Billion Electric BIL-7820NZ Slots ADSL2+ Wireless-N VPN Firewall Router User Manual Users manual 2
Billion Electric Co., Ltd. Slots ADSL2+ Wireless-N VPN Firewall Router Users manual 2
Contents
- 1. Users manual-1
- 2. Users manual-2
- 3. Users manual-3
Users manual-2
96
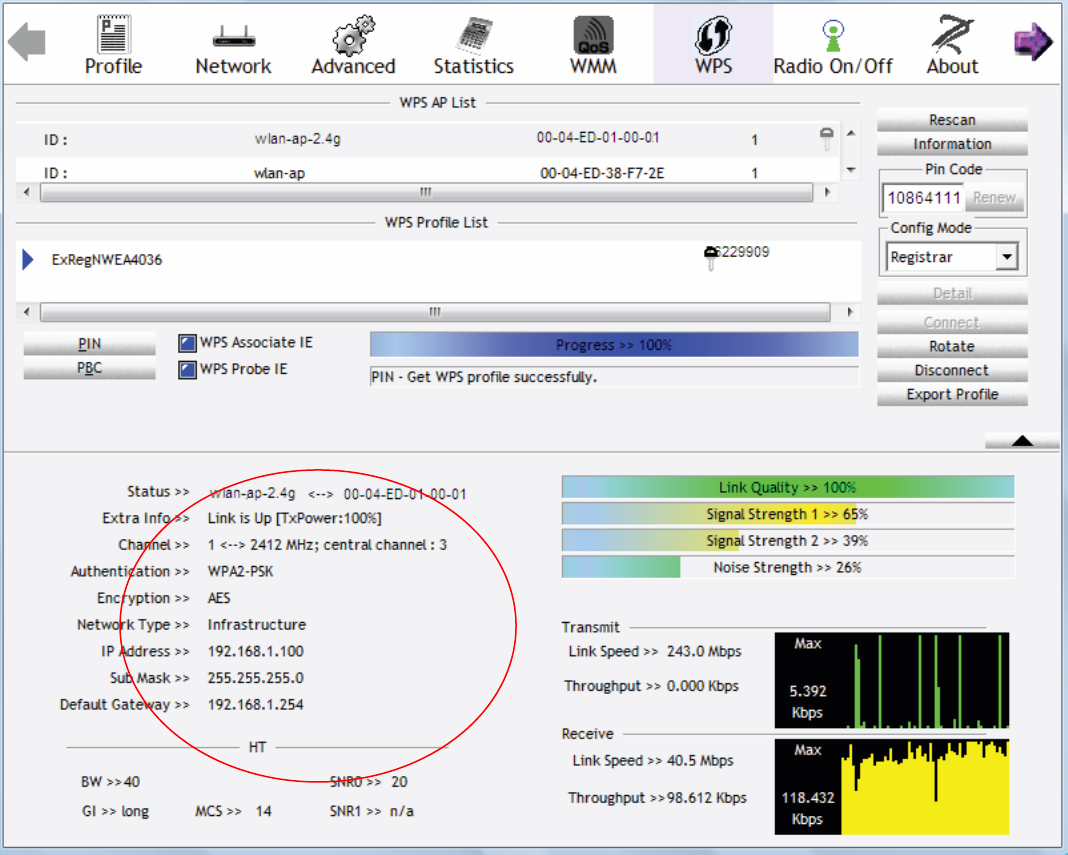
3. The router’s (AP’s) SSID and security setting will now be configured to match the SSID and
security setting of the registrar.
4. Do Web Page refresh after ER complete AP Configuration to check the new parameters setting.
97
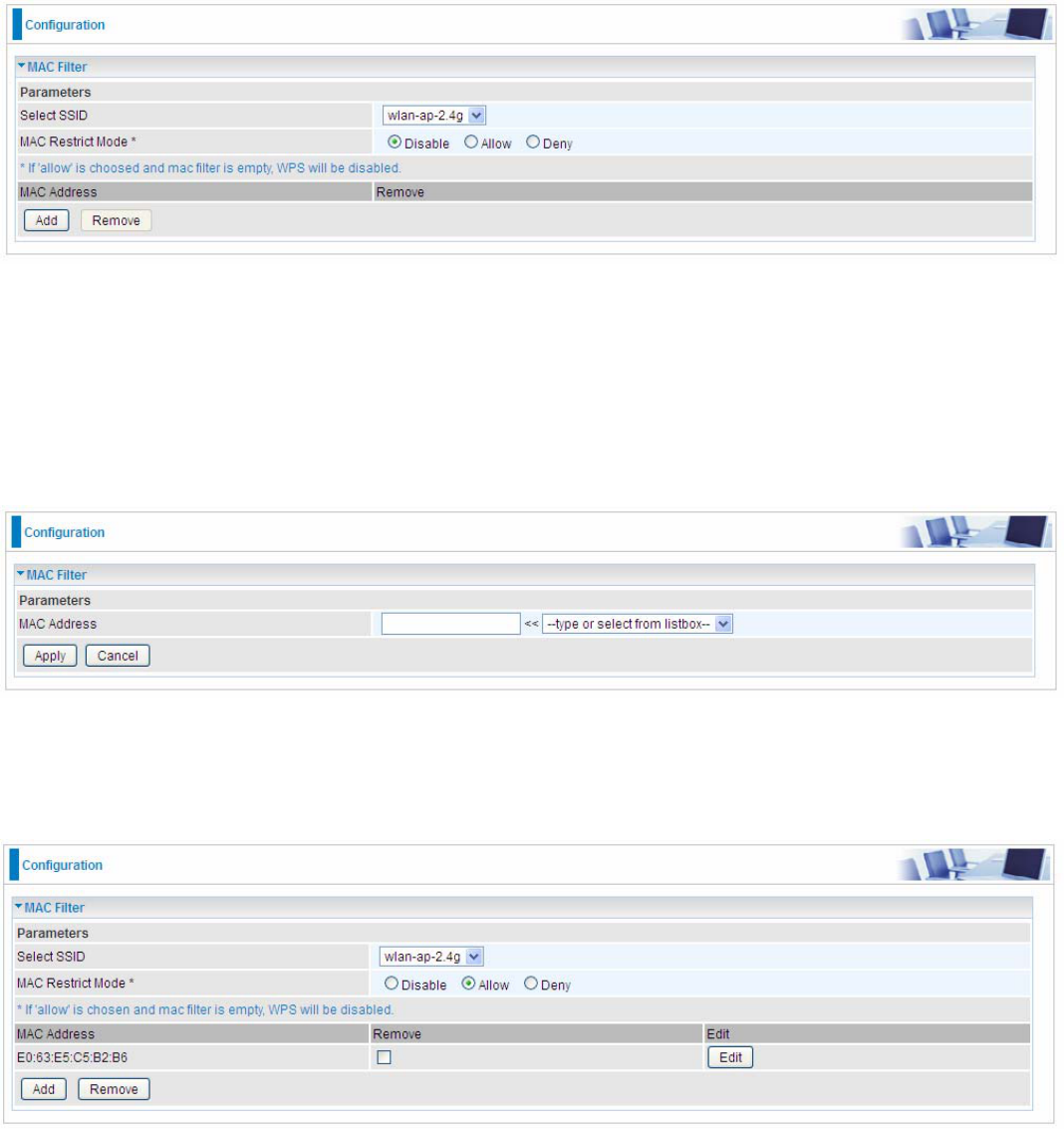
MAC Filter
Select SSID: Select the SSID you want this filter applies to.
MAC Restrict Mode:
Disable: disable the MAC Filter function.
Allow: allow the hosts with the following listed MACs to access the wireless network.
Deny: deny the hosts with the following listed MACs to access the wireless network.
Click Add to add the MACs.
MAC Address: Enter the MAC address(es) or select the MAC address(es). The format of MAC
address could be: xx:xx:xx:xx:xx:xx or xx-xx-xx-xx-xx-xx.
Click Apply to apply your settings and the item will be listed below.
98
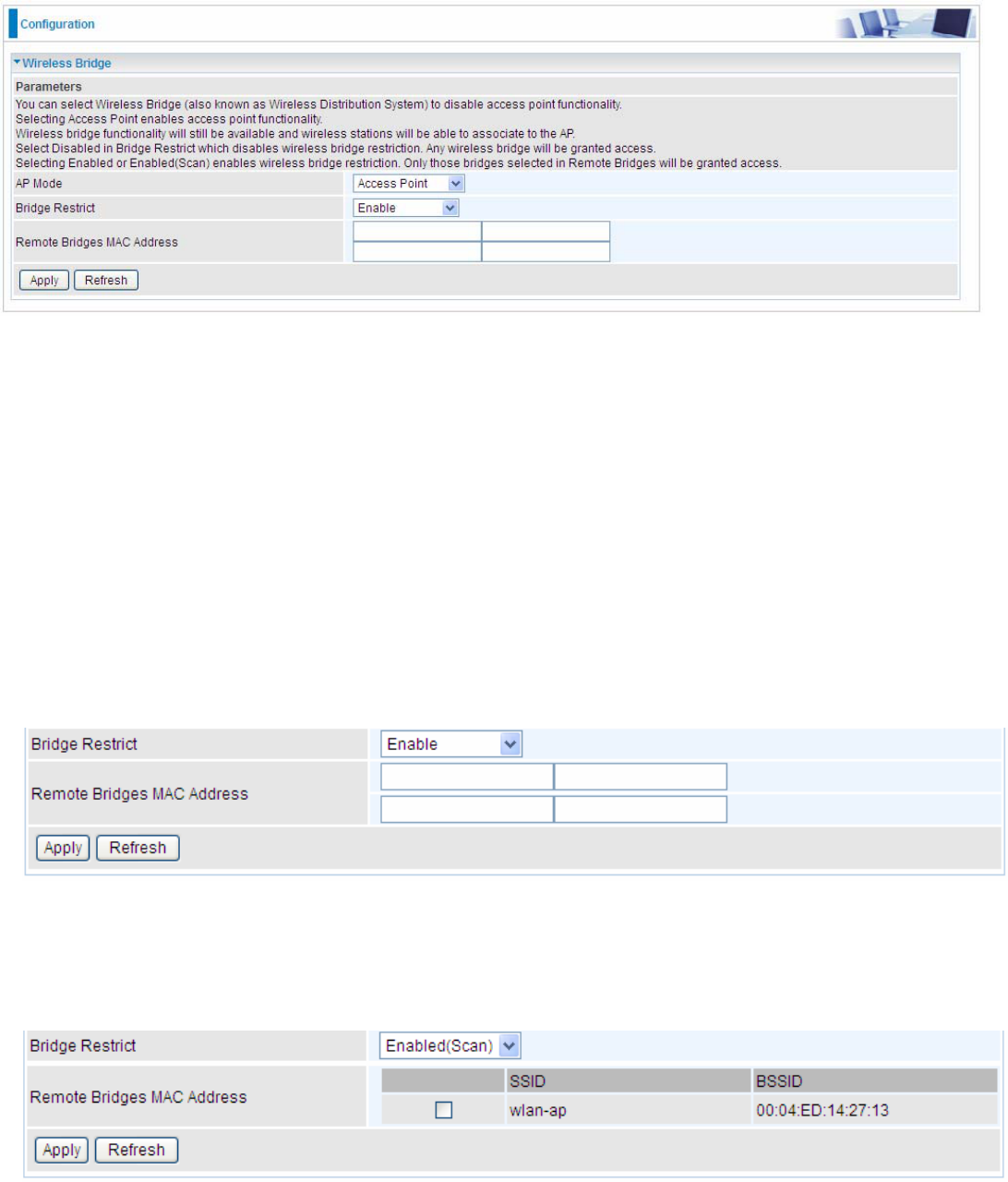
Wireless Bridge
WDS (wireless distributed system) is a wireless access point mode that enables wireless link and
communication with other access points. It’s easy to install, simply define the peer’s MAC address of
the connected AP. WDS takes advantage of cost saving and flexibility with no extra wireless client
device required to bridge between two access points and extending an existing wired or wireless
infrastructure network to create a larger network.
Here you can select what role the AP server has, AP or wireless bridge (WDS).
AP Mode: determines whether the gateway will act as an Access point or as a Bridge.
Access Point: the gateway communicates with both clients and bridges.
Wireless Bridge: the gateway communicates with other WDS devices only. In this mode, the
gateway doesn’t communicate with client devices.
If your wireless network includes repeaters that use WDS, the gateway in wireless bridge mode will
also communicate with your repeaters. The gateway in wireless bridge mode will not communicate
with a repeater that uses a proprietary (non-WDS) mode.
Bridge Restrict: When AP Mode is set to Wireless Bridge, this determines whether the gateway
will communicate with all other bridges or only specific ones:
Enable: to enable wireless bridge restriction. Only those specified in the Remote MAC
Address the gateway can communicate with.
Remote Bridge MAC Address: enter the remote bridge MAC addresses. Here up to 4 bridge
MAC addresses are supported.
Enabled (Scan): to enable wireless bridge restriction. Only those scanned by the gateway
can communicate.
99
Remote Bridge MAC Address: select the remote bridge MAC addresses.
Disable: Does not restrict the gateway communicating with bridges that have their MAC
address listed, but it is still open to communicate with all bridges that are in the same network.
Click Apply to apply your settings.
100
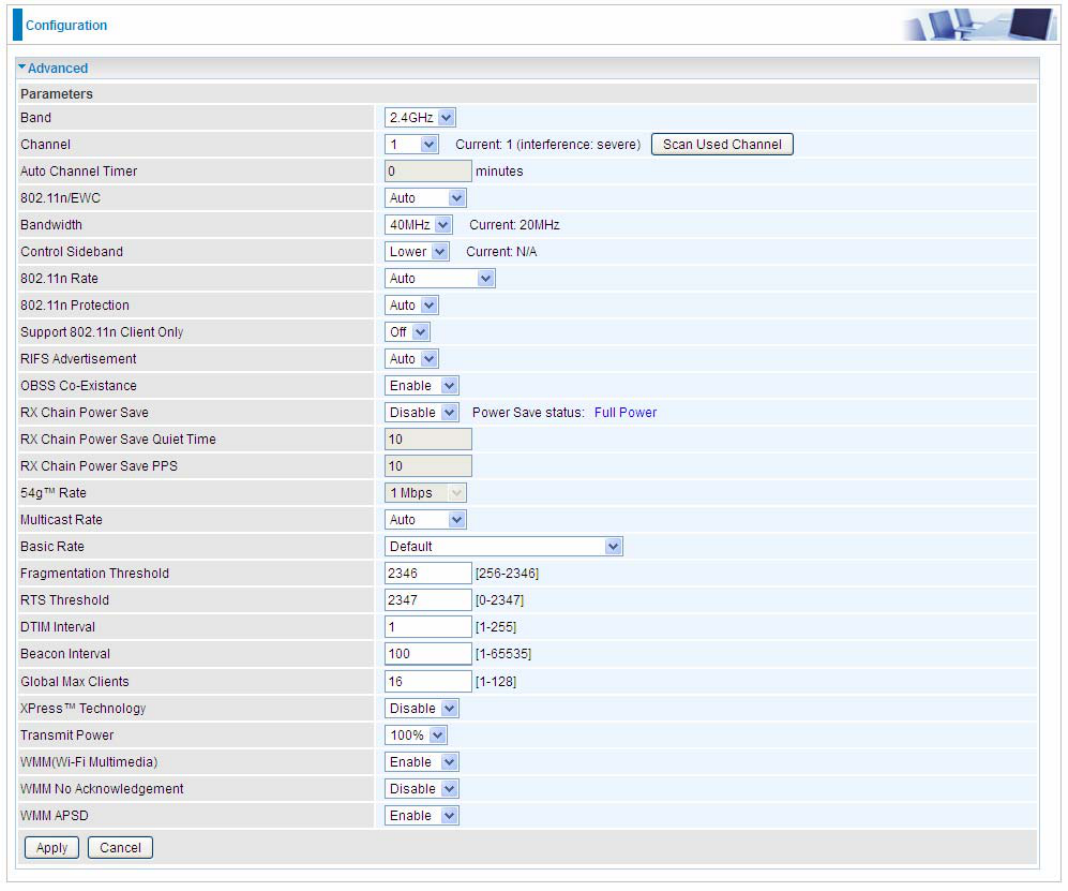
Advanced
Here users can set some advanced parameters about wireless.
Band: select frequency band. Here 2.4GHz.
Channel: Allows channel selection of a specific channel (1-7) or Auto mode.
Scan Used Channel: Press the button to scan and list all channels being used.
Auto Channel Timer (min): The auto channel times length it takes to scan in minutes. Only
available for auto channel mode.
802.11n/EWC: select to auto enable or disable 802.11n.
Bandwidth: Select bandwidth. The higher the bandwidth the better the performance will be.
Control Sideband: only available for 40MHz. It allows you to select upper sideband or lower
sideband. Sideband refers to the frequency band either above (upper sideband) or below (lower
sideband) the carrier frequency, within which fall the spectral components produced by modulation
of a carrier wave.
802.11n Rate: This allows you to select the fixed transmission rate or auto.
802.11n Protection: turn off for maximize throughput. Auto for greater security.
Support 802.11n Client Only: turn on the option to only provide wireless access to the clients
operating at 802.11n speeds.
101
RIFS Advertisement: Reduced Inter-frame Spacing (RIFS) is a 802.11n feature that also improves
performance by reducing the amount of dead time required between OFDM transmissions. Select
Off to disable this function or auto to enable this function.
OBSS Co-Existence: coexistence (or not) between 20 MHZ and 40 MHZ overlapping basic service
sets (OBSS) in wireless local area networks.
RX Chain Power Save: Enabling this feature turns off one of the Receive chains, going from 2x2 to
2x1 to save power.
RX Chain Power Save Quiet Time: The number of seconds the traffic must be below the PPS
value before the Rx Chain Power Save feature activates itself.
RX Chain Power Save PPS: The maximum number of packets per seconds that can be processed
by the WLAN interface for a duration of Quiet Time, described above, before the Rx Chain Power
Save feature activates itself.
Multicast Rate: Setting for multicast packets transmission rate.
Basic Rate: Setting for basic transmission rate. It is not a specific kind of rate, it is a series of rates
supported. When set to Default, the router can transmit with all kinds of standardized rates.
Fragmentation Threshold: A threshold (in bytes) whether the packets will be fragmented and at
what size. Packets succeeding the fragmentation threshold of 802.11n WLAN will be split into
smaller units suitable for circuit size. While the packets smaller than fragmentation threshold will not
be fragmented. Default is 2346, setting the fragmentation too low may result in poor performance.
RTS Threshold: Request to Send (RTS) threshold specifies the packet size, when exceeds the size,
the RTS/CTS will be triggered. The default setting of 2347(max length) will disable the RTS.
DTIM Interval: Delivery Traffic Indication Message (DTIM). The entry range is a value between 1
and 255. A DTIM is countdown variable that informs clients of the next window for listening to
broadcast and multicast messages. When the AP has buffered broadcast or multicast messages for
associated clients, it sends the next DTIM with a DTIM interval value. AP clients hear the beacons
and awaken to receive the broadcast and multicast messages. The default is 1.
Beacon Interval: The amount of time between beacon transmissions in is milliseconds. The default
is 100ms and the acceptable is 1- 65535. The beacon transmissions identify the presence of an
access point.
Global Max Clients: Here you have the option of setting the limit of the number of clients who can
connect to your wireless network.
XPress™ Technology: It has been designed to improve the wireless network efficiency. Default is
disabled.
Transmit Power: select the transmitting power of your wireless signal.
WMM (Wi-Fi Multimedia): you can choose to enable or disable this function which allows for priority
of certain data over wireless network.
WMM No Acknowledgement: Refers to the acknowledge policy at the MAC level. Enabling WMM
No Acknowledgement can result in more efficient throughput but higher error rates in noisy Radio
Frequency (RF) environment.
WMM APSD: Automatic Power Save Delivery. Enable this to save power.
102
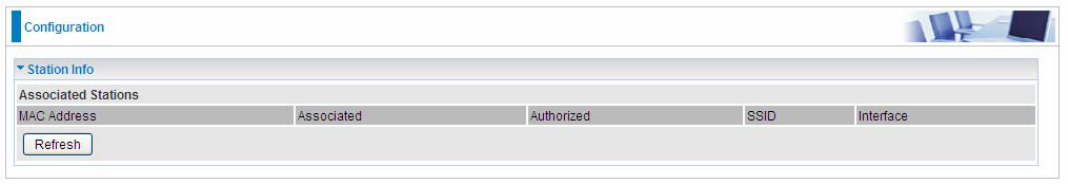
Station Info
Here you can view information about the wireless clients.
MAC Address: The MAC address of the wireless clients.
Associated: List all the stations that are associated with the Access Point. If a station is idle for too
long, it is removed from this list
Authorized: List those devices with authorized access.
SSID: Show the current SSID of the client.
Interface: To show which interface the wireless client is connected to.
Refresh: To get the latest information.
103
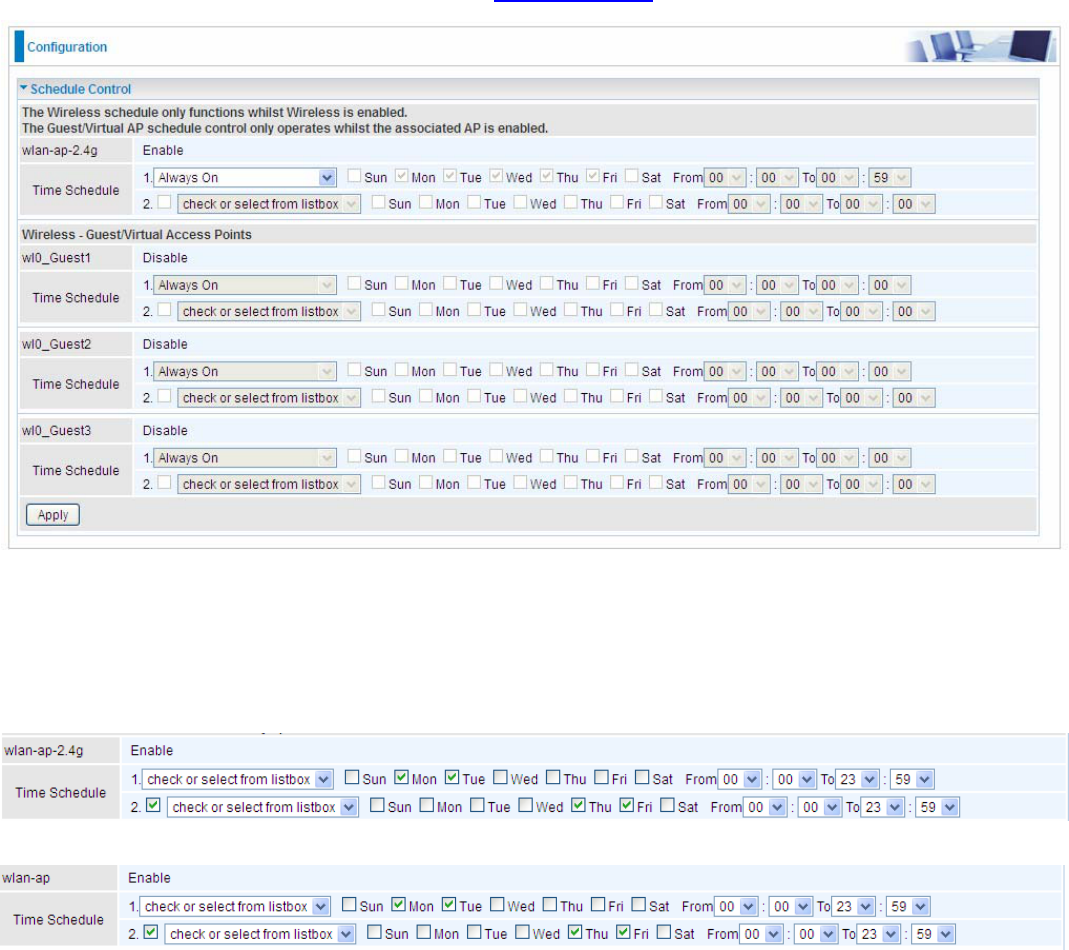
Schedule Control
Schedule control is aimed to offer methods to flexibly control when the wireless network (SSID) is
allowed for access.
The Wireless schedule only functions whilst Wireless is enabled.
The Guest/Virtual AP schedule control only operates whilst the associated AP is enabled.
For detail setting the timeslot, user can turn to Time Schedule .
Time Schedule: Set when the SSID works. If user wants the SSID works all the time, please select
“Always On”; if not, please set or select the exact time your want the SSID works. Here user can set
two separate intervals.
For example: user wants the SSID “wlan-ap-2.4g” to work on weekdays except for Wednesday,
under this circumstance, user can set as shown below. (7820NZ offers a optimal way to set two
separate timeslots when user needs to activate the SSID during separate intervals. )
104
WAN-Wide Area Network
A WAN (Wide Area Network) is a computer network that covers a broad geographical area (eg.
Internet) that is used to connect LAN and other types of network systems.
WAN Service
Two WAN interfaces are provided for WAN connection: DSL and Ethernet.
Click Add to add new WAN connections.
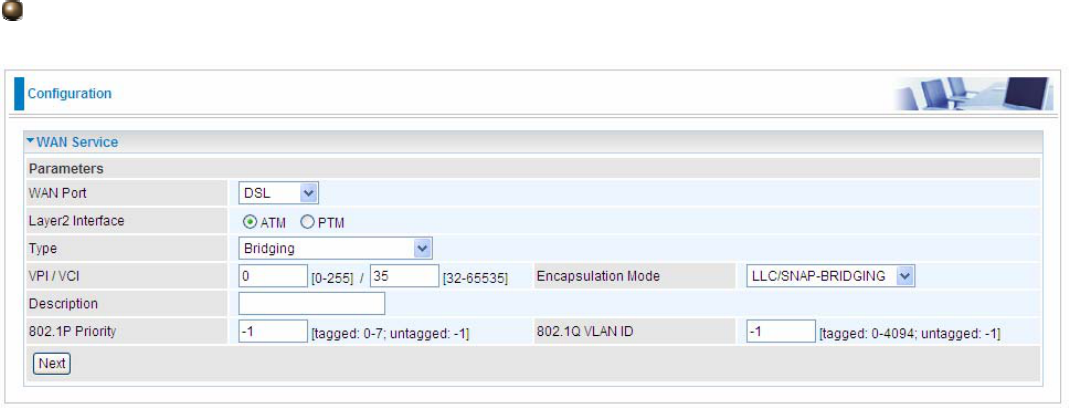
DSL
In DSL mode, there are two transfer modes for you to configure for WAN connection, namely ATM
and PTM, configuration of PTM mode is similar as ATM mode, here take ATM mode WAN
configuration for example.
Layer2 Interface: 2 transfer mode, ATM or PTM.
105
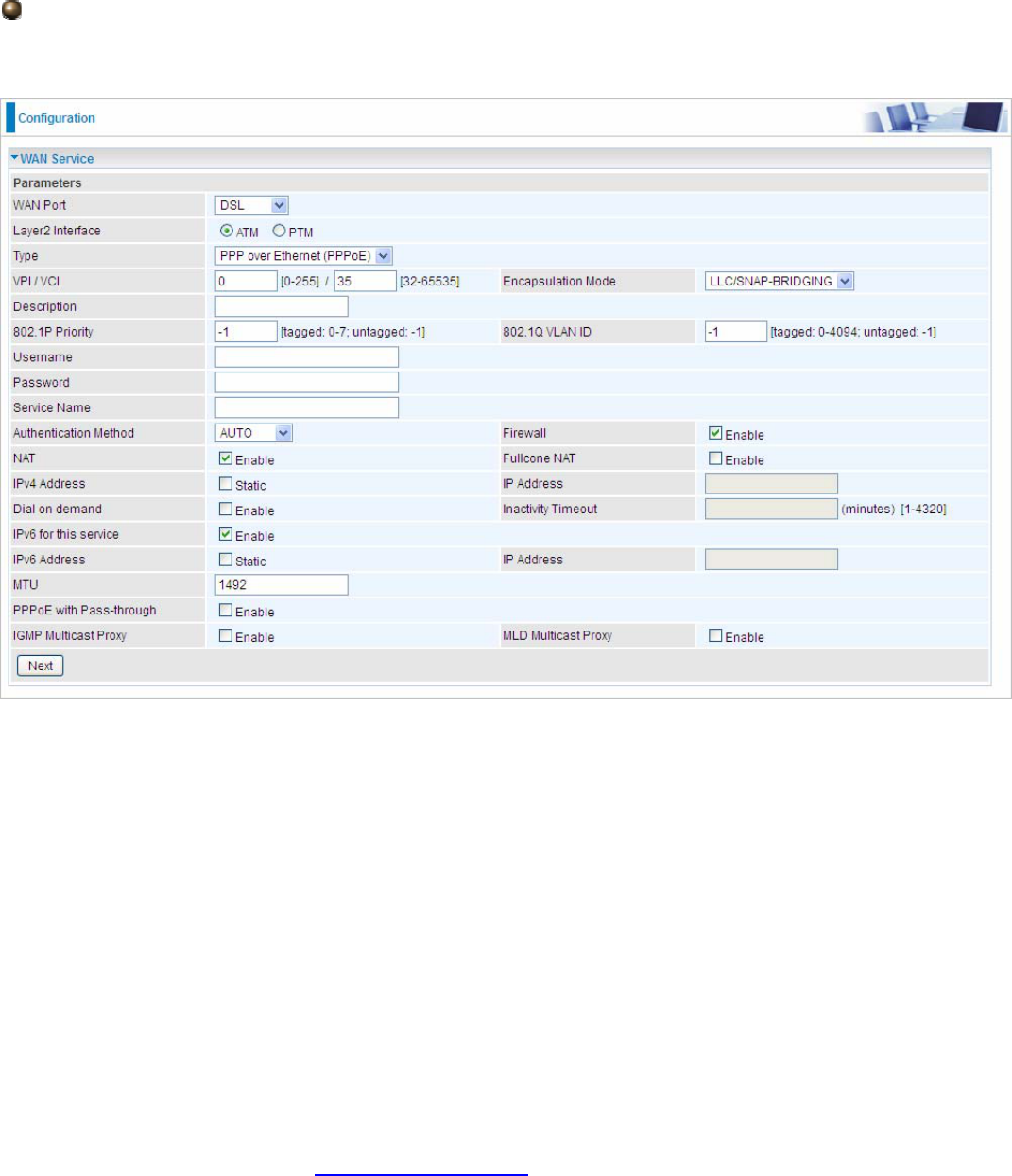
PPPoE
PPPoE (PPP over Ethernet) provides access control in a manner which is similar to dial-up services
using PPP.
VCP/VPI: Enter the VCI/VPI combination from you ISP.
Encapsulation Mode: Select the encapsulation mode, LLC/SNAP-BRIDGING, or VC/MUX.
Description: User-defined description for the connection, commonly for friendly use.
802.1P Priority: The parameter indicates the frame priority level from 0 (lowest) to 7 (highest), which
can be used to prioritize different classes of traffic (voice, video, data, etc). Enter the priority
identification, tagged: 0-1, untagged: -1.
802.1Q VLAN ID: It is a parameter to specify the VLAN which the frame belongs. Enter the VLAN ID
identification, tagged: 0-4094, untagged : -1.
Username: Enter the account obtained from the ISP.
Password: Enter the password obtained from the ISP.
Service Name: The item is for identification purpose, user can define it yourselfe.
Authentication Method: Default is Auto. Or else your ISP will advise you the appropriate mode.
Firewall: Enable to drop all traffic from WAN side. If enabled, all incoming packets by default would
be dropped, and please turn to IP Filtering Incoming to add allowing rules.
NAT: The NAT (Network Address Translation) feature allows multiple users to access the Internet
through a single IP account by sharing the single IP address. If users on your LAN have their own
public IP addresses to access the Internet, NAT function can be disabled. When enabled, a Fullcone
NAT parameter will appear, you can determine whether to enable Fullcone NAT. While only NAT
enabled, the default NAT type Port-Restricted cone NAT will be used.
Fullcone NAT: Enable or disable fullcone NAT. Fullcone is a kind of NAT, in this mode, all requests
from the same internal IP address and port are mapped to the same external IP address and port.
Furthermore, any external host can send a packet to the internal host by sending a packet to the
mapped external address.
106
Note: In PPPoE connection, NAT is enabled by default, you can determine whether to enable
Fullcone NAT or disable Fullcone NAT and only use NAT, the default NAT type is Port Restricted
cone NAT. Of Port-Restricted cone NAT, the restriction includes port numbers. Specifically, an
external host can send a packet, with source IP address X and source port P, to the internal host
only if the internal host had previously sent a packet to IP address X and port P.
IPv4 Address: Select whether to set static IPv4 address or obtain automatically.
IP Address: If Static is enabled in the above field, enter the static IPv4 address get from the ISP.
Dial on demand: It is a parameter to let users to dial for connection to internet themselves. It is
useful when saving internet fees.
Inactivity Timeout: The set Inactivity timeout period, unit: minutes. It is combined use with Dial on
Demand, users should specify the concrete time interval for dial on demand.
IPv6 for this service: Enable to use IPv6 service.
IPv6 Address: Select whether to set static IPv6 address or obtain automatically.
IP Address: If Static is enabled in the above field, enter the static IPv4 address.
