Samsung SRN 472S 1TB User Manual To The 93fe34f1 7922 4b73 9355 5df3d2c87cd0
User Manual: Samsung SRN-472S-1TB to the manual
Open the PDF directly: View PDF ![]() .
.
Page Count: 158 [warning: Documents this large are best viewed by clicking the View PDF Link!]

NETWORK VIDEO RECORDER
User Manual SRN-472S
Copyright
©2014 Samsung Techwin Co., Ltd. All rights reserved.
Trademark
is the registered logo of Samsung Techwin Co., Ltd.
The name of this product is the registered trademark of Samsung Techwin Co., Ltd.
Other trademarks mentioned in this manual are the registered trademark of their respective company.
Restriction
Samsung Techwin Co., Ltd shall reserve the copyright of this document. Under no circumstances, this document shall be reproduced,
distributed or changed, partially or wholly, without formal authorization of Samsung Techwin.
Disclaimer
Samsung Techwin makes the best to verify the integrity and correctness of the contents in this document, but no formal guarantee shall be
provided. Use of this document and the subsequent results shall be entirely on the user’s own responsibility. Samsung Techwin reserves the
right to change the contents of this document without prior notice.
Design and specifications are subject to change without prior notice.
The initial administrator ID is “admin” and the password should be set when logging in for the first time.
Set password for your wireless network if you use the product with a wireless router. Being not protected with password or
using the default wireless router password may expose your video data to potential threat.
Please change your password every three months to safely protect personal information and to prevent the damage of the
information theft.
Please, take note that it’s a user’s responsibility for the security and any other problems caused by mismanaging a password.
Network Video Recorder
User Manual
English _3
● OVERVIEW
IMPORTANT SAFETY INSTRUCTIONS
Read these operating instructions carefully before using the unit.
Follow all the safety instructions listed below.
Keep these operating instructions handy for future reference.
1) Read these instructions.
2) Keep these instructions.
3) Heed all warnings.
4) Follow all instructions.
5) Do not use this apparatus near water.
6) Clean only with dry cloth.
7) Do not block any ventilation openings, Install in accordance with the manufacturer's instructions.
8) Do not install near any heat sources such as radiators, heat registers, stoves, or other apparatus (including
amplifiers) that produce heat.
9) Do not defeat the safety purpose of the polarized or grounding- type plug. A polarized plug has two blades
with one wider than the other. A grounding type plug has two blades and a third grounding prong. The
wide blade or the third prong are provided for your safety. if the provided plug does not fit into your outlet,
consult an electrician for replacement of the obsolete outlet.
10) Protect the power cord from being walked on or pinched particularly at plugs, convenience receptacles,
and the point where they exit from the apparatus.
11) Only use attachments/accessories specified by the manufacturer.
12) Use only with the cart, stand, tripod, bracket, or table specified by the manufacturer,
or sold with the apparatus. When a cart is used, use caution when moving the cart/
apparatus combination to avoid injury from tip-over.
13) Unplug this apparatus during lightning storms or when unused for long periods of
time.
14) Refer all servicing to qualified service personnel. Servicing is required when the
apparatus has been damaged in any way, such as power-supply cord or plug is
damaged, liquid has been spilled or objects have fallen into the apparatus, the apparatus has been
exposed to rain or moisture, does not operate normally, or has been dropped.
Standards Approvals
M
`
This equipment has been tested and found to comply with the limits for a Class A digital device, pursuant to part 15 of the
FCC Rules. These limits are designed to provide reasonable protection against harmful interference when the equipment is
operated in a commercial environment.
This equipment generates, uses, and can radiate radio frequency energy and, if not installed and used in accordance with the
instruction manual, may cause harmful interference to radio communications. Operation of this equipment in a residential area
is likely to cause harmful interference in which case the user will be required to correct the interference at his own expense.
overview
4_ overview
overview
BEFORE START
This manual provides operational information necessary for using the product and contains a description about each
component part and its function as well as menu or network settings.
You have to keep in mind the following notices :
• SAMSUNG retains the copyright on this manual.
• This manual cannot be copied without SAMSUNG's prior written approval.
• We are not liable for any or all losses to the product incurred by your use of non-standard product or violation of
instructions mentioned in this manual.
• Prior to opening the case, please consult a qualified technician first. Whenever this is needed power must be
removed from the unit.
• Before adding a hard disk drive or external storage (USB memory, USB HDD, etc), check if it is compliant with this
product. For the compatibility list, contact the retailer.
Warning
Battery
It is essential that when changing the battery in the unit, the replacement battery must be of the same type
otherwise there may be a possibility of an explosion.
The following are the specifications of the battery you are using now.
• Normal voltage : 3V
• Normal capacity : 170mAh
• Continuous standard load : 0.2mA
• Operating temperature : -20°C ~ +85°C
(-4°F ~ +185°F)
Caution
• Connect the power cord into a grounded outlet.
• The Mains plug is used as a disconnect device and shall stay readily operable at any time.
• Batteries shall not be exposed to excessive heat such as sunshine, fire or the like.
• Risk of Explosion if Battery is replaced by an Incorrect Type. Dispose of Used Batteries According to the
Instructions.
System Shutdown
Turning off the power while the product is in operation, or undertaking improper actions may cause damage or
malfunction to the hard drive or the product.
To safely turn off the power, check <OK> in the system termination pop up window and then remove the power
chord.
You may want to install a UPS system for safe operation in order to prevent damage caused by an unexpected
power stoppage. (Any questions concerning UPS, consult your UPS retailer.)
J `
If powered off abnormally, restarting may take more time for restoring data from hard disk drive for proper operation.
CALIFORNIA USA ONLY
This Perchlorate warning applies only to primary CR (Manganese Dioxide)
Lithium coin cells in the product sold or distributed ONLY in California USA.
"Perchlorate Material - special handling may apply,
See www.dtsc.ca.gov/hazardouswaste/perchlorate."
English _5
● OVERVIEW
Operating Temperature
The guaranteed operating temperature range of this product is 0°C ~ 40°C (32°F ~ 104°F).
This product may not work properly if you run right after a long period of storage at a temperature below the
guaranteed one.
Prior to using a device that has been stored for a long period in low temperatures, allow the product to stand at
room temperature for a period.
Especially for the built-in HDD in the product, its guaranteed temperature range is 5°C ~ 55°C (41°F ~ 131°F).
Likewise, the hard drive may not work at a temperature below the guaranteed one.
Ethernet Port
This equipment is in door use and all the communication wirings are limited to inside of the building.
Security Precautions
The initial administrator ID is “admin” and the password should be set when logging in for the first time.
Set password for your wireless network if you use the product with a wireless router. Being not protected with
password or using the default wireless router password may expose your video data to potential threat.
Please change your password every three months to safely protect personal information and to prevent the
damage of the information theft.
Please, take note that it’s a user’s responsibility for the security and any other problems caused by
mismanaging a password.
6_ overview
overview
CONTENTS
OVERVIEW
3
3 Important Safety Instructions
4 Before Start
6 Contents
8 Features
10 Part Names and Functions (Front)
11 Part Names and Functions (Rear)
12 Remote Control
INSTALLATION
13
13 Checking the installation environment
14 Rack Installation
14 HDD Addition
CONNECTING WITH OTHER DEVICE
17
17 Connecting to an external device
18 Connecting the USB
19 Connecting the Alarm Input/Output
20 Connecting the Network
LIVE
23
23 Getting Started
25 Live Screen Configuration
32 Live Screen Mode
35 Zoom
36 PoE Status
36 Audio ON/OFF
37 Freeze
37 Event Monitoring
38 PTZ control
MENU SETUP
41
41 System Setup
52 Setting the Device
69 Setting the Recording
73 Setting the Event
76 Network Configuration
English _7
● OVERVIEW
SEARCH & PLAY
88
88 Search
91 Playback
STARTING WEB VIEWER
93
93 What is Web Viewer?
94 Connecting Web Viewer
LIVE VIEWER
96
96 Live Viewer
98 Live Screen Configuration
103 Controlling a Connected Network Camera
SEARCH VIEWER
105
105 Search Viewer
SETUP VIEWER
109
109 Setup Viewer
BACKUP VIEWER
127
127 SEC Backup Viewer
APPENDIX
129
129 Product Specification
134 Product Overview
135 Default Setting
138 Troubleshooting
142 Open Source License Report on the Product
8_ overview
overview
FEATURES
The product records video and audio from network cameras to a hard disk, and enables playback from the hard disk.
It also provides remote monitoring environment for video and audio over the network using a remote computer.
• User-friendly UI
• VGA, 4CIF, record in a max of 2592X1944 (5M pixel) supported
• Record and play video
• Record and play audio
• Supports ONVIF Pofile S standard and RTP / RTSP protocols
• Play high-definition video using the HDMI cable
• Display the HDD operation status by HDD SMART
• HDD overwrite enabled
• Backup using USB 2.0 protocols and external HDD
• Simultaneous play of 4 channels
• Various Search Modes (Search by Time, Event, Backup)
• Various Recording Modes (Normal, Event, Scheduled Recording)
• Alarm Input / Output
• Remote Monitoring function by Windows Network Viewer
• Live monitoring of the network camera
• Installation Wizard Function (Easy Setup, Quick Setup)
English _9
● OVERVIEW
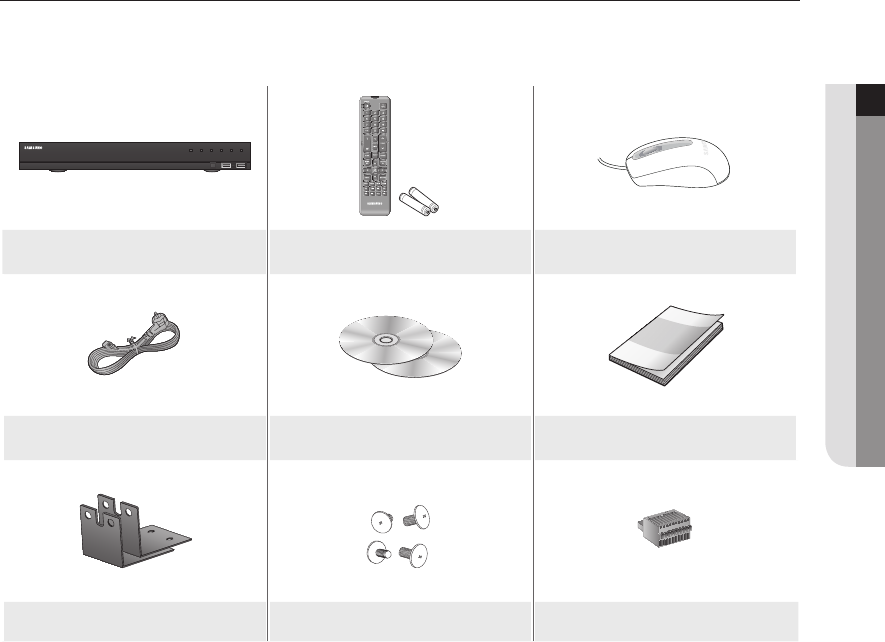
Package Contents
Please unwrap the product, and place the product on a flat place or in the place to be installed.
Please check the following contents are included in addition to the main unit.
'9
6516
1(7:25.9,'(25(&25'(5
REC HDD ALARM
NETWORK BACKUP
POWER
NVR Remote Control /
Remote Control Battery (AAA) Mouse
Power Cable Network Viewer Software /
User Manual CD User Manual or Quick Manual
Bracket rack Bracket mounting screws Terminal block
10_ overview
overview
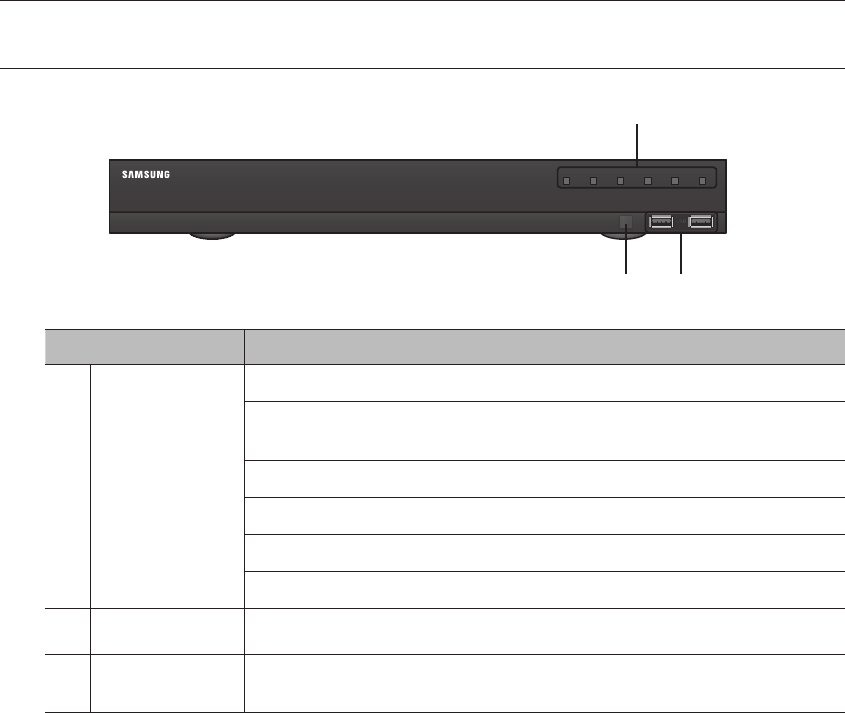
PART NAMES AND FUNCTIONS (FRONT)
Part Names Functions
LED Indicator
REC : Lights on when recording is in progress.
HDD : Displays the normal access to HDD.
LED turns on when accessing the hard disk.
ALARM : Lights on when an event occurs.
NETWORK : Displays both network connection and data transfer status.
BACKUP : Displays when Backup is in progress.
POWER : Shows the power ON/OFF status.
b
USB Connects the USB devices.
c
Remote Reception
System Receive the signal from the remote control.
'9
6516
1(7:25.9,'(25(&25'(5
REC HDD ALARM
NETWORK BACKUP
POWER
c b
English _11
● OVERVIEW
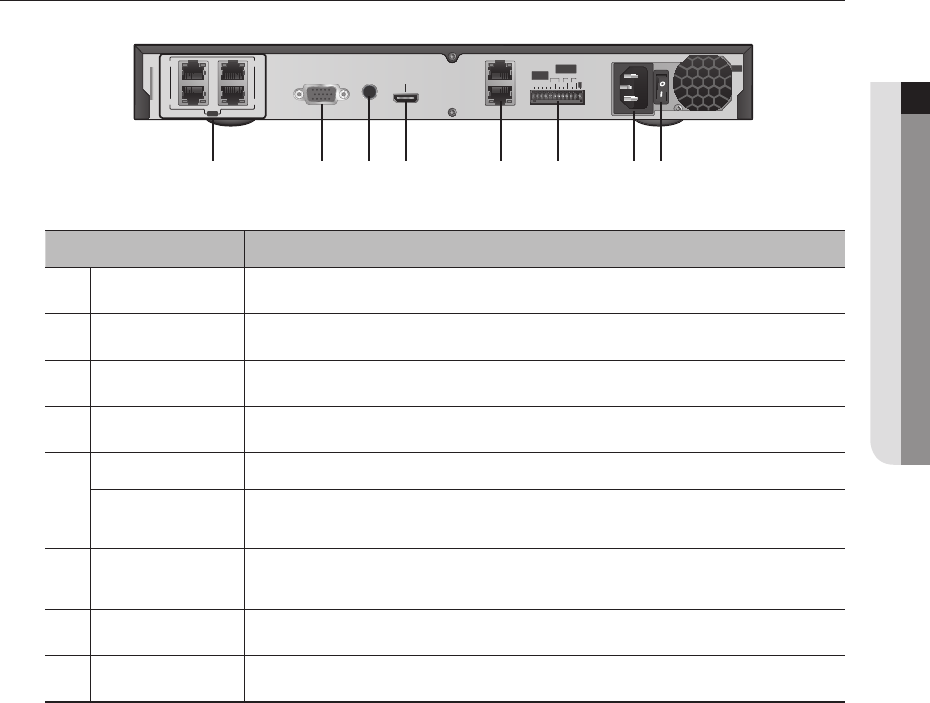
PART NAMES AND FUNCTIONS (REAR)
Part Names Functions
PoE 1/2/3/4 Power supply port to connect to a camera.
b
VGA OUT VGA Video Signal Output Port.
c
AUDIO OUT Audio Signal Output Port (RCA jack).
HDMI HDMI connector port.
NETWORK 2 Port used to send video to the web viewer.
NETWORK 1 Port connected to a camera, and you can access the camera's web viewer to setup detailed
camera settings.
ALARM - ALARM IN : Alarm input ports.
- ALARM OUT : Alarm output ports.
Power Terminal to connect power to.
Power Switch Power on/off switch.
G
1&12 12 12
&20 &20 &20
ALARM
OUT
ALARM
IN
AC 100
240~IN
3R(
3R(
3R(
3R(
9*$287
$8',2
287 +'0,
1(7:25.
1(7:25.
3R(
cb
12_ overview
overview
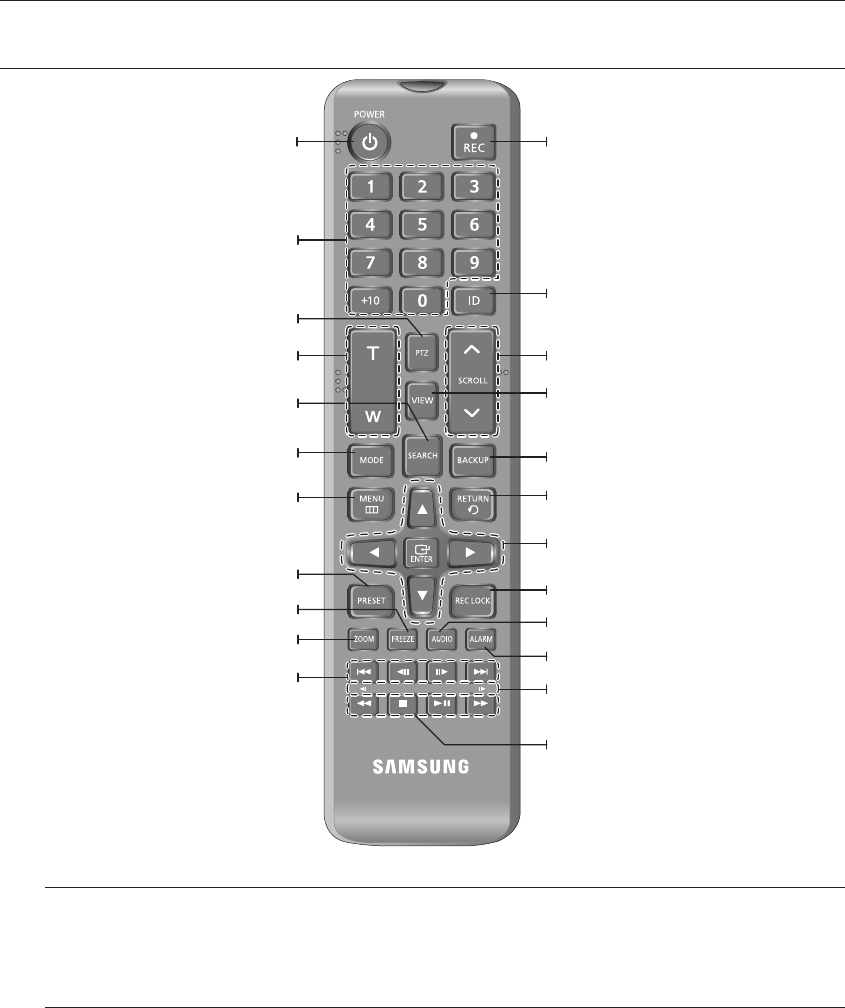
REMOTE CONTROL
Using the Numeric buttons
1. Select a number between 1 and 4.
2. Move to the selected channel number.
Changing the Remote Control ID
Remote control’s ID and NVR’s ID should be matched for proper operation.
1. Press the [ID] button of the remote control and check the ID displayed on the NVR screen.
The factory default ID of the remote control is 00.
2. Enter 2 digits of your selection in order, while pressing the [ID] button of the remote control.
3. When ID input is done, press the [ID] button of the remote control again to check the setting.
M
`If you want to change the remote control ID to 08: Press 0 and 8 in order while the [ID] button of the remote control is
pressed.
For changing the ID of remote device, refer to “Remote Devices”. (Page 67)
POWER
Displays the Exit pop up screen.
REC
Starts or ends the live recording.
ID
Sets the ID of the system.
Select 2 digits from 0 ~ 9 while pressing the ID Key.
VIEW
Runs the View function in the PTZ mode.
BACKUP
Displays the Backup Menu.
RETURN
Returns to the previous screen.
REC LOCK
Selects the recording lock function.
AUDIO
Turns Audio on/off.
Up/Down/Left/Right(▲▼◄ ►)/ENTER
Moves the cursor up/down/left/right, and runs the
Select Menu.
Move Frame
While paused, moves to the previous/next frame.
SCROLL ,.
Moves the menu scroll.
FR, STOP, PLAY/PAUSE, FF
MODE
Changes the screen mode.
MENU
Display the live screen menu.
ZOOM
Runs the digital zoom (x2) function.
NUMBER [0~+10]
Used as the numeric input keys, or displays a single
channel.
T/W
Zooms in or out.
PTZ
Displays or ends PTZ.
SEARCH
Displays the search menu.
PRESET
Displays the Preset Setup.
FREEZE
Freezes the screen temporarily.
Skip Backward (by unit time),
Slow Rewind, Slow Forward,
Skip Forward (by unit time)
ALARM
Cancels the Alarm.
English _13
● INSTALLATION
installation
Please take note of the followings before using this product.
• Do not use the product outdoor.
• Do not spill water or liquid in the connection part of the product.
• Do not impose the system to excessive shock or force.
• Do not pull out the power plug forcefully.
• Do not disassemble the product on your own.
• Do not exceed the rated input/output range.
• Use a certified power cord only.
• For the product with an input ground, use a grounded power plug.
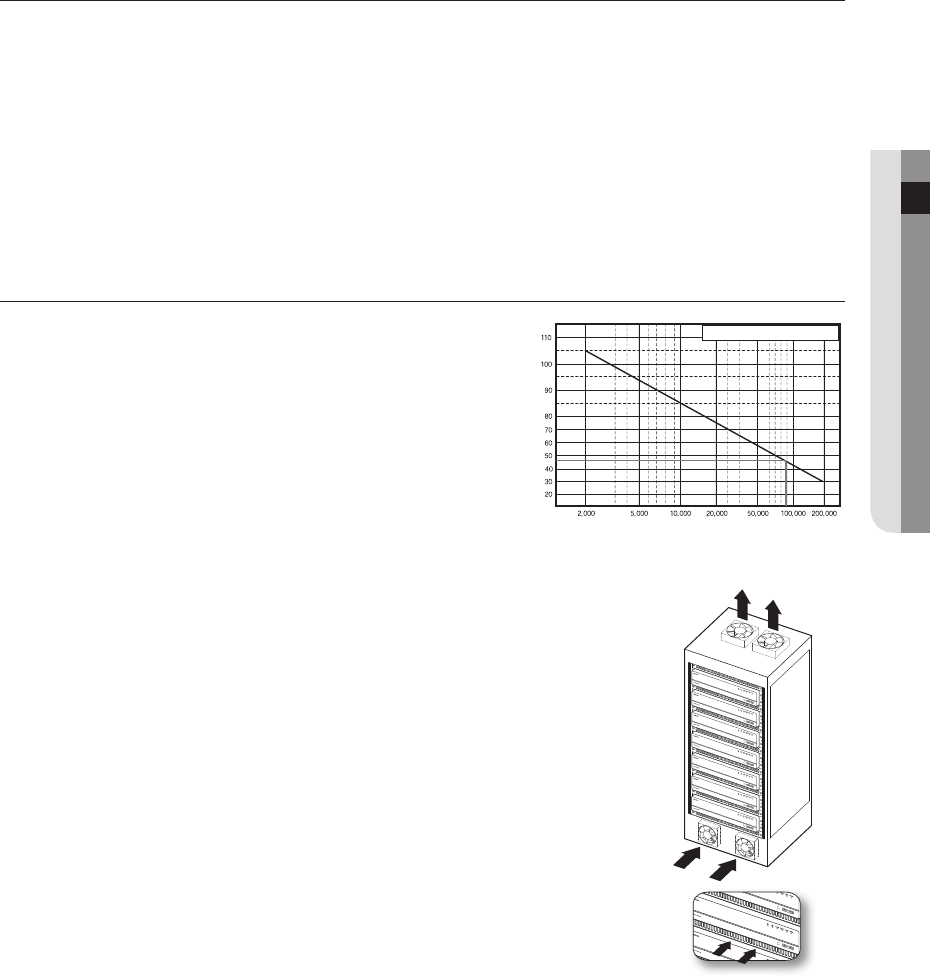
CHECKING THE INSTALLATION ENVIRONMENT
This product is a top-notch security device that is equipped
with a high-capacity HDD and other key circuit boards.
Note that an excessive internal temperature of the product may
cause a system failure or a shortened product life (see the right
figure). Keep in mind the following instructions before installing
the product.
When mounting the product on a rack, comply with the following instructions.
1. Please ensure that the rack inside is not sealed.
2. Please ensure the air is circulated through the inlet/outlet as shown in the picture.
3. If you pile up the prudcts or other rack-mount devices as shown in figure 2, secure
room for ventilation or install a vent.
4. For natural air convection, place the inlet at the bottom of the rack and the outlet on
top.
5. It is strongly recommended that a fan motor is installed at the inlet and the outlet for air
circulation. (Please fit a filter at the inlet to screen dust or foreign substances.)
6. Please maintain the temperature inside the rack or surrounding areas between 0°C ~
40°C (32°F ~ 104°F) as shown in the figure 1.
Rack Mount Instructions - The following or similar rack-mount instructions are
included with the installation instructions :
A) Elevated Operating Ambient - If installed in a closed or multi-unit rack assembly, the
operating ambient temperature of the rack environment may be greater than room
ambient. Therefore, consideration should be given to installing the equipment in an
environment compatible with the maximum ambient temperature (Tma) specified by the manufacturer.
B) Reduced Air Flow - Installation of the equipment in a rack should be such that the amount of air flow required
for safe operation of the equipment is not compromised.
C) Mechanical Loading - Mounting of the equipment in the rack should be such that a hazardous condition is
not achieved due to uneven mechanical loading.
D) Circuit Overloading - Consideration should be given to the connection of the equipment to the supply circuit
and the effect that overloading of the circuits might have on overcurrent protection and supply wiring.
Appropriate consideration of equipment nameplate ratings should be used when addressing this concern.
E) Reliable Earthing - Reliable earthing of rack-mounted equipment should be maintained. Particular attention should
be given to supply connections other than direct connections to the branch circuit (e.g. use of power strips).
One Year: 24HR X 365 DAY =8,760 HR
Temperature
Unit: ºC
Life (Unit: HOURS)
[Figure 1]
[Figure 2]
[Fi 2
]
14_ installation
installation
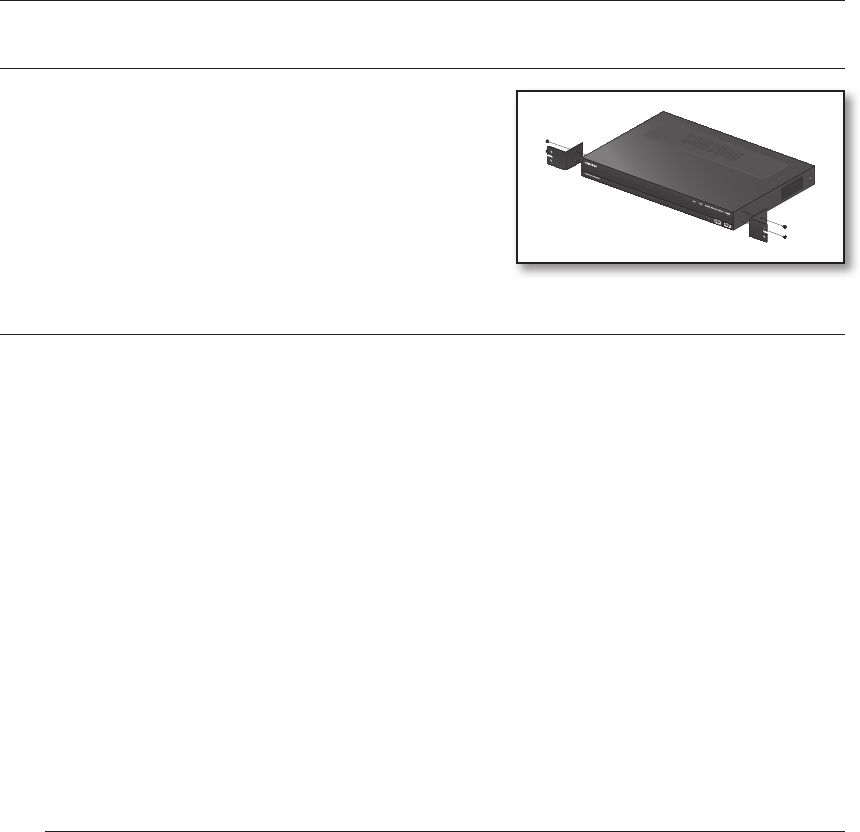
RACK INSTALLATION
Install the Bracket-Rack as shown in the figure, and then fasten the
screws on both sides (2 screws on each side).
`Fix the screws not to be loosened by vibrations.
HDD ADDITION
Make sure to unplug the power cord from the wall outlet to prevent possible electric shock, injury or product damage.
Please consult your provider for further information on HDD installation since improper installation or settings may
damage the product.
`Number of HDDs supported : Basic 1 EA + max 1 can be added.
`Make sure to unplug the power cord from the wall outlet before proceeding with the installation.
J `Cautions for data loss (HDD care)
Please pay attention so that the data inside the HDD is not damaged.
Before adding a HDD, please check the compatibility with this product.
HDD is vulnerable to malfunction due to its sensitive nature especially against shock when operating.
Please ensure that the HDD is free from such shock.
We are not liable for any damage to the HDD incurred by user's carelessness or miss use.
`Cases might cause damage to HDD or recorded data
To minimize the risk of data loss from a damaged HDD, please backup data as often as possible.
If exposed to shock when disassembling or installing, data stored in the hard disk may be damaged.
A sudden power failure or turning off the product while in HDD operation may damage the hard disk drive.
HDD or files stored inside may be damaged if the main body is moved or impacted during the HDD operation.
Cautions when installing a HDD
1. Do not apply excessive force to the HDD.
2. Pay attention so as not to lose the disassembly screws or accessories.
`If the screws or accessories are not put together correctly, the product may breakdown or not operate properly.
3. Please check the HDD compatibility before adding a HDD.
`Please contact your nearest dealer to obtain the list of compatible devices.
English _15
● INSTALLATION
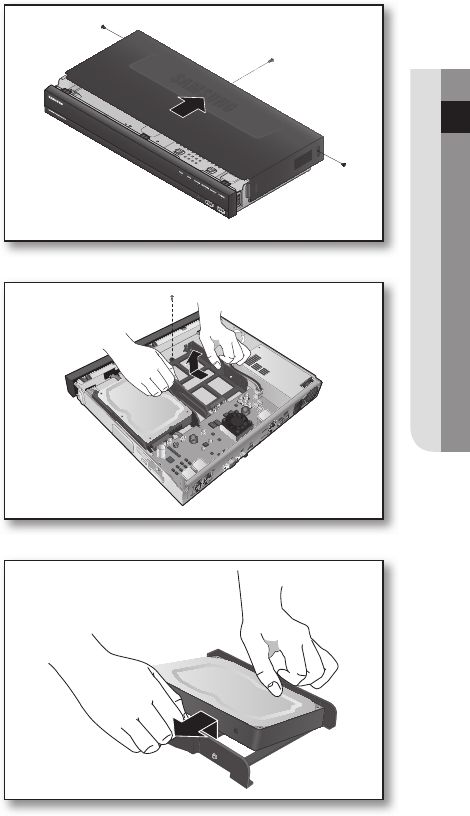
When you mount an HDD
1. Unfasten the screws on the side and in the rear and
remove the cover.
2. Unfasten the screws on the HDD bracket and
remove the bracket.
`Press the handle on both sides of the bracket and pull it
forward. The main body and the bracket will separate.
3. First combine the HDD bracket and one side of the
HDD and open the bracket on the other side to
mount the HDD.
`Insert the screws from the HDD bracket into the HDD screw
hole.
G
1&
12 12 12
&20 &20&20
ALARM
OUT
ALARM
IN
16_ installation
installation
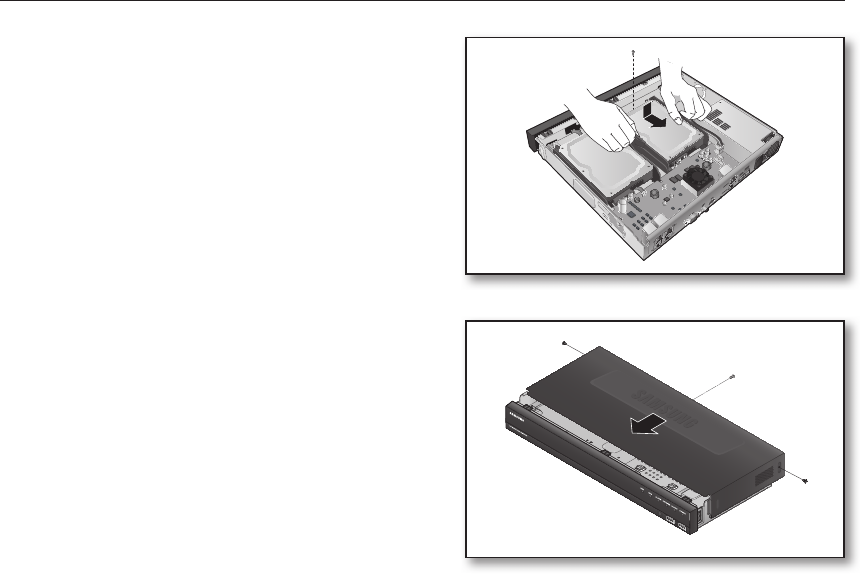
4. Press the bracket where the HDD is mounted and fix
it in with screws.
5. Close the cover and use the screws to fix it.
G
1&12 12 12
&20 &20&20
ALARM
OUT
ALARM
IN
English _17
● CONNECTING WITH OTHER DEVICE
connecting with other device
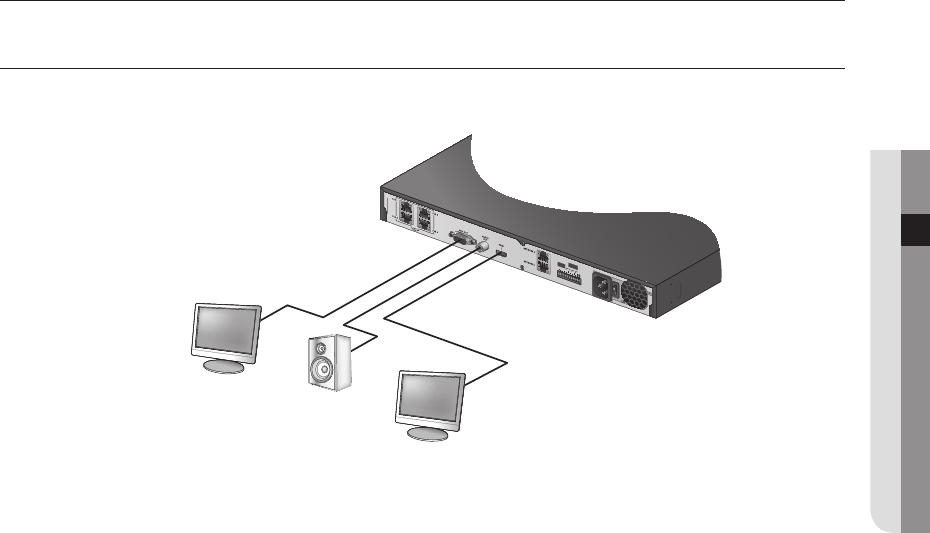
CONNECTING TO AN EXTERNAL DEVICE
J `Unrated or improper power source may cause damage to the system. Ensure that you use only the rated power source
before pressing the POWER button.
G
1&
12 12 12
&20&20 &20
ALARM
OUT
ALARM
IN
VIDEO OUT
(VGA) AUDIO OUT
HDMI OUT
18_ connecting with other device
connecting with other device
CONNECTING THE USB
1. On the front of the product, there is a USB port.
2. You can connect a USB HDD, USB CD/DVD player, USB memory or mouse to the USB port.
3.
If a USB HDD is connected to the system, recognition and settings are available in "Menu Setup > Device >
Storage Device". (Page 65)
4. The product supports hot plugging function that enables connecting/disconnecting USB devices while in
operating the system.
J `If you use the USB device for Backup purposes, format it with FAT32 on PC if it is not formatted on the NVR.
`Some USB devices may fail to function properly due to compatibility issue, please check the device before using.
`Only USB storage devices that comply with the standards (having a metal cover) are guaranteed for data transfer.
`In case if the USB device’s electric contacts have been worn out, data transfer between the devices may not properly
function.
English _19
● CONNECTING WITH OTHER DEVICE
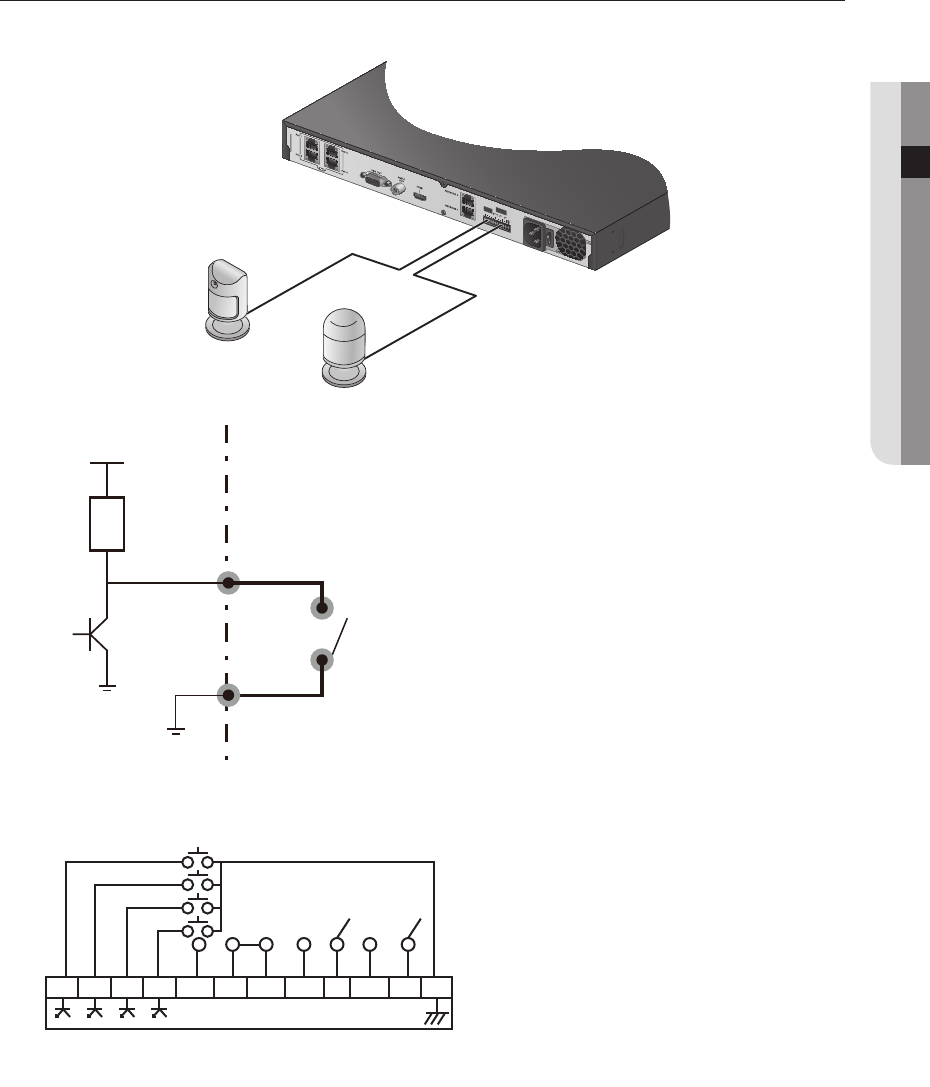
CONNECTING THE ALARM INPUT/OUTPUT
The Alarm In/Out port at the back is composed of the following.
• ALARM IN 1 ~ 4 : Alarm Input Port
• ALARM OUT 1 ~ 3 : Alarm Output Port
Open collector
output device
Mechanical
switch
I/O
1.2KΩ
GND
VDD
GND
or
G
1&12 1212
&20 &20 &20
ALARM
OUT
ALARM
IN
Sensors
Alarm
1 2 3 4 N.O C N.C N.O C N.O C G
ALARM OUT
(30VDC 2A,
125VAC 0.5A MAX)
ALARM IN
(5mA sink)
20_ connecting with other device
connecting with other device
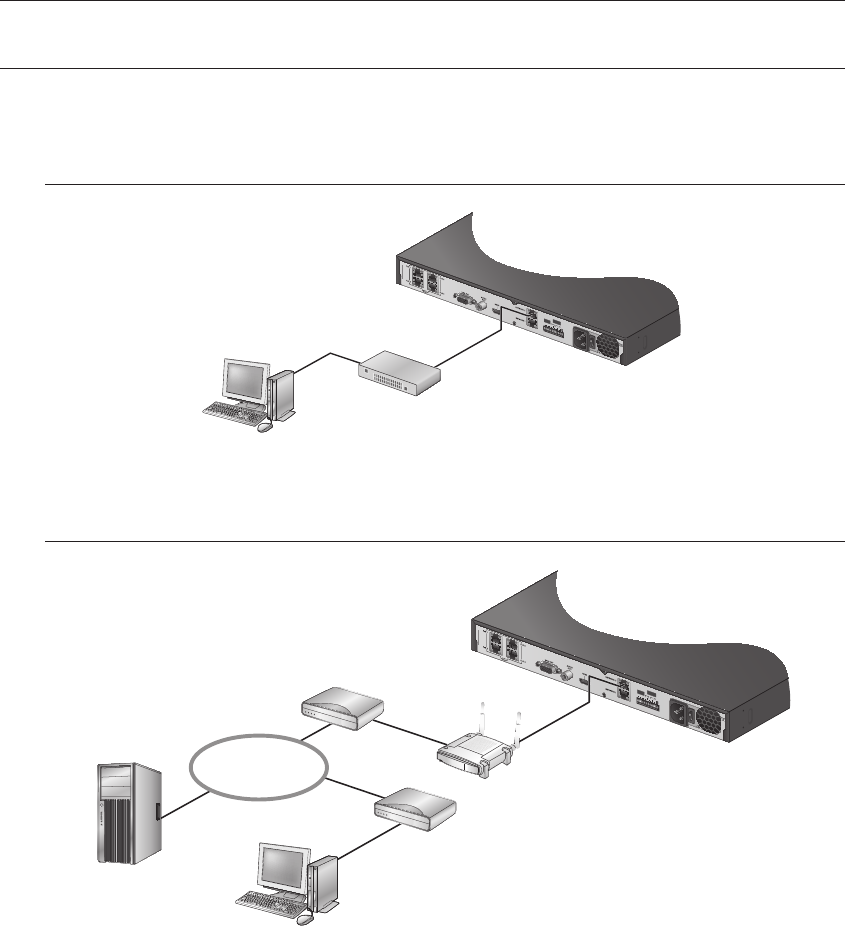
CONNECTING THE NETWORK
M
`For more information about network connection, refer to "Network Configuration". (Page 76)
Network connection via Ethernet (10/100BaseT)
Network connection via router
G
1&
12 12 12
&20 &20 &20
ALARM
OUT
ALARM
IN
Windows
Network Viewer
Switch
G
1&
12 12 12
&20 &20 &20
ALARM
OUT
ALARM
IN
Brodband router
xDSL or Cable
Modem
xDSL or Cable
Modem
Windows
Network Viewer
DDNS Server
(Data Center)
NETWORK
English _21
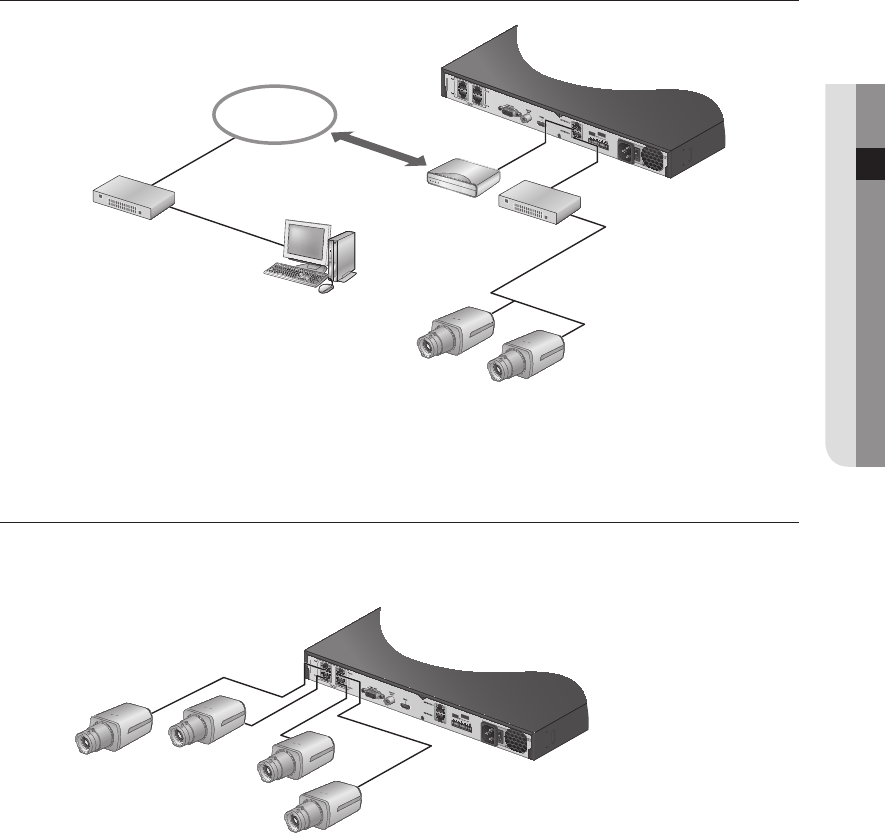
● CONNECTING WITH OTHER DEVICE
Connecting to Internet through PPPoE
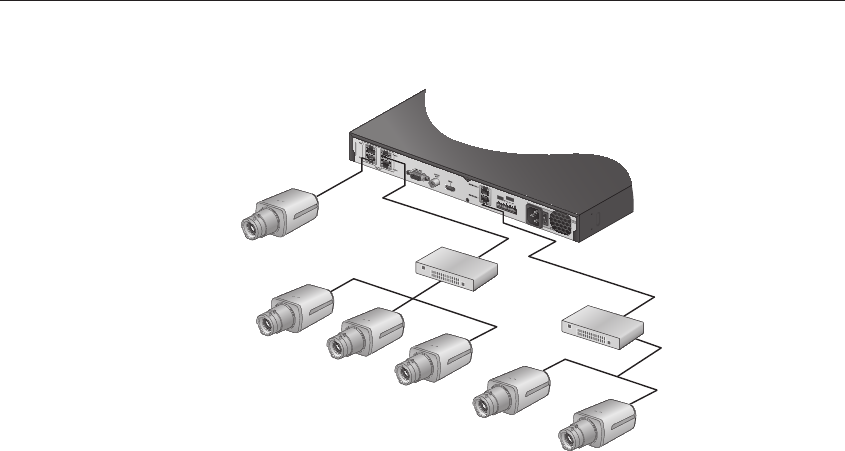
Connecting the network camera
PnP mode
G
1&
12 12 12
&20 &20 &20
ALARM
OUT
ALARM
IN
Network Camera
ex) IP : 192.168.231.20
Network Camera
ex) IP : 192.168.231.40
Network Camera
ex) IP : 192.168.231.30
Network Camera
ex) IP : 192.168.231.10
ex
ex
)
)
IP
IP
:
:
192.168.231.100
192.168.231.100
G
1&
12 12 12
&20 &20 &20
ALARM
OUT
ALARM
IN
Windows
Network Viewer
NETWORK
PPPoE MODEM
Switch
Phone(PPPoE)
Line
Switch
Network Camera
Network Camera
22_ connecting with other device
connecting with other device
Manual mode
G
1&
12 1212
&20 &20&20
ALARM
OUT
ALARM
IN
Switch
Switch
Network Camera
Network Camera
ex) IP : 192.168.1.20 Network Camera
ex) IP : 192.168.1.10
Network Camera
Network Camera
Network Camera
ex
ex
)
)
IP
IP
:
:
192.168.1.100
192.168.1.100
English _23
● LIVE
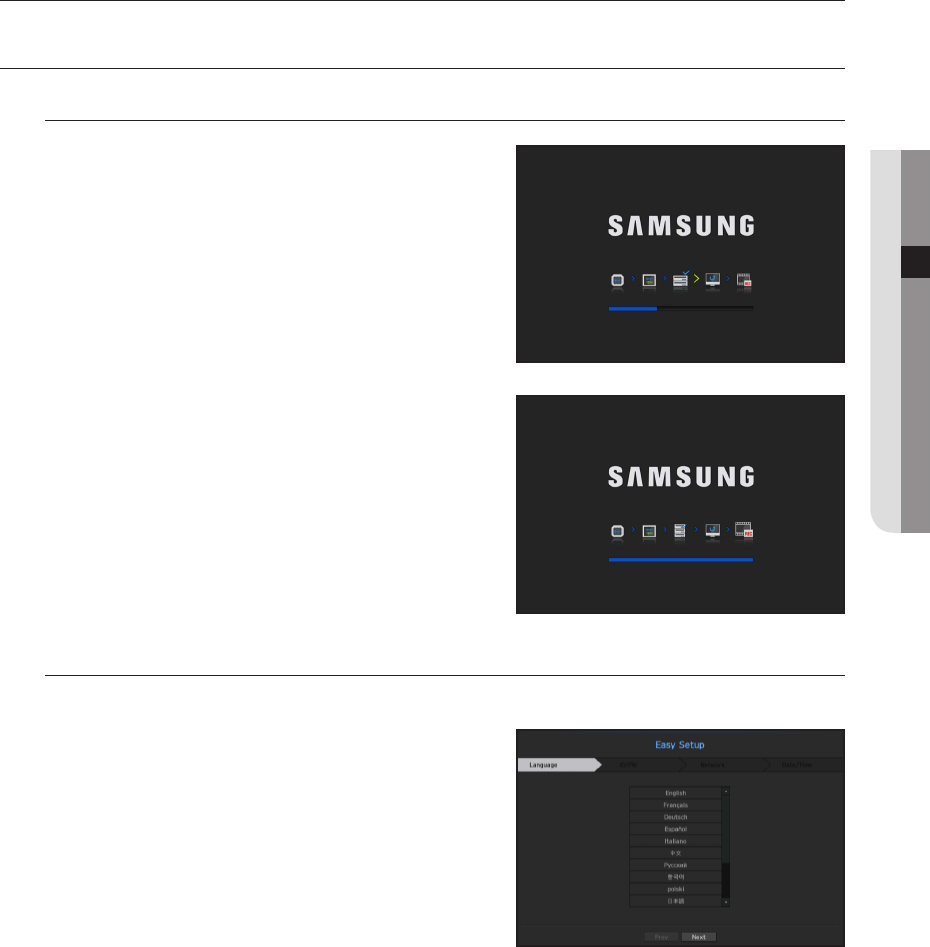
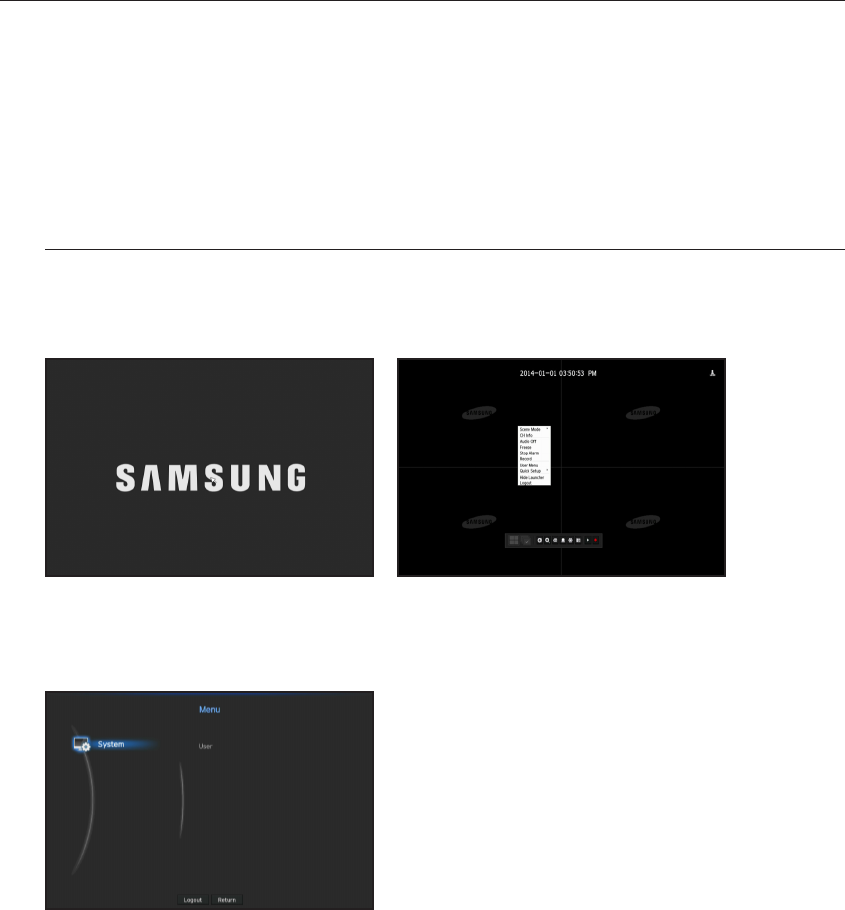
GETTING STARTED
Starting the system
1. Connect the power cable of the NVR to the wall outlet.
2. You will see the initialization screen.
The initialization process will last about 2 minute.
If a new HDD is installed, the initialization process may take
longer.
Easy Setup
This setting makes it easy to set language, ID/password, networks, and date/time.
1. When you start the product, the initialization screen will
appear. Then the <Easy Setup> screen will appear.
Select language to use and then click the <Next> button to
proceed to the next step.
2. After entering and confirming <Password>, press the
<Next> button to move onto the next step.
3. After setting the network access environment, press the
<Next> button to move onto the next step.
4. After setting the date/time, press the <Next> button to
launch the camera registration popup window.
Press the <OK> button to launch the camera registration screen and press the <Cancel> button to launch
the live screen.
`For more on how to register a camera, refer to “To register a camera”. (Page 52)
M
`The camera registration window only appears when there is no camera registered in a channel.
`If one or more channel is registered, the recording setting popup screen will appear.
`After all the steps are finished using the IPv4 information of the network set in step 4, the DHCP server will automatically
start operating again.
Camera may be searched within 1 minute after DHCP Server started.
live

24_ live
live
Shutting Down the System
1. Press the [POWER] button for your remote controller or
select <Shutdown> in the live screen menu.
2. The “Shutdown” confirmation pop-up window will appear.
3. Using the directional button on your remote control, select
<OK> and press the [ENTER] button or click on <OK>.
The system will shut down.
M
`Only the user with the "shutdown" permission can shut down
the system.
`For the permission management, refer to "User > Setting Permissions". (Page 45)
Login
If you want to use the NVR menu, you need to login as a user with the privileges to access it.
1. In the live mode screen, right click the mouse button or press
the [MENU] button on your remote control.
You will see the context menu on the screen as shown.
2. Select <Login>.
The login dialog appears.
J `Even if you press the menu button that requires a login with the
remote control, the login screen will appear.
`The first administator ID is "admin" and the password must be set
in the Installation Wizard.
`Set password for your wireless network if you use the product with
a wireless router. Being not protected with password or using the
default wireless router password may expose your video data to
potential threat.
`Please change your password every three months to safely protect personal information and to prevent the damage of the
information theft.
Please, take note that it’s a user’s responsibility for the security and any other problems caused by mismanaging a password.
M
`To change access privileges, refer to "User > Setting Permissions". (Page 45)
Scene Mode ►
CH Info
Live Status
Record Status
PoE Status
Audio Off
Freeze
Stop Alarm
Record
Play
Search
Backup
Menu
Quick Setup ►
Shutdown
Hide Launcher
Login
English _25
● LIVE
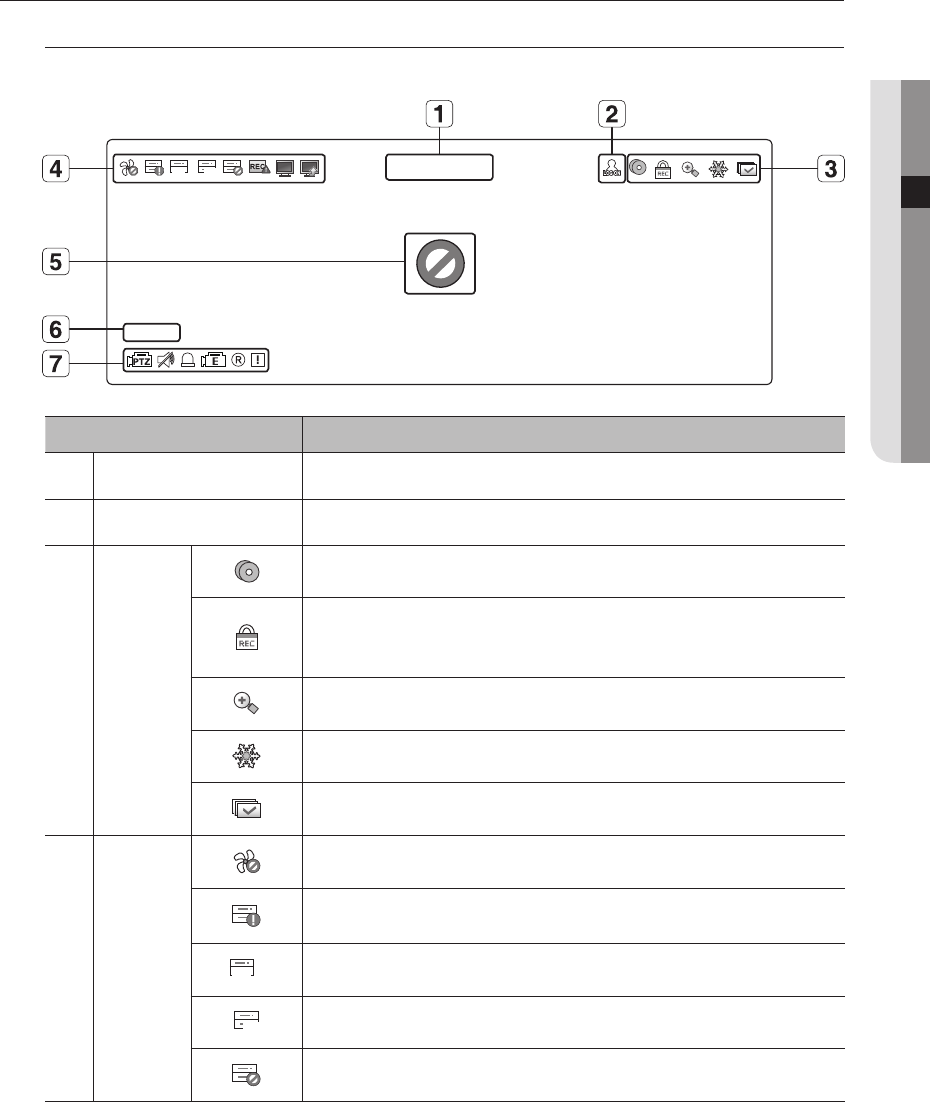
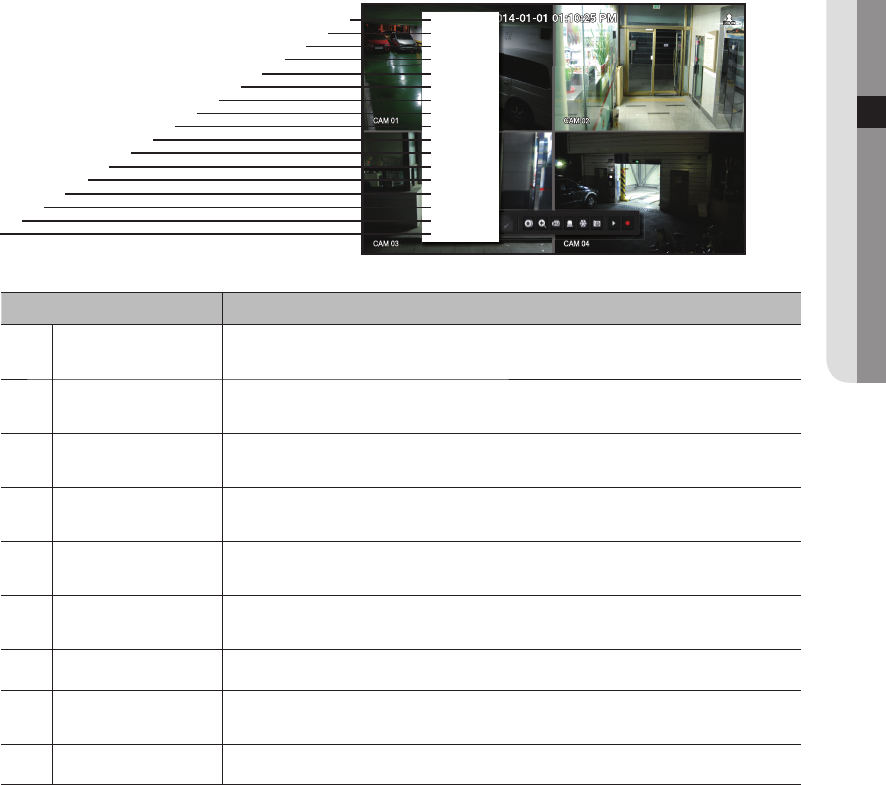
LIVE SCREEN CONFIGURATION
Icons on the Live Screen
You can check the status or operation of the NVR with the icons on the live screen.
