Siemens Communications BSIP1US DECT Basestation User Manual bk
Siemens Communications, Inc. DECT Basestation bk
User Manual
Communication for the open minded
Siemens Enterprise Communications
www.siemens.com/open
Documentation
HiPath OpenOffice ME/EE
HiPath Cordless IP
Service Manual
A31003-C1010-S100-2-7620

Copyright ©
Siemens Enterprise
Communications GmbH & Co. KG 2010
Hofmannstr. 51, 80200 München
Siemens Enterprise Communications GmbH & Co. KG
is a Trademark Licensee of Siemens AG
Reference No.: A31003-C1010-S100-2-7620
The information provided in this document contains
merely general descriptions or characteristics of
performance which in case of actual use do not
always apply as described or which may change as
a result of further development of the products. An
obligation to provide the respective characteristics
shall only exist if expressly agreed in the terms of
contract. Availability and technical specifications are
subject to change without notice.
OpenScape, OpenStage and HiPath are registered
trademarks of Siemens Enterprise
Communications GmbH & Co. KG.
All other company, brand, product and service
names are trademarks or registered trademarks of
their respective holders.
Siemens Enterprise Communications
www.siemens.com/open
Communication for the open minded

bkTOC.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 3
Nur für den internen Gebrauch Contents
Contents 0
List of Tables . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8
List of Figures . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
1 Introduction and Important Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10
1.1 Safety Information and Warnings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10
1.2 Correct Use . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12
1.3 Proper disposal and recycling . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
1.4 Standards and Guidelines on Installation. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14
1.4.1 Labeling . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14
1.5 Data Protection and Data Security. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
1.6 Documentation Feedback . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16
2 Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
2.1 Einleitung . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
2.1.1 DECT IP Base Station (BSIP1). . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
2.1.2 HiPath Cordless IP Server Software. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
2.1.2.1 Communication Interfaces. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
2.2 System Configuration. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
2.2.1 Scenario - HiPath Cordless IP server software is activated on a DECT IP base station . . . . . . . . . . . 24
2.3 DECT IP Base Station Data. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
2.3.1 Outdoor Case . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26
2.3.2 Powering the DECT IP Base Stations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 27
2.4 Network Requirement . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 28
3 Planning a HiPath Cordless IP System. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29
3.1 Planning According to Call Traffic Load . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29
3.2 General . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30
3.3 Propagation Conditions for Radio Traffic . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 31
3.3.1 In the Open with Visibility . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32
3.3.2 Industrial Sites . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32
3.3.3 Indoor Areas in Buildings in Brick and Light Construction Materials . . . . . . . . . . . . . . . . . . . . . . . . . . 33
3.3.4 Indoor Areas in Reinforced Concrete Buildings with Diverse Interior Layout . . . . . . . . . . . . . . . . . . . . 34
3.4 Determining the Installation Site . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 36
3.4.1 Indoors . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 36
3.4.1.1 In Buildings of Brick or Light Construction Materials . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 36
3.4.1.2 In Steel/Concrete Buildings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38
3.4.1.3 Factory Halls and Open-Plan Offices . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
3.4.2 Outdoors . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
3.5 Installing Base Stations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
3.5.1 Ethernet Connection Cable. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
3.5.2 Where Not To Install DECT IP base stations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
3.5.3 Where Should DECT IP base stations be installed? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 47
3.5.4 Indoors . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 48
3.5.4.1 Wall Mounting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 48
3.5.4.2 Ethernet Socket Allocation in the DECT IP Base Station . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 49
3.5.5 Tools/Aids . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 50
3.5.6 Outdoors . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 50

Contents Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
4HiPath Cordless IP, Service Manual
bkTOC.fm
3.5.6.1 Preparatory Tasks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 51
3.5.6.2 Mast Installation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52
3.5.6.3 Wall Installation with Mounting Plate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 54
3.5.6.4 Wall Mounting Without Mounting Plate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 56
4 Putting Into Service . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 57
4.1 Preparation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 57
4.2 Entering the DECT System Number (DECT ARI). . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 58
4.3 Overview IP adresses. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 59
5 Installation and Administration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 60
5.1 Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 60
5.2 Network Concept . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 61
5.2.1 Overview of reserved networks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 62
5.3 Synchronisation over air concept . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 62
5.4 WBM related issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 63
5.4.1 Supported Web Browser . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 63
5.4.2 General WBM issues. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 63
5.4.3 Multiple WBM sessions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 63
5.4.4 Marking changed values . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 64
5.5 Phone related issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 65
5.5.1 Date / time for phone idle display . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 65
5.6 Partition concept of BSIP1 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 65
5.7 Factory reset of BSIP1 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 66
5.8 Release notes. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 67
5.9 Quick Start . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 67
5.10 Quick start overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 67
5.11 Prepare and connect hardware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 68
5.12 Configure BSIP1 for IWU mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 68
5.13 Configuration of VoIP (Infrastructure) network . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 72
5.14 Configuration of DECT network . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 73
5.15 Configuration of users at the PBX . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75
5.16 Configuration of users at the BSIP IWU . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75
5.16.1 Gateway and Group . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75
5.16.2 User. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 76
5.17 Start system services and register handsets . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 78
5.17.1 Start system services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 78
5.17.2 Register handsets . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 78
5.18 Configure further BSIP Only to the system. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 81
5.19 "Quick Start" Completion . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 84
5.20 Further steps. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 84
5.20.1 Radio frequency site survey . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 84
5.20.2 Synchronisation implementation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 84
5.21 Configuration reference . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 84
5.22 WBM overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 85
5.22.1 Different WBM modes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 85
5.22.2 Features in WBM mode Siemens Admin. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 85
5.22.3 Login to WBM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 86
5.22.3.1 Multiple WBM sessions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 86
5.22.3.2 Login and Password change . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 86
5.22.3.3 Changing a WBM User's password . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 86
5.22.4 General objects . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 88
5.22.5 Configuration Systematic. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 89

bkTOC.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 5
Nur für den internen Gebrauch Contents
5.22.6 Changing values . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 89
5.22.6.1 Debug windows . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 90
5.23 Administration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 91
5.23.1 Frame Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 91
5.23.1.1 Button [Restore Config] . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 91
5.23.1.2 Button [Backup Config] . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 93
5.23.2 Frame Program Info . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 94
5.23.2.1 [System Update] . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 95
5.23.2.2 Other options. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 96
5.24 "Network/Gateways" Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 98
5.24.1 Gateway configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 98
5.24.2 Network configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 100
5.25 "Group" Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 104
5.26 Users Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 106
5.26.1 General user configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 106
5.26.2 Configuration Page "User - User" . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 107
5.26.3 Configuration Page "User - VoiP" . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 108
5.26.4 Configuration Page "User - Dect" . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 109
5.26.5 Auto Entry users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 111
5.27 Dect Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 112
5.27.1 Configuration Page "Dect - Device" . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 112
5.27.2 Configuration Page "Dect - Sync". . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 113
5.27.3 Configuration Page "Dect - ARI". . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 115
5.27.4 Configuration Page "Dect - About" . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 116
5.27.5 Configuration Page "Dect - Radio" (Advanced mode) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 117
5.27.6 Configuration Page "Dect - Call" (Advanced mode) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 117
5.27.7 Configuration Page "Dect - Debug" (Advanced mode). . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 118
5.27.8 General DECT configuration. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 118
5.27.8.1 Adding, deleting and scanning . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 119
5.27.8.2 General configuration options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 120
5.28 Debugging Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 121
5.29 "Status" Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 125
5.29.1 Configuration Page "Status - Modules 1" . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 126
5.29.2 Configuration Page "Status - Modules 2" . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 127
5.29.3 Configuration Page "Status - Calls Dect" . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 128
5.29.4 Configuration Page "Status - RSSI" . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 130
5.30 "System" Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 132
5.31 Configuration Hints for PBXs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 133
5.32 HiPath OpenOffice EE . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 133
5.32.1 Base Configuration - HiPath OpenOffice EE . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 133
5.32.2 Base Configuration - BSIP IWU . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 135
5.32.3 Station Configuration - HiPath OpenOffice EE . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 135
5.32.3.1 Step 1 - User Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 136
5.32.3.2 Step 2 - Workpointclient Data . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 136
5.32.4 Station Configuration - BSIP IWU. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 137
5.32.5 Time server configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 138
5.33 HiPath OpenOffice ME. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 138
5.33.1 Base Configuration - HiPath OpenOffice ME . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 138
5.33.2 Base Configuration - BSIP IWU . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 140
5.33.3 Station Configuration - HiPath OpenOffice ME. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 141
5.33.3.1 Step 1 - User Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 141
5.33.3.2 Step 2 - Workpointclient Data . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 142

Contents Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
6HiPath Cordless IP, Service Manual
bkTOC.fm
tation Configuration - IP-DECT IWU . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 143
5.33.5 Time server configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 144
5.34 Troubleshooting / FAQ . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 144
5.34.1 BSIP1 Only is not found using "Scan". . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 144
5.34.2 Registration of the handsets not successful . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 145
5.34.3 Idle display of handset is blinking . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 145
5.34.4 Display message "Netzfehler" / "Out of Order" . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 145
5.35 Configuration hints for Web Browser . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 145
5.35.1 Mozilla Firefox . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 145
5.35.2 Microsoft Internet Explorer . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 146
6 Technical Data . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 147
6.1 BSIP1 DECT standard EU . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 147
6.2 BSIP1US DECT standard USA . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 148
6.3 Base Stations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 149
6.3.1 Mobile Telephones . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 152
6.3.1.1 Gigaset S3 professional. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 152
6.3.1.2 Gigaset SL3 professional . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 154
6.3.1.3 Gigaset M2 professional, Gigaset M2 plus professional . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 156
6.3.1.4 Gigaset M2 Ex professional . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 157
6.3.2 PoE Injector. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 158
6.3.3 Item Number Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 159
6.4 Measuring Equipment. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 160
6.5 Operating Manuals . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 160
7 Diagnosis and Maintenance . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 161
7.1 Checking the Base Stations and the Radio Coverage . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 161
7.1.1 Base Stations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 162
7.1.2 Quick Verification of Area Coverage . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 163
7.2 Testing the Radio Area . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 164
7.2.1 Significance of Results Obtained. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 164
7.2.2 Gigaset Family. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 166
7.2.2.1 Activating Measuring Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 166
7.2.2.2 Deactivating Measuring Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 168
7.2.3 Documentation of Results . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 170
7.3 Troubleshooting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 173
7.3.1 Checking HiPath Cordless IP Components . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 173
7.3.2 What Happens If ... . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 174
7.3.2.1 Synchronism Symbol on Handset Display: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 174
7.3.2.2 Handset Cannot Be Reached . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 175
7.3.2.3 Connection Handover . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 175
7.3.2.4 Handset: Problems Logging On . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 176
7.3.3 Deactivating the PIN Lock on Gigaset S3, SL3. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 177
8 Open Source Software used in the Product . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 178
8.1 General Conditions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 178
8.2 Open Source Software Used . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 180
8.3 Acknowledgements. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 181
8.4 Text of the used Open Source Software Licenses . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 182
8.4.1 GPL . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 182
8.4.2 LGPL . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 189
8.4.3 Libpcap . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 199

bkTOC.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 7
Nur für den internen Gebrauch Contents
8.4.4 OpenSSL . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 200
8.4.5 Net-SNMP. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 203
8.4.6 Zlib . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 207
8.4.7 Mini Httpd . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 210
8.4.8 Ipsec Tools . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 211
8.4.9 OpenSSH . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 212
8.4.10 JSON-C . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 221
8.4.11 lsof License. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 221
Index . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 225

List of Tables Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
8HiPath Cordless IP, Service Manual
bkLOT.fm
List of Tables 0
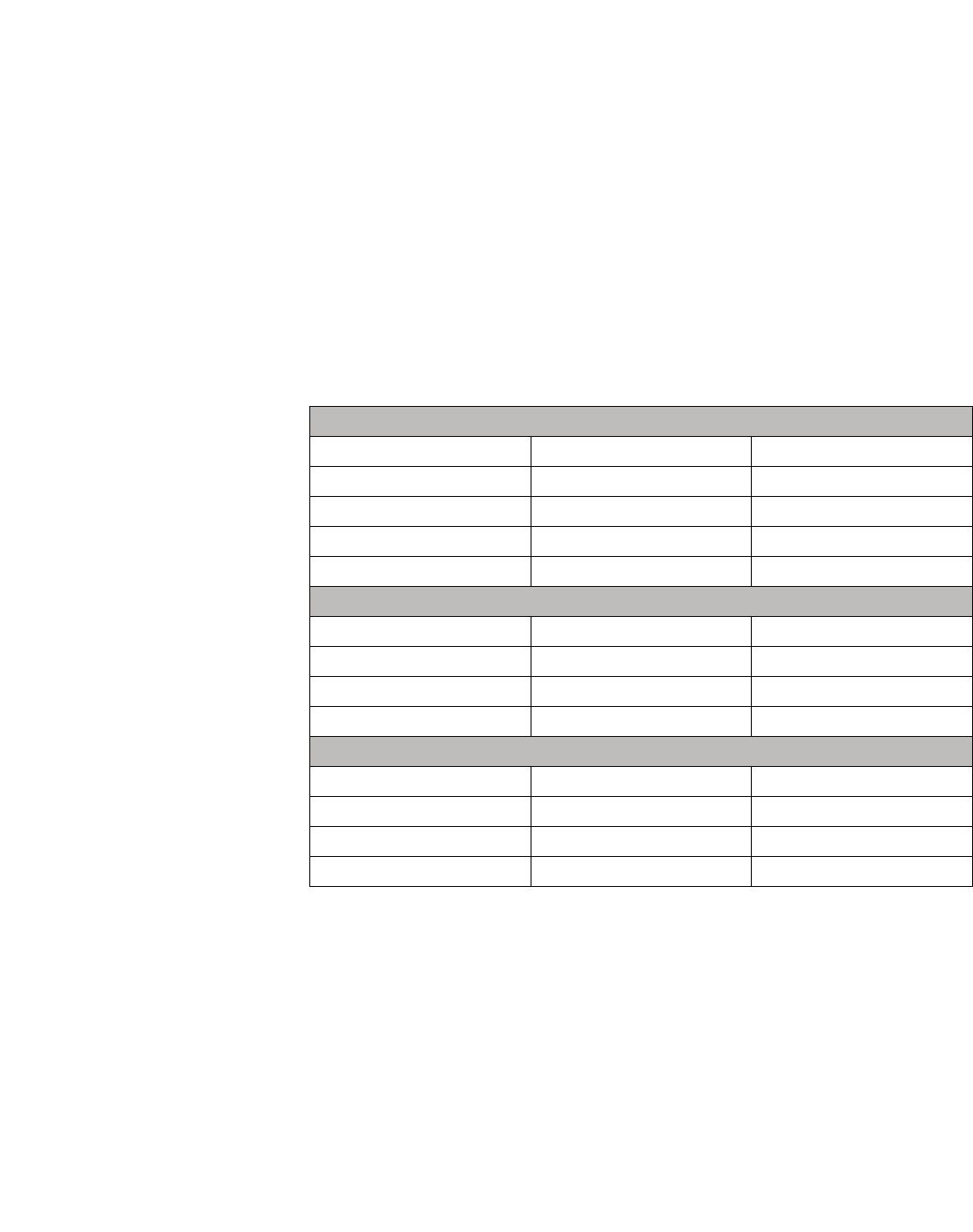
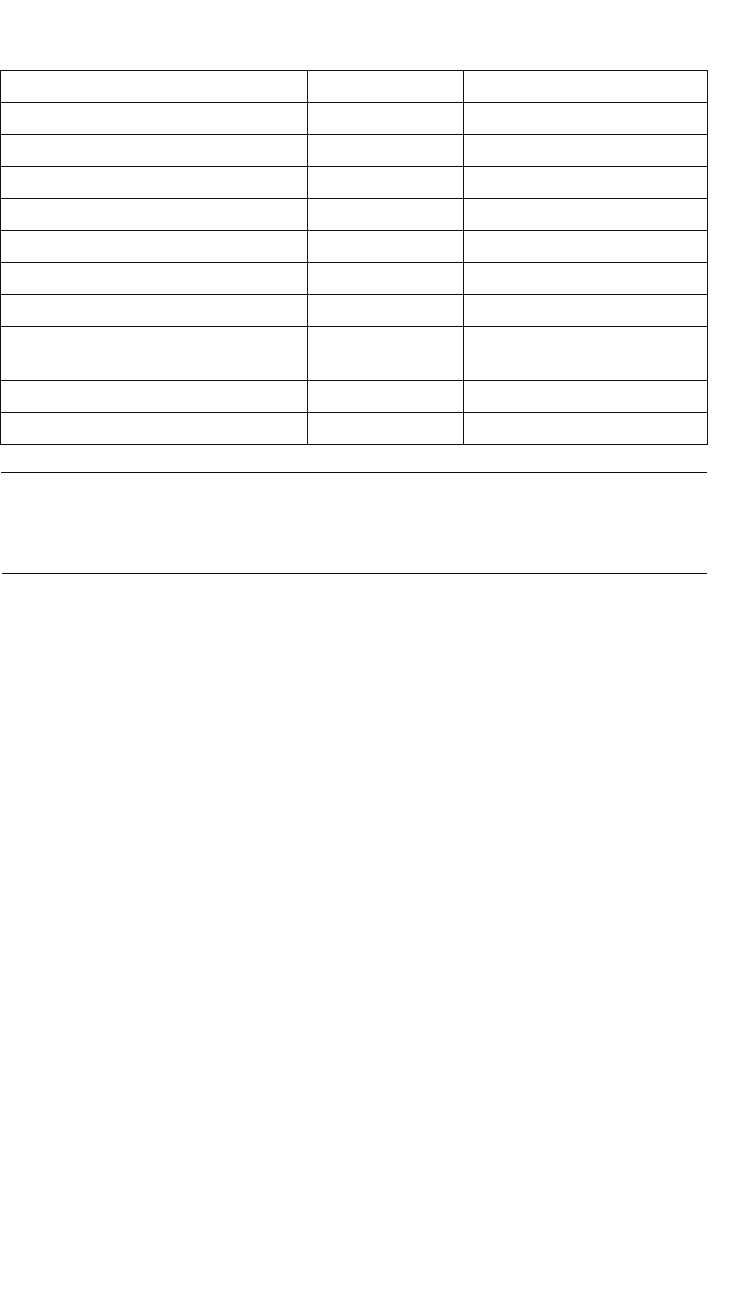
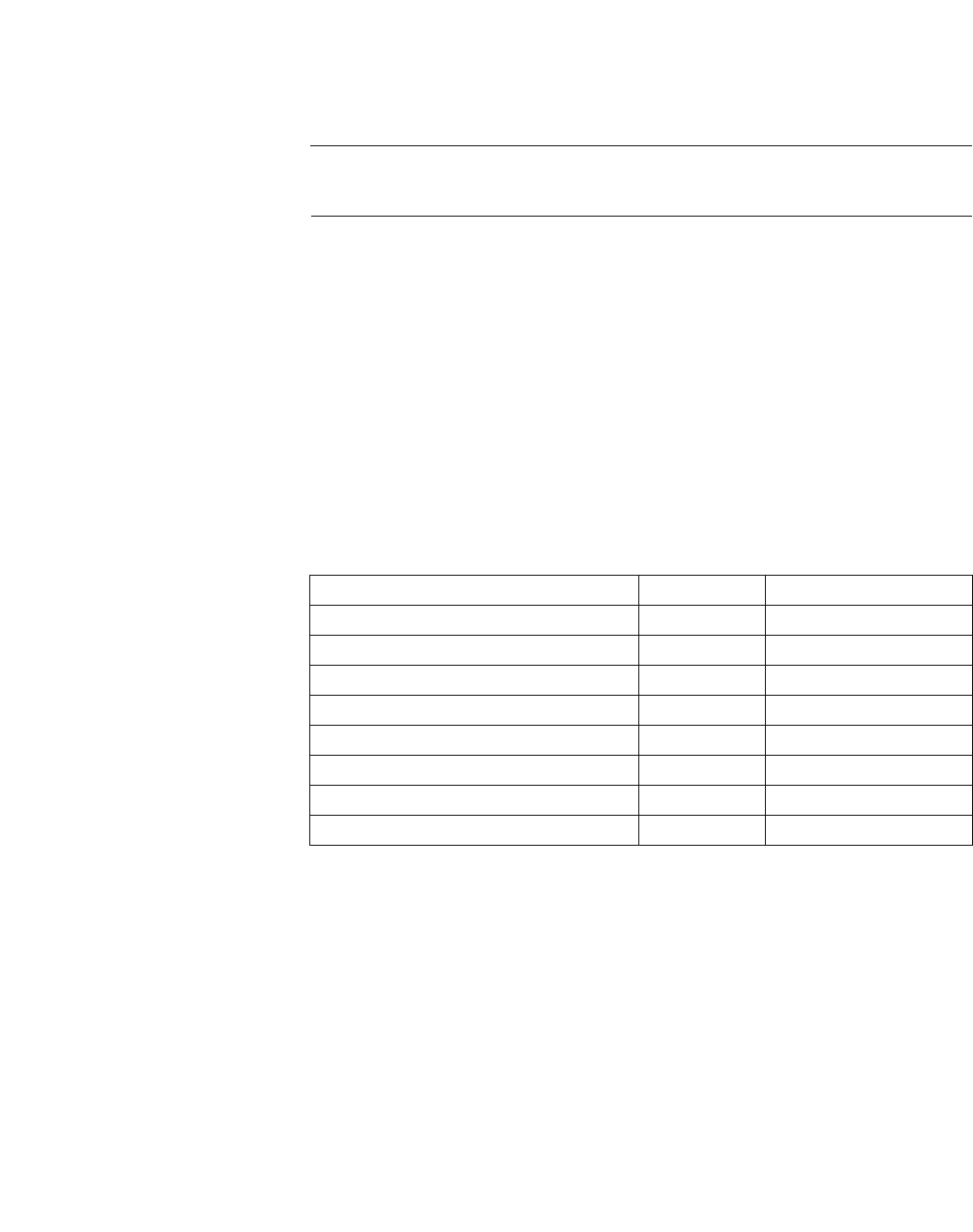
Table 1 Technical data DECT IP base station . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
Table 2 Recommended amount of users at 10 voice channels . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29
Table 3 Insertion loss (ae)/range loss in the radio area . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34
Table 4 Insertion loss (ae)/range loss in the radio area . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 35
Table 5 Belegung der Ethernetbuchse. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 49
Table 6 Tools/aids . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 50
Table 7 LED status displays on the base station . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 150

bkLOF.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 9
Nur für den internen Gebrauch List of Figures
List of Figures 0
Figure 1 General Overview of the HiPath Cordless IP System . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
Figure 2 Optimum system synchronization over DECT . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Figure 3 Not optimally synchronized, each DECT IP base station has only one synchronization partner
21
Figure 4 Protocols of the path between Handset and Communication Server. . . . . . . . . . . . . . . . . . 22
Figure 5 Depicts all communication channels of the HiPath Cordless IP System . . . . . . . . . . . . . . . 22
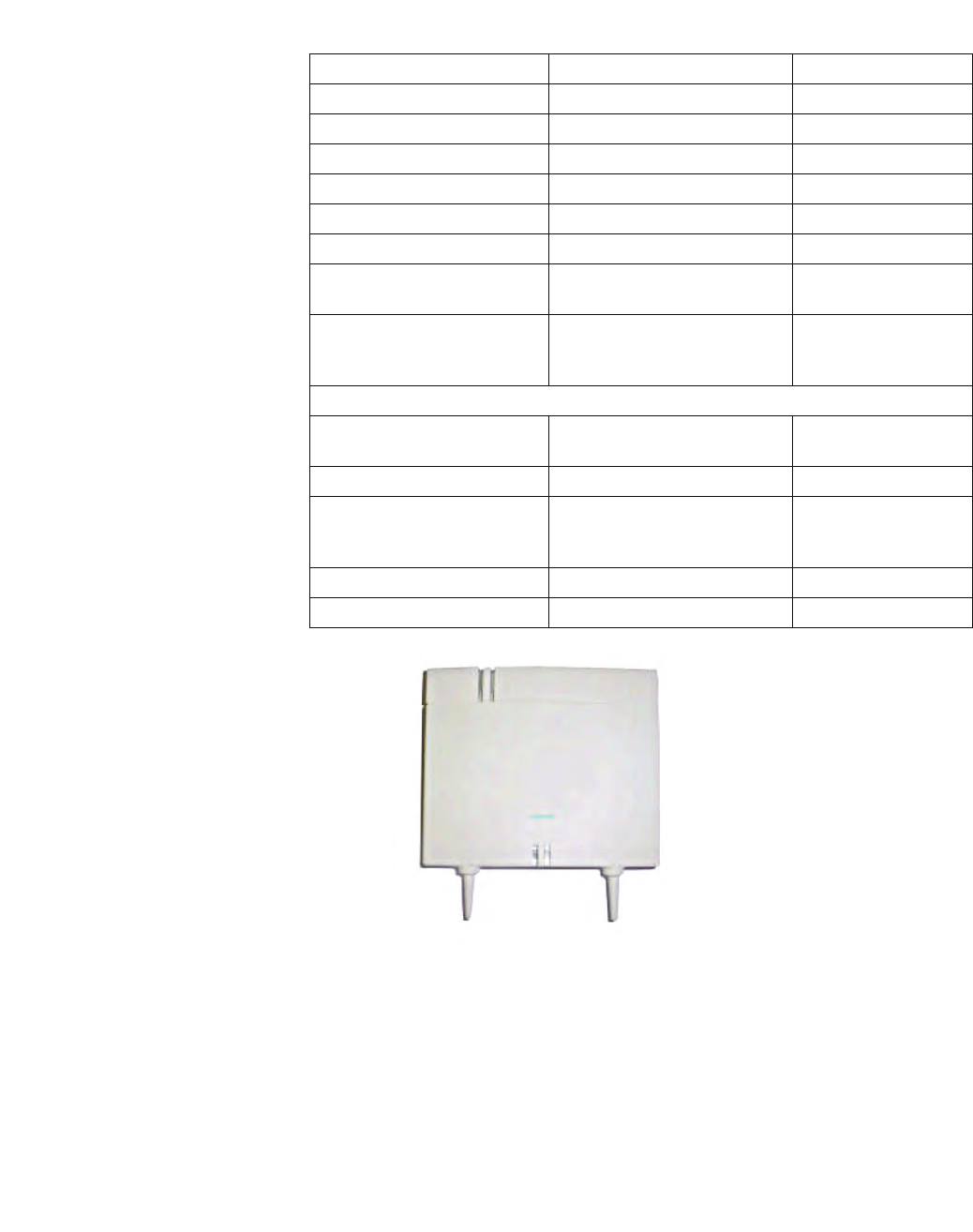
Figure 6 DECT IP base station BSIP1 (Item number: U30807-S5494-X) . . . . . . . . . . . . . . . . . . . . . 25
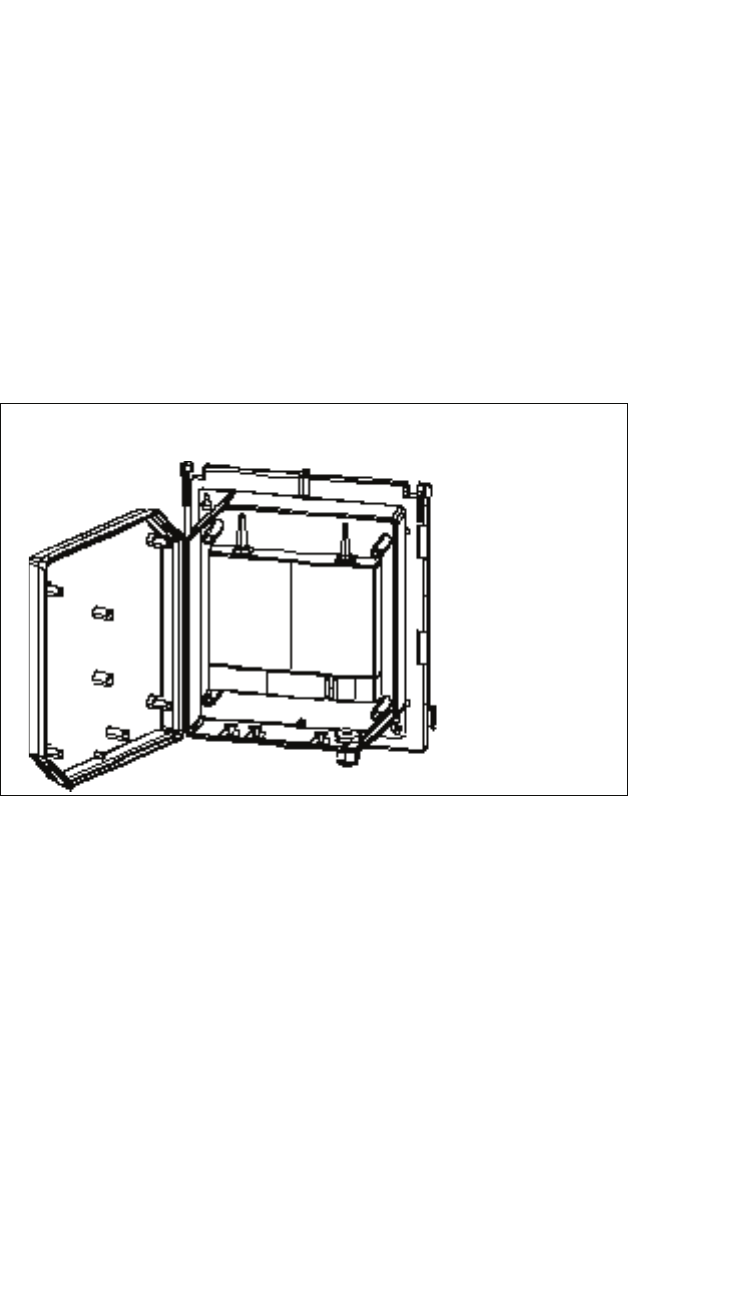
Figure 7 Outdoor case with DECT IP base station. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26
Figure 8 PoE Injector . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 27
Figure 9 Base station distribution in buildings of brick and light construction materials . . . . . . . . . . . 37
Figure 10 Base station distribution in interiors of brick and light construction materials. . . . . . . . . . . . 39
Figure 11 Base station distribution in interiors with concrete and steel dividing walls . . . . . . . . . . . . . 41
Figure 12 Base station distribution for base stations with housing for outdoor use . . . . . . . . . . . . . . . 43
Figure 13 Base station distribution for coverage of an outdoor area . . . . . . . . . . . . . . . . . . . . . . . . . . 45
Figure 14 Components for outdoor installation. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 51
Figure 15 Outdoor housing with base station . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52
Figure 16 Outdoor housing with mounting plate and mast blocks . . . . . . . . . . . . . . . . . . . . . . . . . . . . 53
Figure 17 Mast installation – plan view. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 54
Figure 18 Wall mounting without mounting plate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 56
Figure 19 LED position on the base station . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 151
Figure 20 Measurement result . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 165
Figure 21 Building - Base station installation site/radio area . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 171
Figure 22 Outdoors - Base station installation site/radio area . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 172

c01.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 10
Introduction and Important Notes
Safety Information and Warnings
1 Introduction and Important Notes
1.1 Safety Information and Warnings
Work on communication systems and devices may only be carried out by
qualified persons.
For the purposes of safety information and warnings, qualified persons are
persons who are authorized to place into operation, ground, and label systems,
devices, and lines in accordance with applicable safety procedures and
standards.
It is absolutely essential that you read and understand the following safety infor-
mation and warnings before starting installation and implementation work on the
communication system or device.
You should also carefully read and observe all safety information and warnings
on the communication systems and devices themselves.
Familiarize yourself with emergency numbers.
c01.fm
Introduction and Important Notes
Safety Information and Warnings
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 11
Types of safety information and warnings
The following grades of safety information/warnings are used in this manual:
7
DANGER
Indicates an immediate danger that could result in death or serious injury.
7
WARNING
Indicates a general danger that could result in death or serious injury.
7
CAUTION
Indicates a danger that could result in injury.
NOTE: Indicates situations that could result in damage to property and/or loss of
data.
Symbols for specifying the source of danger more exactly
The following symbols are not usually used in the manual. They explain symbols
that may be depicted on the communication systems and equipment.
•

Introduction and Important Notes
c01.fm
Correct Use
A31003-C1010-S100-2-7620, 08/2010
12 HiPath Cordless IP, Service Manual
1.2 Correct Use
The communications system may only be used for the purpose described in this
document and only in connection with the additional devices and components as
recommended and permitted by
Siemens Enterprise Communications GmbH & Co. KG under Trademark License
of Siemens AG 2008.
The proper use of the communications system assumes correct
transport,storage, assembly and setup as well as careful operation and mainte-
nance.
c01.fm
Introduction and Important Notes
Proper disposal and recycling
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 13
1.3 Proper disposal and recycling
All electrical and electronic products should be disposed of
separately from the municipal waste stream via designated collection
facilities appointed by the government or the local authorities.
The correct disposal and separate collection of your old appliance will
help prevent potential negative consequences for the environment
and human health. It is a precondition for reuse and recycling of used
electrical and electronic equipment.
For more detailed information about disposal of your old appliance,
please contact your city office, waste disposal service, the shop
where you purchased the product or your sales representative.
The statements quoted above are only fully valid for equipment which
is installed and sold in the countries of the European Union and is
covered by the directive 2002/96/EC. Countries outside the
European Union may have other regulations regarding the disposal
of electrical and electronic equipment.
Used accumulators and batteries with this sign are valuable
economic goods and must be recycled. Used accumulators and
batteries that are not recycled must be disposed of as hazardous
waste with full observance of all regulations.
Introduction and Important Notes
c01.fm
Standards and Guidelines on Installation
A31003-C1010-S100-2-7620, 08/2010
14 HiPath Cordless IP, Service Manual
1.4 Standards and Guidelines on Installation
1.4.1 Labeling
This device complies with the EU guideline 1999/5/EEC as
confirmed by the CE certificate.
This device has been manufactured in accordance with our
certified environmental management system (ISO 14001). This
process ensures that energy consumption and the use of
primary raw materials are kept to a minimum, thus reducing
waste production.
c01.fm
Introduction and Important Notes
Data Protection and Data Security
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 15
1.5 Data Protection and Data Security
This system processes and uses personal data for purposes such as call detail
recording, displays, and customer data acquisition.
In Germany, the processing and use of such data is subject to various regulations,
including those of the Federal Data Protection Law (Bundesdatenschutzgesetz,
BDSG). For other countries, please follow the appropriate national laws.
The aim of data protection is to protect the rights of individuals from being
adversely affected by use of their personal data.
In addition, the aim of data protection is to prevent the misuse of data when it is
processed and to ensure that one’s own interests and the interests of other
parties which need to be protected are not affected.
The customer is responsible for ensuring that the system is installed,
operated and maintained in accordance with all applicable labor laws and
regulations and all laws and regulations relating to data protection, privacy
and safe labor environment.
Employees of Siemens Enterprise Communications GmbH & Co. KG are bound
to safeguard trade secrets and personal data under the terms of the company’s
work rules.
In order to ensure that the statutory requirements are consistently met during
service – whether on-site or remote – you should always observe the following
rules. You will not only protect the interests of your and our customers, you will
also avoid personal consequences.
A conscientious and responsible approach helps protect data and ensure
privacy:
•Ensure that only authorized persons have access to customer data.
•Take full advantage of password assignment options; Never give passwords
to an unauthorized person orally or in writing.
•Ensure that no unauthorized person is able to process (store, modify,
transmit, disable, delete) or use customer data in any way.
•Prevent unauthorized persons from gaining access to storage media, such as
backup CDs or log printouts. This applies to service calls as well as to storage
and transport.
•Ensure that storage media which are no longer required are completely
destroyed. Ensure that no sensitive documents are left unprotected.
Work closely with your customer contact; this promotes trust and reduces
your workload.

Introduction and Important Notes
c01.fm
Documentation Feedback
A31003-C1010-S100-2-7620, 08/2010
16 HiPath Cordless IP, Service Manual
1.6 Documentation Feedback
If you have questions that are not answered by this document:
•Internal employees should contact their National Support Center.
•Customers should contact their retailer or the Siemens Customer Support
Center.
When you call, state the title, ID number, and issue of the document.
Example:
•Title: HiPath Cordless IP, Service Documentation
•ID number: A31003-C1010-S100-1-7620
•Issue: 1
c02.fm
Overview
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 17
2 Overview
The HiPath Cordless IP solution extends the scope of the DECT standard
introduced for voice communication, making it now available for Voice over IP
infrastructures.
The radio range covered by the HiPath Cordless IP system is made up of DECT
IP base stations that together form either an seamless network of overlapping
and synchronous radio cells or individual radio islands. The size of a radio cell
depends on local/structural factors.
Voice over IP infrastructures are connected via the SIP protocol. In their capacity
as mobile communication solutions, DECT radio cells are therefore an optimal
enhancement to SIP-compliant Voice over IP systems.
The DECT IP base stations support seamless handover in ongoing voice
connections, that is, moving from one radio cell to another during a call with a
DECT handset. The roaming function is also available for mobile stations.
HiPath Cordless IP also supports the DECT protocol GAP (Generic Access
Profile) and the radio protocol PN-CAP. The basic function scope required by
ETSI is thus extended to include a number of Siemens-specific features.
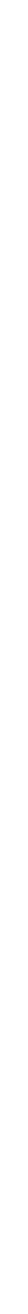
Figure 1 General Overview of the HiPath Cordless IP System

Overview
c02.fm
A31003-C1010-S100-2-7620, 08/2010
18 HiPath Cordless IP, Service Manual
The HiPath Cordless IP System contains the following main components, see
also Figure 1:
• Handset: Gigaset professional DECT handsets with PN-CAP
functionality
• BSIP1: DECT IP Basestations with GAP/ PN-CAP functionality to the
handset and IP interface to the Ethernet network.
• HiPath Cordless IP Server SW: central Server SW component for
control of the DECT IP Basestations, SIP interworking with the
communication server, and the common administration and configuration
interface of the whole HiPath Cordless IP solution.

c02.fm
Overview
Einleitung
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 19
2.1 Einleitung
The HiPath Cordless IP solution is designed as a DECT system with an SIP
interface to the communication server.
The following platforms are supported with the current release
•HiPath OpenOffice EE from V1.0
•HiPath OpenOffice ME from V1.0
2.1.1 DECT IP Base Station (BSIP1)
DECT IP base stations combine to form a network of radio cells. Roaming
between radio cells is possible for DECT handsets during a voice connection if
the radio cells are synchronized and overlap.
DECT IP base stations come with all necessary software for the DECT and IP
functions. This software is configured and administered via the HiPath Cordless
IP server software.
2.1.2 HiPath Cordless IP Server Software
HiPath Cordless IP server software is installed once on a system and runs on a
DECT IP base station. It supports the following functions:
Function: Router and protocol converter
The HiPath Cordless IP server software serves as the interface between the IP
DECT base stations and the communication server.
It manages the voice connections between the communication server and the
relevant DECT IP base station and converts these into a data format that can be
reed by the DECT IP base stations. At DECT layer the media packets are
enhanced with DECT signaling (time frame, frequency) information. The HiPath
Cordless IP Server SW converts incoming RTP media data into UDP packets via
DECT codec G726.
Only HiPath Cordless IP Server SW knows, at which DECT IP Basestation a
special DECT handset is located. For the communication server or any other
phone, the HiPath Cordless IP Server SW is the endpoint. Whenever a handset
performs a handover, this process is invisible outside the HiPath Cordless IP
System. In the view of the communication server the HiPath Cordless IP Server
SW is like a Gateway User-Agent that manages lots of handsets. Handsets use
the HiPath Cordless IP server software for registration at the communication
server. This software regulates the check-in procedure for the DECT handsets
and their management.

Overview
c02.fm
Einleitung
A31003-C1010-S100-2-7620, 08/2010
20 HiPath Cordless IP, Service Manual
Function: Configuration and administration interface
All administrative functionality for the DECT IP Basestations as well as for HiPath
Cordless IP Server SW itself is performed via a Web Based Management to the
HiPath Cordless IP Server SW, i.e., all DECT IP Basestations are administered
via HiPath Cordless IP Server SW.
Function: Synchronization management
DECT IP base stations must be perfectly synchronized as a prerequisite for
seamless handover. If the DECT IP base stations are synchronized, they
combine to form a seamless handover cluster. The synchronization management
function only works in this cluster. Additional clusters are possible but not
synchronized. Seamless handover is not possible between different
asynchronous clusters.
In DECT systems with line-switched connections such as HiPath Cordless
systems, the synchronization information needed for synchronizing the DECT IP
base stations is obtained from the UP0 connection. This is not possible in the
HiPath Cordless IP system.
DECT-based synchronization ("synchronization over the air")
This method to synchronize overlapping radio cells runs under SW control
within the DECT part of the DECT IP Basestation. The HiPath Cordless IP
Server SW is acting only as admin point that notices when a base station has
lost its synchronization.
The DECT IP base station must be located in the overlap area of the DECT
IP base station that it wants to synchronize with over the DECT interface. For
every DECT IP Basestation the synchronization "Master" have to be
configured by the configuration Interface of the HiPath Cordless IP Server
SW. DECT information for synchronization are exchanged directly between
the DECT IP Basestations.
A DECT IP base station can also be synchronized with other DECT IP base
stations as this increases the synchronism available in the cluster. It is
important to avoid synchronization loops.
In the event of loss of synchronization, the DECT IP base station stops
accepting calls once all ongoing calls that were being conducted on the
asynchronous DECT IP base station have ended and then it re-synchronizes
the asynchronous DECT IP base station.
c02.fm
Overview
Einleitung
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 21
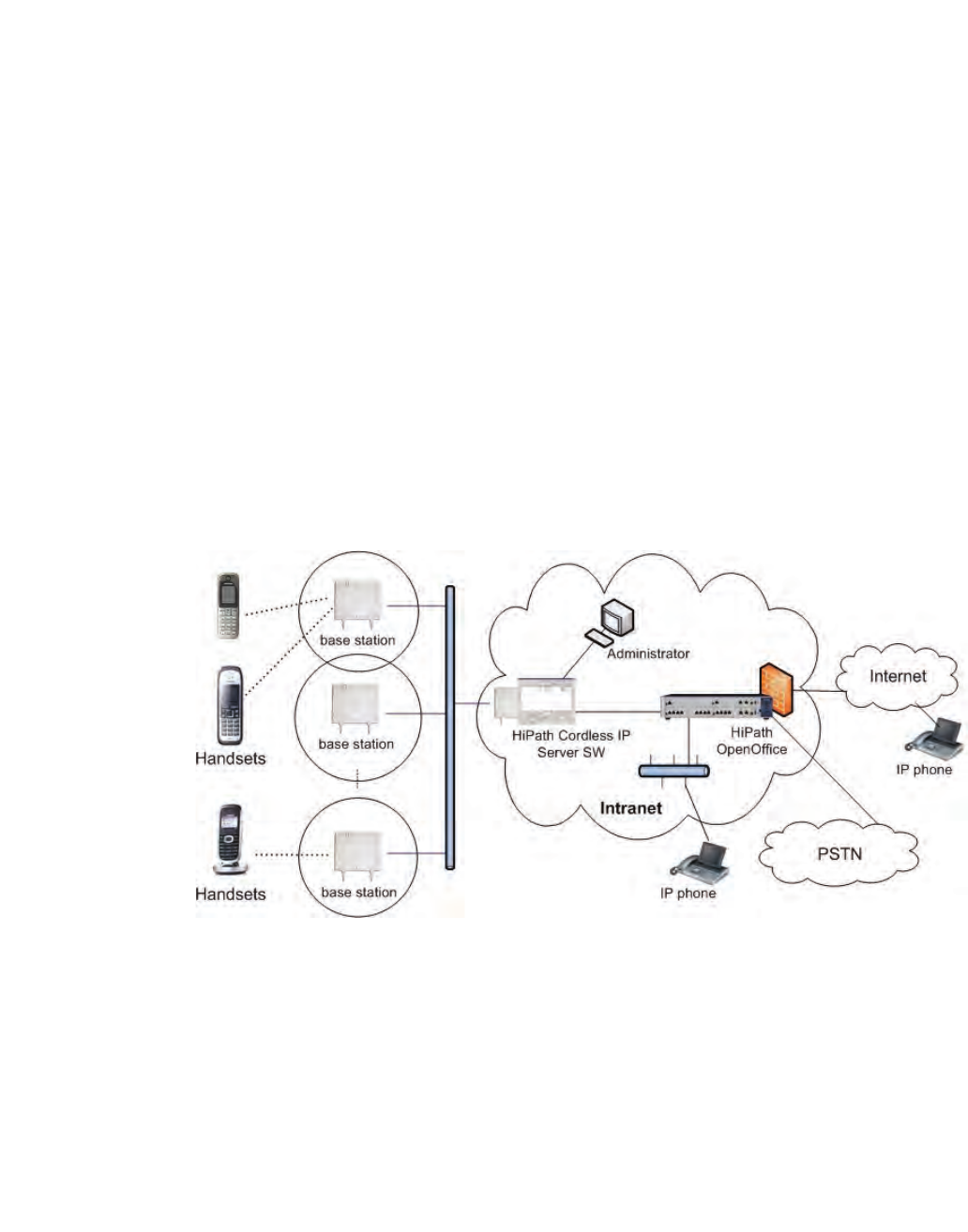
Figure 2 Optimum system synchronization over DECT
Standard synchronization
Alternative synchronization if standard synchronization fails
Figure 3 Not optimally synchronized, each DECT IP base station has only one
synchronization partner
This data is transported in a VPN tunnel to ensure that the signaling and voice
data in active voice connections between a DECT IP base station and HiPath
Cordless IP software is protected against manipulation and interception. For the
VPN encryption IPSec is used.
The DECT IP base stations are set up in communication with the HiPath Cordless
IP server software. As soon as a new DECT IP base station is connected to the
Ethernet, it starts to send multicast packets with its MAC address. The HiPath
Cordless IP server software then activates and takes over control of the DECT IP
base station. The HiPath Cordless IP server software then sends the DECT IP
base station an IP address for communication purposes as well as its own IP
address as a future target address for data traffic.
Overview
c02.fm
Einleitung
A31003-C1010-S100-2-7620, 08/2010
22 HiPath Cordless IP, Service Manual
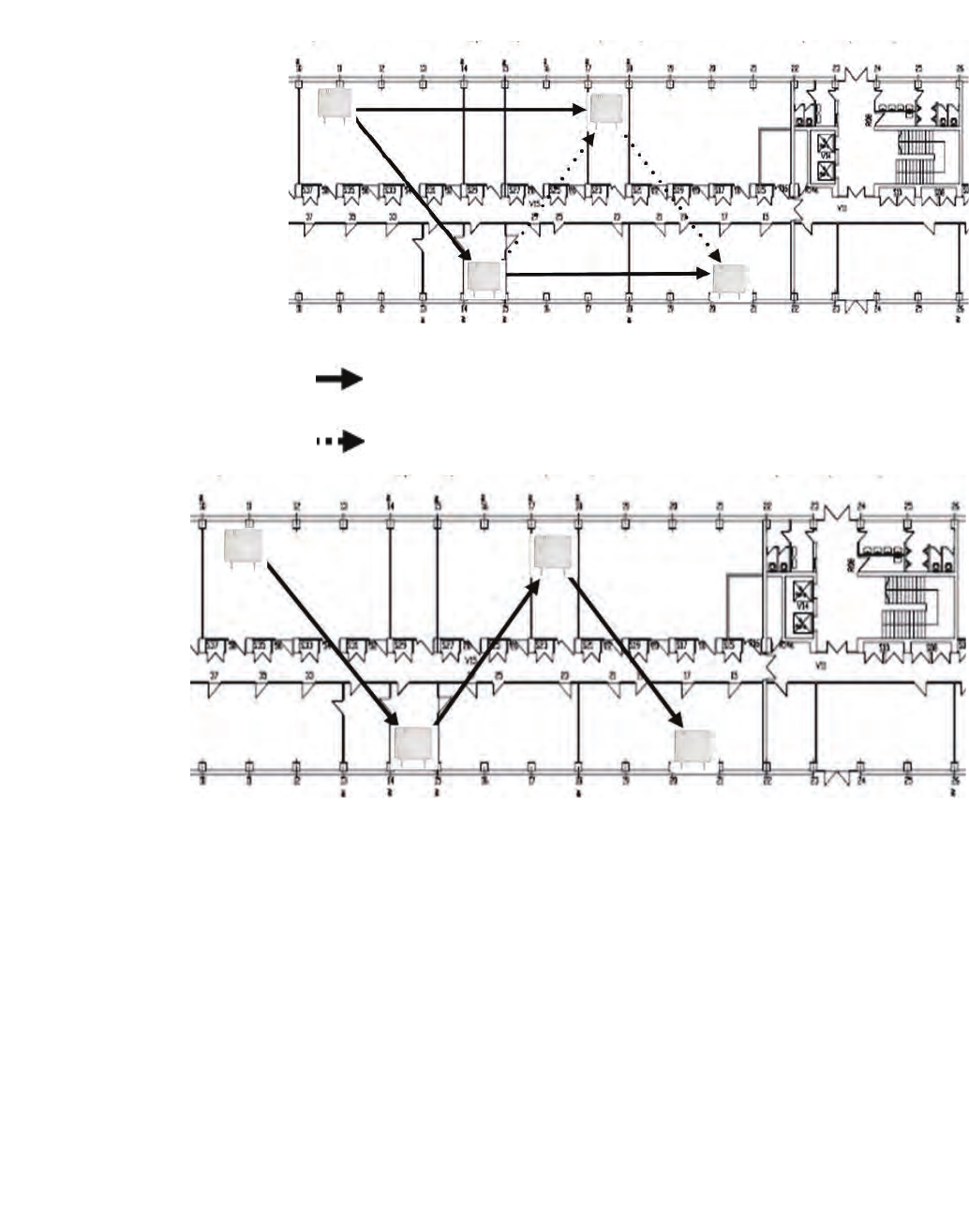
2.1.2.1 Communication Interfaces
The following picture gives an overview of the protocols used between DECT
Handset, DECT IP Basestation, HiPath Cordless IP Server SW and the
communication server.
Figure 4 Protocols of the path between Handset and Communication Server
Figure 5 Depicts all communication channels of the HiPath Cordless IP
System
The following list gives an overview of all communication-channels within the
HiPath Cordless IP System:
DECT Handset - User: Gigaset professional DECT Handsets with PN-CAP
functionality
DECT Handset - BSIP1: In this multicell DECT system, a call can be handed over
seamlessly from one BSIP1 to the other. If seamless handover/ roaming is
impossible and the signal quality is decreasing, at a certain point the handset can
send a warning tone and the connection breaks off.

c02.fm
Overview
Einleitung
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 23
BSIP1 - BSIP1: An accurate synchronization is needed between DECT IP
Basestation for seamless handover.
BSIP1 - HiPath Cordless IP Server SW: BSIP1 is able to handle a tunnel to the
HiPath Cordless IP Server SW, in which the voice data of all active calls and all
signaling data is transported. The connection between BSIP1 and HiPath
Cordless IP Server SW is system-specific, i.e., this protocol is IP based and
performs UDP streaming both ways.
HiPath Cordless IP Server SW - communication server: The SIP interface
between the HiPath Cordless IP Server SW and the communication server is
standard based. Seen from the communication server the DECT over IP System
is a set of SIP subscribers represented by a GW User-Agent, which is the HiPath
Cordless IP Server SW connected to the DECT handsets, i.e. the subscribers are
the DECT handsets.

Overview
c02.fm
System Configuration
A31003-C1010-S100-2-7620, 08/2010
24 HiPath Cordless IP, Service Manual
2.2 System Configuration
The voice and signaling data (RTP/SIP) are always routed over the
HiPath Cordless IP server software because this is the only software that
supports a routing and protocol converter function.
Scenarios are also possible where the HiPath Cordless IP server software is
installed a number of times per communication server. Such scenarios do not
support seamless handover between the different clusters formed with
synchronous DECT IP base stations. Cascading is not available at present for
communication server software.
2.2.1 Scenario - HiPath Cordless IP server software is
activated on a DECT IP base station
All DECT IP base stations always also support the same functions as HiPath
Cordless IP server software. This means that in principle, all DECT IP base
stations can perform HiPath Cordless IP server software functions in addition to
the actual DECT functionality. The HiPath Cordless IP server software must be
activated before the DECT IP base station can perform this function.
The following system limits apply in this scenario based on resource availability
in BSIP1:
– up to 10 DECT IP base stations
– up to 10 parallel calls
These system limits apply to each cluster of synchronous DECT IP base stations
where seamless handover is possible. In the HiPath Cordless IP Server Software
database a maximum of 99 Gigaset professional handsets can be configured. 50
handsets out of the 99 handsets (see calculation above) can be registered in the
HiPath Open Office.
2.3 DECT IP Base Station Data
Table 1 Technical data DECT IP base station
Parameter DECT IP base station BSIP1 Outdoor case
DECT Interface
Max. amount of DECT
channels 120
DECT Signalling GAP/ PN-CAP
IP Interface
Network connection Ethernet 10/100 Base T
c02.fm
Overview
DECT IP Base Station Data
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 25
Figure 6 DECT IP base station BSIP1 (Item number: U30807-S5494-X)
PoE class Class 2 according IEE802.3af
Power consumption < 6,5 W; PoE Class 2
Max. Voice channels 12 (bei G.711)
Codecs G.711/ G.726
QoS 802.1 p/q
Echo Cancellation yes
DHCP Option DCHP on or local entry of IP
addresses
SW Distribution SW Download/ Update central
via HiPath Cordless IP Server
SW
Miscellaneous
Dimensions
(W x H x D in mm) 202 x 256 x 90 296 x 256 x 90
Weight ca. 0,5 kg ca. 1,0 kg
Operating Temperature Indoors:
0 oC bis + 40 oC Outdoors (with outdoor
housing):
- 25 oC bis + 40 oC
Storage temperatur range -5 oC bis + 45 oC
Relative humidity – bis 95 %
Table 1 Technical data DECT IP base station
Parameter DECT IP base station BSIP1 Outdoor case
Overview
c02.fm
DECT IP Base Station Data
A31003-C1010-S100-2-7620, 08/2010
26 HiPath Cordless IP, Service Manual
2.3.1 Outdoor Case
A DECT IP base station must be installed in a weatherproof outdoor case to
guarantee radio coverage in outdoor areas, for example on factory sites. The
outdoor case is suitable for mounting on house walls, roofs or masts.
The outdoor case already used for the HiPath Cordless base station BS4 is also
used for DECT IP base stations (part number: S30122-X7469-X2).
If using the DECT IP base station outdoors, lightning and overvoltage protection
must be provided and guaranteed for the DECT IP base station itself as well as
for the feeder into the DECT IP base station and the building. In compliance with
EN 61000-4-5, the power supply inlet on the DECT IP base station offers up to
0.5 KV overvoltage protection.
Figure 7 Outdoor case with DECT IP base station
Outdoor Case

c02.fm
Overview
DECT IP Base Station Data
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 27
2.3.2 Powering the DECT IP Base Stations
The DECT IP base station can be powered in two different ways:
•Power-over-Ethernet (PoE) Class 2 to 802.3af
•Power-over-Ethernet: PoE injectors
A PoE injector is used if PoE cannot be made available in the network. The
PoE injector must be 802.3af-compatible. Pre-tested and released PoE
injectors are available as optional features within the scope of the HiPath
Cordless IP solution.
The IEEE802.3af standard allows the PoE Injector to be in any location
between the switch and the BSIP1. The maximum allowed distance between
the switch and the BSIP1 for IEEE802.3 compliance is 100 m. It is typical to
deploy the PoE Injector close to the switch, since by doing this one can use
a single UPS (central power supply) to backup both the switch and the PoE
Injector.
If overall efficiency is more important than centralized backup and/or
management, it makes sense to place the PoE Injector closer to the BSIP1,
since the power dissipated at the cable between the PoE Injector and the
BSIP1 is directly proportional to the length of this cable (P = I2 * R).
Figure 8 PoE Injector

Overview
c02.fm
Network Requirement
A31003-C1010-S100-2-7620, 08/2010
28 HiPath Cordless IP, Service Manual
2.4 Network Requirement
Voice connections only work properly over IP networks if the IP network satisfies
all general VoIP network requirements in terms of delay, loss and guaranteed
quality of service features.
The following conditions should also be assured for the DECT IP base stations
and the HiPath Cordless IP server software in the IP network:
•they have to be part of the same Ethernet segment, a layer-3 routing via
an IP router is not supported,
•no devices use the Network Address Translation (NAT) Ethernet segment
•Minimum 2 priority classes acc. to IEEE 802.1 p/q in the IP Network
possible
•Use of 100 Mbps full duplex for all switched LAN ports
•as the solution operates with standard IP addresses, these must be freely
available in the IP network. Refer to Chapter 5.2.1 for this IP address.
Failure to satisfy these conditions can result in delays in the IP network. This
leads to synchronization and voice quality problems in the DECT handsets.
c03.fm
Planning a HiPath Cordless IP System
Planning According to Call Traffic Load
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 29
3 Planning a HiPath Cordless IP System
When planning a cordless system, the position of the base station is critical for
system performance. The load should be optimized using locations with a high
call volumes and radio coverage.
3.1 Planning According to Call Traffic Load
•The borders of base station radio cells should not be located in high traffic
areas because changing base stations during a call (handover) increases
traffic load.
•The best base should be as unique as possible to avoid frequent switching.
10 Voice channels with 100 mErl/user (low traffic)
Grad of Service (GoS) 0,1 % 1 %
Traffic 3,09 Erl 4,46 Erl
User 31 45
10 Voice channels with 150 mErl/user (normal traffic)
Grad of Service (GoS) 0,1 % 1 %
Traffic 3,09 Erl 4,46 Erl
User 21 30
10 Voice channels with 200 mErl/user (high traffic)
Grad of Service (GoS) 0,1 % 1 %
Traffic 3,09 Erl 4,46 Erl
User 15 22
Table 2 Recommended amount of users at 10 voice channels

Planning a HiPath Cordless IP System
c03.fm
General
A31003-C1010-S100-2-7620, 08/2010
30 HiPath Cordless IP, Service Manual
3.2 General
DECT IP Base station (BSIP1)
DECT IP base stations are logically connected to the HiPath Cordless IP server
software over LAN connections. This software is connected to the communication
server via the SIP interface.
•Base station range
– Ethernet cable range (see also Chapter 2.4 for network requirements
between DECT IP base stations and the HiPath Cordless IP server
software)
– Spatial distance
The distance which must be maintained between the different installation
points of the base stations is dependent on
– the range
– the traffic capacity of the radio cells.
You can increase the number of simultaneous calls in a radio cell by
overlapping radio cells (overload).
– Distance
For synchronization over DECT, the DECT IP base stations you want
to synchronize with each other must be able to exchange their
management information (beacons). For this to work, they must be
located in the areas where their radio cells overlap.
– Overlap areas inside/outside buildings (see following chapter),
measurement results (RSSI points) (see Section 7.2.1)
Radio measurement techniques are used to determine the radio range of DECT
IP base stations.
DECT IP base stations inside buildings
– Please note that the base station’s connection cable can be repositioned
as necessary (connection cable plus reserve loop to be factored in).
DECT IP base stations in areas outside buildings (e.g. campuses).
– The base station must be installed in the outdoor case for use is exterior
areas.
– Make sure that adequate lightning and overvoltage protection is provided
for the cable feeder into the building and the DECT IP base station
•Radio propagation
Radio propagation is negatively influenced by

c03.fm
Planning a HiPath Cordless IP System
Propagation Conditions for Radio Traffic
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 31
– obstructions with strong absorption qualities (brick walls, dividing walls,
ceilings, furniture, steel cabinets, bathroom units, elevators, wire-
reinforced glass, leaded windows, blinds and others)
– reflective stationary obstructions (brick buildings, reinforced concrete
buildings, buildings with metal sheathing)
– reflective moving obstructions (people, animals, vehicles)
3.3 Propagation Conditions for Radio Traffic
Radio wave propagation in the DECT frequency range is quasioptical. This
means that a wave is hindered in its propagation if it hits a solid surface and is
thereby reflected to a greater or lesser extent. This reflection is dependent on the
physical qualities of the medium.
In the case of conductive materials, the penetration depth into the medium is
determined mainly by the magnetic quality and the electrical conductivity.
•Metals with a high degree of conductivity
These include copper or steel and prevent most DECT frequency radio waves
from penetrating, reflecting them in the same way as a mirror reflects light.
•Modern construction materials (exceptions, see above)
These have relatively poor conductivity levels with the result that
electromagnetic waves, even if attenuated, still can pass through.
Thus, radio traffic is possible within and through buildings.
•Attenuation qualities
of the construction materials vary greatly resulting in different ranges
depending on the propagation direction and the construction material
penetrated.
This attenuation is mitigated by openings, especially by windows in the
buildings as long as they do not have wire-reinforced or metal-plated glass.
The different levels of radio propagation give rise to various scenarios in which
radio cells are formed:
•in the open with visibility
•industrial sites with reinforced concrete buildings and buildings with metal
facades
– Wood (dry and unprocessed),
glass, plastics (N-conductor) negligible attenuation
– Brick walls,
wood (damp and processed, for example,
particle board) medium range of attenuation
– Reinforced concrete, glass with metal
reinforcement/coating greatest attenuation
Planning a HiPath Cordless IP System
c03.fm
Propagation Conditions for Radio Traffic
A31003-C1010-S100-2-7620, 08/2010
32 HiPath Cordless IP, Service Manual
•indoor areas in buildings made of brick and light construction materials
•indoor areas in reinforced concrete buildings with diverse interior layout,
for example.
3.3.1 In the Open with Visibility
In this scenario, the electromagnetic waves are subject to the lowest amount of
attenuation with the result that they produce the greatest radio wavelength.
In principle, base stations in such a scenario produce a radio coverage range with
a radius of up to 300 m.
This, however, is usually not possible, since trees, bushes and moving
obstructions, such as, people, animals, and vehicles in the direct propagation
route can significantly reduce propagation.
NOTE: A base station installed in an attic directly beside a dormer window
(no metal reinforcement in the window pane) is the alternative to the outdoor
housing for coverage of the outdoor area.
Choose the mounting location carefully:
The base station is often exposed to extreme environmental temperatures, for
example, direct sunlight or extreme cold.
3.3.2 Industrial Sites
Buildings of varying structural materials may be found here, including those:
•of light construction materials,
•of brick,
•of reinforced concrete,
•with metal facades.
The distances between the buildings, however, are rarely greater than 100 m. In
this scenario, outdoor base stations are practical for covering the outdoor area.
•Buildings of brick or light construction materials
are generally penetrable, but the magnetic field reception behind the walls is
extremely low, resulting, quasioptically, in a shadowed area.
For example, in the case of a base station installed on the southern side of a
brick building, the range limit on the northern side would be attained
immediately or after just a few meters, owing to the insertion loss.

c03.fm
Planning a HiPath Cordless IP System
Propagation Conditions for Radio Traffic
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 33
Up to 100 m of the outdoor area can also be supplied through the windows.
For this purpose, the base station must be set up on an upper floor (> 3rd
floor, that is two levels above ground floor). Low-lying obstructions near the
base station, such as, vehicles or a garage (one or two cars) do not, in this
case, cause significant interference.
•Reinforced concrete buildings and/or metal facades:
These have proven to be limiting factors. Penetration into the building is only
possible through windows (up to about 2 m into the building in the case of
standard size windows). The windows cannot be made from wire-reinforced
or metal-plated glass.
Wave conduction is possible in alleys between buildings as well as along
streets. This results in a larger radio area.
3.3.3 Indoor Areas in Buildings in Brick and Light
Construction Materials
•Insertion loss values
In the case of walls of brick or light construction materials, insertion loss
values are relatively small so that even dividing walls of up to 30 m can be
penetrated.
•Vertical attenuation
This is dependent on the ceiling type. In this case, reinforced concrete
ceilings that offer higher attenuation in particular compared to brick play a
decisive role in range evaluation.
These ceilings are dimensioned based on the purpose of the building, for
example,
– single-family residence
– apartment building
– office building
– theater
and so the insertion loss ae also differs accordingly; see Table 3.
Planning a HiPath Cordless IP System
c03.fm
Propagation Conditions for Radio Traffic
A31003-C1010-S100-2-7620, 08/2010
34 HiPath Cordless IP, Service Manual
NOTE: These values show clearly that propagation within buildings is hindered
much less in a horizontal direction than in a vertical direction.
This must be taken into consideration when installing the base station.
3.3.4 Indoor Areas in Reinforced Concrete Buildings
with Diverse Interior Layout
Indoor areas in reinforced concrete buildings can give rise to different scenarios,
depending on the interior layout.
• Scenario 1 - Large factory halls (for manufacturing or office space)
These are either not partitioned (e.g. manufacturing halls) or have mobile
partitions reaching half way to the ceiling (office).
– Propagation conditions
Favorable in this scenario because intervisibility is more frequent than,
for example, in buildings divided into individual offices with no line of sight
between the base station and mobile telephones.
• Scenario 2 - Interior in buildings of brick and light construction materials
– Propagation conditions
Table 3 Insertion loss (ae)/range loss in the radio area
Insertion object ae (dB) Range loss (%)
Brick wall, 10 to 12 cm 2.5 ~ 43.5
Brick wall, 24 cm, small windows 4 ~ 60
Brick wall, 63 to 70 cm 4.0 to 4.5 ~ 60 to 64
Drywall 1.3 to 2.3 ~ 26.5 to 41
Gaseous-concrete wall 6.6 ~ 78
Glass wall 2 ~ 37
Wire-reinforced glass wall 8 ~ 84
Reinforced concrete ceiling
(residence) 6 to 9 ~ 75 to 87
Two reinforced concrete ceilings 26 ~ 99.5
Three reinforced concrete ceilings 46 100
c03.fm
Planning a HiPath Cordless IP System
Propagation Conditions for Radio Traffic
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 35
Similar to buildings with brick outer walls.
However, due to industrial sector requirements, the dimensions of
reinforced concrete ceilings in these buildings are such that insertion loss
values are considerably higher than in brick buildings.
NOTE: The resulting unfavorable vertical wave propagation must be taken into
consideration when installing the base station.
• Scenario 3 - Interior with concrete walls and steel dividing walls
These areas also usually include the heavily steel-reinforced areas of
– stairwells,
– bathroom areas,
– supply shafts, as well as
– elevator shafts.
Table 4 shows several insertion loss values which are relevant to this
scenario, along with the corresponding capacity loss data for the radio area.
– Propagation conditions
Horizontal and vertical values are approximately the same. It has been
determined that in this type of building, transmission usually takes place
along corridors if steel divider walls are installed.
As the relatively high insertion loss values show, individual rooms are
increasingly supplied via reflection if multiple metal walls are in the direct
path.
Concrete walls cause similar conditions to those described above.
Elevator shafts and stairwells must therefore often have their own base
station if they are to be included in the HiPath Cordless IP range.
Table 4 Insertion loss (ae)/range loss in the radio area
Insertion object ae (dB) Range loss (%)
Concrete wall, interior, 10 cm 6 ~ 75
Concrete wall, double, 2 x 20 cm 17 ~ 97.5
Concrete wall, 25 to 30 cm 9.4 to 16 ~ 88 to 97.5
Reinforced concrete ceiling 12 to 14 ~ 91 to 96
Two reinforced concrete ceilings 35 to 47 100
Three reinforced concrete ceilings 42 to 53 100
Steel wall with wire-reinforced glass 6.5 to 10 ~ 75.5 to 90
Steel walls, extending to ceiling, 3.5 m dist. 31 to 41 100
Planning a HiPath Cordless IP System
c03.fm
Determining the Installation Site
A31003-C1010-S100-2-7620, 08/2010
36 HiPath Cordless IP, Service Manual
3.4 Determining the Installation Site
3.4.1 Indoors
3.4.1.1 In Buildings of Brick or Light Construction Materials
•Horizontal direction
A base station must be installed at least every 50 m.
•Central installation in the building
The general rules must be observed.
•Vertical coverage
Care must be taken to ensure that no more than two reinforced concrete
ceilings are in the direct propagation route between the base station and
the area of movement of the handsets.
Other base stations must then be set up in the radio cells if necessary,
based on the concentration of stations or the number of handsets.
Assuming that the distribution of handsets in buildings will be fairly uniform,
additional base stations should preferably be installed on the floors above or
below the minimum required base stations (see Figure 9).
c03.fm
Planning a HiPath Cordless IP System
Determining the Installation Site
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 37
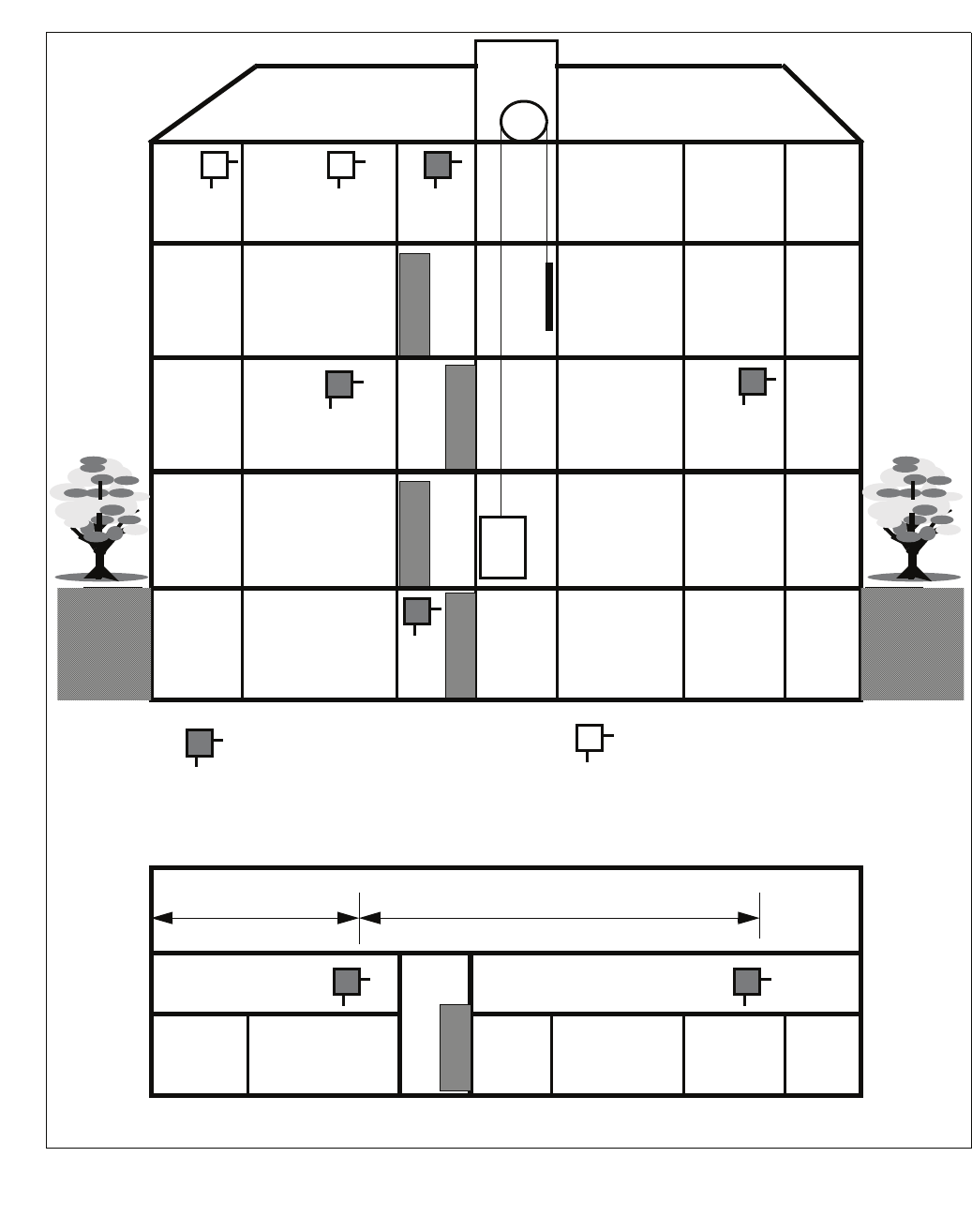
Figure 9 Base station distribution in buildings of brick and light construction materials
BS Z
BS
BS
BS
BS Z
BS BS
Elevator
< 25 m
BS Z
< 50 m
BS
BS
3rd floor
Open-plan office
2nd floor
1st floor
Ground floor
Basement
Elev-
ator
Stair-
well
Minimum required
base station Possible additional base station,
for example, for areas with higher
s
concentration
Floor plan 1st floor
Stair-
well

