Cambium Networks XR630 802.11ac 3x3 AP User Manual xirrus PDF
Xirrus, Inc. 802.11ac 3x3 AP xirrus PDF
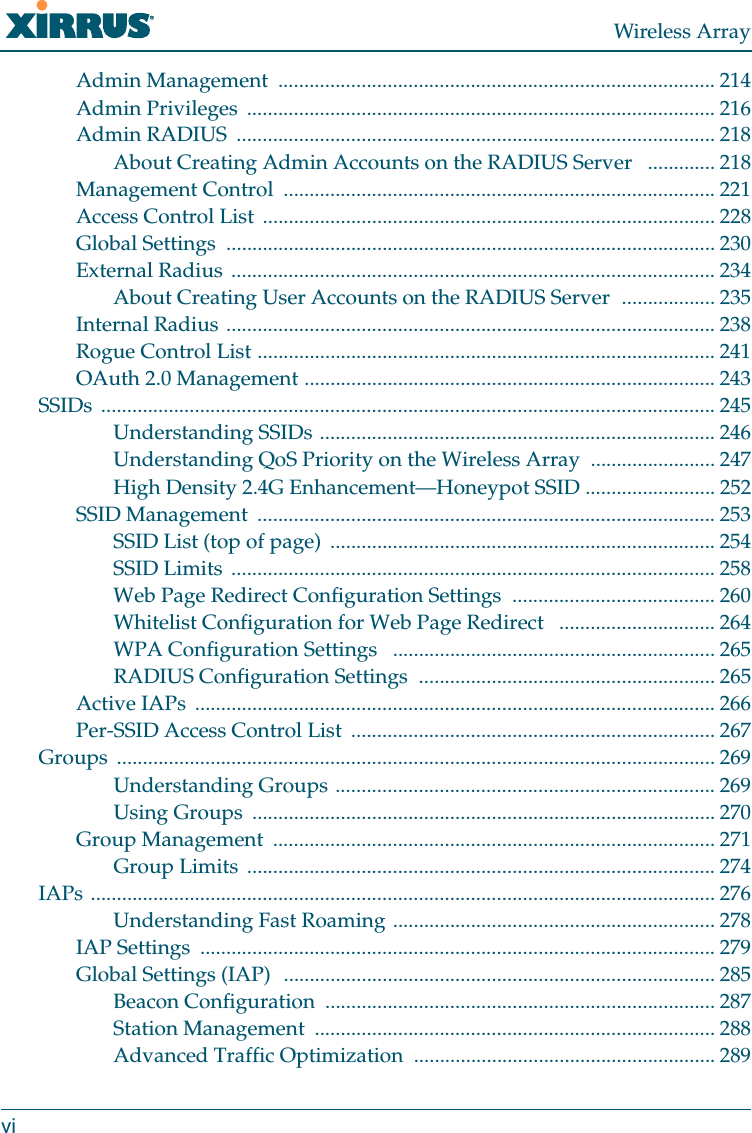