Name Description
Current Date, Time
Displays the current time and date.
b
Login Information
When you are logged in, the "LOG ON" icon will be displayed.
c
Screen Mode
It is displayed when there is ongoing backup in the live condition.
If access to the recording canceling menu is restricted, then it is only displayed when
there is ongoing manual recording.
`Only a user with the right to cancel recording can do so.
It is displayed when the magnifying function is in operation.
This icon is displayed when you press the Freeze button.
It is displayed when all the channels are switched at the set time interval.
System
Operation
It is displayed when there is a problem with the fan.
It is displayed when the recording data cannot be received properly due to a device
problem.
FULL
Displayed if the HDD is full and the NVR has an insufficient space to record.
NO
Displayed if no HDD is installed or the existing HDD should be replaced.
Displayed if the HDD needs a technical examination.
CAM 01
2014-01-01 00:00:01
FULL NO
26_ live
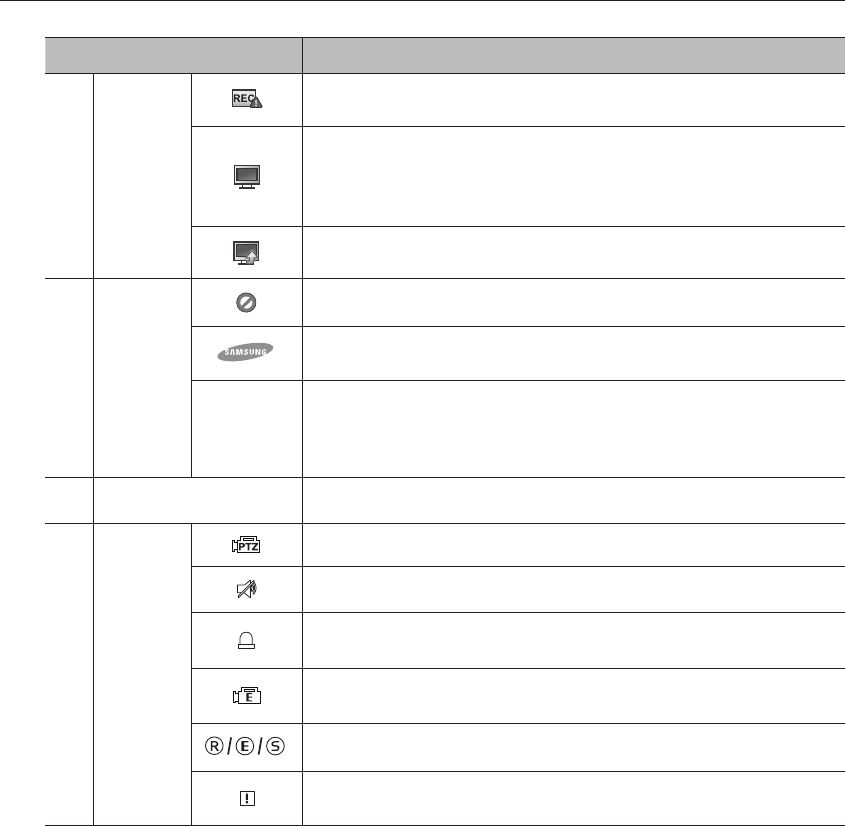
live
Name Description
System
Operation
It is displayed when the max permitted amount of data for each channel is exceeded.
It is displayed when the network is overloaded.
`It occurs when the max receiving allowance is exceeded, causing an overload to the
CPU. It will disappear if you modify the camera settings or delete a camera to reduce
the performance burden.
It is displayed when there is firmware to update the server.
Video Input
Status
Displayed if no input is entered in the condition that the camera is set to <ON>.
Displayed if no permission to live view is granted.
If a camera is <OFF>, or if no camera is registered, or it is in <Covert2> mode, nothing
will be displayed on the screen.
If the camera is set to <Covert1>, the video will be displayed but the OSD menus will not
be displayed.
Camera Title / Channel Display the camera title and channel number.
Camera
Operation
This icon is displayed for a channel that a PTZ-featuring camera is connected to.
Displays AUDIO ON/MUTE. Not displayed in video mode if deactivated.
If the sensor is set to <ON>, the input signal will be displayed on the screen of the
connected channel.
This icon is displayed when Motion Detection is set to <ON> and a camera motion or
camera event occurs.
It displays the status of general/event/scheduled recording.
It is displayed when it fails to decode all the frames due to limited decoding performance
and in this case only the I-Frame is decoded.
English _27
● LIVE
Error Information
• If the built-in HDD is not connected, the “NO HDD” icon ( ) will be displayed in the top left corner. In this
case, make sure you contact the service center for assistance as this may cause a failure of recording,
playback or backup.
• If the cooling fan does not work properly or has a problem, the <Fan Information> window will appear and
the fan error icon ( ) will be displayed on the top left corner.
In this case, check to see if the internal fan works.
As a fan error can shorten the product life, make sure you contact the service center for assistance.
M
`If you see the fan error icon or NO HDD, HDD FAIL icons on the screen, contact the service center for more details.
Live Screen Menu
Beside the functional buttons for your remote control, in the live screen mode, you can right click with the
mouse button or press the [MENU] button on your remote control to launch the live screen menu from where
you can access each menu from.
The context menu differs depending on the state of Log in/out, split mode, and NVR operation status.
M
`Live view, backup, recording, stopping recording, search, PTZ, remote alarlm output, and termination menus can be
restricted in use depending on user privilege settings.
< Single Mode Menu > < Split Mode Menu >
Scene Mode ►
CH Info
Live Status
Record Status
PoE Status
PTZ Control
ZOOM
Audio ►
Freeze
Stop Alarm
Capture
Record
Play
Search
Backup
Menu
Quick Setup ►
Shutdown
Hide Launcher
Logout
Scene Mode ►
CH Info
Live Status
Record Status
PoE Status
Audio Off
Freeze
Stop Alarm
Record
Play
Search
Backup
Menu
Quick Setup ►
Shutdown
Hide Launcher
Logout
28_ live
live
Single Mode Menu
The single mode menu is available only in Single Mode.
If the menu is displayed as <Screen Mode> in the single screen, it is displayed as a <Full Screen> in the
menu where only one channel is selected in the split screen.
Menu Description
Full Screen Select and click a desired channel in Split mode to switch to the full screen of the selected
channel.
b
PTZ Control
Accesses the PTZ Control menu. The PTZ menu will be active on the Live screen after you
select a single channel.
(Page 38)
c
ZOOM You can enlarge the selected screen. (Page 35)
Capture Captures the screen of the selected channel.
< Single Mode Menu >
Scene Mode ►
CH Info
Live Status
Record Status
PoE Status
PTZ Control
ZOOM
Audio ►
Freeze
Stop Alarm
Capture
Record
Play
Search
Backup
Menu
Quick Setup ►
Shutdown
Hide Launcher
Logout
< One channel selection menu in the split screen >
Full Screen
CH Info
Live Status
Record Status
PoE Status
PTZ Control
ZOOM
Audio ►
Freeze
Stop Alarm
Capture
Record
Play
Search
Backup
Menu
Quick Setup ►
Shutdown
Hide Launcher
Logout
b
c
English _29
● LIVE
Split Mode Menu
In Live split mode, right-click to display this context menu as shown.
The context sensitive menu in split mode differs, depending on the login/logout status.
Menu Description
Screen Mode Select a screen mode for the Live screen.
Refer to “Live screen mode”. (Page 32)
b
CH Info It displays the camera connection information for each channel.
Refer to the “Channel Information”. (Page 33)
c
Live Status Shows the live status of connected camera to each channel.
Refer to “Live Status”. (Page 34)
Record Status Shows the record status of each channel.
Refer to “Record Status”. (Page 34)
PoE Status Set the PoE status in each channel.
Refer to the “PoE Status”. (Page 36)
Audio On/Off Turns ON/MUTE the sound of the selected channel.
Refer to “Audio ON/OFF”. (Page 36)
Freeze Stop playing the video temporarily. Refer to “Freeze”. (Page 37)
Stop Alarm Stop the alarm output, deactivate the event icon and release the auto sequencing.
Refer to "Event Monitoring". (Page 37)
Record/Stop Starts/stops the standard recording.
Scene Mode ►
CH Info
Live Status
Record Status
PoE Status
Audio Off
Freeze
Stop Alarm
Record
Play
Search
Backup
Menu
Quick Setup ►
Shutdown
Hide Launcher
Logout
cb
m
q
n
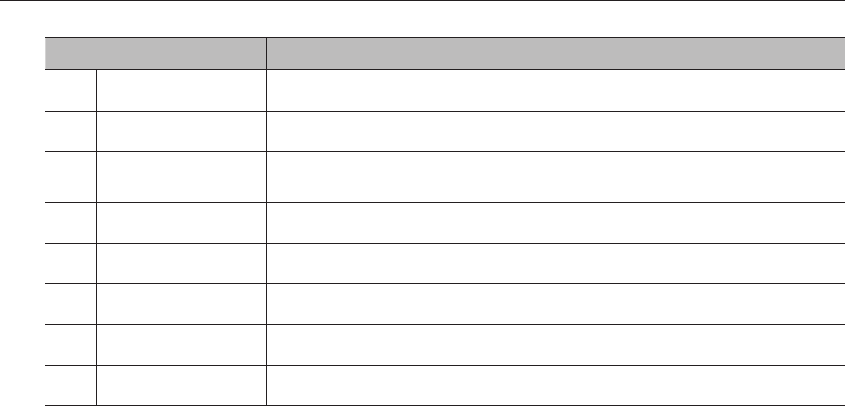
30_ live
live
Menu Description
Play Refer to "Search & Play > Play". (Page 91)
Search Refer to "Search & Play > Search". (Page 88)
Backup Searches for a backup device and runs backup for each channel or schedule backup later at a
more preferable time.
m
Menu Enter the main menu. Refer to the menu settings. (Page 41)
n
Quick Setup The “Camera Register” & “Recording Setup” screen will immediately appear.
Shutdown
The system shutdown dialog will appear.
Show/Hide Launcher
Shows or hides the launcher. Refer to "View the Launcher Menu". (Page 31)
q
Login/Logout You can log in or out.
English _31
● LIVE
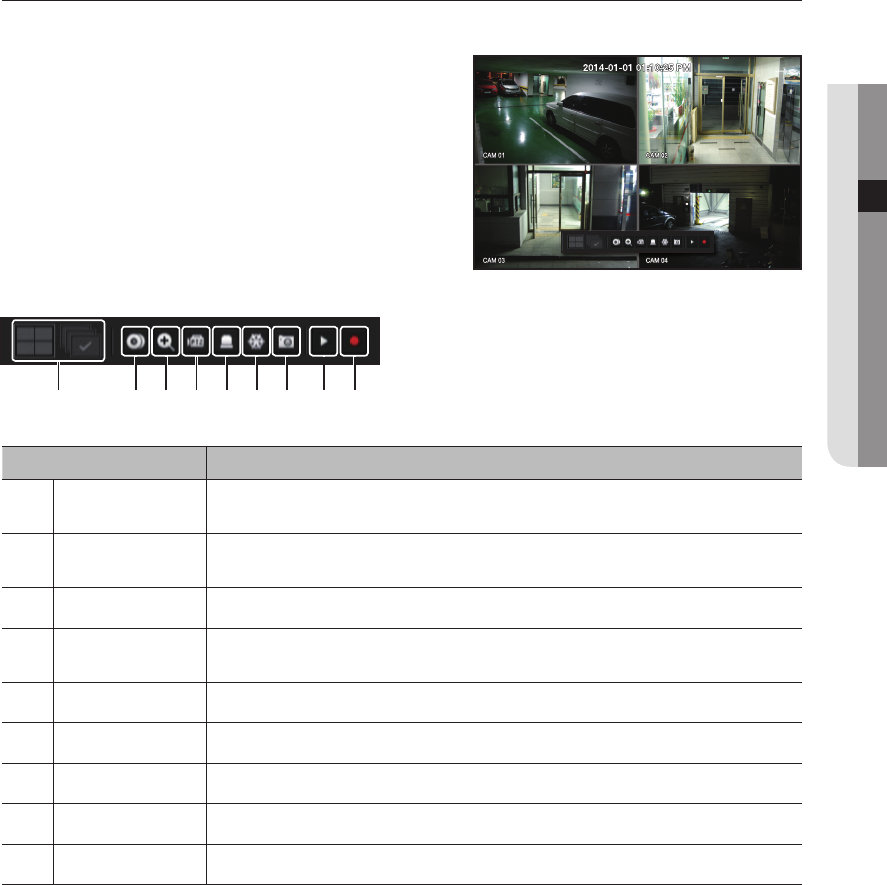
View the Launcher Menu
The Launcher menu appears on the bottom of the live screen.
1. Select <Show Launcher> in the context menu of the Live
screen.
2. Move the cursor to the bottom and click a desired item in
the Launcher menu.
M
`
If no input is entered for 10 seconds, the menu will disappear.
`
The Launcher menu can be accessed only by using the mouse.
Menu Description
Screen Mode Displays a list of split modes available in a bar type.
The current screen mode will be displayed grey.
b
Backup Searches for a backup device and runs backup of each channel or schedule it for later at a more
desirable time.
c
Zoom Enlarges the selected area. This is available only in Single Live mode.
PTZ If the network camera connected to the selected channel supports the PTZ operations, this will run
the PTZ control launcher. This is active only in Live single mode.
Alarm Stops the alarm if it's activated.
Freeze Freezes the Live screen temporarily.
Capture Captures the screen of the selected channel.
Play Enters Play mode if a file to play exist, and if not, enters Search mode.
Record Start/End recording the Live screen.
b c
32_ live
live
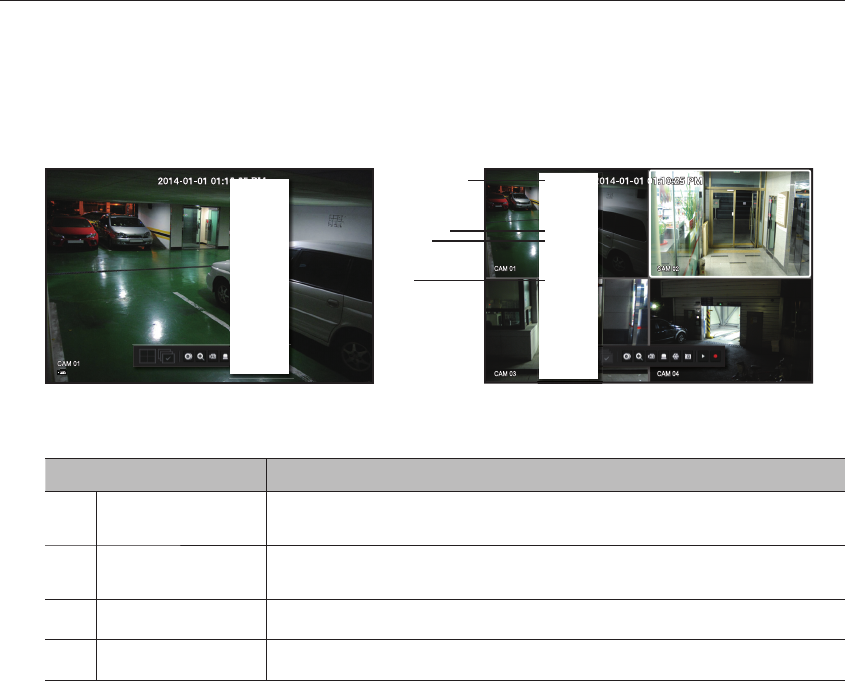
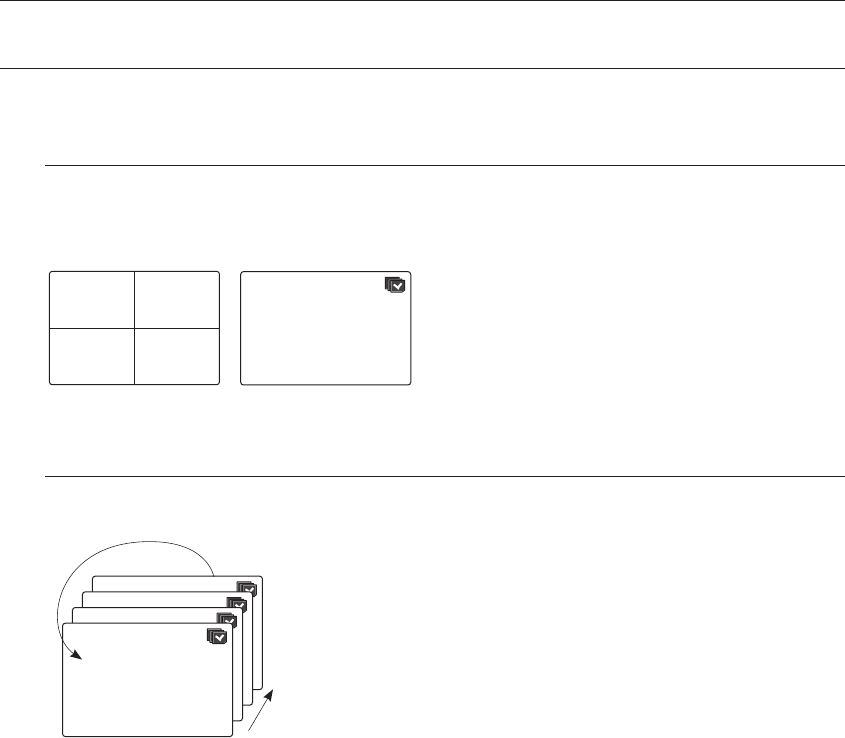
LIVE SCREEN MODE
Four live videos are displayed in the three split screens.
Method for displaying screen mode
If you want to change the split mode, select a screen mode suggested in the launcher menu or right click with
the mouse button and select a split mode in the screen mode menu.
Press the [MODE] button on your remote controller to change it in the order suggested in the launcher menu.
Auto screen switching
You can view the four live videos in the single screen in consecutive order.
M
`In a split mode, If you have set <Sequence switching time> in "Device > Monitor", Auto Sequence will be conducted at
the set interval. (Page 67)
CH1 CH2
CH3 CH4
4-split mode
CH1
Auto Sequence
4
1
Single mode
CH1
CH1
CH1
CH1
English _33
● LIVE
Channel information
Select the <CH Info> in the live screen menu to check the
status of camera connection to each channel.
Channel Setting
You can display the channel in a desired area of a split screen.
1. Place the cursor over the camera name of each channel to display the <
▼
> key to the right on the screen.
2. Click a camera name to display a channel list where you can select a different channel.
3. Select a desired channel and click it.
The selected channel is displayed in the screen.
If you want to change the channel location, you can place your mouse cursor over the desired location.
`Ex : If you want to change channel 1 area to channel 3 area.
Switching to Single Mode
Double click with the mouse button on the desired channel in the split screen to switch the screen to the single
screen.
Press the channel number button on the remote control to switch to single screen.
Refer to "Remote Controller > Using the Number Button". (Page 12)
Ex : With your mouse, double click on channel 3 or press the number 3 on the remote control.
CH1 CH2
CH3 CH4
CH3 CH2
CH1 CH4
CH1 CH2
CH3 CH4 CH3
34_ live
live
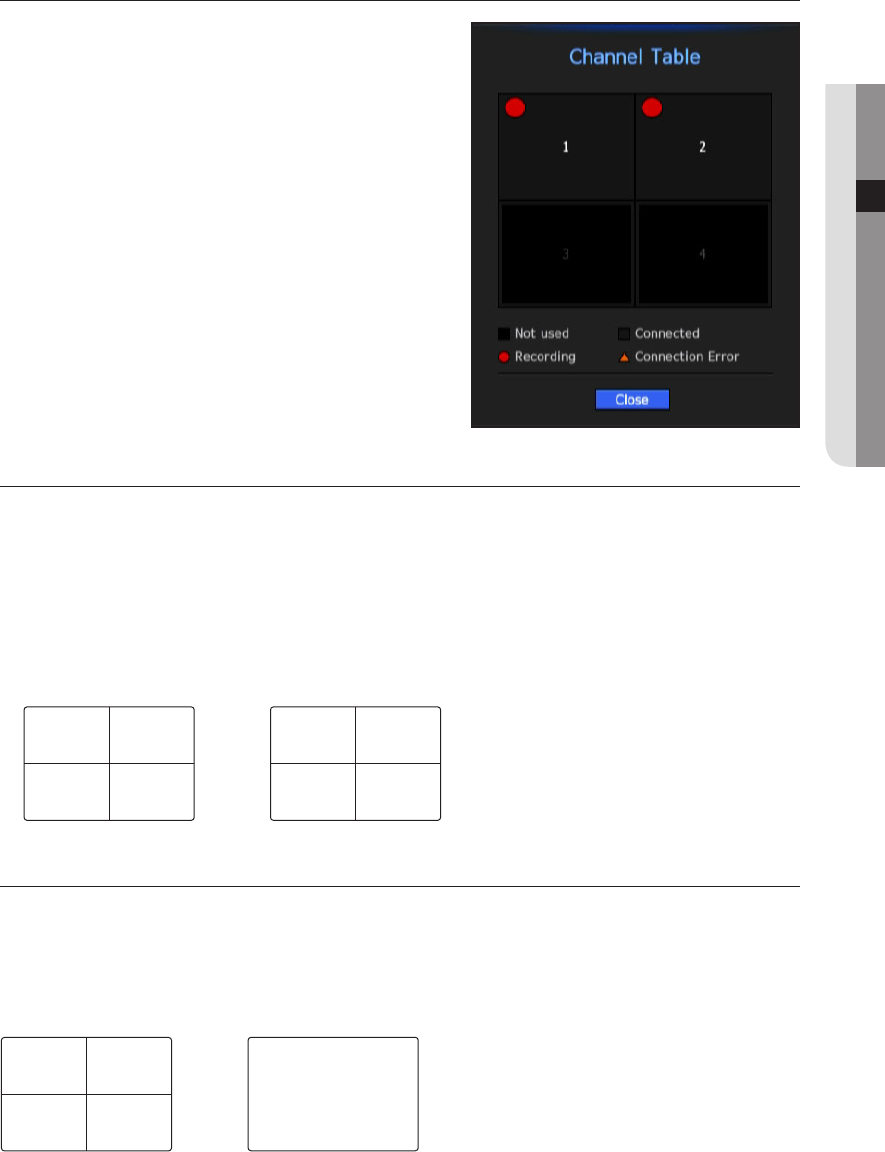
Live Status
Select <Live Status> from the live screen menu to display
status and transfer information of connected camera to each
channel.
• Model : Displays the camera model name connected to each
channel.
• Status : Displays the status of camera connection set to each
channel.
• IP Address : Displays the IP address of a camera set to each channel.
• Codec : Displays the live profile codec information for a camera set to each channel.
• Resolution : Displays the live profile resolution of a camera set to each channel.
• Frame Rate : Displays the live profile transmission rate for a camera set to each channel.
• Quality : Displays the live profile transmission quality of a camera set to each channel.
Record Status
Select <Record Status> from the live screen menu to display
camera profile, input/recording frame rates, input/limit/recording
bps of each channel.
• Total Bitrate (Record/Max) : Record bitrate shows the amount
of actual data recording while Total bitrate shows the
maximum data transfer allowed by the NVR.
• Profile : Shows the video profile configured to each channel.
• Frame (fps) : Show the input/record frames per second for
each channel.
• Bitrate (bps)
- Limit / Input / Record : Shows the amount of limit/input/recording data for each channel.
- Input / Limit : Shows the data ratio of actual data transferred from the camera and allowed maximum
defined by user.
• Current : Shows the recording status information of currently transferred data.
• MAX : Shows recording information of the most biggest recording data out of configured standard and event
recordings.
• : Reloads the recording information.
• Record Setup : The menu screen will switch to the record setting screen.
M
`The warning message on the list's bottom means the NVR replaced the selected recording profile with other available profile,
since the selected one does not produce video data which prohibits screen saving. If the screen displays video, it
automatically resets to the selected profile and its name turns to yellow in the list.
`If Key Frame recording exceeds the allowed data amount specified by limit bitrate, a popup alert and icon appear on the
screen.
The limited recording alert popup does not repeat after displaying once unless camera or recording settings are changed; it
may appear again if settings were changed to notify such status.
If you want to set the alert popup not to appear, change your setting of <Setup Warnings> not to display a message popup.
For further information on bitrate limit of recording data, refer to “Record Setting”. (Page 70)
English _35
● LIVE
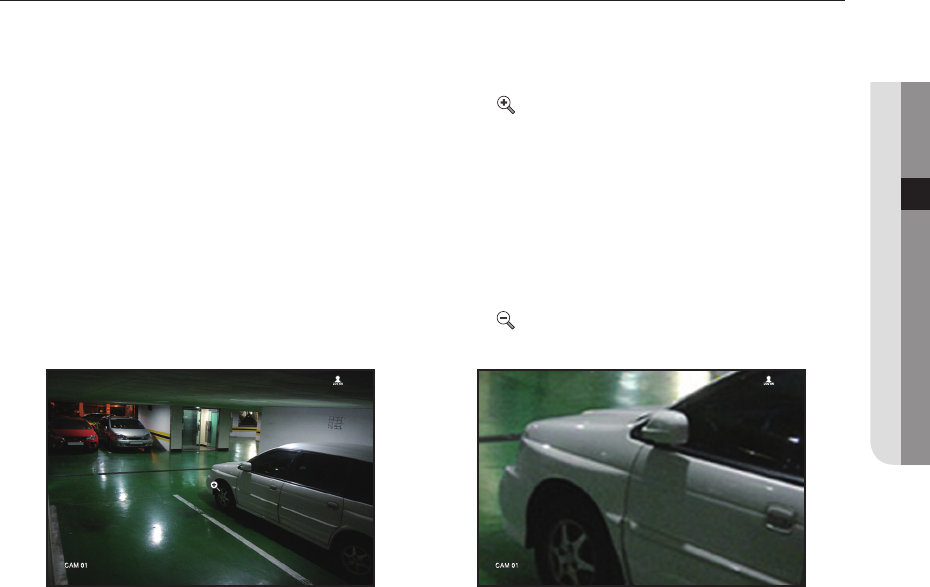
ZOOM
This is activated only in Live Single mode.
After selecting a single screen, if you use the Magnify function, the selected area will be magnified by 2.
1. In the live screen menu, select <ZOOM>.
Press the [ZOOM] button on your remote control or click < > on the launcher menu.
The Magnify icon in the middle of the screen will be displayed.
2. You can use the remote control's directional key(▲▼◄►) or drag with the mouse to set the area of
magnification.
3. Press the [ENTER] button or double click with the mouse to magnify the selected area by two times.
`In the magnified screen, you can drag with the mouse or use the remote control's navigational key (▲▼◄►) to move the
magnified area.
4. In the live screen menu, select <Zoom Out>.
Press the [ZOOM] button on your remote control or click < > on the launcher menu to cancel the
magnification function.
<Normal> <Enlarged twice>
36_ live
live
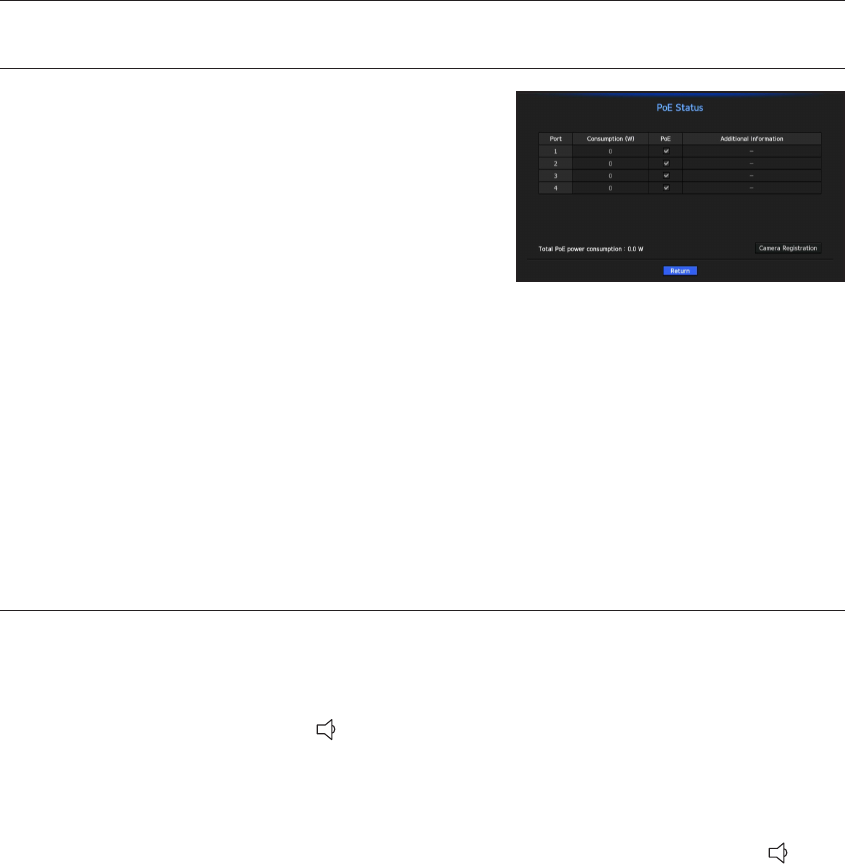
POE STATUS
In the live screen, you can see the PoE status of each port.
1. Select the <PoE Status>.
PoE status view window is displayed.
• Consumption(W) : Displays the power consumption in PoE.
- 0 : No device is connected to the port or a device is using
its own power supply.
- – : Trouble in the port (More detailed trouble information can
be displayed in additional information.)
M
`The max power for each port is 15.4W.
`If each port exceeds 15.4W, the power is automatically cut off.
• PoE : Turns on/off the power supply to the camera.
If checked, it means that the power is on. If not, the power is off.
• Additional information : If there is a problem in the power supply, it is explained here.
Power supply problems include excessive power (class 1 to 4) and voltage errors.
• PoE power consumption total: Display the sum of power consumption for all the ports.
2. Press <Return> to move to the previous screen.
AUDIO ON/OFF
You can turn the sound on/off corresponding to the channel in Live mode.
AUDIO ON/OFF in Single mode
In the screen, click on the audio icon ( ) or in the remote control, press the [AUDIO] button to turn it on/off.
M
`If there is no audio output even if output is activated, check whether the connected network camera supports audio and
audio settings.
The sound icon can be displayed if the sound signal fails to output from noise.
`Only the channel where <AUDIO> is set to <ON> in "Setting the Device > Camera" displays the audio icon ( ) in Live
mode that you can use to turn the sound on/off.
English _37
● LIVE
FREEZE
This is available only in Live mode, this pauses playing the Live image temporarily.
1. Press the [FREEZE] button on your remote control or click < > in launcher mode.
Video playing is paused.
2. Press the [FREEZE] button on your remote control or click < > in launcher mode.
Pause is canceled. Playing is resumed.
EVENT MONITORING
This will display the channel in sync with a specific event (Sensor/Motion/Video Loss) if it occurs.
In "Monitor > Event Display", set the event monitoring to ON/OFF and specify the event display time. (Page 67)
• If multiple events occur simultaneously, the screen will switch to a split mode.
- 2~4 events : 4-split mode
• If the second event occurs within the set time of <Event Display>, the first event will last until the second one
is terminated.
`Ex : If you set <Event Display> to 5 seconds, and only one event occurs in CH 1.
`Ex : If you set <Event Display> to 5 seconds, and the second event occurs in CH 2 within the set time after the first event
occurred in CH 1.
CH1
Event occurrence 5 seconds
Stop alarm
CH1 CH2
CH1
Event occurrence 4 seconds 9 seconds
Stop alarm
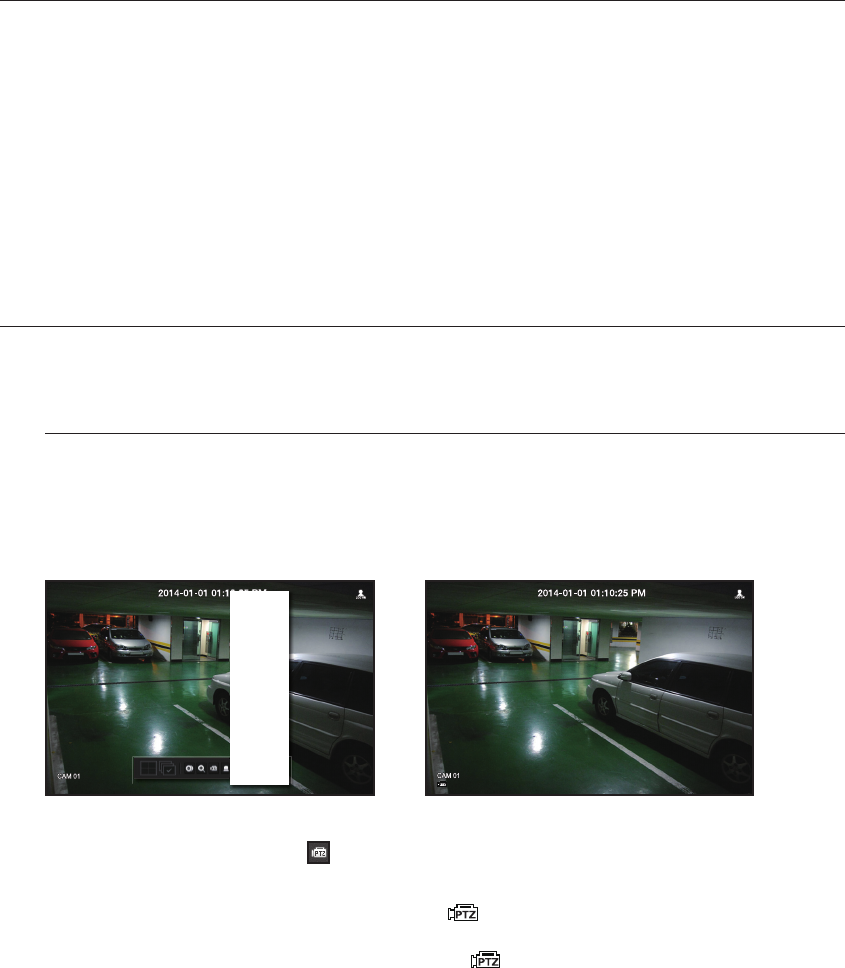
38_ live
live
M
`Press the [ALARM] button or select <Stop Alarm> to initialize the alarm output status and cancel the event function.
`If an alarm is output with the pre-event and post-event times specified together with the event recording settings, the event
recording will perform according to the specified recording type (pre event or post event).
J `In case of continuous events such as motion detection, switching to another split mode display may not immediate if
concatenating events follow, even when you stopped alarm of the event.
`The video may be delayed depending on the network condition.
`The event output can be delayed as the transfer of the alarm event from the network camera takes time.
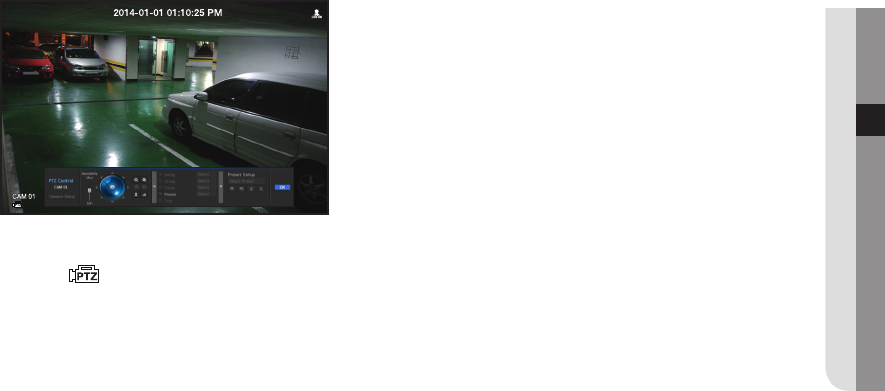
PTZ CONTROL
With this NVR, you can configure the settings of a PTZ camera as well as commercial cameras in the market to your
preference.
PTZ device
This is active only if a channel that a PTZ camera is connected to is selected.
Getting started with PTZ operations
The PTZ camera will be activated only if the channel of the PTZ camera is selected, which can be performed in
the following way:
• Using the remote control : Press the [PTZ] button on your remote control.
• Using the launcher menu : Click < > from the launcher menu of the Live screen.
• Using the Live screen menu : Select <PTZ Control> in the context menu of the Live screen.
• Using the icons on the Live screen : Simply click the < > icon on the Live screen.
M
`This is available only if a PTZ camera is connected and the < > icon is displayed on the screen.
`Even if the connected network camera does not support the PTZ operations, you can configure the PTZ control settings
(if possible) by installing the PTZ driver (physical device).
`It only supports a network camera with Samsung Techwin's PTZ function and a camera registered in the ONVIF.
Scene Mode ►
CH Info
Live Status
Record Status
PoE Status
PTZ Control
ZOOM
Audio ►
Freeze
Stop Alarm
Capture
Record
Play
Search
Backup
Menu
Quick Setup ►
Shutdown
Hide Launcher
Logout
English _39
● LIVE
Using the PTZ camera
You can use a single PTZ camera to perform the Pan, Tilt and Zoom operations to monitor multiple places, and
configure the custom settings of the presets in a desired mode.
1. Open the <PTZ Control> menu.
The < > icon in the left bottom of the screen will turn yellow, indicating that the system accesses "PTZ
Control" mode. You will see the "PTZ Control" launcher menu.
M
`The PTZ working (active) mark can be active even if the PTZ operation is not available in normal mode. So ensure that you
have completed the PTZ settings before proceeding.
2. Adjust the camera recording location by using the PTZ ball in the launcher menu or press the left/right
(▲▼◄►) button on your remote control to move the camera recording location.
• Sensitivity : Adjust sensitivity for Pan, Tilt controls.
• PTZ Wheel : Click a near area from the center to move the camera lens slowly; clicking a far area will move it
fast.
`If clicking and holding the mouse in the left will turn the camera counterclockwise; if clicking and holding the mouse in the right
will move the camera lens clockwise.
• Zoom : Activate the Zoom operation of the PTZ camera.
• Iris : Adjust the amount of light incoming to the camera.
• Focus : You can adjust the focus manually.
• Swing : Swing is a monitoring function that moves between two preset points and enables you to trace the
motion.
• Group : The group function enables you to group various presets before calling them in sequence.
• Trace : Tracking remembers the trace of movements that you instructed and reproduces it for your reference.
• Tour : Monitor all the groups created by a user in turn.
`Some cameras may differ in the menu title and operation with regard to Swing, Group, Tour and Trace.
J `Even if the network camera supports the PTZ operations by default, the PTZ control can be enabled only if the applicable
menu is active in the launcher menu.

40_ live
live
Preset
Preset is a specific position remembered by the PTZ camera. You can use the Preset function to define up to
255 presets for a single PTZ camera.
To add a preset
1. Check the preset checkbox.
2. Select < >.
The virtual keyboard will appear on the screen. Use it to provide the preset name.
`Refer to "Using Virtual Keyboard". (Page 43)
• : You can change the preset settings to your preference.
• : Delete a selected preset.
• : Delete all the existing preset settings.
M
`You can add up to 255 presets, which is the max count supported by the NVR.
`If you replace a camera that saves your preset settings with a different one, you must configure the preset settings again.
3. Select <OK>.
The preset setting will be saved in the provided name.
If you want to change or delete the preset name
1. Check the preset checkbox and select a preset to change or delete.
2. If you selected < >, enter the desired name and press OK.
If you selected < >, press OK to delete it.
• : Delete all the existing preset settings.
J `If you delete the entire presets, the default presets specified in the network camera can be deleted accordingly.
You can setup the system, devices, and options for recording, event and network.
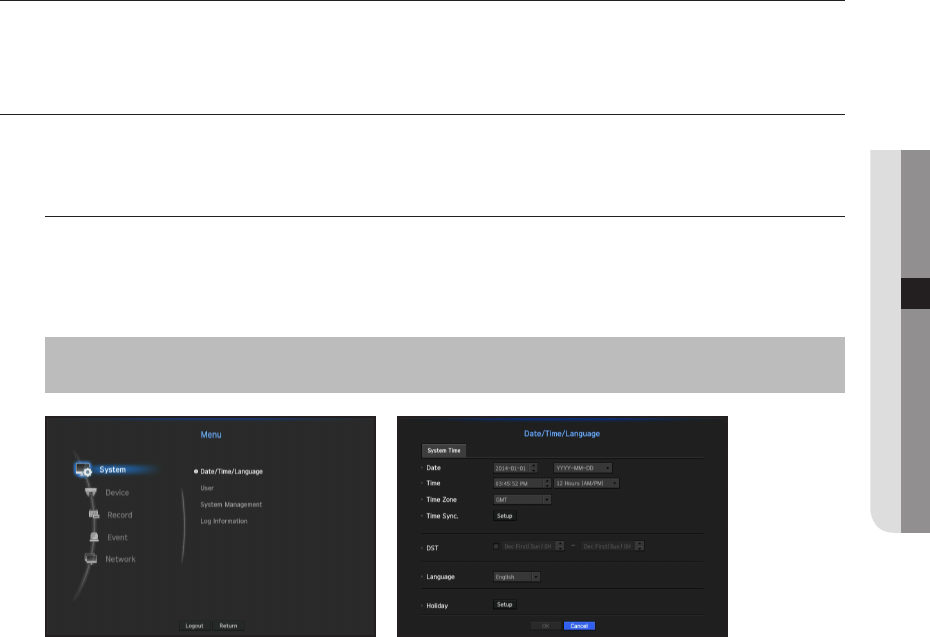
SYSTEM SETUP
You can setup Date/Time/Language, User, System Properties and Log.
Date/Time/Language
Setting the Date/Time/Language
You can check and setup the current Date/Time and time related properties, as well as the language used for
the interface on the screen.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö <System> Ö ► Ö <Date/Time/Language> Ö
[ENTER] Ö ▲▼◄► Ö [ENTER]
•
Date : Sets the date and its format that will appear on the screen.
•
Time : Sets the time and its format that will appear on the screen.
•
Time Zone : Sets the time zone of your area based on the Greenwich Mean Time (GMT).
`GMT (Greenwich Mean Time) is standard World Time and the basis of world time zone.
•
Time Sync. : Specify the use of synchronization with the time server.
Click the <Setup> button to display time synchronization setup screen.
If you select to use the <Time Server>, the current time will be synchronized on a regular basis by the server
defined as <Time Server>.
If this is the case, you cannot change the time setting manually.
-
Synchronization : Specify the use of synchronization with the time server.
-
Time Server : Enter an IP or URL address of the time server.
-
Last Sync Time : Displays the most recent synchronization time from the selected time server.
-
Activate as Server : Set to <Use> to allow the NVR to act as a Time Server for other NVRs.
•
DST : Set up Daylight Saving Time with its period to make the time earlier than the GMT of its time zone by 1
hour during the set period.
•
Language : Select your language. Sets the language for the interface.
English, French, German, Spanish, Italian, Chinese, Russian, Korean, Polish, Japanese, Dutch, Portuguese,
Turkish, Czech, Danish, Swedish, Thai, Romanian, Serbian, Croatian, Hungarian, Greek, Finnish, and
Norwegian are supported.
English _41
● MENU SETUP
menu setup
•
Holiday : A user can select specific dates as holidays according to their own preferences.
Holidays are applied in the <Recording Schedule> or <Alarm Schedule> setting too.
`e.g. every first day of a year is set to be a holiday if you select January 1 and check <1/1>, and every first day of a year and every
first Wednesday of January are set to be holidays if you check <1/1> and <Jan First Wed>.
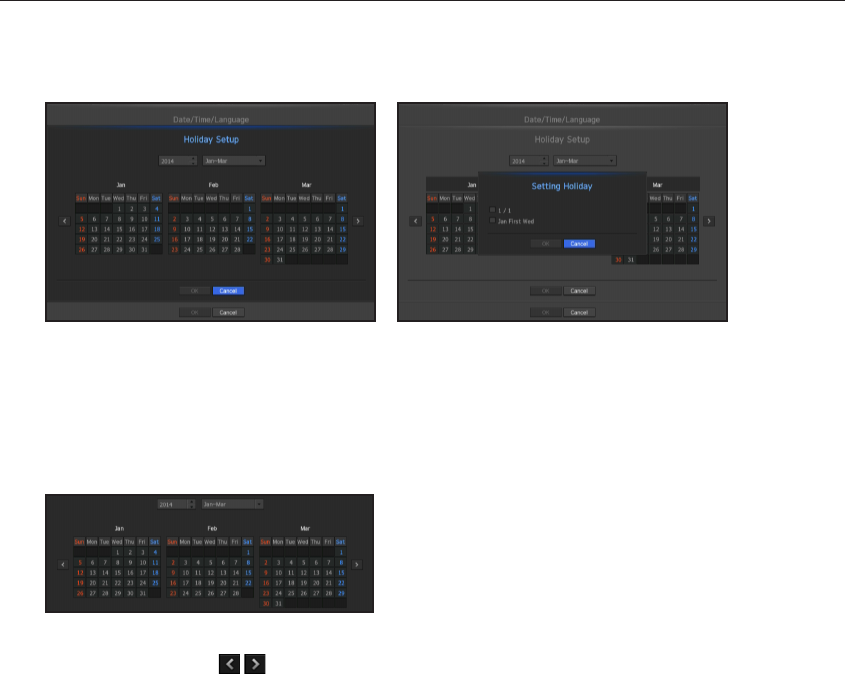
To use the calendar
Use the mouse to select items more easily.
1. Select year and month.
After selecting the < > keys in the screen on the left/right of the wheel, press the [ENTER] button to
move back/forward in increments of three months.
2. Select a date by using the directional button and press the [ENTER] button.
`A date is marked in gray if there exist data for search for system log, event log, time search and event search.
42_ menu setup
menu setup
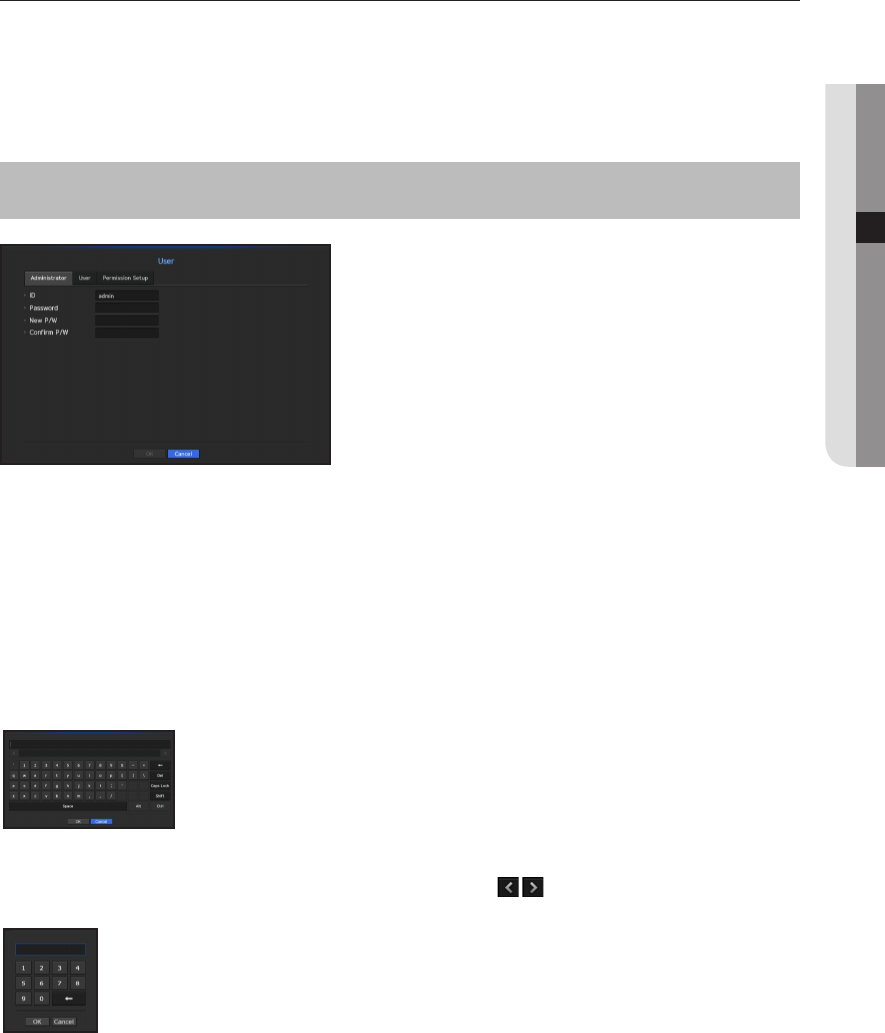
User
You can set permissions of each user over the NVR's specific function and settings.
Setting the Administrator
You can set and change Administrator's ID and password.
The administrator can use and set all menu items and functions.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö <System> Ö ►▼ Ö <User> Ö [ENTER] Ö ▼ Ö
<Administrator> Ö ▲▼◄► Ö [ENTER]
•
ID : Change the admin ID.
•
New P/W : Enter new password.
M
`The first administator ID is "admin" and the password must be set in the Installation Wizard.
`Please change your password every three months to safely protect personal information and to prevent the damage of the
information theft.
Please, take note that it's a user's responsibility for the security and any other problems caused by mismanaging a password.
Using Virtual Keyboard
1. For alphanumeric inputs, the virtual keyboard window appears.
2. Using the directional key(▲▼◄►), move to the desired text tab and press the
[ENTER] button.
3. In the upper text input box of the virtual keyboard, there displays a list of
candidate words containing the selected character.
4. Select a word from the list, or use the keyboard to enter the whole word.
`If there are many of candidate words, use < > buttons to move between them forward
and backward.
5. Select <OK>.
Entered word is applied.
`For upper case letters, use <Caps Lock> button.
`For special characters, use <Shift> button.
`Using the virtual keyboard is the same to a normal keyboard use in your region.
`ID allows alphanumeric characters only.
`A password should be a combination of numbers and letters with eight or more characters.
It must not have special characters such as '&', '#', '<', '>', '{', '}', ''', '~'.
English _43
● MENU SETUP
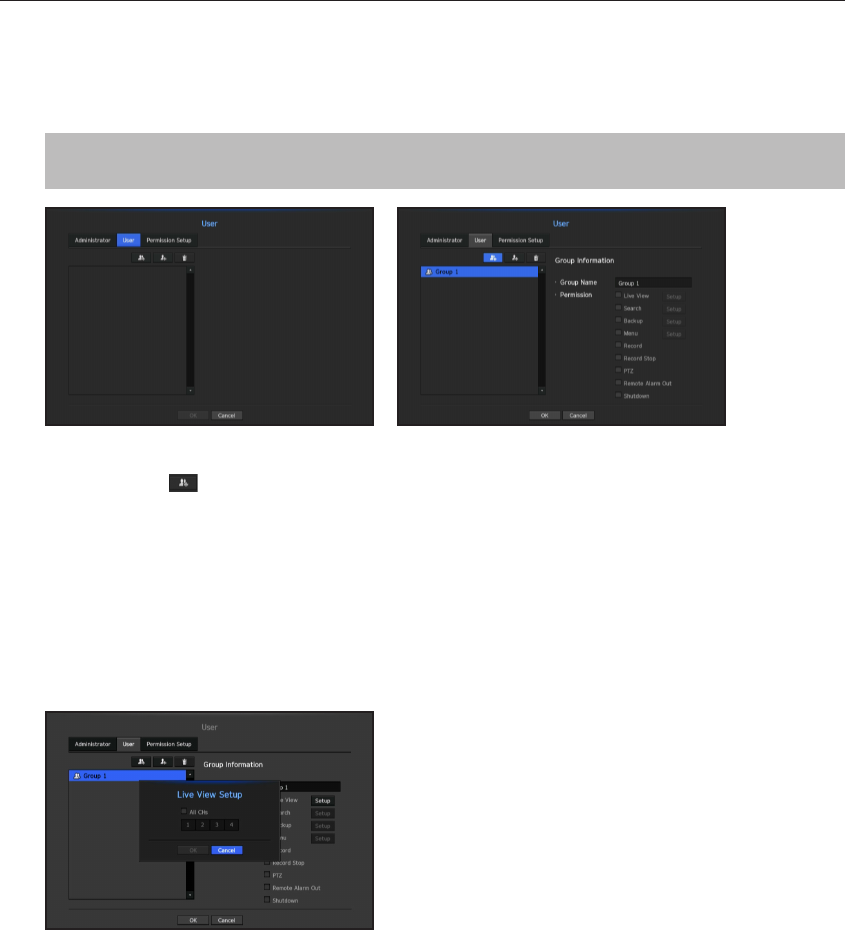
User setting
You can create a group or set permissions for each group.
You can add a user and edit the registered user information.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ►▼ Ö <System> Ö <User> Ö [ENTER] Ö ▼► Ö
<User> Ö ▲▼◄► Ö [ENTER]
If you want to add a group
1. Click on the [ ] button to launch the Group Addition popup window.
If you want to add a group, click on <OK>.
2. Press the group name item to launch the virtual keyboard used to enter group names.
Enter the group name to register.
`You can add a maximum of 10 groups.
If you want to set group permission
Set permission to access each group.
Each group's users can only access items with a check mark beside them.
1. Select the menu to set group permissions.
The menu with access permissions will appear when a user of the group logs in.
•
Live View : You can set permissions to access the live screen for each channel.
•
Search : You can set permissions to access the search menu for each channel.
•
Backup : You can set permissions to access the backup menu for each channel.
•
Menu : You can select and set the setting menu that can be accessed. A group user can only access the
menu selected. If you select the menu, the menu permission setting screen will be displayed.
•
Record, Record Stop, PTZ, Remote Alarm Out, Shutdown : You can select these functions to add to a
group's permissions.
2. Click <OK>.
Check a group user to give them the permission to access the selected item.
44_ menu setup
menu setup
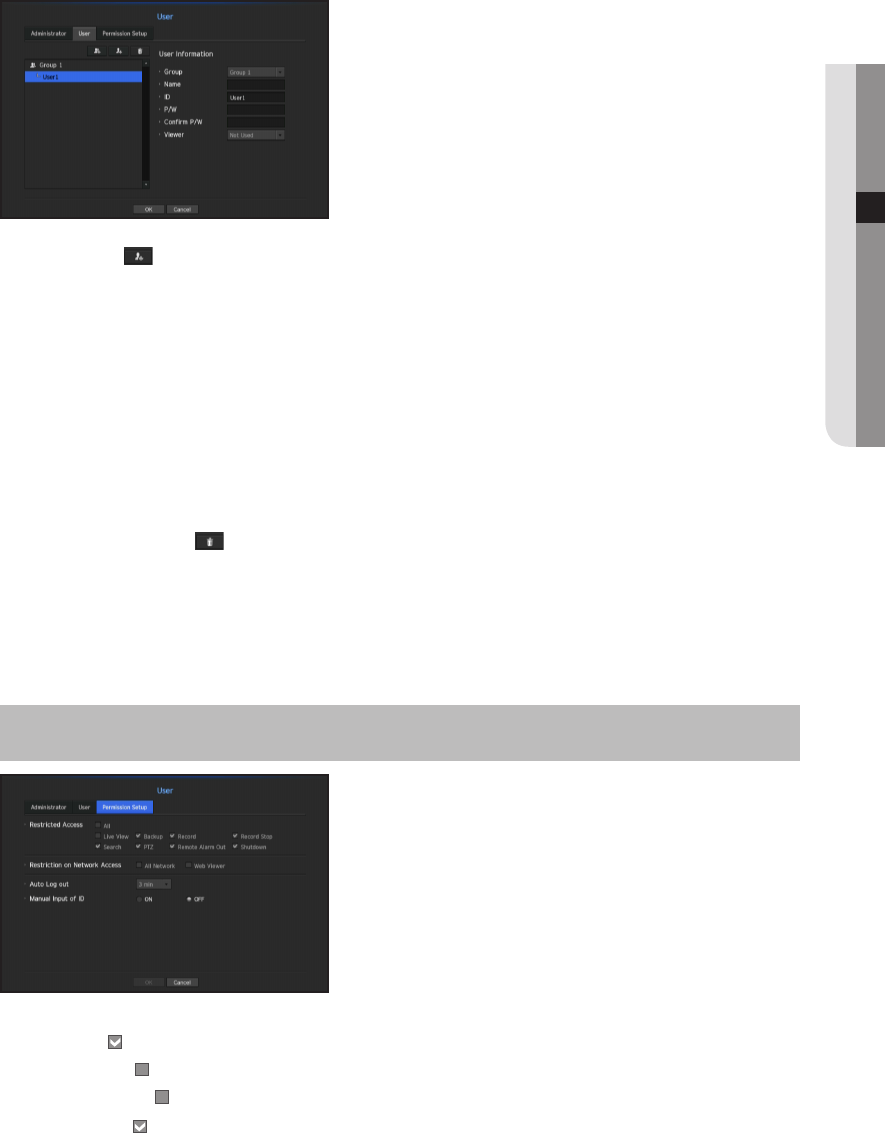
If you want to register a user
1. Click on the [ ] button to launch the user addition popup window.
To add a user, click on <OK>.
2. Select a group.
When registering a user, the selected group will be automatically registered.
`A group can be changed after inputting all required information.
3. Enter name, ID, password and select whether to use the viewer.
If you activate use of <Viewer>, you will have the right to use the web viewer and the network viewer.
4. Click <OK>.
Registered user information will be saved.
When you want to delete the group and user information
1. To delete, click on the [ ] button.
2. The deletion confirmation window will appear and you can select an item to delete and click on <Delete>.
Setting Permissions
You can set restricted access for all general users.
Items with restrictions will require logging in for use.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö <System> Ö ►▼ Ö <User> Ö [ENTER] Ö ▼► Ö
<Permission Setup> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
•
Restricted Access : All menu items allowed for a user can be set with restricted access.
-
Checked ( ) : Restricted
-
Not checked ( ) : Accessible
`If it is not checked ( ) in <Restricted Access>, any user can access the item no matter what the <Permission> setting.
`If it is checked ( ) in <Restricted Access>, a user can access the item only if the user has permission in <Permission>
setting.
English _45
● MENU SETUP
•
Restriction on Network Access : Restricts remote access from a <Restricted Access> network.
-
All Network : Restricts all access instances via Network Viewer and Web Viewer.
-
Web Viewer : Restricts access via the Web Viewer.
•
Auto Log out : A user will be automatically logged out if there is no operation on NVR for over set period of
time.
•
Manual Input of ID : In the login window, select whether to enter ID.
If the user has restricted access
If a new group is restricted to access the entire menus, the users belonging to the group can access only the
basic menus and can change only their respective password.
If all permissions are restricted, you will see only some menu items accessible in the Live screen menu.
To change the user password
If you log in with the user account of a group with restricted access, you just can change your own password.
1. Provide the login information.
2. Select <User Menu>.
The Permission Management screen appears.
3. Select <User>.
The Password dialog shall appear.
4. Provide a new password.
5. Select <OK>.
The old password will be changed to a new one.
46_ menu setup
menu setup
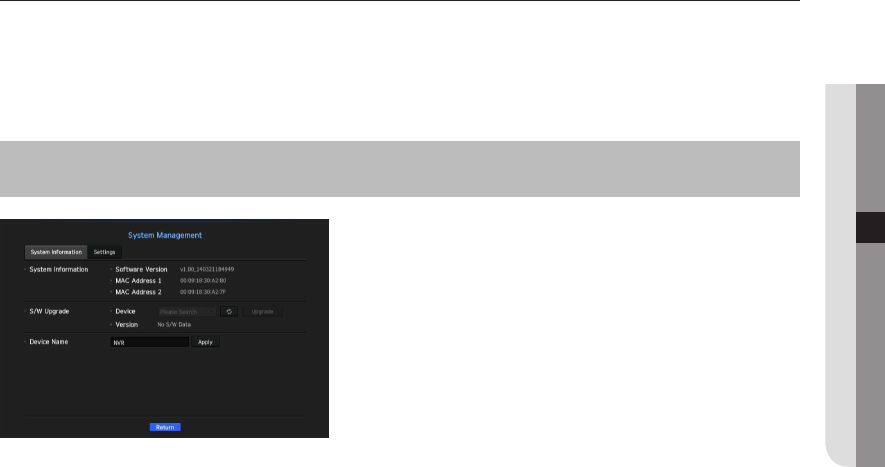
System Management
You can check the system version, update to a newer version, as well as data backup and initialization.
Checking the System Information
You can check the current software version and MAC address before proceeding with the upgrade.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö <System> Ö ►▼ Ö <System Management> Ö
[ENTER] Ö ▼ Ö <System Information> Ö ▲▼◄► Ö [ENTER]
•
System Information : Shows the current system's information.
The values can not be changed by a user.
-
Micom version : This is the micom version.
•
S/W Upgrade : Updates the NVR's software up to date.
•
Device Name : Displayed if the network viewer is connected to NVR.