Planning a HiPath Cordless IP System
c03.fm
Determining the Installation Site
A31003-C1010-S100-2-7620, 08/2010
38 HiPath Cordless IP, Service Manual
3.4.1.2 In Steel/Concrete Buildings
•For interiors of brick or light construction materials (Figure 10)
– Horizontal direction
A base station must be installed at least every 50 m.
– Central installation in the building
The general rules must be observed.
– Vertical coverage
Care must be taken to ensure that not more than one reinforced concrete
ceiling is in the direct propagation route between the base station and the
area where the mobile telephones are used. Adequate coverage cannot
otherwise be guaranteed.
– Stairwells,
– elevator shafts and
– supply shafts
in these buildings usually have strongly-reinforced concrete walls and
stairs. Areas such as these, with poor propagation conditions, often
require additional base stations.
– If additional base stations are needed because of a large number of
mobile telephones, see Figure 10.
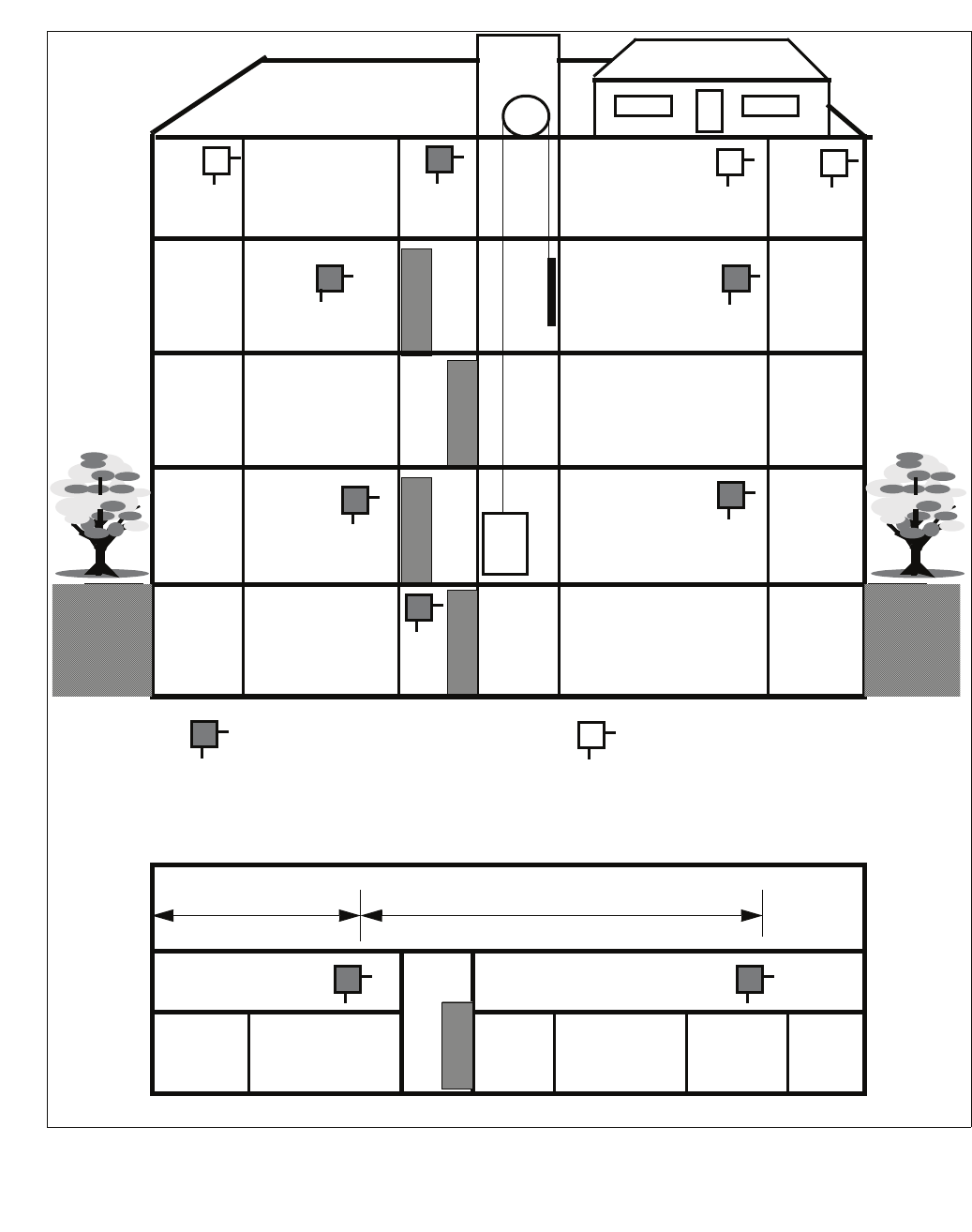
c03.fm
Planning a HiPath Cordless IP System
Determining the Installation Site
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 39
Figure 10 Base station distribution in interiors of brick and light construction materials
BS Z
BS
BS
BS
BS Z
BS
BS BS
Elevator
< 25 m
BS Z
< 50 m
BS
BS Z
BS
BS
3rd floor
Open-plan office
Ground floor
1st floor
Basement
Open-plan office
Minimum required
Base station Possible additional base station,
for example, for areas with higher
s
concentration
Stair-
well
Elev-
ator
Stair-
well
Floor plan 2nd floor
2nd floor

Planning a HiPath Cordless IP System
c03.fm
Determining the Installation Site
A31003-C1010-S100-2-7620, 08/2010
40 HiPath Cordless IP, Service Manual
•For interiors with concrete and steel dividing walls (Figure 11)
– Central installation in the building
The general rules must be observed.
– Horizontal direction
Because of the relatively high attenuation of concrete and steel dividing
walls, a base station must be installed in these buildings at least every 25
m.
– Vertical coverage
Care must be taken to ensure that not more than one reinforced concrete
ceiling is in the direct propagation route between the base station and the
area where the mobile telephones are used. Adequate coverage cannot
otherwise be guaranteed. For
– stairwells,
– elevator shafts and
– supply shafts
additional base stations are also often necessary.
In the case of elevators, a base station can be installed in the elevator
cabin itself.
– If additional base stations are needed because of a large number of
mobile telephones, see Figure 11.
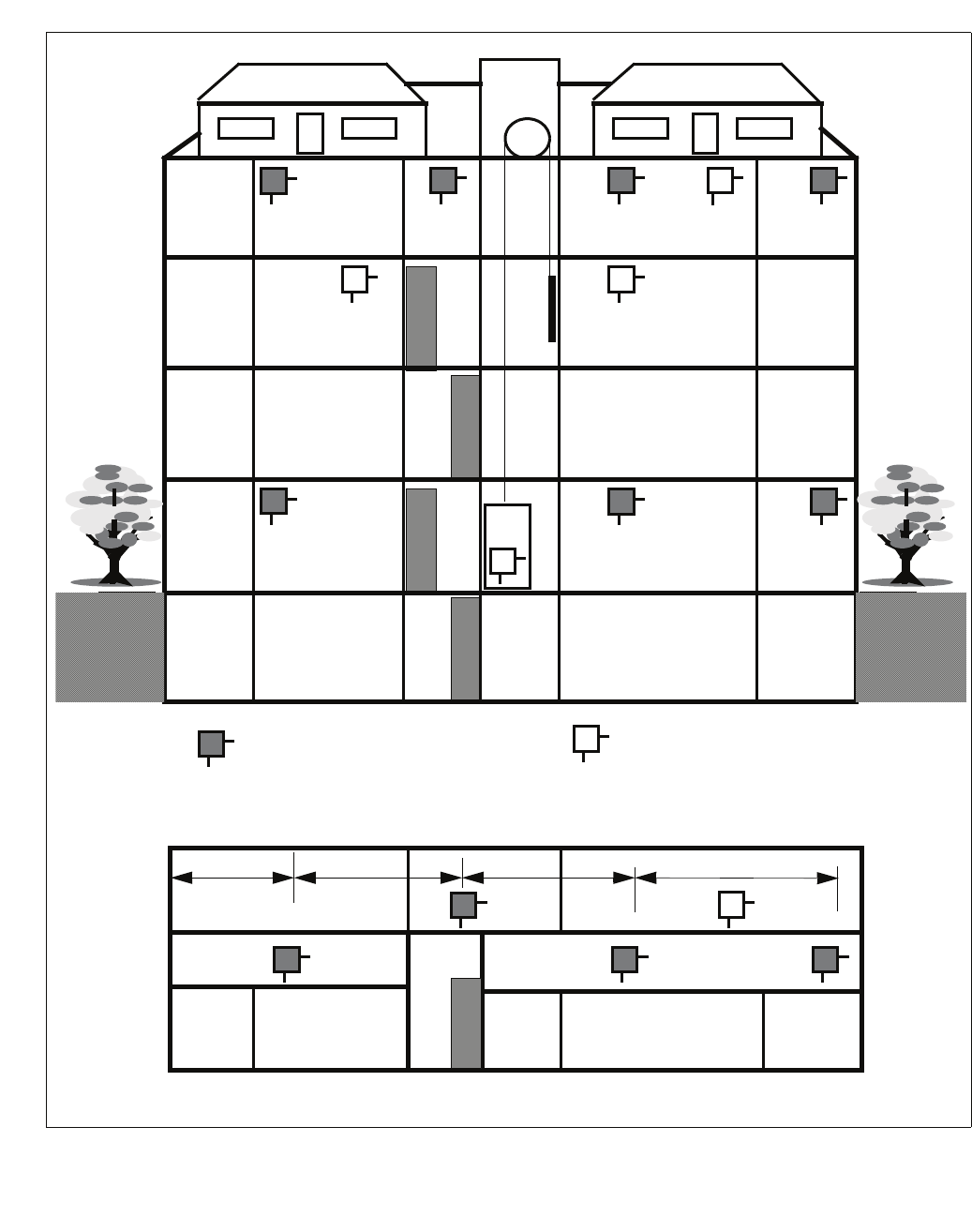
c03.fm
Planning a HiPath Cordless IP System
Determining the Installation Site
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 41
Figure 11 Base station distribution in interiors with concrete and steel dividing walls
BS
BS
BS
BS
Elevator
< 12 m
BS Z
BS BS Z
BS Z
BS Z
BS
BS
< 25 m
BSBS
< 25 m < 25 m
BS
BS
BS BS
Z
Z
3rd floor
Open-plan office
Ground floor
1st floor
Basement
2nd floor
Open-plan office 2
Stair-
well
Elev-
ator
Minimum required
Base station Possible additional base station,
for example, for areas with higher s
concentration
Floor plan 3rd floor
Stair-
well
Planning a HiPath Cordless IP System
c03.fm
Determining the Installation Site
A31003-C1010-S100-2-7620, 08/2010
42 HiPath Cordless IP, Service Manual
3.4.1.3 Factory Halls and Open-Plan Offices
•Within halls or open-plan offices (Figure 10)
Good transmission qualities.
For a hall which is 100 m long, one centrally located base station, suspended
freely from the ceiling (mast, plastic chain), may be sufficient.
7
CAUTION
The base station should not be installed on a reinforced concrete pillar
because the pillar creates a partial shadow which means that a clear line of
sight no longer exists.
In this case, two base stations must be installed 50 m to 75 m apart.
In the case of outer walls or interior siding and/or hall ceilings made of metal
(or metal-clad), it may be necessary to increase the number of base stations
and distribute them in such a way as to virtually exclude radio interference
through reflections.
3.4.2 Outdoors
•Base station with outdoor housing (Figure 12)
Only base stations with weather-resistant housing are suitable for radio
coverage out of doors, e.g. on factory sites.
– Installation
A base station can be installed on a mast made of wood, plastic or
concrete (not metal), on the roof of a building (preferably made of brick or
light construction materials) or on the wall of a house.
– The mast used must be stable and wind-resistant.
NOTE: Choose the installation site to allow maximum visibility from the base
station to the service area.
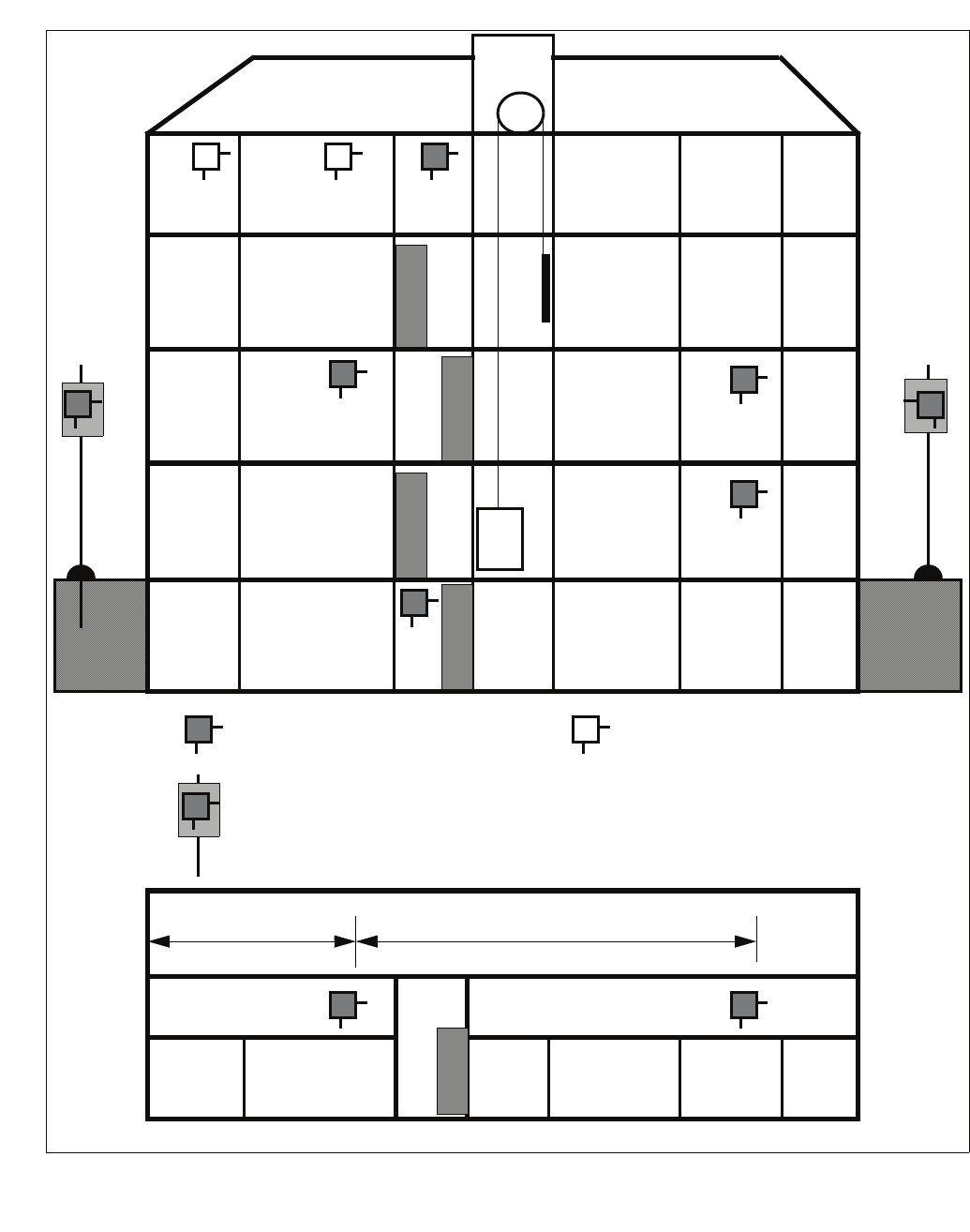
c03.fm
Planning a HiPath Cordless IP System
Determining the Installation Site
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 43
Figure 12 Base station distribution for base stations with housing for outdoor use
BS
BS Z
BS
BS
BS
BS
Z
BS
BS BS
Elevator
< 25 m
BS Z
< 50 m
BS
BS
BS
BS
3rd floor
Open-plan office
Ground floor
1st floor
Basement
2nd floor
Stair-
well
Elev-
ator
Minimum required
Base station
Base station with outdoor
housing
Mast made of wood, plastic,
concrete (not metal)
Possible additional base station,
for example, for areas with higher s
t
concentration
Floor plan 1st floor
Stair-
well

Planning a HiPath Cordless IP System
c03.fm
Determining the Installation Site
A31003-C1010-S100-2-7620, 08/2010
44 HiPath Cordless IP, Service Manual
Example: Planning an outdoor area (Figure 13)
NOTE: A base station installed in an attic directly beside a dormer window (no
metal reinforcement in the window pane) is the alternative to outdoor housing for
coverage of the outdoor area.
•Planning
A site plan, for example, with a scale of 1:300 or 1:1000 is helpful for
determining the base station installation site.
– The customer’s preferred radio area should be indicated on the map
(subject to customer confirmation).
– Additional information about the types and heights of buildings is also
helpful.
– Radio coverage can be adequately determined with the aid of the site
plan and the information above.
•Site plan, see Figure 13
This plan depicts a company’s grounds with buildings A to G. It includes the
type of construction and heights of these buildings.
– Bird’s eye perspective
It is relatively simple to find the point which offers the best possible view
of the grounds without any obstructions.
Placement around the buildings C, E, F, and G is not feasible since the
view from these buildings extends only to a few neighboring buildings.
The view from buildings A and B is better.
In the example, the decision was made to place the base station at
building B rather than A. Note that the areas between buildings C and E
as well as F, G, and A are covered. The radio waves can pass through
brick building A, so that an area of about 10 meters beyond will still be
covered.
In practice, coverage can also be assumed for other outdoor areas as waves
pass through the windows.
•Reinforced concrete buildings or constructions with metal facades
act as limiting factors. Areas behind these buildings are quasioptically
blocked and must be considered not covered by the radio waves.
•Brick buildings
can usually be penetrated so that significant parts of them are reached by the
radio waves.
The supply range, however, often stops less than 10 meters beyond these
buildings.
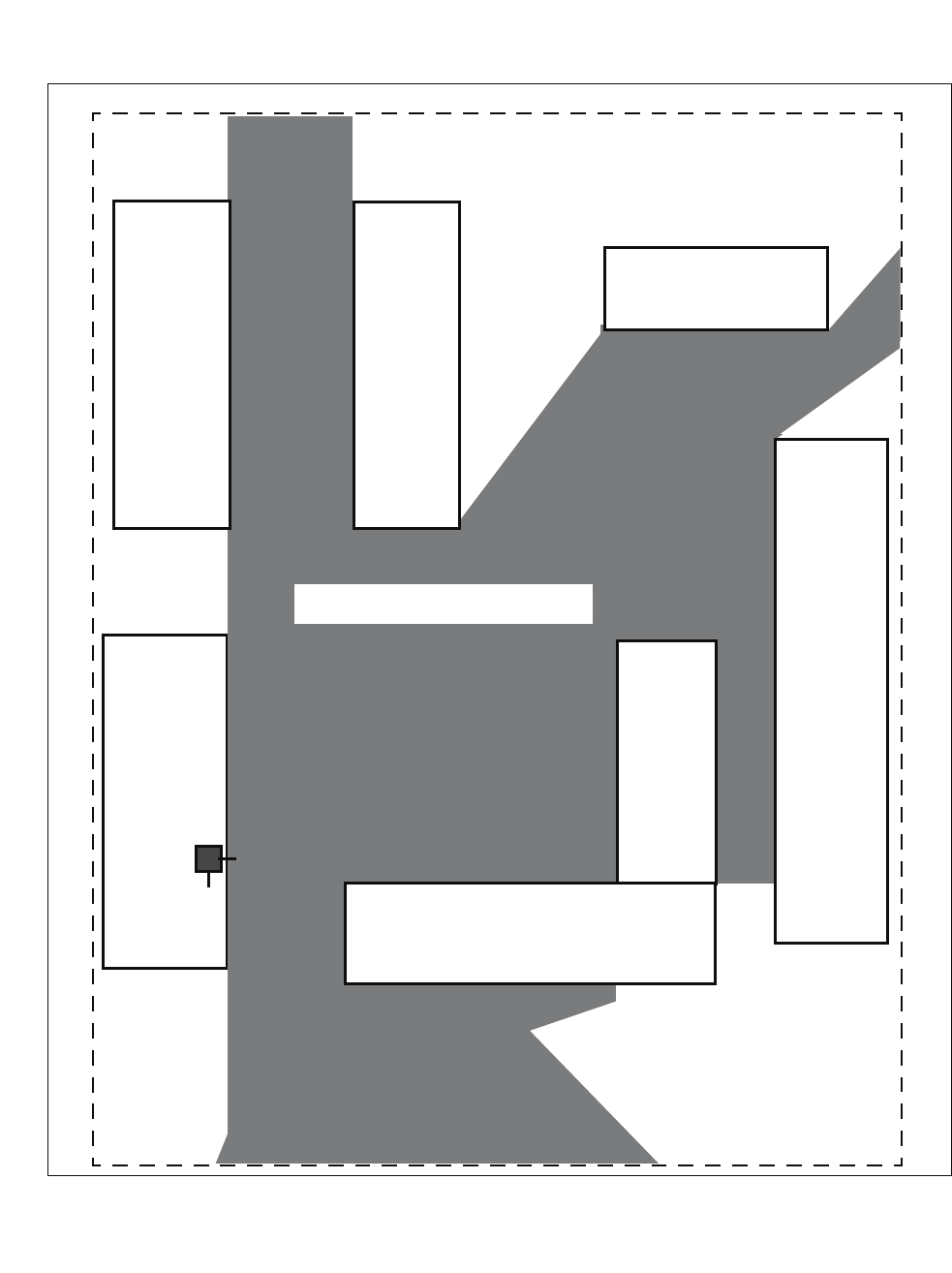
c03.fm
Planning a HiPath Cordless IP System
Determining the Installation Site
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 45
•Streets
act as conductors making greater ranges possible along them.
Figure 13 Base station distribution for coverage of an outdoor area
Bldg
B
concrete/
mounting
height
25 m
Scale 1:1000
BS
Bldg
E
concrete/
27 m
high
Bldg F
concrete/10 m high
Bldg
C
concrete/
27 m
high
Minimum supply range
Property line
Bldg
G
Hall
steel/
10 m
high
Bldg A
brick/15 m high
Planning a HiPath Cordless IP System
c03.fm
Installing Base Stations
A31003-C1010-S100-2-7620, 08/2010
46 HiPath Cordless IP, Service Manual
3.5 Installing Base Stations
3.5.1 Ethernet Connection Cable
The DECT IP base stations are mounted using Ethernet cables that are
terminated with an 8-pin shielded RJ45 connector. The feedthrough in the DECT
IP base station’s protective cover is 14 mm in diameter. Please take this
dimension into account when choosing the RJ45 connector.
3.5.2 Where Not To Install DECT IP base stations
7
CAUTION
Security zones
Areas designated by the customer as security zones, such as, intensive care
units in hospitals or areas behind fire doors.
• Ambient temperature/humidity
– Ambient temperature from +0°C to +40°C
Avoid direct sunlight.
– In damp places, such as bathrooms, laundry rooms, or in the immediate
vicinity of heat sources (for example, heaters).
• Radio area restriction
–In wall recesses or on thick or concrete and metal walls, if the radio supply
area is behind them.
– A base station mounted on a steel or concrete pillar cannot supply the
radio area which lies behind the pillar.
•In lowered ceilings of metal (conductive materials, for example, carbon
fibres).
•On metal walls
Only if there is a safety distance of > 10 cm.
•On metal storage shelves
Only if there is a safety distance of > 3 m.

c03.fm
Planning a HiPath Cordless IP System
Installing Base Stations
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 47
• Electromagnetic compatibility (EMC)
– The installation site should not be in the immediate vicinity of other
electronic equipment, such as, regular (corded) telephones, hi-fi systems
or office or microwave equipment. Only if there is a safety distance1 of >
1 m.
– Directly beside neon/phosphorous lighting tubes, fire alarms, switchgear
cabinets, transformer housings, motor housings.
Only if there is a safety distance1 of > 1 m.
– Directly beside antennas of other communication systems.
Only if there is a safety distance1 of > 3 m.
3.5.3 Where Should DECT IP base stations be
installed?
•Freely accessible,
– but near the ceiling (> 0.5 m away from the ceiling).
(This prevents the base station being blocked by furniture.)
•As centrally as possible in buildings,
– for example, in corridors or on walls of directly adjacent rooms (in the
case of buildings of light construction materials).
•Outdoor areas
may be part of the coverage area.
NOTE: When planning the installation of base stations in buildings (determining
the installation site), architectural plans (scale of about 1:1000) which show the
structural type of the building can be very helpful.
– Near windows facing in the direction of the outdoor area to be covered.
– Outdoor housing, see Section 3.5.6.
1. The safety distance isolates the installation from other equipment, thus im-
proving the electromagnetic compatibility (EMC).
Planning a HiPath Cordless IP System
c03.fm
Installing Base Stations
A31003-C1010-S100-2-7620, 08/2010
48 HiPath Cordless IP, Service Manual
3.5.4 Indoors
3.5.4.1 Wall Mounting
The base station must be freely accessible.
NOTE: When installing a DECT IP base station, the antennas should face
downward.
– Two wall anchors with 5 mm diameter, two screws with 3.5 mm diameter.
1. Drill two holes (5 mm diameter) 110 mm apart in the wall where the base
station is to be mounted. Insert the wall anchors in the hole (see Figure 18).
2. Screw in the screws in such a manner that a clearance of about 4 mm
remains between the head of the screw and the mounting wall. Different
mounting material may be needed depending on the composition of the
mounting wall, for example, wood screws for wooden walls.
Alternative: You can use the housing feet openings in the base plate of the
base station for mounting on wall hooks.
3. Mount the base station on the screw heads or wall hooks.
– Antenna position Antennas pointing towards open space,
in direction of radio area
– DECT IP Base station mounting
position vertical/180° rotated
– Mounting Mounting material not included in scope of
supply
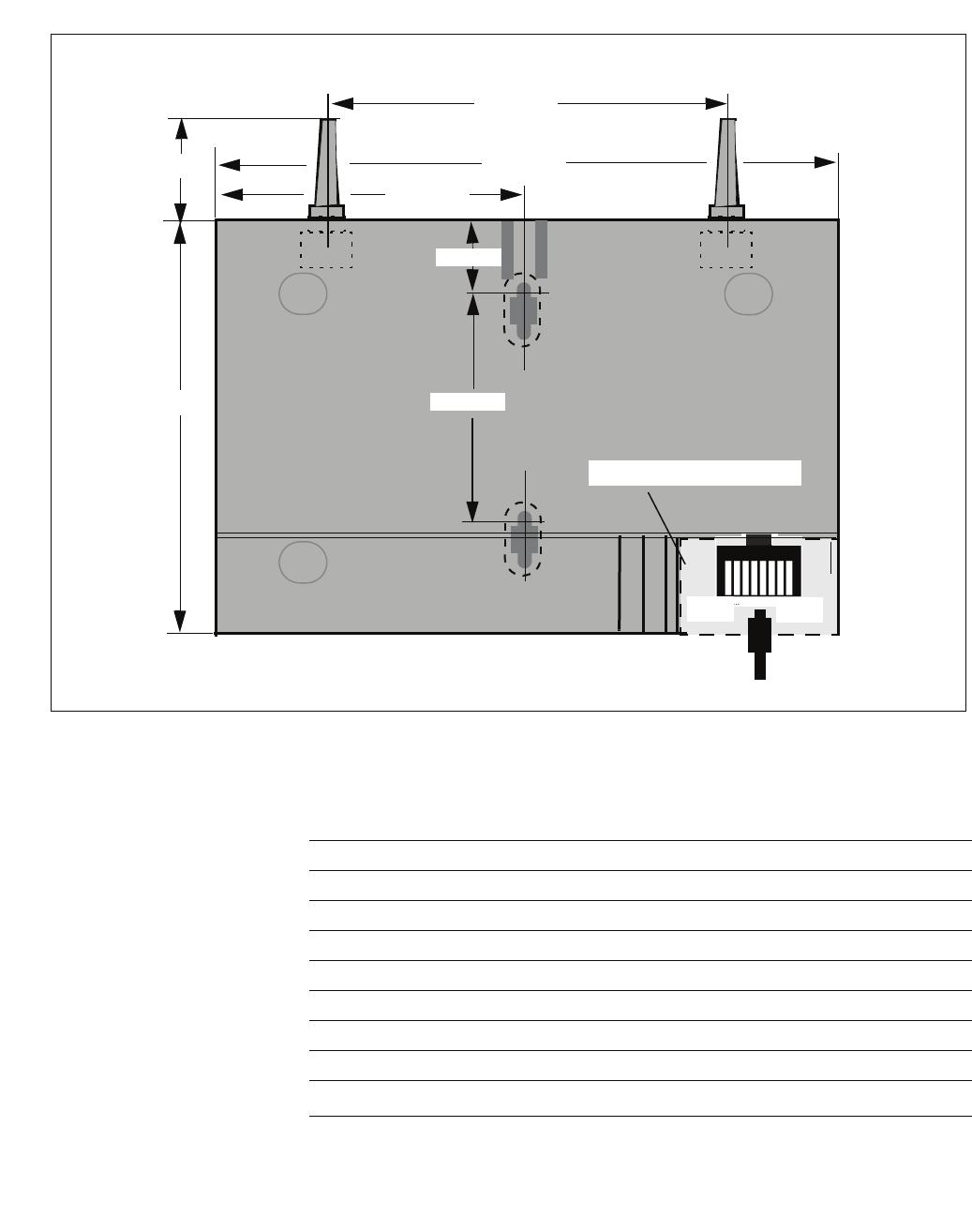
c03.fm
Planning a HiPath Cordless IP System
Installing Base Stations
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 49
3.5.4.2 Ethernet Socket Allocation in the DECT IP Base Station
Antenna 1 Antenna 2
125 mm
202 mm
50 mm
102,5 mm
19 mm
110 mm
Hinged lid on the case
172 mm
Ethernet cable
PIN 8 PIN 1
LED 1/LED 2
PIN Signal MDI Signal MDI-X
1 Tx+ (V+) Rx+ (V-)
2 Tx- (V+) Rx- (V-)
3 Rx+ (V-) Tx+ (V+)
4V+V+
5V+V+
6 Rx- (V-) Tx- (V+)
7V-V-
8V-V-
Table 5 Belegung der Ethernetbuchse
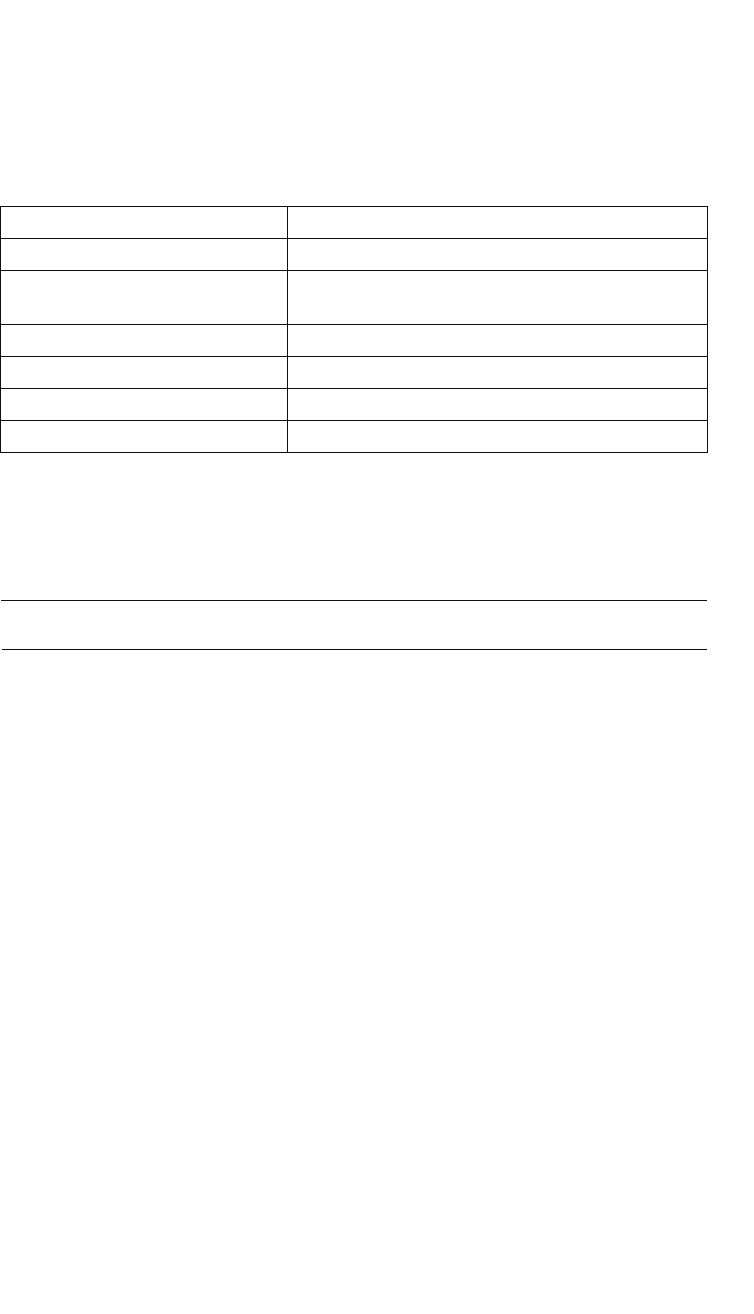
Planning a HiPath Cordless IP System
c03.fm
Installing Base Stations
A31003-C1010-S100-2-7620, 08/2010
50 HiPath Cordless IP, Service Manual
3.5.5 Tools/Aids
The tools and aids listed below will be required when carrying out the activities
described in the following sections. However, they are not included in the delivery
scope.
3.5.6 Outdoors
NOTE: The base station contains an overvoltage protector.
•Features of the outdoor housing
– No special grounding necessary.
The outdoor housing is made of 100% plastic.
– Cable feeder entry.
– Protection against direct sunlight.
– Base station protection at ambient temperature between -25°C and
+40°C (can be operated without heating, +sunlight).
•Figure 14 shows the components of the outdoor housing.
– The outdoor housing is supplied preinstalled.
– The necessary installation material is supplied loose.
– Install the outdoor housing on a mast or on masonry/wood/brick walls.
– Connect the cable from the communication system (see Section 3.5.4.2).
Table 6 Tools/aids
Designation Application
Crosstip screwdriver size 3 To attach installation plate, sun shield
Crosstip screwdriver size 2 To attach mast blocks/mast installation of outdoor
housing
Triangle head screwdriver M 6 To attach and close the housing/outdoors
Aids
Masonry drill, 8 mm diameter To drill holes for wall installation, housing/outdoors
Masonry drill, 5 mm diameter To drill holes for wall installation, housing/indoors
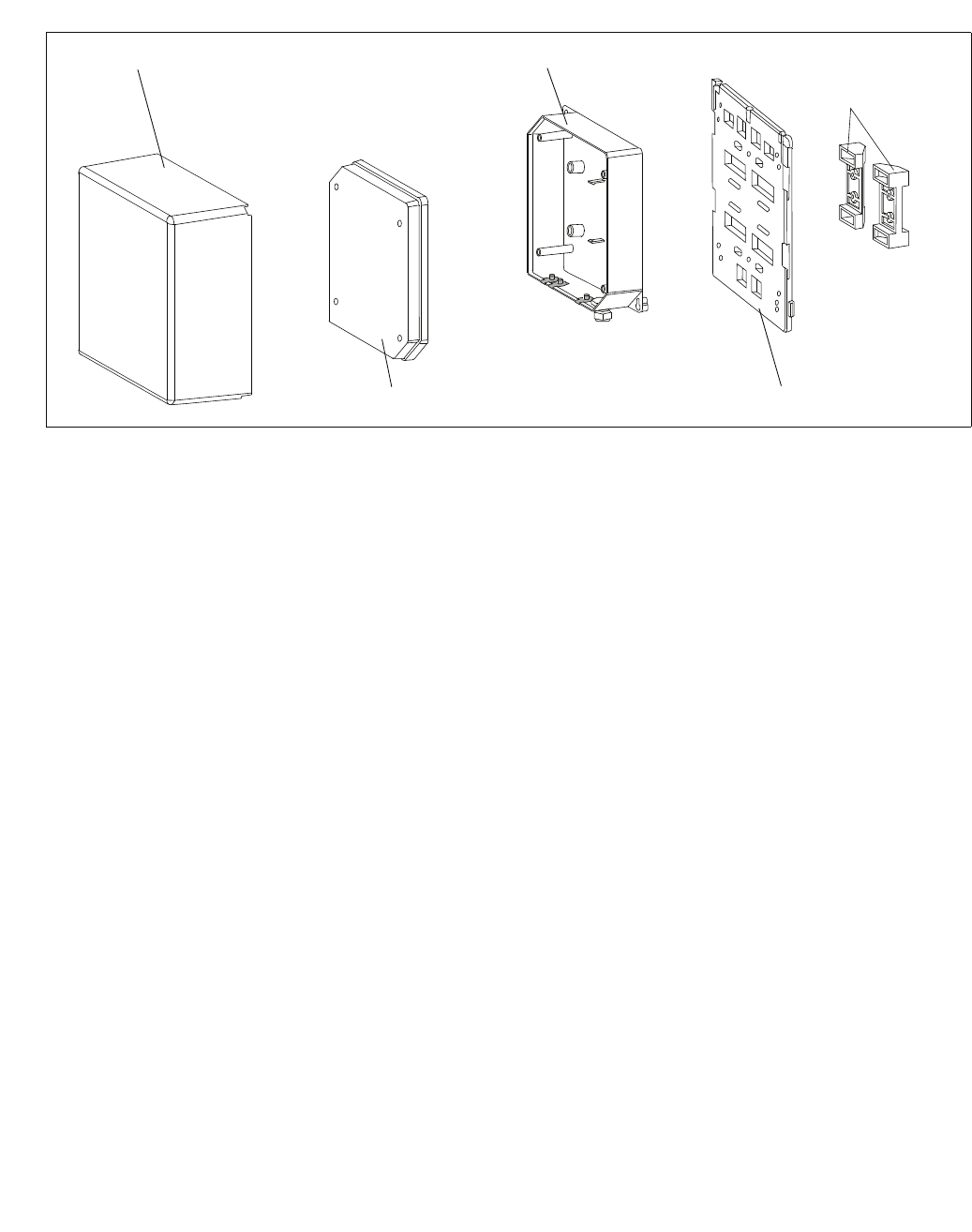
c03.fm
Planning a HiPath Cordless IP System
Installing Base Stations
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 51
3.5.6.1 Preparatory Tasks
The following tasks must be performed with appropriate tools before installing the
outdoor housing:
1. Release the sun shield catches and remove the sun shield.
2. Loosen the special screws that connect the base of the outdoor housing to
the mounting plate and remove the outdoor housing.
3. Open the outdoor housing (four M6 triangle head bolts in the cover).
4. Remove the hinged lid to connection plug X1.
5. Install the base station in the recess provided for this purpose making sure it
locks into place (listen for the latching noise).
Figure 14 Components for outdoor installation
Sun shield Housing base mounted on the
installation plate
Installation plate
Housing cover
Mast blocks, pre-
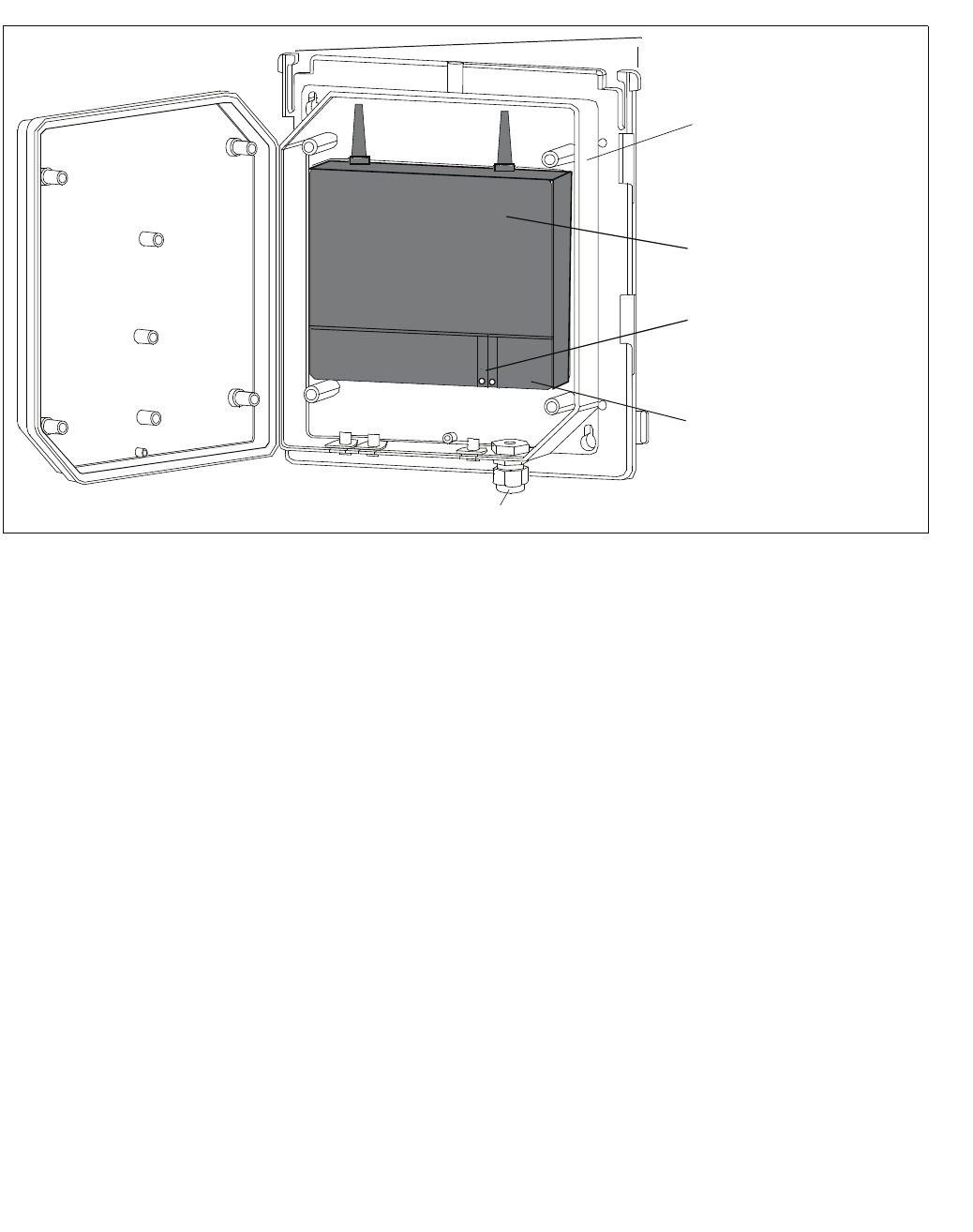
Planning a HiPath Cordless IP System
c03.fm
Installing Base Stations
A31003-C1010-S100-2-7620, 08/2010
52 HiPath Cordless IP, Service Manual
3.5.6.2 Mast Installation
Material required (supplied loose): two metal tightening straps.
1. Loosen the mast block fastening screws.
2. Set the distance of the mast blocks to the necessary mast diameter at the
required height and tighten the screws.
3. Feed the metal tightening straps through the specially-provided holes in the
installation plate, see Figure 16.
4. Attach the base of the outdoor housing to the triangle head bolts on the
installation plate.
5. Screw the triangle head bolts tight.
6. If necessary:
Thread a sealing wire through the lower right fastening hole on the base and
the sealing hole on the mounting plate, see Figure 16.
Seal the wire.
Figure 15 Outdoor housing with base station
Catch for sun shield
Base of outdoor
housing
Base station
LEDs 1/2
(operating mode)
Hinged lid on
connection plug X1
Opening for base station connection line/cable
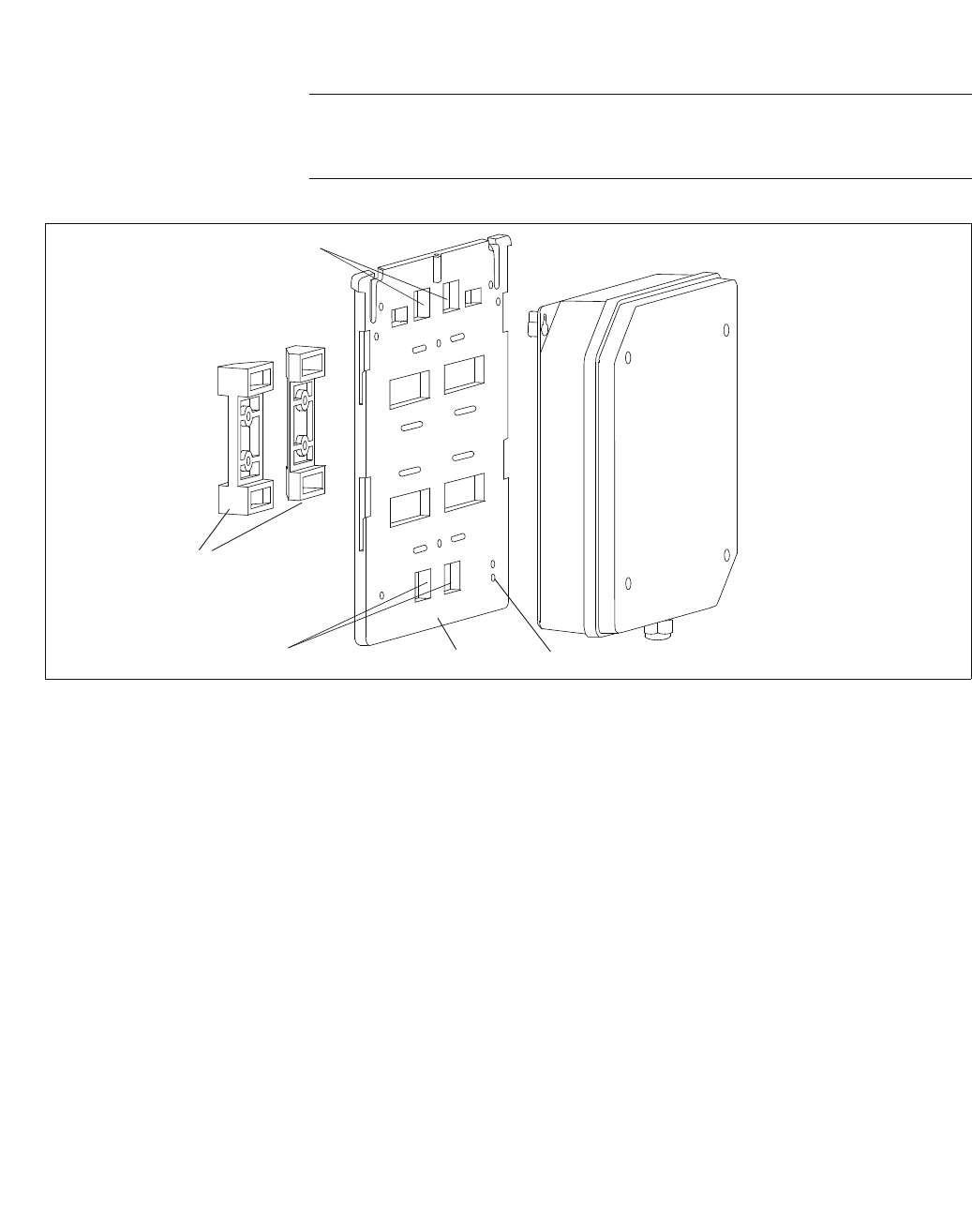
c03.fm
Planning a HiPath Cordless IP System
Installing Base Stations
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 53
7. Attach the installation plate to the mast at the required height with the metal
tightening straps. The mast used must be stable and wind-resistant.
7
CAUTION
Do not install the base station on steel masts.
Figure 16 Outdoor housing with mounting plate and mast blocks
Openings for metal tightening straps Holes for attaching the
outdoor housing
Outdoor housing
Mast blocks
(preinstalled)
Openings for metal tightening straps Installation plate Sealing hole
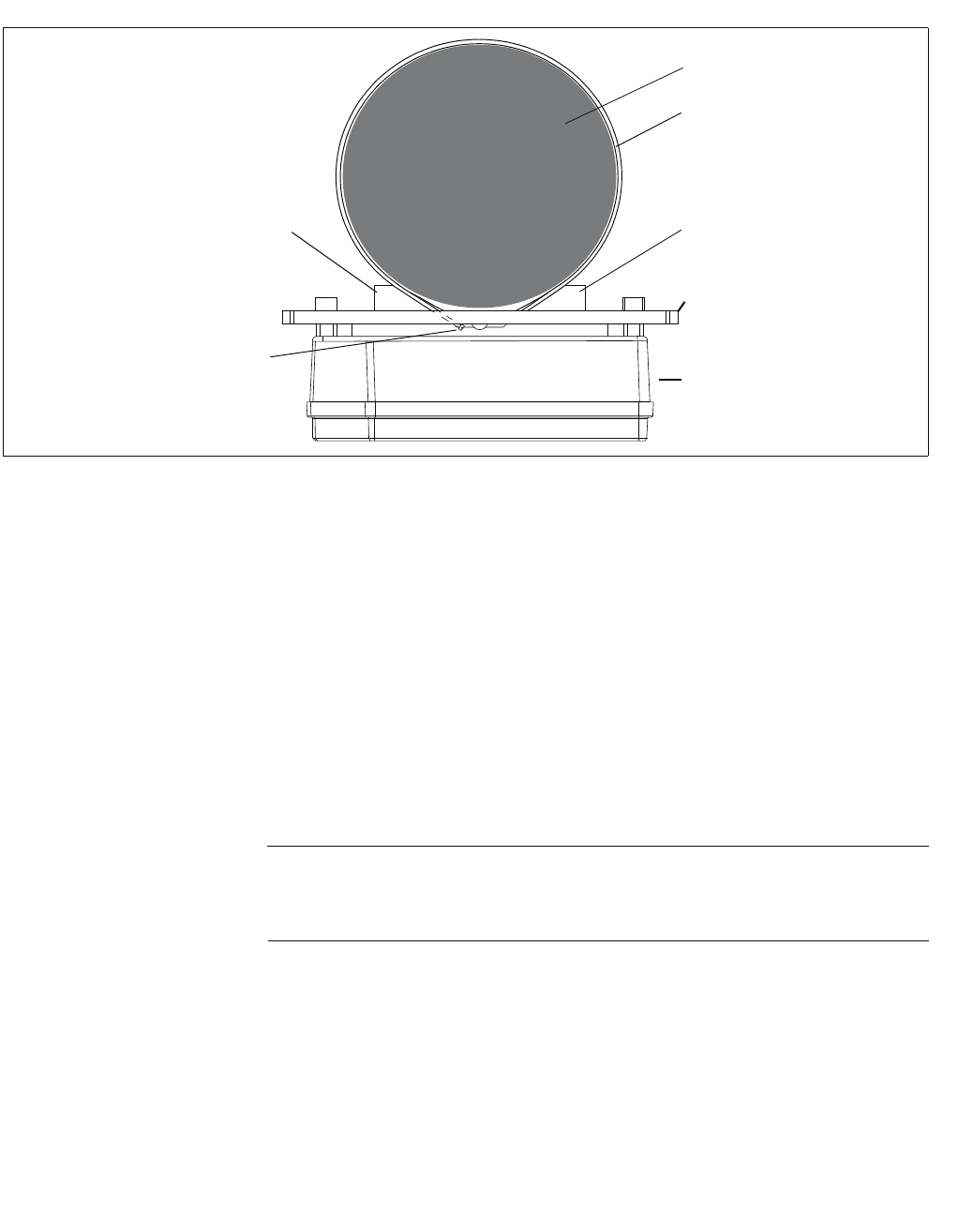
Planning a HiPath Cordless IP System
c03.fm
Installing Base Stations
A31003-C1010-S100-2-7620, 08/2010
54 HiPath Cordless IP, Service Manual
8. Connect the base station connection cable(s) (see Section 3.5.4.2).
9. Secure the housing cover with the four triangle head bolts.
10. If necessary: lock the sun shield into the spaces on the sides of the installation
plate.
3.5.6.3 Wall Installation with Mounting Plate
Material required:
– Two wall anchors of 8 mm diameter, two screws of 6 mm diameter.
NOTE: Different mounting material may be needed depending on the compo-
sition of the mounting wall, for example, wood screws for wooden walls.
In such cases, change/purchase the appropriate mounting material.
1. Drill two holes (8 mm diameter) in the wall where the base station is to be
mounted.
For dimensions, see Figure 18.
– Ensure that there is enough room for the mounting plate.
– Insert the wall anchors in the holes.
2. Remove the mast blocks from the mounting plate.
Figure 17 Mast installation – plan view
Mast block
Mast
Metal tightening strap
Mast block
Installation plate
Outdoor
housing
Locking screw on the
metal tightening strap
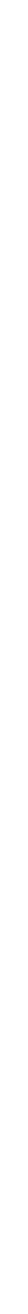
c03.fm
Planning a HiPath Cordless IP System
Installing Base Stations
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 55
3. Attach the mounting plate to the wall with the two screws.
4. Attach the base plate of the outdoor housing to the triangle head bolts on the
mounting plate.
5. Screw the triangle head bolts tight.
6. If necessary:
Thread a sealing wire through the lower right fastening hole on the base and
the sealing hole on the installation plate and seal it (see Figure 16).
7. Connect the base station connection cable(s) (see Section 3.5.4.2).
8. Secure the housing cover with the four triangle head bolts.
9. If necessary: lock the sun shield into the spaces on the sides of the installation
plate.
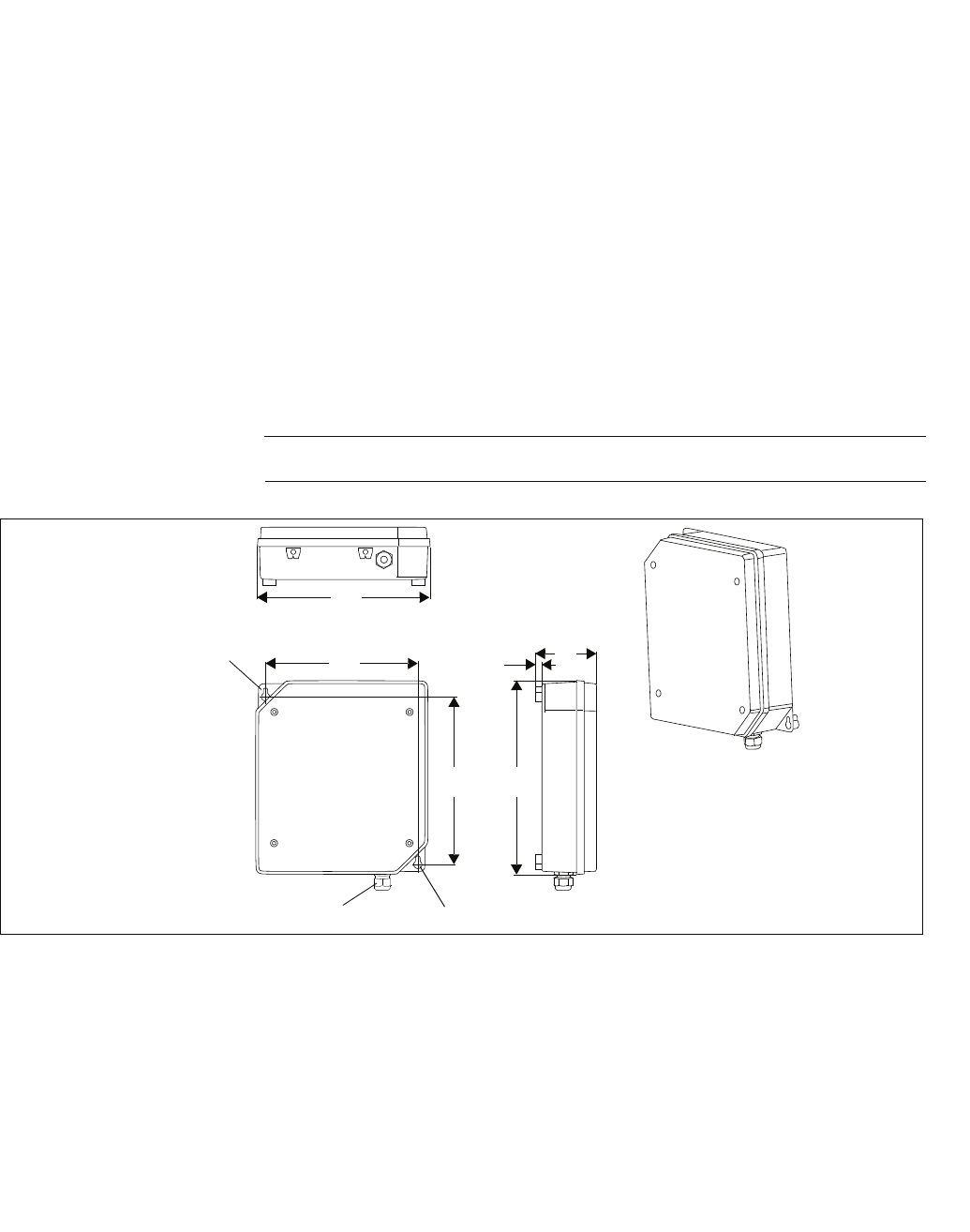
Planning a HiPath Cordless IP System
c03.fm
Installing Base Stations
A31003-C1010-S100-2-7620, 08/2010
56 HiPath Cordless IP, Service Manual
3.5.6.4 Wall Mounting Without Mounting Plate
Material required: two wall anchors of 8 mm diameter
1. Drill two holes (8 mm diameter) in the wall where the base station is to be
mounted.
For dimensions, see Figure 18. Insert the wall anchors in the holes.
2. Screw the two triangle head bolts through the mounting plate and into the wall
anchor so that a clearance of about 12 mm remains between the screw head
and the mounting wall.
3. Hang the base plate of the outdoor housing into the screws by its tabs (upper
left and lower right) and tighten the screws.
4. Connect the base station connection cable(s) (see Section 3.5.4.2).
5. Secure the housing cover with the four triangle head bolts.
NOTE: The sun shield cannot be mounted without the mounting plate.
Figure 18 Wall mounting without mounting plate
256
226
256
90
10
296
Wall attachment
Cable entry to the base station Wall attachment

c04.fm
Putting Into Service
Preparation
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 57
4 Putting Into Service
You can only put your HiPath Cordless IP system into operation after the
•planning,
•coverage,
•installation and cabling,
•installing the communication server and if necessary, the HiPath Cordless
IP server.
requirements have been fulfilled. The installation of the HiPath Cordless IP
system now starts.
4.1 Preparation
1. DECT handsets are charged.
2. DECT system ID is available.
3. LAN suitability for VoIP services is analyzed (refer to Section 3.3).
4. Administration access is available for the HiPath Cordless IP server
software’s Web-Based Management application.
5. Information is available on subscribers, stations numbers, names.
6. There is a sufficiently large number of IP addresses available for use for the
HiPath Cordless IP server software and the DECT IP base stations.
7. The IP address of the communication server, the DHCP server and the DNS
server is determined.
8. The customer data available is backed up.
Optional if these services are to be used:
9. The PoE injectors are available.

Putting Into Service
c04.fm
Entering the DECT System Number (DECT ARI)
A31003-C1010-S100-2-7620, 08/2010
58 HiPath Cordless IP, Service Manual
4.2 Entering the DECT System Number (DECT ARI)
The DECT system number consists of eight hexadecimal characters and is
unique worldwide for each DECT system.
The DECT system number is the number used to identify the individual DECT
systems and therefore to identify the radio signals (radio range). This permits the
synchronization of mobile telephones logged on to the system.
The DECT system number consists of:
•E/ARC (Access Right Code, 4-bit (first digit is always 1)
•EIC (Equipment Installers Code, 16-bit),
•FPN (Fixed Part Number, 8-bit), and
•FPS (Fixed Part Subnumber, 4-bit).
When installing the system for the first time, you must apply for the DECT system
number which then applies to the entire HiPath Cordless IP server software (even
in the event of service).
The DECT system number is stored in the HiPath Cordless IP server software
database.
This system number should be stored safely (loss).
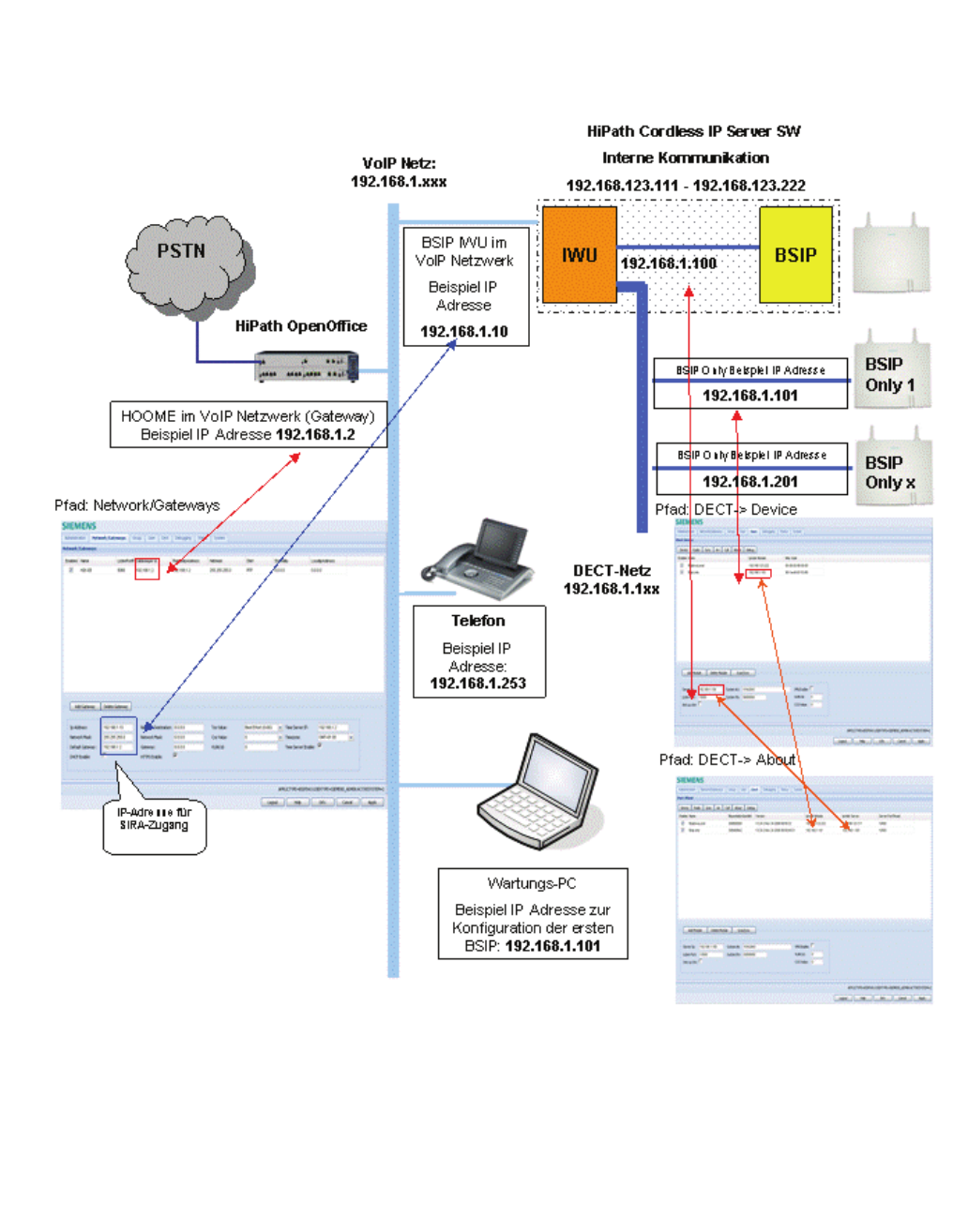
c04.fm
Putting Into Service
Overview IP adresses
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 59
4.3 Overview IP adresses

Installation and Administration
c05_ikon.fm
Terminology
A31003-C1010-S100-2-7620, 08/2010
60 HiPath Cordless IP, Service Manual
5 Installation and Administration
5.1 Terminology
The terms "Voip gateway" and "PBX" are used as a synonym for the supported
HiPath communication servers HiPath OpenOffice ME and HiPath OpenOffice
EE.
The term BSIP Only is used as a synonym for a BSIP1 which is NOT running
the HiPath Cordless IP Server Software.
Therefore the term BSIP IWU is used as a synonym for a BSIP1 which IS
running the HiPath Cordless IP Server Software.

c05_ikon.fm
Installation and Administration
Network Concept
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 61
5.2 Network Concept
The IP network concept of the HiPath Cordless IP solution System is designed
for the separation into three logical networks:
1. VoIP (Infrastructure) network
Here are the existing infrastructure components (default Gateways,
DHCP servers, Time server, ...), the PBX (the VoIP Gateway) and the
BSIP1 running the HiPath Cordless IP Server Software (the Interworking
Unit [IWU] between VoIP and DECT) part of the BSIP1. This network is
used for the connection of the BSIP1 IWU to the IP and VoIP infra-
structure of the company LAN.
The factory-default network address is 192.168.2.0 with a netmask of
255.255.255.0.
The preconfigured IP address of the IWU in this network is 192.168.2.1.
2. DECT network
Here are all BSIP1 Only Base Stations and the BSIP1 running the HiPath
Cordless IP Server Software (IWU) located. This network is solely used
for the communication of the BSIP1 IWU and the BSIP1 Only.
The preconfigured network address of the BSIP1 IWU is 192.168.1.100
with a netmask of 255.255.255.0.
3. BSIP1 internal networks
For internal communication between the different hardware components
of the BSIP1 there are two further networks configured.
Important: These addresses are fixed and cannot be changed. Keep in
mind, that these addresses may not be used for the VoIP network and the
DECT network.
192.168.123.x :
Network between the BSIP1 Local DECT module (.222) and the BSIP1
IWU (.111).
169.254.222.x.
Network between the two main processors (CSP) and 192.168.123.x
(MSP) for internal communication.
Important: All BSIP1 devices must be located inside the same network
segment and therefore MUST NOT be separated by layer 3 routing devices.
Only Layer 2 switches are supported between the BSIPs.