MTU: Maximum Transmission Unit, the size of the largest datagram (excluding media-specific
headers) that IP will attempt to send through the interface.
PPPoE with Pass-through: Enable or disable PPPoE pass-through. If it is enabled, PCs behind the
router can dial itself.
IGMP Multicast Proxy: Check whether to enable this feature. IGMP (Internet Group Management
Protocol) Proxy intercepts the IGMP request from Clients and set up the multicast-forwarding table,
it takes over some of the router’s job, simplifying the router’s job and multicast communication.
MLD Multicast Proxy: check whether to enable this function. MLD (Multicast Listener Discovery
Protocol) Proxy intercepts the MLD request from Clients a set up the multicast-forwarding table. it
takes over some of the router’s job, simplifying the router’s job and multicast communication.
Support MLDv1 and MLDv2.
Click Next to continue to set the default gateway and DNS for IPv4 and IPv6.
107
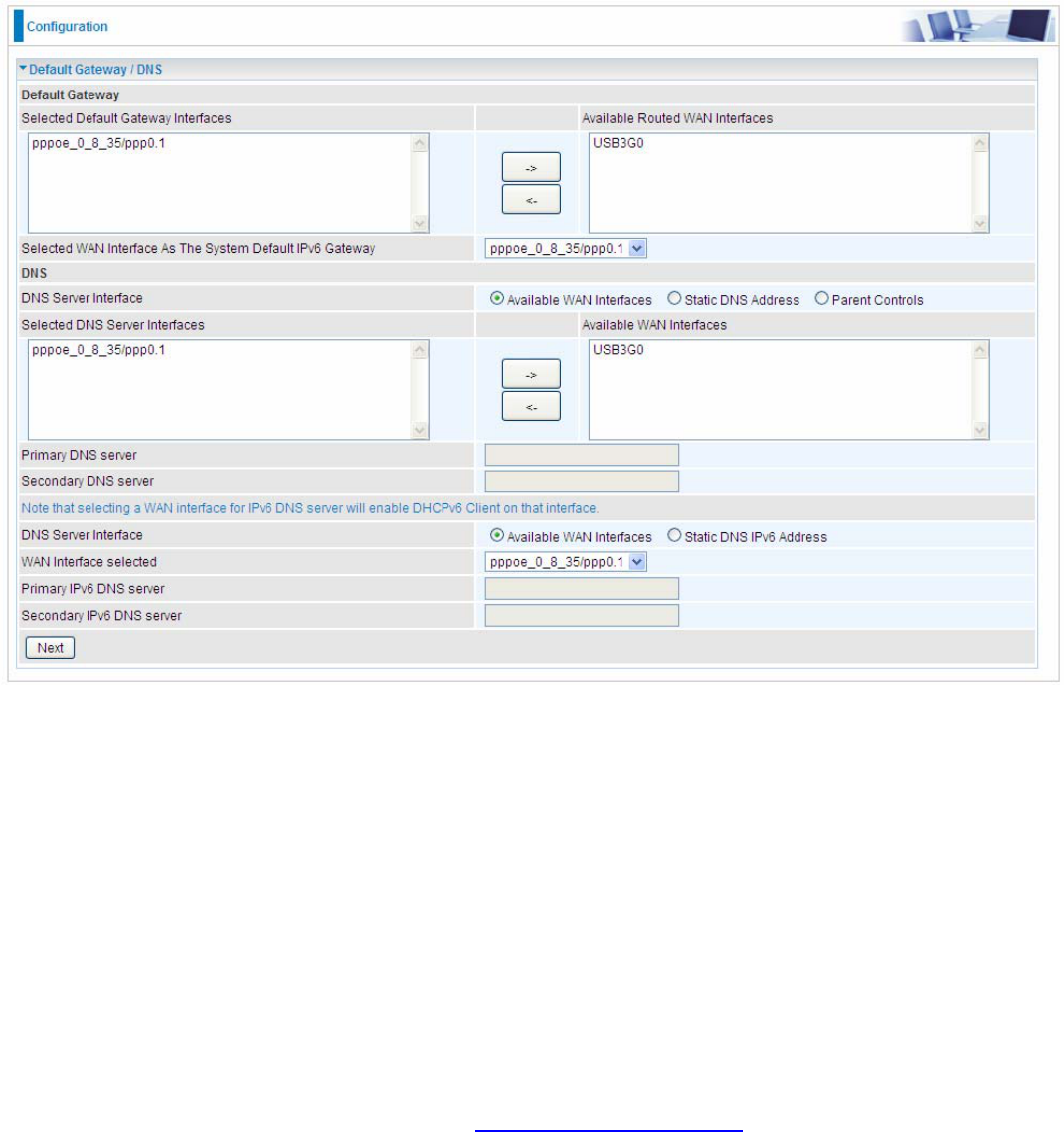
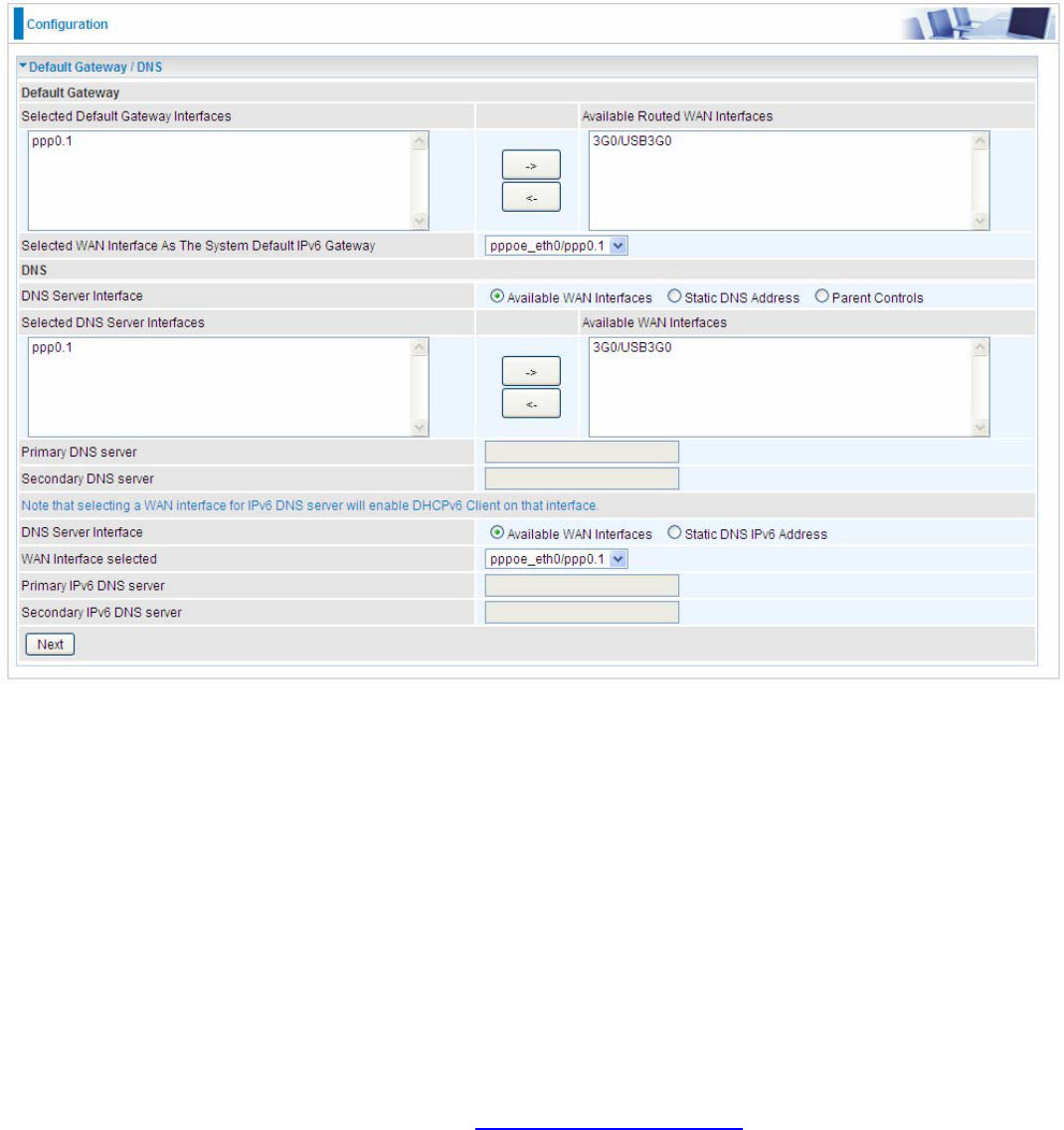
Default Gateway
Select default gateway for you connection (IPv4 and IPv6).
DNS
IPv4
Three ways to set an IPv4 DNS server
Available WAN interfaces: Select a desirable WAN interface as the IPv4 DNS server.
Static DNS Address: To specify DNS server manually by entering your primary and
secondary DNS server addresses.
Parental Controls: If user registers and gets a DNS account in the parental control provider
website, expecting to enjoy a more reliable and safer internet surfing environment, please
select this option (need to configure at Parental Control Provider).
IPv6
Obtain IPv6 DNS info from a WAN interface
WAN Interface selected: Select one configured IPv6 WAN connection from the menu to be as an
IPv6 DNS.
Static DNS IPv6 Address
Primary IPv6 DNS Server / Secondary IPv6 DNS Server: Type the specific primary and secondary
IPv6 DNS Server address.
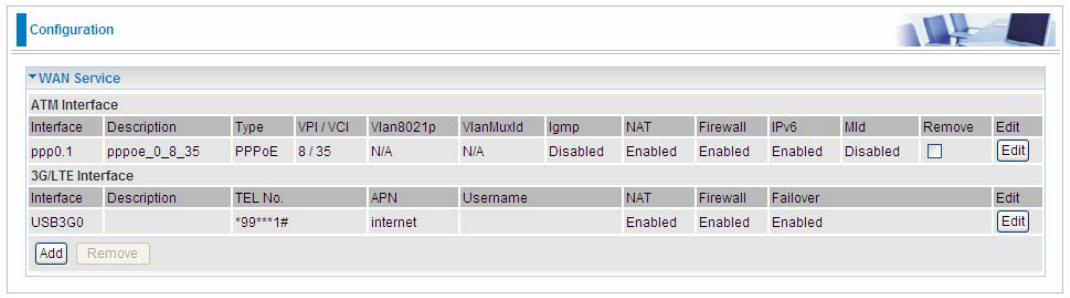
108
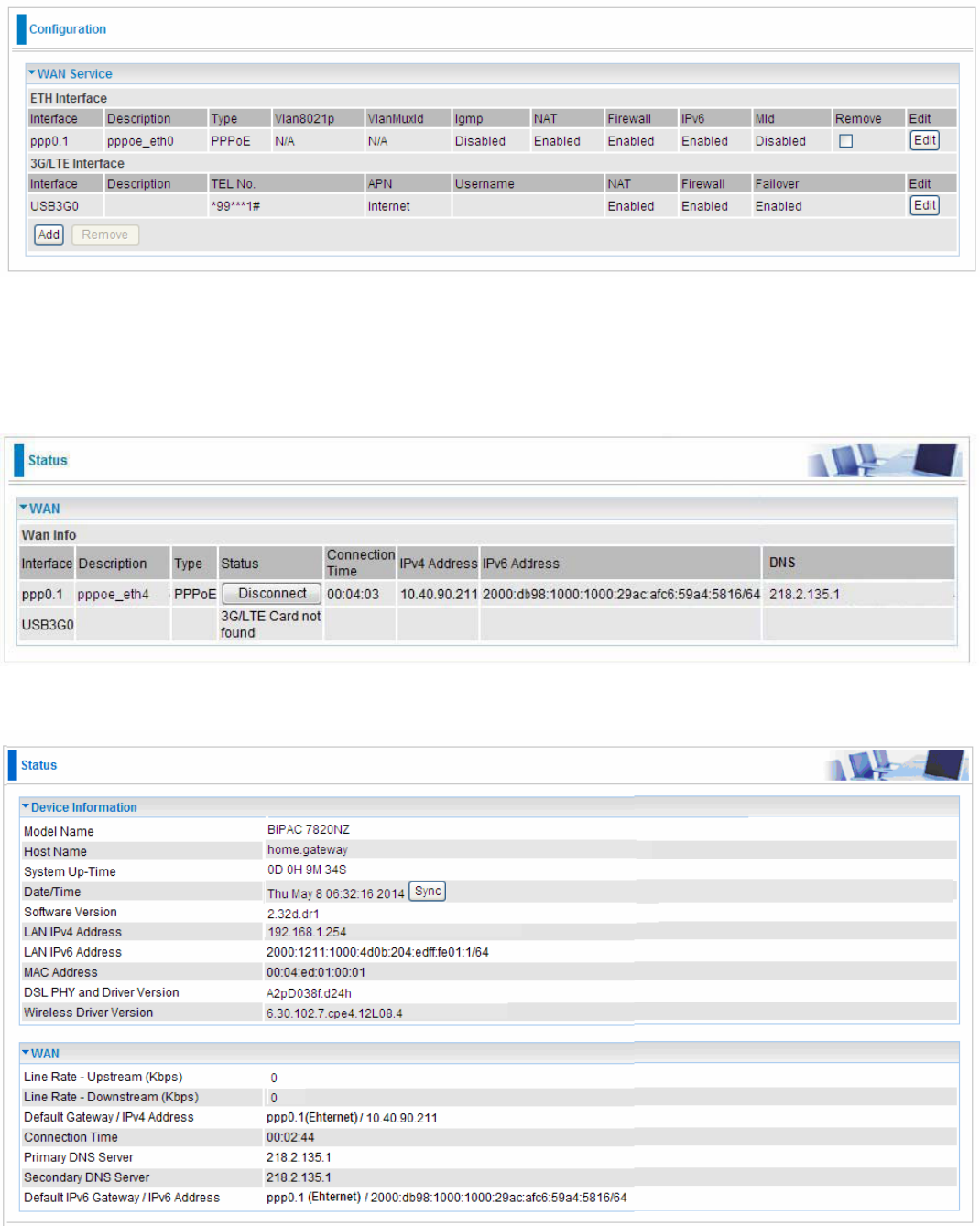
If you don’t need a service, select the item you want to remove, check the checkbox, then press
Remove.
Press Edit button to re-edit this service settings.
109
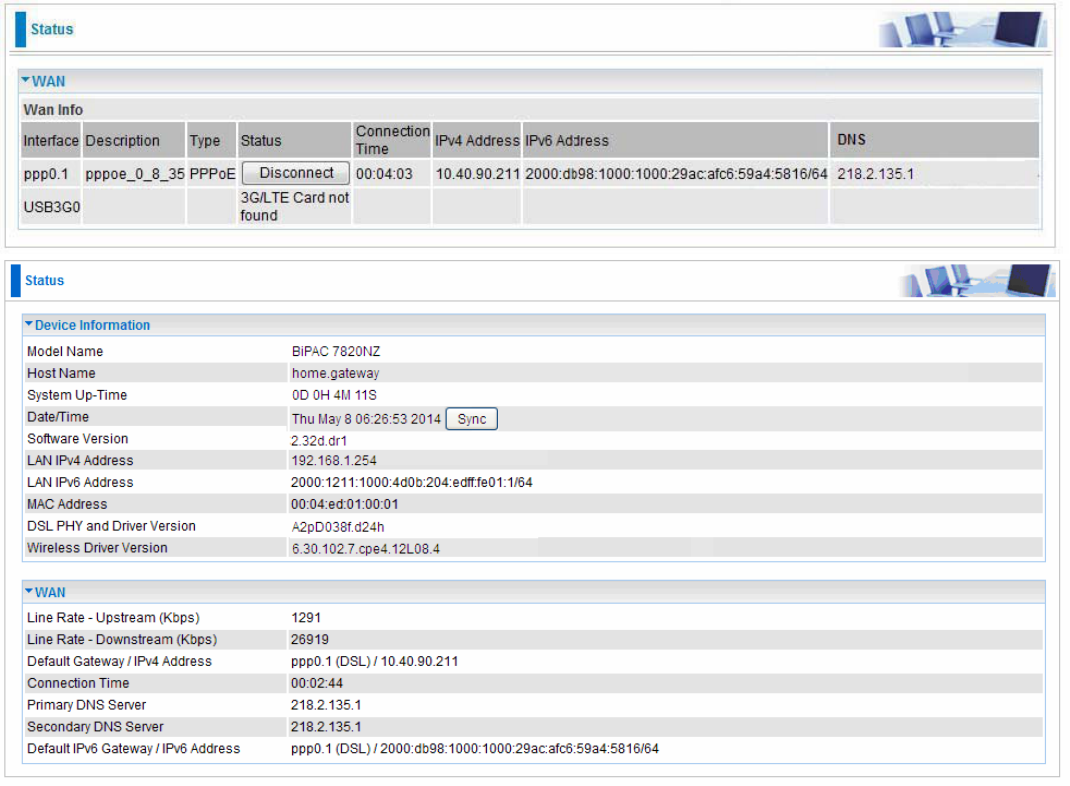
Here you can configure WAN Service, if it is OK, you can access the internet. You can go to Status
>WAN or Summary to view the WAN connection information (if your ISP provides IPv6 service, then
you will obtain an IPv6 address).
(IPv4 or IPv6)
110
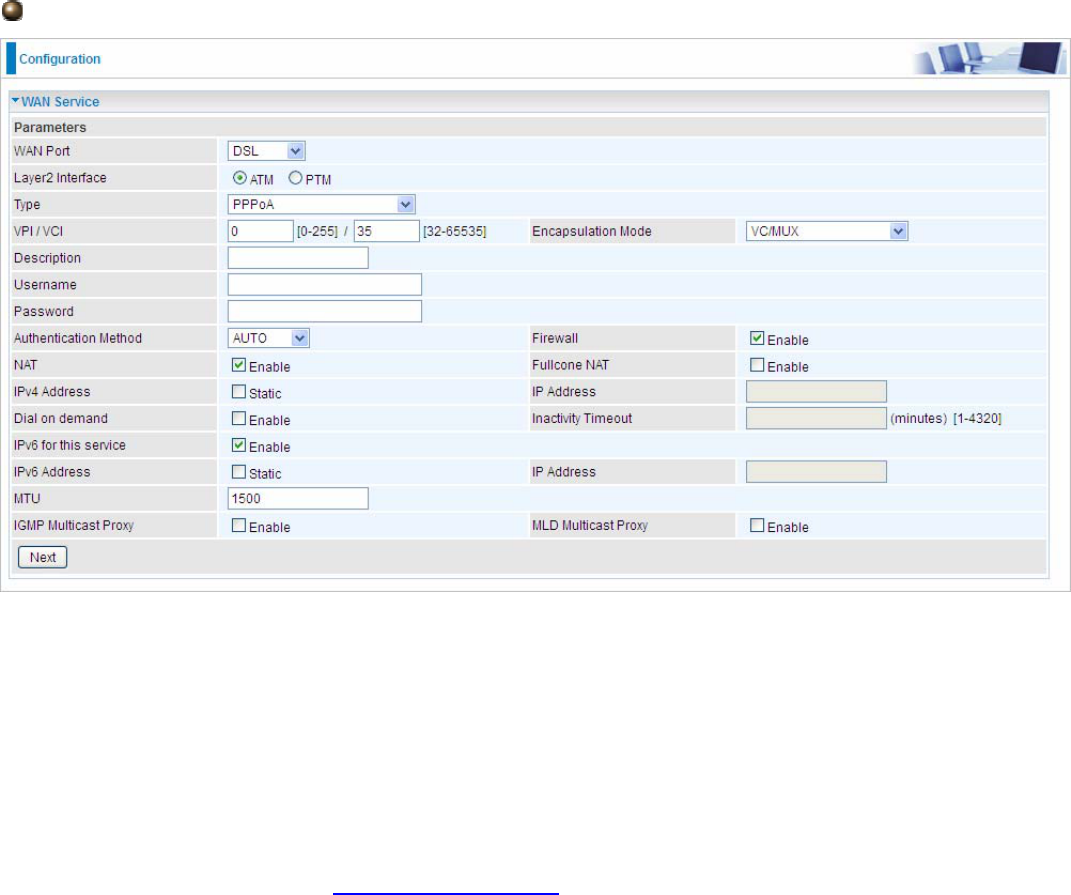
PPPoA
VCP/VPI: Enter the VCI/VPI combination from you ISP.
Encapsulation Mode: Select the encapsulation mode, LLC/SNAP-BRIDGING, or VC/MUX.
Description: User-defined description for the connection.
Username: Enter the account obtained from the ISP.
Password: Enter the password obtained from the ISP.
Authentication Method: Default is Auto. Or else your ISP will advise you the appropriate mode.
Firewall: Enable to drop all traffic from WAN side. If enabled, all incoming packets by default would
be dropped, and please turn to IP Filtering Incoming to add allowing rules.
NAT: The NAT (Network Address Translation) feature allows multiple users to access the Internet
through a single IP account by sharing the single IP address. If users on your LAN have their own
public IP addresses to access the Internet, NAT function can be disabled. When enabled, a Fullcone
NAT parameter will appear, you can determine whether to enable Fullcone NAT. While only NAT
enabled, the default NAT type Port-Restricted cone NAT will be used.
Fullcone NAT: Enable or disable fullcone NAT. Fullcone is a kind of NAT, in this mode, all requests
from the same internal IP address and port are mapped to the same external IP address and port.
Furthermore, any external host can send a packet to the internal host by sending a packet to the
mapped external address.
Note: In this connection, NAT is enabled by default, you can determine whether to enable Fullcone
NAT or disable Fullcone NAT and only use NAT, the default NAT type is Port Restricted cone NAT.
With Port-Restricted cone NAT, the restriction includes port numbers. Specifically, an external host
can send a packet, with source IP address X and source port P, to the internal host only if the
internal host had previously sent a packet to IP address X and port P
IPv4 Address: Select whether to set static IPv4 address or obtain automatically.
IP Address: If Static is enabled in the above field, enter the static IPv4 address get from the ISP.
Dial on demand: It is a parameter to let users to dial for connection to internet themselves. It is
useful when saving internet fees.
Inactivity Timeout: The set Inactivity timeout period, unit: minutes. It is combined use with Dial on
Demand, users should specify the concrete time interval for dial on demand.
111
IPv6 for this service: Enable to use IPv6 service.
IPv6 Address: Select whether to set static IPv6 address or obtain automatically.
IP Address: If Static is enabled in the above field, enter the static IPv4 address.
MTU: Maximum Transmission Unit, the size of the largest datagram (excluding media-specific
headers) that IP will attempt to send through the interface.
IGMP Multicast Proxy: Check whether to enable this feature. IGMP (Internet Group Management
Protocol) Proxy intercepts the IGMP request from Clients and set up the multicast-forwarding table,
it takes over some of the router’s job, simplifying the router’s job and multicast communication.
MLD Multicast Proxy: check whether to enable this function. MLD (Multicast Listener Discovery
Protocol) Proxy intercepts the MLD request from Clients a set up the multicast-forwarding table. it
takes over some of the router’s job, simplifying the router’s job and multicast communication.
Support MLDv1 and MLDv2.
Click Next to continue to set the default gateway and DNS for IPv4 and IPv6.
112
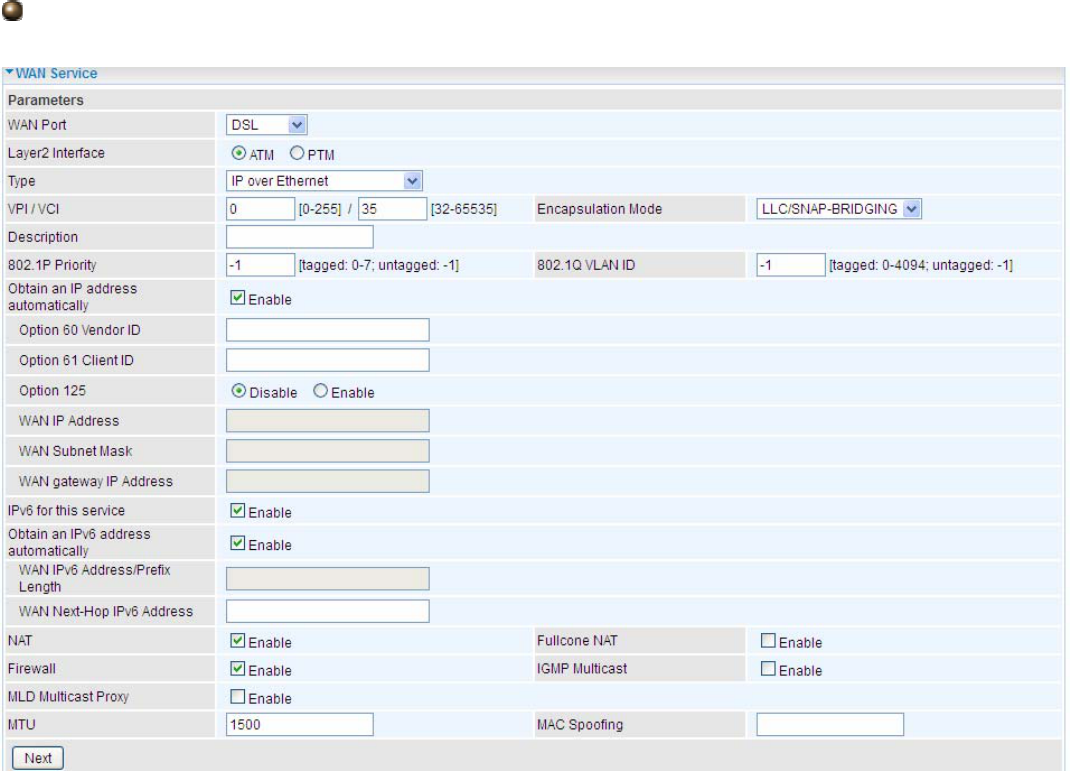
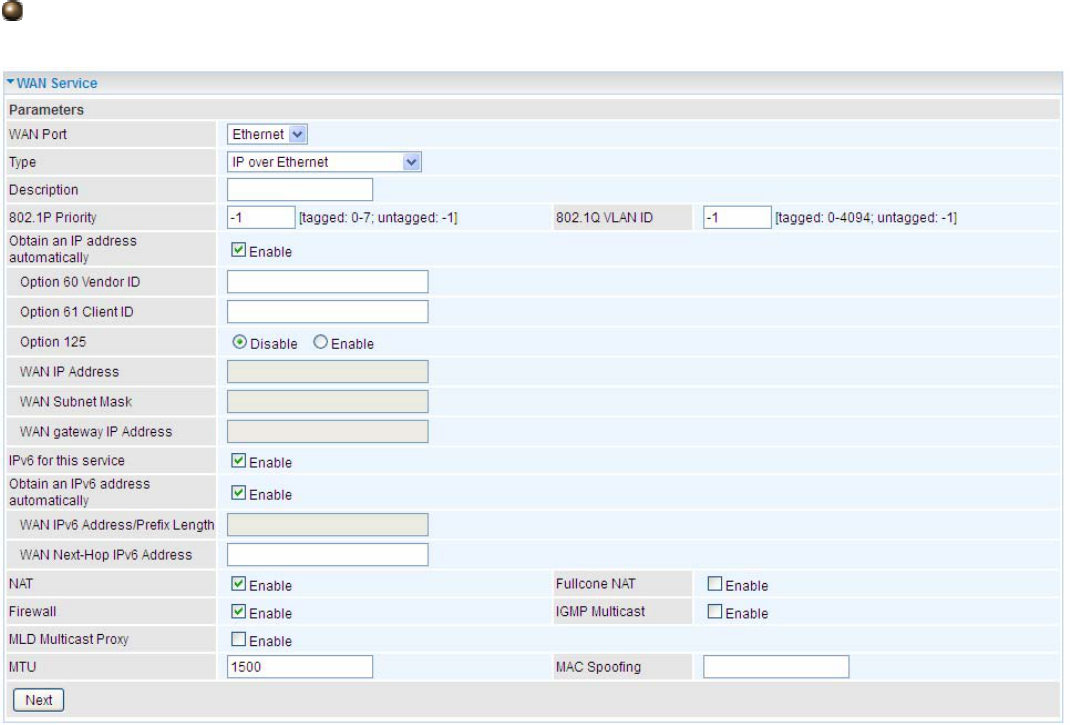
IP over Ethernet
VCP/VPI: Enter the VCI/VPI combination from you ISP.
Encapsulation Mode: Select the encapsulation mode, LLC/SNAP-BRIDGING, or VC/MUX.
Description: User-defined description for the connection, commonly for friendly use.
Authentication Method: Default is Auto. Or else your ISP will advise you the appropriate mode.
802.1P Priority: The parameter indicates the frame priority level from 0 (lowest) to 7 (highest), which
can be used to prioritize different classes of traffic (voice, video, data, etc). Enter the priority
identification, tagged: 0-1, untagged: -1.
802.1Q VLAN ID: It is a parameter to specify the VLAN which the frame belongs. Enter the VLAN ID
identification, tagged: 0-4094, untagged : -1.
Here two modes are supported for users to deal with the IP and DNS. You can select obtain
automatically or manually input the information according to your ISP.
Obtain an IP address automatically: Check whether to enable this function.
Option 60 Vendor ID: Enter the associated information by your ISP. This option is used by DHCP
clients to optionally identify the vendor type and configuration of a DHCP client. The information is a
string of n octets, interpreted by servers. Vendors may choose to define specific vendor class
identifiers to convey particular configuration or other identification information about a client.
Option 61 Client ID: Enter the associated information provided by your ISP.
Option 125: Option 125 is a complementary standard of DHCP protocol, it is used to encapsulate
option 125 message into DHCP offer packet before forward it to clients. After the clients receive the
packet, it check the option 125 field in the packet with the prestored message, if it is matched, then
the client accepts this offer, otherwise it will be abandoned. Check Enable or Disable this function.

113
Default setting is Disable.
WAN IP Address: Enter your IPv4 address to the device provided by your ISP.
WAN Subnet Mask: Enter your submask to the device provided by your ISP.
WAN gateway IP Address: Enter your gateway IP address to the device provided by your ISP.
IPv6 for this service: Enable to use IPv6 service.
Obtain an IPv6 address automatically: check whether to enable or disable this feature.
WAN IPv6 Address/Prefix Length: Enter the WAN IPv6 Address/Prefix Length from your ISP.
WAN Next-Hop IPv6 Address: Enter the WAN Next-Hop IPv6 Address from your ISP.
Note: If you don’t know well about the DHCP Option, you can leave it empty or leave it as default.
NAT: The NAT (Network Address Translation) feature allows multiple users to access the Internet
through a single IP account by sharing the single IP address. If users on your LAN have their own
public IP addresses to access the Internet, NAT function can be disabled. When enabled, a Fullcone
NAT parameter will appear, you can determine whether to enable Fullcone NAT. While only NAT
enabled, the default NAT type Port-Restricted cone NAT will be used.
Fullcone NAT: Enable or disable fullcone NAT. Fullcone is a kind of NAT, in this mode, all requests
from the same internal IP address and port are mapped to the same external IP address and port.
Furthermore, any external host can send a packet to the internal host, by sending a packet to the
mapped external address.
Firewall: Enable to drop all traffic from WAN side. If enabled, all incoming packets by default would
be dropped, and please turn to IP Filtering Incoming to add allowing rules.
IGMP Multicast: IGMP (Internet Group Membership Protocol) is a protocol used by IP hosts to
report their multicast group memberships to any immediately neighboring multicast routers. Check
this item to enable IGMP multicast on that WAN interface for multicast forwarding.
MLD Multicast Proxy: check whether to enable this function. MLD (Multicast Listener Discovery
Protocol) Proxy intercepts the MLD request from Clients a set up the multicast-forwarding table. it
takes over some of the router’s job, simplifying the router’s job and multicast communication.
Support MLDv1 and MLDv2.
MTU: Maximum Transmission Unit, the size of the largest datagram (excluding media-specific
headers) that IP will attempt to send through the interface.
MAC Spoofing: This option is required by some service providers specifying some specific MAC
allowed for connecting in network. You must fill in the MAC address specified by your service
provider when this information is required.
Click Next to continue to set the default gateway and DNS for IPv4 and IPv6.
