your
Amazon AWS environment, where your machines are provisioned, and your vRealize Automation
environment, where the agents download packages and receive instructions.
When you use vRealize Automation to provision Amazon AWS machines with the vRealize Automation
guest agent and Software bootstrap agent, you must set up network-to-Amazon VPC connectivity so your
provisioned machines can communicate back to vRealize Automation to customize your machines.
For more information about Amazon AWS VPC connectivity options, see the Amazon AWS
documentation.
Using Optional Amazon Features
vRealize Automation supports several Amazon features, including Amazon Virtual Private Cloud, elastic
load balancers, elastic IP addresses, and elastic block storage.
Using Amazon Security Groups
Specify at least one security group when creating an Amazon reservation. Each available region requires
at least one specified security group.
A security group acts as a firewall to control access to a machine. Every region includes at least the
default security group. Administrators can use the Amazon Web Services Management Console to create
additional security groups, configure ports for Microsoft Remote Desktop Protocol or SSH, and set up a
virtual private network for an Amazon VPN.
When you create an Amazon reservation or configure a machine component in the blueprint, you can
choose from the list of security groups that are available to the specified Amazon account region. Security
groups are imported during data collection.
For information about creating and using security groups in Amazon Web Services, see Amazon
documentation.
Configuring vRealize Automation
VMware, Inc. 15
Understanding Amazon Web Service Regions
Each Amazon Web Services account is represented by a cloud endpoint. When you create an
Amazon Elastic Cloud Computing endpoint in vRealize Automation, regions are collected as compute
resources. After the IaaS administrator selects compute resources for a business group, inventory and
state data collections occur automatically.
Inventory data collection, which occurs automatically once a day, collects data about what is on a
compute resource, such as the following data:
nElastic IP addresses
nElastic load balancers
nElastic block storage volumes
State data collection occurs automatically every 15 minutes by default. It gathers information about the
state of managed instances, which are instances that vRealize Automation creates. The following are
examples of state data:
nWindows passwords
nState of machines in load balancers
nElastic IP addresses
A fabric administrator can initiate inventory and state data collection and disable or change the frequency
of inventory and state data collection.
Using Amazon Virtual Private Cloud
Amazon Virtual Private Cloud allows you to provision Amazon machine instances in a private section of
the Amazon Web Services cloud.
Amazon Web Services users can use Amazon VPC to design a virtual network topology according to your
specifications. You can assign an Amazon VPC in vRealize Automation. However, vRealize Automation
does not track the cost of using the Amazon VPC.
When you provision using Amazon VPC, vRealize Automation expects there to be a VPC subnet from
which Amazon obtains a primary IP address. This address is static until the instance is terminated. You
can also use the elastic IP pool to also attach an elastic IP address to an instance in
vRealize Automation. That would allow the user to keep the same IP if they are continually provisioning
and tearing down an instance in Amazon Web Services.
Use the AWS Management Console to create the following elements:
nAn Amazon VPC, which includes Internet gateways, routing table, security groups and subnets, and
available IP addresses.
nAn Amazon Virtual Private Network if users need to log in to Amazon machines instances outside of
the AWS Management Console.
vRealize Automation users can perform the following tasks when working with an Amazon VPC:
nA fabric administrator can assign an Amazon VPC to a cloud reservation. See Create an Amazon
Reservation.
Configuring vRealize Automation
VMware, Inc. 16
nA machine owner can assign an Amazon machine instance to an Amazon VPC.
For more information about creating an Amazon VPC, see Amazon Web Services documentation.
Using Elastic Load Balancers for Amazon Web Services
Elastic load balancers distribute incoming application traffic across Amazon Web Services instances.
Amazon load balancing enables improved fault tolerance and performance.
Amazon makes elastic load balancing available for machines provisioned using Amazon EC2 blueprints.
The elastic load balancer must be available in the Amazon Web Services,
Amazon Virtual Private Network and at the provisioning location. For example, if a load balancer is
available in us-east1c and a machine location is us-east1b, the machine cannot use the available load
balancer.
vRealize Automation does not create, manage, or monitor the elastic load balancers.
For information about creating Amazon elastic load balancers by using the
Amazon Web Services Management Console, see Amazon Web Services documentation.
Using Elastic IP Addresses for Amazon Web Services
Using an elastic IP address allows you to rapidly fail over to another machine in a dynamic
Amazon Web Services cloud environment. In vRealize Automation, the elastic IP address is available to
all business groups that have rights to the region.
An administrator can allocate elastic IP addresses to your Amazon Web Services account by using the
AWS Management Console. There are two groups of elastic IP addresses in any given a region, one
range is allocated for non-Amazon VPC instances and another range is for Amazon VPCs. If you allocate
addresses in a non-Amazon VPC region only, the addresses are not available in an Amazon VPC. The
reverse is also true. If you allocate addresses in an Amazon VPC only, the addresses are not available in
a non-Amazon VPC region.
The elastic IP address is associated with your Amazon Web Services account, not a particular machine,
but only one machine at a time can use the address. The address remains associated with your
Amazon Web Services account until you choose to release it. You can release it to map it to a specific
machine instance.
An IaaS architect can add a custom property to a blueprint to assign an elastic IP address to machines
during provisioning. Machine owners and administrators can view the elastic IP addresses assigned to
machines, and machine owners or administrators with rights to edit machines can assign an elastic IP
addresses after provisioning. However, if the address is already associated to a machine instance, and
the instance is part of the Amazon Virtual Private Cloud deployment, Amazon does not assign the
address.
For more information about creating and using Amazon elastic IP addresses, see Amazon Web Services
documentation.
Configuring vRealize Automation
VMware, Inc. 17
Using Elastic Block Storage for Amazon Web Services
Amazon elastic block storage provides block level storage volumes to use with an Amazon machine
instance and Amazon Virtual Private Cloud. The storage volume can persist past the life of its associated
Amazon machine instance in the Amazon Web Services cloud environment.
When you use an Amazon elastic block storage volume in conjunction with vRealize Automation, the
following caveats apply:
nYou cannot attach an existing elastic block storage volume when you provision a machine instance.
However, if you create a new volume and request more than one machine at a time, the volume is
created and attached to each instance. For example, if you create one volume named volume_1 and
request three machines, a volume is created for each machine. Three volumes named volume_1 are
created and attached to each machine. Each volume has a unique volume ID. Each volume is the
same size and in the same location.
nThe volume must be of the same operating system and in the same location as the machine to which
you attach it.
nvRealize Automation does not manage the primary volume of an elastic block storage-backed
instance.
For more information about Amazon elastic block storage, and details on how to enable it by using
Amazon Web Services Management Console, see Amazon Web Services documentation.
Scenario: Configure Network-to-Amazon VPC Connectivity for a Proof of
Concept Environment
As the IT professional setting up a proof of concept environment to evaluate vRealize Automation, you
want to temporarily configure network-to-Amazon VPC connectivity to support the vRealize Automation
Software feature.
Network-to-Amazon VPC connectivity is only required if you want to use the guest agent to customize
provisioned machines, or if you want to include Software components in your blueprints. For a production
environment, you would configure this connectivity officially through Amazon Web Services, but because
you are working in a proof of concept environment, you want to create temporary network-to-Amazon
VPC connectivity. You establish the SSH tunnel and then configure an Amazon reservation in
vRealize Automation to route through your tunnel.
Prerequisites
nInstall and fully configure vRealize Automation. See Installing and Configuring vRealize Automation
for the Rainpole Scenario.
nCreate an Amazon AWS security group called TunnelGroup and configure it to allow access on port
22.
nCreate or identify a CentOS machine in your Amazon AWS TunnelGroup security group and note the
following configurations:
nAdministrative user credentials, for example root.
Configuring vRealize Automation
VMware, Inc. 18
nPublic IP address.
nPrivate IP address.
nCreate or identify a CentOS machine on the same local network as your vRealize Automation
installation.
nInstall OpenSSH SSHD Server on both tunnel machines.
Procedure
1Log in to your Amazon AWS tunnel machine as the root user or similar.
2Disable iptables.
# service iptables save
# service iptables stop
# chkconfig iptables off
3Edit /etc/ssh/sshd_config to enable AllowTCPForwarding and GatewayPorts.
4Restart the service.
/etc/init.d/sshd restart
5Log in to the CentOS machine on the same local network as your vRealize Automation installation as
the root user.
6Invoke the SSH Tunnel from the local network machine to the Amazon AWS tunnel machine.
ssh -N -v -o "ServerAliveInterval 30" -o "ServerAliveCountMax 40" -o "TCPKeepAlive yes” \
-R 1442:vRealize_automation_appliance_fqdn:5480 \
-R 1443:vRealize_automation_appliance_fqdn:443 \
-R 1444:manager_service_fqdn:443 \
User of Amazon tunnel machine@Public IP Address of Amazon tunnel machine
You configured port forwarding to allow your Amazon AWS tunnel machine to access
vRealize Automation resources, but your SSH tunnel does not function until you configure an Amazon
reservation to route through the tunnel.
What to do next
1 Install the software bootstrap agent and the guest agent on a Windows or Linux reference machine to
create an Amazon Machine Image that your IaaS architects can use to create blueprints. See
Preparing for Software Provisioning.
2 Configure your Amazon reservation in vRealize Automation to route through your SSH tunnel. See
Scenario: Create an Amazon Reservation for a Proof of Concept Environment.
Configuring vRealize Automation
VMware, Inc. 19
Preparing Red Hat OpenStack Network and Security Features
vRealize Automation supports several features in OpenStack including security groups and floating IP
addresses. Understand how these features work with vRealize Automation and configure them in your
environment.
Using OpenStack Security Groups
Security groups allow you to specify rules to control network traffic over specific ports.
You can specify security groups when creating a reservation and also in the blueprint canvas. You can
also specify security groups when requesting a machine.
Security groups are imported during data collection.
Each available region requires at least one specified security group. When you create a reservation, the
available security groups that are available to you in that region are displayed. Every region includes at
least the default security group.
Additional security groups must be managed in the source resource. For more information about
managing security groups for the various machines, see the OpenStack documentation.
Using Floating IP Addresses with OpenStack
You can assign floating IP addresses to a running virtual instance in OpenStack.
To enable assignment of floating IP addresses, you must configure IP forwarding and create a floating IP
pool in Red Hat OpenStack. For more information, see the Red Hat OpenStack documentation.
You must entitle the Associate Floating IP and Disassociate Floating IP actions to machine owners. The
entitled users can then associate a floating IP address to a provisioned machine from the external
networks attached to the machine by selecting an available address from the floating IP address pool.
After a floating IP address has been associated with a machine, a vRealize Automation user can select a
Disassociate Floating IP option to view the currently assigned floating IP addresses and disassociate an
address from a machine.
Preparing Your SCVMM Environment
Before you begin creating SCVMM templates and hardware profiles for use in vRealize Automation
machine provisioning, you must understand the naming restrictions on template and hardware profile
names, and configure SCVMM network and storage settings.
Template and Hardware Profile Naming
Because of naming conventions that SCVMM and vRealize Automation use for templates and hardware
profiles, do not start your template or hardware profile names with the words temporary or profile. For
example, the following words are ignored during data collection:
nTemporaryTemplate
nTemporary Template
Configuring vRealize Automation
VMware, Inc. 20
nTemporaryProfile
nTemporary Profile
nProfile
Required Network Configuration for SCVMM Clusters
SCVMM clusters only expose virtual networks to vRealize Automation, so you must have a 1:1
relationship between your virtual and logical networks. Using the SCVMM console, map each logical
network to a virtual network and configure your SCVMM cluster to access machines through the virtual
network.
Required Storage Configuration for SCVMM Clusters
On SCVMM Hyper-V clusters, vRealize Automation collects data and provisions on shared volumes only.
Using the SCVMM console, configure your clusters to use shared resource volumes for storage.
Required Storage Configuration for Standalone SCVMM Hosts
For standalone SCVMM hosts, vRealize Automation collects data and provisions on the default virtual
machine path. Using the SCVMM console, configure default virtual machine paths for your standalone
hosts.
Preparing for Machine Provisioning
Depending on your environment and the method of machine provisioning you want to use, you might
have to configure elements outside of vRealize Automation, such as machine templates, machine
images, or boot environments, to prepare for machine provisioning.
Choosing a Machine Provisioning Method to Prepare
For most machine provisioning methods, you must prepare some elements outside of
vRealize Automation.
Configuring vRealize Automation
VMware, Inc. 21

Table 1‑3. Choosing a Machine Provisioning Method to Prepare
Scenario
Supported
Endpoint Agent Support Provisioning Method Pre-provisioning Preparations
Configure
vRealize Automation to run
custom Visual Basic scripts
as additional steps in the
machine life cycle, either
before or after machine
provisioning. For example,
you could use a pre-
provisioning script to
generate certificates or
security tokens before
provisioning, and then a
post-provisioning script to
use the certificates and
tokens after machine
provisioning.
You can run
Visual Basic
scripts with
any
supported
endpoint
except
Amazon
AWS.
Depends on the
provisioning
method you
choose.
Supported as an
additional step in any
provisioning method,
but you cannot use
Visual Basic scripts
with Amazon AWS
machines.
Checklist for Running Visual Basic
Scripts During Provisioning
Provision application
blueprints that automate
the installation,
configuration, and life cycle
management of
middleware and application
deployment components
such as Oracle, MySQL,
WAR, and database
Schemas.
nvSphere
nvCloud
Air
nvCloud
Director
nAmazon
AWS
n(Required)
Guest agent
n(Required)
Software
bootstrap agent
and guest
agent
nClone
nClone (for
vCloud Air or
vCloud Director)
nLinked clone
nAmazon Machine
Image
If you want the ability to use Software
components in your blueprints,
prepare a provisioning method that
supports the guest agent and
Software bootstrap agent. For more
information about preparing for
Software, see Preparing for Software
Provisioning.
Further customize
machines after provisioning
by using the guest agent.
All virtual
endpoints
and
Amazon
AWS.
n(Required)
Guest agent
n(Optional)
Software
bootstrap agent
and guest
agent
Supported for all
provisioning methods
except Virtual
Machine Image.
If you want the ability to customize
machines after provisioning, select a
provisioning method that supports
the guest agent. For more
information about the guest agent,
see Using vRealize Automation
Guest Agent in Provisioning.
Provision machines with no
guest operating system.
You can install an
operating system after
provisioning.
All virtual
machine
endpoints.
Not supported Basic No required pre-provisioning
preparations outside of
vRealize Automation.
Provision a space-efficient
copy of a virtual machine
called a linked clone.
Linked clones are based
on a snapshot of a VM and
use a chain of delta disks
to track differences from a
parent machine.
vSphere n(Optional)
Guest agent
n(Optional)
Software
bootstrap agent
and guest
agent
Linked Clone You must have an existing vSphere
virtual machine.
If you want to support Software, you
must install the guest agent and
software bootstrap agent on the
machine you intend to clone.
Configuring vRealize Automation
VMware, Inc. 22
Table 1‑3. Choosing a Machine Provisioning Method to Prepare (Continued)
Scenario
Supported
Endpoint Agent Support Provisioning Method Pre-provisioning Preparations
Provision a space-efficient
copy of a virtual machine
by using
Net App FlexClone
technology.
vSphere (Optional) Guest
agent
NetApp FlexClone Checklist for Preparing to Provision
by Cloning
Provision machines by
cloning from a template
object created from an
existing Windows or Linux
machine, called the
reference machine, and a
customization object.
nvSphere
nKVM
(RHEV)
nSCVMM
n(Optional)
Guest agent
n(Optional for
vSphere only)
Software
bootstrap agent
and guest
agent
Clone See Checklist for Preparing to
Provision by Cloning.
If you want to support Software, you
must install the guest agent and
software bootstrap agent on the
vSpheremachine you intend to clone.
Provision vCloud Air or
vCloud Director machines
by cloning from a template
and customization object.
nvCloud
Air
nvCloud
Director
n(Optional)
Guest agent
n(Optional)
Software
bootstrap agent
and guest
agent
vCloud Air or
vCloud Director
Cloning
See Preparing for vCloud Air and
vCloud Director Provisioning.
If you want to support Software,
create a template that contains the
guest agent and software bootstrap
agent. For vCloud Air, configure
network connectivity between your
vRealize Automation environment
and your vCloud Air environment.
Provision a machine by
booting from an ISO
image, using a kickstart or
autoYaSt configuration file
and a Linux distribution
image to install the
operating system on the
machine.
nAll
virtual
endpoint
s
nRed Hat
OpenSt
ack
Guest agent is
installed as part of
the preparation
instructions.
Linux Kickstart Preparing for Linux Kickstart
Provisioning
Provision a machine and
pass control to an SCCM
task sequence to boot from
an ISO image, deploy a
Windows operating
system, and install the
vRealize Automation guest
agent.
All virtual
machine
endpoints.
Guest agent is
installed as part of
the preparation
instructions.
SCCM Preparing for SCCM Provisioning
Configuring vRealize Automation
VMware, Inc. 23
Table 1‑3. Choosing a Machine Provisioning Method to Prepare (Continued)
Scenario
Supported
Endpoint Agent Support Provisioning Method Pre-provisioning Preparations
Provision a machine by
booting into a WinPE
environment and installing
an operating system using
a Windows Imaging File
Format (WIM) image of an
existing Windows
reference machine.
nAll
virtual
endpoint
s
nRed Hat
OpenSt
ack
Guest agent is
required. You can
use PEBuilder to
create a WinPE
image that includes
the guest agent.
You can create the
WinPE image by
using another
method, but you
must manually
insert the guest
agent.
WIM Preparing for WIM Provisioning
Launch an instance from a
virtual machine image.
Red Hat
OpenStack
Not supported Virtual Machine Image See Preparing for Virtual Machine
Image Provisioning.
Launch an instance from
an Amazon Machine
Image.
Amazon
AWS
n(Optional)
Guest agent
n(Optional)
Software
bootstrap agent
and guest
agent
Amazon Machine
Image
Associate Amazon machine images
and instance types with your
Amazon AWS account.
If you want to support Software,
create an Amazon Machine Image
that contains the guest agent and
software bootstrap agent, and
configure network-to-VPC
connectivity between your
Amazon AWS and
vRealize Automation environments.
Checklist for Running Visual Basic Scripts During Provisioning
You can configure vRealize Automation to run your custom Visual Basic scripts as additional steps in the
machine life cycle, either before or after machine provisioning. For example, you could use a pre-
provisioning script to generate certificates or security tokens before provisioning, and then a post-
provisioning script to use the certificates and tokens after machine provisioning. You can run Visual Basic
scripts with any provisioning method, but you cannot use Visual Basic scripts with Amazon AWS
machines.
Configuring vRealize Automation
VMware, Inc. 24
Table 1‑4. Running Visual Basic Scripts During Provisioning Checklist
Task Location Details
Install and configure the EPI agent for
Visual Basic scripts.
Typically the Manager Service host See Installing vRealize Automation 7.0.
Create your visual basic scripts. Machine where EPI agent is installed vRealize Automation includes a sample
Visual Basic script
PrePostProvisioningExample.vbs in
the Scripts subdirectory of the EPI agent
installation directory. This script contains a
header to load all arguments into a
dictionary, a body in which you can
include your functions, and a footer to
return updated custom properties to
vRealize Automation.
When executing a Visual Basic script, the
EPI agent passes all machine custom
properties as arguments to the script. To
return updated property values to
vRealize Automation, place these
properties in a dictionary and call a
function provided by vRealize Automation.
Gather the information required to
include your scripts in blueprints.
Capture information and transfer to your
infrastructure architects
Note A fabric administrator can create
a property group by using the property
sets ExternalPreProvisioningVbScript
and ExternalPostProvisioningVbScript to
provide this required information. Doing
so makes it easier for blueprint architects
to include this information correctly in
their blueprints.
nThe complete path to the Visual Basic
script, including the filename and
extension. For example, %System
Drive%Program Files
(x86)\VMware\vCAC
Agents\EPI_Agents\Scripts\Send
Email.vbs.
nTo run a script before provisioning,
instruct infrastructure architects to
enter the complete path to the script
as the value of the custom property
ExternalPreProvisioningVbScrip
t. To run a script after provisioning,
they need to use the custom property
ExternalPostProvisioningVbScri
pt..
Using vRealize Automation Guest Agent in Provisioning
You can install the guest agent on reference machines to further customize a machine after deployment.
You can use the reserved guest agent custom properties to perform basic customizations such as adding
and formatting disks, or you can create your own custom scripts for the guest agent to run within the
guest operating system of a provisioned machine.
After the deployment is completed and the customization specification is run (if you provided one), the
guest agent creates an XML file that contains all of the deployed machine's custom properties
c:\VRMGuestAgent\site\workitem.xml, completes any tasks assigned to it with the guest agent
custom properties, and then deletes itself from the provisioned machine.
Configuring vRealize Automation
VMware, Inc. 25
You can write your own custom scripts for the guest agent to run on deployed machines, and use custom
properties on the machine blueprint to specify the location of those scripts and the order in which to run
them. You can also use custom properties on the machine blueprint to pass custom property values to
your scripts as parameters.
For example, you could use the guest agent to make the following customizations on deployed machines:
nChange the IP address
nAdd or format drives
nRun security scripts
nInitialize another agent, for example Puppet or Chef
Your custom scripts do not have to be locally installed on the machine. As long as the provisioned
machine has network access to the script location, the guest agent can access and run the scripts. This
lowers maintenance costs because you can update your scripts without having to rebuild all of your
templates.
If you choose to install the guest agent to run custom scripts on provisioned machines, your blueprints
must include the appropriate guest agent custom properties. For example, if you install the guest agent
on a template for cloning, create a custom script that changes the provisioned machine's IP address, and
place the script in a shared location, you need to include a number of custom properties in your blueprint.
Table 1‑5. Custom Properties for Changing IP Address of a Provisioned Machine with a Guest
Agent
Custom Property Description
VirtualMachine.Admin.UseGuestAgent Set to true to initialize the guest agent when the provisioned
machine is started.
VirtualMachine.Customize.WaitComplete Set to True to prevent the provisioning workflow from sending
work items to the guest agent until all customizations have been
completed.
VirtualMachine.SoftwareN.ScriptPath Specifies the full path to an application's install script. The path
must be a valid absolute path as seen by the guest operating
system and must include the name of the script file name.
You can pass custom property values as parameters to the
script by inserting {YourCustomProperty} in the path string. For
example, entering the
value \\vra-
scripts.mycompany.com\scripts\changeIP.bat runs the
changeIP.bat script from a shared location, but entering the
value \\vra-
scripts.mycompany.com\scripts\changeIP.bat
{VirtualMachine.Network0.Address} runs the changeIP
script but also passes the value of the
VirtualMachine.Network0.Address property to the script as
a parameter.
For more information about custom properties you can use with the guest agent, see Custom Properties
Reference.
Configuring vRealize Automation
VMware, Inc. 26
Install the Guest Agent on a Linux Reference Machine
Install the Linux guest agent on your reference machines to further customize machines after deployment.
Prerequisites
nIdentify or create the reference machine.
nThe guest agent files you download contain both tar.gz and RPM package formats. If your operating
system cannot install tar.gz or RPM files, use a conversion tool to convert the installation files to your
preferred package format.
Procedure
1Navigate to the vCloud Automation Center Appliance management console installation page.
For example: https://vcac-hostname.domain.name:5480/installer/.
2Download and save the Linux Guest Agent Packages.
3Unpack the LinuxGuestAgentPkgs file.
4Install the guest agent package that corresponds to the guest operating system you are deploying
during provisioning.
a Navigate to the LinuxGuestAgentPkgs subdirectory for your guest operating system.
b Locate your preferred package format or convert a package to your preferred package format.
c Install the guest agent package on your reference machine.
For example, to install the files from the RPM package, run rpm -i
gugent-7.0.0-012715.x86_64.rpm.
5Configure the guest agent to communicate with the Manager Service by running installgugent.sh
Manager_Service_Hostname_fdqn:portnumber ssl platform.
The default port number for the Manager Service is 443. Accepted platform values are ec2, vcd, vca,
and vsphere.
Option Description
If you are using a load balancer Enter the fully qualified domain name and port number of your Manager Service
load balancer. For example:
cd /usr/share/gugent
./installgugent.sh load_balancer_manager_service.mycompany.com:
443 ssl ec2
With no load balancer Enter the fully qualified domain name and port number of your Manager Service
machine. For example:
cd /usr/share/gugent
./installgugent.sh manager_service_machine.mycompany.com:443
ssl vsphere
Configuring vRealize Automation
VMware, Inc. 27
6If deployed machines are not already configured to trust the Manager Service SSL certificate, you
must install the cert.pem file on your reference machine to establish trust.
nFor the most secure approach, obtain the cert.pem certificate and manually install the file on the
reference machine.
nFor a more convenient approach, you can connect to the manager service load balancer or
manager service machine and download the cert.pem certificate.
Option Description
If you are using a load balancer As the root user on the reference machine, run the following command:
echo | openssl s_client -connect
manager_service_load_balancer.mycompany.com:443 | sed -ne '/-
BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p' > cert.pem
With no load balancer As the root user on the reference machine, run the following command:
echo | openssl s_client -connect
manager_service_machine.mycompany.com:443 | sed -ne '/-BEGIN
CERTIFICATE-/,/-END CERTIFICATE-/p' > cert.pem
7If you are installing the guest agent on a Ubuntu operating system, create symbolic links for shared
objects by running one of the following command sets.
Option Description
64-bit systems cd /lib/x86_64-linux-gnu
sudo ln -s libssl.so.1.0.0 libssl.so.10
sudo ln -s libcrypto.so.1.0.0 libcrypto.so.10
32-bit systems cd /lib/i386-linux-gnu
sudo ln -s libssl.so.1.0.0 libssl.so.10
sudo ln -s libcrypto.so.1.0.0 libcrypto.so.10
What to do next
Convert your reference machine into a template for cloning, an Amazon Machine Image, or a snapshot
that your IaaS architects can use when creating blueprints.
Install the Guest Agent on a Windows Reference Machine
Install the Windows guest agent on a Windows reference machines to run as a Windows service and
enable further customization of machines.
Prerequisites
nIdentify or create the reference machine.
nIf you want to use the most secure approach for establishing trust between the guest agent and your
Manager Service machine, obtain the SSL certificate in PEM format from your Manager Service
machine. For more information about how the guest agent establishes trust, see Configuring the
Windows Guest Agent to Trust a Server.
Configuring vRealize Automation
VMware, Inc. 28
Procedure
1Navigate to the vCloud Automation Center Appliance management console installation page.
For example: https://vcac-hostname.domain.name:5480/installer/.
2Download and save the Windows guest agent installation file to the C drive of your reference
machine.
nWindows guest agent files (32-bit.)
nWindows guest agent files (64-bit.)
3Install the guest agent on the reference machine.
a Right-click the file and select Properties.
b Click General.
c Click Unblock.
d Extract the files.
This produces the directory C:\VRMGuestAgent. Do not rename this directory.
4Configure the guest agent to communicate with the Manager Service.
a Open an elevated command prompt.
b Navigate to C:\VRMGuestAgent.
c Configure the guest agent to trust your Manager Service machine.
Option Description
Allow the guest agent to trust the
first machine to which it connects.
No configuration required.
Manually install the trusted PEM file. Place the Manager Service PEM file in the C:\VRMGuestAgent\ directory.
d Run winservice -i -h Manager_Service_Hostname_fdqn:portnumber -p ssl.
The default port number for the Manager Service is 443.
Option Description
If you are using a load balancer Enter the fully qualified domain name and port number of your Manager
Service load balancer. For example, winservice -i -h
load_balancer_manager_service.mycompany.com:443 -p ssl.
With no load balancer Enter the fully qualified domain name and port number of your Manager
Service machine. For example, winservice -i -h
manager_service_machine.mycompany.com:443 -p ssl.
If you are preparing an Amazon
machine image
You need to specify that you are using Amazon. For example, winservice -i
-h manager_service_machine.mycompany.com:443:443 -p ssl -c ec2
The name of the Windows service is VCACGuestAgentService. You can find the installation log VCAC-
GuestAgentService.log in C:\VRMGuestAgent.
Configuring vRealize Automation
VMware, Inc. 29
What to do next
Convert your reference machine into a template for cloning, an Amazon machine image, or a snapshot so
your IaaS architects can use your template when creating blueprints.
Configuring the Windows Guest Agent to Trust a Server
The most secure approach is to install the trusted PEM file manually on each template that uses the
guest agent, but you can also allow the guest agent to trust the first machine to which it connects.
Installing the PEM file for the trusted server on each template along with the guest agent is the most
secure approach. For security, the guest agent does not check for a certificate if a PEM file already exists
in the VRMGuestAgent directory. If the server certificates change, you must manually rebuild your
templates with the new PEM files.
You can also configure the guest agent to populate the trusted PEM file on first use. This is less secure
than manually installing the PEM files on each template, but is more flexible for environments where you
might use a single template for multiple servers. To allow the guest agent to trust the first server it
connects to, you create a template with no PEM files in the VRMGuestAgent directory. The guest agent
populates the PEM file the first time it connect to a server. The template always trusts the first system to
which it connects. For security, the guest agent does not check for a certificate if a PEM file already exists
in the VRMGuestAgent directory. If the server certificate changes, you must remove the PEM file from
your VRMGuestAgent directory. The guest agent installs the new PEM file the next time it connects to the
server.
Checklist for Preparing to Provision by Cloning
You must perform some preparation outside of vRealize Automation to create the template and the
customization objects used to clone Linux and Windows virtual machines.
Cloning requires a template to clone from, created from a reference machine.
Configuring vRealize Automation
VMware, Inc. 30
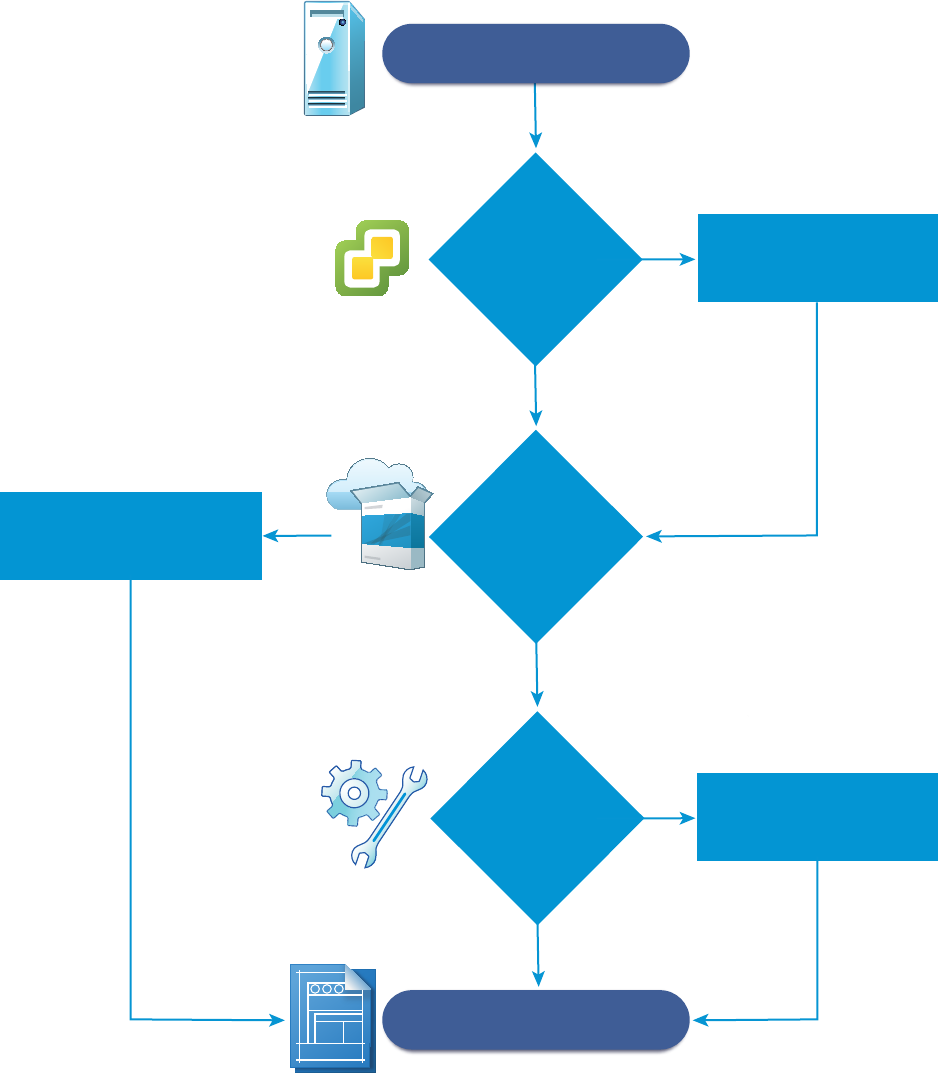
TEMPLATE
Identify or create
a reference machine.
No
Yes
No
No
Convert your reference
machine to a template.
Install the guest agent and
the software bootstrap
agent.
Install the guest agent.
Install VMware Tools.
Yes
Are you working in
vCenter Server?
Do you want
to support software
components in
your blueprints?
Do you want
the ability to
customize
machines after
deployment?
Yes
If you are provisioning a Windows machine by cloning, the only way to join the provisioned machine to an
Active Directory domain is by using the customization specification from vCenter Server or by including a
guest operating system profile with your SCVMM template. Machines provisioned by cloning cannot be
placed in an Active Directory container during provisioning. You must do this manually after provisioning.
Configuring vRealize Automation
VMware, Inc. 31
Table 1‑6. Checklist for Preparing to Provision by Cloning
Task Location Details
Identify or create the reference machine. Hypervisor See the documentation provided by your
hypervisor.
(Optional) If you want your clone template to
support Software components, install the
vRealize Automation guest agent and software
bootstrap agent on your reference machine.
Reference machine For Windows reference machines, see Prepare
a Windows Reference Machine to Support
Software.
For Linux reference machines, see Prepare a
Linux Reference Machine to Support Software.
(Optional) If you do not need your clone template
to support Software components, but you do want
the ability to customize deployed machines, install
the vRealize Automation guest agent on your
reference machine.
Reference machine See Using vRealize Automation Guest Agent in
Provisioning.
If you are working in a vCenter Server
environment, install VMware Tools on the reference
machine.
vCenter Server See the VMware Tools documentation.
Use the reference machine to create a template
for cloning.
Hypervisor The reference machine may be powered on or
off. If you are cloning in vCenter Server, you can
use a reference machine directly without
creating a template.
See the documentation provided by your
hypervisor.
Create the customization object to configure
cloned machines by applying System Preparation
Utility information or a Linux customization.
Hypervisor If you are cloning for Linux you can install the
Linux guest agent and provide external
customization scripts instead of creating a
customization object. If you are cloning with
vCenter Server, you must provide the
customization specification as the customization
object.
See the documentation provided by your
hypervisor.
Gather the information required to create
blueprints that clone your template.
Capture information and
transfer to your IaaS
architects.
See Worksheet for Virtual Provisioning by
Cloning.
Worksheet for Virtual Provisioning by Cloning
Complete the knowledge transfer worksheet to capture information about the template, customizations,
and custom properties required to create clone blueprints for the templates you prepared in your
environment. Not all of this information is required for every implementation. Use this worksheet as a
guide, or copy and paste the worksheet tables into a word processing tool for editing.
Configuring vRealize Automation
VMware, Inc. 32
Required Template and Reservation Information
Table 1‑7. Template and Reservation Information Worksheet
Required Information My Value Details
Template name
Reservations on which the template
is available, or reservation policy to
apply
To avoid errors during provisioning, ensure that
the template is available on all reservations or
create reservation policies that architects can
use to restrict the blueprint to reservations
where the template is available.
(vSphere only) Type of cloning
requested for this template
nClone
nLinked Clone
nNetApp FlexClone
Customization specification name
(Required for cloning with static IP
addresses)
You cannot perform customizations of Windows
machines without a customization specification
object.
(SCVMM only) ISO name
(SCVMM only) Virtual hard disk
(SCVMM only) Hardware profile to
attach to provisioned machines
Required Property Groups
You can complete the custom property information sections of the worksheet, or you can create property
groups and ask architects to add your property groups to their blueprints instead of numerous individual
custom properties.
Required vCenter Server Operating System
You must supply the guest operating system custom property for vCenter Server provisioning.
Table 1‑8. vCenter Server Operating System
Custom Property My Value Description
VMware.VirtualCenter.OperatingSy
stem
Specifies the vCenter Server guest
operating system version
(VirtualMachineGuestOsIdentifier)
with which vCenter Server creates the
machine. This operating system version
must match the operating system version
to be installed on the provisioned machine.
Administrators can create property groups
using one of several property sets, for
example,
VMware[OS_Version]Properties, that
are predefined to include the correct
VMware.VirtualCenter.OperatingSyst
em values. This property is for virtual
provisioning.
Configuring vRealize Automation
VMware, Inc. 33
Visual Basic Script Information
If you configured vRealize Automation to run your custom Visual Basic scripts as additional steps in the
machine life cycle, you must include information about the scripts in the blueprint.
Note A fabric administrator can create a property group by using the property sets
ExternalPreProvisioningVbScript and ExternalPostProvisioningVbScript to provide this required
information. Doing so makes it easier for blueprint architects to include this information correctly in their
blueprints.
Table 1‑9. Visual Basic Script Information
Custom Property My Value Description
ExternalPreProvisioningVbScript Run a script before provisioning. Enter the
complete path to the script including the
filename and extension. %System Drive
%Program Files (x86)\VMware\vCAC
Agents\EPI_Agents\Scripts\SendEmai
l.vbs.
ExternalPostProvisioningVbScript Run a script after provisioning. Enter the
complete path to the script including the
filename and extension. %System Drive
%Program Files (x86)\VMware\vCAC
Agents\EPI_Agents\Scripts\SendEmai
l.vbs
Linux Guest Agent Customization Script Information
If you configured your Linux template to use the guest agent for running customization scripts, you must
include information about the scripts in the blueprint.
Configuring vRealize Automation
VMware, Inc. 34
Table 1‑10. Linux Guest Agent Customization Script Information Worksheet
Custom Property My Value Description
Linux.ExternalScript.Name Specifies the name of an optional
customization script, for example
config.sh, that the Linux guest agent
runs after the operating system is
installed. This property is available for
Linux machines cloned from templates on
which the Linux agent is installed.
If you specify an external script, you must
also define its location by using the
Linux.ExternalScript.LocationType
and Linux.ExternalScript.Path
properties.
Linux.ExternalScript.LocationTy
pe
Specifies the location type of the
customization script named in the
Linux.ExternalScript.Name property.
This can be either local or nfs.
You must also specify the script location
using the Linux.ExternalScript.Path
property. If the location type is nfs, also
use the Linux.ExternalScript.Server
property.
Linux.ExternalScript.Server Specifies the name of the NFS server, for
example lab-ad.lab.local, on which the
Linux external customization script
named in Linux.ExternalScript.Name
is located.
Linux.ExternalScript.Path Specifies the local path to the Linux
customization script or the export path to
the Linux customization on the NFS
server. The value must begin with a
forward slash and not include the file
name, for
example /scripts/linux/config.sh.
Other Guest Agent Custom Properties
If you installed the guest agent on your reference machine, you can use custom properties to further
customize machines after deployment.
Configuring vRealize Automation
VMware, Inc. 35
Table 1‑11. Custom Properties for Customizing Cloned Machines with a Guest Agent
Worksheet
Custom Property My Value Description
VirtualMachine.Admin.AddOwnerToAd
mins
Set to True (default) to add the machine’s
owner, as specified by the
VirtualMachine.Admin.Owner property, to
the local administrators group on the
machine.
VirtualMachine.Admin.AllowLogin Set to True (default) to add the machine
owner to the local remote desktop users
group, as specified by the
VirtualMachine.Admin.Owner property.
VirtualMachine.Admin.UseGuestAgen
t
If the guest agent is installed as a service on
a template for cloning, set to True on the
machine blueprint to enable the guest agent
service on machines cloned from that
template. When the machine is started, the
guest agent service is started. Set to False
to disable the guest agent. If set to False,
the enhanced clone workfow will not use the
guest agent for guest operating system
tasks, reducing its functionality to
VMwareCloneWorkflow. If not specified or
set to anything other than False, the
enhanced clone workflow will send work
items to the guest agent.
VirtualMachine.DiskN.Active Set to True (default) to specify that the
machine's disk N is active. Set to False to
specify that the machine's disk N is not
active.
Configuring vRealize Automation
VMware, Inc. 36

Table 1‑11. Custom Properties for Customizing Cloned Machines with a Guest Agent
Worksheet (Continued)
Custom Property My Value Description
VirtualMachine.DiskN.Size Defines the size in GB of disk N. For
example, to give a size of 150 GB to a disk
G, define the custom property
VirtualMachine.Disk0.Size and enter a
value of 150. Disk numbering must be
sequential. By default a machine has one
disk referred to by
VirtualMachine.Disk0.Size, where size
is specified by the storage value on the
blueprint from which the machine is
provisioned. The storage value on the
blueprint user interface overwrites the value
in the VirtualMachine.Disk0.Size
property. The
VirtualMachine.Disk0.Size property is
not available as a custom property because
of its relationship with the storage option on
the blueprint. More disks can be added by
specifying VirtualMachine.Disk1.Size,
VirtualMachine.Disk2.Size and so on.
VirtualMachine.Admin.TotalDiskUsage
always represents the total of
the .DiskN.Size properties plus the
VMware.Memory.Reservation size
allocation.
VirtualMachine.DiskN.Label Specifies the label for a machine’s disk N.
The disk label maximum is 32 characters.
Disk numbering must be sequential. When
used in conjunction with a guest agent,
specifies the label of a machine's disk N
inside the guest operating system.
VirtualMachine.DiskN.Letter Specifies the drive letter or mount point of a
machine’s disk N. The default is C. For
example, to specify the letter D for Disk 1,
define the custom property as
VirtualMachine.Disk1.Letter and enter
the value D. Disk numbering must be
sequential. When used in conjunction with a
guest agent, this value specifies the drive
letter or mount point under which an
additional disk N is mounted by the guest
agent in the guest operating system.
Configuring vRealize Automation
VMware, Inc. 37

Table 1‑11. Custom Properties for Customizing Cloned Machines with a Guest Agent
Worksheet (Continued)
Custom Property My Value Description
VirtualMachine.Admin.CustomizeGue
stOSDelay
Specifies the time to wait after customization
is complete and before starting the guest
operating system customization. The value
must be in HH:MM:SS format. If the value is
not set, the default value is one minute
(00:01:00). If you choose not to include this
custom property, provisioning can fail if the
virtual machine reboots before guest agent
work items are completed, causing
provisioning to fail.
VirtualMachine.Customize.WaitComp
lete
Set to True to prevent the provisioning
workflow from sending work items to the
guest agent until all customizations have
been completed.
VirtualMachine.SoftwareN.Name Specifies the descriptive name of a software
application N or script to install or run during
provisioning. This is an optional and
information-only property. It serves no real
function for the enhanced clone workflow or
the guest agent but it is useful for a custom
software selection in a user interface or for
software usage reporting.
VirtualMachine.SoftwareN.ScriptPa
th
Specifies the full path to an application's
install script. The path must be a valid
absolute path as seen by the guest
operating system and must include the
name of the script file name.
You can pass custom property values as
parameters to the script by inserting
{CustomPropertyName} in the path string.
For example, if you have a custom property
named ActivationKey whose value is
1234, the script path is
D:\InstallApp.bat –key
{ActivationKey}. The guest agent runs
the command D:\InstallApp.bat –key
1234. Your script file can then be
programmed to accept and use this value.
Configuring vRealize Automation
VMware, Inc. 38
Table 1‑11. Custom Properties for Customizing Cloned Machines with a Guest Agent
Worksheet (Continued)
Custom Property My Value Description
VirtualMachine.SoftwareN.ISOName Specifies the path and file name of the ISO
file relative to the data store root. The format
is /folder_name/subfolder_name/file_
name.iso. If a value is not specified, the
ISO is not mounted.
VirtualMachine.SoftwareN.ISOLocat
ion
Specifies the storage path that contains the
ISO image file to be used by the application
or script. Format the path as it appears on
the host reservation, for example
netapp-1:it_nfs_1. If a value is not
specified, the ISO is not mounted.
Networking Custom Properties
If you are not integrating with NSX, you can still specify configuration for specific network devices on a
machine by using custom properties.
Table 1‑12. Custom Properties for Networking Configuration
Custom Property My Value Description
VirtualMachine.NetworkN.Address Specifies the IP address of network
device N in a machine provisioned with a
static IP address.
VirtualMachine.NetworkN.MacAddr
essType
Indicates whether the MAC address of
network device N is generated or user-
defined (static). This property is available
for cloning.
The default value is generated. If the
value is static, you must also use
VirtualMachine.NetworkN.MacAddres
s to specify the MAC address.
VirtualMachine.NetworkN custom
properties are designed to be specific to
individual blueprints and machines. When
a machine is requested, network and IP
address allocation is performed before
the machine is assigned to a reservation.
Because blueprints are not guaranteed to
be allocated to a specific reservation, do
not use this property on a reservation.
Configuring vRealize Automation
VMware, Inc. 39
Table 1‑12. Custom Properties for Networking Configuration (Continued)
Custom Property My Value Description
VirtualMachine.NetworkN.MacAddr
ess
Specifies the MAC address of a network
device N. This property is available for
cloning.
If the value of
VirtualMachine.NetworkN.MacAddres
sType is generated, this property contains
the generated address.
If the value of
VirtualMachine.NetworkN.MacAddres
sType is static, this property specifies the
MAC address. For virtual machines
provisioned on ESX server hosts, the
address must be in the range specified by
VMware. For details, see vSphere
documentation.
VirtualMachine.NetworkN custom
properties are designed to be specific to
individual blueprints and machines. When
a machine is requested, network and IP
address allocation is performed before
the machine is assigned to a reservation.
Because blueprints are not guaranteed to
be allocated to a specific reservation, do
not use this property on a reservation.
Configuring vRealize Automation
VMware, Inc. 40

Table 1‑12. Custom Properties for Networking Configuration (Continued)
Custom Property My Value Description
VirtualMachine.NetworkN.Name Specifies the name of the network to
connect to, for example the network
device N to which a machine is attached.
This is equivalent to a network interface
card (NIC).
By default, a network is assigned from the
network paths available on the
reservation on which the machine is
provisioned. Also see
VirtualMachine.NetworkN.AddressTy
pe.
You can ensure that a network device is
connected to a specific network by setting
the value of this property to the name of a
network on an available reservation. For
example, If you give properties for N= 0
and 1, you get 2 NICs and their assigned
value, provided the network is selected in
the associated reservation.
VirtualMachine.NetworkN custom
properties are designed to be specific to
blueprints and machines. When a
machine is requested, network and IP
address allocation is performed before
the machine is assigned to a reservation.
Because blueprints are not guaranteed to
be allocated to a specific reservation, do
not use this property on a reservation.
You can add this property to a vCloud Air
or vCloud Director machine component in
a blueprint.
VirtualMachine.NetworkN.PortID Specifies the port ID to use for network
device N when using a dvPort group with
a vSphere distributed switch.
VirtualMachine.NetworkN custom
properties are designed to be specific to
individual blueprints and machines. When
a machine is requested, network and IP
address allocation is performed before
the machine is assigned to a reservation.
Because blueprints are not guaranteed to
be allocated to a specific reservation, do
not use this property on a reservation.
Configuring vRealize Automation
VMware, Inc. 41
Table 1‑12. Custom Properties for Networking Configuration (Continued)
Custom Property My Value Description
VirtualMachine.NetworkN.Profile
Name
Specifies the name of a network profile
from which to assign a static IP address
to network device N or from which to
obtain the range of static IP addresses
that can be assigned to network device N
of a cloned machine, where N=0 for the
first device, 1 for the second, and so on.
If a network profile is specified in the
network path in the reservation on which
the machine is provisioned, a static IP
address is assigned from that network
profile. You can ensure that a static IP
address is assigned from a specific profile
by setting the value of this property to the
name of a network profile.
nVirtualMachine.NetworkN.Subn
etMask
nVirtualMachine.NetworkN.Gate
way
nVirtualMachine.NetworkN.Prim
aryDns
nVirtualMachine.NetworkN.Seco
ndaryDns
nVirtualMachine.NetworkN.Prim
aryWins
nVirtualMachine.NetworkN.Seco
ndaryWins
nVirtualMachine.NetworkN.DnsS
uffix
nVirtualMachine.NetworkN.DnsS
earchSuffixes
Appending a name allows you to create
multiple versions of a custom property.
For example, the following properties
might list load balancing pools set up for
general use and machines with high,
moderate, and low performance
requirements:
nVCNS.LoadBalancerEdgePool.Name
s
nVCNS.LoadBalancerEdgePool.Name
s.moderate
nVCNS.LoadBalancerEdgePool.Name
s.high
nVCNS.LoadBalancerEdgePool.Name
s.low
Configures attributes of the network
profile specified in
VirtualMachine.NetworkN.ProfileNa
me.
Configuring vRealize Automation
VMware, Inc. 42
Table 1‑12. Custom Properties for Networking Configuration (Continued)
Custom Property My Value Description
VCNS.LoadBalancerEdgePool.Names.
name
Specifies the
vCloud Networking and Security load
balancing pools to which the virtual
machine is assigned during provisioning.
The virtual machine is assigned to all
service ports of all specified pools. The
value is an edge/pool name or a list of
edge/pool names separated by commas.
Names are case-sensitive.
Appending a name allows you to create
multiple versions of a custom property.
For example, the following properties
might list load balancing pools set up for
general use and machines with high,
moderate, and low performance
requirements:
nVCNS.LoadBalancerEdgePool.Name
s
nVCNS.LoadBalancerEdgePool.Name
s.moderate
nVCNS.LoadBalancerEdgePool.Name
s.high
nVCNS.LoadBalancerEdgePool.Name
s.low
Configuring vRealize Automation
VMware, Inc. 43
Table 1‑12. Custom Properties for Networking Configuration (Continued)
Custom Property My Value Description
VCNS.SecurityGroup.Names.name Specifies the
vCloud Networking and Security security
group or groups to which the virtual
machine is assigned during provisioning.
The value is a security group name or a
list of names separated by commas.
Names are case-sensitive.
Appending a name allows you to create
multiple versions of the property, which
can be used separately or in combination.
For example, the following properties can
list security groups intended for general
use, for the sales force, and for support:
nVCNS.SecurityGroup.Names
nVCNS.SecurityGroup.Names.sales
nVCNS.SecurityGroup.Names.suppo
rt
VCNS.SecurityTag.Names.name Specifies the
vCloud Networking and Security security
tag or tags to which the virtual machine is
associated during provisioning. The value
is a security tag name or a list of names
separated by commas. Names are case-
sensitive.
Appending a name allows you to create
multiple versions of the property, which
can be used separately or in combination.
For example, the following properties can
list security tags intended for general use,
for the sales force, and for support:
nVCNS.SecurityTag.Names
nVCNS.SecurityTag.Names.sales
nVCNS.SecurityTag.Names.support
Preparing for vCloud Air and vCloud Director Provisioning
To prepare for provisioning vCloud Air and vCloud Director machines by using vRealize Automation, you
must configure the organization virtual data center with templates and customization objects.
To provision vCloud Air and vCloud Director resources using vRealize Automation, the organization
requires a template to clone from that consists of one or more machine resources.
Configuring vRealize Automation
VMware, Inc. 44

Templates that are to be shared across organizations must be public. Only reserved templates are
available to vRealize Automation as a cloning source.
Note When you create a blueprint by cloning from a template, that template's unique identifier becomes
associated with the blueprint. When the blueprint is published to the vRealize Automation catalog and
used in the provisioning and data collection processes, the associated template is recognized. If you
delete the template in vCloud Air or vCloud Director, subsequent vRealize Automation provisioning and
data collection fails because the associated template no longer exists. Instead of deleting and recreating
a template, for example to upload an updated version, replace the template using the vCloud Air
vCloud Director template replacement process. Using vCloud Air or vCloud Director to replace the
template, rather than deleting and recreating the template, keeps the template's unique ID intact and
allows provisioning and data collection to continue functioning.
The following overview illustrates the steps you need to perform before using vRA to create endpoints,
and define reservations and blueprints. For more information about these administrative tasks, see
vCloud Air and vCloud Director product documentation.
1 In vCloud Air or vCloud Director, create a template for cloning and add it to the organization catalog.
2 In vCloud Air or vCloud Director, use the template to specify custom settings such as passwords,
domain, and scripts for the guest operating system on each machine.
You can use vRealize Automation to override some of these settings.
Customization can vary depending on the guest operating system of the resource.
3 In vCloud Air or vCloud Director, configure the catalog to be shared with everyone in the organization.
In vCloud Air or vCloud Director, configure account administrator access to applicable organizations
to allow all users and groups in the organization to have access to the catalog. Without this sharing
designation, the catalog templates are not be visible to endpoint or blueprint architects in
vRealize Automation.
4 Gather the following information so that you can include it in blueprints:
nName of the vCloud Air or vCloud Director template.
nAmount of total storage specified for the template.
Preparing for Linux Kickstart Provisioning
Linux Kickstart provisioning uses a configuration file to automate a Linux installation on a newly
provisioned machine. To prepare for provisioning you must create a bootable ISO image and a Kickstart
or autoYaST configuration file.
The following is a high-level overview of the steps required to prepare for Linux Kickstart provisioning:
1 Verify that a DHCP server is available on the network. vRealize Automation cannot provision
machines by using Linux Kickstart provisioning unless DHCP is available.
2 Prepare the configuration file. In the configuration file, you must specify the locations of the
vRealize Automation server and the Linux agent installation package. See Prepare the Linux Kickstart
Configuration Sample File.
Configuring vRealize Automation
VMware, Inc. 45
3 Edit the isolinux/isolinux.cfg or loader/isolinux.cfg to specify the name and location of the
configuration file and the appropriate Linux distribution source.
4 Create the boot ISO image and save it to the location required by your virtualization platform. See the
documentation provided by your hypervisor for information about the required location.
5 (Optional) Add customization scripts.
a To specify post-installation customization scripts in the configuration file, see Specify Custom
Scripts in a kickstart/autoYaST Configuration File.
b To call Visual Basic scripts in blueprint, see Checklist for Running Visual Basic Scripts During
Provisioning.
6 Gather the following information so that blueprint architects can include it in their blueprints:
a The name and location of the ISO image.
b For vCenter Server integrations, the vCenter Server guest operating system version with which
vCenter Server is to create the machine.
Note You can create a property group with the property set BootIsoProperties to include the required
ISO information. This makes it easier to include this information correctly on blueprints.
Prepare the Linux Kickstart Configuration Sample File
vRealize Automation provides sample configuration files that you can modify and edit to suit your needs.
There are several changes required to make the files usable.
Procedure
1Navigate to the vCloud Automation Center Appliance management console installation page.
For example: https://vcac-hostname.domain.name:5480/installer/.
2Download and save the Linux Guest Agent Packages.
3Unpack the LinuxGuestAgentPkgs file.
4Navigate to the LinuxGuestAgentPkgs file and locate the subdirectory that corresponds to the guest
operating system that you are deploying during provisioning.
5Open the sample-https.cfg file.
6Replace all instances of the string host=dcac.example.net with the IP address or fully qualified
domain name and port number for the vRealize Automation server host.
Platform Required Format
vSphere ESXi IP Address, for example: --host=172.20.9.59
vSphere ESX IP Address, for example: --host=172.20.9.58
SUSE 10 IP Address, for example: --host=172.20.9.57
All others FQDN, for example: --host=mycompany-host1.mycompany.local:443
Configuring vRealize Automation
VMware, Inc. 46

7Locate each instance of gugent.rpm or gugent.tar.gz and replace the URL rpm.example.net
with the location of the guest agent package.
For example:
rpm -i nfs:172.20.9.59/suseagent/gugent.rpm
8Save the file to a location accessible to newly provisioned machines.
Specify Custom Scripts in a kickstart/autoYaST Configuration File
You can modify the configuration file to copy or install custom scripts onto newly provisioned machines.
The Linux agent runs the scripts at the specified point in the workflow.
Your script can reference any of the ./properties.xml files in
the /usr/share/gugent/site/workitem directories.
Prerequisites
nPrepare a kickstart or autoYaST configuration file. See Prepare the Linux Kickstart Configuration
Sample File.
nYour script must return a non-zero value on failure to prevent machine provisioning failure.
Procedure
1Create or identify the script you want to use.
2Save the script as NN_scriptname.
NN is a two digit number. Scripts are executed in order from lowest to highest. If two scripts have the
same number, the order is alphabetical based on scriptname.
3Make your script executable.
4Locate the post-installation section of your kickstart or autoYaST configuration file.
In kickstart, this is indicated by %post. In autoYaST, this is indicated by post-scripts.
5Modify the post-installation section of the configuration file to copy or install your script into
the /usr/share/gugent/site/workitem directory of your choice.
Custom scripts are most commonly run for virtual kickstart/autoYaST with the work items SetupOS
(for create provisioning) and CustomizeOS (for clone provisioning), but you can run scripts at any
point in the workflow.
For example, you can modify the configuration file to copy the script 11_addusers.sh to
the /usr/share/gugent/site/SetupOS directory on a newly provisioned machine by using the
following command:
cp nfs:172.20.9.59/linuxscripts/11_addusers.sh /usr/share/gugent/site/SetupOS
The Linux agent runs the script in the order specified by the work item directory and the script file name.
Configuring vRealize Automation
VMware, Inc. 47
Preparing for SCCM Provisioning
vRealize Automation boots a newly provisioned machine from an ISO image, and then passes control to
the specified SCCM task sequence.
SCCM provisioning is supported for the deployment of Windows operating systems. Linux is not
supported. Software distribution and updates are not supported.
The following is a high-level overview of the steps required to prepare for SCCM provisioning:
1 Consult with your network administrator to ensure that the following network requirements are met:
nCommunication with SCCM requires the NetBios name of the SCCM server. At least one
Distributed Execution Manager (DEM) must be able to resolve the fully qualified name of the
SCCM server to its NetBios name.
nThe SCCM server and the vRealize Automation server must be on the same network and
available to each other.
2 Create a software package that includes the vRealize Automation guest agent. See Create a
Software Package for SCCM Provisioning.
3 In SCCM, create the desired task sequence for provisioning the machine. The final step must be to
install the software package you created that contains the vRealize Automation guest agent. For
information about creating task sequences and installing software packages, see SCCM
documentation.
4 Create a zero touch boot ISO image for the task sequence. By default, SCCM creates a light touch
boot ISO image. For information about configuring SCCM for zero touch ISO images, see SCCM
documentation.
5 Copy the ISO image to the location required by your virtualization platform. If you do not know the
appropriate location, refer to the documentation provided by your hypervisor.
6 Gather the following information so that blueprint architects can include it on blueprints:
a The name of the collection containing the task sequence.
b The fully qualified domain name of the SCCM server on which the collection containing the
sequence resides.
c The site code of the SCCM server.
d Administrator-level credentials for the SCCM server.
e (Optional) For SCVMM integrations, the ISO, virtual hard disk, or hardware profile to attach to
provisioned machines.
Note You can create a property group with the SCCMProvisioningProperties property set to include
all of this required information. This makes it easier to include the information on blueprints.
Configuring vRealize Automation
VMware, Inc. 48
Create a Software Package for SCCM Provisioning
The final step in your SCCM task sequence must be to install a software package that includes the
vRealize Automation guest agent.
Procedure
1Navigate to the vCloud Automation Center Appliance management console installation page.
For example: https://vcac-hostname.domain.name:5480/installer/.
2Download and save the Windows guest agent files.
nWindows guest agent files (32-bit.)
nWindows guest agent files (64-bit.)
3Extract the Windows guest agent files to a location available to SCCM.
4Create a software package from the definition file SCCMPackageDefinitionFile.sms.
5Make the software package available to your distribution point.
6Select the contents of the extracted Windows guest agent files as your source files.
Preparing for WIM Provisioning
Provision a machine by booting into a WinPE environment and then install an operating system using a
Windows Imaging File Format (WIM) image of an existing Windows reference machine.
The following is a high-level overview of the steps required to prepare for WIM provisioning:
1 Identify or create the staging area. This should be a network directory that can be specified as a UNC
path or mounted as a network drive by the reference machine, the system on which you build the
WinPE image, and the virtualization host on which machines are provisioned.
2 Ensure that a DHCP server is available on the network. vRealize Automation cannot provision
machines by using a WIM image unless DHCP is available.
3 Identify or create the reference machine within the virtualization platform you intend to use for
provisioning. For vRealize Automation requirements, see Reference Machine Requirements for WIM
Provisioning. For information about creating a reference machine, see the documentation provided by
your hypervisor.
4 Using the System Preparation Utility for Windows, prepare the reference machine's operating system
for deployment. See SysPrep Requirements for the Reference Machine.
5 Create the WIM image of the reference machine. Do not include any spaces in the WIM image file
name or provisioning fails.
6 Create a WinPE image that contains the vRealize Automation guest agent. You can use the
vRealize Automation PEBuilder to create a WinPE image that includes the guest agent.
nInstall PEBuilder.
Configuring vRealize Automation
VMware, Inc. 49
n(Optional) Create any custom scripts you want to use to customize provisioned machines and
place them in the appropriate work item directory of your PEBuilder installation. See Specify
Custom Scripts in a PEBuilder WinPE.
nIf you are using VirtIO for network or storage interfaces, you must ensure that the necessary
drivers are included in your WinPE image and WIM image. See Preparing for WIM Provisioning
with VirtIO Drivers.
nCreate a WinPE Image by Using PEBuilder.
You can create the WinPE image by using another method, but you must manually insert the
vRealize Automation guest agent. See Manually Insert the Guest Agent into a WinPE Image.
7 Place the WinPE image in the location required by your virtualization platform. If you do not know the
location, see the documentation provided by your hypervisor.
8 Gather the following information so that you can include it the blueprint:
a The name and location of the WinPE ISO image.
b The name of the WIM file, the UNC path to the WIM file, and the index used to extract the desired
image from the WIM file.
c The user name and password under which to map the WIM image path to a network drive on the
provisioned machine.
d (Optional) If you do not want to accept the default, K, the drive letter to which the WIM image path
is mapped on the provisioned machine.
e For vCenter Server integrations, the vCenter Server guest operating system version with which
vCenter Server is to create the machine.
f (Optional) For SCVMM integrations, the ISO, virtual hard disk, or hardware profile to attach to
provisioned machines.
Note You can create a property group to include all of this required information. Using a property
group makes it easier to include all the information correctly in blueprints.
Reference Machine Requirements for WIM Provisioning
WIM provisioning involves creating a WIM image from a reference machine. The reference machine must
meet basic requirements for the WIM image to work for provisioning in vRealize Automation.
The following is a high-level overview of the steps to prepare a reference machine:
1 If the operating system on your reference machine is Windows Server 2008 R2, Windows Server
2012, Windows 7, or Windows 8, the default installation creates a small partition on the system's hard
disk in addition to the main partition. vRealize Automation does not support the use of WIM images
created on such multi-partitioned reference machines. You must delete this partition during the
installation process.
2 Install NET 4.5 and Windows Automated Installation Kit (AIK) for Windows 7 (including WinPE 3.0) on
the reference machine.
Configuring vRealize Automation
VMware, Inc. 50
3 If the reference machine operating system is Windows Server 2003 or Windows XP, reset the
administrator password to be blank. (There is no password.)
4 (Optional) If you want to enable XenDesktop integration, install and configure a
Citrix Virtual Desktop Agent.
5 (Optional) A Windows Management Instrumentation (WMI) agent is required to collect certain data
from a Windows machine managed by vRealize Automation, for example the Active Directory status
of a machine’s owner. To ensure successful management of Windows machines, you must install a
WMI agent (typically on the Manager Service host) and enable the agent to collect data from
Windows machines. See Installing vRealize Automation 7.0.
SysPrep Requirements for the Reference Machine
A SysPrep answer file contains several required settings that are used for WIM provisioning.
Table 1‑13. Windows Server or Windows XP reference machine SysPrep required settings
GuiUnattended Settings Value
AutoLogon Yes
AutoLogonCount 1
AutoLogonUsername username
(username and password are the credentials used for auto
logon when the newly provisioned machine boots into the guest
operating system. Administrator is typically used.)
AutoLogonPassword password corresponding to the AutoLogonUsername.
Table 1‑14. Required SysPrep Settings for reference machine that are not using Windows
Server 2003 or Windows XP:
AutoLogon Settings Value
Enabled Yes
LogonCount 1
Configuring vRealize Automation
VMware, Inc. 51
Table 1‑14. Required SysPrep Settings for reference machine that are not using Windows
Server 2003 or Windows XP: (Continued)
AutoLogon Settings Value
Username username
(username and password are the credentials used for auto
logon when the newly provisioned machine boots into the guest
operating system. Administrator is typically used.)
Password password
(username andpassword are the credentials used for auto logon
when the newly provisioned machine boots into the guest
operating system. Administrator is typically used.)
Note For reference machines that use a Windows platform
newer than Windows Server 2003/Windows XP, you must set
the autologon password by using the custom property
Sysprep.GuiUnattended.AdminPassword. A convenient way
to ensure this is done is to create a property group that includes
this custom property so that tenant administrators and business
group managers can include this information correctly in their
blueprints.
Install PEBuilder
The PEBuilder tool provided by vRealize Automation provides a simple way to include the
vRealize Automation guest agent in your WinPE images.
PEBuilder has a 32 bit guest agent. If you need to run commands specific to 64 bit, install PEBuilder and
then get the 64 bit files from the GugentZipx64.zip file.
Install PEBuilder in a location where you can access your staging environment.
Prerequisites
nInstall NET Framework 4.5.
nWindows Automated Installation Kit (AIK) for Windows 7 (including WinPE 3.0) is installed.
Procedure
1Navigate to the vCloud Automation Center Appliance management console installation page.
For example: https://vcac-hostname.domain.name:5480/installer/.
2Download the PEBuilder.
3(Optional) Download the Windows 64-bit guest agent package if you want to include the Windows 64-
bit guest agent in your WinPE instead of the Windows 32-bit guest agent.
4Run vCAC-WinPEBuilder-Setup.exe.
5Follow the prompts to install PEBuilder.
6(Optional) Replace the Windows 32-bit guest agent files located in \PE Builder\Plugins\VRM
Agent\VRMGuestAgent with the 64-bit files to include the 64-bit agent in your WinPE.
Configuring vRealize Automation
VMware, Inc. 52
You can use PEBuilder to create a WinPE for use in WIM provisioning.
Specify Custom Scripts in a PEBuilder WinPE
You can use PEBuilder to customize machines by running custom bat scripts at specified points in the
provisioning workflow.
Prerequisites
Install PEBuilder.
Procedure
1Create or identify the bat script you want to use.
Your script must return a non-zero value on failure to prevent machine provisioning failure.
2Save the script as NN_scriptname.
NN is a two digit number. Scripts are executed in order from lowest to highest. If two scripts have the
same number, the order is alphabetical based on scriptname.
3Make your script executable.
4Place the scripts in the work item subdirectory that corresponds to the point in the provisioning
workflow you want the script to run.
For example, C:\Program Files (x86)\VMware\vRA\PE Builder\Plugins\VRM
Agent\VRMGuestAgent\site\SetupOS.
The agent runs the script in the order specified by the work item directory and the script file name.
Preparing for WIM Provisioning with VirtIO Drivers
If you are using VirtIO for network or storage interfaces, you must ensure that the necessary drivers are
included in your WinPE image and WIM image. VirtIO generally offers better performance when
provisioning with KVM (RHEV).
Windows drivers for VirtIO are included as part of the Red Hat Enterprise Virtualization and are located in
the /usr/share/virtio-win directory on the file system of the Red Hat Enterprise Virtualization
Manager. The drivers are also included in the Red Hat Enterprise Virtualization Guest Tools
located /usr/share/rhev-guest-tools-iso/rhev-tools-setup.iso.
The high-level process for enabling WIM-based provisioning with VirtIO drivers is as follows:
1 Create a WIM image from a Windows reference machine with the VirtIO drivers installed or insert the
drivers into an existing WIM image.
2 Copy the VirtIO driver files to the Plugins subdirectory of your PEBuilder installation directory before
creating a WinPE image, or insert the drivers into a WinPE image created using other means.
3 Upload the WinPE image ISO to the Red Hat Enterprise Virtualization ISO storage domains using the
rhevm-iso-uploader command. For more information about managing ISO images in RHEV refer
to the Red Hat documentation.
Configuring vRealize Automation
VMware, Inc. 53
4 Create a KVM (RHEV) blueprint for WIM provisioning and select the WinPE ISO option. The custom
property VirtualMachine.Admin.DiskInterfaceType must be included with the value VirtIO. A
fabric administrator can include this information in a property group for inclusion on blueprints.
The custom properties Image.ISO.Location and Image.ISO.Name are not used for KVM (RHEV)
blueprints.
Create a WinPE Image by Using PEBuilder
Use the PEBuilder tool provided by vRealize Automation to create a WinPE ISO file that includes the
vRealize Automation guest agent.
Prerequisites
nInstall PEBuilder.
n(Optional) Configure PEBuilder to include the Windows 64-bit guest agent in your WinPE instead of
the Windows 32-bit guest agent. See Install PEBuilder.
n(Optional) Add any third party plugins you want to add to the WinPE image to the PlugIns
subdirectory of the PEBuilder installation directory.
n(Optional) Specify Custom Scripts in a PEBuilder WinPE.
Procedure
1Run PEBuilder.
2Enter the IaaS Manager Service host information.
Option Description
If you are using a load balancer a Enter the fully qualified domain name of the load balancer for the IaaS
Manager Service in the vCAC Hostname text box. For example,
manager_service_LB.mycompany.com.
b Enter the port number for the IaaS Manager Service load balancer in the
vCAC Port text box. For example, 443.
With no load balancer a Enter the fully qualified domain name of the IaaS Manager Service machine
in the vCAC Hostname text box. For example,
manager_service.mycompany.com.
b Enter the port number for the IaaS Manager Service machine in the vCAC
Port text box. For example, 443.
3Enter the path to the PEBuilder plugins directory.
This depends on the installation directory specified during installation. The default is C:\Program
Files (x86)\VMware\vCAC\PE Builder\PlugIns.
4Enter the output path for the ISO file you are creating in the ISO Output Path text box.
This location should be on the staging area you prepared.
Configuring vRealize Automation
VMware, Inc. 54
5Click File > Advanced.
Note Do not change the WinPE Architecture or Protocol settings.
6Select the Include vCAC Guest Agent in WinPE ISO check box.
7Click OK.
8Click Build.
What to do next
Place the WinPE image in the location required by your integration platform. If you do not know the
location, please see the documentation provided by your platform.
If you are provisioning HP iLO machines, place the WinPE image in a web-accessible location. For
Dell iDRAC machines, place the image in a location available to NFS or CIFS. Record the address.
Manually Insert the Guest Agent into a WinPE Image
You do not have to use the vRealize Automation PEBuilder to create your WinPE. However, if you do not
use the PEBuilder you must manually insert the vRealize Automation guest agent into your WinPE image.
Prerequisites
nSelect a Windows system from which the staging area you prepared is accessible and on which .NET
4.5 and Windows Automated Installation Kit (AIK) for Windows 7 (including WinPE 3.0) are installed.
nCreate a WinPE.
Procedure
1Install the Guest Agent in a WinPE
If you choose not to use the vRealize Automation PEBuilder to create you WinPE, you must install
PEBuilder to manually copy the guest agent files to your WinPE image.
2Configure the doagent.bat File
If you choose not to use the vRealize Automation PEBuilder, you must manually configure the
doagent.bat file.
3Configure the doagentc.bat File
If you choose not to use the vRealize Automation PEBuilder, you must manually configure the
doagentc.bat file.
4Configure the Guest Agent Properties Files
If you choose not to use the vRealize Automation PEBuilder, you must manually configure the guest
agent properties files.
Install the Guest Agent in a WinPE
If you choose not to use the vRealize Automation PEBuilder to create you WinPE, you must install
PEBuilder to manually copy the guest agent files to your WinPE image.
Configuring vRealize Automation
VMware, Inc. 55
PEBuilder has a 32 bit guest agent. If you need to run commands specific to 64 bit, install PEBuilder and
then get the 64 bit files from the GugentZipx64.zip file.
Prerequisites
nSelect a Windows system from which the staging area you prepared is accessible and on which .NET
4.5 and Windows Automated Installation Kit (AIK) for Windows 7 (including WinPE 3.0) are installed.
nCreate a WinPE.
Procedure
1Navigate to the vCloud Automation Center Appliance management console installation page.
For example: https://vcac-hostname.domain.name:5480/installer/.
2Download the PEBuilder.
3(Optional) Download the Windows 64-bit guest agent package if you want to include the Windows 64-
bit guest agent in your WinPE instead of the Windows 32-bit guest agent.
4Execute vCAC-WinPEBuilder-Setup.exe.
5Deselect both Plugins and PEBuilder.
6Expand Plugins and select VRMAgent.
7Follow the prompts to complete the installation.
8(Optional) After installation is complete, replace the Windows 32-bit guest agent files located in \PE
Builder\Plugins\VRM Agent\VRMGuestAgent with the 64-bit files to include the 64-bit agent in
your WinPE.
9Copy the contents of %SystemDrive%\Program Files (x86)\VMware\PE Builder\Plugins\VRM
Agent\VRMGuestAgent to a new location within your WinPE Image.
For example: C:\Program Files (x86)\VMware\PE Builder\Plugins\VRM
Agent\VRMGuestAgent.
Configure the doagent.bat File
If you choose not to use the vRealize Automation PEBuilder, you must manually configure the
doagent.bat file.
Prerequisites
Install the Guest Agent in a WinPE.
Procedure
1Navigate to the VRMGuestAgent directory within your WinPE Image.
For example: C:\Program Files (x86)\VMware\PE Builder\Plugins\VRM
Agent\VRMGuestAgent.
2Make a copy of the file doagent-template.bat and name it doagent.bat.
Configuring vRealize Automation
VMware, Inc. 56
3Open doagent.bat in a text editor.
4Replace all instances of the string #Dcac Hostname# with the fully qualified domain name and port
number of the IaaS Manager Service host.
Option Description
If you are using a load balancer Enter the fully qualified domain name and port of the load balancer for the IaaS
Manager Service. For example,
manager_service_LB.mycompany.com:443
With no load balancer Enter the fully qualified domain name and port of the machine on which the IaaS
Manager Service is installed. For example,
manager_service.mycompany.com:443
5Replace all instances of the string #Protocol# with the string /ssl.
6Replace all instances of the string #Comment# with REM (REM must be followed by a trailing space).
7(Optional) If you are using self-signed certificates, uncomment the openSSL command.
echo QUIT | c:\VRMGuestAgent\bin\openssl s_client –connect
8Save and close the file.
9Edit the Startnet.cmd script for your WinPE to include the doagent.bat as a custom script.
Configure the doagentc.bat File
If you choose not to use the vRealize Automation PEBuilder, you must manually configure the
doagentc.bat file.
Prerequisites
Configure the doagent.bat File.
Procedure
1Navigate to the VRMGuestAgent directory within your WinPE Image.
For example: C:\Program Files (x86)\VMware\PE Builder\Plugins\VRM
Agent\VRMGuestAgent.
2Make a copy of the file doagentsvc-template.bat and name it doagentc.bat.
3Open doagentc.bat in a text editor.
4Remove all instance of the string #Comment#.
Configuring vRealize Automation
VMware, Inc. 57
5Replace all instances of the string #Dcac Hostname# with the fully qualified domain name and port
number of the Manager Service host.
The default port for the Manager Service is 443.
Option Description
If you are using a load balancer Enter the fully qualified domain name and port of the load balancer for the
Manager Service. For example,
load_balancer_manager_service.mycompany.com:443
With no load balancer Enter the fully qualified domain name and port of the Manager Service. For
example,
manager_service.mycompany.com:443
6Replace all instances of the string #errorlevel# with the character 1.
7Replace all instances of the string #Protocol# with the string /ssl.
8Save and close the file.
Configure the Guest Agent Properties Files
If you choose not to use the vRealize Automation PEBuilder, you must manually configure the guest
agent properties files.
Prerequisites
Configure the doagentc.bat File.
Procedure
1Navigate to the VRMGuestAgent directory within your WinPE Image.
For example: C:\Program Files (x86)\VMware\PE Builder\Plugins\VRM
Agent\VRMGuestAgent.
2Make a copy of the file gugent.properties and name it gugent.properties.template.
3Make a copy of the file gugent.properties.template and name it gugentc.properties.
4Open gugent.properties in a text editor.
5Replace all instances of the string GuestAgent.log the string
X:/VRMGuestAgent/GuestAgent.log.
6Save and close the file.
7Open gugentc.properties in a text editor.
8Replace all instances of the string GuestAgent.log the string
C:/VRMGuestAgent/GuestAgent.log.
9Save and close the file.
Configuring vRealize Automation
VMware, Inc. 58
Preparing for Virtual Machine Image Provisioning
Before you provision instances with OpenStack, you must have virtual machine images and flavors
configured in the OpenStack provider.
Virtual Machine Images
You can select an virtual machine image from a list of available images when creating blueprints for
OpenStack resources.
A virtual machine image is a template that contains a software configuration, including an operating
system. Virtual machine images are managed by the OpenStack provider and are imported during data
collection.
If an image that is used in a blueprint is later deleted from the OpenStack provider, it is also removed from
the blueprint. If all the images have been removed from a blueprint, the blueprint is disabled and cannot
be used for machine requests until it is edited to add at least one image.
OpenStack Flavors
You can select one or more flavors when creating OpenStack blueprints.
OpenStack flavors are virtual hardware templates that define the machine resource specifications for
instances provisioned in OpenStack. Flavors are managed by the OpenStack provider and are imported
during data collection.
vRealize Automation supports several flavors of OpenStack. For the most current information about
OpenStack flavor support, see the vRealize Automation Support Matrix at
https://www.vmware.com/support/pubs/vcac-pubs.html.
Preparing for Amazon Machine Image Provisioning
Prepare your Amazon Machine Images and instance types for provisioning in vRealize Automation.
Understanding Amazon Machine Images
You can select an Amazon machine image from a list of available images when creating Amazon
machine blueprints.
An Amazon machine image is a template that contains a software configuration, including an operating
system. They are managed by Amazon Web Services accounts. vRealize Automation manages the
instance types that are available for provisioning.
The Amazon machine image and instance type must be available in an Amazon region. Not all instance
types are available in all regions.
You can select an Amazon machine image provided by Amazon Web Services, a user community, or the
AWS Marketplace site. You can also create and optionally share your own Amazon machine images. A
single Amazon machine image can be used to launch one or many instances.
Configuring vRealize Automation
VMware, Inc. 59
The following considerations apply to Amazon machine images in the Amazon Web Services accounts
from which you provision cloud machines:
nEach blueprint must specify an Amazon machine image.
A private Amazon machine image is available to a specific account and all its regions. A public
Amazon machine image is available to all accounts, but only to a specific region in each account.
nWhen the blueprint is created, the specified Amazon machine image is selected from regions that
have been data-collected. If multiple Amazon Web Services accounts are available, the business
group manager must have rights to any private Amazon machine images. The Amazon machine
image region and the specified user location restrict provisioning request to reservations that match
the corresponding region and location.
nUse reservations and policies to distribute Amazon machine images in your Amazon Web Services
accounts. Use policies to restrict provisioning from a blueprint to a particular set of reservations.
nvRealize Automation cannot create user accounts on a cloud machine. The first time a machine
owner connects to a cloud machine, she must log in as an administrator and add her
vRealize Automation user credentials or an administrator must do that for her. She can then log in
using her vRealize Automation user credentials.
If the Amazon machine image generates the administrator password on every boot, the Edit Machine
Record page displays the password. If it does not, you can find the password in the Amazon Web
Services account. You can configure all Amazon machine images to generate the administrator
password on every boot. You can also provide administrator password information to support users
who provision machines for other users.
nTo allow remote Microsoft Windows Management Instrumentation (WMI) requests on cloud machines
provisioned in Amazon Web Services accounts, enable a Microsoft Windows Remote Management
(WinRM) agent to collect data from Windows machines managed by vRealize Automation. See
Installing vRealize Automation 7.0.
nA private Amazon machine image can be seen across tenants.
For related information, see Amazon Machine Images (AMI) topics in Amazon documentation.
Understanding Amazon Instance Types
An IaaS architect selects one or more Amazon instance types when creating Amazon EC2 blueprints. An
IaaS administrator can add or remove instance types to control the choices available to the architects.
An Amazon EC2 instance is a virtual server that can run applications in Amazon Web Services. Instances
are created from an Amazon machine image and by choosing an appropriate instance type.
Configuring vRealize Automation
VMware, Inc. 60