English _47
● MENU SETUP
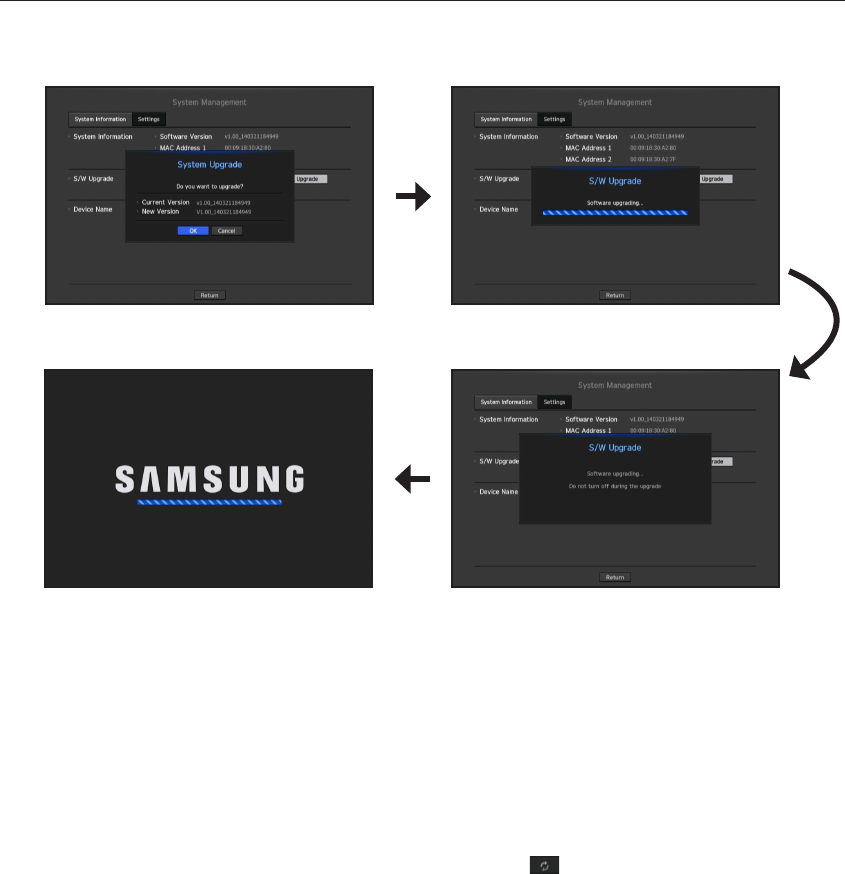
To upgrade the current software version
1. Connect a device storing the software to be updated.
`It may take about 10 seconds to recognize the device.
`Upgradeable devices include USB memory, and network device.
`To update the network, the current NVR should have been connected to the network.
Upgrade via the proxy server may not be enabled due to the restricted access.
2. Select <System Management> from <System> window.
3. Select <System Information>.
4. When the recognized device appears, select <Upgrade>.
`If you connect a device in the upgrade menu window, you can press the < > button to search for available software.
`If there is an upgrade image on the network, the popup window will appear.
`The <Upgrade> button will be activated only if the current <Software Version> of the <System Information> is same to or
older than that of <S/W Upgrade>.
5. Press <OK> in the "S/W Upgrade" window.
`While updating, it shows the progress.
6. When the updating is done, it automatically restarts.
Do not turn the power off until it finishes restarting.
M
`If "Upgrade Failed" appears, retry from the step 4.
When you experience continued failure, consult the service center for assistance.
48_ menu setup
menu setup
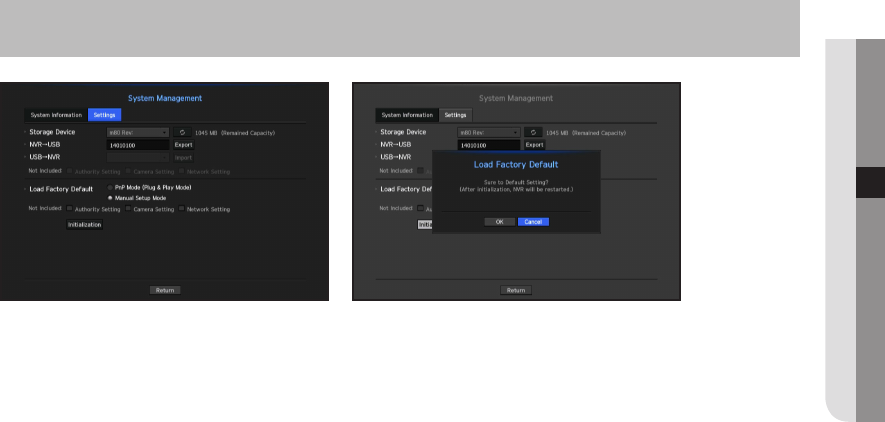
Settings
You can copy and import the NVR settings by using a storage media.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö <System> Ö ►▼ Ö <System Management> Ö
[ENTER] Ö ▼► Ö <Settings> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
•
Storage Device : Shows the connected storage device.
•
Export : Exports NVR settings to the connected storage device.
•
Import : Imports NVR settings from the storage device and applies to the NVR.
-
Uncheck the checkbox of an item(s) that you want to import.
Only the other items than the selected one will be applied to the NVR.
-
You cannot retrieve the configuration file from another mode. In other words, in PnP mode, you cannot
retrieve the manual setting information. In manual setting mode, you cannot retrieve the PnP setting
information.
•
Load Factory Default : Restore the factory default settings of NVR.
Uncheck the checkbox of an item(s) that you want to reset. Then, only the other items than the selected one
will return to the factory default.
If <Initialization> is selected, a confirmation dialog for "Load Factory Default" prompts. Press <OK> to
initialize the system to the factory default.
`After changing the mode, reboot to initialize. (PnP mode < -> manual setup mode)
M
`If you want to initialize the <Authority Setting>, you need to reset the password.
In case you reboot, reset it the Installation Wizard and if not, use the guide screen to reset it.
English _49
● MENU SETUP
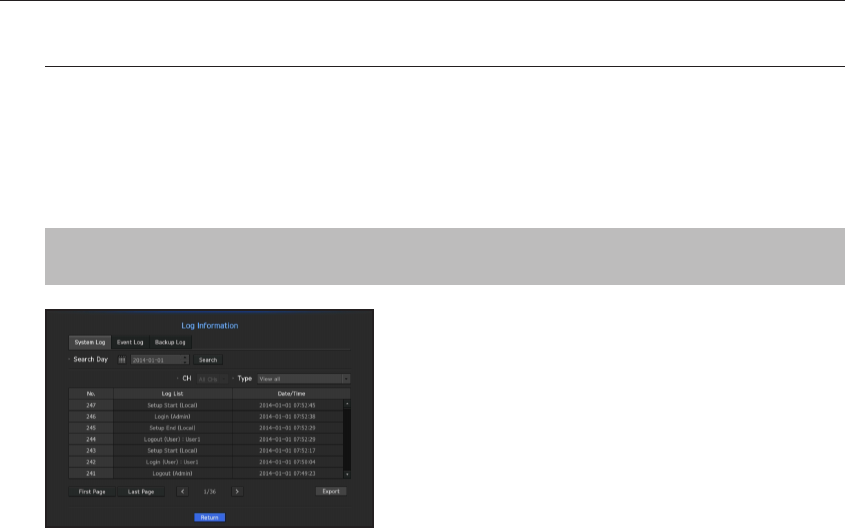
Log Information
You can browse logs on the system and events.
Checking the system log
System Log shows log and timestamp on every system start up, system shutdown, and changes on system
settings.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö <System> Ö ►▼ Ö <Log Information> Ö [ENTER]
Ö ▼ Ö <System Log> Ö ▲▼◄► Ö [ENTER]
•
Search Day : Click the Calendar icon to display the calendar window, or use the direction buttons to specify
the search period of the system log.
`For using the calendar, refer to "To use the calendar". (Page 42)
•
Search : Specify the date and press this button to display the search result in the log list.
•
Type : When there are too many logs, you can display logs of the desired format by selecting the type.
•
Export : Save all the logged information recorded in the NVR into the storage media.
50_ menu setup
menu setup

Checking the event log
You can search recorded events including alarms, camera events and video loss.
It also shows the log and its timestamp.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö <System> Ö ►▼ Ö <Log Information> Ö [ENTER]
Ö ▼► Ö <Event Log> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
•
Search Day : Click the Calendar icon to display the calendar window, or use the direction buttons to specify
the search period of the system log.
`For using the calendar, refer to "To use the calendar". (Page 42)
•
Search : Specify the date and press this button to display the search result in the log list.
•
Type : When there are too many logs, you can display logs of the desired format by selecting the type.
•
Export : Save all the logged information recorded in the NVR into the storage media.
Checking the backup log
You can find out who backed up and the details (backup time, channel, device to use, file format, etc.).
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö <System> Ö ►▼ Ö <Log Information> Ö [ENTER]
Ö ▼► Ö <Backup Log> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
•
Search Day : Click the Calendar icon to display the calendar window, or use the direction buttons to specify
the search period of the system log.
`For using the calendar, refer to "To use the calendar". (Page 42)
•
Search : Specify the date and press this button to display the search result in the log list.
English _51
● MENU SETUP
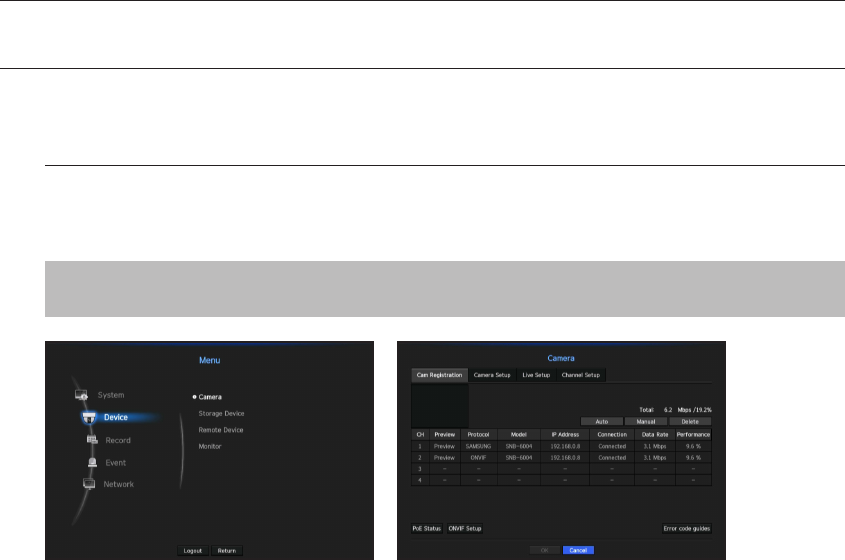
SETTING THE DEVICE
You can setup Camera, Storage Device and Monitor.
Camera
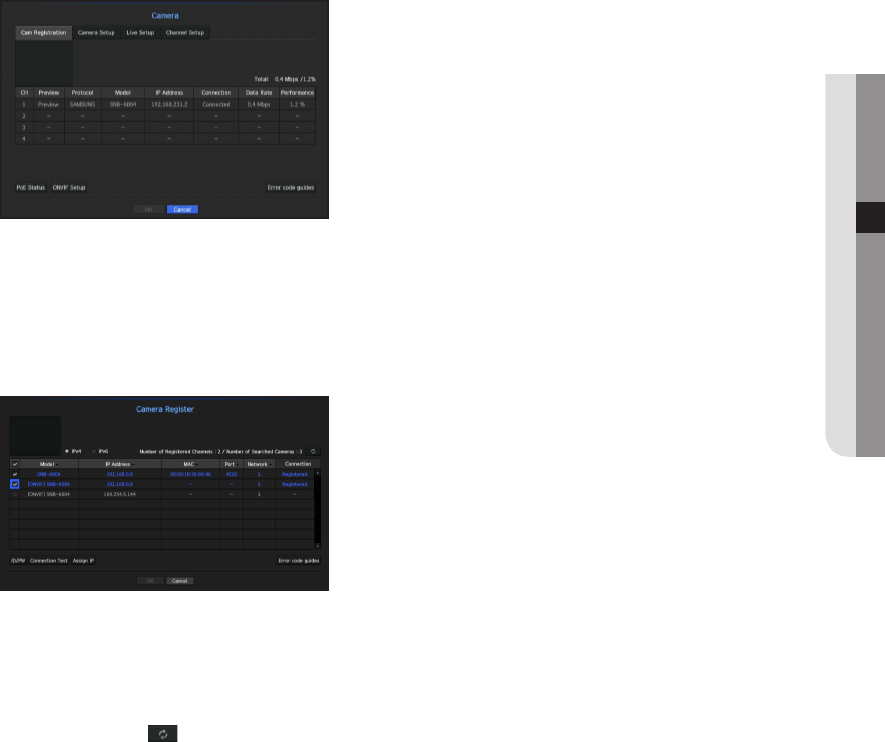
To register a camera
You can register a network camera for each channel and make connection between.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Device> Ö ► Ö <Camera> Ö [ENTER] Ö ▼
Ö <Cam Registration> Ö ▲▼◄► Ö [ENTER]
•
Preview : View the video of the channel as a current image.
•
Protocol : Show the protocol information of a registered network camera.
•
Model : Show the camera model name.
•
IP Address : Display the IP address of a network camera.
•
Connection : Display the connection status.
•
Data Rate : Displays the total amount of data received by the channel.
•
Performance : Displays the necessary performance occupancy rate for receiving the amount of data.
`A camera registered with the RTSP, ONVIF protocols can occupy twice the capacity of the existing amount of data.
M
`If the NVR has been initialized, it may not connect to cameras. Configure the network settings first and add cameras.
For more information on network settings, refer to "Network Configuration". (Page 76)
52_ menu setup
menu setup
If you want to register a camera in PnP mode
J
`When you connect a camera in PnP mode, the initial ID, password and DHCP mode should be set in advance.
`Samsung cameras are registered for Samsung protocols and other cameras are registered by using the Onvif protocol.
`In PnP mode, you cannot connect a device that runs the DHCP server in PoE port or camera setting port. (Ex: hub)
To auto-search for and register a network camera
1. In the <Cam Registration> field, click on the <Auto> button.
2. Search for a network camera connected.
`An already registered camera will be marked in blue in the list.
`If you search for the camera again or if the IP is an old IP that was not assigned by the DHCP server (such as -192.168.1.100),
then press the < > button to check if a new IP has been assigned. If the IP is still the same, then select Assign IP to
assign the IP manually.
3. Select a camera from the camera list to see a preview of its current video feed.
`Camera searched with ONVIF does not provide previews.
English _53
● MENU SETUP
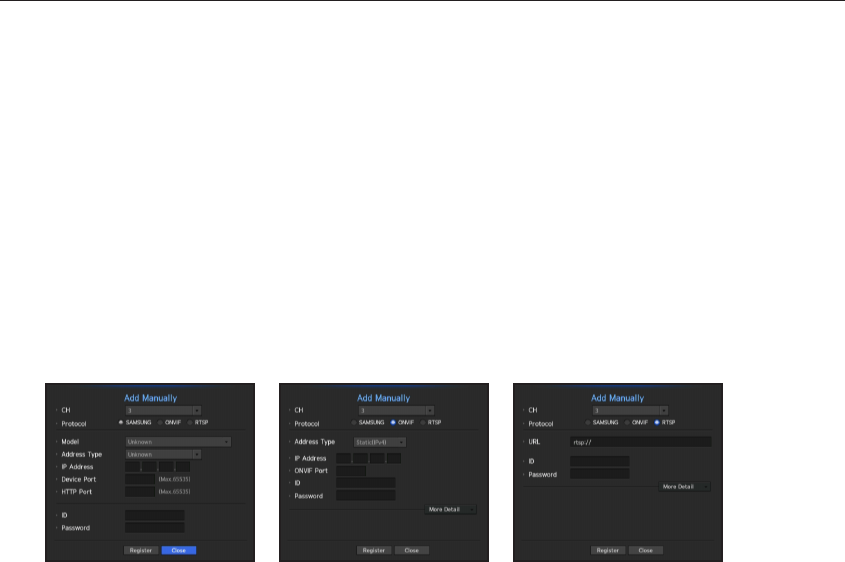
4. Check the checkbox next to a network camera that you want to connect to.
`You can select all of the network cameras in the list and provide <ID> and <Password> all at once.
`Click a header at the top of the list to sort the list according to that header.
J
`Registering camera with user account other than admin may restrict camera function.
`When you change the camera ID/password in the camera web viewer, if the camera is already registered in NVR, you also
have to change the camera ID/passowrd information registered in NVR.
5. Click on the <ID/PW> button to enter the selected network camera's <ID> and <Password>.
6. Press the <Connection Test> button to make a connection to a camera.
7. Press <Register> to register the selected camera.
To manually search for and register a network camera
1. In the <Register> menu, click on the <Manual> button.
2. The manual search window will appear.
3. Select a channel and protocol used to connect to a camera.
The input items may differ depending on the selected protocol.
•
SAMSUNG : Comply with the internal network protocols adopted by Samsung Techwin.
•
ONVIF : Means the camera supports ONVIF protocols. When connecting a camera that its name cannot be
found from the list, select <ONVIF>.
•
RTSP : Comply with RFC 2326, one of "Real Time Streaming Protocol (RTSP)" for real-time streaming.
54_ menu setup
menu setup
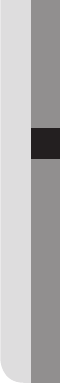
4. If you select the <SAMSUNG> protocol, check options as necessary.
•
Model : Select a camera model.
-
Samsung Network Camera/Encoder : Means the camera/encoder supports Samsung Techwin's SVNP
protocol. When connecting a camera that does not appear in the camera list, select Samsung Netowrk
Camera/Encoder.
`However, you must select the correct model name of the camera, if it's in the list. Some of obsolete camera models may not be
supported.
`The below models are discontinued. If you register them with ONVIF, some camera functions will be restricted or cause errors.
It is recommended you register the Samsung protocol.
- SNB-2000, SNB-3000, SNC-B2315, SNC-B2331, SNC-B2335, SNC-B5368, SNC-B5395, SNC-B5399, SNC-570,
SNC-1300, SND-460V, SND-560, SND-3080, SND-3080C, SND-3080CF, SND-3080F, SND-3081, SNP-3301, SNP-3301H,
SNP-3350, SNP-3370, SNP-3370TH, SNP-3750, SNV-3080, SNP-3430
•
Address type : Select an address type of the camera.
`Address type can be different dependingon connected product model.
-
Static(IPv4)/Static(IPv6) : Used to provide the IP address of the camera manually.
-
iPOLiS DDNS : This is available only if the camera is registered with the iPOLiS DDNS(www.samsungipolis.
com) server. Provide the registered domain for DDNS ID.
`Ex) http://www.samsungipolis.com/snb5000 provide "snb5000" for iPOLiS DDNS
-
URL : Used for URL address input.
M
`Refer to the user manual of the connected camera and check the DDNS specification that is supported by the camera.
•
IP Address : Provide the IP address of the camera.
•
Device Port : Provide the device port of the camera.
•
HTTP Port : Provide the HTTP port of the camera.
•
ID : Provide the ID of the camera that you want to register.
•
Password : Enter the password of the camera to be registered.
5. Select <ONVIF> or <RTSP> for the protocol and enter your input for each field appears.
•
ONVIF Address / RTSP URL : Enter the camera's RTSP access address that supports ONVIF or RTSP.
For more information about the RTSP address, refer to the manual of each applicable network camera.
•
ID : Enter the ID for accessing via ONVIF/RTSP protocol.
•
Password : Enter the password for accessing via ONVIF/RTSP protocol.
•
Mode : If <More Detail> button clicked, setup window will appear. Select a mode that is supported by the
network camera in RTSP connection mode.
-
TCP : The connection type with the network camera will switch to "RTP over TCP".
-
UDP : The connection type with the network camera will switch to "RTP over UDP".
-
HTTP : The connection type with the network camera will switch to "RTP over TCP (HTTP)".
-
HTTPS : The connection type with the network camera will switch to "RTP over TCP (HTTPS)".
English _55
● MENU SETUP

If you want to check the error details of camera registration
If you failed to register a camera, the reason for the failure will be displayed.
•
Connection failed due to unknown error. : This message appears if the camera has failed to be registered
due to unknown connection status.
•
Due to the camera account locking, access has failed. : When you enter a wrong ID/password 5 times to
login to the camera account, this message is displayed.
Try to log in again after 30 seconds. If the same message appears, you may need to check whether someone
has tried to access your camera account from the outside.
•
Connected successfully. : This message appears if the camera is connected successfully.
•
Incorrect model information. Provide the correct model information. : This message appears if the
model information provided for registering the camera is incorrect.
•
Authentication has failed : This message appears if the ID or password provided for registering the camera
is incorrect.
•
Connection has failed due to excessive concurrent users. : This message appears if the concurrent user
count exceeds the upper limit.
•
Connection has failed due to incorrect HTTP port information. : This message appears if the HTTP port
number of the camera is invalid.
•
Connection has failed. Unknown connection status. : This message appears if the camera has failed to
be connected due to a unknown error.
•
User Model Modification : When registering a new camera, it is named according to the device's default if
user set the model to <Samsung Network Camera/Encoder>. In case if automatic registration fails, user
can change the model name of camera to be registered.
To edit camera profile
When a camera is added for the first time, it is added as the default profile of H.264, MPEG4 and MJPEG in
order temporarily.
To change its profile, refer to "Setting the camera recording profile" (Page 71) or "Live Setting" (Page 63).
M
`
In case of NVR, if you set 3 different profiles for live, recording and network profile, one camera will produce video streams
accordingly, having different stream formats. Especially, note that the live profile may vary depending on the used screen split mode.
`For cameras, if applied with one profile only, the produced frame rate is fixed as the profile specifies; if applied with multiple
profiles, produced video stream's frame rate is not guaranteed. For example, if applied with 2 profiles of 30fps, the camera
may transmit streams at 20fps.
56_ menu setup
menu setup
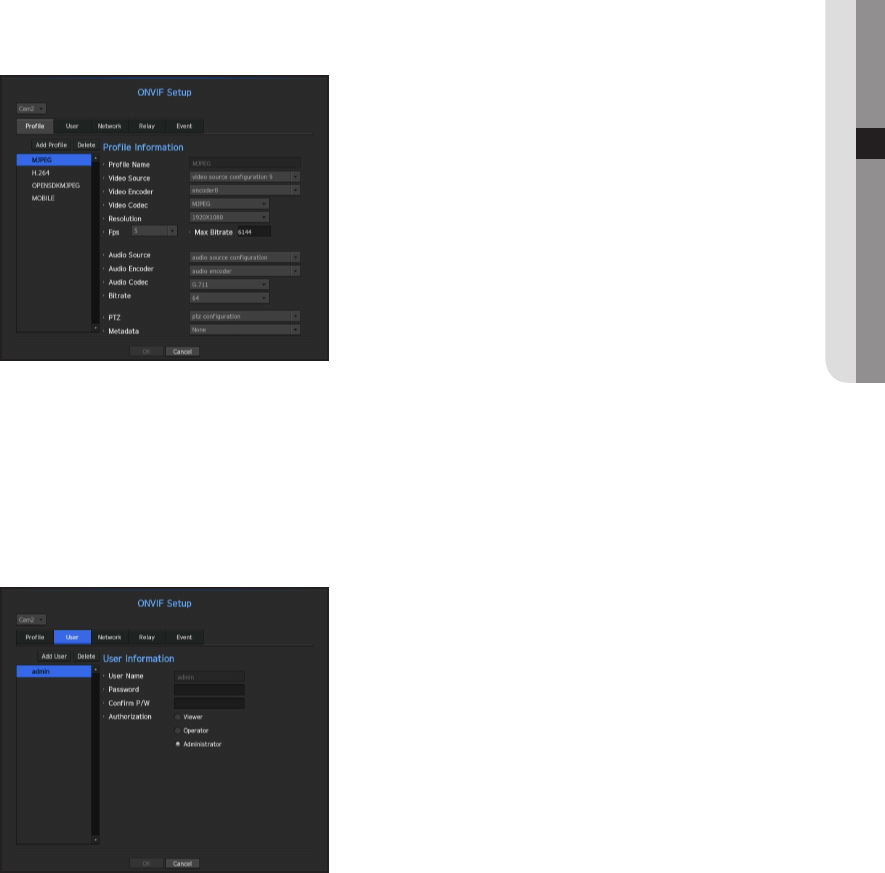
ONVIF Setup
In the bottom of the camera addition screen, click on the <ONVIF Setup> button to set additional settings for
cameras with the ONVIF protocol.
`You can change the information only if the user account (camera account used for camera registration) is used to read the user
information and a connection is made with the admin privilege.
Profile
• CH : It shows the list of registered camera with the ONVIF setting.
• Add Profile : You can add camera profile.
After adding a profile, click on the <OK> button to add it to the list.
• Delete : After selecting the profile to delete, click on the <Delete> button to delete the selected profile.
• Profile information : You can set the details of the selected profile.
After finishing setting each item, click on the <OK> button to save changes.
User
• Add User : You can add a camera user.
After adding a user, click on the <OK> button to add them to the list.
• Delete : After selecting the user to delete, click on the <Delete> button to delete the selected user.
• User Information : You can set the details of the selected user.
English _57
● MENU SETUP
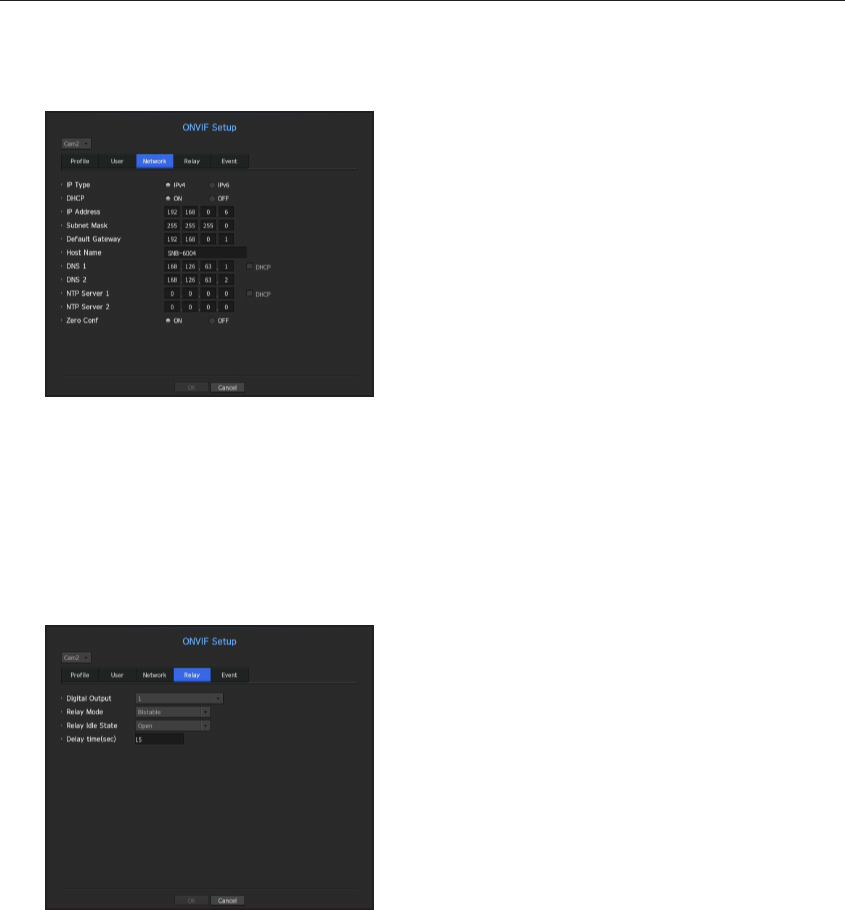
Network
You can set the details of the network.
• IP Type : Select from either the IPv4/IPv6 IP types.
• DHCP : Select whether to use the DHCP.
• DNS / NTP Server : Only if the DHCP setting is <ON>, the DHCP checkbox will be activated.
`If the DHCP is checked, you can manually enter the IP address.
Relay
You can set details of the relay.
• Digital Output : You can select a digital output channel.
• Relay Mode : Select either bi or mono stable modes.
• Relay Idle State : Select either open or closed relay standby modes.
• Delay Time : Select the relay operation waiting time.
58_ menu setup
menu setup
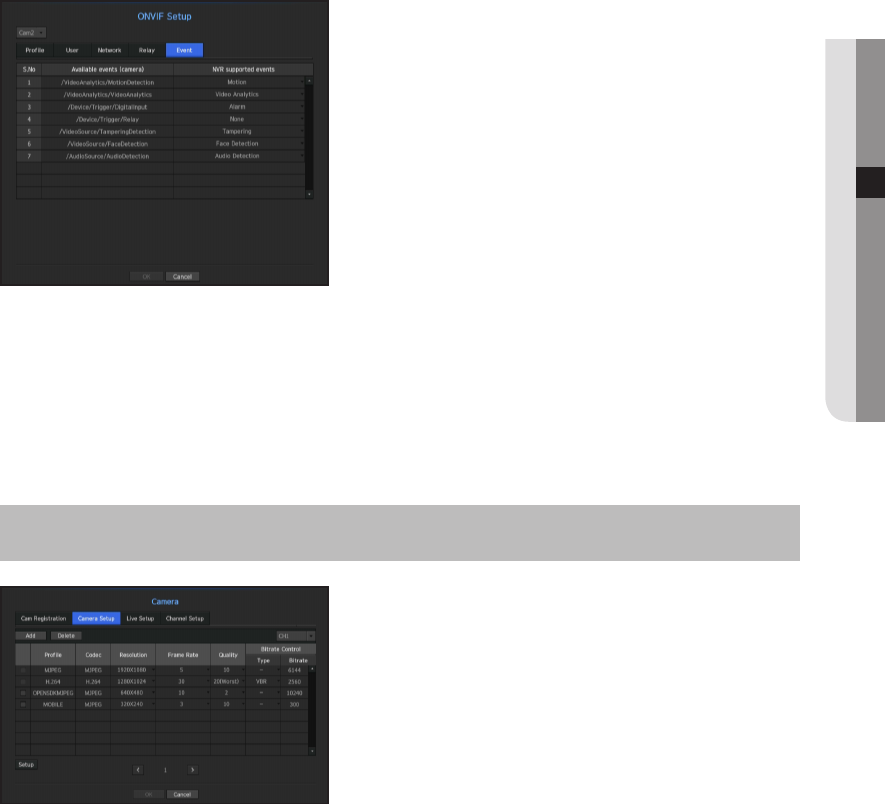
Event
You can set details of the event.
• Available events (camera) : It shows the list of all the events supported by a camera by using the ONVIF
protocol.
• NVR supported events : You can map the list of events supported by a camera to events that the NVR can
detect. There is no default value. It only shows the value sent by a camera.
Camera Setting
You can change the video settings of a registered network camera for each channel.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Device> Ö ► Ö <Camera> Ö [ENTER] Ö ▼►
Ö <Camera Setup> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
•
Add : You can add camera profile. Click on the Add button to launch the addition window.
Enter the information and click on the <OK> button to add it to the list.
•
Delete : You can delete the selected profile from the list.
•
Select Camera : Select the camera channel to change the video transmission settings.
•
Profile : Show a video profile for the connected camera.
•
Codec : Show the codec information for the selected profile.
•
Resolution : You can change the resolution of the selected profile.
•
Frame Rate : You can change the baud rate of the selected profile.
•
Quality : You can change the video quality of the selected profile.
•
Bitrate Control : You can change the bit rate for video transmission of the selected profile.
English _59
● MENU SETUP
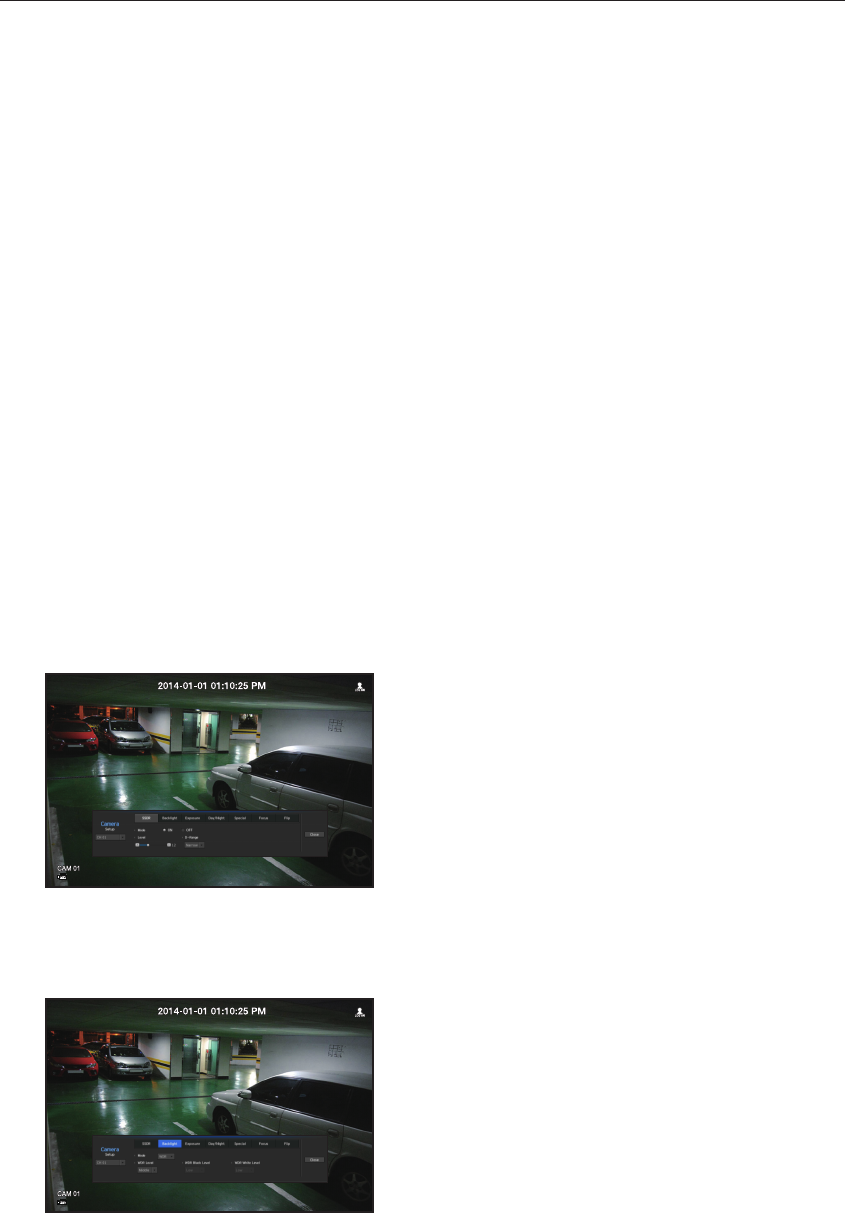
M
`If you change the settings of a specific profile for each model, the effective range of the baud rate may be changed
accordingly.
Ex) if you set the baud rate of the first profile to 30fps, the send rate of the second profile will be changed to 15fps.
`Menu items except Codec, Resolution, Transfer Rate, and Transfer Quality can be configured in the network camera's
settings menu.
`If you change the current profile settings, you may encounter an interrupted playback on the recording or live screen for a
certain time.
`Changes made in Camera Setup page are applied immediately, while changes made through the camera's web page may
require up to 3 minutes.
Setup
In the bottom of the camera setting screen, press the <Setup> button to set your camera while watching the
live video of the selected camera.
M
`SUNAPI (Samsung Unified Network API) : Camera that supports the communication protocols provided by Samsung
1. Camera supporting SUNAPI.
2. A camera connected with admin privileges.
3. A camera connected to Samsung protocols.
In the above cases, you can use the function.
`For more details on camera settings, refer to the camera user manual.
Settings and operational spec vary depending on each camera.
SSDR
If there is a significant difference between the dark and the bright areas, increase the brightness of the dark
areas to maintain the level of brightness of the entire area.
Mode, level, D-Range can be set.
Backlight
You can view both bright and dark areas.
Mode, WDR level, WDR black/white levels can be set.
60_ menu setup
menu setup

Exposure
You can adjust the exposure of your camera.
Brightness control, shutter, SSNR, Sens-up, shutter/lens, and gains can be set.
Day/Night
You can change the mode to adjust the color and contrast.
Mode, switching time, brightness change, alarm time, alarm input/output, negative color, daytime/nighttime
switching and simple focus, and activation time can be set.
Special
DIS (shaking compensation), use of Defog levels can be set.
English _61
● MENU SETUP
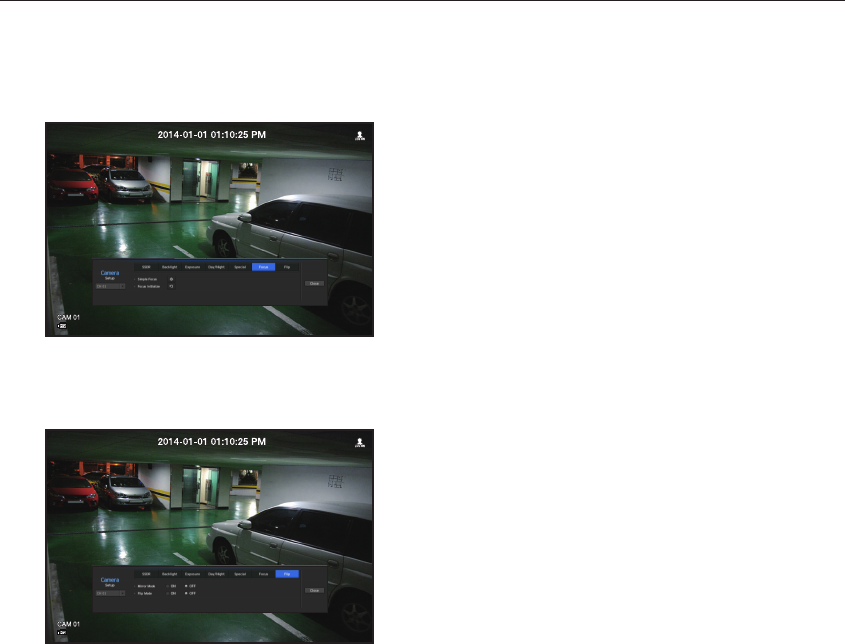
Focus
You can adjust the focus of you camera's video.
Items of Simple Focus and Focus-Initialize Setting can be set.
Flip
You can set the mirror mode (horizontal flipping) and the flip mode (vertical flipping).
After finishing with setting camera, click on the <Close> button to move back to the previous screen.
62_ menu setup
menu setup
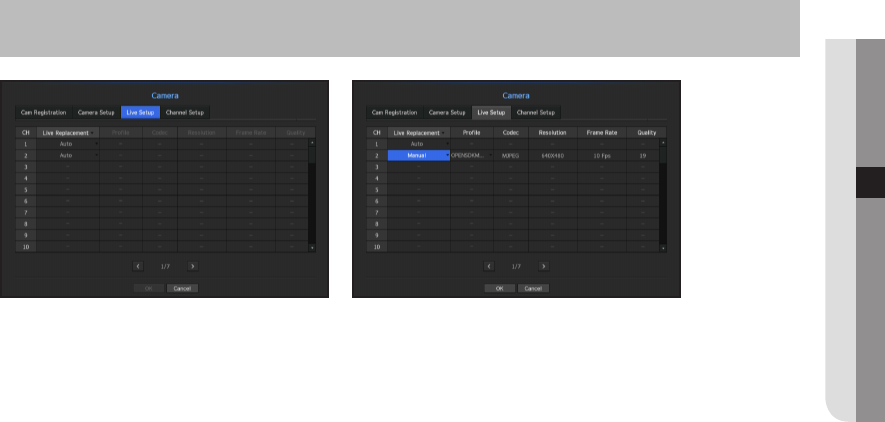
Live Setting
You can change the live transfer settings of the network camera.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Device> Ö ► Ö <Camera> Ö [ENTER] Ö ▼►
Ö <Live Setup> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
•
Live Replacement : You can select the live profile setup mode.
If you select <Manual>, the profile setup items are enabled, and you can change settings manually.
-
Auto : For live monitoring, the profile which is approximate to the output resolution of each channel must be
selected automatically.
e.g., Camera profile : Three profiles (1280x720, 800x600 and 640x480) are supported.
If the resolution of the output screen is 1920x1080:
1280x720 is selected automatically if the channel resolution of the single channel is 1920x1080.
640x480 is selected automatically if the channel resolution of 16-split channel is 480x270.
-
Manual : Live monitoring is performed with the profile selected by the user from the registered camera
profiles.
-
Record : Live monitoring is performed with the profile set for recording.
•
Profile : You can select the video profile of the connected camera setting.
•
Codec : Show the codec of the selected recording profile.
•
Resolution : Show the resolution of the selected profile.
•
Frame Rate : Show the frame rate of the selected profile.
•
Quality : Show the quality of transfer video of the selected profile.
English _63
● MENU SETUP
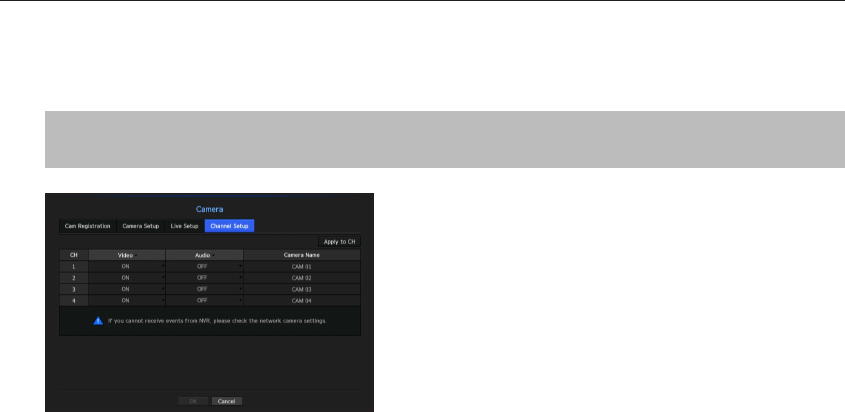
Channel Setting
You can configure the video settings for each channel.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Device> Ö ► Ö <Camera> Ö [ENTER] Ö ▼►
Ö <Channel Setup> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
• Apply to CH : If you select <Apply to CH>, the "Apply to CH" confirmation window will appear.
After selecting channels that the settings will be applied to, click on <OK> to apply them to the selected
channels.
•
Video
-
<ON/OFF> : You can turn ON/OFF the selected channel's camera.
-
<Covert1> : Shows information other than the video of the selected channel.
For privacy protection, it does not display the video while the recording continues.
-
<Covert2> : Shows nothing but an empty screen while the recording continues.
M
`If the channel is set to <Covert1> or <Covert2> mode, the channel's sound is not hearable.
However, the channel's sound is recorded if its Audio setting is set to <ON>, even the sound is not heard in Live mode.
•
Audio
-
If set to <ON>, you can turn the audio of the channel ON/OFF on the Live screen.
-
If set to <OFF>, the channel's audio is off on the Live screen and not recorded.
•
Camera Name : Provide a camera Name.
`You can enter up to 15 characters including space.
64_ menu setup
menu setup
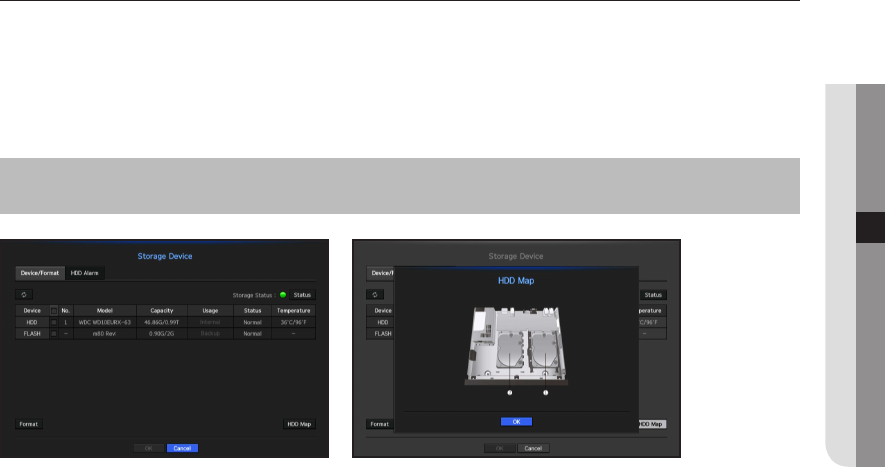
Storage Device
You can check information on storage devices.
Device/Format
You can check storage devices and their capacity, usage as well as status.
Devices available are HDD, and USB devices (Memory, HDD).
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Device> Ö ►▼ Ö <Storage Device> Ö
[ENTER] Ö ▼ Ö <Device/Format> Ö ▲▼◄► Ö [ENTER]
• Storage Status : Displays the working status of a storage device.
-
Red : Displays the situation of video loss.
-
Green : Displays the normal situation without video recording losses.
-
Status
`Full BPS : Displays the current rate of recording.
`Current Loss Rate : Displays the current recording loss rate.
`Max Loss Amount : Displays the maximum amount of losses up until now.
• No. : You can check the designated number for the built-in HDD.
`If you want the find out about the location corresponding to the HDD number, refer to the <HDD Map>.
• Capacity : Displays the amount of storage device use and the full capacity.
• Usage : Designate the purpose of use for a storage device.
• Status : Displays the current working condition of a storage device.
For inspection or replacement of HDD alarms, please refer to "HDD Alarm Setting." (Page 66)
-
Normal : It is displayed during normal operation.
-
Inspection : Operating with partial problems.
-
Replacement : It is displayed when you can no longer use it.
• Temperature : You can check the temperature of the HDD mounted in the NVR.
English _65
● MENU SETUP
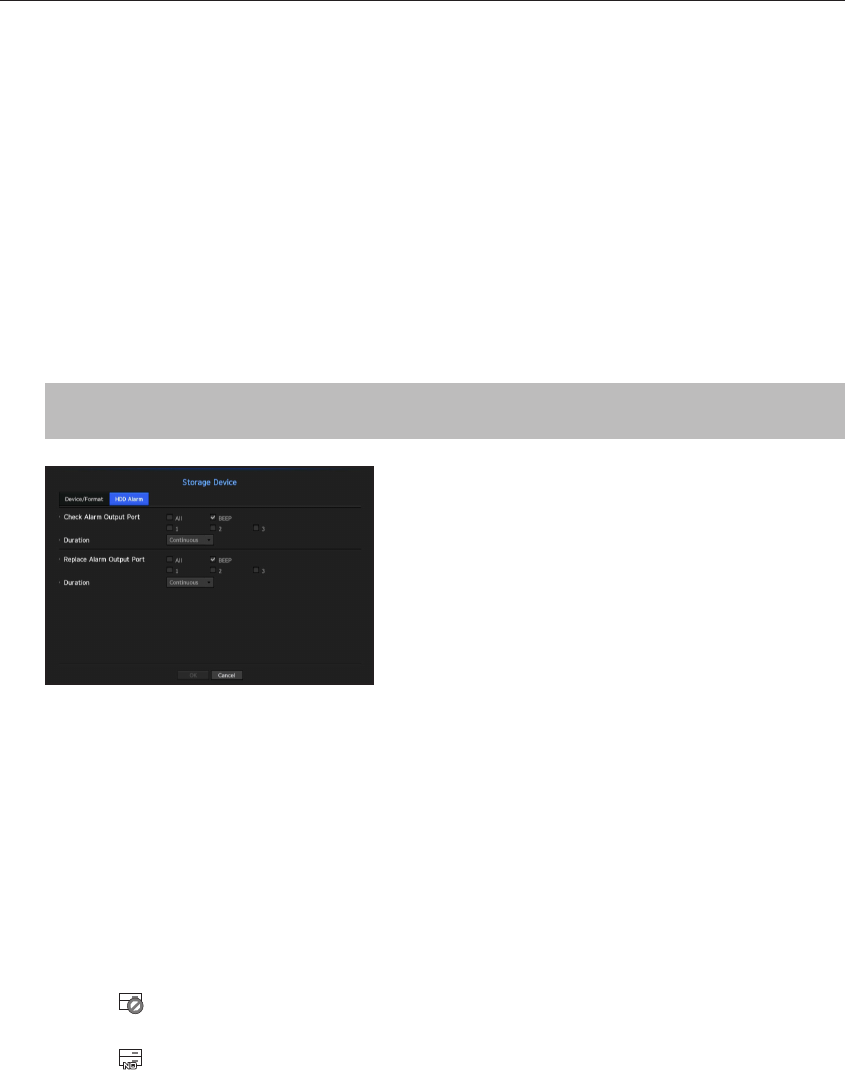
• Format : Select a device and click on format after which a format confirmation window appears.
Click on the <OK> button to format the selected storage device.
J
`Formatting will delete all the recording data that has been saved. Be careful.
`While formatting is ongoing, you cannot record video.
`Do not remove a formatting device until it is finished.
• HDD Map : You can check the location according to the assigned number for the HDDs installed inside.
`Refer to this when servicing or installing an additional HDD.
HDD Alarm Setting
You can set the inspection alarm output terminal, the replacement alarm output terminal and the alarm time for
HDD defects.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Device> Ö ►▼ Ö <Storage Device> Ö
[ENTER] Ö ▼► Ö <HDD Alarm> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
•
Alarm
-
Alarm signal will output through the alarm out port on the rear side when selected <1>, <2>, <3>.
-
If <BEEP> was selected, a beep will sound.
-
If <All> was selected, both beep sound and alarm signal through rear side ports will output.
•
Check Alarm Output Port : If HDD generates check alarm, the alarm signal will output to the specified alarm
output port.
•
Replace Alarm Output Port : If HDD generates replace alarm, the alarm signal will output to the specified
alarm output port.
•
Duration : Sets the alarm duration for the alarm signal and beep sound.
M
`<Check> status means that the HDD is operating but it has problems that require technical examination.
() appears on the Live screen.
`<Replace> status means that the HDD has defect and requires immediate replacement.
() appears on the Live screen.
66_ menu setup
menu setup
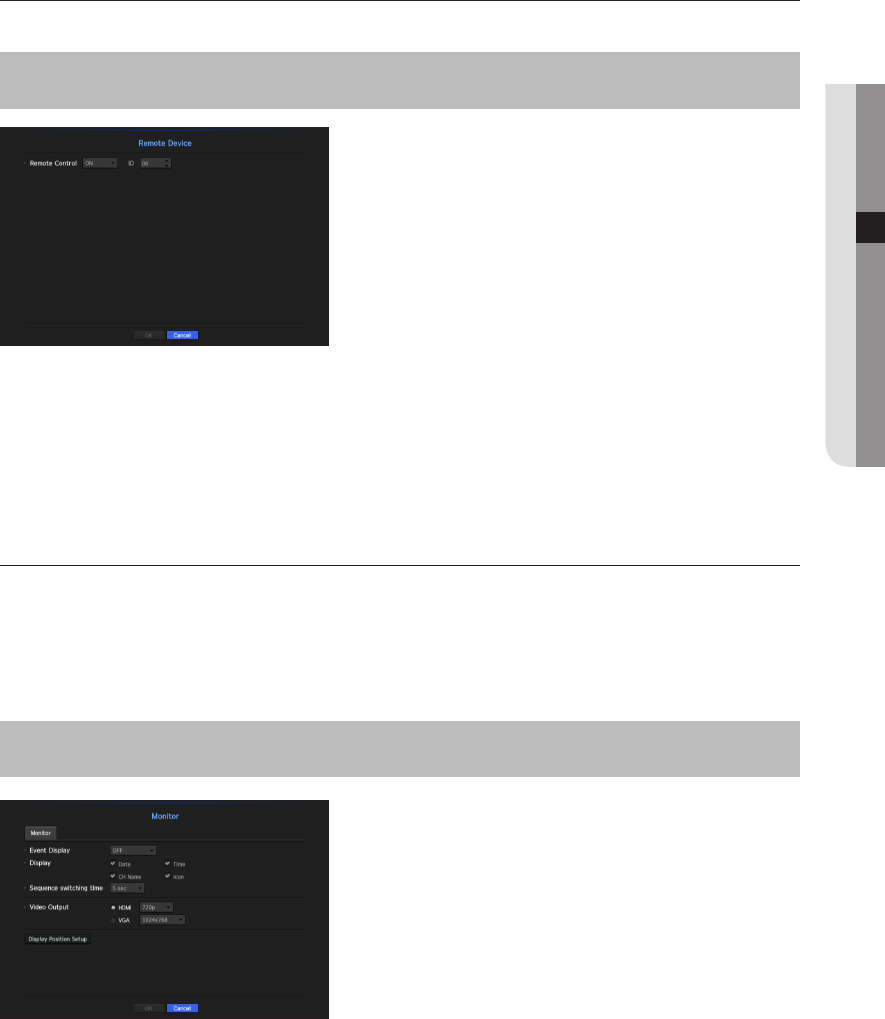
Remote Devices
You can adjust the ID for a remote control to be used in connection with NVR.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Device> Ö ►▼ Ö <Remote Device> Ö
[ENTER] Ö ▲▼◄► Ö [ENTER]
• Remote control: Select whether to use a remote control.
• ID: Select an ID number linked to a camera.
If the remote control ID does not match, it will not operate properly.
M
`To change the remote control ID, refer to "Changing the Remote Control ID". (Page 12)
Monitor
You can set the information displayed on the monitor as well as the output system.
Monitor settings
You can configure the monitor output-related settings including the displayed information, dwell time and output
system.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Device> Ö ►▼ Ö <Monitor> Ö ▲▼◄► Ö
[ENTER]
•
Event Display : Sets the dwell time of the event channel display on the monitor when an event occurs.
If you set it to <Continuous>, it will continue to display, until you press the [ALARM] button to cancel it.
•
Display : Displays only checked items on the monitor screen.
•
Sequence switching time : Set the automatic switching time for the segmented screen in live mode.
English _67
● MENU SETUP
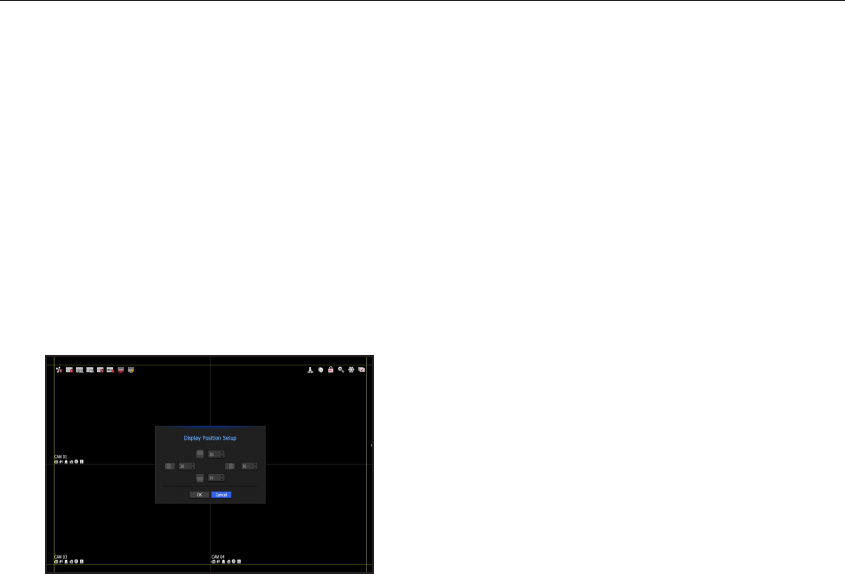
•
Video Output : Select a video output type from <HDMI> and <VGA>.
If your selection of <HDMI> or <VGA> does not match with the monitor setting, the video may not be output.
If you press the [STOP
(@)] [ZOOM] [STOP
(@)] [ZOOM] [MENU] button on your remote control,
the basic resolution pop up will appear. You can adjust the desired resolution in it.
`If the changed resolution is not supported by the monitor, the video may not be displayed properly. If this is the case, the screen
will restore the default resolution after a certain time. Then, you can change it to a different resolution.
M
`Specify the event display time and dwell time in consideration of the video delay depending on the network environment.
To adjust the display position
Some monitors many not display information (camera name, icon, time information, etc.) about the NVR,
depending on the condition. Then, you can change the display position of the data.
1. From the monitor setup menu, select <Display Position Setup>.
2. Using the directional key or number button on the remote control, you can adjust the screen.
3. Press <OK>.
68_ menu setup
menu setup
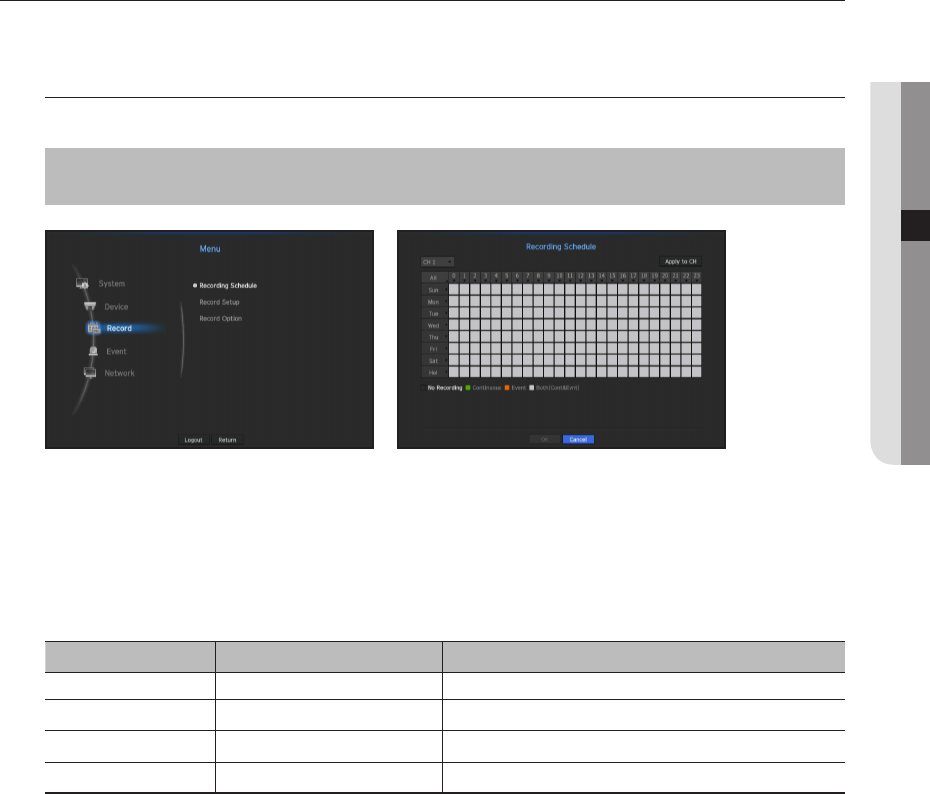
SETTING THE RECORDING
You can setup scheduled recording, event recording and other recording related settings.
Recording Schedule
Make your reservation on a date and time to schedule the recording on specified time.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Record> Ö ► Ö <Recording Schedule> Ö
[ENTER] Ö ▲▼◄► Ö [ENTER]
•
All : The entire time range (Monday through Sunday including holidays, AM 0~ PM 23) will be reserved with
the same recording schedule
•
Apply to CH : If you select <Apply to CH>, the "Apply to CH" confirmation pop-up window will appear.
After selecting channels that the settings will be applied to, click on <OK> to apply them to the selected
channels.
Record setting by the color
Color Function Description
No Color No Recording No schedule / event recording
Green Continuous Scheduled recording only
Orange Event Event recording only
White Both(Cont&Evnt) Both scheduled / event recordings
Each press of a selected cell will cycle through <No Recording>-<Continuous>-<Event>-<Both(Cont&Evnt)>.
English _69
● MENU SETUP
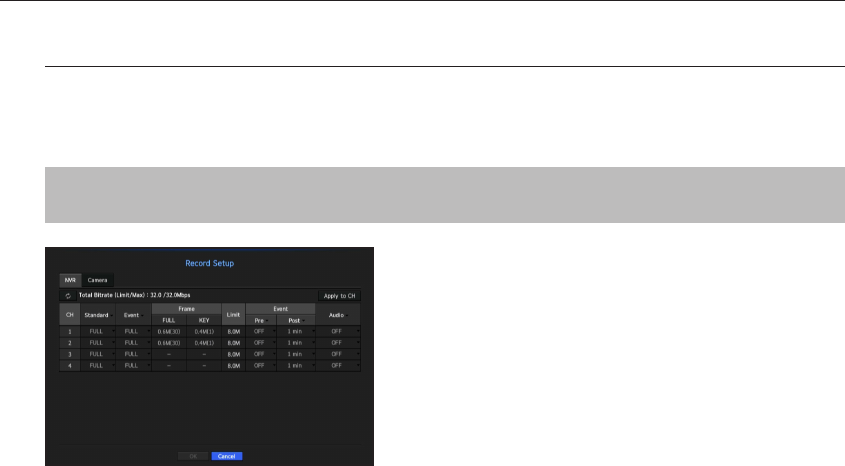
Record Setting
You can set resolution, IPS, and quality of recordings by channel, and by recording type of standard / event.
You can check frame rates and data transfer amount of Full Frame and Key Frame recordings for each channel,
and set the transfer limit for recordings.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Record> Ö ►▼ Ö <Record Setup> Ö
[ENTER] Ö ▼ Ö <NVR> Ö ▲▼◄► Ö [ENTER]
•
Apply to CH : If you select <Apply to CH>, the "Apply to CH" confirmation window will appear.
After selecting channels that the settings will be applied to, click on <OK> to apply them to the selected
channels.
•
Standard, Event : Configures Standard recording and Event recording.
-
FULL : Records all frames fed by the camera.
-
KEY : Records only key frames fed by the camera.
Actual recording rate may differ from camera settings. In general, 1 to 2 frames per second are recorded.
-
OFF : No recording is made.
• Frame
-
FULL : Shows the amount of data for all the scene recordings.
-
KEY : Shows the amount of data for the main scene recordings.
• Limit : Set the amount of data allowed for input for each channel.
• Event : When an event occurs, you can set which point you will start or stop recording.
-
Pre : When an event occurs, recording will be started regardless of the time set.
If you set it to five seconds, recording will start at five seconds before an event occurs.
-
Post : When an event occurs, recording will continue after the time set.
If you set it to five seconds, recording will continue for a further five seconds after an event is finished.
• Audio : Specify whether to record the sound received from the camera or not.
M
`
If a channel's data transfer exceeds defined allowed limit, then it may affect to other channels, and may force switching to
<KEY> recording even when the channel is configured to <FULL> recording mode. For Key Frame recording channels, the
icon for limited recording appears on the live screen's top side.