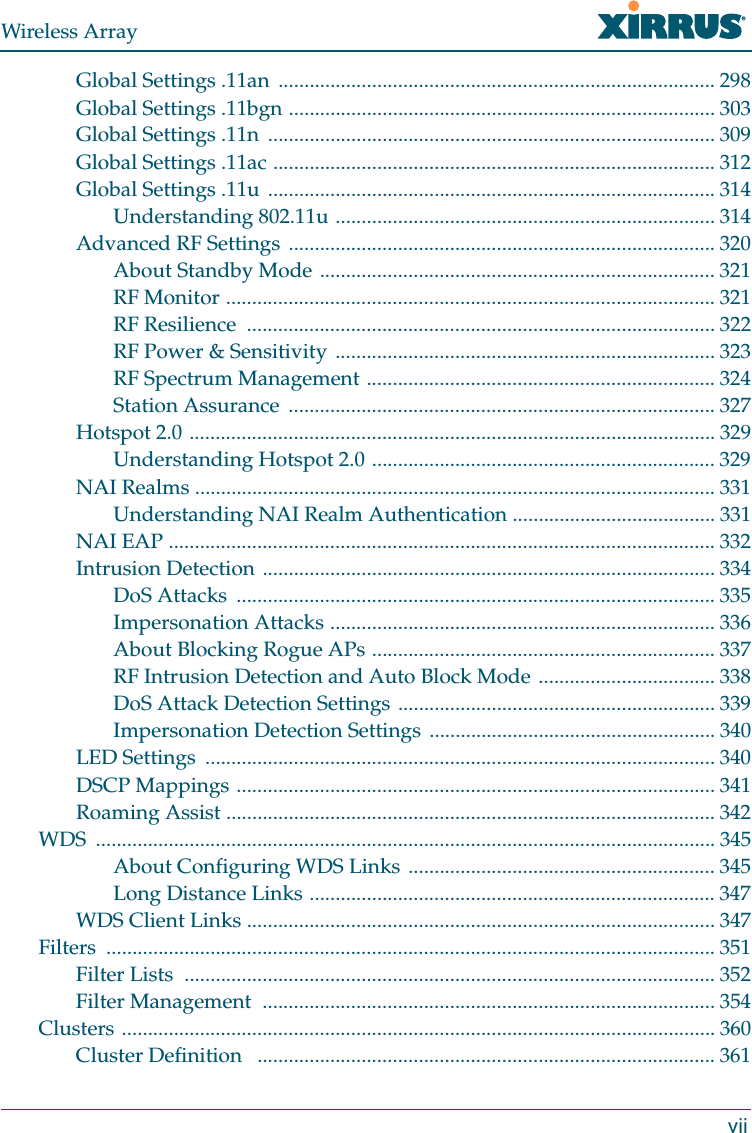
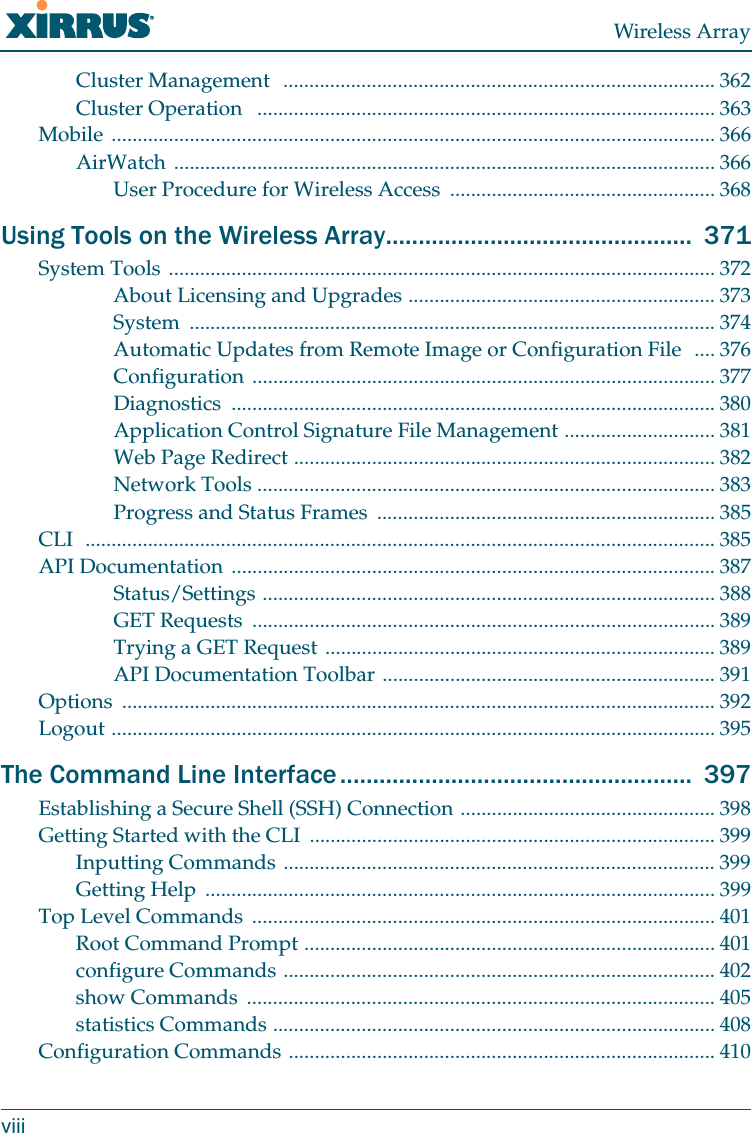
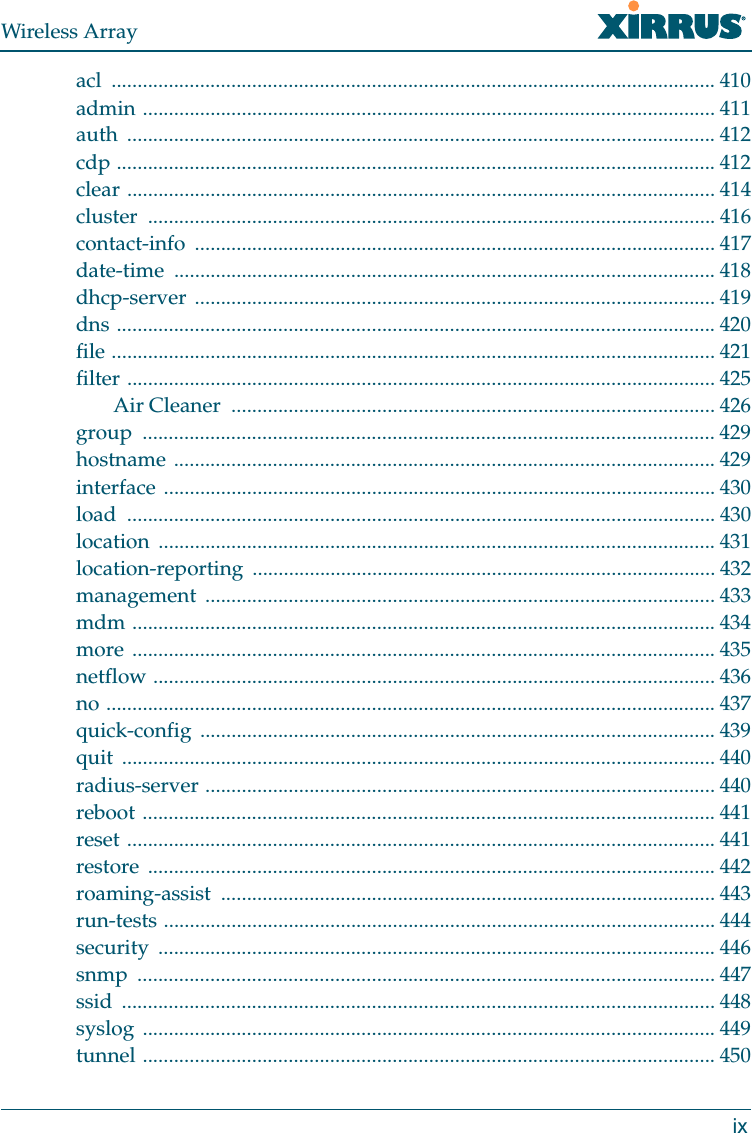
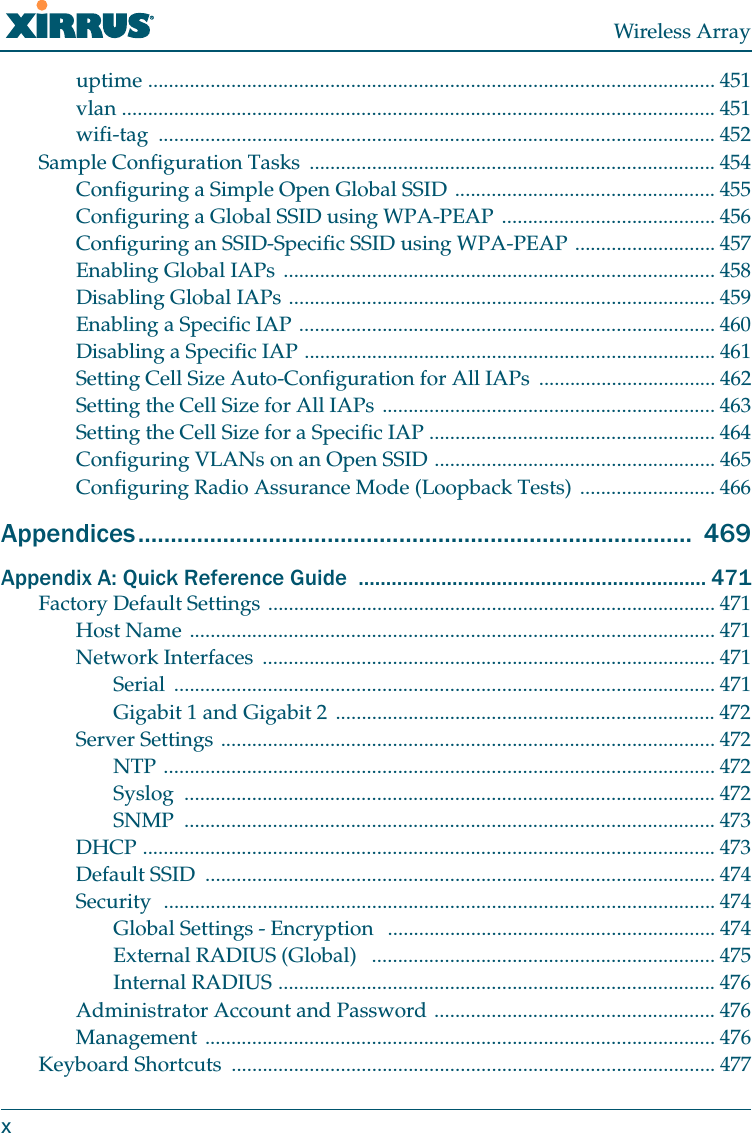