To provision a machine in an Amazon Web Services account, an instance type is applied to the specified
Amazon machine image. The available instance types are listed when architects create the Amazon EC2
blueprint. Architects select one or more instance types, and those instance types become choices
available to the user when they request to provision a machine. The instance types must be supported in
the designated region.
For related information, see Selecting Instance Types and Amazon EC2 Instance Details topics in
Amazon documentation.
Add an Amazon Instance Type
Several instance types are supplied with vRealize Automation for use with Amazon blueprints. An
administrator can add and remove instance types.
The machine instance types managed by IaaS administrators are available to blueprint architects when
they create or edit an Amazon blueprint. Amazon machine images and instance types are made available
through the Amazon Web Services product.
Prerequisites
Log in to the vRealize Automation console as an IaaS administrator.
Procedure
1Click Infrastructure > Administration > Instance Types.
2Click New Instance Type.
3Add a new instance type, specifying the following parameters.
Information about the available Amazon instances types and the setting values that you can specify
for these parameters is available from Amazon Web Services documentation in EC2 Instance Types -
Amazon Web Services (AWS) at aws.amazon.com/ec2 and Instance Types at
docs.aws.amazon.com.
nName
nAPI name
nType Name
nIO Performance Name
nCPUs
nMemory (GB)
nStorage (GB)
nCompute Units
4Click the Save icon ( ).
When IaaS architects create Amazon Web Services blueprints, they can use your custom instance types.
Configuring vRealize Automation
VMware, Inc. 61
What to do next
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Scenario: Prepare vSphere Resources for Machine Provisioning in
Rainpole
As the vSphere administrator creating templates for vRealize Automation, you want to use the vSphere
Web Client to prepare for cloning CentOS machines in vRealize Automation.
TEMPLATE
You are here
Prepare
Installation Install Prepare
Template
Request Initial
Content
You want to convert an existing CentOS reference machine into a vSphere template so you and your
Rainpole architects can create blueprints for cloning CentOS machines in vRealize Automation. To
prevent any conflicts that might arise from deploying multiple virtual machines with identical settings, you
also want to create a general customization specification that you and your architects can use to create
clone blueprints for Linux templates.
Procedure
1Scenario: Convert Your CentOS Reference Machine into a Template for Rainpole
Using the vSphere Client, you convert your existing CentOS reference machine into a vSphere
template for your vRealize Automation IaaS architects to reference as the base for their clone
blueprints.
2Scenario: Create a Customization Specification for Cloning Linux Machines in Rainpole
Using the vSphere Client, you create a standard customization specification for your
vRealize Automation IaaS architects to use when they create clone blueprints for Linux machines.
Scenario: Convert Your CentOS Reference Machine into a Template for
Rainpole
Using the vSphere Client, you convert your existing CentOS reference machine into a vSphere template
for your vRealize Automation IaaS architects to reference as the base for their clone blueprints.
Configuring vRealize Automation
VMware, Inc. 62
Procedure
1Log in to your reference machine as the root user and prepare the machine for conversion.
a Remove udev persistence rules.
/bin/rm -f /etc/udev/rules.d/70*
b Enable machines cloned from this template to have their own unique identifiers.
/bin/sed -i '/^\(HWADDR\|UUID\)=/d'
/etc/sysconfig/network-scripts/ifcfg-eth0
c Power down the machine.
shutdown -h now
2Log in to the vSphere Web Client as an administrator.
3Click the VM Options tab.
4Right-click your reference machine and select Edit Settings.
5Enter Rainpole_centos_63_x86 in the VM Name text box.
6Even though your reference machine has a CentOS guest operating system, select Red Hat
Enterprise Linux 6 (64-bit) from the Guest OS Version drop-down menu.
If you select CentOS, your template and customization specification might not work as expected.
7Right-click your Rainpole_centos_63_x86 reference machine in the vSphere Web Client and select
Template > Convert to Template.
vCenter Server marks your Rainpole_centos_63_x86 reference machine as a template and displays the
task in the Recent Tasks pane.
What to do next
To prevent any conflicts that might arise from deploying multiple virtual machines with identical settings,
you create a general customization specification that you and your Rainpole architects can use to create
clone blueprints for Linux templates.
Scenario: Create a Customization Specification for Cloning Linux Machines in
Rainpole
Using the vSphere Client, you create a standard customization specification for your vRealize Automation
IaaS architects to use when they create clone blueprints for Linux machines.
Procedure
1On the home page, click Customization Specification Manager to open the wizard.
2Click the New icon.
Configuring vRealize Automation
VMware, Inc. 63
3Specify properties.
a Select Linux from the Target VM Operating System drop-down menu.
b Enter Linux in the Customization Spec Name text box.
c Enter Rainpole Linux cloning with vRealize Automation in the Description text box.
d Click Next.
4Set computer name.
a Select Use the virtual machine name.
b Enter the domain on which cloned machines are going to be provisioned in the Domain name
text box.
For example, rainpole.local.
c Click Next.
5Configure time zone settings.
6Click Next.
7Select Use standard network settings for the guest operating system, including enabling
DHCP on all network interfaces.
8Follow the prompts to enter the remaining required information.
9On the Ready to complete page, review your selections and click Finish.
You have a general customization specification that you can use to create blueprints for cloning Linux
machines.
What to do next
Log in to the vRealize Automation console as the configuration administrator you created during the
installation and request the catalog items that quickly set up your proof of concept.
Preparing for Software Provisioning
Use Software to deploy applications and middleware as part of the vRealize Automation provisioning
process for vSphere, vCloud Director,vCloud Air, and Amazon AWS machines.
You can deploy Software on machines if your blueprint supports Software and if you install the guest
agent and software bootstrap agent on your reference machines before you convert them into templates,
snapshots, or Amazon Machine Images.
Configuring vRealize Automation
VMware, Inc. 64
Table 1‑15. Provisioning Methods that Support Software
Machine Type
Provisioning
Method Required Preparation
vSphere Clone A clone blueprint provisions a complete and independent virtual machine based on a
vCenter Server virtual machine template. If you want your templates for cloning to support
Software components, install the guest agent and software bootstrap agent on your
reference machine as you prepare a template for cloning. See Checklist for Preparing to
Provision by Cloning.
vSphere Linked Clone A linked clone blueprint provisions a space-efficient copy of a vSphere machine based on a
snapshot, using a chain of delta disks to track differences from the parent machine. If you
want your linked clone blueprints to support Software components, install the guest agent
and software bootstrap agent on the machine before you take the snapshot.
If your snapshot machine was cloned from a template that supports Software, the required
agents are already installed.
vCloud Director Clone A clone blueprint provisions a complete and independent virtual machine based on a
vCenter Server virtual machine template. If you want your templates for cloning to support
Software components, install the guest agent and software bootstrap agent on your
reference machine as you prepare a template for cloning. See Checklist for Preparing to
Provision by Cloning.
vCloud Air Clone A clone blueprint provisions a complete and independent virtual machine based on a
vCenter Server virtual machine template. If you want your templates for cloning to support
Software components, install the guest agent and software bootstrap agent on your
reference machine as you prepare a template for cloning. See Checklist for Preparing to
Provision by Cloning.
Amazon AWS Amazon
Machine
Image
An Amazon machine image is a template that contains a software configuration, including
an operating system. If you want to create an Amazon machine image that supports
Software, connect to a running Amazon AWS instance that uses an EBS volume for the root
device. Install the guest agent and software bootstrap agent on the reference machine, then
create an Amazon Machine Image from your instance. For instruction on creating Amazon
EBS-backed AMIs, see the Amazon AWS documentation.
For the guest agent and Software bootstrap agent to function on provisioned machines, you
must configure network-to-VPC connectivity.
Preparing to Provision Machines with Software
To support Software components, you must install the guest agent and Software bootstrap agent on your
reference machine before you convert to a template for cloning, create an Amazon machine image, or
take a snapshot.
Prepare a Windows Reference Machine to Support Software
You install the supported Java Runtime Environment, the guest agent, and the Software bootstrap agent
on your Windows reference machine to create a template, snapshot, or Amazon Machine Instance that
supports Software components.
Configuring vRealize Automation
VMware, Inc. 65
Software supports scripting with Windows CMD, PowerShell 2.0.
Important Because the boot process must not be interrupted, configure the virtual machine so that
nothing causes the virtual machine's boot process to pause before reaching the final operating system
login prompt. For example, verify that no processes or scripts prompt for user interaction when the virtual
machine starts.
Prerequisites
nIdentify or create a reference machine.
nIf you have previously installed the guest agent or Software bootstrap agent on this machine, remove
the agents and runtime logs. See Updating Existing Virtual Machine Templates in vRealize
Automation.
nIf you plan to remotely access the virtual machine Windows remote desktop for troubleshooting or for
other reasons, install the Remote Desktop Services (RDS) for Windows.
nVerify that all of the network configuration artifacts are removed from the network configuration files.
nIf you want to use the most secure approach for establishing trust between the guest agent and your
Manager Service machine, obtain the SSL certificate in PEM format from your Manager Service
machine. For more information about how the guest agent establishes trust, see Configuring the
Windows Guest Agent to Trust a Server.
nVerify that the Darwin user has Log on as a service access rights on the Windows reference
machine.
Procedure
1Log in to your Windows reference machine as a Windows Administrator and open a command
prompt.
2Download and install the supported Java Runtime Environment from
https://vRealize_VA_Hostname_fqdn:5480/service/software/index.html.
a Download the Java SE Runtime Environment zip file https://vRealize_VA_Hostname_fqdn:
5480/service/software/download/jre-version-win64.zip.
b Create a \opt\vmware-jre folder and unzip the JRE file to the folder.
c Open a PowerShell command window and enter type \opt\vmware-jre\bin\java -version
to verify the installation.
The installed version of Java appears.
3Download and install the vRealize Automation guest agent from
https://vRealize_VA_Hostname_fqdn:5480/installer/.
a Download GugentZip_version to the C drive on the reference machine.
b Right-click the file and select Properties.
c Click General.
Configuring vRealize Automation
VMware, Inc. 66
d Click Unblock.
e Extract the files.
f Unzip the installation file to C:\.
This produces the directory C:\VRMGuestAgent. Do not rename this directory.
4Configure the guest agent to communicate with the Manager Service.
a Open an elevated command prompt.
b Navigate to C:\VRMGuestAgent.
c Configure the guest agent to trust your Manager Service machine.
Option Description
Allow the guest agent to trust the
first machine to which it connects.
No configuration required.
Manually install the trusted PEM file. Place the Manager Service PEM file in the C:\VRMGuestAgent\ directory.
d Run winservice -i -h Manager_Service_Hostname_fdqn:portnumber -p ssl.
The default port number for the Manager Service is 443.
Option Description
If you are using a load balancer Enter the fully qualified domain name and port number of your Manager
Service load balancer. For example, winservice -i -h
load_balancer_manager_service.mycompany.com:443 -p ssl.
With no load balancer Enter the fully qualified domain name and port number of your Manager
Service machine. For example, winservice -i -h
manager_service_machine.mycompany.com:443 -p ssl.
If you are preparing an Amazon
machine image
You need to specify that you are using Amazon. For example, winservice -i
-h manager_service_machine.mycompany.com:443:443 -p ssl -c ec2
5Download the Software agent bootstrap file from https://vRealize_VA_Hostname_fqdn:
5480/service/software/index.html.
a Download the Software bootstrap agent file https://vRealize_VA_Hostname_fqdn:
5480/service/software/download/vmware-vra-software-agent-bootstrap-
windows_version.zip.
b Right-click the file and select Properties.
c Click General.
d Click Unblock.
Important If you do not disable this Windows security feature, you cannot use the Software
agent bootstrap file.
e Unzip the vmware-vra-software-agent-bootstrap-windows_version.zip file to the \temp
folder.
Configuring vRealize Automation
VMware, Inc. 67
6Install the Software bootstrap agent.
a Open a Windows CMD console and navigate to the \temp folder.
b Enter the command to install the agent bootstrap.
install.bat password=Password managerServiceHost=manager_service_machine.mycompany.com
managerServicePort=443 httpsMode=true cloudProvider=ec2|vca|vcd|vsphere
The default port number for the Manager Service is 443. Accepted values for cloudprovider are
ec2, vca, vcd, and vsphere. The install.bat script creates a user account called darwin for
the software bootstrap agent using the password you set in the install command. The Password
you set must meet the Windows password requirements.
7Verify that the user darwin_user exists.
a Enter lusrmgr.msc at a command prompt.
b Verify that the user darwin_user exists and belongs to the administrator group.
c Set the password to never expire.
The setting ensures that the template remains usable after 30 days.
If the user is not available, verify that the Windows server password is accurate.
8Shut down the Windows virtual machine.
What to do next
Convert your reference machine into a template for cloning, an Amazon machine image, or a snapshot so
your IaaS architects can use your template when creating blueprints.
Prepare a Linux Reference Machine to Support Software
You use a single script to install the supported Java Runtime Environment, the guest agent, and the
Software bootstrap agent on your Linux reference machine to create a template, snapshot, or Amazon
Machine Instance that supports Software components.
Software supports scripting with Bash.
Important Because the boot process must not be interrupted, configure the virtual machine so that
nothing causes the virtual machine's boot process to pause before reaching the final operating system
login prompt. For example, verify that no processes or scripts prompt for user interaction when the virtual
machine starts.
Prerequisites
nIdentify or create a Linux reference machine and verify that the following commands are available:
nwget
nunzip
nsha256sum
Configuring vRealize Automation
VMware, Inc. 68
ngrep
nsed
nsetsid
nawk
nifconfig
napt-get
nyum
nchkconfig
ndmidecode
nperl
nIf you plan to remotely access the virtual machine using Linux ssh logging for troubleshooting or for
other reasons, install the OpenSSH server and client for Linux.
nRemove network configuration artifacts from the network configuration files.
Procedure
1Log in to your reference machine as the root user.
2Download the installation script from your vRealize Automation appliance.
wget https://vRealize_VA_Hostname_fqdn:5480/service/software/download/prepare_vra_template.sh
If your environment is using self-signed certificates, you might have to use the wget option --no-
check-certificate option. For example:
wget --no-check-certificate https://vRealize_VA_Hostname_fqdn:
5480/service/software/download/prepare_vra_template.sh
3Make the prepare_vra_template.sh script executable.
chmod +x prepare_vra_template.sh
4Run the prepare_vra_template.sh installer script.
./prepare_vra_template.sh
You can run the help command ./prepare_vra_template.sh --help for information about non-
interactive options and expected values.
5Follow the prompts to complete the installation.
You see a confirmation message when the installation is successfully completed. If you see an error
message and logs in the console, resolve the errors and run the installer script again.
Configuring vRealize Automation
VMware, Inc. 69
6Shut down the Linux virtual machine.
The script removes any previous installations of the Software bootstrap agent and installs the supported
versions of the Java Runtime Environment, the guest agent, and the Software bootstrap agent.
What to do next
On your hypervisor or cloud provider, turn your reference machine into a template, snapshot, or Amazon
Machine Image that your infrastructure architects can use when creating blueprints.
Updating Existing Virtual Machine Templates in vRealize Automation
If you are updating your templates, Amazon Machine Images, or snapshots for the latest version of the
Windows Software bootstrap agent, or if you are manually updating to the latest Linux Software bootstrap
agent instead of using the prepare_vra_template.sh script, you need to remove any existing
versions and delete any logs.
Linux
For Linux reference machines, running the prepare_vra_template.sh script script resets the agent
and removes any logs for you before reinstalling. However, if you intend to manually install, you need to
log into the reference machine as the root user and run the command to reset and remove the artifacts.
/opt/vmware-appdirector/agent-bootstrap/agent_reset.sh
Windows
For Windows reference machines, you remove the existing Software agent bootstrap and
vRealize Automation 6.0 or later guest agent, and delete any existing runtime log files. In a PowerShell
command window, run the commands to remove the agent and artifacts.
\opt\vmware-appdirector\agent-bootstrap\agent_bootstrap_removal.bat
\opt\vmware-appdirector\agent-bootstrap\agent_reset.bat
Scenario: Prepare a vSphere CentOS Template for Clone Machine
and Software Component Blueprints
As a vCenter Server administrator, you want to prepare a vSphere template that your
vRealize Automation architects can use to clone Linux CentOS machines. You want to ensure that your
template supports blueprints with software components, so you install the guest agent and the software
bootstrap agent before you turn your reference machine into a template.
Prerequisites
nIdentify or create a Linux CentOS reference machine with VMware Tools installed. Include at least
one Network Adapter to provide internet connectivity in case blueprint architects do not add this
functionality at the blueprint level. For information about creating virtual machines, see the vSphere
documentation.
Configuring vRealize Automation
VMware, Inc. 70
nYou must be connected to a vCenter Server to convert a virtual machine to a template. You cannot
create templates if you connect the vSphere Client directly to an vSphere ESXi host.
Procedure
1Scenario: Prepare Your Reference Machine for Guest Agent Customizations and Software
Components
You want your template to support software components, so you must install both the guest agent
and the software bootstrap agent on your reference machine. To simplify the process, you download
and run a vRealize Automation script that installs both the guest agent and the software bootstrap
agent instead of downloading and installing the packages separately.
2Scenario: Convert Your CentOS Reference Machine into a Template
After you install the guest agent and software bootstrap agent onto your reference machine, you turn
your reference machine into a template that vRealize Automation architects can use to create clone
machine blueprints.
3Scenario: Create a Customization Specification for vSphere Cloning
Create a customization specification for your blueprint architects to use with your
cpb_centos_63_x84 template.
You created a template and customization specification from your reference machine that blueprint
architects can use to create vRealize Automation blueprints that clone Linux CentOS machines. Because
you installed the Software bootstrap agent and the guest agent on your reference machine, architects can
use your template to create elaborate catalog item blueprints that include Software components or other
guest agent customizations such as running scripts or formatting disks. Because you installed
VMware Tools, architects and catalog administrators can allow users to perform actions against
machines, such as reconfigure, snapshot, and reboot.
What to do next
After you configure vRealize Automation users, groups, and resources, you can use your template and
customization specification to create a machine blueprint for cloning. See Scenario: Create a vSphere
CentOS Blueprint for Cloning in Rainpole.
Scenario: Prepare Your Reference Machine for Guest Agent Customizations
and Software Components
You want your template to support software components, so you must install both the guest agent and the
software bootstrap agent on your reference machine. To simplify the process, you download and run a
vRealize Automation script that installs both the guest agent and the software bootstrap agent instead of
downloading and installing the packages separately.
Procedure
1Log in to your reference machine as the root user.
Configuring vRealize Automation
VMware, Inc. 71
2Download the installation script from your vRealize Automation appliance.
wget https://vRealize_VA_Hostname_fqdn:5480/service/software/download/prepare_vra_template.sh
If your environment is using self-signed certificates, you might have to use the wget option --no-
check-certificate option. For example:
wget --no-check-certificate https://vRealize_VA_Hostname_fqdn:
5480/service/software/download/prepare_vra_template.sh
3Make the prepare_vra_template.sh script executable.
chmod +x prepare_vra_template.sh
4Run the prepare_vra_template.sh installer script.
./prepare_vra_template.sh
You can run the help command ./prepare_vra_template.sh --help for information about non-
interactive options and expected values.
5Follow the prompts to complete the installation.
You see a confirmation message when the installation is successfully completed. If you see an error
message and logs in the console, resolve the errors and run the installer script again.
You installed both the software bootstrap agent and its prerequisite, the guest agent, to ensure
vRealize Automation architects who use your template can include software components in their
blueprints. The script also connected to your Manager Service instance and downloaded the SSL
certificate to establish trust between the Manager Service and machines deployed from your template.
This is a less secure approach than obtaining the Manager Service SSL certificate and manually installing
it on your reference machine in /usr/share/gugent/cert.pem.
Scenario: Convert Your CentOS Reference Machine into a Template
After you install the guest agent and software bootstrap agent onto your reference machine, you turn your
reference machine into a template that vRealize Automation architects can use to create clone machine
blueprints.
After you convert your reference machine to a template, you cannot edit or power on the template unless
you convert it back to a virtual machine.
Configuring vRealize Automation
VMware, Inc. 72
Procedure
1Log in to your reference machine as the root user and prepare the machine for conversion.
a Remove udev persistence rules.
/bin/rm -f /etc/udev/rules.d/70*
b Enable machines cloned from this template to have their own unique identifiers.
/bin/sed -i '/^\(HWADDR\|UUID\)=/d'
/etc/sysconfig/network-scripts/ifcfg-eth0
c If you rebooted or reconfigured the reference machine after installing the software bootstrap
agent, reset the agent.
/opt/vmware-appdirector/agent-bootstrap/agent_reset.sh
d Power down the machine.
shutdown -h now
2Log in to the vSphere Web Client as an administrator.
3Right-click your reference machine and select Edit Settings.
4Enter cpb_centos_63_x84 in the VM Name text box.
5Even though your reference machine has a CentOS guest operating system, select Red Hat
Enterprise Linux 6 (64-bit) from the Guest OS Version drop-down menu.
If you select CentOS, your template and customization specification might not work as expected.
6Right-click your reference machine in the vSphere Web Client and select Template > Convert to
Template.
vCenter Server marks your cpb_centos_63_x84 reference machine as a template and displays the task in
the Recent Tasks pane. If you have already brought your vSphere environment under
vRealize Automation management, your template is discovered during the next automated data
collection. If you have not configured your vRealize Automation yet, the template is collected during that
process.
Scenario: Create a Customization Specification for vSphere Cloning
Create a customization specification for your blueprint architects to use with your cpb_centos_63_x84
template.
Procedure
1Log in to the vSphere Web Client as an administrator.
2On the home page, click Customization Specification Manager to open the wizard.
Configuring vRealize Automation
VMware, Inc. 73
3Click the New icon.
4Click the New icon.
5Specify properties.
a Select Linux from the Target VM Operating System drop-down menu.
b Enter Customspecs in the Customization Spec Name text box.
c Enter cpb_centos_63_x84 cloning with vRealize Automation in the Description text box.
d Click Next.
6Set computer name.
a Select Use the virtual machine name.
b Enter the domain on which cloned machines are going to be provisioned in the Domain name
text box.
c Click Next.
7Configure time zone settings.
8Click Next.
9Select Use standard network settings for the guest operating system, including enabling
DHCP on all network interfaces.
Fabric administrators and infrastructure architects handle network settings for provisioned machine by
creating and using Network profiles in vRealize Automation.
10 Follow the prompts to enter the remaining required information.
11 On the Ready to complete page, review your selections and click Finish.
Scenario: Prepare for Importing the Dukes Bank for vSphere
Sample Application Blueprint
As a vCenter Server administrator, you want to prepare a vSphere CentOS 6.x Linux template and
customization specification that you can use to provision the vRealize Automation Dukes Bank sample
application.
You want to ensure that your template supports the sample application software components, so you
install the guest agent and the software bootstrap agent onto your Linux reference machine before you
convert it to a template and create a customization specification. You disable SELinux on your reference
machine to ensure your template supports the specific implementation of MySQL used in the Dukes Bank
sample application.
Prerequisites
nInstall and fully configure vRealize Automation. See Installing and Configuring vRealize Automation
for the Rainpole Scenario.
Configuring vRealize Automation
VMware, Inc. 74
nIdentify or create a CentOS 6.x Linux reference machine with VMware Tools installed. For information
about creating virtual machines, see the vSphere documentation.
nYou must be connected to a vCenter Server to convert a virtual machine to a template. You cannot
create templates if you connect the vSphere Client directly to an vSphere ESXi host.
Procedure
1Scenario: Prepare Your Reference Machine for the Dukes Bank vSphere Sample Application
You want your template to support the Dukes Bank sample application, so you must install both the
guest agent and the software bootstrap agent on your reference machine so vRealize Automation
can provision the software components. To simplify the process, you download and run a
vRealize Automation script that installs both the guest agent and the software bootstrap agent
instead of downloading and installing the packages separately.
2Scenario: Convert Your Reference Machine into a Template for the Dukes Bank vSphere Application
After you install the guest agent and software bootstrap agent on your reference machine, you
disable SELinux to ensure your template supports the specific implementation of MySQL used in the
Dukes Bank sample application. You turn your reference machine into a template that you can use
to provision the Dukes Bank vSphere sample application.
3Scenario: Create a Customization Specification for Cloning the Dukes Bank vSphere Sample
Application Machines
You create a customization specification to use with your Dukes Bank machine template.
You created a template and customization specification from your reference machine that supports the
vRealize Automation Dukes Bank sample application.
Scenario: Prepare Your Reference Machine for the Dukes Bank vSphere
Sample Application
You want your template to support the Dukes Bank sample application, so you must install both the guest
agent and the software bootstrap agent on your reference machine so vRealize Automation can provision
the software components. To simplify the process, you download and run a vRealize Automation script
that installs both the guest agent and the software bootstrap agent instead of downloading and installing
the packages separately.
Procedure
1Log in to your reference machine as the root user.
2Download the installation script from your vRealize Automation appliance.
wget https://vRealize_VA_Hostname_fqdn:5480/service/software/download/prepare_vra_template.sh
If your environment is using self-signed certificates, you might have to use the wget option --no-
check-certificate option. For example:
wget --no-check-certificate https://vRealize_VA_Hostname_fqdn:
5480/service/software/download/prepare_vra_template.sh
Configuring vRealize Automation
VMware, Inc. 75
3Make the prepare_vra_template.sh script executable.
chmod +x prepare_vra_template.sh
4Run the prepare_vra_template.sh installer script.
./prepare_vra_template.sh
You can run the help command ./prepare_vra_template.sh --help for information about non-
interactive options and expected values.
5Follow the prompts to complete the installation.
You see a confirmation message when the installation is successfully completed. If you see an error
message and logs in the console, resolve the errors and run the installer script again.
You installed both the software bootstrap agent and its prerequisite, the guest agent, to ensure the Dukes
Bank sample application successfully provisions software components. The script also connected to your
Manager Service instance and downloaded the SSL certificate to establish trust between the Manager
Service and machines deployed from your template. This is a less secure approach than obtaining the
Manager Service SSL certificate and manually installing it on your reference machine
in /usr/share/gugent/cert.pem, and you can manually replace this certificate now if security is a high
priority.
Scenario: Convert Your Reference Machine into a Template for the Dukes
Bank vSphere Application
After you install the guest agent and software bootstrap agent on your reference machine, you disable
SELinux to ensure your template supports the specific implementation of MySQL used in the Dukes Bank
sample application. You turn your reference machine into a template that you can use to provision the
Dukes Bank vSphere sample application.
After you convert your reference machine to a template, you cannot edit or power on the template unless
you convert it back to a virtual machine.
Procedure
1Log in to your reference machine as the root user.
a Edit your /etc/selinux/config file to disable SELinux.
SELINUX=disabled
If you do not disable SELinux, the MySQL software component of the Duke's Bank Sample
application might not work as expected.
b Remove udev persistence rules.
/bin/rm -f /etc/udev/rules.d/70*
Configuring vRealize Automation
VMware, Inc. 76
c Enable machines cloned from this template to have their own unique identifiers.
/bin/sed -i '/^\(HWADDR\|UUID\)=/d'
/etc/sysconfig/network-scripts/ifcfg-eth0
d If you rebooted or reconfigured the reference machine after installing the software bootstrap
agent, reset the agent.
/opt/vmware-appdirector/agent-bootstrap/agent_reset.sh
e Power down the machine.
shutdown -h now
2Log in to the vSphere Web Client as an administrator.
3Right-click your reference machine and select Edit Settings.
4Enter dukes_bank_template in the VM Name text box.
5If your reference machine has a CentOS guest operating system, select Red Hat Enterprise Linux 6
(64-bit) from the Guest OS Version drop-down menu.
If you select CentOS, your template and customization specification might not work as expected.
6Click OK.
7Right-click your reference machine in the vSphere Web Client and select Template > Convert to
Template.
vCenter Server marks your dukes_bank_template reference machine as a template and displays the task
in the Recent Tasks pane. If you have already brought your vSphere environment under
vRealize Automation management, your template is discovered during the next automated data
collection. If you have not configured your vRealize Automation yet, the template is collected during that
process.
Scenario: Create a Customization Specification for Cloning the Dukes Bank
vSphere Sample Application Machines
You create a customization specification to use with your Dukes Bank machine template.
Procedure
1Log in to the vSphere Web Client as an administrator.
2On the home page, click Customization Specification Manager to open the wizard.
3Click the New icon.
4Specify properties.
a Select Linux from the Target VM Operating System drop-down menu.
b Enter Customspecs_sample in the Customization Spec Name text box.
Configuring vRealize Automation
VMware, Inc. 77
c Enter Dukes Bank customization spec in the Description text box.
d Click Next.
5Set computer name.
a Select Use the virtual machine name.
b Enter the domain on which you want to provision the Dukes Bank sample application in the
Domain name text box.
c Click Next.
6Configure time zone settings.
7Click Next.
8Select Use standard network settings for the guest operating system, including enabling
DHCP on all network interfaces.
Fabric administrators and infrastructure architects handle network settings for provisioned machine by
creating and using Network profiles in vRealize Automation.
9Follow the prompts to enter the remaining required information.
10 On the Ready to complete page, review your selections and click Finish.
You created a template and customization specification that you can use to provision the Dukes Bank
sample application.
What to do next
1 Create an external network profile to provide a gateway and a range of IP addresses. See Create a
Network Profile for Static IP Address Assignment.
2 Map your external network profile to your vSphere reservation. See Create a Reservation for Hyper-V,
KVM, SCVMM, vSphere, or XenServer. The sample application cannot provision successfully without
an external network profile.
3 Import the Duke's Bank sample application into your environment. See Scenario: Importing the Dukes
Bank for vSphere Sample Application and Configuring for Your Environment.
Configuring vRealize Automation
VMware, Inc. 78
Configuring Tenant Settings 2
Tenant administrators configure tenant settings such as user authentication, and manage user roles and
business groups. System administrators and tenant administrators configure options such as email
servers to handle notifications, and branding for the vRealize Automation console.
You can use the Configuring Tenant Settings Checklist to see a high-level overview of the sequence of
steps required to configure tenant settings.
Table 2‑1. Checklist for Configuring Tenant Settings
Task
vRealize
Automation Role Details
Create local user accounts and assign a tenant
administrator.
System
administrator
For an example of creating local user
accounts, see Scenario: Create Local User
Accounts for Rainpole.
Configure Directories Management to set up tenant identity
management and access control settings.
Tenant
administrator
Choosing Directories Management
Configuration Options
Create business groups and custom groups, and grant
user access rights to the vRealize Automation console.
Tenant
administrator
Configuring Groups and User Roles
(Optional) Create additional tenants so users can access
the appropriate applications and resources they need to
complete their work assignments.
System
administrator
Create Additional Tenants
(Optional) Configure custom branding on the tenant login
and application pages of the vRealize Automation console.
nSystem
administrator
nTenant
administrator
Configuring Custom Branding
(Optional) Configure vRealize Automation to send users
notifications when specific events occur.
nSystem
administrator
nTenant
administrator
Checklist for Configuring Notifications
(Optional) Configure vRealize Orchestrator to support
XaaS and other extensibility.
nSystem
administrator
nTenant
administrator
Configuring vRealize Orchestrator and Plug-
Ins
VMware, Inc. 79
Table 2‑1. Checklist for Configuring Tenant Settings (Continued)
Task
vRealize
Automation Role Details
(Optional) Create a custom remote desktop protocol file
that IaaS architects use in blueprints to configure RDP
settings.
System
administrator
Create a Custom RDP File to Support RDP
Connections for Provisioned Machines
(Optional) Define datacenter locations that your fabric
administrators and IaaS architects can leverage to allow
users to select an appropriate location for provisioning when
they request machines.
System
administrator
For an example of adding datacenter
locations, see Scenario: Add Datacenter
Locations for Cross Region Deployments.
This chapter includes the following topics:
nChoosing Directories Management Configuration Options
nScenario: Configure an Active Directory Link for a Highly Available vRealize Automation
nScenario: Configure Smart Card Authentication for vRealize Automation
nConfiguring Groups and User Roles
nScenario: Configure the Default Tenant for Rainpole
nCreate Additional Tenants
nConfiguring Custom Branding
nChecklist for Configuring Notifications
nCreate a Custom RDP File to Support RDP Connections for Provisioned Machines
nScenario: Add Datacenter Locations for Cross Region Deployments
nConfiguring vRealize Orchestrator and Plug-Ins
Choosing Directories Management Configuration Options
You can use vRealize Automation Directories Management features to configure an Active Directory link
in accordance with your user authentication requirements.
Directories Management provides many options to support a highly customized user authentication.
Table 2‑2. Choosing Directories Management Configuration Options
Configuration Option Procedure
Required. Configure a link to your Active Directory. 1 Configure a link to your Active Directory. See Configure a
Link to Active Directory.
2 If you configured vRealize Automation for high availability,
see Configure Directories Management for High Availability.
(Optional) Enhance security of a user ID and password based
directory link by configuring bi-directional integration with Active
Directory Federated Services.
Configure a Bi Directional Trust Relationship Between vRealize
Automation and Active Directory
(Optional) Add users and groups to an existing Active Directory
Link .
Add Users or Groups to an Active Directory Connection
Configuring vRealize Automation
VMware, Inc. 80
Table 2‑2. Choosing Directories Management Configuration Options (Continued)
Configuration Option Procedure
(Optional) Edit the default policy to apply custom rules for an
Active Directory link.
Manage the User Access Policy
(Optional) Configure network ranges to restrict the IP addresses
through which users can log in to the system, manage login
restrictions (timeout, number of login attempts before lock-out).
Add or Edit a Network Range
Directories Management Overview
Tenant administrators can configure tenant identity management and access control settings using the
Directories Management options on the vRealize Automation application console.
You can manage the following settings from the Administration > Directories Management tab.
Table 2‑3. Directories Management Settings
Setting Description
Directories The Directories page enables you to create and manage Active Directory links to support
vRealize Automation tenant user authentication and authorization. You create one or more
directories and then sync those directories with your Active Directory deployment. This page
displays the number of groups and users that are synced to the directory and the last sync time.
You can click Sync Now, to manually start the directory sync.
See Using Directories Management to Create an Active Directory Link.
When you click on a directory and then click the Sync Settings button, you can edit the sync
settings, navigate the Identity Providers page, and view the sync log.
From the directories sync settings page you can schedule the sync frequency, see the list of
domains associated with this directory, change the mapped attributes list, update the user and
groups list that syncs, and set the safeguard targets.
Connectors The Connectors page lists deployed connectors for your enterprise network. A connector syncs
user and group data between Active Directory and the Directories Management service, and when
it is used as the identity provider, authenticates users to the service. Each vRealize Automation
appliance contains a connector by default. See Managing Connectors.
User Attributes The User Attributes page lists the default user attributes that sync in the directory and you can add
other attributes that you can map to Active Directory attributes. See Select Attributes to Sync with
Directory.
Network Ranges This page lists the network ranges that are configured for your system. You configure a network
range to allow users access through those IP addresses. You can add additional network ranges
and you can edit existing ranges. See Add or Edit a Network Range.
Identity Providers The Identity Providers page lists identity providers that are available on your system. vRealize
Automation systems contain a connector that serves as the default identity provider and that
suffices for many user needs. You can add third-party identity provider instances or have a
combination of both.
See Configure an Identity Provider Instance.
Policies The Policies page lists the default access policy and any other web application access policies you
created. Policies are a set of rules that specify criteria that must be met for users to access their
application portals or to launch Web applications that are enabled for them. The default policy
should be suitable for most vRealize Automation deployments, but you can edit it if needed. See
Manage the User Access Policy.
Configuring vRealize Automation
VMware, Inc. 81
Important Concepts Related to Active Directory
Several concepts related to Active Directory are integral to understanding how Directories Management
integrates with your Active Directory environments.
Connector
The connector, a component of the service, performs the following functions.
nSyncs user and group data between Active Directory and the service.
nWhen being used as an identity provider, authenticates users to the service.
The connector is the default identity provider. For the authentication methods the connector supports,
see VMware Identity Manager Administration. You can also use third-party identity providers that
support the SAML 2.0 protocol. Use a third-party identity provider for an authentication type the
connector does not support or for an authentication type the connector does support, if the third-party
identity provider is preferable based on your enterprise security policy.
Note Even if you use third-party identity providers, you must configure the connector to sync user
and group data.
Directory
The Directories Management service has its own concept of a directory, which uses Active Directory
attributes and parameters to define users and groups. You create one or more directories and then sync
those directories with your Active Directory deployment. You can create the following directory types in
the service.
nActive Directory over LDAP. Create this directory type if you plan to connect to a single Active
Directory domain environment. For the Active Directory over LDAP directory type, the connector
binds to Active Directory using simple bind authentication.
nActive Directory, Integrated Windows Authentication. Create this directory type if you plan to connect
to a multi-domain or multi-forest Active Directory environment. The connector binds to Active
Directory using Integrated Windows Authentication.
The type and number of directories that you create varies depending on your Active Directory
environment, such as single domain or multi-domain, and on the type of trust used between domains. In
most environments, you create one directory.
The service does not have direct access to Active Directory. Only the connector has direct access to
Active Directory. Therefore, you associate each directory created in the service with a connector instance.
Worker
When you associate a directory with a connector instance, the connector creates a partition for the
associated directory called a worker. A connector instance can have multiple workers associated with it.
Each worker acts as an identity provider. You define and configure authentication methods per worker.
Configuring vRealize Automation
VMware, Inc. 82
The connector syncs user and group data between Active Directory and the service through one or more
workers.
You cannot have two workers of the Integrated Windows Authentication type on the same connector
instance.
Active Directory Environments
You can integrate the service with an Active Directory environment that consists of a single Active
Directory domain, multiple domains in a single Active Directory forest, or multiple domains across multiple
Active Directory forests.
Single Active Directory Domain Environment
A single Active Directory deployment allows you to sync users and groups from a single Active Directory
domain.
See Configure a Link to Active Directory. For this environment, when you add a directory to the service,
select the Active Directory over LDAP option.
Multi-Domain, Single Forest Active Directory Environment
A multi-domain, single forest Active Directory deployment allows you to sync users and groups from
multiple Active Directory domains within a single forest.
You can configure the service for this Active Directory environment as a single Active Directory, Integrated
Windows Authentication directory type or, alternatively, as an Active Directory over LDAP directory type
configured with the global catalog option.
nThe recommended option is to create a single Active Directory, Integrated Windows Authentication
directory type.
See Configure a Link to Active Directory. When you add a directory for this environment, select the
Active Directory (Integrated Windows Authentication) option.
Multi-Forest Active Directory Environment with Trust Relationships
A multi-forest Active Directory deployment with trust relationships allows you to sync users and groups
from multiple Active Directory domains across forests where two-way trust exists between the domains.
See Configure a Link to Active Directory. When you add a directory for this environment, select the Active
Directory (Integrated Windows Authentication) option.
Multi-Forest Active Directory Environment Without Trust Relationships
A multi-forest Active Directory deployment without trust relationships allows you to sync users and groups
from multiple Active Directory domains across forests without a trust relationship between the domains. In
this environment, you create multiple directories in the service, one directory for each forest.
See Configure a Link to Active Directory. The type of directories you create in the service depends on the
forest. For forests with multiple domains, select the Active Directory (Integrated Windows Authentication)
option. For a forest with a single domain, select the Active Directory over LDAP option.
Configuring vRealize Automation
VMware, Inc. 83
Using Directories Management to Create an Active Directory Link
After you create vRealize Automation tenants, you must log in to the system console as a tenant
administrator and create an Active Directory link to support user authentication.
Configure a Link to Active Directory
You must use the Directories Management feature to configure a link to Active Directory to support user
authentication for all tenants and select users and groups to sync with the Directories Management
directory.
There are two Active Directory connection options: Active Directory over LDAP, and Active Directory
(Integrated Windows Authentication). An Active Directory over LDAP connection supports DNS Service
Location lookup by default. With Active Directory (Integrated Windows Authentication), you configure the
domain to join.
Prerequisites
nConnector installed and the activation code activated.
nSelect the required default attributes and add additional attributes on the User Attributes page. See
Select Attributes to Sync with Directory.
nList of the Active Directory groups and users to sync from Active Directory.
nFor Active Directory over LDAP, information required includes the Base DN, Bind DN, and Bind DN
password.
nFor Active Directory Integrated Windows Authentication, the information required includes the
domain's Bind user UPN address and password.
nIf Active Directory is accessed over SSL, a copy of the SSL certificate is required.
nFor Active Directory (Integrated Windows Authentication), when you have multi-forest Active Directory
configured and the Domain Local group contains members from domains in different forests, make
sure that the Bind user is added to the Administrators group of the domain in which the Domain Local
group resides. If this is not done, these members will be missing from the Domain Local group.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Directories Management > Directories.
2Click Add Directory.
3On the Add Directory page, specify the IP address for the Active Directory server in the Directory
Name text box.
Configuring vRealize Automation
VMware, Inc. 84
4Select the appropriate Active Directory communication protocol using the radio buttons under the
Directory Name text box.
Option Description
Windows Authentication Select Active Directory (Integrated Windows Authentication)
LDAP Select Active Directory over LDAP.
5Configure the connector that synchronizes users from the Active Directory to the VMware
Directories Management directory in the Directory Sync and Authentication section.
Option Description
Sync Connector Select the appropriate connector to use for your system. Each vRealize
Automation appliance contains a default connector. Consult your system
administrator if you need help in choosing the appropriate connector.
Authentication Click the appropriate radio button to indicate whether the selected connector also
performs authentication.
Directory Search Attribute Select the appropriate account attribute that contains the user name.
6Enter the appropriate information in the Server Location text box if you selected Active Directory over
LDAP or in the Join Domain Details text boxes if you selected Active Directory (Integrated Windows
Authentication)
Option Description
Server Location - Displayed when
Active Directory over LDAP is selected
nIf you want to use DNS Service Location to locate Active Directory domains,
leave the This Directory supports DNS Service Location check box
selected.
nIf the specified Active Directory does not use DNS Service Location lookup,
deselect the check box beside This Directory supports DNS Service
Location in the Server Location fields and enter the Active Directory server
host name and port number in the appropriate text boxes.
nIf Active Directory requires access over SSL, select the This Directory
requires all connections to use SSL check box under the Certificates
heading and provide the Active Directory SSL certificate.
Join Domain Details - Displayed when
Active Directory (integrated Windows
Authentication) is selected
Enter the appropriate credentials in the Domain Name, Domain Admin User
Name, and Domain Admin Password text boxes.
Configuring vRealize Automation
VMware, Inc. 85
7In the Bind User Details section, enter the appropriate credentials to facilitate directory
synchronization.
For Active Directory over LDAP:
Option Description
Base DN Enter the search base distinguished name. For example,
cn=users,dc=corp,dc=local.
Bind DN Enter the bind distinguished name. For example,
cn=fritz infra,cn=users,dc=corp,dc=local
For Active Directory (Integrated Windows Authentication):
Option Description
Bind User UPN Enter the User Principal Name of the user who can authenticate with the domain.
For example, UserName@example.com.
Bind DN Password Enter the Bind User password.
8Click Test Connection to test the connection to the configured directory.
9Click Save & Next.
The Select the Domains page appears with the list of domains.
10 Review and update the domains listed for the Active Directory connection.
nFor Active Directory (Integrated Windows Authentication), select the domains that should be
associated with this Active Directory connection.
nFor Active Directory over LDAP, the domains are listed with a checkmark.
Note If you add a trusting domain after the directory is created, the service does not
automatically detect the newly trusting domain. To enable the service to detect the domain, the
connector must leave and then rejoin the domain. When the connector rejoins the domain, the
trusting domain appears in the list.
11 Click Next.
12 Verify that the Directories Management directory attribute names are mapped to the correct Active
Directory attributes.
If the directory attribute names are not mapped correctly, select the correct Active Directory attribute
from the drop-down menu.
13 Click Next.
Configuring vRealize Automation
VMware, Inc. 86

14 Click to select the groups you want to sync from Active Directory to the directory.
When you add a group from Active Directory, if members of that group are not in the Users list, they
are added.
Note The Directories Management user authentication system imports data from Active Directory
when adding groups and users, and the speed of the system is limited by Active Directory
capabilities. As a result, import operations may require a significant amount of time depending on the
number of groups and users being added. To minimize the potential for delays or problems, limit the
number of groups and users to only those required for vRealize Automation operation. If your system
performance degrades or if errors occur, close any unneeded applications and ensure that your
system has appropriate memory allocated to Active Directory. If problems persist, increase the Active
Directory memory allocation as needed. For systems with large numbers of users and groups, you
may need to increase the Active Directory memory allocation to as much as 24 GB.
15 Click Next.
16 Click to add additional users. For example, enter as
CN-username,CN=Users,OU-myUnit,DC=myCorp,DC=com.
To exclude users, click to create a filter to exclude some types of users. You select the user
attribute to filter by, the query rule, and the value.
17 Click Next.
18 Review the page to see how many users and groups are syncing to the directory.
If you want to make changes to users and groups, click the Edit links.
19 Click Push to Workspace to start the synchronization to the directory.
The connection to the Active Directory is complete and the selected users and groups are added to the
directory.
What to do next
If your vRealize Automation environment is configured for high availability, you must specifically configure
Directories Management for high availability. See Configure Directories Management for High Availability.
nSet up authentication methods. After users and groups sync to the directory, if the connector is also
used for authentication, you can set up additional authentication methods on the connector. If a third
party is the authentication identity provider, configure that identity provider in the connector.
nReview the default access policy. The default access policy is configured to allow all appliances in all
network ranges to access the Web browser, with a session time out set to eight hours or to access a
client app with a session time out of 2160 hours (90 days). You can change the default access policy
and when you add Web applications to the catalog, you can create new ones.
nApply custom branding to the administration console, user portal pages and the sign-in screen.
See the Directories Management Administration Guide for information about configuring these features.
Configuring vRealize Automation
VMware, Inc. 87
Configure Directories Management for High Availability
You can use Directories Management to configure a high availability Active Directory connection in
vRealize Automation.
Each vRealize Automation appliance includes a connector that supports user authentication, although
only one connector is typically configured to perform directory synchronization. It does not matter which
connector you choose to serve as the sync connector. To support Directories Management high
availability, you must configure a second connector that corresponds to your second vRealize Automation
appliance, which connects to your Identity Provider and points to the same Active Directory. With this
configuration, if one appliance fails, the other takes over management of user authentication.
In a high availability environment, all nodes must serve the same set of Active Directories, users,
authentication methods, etc. The most direct method to accomplish this is to promote the Identity Provider
to the cluster by setting the load balancer host as the Identity Provider host. With this configuration, all
authentication requests are directed to the load balancer, which forwards the request to either connector
as appropriate.
Prerequisites
nConfigure your vRealize Automation deployment with at least two instance of the vRealize
Automation appliance.
nInstall vRealize Automation in Enterprise mode operating in a single domain with two instances of
thevRealize Automation appliance.
nInstall and configure an appropriate load balancer to work with your vRealize Automation deployment.
nConfigure tenants and Directories Management using one of the connectors supplied with the
installed instances of the vRealize Automation appliance. For information about tenant configuration,
see Chapter 2 Configuring Tenant Settings.
Procedure
1Log in to the load balancer for your vRealize Automation deployment as a tenant administrator.
The load balancer URL is <load balancer address>/vcac/org/tenant_name.
2Select Administration > Directories Management > Identity Providers.
3Click the Identity Provider that is currently in use for your system.
The existing directory and connector that provide basic identity management for your system
appears.
4On the Identity Provider properties page, click the Add a Connector drop-down list, and select the
connector that corresponds to your secondary vRealize Automation appliance.
5Enter the appropriate password in the Bind DN Password text box that appears when you select the
connector.
6Click Add Connector.
Configuring vRealize Automation
VMware, Inc. 88
7The main connector appears in the IdP Hostnametext box by default. Change the host name to point
to the load balancer.
Configure a Bi Directional Trust Relationship Between vRealize Automation
and Active Directory
You can enhance system security of a basic vRealize Automation Active Directory connection by
configuring a bi directional trust relationship between your identity provider and Active Directory
Federated Services.
To configure a bi-directional trust relationship between vRealize Automation and Active Directory, you
must create a custom identity provider and add Active Directory metadata to this provider. Also, you must
modify the default policy used by your vRealize Automation deployment. Finally, you must configure
Active Directory to recognize your identity provider.
Prerequisites
nVerify that you have configured tenants for your vRealize Automation deployment set up an
appropriate Active Directory link to support basic Active Directory user ID and password
authentication.
nActive Directory is installed and configured for use on your network.
nObtain the appropriate Active Directory Federated Services (ADFS) metadata.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Obtain the Federation Metadata file.
You can download this file from
https://servername.domain/FederationMetadata/2007-06/FederationMetadata.xml
2Search for the word logout, and edit the location of each instance to point to
https://servername.domain/adfs/ls/logout.aspx
For example, the following:
SingleLogoutService
Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST"
Location="https://servername.domain/adfs/ls/ "/>
Should be changed to:
SingleLogoutService
Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST"
Location="https://servername.domain/adfs/ls/logout.aspx"/>
Configuring vRealize Automation
VMware, Inc. 89
3Create a new Identity Provider for you deployment.
a Select Administration > Directories Management > Identity Providers.
b Click Add Identity Provider and complete the fields as appropriate.
Option Description
Identity Provider Name Enter a name for the new identity provider
Identity Provider Metadata (URI or
XML)
Paste the contents of your Active Directory Federated Services metadata file
here.
Name ID Policy in SAML Request
(Optional)
If appropriate, enter a name for the identity policy SAML request.
Users Select the domains to which you want users to have access privileges.
Process IDP Metadata Click to process the metadata file that you added.
Network Select the network ranges to which you want users to have access.
Authentication Methods Enter a name for the authentication method used by this identity provider.
SAML Context Select the appropriate context for your system.
SAML Signing Certificate Click the link beside the SAML Metadata heading to download the Directories
Management metadata.
c Save the Directories Management metadata file as sp.xml.
d Click Add.
4Add a rule to the default policy.
a Select Administration > Directories Management > Policies.
b Click the default policy name.
c Click the + icon under the Policy Rules heading to add a new rule.
Use the fields on the Add a Policy Rule page to create a rule that specifies the appropriate
primary and secondary authentication methods to use for a specific network range and device.
For example, if the user's network range is "My Machine", and the user needs to access content
from "All Device Types," then, for a typical deployment, that user must authenticate using the
following method: ADFS Username and Password.
d Click Save to save your policy updates.
e On the Default Policy page, drag the new rule to the top of the table so that it takes precedence
over existing rules.
Configuring vRealize Automation
VMware, Inc. 90

5Using the Active Directory Federated Services management console, or another appropriate tool, set
up a relying party trust relationship with the vRealize Automation identity provider.
To set up this trust, you must import the Directories Management metadata that you previously
downloaded. See the Microsoft Active Directory documentation for more information about
configuring Active Directory Federated Services for bi-directional trust relationships. As part of this
process, you must do the following:
nSet up a Relying Party Trust. When you set up this trust, you must import the VMware Identity
Provider service provider metadata XML file that you copied and saved
nCreate a claim rule that transforms the attributes retrieved from LDAP in the Get Attributes rule
into the desired SAML format. After you create the rule,. you must edit the rule by adding the
following text:
c:[Type == "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress"]
=> issue(Type = "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier", Issuer
= c.Issuer, OriginalIssuer = c.OriginalIssuer, Value = c.Value, ValueType = c.ValueType,
Properties["http://schemas.xmlsoap.org/ws/2005/05/identity/claimproperties/format"] =
"urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress",
Properties["http://schemas.xmlsoap.org/ws/2005/05/identity/claimproperties/spnamequalifier"] =
"vmwareidentity.domain.com");
Configure SAML Federation Between Directories Management and SSO2
You can establish federation between vRealize Automation Directories Management and systems that
use SSO2.
Establish federation between Directories Management and SSO2 by creating a SAML connection
between the two parties. Currently, the only supported end-to-end flow is where SSO2 acts as the Identity
Provider (Idp) and Directories Management acts as the service provider (SP).
For users to be authenticated by SSO2, the same account must exist in both Directories Management
and SSO2. At least the UserPrinicpalName (UPN) of the user has to match on both ends. Other attributes
can differ as they are required to identify the SAML subject.
For local users in SSO2, such as admin@vsphere.local, corresponding accounts must be created in
Directories Management as well (where at least the UPN of the user matches). For now, this must be
done manually or by a script using the Directories Management local user creation APIs.
Setting up SAML between SSO2 and Directories Management involves configuration on the Directories
Management and SSO components.
Configuring vRealize Automation
VMware, Inc. 91
Table 2‑4. SAML Federation Component Configuration
Component Configuration
Directories Management Configure SSO2 as a third-party Identity Provider on Directories Management and update the
default authentication policy. You can create an automated script to set up
Directories Management.
SSO2 component Configure Directories Management as a service provider by importing the
Directories Management sp.xml file. This file enables you to configure SSO2 to use
Directories Management as the Service Provider (SP).
Prerequisites
nYou have configured tenants for your vRealize Automation deployment set up an appropriate Active
Directory link to support basic Active Directory user ID and password authentication.
nActive Directory is installed and configured for use on your network.
nObtain the appropriate Active Directory Federated Services (ADFS) metadata.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Download SSO2 Identity Provider metadata through the SSO2 user interface.
a Login to vCenter as a an Administrator at https://<cloudvm-hostnamte>/.
b Click the Log in to vSphere Web Client link
c On the left navigation pane, select Administration > Single Sign On > Configuration.
d Click Download adjacent to the Metadata for your SAML service provider heading.
The vsphere.local.xml file should begin downloading.
e Copy the contents of the vsphere.local.xml file.
2Use the vRealize Automation Directories Management Identity Providers page to create a new
Identity Provider.
a Log in to vRealize Automation as a tenant administrator.
b Select Administration > Directories Management > Identity Providers.
c Click Add Identity Provider.
d Enter a name for the new Identity Provider in the Identity Provider Name text box.
e Paste the contents of your SSO2 idp.xml metadata file into the Identity Provider Metadata
(URI or XML) text box.
f Click Process IDP Metadata.
g Enter the following in the Name ID Policy in SAML Request (Optional) text box.
http://schemas.xmlsoap.org/claims/UPN
h Select the domains to which you want users to have access privileges in the Users text box.
Configuring vRealize Automation
VMware, Inc. 92
i Select the network ranges from which you want users to have access privileges to this identity
provider in the Network text box.
If you want to authenticate users from an IP addresses, select All Ranges.
j Enter a name for the authentication method in the Authentication Methods text box.
k Use the SAML Context drop down menu to the right of the Authentication Methods text box to
map the authentication method to urn:oasis:names:tc:SAML:2.0:ac:classes:Password.
l Click the link beside the SAML Metadata heading under the SAML Signing Certificate text box,
to download the Directories Management metadata.
m Save the Directories Management metadata file as sp.xml.
n Click Add.
3Update the relevant authentication policy using the Directories Management Policies page to redirect
authentication to the third party SSO2 identity provider.
a Select Administration > Directories Management > Policies.
b Click the default policy name.
c Click authentication method under the Policy Rules heading to edit the existing authentication
rule.
Use the fields on the Edit a Policy Rule page to change the authentication method from password
to the appropriate method. In this case, the method should be SSO2.
d Click Save to save your policy updates.
4On the left navigation pane, select Administration > Single Sign On > Configuration, and click
Update to upload the sp.xml file to vSphere.
Add Users or Groups to an Active Directory Connection
You can add users or groups to an existing Active Directory connection.
The Directories Management user authentication system imports data from Active Directory when adding
groups and users, and the speed of the system is limited by Active Directory capabilities. As a result,
import operations may require a significant amount of time depending on the number of groups and users
being added. To minimize the potential for delays or problems, limit the number of groups and users to
only those required for vRealize Automation operation. If performance degrades or if errors occur, close
any unneeded applications and ensure that your deployment has appropriate memory allocated to Active
Directory. If problems persist, increase the Active Directory memory allocation as needed. For
deployments with large numbers of users and groups, you may need to increase the Active Directory
memory allocation to as much as 24 GB.
Configuring vRealize Automation
VMware, Inc. 93
When running a synchronize operation for a vRealize Automation deployment with a many users and
groups, there may be a delay after the Sync is in progress message disappears before the Sync Log
details are displayed. Also, the time stamp on the log file may differ from the time that the user interface
indicates that the synchronize operation completed.
Note You cannot cancel a synchronize operation after it has been initiated.
Prerequisites
nConnector installed and the activation code activated. Select the required default attributes and add
additional attributes on the User Attributes page.
nList of the Active Directory groups and users to sync from Active Directory.
nFor Active Directory over LDAP, information required includes the Base DN, Bind DN, and Bind DN
password.
nFor Active Directory Integrated Windows Authentication, the information required includes the
domain's Bind user UPN address and password.
nIf Active Directory is accessed over SSL, a copy of the SSL certificate is required.
nFor Active Directory Integrated Windows Authentication, when you have multi-forest Active Directory
configured and the Domain Local group contains members from domains in different forests, make
sure that the Bind user is added to the Administrators group of the domain in which the Domain Local
group resides. If this is not done, these members are missing from the Domain Local group.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Directories Management > Directories
2Click the desired directory name.
3Click Sync Settings to open a dialog with synchronization options.
4Click the appropriate icon depending on whether you want to change the user or group configuration.
To edit the group configuration:
nTo add groups, click the + icon to add a new line for group DN definitions and enter the
appropriate group DN.
nIf you want to delete a group DN definition, click the x icon for the desired group DN.
To edit the user configuration:
uTo add users, click the + icon to add a new line for user DN definition and enter the appropriate
user DN.
If you want to delete a user DN definition, click the x icon for the desired user DN.
5Click Save to save your changes without synchronizing to make your updates immediately, or click
Save & Sync to save your changes and synchronize to implement your updates immediately.
Configuring vRealize Automation
VMware, Inc. 94
Select Attributes to Sync with Directory
When you set up the Directories Management directory to sync with Active Directory, you specify the user
attributes that sync to the directory. Before you set up the directory, you can specify on the User Attributes
page which default attributes are required and, if you want, add additional attributes that you want to map
to Active Directory attributes.
When you configure the User Attributes page before the directory is created, you can change default
attributes from required to not required, mark attributes as required, and add custom attributes.
For a list of the default mapped attributes, see Managing User Attributes that Sync from Active Directory.
After the directory is created, you can change a required attribute to not be required, and you can delete
custom attributes. You cannot change an attribute to be a required attribute.
When you add other attributes to sync to the directory, after the directory is created, go to the directory's
Mapped Attributes page to map these attributes to Active Directory Attributes.
Procedure
1Log in to vRealize Automation as a system or tenant administrator.
2Click the Administration tab.
3Select Directories Management > User Attributes
4In the Default Attributes section, review the required attribute list and make appropriate changes to
reflect what attributes should be required.
5In the Attributes section, add the Directories Management directory attribute name to the list.
6Click Save.
The default attribute status is updated and attributes you added are added on the directory's Mapped
Attributes list.
7After the directory is created, go to the Identity Stores page and select the directory.
8Click Sync Settings > Mapped Attributes.
9In the drop-down menu for the attributes that you added, select the Active Directory attribute to map
to.
10 Click Save.
The directory is updated the next time the directory syncs to the Active Directory.
Add Memory to Directories Management
You may need to allocate additional memory to Directories Management if you have Active Directory
connections that contain a large number of users or groups.
Configuring vRealize Automation
VMware, Inc. 95

By default, 4 GB of memory is allocated to the Directories Management service. This is sufficient for many
small to medium sized deployments. If you have an Active Directory connection that uses a large number
of users or groups, you may need to increase this memory allocation. Increased memory allocation is
appropriate for systems with more than 100,000 users , each in 30 groups and 750 groups overall. For
these system, VMware recommends increasing the Directories Management memory allocation to 6 GB.
Directories Management memory is calculated based on the total memory allocated to the vRealize
Automation appliance The following table shows memory allocations for relevant components.
Table 2‑5. vRealize Automation appliance Memory Allocation
Virtual Appliance Memory vRA service memory vIDM service memory
18 GB 3.3 GB 4 GB
24 GB 4.9 GB 6 GB
30 GB 7.4 GB 9.1 GB
Note These allocations assume that all default services are enabled and running on the virtual
appliance. They may change if some services are stopped.
Prerequisites
nAn appropriate Active Directory connection is configured and functioning on your
vRealize Automation deployment.
Procedure
1Stop each machine on which a vRealize Automation appliance is running.
2Increase the virtual appliance memory allocation on each machine.
If you are using the default memory allocation of 18 GB, VMware recommends increasing the
memory allocation to 24 GB.
3Restart the vRealize Automation appliance machines.
Create a Domain Host Lookup File to Override DNS Service Location (SRV)
Lookup
When you enable Integrated Windows Authentication, the Directory configuration is changed to enable
the DNS Service Location field. The connector service location lookup is not site aware. If you want to
override the random DC selection, you can create a file called domain_krb.properties and add the
domain to host values that take precedence over SRV lookup.
Procedure
1From the appliance-va command line, log in as the user with root privileges.
2Change directories to /usr/local/horizon/conf and create a file called
domain_krb.properties.
Configuring vRealize Automation
VMware, Inc. 96
3Edit the domain_krb.properties file to add the list of the domain to host values. Add the information as
<AD Domain>=<host:port>, <host2:port2>, <host2:port2>.
For example, enter the list as example.com=examplehost.com:636,
examplehost2.example.com:389
4Change the owner of the domain_krb.properties file to horizon and group to www. Enter
chown horizon:www /usr/local/horizon/conf/domain_krb.properties.
5Restart the service. Enter service horizon-workspace restart.
Managing User Attributes that Sync from Active Directory
The Directories Management User Attributes page lists the user attributes that sync to your Active
Directory connection.
Changes that are made and saved in the User Attributes page are added to the Mapped Attributes page
in the Directories Management directory. The attributes changes are updated to the directory with the next
sync to Active Directory.
The User Attributes page lists the default directory attributes that can be mapped to Active Directory
attributes. You select the attributes that are required, and you can add other Active Directory attributes
that you want to sync to the directory.
Table 2‑6. Default Active Directory Attributes to Sync to Directory
Directory Attribute Name Default Mapping to Active Directory Attribute
userPrincipalName userPrincipalName
distinguishedName distinguishedName
employeeId employeeID
domain canonicalName. Adds the fully qualified domain name of object.
disabled (external user disabled) userAccountControl. Flagged with UF_Account_Disable
When an account is disabled, users cannot log in to access their
applications and resources. The resources that users were entitled
to are not removed from the account so that when the flag is
removed from the account users can log in and access their entitled
resources
phone telephoneNumber
lastName sn
firstName givenName
email mail
userName sAMAccountName.
The User Attributes page lists the default directory attributes that can be mapped to Active Directory
attributes. You select the attributes that are required, and you can add other Active Directory attributes
that you want to sync to the directory.
Configuring vRealize Automation
VMware, Inc. 97
Table 2‑7. Default Active Directory Attributes to Sync to Directory
Directory Attribute Name Default Mapping to Active Directory Attribute
userPrincipalName userPrincipalName
distinguishedName distinguishedName
employeeId employeeID
domain canonicalName. Adds the fully qualified domain name of object.
disabled (external user disabled) userAccountControl. Flagged with UF_Account_Disable
When an account is disabled, users cannot log in to access their
applications and resources. The resources that users were entitled
to are not removed from the account so that when the flag is
removed from the account users can log in and access their entitled
resources
phone telephoneNumber
lastName sn
firstName givenName
email mail
userName sAMAccountName.
Managing Connectors
The Connectors page lists deployed connectors for your enterprise network. A connector syncs user and
group data between Active Directory and the Directories Management service, and when it is used as the
identity provider, authenticates users to the service.
In vRealize Automation, each vRealize Automation appliance appliance contains its own connector, and
these connectors are suitable for most deployments.
When you associate a directory with a connector instance, the connector creates a partition for the
associated directory called a worker. A connector instance can have multiple workers associated with it.
Each worker acts as an identity provider. The connector syncs user and group data between Active
Directory and the service through one or more workers. You define and configure authentication methods
on a per worker basis.
You can manage various aspects of an Active Directory link from the Connectors page. This page
contains a table and several buttons that enable you to complete various management tasks.
nIn the Worker column, select a worker to view the connector's details and navigate to the Auth
Adapters page to see the status of the available authentication methods. For information about
authentication, see Integrating Alternative User Authentication Products with Directories
Management.
nIn the Identity Provider column, select the IdP to view, edit or disable. See Configure an Identity
Provider Instance.
nIn the Associated Directory column, access the directory associated with this worker.
Configuring vRealize Automation
VMware, Inc. 98
nClick Join Domain to join the connector to a specific Active Directory domain. For example when you
configure Kerberos authentication, you must join the Active Directory domain either containing users
or having trust relationship with the domains containing users.
nWhen you configure a directory with an Integrated Windows Authentication Active Directory, the
connector joins the domain according to the configuration details.
Join a Connector Machine to a Domain
In some cases, you may need to join a machine containing a Directories Management connector to a
domain.
For Active Directory over LDAP directories, you can join a domain after creating the directory. For Active
Directory (Integrated Windows Authentication) directories, the connector is joined to the domain
automatically when you create the directory. In both cases, you must supply the appropriate credentials.
To join a domain, you need Active Directory credentials that have the privilege to "join computer to AD
domain". This is configured in Active Directory with the following rights:
nCreate Computer Objects
nDelete Computer Objects
When you join a domain, a computer object is created in the default location in Active Directory.
If you do not have the rights to join a domain, or if your company policy requires a custom location for the
computer object, you must ask your administrator to create the object and then join the connector
machine to the domain.
Procedure
1Ask you Active Directory administrator to create the computer object in Active Directory, in a location
determined by your company policy. Provide the host name of the connector, Ensure that you provide
the fully-qualified domain name. For example: server.example.com
You can find the host name in the Host Name column on the Connectors page in the administrative
console. Select Administration > Directories Management > Connectors
2After the computer object is created, click Join Domain on the Connectors page to join the domain
using any domain user account available in Directories Management.
About Domain Controller Selection
The domain_krb.properties file determines which domain controllers are used for directories that have
DNS Service Location (SRV records) lookup enabled. It contains a list of domain controllers for each
domain. The connector creates the file initially, and you must maintain it subsequently. The file overrides
DNS Service Location (SRV) lookup.
The following types of directories have DNS Service Location lookup enabled.
nActive Directory over LDAP with the This Directory supports DNS Service Location option
selected
Configuring vRealize Automation
VMware, Inc. 99
nActive Directory (Integrated Windows Authentication), which always has DNS Service Location
lookup enabled
When you first create a directory that has DNS Service Location lookup enabled, a
domain_krb.properties file is created automatically in the /usr/local/horizon/conf directory of the
virtual machine and is auto-populated with domain controllers for each domain. To populate the file, the
connector attempts to find domain controllers that are at the same site as the connector and selects two
that are reachable and that respond the fastest.
When you create additional directories that have DNS Service Location enabled, or add new domains to
an Integrated Windows Authentication directory, the new domains, and a list of domain controllers for
them, are added to the file.
You can override the default selection at any time by editing the domain_krb.properties file. As a best
practice, after you create a directory, view the domain_krb.properties file and verify that the domain
controllers listed are the optimal ones for your configuration. For a global Active Directory deployment that
has multiple domain controllers across different geographical locations, using a domain controller that is
in close proximity to the connector ensures faster communication with Active Directory.
You must also update the file manually for any other changes. The following rules apply.
nThe domain_krb.properties file is created in the virtual machine that contains the connector. In a
typical deployment, with no additional connectors deployed, the file is created in the
Directories Management service virtual machine. If you are using an additional connector for the
directory, the file is created in the connector virtual machine. A virtual machine can only have one
domain_krb.properties file.
nThe file is created, and auto-populated with domain controllers for each domain, when you first create
a directory that has DNS Service Location lookup enabled.
nDomain controllers for each domain are listed in order of priority. To connect to Active Directory, the
connector tries the first domain controller in the list. If it is not reachable, it tries the second one in the
list, and so on.
nThe file is updated only when you create a new directory that has DNS Service Location lookup
enabled or when you add a domain to an Integrated Windows Authentication directory. The new
domain and a list of domain controllers for it are added to the file.
Note that if an entry for a domain already exists in the file, it is not updated. For example, if you
created a directory, then deleted it, the original domain entry remains in the file and is not updated.
nThe file is not updated automatically in any other scenario. For example, if you delete a directory, the
domain entry is not deleted from the file.
nIf a domain controller listed in the file is not reachable, edit the file and remove it.
nIf you add or edit a domain entry manually, your changes will not be overwritten.
Configuring vRealize Automation
VMware, Inc. 100

How Domain Controllers are Selected to Auto-Populate the
domain_krb.properties File
To auto-populate the domain_krb.properties file, domain controllers are selected by first determining
the subnet on which the connector resides (based on the IP address and netmask), then using the Active
Directory configuration to identify the site of that subnet, getting the list of domain controllers for that site,
filtering the list for the appropriate domain, and picking the two domain controllers that respond the
fastest.
To detect the domain controllers that are the closest, VMware Identity Manager has the following
requirements.
nThe subnet of the connector must be present in the Active Directory configuration, or a subnet must
be specified in the runtime-config.properties file.
The subnet is used to determine the site.
nThe Active Directory configuration must be site aware.
If the subnet cannot be determined or if your Active Directory configuration is not site aware, DNS Service
Location lookup is used to find domain controllers, and the file is populated with a few domain controllers
that are reachable. Note that these domain controllers may not be at the same geographical location as
the connector, which can result in delays or timeouts while communicating with Active Directory. In this
case, edit the domain_krb.properties file manually and specify the correct domain controllers to use
for each domain.
Sample domain_krb.properties File
example.com=host1.example.com:389,host2.example.com:389
nOverride the Default Subnet Selection
To auto-populate the domain_krb.properties file, the connector attempts to find domain
controllers that are at the same site so there is minimal latency between the connector and Active
Directory.
nEdit the domain_krb.properties file
The /usr/local/horizon/conf/domain_krb.properties file determines the domain controllers
to use for directories that have DNS Service Location lookup enabled. You can edit the file at any
time to modify the list of domain controllers for a domain, or to add or delete domain entries. Your
changes will not be overridden.
nTroubleshooting domain_krb.properties
Use this information to troubleshoot the domain_krb.properties file.
Override the Default Subnet Selection
To auto-populate the domain_krb.properties file, the connector attempts to find domain controllers that
are at the same site so there is minimal latency between the connector and Active Directory.
Configuring vRealize Automation
VMware, Inc. 101