114
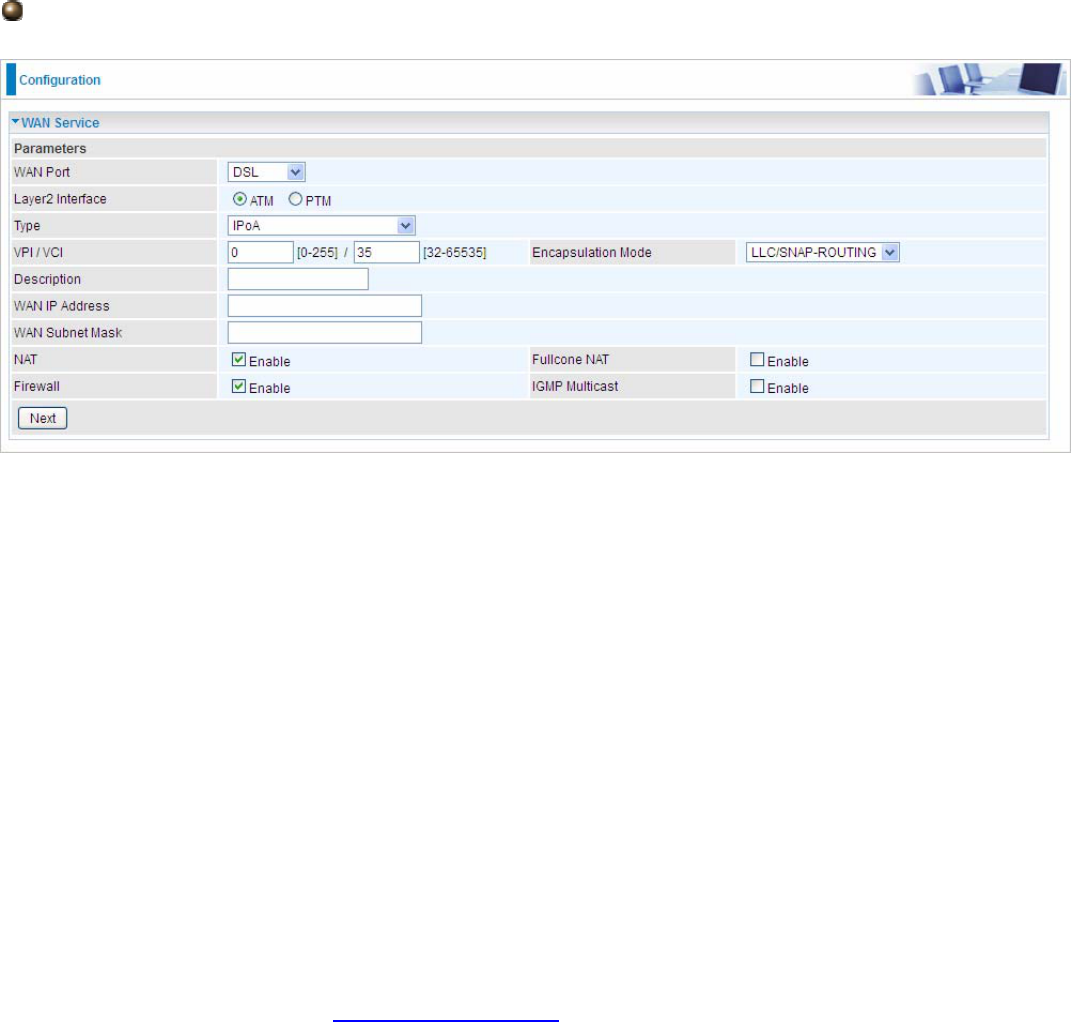
IPoA
VCP/VPI: Enter the VCI/VPI combination from you ISP.
Encapsulation Mode: Select the encapsulation mode, LLC/SNAP-BRIDGING, or VC/MUX.
Description: User-defined description for the connection, commonly for friendly use.
WAN IP: Enter the WAN IP from the ISP.
WAN Subnet Mask: Enter the WAN Subnet Mask from the ISP.
NAT: The NAT (Network Address Translation) feature allows multiple users to access the Internet
through a single IP account by sharing the single IP address. If users on your LAN have their own
public IP addresses to access the Internet, NAT function can be disabled. When enabled, a Fullcone
NAT parameter will appear, you can determine whether to enable Fullcone NAT. While only NAT
enabled, the default NAT type Port-Restricted cone NAT will be used.
Fullcone NAT: Enable or disable fullcone NAT. Fullcone is a kind of NAT, in this mode, all requests
from the same internal IP address and port are mapped to the same external IP address and port.
Furthermore, any external host can send a packet to the internal host, by sending a packet to the
mapped external address.
Firewall: Enable to drop all traffic from WAN side. If enabled, all incoming packets by default would
be dropped, and please turn to IP Filtering Incoming to add allowing rules.
IGMP Multicast: IGMP (Internet Group Membership Protocol) is a protocol used by IP hosts to
report their multicast group memberships to any immediately neighboring multicast routers. Check
this item to enable IGMP multicast on that WAN interface for multicast forwarding.
115
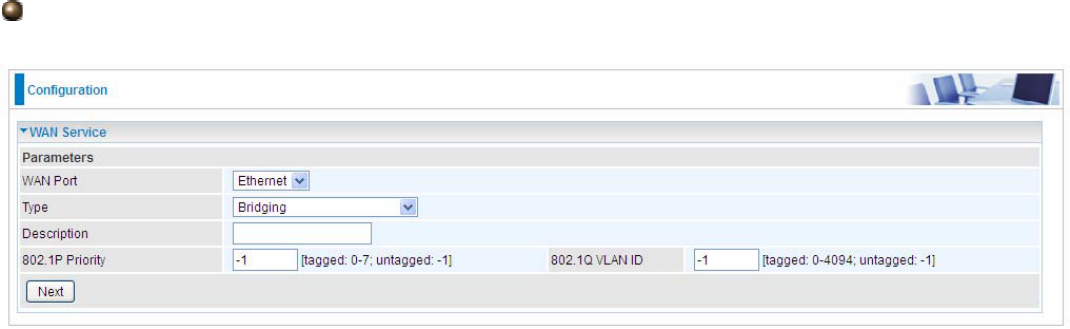
Bridging
VCP/VPI: Enter the VCI/VPI combination from you ISP.
Encapsulation Mode: Select the encapsulation mode, LLC/SNAP-BRIDGING, or VC/MUX.
Description: User-defined description for the connection, commonly for friendly use.
802.1P Priority: The parameter indicates the frame priority level from 0 (lowest) to 7 (highest), which
can be used to prioritize different classes of traffic (voice, video, data, etc). Enter the priority
identification, tagged: 0-1, untagged: -1.
802.1Q VLAN ID: It is a parameter to specify the VLAN which the frame belongs. Enter the VLAN ID
identification, tagged: 0-4094, untagged : -1.
116
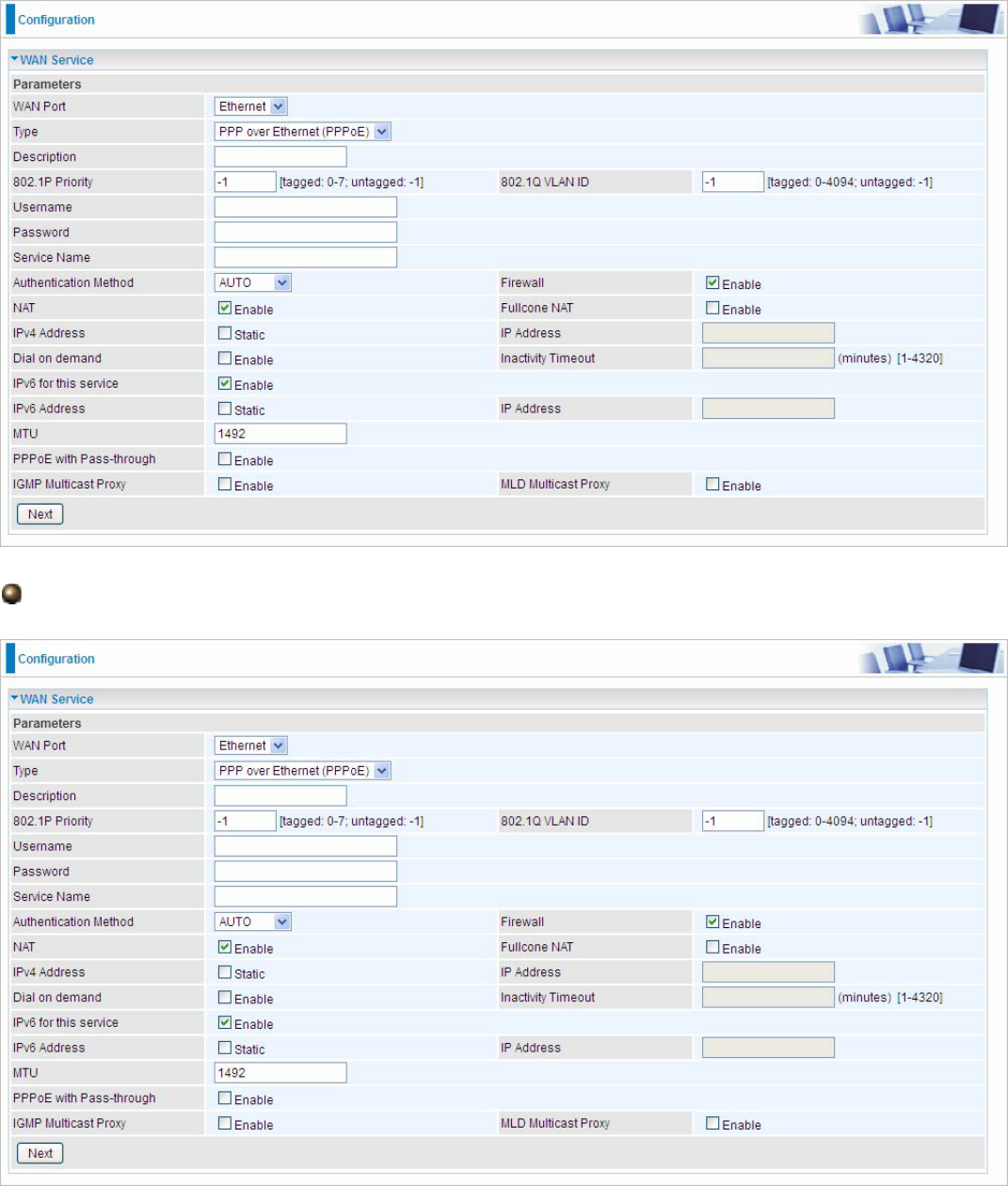
Ethernet
Ethernet WAN connection is well known as directly broadband WAN connection.
PPPoE
Description: User-defined description for the connection, commonly for friendly use.
802.1P Priority: The parameter indicates the frame priority level from 0 (lowest) to 7 (highest), which
can be used to prioritize different classes of traffic (voice, video, data, etc). Enter the priority
identification, tagged: 0-1, untagged: -1.
802.1Q VLAN ID: It is a parameter to specify the VLAN which the frame belongs. Enter the VLAN ID

117
identification, tagged: 0-4094, untagged : -1.
Username: Enter the account obtained from the ISP.
Password: Enter the password obtained from the ISP.
Service Name: The item is for identification purpose, user can define it yourselfe.
Authentication Method: Default is Auto. Or else your ISP will advise you the appropriate mode.
Firewall: Enable to drop all traffic from WAN side. If enabled, all incoming packets by default would
be dropped, and please turn to IP Filtering Incoming to add allowing rules.
NAT: The NAT (Network Address Translation) feature allows multiple users to access the Internet
through a single IP account by sharing the single IP address. If users on your LAN have their own
public IP addresses to access the Internet, NAT function can be disabled. When enabled, a Fullcone
NAT parameter will appear, you can determine whether to enable Fullcone NAT. While only NAT
enabled, the default NAT type Port-Restricted cone NAT will be used.
Fullcone NAT: Enable or disable fullcone NAT. Fullcone is a kind of NAT, in this mode, all requests
from the same internal IP address and port are mapped to the same external IP address and port.
Furthermore, any external host can send a packet to the internal host by sending a packet to the
mapped external address.
Note: In PPPoE connection, NAT is enabled by default, you can determine whether to enable
Fullcone NAT. and while you disable Fullcone NAT and only use NAT, the default NAT type is Port
Restricted or Port-Restricted cone NAT, the restriction includes port numbers. Specifically, an
external host can send a packet, with source IP address X and source port P, to the internal host
only if the internal host had previously sent a packet to IP address X and port P
IPv4 Address: Select whether to set static IPv4 address or obtain automatically.
IP Address: If Static is enabled in the above field, enter the static IPv4 address get from the ISP.
Dial on demand: It is a parameter to let users to dial for connection to internet themselves. It is
useful when saving internet fees.
Inactivity Timeout: The set Inactivity timeout period, unit: minutes. It is combined use with Dial on
Demand, users should specify the concrete time interval for dial on demand.
IPv6 for this service: Enable to use IPv6 service.
IPv6 Address: Select whether to set static IPv6 address or obtain automatically.
IP Address: If Static is enabled in the above field, enter the static IPv4 address.
MTU: Maximum Transmission Unit, the size of the largest datagram (excluding media-specific
headers) that IP will attempt to send through the interface.
PPPoE with Pass-through: Enable or disable PPPoE pass-through. If it is enabled, PCs behind the
router can dial itself.
IGMP Multicast Proxy: Check whether to enable this feature. IGMP (Internet Group Management
Protocol) Proxy intercepts the IGMP request from Clients and set up the multicast-forwarding table,
it takes over some of the router’s job, simplifying the router’s job and multicast communication.
MLD Multicast Proxy: check whether to enable this function. MLD (Multicast Listener Discovery
Protocol) Proxy intercepts the MLD request from Clients a set up the multicast-forwarding table. it
takes over some of the router’s job, simplifying the router’s job and multicast communication.
Support MLDv1 and MLDv2.
118
Click Next to continue to set the default gateway and DNS for IPv4 and IPv6.
Default Gateway
Select default gateway for you connection (IPv4 and IPv6).
DNS
IPv4
Three ways to set an IPv4 DNS server
Available WAN interfaces: Select a desirable WAN interface as the IPv4 DNS server.
Static DNS Address: To specify DNS server manually by entering your primary and
secondary DNS server addresses.
Parental Controls: If user registers and gets a DNS account in the parental control provider
website, expecting to enjoy a more reliable and safer internet surfing environment, please
select this option (need to configure at Parental Control Provider).
IPv6
Obtain IPv6 DNS info from a WAN interface
WAN Interface selected: Select one configured IPv6 WAN connection from the menu to be as an
IPv6 DNS.
Static DNS IPv6 Address
Primary IPv6 DNS Server / Secondary IPv6 DNS Server: Type the specific primary and secondary
IPv6 DNS Server address.
119
If you don’t need the service, select the item you want to remove, check the checkbox, then press
Remove, it will be OK.
Press Edit button to re-edit this service settings.
Here the corresponding WAN Service have been configured, if it is OK, you can access the internet.
You can go to Status>WAN or Summary to view the WAN connection information (if your ISP
provides IPv6 service, then you will obtain an IPv6 address).
(IPv4 or IPv6)
The device summary information
120
IP over Ethernet
Description: User-defined description for the connection, commonly for friendly use.
802.1P Priority: The parameter indicates the frame priority level from 0 (lowest) to 7 (highest), which
can be used to prioritize different classes of traffic (voice, video, data, etc). Enter the priority
identification, tagged: 0-1, untagged: -1.
802.1Q VLAN ID: It is a parameter to specify the VLAN which the frame belongs. Enter the VLAN ID
identification, tagged: 0-4094, untagged : -1.
Here two modes are supported for users to deal with the IP and DNS. You can select obtain
automatically or manually input the information according to your ISP.
Obtain an IP address automatically: Check whether to enable this function.
Option 60 Vendor ID: Enter the associated information by your ISP. This option is used by DHCP
clients to optionally identify the vendor type and configuration of a DHCP client. The information is a
string of n octets, interpreted by servers. Vendors may choose to define specific vendor class
identifiers to convey particular configuration or other identification information about a client.
Option 61 Client ID: Enter the associated information provided by your ISP.
Option 125: Option 125 is a complementary standard of DHCP protocol, it is used to encapsulate
option 125 message into DHCP offer packet before forward it to clients. After the clients receive the
packet, it check the option 125 field in the packet with the pre-stored message, if it is matched, then
the client accepts this offer, otherwise it will be abandoned. Check Enable or Disable this function.
Default setting is Disable.
WAN IP Address: Enter your IPv4 address to the device provided by your ISP.
WAN Subnet Mask: Enter your submask to the device provided by your ISP.
WAN gateway IP Address: Enter your gateway IP address to the device provided by your ISP.
IPv6 for this service: Enable to use IPv6 service.

121
Obtain an IPv6 address automatically: check whether to enable or disable this feature.
WAN IPv6 Address/Prefix Length: Enter the WAN IPv6 Address/Prefix Length from your ISP.
WAN Next-Hop IPv6 Address: Enter the WAN Next-Hop IPv6 Address from your ISP.
Note: If you don’t know well about the DHCP Option, you can leave it empty or leave it as default.
NAT: The NAT (Network Address Translation) feature allows multiple users to access the Internet
through a single IP account by sharing the single IP address. If users on your LAN have their own
public IP addresses to access the Internet, NAT function can be disabled. When enabled, a Fullcone
NAT parameter will appear, you can determine whether to enable Fullcone NAT. While only NAT
enabled, the default NAT type Port-Restricted cone NAT will be used.
Fullcone NAT: Enable or disable fullcone NAT. Fullcone is a kind of NAT, in this mode, all requests
from the same internal IP address and port are mapped to the same external IP address and port.
Furthermore, any external host can send a packet to the internal host, by sending a packet to the
mapped external address.
Firewall: Enable to drop all traffic from WAN side. If enabled, all incoming packets by default would
be dropped, and please turn to IP Filtering Incoming to add allowing rules.
IGMP Multicast: IGMP (Internet Group Membership Protocol) is a protocol used by IP hosts to
report their multicast group memberships to any immediately neighboring multicast routers. Check
this item to enable IGMP multicast on that WAN interface for multicast forwarding.
MLD Multicast Proxy: check whether to enable this function. MLD (Multicast Listener Discovery
Protocol) Proxy intercepts the MLD request from Clients a set up the multicast-forwarding table. it
takes over some of the router’s job, simplifying the router’s job and multicast communication.
Support MLDv1 and MLDv2.
MTU: Maximum Transmission Unit, the size of the largest datagram (excluding media-specific
headers) that IP will attempt to send through the interface.
MAC Spoofing: This option is required by some service providers specifying some specific MAC
allowed to join in network. You must fill in the MAC address specified by your service provider when
this information is required.
122
Bridging
Description: User-defined description for the connection, commonly for friendly use.
802.1P Priority: The parameter indicates the frame priority level from 0 (lowest) to 7 (highest), which
can be used to prioritize different classes of traffic (voice, video, data, etc). Enter the priority
identification, tagged: 0-1, untagged: -1.
802.1Q VLAN ID: It is a parameter to specify the VLAN which the frame belongs. Enter the VLAN ID
identification, tagged: 0-4094, untagged : -1.
123
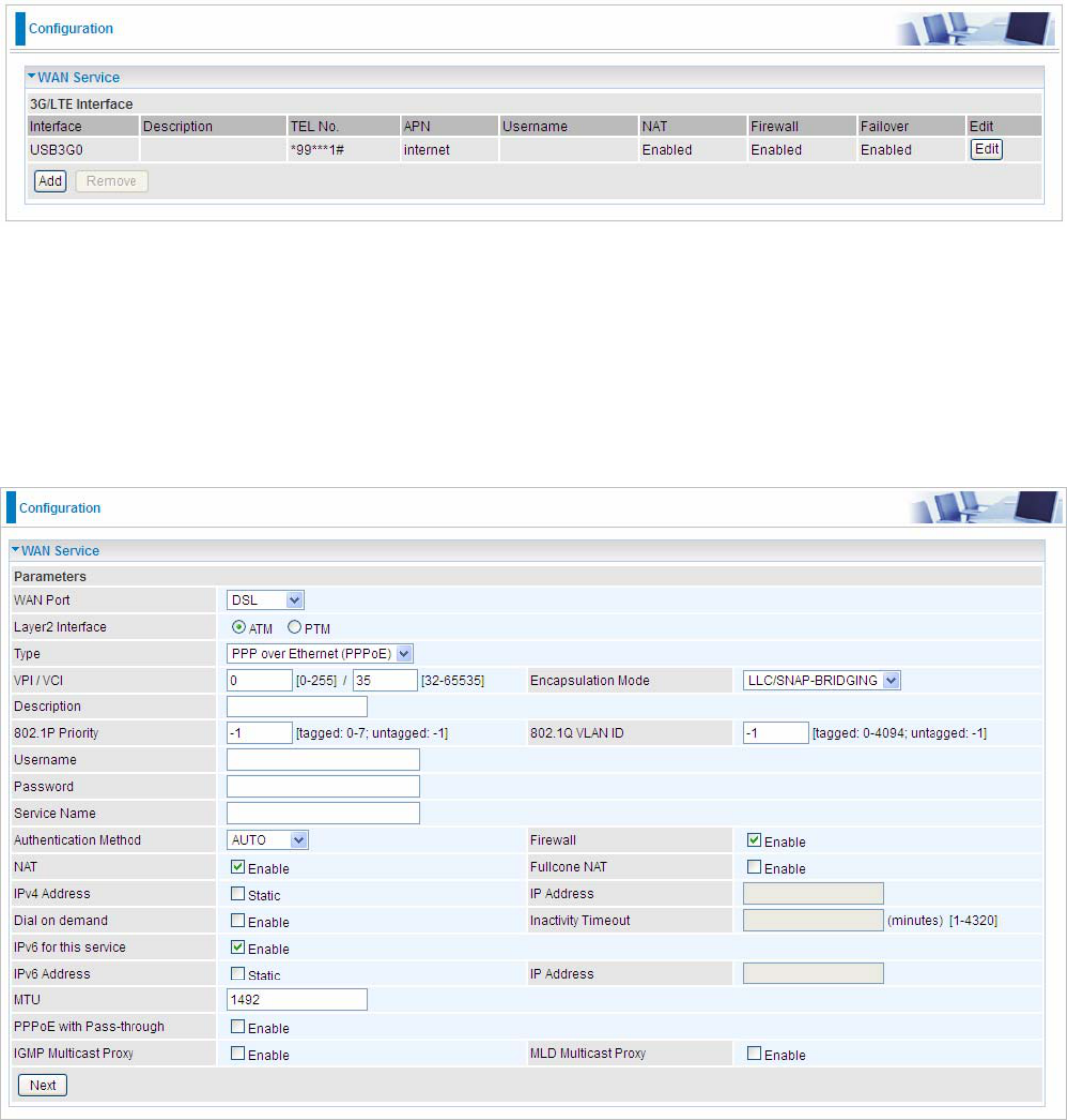
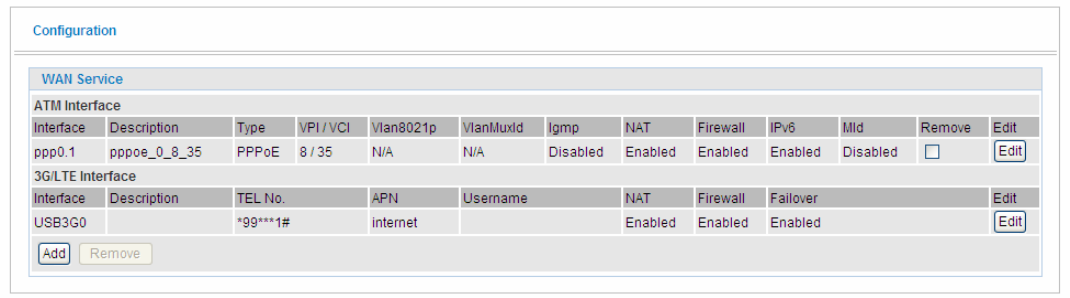
3G/LTE
Select 3G/LTE to configure the route to enjoy the mobility. Given that BiPAC 7820NZ supports dual -
SIM mobile connectivity, please determine which SIM you are gonna use or both (3G/LTE failover),
and set the exact required connecting information for each SIM (SIM1 and SIM2). By default the
3G/LTE interface is on, user can edit the parameters to meet your own requirements.
Click Edit button to enter the 3G/LTE configuration page.
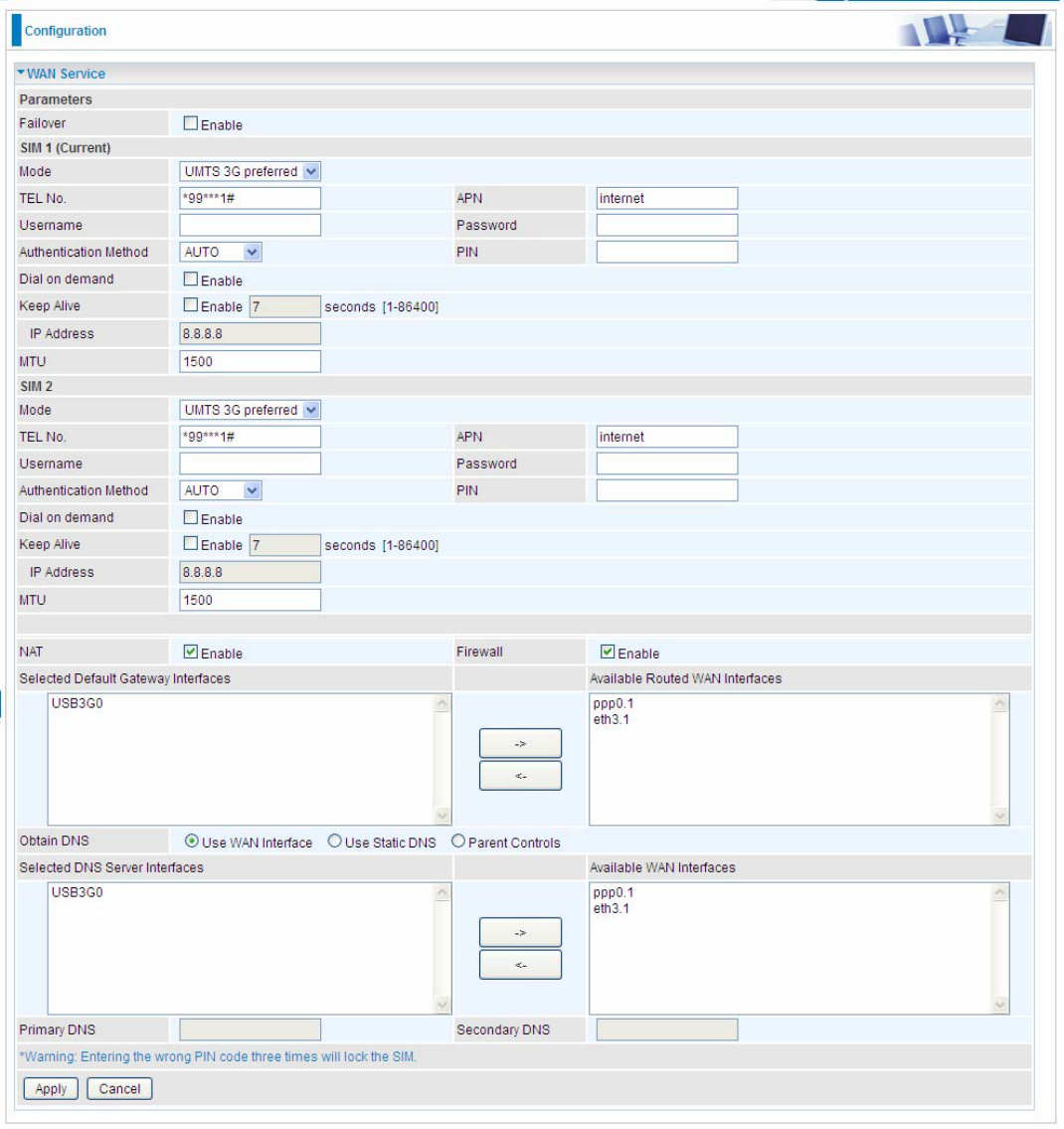
124
Failover: If enabled, the 3G/LTE will work in failover mode and be brought up only when there is no
active default route. In this mode, 3G/LTE work as a backup for the WAN connectivity. While if
disabled, 3G/LTE serves as a normal interface, and can only be brought up when it has been
configured to achieve a mobile connectivity.
SIM 1 & SIM 2
Mode: There are 6 options of phone service standards: GSM 2G only, UTMS 3G only, GSM 2G
preferred, UMTS 3G preferred, Automatic, and Use 3G/LTE 3g dongle settings. If you are uncertain
what services are available to you, and then please select Automatic.
TEL No.: The dial string to make a 3G/LTE user internetworking call. It may provide by your mobile
service provider.
APN: An APN is similar to a URL on the WWW, it is what the unit makes a GPRS / UMTS call. The
125
service provider is able to attach anything to an APN to create a data connection, requirements for
APNs varies between different service providers. Most service providers have an internet portal
which they use to connect to a DHCP Server, thus giving you access to the internet i.e. some 3G
operators use the APN ‘internet’ for their portal. The default value is “internet”.
Username/Password: Enter the username and password provided by your service provider. The
username and password are case sensitive.
Authentication Protocol: Default is Auto. Please consult your service provider on whether to use
PAP, CHAP or MSCHAP.
PIN: PIN stands for Personal Identification Number. A PIN code is a numeric value used in certain
systems as a password to gain access, and authenticate. In mobile phones a PIN code locks the
SIM card until you enter the correct code. If you enter the PIN code incorrectly into the phone 3 times
in a row, then the SIM card will be blocked and you will require a PUK code from your network/
service provider.
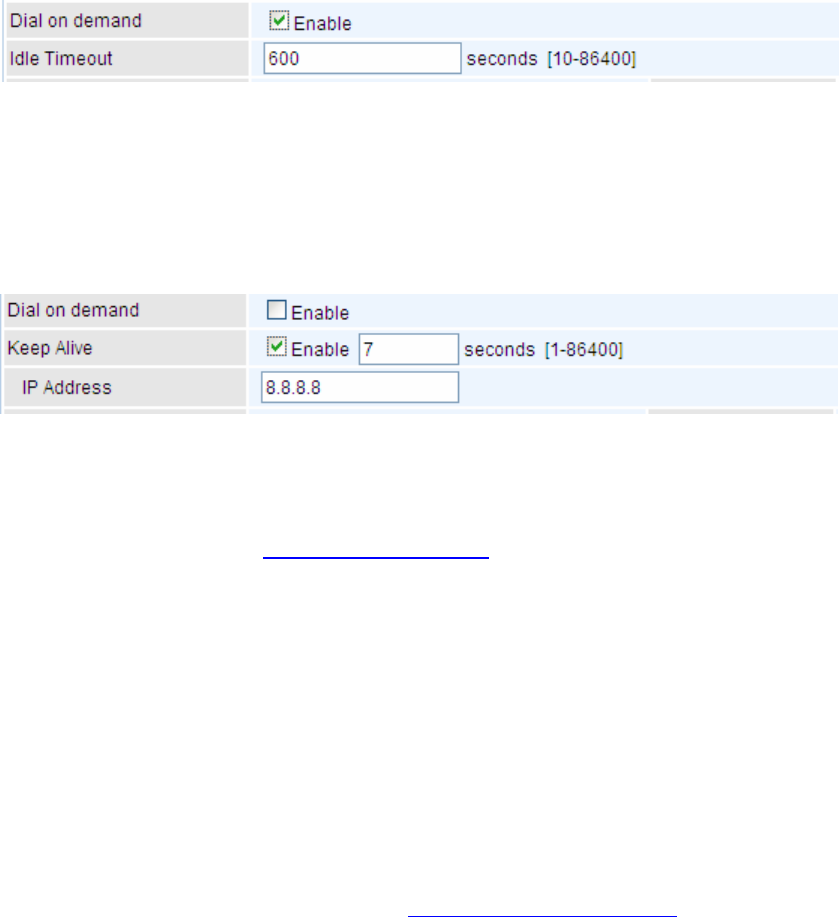
Connect on Demand: If you want to make UMTS/GPRS call only when there is a packet
requesting access to the Internet (i.e. when a program on your computer attempts to access
the Internet). In this mode, you must set Idle Timeout value at same time. Click on Connect on
Demand, the Idle Timeout field will display.
Idle Timeout: Auto-disconnect the broadband firewall gateway when there is no activity on
the line for a predetermined period of time. Default is 600 seconds.
Keep Alive: Check Enable to allow the router to check the mobile connectivity every 7 (can
be changed based on need) seconds by ping the IP address set below the keep the 3G/LTE
link active.
IP Address: The IP address is used to “ping”, and router will ping the IP to find whether the
connection is still on.
NAT: Check to enable the NAT function.
Firewall: Enable to drop all traffic from WAN side. If enabled, all incoming packets by default would
be dropped, and please turn to IP Filtering Incoming to add allowing rules.
MTU: MTU (Maximum Transmission Unit) is the size of the largest datagram that IP will attempt to
send through the interface.
Select default gateway interfaces: Select from the interfaces the default gateway, here commonly
we select ppp3g0.
Selected DNS Server Interfaces: Three ways to set a DNS server.
Available WAN interfaces: Select a desirable WAN interface as the DNS server.
Static DNS Address: To specify DNS server manually by entering your primary and
secondary DNS server addresses.
Parental Controls: If user registers and gets a DNS account in the parental control provider
website, expecting to enjoy a more reliable and safer internet surfing environment, please
select this option (need to configure at Parental Control Provider).

126
Click Apply to confirm the settings.
Here you can configure WAN Service, if it is OK, you can access the internet. You can go to Status
>WAN or Summary to view the WAN connection information (Here user can see the 3G/LTE
failover).
127
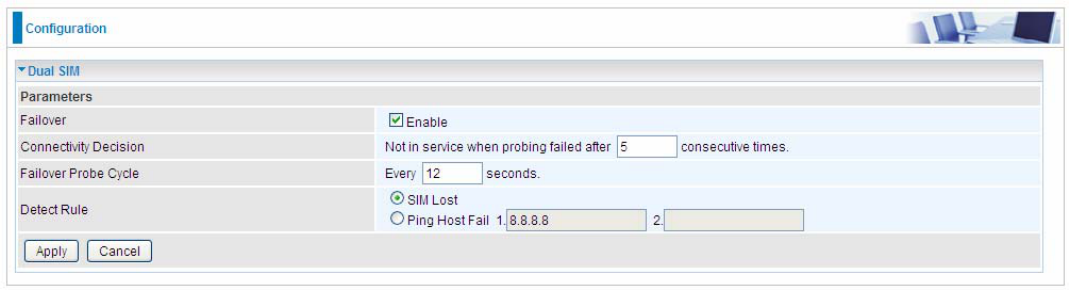
Dual SIM
BiPAC 7820NZ offers dual-SIM slots for two mobile SIM cards. The SIM 1 will be in use when two
SIM cards are both up. The current SIM connection will fail over to the other SIM connection when
the situation below happens. But note when the failover is done, the connection cannot fail back to
the previous SIM connection.
