Fujitsu Client Computing WB0001 S6120D, S6130 LIFEBOOK FUJITSU LAPTOP PC's User Manual Calexico Manual
Fujitsu Limited S6120D, S6130 LIFEBOOK FUJITSU LAPTOP PC's Calexico Manual
Contents
- 1. Bluetooth User Manual
- 2. Calexico Manual
Calexico Manual
Intel(R) PRO/Wireless LAN Mini PCI Adapter
User's Guide
This document provides information for the following wireless devices:
• Intel(R) PRO/Wireless LAN 2100 3B Mini PCI Adapter, operating at 2.4 GHz
These wireless adapters operate with high-capacity networks using multiple access points
within large or small environments. Using the Intel(R) PROSet Windows utility you can configure,
manage wireless local area network (WLAN) management tasks, adapter switching functions,
and connections.
Wireless LAN General Information
1.About Wireless LAN Technology
Adapter Setup and Configuration
2.Software Installation
3.Using Intel(R) PROSet
4.Connecting to a Network using Intel® PROSet
5.Security Overview
6.Setting Up WEP Encryption and Authentication
7.Troubleshooting
8.Specifications
9.Glossary
Support and Warranty
10.Customer Support
11.Software License
12.Safety and Regulatory Notices
13.Limited Warranty
14.Legal Notices
Copyright (c) 2003 Intel Corporation. All rights reserved.
Intel Corporation, 5200 N.E. Elam Young Parkway, Hillsboro, OR 97124-6497 USA
Intel Corporation assumes no responsibility for errors or omissions in this document. Nor does Intel make any commitment to
update the information contained herein.
Intel, Itanium, and Pentium are trademarks or registered trademarks of Intel Corporation or its subsidiaries in the United States
and other countries.
*Other names and brands may be claimed as the property of others.
1.About Wireless LAN Technology
A wireless network connects computers without using network cables. Computers use radio
communications to send data between each other. You can communicate directly with other
wireless computers, or connect to an existing network through a wireless access point. When
you set up your wireless adapter, you select the operating mode for the kind of wireless network
you want. You can use your Intel(R) PRO/Wireless adapter to connect to other similar wireless
devices that comply with the 802.11 standard for wireless networking.
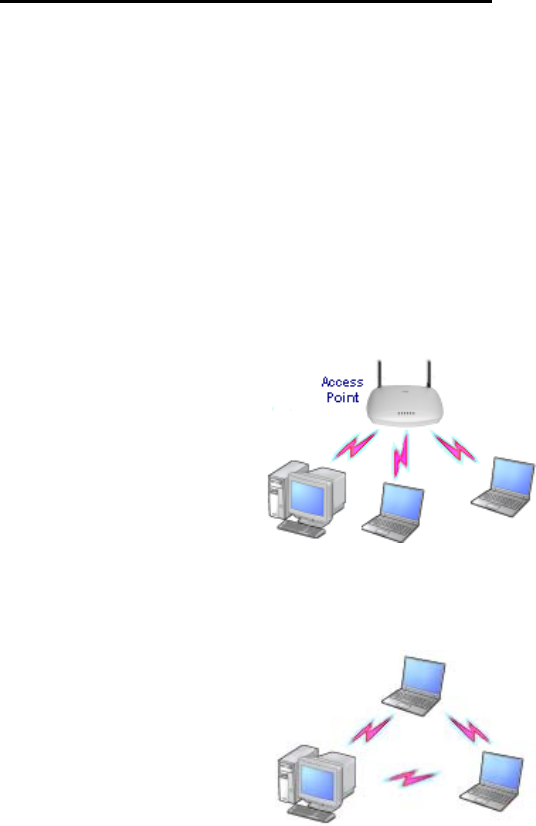
Choosing a Wireless LAN Mode
Wireless LANs can operate with or without access points, depending on the number of users in
the network. Infrastructure mode uses access points to allow wireless computers to send and
receive information. Wireless computers transmit to the access point, the access point receives
the information and rebroadcasts it to other computers. The access point can also connect to a
wired network or to the Internet. Multiple access points can work together to provide coverage
over a wide area.
Peer-to-Peer mode, also called Ad Hoc mode, works without access points and allows wireless
computers to send information directly to other wireless computers. You can use Peer-to-Peer
mode to network computers in a home or small office or to set up a temporary wireless network
for a meeting.
Configuring a Wireless LAN
There are three basic components that must be configured for a wireless LAN to operate
properly:
• Network Name—Each wireless network uses a unique Network Name to identify the
network. This name is called the Service Set Identifier (SSID). When you set up your
wireless adapter, you specify the SSID. If you want to connect to an existing network,
you must use the name for that network. If you are setting up your own network you can
make up your own name and use it on each computer. The name can be up to 32
characters long and contain letters and numbers.
• Profiles—When you set up your computer to access a wireless network, Intel(R)
PROSet creates a profile for the wireless settings that you specify. If you want to
connect to another network, you can scan for existing networks and make a temporary
connection, or create a new profile for that network. After you create profiles, your
computer will automatically connect when you change locations.

• Security—The 802.11 wireless networks use encryption to help protect your data.
Wired equivalent privacy (WEP) uses a 64-bit or 128-bit shared encryption key to
scramble data. Before a computer transmits data, it scrambles the data using the secret
encryption key. The receiving computer uses this same key to unscramble the data. If
you are connecting to an existing network, use the encryption key provided by the
administrator of the wireless network. If you are setting up your own network you can
make up your own key and use it on each computer.
Identifying a Wireless Network
Depending on the size and components of a wireless LAN, there are many ways to identify a
wireless LAN:
• The Network Name or Service Set Identifier (SSID)—Identifies a wireless network. All
wireless devices on the network must use the same SSID.
• Extended Service Set Identifier (ESSID)—A special case of SSID used to identify a
wireless network that includes access points.