`
A channel displayed in yellow indicates that the recorded data is not being transferred from the camera and that the recording
is being performed temporarily using another profile on the camera.
Check the channel information to see the applied profile to the channel listed in yellow.
A channel displayed in orange indicates that the amount of inputted data is greater than the permitted data amount.
In this case, it is impossible to record all of the incoming frames.
Instead, only part of the frames (1 or 2 frames per second) can be recorded. To resolve this issue, you must set the permitted
data amount to be greater than the amount of inputted data.
Refer to notes on "Record status". (Page 34)
70_ menu setup
menu setup
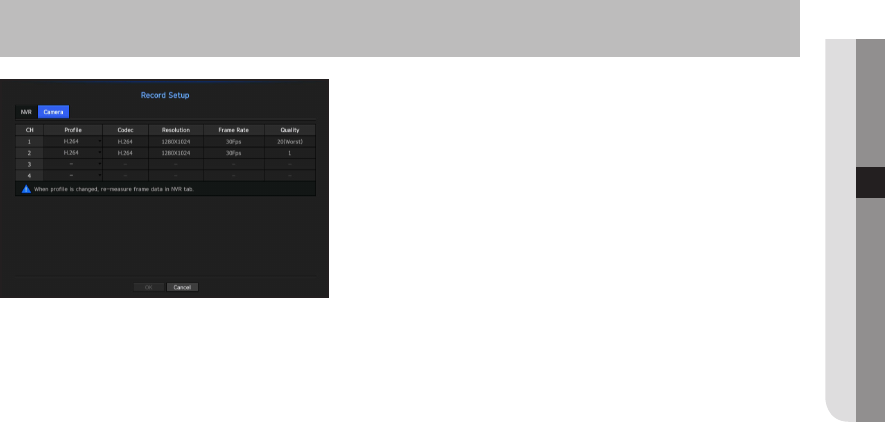
Setting the camera recording profile
You can set the video profile to perform recording on your camera connected to each channel.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Record> Ö ►▼ Ö <Record Setup> Ö
[ENTER] Ö ▼► Ö <Camera> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
M
`You can configure the settings only for the profiles that are supported by the camera.
`If the profiles used for recording and network are different, camera's video feed may not comply with the frame rate as
specified in the camera.
•
Profile : Select a record profile for the connected camera.
•
Codec : Show the codec information for the selected record profile.
•
Resolution : Display the resolution for the selected record profile.
•
Frame Rate : Display the baud rate for the selected record profile.
•
Quality : Display the video quality for the selected record profile.
English _71
● MENU SETUP
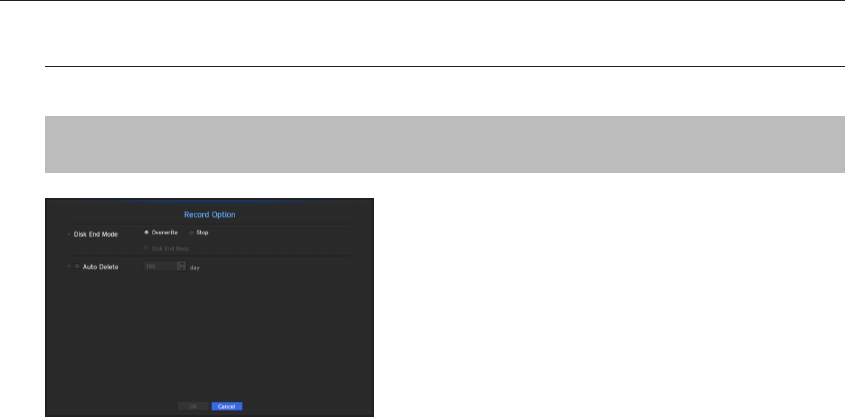
Record Option
When the HDD capacity is full, you can set whether to stop recording or start overwriting.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Record> Ö ►▼ Ö <Record Option> Ö
[ENTER] Ö ▲▼◄► Ö [ENTER]
•
Disk End Mode : Select a HDD repetitive recording type.
-
Overwrite : If the HDD is full, this will overwrite the existing data and keep recording.
-
Stop : If the HDD is full, this will stop recording automatically.
•
Disk End Beep : If you select <Stop> for the disk end mode, this button will be active. Specify the use of
beep when the HDD recording ends.
If you check it, the beep will sound on the disk full and the recording stops.
•
Auto Delete : If you check this option, the period list box is active. Specify the deletion period to delete any
earlier data than the specified date. However, you can search for data from the current time to the selected
date.
J
`If you press <OK> when you have completed your settings, all the existing data earlier than the specified period will be
deleted automatically. So it is recommend to backup the previous data if necessary for later use.
72_ menu setup
menu setup
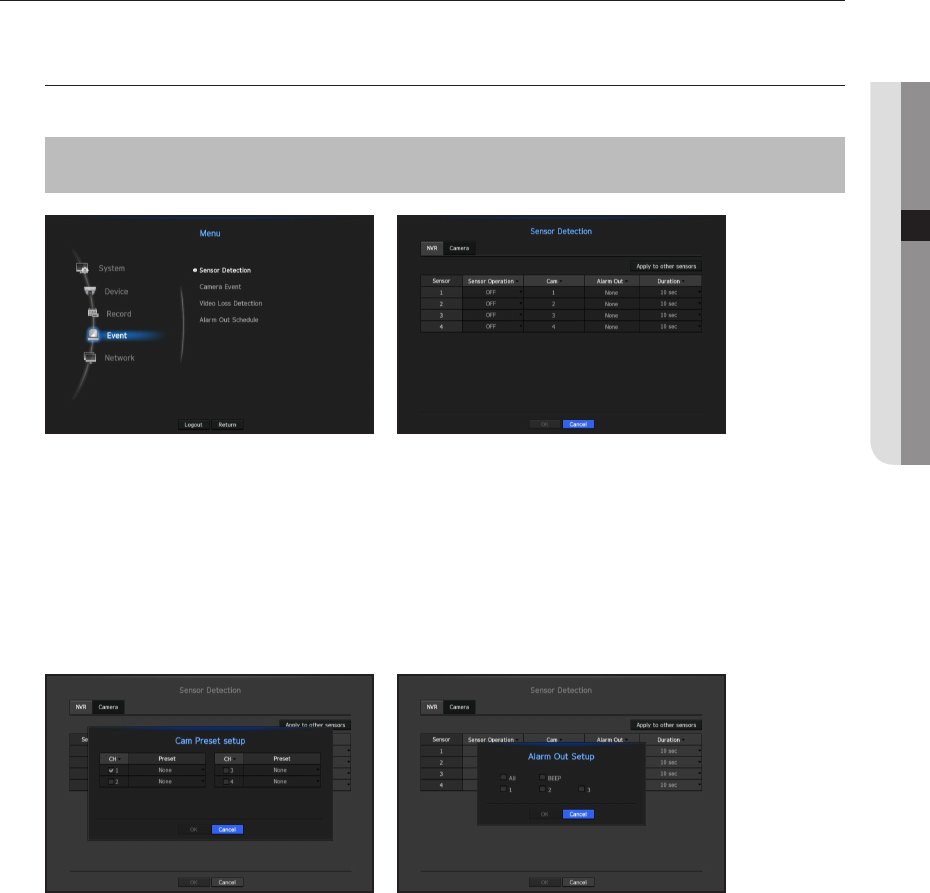
SETTING THE EVENT
You can make the setup for record in case of sensor detection, camera event or video loss detection.
Sensor Detection
You can set the sensor's operating condition and connected camera, as well as alarm output and its duration.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Event> Ö ► Ö <Sensor Detection> Ö
[ENTER] Ö ▼ Ö <NVR> Ö ▲▼◄► Ö [ENTER]
•
Apply to other sensors : If you select <Apply to other sensors>, the "Apply to other sensors" confirmation
window will appear.
After selecting channels that the settings will be applied to, click on <OK> to apply them to the selected
channels.
•
Sensor Operation : Sets the operation mode of sensors.
`In the <Camera> tab, you can set whether or not to use a sensor.
-
<N.O (Normal Open)> : Sensor is opened. If the sensor is closed, it generates alarm.
-
<N.C (Normal Close)> : Sensor is closed. If the sensor is open, it generates alarm.
•
Cam : Select a channel to be connected to the sensor.
If selected camera, "Cam Preset setup" window appears.
Select a channel and setup the preset.
`Preset setup can be done in PTZ mode.
•
Alarm out : Sets the alarm output method.
`For further information on alarm output, refer to "HDD Alarm > Alarm". (Page 66)
•
Duration : Sets the duration of alarm signal and alarm sound.
M
`
If you select <Camera> tab, you can configure the sensor operation settings of the network camera connected to each channel.
`
If the connected network camera that has configured the alarm in/out settings triggers an alarm, NVR will perform the alarm out.
English _73
● MENU SETUP
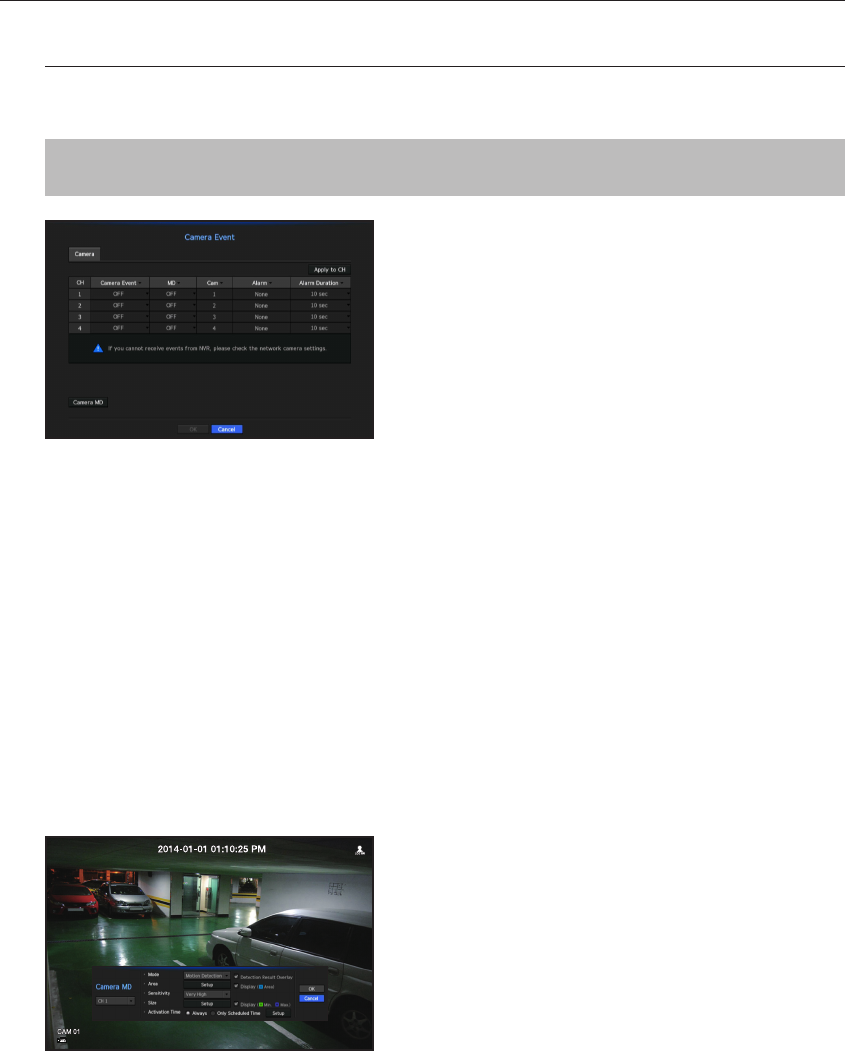
Camera Event
You can specify operation of events sent from your camera (motion detection, video analysis events, audio
events), alarm display methods, and alarm time.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Event> Ö ►▼ Ö <Camera Event> Ö [ENTER]
Ö ▲▼◄► Ö [ENTER]
• Apply to CH : If you select <Apply to CH>, the "Apply to CH" confirmation window will appear.
After selecting channels that the settings will be applied to, click on <OK> to apply them to the selected
channels.
• Camera Event : Select whether or not to use a camera event.
• MD : Select whether or not to use motion detection from camera.
• Cam : Select an event detection channel.
• If you select a camera item, the "Camera preset" screen will appear. Select a channel to connect and set the
preset.
`You can set the preset in PTZ mode.
• Alarm : Select the method for alarm output.
`For more details, refer to "HDD alarm > Alarm". (Page 66)
• Alarm Duration : Set the duration of alarm.
• Camera MD : You can set the detailed setting of motion detection for a network camera connected.
-
Mode : Set the motion detection mode.
-
Area : Click on <Setup> and when the detailed setup menu appears, set the motion detection area.
-
Sensitivity : Set the sensitivity for motion detection. (very low/low//medium/high/very high).
-
Size : Click on <Setup>. When the detailed setup menu appears, set the max/min size of the object to be
detected.
-
Activation Time : Select the operation time of motion detection.
After finishing with setup, click on the <OK> button to move back to the previous screen after saving the setup.
74_ menu setup
menu setup
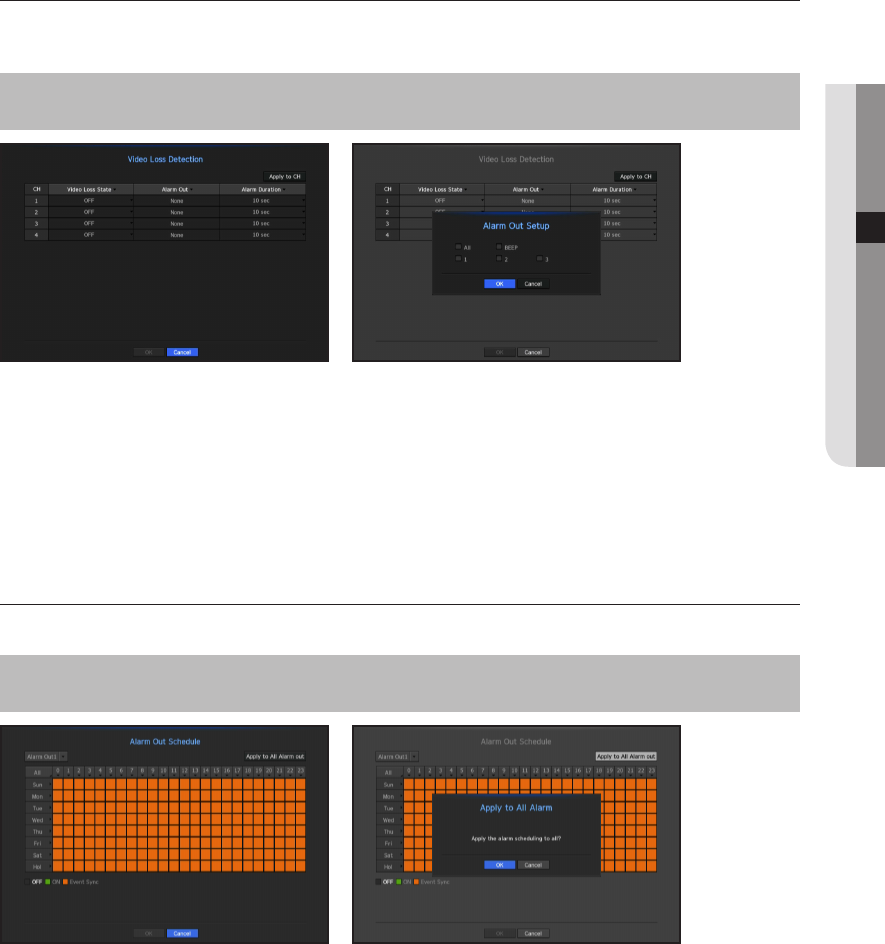
Video Loss Detection
You can set the camera so that the camera can trigger the alarm if it is disconnected or the video is lost due to
unstable network connection.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Event> Ö ►▼ Ö <Video Loss Detection> Ö
[ENTER] Ö ▲▼◄► Ö [ENTER]
• Apply to CH : If you select <Apply to CH>, the "Apply to CH" confirmation window will appear.
After selecting channels that the settings will be applied to, click on <OK> to apply them to the selected
channels.
•
Video Loss State : Specify the use of video loss detection.
•
Alarm Out : Select an alarm output method.
`For further information on alarm output, refer to "HDD Alarm > Alarm". (Page 66)
•
Alarm Duration : Specify the duration of the alarm output with the beep.
Alarm Out Schedule
You can set the conditions and operating hours for scheduled alarms.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Event> Ö ►▼ Ö <Alarm Out Schedule> Ö
[ENTER] Ö ▲▼◄► Ö [ENTER]
•
Alarm Out : Sets the alarm output method.
`For further information on alarm output, refer to "HDD Alarm > Alarm". (Page 66)
-
<ON> : Marked in green, and always generates alarm on scheduled time.
-
<OFF> : Marked in black, no alarm is generated even if an event occurs.
-
<Event Sync> : Marked in orange, generates alarm only when an event occurs.
•
Apply to All Alarm out : Applies the configured schedule to all alarms.
M
`When the alarm is generated on the scheduled time, you can stop the alarm by canceling the schedule.
English _75
● MENU SETUP
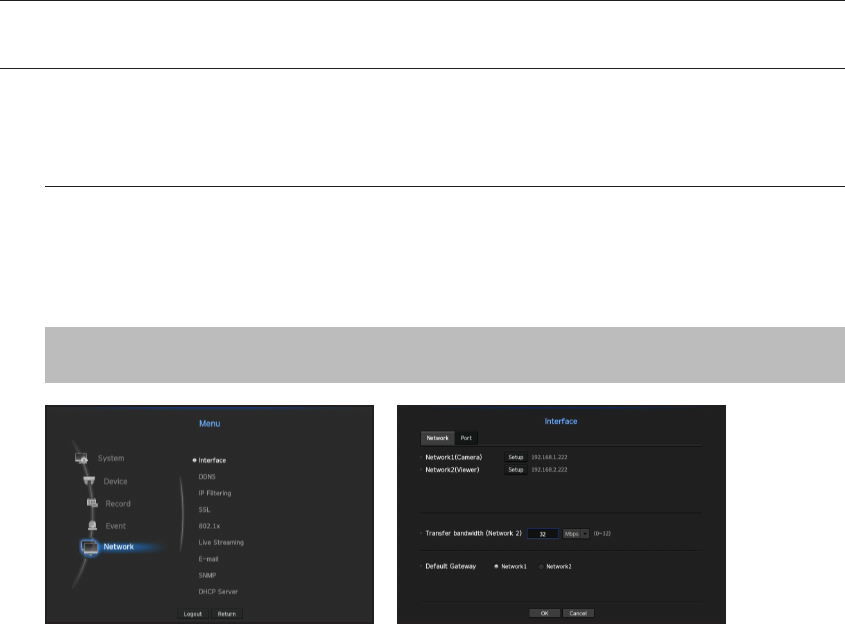
NETWORK CONFIGURATION
It provides networked monitoring of Live screen from a remote place, and supports mail forwarding function with
events. You can configure the network environment which enables such functions.
Interface
You can set the network connection route and protocol.
Setting a network connection
Sets the protocol and environment of the network.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ► Ö <Interface> Ö [ENTER] Ö ▼
Ö <Network> Ö ▲▼◄► Ö [ENTER]
• Network1 (Camera) : Port for camera connections; it receives video from a camera.
• Network2 (Viewer) : Port used to send video to the web viewer.
• Network1 (Camera) / Network2 (Viewer) setup
-
IP Type : Select a network connection type.
-
IP Address, Subnet Mask, Gateway, DNS
<Static> : You can manually enter IP address, subnet mask, gateway and DNS.
<DHCP> : IP address, subnet mask and gateway values will be automatically set.
<PPPoE> : IP address, subnet mask and gateway values will be automatically set.
-
User ID, Password : If you set the connection mode to PPPoE, you need to enter "User ID" and
"Password" to register in PPPoE.
• Transfer bandwidth (Network3) : Enter the maximum amount of upload data bandwidth.
Check the assigned setting in Connection Mode before entering your value.
`If the sum of the network TX/RX is less than 32Mbps, there is a max transmission rate of 32Mbps.
• Default Gateway : Set the basic gateway by using Network1 (Camera) / Network2 (Viewer) setup.
M
`You can manually input DNS of <DHCP> and <PPPoE> when it selected to <Manual>.
76_ menu setup
menu setup
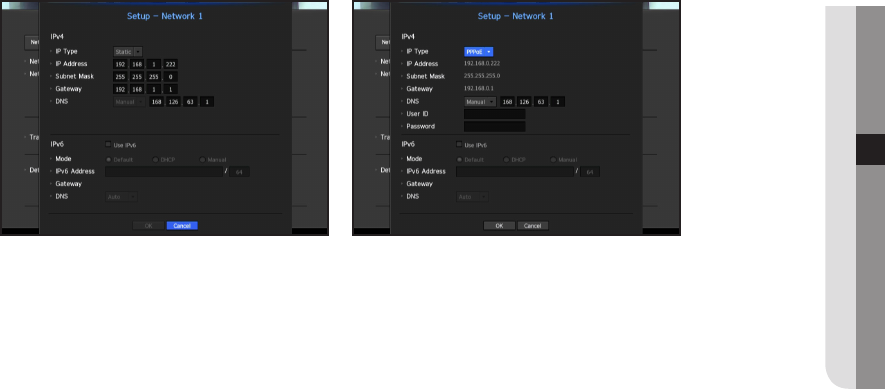
Connecting and Setting the Network
Networking may differ from the connection method, check your environment before setting the connection
mode.
When no router is used
•
Static IP mode
-
Internet connection : Static IP, leased line, and LAN environments allows connection between the NVR and
remote user.
-
NVR Network Settings : Set the <Network> in <Interface> menu of the connected NVR to <Static>.
`Consult your network manager for IP, Gateway and Subnet Mask.
•
DHCP mode
-
Internet connection : Connect the NVR directly to a cable modem, DHCP ADSL modem or FTTH network.
-
NVR Network Settings : Set the <Network> in <Interface> menu of the connected NVR to <DHCP>.
•
PPPoE
-
Internet connection : An PPPoE modem is directly connected to the NVR, where the PPPoE connection
requires user ID and password.
-
NVR Network Settings : Set the <Network> in <Interface> menu of the connected NVR to <PPPoE>.
`PPPoE <User ID> and <Password> should be the same to the PPPoE user information.
If you don't know the ID and password, consult your PPPoE service provider.
English _77
● MENU SETUP

When a router is used
J
`To avoid IP address conflict with the NVR's static IP, check followings :
•
Setting the NVR with a static IP
-
Internet connection : You can connect the NVR to a router which is connected to an PPPoE/Cable modem
or a router in a Local Area Network (LAN) environment.
•
Setting the NVR Network
1. Set the <Connection Mode> in <Connection> menu of the connected NVR to <Static>.
2. Check whether the set IP address is in the static IP range provided by the Broadband Router.
IP Address, Gateway, and Subnet Mask : Consult your network manager.
`Check whether the set IP address is in the static IP range provided by the Broadband Router.
J
`If a DHCP server is configured with starting address (192.168.0.100) and end address (192.168.0.200), you should set the
IP address out of the configured DHCP range (192.168.0.2 ~ 192.168.0.99 and 192.168.0.201 ~ 192.168.0.254).
3. Check the Gateway address and subnet mask are equal to those set in the Broadband Router.
•
Setting the DHCP IP Address of the Broadband Router
1. To access the Broadband Router's configurations, open a web browser on the local PC that is connected
to the Broadband Router and enter the router's address (ex : http://192.168.1.1).
2. At this stage, make the local PC's windows network configurations to the below example :
Ex) IP : 192.168.1.2
Subnet Mask : 255.255.255.0
Gateway : 192.168.1.1
-
Once connected to the Broadband Router, it prompts with password. While entering nothing to the User
Name field, enter "admin" into the password field and press <OK> to access the router configurations.
-
Access the router's DHCP configuration menu and set its DHCP server activation, and provide the start
and end address.
Set the start address (192.168.0.100) and end address (192.168.0.200).
M
`Above steps may differ from the router devices depending on the manufacturer.
78_ menu setup
menu setup
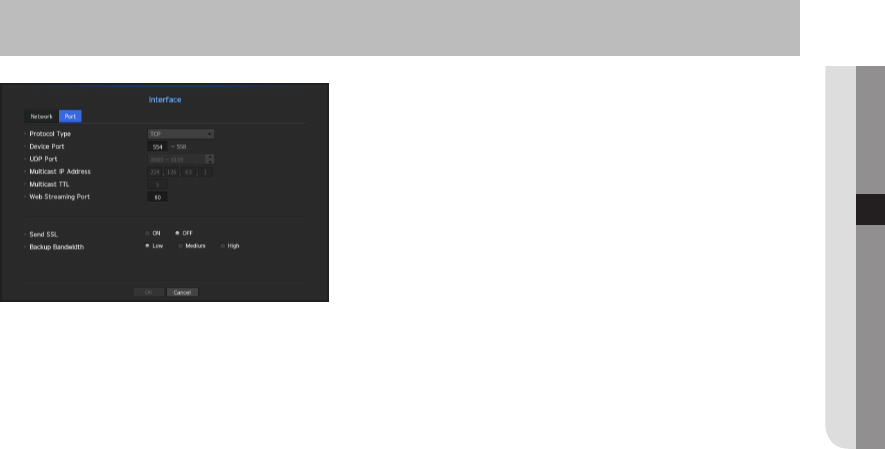
Port Setting
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ► Ö <Interface> Ö [ENTER] Ö
▼► Ö <Port> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
•
Protocol Type : Select the protocol type among TCP, UDP - Unicast and UDP - Multicast.
•
Device Port : Enter the connectable port number. Initially, <554> is set.
-
TCP : It has better stability and lower speed when compared to UDP, and recommended for internet
environments.
•
UDP Port : Initially, <8000~8159> is set. It increases / decreases by 160.
-
UDP : It has less stability and faster speed when compared to TCP, and recommended for local area
network (LAN) environments.
•
Multicast IP Address : User can directly input.
•
Multicast TTL : Select from 0 ~ 255. Initial value for the TTL is set to <5>.
•
Web Streaming Port : Enter the port number for the Web Viewer. Initially, it is set to <80>.
•
Send SSL : Select this option to send SSL.
•
Backup Bandwidth : Select the degree of backup bandwidth.
English _79
● MENU SETUP
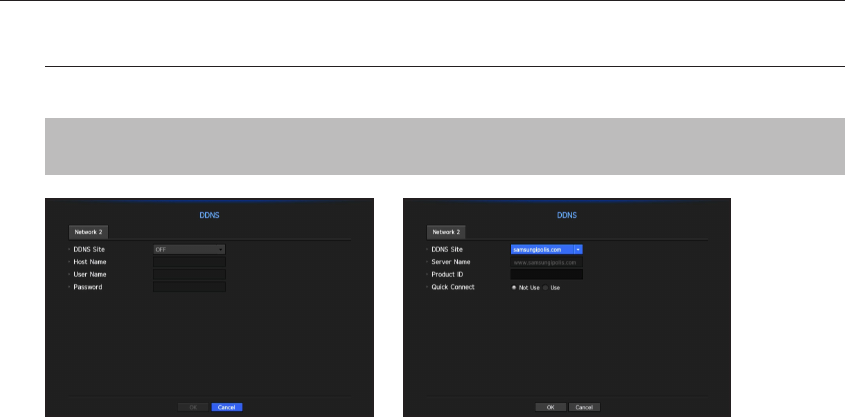
DDNS
If a remote user accesses the network, you can set whether or not to use DDNS and the site to be connected.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ►▼ Ö <DDNS> Ö [ENTER] Ö ▼
Ö <Network 2> Ö ▲▼◄► Ö [ENTER]
•
DDNS Site : Specify the use of DDNS and select a site that you registered.
•
Host Name : Provide the host name that you registered with the DDNS site.
•
User Name : Provide the user ID that you registered with the DDNS Site.
•
Password : Provide the password that you registered with the DDNS site.
M
`Refer to "Using Virtual Keyboard". (Page 43)
`If you select <OFF>, the input box will be inactive.
`If you select <iPOLiS>, the host name input box will be inactive. The user name input box will be active.
•
Quick Connect : Appears if the <samsungipolis.com> is selected for a <DDNS Site>.
To use the function, set to <Use> after connecting the NVR to a UPnP router.
M
`If canceled during Quick Connect configuration, it automatically switches to <Not Use> and saved.
To check Quick Connect status
A progress bar and its message appears for a Quick Connect.
•
Quick Connect Success : Message for a successful connection.
•
Invalid Network Configuration : Message appears if the network configuration is not valid. Check the
configuration.
•
Please enable UPnP function of the router : Message appears if the router requires UPnP function
enabled.
•
Failed to find the router : Message appears if the router is not found. Check the router's configurations.
•
Please restart the router : Message appears if the router should be restarted.
80_ menu setup
menu setup
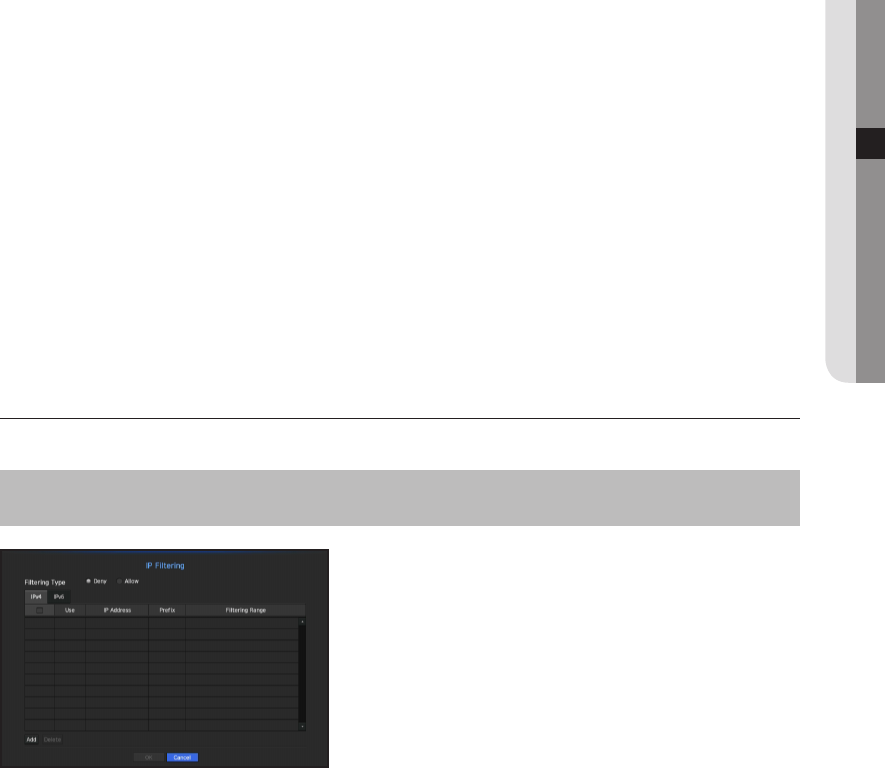
DDNS Setting
DDNS is a short form of Dynamic Domain Naming System.
DNS (Domain Name System) is a service that routes a domain name consisting of user friendly characters (ex :
www.google.com) to an IP address consisting of numbers (64.233.189.104).
DDNS (Dynamic DNS) is a service that registers a domain name and the floating IP address with the DDNS
server so that the domain name can be routed to the IP address even if the IP is changed in a dynamic IP
system.
•
Setting DDNS in the NVR
Set <Protocol Type> in the <Protocol> menu of the connected NVR to the following :
Ex) Protocol Type : TCP
Port (TCP) : 554, 555, 556, 557, 558
DDNS Site : iPOLiS
•
DDNS Settings of the Router
Select the corresponding menu for the network transfer protocol of the router.
•
Setting up UPnP of Router
Refer to the router's documentation to enable the UPnP function of the router.
IP Filtering
You can prepare the list of IP addresses to allow or block access to a specific IP address.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ►▼ Ö <IP Filtering> Ö [ENTER]
Ö ▲▼◄► Ö [ENTER]
• Filtering Type :
-
Deny : If you select reject, access to the registered IP address will be limited.
-
Allow : If you choose permit, then they can only access the registered IP addresses.
• Use : Select the checkbox for the IP address that will use IP filtering.
• IP Address : Enter the IP address for filtering.
• Filtering Range : If you enter an IP address or prefix, then the range of IP addresses blocked or permitted will
be displayed.
J
`If a camera's IP address is not included in the Permit list or is in the Reject list access to it will be rejected.
English _81
● MENU SETUP
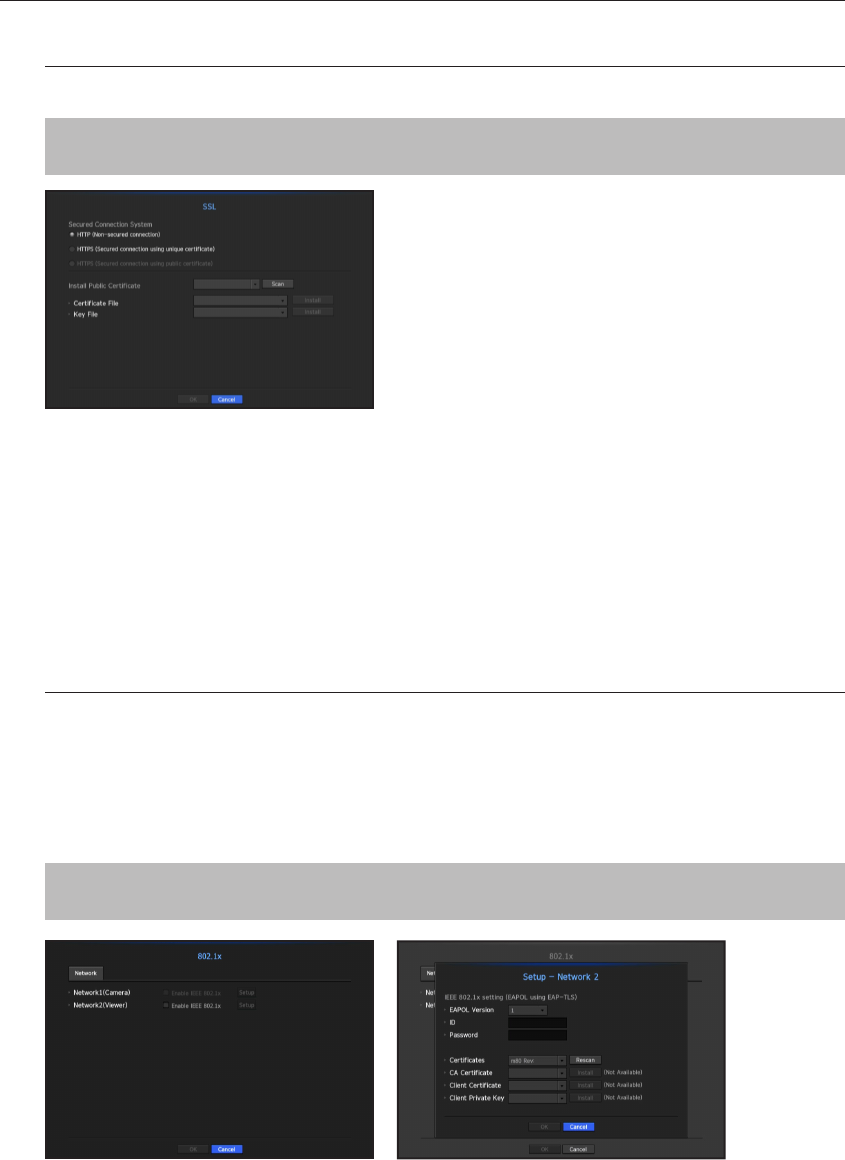
SSL
You can select a security connection system or install public certificates.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ►▼ Ö <SSL> Ö [ENTER] Ö
▲▼◄► Ö [ENTER]
• Secured Connection System : You can select a type of security connection system.
-
HTTP (Non-secured connection)
-
HTTPS (Secured connection using unique certificate)
-
HTTPS (Secured connection using public certificate)
• Install Public Certificate : You can scan and register public certificates to be installed.
If you want to use a certificate, you need to install a certificate file along with and an encryption file.
`The <HTTPS (Secured connection using public certificate)> menu can be selected only if there is a registered public
certificate.
802.1x
When connecting to a network, you can select whether to use the 802.1x protocol and install a corresponding
certificate.
802.1x is a certificate system for the server and the client. It can guarantee robust performance against hacking
into the Tx/Rx network data, virus or information leaks.
By using this system, you can block access from a client who is not certified and only allow communication to
certified users and thus increase the level of security.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ►▼ Ö <802.1x> Ö [ENTER] Ö ▼
Ö <Network> Ö ▲▼◄► Ö [ENTER]
• EAPOL Version : Select the EAPOL version to be used as protocol.
`Some switch hubs will not operate if you set them to version <2>. Select version <1>.
82_ menu setup
menu setup
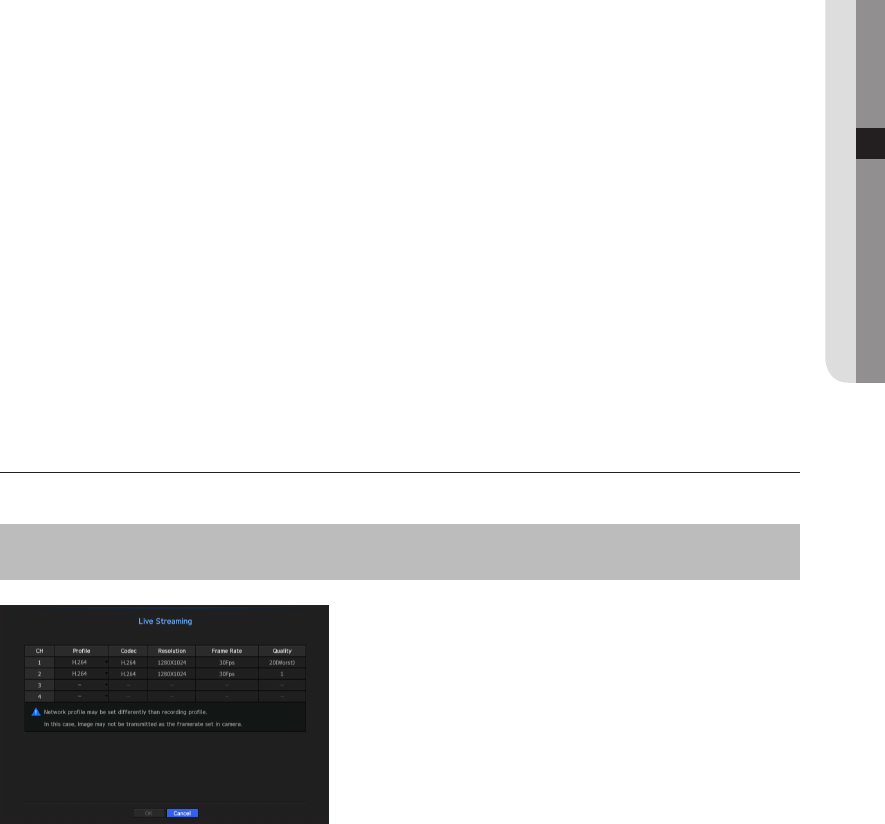
• ID : Enter the ID provided by the RADIUS server administrator.
`If the entered ID does not match the ID of the client's certificate, it won't be processed properly.
• Password : Enter the password provided by the RADIUS server administrator.
`If the password you entered does not match that of the client's private key, it won't be processed properly.
• Certificates : Search for a device. Click on <Rescan> to search for a device again.
• CA Certificate : Select this only if your public certificate includes the public key.
• Client Certificate : Select if the public certificate includes a client's authentication key.
• Client Private Key : Select it if the public certificate contains the client private key.
M
`For successful implementation of the 802.1x operating environment, the administrator must use the RADIUS server.
In addition, the switch hub connected to the server must be a device that supports 802.1x.
`If the time setting of the RADIUS server, the switch hub and an NVR device do not match, communication between them can
fail.
`If a password is assigned to the client's private key, the server administrator should confirm the ID and password.
The ID and password allow up to 30 characters each. (But it only supports letters, numbers and special characters ("-", "_",
"." 3 types) only.
Accessing non password-protected files is allowed without entering a password.
`The 802.1x protocol adopted by the NVR is EAP-TLS.
`You need to install all three certificates to use 802.1x.
Live Streaming Setting
You can configure the profile to transfer the live video of each channel via the network.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ►▼ Ö <Live Streaming> Ö
[ENTER] Ö ▲▼◄► Ö [ENTER]
•
Profile : Select a network profile for the connected camera.
•
Codec : Show the codec information for the selected network profile.
•
Resolution : Display the resolution for the selected network profile.
•
Frame Rate : Display the baud rate for the selected network profile.
•
Quality : Display the video quality for the selected network profile.
M
`If the profiles used for network and recording are different, camera's video feed may not comply with the frame rate as
specified in the camera.
English _83
● MENU SETUP
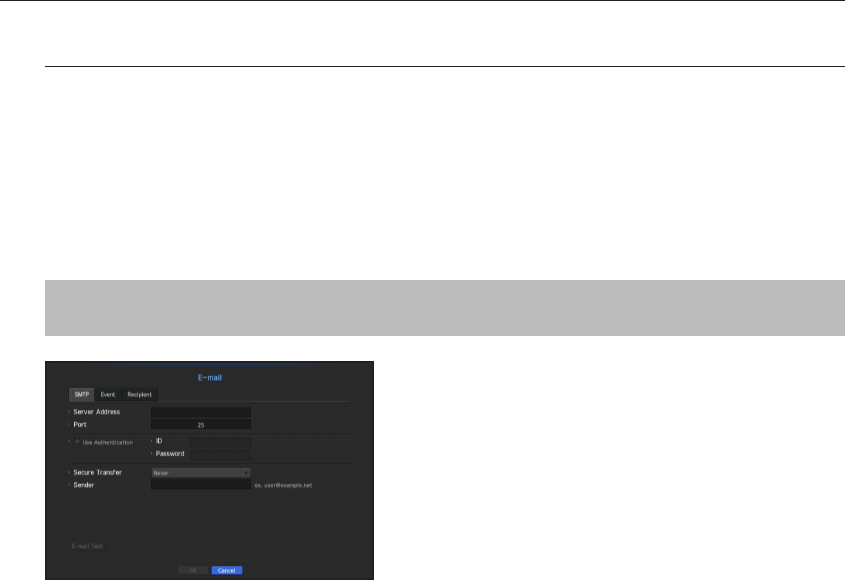
E-mail
You can send an e-mail to a NVR-registered user at a specific time interval, or if an event occurs.
M
`If the camera is set to <OFF> or the channel's event is Video Loss, a notification is sent to the designated email address
only in text.
SMTP Setting
Sets the SMTP mail server.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ►▼ Ö <E-mail> Ö [ENTER] Ö ▼
Ö <SMTP> Ö ▲▼◄► Ö [ENTER]
•
Server Address : Enter the SMTP server address to connect to.
•
Port : Sets the communication port.
•
Use Authentication : Check this if the SMTP server uses user authentication.
The account input box will be activated.
•
ID : Enter a ID to use authentication when connecting to the SMTP server.
•
Password : Enter the password of the SMTP server user.
•
Secure Transfer : Select one from <Never> and <TLS (if available)>.
•
Sender : Use the virtual keyboard to enter the sender's e-mail address.
`Refer to "Using Virtual Keyboard". (Page 43)
•
E-mail Test : Conducts the test on the server settings.
84_ menu setup
menu setup
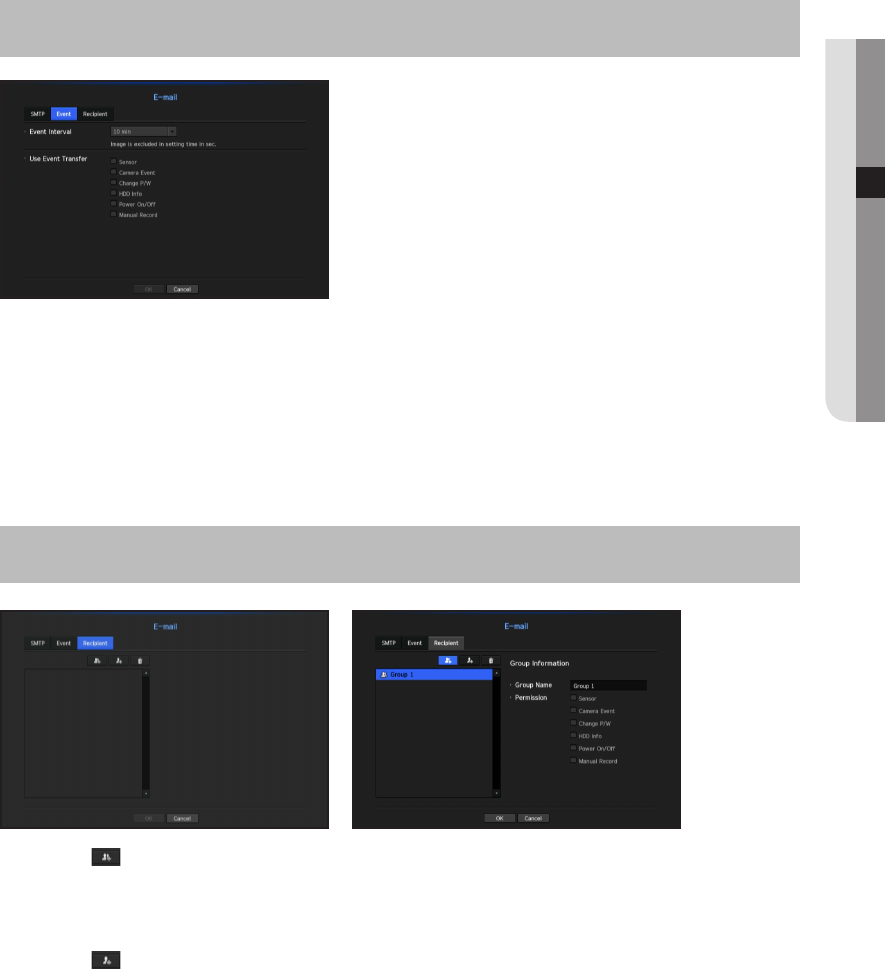
Event Setting
You can set the interval and type of the event that will be sent to the user.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ►▼ Ö <E-mail> Ö [ENTER] Ö
▼► Ö <Event> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
•
Event Interval : Set the event interval.
`If a series of events occurs, the e-mail will be sent at the specified interval, not on each event.
•
Use Event Transfer : Select an event type to send if an event occurs.
If the selected event occurs, the e-mail will be sent to the group that has the recipient authority.
Recipient Setting
You can create a group and add users to it or; you can delete users and change a group.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ►▼ Ö <E-mail> Ö [ENTER] Ö
▼► Ö <Recipient> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
• Click on < > to add a group.
Select a group name and the privilege.
• Select a recipient group to receive emails.
If a group is added, it will appear in the group list.
• Click on < > to add a recipient.
Select a group and enter names and email addresses.
If a group is created, you can add a recipient.
`For inputting the recipient name and email address, refer to "Using Virtual Keyboard". (Page 43)
English _85
● MENU SETUP
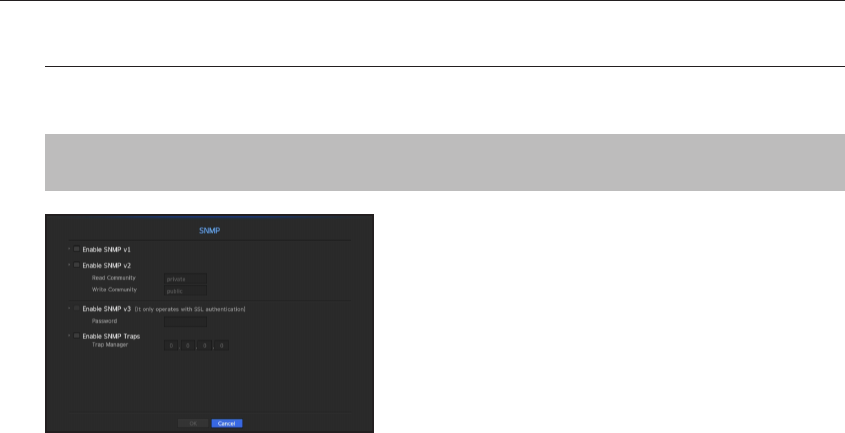
SNMP
Using the SNMP protocol, the system or network administrator can monitor the network devices remotely as
well as the operating environment.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ►▼ Ö <SNMP> Ö [ENTER] Ö
▲▼◄► Ö [ENTER]
• Enable SNMP v1 : SNMP version 1 is used.
• Enable SNMP v2 : SNMP version 2 is used.
-
Read Community : Enter the name of read-only community to access the SNMP information. By default it is
set to <private>.
-
Write Community : Enter the name of write-only community to access the SNMP information. By default, it
is set to <public>.
• Enable SNMP v3 : SNMP version 3 is used.
-
Password : Set the initial user password for SNMP version 3.
• Enable SNMP Traps : SNMP trap is used to send important events and conditions to the Admin System.
-
Trap Manager : Enter the IP address to which messages will be sent.
J
`SNMP v3 can be set only if the security connection method is set to HTTPS mode.
Refer to "SSL" for more details. (Page 82)
86_ menu setup
menu setup
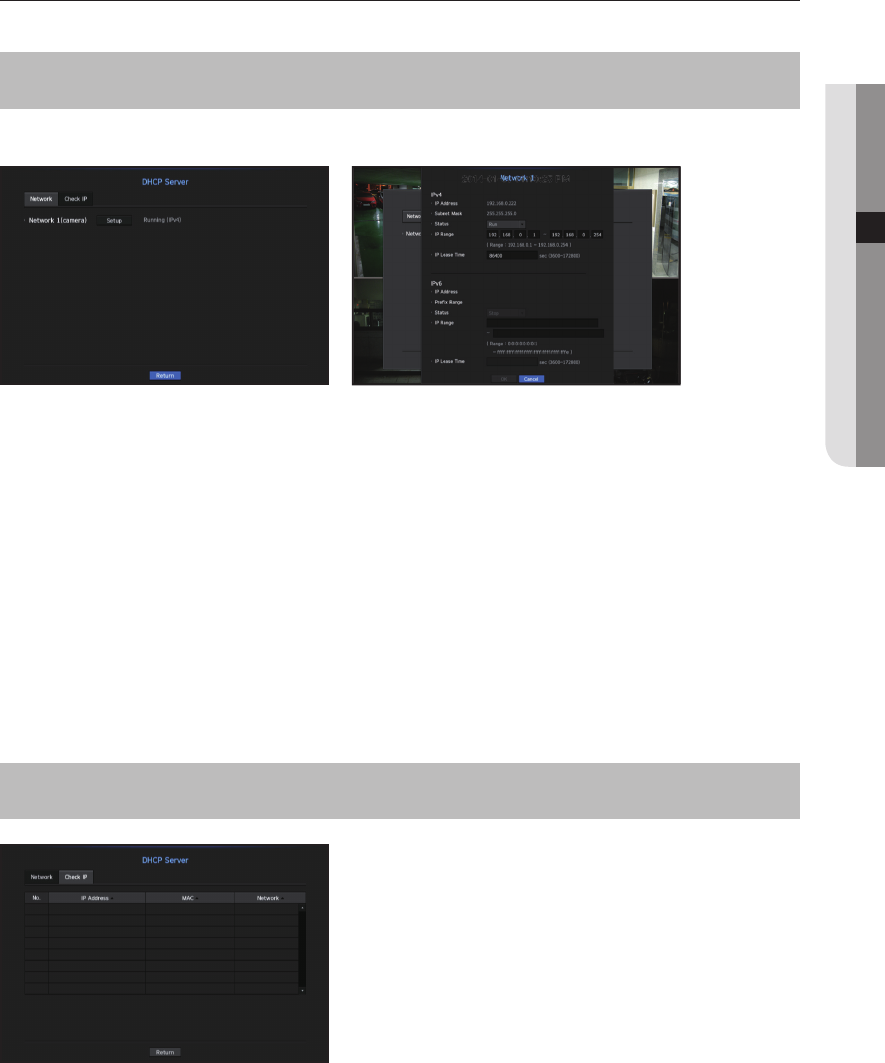
DHCP Server
You can set the internal DHCP server and assign an IP address to the network camera.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ►▼ Ö <DHCP Server> Ö
[ENTER] Ö ▼ Ö <Network> Ö ▲▼◄► Ö [ENTER]
Network Setting
•
Network 1 : Select <Setup>, and you can set the IP range operated by the server and time.
To set the DHCP server
1. On the DHCP Server Setup window, click <Setup>.
2. Select <Run> in the <Status> field.
3. Enter the starting IP and end IP in the <IP Range> field.
4. Fill in the <IP Lease Time> field.
5. Click <OK>.
The IP range entered is set as the DHCP server address of the network.
Check IP
You can check the IP Address and Mac currently used through the DHCP server, and the connected network
port.
[MENU] Ö [ENTER] Ö ▼ Ö <Menu> Ö [ENTER] Ö ▼ Ö <Network> Ö ►▼ Ö <DHCP Server> Ö
[ENTER] Ö ▼► Ö <Check IP> Ö [ENTER] Ö ▲▼◄► Ö [ENTER]
•
Network : Select the network port to check the information on IP and others.
English _87
● MENU SETUP
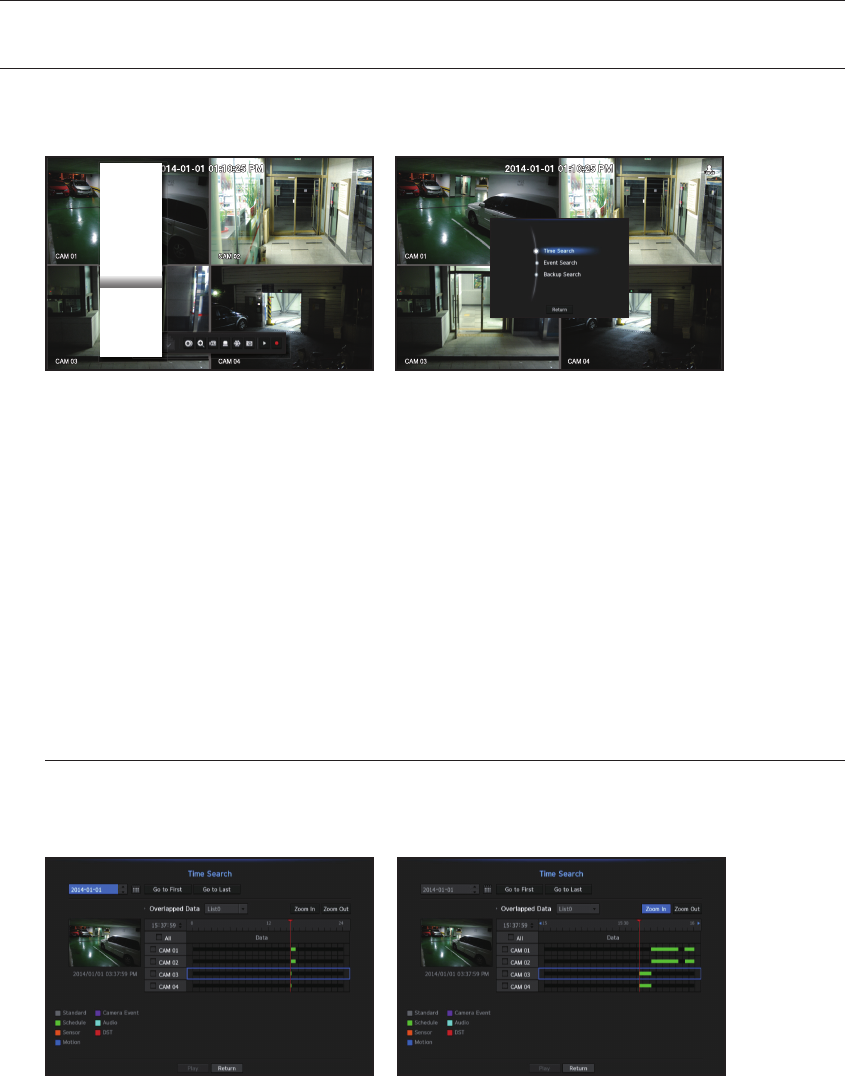
SEARCH
You can perform the search for recorded data by the time or by the search criteria such as an event.
You can access the <Search> menu directly in Live mode.
1. In live mode, right click with the mouse button or press the [MENU] button on your remote control.
The Live menu appears.
2. Select <Search>.
Or press the [SEARCH] button on your remote control
3. The Search menu should appear.
4. The search can be restricted by the Auto Delete function.
Refer to "Setting the Recording > Record Option". (Page 72)
M
`Overlapped data : It only appears if there exists overlapped data on a certain time, produced due to the change of NVR's time
setup. The latest data comes first, from <List0>.
It does not appear in <Backup Search>.
`The search time is based on the time specified by NVR.
Time Search
You can search for recorded data of a desired time.
The displayed time is based on the local time zone and the daylight saving time (DST). Therefore, data recorded
at the same time from different areas may differ based on the time zone and the DST.
1. Select <Time Search> in the <Search> menu.
2. In the date selection window, click on the < > > button to select a search date.
`For using the calendar, refer to "To use the calendar". (Page 42)
88_ search & play
search & play
Scene Mode ►
CH Info
Live Status
Record Status
PoE Status
Audio Off
Freeze
Stop Alarm
Record
Play
Search
Backup
Menu
Quick Setup ►
Shutdown
Hide Launcher
Logout
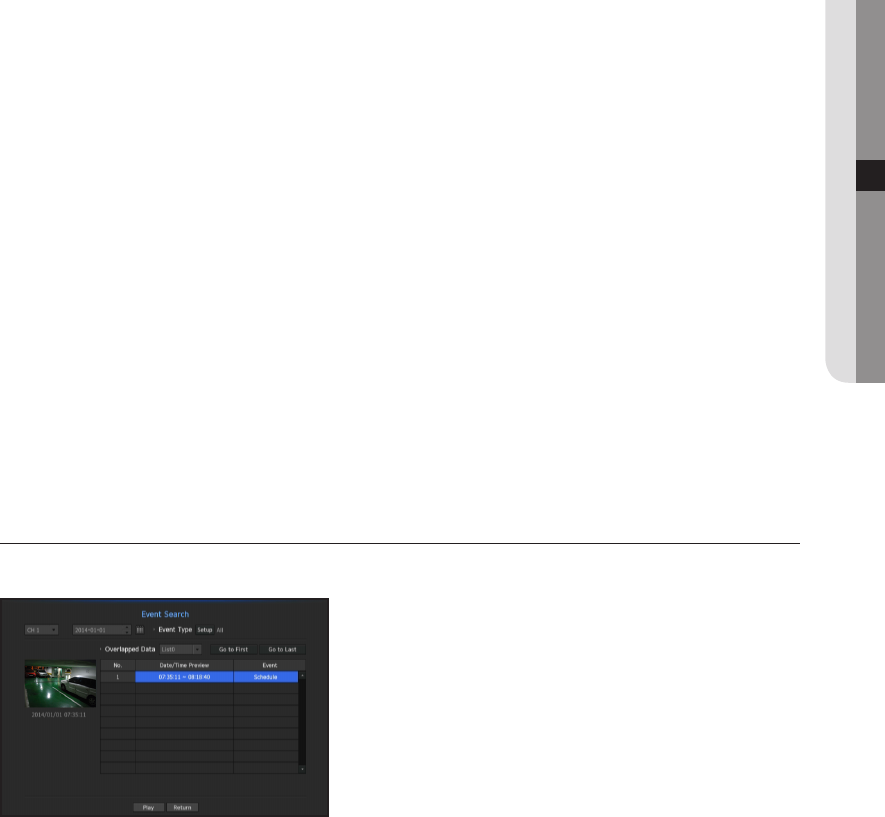
3. The record data on the specific date will be listed.
The display bar is different according to the data type. So check the data type for the color in the left pane.
M
`If DST (Daylight Saving Time) is configured, overlapping multiple recordings may be produced for a certain moment of time.
Such a time section is distinguished with red color to mark DST section.
4. Using the directional button(▲▼◄►) on your remote control, you can set the search condition or press the
[ENTER] button.
•
Go to First : Move to the earliest recording date.
•
Go to Last : Move to the latest recording date.
•
Time : Enter a time to perform the search or use the up/down button <
>
> to select one.
•
Zoom In : The map enlarges in detail.
It will switch in the sequence of 24hours - 12 hours - 6 hours - 2hours - 1hour.
•
Zoom Out : The map will switch in the reverse order of the detailed mode above.
It will switch in the sequence of 1hour - 2 hours - 6 hours - 12 hours - 24 hours.
•
Preview : Click <Channel> and select (click, drag) a time in <Duration> to display a still image for the
portion.
-
If the selected channel does not contain any recorded data, it will be marked black.
5. Select a data item and click <Play>.
The screen switches to the data playback mode.
Color indications depending on current recording status
The recorded data types are represented through the use of different colors. Each color corresponds to a
certain recording type.
Event Search
You can search for events by the channel and play them.
1. Select <Event Search> in the <Search> menu.
2. Using the directional button(▲▼◄►) on your remote control, you can set the channel, the search date, and
the search condition and then press the [ENTER] button.
`Depending on the menu selected, it will search for all/motion detection/video analysis/audio detection/sensors/reservation/
general recording events.
•
Date/Time Preview : If you select a data item in the list, the still image of the selected data will be displayed in
the left preview pane.
•
Event : Displays the type of the event that occurred.
3. Select a data item and click <Play>.
The screen switches to the event data playback mode.
