Cambium Networks XR520 Xirrus Wireless Array User Manual xirrus PDF
Xirrus, Inc. Xirrus Wireless Array xirrus PDF
Contents
User manual 2 rev

Wireless Array
The Command Line Interface 377
The Command Line Interface
This section covers the commands and the command structure used by the
Wireless Array’s Command Line Interface (CLI), and provides a procedure for
establishing an SSH connection to the Array. Topics discussed include:
“Establishing a Secure Shell (SSH) Connection” on page 377.
“Getting Started with the CLI” on page 379.
“Top Level Commands” on page 381.
“Configuration Commands” on page 390.
“Sample Configuration Tasks” on page 426.
See Also
Establishing Communication with the Array
Network Map
System Tools
Establishing a Secure Shell (SSH) Connection
Use this procedure to initialize the system and log in to the Command Line
Interface (CLI) via a Secure Shell (SSH) utility, such as PuTTY. When connecting to
the unit’s Command Line Interface over a network connection, you must use a
Secure SHell version 2 (SSH-2) utility. Make sure that your SSH utility is set up to
use SSH-2.
1. Start your SSH session and communicate with the Array via its IP
address.
•If the Array is connected to a network that uses DHCP, use the
address assigned by DHCP. We recommend that you have the
Some commands are only available if the Array’s license includes
appropriate Xirrus Advanced Feature Sets. If a command is unavailable,
an error message will notify you that your license does not support the
feature. See “About Licensing and Upgrades” on page 361.
Wireless Array
378 The Command Line Interface
network administrator assign a reserved address to the Array for ease
of access in the future.
•If the network does not use DHCP, use the factory default address
10.0.2.1 to access either the Gigabit 1 or Gigabit 2 Ethernet port. You
may need to change the IP address of the port on your computer that
is connected to the Array — change that port’s IP address so that it is
on the same 10.0.2.xx subnet as the Array port.
•If your Array is an 8-, 12-, or 16-port model, it has a 10/100Mb
Ethernet port called Ethernet0. This management port has a default
IP address of 10.0.1.1. You may connect your computer directly to this
port, but you will need to set the IP address of the connected port on
your computer to the 10.0.1.xx subnet.
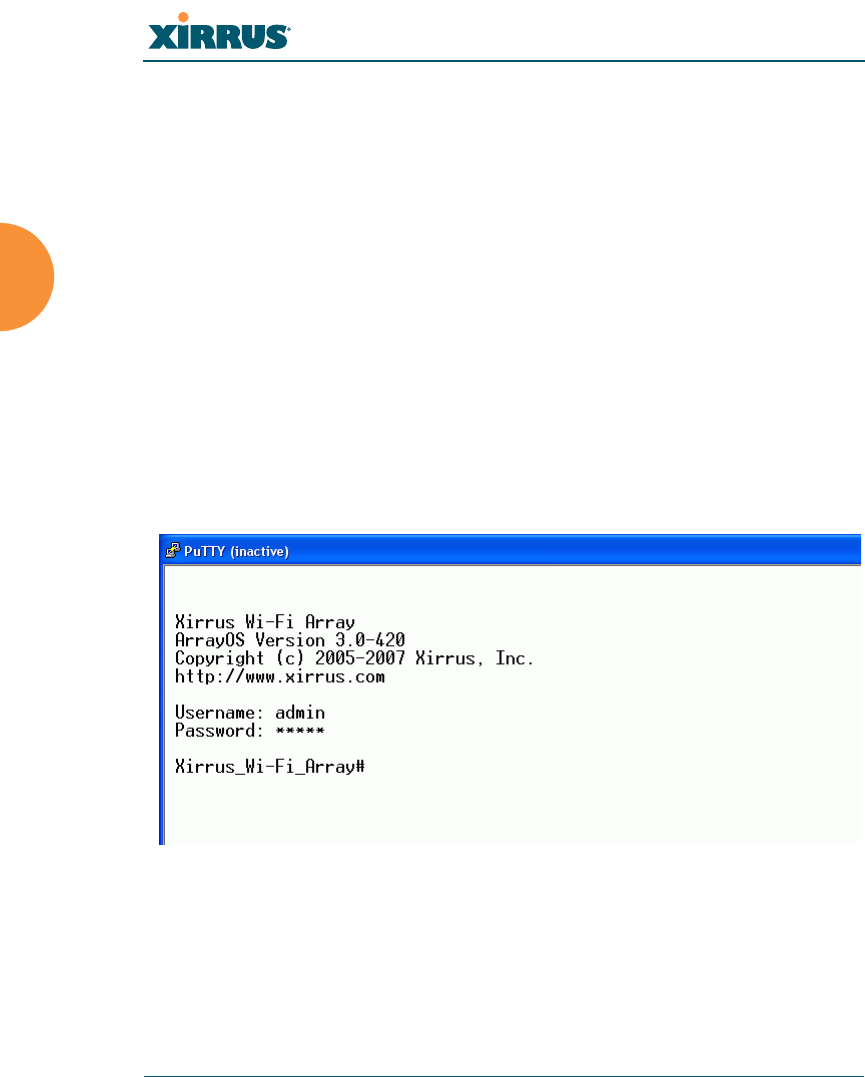
2. At the login prompt, enter your user name and password (the default for
both is admin). Login names and passwords are case-sensitive. You are
now logged in to the Array’s Command Line Interface.
Figure 184. Logging In
Wireless Array
The Command Line Interface 379
Getting Started with the CLI
The root command prompt (Root Command Prompt) is the first prompt you see
after logging in to the CLI. If you are at a level other than the root command
prompt you can return to this prompt at any time by using the exit command to
step back through each command prompt level. The root command prompt you
see in the CLI window is determined by the host name you assigned to your
Array. The prompt Xirrus_Wi-Fi_Array is displayed throughout this document
simply because this is the host name assigned to the Array used for development.
To terminate your session at any time, use the quit command.
Inputting Commands
When inputting commands you need only type as many characters as the system
requires before it recognizes your input. For example, you can type the
abbreviated term config to access the configure prompt.
Getting Help
The CLI offers the following two levels of assistance:
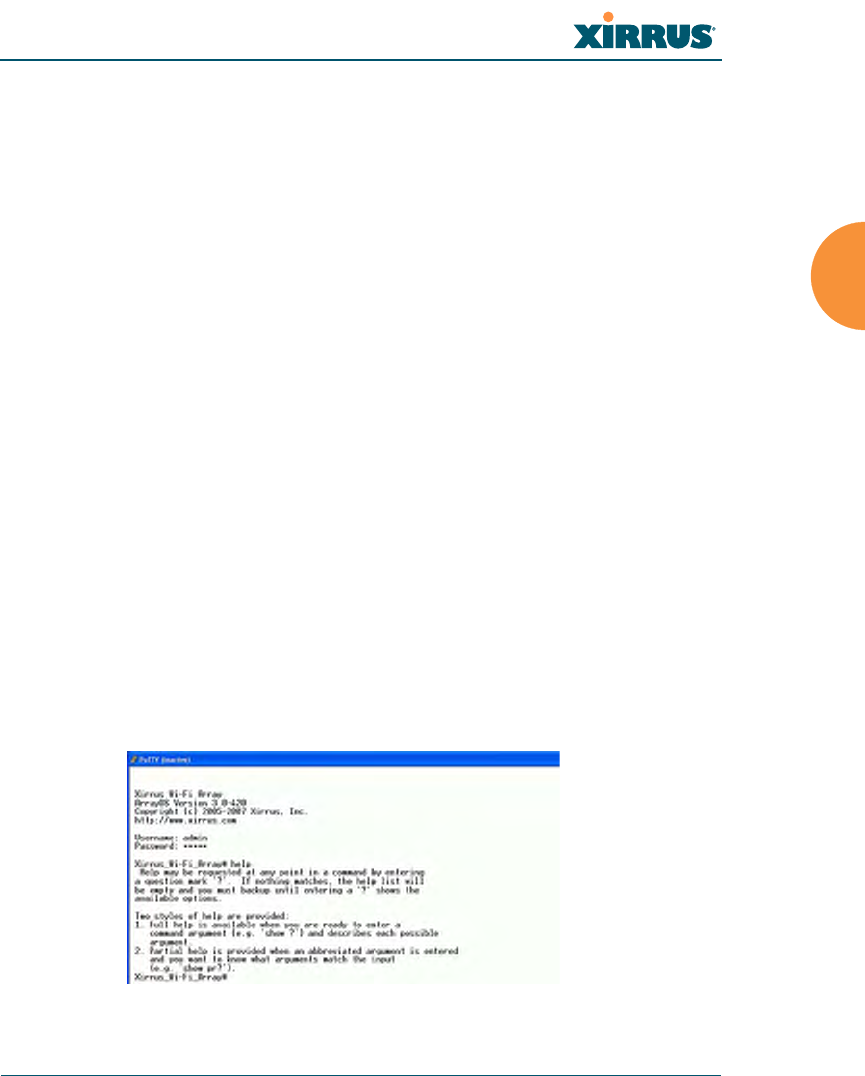
help Command
The help command is only available at the root command prompt.
Initiating this command generates a window that provides information
about the types of help that are available with the CLI.
Figure 185. Help Window
Wireless Array
380 The Command Line Interface
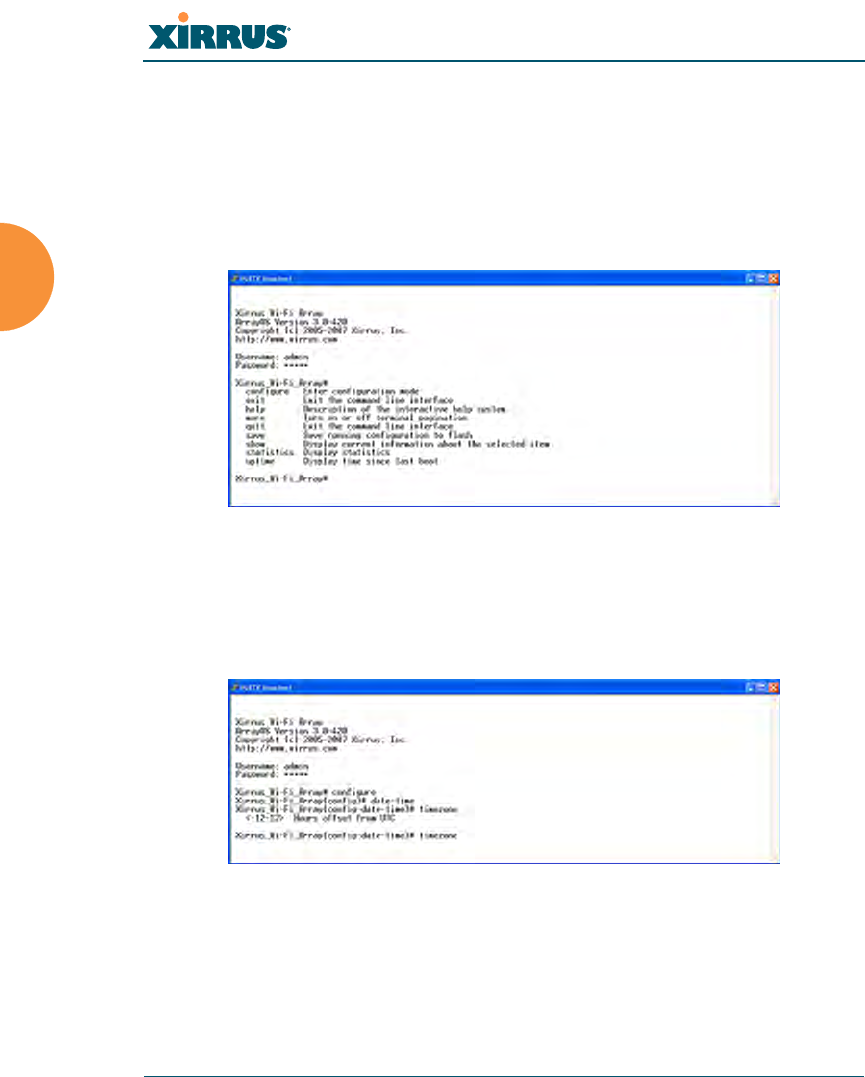
? Command
This command is available at any prompt and provides either FULL or
PARTIAL help. Using the ? (question mark) command when you are
ready to enter an argument will display all the possible arguments (full
help). Partial help is provided when you enter an abbreviated argument
and you want to know what arguments will match your input.
Figure 186. Full Help
Figure 187 shows an example of how the Help system can provide the
argument and format when specifying the time zone under the date-time
command.
Figure 187. Partial Help