• Independent Basic Service Set Identifier (IBSSID)—A special case of SSID used to
identify a network of wireless computers configured to communicate directly with one
another without using an access point.
• Basic Service Set Identifier (BSSID)—A unique identifier for each wireless device.
The BSSID is the Ethernet MAC address of the device.
• Broadcast SSID—An access point can respond to computers sending probe packets
with the broadcast SSID. If this feature is enabled on the access point, any wireless
user can associate with the access point by using a blank (null) SSID.
Surveying the Site of Your Wireless LAN
Conducting a site survey for your wireless LAN is the most crucial step in the process of setting
up a wireless network. It greatly reduces the amount of troubleshooting you will have to do once
you have the wireless LAN set up and ready for connection testing. To conduct a site survey,
you will need the following tools:
• An access point (or laptop computer) that is set up to be the transmitter. It should be
mounted near and at the same height as the designated location of your wireless LAN.
• A laptop that will act as the mobile receiver. It must contain your site survey software.
• An area or building map, which will be used to plot the strength of your signals.
Once you have the tools you need, you are ready to survey the inside of the building. Launch
the site survey software on the mobile receiver laptop and carry it around in the intended
wireless LAN area to test the signal strength. Be sure to also check the signal strength of each
intended access point location. If you encounter problems while surveying the site, make sure
your transmitter laptop is not located on a wall containing metal, such as an air-conditioning
duct, which will interfere with the range of your signal. Simply move the transmitter and test the
signal strength again. For users to have seamless coverage when moving from access point to
access point, the signal levels at each point must overlap. There is software available that will
seamlessly hand off changing signal levels from one access point to another.
Your building's infrastructure can sometimes interfere with the microwave signal, but finding the
location and cause of the interference will allow you to figure out the best place to mount your
access points for optimal area coverage. Microwave signals travel in all directions, which means
there is one access point for a multi-floor building. However, the range is highly dependent on
the material used to construct the flooring, especially metal materials. Once your signal strength
is strong inside the building, you are ready to check the strength outside the building. To do so,

simply carry the mobile receiver laptop as far down the street or around the building as you can
go without losing significant signal strength.
If possible, you should be aware of the types of networks being used by the companies on the
floors above and below you, so that you can work together in harmony. With wireless networks,
security is very important and if you communicate with those around you, you are better
prepared to select the right channels, as well as the best location for access points.
Factors Affecting Range
Although access points can transmit signals up to 60 feet away in an area with many walled
barriers or as much as 500 feet away in a large open area, the range is affected by the
following factors:
• Building materials, such as steel and drywall, can shorten the range of the radio signals.
• Physical layout of the area can interfere with the signals and cause them to be dropped.
• Electronic noise from cell phones, microwave ovens, or other devices on the same
frequency can interfere with the transmission of the signals.
• Range is inversely proportional to data rate, so the faster that the signals are sent, the
less distance they will travel.
Taking these factors into consideration when you survey the site for your WLAN is key to
providing all of your users with undisturbed mobile connectivity. Using multiple access points will,
of course, reduce the impact of these factors if your area has dividing walls throughout.
Stronger Security
Although wireless networks are easy to use, the main issue lies with security. Even if you
enable the security settings defined in the 802.11b standard, as well as the security settings of
your hardware, your network is still vulnerable. There are a few things you can do to make it
more difficult for outsiders to access your network:
• Change the default network name of your WLAN. Every manufacturer's default settings
are public knowledge.
• Do not allow the name of your network to be broadcasted by your access points. This
makes it more difficult for hackers to identify your network.
• Enable Wired Equivalent Privacy (WEP) encryption, which is the same security feature
used by online shopping websites.
• Change your encryption keys as often as possible. Temporal Key Integrity Protocol
(TKIP), which is being developed by a IEEE task group, will change the keys
automatically.
• Enable MAC address filtering so that each access point can generate a list of approved
MAC addresses for your WLAN.
• If you have a small network, use virtual private network encryption for additional security.
If you have a large network, you may want to install a gateway between your access
points and network clients.
2.Software Installation
Installing Drivers and Intel(R) PROSet Software
See the instructions for your operating system:

-Installation under Windows XP
Preliminary Notes
The installation instructions in this section are based on the following assumptions:
• The wireless adapter hardware has already been installed in the computer in
accordance with the computer manufacturer's instructions.
• The computer has not been powered on since the hardware installation was completed.
• No other wireless LAN card is installed in this computer.
To install the driver before installing hardware, use Start > Run and browse to the file
SetupWLD.exe in the path PROW7100\WINXP on the Intel CD. After running SetupWLD.exe,
shut down the computer and install the hardware. When the computer restarts, the driver will be
automatically installed.
Before proceeding, make sure that you are operating Windows XP with administrative
rights. If you log in to Windows XP without administrative rights, you may run into problems
during the installation.
The Intel(R) PROSet utility or the Windows XP wireless configuration feature can be used
to configure wireless network settings. The instructions below include steps for installing the
Intel(R) PROSet utility and for turning off the Windows XP configuration feature. If you do not
turn off the Windows XP feature, you will not be able to use Intel(R) PROSet to configure
wireless network settings. For information on how to use the Windows XP feature, see your
Windows XP documentation.
Driver Installation
To install drivers under Windows* XP, follow these steps:
1. Power up the computer in which the wireless adapter hardware has just been installed.
2. Log in with administrative rights if prompted by Windows XP.
3. Wait for Windows to detect the newly installed hardware and display the Found New
Hardware Wizard dialog. Verify that Install the software automatically
(Recommended) is selected. If Windows does not detect the new hardware, see
Troubleshooting.
4. Insert the Intel CD into your CD drive. The New Hardware Found Wizard searches for
the correct driver files and copies them to your hard drive.