English _89
● SEARCH & PLAY
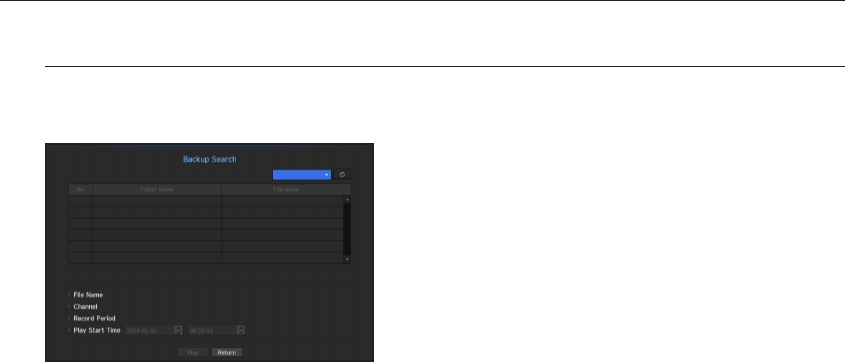
Backup Search
Searches for backup data in the connected backup device.
Only data in the format of NVR is included in the search.
1. Select <Backup Search> in the <Search> menu.
2. Using the directional button(▲▼◄►) on your remote control, you can set the channel, the search date, and
the search condition and then press the [ENTER] button.
•
Channel : Displays the recorded channel.
•
Record Period : Displays the record period.
•
Play Start Time : Select a time that you start playing.
3. Select a data item and click <Play>.
The screen switches to the backup data playback mode.
90_ search & play
search & play
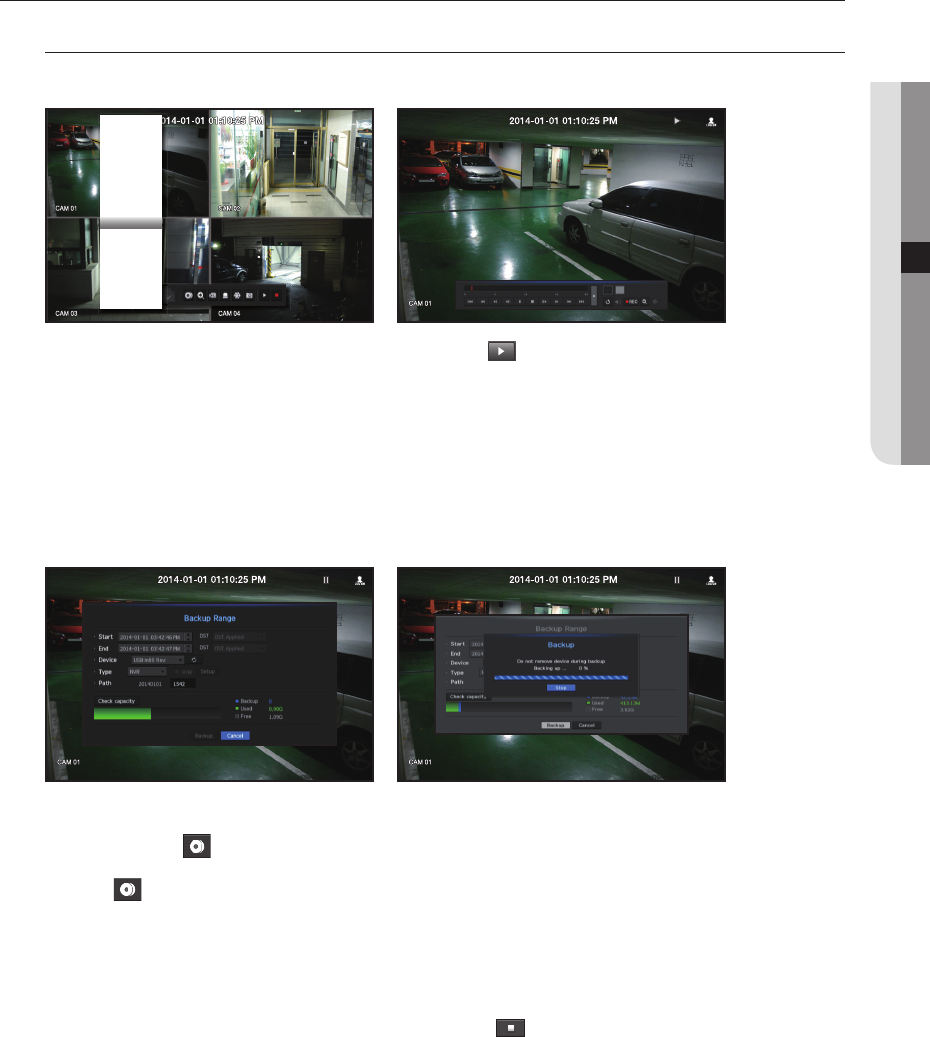
PLAYBACK
Play
You can play data stored in the HDD and backup a desired portion of the data.
1. In the live menu screen, select <Play> menu or click on < > in the launcher menu or press the [+]
button on your remote control.
2. Using the up/down(▲▼) button, select the search menu.
`If this is the first time you try to play, you will start with the data search window.
For data search, refer to "Search". (Page 88)
3. Select a data item and click <Play> in the Search menu.
The selected data is played and the play launcher appears on the screen.
`If there is an existing data, <Play> will start immediately without performing the search.
•
Playback Information : Displays the date and time of the current data in the top corner.
•
Backup : Click < > to set the current time to the start time of backup; you can specify a backup area
using the mouse (yellow triangle).
Click < > again to set the current time to the end time of the backup and the "Backup Range" window
appears.
-
Type : Supports formats of NVR and SEC.
-
Device : Select a backup device.
-
Check Capacity : Enables you to check the capacity of the selected storage device.
4. If you want to return to the live screen while playing, click < > on the launcher menu or press the [@]
button on your remote control.
English _91
● SEARCH & PLAY
Scene Mode ►
CH Info
Live Status
Record Status
PoE Status
Audio Off
Freeze
Stop Alarm
Record
Play
Search
Backup
Menu
Quick Setup ►
Shutdown
Hide Launcher
Logout
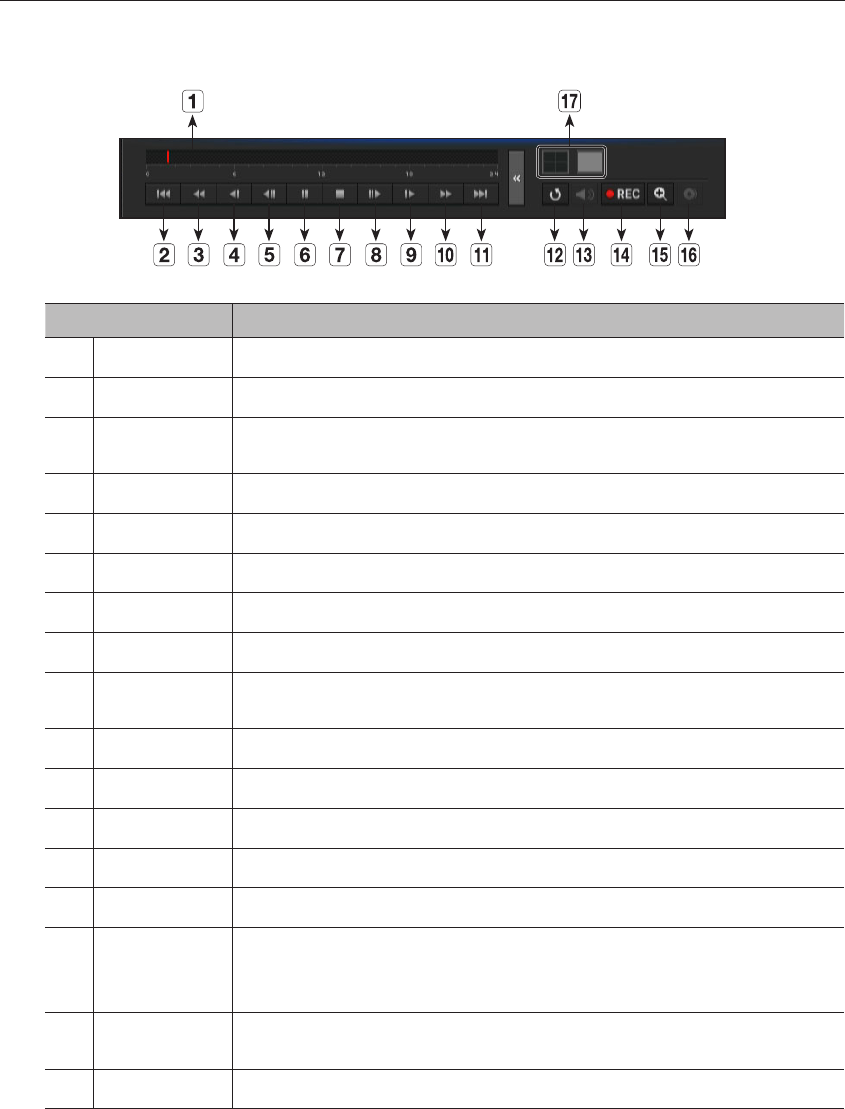
Using the Playback Button
Name Description
Play Timeline Indicates the current playback point, and can be used to move.
b
Skip Backward Moves backward by unit time.
c
Backward Fast
Play Used for quick backward search while in Play.
Backward Slow Play
Used for backward frame-by-frame search while in PAUSE.
Step Backward Moves backward by one frame at a time.
Pause Stops playing the current video temporarily.
Stop Stops playback and moves to the live screen.
Step Forward Moves forward by one frame at a time.
Forward Slow Play In a split mode, the real time playback may not be supported, depending on the record quality,
resolution and number of channels. And some frame rates may be supported.
Forward Fast Play Used for quick forward playback.
Skip Forward Moves forward by unit time.
Return Return to the search setup screen.
m
Audio Sets Audio ON/OFF.
n
REC Records all channels in Live mode.
ZOOM
This is available in Single mode, which will enlarge the video from a selected channel.
To cancel the zooming, simply double-click the enlarged image or select <Close Zoom> in the Live
screen menu.
Partial Backup Begins backup of the selected section of the video being played, with the specified starting/ending
point.
q
Mode Switch Click on the desired playing mode or press the [MODE] button to change the split mode.
92_ search & play
search & play
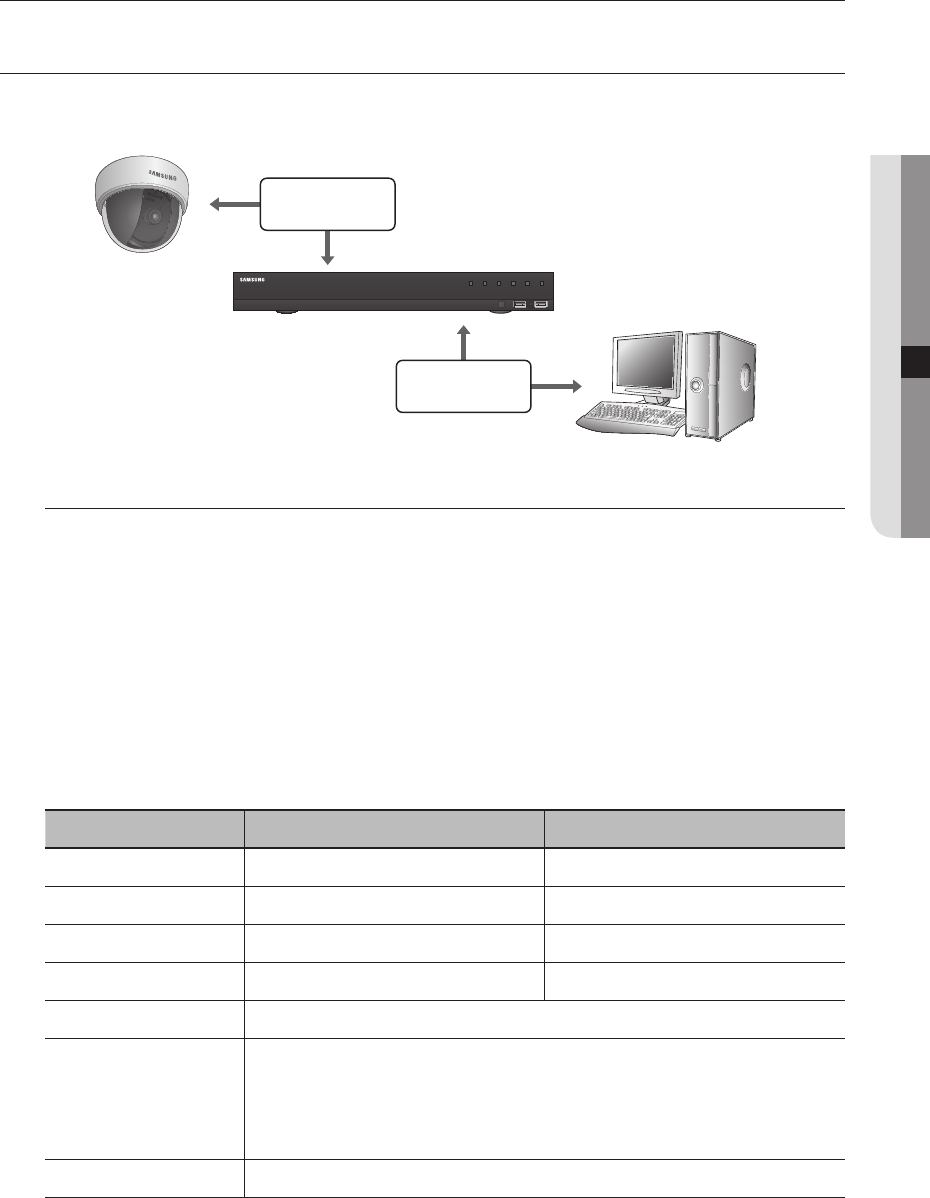
WHAT IS WEB VIEWER?
WebViewer is a software program with which the operator can access a remote NVR (Network Video Recorder) for
real-time monitoring, PTZ control (if configured) or search.
Product Features
•
Remote connection using the browser
•
PTZ camera control enabled
•
Supports 1, 4 camera viewing formats (maximum of 4 cameras in the list).
•
Saving function in JPEG/BMP/PNG image format for printing and storage.
•
Record video in AVI format-compatible with popular media players. (The integrated codec is needed)
•
To play the video in Windows Media Player, you must download and install the relevant codec from www.
windows7codecs.com. (version 4.0.3 or higher)
System Requirements
The following lists the minimum suggested hardware and operating system requirements needed to run the
Web Viewer.
Item Minimum Recommended
CPU Intel Core 2 Quad 2.5GHz or higher Intel i7 (3.5GHz) or more
RAM 2GB or more 4GB or more
HDD 200GB or more 500GB or more
VGA Memory 512MB or more 1GB or more
Display Resolution 1280 x 1024 or higher
OS
Window XP(service pack 2 or above), Vista, 7, 8, Mac OS X(10.6 or above)
OpenGL (GPU Accelerator supported)
Web browser Windows environment : Latest security patch, IE 8 or higher with bug patches
(IE 9 recommended), IE 10, Chrome 26.x or higher, FireFox 19.x version or higher
Mac OS X environment : Latest security patch, Safari 6.0.3 or higher with bug patches
Network 10/100 Ethernet NIC
English _93
● STARTING WEB VIEWER
starting web viewer
'9
6516
1(7:25.9,'(25(&25'(5
REC HDD ALARM
NETWORK BACKUP
POWER
NETWORK
NETWORK
NVR
Network Camera
Remote PC
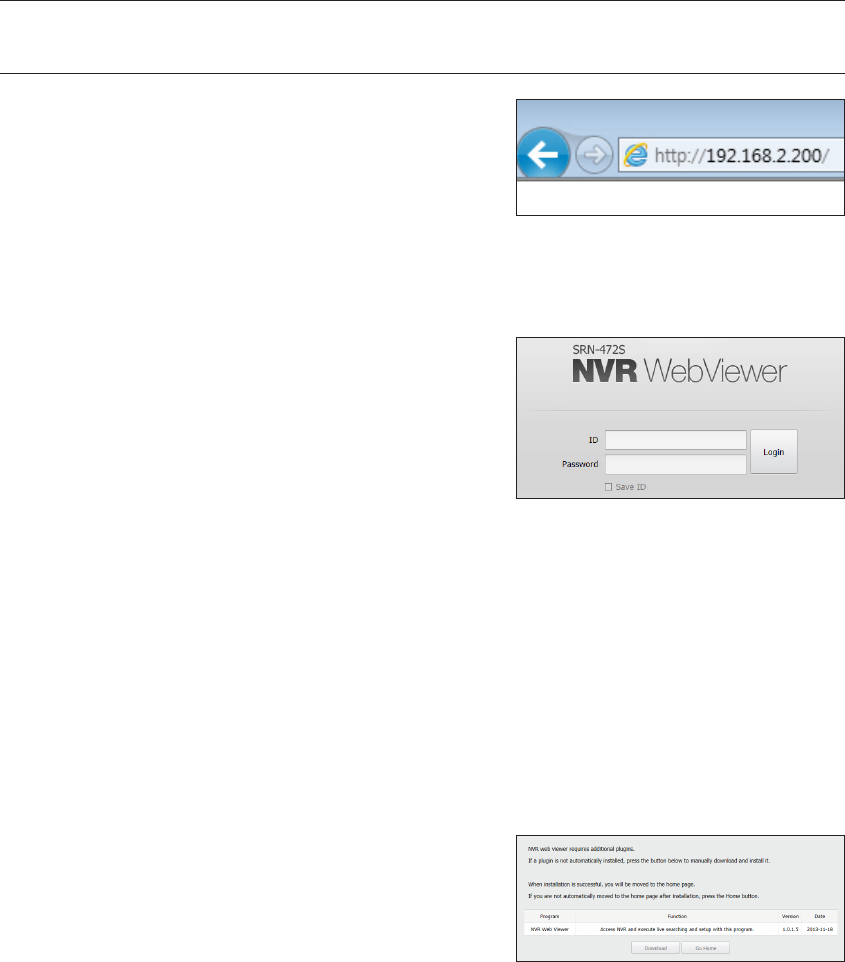
CONNECTING WEB VIEWER
1. Open your web browser and type the IP address or URL of
NVR into the URL address box.
M
`You need to connect network 2 before you can access the web
viewer.
`"192.168.2.200" is set to IP by default.
`You must have specified the IP address in "Network > Interface".
`The URL connection will be enabled only when the DDNS connection settings have been completed.
For more information, refer to "Network Configuration > DDNS". (Page 80)
2. A user with the admin permissions should provide the admin
ID and password. A registered user should provide the user
ID and password.
J
`The initial admin ID/password for your web viewer are "admin" and
"4321" and you need to reset them in the easy setup phase.
Easy setup can be used only in the initial setup of the product.
`Set password for your wireless network if you use the product with
a wireless router. Being not protected with password or using the default wireless router password may expose your video
data to potential threat.
`Please change your password every three months to safely protect personal information and to prevent the damage of the
information theft.
Please, take note that it's a user's responsibility for the security and any other problems caused by mismanaging a
password.
M
`It allow s up to 10 simultaneous access including the Admin and general users.
`Password of the Admin and general users can be changed in <Permission Setup> menu of the NVR.
`Normal users should have set <Webviewer> under <Restriction on Network Access> to Use before connecting to the
Web Viewer. (Page 45)
`All settings are applied by the NVR's settings.
3. The plugin installation confirmation pop-up window will
appear.
94_ starting web viewer
starting web viewer
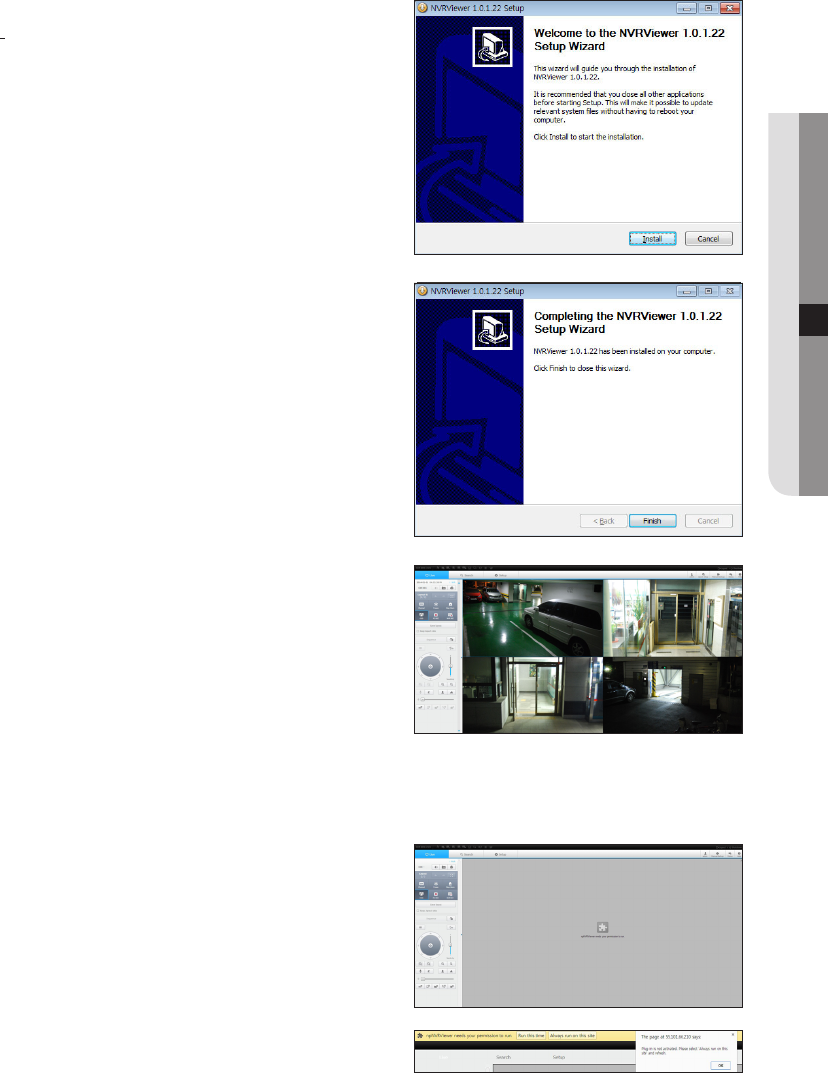
4. When a program installation wizard window appears, press
the [Install] button to install the program.
`The version of the program installed may vary depending on the update
version.
5. When program installation is complete, click on the [Finish]
button.
6. When installation is finished, and you are successfully logged
in, the live viewer main screen will appear.
If you want to access the web viewer with multiple browsers
Set auto execution of plugin (npNVRViewer) in the browser menu
that you first access and refresh the screen after activating the
plugin or selecting plugin reliability.
Each time the browser is upgraded in the future, the plugin activation
method can be changed. Plug in setting menu can be referred to in the
browser manual.
J
`For chrome browsers, "Plug in is not activated. Please select
'Always run on this site' and refresh", then select the 'always
execute on this site' button in the top of the browser.
English _95
● STARTING WEB VIEWER
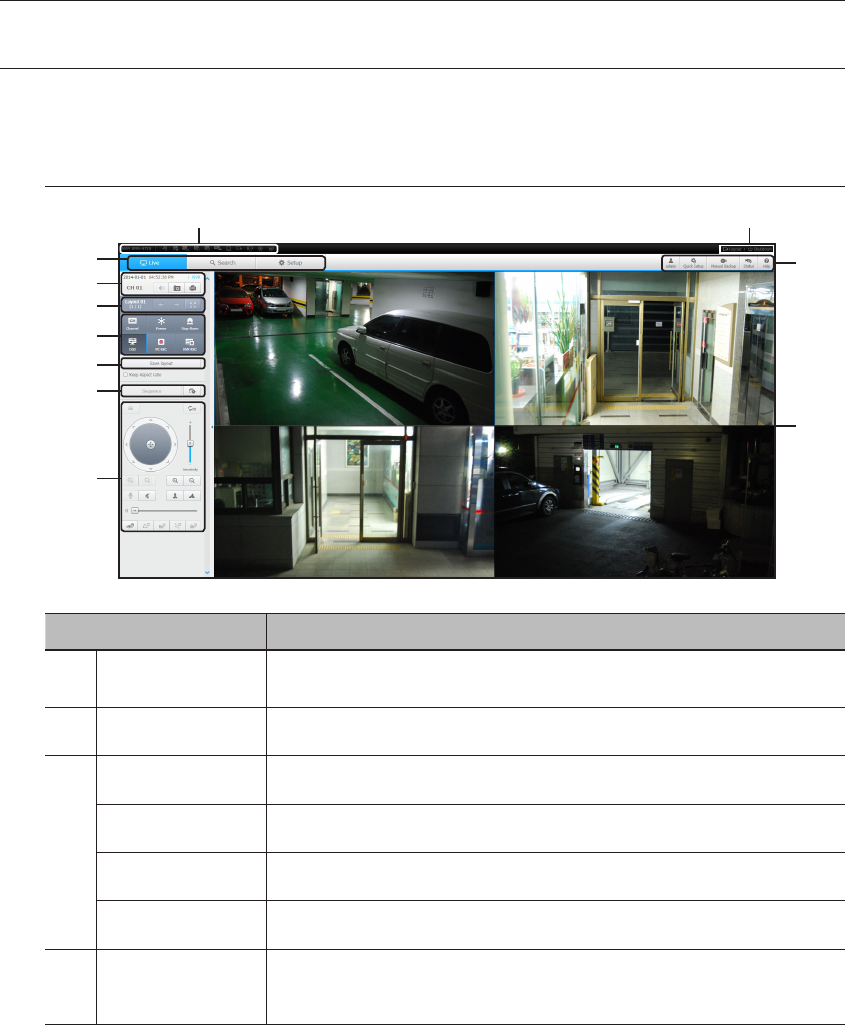
LIVE VIEWER
You can check the video from camera registered in the NVR connected from a remote PC. Also, you can adjust the
camera and check the network transfer status.
Live Viewer Screen
Menu Description
System Stauts
Indicator
Displays icons to display the screen or system status.
bMenu Selection
Switches into corresponding menu screen by clicking each menu.
c
Date/channel
Shows the access date/time and the selected channel.
Sound
Sets the sound connected to each channel to either ON/OFF.
Capture
Saves current video for the selected channel in the path designated by the user.
Print
Prints current video image for the selected channel through designated printer.
Channel change/full
screen
Switches to the previous/next channel group.
Switch from the full screen to the split screen.
96_ live viewer
live viewer
b
c
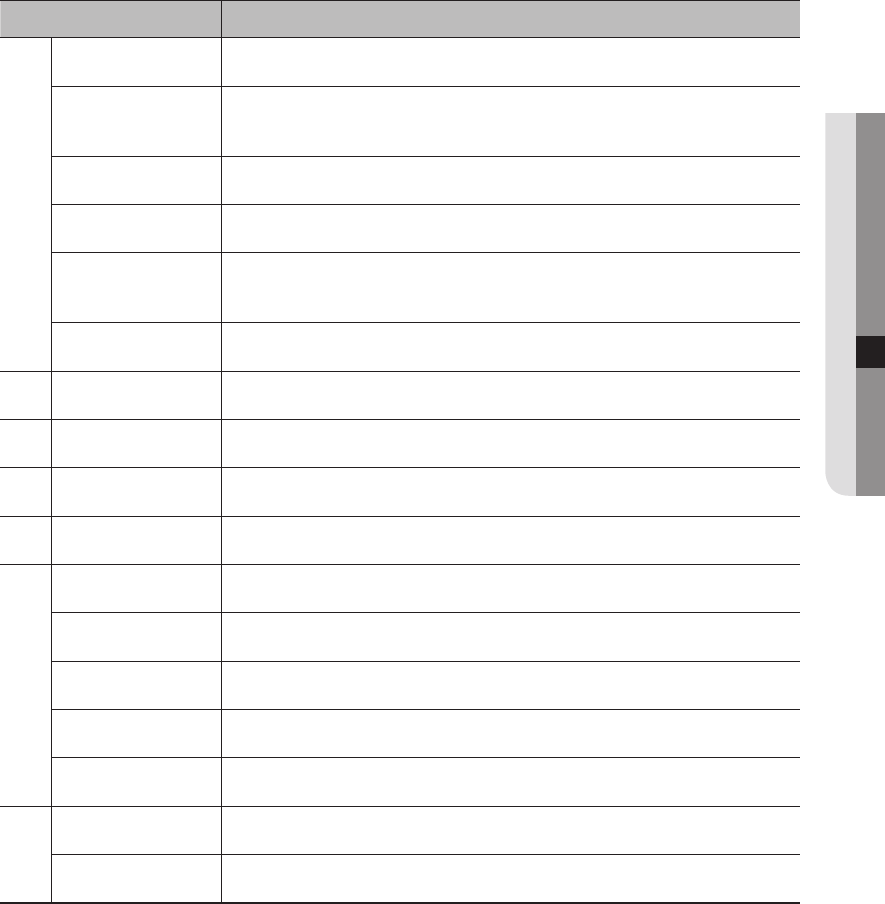
Menu Description
Channel information
Shows the channel information selected.
Pause
Temporarily stops the videos in all the channels or deactivates the Pause function in
suspending status.
Stop Alarm
Deactivates an alarm when it occurs.
OSD
Check the OSD item to display the OSD screen information in the web viewer window.
PC recording
Saves the real-time video, in AVI format, from the selected channel in a designated folder on
the PC.
NVR recording
Start and stop NVR recording.
Save layout
Save layout.
Switching
Set the sequence.
PTZ
Controls connect PTZ camera(s).
Display Pane
Displays the video of camera connected to NVR.
ID
Display the ID of user connected.
Quick setup
Simple camera registration and recording settings.
Manual backup
Manually backup the video of the camera connected.
Status
Shows the camera live and recording status.
Help
Move to the help window.
Logout
Performs logout process.
Close
Turn off the NVR system.
English _97
● LIVE VIEWER
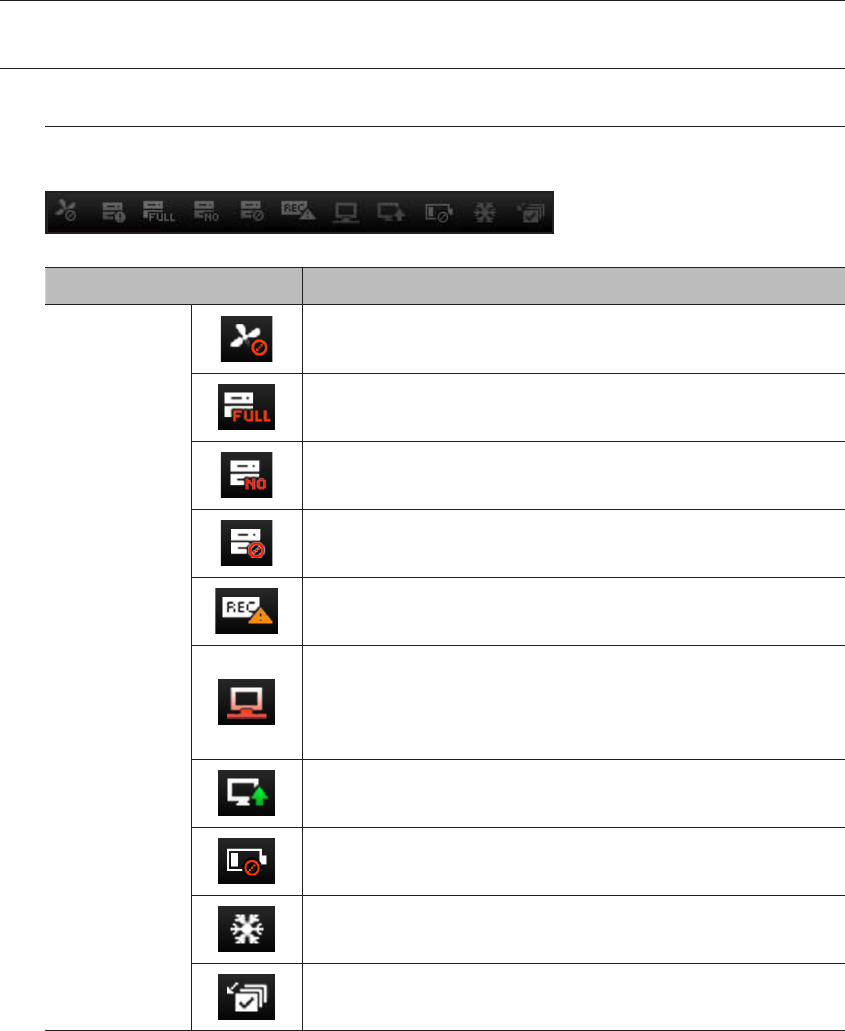
LIVE SCREEN CONFIGURATION
System Status
You can check the status or operation of the NVR with the icons on the live screen.
Item Description
System Operation
It is displayed when there is a problem with the fan.
Displayed if the HDD is full and the NVR has an insufficient space to
record.
Displayed if no HDD is installed or the existing HDD should be replaced.
Displayed if the HDD needs a technical examination.
It is displayed when the max permitted amount of data for each channel is exceeded.
It is displayed when the network is overloaded. It is displayed when the network is
overloaded.
`It occurs when the max receiving performance is exceeded, causing an overload to the
CPU. It will disappear if you modify the camera setting or delete a camera to reduce
the level of performance overload.
It is displayed when there is firmware to update the server. It is displayed when there
is firmware to update the server.
It is displayed if the battery level for an NVR device is empty.
If you press the screen stop button, it is displayed.
It is displayed when all the channels are switched at the set time interval.
98_ live viewer
live viewer
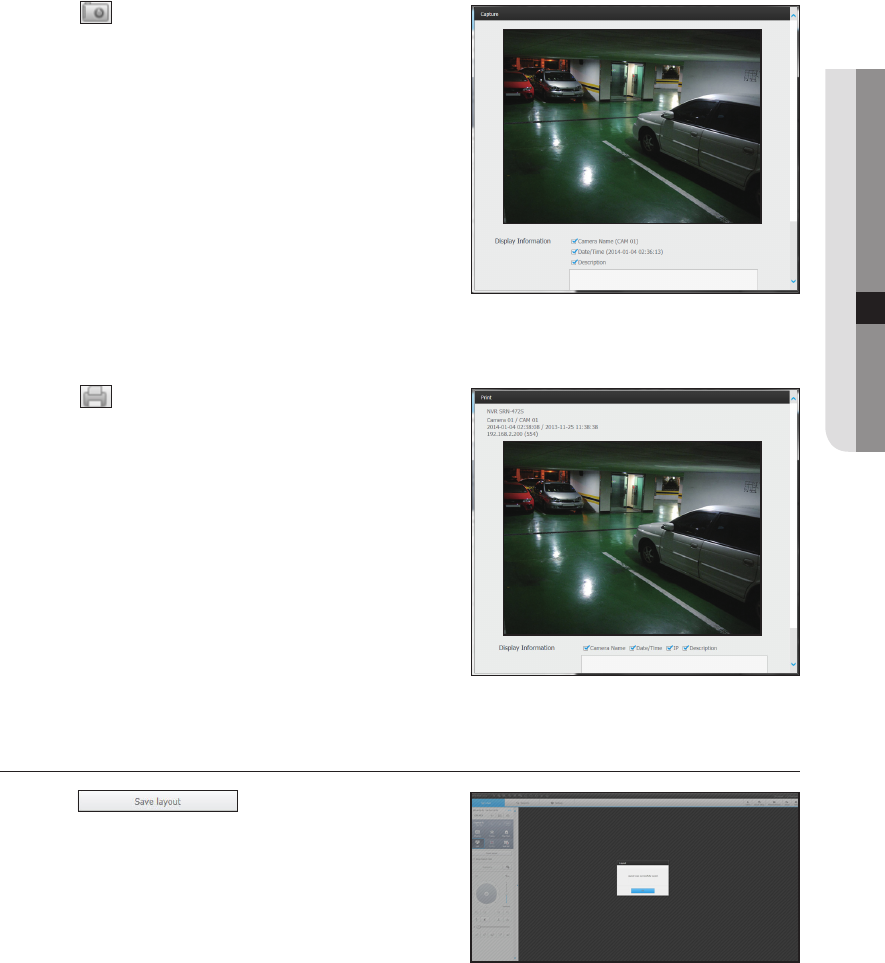
To capture a screen
1. Click < > button.
When a pop-up window appears, select the saving path for
captured image.
2. Select the path and name the file. And then click the [OK]
button.
3. Save current camera's video image as .bmp, .jpg or .png file.
J
`If the viewer is running without the administrator's permission in
Windows Vista/7, you may not save the captured image as .bmp, .
jpg or .png file.
To print a screen
1. Click < > button.
2. Print current camera's video image with the printer
connected to the PC operating the Web Viewer.
Saving layout
Click on < >.
The changed layout will be saved.
English _99
● LIVE VIEWER
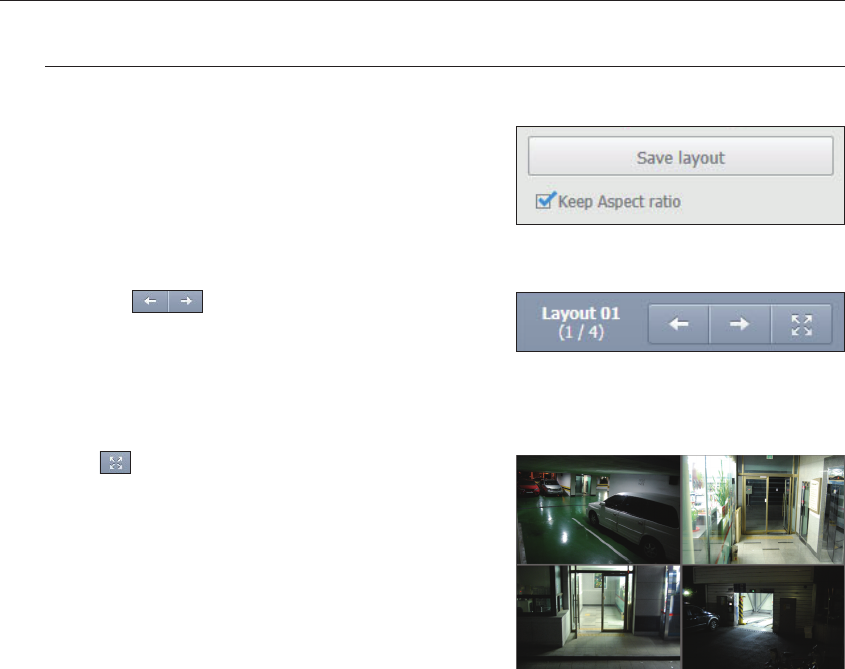
Changing Split Mode
If you want to maintain the current screen ratio
When you change from a split screen, check <Keep Aspect
ratio> to maintain the ratio and change to a different size.
To go to your desired channel screen
Press the < > button to move to the previous/next
channel group.
To switch to full screen mode
Click < >.
Current split screen appears in full screen.
Press the [ESC] key to exit the full screen mode.
MAC Safari does not support full screen.
100_ live viewer
live viewer
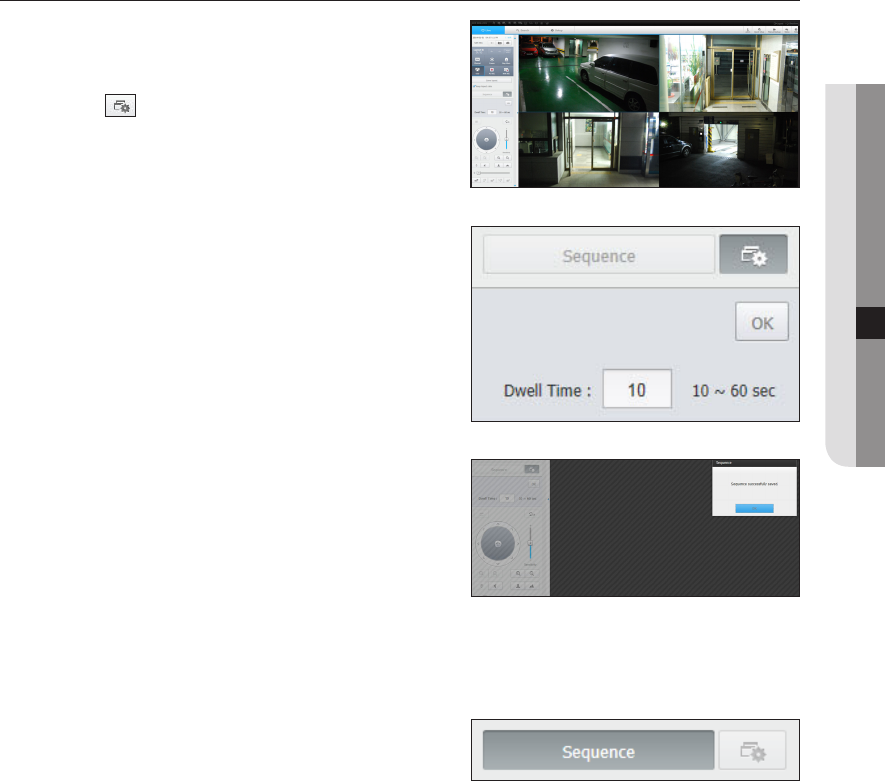
Setting screen switching
If you don't register the layout, the screen switching function will
not operate.
You can view the layouts one by one.
Click on the < > button to launch the switching setting
window.
1. Enter the desired screen switching time.
2. Click on the <OK> button to save the designated sequence.
To perform switching
Click on the <Sequence> button to activate the switching mode
and run a sequence.
English _101
● LIVE VIEWER
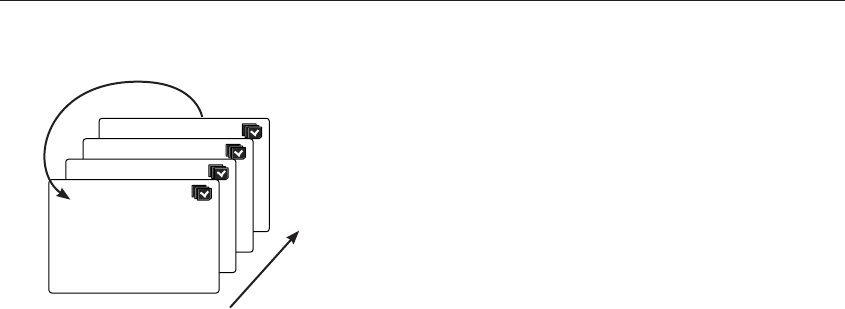
Auto Sequence
M
`When switching to another channel, the video may be slightly delayed depending on network status.
`If you perform automatic switching of a single screen, the layout setting menu will be deactivated during operation.
CH1
CH1
CH1
CH1
4
1
Single mode
102_ live viewer
live viewer
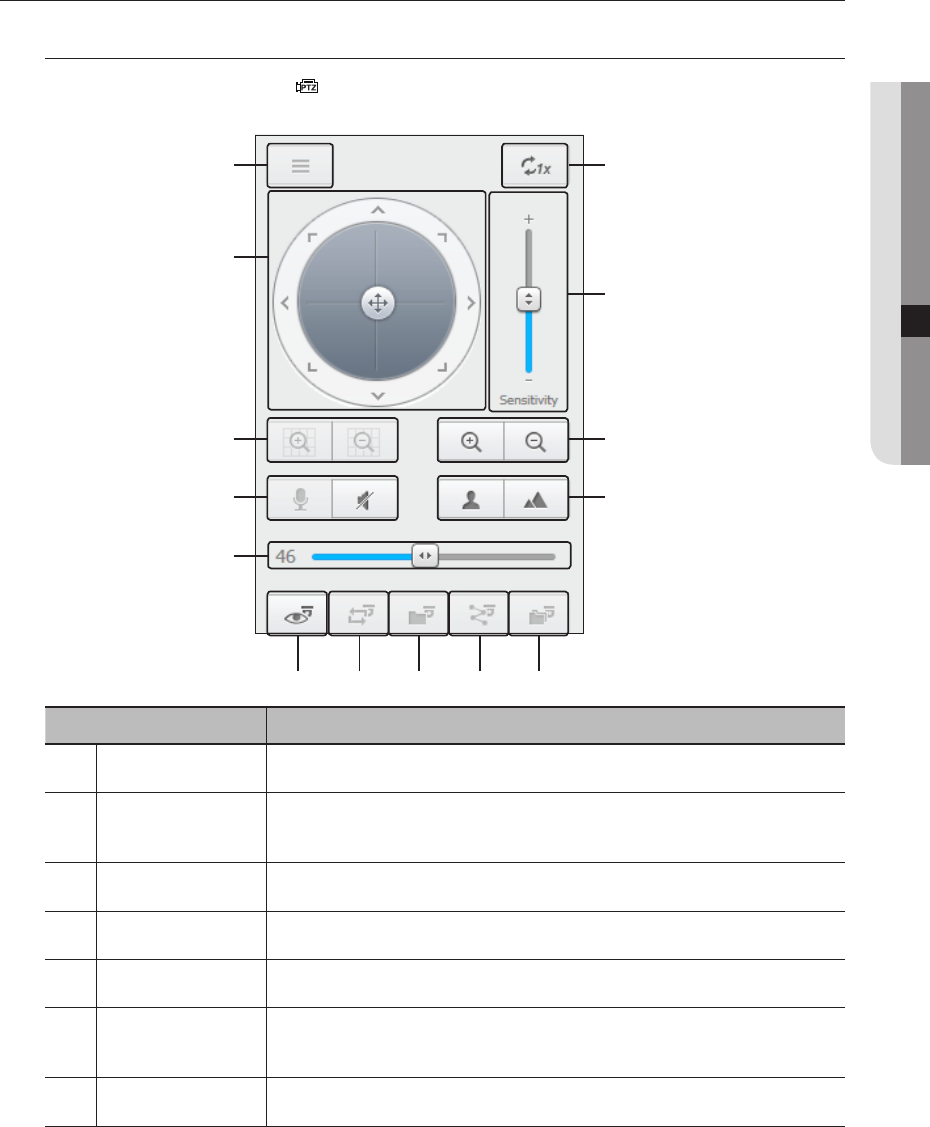
CONTROLLING A CONNECTED NETWORK CAMERA
Controlling PTZ
If PTZ camera is connected, the < > icon appears on screen. When selecting corresponding camera
channel, the PTZ tab is provided to allow you to control the PTZ.
Item Description
Camera menu
Displays the camera settings menu.
bDirection Adjustment
Use this to adjust the direction of the camera or click the crosshair in the center to use it as an
OK button.
cDigital zoom
Adjust digital zooming to make an image larger or smaller.
Sound Set audio mute for the PC and camera's audio talk.
Volume control
Change the PC volume between 0 and 100.
Preset
Sets the preset position for camera framing and moves to designated preset position when
selecting a desired preset.
Swing
Moves between the preset start point and end point.
m
n
b
c
English _103
● LIVE VIEWER
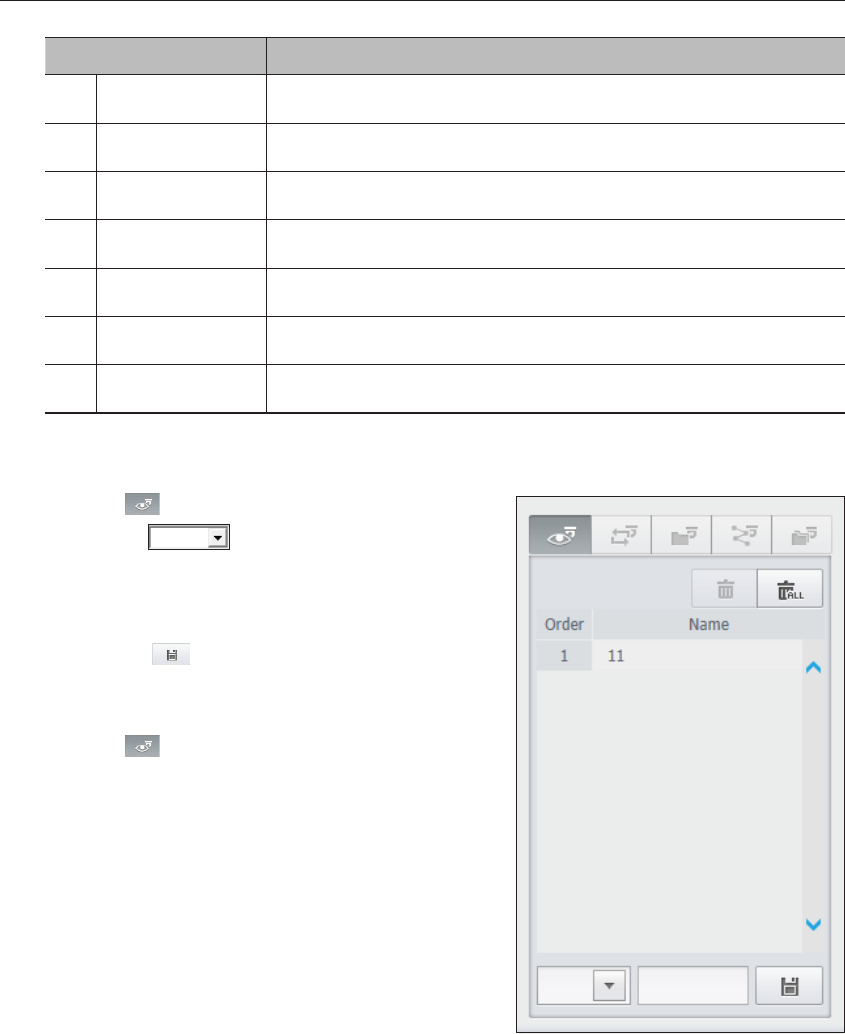
Item Description
Group
Moves in the path specified by combining the preset.
Trace
Moves camera's framing in the predefined path.
Tour
Moves in the path specified by combining multiple groups.
Focus
Adjusts the focus of the camera.
Zoom
Zooms in/out the image by controling camera's zoom.
mSensitivity Adjust the sensitivity of your camera operation.
nDigital Zoom Off Returns to the original size from the zoomed state.
To set a preset
1. Click < > button to display "Preset" window.
2. Click on < > to select the preset order.
3. Enter the name of preset.
4. Use direction keys to adjust the direction which camera
aims at.
5. Click the < > button.
To activate the preset
1. Click < > button to display "Preset" window.
2. Select a desired preset to activate from the list.
The camera's framing moves to the preset position.
To activate Swing(Auto-pan), Group(Scan), Trace(Pattern) and Tour
You can activate listed functions in the same manner as using a preset. For more information, refer to
corresponding user manul of applicable camera.
M
`Only selective functions of the camera can be supported, depending on camera.
104_ live viewer
live viewer
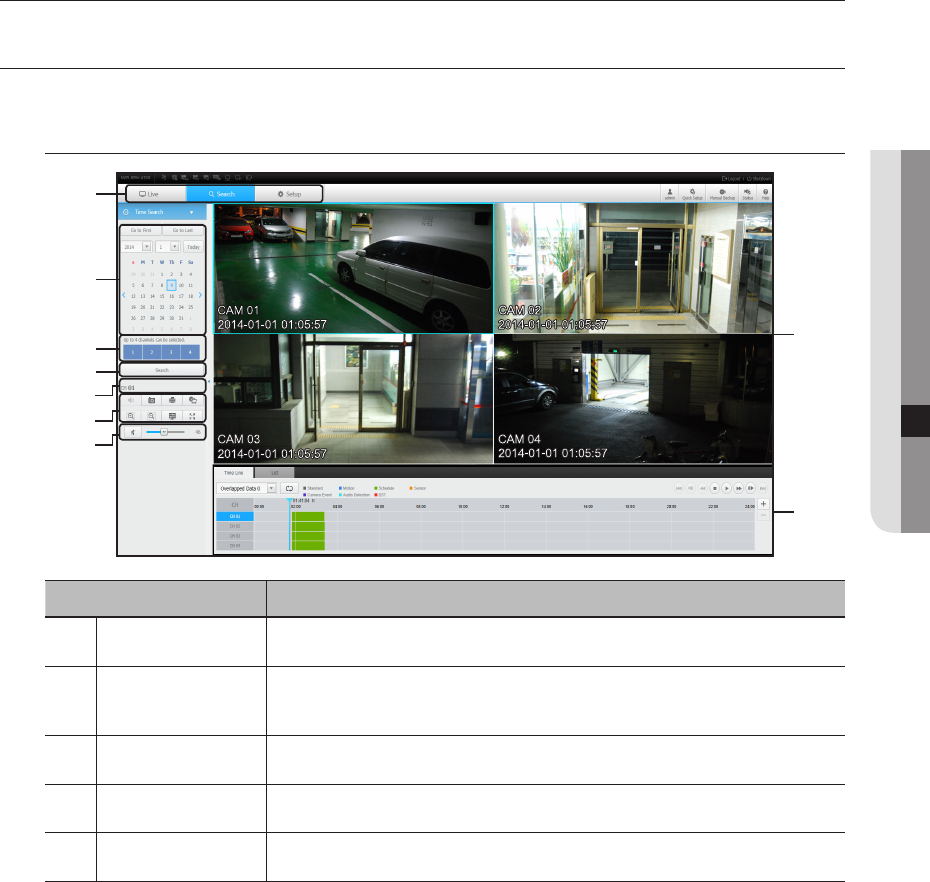
SEARCH VIEWER
You can search and play the video record saved in NVR by accessing NVR remotely.
Search Viewer Screen
Item Description
Menu Selection
Switches to the corresponding menu screen by clicking each menu.
bCalendar
Displays the video-recorded date in blue and today in red. Click the date in blue color to display
the recorded video information in timeline.
cChannel selection
Displays the search channels.
Search
Search for the user designated channel for the selected date.
Channel displays
Display the selected channel number.
b
c
English _105
● SEARCH VIEWER
search viewer
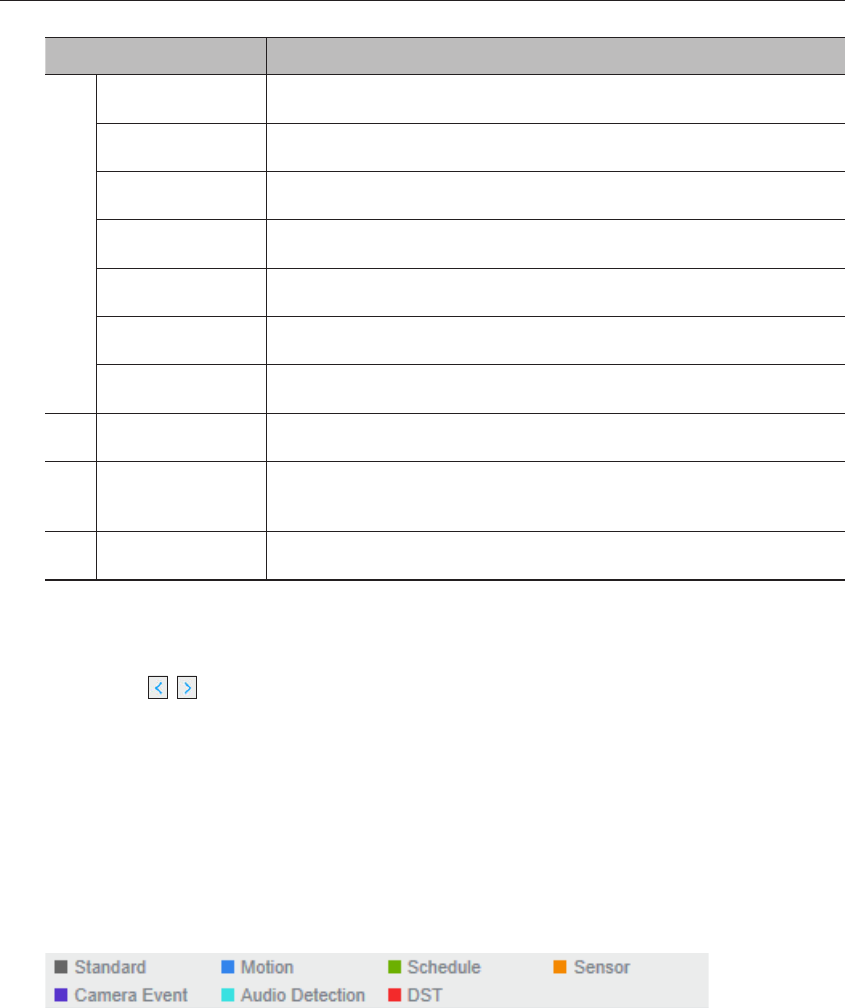
Item Description
Sound
Change the PC volume between 0 and 100.
Capture
Saves current video for selected channel in the designated path.
Print
Prints current video image for selected channel through the assigned printer.
Section backup
Backup the video for the selected section.
Magnify/Shrink
Magnify or shrink the current video for the selected channel.
OSD
Displays the channel information.
Full screen
Show the four way split screen in the full screen.
Sound control
Adjust the audio for the video searched.
Recording Color
Displays the corresponding color depending on recorded data type if you place your mouse
cursor on that area.
Display Pane
Plays corresponding data on the screen if you select a search result.
To search by date
You can select the search date by using calendar.
1. Click on < , > to select the year/month for your search.
If a date has data associated with it, it is displayed in blue. The current date is displayed as a blue box.
2. Click the date to search in calendar.
The first image of searched video data on the date is displayed on screen and the data is displayed in the
timeline.
3. To search video data on today, click <Today>.
Today's date is selected.
Color indications depending on current recording status
Displays the corresponding color according to the recorded data type.
M
`If 2 or more kinds of recording type are mixed for the same timeline, only the recording type with higher priority is displayed.
(Priority: Standard > Motion > Schedule > Sensor > Camera Event > Audio Detection > DST)
106_ search viewer
search viewer
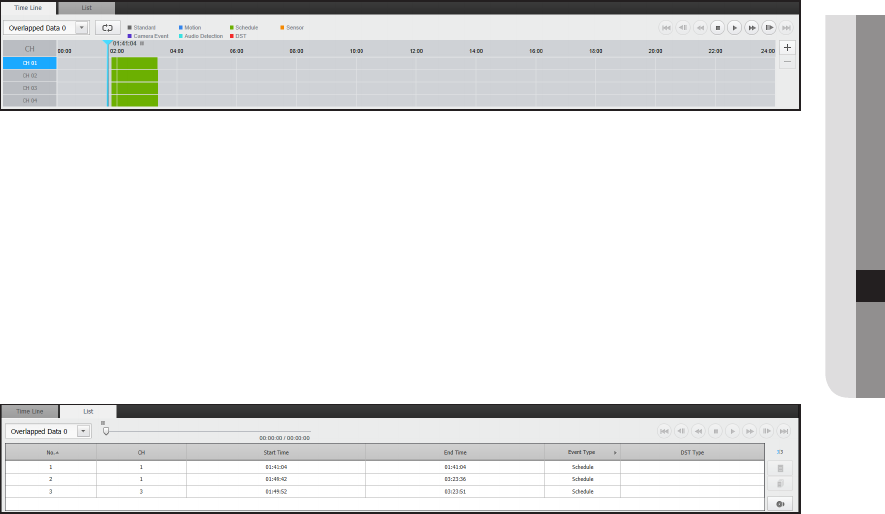
To adjust timeline
If searched data are overlapping, you can select a desired data, move its playback time point, and zoom in/out
the timeline.
1. Select the number of data to search if data is overlapping.
It appears only when data are overlapped and assigns <0> to the most recent data.
2. Click your desired time point to play on the timeline.
The playback start point is moved.
3. Click <+> / <-> to zoom in/out the zoom factor to display time.
4. When magnified, if you want to view the pre/post timeline, click on the timeline and drag it in the direction
you want to move it.
If you want to check the recording list
The results for each recording section will be displayed.
English _107
● SEARCH VIEWER
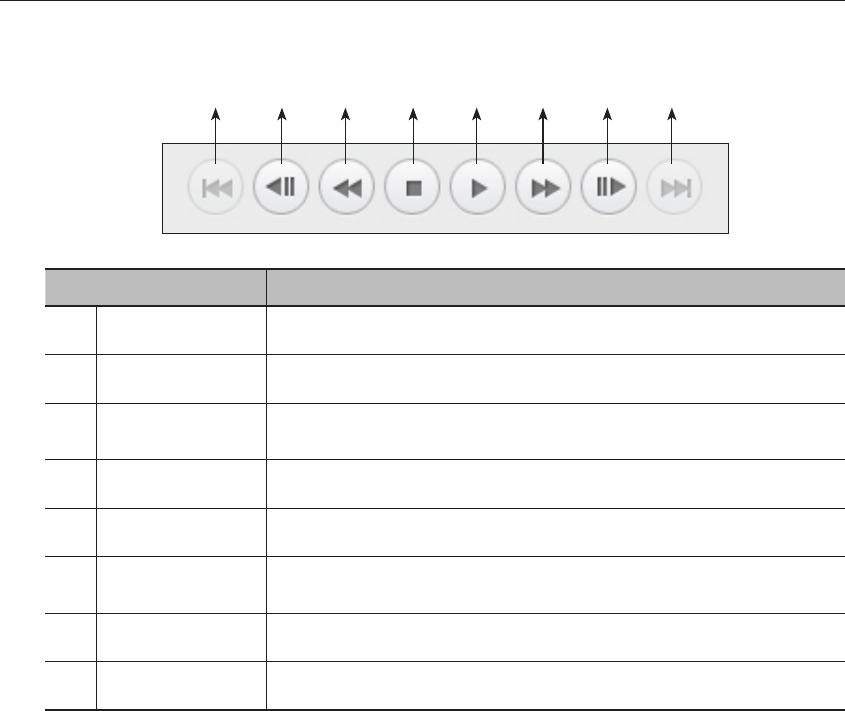
Names and Functions of Play Buttons
Item Description
Back
Returns to the previous event.
bPrevious frame
Move backward one sec.
cBackward X times
speed playing
Used to rewind at X times the speed.
Stop
After finishing playing, move to the live mode.
Play/Pause
Video is played and paused.
Forward X times
speed playing
Play the video forward at X times the speed.
Next frame
Move forward one sec.