Wireless Array
The Command Line Interface 381
Top Level Commands
This section offers an at-a-glance view of all top level commands — organized
alphabetically. Top level commands are defined here as commands that are
directly accessible from the root command prompt (Xirrus_Wi-Fi_Array#). The
root command prompt is based on the host name assigned to your Array. When
inputting commands, be aware that all commands are case-sensitive.
All other commands are considered second level configuration commands —
these are the commands you use to configure specific elements of the Array’s
features and functionality. For a listing of these commands with examples of
command formats and structure, go to “Configuration Commands” on page 390.
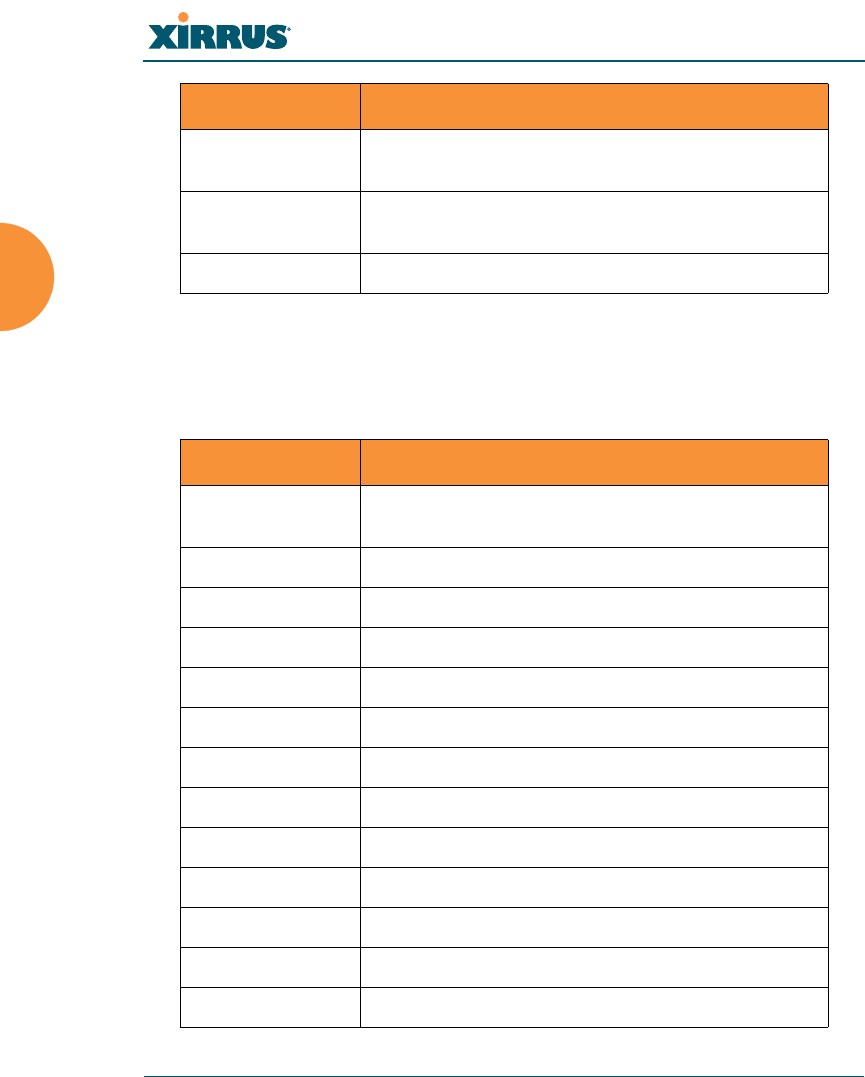
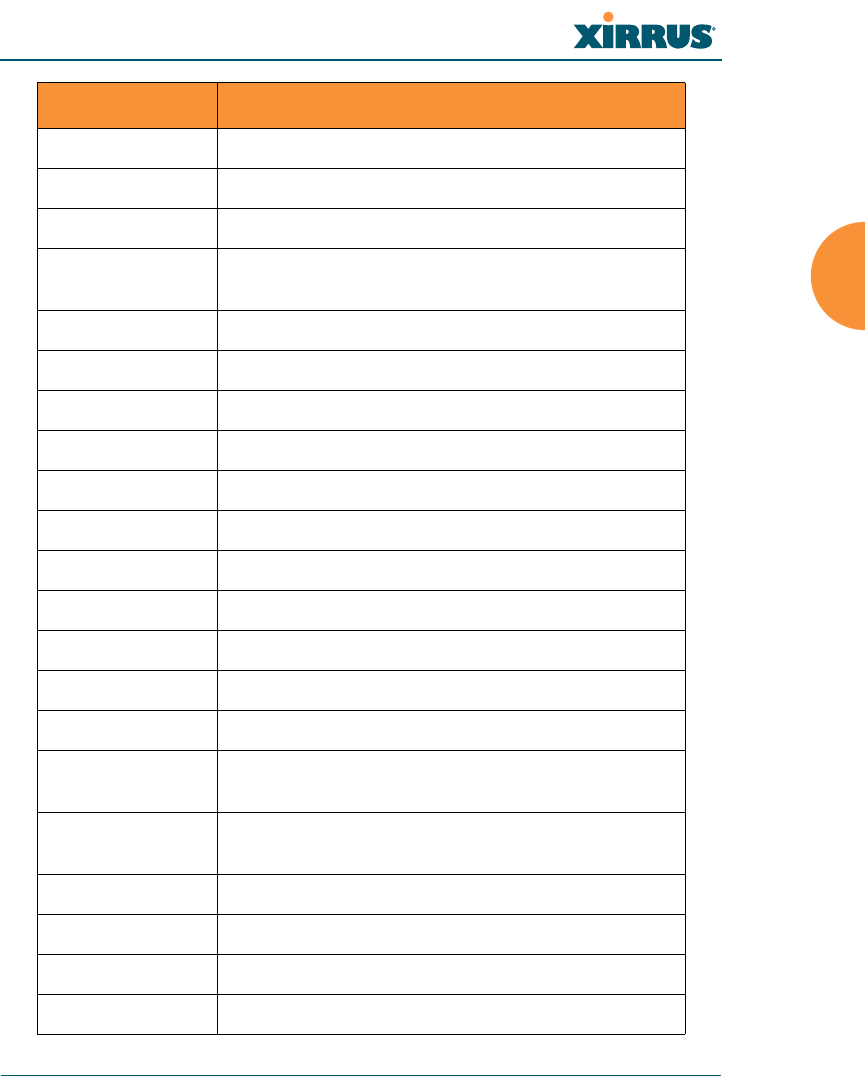
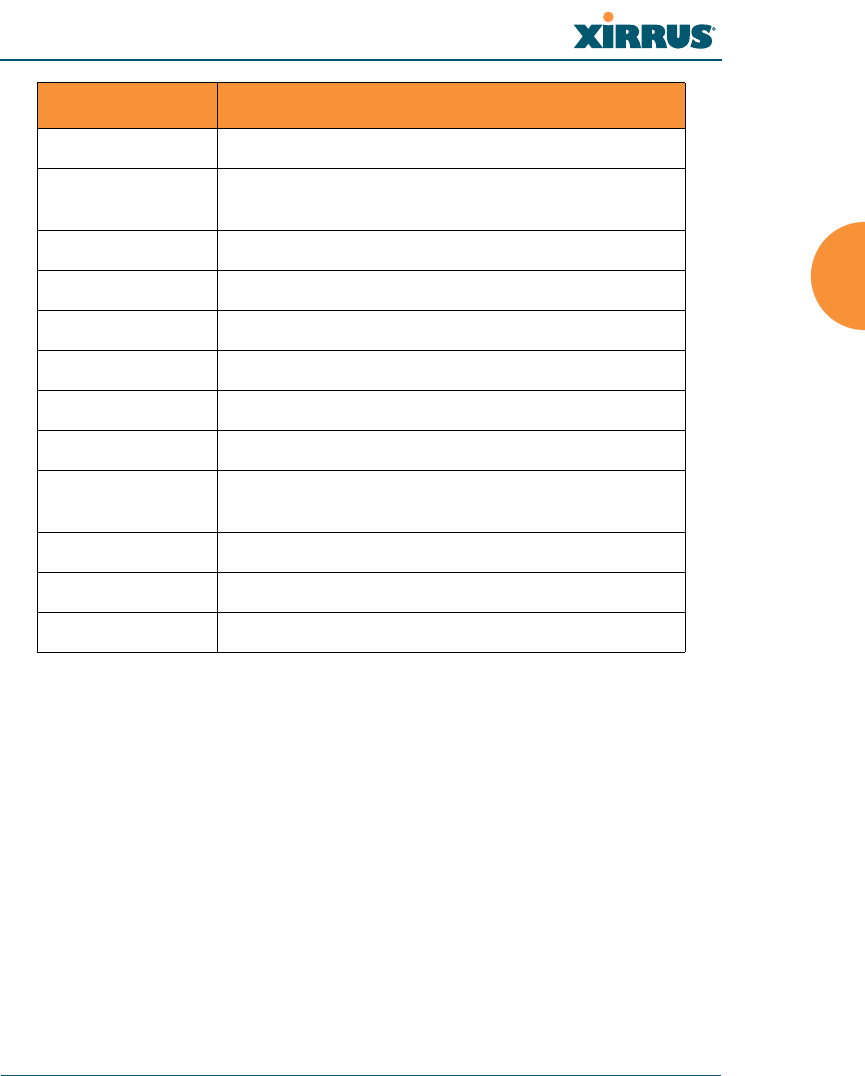
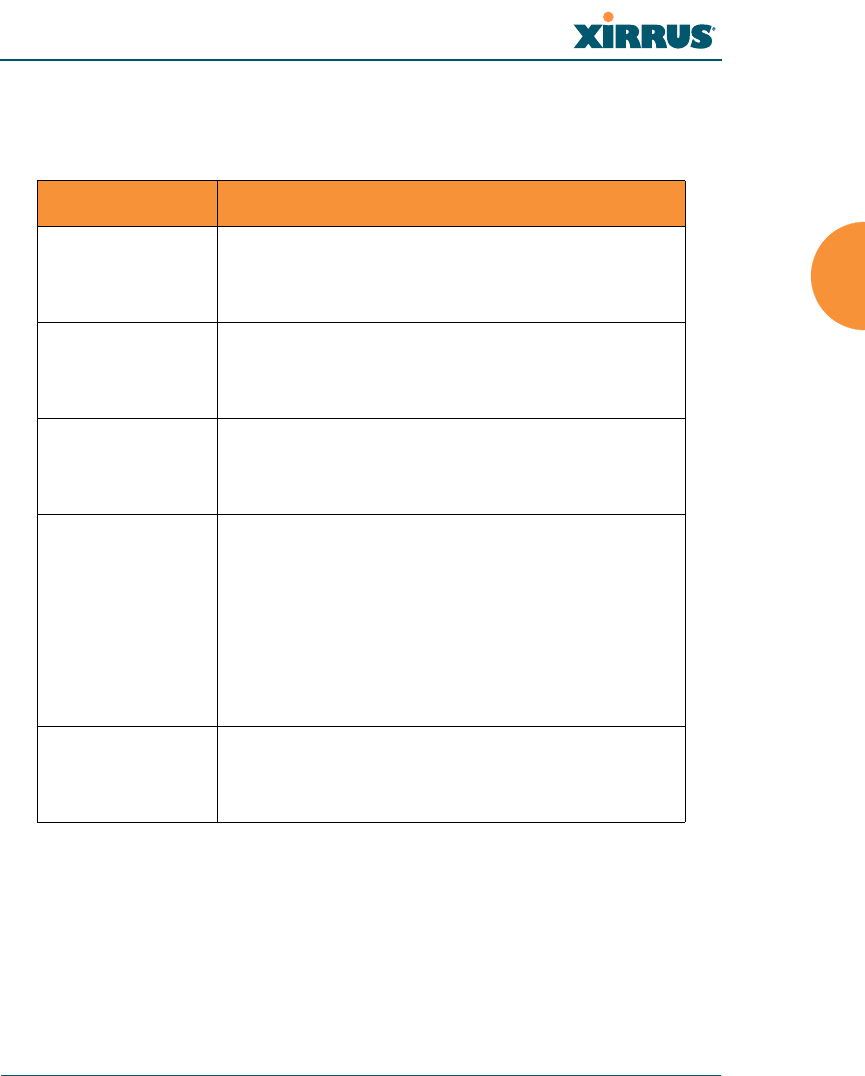
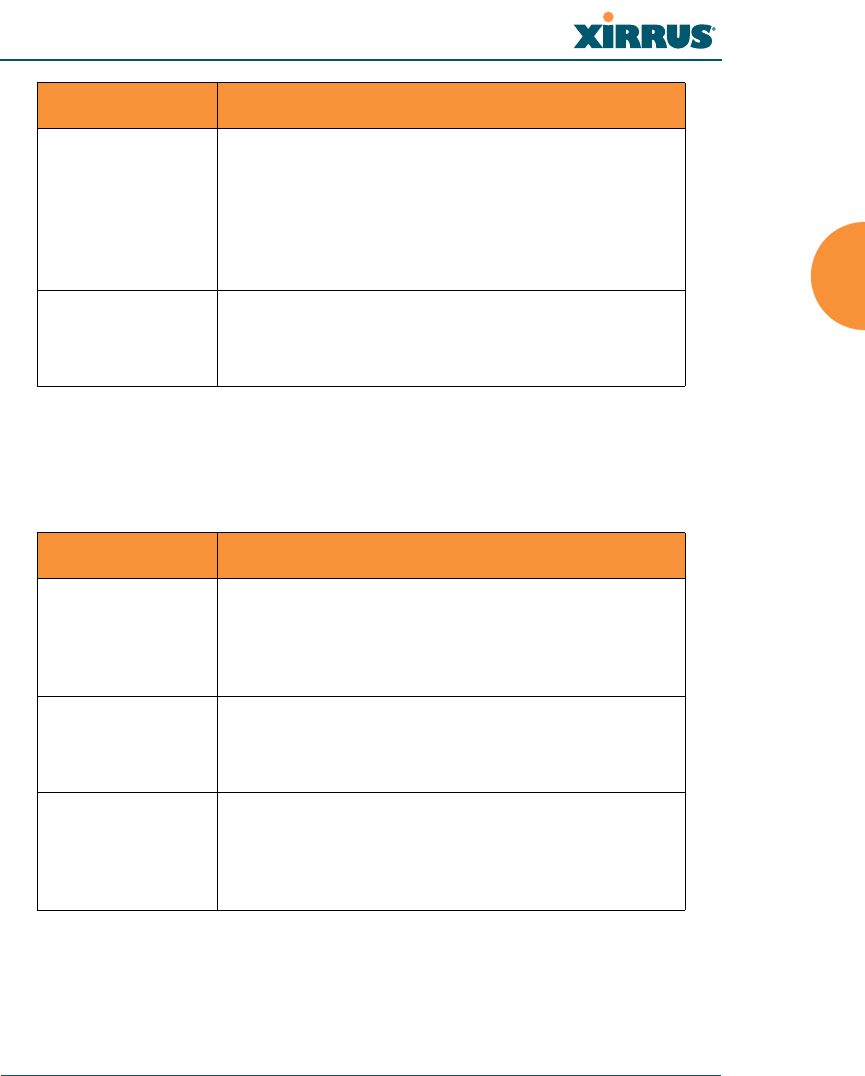
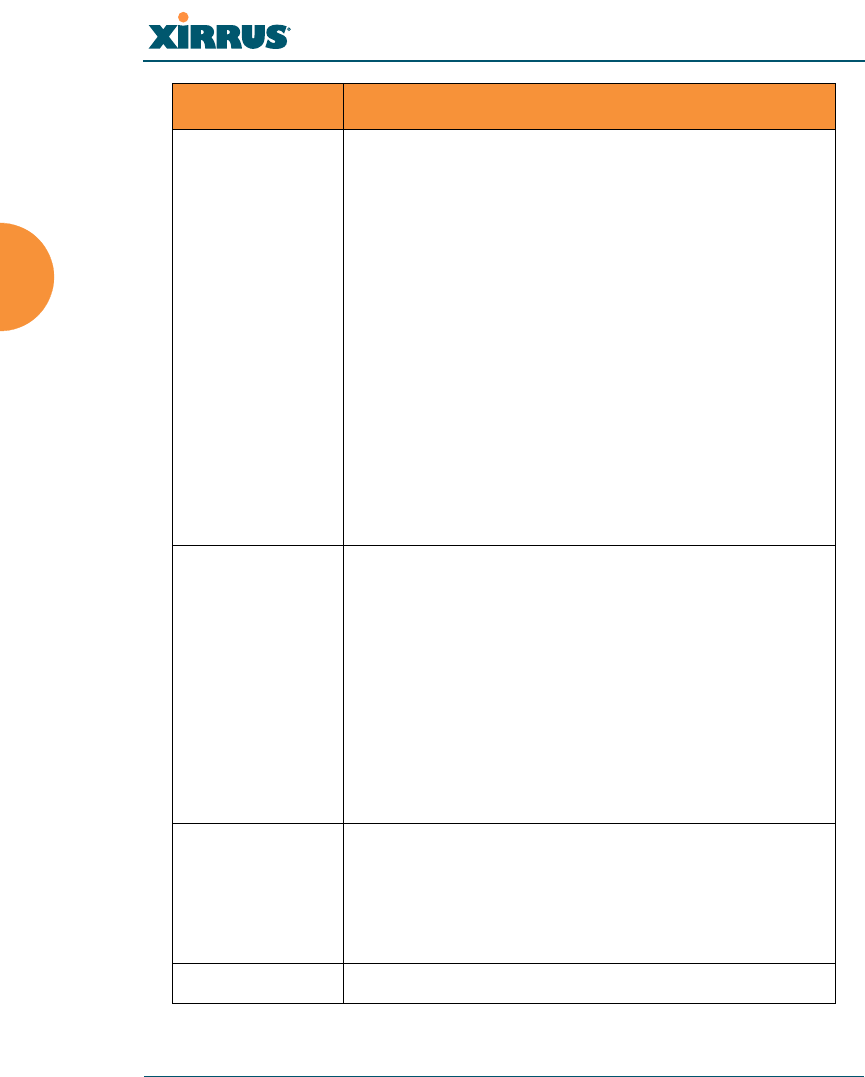
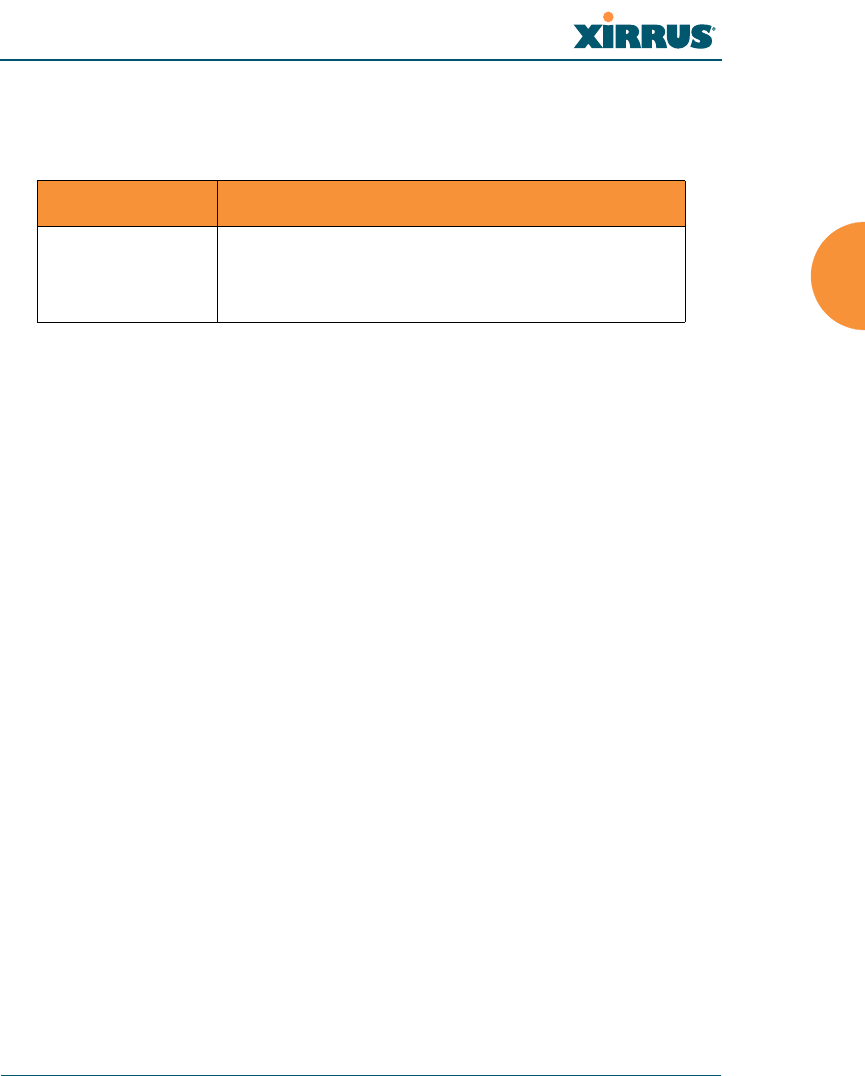
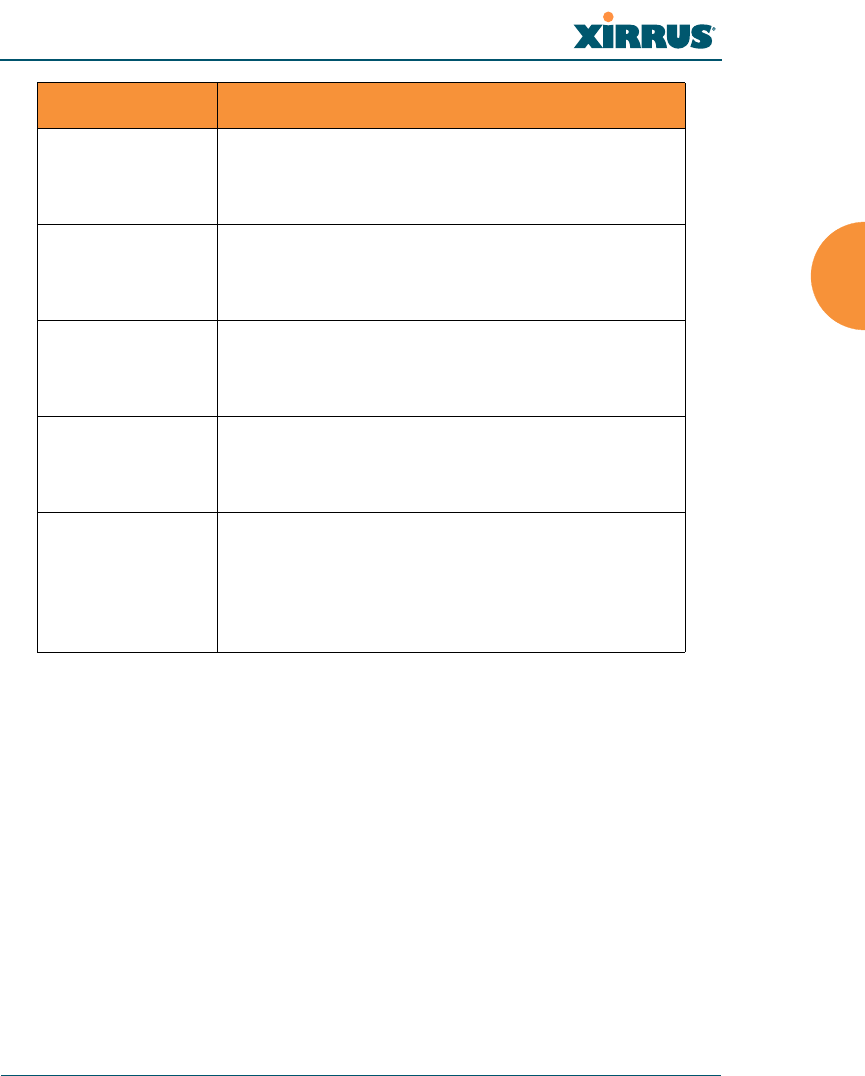
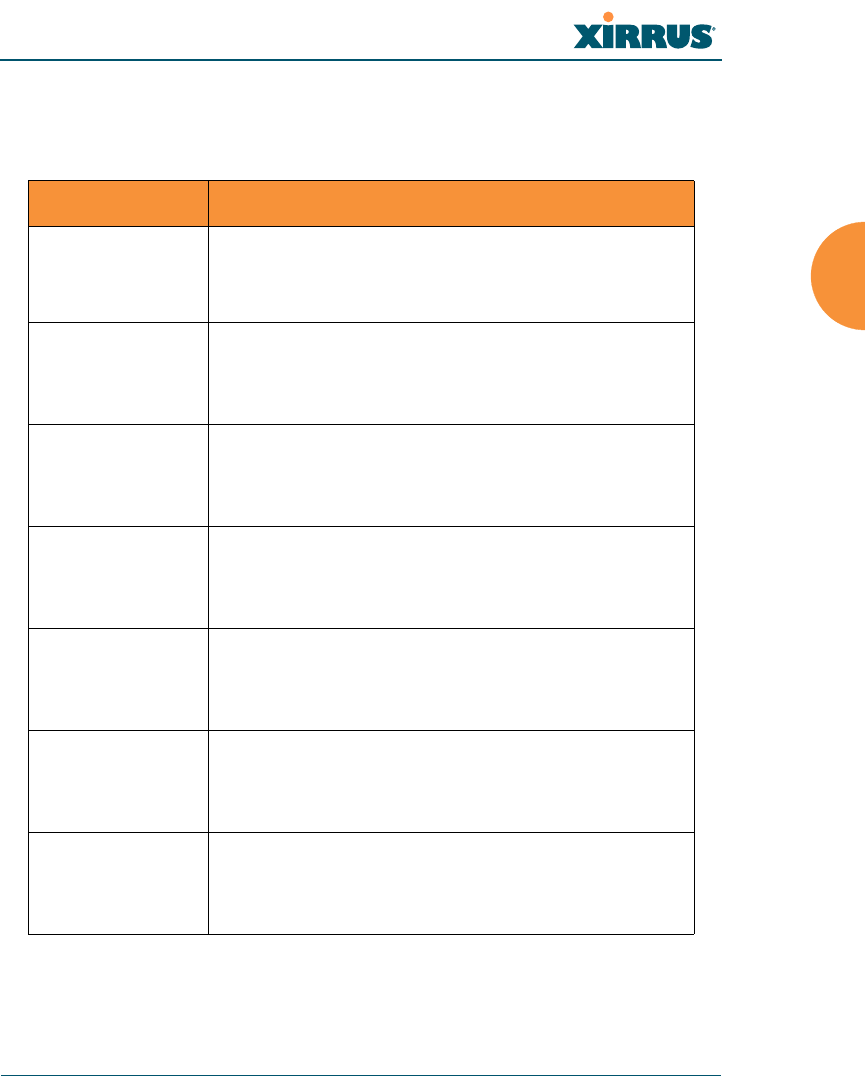
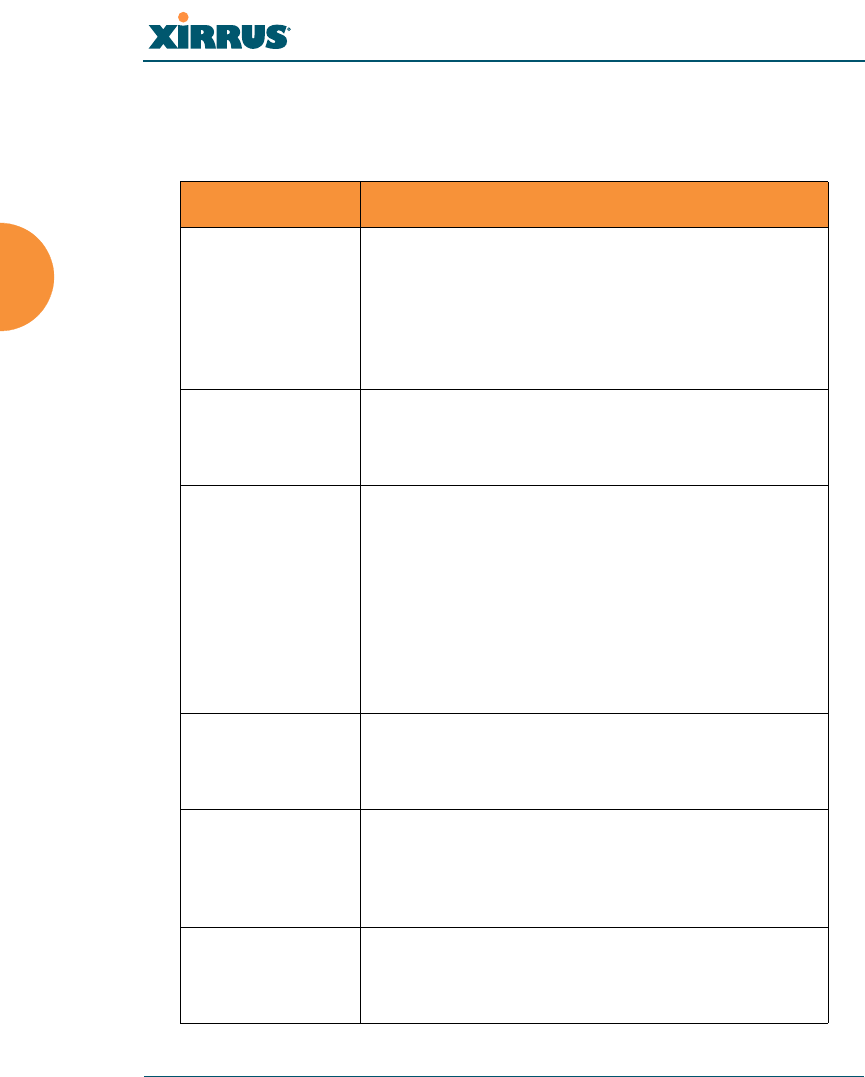
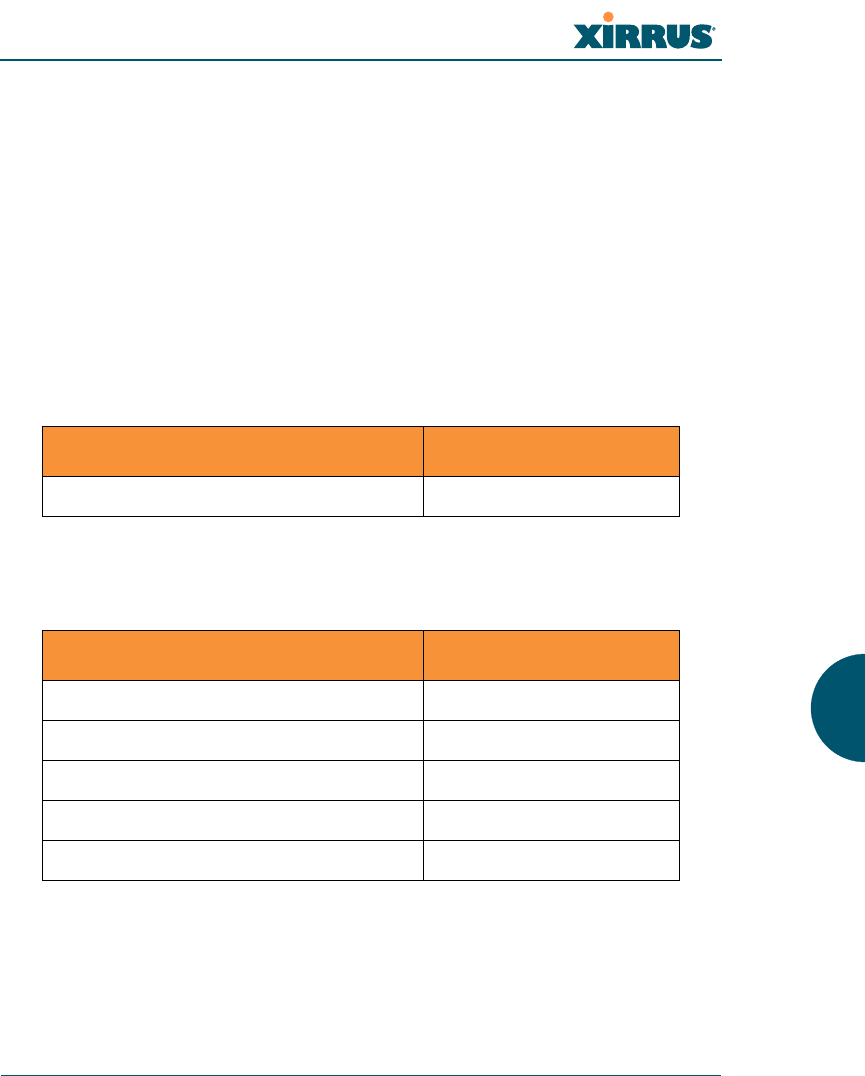
Root Command Prompt
The following table shows the top level commands that are available from the
root command prompt [Xirrus_Wi-Fi_Array].
Command Description
@ Type @n to execute command n (as shown by the
history command).
configure Enter the configuration mode. See “Configuration
Commands” on page 390.
exit Exit the CLI and terminate your session — if this
command is used at any level other than the root
command prompt you will simply exit the current
level (step back) and return to the previous level.
help Show a description of the interactive help system.
See also, “Getting Help” on page 379.
history List history of commands that have been
executed.
more Turn terminal pagination ON or OFF.
quit Exit the Command Line Interface (from any level).
search Search for pattern in show command output.
Wireless Array
382 The Command Line Interface
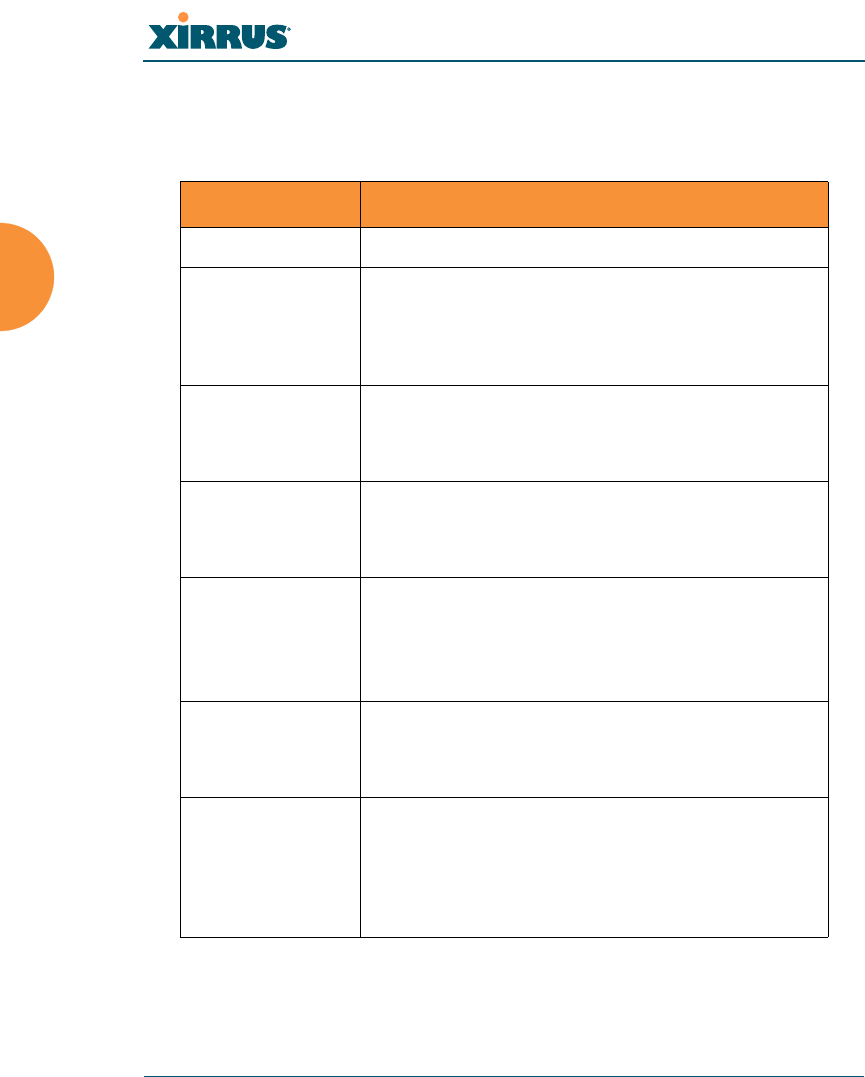
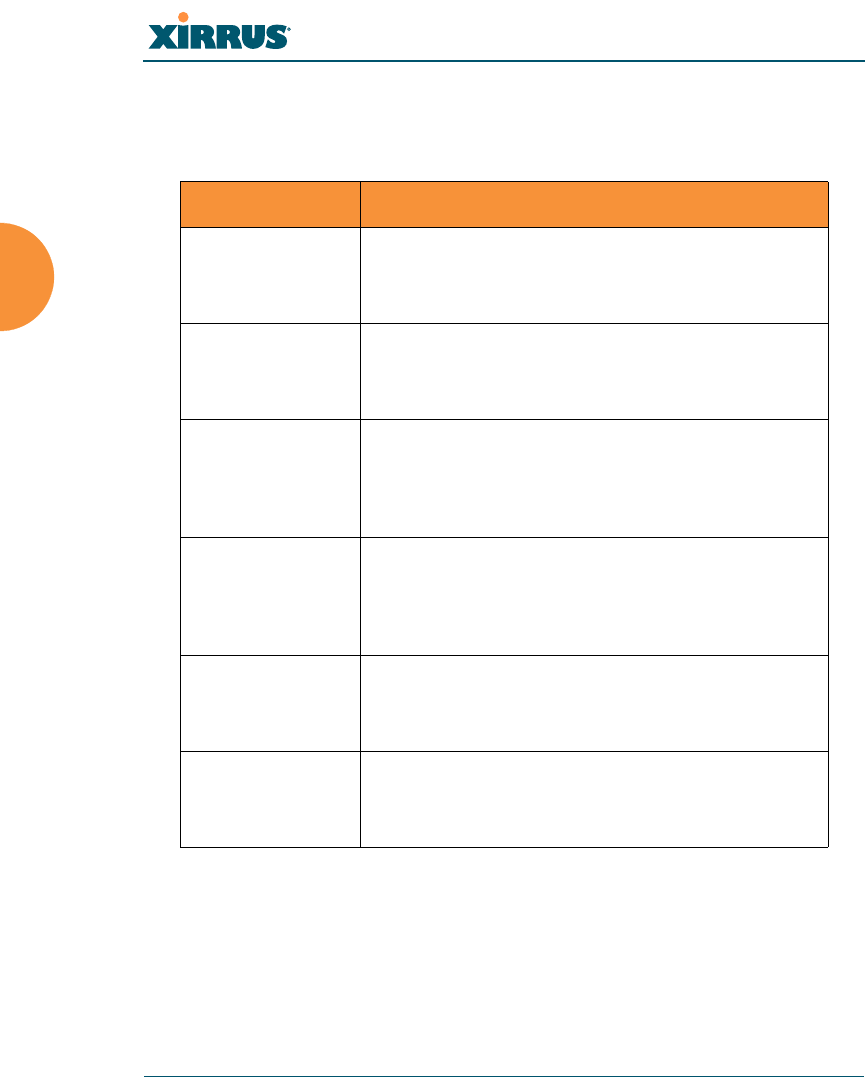
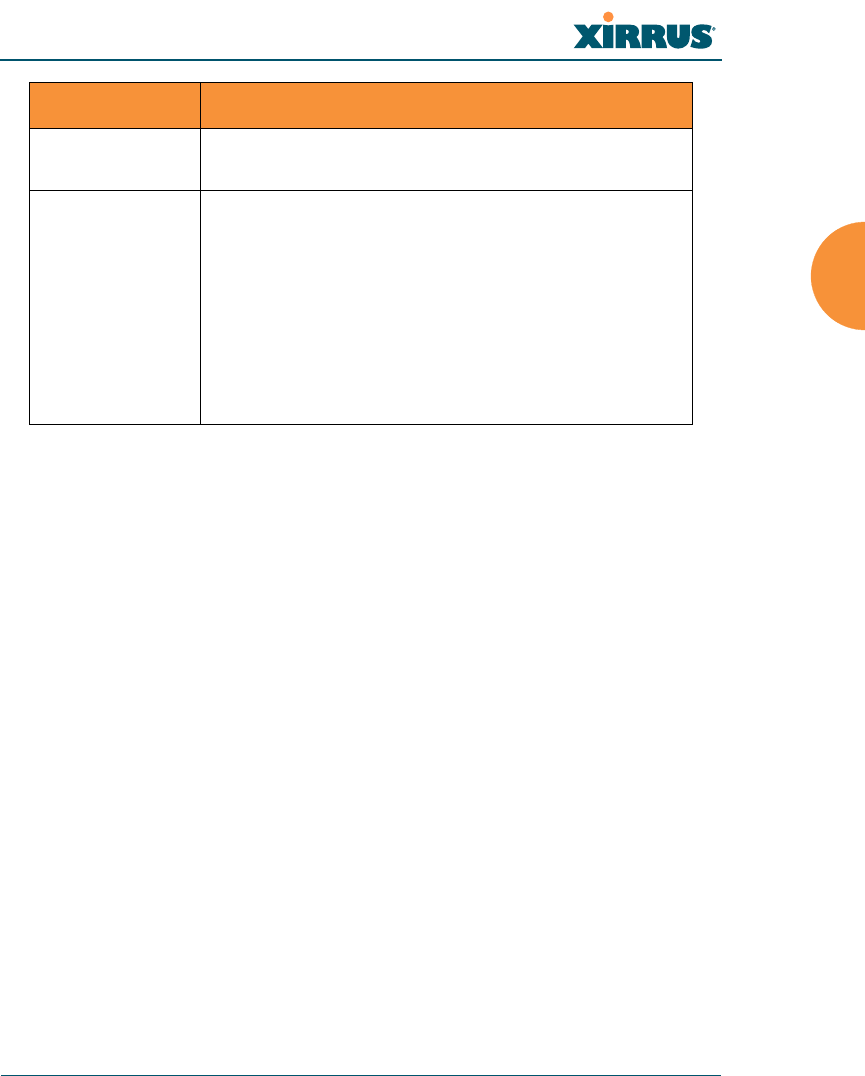
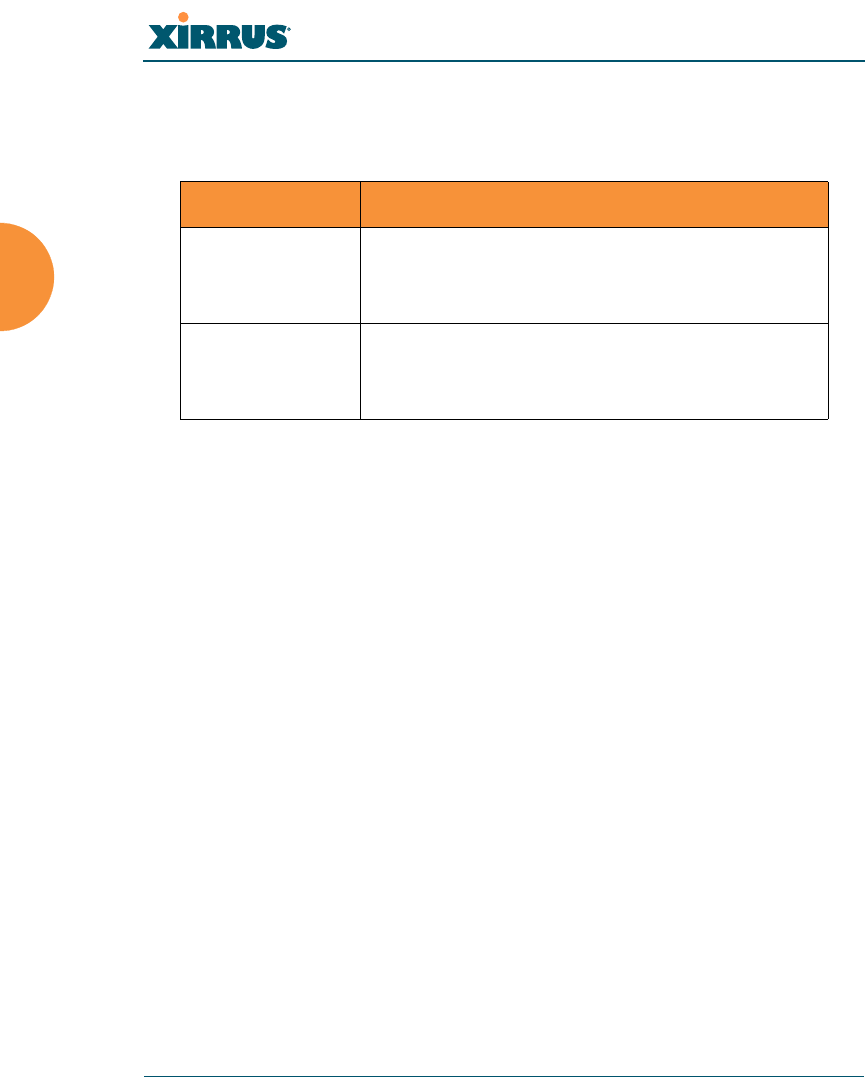
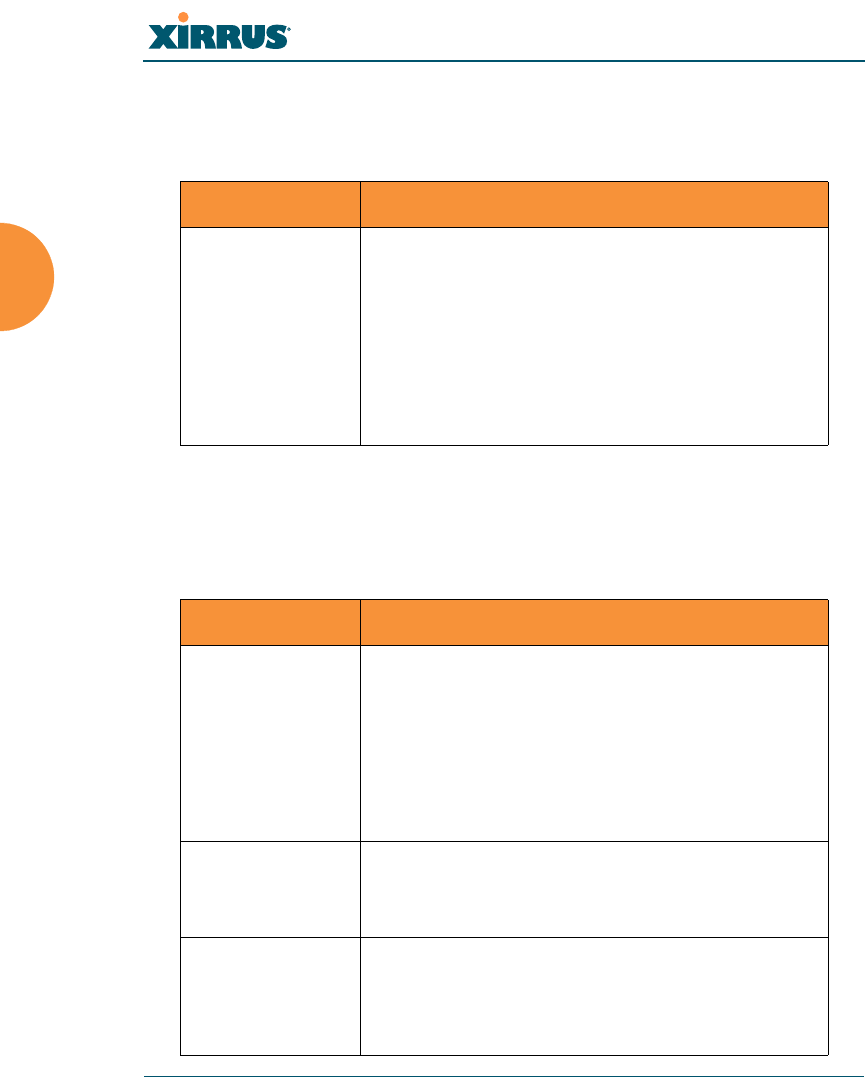
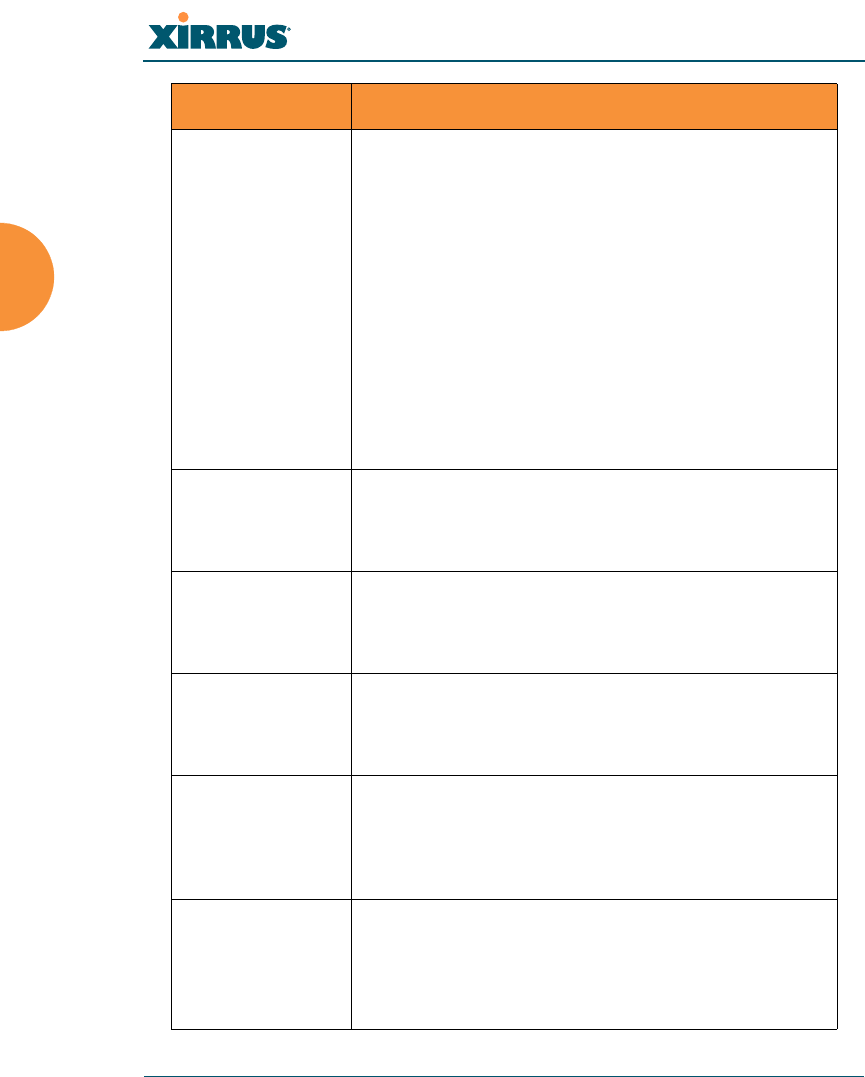
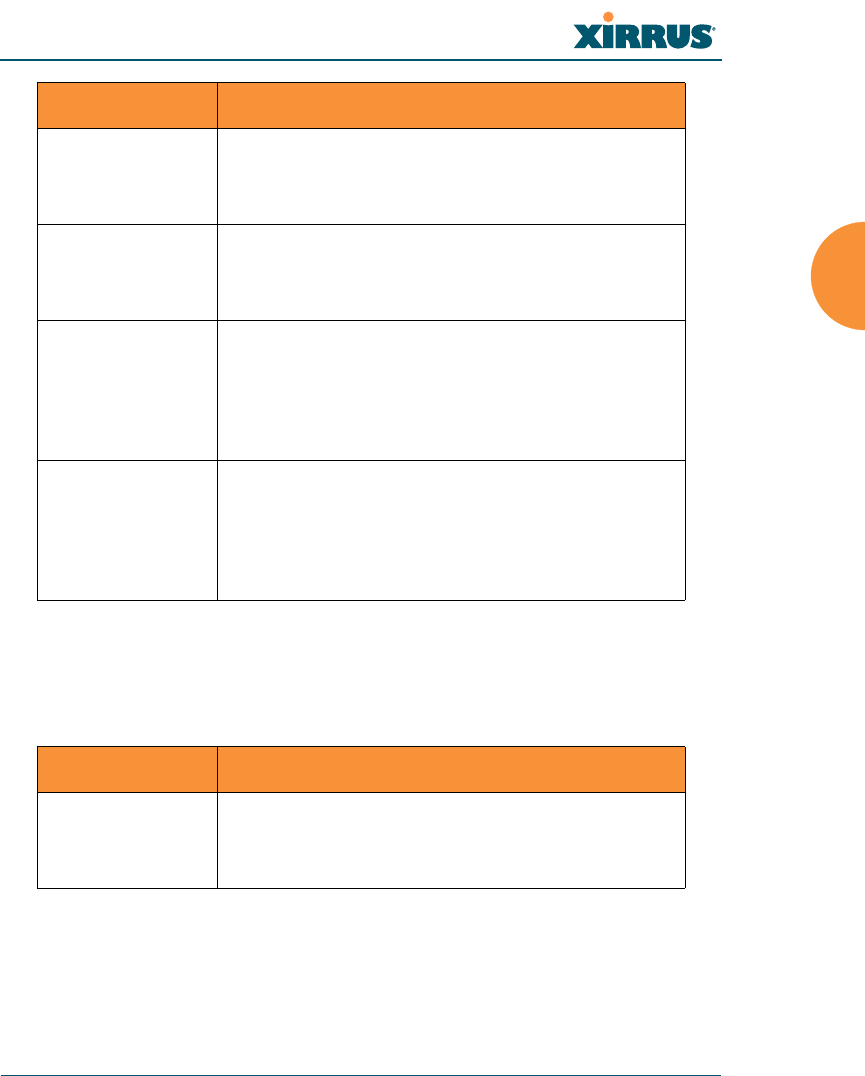
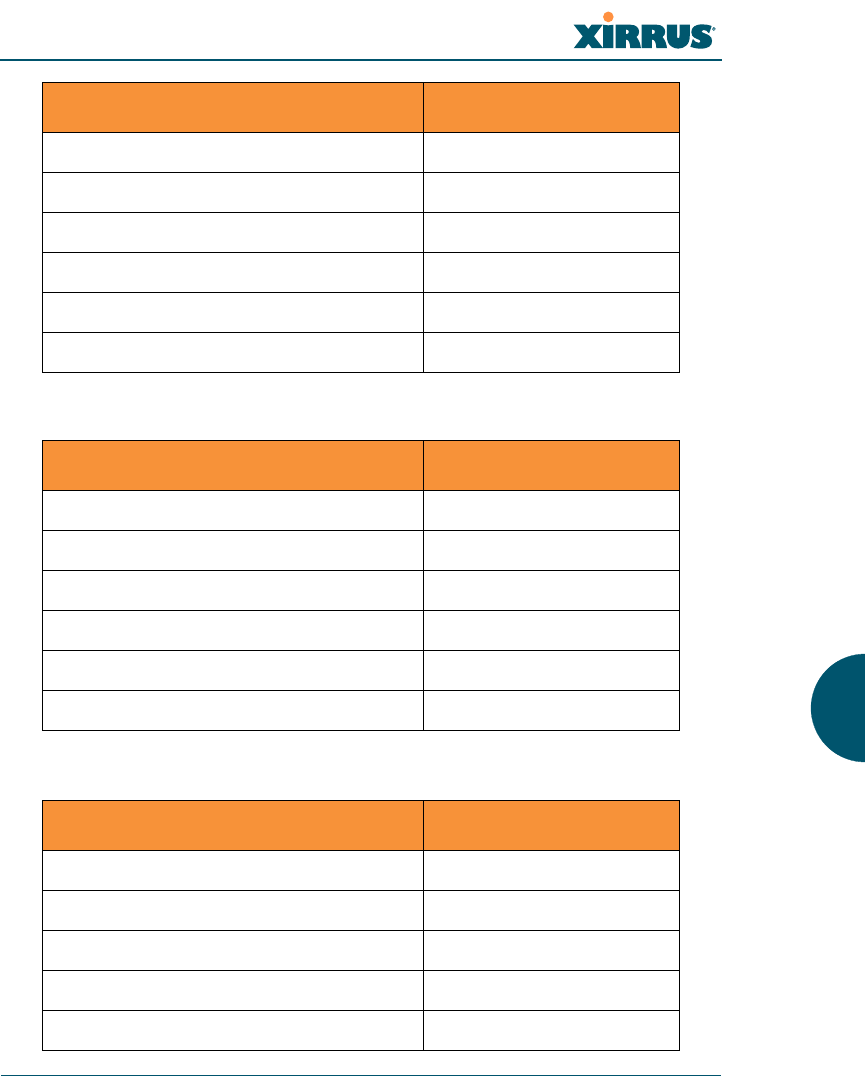
configure Commands
The following table shows the second level commands that are available with the
top level configure command [Xirrus_Wi-Fi_Array(config)#].
show Display information about the selected item. See
“show Commands” on page 385.
statistics Display statistical data about the Array. See
“statistics Commands” on page 388.
uptime Display the elapsed time since the last boot.
Command Description
@ Type @n to execute command n (as shown by the
history command).
acl Configure the Access Control List.
admin Define administrator access parameters.
cdp Configure Cisco Discovery Protocol settings.
clear Remove/clear the requested elements.
cluster Make configuration changes to multiple Arrays.
contact-info Contact information for assistance on this Array.
date-time Configure date and time settings.
dhcp-server Configure the DHCP Server.
dns Configure the DNS settings.
end Exit the configuration mode.
exit Go UP one mode level.
file Manage the file system.
Command Description
Wireless Array
The Command Line Interface 383
filter Define protocol filter parameters.
group Define user groups with parameter settings
help Description of the interactive Help system.
history List history of commands that have been
executed.
hostname Host name for this Array.
interface Select the interface to configure.
load Load running configuration from flash
location Location name for this Array.
management Configure array management parameters
more Turn ON or OFF terminal pagination.
netflow Configure NetFlow data collector.
no Disable (if enabled) or set to default value.
quit Exit the Command Line Interface.
radius-server Configure the RADIUS server parameters.
reboot Reboot the Array.
reset Reset all settings to their factory default values
and reboot.
restore Reset all settings to their factory default values
and reboot.
run-tests Run selective tests.
save Save the running configuration to FLASH.
search Search for pattern in show command output.
security Set the security parameters for the Array.
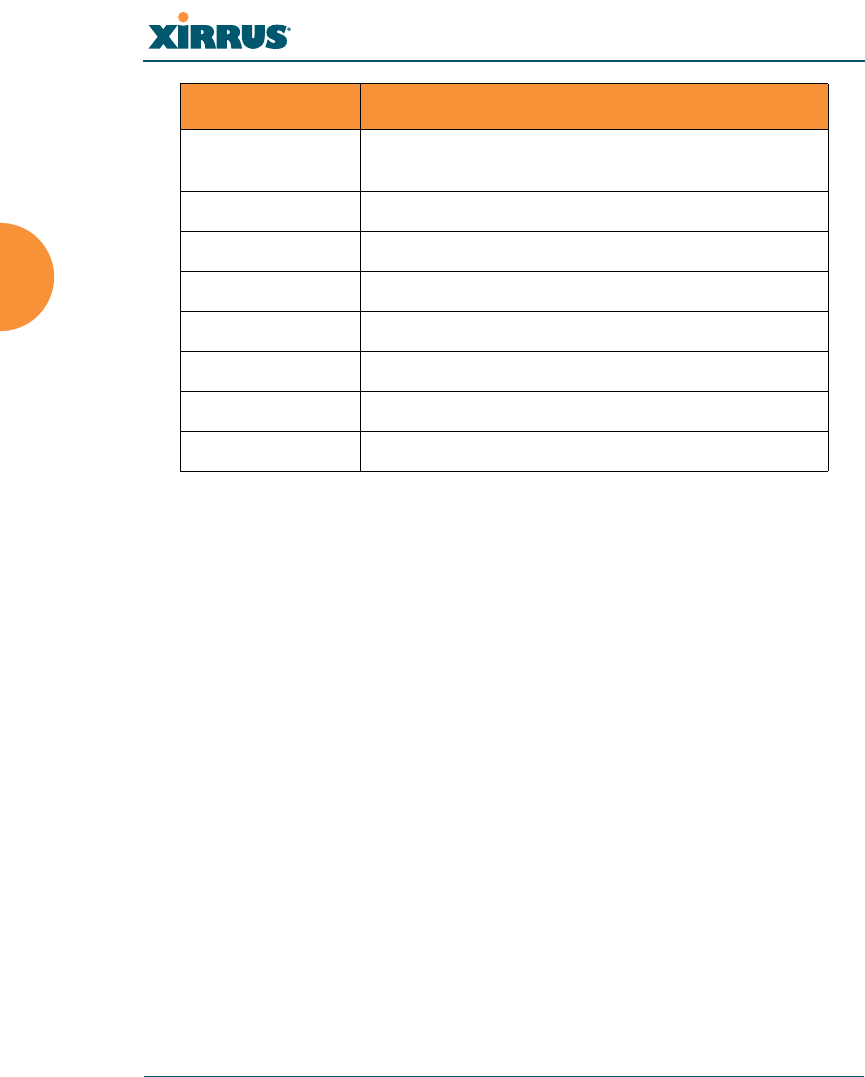
Command Description
Wireless Array
384 The Command Line Interface
show Display current information about the selected
item.
snmp Enable, disable or configure SNMP.
ssid Configure the SSID parameters.
statistics Display statistics.
syslog Enable, disable or configure the Syslog Server.
uptime Display time since the last boot.
vlan Configure VLAN parameters.
wifi-tag Configure VLAN parameters.
Command Description
Wireless Array
The Command Line Interface 385
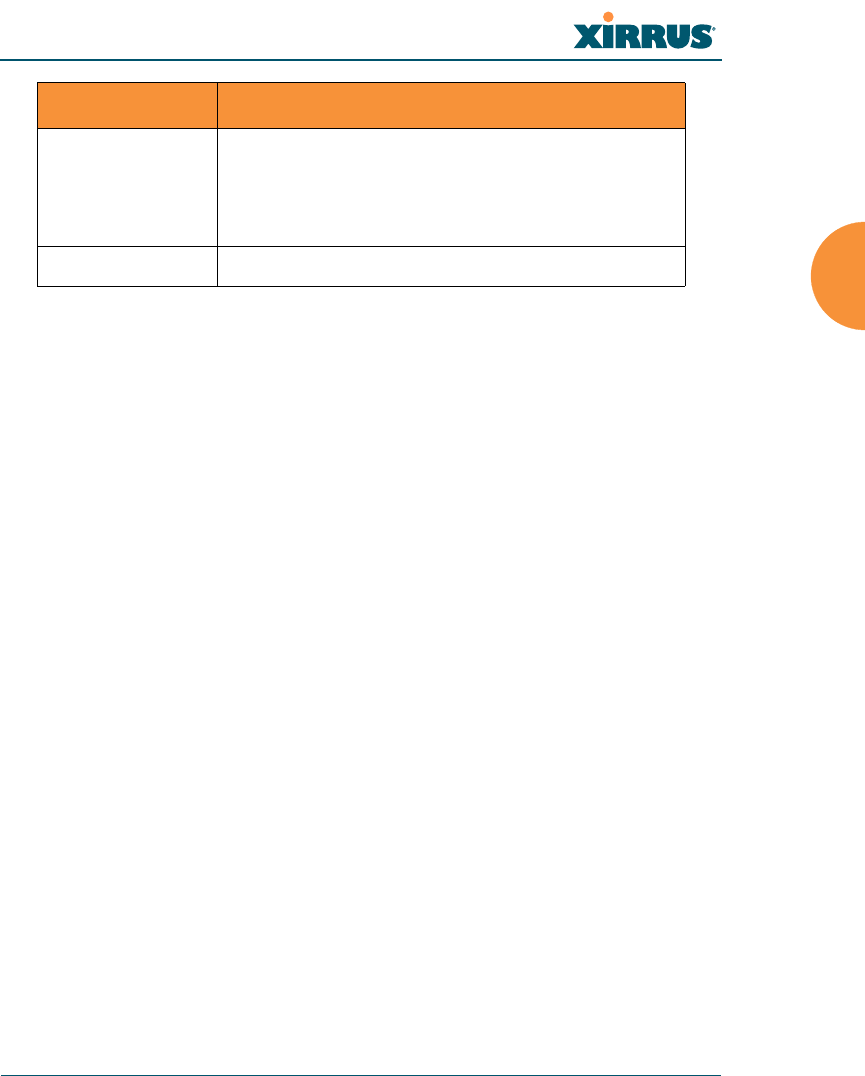
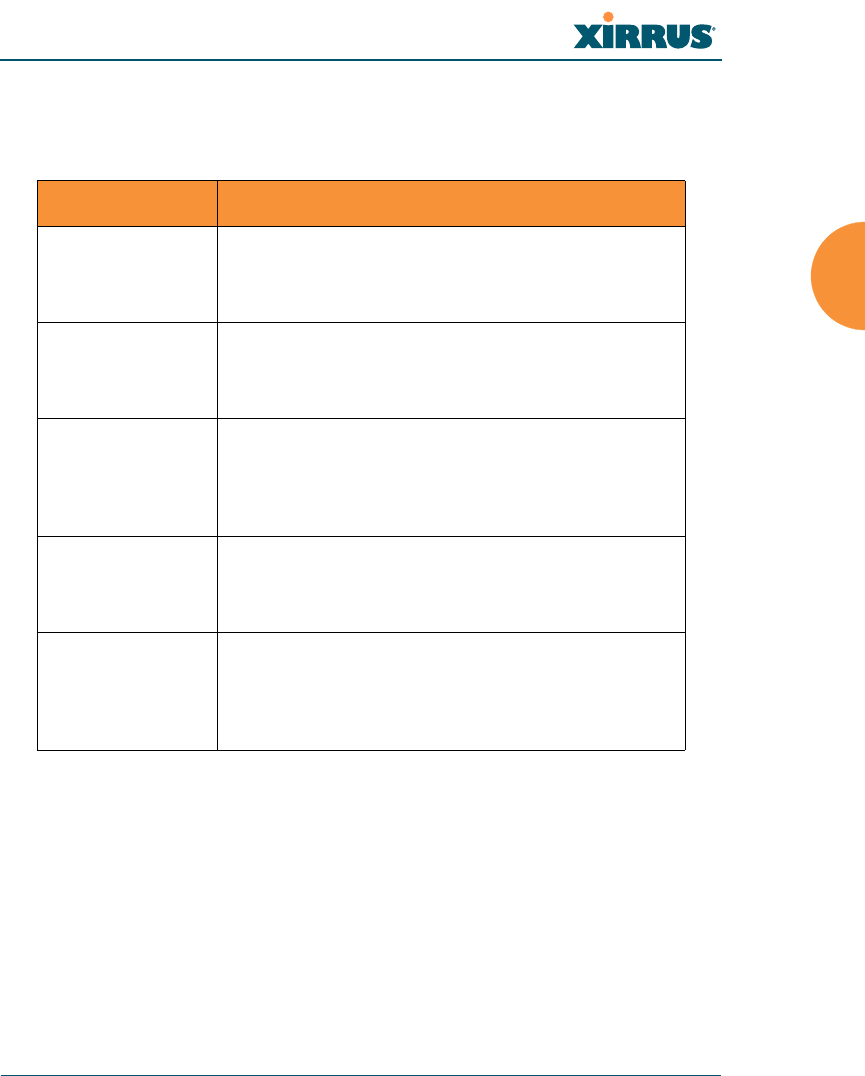
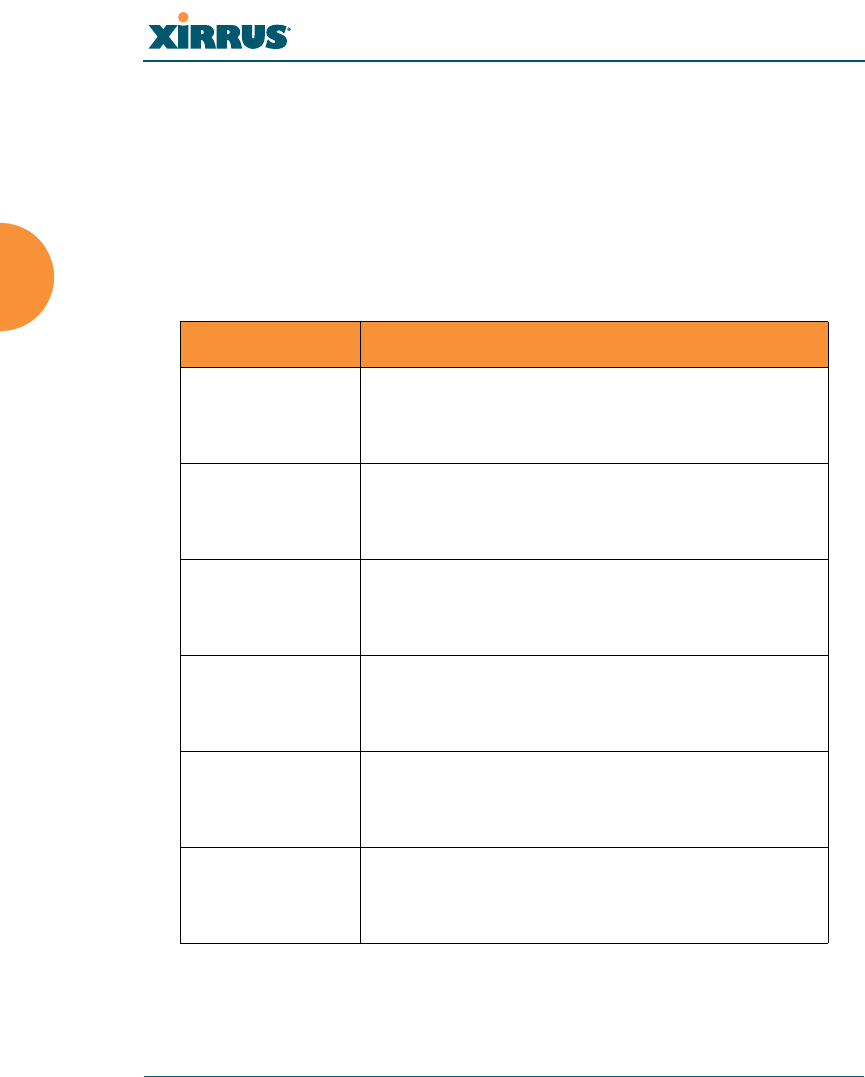
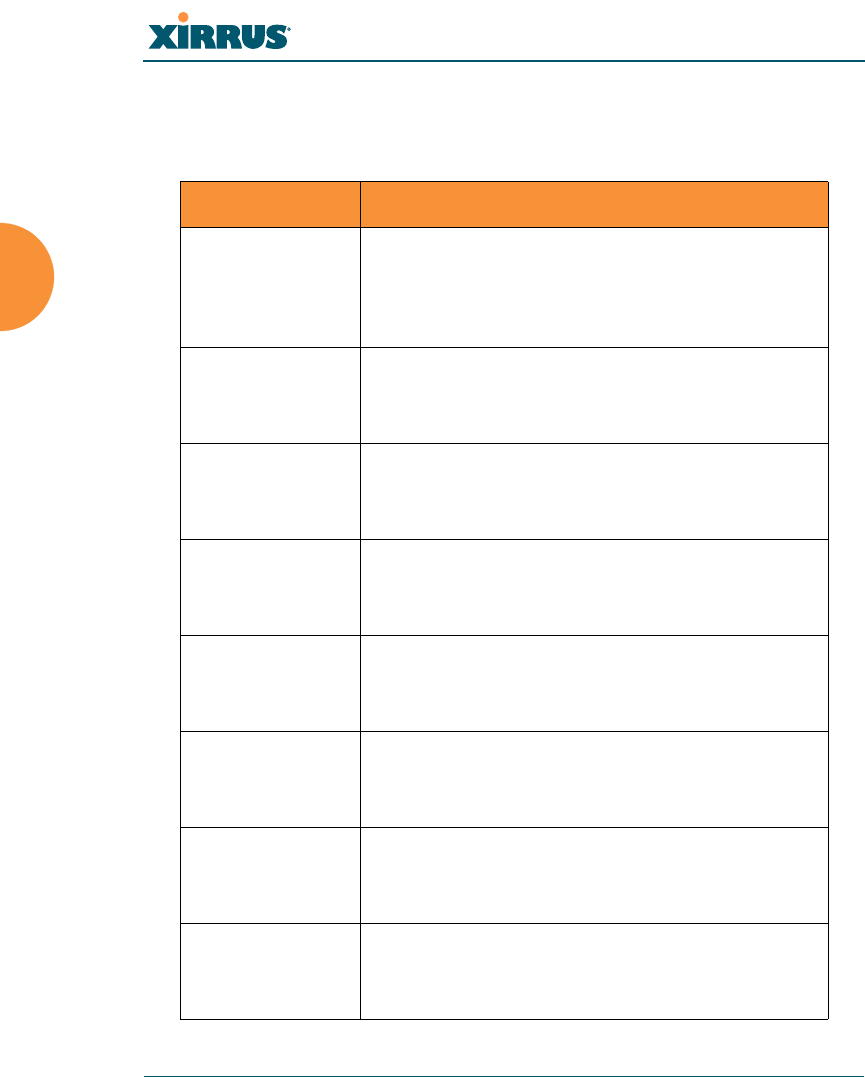
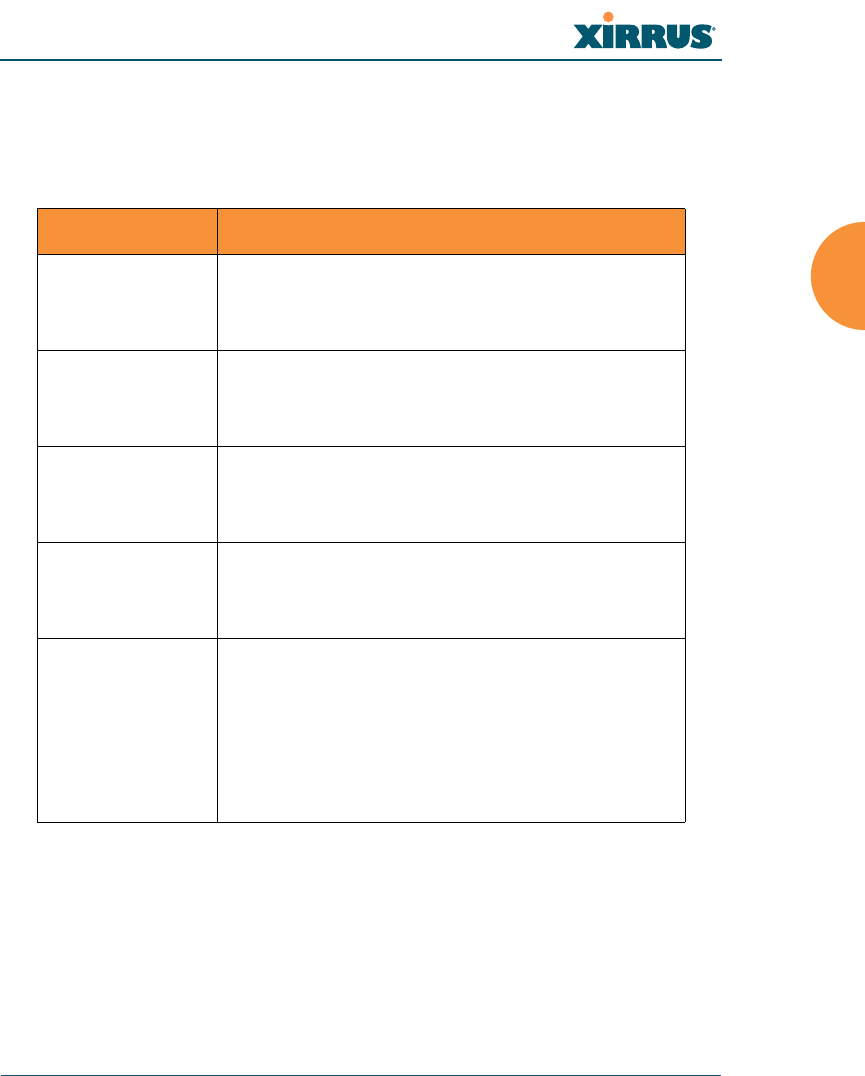
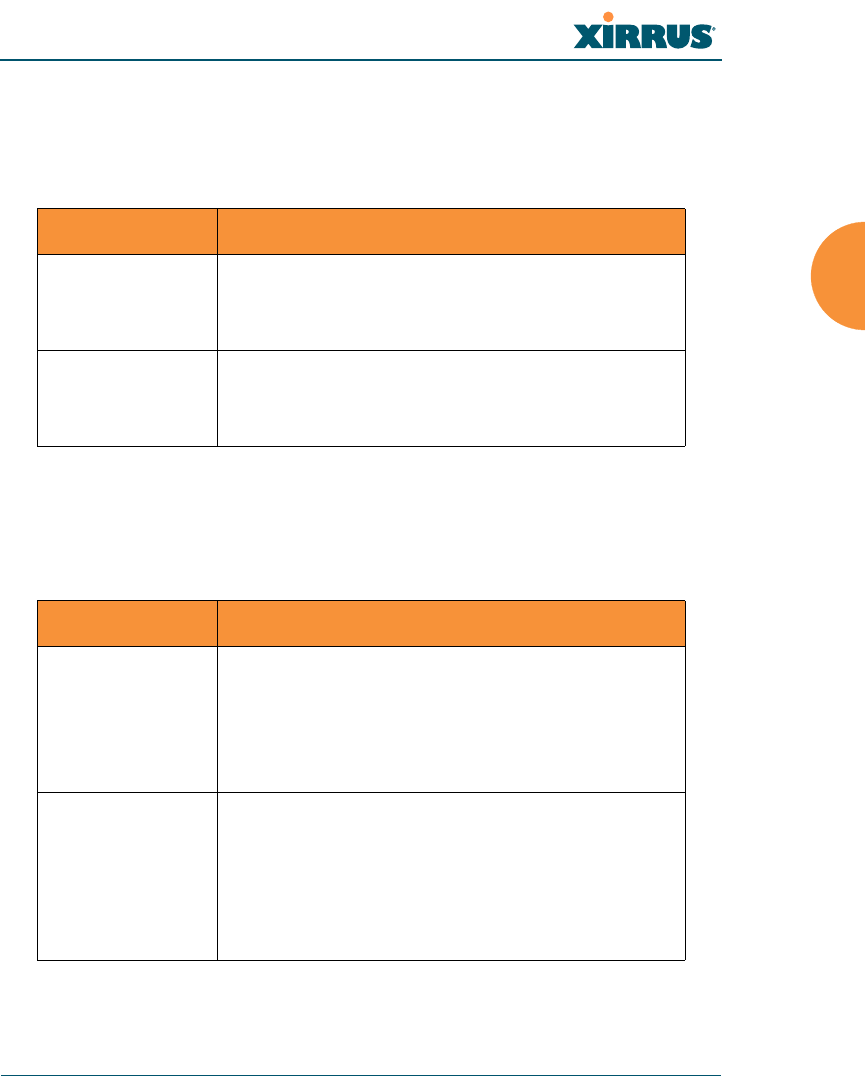
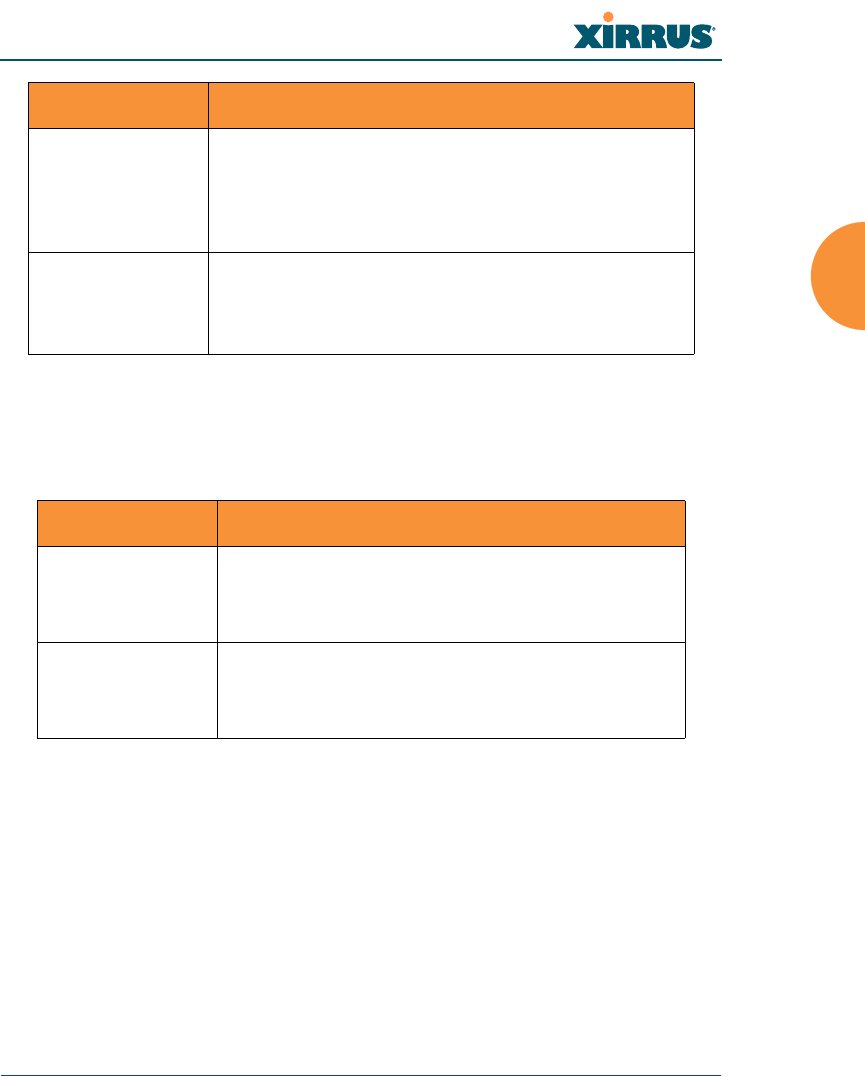
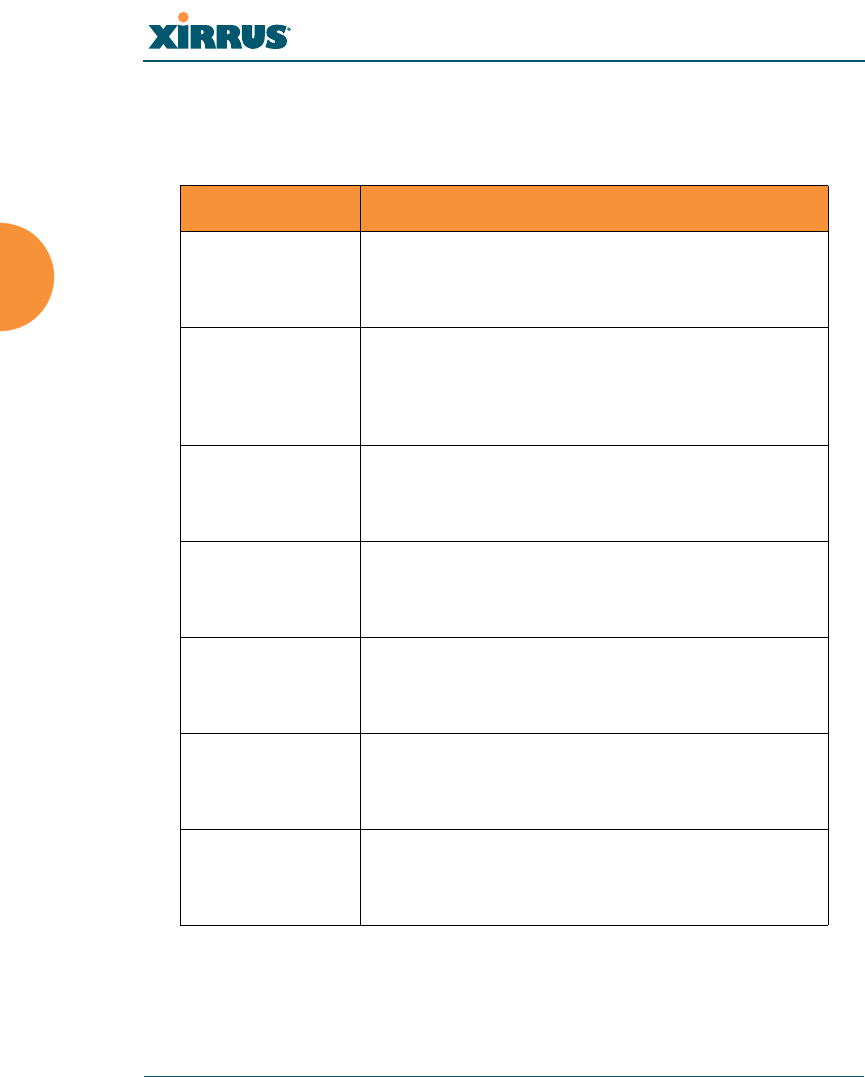
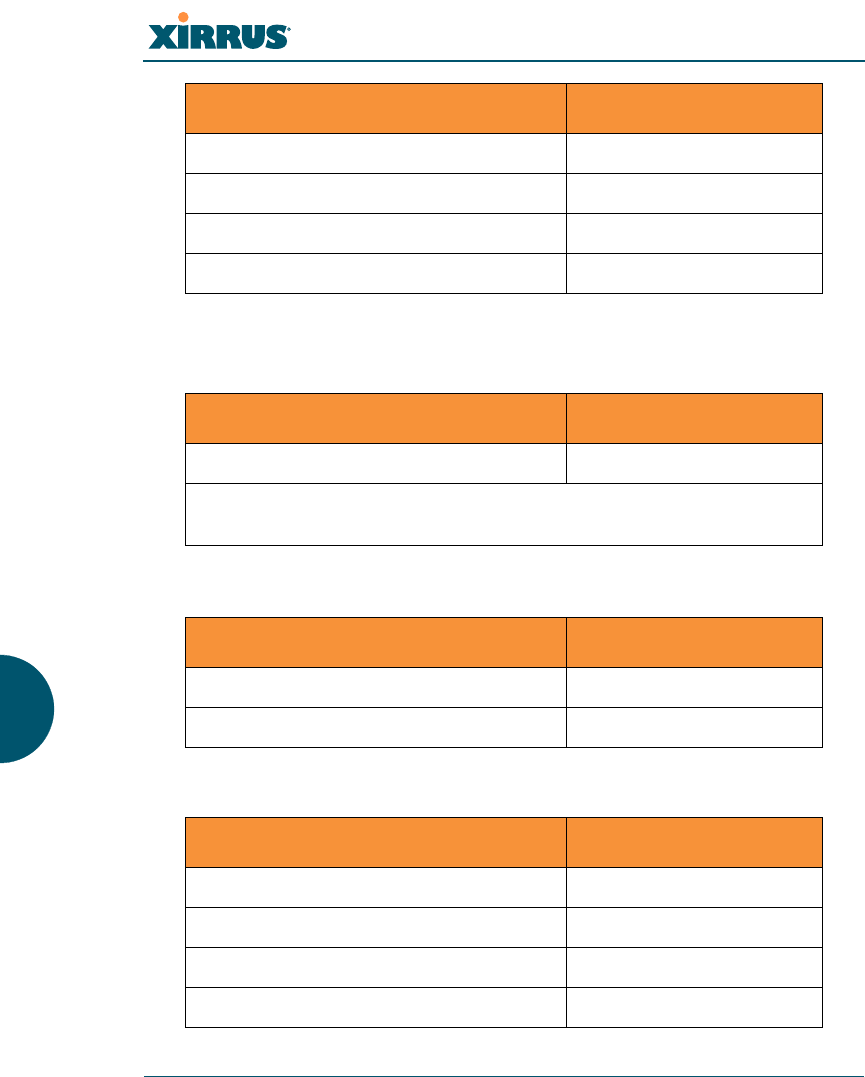
show Commands
The following table shows the second level commands that are available with the
top level show command [Xirrus_Wi-Fi_Array# show].
Command Description
acl Display the Access Control List.
admin Display the administrator list or login
information.
array-info Display system information.
associated-
stations
Display stations that have associated to the Array.
boot-env Display Boot loader environment variables.
capabilities Display detailed station capabilities.
cdp Display Cisco Discovery Protocol settings.
channel-list Display list of Array’s 802.11an and bgn channels.
clear-text Display and enter passwords and secrets in the
clear.
conntrack Display the Connection Tracking table.
console Display terminal settings.
contact-info Display contact information.
date-time Display date and time settings summary.
dhcp-leases Display IP addresses (leases) assigned to stations
by the DHCP server.
dhcp-pool Display internal DHCP server settings summary
information.
diff Display the difference between configurations.
dns Display DNS summary information.
Wireless Array
386 The Command Line Interface
error-numbers Display the detailed error number in error
messages.
ethernet Display Ethernet interface summary information.
external-radius Display summary information for the external
RADIUS server settings.
factory-config Display the Array factory configuration
information.
filters Display filter information.
iap Display IAP configuration information.
internal-radius Display the users defined for the embedded
RADIUS server.
lastboot-config Display Array configuration at the time of the last
boot-up.
management Display settings for managing the Array, plus
Standby, FIPS, and other information.
network-map Display network map information.
realtime-monitor Display realtime statistics for all IAPs.
rogue-ap Display rogue AP information.
route Display the routing table.
rssi-map Display RSSI map by IAP for station.
running-config Display configuration information for the Array
currently running.
saved-config Display the last saved Array configuration.
security Display security settings summary information.
self-test Display self test results.
snmp Display SNMP summary information.
Command Description
Wireless Array
The Command Line Interface 387
spanning-tree Display spanning tree information.
spectrum-
analyzer
Display spectrum analyzer measurements.
ssid Display SSID summary information.
stations Display station information.
statistics Display statistics.
syslog Display the system log.
syslog-settings Display the system log (Syslog) settings.
temperature Display the current board temperatures.
unassociated-
stations
Display unassociated station information.
vlan Display VLAN information.
wds Display WDS information.
<cr> Display configuration or status information.
Command Description
Wireless Array
388 The Command Line Interface
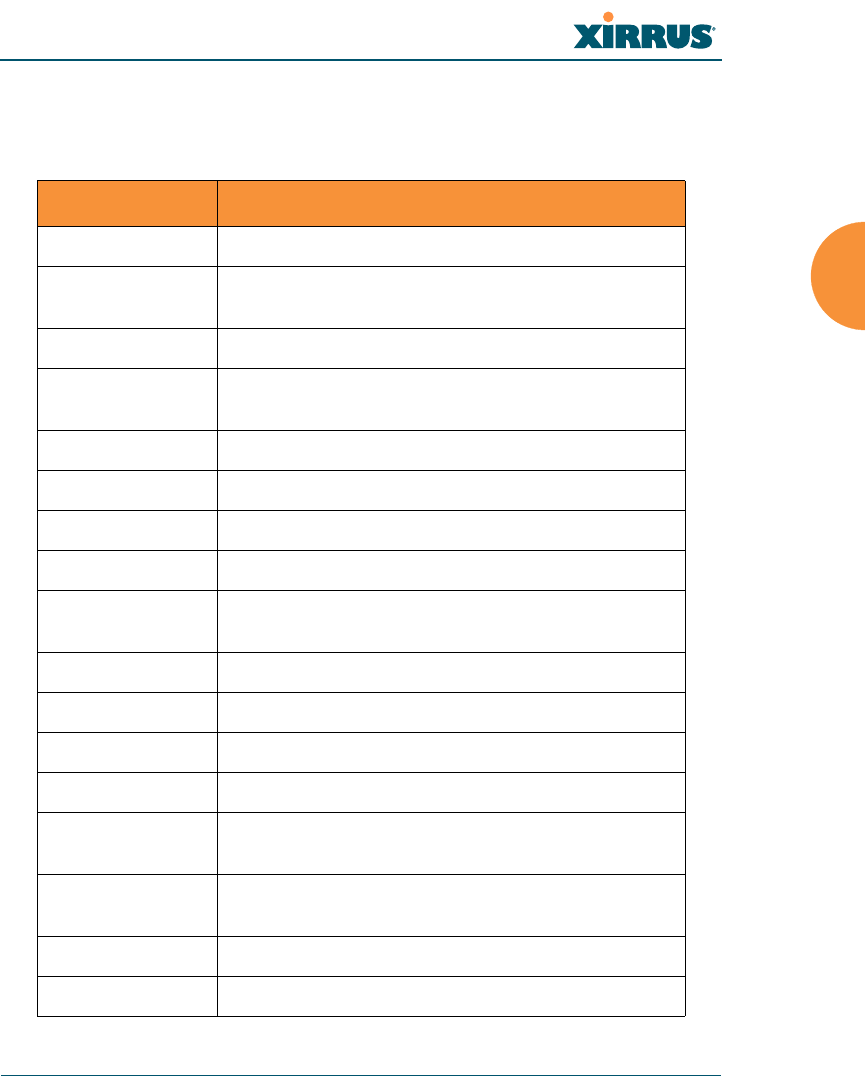
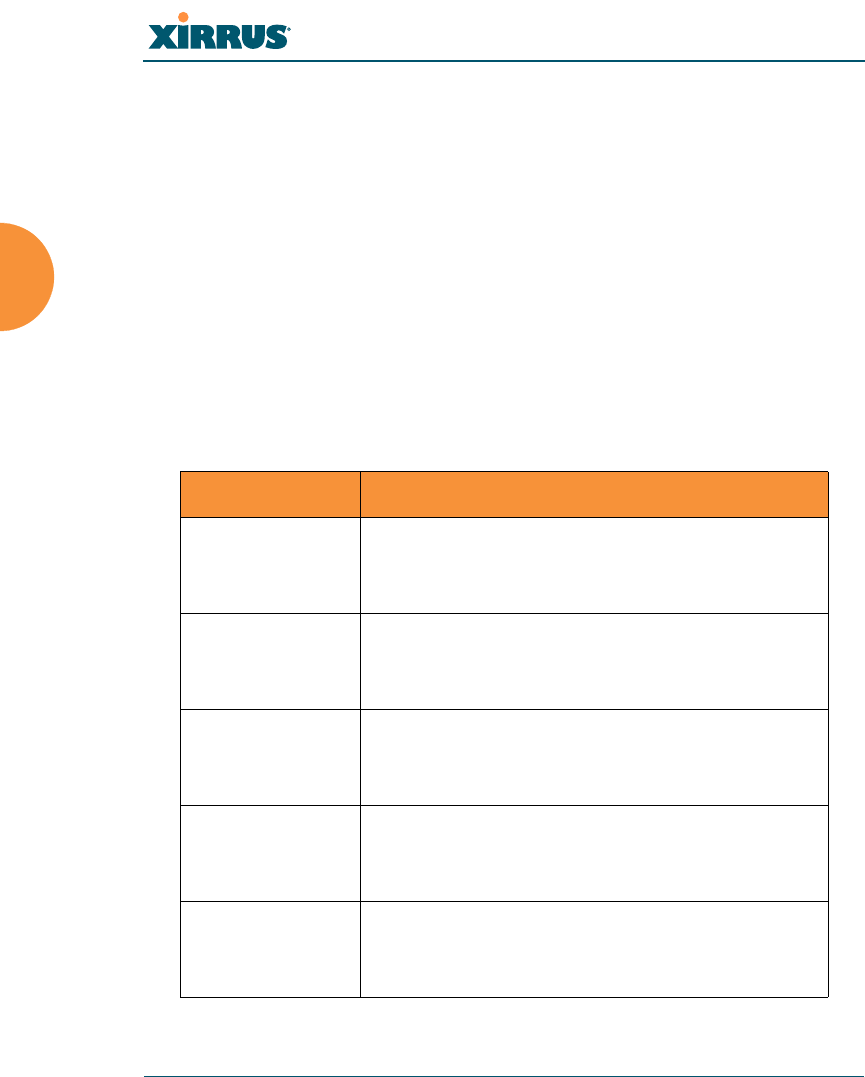
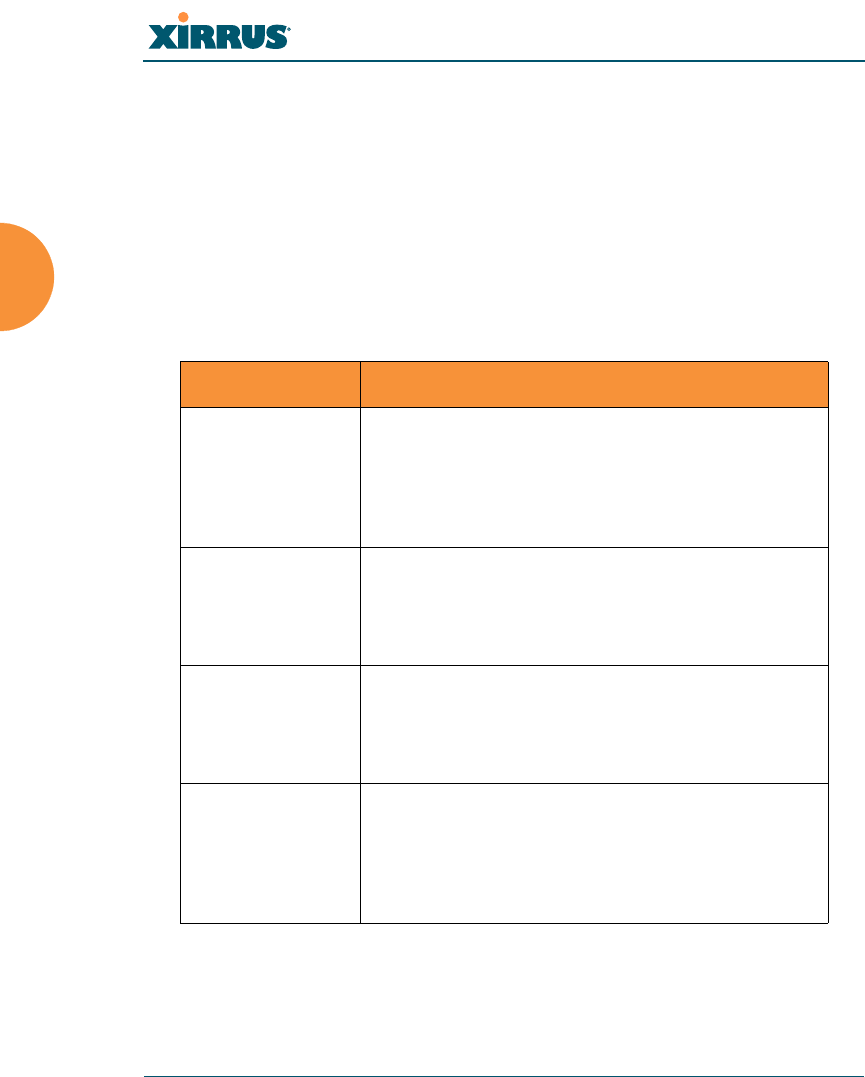
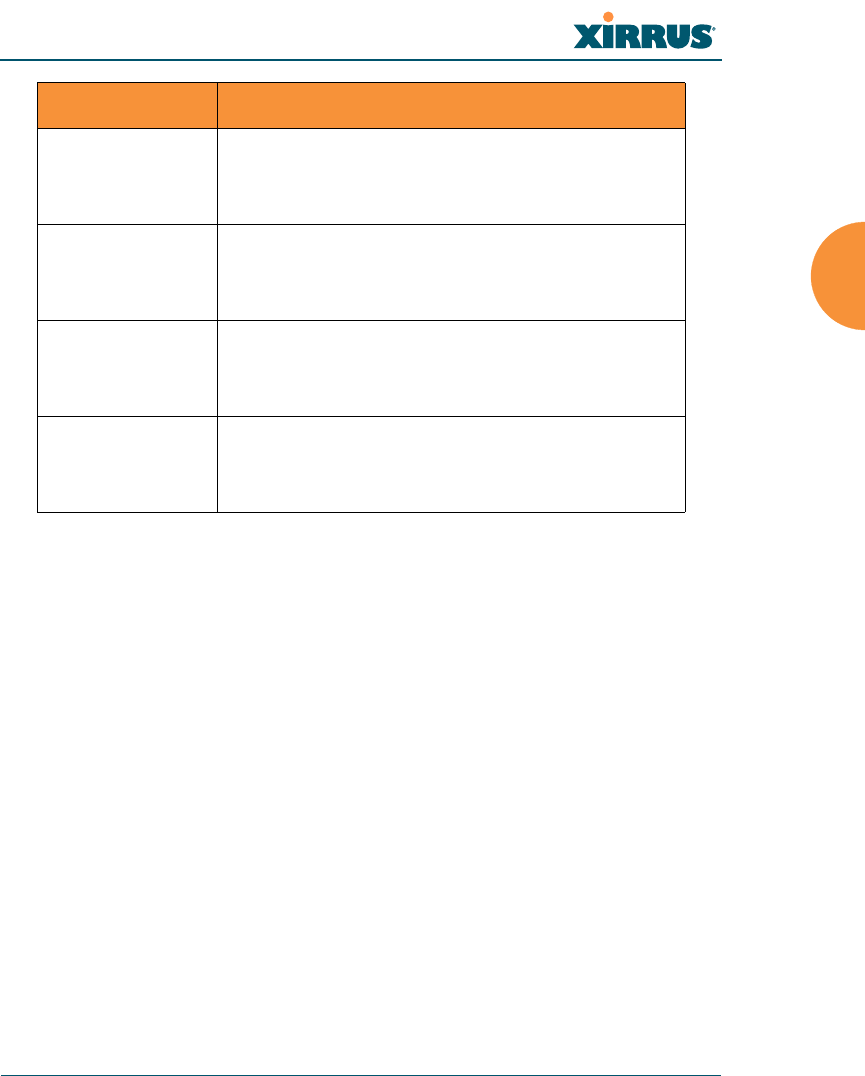
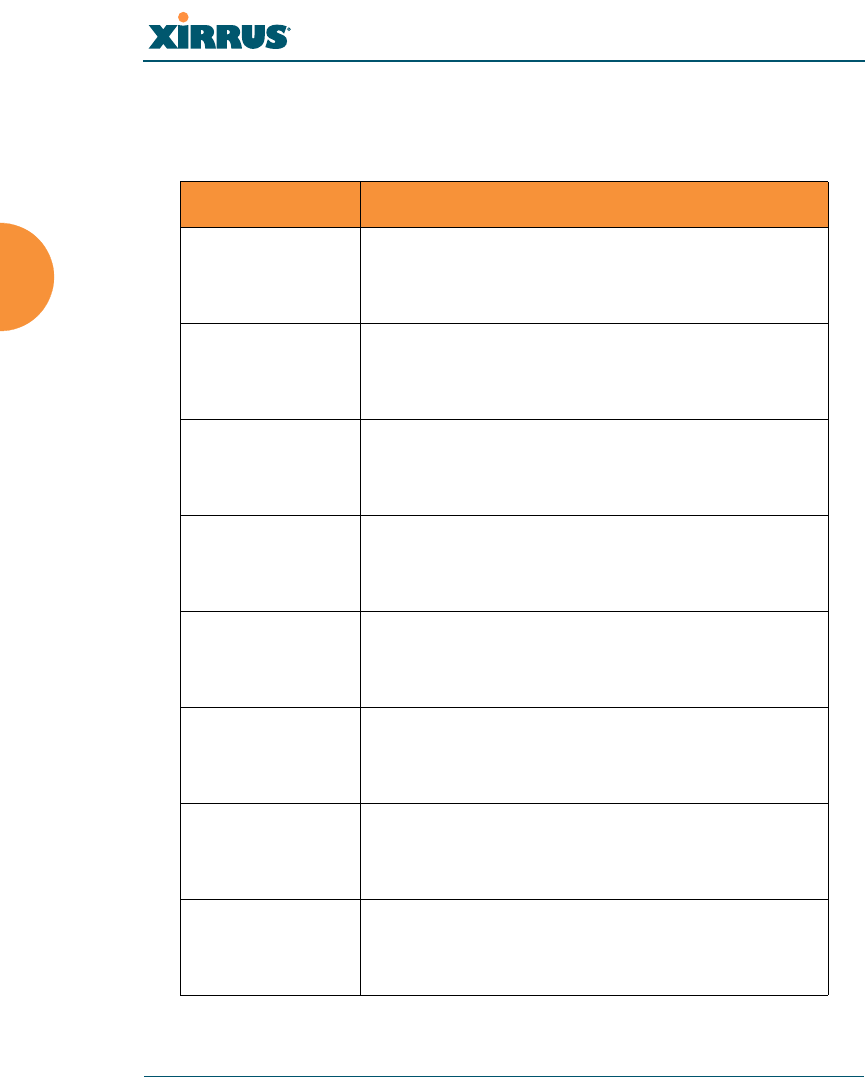
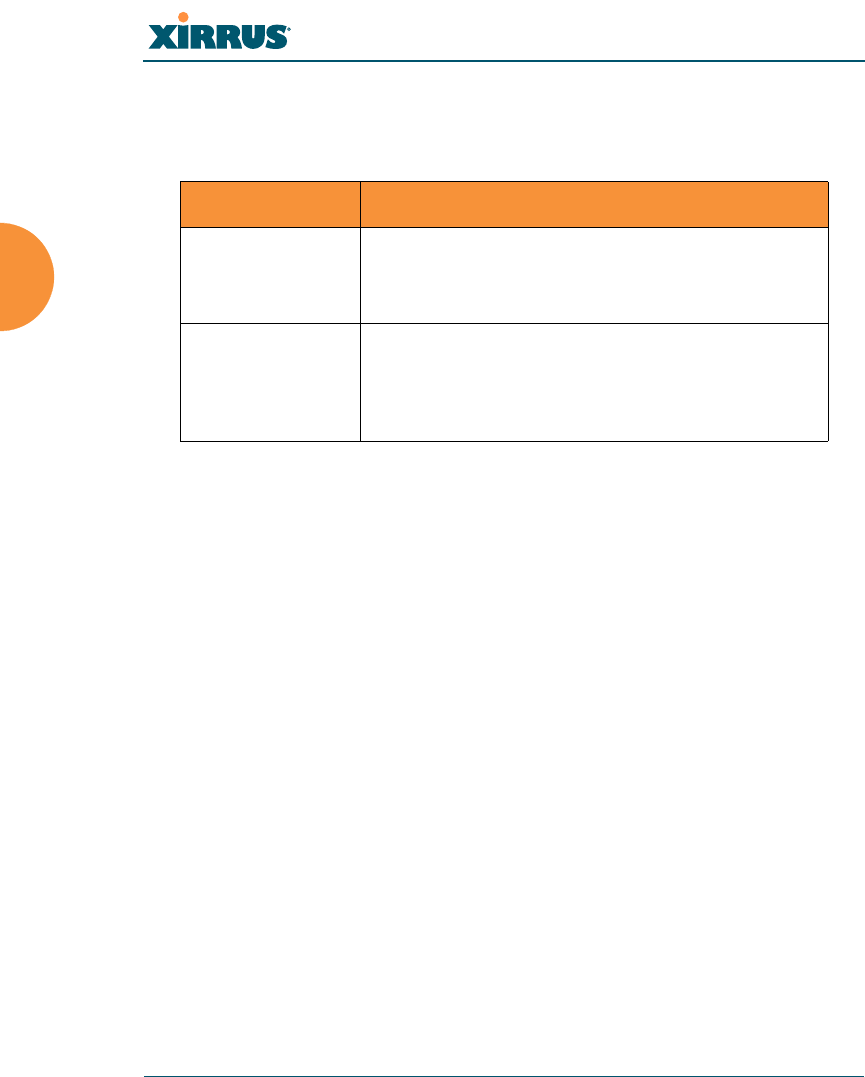
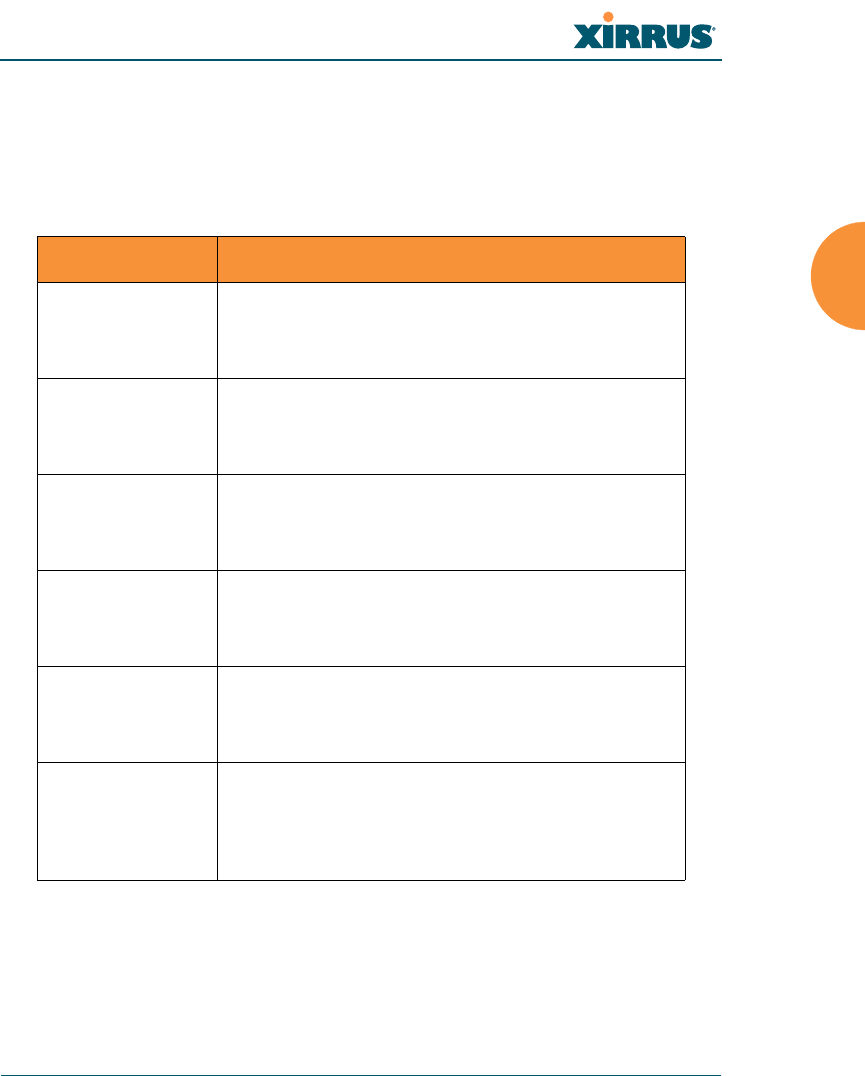
statistics Commands
The following table shows the second level commands that are available with the
top level statistics command [Xirrus_Wi-Fi_Array# statistics].
Command Description
ethernet Display statistical data for all Ethernet interfaces.
Ethernet Name
eth0, gig1, gig2
Display statistical data for the defined Ethernet
interface (either eth0, gig1 or gig2).
FORMAT:
statistics gig1
filter Display statistics for defined filters (if any).
FORMAT:
statistics filter [detail]
filter-list Display statistics for defined filter list (if any).
FORMAT:
statistics filter <filter-list>
iap Display statistical data for the defined IAP.
FORMAT:
statistics iap iap2
statistics iap abgn4
station Display statistical data about associated stations.
FORMAT:
statistics station billw
vlan Display statistical data for the defined VLAN. You
must use the VLAN number (not its name) when
defining a VLAN.
FORMAT:
statistics vlan 1
Wireless Array
The Command Line Interface 389
wds Display statistical data for the defined active WDS
(Wireless Distribution System) links.
FORMAT:
statistics wds 1
<cr> Display configuration or status information.
Command Description
Wireless Array
390 The Command Line Interface
Configuration Commands
All configuration commands are accessed by using the configure command at the
root command prompt (Xirrus_Wi-Fi_Array#). This section provides a brief
description of each command and presents sample formats where deemed
necessary. The commands are organized alphabetically. When inputting
commands, be aware that all commands are case-sensitive.
To see examples of some of the key configuration tasks and their associated
commands, go to “Sample Configuration Tasks” on page 426.
acl
The acl command [Xirrus_Wi-Fi_Array(config)# acl] is used to configure the
Access Control List.
Command Description
add Add a MAC address to the list.
FORMAT:
acl add AA:BB:CC:DD:EE:FF
del Delete a MAC address from the list.
FORMAT:
acl del AA:BB:CC:DD:EE:FF
disable Disable the Access Control List
FORMAT:
acl disable
enable Enable the Access Control List
FORMAT:
acl enable
reset Delete all MAC addresses from the list.
FORMAT:
acl reset
Wireless Array
The Command Line Interface 391
admin
The admin command [Xirrus_Wi-Fi_Array(config-admin)#] is used to configure
the Administrator List.
Command Description
add Add a user to the Administrator List.
FORMAT:
admin add [userID]
del Delete a user to the Administrator List.
FORMAT:
admin del [userID]
edit Modify user in the Administrator List.
FORMAT:
admin edit [userID]
radius Define a RADIUS server to be used for
authenticating administrators.
FORMAT:
admin radius [disable | enable | off | on |
timeout <seconds> | auth-type [PAP | CHAP]]
admin radius [primary |secondary]
port <portid> server [<ip-addr> | <host>]
secret <shared-secret>
reset Delete all users and restore the default user.
FORMAT:
admin reset
Wireless Array
392 The Command Line Interface
cdp
The cdp command [Xirrus_Wi-Fi_Array(config)# cdp] is used to configure the
Cisco Discovery Protocol.
Command Description
disable Disable the Cisco Discovery Protocol
FORMAT:
cdp disable
enable Enable the Cisco Discovery Protocol
FORMAT:
cdp enable
hold-time Select CDP message hold time before messages
received from neighbors expire.
FORMAT:
cdp hold-time [# seconds]
interval The Array sends out CDP announcements at this
interval.
FORMAT:
cdp interval [# seconds]
off Disable the Cisco Discovery Protocol
FORMAT:
cdp off
on Enable the Cisco Discovery Protocol
FORMAT:
cdp on
Wireless Array
The Command Line Interface 393
clear
The clear command [Xirrus_Wi-Fi_Array(config)# clear] is used to clear
requested elements.
Command Description
authentication Deauthenticate a station.
FORMAT:
clear station [authenticated station]
history Clear the history of CLI commands executed.
FORMAT:
clear history
screen Clear the screen where you’re viewing CLI
output.
FORMAT:
clear syslog
statistics Clear the statistics for a requested interface.
FORMAT:
clear statistics [eth0]
syslog Clear all Syslog messages, but continue to log new
messages.
FORMAT:
clear syslog
Wireless Array
394 The Command Line Interface
cluster
The cluster command [Xirrus_Wi-Fi_Array(config)# cluster] is used to create and
operate clusters. Clusters allow you to configure multiple Arrays at the same
time. Using CLI (or WMI), you may define a set of Arrays that are members of the
cluster. Then you may switch the Array to Cluster operating mode for a selected
cluster, which sends all successive configuration commands issued via CLI or
WMI to all of the member Arrays. When you exit cluster mode, configuration
commands revert to applying only to the Array to which you are connected.
For more information, see “Clusters” on page 352.
Command Description
add Create a new Array cluster. Enters edit mode for
that cluster to allow you to specify the Arrays that
belong to the cluster.
FORMAT:
cluster add [cluster-name]
del Delete an Array cluster. Type del ? to list the
existing clusters.
FORMAT:
cluster del [cluster-name]
edit Enter edit mode for selected cluster to add or
delete Arrays that belong to the cluster.
FORMAT:
cluster edit [cluster-name]
end Exit Cluster configuration mode. Configuration
returns to normal operation, affecting this Array
only.
FORMAT:
cluster end
Wireless Array
The Command Line Interface 395
contact-info
The contact-info command [Xirrus_Wi-Fi_Array(config)# contact-info] is used
for managing administrator contact information.
operate Enter Cluster operation mode. All configuration
commands are applied to all of the selected
cluster’s member Arrays until you give the end
command (see above).
FORMAT:
cluster operate [cluster-name]
reset Delete all clusters.
FORMAT:
cluster reset
Command Description
email Add an email address for the contact (must be in
quotation marks).
FORMAT:
contact-info email [“contact@mail.com”]
name Add a contact name (must be in quotation marks).
FORMAT:
contact-info name [“Contact Name”]
phone Add a telephone number for the contact (must be
in quotation marks).
FORMAT:
contact-info phone [“8185550101”]
Command Description
Wireless Array
396 The Command Line Interface
date-time
The date-time command [Xirrus_Wi-Fi_Array(config-date-time)#] is used to
configure the date and time parameters. Your Array supports the Network Time
Protocol (NTP) in order to ensure that the Array’s internal time is accurate. NTP is
set to UTC time by default; however, you can set the time zone so that your Array
will display local time. This is done by defining an offset from the UTC value. For
example, Pacific Standard Time is 8 hours behind UTC time, so the offset from
UTC time would be -8.
Command Description
dst_adjust Enable adjustment for daylight savings.
FORMAT:
date-time dst_adjust
no Disable daylight savings adjustment.
FORMAT:
date-time no dst_adjust
ntp Enable the NTP server.
FORMAT:
date-time ntp on (or off to disable)
offset Set an offset from Greenwich Mean Time.
FORMAT:
date-time no dst_adjust
set Set the date and time for the Array.
FORMAT:
date-time set [10:24 10/23/2007]
timezone Configure the time zone.
FORMAT:
date-time timezone [-8]
Wireless Array
The Command Line Interface 397
dhcp-server
The dhcp-server command [Xirrus_Wi-Fi_Array(config-dhcp-server)#] is used to
add, delete and modify DHCP pools.
Command Description
add Add a DHCP pool.
FORMAT:
dhcp-server add [dhcp pool]
del Delete a DHCP pool.
FORMAT:
dhcp-server del [dhcp pool]
edit Edit a DHCP pool
FORMAT:
dhcp-server edit [dhcp pool]
reset Delete all DHCP pools.
FORMAT:
dhcp-server reset