To find the site, the connector determines the subnet on which it resides, based on its IP address and
netmask, then uses the Active Directory configuration to identify the site for that subnet. If the subnet of
the virtual machine is not in Active Directory, or if you want to override the automatic subnet selection, you
can specify a subnet in the runtime-config.properties file.
Procedure
1Log in to the Directories Management virtual machine as the root user.
Note If you are using an additional connector for the directory, log in to the connector virtual
machine.
2Edit the /usr/local/horizon/conf/runtime-config.properties file and add the following
attribute.
siteaware.subnet.override=subnet
where subnet is a subnet for the site whose domain controllers you want to use. For example:
siteaware.subnet.override=10.100.0.0/20
3Save and close the file.
4Restart the service.
service horizon-workspace restart
Edit the domain_krb.properties file
The /usr/local/horizon/conf/domain_krb.properties file determines the domain controllers to
use for directories that have DNS Service Location lookup enabled. You can edit the file at any time to
modify the list of domain controllers for a domain, or to add or delete domain entries. Your changes will
not be overridden.
The file is initially created and auto-populated by the connector. You need to update it manually in some
scenarios.
nIf the domain controllers selected by default are not the optimal ones for your configuration, edit the
file and specify the domain controllers to use.
nIf you delete a directory, delete the corresponding domain entry from the file.
nIf any domain controllers in the file are not reachable, remove them from the file.
See also About Domain Controller Selection.
Procedure
1Log in to the Directories Management virtual machine as the root user.
Note If you are using an additional connector for the directory, log in to the connector virtual
machine.
2Change directories to /usr/local/horizon/conf.
Configuring vRealize Automation
VMware, Inc. 102
3Edit the domain_krb.properties file to add or edit the list of domain to host values.
Use the following format:
domain=host:port,host2:port,host3:port
For example:
example.com=examplehost1.example.com:389,examplehost2.example.com:389
List the domain controllers in order of priority. To connect to Active Directory, the connector tries the
first domain controller in the list. If it is not reachable, it tries the second one in the list, and so on.
Important Domain names must be in lowercase.
4Change the owner of the domain_krb.properties file to horizon and group to www using the
following command:
chown horizon:www /usr/local/horizon/conf/domain_krb.properties
5Restart the service.
service horizon-workspace restart
Troubleshooting domain_krb.properties
Use this information to troubleshoot the domain_krb.properties file.
"Error resolving domain" error
If the domain_krb.properties file already includes an entry for a domain, and you try to create a new
directory of a different type for the same domain, an "Error resolving domain" error occurs. You must edit
the domain_krb.properties file and manually remove the domain entry before creating the new
directory.
Domain controllers are unreachable
Once a domain entry is added to the domain_krb.properties file, it is not updated automatically. If any
domain controllers listed in the file become unreachable, edit the file manually and remove them.
Managing Access Policies
The Directories Management policies are a set of rules that specify criteria that must be met for users to
access their app portal or to launch specified Web applications.
You create the rule as part of a policy. Each rule in a policy can specify the following information.
nThe network range, where users are allowed to log in from, such as inside or outside the enterprise
network.
nThe device type that can access through this policy.
nThe order that the enabled authentication methods are applied.
Configuring vRealize Automation
VMware, Inc. 103
nThe number of hours the authentication is valid.
Note The policies do not control the length of time that a Web application session lasts. They control the
amount of time that users have to launch a Web application.
The Directories Management service includes a default policy that you can edit. This policy controls
access to the service as a whole. See Applying the Default Access Policy. To control access to specific
Web applications, you can create additional policies. If you do not apply a policy to a Web application, the
default policy applies.
Configuring Access Policy Settings
A policy contains one or more access rules. Each rule consists of settings that you can configure to
manage user access to their application portals as a whole or to specified Web applications.
Each identity provider instance in your Directories Management deployment links network ranges with
authentication methods. When you configure a policy rule, ensure that the network range is covered by
an existing identity provider instance.
Network Range
For each rule, you determine the user base by specifying a network range. A network range consists of
one or more IP ranges. You create network ranges from the Identity & Access Management tab, Setup >
Network Ranges page prior to configuring access policy sets.
Device Type
Select the type of device that the rule manages. The client types are Web Browser, Identity Manager
Client App, iOS, Android, and All device types.
Authentication Methods
Set the priority of the authentication methods for the policy rule. The authentication methods are applied
in the order they are listed. The first identity provider instances that meets the authentication method and
network range configuration in the policy is selected, and the user authentication request is forwarded to
the identity provider instance for authentication. If authentication fails, the next authentication method in
the list is selected. If Certificate authentication is used, this method must be the first authentication
method in the list.
You can configure access policy rules to require users to pass credentials through two authentication
methods before they can sign in. If one or both authentication method fails and fallback methods are also
configured, users are prompted to enter their credentials for the next authentication methods that are
configured. The following two scenarios describe how authentication chaining can work.
nIn the first scenario, the access policy rule is configured to require users to authenticate with their
password and with their Kerberos credential. Fallback authentication is set up to require the password
and the RADIUS credential for authentication. A user enters the password correctly, but fails to enter
the correct Kerberos authentication credential. Since the user entered the correct password, the
fallback authentication request is only for the RADIUS credential. The user does not need to re-enter
the password.
Configuring vRealize Automation
VMware, Inc. 104
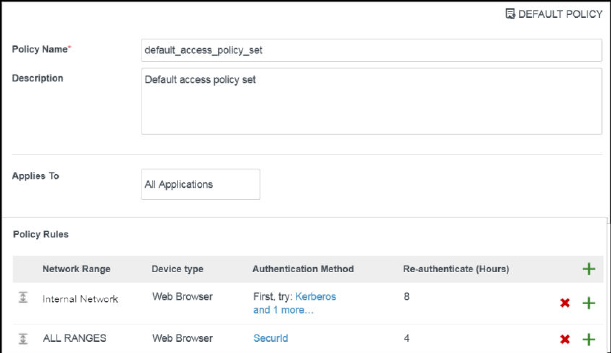
nIn the second scenario, the access policy rule is configured to require users to authenticate with their
password and their Kerberos credential. Fallback authentication is set up to require RSA SecurID and
a RADIUS for authentication. A user enters the password correctly but fails to enter the correct
Kerberos authentication credential. The fallback authentication request is for both the RSA SecurID
credential and the RADIUS credential for authentication.
Authentication Session Length
For each rule, you set the length that this authentication is valid. The value determines the maximum
amount of time users have since their last authentication event to access their portal or to launch a
specific Web application. For example, a value of 4 in a Web application rule gives users four hours to
launch the web application unless they initiate another authentication event that extends the time.
Example Default Policy
The following policy serves as an example of how you can configure the default policy to control access
to the apps portal. See Manage the User Access Policy
The policy rules are evaluated in the order listed. You can change the order of the policy by dragging and
dropping the rule in the Policy Rules section.
In the following use case, this policy example applies to all applications.
1nFor the internal network (Internal Network Range), two authentication methods are configured for
the rule, Kerberos and password authentication as the fallback method. To access the apps portal
from an internal network, the service attempts to authenticate users with Kerberos authentication
first, as it is the first authentication method listed in the rule. If that fails, users are prompted to
enter their Active Directory password. Users log in using a browser and now have access to their
user portals for an eight-hour session.
nFor access from the external network (All Ranges), only one authentication method is configured,
RSA SecurID. To access the apps portal from an external network, users are required to log in
with SecurID. Users log in using a browser and now have access to their apps portals for a four-
hour session.
Configuring vRealize Automation
VMware, Inc. 105
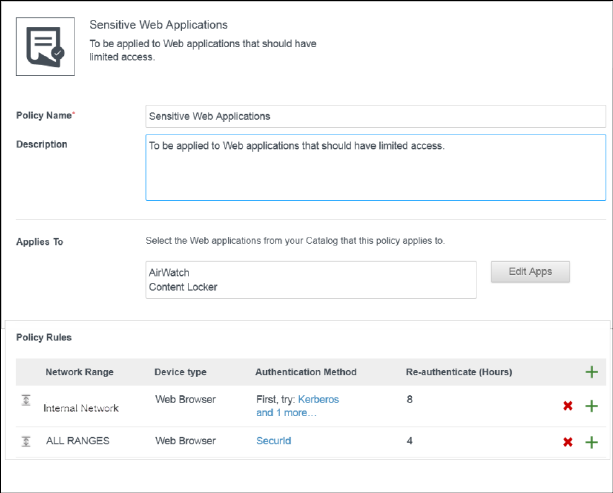
2 When a user attempts to access a resource, except for Web applications covered by a Web-
application-specific policy, the default portal access policy applies.
For example, the re-authentication time for such resources matches the re-authentication time of the
default access policy rule. If the time for a user who logs in to the apps portal is eight hours according
to the default access policy rule, when the user attempts to launch a resource during the session, the
application launches without requiring the user to re-authenticate.
Managing Web-Application-Specific Policies
When you add Web applications to the catalog, you can create Web-application-specific access policies.
For example, you can create an policy with rules for a Web application that specifies which IP addresses
have access to the application, using which authentication methods, and for how long until
reauthentication is required.
The following Web-application-specific policy provides an example of a policy you can create to control
access to specified Web applications.
Example 1 Strict Web-Application-Specific Policy
In this example, a new policy is created and applied to a sensitve Web application.
1 To access the service from outside the enterprise network, the user is required to log in with RSA
SecurID. The user logs in using a browser and now has access to the apps portal for a four hour
session as provided by the default access rule.
2 After four hours, the user tries to launch a Web application with the Sensitive Web Applications policy
set applied.
Configuring vRealize Automation
VMware, Inc. 106
3 The service checks the rules in the policy and applies the policy with the ALL RANGES network
range since the user request is coming from a Web browser and from the ALL RANGES network
range.
The user logs in using the RSA SecurID authentication method, but the session just expired. The user
is redirected for reauthentication. The reauthentication provides the user with another four hour
session and the ability to launch the application. For the next four hours, the user can continue to
launch the application without having to reauthenticate.
Example 2 Stricter Web-Application-Specific Policy
For a stricter rule to apply to extra sensitve Web applications, you could require re-authentication With
SecureId on any device after 1 hour. The following is an example of how this type of policy access rule is
implemented.
1 User logs in from an inside the enterprise network using the password authentication method.
Now, the user has access to the apps portal for eight hours, as set up in Example 1.
2 The user immediately tries to launch a Web application with the Example 2 policy rule applied, which
requires RSA SecurID authentication.
3 The user is redirected to an identity provider that provides RSA SecurID authentication.
4 After the user successfully logs in, the service launches the application and saves the authentication
event.
The user can continue to launch this application for up to one hour but is asked to reauthenticate after
an hour, as dictated by the policy rule.
Manage the User Access Policy
vRealize Automation is supplied with a default user access policy that you can use as is or edit as needed
to manage tenant access to applications.
vRealize Automation is supplied with a default user access policy, and you cannot add new policies. You
can edit the existing policy to add rules.
Prerequisites
nSelect or configure the appropriate identity providers for your deployment. See Configure an Identity
Provider Instance.
nConfigure the appropriate network ranges for your deployment. See Add or Edit a Network Range.
nConfigure the appropriate authentication methods for your deployment. See Integrating Alternative
User Authentication Products with Directories Management.
nIf you plan to edit the default policy (to control user access to the service as a whole), configure it
before creating Web-application-specific policy.
nAdd Web applications to the Catalog. The Web applications must be listed in the Catalog page before
you can add a policy.
Configuring vRealize Automation
VMware, Inc. 107
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Directories Management > Policies.
2Click Edit Policy to add a new policy.
3Add a policy name and description in the respective text boxes.
4In the Applies To section, click Select and in the page that appears, select the Web applications that
are associated with this policy.
5In the Policy Rules section, click + to add a rule.
The Add a Policy Rule page appears.
a Select the network range to apply to this rule.
b Select the type of device that can access the web applications for this rule.
c Select the authentication methods to use in the order the method should be applied.
d Specify the number of hours a Web application session open.
e Click Save.
6Configure additional rules as appropriate.
7Click Save.
Integrating Alternative User Authentication Products with
Directories Management
Typically, when you initially configure Directories Management, you use the connectors supplied with your
existing vRealize Automation infrastructure to create an Active Directory connection for user ID and
password based authentication and management. Alternatively, you can integrate Directories
Management with other authentication solutions such as Kerberos or RSA SecurID.
The identity provider instance can be the Directories Management connector instance, third-party identity
provider instances, or a combination of both.
Configuring vRealize Automation
VMware, Inc. 108
Table 2‑8. User Authentication Types Supported by Directories Management
Authentication Types Description
Kerberos Kerberos authentication provides domain users with single sign-on access to their apps
portal, eliminating the requirement for domain users to sign in to their apps portal again
after they log in to the enterprise network. The Directories Management validates user
desktop credentials using Kerberos tickets distributed by the key distribution center
(KDC).
Certificate Certificate-based authentication can be configured to allow clients to authenticate with
certificates on their desktop and mobile devices or to use a smart card adapter for
authentication.
Certificate-based authentication is based on what the user has and what the person
knows. A X.509 certificate uses the public key infrastructure standard to verify that a
public key contained within the certificate belongs to the user.
Certificate-based authentication is based on what the user has and what the person
knows. A X.509 certificate uses the public key infrastructure standard to verify that a
public key contained within the certificate belongs to the user.
RSA SecurID When RSA SecurID authentication is configured, Directories Management is configured
as the authentication agent in the RSA SecurID server. RSA SecurID authentication
requires users to use a token-based authentication system. RSA SecurID is a
recommended authentication method for users accessing Directories Management from
outside the enterprise network.
RADIUS RADIUS authentication provides two-factor authentication options. You set up the
RADIUS server that is accessible to the Directories Management service. When users
sign in with their user name and passcode, an access request is submitted to the RADIUS
server for authentication.
RSA Adaptive Authentication RSA authentication provides a stronger multi-factor authentication than only user name
and password authentication against Active Directory. When RSA Adaptive Authentication
is enabled, the risk indicators specified in the risk policy set up in the RSA Policy
Management application and the Directories Management service configuration of
adaptive authentication are used to determine the required authentication prompts.
Configuring SecurID for Directories Management
When you configure RSA SecurID server, you must add the Directories Management service information
as the authentication agent on the RSA SecurID server and configure the RSA SecurID server
information on the Directories Management service.
When you configure SecurID to provide additional security, you must ensure that your network is properly
configured for your Directories Management deployment. For SecurID specifically, you must ensure that
the appropriate port is open to enable SecurID to authenticate users outside your network.
After you run the Directories Management Setup wizard and configured your Active Directory connection,
you have the information necessary to prepare the RSA SecurID server. After you prepare the RSA
SecurID server for Directories Management, you enable SecurID in the administration console.
nPrepare the RSA SecurID Server
The RSA SecurID server must be configured with information about the Directories Management
appliance as the authentication agent. The information required is the host name and the IP
addresses for network interfaces.
Configuring vRealize Automation
VMware, Inc. 109
nConfigure RSA SecurID Authentication
After Directories Management is configured as the authentication agent in the RSA SecurID server,
you must add the RSA SecurID configuration information to the connector.
Prepare the RSA SecurID Server
The RSA SecurID server must be configured with information about the Directories Management
appliance as the authentication agent. The information required is the host name and the IP addresses
for network interfaces.
Prerequisites
nVerify that one of the following RSA Authentication Manager versions is installed and functioning on
the enterprise network: RSA AM 6.1.2, 7.1 SP2 and later, and 8.0 and later. The
Directories Management server uses AuthSDK_Java_v8.1.1.312.06_03_11_03_16_51 (Agent API
8.1 SP1), which only supports the preceding versions of RSA Authentication Manager (the RSA
SecurID server). For information about installing and configuring RSA Authentication Manager (RSA
SecurID server), see RSA documentation.
Procedure
1On a supported version of the RSA SecurID server, add the Directories Management connector as an
authentication agent. Enter the following information.
Option Description
Hostname The host name of Directories Management.
IP address The IP address of Directories Management.
Alternate IP address If traffic from the connector passes through a network address translation (NAT)
device to reach the RSA SecurID server, enter the private IP address of the
appliance.
2Download the compressed configuration file and extract the sdconf.rec file.
Be prepared to upload this file later when you configure RSA SecurID in Directories Management.
What to do next
Go to the administration console and in the Identity & Access Management tab Setup pages, select the
connector and in the AuthAdapters page configure SecurID.
Configure RSA SecurID Authentication
After Directories Management is configured as the authentication agent in the RSA SecurID server, you
must add the RSA SecurID configuration information to the connector.
Prerequisites
nVerify that RSA Authentication Manager (the RSA SecurID server) is installed and properly
configured.
nDownload the compressed file from the RSA SecurID server and extract the server configuration file.
Configuring vRealize Automation
VMware, Inc. 110
Procedure
1As a tenant administrator, navigate to Administration > Directories Management > Connectors
2On the Connectors page, select the Worker link for the connector that is being configured with RSA
SecurID.
3Click Auth Adapters and then click SecurIDldpAdapter.
You are redirected to the identity manager sign in page.
4In the Authentication Adapters page SecurIDldpAdapter row, click Edit.
5Configure the SecurID Authentication Adapter page.
Information used and files generated on the RSA SecurID server are required when you configure the
SecurID page.
Option Action
Name A name is required. The default name is SecurIDldpAdapter. You can change this.
Enable SecurID Select this box to enable SecurID authentication.
Number of
authentication
attempts
allowed
Enter the maximum number of failed login attempts when using the RSA SecurID token. The default is five
attempts.
Connector
Address
Enter the IP address of the connector instance. The value you enter must match the value you used when
you added the connector appliance as an authentication agent to the RSA SecurID server. If your RSA
SecurID server has a value assigned to the Alternate IP address prompt, enter that value as the connector
IP address. If no alternate IP address is assigned, enter the value assigned to the IP address prompt.
Agent IP
Address
Enter the value assigned to the IP address prompt in the RSA SecurID server.
Server
Configuration
Upload the RSA SecurID server configuration file. First, you must download the compressed file from the
RSA SecurID server and extract the server configuration file, which by default is named sdconf.rec.
Node Secret Leaving the node secret field blank allows the node secret to auto generate. It is recommended that you
clear the node secret file on the RSA SecurID server and intentionally do not upload the node secret file.
Ensure that the node secret file on the RSA SecurID server and on the server connector instance always
match. If you change the node secret at one location, change it at the other location.
6Click Save.
What to do next
Add the authentication method to the default access policy. Navigate to Administration > Directories
Management > Policies and click Edit Default Policy to edit the default policy rules to add the SecurID
authentication method to the rule in the correct authentication order.
Configuring RADIUS for Directories Management
You can configure Directories Management so that users are required to use RADIUS (Remote
Authentication Dial-In User Service) authentication. You configure the RADIUS server information on the
Directories Management service.
Configuring vRealize Automation
VMware, Inc. 111
RADIUS support offers a wide range of alternative two-factor token-based authentication options.
Because two-factor authentication solutions, such as RADIUS, work with authentication managers
installed on separate servers, you must have the RADIUS server configured and accessible to the identity
manager service.
When users sign in to their My Apps portal and RADIUS authentication is enabled, a special login dialog
box appears in the browser. Users enter their RADUS authentication user name and passcode in the
login dialog box. If the RADIUS server issues an access challenge, the identity manager service displays
a dialog box prompting for a second passcode. Currently support for RADIUS challenges is limited to
prompting for text input.
After a user enters credentials in the dialog box, the RADIUS server can send an SMS text message or
email, or text using some other out-of-band mechanism to the user's cell phone with a code. The user can
enter this text and code into the login dialog box to complete the authentication.
If the RADIUS server provides the ability to import users from Active Directory, end users might first be
prompted to supply Active Directory credentials before being prompted for a RADIUS authentication
username and passcode.
Prepare the RADIUS Server
Set up the RADIUS server and then configure it to accept RADIUS requests from the
Directories Management service.
Refer to your RADIUS vendor's setup guides for information about setting up the RADIUS server. Note
your RADIUS configuration information as you use this information when you configure RADIUS in the
service. To view the type of RADIUS information required to configure Directories Management see
Configure RADIUS Authentication in Directories Management.
You can set up a secondary Radius authentication server to be used for high availability. If the primary
RADIUS server does not respond within the server timeout configured for RADIUS authentication, the
request is routed to the secondary server. When the primary server does not respond, the secondary
server receives all future authentication requests.
Configure RADIUS Authentication in Directories Management
You enable RADIUS software on an authentication manager server. For RADIUS authentication, follow
the vendor's configuration documentation.
Prerequisites
Install and configure the RADIUS software on an authentication manager server. For RADIUS
authentication, follow the vendor's configuration documentation.
You need to know the following RADIUS server information to configure RADIUS on the service.
nIP address or DNS name of the RADIUS server.
nAuthentication port numbers. Authentication port is usually 1812.
nAuthentication type. The authentication types include PAP (Password Authentication Protocol), CHAP
(Challenge Handshake Authentication Protocol), MSCHAP1, MSCHAP2 (Microsoft Challenge
Handshake Authentication Protocol, versions 1 and 2).
Configuring vRealize Automation
VMware, Inc. 112
nRADIUS shared secret that is used for encryption and decryption in RADIUS protocol messages.
nSpecific timeout and retry values needed for RADIUS authentication
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Directories Management > Connectors.
2On the Connectors page, select the Worker link for the connector that is being configured for RADIUS
authentication.
3Click Auth Adapters and then click RadiusAuthAdapter.
You are redirected to the identity manager sign-in page.
4Click Edit to configure these fields on the Authentication Adapter page.
Option Action
Name A name is required. The default name is RadiusAuthAdapter. You can change this.
Enable Radius
Adapter
Select this box to enable RADIUS authentication.
Number of
authentication
attempts
allowed
Enter the maximum number of failed login attempts when using RADIUS to log in. The default is five
attempts.
Number of
attempts to
Radius server
Specify the total number of retry attempts. If the primary server does not respond, the service waits for the
configured time before retrying again.
Radius server
hostname/addr
ess
Enter the host name or the IP address of the RADIUS server.
Authentication
port
Enter the Radius authentication port number. This is usually 1812.
Accounting port Enter 0 for the port number. The accounting port is not used at this time.
Authentication
type
Enter the authentication protocol that is supported by the RADIUS server. Either PAP, CHAP, MSCHAP1,
OR MSCHAP2.
Shared secret Enter the shared secret that is used between the RADIUS server and the VMware Identity Manager service.
Server timeout
in seconds
Enter the RADIUS server timeout in seconds, after which a retry is sent if the RADIUS server does not
respond.
Realm Prefix (Optional) The user account location is called the realm.
If you specify a realm prefix string, the string is placed at the beginning of the user name when the name is
sent to the RADIUS server. For example, if the user name is entered as jdoe and the realm prefix DOMAIN-
A\ is specified, the user name DOMAIN-A\jdoe is sent to the RADIUS server. If you do not configure these
fields, only the user name that is entered is sent.
Configuring vRealize Automation
VMware, Inc. 113
Option Action
Realm Suffix (Optional) If you specify a realm suffix, the string is placed at end of the user name. For example, if the suffix
is @myco.com, the username jdoe@myco.com is sent to the RADIUS server.
Login page
passphrase
hint
Enter the text string to display in the message on the user login page to direct users to enter the correct
Radius passcode. For example, if this field is configured with AD password first and then SMS passcode,
the login page message would read Enter your AD password first and then SMS passcode. The default
text string is RADIUS Passcode.
5You can enable a secondary RADIUS server for high availability.
Configure the secondary server as described in step 4.
6Click Save.
What to do next
Add the RADIUS authentication method to the default access policy. Select Administration >
Directories Management > Policies and click Edit Default Policy to edit the default policy rules to add
the RADIUS authentication method to the rule in the correct authentication order.
Configuring a Certificate or Smart Card Adapter for Use with
Directories Management
You can configure x509 certificate authentication to allow clients to authenticate with certificates on their
desktop and mobile devices or to use a smart card adapter for authentication. Certificate-based
authentication is based on what the user has (the private key or smart card), and what the person knows
(the password to the private key or the smart-card PIN.) An X.509 certificate uses the public key
infrastructure (PKI) standard to verify that a public key contained within the certificate belongs to the user.
With smart card authentication, users connect the smart card with the computer and enter a PIN.
The smart card certificates are copied to the local certificate store on the user's computer. The certificates
in the local certificate store are available to all the browsers running on this user's computer, with some
exceptions, and therefore, are available to a Directories Management instance in the browser.
Using User Principal Name for Certificate Authentication
You can use certificate mapping in Active Directory. Certificate and smart card logins uses the user
principal name (UPN) from Active Directory to validate user accounts. The Active Directory accounts of
users attempting to authenticate in the Directories Management service must have a valid UPN that
corresponds to the UPN in the certificate.
You can configure the Directories Management to use an email address to validate the user account if the
UPN does not exist in the certificate.
You can also enable an alternate UPN type to be used.
Certificate Authority Required for Authentication
To enable logging in using certificate authentication, root certificates and intermediate certificates must be
uploaded to the Directories Management.
Configuring vRealize Automation
VMware, Inc. 114
The certificates are copied to the local certificate store on the user's computer. The certificates in the local
certificate store are available to all the browsers running on this user's computer, with some exceptions,
and therefore, are available to a Directories Management instance in the browser.
For smart-card authentication, when a user initiates a connection to a the Directories Management
instance, the Directories Management service sends a list of trusted certificate authorities (CA) to the
browser. The browser checks the list of trusted CAs against the available user certificates, selects a
suitable certificate, and then prompts the user to enter a smart card PIN. If multiple valid user certificates
are available, the browser prompts the user to select a certificate.
If a user cannot authenticate, the root CA and intermediate CA might not be set up correctly, or the
service has not been restarted after the root and intermediate CAs were uploaded to the server. In these
cases, the browser cannot show the installed certificates, the user cannot select the correct certificate,
and certificate authentication fails.
Using Certificate Revocation Checking
You can configure certificate revocation checking to prevent users who have their user certificates
revoked from authenticating. Certificates are often revoked when a user leaves an organization, loses a
smart card, or moves from one department to another.
Certificate revocation checking with certificate revocation lists (CRLs) and with the Online Certificate
Status Protocol (OCSP) is supported. A CRL is a list of revoked certificates published by the CA that
issued the certificates. OCSP is a certificate validation protocol that is used to get the revocation status of
a certificate.
You can configure certificate revocation checking in the administration console Connectors > Auth
Adapters > CertificateAuthAdapter page when you configure certificate authentication.
You can configure both CRL and OCSP in the same certificate authentication adapter configuration.
When you configure both types of certificate revocation checking and the Use CRL in case of OCSP
failure checkbox is enabled, OCSP is checked first and if OCSP fails, revocation checking falls back to
CRL. Revocation checking does not fall back to OCSP if CRL fails.
Logging in with CRL Checking
When you enable certificate revocation, the Directories Management server reads a CRL to determine
the revocation status of a user certificate.
If a certificate is revoked, authentication through the certificate fails.
Logging in with OCSP Certificate Checking
When you configure Certificate Status Protocol (OCSP) revocation checking, Directories Management
sends a request to an OCSP responder to determine the revocation status of a specific user certificate.
The Directories Management server uses the OCSP signing certificate to verify that the responses it
receives from the OCSP responder are genuine.
Configuring vRealize Automation
VMware, Inc. 115
If the certificate is revoked, authentication fails.
You can configure authentication to fall back to CRL checking if it does not receive a response from the
OSCP responder or if the response is invalid.
Configure Certificate Authentication for Directories Management
You enable and configure certificate authentication from the vRealize Automation administration console
Directories Management feature.
Prerequisites
nObtain the Root certificate and intermediate certificates from the CA that signed the certificates
presented by your users.
n(Optional) List of Object Identifier (OID)s of valid certificate policies for certificate authentication.
nFor revocation checking, the file location of the CRL, the URL of the OCSP server.
n(Optional) OCSP Response Signing certificate file location.
nConsent form content, if enabling a consent form to display before authentication.
Procedure
1As a tenant administrator, navigate to Administration > Directories Management > Connectors
2On the Connectors page, select the Worker link for the connector that is being configured.
3Click Auth Adapters and then click CertificateAuthAdapter.
You are redirected to the identity manager sign in page.
4In the CertificateAuthAdapter row, click Edit.
5Configure the Certificate Authentication Adapter page.
Note An asterisk indicates a required field. All other fields are optional.
Option Description
*Name A name is required. The default name is CertificateAuthAdapter. You can change
this name.
Enable certificate adapter Select the check box to enable certificate authentication.
*Root and intermediate CA certificates Select the certificate files to upload. You can select multiple root CA and
intermediate CA certificates that are encoded as DER or PEM.
Uploaded CA certificates The uploaded certificate files are listed in the Uploaded Ca Certificates section of
the form.
You must restart the service before the new certificates are made available.
Click Restart Web Service to restart the service and add the certificates to the
trusted service.
Note Restarting the service does not enable certificate authentication. After the
service is restarted, continue configuring this page. Clicking Save at the end of
the page enables certificate authentication on the service.
Configuring vRealize Automation
VMware, Inc. 116
Option Description
Use email if no UPN in certificate If the user principal name (UPN) does not exist in the certificate, select this
checkbox to use the emailAddress attribute as the Subject Alternative Name
extension to validate user accounts.
Certificate policies accepted Create a list of object identifiers that are accepted in the certificate policies
extensions.
Enter the object ID numbers (OID) for the Certificate Issuing Policy. Click Add
another value to add additional OIDs.
Enable cert revocation Select the check box to enable certificate revocation checking. This prevents
users who have revoked user certificates from authenticating.
Use CRL from certificates Select the check box to use the certificate revocation list (CRL) published by the
CA that issued the certificates to validate a certificate's status, revoked or not
revoked.
CRL Location Enter the server file path or the local file path from which to retrieve the CRL.
Enable OCSP Revocation Select the check box to use the Online Certificate Status Protocol (OCSP)
certificate validation protocol to get the revocation status of a certificate.
Use CRL in case of OCSP failure If you configure both CRL and OCSP, you can check this box to fall back to using
CRL if OCSP checking is not available.
Send OCSP Nonce Select this check box if you want the unique identifier of the OCSP request to be
sent in the response.
OCSP URL If you enabled OCSP revocation, enter the OCSP server address for revocation
checking.
OCSP responder's signing certificate Enter the path to the OCSP certificate for the responder, /path/to/file.cer.
Enable consent form before
authentication
Select this check box to include a consent form page to appear before users log
in to their My Apps portal using certificate authentication.
Consent form content Type the text that displays in the consent form in this text box.
6Click Save.
What to do next
nAdd the certificate authentication method to the default access policy.Navigate to Administration >
Directories Management > Policies and click Edit Default Policy to edit the default policy rules and
add Certificate and make it the first authentication method for the default policy. Certificate must be
first authentication method listed in the policy rule, otherwise certificate authentication fails.
nWhen Certificate Authentication is configured, and the service appliance is set up behind a load
balancer, make sure that the Directories Management connector is configured with SSL pass-through
at the load balancer and not configured to terminate SSL at the load balancer. This configuration
ensures that the SSL handshake is between the connector and the client in order to pass the
certificate to the connector.
Configuring a Third-Party Identity Provider Instance to Authenticate Users
You can configure a third-party identity provider to be used to authenticate users in the
Directories Management service.
Configuring vRealize Automation
VMware, Inc. 117
Complete the following tasks prior to using the administration console to add the third-party identity
provider instance.
nVerify that the third-party instances are SAML 2.0 compliant and that the service can reach the third-
party instance.
nObtain the appropriate third-party metadata information to add when you configure the identity
provider in the administration console. The metadata information you obtain from the third-party
instance is either the URL to the metadata or the actual metadata.
Configure an Identity Provider Instance
vRealize Automation is supplied with a default identity provider instance. Users may want to create
additional identity provider instances.
vRealize Automation is supplied with an default identity provider. In most cases, the default provider is
sufficient for customer needs. If you use an existing enterprise identity management solution, however,
you can set up a custom identity provider to redirect users to your existing identity solution.
Prerequisites
nConfigure the network ranges that you want to direct to this identity provider instance for
authentication. See Add or Edit a Network Range.
nAccess to the third-party metadata document. This can be either the URL to the metadata or the
actual metadata.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Navigate to the Administration > Directories Management > Identity Providers.
This page displays all configured Identity Providers.
2Click Add Identity Provider and edit the identity provider instance settings.
Form Item Description
Identity Provider Name Enter a name for this identity provider instance.
SAML Metadata Add the third party IdPs XML-based metadata document to establish trust with the identity
provider.
1 Enter the SAML metadata URL or the xml content into the text box.
2 Click Process IdP Metadata. The NameID formats supported by the IdP are extracted from
the metadata and added to the Name ID Format table.
3 In the Name ID value column, select the user attribute in the service to map to the ID formats
displayed. You can add custom third-party name ID formats and map them to the user
attribute values in the service.
4 (Optional) Select the NameIDPolicy response identifier string format.
Users Select the Directories Management directories of the users that can authenticate using this
identity provider.
Configuring vRealize Automation
VMware, Inc. 118
Form Item Description
Network The existing network ranges configured in the service are listed.
Select the network ranges for the users, based on their IP addresses, that you want to direct to
this identity provider instance for authentication.
Authentication Methods Add the authentication methods supported by the third-party identity provider. Select the SAML
authentication context class that supports the authentication method.
SAML Signing Certificate Click Service Provider (SP) Metadata to see URL to Directories Management SAML service
provider metadata URL . Copy and save the URL. This URL is configured when you edit the
SAML assertion in the third-party identity provider to map Directories Management users.
Hostname If the Hostname field displays, enter the hostname where the identity provider is redirected to for
authentication. If you are using a non-standard port other than 443, you can set this as
Hostname:Port. For example, myco.example.com:8443.
3Click Add.
What to do next
nCopy and save the Directories Management service provider metadata that is required to configure
the third-party identity provider instance. This metadata is available either in the SAML Signing
Certificate section of the Identity Provider page.
nAdd the authentication method of the identity provider to the services default policy.
See the Setting Up Resources in Directories Management guide for information about adding and
customizing resources that you add to the catalog.
Managing Authentication Methods to Apply to Users
The Directories Management service attempts to authenticate users based on the authentication
methods, the default access policy, network ranges, and the identity provider instances you configure.
When users attempt to log in, the service evaluates the default access policy rules to select which rule in
the policy to apply. The authentication methods are applied in the order they are listed in the rule. The first
identity provider instance that meets the authentication method and network range requirements of the
rule is selected and the user authentication request is forwarded to the identity provider instance for
authentication. If authentication fails, the next authentication method configured in the rule is applied.
You can set up authentication methods to be different for internal user and external user log ins. For
example, you could set up the Active Directory password or Kerberos authentication methods for internal
users and RSA SecurID authentication method for external users. Users attempting to access their apps
portal from inside the organization's network are directed to an identity provider instance that provides
Kerberos authentication or password authentication. Users outside the network are directed to an identity
provider instance that provides RSA SecurID authentication.
Add or Edit a Network Range
You can manage the network ranges to define the IP addresses from which users can log in via an Active
Directory link. You add the network ranges you create to specific identity provider instances and to access
policy rules.
Configuring vRealize Automation
VMware, Inc. 119
Define network ranges for your Directories Management deployment based on your network topology.
One network range, called ALL RANGES, is created as the default. This network range includes every IP
address available on the Internet, 0.0.0.0 to 255.255.255.255. Even if your deployment has a single
identity provider instance, you can change the IP address range and add other ranges to exclude or
include specific IP addresses to the default network range. You can create other network ranges with
specific IP addresses that you can apply for specific purpose.
Note The default network range, ALL RANGES, and its description, "a network for all ranges," are
editable. You can edit the name and description, including changing the text to a different language, by
clicking the network range name on the Network Ranges page.
Prerequisites
nYou have configured tenants for your vRealize Automation deployment set up an appropriate Active
Directory link to support basic Active Directory user ID and password authentication.
nActive Directory is installed and configured for use on your network.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Directories Management > Network Ranges.
2Edit an existing network range or add a new network range.
Option Description
Edit an existing range Click the network range name to edit.
Add a range Click Add Network Range to add a new range.
3Complete the form.
Form Item Description
Name Enter a name for the network range.
Description Enter a description for the Network Range.
View Pods The View Pods option only appears when the View module is enabled.
Client Access URL Host. Enter the correct Horizon Client access URL for the network range.
Client Access Port. Enter the correct Horizon Client access port number for the network range.
IP Ranges Edit or add IP ranges until all desired and no undesired IP addresses are included.
What to do next
nAssociate each network range with an identity provider instance.
nAssociate network ranges with access policy rule as appropriate. See Configuring Access Policy
Settings.
Configuring vRealize Automation
VMware, Inc. 120
Select Attributes to Sync with Directory
When you set up the Directories Management directory to sync with Active Directory, you specify the user
attributes that sync to the directory. Before you set up the directory, you can specify on the User Attributes
page which default attributes are required and, if you want, add additional attributes that you want to map
to Active Directory attributes.
When you configure the User Attributes page before the directory is created, you can change default
attributes from required to not required, mark attributes as required, and add custom attributes.
For a list of the default mapped attributes, see Managing User Attributes that Sync from Active Directory.
After the directory is created, you can change a required attribute to not be required, and you can delete
custom attributes. You cannot change an attribute to be a required attribute.
When you add other attributes to sync to the directory, after the directory is created, go to the directory's
Mapped Attributes page to map these attributes to Active Directory Attributes.
Procedure
1Log in to vRealize Automation as a system or tenant administrator.
2Click the Administration tab.
3Select Directories Management > User Attributes
4In the Default Attributes section, review the required attribute list and make appropriate changes to
reflect what attributes should be required.
5In the Attributes section, add the Directories Management directory attribute name to the list.
6Click Save.
The default attribute status is updated and attributes you added are added on the directory's Mapped
Attributes list.
7After the directory is created, go to the Identity Stores page and select the directory.
8Click Sync Settings > Mapped Attributes.
9In the drop-down menu for the attributes that you added, select the Active Directory attribute to map
to.
10 Click Save.
The directory is updated the next time the directory syncs to the Active Directory.
Applying the Default Access Policy
The Directories Management service includes a default access policy that controls user access to their
apps portals. You can edit the policy to change the policy rules as necessary.
When you enable authentication methods other than password authentication, you must edit the default
policy to add the enabled authentication method to the policy rules.
Configuring vRealize Automation
VMware, Inc. 121
Each rule in the default access policy requires that a set of criteria be met in order to allow user access to
the apps portal. You apply a network range, select which type of user can access content and select the
authentication methods to use. See Managing Access Policies.
The number of attempts the service makes to login a user using a given authentication method varies.
The services only makes one attempt at authentication for Kerberos or certificate authentication. If the
attempt is not successful in logging in a user, the next authentication method in the rule is attempted. The
maximum number of failed login attempts for Active Directory password and RSA SecurID authentication
is set to five by default. When a user has five failed login attempts, the service attempts to log in the user
with the next authentication method on the list. When all authentication methods are exhausted, the
service issues an error message.
Apply Authentication Methods to Policy Rules
Only the password authentication method is configured in the default policy rules. You must edit the policy
rules to select the other authentication methods you configured and set the order in which the
authentication methods are used for authentication.
Prerequisites
Enable and configure the authentication methods that your organization supports. See Integrating
Alternative User Authentication Products with Directories Management
Procedure
1Select Administration > Directories Management > Policies
2Click the default access policy to edit.
3To edit a policy rule, click the authentication method to edit in the Policy Rules, Authentication Method
column.
The add a new policy rule, click the + icon.
4If adding a new rule, select the network range for this policy and the device type that the rule
manages.
5To configure the authentication order, in the then the user must authenticate using the following
method drop-down menu, select the authentication method to apply first. To require users to
authenticate through two authentication methods, in the next drop down menu, select and and enter
a second authentication method.
Note All the authentication methods are listed in the drop-down menu, even if they are not enabled.
Select only from the authentication methods that are enabled on the Connector > Auth Adapters
page.
6(Optional) To configure a fallback authentication method if the first authentication fails, select another
enabled authentication method from the next drop-down menu.
You can add multiple fallback authentication methods to a rule.
7Click Save and click Save again on the Policy page.
Configuring vRealize Automation
VMware, Inc. 122
Configuring Kerberos for Directories Management
Kerberos authentication provides users who are successfully signed in to their Active Directory domain to
access their apps portal without additional credential prompts. You enable Windows authentication to
allow the Kerberos protocol to secure interactions between users' browsers and the
Directories Management service. You do not need to directly configure Active Directory to make Kerberos
function with your deployment.
Currently, interactions between a user's browser and the service are authenticated by Kerberos on the
Windows operating systems only. Accessing the service from other operating systems does not take
advantage of Kerberos authentication.
nConfigure Kerberos Authentication
To configure the Directories Management service to provide Kerberos authentication, you must join
to the domain and enable Kerberos authentication on the Directories Management connector.
nConfigure Internet Explorer to Access the Web Interface
You must configure the Internet Explorer browser if Kerberos is configured for your deployment and
if you want to grant users access to the Web interface using Internet Explorer.
nConfigure Firefox to Access the Web Interface
You must configure the Firefox browser if Kerberos is configured for your deployment and you want
to grant users access to the Web interface using Firefox.
nConfigure the Chrome Browser to Access the Web Interface
You must configure the Chrome browser if Kerberos is configured for your deployment and if you
want to grant users access to the Web interface using the Chrome browser.
Configure Kerberos Authentication
To configure the Directories Management service to provide Kerberos authentication, you must join to the
domain and enable Kerberos authentication on the Directories Management connector.
Procedure
1As a tenant administrator, navigate to Administration > Directories Management > Connectors
2On the Connectors page, for the connector that is being configured for Kerberos authentication, click
Join Domain.
Configuring vRealize Automation
VMware, Inc. 123
3On the Join Domain page, enter the information for the Active Directory domain.
Option Description
Domain Enter the fully qualified domain name of the Active Directory. The domain name you enter must be the same
Windows domain as the connector server.
Domain User Enter the user name of an account in the Active Directory that has permissions to join systems to that Active
Directory domain.
Domain
Password
Enter the password associated with the AD Username. This password is not stored by
Directories Management
.
Click Save.
The Join Domain page is refreshed and displays a message that you are currently joined to the
domain.
4In the Worker column for the connector click Auth Adapters.
5Click KerberosIdpAdapter
You are redirected to the identity manager sign in page.
6Click Edit in the KerberosldpAdapter row and configure the Kerberos authentication page.
Option Description
Name A name is required. The default name is KerberosIdpAdapter. You can change this.
Directory UID
Attribute
Enter the account attribute that contains the user name.
Enable
Windows
Authentication
Select this to extend authentication interactions between users' browsers and Directories Management.
Enable NTLM Select this to enable NT LAN Manager (NTLM) protocol-based authentication only if your Active Directory
infrastructure relies on NTLM authentication.
Enable
Redirect
Select this if round-robin DNS and load balancers do not have Kerberos support. Authentication requests
are redirected to Redirect Host Name. If this is selected, enter the redirect host name in Redirect Host
Name text box. This is usually the hostname of the service.
7Click Save.
What to do next
Add the authentication method to the default access policy. Navigate to Administration > Directories
Management > Policies and click Edit Default Policy to edit the default policy rules to add the Kerberos
authentication method to the rule in the correct authentication order.
Configure Internet Explorer to Access the Web Interface
You must configure the Internet Explorer browser if Kerberos is configured for your deployment and if you
want to grant users access to the Web interface using Internet Explorer.
Configuring vRealize Automation
VMware, Inc. 124
Kerberos authentication works in conjunction with Directories Management on Windows operating
systems.
Note Do not implement these Kerberos-related steps on other operating systems.
Prerequisites
Configure the Internet Explorer browser for each user or provide users with the instructions after you
configure Kerberos.
Procedure
1Verify that you are logged into Windows as a user in the domain.
2In Internet Explorer, enable automatic log in.
a Select Tools > Internet Options > Security.
b Click Custom level.
c Select Automatic login only in Intranet zone.
d Click OK.
3Verify that this instance of the connector virtual appliance is part of the local intranet zone.
a Use Internet Explorer to access the Directories Management sign in URL at
https://myconnectorhost.domain/authenticate/.
b Locate the zone in the bottom right corner on the status bar of the browser window.
If the zone is Local intranet, Internet Explorer configuration is complete.
4If the zone is not Local intranet, add the Directories Management sign in URL to the intranet zone.
a Select Tools > Internet Options > Security > Local intranet > Sites.
b Select Automatically detect intranet network.
If this option was not selected, selecting it might be sufficient for adding the to the intranet zone.
c (Optional) If you selected Automatically detect intranet network, click OK until all dialog boxes
are closed.
d In the Local Intranet dialog box, click Advanced.
A second dialog box named Local intranet appears.
e Enter the Directories Management URL in the Add this Web site to the zone text box.
https://myconnectorhost.domain/authenticate/
f Click Add > Close > OK.
Configuring vRealize Automation
VMware, Inc. 125
5Verify that Internet Explorer is allowed to pass the Windows authentication to the trusted site.
a In the Internet Options dialog box, click the Advanced tab.
b Select Enable Integrated Windows Authentication.
This option takes effect only after you restart Internet Explorer.
c Click OK.
6Log in to the Web interface to check access.
If Kerberos authentication is successful, the test URL goes to the Web interface.
The Kerberos protocol secures all interactions between this Internet Explorer browser instance and
Directories Management. Now, users can use single sign-on to access their My Apps portal.
Configure Firefox to Access the Web Interface
You must configure the Firefox browser if Kerberos is configured for your deployment and you want to
grant users access to the Web interface using Firefox.
Kerberos authentication works in conjunction with Directories Management on Windows operating
systems.
Prerequisites
Configure the Firefox browser, for each user, or provide users with the instructions, after you configure
Kerberos.
Procedure
1In the URL text box of the Firefox browser, enter about:config to access the advanced settings.
2Click I'll be careful, I promise!.
3Double-click network.negotiate-auth.trusted-uris in the Preference Name column.
4Enter your Directories Management URL in the text box.
https://myconnectorhost.domain.com
5Click OK.
6Double-click network.negotiate-auth.delegation-uris in the Preference Name column.
7Enter your Directories Management URL in the text box.
https://myconnectorhost.domain.com/authenticate/
8Click OK.
9Test Kerberos functionality by using the Firefox browser to log in to login URL. For example,
https://myconnectorhost.domain.com/authenticate/.
If the Kerberos authentication is successful, the test URL goes to the Web interface.
Configuring vRealize Automation
VMware, Inc. 126
The Kerberos protocol secures all interactions between this Firefox browser instance and
Directories Management. Now, users can use single sign-on access their My Apps portal.
Configure the Chrome Browser to Access the Web Interface
You must configure the Chrome browser if Kerberos is configured for your deployment and if you want to
grant users access to the Web interface using the Chrome browser.
Kerberos authentication works in conjunction with Directories Management on Windows operating
systems.
Note Do not implement these Kerberos-related steps on other operating systems.
Prerequisites
nConfigure Kerberos.
nSince Chrome uses the Internet Explorer configuration to enable Kerberos authentication, you must
configure Internet Explorer to allow Chrome to use the Internet Explorer configuration. See Google
documentation for information about how to configure Chrome for Kerberos authentication.
Procedure
1Test Kerberos functionality by using the Chrome browser.
2Log in to Directories Management at https://myconnectorhost.domain.com/authenticate/.
If Kerberos authentication is successful, the test URL connects with the Web interface.
If all related Kerberos configurations are correct, the relative protocol (Kerberos) secures all interactions
between this Chrome browser instance and Directories Management. Users can use single sign-on
access their My Apps portal.
Scenario: Configure an Active Directory Link for a Highly
Available vRealize Automation
As a tenant administrator, you want to configure an Active Directory over LDAP directory connection to
support user authentication for your highly available vRealize Automation deployment.
Each vRealize Automation appliance includes a connector that supports user authentication, although
only one connector is typically configured to perform directory synchronization. It does not matter which
connector you choose to serve as the sync connector. To support Directories Management high
availability, you must configure a second connector that corresponds to your second vRealize Automation
appliance, which connects to your Identity Provider and points to the same Active Directory. With this
configuration, if one appliance fails, the other takes over management of user authentication.
Configuring vRealize Automation
VMware, Inc. 127
In a high availability environment, all nodes must serve the same set of Active Directories, users,
authentication methods, etc. The most direct method to accomplish this is to promote the Identity Provider
to the cluster by setting the load balancer host as the Identity Provider host. With this configuration, all
authentication requests are directed to the load balancer, which forwards the request to either connector
as appropriate.
Prerequisites
nInstall a distributed vRealize Automation deployment with appropriate load balancers. See Installing
vRealize Automation 7.0.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Directories Management > Directories.
2Click Add Directory.
3Enter your specific Active Directory account settings, and accept the default options.
Option Sample Input
Directory Name Add the IP address of your active directory domain name.
Sync Connector Every vRealize Automation appliance contains a connector. Use any of the
available connectors.
Base DN Enter the Distinguished Name (DN) of the starting point for directory server
searches. For example, cn=users,dc=corp,dc=local.
Bind DN Enter the full distinguished name (DN), including common name (CN), of an
Active Directory user account that has privileges to search for users. For
example, cn=config_admin infra,cn=users,dc=corp,dc=local.
Bind DN Password Enter the Active Directory password for the account that can search for users.
4Click Test Connection to test the connection to the configured directory.
If the connection fails, check your entries in all fields and consult your system administrator if
necessary.
5Click Save & Next.
The Select the Domains page with the list of domains appears.
6Leave the default domain selected and click Next.
7Verify that the attribute names are mapped to the correct Active Directory attributes. If not, select the
correct Active Directory attribute from the drop-down menu. Click Next.
8Select the groups and users you want to sync.
aClick the Add icon ( ).
b Enter the user domain and click Find Groups.
For example, cn=users,dc=corp,dc=local.
Configuring vRealize Automation
VMware, Inc. 128

c Select the Select All check box.
d Click Select.
e Click Next.
fClick to add additional users. For example, enter as
CN-username,CN=Users,OU-myUnit,DC=myCorp,DC=com.
To exclude users, click + to create a filter to exclude some types of users. You select the user
attribute to filter by, the query rule, and the value.
g Click Next.
9Review the page to see how many users and groups are syncing to the directory and click Sync
Directory.
The directory sync process takes some time, but it happens in the background and you can continue
working.
10 Configure a second connector to support high availability.
a Log in to the load balancer for your vRealize Automation deployment as a tenant administrator.
The load balancer URL is load balancer address/vcac/org/tenant_name.
b Select Administration > Directories Management > Identity Providers.
c Click the Identity Provider that is currently in use for your system.
The existing directory and connector that provide basic identity management for your system
appears.
d Click the Add a Connector drop-down list, and select the connector that corresponds to your
secondary vRealize Automation appliance.
e Enter the appropriate password in the Bind DN Password text box that appears when you select
the connector.
f Click Add Connector.
g Edit the host name to point to your load balancer.
You connected your corporate active directory to vRealize Automation and configured directories
management for high availability.
What to do next
To provide enhanced security, you can configure bi-directional trust between your identity provider and
your Active Directory. See Configure a Bi Directional Trust Relationship Between vRealize Automation
and Active Directory.
Configuring vRealize Automation
VMware, Inc. 129
Scenario: Configure Smart Card Authentication for
vRealize Automation
As a system administrator, you must configure smart card authentication for your vRealize Automation
deployment using Directories Management.
Directories Management supports multiple identity providers and connector clusters for each configured
Active Directory. To use smart card authentication, you can set up either a single external connector or a
connector cluster with an appropriate identity provider behind a load balancer that permits SSL
passthrough.
There are various certificate configuration options available for use with smart card authentication. See
Configuring a Certificate or Smart Card Adapter for Use with Directories Management.
Prerequisites
nConfigure an appropriate Active Directory connection for use with your vRealize Automation
deployment.
nDownload the OVA file required to configure a connector from VMware vRealize Automation Tools
and SDK.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Generate a Connector Activation Token
Before you deploy the connector virtual appliance to use for smart card authentication, generate an
activation code for the new connector from the vRealize Automation console. The activation code is
used to establish communication between Directories Management and the connector.
2Deploy the Connector OVA File
After downloading a connector OVA file, you can deploy it using the VMware vSphere Client or
vSphere Web Client.
3Configure Connector Settings
After deploying the connector OVA, you must run the Setup wizard to activate the appliance and
configure the administrator passwords.
4Apply Public Certificate Authority
When Directories Management is installed, a default SSL certificate is generated. You can use the
default certificate for testing purposes, but you should generate and install commercial SSL
certificates for production environments.
5Create a Workspace Identity Provider
You must create a Workspace identity provider for use with an external connector.
6Configure Certificate Authentication and Configure Default Access Policy Rules
You must configure your external connection for use with your vRealize Automation Active Directory
and domain.
Configuring vRealize Automation
VMware, Inc. 130
Generate a Connector Activation Token
Before you deploy the connector virtual appliance to use for smart card authentication, generate an
activation code for the new connector from the vRealize Automation console. The activation code is used
to establish communication between Directories Management and the connector.
You can configure a single connector or a connector cluster. If you want to use a connector cluster, repeat
this procedure for each connector that you need.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Directories Management > Connectors
2Type a name for the new connector in the Connector ID Name text box.
3Press Enter.
The activation code for the connector is displayed in the Connector Activation Code box.
4Copy the activation code for use in configuring the connector using the OVA file.
Deploy the Connector OVA File
After downloading a connector OVA file, you can deploy it using the VMware vSphere Client or vSphere
Web Client.
You deploy the OVA file using the vSphere Client or the vSphere Web Client.
Prerequisites
nIdentify the DNS records and host name to use for your connector OVA deployment.
nIf using the vSphere Web Client, use either Firefox or Chrome browsers. Do not use Internet Explorer
to deploy the OVA file.
nDownload the OVA file required to configure a connector from VMware vRealize Automation Tools
and SDK.
Procedure
1In the vSphere Client or the vSphere Web Client, select File > Deploy OVF Template.
2In the Deploy OVF Template pages, enter the information specific to your deployment of the
connector.
Page Description
Source Browse to the OVA package location, or enter a specific URL.
OVA Template Details Verify that you selected the correct version.
License Read the End User License Agreement and click Accept.
Configuring vRealize Automation
VMware, Inc. 131
Page Description
Name and Location Enter a name for the virtual appliance. The name must be unique within the
inventory folder and can contain up to 80 characters. Names are case sensitive.
Select a location for the virtual appliance.
Host / Cluster Select the host or cluster to run the deployed template.
Resource Pool Select the resource pool.
Storage Select the location to store the virtual machine files.
Disk Format Select the disk format for the files. For production environments, select a Thick
Provision format. Use the Thin Provision format for evaluation and testing.
Network Mapping Map the networks in your environment to the networks in the OVF template.
Properties a In the Timezone setting field, select the correct time zone.
b The Customer Experience Improvement Program checkbox is selected by
default. VMware collects anonymous data about your deployment in order to
improve VMware's response to user requirements. Deselect the checkbox if
you do not want the data collected.
c In the Host Name text box, enter the host name to use. If this is blank,
reverse DNS is used to look up the host name.
d To configure the static IP address for connector, enter the address for each of
the following: Default Gateway, DNS, IP Address, and Netmask.
Important If any of the four address fields, including Host Name, are left
blank, DHCP is used.
To configure DHCP, leave the address fields blank.
Ready to Complete Review your selections and click Finish.
Depending on your network speed, the deployment can take several minutes. You can view the
progress in the progress dialog box.
3When the deployment is complete, select the appliance, right-click, and select Power > Power on.
The appliance is initialized. You can go to the Console tab to see the details. When the virtual
appliance initialization is complete, the console screen displays the version and URLs to log in to the
Setup wizard to complete the set up.
What to do next
Use the Setup wizard to add the activation code and administrative passwords.
Configure Connector Settings
After deploying the connector OVA, you must run the Setup wizard to activate the appliance and configure
the administrator passwords.
Prerequisites
nYou have generated an activation code for the connector.
nEnsure the connector appliance is powered on and you know the connector URL.
nCollect a list of password to use for the connector administrator, root account, and sshuser account.
Configuring vRealize Automation
VMware, Inc. 132
Procedure
1To run the Setup wizard, enter the connector URL that was displayed in the Console tab after the
OVA was deployed.
2On the Welcome Page, click Continue.
3Create strong passwords for the following connector virtual appliance administrator accounts.
Strong passwords should be at least eight characters long and include uppercase and lowercase
characters and at least one digit or special character.
Option Description
Appliance Administrator Create the appliance administrator password. The user name is admin and
cannot be changed. You use this account and password to log into the connector
services to manage certificates, appliance passwords and syslog configuration.
Important The admin user password must be at least 6 characters in length.
Root Account A default VMware root password was used to install the connector appliance.
Create a new root password.
sshuser Account Create the password to use for remote access to the connector appliance.
4Click Continue.
5On the Activate Connector page, paste in the activation code and click Continue.
6If you are using a self-signed certificate on the vRealize Automation internal connector, you must
enter the Root CA Certificate information as well.
You can get the root CA from https://:8443/cfg/ssl. Select the Terminate SSL on a Load
Balancer tab, and then click the link for /horizon_workspace_rootca.pem.
The activation code is verified and communication between the service and the connector instance is
established to complete the connector configuration.
What to do next
In the service, set up your environment based on your needs. For example, if you added an additional
connector because you want to sync two Integrated Windows Authentication directories, create the
directory and associate it with the new connector.
Apply Public Certificate Authority
When Directories Management is installed, a default SSL certificate is generated. You can use the default
certificate for testing purposes, but you should generate and install commercial SSL certificates for
production environments.
Note If the Directories Management points to a load balancer, the SSL certificate is applied to the load
balancer.
Configuring vRealize Automation
VMware, Inc. 133
Prerequisites
Generate a Certificate Signing Request (CSR) and obtain a valid, signed certificate from a CA. If your
organization provides SSL certificates that are signed by a CA, you can use these certificates. The
certificate must be in the PEM format.
Procedure
1Log in to the connector appliance administrative page as an admin user at the following location:
Https://myconnector.mycompany:8443/cfg
2In the administration console, click Appliance Settings.
VA configuration is selected by default.
3Click Manage Configuration.
4In the dialog box that appears, enter the Directories Management server admin user password.
5Select Install Certificate.
6In the Terminate SSL on Identity Manager Appliance tab, select Custom Certificate.
7In the SSL Certificate Chain text box, paste the host, intermediate, and root certificates, in that
order.
The SSL certificate works only if you include the entire certificate chain in the correct order. For each
certificate, copy everything between and including the lines -----BEGIN CERTIFICATE----- and -----
END CERTIFICATE----
Ensure that the certificate includes the FQDN hostname.
8Paste the private key in the Private Key text box. Copy everything between ----BEGIN RSA PRIVATE
KEY and ---END RSA PRIVATE KEY.
9Click Save.
Example: Certificate Examples
Certificate Chain Example
-----BEGIN CERTIFICATE-----
jlQvt9WdR9Vpg3WQT5+C3HU17bUOwvhp/r0+
...
...
...
W53+O05j5xsxzDJfWr1lqBlFF/OkIYCPcyK1
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
Configuring vRealize Automation
VMware, Inc. 134
Certificate Chain Example
WdR9Vpg3WQT5+C3HU17bUOwvhp/rjlQvt90+
...
...
...
O05j5xsxzDJfWr1lqBlFF/OkIYCPW53+cyK1
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
dR9Vpg3WQTjlQvt9W5+C3HU17bUOwvhp/r0+
...
...
...
5j5xsxzDJfWr1lqW53+O0BlFF/OkIYCPcyK1
-----END CERTIFICATE-----
Private Key Example
-----BEGIN RSA PRIVATE KEY-----
jlQvtg3WQT5+C3HU17bU9WdR9VpOwvhp/r0+
...
...
...
1lqBlFFW53+O05j5xsxzDJfWr/OkIYCPcyK1
-----END RSA PRIVATE KEY-----
Create a Workspace Identity Provider
You must create a Workspace identity provider for use with an external connector.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Directories Management > Identity Providers.
2Select Add Identity Provider.
3Select Create Workspace IDP on the displayed menu.
4Type a name for the identity provider in the Identity Provider Name field.
5Select the directory that corresponds to the users that will use this identity provider.
The directory selected determine which connectors are displayed for selection with this identity
provider.
Configuring vRealize Automation
VMware, Inc. 135
6Select the external connector or connectors that you configured for smart card authentication.
Note If the deployment is located behind a load balancer, enter the load balancer URL.
7Select the network for access to this identity provider.
8Click Add.
Configure Certificate Authentication and Configure Default
Access Policy Rules
You must configure your external connection for use with your vRealize Automation Active Directory and
domain.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Directories Management > Connectors
2Select the Desired connector in the Worker column.
The selected worker is shown in the Worker Name text box on the Connector Detail tab and
connector type information appears in the Connector Type text box.
3Ensure that the connector links to the desired Active Directory by specifying that Directory in the
Associated Directory text box.
4Type the appropriate domain name in the Associated Domains text box.
5Select the AuthAdapters tab and enable CertificateAuthAdapter.
6Configure certificate authentication as appropriate for your deployment.
See Configure Certificate Authentication for Directories Management.
7Select Administration > Directories Management > Policies
8Click Edit Default Policy.
9Add Certificate to the policy rules and make it the first authentication method.
Certificate must be the first authentication method listed in the policy rule, otherwise certificate
authentication fails.
Configuring Groups and User Roles
Tenant administrators create business groups and custom groups, and grant user access rights to the
vRealize Automation console.
Assign Roles to Directory Users or Groups
Tenant administrators grant users access rights by assigning roles to users or groups.
Configuring vRealize Automation
VMware, Inc. 136

Prerequisites
Log in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Users & Groups > Directory Users & Groups.
2Enter a user or group name in the Search box and press Enter.
Do not use an at sign (@), backslash (\), or slash (/) in a name. You can optimize your search by
typing the entire user or group name in the form user@domain.
3Click the name of the user or group to which you want to assign roles.
4Select one or more roles from the Add Roles to this User list.
The Authorities Granted by Selected Roles list indicates the specific authorities you are granting.
5(Optional) Click Next to view more information about the user or group.
6Click Update.
Users who are currently logged in to the vRealize Automation console must log out and log back in to the
vRealize Automation console before they can navigate to the pages to which they have been granted
access.
What to do next
Optionally, you can create your own custom groups from users and groups in your Active Directory
connections. See Create a Custom Group.
Create a Custom Group
Tenant administrators can create custom groups by combining other custom groups, identity store groups,
and individual identity store users.
You can assign roles to your custom group, but it is not necessary in all cases. For example, you can
create a custom group called Machine Specification Approvers, to use for all machine pre-approvals. You
can also create custom groups to map to your business groups so that you can manage all groups in one
place. In those cases, you do not need to assign roles.
Prerequisites
Log in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Users & Groups > Custom Groups.
2Click the Add icon ( ).
3Enter a group name in the New Group Name text box.
Custom group names cannot contain the combination of a semicolon (;) followed by an equal sign (=).
Configuring vRealize Automation
VMware, Inc. 137
4(Optional) Enter a description in the New Group Description text box.
5Select one or more roles from the Add Roles to this Group list.
The Authorities Granted by Selected Roles list indicates the specific authorities you are granting.
6Click Next.
7Add users and groups to create your custom group.
a Enter a user or group name in the Search box and press Enter.
Do not use an at sign (@), backslash (\), or slash (/) in a name. You can optimize your search by
typing the entire user or group name in the form user@domain.
b Select the user or group to add to your custom group.
8Click Add.
Users who are currently logged in to the vRealize Automation console must log out and log back in to the
vRealize Automation console before they can navigate to the pages to which they have been granted
access.
Create a Business Group
Business groups are used to associate a set of services and resources to a set of users, often
corresponding to a line of business, department, or other organizational unit. You create a business group
so that you can configure reservations and entitle users to provision service catalog items for the
business group members.
To add multiple users to a business group role, you can add multiple individual users, or you can add
multiple users at the same time by adding an identity store group or a custom group to a role. For
example, you can create a custom group Sales Support Team and add that group to the support role. You
can also use existing identity store user groups. The users and groups you choose must be valid in the
identity store.
To support vCloud Director integration, the same business group members in the vRealize Automation
business group must also be members of the vCloud Director organization.
After a tenant administrator creates the business group, the business group manager has permission to
modify the manager email address and the members. The tenant administrator can modify all the options.
This procedure assumes that IaaS is installed and configured.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator.
nIf you want to specify a default machine prefix that is prepended to machine names for machines
provisioned by a member of the business group, request a machine prefix from a fabric administrator.
See Configure Machine Prefixes. Machine prefixes are not applicable to XaaS requests.
Configuring vRealize Automation
VMware, Inc. 138
Procedure
1Select Administration > Users and Groups > Business Groups.
2Click the Add icon ( ).
3Configure the business group details.
a Enter a name in the Name text box.
b Enter a description in the Description text box.
c Type one or more user names or group names in the Send manager emails to text box and
press Enter.
Multiple entries must be separated with commas. For example,
JoeAdmin@mycompany.com,WeiMgr@mycompany.com.
d Add custom properties.
e Click Next.
4Enter a user name or custom user group name and press Enter.
You can add one or more individuals or custom user groups to the business group. You do not have
to specify users at this time. You can create empty business groups to populate later.
Option Description
Group Manager Role Can create entitlements and assign approval policies for the group.
Support Role Can request and manage service catalog items on behalf of the other members of
the business group.
User Role Can request service catalog items to which they are entitled.
5Click Next.
6Configure default infrastructure options.
Option Description
Default machine prefix Select a preconfigured machine prefix for the business group.
This prefix is used by machine blueprints. If the blueprint is configured to use the
default prefix and you do not specify the default here, a machine prefix is created
for you based on the business group name. The best practice is to provide a
default prefix. You can still configure blueprints with specific prefixes or allow
service catalog users to override it when they request a blueprint.
XaaS blueprints do not use default machine prefixes. If you configure a prefix
here and entitle an XaaS blueprint to this business group, it does not affect the
provisioning of an XaaS machine.
Active Directory container Enter an Active Directory container. This option applies only to WIM provisioning.
Other provisioning methods require additional configuration to join provisioned
machines to an AD container.
7Click Add.
Configuring vRealize Automation
VMware, Inc. 139
Fabric administrators can allocate resources to your business group by creating a reservation. Business
group managers can create entitlements for members of the business group.
What to do next
nCreate a reservation for your business group based on where the business group provisions
machines. See Choosing a Reservation Scenario.
nIf the catalog items are published and the services exist, you can create an entitlement for the
business group members. See Entitle Users to Services, Catalog Items, and Actions.
Troubleshooting Missing Business Group Data
Business groups are missing or data is missing from business groups.
Problem
When you look for known business groups, the business group is missing from Administration > Users
and Groups > Business Groups or the business group is not interacting with reservations or
entitlements as expected.
Cause
Business group information exists in two databases, CAFE and IaaS, and the information must be the
same. During standard operations, the databases remain synchronized. If you encounter this problem,
you might need to force a synchronization.
The problem can appear after you upgrade if the synchronization does to run as expected. It can also
appear if you use the API to update the IaaS database with a new or modified business group.
Solution
Prerequisites
Ensure that you can run command line commands. See Programming Guide.
Procedure
uEnter the command string on the vcac-cli command line.
What the command updates Command Shortened version of command
To synchronize the CAFE database to
with the IaaS values.
Vcac-Config.exe
SynchronizeDatabases --
DatabaseSyncSource IaaS -v
Vcac-Config.exe
SynchronizeDatabases -dss IaaS
-v
To synchronize the IaaS database to
with the CAFE values.
Vcac-Config.exe
SynchronizeDatabases --
DatabaseSyncSource Cafe -v
Vcac-Config.exe
SynchronizeDatabases -dss Cafe
-v
Troubleshooting Slow Performance When Displaying Group
Members
The business group or custom group members are slow to display when viewing a group's details.
Configuring vRealize Automation
VMware, Inc. 140

Problem
When you view user information in environments with a large number of users, the user names are slow
to load in the user interface.
Cause
The extended time required to load the names occurs in environments with a large Active Directory
environment.
Solution
uTo reduce the retrieval workload, use Active Directory groups or custom groups whenever possible
rather than adding hundreds of individual members by name.
Scenario: Configure the Default Tenant for Rainpole
As the system administrator, you want to configure your vRealize Automation instance as an ongoing
development environment. You create local user accounts and assign yourself to the tenant administrator
role. Using the tenant administrator privileges, you start configuring vRealize Automation as a
development environment for building and testing blueprints.
You are here
Configure
Tenant
Configure IaaS
Resources
Design On-
Demand Services
Procedure
1Scenario: Create Local User Accounts for Rainpole
Using your default system administrator privileges, you create two local user accounts in the default
tenant. Assign one of these accounts to the tenant administrator role so you can start configuring the
default tenant. You can use the second account later as a shared login for your architects to test
blueprint and catalog access.
2Scenario: Connect Your Corporate Active Directory to vRealize Automation for Rainpole
As a tenant administrator, you want vRealize Automation to authenticate logins against your
corporate active directory. You configure a connection between vRealize Automation and your single
domain active directory over LDAP.
3Scenario: Configure Branding for the Default Tenant for Rainpole
Using your tenant administrator privileges, you customize the look and feel of the
vRealize Automation console. You upload a new logo, change the colors, update the header and
footer information, and configure the login screen branding.
Configuring vRealize Automation
VMware, Inc. 141
4Scenario: Create a Custom Group for Your Rainpole Architects
Using your tenant administrator privileges, you create a custom group for members of your IT
organization who need highly privileged access to vRealize Automation. You assign roles to this
custom group as you configure vRealize Automation.
5Scenario: Assign IaaS Administrator Privileges to Your Custom Group of Rainpole Architects
Using your default system administrator privileges, you assign your custom group to the IaaS
administrator role to allow the group to configure IaaS resources.
Scenario: Create Local User Accounts for Rainpole
Using your default system administrator privileges, you create two local user accounts in the default
tenant. Assign one of these accounts to the tenant administrator role so you can start configuring the
default tenant. You can use the second account later as a shared login for your architects to test blueprint
and catalog access.
Procedure
1Navigate to the vRealize Automation console, https://vra01svr01.rainpole.local/vcac.
2Enter the default system administrator username, administrator, and password, VMware1!.
3Select Administration > Tenants.
4Click vsphere.local.
5Select the Local Users tab.
6Click the New icon ( ).
7Create a local user account to assign to the tenant administrator role.
Option Input
First Name Rainpole
Last Name tenant admin
Email Enter your email address or use the placeholder
rainpole_tenant_admin@rainpole.com.
Username Rainpole tenant admin
Password VMware1!
8Click OK.
9Click the New icon ( ).
10 Create a local user account that you and your architects can later configure for testing blueprints and
catalog access.
Option Input
First Name test
Last Name user
Configuring vRealize Automation
VMware, Inc. 142

Option Input
Email Enter an email address or use the placeholder test_user@rainpole.com.
Username test_user
Password VMware1!
11 Click OK.
12 Click the Administrators tab.
13 Enter Rainpole in the Tenant administrators search box and press Enter. Select your Rainpole
tenant admin user.
The tenant administrator role is assigned to your Rainpole tenant admin user.
14 Click Finish.
15 Log out of the console.
You can use the Rainpole tenant admin local user to access the tenant administration settings and
configure your tenant. The test_user account is useful as a shared login for your architects and catalog
administrators. They can configure the account as a basic user and verify blueprint and catalog access
and test approval behaviors.
What to do next
Configure vRealize Automation to authenticate logins against your existing corporate active directory.
Scenario: Connect Your Corporate Active Directory to
vRealize Automation for Rainpole
As a tenant administrator, you want vRealize Automation to authenticate logins against your corporate
active directory. You configure a connection between vRealize Automation and your single domain active
directory over LDAP.
Procedure
1Navigate to the vRealize Automation console, https://vra01svr01.rainpole.local/vcac.
2Enter the username Rainpole tenant admin and password VMware1!.
3Select Administration > Directories Management > Directories.
4Click Add Directory.
5Enter your specific Active Directory account settings, and accept the default options.
Option Sample Input
Directory Name Add the IP address of your active directory domain name.
Sync Connector vra01svr01.rainpole.local
Base DN Enter the Distinguished Name (DN) of the starting point for directory server
searches. For example, cn=users,dc=rainpole,dc=local.
Configuring vRealize Automation
VMware, Inc. 143
Option Sample Input
Bind DN Enter the full distinguished name (DN), including common name (CN), of an
Active Directory user account that has privileges to search for users. For
example, cn=config_admin infra,cn=users,dc=rainpole,dc=local.
Bind DN Password Enter the Active Directory password for the account that can search for users.
6Click the Test Connection button to test the connection to the configured directory.
7Click Save & Next.
The Select the Domains page with the list of domains appears.
8Accept the default domain setting and click Next.
9Verify that the attribute names are mapped to the correct Active Directory attributes and click Next.
10 Select the groups and users you want to sync.
aClick the Add icon ( ).
b Enter the user domain and click Find Groups.
For example, cn=users,dc=rainpole,dc=local.
c Select the Select All check box.
d Click Select.
e Click Next.
f Accept the defaults on the Select Users page and click Next.
11 Review the page to see how many users and groups are syncing to the directory and click Sync
Directory.
The directory sync process takes some time, but it happens in the background and you can continue
working.
You can assign privileges and grant access to any of the Active Directory users and groups you synced to
vRealize Automation.
What to do next
Using your tenant administrator privileges, customize the look and feel of the vRealize Automation
console.
Scenario: Configure Branding for the Default Tenant for Rainpole
Using your tenant administrator privileges, you customize the look and feel of the vRealize Automation
console. You upload a new logo, change the colors, update the header and footer information, and
configure the login screen branding.
Procedure
1Select Administration > Branding > Header & Footer Branding.
Configuring vRealize Automation
VMware, Inc. 144
2Deselect the Use default check box.
3Follow the prompts to create a header.
4Click Next.
5Follow the prompts to create a footer.
6Click Finish.
The console is updated with your changes.
7Select Administration > Branding > Login Screen Branding.
8Follow the prompts to customize the login screen branding.
9Click Save.
The console is updated with your changes.
You updated the look and feel of the console for the default tenant.
What to do next
Create a custom group for members of your IT organization who need highly privileged access to
vRealize Automation.
Scenario: Create a Custom Group for Your Rainpole Architects
Using your tenant administrator privileges, you create a custom group for members of your IT
organization who need highly privileged access to vRealize Automation. You assign roles to this custom
group as you configure vRealize Automation.
If you want to add or disable this high-level access for users, you can change the membership of the
group instead of editing settings for each user in multiple locations.
Procedure
1Select Administration > Users & Groups > Custom Groups.
2Click the New icon ( ).
3Enter Rainpole architects in the Name text box.
4Select roles from the Add Roles to this Group list.
You cannot assign IaaS administrator, fabric administrator, business group manager, or business user
roles on this page. You assign those roles while you configure vRealize Automation.
Option Description
Tenant administrator Responsible for user and group management, tenant branding and notifications,
and business policies such as approvals and entitlements. They also track
resource usage by all users within the tenant and initiate reclamation requests for
virtual machines.
Infrastructure (IaaS) architect Create and manage machine blueprints and application blueprints.
Configuring vRealize Automation
VMware, Inc. 145
Option Description
XaaS architect For Advanced and Enterprise licensed users, create and manage XaaS
blueprints.
Software architect For Enterprise licensed users, create and manage software components and
application blueprints.
5Click Next.
6Search for corporate active directory users and select users to add to your custom group.
You assign yourself and anyone who needs an extremely high level of access to your
vRealize Automation development environment to this group.
7Click Finish.
You granted your custom group the rights to manage the default tenant, create blueprints, and manage
the service catalog. As you configure vRealize Automation, you add permissions and roles to your custom
group.
What to do next
Assign your custom group to the IaaS administrator role.
Scenario: Assign IaaS Administrator Privileges to Your Custom
Group of Rainpole Architects
Using your default system administrator privileges, you assign your custom group to the IaaS
administrator role to allow the group to configure IaaS resources.
Procedure
1Log out of the vRealize Automation console.
2Select the vsphere.local domain and click Next.
3Enter the default system administrator username, administrator, and password, vmware.
4Select Administration > Tenants.
5Click the default tenant name vsphere.local.
6Click the Administrators tab.
7Search for Rainpole architects in the IaaS administrators search box and select your custom
group.
8Click Finish.
9Log out of the console.
Any member of your custom group can now manage cloud, virtual, networking, and storage infrastructure
for all tenants in your vRealize Automation instance. You can update membership of the group at any time
to grant or revoke these privileges.
Configuring vRealize Automation
VMware, Inc. 146
What to do next
Using the IaaS administrator privileges you granted your custom group, you can configure your IaaS
resources.
Create Additional Tenants
As a system administrator, you can create additional vRealize Automation tenants so that users can
access the appropriate applications and resources that they need to complete their work assignments.
A tenant is a group of users with specific privileges who work within a software instance. Typically, a
default vRealize Automation tenant is created during system installation and initial configuration. After
that, administrators can create additional tenants so that users can log in and complete their work
assignments. Administrators can create as many tenants as needed for system operation. When creating
tenants, administrators must specify basic configuration such as name, login URL, local users, and
administrators. After configuring basic tenant information, the tenant administrator must log in and set up
an appropriate Active Directory connection using the Directories Management functionality on the
Administrative tab of the vRealize Automation console. In addition, tenant administrators can apply
custom branding to tenants.
Prerequisites
Log in to the vRealize Automation console as a system administrator.
Procedure
1Specify Tenant Information
The first step to configuring a tenant is to name the new tenant and add it to vRealize Automation
and create the tenant-specific access URL.
2Configure Local Users
The vRealize Automation system administrator must configure local users for each applicable
tenant.
3Appoint Administrators
You can appoint one or more tenant administrators and IaaS administrators from the identity stores
you configured for a tenant.
Specify Tenant Information
The first step to configuring a tenant is to name the new tenant and add it to vRealize Automation and
create the tenant-specific access URL.
Prerequisites
Log in to the vRealize Automation console as a system administrator.
Procedure
1Select Administration > Tenants.
Configuring vRealize Automation
VMware, Inc. 147
2Click the Add icon ( ).
3Enter a name in the Name text box.
4(Optional) Enter a description in the Description text box.
5Enter a unique identifier for the tenant in the URL Name text box.
This URL token is used to append a tenant-specific identifier to the vRealize Automation console
URL.
For example, enter mytenant to create the URL https://vrealize-appliance-
hostname.domain.name/vcac/org/mytenant.
Note The tenant URL must use lowercase characters only in vRealize Automation 7.0 and 7.1.
6(Optional) Enter an email address in the Contact Email text box.
7Click Submit and Next.
Your new tenant is saved and you are automatically directed to the Identity Stores tab for the next step
in the process.
Configure Local Users
The vRealize Automation system administrator must configure local users for each applicable tenant.
After an administrator creates the general information for a tenant, the Local users tab becomes active,
and the administrator can designate users who can access the tenant. When tenant configuration is
complete, local tenant users can log in to their respective tenants to complete work assignments.
Prerequisites
Procedure
1Click the Add button on the Local users tab.
2Enter the users first and last names into the First name and Last name fields on the User Details
dialog.
3Enter the user email address into the Email field.
4Enter the user ID and password for the user in the User name and Password fields.
5Click the Add button.
6Repeat these steps as applicable for all local users of the tenant.
The specified local users are created for the tenant.
Configuring vRealize Automation
VMware, Inc. 148
Appoint Administrators
You can appoint one or more tenant administrators and IaaS administrators from the identity stores you
configured for a tenant.
Tenant administrators are responsible for configuring tenant-specific branding, as well as managing
identity stores, users, groups, entitlements, and shared blueprints within the context of their tenant. IaaS
Administrators are responsible for configuring infrastructure source endpoints in IaaS, appointing fabric
administrators, and monitoring IaaS logs.
Prerequisites
n
nBefore you appoint IaaS administrators, you must install IaaS. For more information about installing
IaaS, see Installing vRealize Automation 7.0.
Procedure
1Enter the name of a user or group in the Tenant Administrators search box and press Enter.
For faster results, enter the entire user or group name, for example myAdmins@mycompany.domain.
Repeat this step to appoint additional tenant administrators.
2If you have installed IaaS, enter the name of a user or group in the IaaS Administrators search box
and press Enter.
For faster results, enter the entire user or group name, for example
IaaSAdmins@mycompany.domain. Repeat this step to appoint additional infrastructure
administrators.
3Click Add.
(Optional) Configuring Custom Branding
vRealize Automation enables you to apply custom branding to tenant login and application pages.
Custom branding can include text and background colors, business logos, company name, privacy
policies, copyright statements and other relevant information that you want to appear on tenant login or
application pages.
Custom Branding for Tenant Login Page
Use the Login Screen Branding page to apply custom branding to your vRealize Automation tenant login
pages.
You can use default vRealize Automation branding on your tenant login pages, or you can configure
custom branding using the Login Screen Branding page. Note that custom branding applies in the same
manner to all of your tenant applications.
This page enables you to configure branding on all tenant login pages.
Configuring vRealize Automation
VMware, Inc. 149
The Login Screen Branding page displays the currently implemented tenant login branding in the Preview
pane.
Note After saving new tenant login page branding, there may be a delay of up to five minutes before it
becomes visible on all login pages.
Prerequisites
To use a custom logo or other image with your branding, you must have the appropriate files available.
Procedure
1Log in to vRealize Automation as a system or tenant administrator.
2Click the Administration tab.
3Select the desired visual effects using the check boxes under the Effects heading.
All effects are optional.
4Select Branding > Login Screen Branding
5Click Upload beneath the Logo field, then navigate to the appropriate folder and select a logo image
file.
6If desired, click Upload beneath the Image (optional) field, then navigate to the appropriate folder and
select an additional image file.
7If desired, enter the appropriate hex codes in the Background color, Masthead color, Login button
background color and Login button foreground color fields.
Search the internet for a list of hex color codes if needed.
8Click Save to apply your settings.
Tenant users see the custom branding on their login pages.
Custom Branding for Tenant Applications
Use the Application Branding page to apply custom branding to vRealize Automation tenant applications.
You can use default vRealize Automation branding on your user applications, or you can configure
custom branding using the Application Branding page. This page enables you to configure branding on
the header and footer of application pages. Note that custom branding applies in the same manner to all
of your user applications.
The Application Branding page displays the currently implemented header or footer branding at the
bottom of the page.
Prerequisites
If you want to use a custom logo with your branding, you must have the logo image file available.
Configuring vRealize Automation
VMware, Inc. 150
Procedure
1Log in to vRealize Automation as a system or tenant administrator.
2Click the Administration tab.
3Select Branding > Application Branding
4Click the Header tab if it is not already active.
5If you want to use the default vRealize Automation branding, click the Use Default check box.
6To implement custom branding, make the appropriate selections in the fields on the Header and
Footer tabs.
a Click the Browse button in the Header Logo field, then navigate to the appropriate folder and
select an logo image file.
b Type the appropriate company name in the Company name field.
The specified name appears when a user mouses over the logo.
c Type the appropriate name into the Product name field.
The name you enter here appears in the application header adjacent to the logo.
d Enter the appropriate hex color code for the application perimeter background color in the
Background hex color field.
Search the internet for a list of hex color codes if needed.
e Enter the appropriate hex code for the text color in the Text hex color field.
Search the internet for a list of hex text color codes if needed.
f Click Next to activate the Footer tab.
g Type the desired statement into the Copyright notice field.
h Type the link to you company privacy policy statement in the Privacy policy link field.
i Type the desired company contact information in the Contact link field.
7Click Update to implement your branding configuration.
Tenant users see the custom branding on their application pages.
(Optional) Checklist for Configuring Notifications
You can configure vRealize Automation to send users notifications when specific events occur. Users can
choose which notifications to subscribe to, but they can only select from events you enable as notification
triggers.
Configuring vRealize Automation
VMware, Inc. 151
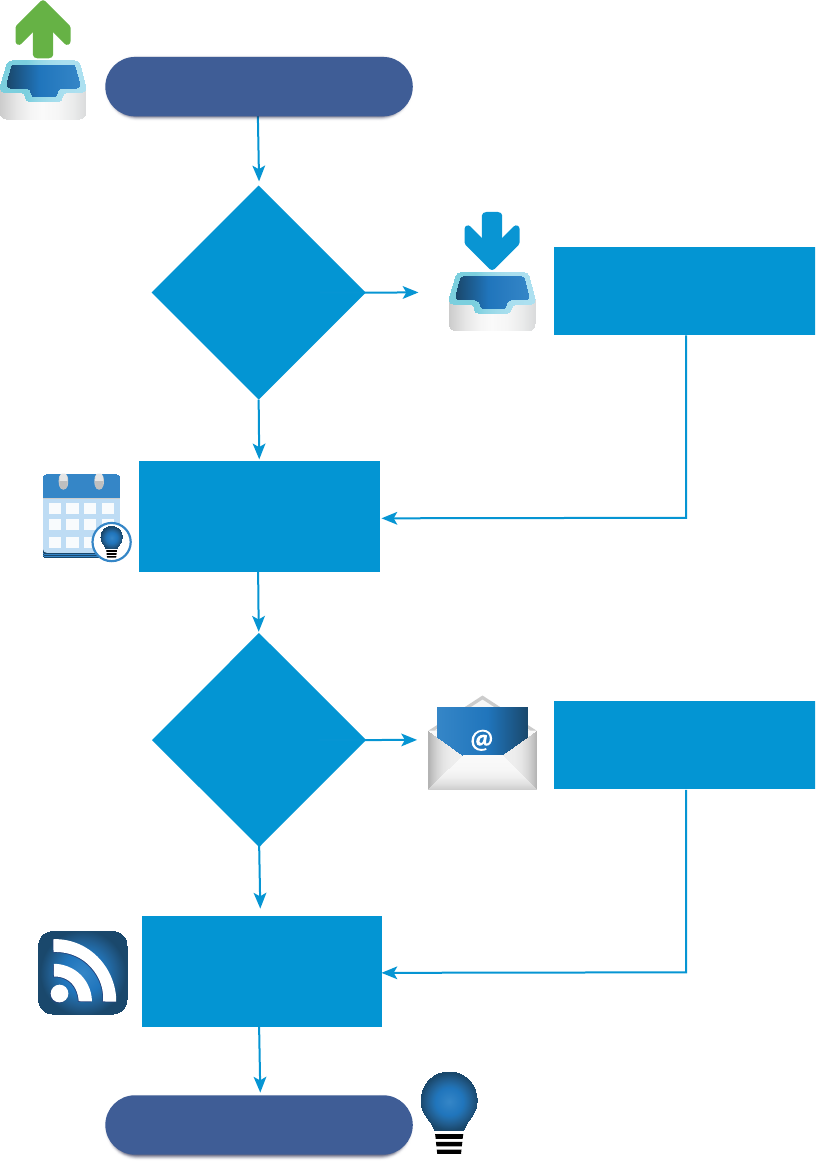
!
TEMPLATE
Configure an outbound mail
server to send notifications.
No
Yes
No
Users get the
notifications they want.
Edit the configuration files
that control IaaS notifications.
Enable notifications for
any events you want
to allow users to
receive updates for.
Configure an inbound mail
server to receive notifications.
Yes
Do you want users
to be able to respond
to notifications?
Do you want to
customize the
templates for IaaS
notifications?
Tell your users how to
subscribe to the
notifications you enabled.
The Configuring Notifications Checklist provides a high-level overview of the sequence of steps required
to configure notifications and provides links to decision points or detailed instructions for each step.
Configuring vRealize Automation
VMware, Inc. 152
Table 2‑9. Checklist for Configuring Notifications
Task Required Role Details
Configure an outbound email server to send notifications. nSystem
administrators
configure
default global
servers.
nTenant
administrators
configure
servers for their
tenants.
To configure a server for your tenant for the
first time, see Add a Tenant-Specific
Outbound Email Server. If you need to
override a default global server, see
Override a System Default Outbound Email
Server. To configure global default servers
for all tenants, see Create a Global
Outbound Email Server.
(Optional) Configure an inbound email server so that users
can complete tasks by responding to notifications.
nSystem
administrators
configure
default global
servers.
nTenant
administrators
configure
servers for their
tenants.
To configure a server for your tenant for the
first time, see Add a Tenant-Specific
Inbound Email Server. If you need to
override a default global server, see
Override a System Default Inbound Email
Server. To configure a global default server
for all tenants, see Create a Global Inbound
Email Server.
Select the vRealize Automation events to trigger user
notifications. Users can only subscribe to notifications for
events you enable as notification triggers.
Tenant
administrator
See Configure Notifications.
(Optional) Configure the templates for notifications sent to
machine owners concerning events that involve their
machines, such as lease expiration.
Anyone with access
to the
directory \Templat
es under the
vRealize
Automation server
install directory
(typically
%SystemDrive
%\Program Files
x86\VMware\vCA
C\Server) can
configure the
templates for these
email notifications.
See Configuring Templates for Automatic
IaaS Emails.
Provide your users with instructions about how to
subscribe to the notifications that you enabled. They can
choose to subscribe to only the notifications that are relevant
to their roles.
All users See Subscribe to Notifications.
Configuring vRealize Automation
VMware, Inc. 153

Configuring Global Email Servers for Notifications
Tenant administrators can add email servers as part of configuring notifications for their own tenants. As a
system administrator, you can set up global inbound and outbound email servers that appear to all
tenants as the system defaults. If tenant administrators do not override these settings before enabling
notifications, vRealize Automation uses the globally configured email servers.
Create a Global Inbound Email Server
System administrators create a global inbound email server to handle inbound email notifications, such as
approval responses. You can create only one inbound server, which appears as the default for all tenants.
If tenant administrators do not override these settings before enabling notifications, vRealize Automation
uses the globally configured email server.
Prerequisites
Log in to the vRealize Automation console as a system administrator.
Procedure
1Select Administration > Email Servers.
2Click the Add icon ( ).
3Select Email – Inbound.
4Click OK.
5Enter a name in the Name text box.
6(Optional) Enter a description in the Description text box.
7(Optional) Select the SSL check box to use SSL for security.
8Choose a server protocol.
9Type the name of the server in the Server Name text box.
10 Type the server port number in the Server Port text box.
11 Type the folder name for emails in the Folder Name text box.
This option is required only if you choose IMAP server protocol.
12 Enter a user name in the User Name text box.
13 Enter a password in the Password text box.
14 Type the email address that vRealize Automation users can reply to in the Email Address text box.
15 (Optional) Select Delete From Server to delete from the server all processed emails that are
retrieved by the notification service.
16 Choose whether vRealize Automation can accept self-signed certificates from the email server.
17 Click Test Connection.
Configuring vRealize Automation
VMware, Inc. 154

18 Click Add.
Create a Global Outbound Email Server
System administrators create a global outbound email server to handle outbound email notifications. You
can create only one outbound server, which appears as the default for all tenants. If tenant administrators
do not override these settings before enabling notifications, vRealize Automation uses the globally
configured email server.
Prerequisites
Log in to the vRealize Automation console as a system administrator.
Procedure
1Select Administration > Email Servers.
2Click the Add icon ( ).
3Select Email – Outbound.
4Click OK.
5Enter a name in the Name text box.
6(Optional) Enter a description in the Description text box.
7Type the name of the server in the Server Name text box.
8Choose an encryption method.
nClick Use SSL.
nClick Use TLS.
nClick None to send unencrypted communications.
9Type the server port number in the Server Port text box.
10 (Optional) Select the Required check box if the server requires authentication.
a Type a user name in the User Name text box.
b Type a password in the Password text box.
11 Type the email address that vRealize Automation emails should appear to originate from in the
Sender Address text box.
This email address corresponds to the user name and password you supplied.
12 Choose whether vRealize Automation can accept self-signed certificates from the email server.
13 Click Test Connection.
14 Click Add.
Configuring vRealize Automation
VMware, Inc. 155

Add a Tenant-Specific Outbound Email Server
Tenant administrators can add an outbound email server to send notifications for completing work items,
such as approvals.
Each tenant can have only one outbound email server. If your system administrator has already
configured a global outbound email server, see Override a System Default Outbound Email Server.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator.
nIf the email server requires authentication, the specified user must be in an identity store and the
business group.
Procedure
1Select Administration > Notifications > Email Servers.
2Click the Add icon ( ).
3Select Email – Outbound.
4Click OK.
5Enter a name in the Name text box.
6(Optional) Enter a description in the Description text box.
7Type the name of the server in the Server Name text box.
8Choose an encryption method.
nClick Use SSL.
nClick Use TLS.
nClick None to send unencrypted communications.
9Type the server port number in the Server Port text box.
10 (Optional) Select the Required check box if the server requires authentication.
a Type a user name in the User Name text box.
b Type a password in the Password text box.
11 Type the email address that vRealize Automation emails should appear to originate from in the
Sender Address text box.
This email address corresponds to the user name and password you supplied.
Configuring vRealize Automation
VMware, Inc. 156
12 Choose whether vRealize Automation can accept self-signed certificates from the email server.
This option is available only if you enabled encryption.
nClick Yes to accept self-signed certificates.
nClick No to reject self-signed certificates.
13 Click Test Connection.
14 Click Add.
Add a Tenant-Specific Inbound Email Server
Tenant administrators can add an inbound email server so that users can respond to notifications for
completing work items, such as approvals.
Each tenant can have only one inbound email server. If your system administrator already configured a
global inbound email server, see Override a System Default Inbound Email Server.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator.
nVerify that the specified user is in an identity store and in the business group.
Procedure
1Select Administration > Notifications > Email Servers.
2Click the Add icon ( ).
3Select Email - Inbound and click OK.
4Configure the following inbound email server options.
Option Action
Name Enter a name for the inbound email server.
Description Enter a description of the inbound email server.
Security Select the Use SSL check box.
Protocol Choose a server protocol.
Server Name Enter the server name.
Server Port Enter the server port number.
5Type the folder name for emails in the Folder Name text box.
This option is required only if you choose IMAP server protocol.
6Enter a user name in the User Name text box.
7Enter a password in the Password text box.
8Type the email address that vRealize Automation users can reply to in the Email Address text box.
Configuring vRealize Automation
VMware, Inc. 157
9(Optional) Select Delete From Server to delete from the server all processed emails that are
retrieved by the notification service.
10 Choose whether vRealize Automation can accept self-signed certificates from the email server.
This option is available only if you enabled encryption.
nClick Yes to accept self-signed certificates.
nClick No to reject self-signed certificates.
11 Click Test Connection.
12 Click Add.
Override a System Default Outbound Email Server
If the system administrator configured a system default outbound email server, the tenant administrator
can override this global setting.
Prerequisites
Log in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Notifications > Email Servers.
2Select the Outbound email server.
3Click Override Global.
4Enter a name in the Name text box.
5(Optional) Enter a description in the Description text box.
6Type the name of the server in the Server Name text box.
7Choose an encryption method.
nClick Use SSL.
nClick Use TLS.
nClick None to send unencrypted communications.
8Type the server port number in the Server Port text box.
9(Optional) Select the Required check box if the server requires authentication.
a Type a user name in the User Name text box.
b Type a password in the Password text box.
10 Type the email address that vRealize Automation emails should appear to originate from in the
Sender Address text box.
This email address corresponds to the user name and password you supplied.
Configuring vRealize Automation
VMware, Inc. 158
11 Choose whether vRealize Automation can accept self-signed certificates from the email server.
This option is available only if you enabled encryption.
nClick Yes to accept self-signed certificates.
nClick No to reject self-signed certificates.
12 Click Test Connection.
13 Click Add.
Override a System Default Inbound Email Server
If the system administrator has configured a system default inbound email server, tenant administrators
can override this global setting.
Prerequisites
Log in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Notifications > Email Servers.
2Select the Inbound email server in the Email Servers table.
3Click Override Global.
4Enter the following inbound email server options.
Option Action
Name Enter the name of the inbound email server.
Description Enter a description of the inbound email server.
Security Select the SSL check box to use SSL for security.
Protocol Choose a server protocol.
Server Name Enter the server name.
Server Port Enter the server port number.
5Type the folder name for emails in the Folder Name text box.
This option is required only if you choose IMAP server protocol.
6Enter a user name in the User Name text box.
7Enter a password in the Password text box.
8Type the email address that vRealize Automation users can reply to in the Email Address text box.
9(Optional) Select Delete From Server to delete from the server all processed emails that are
retrieved by the notification service.
Configuring vRealize Automation
VMware, Inc. 159
10 Choose whether vRealize Automation can accept self-signed certificates from the email server.
This option is available only if you enabled encryption.
nClick Yes to accept self-signed certificates.
nClick No to reject self-signed certificates.
11 Click Test Connection.
12 Click Add.
Revert to System Default Email Servers
Tenant administrators who override system default servers can revert the settings back to the global
settings.
Prerequisites
Log in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > Notifications > Email Servers.
2Select the email server to revert.
3Click Revert to Global.
4Click Yes.
Configure Notifications
Each user determines whether to receive notifications, but tenant administrators determine which events
trigger notifications.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator.
nVerify that a tenant administrator or system administrator configured an outbound email server. See
Add a Tenant-Specific Outbound Email Server.
Procedure
1Select Administration > Notifications > Scenarios.
2Select one or more notifications.
3Click Activate.
Users who subscribe to notifications in their preference settings now receive the notifications.
Configuring vRealize Automation
VMware, Inc. 160

Configuring Templates for Automatic IaaS Emails
You can configure the templates for automatic notification emails sent to machine owners by the IaaS
service about events involving their machines.
The events that trigger these notifications include, for example, the expiration or approaching expiration of
archive periods and virtual machine leases.
Tenant administrators can enable or disable IaaS email notifications for machine owners, and machine
owners can choose to receive or not receive email notifications. Anyone with access to the
directory \Templates under the vRealize Automation server install directory (typically %SystemDrive
%\Program Files x86\VMware\vCAC\Server) can configure the templates for these email notifications.
Email Template Object Reference
You can add email template objects to automatic email templates to return information about URIs,
machines, blueprints, costs, and requests.
You can use the following email template objects to return information to automatic email templates.
nWebsiteURIItems
nWebsiteURIInbox
nVirtualMachineEx
nVirtualMachineTemplateEx
nReservationHelper
nRequest
nRequestWithAudit
The WebsiteURIItems object returns the URL of the Items tab on the vRealize Automation console, for
example https://vcac.mycompany.com/shell-ui-app/org/mytenant/#csp.catalog.item.list.
To use this object to provide a link to the My Items page in the console, consider the following sample
lines.
Click
<a>
<xsl:attribute name="href">
<xsl:value-of select="//WebsiteURIItems"/>
</xsl:attribute><xsl:value-of select="//WebsiteURIItems"/>here</a>
for your provisioned items.
Configuring vRealize Automation
VMware, Inc. 161
The WebsiteURIInbox object returns the URL of the Inbox tab on the vRealize Automation console, for
example https://vcac.mycompany.com/shell-ui-app/org/mytenant/#cafe.work.items.list. To
use this object to provide a link to the My Inbox page in the console, consider the following sample lines.
Click
<a>
<xsl:attribute name="href">
<xsl:value-of select="//WebsiteURIInbox"/></xsl:attribute><xsl:value-of
select="//WebsiteURIInbox"/>here</a>
for your assigned tasks.
The VirtualMachineEx object returns a specific item of information about the machine associated with the
event triggering the email. The information is determined by the attribute provided with the object; see the
table Selected Attributes of the VirtualMachineEx Object for more information. For example, you could
use the following line to include the expiration date of the machine in an email.
<xsl:value-of select="//VirtualMachineEx/Expires"/>
Table 2‑10. Selected Attributes of the VirtualMachineEx Object
Attribute Returns
Name Name of machine as generated by vRealize Automation
Description Machine’s description
DnsName Machine’s DNS name
TemplateName Name of blueprint from which machine was provisioned
StoragePath If a virtual machine, name of storage path on which machine was provisioned
State/Name Status of machine
Owner Owner of machine
Expires Date on which machine expires
ExpireDays Number of days until machine expires
CreationTime Date and time at which machine was provisioned
HostName If a virtual machine, name of host where machine was provisioned
GroupName Name of business group in which machine was provisioned
ReservationName Name of reservation on which machine was provisioned
Group/AdministratorE
mail
Names of users or groups who receive group manager emails for business group for which machine was
provisioned
In addition, the special attribute Properties lets you search the custom properties associated with the
machine for a specific property and return the value if found. For example, to include the value of
Image.WIM.Name, which specifies the name of the WIM image from which a machine was provisioned,
you could use the following lines.
<xsl:for-each select="//VirtualMachineEx/Properties/NameValue">
<xsl:if test="starts-with(Name, 'Image.WIM.Name')">
<xsl:value-of select="Value"/>
Configuring vRealize Automation
VMware, Inc. 162
If the machine does not have the Image.WIM.Name property, nothing is returned.
The VirtualMachineTemplateEx object returns a specific item of information about the source blueprint of
the machine associated with the even triggering the email. The information is determined by the attribute
provided with the object; see the table Selected Attributes of the VirtualMachineTemplateEx Email Object
for more information. For example, to include the daily cost specified in the source blueprint you could
use the following line:
<xsl:value-of select="//VirtualMachineTemplateEx/Cost"/>
Table 2‑11. Selected Attributes of the VirtualMachineTemplateEx Email Object
Attribute Returns
Name Name of blueprint
Description Blueprint’s description
MachinePrefix Machine prefix specified in blueprint
LeaseDays Number of lease days specified in blueprint
ExpireDays If a virtual blueprint, number of archive days specified
Cost Daily cost specified in blueprint
VirtualMachineTemplateEx also takes the special attribute Properties to let you search the custom
properties included in the blueprint for a specific property and return the value if found, as described for
the VirtualMachineEx object.
The ReservationHelper object returns information about the daily cost of the machine, as specified by the
attributes in the table Selected Attributes of the ReservationHelper Email Object, when a cost profile
applies to the machine associated with the event triggering the email.
Table 2‑12. Selected Attributes of the ReservationHelper Email Object
Attribute Returns
DailyCostFormatted Daily cost of machine
LeaseCostFormatted Daily cost times the number of days in the machine’s lease.
Modify an Existing Automatic Email Template
You can edit the automatic email templates used by the IaaS service when notifying machine owners and
managers.
You can customize the text and format of the automatic email for an IaaS event by editing the XSLT
template for the event. You can find the following IaaS templates in the directory \Templates under the
vRealize Automation server install directory (typically %SystemDrive%\Program Files
x86\VMware\vCAC\Server).
nArchivePeriodExpired
nEpiRegister
nEpiUnregister
Configuring vRealize Automation
VMware, Inc. 163
nLeaseAboutToExpire
nLeaseExpired
nLeaseExpiredPowerOff
nManagerLeaseAboutToExpire
nManagerLeaseExpired
nManagerReclamationExpiredLeaseModified
nManagerReclamationForcedLeaseModified
nReclamationExpiredLeaseModified
nReclamationForcedLeaseModified
nVdiRegister
nVdiUnregister
Prerequisites
Log in to the IaaS Manager Service host using administrator credentials.
Procedure
1Change to the directory \Templates.
2Edit an XSLT template as required.
Customize the Date for Email Notification for Machine Expiration
You can specify when to send an email notification prior to a machine expiration date.
You can change the setting that defines the number of days before a machine's expiration date that
vRealize Automation sends an expiration notification email. The email notifies users of a machine's
expiration date. By default, the setting is 7 days prior to machine expiration.
Procedure
1Log in to the vRealize Automation server by using credentials with administrative access.
2Navigate to and open the /etc/vcac/setenv-user file.
3Add the following line to the file to specify the number of days prior to machine expiration, where 3 in
this example specifies 3 days prior to machine expiration.
VCAC_OPTS="$VCAC_OPTS -Dlease.enforcement.prearchive.notification.days=3"
4Restart the vCAC services on the virtual appliance by running the following command:
service vcac-server restart
Configuring vRealize Automation
VMware, Inc. 164
What to do next
If you are working in a high availability load balancer environment, repeat this procedure for all the virtual
appliances in the HA environment.
Subscribe to Notifications
If your administrators have configured notifications, you can subscribe to receive notifications from
vRealize Automation. Notification events can include the successful completion of a catalog request or a
required approval.
Prerequisites
Log in to the vRealize Automation console.
Procedure
1Click Preferences.
2Select the Enabled check box for the Email protocol in the Notifications table.
3Click Apply.
4Click Close.
(Optional) Create a Custom RDP File to Support RDP
Connections for Provisioned Machines
System administrators create a custom remote desktop protocol file that IaaS architects use in blueprints
to configure RDP settings. You create the RDP file and provide architects with the full pathname for the
file so they can include it in blueprints, then a catalog administrator entitles users to the RDP action.
Note If you are using Internet Explorer with Enhanced Security Configuration enabled, you cannot
download .rdp files.
Prerequisites
Log in to the IaaS Manager Service as an administrator.
Procedure
1Set your current directory to <vRA_installation_dir>\Rdp.
2Copy the file Default.rdp and rename it to Console.rdp in the same directory.
3Open the Console.rdp file in an editor.
4Add RDP settings to the file.
For example, connect to console:i:1.
5If you are working in a distributed environment, log in as a user with administrative privileges to the
IaaS Host Machine where the Model Manager Website component is installed.
Configuring vRealize Automation
VMware, Inc. 165

6Copy the Console.rdp file to the directory vRA_installation_dir\Website\Rdp.
Your IaaS architects can add the RDP custom properties to Windows machine blueprints, and then
catalog administrators can entitle users to the Connect Using RDP action. See Add RDP Connection
Support to Your Windows Machine Blueprints.
(Optional) Scenario: Add Datacenter Locations for Cross
Region Deployments
As a system administrator, you want to define locations for your Boston and London datacenters so your
fabric administrators can apply the appropriate locations to compute resources in each datacenter. When
your blueprint architects create blueprints, they can enable the locations feature so users can choose to
provision machines in Boston or London when they fill out their catalog item request forms.
You have a datacenter in London, and a datacenter in Boston, and you do not want users in Boston
provisioning machines on your London infrastructure or vice versa. To ensure that Boston users provision
on your Boston infrastructure, and London users provision on your London infrastructure, you want to
allow users to select an appropriate location for provisioning when they request machines.
Procedure
1Log in to your IaaS Web Server host using administrator credentials.
This is the machine on which you installed the IaaS Website component.
2Edit the file WebSite\XmlData\DataCenterLocations.xml in the Windows server install directory
(typically %SystemDrive%\Program Files x86\VMware\vCAC\Server).
3Edit the CustomDataType section of the file to create Data Name entries for each location.
<CustomDataType>
<Data Name="London" Description="London datacenter" />
<Data Name="Boston" Description="Boston datacenter" />
</CustomDataType
4Save and close the file.
5Restart the manager service.
6If you have more than one IaaS Web Server host, repeat this procedure on each redundant instance.
Configuring vRealize Automation
VMware, Inc. 166
Your fabric administrator can apply the appropriate location to compute resources located in each
datacenter. See Scenario: Apply a Location to a Compute Resource for Cross Region Deployments.
Configuring vRealize Orchestrator and Plug-Ins
VMware vRealize ™ Orchestrator ™ is an automation and management engine that extends
vRealize Automation to support XaaS and other extensibility.
vRealize Orchestrator allows administrators and architects to develop complex automation tasks by using
the workflow designer, and then access and run the workflows from vRealize Automation.
vRealize Orchestrator can access and control external technologies and applications by using
vRealize Orchestrator plug-ins.
Configuration Privileges
System and tenant administrators can configure vRealize Automation to use an external
vRealize Orchestrator server.
In addition, system administrators can also determine the workflow folders that are available to each
tenant.
Tenant administrators can configure the vRealize Orchestrator plug-ins as endpoints.
Role vRealize Orchestrator-Related Configuration Privileges
System administrators nConfigure the vRealize Orchestrator server for all tenants.
nDefine the default vRealize Orchestrator workflow folders per tenant.
Tenant administrators nConfigure the vRealize Orchestrator server for their own tenant.
nAdd vRealize Orchestrator plug-ins as endpoints.
Configure the Default Workflow Folder for a Tenant
System administrators can group workflows in different folders and then define workflow categories per
tenant. By doing this, a system administrator can grant users from different tenants access to different
workflow folders on the same vRealize Orchestrator server.
Prerequisites
Log in to the vRealize Automation console as a system administrator.
Procedure
1Select Administration > Advanced Services > Default vRO Folder.
2Click the name of the tenant you want to edit.
3Browse the vRealize Orchestrator workflow library and select a folder.
4Click Add.
You defined the default vRealize Orchestrator workflow folder for a tenant.
Configuring vRealize Automation
VMware, Inc. 167