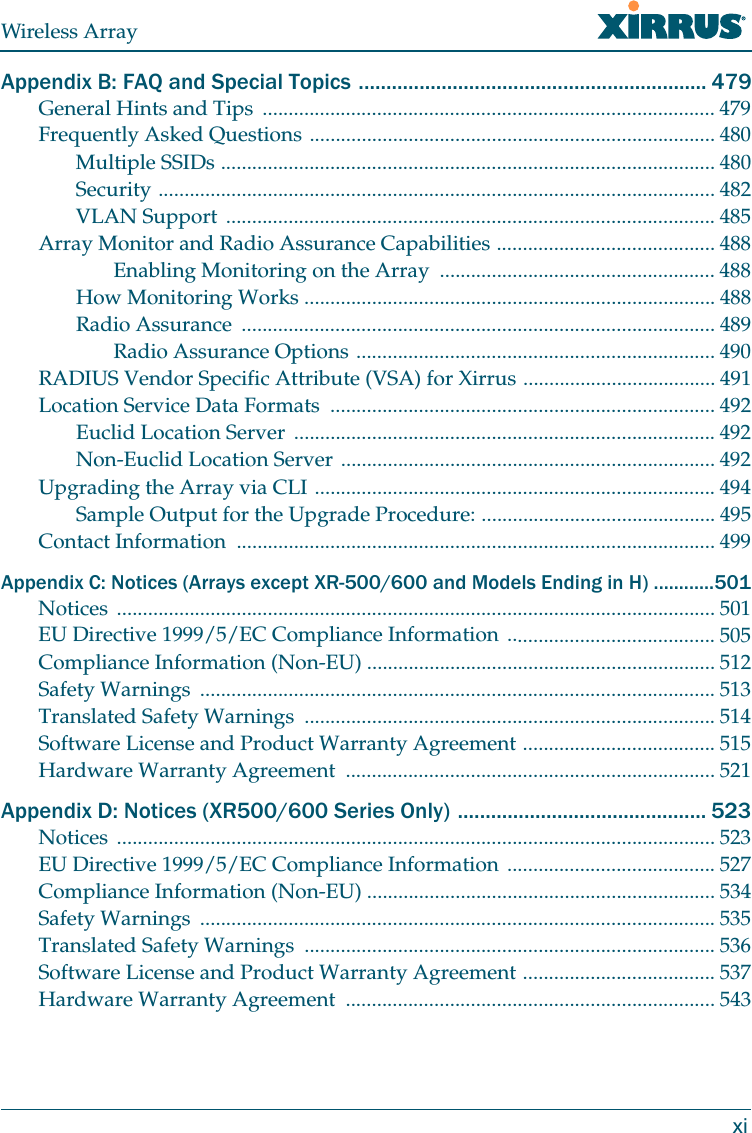
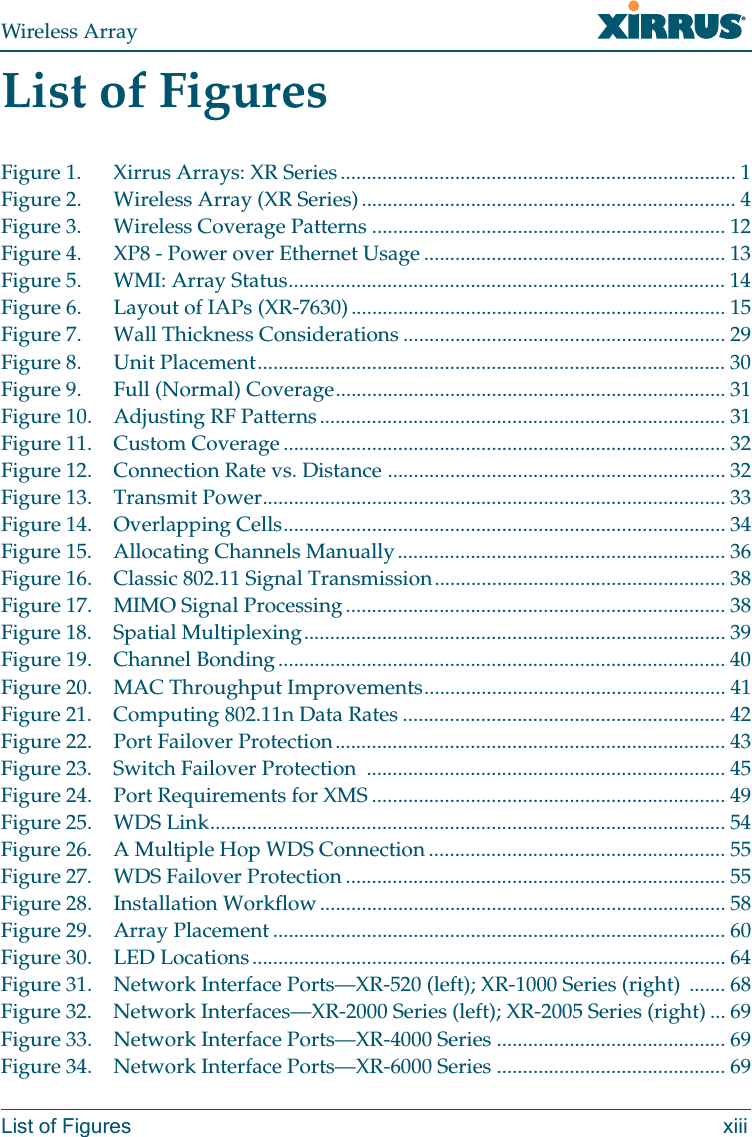
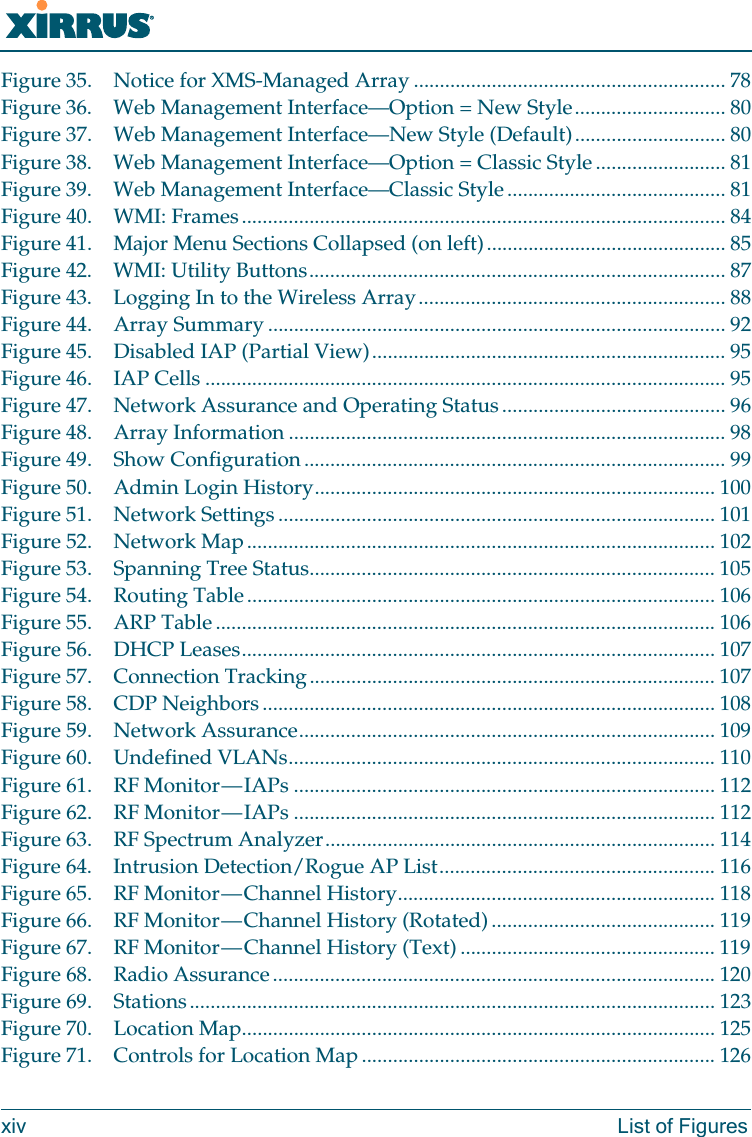
Contents
- 1. User Manual (1 of 2).pdf
- 2. User Manual (2 of 2).pdf