Wireless Array
398 The Command Line Interface
dns
The dns command [Xirrus_Wi-Fi_Array(config-dns)#] is used to configure your
DNS parameters.
Command Description
domain Enter your domain name.
FORMAT:
dns domain [www.mydomain.com]
server1 Enter the IP address of the primary DNS server.
FORMAT:
dns server1 [1.2.3.4]
server2 Enter the IP address of the secondary DNS server.
FORMAT:
dns server1 [2.3.4.5]
server3 Enter the IP address of the tertiary DNS server.
FORMAT:
dns server1 [3.4.5.6]
Wireless Array
The Command Line Interface 399
file
The file command [Xirrus_Wi-Fi_Array(config-file)#] is used to manage files.
Command Description
active-image Validate and commit a new array software image.
backup-image Validate and commit a new backup software image.
check-image Validate a new array software image.
chkdsk Check flash file system.
copy
cp
Copy a file to another file.
FORMAT:
file copy [sourcefile destinationfile]
dir List the contents of a directory.
FORMAT:
file dir [directory]
erase Delete a file from the FLASH file system.
FORMAT:
file erase [filename]
format Format flash file system.
ftp Open an FTP connection with a remote server. Files
will be transferred in binary mode.
FORMAT:
file ftp host {<hostname> |<ip>} [port <port_#>]
[user {anonymous | <username> password
<passwd> } ] { put <source_file> [<dest_file>] |
get <source_file> [<dest_file>] }
Note: Any time you transfer any kind of software
image file for the Array, it must be transferred in
binary mode, or the file may be corrupted.
list List the contents of a file.
FORMAT:
file list [filename]
Wireless Array
400 The Command Line Interface
remote-config When the Array boots up, it fetches the specified
configuration file from the TFTP server defined in
the file remote-server command, and uses this
configuration. This must be an Array configuration
file with a .conf extension.
A partial configuration file may be used. For
instance, if you wish to use a single configuration file
for all of your Arrays but don't want to have the
same IP address for each Array, you may remove the
ipaddr line from the file. You can then load the file on
each array and the local IP addresses will not change.
FORMAT:
file remote-config <config-file.conf>
Note: If you enter file remote-config ?, the help
response suggests possibilities by listing all of the
configuration files that are currently in the Array’s
flash.
remote-image When the Array boots up, it fetches the named image
file from the TFTP server defined in the file remote-
server command, and upgrades to this file before
booting. This must be an Array image file with a .bin
extension.
FORMAT:
file remote-image <image-file.bin>
Note: This will happen every time that the Array
reboots. If you only want to fetch the remote-image
one time be sure to turn off the remote image option
after the initial download.
remote-server Sets up a TFTP server to be used for automated
remote update of software image and configuration
files when rebooting.
FORMAT:
file remote-server A.B.C.D
rename Rename a file.
Command Description
Wireless Array
The Command Line Interface 401
scp Copy a file to or from a remote system. You may
specify the port to use.
tftp Open a TFTP connection with a remote server.
FORMAT:
file tftp host {<hostname> |<ip>} [port <port_#>]
[user {anonymous | <username> password
<passwd> } ] { put <source_file> [<dest_file>] |
get <source_file> [<dest_file>] }
Note: Any time you transfer any kind of software
image file for the Array, it must be transferred in
binary mode, or the file may be corrupted.
Command Description
Wireless Array
402 The Command Line Interface
filter
The filter command [Xirrus_Wi-Fi_Array(config-filter)#] is used to manage
protocol filters and filter lists.
Command Description
add Add a filter. Details about the air cleaner feature
are after the end of this table.
FORMAT:
filter add [air-cleaner |name]
add-list Add a filter list.
FORMAT:
filter add-list [name]
del Delete a filter.
FORMAT:
filter del [name]
del-list Delete a filter list.
FORMAT:
filter del-list [name]
edit Edit a filter.
FORMAT:
filter edit [name type]
edit-list Edit a filter list
FORMAT:
filter edit-list [name type]
enable Enable a filter list.
FORMAT:
filter enable
move Change a filter priority.
FORMAT:
filter move [name priority]
Wireless Array
The Command Line Interface 403
Air Cleaner
The air cleaner feature offers a number of predetermined filter rules that eliminate
a great deal of unnecessary wireless traffic, resulting in improved performance.
You may select all of the air cleaner rules for the greatest effect, or only specific
rules, such as broadcast or multicast, to eliminate only a particular source of
traffic. The following options are offered:
MyArray(config)# filter add air-cleaner
all All air cleaner filters
arp Eliminate station to station ARPs over the air
broadcast Eliminate broadcast traffic from the air
dhcp Eliminate stations serving DHCP addresses from the air
multicast Eliminate chatty multicast traffic from the air
netbios Eliminate NetBIOS traffic from the air
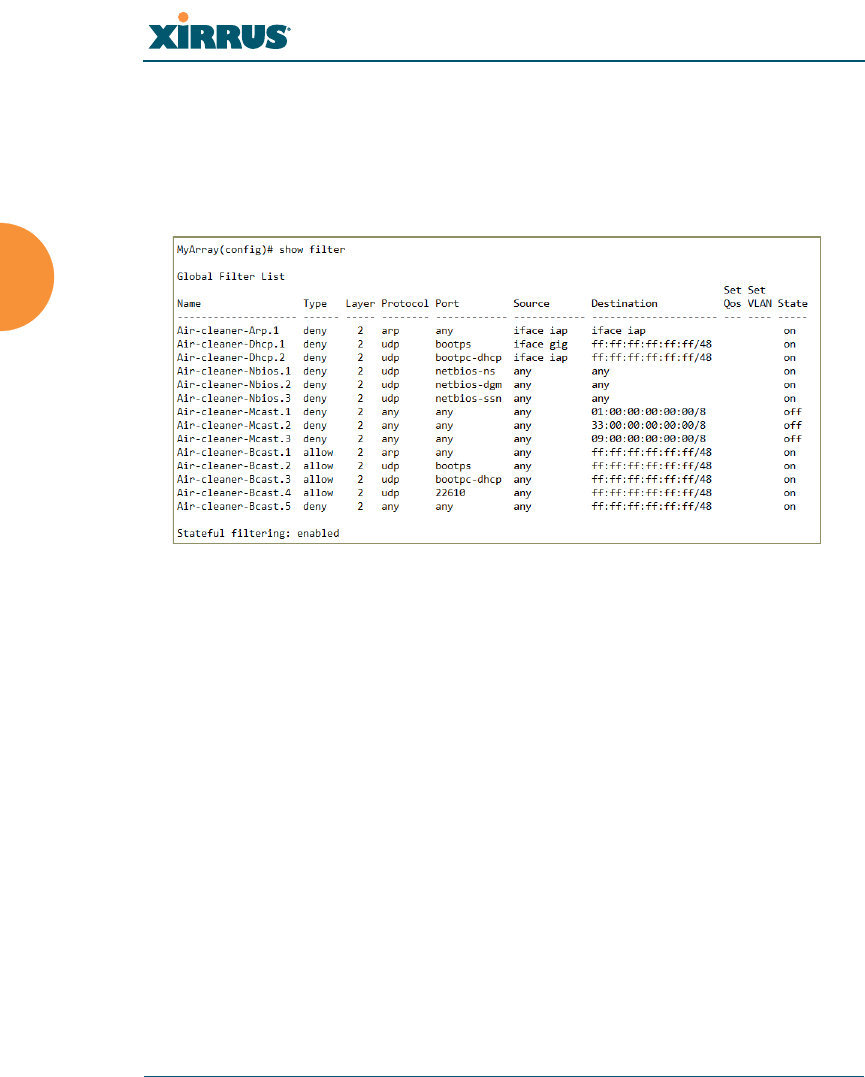
If you select all, the rules shown in Figure 188 are added to the predefined filter
list named Global. These rules assume that you have station-to-station blocking
enabled, that a DHCP server is on the Array’s wired connection, and that you
want to block most all multicast and all broadcast traffic not vital to normal
off Disable a filter list.
FORMAT:
filter off
on Enable a filter list.
FORMAT:
filter on
reset Delete all protocol filters and filter lists.
FORMAT:
filter reset
stateful Enable or disable stateful filtering (firewall).
FORMAT:
Stateful [enable | disable | on |off]
Command Description
Wireless Array
404 The Command Line Interface
operation. If you find that there is a particular type of multicast or broadcast
traffic that you want to allow, just add a specific allow filter for it before the deny
filter in this list that would normally block it. Add or delete any of the Multicast
rules as necessary for a specific site. Remember that the order of the rules is
important.
Figure 188. Air Cleaner Filter Rules
Explanations of some sample rules are below.
Air-cleaner-Arp.1 blocks ARPs from one client from being transmitted to
clients via all of the radios. The station to station block setting doesn't
block this traffic, so this filter eliminates this unnecessary traffic.
Air-cleaner-Dhcp.1 drops all DHCP client traffic coming in from the
gigabit interface. This traffic doesn't need to be transmitted by the radios
since there shouldn't be any DHCP server associated to the radios and
offering DHCP addresses. For large subnets the DHCP discover/request
broadcast traffic can be significant.
Air-cleaner-Dhcp.2 drops all DHCP server traffic coming in from the
radio interfaces. There should not be any DHCP server associated to the
radios. These rogue DHCP servers are blocked from doing any damage
with this filter. There have been quite a few cases in public venues like
schools and conventions where such traffic is seen.