What to do next
Repeat the procedure for all of the tenants for which you want to define a default workflow folder.
Configure an External vRealize Orchestrator Server
You can set up vRealize Automation to use an external vRealize Orchestrator server.
System administrators can configure the default vRealize Orchestrator server globally for all tenants.
Tenant administrators can configure the vRealize Orchestrator server only for their tenants.
Connections to external vRealize Orchestrator server instances require the user account to have view
and execute permissions in vRealize Orchestrator.
nSingle Sign-On authentication. The user information is passed to vRealize Orchestrator with the XaaS
request and the user is granted view and execute permissions for the requested workflow.
nBasic authentication. The provided user account must be a member of a vRealize Orchestrator group
with view and execute permissions or the member of the vcoadmins group.
Prerequisites
nInstall and configure an external vRealize Orchestrator server. You can also deploy the
vRealize Orchestrator Appliance. See Installing and Configuring VMware vCenter Orchestrator.
nLog in to the vRealize Automation console as a system administrator or tenant administrator.
Procedure
1Select Administration > vRO Configuration > Server Configuration.
2Click Use an external Orchestrator server.
3Enter a name and, optionally, a description.
4Enter the IP or the DNS name of the machine on which the vRealize Orchestrator server runs in the
Host text box.
5Enter the port number to communicate with the external vRealize Orchestrator server in the Port text
box.
8281 is the default port for vRealize Orchestrator.
6Select the authentication type.
Option Description
Single Sign-On Connects to the vRealize Orchestrator server by using vCenter Single Sign-On.
This option is applicable only if you configured the vRealize Orchestrator and
vRealize Automation to use one common vCenter Single Sign-On instance.
Basic Connects to the vRealize Orchestrator server with the user name and password
that you enter in the User name and Password text boxes.
The account that you provide must be a member of the vRealize Orchestrator
vcoadmins group or a member of a group with view and execute permissions.
7Click Test Connection.
Configuring vRealize Automation
VMware, Inc. 168
8Click Update.
You configured the connection to the external vRealize Orchestrator server, and the vCAC workflows
folder and the related utility actions are automatically imported. The vCAC > ASD workflows folder
contains workflows for configuring endpoints and creating resource mappings.
What to do next
Configure the vRealize Orchestrator plug-ins as endpoints. See Configuring XaaS Resources.
Log in to the vRealize Orchestrator Configuration Interface
To edit the configuration of the default vRealize Orchestrator instance embedded in vRealize Automation,
you must start the vRealize Orchestrator configuration service and log in to the vRealize Orchestrator
configuration interface.
The vRealize Orchestrator configuration service is not started by default in the vRealize Automation
appliance. You must start the vRealize Orchestrator configuration service to access the
vRealize Orchestrator configuration interface.
Procedure
1Start the vRealize Orchestrator Configuration service.
a Log in to the vRealize Automation appliance Linux console as root.
b Enter service vco-configurator start and press Enter.
2Navigate to the vRealize Automation appliance management console by using its fully qualified
domain name, https://vra-va-hostname.domain.name.
3Click vRealize Orchestrator Control Center.
You are redirected to https://vra-va-hostname.domain.name:8283/vco-controlcenter.
4Log in to the vRealize Orchestrator Control Center.
The user name is configured by the vRealize Automation appliance administrator.
5(Optional) If this is the first time you are logging in, change the default password and click Apply
changes.
Your new password must be at least eight characters long, and must contain at least one digit, one
special character, and one uppercase letter.
Log in to the vRealize Orchestrator Client
To perform general administration tasks or to edit and create workflows in the default
vRealize Orchestrator instance, you must log in to the vRealize Orchestrator client.
The vRealize Orchestrator client interface is designed for developers with administrative rights who want
to develop workflows, actions, and other custom elements.
Configuring vRealize Automation
VMware, Inc. 169
Procedure
1Navigate to the vRealize Automation appliance management console by using its fully qualified
domain name, https://vra-va-hostname.domain.name.
2Click vRealize Orchestrator Client.
The client file is downloaded.
3Click the download and following the prompts.
4On the vRealize Orchestrator log in page, enter the IP or the domain name of the vRealize
Automation appliance in the Host name text box, and 443 as the default port number.
For example, enter vrealize_automation_appliance_ip:443.
5Log in by using the vRealize Orchestrator Client user name and password.
The credentials are the default tenant administrator user name and password.
6In the Certificate Warning window select an option to handle the certificate warning.
The vRealize Orchestrator client communicates with the vRealize Orchestrator server by using an
SSL certificate. A trusted CA does not sign the certificate during installation. You receive a certificate
warning each time you connect to the vRealize Orchestrator server.
Option Description
Ignore Continue using the current SSL certificate.
The warning message appears again when you reconnect to the same
vRealize Orchestrator server, or when you try to synchronize a workflow with a
remote Orchestrator server.
Cancel Close the window and stop the login process.
Install this certificate and do not
display any security warnings for it
anymore.
Select this check box and click Ignore to install the certificate and stop receiving
security warnings.
You can change the default SSL certificate with a certificate signed by a CA. For more information
about changing SSL certificates, see Installing and Configuring VMware vRealize Orchestrator.
What to do next
You can import a package, develop workflows, or set root access rights on the system. See Using the
VMware vRealize Orchestrator Client and Developing with VMware vRealize Orchestrator.
Configuring vRealize Automation
VMware, Inc. 170
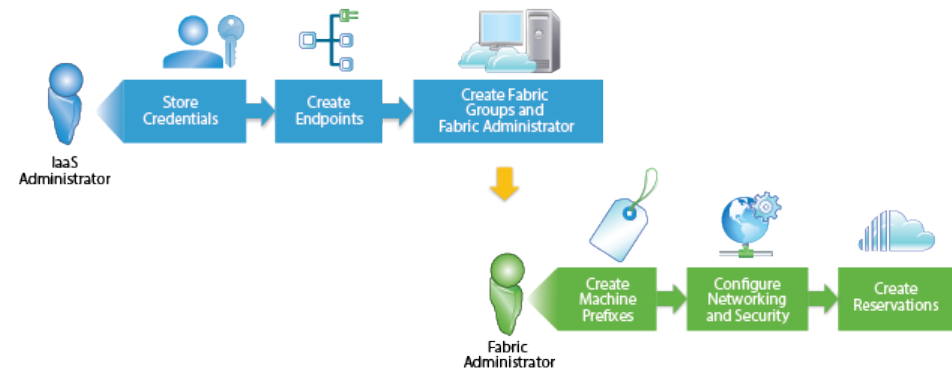
Configuring Resources 3
You can configure resources such as endpoints, reservations, and network profiles to support
vRealize Automation blueprint definition and machine provisioning.
This chapter includes the following topics:
nChecklist for Configuring IaaS Resources
nConfiguring XaaS Resources
nInstalling Additional Plug-Ins on the Default vRealize Orchestrator Server
Checklist for Configuring IaaS Resources
IaaS administrators and fabric administrators configure IaaS resources to integrate existing infrastructure
with vRealize Automation and to allocate infrastructure resources to vRealize Automation business
groups.
You can use the Configuring IaaS Resources Checklist to see a high-level overview of the sequence of
steps required to configure IaaS resources.
VMware, Inc. 171
Table 3‑1. Checklist for Configuring IaaS Resources
Task
vRealize
Automation Role Details
Store administrator-level credentials to your infrastructure. IaaS administrator Store User Credentials.
You do not have to provide credentials if you
are integrating one of the following
platforms:
nXen pool on a XenServer
nXenServer
nvSphere, and your system administrator
configured the proxy agent to use
integrated credentials
Create endpoints for your infrastructure to bring resources
under vRealize Automation management.
IaaS administrator Choosing an Endpoint Scenario.
Create a fabric group to organize infrastructure resources
into groups and assign one or more administrators to manage
those resources as your vRealize Automation fabric
administrators.
IaaS administrator Create a Fabric Group.
Configure machine prefixes used to create names for
machines provisioned through vRealize Automation.
Fabric administrator Configure Machine Prefixes.
(Optional) Create network profiles to configure network
settings for provisioned machines.
Fabric administrator Creating a Network Profile.
Allocate infrastructure resources to business groups by
creating reservations and, optionally, reservation and storage
reservation profiles.
nIaaS
administrator if
also configured
as a Fabric
Administrator
nFabric
administrator
Configuring Reservations and Reservation
Policies.
Store User Credentials
You must store administrator-level credentials for your environment so that vRealize Automation can
communicate with your endpoints. Because the same credentials can be used for multiple endpoints,
credentials are managed separately from endpoints and associated when endpoints are created or
edited.
Prerequisites
Log in to the vRealize Automation console as an IaaS administrator.
Procedure
1Select Infrastructure > Endpoints > Credentials.
2Click New Credentials.
3Enter a name in the Name text box.
4(Optional) Enter a description in the Description text box.
Configuring vRealize Automation
VMware, Inc. 172
5Enter the user name in the User name text box.
Platform Format and Details
vSphere domain\username
Provide credentials with permission to modify custom attributes.
vCloud Air username as specified in the endpoint user interface
Provide credentials for an organization administrator with rights to connect by
using VMware Remote Console.
vCloud Director username as specified in the endpoint user interface
Provide credentials with rights to connect by using VMware Remote Console.
nTo manage all organizations with a single endpoint, provide credentials for a
system administrator.
nTo manage each organization virtual datacenter (vDC) with a separate
endpoint, create separate organization administrator credentials for each
vDC.
Do not create a single system-level endpoint and individual organization
endpoints for the same vCloud Director instance.
vRealize Orchestrator username@domain
Provide credentials for each of your vRealize Orchestrator instances with Execute
permissions on all workflows you want to call from vRealize Automation.
vCloud Networking and Security
(vSphere only)
domain\username
NSX (vSphere only) username
Amazon AWS Enter your access key ID. For information about obtaining your access key ID and
secret access key, see the Amazon AWS documentation.
Cisco UCS Manager username
Dell iDRAC username
HP iLO username
Hyper-V (SCVMM) domain\username
KVM (RHEV) username@domain
NetApp ONTAP username
Red Hat OpenStack username
Provide credentials for a single user who is an administrator in all your
Red Hat OpenStack tenants, or create separate credentials for each tenant.
6Enter the password in the Password text boxes.
Platform Format
Amazon AWS Enter your Secret access key. For information about obtaining your access key ID
and secret access key, see the Amazon AWS documentation.
All others Enter the password for the user name you provided.
7Click the Save icon ( ).
Configuring vRealize Automation
VMware, Inc. 173
What to do next
Now that your credentials are stored, you are ready to create an endpoint. See Choosing an Endpoint
Scenario.
Choosing an Endpoint Scenario
You create the endpoints that allow vRealize Automation to communicate with your infrastructure.
Depending on your machine provisioning needs, the procedure to create an endpoint differs.
Choose an endpoint scenario based on the target endpoint type.
Table 3‑2. Choosing an Endpoint Scenario
Environment Create Endpoint
vSphere Create a vSphere Endpoint
vSphere with vCloud Networking and Security or NSX nCreate a vRealize Orchestrator Endpoint
nCreate a vSphere Endpoint with Network and Security
Integration
vRealize Orchestrator Create a vRealize Orchestrator Endpoint
vCloud Air Subscription or OnDemand Create a vCloud Air Endpoint
vCloud Director Create a vCloud Director Endpoint
Amazon cloud service account nCreate an Amazon Endpoint
n(Optional) Add an Amazon Instance Type
Standalone Hyper-V Create a Standalone Endpoint for Hyper-V
Hyper-V with SCVMM
(Microsoft Center Virtual Machine Manager)
Create a Hyper-V (SCVMM) Endpoint
KVM (RHEV) Create a KVM (RHEV) Endpoint
vSphere with Net App FlexClone technology for storage Create a NetApp ONTAP Endpoint
OpenStack tenant Create an OpenStack Endpoint
Xen pool on a XenServer Create a Xen Pool Endpoint
XenServer Create a XenServer Endpoint
Import a list of endpoints nPreparing an Endpoint CSV File for Import
nImport a List of Endpoints
Create an Amazon Endpoint
You can create an endpoint to connect to an Amazon Web Services instance.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nStore User Credentials.
Configuring vRealize Automation
VMware, Inc. 174
Procedure
1Select Infrastructure > Endpoints > Endpoints.
2Select New Endpoint > Cloud > Amazon EC2.
3Enter a name and, optionally, a description.
Typically this name indicates the Amazon Web Services account that corresponds to this endpoint.
4Select the Credentials for the endpoint.
Only one endpoint can be associated with an Amazon access key ID.
5(Optional) Click the Use proxy server checkbox to configure additional security and force
connections to Amazon Web Services to pass through a proxy server.
a Enter the host name of your proxy server in the Hostname text box.
b Enter the port number to use for connecting to the proxy server in the Port text box.
c (Optional) Click the Browse icon next to the Credentials text box.
Select or create credentials that represent the user name and password for the proxy server, if
required by the proxy configuration.
6(Optional) Add custom properties.
7Click OK.
After the endpoint is created, vRealize Automation begins collecting data from the Amazon Web Services
regions.
What to do next
vRealize Automation provides several Amazon Web Services instance types for you to use when creating
blueprints, but if you want to import your own instance types see Add an Amazon Instance Type.
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Add an Amazon Instance Type
Several instance types are supplied with vRealize Automation for use with Amazon blueprints. An
administrator can add and remove instance types.
The machine instance types managed by IaaS administrators are available to blueprint architects when
they create or edit an Amazon blueprint. Amazon machine images and instance types are made available
through the Amazon Web Services product.
Prerequisites
Log in to the vRealize Automation console as an IaaS administrator.
Procedure
1Click Infrastructure > Administration > Instance Types.
2Click New Instance Type.
Configuring vRealize Automation
VMware, Inc. 175

3Add a new instance type, specifying the following parameters.
Information about the available Amazon instances types and the setting values that you can specify
for these parameters is available from Amazon Web Services documentation in EC2 Instance Types -
Amazon Web Services (AWS) at aws.amazon.com/ec2 and Instance Types at
docs.aws.amazon.com.
nName
nAPI name
nType Name
nIO Performance Name
nCPUs
nMemory (GB)
nStorage (GB)
nCompute Units
4Click the Save icon ( ).
When IaaS architects create Amazon Web Services blueprints, they can use your custom instance types.
What to do next
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Create an OpenStack Endpoint
You can create an endpoint to connect to an OpenStack instance.
vRealize Automation supports several flavors of OpenStack. For the most current information about
OpenStack flavor support, see the Support Matrix at https://www.vmware.com/support/pubs/vcac-
pubs.html.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nStore User Credentials.
Procedure
1Select Infrastructure > Endpoints > Endpoints.
2Select New Endpoint > Cloud > OpenStack.
3Enter a name and, optionally, a description.
Configuring vRealize Automation
VMware, Inc. 176

4Enter the URL for the endpoint in the Address text box.
This specifies the fully qualified host name or IP address of the OpenStack keystone identity server.
The URL must be of the format FQDN:5000 or IP_address:5000.
For example: http://openstack.mycompany.com:5000.
Note Do not include the /v2.0 suffix in the endpoint address.
5Select the Credentials for the endpoint.
The credentials you provide must have the administrator role in the OpenStack tenant associated with
the endpoint.
6Enter an OpenStack tenant name in the OpenStack project text box.
If you set up multiple endpoints with different OpenStack tenants, create reservation policies for each
tenant. This ensures that machines are provisioned to the appropriate tenant resources.
7(Optional) Add custom properties.
8Click OK.
What to do next
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Create a vCloud Air Endpoint
You can create a vCloud Air endpoint for a an OnDemand or subscription service.
For information about vCloud Air Management Console, see vCloud Air documentation.
Note vCloud Air endpoints and vCloud Director endpoints do not support network profiles in a machine
deployment.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nVerify that you have Virtual Infrastructure Administrator authorization for your vCloud Air
subscription service or OnDemand account.
nStore User Credentials.
Procedure
1Select Infrastructure > Endpoints > Endpoints.
2Select New Endpoint > Cloud > vCloud Air.
3Enter a name and, optionally, a description.
Configuring vRealize Automation
VMware, Inc. 177
4Accept the default vCloud Air endpoint address in the Address text box or enter a new one.
The default vCloud Air endpoint address is https://vca.vmware.com, as specified in the Default URL
for vCloud Air endpoint global property.
5Select the Credentials for the endpoint.
The credentials must be those of thevCloud Air subscription service or OnDemand account
administrator.
6(Optional) Select the Use proxy server check box to configure additional security and force
connections to pass through a proxy server.
a Enter the host name of your proxy server in the Hostname text box.
b Enter the port number to use for connecting to the proxy server in the Port text box.
c (Optional) Click the Browse icon next to the Credentials text box.
Select or create credentials that represent the user name and password for the proxy server, if
required by the proxy configuration.
7(Optional) Add custom properties.
8Click OK.
What to do next
Create a Fabric Group.
Create a vCloud Director Endpoint
You can create a vCloud Director endpoint to manage all of the vCloud Director virtual data centers
(vDCs) in your environment, or you can create separate endpoints to manage each vCloud Director
organization.
For information about Organization vDCs, see vCloud Director documentation.
Do not create a single endpoint and individual organization endpoints for the same vCloud Director
instance.
vRealize Automation uses a proxy agent to manage vSphere resources.
Note vCloud Air endpoints and vCloud Director endpoints do not support network profiles in a machine
deployment.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nStore User Credentials.
Procedure
1Select Infrastructure > Endpoints > Endpoints.
Configuring vRealize Automation
VMware, Inc. 178
2Select New Endpoint > Cloud > vCloud Director.
3Enter a name and, optionally, a description.
4Enter the URL of the vCloud Director server in the Address text box.
The URL must be of the type FQDN or IP_address.
For example, https://mycompany.com.
5Select the Credentials for the endpoint.
nTo connect to the vCloud Director server and specify the organization for which the user has the
administrator role, use organization administrator credentials. With these credentials, the
endpoint can access only the associated organization vDCs. You can add endpoints for each
additional organization in the vCloud Director instance to integrate with vRealize Automation.
nTo allow access to all Organization vDCs in the vCloud Director instance, use system
administrator credentials for a vCloud Director and leave the Organization text box empty.
6If you are an organization administrator, you can enter a vCloud Director organization name in the
Organization text box.
Option Description
Discover all Organization vCDs If you have implemented vCloud Director in a private cloud, you can leave the
Organization text box blank to allow the application to discover all the available
Organization vDCs.
Separate endpoints for each
Organization vCD
Enter a vCloud Director organization name in the Organization text box.
The Organization name matches your vCloud Director Organization name, which might also appear
as your virtual data center (vDC) name. If you are using a Virtual Private Cloud, then this name is a
unique identifier in the M123456789-12345 format. In a dedicated cloud, it is the given name of the
target vDC.
You cannot leave the Organization text box empty.
7(Optional) Select the Use proxy server check box to configure additional security and force
connections to pass through a proxy server.
a Enter the host name of your proxy server in the Hostname text box.
b Enter the port number to use for connecting to the proxy server in the Port text box.
c (Optional) Click the Browse icon next to the Credentials text box.
Select or create credentials that represent the user name and password for the proxy server, if
required by the proxy configuration.
8(Optional) Add custom properties.
9Click OK.
Configuring vRealize Automation
VMware, Inc. 179

What to do next
Create a Fabric Group.
Create a vRealize Orchestrator Endpoint
You can configure multiple endpoints to connect to different vRealize Orchestrator servers, but you must
configure a priority for each endpoint.
When executing vRealize Orchestrator workflows, vRealize Automation tries the highest priority
vRealize Orchestrator endpoint first. If that endpoint is not reachable, then it proceeds to try the next
highest priority endpoint until a vRealize Orchestrator server is available to run the workflow.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nConfigure the user credentials. See Configuring vRealize Automation.
Procedure
1Select Infrastructure > Endpoints > Endpoints.
2Select New Endpoint > Orchestration > vCenter Orchestrator.
3Enter a name and, optionally, a description.
4Type a URL with the fully qualified name or IP address of the vRealize Orchestrator server and the
vRealize Orchestrator port number.
The transport protocol must be HTTPS. If no port is specified, the default port 443 is used.
To use the default vRealize Orchestrator instance embedded in the vRealize Automation appliance,
type https://vrealize-automation-appliance-hostname:443/vco.
5Specify the endpoint priority.
a Click New Property.
b Type VMware.VCenterOrchestrator.Priority in the Name text box.
The property name is case sensitive.
c Type an integer greater than or equal to 1 in the Value text box.
Lower value means higher priority.
dClick the Save icon ( ).
6Click OK.
Configuring vRealize Orchestrator Endpoints for Networking
If you are using vRealize Automation workflows to call vRealize Orchestrator workflows, you must
configure the vRealize Orchestrator instance or server as an endpoint.
For information about adding a vRealize Orchestrator endpoint, see Create a vRealize Orchestrator
Endpoint.
Configuring vRealize Automation
VMware, Inc. 180
You can associate a vRealize Orchestrator endpoint with a machine blueprint to make sure that all of the
vRealize Orchestrator workflows for machines provisioned from that blueprint are run using that endpoint.
vRealize Automation by default includes an embedded vRealize Orchestrator instance. It is
recommended that you use this as your vRealize Orchestrator endpoint for running vRealize Automation
workflows in a test environment or creating a proof of concept.
You can also install a plug-in on an external vRealize Orchestrator server.
It is recommended that you use this vRealize Orchestrator endpoint for running vRealize Automation
workflows in a production environment.
To install the plug-in, see the README available with the plug-in installer file from the VMware product
download site at http://vmware.com/web/vmware/downloads under the vCloud Networking and Security
or NSX links.
Create a NetApp ONTAP Endpoint
You can create endpoints to allow vRealize Automation to communicate with storage devices that use
Net App FlexClone technology.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nStore User Credentials.
Procedure
1Select Infrastructure > Endpoints > Endpoints.
2Select New Endpoint > Storage > NetApp ONTAP.
3Enter a name in the Name text box.
4(Optional) Enter a description in the Description text box.
5Enter the URL for the endpoint in the Address text box.
The URL must be of the type: FQDN or IP_address.
For example: netapp-1.mycompany.local.
6Select the Credentials for the endpoint.
If you did not already store the credentials, you can do so now.
7(Optional) Add custom properties.
8Click OK.
vRealize Automation can now discover your compute resources.
What to do next
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Configuring vRealize Automation
VMware, Inc. 181
Create a Hyper-V (SCVMM) Endpoint
IaaS administrators create endpoints to allow vRealize Automation to communicate with your SCVMM
environment and discover compute resources, collect data, and provision machines.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nStore User Credentials.
Procedure
1Select Infrastructure > Endpoints > Endpoints.
2Select New Endpoint > Virtual > Hyper-V (SCVMM).
3Enter a name in the Name text box.
4(Optional) Enter a description in the Description text box.
5Enter the URL for the endpoint in the Address text box.
The URL must be of the type: FQDN or IP_address.
For example: mycompany-scvmm1.mycompany.local.
6Select the Credentials for the endpoint.
If you did not already store the credentials, you can do so now.
7(Optional) Add custom properties.
8Click OK.
vRealize Automation can now discover your compute resources.
What to do next
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Create a Standalone Endpoint for Hyper-V
You can create endpoints to allow vRealize Automation to communicate with the Hyper-V server
environment and discover compute resources, collect data, and provision machines.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nA system administrator must install a proxy agent with stored credentials that correspond to your
endpoint. See Installing vRealize Automation 7.0.
Procedure
1Select Infrastructure > Endpoints > Agents.
Configuring vRealize Automation
VMware, Inc. 182
2Enter the fully qualified DNS name of your Hyper-V server in the Compute resource text box.
3Select the proxy agent that your system administrator installed for this endpoint from the Proxy agent
name drop-down menu.
4(Optional) Enter a description in the Description text box.
5Click OK.
vRealize Automation can now discover your compute resources.
What to do next
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Create a KVM (RHEV) Endpoint
You can create endpoints to allow vRealize Automation to communicate with the KVM (RHEV)
environment and discover compute resources, collect data, and provision machines.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nStore User Credentials.
Procedure
1Select Infrastructure > Endpoints > Endpoints.
2Select New Endpoint > Virtual > KVM (RHEV).
3Enter a name in the Name text box.
4(Optional) Enter a description in the Description text box.
5Enter the URL for the endpoint in the Address text box.
The URL must be of the type: https://FQDN or https://IP_address
For example, https://mycompany-kvmrhev1.mycompany.local.
6Select the Credentials for the endpoint.
If you did not already store the credentials, you can do so now.
7(Optional) Add custom properties.
8Click OK.
vRealize Automation can now discover your compute resources.
What to do next
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Configuring vRealize Automation
VMware, Inc. 183
Create a vSphere Endpoint
You can create endpoints that allow vRealize Automation to communicate with the vSphere environment
and discover compute resources, collect data, and provision machines.
For configurations that support vCloud Networking and Security or NSX, see Create a vSphere Endpoint
with Network and Security Integration.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nA system administrator must install a vSphere agent to correspond to your vSphere endpoints and
credentials. See Installing vRealize Automation 7.0.
nThe endpoint name you configure in vRealize Automation must match the endpoint name provided to
the vSphere proxy agent during installation. If you do not know the endpoint name your system
administrator provided to the proxy agent, see Troubleshooting Attached vSphere Endpoint Cannot
be Found.
nIf your system administrator did not configure the proxy to use integrated credentials, you must store
administrator-level credentials for your endpoint. See Store User Credentials.
Procedure
1Select Infrastructure > Endpoints > Endpoints.
2Select New Endpoint > Virtual > vSphere.
3Enter a name in the Name text box.
This must match the endpoint name provided to the vSphere proxy agent during installation or data
collection fails.
4(Optional) Enter a description in the Description text box.
5Enter the URL for the vCenter Server instance in the Address text box.
The URL must be of the type: https://hostname/sdk or https://IP_address/sdk.
For example, https://vsphereA/sdk.
6Select the Credentials for the endpoint.
If your system administrator configured the vSphere proxy agent to use integrated credentials, you
can select the Integrated credentials.
7Do not select Specify manager for network and security platform unless your configuration
supports vCloud Networking and Security or NSX.
This setting is for implementations that use vCloud Networking and Security or NSX and requires
additional configuration.
8(Optional) Add any custom properties.
9Click OK.
Configuring vRealize Automation
VMware, Inc. 184
vRealize Automation can now discover your compute resources.
Important Renaming vSphere assets after discovery can cause provisioning to fail.
What to do next
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Create a vSphere Endpoint with Network and Security Integration
You can create endpoints that allow vRealize Automation to communicate with the vSphere environment,
and a vCloud Networking and Security or NSX instance.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nA system administrator must install a vSphere agent to correspond to your vSphere endpoints and
credentials. See Installing vRealize Automation 7.0.
nThe endpoint name you configure in vRealize Automation must match the endpoint name provided to
the vSphere proxy agent during installation. If you do not know the endpoint name your system
administrator provided to the proxy agent, see Troubleshooting Attached vSphere Endpoint Cannot
be Found.
nIf your system administrator did not configure the proxy to use integrated credentials, you must store
administrator-level credentials for your endpoint. See Store User Credentials.
nConfigure your NSX or vCloud Networking and Security network settings. See Configuring Network
and Security Component Settings.
Procedure
1Select Infrastructure > Endpoints > Endpoints.
2Select New Endpoint > Virtual > vSphere.
3Enter a name in the Name text box.
This must match the endpoint name provided to the vSphere proxy agent during installation or data
collection fails.
4(Optional) Enter a description in the Description text box.
5Enter the URL for the vCenter Server instance in the Address text box.
The URL must be of the type: https://hostname/sdk or https://IP_address/sdk.
For example, https://vsphereA/sdk.
6Select the Credentials for the endpoint.
If your system administrator configured the vSphere proxy agent to use integrated credentials, you
can select the Integrated credentials.
Configuring vRealize Automation
VMware, Inc. 185

7Configure a networking solution platform.
This step is required for enabling NSX networking and security features.
a Select Specify manager for network and security platform.
b Enter the URL for the vCloud Networking and Security or NSX instance in the Address text box.
The URL must be of the type: https://hostname or https://IP_address.
For example, https://nsx-manager.
c Select the Credentials for the endpoint.
8(Optional) Add any custom properties.
9Click OK.
vRealize Automation can now discover your compute resources.
Important Renaming vSphere assets after discovery can cause provisioning to fail.
What to do next
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Create a Xen Pool Endpoint
You can create endpoints to allow vRealize Automation to communicate with the Xen pool master and
discover compute resources, collect data, and provision machines.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nA system administrator must install a proxy agent with stored credentials that correspond to your
endpoint. See Installing vRealize Automation 7.0.
Procedure
1Select Infrastructure > Endpoints > Agents.
2Enter the name of your Xen pool master in the Compute resource text box.
Note Do not enter the name of the Xen pool. You must enter the name of the pool master.
To avoid duplicate entries in the vRealize Automation compute resource table, specify an address
that matches the configured Xen pool master address. For example, if the Xen pool master address
uses the host name, enter the host name and not the FQDN. If the Xen pool master address uses
FQDN, then enter the FQDN.
3Select the proxy agent that your system administrator installed for this endpoint from the Proxy agent
name drop-down menu.
4(Optional) Enter a description in the Description text box.
Configuring vRealize Automation
VMware, Inc. 186
5Click OK.
vRealize Automation can now discover your compute resources.
What to do next
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Create a XenServer Endpoint
You can create endpoints to allow vRealize Automation to communicate with the XenServer environment
and discover compute resources, collect data, and provision machines.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nA system administrator must install a proxy agent with stored credentials that correspond to your
endpoint. See Installing vRealize Automation 7.0.
Procedure
1Select Infrastructure > Endpoints > Agents.
2Enter the fully qualified DNS name of your XenServer server in the Compute resource text box.
3Select the proxy agent that your system administrator installed for this endpoint from the Proxy agent
name drop-down menu.
4(Optional) Enter a description in the Description text box.
5Click OK.
vRealize Automation can now discover your compute resources.
What to do next
Add the compute resources from your endpoint to a fabric group. See Create a Fabric Group.
Preparing an Endpoint CSV File for Import
Instead of adding endpoints one at a time by using the vRealize Automation console, you can import a list
of endpoints by uploading a CSV file.
The CSV file must contain a header row with the expected fields. Fields are case sensitive and must be in
a specific order. You can upload multiple endpoints of varying types with the same CSV file. For
vCloud Director, system administrator accounts are imported, rather than organization administrator
endpoints.
Configuring vRealize Automation
VMware, Inc. 187
Table 3‑3. CSV File Fields and Their Order for Importing Endpoints
Field Description
InterfaceType (Required)
You can upload multiple types of endpoints in a single file.
nvCloud Air
nvCloud Director
nvRealize Orchestrator
nvSphere
nAmazon EC2
nOpenStack
nNetAppOnTap
nSCVMM
nKVM
Address (Required for all interface types except Amazon) URL for the endpoint. For information about the
required format for your platform type, see the appropriate procedure to create an endpoint for
your platform.
Credentials (Required) Name you gave the user credentials when you stored them in vRealize Automation.
Name (Required) Provide a name for the endpoint. For OpenStack, the address is used as the default
name.
Description (Optional) Provide a description for the endpoint.
OpenstackProject (Required for OpenStack only) Provide the project name for the endpoint.
Import a List of Endpoints
Importing a CSV file of endpoints can be more efficient than adding endpoints one at a time by using the
vRealize Automation console.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nStore the credentials for your endpoints.
nPrepare an Endpoint CSV file for import.
Procedure
1Select Infrastructure > Endpoints > Endpoints.
2Click Import Endpoints.
3Click Browse.
4Locate the CSV file that contains your endpoints.
Configuring vRealize Automation
VMware, Inc. 188
5Click Open.
A CSV file opens that contains a list of endpoints in the following format:
InterfaceType,Address,Credentials,Name,Description
vCloud,https://abxpoint2vco,svc-admin,abxpoint2vco,abxpoint
6Click Import.
You can edit and manage your endpoints through the vRealize Automation console.
Troubleshooting Attached vSphere Endpoint Cannot be Found
When data collection fails for a vSphere endpoint, it is often due to a mismatch between the proxy name
and the endpoint name.
Problem
Data collection fails for a vSphere endpoint. The log messages return an error similar to the following:
This exception was caught: The attached endpoint
'vCenter' cannot be found.
Cause
The endpoint name you configure in vRealize Automation must match the endpoint name provided to the
vSphere proxy agent during installation. Data collection fails for a vSphere endpoint if there is a mismatch
between the endpoint name and the proxy agent name. Until an endpoint with a matching name is
configured, the log messages return an error similar to the following:
This exception was caught: The attached endpoint
'expected endpoint name' cannot be found.
Solution
1Select Infrastructure > Monitoring > Log.
2Look for an Attached Endpoint Cannot be Found error message.
For example,
This exception was caught: The attached endpoint
'expected endpoint name' cannot be found.
3Edit your vSphere endpoint to match the expected endpoint name shown in the log message.
a Select Infrastructure > Endpoints > Endpoints.
b Click the name of the endpoint to edit.
Configuring vRealize Automation
VMware, Inc. 189
c Enter the expected endpoint name in the Name text box.
d Click OK.
The proxy agent can commute with the endpoint and data collection is successful.
Troubleshooting Locate the vCloud Air Management URL for an Organization
Virtual Data Center
To create a vCloud Air endpoint, you must provide vRealize Automation with the required vCloud Air
region and the management URL.
Solution
The vCloud Air management URL is also the URL of the vCloud Director server used to manage a
specific virtual data center (vDC). You can use the region information and the management URL to
configure your vCloud Air endpoint.
Locate the Management URL for each region vDC from the vCloud Air Console.
Procedure
1Log in to vCloud Air console with administrative privileges.
2From the vCloud Air dashboard, select your virtual data center.
3Click the link to display a URL for the virtual data center for use in API commands.
For example: https://mycompany.com:443/cloud/org/vCloudAutomation/.
The Management URL that you need to provide to vRealize Automation is the host and port
portion of the API command URL, and the region is the portion of the URL that follows
cloud/org/. In the example provided, the Management URL is https://mycompany.com:443,
and the region is vCloudAutomation.
Create a Fabric Group
You can organize infrastructure resources into fabric groups and assign one or more fabric administrators
to manage the resources in the fabric group.
Fabric groups are required for virtual and cloud endpoints. You can grant the fabric administrator role to
multiple users by either adding multiple users one at a time or by choosing an identity store group or
custom group as your fabric administrator.
Prerequisites
nLog in to the vRealize Automation console as an IaaS administrator.
nCreate at least one endpoint.
Procedure
1Select Infrastructure > Fabric Groups.
2Click New Fabric Group.
Configuring vRealize Automation
VMware, Inc. 190
3Enter a name in the Name text box.
4(Optional) Enter a description in the Description text box.
5Enter a user name or group name in the Fabric administrators text box and press Enter.
Repeat this step to add multiple users or groups to the role.
6Click one or more Compute resources to include in your fabric group.
Only resources that exist on the clusters you select for your fabric group are discovered during data
collection. For example, only templates that exist on the clusters you select are discovered and
available for cloning on reservations you create for business groups.
7Click OK.
Fabric administrators can now configure machine prefixes. See Configure Machine Prefixes.
Users who are currently logged in to the vRealize Automation console must log out and log back in to the
vRealize Automation console before they can navigate to the pages to which they have been granted
access.
Configure Machine Prefixes
You can create machine prefixes that are used to create names for machines provisioned through
vRealize Automation. A machine prefix is required when defining a machine component in the blueprint
design canvas.
A prefix is a base name to be followed by a counter of a specified number of digits. When the digits are all
used, vRealize Automation rolls back to the first number.
Machine prefixes must conform to the following limitations:
nContain only the case-insensitive ASCII letters a through z, the digits 0 through 9, and the hyphen (-).
nNot begin with a hyphen.
nNo other symbols, punctuation characters, or blank spaces can be used.
nNo longer than 15 characters, including the digits, to conform to the Windows limit of 15 characters in
host names.
Longer host names are truncated when a machine is provisioned, and updated the next time data
collection is run. However, for WIM provisioning names are not truncated and provisioning fails when
the specified name is longer than 15 characters.
nvRealize Automation does not support multiple virtual machines of the same name in a single
instance. If you choose a naming convention that causes an overlap in machine names,
vRealize Automation does not provision a machine with the redundant name. If possible,
vRealize Automation skips the name that is already in use and generates a new machine name using
the specified machine prefix. If a unique name cannot be generated, provisioning fails.
Prerequisites
Log in to the vRealize Automation console as a fabric administrator.
Configuring vRealize Automation
VMware, Inc. 191

Procedure
1Click Infrastructure > Administration > Machine Prefixes.
2Click New.
3Enter the machine prefix in the Name text box.
4Enter the number of counter digits in the Number of Digits text box.
5Enter the counter start number in the Next Number text box.
6Click the Save icon ( ).
Tenant administrators can create business groups so that users can access vRealize Automation to
request machines.
Managing Key Pairs
Key pairs are used to provision and connect to a cloud instance. A key pair is used to decrypt Windows
passwords or to log in to a Linux machine.
Key pairs are required for provisioning with Amazon AWS. For Red Hat OpenStack, key pairs are
optional.
Existing key pairs are imported as part of data collection when you add a cloud endpoint. A fabric
administrator can also create and manage key pairs by using the vRealize Automation console. If you
delete a key pair from the vRealize Automation console, it is also deleted from the cloud service account.
In addition to managing key pairs manually, you can configure vRealize Automation to generate key pairs
automatically per machine or per business group.
nA fabric administrator can configure the automatic generation of key pairs at a reservation level.
nIf the key pair is going to be controlled at the blueprint level, the fabric administrator must select Not
Specified on the reservation.
nA tenant administrator or business group manager can configure the automatic generation of key
pairs at a blueprint level.
nIf key pair generation is configured at both the reservation and blueprint level, the reservation setting
overrides the blueprint setting.
Create a Key Pair
You can create key pairs for use with endpoints by using vRealize Automation.
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nCreate a cloud endpoint and add your cloud compute resources to a fabric group. See Choosing an
Endpoint Scenario and Create a Fabric Group.
Configuring vRealize Automation
VMware, Inc. 192

Procedure
1Select Infrastructure > Reservations > Key Pairs.
2Click New.
3Enter a name in the Name text box.
4Select a cloud region from the Compute resource drop-down menu.
5Click the Save icon ( ).
The key pair is ready to use when the Secret Key column has the value ************.
Upload the Private Key for a Key Pair
You can upload the private key for a key pair in PEM format.
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nYou must already have a key pair. See Create a Key Pair.
Procedure
1Select Infrastructure > Reservations > Key Pairs.
2Locate the key pair for which you want to upload a private key.
3Click the Edit icon ( ).
4Use one of the following methods to upload the key.
nBrowse for a PEM-encoded file and click Upload.
nPaste the text of the private key, beginning with -----BEGIN RSA PRIVATE KEY----- and
ending with -----END RSA PRIVATE KEY-----.
5Click the Save icon ( ).
Export the Private Key from a Key Pair
You can export the private key from a key pair to a PEM-encoded file.
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nA key pair with a private key must exist. See Upload the Private Key for a Key Pair.
Procedure
1Select Infrastructure > Reservations > Key Pairs.
2Locate the key pair from which to export the private key.
Configuring vRealize Automation
VMware, Inc. 193

3Click the Export icon ( ).
4Browse to the location that you want to save the file and click Save.
Creating a Network Profile
You can use network profiles to specify network settings in reservations, relative to a network path. With
some machine types, you can specify a network profile when you work with blueprints in the design
canvas.
You specify an external network profile when you create reservations and blueprints.
If a network profile is specified in the blueprint (by using the VirtualMAchine.NetworkN.ProfileName
custom property) and by a reservation that is used by the blueprint, the network profile specified in the
blueprint takes precedence. However, if the custom property is not used in the blueprint, and you select a
network profile for a machine NIC, vRealize Automation uses a reservation network path for the machine
NIC for which the network profile is specified.
Network profiles are used to configure network settings when machines are provisioned, and to specify
the configuration of NSX Edge devices that are created when you provision machines. In a reservation,
you can assign a network profile to a network path and specify any one of those paths for a machine
component in a blueprint.
You can create a network profile to define a type of available network, including external network profiles
and templates for network address translation (NAT) and routed network profiles that will build NSX
logical switches and appropriate routing settings for a new network path to be used by provisioned
machine as assigned in blueprint.
You can specify the ranges of IP addresses that network profiles can use. Each IP address in the
specified ranges that are allocated to a machine is reclaimed for reassignment when the machine is
destroyed.
A blueprint creator specifies NAT, external, and routed network profiles in blueprints for use in configuring
network adapters and load balancers for the provisioning machine.
Configuring vRealize Automation
VMware, Inc. 194
Table 3‑4. Available Network Types for a vRealize Automation Network Profile
Network Type Description
External Existing physical or logical networks configured on the vSphere server. They are the external part of the NAT
and routed networks types. An external network profile can define a range of static IP addresses available on
the external network. An external network profile with a static IP range is a prerequisite for NAT and routed
networks.
NAT Created during provisioning. They are networks that use one set of IP addresses for external communication
and another set for internal communications. With one-to-one NAT networks, every virtual machine is assigned
an external IP address from the external network profile and an internal IP address from the NAT network
profile. With one-to-many NAT networks, all machines share a single IP address from the external network
profile for external communication. A NAT network profile defines local and external networks that use a
translation table for mutual communication.
Routed Created during provisioning. They represent a routable IP space divided across subnets that are linked
together using Distributed Logical Router (DLR). Every new routed network has the next available subnet
assigned to it and is associated with other routed networks that use the same network profile. The virtual
machines that are provisioned with routed networks that have the same routed network profile can
communicate with each other and the external network. A routed network profile defines a routable space and
available subnets. For more information about Distributed Logical Router, see NSX Administration Guide.
vRealize Automation uses vSphere DHCP to assign IP addresses to the machines it provisions,
regardless of which provisioning method is used. When provisioning virtual machines by cloning (with a
customization specified) or by using kickstart/autoYaST provisioning, the requesting machine owner can
assign static IP addresses from a predetermined range.
Assigning a Static IP Address Range
You can assign static IP addresses from a predefined range to virtual machines that are provisioned by
cloning, by using Linux kickstart/autoYaST, or to cloud machines that are provisioned in OpenStack by
using kickstart.
By default, vRealize Automation uses Dynamic Host Configuration Protocol (DHCP) to assign IP
addresses to provisioned machines.
An administrator can create network profiles to define a range of static IP addresses that you can assign
to machines. You can assign network profiles to specific network paths on a reservation. Any cloud
machine or virtual machine that is provisioned by cloning or by kickstart/autoYaST that is attached to a
network path with an associated network profile is provisioned with an assigned static IP address. For
provisioning with a static IP address assignment, you must use a customization specification.
You can assign a network profile to vSphere machine component in a blueprint by adding an existing, on-
demand NAT, or on-demand routed network component to the design canvas and then selecting a
network profile to which to connect the vSphere machine component. You can also assign network
profiles to blueprints by using the custom property VirtualMachine.NetworkN.ProfileName, where N
is the network identifier.
Configuring vRealize Automation
VMware, Inc. 195
If a network profile is specified in the blueprint (by using the VirtualMAchine.NetworkN.ProfileName
custom property) and by a reservation that is used by the blueprint, the network profile specified in the
blueprint takes precedence. However, if the custom property is not used in the blueprint, and you select a
network profile for a machine NIC, vRealize Automation uses a reservation network path for the machine
NIC for which the network profile is specified.
When you destroy a machine that has a static IP address, its IP address is made available for other
machines to use. Unused addresses might not be available immediately after the machines using them
are destroyed because the process to reclaim static IP addresses runs every 30 minutes. If IP addresses
are not available in the network profile, machines cannot be provisioned with static IP assignment on the
associated network path.
Create a Network Profile for Static IP Address Assignment
You can create network profiles to define a range of static IP addresses that the provisioning request can
assign to machines.
Procedure
1Specify Network Profile Information for a Static IP Range
The network profile information identifies the external network profile and specifies settings for an
existing network.
2Configure a Static IP Range in a Network Profile
You can define one or more ranges of static IP addresses in the network profile for use in
provisioning a machine. If you do not specify a range, you can use a network profile as a network
reservation policy to select a reservation network path for a machine network card (NIC).
What to do next
You can assign a network profile to a network path in a reservation or a blueprint creator can specify the
network profile in a blueprint.
Specify Network Profile Information for a Static IP Range
The network profile information identifies the external network profile and specifies settings for an existing
network.
Prerequisites
Log in to the vRealize Automation console as a fabric administrator.
Procedure
1Select Infrastructure > Reservations > Network Profiles.
2Select New Network Profile > External.
3Enter a name and, optionally, a description.
4Enter an IP subnet mask address in the Subnet mask text box.
For example, 255.255.0.0.
Configuring vRealize Automation
VMware, Inc. 196
5(Optional) Enter the default IP gateway address in the Gateway text box.
The gateway address is required for a one-to-one NAT network profile.
6(Optional) In the DNS/WINS group, enter values as needed.
The external network profile provides these values.
Configure a Static IP Range in a Network Profile
You can define one or more ranges of static IP addresses in the network profile for use in provisioning a
machine. If you do not specify a range, you can use a network profile as a network reservation policy to
select a reservation network path for a machine network card (NIC).
Prerequisites
Specify Network Profile Information for a Static IP Range.
Procedure
1Click the IP Ranges tab.
2Click New Network Range.
The New Network Range dialog box appears.
3Enter a name and, optionally, a description.
4Enter an IP address in the Starting IP address text box.
5Enter an IP address in the Ending IP address text box.
6Click OK.
The newly defined IP address range appears in the Defined Ranges list. The IP addresses in the
range appear in the Defined IP Addresses list.
7(Optional) Upload one or more IP addresses from a CSV file.
A row in the CSV file has the format ip_address,mname,status.
CSV Field Description
ip_address An IP address
mname Name of a managed machine in vRealize Automation. If the field is empty, defaults to no name.
status Allocated or Unallocated, case-sensitive. If the field is empty, defaults to Unallocated.
a Click Browse next to the Upload CSV text box.
b Navigate to the CSV file and click Open.
c Click Process CSV File.
The uploaded IP addresses appear in the Defined IP Addresses list. If the upload fails, diagnostic
messages appear that identify the problems.
Configuring vRealize Automation
VMware, Inc. 197
8(Optional) Filter IP address entries to only those that match.
a Click in the Defined IP Addresses text boxes.
b Enter a partial IP address or machine name, or select a date from the Last Modified drop-down
calendar.
The IP addresses that match the filter criteria appear.
9Click OK.
What to do next
You can assign a network profile to a network path in a reservation or a blueprint creator can specify the
network profile in a blueprint.
Create an External Network Profile
You can create an external network profile to define external network properties and a range of static IP
addresses to use when provisioning machines.
Procedure
1Configure External Network Profile Information
The network profile information identifies the external network properties and specifies settings for
an existing network. An external network profile is a requirement of NAT and routed network profiles.
2Configure External Network Profile IP Ranges
You can define zero or more ranges of static IP addresses for use in provisioning a network. An
external network profile must have at least one static IP range for use with routed and NAT network
profiles.
Configure External Network Profile Information
The network profile information identifies the external network properties and specifies settings for an
existing network. An external network profile is a requirement of NAT and routed network profiles.
Prerequisites
nVerify that you have a gateway IP address.
nLog in to the vRealize Automation console as a fabric administrator.
Procedure
1Select Infrastructure > Reservations > Network Profiles.
2Select New Network Profile > External.
3Enter a name and, optionally, a description.
4Enter an IP subnet mask address in the Subnet mask text box.
For example, 255.255.0.0.
5Enter an IP address in the Gateway text box.
Configuring vRealize Automation
VMware, Inc. 198
6In the DNS/WINS group, enter values as needed.
What to do next
You can configure IP ranges for static IP addresses. See Configure External Network Profile IP Ranges.
Configure External Network Profile IP Ranges
You can define zero or more ranges of static IP addresses for use in provisioning a network. An external
network profile must have at least one static IP range for use with routed and NAT network profiles.
If an external network profile does not have IP ranges defined, you can use it to specify which network is
picked for a network card (NIC).
Prerequisites
Configure External Network Profile Information.
Procedure
1Click the IP Ranges tab.
2Click New Network Range.
The New Network Range dialog box appears.
3Enter a name and, optionally, a description.
4Enter an IP address in the Starting IP address text box.
5Enter an IP address in the Ending IP address text box.
6Click OK.
The newly defined IP address range appears in the Defined Ranges list. The IP addresses in the
range appear in the Defined IP Addresses list.
7(Optional) Upload one or more IP addresses from a CSV file.
A row in the CSV file has the format ip_address,mname,status.
CSV Field Description
ip_address An IP address
mname Name of a managed machine in vRealize Automation. If the field is empty, defaults to no name.
status Allocated or Unallocated, case-sensitive. If the field is empty, defaults to Unallocated.
a Click Browse next to the Upload CSV text box.
b Navigate to the CSV file and click Open.
c Click Process CSV File.
The uploaded IP addresses appear in the Defined IP Addresses list. If the upload fails, diagnostic
messages appear that identify the problems.
Configuring vRealize Automation
VMware, Inc. 199
8(Optional) Filter IP address entries to only those that match.
a Click in the Defined IP Addresses text boxes.
b Enter a partial IP address or machine name, or select a date from the Last Modified drop-down
calendar.
The IP addresses that match the filter criteria appear.
9Click OK.
Create a NAT Network Profile
You can create a NAT network profile template to define a NAT network and assign ranges of static IP
and DHCP addresses to it.
Procedure
1Specify NAT Network Profile Information
The network profile information identifies the NAT network properties, its underlying external network
profile, the NAT type, and other values used in provisioning the network.
2Configure NAT Network Profile IP Ranges
You can define one or more ranges of static IP addresses for use in provisioning a network.
Specify NAT Network Profile Information
The network profile information identifies the NAT network properties, its underlying external network
profile, the NAT type, and other values used in provisioning the network.
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nCreate an External Network Profile.
Procedure
1Select Infrastructure > Reservations > Network Profiles.
2Select New Network Profile > NAT.
3Enter a name and, optionally, a description.
4Select a network profile from the drop-down menu.
Configuring vRealize Automation
VMware, Inc. 200
5Select a NAT type from the drop-down menu.
Option Description
One-to-One Assign an external static IP address to each network adapter. Every machine can
access the external network and is accessible from the external network.
One-to-Many One external IP address is shared among all machines on the network. An
internal machine can have either DHCP or static IP addresses. Every machine
can access the external network, but no machine is accessible from the external
network. Selecting this option enables the Enabled check box in the DHCP
group.
6Enter an IP subnet mask address in the Subnet mask text box.
For example, 255.255.0.0.
7Type an IP address in the Gateway text box.
The gateway address is required for a one-to-one NAT network profile.
8(Optional) In the DNS/WINS group, enter values as needed.
The external network profile provides these values.
9(Optional) In the DHCP group, select the Enabled check box and enter the values as needed.
You can select the check box only if you set the NAT type to one-to-many.
10 (Optional) Set a lease time to define how long a machine can use an IP address.
What to do next
A NAT network profile requires DHCP information or an IP range. For information about how to create an
IP range, see Configure NAT Network Profile IP Ranges.
Configure NAT Network Profile IP Ranges
You can define one or more ranges of static IP addresses for use in provisioning a network.
Prerequisites
Configure External Network Profile Information.
Procedure
1Click the IP Ranges tab.
2Click New Network Range.
The New Network Range dialog box appears.
3Enter a name and, optionally, a description.
4Enter an IP address in the Starting IP address text box.
5Enter an IP address in the Ending IP address text box.
Configuring vRealize Automation
VMware, Inc. 201
6Click OK.
The newly defined IP address range appears in the Defined Ranges list. The IP addresses in the
range appear in the Defined IP Addresses list.
7(Optional) Upload one or more IP addresses from a CSV file.
A row in the CSV file has the format ip_address,mname,status.
CSV Field Description
ip_address An IP address
mname Name of a managed machine in vRealize Automation. If the field is empty, defaults to no name.
status Allocated or Unallocated, case-sensitive. If the field is empty, defaults to Unallocated.
a Click Browse next to the Upload CSV text box.
b Navigate to the CSV file and click Open.
c Click Process CSV File.
The uploaded IP addresses appear in the Defined IP Addresses list. If the upload fails, diagnostic
messages appear that identify the problems.
8(Optional) Filter IP address entries to only those that match.
a Click in the Defined IP Addresses text boxes.
b Enter a partial IP address or machine name, or select a date from the Last Modified drop-down
calendar.
The IP addresses that match the filter criteria appear.
9Click OK.
Create a Routed Network Profile
You can create a routed network profile to define a routable IP space and available subnets for routed
networks.
Procedure
1Specify Routed Network Profile Information
The network profile information identifies the routed network properties, its underlying external
network profile, and other values used in provisioning the network.
2Configure Routed Network Profile IP Ranges
You can define one or more ranges of static IP addresses for use in provisioning a network.
Specify Routed Network Profile Information
The network profile information identifies the routed network properties, its underlying external network
profile, and other values used in provisioning the network.
Configuring vRealize Automation
VMware, Inc. 202
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nCreate an External Network Profile.
nVerify that the NSX logical router is configured in the vSphere Client to use the routed network profile.
See NSX Administration Guide.
Procedure
1Select Infrastructure > Reservations > Network Profiles.
2Select New Network Profile > Routed.
3Enter a name and, optionally, a description.
4Select a network profile from the drop-down menu.
5Enter an IP subnet mask address in the Subnet mask text box.
For example, 255.255.0.0.
6Type a mask address in the Range subnet mask text box.
For example, 255.255.255.0.
7Type an IP address in the Base IP text box.
8(Optional) In the DNS/WINS group, enter values as needed.
The external network profile provides these values.
What to do next
A routed network profile requires an IP range. For information on creating an IP range, see Configure
Routed Network Profile IP Ranges.
Configure Routed Network Profile IP Ranges
You can define one or more ranges of static IP addresses for use in provisioning a network.
During provisioning, every new routed network allocates the next available subnet range and uses it as its
IP space.
When a deployment is deleted, its allocated routed network profile range is released after the next static
IP addresses workflow runs.
Prerequisites
Configure External Network Profile Information.
Procedure
1Click the IP Ranges tab.
Configuring vRealize Automation
VMware, Inc. 203
2Click Generate Ranges.
You must enter the subnet mask, range subnet mask, and base IP addresses on the Network Profile
Information tab before you can generate IP ranges. Starting with the base IP address,
vRealize Automation generates ranges based on the range subnet mask.
For example, vRealize Automation generates ranges of 254 IP addresses if the subnet mask is
255.255.0.0 and the range subnet mask is 255.255.255.0.
3Click New Network Range.
The New Network Range dialog box appears.
4Enter a name and, optionally, a description.
5Enter an IP address in the Starting IP address text box.
This IP address must match the base IP address in the routed network profile.
6Enter an IP address in the Ending IP address text box.
7Click OK.
The IP address range appears in the Defined Ranges list.
8Click OK.
Configuring Reservations and Reservation Policies
A vRealize Automation reservation can define policies, priorities, and quotas that determine machine
placement for provisioning requests. Reservation policies restrict machine provisioning to a subset of
available reservations. Storage reservation policies allow blueprint architects to assign machine volumes
to different datastores.
Reservations
You can create a vRealize Automation reservation to allocate provisioning resources in the fabric group to
a specific business group.
For example, you can use reservations to specify that a share of the memory, CPU, networking, and
storage resources of a single compute resource belongs to a particular business group or that certain
machines be allocated to a specific business group.
You can create a reservation for the following machine types:
nvSphere
nvCloud Air
nvCloud Director
nAmazon
nHyper-V
nKVM
Configuring vRealize Automation
VMware, Inc. 204
nOpenStack
nSCVMM
nXenServer
Choosing a Reservation Scenario
You can create reservations to allocate resources to business groups. Depending on your scenario, the
procedure to create a reservation differs.
Choose a reservation scenario based on the target endpoint type.
Each business group must have at least one reservation for its members to provision machines of that
type. For example, a business group with an OpenStack reservation but not an Amazon reservation,
cannot request a machine from Amazon. In this example, the business group must be allocated a
reservation specifically for Amazon resources.
Table 3‑5. Choosing a Reservation Scenario
Scenario Procedure
Create a vSphere reservation. Create a Reservation for Hyper-V, KVM, SCVMM, vSphere, or
XenServer
Create a reservation to allocate resources for a vCloud Air
endpoint.
Create a vCloud Air Reservation
Create a reservation to allocate resources for a vCloud Director
endpoint.
Create a vCloud Director Reservation
Create a reservation to allocate resources on an Amazon
resource (with or without using Amazon Virtual Private Cloud).
Create an Amazon Reservation
Create a reservation to allocate resources on an OpenStack
resource.
Create an OpenStack Reservation
Create a reservation to allocate resources for Hyper-V. Create a Reservation for Hyper-V, KVM, SCVMM, vSphere, or
XenServer
Create a reservation to allocate resources for KVM. Create a Reservation for Hyper-V, KVM, SCVMM, vSphere, or
XenServer
Create a reservation to allocate resources on an OpenStack.
resource.
Create an OpenStack Reservation
Create a reservation to allocate resources for SCVMM. Create a Reservation for Hyper-V, KVM, SCVMM, vSphere, or
XenServer
Create a reservation to allocate resources for XenServer. Create a Reservation for Hyper-V, KVM, SCVMM, vSphere, or
XenServer
Creating Cloud Category Reservations
A cloud category type reservation provides access to the provisioning services of a cloud service account
for a particular vRealize Automation business group. Available cloud reservation types include Amazon,
OpenStack, vCloud Air, and vCloud Director.
A reservation is a share of the memory, CPU, networking, and storage resources of one compute
resource allocated to a particular vRealize Automation business group.
Configuring vRealize Automation
VMware, Inc. 205
A business group can have multiple reservations on one endpoint or reservations on multiple endpoints.
The allocation model for a reservation depends on the allocation model in the associated datacenter.
Available allocation models are Allocation Pool, Pay As You Go, and reservation pool. For information
about allocation models, see thevCloud Director or vCloud Air documentation.
In addition to defining the share of fabric resources allocated to the business group, a reservation can
define policies, priorities, and quotas that determine machine placement.
Understanding Selection Logic for Cloud Reservations
When a member of a business group creates a provisioning request for a cloud machine,
vRealize Automation selects a machine from one of the reservations that are available to that business
group. Cloud reservations include Amazon, OpenStack, vCloud Air, and vCloud Director.
The reservation for which a machine is provisioned must satisfy the following criteria:
nThe reservation must be of the same platform type as the blueprint from which the machine was
requested.
nThe reservation must be enabled.
nThe reservation must have capacity remaining in its machine quota or have an unlimited quota.
The allocated machine quota includes only machines that are powered on. For example, if a
reservation has a quota of 50, and 40 machines have been provisioned but only 20 of them are
powered on, the reservation’s quota is 40 percent allocated, not 80 percent.
nThe reservation must have the security groups specified in the machine request.
nThe reservation must be associated with a region that has the machine image specified in the
blueprint.
nThe reservation must have sufficient unallocated memory and storage resources to provision the
machine.
In a Pay As You Go reservation, resources can be unlimited.
nFor Amazon machines, the request specifies an availability zone and whether the machine is to be
provisioned a subnet in a Virtual Private Cloud (VPC) or a in a non-VPC location. The reservation
must match the network type (VPC or non-VPC).
nFor vCloud Air or vCloud Director, if the request specifies an allocation model, the virtual datacenter
associated with the reservation must have the same allocation model.
nFor vCloud Director or vCloud Air, the specified organization must be enabled.
nAny blueprint templates must be available on the reservation. If the reservation policy maps to more
than one resources, the templates should be public.
nIf the cloud provider supports network selection and the blueprint has specific network settings, the
reservation must have the same networks.
If the blueprint or reservation specifies a network profile for static IP address assignment, an IP
address must be available to assign to the new machine.
Configuring vRealize Automation
VMware, Inc. 206
nIf the request specifies an allocation model, the allocation model in the reservation must match the
allocation model in the request.
nIf the blueprint specifies a reservation policy, the reservation must belong to that reservation policy.
Reservation policies are a way to guarantee that the selected reservation satisfies any additional
requirements for provisioning machines from a specific blueprint. For example, if a blueprint uses a
specific machine image, you can use reservation policies to limit provisioning to reservations
associated with the regions that have the required image.
If no reservation is available that meets all of the selection criteria, provisioning fails.
If multiple reservations meet all of the criteria, the reservation from which to provision a requested
machine is determined by the following logic:
nReservations with higher priority are selected over reservations with lower priority.
nIf multiple reservations have the same priority, the reservation with the lowest percentage of its
machine quota allocated is selected.
nIf multiple reservations have the same priority and quota usage, machines are distributed among
reservations in round-robin fashion.
If multiple storage paths are available on a reservation with sufficient capacity to provision the machine
volumes, storage paths are selected according to the following logic.
nIf the blueprint or request specifies a storage reservation policy, the storage path must belong to that
storage reservation policy.
If the custom property VirtualMachine.DiskN.StorageReservationPolicyMode is set to Not
Exact, and no storage path with sufficient capacity is available in the storage reservation policy, then
provisioning proceeds with a storage path outside the specified storage reservation policy. The
default value of VirtualMachine.DiskN.StorageReservationPolicyMode is Exact.
nStorage paths with higher priority are selected over reservations with lower priority.
nIf multiple storage paths have the same priority, machines are distributed among storage paths by
using round-robin scheduling.
Using Amazon Security Groups
Specify at least one security group when creating an Amazon reservation. Each available region requires
at least one specified security group.
A security group acts as a firewall to control access to a machine. Every region includes at least the
default security group. Administrators can use the Amazon Web Services Management Console to create
additional security groups, configure ports for Microsoft Remote Desktop Protocol or SSH, and set up a
virtual private network for an Amazon VPN.
Configuring vRealize Automation
VMware, Inc. 207

When you create an Amazon reservation or configure a machine component in the blueprint, you can
choose from the list of security groups that are available to the specified Amazon account region. Security
groups are imported during data collection.
For information about creating and using security groups in Amazon Web Services, see Amazon
documentation.
Create an Amazon Reservation
You must allocate resources to machines by creating a reservation before members of a business group
can request machine provisioning.
You can work with Amazon reservations for Amazon Virtual Private Cloud or Amazon non-VPC.
Amazon Web Services users can create a Amazon Virtual Private Cloud to design a virtual network
topology according to your specifications. If you plan to use Amazon VPC, you must assign an
Amazon VPC to a vRealize Automation reservation. See .
Note After you create a reservation, you cannot change the business group or compute resource
associations.
For information about creating an Amazon VPC by using the AWS Management Console, see
Amazon Web Services documentation.
Procedure
1Specify Amazon Reservation Information
Each reservation is configured for a specific business group to grant them access to request
machines on a specified compute resource.
2Specify Resource and Network Settings for Amazon Reservations
Specify resource and network settings for provisioning machines from this vRealize Automation
reservation.
3Specify Custom Properties and Alerts for Amazon Reservations
You can associate custom properties with a vRealize Automation reservation. You can also
configure alerts to send email notifications when reservation resources are low.
Specify Amazon Reservation Information
Each reservation is configured for a specific business group to grant them access to request machines on
a specified compute resource.
Note After you create a reservation, you cannot change the business group or compute resource
associations.
You can control the display of reservations when adding, editing, or deleting by using the Filter By
Category option on the Reservations page. Note that test agent reservations do not appear in the
reservations list when filtering by category.
Configuring vRealize Automation
VMware, Inc. 208

Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nVerify that a tenant administrator created at least one business group.
nVerify that a compute resource exists.
nConfigure network settings.
n(Optional) Configure network profile information.
nVerify that you have access to a desired Amazon network. For example, if you want to use VPC,
verify that you have access to an Amazon Virtual Private Cloud (VPC) network.
nVerify that any required key pairs exist. See Managing Key Pairs.
Procedure
1Select Infrastructure > Reservations > Reservations.
2Click the New icon ( ) and select the type of reservation to create.
Select Amazon.
3(Optional) Select an existing reservation from the Copy from existing reservation drop-down menu.
Data from the selected reservation appears. You can make changes as required for your new
reservation.
4Enter a name in the Name text box.
5Select a tenant from the Tenant drop-down menu.
6Select a business group from the Business group drop-down menu.
Only users in this business group can provision machines by using this reservation.
7(Optional) Select a reservation policy from the Reservation policy drop-down menu.
This option requires that one or more reservation policies exist. You can edit the reservation later to
specify a reservation policy.
You use a reservation policy to restrict provisioning to specific reservations.
8Enter a number in the Priority text box to set the priority for the reservation.
The priority is used when a business group has more than one reservation. A reservation with priority
1 is used for provisioning over a reservation with priority 2.
9(Optional) Deselect the Enable this reservation check box if you do not want this reservation active.
Do not navigate away from this page. Your reservation is not complete.
Specify Resource and Network Settings for Amazon Reservations
Specify resource and network settings for provisioning machines from this vRealize Automation
reservation.
Configuring vRealize Automation
VMware, Inc. 209
For related information about load balancers, see Configuring vRealize Automation.
Prerequisites
Specify Amazon Reservation Information.
Procedure
1Click the Resouces tab.
2Select a compute resource on which to provision machines from the Compute resource drop-down
menu.
Available Amazon regions are listed.
3(Optional) Enter a number in the Machine quota text box to set the maximum number of machines
that can be provisioned on this reservation.
Only machines that are powered on are counted towards the quota. Leave blank to make the
reservation unlimited.
4Select a method of assigning key pairs to compute instances from the Key pair drop-down menu.
Option Description
Not Specified Controls key pair behavior at the blueprint level rather than the reservation level.
Auto-Generated per Business Group Every machine provisioned in the same business group has the same key pair,
including machines provisioned on other reservations when the machine has the
same compute resource and business group. Because key pairs generated this
way are associated with a business group, the key pairs are deleted when the
business group is deleted.
Auto-Generated per Machine Each machine has a unique key pair. This is the most secure method because no
key pairs are shared among machines.
Specific Key Pair Every machine provisioned on this reservation has the same key pair. Browse for
a key pair to use for this reservation.
5If you selected Specific key Pair in the Key pair drop-down menu, select a key pair value from the
Specific key pair drop-down menu.
6If you are configured for Amazon Virtual Private Cloud, enable the Assign to a subnet in a VPC
check mark box. Otherwise, leave the box unchecked.
If you select Assign to a subnet in a VPC, the following locations or subnets, security groups, and
load balancers options appear in a popup menu rather than on this same page.
7Select one or more available locations (non-VPC) or subnets (VPC) from the Locations or Subnets
list.
Select each available location or subnet that you want to be available for provisioning.
8Select one or more security groups that can be assigned to a machine during provisioning from the
Security groups list.
Select each security group that can be assigned to a machine during provisioning.
Configuring vRealize Automation
VMware, Inc. 210
9Select one or more available load balancers from the Load balancers list.
If you are using the elastic load balancer feature, select one or more available load balancers that
apply to the selected locations or subnets.
You can save the reservation now by clicking Save. Or you can add custom properties to further control
reservation specifications. You can also configure email alerts to send notifications when resources
allocated to this reservation become low.
Specify Custom Properties and Alerts for Amazon Reservations
You can associate custom properties with a vRealize Automation reservation. You can also configure
alerts to send email notifications when reservation resources are low.
Custom properties and email alerts are optional configurations for the reservation. If you do not want to
associate custom properties or set alerts, click Save to finish creating the reservation.
You can add as many custom properties as apply to your needs.
If configured, alerts are generated daily, rather than when the specified thresholds are reached.
Important Notifications are only sent if email alerts are configured and notifications are enabled.
Prerequisites
Specify Resource and Network Settings for Amazon Reservations.
Procedure
1Click the Properties tab.
2Click New.
3Enter a valid custom property name.
4If applicable, enter a property value.
5Click Save.
6(Optional) Add any additional custom properties.
7Click the Alerts tab.
8Enable the Capacity Alerts check box to configure alerts to be sent.
9Use the slider to set thresholds for available resource allocation.
10 Enter one or more user email addresses or group names to receive alert notifications in the
Recipients text box.
Press Enter to separate multiple entries.
11 Select Send alerts to group manager to include group managers in the email alerts.
12 Specify a reminder frequency (days).
13 Click Save.
Configuring vRealize Automation
VMware, Inc. 211
The reservation is saved and appears in the Reservations list.
What to do next
You can configure optional reservation policies or begin preparing for provisioning.
Users who are authorized to create blueprints can create them now.
Create an OpenStack Reservation
You must allocate resources to machines by creating a reservation before members of a business group
can request machine provisioning.
Create an OpenStack reservation.
Procedure
1Specify OpenStack Reservation Information
Each reservation is configured for a specific business group to grant them access to request
machines on a specified compute resource.
2Specify Resources and Network Settings for OpenStack Reservations
Specify resource and network settings available to machines that are provisioned from this
vRealize Automation reservation.
3Specify Custom Properties and Alerts for OpenStack Reservations
You can associate custom properties with a vRealize Automation reservation. You can also
configure alerts to send email notifications when reservation resources are low.
Specify OpenStack Reservation Information
Each reservation is configured for a specific business group to grant them access to request machines on
a specified compute resource.
Note After you create a reservation, you cannot change the business group or compute resource
associations.
You can control the display of reservations when adding, editing, or deleting by using the Filter By
Category option on the Reservations page. Note that test agent reservations do not appear in the
reservations list when filtering by category.
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nVerify that a tenant administrator created at least one business group.
nVerify that a compute resource exists.
nVerify that any optional security groups or floating IP addresses are configured.
nVerify that any required key pairs exist. See Managing Key Pairs.
nVerify that a compute resource exists.
Configuring vRealize Automation
VMware, Inc. 212

nConfigure network settings.
Procedure
1Select Infrastructure > Reservations > Reservations.
2Click the New icon ( ) and select the type of reservation to create.
Select OpenStack.
3(Optional) Select an existing reservation from the Copy from existing reservation drop-down menu.
Data from the selected reservation appears. You can make changes as required for your new
reservation.
4Enter a name in the Name text box.
5Select a tenant from the Tenant drop-down menu.
6Select a business group from the Business group drop-down menu.
Only users in this business group can provision machines by using this reservation.
7(Optional) Select a reservation policy from the Reservation policy drop-down menu.
This option requires that one or more reservation policies exist. You can edit the reservation later to
specify a reservation policy.
You use a reservation policy to restrict provisioning to specific reservations.
8Enter a number in the Priority text box to set the priority for the reservation.
The priority is used when a business group has more than one reservation. A reservation with priority
1 is used for provisioning over a reservation with priority 2.
9(Optional) Deselect the Enable this reservation check box if you do not want this reservation active.
Do not navigate away from this page. Your reservation is not complete.
Specify Resources and Network Settings for OpenStack Reservations
Specify resource and network settings available to machines that are provisioned from this
vRealize Automation reservation.
Prerequisites
Specify OpenStack Reservation Information.
Procedure
1Click the Resouces tab.
2Select a compute resource on which to provision machines from the Compute resource drop-down
menu.
Only templates located on the cluster you select are available for cloning with this reservation.
Configuring vRealize Automation
VMware, Inc. 213
3(Optional) Enter a number in the Machine quota text box to set the maximum number of machines
that can be provisioned on this reservation.
Only machines that are powered on are counted towards the quota. Leave blank to make the
reservation unlimited.
4Select a method of assigning key pairs to compute instances from the Key pair drop-down menu.
Option Description
Not Specified Controls key pair behavior at the blueprint level rather than the reservation level.
Auto-Generated per Business Group Every machine provisioned in the same business group has the same key pair,
including machines provisioned on other reservations when the machine has the
same compute resource and business group. Because key pairs generated this
way are associated with a business group, the key pairs are deleted when the
business group is deleted.
Auto-Generated per Machine Each machine has a unique key pair. This is the most secure method because no
key pairs are shared among machines.
Specific Key Pair Every machine provisioned on this reservation has the same key pair. Browse for
a key pair to use for this reservation.
5If you selected Specific key Pair in the Key pair drop-down menu, select a key pair value from the
Specific key pair drop-down menu.
6Select one or more security groups that can be assigned to a machine during provisioning from the
Security groups list.
7Click the Network tab.
8Configure a network path for machines provisioned by using this reservation.
a (Optional) If the option is available, select a storage endpoint from the Endpoint drop-down
menu.
The FlexClone option is visible in the endpoint column if a NetApp ONTAP endpoint exists and if
the host is virtual. If there is a NetApp ONTAP endpoint, the reservation page displays the
endpoint assigned to the storage path. When you add, update, or delete an endpoint for a storage
path, the change is visible in all the applicable reservations.
When you add, update, or delete an endpoint for a storage path, the change is visible in the
reservation page.
b Select a network paths for machines provisioned by this reservation from the Network Paths list.
c (Optional) Select a listed network profile from the Network Profile drop-down menu.
This option requires that one or more network profiles exists.
You can select more than one network path on a reservation, but only one network is used when
provisioning a machine.
You can save the reservation now by clicking Save. Or you can add custom properties to further control
reservation specifications. You can also configure email alerts to send notifications when resources
allocated to this reservation become low.
Configuring vRealize Automation
VMware, Inc. 214
Specify Custom Properties and Alerts for OpenStack Reservations
You can associate custom properties with a vRealize Automation reservation. You can also configure
alerts to send email notifications when reservation resources are low.
Custom properties and email alerts are optional configurations for the reservation. If you do not want to
associate custom properties or set alerts, click Save to finish creating the reservation.
You can add as many custom properties as apply to your needs.
Important Notifications are only sent if email alerts are configured and notifications are enabled.
If configured, alerts are generated daily, rather than when the specified thresholds are reached.
Prerequisites
Specify Resources and Network Settings for OpenStack Reservations.
Procedure
1Click the Properties tab.
2Click New.
3Enter a valid custom property name.
4If applicable, enter a property value.
5Click Save.
6(Optional) Add any additional custom properties.
7Click the Alerts tab.
8Enable the Capacity Alerts check box to configure alerts to be sent.
9Use the slider to set thresholds for available resource allocation.
10 Enter one or more user email addresses or group names to receive alert notifications in the
Recipients text box.
Press Enter to separate multiple entries.
11 Select Send alerts to group manager to include group managers in the email alerts.
12 Specify a reminder frequency (days).
13 Click Save.
The reservation is saved and appears in the Reservations list.
What to do next
You can configure optional reservation policies or begin preparing for provisioning.
Users who are authorized to create blueprints can create them now.
Configuring vRealize Automation
VMware, Inc. 215
Create a vCloud Air Reservation
You must allocate resources to machines by creating a vRealize Automation reservation before members
of a business group can request machine provisioning.
Each business group must have at least one reservation for its members to provision machines of that
type.
Procedure
1Specify vCloud Air Reservation Information
You can create a reservation for each vCloud Air machine subscription or OnDemand resource.
Each reservation is configured for a specific business group to grant them access to request
machines.
2Specify Resources and Network Settings for a vCloud Air Reservation
Specify resource and network settings available to vCloud Air machines that are provisioned from
this vRealize Automation reservation.
3Specify Custom Properties and Alerts for a vCloud Air Reservation
You can associate custom properties with a vRealize Automation reservation. You can also
configure alerts to send email notifications when reservation resources are low.
What to do next
You can configure optional reservation policies or begin preparing for provisioning.
Users who are authorized to create blueprints can create them now.
Specify vCloud Air Reservation Information
You can create a reservation for each vCloud Air machine subscription or OnDemand resource. Each
reservation is configured for a specific business group to grant them access to request machines.
You can control the display of reservations when adding, editing, or deleting by using the Filter By
Category option on the Reservations page. Note that test agent reservations do not appear in the
reservations list when filtering by category.
Note After you create a reservation, you cannot change the business group or compute resource
associations.
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nVerify that a tenant administrator created at least one business group.
nVerify that a compute resource exists.
nConfigure network settings.
n(Optional) Configure network profile information.
Configuring vRealize Automation
VMware, Inc. 216

Procedure
1Select Infrastructure > Reservations > Reservations.
2Click the New icon ( ) and select the type of reservation to create.
The available cloud reservation types are Amazon, OpenStack, vCloud Air, and vCloud Director.
Select vCloud Air.
3(Optional) Select an existing reservation from the Copy from existing reservation drop-down menu.
Data from the selected reservation appears. You can make changes as required for your new
reservation.
4Enter a name in the Name text box.
5Select a tenant from the Tenant drop-down menu.
6Select a business group from the Business group drop-down menu.
Only users in this business group can provision machines by using this reservation.
7(Optional) Select a reservation policy from the Reservation policy drop-down menu.
This option requires that one or more reservation policies exist. You can edit the reservation later to
specify a reservation policy.
You use a reservation policy to restrict provisioning to specific reservations.
8Enter a number in the Priority text box to set the priority for the reservation.
The priority is used when a business group has more than one reservation. A reservation with priority
1 is used for provisioning over a reservation with priority 2.
9(Optional) Deselect the Enable this reservation check box if you do not want this reservation active.
Do not navigate away from this page. Your reservation is not complete.
Specify Resources and Network Settings for a vCloud Air Reservation
Specify resource and network settings available to vCloud Air machines that are provisioned from this
vRealize Automation reservation.
The available resource allocation models for machines provisioned from a vCloud Director reservation are
Allocation Pool, Pay As You Go, and Reservation Pool. For Pay As You Go, you do not need to specify
storage or memory amounts but do need to specify a priority for the storage path. For details about these
allocation models, see vCloud Air documentation.
You can specify a standard or disk-level storage profile. Multi-level disk storage is available vCloud Air
endpoints.
Configuring vRealize Automation
VMware, Inc. 217
For integrations that use Storage Distributed Resource Scheduler (SDRS) storage, you can select a
storage cluster to allow SDRS to automatically handle storage placement and load balancing for
machines provisioned from this reservation. The SDRS automation mode must be set to Automatic.
Otherwise, select a datastore within the cluster for standalone datastore behavior. SDRS is not supported
for FlexClone storage devices.
Prerequisites
Specify vCloud Director Reservation Information.
Procedure
1Click the Resouces tab.
2Select a compute resource on which to provision machines from the Compute resource drop-down
menu.
Only templates located on the cluster you select are available for cloning with this reservation.
3Select an allocation model.
4(Optional) Enter a number in the Machine quota text box to set the maximum number of machines
that can be provisioned on this reservation.
Only machines that are powered on are counted towards the quota. Leave blank to make the
reservation unlimited.
5Specify the amount of memory, in GB, to be allocated to this reservation from the Memory table.
The overall memory value for the reservation is derived from your compute resource selection.
6Select one or more listed storage paths.
The available storage path options are derived from your compute resource selection.
a Enter a value in the This Reservation Reserved text box to specify how much storage to
allocate to this reservation.
b Enter a value in the Priority text box to specify the priority value for the storage path relative to
other storage paths that pertain to this reservation.
The priority is used for multiple storage paths. A storage path with priority 0 is used before a path
with priority 1.
c Click the Disable option if you do not want to enable the storage path for use by this reservation.
d Repeat this step to configure clusters and datastores as needed.
7Click the Network tab.
Configuring vRealize Automation
VMware, Inc. 218
8Configure a network path for machines provisioned by using this reservation.
a (Optional) If the option is available, select a storage endpoint from the Endpoint drop-down
menu.
The FlexClone option is visible in the endpoint column if a NetApp ONTAP endpoint exists and if
the host is virtual. If there is a NetApp ONTAP endpoint, the reservation page displays the
endpoint assigned to the storage path. When you add, update, or delete an endpoint for a storage
path, the change is visible in all the applicable reservations.
When you add, update, or delete an endpoint for a storage path, the change is visible in the
reservation page.
b Select a network paths for machines provisioned by this reservation from the Network Paths list.
c (Optional) Select a listed network profile from the Network Profile drop-down menu.
This option requires that one or more network profiles exists.
You can select more than one network path on a reservation, but only one network is used when
provisioning a machine.
You can save the reservation now by clicking Save. Or you can add custom properties to further control
reservation specifications. You can also configure email alerts to send notifications when resources
allocated to this reservation become low.
Specify Custom Properties and Alerts for a vCloud Air Reservation
You can associate custom properties with a vRealize Automation reservation. You can also configure
alerts to send email notifications when reservation resources are low.
Custom properties and email alerts are optional configurations for the reservation. If you do not want to
associate custom properties or set alerts, click Save to finish creating the reservation.
You can add as many custom properties as apply to your needs.
If configured, alerts are generated daily, rather than when the specified thresholds are reached.
Important Notifications are only sent if email alerts are configured and notifications are enabled.
Alerts are not available for Pay As You Go reservations that were created with no specified limits.
Prerequisites
Specify Resources and Network Settings for a vCloud Air Reservation
Procedure
1Click the Properties tab.
2Click New.
3Enter a valid custom property name.
4If applicable, enter a property value.
Configuring vRealize Automation
VMware, Inc. 219
5(Optional) Check the Encrypted check box to encrypt the property value.
6(Optional) Check the Prompt User check box to require that the user enter a value.
This option cannot be overridden when provisioning.
7Click Save.
8(Optional) Add any additional custom properties.
9Click the Alerts tab.
10 Enable the Capacity Alerts check box to configure alerts to be sent.
11 Use the slider to set thresholds for available resource allocation.
12 Enter one or more user email addresses or group names to receive alert notifications in the
Recipients text box.
Press Enter to separate multiple entries.
13 Select Send alerts to group manager to include group managers in the email alerts.
14 Specify a reminder frequency (days).
15 Click Save.
The reservation is saved and appears in the Reservations list.
Create a vCloud Director Reservation
You must allocate resources to machines by creating a vRealize Automation reservation before members
of a business group can request machine provisioning.
Each business group must have at least one reservation for its members to provision machines of that
type.
Procedure
1Specify vCloud Director Reservation Information
You can create a reservation for each vCloud Director organization virtual datacenter (VDC). Each
reservation is configured for a specific business group to grant them access to request machines on
a specified compute resource.
2Specify Resources and Network Settings for a vCloud Director Reservation
Specify resource and network settings available to vCloud Director machines that are provisioned
from this vRealize Automation reservation.
3Specify Custom Properties and Alerts for vCloud Director Reservations
You can associate custom properties with a vRealize Automation reservation. You can also
configure alerts to send email notifications when reservation resources are low.
What to do next
You can configure optional reservation policies or begin preparing for provisioning.
Users who are authorized to create blueprints can create them now.
Configuring vRealize Automation
VMware, Inc. 220
Specify vCloud Director Reservation Information
You can create a reservation for each vCloud Director organization virtual datacenter (VDC). Each
reservation is configured for a specific business group to grant them access to request machines on a
specified compute resource.
You can control the display of reservations when adding, editing, or deleting by using the Filter By
Category option on the Reservations page. Note that test agent reservations do not appear in the
reservations list when filtering by category.
Note After you create a reservation, you cannot change the business group or compute resource
associations.
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nVerify that a tenant administrator created at least one business group.
nVerify that a compute resource exists.
nConfigure network settings.
n(Optional) Configure network profile information.
Procedure
1Select Infrastructure > Reservations > Reservations.
2Click the New icon ( ) and select the type of reservation to create.
The available cloud reservation types are Amazon, OpenStack, vCloud Air, and vCloud Director.
Select vCloud Director.
3(Optional) Select an existing reservation from the Copy from existing reservation drop-down menu.
Data from the selected reservation appears. You can make changes as required for your new
reservation.
4Enter a name in the Name text box.
5Select a tenant from the Tenant drop-down menu.
6Select a business group from the Business group drop-down menu.
Only users in this business group can provision machines by using this reservation.
7(Optional) Select a reservation policy from the Reservation policy drop-down menu.
This option requires that one or more reservation policies exist. You can edit the reservation later to
specify a reservation policy.
You use a reservation policy to restrict provisioning to specific reservations.
Configuring vRealize Automation
VMware, Inc. 221
8Enter a number in the Priority text box to set the priority for the reservation.
The priority is used when a business group has more than one reservation. A reservation with priority
1 is used for provisioning over a reservation with priority 2.
9(Optional) Deselect the Enable this reservation check box if you do not want this reservation active.
Do not navigate away from this page. Your reservation is not complete.
Specify Resources and Network Settings for a vCloud Director Reservation
Specify resource and network settings available to vCloud Director machines that are provisioned from
this vRealize Automation reservation.
The available resource allocation models for machines provisioned from a vCloud Director reservation are
Allocation Pool, Pay As You Go, and Reservation Pool. For Pay As You Go, you do not need to specify
storage or memory amounts but do need to specify a priority for the storage path. For details about these
allocation models, see vCloud Director documentation.
You can specify a standard or disk-level storage profile. Multi-level disk storage is available for
vCloud Director 5.6 and greater endpoints. Multi-level disk storage is not supported for vCloud Director
5.5 endpoints.
For integrations that use Storage Distributed Resource Scheduler (SDRS) storage, you can select a
storage cluster to allow SDRS to automatically handle storage placement and load balancing for
machines provisioned from this reservation. The SDRS automation mode must be set to Automatic.
Otherwise, select a datastore within the cluster for standalone datastore behavior. SDRS is not supported
for FlexClone storage devices.
Prerequisites
Specify vCloud Director Reservation Information.
Procedure
1Click the Resouces tab.
2Select a compute resource on which to provision machines from the Compute resource drop-down
menu.
Only templates located on the cluster you select are available for cloning with this reservation.
3Select an allocation model.
4(Optional) Enter a number in the Machine quota text box to set the maximum number of machines
that can be provisioned on this reservation.
Only machines that are powered on are counted towards the quota. Leave blank to make the
reservation unlimited.
5Specify the amount of memory, in GB, to be allocated to this reservation from the Memory table.
The overall memory value for the reservation is derived from your compute resource selection.
Configuring vRealize Automation
VMware, Inc. 222
6Select one or more listed storage paths.
The available storage path options are derived from your compute resource selection.
a Enter a value in the This Reservation Reserved text box to specify how much storage to
allocate to this reservation.
b Enter a value in the Priority text box to specify the priority value for the storage path relative to
other storage paths that pertain to this reservation.
The priority is used for multiple storage paths. A storage path with priority 0 is used before a path
with priority 1.
c Click the Disable option if you do not want to enable the storage path for use by this reservation.
d Repeat this step to configure clusters and datastores as needed.
7Click the Network tab.
8Configure a network path for machines provisioned by using this reservation.
a (Optional) If the option is available, select a storage endpoint from the Endpoint drop-down
menu.
The FlexClone option is visible in the endpoint column if a NetApp ONTAP endpoint exists and if
the host is virtual. If there is a NetApp ONTAP endpoint, the reservation page displays the
endpoint assigned to the storage path. When you add, update, or delete an endpoint for a storage
path, the change is visible in all the applicable reservations.
When you add, update, or delete an endpoint for a storage path, the change is visible in the
reservation page.
b Select a network paths for machines provisioned by this reservation from the Network Paths list.
c (Optional) Select a listed network profile from the Network Profile drop-down menu.
This option requires that one or more network profiles exists.
You can select more than one network path on a reservation, but only one network is used when
provisioning a machine.
You can save the reservation now by clicking Save. Or you can add custom properties to further control
reservation specifications. You can also configure email alerts to send notifications when resources
allocated to this reservation become low.
Specify Custom Properties and Alerts for vCloud Director Reservations
You can associate custom properties with a vRealize Automation reservation. You can also configure
alerts to send email notifications when reservation resources are low.
Custom properties and email alerts are optional configurations for the reservation. If you do not want to
associate custom properties or set alerts, click Save to finish creating the reservation.
You can add as many custom properties as apply to your needs.
Configuring vRealize Automation
VMware, Inc. 223
If configured, alerts are generated daily, rather than when the specified thresholds are reached.
Important Notifications are only sent if email alerts are configured and notifications are enabled.
Alerts are not available for Pay As You Go reservations that were created with no specified limits.
Prerequisites
Specify Resources and Network Settings for a vCloud Director Reservation.
Procedure
1Click the Properties tab.
2Click New.
3Enter a valid custom property name.
4If applicable, enter a property value.
5(Optional) Check the Encrypted check box to encrypt the property value.
6(Optional) Check the Prompt User check box to require that the user enter a value.
This option cannot be overridden when provisioning.
7Click Save.
8(Optional) Add any additional custom properties.
9Click the Alerts tab.
10 Enable the Capacity Alerts check box to configure alerts to be sent.
11 Use the slider to set thresholds for available resource allocation.
12 Enter one or more user email addresses or group names to receive alert notifications in the
Recipients text box.
Press Enter to separate multiple entries.
13 Select Send alerts to group manager to include group managers in the email alerts.
14 Specify a reminder frequency (days).
15 Click Save.
The reservation is saved and appears in the Reservations list.
Scenario: Create an Amazon Reservation for a Proof of Concept Environment
Because you used an SSH tunnel to temporarily establish network-to-Amazon VPC connectivity for your
proof of concept environment, you have to add custom properties to your Amazon reservations to ensure
the Software bootstrap agent and guest agent run communications through the tunnel.
Configuring vRealize Automation
VMware, Inc. 224
Network-to-Amazon VPC connectivity is only required if you want to use the guest agent to customize
provisioned machines, or if you want to include Software components in your blueprints. For a production
environment, you would configure this connectivity officially through Amazon Web Services, but because
you are working in a proof of concept environment, you configured a temporary SSH tunnel instead.
Using your fabric administrator privileges, you create a reservation to allocate your Amazon Web Services
resources and you include several custom properties to support the SSH tunneling. You also configure
the reservation on the same region and VPC as your tunnel machine.
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nConfigure an SSH tunnel to establish network-to-Amazon VPC connectivity. Make a note of the
subnet, security group, and private IP address of your Amazon AWS tunnel machine. See Scenario:
Configure Network-to-Amazon VPC Connectivity for a Proof of Concept Environment.
nCreate a business group for members of your IT organization who need to architect blueprints in your
proof of concept environment. See Create a Business Group.
nVerify that a tenant administrator created at least one business group.
Procedure
1Scenaro: Specify Amazon AWS Reservation Information for a Proof of Concept Environment
You want to reserve resources for your team of blueprint architects so they can test the functionality
in your proof of concept environment, so you configure this reservation to allocate resources to your
architects business group.
2Scenario: Specify Amazon AWS Network Settings for a Proof of Concept Environment
You configure the reservation to use the same region and networking settings that your tunnel
machine is using, and you restrict the number of machines that can be powered on for this
reservation to manage resource usage.
3Scenario: Specify Custom Properties to Run Agent Communications Through Your Tunnel
When you configured network-to-Amazon VPC connectivity, you configured port forwarding to allow
your Amazon AWS tunnel machine to access vRealize Automation resources. You need to add
custom properties on the reservation to configure the agents to access those ports.
Scenaro: Specify Amazon AWS Reservation Information for a Proof of Concept Environment
You want to reserve resources for your team of blueprint architects so they can test the functionality in
your proof of concept environment, so you configure this reservation to allocate resources to your
architects business group.
Note After you create a reservation, you cannot change the business group or compute resource
associations.
Procedure
1Select Infrastructure > Reservations > Reservations.
Configuring vRealize Automation
VMware, Inc. 225