Move forward
Proceeds to the next event.
b c
108_ search viewer
search viewer
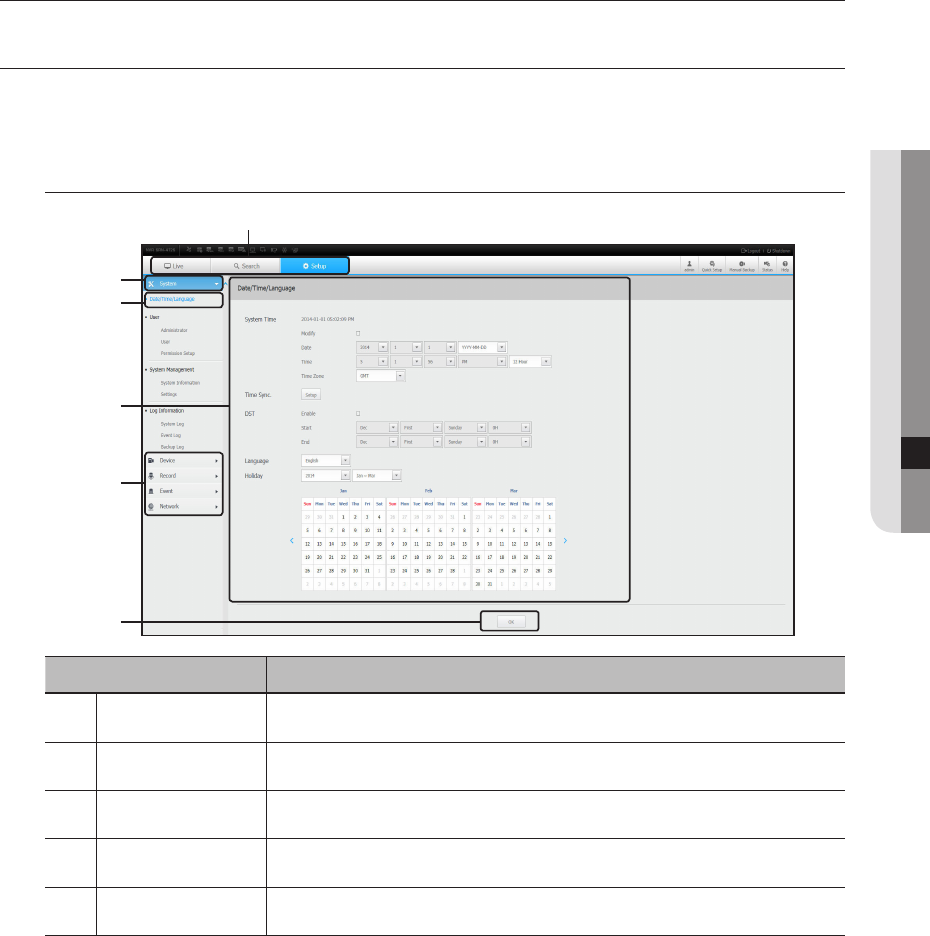
setup viewer
SETUP VIEWER
You can configure the NVR settings remotely on the network.
To configure the NVR settings, click <Setup>.
Settings Screen
Item Description
Menu Selection
Click each menu to switch into corresponding menu screen.
bParent Menu
Configure the settings or select a parent item to change the existing settings.
cSub-Menu
Among the sub-menus of selected parent menu, select a desired item to set.
Detailed Menu
Click desired item's input field to change and enter a desired value.
OK
Apply the modified settings.
b
c
b
English _109
● SETUP VIEWER
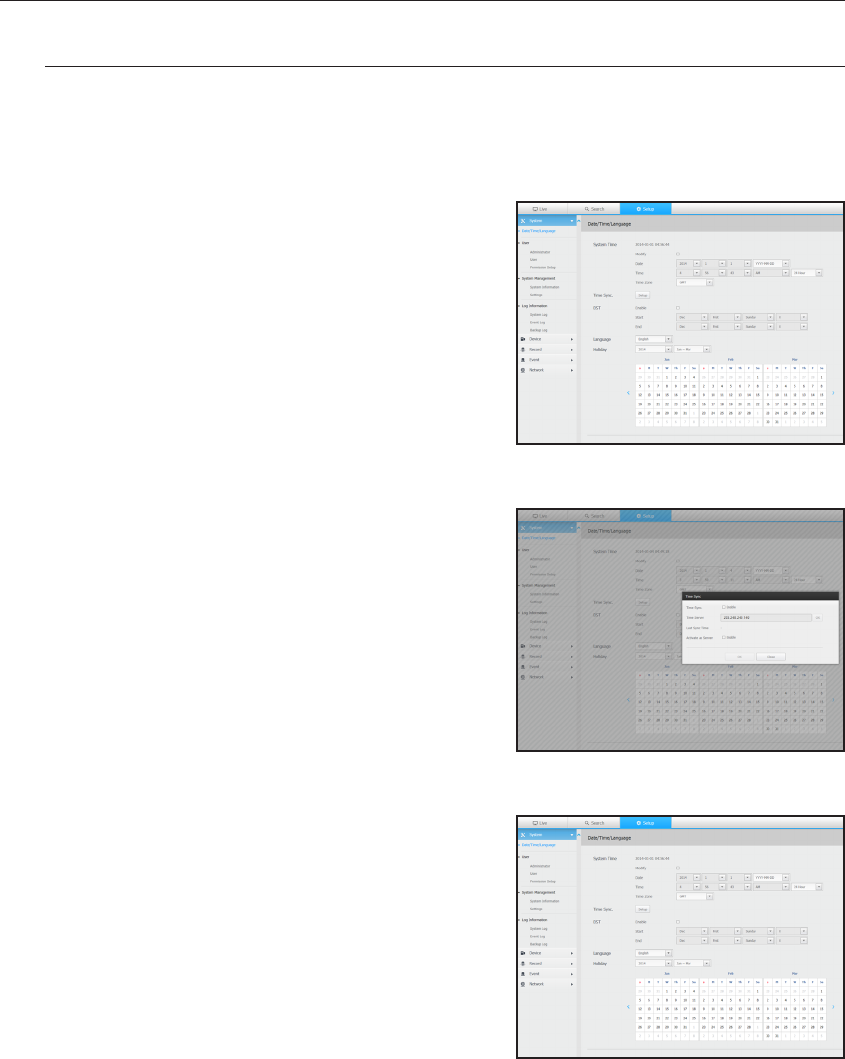
System
You can configure the various settings of the NVR system.
Date/Time/Language
For more information, refer to "Date/Time/Language" in the "System" menu. (Page 41)
Date/Time
Set the date and time.
Time Synchronization Setup
Set the time synchronization.
DST (Daylight Saving Time)
During the summer, Daylight Saving Time (DST) advances
clocks one hour forwards from the standard local time zone.
Language
Select a preferred language for the NVR.
Holiday
A user can select specific dates as holidays according to their
own preferences.
110_ setup viewer
setup viewer
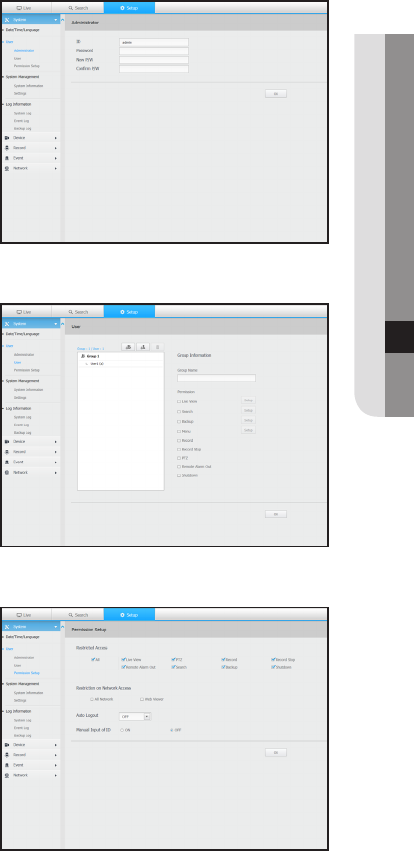
Permission Management
For more information, refer to "User" in the "System Setup" menu. (Page 43)
Admin
You can change the admin ID or the password.
ID allows alphanumeric characters only.
`If the admin ID is not used for access, you cannot change the ID.
`If the ID being used is changed, you will be automatically logged out.
User
You can add, change or remove a user or users.
Permission Setup
You can set the user permission.
English _111
● SETUP VIEWER
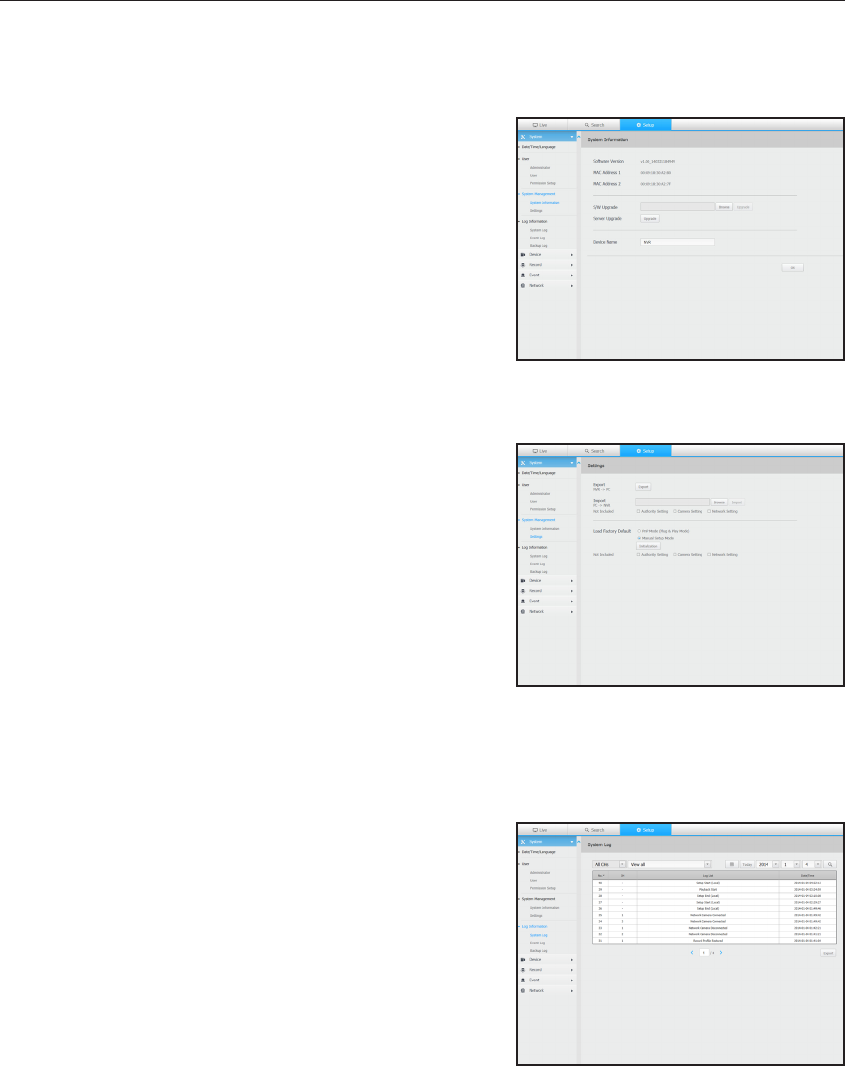
System Management
For more information, refer to "System Management" in the "System" menu. (Page 47)
System Information
You can see information of the current system.
Check the software version and MAC address.
Settings
Using a storage device, you can apply the current configuration
of NVR to another NVR.
Press the Initialize button to return the network settings to their
factory default state. Items in the <Not Included> category are
excluded from the initialization.
Log information
System log
Data recorded in the system log displays various system-related
logs/date/time such as system starts, system ending and menu
setting changes.
112_ setup viewer
setup viewer
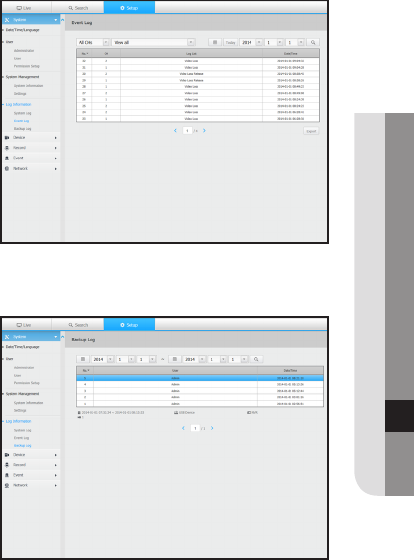
Event log
The event log lists recorded events, such as sensor events,
camera events, or image losses.
Backup log
You can inquire about a user who performed a backup,
execution time, details (backup time, channel, backup device,
backup file type).
English _113
● SETUP VIEWER
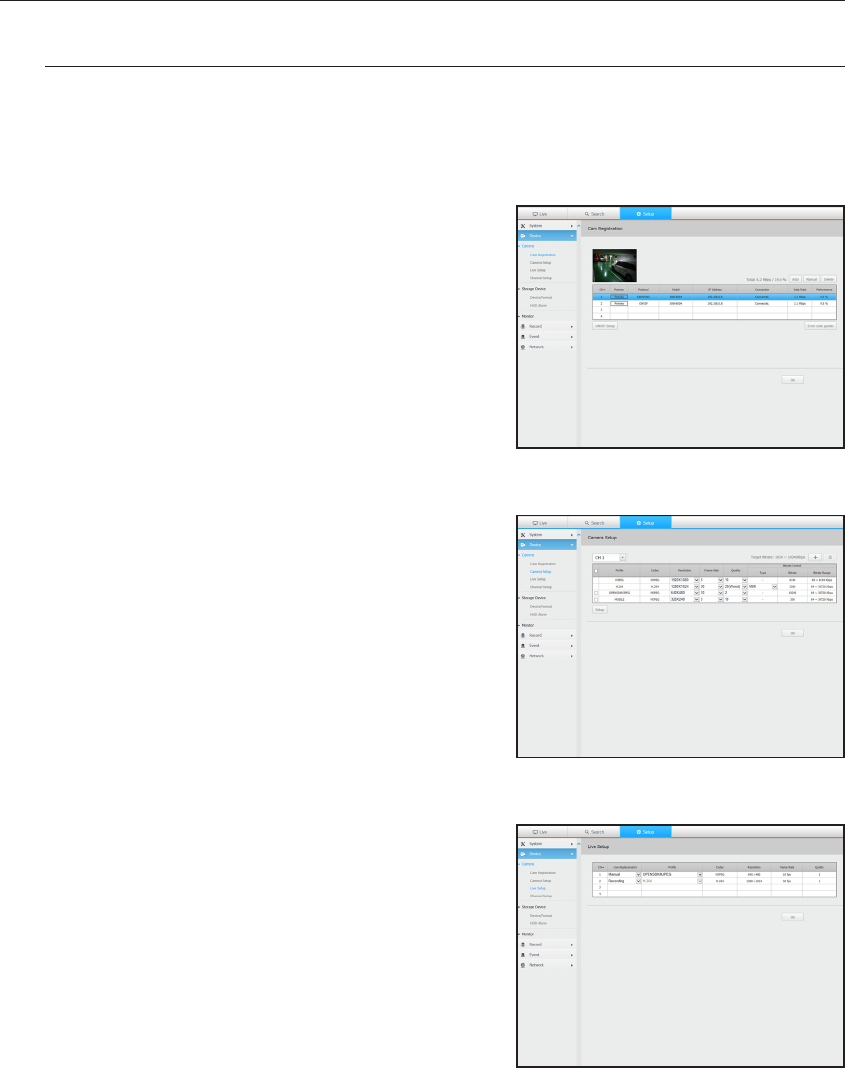
Device
You can check a list of devices that are connected to the NVR and configure the necessary settings.
Click <Device> in the menu screen.
For more information, refer to "Setting the Device". (Page 52)
Camera
Cam Registration
You can add a network camera(s).
Camera Setup
You can change the settings of a connected network camera.
Live Setup
You can change the life transfer settings of the network camera.
114_ setup viewer
setup viewer
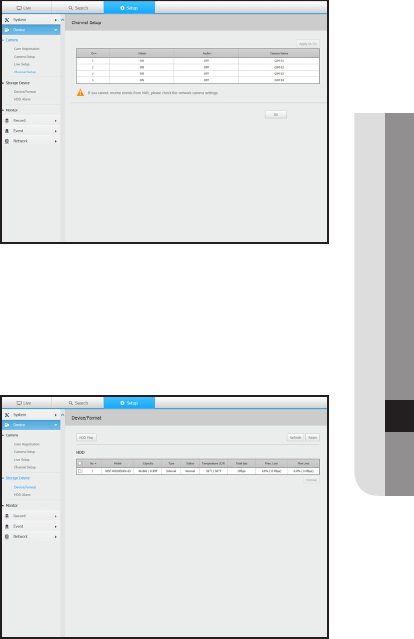
Channel Setup
You can configure the video settings for each channel.
Storage Device
You can check and change the settings related to the data storage device.
Device/format
You can check a storage device, amount of use, type of use
and status of storage device.
English _115
● SETUP VIEWER
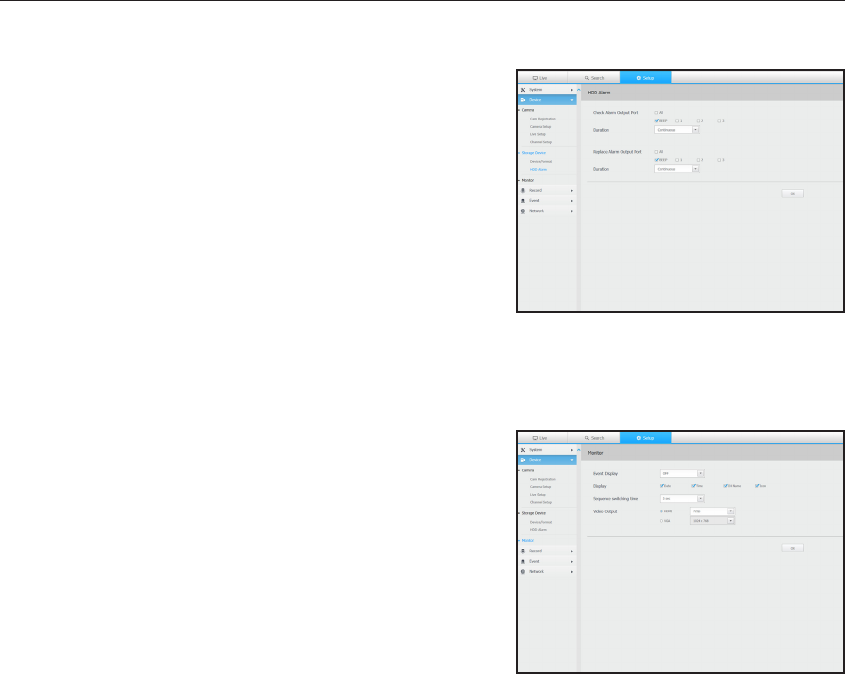
HDD Alarm
You can set the alarm output port and the duration in case an
error occurs.
Monitor
Monitor
You can configure the monitoring screen settings and set the
output system.
M
`If the video is not played properly, refer to the troubleshooting
section later in this manual. (Page 138)
`The Monitor Setup settings control the monitor connected to the
NVR.
116_ setup viewer
setup viewer
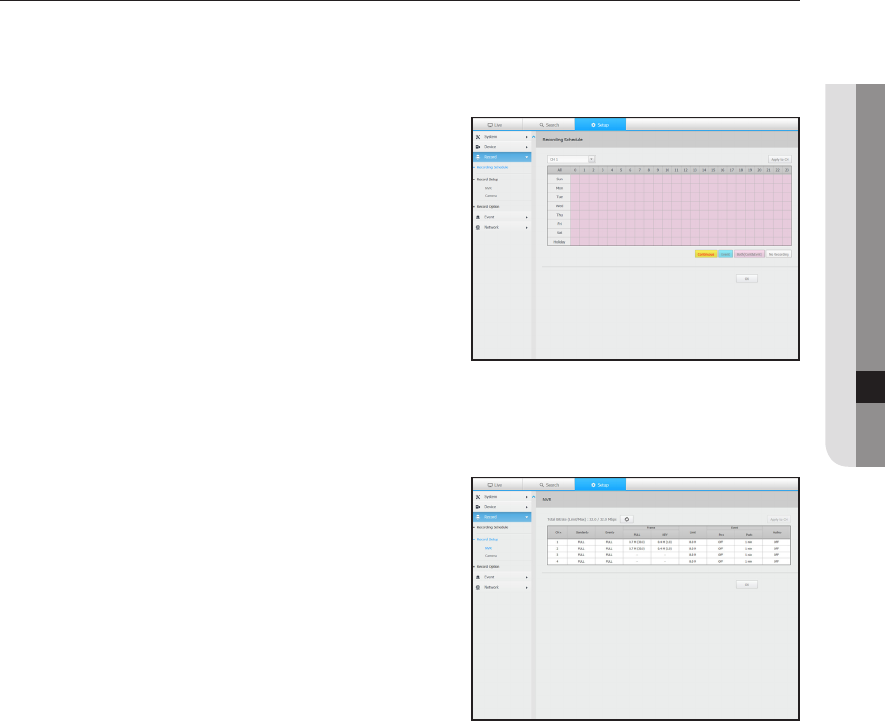
Record
For more information, refer to "Setting the Recording". (Page 69)
Recording Schedule
If you set a recording schedule for a specific date and time, the
recording will start at that specific time.
Record Setup
NVR
Select a type of the normal/event recording frame rate for each
channel.
English _117
● SETUP VIEWER
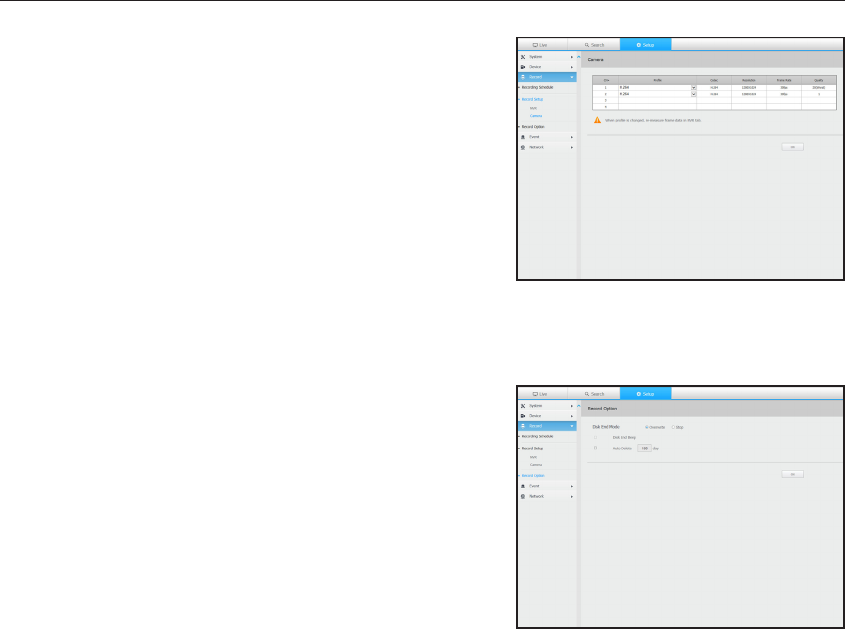
Camera
You can set the recording profile for a network camera.
Record Option
You can set the Disk End Mode.
118_ setup viewer
setup viewer
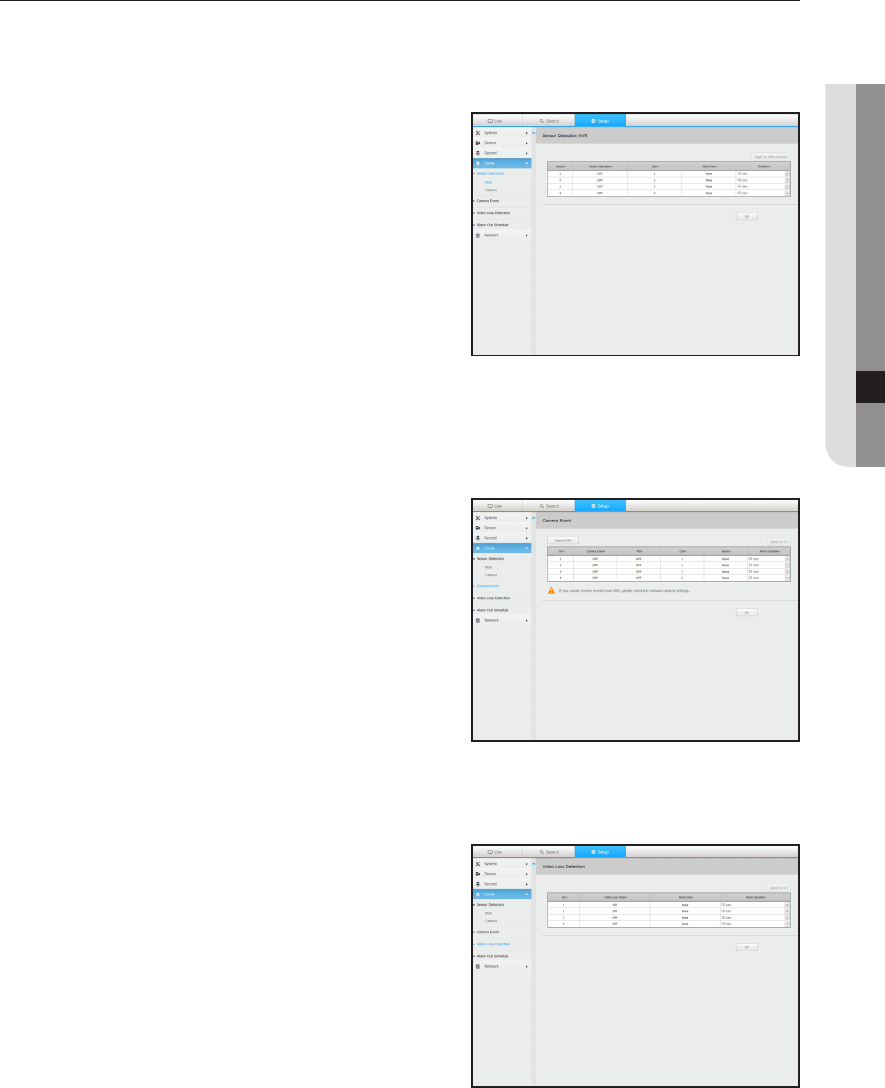
Event
For more information, refer to "Setting the Event". (Page 73)
Sensor Detection
NVR / Camera
You can set the sensor operation mode and the synchronized
camera as well as the alarm output type and the duration.
`If the connected network camera that has configured the alarm in/out
settings triggers an alarm, NVR will perform the alarm out.
Camera Event
You can set the camera event mode, the alarm output type and
the alarm time.
Video Loss Detection
You can set to trigger the alarm if a video loss occurs.
English _119
● SETUP VIEWER
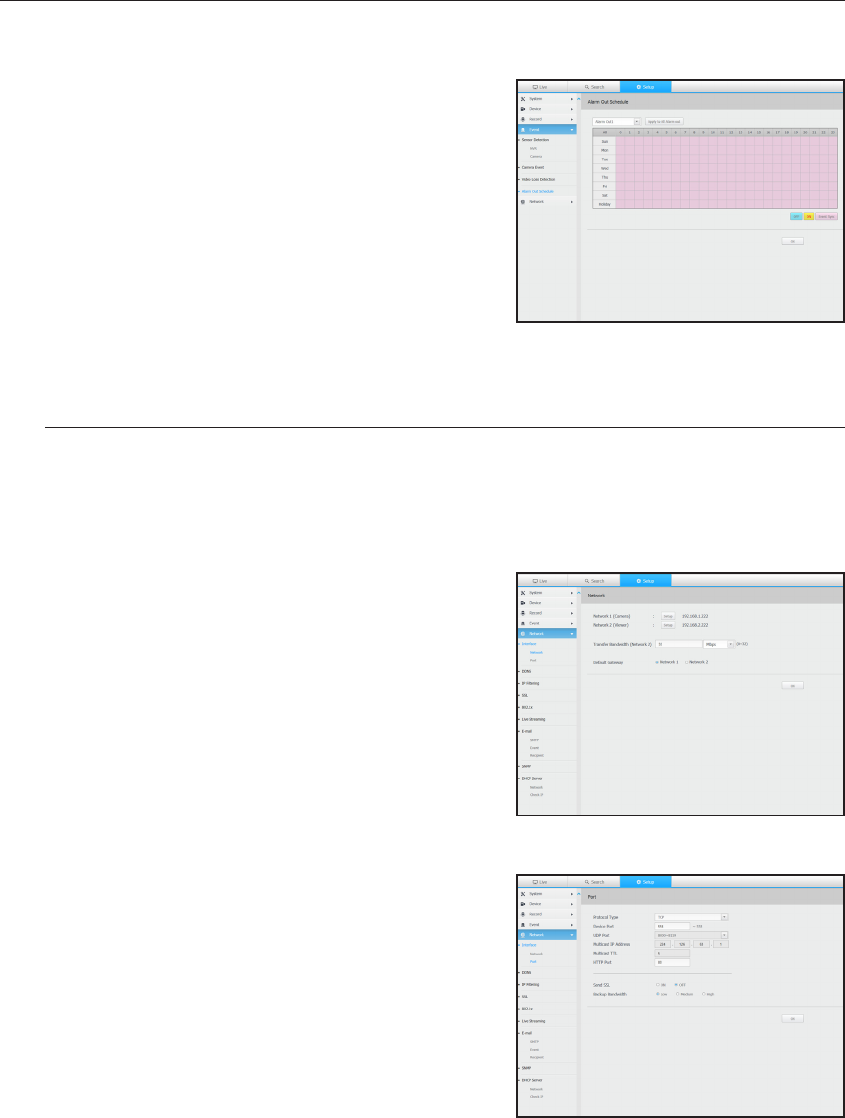
Alarm Out Schedule
You can schedule the alarm output according to the day of the
week and the time.
The default setting is Event Sync, which activates the alarm only
if an event occurs.
Network
For more information, refer to "Network Configuration". (Page 76)
Interface
A remote user can access the NVR via the network to check the current mode and the IP address.
Network
Specify the network connection path.
Port
You can configure the protocol related settings.
120_ setup viewer
setup viewer
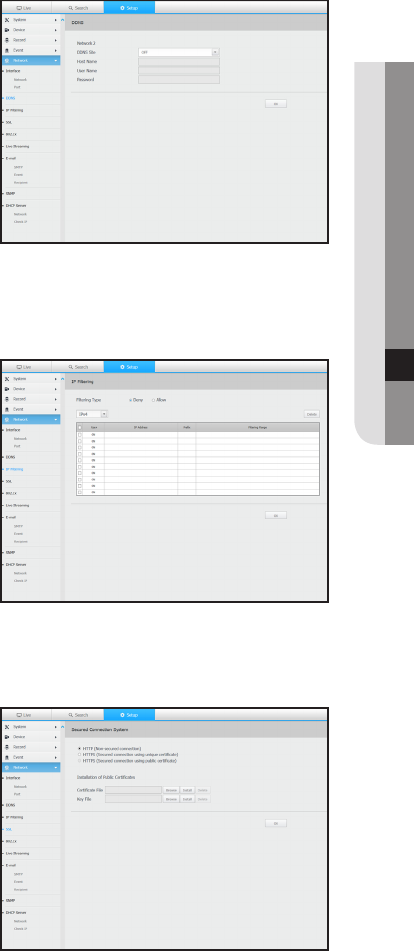
DDNS
Network2
You can check the DDNS settings.
IP Filtering
You can prepare the list of IP address to allow or block
accesses to a specific IP address.
SSL
You can select a security connection system or install public
certificates.
M
`While using HTTPS, if you want to switch to HTTP, then abnormal
operation can take place as the browser contains the setting
values. You need to change the URL to HTTP and reconnect or
initialize the cookie setting of the browser.
English _121
● SETUP VIEWER
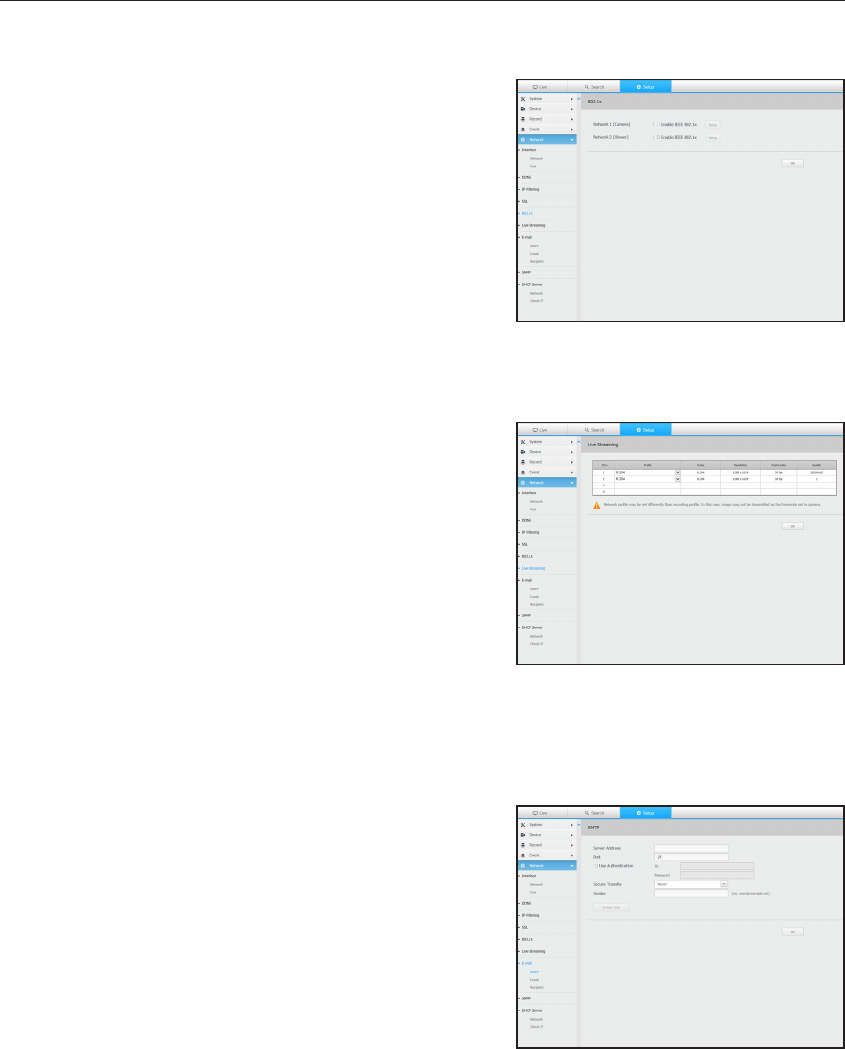
802.1x
When connecting to a network, you can select whether to use
the 802.1x protocol and install corresponding certificate.
Live Streaming
You can configure the network transfer settings of the network
camera.
E-mail
You can specify the SMTP server that sends a mail if an event occurs and set the recipient group and users.
SMTP
You can set the server that sends mails and specify if you use
the authentication process.
122_ setup viewer
setup viewer
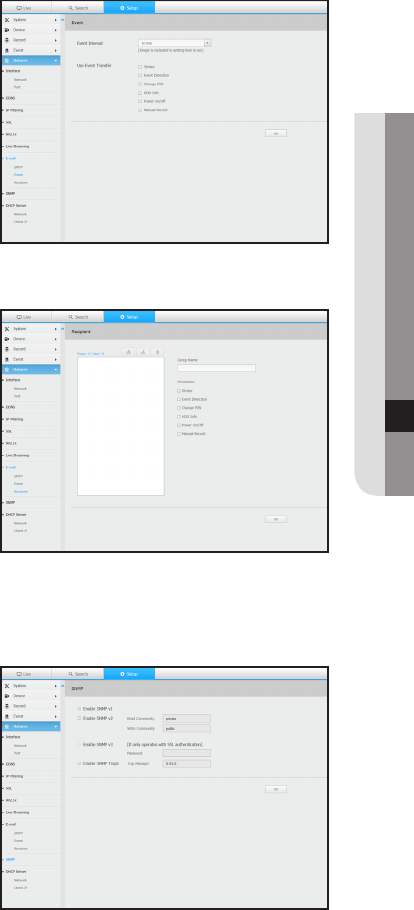
Event
You can set the event interval and specify which events the
server sends mails for.
Recipient
You can set groups and recipients to receive emails.
SNMP
Using the SNMP protocol, the system or network administrator
can remotely monitoring the network devices and sets the
environment.
English _123
● SETUP VIEWER
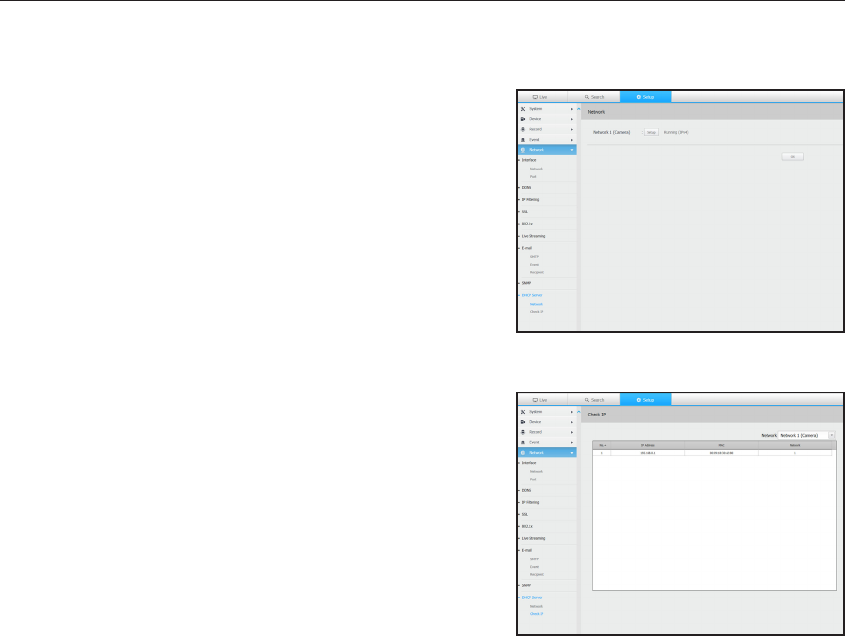
DHCP Server
Network
You can set the internal DHCP server and assign an IP address
to the network camera.
Check IP
You can check the IP and MAC currently used through the
DHCP server, and the connected network port.
124_ setup viewer
setup viewer
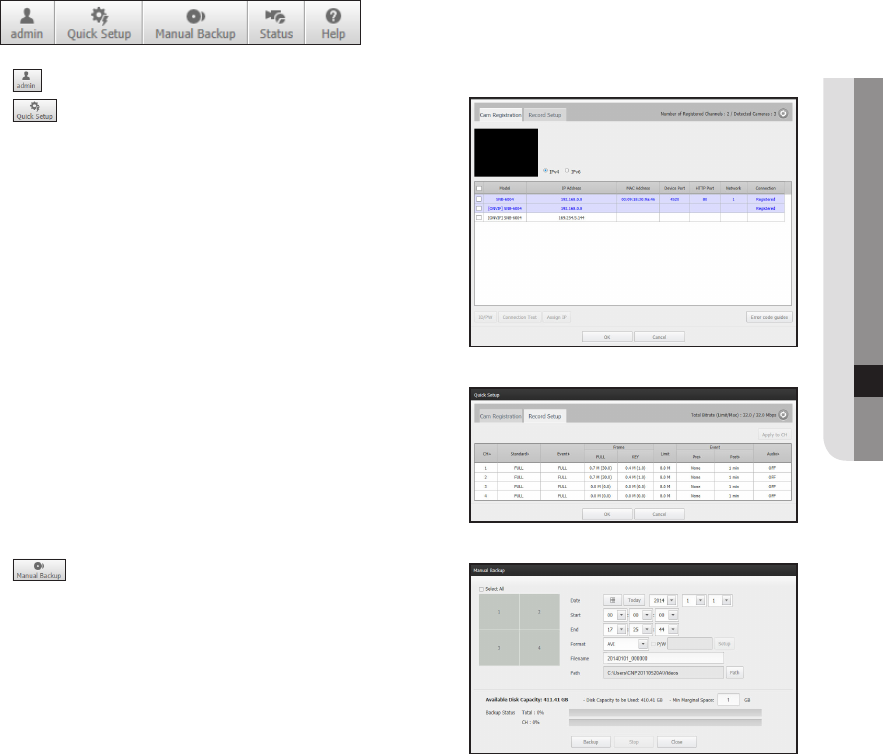
Using the setting icons
• : Display the ID of user connected.
• : You can register a network camera for each channel
and easily set the resolution and the number of shots in case
of event occurrence or manaual recording.
`For more on how to register a camera, refer to "To register a camera".
(Page 52)
• : You can manually enter the desired backup channel
and time/date to backup the recorded video.
English _125
● SETUP VIEWER
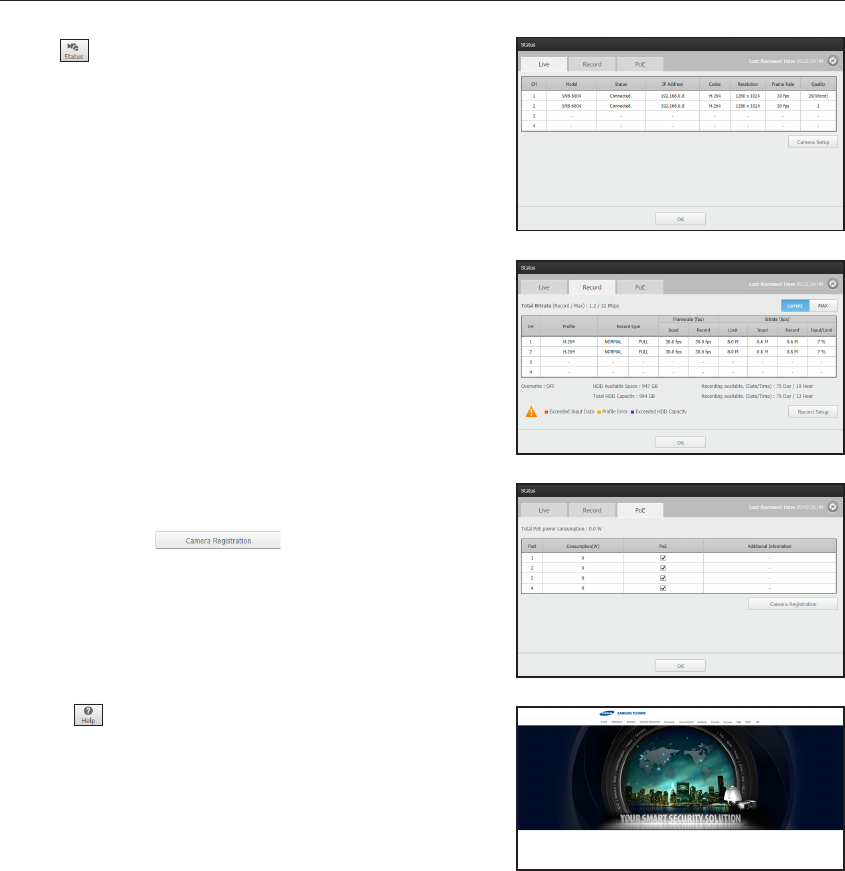
• : You can check the recording status and the status of
camera connected.
-
Live : Select <Live> to check the status of camera
connected to each channel and the transmission
information.
-
Recording : Select <Record> to check the following for
each channel : profile, recording type, inputs / recording
transmission rate, settings / inputs / amount of recorded
data.
-
PoE : Select <PoE> to check the consumption by PoE
connected to each channel.
`Click on < > to move to Device > Camera >
Camera Registration.
For more on camera registration, refer to "To register a camera".
(Page 52)
• < > : You will be immediately directed to the homepage
of Samsung Techwin. (http ://www.samsungcctv.com/).
126_ setup viewer
setup viewer
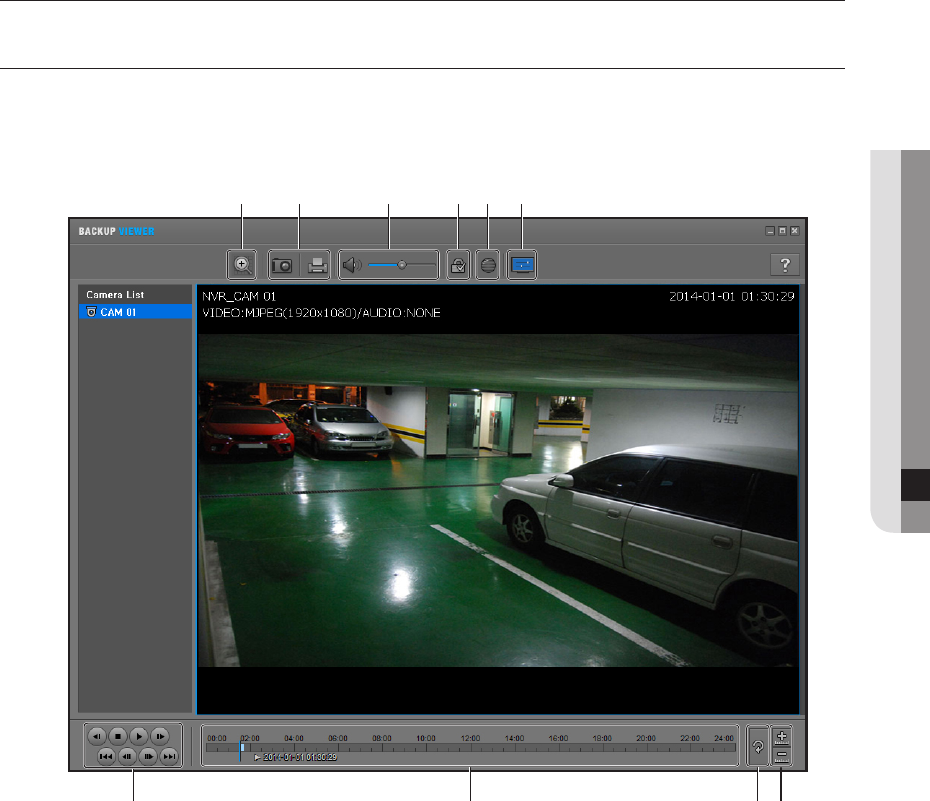
SEC BACKUP VIEWER
You can play a file that is backed up in the format of SEC.
Backup in SEC format produces backup data file, library file and self-executable viewer file.
If you run the backup file viewer, the backup data file will be played.
Recommended System Requirements
PCs with a lower specification than the recommended below may not fully support forward/backward and high-
speed playback.
•
OS : Windows XP professional, Windows Vista, Windows 7
•
CPU : Intel Core 2 Quad 2.5GHz or higher
•
RAM : 3GB or more
•
VGA : Geforce 6200 or higher
b c
English _127
● BACKUP VIEWER
backup viewer
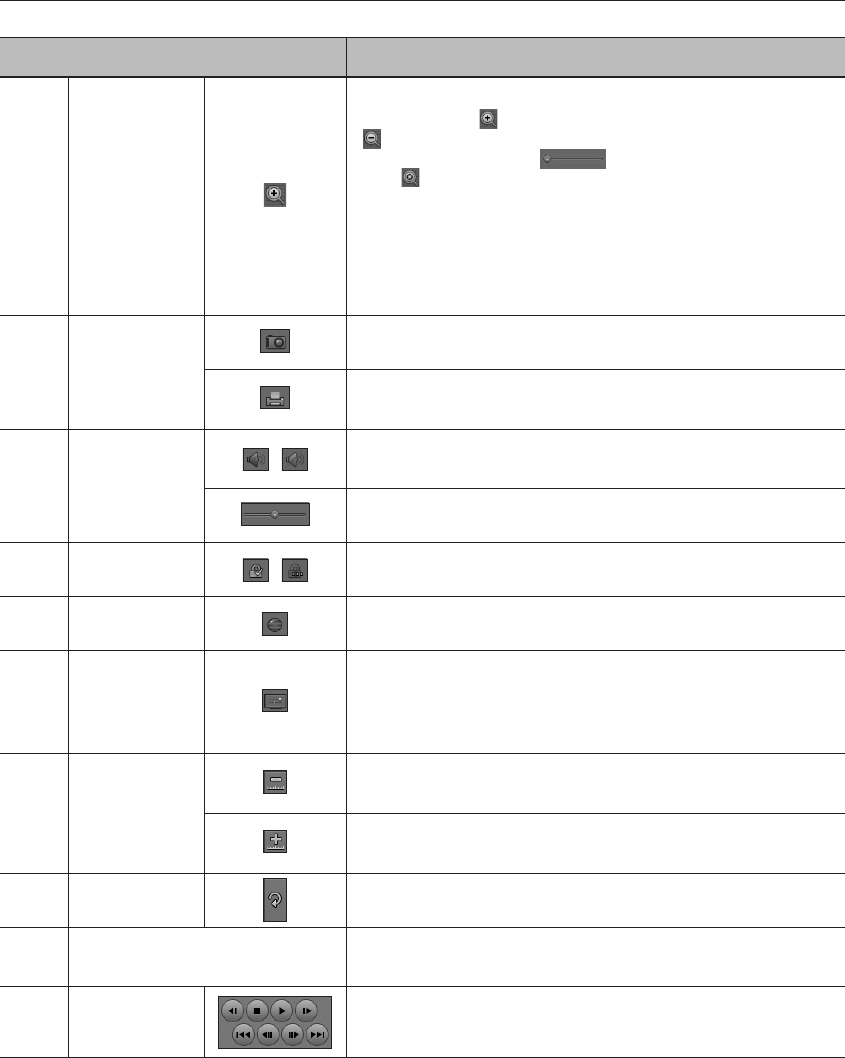
Item Description
Digital Zoom
Enlarge the image by up to 100 times as big as the current one.
Press the Zoom In (
) button the enlarge the image; press the Zoom Out
(
) button to shrink the image.
You can also use the slide bar (
) in the pop-up window to zoom in/out.
Press (
) on a size-changed video to restore the default zoom factor
(100%).
If you enlarge the image by more than 200%, the enlarged area will be
marked on the digital zooming screen. Click on the marked area and move it
to a desired position.
The digital zooming is applied to all backup viewer. When the digital zooming
is canceled, the video size will restore the default rate of 100%.
b
Screen Printout
Saves the current video's image as in an image file. Supports JPEG file format.
Prints out the current screen. You should have installed the appropriate printer
driver before you can print out the screen.
c
Audio
/
A toggle button. Each time you press this button, the audio output will toggle
between activated and deactivated.
You can adjust the volume level from 0 to 100.
Watermark /
Press the button to enable file tampering detection, to detect data file forging.
Deinterlace
You can enable the De-interlace function.
Show OSD
Check the OSD checkbox to display the OSD information on the backup playback
screen.
Information such as backup date, day of the week, time, model name, and
channel number will be displayed on the screen.
Enlarge /
Reduce Timeline
Collapses the time range that is displayed on the range bar of the storage time.
You can collapse the range bar until the overall range is shortened to 24 hours.
Enlarges the time range that is displayed on the range bar of the storage time.
You can enlarge the range bar until the overall range is extended to 1 minute.
Restore Timeline
Restores the timeline to the default.
Display of storage time range
Displays the time range of a stored video file.
You can move the gridline of the range bar to select a time point to play.
Playback Control
You can adjust the video playback of the timeline.