Installation and Administration
c05_ikon.fm
Synchronisation over air concept
A31003-C1010-S100-2-7620, 08/2010
62 HiPath Cordless IP, Service Manual
5.2.1 Overview of reserved networks
192.168.1.1 and 192.168.2.1 are used for factory defaults of BSIP Only and
BSIP IWU
192.168.123.x (.222) for BSIP Local on BSIP Iwu and (.111) corresponding
host ip
169.254.222.x (CSP) and 192.168.123.x (MSP) for internal LINUX communi-
cation
5.3 Synchronisation over air concept
In contrast to a line based synchronisation mechanisms (or a network based
one), synchronisation via air requires special requirements.
Synchronisation signal
Both synchronisation partners are syncing by air. This means that the
synchronisation signal received by the synchronisation client from the
synchronisation master has to have a minimum signal strength. The minimum
signal strength for the synchronisation signal is -85 dB.
Synchronization sequence
For the operation of several synchronized Base Stations the synchronization
sequence shall be configured as a "chain", (chain topology) i.e. the second
Base Station synchronizes to the first, the third Base Station to the second,
the fourth to the third and so on.
If all Base Stations synchronize to one single "Master" Base Station (in a star
topology) a much longer period of time will be needed for the reconstruction
of the system wide synchronization, because of the "Burst" behavior.
In addition to that the distance of a "Sync Slave" to the topmost "Sync Master"
in the synchronization chain shall not be more than 2 hops (Base Stations)
else the "Slip" will be to big and if a Base Station looses synchronization it will
only be (automatically) resynchronized when there are no longer active calls
at this Base Station.
For some topologies it is possible to mix the star topology with the chain
topology.
Avoid using a chain topology which is physically arranged as a circle. In such
a scenario, the drift between the first and the last base station maybe too
large to ensure proper handover between these two basestations.

c05_ikon.fm
Installation and Administration
WBM related issues
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 63
Resynchronisation
Important: If a BSIP loses synchronisation it tries to resync to the configured
synchronisation base station. This process can not start until the last call at
this base station is released and no other calls (at the belonging base station)
are active.
5.4 WBM related issues
5.4.1 Supported Web Browser
Supported Web Browsers are:
•Mozilla Firefox Versions 2 (2.0.0.16 ... 2.0.0.18) and Version 3.0.x (3.01 ..
3.0.6) and
•Microsoft Internet Explorer Version 6.x and Version 7.x
For details refer to chapter 5.35, “Configuration hints for Web Browser”.
5.4.2 General WBM issues
•Don't use special characters inside the objects for WBM. Supported
characters are
0-9, a-z, A-Z, "-" "_". Other characters may prevent the system services
from running correctly.
•Don't configure names for objects with more than 20 Characters.
•Changing of IP addresses of BSIP Only - after changes have been
applied, a manual [Scan/Sync] has to be applied to show the new values
•Configuration and firmware files MUST NOT include spaces in their
filenames
•Do not use multiple WBM session to different BSIPs at a single browser
session. This may influence the behaviour of the WBM sessions.
5.4.3 Multiple WBM sessions
If you login onto the same WBM session on which another user is logged on,
you are informed about that by a message box.
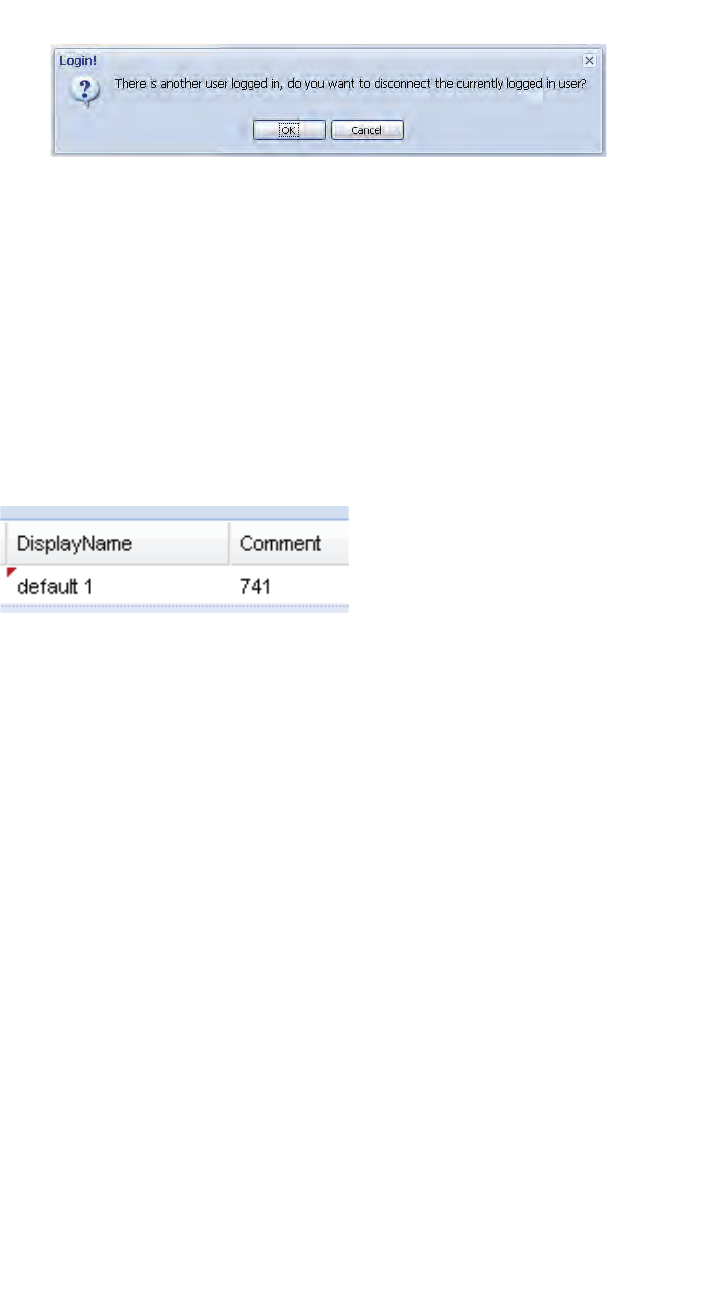
Installation and Administration
c05_ikon.fm
WBM related issues
A31003-C1010-S100-2-7620, 08/2010
64 HiPath Cordless IP, Service Manual
[OK] will logout the currently connected user.
[Cancel] Go back to the Login dialog.
5.4.4 Marking changed values
Changed values are marked with a red triangle at the top left corner of the
corresponding field. But you have to leave the current field for changes to
come in effect (via TAB key or mouse).
Marker for changed values (red triangle):
Please keep in mind that changes are not in effect immediately. You have to
•apply the changes with the [Apply] button and for some changes you have
to
•restart the services or for some changes
•reboot the BSIP1
Information which actions have to be taken to take the changes into effect will
be described in the appropriate chapters.

c05_ikon.fm
Installation and Administration
Phone related issues
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 65
5.5 Phone related issues
5.5.1 Date / time for phone idle display
The handset displays the local system time in its idle display.
The activation of date / time at the phone idle display is initiated by an
outgoing or incoming call (but no active connection is needed therefore).
If the user changed the LocalTime at the handset, the time will be overwritten
with SystemTime after the next incoming or outgoing call.
•Hint: There is neither an activation of the current date / time due to a
Power cycle of the handset nor to a roaming process.
5.6 Partition concept of BSIP1
To guarantee a functional BSIP1 at any time, two bootable systems are imple-
mented at the BSIP1.
A current system and the fallback system. Therefore the BSIP1 has two
different systems partitions: System 1 and System 2.
Both system partitions can hold their own configuration (although it is
copied from one partition to the other during a firmware update).
Both partitions store their application mode (BSIP Only or BSIP IWU)
A factory reset is always applied to the current system partition. It does not
affect the settings of the other partition.
Installation and Administration
c05_ikon.fm
Factory reset of BSIP1
A31003-C1010-S100-2-7620, 08/2010
66 HiPath Cordless IP, Service Manual
5.7 Factory reset of BSIP1
A Factory Reset can be performed by a special "power sequencing" cycle,
which is used to reset the BSIP1 to its default configuration. The factory reset
is applied by the following process:
1. Power on the board (see note)
2. Wait 5s (3s < wait < 7s)
3. Power off the board
4. Repeat steps 1. - 3. three (3) times
5. Boot BSIP1 to OS
The successful factory reset is indicated by fast red flashing of both LEDs.
•Note: If you provide power to the board by connecting the ethernet cable
using a PoE Switch power may NOT provided immediately. Due to the
stages of powering up a PoE link defined in 802.3af it may take up to
some seconds until the power is delivered from the switch to the PoE port.
Take a look at the LEDs or the switch status LEDs to see at which point
the power is available.
After this procedure, the default configuration parameters will be set.
The default application mode after a reset is BSIP Only mode.
•Hint: The factory reset is applied to the currently active partition. It does
not affect the settings of the other partition. But both operation mode
settings (BSIP Only and BSIP IWU) of the active partitions are resetted
Setting Value
Operation mode: BsIP1 Only
IP address of VoIP network 192.168.1.1
Access mode http
User Siemens Username: "Siemens", password "1q21q2"
User SiemensAdmin Username: "SiemensAdmin", password
"1q21q2"
Setting Value
IP address of VoIP network 192.168.2.1
Access mode http
User Siemens Username: "Siemens", password "1q21q2"
User SiemensAdmin Username: "SiemensAdmin", password
"1q21q2"

c05_ikon.fm
Installation and Administration
Release notes
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 67
5.8 Release notes
Check the release notes of the belonging version of the firmware for restric-
tions and special considerations using the BSIP1.
5.9 Quick Start
The quick start chapter describes the initial operation of the HiPath Cordless
IP BSIP1 system for a first functional test including the necessary configu-
ration.
The "Quick Start" assumes the availabilty of
•two BSIP1, a
•functional PoE network switch, (alternatively a switch and Power
injectors ) and CAT.5 cables
• Maintenance PC (Windows XP based) with administration account and a
•supported PBX (e.g. HiPath OpenOffice ME).
Please read the corresponding chapter in the detailed manual parts if you
need further information regarding any step of the "Quick Start".
The following conditions apply:
•For the quick start it is assumed that no VLAN functionality is needed
•No special DECT functionality is configured (Antenna diversity,...).
5.10 Quick start overview
1. Prepare and connect hardware
2. Configure BSIP1 for IWU mode
3. Configuration of IP VoIP (Infrastructure) Network at BSIP IWU
4. Configuration of DECT Network at BSIP IWU
5. Configuration of users at the BSIP IWU
6. Configuration of users at the PBX
7. Start system services and register handsets at the BSIP IWU
8. Attach and configure further BSIP Only to the system
Installation and Administration
c05_ikon.fm
Prepare and connect hardware
A31003-C1010-S100-2-7620, 08/2010
68 HiPath Cordless IP, Service Manual
5.11 Prepare and connect hardware
1. Attach the first BSIP1 to a PoE port of the network switch or via a Power
injector to a standard port of the network switch. Wait about 1 minute until
the LED states of the BSIP1 change to permanently green and red.
2. Meanwhile you may connect the maintenance PC to a switch port via a
ethernet cable.
•Hint: The BSIP1 devices MUST NOT be separated by layer 3 Routing
devices. Only separation via Layer 2 switches is supported.
5.12 Configure BSIP1 for IWU mode
1. The BSIP1 is accessible via its factory default IP address 192.168.1.1 in
BSIP1 Only mode.
To access the BSIP1 Only WBM you have to configure an IP address in
the network 192.168.1.0/255.255.255.0, e.g. 192.168.1.101 on your
maintenance PC.
2. If the IP address 192.168.1.1 is used in your network, you first have to
directly connect the maintenance PC and the BSIP1 via ethernet. This
may be done with a direct ethernet connection via the power injector or
via a separate ethernet switch where only the Maintenance PC and the
BSIP1 are connected.
3. Test via ping, if the BSIP1 is replying to the ping requests at ip address
(ping 192.168.1.1).
4. If not, check all cabling, switch settings, (e.g VLAN configuration).
5. Ensure that the configured local IP of the maintenance PC adress is up
(e.g ping 192.168.1.101).
6. If you don't get replies consider to reset the BSIP to its factory defaults
(see chapter 5.7, “Factory reset of BSIP1”).
7. Start the Web browser at the Maintenance PC
8. Access the WBM (Web based management) at the following URL: http://
192.168.1.1
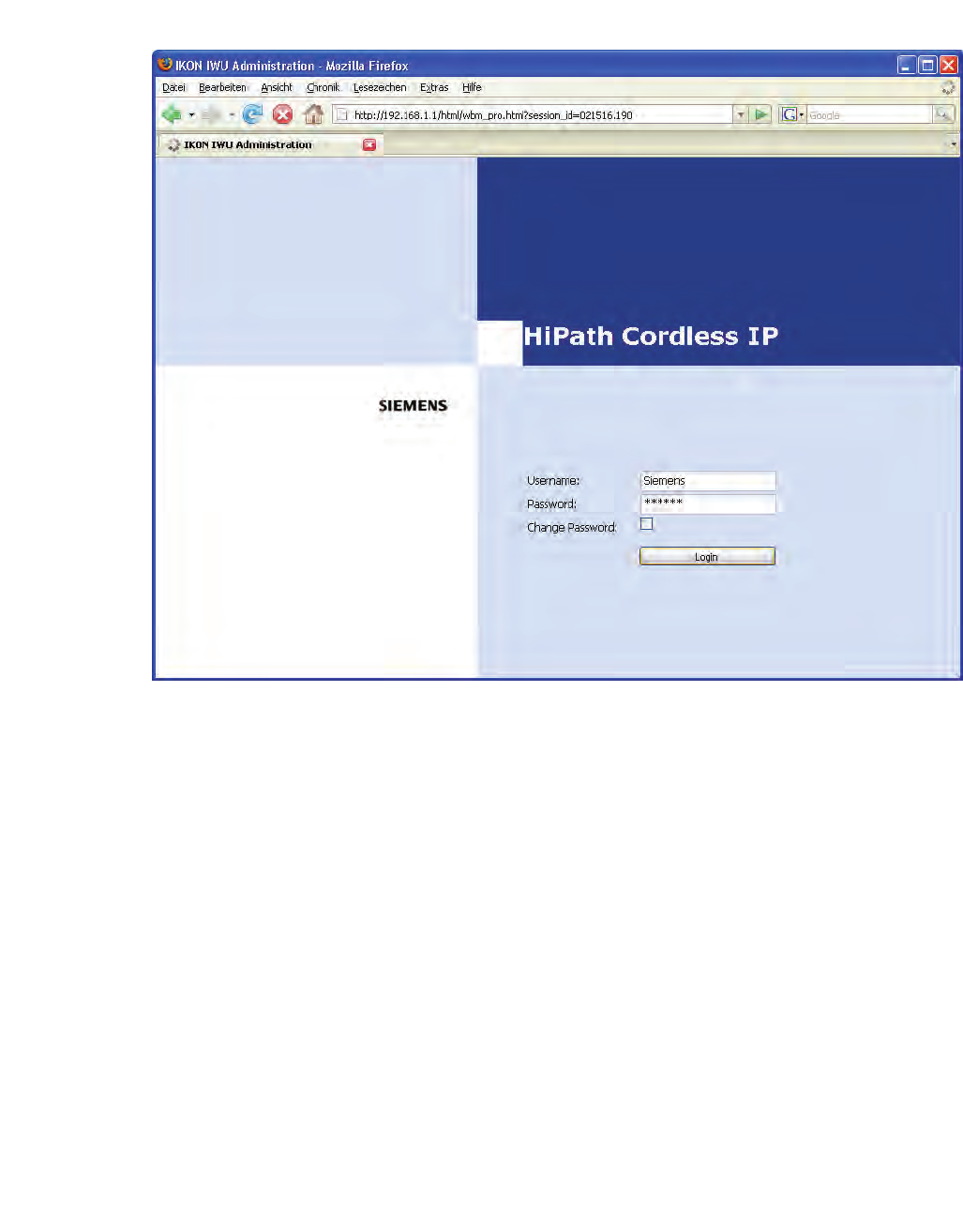
c05_ikon.fm
Installation and Administration
Configure BSIP1 for IWU mode
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 69
9. Log in to the WBM with the following (case-sensitive) credentials:
Username: Siemens, password: 1q21q2
10. Press the [Login] button. The configuration page for the BSIP1 in BSIP
Only mode appears.
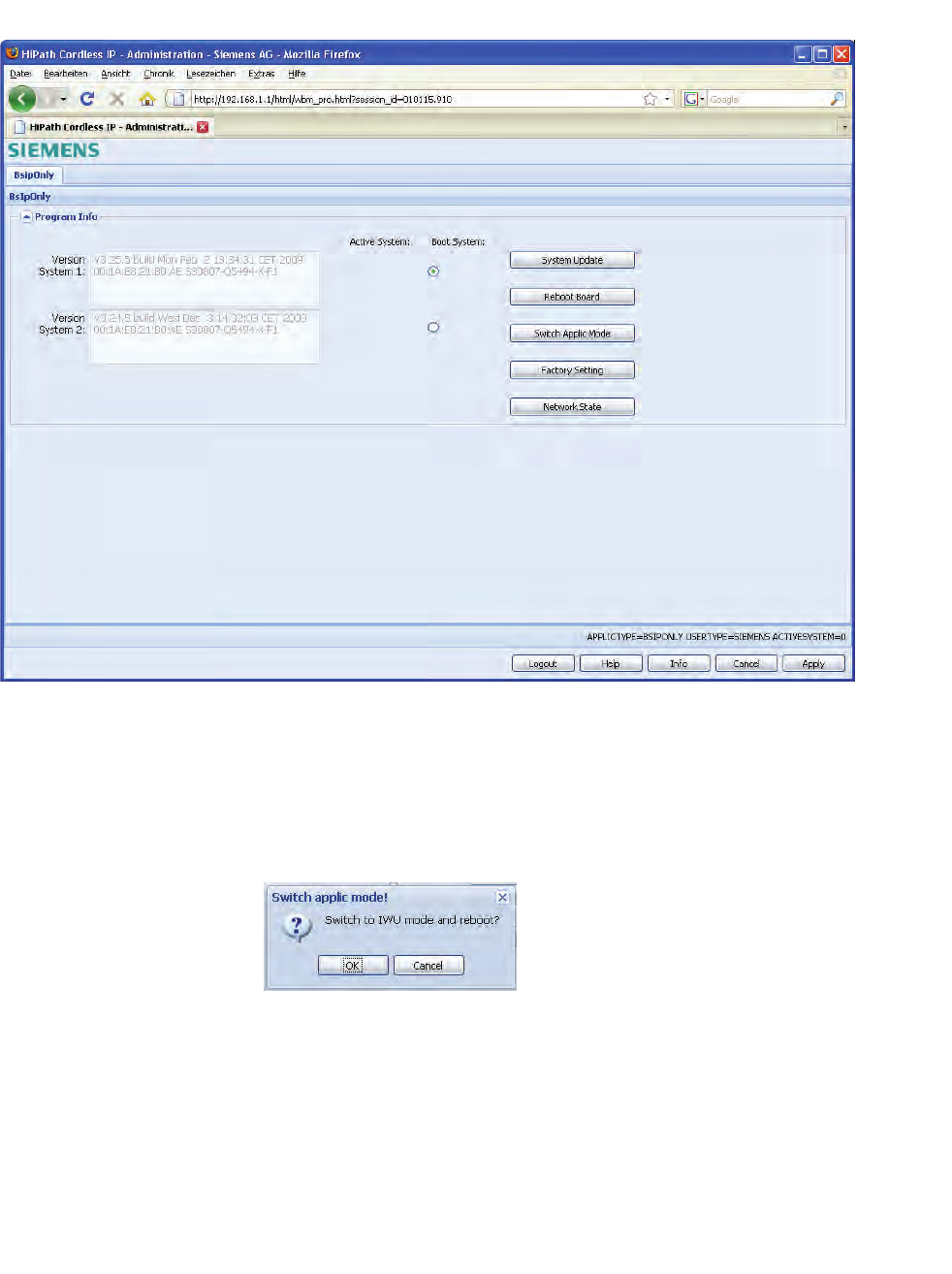
Installation and Administration
c05_ikon.fm
Configure BSIP1 for IWU mode
A31003-C1010-S100-2-7620, 08/2010
70 HiPath Cordless IP, Service Manual
11. To change the application mode of the BSIP1 from BSIP1 Only to BSIP1
IWU select [Switch Applic Mode].
•Hint: The current application mode is indicated at the bottom status
line (APPLICTYPE=BSIPONLY or BSIPIWU)
After changing the application mode, the following message box will appear.
12. Press [OK] to reboot the BSIP1 and start it in application mode BSIP1
IWU.
•Important note: After changing the application mode, the BSIP1 will start
in BSIP1 IWU mode and therefore has a different default IP address. The
default IP address in IWU mode is 192.168.2.1.
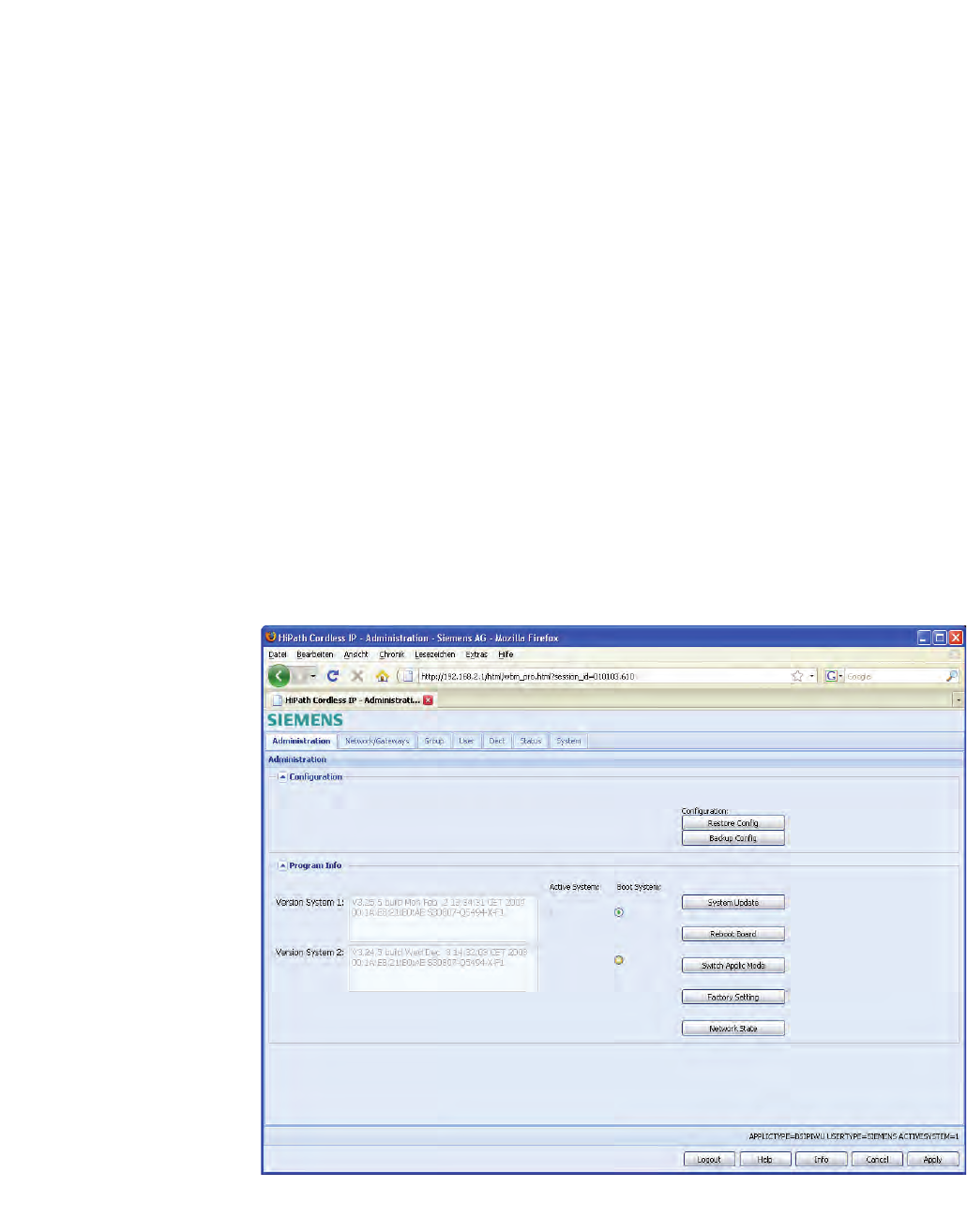
c05_ikon.fm
Installation and Administration
Configure BSIP1 for IWU mode
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 71
The BSIP1 is accessible via the factory default IP address 192.168.2.1 in
BSIP1 IWU mode. To access the BSIP1 IWU WBM you have to configure an
IP address in the network 192.168.2.0/255.255.255.0, e.g. 192.168.2.101 on
your Maintenance PC.
1. If the IP address 192.168.2.1 is used in your network, you first have to
directly connect the Maintenance PC and the BSIP1 via ethernet. This
may be done with a direct ethernet connection via the power injector or
via a separate ethernet switch where only the Maintenance PC and the
BSIP1 are connected.
2. Test via ping, if the BSIP1 is replying to the ping requests at ip address
(ping 192.168.2.1).
3. If not, check all cabling, switch settings, (e.g VLAN configuration).
4. Ensure that the configured local IP of the maintenance PC adress is up
(e.g ping 192.168.2.101).
5. Access the WBM (Web based management) at the following URL: http://
192.168.2.1
6. Log in to the WBM with the following (case-sensitive) credentials:
7. Username: Siemens, Password: 1q21q2
8. Press the [Login] button. The configuration page for the BSIP1 in BSIP1
Only mode appears.
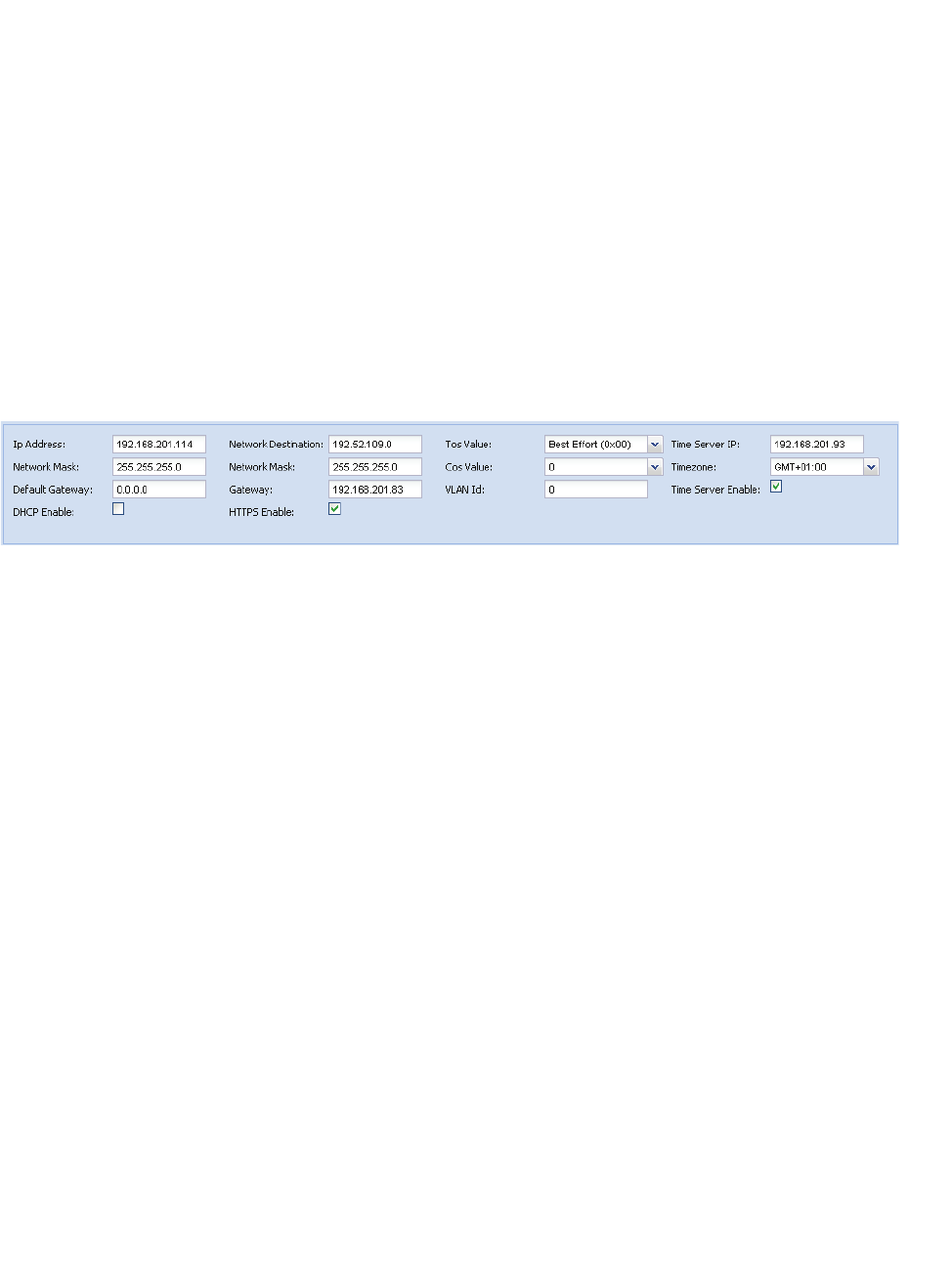
Installation and Administration
c05_ikon.fm
Configuration of VoIP (Infrastructure) network
A31003-C1010-S100-2-7620, 08/2010
72 HiPath Cordless IP, Service Manual
5.13 Configuration of VoIP (Infrastructure) network
Since configuration of the IP VoIP (Infrastructure) Network settings requires
a reboot of the BSIP1, the settings are configured before the BSIP hardware
is attached to the designated network segment.
To allow direct IP communication between the BSIP1 and the PBX both
devices have to be located in the same IP network. Therefore it is necessary
to adapt the IP address of the BSIP1 to the network of the VoIP (Infra-
structure) . You need at least one unused IP address of the Infrastructure
network, which has to be configured at the BSIP1.
1. Select the configuration page "Network/Gateways".
2. Change the configuration in the bottom frame to the designated values of
the BSIP1 IWU.
Change the following values according your needs:
Ip address:
Here you have to configure the ip address at which the BSIP IWU should
be available inside the VoIP (Infrastructure) Network. This also is the
address at which the BSIP1 IWU is accessible via WBM.
Network mask
Enter the corresponding netmask for the IP address as configured above.
(Default for Class C networks: 255.255.255.0).
Time Server Ip
Since the BSIP1 has no hardware clock, time has to be set according a
NTP (or SNTP) time server. After activating the NTP Server at the PBX,
it may take some minutes upon activation of the NTP service. This is due
to the nature of time synchronisation between NTP server and NTP client.
For details configuring time server at the PBX refer to "chapter 5.31,
“Configuration Hints for PBXs”.
https
Activate the https access mode.
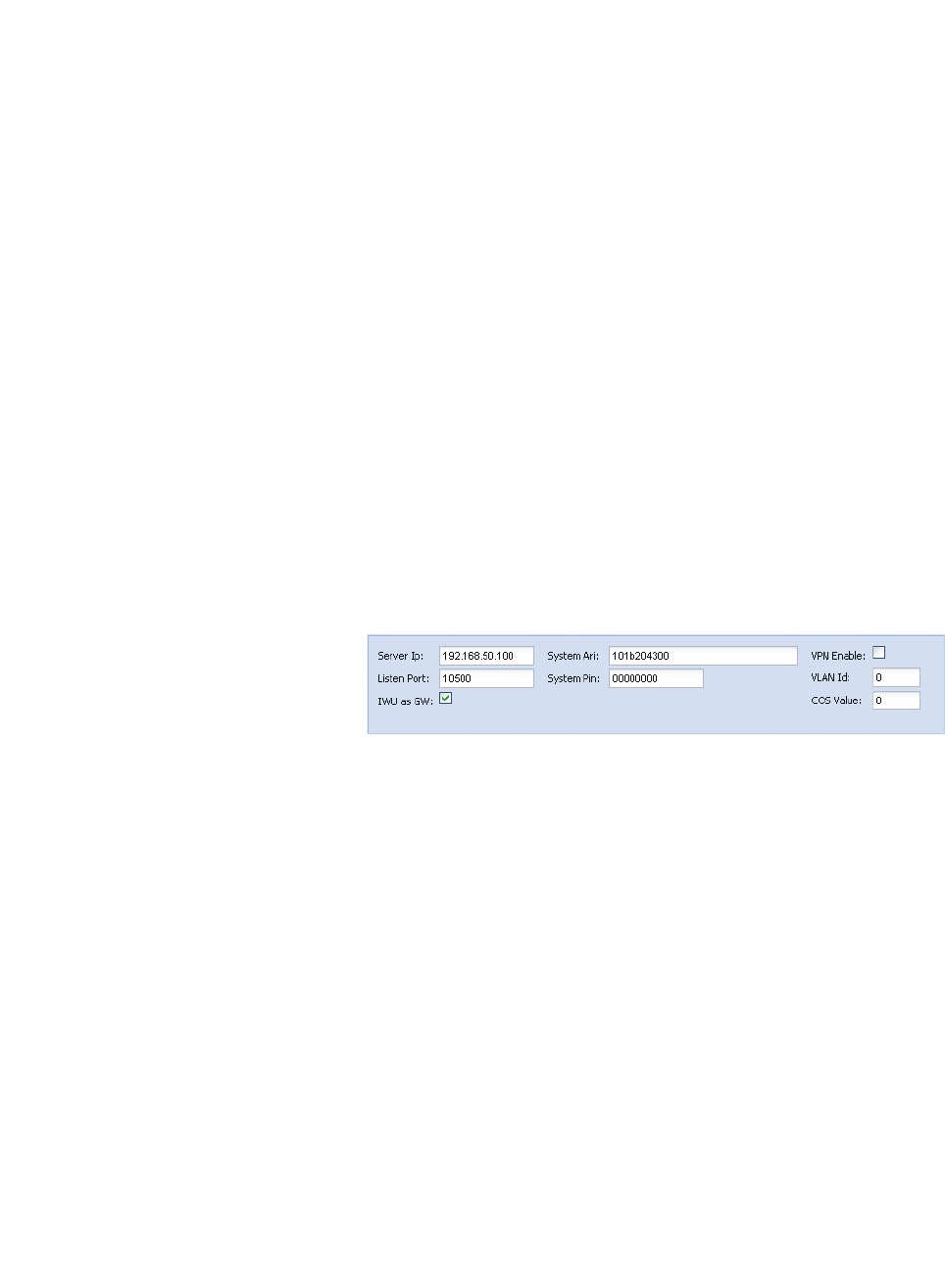
c05_ikon.fm
Installation and Administration
Configuration of DECT network
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 73
Routing entries
If you need routing to another network (e.g. access from maintenance PC
to the IP VoIP (Infrastructure) Network, you can configure the corres-
ponding values either by setting the "Default Gateway" or by a special
"Network destination".
If using the "Network destination" method, you have to configure the fields
"Network destination", "Network mask" and "Gateway" and additionaly
you have to add a route at the maintenance PC.
• Important: Ensure that the ip configuration is configured correctly.
Otherwise - after rebooting the board - it may not be accessible without
resetting it to its factory defaults (which have a fixed IP setting of
192.168.1.1).
5.14 Configuration of DECT network
Since configuration of the DECT Network settings requires a reboot of the
BSIP1, the settings are configured before the BSIP1 hardware is attached to
the designated network segment.
1. Select the the configuration page "Dect".
2. Change the configuration in the bottom frame to the designated values of
the BSIP1 IWU.
Server Ip
This field contains the IP address of the server (the IWU) in the DECT
network.
It is used for communication between all BSIP Only and the BSIP IWU.
SystemAri
In this field the System ARI (DECT ID) which has to be unique at each
DECT system and has been assigned to the system has to be configured.
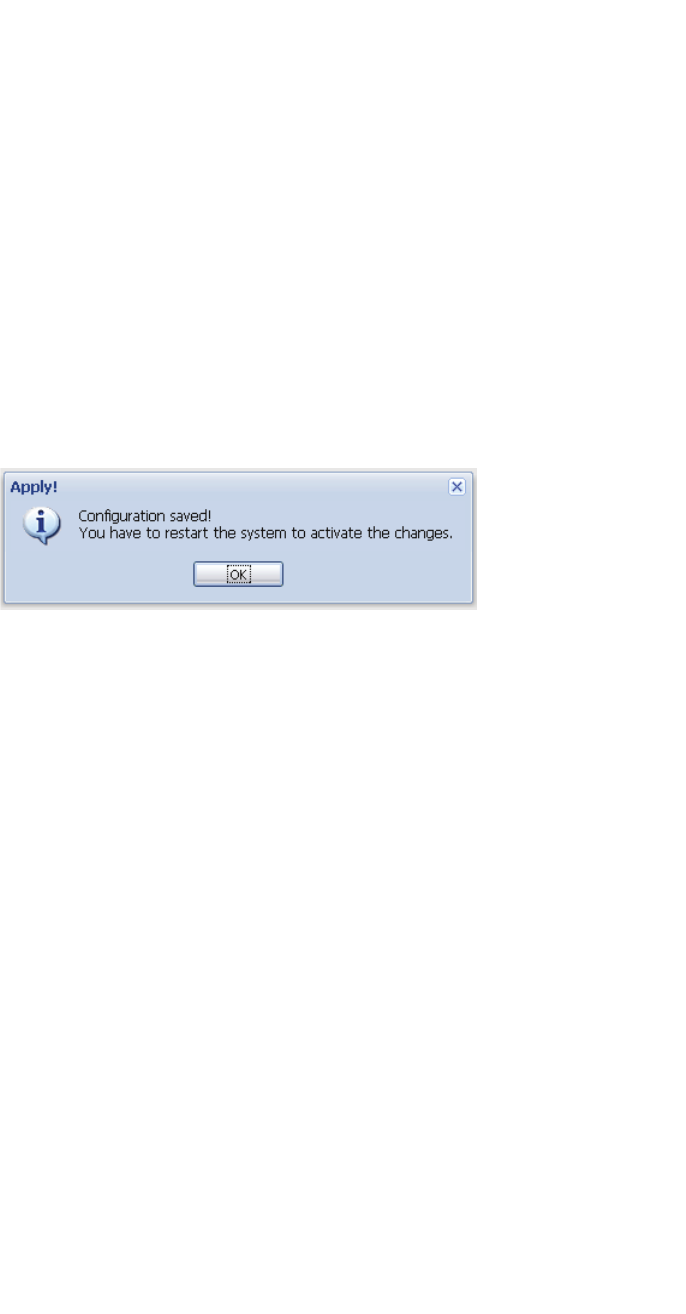
Installation and Administration
c05_ikon.fm
Configuration of DECT network
A31003-C1010-S100-2-7620, 08/2010
74 HiPath Cordless IP, Service Manual
System Pin
The "PIN" is a 8-digit number and it is needed for the registration of
handsets. It is preconfigured with "00000000" and may be configured
systemwide here. You can change the system pin to another decimal
value.
IWU as GW
Activate this option to use the BSIP1 IWU as a router to the BSIP1 Only.
•Background: Using the option "IWU as GW" enables the routing (ip
forwarding) via the IP VoIP (Infrastructure) Network to the DECT Network.
This ensures access to the network in which the BSIP Only are located,
without having an ip address (in the DECT network) configured at the
maintenance PC. Additionaly you have to add a route at the maintenance
PC
3. Apply the changes by clicking the [Apply] button at the bottom section.
4. Confirm the message box by clicking on [OK].
As stated above, for the changes to become active, the BSIP1 has to be
rebooted.
•Important: After rebooting, the BSIP1 will not be accessible by its the ip
address 192.168.2.1 anymore. Instead it is accessible by the ip address
of the IP VoIP (Infrastructure) Network (configured at the step above). If
you have attached the BSIP1 directly via a ethernet cable you have to
attach the BSIP1 physically to the designated network segment after
rebooting it.
5. Select the configuration page "Administration".
6. Initiate the reboot by clicking the [Reboot Board] button.
Wait about 1 minute for the board to come up again. The board LEDs
should change to permanently orange / orange.
7. Access the WBM (Web based management) by the in address you have
configured before for the IP VoIP (Infrastructure) Network.
Depending on the http access mode you have to use http:// or https://
mode
HTTPS Enabled = [ ]use http://{Server Ip of IP VoIP (Infrastructure)
Network}
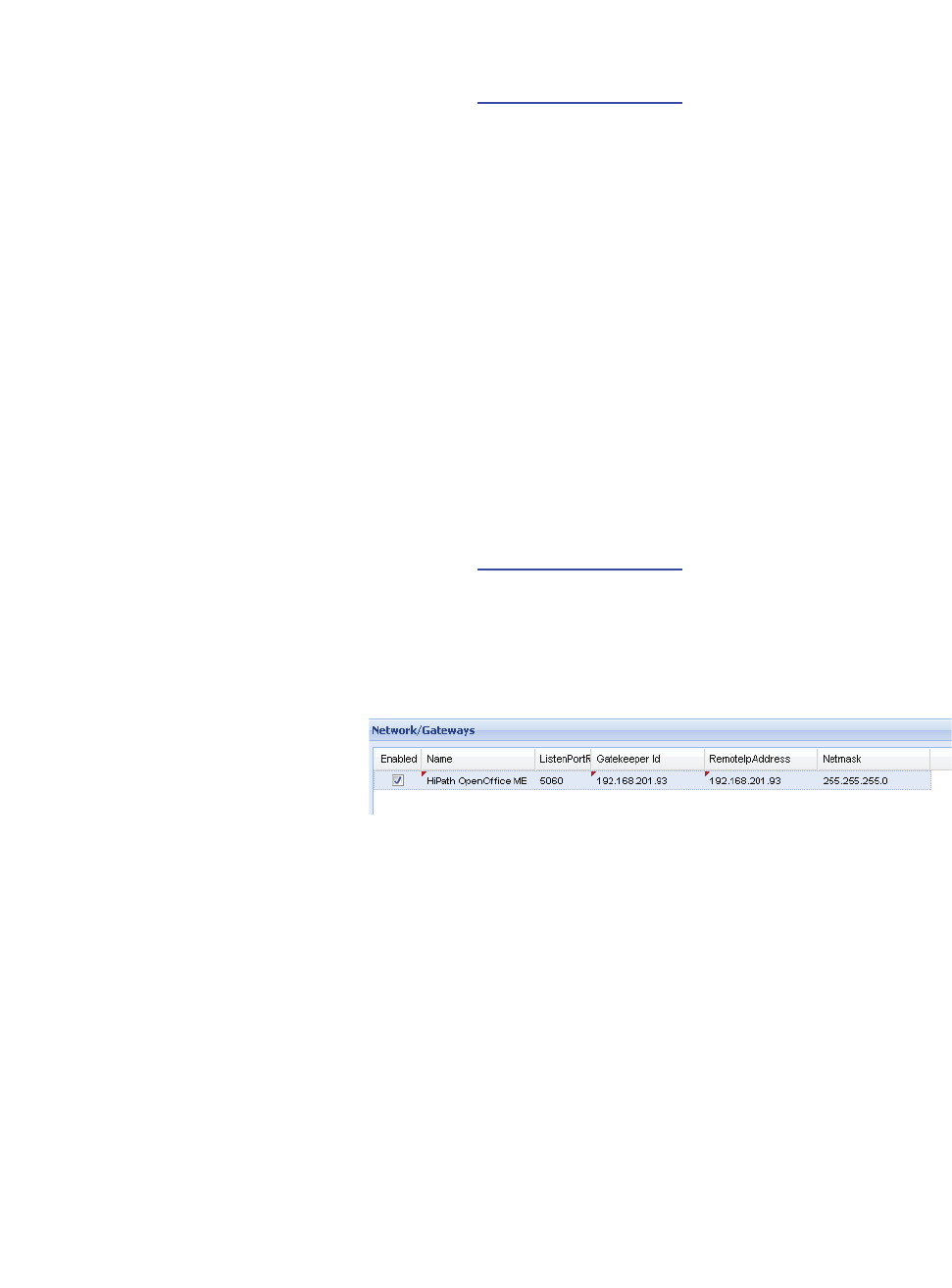
c05_ikon.fm
Installation and Administration
Configuration of users at the PBX
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 75
HTTPS Enabled = [X]use https://{Server Ip of IP VoIP (Infrastructure)
Network}
Example: https://192.168.201.114
5.15 Configuration of users at the PBX
It is assumed that the VoIP users at the PBX are already configured. For detail
refer to Section 5.31.
5.16 Configuration of users at the BSIP IWU
5.16.1 Gateway and Group
1. Access the WBM of the BSIP1 IWU WBM via the web browser at the
maintenance PC.
Example: https://192.168.201.114
2. Log in to the WBM with Username "Siemens".
3. Switch to configuration page "Network/Gateways".
4. Add a new gateway entry by clicking on the button [Add Gateway].
5. Change the following values:
Name
Change the preconfigured name of the PBX to a descriptive name for the
VoIP Gateway. This name is only used for the internal configuration of the
BSIP Software.
Remote IP address and Netmask
Change the preconfigured "Remote IP address" as well as the corres-
ponding "Netmask" to the ip address of your PBX.
6. Switch to configuration page "Group"
Groups are the connecting link between the "Gateways" and the VoIP
Users. A User is assigned to a Group and a Group is assigned to a
"Gateway".
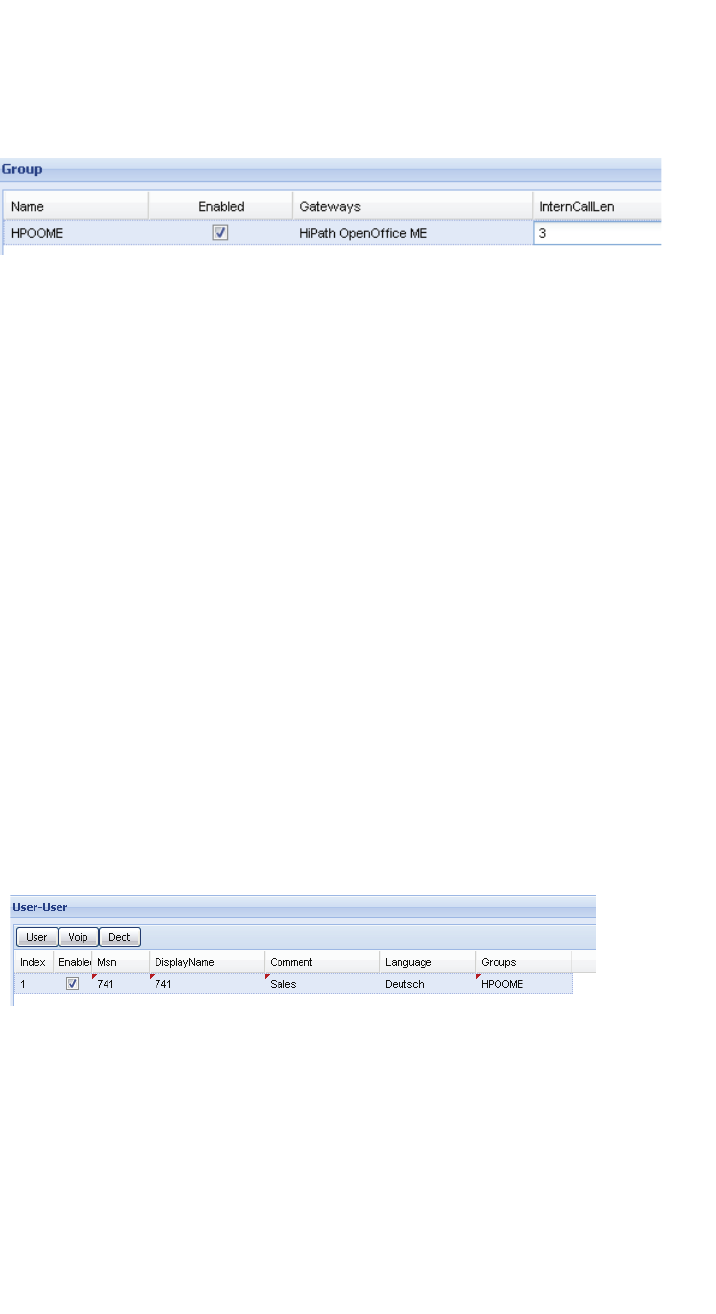
Installation and Administration
c05_ikon.fm
Configuration of users at the BSIP IWU
A31003-C1010-S100-2-7620, 08/2010
76 HiPath Cordless IP, Service Manual
The default configuration already contains an entry for a Group, which is
used for assigning the Users to the Gateways, so you do not need to
make changes here.
7. Add a new group by clicking on the button [Add Group].
8. Change the contents of the following fields.
Name
Change the preconfigured name of the Group (e.g. to the name of the
corresponding PBX) . This name is only used for the internal configuration
of the BSIP Software.
Gateways
Select the gateway from the dropdown field which you have configured in
the last step.
5.16.2 User
1. Switch to configuration page "User", sub page User ("User -User").
Set up one or several Users according the user configuration at the PBX
for the connection with the BSIP1. Please take care of the consistency of
the entries between the PBX and the BSIP1.
2. Add a new user by clicking on the button [Add User].
•Hint: For the correlation of the fields between the BSIP and the PBX refer
to chapter 5.33.4, “Station Configuration - IP-DECT IWU”.
3. Change the contents of the following fields:
Msn (necessary)
The MSN has to correlate with the Callnumber of the User at the PBX.
DisplayName (necessary)
This information is shown at the idle display of the corresponding
handset.
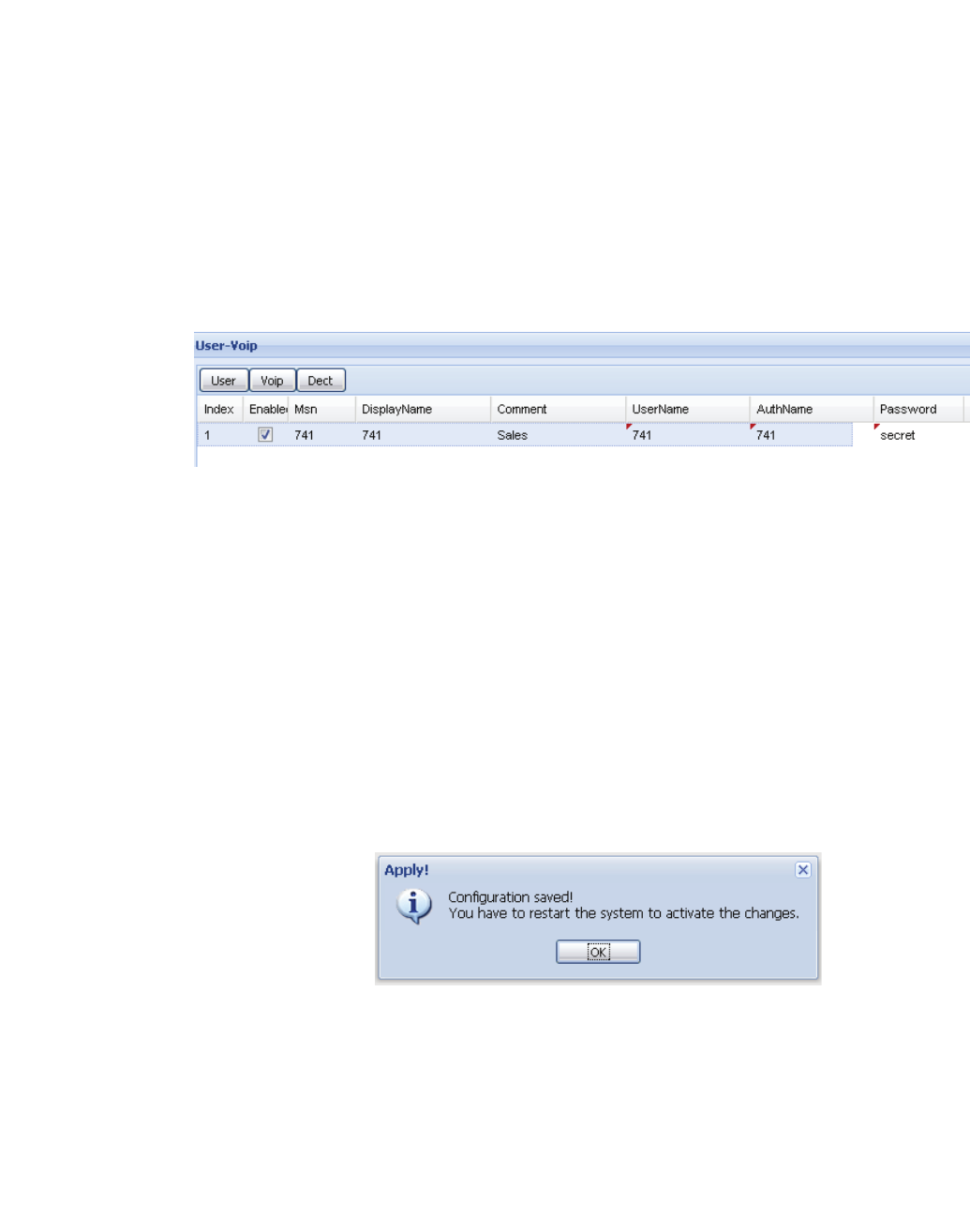
c05_ikon.fm
Installation and Administration
Configuration of users at the BSIP IWU
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 77
Comment (optional)
Here you may enter any desired text for administration purposes.
Language
The language used for display messages of the handset can is selected
here
Groups
Choose a Group (and with that a Gateway) from the dropdown box to
which the user is associated to.
4. Switch to configuration page "User", sub page Voip ("User -Voip").
5. Change the contents of the following fields:
UserName (necessary)
Name or Number for the registration of the User at the PBX.
AuthName (optional)
Name which is used for the authentification at the PBX (together with
"Password").
Password
Optional, but necessary if an "AuthName" is entered; The password
which is used for the authentification at the PBX (together with
"AuthName".
6. Apply the changes by clicking the [Apply] button at the bottom section.
7. Confirm the message box by clicking on [OK].
8. To append further users to the configuration, repeat the steps above.
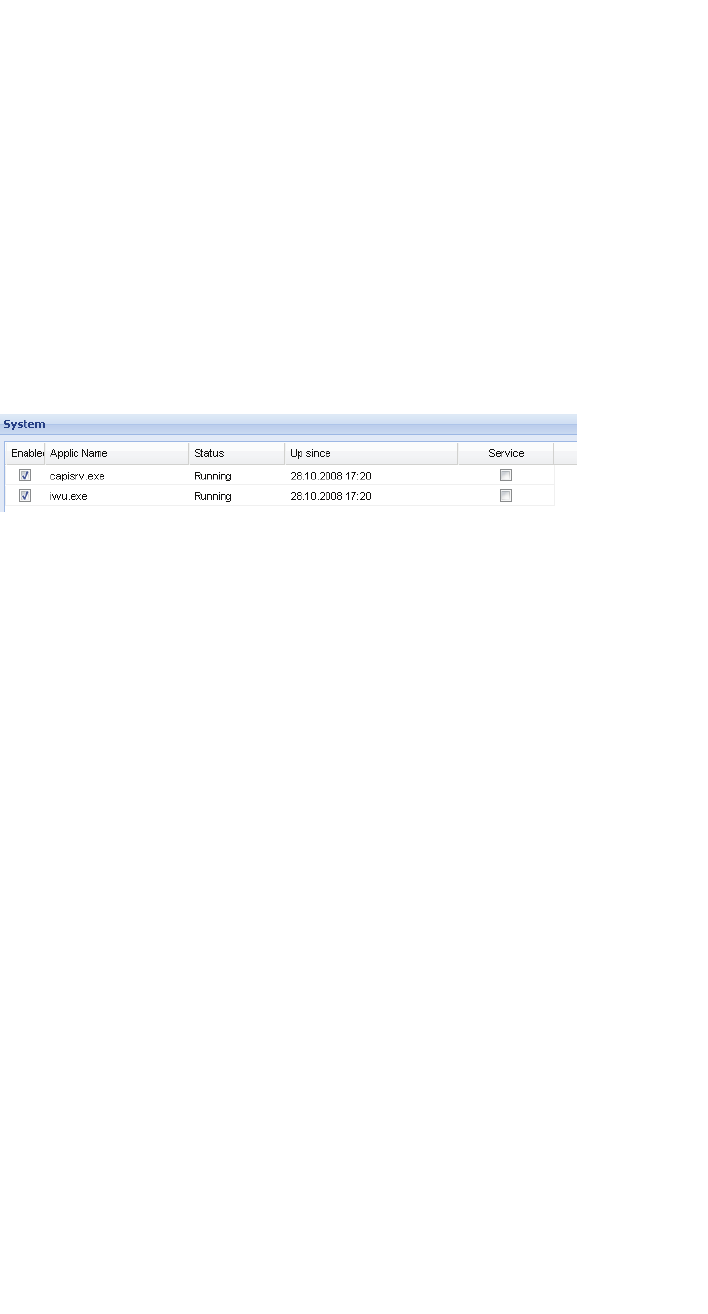
Installation and Administration
c05_ikon.fm
Start system services and register handsets
A31003-C1010-S100-2-7620, 08/2010
78 HiPath Cordless IP, Service Manual
5.17 Start system services and register handsets
5.17.1 Start system services
1. Switch to configuration page "System".
To start the functionality of the BSIP1 IWU you first have to start the
system services.
2. Start the services by clicking the [System Start] button at the bottom
section.
3. Check if the system services are running by clicking at the [Refresh]
button several times.
If the system services are started correctly (both states displayed as
"Running", the LED state at the BSIP1 IWU should change from orange/
orange to green/off.
If a time server is configured correctly and can be contacted, the field "Up
since" should display actual local time values, otherwise time will start at
"01.01.1970 00:00".
5.17.2 Register handsets
1. Switch to configuration page "User-Dect".
•Prepare one handset for the registration process.
•Attention: Do not confirm the following procedure at the Handset right
now!
Start the Registration procedure via the menu at the Handset. Choose
any Base Station for the Registration at the handset. Enter the
SystemPIN (preconfigured to "00000000" at configuration page "DECT"
as PIN at the handset (Attention: Do not confirm yet!).
2. Select the corresponding user in the WBM to which the handset has to be
assigned to.
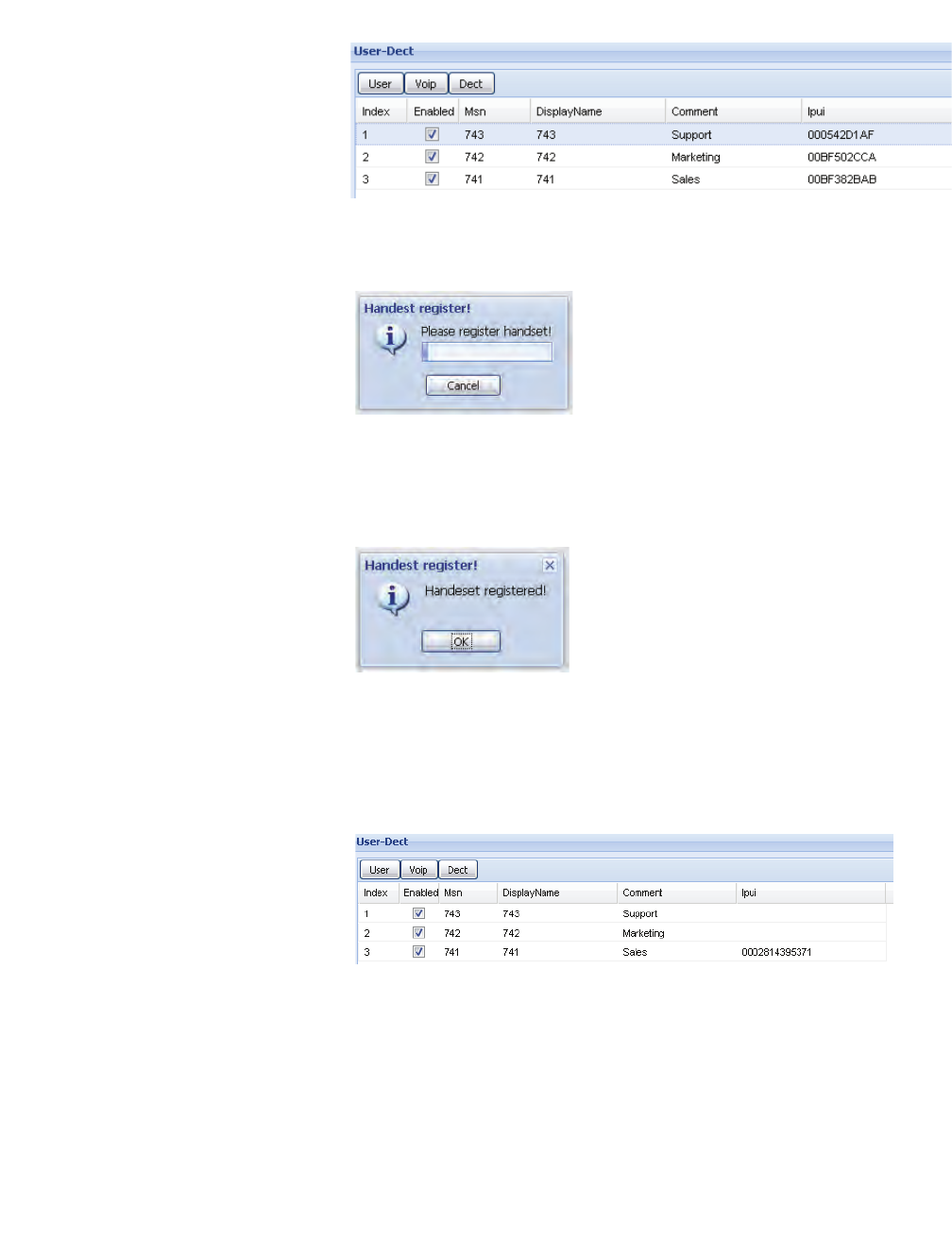
c05_ikon.fm
Installation and Administration
Start system services and register handsets
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 79
3. Activate the Registration procedure at the WBM by clicking at [Register]
at the bottom section of page "User-Dect".
4. Now confirm the already entered PIN at the Handset (normally with
softbutton "OK").
•"The WBM displays the successful Registration of the Handset.
•If the handset does not ring please read chapter 5.34, “Troubles-
hooting / FAQ” concerning possible reasons.
•"The IPUI of the registered handset is displayed in hexadecimal notation
in the user entry.
5. Select the user again and click on [TestCall]. The registered Handset will
start ringing. You can accept the call at your handset (no voice data will
be transferred) or terminate the test call by clicking [HangUp].

Installation and Administration
c05_ikon.fm
Start system services and register handsets
A31003-C1010-S100-2-7620, 08/2010
80 HiPath Cordless IP, Service Manual
6. Confirm the message box by clicking on [OK].
•If the handset does not ring please read chapter 5.34, “Troubles-
hooting / FAQ” concerning possible reasons.
You can register further handsets for already configured VoIP users now or to
a later time.
• Important note: Telephony functionality is not available before the
system services have been started succesfully.
7. To test the telephony integration, go to configuration page "System" and
restart the services.
After the services are running, telephony functionality should be available.
You should be able to establish calls between the handsets.
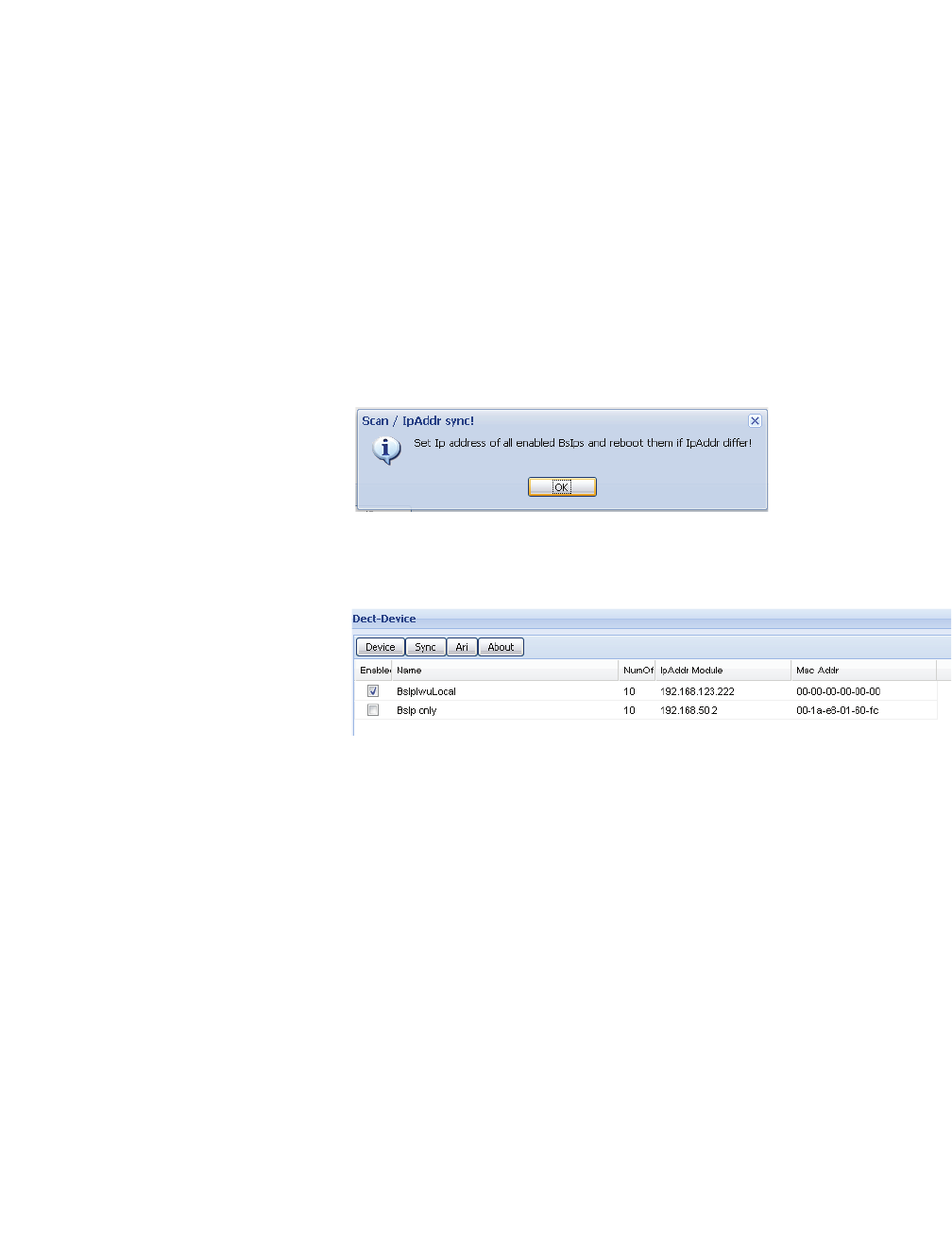
c05_ikon.fm
Installation and Administration
Configure further BSIP Only to the system
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 81
5.18 Configure further BSIP Only to the system
1. Attach the second BSIP1 to a PoE port of the network switch of the DECT
Network or via a power injector to a standard port of the network switch.
It is assumed that the first Base Station is the synchronization master for
the Over-Air synchronization of the second Base Station.
2. Wait about 1 minute until the LED states at the BSIP Only change to
permanently green and red.
3. At the WBM of the BSIP1 IWU switch to configuration page "Dect-
Device".
4. To scan the newly attached second BSIP click on the button [Scan/Sync].
5. Confirm the message box by clicking on [OK].
The newly attached second BSIP1 should be found automatically and a
record will be appended for it in the table of DECT devices.
•If the BSIP1 is not found please read the chapter 5.34, “Troubleshooting
/ FAQ” concerning possible reasons.
The BSIP1 Only has to be configured for usage within the HiPath Cordless IP
system by the following procedure:
6. Select the newly created entry for BSIP Only and change the contents of
the following fields:
Enabled (necessary)
Set to Enabled for usage within the HiPath Cordless IP system.
Name (necessary)
Descriptive name for the BSIP1. Change the preconfigured name of the
BSIP1 (e.g. to the name of the physical location it is destinated for). This
name is only used for the internal configuration of the BSIP1.
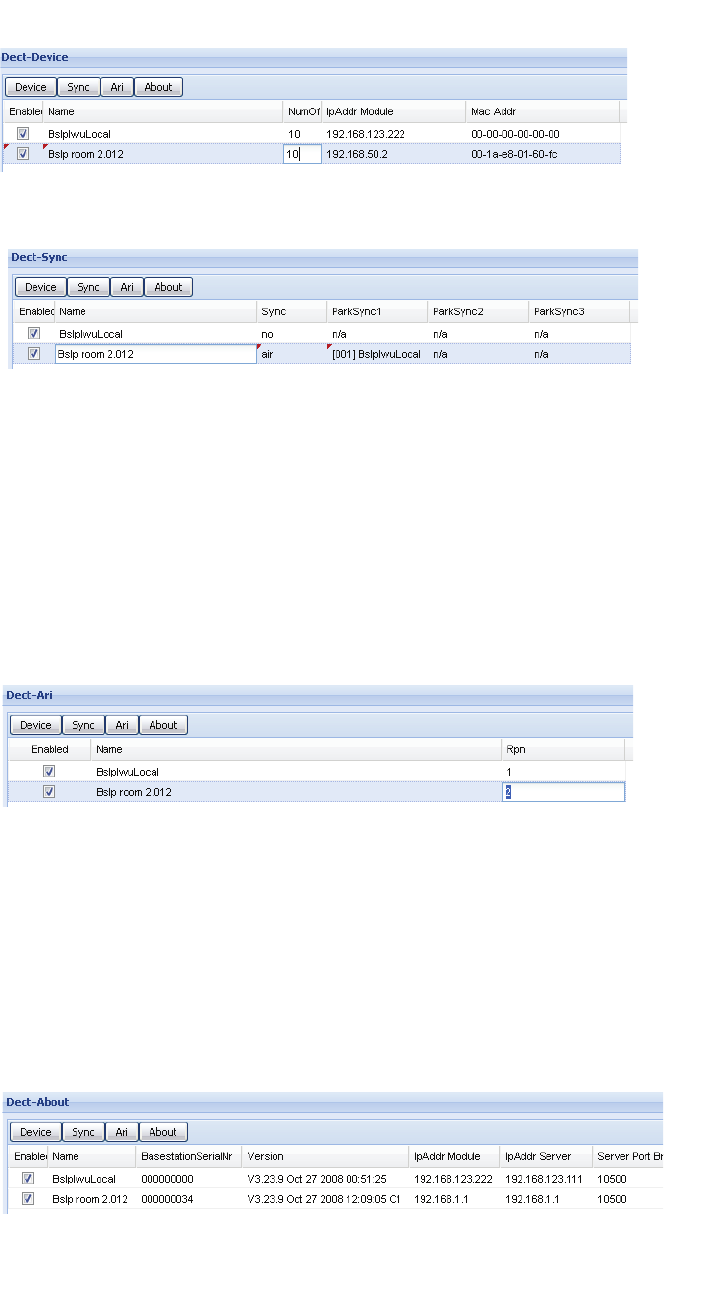
Installation and Administration
c05_ikon.fm
Configure further BSIP Only to the system
A31003-C1010-S100-2-7620, 08/2010
82 HiPath Cordless IP, Service Manual
7. At the WBM of the BSIP1 IWU switch to configuration page "Dect-Sync".
8. Select the newly created entry for BSIP Only and change the contents of
the following fields:
Sync (necessary)
Set to "air" to synchronise the actual BSIP1 to another BSIP1 via air.
ParkSync1 (necessary)
9. Select from the dropdown to which BSIP the selected BSIP1 should be
synchronised to.
10. At the WBM of the BSIP1 IWU switch to configuration page "Dect-Ari".
11. Select the newly created entry for BSIP Only and change the contents of
the following fields:
Rpn (necessary)
12. Change the "Rpn" for the selected first entry from "0" to "1".
•Note: When using several Base Stations they have to be configured with
a unique "Rpn" different from "0". Valid RPNs for a class B Ari are 1 ... 255.
13. At the WBM of the BSIP1 IWU switch to configuration page "Dect-About".
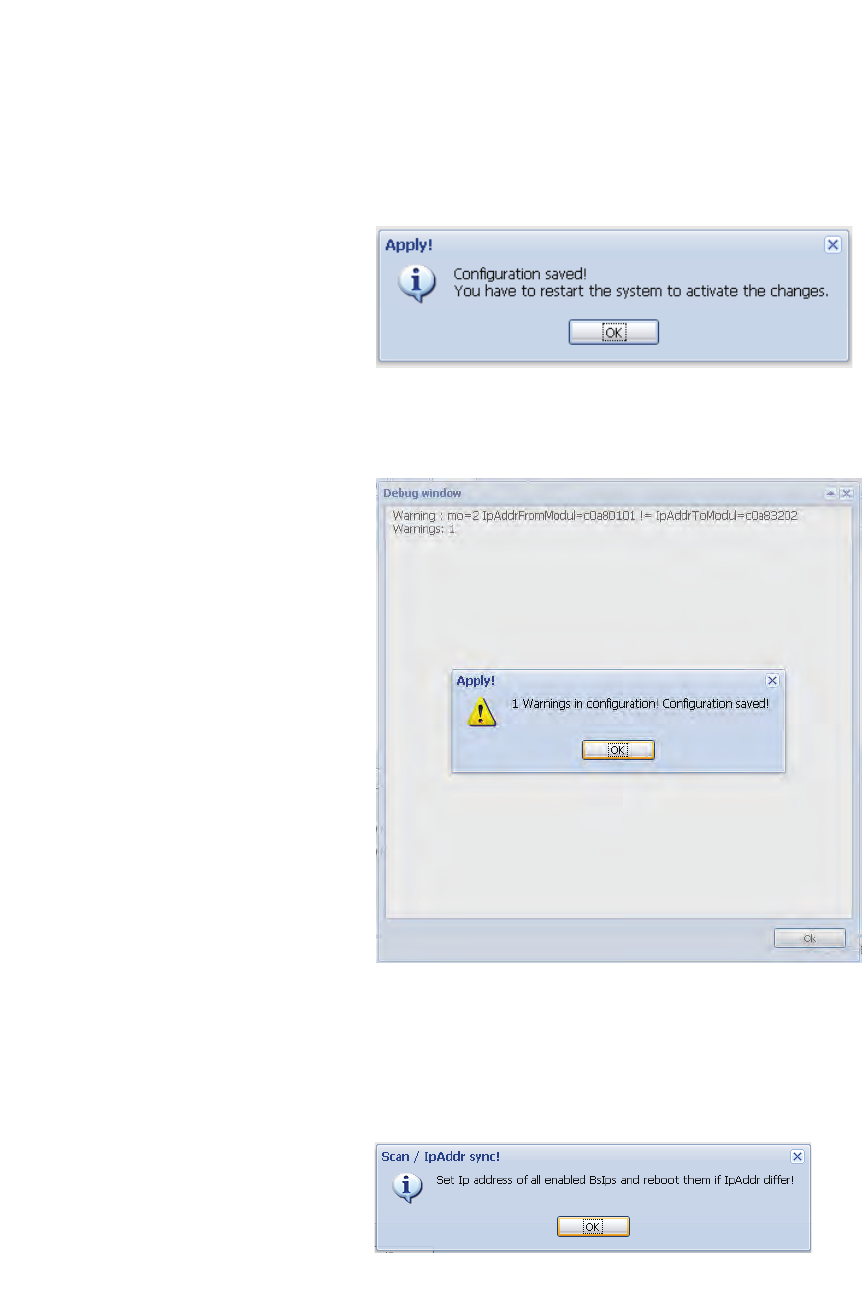
c05_ikon.fm
Installation and Administration
Configure further BSIP Only to the system
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 83
The fields IpAddr Module and IpAddr Server display the current (default)
values for the selected BSIP1.
14. To apply all the changes to the BSIP1, the BSIP1 has to be synchronized.
During the synchronization process the BSIP1 Only will receive its confi-
guration values from the BSIP1 IWU.
15. Apply the changes by clicking the [Apply] button at the bottom section.
16. Confirm the message box by clicking on [OK].
A debug window will appear.
17. Confirm the Debug window by clicking on [OK].
18. Start the synchronisation process by clicking the [Scan/Sync] button at
the bottom section.
A message box will appear.