Wireless Array
The Command Line Interface 405
Air-cleaner-Mcast.1 drops all multicast traffic with a destination MAC
address starting with 01. This filters out a lot of IP multicast traffic that
starts with 224.
Air-cleaner-Mcast.2 drops all multicast traffic with a destination MAC
address starting with 33. A lot of IPv6 traffic and other multicast traffic is
blocked by this filter.
Air-cleaner-Mcast.3 drops all multicast traffic with a destination MAC
address starting with 09. A lot of Appletalk traffic and other multicast
traffic is blocked by this filter. Note that for OSX 10.6.* Snow Leopard no
longer supports Appletalk.
Air-cleaner-Bcast.1 allows all ARP traffic (other than the traffic that was
denied by Air-cleaner-Arp.1). This is needed because Air-cleaner-Bcast.5
would drop this valid traffic.
Air-cleaner-Bcast.4 allows all XRP traffic from Arrays to be received from
the wire. This is needed because Air-cleaner-Bcast.5 would drop this
valid traffic.
Air-cleaner-Bcast.5 drops all other broadcast traffic that hasn't previously
been explicitly allowed. This filter will catch all UDP broadcast traffic as
well as all other known and unknown protocol broadcast traffic.
Wireless Array
406 The Command Line Interface
group
The group command [Xirrus_Wi-Fi_Array(config)# group] is used to create and
configure user groups. User groups allow administrators to assign specific
network parameters to users through RADIUS privileges rather than having to
map users to a specific SSID. Groups provide flexible control over user privileges
without the need to create large numbers of SSIDs. For more information, see
“Groups” on page 264.
hostname
The hostname command [Xirrus_Wi-Fi_Array(config)# hostname] is used to
change the hostname used by the Array.
Command Description
add Create a new user group.
FORMAT:
group add [group-name]
del Delete a user group.
FORMAT:
group del [group-name]
edit Set parameters values for a group.
FORMAT:
group edit [group-name]
reset Reset the group.
FORMAT:
group reset
Command Description
hostname Change the hostname of the Array.
FORMAT:
hostname [name]
Wireless Array
The Command Line Interface 407
interface
The interface command [Xirrus_Wi-Fi_Array(config)# interface] is used to select
the interface that you want to configure. To see a listing of the commands that are
available for each interface, use the ? command at the selected interface prompt.
For example, using the ? command at the Xirrus_Wi-Fi_Array(config-gig1}#
prompt displays a listing of all commands for the gig1 interface.
Command Description
console Select the console interface. The console interface
is used for management purposes only.
FORMAT:
interface console
eth0 Select the Fast Ethernet interface. The Fast
Ethernet interface is used for management
purposes only.
FORMAT:
interface eth0
Note: To configure a static route for management
traffic, next enter:
static-route addr [ip-addr]
static-route mask [subnet-mask]
gig1 Select the Gigabit 1 interface.
FORMAT:
interface gig1
gig2 Select the Gigabit 2 interface.
FORMAT:
interface gig2
iap Select an IAP.
FORMAT:
interface iap
Wireless Array
408 The Command Line Interface
load
The load command [Xirrus_Wi-Fi_Array(config)# load] loads a configuration
file.
location
The location command [Xirrus_Wi-Fi_Array(config)# location] is used to set the
location for the Array.
Command Description
factory.conf Load the factory settings configuration file.
FORMAT:
load [factory.conf]
lastboot.conf Load the configuration file from the last boot-up.
FORMAT:
load [lastboot.conf]
[myfile].conf If you have saved a configuration, enter its name
to load it.
FORMAT:
load [myfile.conf]
saved.conf Load the configuration file with the last saved
settings.
FORMAT:
load [saved.conf]
Command Description
<cr> Set the location for the Array.
FORMAT:
location [newlocation]
Wireless Array
The Command Line Interface 409
management
The management command [Xirrus_Wi-Fi_Array(config)# management] enters
management mode, where you may configure management parameters.
The following types of settings may be configured in management mode:
banner Configure login banner messages
console Configure console management parameters
https Enable/disable HTTPS access
license Set array software license key
load Load running configuration from flash
max-auth-attempts Maximum number of authentication (login)
attempts (0 means unlimited)
network-assurance Enable/disable network assurance
reauth-period Time between failed CLI login attempts
restore Restore to previous saved config
revert Revert to saved configuration after delay if
configuration not saved
save Save running configuration to flash
ssh Enable/disable SSH access
standby Configure standby parameters
telnet Enable/disable telnet access
uptime Display time since last boot
xircon Enable/disable xircon access. See Xircon User’s
Guide for more information. Not available for XN Arrays.
Command Description
<cr> Enter management mode.
FORMAT:
management <cr>
Wireless Array
410 The Command Line Interface
more
The more command [Xirrus_Wi-Fi_Array(config)# more] is used to turn terminal
pagination ON or OFF.
Command Description
off Turn OFF terminal pagination.
FORMAT:
more off
on Turn ON terminal pagination.
FORMAT:
more on
Wireless Array
The Command Line Interface 411
netflow
The netflow command [Xirrus_Wi-Fi_Array(config-netflow)#] is used to enable
or disable, or configure sending IP flow information (traffic statistics) to the
collector you specify.
Command Description
disable Disable netflow.
FORMAT:
netflow disable
enable Enable netflow.
FORMAT:
netflow enable
off Disable netflow.
FORMAT:
netflow off
on Enable netflow.
FORMAT:
netflow on
collector Set the netflow collector IP address or fully
qualified domain name (host.domain). Only one
collector may be set. If port is not specified, the
default is 2055.
FORMAT:
netflow collector host {<ip-addr> | <domain>}
[port <port#>]
Wireless Array
412 The Command Line Interface
no
The no command [Xirrus_Wi-Fi_Array(config)# no] is used to disable a selected
element or set the element to its default value.
Command Description
acl Disable the Access Control List.
FORMAT:
no acl
dot11a Disable all 802.11an IAPs (radios).
FORMAT:
no dot11a
dot11bg Disable all 802.11bgn IAPs (radios).
FORMAT:
no dot11bg
https Disable https access.
FORMAT:
no https
intrude-detect Disable intrusion detection.
FORMAT:
no intrude-detect
management Disable management on all Ethernet interfaces.
FORMAT:
no management
more Disable terminal pagination.
FORMAT:
no more
ntp Disable the NTP server.
FORMAT:
no ntp
Wireless Array
The Command Line Interface 413
snmp Disable SNMP features.
FORMAT:
no snmp
ssh Disable ssh access.
FORMAT:
no ssh
syslog Disable the Syslog services.
FORMAT:
no syslog
telnet Disable Telnet access.
FORMAT:
no telnet
ETH-NAME Disable the selected Ethernet interface (eth0, gig1
or gig2). You cannot disable the console interface.
with this command.
FORMAT:
no eth0 (gig1 or gig2)
Command Description
Wireless Array
414 The Command Line Interface
quit
The quit command [Xirrus_Wi-Fi_Array(config)# quit] is used to exit the
Command Line Interface.
radius-server
The radius-server command [Xirrus_Wi-Fi_Array(config-radius-server)#] is
used to configure the external and internal RADIUS server parameters.
Command Description
<cr> Exit the Command Line Interface.
FORMAT:
quit
If you have made any configuration changes and
your changes have not been saved, you are
prompted to save your changes to Flash.
At the prompt, answer Yes to save your changes,
or answer No to discard your changes.
Command Description
external Configure an external RADIUS server.
FORMAT:
radius-server external
To configure a RADIUS server (primary,
secondary, or accounting server, by IP address or
host name), and the reporting interval use:
radius-server external accounting
internal Configure the external RADIUS server.
FORMAT:
radius-server internal
use Choose the active RADIUS server (either external
or internal).
FORMAT:
use external (or internal)
Wireless Array
The Command Line Interface 415
reboot
The reboot command [Xirrus_Wi-Fi_Array(config)# reboot] is used to reboot the
Array. If you have unsaved changes, the command will notify you and give you a
chance to cancel the reboot.
reset
The reset command [Xirrus_Wi-Fi_Array(config)# reset] is used to reset all
settings to their default values then reboot the Array.
Command Description
<cr> Reboot the Array.
FORMAT:
reboot
delay Reboot the Array after a delay of 1 to 60 seconds.
FORMAT:
reboot delay [n]
Command Description
<cr> Reset all configuration parameters to their factory
default values.
FORMAT:
reset
The Array is rebooted automatically.
preserve-ip-
settings
Preserve all ethernet and VLAN settings and reset
all other configuration parameters to their factory
default values.
FORMAT:
reset preserve-ip-settings
The Array is rebooted automatically.
Wireless Array
416 The Command Line Interface
restore
The restore command [Xirrus_Wi-Fi_Array(config)# restore] is used to restore
configuration to a version that was previously saved locally.
Command Description
?Use this to display the list of available config files.
FORMAT:
restore ?
<filename> Enter the name of the locally saved configuration
to restore.
FORMAT:
restore <config-filename>
Wireless Array
The Command Line Interface 417
run-tests
The run-tests command [Xirrus_Wi-Fi_Array(run-tests)#] is used to enter run-
tests mode, which allows you to perform a range of tests on the Array.
Command Description
<cr> Enter run-tests mode.
FORMAT:
run-tests
iperf Execute iperf utility.
FORMAT:
run-tests iperf
kill-beacons Turn off beacons for selected single IAP.
FORMAT:
run-tests kill-beacons [off | iap-name]
kill-probe-
responses
Turn off probe responses for selected single IAP.
FORMAT:
run-tests kill-probe-responses [off | iap-name]
led LED test.
FORMAT:
run-tests led [flash | rotate]
memtest Execute memory tests.
FORMAT:
run-tests memtest
ping Execute ping utility.
FORMAT:
run-tests ping [host-name | ip-addr]
Wireless Array
418 The Command Line Interface
radius-ping Special ping utility to test the connection to a
RADIUS server.
FORMAT:
run-tests radius-ping [external | ssid <ssidnum>]
[primary | secondary] user <raduser> password
<radpasswd> auth-type [CHAP | PAP]
run-tests radius-ping [internal | server
<radserver> port <radport> secret <radsecret> ]
user <raduser> password <radpasswd>
auth-type [CHAP | PAP]
You may select a RADIUS server that you have
already configured (ssid or external or internal) or
specify another server.
rlb Run manufacturing radio loopback test.
FORMAT:
run-tests rlb {optional command line switches}
self-test Execute self-test.
FORMAT:
run-tests self-test {logfile-name (optional)]
site-survey Enable or disable site survey mode.
FORMAT:
run-tests site-survey [on | off | enable | disable]
ssh Execute ssh utility.
FORMAT:
run-tests ssh [hostname | ip-addr]
[command-line-switches (optional)]
tcpdump Execute tcpdump utility to dump traffic for selected
interface or VLAN. Supports 802.11 headers.
FORMAT:
run-tests tcpdump
Command Description
Wireless Array
The Command Line Interface 419
security
The security command [Xirrus_Wi-Fi_Array(config-security)#] is used to
establish the security parameters for the Array.
telnet Execute telnet utility.
FORMAT:
run-tests telnet [hostname | ip-addr]
[command-line-switches (optional)]
traceroute Execute traceroute utility.
FORMAT:
run-tests traceroute [host-name | ip-addr]
Command Description
wep Set the WEP encryption parameters.
FORMAT:
security wep
wpa Set the WEP encryption parameters.
FORMAT:
security wpa
Command Description
Wireless Array
420 The Command Line Interface
snmp
The snmp command [Xirrus_Wi-Fi_Array(config-snmp)#] is used to enable,
disable, or configure SNMP.
Command Description
v2 Enable SNMP v2.
FORMAT:
snmp v2
v3 Enable SNMP v3.
FORMAT:
snmp v3
trap Configure traps for SNMP. Up to four trap
destinations may be configured, and you may
specify whether to send traps for authentication
failure.
FORMAT:
snmp trap

Wireless Array
The Command Line Interface 421
ssid
The ssid command [Xirrus_Wi-Fi_Array(config-ssid)#] is used to establish your
SSID parameters.
Command Description
add Add an SSID.
FORMAT:
ssid add [newssid]
del Delete an SSID.
FORMAT:
ssid del [oldssid]
edit Edit an existing SSID.
FORMAT:
ssid edit [existingssid]
reset Delete all SSIDs and restore the default SSID.
FORMAT:
ssid reset
Wireless Array
422 The Command Line Interface
syslog
The syslog command [Xirrus_Wi-Fi_Array(config-syslog)#] is used to enable,
disable, or configure the Syslog server.
Command Description
console Enable or disable the display of Syslog messages
on the console, and set the level to be displayed.
All messages at this level and lower (i.e., more
severe) will be displayed.
FORMAT:
syslog console [on/off] level [0-7]
disable Disable the Syslog server.
FORMAT:
syslog disable
email Disable the Syslog server.
FORMAT:
syslog email from [email-from-address]
level [0-7]
password [email-acct-password]
server [email-server-IPaddr]
test [test-msg-text]
to-list [recipient-email-addresses]
user [email-acct-username]
enable Enable the Syslog server.
FORMAT:
syslog enable
local-file Set the size and/or severity level (all messages at
this level and lower will be logged).
FORMAT:
syslog local-file size [1-500] level [0-7]
no Disable the selected feature.
FORMAT:
syslog no [feature]
Wireless Array
The Command Line Interface 423
uptime
The uptime command [Xirrus_Wi-Fi_Array(config)# uptime] is used to display
the elapsed time since you last rebooted the Array.
off Disable the Syslog server.
FORMAT:
syslog off
on Enable the Syslog server.
FORMAT:
syslog on
primary Set the IP address of the primary Syslog server
and/or the severity level of messages to be
logged.
FORMAT:
syslog primary [1.2.3.4] level [0-7]
secondary Set the IP address of the secondary (backup)
Syslog server and/or the severity level of
messages to be logged.
FORMAT:
syslog primary [1.2.3.4] level [0-7]
Command Description
<cr> Display time since last reboot.
FORMAT:
uptime
Command Description
Wireless Array
424 The Command Line Interface
vlan
The vlan command [Xirrus_Wi-Fi_Array(config-vlan)#] is used to establish your
VLAN parameters.
Command Description
add Add a VLAN.
FORMAT:
vlan add [newvlan]
default-route Assign a VLAN for the default route (for
outbound management traffic).
FORMAT:
vlan default-route [defaultroute]
delete Delete a VLAN.
FORMAT:
vlan delete [oldvlan]
edit Modify an existing VLAN.
FORMAT:
vlan edit [existingvlan]
native-vlan Assign a native VLAN (traffic is untagged).
FORMAT:
vlan native-vlan [nativevlan]
no Disable the selected feature.
FORMAT:
vlan no [feature]
reset Delete all existing VLANs.
FORMAT:
vlan reset
Wireless Array
The Command Line Interface 425
wifi-tag
The wifi-tag command [Xirrus_Wi-Fi_Array(config-wifi-tag)#] is used to enable
or disable Wi-Fi tag capabilities. When enabled, the Array listens for and collects
information about Wi-Fi RFID tags sent on the designated channels. See also “Wi-
Fi Tag” on page 188.
Command Description
disable Disable wifi-tag.
FORMAT:
wifi-tag disable
enable Enable wifi-tag.
FORMAT:
wifi-tag enable
off Disable wifi-tag.
FORMAT:
wifi-tag off
on Enable wifi-tag.
FORMAT:
wifi-tag on
tag-channel-bg Set an 802.11b or g channel for listening for tags.
FORMAT:
wifi-tag tag-channel-bg <1-255>
udp-port Set the UDP port which a tagging server will use
to query the Array for tagging information.
FORMAT:
wifi-tag udp-port <1025-65535>