2Click the New icon ( ) and select the type of reservation to create.
Select Amazon.
3Enter Amazon Tunnel POC in the Name text box.
4Select the business group you created for your blueprint architects from the Business Group drop-
down menu.
5Enter a 1 in the Priority text box to set this reservation as the highest priority.
You configured the business group and the priority for the reservation, but you still need to allocate
resources and configure the custom properties for the SSH tunnel.
Scenario: Specify Amazon AWS Network Settings for a Proof of Concept Environment
You configure the reservation to use the same region and networking settings that your tunnel machine is
using, and you restrict the number of machines that can be powered on for this reservation to manage
resource usage.
Procedure
1Click the Resouces tab.
2Select a compute resource on which to provision machines from the Compute resource drop-down
menu.
Select the Amazon AWS region where your tunnel machine is located.
3(Optional) Enter a number in the Machine quota text box to set the maximum number of machines
that can be provisioned on this reservation.
Only machines that are powered on are counted towards the quota. Leave blank to make the
reservation unlimited.
4Select Specify Key Pair from the Key pair drop-down menu.
Because this is a proof of concept environment, you choose to share a single key pair for all
machines provisioned by using this reservation.
5Select the key pair you want to share with your architect users from the Key Pair drop-down menu.
6Enable the Assign to a subnet in a VPC checkbox.
7Select the same subnet and security groups that your tunnel machine is using.
You configured the reservation to use the same region and networking settings as your tunnel machine,
but you still need to add custom properties to ensure the Software bootstrap agent and guest agent run
communications through the tunnel.
Scenario: Specify Custom Properties to Run Agent Communications Through Your Tunnel
When you configured network-to-Amazon VPC connectivity, you configured port forwarding to allow your
Amazon AWS tunnel machine to access vRealize Automation resources. You need to add custom
properties on the reservation to configure the agents to access those ports.
Configuring vRealize Automation
VMware, Inc. 226
Procedure
1Click the Properties tab.
2Click New.
3Configure the tunnel custom properties.
Use the private IP address of your Amazon AWS tunnel machine and port 1443, which you assigned
for vRealize_automation_appliance_fqdn when you invoked the SSH tunnel.
Option Value
software.ebs.url https://Private_IP:1443/event-broker-service/api
software.agent.service.url https://Private_IP:1443/software-service/api
agent.download.url https://Private_IP:1443/software-service/resources/nobel-
agent.jar
4Click Save.
You created a reservation to allocate Amazon AWS resources to your architects business group. You
configured the reservation to support the guest agent and the Software bootstrap agent. Your architects
can create blueprints that leverage the guest agent to customize deployed machines or include Software
components.
Creating Virtual Category Reservations
A virtual category type reservation provides access to the provisioning services of a virtual machine
deployment for a particular vRealize Automation business group. Available virtual reservation types
include vSphere, Hyper-V, KVM, SCVMM, and XenServer.
A reservation is a share of the memory, CPU, networking, and storage resources of one compute
resource allocated to a particular vRealize Automation business group.
A business group can have multiple reservations on one endpoint or reservations on multiple endpoints.
To provision virtual machines, a business group must have at least one reservation on a virtual compute
resource. Each reservation is for one business group only, but a business group can have multiple
reservations on a single compute resource, or multiple reservations on compute resources of different
types.
In addition to defining the share of fabric resources allocated to the business group, a reservation can
define policies, priorities, and quotas that determine machine placement.
Understanding Selection Logic for Reservations
When a member of a business group create a provisioning request for a virtual machine,
vRealize Automation selects a machine from one of the reservations that are available to that business
group.
Configuring vRealize Automation
VMware, Inc. 227
The reservation for which a machine is provisioned must satisfy the following criteria:
nThe reservation must be of the same platform type as the blueprint from which the machine was
requested.
A generic virtual blueprint can be provisioned on any type of virtual reservation.
nThe reservation must be enabled.
nThe compute resource must be accessible and not in maintenance mode.
nThe reservation must have capacity remaining in its machine quota or have an unlimited quota.
The allocated machine quota includes only machines that are powered on. For example, if a
reservation has a quota of 50, and 40 machines have been provisioned but only 20 of them are
powered on, the reservation’s quota is 40 percent allocated, not 80 percent.
nThe reservation must have sufficient unallocated memory and storage resources to provision the
machine.
When a virtual reservation’s machine quota, memory, or storage is fully allocated, no further virtual
machines can be provisioned from it. Resources may be reserved beyond the physical capacity of a
virtualization compute resource (overcommitted), but when the physical capacity of a compute
resource is 100% allocated, no further machines can be provisioned on any reservations with that
compute resource until the resources are reclaimed.
nIf the blueprint has specific network settings, the reservation must have the same networks.
If the blueprint or reservation specifies a network profile for static IP address assignment, an IP
address must be available to assign to the new machine.
nIf the blueprint or request specifies a location, the compute resource must be associated with that
location.
If the value of the custom property VRM.Datacenter.Policy is Exact and there is no reservation for a
compute resource associated with that location that satisfies all the other criteria, then provisioning
fails.
If the value of VRM.Datacenter.Policy is NotExact and there is no reservation for a compute resource
associated with that location that satisfies all the other criteria, provisioning can proceed on another
reservation regardless of location. This option is the default.
nIf the blueprint or request specifies the custom property VirtualMachine.Host.TpmEnabled, trusted
hardware must be installed on the compute resource for the reservation.
nIf the blueprint specifies a reservation policy, the reservation must belong to that reservation policy.
Reservation policies are a way to guarantee that the selected reservation satisfies any additional
requirements for provisioning machines from a specific blueprint. For example, you can use
reservation policies to limit provisioning to compute resources with a specific template for cloning.
If no reservation is available that meets all of the selection criteria, provisioning fails.
Configuring vRealize Automation
VMware, Inc. 228
If multiple reservations meet all of the criteria, the reservation from which to provision a requested
machine is determined by the following logic:
nReservations with higher priority are selected over reservations with lower priority.
nIf multiple reservations have the same priority, the reservation with the lowest percentage of its
machine quota allocated is selected.
nIf multiple reservations have the same priority and quota usage, machines are distributed among
reservations in round-robin fashion.
If multiple storage paths are available on a reservation with sufficient capacity to provision the machine
volumes, storage paths are selected according to the following logic:
nIf the blueprint or request specifies a storage reservation policy, the storage path must belong to that
storage reservation policy.
If the value of the custom property VirtualMachine.DiskN.StorageReservationPolicyMode is NotExact
and there is no storage path with sufficient capacity within the storage reservation policy, then
provisioning can proceed with a storage path outside the specified storage reservation policy. The
default value of VirtualMachine.DiskN.StorageReservationPolicyMode is Exact.
nIf multiple storage paths have the same priority, machines are distributed among storage paths in
round-robin fashion.
Creating a vSphere Reservation for NSX Network and Security Virtualization
You can create a vSphere reservation to assign external networks and routed gateways to network
profiles for networks, specify the transport zone, and assign security groups to machine components.
If you have configured VMware NSX, and installed the NSX plug-in for vRealize Automation, you can
specify NSX transport zone, gateway reservation policy, and app isolation settings when you create or
edit a blueprint. These settings are available on the NSX Settings tab on the New Blueprint and
Blueprint Properties pages.
The network and security component settings that you add to the blueprint design canvas are derived
from your NSX configuration and require that you have installed the NSX plug-in and run data collection
for the NSX inventory for vSphere clusters. Network and security components are specific to NSX and are
available for use with vSphere machine components only. For information about configuring NSX, see
NSX Administration Guide.
When vRealize Automation provisions machines with NAT or routed networking, it provisions a routed
gateway as the network router. The routed gateway is a management machine that consumes compute
resources. It also manages the network communications for the provisioned machine components. The
reservation used to provision the routed gateway determines the external network used for NAT and
routed network profiles. It also determines the reservation routed gateway used to configure routed
networks. The reservation routed gateway links routed networks together with entries in the routing table.
You can specify a routed gateway reservation policy to identify which reservations to use when
provisioning the machines using the routed gateway. By default, vRealize Automation uses the same
reservations for the routed gateway and the machine components.
Configuring vRealize Automation
VMware, Inc. 229
You select one or more security groups in the reservation to enforce baseline security policy for all
component machines provisioned with that reservation in vRealize Automation. Every provisioned
machine is added to these specified security groups.
Successful provisioning requires the transport zone of the reservation to match the transport zone of a
machine blueprint when that blueprint defines machine networks. Similarly, provisioning a machine's
routed gateway requires that the transport zone defined in the reservation matches the transport zone
defined for the blueprint.
When you select a routed gateway and network profile on a reservation when configuring routed
networks, select the network path to be used in linking routed networks together and assign it the external
network profile used to configure the routed network profile. The list of network profiles available to be
assigned to a network path is filtered to match the subnet of the network path based on the subnet mask
and primary IP address selected for the network interface.
If you want to use a routed gateway in vRealize Automation reservations, configure the routed gateway
externally in the NSX or vCloud Networking and Security environment and then run inventory data
collection. For NSX, you must have a working NSX Edge instance before you can configure the default
gateway for static routes or dynamic routing details for an Edge services gateway or distributed router.
See NSX Administration Guide or vCloud Networking and Security product documentation.
Create a Reservation for Hyper-V, KVM, SCVMM, vSphere , or XenServer
You must allocate resources to machines by creating a reservation before members of a business group
can request machine provisioning.
Each business group must have at least one reservation for its members to provision machines of that
type. For example, a business group with a vSphere reservation, but not a KVM (RHEV) reservation,
cannot request a KVM (RHEV) virtual machine. In this example, the business group must be allocated a
reservation specifically for KVM (RHEV) resources.
Procedure
1Specify Virtual Reservation Information
Each reservation is configured for a specific business group to grant users access to request
machines on a specified compute resource.
2Specify Resource and Networking Settings for a Virtual Reservation
Specify resource and network settings for provisioning machines from this vRealize Automation
reservation.
3Specify Custom Properties and Alerts for Virtual Reservations
You can associate custom properties with a vRealize Automation reservation. You can also
configure alerts to send email notifications when reservation resources are low.
Specify Virtual Reservation Information
Each reservation is configured for a specific business group to grant users access to request machines
on a specified compute resource.
Configuring vRealize Automation
VMware, Inc. 230
You can control the display of reservations when adding, editing, or deleting by using the Filter By
Category option on the Reservations page. Note that test agent reservations do not appear in the
reservations list when filtering by category.
Note After you create a reservation, you cannot change the business group or compute resource
associations.
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nVerify that a tenant administrator created at least one business group.
nVerify that a compute resource exists.
nConfigure network settings.
n(Optional) Configure network profile information.
Procedure
1Select Infrastructure > Reservations > Reservations.
2Click the New icon ( ) and select the type of reservation to create.
The available virtual reservation types are Hyper-V, KVM, SCVMM, vSphere, and XenServer.
For example, select vSphere.
3(Optional) Select an existing reservation from the Copy from existing reservation drop-down menu.
Data from the selected reservation appears. You can make changes as required for your new
reservation.
4Enter a name in the Name text box.
5Select a tenant from the Tenant drop-down menu.
6Select a business group from the Business group drop-down menu.
Only users in this business group can provision machines by using this reservation.
7(Optional) Select a reservation policy from the Reservation policy drop-down menu.
This option requires that one or more reservation policies exist. You can edit the reservation later to
specify a reservation policy.
You use a reservation policy to restrict provisioning to specific reservations.
8Enter a number in the Priority text box to set the priority for the reservation.
The priority is used when a business group has more than one reservation. A reservation with priority
1 is used for provisioning over a reservation with priority 2.
9(Optional) Deselect the Enable this reservation check box if you do not want this reservation active.
Do not navigate away from this page. Your reservation is not complete.
Configuring vRealize Automation
VMware, Inc. 231
Specify Resource and Networking Settings for a Virtual Reservation
Specify resource and network settings for provisioning machines from this vRealize Automation
reservation.
You can select a FlexClone datastore in your reservation if you have a vSphere environment and storage
devices that use Net App FlexClone technology. SDRS is not supported for FlexClone storage devices.
Prerequisites
Specify Virtual Reservation Information.
Procedure
1Click the Resouces tab.
2Select a compute resource on which to provision machines from the Compute resource drop-down
menu.
Only templates located on the cluster you select are available for cloning with this reservation.
3(Optional) Enter a number in the Machine quota text box to set the maximum number of machines
that can be provisioned on this reservation.
Only machines that are powered on are counted towards the quota. Leave blank to make the
reservation unlimited.
4Specify the amount of memory, in GB, to be allocated to this reservation from the Memory table.
The overall memory value for the reservation is derived from your compute resource selection.
5Select one or more listed storage paths.
The available storage path options are derived from your compute resource selection.
For integrations that use Storage Distributed Resource Scheduler (SDRS) storage, you can select a
storage cluster to allow SDRS to automatically handle storage placement and load balancing for
machines provisioned from this reservation. The SDRS automation mode must be set to Automatic.
Otherwise, select a datastore within the cluster for standalone datastore behavior. SDRS is not
supported for FlexClone storage devices.
6If available for the compute resource, select a resource pool in the Resource Pool drop-down menu.
7Click the Network tab.
Configuring vRealize Automation
VMware, Inc. 232
8Configure a network path for machines provisioned by using this reservation.
a (Optional) If the option is available, select a storage endpoint from the Endpoint drop-down
menu.
The FlexClone option is visible in the endpoint column if a NetApp ONTAP endpoint exists and if
the host is virtual. If there is a NetApp ONTAP endpoint, the reservation page displays the
endpoint assigned to the storage path. When you add, update, or delete an endpoint for a storage
path, the change is visible in all the applicable reservations.
When you add, update, or delete an endpoint for a storage path, the change is visible in the
reservation page.
b Select a network paths for machines provisioned by this reservation from the Network Paths list.
c (Optional) Select a listed network profile from the Network Profile drop-down menu.
This option requires that one or more network profiles exists.
You can select more than one network path on a reservation, but only one network is used when
provisioning a machine.
You can save the reservation now by clicking Save. Or you can add custom properties to further control
reservation specifications. You can also configure email alerts to send notifications when resources
allocated to this reservation become low.
Specify Custom Properties and Alerts for Virtual Reservations
You can associate custom properties with a vRealize Automation reservation. You can also configure
alerts to send email notifications when reservation resources are low.
Custom properties and email alerts are optional configurations for the reservation. If you do not want to
associate custom properties or set alerts, click Save to finish creating the reservation.
You can add as many custom properties as apply to your needs.
Important Notifications are only sent if email alerts are configured and notifications are enabled.
If configured, alerts are generated daily, rather than when the specified thresholds are reached.
Prerequisites
Specify Resource and Networking Settings for a Virtual Reservation.
Procedure
1Click the Properties tab.
2Click New.
3Enter a valid custom property name.
4If applicable, enter a property value.
5(Optional) Check the Encrypted check box to encrypt the property value.
Configuring vRealize Automation
VMware, Inc. 233
6(Optional) Check the Prompt User check box to require that the user enter a value.
This option cannot be overridden when provisioning.
7(Optional) Add any additional custom properties.
8Click the Alerts tab.
9Enable the Capacity Alerts check box to configure alerts to be sent.
10 Use the slider to set thresholds for available resource allocation.
11 Enter one or more user email addresses or group names to receive alert notifications in the
Recipients text box.
Press Enter to separate multiple entries.
12 Select Send alerts to group manager to include group managers in the email alerts.
13 Specify a reminder frequency (days).
14 Click Save.
The reservation is saved and appears in the Reservations list.
What to do next
You can configure optional reservation policies or begin preparing for provisioning.
Users who are authorized to create blueprints can create them now.
Edit a Reservation to Assign a Network Profile
You can assign a network profile to a reservation, for example to enable static IP assignment for
machines that are provisioned on that reservation.
You can also assign a network profile to a blueprint by using the custom property
VirtualMachine.NetworkN.ProfileName on the Properties tab of the New Blueprint or Blueprint
Properties page.
If a network profile is specified in the blueprint (by using the VirtualMAchine.NetworkN.ProfileName
custom property) and by a reservation that is used by the blueprint, the network profile specified in the
blueprint takes precedence. However, if the custom property is not used in the blueprint, and you select a
network profile for a machine NIC, vRealize Automation uses a reservation network path for the machine
NIC for which the network profile is specified.
Note This information does not apply to Amazon Web Services.
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
nCreate a network profile. See Creating a Network Profile.
Configuring vRealize Automation
VMware, Inc. 234
Procedure
1Select Infrastructure > Reservations > Reservations.
2Point to a reservation and click Edit.
3Click the Network tab.
4Assign a network profile to a network path.
a Select a network path on which to enable static IP addresses.
The network path options are derived from settings on the Resources tab.
b Map an available network profile to the path by selecting a profile from the Network Profile drop-
down menu.
c (Optional) Repeat this step to assign network profiles to additional network paths on this
reservation.
5Click OK.
Reservation Policies
You can use a reservation policy to control how reservation requests are processed. When you provision
machines from the blueprint, provisioning is restricted to the resources specified in your reservation
policy.
Reservation policies provide an optional means of controlling how reservation requests are processed.
You can apply a reservation policy to a blueprint to restrict the machines provisioned from that blueprint to
a subset of available reservations.
You can use a reservation policy to collect resources into groups for different service levels, or to make a
specific type of resource easily available for a particular purpose. When a user requests a machine, it can
be provisioned on any reservation of the appropriate type that has sufficient capacity for the machine. The
following scenarios provide a few examples of possible uses for reservation policies:
nTo ensure that provisioned machines are placed on reservations with specific devices that support
NetApp FlexClone.
nTo restrict provisioning of cloud machines to a specific region containing a machine image that is
required for a specific blueprint.
nAs an additional means of using a Pay As You Go allocation model for machine types that support
that capability.
Configuring vRealize Automation
VMware, Inc. 235

You can add multiple reservations to a reservation policy, but a reservation can belong to only one policy.
You can assign a single reservation policy to more than one blueprint. A blueprint can have only one
reservation policy.
Note If you have SDRS enabled on your platform, you can allow SDRS to load balance storage for
individual virtual machine disks, or all storage for the virtual machine. If you are working with SDRS
datastore clusters, conflicts can occur when you use reservation policies and storage reservation policies.
For example, if a standalone datastore or a datastore within an SDRS cluster is selected on one of the
reservations in a policy or storage policy, your virtual machine storage might be frozen instead of driven
by SDRS. If you request reprovisioning for a machine with storage placement on an SDRS cluster, the
machine is deleted if the SDRS automation level is disabled.
Note vCloud Air endpoints and vCloud Director endpoints do not support network profiles in a machine
deployment.
Configure a Reservation Policy
You can create reservation policies to collect resources into groups for different service levels, or to make
a specific type of resource easily available for a particular purpose. After you create the reservation policy,
you then must populate it with reservations before tenant administrators and business group managers
can use the policy effectively in a blueprint.
A reservation policy can include reservations of different types, but only reservations that match the
blueprint type are considered when selecting a reservation for a particular request.
Procedure
1Create a Reservation Policy
You can use reservation policies to group similar reservations together.
2Assign a Reservation Policy to a Reservation
You can assign a reservation policy to a reservation when you create the reservation. They can also
edit an existing reservation to assign a reservation policy to it, or change its reservation policy
assignment.
Create a Reservation Policy
You can use reservation policies to group similar reservations together.
Create the reservation policy first, then add the policy to reservations to allow a blueprint creator to use
the reservation policy in a blueprint.
The policy is created as an empty container.
You can control the display of reservation policies when adding, editing, or deleting by using the Filter By
Type option on the Reservation Policies page.
Prerequisites
Log in to the vRealize Automation console as a fabric administrator.
Configuring vRealize Automation
VMware, Inc. 236
Procedure
1Select Infrastructure > Reservations > Reservation Policies.
2Click Add.
3Enter a name in the Name text box.
4Select Reservation Policy from the Type drop-down menu.
5Enter a description in the Description text box.
6Click Update to save the policy.
Assign a Reservation Policy to a Reservation
You can assign a reservation policy to a reservation when you create the reservation. They can also edit
an existing reservation to assign a reservation policy to it, or change its reservation policy assignment.
Prerequisites
Create a Reservation Policy.
Procedure
1Select Infrastructure > Reservations > Reservations.
2Point to a reservation and click Edit.
3Select a reservation policy from the Reservation Policy drop-down menu.
4Click Save.
Storage Reservation Policies
You can create storage reservation policies to allow blueprint architects to assign the volumes of a virtual
machine to different datastores for the vSphere, KVM (RHEV), and SCVMM platform types or different
storage profiles for other resources, such as vCloud Air or vCloud Director resources.
Assigning the volumes of a virtual machine to different datastores or to a different storage profile allows
blueprint architects to control and use storage space more effectively. For example, they might deploy the
operating system volume to a slower, less expensive datastore, or storage profile, and the database
volume to a faster datastore or storage profile.
Some machine endpoints only support a single storage profile, while others support multi-level disk
storage. Multi-level disk storage is available for vCloud Director 5.6 and greater endpoints and for
vCloud Air endpoints. Multi-level disk storage is not supported for vCloud Director 5.5 endpoints.
When you create a blueprint, you can assign a single datastore or a storage reservation policy that
represents multiple datastores to a volume. When they assign a single datastore, or storage profile, to a
volume, vRealize Automation uses that datastore or storage profile at provisioning time, if possible. When
they assign a storage reservation policy to a volume, vRealize Automation uses one of its datastores, or
storage profiles if working with other resources, such as vCloud Air or vCloud Director, at provisioning
time.
Configuring vRealize Automation
VMware, Inc. 237
A storage reservation policy is essentially a tag applied to one or more datastores or storage profiles by a
fabric administrator to group datastores or storage profiles that have similar characteristics, such as
speed or price. A datastore or storage profile can be assigned to only one storage reservation policy at a
time, but a storage reservation policy can have many different datastores or storage profiles.
You can create a storage reservation policy and assign it to one or more datastores or storage profiles. A
blueprint creator can then assign the storage reservation policy to a volume in a virtual blueprint. When a
user requests a machine that uses the blueprint, vRealize Automation uses the storage reservation policy
specified in the blueprint to select a datastore or storage profile for the machine’s volume.
Note If you have SDRS enabled on your platform, you can allow SDRS to load balance storage for
individual virtual machine disks, or all storage for the virtual machine. If you are working with SDRS
datastore clusters, conflicts can occur when you use reservation policies and storage reservation policies.
For example, if a standalone datastore or a datastore within an SDRS cluster is selected on one of the
reservations in a policy or storage policy, your virtual machine storage might be frozen instead of driven
by SDRS. If you request reprovisioning for a machine with storage placement on an SDRS cluster, the
machine is deleted if the SDRS automation level is disabled.
Configure a Storage Reservation Policy
You can create storage reservation policies to group datastores that have similar characteristics, such as
speed or price. After you create the storage reservation policy, you must populate it with datastores
before using the policy in a blueprint.
Procedure
1Create a Storage Reservation Policy
You can use a storage reservation policy to group datastores that have similar characteristics, such
as speed or price.
2Assign a Storage Reservation Policy to a Datastore
You can associate a storage reservation policy to a compute resource. After the storage reservation
policy is created, populate it with datastores. A datastore can belong to only one storage reservation
policy. Add multiple datastores to create a group of datastores for use with a blueprint.
Create a Storage Reservation Policy
You can use a storage reservation policy to group datastores that have similar characteristics, such as
speed or price.
The policy is created as an empty container.
You can control the display of reservation policies when adding, editing, or deleting by using the Filter By
Type option on the Reservation Policies page.
Prerequisites
Log in to the vRealize Automation console as a fabric administrator.
Configuring vRealize Automation
VMware, Inc. 238

Procedure
1Select Infrastructure > Reservations > Reservation Policies.
2Click Add.
3Enter a name in the Name text box.
4Select Storage Reservation Policy from the Type drop-down menu.
5Enter a description in the Description text box.
6Click Update to save the policy.
Assign a Storage Reservation Policy to a Datastore
You can associate a storage reservation policy to a compute resource. After the storage reservation
policy is created, populate it with datastores. A datastore can belong to only one storage reservation
policy. Add multiple datastores to create a group of datastores for use with a blueprint.
Prerequisites
Create a Storage Reservation Policy.
Procedure
1Select Infrastructure > Compute Resources > Compute Resources.
2Point to a compute resource and click Edit.
3Click the Configuration tab.
4Locate the datastore to add to your storage reservation policy in the Storage table.
5Click the Edit icon ( ) next to the desired Storage Path object.
6Select a storage reservation policy from the Storage Reservation Policy column drop-down menu.
After you provision a machine, you cannot change its storage reservation policy if doing so would
change the storage profile on a disk.
7Click the Save icon ( ).
8Click OK.
9(Optional) Assign additional datastores to your storage reservation policy.
Scenario: Configure IaaS Resources for Rainpole
Using a combination of your IaaS administrator and tenant administrator privileges, you create a prefix to
prepend to vSphere machines created in vRealize Automation, organize your vSphere resources into a
fabric group, and allocate resources to your custom group of vRealize Automation architects.
Configuring vRealize Automation
VMware, Inc. 239

You are here
Configure
Tenant
Configure IaaS
Resources
Design On-
Demand Services
Procedure
1Scenario: Create a Fabric Group for Rainpole
Using your IaaS administrator privileges, you create a fabric group that contains the compute
resources discovered when you created the vSphere endpoint. Assign your custom group of
vRealize Automation architects and developers to the fabric administrator role for this group.
2Scenario: Configure Machine Prefixes for Rainpole
Using your fabric administrator privileges, you create a prefix that you can configure to prepend to
machines provisioned by your vRealize Automation architects and developers during development
and testing.
3Scenario: Create a Business Group for Your Rainpole Architects to Test Catalog Items
Using your tenant administrator privileges, you create a business group for the IT team responsible
for designing and testing vRealize Automation blueprints.
4Scenario: Create a Reservation to Assign Resources to Your Rainpole Architects
Using your fabric administrator privileges, you create a reservation for your Rainpole business group
to allocate them vSphere resources.
Scenario: Create a Fabric Group for Rainpole
Using your IaaS administrator privileges, you create a fabric group that contains the compute resources
discovered when you created the vSphere endpoint. Assign your custom group of vRealize Automation
architects and developers to the fabric administrator role for this group.
You do not need to create a vSphere endpoint, because you already created one when you requested the
initial content catalog item.
Procedure
1Select Infrastructure > Fabric Groups.
2Click the New icon ( ).
3Enter Rainpole fabric in the Name text box.
4Search for Rainpole architects in the Fabric administrators search box and select your custom
group.
5Select the compute resource from your vSphere environment to include in your fabric group.
6Click OK.
7Refresh your browser to view the new menu options available to you as a fabric administrator.
Configuring vRealize Automation
VMware, Inc. 240
What to do next
Using your fabric administrator privileges, you create a machine prefix for your Rainpole architects to use
so any machines they provision during development and testing are easily identified.
Scenario: Configure Machine Prefixes for Rainpole
Using your fabric administrator privileges, you create a prefix that you can configure to prepend to
machines provisioned by your vRealize Automation architects and developers during development and
testing.
Procedure
1Select Infrastructure > Administration > Machine Prefixes.
2Click New.
3Enter Rainpole in the Machine Prefix text box.
4Enter 3 in the Number of Digits text box.
5Enter 1 in the Next Number text box.
6Click the Save icon ( ).
What to do next
Using your tenant administrator privileges, you create a business group for the IT team that is responsible
for designing and testing your vRealize Automation blueprints.
Scenario: Create a Business Group for Your Rainpole Architects to Test
Catalog Items
Using your tenant administrator privileges, you create a business group for the IT team responsible for
designing and testing vRealize Automation blueprints.
Procedure
1Select Administration > Users and Groups > Business Groups.
2Click the New icon ( ).
3Enter Rainpole business group in the Name text box.
4Enter one or more email addresses in the Send manager emails to text box.
For example, enter your own email address, or the email address of your IT manager.
5Add a custom property to assist your architects with troubleshooting their blueprints.
aClick the New icon ( ).
b Enter _debug_deployment in the Name text box.
Configuring vRealize Automation
VMware, Inc. 241
c Enter true in the Value text box.
d Select Prompt User to allow your architects to turn this feature on or off when they request a
catalog item.
Typically, if one component of a catalog item fails to provision vRealize Automation rolls back all
resources for the whole catalog item. You use this custom property to override that behavior so your
architects can pinpoint where their blueprints are failing. You add this custom property to the business
group instead of the blueprints to ensure that architects can always choose to override this behavior,
but the choice is never accidentally provided to users.
6Click Next.
7Search Rainpole architects in the Group manager role search box and select your custom
group.
8Search test_user in the User role search box and select the local user you set up as a shared login
for testing blueprints.
9Click Next.
10 Select Rainpole as the default machine prefix from the drop-down menu.
11 Click Finish.
What to do next
Using your fabric administrator privileges, you allocate IaaS resources to your Rainpole business group
by creating a reservation.
Scenario: Create a Reservation to Assign Resources to Your Rainpole
Architects
Using your fabric administrator privileges, you create a reservation for your Rainpole business group to
allocate them vSphere resources.
Note After you create a reservation, you cannot change the business group or the compute resource.
Procedure
1Select Infrastructure > Reservations > Reservations.
2Click the New icon ( ).
3Select vSphere from the drop-down menu.
4Enter the reservation information.
Option Input
Name Rainpole reservation
Tenant vsphere.local
Business Group Rainpole business group
Priority 1
Configuring vRealize Automation
VMware, Inc. 242
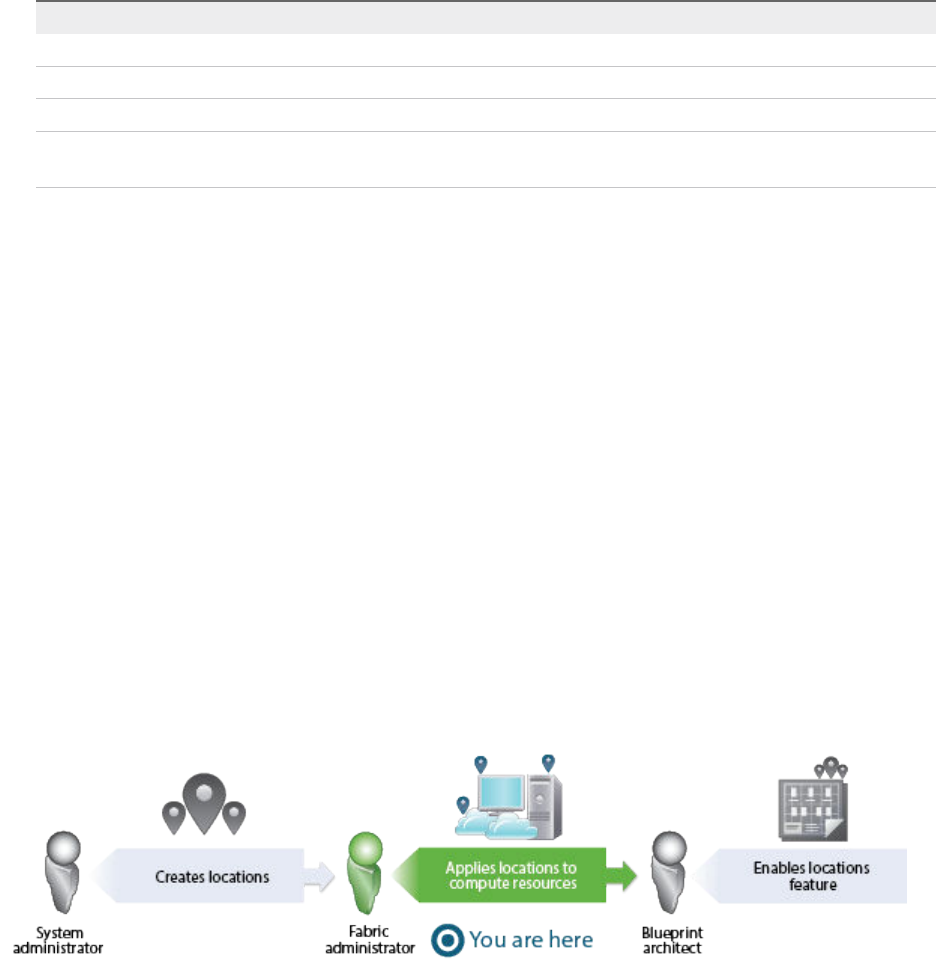
5Select the Resources tab.
6Enter the resources information from your deployment environment.
Option Input
Compute resources Select a resource cluster from the drop-down menu.
Machine quota Specify the maximum number of powered on machines for this reservation.
Memory Specify the maximum amount of memory (MB) this reservation can consume.
Storage Select one or more storage paths and reserve space (GB) for this reservation.
Prioritize the storage paths, with 1 being the highest priority.
7Select the Network tab.
8Select at least one vSphere network path.
9Click OK.
You have brought your vSphere infrastructure under vRealize Automation management and allocated
vSphere resources to your team.
What to do next
Using your IaaS architect privileges, you create a machine blueprint to clone vSphere CentOS machines.
Scenario: Apply a Location to a Compute Resource for Cross
Region Deployments
As a fabric administrator, you want to label your compute resources as belonging to your Boston or
London datacenter to support cross region deployments. When your blueprint architects enable the
locations feature on their blueprints, users are able to choose whether to provision machines in your
Boston or London datacenter.
You have a datacenter in London, and a datacenter in Boston, and you don't want users in Boston
provisioning machines on your London infrastructure or vice versa. To ensure that Boston users provision
on your Boston infrastructure, and London users provision on your London infrastructure, you want to
allow users to select an appropriate location for provisioning when they request machines.
Prerequisites
nLog in to the vRealize Automation console as a fabric administrator.
Configuring vRealize Automation
VMware, Inc. 243
nAs a system administrator, define the datacenter locations. See Scenario: Add Datacenter Locations
for Cross Region Deployments.
Procedure
1Select Infrastructure > Compute Resources > Compute Resources.
2Point to the compute resource located in your Boston datacenter and click Edit.
3Select Boston from the Locations drop-down menu.
4Click OK.
5Repeat this procedure as necessary to associate your compute resources to your Boston and London
locations.
IaaS architects can enable the locations feature so users can choose to provision machines in Boston or
London when they fill out their catalog item request forms. See Scenario: Enable Users to Select
Datacenter Locations for Cross Region Deployments.
Configuring XaaS Resources
By configuring XaaS endpoints you can connect the vRealize Automation to your environment. When you
configure vRealize Orchestrator plug-ins as endpoints, you use the vRealize Automation user interface to
configure the plug-ins instead of using the vRealize Orchestrator configuration interface.
To use vRealize Orchestrator capabilities and the vRealize Orchestrator plug-ins to expose VMware and
third-party technologies to vRealize Automation, you can configure the vRealize Orchestrator plug-ins by
adding the plug-ins as endpoints. This way, you create connections to different hosts and servers, such
as vCenter Server instances, a Microsoft Active Directory host, and so on.
When you add a vRealize Orchestrator plug-in as an endpoint by using the vRealize Automation UI, you
run a configuration workflow in the default vRealize Orchestrator server. The configuration workflows are
located in the vRealize Automation > XaaS > Endpoint Configuration workflows folder.
Important Configuring a single plug-in in vRealize Orchestrator and in the vRealize Automation console
is not supported and results in errors.
Configure the Active Directory Plug-In as an Endpoint
You can add an endpoint and configure the Active Directory plug-in to connect to a running Active
Directory instance and manage users and user groups, Active Directory computers, organizational units,
and so on.
Important By using the Microsoft Active Directory plug-in, you can orchestrate only one connection to
an Active Directory host. You cannot add multiple Microsoft Active Directory instances as endpoints. You
cannot delete an Active Directory endpoint. After you add an Active Directory endpoint, you can update it
at any time.
Configuring vRealize Automation
VMware, Inc. 244
Prerequisites
nVerify that you have access to a Microsoft Active Directory instance. See the Microsoft Active
Directory documentation.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > vRO Configuration > Endpoints.
2Click the New icon ( ).
3Select Active Directory from the Plug-in drop-down menu.
4Click Next.
5Enter a name and, optionally, a description.
6Click Next.
7Configure the Active Directory server details.
a Enter the IP address or the DNS name of the host on which Active Directory runs in the Active
Directory host IP/URL text box.
b Enter the lookup port of your Active Directory server in the Port text box.
vRealize Orchestrator supports the Active Directory hierarchical domains structure. If your
domain controller is configured to use Global Catalog, you must use port 3268. You cannot use
the default port 389 to connect to the Global Catalog server.
c Enter the root element of the Active Directory service in the Root text box.
For example, if your domain name is mycompany.com, then your root Active Directory is
dc=mycompany,dc=com.
This node is used for browsing your service directory after entering the appropriate credentials.
For large service directories, specifying a node in the tree narrows the search and improves
performance. For example, rather than searching in the entire directory, you can specify
ou=employees,dc=mycompany,dc=com. This root element displays all the users in the
Employees group.
d (Optional) To activate encrypted certification for the connection between vRealize Orchestrator
and Active Directory, select Yes from the Use SSL drop-down menu.
Note The SSL certificate is automatically imported without prompting for confirmation even if the
certificate is self-signed.
e (Optional) Enter the default domain in the Default Domain text box.
For example, if your domain name is mycompany.com, type @mycompany.com.
Configuring vRealize Automation
VMware, Inc. 245

8Configure the shared session settings.
a Enter the user name for the shared session in the User name for the shared session text box.
a Enter the password for the shared session in the Password for the shared session text box.
9Click Finish.
You added an Active Directory instance as an endpoint. XaaS architects can use XaaS to publish Active
Directory plug-in workflows as catalog items and resource actions.
Configure the HTTP-REST Plug-In as an Endpoint
You can add an endpoint and configure the HTTP-REST plug-in to connect to a REST host.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator.
nVerify that you have access to a REST host.
Procedure
1Select Administration > vRO Configuration > Endpoints.
2Click the New icon ( ).
3Select HTTP-REST from the Plug-in drop-down menu.
4Click Next.
5Enter a name and, optionally, a description.
6Click Next.
7Provide information about the REST host.
a Enter the name of the host in the Name text box.
b Enter the address of the host in the URL text box.
Note If you use Kerberos access authentication, you must provide the host address in FDQN
format.
c (Optional) Enter the number of seconds before a connection times out in the Connection
timeout (seconds) text box.
The default value is 30 seconds.
d (Optional) Enter the number of seconds before an operation times out in the Operation timeout
(seconds) text box.
The default value is 60 seconds.
Configuring vRealize Automation
VMware, Inc. 246
8(Optional) Configure proxy settings.
a Select Yes to use a proxy from the Use Proxy drop-down menu.
b Enter the IP of the proxy server in the Proxy address text box.
c Enter the port number to communicate with the proxy server in the Proxy port text box.
9Click Next.
10 Select the authentication type.
Option Action
None No authentication is required.
OAuth 1.0 Uses OAuth 1.0 protocol. You must provide the required authentication
parameters under OAuth 1.0.
a Enter the key used to identify the consumer as a service provider in the
Consumer key text box.
b Enter the secret to establish ownership of the consumer key in the
Consumer secret text box.
c (Optional) Enter the access token that the consumer uses to gain access to
the protected resources in the Access token text box.
d (Optional) Enter the secret that the consumer uses to establish ownership of
a token in the Access token secret text box.
OAuth 2.0 Uses OAuth 2.0 protocol.
Enter the authentication token in the Token text box.
Basic Provides basic access authentication. The communication with the host is in
shared session mode.
a Enter the user name for the shared session in the Authentication user
name text box.
b Enter the password for the shared session in the Authentication password
text box.
Digest Provides digest access authentication that uses encryption. The communication
with the host is in shared session mode.
a Enter the user name for the shared session in the Authentication user
name text box.
b Enter the password for the shared session in the Authentication password
text box.
Configuring vRealize Automation
VMware, Inc. 247

Option Action
NTLM Provides NT LAN Manager (NTLM) access authentication within the Window
Security Support Provider (SSP) framework. The communication with the host is
in shared session mode.
a Provide the user credentials for the shared session.
nEnter the user name for the shared session in the Authentication user
name text box.
nEnter the password for the shared session in the Authentication
password text box.
b Configure the NTLM details
n(Optional) Enter the workstation name in the Workstation for NTLM
authentication text box.
nEnter the domain name in the Domain for NTLM authentication text
box.
Kerberos Provides Kerberos access authentication. The communication with the host is in
shared session mode.
a Enter the user name for the shared session in the Authentication user
name text box.
b Enter the password for the shared session in the Authentication password
text box.
11 Click Finish.
You configured the endpoint and added a REST host. XaaS architects can use XaaS to publish HTTP-
REST plug-in workflows as catalog items and resource actions.
Configure the PowerShell Plug-In as an Endpoint
You can add an endpoint and configure the PowerShell plug-in to connect to a running PowerShell host,
so that you can call PowerShell scripts and cmdlets from vRealize Orchestrator actions and workflows,
and work with the result.
Prerequisites
nVerify that you have access to a Windows PowerShell host. For more information about Microsoft
Windows PowerShell, see the Windows PowerShell documentation.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > vRO Configuration > Endpoints.
2Click the New icon ( ).
3Select PowerShell from the Plug-in drop-down menu.
4Click Next.
5Enter a name and, optionally, a description.
6Click Next.
Configuring vRealize Automation
VMware, Inc. 248
7Specify the PowerShell host details.
a Enter the name of the host in the Name text box.
b Enter the IP address or the FDQN of the host in the Host/IP text box.
8Select the PowerShell host type to which the plug-in connects.
Option Action
WinRM a Enter the port number to use for communication with the host in the Port text
box under the PowerShell host details.
b Select a transport protocol from the Transport protocol drop-down menu.
Note If you use the HTTPS transport protocol, the certificate of the remote
PowerShell host is imported to the vRealize Orchestrator keystore.
c Select the authentication type from the Authentication drop-down menu.
Note To use Kerberos authentication, enable it on the WinRM service. For
information about configuring Kerberos authentication, see Using the
PowerShell Plug-In.
SSH None.
9Enter the credentials for a shared session communication with the PowerShell host in the User name
and Password text boxes.
10 Click Finish.
You added an Windows PowerShell host as an endpoint. XaaS architects can use the XaaS to publish
PowerShell plug-in workflows as catalog items and resource actions.
Configure the SOAP Plug-In as an Endpoint
You can add an endpoint and configure the SOAP plug-in to define a SOAP service as an inventory
object, and perform SOAP operations on the defined objects.
Prerequisites
nVerify that you have access to a SOAP host. The plug-in supports SOAP Version 1.1 and 1.2, and
WSDL 1.1 and 2.0.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > vRO Configuration > Endpoints.
2Click the New icon ( ).
3From the Plug-in drop-down menu, select SOAP.
4Click Next.
5Enter a name and, optionally, a description.
6Click Next.
Configuring vRealize Automation
VMware, Inc. 249
7Provide the details about the SOAP host.
a Enter the name of the host in the Name text box.
b Select whether to provide the WSDL content as text from the Provide WSDL content drop-down
menu.
Option Action
Yes Enter the WSDL text in the WSDL content text box.
No Enter the correct path in the WSDL URL text box.
c (Optional) Enter the number of seconds before a connection times out in the Connection
timeout (in seconds) text box.
The default value is 30 seconds.
d (Optional) Enter the number of seconds before an operation times out in the Request timeout (in
seconds) text box.
The default value is 60 seconds.
8(Optional) Specify the proxy settings.
a To use a proxy, select Yes from the Proxy drop-down menu.
b Enter the IP of the proxy server in the Address text box.
c Enter the port number to communicate with the proxy server in the Port text box.
9Click Next.
10 Select the authentication type.
Option Action
None No authentication is required.
Basic Provides basic access authentication. The communication with the host is in
shared session mode.
a Enter the user name for the shared session in the User name text box.
b Enter the password for the shared session in the Password text box.
Digest Provides digest access authentication that uses encryption. The communication
with the host is in shared session mode.
a Enter the user name for the shared session in the User name text box.
b Enter the password for the shared session in the Password text box.
Configuring vRealize Automation
VMware, Inc. 250

Option Action
NTLM Provides NT LAN Manager (NTLM) access authentication in the Window Security
Support Provider (SSP) framework. The communication with the host is in shared
session mode.
a Provide the user credentials.
nEnter the user name for the shared session in the User name text box.
nEnter the password for the shared session in the Password text box.
b Provide the NTLM settings.
nEnter the domain name in the NTLM domain text box.
n(Optional) Enter the workstation name in the NTLM workstation text box.
Negotiate Provides Kerberos access authentication. The communication with the host is in
shared session mode.
a Provide the user credentials.
1 Enter the user name for the shared session in the User name text box.
2 Enter the password for the shared session in the Password text box.
b Enter the Kerberos service SPN in the Kerberos service SPN text box.
11 Click Finish.
You added a SOAP service. XaaS architects can use XaaS to publish SOAP plug-in workflows as catalog
items and resource actions.
Configure the vCenter Server Plug-In as an Endpoint
You can add an endpoint and configure the vCenter Server plug-in to connect to a running vCenter Server
instance to create XaaS blueprints to manage vSphere inventory objects.
Prerequisites
nInstall and configure vCenter Server. See vSphere Installation and Setup.
nLog in to the vRealize Automation console as a tenant administrator.
Procedure
1Select Administration > vRO Configuration > Endpoints.
2Click the New icon ( ).
3Select vCenter Server from the Plug-in drop-down menu.
4Click Next.
5Enter a name and, optionally, a description.
6Click Next.
Configuring vRealize Automation
VMware, Inc. 251
7Provide information about the vCenter Server instance.
a Enter the IP address or the DNS name of the machine in the IP or host name of the vCenter
Server instance to add text box.
This is the IP address or DNS name of the machine on which the vCenter Server instance you
want to add is installed.
b Enter the port to communicate with the vCenter Server instance in the Port of the vCenter
Server instance text box.
The default port is 443.
c Enter the location of the SDK to use for connecting to your vCenter Server instance in the
Location of the SDK that you use to connect to the vCenter Server instance text box.
For example, /sdk.
8Click Next.
9Define the connection parameters.
a Enter the HTTP port of the vCenter Server instance in the HTTP port of the vCenter Server
instance - applicable for VC plugin version 5.5.2 or earlier text box.
b Enter the credentials for vRealize Orchestrator to use to establish the connection to the
vCenter Server instance in the User name of the user that Orchestrator will use to connect to
the vCenter Server instance and Password of the user that Orchestrator will use to
connect to the vCenter Server instance text boxes.
The user that you select must be a valid user with privileges to manage vCenter Server
extensions and a set of custom defined privileges.
10 Click Finish.
You added a vCenter Server instance as an endpoint. XaaS architects can use the XaaS to publish
vCenter Server plug-in workflows as catalog items and resource actions.
Installing Additional Plug-Ins on the Default
vRealize Orchestrator Server
You can install additional plug-ins on the default vRealize Orchestrator server by using the
vRealize Orchestrator configuration interface.
Additional plug-ins are not supported for configuration as vRealize Automation endpoints, but you can
install additional plug-ins on the default vRealize Orchestrator server and use the workflows with XaaS.
Plug-in installation files are available as .vmoapp or .dar files from either the VMware Solution Exchange
website or the vCenter Orchestrator Plug-Ins Documentation.
For more information about installing new plug-ins, see Installing and Configuring VMware vCenter
Orchestrator
Configuring vRealize Automation
VMware, Inc. 252
Providing On-Demand Services
to Users 4
You deliver on-demand services to users by creating catalog items and actions, then carefully controlling
who can request those services by using entitlements and approvals.
This chapter includes the following topics:
nDesigning Blueprints
nExporting and Importing Blueprints
nBuilding Your Design Library
nAssembling Application Blueprints
nManaging the Service Catalog
Designing Blueprints
Blueprint architects build Software components, machine blueprints, and custom XaaS blueprints and
assemble those components into the blueprints that define the items users request from the catalog.
You can create and publish blueprints for a single machine, or a single custom XaaS blueprint, but you
can also combine machine components and XaaS blueprints with other building blocks to design
elaborate catalog item blueprints that include multiple machines, networking and security, software with
full life cycle support, and custom XaaS functionality.
Depending on the catalog item you want to define, the process can be as simple as a single infrastructure
architect publishing one machine component as a blueprint, or the process can include multiple architects
creating many different types of components to design a complete application stack for users to request.
VMware, Inc. 253

Software Components
You can create and publish software components to install software during the machine provisioning
process and support the software life cycle. For example, you can create a blueprint for developers to
request a machine with their development environment already installed and configured. Software
components are not catalog items by themselves, and you must combine them with a machine
component to create a catalog item blueprint.
Machine Blueprints
You can create and publish simple blueprints to provision single machines, or you can create multi-
machine blueprints that contain several different types of machine components. You can also add
networking and security components to machine blueprints, such as security groups or network profiles.
Configuring vRealize Automation
VMware, Inc. 254
XaaS Blueprints
You can publish your vRealize Orchestrator workflows as XaaS blueprints. For example, you can create a
custom resource for Active Directory users, and design an XaaS blueprint to allow managers to provision
new users in their Active Directory group. You create and manage XaaS components outside of the
design tab. You can reuse published XaaS blueprints to create application blueprints, but only in
combination with at least one machine component.
Application Blueprints with Multi-Machine, XaaS , and Software
Components.
You can add any number of machine components, Software components, and XaaS blueprints to a
machine blueprint to deliver elaborate functionality to your users. For example, you can create a blueprint
for managers to provision a new hire setup. You can combine multiple machine components, software
components, and a XaaS blueprint for provisioning new Active Directory users. The QE Manager can
request your New Hire catalog item, and their new quality engineering employee is provisioned in Active
Directory and given two working virtual machines, one Windows and one Linux, each with all the required
software for running test cases in these environments.
Exporting and Importing Blueprints
You can programmatically export content from one vRealize Automation environment to another by using
the vRealize Automation REST API or by using the vRealize CloudClient.
For example, you can create and test your blueprints in a development environment and then import them
into your production environment, or you could import a property definition from a community forum. You
can programmatically import and export any of the following vRealize Automation content:
nApplication blueprints and all their components
nIaaS machine blueprints
nSoftware components
nXaaS blueprints
nProperty definitions
nProperty groups
Configuring vRealize Automation
VMware, Inc. 255
Table 4‑1. Choosing Your Import and Export Tool
Tool More information
vRealize CloudClient https://developercenter.vmware.com/tools
vRealize Automation REST API See Programming Guide and REST API Reference in the
vRealize Automation documentation at
https://www.vmware.com/support/pubs/vcac-pubs.html.
Note When exporting and importing blueprints programmatically across vRealize Automation
deployments, for example from a test to a production environment or from one organization to another, it
is important to recognize that clone template data is included in the package. When you import the
blueprint package, default settings are populated based on information in the package. For example, if
you export and then import a blueprint that was created using a clone-style workflow, and the template
from which that clone data was derived does not exist in an endpoint within the vRealize Automation
deployment in which you import the blueprint, some blueprint settings will not be applicable for that
deployment.
Scenario: Importing the Dukes Bank for vSphere Sample
Application and Configuring for Your Environment
As an IT professional evaluating or learning vRealize Automation, you want to import a robust sample
application into your vRealize Automation instance so you can quickly explore the available functionality
and determine how you might build vRealize Automation blueprints that suit the needs of your
organization.
Prerequisites
nPrepare a CentOS 6.x Linux reference machine, convert it to a template, and create a customization
specification. See Scenario: Prepare for Importing the Dukes Bank for vSphere Sample Application
Blueprint.
nCreate an external network profile to provide a gateway and a range of IP addresses. See Create a
Network Profile for Static IP Address Assignment.
nMap your external network profile to your vSphere reservation. See Create a Reservation for Hyper-V,
KVM, SCVMM, vSphere, or XenServer. The sample application cannot provision successfully without
an external network profile.
nVerify that you have both the infrastructure architect and software architect privileges. Both roles
are required to import the Dukes Bank sample application and to interact with the Dukes Bank
blueprints and software components.
Configuring vRealize Automation
VMware, Inc. 256

Procedure
1Scenario: Import the Dukes Bank for vSphere Sample Application
You download the Dukes Bank for vSphere application from your vRealize Automation appliance.
You import the sample application into your vRealize Automation tenant to view a working sample of
a multi-tiered vRealize Automation blueprint that includes multiple machine components with
networking and software components.
2Scenario: Configure Dukes Bank vSphere Sample Components for Your Environment
Using your infrastructure architect privileges, you configure each of the Dukes Bank machine
components to use the customization specification, template, and machine prefixes that you created
for your environment.
You have configured the Dukes Bank for vSphere sample application for your environment to use as a
starting point for developing your own blueprints, as a tool to evaluate vRealize Automation, or as a
learning resource to assist you in understanding vRealize Automation functionality and components.
Scenario: Import the Dukes Bank for vSphere Sample Application
You download the Dukes Bank for vSphere application from your vRealize Automation appliance. You
import the sample application into your vRealize Automation tenant to view a working sample of a multi-
tiered vRealize Automation blueprint that includes multiple machine components with networking and
software components.
Procedure
1Log in to your vRealize Automation appliance as root by using SSH.
2Download the Dukes Bank for vSphere sample application from your vRealize Automation appliance
to /tmp.
wget --no-check-certificate https://vRealize_VA_Hostname_fqdn:
5480/blueprints/DukesBankAppForvSphere.zip
Do not unzip the package.
3Download Cloud Client version 4.x from http://developercenter.vmware.com/tool/cloudclient to /tmp.
4Unzip the cloudclient-4x-dist.zip package.
5Run Cloud Client under the /bin directory.
$>./bin/cloudclient.sh
6If prompted, accept the license agreement.
7Using Cloud Client, log in to the vRealize Automation appliance as a user with software architect
and infrastructure architect privileges.
CloudClient>vra login userpass --server https://vRealize_VA_Hostname_fqdn --user <user@domain.com>
--tenant <TenantName>
Configuring vRealize Automation
VMware, Inc. 257
8When prompted, enter your login password.
9Validate that the DukesBankAppForvSphere.zip content is available.
vra content import --path /<Path>/DukesBankAppForvSphere.zip --dry-run true --resolution overwrite
By configuring the resolution to overwrite instead of skip, you allow vRealize Automation to correct
conflicts when possible.
10 Import the Dukes Bank sample application.
vra content import --path /<Path>/DukesBankAppForvSphere.zip --dry-run false --resolution overwrite
When you log on to the vRealize Automation console as a user with software architect and
infrastructure architect privileges, you see Dukes Bank blueprints and software components on the
Design > Blueprints tab and the Design > Software Components tab.
Scenario: Configure Dukes Bank vSphere Sample Components for Your
Environment
Using your infrastructure architect privileges, you configure each of the Dukes Bank machine components
to use the customization specification, template, and machine prefixes that you created for your
environment.
This scenario configures the machine components to clone machines from the template you created in
the vSphere Web Client. If you want to create space-efficient copies of a virtual machine based on a
snapshot, the sample application also supports linked clones. Linked clones use a chain of delta disks to
track differences from a parent machine, are provisioned quickly, reduce storage cost, and are ideal to
use when performance is not a high priority.
Procedure
1Log in to the vRealize Automation console as an infrastructure architect.
You can configure the Dukes Bank sample application to work in your environment with only the
infrastructure architect role, but if you want to view or edit the sample software components you
also need the software architect role.
2Select Design > Blueprints.
3Select the DukesBankApplication blueprint and click the Edit icon.
4Edit the appserver-node so vRealize Automation can provision this machine component in your
environment.
You configure the blueprint to provision multiple instances of this machine component so you can
verify the load balancer node functionality.
a Click the appserver-node component on the design canvas.
Configuration details appear in the bottom panel.
b Select your machine prefix from the Machine prefix drop-down menu.
Configuring vRealize Automation
VMware, Inc. 258
c Configure your blueprint to provision at least two instances of this node by selecting a minimum of
2 instances and a maximum of 10.
On the request form, users are able to select to provision at least two and up to ten appserver
nodes.
d Click the Build Information tab.
e Select Cloneworkflow from the Provisioning workflow drop-down menu.
f Select your dukes_bank_template from the Clone from dialog.
g Enter your Customspecs_sample in the Customization spec text box.
This field is case sensitive.
h Click the Machine Resources tab.
i Verify that memory settings are at least 2048 MB.
5Edit the loadbalancer-node so vRealize Automation can provision this machine component in your
environment.
a Click the loadbalancer-node component on the design canvas.
b Select your machine prefix from the Machine prefix drop-down menu.
c Click the Build Information tab.
d Select Cloneworkflow from the Provisioning workflow drop-down menu.
e Select your dukes_bank_template from the Clone from dialog.
f Enter your Customspecs_sample in the Customization spec text box.
This field is case sensitive.
g Click the Machine Resources tab.
h Verify that memory settings are at least 2048 MB.
6Repeat Step 5 for the database-node machine component.
7Click Save and Finish.
Your changes are saved and you return to the Blueprints tab.
8Select the DukesBankApplication blueprint and click Publish.
You configured the Dukes Bank sample application blueprint for your environment and published the
finished blueprint.
What to do next
Published blueprints do not appear to users in the catalog until you configure a catalog service, add the
blueprint to a service, and entitle users to request your blueprint. See Checklist for Configuring the
Service Catalog.
Configuring vRealize Automation
VMware, Inc. 259
After you configure your Dukes Bank blueprint to display in the catalog, you can request to provision the
sample application. See Scenario: Test the Dukes Bank Sample Application.
Scenario: Test the Dukes Bank Sample Application
You request the Dukes Bank catalog item, and log in to the sample application to verify your work and
view vRealize Automation blueprint functionality.
Prerequisites
nImport the Dukes Bank sample application and configure the blueprint components to work in your
environment. See Scenario: Importing the Dukes Bank for vSphere Sample Application and
Configuring for Your Environment.
nConfigure the service catalog and make your published Dukes Bank blueprint available for users to
request. See Checklist for Configuring the Service Catalog.
nVerify that virtual machines you provision can reach the yum repository.
Procedure
1Log in to the vRealize Automation console as a user who is entitled to the Dukes Bank catalog item.
2Click the Catalog tab.
3Locate the Dukes Bank sample application catalog item and click Request.
4Fill in the required request information for each component that has a red asterisk.
a Navigate to the JBossAppServer component to fill in the required request information.
b Enter the fully qualified domain name of your vRealize Automation appliance in the
app_content_server_ip text box.
c Navigate to the Dukes_Bank_App software components to fill in the required request information.
d Enter the fully qualified domain name of your vRealize Automation appliancein the
app_content_server_ip text boxes.
5Click Submit.
Depending on your network and your vCenter Server instance, it can take approximately 15-20
minutes for the Dukes Bank sample application to fully provision. You can monitor the status under
the Requests tab, and after the application provisions you can view the catalog item details on the
Items tab.
6After the application provisions, locate the IP address of the load balancer server so you can access
the Dukes Bank sample application.
a Select Items > Deployments.
b Expand your Dukes Bank sample application deployment and select the Apache load balancer
server.
c Click View Details.
Configuring vRealize Automation
VMware, Inc. 260
d Select the Network tab.
e Make a note of the IP address.
7Log in to the Dukes Bank sample application.
a Navigate to your load balancer server at http://IP_Apache_Load_Balancer:8081/bank/main.faces.
If you want to access the application servers directly, you can navigate to http://IP_AppServer:
8080/bank/main.faces.
b Enter 200 in the Username text box.
c Enter foobar in the Password text box.
You have a working Dukes Bank sample application to use as a starting point for developing your own
blueprints, as a tool to evaluate vRealize Automation, or as a learning resource to assist you in
understanding vRealize Automation functionality and components.
Building Your Design Library
You can build out a library of reusable blueprint components that your architects can assemble into
application blueprints for delivering elaborate on-demand services to your users.
Build out a library of the smallest blueprint design components: single machine blueprints, Software
components, and XaaS blueprints, then combine these base building blocks in new and different ways to
create elaborate catalog items that deliver increasing levels of functionality to your users.
If you have not yet built out your design library, your workflow for creating an application blueprint
depends on the purpose and extent of the catalog item you are designing. You might create Software
components, XaaS blueprints, or machine blueprints before you assemble the final application blueprint
you want your users to see as a catalog item.
Configuring vRealize Automation
VMware, Inc. 261
Table 4‑2. Building Your Design Library
Catalog Item Role Components Description Details
Machines Infrastructur
e architect
Create machine
blueprints on the
Blueprints tab.
You can create machine blueprints to rapidly
deliver virtual, private and public, or hybrid cloud
machines to your users.
Published machine blueprints are available for
catalog administrators to include in the catalog as
standalone blueprints, but you can also combine
machine blueprints with other components to
create more elaborate catalog items that include
multiple machine blueprints, Software, or XaaS
blueprints.
Configure a Machine
Blueprint
NSX Network
and security
on machines
Infrastructur
e architect
Add NSX
network and
security
components to
vSphere
machine
blueprints on the
Blueprints tab.
You can configure network and security
components such as network profiles and security
groups, to allow virtual machines to communicate
with each other over physical and virtual networks
securely and efficiently.
You must combine network and security
components with at least one vSphere machine
component before catalog administrators can
include them in the catalog. You can only apply
NSX network and security components to
vSphere machine blueprints.
Designing Machine
Blueprints with NSX
Networking and Security
Software on
machines
Software
architect
Create and
publish Software
Components on
the Software
tab, then
combine them
with machine
blueprints on the
Blueprints tab.
Add Software components to your machine
blueprints to standardize, deploy, configure,
update, and scale complex applications in cloud
environments. These applications can range from
simple Web applications to elaborate custom
applications and packaged applications.
Software components cannot appear in the
catalog alone. You must create and publish your
Software components and then assemble an
application blueprint that contains at least one
machine.
Create a Software
Component
Configuring vRealize Automation
VMware, Inc. 262
Table 4‑2. Building Your Design Library (Continued)
Catalog Item Role Components Description Details
Custom IT
Services
XaaS
architects
Create and
publish XaaS
blueprints on the
XaaS tab.
You can create XaaS catalog items that extend
vRealize Automation functionality beyond
machine, networking, security, and software
provisioning. Using existing vRealize Orchestrator
workflows and plug-ins, or custom scripts you
develop in vRealize Orchestrator, you can
automate the delivery of any IT services.
Published XaaS blueprints are available for
catalog administrators to include in the catalog as
standalone blueprints, but you can also combine
them with other components on the Blueprints
tab to create more elaborate catalog items.
Creating XaaS Blueprints
and Resource Actions
Assemble
published
blueprint
building
blocks into
new catalog
items
nApplicati
on
architect
nInfrastru
cture
architect
nSoftwar
e
architect
Combine
additional
machine
blueprints, XaaS
blueprints, and
Software
components with
at least one
machine
component or
machine
blueprint on the
Blueprints tab.
You can reuse published components and
blueprints, combining them in new ways to create
IT service packages that deliver elaborate
functionality to your users.
Assembling Application
Blueprints
Designing Machine Blueprints
Machine blueprints are the complete specification for a machine, determining a machine's attributes, the
manner in which it is provisioned, and its policy and management settings. Depending on the complexity
of the catalog item you are building, you can combine one or more machine components in the blueprint
with other components in the design canvas to create more elaborate catalog items that include
networking and security, Software components, XaaS components, and other blueprint components.
Space-Ecient Storage for Virtual Provisioning
Space-efficient storage technology eliminates the inefficiencies of traditional storage methods by using
only the storage actually required for a machine's operations. Typically, this is only a fraction of the
storage actually allocated to machines. vRealize Automation supports two methods of provisioning with
space-efficient technology, thin provisioning and FlexClone provisioning.
When standard storage is used, the storage allocated to a provisioned machine is fully committed to that
machine, even when it is powered off. This can be a significant waste of storage resources because few
virtual machines actually use all of the storage allocated to them, just as few physical machines operate
with a 100% full disk. When a space-efficient storage technology is used, the storage allocated and the
storage used are tracked separately and only the storage used is fully committed to the provisioned
machine.
Configuring vRealize Automation
VMware, Inc. 263
Thin Provisioning
Thin provisioning is supported for all virtual provisioning methods. Depending on your virtualization
platform, storage type, and default storage configuration, thin provisioning might always be used during
machine provisioning. For example, for vSphere ESX Server integrations using NFS storage, thin
provisioning is always employed. However, for vSphere ESX Server integrations that use local or iSCSI
storage, thin provisioning is only used to provision machines if the custom property
VirtualMachine.Admin.ThinProvision is specified in the blueprint. For more information about thin
provisioning, please see the documentation provided by your virtualization platform.
Net App FlexClone Provisioning
You can create a blueprint for Net App FlexClone provisioning if you are working in a vSphere
environment that uses Network File System (NFS) storage and FlexClone technology.
You can only use NFS storage, or machine provisioning fails. You can specify a FlexClone storage path
for other types of machine provisioning, but the FlexClone storage path behaves like standard storage.
The following is a high-level overview of the sequence of steps required to provision machines that use
FlexClone technology:
1 An IaaS administrator creates a NetApp ONTAP endpoint. See Create a NetApp ONTAP Endpoint.
2 An IaaS administrator runs data collection on the endpoint to enable the endpoint to be visible on the
compute resource and reservation pages.
The FlexClone option is visible on a reservation page in the endpoint column if a NetApp ONTAP
endpoint exists and if the host is virtual. If there is a NetApp ONTAP endpoint, the reservation page
displays the endpoint assigned to the storage path.
3 A fabric administrator creates a vSphere reservation, enables FlexClone storage, and specifies an
NFS storage path that uses FlexClone technology.
4 An Infrastructure Architect or other authorized user creates a blueprint for FlexClone provisioning.
Configure a Machine Blueprint
Configure and publish a machine component as a standalone blueprint that other architects can reuse as
a component in application blueprints, and catalog administrators can include in catalog services.
Prerequisites
nLog in to the vRealize Automation console as an infrastructure architect.
nComplete external preparations for provisioning, such as creating templates, WinPE's, and ISO's, or
gather the information about external preparations from your administrators.
nConfigure your tenant. Chapter 2 Configuring Tenant Settings.
nConfigure your IaaS resources. Checklist for Configuring IaaS Resources.
nSee Configuring vRealize Automation.
Configuring vRealize Automation
VMware, Inc. 264
Procedure
1Select Design > Blueprints.
2Click the New icon ( ).
3Follow the prompts on the New Blueprint dialog box to configure general settings.
4Click OK.
5Click Machine Types in the Categories area to display a list of available machine types.
6Drag the type of machine you want to provision onto the design canvas.
7Follow the prompts on each of the tabs to configure machine provisioning details.
8Click Finish.
9Select your blueprint and click Publish.
You configured and published a machine component as a standalone blueprint. Catalog administrators
can include this machine blueprint in catalog services and entitle users to request this blueprint. Other
architects can reuse this machine blueprint to create more elaborate application blueprints that include
Software components, XaaS blueprints, or additional machine blueprints.
What to do next
You can combine a machine blueprint with Software components, XaaS blueprints, or additional machine
blueprints to create more elaborate application blueprints. See Assembling Application Blueprints.
Machine Blueprint Settings
Understand the settings and options you can configure when you create machine blueprints.
New Blueprint and Blueprint Properties Settings
Understand the settings and options that you can configure in the New Blueprint dialog box. After you
create the blueprint, you can edit these settings on the Blueprint Properties dialog box.
General Tab
Apply settings across your entire blueprint, including all components you intend to add now or later.
Table 4‑3. General Tab Settings
Setting Description
Name Enter a name for your blueprint.
Identifier The identifier field automatically populates based on the name you entered.
You can edit this field now, but after you save the blueprint you can never
change it. Because identifiers are permanent and unique within your tenant,
you can use them to programmatically interact with blueprints and to create
property bindings.
Description Summarize your blueprint for the benefit of other architects. This description
also appears to users on the request form.
Configuring vRealize Automation
VMware, Inc. 265
Table 4‑3. General Tab Settings (Continued)
Setting Description
Archive days You can specify an archival period to temporarily retain deployments instead
of destroying deployments as soon as their lease expires. Specify 0 (default)
to destroy the deployment when its lease expires. The archival period begins
on the day the lease expires. When the archive period ends, the deployment
is destroyed.
Lease days: Minimum and Maximum Enter a minimum and a maximum value to allow users to choose from a
range of lease lengths. When the lease ends, the deployment is either
destroyed or archived.
NSX Settings Tab
If you have configured VMware NSX, and installed the NSX plug-in for vRealize Automation, you can
specify NSX transport zone, gateway reservation policy, and app isolation settings when you create or
edit a blueprint. These settings are available on the NSX Settings tab on the New Blueprint and
Blueprint Properties pages.
For information about NSX settings, see New Blueprint and Blueprint Properties Settings with NSX.
Properties Tab
Custom properties you add at the blueprint level apply to the entire blueprint, including all components.
However, they can be overridden by custom properties assigned later in the precedence chain. For more
information about order of precedence for custom properties, see Custom Properties Reference.
Table 4‑4. Properties Tab Settings
Tab Setting Description
Property Groups Property groups are reusable groups of properties that are designed to simplify the
process of adding custom properties to blueprints. Your tenant administrators and fabric
administrators can group properties that are often used together so you can add the
property group to a blueprint instead of individually inserting custom properties.
Move up /Move down Control the order of precedence given to each
property group in relation to one another by
prioritizing the groups. The first group in the
list has the highest priority, and its custom
properties have first precedence. You can also
drag and drop to reorder.
View properties View the custom properties in the selected
property group.
View merged properties If a custom property is included in more than
one property group, the value included in the
property group with the highest priority takes
precedence. You can view these merged
properties to assist you in prioritizing property
groups.
Custom Properties You can add individual custom properties instead of property groups.
Configuring vRealize Automation
VMware, Inc. 266
Table 4‑4. Properties Tab Settings (Continued)
Tab Setting Description
Name For a list of custom property names and
behaviors, see Custom Properties Reference.
Value Enter the value for the custom property.
Encrypted You can choose to encrypt the property value,
for example, if the value is a password.
Overridable You can specify that the property value can be
overridden by the next or subsequent person
who uses the property. Typically, this is
another architect, but if you select Show in
request, your business users are able to see
and edit property values when they request
catalog items.
Show in request If you want to display the property name and
value to your end users, you can select to
display the property on the request form when
requesting machine provisioning. You must
also select overridable if you want users to
provide a value.
vSphere Machine Component Settings
Understand the settings and options that you can configure for a vSphere machine component in the
vRealize Automation blueprint design canvas. vSphere is the only machine component type that can use
NSX network and security component settings in the design canvas.
General Tab
Configure general settings for a vSphere machine component.
Table 4‑5. General Tab Settings
Setting Description
ID Enter a name for your machine component, or accept the default.
Description Summarize your machine component for the benefit of other architects.
Display location on request In a cloud environment, such as vCloud Air, this allows users to select a
region for their provisioned machines.
For a virtual environment, such as vSphere, you can configure the locations
feature to allow users to select a particular data center location at which to
provision a requested machine. To fully configure this option, a system
administrator adds data center location information to a locations file and a
fabric administrator edits a compute resource to associate it with a location.
Configuring vRealize Automation
VMware, Inc. 267
Table 4‑5. General Tab Settings (Continued)
Setting Description
Reservation policy Apply a reservation policy to a blueprint to restrict the machines provisioned
from that blueprint to a subset of available reservations. Fabric
administrators create reservation policies to provide an optional and helpful
means of controlling how reservation requests are processed, for example to
collect resources into groups for different service levels, or to make a specific
type of resource easily available for a particular purpose. If your fabric
administrator did not configure reservation policies, you do not see any
available options in this drop-down menu.
Machine prefix Machine prefixes are created by fabric administrators and are used to create
the names of provisioned machines. If you select Use group default,
machines provisioned from your blueprint are named according to the
machine prefix configured as the default for the user's business group. If no
machine prefix is configured, one is generated for you based on the name of
the business group.
If your fabric administrator configures other machine prefixes for you to
select, you can apply one prefix to all machines provisioned from your
blueprint, no matter who the requestor is.
Instances: Minimum and Maximum To support clustering, you can provision multiple instances of the same
machine component as part of your blueprint. Enter a minimum and
maximum value to allow users to select from a range of instances.
Build Information Tab
Configure build information settings for a vSphere machine component.
Configuring vRealize Automation
VMware, Inc. 268
Table 4‑6. Build Information Tab
Setting Description
Blueprint type For record-keeping and licensing purposes, select whether
machines provisioned from this blueprint are classified as
Desktop or Server.
Action The options you see in the action drop-down menu depend on
the type of machine you select.
The following actions are available:
nCreate
Create the machine component specification without use of
a cloning option.
nClone
Make copies of a virtual machine from a template and
customization object.
nLinkedClone
Provision a space-efficient copy of a virtual machine called a
linked clone. Linked clones are based on a snapshot of a
VM and use a chain of delta disks to track differences from a
parent machine.
nNetAppFlexClone
If your fabric administrators configured your reservations to
use NetApp Flexclone storage, you can clone space-
efficient copies of machines using this technology.
Provisioning workflow The options you see in the provisioning workflow drop-down
menu depend on the type of machine you select, and the action
you select.
nCloudLinuxKickstartWorkflow
Provision a machine by booting from an ISO image, using a
kickstart or autoYaSt configuration file and a Linux
distribution image to install the operating system on the
machine.
nCloudProvisioningWorkflow
Create a machine by starting from either a virtual machine
instance or cloud-based image.
nCloudWIMImageWorkflow
Provision a machine by booting into a WinPE environment
and installing an operating system using a Windows Imaging
File Format (WIM) image of an existing Windows reference
machine.
When using a WIM provisioning workflow in a blueprint,
specify a storage value that accounts for the size of each
disk to be used on the machine. Use the total value of all
disks as the minimum storage value for the machine
component. Also specify a size for each disk that is large
enough to accommodate the operating system.
Configuring vRealize Automation
VMware, Inc. 269
Table 4‑6. Build Information Tab (Continued)
Setting Description
Clone from For clone or NetApp FlexClone, select a machine template to
clone from.
For linked clones, select a machine from the list of machines.
You only see machines that have available snapshots to clone
from, that you manage as a tenant administrator or business
group manager.
Clone from snapshot For linked clones, select an existing snapshot to clone from
based on the selected machine template. Machines only appear
in the list if they already have an existing snapshot, and if you
manage that machine as a tenant administrator or business
group manager.
This option is available for the Linked Clone action.
Customization spec Specify an available customization specification. A
customization spec is required only if you are cloning with static
IP addresses.
You cannot perform customization of Windows machines without
a customization specification. For Linux clone machines, you
can perform customization by using a customization spec, an
external script, or both.
Machine Resources Tab
Specify CPU, memory, and storage settings for your vSphere machine component.
Table 4‑7. Machine Resources Tab
Setting Description
CPUs: Minimum and Maximum Enter a minimum and maximum number of CPUs that can be
provisioned by this machine component.
Memory (MB): Minimum and Maximum Enter a minimum and maximum amount of memory that can be
consumed by machines that are provisioned by this machine
component.
Storage (GB): Minimum and Maximum Enter a minimum and maximum amount of storage that can be
consumed by machines that are provisioned by this machine
component. For vSphere, KVM (RHEV), SCVMM, vCloud Air,
and vCloud Director, minimum storage is set based on what you
enter on the Storage tab.
When using a WIM provisioning workflow in a blueprint, specify
a storage value that accounts for the size of each disk to be
used on the machine. Use the total value of all disks as the
minimum storage value for the machine component. Also specify
a size for each disk that is large enough to accommodate the
operating system.
Storage Tab
You can add storage volume settings, including one or more storage reservation policies, to the machine
component to control storage space.
Configuring vRealize Automation
VMware, Inc. 270
Table 4‑8. Storage Tab Settings
Setting Description
ID Enter an ID or name for the storage volume.
Capacity (GB) Enter the storage capacity for the storage volume.
Drive Letter/Mount Path Enter a drive letter or mount path for the storage volume.
Label Enter a label for the drive letter and mount path for the storage
volume.
Storage Reservation Policy Enter the existing storage reservation policy to use with this storage
volume.
Custom Properties Enter any custom properties to use with this storage volume.
Maximum volumes Enter the maximum number of allowed storage volumes that can be
used when provisioning from the machine component. Enter 0 to
prevent others from adding storage volumes. The default value is
60.
Allow users to see and change storage reservation
policies
Select the check box to allow users to remove an associated
reservation policy or specify a different reservation policy when
provisioning.
Network Tab
You can configure network settings for a vSphere machine component based on NSX network and load
balancer settings that are configured outside vRealize Automation. You can use settings from one or
more existing and on-demand NSX network components in the blueprint design canvas.
For information about adding and configuring NSX network and security components before using
network tab settings on a vSphere machine component, see Configuring Network and Security
Component Settings.
For information about specifying blueprint-level NSX settings that apply to vSphere machine components,
see New Blueprint and Blueprint Properties Settings with NSX.
Table 4‑9. Network Tab Settings
Setting Description
Network Select a network component from the drop-down menu. Only
network components that exist in the blueprint design canvas
are listed.
Assignment Type Accept the default assignment derived from the network
component or select an assignment type from the drop-down
menu. The DCHP and Static option values are derived from
settings in the network component.
Address Specify the IP address for the network. The option is available
only for the static address type.
Load Balancing Enter the service to use for load balancing.
Configuring vRealize Automation
VMware, Inc. 271
Table 4‑9. Network Tab Settings (Continued)
Setting Description
Custom Properties Display custom properties that are configured for the selected
network component or network profile.
Maximum network adapters Specify the maximum number of network adapters, or NICs, to
allow for this machine component. The default is unlimited. Set
to 0 to disable adding NICs for the machine components.
Security Tab
You can configure security settings for a vSphere machine component based on NSX settings that are
configured outside vRealize Automation. You an optionally use settings from existing and on-demand
NSX security components in the blueprint design canvas.
The security settings from existing and on-demand security group and security tag components in the
blueprint design canvas are automatically available.
For information about adding and configuring NSX network and security components before using
security tab settings on a vSphere machine component, see Configuring Network and Security
Component Settings.
For information about specifying blueprint-level NSX information that applies to vSphere machine
components, see New Blueprint and Blueprint Properties Settings with NSX.
Table 4‑10. Security Tab Settings
Setting Description
Name Display the name of an NSX security group or tag. The names
are derived from security components in the blueprint design
canvas.
Select the check box next to a listed security group or tag to use
that group or tag for provisioning from this machine component.
Type Indicate if the security element is an on-demand security group,
an existing security group, or a security tag.
Description Display the description defined for the security group or tag.
Endpoint Display the endpoint used by the NSX security group or tag.
Properties Tab
Optionally specify custom property and property group information for your vSphere machine component.
You can add individual and groups of custom properties to the machine component by using the
Properties tab. You can add also custom properties and property groups to the overall blueprint by using
the Properties tab when you create or edit a blueprint by using the New Blueprint or Blueprint
Properties page, respectively.
You can use the Custom Properties tab to add and configure options for existing custom properties.
Custom properties are supplied with vRealize Automation and you can also create property definitions.
Configuring vRealize Automation
VMware, Inc. 272
Table 4‑11. Properties > Custom Properties Tab Settings
Setting Description
Name Enter the name of a custom property or select an available
custom property from the drop-down menu. For example, enter
the custom property name Machine.SSH to specify whether
machines provisioned by using this blueprint allow SSH
connections. Properties only appear in the drop-down menu if
your tenant administrator or fabric administrator created property
definitions.
Value Enter or edit a value to associate with the custom property
name. For example, set the value as true to allow entitled users
to connect by using SSH to machines provisioned by using your
blueprint.
Encrypted You can choose to encrypt the property value, for example, if the
value is a password.
Overridable You can specify that the property value can be overridden by the
next or subsequent person who uses the property. Typically, this
is another architect, but if you select Show in request, your
business users are able to see and edit property values when
they request catalog items.
Show in Request If you want to display the property name and value to your end
users, you can select to display the property on the request form
when requesting machine provisioning. You must also select
overridable if you want users to provide a value.
You can use the Property Groups tab to add and configure settings for existing custom property groups.
You can create your own property groups or use property groups that have been created for you.
Table 4‑12. Properties > Property Groups Tab Settings
Setting Description
Name Select an available property group from the drop-down menu.
Move Up and Move Down Control the precedence level of listed property groups in
descending order. The first-listed property group has
precedence over the next-listed property group and so on.
View Properties Display the custom properties in the selected property group.
View Merged Properties Display all the custom properties in the listed property groups in
the order in which they appear in the list of property groups.
Where the same property appears in more than one property
group, the property name appears only once in the list based on
when it is first encountered in the list.
vCloud Air Machine Component Settings
Understand the settings and options that you can configure for a vCloud Air machine component in the
vRealize Automation blueprint design canvas.
Configuring vRealize Automation
VMware, Inc. 273
General Tab
Configure general settings for a vCloud Air machine component.
Table 4‑13. General Tab Settings
Setting Description
ID Enter a name for your machine component, or accept the default.
Description Summarize your machine component for the benefit of other architects.
Display location on request In a cloud environment, such as vCloud Air, this allows users to select a
region for their provisioned machines.
For a virtual environment, such as vSphere, you can configure the locations
feature to allow users to select a particular data center location at which to
provision a requested machine. To fully configure this option, a system
administrator adds data center location information to a locations file and a
fabric administrator edits a compute resource to associate it with a location.
Reservation policy Apply a reservation policy to a blueprint to restrict the machines provisioned
from that blueprint to a subset of available reservations. Fabric
administrators create reservation policies to provide an optional and helpful
means of controlling how reservation requests are processed, for example to
collect resources into groups for different service levels, or to make a specific
type of resource easily available for a particular purpose. If your fabric
administrator did not configure reservation policies, you do not see any
available options in this drop-down menu.
Machine prefix Machine prefixes are created by fabric administrators and are used to create
the names of provisioned machines. If you select Use group default,
machines provisioned from your blueprint are named according to the
machine prefix configured as the default for the user's business group. If no
machine prefix is configured, one is generated for you based on the name of
the business group.
If your fabric administrator configures other machine prefixes for you to
select, you can apply one prefix to all machines provisioned from your
blueprint, no matter who the requestor is.
Instances: Minimum and Maximum To support clustering, you can provision multiple instances of the same
machine component as part of your blueprint. Enter a minimum and
maximum value to allow users to select from a range of instances.
Build Information Tab
Configure build information settings for a vCloud Air machine component.
Configuring vRealize Automation
VMware, Inc. 274
Table 4‑14. Build Information Tab
Setting Description
Blueprint type For record-keeping and licensing purposes, select whether
machines provisioned from this blueprint are classified as
Desktop or Server.
Action The options you see in the action drop-down menu depend on
the type of machine you select.
The following actions are available:
nClone
Make copies of a virtual machine from a template and
customization object.
Provisioning workflow The options you see in the provisioning workflow drop-down
menu depend on the type of machine you select, and the action
you select.
The following actions are available:
nCloneWorkflow
Make copies of a virtual machine, either by clone, linked
clone, or Netapp Flexclone.
Clone from For clone or NetApp FlexClone, select a machine template to
clone from.
For linked clones, select a machine from the list of machines.
You only see machines that have available snapshots to clone
from, that you manage as a tenant administrator or business
group manager.
Machine Resources Tab
Specify CPU, memory and storage settings for your vCloud Air machine component.
Table 4‑15. Machine Resources Tab
Setting Description
CPUs: Minimum and Maximum Enter a minimum and maximum number of CPUs that can be
provisioned by this machine component.
Memory (MB): Minimum and Maximum Enter a minimum and maximum amount of memory that can be
consumed by machines that are provisioned by this machine
component.
Storage (GB): Minimum and Maximum Enter a minimum and maximum amount of storage that can be
consumed by machines that are provisioned by this machine
component. For vSphere, KVM (RHEV), SCVMM, vCloud Air,
and vCloud Director, minimum storage is set based on what you
enter on the Storage tab.
Storage Tab
You can add storage volume settings, including one or more storage reservation policies, to the machine
component to control storage space.
Configuring vRealize Automation
VMware, Inc. 275
Table 4‑16. Storage Tab Settings
Setting Description
ID Enter an ID or name for the storage volume.
Capacity (GB) Enter the storage capacity for the storage volume.
Drive Letter/Mount Path Enter a drive letter or mount path for the storage volume.
Label Enter a label for the drive letter and mount path for the storage
volume.
Storage Reservation Policy Enter the existing storage reservation policy to use with this storage
volume.
Custom Properties Enter any custom properties to use with this storage volume.
Maximum volumes Enter the maximum number of allowed storage volumes that can be
used when provisioning from the machine component. Enter 0 to
prevent others from adding storage volumes. The default value is
60.
Allow users to see and change storage reservation
policies
Select the check box to allow users to remove an associated
reservation policy or specify a different reservation policy when
provisioning.
Properties Tab
Optionally specify custom property and property group information for your vCloud Air machine
component.
You can add individual and groups of custom properties to the machine component by using the
Properties tab. You can add also custom properties and property groups to the overall blueprint by using
the Properties tab when you create or edit a blueprint by using the New Blueprint or Blueprint
Properties page, respectively.
You can use the Custom Properties tab to add and configure options for existing custom properties.
Custom properties are supplied with vRealize Automation and you can also create property definitions.
Table 4‑17. Properties > Custom Properties Tab Settings
Setting Description
Name Enter the name of a custom property or select an available
custom property from the drop-down menu. For example, enter
the custom property name Machine.SSH to specify whether
machines provisioned by using this blueprint allow SSH
connections. Properties only appear in the drop-down menu if
your tenant administrator or fabric administrator created property
definitions.
Value Enter or edit a value to associate with the custom property
name. For example, set the value as true to allow entitled users
to connect by using SSH to machines provisioned by using your
blueprint.
Encrypted You can choose to encrypt the property value, for example, if the
value is a password.
Configuring vRealize Automation
VMware, Inc. 276
Table 4‑17. Properties > Custom Properties Tab Settings (Continued)
Setting Description
Overridable You can specify that the property value can be overridden by the
next or subsequent person who uses the property. Typically, this
is another architect, but if you select Show in request, your
business users are able to see and edit property values when
they request catalog items.
Show in Request If you want to display the property name and value to your end
users, you can select to display the property on the request form
when requesting machine provisioning. You must also select
overridable if you want users to provide a value.
You can use the Property Groups tab to add and configure settings for existing custom property groups.
You can create your own property groups or use property groups that have been created for you.
Table 4‑18. Properties > Property Groups Tab Settings
Setting Description
Name Select an available property group from the drop-down menu.
Move Up and Move Down Control the precedence level of listed property groups in
descending order. The first-listed property group has
precedence over the next-listed property group and so on.
View Properties Display the custom properties in the selected property group.
View Merged Properties Display all the custom properties in the listed property groups in
the order in which they appear in the list of property groups.
Where the same property appears in more than one property
group, the property name appears only once in the list based on
when it is first encountered in the list.
Amazon Machine Component Settings
Understand the settings and options that you can configure for an Amazon machine component in the
vRealize Automation blueprint design canvas.
General Tab
Configure general settings for an Amazon machine component.
Table 4‑19. General Tab Settings
Setting Description
ID Enter a name for your machine component, or accept the default.
Description Summarize your machine component for the benefit of other architects.
Display location on request In a cloud environment, such as vCloud Air, this allows users to select a
region for their provisioned machines.
For a virtual environment, such as vSphere, you can configure the locations
feature to allow users to select a particular data center location at which to
provision a requested machine. To fully configure this option, a system
administrator adds data center location information to a locations file and a
fabric administrator edits a compute resource to associate it with a location.
Configuring vRealize Automation
VMware, Inc. 277
Table 4‑19. General Tab Settings (Continued)
Setting Description
Reservation policy Apply a reservation policy to a blueprint to restrict the machines provisioned
from that blueprint to a subset of available reservations. Fabric
administrators create reservation policies to provide an optional and helpful
means of controlling how reservation requests are processed, for example to
collect resources into groups for different service levels, or to make a specific
type of resource easily available for a particular purpose. If your fabric
administrator did not configure reservation policies, you do not see any
available options in this drop-down menu.
Machine prefix Machine prefixes are created by fabric administrators and are used to create
the names of provisioned machines. If you select Use group default,
machines provisioned from your blueprint are named according to the
machine prefix configured as the default for the user's business group. If no
machine prefix is configured, one is generated for you based on the name of
the business group.
If your fabric administrator configures other machine prefixes for you to
select, you can apply one prefix to all machines provisioned from your
blueprint, no matter who the requestor is.
Instances: Minimum and Maximum To support clustering, you can provision multiple instances of the same
machine component as part of your blueprint. Enter a minimum and
maximum value to allow users to select from a range of instances.
Build Information Tab
Configure build information settings for an Amazon machine component.
Table 4‑20. Build Information Tab
Setting Description
Blueprint type For record-keeping and licensing purposes, select whether
machines provisioned from this blueprint are classified as
Desktop or Server.
Provisioning workflow The only provisioning workflow available for an Amazon
machine component is CloudProvisioningWorkflow.
Create a machine by starting from either a virtual machine
instance or cloud-based image.
Amazon Machine Image Select an available Amazon machine image. An Amazon
machine image is a template that contains a software
configuration, including an operating system. Machine images
are managed by Amazon Web Services accounts.
Configuring vRealize Automation
VMware, Inc. 278
Table 4‑20. Build Information Tab (Continued)
Setting Description
Key Pair Key pairs are required for provisioning with Amazon Web
Services.
Key pairs are used to provision and connect to a cloud instance.
They are also used to decrypt Windows passwords and to log in
to a Linux machine.
The following key pair options are available:
nNot specified
Controls key pair behavior at the blueprint level rather than
at the reservation level.
nAuto-generated per business group
Specifies that each machine provisioned in the same
business group has the same key pair, including machines
provisioned on other reservations when the machine has the
same compute resource and business group. Because the
key pairs are associated with a business group, the key
pairs are deleted when the business group is deleted.
nAuto-generated per machine
Specifies that each machine has a unique key pair. The
auto-generated per machine option is the most secure
method because no key pairs are shared among machines.
Enable Amazon network options on machine Choose whether to allow users to provision a machine in a
virtual private cloud (VPC) or a non-VPC location when they
submit the request.
Instance Types Select one or more Amazon instance types. An Amazon
instance is a virtual server that can run applications in Amazon
Web Services. Instances are created from an Amazon machine
image and by choosing an appropriate instance type.
vRealize Automation manages the machine image instance
types that are available for provisioning.
Machine Resources Tab
Specify CPU, memory, storage, and EBS volume settings for your Amazon machine component.
Table 4‑21. Machine Resources Tab
Setting Description
CPUs: Minimum and Maximum Enter a minimum and maximum number of CPUs that can be
provisioned by this machine component.
Memory (MB): Minimum and Maximum Enter a minimum and maximum amount of memory that can be
consumed by machines that are provisioned by this machine
component.
Configuring vRealize Automation
VMware, Inc. 279
Table 4‑21. Machine Resources Tab (Continued)
Setting Description
Storage (GB): Minimum and Maximum Enter a minimum and maximum amount of storage that can be
consumed by machines that are provisioned by this machine
component. For vSphere, KVM (RHEV), SCVMM, vCloud Air,
and vCloud Director, minimum storage is set based on what you
enter on the Storage tab.
EBS Storage (GB): Minimum and Maximum Enter a minimum and maximum amount of Amazon Elastic
Block Store (EBS) storage volume that can be consumed by
machine resources that are provisioned by this machine
component.
When destroying a deployment that contains an Amazon
machine component, all EBS volumes that were added to the
machine during its life cycle are detached, rather than
destroyed. vRealize Automation does not provide an option for
destroying the EBS volumes.
Properties Tab
Optionally specify custom property and property group information for your Amazon machine component.
You can add individual and groups of custom properties to the machine component by using the
Properties tab. You can add also custom properties and property groups to the overall blueprint by using
the Properties tab when you create or edit a blueprint by using the New Blueprint or Blueprint
Properties page, respectively.
You can use the Custom Properties tab to add and configure options for existing custom properties.
Custom properties are supplied with vRealize Automation and you can also create property definitions.
Table 4‑22. Properties > Custom Properties Tab Settings
Setting Description
Name Enter the name of a custom property or select an available
custom property from the drop-down menu. For example, enter
the custom property name Machine.SSH to specify whether
machines provisioned by using this blueprint allow SSH
connections. Properties only appear in the drop-down menu if
your tenant administrator or fabric administrator created property
definitions.
Value Enter or edit a value to associate with the custom property
name. For example, set the value as true to allow entitled users
to connect by using SSH to machines provisioned by using your
blueprint.
Encrypted You can choose to encrypt the property value, for example, if the
value is a password.
Configuring vRealize Automation
VMware, Inc. 280
Table 4‑22. Properties > Custom Properties Tab Settings (Continued)
Setting Description
Overridable You can specify that the property value can be overridden by the
next or subsequent person who uses the property. Typically, this
is another architect, but if you select Show in request, your
business users are able to see and edit property values when
they request catalog items.
Show in Request If you want to display the property name and value to your end
users, you can select to display the property on the request form
when requesting machine provisioning. You must also select
overridable if you want users to provide a value.
You can use the Property Groups tab to add and configure settings for existing custom property groups.
You can create your own property groups or use property groups that have been created for you.
Table 4‑23. Properties > Property Groups Tab Settings
Setting Description
Name Select an available property group from the drop-down menu.
Move Up and Move Down Control the precedence level of listed property groups in
descending order. The first-listed property group has
precedence over the next-listed property group and so on.
View Properties Display the custom properties in the selected property group.
View Merged Properties Display all the custom properties in the listed property groups in
the order in which they appear in the list of property groups.
Where the same property appears in more than one property
group, the property name appears only once in the list based on
when it is first encountered in the list.
OpenStack Machine Component Settings
Understand the settings and options you can configure for an OpenStack machine component in the
vRealize Automation blueprint design canvas.
General Tab
Configure general settings for an OpenStack machine component.
Table 4‑24. General Tab Settings
Setting Description
ID Enter a name for your machine component, or accept the default.
Description Summarize your machine component for the benefit of other architects.
Display location on request In a cloud environment, such as vCloud Air, this allows users to select a
region for their provisioned machines.
For a virtual environment, such as vSphere, you can configure the locations
feature to allow users to select a particular data center location at which to
provision a requested machine. To fully configure this option, a system
administrator adds data center location information to a locations file and a
fabric administrator edits a compute resource to associate it with a location.
Configuring vRealize Automation
VMware, Inc. 281
Table 4‑24. General Tab Settings (Continued)
Setting Description
Reservation policy Apply a reservation policy to a blueprint to restrict the machines provisioned
from that blueprint to a subset of available reservations. Fabric
administrators create reservation policies to provide an optional and helpful
means of controlling how reservation requests are processed, for example to
collect resources into groups for different service levels, or to make a specific
type of resource easily available for a particular purpose. If your fabric
administrator did not configure reservation policies, you do not see any
available options in this drop-down menu.
Machine prefix Machine prefixes are created by fabric administrators and are used to create
the names of provisioned machines. If you select Use group default,
machines provisioned from your blueprint are named according to the
machine prefix configured as the default for the user's business group. If no
machine prefix is configured, one is generated for you based on the name of
the business group.
If your fabric administrator configures other machine prefixes for you to
select, you can apply one prefix to all machines provisioned from your
blueprint, no matter who the requestor is.
Instances: Minimum and Maximum To support clustering, you can provision multiple instances of the same
machine component as part of your blueprint. Enter a minimum and
maximum value to allow users to select from a range of instances.
Build Information Tab
Configure build information settings for an OpenStack machine component.
Configuring vRealize Automation
VMware, Inc. 282
Table 4‑25. Build Information Tab
Setting Description
Blueprint type For record-keeping and licensing purposes, select whether
machines provisioned from this blueprint are classified as
Desktop or Server.
Provisioning workflow The following provisioning workflows are available for an
OpenStack machine component:
nCloudLinuxKickstartWorkflow
Provision a machine by booting from an ISO image, using a
kickstart or autoYaSt configuration file and a Linux
distribution image to install the operating system on the
machine.
nCloudProvisioningWorkflow
Create a machine by starting from either a virtual machine
instance or cloud-based image.
nCloudWIMImageWorkflow
Provision a machine by booting into a WinPE environment
and installing an operating system using a Windows Imaging
File Format (WIM) image of an existing Windows reference
machine.
When using a WIM provisioning workflow in a blueprint,
specify a storage value that accounts for the size of each
disk to be used on the machine. Use the total value of all
disks as the minimum storage value for the machine
component. Also specify a size for each disk that is large
enough to accommodate the operating system.
OpenStack Image Select an available OpenStack machine image. An OpenStack
machine image is a template that contains a software
configuration, including an operating system. Machine images
are managed by OpenStack accounts.
Configuring vRealize Automation
VMware, Inc. 283
Table 4‑25. Build Information Tab (Continued)
Setting Description
Key Pair Key pairs are optional for provisioning with OpenStack.
Key pairs are used to provision and connect to a cloud instance.
They are also used to decrypt Windows passwords and to log in
to a Linux machine.
The following key pair options are available:
nNot specified
Controls key pair behavior at the blueprint level rather than
at the reservation level.
nAuto-generated per business group
Specifies that each machine provisioned in the same
business group has the same key pair, including machines
provisioned on other reservations when the machine has the
same compute resource and business group. Because the
key pairs are associated with a business group, the key
pairs are deleted when the business group is deleted.
nAuto-generated per machine
Specifies that each machine has a unique key pair. The
auto-generated per machine option is the most secure
method because no key pairs are shared among machines.
Flavors Select one or more OpenStack flavors. An OpenStack flavor is a
virtual hardware template that defines the machine resource
specifications for instances provisioned in OpenStack. Flavors
are managed within the OpenStack provider and are imported
during data collection.
Machine Resources Tab
Specify CPU, memory and storage settings for your OpenStack machine component.
Configuring vRealize Automation
VMware, Inc. 284
Table 4‑26. Machine Resources Tab
Setting Description
CPUs: Minimum and Maximum Enter a minimum and maximum number of CPUs that can be
provisioned by this machine component.
Memory (MB): Minimum and Maximum Enter a minimum and maximum amount of memory that can be
consumed by machines that are provisioned by this machine
component.
Storage (GB): Minimum and Maximum Enter a minimum and maximum amount of storage that can be
consumed by machines that are provisioned by this machine
component. For vSphere, KVM (RHEV), SCVMM, vCloud Air,
and vCloud Director, minimum storage is set based on what you
enter on the Storage tab.
When using a WIM provisioning workflow in a blueprint, specify
a storage value that accounts for the size of each disk to be
used on the machine. Use the total value of all disks as the
minimum storage value for the machine component. Also specify
a size for each disk that is large enough to accommodate the
operating system.
Properties Tab
Optionally specify custom property and property group information for your OpenStack machine
component.
You can add individual and groups of custom properties to the machine component by using the
Properties tab. You can add also custom properties and property groups to the overall blueprint by using
the Properties tab when you create or edit a blueprint by using the New Blueprint or Blueprint
Properties page, respectively.
You can use the Custom Properties tab to add and configure options for existing custom properties.
Custom properties are supplied with vRealize Automation and you can also create property definitions.
Table 4‑27. Properties > Custom Properties Tab Settings
Setting Description
Name Enter the name of a custom property or select an available
custom property from the drop-down menu. For example, enter
the custom property name Machine.SSH to specify whether
machines provisioned by using this blueprint allow SSH
connections. Properties only appear in the drop-down menu if
your tenant administrator or fabric administrator created property
definitions.
Value Enter or edit a value to associate with the custom property
name. For example, set the value as true to allow entitled users
to connect by using SSH to machines provisioned by using your
blueprint.
Encrypted You can choose to encrypt the property value, for example, if the
value is a password.
Configuring vRealize Automation
VMware, Inc. 285
Table 4‑27. Properties > Custom Properties Tab Settings (Continued)
Setting Description
Overridable You can specify that the property value can be overridden by the
next or subsequent person who uses the property. Typically, this
is another architect, but if you select Show in request, your
business users are able to see and edit property values when
they request catalog items.
Show in Request If you want to display the property name and value to your end
users, you can select to display the property on the request form
when requesting machine provisioning. You must also select
overridable if you want users to provide a value.
You can use the Property Groups tab to add and configure settings for existing custom property groups.
You can create your own property groups or use property groups that have been created for you.
Table 4‑28. Properties > Property Groups Tab Settings
Setting Description
Name Select an available property group from the drop-down menu.
Move Up and Move Down Control the precedence level of listed property groups in
descending order. The first-listed property group has
precedence over the next-listed property group and so on.
View Properties Display the custom properties in the selected property group.
View Merged Properties Display all the custom properties in the listed property groups in
the order in which they appear in the list of property groups.
Where the same property appears in more than one property
group, the property name appears only once in the list based on
when it is first encountered in the list.
Troubleshooting Blueprints for Clone and Linked Clone
When creating a linked clone or clone blueprint, machine or templates are missing. Using your shared
clone blueprint to request machines fails to provision machines.
Problem
When working with clone or linked clone blueprints, you might encounter one of the following problems:
nWhen you create a linked clone blueprint, no machines appear in the list to clone, or the machine you
want to clone does not appear.
nWhen you create a clone blueprint for a business group, no templates appear in the list of templates
to clone, or the template you want does not appear.
nWhen machines are requested by using your shared clone blueprint, provisioning fails.
Cause
There are multiple possible causes for common clone and linked clone blueprint problems.
Configuring vRealize Automation
VMware, Inc. 286