- 3. User manual (Statement)
- 4. User manual-1
- 5. User manual-2
- 6. User Manual
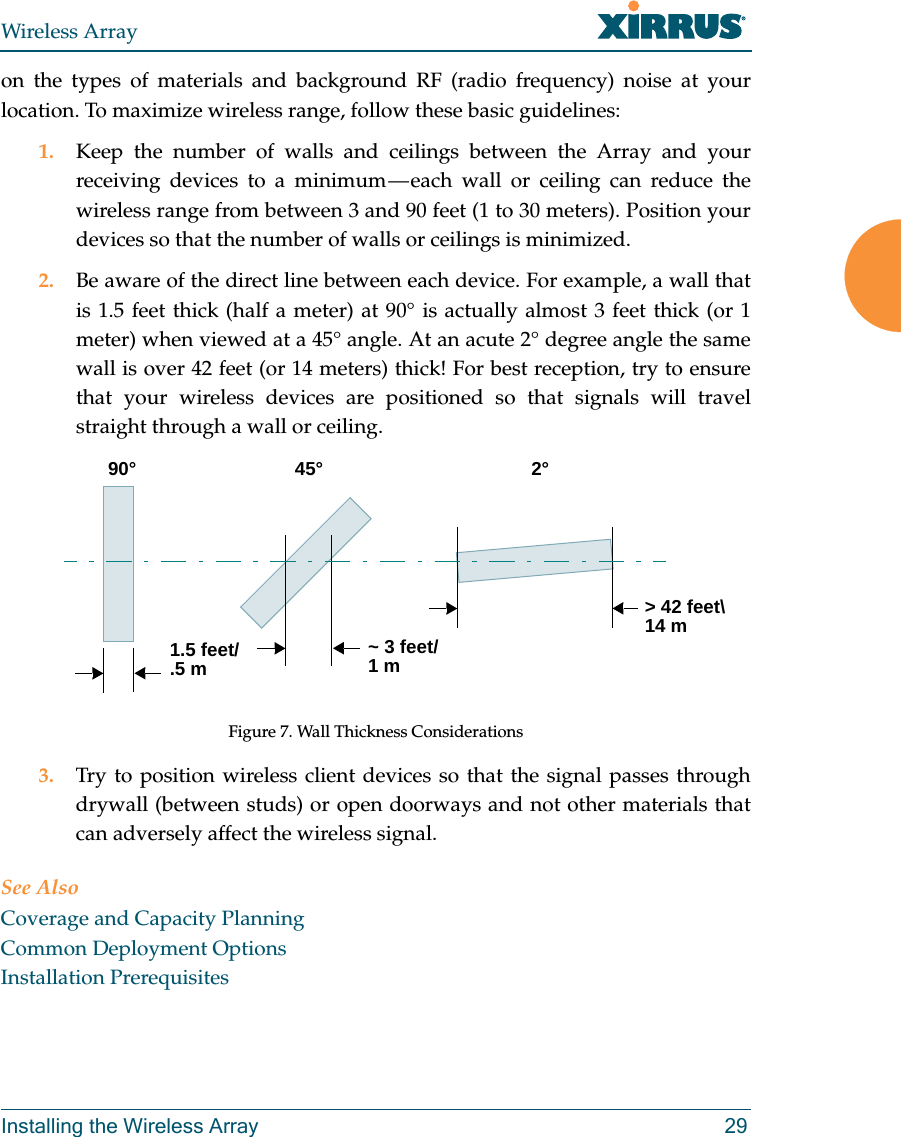
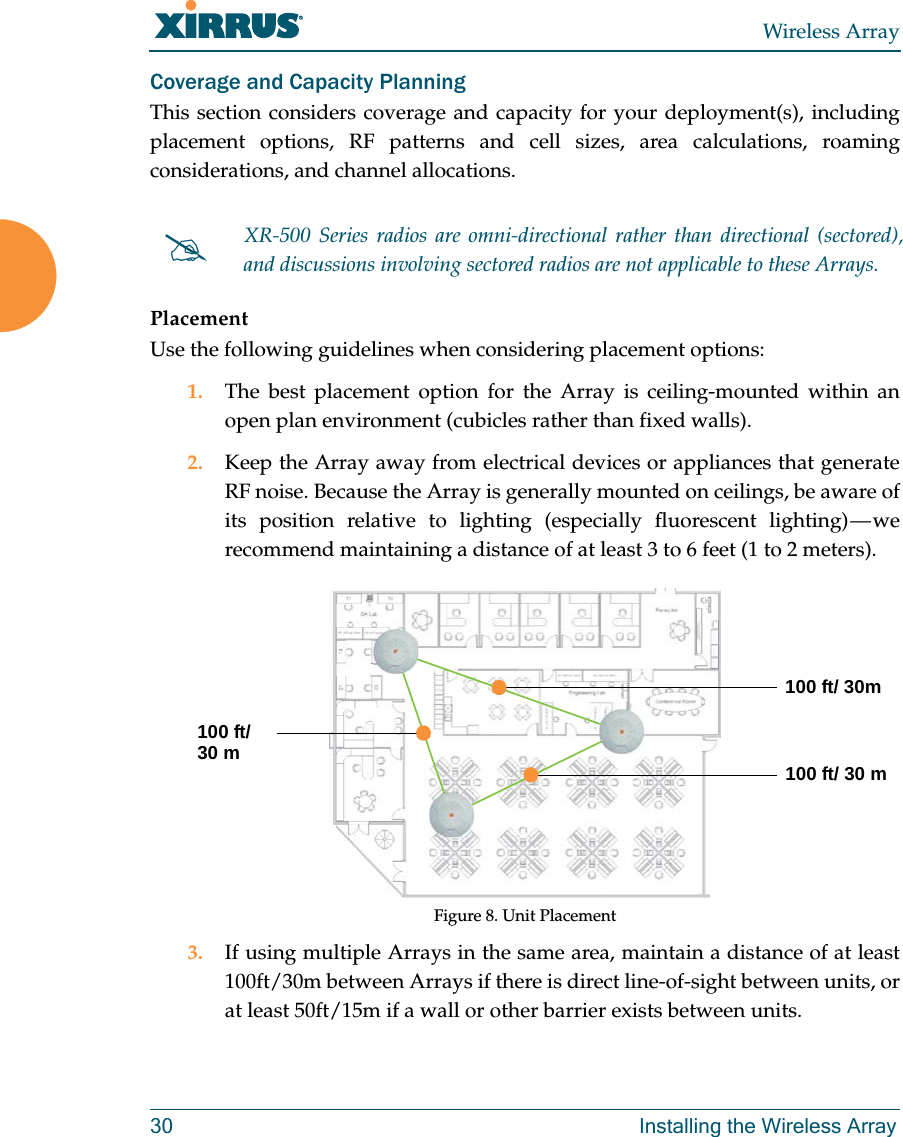