5. On the Network Name screen, click Next to accept the default Network Name (SSID),
or enter a specific SSID for your network, then click Next.
6. On the
Data Encryption screen, click Next to accept the default encryption setting
None, or enter specific encryption settings for your network, then click Next.
7. On the Found New Hardware Wizard screen, click Finish. Proceed to disable the
Windows XP wireless configuration feature.
Disable Windows XP Wireless Configuration (Required)
To disable the Windows XP wireless configuration feature so that you can use Intel(R) PROSet
for wireless configuration, continue as follows:
Instructions are written for use with the Windows XP Start Menu and Control Panel
Category View, not with "Classic" Start Menu or Control Panel views.

8. Click Start and Control Panel.
9. On the Pick a category screen, click Network and Internet Connections, then under
the heading or pick a Control Panel icon click Network Connections.
10. In the Network Connections window, right-click your Wireless Network Connection
and select Properties.
11. Select the Wireless Networks tab.
12. Click to clear ("deselect") the check box Use Windows to configure my wireless
network settings, then click OK on the Wireless Network tab. Do not click any other
tabs. Continue with the installation of Intel(R) PROSet.
Intel(R) PROSet Installation (Required)
Continue with the following steps to install the Intel(R) PROSet wireless configuration utility
(required):
Some versions of this product do not support the Intel(R) PRO Network Connections
menu screen for installation of utility software. If the Intel(R) PRO Network Connections menu
screen does not appear, or if it does not have a menu item for Wireless LAN Adapters, you can
start the Intel(R) PROSet installer manually using Start > Run and browsing to the file
PROSet.msi in the path APPS/PROSet/2K-NET32 on the Intel CD supplied with the product.
Skip Steps 13 and 14 below and continue with Step 15.
13. Display the Intel(R) PRO Network Connections screen by removing and re-inserting
the Intel CD, or by running autorun.exe from the CD. Click Wireless LAN Adapters.
14. On the
Intel PRO/Wireless LAN Adapters menu screen, click Install Software.
15. On the
Welcome to the InstallShield Wizard for Intel(R) PROSet screen, click Next.
16. On the License Agreement screen, after reading the license agreement, select I
accept the terms in the license agreement and click Next.
17. On the Setup Type screen, select Typical and then click Next. This is the
recommended setting for a first-time installation.
18. On the Ready to Install the Program screen click Install.
19. After the software is installed on your computer, click Finish. Click Exit to close the
Intel(R) PRO Network Connections screen or leave it open if you wish to install
Wireless Administration Tools.
20. To launch Intel(R) PROSet, double-click the Intel(R) PROSet icon in the system tray or
follow the path Start > Programs > Intel Network Adapters > Intel(R) PROSet. For
additional information on the program, press F1 or click Help while the program is
running.
Administration Tools Installation (Optional)
Continue with the following steps to install the Intel(R) Wireless Administration Tools Site
Survey and AP Discovery (optional):
Some versions of this product do not support the Intel(R) PRO Network Connections
menu screen for installation of the Administration Tools. If the Intel(R) PRO Network
Connections menu screen does not appear, or if it does not have a menu item for Wireless LAN
Adapters, you can start the Administration Tools installer manually using Start > Run and

browsing to the file APAdmin.msi in the path APPS/PROSet/2K-NET32 on the Intel CD
supplied with the product. Skip Steps 21 and 22 below and continue with Step 23.
21. On the
Intel(R) PRO Network Connections screen, click Wireless LAN Adapters.
You can display this screen by removing and re-inserting the Intel CD, or by
running autorun.exe from the CD.
22. On the Intel PRO/Wireless LAN Adapters menu screen, click Install AP Admin Tools.
23. On the Welcome to the InstallShield Wizard for Intel(R) Wireless Administration
Tools screen, click Next.
24. On the
License Agreement screen, after reading the license agreement, select I
accept the terms in the license agreement and click Next.
25. On the Setup Type screen, verify that Typical is selected, then click Next.
26. On the Ready to Install the Program screen click Install.
27. After the software is installed on your computer, click Finish. Click Exit to close the
Intel(R) PRO Network Connections screen.
28. To launch the Wireless Administration Tools, follow the path Start > Programs >
Intel(R) PRO Wireless > Access Point Administration Tools and select AP
Discovery or Site Survey. For additional information on either program, press F1 or
click Help while the program is running.
-Installation under Windows 2000
Preliminary Notes
The installation instructions in this section are based on the following assumptions:
• The wireless adapter hardware has already been installed in the computer in
accordance with the computer manufacturer's instructions.
• The computer has not been powered on since the hardware installation was completed.
• No other wireless LAN card is installed in this computer.
To install the driver before installing hardware, use Start > Run and browse to the file
SetupWLD.exe in the path PROW7100\WIN2K on the Intel CD. After running SetupWLD.exe,
shut down the computer and install the hardware. When the computer restarts, the driver will be
automatically installed.
After loading the Windows 2000 operating system, be sure to log in with administrative
rights. If you log in to Windows 2000 without administrative rights, you may run into problems
during the installation.
During initial adapter installation and configuration, it may take up to two minutes for
adapter settings to be confirmed.
Driver Installation
To install driver software in Windows* 2000, follow these steps:

1. Power up the computer in which the wireless adapter hardware has just been installed.
2. Log in with administrative rights when prompted by Windows 2000.
3. Wait for Windows to detect the newly installed hardware and display the Found New
Hardware Wizard dialog. If Windows does not detect the new hardware, see
Troubleshooting.
4. Insert the Intel CD-ROM into your CD-ROM drive. If the Intel(R) PRO Network
Connections menu screen appears, leave it open and click the Found New Hardware
Wizard dialog to make that the active window.
5. On the Install Hardware Device Drivers screen verify that Search for a suitable
driver for my device (recommended) is selected, then click Next.