Failover: Check Enable to activate failover feature.
Connectivity Decision: Set how many times of probing failure to switch to the other SIM.
Failover Probe Cycle: Set the time duration for the Probe Cycle to determine when the router will
switch to the other SIM once the current SIM connection fails. For example, when set to 12 seconds,
the probe will be conducted every 12 seconds.
Detect Rule: Choose the probe policy, to Ping Host or when SIM lost
SIM Lost: SIM card absent or not be able to establish connection.
Ping Host Fail: It will send ping packets to host pre-set, and wait for response from it in every
“Probe Cycle” to check the connectivity to the mail SIM.
Note:
The time set is for each probe cycle, but the decision to change to the other SIM is determined by
Probe Cycle multiplied by connection Decision amount (e.g. From the image above it will be 12
seconds multiplied by 5 consecutive fails, the router will determine failover to another SIM).
128
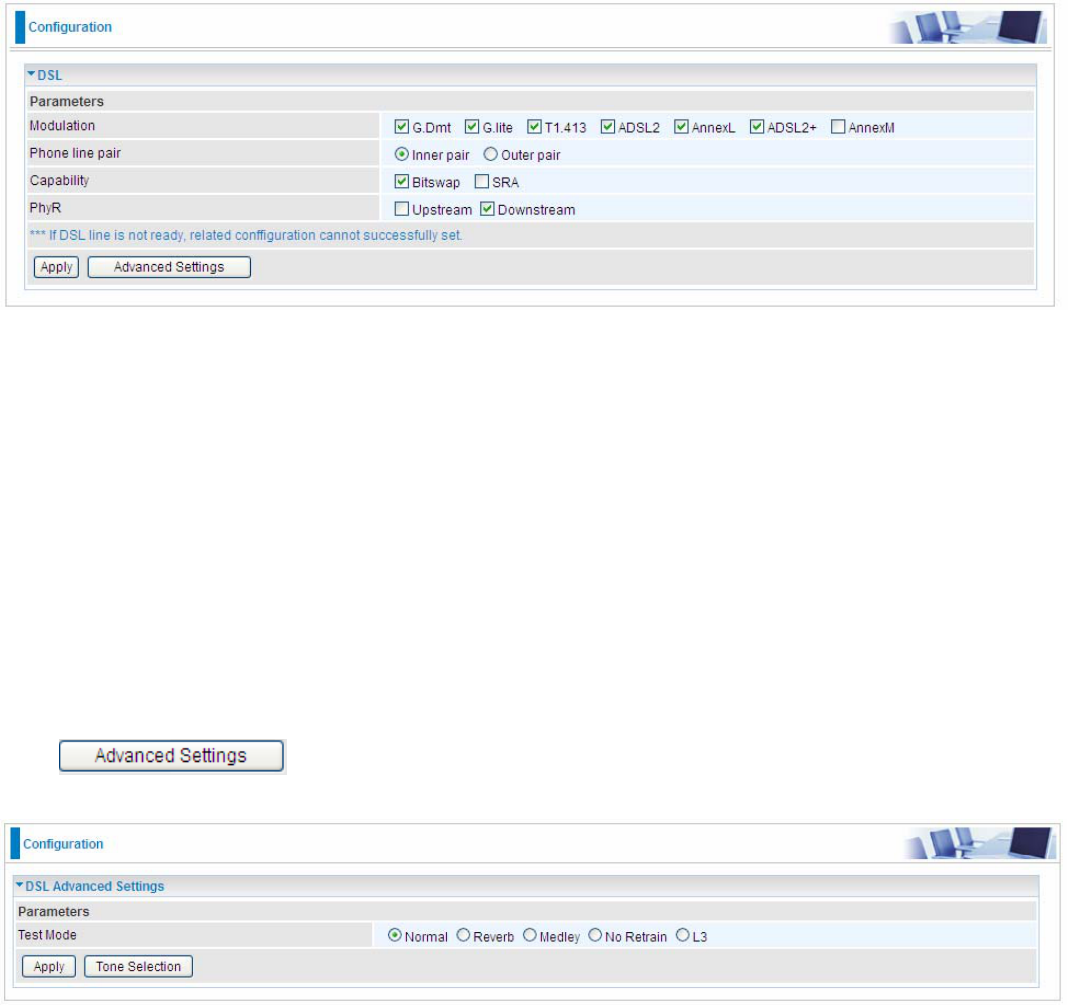
DSL
This screen allows you to set DSL parameters. DSL knowledge is required to configure these
settings. Contact your ISP to make sure that these parameters are correct.
Modulation: There are 7 modes “G.Dmt”, “G.lite”, “T1.413”, “ADSL2”, “AnnexL”, ”ADSL2+”,
“AnnexM” that user can select for this connection.
Phone line pair: This is for reserved only. You can choose "Inner Pair" or "Outer Pair".
Capability: There are 2 options “Bitswap Enable” and “SRA Enable” that user can select for this
connection.
Bitswap Enable: Allows bitswaping function.
SRA Enable: Allows seamless rate adaptation.
PhyR: A new technology to control impulse and noise to improve the BER and DSL data quality.
Click Apply to confirm the settings.
Click to future configure DSL.
Select the Test Mode, or leave it as default.
Tone Selection: This should be left as default or be configured by an advanced user.
The frequency band of ADSL is split up into 256 separate tones, each spaced 4.3125 kHz apart.
129
With each tone carrying separate data, the technique operates as if 256 separate modems were
running in parallel. The tone range is from 0 to 31 for upstream and from 32 to 255 for
downstream。
130
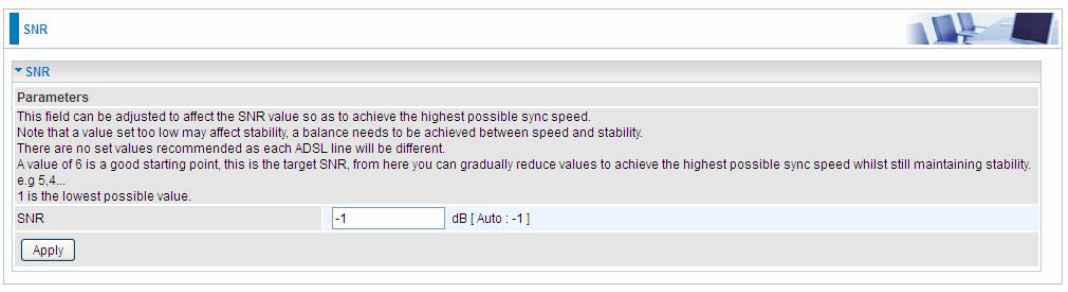
SNR
Signal-to-noise ratio (often abbreviated SNR or S/N) is a measure used in science and engineering
that compares the level of a desired signal to the level of background noise. It is defined as the ratio
of signal power to the noise power.
SNR: Change the value to adjust the DSL link rate, more suitable for an advanced user.
131
System
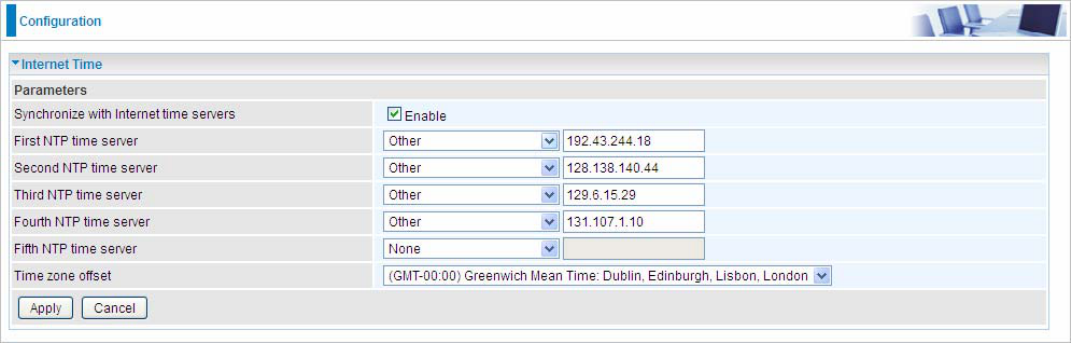
Internet Time
The router does not have a real time clock on board; instead, it uses the Network Time Protocol
(NTP) to get the most current time from an NTP server.
NTP is a protocol for synchronization of computers. It can enable computers synchronize to the NTP
server or clock source with a high accuracy.
Choose the NTP time server from the drop-down menu, if you prefer to specify an NTP server other
than those in the drop-down list, simply enter its IP address in their appropriate blanks provided as
shown above. Your ISP may also provide an SNTP server for you to use.
Choose your local time zone from the drop-down menu. After a successful connection to the Internet,
the router will retrieve the correct local time from the NTP server you have specified. If you prefer to
specify an NTP server other than those in the drop-down list, simply enter its IP address in their
appropriate blanks provided as shown above. Your ISP may also provide an NTP server for you to
use.
Click Apply to apply your settings.
132
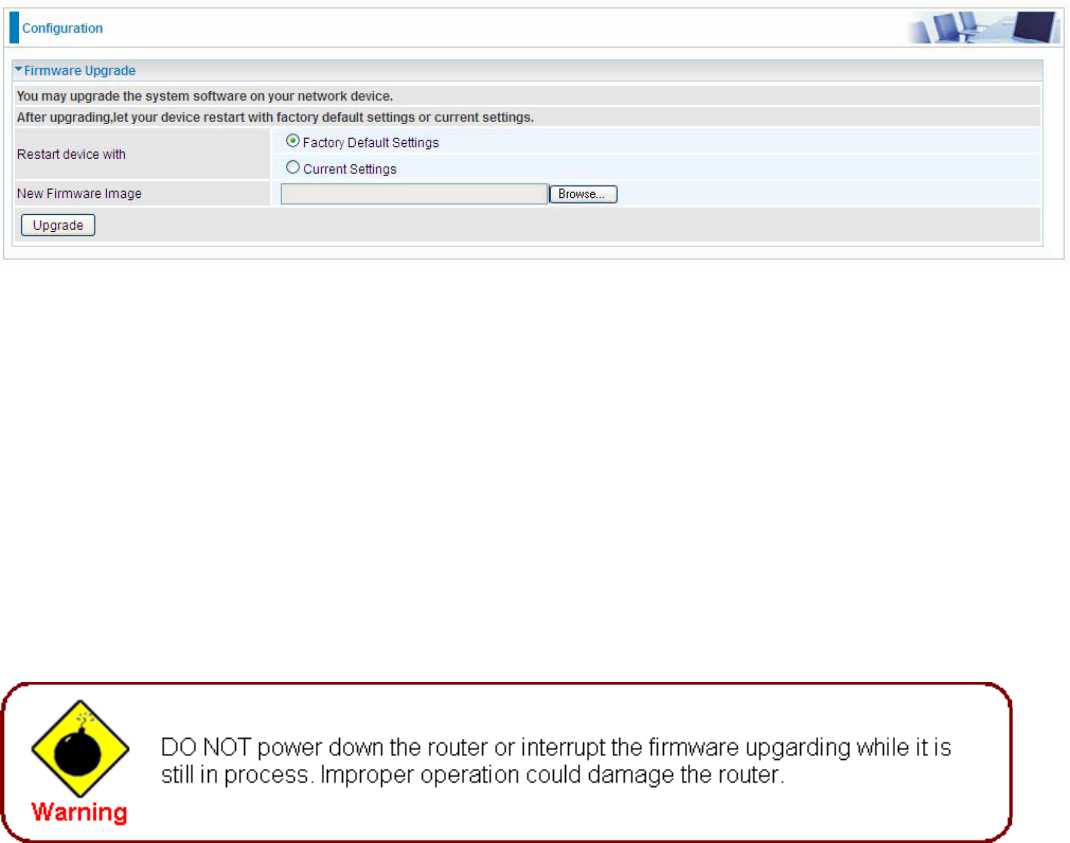
Firmware Upgrade
Software upgrading lets you experience new and integral functions of your router.
Restart device with:
Factory Default Settings: Restart the device with factory default settings automatically when
finishing upgrading.
Current Settings: Restart the device with the current settings automatically when finishing
upgrading.
Your router’s “firmware” is the software that allows it to operate and provides all its functionality.
Think of your router as a dedicated computer, and the firmware as the software it runs. Over time
this software may be improved and revised, and your router allows you to upgrade the software it
runs to take advantage of these changes.
Clicking on Browse will allow you to select the new firmware image file you have downloaded to
your PC. Once the correct file is selected, click Upgrade to update the firmware in your router.
133
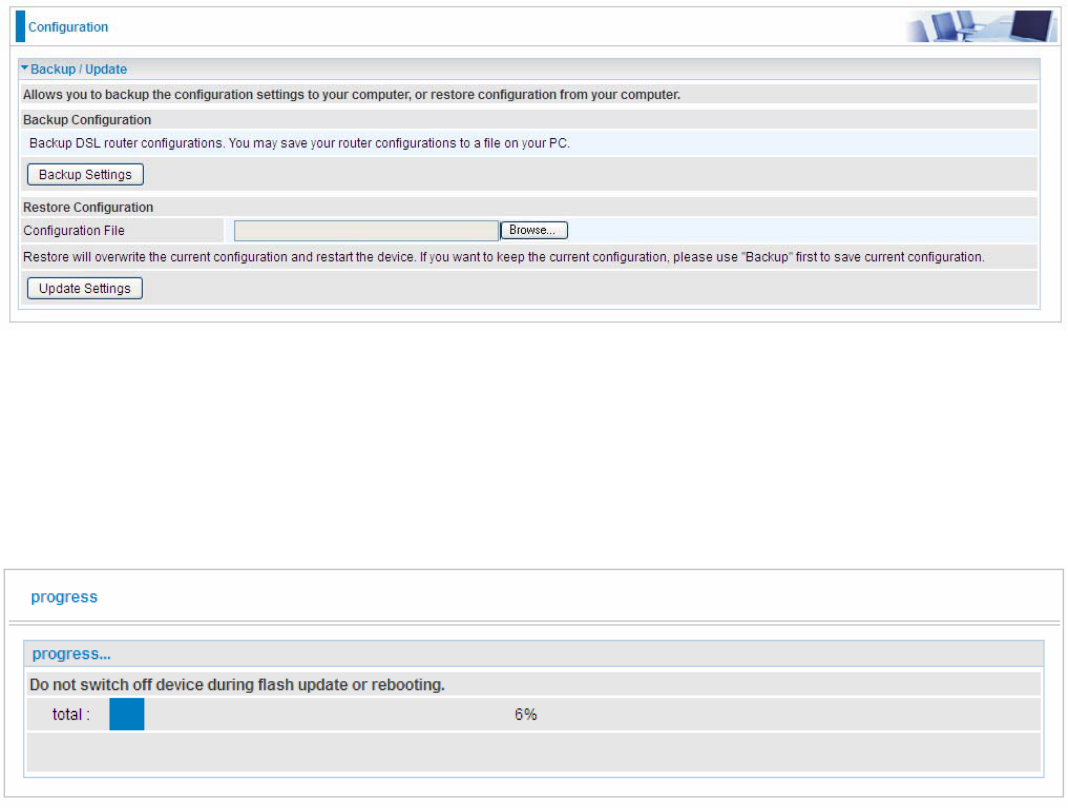
Backup / Update
These functions allow you to save and backup your router’s current settings to a file on your PC, or
to restore from a previously saved backup. This is useful if you wish to experiment with different
settings, knowing that you have a backup handy in the case of any mistakes. It is advisable to
backup your router’s settings before making any significant changes to your router’s configuration.
Click Backup Settings, a window appears, click save , then browse the location where you want to
save the backup file.
Click Browse and browse to the location where your backup file is saved, the click Open. Then in
the above page, click Update Settings, the following process indicating screen will appear. Let it
update to 100%, it will automatically turn to the Device Info page.
134
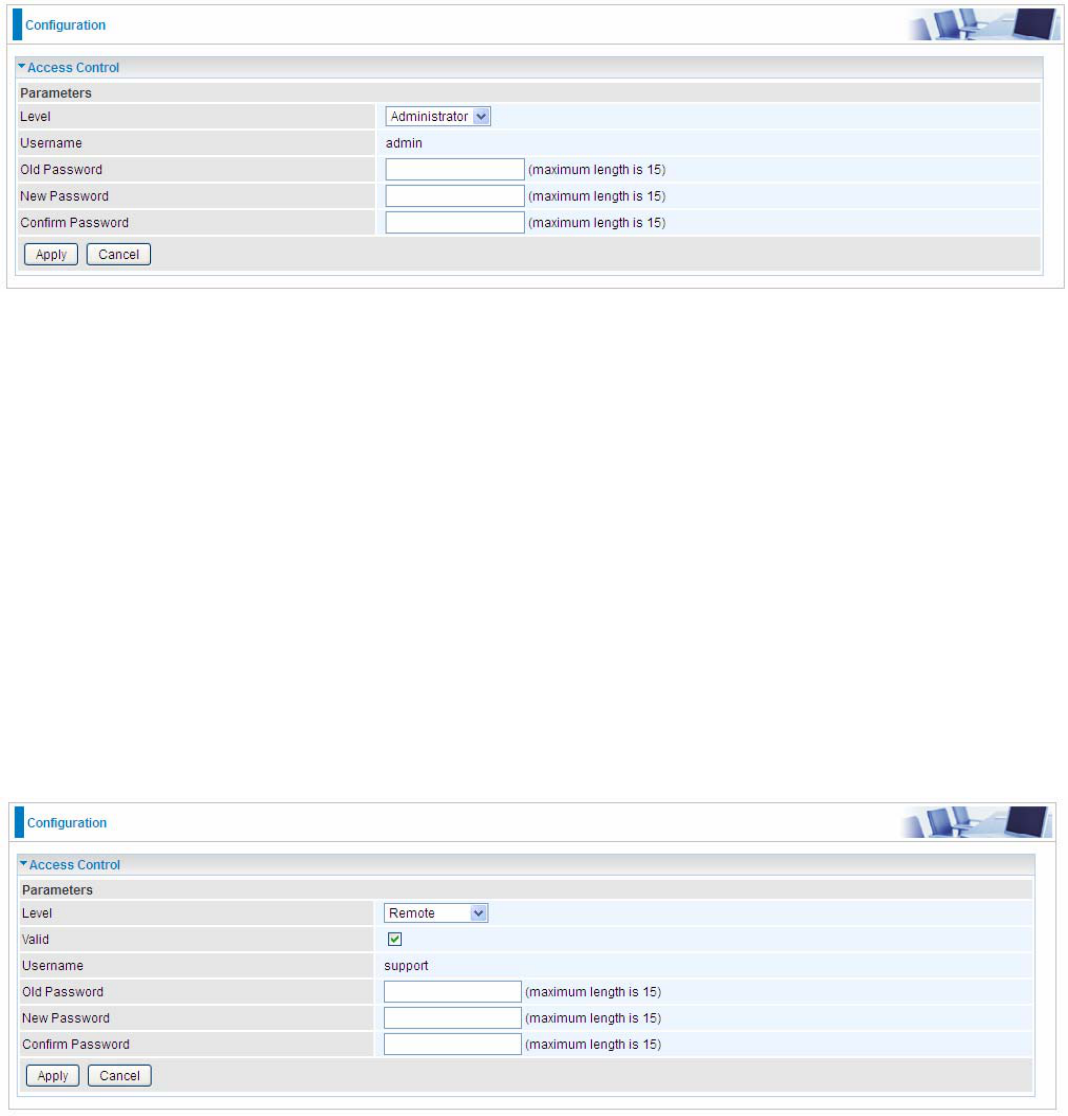
Access Control
Access Control is used to prevent unauthorized access to the router configuration page. Here you
can change the login user password. Three user levels are provided here. Each user level there’s a
default provided user. You must access the router with the appropriate username and password.
Here the corresponding passwords are allowed to change.
Level: select which level you want to change password to. There are three default levels.
Administrator: the root user, corresponding default username and password are admin and
admin respectively.
Remote: username for the remote user to login, corresponding default username and
password are support and support respectively.
Local: username for the general user, when logon to the web page, only lit items would be
listed for common user, corresponding default username password are user and user
respectively.
Username: the default username for each user level.
Old Password: Enter the old password.
New Password: Enter the new password.
Confirm Password: Enter again the new password to confirm.
Note: By default the accounts of Remote and Local are disabled, please click Valid check-box to
activate the accounts.
Click Apply to apply your new settings.
135
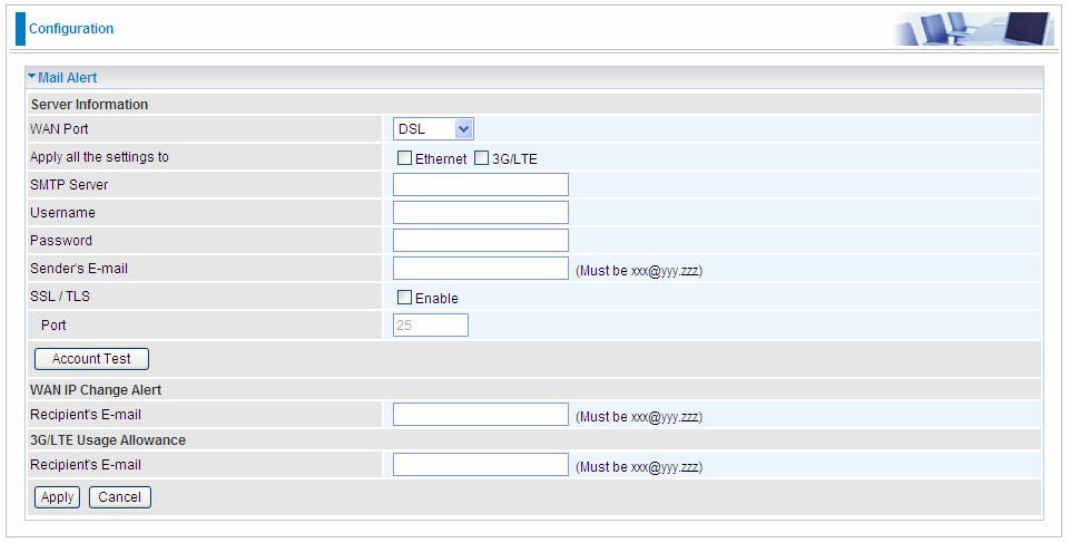
Mail Alert
Mail alert is designed to keep system administrator or other relevant personnel alerted of any
unexpected events that might have occurred to the network computers or server for monitoring
efficiency. With this alert system, appropriate solutions may be tackled to fix problems that may have
arisen so that the server can be properly maintained.
WAN Port: Mail Alert feature can be applicable to every WAN mode: Ethernet,DSL and 3G/LTE.
Select the port you want to use Mail Alert.
For example DSL, then when the WAN connection is in DSL mode and when there is any
unexpected event, the alert message will be sent to your specified E-mail.
Apply all settings to: check whether you want to have a copy of the settings to apply to other WAN
port, suppose the above Main port is DSL, then if you enable this function, then Ethernet port will
have the same configuration.
SMTP Server: Enter the SMTP server that you would like to use for sending emails.
Username: Enter the username of your email account to be used by the SMTP server.
Password: Enter the password of your email account.
Sender’s Email: Enter your email address.
SSL: check to whether to enable SSL encryption feature.
Port: the port, default is 25.
Account Test: Press this button to test the connectivity and feasibility to your sender’s e-mail.
Recipient’s Email (WAN IP Change Alert): Enter the email address that will receive the alert
message once a WAN IP change has been detected.
Recipient’s Email (3G/LTE Usage Allowance): Enter the email address that will receive the alert
message once the 3G over Usage Allowance occurs.
136
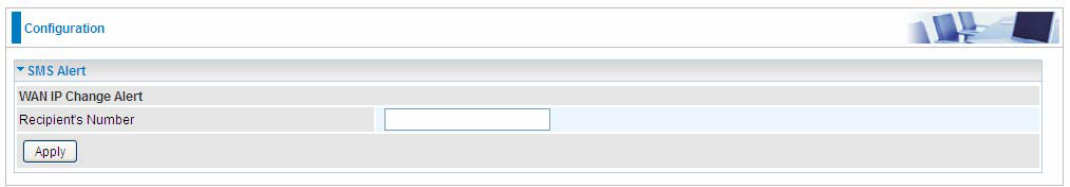
SMS Alert
SMS, Short Message Service, is to inform clients the information clients subscribe. The BiPAC
7820NZ offers SMS alert sending clients alert messages when a WAN IP change is detected.
Recipient’s Number (WAN IP Change Alert): Enter the Recipient’s number that will receive the
alert message once a WAN IP change has been detected.
137
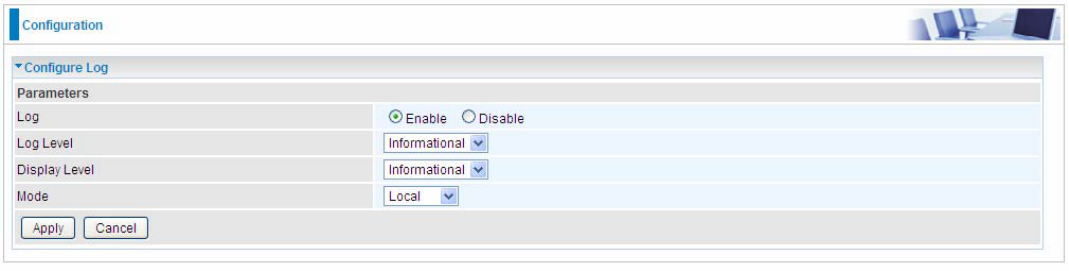
Configure Log
Log: Enable or disable this function.
Log level: Select your log level. The log level allows you to configure which types of events are
logged. There are eight log levels from high to low are displayed below:
Emergency = system is unusable
Alert = action must be taken immediately
Critical = critical conditions
Error = error conditions
Warning = warning conditions
Notice = normal but significant conditions
Informational = information events
Debugging = debug-level messages
The gateway records all log events at the chosen level and above. For instance, if you set the log
level to Critical, all critical, alert, and emergency events are logged, but none of the others are
recorded
Display Level: Display the log according to the level you set when you view system log. Once you
set the display level, the logs of the same or higher priority will be displayed.
Mode: Select the mode the system log adopted. Three modes: local, Remote and Both.
Local: Select this mode to store the logs in the router’s local memory.
Remote: Select this mode to send the log information to a remote log server. Then you must
assign the remote log server and port, 514 is often used.
Both: Logs stored adopting above two ways.
Click Apply to save your settings.
138
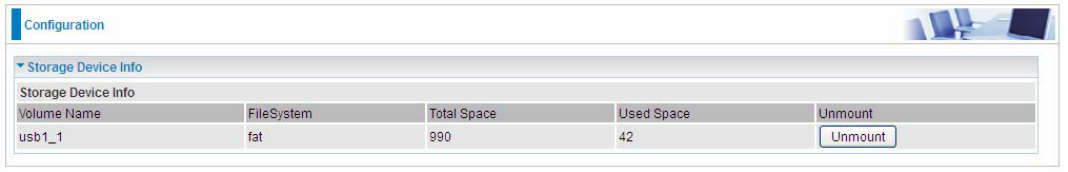
USB
Storage here refers to network sharing in the network environment, USB devices act as the storage
carrier for DLNA, NAS (Samba server, FTP server).
Storage Device Info
This part provides users direct access to the storage information like the total volume, the used and
the remaining capacity of the device.
Volume Name: Display the storage volume name
FileSystem: Display the storage device’s file system format, well-known is FAT.
Total Space: Display the total space of the storage, with unit MB.
Used Space: Display the remaining space of each partition, unit MB.
Unmount: Click Unmount button if you want to uninstall the USB device. Please Note that first click
Unmount before you uninstall your USB storage.
139
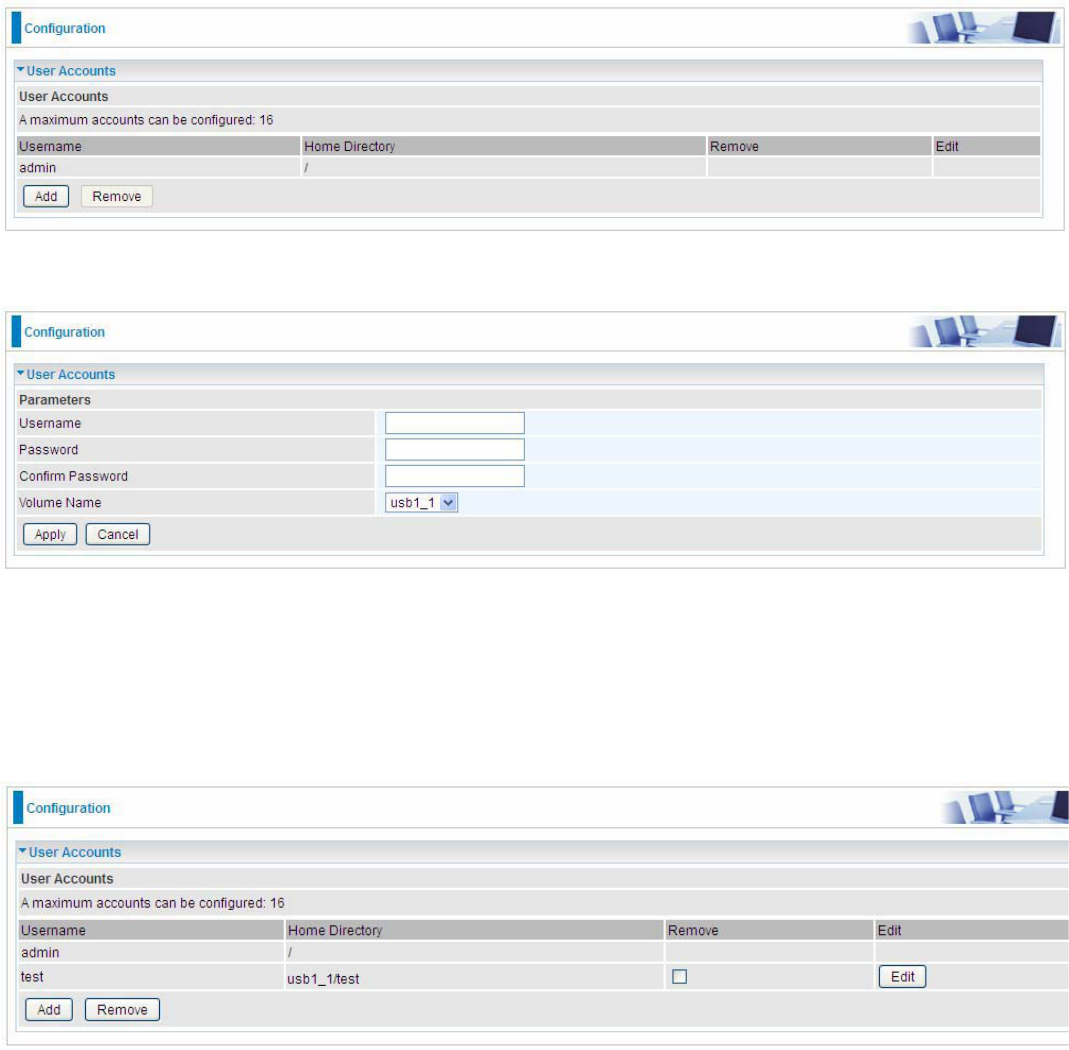
User Account
Users here can add user accounts for access to the storage, in this way users can access the
network sharing storage with the specified account, and again protect their own data.
Users added here are entitled to have access to both Samba server and FTP server.
Default user admin.
Click Add button, enter the user account-adding page:
Username: user-defined name, but simpler and more convenient to remember would be favorable.
Password: Set the password.
Confirm Password: Reset the password for confirmation.
Volume Name: Select Volume name, as to create access to the volume of the specified partition of
the storage.
For example, a user test is setup behind the usb1_1.
The user “test” has the right to access both Samba and FTP server.