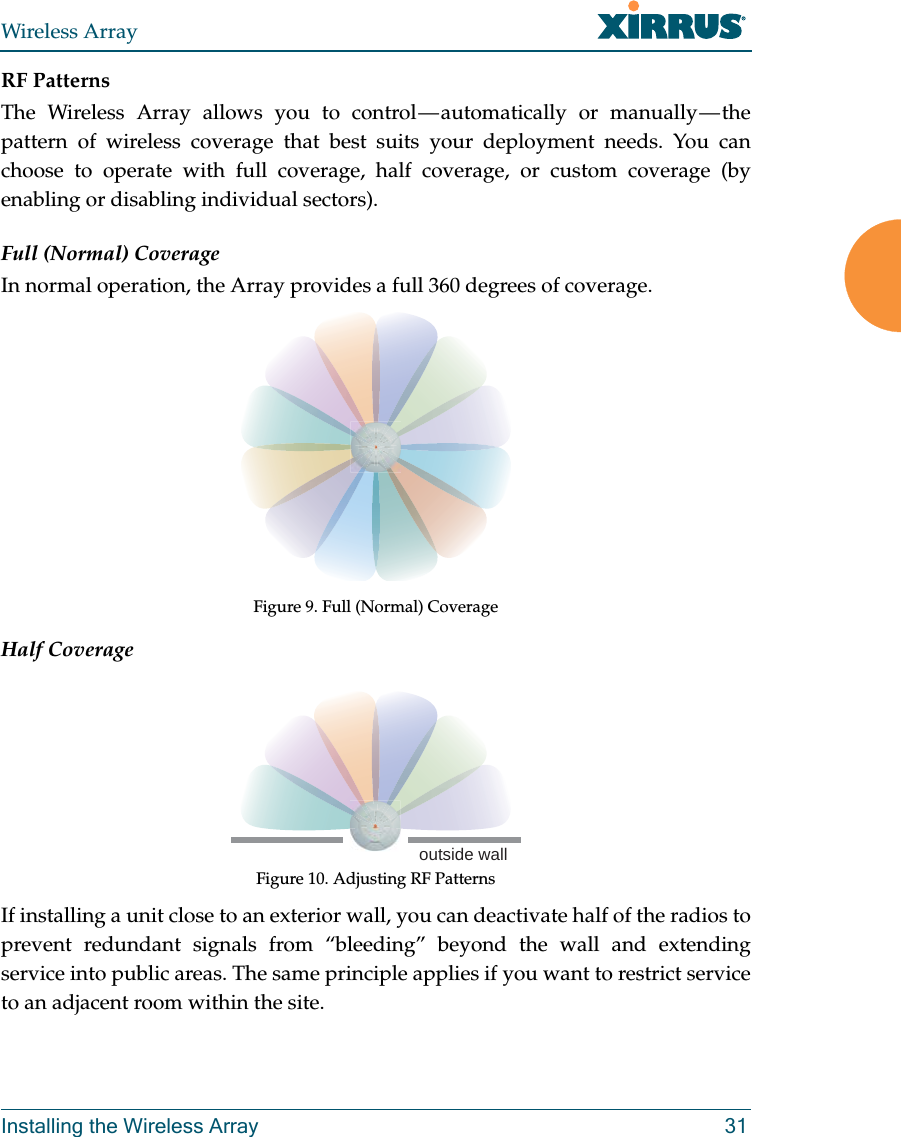
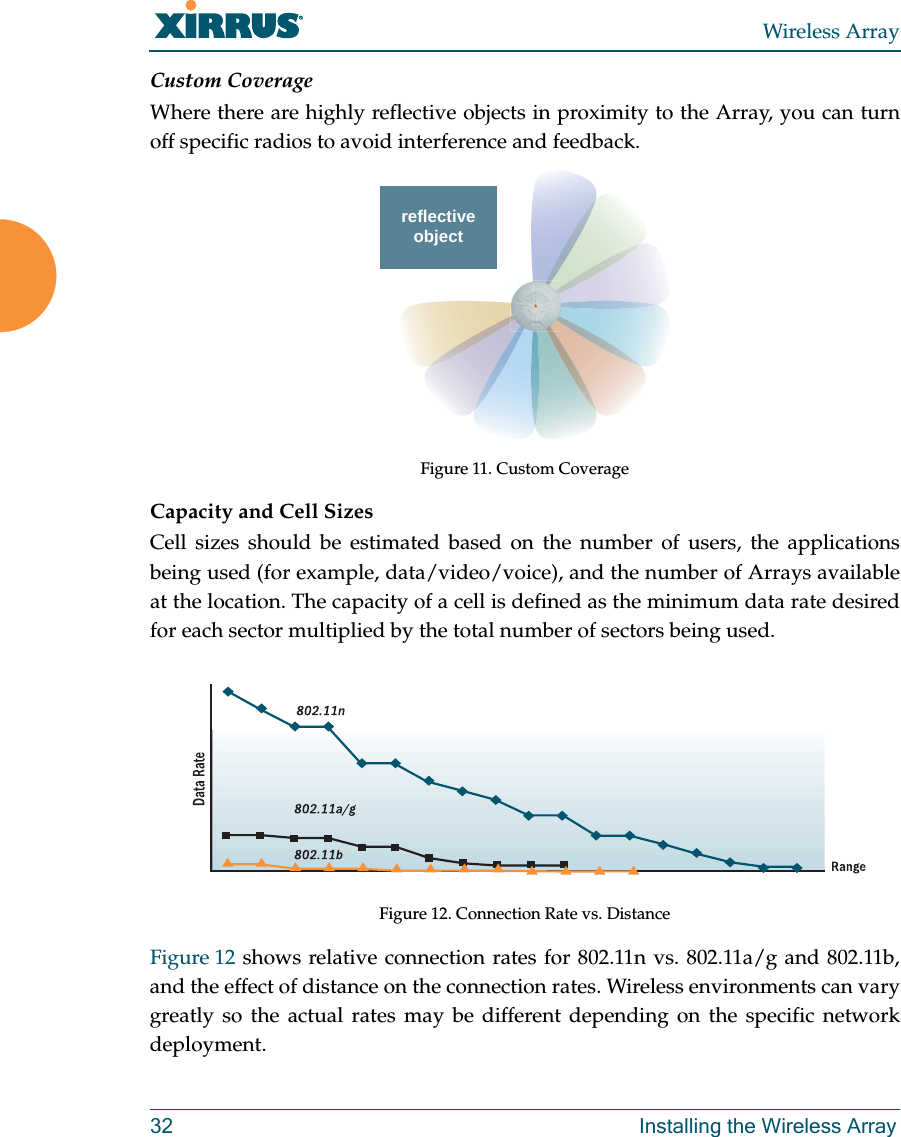
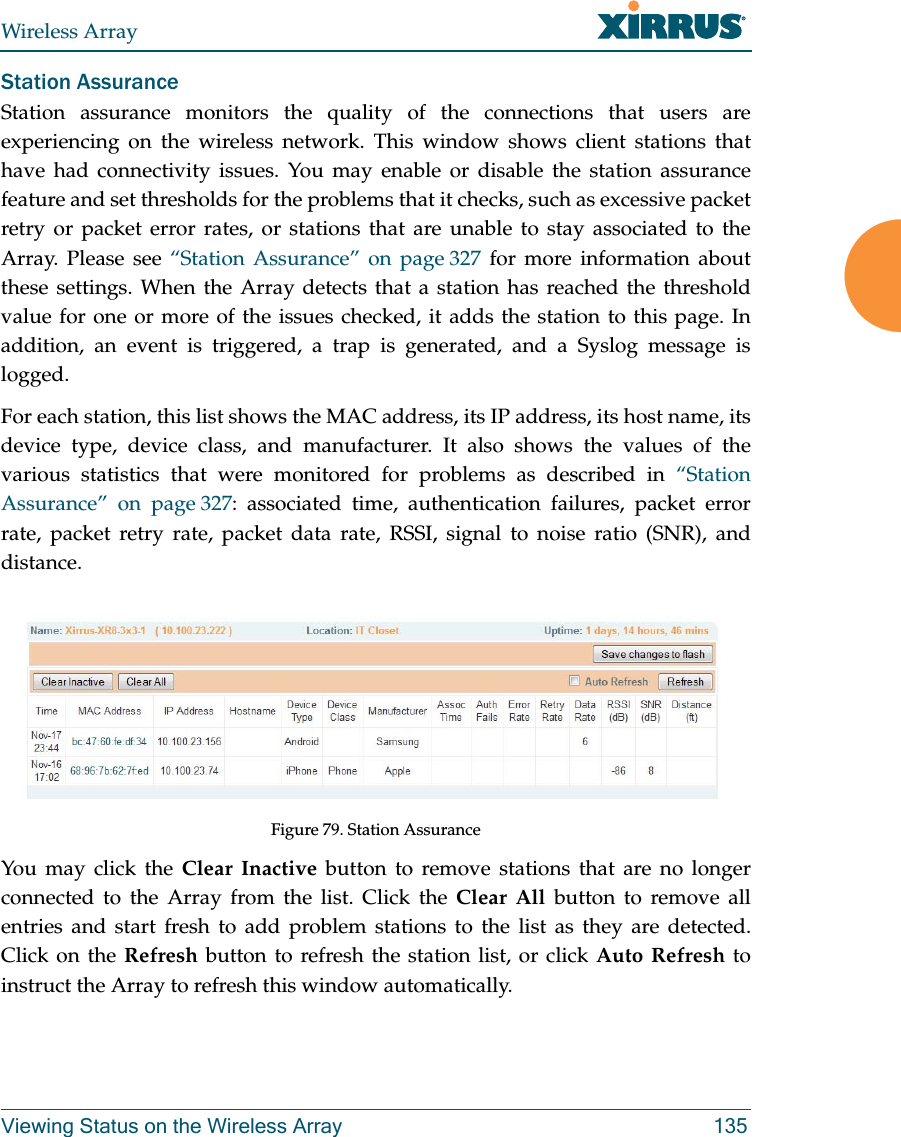
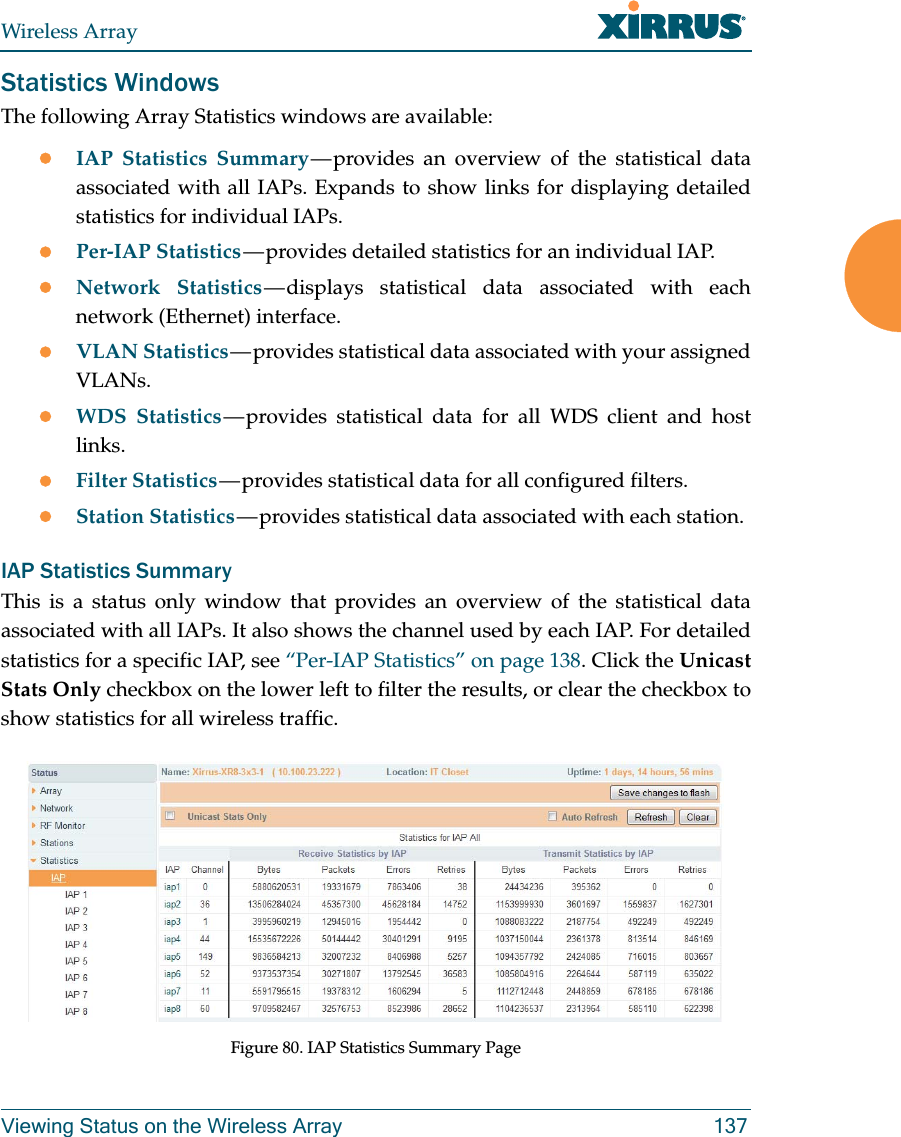