6. When the Locate Driver Files dialog appears, verify that the item CD-ROM drives is
checked and click Next.
7. When the Driver Files Search Results dialog appears, indicating that a driver was
found, click Next.
8. On the Network Name screen, click Next to accept the default Network Name (SSID),
or enter a specific SSID for your network, then click Next.
9. On the
Data Encryption screen, click Next to accept the default encryption setting
None, or enter specific encryption settings for your network, then click Next.
10. On the Found New Hardware Wizard screen, click Finish. Proceed to install Intel(R)
PROSet.
Intel(R) PROSet Installation (Required)
Continue with the following steps to install the Intel(R) PROSet wireless configuration utility
(required):
Some versions of this product do not support the Intel(R) PRO Network Connections
menu screen for installation of utility software. If the Intel(R) PRO Network Connections menu
screen does not appear, or if it does not have a menu item for Wireless LAN Adapters, you can
start the Intel(R) PROSet installer manually using Start > Run and browsing to the file
PROSet.msi in the path APPS/PROSet/2K-NET32 on the Intel CD supplied with the product.
Skip Steps 11 and 12 below and continue with Step 13.
11. On the Intel(R) PRO Network Connections screen, click Wireless LAN Adapters.
This screen may have been launched in step 4 above. If the screen is not visible
when you close the Found New Hardware Wizard dialog, display it by removing and
re-inserting the Intel CD, or by running autorun.exe from the CD.
12. On the
Intel PRO/Wireless LAN Adapters menu screen, click Install Software.
13. On the Welcome to the InstallShield Wizard for Intel(R) PROSet screen, click Next.
14. On the License Agreement screen, after reading the license agreement, select I
accept the terms in the license agreement and click Next.
15. On the
Setup Type screen, verify that Typical is selected, then click Next. This is the
recommended setting for a first-time installation.
16. On the Ready to Install the Program screen click Install.

17. After the software is installed on your computer, click Finish. Click Exit to close the
Intel(R) PRO Network Connections screen or leave it open if you wish to install
Wireless Administration Tools.
18. To launch Intel(R) Intel(R) PROSet, double-click the Intel(R) PROSet icon in the system
tray or follow the path Start > Programs > Intel Network Adapters > Intel(R) PROSet.
For additional information on the program, press F1 or click Help while the program is
running.
During initial adapter installation and configuration, it may take up to two minutes for
adapter settings to be confirmed.
Administration Tools Installation (Optional)
Continue with the following steps to install the Intel(R) Wireless Administration Tools Site
Survey and AP Discovery (optional):
Some versions of this product do not support the Intel(R) PRO Network Connections
menu screen for installation of the Administration Tools. If the Intel(R) PRO Network
Connections menu screen does not appear, or if it does not have a menu item for Wireless LAN
Adapters, you can start the Administration Tools installer manually using Start > Run and
browsing to the file APAdmin.msi in the path APPS/PROSet/2K-NET32 on the Intel CD
supplied with the product. Skip Steps 19 and 20 below and continue with Step 21.
19. On the
Intel(R) PRO Network Connections screen, click Wireless LAN Adapters.
This screen may have been launched in step 4 above. If the screen is not visible
when you close the Found New Hardware Wizard dialog, display it by removing and
re-inserting the Intel CD, or by running autorun.exe from the CD.
20. On the Intel PRO/Wireless LAN Adapters menu screen, click Install AP Admin
Tools.
21. On the Welcome to the InstallShield Wizard for Intel(R) Wireless Administration
Tools screen, click Next.
22. On the
License Agreement screen, after reading the license agreement, select I
accept the terms in the license agreement and click Next.
23. On the Setup Type screen, verify that Typical is selected, then click Next.
24. On the Ready to Install the Program screen click Install.
25. After the software is installed on your computer, click Finish. Click Exit to close the
Intel(R) PRO Network Connections screen.
26. To launch the Wireless Administration Tools, follow the path Start > Programs >
Intel(R) PRO Wireless > Access Point Administration Tools and select AP
Discovery or Site Survey. For additional information on either program, press F1 or
click Help while the program is running.
-Installation under Windows NT 4.0
Preliminary Notes

The installation instructions in this section are based on the following assumptions:
• The wireless adapter hardware has already been installed in the computer in
accordance with the computer manufacturer's instructions.
• The computer has not been powered on since the hardware installation was completed.
• No other wireless LAN card is installed in the computer in which the Mini PCI Adapter
hardware has been installed.
Install Network Drivers for Windows* NT* 4.0
NOTE: Before installing drivers, install Service Pack 6 or later. Advanced features for
Intel adapters require Service Pack 6a or later.
NOTE: Use the following information if NT Networking has already been installed on the
PC. If NT Networking is not installed, please refer to your Windows NT documentation or
consult your network administrator for instructions. Also refer to your Windows NT
documentation for information about installing the TCP/IP protocol.
1. Power up the computer in which the wireless adapter hardware has just been installed.
2. Wait for Windows NT to start, then log in as administrator.
3. Insert the Intel CD into your CD-ROM drive. If the Intel(R) PRO Network Connections
screen displays, you may disregard it or close it (you will redisplay it later to install
Intel(R) PROSet II).
4. Click Start, Settings, Control Panel, then double-click the Network icon.
5. When the Networking dialog appears, select the Adapters tab and click the Add button.
6. Click the Have Disk button after the available network adapters display.
7. Enter the path D:\PROW2100\WINNT4\ (where D: is your CD-ROM drive) and click OK.
8. Select “Intel(R) PRO/Wireless 2100 Mini PCI Adapter” from the list of supported
adapters and click OK.
9. If prompted for additional Windows NT files, re-enter the path to your CD drive (for
example, D:\).