140
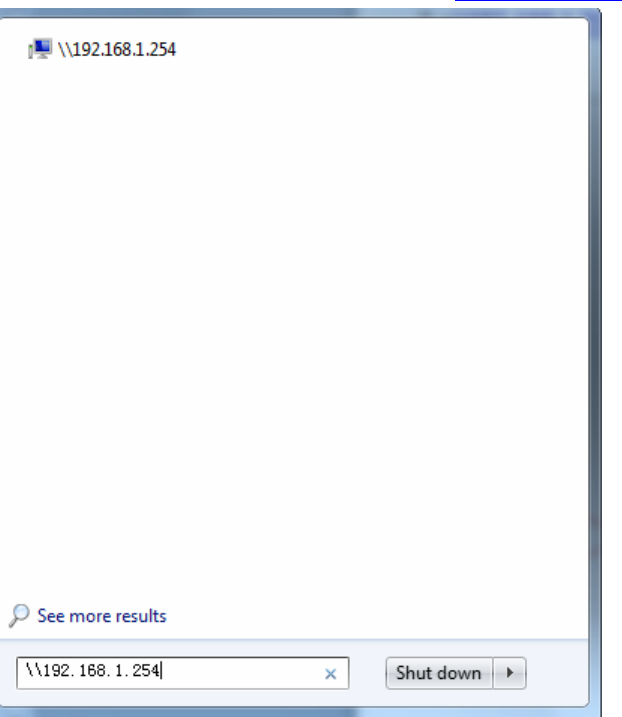
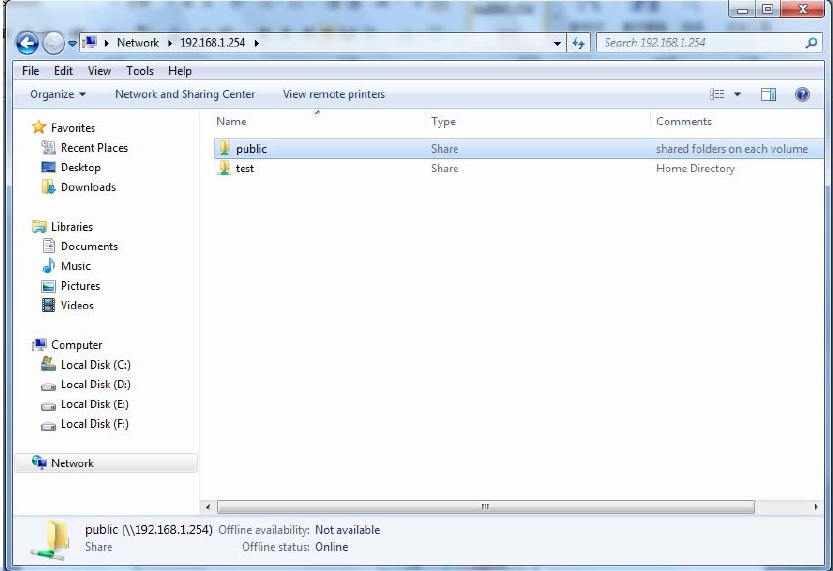
How to access Samba:
In your computer, Click Start > Run, enter \\192.168.1.254 (LAN IP)
141
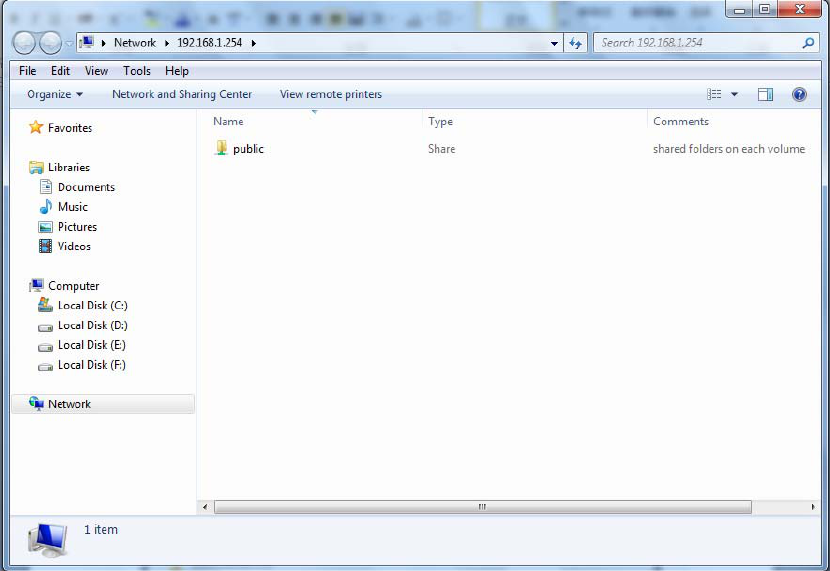
When accessing the network storage, you can see a folder named “public”, users should have the
account to enter, and the account can be set at the User Accounts section.
When first logged on to the network folder, you will see the “public” folder.
Public: The public sharing space for each user in the USB Storage.
When user register a USB account and log successfully, a private folder (the same name as the user
account registered) exclusive for each user is established. Go on to see the details.
142
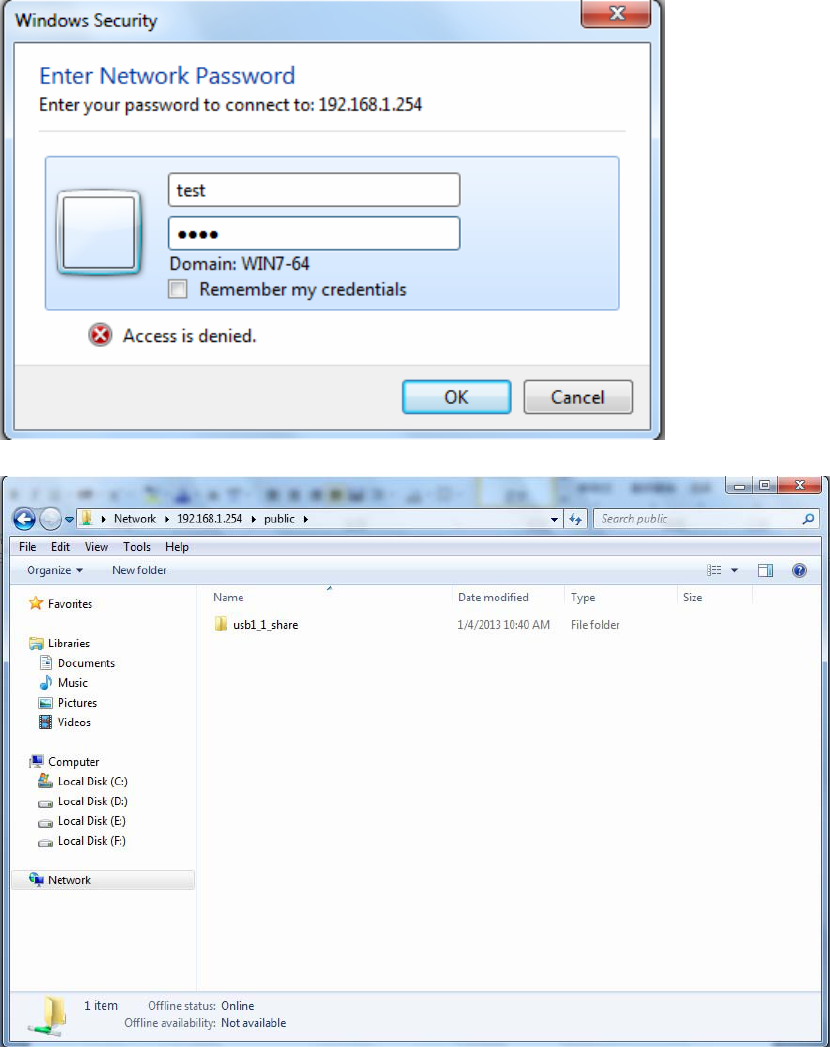
Access the folder public.
143
When successfully accessed, the private folder of each user is established, and user can see from
the following picture. The test fold in the picture is the private space for each user.
144
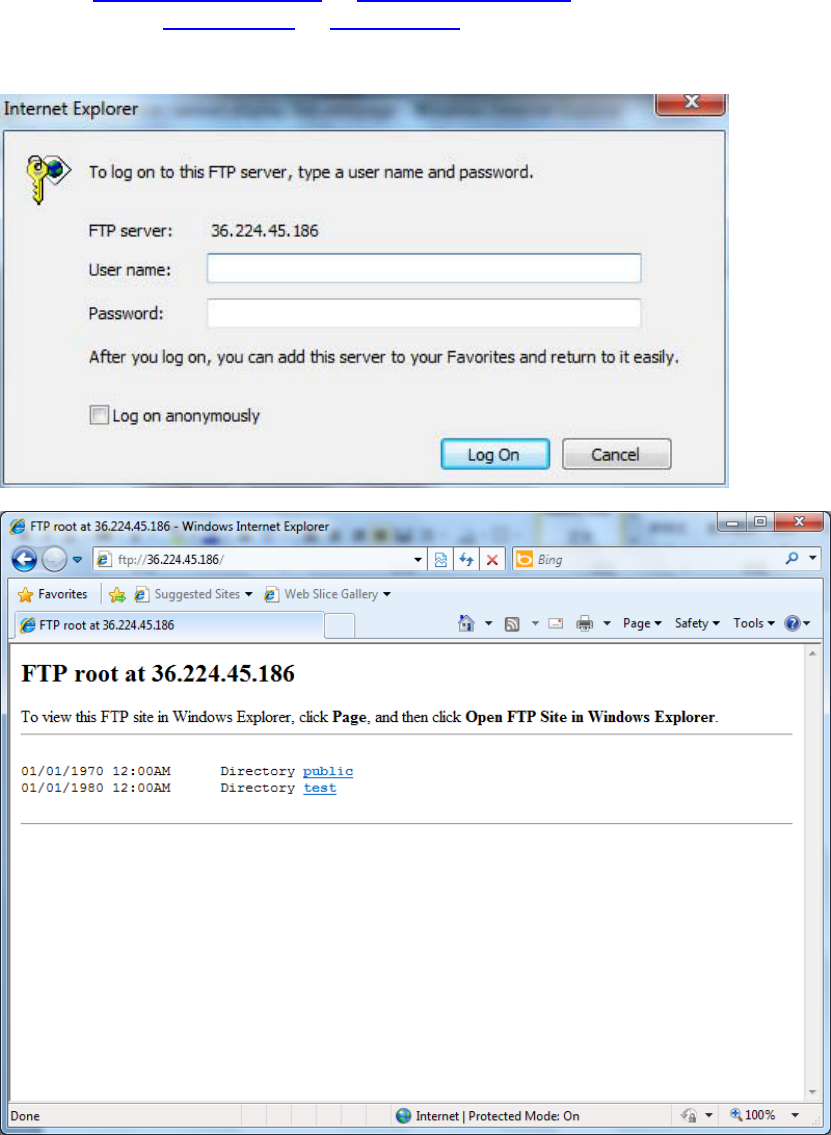
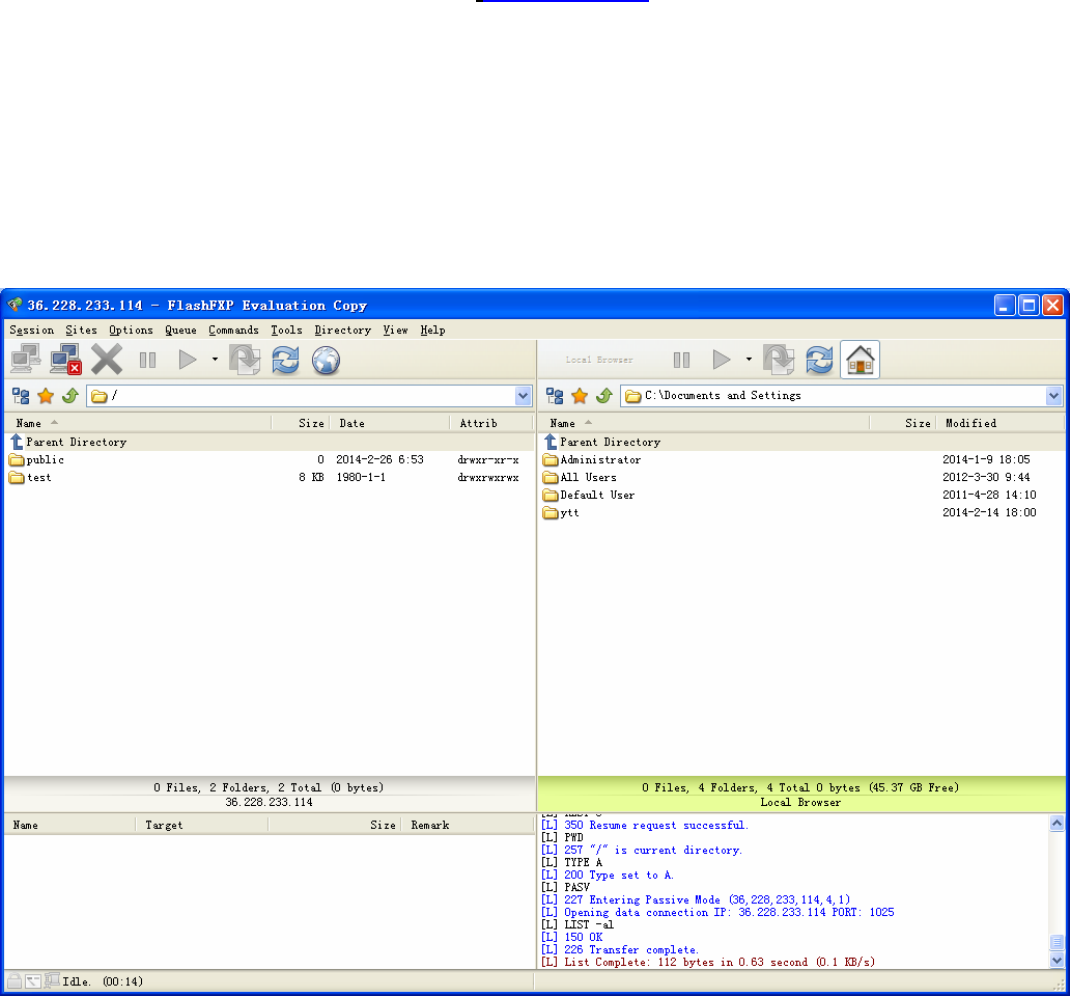
How to use FTP:
Please note to enable remote FTP access in Remote Access.
1. Access via FTP tools
Take popular FTP tool of FlashFXP for example:
1) Open FlashFXP
2) Create ftp sites (LAN IP / WAN IP, and set the account, port).
3) Connect to the ftp site.
146
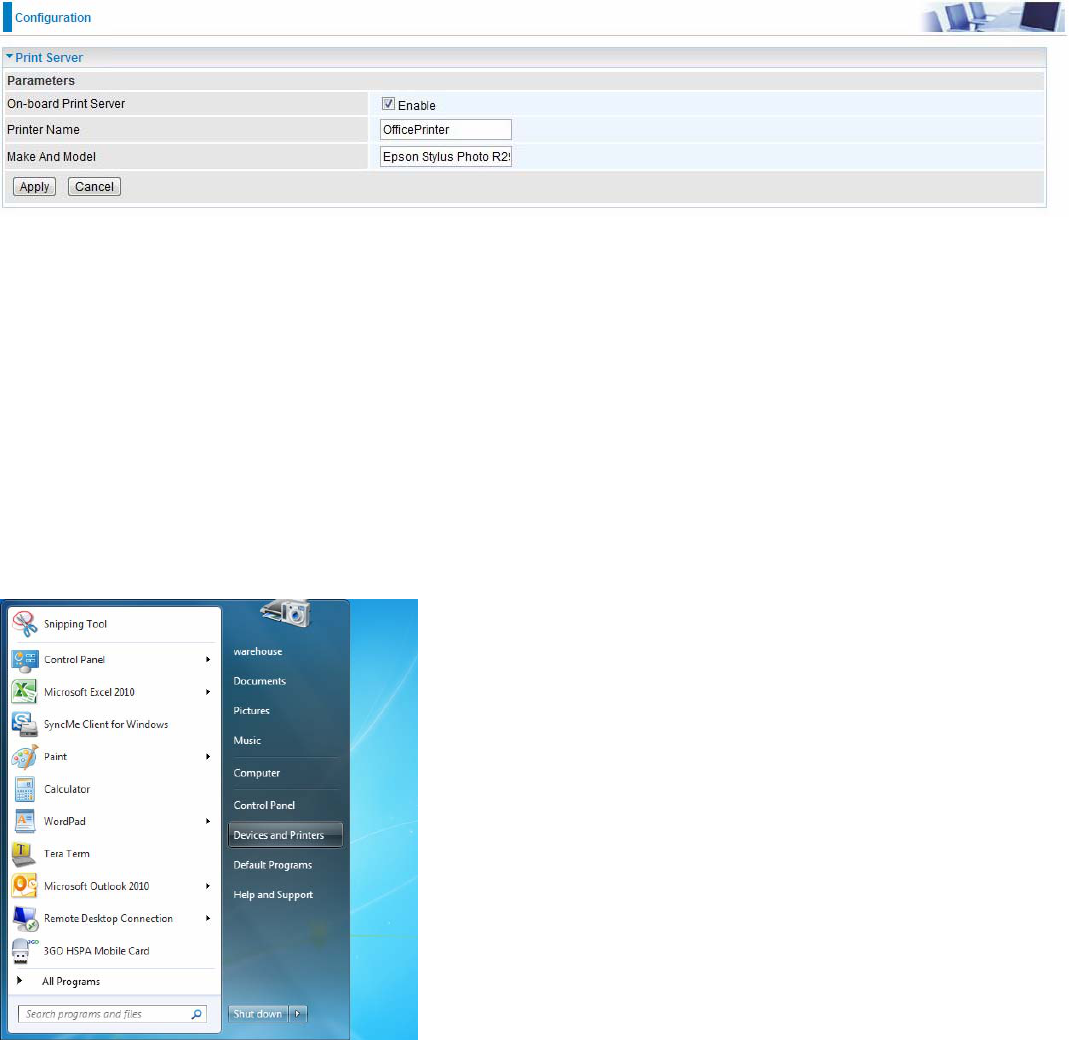
Print Server
The Print Server feature allows you to share a printer on your network by connecting a USB cable
from your printer to the USB port on the 7820NZ. This allows you to print from any location on your
network.
Note: Only USB printers are supported
Setup of the printer is a 3 step process (7820NZ for example)
1. Connect the printer to the 7820NZ’s USB port
2. Enable the print server on the 7820NZ
3. Install the printer drivers on the PC you want to print from
On-board Print Server: Check Enable to activate the print server
Printer Name: Enter the Printer name, for example, OfficePrinter
Make and Model: Enter in the Make and Model information for the printer, for example, Epson
Stylus Photo R290
Note:
The Printer name can be any text string up to 40 characters. It cannot contain spaces.
The Make and Model can be any text string up to 128 characters.
Set up of Printer client (Windows 7)
Step 1: Click Start and select “Devices and Printers”
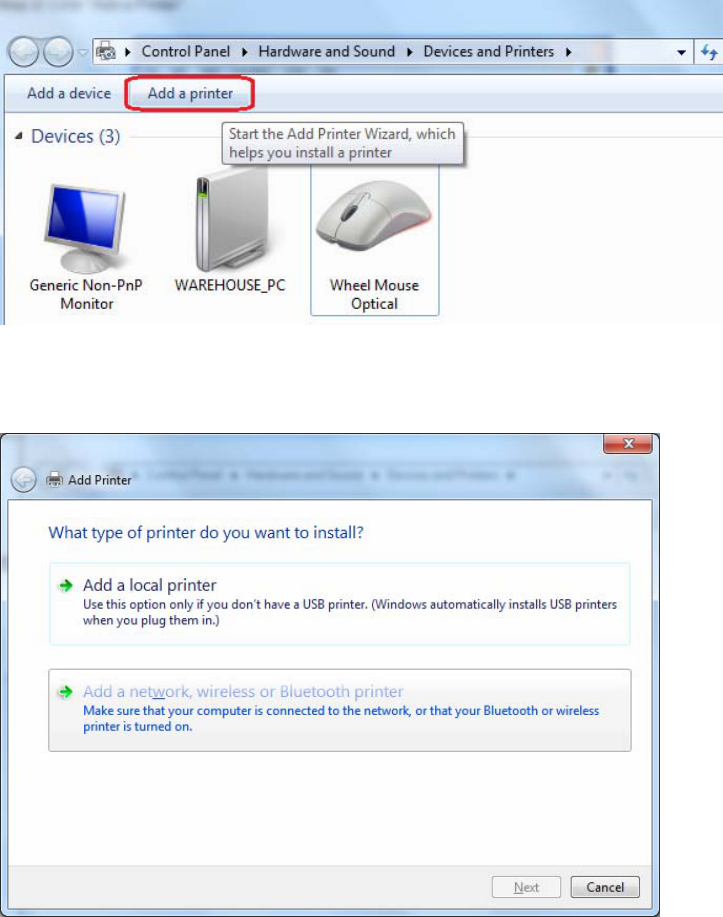
147
Step 2: Click ‘’Add a Printer’’.
Step 3: Click “Add a network, wireless or Bluetooth printer
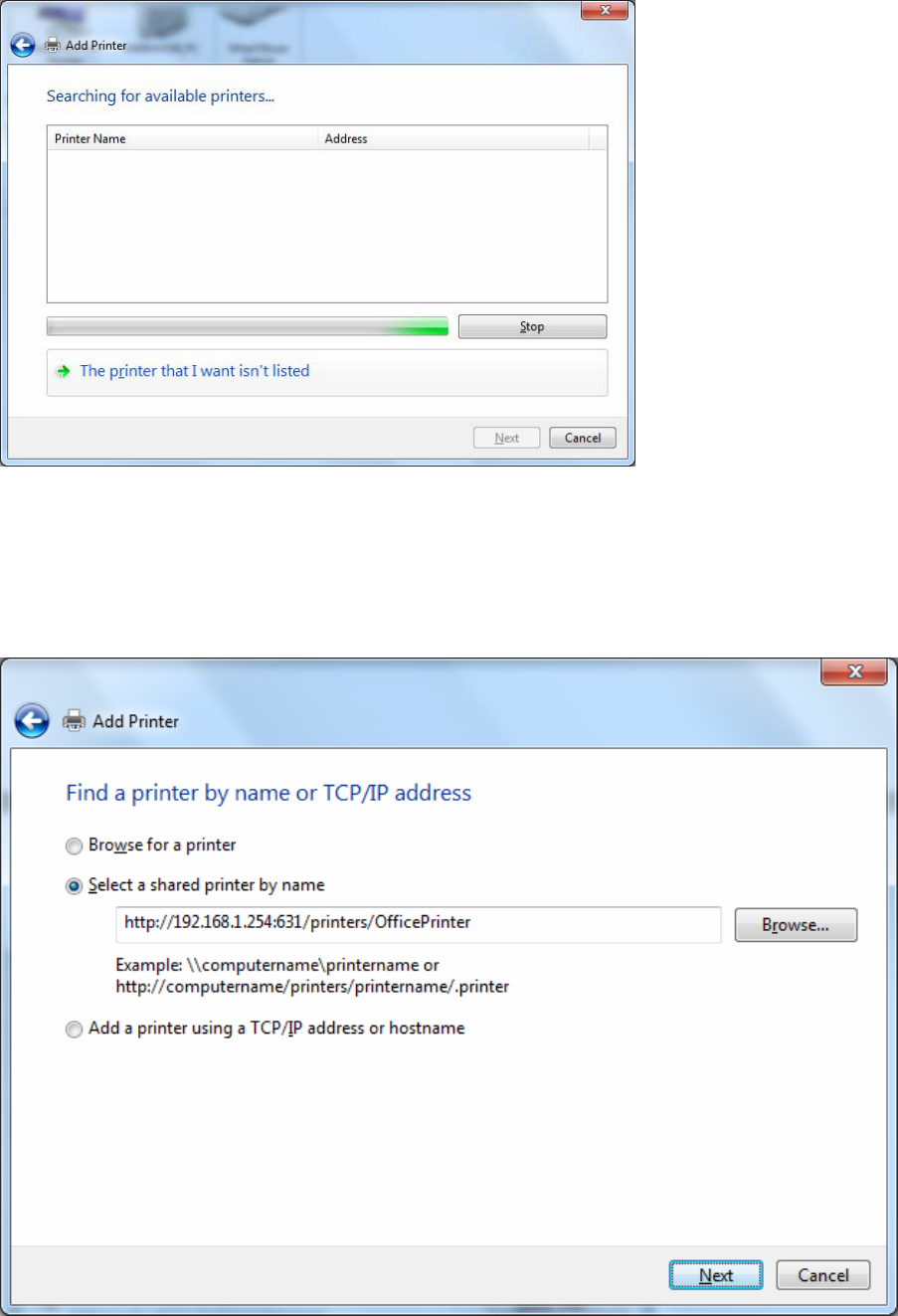
148
Step 4: Click “The printer that I want isn’t listed”
Step 5: Select “Select a shared printer by name”
Enter http://7820NZ- LAN-IP:631/printers/printer-name or. Make sure printer’s name is the same as what you set in
the 7820NZ earlier
For Example: http://192.168.1.254:631/printers/OfficePrinter
OfficePrinter is the Printer Name we setup earlier
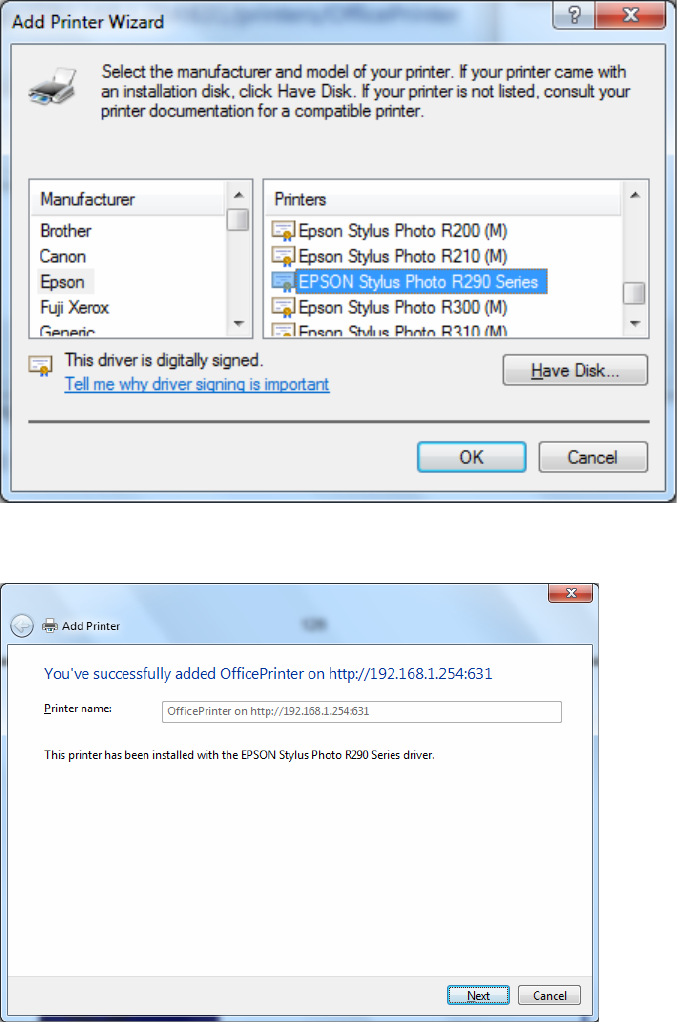
149
Step 6: Click “Next” to add the printer driver. If your printer is not listed and your printer came with an installation
disk, click “Have Disk” find it and install the driver.
Step 7: Click “Next”
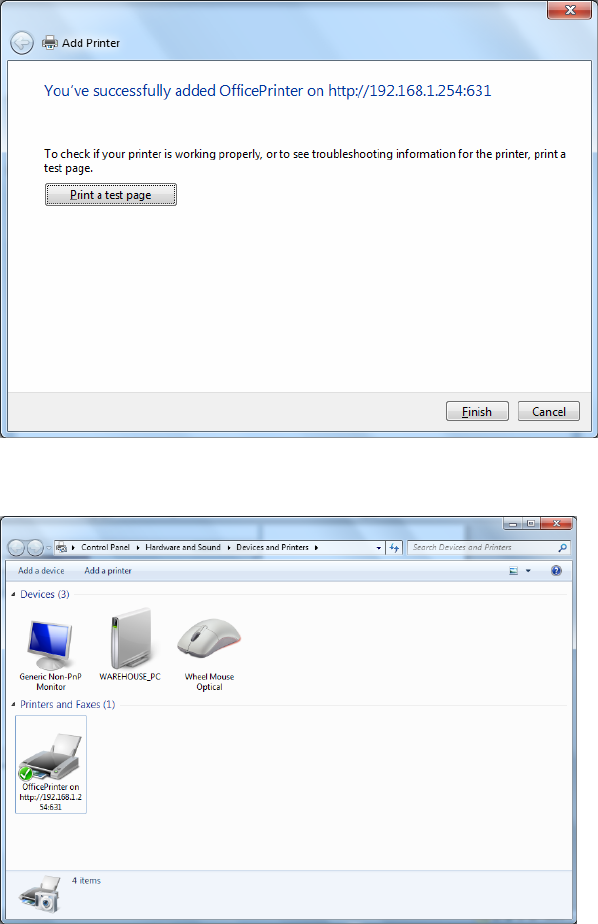
150
Step 8: Click “Next” and you are done
You will now be able to see your printer on the Devices and Printers Page
151
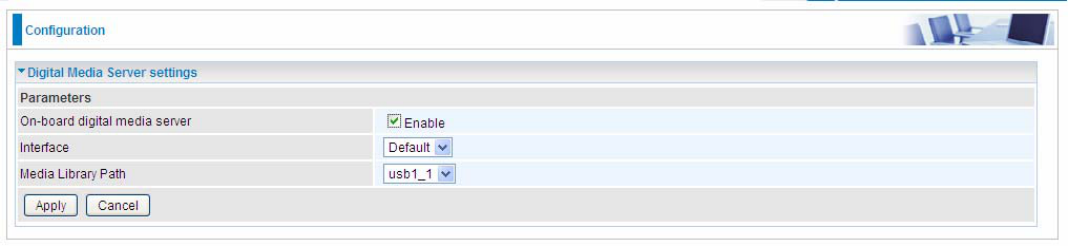
DLNA
The Digital Living Network Alliance (DLNA) is a non-profit collaborative trade organization
established by Sony in June 2003, which is responsible for defining interoperability guidelines to
enable sharing of digital media between consumer devices such as computers, printers, cameras,
cell phones and other multiple devices.
DLNA uses Universal Plug and Play (UPnP) for media management, discovery and control. UPnP
defines the types of devices (‘server’, ‘renderer’, ‘controller’) that DLNA supports and the mechanism
for accessing media over a network.
Overall, DLNA allows more convenience, more choices and enjoyment of your digital content
through DLNA certified devices. Any DLNA certified devices or software can access the DLNA
server.
With USB storage, 7820NZ can serve as a DLNA server.
On-board digital media server: Enable to share the device as a DLNA server.
Interface: The VLAN group, it is the bound interface for DLNA server accessing.
Media Library Path: Default is usb1_1, total USB space (pictures, videos, music, etc, all can be
accessed with this path).
152
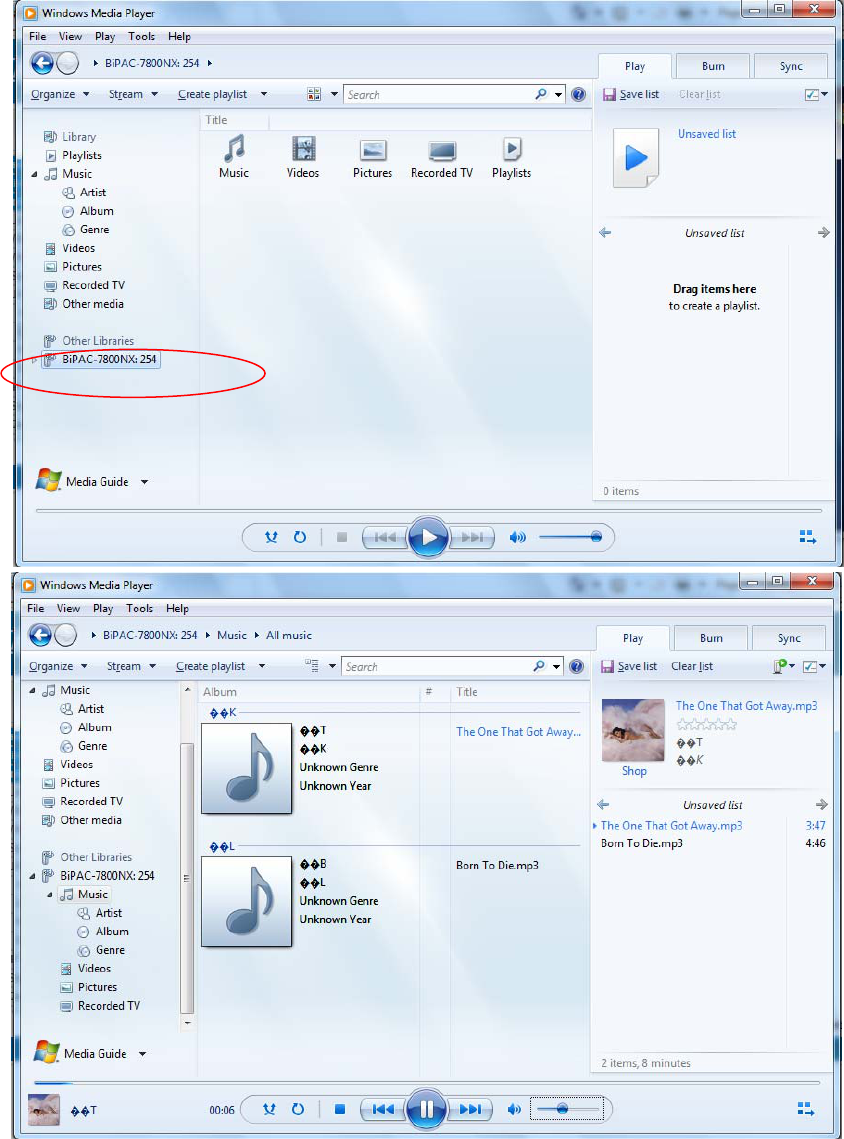
Take Windows media player in Windows 7 accessing the DLNA server for example for usage of
DLNA .