Wireless Array
426 The Command Line Interface
Sample Configuration Tasks
This section provides examples of some of the common configuration tasks used
with the Wireless Array, including:
“Configuring a Simple Open Global SSID” on page 427.
“Configuring a Global SSID using WPA-PEAP” on page 428.
“Configuring an SSID-Specific SSID using WPA-PEAP” on page 429.
“Enabling Global IAPs” on page 430.
“Disabling Global IAPs” on page 431.
“Enabling a Specific IAP” on page 432.
“Disabling a Specific IAP” on page 433.
“Setting Cell Size Auto-Configuration for All IAPs” on page 434
“Setting the Cell Size for All IAPs” on page 435.
“Setting the Cell Size for a Specific IAP” on page 436.
“Configuring VLANs on an Open SSID” on page 437.
“Configuring Radio Assurance Mode (Loopback Tests)” on page 438.
To facilitate the accurate and timely management of revisions to this section, the
examples shown here are presented as screen images taken from a Secure Shell
(SSH) session (in this case, PuTTY). Depending on the application you are using
to access the Command Line Interface, and how your session is set up (for
example, font and screen size), the images presented on your screen may be
different than the images shown in this section. However, the data displayed will
be the same.
Some of the screen images shown in this section have been modified for clarity.
For example, the image may have been “elongated” to show all data without the
need for additional images or scrolling. We recommend that you use the Adobe
PDF version of this User’s Guide when reviewing these examples — a hard copy
document may be difficult to read.
As mentioned previously, the root command prompt is determined by the host
name assigned to your Array.
Wireless Array
The Command Line Interface 427
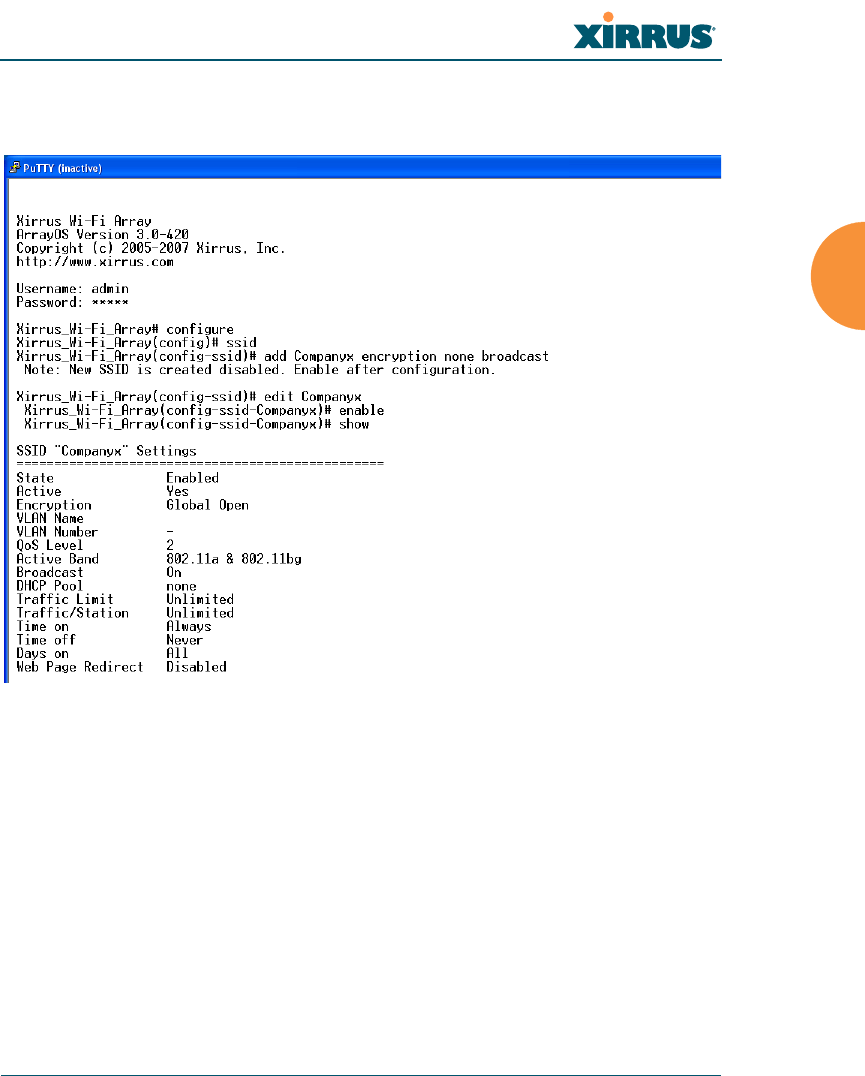
Configuring a Simple Open Global SSID
This example shows you how to configure a simple open global SSID.
Figure 189. Configuring a Simple Open Global SSID
Wireless Array
428 The Command Line Interface
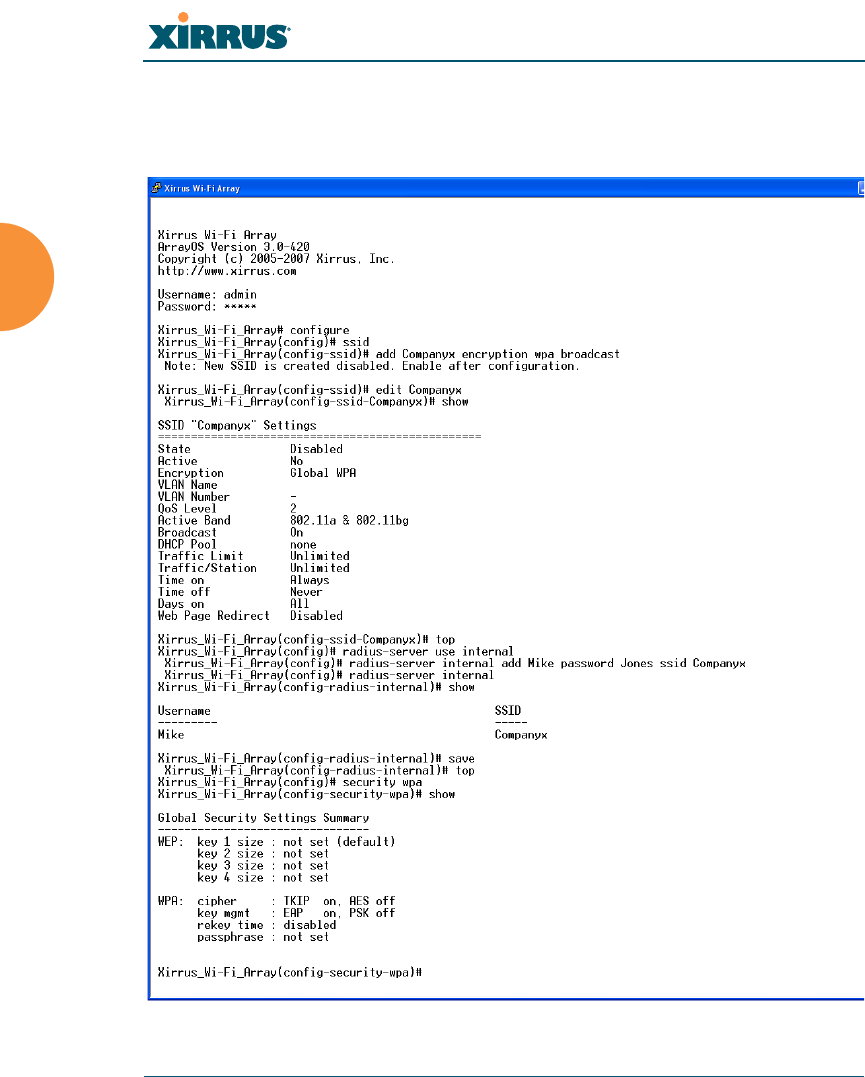
Configuring a Global SSID using WPA-PEAP
This example shows you how to configure a global SSID using WPA-PEAP
encryption in conjunction with the Array’s Internal RADIUS server.
Figure 190. Configuring a Global SSID using WPA-PEAP
Wireless Array
The Command Line Interface 429
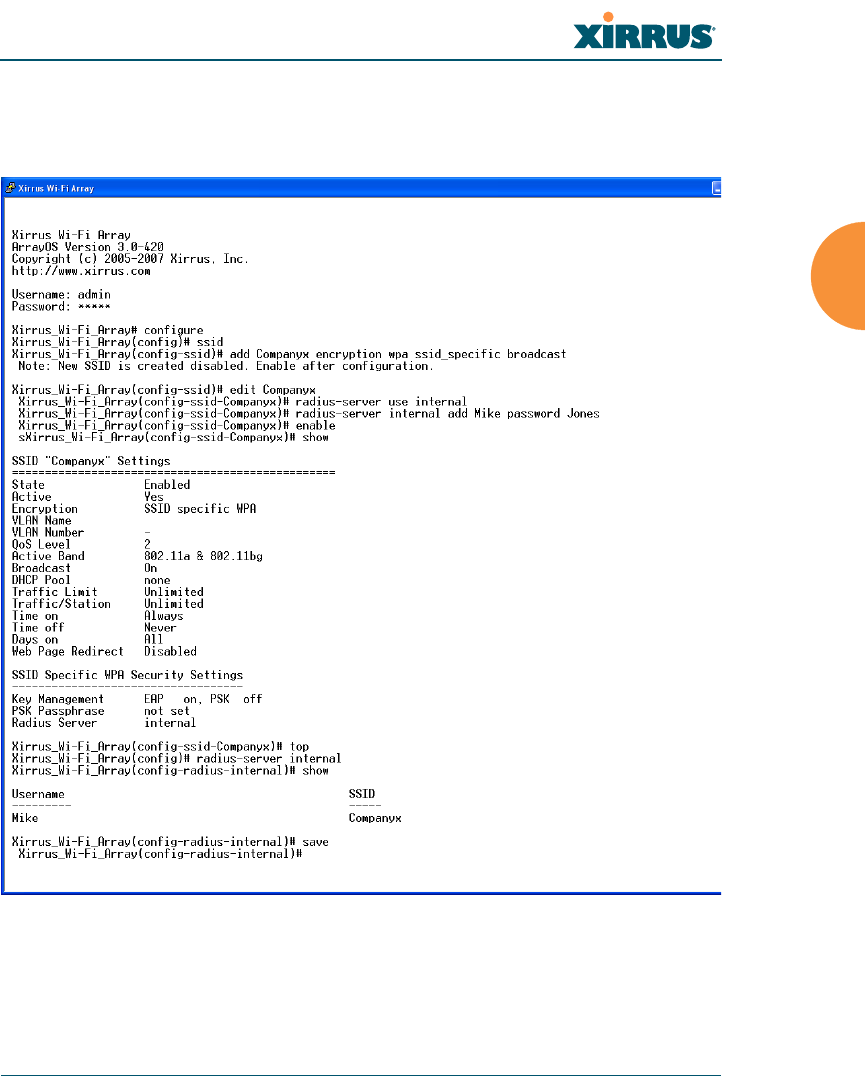
Configuring an SSID-Specific SSID using WPA-PEAP
This example shows you how to configure an SSID-specific SSID using WPA-
PEAP encryption in conjunction with the Array’s Internal RADIUS server.
Figure 191. Configuring an SSID-Specific SSID using WPA-PEAP
Wireless Array
430 The Command Line Interface
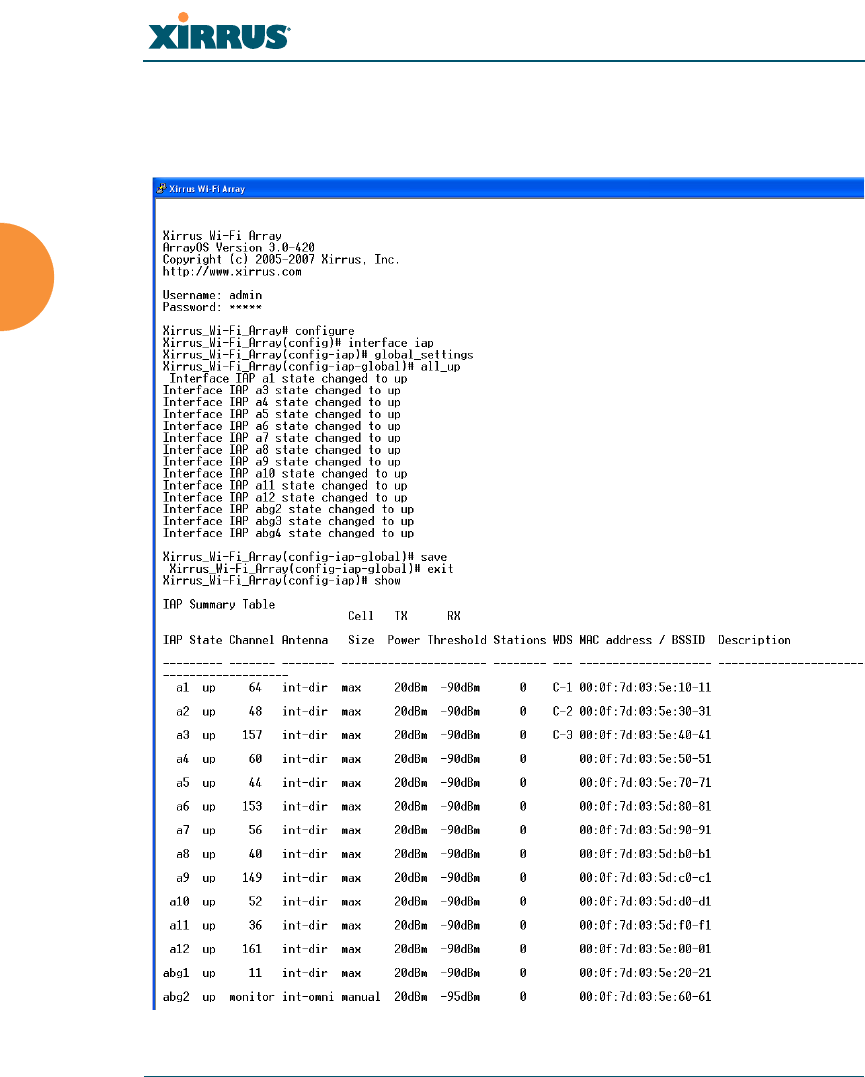
Enabling Global IAPs
This example shows you how to enable all IAPs (radios), regardless of the
wireless technology they use.
Figure 192. Enabling Global IAPs
Wireless Array
The Command Line Interface 431
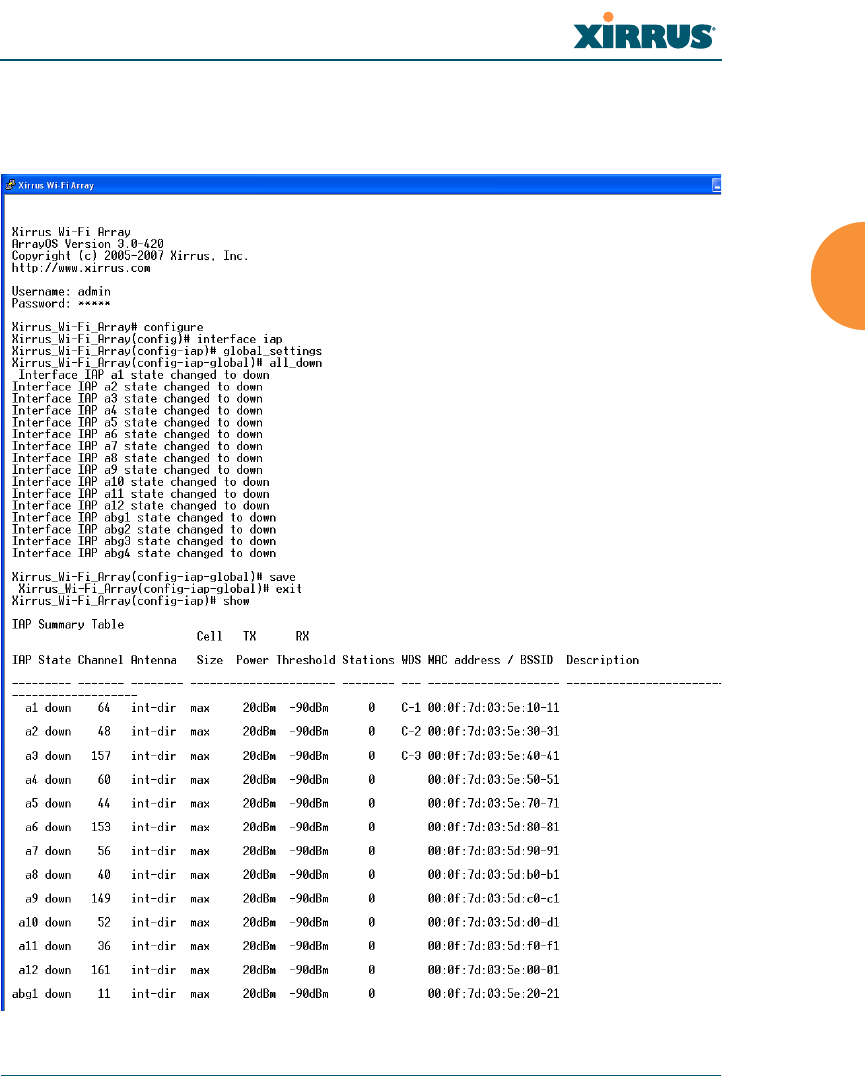
Disabling Global IAPs
This example shows you how to disable all IAPs (radios), regardless of the
wireless technology they use.
Figure 193. Disabling Global IAPs
Wireless Array
432 The Command Line Interface
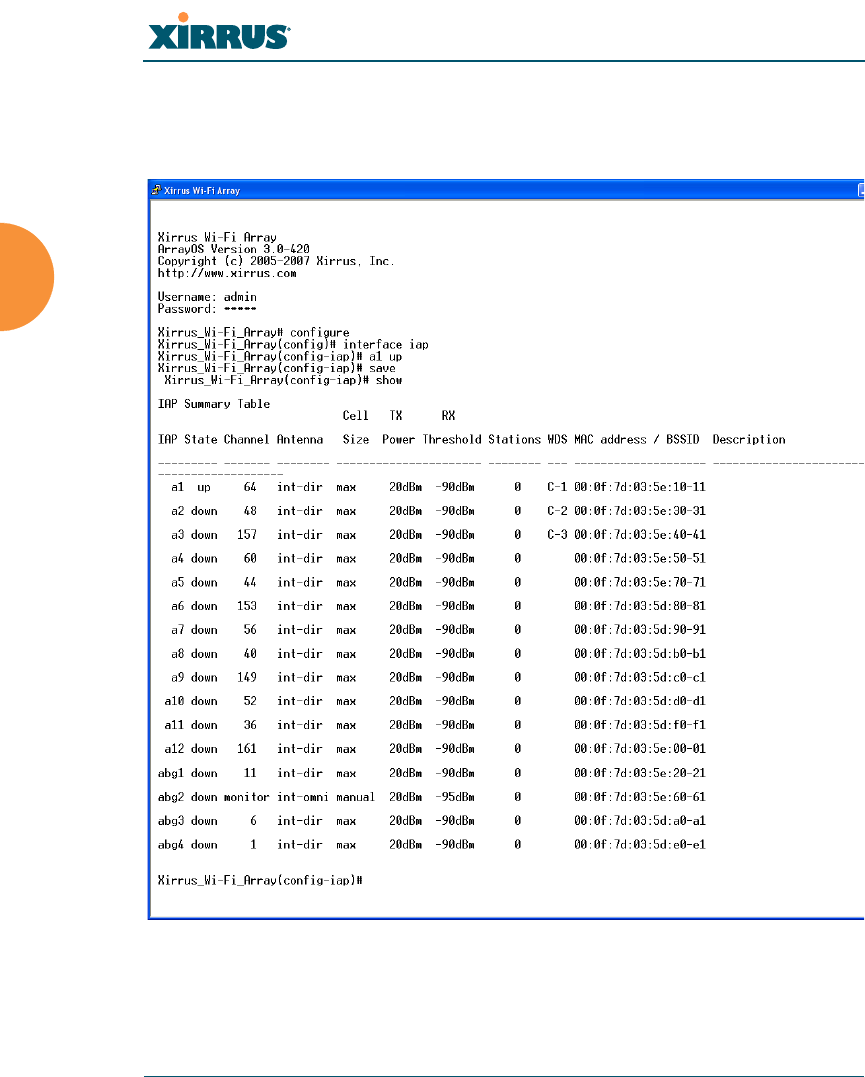
Enabling a Specific IAP
This example shows you how to enable a specific IAP (radio). In this example, the
IAP that is being enabled is a1 (the first IAP in the summary list).
Figure 194. Enabling a Specific IAP
Wireless Array
The Command Line Interface 433
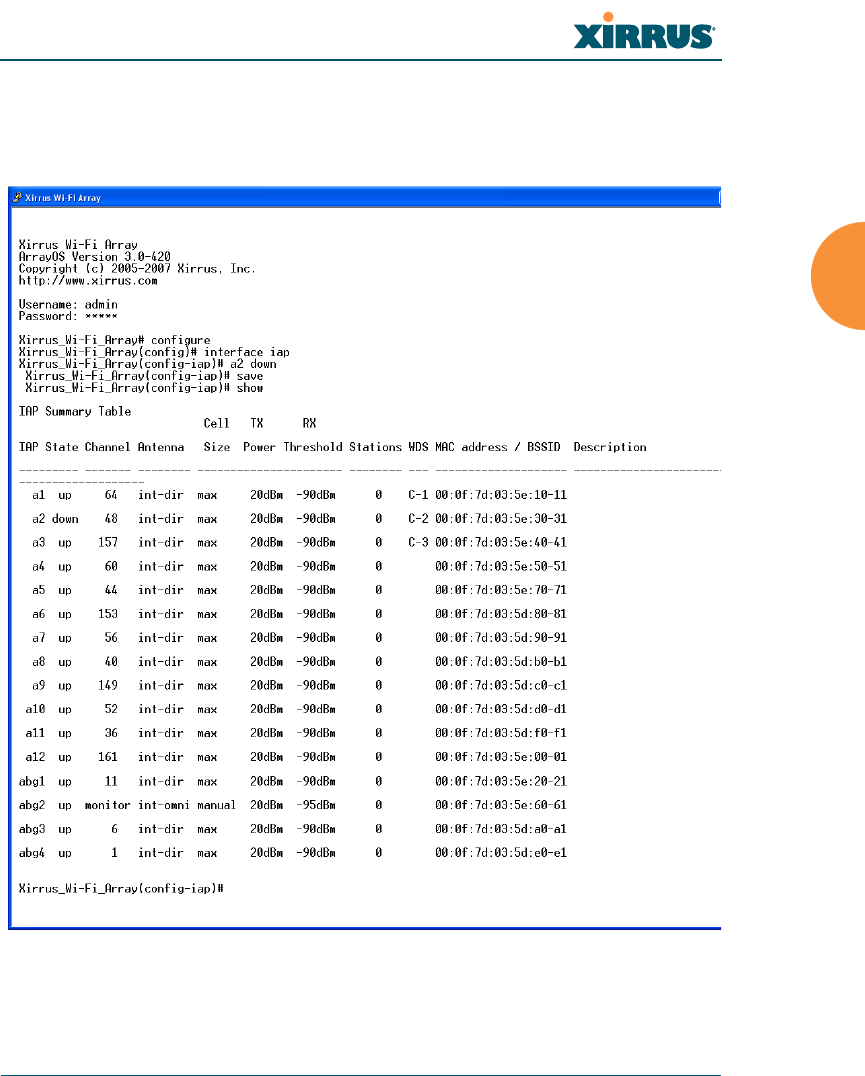
Disabling a Specific IAP
This example shows you how to disable a specific IAP (radio). In this example,
the IAP that is being disabled is a2 (the second IAP in the summary list).
Figure 195. Disabling a Specific IAP
Wireless Array
434 The Command Line Interface
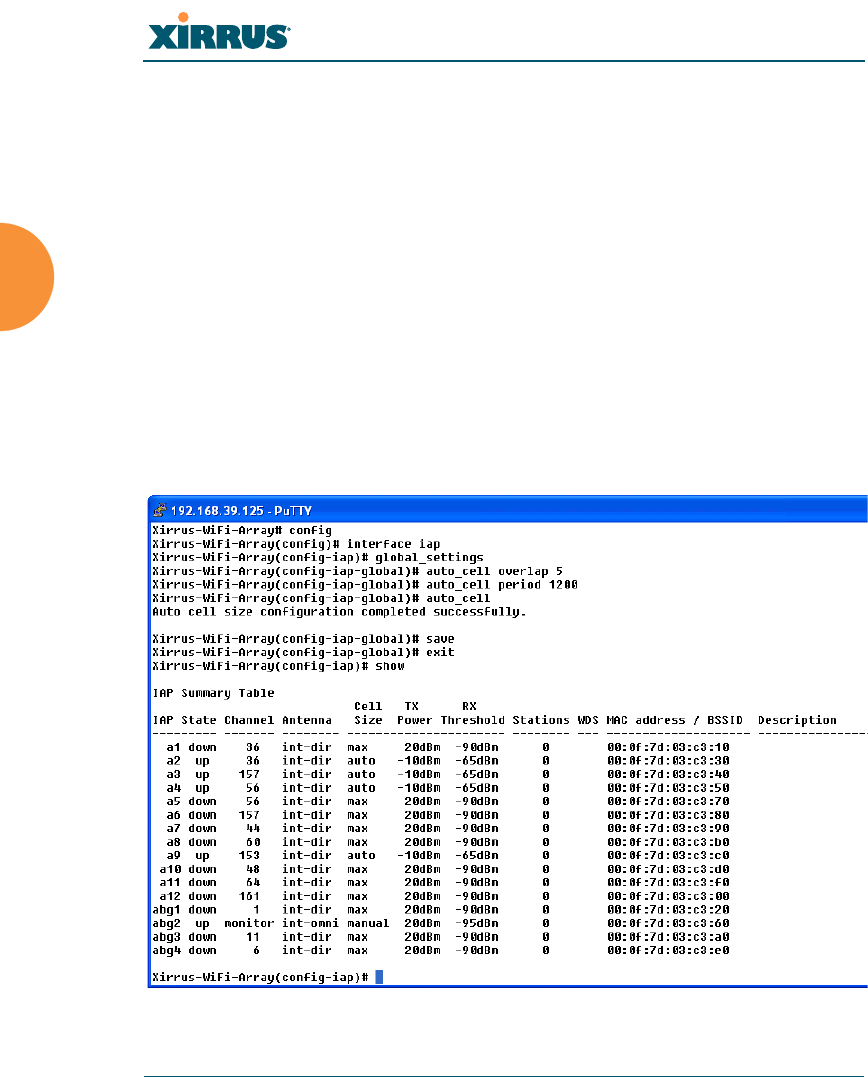
Setting Cell Size Auto-Configuration for All IAPs
This example shows how to set the cell size for all enabled IAPs to be auto-
configured (auto). (See “Fine Tuning Cell Sizes” on page 31.) The auto_cell option
may be used with global_settings, global_a_settings, or global_bg_settings. It
sets the cell size of the specified IAPs to auto, and it launches an auto-
configuration to adjust the sizes. Be aware that if the intrude-detect feature is
enabled on the monitor radio, its cell size is unaffected by this command. Also,
any IAPs used in WDS links are unaffected.
Auto-configuration may be set to run periodically at intervals specified by
auto_cell period (in seconds) if period is non-zero. The percentage of overlap
allowed between cells in the cell size computation is specified by auto_cell
overlap (0 to 100). This example sets auto-configuration to run every 1200 seconds
with an allowed overlap of 5%. It sets the cell size of all IAPs to auto, and runs a
cell size auto-configure operation which completes successfully.
Figure 196. Setting the Cell Size for All IAPs
Wireless Array
The Command Line Interface 435
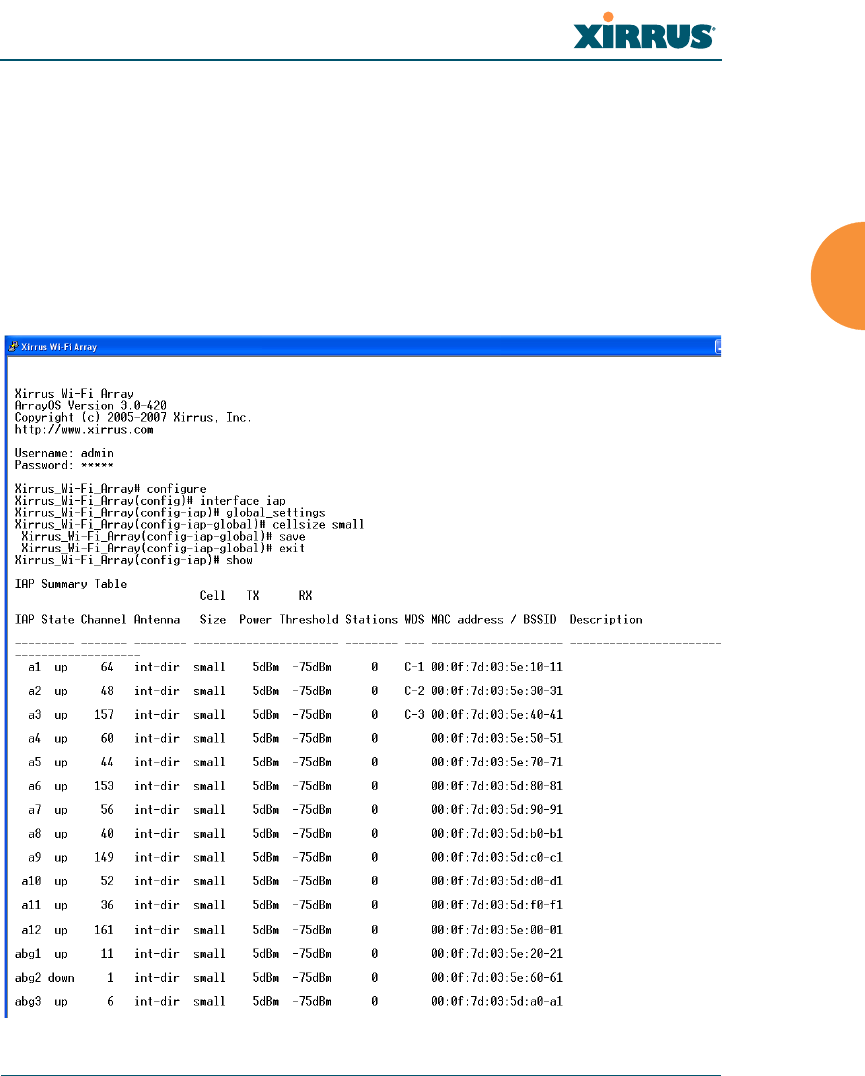
Setting the Cell Size for All IAPs
This example shows you how to establish the cell size for all IAPs (radios),
regardless of the wireless technology they use. Be aware that if the intrude-detect
feature is enabled on the monitor radio the cell size cannot be set globally — you
must first disable the intrude-detect feature on the monitor radio.
In this example, the cell size is being set to small for all IAPs. You have the option
of setting IAP cell sizes to small, medium, large, or max. See also, “Fine Tuning
Cell Sizes” on page 31.
Figure 197. Setting the Cell Size for All IAPs
Wireless Array
436 The Command Line Interface
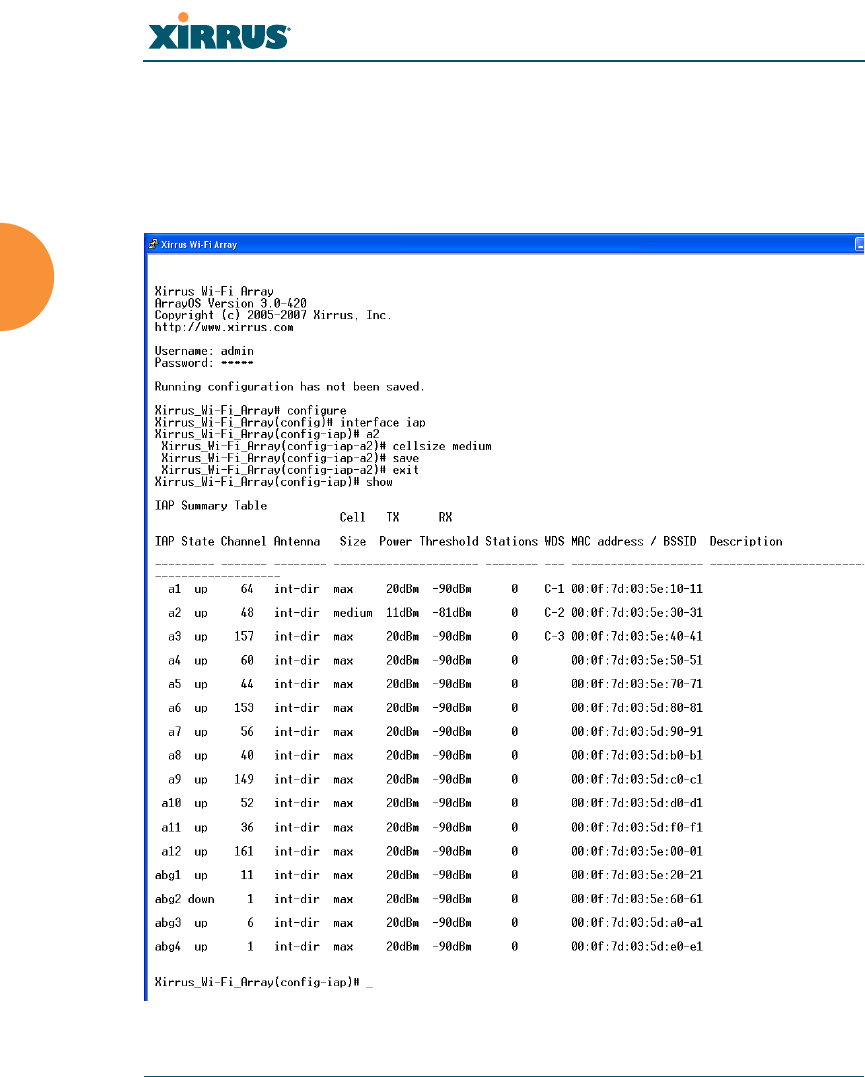
Setting the Cell Size for a Specific IAP
This example shows you how to establish the cell size for a specific IAP (radio). In
this example, the cell size for a2 is being set to medium. You have the option of
setting IAP cell sizes to small, medium, large, or max (the default is max). See
also, “Fine Tuning Cell Sizes” on page 31.
Figure 198. Setting the Cell Size for a Specific IAP
Wireless Array
The Command Line Interface 437
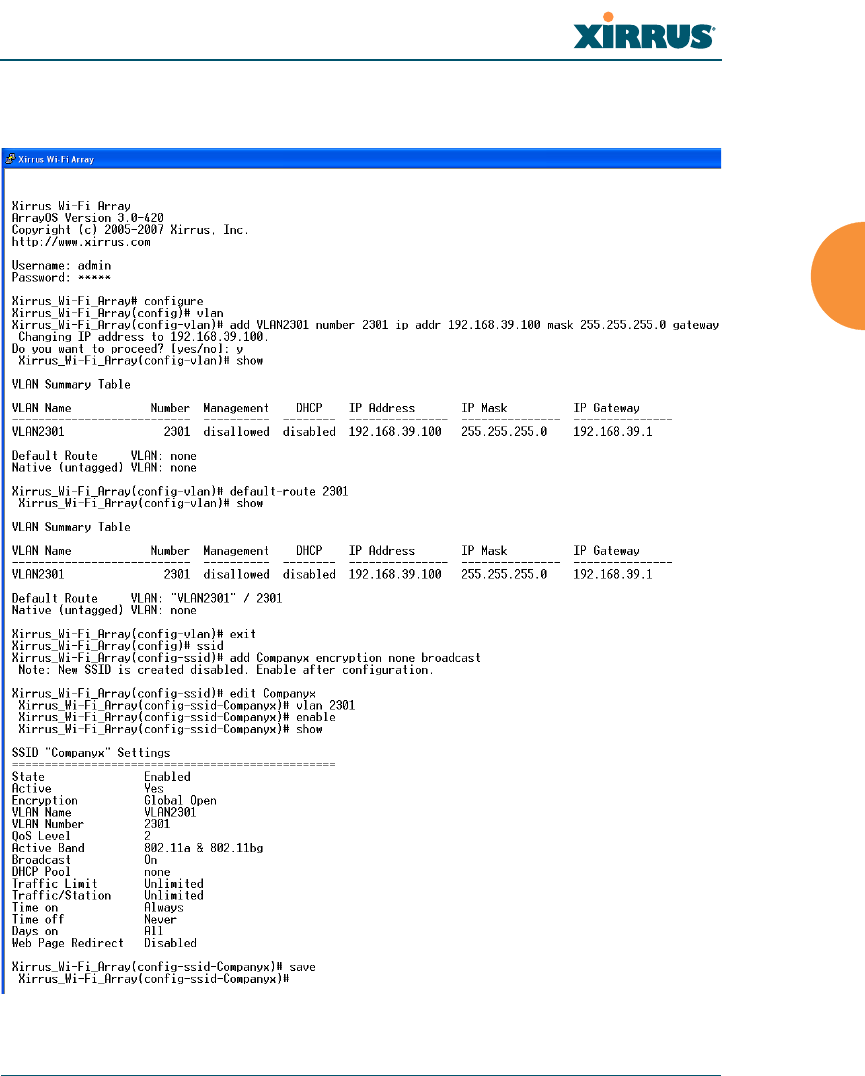
Configuring VLANs on an Open SSID
This example shows you how to configure VLANs on an Open SSID.
Figure 199. Configuring VLANs on an Open SSID
Setting the default route
enables the Array to send
management traffic, such as
Syslog messages and SNMP
information to a destination
behind a router.