Installation and Administration
c05_ikon.fm
"Quick Start" Completion
A31003-C1010-S100-2-7620, 08/2010
84 HiPath Cordless IP, Service Manual
19. Confirm the message box by clicking on [OK].
The following process will transfer the new settings to the BSIP1 Only.
Therefore, the BSIP1 Only will rebooted automatically by the system.
20. Wait about 1 minute until the BSIP1 is started completely (LED states
should be green/red)
21. At the WBM of the BSIP1 IWU switch to configuration page "System".
22. Start the services by clicking the [System Start] button at the bottom
section.
After the system services are started successfully, telephony functionality is
available.
5.19 "Quick Start" Completion
After you have accomplished some successful test calls you may configure
all additional Users and additional BSIP1 Only in your System.
At this step it's a good idea to backup the configuration. For details refer to
chapter 5.23.1.2, “Button [Backup Config]”
5.20 Further steps
5.20.1 Radio frequency site survey
A radio frequency site survey has to be performed. Within this step, also the
synchronisation concept has to be designed, implemented and tested.
5.20.2 Synchronisation implementation
The syncronisation implementation should be part of the radio frequency site
survey.
For details of synchronisation via air refer to chapter 5.3, “Synchronisation
over air concept”.
5.21 Configuration reference
For the configuration of the HiPath Cordless IP system you have to connect
via a Browser to the BSIP1 IWU.
c05_ikon.fm
Installation and Administration
WBM overview
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 85
5.22 WBM overview
5.22.1 Different WBM modes
•Hint: Where not other stated, all documentation is described for WBM
mode Siemens Standard.
The system has two built-in factory default WBM users:
Using the WBM mode Siemens Administration, more or changed configu-
ration options are available.
For most configuration tasks, WBM mode Siemens Standard is sufficient.
5.22.2 Features in WBM mode Siemens Admin
Configuration page Network-Gateways
•GW specific Options: Fields "Gatekeeper Id", "Dtmf", "StunnelIp", "LocalI-
pAddress" available
Configuration page Dect-Call
•Field "NumofChannel" moved from sub-page Device
Configuration page Dect-Radio
•Field "Diversity" available
•Dropdown Field "Frequency" (Default: "1.88 - 1.90" for Europe, other
available values: "1.91 - 1.93"). Changig this option from its default "off"
is not supported yet.
Configuration page Dect-Ari
•Field "Cipher"
WBM mode Username Default password
Siemens Standard Siemens 1q21q2
Siemens Administration SiemensAdmin 1q21q2
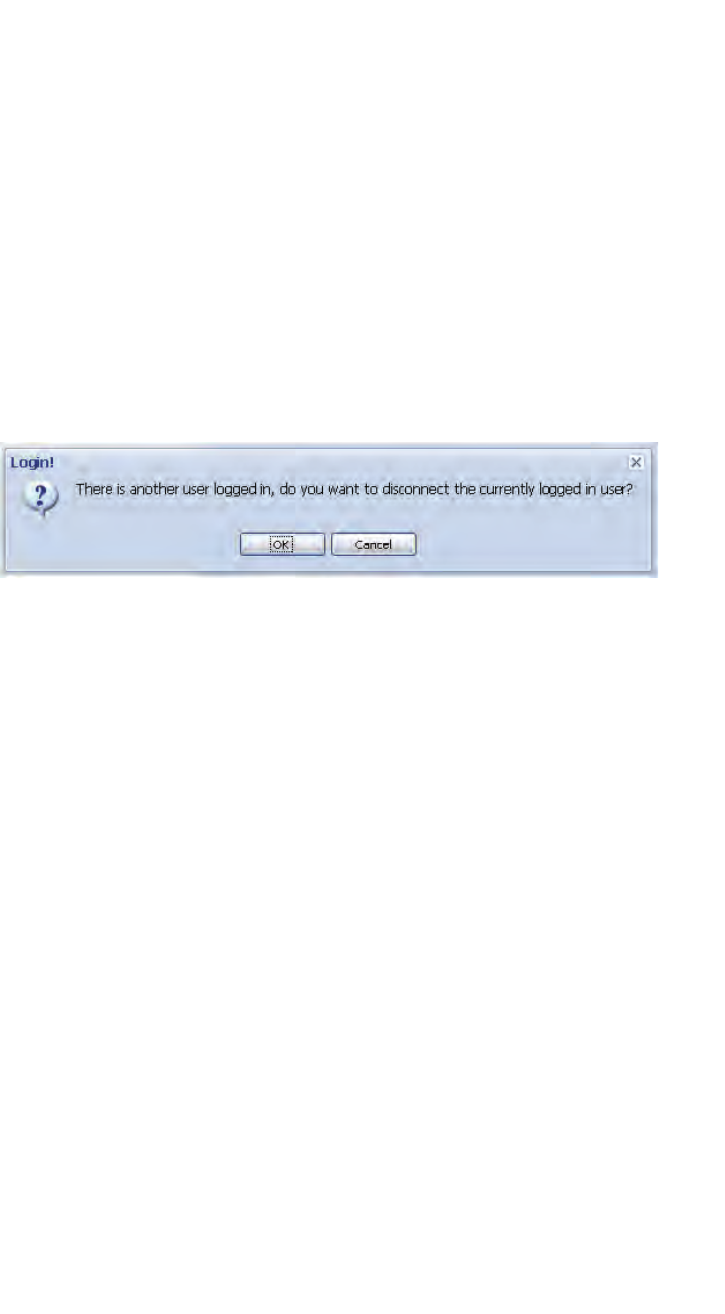
Installation and Administration
c05_ikon.fm
WBM overview
A31003-C1010-S100-2-7620, 08/2010
86 HiPath Cordless IP, Service Manual
Configuration page Dect-Debug
•only available in WBM mode Siemens Admin
Configuration page Debugging
•only available in WBM mode Siemens Admin
5.22.3 Login to WBM
5.22.3.1 Multiple WBM sessions
If you login onto the same WBM session on which another user was logged
on, you are informed about that by a message box.
[OK] will logout the currently connected user.
[Cancel] Go back to the Login dialog.
After a timeout of 30 minutes after the last WBM access the user will be
logged out automatically by the WBM.
5.22.3.2 Login and Password change
•Hint: Password and Username are handled Case sensitive.
The WBM configuration mode is chosen according the Login username.
Concurrent Logins are not possible. The users who tries to login last is given
the ability to logout the already logged in user.
5.22.3.3 Changing a WBM User's password
•Important note: Please note down the new password at a secure place.
Passwords are stored at system level and also used when updating the
system at a later time. If you forgot the password, you only may overcome
the situation by resetting the system to factory defaults.
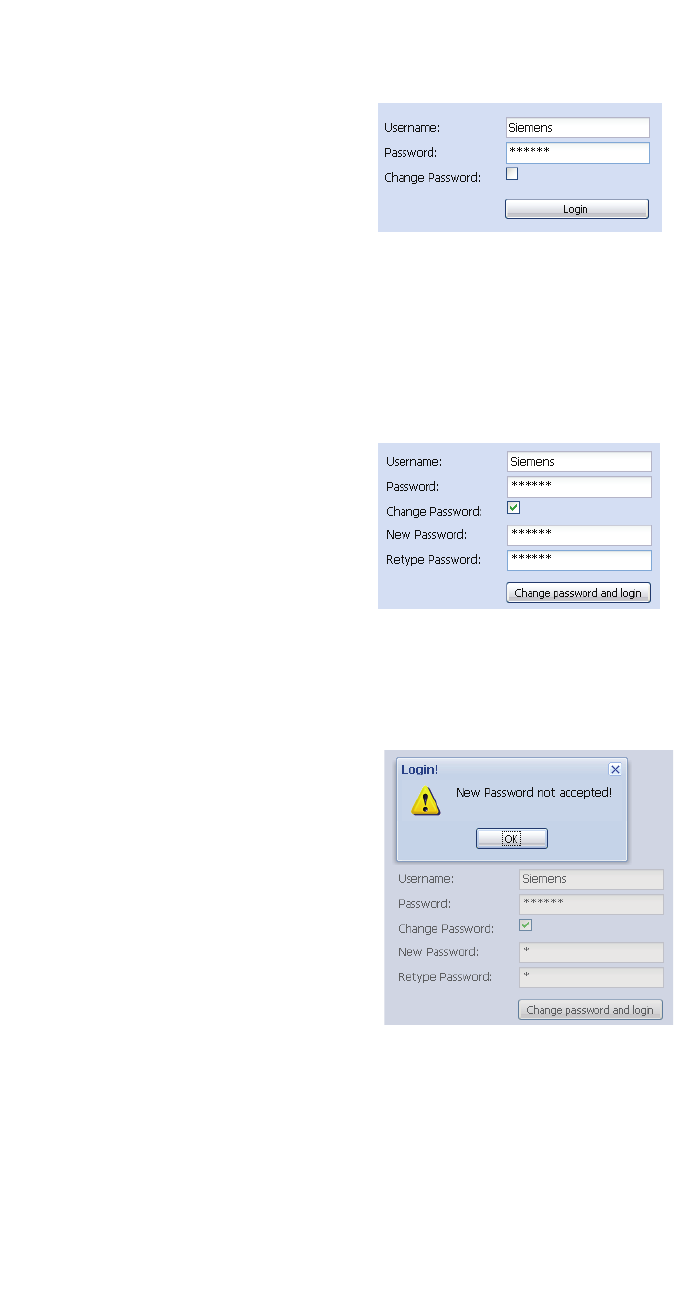
c05_ikon.fm
Installation and Administration
WBM overview
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 87
1. On the Login page, enter the Username and current password for the
destinated user which has to be changed.
2. Activate the checkbox "Change Password".
3. Two new fields will be displayed: "New password" and "Retype
password". Type in the new password in both fields.
•Hint: Username and passwords are case sensitive, the minimum
password length is 6 (six) characters.
4. Click on [Change password and login].
If both new passwords are equal and valid, you will be logged in onto the
WBM. Otherwise a error message will appear.

Installation and Administration
c05_ikon.fm
WBM overview
A31003-C1010-S100-2-7620, 08/2010
88 HiPath Cordless IP, Service Manual
5.22.4 General objects
The WBM consists of several pages with topically structured configuration
options of the IWU Software. These pages can be selected via the Tabs in the
upper part of the WBM.
The buttons on all configuration pages on the bottom right have the following
meaning:
Logout
This functionality will logout the currently user from the WBM session. After
you have finished configuration, it is good practice to logout from the WBM
session.
Help
The Help button starts the browser based online help system.
Info
Displays version information and the software license agreement.
Cancel
With [Cancel] the Configuration Utility is closed, modifications are discarded.
Apply
With this Button, all configuration is updated and iternally saved. Also current
changes at a WBM page (which is not already applied) is applied and stored
to the configuration of WBM.
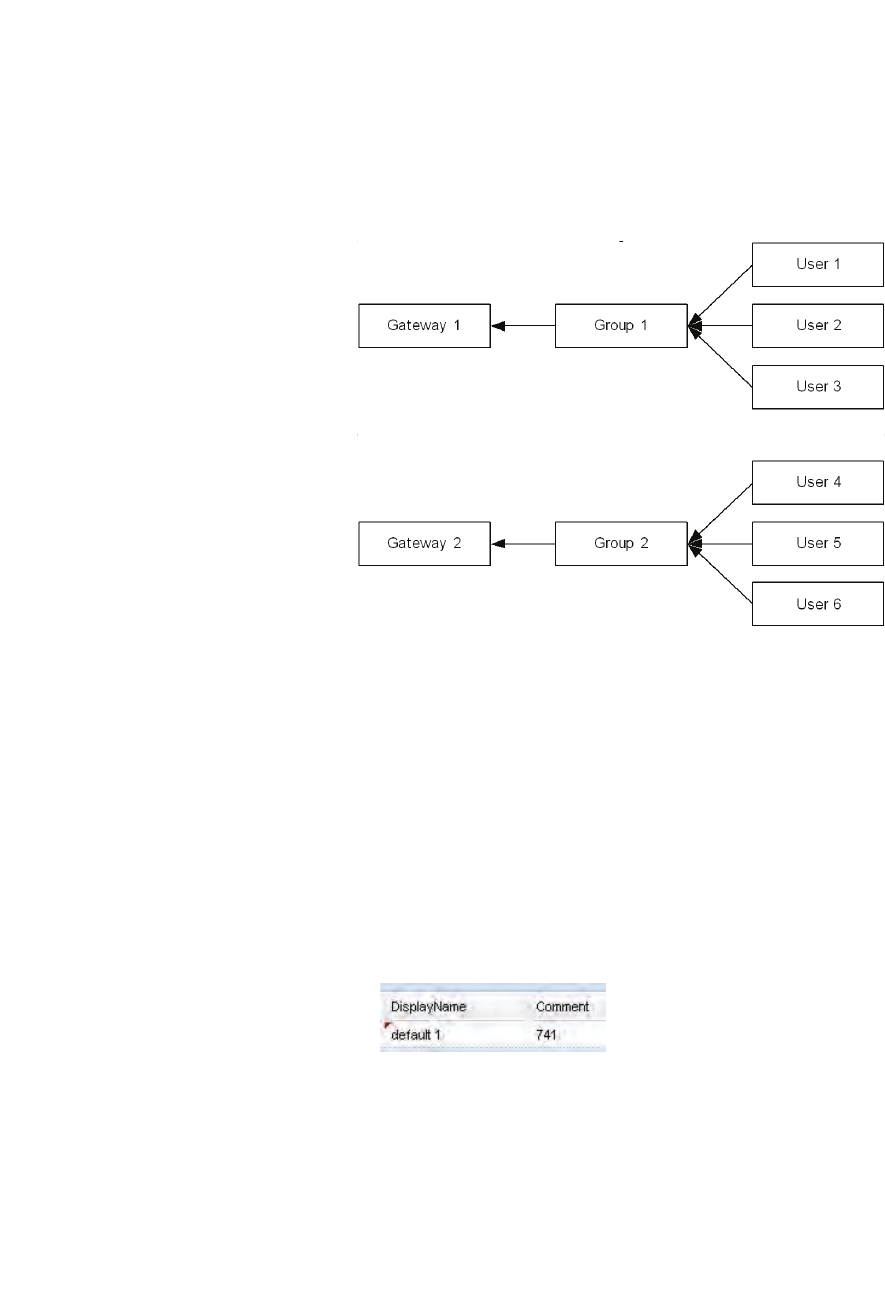
c05_ikon.fm
Installation and Administration
WBM overview
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 89
5.22.5 Configuration Systematic
Several "Gateways" (PBXs) are supported per HiPath Cordless IP system.
For establishing a call over a VoIP gateway, a Group has to be assigned to
the Gateway and a User has to be assigned to this Group.
The following figure shows the relationships between Gateways, Groups and
Users.
According to the figure above the following relations exist:
•One ore more Users can be assigned to a Group (n:1).
•One Group can be assigned to a Gateway (1:1).
Usually only 1 Gateway (the PBX) is configured for the IP-DECT System.
5.22.6 Changing values
Changed values are marked with a red triangle at the top left corner of the
corresponding filed.
But you have to leave the current filed for changes to come in effect (via TAB
key or mouse).
Please keep in mind that changes are not in effect immediately.
You have to
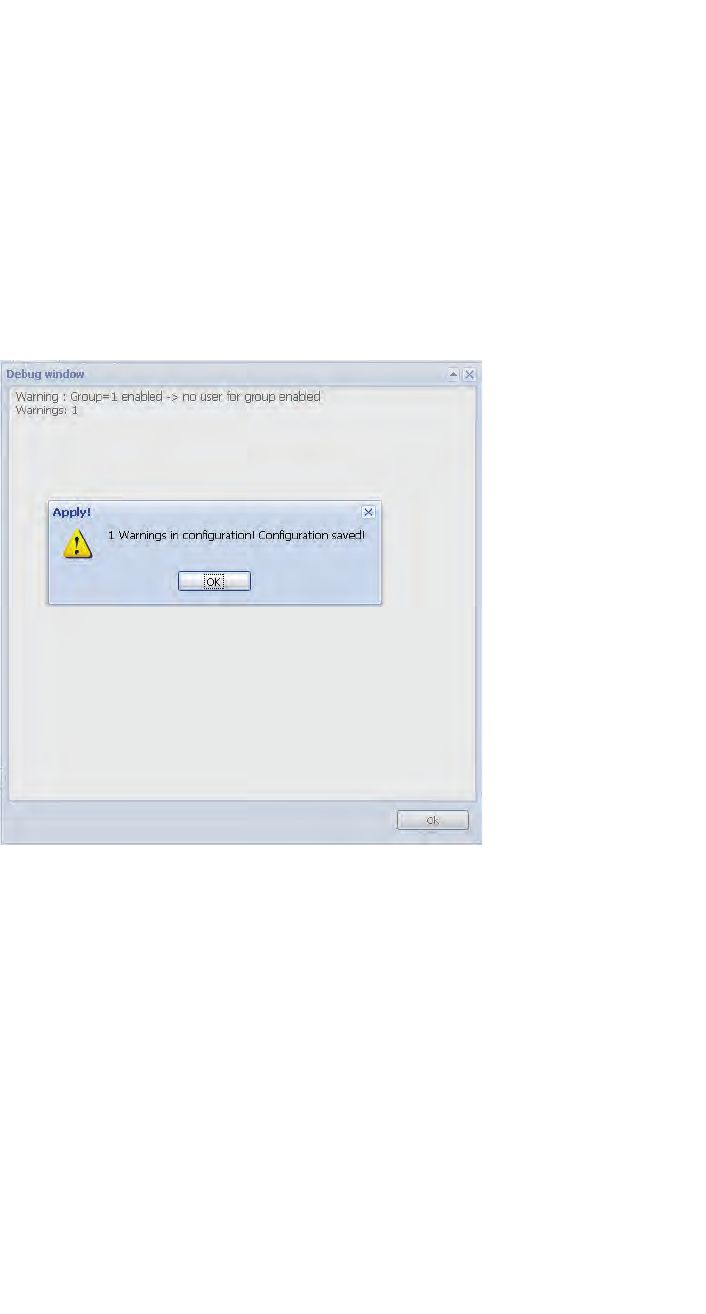
Installation and Administration
c05_ikon.fm
WBM overview
A31003-C1010-S100-2-7620, 08/2010
90 HiPath Cordless IP, Service Manual
1. apply the changes with the [Apply] button and for some changes you
have to
2. restart the services
5.22.6.1 Debug windows
To inform the user about special events (e.g configuration warnings and/or
errors) a Debug window will display the corresponding messages to the user.
After changing (and/or applying) changes to configuration objects, the WBM
displays the debug windows with warnings and/or errors.
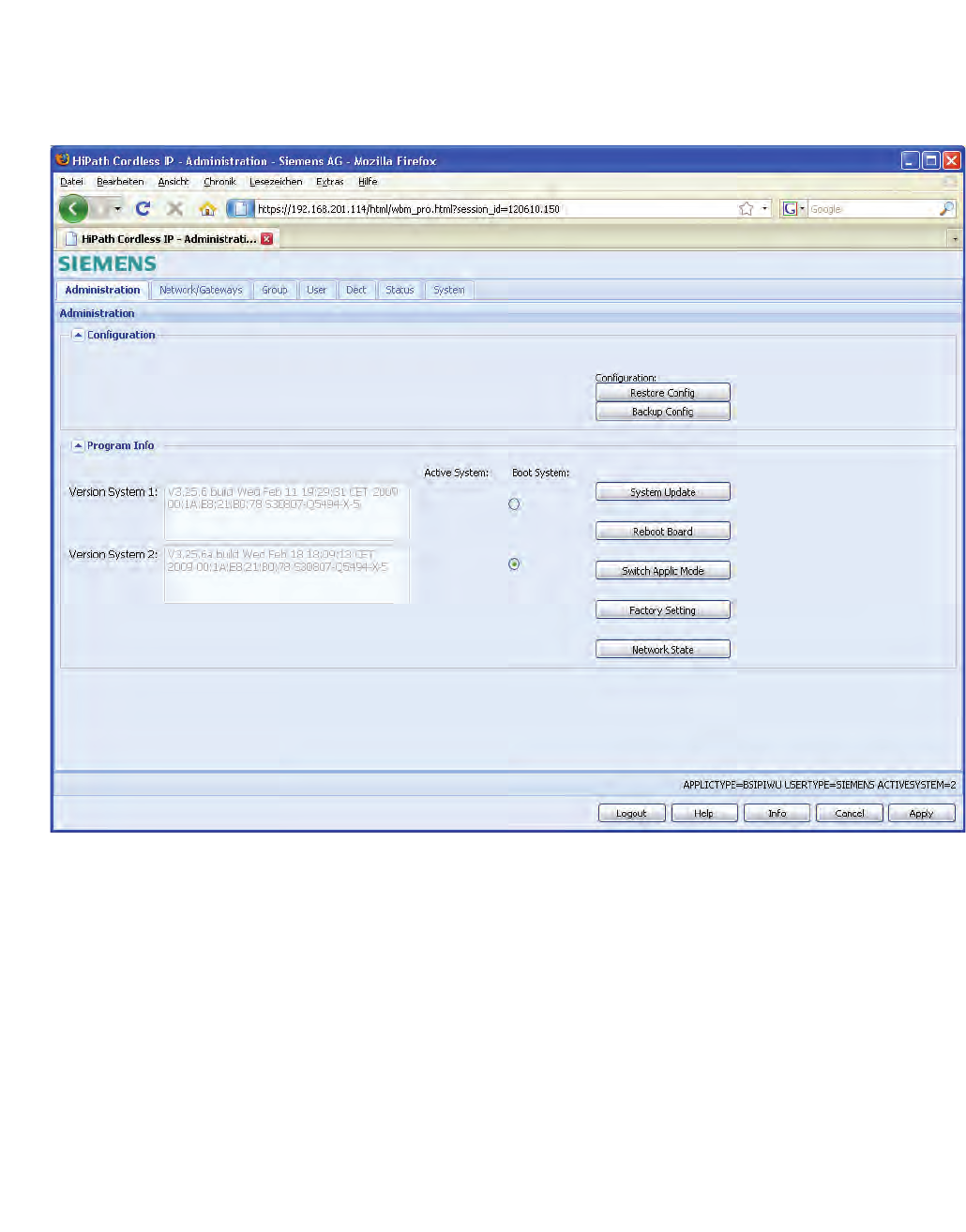
c05_ikon.fm
Installation and Administration
Administration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 91
5.23 Administration
On the Administration page, administrative configuration and information
about the BSIP1 is provided.
5.23.1 Frame Configuration
5.23.1.1 Button [Restore Config]
1. With the Button [Restore Config] the complete configuration of the BSIP
IWU can be restored from a previously backuped configuration from a file.
•Hints:The system services have to be stopped to use this feature.
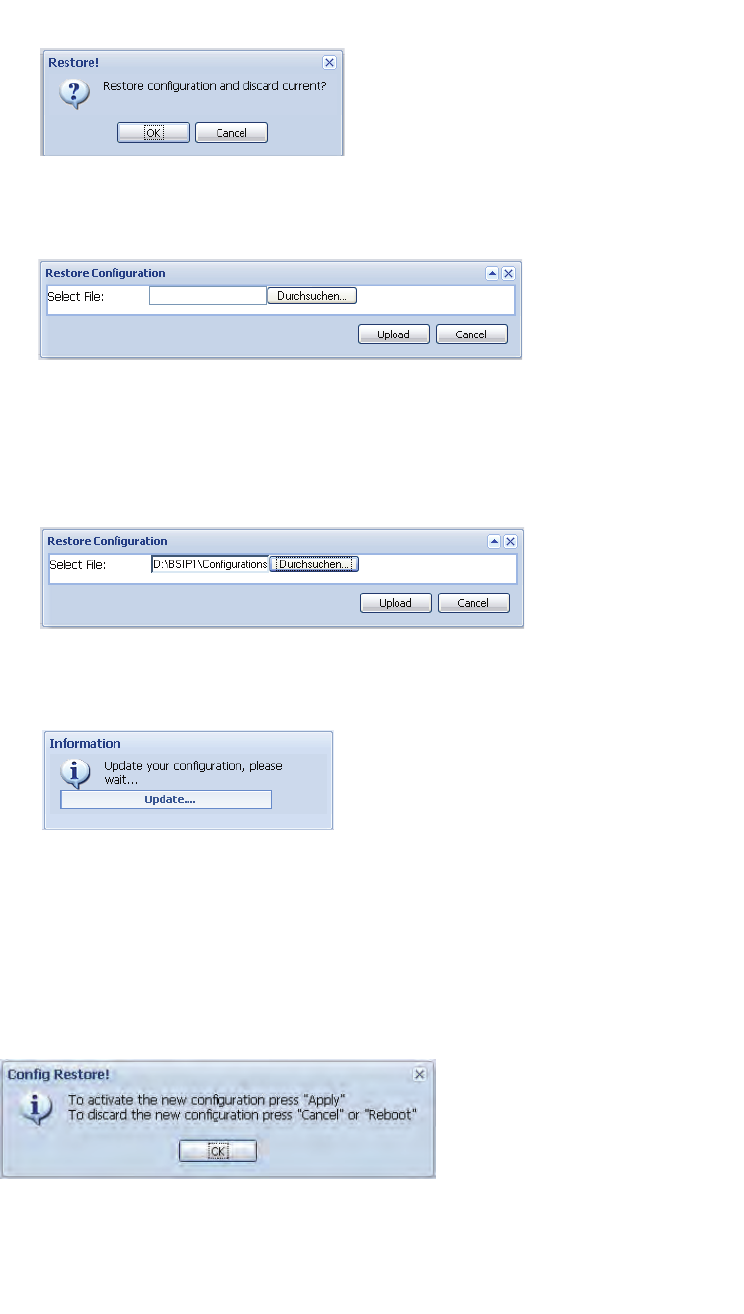
Installation and Administration
c05_ikon.fm
Administration
A31003-C1010-S100-2-7620, 08/2010
92 HiPath Cordless IP, Service Manual
2. After confirming the action with button [OK], a file "Restore Configuration"
Dialog opens.
3. After clicking on [Durchsuchen] you can select a configuration file using
an browser based file open dialog. ( by default "iwu_config.tgz ").
4. After you have selected the desired configuration file you can load it into
the BSIP1 using the [Upload] button.
During the upload process, a message box with a progress bar will be
displayed.
•Important: All stored configuration is loaded into the WBM. Ensure that
you have loaded the correct configuration file. Particularly ensure that all
relevant ip address values are correct (otherwise you won't be able to
access the WBM after a reboot).
•After the configuration file is downloaded, you have to apply or discard the
changes. For both actions, a reboot has to be performed.
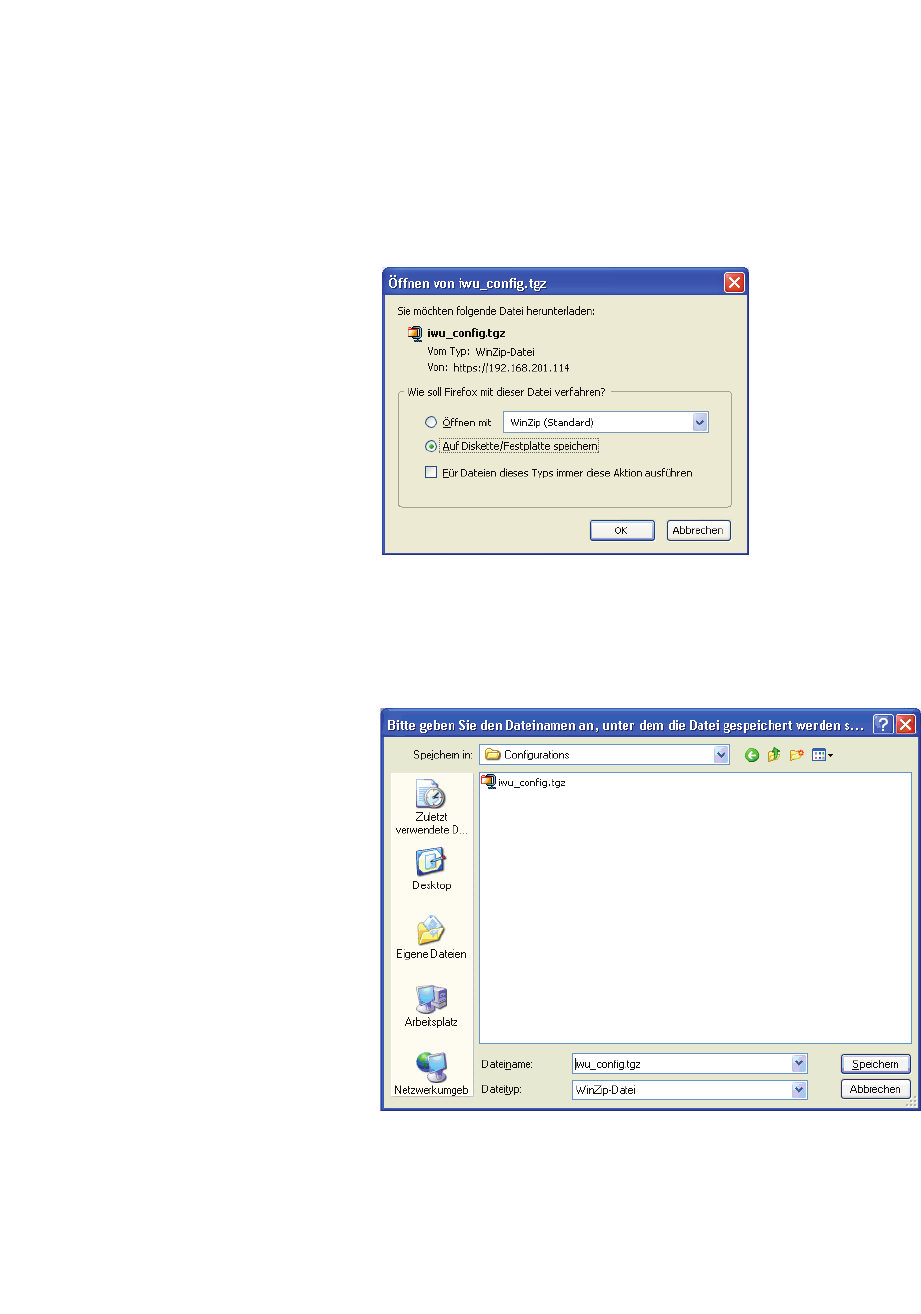
c05_ikon.fm
Installation and Administration
Administration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 93
5.23.1.2 Button [Backup Config]
With this Button the complete configuration of the BSIP can be backuped and
stored on the file system of the maintenance PC.
•Hint: The system services have to be stopped to use this feature.
1. After clicking on the button [Backup Config], a browser based file open
dialog will be displayed immediately.
2. You have to select the store method of the dialog, click on button [OK]
and select from the following "save as" dialog a folder to store the confi-
guration files on the maintenance PC or a directory available via the
network.
3. Save the configuration file using the default name "iwu_config.tgz " or
change it according your needs (Don't use blanks in the filename).
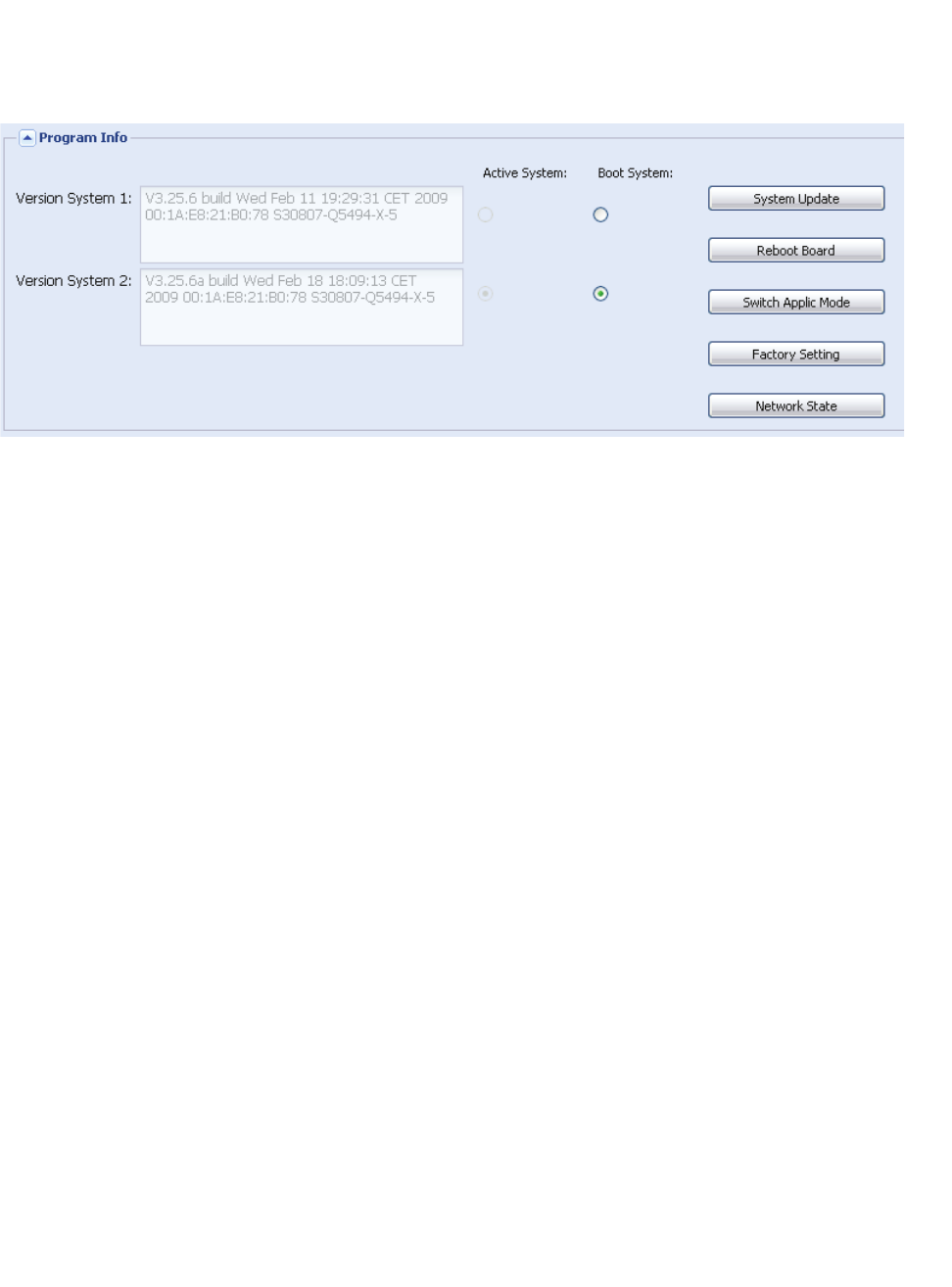
Installation and Administration
c05_ikon.fm
Administration
A31003-C1010-S100-2-7620, 08/2010
94 HiPath Cordless IP, Service Manual
5.23.2 Frame Program Info
Version system 1 and Version system 2
System1 and System2 partitions
To guarantee a functional BSIP1 at any time, two bootable systems are
present on the BSIP.
The current (active) system and the fallback (non active) system.
Therefore the BSIP1 has two different systems partitions: System 1 and
System 2.
Version Systemx:
Displays information about SW version , MAC address
Active system
The radio buttons below "Active system" indicate, which of the both System
partition is the currently ACTIVE System partition. In the example of the
screenshot above System 2 is the active partition.
Boot system
The radio buttons below "Boot system" determine, which of the both System
partition will be booted and therefore be the active partition AFTER a reboot
of the board..
•Hint: Don't activate a system partition whose displayed version is "n/a" or
"update unsuccessfull". This may lead to a unusable system.

c05_ikon.fm
Installation and Administration
Administration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 95
5.23.2.1 [System Update]
Updating the system software
•Important: If you update the system software, the Update is always
applied to the NON-active system. Furthermore, the current configuration
of the active system will be applied to the NON-active system. You have
to ensure to use the SAME software version at all BSIPs. Therefore,
updating the software has to take place at the BSIP IWU AND at all BSIP
Only.
A downgrade is not fully supported. In need of a downgrade, a factory reset
is applied automatically. Please refer to the delivered Release notes of the
new version for details of the update process.
Create a backup of the old configuration (Page Registration - [Backup Config].
Update instructions
1. Please create a backup of the old configuration (Page Registration -
[Backup Config].
2. Ensure that you have a firmware file of the old version available (in case
of a necessary downgrade).
3. Start with the update for the BSIP1 running the HiPath Cordless IP Server
Software (BSIP1 IWU) and reboot the BSIP1 IWU as described in
chapter 5.23.2.2, “Other options”.
Hint: Don’t forget to clear the browser cache after updating a partition.
4. Apply the update to all BSIP1 Only modules and reboot them.
Hint: Don’t forget to clear the browser cache after updating a partition.
5. Restart the services at the BSIP1 IWU.
6. Clear cache of Browser (Very Important). After updating to the new
version the cache of the browser has to be cleared. Otherwise sporadic
problems with the new version will occure since old (cached) configu-
ration pages are used by the browser.
To clear the cache of your browser:
1. Restart your browser.
2. Clear the browser cache of MS Internet Explorer MSIE6:
Tools -> Internet Options -> General -> Temporary Internet Files -> Delete
MSIE7: Tools - Internet Options - General - Browsing history - Delete -
Temporary Internet Files.
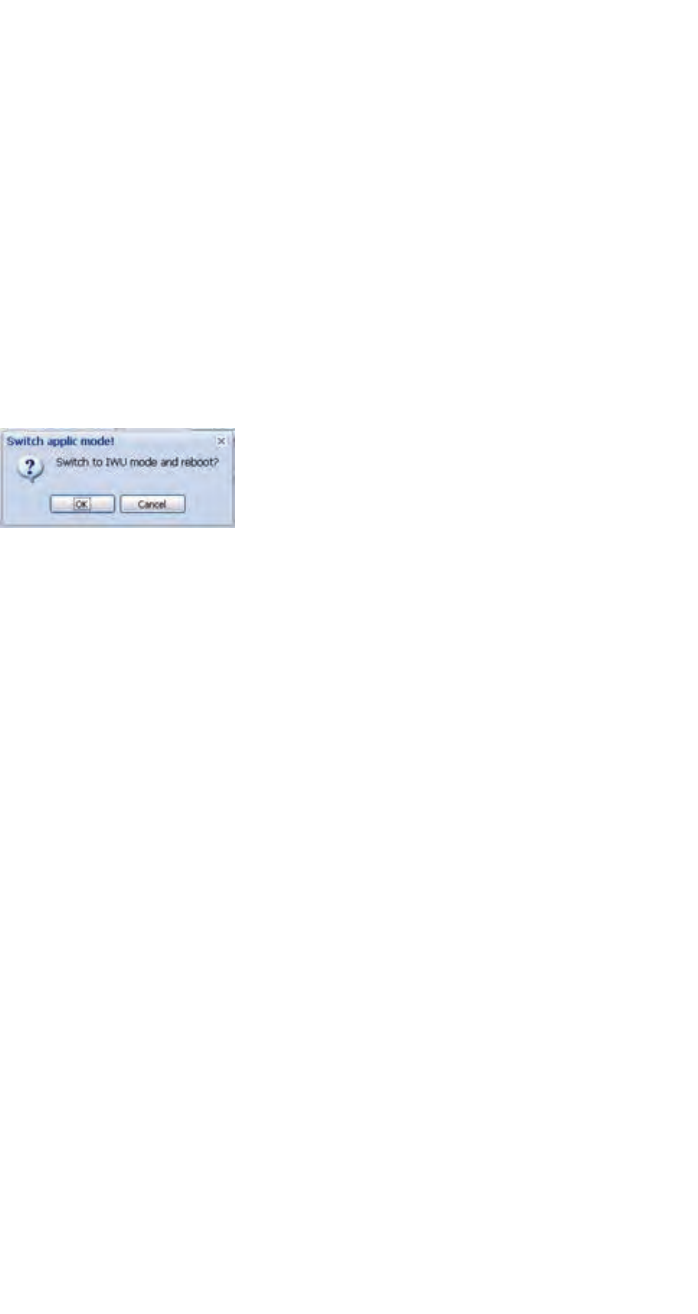
Installation and Administration
c05_ikon.fm
Administration
A31003-C1010-S100-2-7620, 08/2010
96 HiPath Cordless IP, Service Manual
5.23.2.2 Other options
[Reboot Board]
Using this Button the BSIP1 will start the reboot process after a confirmation
dialog.
[Switch Applic Mode]
To change the mode of the BSIP1 between BSIP1 Only to BSIP1 IWU select
[Switch Applic Mode].
•Hint: The current working mode is printed out at the bottom sstaus line
(APPLICTYPE=BSIPONLY or BSIPIWU) and in the output of [Network
State].
After changing the application mode, the following message box will appear.
Press [OK] to reboot the BSIP1 and start it in the other application mode.
• Important note: After changing the application mode the BSIP1 will start
with the IP configuration which was configured last for the corresponding
application mode. This may be the default configuration for the mode or
the already configured addresses for the mode.
[Factory setting]
Using this functionality, a factory reset of the BSIP1 may be initiated.
This functionality may be used alternatively to the procedure of factory reset
by power sequencing described in chapter 5.7, “Factory reset of BSIP1”.
[Network State]
The output of the Network states functionality displays summarised infor-
mation about the systems network configuration.
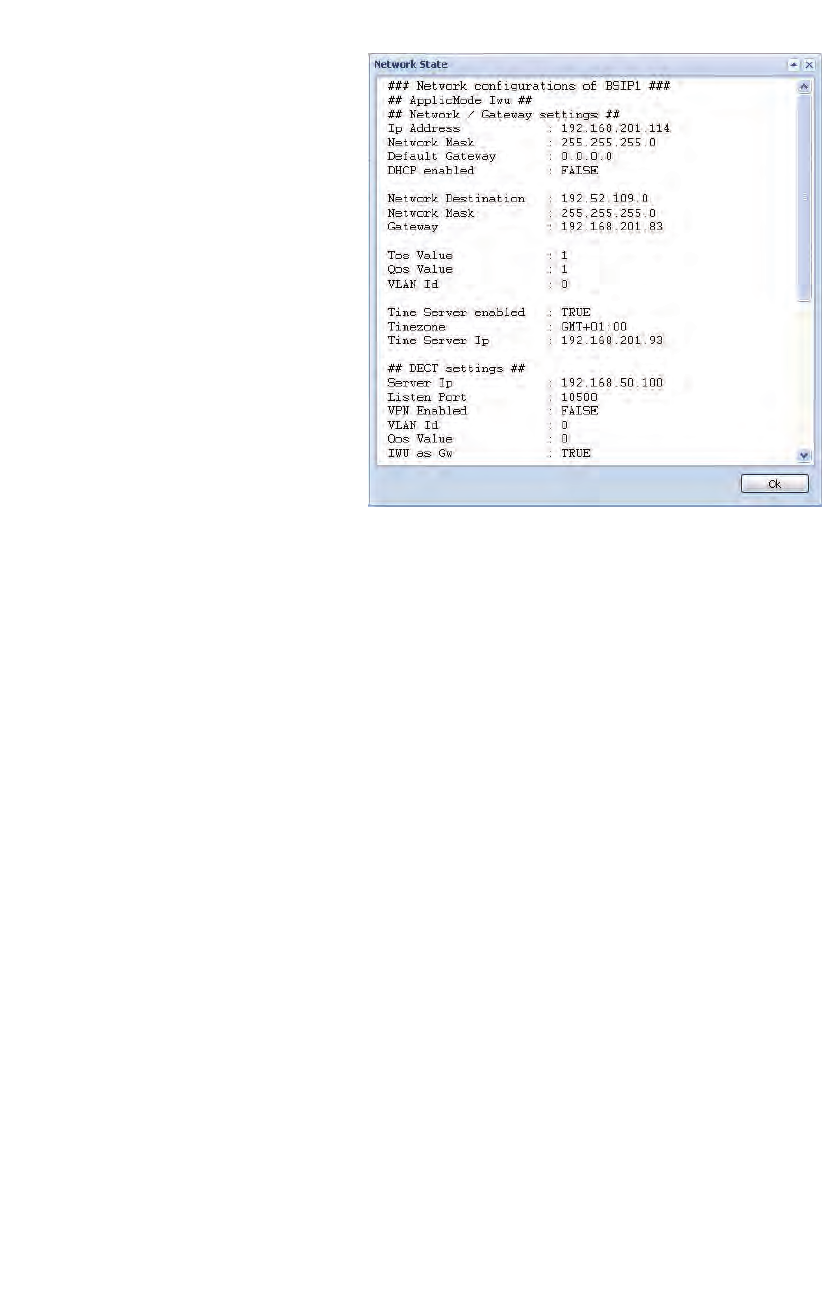
c05_ikon.fm
Installation and Administration
Administration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 97
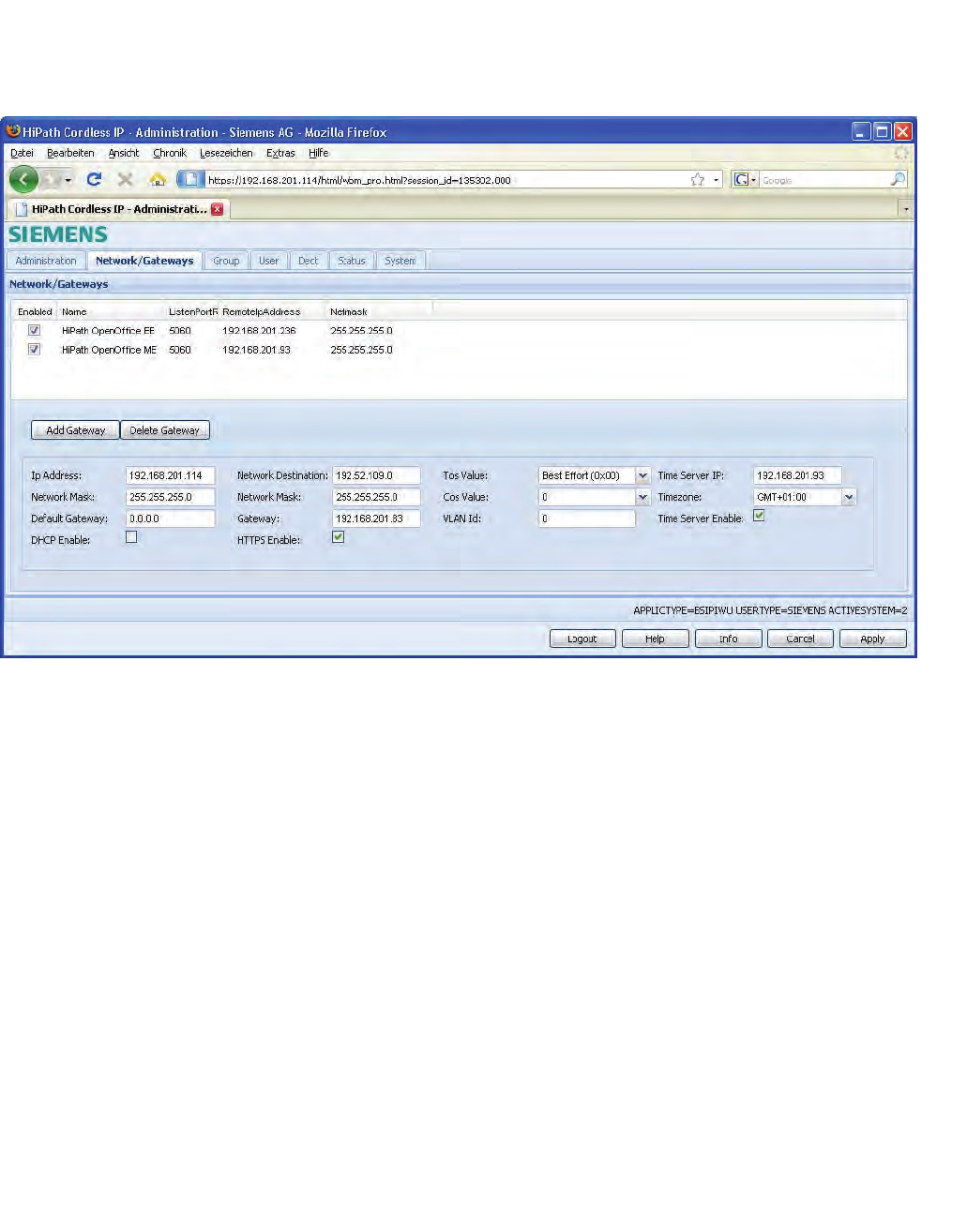
Installation and Administration
c05_ikon.fm
"Network/Gateways" Configuration
A31003-C1010-S100-2-7620, 08/2010
98 HiPath Cordless IP, Service Manual
5.24 "Network/Gateways" Configuration
The configuration page “Network/Gateways” is divided into two parts.
In the table view at the top, the VoIP gateways (PBX) are assigned to the
"VoIP" connections.
At the bottom of the page, the general network configuration of the BSIP IWU
network is done.
5.24.1 Gateway configuration
•Hints: To add or delete a Gateway entry, the system services have to be
stopped before. All changes will be activated after a restart of the system
services.
1. To add a new entry for a gateway, click on [Add Gateway]. A new entry
line with default values is appended, which have to be modified according
to your system needs.
The new entry line is either inserted above the selected Gateway or inserted
at the top of the list if no Gateway is selected.
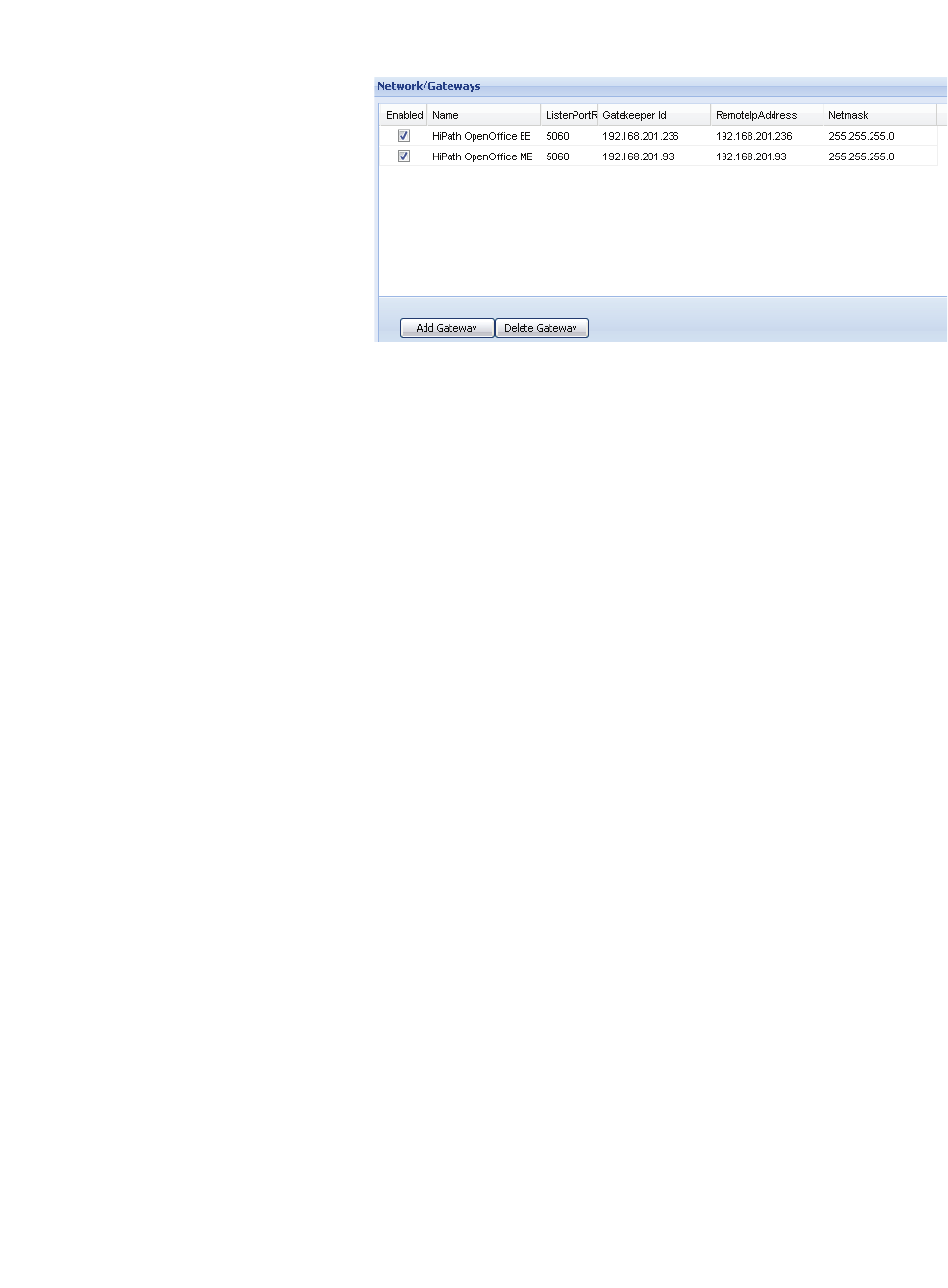
c05_ikon.fm
Installation and Administration
"Network/Gateways" Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 99
1. A selected Gateway entry may be deleted by clicking [Delete Gateway].
The columns of the configuration page have the following meaning:
Enabled
When activating this element ( ) the selected Gateway (the PBX) is added to
the configuration and can be selected when configuring the Groups later on.
Name
Enter a unique name here for the Gateway. This name will be displayed in the
dropdown box of the available Gateways when configuring the Groups.
ListenPortRemote
This entry determines the common SIP listen port of the configured gateway.
There is no need to change this port to another value than 5060. The default
setting is "5060".
If adding new entries, the value is duplicated from the field
“Remote IpAddress”. If changing the value in Field “RemoteIPAddress”, the
value is only duplicated, if both values didn’t differ before. Otherwise the field
“GatekeeperId” remains unchanged.
Gatekeeper Id
The field “Gatekeeper Id“ is only displayed in SiemensAdmin mode . The
value is equal to the IP address of the VoIP Gateway. By default, enter the
same value as in field “Remote IP address“.
Remote IP Address
Enter the IP address of the Gateway (the PBX) here. It shall be located in the
IP Infrastructure network (see chapter 5.2, “Network Concept”). At the BSIP1
a corresponding IP Infrastructure address has to be configured.
Netmask
Enter the netmask for the IP address for the Gateway here. (Default for Class
C networks: 255.255.255.0).
Dtmf (only in advanced config. Mode)
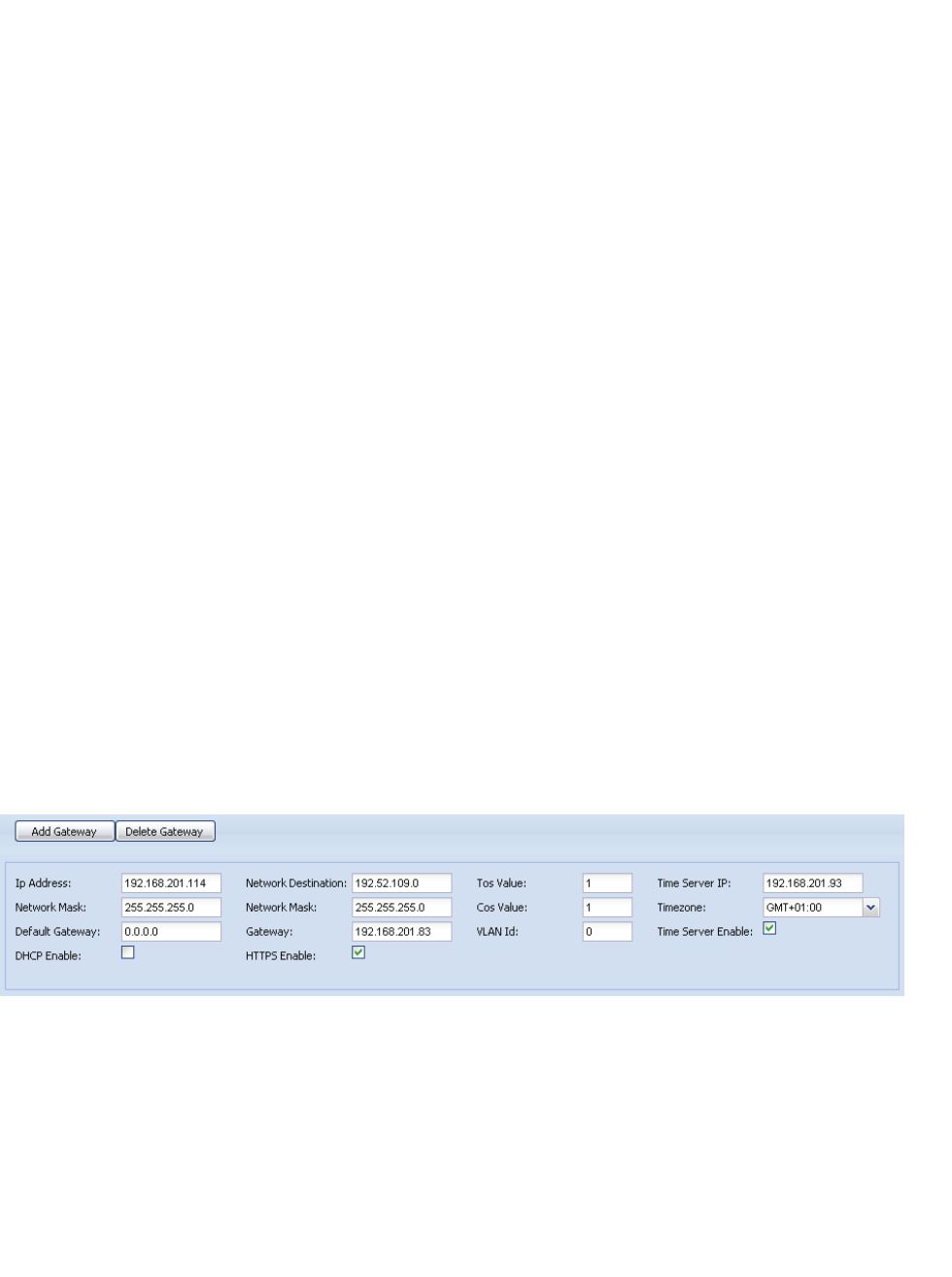
Installation and Administration
c05_ikon.fm
"Network/Gateways" Configuration
A31003-C1010-S100-2-7620, 08/2010
100 HiPath Cordless IP, Service Manual
Selects the method for the transmission of DTMF digits ("tones") to the
Gateway:
"Signaling": The DTMF Digits are transmitted via the Signaling protocol to the
Gateway (For SIP via the INFO method).
"RTP": The DTMF Digits are transmitted to the Gateway via the Voice (RTP)
channel (e.g. for SIP embedded in the RTP protocol according to RFC2833).
There is no need to change this setting for the supported gateways. The
default setting is "RTP".
Stunnel IP (only in advanced config. Mode)
Optional - The ip address of the Stun Server for the VoIP gateway SIP
Registrar or the Proxy Server. This configuration is depending on the used
PBX. There is no need to change this setting for the supported gateways. The
default setting is "0.0.0.0".
LocalIPAddress (only in advanced config. Mode)
Optional IP address to which the communication to the gateway should be
bound to. There is no need to change this setting for the supported gateways.
The default setting is "0.0.0.0".
5.24.2 Network configuration
At the bottom of the configuration page "Network/Gateways", the general
network configuration of the BSIP IWU network is done.
Refer to the concepts of networking described in chapter 5.2, “Network
Concept”.
•Hint: All changes will be activated after a reboot of the BSIP1.
IP settings for the BSIP IWU
Ip Address
Here you have to configure the ip address at which the BSIP IWU should be
configured inside the VoIP (Infrastructure) Network. This is also the ip
address at which the BSIP1 IWU is accessible via WBM.
c05_ikon.fm
Installation and Administration
"Network/Gateways" Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 101
Network Mask
Enter the corresponding netmask for the IP address as configured above.
(Default for Class C networks: 255.255.255.0).
Default Gateway
If all other routing is done via a default gateway , it can be configured here.
Alternatively, a dedicated route may be configured using the settings
"Network destination", "Network Mask" and "Gateway" as described below.
Hint: The Default gateway is functional only for neworks outside 192.168.0.0/
255.255.0.0. (Since 192.168.x.y. is a reserved local network for DECT
Basestations).
•Important: All BSIP1 devices must be located inside the same network
segment and therefore MUST NOT be separated by layer 3 Routing
devices. Only Layer 2 switches are supported between the BSIP.
DHCP Enable
Activate this option if the BSIP VoIP (Infrastructure) network has to be confi-
gured by a DHCP server. The BSIP IWU settings for the VoIP (Infrastructure)
network will be assigned by the DHCP server.
•Important notes:
•If using DHCP for the VoIP (Infrastructure) network, the configuration
of the DECT network has to be done manually (since not distributed
by the DHCP server).
•After applying the DHCP changes (reboot of BSIP1), the BSIP1 will
be assigned a new IP address by the DHCP server. Since there is no
local console access at BSIP1 possible, the only method to get the
assigned IP address is to have access to the DHCP servers lease
information! Contact the administrator of the DHCP server before
activating this option.
Network Destination
Alternatively, if a default gateway should not be used, a dedicated route to
another network may be configured here (e.g. using a Time server or access
to a maintenance network, ...). In the following three fields, you have to
configure the routing information to the other IP network.
Network destination
The destination address for the other IP network (e.g. 192.52.109.0).
Network Mask
The corresponding network mask for the other Network destination. (e.g.
255.255.255.0).
Gateway

Installation and Administration
c05_ikon.fm
"Network/Gateways" Configuration
A31003-C1010-S100-2-7620, 08/2010
102 HiPath Cordless IP, Service Manual
The IP address of the gateway inside the VoIP (Infrastructure) network which
handles the routing to the other network.
HTTPS Enable
Determines if https (Hypertext Transfer Protocol over Secure Socket Layer)
should be used for WBM communication between the browser and the
BSIP1. Using https encrypts the communication between the browser and the
WBM. It is suggested to use https mode.
Depending on the http access mode you have to use http:// or https:// mode
at the browser.
HTTPS Enabled = [ ] use http://{Server Ip IP VoIP (Infrastructure) Network}
HTTPS Enabled = [X] use
https://
{Server Ip IP VoIP (Infrastructure) Network}
Example: https://192.168.201.114
Tos Value
With the “TOS Value“ you can configure the prioritization of the IP packets via
TCP/IP (Layer3 ) according to DSCP. It is only used for the IP DSCP field for
VoIP Signalling (SIP) and VoIP data (RTP) packets towards the PBX (VoIP
Infrastructure Network).
Other IP packets e.g.
•WBM or SSH towards the VoIP Infrastructure network or
•packets between BSIP1 Only and BSIP1 IWU (DECT Network)
are NOT tagged with configured the DSCP value. (Default = “0“, i.e. no priori-
tization).
Using the dropdown you may select one of the pre-configured ToS values.
Cos Value
With the “CoS Value“ (decimal) you can configure the prioritization of the
ethernet packets via ethernet (Layer2) according to 802.1p. (Default = “0“, i.e.
no prioritization).
Using the dropdown you may select one of the pre-configured CoS values.
VLAN Id
The corresponding VLAN Id is configured here. If VLANs are used (value
unequal to "0"), the switch port connected with the BSIP IWU has to be confi-
gured to tag the ethernet frames.
If a value of zero (0) is configured here, the BSIP IWU will not tag the ethernet
frames. Otherwise, the frames are tagged according to their destination.
All frames inside the destinated VoIP (Infrastructure) network will be tagged
with the configured VLAN Id. All frames destinated to the DECT network will
be tagged with the VLAN Id configured at the DECT page.
Hint: The BSIP1 ethernet tagging feature is only activated for VLANId <> "0".