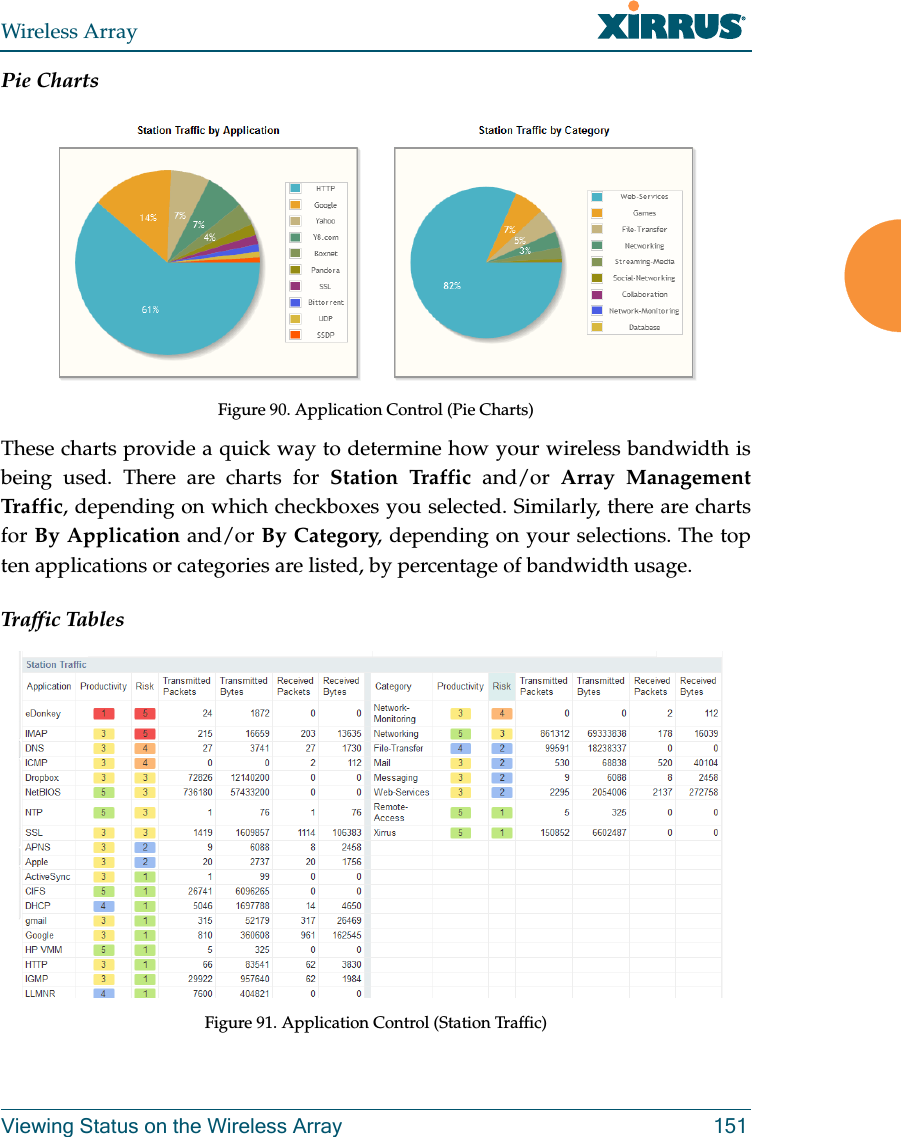
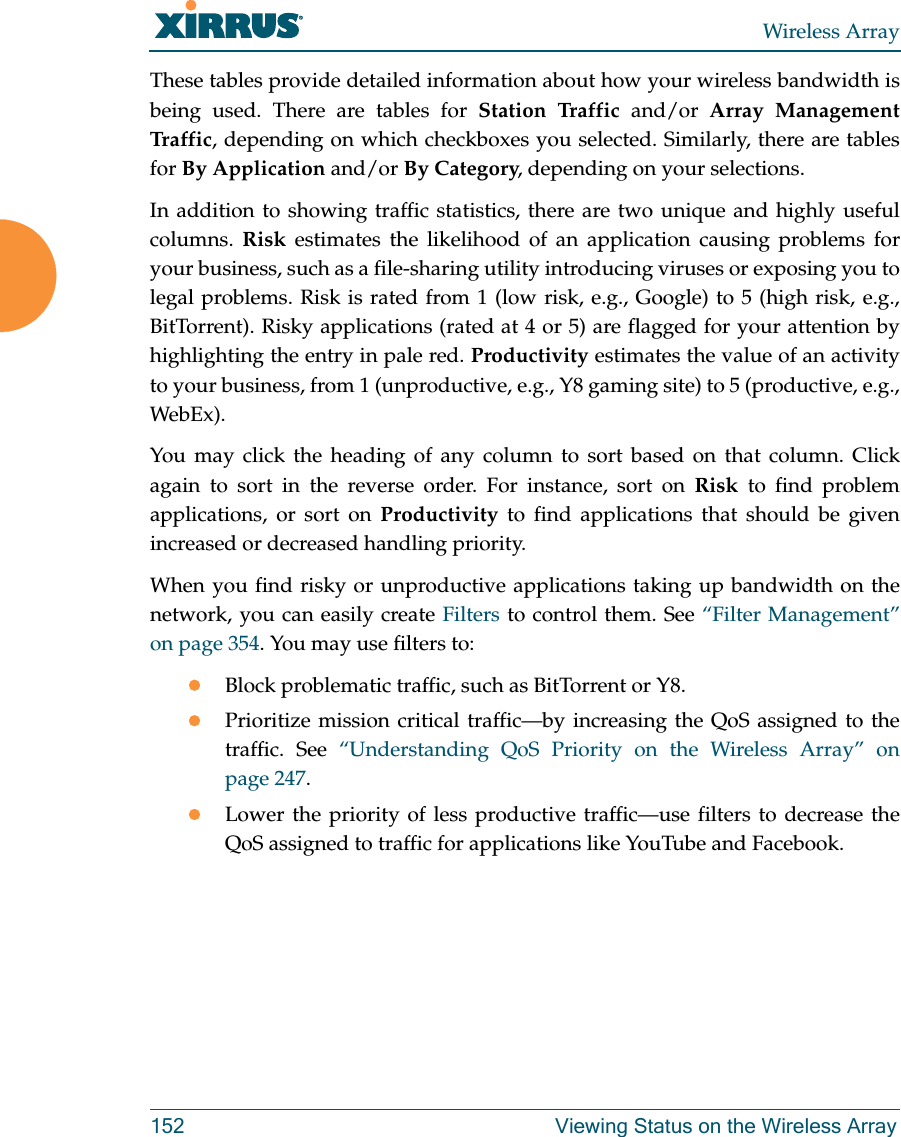
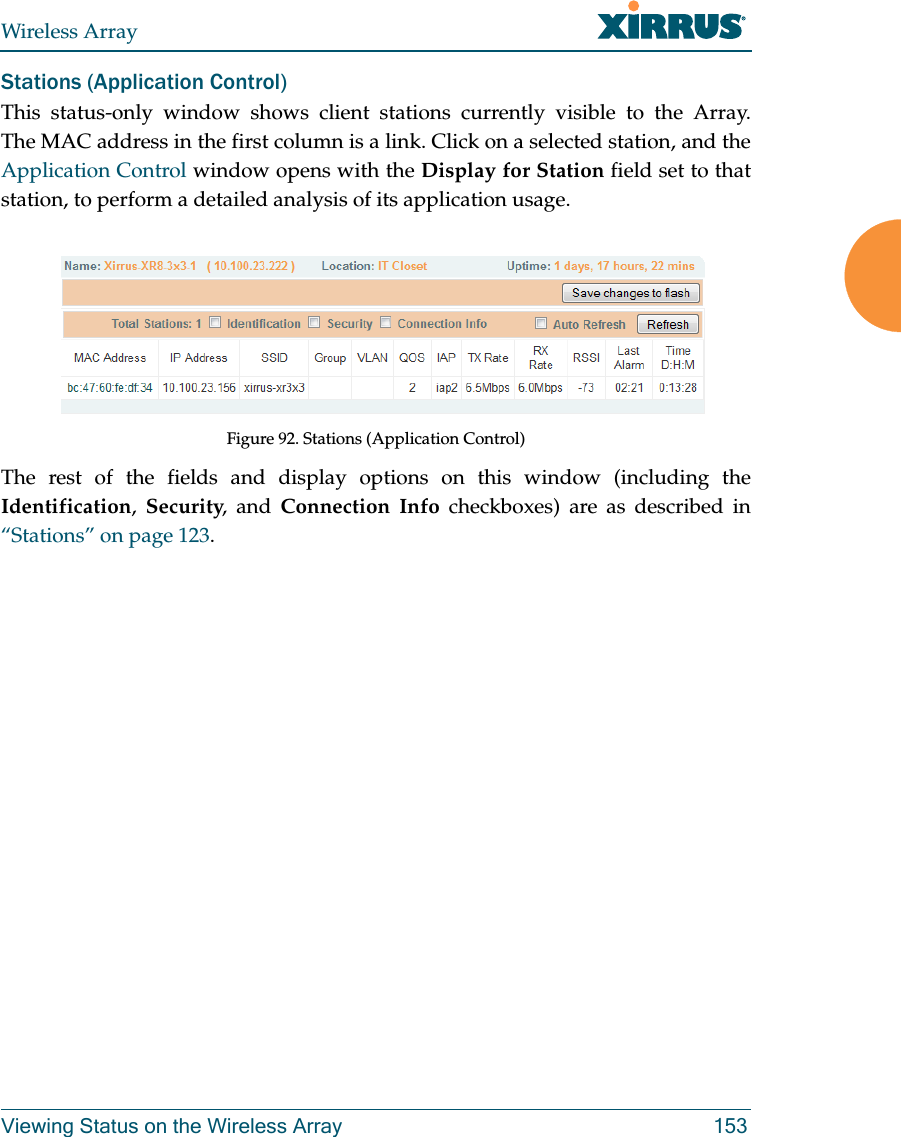
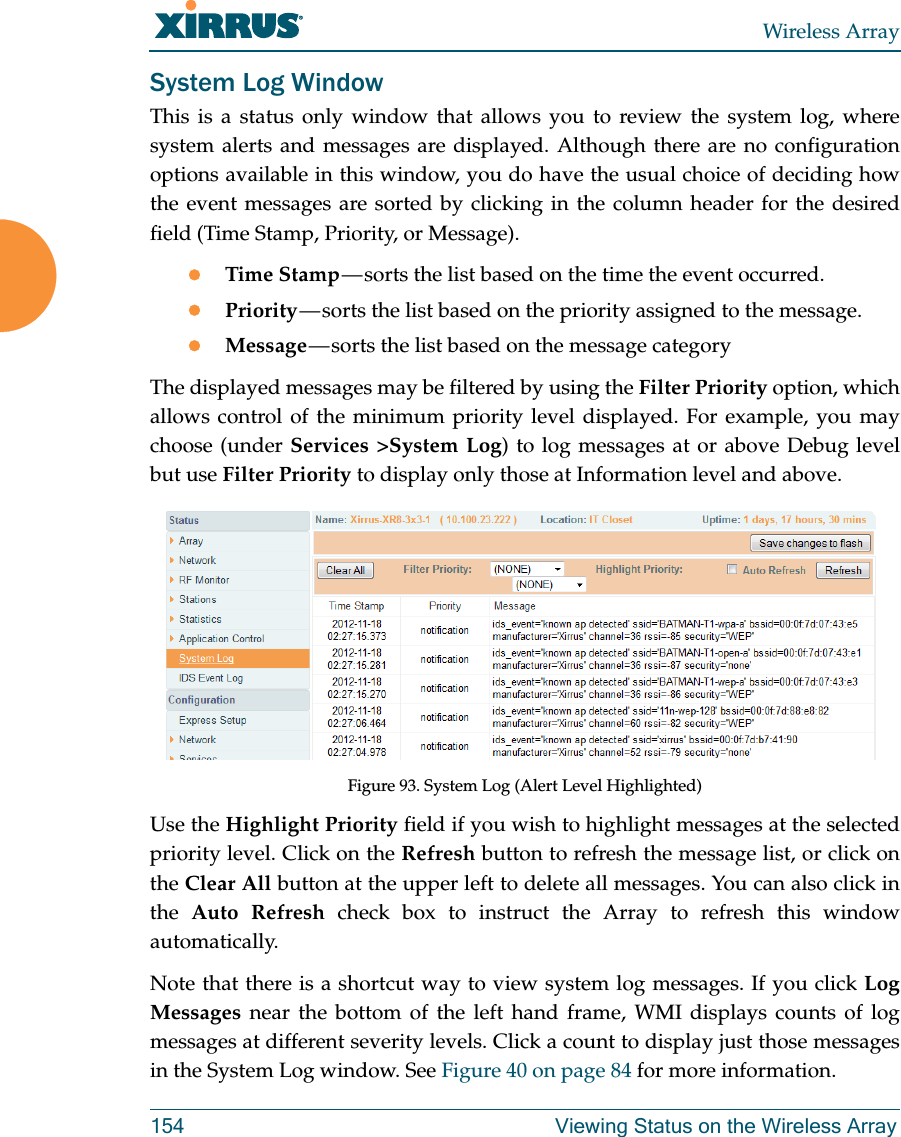