Wireless Array
438 The Command Line Interface
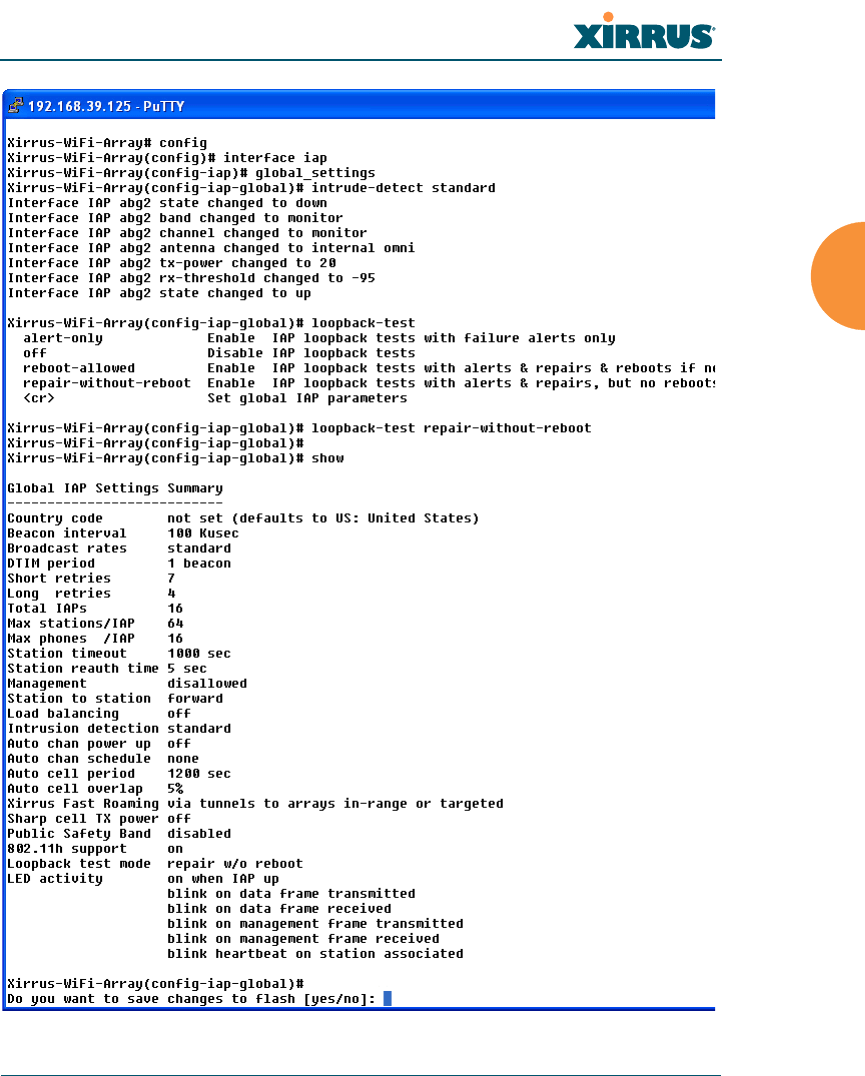
Configuring Radio Assurance Mode (Loopback Tests)
The Array uses its built-in monitor radio to monitor other radios in the Array.
Tests include sending probes on all channels and checking for a response, and
checking whether beacons are received from the other radio. If a problem is
detected, corrective actions are taken to recover. Loopback mode operation is
described in detail in “Array Monitor and Radio Assurance Capabilities” on
page 460.
The following actions may be configured:
alert-only — the Array will issue an alert in the Syslog.
repair-without-reboot — the Array will issue an alert and reset radios at
the Physical Layer (Layer 1) and possibly at the MAC layer. The reset
should not be noticed by users, and they will not need to reassociate.
reboot-allowed — the Array will issue an alert, reset the radios, and
schedule the Array to reboot at midnight (per local Array time) if
necessary. All stations will need to reassociate to the Array.
off — Disable IAP loopback tests (no self-monitoring occurs). Radio
Assurance mode is off by default.
This is a global IAPs setting — the monitor radio will monitor all other radios
according to the settings above, and it cannot be set up to monitor particular
radios. Radio assurance mode requires Intrusion Detection to be set to Standard.
The following example shows you how to configure a loopback test.
Wireless Array
The Command Line Interface 439
Figure 200. Configuring Radio Assurance Mode (Loopback Testing)

Wireless Array
440 The Command Line Interface

Wireless Array
Appendices 441
Appendices

Wireless Array
442 Appendices
Page is intentionally blank
Wireless Array
443
Appendix A: Quick Reference Guide
This section contains product reference information. Use this section to locate the
information you need quickly and efficiently. Topics include:
“Factory Default Settings” on page 443.
“Keyboard Shortcuts” on page 449.
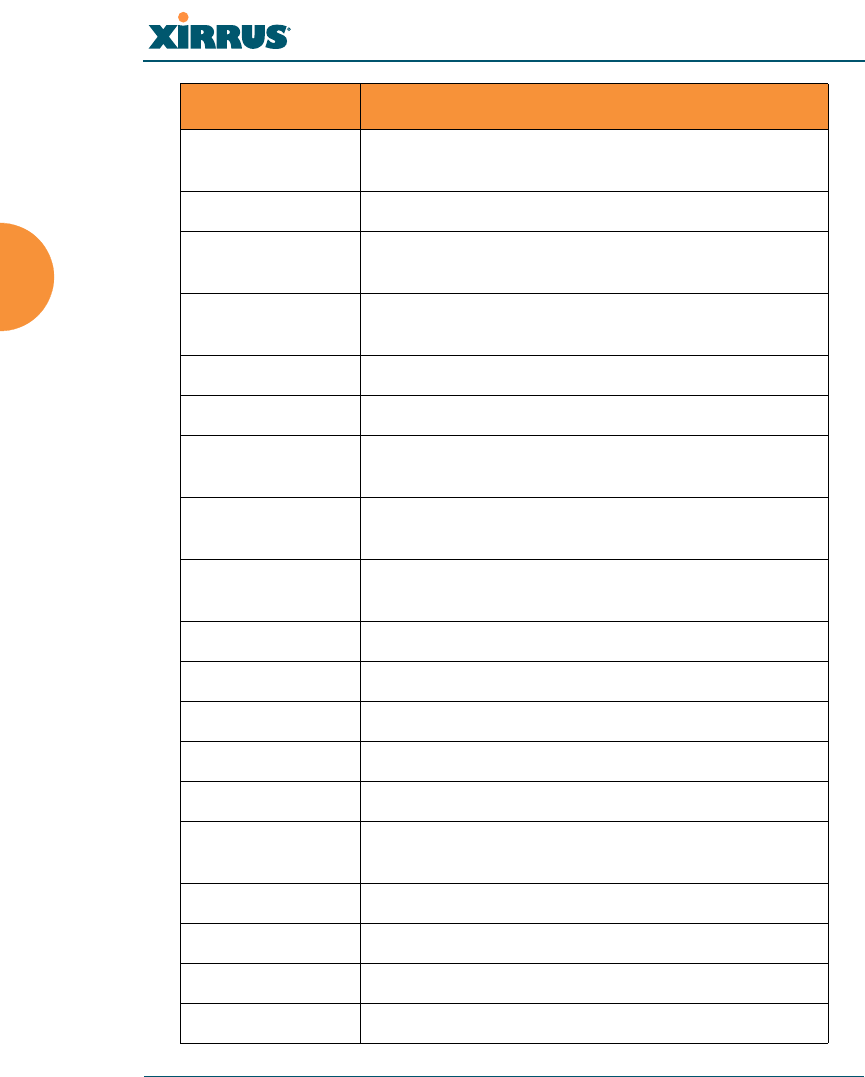
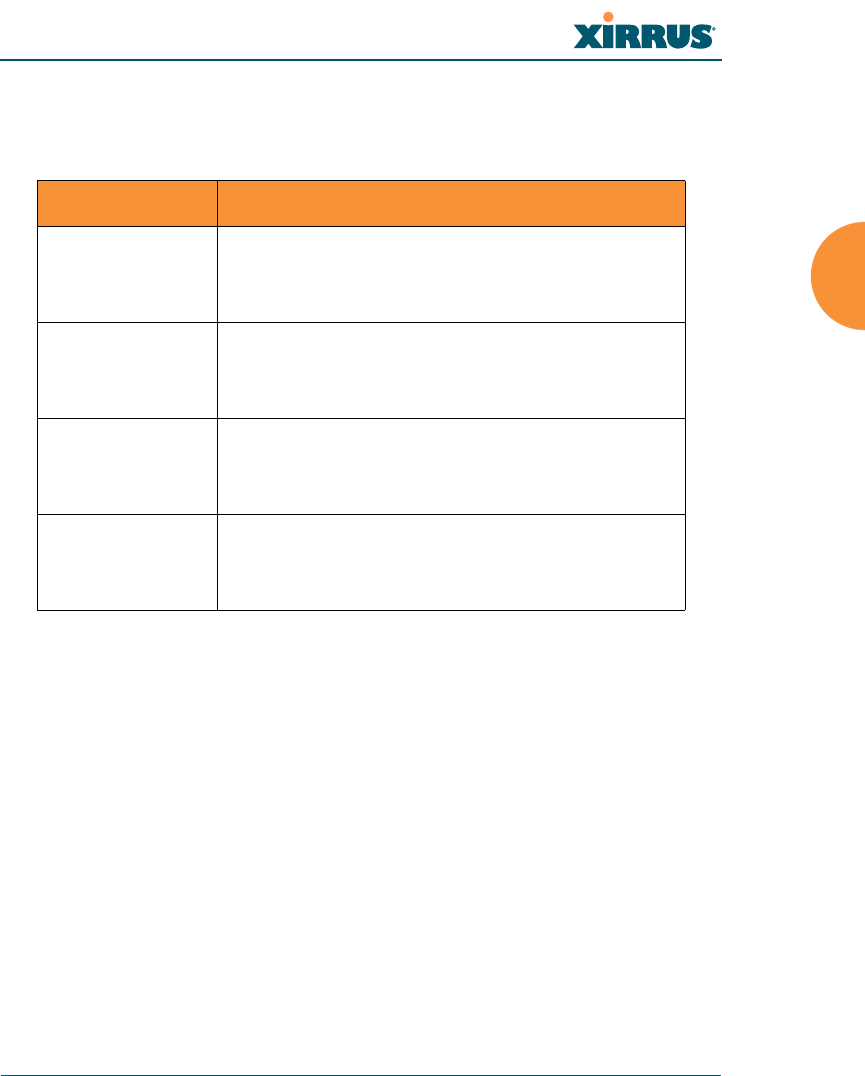
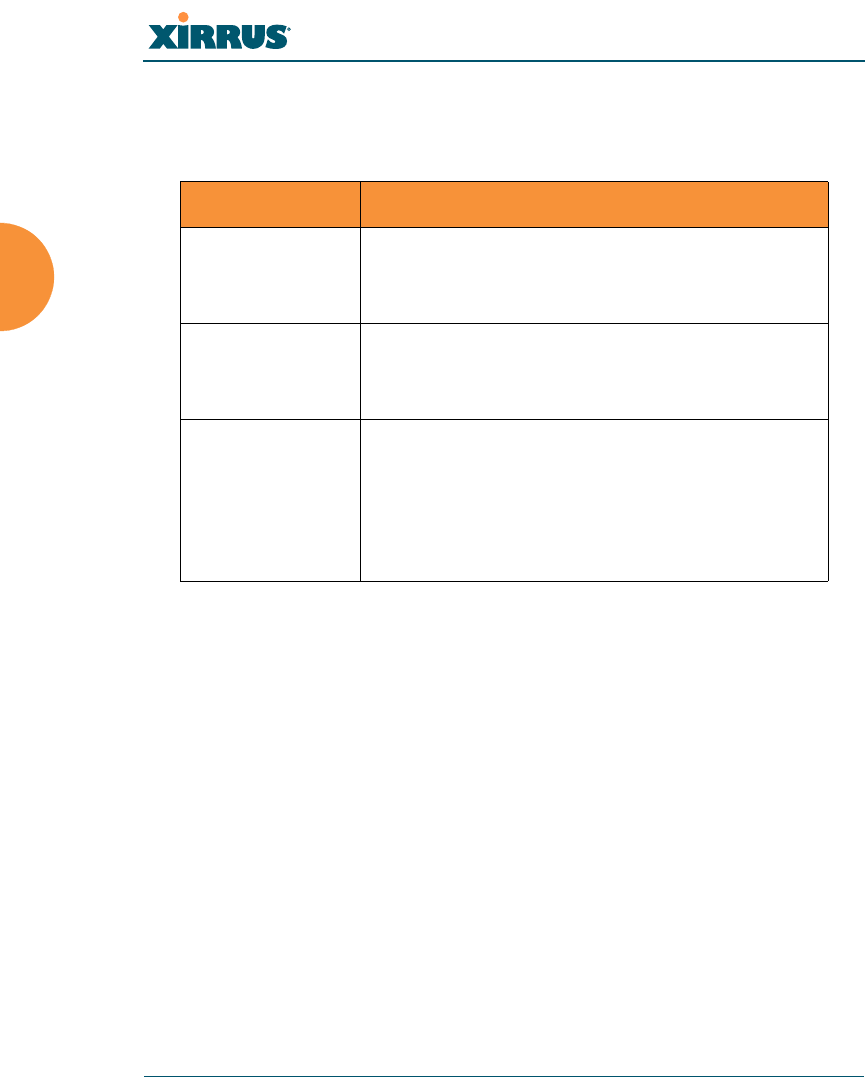
Factory Default Settings
The following tables show the Wireless Array’s factory default settings.
Host Name
Network Interfaces
Serial
Setting Default Value
Host name Xirrus-WiFi-Array
Setting Default Value
Baud Rate 115200
Word Size 8 bits
Stop Bits 1
Parity No parity
Time Out 10 seconds

Wireless Array
444
Gigabit 1 and Gigabit 2
Server Settings
NTP
Syslog
Setting Default Value
Enabled Yes
DHCP Bind Yes
Default IP Address 10.0.2.1
Default IP Mask 255.255.255.0
Default Gateway None
Auto Negotiate On
Duplex Full
Speed 1000 Mbps
MTU Size 1500
Management Enabled Yes
Setting Default Value
Enabled No
Primary time.nist.gov
Secondary pool.ntp.org
Setting Default Value
Enabled Yes
Wireless Array
445
SNMP
DHCP
Local Syslog Level Information
Maximum Internal Records 500
Primary Server None
Primary Syslog Level Information
Secondary Server None
Secondary Syslog Level Information
Setting Default Value
Enabled Yes
Read-Only Community String xirrus_read_only
Read-Write Community String xirrus
Trap Host null (no setting)
Trap Port 162
Authorization Fail Port On
Setting Default Value
Enabled No
Maximum Lease Time 300 minutes
Default Lease Time 300 minutes
IP Start Range 192.168.1.2
IP End Range 192.168.1.254
Setting Default Value

Wireless Array
446
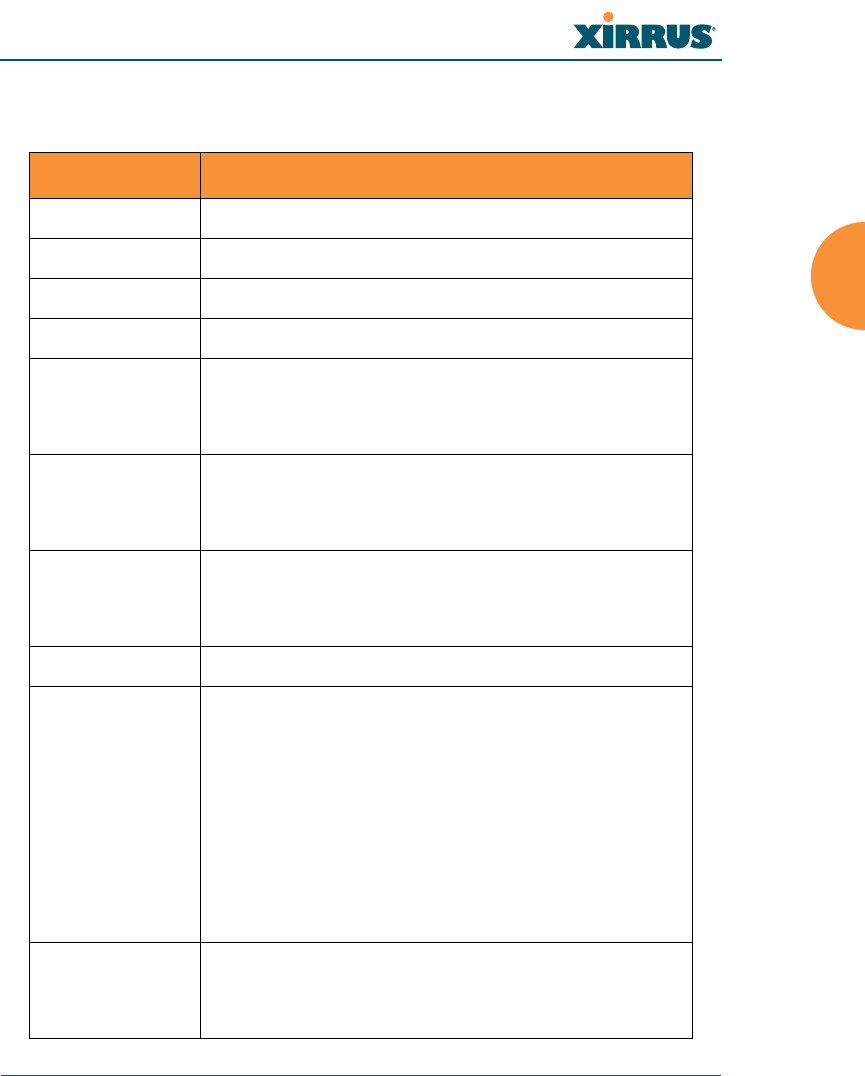
Default SSID
Security
Global Settings - Encryption
NAT Disabled
IP Gateway None
DNS Domain None
DNS Server (1 to 3) None
Setting Default Value
ID xirrus
VLAN None
Encryption Off
Encryption Type None
QoS 2
Enabled Yes
Broadcast On
Setting Default Value
Enabled Yes
WEP Keys null (all 4 keys)
WEP Key Length null (all 4 keys)
Default Key ID 1
Setting Default Value

Wireless Array
447
External RADIUS (Global)
WPA Enabled No
TKIP Enabled Yes
AES Enabled Yes
EAP Enabled Yes
PSK Enabled No
Pass Phrase null
Group Rekey Disabled
Setting Default Value
Enabled Yes
Primary Server None
Primary Port 1812
Primary Secret xirrus
Secondary Server null (no IP address)
Secondary Port 1812
Secondary Secret null (no secret)
Time Out (before primary server is
retired) 600 seconds
Accounting Disabled
Interval 300 seconds
Primary Server None
Primary Port 1813
Setting Default Value
Wireless Array
448
Internal RADIUS
Administrator Account and Password
Management
Primary Secret null (no secret)
Secondary Server None
Secondary Port 1813
Secondary Secret null (no secret)
Setting Default Value
Enabled No
The user database is cleared upon reset to the factory defaults. For the
Internal RADIUS Server you have a maximum of 1,000 entries.
Setting Default Value
ID admin
Password admin
Setting Default Value
SSH On
SSH timeout 300 seconds
Telnet Off
Telnet timeout 300 seconds
Setting Default Value

Wireless Array
449
Keyboard Shortcuts
The following table shows the most common keyboard shortcuts used by the
Command Line Interface.
See Also
An Overview
Serial On
Serial timeout 300 seconds
Management over IAPs Off
http timeout 300 seconds
Action Shortcut
Cut selected data and place it on the
clipboard. Ctrl + X
Copy selected data to the clipboard. Ctrl + C
Paste data from the clipboard into a
document (at the insertion point). Ctrl + V
Go to top of screen. Ctrl + Z
Copy the active window to the
clipboard. Alt + Print Screen
Copy the entire desktop image to the
clipboard. Print Screen
Abort an action at any time. Esc
Go back to the previous screen. b
Access the Help screen. ?
Setting Default Value

Wireless Array
450
Use this Space for Your Notes

Wireless Array
451
Appendix B: Technical Support
This appendix provides valuable support information that can help you resolve
technical difficulties. Before contacting Xirrus, review all topics below and try to
determine if your problem resides with the Wireless Array or your network
infrastructure. Topics include:
“General Hints and Tips” on page 451
“Frequently Asked Questions” on page 452
“Array Monitor and Radio Assurance Capabilities” on page 460
“RADIUS Vendor Specific Attribute (VSA) for Xirrus” on page 463
“Upgrading the Array via CLI” on page 464
“Contact Information” on page 469
General Hints and Tips
This section provides some useful tips that will optimize the reliability and
performance of your Wireless Arrays.
The Wireless Array requires careful handling. For best performance, units
should be mounted in a dust-free and temperature-controlled
environment.
If using multiple Arrays in the same area, maintain a distance of at least
100 feet (30m) between Arrays if there is direct line-of-sight between the
units, or at least 50 feet (15 m) if a wall or other barrier exists between the
units.
Keep the Wireless Array away from electrical devices or appliances that
generate RF noise. Because the Array is generally mounted on ceilings, be
aware of its position relative to lighting (especially fluorescent lighting).
If you are deploying multiple units, the Array should be oriented so that
the monitor abgn2 radio is oriented in the direction of the least required
coverage, because when in monitor mode the radio does not function as
an AP servicing stations.

Wireless Array
452
The Wireless Array should only be used with Wi-Fi certified client
devices.
See Also
Contact Information
Multiple SSIDs
Security
VLAN Support
Frequently Asked Questions
This section answers some of the most frequently asked questions, organized by
functional area.
Multiple SSIDs
Q. What Are BSSIDs and SSIDs?
A. BSSID (Basic Service Set Identifier) refers to an individual access point
radio and its associated clients. The identifier is the MAC address of the
access point radio that forms the BSS.
A group of BSSs can be formed to allow stations in one BSS to
communicate to stations in another BSS by way of a backbone that
interconnects each access point.
The Extended Service Set (ESS) refers to the group of BSSIDs that are
grouped together to form one ESS. The ESSID (often referred to as SSID or
“wireless network name”) identifies the Extended Service Set. Clients
must associate to a single ESS at any given time. Clients ignore traffic
from other Extended Service Sets that do not have the same SSID.
Legacy access points typically support one SSID per access point. Xirrus
Wireless Arrays support the ability for multiple SSIDs to be defined and
used simultaneously.
Q. What would I use SSIDs for?

Wireless Array
453
A. The creation of different wireless network names allows system
administrators to separate types of users with different requirements. The
following policies can be tied to an SSID:
Minimum security required to join this SSID.
The wireless Quality of Service (QoS) desired for this SSID.
The wired VLAN associated with this SSID.
As an example, one SSID named accounting might require the highest
level of security, while another SSID named guests might have low
security requirements.
Another example may define an SSID named voice that supports voice
over Wireless LAN phones with the highest possible Quality of Service
(QoS) definition. This type of SSID might also forward traffic to specific
VLANs on the wired network.
Q. How do I set up SSIDs?
A. Use the following procedure as a guideline. For more detailed
information, go to “SSIDs” on page 242.
1. From the Web Management Interface, go to the SSID
Management page.
2. Select Yes to make the SSID visible to all clients on the network.
Although the Wireless Array will not broadcast SSIDs that are
hidden, clients can still associate to a hidden SSID if they know
the SSID name to connect to it.
3. Select the minimum security that will be required by users for
this SSID.
4. If desired (optional), select a Quality of Service (QoS) setting for
this SSID. The QoS setting you define here will prioritize wireless
traffic for this SSID over other SSID wireless traffic.
5. If desired (optional), select a VLAN that you want this traffic to
be forwarded to on the wired network.

Wireless Array
454
6. If desired (optional), you can select which radios this SSID will
not be available on — the default is to make this SSID available on
all radios.
7. Click on the Save changes to flash if you wish to make your
changes permanent.
8. If you need to edit any of the SSID settings, you can do so from
the SSID Management page.
See Also
Contact Information
General Hints and Tips
Security
SSIDs
SSID Management
VLAN Support
Security
Q. How do I know my management session is secure?
A. Follow these guidelines:
Administrator passwords
Always change the default administrator password (the default
is admin), and choose a strong replacement password. When
appropriate, issue read only administrator accounts.
SSH versus Telnet
Be aware that Telnet is not secure over network connections and
should be used only with a direct serial port connection. When
connecting to the unit’s Command Line Interface over a network
connection, you must use a Secure SHell (SSH) utility. The most
commonly used freeware providing SSH tools is PuTTY. The
Array only allows SSH-2 connections, so your SSH utility must
be set up to use SSH-2.

Wireless Array
455
Configuration auditing
Do not change approved configuration settings. The optional
Xirrus Management System (XMS) offers powerful management
features for small or large Wireless Array deployments, and can
audit your configuration settings automatically. In addition,
using the XMS eliminates the need for an FTP server.
Q. Which wireless data encryption method should I use?
A. Wireless data encryption prevents eavesdropping on data being
transmitted or received over the airwaves. The Wireless Array allows you
to establish the following data encryption configuration options:
Open
This option offers no data encryption and is not recommended,
though you might choose this option if clients are required to use
a VPN connection through a secure SSH utility, like PuTTy.
WEP (Wired Equivalent Privacy)
This option provides minimal protection (though much better
than using an open network). An early standard for wireless data
encryption and supported by all Wi-Fi certified equipment, WEP
is vulnerable to hacking and is therefore not recommended for
use by Enterprise networks.
WPA (Wi-Fi Protected Access)
This is a much stronger encryption model than WEP and uses
TKIP (Temporal Key Integrity Protocol) with AES (Advanced
Encryption Standard) to prevent WEP cracks.
TKIP solves security issues with WEP. It also allows you to
establish encryption keys on a per-user-basis, with key rotation
for added security. In addition, TKIP provides Message Integrity
Check (MIC) functionality and prevents active attacks on the
wireless network.
AES is the strongest encryption standard and is used by
government agencies; however, old legacy hardware may not be
capable of supporting the AES mode (it probably won’t work on

Wireless Array
456
older wireless clients). Because AES is the strongest encryption
standard currently available, it is highly recommended for
Enterprise networks.
Any of the above encryption modes can be used (and can be used at
the same time).
Q. Which user authentication method should I use?
A. User authentication ensures that users are who they say they are. For
example, the most obvious example of authentication is logging in with a
user name and password. The Wireless Array allows you to choose
between the following user authentication methods:
Pre-Shared Key
Users must manually enter a key (pass phrase) on the client side
of the wireless network that matches the key stored by the
administrator in your Wireless Arrays.
RADIUS 802.1x with EAP
802.1x uses a RADIUS server to authenticate large numbers of
clients, and can handle different EAP (Extensible Authentication
Protocol) authentication methods, including EAP-TLS, EAP-
TTLS and EAP-PEAP. The RADIUS server can be internal
(provided by the Wireless Array) or external. An external
RADIUS server offers more functionality and is recommended
for large Enterprise deployments.
When using this method, user names and passwords must be
entered into the RADIUS server for user authentication.
MAC Address ACLs (Access Control Lists)
MAC address ACLs provide a list of client adapter MAC
addresses that are allowed or denied access to the wireless
TKIP encryption does not support high throughput rates, per the
IEEE 802.11n.
TKIP should never be used for WDS links on XN arrays.

Wireless Array
457
network. Access Control Lists work well when there are a limited
number of users — in this case, enter the MAC addresses of each
user in the Allow list. In the event of a lost or stolen MAC
adapter, enter the affected MAC address in the Deny list.
Q. Why do I need to authenticate my Wireless Array units?
A. When deploying multiple Wireless Arrays, you may need to define which
units are part of which wireless network (for example, if you are
establishing more than one network). In this case, you need to employ the
Xirrus Management System (XMS) which can authenticate your Arrays
automatically and ensure that only authorized units are associated with
the defined wireless network.
Q. What is rogue AP (Access Point) detection?
A. The Wireless Array has integrated monitor capabilities, which can
constantly scan the local wireless environment for rogue APs (non-Xirrus
devices that are not part of your wireless network), unencrypted
transmissions, and other security issues. Administrators can then classify
each rogue AP and ensure that these devices do not interrupt or interfere
with the network.
See Also
Contact Information
General Hints and Tips
Multiple SSIDs
VLAN Support
VLAN Support
Q. What Are VLANs?
A. VLANs (Virtual Local Area Networks) are a logical grouping of network
devices that share a common network broadcast domain. Members of a
particular VLAN can be on any segment of the physical network but
logically only members of a particular VLAN can see each other.

Wireless Array
458
VLANs are defined and implemented using the wired network switches
that are VLAN capable. Packets are tagged for transmission on a
particular VLAN according to the IEEE 802.1Q standard, with VLAN
switches processing packets according to the tag.
Q. What would I use VLANs for?
A. Logically separating different types of users, systems, applications, or
other logical division aids in performance and management of different
network devices. Different VLANs can also be assigned with different
packet priorities to prioritize packets from one VLAN over packets from
another VLAN.
VLANs are managed by software settings — instead of physically
plugging in and moving network cables and users — which helps to ease
network management tasks.
Q. What are Wireless VLANs?
A. Wireless VLANs allow similar functionality to the wired VLAN
definitions and extend the operation of wired VLANs to the wireless side
of the network.
Wireless VLANs can be mapped to wireless SSIDs so that traffic from
wired VLANs can be sent to wireless users of a particular SSID. The
reverse is also true, where wireless traffic originating from a particular
SSID can be tagged for transmission on a particular wired VLAN.
Sixteen SSIDs can be defined on your Wireless Array, allowing a total of
sixteen VLANs to be accessed (one per SSID).
As an example, to provide guest user access an SSID of guest might be
created. This SSID could be mapped to a wired VLAN that segregates
unknown users from the rest of the wired network and restricts them to
Internet access only. Wireless users could then associate to the wireless
network via the guest SSID and obtain access to the Internet through the
selected VLAN, but would be unable to access other privileged network
resources.
See Also

Wireless Array
459
Contact Information
General Hints and Tips
Multiple SSIDs
Security

Wireless Array
460
Array Monitor and Radio Assurance Capabilities
All models of the Wireless Array have integrated monitoring capabilities to check
that the Array’s radios are functioning correctly, and act as a threat sensor to
detect and prevent intrusion from rogue access points.
Enabling Monitoring on the Array
Any radio IAP abgn2 may be set to monitor the Array or to be a normal IAP radio.
In order to enable the functions required for intrusion detection and for
monitoring the other Array radios, you must configure one monitor radio on the
IAP Settings window as follows:
Check the Enabled checkbox.
Set Mode to Monitor.
Set Channel to Monitor.
The settings above will automatically set the Antenna selection to
Internal-Omni., also required for monitoring. See the “IAP Settings” on page 274
for more details. The values above are the factory default settings for the Array.
How Monitoring Works
When the monitor radio has been configured as just described, it performs these
steps continuously (24/7) to check the other radios on the Array and detect
possible intrusions:
1. The monitor radio scans all channels with a 200ms dwell time, hitting all
channels about once every 10 seconds.
2. Each time it tunes to a new channel it sends out a probe request in an
attempt to smoke out rogues.
3. It then listens for all probe responses and beacons to detect any rogues
within earshot.
4. Array radios respond to that probe request with a probe response.
Intrusion Detection is enabled or disabled separately from monitoring. See Step 1
in “Advanced RF Settings” on page 313.

Wireless Array
461
Radio Assurance
The Array is capable of performing continuous, comprehensive tests on its radios
to assure that they are operating properly. Testing is enabled using the Radio
Assurance Mode setting on the Advanced RF Settings window (Step 2 in
“Advanced RF Settings” on page 313). When this mode is enabled, the monitor
radio performs loopback tests on the Array. Radio Assurance Mode requires
Intrusion Detection to be set to Standard (See Step 1 in “Advanced RF Settings”
on page 313).
When Radio Assurance Mode is enabled:
1. The Array keeps track of whether or not it hears beacons and probe
responses from the Array’s radios.
2. After 10 minutes (roughly 60 passes on a particular channel by the
monitor radio), if it has not heard beacons or probe responses from one of
the Array’s radios it issues an alert in the Syslog. If repair is allowed (see
“Radio Assurance Options” on page 462), the Array will reset and
reprogram that particular radio at the Physical Layer (PHY — Layer 1).
This action takes under 100ms and stations are not deauthenticated, thus
users should not be impacted.
3. After another 10 minutes (roughly another 60 passes), if the monitor still
has not heard beacons or probe responses from the malfunctioning radio
it will again issue an alert in the Syslog. If repair is allowed, the Array will
reset and reprogram the MAC (the lower sublayer of the Data Link Layer)
and then all of the PHYs. This is a global action that affects all radios. This
action takes roughly 300ms and stations are not deauthenticated, thus
users should not be impacted.
4. After another 10 minutes, if the monitor still has not heard beacons or
probe responses from that radio, it will again syslog the issue. If reboot is
allowed (see “Radio Assurance Options” on page 462), the Array will
schedule a reboot. This reboot will occur at one of the following times,
whichever occurs first:
•When no stations are associated to the Array
•Midnight

Wireless Array
462
Radio Assurance Options
If the monitor detects a problem with an Array radio as described above, it will
take action according to the preference that you have specified in the Radio
Assurance Mode setting on the Advanced RF Settings window (see Step 2
page 315):
Failure alerts only — The Array will issue alerts in the Syslog, but will not
initiate repairs or reboots.
Failure alerts & repairs, but no reboots — The Array will issue alerts and
perform resets of the PHY and MAC as described above.
Failure alerts & repairs & reboots if needed — The Array will issue
alerts, perform resets of the PHY and MAC, and schedule reboots as
described above.
Disabled — Disable IAP loopback tests (no self-monitoring occurs).
Loopback tests are disabled by default.

Wireless Array
463
RADIUS Vendor Specific Attribute (VSA) for Xirrus
A RADIUS VSA is defined for Xirrus Arrays to control administrator privileges
settings for user accounts. The RADIUS VSA is used by Arrays to define the
following attribute for administrator accounts:
Array administrators — the Xirrus-Admin-Role attribute sets the
privilege level for this account. Set the value to the string defined in
Privilege Level Name as described in “About Creating Admin Accounts
on the RADIUS Server” on page 218.

Wireless Array
464
Upgrading the Array via CLI
If you are experiencing difficulties communicating with the Array using the Web
Management Interface, the Array provides lower-level facilities that may be used
to accomplish an upgrade via the CLI and the Xirrus Boot Loader (XBL).
1. Download the latest software update from the Xirrus FTP site using your
Enhanced Care FTP username and password. If you do not have an FTP
username and password, contact Xirrus Customer Service for assistance
(support@xirrus.com). The software update is provided as a zip file.
Unzip the contents to a local temp directory. Take note of the extracted file
name in case you need it later on — you may also need to copy this file
elsewhere on the network depending on your situation.
2. Install a TFTP server software package if you don't have one running. It
may be installed on any PC on your network, including your desktop or
laptop. The Solar Winds version is freeware and works well.
http://support.solarwinds.net/updates/New-customerFree.cfm?ProdId=52
The TFTP install process creates the TFTP-Root directory on your C:
drive, which is the default target for sending and receiving files. This may
be changed if desired. This directory is where you will place the extracted
Xirrus software update file(s). If you install the TFTP server on the same
computer to which you extracted the file, you may change the TFTP
directory to C:\xirrus if desired.
You must make the following change to the default configuration of the
Solar Winds TFTP server. In the File/Configure menu, select Security,
then select Transmit only and click OK.
3. Determine the IP address of the computer hosting the TFTP server. (To
display the IP address, open a command prompt and type ipconfig)
4. Connect your Array to the computer running TFTP using a serial cable,
and open a terminal program if you haven't already. Attach a network
cable to the Array’s GIG1 port, if it is not already part of your network.