128_ backup viewer
backup viewer
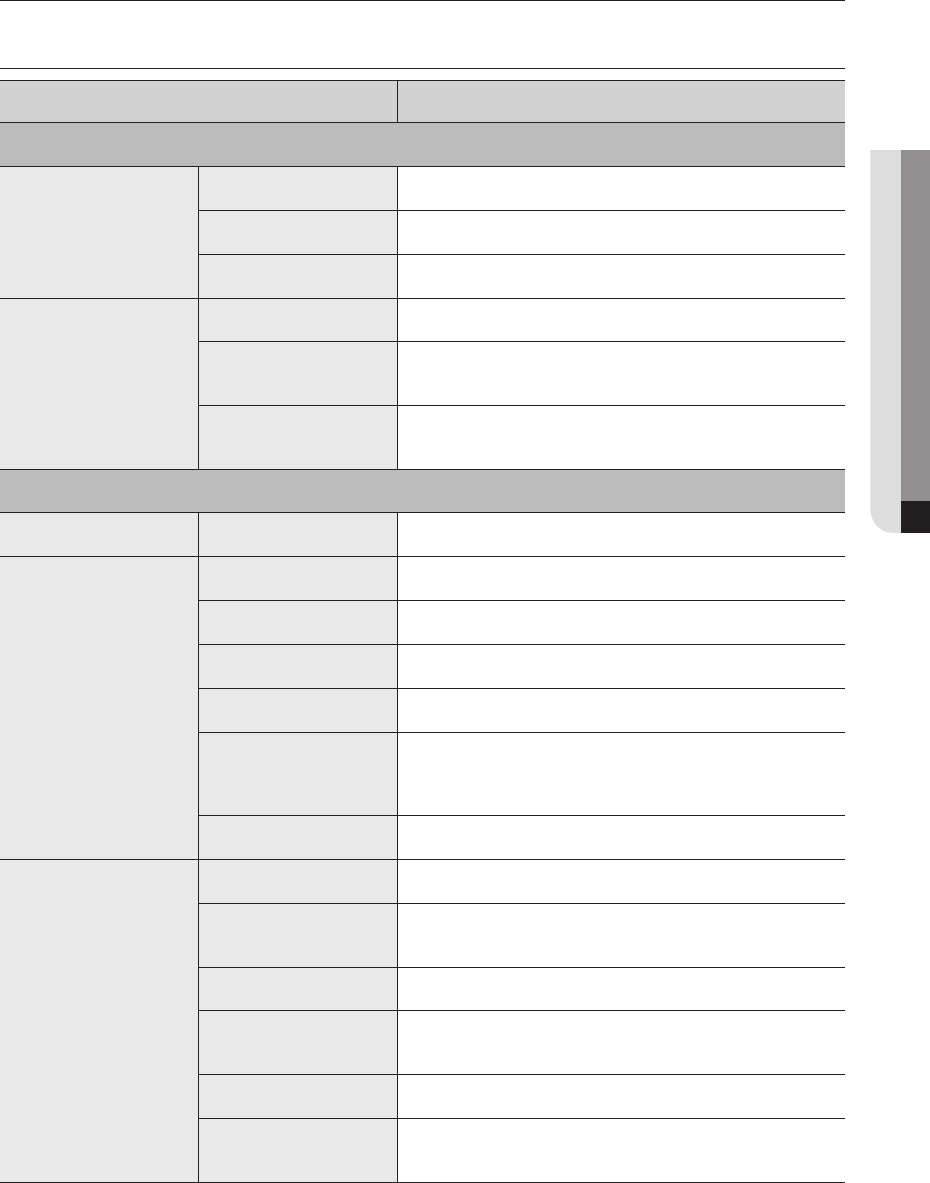
PRODUCT SPECIFICATION
Item Details
Display
Network Camera
Inputs Max. 4CH
Resolution CIF ~ 5MP
Protocols Samsung(SVNP), ONVIF supporting version(1.0 ~ 2.22)
Live
Local Display HDMI/VGA
Multi-Channel Display [Local Monitor] 1 / 4 / Auto Sequence
[Web] 1 / 4 / Auto Sequence
Performance [Local Monitor] 5MP(30fps), 3MP(30fps), 2MP(120fps)
[Web] 5MP(30fps), 3MP(60fps), 2MP(120fps)
Performance
Operating System Embedded Linux
Record
Compression H.264, MJPEG
Recording Bandwidth 32Mbps(2MP 4camera real-time recording)
Resolution CIF ~ 5MP
Type Manual, Schedule, Event (Pre/Post)
Event Trigger
- Alarm Input(4)
- Video Loss
- Camera Event(MD, Video Analytics)
Event Action e-Mail, PTZ Preset, Alarm Out, Buzzer, Monitor Out
Search & Play
Playback Bandwidth 32Mbps(4ch simultaneously)
Performance [Local Monitor] 5MP(30fps), 3MP(30fps), 2MP(120fps)
[Web] 5MP(30fps), 3MP(60fps), 2MP(120fps)
Mode Date & Time(Calendar)/Event Log list
Simultaneous playback 4 channels(Local Monitor)
4 ch(Web), 4 ch(CMS)
Resolution CIF ~ 5MP
Playback Control Fast Forward/Fast Backward, Move one step up/Move one step
down
English _129
● APPENDIX
appendix
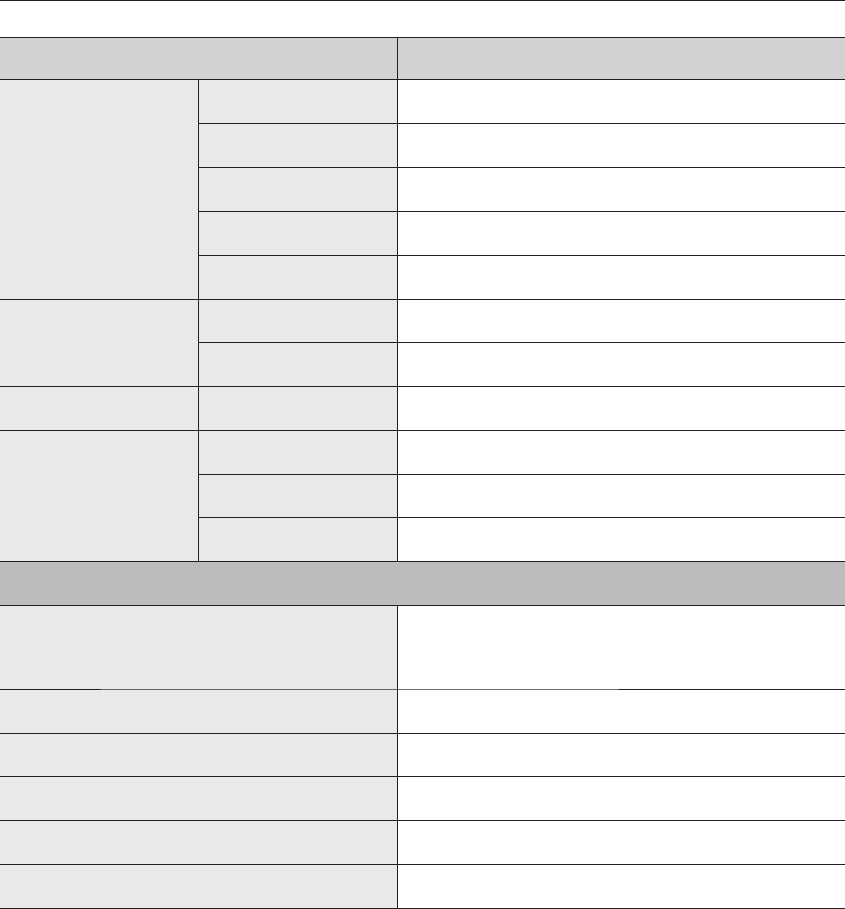
Item Details
Storage
Internal HDD Up to 2 SATA HDDs
External (DAS) N/A
External (NAS) N/A
Capacity Internal (8TB)
RAID N/A
Backup
File backup BU/Exe(USB), JPG, AVI(Web, CMS)
Function Single channel Play, Date-Time/Title display
Sensor I/O 4/3 (NO/NC Selectable)
Audio
Input 4 channels (network)
Compression G.711, G.726
Audio Communication 2-Way
Network
Protocol
TCP/IP, UDP/IP, RTP(UDP), RTP(TCP), RTSP, NTP, HTTP, DHCP(Server,
Client), PPPoE, SMTP, ICMP, IGMP, ARP, DNS, DDNS, uPnP, HTTPS,
SNMP, ONVIF
DDNS Samsung iPOLiS DDNS
Transmission Bandwidth MIN 32Mbps
Max Remote Users Search(3) / Live unicast(10) / Live multicast(20)
IP Version IPv4/v6
Security User access Log, IP Filtering, 802.1x, Encryption
130_ appendix
appendix
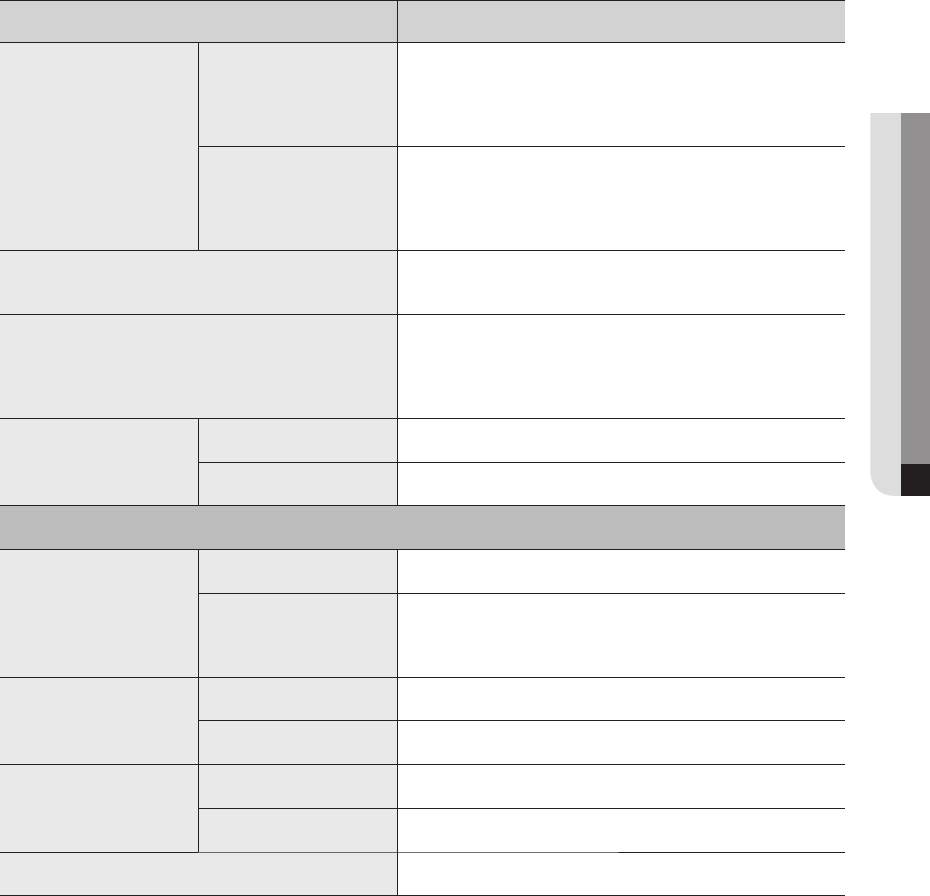
Item Details
Language
GUI
English, French, German, Italian, Spanish, Russian, Turkish, Polish,
Dutch, Swedish, Czech, Portuguese, Danish, Rumanian, Serbian,
Croatian, Hungarian, Greek, Norwegian, Finnish, Korean, Chinese,
Japanese, Thai (24)
Webviewer
English, French, German, Italian, Spanish, Russian, Turkish, Polish,
Dutch, Swedish, Czech, Portuguese, Danish, Rumanian, Serbian,
Croatian, Hungarian, Greek, Norwegian, Finnish, Korean, Chinese,
Japanese, Thai (24)
OS Supported OS : Window XP(service pack 2 or above), Vista, 7, 8, 8.1,
Mac OS X(10.7 or above)
Web Browser
Microsoft Internet Explorer (Ver. 8~11),
Mozilla Firefox (Ver. 19.x or higher),
Google Chrome (Ver. 26.x or higher),
Apple Safari (Ver. 6.0.3 or higher (Mac OS X 10.6 or higher))
Viewer Software
Type SSM., Webviewer, Smart Viewer, Mobile Viewer
CMS Support Support SDK/CGI
Functions
Camera Setup
Register 1) PnP mode 2) Semi-Auto 3) Manual
Setup Items
- IP Address, Add Profile Edit, Bitrate, Compression, Quality
- Video Setup(MD, ABF, Brightness/Contrast, Flip/Mirror, IRIS, WDR,
D&N, SSNR, Shutter)
PTZ
Control Via GUI, Webviewer
Preset 256 Presets
Smart phone
Support Model I-Phone, Android
Control Live(4ch) / Playback(1ch)
System Control Mouse, Web
English _131
● APPENDIX
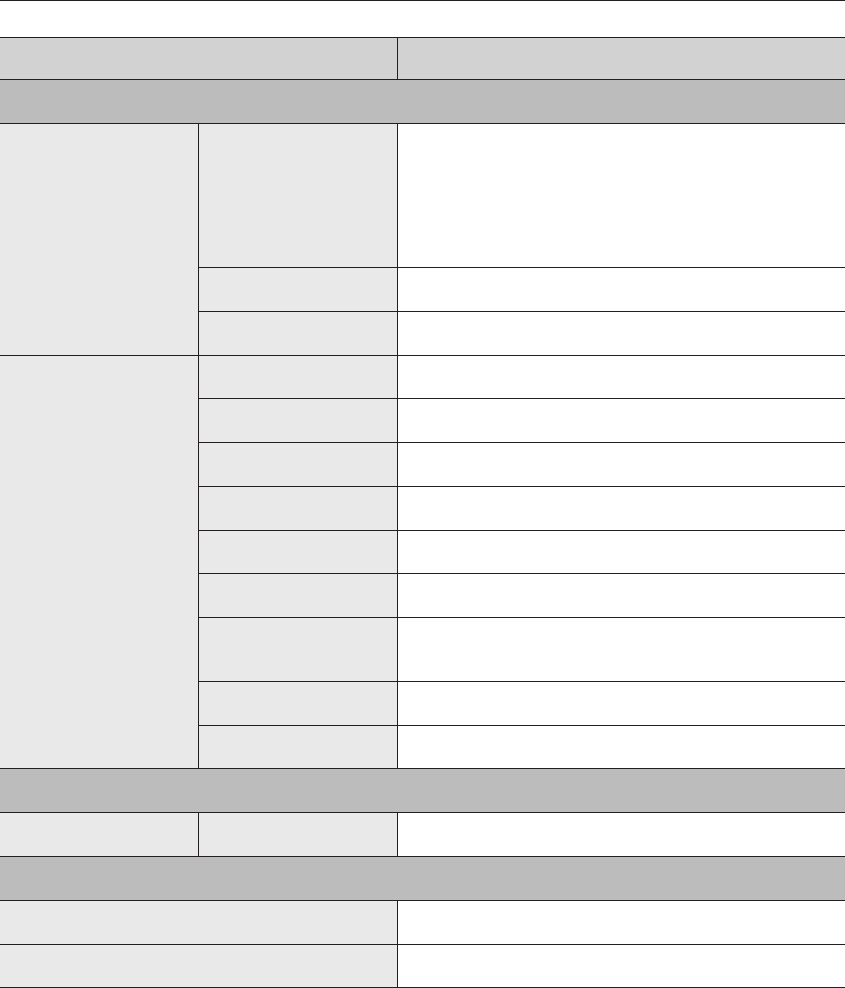
Item Details
Indicator/Interface
Front
Indicator
Power Status LED 1EA
HDD Action LED 1EA
Alarm Status LED 1EA
Record Status LED 1EA
Network Action LED 1EA
BACKUP Status LED 1EA
USB 2EA
Switch N/A
Connectors
VGA 1 EA
HDMI 1 EA
Audio Out(1EA, RCA, Line)
DVD N/A
Serial N/A
Ethernet 4EA (PoE, 10/100Mbps), 2EA (LAN, WAN, 100Mbps)
Alarm In(4EA, Terminal Block)
Out(3EA, Terminal Block)
Reset N/A
Power Cord AC Inlet
System
Log Log List Max. 20000 (System Log, Event Log, Backup Log each)
Environmental
Operating Temperature / Humidity +0°C to +40°C
Humidity 20% ~ 85%
132_ appendix
appendix
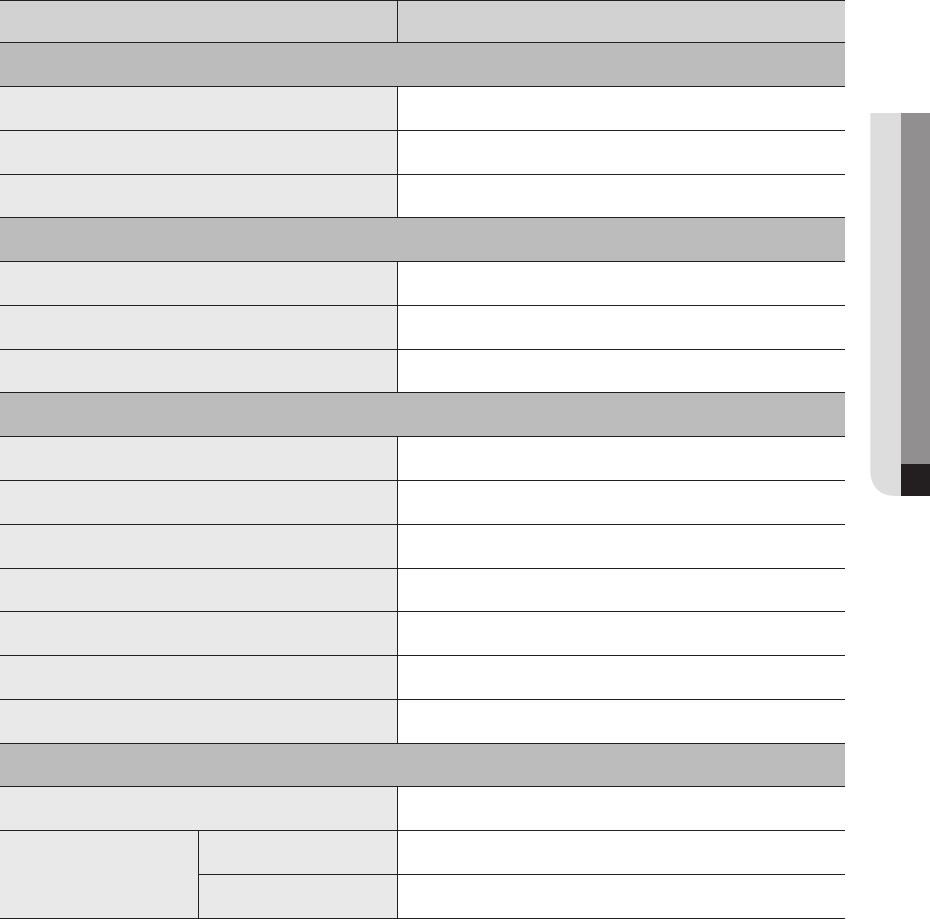
Item Details
Electrical
Input Voltage /Current 100-240V / 3.5A 50Hz-60Hz
NVR Power consumption Max. 30W
Camera Power Output Max. 15.4W per channel, Total 61.6W (PoE, IEEE 802.3af)
Mechanical
Color / Material Black / Metal
Dimension (WxDxH) W370xD44xH320mm(1U)
Weight 2.73Kg(without HDD)
Accessories
IR remote control Included
Mouse Included
Viewer CD Backup viewer, installation manuals
IB Included
Power Cord Included
Terminal block Included
Bracket mounting screws Included
Standards
Regulation R82(France)
Approvals
Safety UL,KC
EMC CE, FCC, KCC, CCC, Gost-R
English _133
● APPENDIX
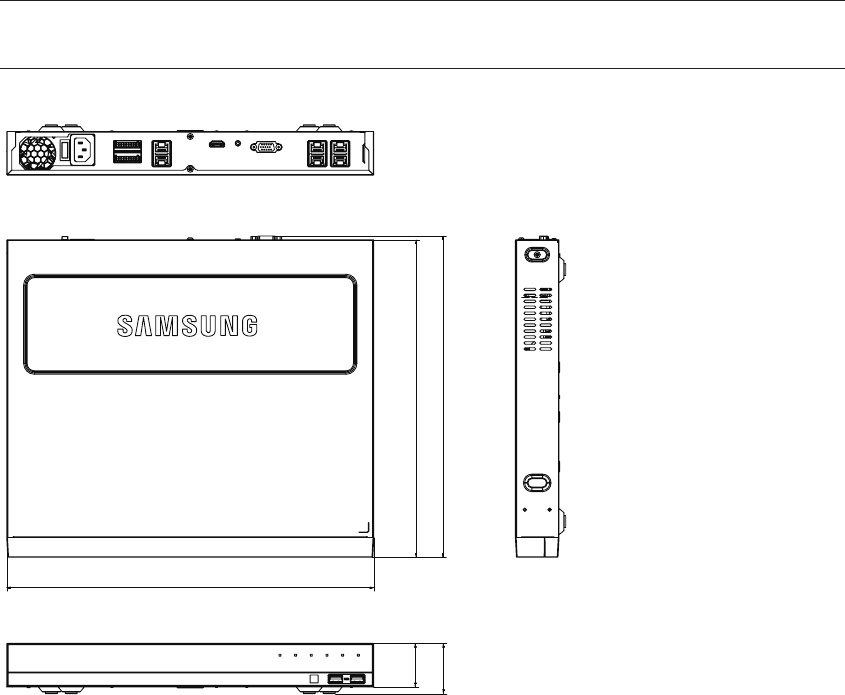
PRODUCT OVERVIEW
unit : mm (inches)
320 [12.6]
323.9 [12.75]
370 [14.57]
44 [1.73]
50.7 [2]
134_ appendix
appendix
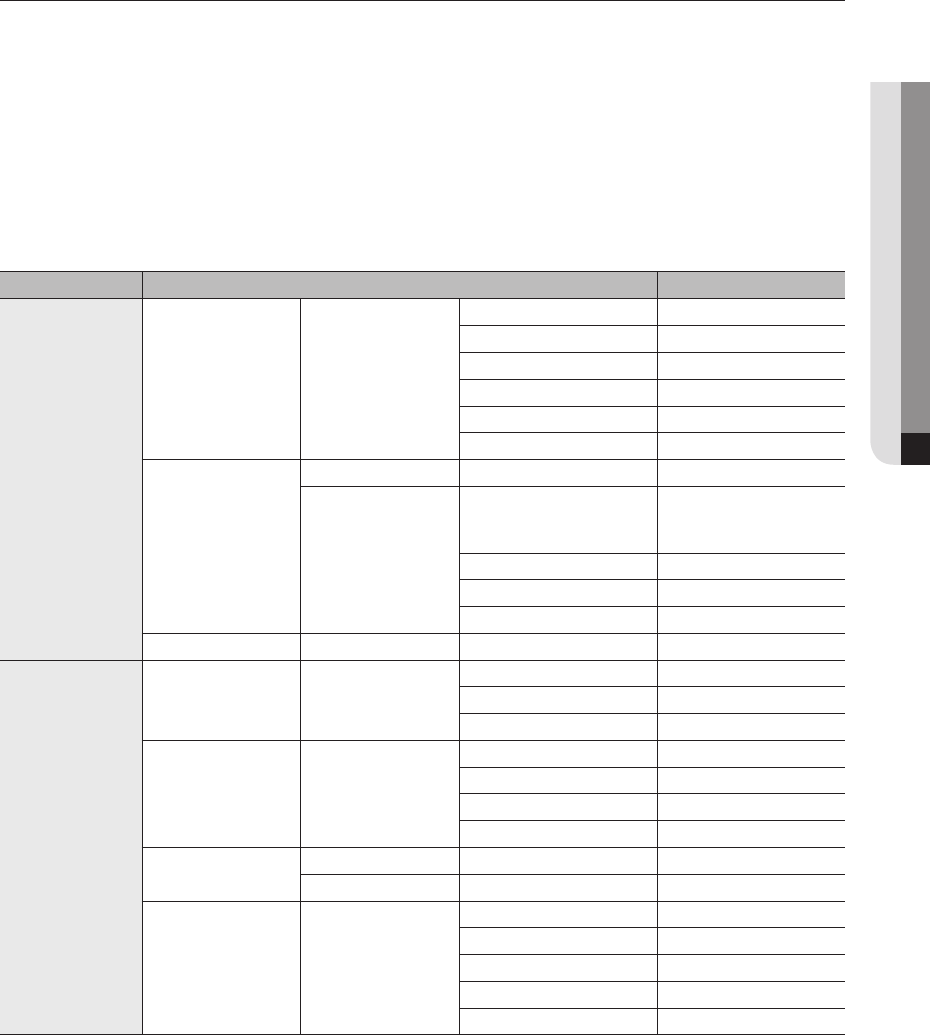
DEFAULT SETTING
To reset the system, move to "System Management > Settings > Load Factory Default" and press the
<Initialization> button.
This returns the factory default settings.
M
`When you initialize the system without changing the <Authority Setting>, you must enter the ID and password to log into the
system after it reboots. The ID and password are "admin" and "4321", respectively.
Please change the password after you log in.
`The initial administrator ID is "admin" and the password should be set when logging in for the first time.
`Please change your password every three months to safely protect personal information and to prevent the damage of the information theft.
Please, take note that it's a user's responsibility for the security and any other problems caused by mismanaging a password.
Category Details Factory Default
System
Date/Time/Language Date/Time/Language
Date YYYY-MM-DD
Time 24 hours
Time Zone GMT
Time Sync. OFF
DST OFF
Language English
User
Admin ID admin
Permission Setup
Restricted Access
Backup/Record/Record
Stop/Search/PTZ/Remote
Alarm Out/Shutdown
Restriction on Network Access
None
Auto Log out 3 Min
Manual Input of ID OFF
System Management System Information Device Name NVR
Device
Camera Channel Setup
Video ON
Audio OFF
Camera Name CAM 01 ~ CAM 04
Storage Device HDD Alarm
Check Alarm Output Port BEEP
Duration Continuous
Replace Alarm Output Port BEEP
Duration Continuous
Remote Device Remote Control ON
ID 00
Monitor Monitor
Event Display OFF
Display All
Multi CH SEQ Time 5 sec
Video Output VGA(1280x1024)
Display Position Setup 30
English _135
● APPENDIX
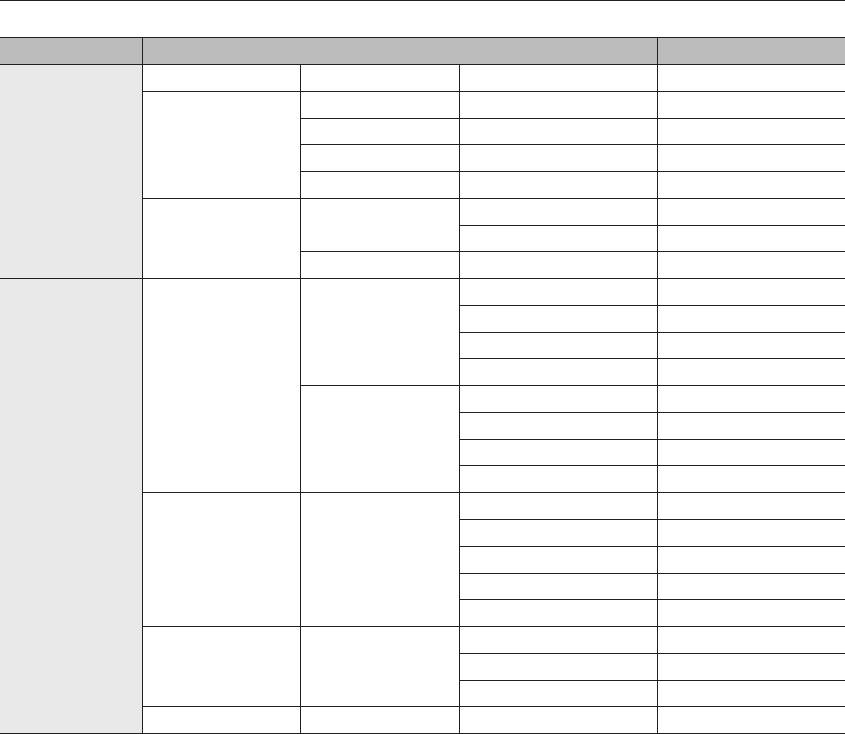
Category Details Factory Default
Record
Recording Schedule CH1~CH4Both(Cont&Evnt)
Record Setup
Standard Full
Event Full
Pre Event OFF
POST Event 1 min
Record Option Disk End Mode Overwrite
Disk End Beep OFF
Auto Delete 180
Event
Sensor Detection
NVR
Sensor Operation OFF
Cam Camera No.
Alarm Out None
Duration 10 sec
Network Camera
Sensor Operation OFF
Cam Camera No.
Alarm Out None
Duration 10 sec
Camera Event
Camera Event OFF
MD OFF
Cam Camera No.
Alarm None
Alarm Duration 10 sec
Video loss detection
Video loss status OFF
Alarm Out None
Alarm Duration 10 sec
Alarm Out Schedule Alarm Out1
136_ appendix
appendix
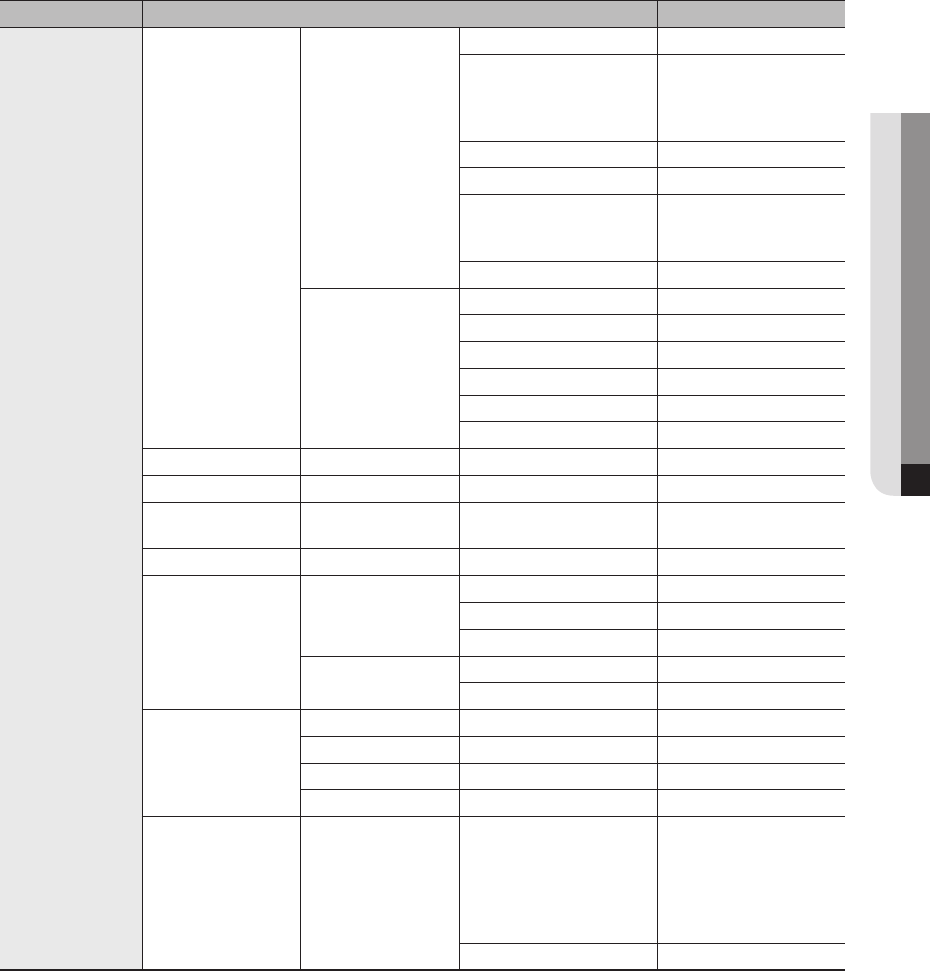
Category Details Factory Default
Network
Interface
Network
IP Type Static
Network 1(Camera)
PnP mode :
192.168.231.200
Manual mode :
192.168.1.200
Network 2(Viewer) 192.168.2.200
Subnet Mask 255.255.255.0
Gateway
PnP mode : 192.168.2.1
Manual mode :
192.168.1.1
DNS 168.126.63.1
Port
Protocol Type TCP
Device Type 554
UDP Port 8000~8159
Multicast IP Address 224.126.63.1
Multicast TTL 5
Web Streaming Port 80
DDNS Network2DDNS Site OFF
IP Filtering Filtering Type Deny
SSL Secured Connection System HTTP (Non-secured
connection)
802.1x Network2Enable IEEE 802.1x OFF
E-Mail
SMTP
Port 25
Use Authentication OFF
Secure Transfer Never
Event Event Interval 10 min
Use Event Transfer OFF
SNMP
Enable SNMP v1 OFF
Enable SNMP v2 OFF
Enable SNMP v3 OFF
Enable SNMP Traps OFF
DHCP Server Network 1(camera) IP Range
PnP mode :
192.168.231.1
~ 192.168.231.254
Manual mode :
192.168.1.1
~192.168.1.254
IP Lease time 86400
English _137
● APPENDIX
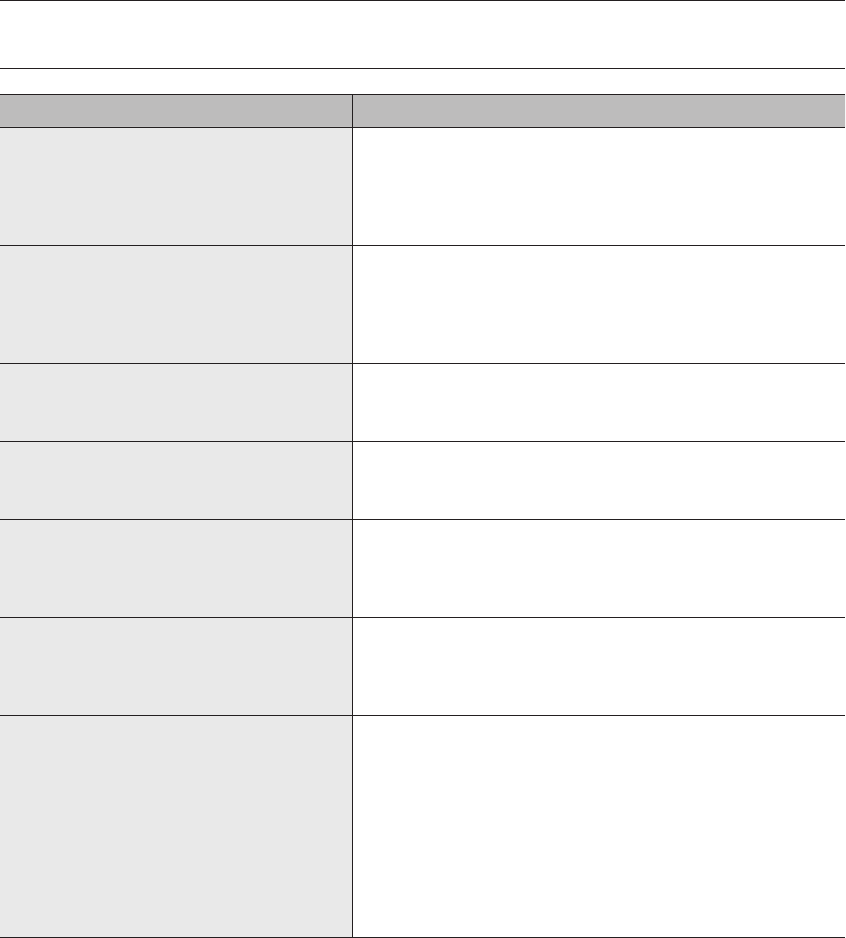
TROUBLESHOOTING
Problem Action
The system does not turn on and the indicator on the
front panel does not work at all.
y
Check if the power supply system is properly connected.
y
Check the system for the input voltage from the power source.
yIf the problem persists even after you have taken the above actions, check
the power supplier and replace it with a new one if neccessary.
yCheck inside if the cables are properly connected. (SMPS, FRONT)
Some channels display just a black screen even if
they receive video sources.
yCheck if the camera is properly supplied with power.
yCheck the video output connecting the camera's webviewer.
yCheck if the network port is properly connected and the network setting is
set correctly.
yChange the hub supporting Gigabit, it may solves.
Even if you press the [REC] button on your remote
control, the REC LED does not turn on and no
recording is done.
yCheck if there is recording space in the HDD.
yIn the menu, check if the recording mode is set to ON.
yIn the menu, check if the number of general recordings is turned <OFF>.
The screen displays the logo image repeatedly. y
This may occur from a problem with the main board, or the related software is
corrupt.
Contact the nearest service center for more information.
The Channel button does not work on the Live
screen.
y
The Channel button does not work if the current screen is in the event
monitoring mode.
If it is the event monitoring screen, press the [ALARM] button to terminate the
event screen and select a channel.
The cursor will not move to the Start button when I
start the calendar search.
y
Check if the channel and the date that you want to play are marked with the V
symbol.
Both channel and date should be checked before you can start playing with
the Start button.
No video is played on the connected monitor. y
Check if the necessary cables are connected to the monitor properly.
y
If the screen is not displayed even when a connection is made, then check the
remote control, and press the [STOP (@)] [ZOOM] [STOP (@)]
[ZOOM] [MENU] button to launch the basic resolution information window.
You can set the desired resolution here. If the screen is not displayed after a
while, then wait until the basic resolution window appear. Again, switch to
another resolution and and finally switch to the final output resolution.
y
Some monitors do not support the NVR output (HDMI or VGA).
(NVR output resolution : VGA : 1024*768, 1280*1024, HDMI : 720P, 1080P)
Check the monitor resolution
138_ appendix
appendix
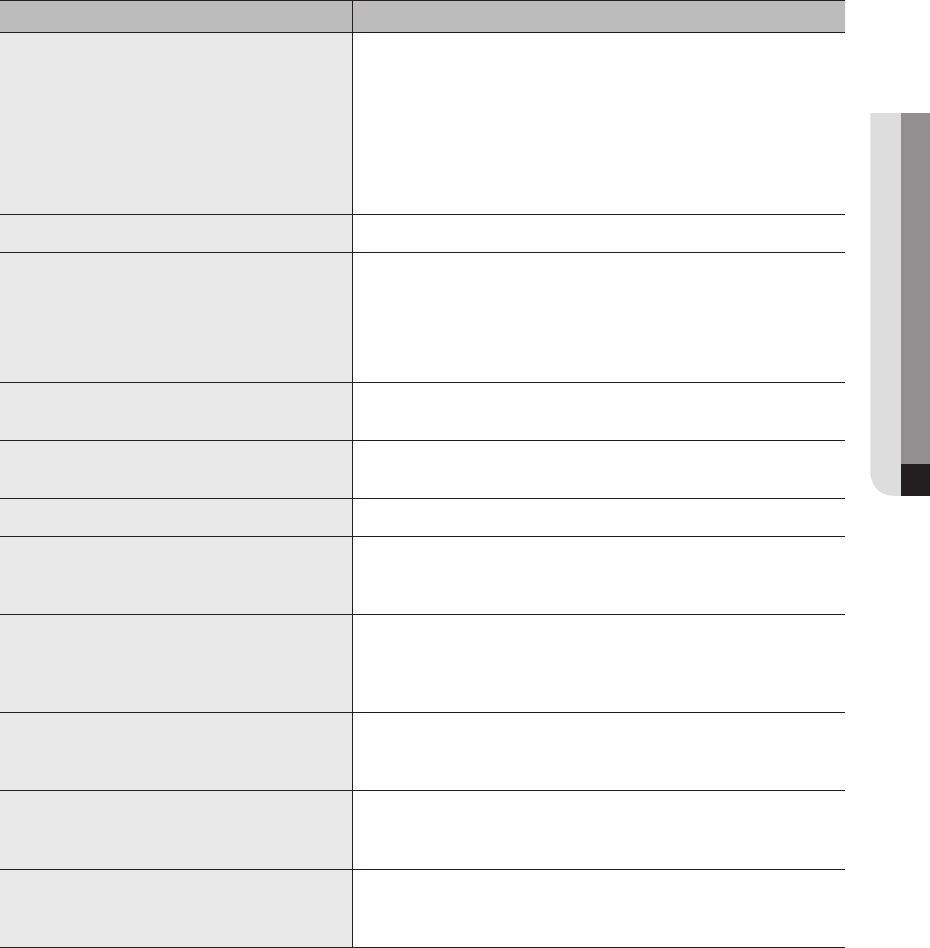
Problem Action
When an alarm occurs, I try to press the [ALARM]
button on my remote control to cancel it but an
alarm keeps running and it cannot be cancelled.
yPress the [MENU] button on your remote control to cancel the alarm.
1) Event monitoring screen cancellation: monitoring mode - Turn off the event
monitoring time.
2) Canceling alarm sounds: event recording mode - alarm (camera event/
video loss) - Mute the alarm output.
3) Canceling events: event recording mode - alarm (camera event/video loss)
- Turn off the mode.
No response controlling PTZ in the live viewer. yCheck the registered Camera if it support PTZ function.
The camera is not connected or the PC fails to
connect to the product.
y
Check if the network cable is connected properly.
y
Ensure that you have set Network – Connection Mode.
y
Check the IP setting of the PC or camera.
y
Try the Ping Test.
y
Check if there is a different device near the product uses the same IP.
I registered a camera, but the web viewer does not
show live video.
y
After registering a camera, a user need to edit/save the desired layout, before
the screen split mode and live screen fit for the setting appears.
In the web viewer, the screen does not switch
automatically.
y
You need to select the desired layout for sequence operation, in the automatic
switching menu.
The Live screen is too bright or too dark. y
Check the video settings of the registered camera.
A message of "Need to reset date/time." Is displayed
on the screen.
y
This message is displayed if there occurs a problem with the time setting of
the internal clock or an error in the clock itself.
Contact the retailer or the service center for more information.
The time bar is not displayed in Search mode. y
The timeline can switch between normal and extension mode.
In extension mode, the time bar may not be displayed in the current timeline.
Switch to normal mode or use the left or right button to navigate through the
time bar.
The "NO HDD" icon and an error message are
displayed.
y
Check the HDD for connection. If the problem persists in a normal condition,
contact the nearest service center to have the HDD checked by the service
personnel.
I have installed an additional HDD on the NVR but it
does not recognize the HDD.
y
See the compatibilty list to check if the additional HDD is supported by the
NVR. For the compatibility list, contact the retailer where you purchased the
NVR.
I have connected an external storage device (USB
Memory, USB HDD) to the NVR but the NVR seems
not to recognize it.
y
See the compatibility list of external storage devices to check if the connected
device is supported by the NVR. For the compatibility list, contact the retailer
where you purchased the NVR.
English _139
● APPENDIX
Problem Action
If I press the ESC key in full screen mode of the
WebViewer, the system does not switch to a normal
split mode.
y
Press the ALT+TAB keys to select 'ACTIVE MOVIE' and press the ESC key
again. The system will switch to a normal split mode.
I found it difficult to configure the network settings if
using the default search, backup and router settings.
y
For more information, refer to the user manual.
y
If you want to check the basics of the product for a quick start, refer to the
quick start guide (backup, search).
yIf you use the router for network connection, refer to the "Connecting
and Setting the Network" section in this manual.
I forgot the password. y
Contact the NVR administrator for help.
Backup data is just not played by the PC or NVR. y
When you are backing up data, you have choices about the player either: PC
or NVR. Make your selection before proceeding.
y
If you are using the PC to play the data, the format of the backup file should
be either SEC.
y
If you are using the NVR for this purpose, formatting backup files should be
done by the NVR.
You cannot move to live while playing video. y
On the remote control, press the Stop [
] button or press the [@]
button in the launcher to immediately move to the live screen.
Recording does not work. y
If your player does not display a Live image at all, that indicates recording
does not work so first check if you see an image on the screen.
y
Recording does not work if the recording settings are not properly configured.
1) Direct recording: press the [REC] button on the NVR remote control to start
recording immediately.
2) Scheduled recording: In menu/recording/scheduled recording, set the
desired recording time to start recording at that time.
-<Continuous> recording: Must start recording at the time.
-<Event> recording: When an event occurs (alarm, motion detection,
video loss), recording is started. If there is no event, there is no
recording.
-<Continuous/event> recording: If there is no event, continuous
recording is done and when events occur, event recording is done.
The image quality of the recording data is not good. y
Increase the resolution and quality level in Menu – Record – Quality /
Resolution.
1) Resolution: Select a bigger size when specifying the recording size.
The recording image in the CIF format shows a deteriorated quality as
it is enlarged from a small-sized image.
2) Record Quality: Specify a bigger level for the recording quality.
y
If you increase the resolution and the recording quality, the data size
increases accordingly. So the HDD will be filled faster. Overwriting will
overwrite the existing data so recording will proceed at a shorter interval.
140_ appendix
appendix
Problem Action
Frame rate of the actual recording does not match
that of configured to the camera.
y
If multiple profiles were applied to one camera for video transmission, the
actual video stream can be serviced by the camera at a lower frame rate than
specified.
Configure your camera to use one profile for data streaming as possible.
For example, if you set the same profile for recording and network profiles,
the actual recording is made at the specified frame rate.
Still, live video display using split screen mode may apply yet another profile
to camera in accordance with the used screen mode.
Note that allowed limit bitrate for recording / recording settings should be set
to be bigger values than that of camera's feed.
Recording is not performed in accordance with the
settings.
y
If the recording status shows that the input data is exceeded.
Then go to Menu – Recording – Recording Setting, and set the max data
capacity to greater than the input data.
The recording screen will slow down. y
Check if the recording spec for each HDD condition (refer to the recording
setting in menu) is appropriate for the actual recording setting.
y
Only main video frames will play if the data data processing rate exceeds the
play performance (refer to the product specifications in menu).
English _141
● APPENDIX

OPEN SOURCE LICENSE REPORT ON THE PRODUCT
The software included in this product contains copyrighted software that is licensed under the GPL/LGPL. You may obtain the
complete Corresponding Source code from us for a period of three years after our last shipment of this product by sending email to
help.cctv@samsung.com
If you want to obtain the complete Corresponding Source code in the physical medium such as CD-ROM, the cost of physically
performing source distribution might be charged.
M
`For more details about Open Source, refer to the CD.
•
GPL Software : Linux Kernel 2.6.37, uboot, busybox 1.21.1, Net-SNMP 5.6.2, wpa_supplicant 0.7.3, smartmontools 5.37,
xfsprogs 3.1.8, msmtp 1.4.30, parted 3.1, dosfstools 3.0.24, wget 1.14, dibbler 0.8.4, Udhcp 0.98
•
LGPL Software : ffmpeg, QT 4.7.2, Live555, ntp 4.2.6p1
•
BSD : pcre 8.31, pppd 2.4.5
•
BSD 2.0 : lighttpd 1.4.26
•
Boost Software License : boost 1.43.0
•
PHP 3.01 License : PHP 5.2.0
•
UNDER THE ZLIB : tinyxml 2.6.2
GNU GENERAL PUBLIC LICENSE
Version 2, June 1991
Copyright (C) 1989, 1991 Free Software Foundation, Inc.
51 Franklin St, Fifth Floor, Boston, MA 02110-1301 USA
Everyone is permitted to copy and distribute verbatim copies of this
license document, but changing it is not allowed.
Preamble
The licenses for most software are designed to take away your freedom
to share and change it. By contrast, the GNU General Public License is
intended to guarantee your freedom to share and change free software--
to make sure the software is free for all its users. This General Public
License applies to most of the Free Software Foundation's software and
to any other program whose authors commit to using it. (Some other
Free Software Foundation software is covered by the GNU Library
General Public License instead.) You can apply it to your programs, too.
When we speak of free software, we are referring to freedom, not price.
Our General Public Licenses are designed to make sure that you have
the freedom to distribute copies of free software (and charge for this
service if you wish), that you receive source code or can get it if you want
it, that you can change the software or use pieces of it in new free
programs; and that you know you can do these things.
To protect your rights, we need to make restrictions that forbid anyone to
deny you these rights or to ask you to surrender the rights.
These restrictions translate to certain responsibilities for you if you
distribute copies of the software, or if you modify it.
For example, if you distribute copies of such a program, whether gratis
or for a fee, you must give the recipients all the rights that you have. You
must make sure that they, too, receive or can get the source code. And
you must show them these terms so they know their rights.
We protect your rights with two steps: (1) copyright the software, and (2)
offer you this license which gives you legal permission to copy, distribute
and/or modify the software.
Also, for each author's protection and ours, we want to make certain that
everyone understands that there is no warranty for this free software. If the
software is modified by someone else and passed on, we want its recipients
to know that what they have is not the original, so that any problems
introduced by others will not reflect on the original authors' reputations.
Finally, any free program is threatened constantly by software patents.
We wish to avoid the danger that redistributors of a free program will
individually obtain patent licenses, in effect making the program
proprietary. To prevent this, we have made it clear that any patent must
be licensed for everyone's free use or not licensed at all.
The precise terms and conditions for copying, distribution and
modification follow.
GNU GENERAL PUBLIC LICENSE
TERMS AND CONDITIONS FOR COPYING,
DISTRIBUTION AND MODIFICATION
0. This License applies to any program or other work which contains a
notice placed by the copyright holder saying it may be distributed under
the terms of this General Public License. The "Program", below, refers to
any such program or work, and a "work based on the Program" means
either the Program or any derivative work under copyright law: that is to
say, a work containing the Program or a portion of it, either verbatim or
with modifications and/or translated into another language. (Hereinafter,
translation is included without limitation in the term "modification".) Each
licensee is addressed as "you".
Activities other than copying, distribution and modification are not
covered by this License; they are outside its scope. The act of running
the Program is not restricted, and the output from the Program is
covered only if its contents constitute a work based on the Program
(independent of having been made by running the Program).
Whether that is true depends on what the Program does.
1. You may copy and distribute verbatim copies of the Program's source
code as you receive it, in any medium, provided that you conspicuously
and appropriately publish on each copy an appropriate copyright notice
and disclaimer of warranty; keep intact all the notices that refer to this
License and to the absence of any warranty; and give any other
recipients of the Program a copy of this License along with the Program.
You may charge a fee for the physical act of transferring a copy, and you
may at your option offer warranty protection in exchange for a fee.
2. You may modify your copy or copies of the Program or any portion of
it, thus forming a work based on the Program, and copy and distribute
such modifications or work under the terms of Section 1 above, provided
that you also meet all of these conditions:
a) You must cause the modified files to carry prominent notices stating
that you changed the files and the date of any change.
b) You must cause any work that you distribute or publish, that in whole
or in part contains or is derived from the Program or any part thereof, to
be licensed as a whole at no charge to all third parties under the terms of
this License.
c) If the modified program normally reads commands interactively when
run, you must cause it, when started running for such interactive use in
the most ordinary way, to print or display an announcement including an
appropriate copyright notice and a notice that there is no warranty (or
else, saying that you provide a warranty) and that users may redistribute
the program under these conditions, and telling the user how to view a
copy of this License. (Exception: if the Program itself is interactive but
does not normally print such an announcement, your work based on the
Program is not required to print an announcement.)
These requirements apply to the modified work as a whole. If identifiable
sections of that work are not derived from the Program, and can be
reasonably considered independent and separate works in themselves,
then this License, and its terms, do not apply to those sections when
you distribute them as separate works. But when you distribute the
same sections as part of a whole which is a work based on the Program,
the distribution of the whole must be on the terms of this License, whose
permissions for other licensees extend to the entire whole, and thus to
each and every part regardless of who wrote it.
Thus, it is not the intent of this section to claim rights or contest your
rights to work written entirely by you; rather, the intent is to exercise the
right to control the distribution of derivative or collective works based on
the Program.
In addition, mere aggregation of another work not based on the Program
with the Program (or with a work based on the Program) on a volume of
a storage or distribution medium does not bring the other work under the
scope of this License.
3. You may copy and distribute the Program (or a work based on it,
under Section 2) in object code or executable form under the terms of
Sections 1 and 2 above provided that you also do one of the following:
a) Accompany it with the complete corresponding machine-readable
source code, which must be distributed under the terms of Sections 1
and 2 above on a medium customarily used for software interchange; or,
b) Accompany it with a written offer, valid for at least three years, to give
any third party, for a charge no more than your cost of physically
performing source distribution, a complete machine-readable copy of the
corresponding source code, to be distributed under the terms of
Sections 1 and 2 above on a medium customarily used for software
interchange; or,
c) Accompany it with the information you received as to the offer to
distribute corresponding source code. (This alternative is allowed only for
noncommercial distribution and only if you received the program in object
code or executable form with such an offer, in accord with Subsection b
above.)
The source code for a work means the preferred form of the work for
making modifications to it. For an executable work, complete source
code means all the source code for all modules it contains, plus any
associated interface definition files, plus the scripts used to control
compilation and installation of the executable. However, as a special
exception, the source code distributed need not include anything that is
normally distributed (in either source or binary form) with the major
components (compiler, kernel, and so on) of the operating system on
which the executable runs, unless that component itself accompanies
the executable.
If distribution of executable or object code is made by offering access to
copy from a designated place, then offering equivalent access to copy
the source code from the same place counts as distribution of the
source code, even though third parties are not compelled to copy the
source along with the object code.
4. You may not copy, modify, sublicense, or distribute the Program
except as expressly provided under this License. Any attempt otherwise
to copy, modify, sublicense or distribute the Program is void, and will
automatically terminate your rights under this License.
However, parties who have received copies, or rights, from you under
this License will not have their licenses terminated so long as such
parties remain in full compliance.
5. You are not required to accept this License, since you have not signed
it. However, nothing else grants you permission to modify or distribute
the Program or its derivative works. These actions are prohibited by law if
you do not accept this License. Therefore, by modifying or distributing
the Program (or any work based on the Program), you indicate your
acceptance of this License to do so, and all its terms and conditions for
copying, distributing or modifying the Program or works based on it.
6. Each time you redistribute the Program (or any work based on the
Program), the recipient automatically receives a license from the original
licensor to copy, distribute or modify the Program subject to these terms
and conditions. You may not impose any further restrictions on the
recipients' exercise of the rights granted herein.
You are not responsible for enforcing compliance by third parties to this
License.
7. If, as a consequence of a court judgment or allegation of patent
infringement or for any other reason (not limited to patent issues),
conditions are imposed on you (whether by court order, agreement or
otherwise) that contradict the conditions of this License, they do not
excuse you from the conditions of this License. If you cannot distribute
so as to satisfy simultaneously your obligations under this License and
any other pertinent obligations, then as a consequence you may not
distribute the Program at all. For example, if a patent license would not
permit royalty-free redistribution of the Program by all those who receive
copies directly or indirectly through you, then the only way you could
satisfy both it and this License would be to refrain entirely from
distribution of the Program.
If any portion of this section is held invalid or unenforceable under any
particular circumstance, the balance of the section is intended to apply
and the section as a whole is intended to apply in other circumstances.
It is not the purpose of this section to induce you to infringe any patents
or other property right claims or to contest validity of any such claims;
this section has the sole purpose of protecting the integrity of the free
software distribution system, which is implemented by public license
practices. Many people have made generous contributions to the wide
range of software distributed through that system in reliance on
consistent application of that system; it is up to the author/donor to
decide if he or she is willing to distribute software through any other
system and a licensee cannot impose that choice.
This section is intended to make thoroughly clear what is believed to be
a consequence of the rest of this License.
8. If the distribution and/or use of the Program is restricted in certain
countries either by patents or by copyrighted interfaces, the original
copyright holder who places the Program under this License may add an
explicit geographical distribution limitation excluding those countries, so
that distribution is permitted only in or among countries not thus
excluded. In such case, this License incorporates the limitation as if
written in the body of this License.
9. The Free Software Foundation may publish revised and/or new
versions of the General Public License from time to time. Such new
versions will be similar in spirit to the present version, but may differ in
detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Program
specifies a version number of this License which applies to it and "any
later version", you have the option of following the terms and conditions
either of that version or of any later version published by the Free
Software Foundation. If the Program does not specify a version number
of this License, you may choose any version ever published by the Free
Software Foundation.
10. If you wish to incorporate parts of the Program into other free
programs whose distribution conditions are different, write to the author
to ask for permission. For software which is copyrighted by the Free
Software Foundation, write to the Free Software Foundation; we
sometimes make exceptions for this. Our decision will be guided by the
two goals of preserving the free status of all derivatives of our free
software and of promoting the sharing and reuse of software generally.
NO WARRANTY
11. BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE,
THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT
PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE
STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER
PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY OF
ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT
LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND
FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO
THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU.
SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE
COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
12. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR
AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY
OTHER PARTY WHO MAY MODIFY AND/OR REDISTRIBUTE THE
PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR
DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR
CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR
INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO
LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR
LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF
THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN
IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE
POSSIBILITY OF SUCH DAMAGES.
END OF TERMS AND CONDITIONS
How to Apply These Terms to Your New
Programs
If you develop a new program, and you want it to be of the greatest
possible use to the public, the best way to achieve this is to make it free
software which everyone can redistribute and change under these terms.
To do so, attach the following notices to the program. It is safest to
attach them to the start of each source file to most effectively convey the
exclusion of warranty; and each file should have at least the "copyright"
line and a pointer to where the full notice is found.
<one line to give the program's name and a brief idea of what it does.>
Copyright (C) <year> <name of author>
This program is free software; you can redistribute it and/or modify it
under the terms of the GNU General Public License as published by the
Free Software Foundation; either version 2 of the License, or (at your
option) any later version.
This program is distributed in the hope that it will be useful, but
WITHOUT ANY WARRANTY; without even the implied warranty of
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See
the GNU General Public License for more details.
You should have received a copy of the GNU General Public License
along with this program; if not, write to the Free Software Foundation,
Inc., 51 Franklin St, Fifth Floor, Boston, MA 02110-1301 USA
Also add information on how to contact you by electronic and paper
mail.
If the program is interactive, make it output a short notice like this when it
starts in an interactive mode:
Gnomovision version 69, Copyright (C) year name of author
Gnomovision comes with ABSOLUTELY NO WARRANTY; for details
type `show w'.
This is free software, and you are welcome to redistribute it under certain
conditions; type `show c' for details.
The hypothetical commands `show w' and `show c' should show the
appropriate parts of the General Public License. Of course, the
commands you use may be called something other than `show w' and
`show c'; they could even be mouse-clicks or menu items--whatever
suits your program.
You should also get your employer (if you work as a programmer) or your
school, if any, to sign a "copyright disclaimer" for the program, if
necessary. Here is a sample; alter the names:
Yoyodyne, Inc., hereby disclaims all copyright interest in the program
`Gnomovision' (which makes passes at compilers) written by James
Hacker.
<signature of Ty Coon>, 1 April 1989
Ty Coon, President of Vice
This General Public License does not permit incorporating your program
into proprietary programs. If your program is a subroutine library, you
may consider it more useful to permit linking proprietary applications with
the library. If this is what you want to do, use the GNU Library General
Public License instead of this License.
GNU LESSER GENERAL PUBLIC LICENSE
Version 2.1, February 1999
Copyright (C) 1991, 1999 Free Software Foundation, Inc.
51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA
Everyone is permitted to copy and distribute verbatim copies of this
license document, but changing it is not allowed.
[This is the first released version of the Lesser GPL. It also counts as the
successor of the GNU Library Public License, version 2, hence the
version number 2.1.]
Preamble
The licenses for most software are designed to take away your freedom
to share and change it. By contrast, the GNU General Public Licenses
are intended to guarantee your freedom to share and change free
software--to make sure the software is free for all its users.
This license, the Lesser General Public License, applies to some specially
designated software packages--typically libraries--of the Free Software
Foundation and other authors who decide to use it. You can use it too,
but we suggest you first think carefully about whether this license or the
ordinary General Public License is the better strategy to use in any
particular case, based on the explanations below.
When we speak of free software, we are referring to freedom of use, not
price. Our General Public Licenses are designed to make sure that you
have the freedom to distribute copies of free software (and charge for
this service if you wish); that you receive source code or can get it if you
want it; that you can change the software and use pieces of it in new free
programs; and that you are informed that you can do these things.
To protect your rights, we need to make restrictions that forbid
distributors to deny you these rights or to ask you to surrender these
rights. These restrictions translate to certain responsibilities for you if you
distribute copies of the library or if you modify it.
For example, if you distribute copies of the library, whether gratis or for a
fee, you must give the recipients all the rights that we gave you. You
must make sure that they, too, receive or can get the source code. If you
link other code with the library, you must provide complete object files to
the recipients, so that they can relink them with the library after making
changes to the library and recompiling it. And you must show them these
terms so they know their rights.
We protect your rights with a two-step method: (1) we copyright the
library, and (2) we offer you this license, which gives you legal permission
to copy, distribute and/or modify the library.
To protect each distributor, we want to make it very clear that there is no
warranty for the free library. Also, if the library is modified by someone
else and passed on, the recipients should know that what they have is
not the original version, so that the original author's reputation will not be
affected by problems that might be introduced by others.
Finally, software patents pose a constant threat to the existence of any
free program. We wish to make sure that a company cannot effectively
restrict the users of a free program by obtaining a restrictive license from
a patent holder. Therefore, we insist that any patent license obtained for
a version of the library must be consistent with the full freedom of use
specified in this license.
Most GNU software, including some libraries, is covered by the ordinary
GNU General Public License. This license, the GNU Lesser General
Public License, applies to certain designated libraries, and is quite
different from the ordinary General Public License. We use this license for
certain libraries in order to permit linking those libraries into non-free
programs.
When a program is linked with a library, whether statically or using a
shared library, the combination of the two is legally speaking a combined
work, a derivative of the original library. The ordinary General Public
License therefore permits such linking only if the entire combination fits
its criteria of freedom. The Lesser General Public License permits more
lax criteria for linking other code with the library.
We call this license the "Lesser" General Public License because it does
Less to protect the user's freedom than the ordinary General Public
License. It also provides other free software developers Less of an
advantage over competing non-free programs. These disadvantages are
the reason we use the ordinary General Public License for many libraries.
However, the Lesser license provides advantages in certain special
circumstances.
For example, on rare occasions, there may be a special need to
encourage the widest possible use of a certain library, so that it becomes
a de-facto standard. To achieve this, non-free programs must be allowed
to use the library. A more frequent case is that a free library does the
same job as widely used non-free libraries. In this case, there is little to
gain by limiting the free library to free software only, so we use the Lesser
General Public License.
In other cases, permission to use a particular library in non-free programs
enables a greater number of people to use a large body of free software.
For example, permission to use the GNU C Library in non-free programs
enables many more people to use the whole GNU operating system, as
well as its variant, the GNU/Linux operating system.
Although the Lesser General Public License is Less protective of the
users' freedom, it does ensure that the user of a program that is linked
with the Library has the freedom and the wherewithal to run that program
using a modified version of the Library.
The precise terms and conditions for copying, distribution and
modification follow. Pay close attention to the difference between a "work
based on the library" and a "work that uses the library". The former
contains code derived from the library, whereas the latter must be
combined with the library in order to run.
GNU LESSER GENERAL PUBLIC LICENSE
TERMS AND CONDITIONS FOR COPYING,
DISTRIBUTION AND MODIFICATION
0. This License Agreement applies to any software library or other
program which contains a notice placed by the copyright holder or other
authorized party saying it may be distributed under the terms of this
Lesser General Public License (also called "this License").
Each licensee is addressed as "you".
A "library" means a collection of software functions and/or data prepared
so as to be conveniently linked with application programs (which use
some of those functions and data) to form executables.
The "Library", below, refers to any such software library or work which
has been distributed under these terms. A "work based on the Library"
means either the Library or any derivative work under copyright law: that
is to say, a work containing the Library or a portion of it, either verbatim
or with modifications and/or translated straightforwardly into another
language. (Hereinafter, translation is included without limitation in the
term "modification".)
"Source code" for a work means the preferred form of the work for
making modifications to it. For a library, complete source code means all
the source code for all modules it contains, plus any associated interface
definition files, plus the scripts used to control compilation and installation
of the library.
Activities other than copying, distribution and modification are not
covered by this License; they are outside its scope. The act of running a
program using the Library is not restricted, and output from such a
program is covered only if its contents constitute a work based on the
Library (independent of the use of the Library in a tool for writing it).
Whether that is true depends on what the Library does and what the
program that uses the Library does.
1. You may copy and distribute verbatim copies of the Library's complete
source code as you receive it, in any medium, provided that you
conspicuously and appropriately publish on each copy an appropriate
copyright notice and disclaimer of warranty; keep intact all the notices
that refer to this License and to the absence of any warranty; and
distribute a copy of this License along with the Library.
You may charge a fee for the physical act of transferring a copy, and you
may at your option offer warranty protection in exchange for a fee.
2. You may modify your copy or copies of the Library or any portion of it,
thus forming a work based on the Library, and copy and distribute such
modifications or work under the terms of Section 1 above, provided that
you also meet all of these conditions:
a) The modified work must itself be a software library.
b) You must cause the files modified to carry prominent notices stating
that you changed the files and the date of any change.
c) You must cause the whole of the work to be licensed at no charge to
all third parties under the terms of this License.
d) If a facility in the modified Library refers to a function or a table of data
to be supplied by an application program that uses the facility, other than
as an argument passed when the facility is invoked, then you must make
a good faith effort to ensure that, in the event an application does not
supply such function or table, the facility still operates, and performs
whatever part of its purpose remains meaningful.
(For example, a function in a library to compute square roots has a
purpose that is entirely well-defined independent of the application.
Therefore, Subsection 2d requires that any application-supplied function
or table used by this function must be optional: if the application does
not supply it, the square root function must still compute square roots.)
These requirements apply to the modified work as a whole. If identifiable
sections of that work are not derived from the Library, and can be
reasonably considered independent and separate works in themselves,
then this License, and its terms, do not apply to those sections when
you distribute them as separate works. But when you distribute the
same sections as part of a whole which is a work based on the Library,
the distribution of the whole must be on the terms of this License, whose
permissions for other licensees extend to the entire whole, and thus to
each and every part regardless of who wrote it.
Thus, it is not the intent of this section to claim rights or contest your
rights to work written entirely by you; rather, the intent is to exercise the
right to control the distribution of derivative or collective works based on
the Library.
In addition, mere aggregation of another work not based on the Library
with the Library (or with a work based on the Library) on a volume of a
storage or distribution medium does not bring the other work under the
scope of this License.
3. You may opt to apply the terms of the ordinary GNU General Public
License instead of this License to a given copy of the Library. To do this,
you must alter all the notices that refer to this License, so that they refer
to the ordinary GNU General Public License, version 2, instead of to this
License. (If a newer version than version 2 of the ordinary GNU General
Public License has appeared, then you can specify that version instead if
you wish.) Do not make any other change in these notices.
Once this change is made in a given copy, it is irreversible for that copy,
so the ordinary GNU General Public License applies to all subsequent
copies and derivative works made from that copy.
This option is useful when you wish to copy part of the code of the
Library into a program that is not a library.
4. You may copy and distribute the Library (or a portion or derivative of it,
under Section 2) in object code or executable form under the terms of
Sections 1 and 2 above provided that you accompany it with the
complete corresponding machine-readable source code, which must be
distributed under the terms of Sections 1 and 2 above on a medium
customarily used for software interchange.
If distribution of object code is made by offering access to copy from a
designated place, then offering equivalent access to copy the source
code from the same place satisfies the requirement to distribute the
source code, even though third parties are not compelled to copy the
source along with the object code.
5.
A program that contains no derivative of any portion of the Library, but is
designed to work with the Library by being compiled or linked with it, is called
a "work that uses the Library". Such a work, in isolation, is not a derivative
work of the Library, and therefore falls outside the scope of this License.
However, linking a "work that uses the Library" with the Library creates
an executable that is a derivative of the Library (because it contains
portions of the Library), rather than a "work that uses the library". The
executable is therefore covered by this License.
Section 6 states terms for distribution of such executables.
When a "work that uses the Library" uses material from a header file that
is part of the Library, the object code for the work may be a derivative
work of the Library even though the source code is not.
Whether this is true is especially significant if the work can be linked
without the Library, or if the work is itself a library. The threshold for this to
be true is not precisely defined by law.
If such an object file uses only numerical parameters, data structure
layouts and accessors, and small macros and small inline functions (ten
lines or less in length), then the use of the object file is unrestricted,
regardless of whether it is legally a derivative work. (Executables containing
this object code plus portions of the Library will still fall under Section 6.)
Otherwise, if the work is a derivative of the Library, you may distribute the
object code for the work under the terms of Section 6.
Any executables containing that work also fall under Section 6, whether
or not they are linked directly with the Library itself.
6. As an exception to the Sections above, you may also combine or link
a "work that uses the Library" with the Library to produce a work
containing portions of the Library, and distribute that work under terms of
your choice, provided that the terms permit modification of the work for
the customer's own use and reverse engineering for debugging such
modifications.
You must give prominent notice with each copy of the work that the
Library is used in it and that the Library and its use are covered by this
License. You must supply a copy of this License. If the work during
execution displays copyright notices, you must include the copyright
notice for the Library among them, as well as a reference directing the
user to the copy of this License. Also, you must do one of these things:
a) Accompany the work with the complete corresponding machine-
readable source code for the Library including whatever changes were
used in the work (which must be distributed under Sections 1 and 2
above); and, if the work is an executable linked with the Library, with the
complete machine-readable "work that uses the Library", as object code
and/or source code, so that the user can modify the Library and then
relink to produce a modified executable containing the modified Library.
(It is understood that the user who changes the contents of definitions
files in the Library will not necessarily be able to recompile the application
to use the modified definitions.)
b) Use a suitable shared library mechanism for linking with the Library. A
suitable mechanism is one that (1) uses at run time a copy of the library
already present on the user's computer system, rather than copying
library functions into the executable, and (2) will operate properly with a
modified version of the library, if the user installs one, as long as the
modified version is interface-compatible with the version that the work
was made with.
c) Accompany the work with a written offer, valid for at least three years,
to give the same user the materials specified in Subsection 6a, above, for
a charge no more than the cost of performing this distribution.
d) If distribution of the work is made by offering access to copy from a
designated place, offer equivalent access to copy the above specified
materials from the same place.
e) Verify that the user has already received a copy of these materials or
that you have already sent this user a copy.
For an executable, the required form of the "work that uses the Library"
must include any data and utility programs needed for reproducing the
executable from it. However, as a special exception, the materials to be
distributed need not include anything that is normally distributed (in either
source or binary form) with the major components (compiler, kernel, and
so on) of the operating system on which the executable runs, unless that
component itself accompanies the executable.
It may happen that this requirement contradicts the license restrictions of
other proprietary libraries that do not normally accompany the operating
system. Such a contradiction means you cannot use both them and the
Library together in an executable that you distribute.
7. You may place library facilities that are a work based on the Library
side-by-side in a single library together with other library facilities not
covered by this License, and distribute such a combined library, provided
that the separate distribution of the work based on the Library and of the
other library facilities is otherwise permitted, and provided that you do
these two things:
a) Accompany the combined library with a copy of the same work based
on the Library, uncombined with any other library facilities. This must be
distributed under the terms of the Sections above.
b) Give prominent notice with the combined library of the fact that part of
it is a work based on the Library, and explaining where to find the
accompanying uncombined form of the same work.
8. You may not copy, modify, sublicense, link with, or distribute the
Library except as expressly provided under this License. Any attempt
otherwise to copy, modify, sublicense, link with, or distribute the Library is
void, and will automatically terminate your rights under this License.
However, parties who have received copies, or rights, from you under
this License will not have their licenses terminated so long as such
parties remain in full compliance.
9. You are not required to accept this License, since you have not signed
it. However, nothing else grants you permission to modify or distribute
the Library or its derivative works. These actions are prohibited by law if
you do not accept this License. Therefore, by modifying or distributing
the Library (or any work based on the Library), you indicate your
acceptance of this License to do so, and all its terms and conditions for
copying, distributing or modifying the Library or works based on it.
10. Each time you redistribute the Library (or any work based on the
Library), the recipient automatically receives a license from the original
licensor to copy, distribute, link with or modify the Library subject to
these terms and conditions. You may not impose any further restrictions
on the recipients' exercise of the rights granted herein.
You are not responsible for enforcing compliance by third parties with this
License.
11. If, as a consequence of a court judgment or allegation of patent
infringement or for any other reason (not limited to patent issues),
conditions are imposed on you (whether by court order, agreement or
otherwise) that contradict the conditions of this License, they do not
excuse you from the conditions of this License. If you cannot distribute
so as to satisfy simultaneously your obligations under this License and
any other pertinent obligations, then as a consequence you may not
distribute the Library at all. For example, if a patent license would not
permit royalty-free redistribution of the Library by all those who receive
copies directly or indirectly through you, then the only way you could
satisfy both it and this License would be to refrain entirely from
distribution of the Library.