10. The Adapter Properties dialog displays. Click the Configure button.
11. On the Wireless Network tab, click Next to accept the default Network Name (SSID),
or enter a specific SSID for your network, then click OK to continue. (Default setting
under the Advanced button is no security; consult your network administrator if security
is required.)
12. Click Close.
13. Enter TCP/IP settings for your network and click OK.
14. When prompted to restart the computer, remove the CD-ROM and click Yes.

15. After the computer has restarted, double-click the Network Neighborhood icon on
your desktop. Make sure that you have access to the network. If you can log on your
adapter has been properly installed.
16. Proceed to Install Intel(R) PROSet II.
Install Intel(R) PROSet II (Required)
Intel Intel(R) PROSet II enables you to test and configure Intel network adapters on computers
running Windows* NT with Service Pack 5 or later. For details about installing Intel Intel(R)
PROSet II, see the instructions below.
When you run the Intel(R) PROSet Installer, it checks to see if a previously installed
version of Intel(R) PROSet exists on your computer. If another installation is detected, you will
be asked to remove it before proceeding with the installation of Intel(R) PROSet II. Use
Add/Remove Programs in the Control Panel to find and remove any previous versions of
Intel(R) PROSet software.
Some versions of this product do not support the Intel(R) PRO Network Connections
menu screen for installation of Intel(R) PROSet II. If the Intel(R) PRO Network Connections
menu screen does not appear when you insert the Intel CD, or if it appears but does not have a
menu item for Wireless LAN Adapters, you can start the Intel(R) PROSet II installer manually
using Start > Run and browsing to the file WSetup.exe in the path APPS\PROSet\WINNT4 on
the Intel CD. Then skip to Step 4 below and continue with the installation.
1. Insert the Intel CD into your CD-ROM drive. The Intel(R) PRO Network Connections
screen displays. (If it doesn't display, use Start, Run and launch the file autorun.exe
from the Intel CD.)
2. On the Intel(R) PRO Network Connections screen, click Wireless LAN Adapters.
3. On the Intel PRO/Wireless LAN Adapters menu screen, click Install Software.
4. On the Welcome to the InstallShield Wizard for Intel(R) PROSet screen, click Next.
5. On the License Agreement screen, after reading the license agreement, select I
accept the terms in the license agreement and click Next.
6. On the Setup Type screen, verify that Typical is selected, then click Next. This is the
recommended setting for a first-time installation. Click Custom if you wish to install
Intel(R) PROSet in a nondefault location.
7. On the Ready to Install the Program screen click Install.
8. After the software is installed on your computer, click Finish. Click Exit to close the
Intel(R) PRO Network Connections screen, if displayed.
9. To launch Intel(R) PROSet II, double-click the Intel(R) PROSet II icon in the system tray
or in the Control Panel. For additional information, press F1 or click Help while the
program is running.
10.
Restart the computer if prompted.
Install Administration Tools (Optional)
Continue with the following steps to install the Intel(R) Wireless Administration Tools Site
Survey and AP Discovery (optional):
1. Insert the Intel CD into your CD-ROM drive. The Intel(R) PRO Network Connections
screen displays. (If it doesn't display, use Start, Run and launch the file autorun.exe
from the Intel CD.)
2. On the Intel(R) PRO Network Connections screen, click Wireless LAN Adapters.
3. On the Intel PRO/Wireless LAN Adapters menu screen, click Install AP Admin
Tools.
4. On the
Welcome to the InstallShield Wizard for Intel(R) Wireless Administration
Tools screen, click Next.
5. On the License Agreement screen, after reading the license agreement, select I
accept the terms in the license agreement and click Next.
6. On the Setup Type screen, verify that Typical is selected, then click Next.
7. On the Ready to Install the Program screen click Install.
8. After the software is installed on your computer, click Finish. Click Exit to close the
Intel(R) PRO Network Connections screen.
9. To launch the Wireless Administration Tools, follow the path Start > Programs >
Intel(R) PRO Wireless > Access Point Administration Tools and select AP
Discovery or Site Survey. For additional information on either program, press F1 or
click Help while the program is running.
-Installation under Windows Me
Preliminary Notes
The installation instructions in this section are based on the following assumptions:
• The wireless adapter hardware has already been installed in the computer in
accordance with the computer manufacturer's instructions.
• The computer has not been powered on since the hardware installation was completed.
• No other wireless LAN card is installed in this computer.
To install the driver before installing hardware, use Start > Run and browse to the file
SetupWLD.exe in the path PROW7100\WINSE-ME on the Intel CD. After running
SetupWLD.exe, shut down the computer and install the hardware. When the computer restarts,
the driver will be automatically installed.
Driver Installation
To install the software in Windows* Me (Millennium Edition), follow these steps:
1. Power up the computer in which the wireless adapter hardware has just been installed.
2. Wait for Windows to detect the newly installed hardware and display the Add New
Hardware Wizard dialog. DO NOT click Next. Verify that Automatic search for a
better driver (Recommended) is selected. If Windows does not detect the new
hardware, see Troubleshooting.

3. Insert the Intel CD into your CD drive. Windows installs the driver from the CD. If the
installation does not start automatically, click Next on the Add New Hardware Wizard
screen.
4. On the Network Name screen, click Next to accept the default Network Name (SSID)
101, or enter a specific SSID for your network, then click Next.
5. On the
Data Encryption screen, click Next to accept the default encryption setting
None, or enter specific encryption settings for your network, then click Next.
6. Click Finish on the Add New Hardware Wizard screen when the driver installation is
complete.
7. When prompted to restart the computer, click No. You will restart it manually later.
Proceed to install Intel(R) PROSet.