Wireless Array
465
Boot your Array and watch the progress messages. When Press space bar
to exit to bootloader: is displayed, press the space bar. The rest of this
procedure is performed using the bootloader.
The following steps assume that you are running DHCP on your local
network.
5. Type dhcp and hit return. This instructs the Array to obtain a DHCP
address and use it during this boot in the bootloader environment.
6. Type dir and hit return to see what's currently in the compact flash.
7. Type del and hit return to delete the contents of the compact flash.
8. Type update server <TFTP-server-ip-addr> XS-5.x-xxxx.bin (the actual
Xirrus file name will vary depending on Array model number and
software version — use the file name from your software update) and hit
return. The software update will be transferred to the Array's memory
and will be written to the compact flash card. (See output below.)
9. Type reset and hit return. Your Array will reboot, running your new
version of software.
Sample Output for the Upgrade Procedure:
The user actions are highlighted in the output below, for clarity.
Username: admin
Password: *****
Xirrus-WiFi-Array# configure
Xirrus-WiFi-Array(config)# reboot
Are you sure you want to reboot? [yes/no]: yes
Array is being rebooted.
Xirrus Boot Loader 1.0.0 (Oct 17 2006 - 13:11:42), Build: 2725
Processor | Motorola PowerPC, PVR=80200020 SVR=80300020
Board | Xirrus MPC8540 CPU Board
Clocks | CPU : 825 MHz DDR : 330 MHz Local Bus: 41 MHz

Wireless Array
466
L1 cache | Data: 32 KB Inst: 32 KB Status : Enabled
Watchdog | Enabled (5 secs)
I2C Bus | 400 KHz
DTT | CPU:34C RF0:34C RF1:34C RF2:27C RF3:29C
RTC | Wed 2007-Nov-05 6:43:14 GMT
System DDR | 256 MB, Unbuffered Non-ECC (2T)
L2 cache | 256 KB, Enabled
FLASH | 4 MB, CRC: OK
FPGA | 2 Devices programmed
Packet DDR | 256 MB, Unbuffered Non-ECC, Enabled
Network | Mot FEC Mot TSEC1 [Primary] Mot TSEC2
IDE Bus 0 | OK
CFCard | 122 MB, Model: Hitachi XXM2.3.0
Environment| 4 KB, Initialized
In: serial
Out: serial
Err: serial
Press space bar to exit to bootloader:
XBL>dhcp
[DHCP ] Device : Mot TSEC1 1000BT Full Duplex
[DHCP ] IP Addr : 192.168.39.195
XBL>dir
[CFCard] Directory of /
Date Time Size File or Directory name
----------- -------- -------- ---------------------------
2007-Nov-05 6:01:56 29 lastboot
2007-Apr-05 15:47:46 28210390 xs-3.1-0433.bak
2007-Mar-01 16:39:42 storage/
2007-Apr-05 15:56:38 28210430 xs-3.1-0440.bin
2007-Mar-03 0:56:28 wpr/
3 file(s), 2 dir(s)

Wireless Array
467
XBL>del *
[CFCard] Delete : 2 file(s) deleted
XBL>update server 192.168.39.102 xs-3.0-0425.bin
[TFTP ] Device : Mot TSEC1 1000BT Full Duplex
[TFTP ] Client : 192.168.39.195
[TFTP ] Server : 192.168.39.102
[TFTP ] File : xs-3.0-0425.bin
[TFTP ] Address : 0x1000000
[TFTP ] Loading : ##################################################
[TFTP ] Loading : ##################################################
[TFTP ] Loading : ###### done
[TFTP ] Complete: 12.9 sec, 2.1 MB/sec
[TFTP ] Bytes : 27752465 (1a77811 hex)
[CFCard] File : xs-3.0-0425.bin
[CFCard] Address : 0x1000000
[CFCard] Saving : ############################################### done
[CFCard] Complete: 137.4 sec, 197.2 KB/sec
[CFCard] Bytes : 27752465 (1a77811 hex)
XBL>reset
[RESET ]
Xirrus Boot Loader 1.0.0 (Oct 17 2006 - 13:11:42), Build: 2725
Processor | Motorola PowerPC, PVR=80200020 SVR=80300020
Board | Xirrus MPC8540 CPU Board
Clocks | CPU : 825 MHz DDR : 330 MHz Local Bus: 41 MHz
L1 cache | Data: 32 KB Inst: 32 KB Status : Enabled
Watchdog | Enabled (5 secs)
I2C Bus | 400 KHz
DTT | CPU:33C RF0:32C RF1:31C RF2:26C RF3:27C
RTC | Wed 2007-Nov-05 6:48:44 GMT
System DDR | 256 MB, Unbuffered Non-ECC (2T)

Wireless Array
468
L2 cache | 256 KB, Enabled
FLASH | 4 MB, CRC: OK
FPGA | 2 Devices programmed
Packet DDR | 256 MB, Unbuffered Non-ECC, Enabled
Network | Mot FEC Mot TSEC1 [Primary] Mot TSEC2
IDE Bus 0 | OK
CFCard | 122 MB, Model: Hitachi XXM2.3.0
Environment| 4 KB, Initialized
In: serial
Out: serial
Err: serial
Press space bar to exit to bootloader:
[CFCard] File : xs*.bin
[CFCard] Address : 0x1000000
[CFCard] Loading : ############################################### done
[CFCard] Complete: 26.9 sec, 1.0 MB/sec
[CFCard] Bytes : 27752465 (1a77811 hex)
[Boot ] Address : 0x01000000
[Boot ] Image : Verifying checksum .... OK
[Boot ] Unzip : Multi-File Image .... OK
[Boot ] Initrd : Loading RAMDisk Image
[Boot ] Initrd : Verifying checksum .... OK
[Boot ] Execute : Transferring control to OS
Initializing hardware ........................................ OK
Xirrus Wi-Fi Array
ArrayOS Version 3.0-425
Copyright (c) 2005-2007 Xirrus, Inc.
http://www.xirrus.com
Username:

Wireless Array
469
Contact Information
Xirrus, Inc. is located in Thousand Oaks, California, just 55 minutes northwest of
downtown Los Angeles and 40 minutes southeast of Santa Barbara.
Xirrus, Inc.
2101 Corporate Center Drive
Thousand Oaks, CA 91320
USA
Tel: 1.805.262.1600
1.800.947.7871 Toll Free in the US
Fax: 1.866.462.3980
www.xirrus.com
support.xirrus.com

Wireless Array
470

Wireless Array
471
Appendix C: Notices
This appendix contains the following information:
“Notices” on page 471
“EU Directive 1999/5/EC Compliance Information” on page 475
“Compliance Information (Non-EU)” on page 482
“Safety Warnings” on page 483
“Translated Safety Warnings” on page 484
“Software License and Product Warranty Agreement” on page 485
“Hardware Warranty Agreement” on page 491
Notices
Wi-Fi Alliance Certification
www.wi-fi.org
FCC Notice
This device complies with Part 15 of the FCC Rules, with operation subject to the
following two conditions: (1) This device may not cause harmful interference, and
(2) this device must accept any interference received, including interference that
may cause unwanted operation.
This equipment has been tested and found to comply with the limits for a Class B
digital device, pursuant to Part 15 of the FCC rules. These limits are designed to
provide reasonable protection against harmful interference in a residential
installation. This equipment generates, uses and can radiate RF energy and, if not
installed and used in accordance with the instructions, may cause harmful
interference to radio communications. However, there is no guarantee that
interference will not occur in a particular installation. If this equipment does
cause harmful interference to radio or television reception, which can be

Wireless Array
472
determined by turning the equipment off and on, the user is encouraged to try to
correct the interference by one or more of the following safety measures:
Reorient or relocate the receiving antenna.
Increase the separation between the equipment and the receiver.
Connect the equipment into an outlet on a circuit different from that to
which the receiver is connected.
Consult the dealer or an experienced wireless technician for help.
Use of a shielded twisted pair (STP) cable must be used for all Ethernet
connections in order to comply with EMC requirements.
This transmitter must not be co-located or operating in conjunction with any
other antenna or transmitter.
Operations in the 5.15-5.25GHz band are restricted to indoor usage only.
High Power Radars
High power radars are allocated as primary users (meaning they have priority) in
the 5250MHz to 5350MHz and 5650MHz to 5850MHz bands. These radars could
cause interference and/or damage to LE-LAN devices.
Non-Modification Statement
Unauthorized changes or modifications to the device are not permitted. Use only
the supplied internal antenna, or external antennas supplied by the manufacturer.
Modifications to the device will void the warranty and may violate FCC
regulations. Please go to the Xirrus Web site for a list of all approved antennas.
Cable Runs for Power over Gigabit Ethernet (PoGE)
If using PoGE, the Array must be connected to PoGE networks without routing
cabling to the outside plant — this ensures that cabling is not exposed to lightning
strikes or possible cross over from high voltage.
!FCC Caution: Any changes or modifications not expressly approved by the
party responsible for compliance could void the user's authority to operate this
equipment.

Wireless Array
473
Battery Warning
UL Statement
Use only with listed ITE product.
RF Radiation Hazard Warning
To ensure compliance with FCC and Industry Canada RF exposure requirements,
this device must be installed in a location where the antennas of the device will
have a minimum distance of at least 30 cm (12 inches) from all persons. Using
higher gain antennas and types of antennas not certified for use with this product
is not allowed. The device shall not be co-located with another transmitter.
Installez l'appareil en veillant à conserver une distance d'au moins 30 cm entre les
éléments rayonnants et les personnes. Cet avertissement de sécurité est conforme
aux limites d'exposition définies par la norme CNR-102 at relative aux fréquences
radio.
Industry Canada Statement
This device complies with RSS-210 of the Industry Canada Rules. Operation is
subject to the following two conditions: (1) This device may not cause harmful
interference, and (2) this device must accept any interference received, including
interference that may cause undesired operation.
Ce dispositif est conforme à la norme CNR-210 d'Industrie Canada applicable aux
appareils radio exempts de licence. Son fonctionnement est sujet aux deux
conditions suivantes: (1) le dispositif ne doit pas produire de brouillage
préjudiciable, et (2) ce dispositif doit accepter tout brouillage reçu, y compris un
brouillage susceptible de provoquer un fonctionnement indésirable.
!Caution! The Array contains a battery which is not to be replaced by the
customer. Danger of Explosion exists if the battery is incorrectly replaced.
Replace only with the same or equivalent type recommended by the
manufacturer. Dispose of used batteries according to the manufacturer's
instructions.

Wireless Array
474
Caution :
(i) the device for operation in the band 5150-5250 MHz is only for indoor use to
reduce the potential for harmful interference to co-channel mobile satellite
systems;
(ii) high-power radars are allocated as primary users (i.e. priority users) of the
bands 5250-5350 MHz and 5650-5850 MHz and that these radars could cause
interference and/or damage to LE-LAN devices.
Avertissement:
(i) les dispositifs fonctionnant dans la bande 5 150-5 250 MHz sont réservés
uniquement pour une utilisation à l'intérieur afin de réduire les risques de
brouillage préjudiciable aux systèmes de satellites mobiles utilisant les mêmes
canaux;
(ii) De plus, les utilisateurs devraient aussi être avisés que les utilisateurs de
radars de haute puissance sont désignés utilisateurs principaux (c.-à-d., qu'ils ont
la priorité) pour les bandes 5 250-5 350 MHz et 5 650-5 850 MHz et que ces radars
pourraient causer du brouillage et/ou des dommages aux dispositifs LAN-EL.
High Power Radars
High power radars are allocated as primary users (meaning they have priority) in
the 5250MHz to 5350MHz and 5650MHz to 5850MHz bands. These radars could
cause interference and/or damage to LELAN devices used in Canada.
Les utilisateurs de radars de haute puissance sont désignés utilisateurs
principaux (c.-à-d., qu’ils ont la priorité) pour les bandes 5 250 - 5 350 MHz et
5 650 - 5 850 MHz. Ces radars pourraient causer du brouillage et/ou des
dommages aux dispositifs LAN-EL.

Wireless Array
475
EU Directive 1999/5/EC Compliance Information
This section contains compliance information for the Xirrus Wireless Array family
of products. The compliance information contained in this section is relevant to
the European Union and other countries that have implemented the EU Directive
1999/5/EC.
Declaration of Conformity
Cesky [Czech] Toto zahzeni je v souladu se základnimi požadavky a
ostatnimi odpovidajcimi ustano veni mi Směrnice
1999/5/EC.
Dansk [Danish] Dette udstyr er i overensstemmelse med de
væsentlige krav og andre relevante bestemmelser i
Direktiv 1999/5/EF.
Deutsch [German] Dieses Gerat entspricht den grundlegenden
Anforderungen und den weiteren entsprechenden
Vorgaben der Richtinie 1999/5/EU.
Eesti [Estonian] See seande vastab direktiivi 1999/5/EU olulistele
nöuetele ja teistele as jakohastele sätetele.
English This equipment is in compliance with the essential
requirements and other relevant provisions of
Directive 1999/5/EC.
Español [Spain] Este equipo cump le con los requisitos esenciales asi
como con otras disposiciones de la Directiva 1999/5/
CE.
Ελληνυκη [Greek] Αυτόζ ο εξοπλτσμόζ είναι σε συμμόρφωση με τιζ
ουσιώδειζ απαιτήσειζ και ύλλεζ σχετικέζ διατάξειζ τηζ
Οδηγιαζ 1999/5/EC.
Français [French] Cet appareil est conforme aux exigences essentielles
et aux autres dispositions pertinentes de la Directive
1999/5/EC.

Wireless Array
476
ĺslenska [Icelandic] Þetta tæki er samkvæmt grunnkröfum og öðrum
viðeigandi ákvæðum Tilskipunar 1999/5/EC.
Italiano [Italian] Questo apparato é conforme ai requisiti essenziali ed
agli altri principi sanciti dalla Direttiva 1999/5/CE.
Latviski [Latvian] Šī iekārta atbilst Direktīvas 1999/5/EK būtiskajā
prasībām un citiem ar to saistītajiem noteikumiem.
Lietuvių [Lithuanian] Šis įrenginys tenkina 1995/5/EB Direktyvos
esminius reikalavimus ir kitas šios direktyvos
nuostatas.
Nederlands [Dutch] Dit apparant voldoet aan de essentiele eisen en
andere van toepassing zijnde bepalingen van de
Richtlijn 1995/5/EC.
Malti [Maltese] Dan l-apparant huwa konformi mal-htigiet essenzjali
u l-provedimenti l-ohra rilevanti tad-Direttiva 1999/
5/EC.
Margyar [Hungarian] Ez a készülék teljesiti az alapvetö követelményeket
és más 1999/5/EK irányelvben meghatározott
vonatkozó rendelkezéseket.
Norsk [Norwegian] Dette utstyret er i samsvar med de grunnleggende
krav og andre relevante bestemmelser i EU-direktiv
1999/5/EF.
Polski [Polish] Urządzenie jest zgodne z ogólnymi wymaganiami
oraz sczególnymi mi warunkami określony mi
Dyrektywą. UE:1999/5/EC.
Portuguès [Portuguese] Este equipamento está em conformidade com os
requisitos essenciais e outras provisões relevantes da
Directiva 1999/5/EC.
Slovensko [Slovenian] Ta naprava je skladna z bistvenimi zahtevami in
ostalimi relevantnimi popoji Direktive 1999/5/EC.
Wireless Array
477
Assessment Criteria
The following standards were applied during the assessment of the product
against the requirements of the Directive 1999/5/EC:
Radio: EN 301 893 and EN 300 328 (if applicable)
EMC: EN 301 489-1 and EN 301 489-17
Safety: EN 50371 to EN 50385 and EN 60601
CE Marking
For the Xirrus Wireless Array, the CE mark and Class-2 identifier opposite are
affixed to the equipment and its packaging:
Slovensky [Slovak] Toto zariadenie je v zhode so základnými
požadavkami a inými prislušnými nariadeniami
direktiv: 1999/5/EC.
Suomi [Finnish] Tämä laite täyttää direktiivin 1999/5//EY olennaiset
vaatimukset ja on siinä asetettujen muiden laitetta
koskevien määräysten mukainen.
Svenska [Swedish] Denna utrustning är i överensstämmelse med de
väsentliga kraven och andra relevanta bestämmelser
i Direktiv 1999/5/EC.
Wireless Array
478
WEEE Compliance
Natural resources were used in the production of
this equipment.
This equipment may contain hazardous
substances that could impact the health of the
environment.
In order to avoid harm to the environment and
consumption of natural resources, we encourage
you to use appropriate take-back systems when
disposing of this equipment.
The appropriate take-back systems will reuse or
recycle most of the materials of this equipment in
a way that will not harm the environment.
The crossed-out wheeled bin symbol (in
accordance with European Standard EN 50419)
invites you to use those take-back systems and
advises you not to combine the material with
refuse destined for a land fill.
If you need more information on collection, re-
use and recycling systems, please contact your
local or regional waste administration.
Please contact Xirrus for specific information on
the environmental performance of our products.
Wireless Array
479
National Restrictions
In the majority of the EU and other European countries, the 2.4 GHz and 5 GHz
bands have been made available for the use of Wireless LANs. The following table
provides an overview of the regulatory requirements in general that are
applicable for the 2.4 GHz and 5 GHz bands.
*Dynamic frequency selection and Transmit Power Control is required in these
frequency bands.
**France is indoor use only in the upper end of the band.
The requirements for any country may change at any time. Xirrus recommends
that you check with local authorities for the current status of their national
regulations for both 2.4 GHz and 5 GHz wireless LANs.
The following countries have additional requirements or restrictions than those
listed in the above table:
Belgium
The Belgian Institute for Postal Services and Telecommunications (BIPT) must
be notified of any outdoor wireless link having a range exceeding 300 meters.
Xirrus recommends checking at www.bipt.be for more details.
Draadloze verbindingen voor buitengebruik en met een reikwijdte van meer dan 300
meter dienen aangemeld te worden bij het Belgisch Instituut voor postdiensten en
telecommunicatie (BIPT). Zie www.bipt.be voor meer gegevens.
Frequency
Band (MHz) Max Power Level
(EIRP) (mW) Indoor Outdoor
2400–2483.5 100 X X**
5250–5350* 200 X N/A
5470–5725* 1000 X X

Wireless Array
480
Les liasons sans fil pour une utilisation en extérieur d’une distance supérieure à 300
mèters doivent être notifiées à l’Institut Belge des services Postaux et des
Télécommunications (IBPT). Visitez www.bipt.be pour de plus amples détails.
Greece
A license from EETT is required for the outdoor operation in the 5470 MHz to
5725 MHz band. Xirrus recommends checking www.eett.gr for more details.
Η δη ιουργβάικτ ωνεξωτερικο ρουστη ζ νησυ νοτ των 5470–5725 ΜΗz ε ιτρ ετάιωνο
ετάά όάδειά της ΕΕΤΤ, ου ορηγεβτάι στερά ά ό σ φωνη γν η του ΓΕΕΘΑ. ερισσότερες
λε τομ ρειεωστο www.eett.gr
Italy
This product meets the National Radio Interface and the requirements
specified in the National Frequency Allocation Table for Italy. Unless this
wireless LAN product is operating within the boundaries of the owner’s
property, its use requires a “general authorization.” Please check with
www.communicazioni.it/it/ for more details.
Questo prodotto é conforme alla specifiche di Interfaccia Radio Nazionali e rispetta il
Piano Nazionale di ripartizione delle frequenze in Italia. Se non viene installato
all’interno del proprio fondo, l’utilizzo di prodotti wireless LAN richiede una
“autorizzazione Generale.” Consultare www.communicazioni.it/it/ per maggiori
dettagli.
Norway, Switzerland and Liechtenstein
Although Norway, Switzerland and Liechtenstein are not EU member states,
the EU Directive 1999/5/EC has also been implemented in those countries.
Calculating the Maximum Output Power
The regulatory limits for maximum output power are specified in EIRP (radiated
power). The EIRP level of a device can be calculated by adding the gain of the
antenna used (specified in dBi) to the output power available at the connector
(specified in dBm).

Wireless Array
481
Antennas
The Xirrus Wireless Array employs integrated antennas that cannot be removed
and which are not user accessible. Nevertheless, as regulatory limits are not the
same throughout the EU, users may need to adjust the conducted power setting
for the radio to meet the EIRP limits applicable in their country or region.
Adjustments can be made from the product’s management interface — either Web
Management Interface (WMI) or Command Line Interface (CLI).
Operating Frequency
The operating frequency in a wireless LAN is determined by the access point. As
such, it is important that the access point is correctly configured to meet the local
regulations. See National Restrictions in this section for more information.
If you still have questions regarding the compliance of Xirrus products or you
cannot find the information you are looking for, please contact us at:
Xirrus, Inc.
2101 Corporate Center Drive
Thousand Oaks, CA 91320
USA
Tel: 1.805.262.1600
1.800.947.7871 Toll Free in the US
Fax: 1.866.462.3980
www.xirrus.com

Wireless Array
482
Compliance Information (Non-EU)
This section contains compliance information for the Xirrus Wireless Array family
of products. The compliance information contained in this section is relevant to
the listed countries (outside of the European Union and other countries that have
implemented the EU Directive 1999/5/EC).
Declaration of Conformity
Mexico XN16: Cofetel Cert #: RCPXIXN10-1052
XN12: Cofetel Cert #: RCPXIXN10-1052-A1
XN8: Cofetel Cert #: RCPXIXN10-1052-A2
XN4: Cofetel Cert #: RCPXIXN10-1052-A3
Thailand This telecommunication equipment conforms to
NTC technical requirement.

Wireless Array
483
Safety Warnings
Translated safety warnings appear on the following page.
!Safety Warnings
Read all user documentation before powering this device. All Xirrus
interconnected equipment should be contained indoors. This product is
not suitable for outdoor operation. Please verify the integrity of the
system ground prior to installing Xirrus equipment. Additionally,
verify that the ambient operating temperature does not exceed 40°C.
!Explosive Device Proximity Warning
Do not operate the XR Series Wireless Array near unshielded blasting
caps or in an explosive environment unless the device has been
modified to be especially qualified for such use.
!Lightning Activity Warning
Do not work on the XR Series Wireless Array or connect or disconnect
cables during periods of lightning activity.
!Circuit Breaker Warning
The XR Series Wireless Array relies on the building’s installation for
over current protection. Ensure that a fuse or circuit breaker no larger
than 120 VAC, 15A (U.S.) or 240 VAC, 10A (International) is used on all
current-carrying conductors.

Wireless Array
484
Translated Safety Warnings
Avertissements de Sécurité
!Sécurité
Lisez l'ensemble de la documentation utilisateur avant de mettre cet
appareil sous tension. Tous les équipements Xirrus interconnectés
doivent être installés en intérieur. Ce produit n'est pas conçu pour être
utilisé en extérieur. Veuillez vérifier l'intégrité de la terre du système
avant d'installer des équipements Xirrus. Vérifiez également que la
température de fonctionnement ambiante n'excède pas 40°C.
!Proximité d'appareils explosifs
N'utilisez pas l'unité XR Wireless Array à proximité d'amorces non
blindées ou dans un environnement explosif, à moins que l'appareil
n'ait été spécifiquement modifié pour un tel usage.
!Foudre
N'utilisez pas l'unité XR Wireless Array et ne branchez pas ou ne
débranchez pas de câbles en cas de foudre.
!Disjoncteur
L'unité XR Wireless Array dépend de l'installation du bâtiment pour ce
qui est de la protection contre les surintensités. Assurez-vous qu'un
fusible ou qu'un disjoncteur de 120 Vca, 15 A (États-Unis) ou de 240
Vca, 10 A (International) maximum est utilisé sur tous les conducteurs
de courant.

Wireless Array
485
Software License and Product Warranty Agreement
THIS SOFTWARE LICENSE AGREEMENT (THE “AGREEMENT”) IS A LEGAL
AGREEMENT BETWEEN YOU (“CUSTOMER”) AND LICENSOR (AS DEFINED
BELOW) AND GOVERNS THE USE OF THE SOFTWARE INSTALLED ON THE
PRODUCT (AS DEFINED BELOW). IF YOU ARE AN EMPLOYEE OR AGENT
OF CUSTOMER, YOU HEREBY REPRESENT AND WARRANT TO LICENSOR
THAT YOU HAVE THE POWER AND AUTHORITY TO ACCEPT AND TO
BIND CUSTOMER TO THE TERMS AND CONDITIONS OF THIS AGREEMENT
(INCLUDING ANY THIRD PARTY TERMS SET FORTH HEREIN). IF YOU DO
NOT AGREE TO ALL OF THE TERMS OF THIS AGREEMENT RETURN THE
PRODUCT AND ALL ACCOMPANYING MATERIALS (INCLUDING ALL
DOCUMENTATION) TO THE RELEVANT VENDOR FOR A FULL REFUND OF
THE PURCHASE PRICE THEREFORE.
CUSTOMER UNDERSTANDS AND AGREES THAT USE OF THE PRODUCT
AND SOFTWARE SHALL BE DEEMED AN AGREEMENT TO THE TERMS
AND CONDITIONS GOVERNING SUCH SOFTWARE AND THAT CUSTOMER
IS BOUND BY AND BECOMES A PARTY TO THIS AGREEMENT.
1.0 DEFINITIONS
1.1 “Documentation” means the user manuals and all other all documentation,
instructions or other similar materials accompanying the Software covering
the installation, application, and use thereof.
1.2 “Licensor” means XIRRUS and its suppliers.
1.3 “Product” means a multi-radio access point containing four or more distinct
radios capable of simultaneous operation on four or more non-overlapping
channels.
1.4 “Software” means, collectively, each of the application and embedded
software programs delivered to Customer in connection with this Agreement.
For purposes of this Agreement, the term Software shall be deemed to include
any and all Documentation and Updates provided with or for the Software.
1.5 “Updates” means any bug-fix, maintenance or version release to the Software
that may be provided to Customer from Licensor pursuant to this Agreement
or pursuant to any separate maintenance and support agreement entered into
by and between Licensor and Customer.
2.0 GRANT OF RIGHTS
2.1 Software. Subject to the terms and conditions of this Agreement, Licensor
hereby grants to Customer a perpetual, non-exclusive, non-sublicenseable,
non-transferable right and license to use the Software solely as installed on

Wireless Array
486
the Product in accordance with the accompanying Documentation and for no
other purpose.
2.2 Ownership. The license granted under Sections 2.1 above with respect to the
Software does not constitute a transfer or sale of Licensor's or its suppliers'
ownership interest in or to the Software, which is solely licensed to Customer.
The Software is protected by both national and international intellectual
property laws and treaties. Except for the express licenses granted to the
Software, Licensor and its suppliers retain all rights, title and interest in and
to the Software, including (i) any and all trade secrets, copyrights, patents and
other proprietary rights therein or thereto or (ii) any Marks (as defined in
Section 2.3 below) used in connection therewith. In no event shall Customer
remove, efface or otherwise obscure any Marks contained on or in the
Software. All rights not expressly granted herein are reserved by Licensor.
2.3 Copies. Customer shall not make any copies of the Software but shall be
permitted to make a reasonable number of copies of the related
Documentation. Whenever Customer copies or reproduces all or any part of
the Documentation, Customer shall reproduce all and not efface any titles,
trademark symbols, copyright symbols and legends, and other proprietary
markings or similar indicia of origin (“Marks”) on or in the Documentation.
2.4 Restrictions. Customer shall not itself, or through any parent, subsidiary,
affiliate, agent or other third party (i) sell, rent, lease, license or sublicense,
assign or otherwise transfer the Software, or any of Customer's rights and
obligations under this Agreement except as expressly permitted herein; (ii)
decompile, disassemble, or reverse engineer the Software, in whole or in part,
provided that in those jurisdictions in which a total prohibition on any
reverse engineering is prohibited as a matter of law and such prohibition is
not cured by the fact that this Agreement is subject to the laws of the State of
California, Licensor agrees to grant Customer, upon Customer's written
request to Licensor, a limited reverse engineering license to permit
interoperability of the Software with other software or code used by
Customer; (iii) allow access to the Software by any user other than by
Customer's employees and contractors who are bound in writing to
confidentiality and non-use restrictions at least as protective as those set forth
herein; (iv) except as expressly set forth herein, write or develop any
derivative software or any other software program based upon the Software;
(v) use any computer software or hardware which is designated to defeat any
copy protection or other use limiting device, including any device intended to
limit the number of users or devices accessing the Product; (vi) disclose
information about the performance or operation of the Product or Software to
any third party without the prior written consent of Licensor; or (vii) engage a
third party to perform benchmark or functionality testing of the Product or
Software.

Wireless Array
487
3.0 LIMITED WARRANTY AND LIMITATION OF LIABILITY
3.1 Limited Warranty & Exclusions. Licensor warrants that the Software will
perform in substantial accordance with the specifications therefore set forth in
the Documentation for a period of ninety [90] days after Customer's
acceptance of the terms of this Agreement with respect to the Software
(“Warranty Period”). If during the Warranty Period the Software or Product
does not perform as warranted, Licensor shall, at its option, correct the
relevant Product and/or Software giving rise to such breach of performance
or replace such Product and/or Software free of charge. THE FOREGOING
ARE CUSTOMER'S SOLE AND EXCLUSIVE REMEDIES FOR BREACH OF
THE FOREGOING WARRANTY. THE WARRANTY SET FORTH ABOVE IS
MADE TO AND FOR THE BENEFIT OF CUSTOMER ONLY. The warranty
will apply only if (i) the Software has been used at all times and in accordance
with the instructions for use set forth in the Documentation and this
Agreement; (ii) no modification, alteration or addition has been made to the
Software by persons other than Licensor or Licensor's authorized
representative; and (iii) the Software or Product on which the Software is
installed has not been subject to any unusual electrical charge.
3.2 DISCLAIMER. EXCEPT AS EXPRESSLY STATED IN THIS SECTION 3, ALL
ADDITIONAL CONDITIONS, REPRESENTATIONS, AND WARRANTIES,
WHETHER IMPLIED, STATUTORY OR OTHERWISE, INCLUDING,
WITHOUT LIMITATION, ANY IMPLIED WARRANTIES OR CONDITIONS
OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE,
SATISFACTORY QUALITY, ACCURACY, AGAINST INFRINGEMENT OR
ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE
PRACTICE, ARE HEREBY DISCLAIMED BY LICENSOR AND ITS
SUPPLIERS. THIS DISCLAIMER SHALL APPLY EVEN IF ANY EXPRESS
WARRANTY AND LIMITED REMEDY OFFERED BY LICENSOR FAILS OF
ITS ESSENTIAL PURPOSE. ALL WARRANTIES PROVIDED BY LICENSOR
ARE SUBJECT TO THE LIMITATIONS OF LIABILITY SET FORTH IN THIS
AGREEMENT.
3.3 HAZARDOUS APPLICATIONS. THE SOFTWARE IS NOT DESIGNED OR
INTENDED FOR USE IN HAZARDOUS ENVIRONMENTS REQUIRING
FAIL SAFE PERFORMANCE, SUCH AS IN THE OPERATION OF A
NUCLEAR FACILITY, AIRCRAFT NAVIGATION OR COMMUNICATIONS
SYSTEMS, AIR TRAFFIC CONTROLS OR OTHER DEVICES OR SYSTEMS
IN WHICH A MALFUNCTION OF THE SOFTWARE WOULD RESULT IN
FORSEEABLE RISK OF INJURY OR DEATH TO THE OPERATOR OF THE
DEVICE OR SYSTEM OR TO OTHERS (“HAZARDOUS APPLICATIONS”).
CUSTOMER ASSUMES ANY AND ALL RISKS, INJURIES, LOSSES, CLAIMS
AND ANY OTHER LIABILITIES ARISING OUT OF THE USE OF THE
SOFTWARE IN ANY HAZARDOUS APPLICATIONS.

Wireless Array
488
3.4 Limitation of Liability.
(a) TOTAL LIABILITY. NOTWITHSTANDING ANYTHING ELSE HEREIN,
ALL LIABILITY OF LICENSOR AND ITS SUPPLIERS UNDER THIS
AGREEMENT SHALL BE LIMITED TO THE AMOUNT PAID BY
CUSTOMER FOR THE RELEVANT SOFTWARE, OR PORTION
THEREOF, THAT GAVE RISE TO SUCH LIABILITY OR ONE
HUNDRED UNITED STATES DOLLARS (US$100), WHICHEVER IS
GREATER. THE LIABILITY OF LICENSOR AND ITS SUPPLIERS
UNDER THIS SECTION SHALL BE CUMULATIVE AND NOT PER
INCIDENT.
(b) DAMAGES. IN NO EVENT SHALL LICENSOR, ITS SUPPLIERS OR
THEIR RELEVANT SUBCONTRACTORS BE LIABLE FOR (A) ANY
INCIDENTAL, SPECIAL, PUNITIVE OR CONSEQUENTIAL
DAMAGES, LOST PROFITS OR LOST OR DAMAGED DATA, OR ANY
INDIRECT DAMAGES, WHETHER ARISING IN CONTRACT, TORT
(INCLUDING NEGLIGENCE AND STRICT LIABILITY) OR
OTHERWISE OR (B) ANY COSTS OR EXPENSES FOR THE
PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES IN EACH
CASE, EVEN IF LICENSOR OR ITS SUPPLIERS HAVE BEEN
INFORMED OF THE POSSIBILITY OF SUCH DAMAGES.
3.5 Exclusions. SOME JURISDICTIONS DO NOT PERMIT THE LIMITATIONS
OF LIABILITY AND LIMITED WARRANTIES SET FORTH UNDER THIS
AGREEMENT. IN THE EVENT YOU ARE LOCATED IN ANY SUCH
JURISDICTION, THE FOREGOING LIMITATIONS SHALL APPLY ONLY
TO THE MAXIMUM EXTENT PERMITTED IN SUCH JURISDICTIONS. IN
NO EVENT SHALL THE FOREGOING EXCLUSIONS AND LIMITATIONS
ON DAMAGES BE DEEMED TO APPLY TO ANY LIABILITY BASED ON
FRAUD, WILLFUL MISCONDUCT, GROSS NEGLIGENCE OR PERSONAL
INJURY OR DEATH.
4.0 CONFIDENTIAL INFORMATION
4.1 Generally. The Software (and its accompanying Documentation) constitutes
Licensor's and its suppliers' proprietary and confidential information and
contains valuable trade secrets of Licensor and its suppliers (“Confidential
Information”). Customer shall protect the secrecy of the Confidential
Information to the same extent it protects its other valuable, proprietary and
confidential information of a similar nature but in no event shall Customer
use less than reasonable care to maintain the secrecy of the Confidential
Information. Customer shall not use the Confidential Information except to
exercise its rights or perform its obligations as set forth under this Agreement.
Customer shall not disclose such Confidential Information to any third party
other than subject to non-use and non-disclosure obligations at least as

Wireless Array
489
protective of a party's right in such Confidential Information as those set forth
herein.
4.2 Return of Materials. Customer agrees to (i) destroy all Confidential
Information (including deleting any and all copies contained on any of
Customer's Designated Hardware or the Product) within fifteen (15) days of
the date of termination of this Agreement or (ii) if requested by Licensor,
return, any Confidential Information to Licensor within thirty (30) days of
Licensor's written request.
5.0 TERM AND TERMINATION
5.1 Term. Subject to Section 5.2 below, this Agreement will take effect on the
Effective Date and will remain in force until terminated in accordance with
this Agreement.
5.2 Termination Events. This Agreement may be terminated immediately upon
written notice by either party under any of the following conditions:
(a) If the other party has failed to cure a breach of any material term or
condition under the Agreement within thirty (30) days after receipt of
notice from the other party; or
(b) Either party ceases to carry on business as a going concern, either party
becomes the object of the institution of voluntary or involuntary
proceedings in bankruptcy or liquidation, which proceeding is not
dismissed within ninety (90) days, or a receiver is appointed with respect
to a substantial part of its assets.
5.3 Effect of Termination.
(a) Upon termination of this Agreement, in whole or in part, Customer shall
pay Licensor for all amounts owed up to the effective date of termination.
Termination of this Agreement shall not constitute a waiver for any
amounts due.
(b) The following Sections shall survive the termination of this Agreement
for any reason: Sections 1, 2.2, 2.4, 3, 4, 5.3, and 6.
(c) No later than thirty (30) days after the date of termination of this
Agreement by Licensor, Customer shall upon Licensor's instructions
either return the Software and all copies thereof; all Documentation
relating thereto in its possession that is in tangible form or destroy the
same (including any copies thereof contained on Customer's Designated
Hardware). Customer shall furnish Licensor with a certificate signed by
an executive officer of Customer verifying that the same has been done.

Wireless Array
490
6. MISCELLANEOUS
If Customer is a corporation, partnership or similar entity, then the license to the
Software and Documentation that is granted under this Agreement is expressly
conditioned upon and Customer represents and warrants to Licensor that the
person accepting the terms of this Agreement is authorized to bind such entity to
the terms and conditions herein. If any provision of this Agreement is held to be
invalid or unenforceable, it will be enforced to the extent permissible and the
remainder of this Agreement will remain in full force and effect. During the
course of use of the Software, Licensor may collect information on your use
thereof; you hereby authorize Licensor to use such information to improve its
products and services, and to disclose the same to third parties provided it does
not contain any personally identifiable information. The express waiver by either
party of any provision, condition or requirement of this Agreement does not
constitute a waiver of any future obligation to comply with such provision,
condition or requirement. Customer and Licensor are independent parties.
Customer may not export or re-export the Software or Documentation (or other
materials) without appropriate United States, European Union and foreign
government licenses or in violation of the United State's Export Administration
Act or foreign equivalents and Customer shall comply with all national and
international laws governing the Software. This Agreement will be governed by
and construed under the laws of the State of California and the United States as
applied to agreements entered into and to be performed entirely within
California, without regard to conflicts of laws provisions thereof and the parties
expressly exclude the application of the United Nations Convention on Contracts
for the International Sales of Goods and the Uniform Computer Information
Transactions Act (as promulgated by any State) to this Agreement. Suits or
enforcement actions must be brought within, and each party irrevocably commits
to the exclusive jurisdiction of, the state and federal courts located in Ventura
County, California. Customer may not assign this Agreement by operation of law
or otherwise, without the prior written consent of Licensor and any attempted
assignment in violation of the foregoing shall be null and void. This Agreement
cancels and supersedes all prior agreements between the parties. This Agreement
may not be varied except through a document agreed to and signed by both
parties. Any printed terms and conditions contained in any Customer purchase
order or in any Licensor acknowledgment, invoice or other documentation
relating to the Software shall be deemed deleted and of no force or effect and any
additional typed and/or written terms and conditions contained shall be for
administrative purposes only, i.e. to identify the types and quantities of Software
to be supplied, line item prices and total price, delivery schedule, and other
similar ordering data, all in accordance with the provisions of this Agreement.

Wireless Array
491
Hardware Warranty Agreement
PLEASE READ THIS AGREEMENT CAREFULLY BEFORE USING THIS
PRODUCT
BY USING THIS PRODUCT, YOU ACKNOWLEDGE THAT YOU HAVE READ
AND UNDERSTOOD ALL THE TERMS AND CONDITIONS OF THIS
AGREEMENT AND THAT YOU ARE CONSENTING TO BE BOUND BY THIS
AGREEMENT. IF YOU DO NOT AGREE TO ALL OF THE TERMS OF THIS
AGREEMENT, RETURN THE UNUSED PRODUCT TO THE PLACE OF
PURCHASE FOR A FULL REFUND.
LIMITED WARRANTY. Xirrus warrants that for a period of five years from the
date of purchase by the original purchaser (“Customer”): (i) the Xirrus Equipment
(“Equipment”) will be free of defects in materials and workmanship under
normal use; and (ii) the Equipment substantially conforms to its published
specifications. Except for the foregoing, the Equipment is provided AS IS. This
limited warranty extends only to Customer as the original purchaser. Customer's
exclusive remedy and the entire liability of Xirrus and its suppliers under this
limited warranty will be, at Xirrus' option, repair, replacement, or refund of the
Equipment if reported (or, upon request, returned) to the party supplying the
Equipment to Customer. In no event does Xirrus warrant that the Equipment is
error free or that Customer will be able to operate the Equipment without
problems or interruptions.
This warranty does not apply if the Equipment (a) has been altered, except by
Xirrus, (b) has not been installed, operated, repaired, or maintained in accordance
with instructions supplied by Xirrus, (c) has been subjected to abnormal physical
or electrical stress, misuse, negligence, or accident, or (d) is used in ultra-
hazardous activities.
DISCLAIMER. EXCEPT AS SPECIFIED IN THIS WARRANTY, ALL EXPRESS OR
IMPLIED CONDITIONS, REPRESENTATIONS, AND WARRANTIES
INCLUDING, WITHOUT LIMITATION, ANY IMPLIED WARRANTY OF
MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE,
NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE,
OR TRADE PRACTICE, ARE HEREBY EXCLUDED TO THE EXTENT
ALLOWED BY APPLICABLE LAW.
IN NO EVENT WILL XIRRUS OR ITS SUPPLIERS BE LIABLE FOR ANY LOST
REVENUE, PROFIT, OR DATA, OR FOR SPECIAL, INDIRECT,
CONSEQUENTIAL, INCIDENTAL, OR PUNITIVE DAMAGES HOWEVER
CAUSED AND REGARDLESS OF THE THEORY OF LIABILITY ARISING OUT
OF THE USE OF OR INABILITY TO USE THE EQUIPMENT EVEN IF XIRRUS
OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH
DAMAGES. In no event shall Xirrus' or its suppliers' liability to Customer,

Wireless Array
492
whether in contract, tort (including negligence), or otherwise, exceed the price
paid by Customer.
The foregoing limitations shall apply even if the above-stated warranty fails of its
essential purpose. SOME STATES DO NOT ALLOW LIMITATION OR
EXCLUSION OF LIABILITY FOR CONSEQUENTIAL OR INCIDENTAL
DAMAGES.
The above warranty DOES NOT apply to any evaluation Equipment made
available for testing or demonstration purposes. All such Equipment is provided
AS IS without any warranty whatsoever.
Customer agrees the Equipment and related documentation shall not be used in
life support systems, human implantation, nuclear facilities or systems or any
other application where failure could lead to a loss of life or catastrophic property
damage, or cause or permit any third party to do any of the foregoing.
All information or feedback provided by Customer to Xirrus with respect to the
Product shall be Xirrus' property and deemed confidential information of Xirrus.
Equipment including technical data, is subject to U.S. export control laws,
including the U.S. Export Administration Act and its associated regulations, and
may be subject to export or import regulations in other countries. Customer
agrees to comply strictly with all such regulations and acknowledges that it has
the responsibility to obtain licenses to export, re-export, or import Equipment.
This Agreement shall be governed by and construed in accordance with the laws
of the State of California, United States of America, as if performed wholly within
the state and without giving effect to the principles of conflict of law. If any
portion hereof is found to be void or unenforceable, the remaining provisions of
this Warranty shall remain in full force and effect. This Warranty constitutes the
entire agreement between the parties with respect to the use of the Equipment.
Manufacturer is Xirrus, Inc. 2101 Corporate Center Drive Thousand Oaks, CA
91320

Wireless Array
Glossary of Terms 493
Glossary of Terms
802.11a
A supplement to the IEEE 802.11 WLAN specification that describes radio
transmissions at a frequency of 5 GHz and data rates of up to 54 Mbps.
802.11b
A supplement to the IEEE 802.11 WLAN specification that describes radio
transmissions at a frequency of 2.4 GHz and data rates of up to 11 Mbps.
802.11d
A supplement to the Media Access Control (MAC) layer in 802.11 to promote
worldwide use of 802.11 WLANs. It allows Access Points to communicate
information on the permissible radio channels with acceptable power levels for
user devices. Because the 802.11 standards cannot legally operate in some
countries, 802.11d adds features and restrictions to allow WLANs to operate
within the rules of these countries.
802.11g
A supplement to the IEEE 802.11 WLAN specification that describes radio
transmissions at a frequency of 2.4 GHz and data rates of up to 54 Mbps.
802.11n
A supplement to the IEEE 802.11 WLAN specification that describes
enhancements to 802.11a/b/g to greatly enhance reach, speed, and capacity.
802.1Q
An IEEE standard for MAC layer frame tagging (also known as encapsulation).
Frame tagging uniquely assigns a user-defined ID to each frame. It also enables a
switch to communicate VLAN membership information across multiple (and
multi-vendor) devices by frame tagging.
AES
(Advanced Encryption Standard) A data encryption scheme that uses three
different key sizes (128-bit, 192-bit, and 256-bit). AES was adopted by the U.S.
government in 2002 as the encryption standard for protecting sensitive but
unclassified electronic data.