153
IP Tunnel
An IP Tunnel is an Internet Protocol (IP) network communication channels between two networks of
different protocols. It is used to transport another network protocol by encapsulation of its packets.
IP Tunnels are often used to connect two disjoint IP networks that do not have a native routing path
to each other, via an underlying routable protocol across an intermediate transport network, like VPN.
Another prominent use of IP Tunnel is to connect islands of IPv6 installations across the IPv4
internet.
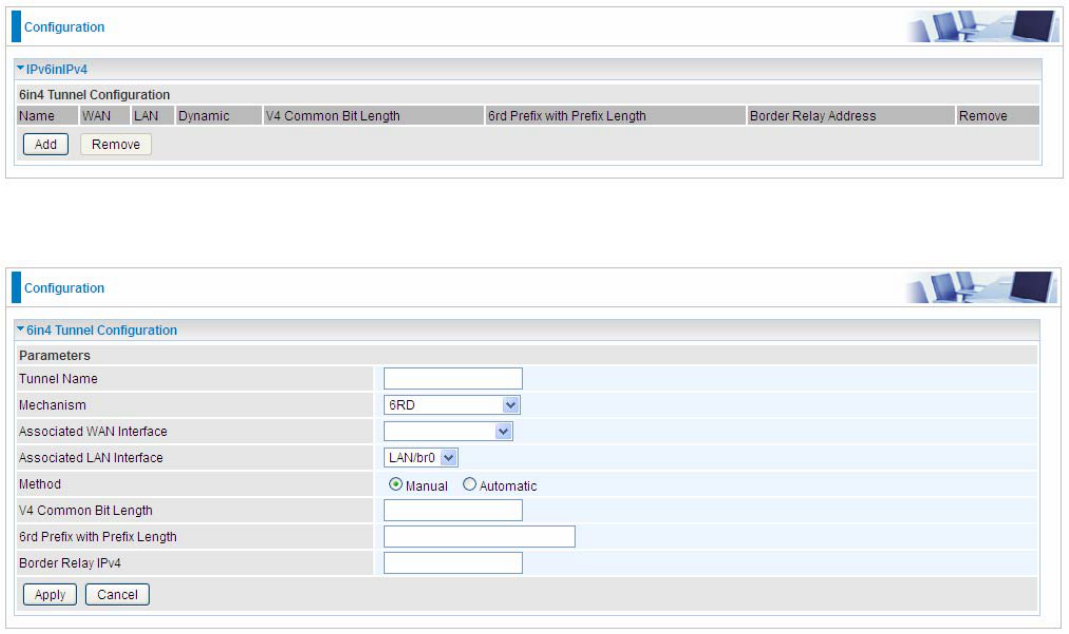
IPv6inIPv4
6in4 is an Internet transition mechanism for migrating from IPv4 to IPv6. 6in4 uses tunneling to
encapsulate IPv6 traffic over explicitly configured IPv4 links. The 6in4 traffic is sent over the IPv4
Internet inside IPv4 packets whose IP headers have the IP Protocol number set to 41. This protocol
number is specifically designated for IPv6 capsulation.
6RD:
6RD is a mechanism to facilitate IPv6 rapid deployment across IPv4 infrastructures of internet
service providers (ISPs).
It is derived from 6to4, a preexisting mechanism to transporting IPv6 packets over IPv4
infrastructure network, with the significant change that it operates entirely within the enduser’s ISP
network, thus avoiding the major architectural problems inherent in the original design of 6to4.
Click Add button to manually add the 6in4 rules.
Tunnel Name: User-defined name.
Mechanism: Here only 6RD.
154
Associated WAN Interface: The applied WAN interface with the set tunnel, thus when there are
packets from/to the WAN interface, the tunnel would be used to transport the packets.
Associated LAN Interface: Set the linked LAN interface with the tunnel.
Method: 6rd operation mechanism: manually configured or automatically configured. If manually,
please fill out the following 6rd parameters.
V4 Common Bit Length: Specify the length of IPv4 address carried in IPv6 prefix, for example, 0
means to carry all the 32 bits of IPv4 address while 8 carries 24 bits of the IPv4 address.
6rd Prefix with Prefix Length: Enter the 6rd prefix and prefix length you uniquely designate to 6rd
by the ISP( The 6rd prefix and prefix length are to replace the standard 6to4 prefix 2002::/16 by an
IPv6 prefix that belongs to the ISP-assigned.)
Border Relay IPv4 Address: The IPv4 address of the border relay. The relay is used to unwrap
capsulated IPv4 packets into IPv6 packets and send them to the IPv6 network.
155
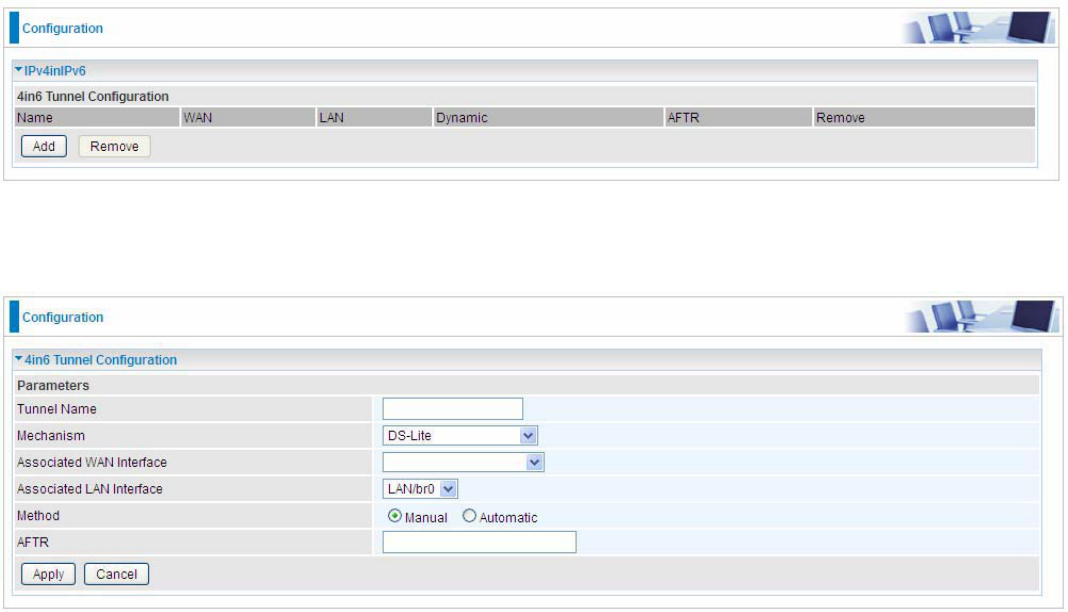
IPv4inIPv6
4in6 refers to tunneling of IPv4 in IPv6. It is an inherent internet interoperation mechanism allowing
IPv4 to be used in an IPv6 only network.
4in6 uses tunneling to encapsulate IPv4 traffic over configured IPv6 tunnels. 4in6 tunnels are usually
manually configured but they can be automated using protocols such as TSP to allow easy
connection to a tunnel broker.
DS – Lite
DS –Lite, or Dual-Stack Lite, is designed to let an ISP omit the deployment of any IPv4 address to
the customer’s CPE. Instead, only global IPv6 addresses are provided (Regular Dual-Stack Lite
deploys global addresses for both IPv4 and IPv6).
The CPE distributes private IPv4 addresses for the LAN clients, the same as a NAT device. The
subnet information is chosen by the customer, identically to the NAT model. However, instead of
performing the NAT itself, the CPE encapsulates the IPv4 packet inside an IPv6 packet.
Click Add button to manually add the 4in6 rules.
Tunnel Name: User-defined tunnel name.
Mechanism: It is the 4in6 tunnel operation technology. Please select DS-Lite.
Associated WAN Interface: The applied WAN interface with the set tunnel, and when there are
packets from/to the WAN interface, the tunnel would be used to transport the packets.
Associated LAN Interface: Specify the linked LAN interface with the tunnel.
Method: Manually to specify the AFTP (Address Family Transition Router) address or Automatic.
AFTR: Specify the address of AFTP (Address Family Transition Router) from your ISP.
156
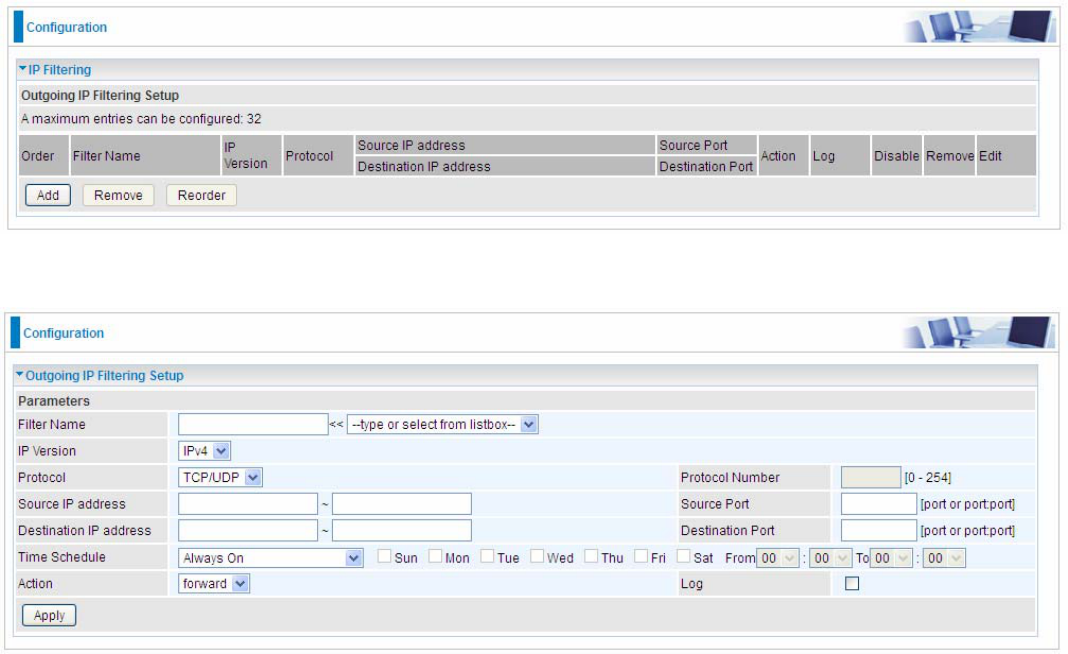
Security
IP Filtering Outgoing
IP filtering enables you to configure your router to block specified internal/external users (IP address)
from Internet access, or you can disable specific service requests (Port number) to /from Internet.
The relationship among all filters is “or” operation, which means that the router checks these
different filter rules one by one, starting from the first rule. As long as one of the rules is satisfied, the
specified action will be taken.
Outbound IP Filtering by default is set to forward all outgoing traffic from LAN to go through the
router, but user can set rules to block the specific outgoing traffic.
Note: The maximum number of entries: 32.
Click Add button to enter the exact rule setting page.
Filter Name: A user-defined rule name. User can select simply from the list box for the application
for quick setup.
IP Version: Select the IP Version, IPv4 or IPv6.
Protocol: Set the traffic type (TCP/UDP, TCP, UDP, ICMP ) that the rule applies to.
Source IP address: This is the Address-Filter used to allow or block traffic to/from particular IP
address(es) featured in the IP range. If you leave empty, it means any IP address.
Source Port [port or port:port]: The port or port range defines traffic from the port (specific
application) or port in the set port range blocked to go through the router. Default is set port from
range 1 – 65535.
Destination IP address: Traffic from LAN with the particular traffic destination address specified in
the IP range is to be blocked from going through the router, similarly set as the Source IP address
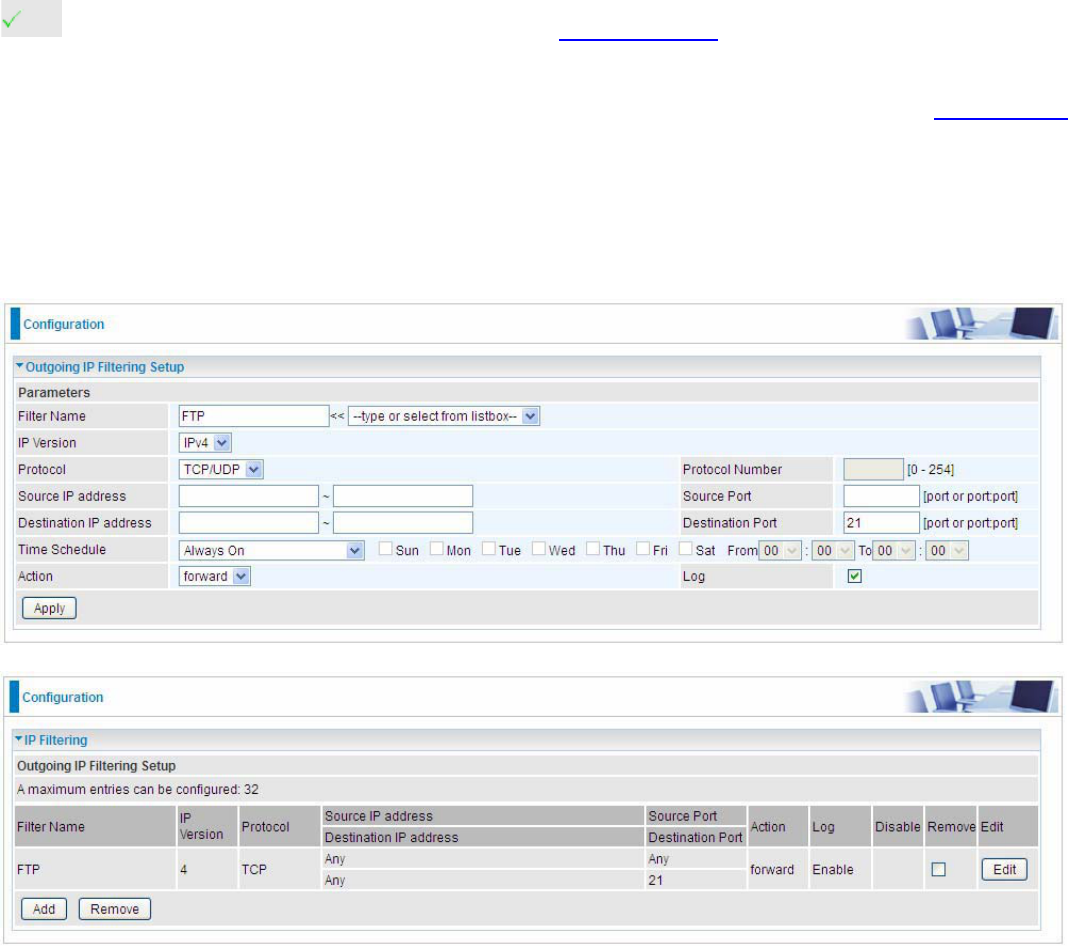
157
above.
Destination Port [port or port: port]: Traffic with the particular set destination port or port in the set
port range is to be blocked from going through the router. Default is set port from port range: 1 –
65535.
Time Schedule: Select or set exactly when the rule works. When set to “Always On”, the rule will
work all time; and also you can set the precise time when the rule works, like 01:00 - 19:00 from
Monday to Friday. Or you can select the already set timeslot in “Time Schedule” during which the
rule works. And when set to “Disable”, the rule is disabled or inactive and there will be an icon”
” in list table indicating the rule is inactive. See Time Schedule.
Action: Select to drop or forward the packets fit the outgoing filtering rule.
Log: check the check-box to record the security log. To check the log, users can turn to Security Log.
Example: For example, if there is an outgoing rule set as follows, then the 21 application between
source IP and destination IP will be forwarded. Or exactly in the rule below, all traffic trying to access
FTP will be forwarded.
(The rule is active; disable field shows the status of the rule, active or inactive)
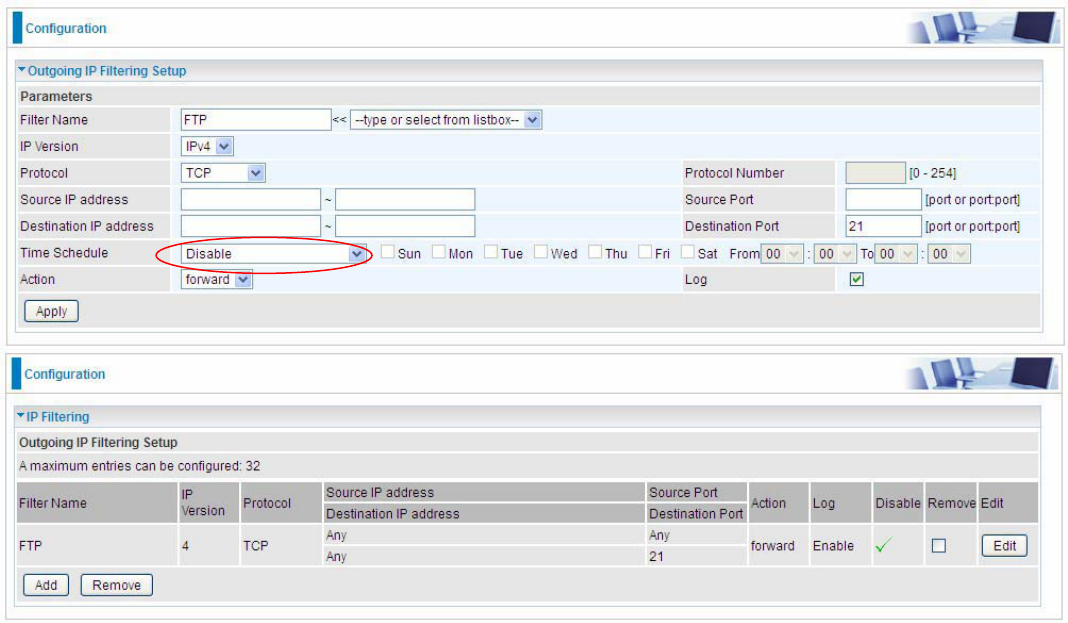
158
(Rule inactive)
159
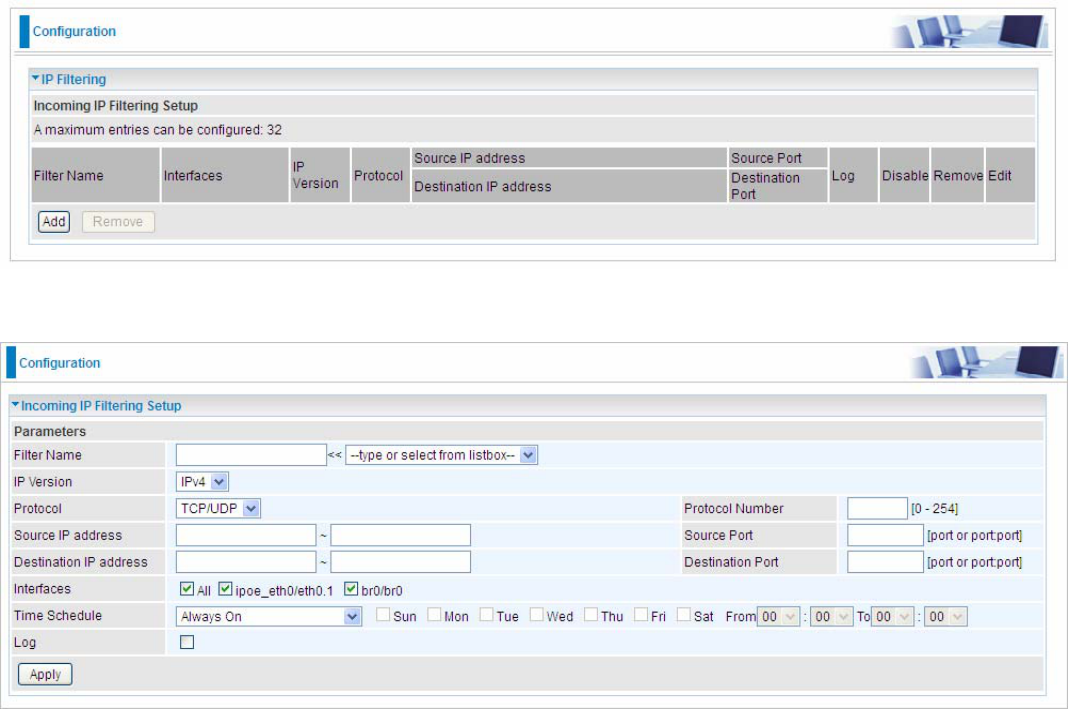
IP Filtering Incoming
Incoming IP Filtering is set by default to block all incoming traffic, but user can set rules to forward
the specific incoming traffic.
Note:
1. The maximum number of entries: 32.
2. When LAN side firewall or firewall in WAN interface(s) is enabled, user can move here to add
allowing rules to pass through the firewall.
Click Add button to enter the exact rule setting page.
Filter Name: A user-defined rule name. User can select simply from the list box for the application
for quick setup.
IP Version: Select the IP Version, IPv4 or IPv6.
Protocol: Set the traffic type (TCP/UDP, TCP, UDP, ICMP ) that the rule applies to.
Source IP address: This is the Address-Filter used to allow or block traffic to/from particular IP
address(es) featured in the IP range.. If you leave empty, it means any IP address.
Source Port [port or port:port]: The port or port range defines traffic from the port (specific
application) or port in the set port range blocked to go through the router. Default is set port from
range 1 – 65535.
Destination IP address: Traffic from LAN with the particular traffic destination address specified in
the IP range is to be blocked from going through the router, similarly set as the Source IP address
above.
Destination Port [port or port : port]: Traffic with the particular set destination port or port in the
set port range is to be blocked from going through the router. Default is set port from port range: 1 –
65535
Interfaces: Check if the filter rule applies to all interfaces. User can base on need select interfaces
to make the rule take effect with those interfaces.

160
Time Schedule: Select or set exactly when the rule works. When set to “Always On”, the rule will
work all time; and also you can set the precise time when the rule works, like 01:00-19:00 from
Monday to Friday. Or you can select the already set timeslot in “Time Schedule” during which the
rule works. And when set to “Disable”, the rule is disabled or inactive and there will be an icon”
” in the list table indicating the rule is inactive. See Time Schedule.
Log: check the check-box to record the security log. To check the log, users can turn to Security Log.
161
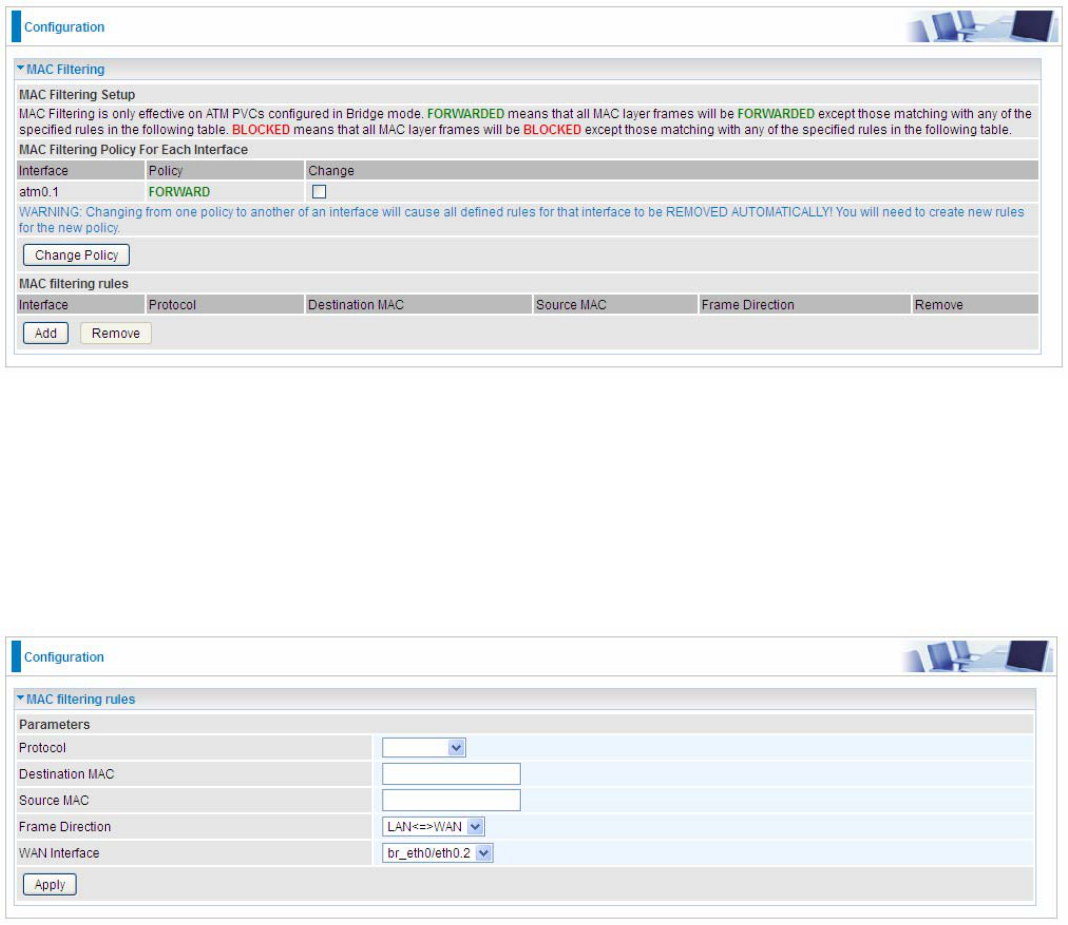
MAC Filtering
MAC Filtering is only effective on ATM PVCs configured in Bridged mode.
FORWARDED means that all MAC layer frames will be forwarded except those matching with any
of the specified rules in the following table.
BLOCKED means that all MAC layer frames will be blocked except those matching with any of the
specified rules in the following table.
By default, all MAC frames of the interface in Bridge Mode will be forwarded, you can check
Change checkbox and then press Change Policy to change the settings to the interface.
For example, from above, the interface atm0.1 is of bridge mode, and all the MAC layer frames will
be forward, but you can set some rules to let some item matched the rules to be blocked.
Click Add button to add the rules.
Protocol type: Select from the drop-down menu the protocol that applies to this rule.
Destination /Source MAC Address: Enter the destination/source address.
Frame Direction: Select the frame direction this rule applies, both LAN and WAN: LAN <=>WAN,
only LAN to WAN: LAN=>WAN, only WAN to LAN: WAN=>LAN.
WAN Interfaces: Select the interfaces configured in Bridge mode.
162
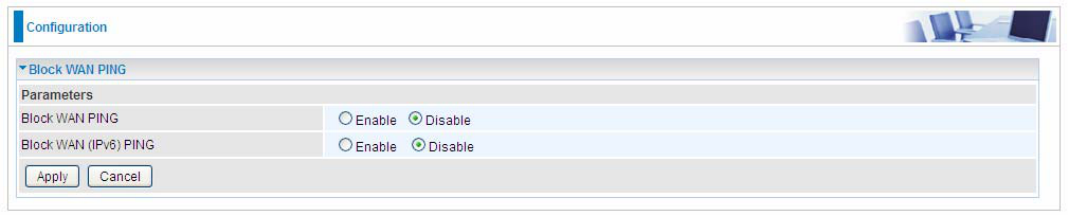
Blocking WAN PING
This feature is enabled to let your router not respond to any ping command when someone others
“Ping” your WAN IP.
163
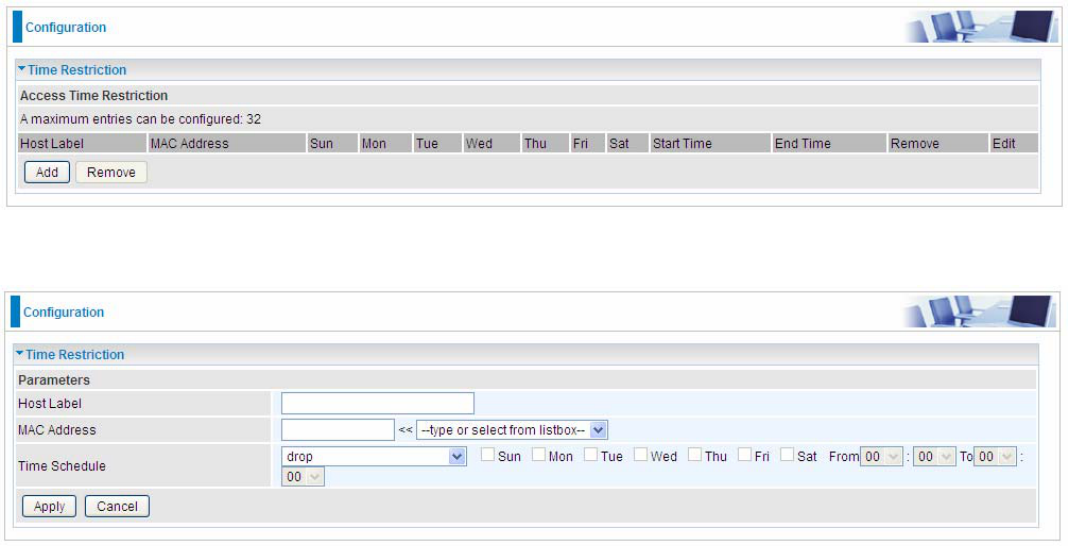
Time Restriction
A MAC (Media Access Control) address is the unique network hardware identifier for each PC on
your network’s interface (i.e. its Network Interface Card or Ethernet card). Using your router’s MAC
Address Filter function, you can configure the network to block specific machines from accessing
your LAN during the specified time.
This page adds time of day restriction to a special LAN device connected to the router. To Restrict
LAN device(s), please click Add button to add the device(s) from accessing internet under some set
time. To find out the MAC address of a window based PC, go to command window, and type
“ipconfig/all”.
Note: The maximum entries configured: 32.
Click Add to add the rules.
Host Label: User-defined name.
MAC Address: Enter the MAC address(es) you want to allow or block to access the router and LAN.
The format of MAC address could be: xx:xx:xx:xx:xx:xx or xx-xx-xx-xx-xx-xx. For convenience, user
can select from the list box.
Time Schedule: To determine when the rule works.
Drop: To drop the MAC entries always; in other words, the MACs are blocked access to router
and internet always.
Forward: To forward the MAC entries always; in other words, the MACs are granted access to
the router and internet always.
Check or select from listbox: To set the time duration during which the MACs are blocked
from access the router and internet. “select from listbox” means that you can select the
already set timeslot in “Time Schedule” section during which the MACs are blocked from
access the router and internet.
Click Apply to confirm your settings. The following prompt window will appear to remind you of the
attention.
164
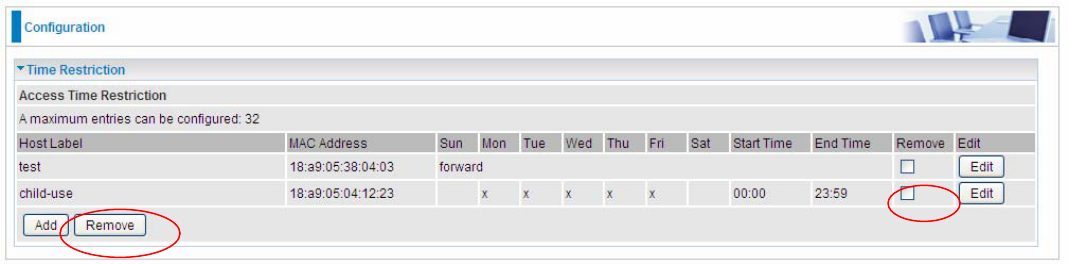
An example:
Here you can see that the user “child-use” with a MAC of 18:a9:05:04:12:23 is blocked to access the
router from 00:00 to 23:59 Monday through Friday.
The “test” can access the internet always.
If you needn’t this rule, you can check the box, press Remove, it will be OK.
.