c05_ikon.fm
Installation and Administration
"Network/Gateways" Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 103
Time Server IP
Since the BSIP1 has no hardware clock, the time has to be set by contacting
a NTP (or SNTP) time server. The IP address of the Time Server is configured
here.
Since the BSIP1 has no hardware clock, the time has to be set by contacting
a NTP (or SNTP) time server. The IP address of the Time Server is configured
here. Hint: The supported platforms may serve as a SNTP server. For details
refer to e.g chapter 5.33.5, “Time server configuration”.
If a time server is not configured correctly and cannot be contacted, local time
will start at "01.01.1970 00:00".
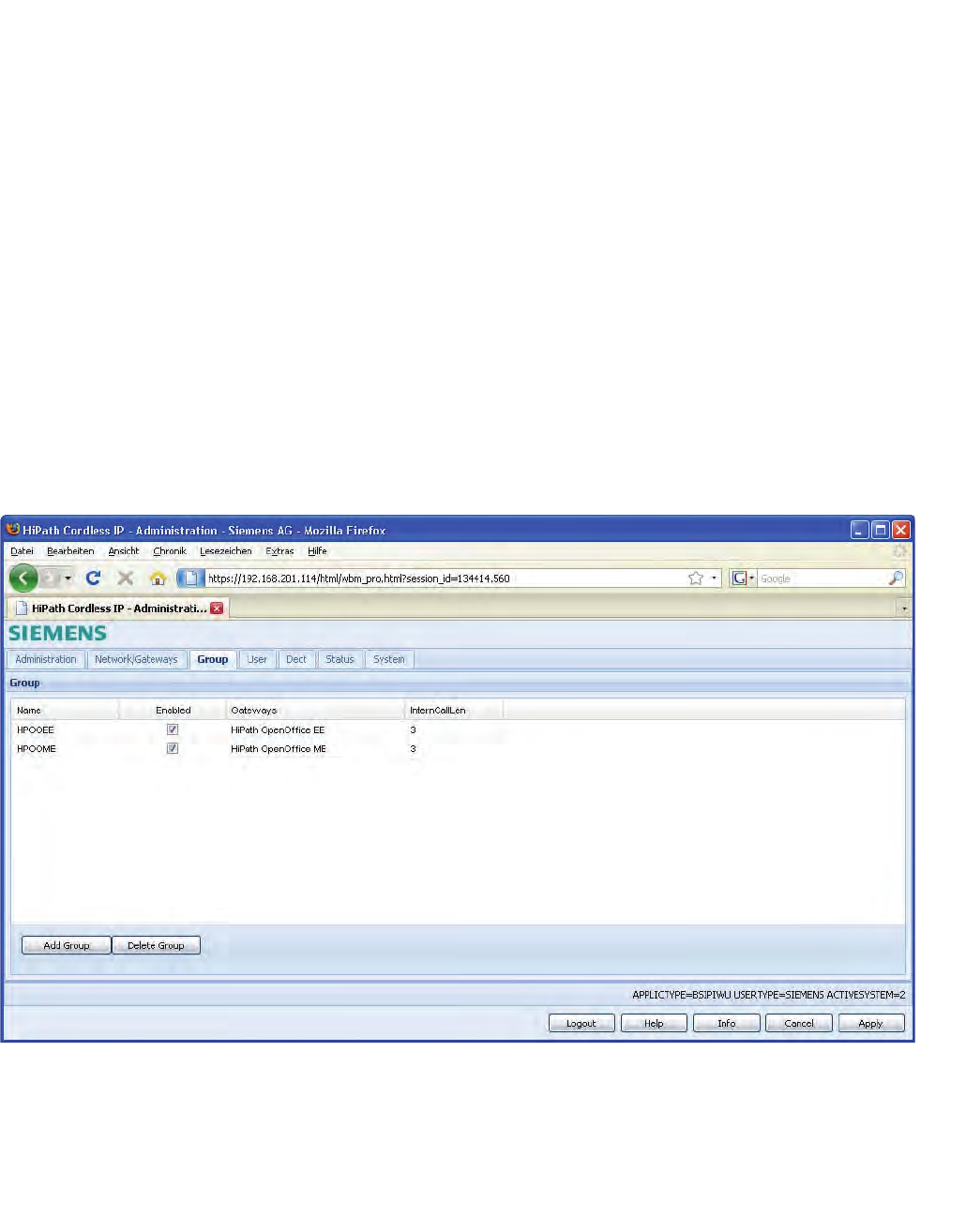
Installation and Administration
c05_ikon.fm
"Group" Configuration
A31003-C1010-S100-2-7620, 08/2010
104 HiPath Cordless IP, Service Manual
Timezone
If using a Time Server, the timezone has to be configured according the
physical location of the HiPath Cordless IP solution (country). Since NTP is
always using UTC time, the local time has to be calculated against the time
zone information to get correct current Local time.
Time Server Enable
Enables the usage of the Time Server.
After activating the NTP Server at the PBX it may take some minutes upon
activation of the NTP service. This is due to the nature of time synchronisation
between NTP server and NTP client.
5.25 "Group" Configuration
On the configuration page "Group" the Groups are defined, which are the
connecting link between the "VoIP Users" and the "Gateways". A User has to
be assigned to a Group and a Group has to be assigned to a Gateway.
•Hints: To add or delete a Group entry, the system services have to be
stopped before. All changes will be activated after a restart of the system
services.

c05_ikon.fm
Installation and Administration
"Group" Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 105
1. To add a new Group entry, click on [Add Group].
A new entry line with default values is appended, which have to be modified
according to your System. The new entry line is either inserted above the
selected Group or inserted at the top of the list if no Group is selected.
2. A selected Group entry may be deleted by clicking [Delete Group].
The columns of the configuration page have the following meaning:
Name
Enter a descriptive name for the Group (e.g the name of the corresponding
gateway). This will be displayed in the dropdown box for the available Groups
when configuring the VoIP Users.
Enabled
When activating this element ( ) the selected Group is enabled and displayed
in the dropdown box for the available Groups when configuring the VoIP
Users.
Gateways
Select the assigned Gateway for this Group via the select box. Hereby the
assignment between the User to a gateway (PBX) is configured.
InternCallLength
With this setting the maximum number of digits of the calling Party number for
internal calls is configured. Calls with a larger number of digits are signalled
as external calls at the handset. The default value is “3”.
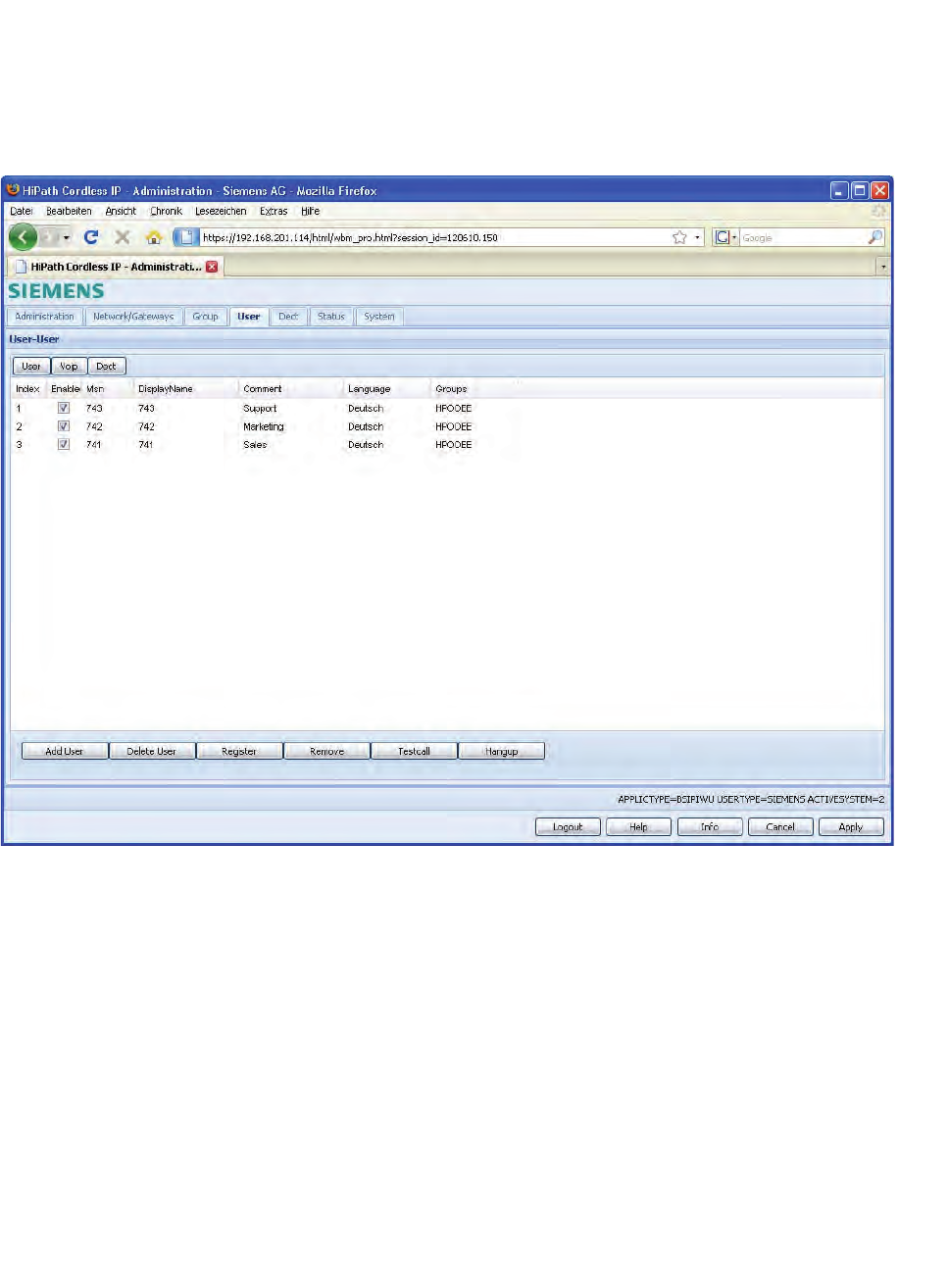
Installation and Administration
c05_ikon.fm
Users Configuration
A31003-C1010-S100-2-7620, 08/2010
106 HiPath Cordless IP, Service Manual
5.26 Users Configuration
On the sub configuration pages below "VoIP Users" ("User", "Voip" and
"Dect") the individual users and their properties regarding "User" (general
user properties), "Voip" (registration via VoIP) and "Dect" can be configured.
5.26.1 General user configuration
•Hint: To add or delete a user entry, the system services have to be
stopped before.
All changes will be activated after a restart of the system services.
1. To add a new user entry, please click on [Add User]. A new entry line with
default values is appended, which have to be modified according to your
system needs. The new entry line is either inserted above the selected
user or inserted at the top of the list if no user is selected.
A selected user entry may be deleted by clicking [Delete User].
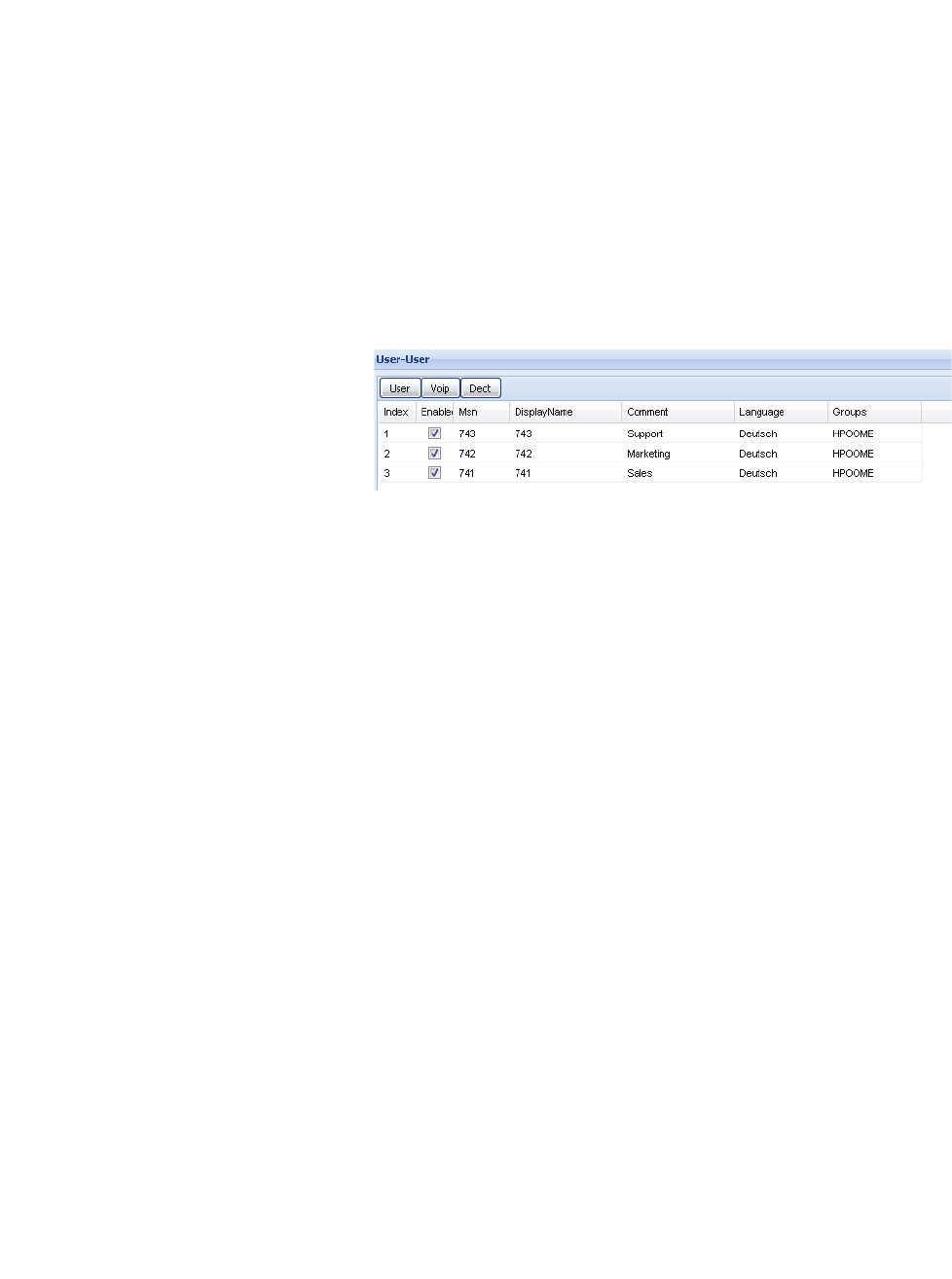
c05_ikon.fm
Installation and Administration
Users Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 107
•Hint: The functionality [Delete user] does not remove the registration of
the handset. It only removes the user entry from the WBM configuration.
Therefore if you delete an user, an “Auto entry” will be added later (for
details refer to chapter 5.26.5, “Auto Entry users”.
The buttons [Register], [Remove], [Testcall] and [Hangup] are described at
a later chapter.
5.26.2 Configuration Page "User - User"
On this page the VoIP parameters for the Users are configured.
The columns of the configuration table have the following meaning:
Index
Current number of the User entry. Automatically incremented by the BSIP.
Enabled
When activating this element ( ) the selected User is enabled at the BSIP
IWU.
MSN
The "MSN" should correspond with the Subscriber Number of the User at the
PBX (usually the "User Name" in the PBX).
DisplayName
The handsets will display this value in their idle display. The activation of the
DisplayInfo is done by an outgoing or incoming call. There is neither an
activation of the DisplayInfo due to a Power cycle of the handset nor to a
roaming process.
The DisplayInfo at the handset is limited to a maximum of 10 Characters.
•Important note: Don't use characters others than 0-9, a-z, A-Z, "-" "_" for
the DisplayInfo configuration. Other characters may prevent that the
DisplayInfo is diplayed correctly or that the system services are running
correctly.
To avoid confusions, the field "DisplayName" should be equal the Msn confi-
gured above.
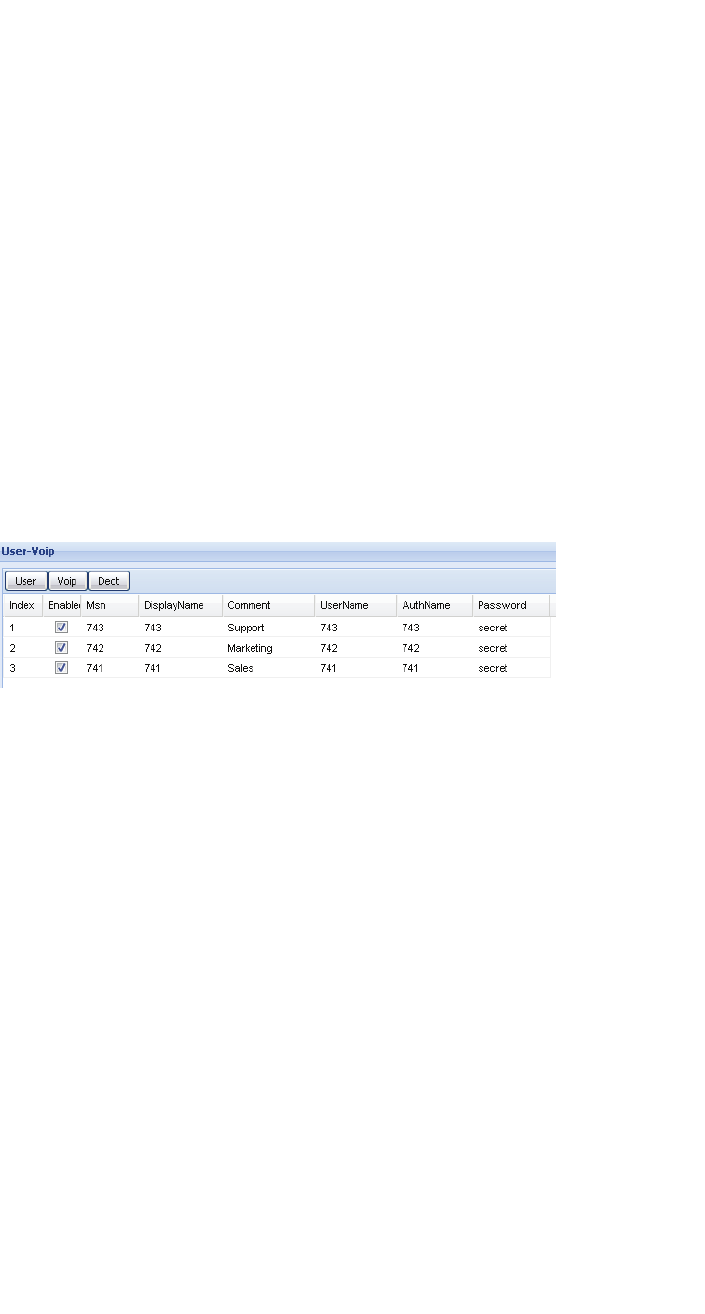
Installation and Administration
c05_ikon.fm
Users Configuration
A31003-C1010-S100-2-7620, 08/2010
108 HiPath Cordless IP, Service Manual
Comment
The field "Comment" serves only as a reference for the system administrator
of the BSIP1. It may e.g. contain the type of the Handset or the name of the
department if the Handset is not associated directly to a person.
This field has no influence on the functionality of the IWU.
Language
The language used for display messages of the handset is selected here.
Groups
Choose a Group (and therefore an associated VoIP gateway) from the
dropdown box to which the user is associated to.
5.26.3 Configuration Page "User - VoiP"
On this page the parameters for the registration of the User at the PBX and
the assignment of the subscriber numbers can be configured.
The columns of the configuration page have the following meaning:
•Note: The columns "Index", "Enabled", "Msn", "DisplayName" and
"Comment" are repeated on all sub pages. A description of these
parameters can be found in chapter 5.26.2, “Configuration Page "User -
User"”.
For the correlation between the values used in the VoIP gateway configu-
ration and in WBM see the corresponding chapter for the used PBX in
chapter 5.31, “Configuration Hints for PBXs”.
UserName
Assign a User Name which is used for the registration at the PBX. This may
be a name or a number depending on the PBX or the provider. For the
supported gateways the phonenumber should be used.
AuthName
The authentication Name is needed as a “Login” name if the registration is
done via “RAS” and the account at the PBX is password protected.
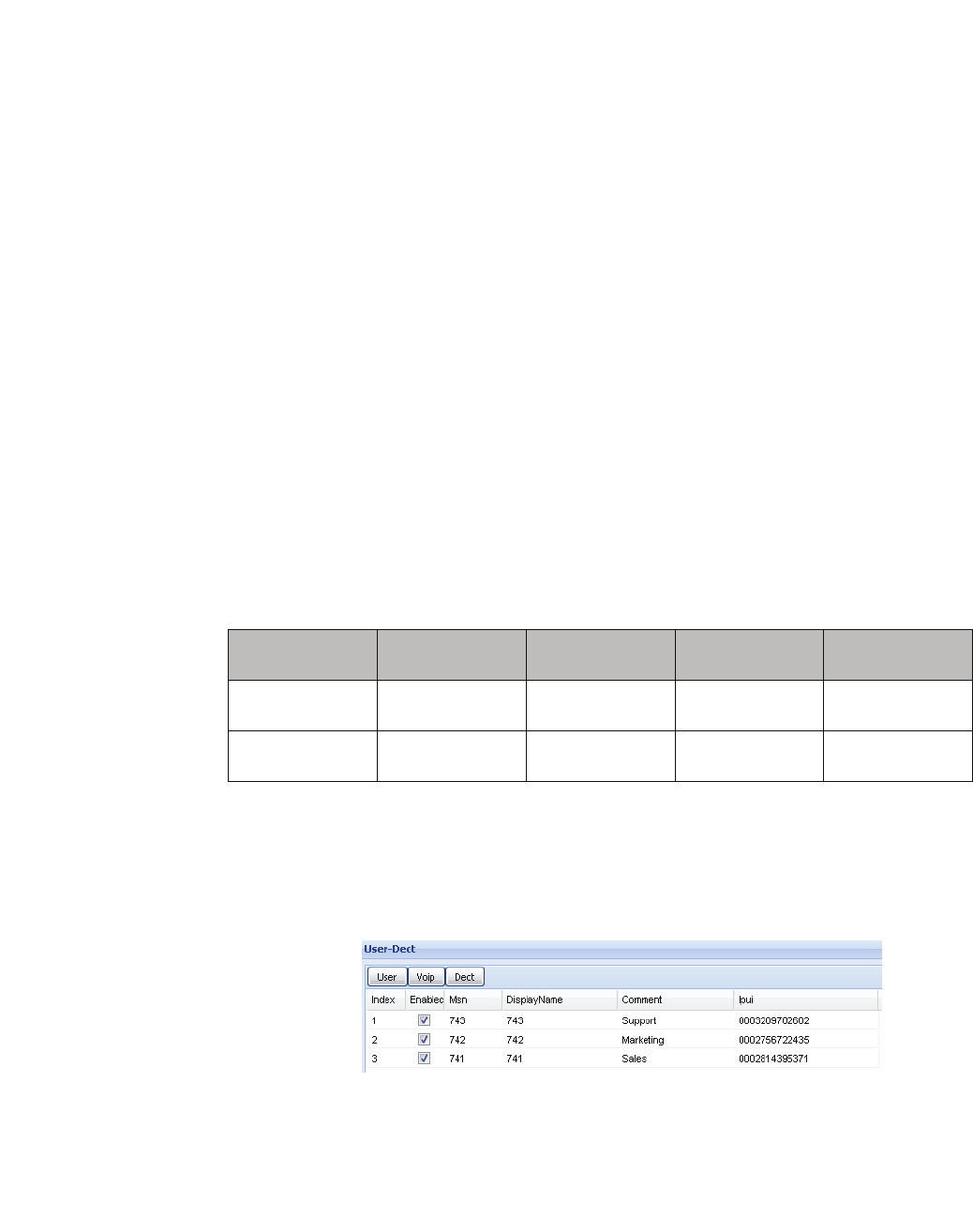
c05_ikon.fm
Installation and Administration
Users Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 109
Password
Enter the Password here which is needed for the registration of the User
(together with the "AuthName").
G729
The usage of low bandwith codec G729 is intended for devices which are
connected to the PBX via low bandwith lines (DSL) e.g. for home office users
using a SIP phone (e.g OptiPoint). Therefore bandwith is an issue for such
scenarios. Inside the LAN efficient bandwith should not be an issue; therefore
codec G711 should generally be used. Therefore there is no need to
configure G729 in the codec list of the PBXs “Gateway - Codec” configuration
page. Activating the codec G729 at the handset changes the codec list from
G711A, G711U to G729ab;G711A,G711U.
To establish a G729 voice connection between a BSIP1 handset (G729
Enabled) and an OptiPoint SIP phone, the following configuration is
necessary:
At the BSIP1, configure G729 for the desired or all user.
At the SIP phone, configure the speech codecs for “G729 preferred” and
activate “Silence suppression” (Silence Supression is needed due to the used
“b” variant of the G729 codec).
Using these settings, calls between the following participiants should use the
following codec:
5.26.4 Configuration Page "User - Dect"
This page contains the user configuration for DECT.
•Note: The columns "Index", "Enabled", "Msn", "DisplayName" and
"Comment" are repeated on all sub pages. A description of these
parameters can be found inchapter 5.26.2, “Configuration Page "User -
User"”.
From / To BSIP1
G729 Enabled BSIP1
G729 Disabled SIP phone TDM user
BSIP1
G729 Enabled G711 G711 G729 G711
BSIP1
G729 Disabled G711 G711 G711 G711

Installation and Administration
c05_ikon.fm
Users Configuration
A31003-C1010-S100-2-7620, 08/2010
110 HiPath Cordless IP, Service Manual
•Hint:All changes will be activated after a restart of the system services.
The buttons in the lower part of the page on the left have the following
functions:
[Register]
Start the DECT registration for the selected User (Registration of the
handset).
For the registration a close by Base Station has to be chosen from the select
box in the column "DectModul" of the User.
The registration mode will be activated for a certain period of time for this
Base Station. At the Handset of the User Registration has to be started and
the PIN number (as configured in chapter 5.27.3, “Configuration Page "Dect
- ARI"”) has to be entered when requested.
•Note: Restart the registration process if you did not succeed registering
your handset in the provided period of time.The time is limited to avoid
foreign handsets registering.
Remove
Remove the DECT registration for the selected User (Deregister the
Handset).
TestCall
Perform a test call. The Handset of the selected User must start ringing (if
already registered). The call can be accepted.
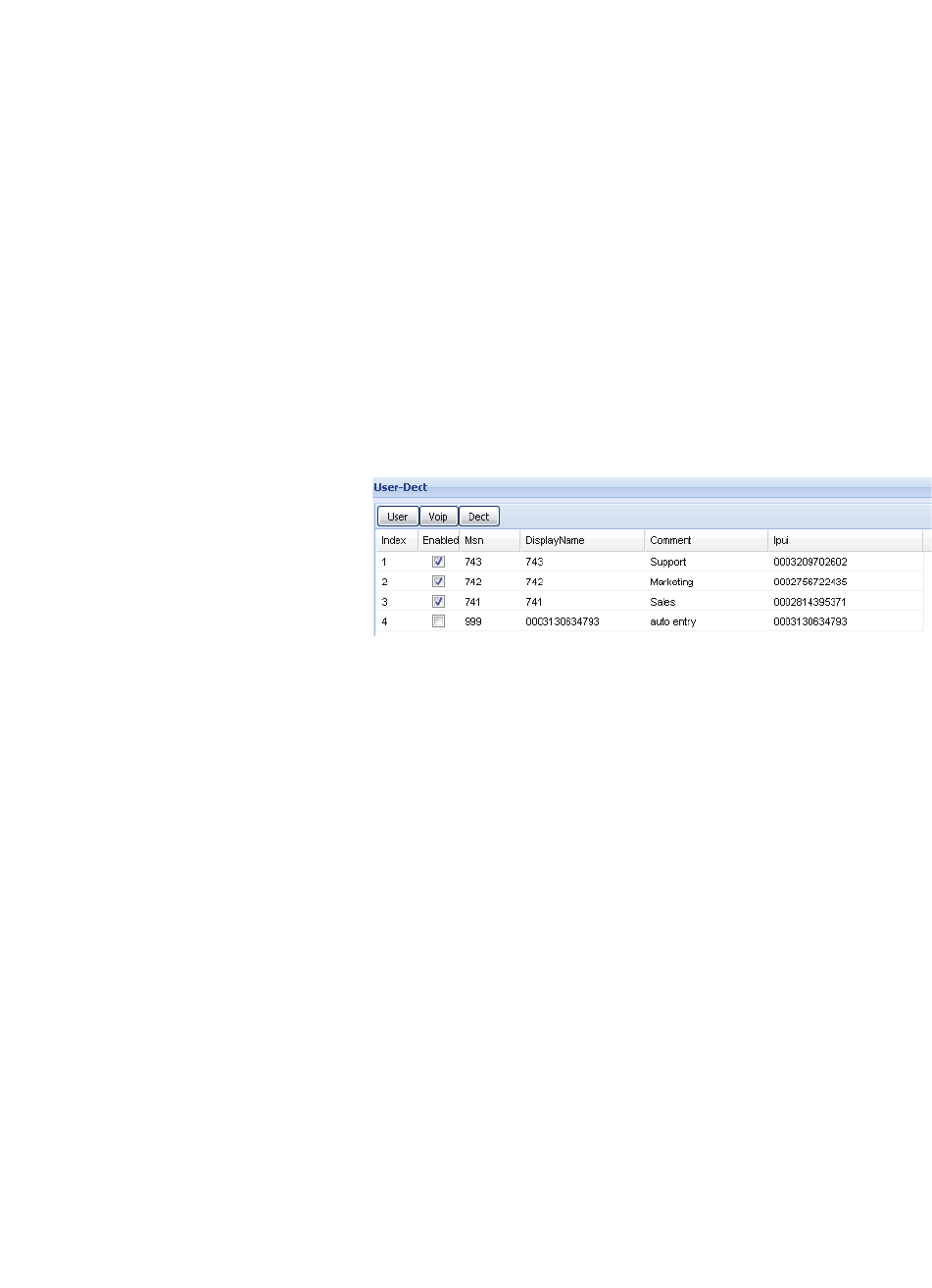
c05_ikon.fm
Installation and Administration
Users Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 111
Hangup
Terminate the test call (Hang up).
Ipui
The IPUI (International Portable User Identity) of the Handset of the User is
automatically recorded during the registration process.
5.26.5 Auto Entry users
The WBM generates a special "Auto entry" user in the following scenarios:
A handset has a valid registration at the BSIP and is registered, but no corre-
sponding User can be found which matches the IPUI of the handset.
The AutoEntry user will be displayed alike a normal user in the user configu-
ration
It is possible to configure the auto entry user as a normal user with the diffe-
rence, that no registration procedure has to be performed (since the DECT
registration at the BSIP was successfull).
•Hint: Auto user entries are stored as normal users in the BSIP configu-
ration.
The auro entry user is also displayed in the status page "Calls Dect".
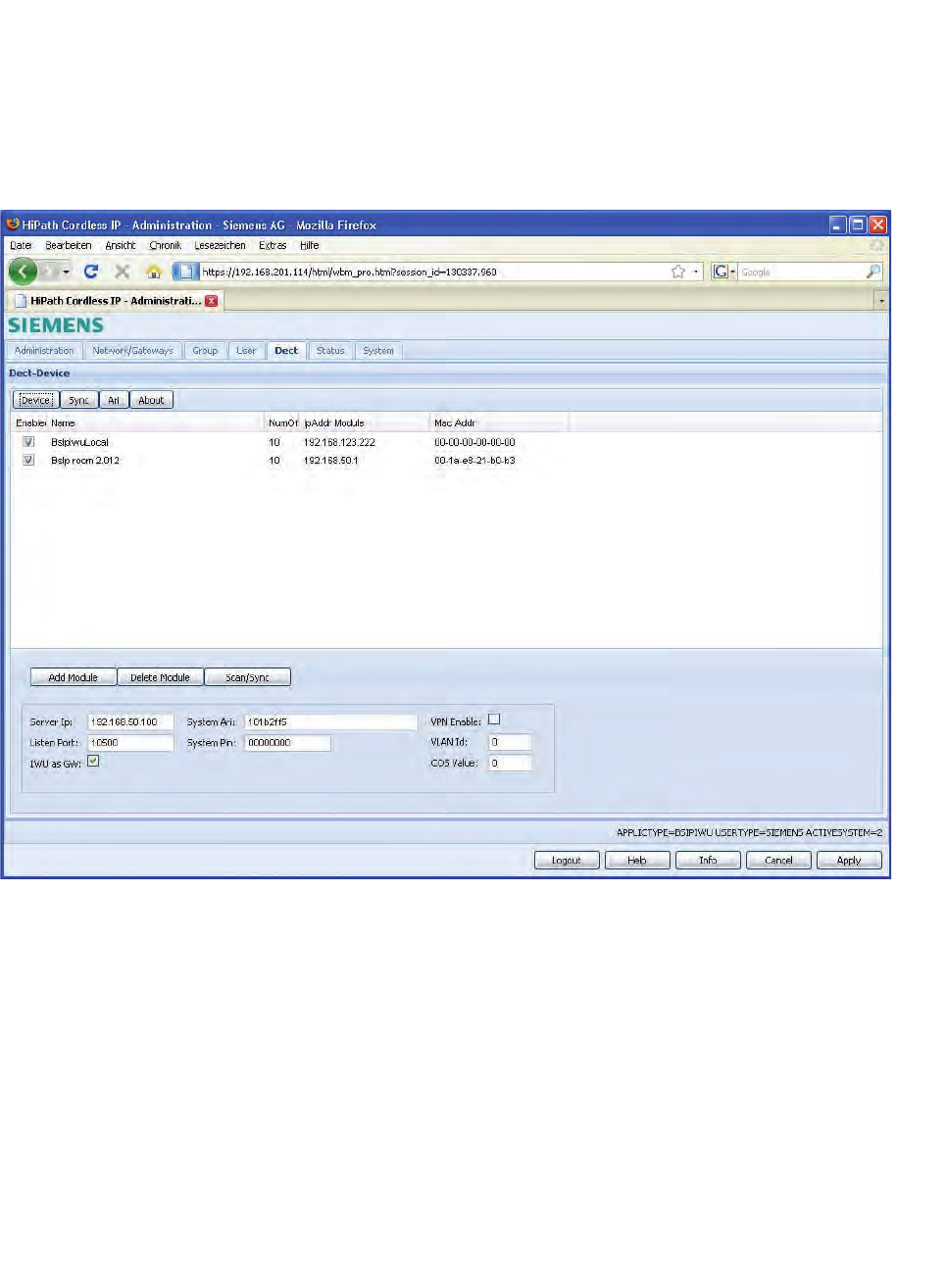
Installation and Administration
c05_ikon.fm
Dect Configuration
A31003-C1010-S100-2-7620, 08/2010
112 HiPath Cordless IP, Service Manual
5.27 Dect Configuration
On the main configuration page "Dect" the IP-DECT ethernet Base Stations
are configured. This page contains the sub configuration pages
"Device",""Sync", "ARI", and , "About".
There are further sub-pages available in WBM mode Siemens Admin.
5.27.1 Configuration Page "Dect - Device"
On this page the properties of the Base Station connections are configured.
The columns of the configuration table have the following meaning:
Enabled
By activating this option this Base Station is enabled at the BSIP IWU.
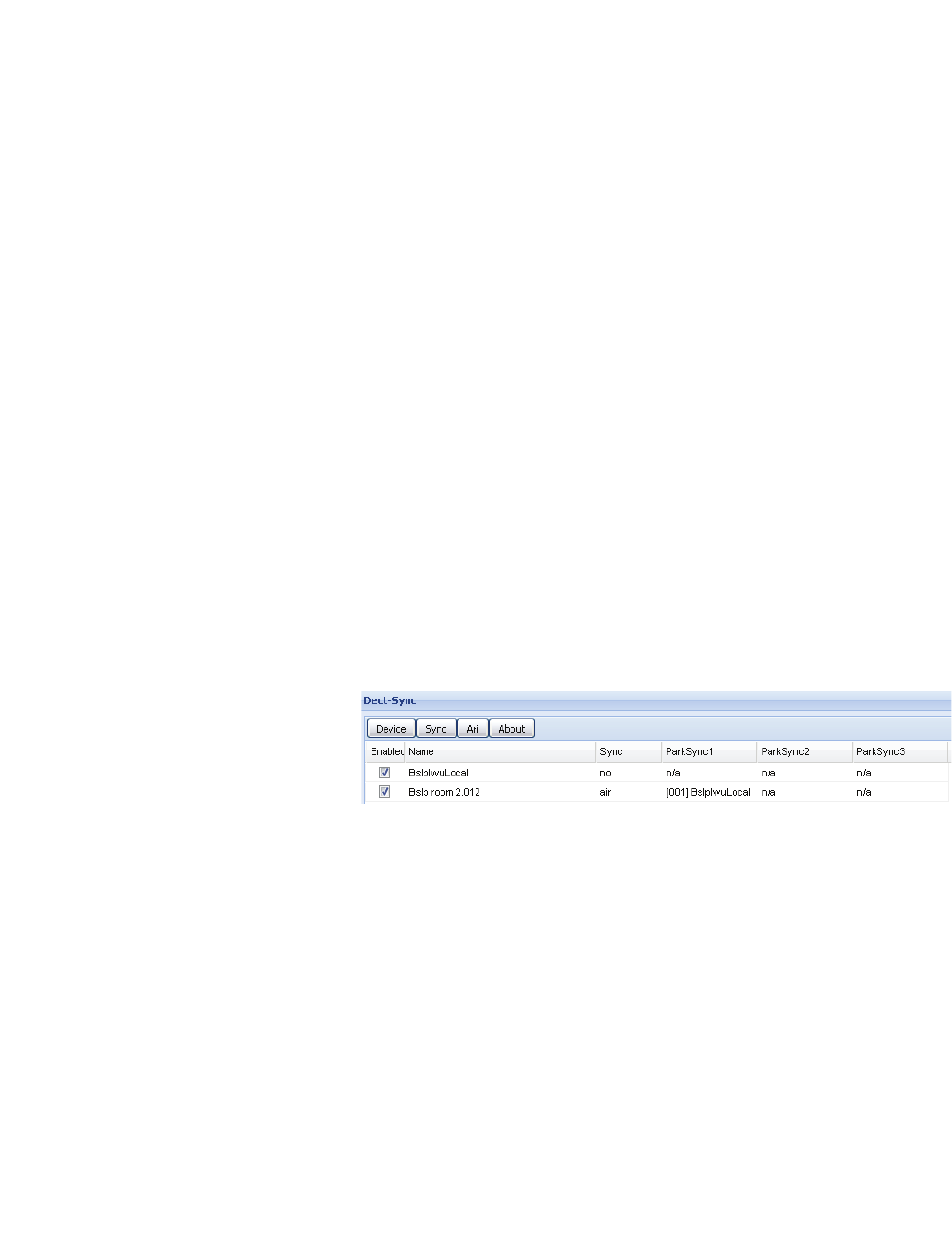
c05_ikon.fm
Installation and Administration
Dect Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 113
Name
The name of the Base Station can be configured here.
NumOfChannel
Number of voice channels of the Base Station in conjunction with the IWU.
The maximum value is "10". If less than "10" parallel voice channels shall be
supported, a smaller value may be configured here. The default value is "10".
IpAddr Module
The IP address of choice for the Base Station in the IP-DECT network is
entered here. Please take care that the "IpAddr Module" address has to be
unique and is in the same subnet as the IP address of the Interworking Unit
("Server Ip").
Please not that the IP address of the Base Station is transmitted to the Base
Station after a [UDP Set] (see chapter 5.27, “Dect Configuration”).
MAC Addr
In this field the ethernet MAC address of the Base Station is displayed as it is
found during a "Scan". It cannot be changed.
5.27.2 Configuration Page "Dect - Sync"
On this configuration page the synchronization of the Base Stations is confi-
gured.
The columns of the configuration page have the following meaning:
•Note: The columns "Enabled" and "Name" are repeated on all sub pages.
A description of thesevalues can be found in chapter 5.27.1, “Configu-
ration Page "Dect - Device"”.
"Sync" (Default value: "air")
Here you can configure the type of synchronization of the Base Station with a
dropdown box. It is important e.g. for the over air-synchronisation and
therefore for the seamless handover between basestations. You can choose
one of the following menu items in the dropdown box:
•"no": No synchronization of the Base Station. This may be configured if
no "seamless handover" is needed or if this BSIP serves as the “Sync
Master” which is the topmost synchronisation source.

Installation and Administration
c05_ikon.fm
Dect Configuration
A31003-C1010-S100-2-7620, 08/2010
114 HiPath Cordless IP, Service Manual
•"air": Synchronization of activated Base Stations over air, i.e. directly via
DECT, but with additional Status information by the IWU.
This method occupies - depending on the Beacon configuration - one or
more available timeslots (which cannot be used for telephony), but it
allows the seamless handover between the radio areas of synchronized
Base Stations.
The Base Station to be synchronized to must be an activated Base Station
at the IWU. This is the standard synchronisation method used.
•"air ext": Synchronization of Base Stations over air, i.e. directly via DECT,
but without additional Status information by the IWU.
This method occupies - depending on the Beacon configuration - one or
more available timeslots (which cannot be used for telephony), but it
allows the seamless handover between the radio areas of synchronized
active Base Stations.
The Base Station to be synchronized to must be a Base Station confi-
gured at the IWU, but it need not be activated.
Alternatively a Base Station may also be synchronized to another Base
Station that is NOT configured at the IWU (e.g. Base Stations of other
manufacturers).
If the PARK of the external Base Station is known, it may be entered as
"PARK Default" of the Base Station to be synchronized on the page "Ari".
For the external Base Station a "Dummy" module has to be configured.
Please notice that this may result in problems regarding the so called
"Beacon Announcement" which may lead to frequent losses of synchro-
nization.
To minimize this problem an (internal) Base Station may be used as
synchronization Base Station. Therefore you have to configure "0"
channels (page "DECT - Device", entry "NumOfChannel"). No voice
connections can be established via this Base Station.
• "ParkSync" (3 columns)
You can choose a Base Station resp. DECT module from the select box
on which the selected Base Station shall synchronize to (synchronization
master). The Base Station will first try to synchronize to the Base Station
in the leftmost "ParkSync" column. If this is not successful or if the
synchronization gets lost while in operation, the Base Station will try to
synchronize to the Base Station in the middle "ParkSync" column and
finally to the rightmost column.
Only when the synchronization to all 3 entered Base Stations is not
successful, a synchronized operation and therefore a seamless handover
will no longer be possible.
•Note regarding the synchronization sequence:
For the operation of several synchronized Base Stations the synchroni-
zation sequence shall be configured as a "chain", i.e. the second Base
Station synchronizes to the first, the third Base Station to the second, the
fourth to the third and so on.
If all Base Stations synchronize to one single "Master" Base Station a
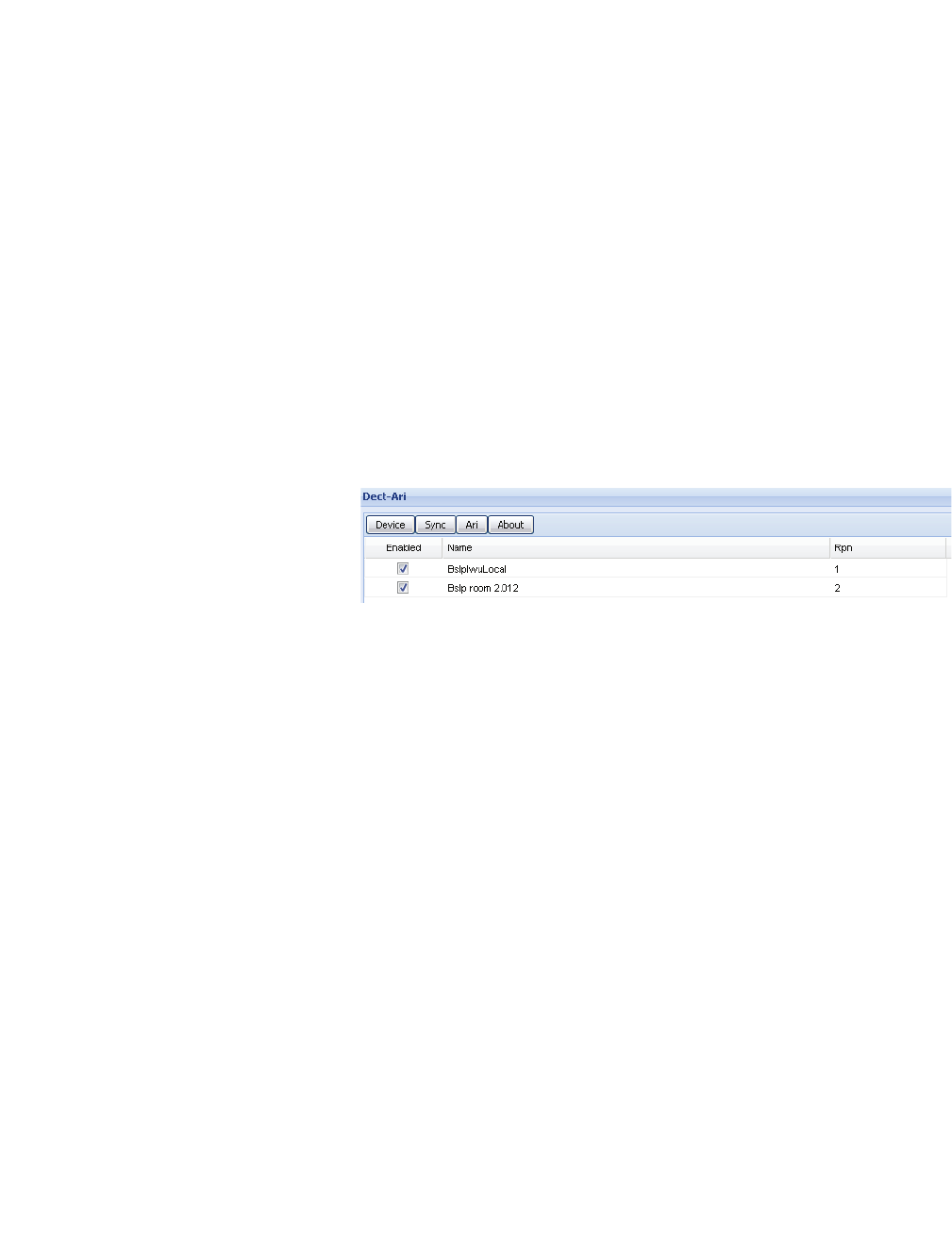
c05_ikon.fm
Installation and Administration
Dect Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 115
much longer period of time will be needed for the reconstruction of the
system wide synchronization, because of the "Burst" behavior.
In addition to that the distance of a "Sync Slave" to the topmost "Sync
Master" in the synchronization chain shall not be more than 5 hops (Base
Stations) else the "Slip" will be to big and if a Base Station looses synchro-
nization it will only be (automatically) resynchronized when there are no
longer active calls at this Base Station.
Important note: If a BSIP looses synchronisation it tries to resync to the
configured synchronisation base station. This process can not start until the
last call at this base station is released and no other calls (at the belonging
base station) are active.
5.27.3 Configuration Page "Dect - ARI"
On this configuration page the access rights (ARI - Access Right Identity) for
the individual Base Stations as seen from the Handsets are configured.
The columns of the configuration page have the following meaning:
•Note: The columns "Enabled" and "Name" are repeated on all sub pages.
A description of these can be found in chapter 5.27.1, “Configuration
Page "Dect - Device"”.)
RPN
When operating the Base Station stand alone and unsynchronized "0"
(default value) has to be entered as RPN ("Radio Fixed Part Number"). For
the setup of a network of synchronized DECT Base Stations this number is
used for a handset to differentiate between the Base Stations for the
seamless handover and it therefore has to be unique in the DECT network.
For DECT Base Stations with an ARI class A (default) the values 1 to 7 are
allowed to differentiate between up to 7 Base Stations, for DECT Base
Stations with an ARI class B the values 1 to 255 are allowed to differentiate
up to 255 Base Stations.
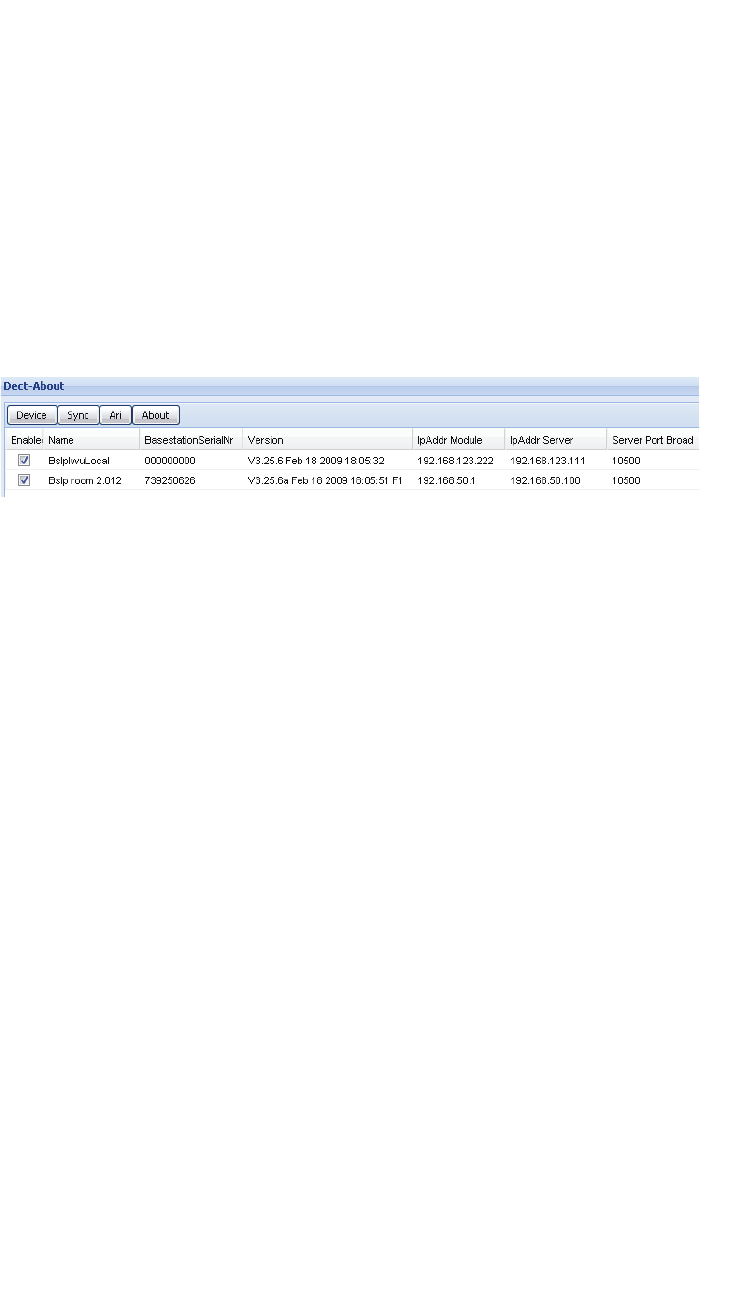
Installation and Administration
c05_ikon.fm
Dect Configuration
A31003-C1010-S100-2-7620, 08/2010
116 HiPath Cordless IP, Service Manual
Cipher (only available in Siemens Admin mode)
By activating the ciphering feature, the communication between the handset
and the configured base station is encrypted.
Configure this setting for all base stations to the same value.
5.27.4 Configuration Page "Dect - About"
This configuration page is only for information purposes on the created DECT
configuration.
1. Click [Scan/Sync] to update all values.
The columns of the configuration page have the following meaning (only
display):
•Note: The columns "Enabled" and "Name" are repeated on all sub pages.
A description of these can be found in chapter 5.27.1, “Configuration
Page "Dect - Device"”.)
BasestationSerialNr."
Serial number of the Base Station as read with "Scan/Sync".
Version
Displays the version number of the Firmware of the DECT module including
version date as read from the Base Station with "Scan/Sync".
IpAddr Module
IP address of the BSIP1 Only , as read with "Scan".
IpAddr Server
IP address of the DECT Server IP (DECT network) read with "Scan/Sync".
Server Port Broad
IP port on which the BSIP IWU communicates with the BSIP Only as read
from the Base Station with "Scan/Sync".
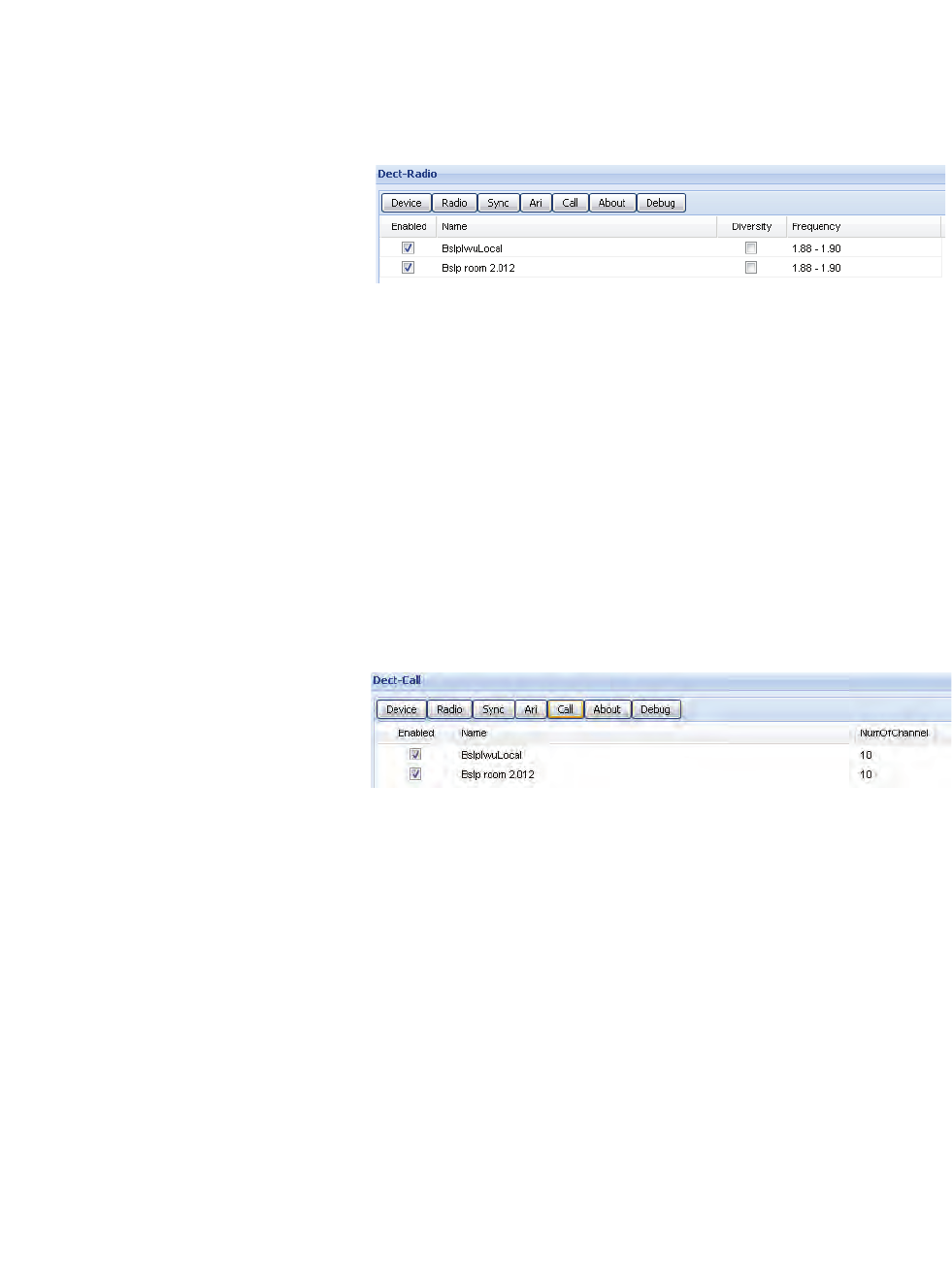
c05_ikon.fm
Installation and Administration
Dect Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 117
5.27.5 Configuration Page "Dect - Radio" (Advanced
mode)
This page is only displayed in Siemens Admin mode at the WBM.
Diversity
Activates the antenna diversity feature for the selected BSIP1.
Frequency
Selects the frequency of the DECT the BSIP1 is working with.
Standard setting: "1.88-1.90". Dont' configure other settings.
5.27.6 Configuration Page "Dect - Call" (Advanced
mode)
This page is only displayed in Siemens Admin mode at the WBM.
NumOfChannel
In SiemensAdmin mode the configuration for number of channels is located
at this sub-page. In Normal mode the configuration may be found at configu-
ration page "Dect - device"
Jitter
In SiemensAdmin mode the jitter buffers for the Dect Module may be confi-
gured here. Don’t change the value from its default “6”.

Installation and Administration
c05_ikon.fm
Dect Configuration
A31003-C1010-S100-2-7620, 08/2010
118 HiPath Cordless IP, Service Manual
5.27.7 Configuration Page "Dect - Debug" (Advanced
mode)
This page is only displayed in Siemens Admin mode at the WBM.
On the sub page "Debug" various logging and debugging functions may be
activated for the individual DECT modules. Based on these functions
potential problems in the DECT section may be isolated. For the analysis of
the Log files profound knowledge of the DECT technologies is essential.
Therefore debugging is intended primarily for our support staff.
•Note: Please note that depending on the activated Logging configuration
big amounts of data may be produced which may have negative influence
on the performance of the IWU Software and the System. Therefore you
should only activate Logging functions when requested by a support
engineer.
The columns of the configuration page have the following meaning:
•Note: The columns "Enabled" and "Name" are repeated on all sub pages.
A description of these can be found in chapter 5.27.1, “Configuration
Page "Dect - Device"”.
Debug Disable (Default value: Deactivated)
When activating this entry ( ) the Logging functionality for the active DECT
module is disabled, independent of the configured Debug level.
Debug Lvl (Default value: "0x00000000")
Debug level of the selected entry. The value may be entered directly
hexadecimal or via the checkboxes on the right.
5.27.8 General DECT configuration
The configuration page "Dect" is divided into two parts.
In the table view at the top, all BSIP1 modules are configured.
At the bottom of the page, the general DECT configuration of the DECT
Network is done.
• All changes will be activated after a reboot of the BSIP1.
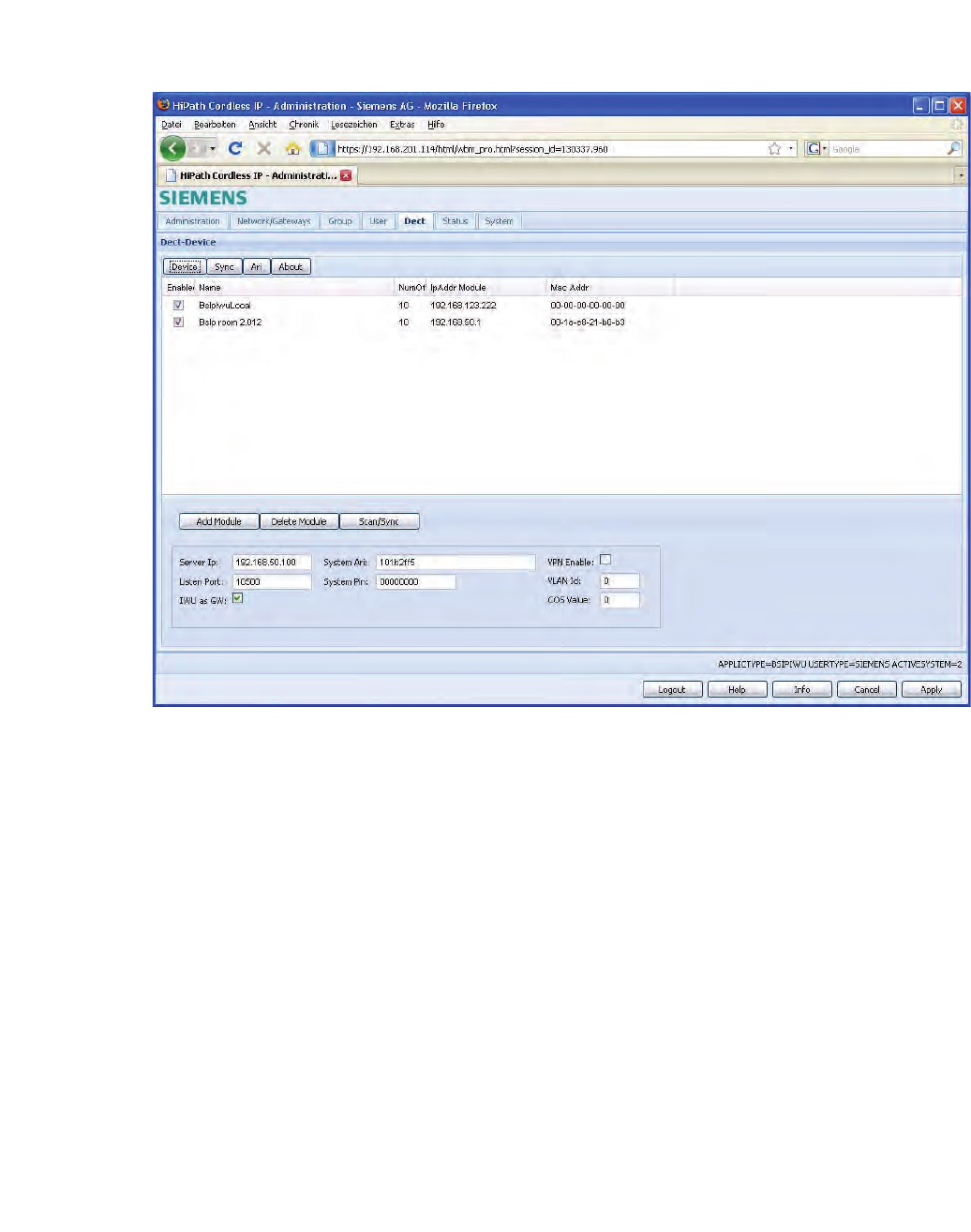
c05_ikon.fm
Installation and Administration
Dect Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 119
5.27.8.1 Adding, deleting and scanning
1. Click on [Add Module] to manually add a new entry for a Base Station
(normally not needed - see [Scan]). You have to configure the new entry.
The new entry is added above the selected Base Station entry or at the
end of the list if no Base Station is selected.
2. By selecting a base station and clicking on [Delete Module], the selected
Base Station entry is deleted.
The button [Scan/Sync] has a dual purpose functionality.
The first functionality is to Scan the network for all BSIPs using an ip
broadcast mechanism. All BSIP Only are answering and sending their actual
configuration information to the BSIP IWU where it is displayed. For BSIPs
which no configuration is assigned, a new entry is automatically added.
Please note that only IP-DECT Base Stations in the same ethernet segment
as the BSIP IWU are found.
The other functionality is to send the configuration to all configured base
stations. Hereby all configured options are transferred to all activated Base
Stations.

Installation and Administration
c05_ikon.fm
Dect Configuration
A31003-C1010-S100-2-7620, 08/2010
120 HiPath Cordless IP, Service Manual
5.27.8.2 General configuration options
Server Ip
This field contains the IP address of the server (the IWU) in the DECT
network. It is used by the BSIP Only as the destination ip address for ip
packets.
Listen Port
This field defines the IP port on which the communication between the BSIP1
IWU and BSIP1 Only is established. The default value is 10500.
SystemAri
In this field the System ARI (DECT ID) which has to be unique at each DECT
system has to be configured. The SystemAri is provided by the system imple-
mentor. Supported System Ari’s are Class A and ClassB Ari.
SystemPIN
The "PIN" is a 8-digit number and it is needed for the registration of Handsets.
It is preconfigured with "00000000" and may be configured systemwide here.
IWU as GW
This option is only intended to access the BSIP1 Only when different VLANS
and/or VPNs are configured. It activates the routing functionality between the
VoIP (Infrastructure) network and the DECT network.
Hint: Using the BSIP1 IWU as a router influences the system (e.g. system
load for encryption) and may lead to to unpredictable system bahaviour.
Use this option only in case where other IP access is not available, e.g.
•SSH access to BSIP1 Only
•Access to WBM of BSIP1 Only
•Firmware update of BSIP1 Only
in case where other IP access is not available.
Therefore, you have to add add a route at the maintenance PC (Windows XP):
Example:
IP of BSIP1 IWU is 192.52.109.83, IP-DECT network is 192.168.201.0/
255.255.255.0
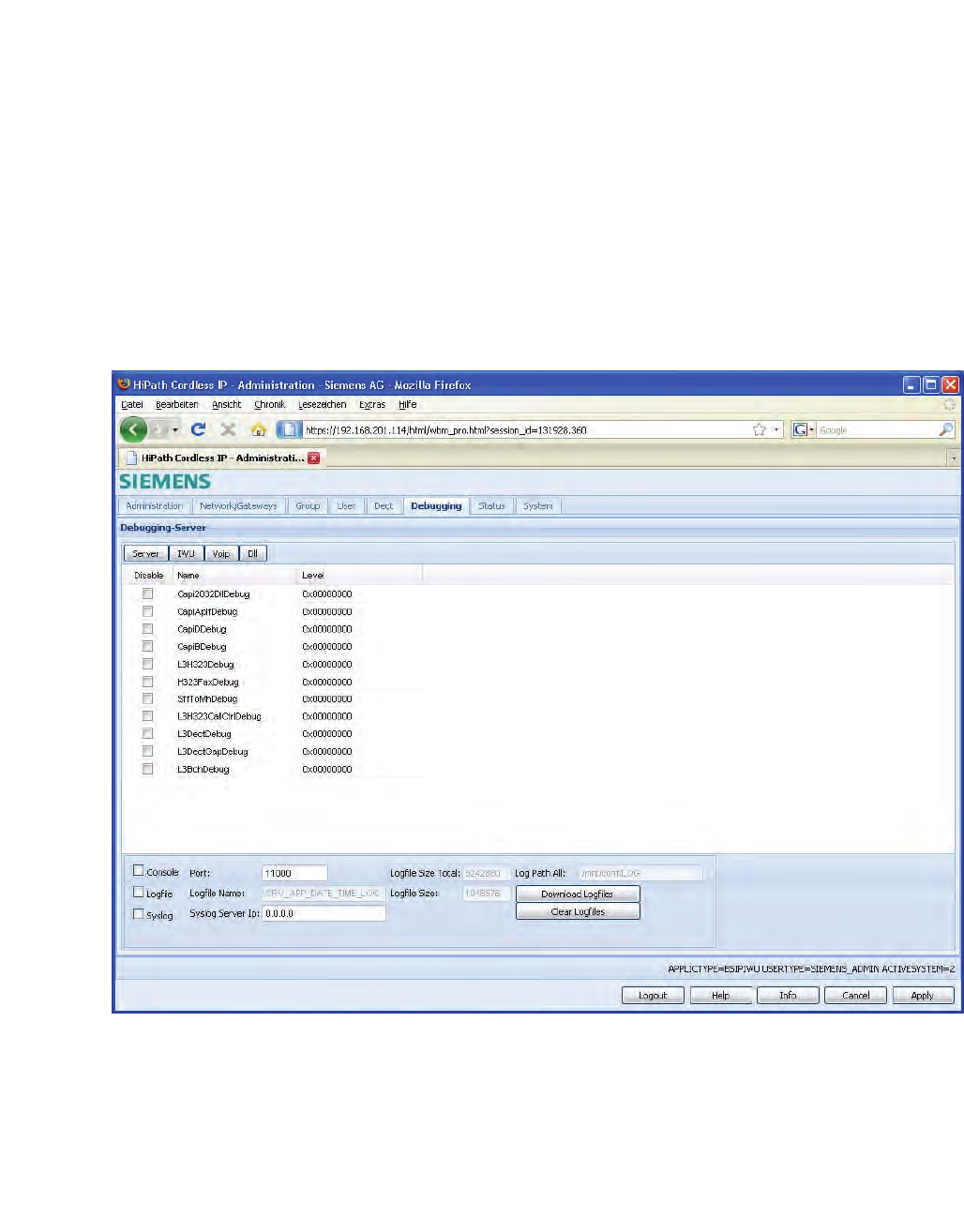
c05_ikon.fm
Installation and Administration
Debugging Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 121
To permanently add a route at the administration XP PC, type in at a
command windows:
route -p add 192.168.201.0 MASK 255.255.255.0
192.52.109.83
Hint: If you have formerly configured an IP address at the maintenance PC
within the DECT network, don't forget to delete this address at the XP PC
before adding the route.
5.28 Debugging Configuration
This page is only displayed with Siemens Admin mode at the WBM.
On the page “Debugging“ various Logging and Debugging functions may be
activated. Based on these functions potential problems regarding DECT,
VoIP or interworking functionality maybe isolated. For the analysis of the Log
files profound knowledge of VoIP and DECT connections is essential.
Therefore they are intended primarily for our support staff.

