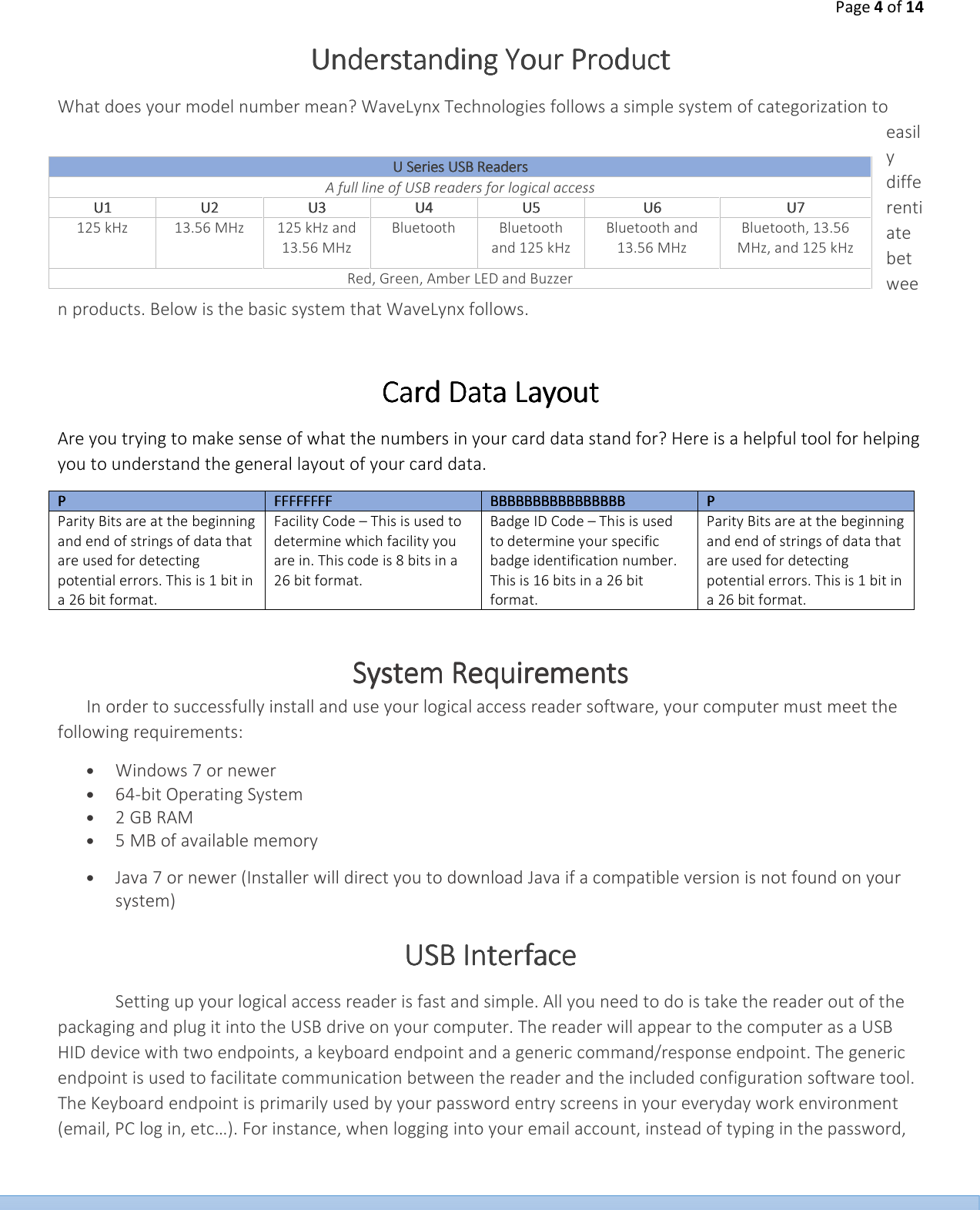
WaveLynx Technologies WLTC-DHMM-11U3 USB 125 kHz and 13.56 MHz RF Front end reader/writer. User Manual UserManual 04 13 2015 042815x