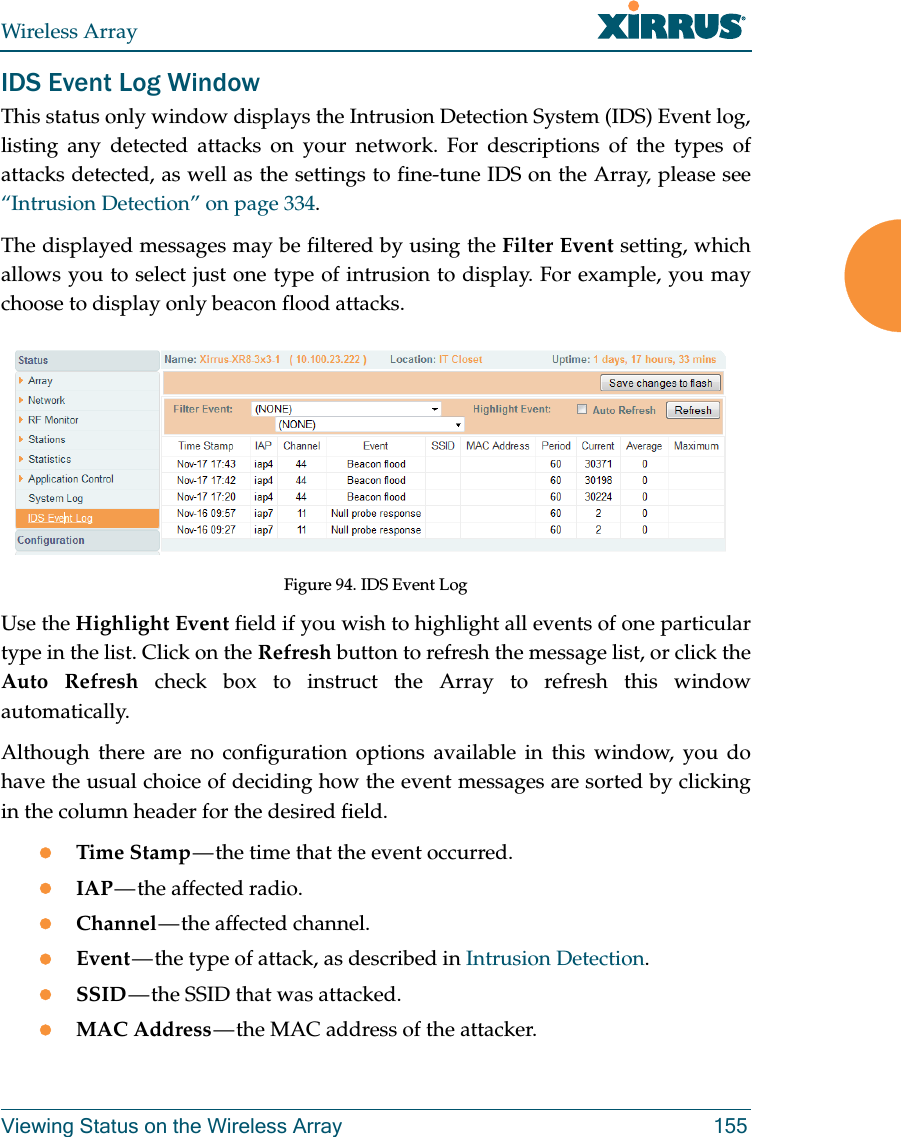
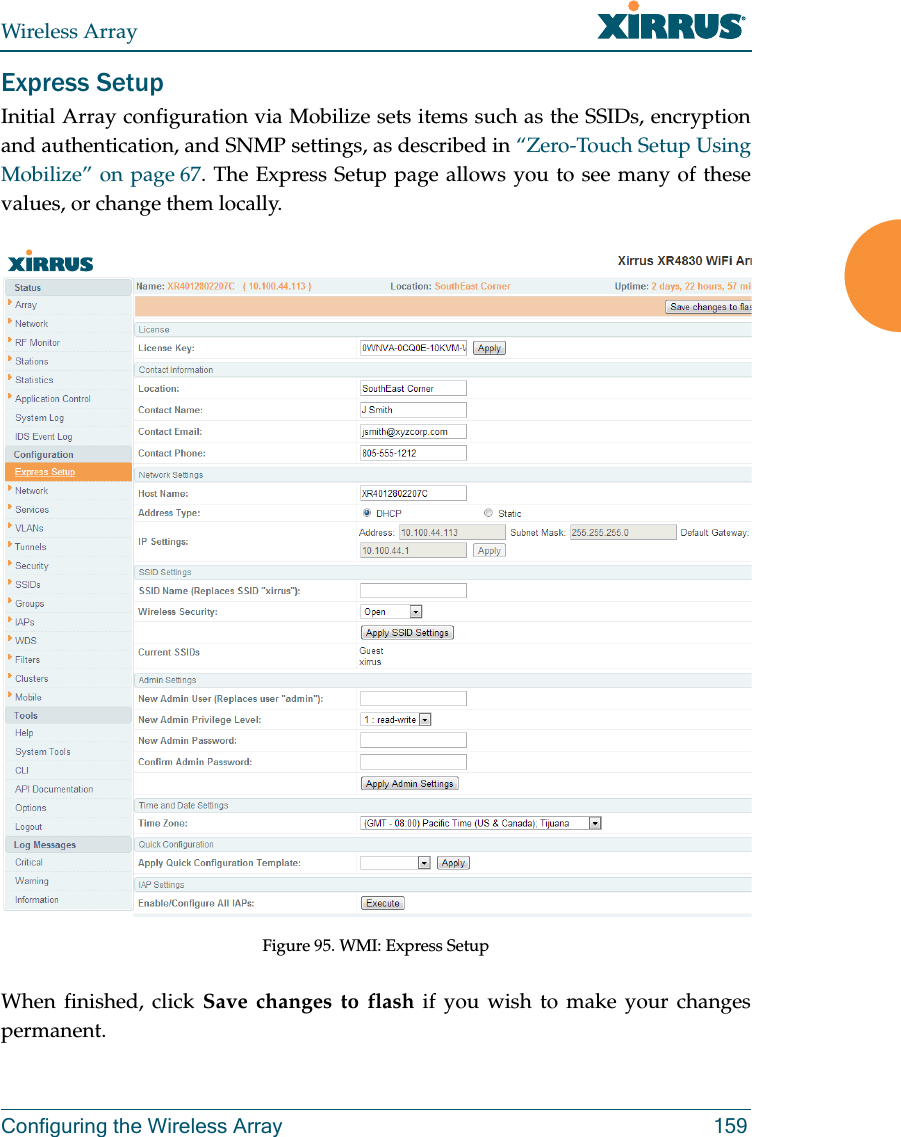
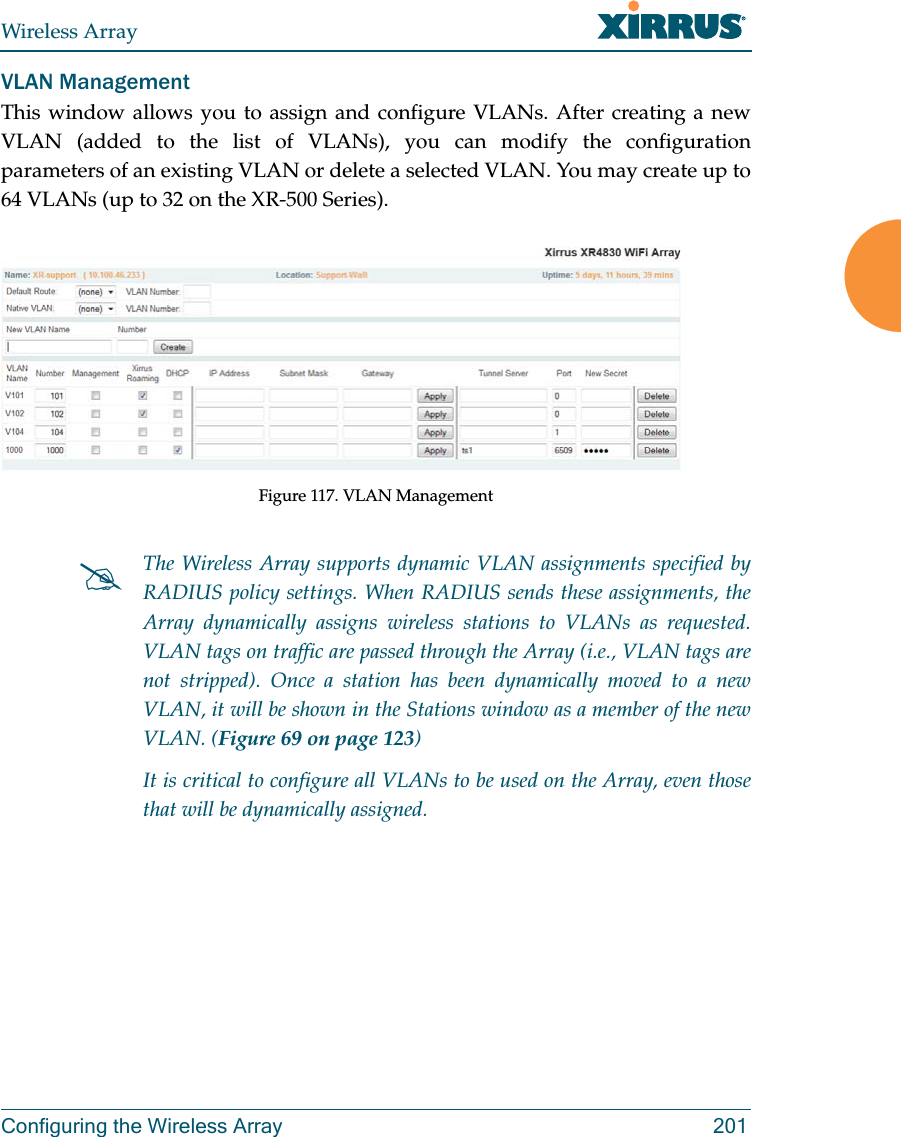
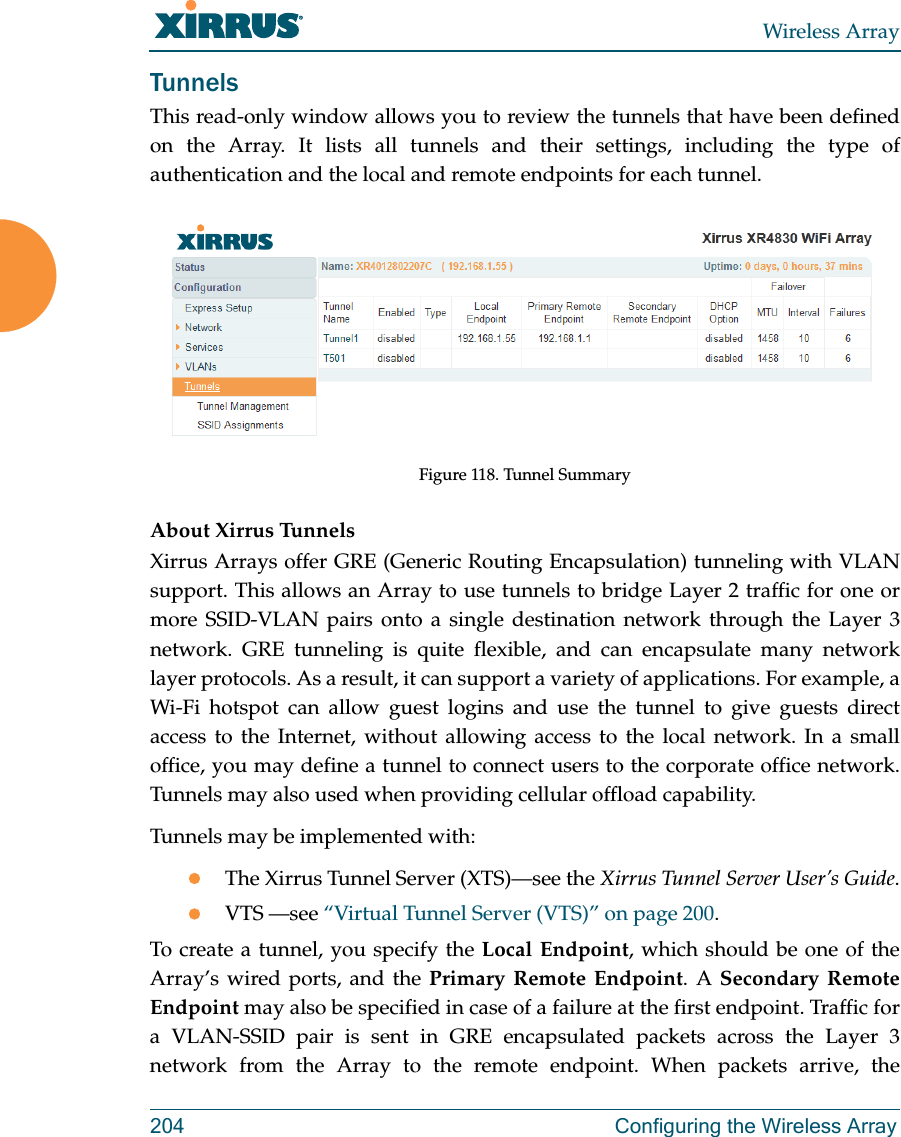