Installation and Administration
c05_ikon.fm
Debugging Configuration
A31003-C1010-S100-2-7620, 08/2010
122 HiPath Cordless IP, Service Manual
The sub pages "Server", "Iwu" "Voip" and "DLL"differentiate the various
parts of the Software for which Debugging can be activated. They differentiate
the names of the Software levels and the according Log file names. You will
get more detailed information from our support engineer when the activation
of a Debug level is requested.
•Note: Please note that depending on the activated Logging configuration
big amounts of data may be produced which may have negative influence
on the performance of the IWU Software and the System. Therefore you
should only activate Logging functions when requested by a support
engineer.
The options of the table have the following meaning:
Disable (Default value: Deactivated)
When activating this entry the logging functionality for the selected entry is
disabled, independent of the configured Debug level.
Name (fixed)
Preconfigured descriptive name of the Software level for which the Debug
level is valid. You will get more detailed information from our support engineer
when the activation of a Debug level is requested.
Level (Default value: "0x00000000")
Debug level of the selected entry. The value may be entered directly
hexadecimal or via the checkboxes on the right.
The options of the lower part of the configuration page have the following
meaning:
Console (Checkbox and entry)
By activating this entry ( ) the Debugging functionality via the Console appli-
cation is enabled.
The entry contains the associated UDP port number for Remote Debugging.
Logfile
By activating this entry ( ) the Debug output is written to the associated Log
files.
You may choose exclusively between Option Logfile or Syslog
Logfilename
This entry shows the name format of the Log file created.
Syslog
By activating this entry ( ) the Debug output is written to the associated Sylog
server.
You may choose exclusively between Option Logfile or Syslog.
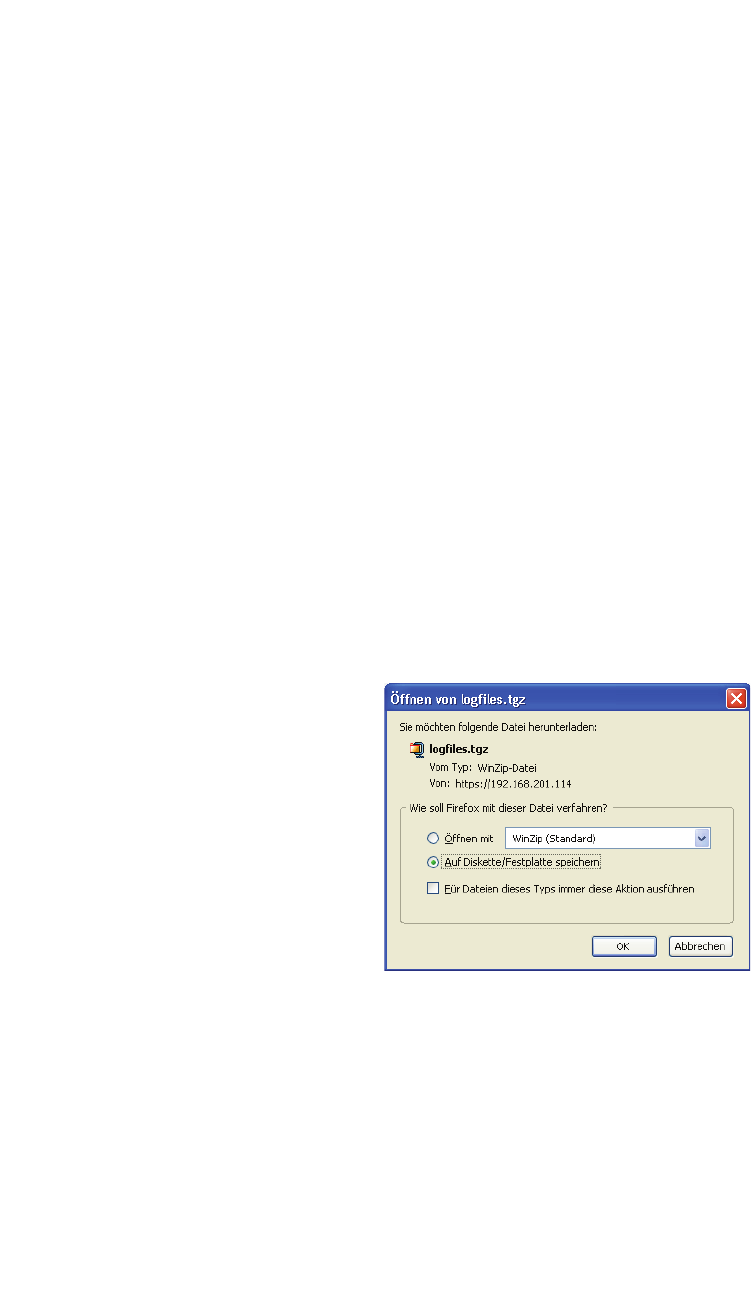
c05_ikon.fm
Installation and Administration
Debugging Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 123
BSIP1 Debugging messages are logged to a configurable syslog daemon
with Facility="LOCAL1" and SEVERTIY Level="ALERT".
Syslog Server IP
The ip address of the syslog server is configured here.
Logfile Size Total
Displays the limit of the the maximum allocated disk space in bytes for all log
files (stored in the “Log Path”) here. A process checks periodically if the total
size is reached. If the limit is reached the oldest Log Files are deleted to free
up disk space.
Logfile Size
Displays the limit of the the maximum file size in bytes of a single logfile here.
As soon as this size is reached the log output is continued in a new file.
LogPath All
Displays the LogPath the files are stored on the BSIP1.
Download logfiles
With this Button all logfiles of the BSIP can be downloaded and stored on the
file system of the maintenance PC.
1. After clicking on the button [Download logfiles], an browser based file
open dialog will be displayed immediately.
2. You have to select the store method of the dialog, click on button [OK]
and select from the following "save as" dialog a folder to store the confi-
guration files on the maintenance PC or a directory available via the
network.
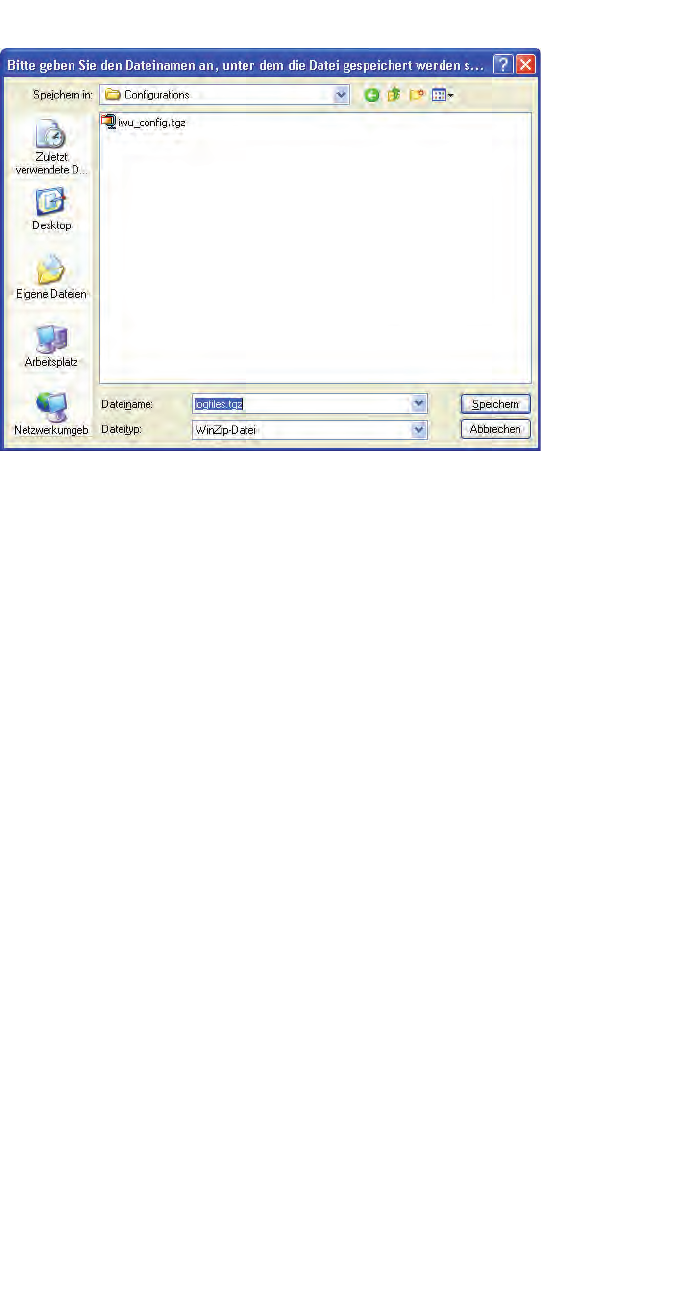
Installation and Administration
c05_ikon.fm
Debugging Configuration
A31003-C1010-S100-2-7620, 08/2010
124 HiPath Cordless IP, Service Manual
3. Save the configuration file using the default name "logfiles" or change it
according your needs (Don't use blanks in the filename).
Clear logfiles
Use this function to clear the logfiles in the log directory.
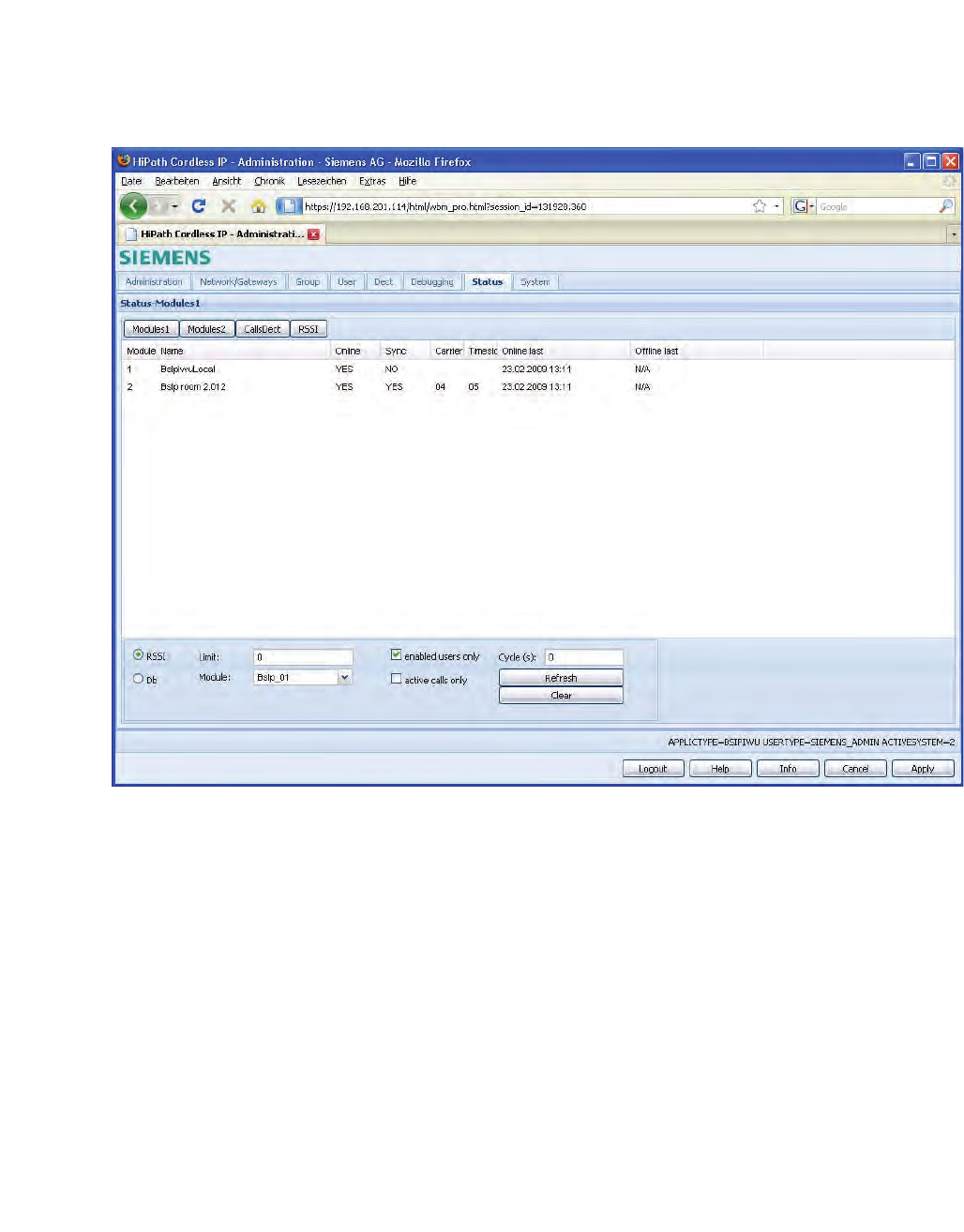
c05_ikon.fm
Installation and Administration
"Status" Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 125
5.29 "Status" Configuration
On the page "Status" of the Configuration Utility various Status information
may be displayed. It consists of several sub pages:
•On the first sub page ([Modules 1]) general information about the base
stations is displayed.
•On the second sub page ([Modules 2]) enhanced information about the
Base Stations is displayed.
•On the third sub page ([Calls Dect]) user specific information about are
displayed.
•On the fourth sub page ([RSSI]) the current allocation of the DECT radio
interface is displayed in a Table (RSSI Table).
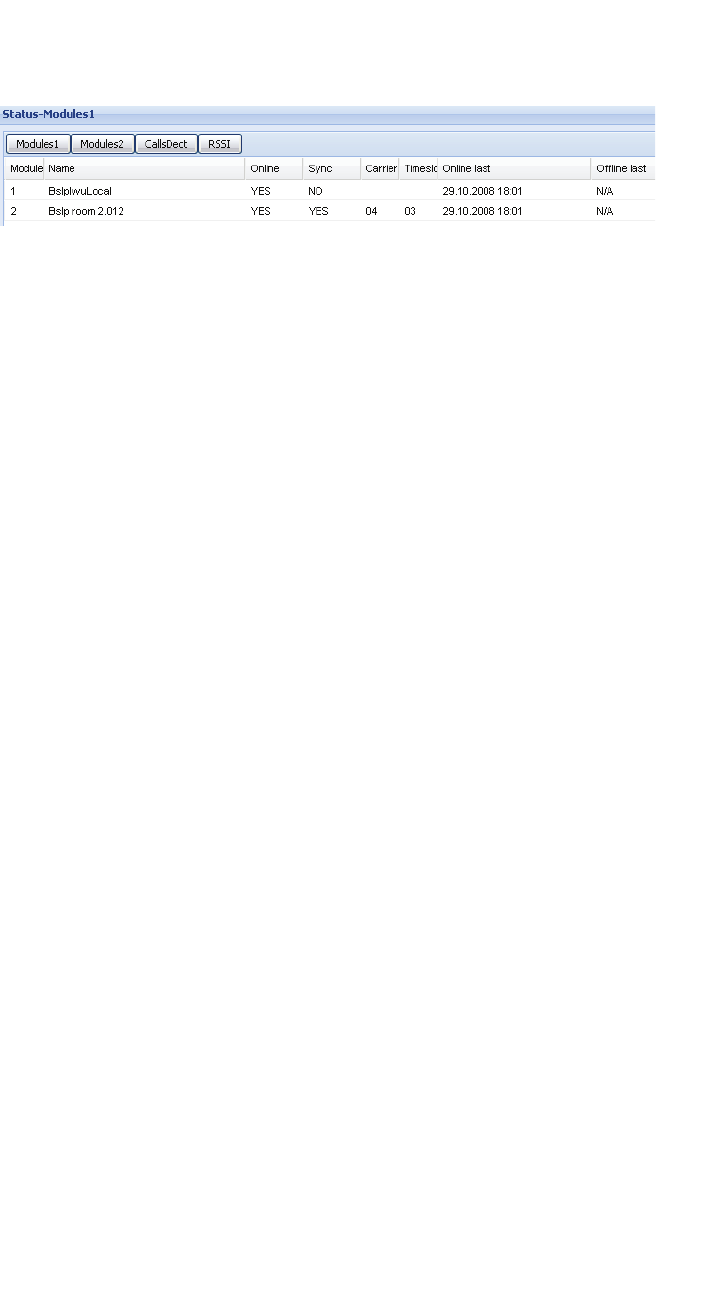
Installation and Administration
c05_ikon.fm
"Status" Configuration
A31003-C1010-S100-2-7620, 08/2010
126 HiPath Cordless IP, Service Manual
5.29.1 Configuration Page "Status - Modules 1"
The columns of the table have the following meaning:
Module
This field contains the consecutive number of the BSIP 1.
Name
The name of the Base Station as read from the Base Station via "Scan".
Online
“Yes” if the selected Base Station is “Online“, “No” if it is “Offline”.
Sync
"Yes" if the selected Base Station is in "Sync" (synchronized), which means
that this base station has synchronised to another base station. At the base
Station which is not synchronized to another base, the value is always "No".
Carrier
Displays the carrier number of the Synchronization channel the BSIP1 is
synchronised to.
Timeslot
Displays the timeslot number of the Synchronization channel the BSIP1 is
synchronised to.
Online last
Displays date/time of the BSIP1 when it lastly changed its state to Online.
Offline last
Displays date/time of the BSIP1 when it lastly changed its state to Offline.
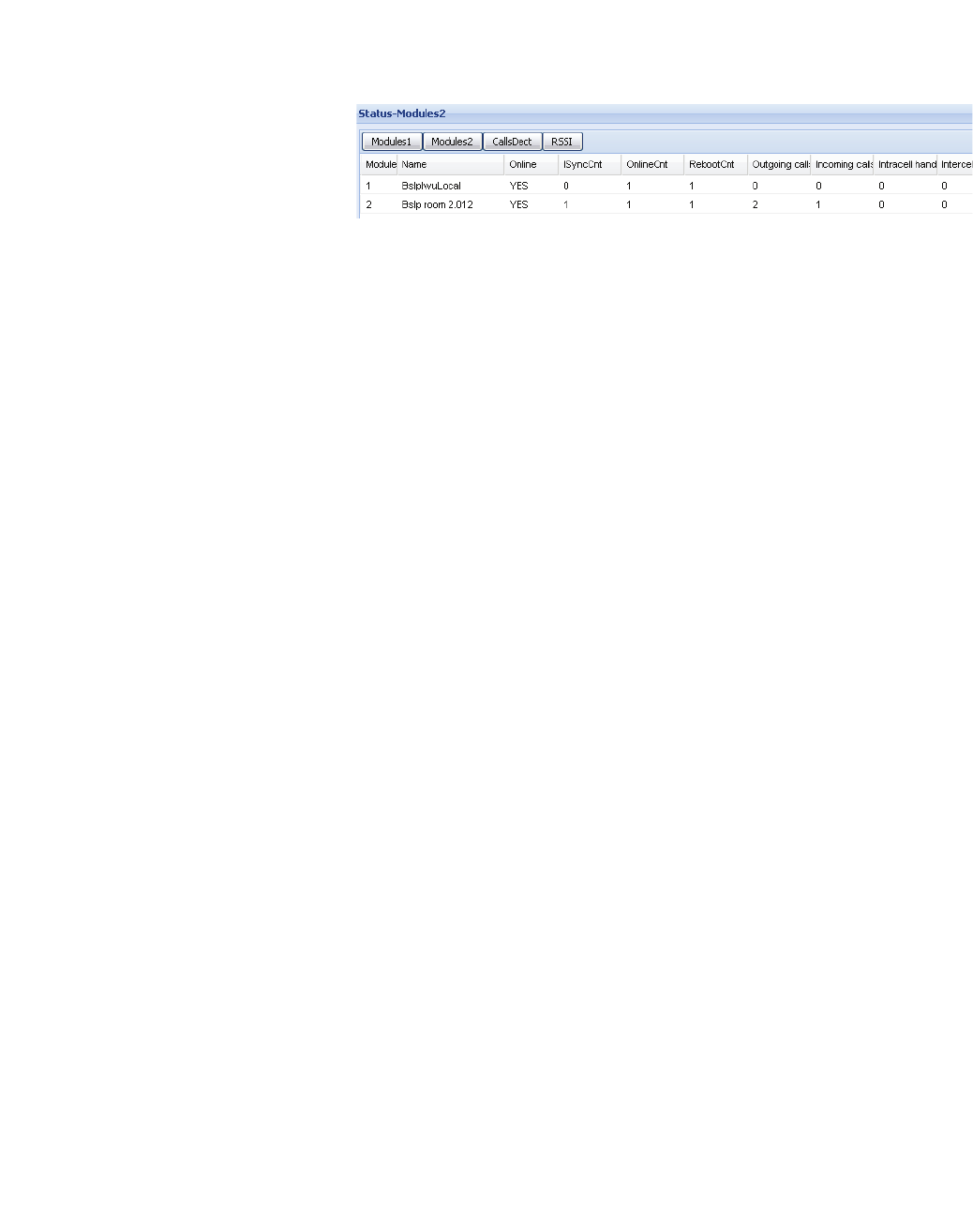
c05_ikon.fm
Installation and Administration
"Status" Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 127
5.29.2 Configuration Page "Status - Modules 2"
Module
This field contains the consecutive number of the BSIP 1.
Name
The name of the Base Station as read from the Base Station via "Scan".
Online
"Yes" if the selected Base Station is "Online".
ISyncCnt (In Sync Count)
Shows how often the Base Station did a resynchronisation since the start of
the system services.
OnlineCnt (Online Count)
Shows how often a Online/Offline change has been detected since the start
of the system services.
BootCnt (Boot Count)
Shows how often the Base Station was booted since the start of the system
services.
Outgoing calls
Shows how often an outgoing connection (from direction BSIP to PBX) has
been signalled.
Incoming calls
Shows how often an incoming connection (from direction PBX to DECT) has
been signalled.
Intracell handover
Shows how often a Intracell handover (transfer of a channel within the same
DECT Base Station ) was detected at the BSIP.
Intercell handover
Shows how often a Intercell handover (transfer of a channel between different
DECT ethernet Base Stations) was detected at the BSIP.

Installation and Administration
c05_ikon.fm
"Status" Configuration
A31003-C1010-S100-2-7620, 08/2010
128 HiPath Cordless IP, Service Manual
5.29.3 Configuration Page "Status - Calls Dect"
On this page user specific information is displayed.
The columns of the table page have the following meaning:
User
DisplayName of the associated User.
Msn
Displays the "Msn" for the current user.
Voip states
Displays the Voip state of the User ("No ras", "Ras up", "Ras down").
Ras changes
Displays the number of ras changes of the user (see Voip states).
Call states
Displays the current Call state of the User ("Located on", "No location",
"Calling out", "Alerting out", "Connected out", "Calling in", "Alerting in",
"Connected in", "Switched off").
Located
Displays the number of the Base Station the User is located on.
Call located
Displays the number of the Base Station on which the current/last call was
located on.
Carrier
Carrier number on which the connection for User "DisplayName" is active.
Timeslot
Timeslot number on which the connection for User "DisplayName" is active.
Incoming calls
Displays the number of incoming connections (from direction PBX to DECT)
which have been signalled for the User.

c05_ikon.fm
Installation and Administration
"Status" Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 129
Outgoing calls
Displays the number of outgoing connections (from direction DECT to
PBX)which have been signalled for the User.
Intracell handover
Shows how often a Intracell handover (transfer of a channel within the same
ethernet Base Station) was detected for the User.
Intercell handover
Shows how often a Intercell handover (transfer of a channel between different
ethernet Base Stations) was detected for the User.
The options at the lower part of the configuration page have the following
meanings:
enabled users only
If activated, only entries for enabled users are displayed (not implemented
yet).
active calls only
If activated, only entries for active calls are displayed (not implemented yet).
Cycles (s)
If a numeric value different than "0" is configured, the display will automati-
cally refresh after the configured number of seconds.
Refresh
Manually refresh the counters displayed.
Clear statistics
Clears (resets) all counters to 0 after a confirmation dialog.
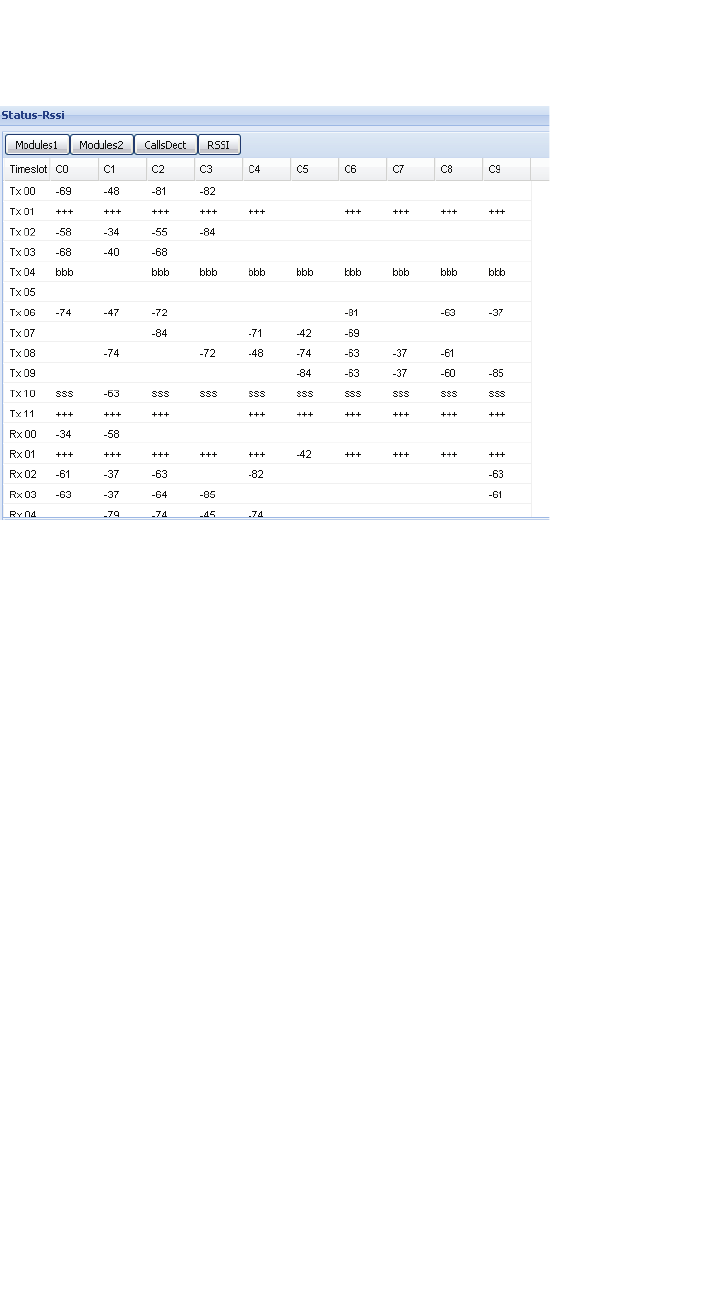
Installation and Administration
c05_ikon.fm
"Status" Configuration
A31003-C1010-S100-2-7620, 08/2010
130 HiPath Cordless IP, Service Manual
5.29.4 Configuration Page "Status - RSSI"
On this page the table with the RSSI values is displayed. The table has the
following structure:
Lines (Tx 00 - Rx 11)
The Timeslots Tx00 - Tx11 and Rx00 - Rx11 are displayed.
Columns (C0 … C9)
Here the Carriers C0 - C9 are displayed.
Cell values:
"bbb"
"bbb" in a line (Timeslot) shows that this is a timeslot with a beacon (sent
signal).
One cell in the line shows the signal level (receive level) of the received value
of the channel allocation of other DECT devices. This value shall be as small
as possible.
"sss"
"sss" in a line (Timeslot) shows that this is a Timeslot with a synchronization
signal (received signal "Sync").
One cell in the line shows the signal level (receive level) of the Sync signal.
This value shall be as high as possible.
For accurate synchronisation over air a minimum signal strength of -85 dB
(resp. 30 [RSSI]) is required.

c05_ikon.fm
Installation and Administration
"Status" Configuration
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 131
"+++"
"+++" in a line (Timeslot) shows that this is a Timeslot with a voice channel
(unidirectional) signal (The Timeslot number of the Rx channel is Tx Channel
+ 12).
One cell in a "Tx" line shows the value of the used Carrier for the voice
channel.
One cell in a "Rx" line shows the receive level of the Base Station in relation
to the active call.
"<value>"
Shows the current value (Receive resp. Send signal of the Rx resp. Tx
Timeslot) depending on the configuration of "RSSI", "Db" and "Limit".
Value ranges:
minimal value (corresponds to poor reception quality) -85 dB (resp. 30
[RSSI])
maximum value (corresponds to good reception quality) -50 dB (resp. 46
[RSSI])
Values outside a bbb, sss, or +++ line display the signal level (receive level)
of other DECT devices. The number of values as well as their value itself shall
be as small as possible.
The options at the lower part of the configuration page have the following
meanings:
"RSSI"
The values displayed in the RSSI table are RSSI values.
"Db"
The values displayed in the RSSI table are Db values.
"Limit"
Here you can configure a minimum value. Only values bigger (in the case of
"Db" only values smaller) than "Limit" are displayed in the RSSI table.
Normally the following default values are used:
RSSI:"30"
Db:"-85"
"Module Rssi"
Here you may select the Base Station which values are displayed at the table.
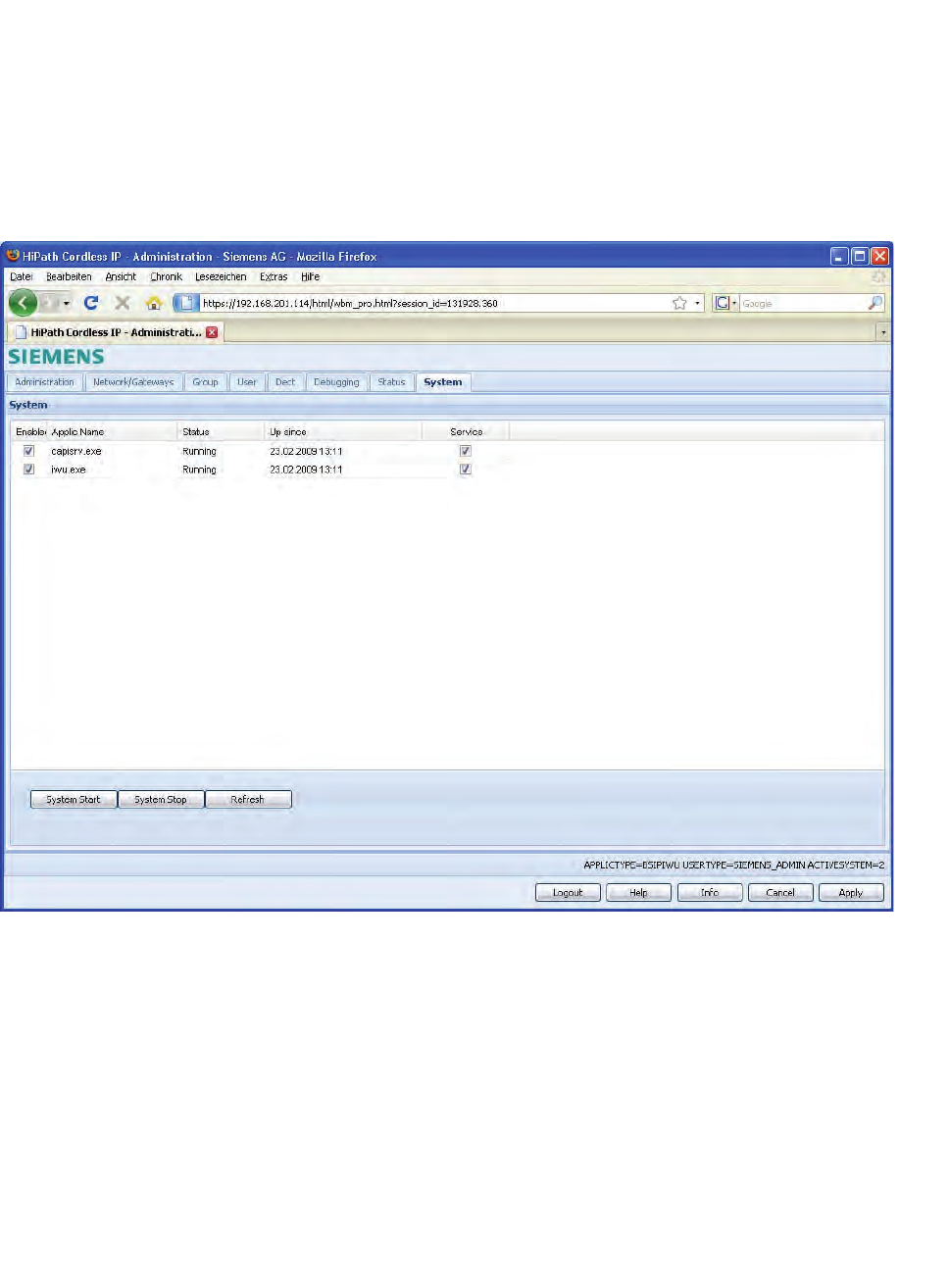
Installation and Administration
c05_ikon.fm
"System" Configuration
A31003-C1010-S100-2-7620, 08/2010
132 HiPath Cordless IP, Service Manual
5.30 "System" Configuration
On the configuration page "System" the two Software processes of the BSIP
can be started and stopped.
1. Click [Start] to start the enabled processes and [Stop] to stop them again.
Activate "Service" if the service should start automatically at system start.
Other modifications are usually not needed here.
The columns of the configuration page have the following meaning:
"Enabled"
Usually both processes are activated ( ). This default configuration should
only be changed for locating problems after consultation of the support team.
"Applic Name"
Both IWU processes are displayed here.
"Status"
In this column the states of the two IWU processes are displayed (“Stopped“,
“Started” or “Running“).
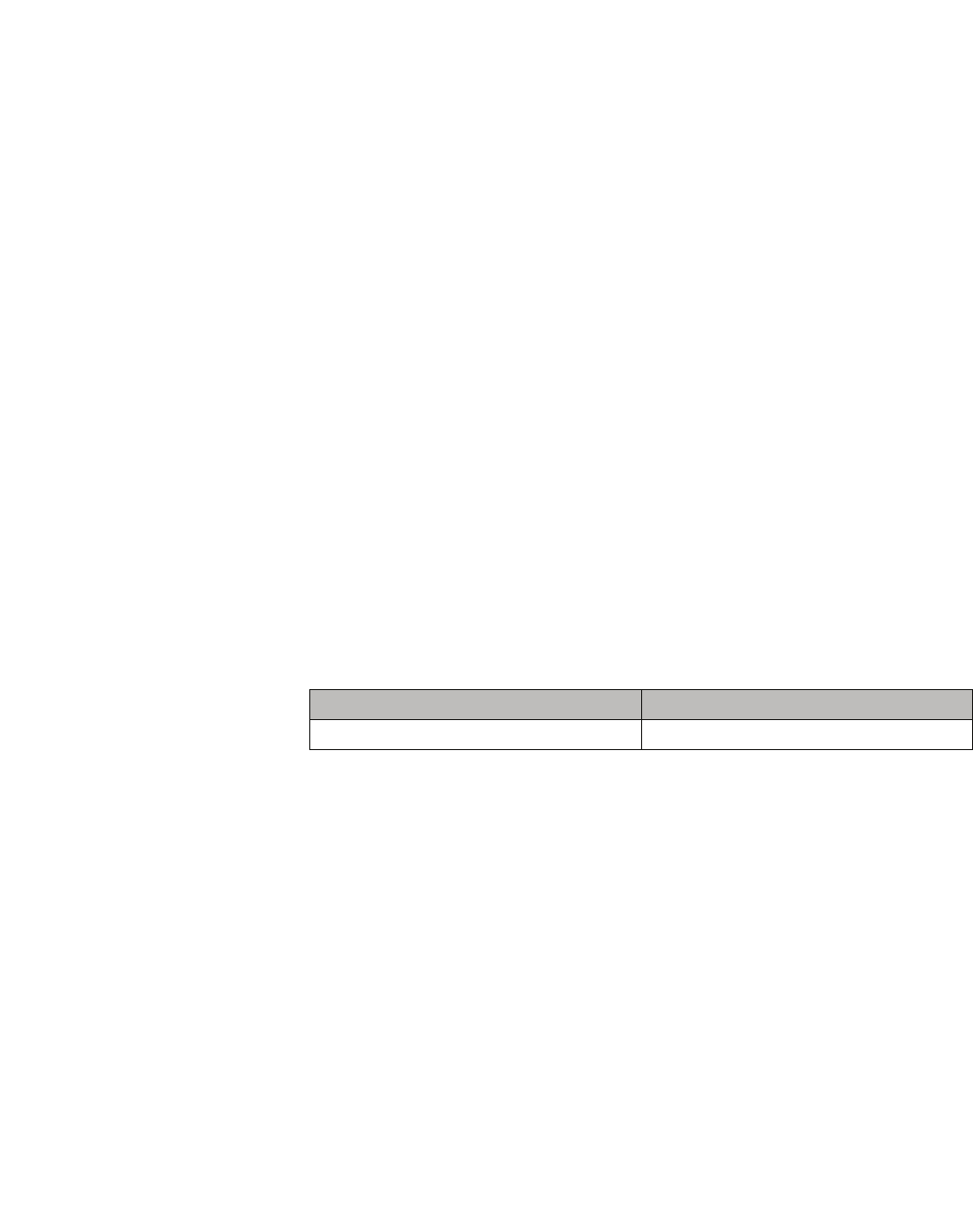
c05_ikon.fm
Installation and Administration
Configuration Hints for PBXs
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 133
Up since
Displays the time the service was started lastt
"Service"
Usually both services are activated which means that the corresponding
process is started automatically after rebooting the BSIP.
5.31 Configuration Hints for PBXs
In the following chapters you can find configuration notes for for different
PBXs which have to be released for usage with the HiPath Cordless IP
system.
5.32 HiPath OpenOffice EE
Here you can find the configuration hints using a HiPath OpenOffice EE (SW-
Version V1) using SIP users.
5.32.1 Base Configuration - HiPath OpenOffice EE
The following value is used for the base configuration:
A detailed configuration instruction for the HiPath OpenOffice EE would go
beyond the scope of this documentation. Therefore only the information
regarding the configuration which is very important and relevant for the Inter-
working is described here.
Detailed documentation for the HiPath OpenOffice EE can be found in the
manual:
•"HiPath OpenOffice EE V1 Administratior Documentation"
1. Please configure the HiPath OpenOffice EE for the usage with SIP Users
and configure the needed number of SIP Users in the Installation
Assistant.
2. Configure the IP address of the HiPath OpenOffice EE to 192.168.0.213
or change the according IP addresses.
3. Configure the following Codec Parameters via "WBM - Explorers - Voice
Gateway - Codec Parameters":
Parameter Value
IP address of the HiPath OpenOffice EE 192.168.0.213
Installation and Administration
c05_ikon.fm
HiPath OpenOffice EE
A31003-C1010-S100-2-7620, 08/2010
134 HiPath Cordless IP, Service Manual
4. Configure the DSP Settings (primarily the Echo Cancellation) via “WBM -
Explorers - Payload - - HW Modules - DSP Settings”:
c05_ikon.fm
Installation and Administration
HiPath OpenOffice EE
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 135
5.32.2 Base Configuration - BSIP IWU
Please make the following configuration settings at the BSIP IWU:
1. Page "Network/Gateways", table gateways
2. Save all modifications with [Apply].
3. Configure one DECT ethernet Base Station for the operation with this
Gateway.
5.32.3 Station Configuration - HiPath OpenOffice EE
The following values are used as a sample for this configuration instruction:
1. The configuration of the HiPath OpenOffice EE is done via Web browser
(Web Based Management - WBM). Please log in to the HiPath
OpenOffice EE, start the Web Based Management in Expert mode and
navigate to the page "WBM - Explorers - Stations - Station - IP Clients -
SIP Clients".
2. Select a free entry (after the base configuration of the
HiPath OpenOffice EE with the assistant free entries should be
available).
If no free entries are available, use the "Subscriber table editor" on the
page "WBM - Explorers - Stations - Station - (Right mouse button ) -
Subscriber table editor", change the "Device Type" of a free entry to "SIP
Client" and store the modifications with [Apply]. After that you should
store the new configuration on the HiPath with the [Save] Button at the
bottom section of the WBM. Now a free SIP User should be available on
"WBM - Explorers - Stations - Station - IP Clients - SIP Clients".
Option Value
Remote IP Address 192.168.0.213
Gatekeeper Id 192.168.0.213
Parameter Value
Name DECT-401
Callnumber 401
Password ikon
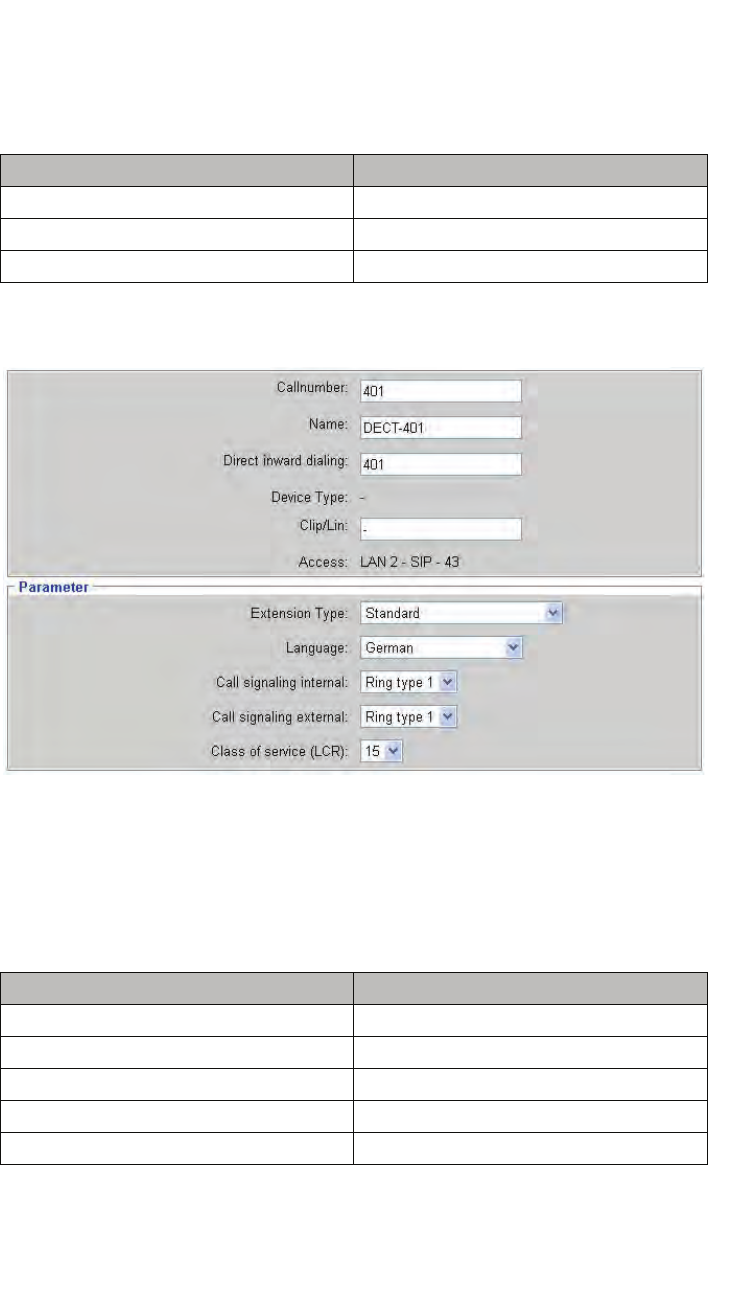
Installation and Administration
c05_ikon.fm
HiPath OpenOffice EE
A31003-C1010-S100-2-7620, 08/2010
136 HiPath Cordless IP, Service Manual
5.32.3.1 Step 1 - User Parameters
1. Select the free entry and choose "Edit station parameter" via click on the
right Mouse Button. Enter the following values in the input mask:
Please do not change the other values. After that the configuration page
should look like this:
5.32.3.2 Step 2 - Workpointclient Data
1. Select the free entry and choose "Edit Workpointclient data" via click on
the right Mouse Button. Enter the following values in the input mask:
Please do not change the other values.
Entry Value
Callnumber: 401
Name: DECT-401
Direct inward dialing: 401
Entry Value
Authentication active: [V]
Password: ikon
Validate password: ikon
User ID: 401
Realm: 401
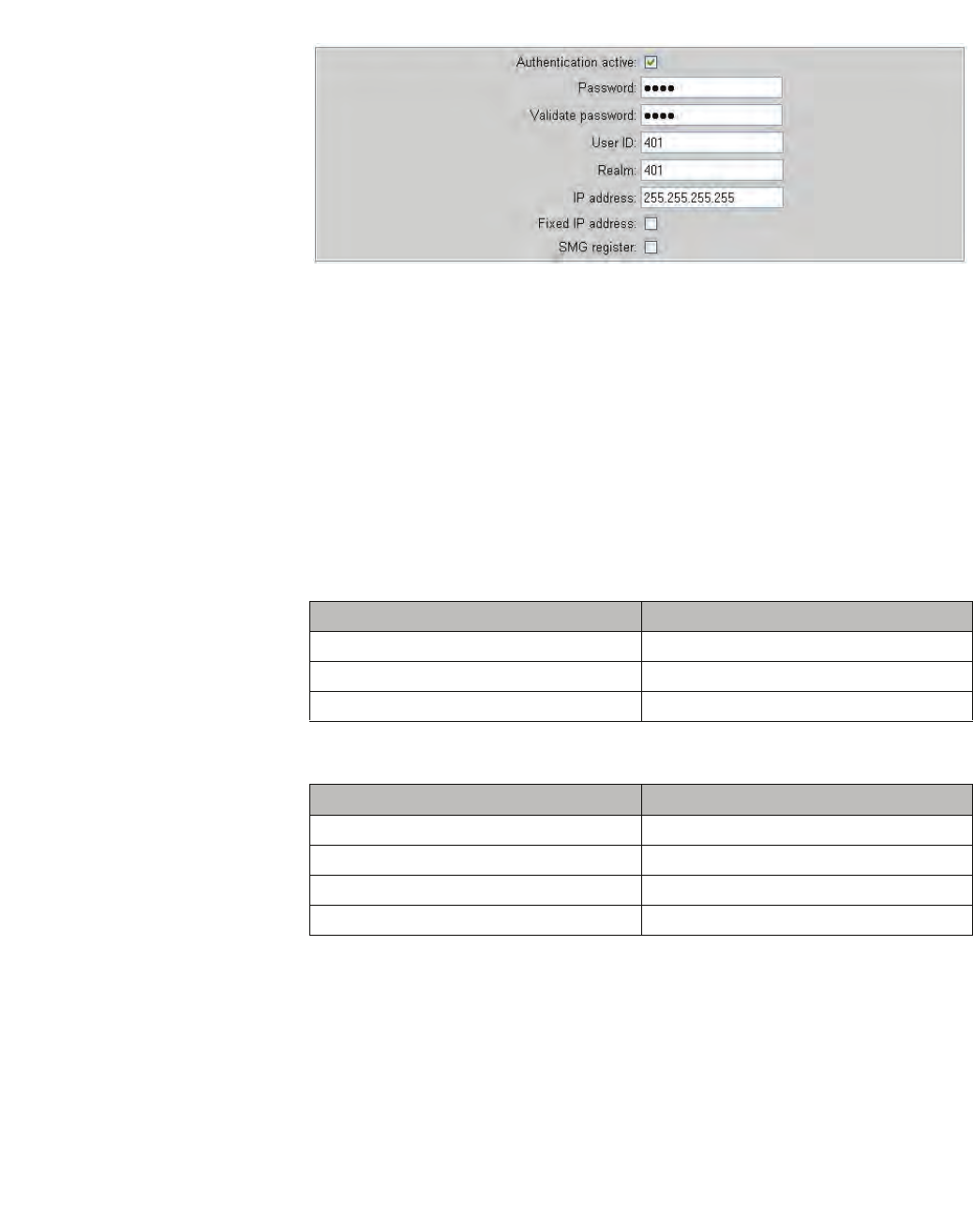
c05_ikon.fm
Installation and Administration
HiPath OpenOffice EE
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 137
2. After that you should save the new configuration on the HiPath with the
[Apply] Button at the bottom of the WBM.
5.32.4 Station Configuration - BSIP IWU
Please make the following configurations at the BSIP IWU:
Page "Users - User"
1. Go to the sub page "User" of "Users" in the Configuration Utility.
2. Select the first entry "DisplayName" and enter the following values:
3. Select the first entry and enter the following values:
4. Save the modifications by clicking [Apply].
Entry Value
DisplayName: 401
Save the modifications by clicking [Apply].
Page "Users - Void "
Entry Value
UserName: 401
AuthName: 401
Password: Ikon
MSN 401

Installation and Administration
c05_ikon.fm
HiPath OpenOffice ME
A31003-C1010-S100-2-7620, 08/2010
138 HiPath Cordless IP, Service Manual
5.32.5 Time server configuration
1. Configure the following settings to activate the time server settings via
“WBM - Explorers - Basic Settings - Date and Time - SNTP settings“:
2. Save the modifications by clicking [Apply].
5.33 HiPath OpenOffice ME
Here you can find the configuration hints using a HiPath OpenOffice ME (SW-
Version V1) using SIP users.
5.33.1 Base Configuration - HiPath OpenOffice ME
•The following value is used for the base configuration:
Detailed configuration instruction for the HiPath OpenOffice ME would go
beyond the scope of this documentation. Therefore only the information
regarding the configuration which is very important and relevant for the Inter-
working is described here.
Detailed documentation for the HiPath OpenOffice ME can be found in the
Siemens manuals:
•"HiPath OpenOffice ME V1 Administrator Documentation"
Entry Value
operating state of SNTP Server: Up
IP address of External Time Server IP adress: 0.0.0.0 if no external time server
is used for time synchronisation, otherwise
the ip address of the external time server.
Poll interval for External Time Server Continuous
Parameter Value
IP address of the HiPath OpenOffice ME 192.168.0.93
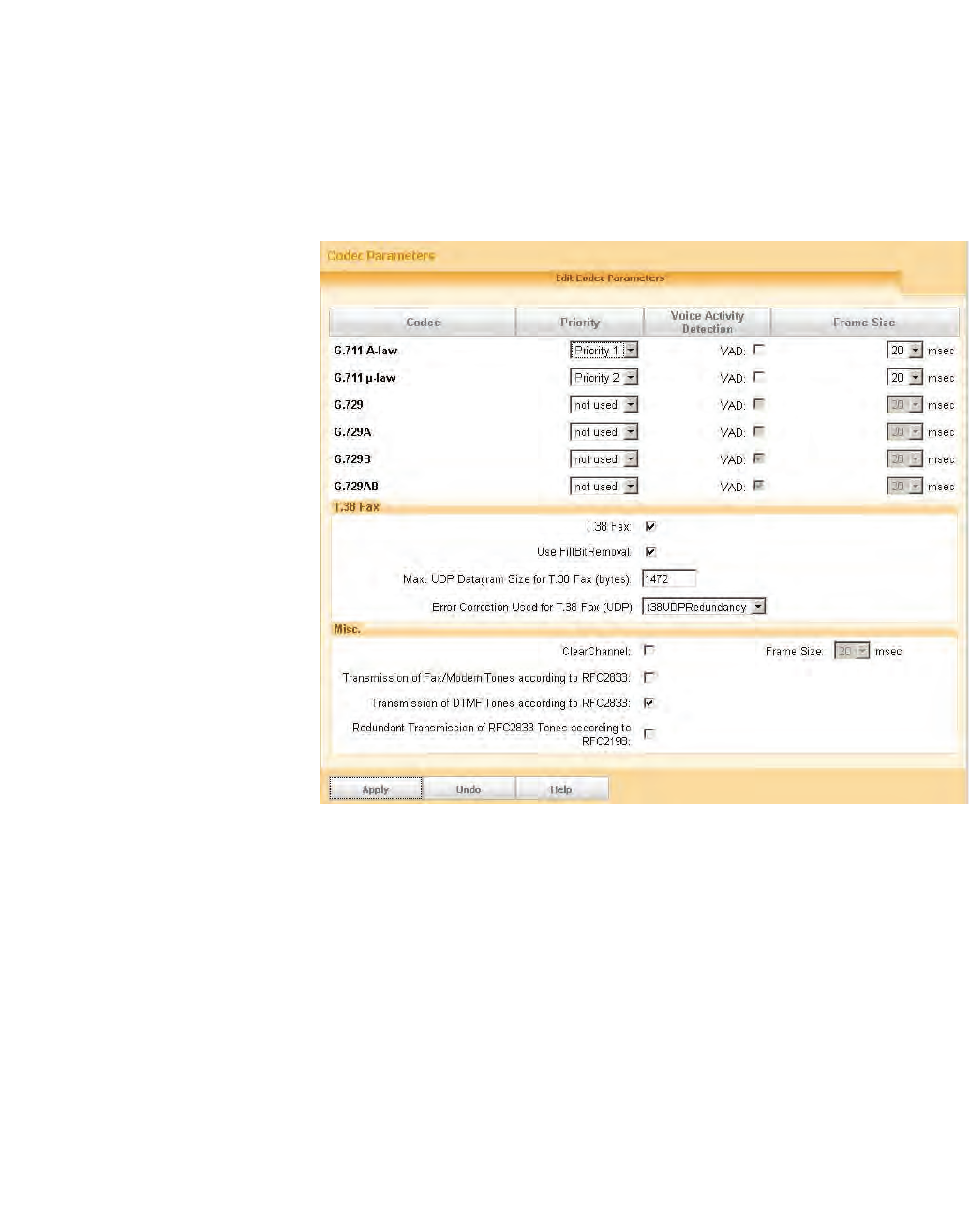
c05_ikon.fm
Installation and Administration
HiPath OpenOffice ME
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 139
1. Please configure the HiPath OpenOffice ME for the usage with SIP Users
and configure the needed number of SIP Users in the Installation
Assistant.
2. Configure the IP address of the HiPath OpenOffice ME to 192.168.0.93
or change the according IP addresses.
3. Configure the following Codec Parameters via "WBM - Expert mode -
Voice Gateway - Codec Parameters":
4. Configure the DSP Settings (primarily the Echo Cancellation) via “WBM -
Expert mode - Payload - HW Modules - Edit DSP Settings”:
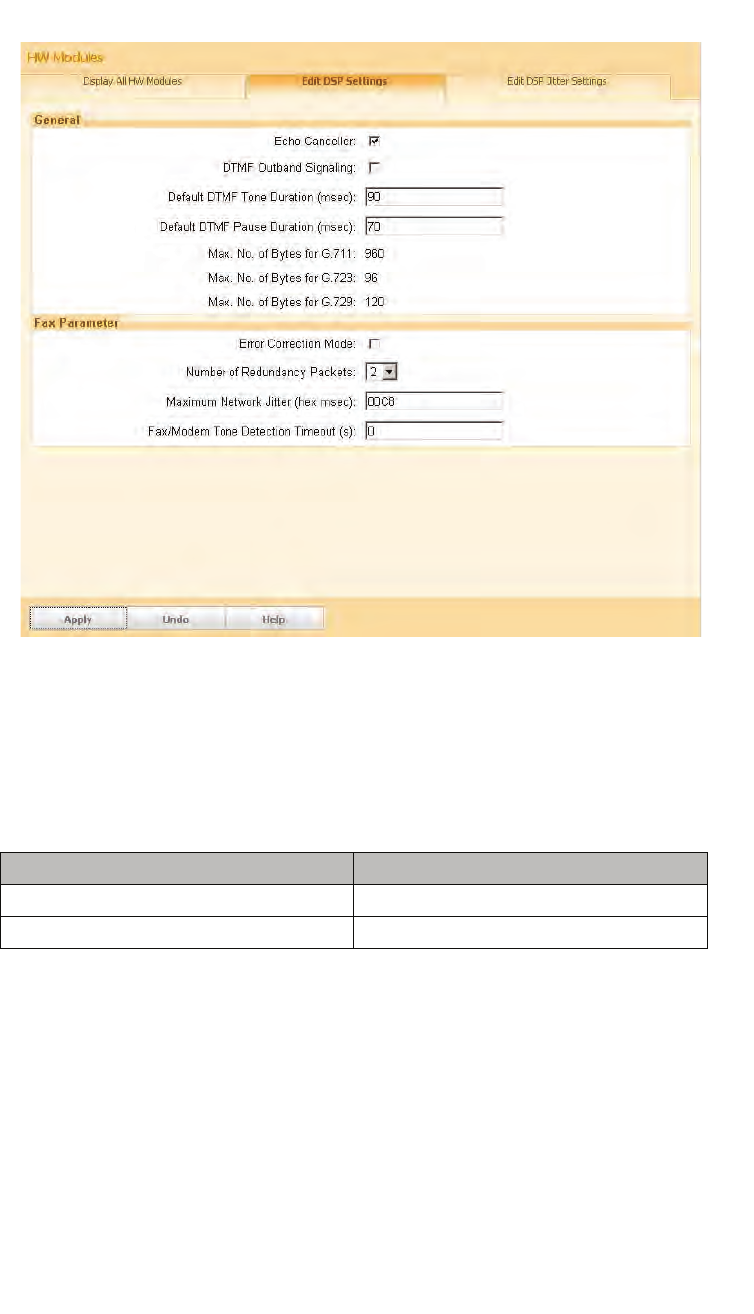
Installation and Administration
c05_ikon.fm
HiPath OpenOffice ME
A31003-C1010-S100-2-7620, 08/2010
140 HiPath Cordless IP, Service Manual
5.33.2 Base Configuration - BSIP IWU
1. Please make the following configuration settings at the BSIP IWU:
Page „Gateways“
2. Save all modifications with [Apply].
3. Configure one DECT ethernet Base Station for the operation with this
Gateway.
Entry Value
Remote IP Address 192.168.0.93
Gatekeeper Id 192.168.0.93
c05_ikon.fm
Installation and Administration
HiPath OpenOffice ME
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 141
5.33.3 Station Configuration - HiPath OpenOffice ME
The following values are used as a sample for this configuration instruction:
1. The configuration of the HiPath OpenOffice ME is done via Web browser
(Web Based Management - WBM). Please log in to the HiPath
OpenOffice ME, start the Web Based Management in Expert mode and
navigate to the page "WBM - Expert mode - Station - IP Clients - SIP
Clients".
2. Select a free entry (after the base configuration of the Siemens HiPath
OpenOffice ME with the Assistant free entries should be available).
If no free entries are available, use the page "WBM - Expert mode -
Stations - Station - IP Clients - Edit subscriber", change the "Device Type"
of a free entry to "SIP Client" and store the modifications with [Apply].
Now a free SIP User should be available on "WBM - Explorers - Stations
- Station - IP Clients - SIP Clients".
5.33.3.1 Step 1 - User Parameters
1. Select the free entry and choose "Edit station parameter". Enter the
following values in the input mask:
Please do not change the other values. After that the configuration page
should look like this:
Parameter Value
Name DECT-401
Callnumber 401
Password ikon
Entry Value
Callnumber: 401
Name: DECT-401
Direct inward dialing: 401
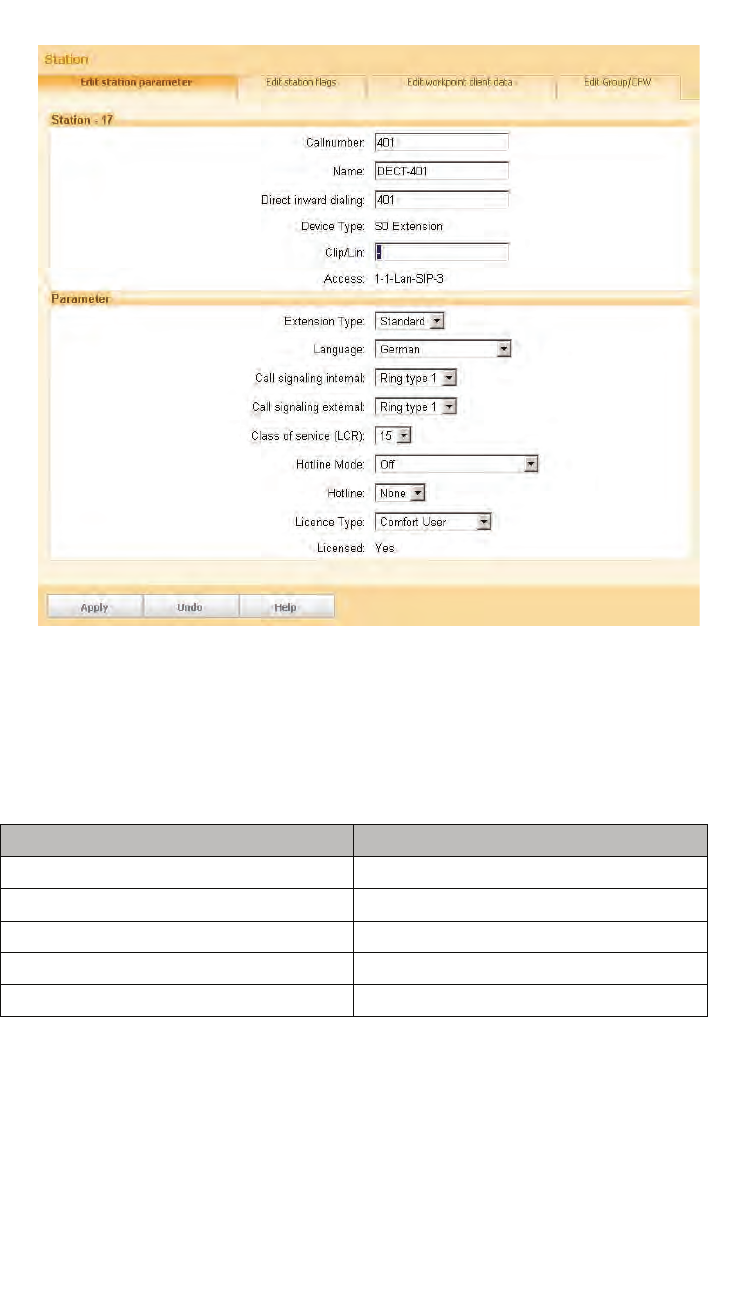
Installation and Administration
c05_ikon.fm
HiPath OpenOffice ME
A31003-C1010-S100-2-7620, 08/2010
142 HiPath Cordless IP, Service Manual
5.33.3.2 Step 2 - Workpointclient Data
1. Select the free entry and choose "Edit Workpointclient data". Enter the
following values in the input mask:
Please do not change the other values.
Entry Value
Authentication active: [V]
Password: ikon
Validate password: ikon
User ID: 401
Realm: 401
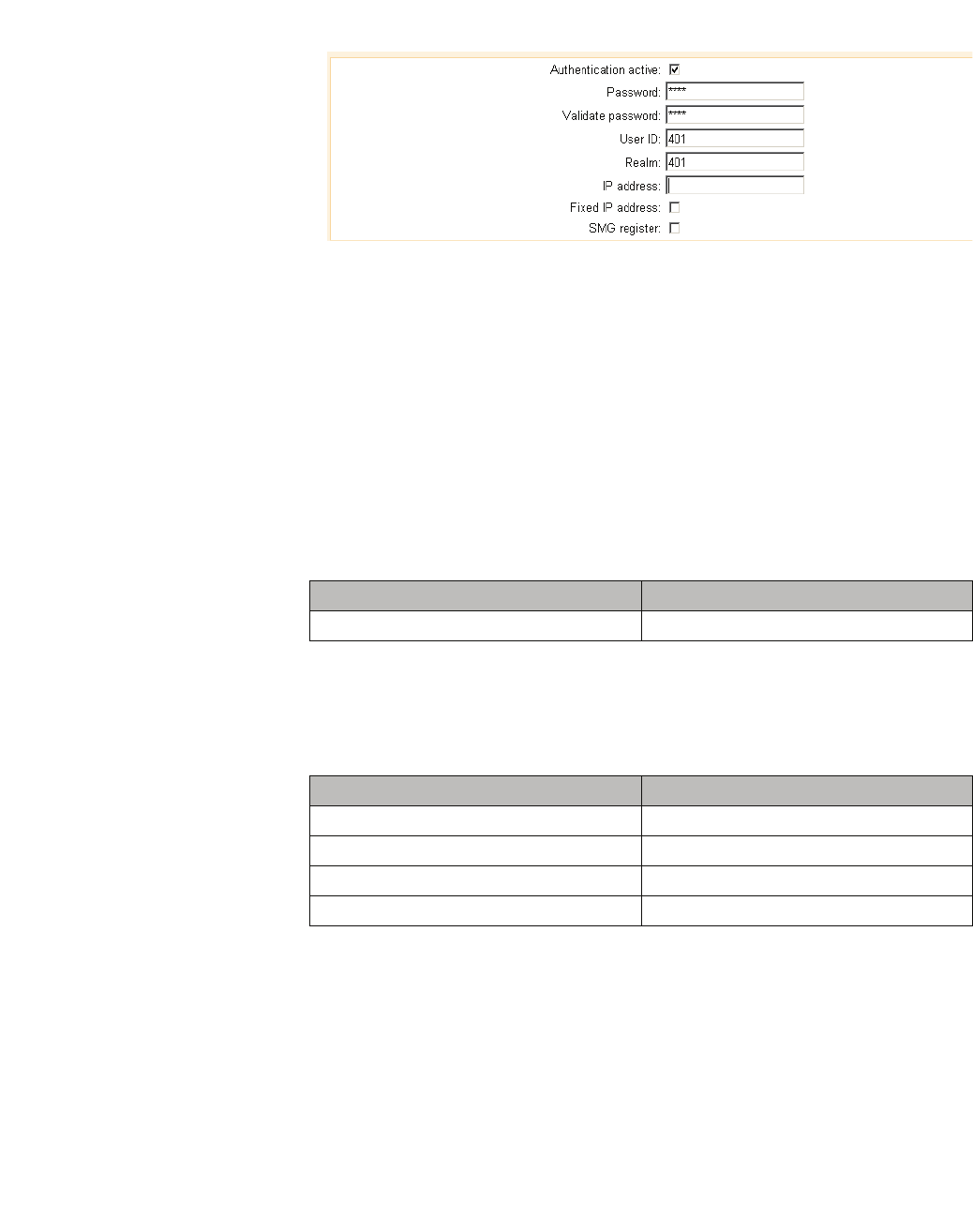
c05_ikon.fm
Installation and Administration
HiPath OpenOffice ME
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 143
2. After that you should save the new configuration on the HiPath with the
[Apply] Button at the bottom of the WBM.
5.33.4 Station Configuration - IP-DECT IWU
Please make the following configurations at the IP-DECT IWU:
Page "Users - User"
1. Go to the sub page "User" of "Users" in the Configuration Utility.
2. Select the first entry "DisplayName" and enter the following values:
Save the modifications by clicking [Apply].
Page "VoIP Users - Ras"
Select the first entry and enter the following values:
3. Save the modifications by clicking [Apply].
Entry Value
DisplayName: DECT-401
Entry Value
UserName: 401
AuthName: 401
Password: ikon
MSN 401
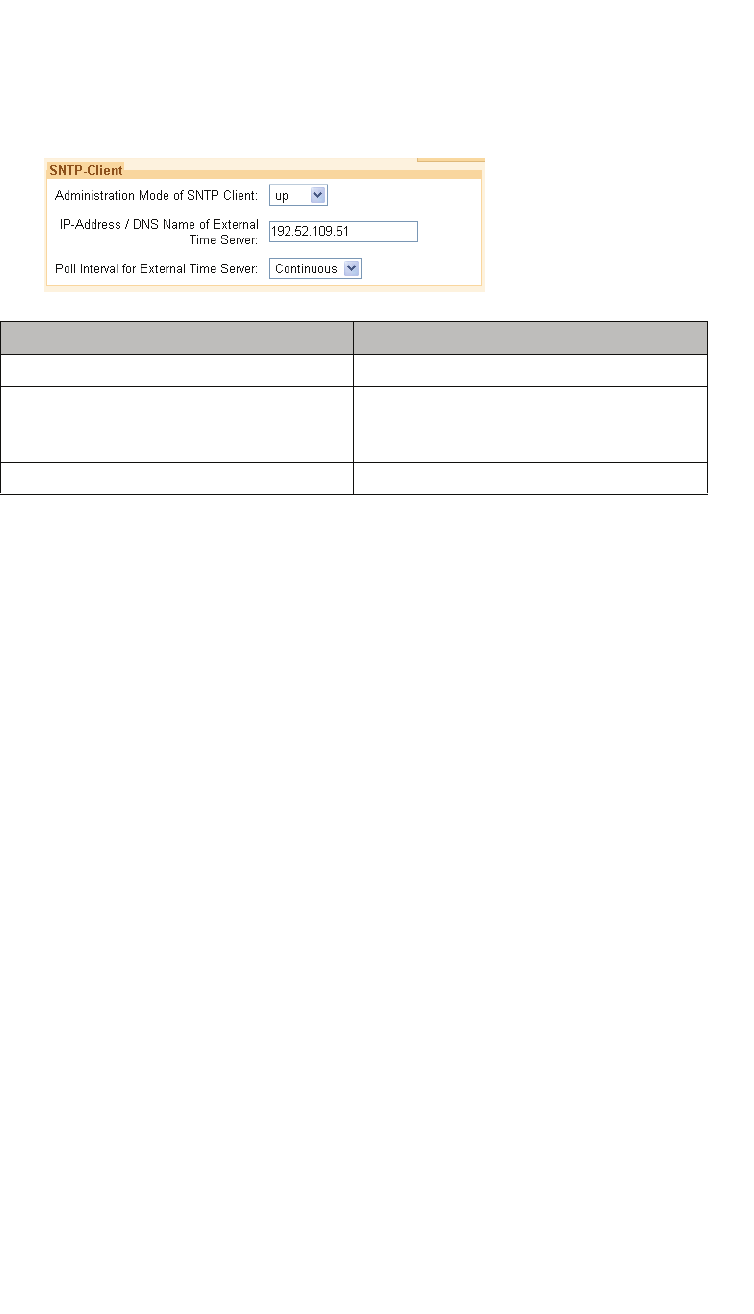
Installation and Administration
c05_ikon.fm
Troubleshooting / FAQ
A31003-C1010-S100-2-7620, 08/2010
144 HiPath Cordless IP, Service Manual
5.33.5 Time server configuration
1. Configure the following settings to activate the time server settings via
"WBM - Expert mode - Basic settings - Date and time - SNTP Settings":
2. Save the modifications by clicking [Apply].
5.34 Troubleshooting / FAQ
5.34.1 BSIP1 Only is not found using "Scan"
Please check the following:
•Is the "missing" BSIP1 connected with the power supply?
(LED states OK?)
•Is the network cable connected at the IP-DECT Base Station?
•Is the network cable connected to an ethernet Switch? Please check the
Status LEDs at the relevant Ports of the ethernet Switch.
•The IP-DECT Base Station must be located in the same ethernet
segment as the IWU. IWU and Base Station cannot operate in different
ethernet segments connected via an IP Router.
•VLAN configuration issues
Entry Value
Administration mode of SNTP client: Up
IP address / DNS Name of External Time
Server: IP adress: 0.0.0.0 if no external time server
is used for time synchronisation, otherwise
the ip address of the external time server.
Poll Interval for External Time Server: Continuous

c05_ikon.fm
Installation and Administration
Configuration hints for Web Browser
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 145
5.34.2 Registration of the handsets not successful
•The PIN configured for the BSIP IWU differs from the PIN entered at the
Handset
(Did you mistype?).
•The handset has no radio connection to the Base Station (too far away
etc.).
•Are all activated Base Station in state "Online" and "InSync" (except the
Base Station which is the Synchronisation masters) ?
5.34.3 Idle display of handset is blinking
The following causes may apply:
•the handset is outside the DECT coverage
•the handset has no DECT registration at the BSIP1
•at the handset the wrong base is selected or
•the system services are not running
5.34.4 Display message "Netzfehler" / "Out of Order"
The RAS registration from the handset at the PBX is down (see Status - Calls
Dect - Voip states)
5.35 Configuration hints for Web Browser
5.35.1 Mozilla Firefox
Mozilla Firefox Versions 2 (2.0.0.16 ... 2.0.0.18) and Version 3.0.x (3.01 .. 3.0.6)
of firefox are supported.
The minimum supported screen resolution the Browser is running on is
1024x768.