WaveLynx Technologies Corporation USB 125 kHz and 13.56 MHz RF Front end reader/writer. UserManual 04 13 2015 042815x
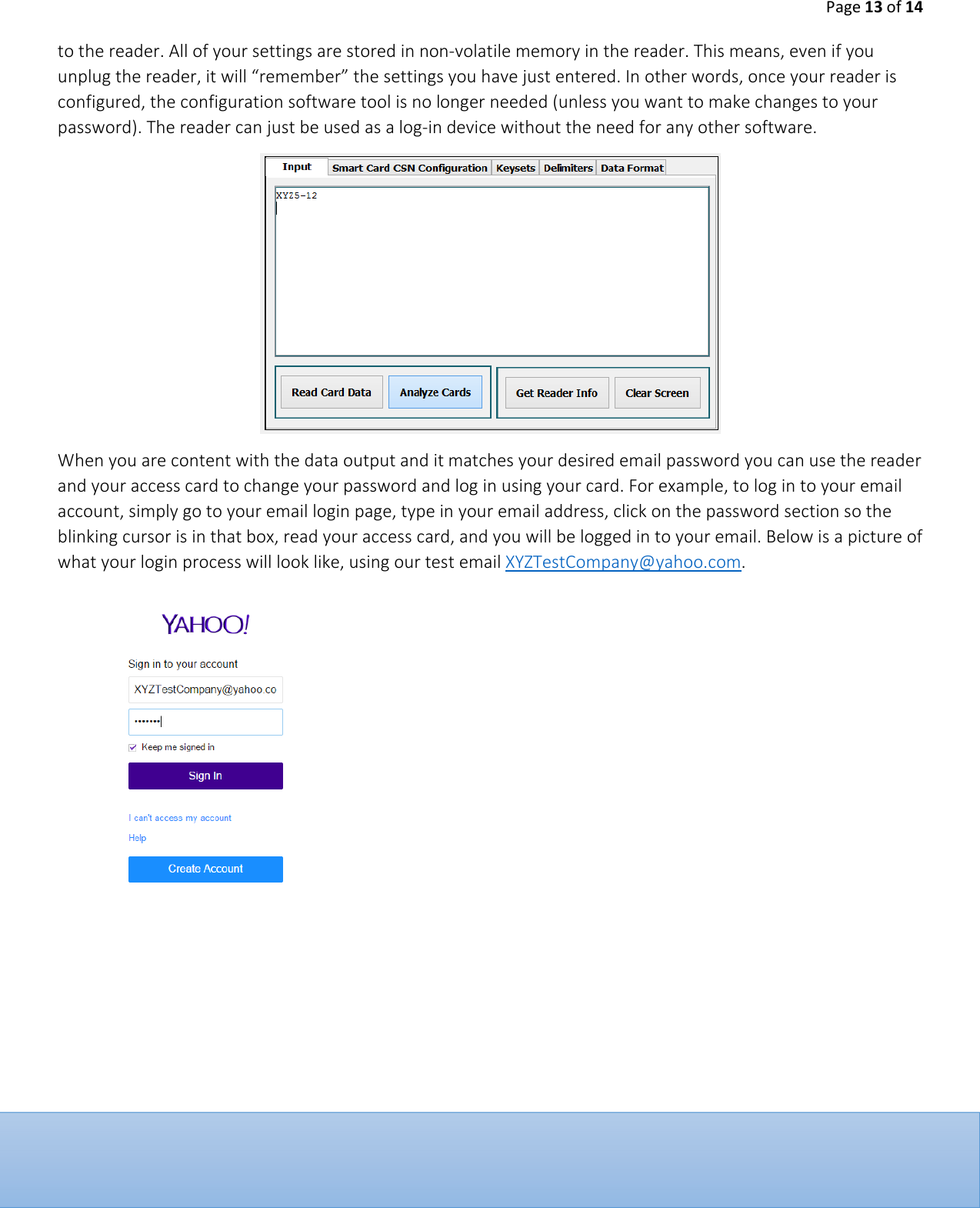
Users Manual