If any portion of this section is held invalid or unenforceable under any
particular circumstance, the balance of the section is intended to apply,
and the section as a whole is intended to apply in other circumstances.
It is not the purpose of this section to induce you to infringe any patents
or other property right claims or to contest validity of any such claims;
this section has the sole purpose of protecting the integrity of the free
software distribution system which is implemented by public license
practices. Many people have made generous contributions to the wide
range of software distributed through that system in reliance on
consistent application of that system; it is up to the author/donor to
decide if he or she is willing to distribute software through any other
system and a licensee cannot impose that choice.
This section is intended to make thoroughly clear what is believed to be
a consequence of the rest of this License.
12. If the distribution and/or use of the Library is restricted in certain
countries either by patents or by copyrighted interfaces, the original
copyright holder who places the Library under this License may add an
explicit geographical distribution limitation excluding those countries, so
that distribution is permitted only in or among countries not thus
excluded. In such case, this License incorporates the limitation as if
written in the body of this License.
13. The Free Software Foundation may publish revised and/or new
versions of the Lesser General Public License from time to time.
Such new versions will be similar in spirit to the present version, but may
differ in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Library
specifies a version number of this License which applies to it and "any
later version", you have the option of following the terms and conditions
either of that version or of any later version published by the Free
Software Foundation. If the Library does not specify a license version
number, you may choose any version ever published by the Free
Software Foundation.
14. If you wish to incorporate parts of the Library into other free
programs whose distribution conditions are incompatible with these,
write to the author to ask for permission. For software which is
copyrighted by the Free Software Foundation, write to the Free Software
Foundation; we sometimes make exceptions for this. Our decision will be
guided by the two goals of preserving the free status of all derivatives of
our free software and of promoting the sharing and reuse of software
generally.
NO WARRANTY
15. BECAUSE THE LIBRARY IS LICENSED FREE OF CHARGE, THERE
IS NO WARRANTY FOR THE LIBRARY, TO THE EXTENT PERMITTED
BY APPLICABLE LAW.
EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
HOLDERS AND/OR OTHER PARTIES PROVIDE THE LIBRARY "AS IS"
WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR
IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED
WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A
PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND
PERFORMANCE OF THE LIBRARY IS WITH YOU. SHOULD THE
LIBRARY PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL
NECESSARY SERVICING, REPAIR OR CORRECTION.
16. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR
AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY
OTHER PARTY WHO MAY MODIFY AND/OR REDISTRIBUTE THE
LIBRARY AS PERMITTED ABOVE, BE LIABLE TO YOU FOR
DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR
CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR
INABILITY TO USE THE LIBRARY (INCLUDING BUT NOT LIMITED TO
LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR
LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF
THE LIBRARY TO OPERATE WITH ANY OTHER SOFTWARE), EVEN IF
SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE
POSSIBILITY OF SUCH DAMAGES.
END OF TERMS AND CONDITIONS
How to Apply These Terms to Your New
Libraries
If you develop a new library, and you want it to be of the greatest
possible use to the public, we recommend making it free software that
everyone can redistribute and change. You can do so by permitting
redistribution under these terms (or, alternatively, under the terms of the
ordinary General Public License).
To apply these terms, attach the following notices to the library. It is
safest to attach them to the start of each source file to most effectively
convey the exclusion of warranty; and each file should have at least the
"copyright" line and a pointer to where the full notice is found.
<one line to give the library's name and a brief idea of what it does.>
Copyright (C) <year> <name of author>
This library is free software; you can redistribute it and/or modify it under
the terms of the GNU Lesser General Public License as published by the
Free Software Foundation; either version 2.1 of the License, or (at your
option) any later version.
This library is distributed in the hope that it will be useful, but WITHOUT
ANY WARRANTY; without even the implied warranty of
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See
the GNU
Lesser General Public License for more details.
You should have received a copy of the GNU Lesser General Public
License along with this library; if not, write to the Free Software
Foundation, Inc., 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301
USA
Also add information on how to contact you by electronic and paper
mail.
You should also get your employer (if you work as a programmer) or your
school, if any, to sign a "copyright disclaimer" for the library, if necessary.
Here is a sample; alter the names:
U-Boot is Free Software. It is copyrighted by Wolfgang Denk and many
others who contributed code (see the actual source code for details).
You can redistribute U-Boot and/or modify it under the terms of version 2
of the GNU General Public License as published by the Free Software
Foundation. Most of it can also be distributed, at your option, under any
later version of the GNU General Public License -- see individual files for
exceptions.
NOTE! This license does *not* cover the so-called "standalone"
applications that use U-Boot services by means of the jump table
provided by U-Boot exactly for this purpose - this is merely considered
normal use of U-Boot, and does *not* fall under the heading of "derived
work".
The header files "include/image.h" and "include/asm-*/u-boot.h" define
interfaces to U-Boot. Including these (unmodified) header files in another
file is considered normal use of U-Boot, and does *not* fall under the
heading of "derived work".
Also note that the GPL below is copyrighted by the Free Software
Foundation, but the instance of code that it refers to (the U-Boot source
code) is copyrighted by me and others who actually wrote it.
-- Wolfgang Denk
GNU GENERAL PUBLIC LICENSE
Version 3, 29 June 2007
Copyright (C) 2007 Free Software Foundation, Inc. <http://fsf.org/>
Everyone is permitted to copy and distribute verbatim copies of this
license document, but changing it is not allowed.
Preamble
The GNU General Public License is a free, copyleft license for software
and other kinds of works.
The licenses for most software and other practical works are designed to
take away your freedom to share and change the works. By contrast, the
GNU General Public License is intended to guarantee your freedom to
share and change all versions of a program--to make sure it remains free
software for all its users. We, the Free Software Foundation, use the
GNU General Public License for most of our software; it applies also to
any other work released this way by its authors. You can apply it to your
programs, too.
When we speak of free software, we are referring to freedom, not price.
Our General Public Licenses are designed to make sure that you have
the freedom to distribute copies of free software (and charge for them if
you wish), that you receive source code or can get it if you want it, that
you can change the software or use pieces of it in new free programs,
and that you know you can do these things.
To protect your rights, we need to prevent others from denying you these
rights or asking you to surrender the rights. Therefore, you have certain
responsibilities if you distribute copies of the software, or if you modify it:
responsibilities to respect the freedom of others.
For example, if you distribute copies of such a program, whether gratis
or for a fee, you must pass on to the recipients the same freedoms that
you received. You must make sure that they, too, receive or can get the
source code. And you must show them these terms so they know their
rights.
Developers that use the GNU GPL protect your rights with two steps: (1)
assert copyright on the software, and (2) offer you this License giving you
legal permission to copy, distribute and/or modify it.
For the developers' and authors' protection, the GPL clearly explains that
there is no warranty for this free software. For both users' and authors'
sake, the GPL requires that modified versions be marked as changed, so
that their problems will not be attributed erroneously to authors of
previous versions.
Some devices are designed to deny users access to install or run
modified versions of the software inside them, although the manufacturer
can do so. This is fundamentally incompatible with the aim of protecting
users' freedom to change the software. The systematic pattern of such
abuse occurs in the area of products for individuals to use, which is
precisely where it is most unacceptable. Therefore, we have designed
this version of the GPL to prohibit the practice for those products. If such
problems arise substantially in other domains, we stand ready to extend
this provision to those domains in future versions of the GPL, as needed
to protect the freedom of users.
Finally, every program is threatened constantly by software patents.
States should not allow patents to restrict development and use of
software on general-purpose computers, but in those that do, we wish
to avoid the special danger that patents applied to a free program could
make it effectively proprietary. To prevent this, the GPL assures that
patents cannot be used to render the program non-free.
The precise terms and conditions for copying, distribution and
modification follow.
TERMS AND CONDITIONS
0. Definitions.
"This License" refers to version 3 of the GNU General Public License.
"Copyright" also means copyright-like laws that apply to other kinds of
works, such as semiconductor masks.
"The Program" refers to any copyrightable work licensed under this
License. Each licensee is addressed as "you". "Licensees" and
"recipients" may be individuals or organizations.
To "modify" a work means to copy from or adapt all or part of the work in
a fashion requiring copyright permission, other than the making of an
exact copy. The resulting work is called a "modified version" of the earlier
work or a work "based on" the earlier work.
A "covered work" means either the unmodified Program or a work based
on the Program.
To "propagate" a work means to do anything with it that, without
permission, would make you directly or secondarily liable for infringement
under applicable copyright law, except executing it on a computer or
modifying a private copy. Propagation includes copying, distribution (with
or without modification), making available to the public, and in some
countries other activities as well.
To "convey" a work means any kind of propagation that enables other
parties to make or receive copies. Mere interaction with a user through a
computer network, with no transfer of a copy, is not conveying.
An interactive user interface displays "Appropriate Legal Notices" to the
extent that it includes a convenient and prominently visible feature that (1)
displays an appropriate copyright notice, and (2) tells the user that there
is no warranty for the work (except to the extent that warranties are
provided), that licensees may convey the work under this License, and
how to view a copy of this License. If the interface presents a list of user
commands or options, such as a menu, a prominent item in the list
meets this criterion.
1. Source Code.
The "source code" for a work means the preferred form of the work for
making modifications to it. "Object code" means any non-source form of
a work.
A "Standard Interface" means an interface that either is an official
standard defined by a recognized standards body, or, in the case of
interfaces specified for a particular programming language, one that is
widely used among developers working in that language.
The "System Libraries" of an executable work include anything, other
than the work as a whole, that (a) is included in the normal form of
packaging a Major Component, but which is not part of that Major
Component, and (b) serves only to enable use of the work with that
Major Component, or to implement a Standard Interface for which an
implementation is available to the public in source code form. A "Major
Component", in this context, means a major essential component
(kernel, window system, and so on) of the specific operating system (if
any) on which the executable work runs, or a compiler used to produce
the work, or an object code interpreter used to run it.
The "Corresponding Source" for a work in object code form means all
the source code needed to generate, install, and (for an executable work)
run the object code and to modify the work, including scripts to control
those activities. However, it does not include the work's System
Libraries, or general-purpose tools or generally available free programs
which are used unmodified in performing those activities but which are
not part of the work. For example, Corresponding Source includes
interface definition files associated with source files for the work, and the
source code for shared libraries and dynamically linked subprograms that
the work is specifically designed to require, such as by intimate data
communication or control flow between those subprograms and other
parts of the work.
The Corresponding Source need not include anything that users can
regenerate automatically from other parts of the Corresponding Source.
The Corresponding Source for a work in source code form is that same
work.
2. Basic Permissions.
All rights granted under this License are granted for the term of copyright
on the Program, and are irrevocable provided the stated conditions are
met. This License explicitly affirms your unlimited permission to run the
unmodified Program. The output from running a covered work is covered
by this License only if the output, given its content, constitutes a covered
work. This License acknowledges your rights of fair use or other
equivalent, as provided by copyright law.
You may make, run and propagate covered works that you do not
convey, without conditions so long as your license otherwise remains in
force. You may convey covered works to others for the sole purpose of
having them make modifications exclusively for you, or provide you with
facilities for running those works, provided that you comply with the
terms of this License in conveying all material for which you do not
control copyright. Those thus making or running the covered works for
you must do so exclusively on your behalf, under your direction and
control, on terms that prohibit them from making any copies of your
copyrighted material outside their relationship with you.
Conveying under any other circumstances is permitted solely under the
conditions stated below. Sublicensing is not allowed; section 10 makes it
unnecessary.
3. Protecting Users' Legal Rights From Anti-Circumvention Law.
No covered work shall be deemed part of an effective technological
measure under any applicable law fulfilling obligations under article 11 of
the WIPO copyright treaty adopted on 20 December 1996, or similar
laws prohibiting or restricting circumvention of such measures.
When you convey a covered work, you waive any legal power to forbid
circumvention of technological measures to the extent such
circumvention is effected by exercising rights under this License with
respect to the covered work, and you disclaim any intention to limit
operation or modification of the work as a means of enforcing, against
the work's users, your or third parties' legal rights to forbid circumvention
of technological measures.
4. Conveying Verbatim Copies.
You may convey verbatim copies of the Program's source code as you
receive it, in any medium, provided that you conspicuously and
appropriately publish on each copy an appropriate copyright notice;
keep intact all notices stating that this License and any non-permissive
terms added in accord with section 7 apply to the code; keep intact all
notices of the absence of any warranty; and give all recipients a copy of
this License along with the Program.
You may charge any price or no price for each copy that you convey, and
you may offer support or warranty protection for a fee.
5. Conveying Modified Source Versions.
You may convey a work based on the Program, or the modifications to
produce it from the Program, in the form of source code under the terms
of section 4, provided that you also meet all of these conditions:
a) The work must carry prominent notices stating that you modified it,
and giving a relevant date.
b) The work must carry prominent notices stating that it is released under
this License and any conditions added under section 7. This requirement
modifies the requirement in section 4 to "keep intact all notices".
c) You must license the entire work, as a whole, under this License to
anyone who comes into possession of a copy. This License will therefore
apply, along with any applicable section 7 additional terms, to the whole
of the work, and all its parts, regardless of how they are packaged. This
License gives no permission to license the work in any other way, but it
does not invalidate such permission if you have separately received it.
d) If the work has interactive user interfaces, each must display
Appropriate Legal Notices; however, if the Program has interactive
interfaces that do not display Appropriate Legal Notices, your work need
not make them do so.
A compilation of a covered work with other separate and independent
works, which are not by their nature extensions of the covered work, and
which are not combined with it such as to form a larger program, in or on
a volume of a storage or distribution medium, is called an "aggregate" if
the compilation and its resulting copyright are not used to limit the
access or legal rights of the compilation's users beyond what the
individual works permit. Inclusion of a covered work in an aggregate
does not cause this License to apply to the other parts of the aggregate.
6. Conveying Non-Source Forms.
You may convey a covered work in object code form under the terms of
sections 4 and 5, provided that you also convey the machine-readable
Corresponding Source under the terms of this License, in one of these
ways:
a) Convey the object code in, or embodied in, a physical product
(including a physical distribution medium), accompanied by the
Corresponding Source fixed on a durable physical medium customarily
used for software interchange.
b) Convey the object code in, or embodied in, a physical product
(including a physical distribution medium), accompanied by a written
offer, valid for at least three years and valid for as long as you offer spare
parts or customer support for that product model, to give anyone who
possesses the object code either (1) a copy of the Corresponding
Source for all the software in the product that is covered by this License,
on a durable physical medium customarily used for software interchange,
for a price no more than your reasonable cost of physically performing
this conveying of source, or (2) access to copy the Corresponding
Source from a network server at no charge.
c) Convey individual copies of the object code with a copy of the written
offer to provide the Corresponding Source. This alternative is allowed
only occasionally and noncommercially, and only if you received the
object code with such an offer, in accord with subsection 6b.
d) Convey the object code by offering access from a designated place
(gratis or for a charge), and offer equivalent access to the Corresponding
Source in the same way through the same place at no further charge.
You need not require recipients to copy the Corresponding Source along
with the object code. If the place to copy the object code is a network
server, the Corresponding Source may be on a different server (operated
by you or a third party) that supports equivalent copying facilities,
provided you maintain clear directions next to the object code saying
where to find the Corresponding Source. Regardless of what server
hosts the Corresponding Source, you remain obligated to ensure that it
is available for as long as needed to satisfy these requirements.
e) Convey the object code using peer-to-peer transmission, provided you
inform other peers where the object code and Corresponding Source of
the work are being offered to the general public at no charge under
subsection 6d.
A separable portion of the object code, whose source code is excluded
from the Corresponding Source as a System Library, need not be
included in conveying the object code work.
A "User Product" is either (1) a "consumer product", which means any
tangible personal property which is normally used for personal, family, or
household purposes, or (2) anything designed or sold for incorporation
into a dwelling. In determining whether a product is a consumer product,
doubtful cases shall be resolved in favor of coverage. For a particular
product received by a particular user, "normally used" refers to a typical
or common use of that class of product, regardless of the status of the
particular user or of the way in which the particular user actually uses, or
expects or is expected to use, the product. A product is a consumer
product regardless of whether the product has substantial commercial,
industrial or non-consumer uses, unless such uses represent the only
significant mode of use of the product.
"Installation Information" for a User Product means any methods,
procedures, authorization keys, or other information required to install
and execute modified versions of a covered work in that User Product
from a modified version of its Corresponding Source. The information
must suffice to ensure that the continued functioning of the modified
object code is in no case prevented or interfered with solely because
modification has been made.
If you convey an object code work under this section in, or with, or
specifically for use in, a User Product, and the conveying occurs as part
of a transaction in which the right of possession and use of the User
Product is transferred to the recipient in perpetuity or for a fixed term
(regardless of how the transaction is characterized), the Corresponding
Source conveyed under this section must be accompanied by the
Installation Information. But this requirement does not apply if neither you
nor any third party retains the ability to install modified object code on the
User Product (for example, the work has been installed in ROM).
The requirement to provide Installation Information does not include a
requirement to continue to provide support service, warranty, or updates
for a work that has been modified or installed by the recipient, or for the
User Product in which it has been modified or installed. Access to a
network may be denied when the modification itself materially and
adversely affects the operation of the network or violates the rules and
protocols for communication across the network.
Corresponding Source conveyed, and Installation Information provided,
in accord with this section must be in a format that is publicly
documented (and with an implementation available to the public in
source code form), and must require no special password or key for
unpacking, reading or copying.
7. Additional Terms.
"Additional permissions" are terms that supplement the terms of this
License by making exceptions from one or more of its conditions.
Additional permissions that are applicable to the entire Program shall be
treated as though they were included in this License, to the extent that
they are valid under applicable law. If additional permissions apply only to
part of the Program, that part may be used separately under those
permissions, but the entire Program remains governed by this License
without regard to the additional permissions.
When you convey a copy of a covered work, you may at your option
remove any additional permissions from that copy, or from any part of it.
(Additional permissions may be written to require their own removal in
certain cases when you modify the work.) You may place additional
permissions on material, added by you to a covered work, for which you
have or can give appropriate copyright permission.
Notwithstanding any other provision of this License, for material you add
to a covered work, you may (if authorized by the copyright holders of that
material) supplement the terms of this License with terms:
a) Disclaiming warranty or limiting liability differently from the terms of
sections 15 and 16 of this License; or
b) Requiring preservation of specified reasonable legal notices or author
attributions in that material or in the Appropriate Legal Notices displayed
by works containing it; or
c) Prohibiting misrepresentation of the origin of that material, or requiring
that modified versions of such material be marked in reasonable ways as
different from the original version; or
d) Limiting the use for publicity purposes of names of licensors or authors
of the material; or
e) Declining to grant rights under trademark law for use of some trade
names, trademarks, or service marks; or
f) Requiring indemnification of licensors and authors of that material by
anyone who conveys the material (or modified versions of it) with
contractual assumptions of liability to the recipient, for any liability that
these contractual assumptions directly impose on those licensors and
authors.
All other non-permissive additional terms are considered "further
restrictions" within the meaning of section 10. If the Program as you
received it, or any part of it, contains a notice stating that it is governed
by this License along with a term that is a further restriction, you may
remove that term. If a license document contains a further restriction but
permits relicensing or conveying under this License, you may add to a
covered work material governed by the terms of that license document,
provided that the further restriction does not survive such relicensing or
conveying.
If you add terms to a covered work in accord with this section, you must
place, in the relevant source files, a statement of the additional terms that
apply to those files, or a notice indicating where to find the applicable
terms.
Additional terms, permissive or non-permissive, may be stated in the
form of a separately written license, or stated as exceptions; the above
requirements apply either way.
8. Termination.
You may not propagate or modify a covered work except as expressly
provided under this License. Any attempt otherwise to propagate or
modify it is void, and will automatically terminate your rights under this
License (including any patent licenses granted under the third paragraph
of section 11).
However, if you cease all violation of this License, then your license from
a particular copyright holder is reinstated (a) provisionally, unless and until
the copyright holder explicitly and finally terminates your license, and (b)
permanently, if the copyright holder fails to notify you of the violation by
some reasonable means prior to 60 days after the cessation.
Moreover, your license from a particular copyright holder is reinstated
permanently if the copyright holder notifies you of the violation by some
reasonable means, this is the first time you have received notice of
violation of this License (for any work) from that copyright holder, and you
cure the violation prior to 30 days after your receipt of the notice.
Termination of your rights under this section does not terminate the
licenses of parties who have received copies or rights from you under
this License. If your rights have been terminated and not permanently
reinstated, you do not qualify to receive new licenses for the same
material under section 10.
9. Acceptance Not Required for Having Copies.
You are not required to accept this License in order to receive or run a
copy of the Program. Ancillary propagation of a covered work occurring
solely as a consequence of using peer-to-peer transmission to receive a
copy likewise does not require acceptance. However, nothing other than
this License grants you permission to propagate or modify any covered
work. These actions infringe copyright if you do not accept this License.
Therefore, by modifying or propagating a covered work, you indicate
your acceptance of this License to do so.
10. Automatic Licensing of Downstream Recipients.
Each time you convey a covered work, the recipient automatically
receives a license from the original licensors, to run, modify and
propagate that work, subject to this License. You are not responsible for
enforcing compliance by third parties with this License.
An "entity transaction" is a transaction transferring control of an
organization, or substantially all assets of one, or subdividing an
organization, or merging organizations. If propagation of a covered work
results from an entity transaction, each party to that transaction who
receives a copy of the work also receives whatever licenses to the work
the party's predecessor in interest had or could give under the previous
paragraph, plus a right to possession of the Corresponding Source of
the work from the predecessor in interest, if the predecessor has it or
can get it with reasonable efforts.
You may not impose any further restrictions on the exercise of the rights
granted or affirmed under this License. For example, you may not
impose a license fee, royalty, or other charge for exercise of rights
granted under this License, and you may not initiate litigation (including a
cross-claim or counterclaim in a lawsuit) alleging that any patent claim is
infringed by making, using, selling, offering for sale, or importing the
Program or any portion of it.
11. Patents.
A "contributor" is a copyright holder who authorizes use under this
License of the Program or a work on which the Program is based. The
work thus licensed is called the contributor's "contributor version".
A contributor's "essential patent claims" are all patent claims owned or
controlled by the contributor, whether already acquired or hereafter
acquired, that would be infringed by some manner, permitted by this
License, of making, using, or selling its contributor version, but do not
include claims that would be infringed only as a consequence of further
modification of the contributor version. For purposes of this definition,
"control" includes the right to grant patent sublicenses in a manner
consistent with the requirements of this License.
Each contributor grants you a non-exclusive, worldwide, royalty-free
patent license under the contributor's essential patent claims, to make,
use, sell, offer for sale, import and otherwise run, modify and propagate
the contents of its contributor version.
In the following three paragraphs, a "patent license" is any express
agreement or commitment, however denominated, not to enforce a
patent (such as an express permission to practice a patent or covenant
not to sue for patent infringement). To "grant" such a patent license to a
party means to make such an agreement or commitment not to enforce
a patent against the party.
If you convey a covered work, knowingly relying on a patent license, and
the Corresponding Source of the work is not available for anyone to
copy, free of charge and under the terms of this License, through a
publicly available network server or other readily accessible means, then
you must either (1) cause the Corresponding Source to be so available,
or (2) arrange to deprive yourself of the benefit of the patent license for
this particular work, or (3) arrange, in a manner consistent with the
requirements of this License, to extend the patent license to downstream
recipients. "Knowingly relying" means you have actual knowledge that,
but for the patent license, your conveying the covered work in a country,
or your recipient's use of the covered work in a country, would infringe
one or more identifiable patents in that country that you have reason to
believe are valid.
If, pursuant to or in connection with a single transaction or arrangement,
you convey, or propagate by procuring conveyance of, a covered work,
and grant a patent license to some of the parties receiving the covered
work authorizing them to use, propagate, modify or convey a specific
copy of the covered work, then the patent license you grant is
automatically extended to all recipients of the covered work and works
based on it.
A patent license is "discriminatory" if it does not include within the scope
of its coverage, prohibits the exercise of, or is conditioned on the
non-exercise of one or more of the rights that are specifically granted
under this License. You may not convey a covered work if you are a party
to an arrangement with a third party that is in the business of distributing
software, under which you make payment to the third party based on the
extent of your activity of conveying the work, and under which the third
party grants, to any of the parties who would receive the covered work
from you, a discriminatory patent license (a) in connection with copies of
the covered work conveyed by you (or copies made from those copies),
or (b) primarily for and in connection with specific products or
compilations that contain the covered work, unless you entered into that
arrangement, or that patent license was granted, prior to 28 March
2007.
Nothing in this License shall be construed as excluding or limiting any
implied license or other defenses to infringement that may otherwise be
available to you under applicable patent law.
12. No Surrender of Others' Freedom.
If conditions are imposed on you (whether by court order, agreement or
otherwise) that contradict the conditions of this License, they do not
excuse you from the conditions of this License. If you cannot convey a
covered work so as to satisfy simultaneously your obligations under this
License and any other pertinent obligations, then as a consequence you
may not convey it at all. For example, if you agree to terms that obligate
you to collect a royalty for further conveying from those to whom you
convey the Program, the only way you could satisfy both those terms
and this License would be to refrain entirely from conveying the Program.
13. Use with the GNU Affero General Public License.
Notwithstanding any other provision of this License, you have permission
to link or combine any covered work with a work licensed under version
3 of the GNU Affero General Public License into a single combined work,
and to convey the resulting work. The terms of this License will continue
to apply to the part which is the covered work, but the special
requirements of the GNU Affero General Public License, section 13,
concerning interaction through a network will apply to the combination
as such.
14. Revised Versions of this License.
The Free Software Foundation may publish revised and/or new versions
of the GNU General Public License from time to time. Such new versions
will be similar in spirit to the present version, but may differ in detail to
address new problems or concerns.
Each version is given a distinguishing version number. If the Program
specifies that a certain numbered version of the GNU General Public
License "or any later version" applies to it, you have the option of
following the terms and conditions either of that numbered version or of
any later version published by the Free Software Foundation. If the
Program does not specify a version number of the GNU General Public
License, you may choose any version ever published by the Free
Software Foundation.
If the Program specifies that a proxy can decide which future versions of
the GNU General Public License can be used, that proxy's public
statement of acceptance of a version permanently authorizes you to
choose that version for the Program.
Later license versions may give you additional or different permissions.
However, no additional obligations are imposed on any author or
copyright holder as a result of your choosing to follow a later version.
15. Disclaimer of Warranty.
THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT
PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE
STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER
PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY OF
ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT
LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND
FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO
THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU.
SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE
COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
16. Limitation of Liability.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED
TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER
PARTY WHO MODIFIES AND/OR CONVEYS THE PROGRAM AS
PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING
ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL
DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE
PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF DATA OR
DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY
YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO
OPERATE WITH ANY OTHER PROGRAMS), EVEN IF SUCH HOLDER
OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
SUCH DAMAGES.
17. Interpretation of Sections 15 and 16.
If the disclaimer of warranty and limitation of liability provided above
cannot be given local legal effect according to their terms, reviewing
courts shall apply local law that most closely approximates an absolute
waiver of all civil liability in connection with the Program, unless a
warranty or assumption of liability accompanies a copy of the Program in
return for a fee.
END OF TERMS AND CONDITIONS
How to Apply These Terms to Your New Programs
If you develop a new program, and you want it to be of the greatest
possible use to the public, the best way to achieve this is to make it free
software which everyone can redistribute and change under these terms.
To do so, attach the following notices to the program. It is safest to
attach them to the start of each source file to most effectively state the
exclusion of warranty; and each file should have at least the "copyright"
line and a pointer to where the full notice is found.
<one line to give the program's name and a brief idea of what it does.>
Copyright (C) <year> <name of author>
This program is free software: you can redistribute it and/or modify it
under the terms of the GNU General Public License as published by the
Free Software Foundation, either version 3 of the License, or (at your
option) any later version.
This program is distributed in the hope that it will be useful, but
WITHOUT ANY WARRANTY; without even the implied warranty of
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See
the GNU General Public License for more details.
You should have received a copy of the GNU General Public License
along with this program. If not, see <http://www.gnu.org/licenses/>.
Also add information on how to contact you by electronic and paper mail.
If the program does terminal interaction, make it output a short notice like
this when it starts in an interactive mode:
<program> Copyright (C) <year> <name of author>
This program comes with ABSOLUTELY NO WARRANTY; for details
type `show w'.
This is free software, and you are welcome to redistribute it under certain
conditions; type `show c' for details.
The hypothetical commands `show w' and `show c' should show the
appropriate parts of the General Public License. Of course, your
program's commands might be different; for a GUI interface, you would
use an "about box".
You should also get your employer (if you work as a programmer) or
school, if any, to sign a "copyright disclaimer" for the program, if
necessary.
For more information on this, and how to apply and follow the GNU GPL,
see <http://www.gnu.org/licenses/>.
The GNU General Public License does not permit incorporating your
program into proprietary programs. If your program is a subroutine
library, you may consider it more useful to permit linking proprietary
applications with the library. If this is what you want to do, use the GNU
Lesser General Public License instead of this License. But first, please
read <http://www.gnu.org/philosophy/why-not-lgpl.html>.
Copyright (C) 1991, 1999 Free Software Foundation, Inc.
51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA
Everyone is permitted to copy and distribute verbatim copies of this
license document, but changing it is not allowed.
[This is the first released version of the Lesser GPL. It also counts as the
successor of the GNU Library Public License, version 2, hence the
version number 2.1.]
NOTE! This copyright does *not* cover user programs that use kernel
services by normal system calls - this is merely considered normal use of
the kernel, and does *not* fall under the heading of "derived work".
Also note that the GPL below is copyrighted by the Free Software
Foundation, but the instance of code that it refers to (the Linux kernel) is
copyrighted by me and others who actually wrote it.
Also note that the only valid version of the GPL as far as the kernel is
concerned is _this_ particular version of the license (ie v2, not v2.2 or
v3.x or whatever), unless explicitly otherwise stated.
Linus Torvalds
PCRE LICENCE
PCRE is a library of functions to support regular expressions whose
syntax and semantics are as close as possible to those of the Perl 5
language.
Release 8 of PCRE is distributed under the terms of the "BSD" licence,
as specified below. The documentation for PCRE, supplied in the "doc"
directory, is distributed under the same terms as the software itself.
The basic library functions are written in C and are freestanding. Also
included in the distribution is a set of C++ wrapper functions, and a
just-in-time compiler that can be used to optimize pattern matching. These
are both optional features that can be omitted when the library is built.
THE BASIC LIBRARY FUNCTIONS
Written by: Philip Hazel
Email local part: ph10
Email domain: cam.ac.uk
University of Cambridge Computing Service, Cambridge, England.
Copyright (c) 1997-2012 University of Cambridge
All rights reserved.
PCRE JUST-IN-TIME COMPILATION SUPPORT
Written by: Zoltan Herczeg
Email local part: hzmester
Emain domain: freemail.hu
Copyright(c) 2010-2012 Zoltan Herczeg
All rights reserved.
STACK-LESS JUST-IN-TIME COMPILER
Written by: Zoltan Herczeg
Email local part: hzmester
Emain domain: freemail.hu
Copyright(c) 2009-2012 Zoltan Herczeg
All rights reserved.
THE C++ WRAPPER FUNCTIONS
Contributed by: Google Inc.
Copyright (c) 2007-2012, Google Inc.
All rights reserved.
THE "BSD" LICENCE
Redistribution and use in source and binary forms, with or without
modification, are permitted provided that the following conditions are
met:
* Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
* Redistributions in binary form must reproduce the above copyright
notice, this list of conditions and the following disclaimer in the
documentation and/or other materials provided with the distribution.
* Neither the name of the University of Cambridge nor the name of
Google Inc. nor the names of their contributors may be used to endorse
or promote products derived from this software without specific prior
written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND
CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED
WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED
WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A
PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE
COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY
DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO,
PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF
USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE
OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS
SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH
DAMAGE.
End
Copyrights:
All of the code can be freely used and redistributed. The individual source
files each have their own copyright and permission notice.
Pppd, pppstats and pppdump are under BSD-style notices.
Some of the pppd plugins are GPL'd. Chat is public domain.
Copyright (c) 2004, Jan Kneschke, incremental
All rights reserved.
Redistribution and use in source and binary forms, with or without
modification, are permitted provided that the following conditions are
met:
- Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
- Redistributions in binary form must reproduce the above copyright
notice, this list of conditions and the following disclaimer in the
documentation and/or other materials provided with the distribution.
- Neither the name of the 'incremental' nor the names of its contributors
may be used to endorse or promote products derived from this
software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND
CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED
WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED
WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A
PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE
COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY
DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO,
PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF
USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE
OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS
SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH
DAMAGE.
Copyright (c) 2005-2009, Thomas BERNARD
All rights reserved.
Redistribution and use in source and binary forms, with or without
modification, are permitted provided that the following conditions are
met:
* Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
* Redistributions in binary form must reproduce the above copyright
notice, this list of conditions and the following disclaimer in the
documentation and/or other materials provided with the distribution.
* The name of the author may not be used to endorse or promote
products derived from this software without specific prior written
permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND
CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED
WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED
WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A
PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE
COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY
DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO,
PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF
USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE
OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS
SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH
DAMAGE.
LICENSE ISSUES
The OpenSSL toolkit stays under a dual license, i.e. both the conditions
of the OpenSSL License and the original SSLeay license apply to the
toolkit.
See below for the actual license texts. Actually both licenses are
BSD-style Open Source licenses. In case of any license issues related to
OpenSSL please contact openssl-core@openssl.org.
OpenSSL License
Copyright (c) 1998-2005 The OpenSSL Project. All rights reserved.
Redistribution and use in source and binary forms, with or without
modification, are permitted provided that the following conditions are
met:
1. Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright
notice, this list of conditions and the following disclaimer in the
documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software
must display the following acknowledgment:
"This product includes software developed by the OpenSSL Project for
use in the OpenSSL Toolkit. (http://www.openssl.org/)"
4. The names "OpenSSL Toolkit" and "OpenSSL Project" must not be
used to endorse or promote products derived from this software without
prior written permission. For written permission, please contact openssl-
core@openssl.org.
5. Products derived from this software may not be called "OpenSSL" nor
may "OpenSSL" appear in their names without prior written permission
of the OpenSSL Project.
6. Redistributions of any form whatsoever must retain the following
acknowledgment:
"This product includes software developed by the OpenSSL Project for
use in the OpenSSL Toolkit (http://www.openssl.org/)"
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT ``AS IS''
AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT
NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY
AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN
NO EVENT SHALL THE OpenSSL PROJECT OR ITS CONTRIBUTORS
BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL,
EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT
NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF
LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT
(INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY
OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE
POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young
(eay@cryptsoft.com). This product includes software written by Tim
Hudson (tjh@cryptsoft.com).
Original SSLeay License
Copyright (C) 1995-1998 Eric Young (eay@cryptsoft.com)
All rights reserved.
This package is an SSL implementation written by Eric Young (eay@
cryptsoft.com).
The implementation was written so as to conform with Netscapes SSL.
This library is free for commercial and non-commercial use as long as the
following conditions are aheared to. The following conditions apply to all
code found in this distribution, be it the RC4, RSA, lhash, DES, etc.,
code; not just the SSL code. The SSL documentation included with this
distribution is covered by the same copyright terms except that the
holder is Tim Hudson (tjh@cryptsoft.com).
Copyright remains Eric Young's, and as such any Copyright notices in
the code are not to be removed.
If this package is used in a product, Eric Young should be given
attribution as the author of the parts of the library used.
This can be in the form of a textual message at program startup or in
documentation (online or textual) provided with the package.
Redistribution and use in source and binary forms, with or without
modification, are permitted provided that the following conditions are
met:
1. Redistributions of source code must retain the copyright notice, this
list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright
notice, this list of conditions and the following disclaimer in the
documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software
must display the following acknowledgement:
"This product includes cryptographic software written by Eric Young
(eay@cryptsoft.com)"
The word 'cryptographic' can be left out if the rouines from the library
being used are not cryptographic related :-).
4. If you include any Windows specific code (or a derivative thereof) from
the apps directory (application code) you must include an
acknowledgement:
"This product includes software written by Tim Hudson (tjh@cryptsoft.
com)"
THIS SOFTWARE IS PROVIDED BY ERIC YOUNG ``AS IS'' AND ANY
EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED
TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS
FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT
SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE FOR ANY
DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO,
PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF
USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE
OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS
SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH
DAMAGE.
The licence and distribution terms for any publically available version or
derivative of this code cannot be changed. i.e. this code cannot simply
be copied and put under another distribution licence [including the GNU
Public Licence.]
Except where otherwise noted in the source code (e.g. the files hash.c,
list.c and the trio files, which are covered by a similar licence but with
different Copyright notices) all the files are:
Copyright (C) 1998-2003 Daniel Veillard. All Rights Reserved.
Permission is hereby granted, free of charge, to any person obtaining a
copy of this software and associated documentation files (the
"Software"), to deal in the Software without restriction, including without
limitation the rights to use, copy, modify, merge, publish, distribute,
sublicense, and/or sell copies of the Software, and to permit persons to
whom the Software is fur-nished to do so, subject to the following
conditions:
The above copyright notice and this permission notice shall be included
in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF
ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO
THE WARRANTIES OF MERCHANTABILITY, FIT-NESS FOR A
PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT
SHALL THE DANIEL VEILLARD BE LIABLE FOR ANY CLAIM,
DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF
CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN
CON-NECTION WITH THE SOFTWARE OR THE USE OR OTHER
DEALINGS IN THE SOFTWARE.
Except as contained in this notice, the name of Daniel Veillard shall not
be used in advertising or otherwise to promote the sale, use or other
deal-ings in this Software without prior written authorization from him.
Boost Software License - Version 1.0 - August 17th, 2003
Permission is hereby granted, free of charge, to any person or
organization obtaining a copy of the software and accompanying
documentation covered by this license (the "Software") to use,
reproduce, display, distribute, execute, and transmit the Software, and to
prepare derivative works of the Software, and to permit third-parties to
whom the Software is furnished to do so, all subject to the following:
The copyright notices in the Software and this entire statement, including
the above license grant, this restriction and the following disclaimer, must
be included in all copies of the Software, in whole or in part, and all
derivative works of the Software, unless such copies or derivative works
are solely in the form of machine-executable object code generated by a
source language processor.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF
ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO
THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A
PARTICULAR PURPOSE, TITLE AND NON-INFRINGEMENT. IN NO
EVENT SHALL THE COPYRIGHT HOLDERS OR ANYONE
DISTRIBUTING THE SOFTWARE BE LIABLE FOR ANY DAMAGES OR
OTHER LIABILITY, WHETHER IN CONTRACT, TORT OR OTHERWISE,
ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE
OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
The MIT License (MIT)
Copyright (c) <year> <copyright holders>
Permission is hereby granted, free of charge, to any person obtaining a
copy of this software and associated documentation files (the
"Software"), to deal in the Software without restriction, including without
limitation the rights to use, copy, modify, merge, publish, distribute,
sublicense, and/or sell copies of the Software, and to permit persons to
whom the Software is furnished to do so, subject to the following
conditions:
The above copyright notice and this permission notice shall be included
in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF
ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO
THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A
PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT
SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR
ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN
ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT
OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR
OTHER DEALINGS IN THE SOFTWARE.
The PHP License, version 3.01
Copyright (c) 1999 - 2006 The PHP Group. All rights reserved.
Redistribution and use in source and binary forms, with or without
modification, is permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright
notice, this list of conditions and the following disclaimer in the
documentation and/or other materials provided with the distribution.
3. The name "PHP" must not be used to endorse or promote products
derived from this software without prior written permission. For written
permission, please contact group@php.net.
4. Products derived from this software may not be called "PHP", nor may
"PHP" appear in their name, without prior written permission from
group@php.net. You may indicate that your software works in
conjunction with PHP by saying "Foo for PHP" instead of calling it "PHP
Foo" or "phpfoo"
5. The PHP Group may publish revised and/or new versions of the
license from time to time. Each version will be given a distinguishing
version number.
Once covered code has been published under a particular version of the
license, you may always continue to use it under the terms of that
version. You may also choose to use such covered code under the terms
of any subsequent version of the license published by the PHP Group.
No one other than the PHP Group has the right to modify the terms
applicable to covered code created under this License.
6. Redistributions of any form whatsoever must retain the following
acknowledgment:
"This product includes PHP software, freely available from
<http://www.php.net/software/>".
THIS SOFTWARE IS PROVIDED BY THE PHP DEVELOPMENT TEAM
``AS IS'' AND ANY EXPRESSED OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
ARE DISCLAIMED. IN NO EVENT SHALL THE PHP DEVELOPMENT
TEAM OR ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT,
INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF
SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR
PROFITS; OR BUSINESS INTERRUPTION)
HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER
IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING
NEGLIGENCE OR OTHERWISE)
ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF
ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
This software consists of voluntary contributions made by many
individuals on behalf of the PHP Group.
The PHP Group can be contacted via Email at group@php.net.
For more information on the PHP Group and the PHP project, please see
<http://www.php.net>.
PHP includes the Zend Engine, freely available at <http://www.zend.com>.
Copyright (c) 2004, Apple Computer, Inc. and The Mozilla Foundation.
All rights reserved.
Redistribution and use in source and binary forms, with or without
modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright
notice, this list of conditions and the following disclaimer in the
documentation and/or other materials provided with the distribution.
3. Neither the names of Apple Computer, Inc. ("Apple") or The Mozilla
Foundation ("Mozilla") nor the names of their contributors may be used to
endorse or promote products derived from this software without specific
prior written permission.
THIS SOFTWARE IS PROVIDED BY APPLE, MOZILLA AND THEIR
CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
DISCLAIMED. IN NO EVENT SHALL APPLE, MOZILLA OR THEIR
CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL,
SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING,
BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF
LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT
(INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT
OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE
POSSIBILITY OF SUCH DAMAGE.
Version: MPL 1.1/GPL 2.0/LGPL 2.1
The contents of this file are subject to the Mozilla Public License Version
1.1 (the "License"); you may not use this file except in compliance with
the License. You may obtain a copy of the License at
http://www.mozilla.org/MPL/
Software distributed under the License is distributed on an "AS IS" basis,
WITHOUT WARRANTY OF ANY KIND, either express or implied. See the
License for the specific language governing rights and limitations under
the License.
The Original Code is mozilla.org code.
The Initial Developer of the Original Code is Netscape Communications
Corporation.
Portions created by the Initial Developer are Copyright (C) 1998 the Initial
Developer. All Rights Reserved.
Contributor(s):
Alternatively, the contents of this file may be used under the terms of
either the GNU General Public License Version 2 or later (the "GPL"), or
the GNU Lesser General Public License Version 2.1 or later (the "LGPL"),
in which case the provisions of the GPL or the LGPL are applicable
instead of those above. If you wish to allow use of your version of this file
only under the terms of either the GPL or the LGPL, and not to allow
others to use your version of this file under the terms of the MPL, indicate
your decision by deleting the provisions above and replace them with the
notice and other provisions required by the GPL or the LGPL. If you do
not delete the provisions above, a recipient may use your version of this
file under the terms of any one of the MPL, the GPL or the LGPL.
TinyXML
TinyXML is a simple, small, C++ XML parser that can be easily integrated
into other programs.
What it does.
In brief, TinyXML parses an XML document, and builds from that a
Document Object Model (DOM) that can be read, modified, and saved.
XML stands for "eXtensible Markup Language." It allows you to create
your own document markups. Where HTML does a very good job of
marking documents for browsers, XML allows you to define any kind of
document markup, for example a document that describes a "to do" list
for an organizer application. XML is a very structured and convenient
format. All those random file formats created to store application data
can all be replaced with XML. One parser for everything. The best place
for the complete, correct, and quite frankly hard to read spec is at http://
www.w3.org/TR/2004/REC-xml-20040204/. An intro to XML (that I really
like) can be found at http://skew.org/xml/tutorial. There are different ways
to access and interact with XML data. TinyXML uses a Document Object
Model (DOM), meaning the XML data is parsed into a C++ objects that
can be browsed and manipulated, and then written to disk or another
output stream. You can also construct an XML document from scratch
with C++ objects and write this to disk or another output stream.
TinyXML is designed to be easy and fast to learn. It is two headers and
four cpp files. Simply add these to your project and off you go. There is
an example file - xmltest.cpp - to get you started. TinyXML is released
under the ZLib license, so you can use it in open source or commercial
code. The details of the license are at the top of every source file.
TinyXML attempts to be a flexible parser, but with truly correct and
compliant XML output. TinyXML should compile on any reasonably C++
compliant system. It does not rely on exceptions or RTTI. It can be
compiled with or without STL support. TinyXML fully supports the UTF-8
encoding, and the first 64k character entities.
What it doesn't do.
TinyXML doesn't parse or use DTDs (Document Type Definitions) or
XSLs (eXtensible Stylesheet Language.) There are other parsers out there
(check out www.sourceforge.org, search for XML) that are much more
fully featured. But they are also much bigger, take longer to set up in your
project, have a higher learning curve, and often have a more restrictive
license. If you are working with browsers or have more complete XML
needs, TinyXML is not the parser for you. The following DTD syntax will
not parse at this time in TinyXML: @verbatim ]> @endverbatim because
TinyXML sees this as a !DOCTYPE node with an illegally embedded
!ELEMENT node. This may be addressed in the future.
Tutorials.
For the impatient, here is a tutorial to get you going. A great way to get
started, but it is worth your time to read this (very short) manual
completely. - @subpage tutorial0
Code Status.
TinyXML is mature, tested code. It is very stable. If you find bugs, please
file a bug report on the sourceforge web site (www.sourceforge.net/
projects/tinyxml). We'll get them straightened out as soon as possible.
There are some areas of improvement; please check sourceforge if you
are interested in working on TinyXML.
Related Projects
TinyXML projects you may find useful! (Descriptions provided by the
projects.)
• TinyXPath (http://tinyxpath.sourceforge.net). TinyXPath is a small
footprint XPath syntax decoder, written in C++.
• TinyXML++ (http://code.google.com/p/ticpp/). TinyXML++ is a
completely new interface to TinyXML that uses MANY of the C++
strengths. Templates, exceptions, and much better error handling.
Features
Using STL
TinyXML can be compiled to use or not use STL. When using STL,
TinyXML uses the std::string class, and fully supports std::istream,
std::ostream, operator<<, and operator>>. Many API methods have
both 'const char*' and 'const std::string&' forms. When STL support is
compiled out, no STL files are included whatsoever. All the string classes
are implemented by TinyXML itself. API methods all use the 'const char*'
form for input. Use the compile time #define: TIXML_USE_STL to
compile one version or the other. This can be passed by the compiler, or
set as the first line of "tinyxml.h". Note: If compiling the test code in Linux,
setting the environment variable TINYXML_USE_STL=YES/NO will
control STL compilation. In the Windows project file, STL and non STL
targets are provided. In your project, It's probably easiest to add the line
"#define TIXML_USE_STL" as the first line of tinyxml.h.
UTF-8
TinyXML supports UTF-8 allowing to manipulate XML files in any
language. TinyXML also supports "legacy mode" - the encoding used
before UTF-8 support and probably best described as "extended ascii".
Normally, TinyXML will try to detect the correct encoding and use it.
However, by setting the value of TIXML_DEFAULT_ENCODING in the
header file, TinyXML can be forced to always use one encoding. TinyXML
will assume Legacy Mode until one of the following occurs:
1. If the non-standard but common "UTF-8 lead bytes" (0xef 0xbb 0xbf)
begin the file or data stream, TinyXML will read it as UTF-8.
2. If the declaration tag is read, and it has an encoding="UTF-8", then
TinyXML will read it as UTF-8.
3. If the declaration tag is read, and it has no encoding specified, then
TinyXML will read it as UTF-8.
4. If the declaration tag is read, and it has an encoding="something
else", then TinyXML will read it as Legacy Mode. In legacy mode,
TinyXML will work as it did before. It's not clear what that mode does
exactly, but old content should keep working.
5. Until one of the above criteria is met, TinyXML runs in Legacy Mode.
What happens if the encoding is incorrectly set or detected? TinyXML will
try to read and pass through text seen as improperly encoded. You may
get some strange results or mangled characters. You may want to force
TinyXML to the correct mode. You may force TinyXML to Legacy Mode
by using LoadFile( TIXML_ENCODING_LEGACY ) or LoadFile( filename,
TIXML_ENCODING_LEGACY ). You may force it to use legacy mode all
the time by setting TIXML_DEFAULT_ENCODING = TIXML_ENCODING_
LEGACY. Likewise, you may force it to TIXML_ENCODING_UTF8 with
the same technique. For English users, using English XML, UTF-8 is the
same as low-ASCII. You don't need to be aware of UTF-8 or change
your code in any way. You can think of UTF-8 as a "superset" of ASCII.
UTF-8 is not a double byte format - but it is a standard encoding of
Unicode! TinyXML does not use or directly support wchar, TCHAR, or
Microsoft's _UNICODE at this time. It is common to see the term
"Unicode" improperly refer to UTF-16, a wide byte encoding of unicode.
This is a source of confusion. For "high-ascii" languages - everything not
English, pretty much - TinyXML can handle all languages, at the same
time, as long as the XML is encoded in UTF-8. That can be a little tricky,
older programs and operating systems tend to use the "default" or
"traditional" code page. Many apps (and almost all modern ones) can
output UTF-8, but older or stubborn (or just broken) ones still output text
in the default code page. For example, Japanese systems traditionally
use SHIFT-JIS encoding. Text encoded as SHIFT-JIS can not be read by
TinyXML. A good text editor can import SHIFT-JIS and then save as
UTF-8. The Skew.org link does a great job covering the encoding issue.
The test file "utf8test.xml" is an XML containing English, Spanish,
Russian, and Simplified Chinese. (Hopefully they are translated correctly).
The file "utf8test.gif" is a screen capture of the XML file, rendered in IE.
Note that if you don't have the correct fonts (Simplified Chinese or
Russian) on your system, you won't see output that matches the GIF file
even if you can parse it correctly. Also note that (at least on my Windows
machine) console output is in a Western code page, so that Print() or
printf() cannot correctly display the file. This is not a bug in TinyXML - just
an OS issue. No data is lost or destroyed by TinyXML. The console just
doesn't render UTF-8.
Entities
TinyXML recognizes the pre-defined "character entities", meaning special
characters. Namely: @verbatim & & < < > > " " ' ' @endverbatim
These are recognized when the XML document is read, and translated to
there UTF-8 equivalents. For instance, text with the XML of: @verbatim
Far & Away @endverbatim will have the Value() of "Far & Away" when
queried from the TiXmlText object, and will be written back to the XML
stream/file as an ampersand. Older versions of TinyXML "preserved"
character entities, but the newer versions will translate them into
characters. Additionally, any character can be specified by its Unicode
code point: The syntax " " or " " are both to the non-breaking space
characher.
Printing
TinyXML can print output in several different ways that all have strengths
and limitations. - Print( FILE* ). Output to a std-C stream, which includes
all C files as well as stdout. - "Pretty prints", but you don't have control
over printing options. - The output is streamed directly to the FILE object,
so there is no memory overhead in the TinyXML code. - used by Print()
and SaveFile() - operator<<. Output to a c++ stream. - Integrates with
standart C++ iostreams. - Outputs in "network printing" mode without
line breaks. Good for network transmission and moving XML between
C++ objects, but hard for a human to read. - TiXmlPrinter. Output to a
std::string or memory buffer. - API is less concise - Future printing
options will be put here. - Printing may change slightly in future versions
as it is refined and expanded.
Streams
With TIXML_USE_STL on TinyXML supports C++ streams (operator
<<,>>) streams as well as C (FILE*) streams. There are some differences
that you may need to be aware of. C style output: - based on FILE* - the
Print() and SaveFile() methods Generates formatted output, with plenty of
white space, intended to be as human-readable as possible. They are
very fast, and tolerant of ill formed XML documents. For example, an
XML document that contains 2 root elements and 2 declarations, will still
print. C style input: - based on FILE* - the Parse() and LoadFile() methods
A fast, tolerant read. Use whenever you don't need the C++ streams.
C++ style output: - based on std::ostream - operator<< Generates
condensed output, intended for network transmission rather than
readability. Depending on your system's implementation of the ostream
class, these may be somewhat slower. (Or may not.) Not tolerant of ill
formed XML: a document should contain the correct one root element.
Additional root level elements will not be streamed out. C++ style input:
- based on std::istream - operator>> Reads XML from a stream, making
it useful for network transmission. The tricky part is knowing when the
XML document is complete, since there will almost certainly be other
data in the stream. TinyXML will assume the XML data is complete after
it reads the root element. Put another way, documents that are ill-
constructed with more than one root element will not read correctly. Also
note that operator>> is somewhat slower than Parse, due to both
implementation of the STL and limitations of TinyXML.
White space
The world simply does not agree on whether white space should be
kept, or condensed. For example, pretend the '_' is a space, and look at
"Hello____world". HTML, and at least some XML parsers, will interpret
this as "Hello_world". They condense white space. Some XML parsers
do not, and will leave it as "Hello____world". (Remember to keep
pretending the _ is a space.) Others suggest that __Hello___world__
should become Hello___world. It's an issue that hasn't been resolved to
my satisfaction. TinyXML supports the first 2 approaches. Call TiXmlBase
::SetCondenseWhiteSpace( bool ) to set the desired behavior. The
default is to condense white space. If you change the default, you should
call TiXmlBase::SetCondenseWhiteSpace( bool ) before making any calls
to Parse XML data, and I don't recommend changing it after it has been
set.
Handles
Where browsing an XML document in a robust way, it is important to
check for null returns from method calls. An error safe implementation
can generate a lot of code like: @verbatim TiXmlElement* root =
document.FirstChildElement( "Document" ); if ( root ) { TiXmlElement*
element = root->FirstChildElement( "Element" ); if ( element ) {
TiXmlElement* child = element->FirstChildElement( "Child" ); if ( child ) {
TiXmlElement* child2 = child->NextSiblingElement( "Child" ); if ( child2 ) {
// Finally do something useful. @endverbatim Handles have been
introduced to clean this up. Using the TiXmlHandle class, the previous
code reduces to: @verbatim TiXmlHandle docHandle( &document );
TiXmlElement* child2 = docHandle.FirstChild( "Document" ).FirstChild(
"Element" ).Child( "Child", 1 ).ToElement(); if ( child2 ) { // do something
useful @endverbatim Which is much easier to deal with. See
TiXmlHandle for more information.
Row and Column tracking
Being able to track nodes and attributes back to their origin location in
source files can be very important for some applications. Additionally,
knowing where parsing errors occured in the original source can be very
time saving. TinyXML can tracks the row and column origin of all nodes
and attributes in a text file. The TiXmlBase::Row() and
TiXmlBase::Column() methods return the origin of the node in the source
text. The correct tabs can be configured in TiXmlDocument::SetTabSize().
Using and Installing
To Compile and Run xmltest: A Linux Makefile and a Windows Visual
C++ .dsw file is provided. Simply compile and run. It will write the file
demotest.xml to your disk and generate output on the screen. It also
tests walking the DOM by printing out the number of nodes found using
different techniques. The Linux makefile is very generic and runs on many
systems - it is currently tested on mingw and MacOSX. You do not need
to run 'make depend'. The dependecies have been hard coded.
Windows project file for VC6
• tinyxml: tinyxml library, non-STL
• tinyxmlSTL: tinyxml library, STL
• tinyXmlTest: test app, non-STL
• tinyXmlTestSTL: test app, STL
Makefile
At the top of the makefile you can set: PROFILE, DEBUG, and
TINYXML_USE_STL. Details (such that they are) are in the makefile. In
the tinyxml directory, type "make clean" then "make". The executable file
'xmltest' will be created.
To Use in an Application:
Add tinyxml.cpp, tinyxml.h, tinyxmlerror.cpp, tinyxmlparser.cpp, tinystr.
cpp, and tinystr.h to your project or make file. That's it! It should compile
on any reasonably compliant C++ system. You do not need to enable
exceptions or RTTI for TinyXML.
How TinyXML works.
An example is probably the best way to go. Take: @verbatim Go to the
Toy store! Do bills @endverbatim Its not much of a To Do list, but it will
do. To read this file (say "demo.xml") you would create a document, and
parse it in: @verbatim TiXmlDocument doc( "demo.xml" ); doc.LoadFile();
@endverbatim And its ready to go. Now lets look at some lines and how
they relate to the DOM. @verbatim @endverbatim The first line is a
declaration, and gets turned into the TiXmlDeclaration class. It will be the
first child of the document node. This is the only directive/special tag
parsed by TinyXML. Generally directive tags are stored in TiXmlUnknown
so the commands wont be lost when it is saved back to disk. @verbatim
@endverbatim A comment. Will become a TiXmlComment object. @
verbatim @endverbatim The "ToDo" tag defines a TiXmlElement object.
This one does not have any attributes, but does contain 2 other
elements. @verbatim @endverbatim Creates another TiXmlElement
which is a child of the "ToDo" element. This element has 1 attribute, with
the name "priority" and the value "1". @verbatim Go to the @endverbatim
A TiXmlText. This is a leaf node and cannot contain other nodes. It is a
child of the "Item" TiXmlElement. @verbatim @endverbatim Another
TiXmlElement, this one a child of the "Item" element. Etc. Looking at the
entire object tree, you end up with: @verbatim TiXmlDocument "demo.
xml" TiXmlDeclaration "version='1.0'" "standalone=no" TiXmlComment "
Our to do list data" TiXmlElement "ToDo" TiXmlElement "Item" Attribtutes:
priority = 1 TiXmlText "Go to the " TiXmlElement "bold" TiXmlText "Toy
store!" TiXmlElement "Item" Attributes: priority=2 TiXmlText "Do bills" @
endverbatim
Documentation
The documentation is build with Doxygen, using the 'dox' configuration
file.
License
TinyXML is released under the zlib license: This software is provided
'as-is', without any express or implied warranty. In no event will the
authors be held liable for any damages arising from the use of this
software. Permission is granted to anyone to use this software for any
purpose, including commercial applications, and to alter it and
redistribute it freely, subject to the following restrictions: 1. The origin of
this software must not be misrepresented; you must not claim that you
wrote the original software. If you use this software in a product, an
acknowledgment in the product documentation would be appreciated
but is not required. 2. Altered source versions must be plainly marked as
such, and must not be misrepresented as being the original software. 3.
This notice may not be removed or altered from any source distribution.
References
The World Wide Web Consortium is the definitive standard body for
XML, and their web pages contain huge amounts of information. The
definitive spec: http://www.w3.org/TR/2004/REC-xml-20040204/ I also
recommend "XML Pocket Reference" by Robert Eckstein and published
by OReilly...the book that got the whole thing started.
Contributors, Contacts, and a Brief History
Thanks very much to everyone who sends suggestions, bugs, ideas, and
encouragement. It all helps, and makes this project fun. A special thanks
to the contributors on the web pages that keep it lively. So many people
have sent in bugs and ideas, that rather than list here we try to give credit
due in the "changes.txt" file. TinyXML was originally written by Lee
Thomason. (Often the "I" still in the documentation.) Lee reviews changes
and releases new versions, with the help of Yves Berquin, Andrew
Ellerton, and the tinyXml community. We appreciate your suggestions,
and would love to know if you use TinyXML. Hopefully you will enjoy it
and find it useful. Please post questions, comments, file bugs, or contact
us at: www.sourceforge.net/projects/tinyxml Lee Thomason, Yves
Berquin, Andrew Ellerton.
Correct Disposal of This Product (Waste Electrical & Electronic Equipment)
(Applicable in the European Union and other European countries with separate collection systems)
This marking on the product, accessories or literature indicates that the product and its electronic accessories (e.g. charger, headset, USB
cable) should not be disposed of with other household waste at the end of their working life. To prevent possible harm to the environment
or human health from uncontrolled waste disposal, please separate these items from other types of waste and recycle them responsibly
to promote the sustainable reuse of material resources.
Household users should contact either the retailer where they purchased this product, or their local government office, for details of
where and how they can take these items for environmentally safe recycling.
Business users should contact their supplier and check the terms and conditions of the purchase contract. This product and its electronic
accessories should not be mixed with other commercial wastes for disposal.
Correct disposal of batteries in this product
(Applicable in the European Union and other European countries with separate battery return systems.)
This marking on the battery, manual or packaging indicates that the batteries in this product should not be disposed of with other household waste at the end of their
working life. Where marked, the chemical symbols Hg, Cd or Pb indicate that the battery contains mercury, cadmium or lead above the reference levels in EC Directive
2006/66. If batteries are not properly disposed of, these substances can cause harm to human health or the environment.
To protect natural resources and to promote material reuse, please separate batteries from other types of waste and recycle them through your local, free battery
return system.
Samsung Techwin cares for the environment at all product manufacturing stages, and is taking measures to provide
customers with more environmentally friendly products.
The Eco mark represents Samsung Techwin's devotion to creating environmentally friendly products, and indicates
that the product satisfies the EU RoHS Directive.
SALES NETWORK
SAMSUNG TECHWIN CO., LTD.
Samsung Techwin R&D Center, 6, Pangyo-ro 319beon-gil, Bundang-gu, Songnam-si, Gyeonggi-do 463-400, Korea
TEL : +82-70-7147-8740~60 FAX : +82-31-8018-3745
SAMSUNG TECHWIN AMERICA Inc.
100 Challenger Rd. Suite 700 Ridgefield Park, NJ 07660
Toll Free : +1-877-213-1222 Direct : +1-201-325-6920
Fax : +1-201-373-0124
www.samsungcctvusa.com
SAMSUNG TECHWIN EUROPE LTD.
Samsung House, 1000 Hillswood Drive, Hillswood Business Park
Chertsey, Surrey, UNITED KINGDOM KT16 OPS
TEL : +44-1932-45-5300 FAX : +44-1932-45-5325
www.samsungtechwin.com
www.samsungsecurity.com
www.samsungipolis.com