Installation and Administration
c05_ikon.fm
Configuration hints for Web Browser
A31003-C1010-S100-2-7620, 08/2010
146 HiPath Cordless IP, Service Manual
5.35.2 Microsoft Internet Explorer
The following version of Microsoft Internet Explorer are supported:
•Version 6.x
•Version 7.x
The minimum supported screen resolution the Browser is running on is
1024x768.
Please keep in mind that the support of IE starts with a running version of BSIP1
v_3.24.3. Updating to version 3.24.3 has to be done with Firefox.
Depending of the security settings of MS IE, the IP address of the BSIP1 has to
be added to the list of Trusted sites (Tools - Internet options - Security - Trusted
sites).
This comes in effect when Backing up a configuration file. If the security settings
are not valid, the configuration file will not be donloaded and the WBM session
will be closed.
For IE7 there is an issue one some installations when backing up the configu-
ration. After initiating the backup process, the information panel will be displayed
and afterwards you are logged out from the WBM. To overcome this situation, you
have to change the following settings in IE7:
1. Select Tools - InternetOptions - Security
2. Select the appropriate zone in which the IWU is located (e.g. "Trusted
sites") and select [Custom level]
3. In the outline view browse to "Downloads" and change the setting of
"Automatic prompting for file downloads" from Disabled to Enabled.
c06.fm
Technical Data
BSIP1 DECT standard EU
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 147
6 Technical Data
6.1 BSIP1 DECT standard EU
•Number of channels 120 duplex channels, freely administered
(10 carriers, each with 12 time-division multiplex
channels)
•Frequency range 1.88 to 1.9 GHz
(send and receive range)
•Channel spacing 1.728 MHz
•Bit rate 1.152 Mbps
•Speech encoding 32 kilobit ADPCM
•GAP standard Specified in DECT specification 300444
•PN CAP Siemens-specific protocol enhancement
•DECT Access EN 301 406 V.1.5.1
DECLARATION OF CONFORMITY
Siemens Enterprise Communications GmbH & Co. KG is a Trademark Licensee of Siemens AG
ZER10008.doc Owner: SEN VA LP Number of Declaration: 10 / 008
We
Siemens Enterprise Communications GmbH & Co. KG
Hofmannstr. 51, D-80200 Munich / Germany
declare that the product
HiPath Cordless Basestation IP1 (BSIP1)
..............................................................................................................................................................................
( name, type, model or version)
to which this declaration relates, conforms to the following European Directives and
European standards:
Directive 99/5/EEC: Radio and Telecommunication Terminal Equipment
EN 50385:2002 EMF
EN 60950-1:2006 Safety
EN 55022:2006+A1:2007 ClassB EMC, Emission ITE Residential Environment
EN 61000-6-2:2005 EMC, Immunity in industrial area
EN 301 406 V1.5.1 DECT Access
EN 301 489-1 V1.8.1 EMC & Radio spectrum Matters for radio Equipment
EN 301 489-6 V1.3.1 EMC & Radio spectrum Matters for radio Equipment (DECT
Equipment)
Other standards or national regulations:
FCC CFR 47, P.15 Class B Radio frequency devices, radiated Emmission
Munich, March 12th, 2010
Siemens Enterprise Communications GmbH & Co. KG
...............................................
(Place and date of issue)
............................................................... ................... ................................................................................
( Name, Function and signature of authorized person ) ( Name, Function and signature of authorized person )

Technical Data
c06.fm
BSIP1US DECT standard USA
A31003-C1010-S100-2-7620, 08/2010
148 HiPath Cordless IP, Service Manual
6.2 BSIP1US DECT standard USA
•This device complies with Part 15 of the FCC rules and with RSS-210 of
Industry Canada.
•Operation is subject to the following two conditions:
1. this device may not cause harmful interference, and
2. this device must accept any interference received, including interference
that may cause undesired operation.
3. Changes or modifications made to this equipment not expressly approved
by (manufacturer name) may void the FCC authorization to operate this
equipment.
•This device is tested and fulfills the Radio Standards Specification RSS-213
Issue 2.
•This device complies with FCC Part 15 Subpart D, unlicensed personal
communication devices.
•Frequency band: 1920-1930 MHz.
•Type of Modulation: multi carrier time division multiple access with Digital
modulation (GFSK).
•Number of channels: 5 RF Channels, 5x12=60TDMA Duplex channels.
•Antenna information: 2 permanent attached antennas, no external connector.
•RF Power: max. +20,5dBm.
•Temperature range: -10 to +45 degree Celsius (ambient).
•FCC ID: AY3-BSIP1US.
NOTE: This equipment has been tested and found to comply with the limits for a
Class B digital device, pursuant to Part 15 of the FCC Rules. These limits are
designed to provide reasonable protection against harmful interference in a
residential installation. This equipment generates, uses and can radiate radio
frequency energy and, if not installed and used in accordance with the
instructions, may cause harmful interference to radio communications. However,
there is no guarantee that interference will not occur in a particular installation. If
this equipment does cause harmful interference to radio or television reception,
which can be determined by turning the equipment off and on, the user is
encouraged to try to correct the interference by one or more of the following
measures:
•Reorient or relocate the receiving antenna.
•Increase the separation between the equipment and receiver.

c06.fm
Technical Data
BSIP1US DECT standard USA
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 149
•Connect the equipment into an outlet on a circuit different from that to which
the receiver is connected.
•Consult the dealer or an experienced radio/TV technician for help.
Radiofrequency radiation exposure Information:
This equipment complies with FCC radiation exposure limits set forth for an
uncontrolled environment. This equipment should be installed and operated with
minimum distance of 20 cm between the radiator and your body.
This transmitter must not be co-located or operating in conjunction with any other
antenna or transmitter.

Technical Data
c06.fm
Base Stations
A31003-C1010-S100-2-7620, 08/2010
150 HiPath Cordless IP, Service Manual
6.3 Base Stations
General
DECT IP Basisstation BSIP1
•Software Can be loaded via the communication system.
•Antennas Two external antennas are mounted on the top of
the housing of the base station.
The base station works with antenna diversity (this
means that the radio receiver is connected to
whichever antenna delivers the greater field
strength).
•Average output power 10 mW to 125 mW
•Radio range Basically dependant on the radio transmission
characteristics of the environment/premises.
– Outdoors Up to 300 m
– Indoors Up to 50 m
•Power supply PoE is used to supply power to the DECT IP base
station
•Accessories Outdoor housing
•Dimensions 202 x 172 x 43 (W x H x D in mm)
•Weight 500 g
•Power supply PoE, according IEEE 802.3af Class 2
•Power consumption < 6,5 W
•Operating temperature indoors
Outdoors (in outdoor housing) + 0°C to + 40°C
- 25°C to + 40°C
•Cabling 10/100 Mbps Ethernet cable, Cat. 5 and higher,
8-pin shielded RJ45 connector
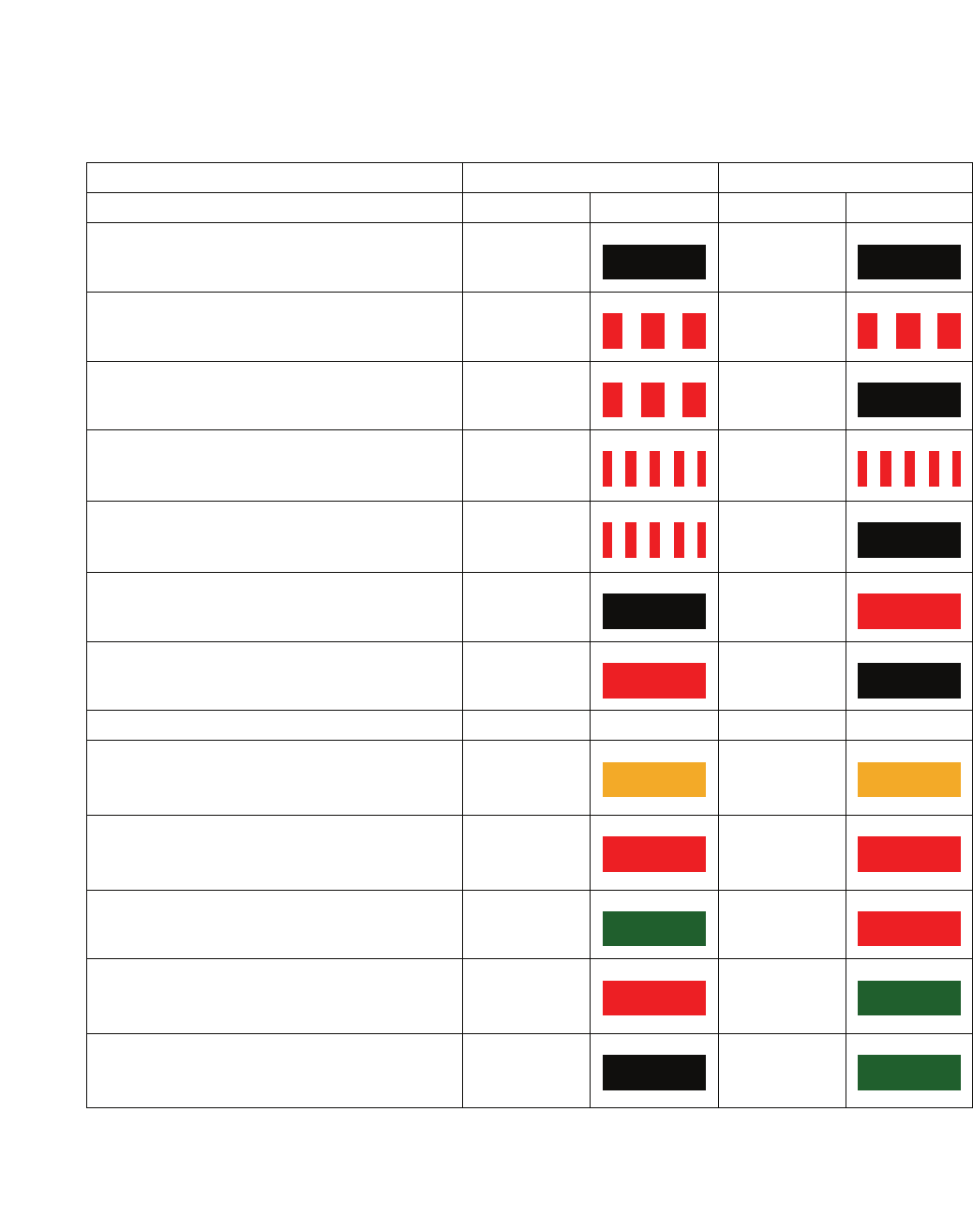
c06.fm
Technical Data
Base Stations
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 151
LED status displays on the base station
•No settings need be made at the base station.
•LED 1/LED 2 on the front of the base station provides the following
information:
Operating State LED 1 LED 2
LED status at booting sequence
No power on Base station off off
BSIP1 is booting the the Active partition red
flashing red
flashing
BSIP1 is booting the the Fallback partition red
flashing off
BSIP1 is booting the Active partition with factory
defaults red
fast flashing red
fast flashing
BSIP1 is booting the Fallback partition with
factory defaults red
fast flashing off
BSIP1 is booting kernel with Active partition off red
BSIP1 is booting kernel with Fallback partition red off
LED status at working process
BSIP1 not ready
Services not started or starting orange orange
BSIP1 ready
No LAN link red red
BSIP1 ready
No Connection to IWU green red
BSIP1 ready
All DECT-frequencies blocked or all available
DECT channels occupied
red green
BSIP1 ready
Link unsynchronized (DECT/LAN), no active call off green
Table 7 LED status displays on the base station
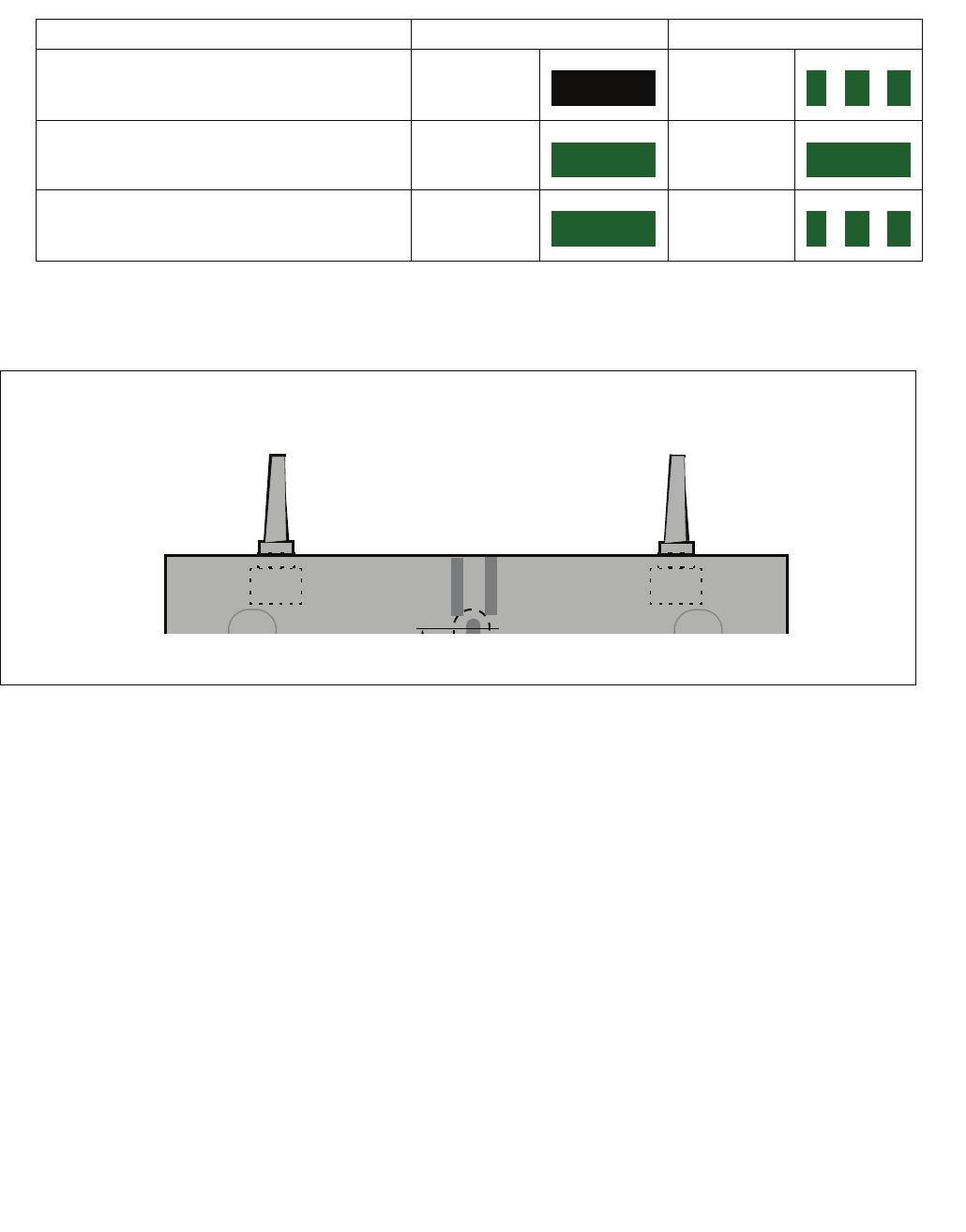
Technical Data
c06.fm
Base Stations
A31003-C1010-S100-2-7620, 08/2010
152 HiPath Cordless IP, Service Manual
Blinking frequency = 500 msec. ON, 500 msec. OFF
Figure 19 LED position on the base station
BSIP1 ready
Link unsynchronized (DECT/LAN), at least one
active call *
off green
flashing
BSIP1 ready
Link synchronized (DECT/LAN), no active call green green
BSIP1 ready
Link synchronized (DECT/LAN), at least one
active call
green green
flashing
* On BSIP IWU means this LED status that a call might by located at another BSIP and be routed via the BSIP IWU
Operating State LED 1 LED 2
Table 7 LED status displays on the base station
LED 1 LED 2

c06.fm
Technical Data
Base Stations
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 153
6.3.1 Mobile Telephones
All the mobile telephones mentioned in this section are suitable for use in normal
environments. The Gigaset M2/M2plus and M2EX mobile telephones may also
be used in industrial environments.
6.3.1.1 Gigaset S3 professional
Do not remove batteries without good reason because charge state monitoring
and the recharge function will not work properly if you do. After the batteries are
removed and reinserted, they must be discharged and recharged as for the initial
startup.
7
CAUTION
The use of any other rechargeable batteries may cause functional
disturbances or may damage the handsets. The manufacturer will not be
held liable in such cases. If replacement batteries are required, be sure to
use only the approved rechargeable types.
•Software Checking, see Section 7.2.2
•Output power Average output power +10 dBm per
channel
Peak output power +24 dBm per channel
•Tone ringing
– Volume control adjustable 5 levels + crescendo ringing
– Tone ringing signal Can be configured separately for internal
and external calls (3 ringtones and 30
melodies)
•User Interface (UI) Menu-driven graphic user interface
•Display Illuminated color display
•Telephone book
(integrated locally) Up to a total of 250 entries
•PIN-lock •4-digit, numeric (see Section 7.3.3)
•Approved ambient conditions + 5°C to + 45°C
20% to 75% relative humidity
•Power supply (state of charge indicated on the display)
– Recommended rechargeable
batteries Nickel Metal Hydride (NiMH), 600 - 1200
mAh
Sanyo NiMH 800
GP 850 mAh
Yuasa Technologies AAA 800
Technical Data
c06.fm
Base Stations
A31003-C1010-S100-2-7620, 08/2010
154 HiPath Cordless IP, Service Manual
Accessories
NOTE: The home version of the Gigaset S3 professional will be classified by the
HiPath Cordless IP system as GAP-device.
Example for a capacity of 800 mAh :
– Talktime Up to 9 hours
– Standby time Up to 175 hours
– Charging time in handset approx. 9 h in charging unit, approx. 7 h in base
station
The times for normal charging and initial charging are comparable.
•Housing approx. 143 x 50 x 30 mm (L x W x H)
•Weight incl. rechargeable battery approx. 119 g
•Charging unit for EU including plug-
in power supply unitt S30852-H1980-R142
•Charging unit for UK including plug-
in power supply unit S30852-H1980-L142
•Charging unit for US including plug-
in power supply unit S30852-H1980-R142
•Charging unit for AUS including
plug-in power supply unit S30852-H1980-C442
c06.fm
Technical Data
Base Stations
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 155
6.3.1.2 Gigaset SL3 professional
Do not remove the battery pack without good reason as charge state monitoring
and the recharge function will not work properly if you do! After the batteriey pack
is removed and reinserted, it must be discharged and recharged as for the initial
startup!
7
CAUTION
The use of any other battery packs may cause functional disturbances or
may damage the handsets. The manufacturer will not be held liable in such
cases. If replacement battery packs are required, be sure to use only the
approved types.
•Software Checking, see Section 7.2.2
•Output power Average output power +10 dBm per channel
Peak output power +24 dBm per channel
•Tone ringing
– Volume control adjustable 5 levels + crescendo ringing
– Tone ringing signal Can be configured separately for internal and
external calls (3 ringtones and 30 melodies)
•User Interface (UI) Menu-driven graphic user interface
•Display Illuminated color display
•Telephone book
(integrated locally) Up to a total of 250 entries
•PIN-lock •4-digit, numeric (see Section 7.3.3)
•Approved ambient conditions + 5°C to + 45°C
20% to 75% relative humidity
•Power supply (state of charge indicated on the display)
•Approved battery pack Lithium-Ion (Li-Ion), 700 mAh
– Talktime Up to 14 hours
– Standby time Up to 350 hours
– Charging time in handset approx. 3,5 h
The times for normal charging and initial charging are comparable.
•Housing approx. 114 x 46,5 x 22,6 mm (L x W x H)
•Weight incl. battery pack approx. 93 g
Technical Data
c06.fm
Base Stations
A31003-C1010-S100-2-7620, 08/2010
156 HiPath Cordless IP, Service Manual
Accessories
NOTE: The home version of the Gigaset SL3 professional will be classified by
the HiPath Cordless IP system as GAP-device.
•Charging unit for EU including plug-in power supply unit S30852-H1982-R141
•Charging unit for UK including plug-in power supply unit S30852-H1982-L141
•Charging unit for US including plug-in power supply unit S30852-H1982-U141
•Charging unit for AUS including plug-in power supply
unit S30852-H1982-C441

c06.fm
Technical Data
Base Stations
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 157
6.3.1.3 Gigaset M2 professional, Gigaset M2 plus professional
Do not remove the battery pack without good reason as charge state monitoring
and the recharge function will not work properly if you do! After the batteriey pack
is removed and reinserted, it must be discharged and recharged as for the initial
startup!
7
CAUTION
The use of any other battery packs may cause functional disturbances or
may damage the handsets. The manufacturer will not be held liable in such
cases. If replacement battery packs are required, be sure to use only the
approved types.
•Software Checking, see Section 7.2.2
•Output power Average output power +10 dBm per channel
Peak output power +24 dBm per channel
•Tone ringing
– Volume control adjustable: 5 levels, levels 4 and 5 for loud
environments.
– Tone ringing signal Can be configured separately for internal and
external calls
20 standard ringtones (3 ringtones / 17 melodies)
16 loadable polyphonic melodies
•User Interface (UI) Menu-driven graphic user interface
•Display Illuminated color display
•Telephone book
(integrated locally) Up to a total of 250 entries
•Voice dialing
(voice telephone book) Up to 30 entries
•PIN-lock •4-digit, numeric (see Section 7.3.3)
•Full functionality of device
guaranteed for -10 °C to +55 °C
100 % relative humidity including splashes and low
pressure jets of water (IP 65)
•Power supply (state of charge indicated on the display)
•Approved battery pack Lithium-Ion, 1000 mAh (A5B00075416005)
Example for a capacity of 850 mAh:
– Talktime Up to 12 hours
– Standby-Time Up to 380 hours, approx. 16 days
– Charging time in handset approx. 3,7 hours
– Initial charging time at least 10 h
•Housing approx. 166,5 x 56,0 x 35,4 mm (L x W x H)

Technical Data
c06.fm
Base Stations
A31003-C1010-S100-2-7620, 08/2010
158 HiPath Cordless IP, Service Manual
Accessories
6.3.1.4 Gigaset M2 Ex professional
•Weight incl. battery pack approx. 180 g
•Charging unit for EU including plug-in power supply unit S30852-H1786-R101
•Charging unit for UK including plug-in power supply unit S30852-H1786-L101
•Software Checking, see Section 7.2.2
•Output power Average output power +10 dBm per channel
Peak output power +24 dBm per channel
•Tone ringing
– Volume control adjustable: 5 levels, levels 4 and 5 for loud
environments.
– Tone ringing signal Can be configured separately for internal and
external calls
20 standard ringtones (3 ringtones / 17 melodies)
16 loadable polyphonic melodies
•User Interface (UI) Menu-driven graphic user interface
•Display Illuminated color display
•Telephone book
(integrated locally) Up to a total of 250 entries
•Voice dialing
(voice telephone book) Up to 30 entries
•PIN-lock •4-digit, numeric (see Section 7.3.3)
•Full functionality of device
guaranteed for -10 °C to +55 °C
100 % relative humidity including splashes and low
pressure jets of water (IP 65)
•Power supply (state of charge indicated on the display)
– Permitted Ex-battery pack Lithium-Ion, 1000 mAh including electronic
components (A5B00075609027)
c06.fm
Technical Data
Base Stations
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 159
Do not remove the Ex-battery pack without good reason as charge state
monitoring and the recharge function will not work properly if you do! After the Ex-
battery pack is removed and reinserted, it must be discharged and recharged as
for the initial startup!
7
CAUTION
Only use approved Ex battery packs . Ex authorisation is only valid and the
handset can only be operated if this battery pack is installed. Other battery
packs are strictly prohibited. If they are used, Ex protection is no longer
valid.
Accessories
6.3.2 PoE Injector
•An injector is needed when operating the DECT IP base station on the
mains,
•Single-port PoE injector in compliance with IEEE 802.3af Class 2
•Injector is included in the scope of features
•The PoE injector ships with startup information and notes on LED status
displays.
Example for a capacity of 850 mAh:
– Talktime Up to 12 hours
– Standby-time Up to 380 hours, approx. 16 days
– Charging time approx. 3,7 h
– Initial charging time at least 10 h
•Housing approx. 166,5 x 56,0 x 35,4 mm (L x W x H)
•Weight incl. battery pack approx. 180 g
•Charging unit for EU including plug-
in power supply unit S30852-H1786-R101
•Charging unit for UK including plug-
in power supply unit S30852-H1786-L101
Technical Data
c06.fm
Base Stations
A31003-C1010-S100-2-7620, 08/2010
160 HiPath Cordless IP, Service Manual
6.3.3 Item Number Overview
•Base stations
– HiPath Cordless IP V1 - Base station BSIP1 S30807-U5494-X
– HiPath Cordless IP V1 - SW License per HiPath
Cordless IP Server*
– HiPath Cordless IP V1 - SW License per DECT IP
Basisstation BSIP1*
– HiPath Cordless IP V1 - CD-ROM with software
– DECT system number (ARI = Access Right Identifier) A31003-G2121-S500-*-
20
– HiPath Cordless IP V1 - HiPath Cordless IP Server
– HiPath Cordless IP V1 - 19" conversation kit for the
HiPath Cordless IP Server
– One-Port PoE Injector S30122-X8009-X20
– Outdoor mounting S30122-X7469-X2
– Power line for PoE injector - EU C39195-Z7001-C11
– Power line for PoE injector - UK C39195-Z7001-C20
– Power line for PoE injector - Switzerland C39195-Z7001-C38
*only needed if the HiPath Cordless IP server software is
installed on dedicated server hardware and not on one of
the DECT IP base stations
•Terminals
–Gigaset M2 professional S30852-S1756-R111
– Charging unit for EU including plug-in power supply unit S30852-H1786-R101
– Charging unit for UK including plug-in power supply unit S30852-H1786-L101
–Gigaset M2 EX professional S30852-S1756-R121
– Charging unit for EU including plug-in power supply unit S30852-H1786-R101
– Charging unit for UKincluding plug-in power supply unit S30852-H1786-L101
–Gigaset M2 plus professional S30852-S1756-R131
– Charging unit for EU including plug-in power supply unit S30852-H1786-R101
– Charging unit for UK including plug-in power supply unit S30852-H1786-L101
–Gigaset S3 professional S30852-H1950-R142
– Charging unit for EU including plug-in power supply unit S30852-H1980-R142
– Charging unit for UK including plug-in power supply unit S30852-H1980-L142
– Charging unit for US including plug-in power supply unit S30852-H1980-R342
– Charging unit for AUS including plug-in power supply
unit S30852-H1980-C442
–Gigaset SL3 professional S30852-H1952-R142
– Charging unit for EU including plug-in power supply unit S30852-H1982-R141
– Charging unit for UK including plug-in power supply unit S30852-H1982-L141
c06.fm
Technical Data
Measuring Equipment
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 161
6.4 Measuring Equipment
6.5 Operating Manuals
See http://apps.g-dms.com:8081/techdoc/search_en.htm
– Charging unit for US including plug-in power supply unit S30852-H1982-U141
– Charging unit for AUS including plug-in power supply
unit S30852-H1982-C441
*
•HiPath Cordless Servicetool HCS DECT
Locater / Locater Pro TIS
Technische Informations-Systeme GmbH
Barloer Weg 190
46397 Bocholt, Germany
Tel.: (0 28 71) 27 22 - 0, (0 28 71) 3 78 62
http://www.tis-gmbh.de/produkte/

c07.fm
Diagnosis and Maintenance
Checking the Base Stations and the Radio Coverage
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 161
7 Diagnosis and Maintenance
7.1 Checking the Base Stations and the Radio Coverage
Do not use Gigaset mobile telephones to check the radio area coverage. This
must be done with the Hicom Cordless Service tool (HCS-DECT).
You can use Gigaset mobile telephones to test the base stations and verify the
radio area coverage.
•A prerequisite is that the mobile telephone being used is logged on to the
system, see the operating manual.
•The radio coverage is tested in two stages:
– Base station test
– Coverage test via the base stations (area coverage)
The following minimum values must be observed for the site survey of the
radio range:
1. Providing handsets with an adequate DECT radio signal
Handsets only receive a sufficiently sized DECT radio signal if they are
located in the radio range of the DECT IP base station, that is:
– RSSI value <-70 dBm
– FRAQ value >95%
2. Distance of DECT IP base stations
For the DECT synchronism function to work, the DECT IP base stations
to be synchronized with each other must be defined in the HiPath
Cordless IP server software. These DECT IP base stations must also be
able to exchange their management information, i.e. they must be at least
<-85 dBm apart.
Failure to maintain these values results in a loss of radio signal or a loss
of synchronism which prevents the handsets from roaming to another
DECT IP base station.
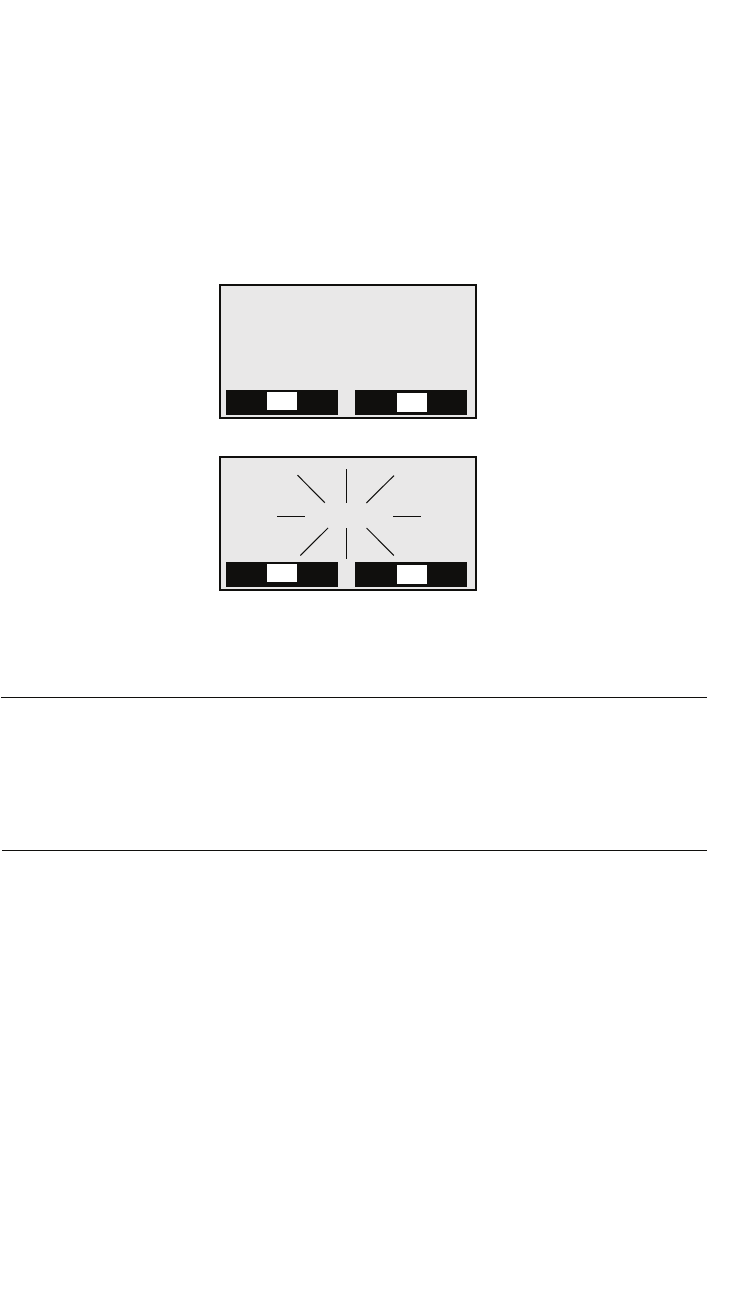
Diagnosis and Maintenance
c07.fm
Checking the Base Stations and the Radio Coverage
A31003-C1010-S100-2-7620, 08/2010
162 HiPath Cordless IP, Service Manual
7.1.1 Base Stations
The purpose of this test is to check the functions of all base stations.
•Take the mobile telephone to each of the base stations.
•Holding the mobile telephone directly below, beside or above each base
station, turn it off and on again.
– Display data, for example:
•Set the mobile telephone to measuring mode.
NOTE: Values recorded with a mobile telephone are not very precise and are
intended to provide a rough assessment only. In addition, different values may be
recorded on each mobile telephone even though the ambient conditions are
identical. If you require more accurate results, we recommended that you use the
Hicom Cordless Service tool (HCS-DECT).
Check:
–RSSI value (field strength value)
–RPN value (base station number)
Does the mobile telephone pick up the connection (synchronization) with
the base station to be tested?
–FRAQ value (transmission quality %)
Synchronization
between mobile
telephone and base
station
Radio connection to the
base station is displayed
on the screen as "Base n",
for example.
No synchronization
between mobile
telephone and base
station
"Base n" flashes, it means
that the radio connection
to the base station has
been lost.
Service
e
z
Base n
Ð
©
Service
e
z
Base n
Ð
©
c07.fm
Diagnosis and Maintenance
Checking the Base Stations and the Radio Coverage
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 163
If the indicated values are not attained, use a second logged-on mobile telephone
to check the value ranges.
If the indicated values are not attained with the second mobile telephone, replace
the base station.
7
WARNING
The customer must be informed about the boundaries of the radio area.
Proceed with the area coverage test once the RSSI value, the availability and
radio quality of all base stations has been checked.
7.1.2 Quick Verification of Area Coverage
The purpose of this test is to check whether the necessary field strength and the
transmission quality is attained throughout the entire radio network.
NOTE: Values recorded with a mobile telephone are not very precise and are
intended to provide a rough assessment only. In addition, different values may be
recorded on each mobile telephone even though the ambient conditions are
identical. If you require more accurate results, we recommended that you use the
Hicom Cordless Service tool (HCS-DECT).
Step 1
The purpose of this step is to provide the basis for step 2 where you will use a
Gigaset mobile telephone to obtain a rough assessment of the area coverage.
•Switch the mobile telephone to measuring mode (see Section 7.2.2.1).
•Establish a voice connection between two mobile telephones. If you wish, you
can use an announcement service (for example "speaking clock").
Step 2
This step involves obtaining a rough assessment of the area coverage.
•With a mobile telephone in measuring mode, move around the area in
question and determine whether an RSSI value > 50 (-60 dBm) and a FRAQ
value > 95% are reached throughout the area.
In the process, the Range Warning feature can be used as an aid for
recognizing the radio area boundaries. A warning tone (range warning) is
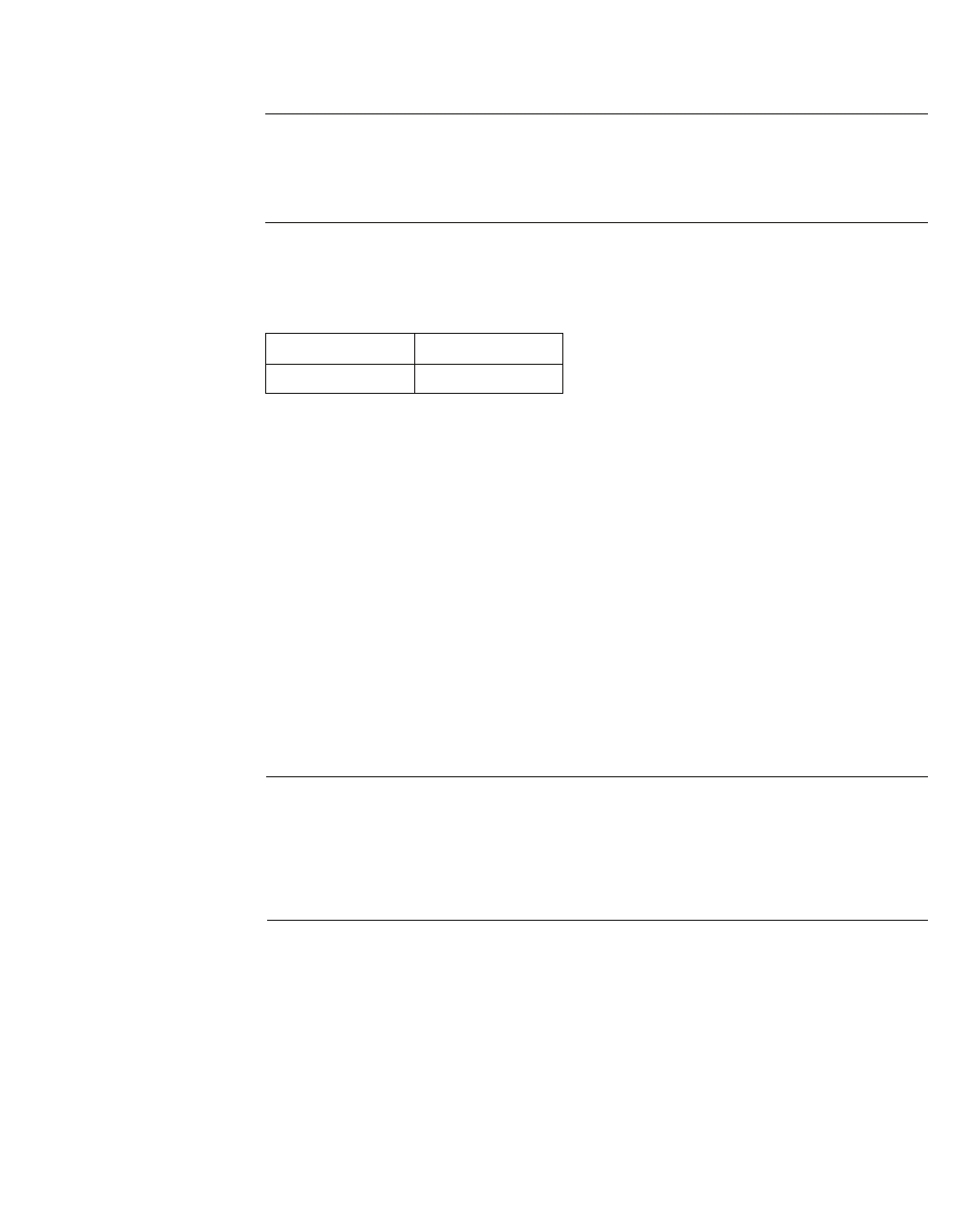
Diagnosis and Maintenance
c07.fm
Testing the Radio Area
A31003-C1010-S100-2-7620, 08/2010
164 HiPath Cordless IP, Service Manual
emitted as soon as you cross the border zone of the radio area. (To activate
the range warning tone, use the "Tones" menu on the mobile telephone
display.)
7
WARNING
Areas in the corners of buildings or behind metal structures should be
carefully checked (check the RSSI values several times).
In these radio area border zones, the radio connection to the base station
may be lost in the case of the following values:
•The measuring sites with RSSI value < 40 (< -80 dBm) should be entered or
marked in the building/site plan.
Step 3
If you require more accurate values than those obtained in step 2, we
recommended that you use the Hicom Cordless Service tool (HCS-DECT).
7.2 Testing the Radio Area
7.2.1 Significance of Results Obtained
NOTE: Values recorded with a mobile telephone are not very precise and are
intended to provide a rough assessment only. In addition, different values may be
recorded on each mobile telephone even though the ambient conditions are
identical. If you require more accurate results, we recommended that you use the
Hicom Cordless Service tool (HCS-DECT)
The following figure shows a sample display of the measuring results for a
Gigaset mobile telephone when a call is in progress:
RSSI < 40 (< -80 dBm)
FRAQ < 95%
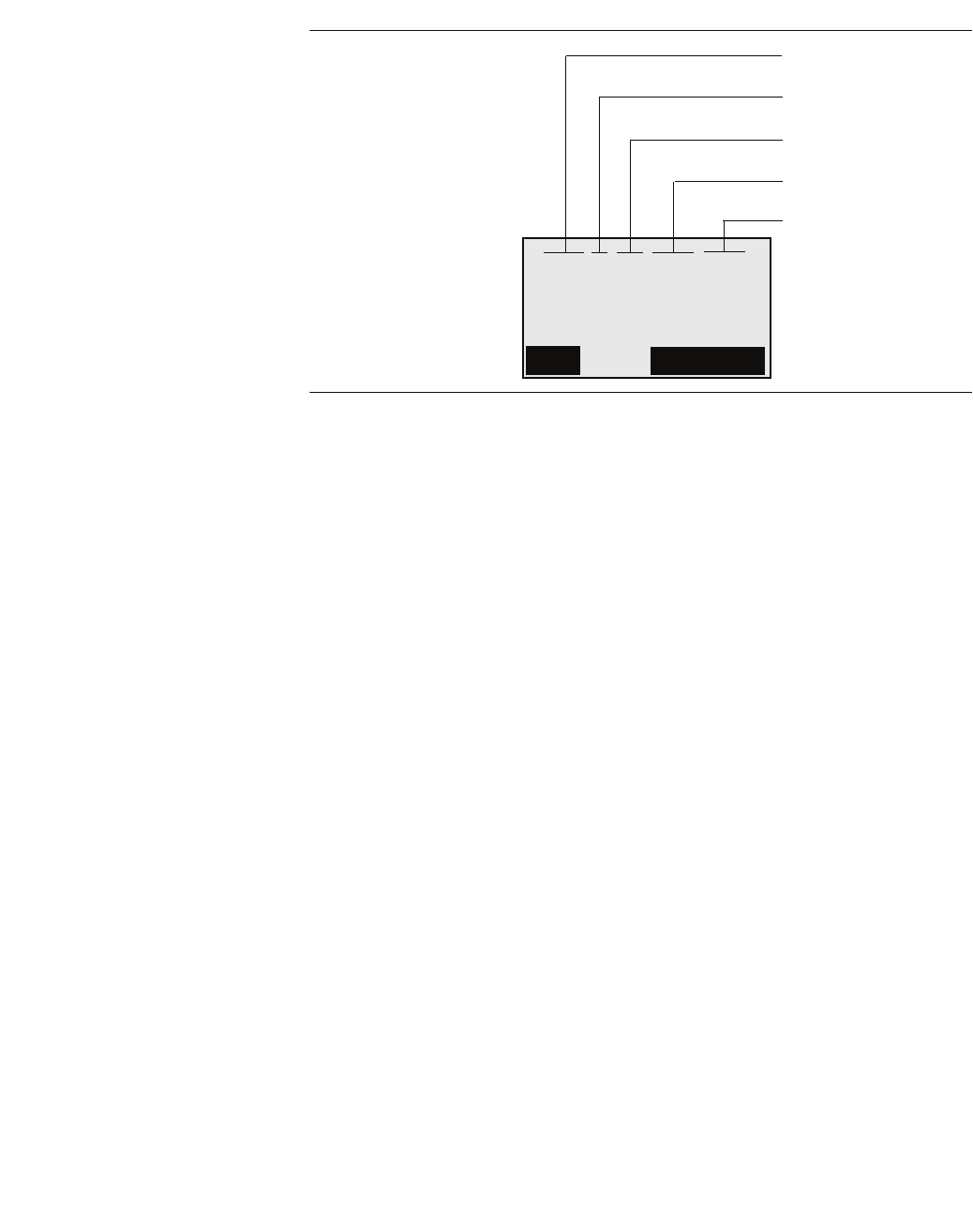
c07.fm
Diagnosis and Maintenance
Testing the Radio Area
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 165
RSSI
(radio signal) Field strength of the radio signals received from the base
station, normalized to a maximum of 100. If the value is < 50, the
radio connection to the base station is no longer guaranteed.
Acceptable field strength is > 50 (> -60 dBm).
Frequency Frequency (0 – 9)
Time slot
(Slot) Time slot (0 – 11) of the receiving channel on which the
measurement is carried out.
RPN
(port number) IDECT IP base station identification based on the RPN (Radio
Fixed Part Number), e.g. 018. If the handset switches on at/over
to an overlapping radio cell/DECT IP base station, the current
DECT IP base station appears on the handset display. The RPN
is indicated in hex format in Gigaset S3 professional and
Gigaset SL3 professional handsets.
Example: RPN 018 will be display in the Gigasets as HEX-value
012H. The identifier "H" shows clearly the hexadecimal
presentation.
FRAQ
(frame quality) Transmission quality in %.
95% to 100% satisfactory (for short periods 90% to 94% non-
critical), < 95% faulty.
095-3-02-012H-100
SAVE
OFF
Measurement result
RSSI
Frequency
Time slot
RPN
FRAQ
Handset display,
forexample
Diagnosis and Maintenance
c07.fm
Testing the Radio Area
A31003-C1010-S100-2-7620, 08/2010
166 HiPath Cordless IP, Service Manual
7.2.2 Gigaset Family
NOTE: The default language for measuring mode is English.
7.2.2.1 Activating Measuring Mode
You must switch off the mobile telephone before you can activate measuring
mode.
Switch off the mobile telephone:
Press the on-hook key until
the confirmation beep is
heard (ascending tone
sequence).
Nothing is displayed
Switch the mobile telephone into service status:
Press keys 1, 4, and 7
simultaneously...
... whilst at the same time...
... pressing the on-hook key.
Activate the "Service" menu:
Enter code 76200.
123
456
789
*0#
Service
12
456
789
*0#
3Service
QS data
SW version
Speechpath test
Service 1
OK
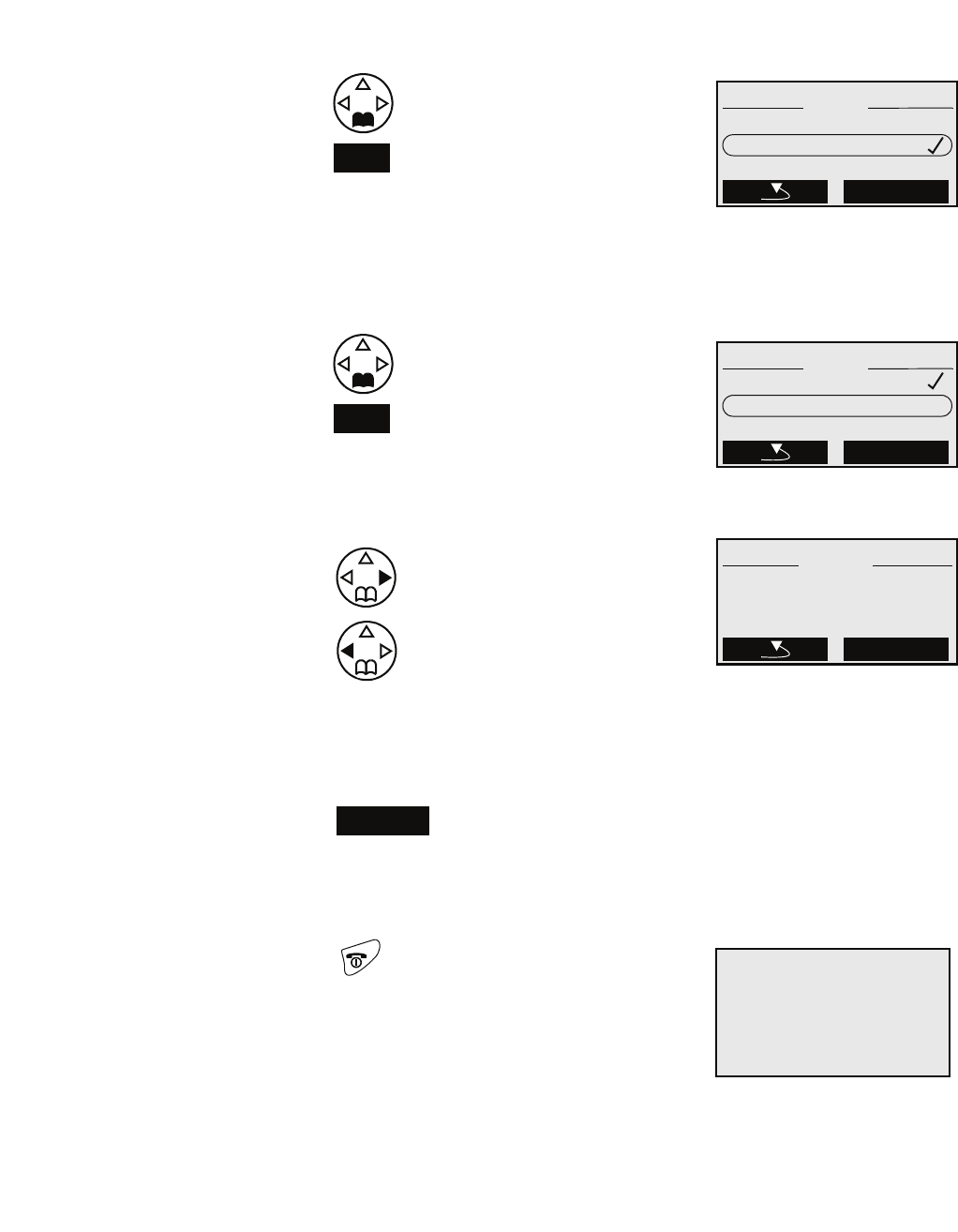
c07.fm
Diagnosis and Maintenance
Testing the Radio Area
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 167
The measurement values are displayed when the mobile telephone is switched
on. Measurements are performed at the set intervals (see Section 7.2.1).
Activate the measuring mode:
Using the navigation key,
scroll down to "Measuring
time".
Confirm with OK.
Measuring mode is switched
on; this is indicated by the
tick next to "Measuring
mode".
Select the measuring time:
Using the navigation key,
scroll down to "Measuring
time".
Confirm with OK.
Set the value range:
Press the navigation key:
to increase the value range
Press the navigation key:
to reduce the value range
Value range: 06 to 16
Recommended value range:
16
(measuring cycle: 1 s to 2.5
s)
Press the Save key
to confirm the value range
set
Switch off the mobile telephone:
Press the on-hook key until
the confirmation beep is
heard (ascending tone
sequence).
Nothing is displayed
OK
Service
Measuring mode
DSP parameters
Measuring time
Service 6
OK
OK
Service
Measuring time
Measuring mode
Service 7
OK
LLLLLLLLLLLLL
Service
Measuring time
Measuring time
Save
<16>
Save
Diagnosis and Maintenance
c07.fm
Testing the Radio Area
A31003-C1010-S100-2-7620, 08/2010
168 HiPath Cordless IP, Service Manual
7
WARNING
Only the specified functions may be activated. Activating other functions
may result in malfunctions.
7.2.2.2 Deactivating Measuring Mode
Switch on the mobile telephone:
Press the on-hook key until the
confirmation beep is heard
(ascending tone sequence). Service
095-3-02-012H-100
z
*Base n
©
Switch off the mobile telephone:
Press the on-hook key until
the confirmation beep is
heard (ascending tone
sequence).
Nothing is displayed
Switch the mobile telephone into service status:
Press keys 1, 4, and 7
simultaneously...
... whilst at the same time...
... pressing the on-hook key.
123
456
789
*0#
Service
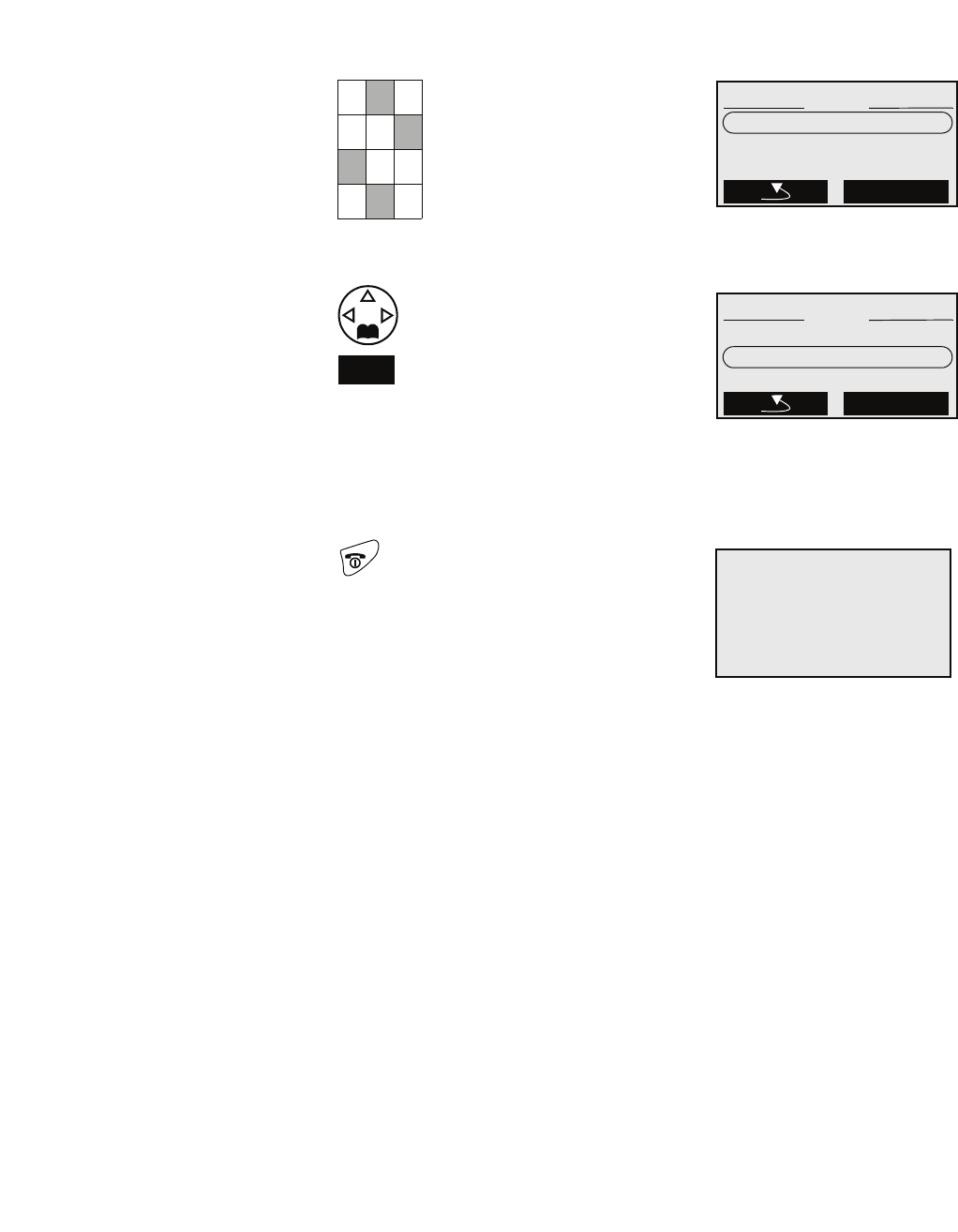
c07.fm
Diagnosis and Maintenance
Testing the Radio Area
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 169
The measurement values are not displayed if the mobile telephone is switched
on.
Activate the "Service" menu:
Enter code 76200.
Deactivate the measuring mode:
Using the navigation key,
scroll down to "Measuring
time".
Confirm with OK.
Measuring mode is switched
off; the tick next to
"Measuring mode"
disappears.
Switch off the mobile telephone:
Press the on-hook key until
the confirmation beep is
heard (ascending tone
sequence).
Nothing is displayed
12
456
789
*0#
3Service
QS data
SW version
Speechpath test
Service 1
OK
OK
Service
Measuring mode
DSP parameters
Measuring time
Service 6
OK
Diagnosis and Maintenance
c07.fm
Testing the Radio Area
A31003-C1010-S100-2-7620, 08/2010
170 HiPath Cordless IP, Service Manual
7.2.3 Documentation of Results
The following points must be documented:
•The installation site of the base stations must be drawn on a customer-
specific building/site plan and the base station number (for example, 016
(RPN in measuring mode)) entered.
•Any deviations from existing building and site plans must be verified with the
Hicom Cordless Service tool (HCS-DECT) and documented.
7
WARNING
Any subsequent structural changes within the radio area (buildings, sites,
facilities, and devices, etc.) might restrict the operation of the mobile
telephones and thus require rearrangement of the base stations.
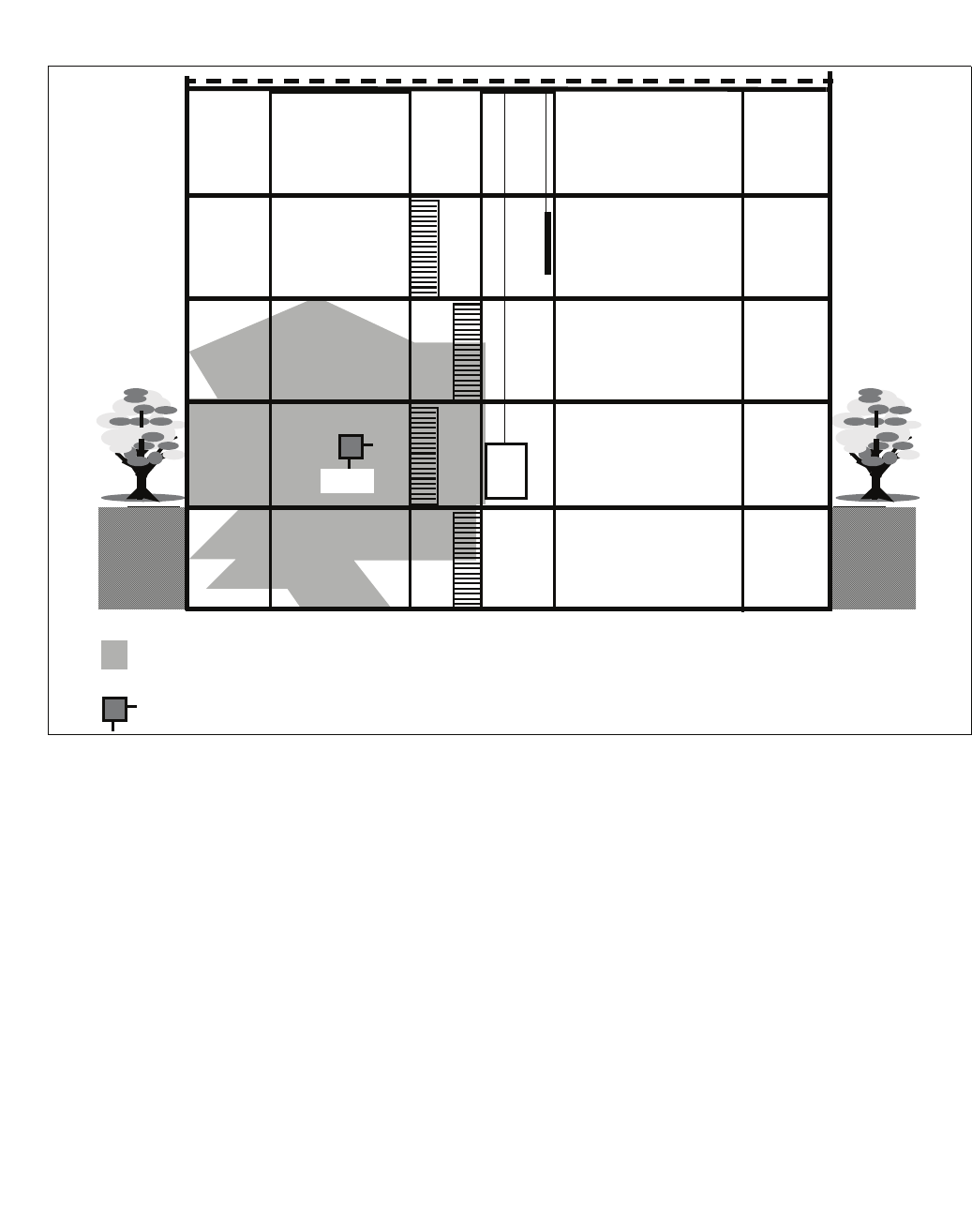
c07.fm
Diagnosis and Maintenance
Testing the Radio Area
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 171
Examples:
Figure 21 Building - Base station installation site/radio area
BS
3rd floor
2nd floor
1st floor
Ground floor
Basement
Elev-
ator
Stair-
well
Radio area for the base station installed
Installation site of the base station
016
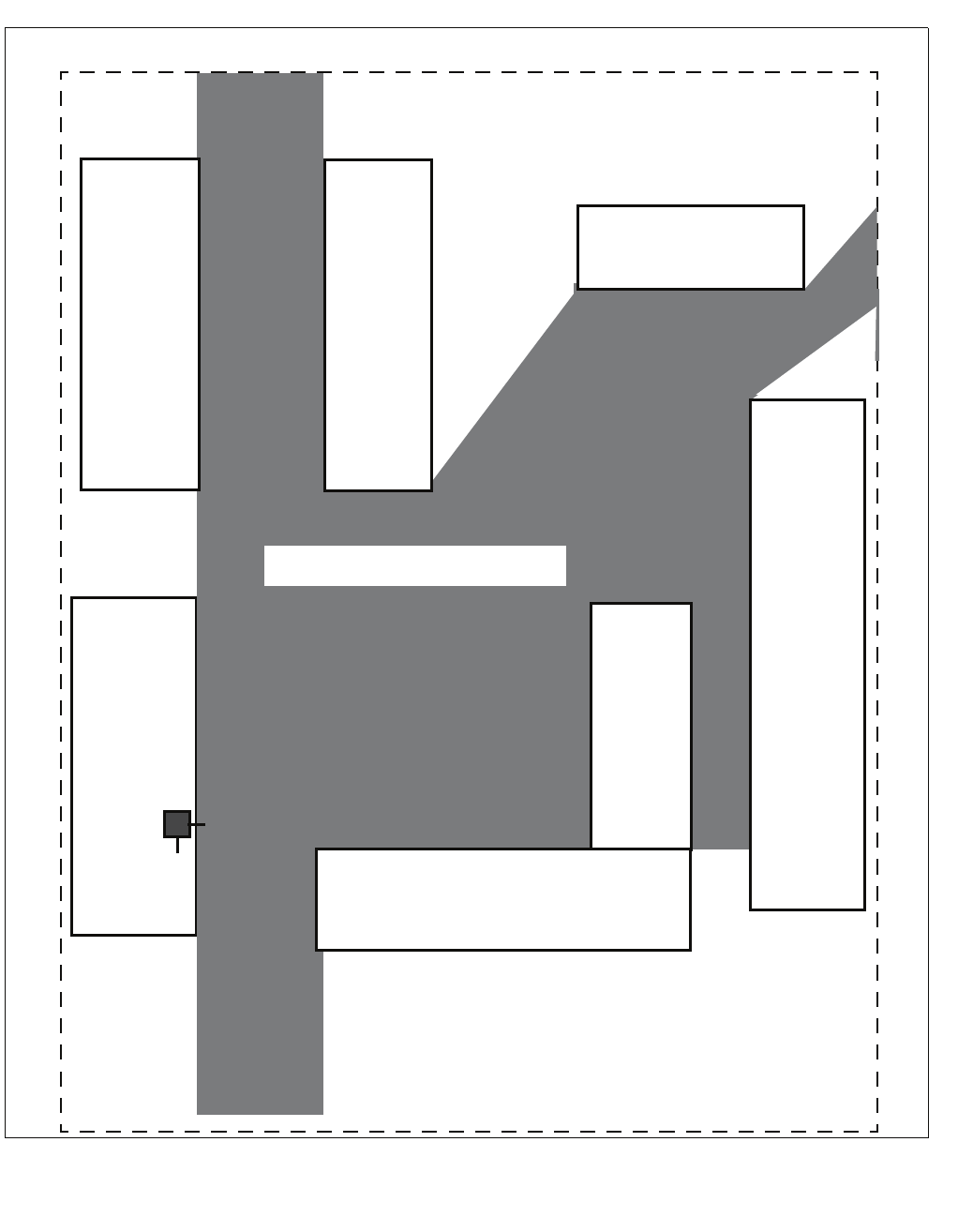
Diagnosis and Maintenance
c07.fm
Testing the Radio Area
A31003-C1010-S100-2-7620, 08/2010
172 HiPath Cordless IP, Service Manual
Figure 22 Outdoors - Base station installation site/radio area
Bldg
B
concrete/
mounting
height
25 m
Scale 1:1000
BS
Bldg
E
concrete/
27 m
high
Bldg F
concrete/10 m high
Bldg
C
concrete/
27 m
high
Minimum supply range
Property line
Bldg
G
Hall
steel/
10 m
high
Bldg A
brick/15 m high

c07.fm
Diagnosis and Maintenance
Troubleshooting
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 173
7.3 Troubleshooting
7.3.1 Checking HiPath Cordless IP Components
•Entire system
– Set up call with the
mobile telephone Operating Manual
Subjective evaluation of voice connection, for example,
background noise
•Check the radio area
coverage See Section 7.1.2
(range warning tone activated)
•DECT IP Base station
(BSIP1)
– LED 1/2 See Section 6.3
– Base station status PC
– Check active status of
base station using the
logged-on mobile
telephone
No synchronism:
"Base n" blinks on handset display.
Handset measuring mode is activated:
- Frequency/slot changes
- RSSI value
If this is not the case, perform the test on a different base
station.
If it is still unsuccessful, use a different handset.
If it is still not possible to synchronize with a base station
after repeated attempts, replace the base station.
•Mobile telephone (MT)
– Logged-on mobile
telephone, synchronized
with base station
Synchronism symbol "Base n" (name = individual
setting) on handset display is continuously visible, does
not blink.

Diagnosis and Maintenance
c07.fm
Troubleshooting
A31003-C1010-S100-2-7620, 08/2010
174 HiPath Cordless IP, Service Manual
7.3.2 What Happens If ...
7.3.2.1 Synchronism Symbol on Handset Display:
–"Base n"
flashes No synchronization to base station
1. Is the mobile telephone not logged on?
2. If the mobile telephone is logged on to multiple
systems, is it switched to the correct system? Is
automatic system selection activated?
Check the base station.
–"Base n"
continuously visible
but no action is
possible
Synchronization to base station
1. An error tone can be heard when the line key is
pressed.
Temporary overload status (all the base station
speech paths are busy).
Wait, and try again.
2. Handset was not able to complete the locations
request successfully (handset contact to the
system).
Workaround:
Repeat locations request by switching off the
handset and then switching it on again.

c07.fm
Diagnosis and Maintenance
Troubleshooting
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 175
7.3.2.2 Handset Cannot Be Reached
1. Handset is called, caller hears ringing (followed by
busy signal).
Causes:
handset being called is switched off
OR
handset is no longer within range
OR
the base station used is in overload status and
there is no other base station within range.
2. Handset is called, call is always switched to another
station.
Handset has inadvertently activated call
forwarding.
7.3.2.3 Connection Handover
– Call disconnected
on handover to
another base
station
1. Check whether or not the base station to which the
call is handed over is in overload status (all radio
channels busy).
2. Check the base station LEDs.
3. Check the overlap sectors.
Is the RSSI value of the other base station OK?
4. Check if the two DECT IP base stations involved in
the handover operation are synchronous. You can
use the Gigaset’s measurement mode for this or
the synchronism display in the HiPath Cordless IP
server software .