Table 4‑29. Causes for Common Clone and Linked Clone Blueprints Problems
Problem Cause Solution
Machines missing You can only create linked clone blueprints by using
machines you manage as a tenant administrator or
business group manager.
A user in your tenant or business
group must request a vSphere
machine. If you have the
appropriate roles, you can do this
yourself.
Templates missing If you are creating a clone blueprint for a business
group, then you only see templates that exist on
compute resources on which the business group has
a reservation.
nVerify that your fabric
administrator created a
reservation for your business
group on the compute resource
containing the templates.
nIf your endpoints are clustered
and contain multiple compute
resources, verify that your IaaS
administrator added the cluster
containing the templates to your
fabric group.
nFor new templates, verify that IT
placed the templates on the
same cluster included in your
fabric group.
Provisioning failure with a shared
blueprint
For shared blueprints, no validation is available to
ensure that the template you select exists in the
reservation used to provision a machine from your
shared clone blueprint.
Consider using entitlements to
restrict the blueprint to users who
have a reservation on the compute
resource where the template exists.
For more information about
entitlements, see Tenant
Administration.
Provisioning failure with a guest
agent
The virtual machine might be rebooting immediately
after the guest operating system customization is
completed, but before the guest agent work items are
completed, causing provisioning to fail. You can use
the custom property
VirtualMachine.Admin.CustomizeGuestOSDelay
to increase the time delay.
Verify that you have added the
custom property
VirtualMachine.Admin.Customi
zeGuestOSDelay. The value must
be in HH:MM:SS format. If the value
is not set, the default value is one
minute (00:01:00).
Linked clone provisioning fails when
using SDRS
When using linked clone provisioning and SDRS, the
new machine must reside on the same cluster. A
provisioning error occurs if the source machine's
disks are on one cluster and you request to provision
a machine on a different cluster.
When using SDRS and linked clone
provisioning, provision machines to
the same cluster as the linked clone
source. Do not provision to a
different cluster.
Adding Network and Security Properties to a Machine Component
Non-vSphere machine components do not have a Network or Security tab. You can add network and
security options to non-vSphere machine components in the blueprint design canvas by using custom
properties.
The Network & Security components are only available for use with vSphere machine components.
Configuring vRealize Automation
VMware, Inc. 287

For machine components that do not have a Network or Security tab, you can add network and security
custom properties, such as VirtualMachine.Network0.Name, to their Properties tab in the blueprint
canvas. However, NSX load balancer properties are only applicable to vSphere machines.
You can define custom properties individually or as part of an existing property group by using the
Properties tab when configuring a machine component in the design canvas. The custom properties that
you define for a machine component pertain to machines of that type that are provisioned from the
blueprint.
For information about the available custom properties, see Custom Properties Reference.
Scenario: Create a vSphere CentOS Blueprint for Cloning in Rainpole
Using your IaaS architect privileges, you create and publish a basic blueprint for cloning vSphere CentOS
machines.
You are here
Configure
Tenant
Configure IaaS
Resources
Design On-
Demand Services
After you publish your blueprint, other architects can reuse it as a component in new blueprints. No one
can see or request your blueprint from the catalog until you use your tenant administrator privileges to
make it available for request.
Procedure
1Scenario: Create a Blueprint for Your Rainpole Machine Component
Using your IaaS architect privileges, create a blueprint and configure the name and description for
your vSphere CentOS machine blueprint. A unique identifier is applied to the blueprint, so you can
programmatically interact with blueprints or create property bindings if you need to. You want users
to have some flexibility with their blueprint leases, so you configure the blueprint to allow users to
choose their lease duration for up to a month.
2Scenario: Configure General Details for Your Rainpole Machine Component
Using your IaaS architect privileges, you drag a vSphere machine component onto the design
canvas and configure the general details for machines provisioned by using your blueprint.
3Scenario: Specify Build Information for Your Rainpole Machine Component
Using your IaaS architect privileges, you configure your blueprint to clone machines from the
CentOS template you created in vSphere.
4Scenario: Configure Machine Resources for Your Rainpole Machines
Using your IaaS architect privileges, you give users minimum and maximum parameters for memory
and the number of allowed CPU's. This conserves resources, but also accommodates your user's
needs.
Configuring vRealize Automation
VMware, Inc. 288

Scenario: Create a Blueprint for Your Rainpole Machine Component
Using your IaaS architect privileges, create a blueprint and configure the name and description for your
vSphere CentOS machine blueprint. A unique identifier is applied to the blueprint, so you can
programmatically interact with blueprints or create property bindings if you need to. You want users to
have some flexibility with their blueprint leases, so you configure the blueprint to allow users to choose
their lease duration for up to a month.
Procedure
1Select Design > Blueprints.
2Click the New icon ( ).
3Enter Centos on vSphere in the Name text box.
4Review the generated unique identifier.
You can edit this field now, but after you save the blueprint you can never change it. Because
identifiers are permanent and unique within your tenant, you can use them to programmatically
interact with blueprints and to create property bindings.
The identifier field automatically populates based on the name you entered.
5Enter Golden Standard CentOS machine configuration in the Description text box.
6Configure a lease range for users to choose from by entering 1 in the Minimum text box and 30 in
the Maximum text box.
7Click OK.
What to do next
You drag a vSphere machine component onto the canvas and configure it to clone the CentOS template
you created in vSphere.
Scenario: Configure General Details for Your Rainpole Machine Component
Using your IaaS architect privileges, you drag a vSphere machine component onto the design canvas and
configure the general details for machines provisioned by using your blueprint.
Only IaaS architects are allowed to configure machine components. Application and Software architects
are only allowed to use machine components by reusing the published machine blueprints that you
create.
Procedure
1Click the Machine Types category in the left navigation pane.
Machine component types appear in the lower panel.
2Drag and drop a vSphere machine component onto the canvas.
3Enter Golden Standard CentOS Machine in the Description text box.
Configuring vRealize Automation
VMware, Inc. 289
4Select Use group default from the Machine prefix drop-down menu.
If you plan to import these blueprints into your other environments, selecting the group default instead
of the specific Rainpole prefix prevents you from configuring your blueprint to work with a machine
prefix that might not be available.
What to do next
You configure the machine component to clone machines from the CentOS template you created.
Scenario: Specify Build Information for Your Rainpole Machine Component
Using your IaaS architect privileges, you configure your blueprint to clone machines from the CentOS
template you created in vSphere.
You configure your machine component to perform the clone action, and select the template you created
as the object to clone from. You specify the customization specification you created to prevent any
conflicts that might arise if you deploy multiple virtual machines with identical settings.
Procedure
1Click the Build Information tab.
2Select whether machines provisioned from this blueprint are classified as Desktop or Server from the
Blueprint type drop-down menu.
This information is for record-keeping and licensing purposes only.
3Select Clone from the Action drop-down menu.
4Select CloneWorkflow from the Provisioning workflow drop-down menu.
5Click the Browse icon next to the Clone from text box.
6Select Rainpole_centos_63_x86 to clone machines from the template you created in vSphere.
7Click OK.
8Enter Linux in the Customization spec text box to use the customization specification you created
in vSphere.
Note This value is case sensitive.
What to do next
You configure CPU, memory, and storage settings for machines provisioned by using your blueprint.
Scenario: Configure Machine Resources for Your Rainpole Machines
Using your IaaS architect privileges, you give users minimum and maximum parameters for memory and
the number of allowed CPU's. This conserves resources, but also accommodates your user's needs.
Configuring vRealize Automation
VMware, Inc. 290

Software architects and application architects are not allowed to configure machine components, but they
can reuse blueprints that contain machines components. When you finish editing your machine
component, you publish your blueprint so other architects can reuse your machine blueprint to design
their own catalog items. Your published blueprint is also available to catalog administrators and tenant
administrators to include in the service catalog.
Procedure
1Click the Machine Resources tab.
2Specify CPU settings for provisioned machines.
a Enter 1 in the Minimum text box.
b Enter 4 in the Maximum text box.
3Specify memory settings for provisioned machines.
a Enter 1024 in the Minimum text box.
This field is automatically populated based on the memory of your template.
b Enter 4096 in the Maximum text box.
4Specify storage settings for provisioned machines.
Some storage information is populated based on the configuration of your template, but you can add
additional storage.
aClick the New icon ( ).
b Enter 10 in the Capacity (GB) text box.
c Click OK.
5Click Finish.
6Select the row containing CentOS on vSphere and click Publish.
You created a catalog-ready blueprint to deliver cloned vSphere CentOS machines to your users and to
reuse in other blueprints as the standard for CentOS machines.
What to do next
Using your tenant administrator privileges, create a catalog service for architects to validate their
blueprints. Publish your CentOS on vSphere machine blueprint as a catalog item and request it to verify
your work.
Scenario: Turn Your Rainpole Machine into a Base for Delivering Software
Components
Using your IaaS architect privileges, you create a blueprint that supports Software components by using a
snapshot of your provisioned machine as the reference machine to clone from. Because you want to
support Software components, you install the guest agent and bootstrap agent on your provisioned
machine before you take the snapshot.
Configuring vRealize Automation
VMware, Inc. 291

You are here
Configure
Tenant
Configure IaaS
Resources
Design On-
Demand Services
Procedure
1Scenario: Install the Guest Agent and Software Bootstrap Agent on Your Rainpole Machine
Using your business group manager privileges, you log into the Rainpole001 machine you
provisioned as the test user. You install the guest agent and the Software bootstrap agent on your
machine to prepare for Software provisioning. When you finish, take a snapshot of the machine to
use as the base for cloning machines to use with Software components.
2Scenario: Create a Linked Clone Blueprint Based on Your Rainpole Snapshot
Using your IaaS architect privileges, you want to provide software architects with space-efficient
copies of the provisioned CentOS machine you prepared.
Scenario: Install the Guest Agent and Software Bootstrap Agent on Your Rainpole Machine
Using your business group manager privileges, you log into the Rainpole001 machine you provisioned as
the test user. You install the guest agent and the Software bootstrap agent on your machine to prepare for
Software provisioning. When you finish, take a snapshot of the machine to use as the base for cloning
machines to use with Software components.
Procedure
1Select Items > Machines.
2Click your CentOS on vSphere item to view item details.
3Click Connect to Remote Console from the Actions menu on the right.
4Log in to the machine as the root user.
5Download the installation script from your vRealize Automation appliance.
wget https://vRealize_VA_Hostname_fqdn:5480/service/software/download/prepare_vra_template.sh
If your environment is using self-signed certificates, you might have to use the wget option --no-
check-certificate option. For example:
wget --no-check-certificate https://vRealize_VA_Hostname_fqdn:
5480/service/software/download/prepare_vra_template.sh
6Make the prepare_vra_template.sh script executable.
chmod +x prepare_vra_template.sh
Configuring vRealize Automation
VMware, Inc. 292

7Run the prepare_vra_template.sh installer script.
./prepare_vra_template.sh
You can run the help command ./prepare_vra_template.sh --help for information about non-
interactive options and expected values.
8Follow the prompts to complete the installation.
You see a confirmation message when the installation is successfully completed. If you see an error
message and logs in the console, resolve the errors and run the installer script again.
9Return to the vRealize Automation console and create the snapshot.
a Click Create Snapshot from the Actions menu on the right and follow the prompts.
b Click the Snapshots tab to monitor the process.
You installed the software bootstrap agent and the guest agent so your snapshot can be used as the
clone base in blueprints that contain software components.
Scenario: Create a Linked Clone Blueprint Based on Your Rainpole Snapshot
Using your IaaS architect privileges, you want to provide software architects with space-efficient copies of
the provisioned CentOS machine you prepared.
You copy your existing CentOS on vSphere blueprint as a starting point, and edit the copy to create linked
clone copies of the snapshot you prepared. Linked clones use a chain of delta disks to track differences
from a parent machine. They are provisioned quickly, reduce storage cost, and are ideal to use when
performance is not a high priority.
Procedure
1Select Design > Blueprints.
2Select the row that contains CentOS on vSphere and click Copy.
You created an independent copy of the CentOS on vSphere machine blueprint.
3Enter CentOS for Software Testing in the Name text box.
4Enter Space-efficient vSphere CentOS for software testing in the Description text box.
5Click OK.
6Select the machine component on your canvas to edit the details.
7Click the Build Information tab.
8Select Linked Clone from the Action drop-down menu.
9Click the Browse icon next to the Clone from text box.
10 Select the provisioned machine Rainpole001 on which you installed the software bootstrap and guest
agents.
11 Select your snapshot from the Clone from snapshot drop-down menu.
Configuring vRealize Automation
VMware, Inc. 293
12 Click Finish.
13 Select the row that contains CentOS for Software Testing and click Publish.
You created a linked clone blueprint that you and your architects can use to deliver software on CentOS
machines.
What to do next
Use your software architect privileges to create a Software component for installing MySQL.
Add RDP Connection Support to Your Windows Machine Blueprints
If you want to allow your catalog administrators to entitle users to the Connect using RDP action for your
Windows blueprints, you must add the RDP custom properties to your machine blueprint, and reference
the custom RDP file your system administrator prepared.
Note If your fabric administrator creates a property group that contains the required custom properties
and you include it in your blueprint, you do not need to individually add the custom properties to the
blueprint.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or business group manager.
nObtain the name of the custom RDP file that your system administrator created for you. See Create a
Custom RDP File to Support RDP Connections for Provisioned Machines.
nCreate at least one Windows machine blueprint.
Procedure
1Select Design > Blueprints.
2Point to the blueprint to update and click Edit.
3Select the machine component on your canvas to edit the details.
4Click the Properties tab.
5Click the Custom Properties tab.
Configuring vRealize Automation
VMware, Inc. 294
6Configure RDP settings.
a Click New Property.
b Enter the RDP custom property names in the Name text box and the corresponding values in the
Value text box.
Option Description and Value
(Required)RDP.File.Name Specifies an RDP file from which to obtain settings, for example
My_RDP_Settings.rdp. The file must reside in the Website\Rdp subdirectory
of the vRealize Automation installation directory.
(Required)
VirtualMachine.Rdp.SettingN
Configures specific RDP settings. N is a unique number used to distinguish
one RDP setting from another. For example, to specify the Authentication
Level so that no authentication requirement is specified, define the custom
property VirtualMachine.Rdp.Setting1 and set the value to authentication
level:i:3. Use to open an RDP link to specify settings.
For a list of available settings and correct syntax, see the Microsoft Windows
RDP documentation.
VirtualMachine.Admin.NameComplet
ion
Specifies the domain name to include in the fully qualified domain name of the
machine that the RDP or SSH files generate for the user interface options
Connect Using RDP or Connect Using SSH option. For example, set the
value to myCompany.com to generate the fully qualified domain name my-
machine-name.myCompany.com in the RDP or SSH file.
c Click Save.
7Select the row containing your blueprint and click Publish.
Your catalog administrators can entitle users to the Connect Using RDP action for machines provisioned
from your blueprint. If users are not entitled to the action, they are not able to connect by using RDP.
Scenario: Add Active Directory Cleanup to Your CentOS Blueprint
As an IaaS architect, you want to configure vRealize Automation to clean up your Active Directory
environment whenever provisioned machines are removed from your hypervisors. So you edit your
existing vSphere CentOS blueprint to configure the Active Directory cleanup plugin.
Using the Active Directory Cleanup Plugin, you can specify the following Active Directory account actions
to occur when a machine is deleted from a hypervisor:
nDelete the AD account
nDisable the AD account
nRename AD account
nMove the AD account to another AD organizational unit (OU)
Prerequisites
Note This information does not apply to Amazon Web Services.
nLog in to the vRealize Automation console as an infrastructure architect.
Configuring vRealize Automation
VMware, Inc. 295
nGather the following information about your Active Directory environment:
nAn Active Directory account user name and password with sufficient rights to delete, disable,
rename, or move AD accounts. The user name must be in domain\username format.
n(Optional) The name of the OU to which to move destroyed machines.
n(Optional) The prefix to attach to destroyed machines.
nCreate a machine blueprint. See Scenario: Create a vSphere CentOS Blueprint for Cloning in
Rainpole.
Procedure
1Select Design > Blueprints.
2Point to your Centos on vSphere blueprint and click Edit.
3Select the machine component on your canvas to bring up the details tab.
4Click the Properties tab.
5Click the Custom properties tab to configure the Active Directory Cleanup Plugin.
a Click New Property.
b Type Plugin.AdMachineCleanup.Execute in the Name text box.
c Type true in the Value text box.
dClick the Save icon ( ).
6Configure the Active Directory Cleanup Plugin by adding custom properties.
Option Description and Value
Plugin.AdMachineCleanup.UserName Enter the Active Directory account user name in the Value text box. This user
must have sufficient privileges to delete, disable, move, and rename Active
Directory accounts. The user name must be in the format domain\username.
Plugin.AdMachineCleanup.Password Enter the password for the Active Directory account user name in the Value text
box.
Plugin.AdMachineCleanup.Delete Set to True to delete the accounts of destroyed machines, instead of disabling
them.
Plugin.AdMachineCleanup.MoveToOu Moves the account of destroyed machines to a new Active Directory
organizational unit. The value is the organization unit to which you are moving the
account. This value must be in ou=OU, dc=dc format, for example
ou=trash,cn=computers,dc=lab,dc=local.
Plugin.AdMachineCleanup.RenamePre
fix
Renames the accounts of destroyed machines by adding a prefix. The value is
the prefix string to prepend, for example destroyed_.
7Click OK.
Whenever machines provisioned from your blueprint are deleted from your hypervisor, your Active
Directory environment is updated.
Configuring vRealize Automation
VMware, Inc. 296
Scenario: Allow Requesters to Specify Machine Host Name
As a blueprint architect, you want to allow your users to choose their own machine names when they
request your blueprints. So you edit your existing CentOS vSphere blueprint to add the Hostname custom
property and configure it to prompt users for a value during their requests.
Note If your fabric administrator creates a property group that contains the required custom properties
and you include it in your blueprint, you do not need to individually add the custom properties to the
blueprint.
Prerequisites
nLog in to the vRealize Automation console as an infrastructure architect.
nCreate a machine blueprint. See Scenario: Create a vSphere CentOS Blueprint for Cloning in
Rainpole.
Procedure
1Select Design > Blueprints.
2Point to your Centos on vSphere blueprint and click Edit.
3Select the machine component on your canvas to bring up the details tab.
4Click the Properties tab.
5Click New Property.
6Enter Hostname in the Name text box.
7Leave the Value text box blank.
8Configure vRealize Automation to prompt users for a hostname value during request.
a Select Overridable.
b Select Show in Request.
Because host names must be unique, users can only request one machine at a time from this
blueprint.
9Click the Save icon ( ).
10 Click OK.
Users who request a machine from your blueprint are required to specify a host name for their machine.
vRealize Automation validates that the specified host name is unique.
Configuring vRealize Automation
VMware, Inc. 297

Scenario: Enable Users to Select Datacenter Locations for Cross Region
Deployments
As a blueprint architect, you want to allow your users to choose whether to provision machines on your
Boston or London infrastructure, so you edit your existing vSphere CentOS blueprint to enable the
locations feature.
You have a datacenter in London, and a datacenter in Boston, and you don't want users in Boston
provisioning machines on your London infrastructure or vice versa. To ensure that Boston users provision
on your Boston infrastructure, and London users provision on your London infrastructure, you want to
allow users to select an appropriate location for provisioning when they request machines.
Prerequisites
nLog in to the vRealize Automation console as an infrastructure architect.
nAs a system administrator, define the datacenter locations. See Scenario: Add Datacenter Locations
for Cross Region Deployments.
nAs a fabric administrator, apply the appropriate locations to your compute resources. See Scenario:
Apply a Location to a Compute Resource for Cross Region Deployments.
nCreate a machine blueprint. See Scenario: Create a vSphere CentOS Blueprint for Cloning in
Rainpole.
Procedure
1Select Design > Blueprints.
2Point to your Centos on vSphere blueprint and click Edit.
3Select the machine component on your canvas to bring up the General details tab.
4Select the Display location on request check box.
5Click Finish.
6Point to your Centos on vSphere blueprint and click Publish.
Business group users are now prompted to select a datacenter location when they request a machine to
be provisioned from your blueprint.
Configuring vRealize Automation
VMware, Inc. 298
Designing Machine Blueprints with NSX Networking and Security
If you have an NSX instance integrated with vRealize Automation, you can configure your vSphere
blueprints to leverage NSX for network and security virtualization.
If you have configured vRealize Automation integration with NSX, you can use network, security, and load
balancer components in the design canvas to configure your blueprint for machine provisioning. You can
also add the following NSX network and security settings to the overall blueprint when you create a new
blueprint or edit an existing blueprint.
nTransport zone - contains the networks used for the provisioned machine deployment
nRouted gateway reservation policy - manages network communication for the provisioned machine
deployment
nApp isolation - allows only internal traffic between machines used in the provisioned machine
deployment
NSX settings are only applicable to vSphere machine component types.
New Blueprint and Blueprint Properties Settings with NSX
You can specify settings that apply to the entire blueprint. After you create the blueprint, you can edit
these settings on the Blueprint Properties dialog box.
General Tab
Apply settings across your entire blueprint, including all components you intend to add now or later.
Table 4‑30. General Tab Settings
Setting Description
Name Enter a name for your blueprint.
Identifier The identifier field automatically populates based on the name you entered.
You can edit this field now, but after you save the blueprint you can never
change it. Because identifiers are permanent and unique within your tenant,
you can use them to programmatically interact with blueprints and to create
property bindings.
Description Summarize your blueprint for the benefit of other architects. This description
also appears to users on the request form.
Archive days You can specify an archival period to temporarily retain deployments instead
of destroying deployments as soon as their lease expires. Specify 0 (default)
to destroy the deployment when its lease expires. The archival period begins
on the day the lease expires. When the archive period ends, the deployment
is destroyed.
Lease days: Minimum and Maximum Enter a minimum and a maximum value to allow users to choose from a
range of lease lengths. When the lease ends, the deployment is either
destroyed or archived.
Configuring vRealize Automation
VMware, Inc. 299
NSX Settings Tab
If you have configured VMware NSX, and installed the NSX plug-in for vRealize Automation, you can
specify NSX transport zone, gateway reservation policy, and app isolation settings when you create or
edit a blueprint. These settings are available on the NSX Settings tab on the New Blueprint and
Blueprint Properties pages.
For information about configuring NSX, see NSX Administration Guide.
Table 4‑31. NSX Settings Tab Settings
Setting Description
Transport zone Select an existing NSX transport zone to contain the network or networks
that the provisioned machine deployment can use.
A transport zone defines which clusters the networks can span. When
provisioning machines, if a transport zone is specified in a reservation and in
a blueprint, the transport zone values must match.
A transport zone is only required for blueprints that have an on-demand
network. For security groups, security tags, and load balancers, the transport
zone is optional. If you do not specify a transport zone, the endpoint is
determined by the location of the security group, security tag, or network that
the load balancer connects to.
Routed gateway reservation policy Select an NSX routed gateway reservation policy. This reservation policy
applies to routed gateways and to all edges that are deployed as part of
provisioning. There is only one edge provisioned per deployment.
For routed networks, edges are not provisioned, but you can use a
reservation policy to select a reservation with the routed gateways to be
used for routed network provisioning.
When vRealize Automation provisions a machine with NAT or routed
networking, it provisions a routed gateway as the network router. The routed
gateway is a management machine that consumes compute resources like
other virtual machines but manages the network communications all
machine in that deployment. The reservation used to provision the routed
gateway determines the external network used for NAT and load balancer
virtual IP addresses. As a best practice, use separate management cluster
for management machines such as NSX Edges.
App isolation Select the App isolation check box to use the app isolation security policy
configured in NSX. The app isolation policy is applied to all vSphere machine
components in the blueprint. You can optionally add NSX security groups
and tags to allow vRealize Orchestrator to open the isolated network
configuration to allow additional paths in and out of the app isolation.
Properties Tab
Custom properties you add at the blueprint level apply to the entire blueprint, including all components.
However, they can be overridden by custom properties assigned later in the precedence chain. For more
information about order of precedence for custom properties, see Custom Properties Reference.
Configuring vRealize Automation
VMware, Inc. 300

Table 4‑32. Properties Tab Settings
Tab Setting Description
Property Groups Property groups are reusable groups of properties that are designed to simplify the
process of adding custom properties to blueprints. Your tenant administrators and fabric
administrators can group properties that are often used together so you can add the
property group to a blueprint instead of individually inserting custom properties.
Move up /Move down Control the order of precedence given to each
property group in relation to one another by
prioritizing the groups. The first group in the
list has the highest priority, and its custom
properties have first precedence. You can also
drag and drop to reorder.
View properties View the custom properties in the selected
property group.
View merged properties If a custom property is included in more than
one property group, the value included in the
property group with the highest priority takes
precedence. You can view these merged
properties to assist you in prioritizing property
groups.
Custom Properties You can add individual custom properties instead of property groups.
Name For a list of custom property names and
behaviors, see Custom Properties Reference.
Value Enter the value for the custom property.
Encrypted You can choose to encrypt the property value,
for example, if the value is a password.
Overridable You can specify that the property value can be
overridden by the next or subsequent person
who uses the property. Typically, this is
another architect, but if you select Show in
request, your business users are able to see
and edit property values when they request
catalog items.
Show in request If you want to display the property name and
value to your end users, you can select to
display the property on the request form when
requesting machine provisioning. You must
also select overridable if you want users to
provide a value.
Applying an NSX Transport Zone to a Blueprint
An NSX administrator can create transport zones to control cluster use of networks.
For an on-demand network, you can specify an NSX transport zone in a blueprint to define the transport
zone that contains the networks used by the provisioned machine deployment.
Configuring vRealize Automation
VMware, Inc. 301

Applying an NSX Routed Gateway Reservation Policy to a Blueprint
You can specify a reservation policy to manage the network communications for machines provisioned by
the blueprint. When requesting machine provisioning, the reservation policy is used to group the
reservations that can be considered for the deployment. The routed gateway reservation policy is also
referred to as an Edge reservation policy.
Networking information is contained in each reservation. When the machines are provisioned, a routed
gateway is allocated as the network router to manage network communications for the provisioned
machines in the deployment. You can add or edit blueprint-level properties by using the blueprint
properties page.
vRealize Automation provisions a routed gateway, for example an edge services gateway, for NAT
networks and for load balancers. For routed networks, vRealize Automation uses existing distributed
routers.
The reservation used to provision the routed gateway determines the external network used for NAT and
routed network profiles, as well as the load balancer virtual IP addresses.
When you use the blueprint to provision a machine deployment, vRealize Automation attempts to use
only the reservations associated with the specified reservation policy to provision the routed gateway.
Applying an NSX App Isolation Security Policy to a Blueprint
An NSX app isolation policy acts as a firewall to block all inbound and outbound traffic to and from the
provisioned machines in the deployment. When you specify a defined NSX app isolation policy, the
machines provisioned by the blueprint can communicate with each other but cannot connect outside the
firewall.
You can apply app isolation at the blueprint level by using the New Blueprint or Blueprint Properties
dialog.
When using an NSX app isolation policy, only internal traffic between the machines provisioned by the
blueprint is allowed. When you request machine provisioning, a security group is created for the
machines to be provisioned. An app isolation security policy is created in NSX and applied to the security
group. Firewall rules are defined in the security policy to allow only internal traffic. For related information,
see Create a vSphere Endpoint with Network and Security Integration.
Note When provisioning with a blueprint that uses both an NSX Edge load balancer and an NSX app
isolation security policy, the dynamically provisioned load balancer is not added to the security group. This
prevents the load balancer from communicating with the machines for which it is meant to handle
connections. Because Edges are excluded from the NSX distributed firewall, they cannot be added to
security groups. To allow load balancing to function properly, use another security group or security policy
that allows the required traffic into the component VMs for load balancing.
Configuring vRealize Automation
VMware, Inc. 302
The app isolation policy has a lower precedence compared to other security policies in NSX. For
example, if the provisioned deployment contains a Web component machine and an App component
machine and the Web component machine hosts a Web service, then the service must allow inbound
traffic on ports 80 and 443. In this case, users must create a Web security policy in NSX with firewall rules
defined to allow incoming traffic to these ports. In vRealize Automation, users must apply the Web
security policy on the Web component of the provisioned machine deployment.
If the Web component machine needs access to the App component machine using a load balancer on
ports 8080 and 8443, the Web security policy should also include firewall rules to allow outbound traffic to
these ports in addition to the existing firewall rules that allow inbound traffic to ports 80 and 443.
For information about security features that can be applied to a machine component in a blueprint, see
Using Security Components in the Blueprint Canvas.
Configuring Network and Security Component Settings
vRealize Automation supports virtualized networks based on the vCloud Networking and Security and
NSX platforms.
Network and security virtualization allows virtual machines to communicate with each other over physical
and virtual networks securely and efficiently.
To integrate network and security with vRealize Automation, an IaaS administrator must install the
vCloud Networking and Security or NSX plug-ins in vRealize Orchestrator and create
vRealize Orchestrator and vSphere endpoints.
For information about external preparation, see Configuring vRealize Automation.
You can create network profiles that specify network settings in reservations and in the blueprint canvas.
External network profiles define existing physical networks. NAT and routed profiles are templates that will
build NSX logical switches and appropriate routing settings for a new network path and for configuring
network interfaces to connect to network path when you provision virtual machines and configure NSX
Edge devices.
The network and security component settings that you add to the blueprint design canvas are derived
from your NSX configuration and require that you have installed the NSX plug-in and run data collection
for the NSX inventory for vSphere clusters. Network and security components are specific to NSX and are
available for use with vSphere machine components only. For information about configuring NSX, see
NSX Administration Guide.
For machine components that do not have a Network or Security tab, you can add network and security
custom properties, such as VirtualMachine.Network0.Name, to their Properties tab in the blueprint
canvas. However, NSX load balancer properties are only applicable to vSphere machines.
If a network profile is specified in the blueprint (by using the VirtualMAchine.NetworkN.ProfileName
custom property) and by a reservation that is used by the blueprint, the network profile specified in the
blueprint takes precedence. However, if the custom property is not used in the blueprint, and you select a
network profile for a machine NIC, vRealize Automation uses a reservation network path for the machine
NIC for which the network profile is specified.
Configuring vRealize Automation
VMware, Inc. 303
Depending on the compute resource, you can select a transport zone that identifies a vSphere endpoint.
A transport zone specifies the hosts and clusters that can be associated with logical switches created
within the zone. A transport zone can span multiple vSphere clusters. The blueprint and the reservations
used in the provisioning must have the same transport zone setting. Transport zones are defined in the
NSX and vCloud Networking and Security environments. See NSX Administration Guide.
Using Security Components in the Blueprint Canvas
You can add NSX security components to the canvas to make their configured settings available to one or
more vSphere machine components in the blueprint.
Security groups, tags, and policies are configured outside of vRealize Automation in the NSX application.
The network and security component settings that you add to the blueprint design canvas are derived
from your NSX configuration and require that you have installed the NSX plug-in and run data collection
for the NSX inventory for vSphere clusters. Network and security components are specific to NSX and are
available for use with vSphere machine components only. For information about configuring NSX, see
NSX Administration Guide.
You can add security controls to blueprints by configuring security groups, tags, and policies for the
vSphere compute resource in NSX. After you run data collection, the security configurations are available
for selection in vRealize Automation.
Security Group
A security group is a collection of assets or grouping objects from the vSphere inventory that is mapped
to a set of security policies, for example distributed firewall rules and third party security service
integrations such as anti-virus and intrusion detection. The grouping feature enables you to create custom
containers to which you can assign resources, such as virtual machines and network adapters, for
distributed firewall protection. After a group is defined, you can add the group as source or destination to
a firewall rule for protection.
You can add security groups to a blueprint, in addition to the security groups specified in the reservation.
Security groups are managed in the source resource. For information about managing security groups for
various resource types, see the vendor documentation.
You can add an NSX existing or on-demand security group to the blueprint canvas.
Security Tag
A security tag is a qualifier object or categorizing entry that you can use as a grouping mechanism. You
define the criteria that an object must meet to be added to the security group you are creating. This gives
you the ability to include machines by defining a filter criteria with a number of parameters supported to
match the search criteria. For example, you can add all of the machines tagged with a specified security
tag to a security group.
You can add a security tag to the blueprint canvas.
Configuring vRealize Automation
VMware, Inc. 304
Security Policy
A security policy is a set of endpoint, firewall, and network introspection services that can be applied to a
security group. You can add security policies to a vSphere virtual machine by using an on-demand
security group in a blueprint. You cannot add a security policy directly to a reservation. After data
collection, the security policies that have been defined in NSX for a compute resource are available for
selection in a blueprint.
App Isolation
When App isolation is enabled, a separate security policy is created. App isolation uses a logical firewall
to block all inbound and outbound traffic to the applications in the blueprint. Component machines that are
provisioned by a blueprint that contains an app isolation policy can communicate with each other but
cannot connect outside the firewall unless other security groups are added to the blueprint with security
policies that allow access.
Add an Existing Security Group Component
You can add an existing security group component to the design canvas in preparation for associating its
settings to one or more machine components or other available component types in the blueprint.
You can use an existing security group component to add an NSX security group to the design canvas
and configure its settings for use with vSphere machine components and Software or XaaS components
that pertain to vSphere.
You can add multiple network and security components to the blueprint design canvas.
Prerequisites
nCreate and configure a security group in NSX. See Configuring vRealize Automation and NSX
Administration Guide.
nVerify that the NSX plug-in for vRealize Automation is installed and that the NSX inventory has
executed successfully for your cluster .
To use NSX configurations in vRealize Automation, you must install the NSX plug-in and run data
collection.
nLog in to the vRealize Automation console as an infrastructure architect.
nOpen a new or existing blueprint in the design canvas by using the Design tab.
Procedure
1Click Network & Security in the Categories section to display the list of available network and
security components.
2Drag an Existing Security Group component onto the design canvas.
3Select an existing security group from the Security Group drop-down menu.
4Click OK.
5Click Finish to save the blueprint as draft or continue configuring the blueprint.
Configuring vRealize Automation
VMware, Inc. 305
You can continue configuring security settings by adding additional security components and by selecting
settings in the Security tab of a vSphere machine component in the blueprint canvas.
Add an On-Demand Security Group Component
You can add an on-demand security group component to the design canvas in preparation for associating
its settings to one or more vSphere machine components or other available component types in the
blueprint.
Prerequisites
nCreate and configure a security policy in NSX. See NSX Administration Guide.
nVerify that the NSX plug-in for vRealize Automation is installed and that the NSX inventory has
executed successfully for your cluster .
To use NSX configurations in vRealize Automation, you must install the NSX plug-in and run data
collection.
nLog in to the vRealize Automation console as an infrastructure architect.
nOpen a new or existing blueprint in the design canvas by using the Design tab.
Procedure
1Click Network & Security in the Categories section to display the list of available network and
security components.
2Drag an On-Demand Security Group component onto the design canvas.
3Enter a name and, optionally, a description.
4Add one or more security policies by clicking the Add icon in the Security policies area and selecting
available security policies.
5Click OK.
6Click Finish to save the blueprint as draft or continue configuring the blueprint.
You can continue configuring security settings by adding additional security components and by selecting
settings in the Security tab of a vSphere machine component in the blueprint canvas.
Add an Existing Security Tag Component
You can add a security tag component to the blueprint design canvas in preparation for associating its
settings to one or more machine components in the blueprint.
You can use a security tag component to add an NSX security tag to the design canvas and configure its
settings for use with vSphere machine components and Software components that pertain to vSphere.
You can add multiple network and security components to the blueprint design canvas.
Prerequisites
nCreate and configure security tags in NSX. See Configuring vRealize Automation and NSX
Administration Guide.
Configuring vRealize Automation
VMware, Inc. 306
nVerify that the NSX plug-in for vRealize Automation is installed and that the NSX inventory has
executed successfully for your cluster .
To use NSX configurations in vRealize Automation, you must install the NSX plug-in and run data
collection.
nVerify that the NSX plug-in for vRealize Automation is installed and that the NSX inventory has
executed successfully for your cluster .
To use NSX configurations in vRealize Automation, you must install the NSX plug-in and run data
collection.
nLog in to the vRealize Automation console as an infrastructure architect.
nOpen a new or existing blueprint in the design canvas by using the Design tab.
Procedure
1Click Network & Security in the Categories section to display the list of available network and
security components.
2Drag a Existing Security Tag component onto the design canvas.
3Click in the Security tag text box and select an existing security tag.
4Click OK.
5Click Finish to save the blueprint as draft or continue configuring the blueprint.
You can continue configuring security settings by adding additional security components and by selecting
settings in the Security tab of a vSphere machine component in the blueprint canvas.
Using Network Components in the Blueprint Canvas
You can add one or more NSX network components to the design canvas and configure their settings for
vSphere machine components in the blueprint.
You can add network components to the canvas to make their configured settings available to one or
more machine components in the blueprint.
The network and security component settings that you add to the blueprint design canvas are derived
from your NSX configuration and require that you have installed the NSX plug-in and run data collection
for the NSX inventory for vSphere clusters. Network and security components are specific to NSX and are
available for use with vSphere machine components only. For information about configuring NSX, see
NSX Administration Guide.
Add an Existing Network Component
You can add an existing NSX network component to the design canvas in preparation for associating its
settings to one or more vSphere machine components in the blueprint.
You can use an existing network component to add an NSX network to the design canvas and configure
its settings for use with vSphere machine components and Software or XaaS components that pertain to
vSphere.
Configuring vRealize Automation
VMware, Inc. 307
When you associate an existing network component or on-demand network component with a machine
component, the NIC information is stored with the machine component. The network profile information
that you specify is stored with the network component.
You can add multiple network and security components to the blueprint design canvas.
For machine components that do not have a Network or Security tab, you can add network and security
custom properties, such as VirtualMachine.Network0.Name, to their Properties tab in the blueprint
canvas. However, NSX load balancer properties are only applicable to vSphere machines.
Prerequisites
nCreate and configure network settings for NSX. See Configuring vRealize Automation and NSX
Administration Guide.
nVerify that the NSX plug-in for vRealize Automation is installed and that the NSX inventory has
executed successfully for your cluster .
To use NSX configurations in vRealize Automation, you must install the NSX plug-in and run data
collection.
nCreate a network profile.
nLog in to the vRealize Automation console as an infrastructure architect.
nOpen a new or existing blueprint in the design canvas by using the Design tab.
Procedure
1Click Network & Security in the Categories section to display the list of available network and
security components.
2Drag an Existing Network component onto the design canvas.
3Click in the Existing network text box and select an existing network profile.
The description, subnet mask and gateway values are populated based on the selected network
profile.
4(Optional) Click the DNS/WINS tab.
5(Optional) Specify or accept provided DNS and WINS settings for the network profile.
nPrimary DNS
nSecondary DNS
nDNS Suffix
nPreferred WINS
nAlternate WINS
You cannot change the DNS or WINS settings for an existing network.
Configuring vRealize Automation
VMware, Inc. 308
6(Optional) Click the IP Ranges tab.
The IP range or ranges specified in the network profile are displayed. You can change the sort order
or column display. For NAT networks, you can also change IP range values.
7Click Finish to save the blueprint as draft or continue configuring the blueprint.
What to do next
You can continue configuring network settings by adding additional network components and by selecting
settings in the Network tab of a vSphere machine component in the blueprint canvas.
Add an On-Demand NAT or On-Demand Routed Network Component
You can add an NSX on-demand NAT network component or NSX on-demand routed network component
to the design canvas in preparation for associating their settings to one or more vSphere machine
components in the blueprint.
When you associate an existing network component or on-demand network component with a machine
component, the NIC information is stored with the machine component. The network profile information
that you specify is stored with the network component.
You can add multiple network and security components to the blueprint design canvas.
For machine components that do not have a Network or Security tab, you can add network and security
custom properties, such as VirtualMachine.Network0.Name, to their Properties tab in the blueprint
canvas. However, NSX load balancer properties are only applicable to vSphere machines.
Prerequisites
nCreate and configure network settings for NSX. See Configuring vRealize Automation and NSX
Administration Guide.
nVerify that the NSX plug-in for vRealize Automation is installed and that the NSX inventory has
executed successfully for your cluster .
To use NSX configurations in vRealize Automation, you must install the NSX plug-in and run data
collection.
nCreate a network profile.
For example, if you are adding an on-demand NAT network component, create a network profile for
NAT.
nLog in to the vRealize Automation console as an infrastructure architect.
nOpen a new or existing blueprint in the design canvas by using the Design tab.
Procedure
1Click Network & Security in the Categories section to display the list of available network and
security components.
2Drag one of the on-demand network components onto the design canvas, depending on whether you
want to configure an on-demand NAT or routed component.
Configuring vRealize Automation
VMware, Inc. 309
3Enter a name and, optionally, a description.
4Select an appropriate network profile from the Network Profile drop-down menu.
For example, if you are adding an On-Demand NAT Network component, select a NAT network
profile.
The following network settings are populated based on your network profile selection. Changes to
these values must be made in the network profile:
nExternal network profile name
nNAT type (On-Demand NAT Network)
nSubnet mask
nRange subnet mask (On-Demand Routed Network)
nRange subnet mask (On-Demand Routed Network)
nBase IP address (On-Demand Routed Network)
5(Optional) Click the DNS/WINS tab.
6(Optional) Specify or accept provided DNS and WINS settings for the network profile.
nPrimary DNS
nSecondary DNS
nDNS Suffix
nPreferred WINS
nAlternate WINS
You cannot change the DNS or WINS settings for an existing network.
7(Optional) For an on-demand NAT network component, click the DCHP tab to specify IP address
range and lease length values.
You can edit the start and end IP address values for the DCHP range. When the virtual machine is
provisioned with DCHP, the network adapter assigns an IP address to the machine that is within this
range. It is a static network adapter by default. The IP address values cannot be those of the network
or broadcast addresses used in the associated subnet. You cannot overlap static IP ranges.
DHCP is available only for on-demand one-to-many NAT network components.
8(Optional) Enter a start IP address value in the IP range start text box.
9(Optional) Enter an end IP address value in the IP range end text box.
10 Enter a DCHP lease length, in seconds, in the Lease time (seconds) text box or leave blank for an
unlimited lease length.
11 (Optional) Click the IP Ranges tab.
The IP range or ranges specified in the network profile are displayed. You can change the sort order
or column display. For NAT networks, you can also change IP range values.
Configuring vRealize Automation
VMware, Inc. 310
12 Click Finish to save the blueprint as draft or continue configuring the blueprint.
What to do next
You can continue configuring network settings by adding additional network components and by selecting
settings in the Network tab of a vSphere machine component in the blueprint canvas.
Using Load Balancer Components in the Blueprint Canvas
You can add one or more on-demand NSX load balancer components to the design canvas to configure
vSphere machine component settings in the blueprint.
The network and security component settings that you add to the blueprint design canvas are derived
from your NSX configuration and require that you have installed the NSX plug-in and run data collection
for the NSX inventory for vSphere clusters. Network and security components are specific to NSX and are
available for use with vSphere machine components only. For information about configuring NSX, see
NSX Administration Guide.
The following rules apply to load balancer pools and VIP network settings in the blueprint:
nIf the pool network profile is NAT, the VIP network profile can be the same NAT network profile in the
same NAT network profile.
nIf the pool network profile is routed, the VIP network profile can only be on the same routed network.
nIf the pool network profile is external, the VIP network profile can only be the same external network
profile.
An NSX Edge resource is also created and load balancer details such as VIP, load-balanced tier, and
configured services are recorded as properties of the Edge resource.
Add an On-Demand Load Balancer Component
You can use an on-demand load balancer component to add an NSX load balancer to the design canvas
and configure its settings for use with vSphere machine components and Software or XaaS components
that pertain to vSphere.
The load balancer settings distribute task processing among provisioned machines in a network.
Prerequisites
nCreate and configure load balancer settings for NSX. See Configuring vRealize Automation and NSX
Administration Guide.
nVerify that the NSX plug-in for vRealize Automation is installed and that the NSX inventory has
executed successfully for your cluster .
To use NSX configurations in vRealize Automation, you must install the NSX plug-in and run data
collection.
nCreate a network profile.
nLog in to the vRealize Automation console as an infrastructure architect.
nOpen a new or existing blueprint in the design canvas by using the Design tab.
Configuring vRealize Automation
VMware, Inc. 311
nVerify that at least one vSphere machine component exists in the blueprint design canvas.
Procedure
1Click Network & Security in the Categories section to display the list of available network and
security components.
2Drag an On-Demand Load Balancer component onto the design canvas.
3Enter a name in the Name text box.
4Select a machine name from the Machine drop-down menu.
The list contains only vSphere machine components in the active blueprint.
5Select a NIC from the NIC drop-down menu.
The list contains NICs that are defined on the selected vSphere machine component.
6Select a VIP network from the VIP Network drop-down menu.
7(Optional) Enter the VIP address for the NIC from the IP Address.
The default setting is the static IP address that is associated with the VIP network. You can specify
another IP address or an IP address range. By default, the next available IP address is allocated for
VIP from the network profile. You can only specify an IP address when VIP is created on a NAT
network.
8Select the check box next to each service that you want to load balance.
Service options include HTTP, HTTPS, and TCP.
9(Optional) Accept or edit the port and health check settings for each selected service.
10 Enter the address for the selected service in the URL for HTTP service text box.
There is only a single URL available for the HTTP service control for each load balancer.
11 Click Finish to save the blueprint as draft or continue configuring the blueprint.
The configured settings are available on the Network tab in the associated vSphere machine component.
Associating Network and Security Components
You can drag network and security components onto the design canvas to make their settings available
for machine component configuration in the blueprint. After you have defined network and security
settings for the machine, you can optionally associate settings from a load balancer component.
After you add an NSX network or security component to the canvas and define its available settings, you
can open the network and security tabs of a vSphere machine component in the canvas and configure its
settings.
Configuring vRealize Automation
VMware, Inc. 312
The network and security component settings that you add to the blueprint design canvas are derived
from your NSX configuration and require that you have installed the NSX plug-in and run data collection
for the NSX inventory for vSphere clusters. Network and security components are specific to NSX and are
available for use with vSphere machine components only. For information about configuring NSX, see
NSX Administration Guide.
For example, you can drag an on-demand NAT network component onto the blueprint's design canvas to
make it available for a vSphere machine component that is also present in the canvas.
Designing Software Components
Software is a model-based application provisioning solution that simplifies creating and standardizing
application deployment topologies.
Software architects create Software components that define middleware and application deployment
components, specifying exactly how they are installed, configured, and uninstalled on machines. Software
architects, IaaS architects, and application architects can use a graphic-based canvas with a drag-and-
drop interface to model application deployment topologies. As a software architect, application architect,
or IaaS architect, you can combine Software components with at least one machine blueprint to define
the structure of the application. You can include installation dependencies and default configurations for
custom and packaged enterprise applications, and provide any configuration values the software architect
designed to be editable, such as environment variables.
Deploying Any Application and Middleware Service
You can deploy Software components on Windows or Linux operating systems on vSphere,
vCloud Director, vCloud Air, and Amazon AWS machines.
nIaaS architects create reusable machine blueprints based on templates, snapshots, or Amazon
machine images that contain the guest agent and Software boostrap agent to support Software
components.
nSoftware architects create reusable software components that define install, configure, start, and
uninstall actions.
nSoftware architects, IaaS architects, and application architects use a graphical interface to visually
model and publish application blueprints that combine Software components and machine blueprints,
reconfiguring Software properties and bindings as required by the software architect.
nCatalog administrators add the published blueprints to a catalog service, and entitle users to request
the catalog item.
nUsers request the catalog item and vRealize Automation deploys the requested application,
provisioning the machine(s) and Software component(s) as defined in the application blueprint.
Configuring vRealize Automation
VMware, Inc. 313
Standardization in Software
With Software, you can create reusable services using standardized configuration properties to meet
strict requirements for IT compliance. Software includes the following standardized configuration
properties:
nModel-driven architecture that enables adding IT certified machine blueprints and middleware
services within the application blueprint.
nA delegation model for overriding configuration name value pairs between software architect,
application architect, and end user to standardize configuration values for application and middleware
service.
Property Types and Setting Options
Software supports string, array, content, boolean, integer, and double properties.
Note The names of properties are case-sensitive and can contain only alphabetic, numeric, hyphen (-),
or underscore (_) characters.
Property Options
You can compute the value of any string property by selecting the computed check box, and you can
make any property encrypted, overridable, or required by selecting the appropriate check boxes when
you configure Software properties. Combine these options with your values to achieve different purposes.
For example, to require blueprint architects to supply a value for a password and encrypt that value, leave
the value text box blank, and select Overridable, Required, and Encrypted.
Option Description
Encrypted Mark properties as encrypted to mask the value and display as
asterisks in vRealize Automation. If you change a property from
encrypted to unencrypted, vRealize Automation resets the
property value. For security, you must set a new value for the
property.
Overridable Allow architects to edit the value of this property when they are
assembling an application blueprint. If you enter a value, it
displays as a default.
Required Require architects to provide a value for this property, or to
accept the default value you supply.
Computed Values for computed properties are assigned by the INSTALL,
CONFIGURE, or START life cycle scripts. The assigned value is
propagated to the subsequent available life cycle stages and to
components that bind to these properties in a blueprint. If select
Computed for a property that is not a string property, the
property type is changed to string.
If you select the computed property option, leave the value for your custom property blank. Design your
scripts for the computed values.
Configuring vRealize Automation
VMware, Inc. 314
Table 4‑33. Scripting Examples for the Computed Property Option
Sample String Property Script Sytax Sample Usage
my_unique_id = "" Bash - $my_unique_id export
my_unique_id="012345678
9"
Windows CMD - %my_unique_id% set
my_unique_id=0123456789
Windows PowerShell - $my_unique_id $my_unique_id =
"0123456789"
String Property
The string property value can be a string or the value bound to another string property. A string value can
contain any ASCII characters. For a bound property, use the Properties tab in the blueprint canvas to
select the appropriate property for binding. The property value is then passed to the action scripts as raw
string data.
Sample String Property Script Syntax Sample Usage
admin_email = "admin@email987.com" Bash - $admin_email echo $admin_email
Windows CMD - %admin_email% echo %admin_email%
Windows PowerShell - $admin_email write-output $admin_email
Array Property
The array property value can be an array of strings defined as [“value1”, “value2”, “value3”…] or the value
bound to another array property. When you define values for an array property you must enclose the
array of strings in square brackets. For an array of strings, the value in the array elements can contain
any ASCIl characters. To properly encode a backslash character in an Array property value, add an extra
backslash, for example, ["c:\\test1\\test2"]. For a bound property, use the Properties tab in the
blueprint canvas to select the appropriate property for binding.
For example, consider a load balancer virtual machine that is balancing the load for a cluster of
application server virtual machines. In such a case, an array property is defined for the load balancer
service and set to the array of IP addresses of the application server virtual machines.
These load balancer service configure scripts use the array property to configure the appropriate load
balancing scheme on the Red Hat, Windows, and Ubuntu operating systems.
Configuring vRealize Automation
VMware, Inc. 315
Sample Array Property Script Syntax Sample Usage
operating_systems = ["Red
Hat","Windows","Ubuntu"]
Bash - ${operating_systems[@]}
for the entire array of strings
${operating_systems[N]}
for the individual array element
for (( i = 0 ; i < $
{#operating_systems[@]}; i++ )); do
echo ${operating_systems[$i]}
done
Windows CMD - %operating_systems_N%
where N represents the position of the element
in the array
for /F "delims== tokens=2" %%A in
('set operating_systems_') do (
echo %%A
)
Windows PowerShell - $operating_systems
for the entire array of strings
$operating_systems[N]
for the individual array element
foreach ($os in $operating_systems){
write-output $os
}
Content Property
The content property value is a URL to a file to download content. Software agent downloads the content
from the URL to the virtual machine and passes the location of the local file in the virtual machine to the
script.
Content properties must be defined as a valid URL with the HTTP or HTTPS protocol. For example, the
JBOSS Application Server Software component in the Dukes Bank sample application specifies a content
property cheetah_tgz_url. The artifacts are hosted in the Software appliance and the URL points to that
location in the appliance. The Software agent downloads the artifacts from the specified location into the
deployed virtual machine.
Sample String Property Script Syntax Sample Usage
cheetah_tgz_url =
"http://app_content_server_ip:port/artifacts/software/jboss/cheetah-2.4.4.tar.gz"
Bash -
$cheetah_tgz_url tar -zxvf
$cheetah_tgz_url
Windows CMD -
%cheetah_tgz_url% start /wait
c:\unzip.exe
%cheetah_tgz_url%
Windows PowerShell
- $cheetah_tgz_url & c:\unzip.exe
$cheetah_tgz_url
Boolean Property
The boolean property type provides True and False choices in the Value drop-down menu.
Integer Property
The integer property type accepts zero, a positive integer, or a negative integer as a value.
Configuring vRealize Automation
VMware, Inc. 316
Binding Software Properties to Other Properties
In several deployment scenarios, a component needs the property value of another component to
customize itself. In vRealize Automation, this process is called binding to other properties. You can design
your components for property bindings, but you configure the binding when you assemble the blueprint.
In addition to setting a property to a hard-coded value, a software architect, IaaS architect, or application
architect can bind Software component properties to other properties in the application blueprint, such as
an IP address or an installation location. When you bind a Software property to another property, you can
customize a script based on the value of another component property or virtual machine property. For
example, a WAR component might need the installation location of the Apache Tomcat server. In your
scripts, you can configure the WAR component to set the server_home property value to the Apache
Tomcat server install_path property value in your script. As long as the architect who assembles the
application blueprint binds the server_home property to the Apache Tomcat server install_path property,
then the server_home property value is set correctly.
Your component scripts can only use properties that you have defined in those scripts.
Passing Property Values Between Life Cycle Stages
You can modify and pass property values between life cycle stages by using the action scripts.
For a computed property, you can modify the value of a property and pass the value to the next life cycle
stage of the action script. For example, if component A has the progress_status value defined as staged,
in the INSTALL and CONFIGURE life cycle stage you change the value to progress_status=installed in
the respective action scripts. If component B is bound to component A, the property values of
progress_status in the life cycle stages of the action script are the same as component A.
Define in the software component that component B depends on A. This dependency defines the passing
of correct property values between components whether they are in the same node or across different
nodes.
For example, you can update a property value in an action script by using the supported scripts.
nBash progress_status="completed"
nWindows CMD set progress_status=completed
nWindows PowerShell $progress_status="completed"
Note Array and content property do not support passing modified property values between action scripts
of life cycle stages.
Best Practices for Developing Components
To familiarize yourself with best practices for defining properties and action scripts, you can download and
import Software components and application blueprints from the VMware Solution Exchange.
Configuring vRealize Automation
VMware, Inc. 317

Follow these best practices when developing Software components.
nFor a script to run without any interruptions, the return value must be set to zero (0). This setting
allows the agent to capture all of the properties and send them to the Software server.
nSome installers might need access to the tty console. Redirect the input from /dev/console. For
example, a RabbitMQ Software component might use the ./rabbitmq_rhel.py --setup-
rabbitmq < /dev/console command in its install script.
nWhen a component uses multiple life cycle stages, the property value can be changed in the
INSTALL life cycle stage. The new value is sent to the next life cycle stage. Action scripts can
compute the value of a property during deployment to supply the value to other dependent scripts.
For example, in the Clustered Dukes Bank sample application, JBossAppServer service computes
the JVM_ROUTE property during the install life cycle stage. This property is used by the
JBossAppServer service to configure the life cycle. Apache load balancer service then binds its
JVM_ROUTE property to the all (appserver:JbossAppServer:JVM_ROUTE) property to get the final
computed value of node0 and node1. If a component requires a property value from another
component to complete an application deployment successfully, you must state explicit dependencies
in the application blueprint.
Note You cannot change the content property value for a component that uses multiple life cycle
stages.
Create a Software Component
Configure and publish a Software component that other software architects, IaaS architects, and
application architects can use to assemble application blueprints.
Prerequisites
Log in to the vRealize Automation console as a software architect.
Procedure
1Select Design > Software Components.
2Click the Add icon ( ).
3Enter a name and, optionally, a description.
Using the name you specified for your Software component, vRealize Automation creates an ID for
the Software component that is unique within your tenant. You can edit this field now, but after you
save the blueprint you can never change it. Because IDs are permanent and unique within your
tenant, you can use them to programmatically interact with blueprints and to create property bindings.
Configuring vRealize Automation
VMware, Inc. 318
4(Optional) If you want to control how your Software component is included in blueprints, select a
container type from the Container drop-down menu.
Option Description
Machines Your Software component must be placed directly on a machine.
One of your published Software
components
If you are designing a Software component specifically to install on top of another
Software component that you created, select that Software component from the
list. For example, if you are designing an EAR component to install on top of your
previously created JBOSS component, select your JBOSS component from the
list.
Software components If you are designing a Software component that should not be installed directly on
a machine, but can be installed on several different Software components, then
select the software components option. For example, if you are designing a WAR
component and you want it to be installed on your Tomcat Server Software
component, and your Tcserver Software component, select the software
components container type.
5Click Next.
6Define any properties you intend to use in your install, configure, start, or uninstall scripts.
aClick the Add icon ( ).
b Enter a name for the property.
c Enter a description for the property.
This description displays to architects who use your Software component in blueprints.
d Select the expected type for the value of your property.
e Define the value for your property.
Option Description
Use the value you supply now nEnter a value.
nDeselect Overridable.
nSelect Required.
Require architects to supply a value nTo provide a default, enter a value.
nSelect Overridable.
nSelect Required.
Allow architects to supply a value if
they choose
nTo provide a default, enter a value.
nSelect Overridable.
nDeselect Required.
Architects can configure your Software properties to show to users in the request form. Architects
can use the Show in Request option to require or request that users fill in values for properties
that you mark as overridable.
7Follow the prompts to provide a script for at least one of the software life cycle actions.
Include exit and status codes for your script. Each supported script type has unique exit and status
code requirements.
Configuring vRealize Automation
VMware, Inc. 319
Script Type Success Status Error Status Unsupported Commands
Bash nreturn 0
nexit 0
nreturn non-zero
nexit non-zero
None
Windows CMD exit /b 0 exit /b non-zero Do not use exit 0 or exit non-zero codes.
PowerShell exit 0 exit non-zero; Do not use warning, verbose, debug, or host calls.
8Select the Reboot checkbox for any script that requires you to reboot the machine.
After the script runs, the machine reboots before starting the next life cycle script.
9Click Finish.
10 Select your Software component and click Publish.
You configured and published a Software component. Other software architects, IaaS architects, and
application architects can use this Software component to add software to application blueprints.
What to do next
Add your published Software component to an application blueprint. See Assembling Application
Blueprints.
Scenario: Create a MySQL Software Component for Rainpole
Using your software architect privileges, create a MySQL Software component to install MySQL on
vSphere CentOS machines. When you design the MySQL Software component for a CentOS virtual
machine, you configure the install, configure, and start parameters, and the scripts for Linux operating
systems.
Procedure
1Select Design > Software Components.
2Click the New icon ( ).
3Enter MySQL for Linux Virtual Machines in the Name text box.
4Verify that the identifier populates based on the provided name.
For example, Software.MySQLforLinuxVirtualMachines
5Enter MySQL installation and configuration in the Description text box.
6Select Machine from the Container drop-down menu.
Because you only want MySQL to install directly on a machine, you restrict architects from dropping
your MySQL Software component on top of other Software components.
7Click Next.
Configuring vRealize Automation
VMware, Inc. 320
8Click New and add and configure each of the following properties for the installation script.
Click OK to save each property.
Architects can configure your Software properties to show to users in the request form. Architects can
use the Show in Request option to require or request that users fill in values for properties that you
mark as overridable.
Name Description Type Value Encrypted
Allow
Override Required Computed
db_root_username Database root
user name
String root No Yes Yes No
JAVA_HOME The directory in
which JRE 1.7 is
installed
String /opt/vmware-
jre
No Yes Yes No
global_ftp_proxy FTP proxy URL,
if any. Not
required.
String No Yes No No
db_port MySQL
database port
String No Yes Yes No
db_root_password Database root
user password
String password Yes Yes Yes No
global_http_proxy HTTP proxy
URL, if any. Not
required.
String No Yes No No
global_https_proxy HTTPS proxy
URL, if any. Not
required.
String No Yes No No
max_allowed_packet_size Server max
allowed packet
size
Integer 1024 No Yes No No
9Click Next.
10 Configure the Install action.
a Select Bash from the Script Type drop-down menu.
b Click Click here to edit.
Configuring vRealize Automation
VMware, Inc. 321

c Paste the following script.
#!/bin/bash
#Setting proxies
export ftp_proxy=${ftp_proxy:-$global_ftp_proxy}
echo "Setting ftp_proxy to $ftp_proxy"
export http_proxy=${http_proxy:-$global_http_proxy}
echo "Setting http_proxy to $http_proxy"
export https_proxy=${https_proxy:-$global_https_proxy}
echo "Setting https_proxy to $https_proxy"
#
# Determine operating system and version
#
export OS=
export OS_VERSION=
if [ -f /etc/redhat-release ]; then
# For CentOS the result will be 'CentOS'
# For RHEL the result will be 'Red'
OS=$(cat /etc/redhat-release | awk {'print $1'})
if [ -n $OS ] && [ $OS = 'CentOS' ]; then
OS_VERSION=$(cat /etc/redhat-release | awk '{print $3}')
else
# RHEL
OS_VERSION=$(cat /etc/redhat-release | awk '{print $7}')
fi
elif [ -f /etc/SuSE-release ]; then
OS=SuSE
MAJOR_VERSION=$(cat /etc/SuSE-release | grep VERSION | awk '{print $3}')
PATCHLEVEL=$(cat /etc/SuSE-release | grep PATCHLEVEL | awk '{print $3}')
OS_VERSION="$MAJOR_VERSION.$PATCHLEVEL"
elif [ -f /usr/bin/lsb_release ]; then
# For Ubuntu the result is 'Ubuntu'
OS=$(lsb_release -a 2> /dev/null | grep Distributor | awk '{print $3}')
OS_VERSION=$(lsb_release -a 2> /dev/null | grep Release | awk '{print $2}')
fi
echo "Using operating system '$OS' and version '$OS_VERSION'"
if [ "x${global_http_proxy}" == "x" ] || [ "x${global_https_proxy}" == "x" ] ||
[ "x${global_ftp_proxy}" == "x" ]; then
echo ""
echo "###############################################################"
echo "# One or more PROXY(s) not set. Network downloads may fail #"
echo "###############################################################"
Configuring vRealize Automation
VMware, Inc. 322

echo ""
fi
export PATH=$PATH:$JAVA_HOME/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
set -e
# Tested on CentOS
if [ -x /usr/sbin/selinuxenabled ] && /usr/sbin/selinuxenabled; then
# SELinux can be disabled by setting "/usr/sbin/setenforce Permissive"
echo 'SELinux in enabled on this VM template. This service requires SELinux to be
disabled to install successfully'
exit 1
fi
if [ "x$OS" != "x" ] && [ "$OS" = 'Ubuntu' ]; then
# Fix the linux-firmware package
export DEBIAN_FRONTEND=noninteractive
apt-get install -y linux-firmware < /dev/console > /dev/console
# Install MySQL package
apt-get install -y mysql-server
else
yum --nogpgcheck --noplugins -y install -x MySQL-server-community mysql-server
fi
# Set Install Path to the default install path (For monitoring)
Install_Path=/usr
echo Install_Path is set to $Install_Path, please modify this script if the install path is
not correct.
d Click OK.
11 Configure the Configure action.
a Select Bash from the Script Type drop-down menu.
b Click Click here to edit.
Configuring vRealize Automation
VMware, Inc. 323

c Paste the following script.
#!/bin/bash
#Setting proxies
export ftp_proxy=${ftp_proxy:-$global_ftp_proxy}
echo "Setting ftp_proxy to $ftp_proxy"
export http_proxy=${http_proxy:-$global_http_proxy}
echo "Setting http_proxy to $http_proxy"
export https_proxy=${https_proxy:-$global_https_proxy}
echo "Setting https_proxy to $https_proxy"
#
# Determine operating system and version
#
export OS=
export OS_VERSION=
if [ -f /etc/redhat-release ]; then
# For CentOS the result will be 'CentOS'
# For RHEL the result will be 'Red'
OS=$(cat /etc/redhat-release | awk {'print $1'})
if [ -n $OS ] && [ $OS = 'CentOS' ]; then
OS_VERSION=$(cat /etc/redhat-release | awk '{print $3}')
else
# RHEL
OS_VERSION=$(cat /etc/redhat-release | awk '{print $7}')
fi
elif [ -f /etc/SuSE-release ]; then
OS=SuSE
MAJOR_VERSION=$(cat /etc/SuSE-release | grep VERSION | awk '{print $3}')
PATCHLEVEL=$(cat /etc/SuSE-release | grep PATCHLEVEL | awk '{print $3}')
OS_VERSION="$MAJOR_VERSION.$PATCHLEVEL"
elif [ -f /usr/bin/lsb_release ]; then
# For Ubuntu the result is 'Ubuntu'
OS=$(lsb_release -a 2> /dev/null | grep Distributor | awk '{print $3}')
OS_VERSION=$(lsb_release -a 2> /dev/null | grep Release | awk '{print $2}')
fi
echo "Using operating system '$OS' and version '$OS_VERSION'"
if [ "x${global_http_proxy}" == "x" ] || [ "x${global_https_proxy}" == "x" ] ||
[ "x${global_ftp_proxy}" == "x" ]; then
echo ""
echo "###############################################################"
echo "# One or more PROXY(s) not set. Network downloads may fail #"
echo "###############################################################"
Configuring vRealize Automation
VMware, Inc. 324

echo ""
fi
export PATH=$PATH:$JAVA_HOME/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
set -e
# Locate the my.cnf file
my_cnf_file=
if [ -f /etc/my.cnf ]; then
my_cnf_file=/etc/my.cnf
elif [ -f /etc/mysql/my.cnf ]; then
my_cnf_file=/etc/mysql/my.cnf
fi
if [ "x$my_cnf_file" = "x" ]; then
echo "Neither /etc/my.cnf nor /etc/mysql/my.cnf can be found, stopping configuration"
exit 1
fi
# update mysql configuration to handle big packets
sed -ie "s/\[mysqld\]/\[mysqld\]\n\
max_allowed_packet=$max_allowed_packet/g" $my_cnf_file
# update listening port
sed -ie "s/\[mysqld\]/\[mysqld\]\n\
port=$db_port/g" $my_cnf_file
sed -i "s/port.*=.*[0-9]*/port=$db_port/g" $my_cnf_file
if [ "x$OS" != "x" ] && [ "$OS" = 'Ubuntu' ]; then
# Make sure that MySQL is started
service mysql restart
else
# set up auto-start on booting
chkconfig mysqld on
# restart mysqld service
service mysqld start
fi
# this will assign a password for mysql admin user 'root'
mysqladmin -u $db_root_username password $db_root_password
d Click OK.
12 Configure the Start action.
a Select Bash from the Script Type drop-down menu.
b Click Click here to edit.
Configuring vRealize Automation
VMware, Inc. 325
c Paste the following script.
#!/bin/sh
echo "The maximum allowed packet size is: "
d Place the cursor between the colon and the quote mark.
e Select max_allowed_packet_size from the Select a property to insert drop-down menu.
The script now includes the property.
#!/bin/sh
echo "The maximum allowed packet size is: $max_allowed_packet_size"
f Click OK.
13 Click Next.
14 Click Finish.
15 Select the row that contains MySQL for Linux Virtual Machines and click Publish.
Your MySQL Software component is available to other architects on the blueprint design page, but you
can't make Software components available until you combine them with a machine.
What to do next
Using your software architect, application architect, or IaaS architect privileges, combine your MySQL
component with the CentOS for Software machine blueprint.
Software Component Settings
Configure general settings, create properties, and write custom action scripts to install, configure, update,
or uninstall your Software component on provisioned machines.
As a software architect, click Design > Software components and click the Add icon to create a new
Software component.
New Software General Settings
Apply general settings to your Software component.
Configuring vRealize Automation
VMware, Inc. 326
Table 4‑34. New Software General Settings
Setting Description
Name Enter a name for your Software component.
ID Using the name you specified for your Software component,
vRealize Automation creates an ID for the Software component
that is unique within your tenant. You can edit this field now, but
after you save the blueprint you can never change it. Because
IDs are permanent and unique within your tenant, you can use
them to programmatically interact with blueprints and to create
property bindings.
Description Summarize your Software component for the benefit of other
architects.
Container Select a container type for your Software component. For
example, selecting Software Component restricts architects
from placing your Software component directly on a machine
without nesting it within another Software component.
New Software Properties
Software component properties are used to parameterize scripts to pass defined properties as
environment variables to scripts running in a machine. Before running your scripts, the Software agent in
the provisioned machine communicates with vRealize Automation to resolve the properties. The agent
then creates script-specific variables from these properties and passes them to the scripts.
Table 4‑35. New Software Properties
Setting Description
Name Enter a name for your Software property. Property names are
case-sensitive and can contain only alphabetic, numeric, hyphen
(-), or underscore (_) characters.
Description For the benefit of other users, summarize your property and any
requirements for the value.
Type Software supports string, array, content, boolean, integer, and
double properties. For a detailed explanation of supported
property types, see Property Types and Setting Options.
Value Select a container for your software component. For example,
selecting Software Component restricts architects from placing
your software component on a machine instead of nesting it
within another software component.
Encrypted Mark properties as encrypted to mask the value and display as
asterisks in vRealize Automation. If you change a property from
encrypted to unencrypted, vRealize Automation resets the
property value. For security, you must set a new value for the
property.
Important If secured properties are printed in the script using
the echo command or other similar commands, these values
appear in plain text in the log files. The values in the log files are
not masked.
Configuring vRealize Automation
VMware, Inc. 327
Table 4‑35. New Software Properties (Continued)
Setting Description
Overridable Allow architects to edit the value of this property when they are
assembling an application blueprint. If you enter a value, it
displays as a default.
Required Require architects to provide a value for this property, or to
accept the default value you supply.
Computed Values for computed properties are assigned by the INSTALL,
CONFIGURE, or START life cycle scripts. The assigned value is
propagated to the subsequent available life cycle stages and to
components that bind to these properties in a blueprint. If select
Computed for a property that is not a string property, the
property type is changed to string.
New Software Actions
You must provide a custom Bash, Windows CMD, or PowerShell script as the action for at least one of
the predefined life cycle stages: Install, Configure, Start, or Uninstall.
You can parameterize a script by declaring, for example, the installer location, installation path, or
environment variables as properties in the script. The parameters render the scripts generic. You can
deploy the service on different environments without modifying these generic scripts. You can also modify
parameter values from the action script. These modified properties can be referred to as property values
for other components.
When you author an action script, the exit and return codes vary between script types. You must set
proper exit codes in the script that are applicable to the application deployment. If the script lacks exit and
return codes, the last command that ran in the script becomes the exit status.
Table 4‑36. New Software Actions
Setting Description
Bash You can use return 0 or exit 0 codes in action scripts to
indicate success status. To indicate error status, you can use
return non-zero or exit non-zero.
cmd Do not use exit 0 and exit non-zero codes in the action
script. If you use these codes in the script, the computed
properties task processing is stopped prematurely. Use exit /b
0 to indicate success status and exit /b non-zero for error
status.
powershell You can use exit 0 to indicate success status and exit non-
zero for error status.
Reboot You can configure your Software component to reboot the
machine at the end of any life cycle stage.
Configuring vRealize Automation
VMware, Inc. 328
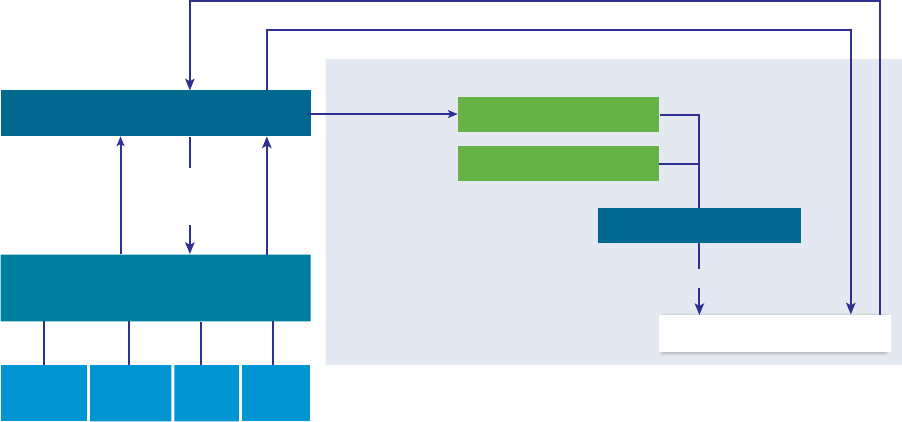
Creating XaaS Blueprints and Resource Actions
The XaaS blueprints can be published as catalog items or used in the blueprint designer. The resource
actions are action that you run on provisioned items.
XaaS is uses vRealize Orchestrator to run workflows that provision items or run actions. For example, you
can configure the workflows to create vSphere virtual machines, Active Directory users in groups, or
PowerShell scripts. If you create a custom vRealize Orchestrator workflow, you can provide that workflow
as an item in the service catalog, allowing the entitled users to run the workflow.
vRealize Orchestrator Integration in vRealize Automation
vRealize Orchestrator is the workflow engine integrated in vRealize Automation.
The vRealize Orchestrator server distributed with vRealize Automation is preconfigured, and therefore
when your system administrator deploys the vRealize Automation Appliance, the vRealize Orchestrator
server is up and running.
Figure 4‑1. Create and Request Catalog Items Included in an XaaS to Provision a Custom
Resource
Map vRealize
Orchestrator
object types
and workflows
to vRealize
Automation
Active
Directory
vCenter
Server SOAP HTTP-
REST
Request a catalog item
Provision the custom resource
XaaS blueprint
vRealize Automation
Catalog
Orchestrator Workflow
Engine and Library
XaaS
Run a
vRealize
Orchestrator
Custom Resource
Expose new
object and
actions in
vRealize
Automation
Publish catalog item
XaaS
XaaS architects add custom resources related to the supported endpoints and provided workflows, and
then create XaaS blueprints and actions based on those resources. Tenant administrators and business
group managers can add the XaaS blueprints and actions to the service catalog. The XaaS blueprint can
also be used in the blueprint designer.
When the service catalog user requests an item, vRealize Automation runs a vRealize Orchestrator
workflow to provision the custom resource.
Configuring vRealize Automation
VMware, Inc. 329
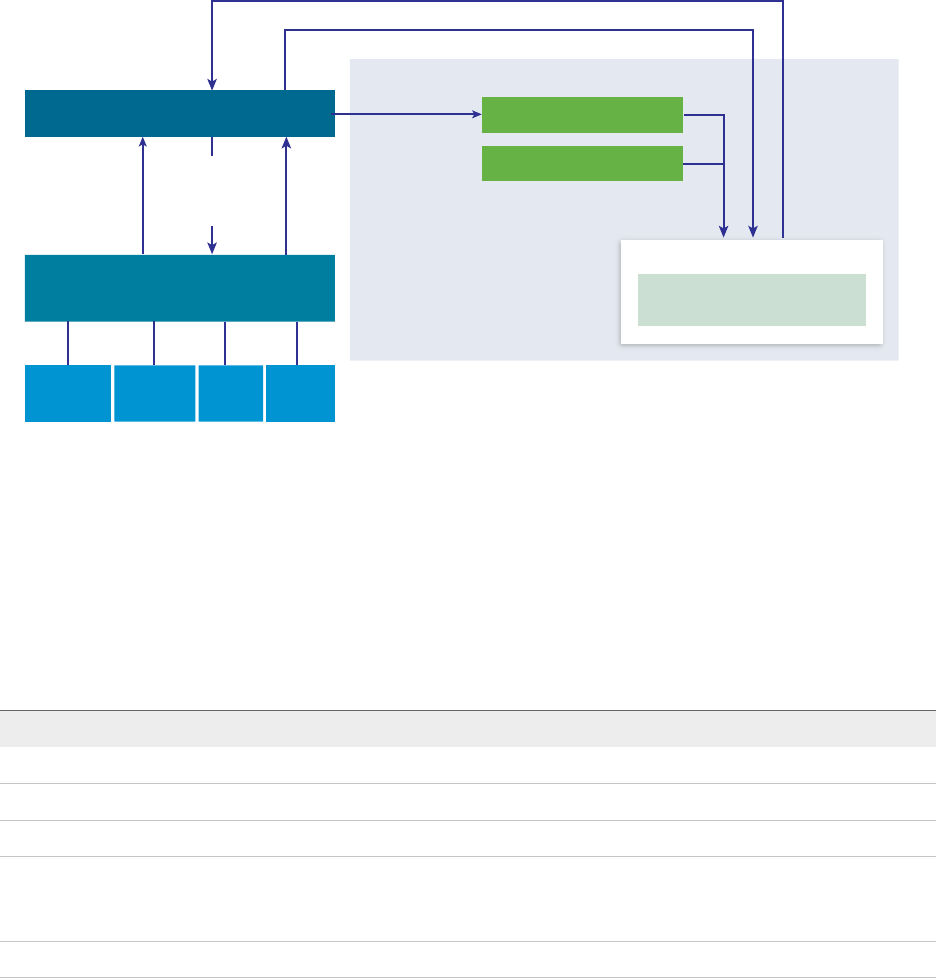
Figure 4‑2. Create and Request Custom Resource Actions to Modify a Custom Resource
Map vRealize
Orchestrator
object types
and workflows
to vRealize
Automation
Active
Directory
vCenter
Server SOAP HTTP-
REST
Request a resource action
Modify the custom resource
Resource Action
vRealize Automation
Catalog
Orchestrator Workflow
Engine and Library
XaaS
Run a
vRealize
Orchestrator
Workflow
Custom Resource
Expose new
object and
actions in
vRealize
Automation
Custom post-provisioning
action
XaaS architects can also add vRealize Orchestrator workflows as resource actions to extend
vRealize Automation capabilities. After the service catalog users provision a custom resource, they can
run post-provisioning action. This way, the consumers run a vRealize Orchestrator workflow and modify
the provisioned custom resource.
When a service catalog user requests an XaaS blueprint or resource action as a catalog item, the XaaS
service runs the corresponding vRealize Orchestrator workflow passing the following data as global
parameters to the workflow:
Table 4‑37. XaaS Global Parameters
Parameter Description
__asd_tenantRef The tenant of the user requesting the workflow.
__asd_subtenantRef The business group of the user requesting the workflow.
__asd_catalogRequestId The request id from the catalog for this workflow run.
__asd_requestedFor The target user of the request. If the request is on behalf of a
user, then this is the user on behalf of whom the workflow is
requested, otherwise it is the user requesting the workflow.
__asd_requestedBy The user requesting the workflow.
If an XaaS blueprint or resource action uses a vRealize Orchestrator workflow that contains a User
Interaction schema element, when a consumer requests the service, the workflow suspends its run and
waits for the user to provide the required data. To answer to a waiting user interaction, the user must
navigate to Inbox > Manual User Action.
The default vRealize Orchestrator server inventory is shared across all tenants and cannot be used per
tenant. For example, if a service architect creates a service blueprint for creating a cluster compute
resource, the consumers from different tenants have to browse through the inventory items of all
vCenter Server instances although they might belong to a different tenant.
Configuring vRealize Automation
VMware, Inc. 330
System administrators can install vRealize Orchestrator or deploy the
VMware vRealize ™ Orchestrator Appliance™ separately to set up an external vRealize Orchestrator
instance and configure vRealize Automation to work with that external vRealize Orchestrator instance.
System administrators can also configure vRealize Orchestrator workflow categories per tenant and
define which workflows are available to each tenant.
In addition, tenant administrators can also configure an external vRealize Orchestrator instance but only
for their own tenants.
For information about configuring an external vRealize Orchestrator instance and vRealize Orchestrator
workflow categories, see Configuring vCenter Orchestrator and Plug-Ins.
List of vRealize Orchestrator Plug-Ins
With plug-ins you can use vRealize Orchestrator to access and control external technologies and
applications. By exposing an external technology in a vRealize Orchestrator plug-in, you can incorporate
objects and functions in workflows that access the objects and functions of the external technology.
The external technologies that you can access by using plug-ins can include virtualization management
tools, email systems, databases, directory services, remote control interfaces, and so on.
You can use the standard set of vRealize Orchestrator plug-ins to incorporate external technologies such
as the vCenter Server API and email capabilities into workflows. In addition, you can use the
vRealize Orchestrator open plug-in architecture to develop plug-ins to access other applications.
Table 4‑38. Plug-Ins Included by Default in vRealize Orchestrator
Plug-In Purpose
vCenter Server Provides access to the vCenter Server API so that you can incorporate all of the
vCenter Server objects and functions into the management processes that you
automate by using vRealize Orchestrator.
Configuration Provides workflows for configuring the vRealize Orchestrator authentication,
database connection, SSL certificates, and so on.
vCO Library Provides workflows that act as basic building blocks for customization and
automation of client processes. The workflow library includes templates for life
cycle management, provisioning, disaster recovery, hot backup, and other
standard processes. You can copy and edit the templates to modify them
according to your needs.
SQL Provides the Java Database Connectivity (JDBC) API, which is the industry
standard for database-independent connectivity between the Java programming
language and a wide range of databases. The databases include SQL databases
and other tabular data sources, such as spreadsheets or flat files. The JDBC API
provides a call-level API for SQL-based database access from workflows.
SSH Provides an implementation of the Secure Shell v2 (SSH-2) protocol. Allows
remote command and file transfer sessions with password and public key-based
authentication in workflows. Supports keyboard-interactive authentication.
Optionally, the SSH plug-in can provide remote file system browsing directly in
the vRealize Orchestrator client inventory.
Configuring vRealize Automation
VMware, Inc. 331
Table 4‑38. Plug-Ins Included by Default in vRealize Orchestrator (Continued)
Plug-In Purpose
XML A complete Document Object Model (DOM) XML parser that you can implement
in workflows. Alternatively, you can use the ECMAScript for XML (E4X)
implementation in the vRealize Orchestrator JavaScript API.
Mail Uses Simple Mail Transfer Protocol (SMTP) to send email from workflows.
Net Wraps the Jakarta Apache Commons Net Library. Provides implementations of
Telnet, FTP, POP3, and IMAP. The POP3 and IMAP part is used for reading
email. In combination with the Mail plug-in, the Net plug-in provides complete
email send and receive capabilities in workflows.
Enumeration Provides common enumerated types that can be used in workflows by other plug-
ins.
Workflow documentation Provides workflows that let you generate information in PDF format about a
workflow or a workflow category.
HTTP-REST Lets you manage REST Web services by providing interaction between vCenter
Orchestrator and REST hosts.
SOAP Lets you manage SOAP Web services by providing interaction between vCenter
Orchestrator and SOAP hosts.
AMQP Lets you interact with Advanced Message Queuing Protocol (AMQP) servers also
known as brokers.
SNMP Enables vCenter Orchestrator to connect and receive information from SNMP-
enabled systems and devices.
Active Directory Provides interaction between vCenter Orchestrator and Microsoft Active
Directory.
vCO WebOperator A Web view that lets you to access the workflows in the vRealize Orchestrator
library and interact with them across a network by using a Web browser.
Dynamic Types Lets you define dynamic types and create and use objects of these dynamic
types.
PowerShell Lets you manage PowerShell hosts and run custom PowerShell operations.
Multi-Node Contains workflows for hierarchical orchestration, management of Orchestrator
instances, and scale-out of Orchestrator activities.
vRealize Automation (only in the instance
embedded in vRealize Automation)
Lets you create and run workflows for interaction between vRealize Orchestrator
and vRealize Automation.
For more information about the vRealize Orchestrator plug-ins that VMware develops and distributes, see
the VMware vRealize ™ Orchestrator ™ Documentation landing page.
Creating Custom Resources
A custom resource maps a vRealize Orchestrator object type as an XaaS resource so that you can create
blueprints and resource actions.
For example, you create a custom resource based on VC:virtual machine so that you can create
blueprints to provision vCenter Server virtual machines and are add resource actions to run on the
machines.
Configuring vRealize Automation
VMware, Inc. 332