Intel(R) PROSet Installation (Required)
To install the Intel(R) PROSet utility, continue with the following steps:
Some versions of this product do not support the Intel(R) PRO Network Connections
menu screen for installation of utility software. If the Intel(R) PRO Network Connections menu
screen does not appear, or if it does not have a menu item for Wireless LAN Adapters, you can
start the Intel(R) PROSet installer manually using Start > Run and browsing to the file
PROSet.msi in the path APPS/PROSet/WN98SEME on the Intel CD supplied with the product.
Skip Steps 8 and 9 below and continue with Step 10.
8. Display the Intel(R) PRO Network Connections screen by removing and re-inserting
the Intel CD, or by running autorun.exe from the CD. Click Wireless Adapters.
9. On the
Intel PRO/Wireless LAN Adapters menu screen, click Install Software.
10. On the Welcome to the InstallShield Wizard for Intel(R) PROSet II screen, click Next.
11. On the License Agreement screen, after reading the license agreement, select I
accept the terms in the license agreement and click Next.
12. On the
Setup Type screen, select Typical and then click Next. This is the
recommended setting for a first-time installation.
13. On the Ready to Install the Program screen click Install.
14. After the software is installed on your computer, click Finish.
15. When prompted to restart the computer, click Yes.
16. To launch Intel(R) PROSet, double-click the Intel(R) PROSet icon in the system tray or
follow the path Start > Programs > Intel Network Adapters > Intel(R) PROSet. For
additional information on the program, press F1 or click Help while the program is
running.
Administration Tools Installation (Optional)
After restarting the computer, continue with the following steps to install the Intel(R) Wireless
Administration Tools Site Survey and AP Discovery (optional):
Some versions of this product do not support the Intel(R) PRO Network Connections
menu screen for installation of the Administration Tools. If the Intel(R) PRO Network
Connections menu screen does not appear, or if it does not have a menu item for Wireless LAN
Adapters, you can start the Administration Tools installer manually using Start > Run and

browsing to the file APAdmin.msi in the path APPS/PROSet/WN98SEME on the Intel CD
supplied with the product. Skip Steps 17 and 18 below and continue with Step 19.
17. On the
Intel(R) PRO Network Connections screen, click Wireless LAN Adapters.
You can display this screen by removing and re-inserting the Intel CD, or by
running autorun.exe from the CD.
18. On the Intel PRO/Wireless LAN Adapters menu screen, click Install AP Admin Tools.
19. On the Welcome to the InstallShield Wizard for Intel(R) Wireless Administration
Tools screen, click Next.
20. On the License Agreement screen, after reading the license agreement, select I
accept the terms in the license agreement and click Next.
21. On the Setup Type screen, verify that Typical is selected, then click Next.
22. On the
Ready to Install the Program screen click Install.
23. After the software is installed on your computer, click Finish.
24. To launch the Wireless Administration Tools, follow the path Start > Programs >
Intel(R) PRO Wireless > Access Point Administration Tools and select AP
Discovery or Site Survey. For additional information on either program, press F1 or
click Help while the program is running.
-Installation under Windows 98SE
Preliminary Notes
The installation instructions in this section are based on the following assumptions:
• The wireless adapter hardware has already been installed in the computer in
accordance with the computer manufacturer's instructions.
• The computer has not been powered on since the hardware installation was completed.
• No other wireless LAN card is installed in the computer.
To install the driver before installing hardware, use Start > Run and browse to the file
SetupWLD.exe in the path PROW7100\WINSE-ME on the Intel CD. After running
SetupWLD.exe, shut down the computer and install the hardware. When the computer restarts,
the driver will be automatically installed.
Driver Installation
To install the software in Windows* 98SE, follow these steps:
1. Power up the computer in which the wireless adapter hardware has just been installed.
2. Wait for Windows to detect the newly installed hardware and display the Add New
Hardware Wizard dialog. Click Next. If Windows does not detect the new hardware,
see Troubleshooting.
3. Insert the Intel CD into your CD drive.

4. On the New Hardware Wizard screen, select Search for the best driver for you
device (Recommended), and click Next, then select CD drive and click Next.
5. On the
Network Name screen, click Next to accept the default Network Name (SSID),
or enter a specific SSID for your network, then click Next.
6. On the Data Encryption screen, click Next to accept the default encryption setting
None, or enter specific encryption settings for your network, then click Next.
7. On the
Add New Hardware Wizard screen, click Finish.
8. When prompted to restart the computer, click No. You will restart it manually later.
Proceed to the installation of Intel(R) PROSet.
Intel(R) PROSet Installation (Required)
To install the Intel(R) PROSet utility, continue with the following steps:
Some versions of this product do not support the Intel(R) PRO Network Connections
menu screen for installation of utility software. If the Intel(R) PRO Network Connections menu
screen does not appear, or if it does not have a menu item for Wireless LAN Adapters, you can
start the Intel(R) PROSet installer manually using Start > Run and browsing to the file
PROSet.msi in the path APPS/PROSet/WN98SEME on the Intel CD supplied with the product.
Skip Steps 9 and 10 below and continue with Step 11.
9. Display the Intel(R) PRO Network Connections screen by removing and re-inserting
the Intel CD, or by running autorun.exe from the CD. Click Wireless Adapters.
10. On the Intel PRO/Wireless LAN Adapters menu screen, click Install Software.
11. On the Welcome to the InstallShield Wizard for Intel(R) PROSet II screen, click Next.
12. On the License Agreement screen, after reading the license agreement, select I
accept the terms in the license agreement and click Next.
13. On the Setup Type screen, select Typical and then click Next. This is the
recommended setting for a first-time installation.
14. On the Ready to Install the Program screen click Install.
15. After the software is installed on your computer, click Finish.
16. When prompted to restart the computer, click Yes.
17. To launch Intel(R) PROSet, double-click the Intel(R) PROSet icon in the system tray or
follow the path Start > Programs > Intel Network Adapters > Intel(R) PROSet. For
additional information on the program, press F1 or click Help while the program is
running.