165
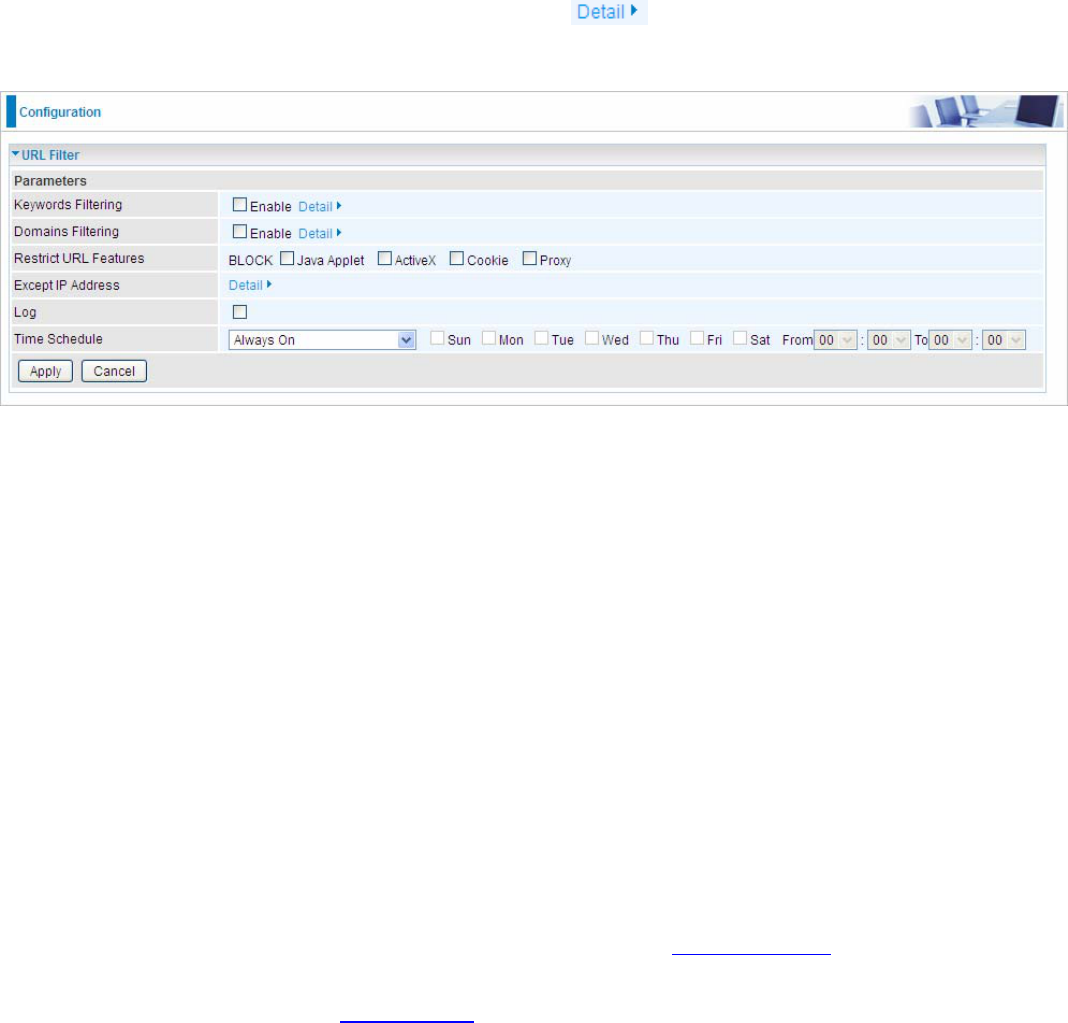
URL Filter
URL (Uniform Resource Locator – e.g. an address in the form of http://www.abcde.com or
http://www.example.com) filter rules allow you to prevent users on your network from accessing
particular websites by their URL. There are no pre-defined URL filter rules; you can add filter rules to
meet your requirements.
Note:
1) URL Filter rules apply to both IPv4 and IPv6 sources.
2) But in Exception IP Address part, user can click to set the exception IP address(es) for
IPv4 and IPv6 respectively.
Keywords Filtering: Allow blocking against specific keywords within a particular URL rather than
having to specify a complete URL (e.g.to block any image called “advertisement.gif”). When enabled,
your specified keywords list will be checked to see if any keywords are present in URLs accessed to
determine if the connection attempt should be blocked. Please note that the URL filter blocks web
browser (HTTP) connection attempts using port 80 only.
Domains Filtering: This function checks the whole URL address but not the IP address against
your list of domains to block or allow. If it is matched, the URL request will either be sent (Trusted) or
dropped (Forbidden).
Restrict URL Features: Click Block Java Applet to filter web access with Java Applet components.
Click Block ActiveX to filter web access with ActiveX components. Click Block Cookie to filter web
access with Cookie components. Click Block Proxy to filter web proxy access.
Exception IP Address: You can input a list of IP addresses as the exception list for URL filtering.
These IPs will not be covered by the URL rules.
Time Schedule: Select or set exactly when the rule works. When set to “Always On”, the rule will
work all time; and also you can set the precise time when the rule works, like 01:00-19:00 from
Monday to Friday. Or you can select the already set timeslot in “Time Schedule” during which the
rule works. And when set to “Disable”, the rule is disabled. See Time Schedule.
Log: Select Enable for this option if you will like to capture the logs for this URL filter policy. To
check the log, users can turn to Security Log.
166
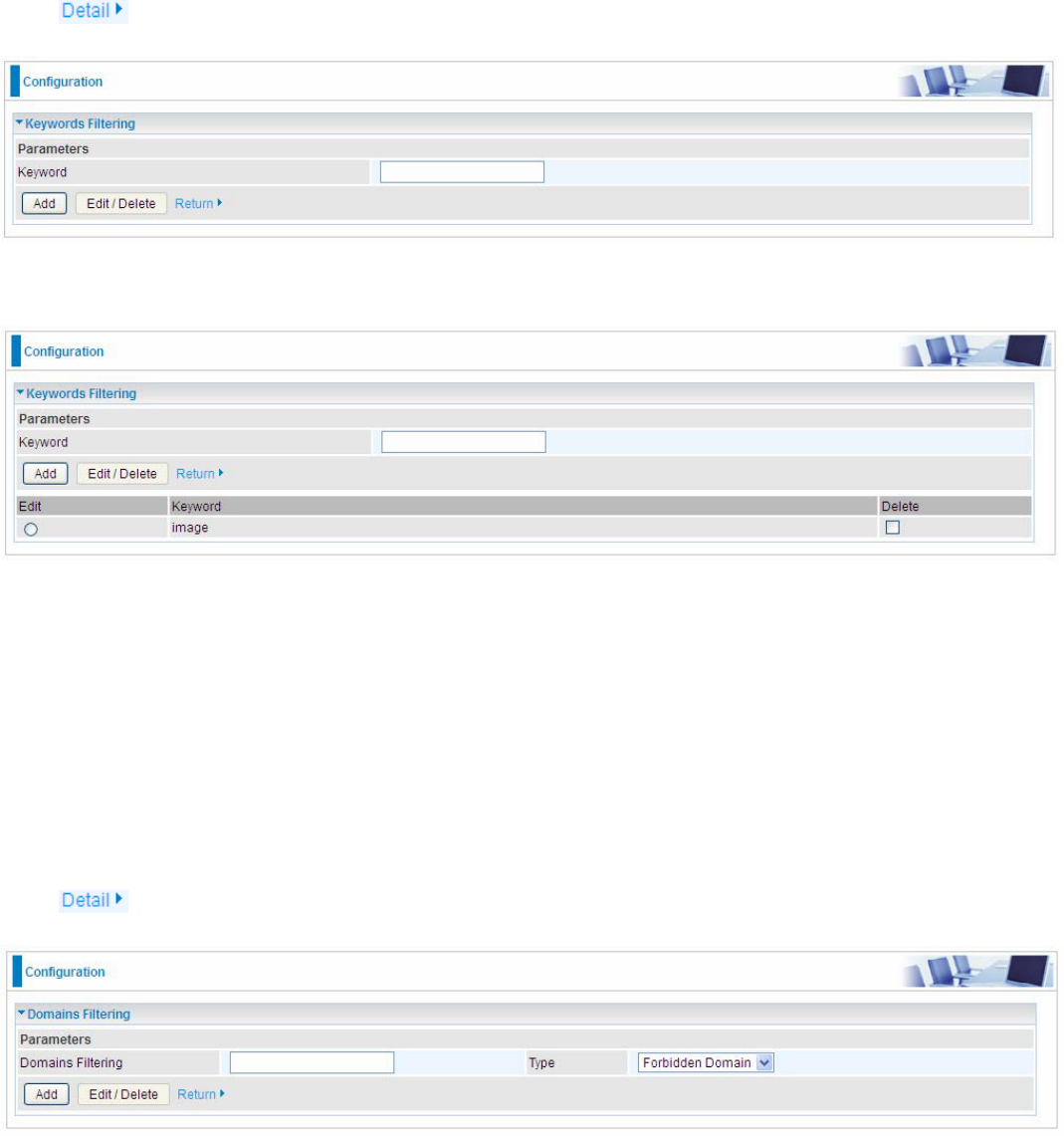
Keywords Filtering
Note: Maximum number of entries: 32.
Click to add the keywords.
Enter the Keyword, for example image, and then click Add.
You can add other keywords like this. The keywords you add will be listed as above. If you want to
reedit the keyword, press the Edit radio button left beside the item, and the word will listed in the
Keyword field, edit, and then press Edit/Delete to confirm. If you want to delete certain keyword,
check Delete checkbox right beside the item, and press Edit/Delete. Click Return to be back to the
previous page.
Domain Filtering
Note: Maximum number of entries: 32.
Click to add Domains.
Domain Filtering: enter the domain you want this filter to apply.
Type: select the action this filter deals with the Domain.
Forbidden Domain: The domain is forbidden access.
Trusted Domain: The domain is trusted and allowed access.
Enter a domain and select whether this domain is trusted or forbidden with the pull-down menu. Next,
click Add. Your new domain will be added to either the Trusted Domain or Forbidden Domain listing,
depending on which you selected previously. For specific process, please refer to Keywords
167
Filtering.
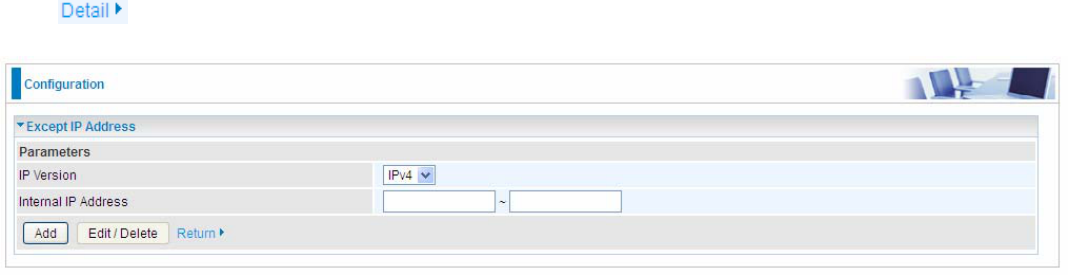
Exception IP Address
In the section, users can set the exception IP respectively for IPv4 and IPv6.
Click to add the IP Addresses.
Enter the except IP address. Click Add to save your changes. The IP address will be entered into
the Exception List, and excluded from the URL filtering rules in effect. For specific process, please
refer to Keywords Filtering.
For example, users can set IPv4 client 192.168.1.103 in your network as a exception address that is
not limited to the rules set in URL filter ( or IPv4 clients (a range) ). And also an IPv6 client
(2000:1211:1002:6ba4:d160:5adb:9009:87ae) or IPv6 clients(a range ) can be the exceptions from
the URL rules.
At the URL Filter page, press Apply to confirm your settings.
168
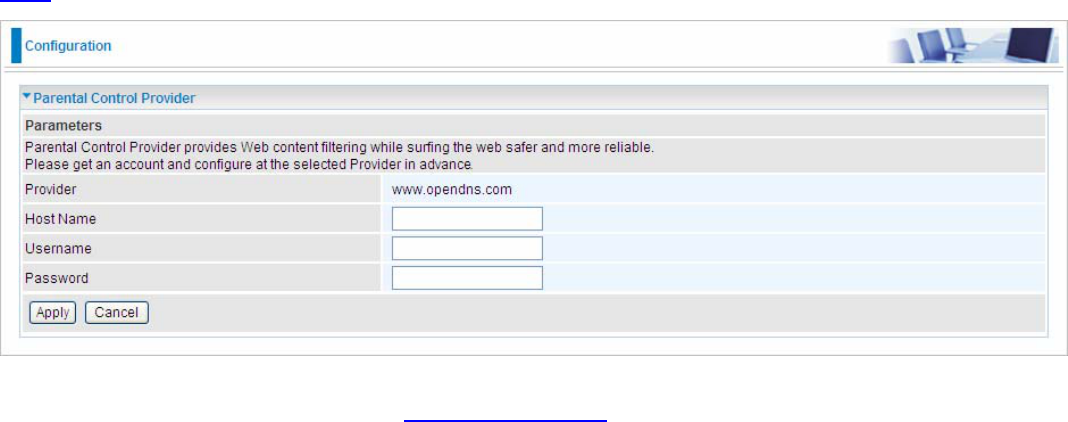
Parental Control Provider
Parental Control Provider provides Web content filtering offering safer and more reliable web surfing
for users. Please get an account and configure at the selected Provider “www.opendns.com” in
advance. To use parental control (DNS), user needs to configure to use parental control (DNS
provided by parental control provider) to access internet at WAN configuration or DNS page(See
DNS).
Host Name, Username and Password: Enter your registered domain name and your username
and password at the provider website www.opendns.com.
169
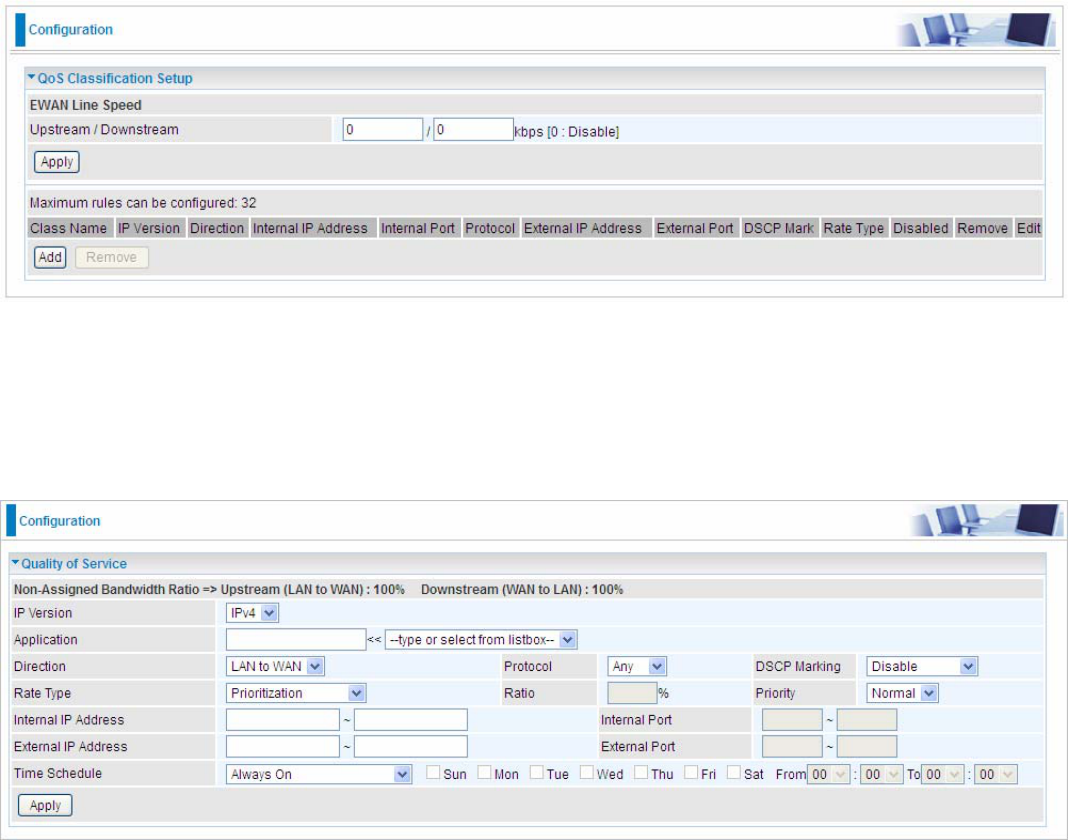
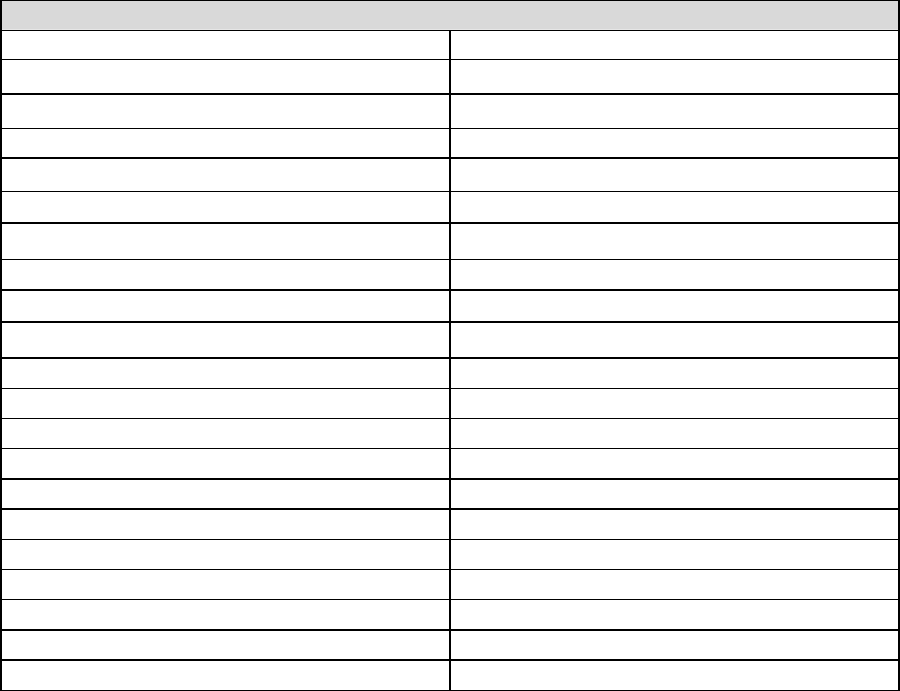
QoS - Quality of Service
QoS helps you to control the data upload traffic of each application from LAN (Ethernet) to WAN
(Internet). This feature allows you to control the quality and speed of throughput for each application
when the system is running with full upstream load.
Note: ADSL line speed is based on the ADSL sync rate. But there is no QoS on 3G/LTE as the
3G/LTE line speed is various and can not be known exactly.
EWAN Line Speed
Upstream / Downstream: Specify the upstream and downstream rate of the EWAN interface.
Click Apply to save the EWAN rate settings.
Click Add to enter QoS rules.
IP Version: Select either IPv4 or IPv6 base on need.
Application: Assign a name that identifies the new QoS application rule. Select from the list box for
quick setup.
Direction: Shows the direction mode of the QoS application.
LAN to WAN: You want to control the traffic from local network to the outside (Upstream).
You can assign the priority for the application or you can limit the rate of the application.
Eg: you have a FTP server inside the local network, and you want to have a limited control by
the QoS policy and so you need to add a policy with LAN to WAN direction setting.
WAN to LAN: Control traffic from WAN to LAN (Downstream).
Protocol: Select the supported protocol from the drop down list.
DSCP Marking: Differentiated Services Code Point (DSCP), it is the first 6 bits in the ToS byte.
DSCP Marking allows users to classify the traffic of the application to be executed according to the
170
DSCP value.
IP Precedence and DSCP Mapping Table
Mapping Table
Default
(
000000
)
Best Effort
EF(101110) Expedited Forwarding
AF11 (001010) Assured Forwarding Class1(L)
AF12 (001100) Assured Forwarding Class1(M)
AF13 (001110) Assured Forwarding Class1(H)
AF21 (010010) Assured Forwarding Class1(L)
AF22 (010100) Assured Forwarding Class1(M)
AF23 (010110) Assured Forwarding Class1(H)
AF31 (011010) Assured Forwarding Class1(L)
AF32 (011100) Assured Forwarding Class1(M)
AF33 (011110) Assured Forwarding Class1(H)
AF41 (100010) Assured Forwarding Class1(L)
AF42 (100100) Assured Forwarding Class1(M)
AF43 (100110) Assured Forwarding Class1(H)
CS1(001000) Class Selector(IP precedence)1
CS2(010000) Class Selector(IP precedence) 2
CS3(011000) Class Selector(IP precedence)3
CS4(100000) Class Selector(IP precedence) 4
CS5(101000) Class Selector(IP precedence) 5
CS6(110000) Class Selector(IP precedence) 6
CS7(111000) Class Selector(IP precedence) 7
DSCP offers three levels of service, Class Selector (CS), Assured Forwarding (AF) and Expedited
Forwarding (EF). AF1, AF2, AF3 and AF4 are four levels of assured forwarding services. Each AF
has three different packet loss priorities from high, medium, to low. Also, CS1-CS7 indicates the IP
precedence.
Rate Type: You can choose Limited or Prioritization.
Limited (Maximum): Specify a limited data rate for this policy. It also is the maximum rate
for this policy. When you choose Limited, type the Ratio proportion. As above FTP server
example, you may want to “throttle” the outgoing FTP speed to 20% of 256K and limit to it,
you may use this type.
Prioritization: Specify the rate type control for the rule to used. If you choose Prioritization
for the rule, you parameter Priority would be available, you can set the priority for this rule.
Set DSCP Marking: When select Set DSCP Marking, the packets matching the rule will be
forwarded according to the pre-set DSCP marking.
Ratio: The rate percent of each application/policy compared to total traffic on the interface with
limited rate type. For example, we want to only allow 20% of the total data for the LAN-to-WAN
direction to be used for FTP server. Then we can specify here with data ratio = 20. If you have ADSL
LINE with 256K/bps.rate, the estimated data rate, in kbps, for this rule is 20%*256*0.9 = 46kbps.
(For 0.9 is an estimated factor for the effective data transfer rate for an ADSL LINE from LAN to
WAN. For WAN-to-LAN, it is 0.85 to 0.8)
Priority: Set the priority given to each policy/application. Specify the priority for the use of bandwidth.
You can specify which application can have higher priority to acquire the bandwidth. Its default
setting is set to Normal. You may adjust this setting to fit your policy / application.
Internal IP Address: The IP address values for Local LAN devices you want to give control.
Internal Port: The Port number on the LAN side, it is used to identify an application.

171
External IP Address: The IP address on remote / WAN side.
External Port: The Port number on the remote / WAN side.
Time Schedule: Select or set exactly when the rule works. When set to “Always On”, the rule will
work all time; and also you can set the precise time when the rule works, like 01:00-19:00 from
Monday to Friday. Or you can select the already set timeslot in “Time Schedule” during which the
rule works. And when set to “Disable”, the rule is disabled or inactive and there will be an icon”
” indicating the rule is inactive. See Time Schedule.
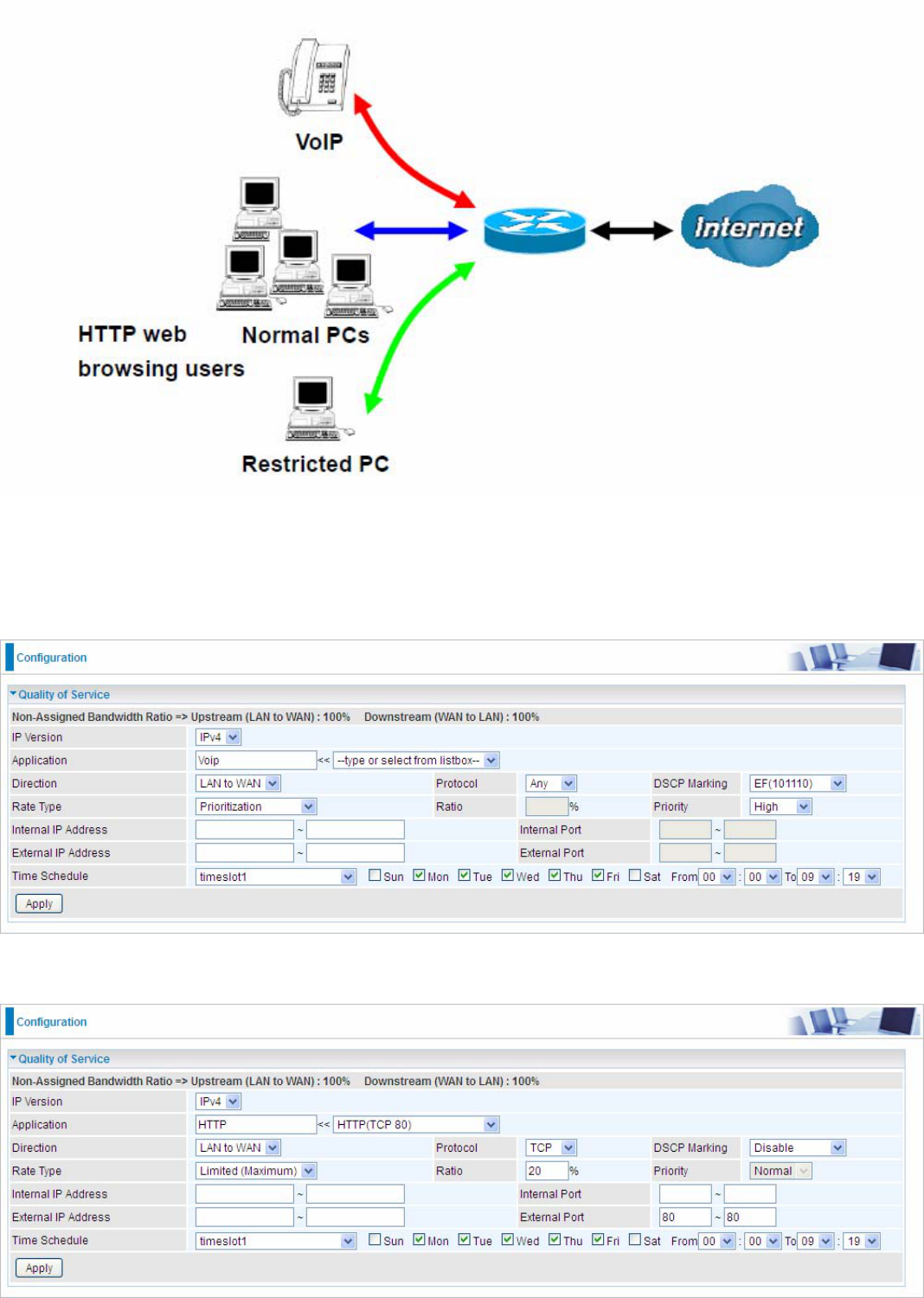
172
Examples: Common usage
1. Give outgoing VoIP traffic more priority.
The default queue priority is normal, so if you have VoIP users in your local network, you can set a
higher priority to the outgoing VoIP traffic.
2. Give regular web http access a limited rate
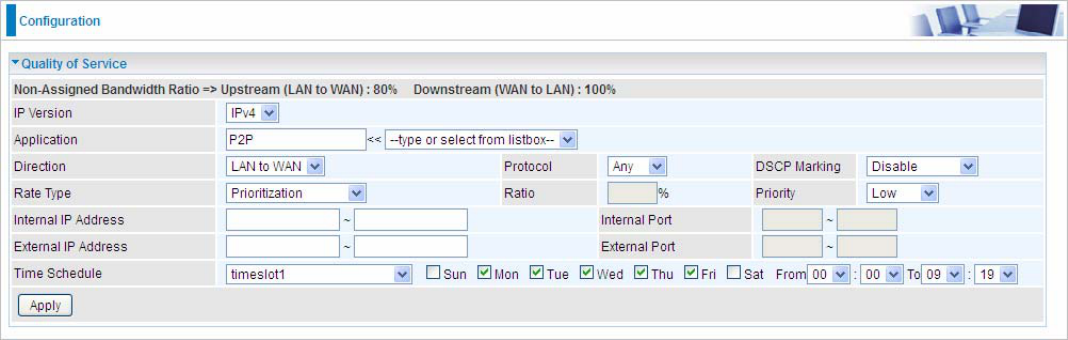
173
3. If you are actively engaged in P2P and are afraid of slowing down internet access for other users
within your network, you can then use QoS to set a rule that has low priority. In this way, P2P
application will not congest the data transmission with other applications.
Other applications, like FTP, Mail access, users can use QoS to control based on need.
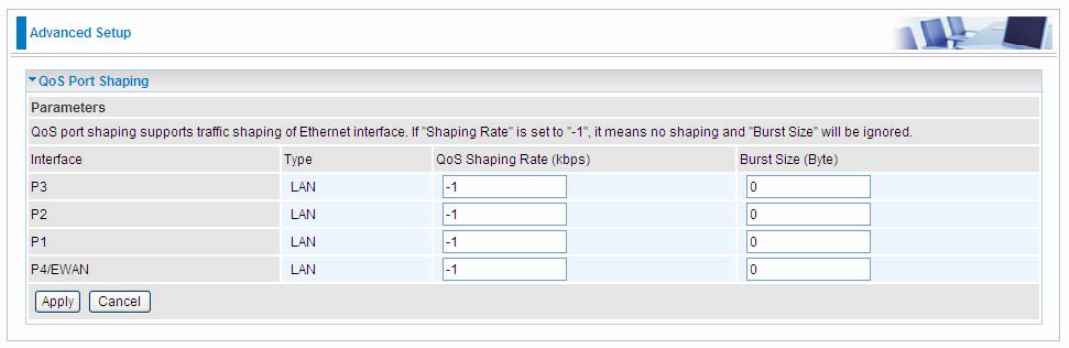
174
QoS Port Shaping
QoS port shaping supports traffic shaping of Ethernet interfaces. It forcefully maximizes the
throughput of the Ethernet interface. When “Shaping Rate” is set to “-1”, no shaping will be in place
and the “Burst Size” is to be ignored.
Interface: P1-P4. P4 used as EWAN also covered.
Type: All LAN when P4 is LAN port; P4 used as EWAN, type WAN and all others LAN.
QoS Shaping Rate (Kbps): Set the forcefully maximum rate.
Burst Size(Bytes): Set the forcefully Burst Size.
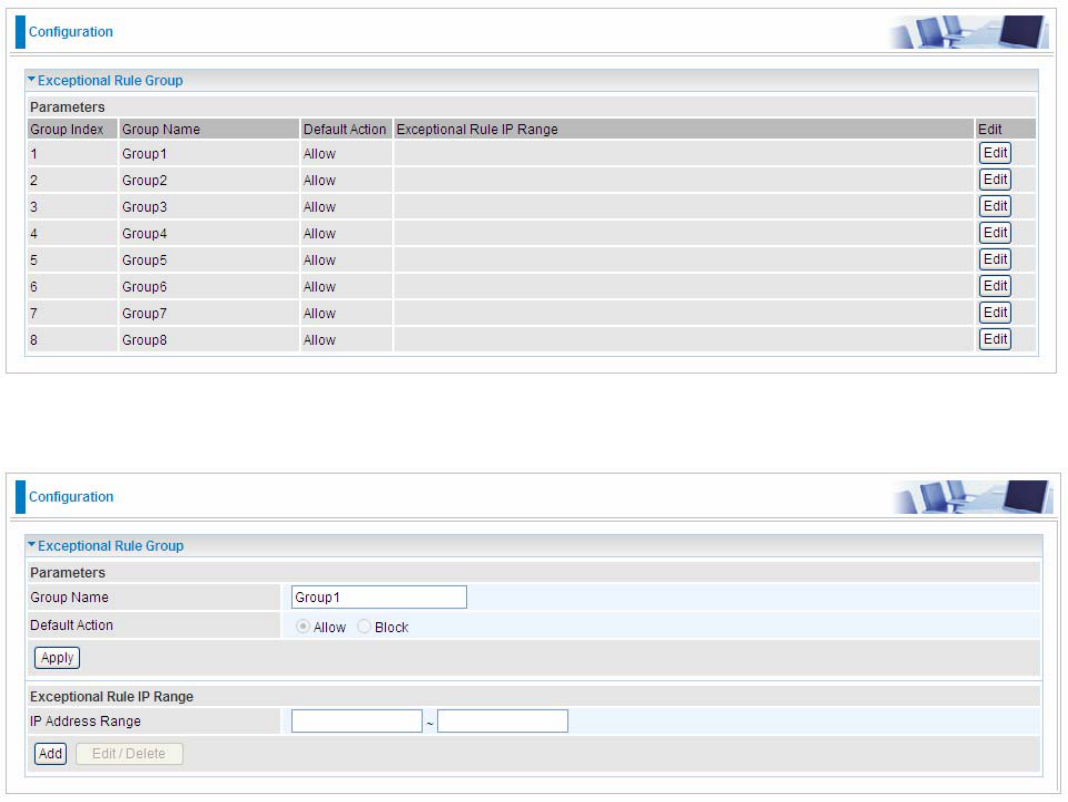
175
NAT
NAT (Network Address Translation) feature translates a private IP to a public IP, allowing multiple
users to access the Internet through a single IP account, sharing the single IP address. It is a natural
firewall for the private network.
Exceptional Rule Group
Exceptional Rule is dedicated to giving or blocking Virtual Server/ DMZ access to some specific IP or
IPs(range). Users are allowed to set 8 different exceptional rule groups at most. In each group, user
can add specific IP or IP range.
Press Edit to set the exceptional IP (IP Range).
Default Action: Please first set the range to make “Default Action” setting available. Set “Allow” to
ban the listed IP or IPs to access the Virtual Server and DMZ Host
Check “Block” to grant access to the listed IP or IPs to Virtual Server and DMZ Host.
Apply: Press Apply button to apply the change.
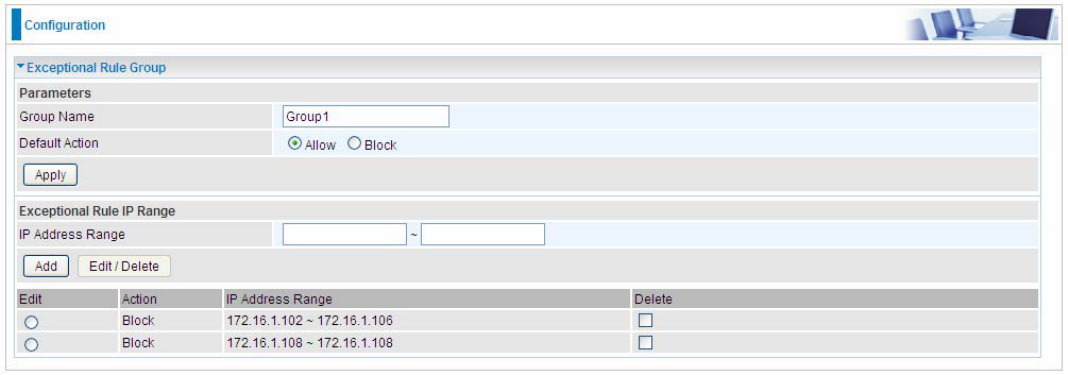
176
Exceptional Rule Range
IP Address Range: Specify the IP address range; IPv4 address range can be supported.