Add a Custom Resource
You create a custom resource to define the XaaS item for provisioning.
By creating a custom resource, you map an object type exposed through the API of a
vRealize Orchestrator plug-in as a resource. You create a custom resource to define the output parameter
of an XaaS blueprint for provisioning and to define an input parameter of a resource action.
During the process of creating a custom resource, on the Details Form page, you can specify the fields of
the read-only form for the resource that displays information on the details view of a provisioned item.
See Designing a Custom Resource Form.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Select Design > XaaS > Custom Resources.
2Click the New icon ( ).
3Enter the vRealize Orchestrator object type In the Orchestrator Type text box and press Enter.
For example, enter v to see all types containing the letter v. To see all types, enter a space and click
Search.
4Enter a name and, optionally, a description.
5Enter a version.
The version supports integers only. The supported format extends to major.minor.micro-revision.
6Click Next.
7Edit the form of the custom resource.
You can edit the custom resource form by deleting, editing, and rearranging elements. You can also
add a new form and form pages and drag elements to the new form and form page.
Option Description
Add a form Click the New Form icon ( ) next to the form name, provide the required
information, and click Submit.
Add a form page Click the New Page icon ( ) next to the form page name, provide the required
information, and click Submit.
Add an element to the form page Drag an element from the New Fields pane on the left to the pane on the right.
You can then provide the required information and click Submit.
The available elements are specific for the vRealize Orchestrator object type.
Edit an element Click the Edit icon ( ) next to the element to edit, make the necessary changes,
and click Submit.
Configuring vRealize Automation
VMware, Inc. 333
Option Description
Delete an element Click the Delete icon ( ) next to the element to delete, and in the confirmation
dialog box click OK.
Delete a form Click the Delete icon ( ) next to the form name, and in the confirmation dialog
box click OK.
8Click Finish.
You created a custom resource and you can see it on the Custom Resources page.
What to do next
Create a XaaS blueprint. See Create an XaaS Blueprint.
Creating XaaS Blueprints and Resource Actions
The XaaS blueprints can be entitled to users as catalog items, or they can be assembled into a composite
blueprints using the design canvas. The resource actions run on the provisioned items to manage the
items after they are provisioned.
For example, you can use an XaaS blueprint to create Active Directory users in a group . You can then
use a resource action to change the require that the user change the password.
Create an XaaS Blueprint as a Catalog Item
An XaaS blueprint is a provisioning blueprint. Some of the provided provisioning workflows include
creating virtual machines, adding users to Active Directory, or taking virtual machine snapshots.
Prerequisites
nLog in to the vRealize Automation console as an XaaS architect.
nCreate a custom resource for the target resource type. See Add a Custom Resource.
Procedure
1Create an XaaS Blueprint
An XaaS blueprint is a complete specification for provisioning. The blueprint can include the input
parameters, submission and read-only forms, sequence of actions, and the provisioning.
2Publish an XaaS Blueprint as a Catalog Item
After you create an XaaS blueprint, it is in a draft state and you can publish it as a catalog item.
Create an XaaS Blueprint
An XaaS blueprint is a complete specification for provisioning. The blueprint can include the input
parameters, submission and read-only forms, sequence of actions, and the provisioning.
You can create service blueprints to provision custom resources that you previously created. When
consumers request these catalog items, the provisioned items are stored on the Items tab and you can
define post-provisioning operations for this type of provisioned resources.
Configuring vRealize Automation
VMware, Inc. 334

If you create a service blueprint for provisioning without specifying the output parameter, when the
consumers request this catalog item, the blueprint does the provisioning but the provisioned items are not
added on the Items tab. You cannot perform post-provisioning operations on this type of provisioned
resource.
You can also create service blueprints for requesting that do not have output parameters and do not result
in provisioning. For example, you can create a service blueprint for sending notifications.
By creating a service blueprint, you publish a vRealize Orchestrator workflow as a catalog item. During
this process you can edit the default generated forms. See Designing an XaaS Blueprint Form.
Prerequisites
nLog in to the vRealize Automation console as an XaaS architect.
nFor items provisioning, create a custom resource corresponding to the output parameter of the
service blueprint. See Add a Custom Resource.
Procedure
1Select Design > XaaS > XaaS Blueprints.
2Click the New icon ( ).
3Navigate through the vRealize Orchestrator workflow library and select a workflow.
You can see the name and description of the selected workflow, and the input and output parameters
as they are defined in vRealize Orchestrator.
4Click Next.
5Enter a name and, optionally, a description.
The Name and Description text boxes are prepopulated with the name and description of the
workflow as they are defined in vRealize Orchestrator.
6(Optional) If you do not want to prompt consumers to enter a description and reason for requesting
this resource action, select the Hide catalog request information page check box.
7Enter a version.
The version supports integers only. The supported format extends to major.minor.micro-revision.
8Click Next.
Configuring vRealize Automation
VMware, Inc. 335
9(Optional) Edit the form of the service blueprint on the Blueprint Form page.
By default, the service blueprint form is mapped to the vRealize Orchestrator workflow presentation.
You can edit the blueprint form by deleting, editing, and rearranging the elements in the form. You can
also add a new form and form pages and drag elements to the new form and form page.
Option Action
Add a form Click the New Form icon ( ) next to the form name, provide the required
information, and click Submit.
Edit a form Click the Edit icon ( ) next to the form name, make the necessary changes,
and click Submit.
Regenerate the workflow presentation Click the Rebuild icon ( ) next to the form name and click OK.
Delete a form Click the Delete icon ( ) next to the form name, and in the confirmation dialog
box click OK.
Add a form page Click the New Page icon ( ) next to the form page name, provide the required
information, and click Submit.
Edit a form page Click the Edit icon ( ) next to the form page name, make the necessary
changes, and click Submit.
Delete a form page Click the Delete icon ( ) next to the form name, and in the confirmation dialog
box click OK.
Add an element to the form page Drag an element from the New Fields pane on the left to the pane on the right.
You can then provide the required information and click Submit.
Edit an element Click the Edit icon ( ) next to the element to edit, make the necessary changes,
and click Submit.
Delete an element Click the Delete icon ( ) next to the element to delete, and in the confirmation
dialog box click OK.
10 Click Next.
11 Select an output parameter from the drop-down menu.
Option Description
A custom resource that you previously
created
When users request this catalog item, the provisioned items are stored on the
Items tab.
No provisioning The service blueprint does not add new items on the Items tab.
12 Click Finish.
You created a service blueprint and you can see it on the XaaS blueprints page.
What to do next
Publish the blueprint as a catalog item. See Publish an XaaS Blueprint as a Catalog Item.
Publish an XaaS Blueprint as a Catalog Item
After you create an XaaS blueprint, it is in a draft state and you can publish it as a catalog item.
Configuring vRealize Automation
VMware, Inc. 336
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Select Design > XaaS > XaaS Blueprints.
2Select the row of the XaaS blueprint to publish, and click Publish.
The status of the XaaS blueprint changes to Published. If you select Administration > Catalog
Management > Catalog Items, you can see that the blueprint is published as a catalog item.
What to do next
nTo make the XaaS blueprint available in the service catalog, you must add the item to a service. See
Creating a Service.
nYou can create a resource action that runs on provisioned items. See Create a Resource Action.
Create an XaaS Resource Action as a Catalog Item
You create a resource action so that you can manage provisioned items using vRealize Orchestrator
workflows.
Prerequisites
nLog in to the vRealize Automation console as an XaaS architect.
nVerify that you have a custom resource that support the action. See Add a Custom Resource.
nIf you are creating actions to run on items not provisioned as XaaS catalog items, verify that you
mapped the target resources. See Mapping Other Resources to Work with XaaS Resource Actions.
Procedure
1Create a Resource Action
A resource action is an XaaS workflow that service catalog users can run on provisioned catalog
items. As an XaaS architect, you can create resource actions to define the operations that
consumers can perform on the provisioned items.
2Publish a Resource Action
The newly created resource action is in draft state, and you must publish the resource action.
3Assign an Icon to a Resource Action
After you create and publish a resource action, you can edit it and assign an icon to the action.
Create a Resource Action
A resource action is an XaaS workflow that service catalog users can run on provisioned catalog items.
As an XaaS architect, you can create resource actions to define the operations that consumers can
perform on the provisioned items.
Configuring vRealize Automation
VMware, Inc. 337

By creating a resource action, you associate a vRealize Orchestrator workflow as a post-provisioning
operation. During this process, you can edit the default submission and read-only forms. See Designing a
Resource Action Form.
Prerequisites
nLog in to the vRealize Automation console as an XaaS architect.
nCreate a custom resource corresponding to the input parameter of the resource action.
Procedure
1Select Design > XaaS > Resource Actions.
2Click the New icon ( ).
3Navigate through the vRealize Orchestrator workflow library and select a workflow.
You can see the name and description of the selected workflow, and the input and output parameters
as they are defined in vRealize Orchestrator.
4Click Next.
5Select the custom resource that you previously created from the Resource type drop-down menu.
6Select the input parameter for the resource action from the Input parameter drop-down menu.
7Click Next.
8Enter a name and, optionally, a description.
The Name and Description text boxes are prepopulated with the name and description of the
workflow as they are defined in vRealize Orchestrator.
9(Optional) If you do not want to prompt consumers to enter a description and reason for requesting
this resource action, select the Hide catalog request information page check box.
10 Enter a version.
The version supports integers only. The supported format extends to major.minor.micro-revision.
Configuring vRealize Automation
VMware, Inc. 338
11 (Optional) Select the type of the action.
Option Description
Disposal The input parameter of the resource action workflow is disposed and the item is
removed from the Items tab. For example, the resource action is for deleting a
provisioned machine.
Provisioning The resource action is for provisioning. For example, the resource action is for
copying a catalog item.
From the drop-down menu, select an output parameter. You can select a custom
resource that you previously created so that when the consumers request this
resource action, the provisioned items are added on the Items tab. If you have
only the No provisioning option, either the resource action is not for provisioning,
or you did not create a proper custom resource for the output parameter, and you
cannot proceed.
Depending on the action workflow, you can select one, both, or none of the options.
12 Select the conditions under which the resource action is available to users, and click Next.
13 (Optional) Edit the form of the resource action on the Form tab.
The form of the resource action maps the vRealize Orchestrator workflow presentation. You can
change the form by deleting, editing, and rearranging the elements. You can also add a new form and
form pages and drag the necessary elements to the new form and form page.
Option Action
Add a form Click the New Form icon ( ) next to the form name, provide the required
information, and click Submit.
Edit a form Click the Edit icon ( ) next to the form name, make the necessary changes,
and click Submit.
Regenerate the workflow presentation Click the Rebuild icon ( ) next to the form name and click OK.
Delete a form Click the Delete icon ( ) next to the form name, and in the confirmation dialog
box click OK.
Add a form page Click the New Page icon ( ) next to the form page name, provide the required
information, and click Submit.
Edit a form page Click the Edit icon ( ) next to the form page name, make the necessary
changes, and click Submit.
Delete a form page Click the Delete icon ( ) next to the form name, and in the confirmation dialog
box click OK.
Add an element to the form page Drag an element from the New Fields pane on the left to the pane on the right.
You can then provide the required information and click Submit.
Edit an element Click the Edit icon ( ) next to the element to edit, make the necessary changes,
and click Submit.
Delete an element Click the Delete icon ( ) next to the element to delete, and in the confirmation
dialog box click OK.
14 Click Finish.
Configuring vRealize Automation
VMware, Inc. 339
You created a resource action and you can see it listed on the Resource Actions page.
What to do next
Publish the resource action. See Publish a Resource Action.
Publish a Resource Action
The newly created resource action is in draft state, and you must publish the resource action.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Select Design > XaaS > Resource Actions.
2Select the row of the resource action to publish, and click Publish.
The status of the resource action changes to Published.
What to do next
Assign an icon to the resource action. See Assign an Icon to a Resource Action. Business group
managers and tenant administrators can then use the action when they create an entitlement.
Assign an Icon to a Resource Action
After you create and publish a resource action, you can edit it and assign an icon to the action.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Select Administration > Catalog Management > Actions.
2Select the resource action that you created.
3Click Configure.
4Click Browse and select the icon to add.
5Click Open.
6Click Update.
You assigned an icon to the resource action. Business group managers and tenant administrators can
use the resource action in an entitlement.
Mapping Other Resources to Work with XaaS Resource Actions
You map items that were not provisioned using XaaS so that you can run resource actions to run on those
items.
Configuring vRealize Automation
VMware, Inc. 340
Create a Resource Mapping
vRealize Automation provides resource mappings for vSphere, vCloud Director, and vCloud Air
machines. You can create additional resource mappings for other types of catalog resources.
Prerequisites
nLog in to the vRealize Automation console as an XaaS architect.
nVerify that the mapping script or workflow is available in vRealize Orchestrator. See Resource
Mapping Script Actions and Workflows
Procedure
1Select Design > XaaS > Resource Mappings.
2Click the New icon ( ).
3Enter a name and, optionally, a description.
4Enter a version.
The version supports integers only. The supported format extends to major.minor.micro-revision.
5Enter the type of the catalog resource in the Catalog Resource Type text box and press enter.
The type of catalog resource appears on the details view of the provisioned item.
6Enter the vRealize Orchestrator object type in the Orchestrator Type text box and press enter.
This is the output parameter of the resource mapping workflow.
7(Optional) Add target criteria to restrict the availability of resource actions created by using this
resource mapping.
Resource actions are also subject to restrictions based on approvals and entitlements.
a Select Available based on conditions.
b Select the type of condition.
Option Description
All of the following If all of the clauses you define are satisfied, resource actions created by using
this resource mapping are available to the user.
Any of the following If any one of the clauses you define are satisfied, resource actions created by
using this resource mapping are available to the user.
Not the following If the clause you define exists, resource actions created by using this resource
mapping are not available.
c Follow the prompts to build your clauses and complete the condition.
8Select your resource mapping script action or workflow from the vRealize Orchestrator library.
9Click OK.
Configuring vRealize Automation
VMware, Inc. 341
Resource Mapping Script Actions and Workflows
You can use the provided resource mappings for vSphere, vCloud Director, or vCloud Air machines or
you can create custom vRealize Orchestrator script actions or workflows to map additional
vRealize Automation catalog resource types to vRealize Orchestrator inventory types.
Depending on your version of vRealize Orchestrator, you can create either a vRealize Orchestrator
workflow or a script action to map resources between vRealize Orchestrator and vRealize Automation.
To develop the resource mapping, you use an input parameter of type Properties, which contains a key-
value pair defining the provisioned resource, and an output parameter of a vRealize Orchestrator
inventory type expected by the corresponding vRealize Orchestrator plug-in. The properties available for
the mapping depend on the type of resource. For example, the EXTERNAL_REFERENCE_ID property is a
common key parameter that defines individual machines, and you can use this property to query a
catalog resource. If you are creating a mapping for a resource that does not use an
EXTERNAL_REFERENCE_ID, you can use one of the other properties that are passed for the individual
machines such as name, description, and so on.
vRealize Automation includes vRealize Orchestrator resource mapping script actions and resource
mapping workflows for each of the provided XaaS resource mappings. Script actions for the provided
resource mappings are located in the com.vmware.vcac.asd.mappings package of the embedded
vRealize Orchestrator server. Workflows for the provided resource mappings are located in the vRealize
Automation > XaaS > Resource Mappings workflows folder of the embedded vRealize Orchestrator
server.
For more information about developing workflows and script actions, see Developing with VMware
vCenter Orchestrator.
Designing Forms for XaaS Blueprints and Actions
The XaaS includes a form designer that you can use to design submission and details forms for
blueprints and resources actions. Based on the presentation of the workflows, the form designer
dynamically generates default forms and fields you can use to modify the default forms.
You can create interactive forms that the users can complete for submission of catalog items and
resource actions. You can also create read-only forms that define what information the users can see on
the details view for a catalog item or a provisioned resource.
As you create XaaS custom resources, XaaS blueprints, and resource actions, forms are generated for
common use cases.
Configuring vRealize Automation
VMware, Inc. 342
Table 4‑39. XaaS Object Types and Associated Forms
Object Type Default Form Additional Forms
Custom resource Resource details form based on the attributes
of the vRealize Orchestrator plug-in inventory
type (read-only).
nNone
XaaS blueprint Request submission form based on the
presentation of the selected workflow.
nCatalog item details (read-only)
nSubmitted request details (read-only)
Resource action Action submission form based on the
presentation of the selected workflow.
nSubmitted action details (read-only)
You can modify the default forms and design new forms. You can drag fields to add and reorder them on
the form. You can place constraints on the values of certain fields, specify default values, or provide
instructional text for the end user who is completing the form.
Because of their different purposes, the operations you can perform to design read-only forms are limited
compared to the operations for designing submission forms.
Fields in the Form Designer
You can extend the workflow presentation and functionality by adding new predefined fields to the default
generated forms of resource actions and XaaS blueprints.
If an input parameter is defined in the vRealize Orchestrator workflow, in vRealize Automation it appears
on the default generated form. If you do not want to use the default generated fields in the form, you can
delete them and drag and drop new fields from the palette. You can replace default generated fields
without breaking the workflow mappings if you use the same ID as the field you are replacing.
You can also add new fields, other than the ones that were generated based on the vRealize Orchestrator
workflow inputs, so that you can extend the workflow presentation and functionality in the following cases:
nAdd constraints to the existing fields
For example, you can create a new drop-down menu and name it dd. You can also create predefined
options of Gold, Silver, Bronze, and Custom. If there is a predefined field, such as CPU, you can add
the following constraints to this field:
nIf dd equals Gold, then CPU is 2000 MHz
nIf dd equals Silver, then CPU is 1000 MHz
nIf dd equals Bronze then CPU is 500 MHz
nIf dd equals Custom, the CPU field is editable, and the consumer can specify a custom value
nAdd external value definitions to fields
You can add an external value definition to a field so that you can run vRealize Orchestrator script
actions and supply additional information to consumers on the forms you design. For instance, you
might want to create a workflow to change the firewall settings of a virtual machine. On the resource
action request page, you want to provide the user with the ability to change the open port settings, but
Configuring vRealize Automation
VMware, Inc. 343
you also want to restrict the options to ports that are open. You can add an external value definition to
a dual list field and select a custom vRealize Orchestrator script action that queries for open ports.
When the request form loads, the script actions runs, and the open ports are presented as options to
the user.
nAdd new fields that are handled in the vRealize Orchestrator workflow as global parameters
For instance, the workflow provides an integration with a third-party system and the workflow
developer defined input parameters to be handled in the general case, but has also provided a way
for passing custom fields. For example, in a scripting box, all global parameters that start with
my3rdparty are handled. Then, if the XaaS architect wants to pass specific values for consumers to
provide, the XaaS architect can add a new field named my3rdparty_CPU.
Table 4‑40. New Fields in the Resource Action or XaaS Blueprint Form
Field Description
Text field Single-line text box
Text area Multi-line text box
Link Field in which consumers enter a URL
Email Field in which consumers enter an email address
Password field Field in which consumers enter a password
Integer field Text box in which consumers entre an integer
You can make this field a slider with a minimum and maximum value, as
well as an increment.
Decimal field Text box in which consumers enter a decimal
You can make this field a slider with a minimum and maximum value, as
well as an increment.
Date & time Text boxes in which consumers specify a date (by selecting a date from
a calendar menu) and can also select the time (by using up and down
arrows)
Dual List A list builder in which consumers move a predefined set of values
between two lists, the first list contains all unselected options and the
second list contains the user's choices.
Check box Check box
Yes/No Drop-down menu for selecting Yes or No
Drop-down Drop-down menu
List List
Check box list Check box list
Radio button group Group of radio buttons
Search Search text box that auto completes the query and where consumers
select an object
Configuring vRealize Automation
VMware, Inc. 344
Table 4‑40. New Fields in the Resource Action or XaaS Blueprint Form (Continued)
Field Description
Tree Tree that consumers use to browse and select available objects
Map Map table that consumers use to define key-value pairs for properties
You can also use the Section header form field to split form pages in sections with separate headings
and the Text form field to add read-only informational texts.
Constraints and Values in the Form Designer
When you edit an element of the blueprint or resource action form, you can apply various constraints and
values to the element.
Constraints
The constraints that you can apply to an element vary depending on the type of element you are editing
or adding to the form. Some constraint values might be configured in the vRealize Orchestrator workflow.
Those values do not appear on the Constraints tab because they are often dependent on conditions that
are evaluated when the workflow runs. Any constraint values that you configure for the blueprint form
overrides any constraints specified in the vRealize Orchestrator workflow.
For each constraint you apply to an element, you can select one of the following options to define the
constraint:
Not set Gets the property from the vRealize Orchestrator workflow presentation.
Constant Sets the element you are editing to required or optional.
Field Binds the element to another element from the form. For example, you can
set the element to be required only when another element, such as a check
box, is selected.
Conditional Applies a condition. By using conditions you can create various clauses
and expressions and apply them to the state or constraints of the element.
External Select a vRealize Orchestrator script action to define the value.
Table 4‑41. Constraints in the forms designer
Constraint Description
Required Indicates whether the element is required.
Read only Indicates whether the field is read-only.
Value Allows you to set a value for the element.
Visible Indicates whether the consumer can see the element.
Minimum length Allows you to set a minimum number of characters of the string input element.
Maximum length Allows you to set a maximum allowed number of characters of the string input
element.
Minimum value Allows you to set a minimum value of the number input element.
Configuring vRealize Automation
VMware, Inc. 345
Table 4‑41. Constraints in the forms designer (Continued)
Constraint Description
Maximum value Allows you to set a maximum value of the number input element.
Increment Allows you to set an increment for an element such as a Decimal or Integer
field. For example, when you want an Integer field to be rendered as a Slider,
you can use the value of the step.
Minimum count Allows you to set a minimum count of items of the element that can be selected.
For example, when you add or edit a Check box list you can set the minimum
number of check boxes that the consumer must select to proceed.
Maximum count Allows you to set a maximum count of items of the element that can be
selected.
For example, when you add or edit a Check box list you can set the maximum
number of check boxes that the consumer must select to proceed.
Values
You can apply values to some of the elements and define what the consumers see for some of the fields.
The options available depend on the type of element you are editing or adding to the form.
Table 4‑42. Values in the Form Designer
Value Description
Not set Get the value of the element you are editing from the
vRealize Orchestrator workflow presentation.
Predefined values Select values from a list of related objects from the
vRealize Orchestrator inventory.
Value Define a static custom values with labels.
External Values Select a vRealize Orchestrator script action to define your value
with information not directly exposed by the workflow.
External Value Definitions in the Form Designer
When you edit some elements in the forms designer, you can assign external value definitions that use
custom vRealize Orchestrator script actions to supply information not directly exposed by the workflow.
For instance, you might want to publish a resource action to install software on a provisioned machine.
Instead of providing the consumer with a static list of all software available for download, you can
dynamically populate that list with software that is relevant for the machine's operating system, software
that the user has not previously installed on the machine, or software that is out of date on the machine
and requires an update.
To provide custom dynamic content for your consumer, you create a vRealize Orchestrator script action
that retrieves the information you want to display to your consumers. You assign your script action to a
field in the form designer as an external value definition. When the resource or service blueprint form is
presented to your consumers, the script action retrieves your custom information and displays it to your
consumer.
Configuring vRealize Automation
VMware, Inc. 346
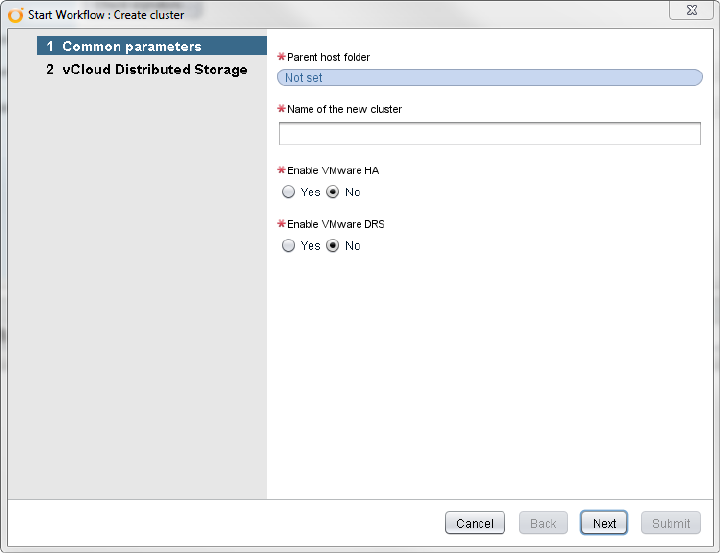
You can use external value definitions to supply default or read-only values, to build boolean expressions,
to define constraints, or to provide options for consumers to select from lists, check boxes, and so on.
Working With the Form Designer
When you create XaaS blueprints, custom resource actions, and custom resources, you can edit the
forms of the blueprints, actions, and resources by using the form designer. You can edit the
representation and define what the consumers of the item or action see when they request the catalog
item or run the post-provisioning operation.
By default, any XaaS blueprint, resource action, or custom resource form is generated based on the
workflow presentation in vRealize Orchestrator.
The steps in the vRealize Orchestrator presentation are represented as form pages and the
vRealize Orchestrator presentation groups are represented as separate sections. The input types of the
selected workflow are displayed as various fields in the form. For example, the vRealize Orchestrator type
string is represented by a text box. A complex type such as VC:VirtualMachine is represented by a
search box or a tree, so that the consumers can type an alphanumeric value to search for a virtual
machine or browse to select a virtual machine.
Configuring vRealize Automation
VMware, Inc. 347
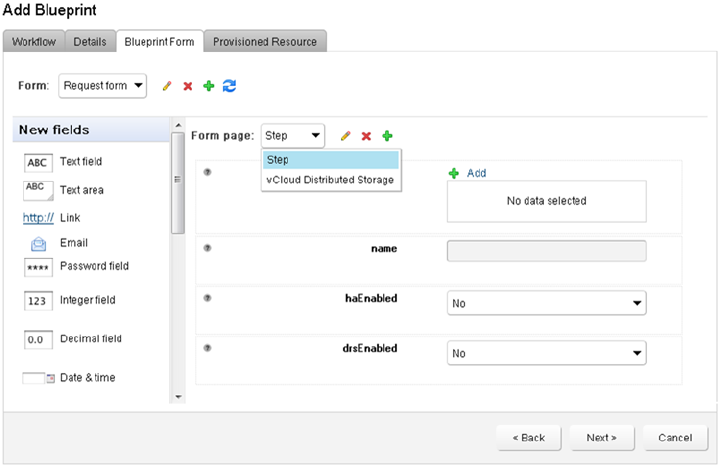
You can edit how an object is represented in the form designer. For example, you can edit the default
VC:VirtualMachine representation and make it a tree instead of a search box. You can also add new
fields such as check boxes, drop-down menus, and so on, and apply various constraints. If the new fields
you add are not valid or are not correctly mapped to the vRealize Orchestrator workflow inputs, when the
consumer runs the workflow, vRealize Orchestrator skips the invalid or unmapped fields.
Designing a Custom Resource Form
All fields on the resource details form are displayed as read-only to the consumer on the item details page
when they provision your custom resource. You can perform basic edit operations to the form, such as
deleting, modifying, or rearranging fields, or you can add new externally defined fields that use
vRealize Orchestrator script actions to supply additional read-only information to consumers.
nEdit a Custom Resource Element
You can edit some of the characteristics of an element on the custom resource Details Form page.
Each default field on the page represents a property of the custom resource. You cannot change the
type of a property or the default values, but you can edit the name, size, description.
nAdd a New Custom Resource Form Page
You can add a new page to rearrange the form into multiple tabs.
nInsert a Section Header in a Custom Resource Form
You can insert a section header to split the form into sections.
nInsert a Text Element in a Custom Resource Form
You can insert a text box to add some descriptive text to the form.
nInsert an Externally Defined Field in a Custom Resource Form
You can insert a new field and assign it an external value definition to dynamically provide read-only
information that consumers can see on the item details page when they provision a custom
resource.
Configuring vRealize Automation
VMware, Inc. 348

Edit a Custom Resource Element
You can edit some of the characteristics of an element on the custom resource Details Form page. Each
default field on the page represents a property of the custom resource. You cannot change the type of a
property or the default values, but you can edit the name, size, description.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nAdd a Custom Resource.
Procedure
1Select Design > XaaS > Custom Resources.
2Click the custom resource to edit.
3Click the Details Form tab.
4Point to the element you want to edit and click the Edit icon.
5Enter a new name for the field in the Label text box to change the label.
6Edit the description in the Description text box.
7Select an option from the Size drop-down menu to change the size of the element.
8Select an option from the Label size drop-down menu to change the size of the label.
9Click Submit.
10 Click Finish.
Add a New Custom Resource Form Page
You can add a new page to rearrange the form into multiple tabs.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nAdd a Custom Resource.
Procedure
1Select Design > XaaS > Custom Resources.
2Click the custom resource to edit.
3Click the Details Form tab.
4Click the New Page icon ( ) next to the Form page name.
5Select the unused screen type and click Submit.
If you already have a resource details or resource list view, you cannot create two of the same type.
6Click Submit.
Configuring vRealize Automation
VMware, Inc. 349
7Configure the form.
8Click Finish.
You can delete some of the elements from the original form page and insert them in the new form page,
or you can add new fields that use external value definitions to provide information to consumers that is
not directly exposed by the vRealize Orchestrator workflow.
Insert a Section Header in a Custom Resource Form
You can insert a section header to split the form into sections.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nAdd a Custom Resource.
Procedure
1Select Design > XaaS > Custom Resources.
2Click the custom resource to edit.
3Click the Details Form tab.
4Drag the Section header element from the Form pane to the Form page pane.
5Type a name for the section.
6Click outside of the element to save the changes.
7Click Finish.
Insert a Text Element in a Custom Resource Form
You can insert a text box to add some descriptive text to the form.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nAdd a Custom Resource.
Procedure
1Select Design > XaaS > Custom Resources.
2Click the custom resource to edit.
3Click the Details Form tab.
4Drag the Text element from the Form pane to the Form page pane.
5Enter the text you want to add.
6Click outside of the element to save the changes.
7Click Finish.
Configuring vRealize Automation
VMware, Inc. 350
Insert an Externally Defined Field in a Custom Resource Form
You can insert a new field and assign it an external value definition to dynamically provide read-only
information that consumers can see on the item details page when they provision a custom resource.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nAdd a Custom Resource.
nDevelop or import a vRealize Orchestrator script action to retrieve the information you want to provide
to consumers.
Procedure
1Select Design > XaaS > Custom Resources.
2Click the custom resource to edit.
3Click the Details Form tab.
4Drag an element from the New Fields pane and drop it to the Form page pane.
5Enter an ID for the element in the ID text box.
6Enter a label in the Label text box.
Labels appear to consumers on the forms.
7(Optional) Select a type for the field from the Type drop-down menu.
8Enter the result type of your vRealize Orchestrator script action in the Entity Type search box and
press Enter.
For example, if you want to use a script action to display the current user, and the script returns a
vRealize Orchestrator result type of LdapUser, enter LdapUser in the Entity Type search box and
press Enter.
9Click Add External Value.
10 Select your custom vRealize Orchestrator script action.
11 Click Submit.
12 Click Submit again.
13 Click Finish.
When the form is presented to your consumers, the script action retrieves your custom information and
displays it to your consumer.
Designing an XaaS Blueprint Form
When you create an XaaS blueprint, you can edit the form of the blueprint by adding new fields to the
form, modifying the existing fields, deleting, or rearranging fields. You can also create new forms and form
pages, and drag and drop new fields to them.
Configuring vRealize Automation
VMware, Inc. 351

nAdd a New XaaS Blueprint Form
When you edit the default generated form of a workflow that you want to publish as a XaaS
blueprint, you can add a new XaaS blueprint form.
nEdit an XaaS Blueprint Element
You can edit some of the characteristics of an element on the Blueprint Form page of a XaaS
blueprint. You can change the type of an element, its default values, and apply various constraints
and values.
nAdd a New Element
When you edit the default generated form of a XaaS blueprint, you can add a predefined new
element to the form. For example, if you do not want to use a default generated field, you can delete
it and replace it with a new one.
nInsert a Section Header in a XaaS Blueprint Form
You can insert a section header to split the form into sections.
nAdd a Text Element to an XaaS Blueprint Form
You can insert a text box to add some descriptive text to the form.
Add a New XaaS Blueprint Form
When you edit the default generated form of a workflow that you want to publish as a XaaS blueprint, you
can add a new XaaS blueprint form.
By adding a new XaaS blueprint form, you define the look and feel of the catalog item details and
submitted request details pages. If you do not add a catalog item details and submitted request details
forms, the consumer sees what is defined in the request form.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nCreate an XaaS Blueprint.
Procedure
1Select Design > XaaS > XaaS Blueprints.
2Click the XaaS blueprint you want to edit.
3Click the Blueprint Form tab.
4Click the New Form icon ( ).
5Enter a name and, optionally, a description.
Configuring vRealize Automation
VMware, Inc. 352
6Select the screen type from the Screen type menu.
Option Description
Catalog item details A catalog item details page that consumers see when they click a catalog item.
Request form The default XaaS blueprint form. The consumers see the request form when they
request the catalog item.
Submitted request details A request details page that consumers see after they request the item and want
to view the request details on the Request tab.
7Click Submit.
What to do next
Add the fields you want by dragging them from the New fields pane to the Form page pane.
Edit an XaaS Blueprint Element
You can edit some of the characteristics of an element on the Blueprint Form page of a XaaS blueprint.
You can change the type of an element, its default values, and apply various constraints and values.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nCreate an XaaS Blueprint.
Procedure
1Select Design > XaaS > XaaS Blueprints.
2Click the XaaS blueprint you want to edit.
3Click the Blueprint Form tab.
4Locate the element you want to edit.
5Click the Edit icon ( ).
6Enter a new name for the field in the Label text box to change the label that consumers see.
7Edit the description in the Description text box.
8Select an option from the Type drop-down menu to change the display type of the element.
The options vary depending on the type of element you edit.
9Select an option from the Size drop-down menu to change the size of the element.
10 Select an option from the Label size drop-down menu to change the size of the label.
Configuring vRealize Automation
VMware, Inc. 353
11 Edit the default value of the element.
Option Description
Not set Gets the value of the element you are editing from the vRealize Orchestrator
workflow presentation.
Constant Sets the default value of the element you are editing to a constant value that you
specify.
Field Binds the default value of the element to a parameter of another element from the
representation.
Conditional Applies a condition. By using conditions you can create various clauses and
expressions and apply them to an element.
External Select a vRealize Orchestrator script action to define the value.
12 Apply constraints to the element on the Constraints tab.
Option Description
Not set Gets the value of the element you are editing from the vRealize Orchestrator
workflow presentation.
Constant Sets the default value of the element you are editing to a constant value that you
specify.
Field Binds the default value of the element to a parameter of another element from the
representation.
Conditional Applies a condition. By using conditions you can create various clauses and
expressions and apply them to an element.
External Select a vRealize Orchestrator script action to define the value.
13 Add one or more values for the element on the Values tab.
The options available depend on the type of element you are editing.
Option Description
Not set Gets the value of the element you are editing from the vRealize Orchestrator
workflow presentation.
Predefined values Select values from a list of related objects from the vRealize Orchestrator
inventory.
a Enter a value in the Predefined values search box to search the
vRealize Orchestrator inventory.
b Select a value from the search results and press Enter.
Value Define custom values with labels.
a Enter a value in the Value text box.
b Enter a label for the value in the Label text box.
cClick the Add icon ( ).
External Values Select a vRealize Orchestrator script action to define your value with information
not directly exposed by the workflow.
nSelect Add External Value.
nSelect your vRealize Orchestrator script action.
nClick Submit.
Configuring vRealize Automation
VMware, Inc. 354
14 Click Submit.
15 Click Finish.
Add a New Element
When you edit the default generated form of a XaaS blueprint, you can add a predefined new element to
the form. For example, if you do not want to use a default generated field, you can delete it and replace it
with a new one.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nCreate an XaaS Blueprint.
Procedure
1Select Design > XaaS > XaaS Blueprints.
2Click the XaaS blueprint you want to edit.
3Click the Blueprint Form tab.
4Drag an element from the New Fields pane and drop it to the Form page pane.
5Enter the ID of a workflow input parameter in the ID text box.
6Enter a label in the Label text box.
Labels appear to consumers on the forms.
7(Optional) Select a type for the field from the Type drop-down menu.
8Enter a vRealize Orchestrator object in the Entity type text box and press Enter.
This step is not required for all field types.
Option Description
Result Type If you are using a script action to define an external value for the field, enter the
result type of your vRealize Orchestrator script action.
Input Parameter If you are using the field to accept consumer input and pass parameters back to
vRealize Orchestrator, enter the type for the input parameter accepted by the
vRealize Orchestrator workflow.
Output Parameter If you are using the field to display information to consumers, enter the type for
the output parameter of the vRealize Orchestrator workflow.
9(Optional) Select the Multiple values check box to allow consumers to select more than one object.
This option is not available for all field types.
10 Click Submit.
11 Click Update.
Configuring vRealize Automation
VMware, Inc. 355
What to do next
You can edit the element to change the default settings and apply various constraints or values.
Insert a Section Header in a XaaS Blueprint Form
You can insert a section header to split the form into sections.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nCreate an XaaS Blueprint.
Procedure
1Select Design > XaaS > XaaS Blueprints.
2Click the XaaS blueprint you want to edit.
3Click the Blueprint Form tab.
4Drag the Section header element from the Form pane to the Form page pane.
5Type a name for the section.
6Click outside of the element to save the changes.
7Click Update.
Add a Text Element to an XaaS Blueprint Form
You can insert a text box to add some descriptive text to the form.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nCreate an XaaS Blueprint.
Procedure
1Select Design > XaaS > XaaS Blueprints.
2Click the XaaS blueprint you want to edit.
3Click the Blueprint Form tab.
4Drag the Text element from the New Fields pane to the Form page pane.
5Enter the text you want to add.
6Click outside of the element to save the changes.
7Click Update.
Configuring vRealize Automation
VMware, Inc. 356
Designing a Resource Action Form
When you create a resource action, you can edit the form of the action by adding new fields to the form,
modifying the existing fields, deleting, or rearranging fields. You can also create new forms and form
pages, and drag and drop new fields to them.
Add a New Resource Action Form
When you edit the default generated form of a workflow you want to publish as a resource action, you can
add a new resource action form.
By adding a new resource action form, you define how the submitted action details page looks. If you do
not add a submitted action details form, the consumer sees what is defined in the action form.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nCreate a Resource Action.
Procedure
1Select Design > XaaS > Resource Actions.
2Click the resource action you want to edit.
3Click the Form tab.
4Click the New Form icon ( ).
5Enter a name and, optionally, a description.
6Select the screen type from the Screen type menu.
Option Description
Action form The default resource action form that consumers see when they decide to run the
post-provisioning action.
Submitted action details A request details page that consumers see when they request the action and
decide to view the request details on the Request tab.
7Click Submit.
What to do next
Add the fields you want by dragging them from the New fields pane to the Form page pane.
Add a New Element to a Resource Action Form
When you edit the default generated form of a resource action, you can add a predefined new element to
the form. For example, if you do not want to use a default generated field, you can delete it and replace it
with a new one.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
Configuring vRealize Automation
VMware, Inc. 357
nCreate a Resource Action.
Procedure
1Select Design > XaaS > Resource Actions.
2Click the resource action you want to edit.
3Click the Form tab.
4Drag an element from the New Fields pane and drop it to the Form page pane.
5Enter the ID of a workflow input parameter in the ID text box.
6Enter a label in the Label text box.
Labels appear to consumers on the forms.
7(Optional) Select a type for the field from the Type drop-down menu.
8Enter a vRealize Orchestrator object in the Entity type text box and press Enter.
This step is not required for all field types.
Option Description
Result Type If you are using a script action to define an external value for the field, enter the
result type of your vRealize Orchestrator script action.
Input Parameter If you are using the field to accept consumer input and pass parameters back to
vRealize Orchestrator, enter the type for the input parameter accepted by the
vRealize Orchestrator workflow.
Output Parameter If you are using the field to display information to consumers, enter the type for
the output parameter of the vRealize Orchestrator workflow.
9(Optional) Select the Multiple values check box to allow consumers to select more than one object.
This option is not available for all field types.
10 Click Submit.
11 Click Finish.
What to do next
You can edit the element to change the default settings and apply various constraints or values.
Edit a Resource Action Element
You can edit some of the characteristics of an element on the resource action Form page. You can
change the type of an element, its default values, and apply various constraints and values.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nCreate a Resource Action.
Configuring vRealize Automation
VMware, Inc. 358
Procedure
1Select Design > XaaS > Resource Actions.
2Click the resource action you want to edit.
3Click the Form tab.
4Locate the element you want to edit.
5Click the Edit icon ( ).
6Enter a new name for the field in the Label text box to change the label that consumers see.
7Edit the description in the Description text box.
8Select an option from the Type drop-down menu to change the display type of the element.
The options vary depending on the type of element you edit.
9Select an option from the Size drop-down menu to change the size of the element.
10 Select an option from the Label size drop-down menu to change the size of the label.
11 Edit the default value of the element.
Option Description
Not set Gets the value of the element you are editing from the vRealize Orchestrator
workflow presentation.
Constant Sets the default value of the element you are editing to a constant value that you
specify.
Field Binds the default value of the element to a parameter of another element from the
representation.
Conditional Applies a condition. By using conditions you can create various clauses and
expressions and apply them to an element.
External Select a vRealize Orchestrator script action to define the value.
12 Apply constraints to the element on the Constraints tab.
Option Description
Not set Gets the value of the element you are editing from the vRealize Orchestrator
workflow presentation.
Constant Sets the default value of the element you are editing to a constant value that you
specify.
Field Binds the default value of the element to a parameter of another element from the
representation.
Conditional Applies a condition. By using conditions you can create various clauses and
expressions and apply them to an element.
External Select a vRealize Orchestrator script action to define the value.
Configuring vRealize Automation
VMware, Inc. 359
13 Add one or more values for the element on the Values tab.
The options available depend on the type of element you are editing.
Option Description
Not set Gets the value of the element you are editing from the vRealize Orchestrator
workflow presentation.
Predefined values Select values from a list of related objects from the vRealize Orchestrator
inventory.
a Enter a value in the Predefined values search box to search the
vRealize Orchestrator inventory.
b Select a value from the search results and press Enter.
Value Define custom values with labels.
a Enter a value in the Value text box.
b Enter a label for the value in the Label text box.
cClick the Add icon ( ).
External Values Select a vRealize Orchestrator script action to define your value with information
not directly exposed by the workflow.
nSelect Add External Value.
nSelect your vRealize Orchestrator script action.
nClick Submit.
14 Click Submit.
15 Click Update.
Insert a Section Header in a Resource Action Form
You can insert a section header to split the form into sections.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nCreate a Resource Action.
Procedure
1Select Design > XaaS > Resource Actions.
2Click the resource action you want to edit.
3Click the Form tab.
4Drag the Section header element from the Form pane to the Form page pane.
5Type a name for the section.
6Click outside of the element to save the changes.
7Click Finish.
Add a Text Element to a Resource Action Form
You can insert a text box to add some descriptive text to the form.
Configuring vRealize Automation
VMware, Inc. 360
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or XaaS architect.
nCreate a Resource Action.
Procedure
1Select Design > XaaS > Resource Actions.
2Click the resource action you want to edit.
3Click the Form tab.
4Drag the Text element from the New Fields pane to the Form page pane.
5Enter the text you want to add.
6Click outside of the element to save the changes.
7Click Finish.
XaaS Examples and Scenarios
The examples and scenarios suggest ways that you can use vRealize Automation to accomplish common
tasks using XaaS blueprints and resource actions.
Create an XaaS Blueprint and Action for Creating and Modifying a User
By using XaaS, you can create and publish a catalog item for provisioning a user in a group. You can also
associate a new post-provisioning operation to the provisioned user, for example, an operation allowing
the consumers to change the user password.
As an XaaS architect, you create a new custom resource, an XaaS blueprint, and publish a catalog item
for creating a user. You also create a resource action for changing the password of the user.
As a catalog administrator, you create a service and include the blueprint catalog item in the service. In
addition, you edit the workflow presentation of the catalog item by using the form designer and change
the way the consumers see the request form.
As a business group manager or a tenant administrator, you entitle the newly created service, catalog
item, and resource action to a consumer.
Prerequisites
Verify that the Active Directory plug-in is properly configured and you have the rights to create users in
Active Directory.
Procedure
1Create a Test User as a Custom Resource
You can create a custom resource and map it to the vRealize Orchestrator object type AD:User.
2Create an XaaS Blueprint for Creating a User
After you created the custom resource, you can create the XaaS blueprint to publish the Create a
user in a group workflow as a catalog item.
Configuring vRealize Automation
VMware, Inc. 361

3Publish the Create a User Blueprint as a Catalog Item
After you create the Create a test user XaaS blueprint, you can publish it as a catalog item.
4Create a Resource Action to Change a User Password
You can create a resource action to allow the consumers of the XaaS create a user blueprint to
change the password of the user after they provision the user.
5Publish the Change a Password Resource Action
To use the Change the password of the Test User resource action as a post-provisioning operation,
you must publish it.
6Create a Catalog Service for Creating a Test User
You can create a service to display the create a user catalog item in the service catalog and allow
consumers to easily locate the catalog item related to creating the test user.
7Associate the Catalog Item with the Create a Test User Service
To include the Create a test user catalog item in the Create a Test User service, you must associate
it with this service.
8Entitle the Service and the Resource Action to a Consumer
Business group managers and tenant administrators can entitle the service and the resource action
to a user or a group of users so that they can see the service in their catalog and request the Create
a test user catalog item included in the service. After the consumers provision the item, they can
request to change the user password.
Create a Test User as a Custom Resource
You can create a custom resource and map it to the vRealize Orchestrator object type AD:User.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Select Design > XaaS > Custom Resources.
2Click the New icon ( ).
3In the Orchestrator Type text box, enter AD:User and press Enter.
4Select AD:User in the list.
5Type a name for the resource.
For example, Test User.
6Type a description for the resource.
For example,
This is a test custom resource that I will use for my catalog item to create a
user in a group.
Configuring vRealize Automation
VMware, Inc. 362

7Click Next.
8Leave the form as is.
9Click Finish.
You created a Test User custom resource and you can see it on the Custom Resources page.
What to do next
Create an XaaS blueprint.
Create an XaaS Blueprint for Creating a User
After you created the custom resource, you can create the XaaS blueprint to publish the Create a user in
a group workflow as a catalog item.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Select Design > XaaS > XaaS Blueprints.
2Click Add ( ).
3Navigate to Orchestrator > Library > Microsoft > Active Directory > User in the
vRealize Orchestrator workflow library, and select the Create a user in a group workflow.
4Click Next.
5Change the name of the blueprint to Create a test user, and leave the description as is.
6Click Next.
7Edit the blueprint form.
a Click The domain name in Win2000 form.
b Click the Constraints tab.
c Click the Value drop-down arrow, select Constant in the drop-down menu, and enter
test.domain.
You set the domain name to a constant value.
d Click the Visible drop-down arrow, select Constant in drop-down menu, and select No in the
drop-down menu.
You made the domain name invisible to the consumer of the catalog item.
e Click Apply to save the changes.
8Click Next.
9Select newUser [Test User] as an output parameter to be provisioned.
10 Click Finish.
Configuring vRealize Automation
VMware, Inc. 363

You created a blueprint for creating a test user and you can see it on the XaaS blueprints page.
What to do next
Publish the Create a test user blueprint to make it an active catalog item.
Publish the Create a User Blueprint as a Catalog Item
After you create the Create a test user XaaS blueprint, you can publish it as a catalog item.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Select Design > XaaS > XaaS Blueprints.
2Select the row of the Create a test user blueprint, and click the Publish button.
The status of the Create a test user blueprint changes to Published. You can navigate to Administration
> Catalog Management > Catalog Items and see that the Create a test user blueprint is published as a
catalog item.
Create a Resource Action to Change a User Password
You can create a resource action to allow the consumers of the XaaS create a user blueprint to change
the password of the user after they provision the user.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Select Design > XaaS > Resource Actions.
2Click Add ( ).
3Navigate to Orchestrator > Library > Microsoft > Active Directory > User in the
vRealize Orchestrator workflow library, and select the Change a user password workflow.
4Click Next.
5Select Test User from the Resource type drop-down menu.
This is the custom resource you created previously.
6Select user from the Input parameter drop-down menu.
7Click Next.
8Change the name of the resource action to Change the password of the Test User, and leave
the description as it appears on the Details tab.
9Click Next.
Configuring vRealize Automation
VMware, Inc. 364

10 (Optional) Leave the form as is.
11 Click Add.
You created a resource action for changing the password of a user and you can see it listed on the
Resource Actions page.
What to do next
Publish the Change the password of the Test User resource action.
Publish the Change a Password Resource Action
To use the Change the password of the Test User resource action as a post-provisioning operation, you
must publish it.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Select Design > XaaS > Resource Actions.
2Select the row of the Change the password of the Test User action, and click the Publish button.
The status of the Change the password of the Test User resource action changes to Published.
What to do next
Assign an icon to the resource action. You can then use the action when you create an entitlement. For
more information about assigning an icon to a resource action, see Assign an Icon to a Resource Action.
Create a Catalog Service for Creating a Test User
You can create a service to display the create a user catalog item in the service catalog and allow
consumers to easily locate the catalog item related to creating the test user.
Prerequisites
Log in to the vRealize Automation console as a tenant administrator or catalog administrator.
Procedure
1Select Administration > Catalog Management > Services.
2Click the New icon ( ).
3Enter Create a Test User as the name of the service.
4Select Active from the Status drop-down menu.
5Leave the other text boxes blank.
6Click OK.
You created the service called Create a Test User, and you can see it on the Services page.
Configuring vRealize Automation
VMware, Inc. 365

What to do next
Edit the Create a test user catalog item to include it in the service.
Associate the Catalog Item with the Create a Test User Service
To include the Create a test user catalog item in the Create a Test User service, you must associate it with
this service.
Prerequisites
Log in to the vRealize Automation console as a tenant administrator or catalog administrator.
Procedure
1Select Administration > Catalog Management > Catalog Items.
2Locate the Create a test user catalog item, and click the catalog item name.
3(Optional) Click Choose File to change the icon of the catalog item.
4Select the Create a Test User service from the Service drop-down menu.
5Click Finish.
You associated the Create a test user catalog item with the Create a Test User service.
What to do next
Business group managers and tenant administrators can entitle the service and the resource action to a
user or a group of users.
Entitle the Service and the Resource Action to a Consumer
Business group managers and tenant administrators can entitle the service and the resource action to a
user or a group of users so that they can see the service in their catalog and request the Create a test
user catalog item included in the service. After the consumers provision the item, they can request to
change the user password.
Prerequisites
Log in to the vRealize Automation console as a tenant administrator or business group manager.
Procedure
1Select Administration > Catalog Management > Entitlements.
2Click the New icon ( ).
3Enter Create a user in the Name text box.
4Leave the Description and Expiration Date text boxes empty.
5Select Active from the Status drop-down menu.
6Select the target business group from the Business Group drop-down menu.
Configuring vRealize Automation
VMware, Inc. 366

7Enter a user name in the Users & Groups text box and press Enter.
The person you select can see the service and the catalog items included in the service in the
catalog.
8Click Next.
9Enter Create a Test User in the Entitled Services text box and press Enter.
10 Enter Change the password of the Test User in the Entitled Actions text box and press Enter.
11 Click Add.
You created an active entitlement and exposed the service to the catalog of the consumers.
When consumers of the service log in to their vRealize Automation consoles, they see the service you
created, Create a test user, on the Catalog tab. They can request the catalog item you created and
included in the service, Create a user in a group. After they create the user, they can change the user
password.
Create and Publish an XaaS Action to Migrate a Virtual Machine
You can create and publish an XaaS resource action to extend the operations that consumers can
perform on IaaS-provisioned vSphere virtual machines.
In this scenario, you create a resource action for quick migration of a vSphere virtual machine.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Create a Resource Action to Migrate a vSphere Virtual Machine
You create a custom resource action to allow the consumers to migrate vSphere virtual machines
after they provision the vSphere virtual machines with IaaS.
2Publish the Action for Migrating a vSphere Virtual Machine
To use the Quick migration of virtual machine resource action as a post-provisioning operation, you
must publish it.
Create a Resource Action to Migrate a vSphere Virtual Machine
You create a custom resource action to allow the consumers to migrate vSphere virtual machines after
they provision the vSphere virtual machines with IaaS.
Procedure
1Select Design > XaaS > Resource Actions.
2Click Add ( ).
3Navigate to Orchestrator > Library > vCenter > Virtual Machine management > Move and
migrate in the vRealize Orchestrator workflow library and select the Quick migration of virtual
machine workflow.
Configuring vRealize Automation
VMware, Inc. 367
4Click Next.
5Select IaaS VC VirtualMachine from the Resource type drop-down menu.
6Select vm from the Input parameter drop-down menu.
7Click Next.
8Leave the name of the resource action and the description as they appear on the Details tab.
9Click Next.
10 Leave the form as is.
11 Click Finish.
You created a resource action for migrating a virtual machine and you can see it listed on the Resource
Actions page.
What to do next
Publish the Action for Migrating a vSphere Virtual Machine
Publish the Action for Migrating a vSphere Virtual Machine
To use the Quick migration of virtual machine resource action as a post-provisioning operation, you must
publish it.
Procedure
1Select Design > XaaS > Resource Actions.
2Select the row of the Quick migration of virtual machine resource action, and click the Publish button.
You created and published a vRealize Orchestrator workflow as a resource action. You can navigate to
Administration > Catalog Management > Actions and see the Quick migration of virtual machine
resource action in the list of actions. You can assign an icon to the resource action. See Assign an Icon to
a Resource Action.
What to do next
Add the action to the entitlements that contain the IaaS-provisioned vSphere virtual machines. See Entitle
Users to Services, Catalog Items, and Actions.
Create an XaaS Action to Migrate a Virtual Machine With vMotion
By using XaaS, you can create and publish a resource action to migrate an IaaS-provisioned virtual
machine with vMotion.
In this scenario, you create a resource action to migrate a vSphere virtual machine with vMotion. In
addition, you edit the workflow presentation by using the form designer and change the way the
consumers see the action when they request it.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Configuring vRealize Automation
VMware, Inc. 368

Procedure
1Create an Action to Migrate a vSphere Virtual Machine With vMotion
You can create a custom resource action to allow the service catalog users to migrate a vSphere
virtual machine with vMotion after they provision the machine with IaaS.
2Edit the Resource Action Form
The resource action form maps the vRealize Orchestrator workflow presentation. You can edit the
form and define what the consumers of the resource action see when they decide to run the post-
provisioning operation.
3Add a Submitted Action Details Form and Save the Action
You can add a new form to the Migrate a virtual machine with vMotion resource action to define what
the consumers see after they request to run the post-provisioning operation.
4Publish the Action for Migrating a Virtual Machine with vMotion
To use the Migrate a virtual machine with vMotion resource action as a post-provisioning operation,
you must publish it.
Create an Action to Migrate a vSphere Virtual Machine With vMotion
You can create a custom resource action to allow the service catalog users to migrate a vSphere virtual
machine with vMotion after they provision the machine with IaaS.
Procedure
1Select Design > XaaS > Resource Actions.
2Click Add ( ).
3Navigate to Orchestrator > Library > vCenter > Virtual Machine management > Move and
migrate in the vRealize Orchestrator workflow library and select the Migrate virtual machine with
vMotion workflow.
4Click Next.
5Select IaaS VC VirtualMachine from the Resource type drop-down menu.
6Select vm from the Input parameter drop-down menu.
7Click Next.
8Leave the name of the resource action and the description as they appear on the Details tab.
9Click Next.
What to do next
Edit the Resource Action Form.
Edit the Resource Action Form
The resource action form maps the vRealize Orchestrator workflow presentation. You can edit the form
and define what the consumers of the resource action see when they decide to run the post-provisioning
operation.
Configuring vRealize Automation
VMware, Inc. 369

Procedure
1Click the Delete icon ( ) to delete the pool element.
2Edit the host element.
aClick the Edit icon ( ) next to the host field.
b Type Target host in the Label text box.
c Select Search from the Type drop-down menu.
d Click the Constraints tab.
e Select Constant from the Required drop-down menu and select Yes.
You made the host field always required.
f Click Submit.
3Edit the priority element.
aClick the Edit icon ( ) next to the priority field.
b Type Priority of the task in the Label text box.
c Select Radio button group from the Type drop-down menu.
d Click the Values tab, and deselect the Not set check box.
e Enter lowPriority in the Predefined values search text box, and press Enter.
f Enter defaultPriority in the Predefined values search text box, and press Enter.
g Enter highPriority in the Predefined values search text box, and press Enter.
h Click Submit.
When the consumers request the resource action, they see a radio button group with three radio
buttons: lowPriority, defaultPriority, and highPriority.
4Edit the state element.
aClick the Edit icon ( ) next to the state field.
b Type Virtual machine state in the Label text box.
c Select Drop-down from the Type drop-down menu.
d Click the Values tab, and deselect the Not set check box.
e Enter poweredOff in the Predefined values search text box, and press Enter.
f Enter poweredOn in the Predefined values search text box, and press Enter.
g Enter suspended in the Predefined values search text box, and press Enter.
h Click Submit.
Configuring vRealize Automation
VMware, Inc. 370

When the consumers request the resource action, they see a drop-down menu with three options:
poweredOff, poweredOn, and suspended.
You edited workflow presentation of the Migrate a virtual machine with vMotion workflow.
What to do next
Add a Submitted Action Details Form and Save the Action.
Add a Submitted Action Details Form and Save the Action
You can add a new form to the Migrate a virtual machine with vMotion resource action to define what the
consumers see after they request to run the post-provisioning operation.
Procedure
1Click the New Form icon ( ) next to the Form drop-down menu.
2Type Submitted action in the Name text box.
3Leave the Description field blank.
4Select Submitted action details from the Screen type menu.
5Click Submit.
6Click the Edit icon ( ) next to the Form page drop-down menu.
7Type Details in the Heading text box.
8Click Submit.
9Drag the Text element from the Form pane and drop it to the Form page.
10 Type
You submitted a request to migrate your machine with vMotion. Wait until the
process completes successfully.
11 Click outside of the text box to save the changes.
12 Click Submit.
13 Click Add.
You created a resource action to migrate a virtual machine with vMotion and you can see it listed on the
Resource Actions page.
What to do next
Publish the Action for Migrating a Virtual Machine with vMotion.
Publish the Action for Migrating a Virtual Machine with vMotion
To use the Migrate a virtual machine with vMotion resource action as a post-provisioning operation, you
must publish it.
Configuring vRealize Automation
VMware, Inc. 371

Procedure
1Select Design > XaaS > Resource Actions.
2Select the row of the Migrate a virtual machine with vMotion action, and lick the Publish button.
You created and published a vRealize Orchestrator workflow as a resource action. You can navigate to
Administration > Catalog Management > Actions and see the Migrate virtual machine with vMotion
resource action in the list of actions. You can assign an icon to the resource action. See Assign an Icon to
a Resource Action.
You also edited the presentation of the workflow and defined the look and feel of the action.
What to do next
Business group managers and tenant administrators can include the Migrate a virtual machine with
vMotion resource action in an entitlement. For more information about how to create and publish IaaS
blueprints for virtual platforms, see Designing Machine Blueprints.
Create and Publish an XaaS Action to Take a Snapshot
By using XaaS, you can create and publish a resource action to take a snapshot of a vSphere virtual
machine that was provisioned with IaaS.
In this scenario, you create a resource action to take a snapshot of a vSphere virtual machine provisioned
withIaaS. In addition, you edit the workflow presentation by using the form designer and change the way
the consumers see the action when they request it.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Create the Action to Take a Snapshot of a vSphere Virtual Machine
You can create a custom resource action to allow the consumers to take a snapshot of a vSphere
virtual machine after they provision the machine with IaaS.
2Publish the Action for Taking a Snapshot
To use the Create a snapshot resource action as a post-provisioning operation, you must publish it.
Create the Action to Take a Snapshot of a vSphere Virtual Machine
You can create a custom resource action to allow the consumers to take a snapshot of a vSphere virtual
machine after they provision the machine with IaaS.
Procedure
1Select Design > XaaS > Resource Actions.
2Click Add ( ).
3Navigate to Orchestrator > Library > vCenter > Virtual Machine management > Snapshot in the
vRealize Orchestrator workflow library and select the Create a snapshot workflow.
Configuring vRealize Automation
VMware, Inc. 372
4Click Next.
5Select IaaS VC VirtualMachine from the Resource type drop-down menu.
6Select vm from the Input parameter drop-down menu.
7Click Next.
8Leave the name of the resource action and the description as they appear on the Details tab.
9Click Next.
10 Leave the form as is.
11 Click Add.
You created a resource action for taking a snapshot of a virtual machine and you can see it listed on the
Resource Actions page.
What to do next
Publish the Action for Taking a Snapshot.
Publish the Action for Taking a Snapshot
To use the Create a snapshot resource action as a post-provisioning operation, you must publish it.
Procedure
1Select Design > XaaS > Resource Actions.
2Select the row of the Create a snapshot action, and click the Publish button.
You created and published a vRealize Orchestrator workflow as a resource action. You can navigate to
Administration > Catalog Management > Actions and see the Create a snapshot resource action in
the list of actions. You can assign an icon to the resource action. See Assign an Icon to a Resource
Action.
What to do next
Business group managers and tenant administrators can include the Create a snapshot resource action
in an entitlement. For more information about how to create and publish IaaS blueprints for virtual
platforms, see Designing Machine Blueprints.
Create and Publish an XaaS Action to Start an Amazon Virtual Machine
By using XaaS, you can create and publish actions to extend the operations that the consumers can
perform on third-party provisioned resources.
In this scenario, you create and publish a resource action for quick starting of Amazon virtual machines.
Prerequisites
nInstall the vRealize Orchestrator plug-in for Amazon Web Services on your default
vRealize Orchestrator server.
nCreate or import a vRealize Orchestrator workflow for resource mapping of Amazon instances.
Configuring vRealize Automation
VMware, Inc. 373

Procedure
1Create a Resource Mapping for Amazon Instances
You can create a resource mapping to associate Amazon instances provisioned by using IaaS with
the vRealize Orchestrator type AWS:EC2Instance exposed by the Amazon Web Services plug-in.
2Create a Resource Action to Start an Amazon Virtual Machine
You can create a resource action so that the consumers can start provisioned Amazon virtual
machines.
3Publish the Action for Starting Amazon Instances
To use the newly created Start Instances resource action for post-provisioning operations on
Amazon virtual machines, you must publish it.
Create a Resource Mapping for Amazon Instances
You can create a resource mapping to associate Amazon instances provisioned by using IaaS with the
vRealize Orchestrator type AWS:EC2Instance exposed by the Amazon Web Services plug-in.
Prerequisites
nLog in to the vRealize Automation console as an XaaS architect.
nCreate or import a vRealize Orchestrator resource mapping workflow or script action.
Procedure
1Select Design > XaaS > Resource Mappings.
2Click Add ( ).
3Enter EC2 Instance in the Name text box.
4Enter Cloud Machine in the Catalog Resource Type text box.
5Enter AWS:EC2Instance in the Orchestrator Type text box.
6Select Always available.
7Select the type of resource mapping to use.
8Select your custom resource mapping script action or workflow from the vRealize Orchestrator library.
9Click Add.
You can use your Amazon resource mapping to create resource actions for Amazon machines
provisioned by using IaaS.
What to do next
Create a Resource Action to Start an Amazon Virtual Machine.
Create a Resource Action to Start an Amazon Virtual Machine
You can create a resource action so that the consumers can start provisioned Amazon virtual machines.
Configuring vRealize Automation
VMware, Inc. 374

Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Select Design > XaaS > Resource Actions.
2Click Add ( ).
3Select Orchestrator > Library > Amazon Web Services > Elastic Cloud > Instances and select
the Start Instances workflow in the workflows folder.
4Click Next.
5Select EC2 Instance from the Resource type drop-down menu.
This is the name of the resource mapping you previously created.
6Select instance from the Input parameter drop-down menu.
This is the input parameter of the resource action workflow to match the resource mapping.
7Click Next.
8Leave the name and the description as they are.
The default name of the resource action is Start Instances.
9Click Next.
10 Leave the fields as they are on the Form tab.
11 Click Add.
You created a resource action for starting Amazon virtual machines and you can see it on the Resource
Actions page.
What to do next
Publish the Action for Starting Amazon Instances.
Publish the Action for Starting Amazon Instances
To use the newly created Start Instances resource action for post-provisioning operations on Amazon
virtual machines, you must publish it.
Prerequisites
Log in to the vRealize Automation console as an XaaS architect.
Procedure
1Select Design > XaaS > Resource Actions.
2Select the row of the Start Instances resource action, and click Publish.
The status of the Start Instances resource action changes to Published.
Configuring vRealize Automation
VMware, Inc. 375

What to do next
Add the start instances action to the entitlement that includes the Amazon catalog item. See Entitle Users
to Services, Catalog Items, and Actions.
Troubleshooting Incorrect Accents and Special Characters in XaaS Blueprints
When you create XaaS blueprints for languages that use non-ASCII strings, the accents and special
characters are displayed as unusable strings.
Cause
A vRealize Orchestrator configuration property that is not set by default, might be enabled.
Solution
1On the Orchestrator server system, navigate to /etc/vco/app-server/.
2Open the vmo.properties configuration file in a text editor.
3Verify that the following property is disabled.
com.vmware.o11n.webview.htmlescaping.disabled
4Save the vmo.properties file.
5Restart the vRealize Orchestrator serv er.
Publishing a Blueprint
Blueprints are saved in the draft state and must be manually published before you can configure them as
catalog items or use them as blueprint components in the design canvas.
After you publish the blueprint, you can entitle it to make it available for provisioning requests in the
service catalog.
You need to publish a blueprint only once. Any changes you make to a published blueprint are
automatically reflected in the catalog.
Publish a Blueprint
You can publish a blueprint for use in machine provisioning and optionally for reuse in another blueprint.
To use the blueprint for requesting machine provisioning, you must entitle the blueprint after publishing it.
Blueprints that are consumed as components in other blueprints do not required entitlement.
Prerequisites
nLog in to the vRealize Automation console as an infrastructure architect.
nCreate a blueprint. See Checklist for Creating vRealize Automation Blueprints.
Procedure
1Click the Design tab.
Configuring vRealize Automation
VMware, Inc. 376
2Click Blueprints.
3Point to the blueprint to publish and click Publish.
4Click OK.
The blueprint is published as a catalog item but you must first entitle it to make it available to users in the
service catalog.
What to do next
Add the blueprint to the catalog service and entitle users to request the catalog item for machine
provisioning as defined in the blueprint.
Assembling Application Blueprints
You can combine a machine blueprint with Software components, XaaS blueprints, or additional machine
blueprints to create more elaborate application blueprints.
nUnderstanding Nested Blueprint Behavior
Nested blueprints allow you to have reuse and modularity control in machine provisioning, but they
do require your understanding of specific rules and considerations. A nested blueprint is a blueprint
that you add to another blueprint and use as a component in that other blueprint.
nSelecting a Machine Blueprint that Supports Software Components
You can assemble an application blueprint that contains Software components, as long as at least
one machine component or machine blueprint that supports Software is included.
nBinding Properties to Other Properties in a Blueprint
You can bind properties of XaaS, machines, Software, and custom properties to other properties in
an application blueprint.
nControlling the Build Order of Blueprint Components
If you have dependencies in your application blueprint, you can configure the blueprint to stagger the
build process by mapping those dependencies directly on the canvas. For example, if you need
properties from your database node to install software on your webserver node, you can configure
your blueprint to provision the database node first.
nScenario: Assemble and Test a Blueprint to Deliver MySQL on Rainpole Linked Clone Machines
Using your application architect, software architect, or IaaS architect privileges, create a blueprint to
combine your MySQL component with the vSphere CentOS linked clone blueprint you created.
Understanding Nested Blueprint Behavior
Nested blueprints allow you to have reuse and modularity control in machine provisioning, but they do
require your understanding of specific rules and considerations. A nested blueprint is a blueprint that you
add to another blueprint and use as a component in that other blueprint.
Configuring vRealize Automation
VMware, Inc. 377
Blueprints can consume other blueprints as components. A blueprint that contains one or more nested
blueprints is referred to as an outer blueprint. Stated another way, when you add a blueprint as a
component to the design canvas while creating or editing another blueprint, the blueprint component is
referred to as a nested blueprint and the container blueprint to which it is added is referred to as the outer
blueprint.
The settings defined in the outer blueprint take precedence over settings in the nested blueprint. Saved
changes to the nested blueprint are reflected in the outer blueprint, except for specified settings in the
outer blueprint that take precedence over settings in the nested blueprint.
Provisioned deployments reflect the current state of the blueprint at the time of provisioning. At the time of
provisioning, the resulting deployment reads current values from the blueprint, including from its nested
blueprints. Once a deployment is created, it is detached from any changes that are subsequently made to
the blueprint from which it was provisioned.
Using nested blueprints presents considerations that are not always obvious. It is important to understand
the following nested blueprint rules and considerations to make the best use of your machine provisioning
capabilities:
nAll networking and security components in outer blueprints can be associated with machines that are
defined in nested blueprints.
nWhen app isolation is applied in the outer blueprint, it overrides app isolation settings specified in
nested blueprints.
nTransport zone settings that are defined in the outer blueprint override transport zone settings that are
specified in nested blueprints.
nAs a best practice to minimize blueprint complexity, limit blueprints to three levels deep, with the top-
level blueprint serving as one of the three levels.
nFor a nested blueprint that contains an on-demand NAT network component, the IP ranges specified
in that on-demand NAT network component are not editable in the outer blueprint.
nThe outer blueprint cannot contain an inner blueprint that contains on-demand network settings or on-
demand load balancer settings. Using an inner blueprint that contains an NSX on-demand network
component or NSX load balancer component is not supported.
nFor a nested blueprint that contains NSX network or security components, you cannot change the
network profile or security policy information specified in the nested blueprint. You can, however,
reuse those settings for other vSphere machine components that you add to the outer blueprint.
nIf a user is entitled to the top-most blueprint, that user is entitled to all aspects of the blueprint,
including nested blueprints.
nYou can apply an approval policy to a blueprint. When approved, the blueprint catalog item and all its
components, including nested blueprints, are provisioned. You can also apply different approval
policies to different components. All the approval policies must be approved before the requested
blueprint is provisioned.
Configuring vRealize Automation
VMware, Inc. 378
nTo ensure that NSX network and security components in nested blueprints are uniquely named in a
composite blueprint, vRealize Automation prefixes the nested blueprint ID to network and security
component names that are not already unique. For example, if you add a blueprint with the ID name
xbp_1 to an outer blueprint and both blueprints contain an on-demand security group component
named OD_Security_Group_1, the component in the nested blueprint is renamed
xbp_1_OD_Security_Group_1 in the blueprint design canvas. Network and security component
names in the outer blueprint are not prefixed.
nYou can change the name of a nested blueprint but you cannot change the name of a machine
component, or any other component, inside a nested blueprint while you are working in the outer
blueprint.
nWhen working in an outer blueprint, you can configure load balancer settings relative to network
component settings and machine component settings that are configured in an inner or nested
blueprint.
nWhen working in an outer blueprint, you can override the Machine Resources settings that are
configured for a machine component in a nested blueprint.
nWhen working in an outer blueprint, you cannot add or delete custom properties for a machine
component in a nested blueprint. However, you can edit those custom properties. You cannot add,
edit or delete property groups for a machine component in a nested blueprint.
nWhen working in an outer blueprint, you can drag and drop a software component onto a machine
component within a nested blueprint.
Selecting a Machine Blueprint that Supports Software
Components
You can assemble an application blueprint that contains Software components, as long as at least one
machine component or machine blueprint that supports Software is included.
While IaaS architects, application architects, and software architects can assemble application blueprints,
only IaaS architects can configure machine components. If you are not an IaaS architect, you cannot
configure your own machine components, but you can reuse machine blueprints that your IaaS architect
created and published. To support Software components, the machine blueprint you select must contain a
machine component based on a template, snapshot, or Amazon machine image that contains the guest
agent and the Software bootstrap agent, and it must use a supported provisioning method. Because the
agents do not support Internet Protocol version 6 (IPv6), ensure that machine blueprints, reservations,
and networking and security components you are using are configured to use IPv4 and not IPv6.
Table 4‑43. Provisioning Methods that Support Software
Machine Type Provisioning Method
vSphere Clone
vSphere Linked Clone
vCloud Director Clone
Configuring vRealize Automation
VMware, Inc. 379
Table 4‑43. Provisioning Methods that Support Software (Continued)
Machine Type Provisioning Method
vCloud Air Clone
Amazon AWS Amazon Machine Image
Binding Properties to Other Properties in a Blueprint
You can bind properties of XaaS, machines, Software, and custom properties to other properties in an
application blueprint.
For example, your software architect might modify property definitions in the life cycle scripts of a WAR
component. A WAR component might need the installation location of the Apache Tomcat server
component, so your software architect configures the WAR component to set the server_home property
value to the Apache Tomcat server install_path property value. As the architect assembling the blueprint,
you have to bind the server_home property to the Apache Tomcat server install_path property for the
Software component to provision successfully.
You set property bindings when you configure components in an application blueprint. On the Blueprint
page, you drag your component onto the canvas and click the Properties tab. To bind a property to
another property in a blueprint, select the Bind checkbox. You can enter
ComponentName~PropertyName in the value text box, or you can use the down arrow to generate a list
of available binding options. You use a tilde character ~ as a delimiter between components and
properties. For example, to bind to the property dp_port, on your MySQL software component, you could
type mysql~db_port.
To bind to properties that are configured during provisioning, such as the IP address of a machine or the
host name of a Software component, you enter _resource~ComponentName~PropertyName. For
example, to bind to the reservation name of a machine, you might enter
_resource~vSphere_Machine_1~MachineReservationName.
See the Examples of String Property Bindings table for examples of a string property value when binding
to different types of properties.
Table 4‑44. Examples of String Property Bindings
Sample Property Type Property Type to Bind Binding Outcome (A binds to B)
String (property A) String (property B="Hi") A="Hi"
String (property A) Content (property
B="http://my.com/content")
A="http://my.com/content"
String (property A) Array (property B=["1","2"]) A="["1","2"]"
String (property A) Computed (property B="Hello") A="Hello"
See the Examples of Array Property Bindings table for examples of an array property value when binding
to different types of properties.
Configuring vRealize Automation
VMware, Inc. 380
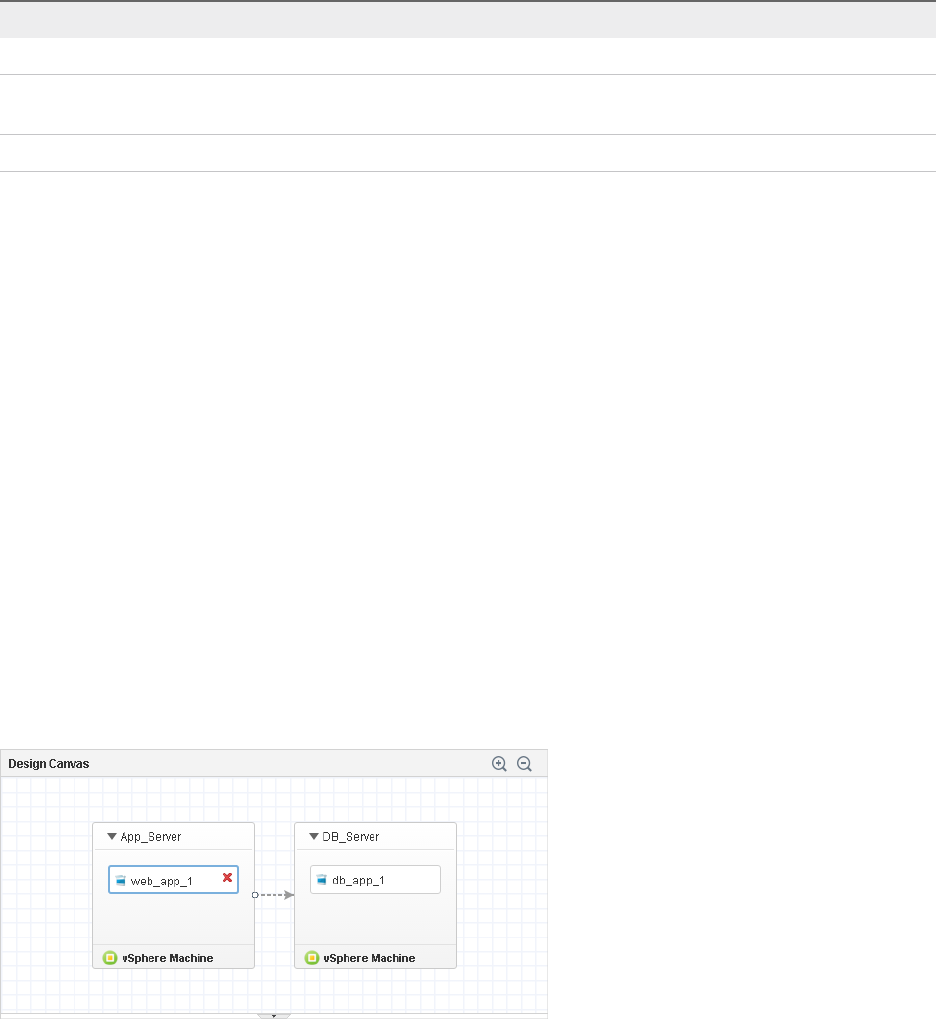
Table 4‑45. Examples of Array Property Bindings
Sample Property Type Property Type to Bind Binding Outcome (A binds to B)
Array (property A) String (property B="Hi") A="Hi"
Array (property A) Content (property
B="http://my.com/content")
A="http://my.com/content"
Array (property A) Computed (property B="Hello") A="Hello"
Controlling the Build Order of Blueprint Components
If you have dependencies in your application blueprint, you can configure the blueprint to stagger the
build process by mapping those dependencies directly on the canvas. For example, if you need
properties from your database node to install software on your webserver node, you can configure your
blueprint to provision the database node first.
When you design blueprints with multiple machines, on which you install and configure applications, you
might have properties you need from one machine to complete an installation on another. For example if
you are building a Web server you might need the IP address or host name of the Database Server
before you can install the application and instantiate the database tables.
To map a dependency on your blueprint canvas, you draw a line from the dependent component to the
component you are depending on. When you are finished, the component you want to build second has
an arrow pointing to the component you want to build first. For example, in the Mapping Dependencies to
Control Build Order figure, the App_Server machine is not provisioned until the DB_Server machine is
built. Alternatively, you could allow both machines to provision and draw the dependency between the
software components instead.
Figure 4‑3. Mapping Dependencies to Control Build Order
Scenario: Assemble and Test a Blueprint to Deliver MySQL on
Rainpole Linked Clone Machines
Using your application architect, software architect, or IaaS architect privileges, create a blueprint to
combine your MySQL component with the vSphere CentOS linked clone blueprint you created.
Configuring vRealize Automation
VMware, Inc. 381