Diagnosis and Maintenance
c07.fm
Troubleshooting
A31003-C1010-S100-2-7620, 08/2010
176 HiPath Cordless IP, Service Manual
7.3.2.4 Handset: Problems Logging On
•Check first if the communication server’s IP board and at least one DECT IP
base station (in range) are operational.
•Is adequate synchronism guaranteed for the DECT IP base station in the
HiPath Cordless IP system?
•Is the handset you want to log on configured on the communication server?
– Test this with a random phone (optiPoint/OpenStage model).
c07.fm
Diagnosis and Maintenance
Troubleshooting
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 177
7.3.3 Deactivating the PIN Lock on Gigaset S3, SL3
A mobile telephone can only be reactivated at the factory or by a service
technician if the user forgets the PIN. The forgotten PIN is deleted on reactivation.
Login data and other data are retained.
Reactivating the PIN requires a programming adapter and the "Win FT" program.
These must be supplied by Gigaset Communications, Bocholt.
Procedure:
1. Connect the adapter to a plug-in power supply unit.
2. Connect the adapter to a PC COM port (PCMCIA in the case of laptops) via
a V.24 (RS232) cable.
3. Start the "Win FT" program.
4. Open the battery compartment and remove the batteries from the mobile
telephone.
5. Insert the mobile telephone into the adapter. "Factorytest" appears on the
display.
6. Open the "EEprom" menu and select the icon to read out the EEPROM (arrow
pointing away from the yellow telephone). The EEPROM is read out.
7. Reset the four-digit PIN to "30 30 30 30". The "30 30 30 30" value is
hexadecimal and corresponds to the decimal value "0000".
7
CAUTION
Modifying any other data in addition to the PIN, for example, the HF or
battery parameters, will disable the mobile telephone. This can only be
reversed at Gigaset Communications, Bocholt.
8. Open the "EEprom" menu and select the icon to write to the EEPROM (arrow
pointing towards the yellow telephone). The EEPROM is re-written.
9. Initiate a reset. The mobile telephone should not request a PIN now.
10. Remove the mobile telephone from the adapter.
11. Insert the batteries into the mobile telephone and close the battery
compartment.
Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
178 HiPath Cordless IP, Service Manual
c08.fm
General Conditions
8 Open Source Software used in the Product
8.1 General Conditions
The Product "HiPath Cordless IP" contains, among other things, Open Source Software, li-
censed under an Open Source Software License and developed by third parties. These Open
Source Software files are protected by copyright. Your rights to use the Open Source Software
beyond the mere execution of Siemens´ program, is governed by the relevant Open Source
Software li-cense conditions.
Your compliance with those license conditions will entitle you to use the Open Source Software
as foreseen in the relevant license. In the event of conflicts between Siemens Enterprise Com-
munication GmbH&Co. KG license conditions and the Open Source Software license condi-
tions, the Open Source Software conditions shall prevail with respect to the Open Source Soft-
ware por-tions of the software. The Open Source Software is licensed royalty-free (i.e., no fees
are charged for exercising the licensed rights, whereas fees may be charged for reimbursement
of costs incurred by Siemens Enterprise Communication GmbH&Co. KG. The license condi-
tions can be found in the following chapters. In addition the license texts can be downloaded
from:
●The BSD License is available on the internet at:
http://www.freebsd.org/copyright/license.html
●The GPL v2 is available on the internet at:
http://www.gnu.org/licenses/old-licenses/gpl-2.0.html
●The LGPL v2.1 is available on the internet at:
http://www.gnu.org/licenses/old-licenses/lgpl-2.1.html
●The OpenSSL license is available on the internet at:
http://www.openssl.org/source/license.html
●The zLib license is available on the internet at:
http://www.zlib.net/zlib_license.html
If programs contained in this product are licensed under GNU General Public License (GPL)
and/or GNU Lesser General Public License (LGPL) and this software is not already delivered
in source code form together with the device, you can request the corresponding source code
from Siemens Enterprise Communication GmbH&Co. KG by paying a fee of 10 Euro for the
physical act of transferring the copy.
Please send your specific request, together with a receipt indicating the date of purchase, with-
in three years of your purchase, together with the MAC ID number of the device and the soft-
ware release number to:

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 179
Nur für den internen Gebrauch Open Source Software used in the Product
General Conditions
Your local Service Organisation of Siemens Enterprise Communication GmbH&Co. KG
Warranty regarding further use of the Open Source Software:
Siemens Enterprise Communication GmbH&Co. KG provides no warranty for the Open Source
Software programs contained in this device, if such programs are used in any manner other
than the program execution intended by Siemens Enterprise Communication GmbH&Co. KG.
The li-censes listed below define the warranty, if any, from the authors or licensors of the Open
Source Software. Siemens Enterprise Communication GmbH&Co. KG specifically disclaims
any warran-ties for defects caused by altering any Open Source Software program or the prod-
uct's configu-ration. You have no warranty claims against Siemens Enterprise Communication
GmbH&Co. KG in the event that the Open Source Software infringes the intellectual property
rights of a third party.
Technical support, if any, will only be provided for unmodified software.
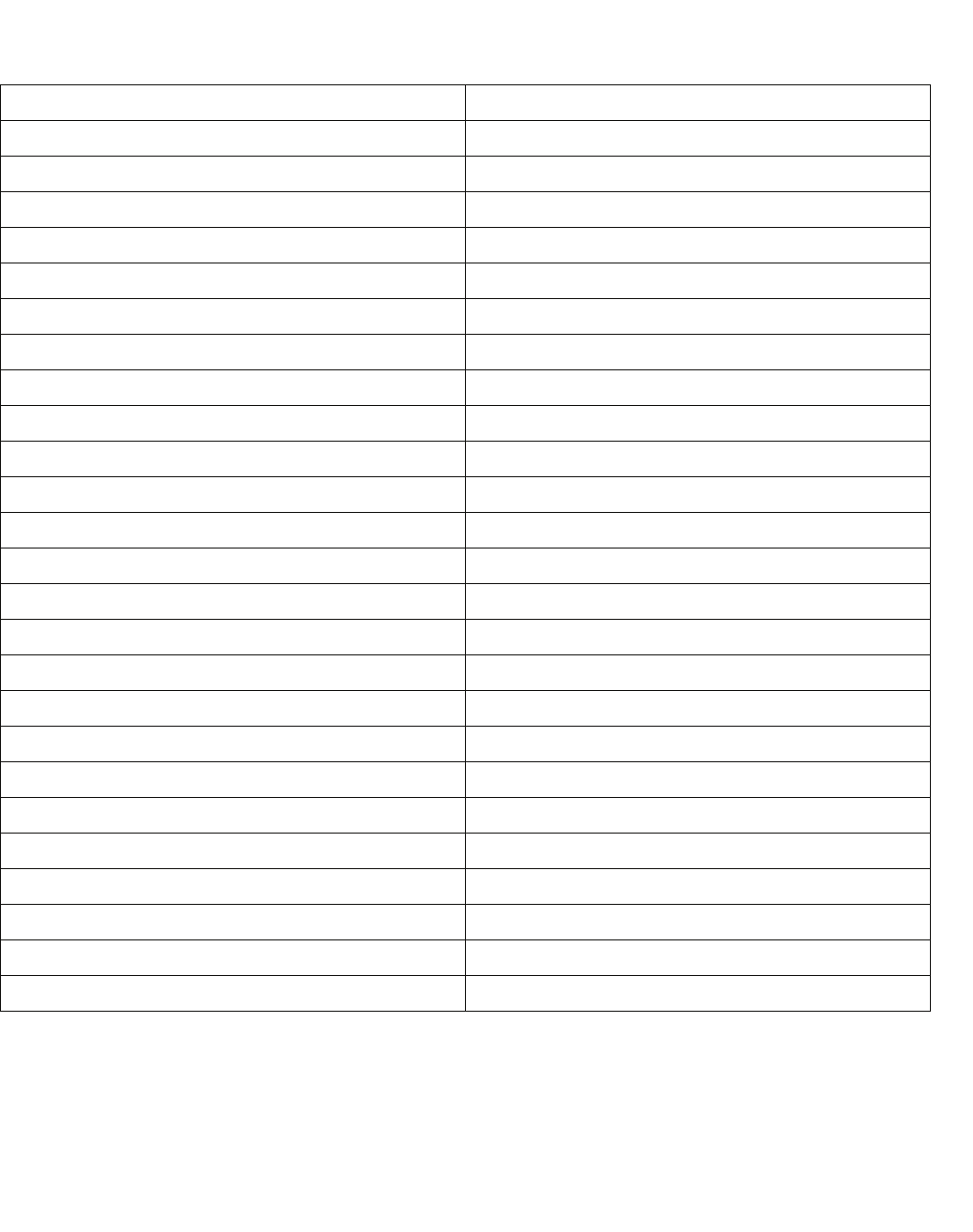
Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
180 HiPath Cordless IP, Service Manual
c08.fm
Open Source Software Used
8.2 Open Source Software Used
Open Source Software Component License
U-Boot GPLv2
Busybox GPLv2
binutils GPLv2
ethtool GPLv2
hotplug2 GPLv2
ipsec-tools X11-License, 3-clause BSD
libelf LGPLv2.1
libpcap BSD License
iptables GPLv2
Isof Isof License
mini_httpd BCD License 2 clause
libpcap BCD License
net-snmp BSD Licenses
openSSL OpenSSL License, SSLeay License
ntp Ntp, without GPLv2 parts
strace BCD License
tcpdump BCD License
mtd-utils GPLv2
gcc 4.* incl. libstdc++ GPLv2
zlib Zlib-license
openSSH BSD Licenses, MIT License
dropbear BSD Licenses
uClibc incl. libpthread LGPLv2.1
linux kernel 2.6.2x GPLv2
JSON-C X11

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 181
Nur für den internen Gebrauch Open Source Software used in the Product
Acknowledgements
8.3 Acknowledgements
OpenSSL:
●This product includes software developed by the OpenSSL Project for use in the
OpenSSL Toolkit. (http://www.openssl.org/)"
●This product includes cryptographic software written by Eric Young
(eay@cryptsoft.com)
Zlib:
●This product includes software developed by Jean-loup Gailly and Mark Adler
Libpcap:
●This product includes software developed by the University of California, Lawrence
Berkeley Laboratory and its contributors.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
182 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
8.4 Text of the used Open Source Software Licenses
8.4.1 GPL
GNU GENERAL PUBLIC LICENSE
Version 2, June 1991
Copyright (C) 1989, 1991 Free Software Foundation, Inc.
59 Temple Place, Suite 330, Boston, MA 02111-1307 USA
Everyone is permitted to copy and distribute verbatim copies
of this license document, but changing it is not allowed.
Preamble
The licenses for most software are designed to take away your freedom to share
and change it. By contrast, the GNU General Public License is intended to
guarantee your freedom to share and change free software--to make sure the
software is free for all its users. This General Public License applies to
most of the Free Software Foundation's software and to any other program whose
authors commit to using it. (Some other Free Software Foundation software
is covered by the GNU Library General Public License instead.) You can apply
it to your programs, too.
When we speak of free software, we are referring to freedom, not price.
Our General Public Licenses are designed to make sure that you have the free-
dom to distribute copies of free software (and charge for this service if you
wish), that you receive source code or can get it if you want it, that you
can change the software or use pieces of it in new free programs; and that
you know you can do these things.
To protect your rights, we need to make restrictions that forbid anyone to
deny you these rights or to ask you to surrender the rights. These restric-
tions translate to certain responsibilities for you if you distribute copies
of the software, or if you modify it.
For example, if you distribute copies of such a program, whether gratis or
for a fee, you must give the recipients all the rights that you have. You
must make sure that they, too, receive or can get the source code. And you
must show them these terms so they know their rights.
We protect your rights with two steps: (1) copyright the software, and (2)
offer you this license which gives you legal permission to copy, distribute
and/or modify the software.

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 183
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
Also, for each author's protection and ours, we want to make certain that
everyone understands that there is no warranty for this free software. If
the software is modified by someone else and passed on, we want its recipients
to know that what they have is not the original, so that any problems intro-
duced by others will not reflect on the original authors' reputations.
Finally, any free program is threatened constantly by software patents. We
wish to avoid the danger that redistributors of a free program will individ-
ually obtain patent licenses, in effect making the program proprietary. To
prevent this, we have made it clear that any patent must be licensed for
everyone's free use or not licensed at all.
The precise terms and conditions for copying, distribution and modification
follow.
GNU GENERAL PUBLIC LICENSE
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
0. This License applies to any program or other work which contains a notice
placed by the copyright holder saying it may be distributed under the terms
of this General Public License. The "Program", below, refers to any such
program or work, and a "work based on the Program" means either the Program
or any derivative work under copyright law: that is to say, a work containing
the Program or a portion of it, either verbatim or with modifications and/or
translated into another language. (Hereinafter, translation is included
without limitation in the term "modification".) Each licensee is addressed
as "you".
Activities other than copying, distribution and modification are not covered
by this License; they are outside its scope. The act of running the Program
is not restricted, and the output from the Program is covered only if its
contents constitute a work based on the Program (independent of having been
made by running the Program).
Whether that is true depends on what the Program does.
1. You may copy and distribute verbatim copies of the Program's source code
as you receive it, in any medium, provided that you conspicuously and appro-
priately publish on each copy an appropriate copyright notice and disclaimer
of warranty; keep intact all the notices that refer to this License and to
the absence of any warranty; and give any other recipients of the Program a
copy of this License along with the Program.
You may charge a fee for the physical act of transferring a copy, and you may
at your option offer warranty protection in exchange for a fee.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
184 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
2. You may modify your copy or copies of the Program or any portion of it,
thus forming a work based on the Program, and copy and distribute such mod-
ifications or work under the terms of Section 1 above, provided that you also
meet all of these conditions:
a) You must cause the modified files to carry prominent notices stating
that you changed the files and the date of any change.
b) You must cause any work that you distribute or publish, that in whole
or in part contains or is derived from the Program or any part thereof, to
be licensed as a whole at no charge to all third parties under the terms of
this License.
c) If the modified program normally reads commands interactively when
run, you must cause it, when started running for such interactive use in the
most ordinary way, to print or display an announcement including an appro-
priate copyright notice and a notice that there is no warranty (or else, say-
ing that you provide a warranty) and that users may redistribute the program
under these conditions, and telling the user how to view a copy of this Li-
cense. (Exception: if the Program itself is interactive but does not normally
print such an announcement, your work based on the Program is not required
to print an announcement.)
These requirements apply to the modified work as a whole. If identifiable
sections of that work are not derived from the Program, and can be reasonably
considered independent and separate works in themselves, then this License,
and its terms, do not apply to those sections when you distribute them as
separate works. But when you distribute the same sections as part of a whole
which is a work based on the Program, the distribution of the whole must be
on the terms of this License, whose permissions for other licensees extend
to the entire whole, and thus to each and every part regardless of who wrote
it.
Thus, it is not the intent of this section to claim rights or contest your
rights to work written entirely by you; rather, the intent is to exercise the
right to control the distribution of derivative or collective works based on
the Program.
In addition, mere aggregation of another work not based on the Program with
the Program (or with a work based on the Program) on a volume of a storage
or distribution medium does not bring the other work under the scope of this
License.
3. You may copy and distribute the Program (or a work based on it, under
Section 2) in object code or executable form under the terms of Sections 1
and 2 above provided that you also do one of the following:
a) Accompany it with the complete corresponding machine-readable source
code, which must be distributed under the terms of Sections 1 and 2 above on
a medium customarily used for software interchange; or,

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 185
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
b) Accompany it with a written offer, valid for at least three years, to
give any third party, for a charge no more than your cost of physically per-
forming source distribution, a complete machine-readable copy of the corre-
sponding source code, to be distributed under the terms of Sections 1 and 2
above on a medium customarily used for software interchange; or,
c) Accompany it with the information you received as to the offer to
distribute corresponding source code. (This alternative is allowed only for
noncommercial distribution and only if you received the program in object
code or executable form with such an offer, in accord with Subsection b
above.)
The source code for a work means the preferred form of the work for making
modifications to it. For an executable work, complete source code means all
the source code for all modules it contains, plus any associated interface
definition files, plus the scripts used to control compilation and installa-
tion of the executable. However, as a special exception, the source code
distributed need not include anything that is normally distributed (in either
source or binary form) with the major components (compiler, kernel, and so
on) of the operating system on which the executable runs, unless that compo-
nent itself accompanies the executable.
If distribution of executable or object code is made by offering access to
copy from a designated place, then offering equivalent access to copy the
source code from the same place counts as distribution of the source code,
even though third parties are not compelled to copy the source along with the
object code.
4. You may not copy, modify, sublicense, or distribute the Program except
as expressly provided under this License. Any attempt otherwise to copy,
modify, sublicense or distribute the Program is void, and will automatically
terminate your rights under this License.
However, parties who have received copies, or rights, from you under this
License will not have their licenses terminated so long as such parties remain
in full compliance.
5. You are not required to accept this License, since you have not signed
it. However, nothing else grants you permission to modify or distribute the
Program or its derivative works. These actions are prohibited by law if you
do not accept this License. Therefore, by modifying or distributing the Pro-
gram (or any work based on the Program), you indicate your acceptance of this
License to do so, and all its terms and conditions for copying, distributing
or modifying the Program or works based on it.
6. Each time you redistribute the Program (or any work based on the Pro-
gram), the recipient automatically receives a license from the original li-
censor to copy, distribute or modify the Program subject to these terms and
conditions. You may not impose any further restrictions on the recipients'
exercise of the rights granted herein. You are not responsible for enforcing
compliance by third parties to this License.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
186 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
7. If, as a consequence of a court judgment or allegation of patent in-
fringement or for any other reason (not limited to patent issues), conditions
are imposed on you (whether by court order, agreement or otherwise) that con-
tradict the conditions of this License, they do not excuse you from the con-
ditions of this License. If you cannot distribute so as to satisfy simulta-
neously your obligations under this License and any other pertinent
obligations, then as a consequence you may not distribute the Program at all.
For example, if a patent license would not permit royalty-free redistribution
of the Program by all those who receive copies directly or indirectly through
you, then the only way you could satisfy both it and this License would be
to refrain entirely from distribution of the Program.
If any portion of this section is held invalid or unenforceable under any
particular circumstance, the balance of the section is intended to apply and
the section as a whole is intended to apply in other circumstances.
It is not the purpose of this section to induce you to infringe any patents
or other property right claims or to contest validity of any such claims;
this section has the sole purpose of protecting the integrity of the free
software distribution system, which is implemented by public license prac-
tices. Many people have made generous contributions to the wide range of
software distributed through that system in reliance on consistent applica-
tion of that system; it is up to the author/donor to decide if he or she is
willing to distribute software through any other system and a licensee cannot
impose that choice.
This section is intended to make thoroughly clear what is believed to be a
consequence of the rest of this License.
8. If the distribution and/or use of the Program is restricted in certain
countries either by patents or by copyrighted interfaces, the original copy-
right holder who places the Program under this License may add an explicit
geographical distribution limitation excluding those countries, so that dis-
tribution is permitted only in or among countries not thus excluded. In such
case, this License incorporates the limitation as if written in the body of
this License.
9. The Free Software Foundation may publish revised and/or new versions of
the General Public License from time to time. Such new versions will be
similar in spirit to the present version, but may differ in detail to address
new problems or concerns.
Each version is given a distinguishing version number. If the Program spec-
ifies a version number of this License which applies to it and "any later
version", you have the option of following the terms and conditions either
of that version or of any later version published by the Free Software Foun-
dation. If the Program does not specify a version number of this License,
you may choose any version ever published by the Free Software Foundation.

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 187
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
10. If you wish to incorporate parts of the Program into other free programs
whose distribution conditions are different, write to the author to ask for
permission. For software which is copyrighted by the Free Software Founda-
tion, write to the Free Software Foundation; we sometimes make exceptions for
this. Our decision will be guided by the two goals of preserving the free
status of all derivatives of our free software and of promoting the sharing
and reuse of software generally.
NO WARRANTY
11. BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY
FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTH-
ERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE
THE PROGRAM "AS IS" WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND
FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND
PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE,
YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
12. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR REDIS-
TRIBUTE THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUD-
ING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF
THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS
OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN
IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH
DAMAGES.
END OF TERMS AND CONDITIONS
How to Apply These Terms to Your New Programs
If you develop a new program, and you want it to be of the greatest possible
use to the public, the best way to achieve this is to make it free software
which everyone can redistribute and change under these terms.
To do so, attach the following notices to the program. It is safest to
attach them to the start of each source file to most effectively convey the
exclusion of warranty; and each file should have at least the "copyright"
line and a pointer to where the full notice is found.
<one line to give the program's name and a brief idea of what it
does.> Copyright (C) <year> <name of author>
This program is free software; you can redistribute it and/or modify
it under the terms of the GNU General Public License as published by
the Free Software Foundation; either version 2 of the License, or
(at your option) any later version.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
188 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
This program is distributed in the hope that it will be useful,
but WITHOUT ANY WARRANTY; without even the implied warranty of
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
GNU General Public License for more details.
You should have received a copy of the GNU General Public License
along with this program; if not, write to the Free Software
Foundation, Inc., 59 Temple Place, Suite 330, Boston,
MA 02111-1307 USA
Also add information on how to contact you by electronic and paper mail.
If the program is interactive, make it output a short notice like this when
it starts in an interactive mode:
Gnomovision version 69, Copyright (C) year name of author’
Gnomovision comes with ABSOLUTELY NO WARRANTY; for details type
`show w'.
This is free software, and you are welcome to redistribute it
under certain conditions; type `show c' for details.
The hypothetical commands `show w' and `show c' should show the appropriate
parts of the General Public License. Of course, the commands you use may be
called something other than `show w' and `show c'; they could even be mouse-
clicks or menu items--whatever suits your program.
You should also get your employer (if you work as a programmer) or your
school, if any, to sign a "copyright disclaimer" for the program, if neces-
sary. Here is a sample; alter the names:
Yoyodyne, Inc., hereby disclaims all copyright interest in the
program `Gnomovision' (which makes passes at compilers) written by
James Hacker.
<signature of Ty Coon>, 1 April 1989
Ty Coon, President of Vice
This General Public License does not permit incorporating your program into
proprietary programs. If your program is a subroutine library, you may con-
sider it more useful to permit linking proprietary applications with the li-
brary. If this is what you want to do, use the GNU Library General
Public License instead of this License.

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 189
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
8.4.2 LGPL
GNU LESSER GENERAL PUBLIC LICENSE
Version 2.1, February 1999
Copyright (C) 1991, 1999 Free Software Foundation, Inc.
59 Temple Place, Suite 330, Boston, MA 02111-1307 USA
Everyone is permitted to copy and distribute verbatim copies
of this license document, but changing it is not allowed.
[This is the first released version of the Lesser GPL. It also counts as the
successor of the GNU Library Public License, version 2, hence the version
number 2.1.]
Preamble
The licenses for most software are designed to take away your freedom to
share and change it. By contrast, the GNU General Public Licenses are in-
tended to guarantee your freedom to share and change free software--to make
sure the software is free for all its users.
This license, the Lesser General Public License, applies to some specially
designated software packages--typically libraries--of the Free Software
Foundation and other authors who decide to use it. You can use it too, but
we suggest you first think carefully about whether this license or the ordi-
nary General Public License is the better strategy to use in any particular
case, based on the explanations below.
When we speak of free software, we are referring to freedom of use, not
price. Our General Public Licenses are designed to make sure that you have
the freedom to distribute copies of free software (and charge for this service
if you wish); that you receive source code or can get it if you want it; that
you can change the software and use pieces of it in new free programs; and
that you are informed that you can do these things.
To protect your rights, we need to make restrictions that forbid distrib-
utors to deny you these rights or to ask you to surrender these rights. These
restrictions translate to certain responsibilities for you if you distribute
copies of the library or if you modify it.
For example, if you distribute copies of the library, whether gratis or for
a fee, you must give the recipients all the rights that we gave you. You
must make sure that they, too, receive or can get the source code. If you
link other code with the library, you must provide complete object files to
the recipients, so that they can relink them with the library after making
changes to the library and recompiling it. And you must show them these terms
so they know their rights.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
190 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
We protect your rights with a two-step method: (1) we copyright the library,
and (2) we offer you this license, which gives you legal permission to copy,
distribute and/or modify the library.
To protect each distributor, we want to make it very clear that there is
no warranty for the free library. Also, if the library is modified by someone
else and passed on, the recipients should know that what they have is not the
original version, so that the original author's reputation will not be af-
fected by problems that might be introduced by others.
Finally, software patents pose a constant threat to the existence of any
free program. We wish to make sure that a company cannot effectively restrict
the users of a free program by obtaining a restrictive license from a patent
holder. Therefore, we insist that any patent license obtained for a version
of the library must be consistent with the full freedom of use specified in
this license.
Most GNU software, including some libraries, is covered by the ordinary GNU
General Public License. This license, the GNU Lesser General Public License,
applies to certain designated libraries, and is quite different from the or-
dinary General Public License. We use this license for certain libraries in
order to permit linking those libraries into non-free programs.
When a program is linked with a library, whether statically or using a
shared library, the combination of the two is legally speaking a combined
work, a derivative of the original library. The ordinary General Public Li-
cense therefore permits such linking only if the entire combination fits its
criteria of freedom. The Lesser General Public License permits more lax cri-
teria for linking other code with the library.
We call this license the "Lesser" General Public License because it does
Less to protect the user's freedom than the ordinary General Public License.
It also provides other free software developers Less of an advantage over
competing non-free programs. These disadvantages are the reason we use the
ordinary General Public License for many libraries. However, the Lesser li-
cense provides advantages in certain special circumstances.
For example, on rare occasions, there may be a special need to encourage
the widest possible use of a certain library, so that it becomes a de-facto
standard. To achieve this, non-free programs must be allowed to use the li-
brary. A more frequent case is that a free library does the same job as
widely used non-free libraries. In this case, there is little to gain by
limiting the free library to free software only, so we use the Lesser General
Public License.

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 191
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
In other cases, permission to use a particular library in non-free programs
enables a greater number of people to use a large body of free software. For
example, permission to use the GNU C Library in non-free programs enables
many more people to use the whole GNU operating system, as well as its vari-
ant, the GNU/Linux operating system.
Although the Lesser General Public License is Less protective of the users'
freedom, it does ensure that the user of a program that is linked with the
Library has the freedom and the wherewithal to run that program using a mod-
ified version of the Library.
The precise terms and conditions for copying, distribution and modification
follow. Pay close attention to the difference between a "work based on the
library" and a "work that uses the library". The former contains code derived
from the library, whereas the latter must be combined with the library in
order to run.
GNU LESSER GENERAL PUBLIC LICENSE
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
0. This License Agreement applies to any software library or other program
which contains a notice placed by the copyright holder or other authorized
party saying it may be distributed under the terms of this Lesser General
Public License (also called "this License"). Each licensee is addressed as
"you".
A "library" means a collection of software functions and/or data prepared
so as to be conveniently linked with application programs (which use some of
those functions and data) to form executables.
The "Library", below, refers to any such software library or work which has
been distributed under these terms. A "work based on the Library" means ei-
ther the Library or any derivative work under copyright law: that is to say,
a work containing the Library or a portion of it, either verbatim or with
modifications and/or translated straightforwardly into another language.
(Hereinafter, translation is included without limitation in the term "modi-
fication".)
"Source code" for a work means the preferred form of the work for making
modifications to it. For a library, complete source code means all the source
code for all modules it contains, plus any associated interface definition
files, plus the scripts used to control compilation and installation of the
library.
Activities other than copying, distribution and modification are not cov-
ered by this License; they are outside its scope. The act of running a pro-
gram using the Library is not restricted, and output from such a program is
covered only if its contents constitute a work based on the Library (inde-
pendent of the use of the Library in a tool for writing it). Whether that
is true depends on what the Library does and what the program that uses the
Library does.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
192 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
1. You may copy and distribute verbatim copies of the Library's complete
source code as you receive it, in any medium, provided that you conspicuously
and appropriately publish on each copy an appropriate copyright notice and
disclaimer of warranty; keep intact all the notices that refer to this License
and to the absence of any warranty; and distribute a copy of this License
along with the Library.
You may charge a fee for the physical act of transferring a copy, and you
may at your option offer warranty protection in exchange for a fee.
2. You may modify your copy or copies of the Library or any portion of it,
thus forming a work based on the Library, and copy and distribute such mod-
ifications or work under the terms of Section 1 above, provided that you also
meet all of these conditions:
a) The modified work must itself be a software library.
b) You must cause the files modified to carry prominent notices stating
that you changed the files and the date of any change.
c) You must cause the whole of the work to be licensed at no charge to
all third parties under the terms of this License.
d) If a facility in the modified Library refers to a function or a table
of data to be supplied by an application program that uses the facil-
ity, other than as an argument passed when the facility is invoked,
then you must make a good faith effort to ensure that, in the event
an application does not supply such function or table, the facility
still operates, and performs whatever part of its purpose remains
meaningful.
(For example, a function in a library to compute square roots has a purpose
that is entirely well-defined independent of the application. Therefore,
Subsection 2d requires that any application-supplied function or table
used by this function must be optional: if the application does not supply
it, the square root function must still compute square roots.)
These requirements apply to the modified work as a whole. If identifiable
sections of that work are not derived from the Library, and can be reasonably
considered independent and separate works in themselves, then this License,
and its terms, do not apply to those sections when you distribute them as
separate works. But when you distribute the same sections as part of a whole
which is a work based on the Library, the distribution of the whole must be
on the terms of this License, whose permissions for other licensees extend
to the entire whole, and thus to each and every part regardless of who wrote
it.

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 193
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
Thus, it is not the intent of this section to claim rights or contest your
rights to work written entirely by you; rather, the intent is to exercise the
right to control the distribution of derivative or collective works based on
the Library.
In addition, mere aggregation of another work not based on the Library with
the Library (or with a work based on the Library) on a volume of a storage
or distribution medium does not bring the other work under the scope of this
License.
3. You may opt to apply the terms of the ordinary GNU General Public License
instead of this License to a given copy of the Library. To do this, you must
alter all the notices that refer to this License, so that they refer to the
ordinary GNU General Public License, version 2, instead of to this License.
(If a newer version than version 2 of the ordinary GNU General Public License
has appeared, then you can specify that version instead if you wish.) Do not
make any other change in these notices.
Once this change is made in a given copy, it is irreversible for that copy,
so the ordinary GNU General Public License applies to all subsequent copies
and derivative works made from that copy.
This option is useful when you wish to copy part of the code of the Library
into a program that is not a library.
4. You may copy and distribute the Library (or a portion or derivative of
it, under Section 2) in object code or executable form under the terms of
Sections 1 and 2 above provided that you accompany it with the complete cor-
responding machine-readable source code, which must be distributed under the
terms of Sections 1 and 2 above on a medium customarily used for software
interchange.
If distribution of object code is made by offering access to copy from a
designated place, then offering equivalent access to copy the source code
from the same place satisfies the requirement to distribute the source code,
even though third parties are not compelled to copy the source along with the
object code.
5. A program that contains no derivative of any portion of the Library, but
is designed to work with the Library by being compiled or linked with it, is
called a "work that uses the Library". Such a work, in isolation, is not a
derivative work of the Library, and therefore falls outside the scope of this
License.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
194 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
However, linking a "work that uses the Library" with the Library creates
an executable that is a derivative of the Library (because it contains por-
tions of the Library), rather than a "work that uses the library". The ex-
ecutable is therefore covered by this License. Section 6 states terms for
distribution of such executables.
When a "work that uses the Library" uses material from a header file that
is part of the Library, the object code for the work may be a derivative work
of the Library even though the source code is not. Whether this is true is
especially significant if the work can be linked without the Library, or if
the work is itself a library. The threshold for this to be true is not pre-
cisely defined by law.
If such an object file uses only numerical parameters, data structure lay-
outs and accessors, and small macros and small inline functions (ten lines
or less in length), then the use of the object file is unrestricted, regard-
less of whether it is legally a derivative work. (Executables containing
this object code plus portions of the Library will still fall under Section
6.)
Otherwise, if the work is a derivative of the Library, you may distribute
the object code for the work under the terms of Section 6. Any executables
containing that work also fall under Section 6, whether or not they are linked
directly with the Library itself.
6. As an exception to the Sections above, you may also combine or link a
"work that uses the Library" with the Library to produce a work containing
portions of the Library, and distribute that work under terms of your choice,
provided that the terms permit modification of the work for the customer's
own use and reverse engineering for debugging such modifications.
You must give prominent notice with each copy of the work that the Library
is used in it and that the Library and its use are covered by this License.
You must supply a copy of this License. If the work during execution displays
copyright notices, you must include the copyright notice for the Library
among them, as well as a reference directing the user to the copy of this
License. Also, you must do one of these things:
a) Accompany the work with the complete corresponding machine-readable
source code for the Library including whatever changes were used in the work
(which must be distributed under Sections 1 and 2 above); and, if the work
is an executable linked with the Library, with the complete machine-readable
"work that uses the Library", as object code and/or source code, so that the
user can modify the Library and then relink to produce a modified executable
containing the modified Library. (It is understood that the user who changes
the contents of definitions files in the Library will not necessarily be able
to recompile the application to use the modified definitions.)

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 195
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
b) Use a suitable shared library mechanism for linking with the Library.
A suitable mechanism is one that (1) uses at run time a copy of the library
already present on the user's computer system, rather than copying library
functions into the executable, and (2) will operate properly with a modified
version of the library, if the user installs one, as long as the modified
version is interface-compatible with the version that the work was made with.
c) Accompany the work with a written offer, valid for at least three
years, to give the same user the materials specified in Subsection 6a, above,
for a charge no more than the cost of performing this distribution.
d) If distribution of the work is made by offering access to copy from a
designated place, offer equivalent access to copy the above specified mate-
rials from the same place.
e) Verify that the user has already received a copy of these materials
or that you have already sent this user a copy.
For an executable, the required form of the "work that uses the Library"
must include any data and utility programs needed for reproducing the exe-
cutable from it. However, as a special exception, the materials to be dis-
tributed need not include anything that is normally distributed (in either
source or binary form) with the major components (compiler, kernel, and so
on) of the operating system on which the executable runs, unless that compo-
nent itself accompanies the executable.
It may happen that this requirement contradicts the license restrictions
of other proprietary libraries that do not normally accompany the operating
system. Such a contradiction means you cannot use both them and the Library
together in an executable that you distribute.
7. You may place library facilities that are a work based on the Library
side-by-side in a single library together with other library facilities not
covered by this License, and distribute such a combined library, provided
that the separate distribution of the work based on the Library and of the
other library facilities is otherwise permitted, and provided that you do
these two things:
a) Accompany the combined library with a copy of the same work based on
the Library, uncombined with any other library facilities. This must be dis-
tributed under the terms of the Sections above.
b) Give prominent notice with the combined library of the fact that part
of it is a work based on the Library, and explaining where to find the ac-
companying uncombined form of the same work.
8. You may not copy, modify, sublicense, link with, or distribute the Li-
brary except as expressly provided under this License. Any attempt otherwise
to copy, modify, sublicense, link with, or distribute the Library is void,

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
196 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
and will automatically terminate your rights under this License. However,
parties who have received copies, or rights, from you under this License will
not have their licenses terminated so long as such parties remain in full
compliance.
9. You are not required to accept this License, since you have not signed
it. However, nothing else grants you permission to modify or distribute the
Library or its derivative works. These actions are prohibited by law if you
do not accept this License. Therefore, by modifying or distributing the Li-
brary (or any work based on the Library), you indicate your acceptance of
this License to do so, and all its terms and conditions for copying, distrib-
uting or modifying the Library or works based on it.
10. Each time you redistribute the Library (or any work based on the Li-
brary), the recipient automatically receives a license from the original li-
censor to copy, distribute, link with or modify the Library subject to these
terms and conditions. You may not impose any further restrictions on the
recipients' exercise of the rights granted herein. You are not responsible
for enforcing compliance by third parties with this License.
11. If, as a consequence of a court judgment or allegation of patent in-
fringement or for any other reason (not limited to patent issues), conditions
are imposed on you (whether by court order, agreement or otherwise) that con-
tradict the conditions of this License, they do not excuse you from the con-
ditions of this License. If you cannot distribute so as to satisfy simulta-
neously your obligations under this License and any other pertinent
obligations, then as a consequence you may not distribute the Library at all.
For example, if a patent license would not permit royalty-free redistribution
of the Library by all those who receive copies directly or indirectly through
you, then the only way you could satisfy both it and this License would be
to refrain entirely from distribution of the Library.
If any portion of this section is held invalid or unenforceable under any
particular circumstance, the balance of the section is intended to apply, and
the section as a whole is intended to apply in other circumstances.
It is not the purpose of this section to induce you to infringe any patents
or other property right claims or to contest validity of any such claims;
this section has the sole purpose of protecting the integrity of the free
software distribution system which is implemented by public license practic-
es. Many people have made generous contributions to the wide range of soft-
ware distributed through that system in reliance on consistent application
of that system; it is up to the author/donor to decide if he or she is willing
to distribute software through any other system and a licensee cannot impose
that choice.

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 197
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
This section is intended to make thoroughly clear what is believed to be a
consequence of the rest of this License.
12. If the distribution and/or use of the Library is restricted in certain
countries either by patents or by copyrighted interfaces, the original copy-
right holder who places the Library under this License may add an explicit
geographical distribution limitation excluding those countries, so that dis-
tribution is permitted only in or among countries not thus excluded. In such
case, this License incorporates the limitation as if written in the body of
this License.
13. The Free Software Foundation may publish revised and/or new versions
of the Lesser General Public License from time to time. Such new versions
will be similar in spirit to the present version, but may differ in detail
to address new problems or concerns.
Each version is given a distinguishing version number. If the Library spec-
ifies a version number of this License which applies to it and "any later
version", you have the option of following the terms and conditions either
of that version or of any later version published by the Free Software Foun-
dation. If the Library does not specify a license version number, you may
choose any version ever published by the Free Software Foundation.
14. If you wish to incorporate parts of the Library into other free programs
whose distribution conditions are incompatible with these, write to the au-
thor to ask for permission. For software which is copyrighted by the Free
Software Foundation, write to the Free Software Foundation; we sometimes make
exceptions for this. Our decision will be guided by the two goals of pre-
serving the free status of all derivatives of our free software and of pro-
moting the sharing and reuse of software generally.
NO WARRANTY
15. BECAUSE THE LIBRARY IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY
FOR THE LIBRARY, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTH-
ERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE
THE LIBRARY "AS IS" WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND
FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND
PERFORMANCE OF THE LIBRARY IS WITH YOU. SHOULD THE LIBRARY PROVE DEFECTIVE,
YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
16. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR REDIS-
TRIBUTE THE LIBRARY AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUD-

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
198 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
ING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF
THE USE OR INABILITY TO USE THE LIBRARY (INCLUDING BUT NOT LIMITED TO LOSS
OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
PARTIES OR A FAILURE OF THE LIBRARY TO OPERATE WITH ANY OTHER SOFTWARE), EVEN
IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH
DAMAGES.
END OF TERMS AND CONDITIONS
How to Apply These Terms to Your New Libraries
If you develop a new library, and you want it to be of the greatest possible
use to the public, we recommend making it free software that everyone can
redistribute and change. You can do so by permitting redistribution under
these terms (or, alternatively, under the terms of the ordinary General Pub-
lic License).
To apply these terms, attach the following notices to the library. It is
safest to attach them to the start of each source file to most effectively
convey the exclusion of warranty; and each file should have at least the
"copyright" line and a pointer to where the full notice is found.
<one line to give the library's name and a brief idea of what it does.>
Copyright (C) <year> <name of author>
This library is free software; you can redistribute it and/or modify it
under the terms of the GNU Lesser General Public License as published by the
Free Software Foundation; either version 2.1 of the License, or (at your op-
tion) any later version.
This library is distributed in the hope that it will be useful, but WITHOUT
ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS
FOR A PARTICULAR PURPOSE. See the GNU Lesser General Public License for more
details.
You should have received a copy of the GNU Lesser General Public License
along with this library; if not, write to the Free Software Foundation, Inc.,
59 Temple Place, Suite 330, Boston, MA 02111-1307 USA
Also add information on how to contact you by electronic and paper mail.
You should also get your employer (if you work as a programmer) or your
school, if any, to sign a "copyright disclaimer" for the library, if neces-
sary. Here is a sample; alter the names:
Yoyodyne, Inc., hereby disclaims all copyright interest in the library
`Frob' (a library for tweaking knobs) written by James Random Hacker.
<signature of Ty Coon>, 1 April 1990
Ty Coon, President of Vice
That's all there is to it!

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 199
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
8.4.3 Libpcap
License: BSD
Redistribution and use in source and binary forms, with or without modifica-
tion, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice,
this list of conditions and the following disclaimer in the documenta-
tion and/or other materials provided with the distribution.
3. The names of the authors may not be used to endorse or promote products
derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED ``AS IS'' AND WITHOUT ANY EXPRESS OR IMPLIED WAR-
RANTIES, INCLUDING, WITHOUT LIMITATION, THE IMPLIED WARRANTIES OF MERCHANT-
ABILITY AND FITNESS FOR A PARTICULAR PURPOSE.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
200 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
8.4.4 OpenSSL
LICENSE ISSUES
================
The OpenSSL toolkit stays under a dual license, i.e. both the conditions
of the OpenSSL License and the original SSLeay license apply to the toolkit.
See below for the actual license texts. Actually both licenses are BSD-style
Open Source licenses. In case of any license issues related to OpenSSL please
contact openssl-core@openssl.org.
OpenSSL License
-----------------
/* ==================================================================
* Copyright (c) 1998-2005 The OpenSSL Project. All rights reserved.
*
* Redistribution and use in source and binary forms, with or without
* modification, are permitted provided that the following conditions
* are met:
*
* 1. Redistributions of source code must retain the above copyright
* notice, this list of conditions and the following disclaimer.
*
* 2. Redistributions in binary form must reproduce the above copyright
* notice, this list of conditions and the following disclaimer in
* the documentation and/or other materials provided with the
* distribution.
*
* 3. All advertising materials mentioning features or use of this
* software must display the following acknowledgment:
* "This product includes software developed by the OpenSSL Project
* for use in the OpenSSL Toolkit. (http://www.openssl.org/)"
*
* 4. The names "OpenSSL Toolkit" and "OpenSSL Project" must not be used to
* endorse or promote products derived from this software without
* prior written permission. For written permission, please contact
* openssl-core@openssl.org.
*
* 5. Products derived from this software may not be called "OpenSSL"
* nor may "OpenSSL" appear in their names without prior written
* permission of the OpenSSL Project.
*
* 6. Redistributions of any form whatsoever must retain the following

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 201
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
* acknowledgment:
* "This product includes software developed by the OpenSSL Project
* for use in the OpenSSL Toolkit (http://www.openssl.org/)"
*
* THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT ``AS IS'' AND ANY
* EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
* IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
* PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL PROJECT OR
* ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL,
* SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT
* NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES;
* LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
* HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT,
* STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE)
* ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED
* OF THE POSSIBILITY OF SUCH DAMAGE.
* ====================================================================
*
* This product includes cryptographic software written by Eric Young
* (eay@cryptsoft.com). This product includes software written by Tim
* Hudson (tjh@cryptsoft.com).
*
Original SSLeay License
-----------------------
/* Copyright (C) 1995-1998 Eric Young (eay@cryptsoft.com)
* All rights reserved.
*
* This package is an SSL implementation written
* by Eric Young (eay@cryptsoft.com).
* The implementation was written so as to conform with Netscapes SSL.
*
* This library is free for commercial and non-commercial use as long as
* the following conditions are aheared to. The following conditions
* apply to all code found in this distribution, be it the RC4, RSA,
* lhash, DES, etc., code; not just the SSL code. The SSL documentation
* included with this distribution is covered by the same copyright terms
* except that the holder is Tim Hudson (tjh@cryptsoft.com).
*
* Copyright remains Eric Young's, and as such any Copyright notices in
* the code are not to be removed.
* If this package is used in a product, Eric Young should be given
* attribution as the author of the parts of the library used.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
202 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
* This can be in the form of a textual message at program startup or
* in documentation (online or textual) provided with the package.
*
* Redistribution and use in source and binary forms, with or without
* modification, are permitted provided that the following conditions
* are met:
* 1. Redistributions of source code must retain the copyright
* notice, this list of conditions and the following disclaimer.
* 2. Redistributions in binary form must reproduce the above copyright
* notice, this list of conditions and the following disclaimer in the
* documentation and/or other materials provided with the distribution.
* 3. All advertising materials mentioning features or use of this software
* must display the following acknowledgement:
* "This product includes cryptographic software written by
* Eric Young (eay@cryptsoft.com)"
* The word 'cryptographic' can be left out if the rouines from the library
* being used are not cryptographic related :-).
* 4. If you include any Windows specific code (or a derivative thereof) from
* the apps directory (application code) you must include an
* acknowledgement: "This product includes software written by Tim Hudson
* (tjh@cryptsoft.com)"
*
* THIS SOFTWARE IS PROVIDED BY ERIC YOUNG ``AS IS'' AND
* ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
* IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
* ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE
* FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
* DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS
* OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
* HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT
* LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY
* OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF
* SUCH DAMAGE.
*
* The licence and distribution terms for any publically available version or
* derivative of this code cannot be changed. i.e. this code cannot simply be
* copied and put under another distribution licence
* [including the GNU Public Licence.]
*/

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 203
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
8.4.5 Net-SNMP
Various copyrights apply to this package, listed in various separate parts
below. Please make sure that you read all the parts.
---- Part 1: CMU/UCD copyright notice: (BSD like) -----
Copyright 1989, 1991, 1992 by Carnegie Mellon University
Derivative Work - 1996, 1998-2000
Copyright 1996, 1998-2000 The Regents of the University of California
All Rights Reserved
Permission to use, copy, modify and distribute this software and its docu-
mentation for any purpose and without fee is hereby granted, provided that
the above copyright notice appears in all copies and that both that copyright
notice and this permission notice appear in supporting documentation, and
that the name of CMU and The Regents of the University of California not be
used in advertising or publicity pertaining to distribution of the software
without specific written permission.
CMU AND THE REGENTS OF THE UNIVERSITY OF CALIFORNIA DISCLAIM ALL WARRANTIES
WITH REGARD TO THIS SOFTWARE, INCLUDING ALL IMPLIED WARRANTIES OF MERCHANT-
ABILITY AND FITNESS. IN NO EVENT SHALL CMU OR THE REGENTS OF THE UNIVERSITY
OF CALIFORNIA BE LIABLE FOR ANY SPECIAL, INDIRECT OR CONSEQUENTIAL DAMAGES
OR ANY DAMAGES WHATSOEVER RESULTING FROM THE LOSS OF USE, DATA OR PROFITS,
WHETHER IN AN ACTION OF CONTRACT, NEGLIGENCE OR OTHER TORTIOUS ACTION, ARIS-
ING OUT OF OR IN CONNECTION WITH THE USE OR PERFORMANCE OF THIS SOFTWARE.
---- Part 2: Networks Associates Technology, Inc copyright notice (BSD) -----
Copyright (c) 2001-2003, Networks Associates Technology, Inc
All rights reserved.
Redistribution and use in source and binary forms, with or without modifica-
tion, are permitted provided that the following conditions are met:
* Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
* Redistributions in binary form must reproduce the above copyright notice,
this list of conditions and the following disclaimer in the documentation
and/or other materials provided with the distribution.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
204 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
* Neither the name of the Networks Associates Technology, Inc nor the names
of its contributors may be used to endorse or promote products derived
from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS ``AS IS''
AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE
LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSE-
QUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT
LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT
OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAM-
AGE.
---- Part 3: Cambridge Broadband Ltd. copyright notice (BSD) -----
Portions of this code are copyright (c) 2001-2003, Cambridge Broadband Ltd.
All rights reserved.
Redistribution and use in source and binary forms, with or without modifica-
tion, are permitted provided that the following conditions are met:
* Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
* Redistributions in binary form must reproduce the above copyright notice,
this list of conditions and the following disclaimer in the documentation
and/or other materials provided with the distribution.
* The name of Cambridge Broadband Ltd. may not be used to endorse or promote
products derived from this software without specific prior written per-
mission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDER ``AS IS'' AND ANY EXPRESS
OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES
OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN
NO EVENT SHALL THE COPYRIGHT HOLDER BE LIABLE FOR ANY DIRECT, INDIRECT, IN-
CIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT
LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA,
OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF
LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLI-
GENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN
IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 205
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
---- Part 4: Sun Microsystems, Inc. copyright notice (BSD) -----
Copyright © 2003 Sun Microsystems, Inc., 4150 Network Circle, Santa Clara,
California 95054, U.S.A. All rights reserved.
Use is subject to license terms below.
This distribution may include materials developed by third parties.
Sun, Sun Microsystems, the Sun logo and Solaris are trademarks or registered
trademarks of Sun Microsystems, Inc. in the U.S. and other countries.
Redistribution and use in source and binary forms, with or without modifica-
tion, are permitted provided that the following conditions are met:
* Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
* Redistributions in binary form must reproduce the above copyright notice,
this list of conditions and the following disclaimer in the documentation
and/or other materials provided with the distribution.
* Neither the name of the Sun Microsystems, Inc. nor the names of its con-
tributors may be used to endorse or promote products derived from this
software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS ``AS IS''
AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE
LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSE-
QUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT
LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT
OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAM-
AGE.
---- Part 5: Sparta, Inc copyright notice (BSD) -----
Copyright (c) 2003-2007, Sparta, Inc
All rights reserved.
Redistribution and use in source and binary forms, with or without modifica-
tion, are permitted provided that the following conditions are met:
* Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
206 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
* Redistributions in binary form must reproduce the above copyright notice,
this list of conditions and the following disclaimer in the documentation
and/or other materials provided with the distribution.
* Neither the name of Sparta, Inc nor the names of its contributors may be
used to endorse or promote products derived from this software without
specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS ``AS IS''
AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE
LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSE-
QUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT
LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT
OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAM-
AGE.
---- Part 6: Cisco/BUPTNIC copyright notice (BSD) -----
Copyright (c) 2004, Cisco, Inc and Information Network
Center of Beijing University of Posts and Telecommunications.
All rights reserved.
Redistribution and use in source and binary forms, with or without modifica-
tion, are permitted provided that the following conditions are met:
* Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
* Redistributions in binary form must reproduce the above copyright notice,
this list of conditions and the following disclaimer in the documentation
and/or other materials provided with the distribution.
* Neither the name of Cisco, Inc, Beijing University of Posts and Telecom-
munications, nor the names of their contributors may be used to endorse
or promote products derived from this software without specific prior
written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS ``AS IS''
AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE
LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSE-
QUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 207
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT
OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAM-
AGE.
---- Part 7: Fabasoft R&D Software GmbH & Co KG copyright notice (BSD) -----
Copyright (c) Fabasoft R&D Software GmbH & Co KG, 2003
oss@fabasoft.com
Author: Bernhard Penz <bernhard.penz@fabasoft.com>
Redistribution and use in source and binary forms, with or without modifica-
tion, are permitted provided that the following conditions are met:
* Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
* Redistributions in binary form must reproduce the above copyright notice,
this list of conditions and the following disclaimer in the documentation
and/or other materials provided with the distribution.
* The name of Fabasoft R&D Software GmbH & Co KG or any of its subsidiaries,
brand or product names may not be used to endorse or promote products de-
rived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDER ``AS IS'' AND ANY EXPRESS
OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES
OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN
NO EVENT SHALL THE COPYRIGHT HOLDER BE LIABLE FOR ANY DIRECT, INDIRECT, IN-
CIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT
LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA,
OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF
LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLI-
GENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN
IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
8.4.6 Zlib
ZLIB DATA COMPRESSION LIBRARY
zlib 1.2.3 is a general purpose data compression library. All the code is
thread safe. The data format used by the zlib library is described by RFCs
(Request for Comments) 1950 to 1952 in the files
http://www.ietf.org/rfc/rfc1950.txt (zlib format), rfc1951.txt (deflate for-
mat) and rfc1952.txt (gzip format). These documents are also available in
other formats from ftp://ftp.uu.net/graphics/png/documents/zlib/zdoc-in-
dex.html

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
208 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
All functions of the compression library are documented in the file zlib.h
(volunteer to write man pages welcome, contact zlib@gzip.org). A usage exam-
ple of the library is given in the file example.c which also tests that the
li-brary is working correctly. Another example is given in the file minigz-
ip.c. The compression library itself is composed of all source files except
exam-ple.c and minigzip.c.
To compile all files and run the test program, follow the instructions given
at the top of Makefile. In short "make test; make install" should work for
most machines. For Unix: "./configure; make test; make install". For MSDOS,
use one of the special makefiles such as Makefile.msc. For VMS, use
make_vms.com.
Questions about zlib should be sent to <zlib@gzip.org>, or to Gilles Vollant
<info@winimage.com> for the Windows DLL version. The zlib home page is http:/
/www.zlib.org or http://www.gzip.org/zlib/ Before reporting a problem,
please check this site to verify that you have the latest version of zlib;
otherwise get the latest version and check whether the problem still exists
or not.
PLEASE read the zlib FAQ http://www.gzip.org/zlib/zlib_faq.html before ask-
ing for help.
Mark Nelson <markn@ieee.org> wrote an article about zlib for the Jan. 1997
issue of Dr. Dobb's Journal; a copy of the article is available in http://
dogma.net/markn/articles/zlibtool/zlibtool.htm
The changes made in version 1.2.3 are documented in the file ChangeLog.
Unsupported third party contributions are provided in directory "contrib".
A Java implementation of zlib is available in the Java Development Kit http:/
/java.sun.com/j2se/1.4.2/docs/api/java/util/zip/package-summary.html
See the zlib home page http://www.zlib.org for details.
A Perl interface to zlib written by Paul Marquess <pmqs@cpan.org> is in the
CPAN (Comprehensive Perl Archive Network) sites http://www.cpan.org/modules/
by-module/Compress/
A Python interface to zlib written by A.M. Kuchling <amk@amk.ca> is available
in Python 1.5 and later versions, see http://www.python.org/doc/lib/module-
zlib.html

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 209
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
A zlib binding for TCL written by Andreas Kupries <a.kupries@westend.com> is
availlable at http://www.oche.de/~akupries/soft/trf/trf_zip.html
An experimental package to read and write files in .zip format, written on
top of zlib by Gilles Vollant <info@winimage.com>, is available in the con-
trib/minizip directory of zlib.
Notes for some targets:
- For Windows DLL versions, please see win32/DLL_FAQ.txt
- For 64-bit Irix, deflate.c must be compiled without any optimization. With
-O, one libpng test fails. The test works in 32 bit mode (with the -n32
compiler flag). The compiler bug has been reported to SGI.
- zlib doesn't work with gcc 2.6.3 on a DEC 3000/300LX under OSF/1 2.1 it
Works when compiled with cc.
- On Digital Unix 4.0D (formely OSF/1) on AlphaServer, the cc option -std1
is necessary to get gzprintf working correctly. This is done by configure.
- zlib doesn't work on HP-UX 9.05 with some versions of /bin/cc. It works
with other compilers. Use "make test" to check your compiler.
- gzdopen is not supported on RISCOS, BEOS and by some Mac compilers.
- For PalmOs, see http://palmzlib.sourceforge.net/
- When building a shared, i.e. dynamic library on Mac OS X, the library must
be installed before testing (do "make install" before "make test"), since
the library location is specified in the library.
Acknowledgments:
The deflate format used by zlib was defined by Phil Katz. The deflate and
zlib specifications were written by L. Peter Deutsch. Thanks to all the people
who reported problems and suggested various improvements in zlib; they are
too numerous to cite here.
Copyright notice:
(C) 1995-2004 Jean-loup Gailly and Mark Adler
This software is provided 'as-is', without any express or implied warranty.
In no event will the authors be held liable for any damages arising from the
use of this software.
Permission is granted to anyone to use this software for any purpose, in-
cluding commercial applications, and to alter it and redistribute it freely,
subject to the following restrictions:

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
210 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
1. The origin of this software must not be misrepresented; you must not
claim that you wrote the original software. If you use this software in
a product, an acknowledgment in the product documentation would be ap-
preciated but is not required.
2. Altered source versions must be plainly marked as such, and must not be
misrepresented as being the original software.
3. This notice may not be removed or altered from any source distribution.
Jean-loup Gailly Mark Adler
jloup@gzip.org madler@alumni.caltech.edu
If you use the zlib library in a product, we would appreciate *not* receiving
lengthy legal documents to sign. The sources are provided for free but without
warranty of any kind. The library has been entirely written by Jean-loup
Gailly and Mark Adler; it does not include third-party code.
If you redistribute modified sources, we would appreciate that you include
in the file ChangeLog history information documenting your changes. Please
read the FAQ for more information on the distribution of modified source ver-
sions.
8.4.7 Mini Httpd
Copyright © 1999, 2000 by Jef Poskanzer <jef@acme.com>. All rights reserved.
Redistribution and use in source and binary forms, with or without modifi-
cati-on, are permitted provided that the following conditions are met:
Redistributions of source code must retain the above copyright notice, this
list of conditions and the following disclaimer.
Redistributions in binary form must reproduce the above copyright notice,
this list of conditions and the following disclaimer in the documentation
and/or other materials provided with the distribution.
THIS SOFTWARE IS PROVIDED BY THE AUTHOR AND CONTRIBUTORS ``AS IS'' AND ANY
EX-PRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED
WAR-RANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DIS-
CLAI-MED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE FOR ANY DI-
RECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (IN-
CLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES;
LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND
ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT
(INCLUDING NEGLI-GENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF
THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 211
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
8.4.8 Ipsec Tools
The ipsec-tools uses the 3 clause BSD license and the follow X11-License
# This originates from X11R5 (mit/util/scripts/install.sh), which was
# later released in X11R6 (xc/config/util/install.sh) with the
# following copyright and license.
#
# Copyright (C) 1994 X Consortium
#
# Permission is hereby granted, free of charge, to any person obtaining a copy
# of this software and associated documentation files (the "Software"), to
# deal in the Software without restriction, including without limitation the
# rights to use, copy, modify, merge, publish, distribute, sublicense, and/or
# sell copies of the Software, and to permit persons to whom the Software is
# furnished to do so, subject to the following conditions:
#
# The above copyright notice and this permission notice shall be included in
# all copies or substantial portions of the Software.
#
# THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
# IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
# FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
# X CONSORTIUM BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN
# AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNEC-
# TION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
#
# Except as contained in this notice, the name of the X Consortium shall not
# be used in advertising or otherwise to promote the sale, use or other deal-
# ings in this Software without prior written authorization from the X Consor-
# tium.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
212 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
8.4.9 OpenSSH
This file is part of the OpenSSH software.
The licences which components of this software fall under are as follows.
First, we will summarize and say that all components are under a BSD licence,
or a licence more free than that.
OpenSSH contains no GPL code.
1)
* Copyright (c) 1995 Tatu Ylonen <ylo@cs.hut.fi>, Espoo, Finland
* All rights reserved
*
* As far as I am concerned, the code I have written for this software
* can be used freely for any purpose. Any derived versions of this
* software must be clearly marked as such, and if the derived work is
* incompatible with the protocol description in the RFC file, it must be
* called by a name other than "ssh" or "Secure Shell".
[Tatu continues]
* However, I am not implying to give any licenses to any patents or
* copyrights held by third parties, and the software includes parts that
* are not under my direct control. As far as I know, all included
* source code is used in accordance with the relevant license agreements
* and can be used freely for any purpose (the GNU license being the most
* restrictive); see below for details.
[However, none of that term is relevant at this point in time. All of
these restrictively licenced software components which he talks about
have been removed from OpenSSH, i.e.,
- RSA is no longer included, found in the OpenSSL library
- IDEA is no longer included, its use is deprecated
- DES is now external, in the OpenSSL library
- GMP is no longer used, and instead we call BN code from OpenSSL
- Zlib is now external, in a library
- The make-ssh-known-hosts script is no longer included
- TSS has been removed
- MD5 is now external, in the OpenSSL library
- RC4 support has been replaced with ARC4 support from OpenSSL
- Blowfish is now external, in the OpenSSL library

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 213
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
[The licence continues]
Note that any information and cryptographic algorithms used in this soft-
ware are publicly available on the Internet and at any major bookstore,
scientific library, and patent office worldwide. More information can
be found e.g. at "http://www.cs.hut.fi/crypto".
The legal status of this program is some combination of all these per-
missions and restrictions. Use only at your own responsibility. You will
be responsible for any legal consequences yourself; I am not making any
claims whether possessing or using this is legal or not in your country,
and I am not taking any responsibility on your behalf.
NO WARRANTY
BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY FOR
THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE
STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PRO-
GRAM "AS IS" WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, IN-
CLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND
FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND
PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE,
YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL
ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR REDISTRIBUTE
THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE
OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF DATA
OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES
OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN IF SUCH
HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
2)
The 32-bit CRC compensation attack detector in deattack.c was contributed
by CORE SDI S.A. under a BSD-style license.
* Cryptographic attack detector for ssh - source code
*
* Copyright (c) 1998 CORE SDI S.A., Buenos Aires, Argentina.
*
* All rights reserved. Redistribution and use in source and binary
* forms, with or without modification, are permitted provided that
* this copyright notice is retained.
*

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
214 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
* THIS SOFTWARE IS PROVIDED ``AS IS'' AND ANY EXPRESS OR IMPLIED
* WARRANTIES ARE DISCLAIMED. IN NO EVENT SHALL CORE SDI S.A. BE
* LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY OR
* CONSEQUENTIAL DAMAGES RESULTING FROM THE USE OR MISUSE OF THIS
* SOFTWARE.
*
* Ariel Futoransky <futo@core-sdi.com>
* <http://www.core-sdi.com>
3)
ssh-keyscan was contributed by David Mazieres under a BSD-style license.
* Copyright 1995, 1996 by David Mazieres <dm@lcs.mit.edu>.
*
* Modification and redistribution in source and binary forms is
* permitted provided that due credit is given to the author and the
* OpenBSD project by leaving this copyright notice intact.
4)
The Rijndael implementation by Vincent Rijmen, Antoon Bosselaers and Paulo
Barreto is in the public domain and distributed with the following li-
cense:
* @version 3.0 (December 2000)
*
* Optimised ANSI C code for the Rijndael cipher (now AES)
*
* @author Vincent Rijmen <vincent.rijmen@esat.kuleuven.ac.be>
* @author Antoon Bosselaers <antoon.bosselaers@esat.kuleuven.ac.be>
* @author Paulo Barreto <paulo.barreto@terra.com.br>
*
* This code is hereby placed in the public domain.
*
* THIS SOFTWARE IS PROVIDED BY THE AUTHORS ''AS IS'' AND ANY EXPRESS
* OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED
* WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
* ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHORS OR CONTRIBUTORS BE
* LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
* CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF
* SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 215
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
* BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY,
* WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE
* OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE,
* EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
5)
One component of the ssh source code is under a 3-clause BSD license,
held by the University of California, since we pulled these parts from
original Berkeley code.
* Copyright (c) 1983, 1990, 1992, 1993, 1995
* The Regents of the University of California. All rights reserved.
*
* Redistribution and use in source and binary forms, with or without
* modification, are permitted provided that the following conditions
* are met:
* 1. Redistributions of source code must retain the above copyright
* notice, this list of conditions and the following disclaimer.
* 2. Redistributions in binary form must reproduce the above copyright
* notice, this list of conditions and the following disclaimer in the
* documentation and/or other materials provided with the distribution.
* 3. Neither the name of the University nor the names of its contributors
* may be used to endorse or promote products derived from this software
* without specific prior written permission.
*
* THIS SOFTWARE IS PROVIDED BY THE REGENTS AND CONTRIBUTORS ``AS IS'' AND
* ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
* IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
* PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE REGENTS OR CONTRIBUTORS
* BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
* CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF
* SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
* INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
* CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE)
* ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF
* THE POSSIBILITY OF SUCH DAMAGE.
6)
Remaining components of the software are provided under a standard
2-term BSD licence with the following names as copyright holders:

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
216 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
Markus Friedl
Theo de Raadt
Niels Provos
Dug Song
Aaron Campbell
Damien Miller
Kevin Steves
Daniel Kouril
Wesley Griffin
Per Allansson
Nils Nordman
Simon Wilkinson
Portable OpenSSH additionally includes code from the following copyright
holders, also under the 2-term BSD license:
Ben Lindstrom
Tim Rice
Andre Lucas
Chris Adams
Corinna Vinschen
Cray Inc.
Denis Parker
Gert Doering
Jakob Schlyter
Jason Downs
Juha Yrjölä
Michael Stone
Networks Associates Technology, Inc.
Solar Designer
Todd C. Miller

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 217
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
Wayne Schroeder
William Jones
Darren Tucker
Sun Microsystems
The SCO Group
Daniel Walsh
* Redistribution and use in source and binary forms, with or without
* modification, are permitted provided that the following conditions
* are met:
* 1. Redistributions of source code must retain the above copyright
* notice, this list of conditions and the following disclaimer.
* 2. Redistributions in binary form must reproduce the above copyright
* notice, this list of conditions and the following disclaimer in the
* documentation and/or other materials provided with the distribution.
*
* THIS SOFTWARE IS PROVIDED BY THE AUTHOR ``AS IS'' AND ANY EXPRESS OR
* IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES
* OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
* IN NO EVENT SHALL THE AUTHOR BE LIABLE FOR ANY DIRECT, INDIRECT,
* INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT
* NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE,
* DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY
* THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT
* (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF
* THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
8) Portable OpenSSH contains the following additional licenses:
a) md5crypt.c, md5crypt.h
* "THE BEER-WARE LICENSE" (Revision 42):

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
218 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
* <phk@login.dknet.dk> wrote this file. As long as you retain this
* notice you can do whatever you want with this stuff. If we meet
* some day, and you think this stuff is worth it, you can buy me a
* beer in return. Poul-Henning Kamp
b) snprintf replacement
* Copyright Patrick Powell 1995
* This code is based on code written by Patrick Powell
* (papowell@astart.com) It may be used for any purpose as long as this
* notice remains intact on all source code distributions
c) Compatibility code (openbsd-compat)
Apart from the previously mentioned licenses, various pieces of code
in the openbsd-compat/ subdirectory are licensed as follows:
Some code is licensed under a 3-term BSD license, to the following
copyright holders:
Todd C. Miller
Theo de Raadt
Damien Miller
Eric P. Allman
The Regents of the University of California
Constantin S. Svintsoff
* Redistribution and use in source and binary forms, with or without
* modification, are permitted provided that the following conditions
* are met:
* 1. Redistributions of source code must retain the above copyright
* notice, this list of conditions and the following disclaimer.
* 2. Redistributions in binary form must reproduce the above copyright
* notice, this list of conditions and the following disclaimer in the
* documentation and/or other materials provided with the distribution.

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 219
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
* 3. Neither the name of the University nor the names of its contributors
* may be used to endorse or promote products derived from this software
* without specific prior written permission.
*
* THIS SOFTWARE IS PROVIDED BY THE REGENTS AND CONTRIBUTORS ``AS IS'' AND
* ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
* IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
* PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE REGENTS OR CONTRIBUTORS
* BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
* CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF
* SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
* INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
* CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE)
* ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF
* THE POSSIBILITY OF SUCH DAMAGE.
Some code is licensed under an ISC-style license, to the following
copyright holders:
Internet Software Consortium.
Todd C. Miller
Reyk Floeter
Chad Mynhier
* Permission to use, copy, modify, and distribute this software for any
* purpose with or without fee is hereby granted, provided that the above
* copyright notice and this permission notice appear in all copies.
*
* THE SOFTWARE IS PROVIDED "AS IS" AND TODD C. MILLER DISCLAIMS ALL
* WARRANTIES WITH REGARD TO THIS SOFTWARE INCLUDING ALL IMPLIED WARRANTIES
* OF MERCHANTABILITY AND FITNESS. IN NO EVENT SHALL TODD C. MILLER BE

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
220 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
* LIABLE FOR ANY SPECIAL, DIRECT, INDIRECT, OR CONSEQUENTIAL DAMAGES OR
* ANY DAMAGES WHATSOEVER RESULTING FROM LOSS OF USE, DATA OR PROFITS,
* WHETHER IN AN ACTION OF CONTRACT, NEGLIGENCE OR OTHER TORTIOUS ACTION,
* ARISING OUT OF OR IN CONNECTION WITH THE USE OR PERFORMANCE OF THIS
* SOFTWARE.
Some code is licensed under a MIT-style license to the following
copyright holders:
Free Software Foundation, Inc.
* Permission is hereby granted, free of charge, to any person obtaining a
* copy of this software and associated documentation files (the
* "Software"), to deal in the Software without restriction, including
* without limitation the rights to use, copy, modify, merge, publish,
* distribute, distribute with modifications, sublicense, and/or sell
* copies of the Software, and to permit persons to whom the Software is
* furnished to do so, subject to the following conditions:
*
* The above copyright notice and this permission notice shall be included
* in all copies or substantial portions of the Software.
*
* THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS
* OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF
* MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT.
* IN NO EVENT SHALL THE ABOVE COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM,
* DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR
* OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR
* THE USE OR OTHER DEALINGS IN THE SOFTWARE.
*
* Except as contained in this notice, the name(s) of the above copyright
* holders shall not be used in advertising or otherwise to promote the

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 221
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses
* sale, use or other dealings in this Software without prior written
* authorization.
------
$OpenBSD: LICENCE,v 1.19 2004/08/30 09:18:08 markus Exp $
8.4.10 JSON-C
X11 like License
Copyright (c) 2004, 2005 Metaparadigm Pte Ltd
Permission is hereby granted, free of charge, to any person obtaining a copy
of this software and associated documentation files (the "Software"), to deal
in the Software without restriction, including without limitation the rights
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
copies of the Software, and to permit persons to whom the Software is fur-
nished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in
all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER
LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM,
OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE
SOFTWARE.
8.4.11 lsof License
Warranty
========
Lsof is provided as-is without any warranty of any kind, either expressed or
implied, including, but not limited to, the implied warranties of merchant-
ability and fitness for a particular purpose. The entire risk as to the qual-
ity and performance of lsof is with you. Should lsof prove defective, you
assume the cost of all necessary servicing, repair, or correction.

Open Source Software used in the Product Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
222 HiPath Cordless IP, Service Manual
c08.fm
Text of the used Open Source Software Licenses
License
========
Lsof has no license. Its use and distribution are subject to these terms and
conditions, found in each lsof source file. (The copyright year in or format
of the notice may vary slightly.)
/*
* Copyright 2002 Purdue Research Foundation, West Lafayette,
* Indiana 47907. All rights reserved.
*
* Written by Victor A. Abell
*
* This software is not subject to any license of the American
* Telephone and Telegraph Company or the Regents of the
* University of California.
*
* Permission is granted to anyone to use this software for
* any purpose on any computer system, and to alter it and
* redistribute it freely, subject to the following
* restrictions:
*
* 1. Neither the authors nor Purdue University are responsible
* for any consequences of the use of this software.
*
* 2. The origin of this software must not be misrepresented,
* either by explicit claim or by omission. Credit to the
* authors and Purdue University must appear in documentation
* and sources.
*
* 3. Altered versions must be plainly marked as such, and must
* not be misrepresented as being the original software.
*
* 4. This notice may not be removed or altered.
*/

c08.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 223
Nur für den internen Gebrauch Open Source Software used in the Product
Text of the used Open Source Software Licenses

Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
224 HiPath Cordless IP, Service Manual
bkIX.fm

bkIX.fm
A31003-C1010-S100-2-7620, 08/2010
HiPath Cordless IP, Service Manual 225
Nur für den internen Gebrauch Index
Index Z
Symbole
"Status" Configuration 125
A
Administration 91
Akku-Zellen 157
Auto Entry users 111
B
Base station
authorized locations 47
installation/indoors 48
installation/outdoors 50
prohibited locations 46
range 30
special installation tools 50
C
Changing values 89
Checking field strength 163
Configuration 118
Configuration "System" 132
Configuration Dect 112
Configuration Hints 133
Configuration Page
"Dect - About" 116
"Dect - ARI" 115
"Dect - Call" 117
"Dect - Debug" 118
"Dect - Device" 112
"Dect - Radio" 117
"Dect - Sync" 113
"Status - Calls Dect" 128
"Status - Modules 1" 126
"Status - Modules 2" 127
"Status - RSSI" 130
"User - Dect" 109
"User - User" 107
"User - VoiP" 108
Configuration reference 84
Configure 68
BSIP1 for IWU mode 68
DECT network 73
Frame 91
further BSIP Only to the system 81
Gateway 98
Network 98
users at the BSIP IWU 75
users at the PBX 75
VoIP (Infrastructure) network 72
D
Data
base station 149
BSIP1 DECT standard EU 147
BSIP1US DECT standard USA 148
Data Protection and Data Security 15
Daten
Ladeschale Gigaset S3 professional 153
Ladeschale Gigaset SL3 professional 155
Ladeschale Gigaset M2 Ex professional 158
Ladeschale Gigaset M2/M2plus professional 157
Deactivating the PIN lock 177
Debug windows 90
Debugging Configuration 121
Documentation Feedback 16
F
Factory reset 66
Frame Program Info 94
G
Gateway configuration 98
General objects 88
Group Configuration 104
H
Hardware
connect 68
prepare 68
HiPath Cordless IP
checking components 173
HiPath cordless IP
tech. data on DECT IP base stations 24
HiPath OpenOffice EE 133
base configuration 133
station configuration 135
Station Configuration - BSIP IWU 137
Time server configuration 138
HiPath OpenOffice ME 138
base configuration 138
Base Configuration - BSIP IWU 140
Station Configuration 141
Station Configuration - IP-DECT IWU 143
Time server configuration 144
HiPath Cordless IP
outdoor case 26

Index Nur für den internen Gebrauch
A31003-C1010-S100-2-7620, 08/2010
226 HiPath Cordless IP, Service Manual
bkIX.fm
I
Item number overview 159
mobile telephones 159
M
Measuring equipment
manufacturer addresses 160
Measuring mode 166
N
Network configuration 100
O
Outdoor case 26
Overview of item code numbers
base stations 159
P
Password change 86
proper disposal and recycling 13
Q
Quick start
overview 67
R
Radio frequency site survey 84
Radio propagation 30, 31
Radio range
measuring radio quality/activating 165
propagation conditions 31
testing/base stations 161
testing/radio quality 164
Radio traffic propagation conditions
indoor areas 33, 34
industrial sites 32
outdoor area 32
Rechargeable batteries 154, 156
Register handsets 78
S
Safety Information and Warnings 10
Standards and Guidelines 14
Start system services 78
Startup
process 57
Synchronisation implementation 84
System number (HC) 58
System Update 95
T
Technical data on DECT IP base stations 24
Test
area coverage 163
base stations 162
base stations, radio propagation 161
correcting possible problems 173
result documentation 170
troubleshooting 174
Troubleshooting 144
U
Users Configuration 106
W
WBM Login 86
WBM modes 85
WBM overview 85