Click Add to add the IP Range.
For instance, if user wants to block IP range of 172.16.1.102-172.16.1.106 from accessing your set
virtual server and DMZ host, you can add this IP range and valid it.
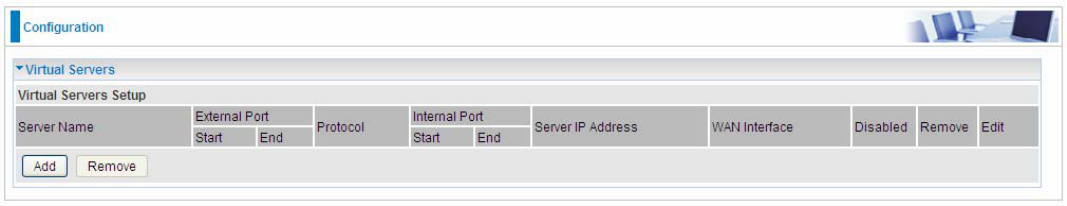
177
Virtual Servers
In TCP/IP and UDP networks a port is a 16-bit number used to identify which application program
(usually a server) incoming connections should be delivered to. Some ports have numbers that are
pre-assigned to them by the IANA (the Internet Assigned Numbers Authority), and these are referred
to as “well-known ports”. Servers follow the well-known port assignments so clients can locate them.
If you wish to run a server on your network that can be accessed from the WAN (i.e. from other
machines on the Internet that are outside your local network), or any application that can accept
incoming connections (e.g. Peer-to-peer/P2P software such as instant messaging applications and
P2P file-sharing applications) and are using NAT (Network Address Translation), then you will
usually need to configure your router to forward these incoming connection attempts using specific
ports to the PC on your network running the application. You will also need to use port forwarding if
you want to host an online game server.
The reason for this is that when using NAT, your publicly accessible IP address will be used by and
point to your router, which then needs to deliver all traffic to the private IP addresses used by your
PCs. Please see the WAN configuration section of this manual for more information on NAT.
The device can be configured as a virtual server so that remote users accessing services such as
Web or FTP services via the public (WAN) IP address can be automatically redirected to local
servers in the LAN network. Depending on the requested service (TCP/UDP port number), the
device redirects the external service request to the appropriate server within the LAN network.
This part is only available when NAT is enabled.
Note: The maximum number of entries: 64.
It is virtual server listing table as you see, Click Add to move on.
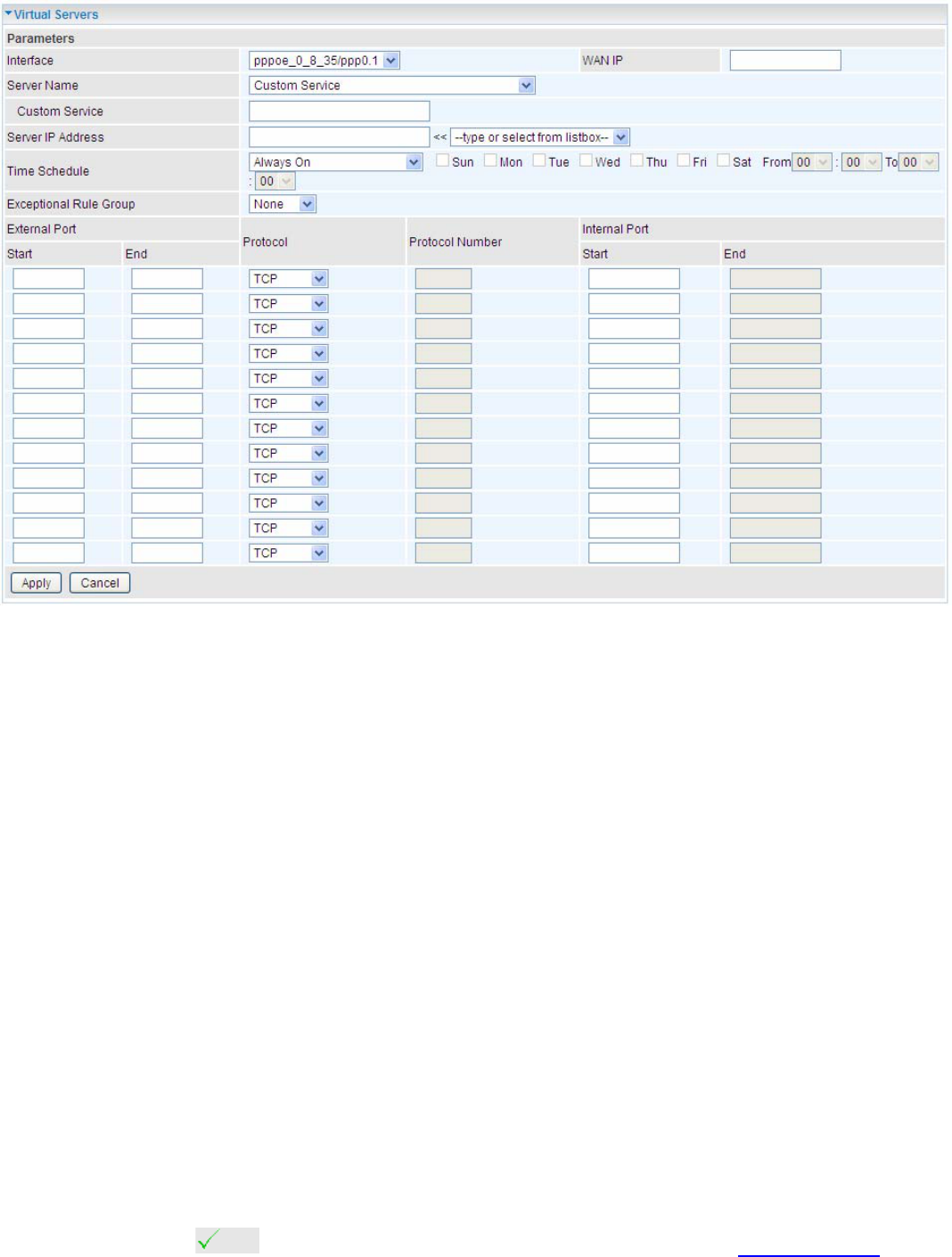
178
The following configuration page will appear to let you configure.
Interface: select from the drop-down menu the interface you want the virtual server(s) to apply.
Server Name: select the server name from the drop-down menu.
Custom Service: It is a kind of service to let users customize the service they want. Enter the user-
defined service name here. It is a parameter only available when users select Custom Service in
the above parameter.
Server IP Address: Enter your server IP Address here. User can select from the list box for quick
setup.
External Port
Start: Enter a port number as the external starting number for the range you want to give
access to internal network.
End: Enter a port number as the external ending number for the range you want to give
access to internal network.
Internal Port
Start: Enter a port number as the internal staring number.
End: Here it will generate automatically according to the End port number of External port
and can’t be modified.
Protocol: select the protocol this service used: TCP/UDP, TCP, UDP.
Time Schedule: Select or set exactly when the Virtual Server works. When set to “Always On”, the
Virtual Server will work all time; and also you can set the precise time when Virtual Server works,
like 01:00 - 19:00 from Monday to Friday. Or you can select the already set timeslot in Time
Schedule during which the Virtual Server works. And when set to “Disable”, the rule is disabled and
there will be an icon in the list table indicating the rule is disabled. See Time Schedule.
Exceptional Rule Group: Select the exceptional group listed. It is to grant or block Virtual Server
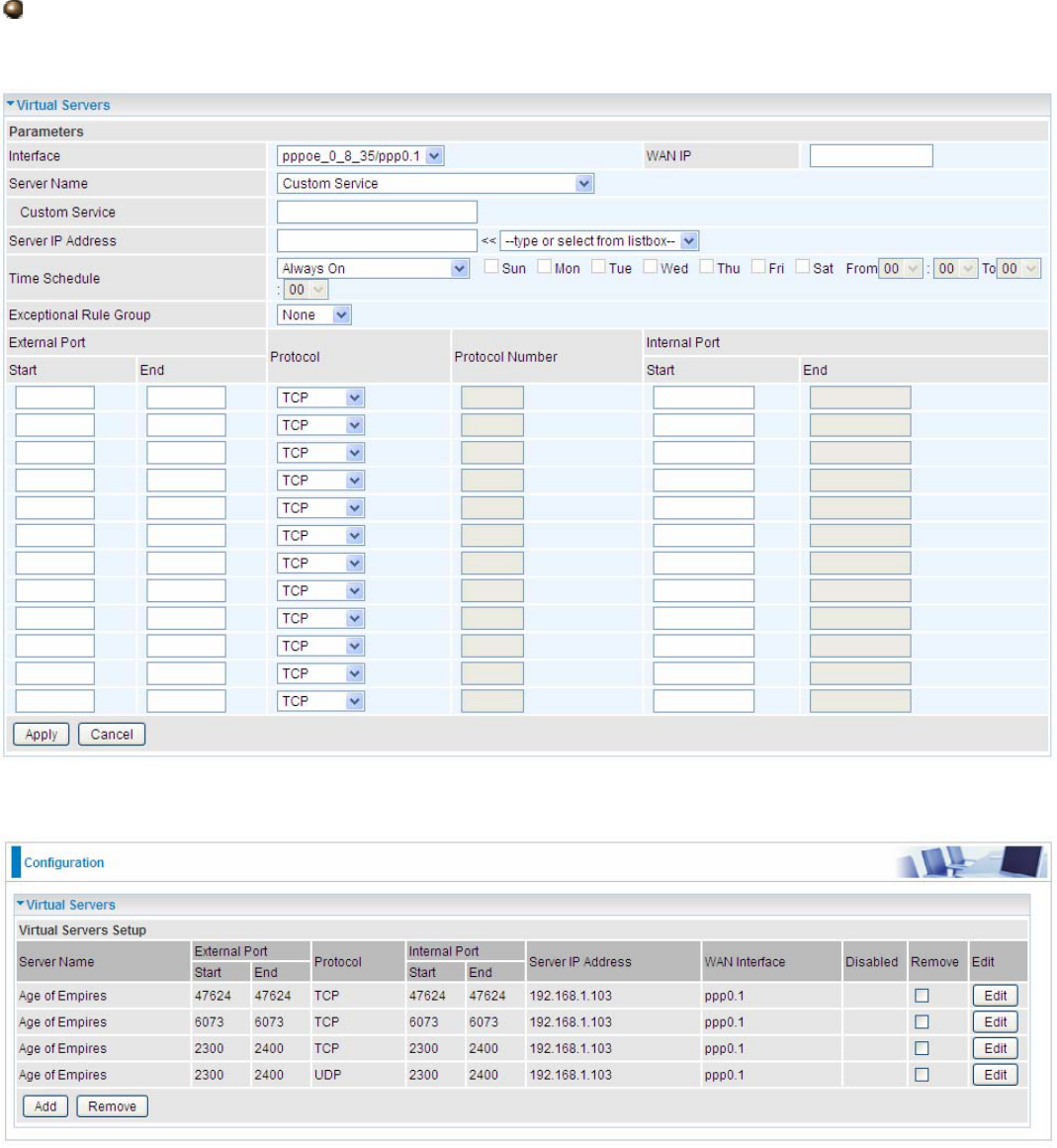
179
access to a group of IPs. For example, as we set previously group 1 blocking access to
172.16.1.102-172.16.1.106. If here you want to block Virtual Server access to this IP range, you can
select Group1.
Set up
1. Select a Server Name from the drop-down menu, then the port will automatically appear, modify
some as you like, or you can just leave it as default. Remember to enter your server IP Address.
2. Press Apply to conform, and the items will be list in the Virtual Servers Setup table.
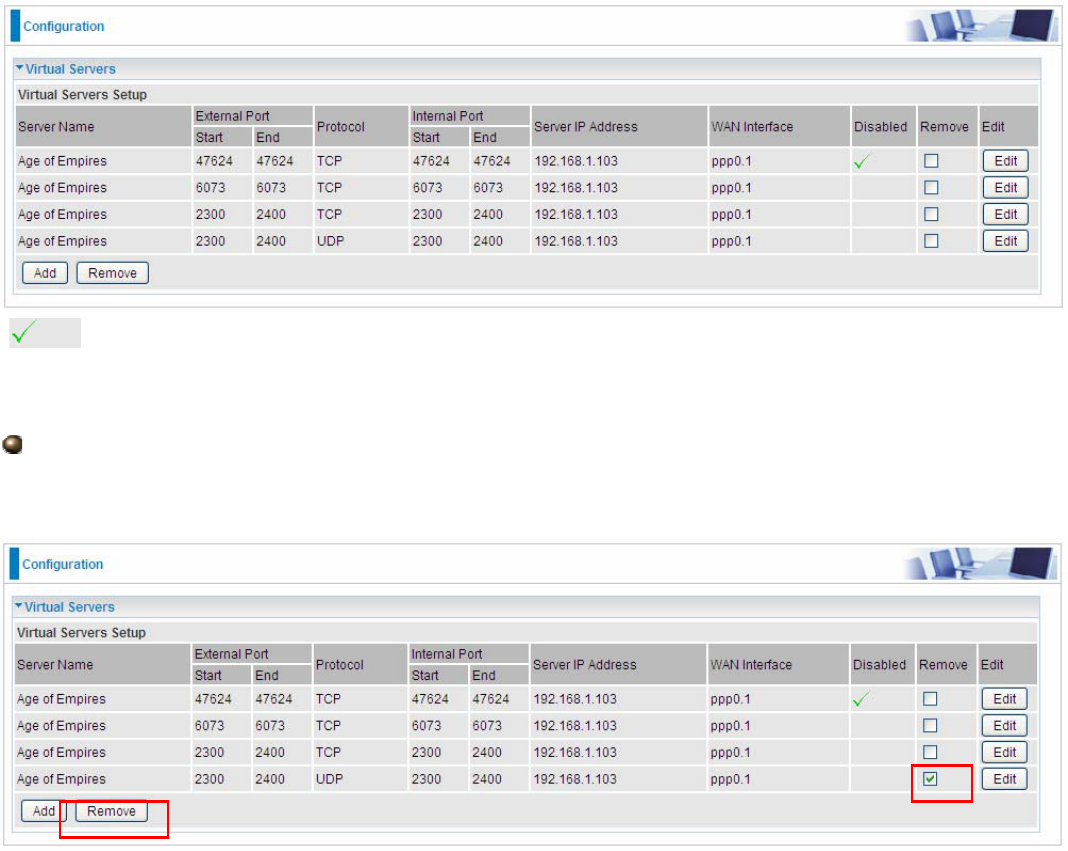
180
(Means the rule is inactive)
Remove
If you don’t need a specified Server, you can remove it. Check the check box beside the item you
want to remove, then press Remove, it will be OK.
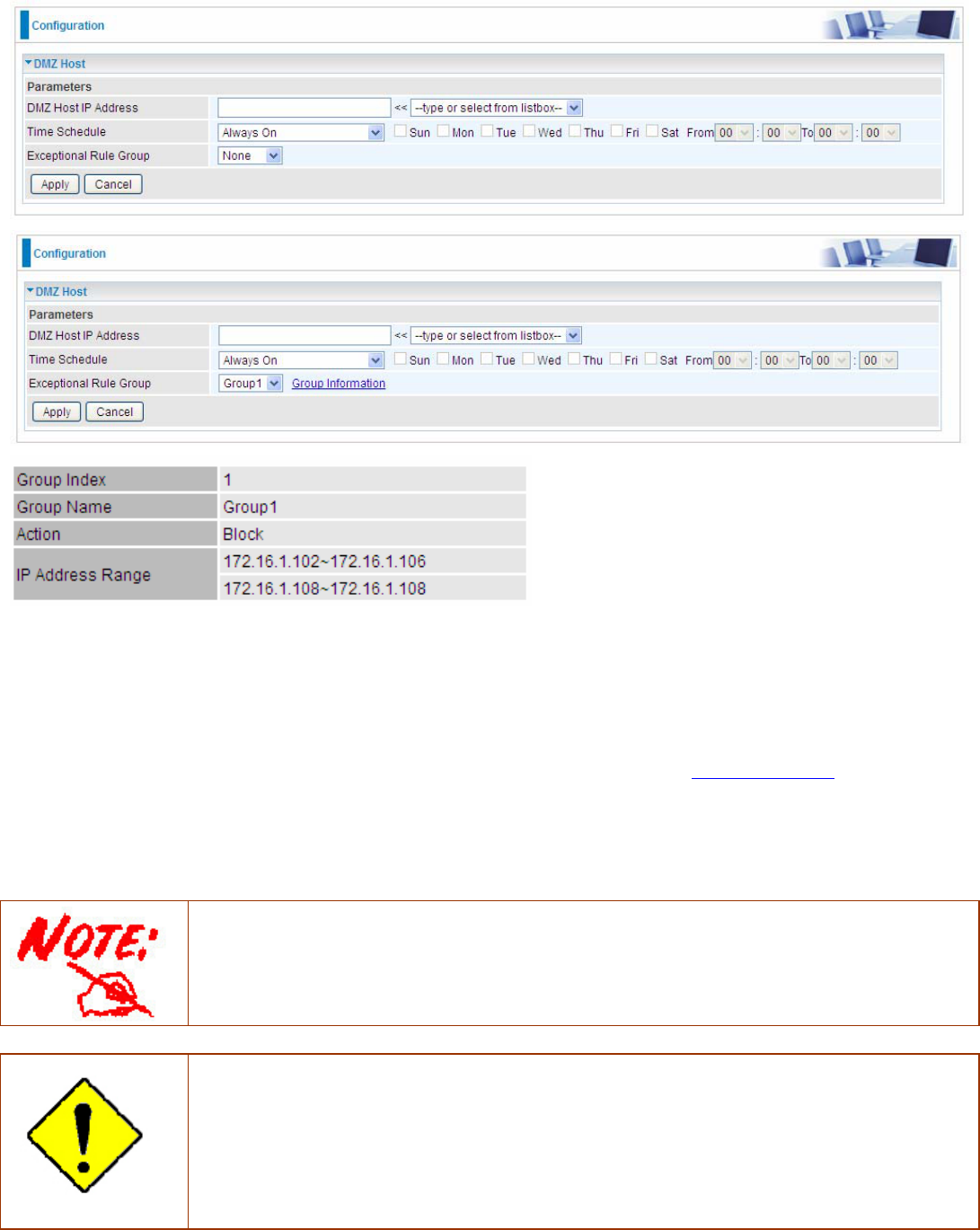
181
DMZ Host
The DMZ Host is a local computer exposed to the Internet. When setting a particular internal IP
address as the DMZ Host, all incoming packets will be checked by Firewall and NAT algorithms
before being passed to the DMZ host, when a packet received does not use a port number used by
any other Virtual Server entries.
(Group Information)
DMZ Host IP Address: Enter the IP Address of a host you want it to be a DMZ host. Select from the
list box to quick set the DMZ.
Time Schedule: Select or set exactly when the DMZ works. When set to “Always On”, the DMZ will
work all time; and also you can set the precise time when DMZ works, like 01:00 - 19:00 from
Monday to Friday. Or you can select the already set timeslot in Time Schedule during which the
DMZ works. And when set to “Disable”, the DMZ Host is disabled. See Time Schedule.
Exceptional Rule Group: Select the exceptional group listed. It is to grant or block DMZ access to
a group of IPs. For example, as we set previously group 1 blocking access to 172.16.1.102-
172.16.1.106. If here you want to block DMZ Access to this IP range, you can select Group1.
Using port mapping does have security implications, since outside users are able to connect
to PCs on your network. For this reason you are advised to use specific Virtual Server
entries just for the ports your application requires instead of simply using DMZ or creating a
Virtual Server entry for “All” protocols, as doing so results in all connection attempts to your
public IP address accessing the specified PC.
Attention
If you have disabled the NAT option in the WAN-ISP section, the Virtual Server function will
hence be invalid.
If the DHCP server option is enabled, you have to be very careful in assigning the IP
addresses of the virtual servers in order to avoid conflicts. The easiest way of configuring
Virtual Servers is to manually assign static IP address to each virtual server PC, with an
address that does not fall into the range of IP addresses that are to be issued by the DHCP
server. You can configure the virtual server IP address manually, but it must still be in the
same subnet as the router.
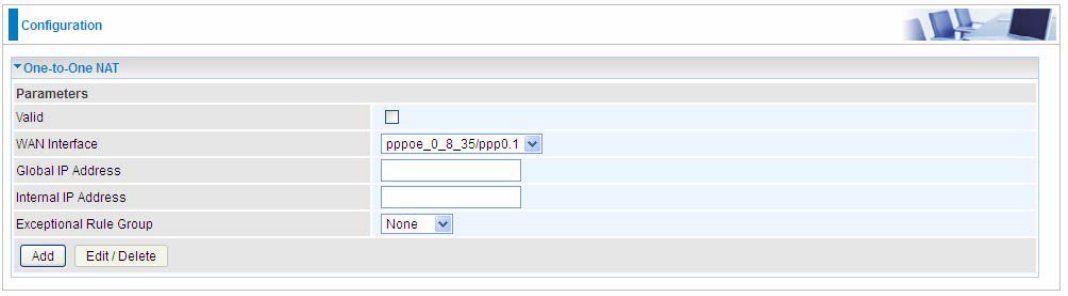
182
One-to-One NAT
One-to-One NAT maps a specific private/local address to a global/public IP address. If user has
multiple global/public IP addresses from your ISP, you are free to use one-to-one NAT to assign
some specific public IP for an internal IP like a public web server mapped with a global/public IP for
outside access.
Valid: Check whether to valid the one-to-one NAT mapping rule.
WAN Interface: Select one based WAN interface to configure the one-to-one NAT.
Global IP address: The Global IP mapped to an internal device. It can be left empty, and under this
circumstance, it can be reached through the WAN IP of interface set in the field above.
Internal Address: The IP address of an internal device in the LAN.
Exceptional Rule Group: Select the exceptional group listed. It is to give or block access to a group
of IPs to the server after One-to-One NAT. For example, a server with 192.168.1.3 is mapped to
123.1.1.2 by One-to-One NAT, then the exceptional group can be designated to have or have not
access to 123.1.1.2.
For example, you have an ADSL connection of pppoe_0_8_35/ppp0.1 interface with three fixed
global IP, and you then can assign the other two global IPs to two internal devices respectively.
If you have a WEB server (IP address: 192.168.1.3) and a FTP server (IP address: 192.168.1.4) in
local network, owning a public IP address range of 123.1.1.2 to 123.1.1.4 assigned by ISP. 123.1.1.2
is used as WAN IP address of the router, 123.1.1.3 is used for WEB server and 123.1.1.4 is used for
FTP server. With One-to-One NAT, the servers with private IP addresses can be accessed at the
corresponding valid public IP addresses.
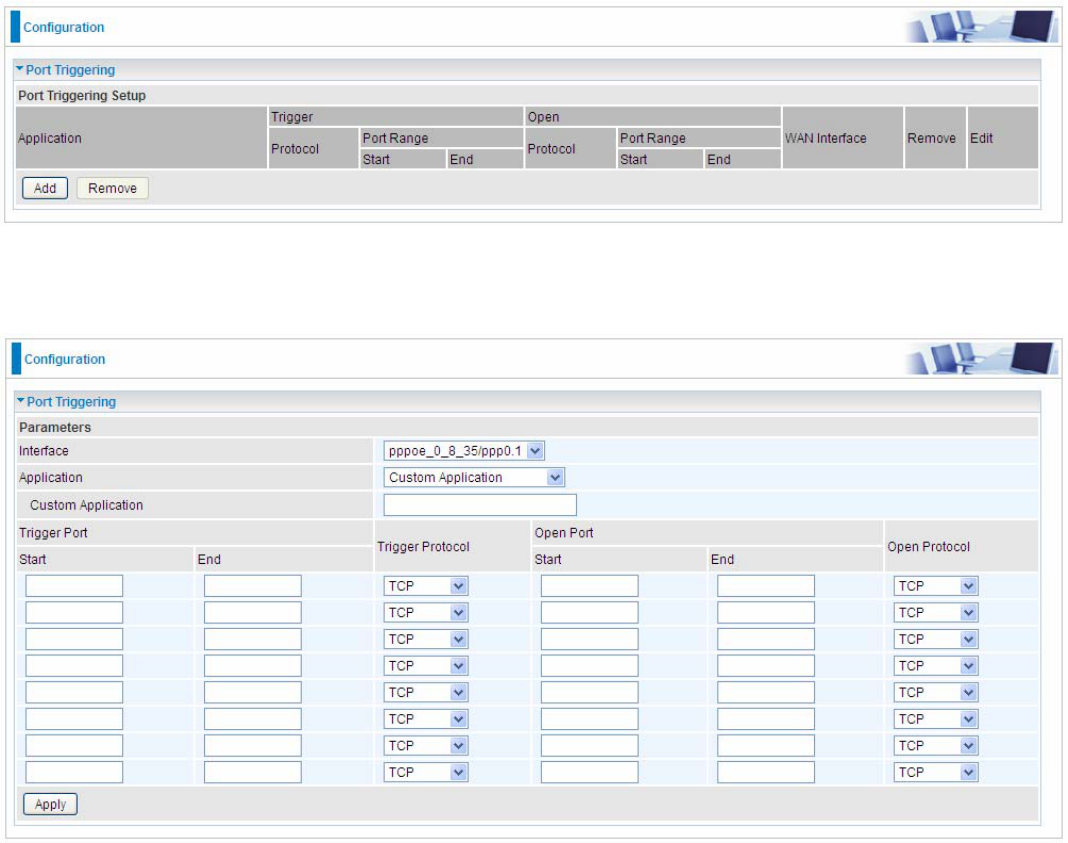
183
Port Triggering
Port triggering is a way to automate port forwarding with outbound traffic on predetermined ports
(‘triggering ports’), incoming ports are dynamically forwarded to the initiating host, while the
outbound ports are in use. Port triggering triggers can open an incoming port when a client on the
local network makes an outgoing connection on a predetermined port or a range of ports.
Click Add to add a port triggering rule.
Interface: Select from the drop-down menu the interface you want the port triggering rules apply to.
Application: Preinstalled applications or Custom Application user can customize the utility yourself.
Custom Application: It is a kind of service to let users themselves customizes the service they
want. Enter the user-defined service name here.
Trigger Port
Start: Enter a port number as the triggering port starting number.
End: Enter a port number as the triggering port ending number.
Any port in the range delimited by the ‘Start’ and ‘End’ would be the trigger port.
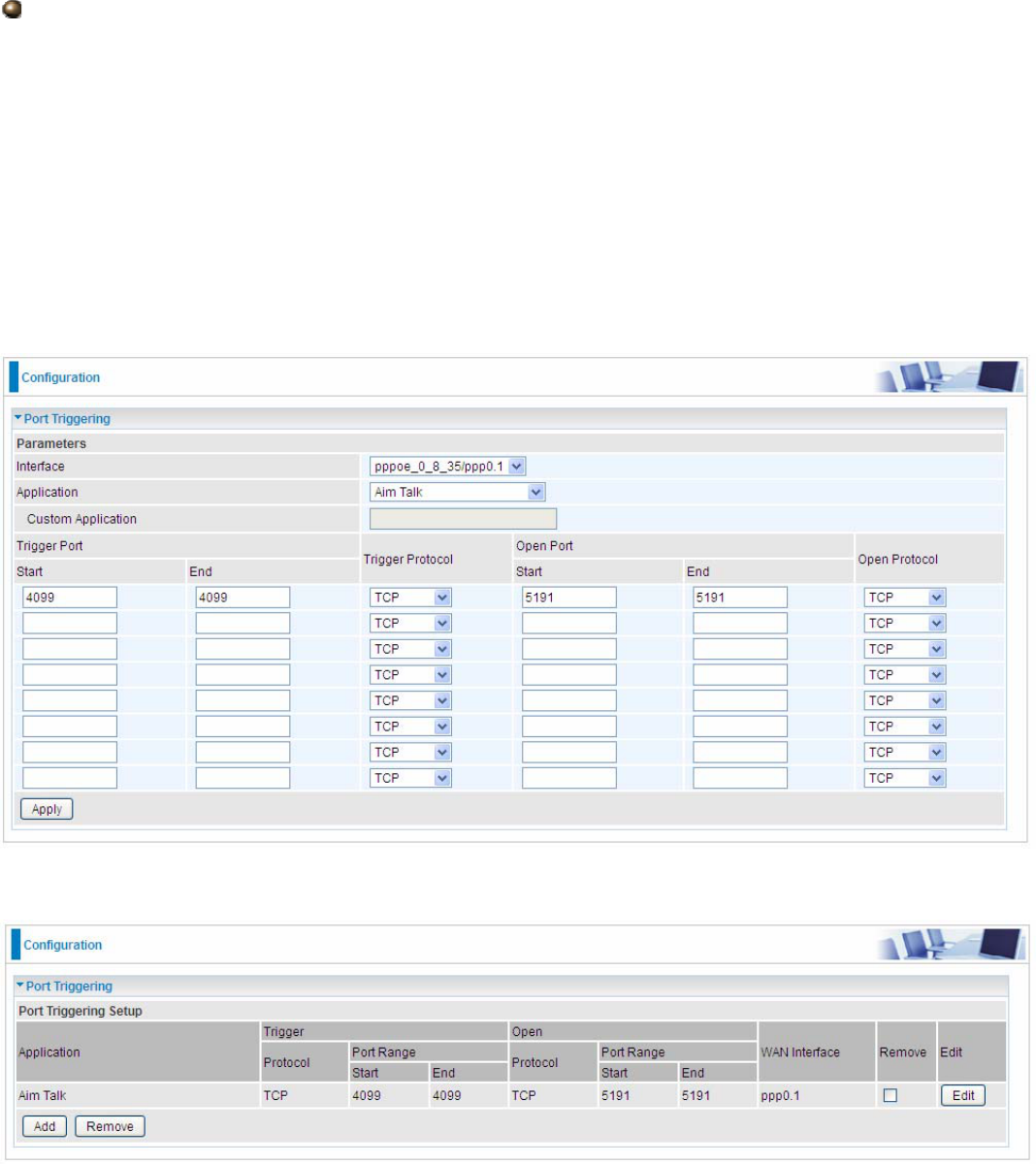
184
Open port
Start: Enter a port number as the open port staring number.
End: Enter a port number as the open port ending number.
Any port in the range delimited by the ‘Start’ and ‘End’ would be the preset forwarding port or open
port.
Protocol: select the protocol this service used: TCP/UDP, TCP, UDP.
Set up
An example of how port triggering works, when a client behind a NAT router connecting to Aim Talk,
it is a TCP connection with the default port 4099.
When connecting to Aim Talk, the client typically makes an outgoing connection on port 4099 to the
Aim Talk server, but when the computer is behind the NAT, the NAT silently drops this connection
because it does not know which computer behind the NAT to send the request to connect.
So, in this case, port triggering in the router is working, when an outbound connection is attempted
on port 4099 (or any port in the range set), it should allow inbound connections to that particular
computer.
1. Select a Server Name from the drop-down menu, then the port will automatically appear, modify
some as you like, or you can just leave it as default. Remember to enter your server IP Address.
2. Press Apply to conform, and the items will be list in the Virtual Servers Setup table.
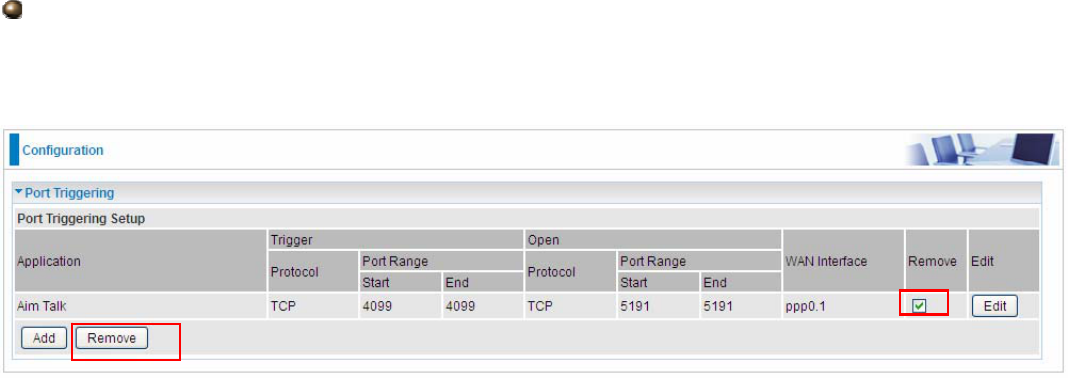
185
Edit/Remove
If you don’t need a specified Server, you can remove it. Check the check box beside the item you
want to remove, and then press Remove.
Click Edit to re-edit your port-triggering rule.