You are here
Configure
Tenant
Configure IaaS
Resources
Design On-
Demand Services
Prerequisites
nCreate a Software component to install MySQL on Linux machines. See Scenario: Create a MySQL
Software Component for Rainpole.
nLog in to the vRealize Automation console as a member of the Rainpole architects custom group.
See Scenario: Create a Custom Group for Your Rainpole Architects.
Procedure
1Scenario: Create a Container for Your MySQL on CentOS Rainpole Blueprint
Using your IaaS, software, or application architect privileges, create a blueprint container and
configure the name, description, and unique identifier for your MySQL on CentOS vSphere blueprint.
2Scenario: Add Software and a Machine to the MySQL on CentOS Blueprint for Rainpole
Using your IaaS, software, or application architect privileges, drag the published CentOS for
Software Testing machine blueprint onto your canvas to reuse that blueprint as your machine. You
drag your published software component onto the virtual machine and configure the Software
properties you specified in the Software component.
3Scenario: Add Your CentOS with MySQL Catalog Item to the Rainpole Service
Using your tenant administrator privileges, add your new blueprint to the Rainpole catalog service so
you can verify your work.
4Scenario: Provision the CentOS with MySQL Catalog Item for Rainpole
Using the test user account, request the service catalog item to provision a CentOS machine with
MySQL.
Scenario: Create a Container for Your MySQL on CentOS Rainpole Blueprint
Using your IaaS, software, or application architect privileges, create a blueprint container and configure
the name, description, and unique identifier for your MySQL on CentOS vSphere blueprint.
Procedure
1Select Design > Blueprints.
2Click the New icon ( ).
3Enter MySQL on CentOS in the Name text box.
Configuring vRealize Automation
VMware, Inc. 382
4Review the generated unique identifier.
The identifier field automatically populates based on the name you entered. You can edit this field
now, but after you save the blueprint you can never change it. Because identifiers are permanent and
unique within your tenant, you can use them to programmatically interact with blueprints and to create
property bindings.
5Enter MySQL Software on vSphere CentOS Machine in the Description text box.
6Configure a lease range for users to choose from by entering 1 in the Minimum text box and 7 in the
Maximum text box.
Users can choose to lease their requested machines for up to 7 days before having to renew their
leases or letting their machines be destroyed.
7Click OK.
What to do next
Drag your MySQL component and your published CentOS for Software machine blueprint onto the
canvas.
Scenario: Add Software and a Machine to the MySQL on CentOS Blueprint for
Rainpole
Using your IaaS, software, or application architect privileges, drag the published CentOS for Software
Testing machine blueprint onto your canvas to reuse that blueprint as your machine. You drag your
published software component onto the virtual machine and configure the Software properties you
specified in the Software component.
Procedure
1Click Blueprints in the Categories list.
2Drag CentOS for Software Testing onto the canvas.
3Click Software Components in the Categories list.
4Drag MySQL for Linux Virtual Machines to the vSphere machine.
5Click the Properties tab.
6Update the db_port property for this blueprint.
a Select the db_port property and click Edit.
b Enter 3308 in the Value text box.
When a service catalog user requests the item, 3308 is the default value.
c Click OK.
7Click Finish.
8Select the row that contains CentOS with MySQL and click Publish.
Configuring vRealize Automation
VMware, Inc. 383

You published a blueprint that includes the CentOS machine and MySQL software component.
Scenario: Add Your CentOS with MySQL Catalog Item to the Rainpole Service
Using your tenant administrator privileges, add your new blueprint to the Rainpole catalog service so you
can verify your work.
Procedure
1Select Administration > Catalog Management > Services.
2Select the Rainpole catalog service row in the Services list and click Manage Catalog Items.
3Click the New icon ( ).
4Select CentOS with MySQL.
Only published blueprints and components that are not yet associated with a service appear in the
list. If you do not see the blueprint, verify that it was published or that it is not included in another
service.
5Click OK.
6Click Close.
Your CentOS with MySQL catalog item is ready for you to request. You do not have to entitle the new
catalog item because you entitled your Rainpole business group to the entire Rainpole service.
What to do next
Request the CentOS with MySQL catalog item to verify your work.
Scenario: Provision the CentOS with MySQL Catalog Item for Rainpole
Using the test user account, request the service catalog item to provision a CentOS machine with
MySQL.
Procedure
1Log out of the vRealize Automation console.
2Log back in with the username test_user and password VMware1!.
3Click the Catalog tab.
4Click the Request button to request a catalog item.
5Enter verifying functionality in the Description text box.
6Click Submit to request the catalog item.
7Click the Requests tab to monitor the status of your request.
When the machine is successfully provisioned, the status message Successful appears.
Configuring vRealize Automation
VMware, Inc. 384
What to do next
nPlan for installing a production environment. See Reference Architecture.
nLearn about more options for configuring vRealize Automation, designing and exporting blueprints,
and governing your service catalog. See Configuring vRealize Automation.
Managing the Service Catalog
The service catalog is where your customers request machines and other items to provision for their use.
You manage user access to the service catalog items based on how you build services, entitle users to
one or more items, and apply governance.
The workflow that you follow to add items to the service catalog varies based on whether you create and
apply approval policies.
Configuring vRealize Automation
VMware, Inc. 385
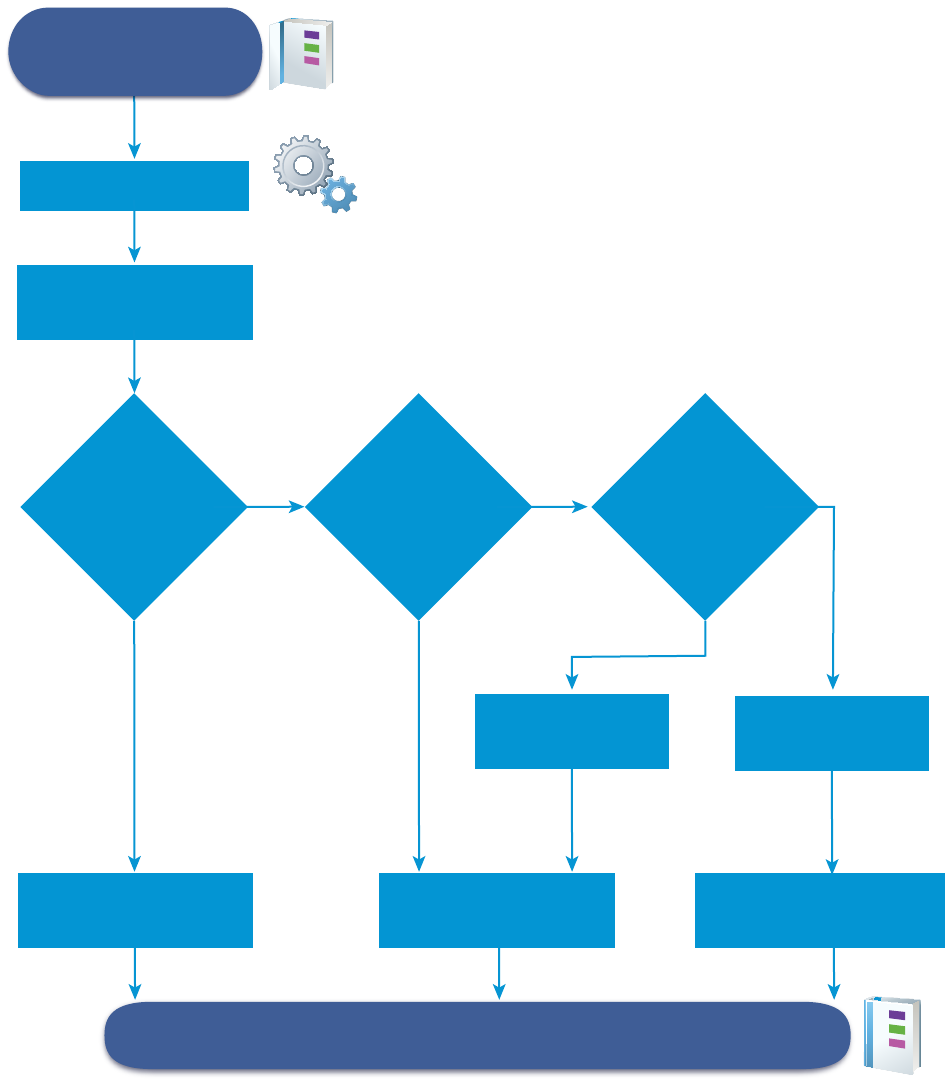
No
Yes
Blueprints and Actions
are published as Catalog
Items and Actions
Add a Catalog Item
to a Service
Create a Service
Do you want
to apply approval
policies to one or more
catalog items that
are included in
the Service?
Create an Entitlement
without approval policies
No
Yes
Do you have an
approval policy
applicable to the
Catalog Items
in Service?
Now Later
Create an approval
policy now or later?
Create an Entitlement
with approval policies
Create or modify
an Approval Policy
Create an
Approval Policy
Modify existing Entitlement
of apply an approval policy
Entitled services and catalog items are available in the Service Catalog.
Verify in the Service Catalog
Checklist for Configuring the Service Catalog
After you create and publish blueprints and actions, you can create a vRealize Automation service,
configure catalog items, and assign entitlements and approvals.
The Configuring the Service Catalog Checklist provides a high-level overview of the steps required to
configure catalog and provides links to decision points or detailed instructions for each step.
Configuring vRealize Automation
VMware, Inc. 386
Table 4‑46. Configuring the Service Catalog Checklist
Task Required Role Details
Add a service. tenant administrator
or catalog
administrator
See Add a Service.
Add a catalog item to a service. tenant administrator
or catalog
administrator
See Add Catalog Items to a Service.
Configure the catalog item in the service. tenant administrator
or catalog
administrator
See Configure a Catalog Item.
Create and apply entitlements to the catalog item. tenant administrator
or business group
manager
See Entitle Users to Services, Catalog
Items, and Actions.
Create and apply approval policies to the catalog item. tenant administrator
or approval
administrator can
create approval
policies
tenant administrator
or business group
manager can apply
approval policies
See Create an Approval Policy.
Creating a Service
A service is a group of catalog items that you want included in the service catalog. You can entitle the
service, which entitles business group users to all the associated catalog items, and you can apply an
approval policy to the service.
A service operates as a dynamic group of catalog items. If you entitle a service, all the catalog items
associated with the service are available in the service catalog to the specified users, and any catalog
items that you add or remove from a service affect the service catalog.
As you create the service, you can use it as a service category so that you can assemble service
offerings for your service catalog users. For example, a Windows desktop service that includes Windows
7, 8, and 10 operating system catalog items, or a Linux service that includes CentOS and RHEL
operating system items.
Add a Service
Add a service to make catalog items available to your service catalog users. All catalog items must be
associated with a service so that you can entitle the items to users.
When the service is entitled to users, the catalog items appear together in the service catalog. You can
also entitle users to the individual catalog items.
Configuring vRealize Automation
VMware, Inc. 387
Prerequisites
Log in to the vRealize Automation console as a tenant administrator or catalog administrator.
Procedure
1Select Administration > Catalog Management > Services.
2Click the New icon ( ).
3Enter a name and description.
These values appear in the service catalog for the catalog users.
4To add a specific icon for the service in the service catalog, click Browse and select an image.
The supported image file types are GIF, JPG, and PNG. The displayed image is 40 x 40 pixels. If you
do not select a custom image, the default icon appears in the service catalog.
5Select a status from the Status drop-down menu.
Option Description
Inactive The service is not available in the service catalog. When a service is in this state,
you can associate catalog items with the service, but you cannot entitle the
service ot users. If you select Inactive for a service that is active and entitled, it is
removed from the service catalog until you reactivate it.
Active (Default) The service and the associated catalog items are available to entitle to
users and, if entitled, are available for in the service catalog for those users.
Deleted Removes the service from vRealize Automation. All associated catalog items are
still present, but any items associated with the service in the service catalog are
not available to the catalog users.
6Configuring the service settings.
The following settings provide information to the service catalog users. The settings do not affect
service availability.
Option Description
Hours Configure the time to coincide with the availability of the support team. The time is
based on your local time.
The hours of service cannot cross from one day to another. For example, you
cannot set the hours of service as 4:00 PM to 4:00 AM. To cross midnight, create
two entitlements. One entitlement for 4:00 PM to 12:00 AM, and another for 12:00
AM to 4:00 AM.
Owner Specify the user or user group who is the primary owner of the service and the
associated catalog items.
Support Team Specify the custom user group or user who is available to support any problems
that the service catalog users encounter when they provision items using the
service.
Change Window Select a date and time when you plan to make a change to the service. The date
and time specified is informational and does not affect the availability of the
service.
Configuring vRealize Automation
VMware, Inc. 388

7Click Add.
What to do next
Associate catalog items with a service so that you can entitle users to the items. See Add Catalog Items
to a Service.
Add Catalog Items to a Service
Add catalog items to services so that you can entitle users to request the items in the service catalog. A
catalog item can be associated with only one service.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or catalog administrator.
nVerify that a service exists. See Add a Service.
nVerify that one or more catalog items are published. See Configure a Catalog Item.
Procedure
1Select Administration > Catalog Management > Services.
2Select the service to which you are adding catalog items and click Manage Catalog Items.
3Click the Catalog Items icon ( ).
a Select the catalog items to include in this service.
The Select Catalog Items dialog box displays only the items that are not already associated with
a service.
b Click Add.
4Click Close.
What to do next
nYou can add a custom icon to the catalog item that will appear with the item in the service catalog.
See Configure a Catalog Item.
nEntitle users to the services or catalog items so that they can request them in the service catalog.
See Creating an Entitlement.
Working with Catalog Items and Actions
Catalog items are published blueprints for machines, software components, and other objects. Actions in
the catalog management area are published actions that you can run on the provisioned catalog items.
You can use the lists to determine what blueprints and actions are published so that you can make them
available to service catalog users.
Configuring vRealize Automation
VMware, Inc. 389
Published Catalog Items
A catalog item is a published blueprint. Published blueprints can also be used in other blueprints. The
reuse of blueprints in other blueprints is not displayed in the catalog items list.
The published catalog items can also include items that are only components of blueprints. For example,
published software components are listed as catalog items, but they are available only as part of a
deployment.
Deployment catalog items must be associated with a service so that you can make them available in the
service catalog to entitled users. Only active items appear in the service catalog. You can configure
catalog items to a different service, disable it if you want to temporarily remove it from the service catalog,
and add a custom icon that appears in the catalog.
Published Actions
Actions are changes that you can make to provisioned catalog items. For example, you can reboot a
virtual machine.
Actions can include built-in actions or actions created using XaaS. Built-in actions are added when you
add a machine or other provided blueprint. XaaS actions must be created and published.
Actions are not associated with services. You must include an action in the entitlement that contains the
catalog item on which the action runs. Actions that are entitled to users do not appear in the service
catalog. The actions are available for the provisioned item on the service catalog user's Items tab based
whether they are applicable to the item and to the current state of the item.
You can add a custom icon to the action that appears on the Items tab.
Configure a Catalog Item
A catalog item is a published blueprint that you can entitle to users. You use the catalog items options to
change the status or associated service. You can also view the entitlements that include the selected
catalog item.
Only catalog items that are associated with a service and entitled to users appear in the service catalog.
Catalog items can be associated with only one service.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or catalog administrator.
nVerify that you have at least one blueprint published as a catalog item. See Publish a Blueprint.
Procedure
1Select Administration > Catalog Management > Catalog Items.
2Select the catalog item and click Configure.
Configuring vRealize Automation
VMware, Inc. 390
3Configure the catalog item settings.
Option Description
Icon Browse for an image. The supported image file types are GIF, JPG, and PNG.
The displayed image is 40 x 40 pixels. If you do not select a custom image, the
default catalog icon appears in the service catalog.
Status Possible values include Active, Inactive, and Staging.
nActive. The catalog item appears in the service catalog and entitled users
can use it to provision resources. The item appears in the catalog item list as
published.
nInactive. The catalog item is not available in the service catalog. The item
appears in the catalog item list as retired.
nStaging. The catalog item is not available in the service catalog. Select this
option if the item was once inactive and you are using staging to indicate that
you are considering reactivating it. Appears in the catalog item list as staging.
Service Select a service. All catalog items must be associated with a service if you want it
to appear in the service catalog for entitled users. The list includes active and
inactive services.
New and noteworthy The catalog item appears in the New & Noteworthy area on the home page.
4To view the entitlements where the catalog item is made available to users, click the Entitlements
tab.
5Click Update.
What to do next
nTo make the catalog item available in the service catalog, you must entitle users to the service
associated with the item or to the individual item. See Creating an Entitlement.
nTo specify the entitlements processing order so that the approval policies for individual users are
applied correctly, set the priority order for multiple entitlements for the same business group. See
Prioritize Entitlements.
Configure an Action for the Service Catalog
An action is a change or workflow that can run on provisioned items. You can add an icon or view the
entitlements that include the selected action.
An action is either a built-in action for a provisioned machine, network, and other blueprint components,
or it is a published XaaS action.
For the icon, the supported image file types are GIF, JPG, and PNG. The displayed image is 40 x 40
pixels. If you do not select a custom image, the default action icon appears on the Items tab.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or catalog administrator.
nVerify that you have at least one published action. See Publish a Blueprint and Publish a Resource
Action.
Configuring vRealize Automation
VMware, Inc. 391
Procedure
1Select Administration > Catalog Management > Actions.
2Select the shared action and click View Details.
3Browse for an image.
4To view the entitlements where the action is made available to users, click the Entitlements tab.
5Click Update.
What to do next
Entitle Users to Services, Catalog Items, and Actions.
Creating an Entitlement
Entitlements control what items and actions are available in the service catalog for the selected business
group members. An entitlement must be active for the items to appear in the service catalog. If you have
items that require governance, you can use entitlements to apply approval policies to different items.
To configure the entitlement, the catalog items must be included in a service. Entitlements can include
catalog items from multiple services.
You must consider the interactions of services, catalog items, actions, and approvals when you create an
entitlement.
Services
An entitled service operates as a dynamic group of catalog items. If a catalog item is added to a service
after it is entitled, the new catalog item is available to the specified users without any additional
configuration. If you apply an approval policy to a service, all the items, when requested, are subject to
the same approval process.
Items
Entitled catalog items can include any of the following items:
nItems from any service that you want to provide to entitled users, even services not included in the
current entitlement.
For example, as a catalog administrator you associated several different versions of the Red Hat
Enterprise Linux with a Red Hat service and entitle the service to the quality engineers for product A.
Then you receive a request to create service catalog items that includes only the latest version of
Linux-based operating systems for the training team. You create an entitlement for the training team
that includes the latest versions of the other operating systems in a service. You already have the
latest version of RHEL associated with another service, so you add RHEL as a catalog item rather
than add the entire Red Hat service.
nItems that are included in a service that is included in the current entitlement, but you want to apply
an approval policy to the individual catalog item that differs from the policy you applied to the service.
Configuring vRealize Automation
VMware, Inc. 392
For example, as a business group manager, you entitle your development team to a service that
includes three virtual machine catalog items. You apply an approval policy that requires the approval
of the virtual infrastructure administrator for machines with more than four CPUs. One of the virtual
machines is used for performance testing, so you add it as a catalog item and apply less restrictive
approval policy for the same group of users.
nItems that are not available for a service catalog user to request on their own because they are a
component of a provisionable item, but to which you want to apply a specific approval policy that
differs from the catalog item in which it is included.
For example, an item includes a machine and software. The machine is available as a provisionable
item and has an approval policy that requires site manager approval. The software is not available as
a standalone, provisionable item, only as part of a machine request, but the approval policy for the
software requires approval from your organization's software licensing administrator. When the
machine is requested in the services catalog, it must be approved by the site administrator and the
software licensing administrator before it is provisioned. After it is provisioned, the machine, with the
software entry, appears in the requestor's Items tab as part of the machine.
Actions
Actions run on provisioned catalog items. To provision a catalog item, you request the item in the service
catalog. To run actions on a provisioned item, the action must be included in the same entitlement as the
catalog item that provisioned the item from the service catalog.
For example, entitlement 1 includes a vSphere virtual machine and a create snapshot action, and
entitlement 2 includes only a vSphere virtual machine. When you deploy a vSphere machine from
entitlement 1, the create snapshot action is available. When you deploy a vSphere machine from
entitlement 2, there is no action. To make the action available to entitlement 2 users, add the create
snapshot action to entitlement 2.
If you select an action that is not applicable to any of the catalog items in the entitlement, it will not appear
as an action on the Items tab. For example, your entitlement includes a vSphere machine and you entitle
a destroy action for a cloud machine. The destroy action is not available to run on the provisioned
machine.
You can apply an approval policy to an action that is different from the policy applied to the catalog item in
the entitlement.
If the service catalog user is the member of multiple business groups, and one group is only entitled to
power on and power off and the other is only entitled to destroy, that user will have all three actions
available to them for the applicable provisioned machine.
Approval Policies
To apply an approval policy when you create the entitlement, the policy must already exist. If it does not,
you can still create the entitlement and leave it in a draft or inactive state until you create the approval
policies needed for the catalog items and actions in this entitlement, and then apply the policies later.
You are not required to apply an approval policy to any of the items or actions. If no approval policy is
applied, the items and actions are deployed when requested without triggering an approval request.
Configuring vRealize Automation
VMware, Inc. 393
Best Practices When Entitling Users to Actions
Blueprints are complex and entitling actions to run on provisioned blueprints can result in unexpected
behavior. Use the following best practices when entitling service catalog users to run actions on their
provisioned items.
nWhen you entitle users to the Destroy Machine action, entitle them to Destroy Deployment. A
provisioned blueprint is a deployment.
A deployment can contain a machine. If the service catalog user is entitled to run the Destroy
Machine action and is not entitled to run the Destroy Deployment, when the user runs the Destroy
Machine action on the last or only machine in a deployment, a message appears indicating that they
do not have permission to run the action. Entitling both actions ensures that the deployment is
removed from your environment. To manage governance on the Destroy Deployment action, you can
create a pre approval policy and apply it to the action. This policy will allow the designated approver
to validate the Destroy Deployment request before it runs.
nWhen you entitle service catalog users to the Change Lease, Change Owner, Expire, Reconfigure
and other actions that can apply to machines and to deployments, entitle them to both actions.
Entitle Users to Services, Catalog Items, and Actions
When you add a service, catalog item, or action to an entitlement, you allow the users and groups
identified in the entitlement to request the provisionable items in the service catalog. Actions are
associated with items and appear on the Items tab for the requesting user.
There are several user roles with permission to create entitlements for business groups.
nTenant administrators can create entitlements for any business group in their tenant.
nBusiness group managers can create entitlements for the groups that they manage.
nCatalog administrators can create entitlements for any business group in their tenant.
When you create an entitlement, you must select a business group and specify individual users and
groups in the business group for the entitlement.
To understand how to create an entitlement so that you can use the interactions of services, catalog
items, and actions with approvals to provide the correct items in the service catalog, see Creating an
Entitlement.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or catalog administrator.
nVerify that the catalog items to which you are entitling users are associated with a service. See Add
Catalog Items to a Service.
nVerify that the business group for which you are defining the entitlement exists and that the member
users and user groups are defined. See Create a Business Group.
Configuring vRealize Automation
VMware, Inc. 394
nVerify that the approval policies exist if you plan to add approvals when you create this entitlement.
See Create an Approval Policy. If you want to entitle users to the items in the service catalog without
approvals, you can modify the entitlement later to add approvals to one or more services, catalog
items, and actions.
Procedure
1Select Administration > Catalog Management > Entitlements.
2Click the New icon ( ).
3Configure the Details options.
Details determine how the entitlement appears in the entitlement list and which users have access to
the items in the service catalog.
Option Description
Name and Description Information about the entitlement that appears in the entitlements list.
Expiration Date Set the date and time if you want the entitlement to become inactive on a
particular date.
Status Possible values include Draft, Active, Inactive.
nDraft. Items are not available in the service catalog and have never been
active. After an entitlement is active, you can never return it to a draft status.
nActive. Items are available in the service catalog. This option is available
when you add or edit entitlements.
nInactive. Items are not available in the service catalog, but the entitlement
was once active. The entitlement was deactivated by the expiration date or by
a user.
Business Group Select a business group. You can create entitlements for only one business group
and entitled users must be members of the business group.
If you want an entitlement available to all users, you must either have an All Users
business group and a custom user group that includes all users, or you must
create entitlements for each business group.
If you are logged in as a business group manager, you can create entitlements
only for your business group.
Users and Groups Add one or more users or groups. The available users or groups are limited to
members of the selected business group.
If the status is Draft, you do not need to specify users or groups. To activate an
entitlement, you must specify at least one user or group.
4Click Next.
Configuring vRealize Automation
VMware, Inc. 395
5Click an New icon ( ) to entitle users to services, catalog items, or actions with this entitlement.
You can create an entitlement with various combinations of the services, items, and actions.
Option Description
Entitled Services Add a service when you want to allow entitled users access to all the published
catalog items associated with the service.
An entitled service is a dynamic entitlement. If an item is added to the service at a
later date, it is added to the service catalog for the entitled users. Entitlements
can include both services and individual catalog items.
Entitled Items Add individual items that are available to the entitled users.
Entitlements can include both services and individual catalog items. To apply a
different approval policy to an item that is included in the service, add it as a
catalog item. The approval policy on an item takes precedence over the approval
policy on the service to which it belongs when they are in the same entitlement. If
they are in different entitlements, the order is based on the set priority.
Catalog items must be associated with a service to be available in the service
catalog. The catalog item can be associated with any service, not just a service in
the current entitlement.
Entitled Actions Add actions when you want to allow users to run the actions for a provisioned
item.
Actions that you want to run on the items provisioned from this entitlement must
be included in the same entitlement.
Entitled actions do not appear in the service catalog. They appear on the Items
tab for a provisioned item.
Actions only apply to items defined in
this entitlement
Determines if the entitled actions are entitled for all applicable service catalog
items or only the items in this entitlement.
If selected, the actions are entitled to the business group members for the
applicable items in this entitlement. This method of entitling the actions is
recommended because it allows you to specify the actions for the specific items.
If the option is not selected, the actions are entitled to the users specified in the
entitlement for all applicable catalog items, whether or not the items are included
in this entitlement. Any applied approval policies on these actions are also active.
6Use the drop-down menus in each section to filter the available items.
7Select the check boxes to include items to the entitlement.
8To add an approval policy to the selected service, item, or action, select an approval policy from the
Apply this Policy to selected Items drop-down menu.
If you apply an approval policy to a service, all the items in the service have the same approval policy.
To apply a different policy to an item, add it as a catalog item an apply the appropriate policy.
9Click OK.
The service, item, or action is added to the entitlement.
10 Click Finish to save the entitlement.
If entitlement status is active, the service and items are added to the service catalog.
Configuring vRealize Automation
VMware, Inc. 396
What to do next
Verify that the entitled services and catalog items appear in the service catalog for the entitled users and
that the requested items provision the target objects as expected. You can request the item on behalf of
the selected users.
Prioritize Entitlements
If multiple entitlements exist for the same business group, you can prioritize the entitlements so that when
a service catalog user makes a request, the entitlement and associated approval policy are processed in
the specified order.
If you configure an approval policy for a user group, and you want a group member to have a unique
policy for one or more of the services, catalog items, or actions, prioritize the member entitlement before
the group entitlement. When the member requests an item in the service catalog, the approval policy that
is applied is based on the priority order of the entitlements for the business group. The first time that the
member's name is found, either as part of a custom user group or as an individual user, that is the applied
approval policy.
For example, you create two entitlements for the same catalog item so that you can apply one approval
policy for the accounting user group and a different approval policy for Connie, a member of that group.
Table 4‑47. Example Entitlements
Entitlement 1 Entitlement 2
Business Group: Finance
Users and Groups: Accounting group
Catalog Item 1: Policy A
Business Group: Finance
Users and Groups: Connie
Catalog Item 1: Policy C
Connie requests Catalog Item 1 in the service catalog. Depending on the priority order of the entitlements
for the Finance business group, a different policy is applied to Connie's request.
Table 4‑48. Example Results
Configuration and Result Priority Order Priority Order
Priority Order 1: Entitlement 1
2: Entitlement 2
1: Entitlement 2
2: Entitlement 1
Applied Policy Policy A is applied.
Connie is a member of the
Accounting user group. The
search for Connie as an
entitled user stops at
Entitlement 1 and the
approval policy is applied.
Policy C is applied.
The search for Connie as an
entitled user stops at
Entitlement 2 and the approval
policy is applied.
Prerequisites
Log in to the vRealize Automation console as a tenant administrator or catalog administrator.
Configuring vRealize Automation
VMware, Inc. 397
Procedure
1Select Administration > Catalog Management > Entitlements.
2Click the Prioritize icon ( ).
3Select a business group from the Business Group drop-down list.
4Drag an entitlement to a new location in the list to change its priority.
5Select an update method.
Option Description
Update Saves your changes.
Update & Close Saves your changes and closes the Prioritize Elements window.
Working with Approval Policies
Approval policies are governance that you add to service catalog requests so that you can manage
resources in your environment. Each policy is a defined set of conditions that can be applied to services,
catalog items, and actions when you entitle users to those items.
Approval Policy Process
First, a tenant administrator or approval administrator creates the approval policies where provisioning
governance is needed.
Approval policies are created for approval policy types or specific items. If the policy is based on a policy
type, you can apply it to matching catalog item types. For example, if a policy is based on a software
policy type, then you can define it for and apply it to any software items in the entitlements. If the policy is
for a specific item, you should apply it only to that item. For example, if the item is a specific software
item, then you should apply it only to that specific database software item in the entitlement.
Policies can include pre-approval and post-approval requirements. For pre approval, the request must be
approved before the requested item is provisioned. Post approval policies require that the approver
accept the request before the provisioned item is made available to the requesting user.
The pre and post approval configurations are composed of one or more levels that determine when the
approval policy is triggered and who or how the request is approved. You can include multiple levels. For
example, an approval policy can have one level for manager approval, followed by a level for finance
approval.
Next, a tenant administrator or business group manager applies the approval policies to the services,
catalog items, and actions as appropriate.
Finally, when a service catalog user requests an item to which an approval policy is applied, the
approvers approve or reject the request on their Inbox tab, on Approvals page . The requesting user can
track the approval status for a specific request on their Requests tab.
Configuring vRealize Automation
VMware, Inc. 398
Examples of Approval Policies Based on the Virtual Machine Policy Type
You can create an approval policy that you can apply to the same catalog item type, but it produces
different results when an item is requested in the service catalog. Depending on how the approval policy
is defined and applied, the effect on the service catalog user and the approver varies.
The following table includes examples of different approval policies that are all based on the same
approval policy type. These examples illustrate some of the ways that you can configure approval policies
to accomplish different types of governance.
Table 4‑49. Examples of Approval Policies and Results
Governance
Goals
Selected
Policy Type
Pre or Post
Approval
When is
Approval
Required
Who are the
Approvers
How is the
Policy
Applied in
the
Entitlement
Results When
the Item is
Requested in
the Service
Catalog
The business
group manager
must approve
any virtual
machine
requests.
The approval
policy must be
applicable to
multiple business
groups in
multiple
entitlements.
Service Catalog
- Catalog Item
Request -
Virtual Machine
Add to Pre
Approval tab
Select Always
required
Select
Determine
approvers from
the request.
Select condition
Business
Group >
Managers >
Users >
manager.
Select Anyone
can approve.
Entitlements
are based on
business
groups. This
approval can
be used in any
entitlement
where
manager
approval is
required for
the virtual
machine.
When the service
catalog user
requests a virtual
machine to which
this approval was
applied, the
business group
manager must
approve the
request before
the machine is
provisioned.
The virtual
infrastructure
administrator
must verify the
correct
provisioning of
the virtual
machine and
approve the
request before
the virtual
machine is
released to the
requesting user.
Service Catalog
- Catalog Item
Request -
Virtual Machine
Add to Post
Approval tab
Select Always
required
Select Specific
Users and
Groups.
Select your
virtual
infrastructure
administrators
custom users
group.
Select Anyone
can approve.
This approval
can be used in
any
entitlement
where you
want the
virtual
infrastructure
administrator
to check the
virtual
machine on
the vCenter
Server after it
is provisioned.
When the service
catalog user
requests a virtual
machine to which
this approval was
applied, the
virtual machine is
provisioned. If
each member of
the VI admin
group approves
the request, the
machine is
released to the
user.
Configuring vRealize Automation
VMware, Inc. 399
Table 4‑49. Examples of Approval Policies and Results (Continued)
Governance
Goals
Selected
Policy Type
Pre or Post
Approval
When is
Approval
Required
Who are the
Approvers
How is the
Policy
Applied in
the
Entitlement
Results When
the Item is
Requested in
the Service
Catalog
To manage
virtual
infrastructure
resources and to
control costs,
you add two pre-
approval levels
because one
approval is for
machine
resources and
the other is for
cost of machine
per day.
Service Catalog
- Catalog Item
Request -
Virtual Machine
Add To Pre
Approval tab
Level 1
Select
Required
based on
conditions.
Configure the
conditions
where CPUs >
6 or Memory >
8 or Storage >
100 GB.
Select
Determine
approvers from
the request.
Select condition
Requested by >
manager.
Select .
Click System
Properties and
select CPUs.
Memory, and
Storage so that
the approver can
change the
value to an
acceptable level.
This approval
policy can be
used in an
entitlement
where you
want the
requesting
user's
manager and
a member of
the finance
department to
approve the
request.
When the service
catalog user
requests a virtual
machine, the
request is
evaluated to
determine
whether the
requested CPU,
memory, or
storage amounts
are over the
amounts
specified in level
1. If they are not,
then the level 2
condition is
evaluated. If the
requests
exceeds at least
one of the level 1
conditions, then
the manager
must approve the
request. The
manager has the
option to
decrease the
requested
configuration
amounts and
approve or the
manager can
reject the
request.
Level 2
Select
Required
based on
conditions.
Configure the
condition Cost
> 15.00 per
day.
Select Specific
Users and
Groups.
Select the
finance custom
users group.
Select Anyone
can approve.
Example of Actions with Approval Policies Applied in a Composite
Deployment
When you apply approval policies to actions that can run on various components in a composite blueprint,
the approval process varies depending on how the entitlement is configured and how the approval
policies are applied.
Configuring vRealize Automation
VMware, Inc. 400
This example uses specific details to build the blueprint and then apply approval policies to actions that
you can run from the service catalog on the provisioned blueprint in different entitlements. The blueprint is
a composite blueprint that includes another blueprint. The actions used are to destroy the provisioned
items, destroy a deployment for the blueprints and destroy a virtual machine for the machine. The
resulting behavior includes what is destroyed and when the applied approval policies trigger approval
requests.
Example Blueprint
In this example, you configure a blueprint that includes a nested blueprint with a virtual machine.
nBlueprint 1 - Continuous Integration Blueprint
nBlueprint 2 - Pre-Production Blueprint
nVirtual Machine 1 - TestAsAService vSphere VM
Approval Policies for Destroy Actions
You configure the two approval policies to destroy provisioned items. A Destroy - Deployment action can
run on Blueprint 1 or Blueprint 2 in this example. A Destroy - Virtual machine action can run on Virtual
Machine 1. You create the approval policies so that you can apply them to the actions in the entitlement.
Approval Policy Name Approval Policy Type
Approval Policy A Service Catalog - Resource Action Request - Destroy - Deployment
Approval Policy B Service Catalog - Resource Action Request - Destroy - Virtual Machine
Entitlements and Approval Policies Applied to Actions
You configure three entitlements. Each entitlement includes the composite blueprint. In each entitlement,
you add the destroy actions and apply the approval policies.
Entitlement Name Entitled Action on Provisioned Machine Applied Approval Policy
Entitlement 1 Destroy - Deployment Approval Policy A
Entitlement 2 Destroy - Virtual Machine Approval Policy B
Entitlement 3 Destroy - Deployment
Destroy - Virtual Machine
Approval Policy A
Approval Policy B
User Actions in the Service Catalog
When the service catalog user runs the action, blueprints or machines are destroyed depending on which
item your user ran the action.
Configuring vRealize Automation
VMware, Inc. 401
User Action in the
Service Catalog Selected Action
Destroyed Blueprints or
Machines
Action 1 Destroy - Deployment action runs on Blueprint 1 - Continuous
Integration Blueprint
Blueprint 1, Blueprint 2, and Virtual
Machine 1
Action 2 Destroy - Deployment action runs on the nested Blueprint 2 - Pre-
production Blueprint
Blueprint 2 and Virtual Machine 1
Action 3 Destroy - Virtual Machine action runs on the machine that is inside a
deployment, Virtual Machine 1 - TestAsAService vSphere VM
Virtual Machine 1
Approval Policies Applied to Actions in the Entitlements
You apply the approval policies, the approvers receive an approval request depending on the blueprint or
machine on which your service catalog user ran the action.
Entitlement
Name
Approval Policy on
Actions User Action
Approval Request
Triggered
If Approved,
Destroyed Blueprints
or Machines
Entitlement 1 -
Destroy
Deployment
Approval Policy
Policy A (Destroy
Deployment Approval
Policy) on Destroy -
Deployment action only
Action 1 (Run Destroy -
Deployment action on Blueprint
1)
Approval requests are
triggered for Blueprint 1
only
Blueprint 1, Blueprint
2, and Virtual Machine
1
Action 2 (Run Destroy -
Deployment action on the
Blueprint 2)
Approval requests are
triggered for Blueprint 2
only
Blueprint 2 and Virtual
Machine 1
Action 3 (Destroy - Virtual
Machine action runs on Virtual
Machine 1)
No Approval requests
are triggered
Virtual Machine 1
Entitlement 2 Policy B (Destroy -
Virtual Machine Policy)
on Destroy - Virtual
Machine action only
Action 1 (Run Destroy -
Deployment action on Blueprint
1)
No Approval requests
are triggered
Blueprint 1, Blueprint
2, and Virtual Machine
1
Action 2 (Run Destroy -
Deployment action on the
Blueprint 2)
No Approval requests
are triggered
Blueprint 2 and Virtual
Machine 1
Action 3 (Destroy - Virtual
Machine action runs on Virtual
Machine 1)
Approval requests are
triggered for Virtual
Machine 1 only
Virtual Machine 1
Entitlement 3 Policy A (Destroy
Deployment Approval
Policy) on Destroy -
Deployment action and
Policy B (Destroy -
Virtual Machine Policy)
on Destroy - Virtual
Machine action
Action 1 (Run Destroy -
Deployment action on Blueprint
1)
Approval requests are
triggered for Blueprint 1
only
Blueprint 1, Blueprint
2, and Virtual Machine
1
Configuring vRealize Automation
VMware, Inc. 402

Entitlement
Name
Approval Policy on
Actions User Action
Approval Request
Triggered
If Approved,
Destroyed Blueprints
or Machines
Action 2 (Run Destroy -
Deployment action on the
Blueprint 2)
Approval requests are
triggered for Blueprint 2
only
Blueprint 2 and Virtual
Machine 1
Action 3 (Destroy - Virtual
Machine action runs on Virtual
Machine 1)
Approval requests are
triggered for Virtual
Machine 1 only
Virtual Machine 1
Example of an Approval Policy in Multiple Entitlements
If you apply an approval policy to an item that is used in multiple entitlements that are entitled to same
users in a business group, the approval policy is triggered on the item even in the service where the
approval policy is not explicitly applied in the entitlement.
For example, you create the following blueprints, services, approval policies, and entitlements.
Blueprints
nRHEL vSphere virtual machine
nQE Testing includes RHEL vSphere virtual machine
nQE Training includes RHEL vSphere virtual machine
Services
nThe QE Testing blueprint is associated with the Testing service
nThe QE Training blueprint is associated with the Training service
Entitlements
nEntitlement 1
nEntitlement 2
Table 4‑50. Entitlement Configurations
Entitlement Name Business Group Entitled Service Entitled Item
Entitlement 1 QE Testing Catalog Item
Request - Virtual
Machine applied to
Virtual Machine
Component
Entitlement 2 QE Training
Results
When the user selects QE Training in the service catalog, the approval policy is triggered for RHEL
vSphere virtual machine because it is a blueprint based on virtual machine component that is used in the
QE Training blueprint.
Configuring vRealize Automation
VMware, Inc. 403
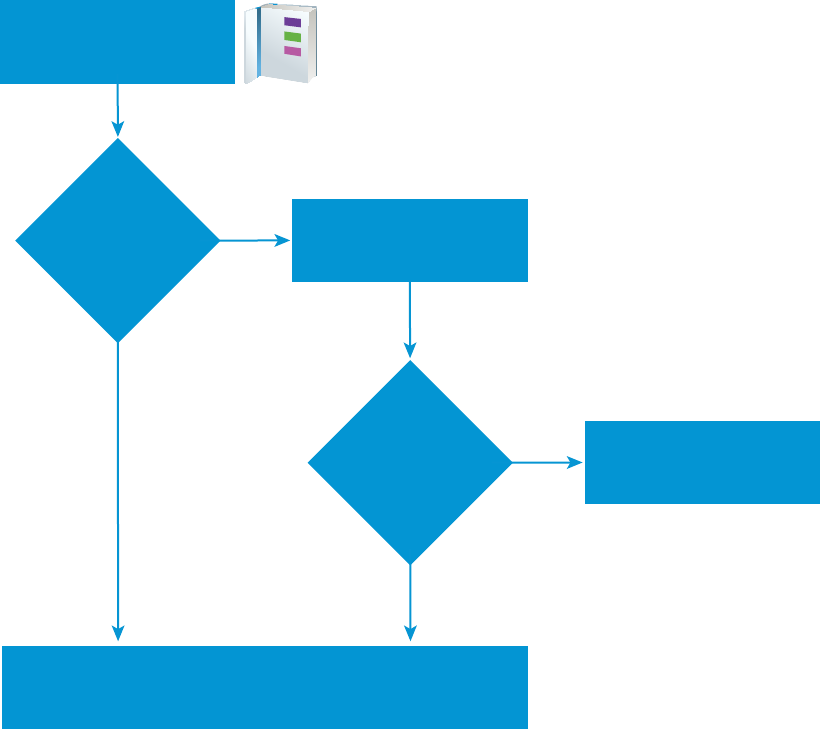
Processing Approval Policies in the Service Catalog
When a user requests an item in the service catalog that has an approval policy applied, the request is
processed by the approver and the requesting user similar to the following workflow
No
Yes
Request item in
the service catalog
Is approval
required on item
or component?
Approval request sent
to approver’s Inbox tab
Yes
Approver
approves
request?
No Requestor notified of
rejection on Requests tab
Item is provisioned
Requester’s Request tab - in progress
Requesters’s Item tab - when provisioned
Create an Approval Policy
Tenant administrators and approval administrators can define approval policies and use them in
entitlements. You can configure the approval policies with multiple levels for pre-approval and post-
approval events.
If you modify a setting in a software component blueprint and an approval policy uses that setting to
trigger an approval request, the approval policy might not work as expected. If you must modify a setting
in a component, verify that your changes do not affect one or more approval policies.
Prerequisites
Log in to the vRealize Automation console as a tenant administrator or approval administrator.
Configuring vRealize Automation
VMware, Inc. 404

Procedure
1Specify Approval Policy Information
When you create an approval policy, define the approval policy type, name, description, and status.
2Create an Approval Level
When you create an approval policy, you can add pre-approval and post-approval levels.
3Configure the Approval Form to Include System and Custom Properties
You can add system and custom properties that appear on an approval form. You add these
properties so that the approvers can change the values of system properties for machine resource
settings such as CPU, lease, or memory, and custom properties before they complete an approval
request.
4Approval Policy Settings
When you create an approval policy, you configure various options that determine when an item
requested by a service catalog users must be approved. The approval can be required before the
request begins provisioning or after the item is provisioned but before it is released to the requesting
user.
Specify Approval Policy Information
When you create an approval policy, define the approval policy type, name, description, and status.
Prerequisites
Log in to the vRealize Automation console as a tenant administrator or approval administrator.
Procedure
1Select Administration > Approval Policies.
2Click the New icon ( ).
Configuring vRealize Automation
VMware, Inc. 405
3Select a policy type or software component.
Option Description
Select an approval policy type Create an approval policy based on the policy request type.
Select this option to define an approval policy that is applicable to all catalog
items of that type. The request type can be a generic request, a catalog item
request, or a resource action request.
The available condition configuration options vary depending on the type. The
more specific the type the more specific the configuration fields. For example,
Service Catalog - Catalog Item Request provides only the fields that are common
to all catalog item requests, but a Service Catalog - Catalog Item Request -
Virtual Machine also includes the common options and options specific to virtual
machines.
The request type limits the catalog items or actions to which you can apply the
approval policy.
Select an item Create an approval policy based on a specific item.
Select this option to define an approval policy that is applicable to specific items
that are not available as individual items in the service catalog, only as part of a
machine or other deployment. For example, software components.
The available condition configuration fields are specific to the item and can be
more detailed than the criteria offered for a policy type item.
List Lists the available policy type or catalog items.
Search or sort the columns to locate a specific item or type.
4Click OK.
5Enter a name and, optionally, a description.
6Select the state of the policy from the Status drop-down menu.
Option Description
Draft Saves the approval policy in an editable state.
Active Saves the approval policy in a read-only state that you can use in an entitlement.
Inactive Saves the approval policy in a read-only state that you cannot use in an
entitlement until you activate the policy.
What to do next
Create the pre-approval and post-approval levels.
Create an Approval Level
When you create an approval policy, you can add pre-approval and post-approval levels.
You can create multiple approval levels for an approval policy. When a service catalog user requests an
item to which an approval policy with multiple levels is applied, each the first level must be accepted
before the approval request is sent to the next approver. See Working with Approval Policies.
Prerequisites
Specify Approval Policy Information.
Configuring vRealize Automation
VMware, Inc. 406
Procedure
1On the Pre Approval or Post Approval tab, click the New icon ( ).
2Enter a name and, optionally, a description.
3Select an approval requirement.
Option Description
Always Required The approval policy is triggered for every request.
Required based on conditions The approval policy is based on one or more condition clauses.
If you select this option, you must create the conditions. When this approval policy
is applied to eligible services, catalog items, or actions in an entitlement, then the
conditions are evaluated. If the conditions are true, then the request must be
approved by the specified approver method before it is provisioned. If the
conditions are false, then the request is provisioned without requiring an approval.
For example, any requests for a virtual machine with 4 or more CPUs must be
approved by the virtual infrastructure administrator.
The availability of the fields on which to base the conditions is determined by the
selected approval policy type or catalog item.
When you enter a value for a condition, the values are case-sensitive.
To configure more than one condition clause, select the Boolean operation for the
clauses.
4Select the approvers.
Option Action
Specific Users and Groups Sends the approval request to the selected users.
Determine approvers from the request Sends the approval request to the users based on the defined condition.
Use event subscription Processes the approval request based on defined event subscriptions.
The workflow subscription must be defined in Adminstration > Events >
Subcriptions. The applicable workflow subscriptions are pre-approval and post-
approval.
5Indicate who must approve the request or action.
Option Description
Anyone can approve Only one of the approvers must approve before the request is processed.
When the item is requested in the service catalog, requests for approval are sent
to all approvers. If one approver approves the request, the request is approved
and the request for approval is removed from the other approvers' inboxes.
All must approve All of the specified approvers must approve before the request is processed.
6Add properties to an approval form or save the level.
nTo add properties to the approval form, click System Properties or Custom Properties.
nTo save the level, click OK.
Configuring vRealize Automation
VMware, Inc. 407
What to do next
To add properties to the approval form, see Configure the Approval Form to Include System and Custom
Properties.
Configure the Approval Form to Include System and Custom Properties
You can add system and custom properties that appear on an approval form. You add these properties so
that the approvers can change the values of system properties for machine resource settings such as
CPU, lease, or memory, and custom properties before they complete an approval request.
The available system properties depend on the approval policy type and how the blueprint is configured.
For some properties, the configured field in the blueprint must include a minimum and maximum value
before the property appears in the system properties list.
Custom properties can be added when you add the approval level. If a custom property is configured and
included in a blueprint, the custom properties you add to the approval form overwrite any other instances
of that custom property for example, in blueprints, property groups, or endpoints.
The approver can modify selected or configured properties in the approval form.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or approval administrator.
nCreate an Approval Level.
Procedure
1On the Pre Approval or Post Approval tab, click the New icon ( ).
2Click the System Properties tab.
3Select the check box for each system property that you want the approver to configure during the
approval process.
4Configure the custom properties.
Add one or more custom properties that you want the approver to configure during the approval
process.
a Click the Custom Properties tab.
bClick the New icon ( ).
c Enter the custom property values.
Option Description
Name Enter the property name.
Label Enter the label that is presented to the approver in the approval form.
Description Enter the extended information for the approver.
This information appears as the field tooltip in the form.
Configuring vRealize Automation
VMware, Inc. 408
d Click Save.
e To delete multiple custom properties, select the rows and click Delete.
5Click OK.
What to do next
nAdd additional pre-approval or post-approval levels.
nSave the approval policy. The policy must be active to apply to services, items, or actions in the
Entitlements.
Approval Policy Settings
When you create an approval policy, you configure various options that determine when an item
requested by a service catalog users must be approved. The approval can be required before the request
begins provisioning or after the item is provisioned but before it is released to the requesting user.
Select Administration > Approval Polices. Click New.
nApproval Policy Type Settings
The approval policy type determines how the approval policy is configured and to what items or
actions you can apply it in the entitlement. When you add approval levels, the policy type or item
affects which fields are available to create conditions for the approval levels.
nAdd Approval Policy Settings
You configure the basic information about the approval policy, including the state to the policy, so
that you can manage the policy.
nAdd Level Information to Approval Policy Settings
An approval level includes the conditions that trigger an approval process when the service catalog
user requests the item, and any system properties and customer properties that you want to include.
When triggered, the approval requests are sent to the designated approvers.
nAdd System Properties to Approval Policy Settings
You selected system properties that you want to add to the approval form and allow the approver to
modify the value.
nAdd Custom Properties to Approval Policy Settings
You configure custom properties that you want to add to the approval form to allow the approver to
modify the value.
Approval Policy Type Settings
The approval policy type determines how the approval policy is configured and to what items or actions
you can apply it in the entitlement. When you add approval levels, the policy type or item affects which
fields are available to create conditions for the approval levels.
Select Administration > Approval Polices. Click New.
Configuring vRealize Automation
VMware, Inc. 409
Table 4‑51. Approval Policy Type Options
Option Description
Select an approval policy type Create an approval policy based on the policy request type.
Select this option to define an approval policy that is applicable
to all catalog items of that type. The request type can be a
generic request, a catalog item request, or a resource action
request.
The available condition configuration options vary depending on
the type. The more specific the type the more specific the
configuration fields. For example, Service Catalog - Catalog Item
Request provides only the fields that are common to all catalog
item requests, but a Service Catalog - Catalog Item Request -
Virtual Machine also includes the common options and options
specific to virtual machines.
The request type limits the catalog items or actions to which you
can apply the approval policy.
Select an item Create an approval policy based on a specific item.
Select this option to define an approval policy that is applicable
to specific items that are not available as individual items in the
service catalog, only as part of a machine or other deployment.
For example, software components.
The available condition configuration fields are specific to the
item and can be more detailed than the criteria offered for a
policy type item.
List Lists the available policy type or catalog items.
Search or sort the columns to locate a specific item or type.
Add Approval Policy Settings
You configure the basic information about the approval policy, including the state to the policy, so that you
can manage the policy.
To define the basic approval policy information, select Administration > Approval Polices. Click New.
Select the policy type and click OK.
Table 4‑52. Approval Policy Options
Option Description
Name Name that appears when applying the approval policy in an
entitlement.
Description Provide a verbose description of how the approval policy is
constructed. This information will help you manage your
approval policies.
Configuring vRealize Automation
VMware, Inc. 410
Table 4‑52. Approval Policy Options (Continued)
Option Description
Status Possible values include:
nDraft. The approval policy is not available to apply in
entitlements. After you make a policy active, you can never
return it to draft.
nActive. The approval policy is available to apply in
entitlements.
nInactive. The approval policy is not available to apply in
entitlements. If the policy has not been applied to
entitlements and you make inactive, you can delete the
policy but you cannot reactivate it. If the policy has been
applied and you make inactive, the items to which it applies
must be linked to a different policy or the items are unlinked.
Unlinked items and actions are still entitled to users, but
they do not have an applied approval policy.
Policy Type Displays the approval policy request type.
If you selected a catalog item on which to base the approval
policy, the associated request type is displayed.
Item Displays the selected catalog item.
If you selected a request type on which to base the approval
policy, this field is blank.
Last Updated By Name of the user who made changes to the approval policy.
Last Updated On Date of the last change to the approval policy.
Pre Approval Level To require approval before the requested items is provisioned or
the actions run, configure one or more conditions that trigger an
approval process when the service catalog user requests the
item.
Post Approval Level To require approval after the item is provisioned but before the
provisioned or modified item is released to the requesting
service catalog user, configure one or more conditions that
trigger an approval process.
For example, the virtual infrastructure administrator verifies that
the virtual machine is in a workable state before releasing it to
the service catalog user.
View Linked Entitlements Displays all the entitlements where the approval policy is applied
to services, catalog items, or actions. You can link the items in
one entitlement to a different policy.
This option is only available when you view an active approval
policy.
Add Level Information to Approval Policy Settings
An approval level includes the conditions that trigger an approval process when the service catalog user
requests the item, and any system properties and customer properties that you want to include. When
triggered, the approval requests are sent to the designated approvers.
Configuring vRealize Automation
VMware, Inc. 411
To define the basic approval policy information, select Administration > Approval Polices. Click New.
Select the policy type and click OK. On the Pre Approval or Post Approval tab, click the New icon ( ).
You prioritize levels based on the order that you want them processed. When the approval policy is
triggered, if the first level of approval is rejected, the request is rejected.
Table 4‑53. Level Information Options
Option Description
Name Enter a name.
The level name appears when you are reviewing requests with
approval policies.
Description Enter a level description.
For example, CPU>4 to VI Admin.
When is approval required? Select when the approval policy is triggered.
Always required The approval policy is triggered for every request.
If you select this option and apply this approval policy to eligible
services, catalog items, or actions in an entitlement, then the
request must be approved by the specified approver method
before it is provisioned. For example, all requests must be
approved by the requesting user's manager.
Required based on conditions The approval policy is based on one or more condition clauses.
If you select this option, you must create the conditions. When
this approval policy is applied to eligible services, catalog items,
or actions in an entitlement, then the conditions are evaluated. If
the conditions are true, then the request must be approved by
the specified approver method before it is provisioned. If the
conditions are false, then the request is provisioned without
requiring an approval. For example, any requests for a virtual
machine with 4 or more CPUs must be approved by the virtual
infrastructure administrator.
The availability of the fields on which to base the conditions is
determined by the selected approval policy type or catalog item.
When you enter a value for a condition, the values are case-
sensitive.
To configure more than one condition clause, select the Boolean
operation for the clauses.
nAll of the following. The approval is triggered when all of the
clauses are true. This a Boolean AND operator between
each clause.
nAny of the following. The approval level is triggered when at
least one of clauses is true. This is a Boolean OR operator
between each clause.
nNot the following. The approval level is triggered is none of
the clauses are true. This is a Boolean NOT operator
between each clause.
Approvers Select the approver method.
Configuring vRealize Automation
VMware, Inc. 412
Table 4‑53. Level Information Options (Continued)
Option Description
Specific Users and Groups Sends the approval request to the selected users.
Select the users or user groups that must approve the service
catalog request before it is provisioned or an action runs. For
example, the request goes to the virtual infrastructure
administrator group with Anyone can approve selected.
Determine users from the request Sends the approval request to the users based on the defined
condition.
For example, if you are applying this approval policy across
business groups and you want the business group manger to
approve the request, select Business group > Consumer >
Users > Manager.
Use event subscription Processes the approval request based on defined event
subscriptions.
The workflow subscription must be defined in Adminstration >
Events > Subcriptions. The applicable workflow subscriptions
are pre-approval and post-approval.
Anyone can approve Only one of the approvers must approve before the request is
processed.
When the item is requested in the service catalog, requests for
approval are sent to all approvers. If one approver approves the
request, the request is approved and the request for approval is
removed from the other approvers' inboxes.
If the first approver rejects the request, the requesting user is
notified about the rejection and the approval request is removed
from the approvers' inboxes.
If the first approver approves and the approval request is open
in the second approver's console, the approver is not allowed to
submit the approval request. It was considered completed by the
first approvers response.
If you select Specific Users and Groups or Determine
approvers from the request, and there is more than one
approver, this is one of the additional options. If there is only one
approver, this option to not apply.
All must approve All of the specified approvers must approve before the request is
processed.
If you select Specific Users and Groups or Determine
approvers from the request, and there is more than one
approver, this is one of the additional options. If there is only one
approver, this option to not apply.
Add System Properties to Approval Policy Settings
You selected system properties that you want to add to the approval form and allow the approver to
modify the value.
For example, for a virtual machine approval, select CPU if you want to allow the approver to modify a
request for 6 CPUs to 4 CPUs.
Configuring vRealize Automation
VMware, Inc. 413

To select system properties, select Administration > Approval Polices. Click New. Select the policy
type and click OK. On the Pre Approval or Post Approval tab, click the New icon ( ) and click the
System Properties tab.
Table 4‑54. System Properties Options
Option Description
Properties The list of available system properties depends on the selected
request type or catalog item, and whether system properties
exist for the item.
Some properties are available only when the blueprint is
configured in a particular way. For example, CPUs. The blueprint
to which you are applying the approval policy with the CPU
system property must be configured as a range. For example,
CPU minimum is 2 and the maximum is 8.
Add Custom Properties to Approval Policy Settings
You configure custom properties that you want to add to the approval form to allow the approver to modify
the value.
For example, for a virtual machine approval, add VMware.VirtualCenter.Folder if you want to allow
the approver to specify the folder to which the machine is added in vCenter Server.
You can also add a custom property that is specific to this approval policy form.
To select system properties, select Administration > Approval Polices. Click New. Select the policy
type and click OK. On the Pre Approval or Post Approval tab, click the New icon ( ) and click the
Custom Properties tab.
Table 4‑55. Custom Properties
Option Description
Name Enter the property name.
Label Enter the label that is presented to the approver in the approval
form.
Description Enter the extended information for the approver.
This information appears as the field tooltip in the form.
Modify an Approval Policy
You cannot modify an active or inactive approval policy. You must create a copy of the original policy and
replace the policy that is not producing the required results. Active and inactive approval policies are
read-only. You can modify approval polices that are in a draft state.
When you make the copy of the approval policy, the new policy is based on the original policy type. You
can edit all of the attributes except the policy type. You do this when you want to modify the approval
levels to modify, add, or remove levels, or to add system or custom properties to the forms.
You can create pre-approval and post-approval levels. For instructions about creating an approval level,
see Create an Approval Level.
Configuring vRealize Automation
VMware, Inc. 414
Prerequisites
Log in to the vRealize Automation console as a tenant administrator or approval administrator.
Procedure
1Select Administration > Approval Policies.
2Select the row of the approval policy to copy.
3Click the Copy icon ( ).
A copy of the approval policy is created.
4Select the new approval policy to edit.
5Enter a name in the Name text box.
6(Optional) Enter a description in the Description text box.
7Select the state of the policy from the Status drop-down menu.
Option Description
Draft Saves the approval policy in an editable state.
Active Saves the approval policy in a read-only state that you can use in an entitlement.
Inactive Saves the approval policy in a read-only state that you cannot use in an
entitlement until you activate the policy.
8Edit the pre-approval and post-approval levels.
9Click OK.
You created a new approval policy based on an existing approval policy.
What to do next
Apply the new approval policy in an entitlement. See Entitle Users to Services, Catalog Items, and
Actions.
Deactivate an Approval Policy
When you determine that an approval policy is outdated, you can deactivate the policy so that it is not
available during provisioning.
To deactivate an approval policy, you must assign a new policy for each entitlement to which the approval
policy is currently applied.
You can later reactiveate a deactivated approval policy, or you can delete a deactivated policy.
Prerequisites
Log in to the vRealize Automation console as a tenant administrator or approval administrator.
Procedure
1Select Administration > Approval Policies.
Configuring vRealize Automation
VMware, Inc. 415
2Click the approval policy name.
3Click View Linked Entitlements.
a In the Replace All With drop-down menu, select the new approval policy.
If the list includes more than one entitlement, the new approval policy is applied to all the listed
entitlements.
b Click OK.
4After you verify that no entitlements that are linked to the approval policy, select Inactive from the
Status drop-menu.
5Click OK.
6To delete an approval policy, select the row containing the inactive policy.
a Click Delete.
b Click OK.
The approval policy is unlinked from any entitlements where it is used and deactivated. You can later
reactivate and reapply it to items in an entitlement.
What to do next
If you not longer need the approval policy, you can delete it. See Delete an Approval Policy.
Delete an Approval Policy
If you have approval policies that you deactivated and do not need, you can delete them from
vRealize Automation.
Prerequisites
nUnlink and deactivate approval policies. See Deactivate an Approval Policy.
nLog in to the vRealize Automation console as a tenant administrator or approval administrator.
Procedure
1Select Administration > Approval Policies.
2Select the row containing the inactive policy.
3Click Delete.
4Click OK.
The approval policy is deleted.
Configuring vRealize Automation
VMware, Inc. 416
Scenario: Configure the Catalog for Rainpole Architects to Test
Blueprints
Using your tenant administrator privileges, you create a special catalog service that contains very little
governance, where your Rainpole architects can efficiently test their work before exporting blueprints into
your production environment. You create a Blueprint Testing service, add the vSphere CentOS blueprint
to the service, and entitle your Rainpole architects to all catalog items and any actions associated with the
service so your architects can verify their work by provisioning catalog items.
You are here
Configure
Tenant
Configure IaaS
Resources
Design On-
Demand Services
Procedure
1Scenario: Create a Catalog Service for Rainpole Blueprint Testing
Using your tenant administrator privileges, you create a catalog service called Rainpole service. You
assign yourself as the owner and support contact for this service, so your Rainpole architects can
contact you with any problems.
2Scenario: Add Your vSphere CentOS Catalog Item to the Rainpole Service
Using your tenant administrator privileges, you add the published vSphere CentOS machine
blueprint to your Rainpole service.
3Scenario: Entitle Your Rainpole Architects to Request Catalog Items
Using your tenant administrator privileges, entitle your Rainpole architects to all actions and items
that belong to the Rainpole service.
Scenario: Create a Catalog Service for Rainpole Blueprint Testing
Using your tenant administrator privileges, you create a catalog service called Rainpole service. You
assign yourself as the owner and support contact for this service, so your Rainpole architects can contact
you with any problems.
Procedure
1Select Administration > Catalog Management > Services.
2Click the New icon ( ).
3Enter the name Rainpole service.
4In the Status drop-down menu, select Active.
Configuring vRealize Automation
VMware, Inc. 417

5As the tenant administrator who is creating the service, use the search option to add yourself as the
Owner and Support Team.
6Click OK.
What to do next
Using your tenant administrator privileges, add the published vSphere CentOS machine blueprint to your
Rainpole service.
Scenario: Add Your vSphere CentOS Catalog Item to the Rainpole Service
Using your tenant administrator privileges, you add the published vSphere CentOS machine blueprint to
your Rainpole service.
All published blueprints that you want to provision must be part of a service as a catalog item, but each
blueprint can only be a catalog item in one service at a time. If you need to publish to multiple catalog
services at the same time, create copies of your blueprint.
Procedure
1Select Administration > Catalog Management > Services.
2In the Services list, select the Blueprint Testing row and click Manage Catalog Items.
3Click the New icon ( ).
4Select the check box for CentOS on vSphere.
Only published blueprints and components that are not yet associated with a service appear in the
list. If you do not see the blueprint, verify that it was published or that it is not included in another
service.
5Click OK.
6Click Close.
What to do next
Using your tenant administrator privileges, entitle your Rainpole architects to request catalog items from
the Rainpole service.
Scenario: Entitle Your Rainpole Architects to Request Catalog Items
Using your tenant administrator privileges, entitle your Rainpole architects to all actions and items that
belong to the Rainpole service.
By entitling your Rainpole architects to all actions and items in the service, you make it easier for them to
add new catalog items to the service for testing. In a production environment, you might use entitlements
differently and configure strict governance. You might want to manage which catalog items each user is
allowed to request and which actions they can perform against specific catalog items that they own.
Configuring vRealize Automation
VMware, Inc. 418

Procedure
1Select Administration > Catalog Management > Entitlements.
2Click the New icon ( ).
3Configure the details.
a Enter the name Rainpole architect entitlement
b Select Active from the Status drop-down menu.
c Select the your Rainpole business group from the Business Group drop-down menu.
d Add your Rainpole architects by using the Users & Groups search box.
e Click Next.
4Entitle the Rainpole catalog service.
aClick the Add Services icon ( ) beside the Entitled Services heading.
b Select Rainpole service.
c Click OK.
All the users you included on the entitlement are now entitled to all catalog items in the Rainpole
service.
5Entitle all user actions.
aClick the Add Actions icon ( ) beside the Entitled Actions heading.
b Select the checkbox in the column header to entitle all actions.
c Select the Actions only apply to items in this entitlement checkbox so you can later apply
stricter governance to these users in other catalog services.
d Click OK.
Your architects are entitled to perform any applicable action on catalog items they provision from your
Rainpole service. They are not entitled to perform these actions on any items they might provision
from a different service or through a different entitlement.
6Click Finish.
All of your architects can now see and request the vSphere CentOS machine blueprint and any new
catalog items that are added to their service.
What to do next
Using the local test user account you set up, request to provision the vSphere CentOS catalog item to
test the blueprint and your catalog configuration.
Configuring vRealize Automation
VMware, Inc. 419

Scenario: Test Your Rainpole CentOS Machine
Using the local test user account you created, you request to provision your vSphere CentOS machine.
You log into the provisioned machine and verify that it is working as expected.
You are here
Configure
Tenant
Configure IaaS
Resources
Design On-
Demand Services
Procedure
1Scenario: Request Your Rainpole Virtual Machine
Using your test user account, you request the service catalog item to provision a CentOS on
vSphere virtual machine.
2Scenario: Log in to the Provisioned Rainpole Machine
Using the test user account, you log in to your successfully provisioned vSphere CentOS machine.
Scenario: Request Your Rainpole Virtual Machine
Using your test user account, you request the service catalog item to provision a CentOS on vSphere
virtual machine.
Procedure
1Log out of the vRealize Automation console.
2Log back in with the username test_user and password VMware1!.
3Click the Catalog tab.
4Click the Request button to request a catalog item.
5Enter verifying functionality in the Description text box.
6Click Submit to request the catalog item.
7Click the Requests tab to monitor the status of your request.
When the machine is successfully provisioned, the status message Successful appears.
What to do next
Log in to your provisioned machine.
Scenario: Log in to the Provisioned Rainpole Machine
Using the test user account, you log in to your successfully provisioned vSphere CentOS machine.
Configuring vRealize Automation
VMware, Inc. 420
Procedure
1Select Items > Machines.
2Select the arrow next to the CentOS on vSphere item.
The provisioned machine appears under the expanded item.
3Click the provisioned machine.
4Click Remote Log in to Machine on the right-hand panel.
5Log in to the machine.
You installed vRealize Automation in a minimal deployment, set up a proof of concept, and configured
your environment for ongoing development of blueprints.
What to do next
nIf you purchased a vRealize Automation enterprise license, you can continue reading to learn about
provisioning machines with software components.
nPlan for installing a production environment. See Reference Architecture.
nLearn about more options for configuring vRealize Automation, designing and exporting blueprints,
and governing your service catalog. See Configuring vRealize Automation.
Scenario: Make the CentOS with MySQL Application Blueprint
Available in the Service Catalog
As the tenant administrator, you requested that your blueprint architects create a catalog item to deliver
MySQL on CentOS virtual machines for your development and quality engineering group to run test
cases. Your software architect has informed you that the catalog item is ready for users. To make the item
available to your business users, you need to associate the blueprints and Software component with a
catalog service and then entitle the business group members to request the catalog item.
Prerequisites
nLog in to the vRealize Automation console as a tenant administrator or catalog administrator.
nPublish a blueprint to deliver MySQL on vSphere CentOS virtual machines. See Scenario: Assemble
and Test a Blueprint to Deliver MySQL on Rainpole Linked Clone Machines.
nIf you create blueprints in a development environment, import your blueprint into your production
environment. See Exporting and Importing Blueprints.
nCreate a reservation to allocate vSphere resources to your Dev and QE business group. See Create
a Reservation for Hyper-V, KVM, SCVMM, vSphere, or XenServer.
Configuring vRealize Automation
VMware, Inc. 421

Procedure
1Scenario: Create a Development and Quality Engineering Catalog Service
As the tenant administrator, you want to create a separate catalog service for your development and
quality engineering group so your other groups, such as finance and human resources, don't see the
specialized catalog items. You create a catalog service called Dev and QE Service to publish all the
catalog items development and engineering need to run their test cases.
2Scenario: Add CentOS with MySQL to Your Dev and QE Service
As the tenant administrator, you want to add the CentOS with MySQL catalog item to the Dev and
QE service.
3Scenario: Entitle Users to Request Dev and QE Service Items as a Catalog Item
As the tenant administrator, you create a Dev and QE entitlement and add the catalog items and
some relevant actions so your development and quality engineering users can request the CentOS
with MySQL catalog item, and run actions against the machine and the deployment.
Scenario: Create a Development and Quality Engineering Catalog Service
As the tenant administrator, you want to create a separate catalog service for your development and
quality engineering group so your other groups, such as finance and human resources, don't see the
specialized catalog items. You create a catalog service called Dev and QE Service to publish all the
catalog items development and engineering need to run their test cases.
Procedure
1Select Administration > Catalog Management > Services.
2Click the New icon ( ).
3Enter the name Dev and QE Service in the Name text box.
4Enter the description Dev and QE application catalog items for test cases in the
Description text box.
5Select Active from the Status drop-down menu.
6As the catalog administrator who is creating the service, use the search option to add your name as
the Owner.
7Add the Support Team custom user group.
For example, add a custom user group that includes the IaaS architects and software architects so
that you and the service catalog users have someone to contact if you encounter problems
provisioning the catalog items.
8Click OK.
You created and activated a Dev and QE catalog service, but it doesn't contain any catalog items yet.
Configuring vRealize Automation
VMware, Inc. 422

Scenario: Add CentOS with MySQL to Your Dev and QE Service
As the tenant administrator, you want to add the CentOS with MySQL catalog item to the Dev and QE
service.
Procedure
1Select Administration > Catalog Management > Services.
2Select the Dev and QE Service row in the Services list and click Manage Catalog Items.
3Click the New icon ( ).
4Select CentOS with MySQL.
Only published blueprints and components that are not yet associated with a service appear in the
list. If you do not see the blueprint, verify that it was published or that it is not included in another
service.
5Click OK.
6Click Close.
You published the CentOS with MySQL catalog item to the Dev and QE service, but until you entitle users
to the item or the service, no one can see or request the item.
Scenario: Entitle Users to Request Dev and QE Service Items as a Catalog
Item
As the tenant administrator, you create a Dev and QE entitlement and add the catalog items and some
relevant actions so your development and quality engineering users can request the CentOS with MySQL
catalog item, and run actions against the machine and the deployment.
In this scenario, you entitle the service because you want users to be entitled to any future catalog items
that are added to this service. You also want to allow your users to manage their provisioned deployment,
so you add actions like power on and off, snapshot, and destroy deployment to the entitlement.
Procedure
1Select Administration > Catalog Management > Entitlements.
2Click the New icon ( ).
3Configure the details.
a Enter the name Dev and QE Entitlement in the Name text box.
b In the Status drop-down menu, select Active.
c In the Business Group drop-down menu, select the Dev and QE group.
Configuring vRealize Automation
VMware, Inc. 423
d In the Users and Groups area, add one or more users.
Add yourself only, unless you are certain that the blueprint is working as intended. If it is, you can
add individual users and you can add custom user groups.
e Click Next.
4Add the service.
Although you are adding the CentOS and MySQL catalog items separately, adding the service
ensures that any addition items that you add to the service at a later date are available to the
business group members in the service catalog.
aClick the Add Services icon ( ) beside the Entitled Services heading.
b Select Dev and QE Service.
c Click OK.
Dev and QE service is added to the Entitled Services list.
5Add actions.
aClick the Add Actions icon ( ) beside the Entitled Actions heading.
b Click the Type column header to sort the list.
Select the following actions based on type. These actions are useful to the development and
quality engineering users working with their test case machines, and are the only actions that you
want these business group members to use.
Type Action Name
Machine Power On
Machine Power Off
Virtual Machine Create Snapshot
Virtual Machine Revert To Snapshot
Deployment Destroy
The deployment destroy action destroys the entire deployment and not just the virtual machine.
c Click OK.
The five actions are added to the Entitled Actions list.
6Click Finish.
You added the CentOS with MySQL catalog item to your new Dev and QE catalog service and entitled
your business group members to request and manage the item.
Configuring vRealize Automation
VMware, Inc. 424
What to do next
After you verify your work by provisioning the CentOS with MySQL catalog item, you can add additional
users to the entitlement to make the catalog item publicly available to your development and quality
engineering users. If you want to further govern the provisioning of resources in your environment, you
can create approval policies for the MySQL Software component and the CentOS for Software Testing
machine. See Scenario: Create and Apply CentOS with MySQL Approval Policies.
Scenario: Create and Apply CentOS with MySQL Approval Policies
As the tenant administrator for the development and quality engineering business group, you want to
apply strict governance to catalog item requests. Before your users can provision the CentOS with
MySQL catalog item, you want your vSphere virtual infrastructure administrator to approve the machine
request and you want your software manager to approve the software request.
You create and apply one approval policy for the vSphere CentOS with MySQL service catalog request to
require approval for the machine by a vSphere virtual infrastructure administrator based on specific
conditions, and another approval policy for the MySQL Software component to require approval by your
software manager for every request.
Approval administrators can only create the approvals, and a business group managers can apply them
to entitlements. As a tenant administrator, you can both create the approvals and apply them to
entitlements.
Prerequisites
nLog into the vRealize Automation console as a tenant administrator. Only a tenant administrator can
both create and apply approval policies.
nEnsure that the CentOS with MySQL catalog item is included in a service. See Scenario: Make the
CentOS with MySQL Application Blueprint Available in the Service Catalog.
Procedure
1Scenario: Create a CentOS with MySQL Virtual Machine Approval Policy
As the tenant administrator you want to ensure that the development and quality engineering group
receives virtual machines that are properly provisioned in your environment, so you create an
approval policy that requires pre approval for certain types of requests.
2Scenario: Create a MySQL Software Component Approval Policy
As the tenant administrator, your software managers asked you to create and apply approval
policies for MySQL installations to track licensing usage. You create a policy to notify the software
license manager whenever the MySQL for Linux Virtual Machines Software component is requested.
3Scenario: Apply Approval Policies to CentOS with MySQL Components
As the tenant administrator, you can create approval policies and entitlements. You modify the Dev
and QE entitlement to apply the approval policies that you created so that approvals are triggered
when a service catalog user requests the item.
Configuring vRealize Automation
VMware, Inc. 425
Scenario: Create a CentOS with MySQL Virtual Machine Approval Policy
As the tenant administrator you want to ensure that the development and quality engineering group
receives virtual machines that are properly provisioned in your environment, so you create an approval
policy that requires pre approval for certain types of requests.
Because the CentOS with MySQL virtual machine consumes vCenter Server resources, you want the
vSphere virtual infrastructure administrator to approve requests when the requested memory is more than
2048 MB or more than 2 CPUs to ensure that the resources are consumed wisely. You also you give the
approver the ability to modify the requested CPU and memory values before approving a request.
Procedure
1Select Administration > Approval Policies.
2Create an approval policy for virtual machine provisioning.
aClick the New icon ( ).
b Select Select an approval policy type.
c In the list, select Service Catalog - Catalog Item Request - Virtual Machine.
d Click OK.
e Configure the following options:
Option Configuration
Name Enter CentOS on vSphere CPU or Memory VM.
Description Enter Requires VI Admin approval for CPU>2 or Memory>2048.
Status Select Active.
3On the Pre Approval tab, click the Add icon ( ).
4Configure the Level Information tab with the triggering criteria and the approval actions.
a In the Name text box, enter CPU>2 or Memory>2048 - VI Admin.
b In the Description text box, enter VI Admin approval for CPU and Memory.
c Select Required based on conditions.
d In the Clause drop-down list, select Any of the following.
e In the new Clause drop-down list, select CPUs and configure the clause with the values CPU > 2.
f Click Add expression and configure the clause with the values Memory (MB) > 2048.
g Select Specific Users and Groups.
h Enter the name of the vSphere virtual infrastructure administrator or administrator group in the
search text box and click the search icon ( ).
Configuring vRealize Automation
VMware, Inc. 426
i Select the user or group.
j Select Anyone can approve.
The request only needs one virtual infrastructure administrator to verify the resources and
approve the request.
5Click the System Properties tab and select the properties that allow the approver to modify the
requested CPU and Memory values before approving a request.
a Select the CPUs and Memory (MB) check boxes.
b Click OK.
6Click OK.
You created an approval policy for virtual machine requests, but you still want to create an approval for
the MySQL component. Until you apply the policies to an entitlement, no approvals are triggered.
Scenario: Create a MySQL Software Component Approval Policy
As the tenant administrator, your software managers asked you to create and apply approval policies for
MySQL installations to track licensing usage. You create a policy to notify the software license manager
whenever the MySQL for Linux Virtual Machines Software component is requested.
In some environments you might need this type of approval because license keys must be provided by
the software manager. In this scenario, you only need the software manager to track and approve the
request. After you create the approval policy, you apply the policy to the MySQL for Linux Virtual
Machines catalog item. This approval policy is very specific and can only be applied to the MySQL for
Linux Virtual Machines Software component in the entitlements.
Procedure
1Select Administration > Approval Policies.
2Create an approval policy for the MySQL Software component.
aClick the New icon ( ).
b Select Select an item.
c Select MySQL for Linux Virtual Machines.
d Click OK.
e Configure the following options:
Option Configuration
Name Enter MySQL tracking approval.
Description Enter Approval request sent to software manager.
Status Select Active.
3On the Pre Approval tab, click the Add icon ( ).
Configuring vRealize Automation
VMware, Inc. 427

4Configure the Level Information tab with the triggering criteria and the approval actions.
a In the Name text box, enter MySQL software deployment notice.
b In the Description text box, enter Software mgr approval of software installation.
c Select Always required.
d Select Specific Users and Groups.
eEnter the name of the software manager in the search text box and click the search icon ( ) and
select the user.
f Select Anyone can approve.
The request only needs one software manager to approve the request.
Click OK.
5Click OK.
You created the approval policies for virtual machines and for MySQL for Linux Virtual Machines Software
components. Until you apply the approval policies to an entitlement, no approvals are triggered.
Scenario: Apply Approval Policies to CentOS with MySQL Components
As the tenant administrator, you can create approval policies and entitlements. You modify the Dev and
QE entitlement to apply the approval policies that you created so that approvals are triggered when a
service catalog user requests the item.
While it might be easier to entitle the entire catalog service to your business group, it does not allow you
to have the same control and governance as when you create individual entitlements for catalog items.
For example, if you entitle users to a service, they can request any catalog items that are in the service
and all items that are added to the service in the future. It also means that you can only use very high-
level approval policies that apply to every catalog item in the service, such as always requiring approval
from a manager. If you choose to entitle catalog items individually, you can create and apply very specific
approval policies for each item and tightly control who can request which items in the service. If you
choose to entitle the individual components of catalog items individually, you can have even greater
control.
If you do not know what approval policies you want to apply to items in an entitlement, you can return
later and apply them. In this scenario, you apply different approval policies to two components of the
same published application blueprint.
Procedure
1Select Administration > Catalog Management > Entitlements.
2Click the Dev and QE Entitlement.
3Click the Items and Approvals tab.
Configuring vRealize Automation
VMware, Inc. 428

4Add the CentOS with MySQL machine and apply the approval policy.
aClick the Add Items icon ( ) beside the Entitled Items heading.
b Select the CentOS with MySQL check box.
c Click the Apply this policy to selected items drop-down arrow.
The CentOS on vSphere CPU and Memory policy is not in the list.
d Click Show all and click the down-arrow to view all approval policies.
e Select CentOS on vSphere CPU and Memory [Service Catalog - Catalog Item Request -
Virtual Machine].
The vSphere CentOS machine is a machine blueprint in an application blueprint. Review the
policy names so that you select the one that is appropriate to your catalog item type. If you apply
the wrong policy, the approval policy fails or triggers approval requests based on incorrect
conditions.
f Click OK.
5Add the MySQL for Linux Virtual Machine software component as an item and apply an approval
policy to the MySQL item.
aClick the Add Items icon ( ) beside the Entitled Items heading.
b In the Appears in Catalog drop-down menu, select No.
Software components are always associated with a machine. They are not available to
individually request in the service catalog.
c Select the MySQL for Linux Virtual Machines check box.
d Click the Apply this policy to selected items drop-down arrow.
e Select MySQL tracking approval [Service Catalog - Catalog Item Request - Software
Component].
You do not need the advanced option because the approval policy was created for this specific
software component, which is added to a virtual machine.
f Click OK.
Configuring vRealize Automation
VMware, Inc. 429
6Add actions that the users can run on the provisioned machine.
Approval policies are not applied to actions in this scenario.
aClick the Add Items icon ( ) beside the Entitled Actions heading.
b Select the following actions.
Name / Type Description
Create Snapshot / Virtual Machine Creates a snapshot of the virtual machine, including the installed software.
Allows the developers to create snapshots to which they can revert during
development.
Destroy / Deployment Destroys the entire provisioned blueprint, not just the machine. Use this action
to avoid orphaned components.
Power Off / Machine Turns the virtual machine off.
Power On / Machine Turns the virtual machine on.
Revert to Snapshot / Virtual Machine Reverts to a previously created snapshot.
c Click OK.
7Click Finish.
This entitlement allows you to require different approvals on different blueprint components.
What to do next
Request the CentOS with MySQL item in the service catalog as a member of the business group to verify
that the entitlement and the approvals are behaving as expected.
Configuring vRealize Automation
VMware, Inc. 430