Administration Tools Installation (Optional)
After restarting the computer, continue with the following steps to install the Intel(R) Wireless
Administration Tools Site Survey and AP Discovery (optional):
Some versions of this product do not support the Intel(R) PRO Network Connections
menu screen for installation of the Administration Tools. If the Intel(R) PRO Network
Connections menu screen does not appear, or if it does not have a menu item for Wireless LAN
Adapters, you can start the Administration Tools installer manually using Start > Run and
browsing to the file APAdmin.msi in the path APPS/PROSet/WN98SEME on the Intel CD
supplied with the product. Skip Steps 18 and 19 below and continue with Step 20.
18. On the Intel(R) PRO Network Connections screen, click Wireless LAN Adapters.
You can display this screen by removing and re-inserting the Intel CD, or by
running autorun.exe from the CD.
19. On the
Intel PRO/Wireless LAN Adapters menu screen, click Install AP Admin Tools.
20. On the
Welcome to the InstallShield Wizard for Intel(R) Wireless Administration
Tools screen, click Next.
21. On the License Agreement screen, after reading the license agreement, select I
accept the terms in the license agreement and click Next.
22. On the
Setup Type screen, verify that Typical is selected, then click Next.
23. On the Ready to Install the Program screen click Install.
24. After the software is installed on your computer, click Finish.
25. To launch the Wireless Administration Tools, follow the path Start > Programs >
Intel(R) PRO Wireless > Access Point Administration Tools and select AP
Discovery or Site Survey. For additional information on either program, press F1 or
click Help while the program is running.
3.Using Wireless Profiles in Intel(R) PROSet
A profile is a saved group of network settings. Profiles are displayed in the Profile List in the
Intel(R) PROSet General page. Profiles can be arranged in order of network connection priority.
You can connect to one network using the first profile in the Profile List, then automatically
connect to another network using the next profile. This allows you to stay connected while
roaming freely from one wireless network to another. Although you can assign multiple profiles
to a single network, you can only use one profile per connection.
Profile general settings include, the network name (SSID), channel, security settings, and
TCP/IP settings. The Networks tab allows you to add, edit and delete profiles.
Creating a New Profile
To add a new profile, use the Profile Wizard sequence of dialogs to configure the profile
contents. The following example uses all of the Profile Wizard dialogs. Some settings may not
be required for all profiles.
To create a new profile and connect to a network:
1. Select the wireless adapter in the left-side pane.
2. From the General page, click the Networks tab.
3. Click the Add button. The General Settings dialog displays.
NOTE: If this is the first time you have created a profile, click the profile named Default in
the Profile List, click the Edit button and rename the default profile in the Profile Name
field on the General page.
Step 1 of 4: General Settings

4. Enter a profile name in the Profile Name field.
5. Enter the network SSID, in the Network Name (SSID) field.
6. Click the operating mode to use, Infrastructure or Ad hoc.
7. The Mandatory AP option is only used if Infrastructure mode is selected. Use this option
to connect to a specific access point. Click the Mandatory AP button, enter the
Ethernet address for the access point. Click OK to save the setting and return to the
General Settings page.
8. Click the Configure TCP/IP and VPN settings checkbox to access the TCP/IP and
VPN settings. If these settings are not required, leave the box unchecked, proceed to
step 9.
9. Check the Enable Auto-Import check box to allow this profile to be imported. Refer to
Automatic Profile Distribution for more information.
10. Click Next.
Step 2 of 4: TCP/IP and VPN Client Settings
11. Use these options to configure TCP/IP and VPN settings for a VPN profile. Click Next
when finished.
Step 3 of 4: Security Settings
12. Select
Open or Shared in the Network Authentication drop-down menu. Open, does not
use any authentication method. Shared uses the WEP key as the authentication
method.
13. Click the
Enable data encryption (WEP) checkbox to configure WEP encryption
settings.
14. Click the Password protect this profile checkbox to assign a password to the profile.
15. Click Next.
Step 4 of 4: Password Protection Settings
16. Click the Password protect this profile checkbox.
17. Enter a password in the Password field.
18. Reenter the same password in the Confirm New Password field.
19. Click the
Back button to change or verify the settings or click Finish when you have
completed the profile settings and return to the Networks page.
20. Click the new profile name shown in the Profile List. Use the up and down arrows to
position the priority of the new profile in the priority list.
21. Click the
Advanced button to set the network connection preferences.
22. Click the Connect button to connect to the network.
23. Click OK to close the Intel(R) PROSet dialog.
Creating a VPN Profile
To create a VPN profile:
1. Select the wireless adapter in the left-side pane.
2. From the General page, click the Networks tab.
3. Select the profile to add VPN settings to from the Profile List.
4. Click the
Edit button and the General page appears.
5. Click the
Network tab.
6. Click the Configure button for the TCP/IP Settings. Make sure that Obtain an IP
address automatically and Obtain DNS address automatically is selected.
7. Click the
Close button to close the dialog.
8. Click the
Configure button for the VPN Client Settings.
9. Click Enable VPN for this profile checkbox.
10. Select the VPN client software from the Available VPN Clients drop-down menu.
11. Select the VPN profile if your VPN client software displays the VPN tunnel name.
12. Click the
Close button to close the dialog.
13. Click
OK on any of the pages to save all the settings and return to the Networks page.
14. Click the VPN profile name shown in the Profile List. Use the up and down arrows to
position the priority of new profile in the priority list.
15. Click the
Connect button to connect to the network. The VPN profile name displays a
connect icon. Note: There must be an IP address assigned before the VPN client
software can be launched. Click the Details button to verify that an IP address has
been assigned.