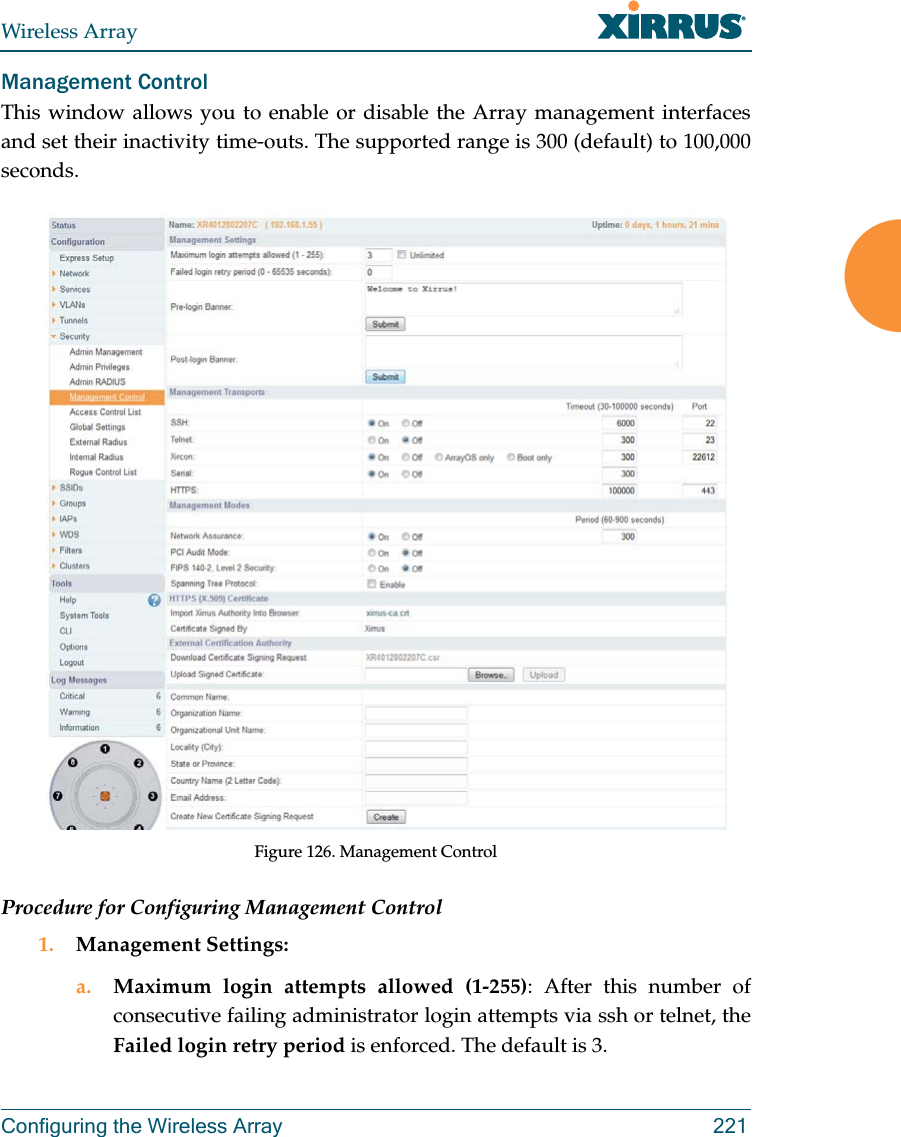
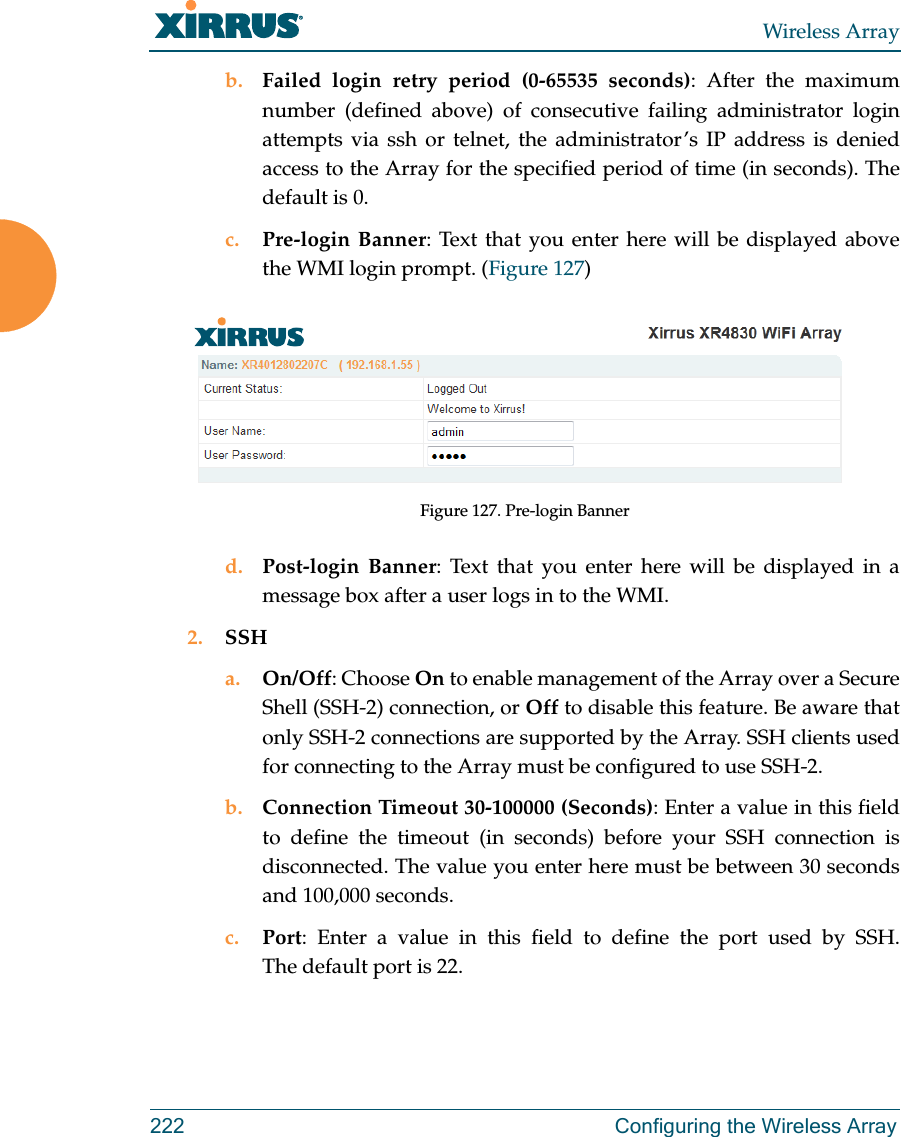
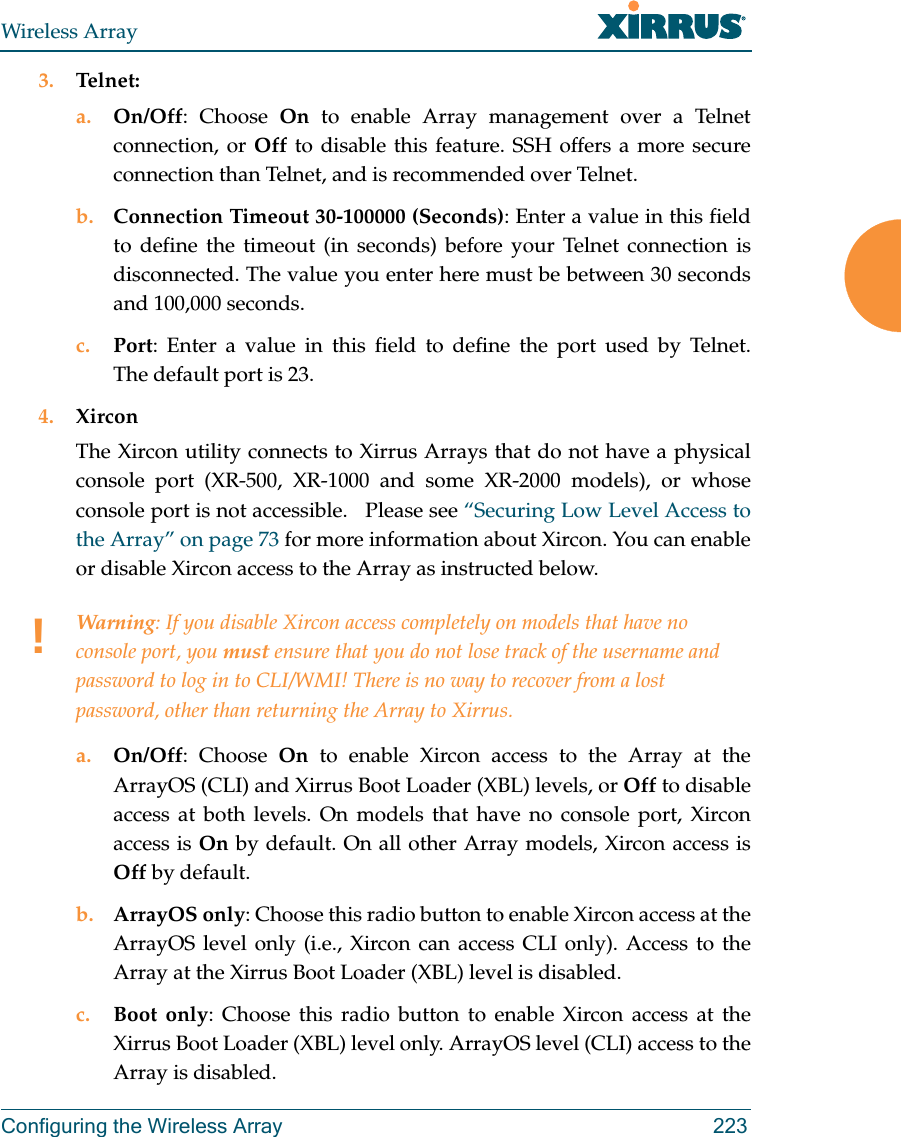
User Manual (1 of 2).pdf