Wireless Array
494 Glossary of Terms
authentication
The process that a station, device, or user employs to announce its identify to
the network which validates it. IEEE 802.11 specifies two forms of authentication,
open system and shared key.
bandwidth
Specifies the amount of the frequency spectrum that is usable for data transfer. In
other words, it identifies the maximum data rate a signal can attain on
the medium without encountering significant attenuation (loss of power).
beacon interval
When a device in a wireless network sends a beacon, it includes with it a beacon
interval, which specifies the period of time before it will send the beacon again.
The interval tells receiving devices on the network how long they can wait in low
power mode before waking up to handle the beacon. Network administrators can
adjust the beacon interval — usually measured in milliseconds (ms) or its
equivalent, kilo-microseconds (Kmsec).
bit rate
The transmission rate of binary symbols ('0' and '1'), equal to the total number of
bits transmitted in one second.
BSS
(Basic Service Set) When a WLAN is operating in infrastructure mode, each access
point and its connected devices are called the Basic Service Set.
BSSID
The unique identifier for an access point in a BSS network. See also, SSID.
CDP
(Cisco Discovery Protocol) CDP is a layer 2 network protocol which runs on most
Cisco equipment and some other network equipment. It is used to share
information with other directly connected network devices. Information such as
the model, network capabilities, and IP address is shared. Wireless Arrays can
both advertise their presence by sending CDP announcements, and gather and
display information sent by neighbors.

Wireless Array
Glossary of Terms 495
cell
The basic geographical unit of a cellular communications system. Service
coverage of a given area is based on an interlocking network of cells, each with a
radio base station (transmitter/receiver) at its center. The size of each cell is
determined by the terrain and forecasted number of users.
channel
A specific portion of the radio spectrum — the channels allotted to one of
the wireless networking protocols. For example, 802.11b and 802.11g use 14
channels in the 2.4 GHz band, only 3 of which don't overlap (1, 6, and 11).
CoS
(Class of Service) A category based on the type of user, type of application,
or some other criteria that QoS systems can use to provide differentiated classes of
service.
default gateway
The gateway in a network that a computer will use to access another network if
a gateway is not specified for use. In a network using subnets, a default gateway
is the router that forwards traffic to a destination outside of the subnet of
the transmitting device.
DHCP
(Dynamic Host Configuration Protocol) A method for dynamically assigning IP
addresses to devices on a network. DHCP issues IP addresses automatically
within a specified range to client devices when they are first powered up.
DHCP lease
The DHCP lease is the amount of time that the DHCP server grants to the DHCP
client for permission to use a particular IP address. A typical DHCP server allows
its administrator to set the lease time.
DNS
(Domain Name System) A system that maps meaningful domain names with
complex numeric IP addresses. DNS is actually a separate network — if one DNS
server cannot translate a domain name, it will ask a second or third until a server
is found with the correct IP address.

Wireless Array
496 Glossary of Terms
domain
The main name/Internet address of a user's Internet site as registered with
the InterNIC organization, which handles domain registration on the Internet. For
example, the “domain” address for Xirrus is: http://www.xirrus.com, broken
down as follows:
http:// represents the Hyper Text Teleprocessing Protocol used by all Web
pages.
www is a reference to the World Wide Web.
xirrus refers to the company.
com specifies that the domain belongs to a commercial enterprise.
DTIM
(Delivery Traffic Indication Message) A DTIM is a signal sent as part of a beacon
by an access point to a client device in sleep mode, alerting the device to a packet
awaiting delivery.
EAP
(Extensible Authentication Protocol) When you log on to the Internet, you're most
likely establishing a PPP connection via a remote access server. The password,
key, or other device you use to prove that you are authorized to do so is controlled
via PPP’s Link Control Protocol (LCP). However, LCP is somewhat inflexible
because it has to specify an authentication device early in the process. EAP allows
the system to gather more information from the user before deciding which
authenticator to use. It is called extensible because it allows more authenticator
types than LCP (for example, passwords and public keys).
EDCF
(Enhanced Distributed Coordinator Function) A QoS extension which uses
the same contention-based access mechanism as current devices but adds “offset
contention windows” that separate high priority packets from low priority
packets (by assigning a larger random backoff window to lower priorities than to
higher priorities). The result is “statistical priority,” where high-priority packets
usually are transmitted before low-priority packets.
encapsulation
A way of wrapping protocols such as TCP/IP, AppleTalk, and NetBEUI in
Ethernet frames so they can traverse an Ethernet network and be unwrapped
when they reach the destination computer.

Wireless Array
Glossary of Terms 497
encryption
Any procedure used in cryptography to translate data into a form that can be
decrypted and read only by its intended receiver.
Fast Ethernet
A version of standard Ethernet that runs at 100 Mbps rather than 10 Mbps.
FCC
(Federal Communications Commission) US wireless regulatory authority.
The FCC was established by the Communications Act of 1934 and is charged with
regulating Interstate and International communications by radio, television, wire,
satellite and cable.
FIPS
The Federal Information Processing Standard (FIPS) Publication 140-2 establishes
a computer security standard used to accredit cryptographic modules.
The standard is a joint effort by the U.S. and Canadian governments.
frame
A packet encapsulated to travel on a physical medium, like Ethernet or Wi-Fi. If a
packet is like a shipping container, a frame is the boat on which the shipping
container is loaded.
Gigabit 1 through 4
The Gigabit Ethernet interfaces on XR Series Arrays. XR-4000 Series Arrays have
two gigabit interfaces, while XR-6000 Series and higher models have four gigabit
interfaces. See also, Gigabit Ethernet.
Gigabit Ethernet
A version of Ethernet with data transfer rates of 1 Gigabit (1,000 Mbps).
Group
A user group, created to define a set of attributes (such as VLAN, traffic limits,
and Web Page Redirect) and privileges (such as fast roaming) that apply to all
users that are members of the group. This allows a uniform configuration to be
easily applied to multiple user accounts. The attributes that can be configured for
user groups are almost identical to those that can be configured for SSIDs.

Wireless Array
498 Glossary of Terms
host name
The unique name that identifies a computer on a network. On the Internet,
the host name is in the form comp.xyz.net. If there is only one Internet site
the host name is the same as the domain name. One computer can have more than
one host name if it hosts more than one Internet site (for example, home.xyz.net
and comp.xyz.net). In this case, comp and home are the host names and xyz.net is
the domain name.
IPsec
A Layer 3 authentication and encryption protocol. Used to secure VPNs.
MAC address
(Media Access Control Address) A 6-byte hexadecimal address assigned by a
manufacturer to a device.
Mbps
(Megabits per second) A standard measure for data transmission speeds (for
example, the rate at which information travels over the Internet). 1 Mbps denotes
one million bits per second.
MTU
(Maximum Transmission Unit) The largest physical packet size — measured in
bytes — that a network can transmit. Any messages larger than the MTU are
divided into smaller packets before being sent. Every network has a different
MTU, which is set by the network administrator. Ideally, you want the MTU to be
the same as the smallest MTU of all the networks between your machine and
a message's final destination. Otherwise, if your messages are larger than one of
the intervening MTUs, they will get broken up (fragmented), which slows down
transmission speeds.
NTP
(Network Time Protocol) An Internet standard protocol (built on top of TCP/IP)
that ensures the accurate synchronization (to the millisecond) of computer clock
times in a network of computers. Running as a continuous background client
program on a computer, NTP sends periodic time requests to servers, obtaining
server time stamps and using them to adjust the client's clock.

Wireless Array
Glossary of Terms 499
packet
Data sent over a network is broken down into many small pieces — packets — by
the Transmission Control Protocol layer of TCP/IP. Each packet contains the
address of its destination as well the data. Packets may be sent on any number of
routes to their destination, where they are reassembled into the original data. This
system is optimal for connectionless networks, such as the Internet, where there
are no fixed connections between two locations.
PLCP
(Physical Layer Convergence Protocol) Defined by IEEE 802.6, a protocol
specified within the Transmission Convergence layer that defines exactly how
cells are formatted within a data stream for a particular type of transmission
facility.
PoGE
This refers to the optional Xirrus-supplied Power over Gigabit Ethernet modules
that provide DC power to Arrays. Power is supplied over the same Cat 5e or Cat 6
cable that supplies the data connection to your gigabit Ethernet switch, thus
eliminating the need to run a power cable.
preamble
Preamble (sometimes called a header) is a section of data at the head of a packet
that contains information that the access point and client devices need when
sending and receiving packets. PLCP Has two structures, a long and a short
preamble. All compliant 802.11b systems have to support the long preamble.
The short preamble option is provided in the standard to improve the efficiency
of a network's throughput when transmitting special data, such as voice, VoIP
(Voice-over IP) and streaming video.
private key
In cryptography, one of a pair of keys (one public and one private) that are created
with the same algorithm for encrypting and decrypting messages and digital
signatures. The private key is provided only to the requestor and never shared.
The requestor uses the private key to decrypt text that has been encrypted with
the public key by someone else.
PSK
(Pre-Shared Key) A TKIP passphrase used to protect your network traffic in WPA.

Wireless Array
500 Glossary of Terms
public key
In cryptography, one of a pair of keys (one public and one private) that are created
with the same algorithm for encrypting and decrypting messages and digital
signatures. The public key is made publicly available for encryption and
decryption.
QoS
(Quality of Service) QoS can be used to describe any number of ways in which
a network provider prioritizes or guarantees a service's performance.
RADIUS
(Remote Authentication Dial-In User Service) A client-server security protocol,
developed to authenticate, authorize, and account for dial-up users. The RADIUS
server stores user profiles, which include passwords and authorization attributes.
RSSI
(Received Signal Strength Indicator) A measure of the energy observed by an
antenna when receiving a signal.
SDMA
(Spatial Division Multiple Access) A wireless communications mode that
optimizes the use of the radio spectrum and minimizes cost by taking advantage
of the directional properties of antennas. The antennas are highly directional,
allowing duplicate frequencies to be used for multiple zones.
SNMP
(Simple Network Management Protocol) A standard protocol that regulates
network management over the Internet.
SNTP
(Simple Network Time Protocol) A simplified version of NTP. SNTP can be used
when the ultimate performance of the full NTP implementation described in RFC
1305 is not needed or justified.

Wireless Array
Glossary of Terms 501
SSH
(Secure SHell) Developed by SSH Communications Security, Secure Shell is a
program to log into another computer over a network, to execute commands in a
remote machine, and to move files from one machine to another. The Array only
allows SSH-2 connections. SSH-2 provides strong authentication and secure
communications over insecure channels. SSH-2 protects a network from attacks,
such as IP spoofing, IP source routing, and DNS spoofing. Attackers who has
managed to take over a network can only force SSH to disconnect — they cannot
“play back” the traffic or hijack the connection when encryption is enabled. When
using SSH-2's slogin (instead of rlogin) the entire login session, including
transmission of password, is encrypted making it almost impossible for an
outsider to collect passwords. Be aware that your SSH utility must be set up to use
SSH-2.
SSID
(Service Set IDentifier) Every wireless network or network subset (such as a BSS)
has a unique identifier called an SSID. Every device connected to that part of the
network uses the same SSID to identify itself as part of the family — when it wants
to gain access to the network or verify the origin of a data packet it is sending over
the network. In short, it is the unique name shared among all devices in a WLAN.
subnet mask
A mask used to determine what subnet an IP address belongs to. An IP address
has two components: (1) the network address and (2) the host address. For
example, consider the IP address 150.215.017.009. Assuming this is part of a Class
B network, the first two numbers (150.215) represent the Class B network address,
and the second two numbers (017.009) identify a particular host on this network.
TKIP
(Temporal Key Integrity Protocol) Provides improved data encryption by
scrambling the keys using a hashing algorithm and, by adding an integrity-
checking feature, ensures that the encryption keys haven’t been tampered with.
transmit power
The amount of power used by a radio transceiver to send the signal out. Transmit
power is generally measured in milliwatts, which you can convert to dBm.
User group
See Group.

Wireless Array
502 Glossary of Terms
VLAN
(Virtual LAN) A group of devices that communicate as a single network, even
though they are physically located on different LAN segments. Because VLANs
are based on logical rather than physical connections, they are extremely flexible.
A device that is moved to another location can remain on the same VLAN
without any hardware reconfiguration.
VLAN tagging
(Virtual LAN tagging) Static port-based VLANs were originally the only way to
segment a network without using routing, but these port-based VLANs could
only be implemented on a single switch (or switches) cabled together. Routing
was required to transfer traffic between unconnected switches. As an alternative
to routing, some vendors created proprietary schemes for sharing VLAN
information across switches. These methods would only operate on that vendor's
equipment and were not an acceptable way to implement VLANs. With the
adoption of the 802.11n standard, traffic can be confined to VLANs that exist on
multiple switches from different vendors. This interoperability and traffic
containment across different switches is the result of a switch's ability to use and
recognize 802.1Q tag headers — called VLAN tagging. Switches that implement
802.1Q tagging add this tag header to the frame directly after the destination and
source MAC addresses. The tag header indicates:
1. That the packet has a tag.
2. Whether the packet should have priority over other packets.
3. Which VLAN it belongs to, so that the switch can forward or filter it
correctly.
WDS (Wireless Distribution System)
WDS creates wireless backhauls between arrays. These links between arrays may
be used rather than having to install data cabling to each array.
WEP
(Wired Equivalent Privacy) An optional IEEE 802.11 function that offers frame
transmission privacy similar to a wired network. The Wired Equivalent Privacy
generates secret shared encryption keys that both source and destination stations
can use to alter frame bits to avoid disclosure to eavesdroppers.

Wireless Array
Glossary of Terms 503
Wi-Fi Alliance
A nonprofit international association formed in 1999 to certify interoperability of
wireless Local Area Network products based on IEEE 802.11 specification. The
goal of the Wi-Fi Alliance's members is to enhance the user experience through
product interoperability.
Wireless Array
A high capacity wireless networking device consisting of multiple radios
arranged in a circular array.
WPA
(Wi-Fi Protected Access) A Wi-Fi Alliance standard that contains a subset of the
IEEE 802.11i standard, using TKIP as an encryption method and 802.1x for
authentication.
WPA2
(Wi-Fi Protected Access 2) WPA2 is the follow-on security method to WPA for
wireless networks and provides stronger data protection and network access
control. It offers Enterprise and consumer Wi-Fi users with a high level of
assurance that only authorized users can access their wireless networks. Like
WPA, WPA2 is designed to secure all versions of 802.11 devices, including
802.11a, 802.11b, 802.11g, and 802.11n, multi-band and multi-mode.
Xirrus Management System (XMS)
A Xirrus product used for managing large Wireless Array deployments from a
centralized Web-based interface.
XP1 and XP8 — Power over Gigabit Ethernet modules
See PoGE.
XPS — Xirrus Power System
A family of optional Xirrus-supplied products that provides power over Gigabit
Ethernet. See PoGE.

Wireless Array
504 Glossary of Terms

Wireless Array
Index 505
Index
Numerics
11n
see IEEE 802.11n 35
802.11a 3, 5, 274, 293
802.11a/b/g 26
802.11a/b/g/n 15
802.11a/n 15, 63, 249
802.11b 3, 5, 298
802.11b/g 274, 298
802.11b/g/n 15, 63, 249
802.11e 16
802.11g 3, 5, 298
802.11i 5, 71, 161
802.11n 5
see IEEE 802.11n 35
WMI page 304
802.11p 16
802.11q 16
802.1x 5, 46, 56, 71, 161, 454
A
abg(n)
nomenclature 2
abg(n)2
intrusion detection 331
self-monitoring
radio assurance (loopback
mode) 314, 315
Access Control List 208
Access Control Lists 454
access control lists (ACLs) 227, 262
ACLs 46, 208, 454
active IAPs
per SSID 261
Address Resolution Protocol
window 109
Address Resolution Protocol (ARP)
290
Admin 454
Admin ID 214
admin ID
authentication via RADIUS 218
Admin Management 214
admin privileges
setting in admin RADIUS account
218
admin RADIUS account
if using Console port 218
admin RADIUS authentication 218
administration 71, 161, 208
Administrator Account 448
Advanced Encryption Standard 46,
454
Advanced RF Analysis Manager
see RAM 18
Advanced RF Performance Manager
see RPM 16
Advanced RF Security Manager
see RSM 17
AeroScout
see WiFi tag 188
AES 5, 16, 46, 56, 71, 161, 446, 454
allow traffic
see filters 344
Analysis Manager
see RAM 18
appearance
WMI options 373
WMI, changing 373
approved
setting rogues 120
APs 56, 119, 240, 454
rogues, blocking 331
APs, rogue
see rogue APs 313, 331
ARP filtering 290

Wireless Array
506 Index
ARP table window 109
Array 28, 62, 63, 84, 161, 171
connecting 62
dismounting 62
management 359
mounting 62
powering up 63
securing 62
Web Management Interface 84
ArrayOS
upgrade 362
Arrays
managing in clusters 352
associated users 28
assurance
network server connectivity 112,
225
assurance (radio loopback testing) 313
assurance, station
see station assurance 320
attack (DoS)
see DoS attack 332
attack (impersonation)
see impersonation attack 333
authentication 16
of admin via RADIUS 218
authority
certificate 212, 225
auto block
rogue APs, settings 331
auto negotiate 171
auto-blocking
rogue APs 331
auto-configuration 71, 280, 293, 298
channel and cell size 313
automatic refresh
setting interval 374
automatic update from remote server
configuration files, boot image 363
B
backhaul
see WDS 53
backup unit
see standby mode 314
band association 249
beacon interval 280
Beacon World Mode 280
beam distribution 15
benefits 14
block
rogue APs, settings 328
block (rogue APs)
see auto block 331
blocking
rogue APs 331
blocking rogue APs 313
boot 362
broadcast 291
fast roaming 291
browser
certificate error 212, 225
BSS 452
BSSID 119, 452
buttons 91
C
capacity
of 802.11n 42
cascading style sheet
sample for web page redirect 369
cdp 392
CDP (Cisco Discovery Protocol)
settings 183
cdp CLI command 392
CDP neighbors 111
cell
sharp cell 313
cell size 28, 274
auto-configuration 313

Wireless Array
Index 507
cell size configuration 313
certificate
about 212, 225
authority 212, 225
error 212, 225
install Xirrus authority 225
X.509 212, 225
channel
auto-configuration 313
configuration 313
list selection 313
channels 28, 119, 274, 280, 293, 298
non-overlapping 15
CHAP (Challenge-Handshake Au-
thentication Protocol)
Admin RADIUS settings 219
web page redirect 258
CHAP Challenge Handshake Authen-
tication Protocol)
RADIUS ping 370
character restrictions 93
Chrome 24
Cisco Discovery Protocol
see cdp 392
Cisco Discovery Protocol (CDP) 183
CLI 5, 56, 59, 66, 377
executing from WMI 371
using to upgrade software image
464
CLI commands
see commands 392
client
web page redirect 368
cluster
CLI command 394
clusters 352
defining 353
management 354
operating in cluster mode 355
command
wifi-tag 425
Command Line Interface 5, 52, 59, 63,
66, 377, 454
configuration commands 390
getting help 379
getting started 379
inputting commands 379
sample configuration tasks 426
SSH 377
top level commands 381
command, utilities
ping, traceroute, RADIUS ping 369
commands
acl 390
admin 391
cdp 392
clear 393
cluster 394
configure 382
contact-info 395
date-time 396
dhcp-server 397
dns 398
file 399
filter 402
group 394, 406
hostname 406
interface 407
load 408
location 408
management 409
more 410
netflow 411
no 412
quit 414
radius-server 414
reboot 415, 423
reset 415
restore 416
run-tests 417

Wireless Array
508 Index
security 419
show 385
snmp 420
ssid 421
statistics 388
syslog 422
vlan 424
Community String 445
configuration 159, 454
express setup 161
reset to factory defaults 366
configuration changes
applying 92
configuration files
automatic update from remote
server 363
download 364
update from local file 364
update from remote file 364
connection
tracking window 110
connectivity
servers, see network assurance
112, 225
Console port
login via 218
Contact Information 469
contact information 469
coverage 28, 59
extended 15
coverage patterns 5
critical messages 89
CTS/RTS 293, 298
D
data rate 293, 298
data rates
increased by 802.11n 41
date/time restrictions
and interactions 268
default gateway 71, 171
default settings 443
Default Value 446
DHCP 445
defaults
reset configuration to factory de-
faults 366
Delivery Traffic Indication Message
280
denial of service
see DoS attack 332
deny traffic
see filters 344
deployment 26, 52, 56, 59, 454
ease of 15
detection
intrusion 331
see DoS attack 332
see impersonation attack 333
see impersonation detection 332
see intrusion detection 332, 333
DHCP 28, 66, 71, 161, 171, 444
default settings 445
leases window 110
DHCP Server 184
diagnostics
log, create file 366
display
WMI options 373
DNS 71, 161, 181
DNS domain 181
DNS server 181
Domain Name System 181
DoS attack detection
settings 332
DTIM 280
DTIM period 280
duplex 171
dynamic VLAN
overridden by group 267

Wireless Array
Index 509
E
EAP 446, 454
EAP-MDS 16
EAP-PEAP 454
EAP-TLS 16, 46, 454
EAP-TTLS 16, 46, 454
EDCF 280
Encryption 446, 454
encryption 16
encryption method
recommended (WPA2 with AES)
210
setting 211
support of multiple methods 210
encryption method (encryption mode)
Open, WEP, WPA, WPA2, WPA-
Both 209
encryption standard
AES, TKIP, both 210
setting 211
Enterprise 1, 3, 454
WLAN 3
Enterprise Class Management 5
Enterprise Class Security 5
ESS 452
ESSID 452
Ethernet 59, 62, 63, 66, 71, 161
event log
IDS (intrusion detection) 157
see system log 150, 156
event messages 89
Express Setup 62, 71, 161
express setup 71, 161
Extended Service Set 452
Extensible Authentication Protocol 454
external RADIUS server 802.1x 25
F
factory default settings 443
factory defaults 444, 445, 446, 448
DHCP 445
reset configuration to 364
factory.conf 364
fail-over
standby mode 314
failover 42, 56
FAQs 452
Fast Ethernet 59, 66, 161, 171, 443
fast roaming 15, 106, 291
about 273
and VLANs 273
features 14, 52, 171, 187, 190, 280, 454
and license key 363
feedback 91
filter list 345
filter name 347
filtering
IPv6 291
filters 344, 345, 347
stateful filtering, disabling 346
statistics 147
Firefox 24
firewall 344
and port usage 48
stateful filtering, disabling 346
fragmentation threshold 293, 298
frequently asked questions 452
FTP 454
FTP server 25
G
General Hints 451
getting started
express setup 161
Gigabit 59, 66, 71, 161, 171, 443
global settings 280, 293, 298
glossary of terms 493
Google Chrome 24
Group
management 266

Wireless Array
510 Index
group 264
CLI command 394, 406
VLAN overrides dynamic VLAN
267
group limits and interactions 268
Group Rekey 446
guard interval
short, for IEEE 802.11n 40
GUI
see WMI 373
H
help
button, bottom of page 91
button, left frame 88
Help button 84
help button 91
host name 71, 84, 161, 181
hs.css 369
HTTPS
certificate, see certificate 225
HTTPS port
web page redirect 255, 259, 260
HyperTerminal 24, 59
I
IAP 28, 63, 71, 161, 274, 293, 298, 334
active SSIDs 261
fast roaming 273
Intrusion Detection (IDS/IPS) 328
naming 2
settings 274
IAP LED 63, 334
IAP LED settings 334
IAPs
auto block rogues 331
intrusion detection 331
IDS
see Intrusion Detection 328
IDS event log
viewing window 157
IEEE 3, 71, 161
IEEE 802.11n
capacity, increased 42
deployment considerations 35
guard interval, short 40
improved MAC throughput 40
increased data rates 41
MIMO 36
multiple data streams 38
spatial multiplexing 38
WMI page 304
IEEE 802.1Q 457
image
upgrade software image 362
impersonation attack detection
settings 333
implementing Voice over Wi-Fi 26,
199, 244
installation 23, 57, 62, 441
installing the MCAP-3616 59
mounting the unit 62
requirements 23
workflow 57
installation workflow 57
interfaces 161
Web 83
internal login page
web page redirect 256
web page redirect, customize 258
internal splash page
web page redirect 257
web page redirect, customize 258
Internet Explorer 24
interval
automatic WMI refresh 374
intrusion detection 119, 331
and auto block settings 331
configuration 313
setting as approved or known 120

Wireless Array
Index 511
intrusion detection (IDS)
viewing event log 157
Intrusion Detection (IDS/IPS) 328
IP Address 28, 71, 84, 92, 119, 161, 171,
181, 190, 194, 359, 444
IP Subnet Mask 71
IPS
see Intrusion Detection 328
IPv6
filtering 291
K
key
upgrade 363
key features 14
Keyboard Shortcuts 449
keyboard shortcuts 449
known
setting rogues 120
L
lastboot.conf 364
Layer 3
fast roaming 273
lease 444
Lease Time 444
leases, DHCP
viewing 110
LEDs 63
sequence 63
settings 334
license Key
upgrading 363
limits
group 268
interactions 268
station 268
traffic 268
list, access control
see access control list 227, 262
list, MAC access
see access control list 227
list, SSID access
see access control list 262
location information 71, 84, 161
log
diagnostics, create file 366
log messages
counters 89
log, IDS(intrusion detection)
viewing window 157
log, system (event)
viewing window 150, 156
logging in 66, 92
Login 92
login
via Console port 218
login page
web page redirect 256, 368
web page redirect, customize 258
logout 376
long retry limit 280
loopback
see radio assurance 438
loopback testing
radio assurance mode 313
M
MAC 46, 66, 452, 454
MAC Access Control Lists 46
MAC Access List 227
MAC address 227, 452, 454
MAC throughput
improved by IEEE 802.11n 40
Management 448, 454
management 95, 159, 359
Array clusters 352
of Arrays 359
Web Management Interface (WMI)
83

Wireless Array
512 Index
maximum lease 444
Maximum Lease Time 444
Megabit 71
menu behavior
WMI 375
Message Integrity Check 454
messages
syslog counters 89
MIC 16, 454
MIMO (Multiple-In Multiple-Out) 36
mode
cluster operating mode 355
monitoring
intrusion detection 119
see intrusion detection 331
mounting 62
mounting plate 62
mounting the unit 62
MTU 171
size 171
multiple data streams 38
N
NAT
table - see connection tracking 110
neighbors, CDP 111
Netflow 187
netflow
CLI command 411
network
interfaces 169
settings 171
network assurance 112, 225
network connections 59, 92, 454
network installation 23, 441
network interface ports 66
network interfaces 171, 443
network status
ARP table window 109
connection
tracking window 110
routing table window 109
viewing leases 110
Network Time Protocol 71, 161, 185
network tools
ping, traceroute, RADIUS ping 369
nomenclature 2
non-overlapping channels 15
NTP 71, 161, 185, 444
NTP Server 185
O
Open (encryption method) 210
optimization, VLAN 291
options
WMI 373
overview 5
P
page loading
WMI 375
PAP (Password Authentication Proto-
col)
Admin RADIUS settings 219
RADIUS ping 370
web page redirect 258
passphrase 46, 71, 161
Password 448, 454
password 92
PEAP 16, 340
performance 14
Performance Manager
see RPM 16
Ping 359
ping 369
planning 42, 45, 46, 52
failover 42
network management 52
port failover 42
power 45

Wireless Array
Index 513
security 46
switch failover 42
WDS 53
PoGE 23
see Power over Gigabit Ethernet 12
PoGE Power Injectors 1
port failover 42
port requirements 48
power outlet 23
Power over Gigabit Ethernet 2, 23, 45,
59
Power over Gigabit Ethernet (PoGE) 12
power planning 45
pre-shared key 46, 56, 454
Print button 84
print button 91
probe
see Netflow 187
product installation 23, 441
product overview 5
product specifications 22
PSK 56, 446
PuTTY 23, 52, 71, 161, 454
PuTTy 24
Q
QoS 16, 249, 446, 452, 500
conflicting values 247
levels defined 250, 267
priority 249
SSID 244, 250
about setting QoS 453
default QoS 446
user group 267
quality
of user experience 320
Quality of Service 16
see QoS 250, 267
quick reference guide 443
quick start
express setup 161
R
radio
assurance (self-test) 314, 315
radio assurance (loopback testing) 313
radio assurance (loopback) mode 314,
315
radio distribution 14
radios
naming 2
RADIUS 5, 23, 46, 56, 208, 227, 262,
444, 454
admin authentication 218
setting admin privileges 218
setting user VSAs 234
Vendor Specific Attributes (VSAs)
463
RADIUS ping
CHAP Challenge Handshake Au-
thentication Protocol) 370
PAP (Password Authentication
Protocol) 370
RADIUS Ping command 369
RADIUS Server 444
RADIUS server 25
RADIUS settings
web page redirect 258
RAM (RF Analysis Manager) 18
reauthentication 280
reboot 362
redirect (WPR) 368
refresh interval
WMI 374
remote boot image
automatic update from remote
TFTP server 363
remote configuration
automatic update from remote
server 363

Wireless Array
514 Index
remote TFTP server
automatic update of boot image,
configuration 363
Reset 359, 444
reset configuration
to factory defaults 366
restore command 416
restrictions
date/time 268
stations 268
traffic 268
RF
intrusion detection 313
spectrum management 313
RF Analysis Manager
see RAM 18
RF configuration 313
RF management
see channel 313
RF Performance Manager
see RPM 16
RF resilience 313
RF Security Manager
see RSM 17
roaming 15, 106, 291
see fast roaming 273
Rogue AP 5, 52, 119, 240, 454
rogue AP
blocking 331
settings for blocking 328
Rogue AP List 119
rogue APs
auto block settings 331
blocking 313
Rogue Control List 240
rogue detection 15
rogues
setting as known or approved 120
root command prompt 381
route
trace route utility 369
routing table window 109
RPM (RF Performance Manager) 16
RSM (RF Security Manager) 17
RSSI 119
RTS 293, 298
RTS threshold 293, 298
S
Safari 24
sample Perl and CSS files for 368
save
with reboot 362
Save button 84
saved.conf 364
scalability 3
schedule
auto channel configuration 313
Secondary Port 444
Secondary Server 444
secret 444
Secure Shell 24
secure Shell 23
security 5, 16, 208, 452, 454
certificate, see certificate 225
Security Manager
see RSM 17
see group 264
self-monitoring 331
radio assurance 438
radio assurance options 314, 315
self-test
radio assurance mode 314, 315
serial port 24, 66, 454
server, VTun
see VTun 203
servers
connectivity, see network assur-
ance 112, 225
Service Set Identifier 71

Wireless Array
Index 515
Services 184, 452
servicing the unit 441
settings 161
setup, express 161
sharp cell 313
setting in WMI 317
short retry limit 280
signal processing
MIMO 36
skin
changing WMI appearance 373
SNMP 5, 13, 71, 161, 171, 184, 194, 445
required for XMS 194, 195
software
upgrade license key 363
software image
upgrading via CLI 464
Software Upgrade 359
software upgrade 362
spatial multiplexing 38
specifications 22
spectrum (RF) management 313
speed 3, 66, 171
11 Mbps 3
54 Mbps 3
splash page
web page redirect 257, 368
web page redirect, customize 258
SSH 23, 24, 52, 71, 161, 171, 209, 448,
454
SSH-2 209
SSID 5, 71, 84, 119, 161, 240, 249, 446,
452, 457
about usage 452
active IAPs 261
QoS 244, 250
about using 453
QoS, about usage 452
web page redirect settings 253
web page redirect settings, about
255, 259, 260
SSID Access List 262
SSID address 262
SSID Management 249, 446, 452
standby mode 314
stateful filtering
disabling 346
static IP 71, 161, 171
station
assurance 320
station assurance 320
station timeout period 280
Stations 452
stations
limits and interactions 268
rogues 120
statistics 148
statistics per station 149
statistics 161
filters 147
netflow 187
per-station 149
stations 148
WDS 145
status bar 84, 91
style
WMI appearance 373
submitting comments 91
subnet 23, 42, 71, 171
switch failover 42
synchronize 71, 161, 185
Syslog 71, 84, 161, 184, 190, 444
time-stamping 71
syslog messages
counters 89
Syslog reporting 190
Syslog Server 190
system commands
ping, trace route, RADIUS ping
369

Wireless Array
516 Index
System Configuration Reset 359
System Log 190
system log
viewing window 150, 156
System Reboot 359
System Tools 359
system tools 360
T
tag, WiFi 188
T-bar 62
T-bar clips 62
TCP
port requirements 48
technical support
contact information 469
frequently asked questions 452
Telnet 209, 448, 454
Temporal Key Integrity Protocol 454
TFTP server
automatic update of boot image,
configuration 363
Time Out 444
time zone 71, 161, 185
timeout 280, 359
Tips 451
TKIP 16, 46, 56, 71, 161, 446, 454
TKIP encryption
and XN Arrays 231
tool
ping, trace route, RADIUS ping
369
Tools 359, 454
tools, network 369
tools, system 360
trace route utility 369
traffic
filtering 344
limits and interactions 268
transmit power 28
Trap Host 445
trap port 194, 445
tunneled
fast roaming 291
Tunnels 204
tunnels
see VTun 199, 203
U
UDP
port requirements 48
Unit 62
attaching 62
mounting 62
unknown
setting rogues 120
upgrade
license key 363
software image 362
upgrading software image
via CLI 464
user accounts
setting RADIUS VSAs 234
user group 264
QoS 267
user group limits and interactions 268
user interface 83
utilities
ping, trace route, RADIUS ping
369
utility buttons 91
V
Vendor Specific Attributes (VSAs)
RADIUS, for Xirrus 463
virtual tunnels
see VTun 203
VLAN 5, 56, 249, 446, 452, 457
broadcast optimization 291
dynamic

Wireless Array
Index 517
overridden by group 267
group (vs. dynamic VLAN) 267
vlan
CLI command 424
VLAN ID 249
VLANs 199
and fast roaming 273
voice
fast roaming 273
implementing on Array 26, 199,
244
Voice-over IP 298
VoIP 298
VoWLAN 16
VPN 71, 161, 454
VTS
Virtual Tunnel Server 199, 203
VTun
specifying tunnel server 199, 203
understanding 199
W
wall thickness considerations 26
warning messages 89
WDS 338, 340
about 53
long distance 278, 339
planning 53
statistics 145
timeouts 278, 339
WDS Client Links 340
Web interface
structure and navigation 88
web interface 83
Web Management Interface 52, 62, 63,
66, 92, 452
Web Management Interface (WMI) 83
web page redirect 368
also called WPR 368
CHAP (Challenge-Handshake Au-
thentication Protocol) 258
customize internal login/splash
page 258
HTTPS port 255, 259, 260
install files for 368
internal login page 256
internal splash page 257
PAP, CHAP 258
RADIUS settings 258
remove files for 369
sample WPR files 369
SSID settings 253
SSID settings, about 255, 259, 260
WEP 16, 46, 71, 161, 208, 249, 446, 454
WEP (Wired Equivalent Privacy)
encryption method 210
WEP encryption
and XN Arrays 232
Wi-Fi Protected Access 5, 46, 71, 161,
454
WiFi tag 188
wifi-tag
CLI command 425
window loading
WMI 375
Wired Equivalent Privacy 71, 454
Wireless Distribution System 338
wireless LAN 3
wireless security 161
WLAN 161
WMI 5, 52, 56, 66, 83, 274
appearance options 373
appearance, changing 373
certificate error 212, 225
executing CLI commands 371
menu behavior 375
options 373
page loading 375
refresh interval 374
workflow 57

Wireless Array
518 Index
WPA 5, 56, 71, 161, 208, 249, 446, 454
WPA (Wi-Fi Protected Access) and
WPA2
encryption method 210
WPA2 5
WPR
see web page redirect 368
wpr.pl 368, 369
X
X.509
certificate 212, 225
Xirrus
certificate authority 225
Xirrus Advanced RF Analysis Manag-
er
see RAM 18
Xirrus Advanced RF Performance
Manager
see RPM 16
Xirrus Advanced RF Security Manager
see RSM 17
Xirrus Management System 5, 13, 15,
23, 25, 52, 454
SNMP required 194, 195
Xirrus Management System (XMS) 1
Xirrus PoGE Power Injectors 1
Xirrus Power over Gigabit Ethernet 23
Xirrus Roaming Protocol 15, 106, 291
XMS 5, 13, 15, 25
port requirements 48
setting IP address of 194
SNMP required 194, 195
XN Array
management 159, 359
XN Arrays
see also IEEE 802.11n 35
XN12 1, 5
XN16 1, 5
management 359
XN4 1, 5
XN8 1, 5
XP PoGE Power Injectors 1
XP1, XP8
see Power over Gigabit Ethernet 12
XPS 23
XRP 15, 106, 291
xs_current.conf 364
xs_diagnostic.log 367
High Performance Wireless Networks
1.800.947.7871 Toll Free in the US
+1.805.262.1600 Sales
+1.805.262.1601 Fax
2101 Corporate Center Drive
Thousand Oaks, CA 91320, USA
To learn more visit:
xirrus.com or
email info@xirrus.com
© 201 Xirrus, Inc. All Rights Reserved. The Xirrus logo is a registered trademark of Xirrus, Inc.
All other trademarks are the property of their respective owners. Content subject to change without notice.
800-0022-001F