16. Follow the on-screen instructions and enter your credentials before connecting.
17. Click OK to close the Intel(R) PROSet dialog.
Importing and Exporting Profiles
Note: A password protected profile can be imported and exported, however, before editing the
profile, the password must be entered.
To import profiles:
1. From the General page, click the Networks tab.
2. Click the
Advanced button.
3. Click the Import/Export button.
4. Click the Import button.
5. Locate the profile to import on your hard disk or enter the profile name in the File name
field. The profile extension is .profile.
6. Click the Import to import the profile into the Profile List.
7. Click OK twice to return to the General page.
8. Click OK to close the Intel(R) PROSet dialog.
To export profiles:
1. From the General page, click the Networks tab.
2. Click the Advanced button.
3. Click the profiles to export from the export profile list.
4. Click the
Browse button and select a directory to save the profiles in. Click OK to return
to the previous dialog.
5. Click the Export button to start exporting the profiles.
6. Click
OK twice to return to the General dialog.
7. Click
OK to close the Intel(R) PROSet dialog.
Automatic Profile Distribution
The Enable Auto-Import feature allows a network administrator to distribute a profile
automatically to computers connected to a network. The Enable Auto-Import box is located on
the Profile Wizard dialogs. When the checkbox is checked the profile must be copied to a
specific directory on the host computer, from there it can be distributed to multiple computers.
Once the profile is received by the remote computer it will automatically be available for use
from the Scan profile list. If an attempt is made to edit a distributed profile that is password
protected, a password prompt will appear.
Automatically importing WLAN profiles is accomplished by monitoring the import folder on your
hard disk for new profile files. Only profiles that have the Enable Auto-Import checked on the
Profile Wizard dialog can be automatically imported. If a profile of the same name already exists
in the Profile List, a dialog is displayed from which you can either reject the import, or accept in
which case the existing profile will be replaced. All imported profiles will be placed at the bottom
of the Profile List, and the profile file will be immediately deleted after the import whether the
import was successful or not.
To distribute a profile to other computers on a network:
1. Select a profile to be edited from the Profile List in the Networks page, and click the
Edit button or click the Add button to create a new profile using the Profile Wizard.
2. Check the
Enable Auto-Import checkbox on the General page.
3. Click OK (Edit a profile) or Finish (Add a profile) to save the setting.
4. Copy the profile to the Programs Files/Intel/PROSet/Import directory. The profile is now
ready to distribute to other computers.
Editing an Existing Profile
To edit an existing profile:
1. Select the wireless adapter in the left-side pane.
2. From the General page, click the Networks tab.
3. Click the Edit button. The General page displays.
4. Click on the General, Security, Network and Password tabs to make the necessary
changes for the network profile settings:
5. Click
OK on any of the pages to save all the settings and return to the Networks page.
6. Click the new profile name shown in the Profile List. Use the up and down arrows to
position the priority of new profile in the priority list.
7. Click the Advanced button to set the network connection preferences.
8. Click the Connect button to connect to the network.
9. Click
OK to close the Intel(R) PROSet dialog.
Deleting a Profile
To delete a profile:
1. Select the wireless adapter in the left-side pane.
2. From the General page, click the Networks tab.
3. Click the profile to be deleted from the Profile List.
4. Click the Delete button.
5. Click Yes to permanently delete the profile.
Connecting to a Network without a Profile
To connect to an available network without a profile:
1. Select the wireless adapter in the left-side pane.
2. From the General page, click the Networks tab.
3. Click the
Scan button.
4. Select the network profile name with <no profile> shown, and click the Connect button.
5. Click the No, connect me directly without creating a profile option. Note, you can
click Yes, create a profile for this network now to create a profile to be used later.
6. Click
OK to connect.
Connecting to a Network if a Blank SSID displays
If the wireless adapter receives a blank network name (SSID) from a stealth access point, both
the blank SSID and <no profile> display in the available networks list. To associate with a
stealth access point, a new profile must first be created before connection. After connection
both the blank SSID and the associated SSID can be viewed in the available networks list.
To connect to an access point that transmits a blank network name (SSID) in the Available
Networks list:
1. From the General page, click the Networks tab.
2. Click the
Scan button.
3. Select the network name with a blank SSID and <no profile> shown in the Available
Networks list.
4. Click the Connect button.
5. Click the Yes, create a profile for this network now option.
6. The Profile Wizard dialog displays. Enter a profile name and Network Name (SSID) and
security settings if required. Click Finish to save the profile settings and return to the
Networks page.
7. Select the new profile from the profile list and click Connect.

Profile Connection Preferences
To access the profile connection preference option:
1. From the General page, click the Networks tab.
2. Click the Advanced button.
3. Under the Auto-connection heading, click the one of the following options:
• Connect to available networks using profiles only (Default setting): Use the profiles in
the Profile List to connect to any available network.
• Connect to any available network if no matching profile is found: Connect to any
available network without using a profile from the Profile List.
4. Click OK to save the setting and return to the previous dialog.
Loading a Profile from the Task Tray
To load a profile from the Task Tray:
1. Right-click Intel(R) PROSet icon in the task tray.
2. Select the Intel PRO/Wireless LAN 7100 3B Mini PCI Adapter or the Intel
PRO/Wireless LAN 2100 3B Mini PCI Adapter.
3. Click
Select Profile and select the profile to be launched.
4.Connecting to a Network using Intel(R) PROSet
Connecting to a Network Automatically
The Configuration Service feature operates in background to automatically display available
networks not listed in the Profile List. This method provides automatic connection in a 2.4 or
5GHz environment to available networks in the range of your wireless adapter. The
Configuration Service constantly monitors your wireless adapter's connection status. If no
matching profiles are found in the Profile List for a network, a dialog automatically displays the
available network access points and computers (ad hoc mode) within range of the wireless
adapter. The Configuration Service can also be used if there is more than one wireless adapter
installed using 802.11a and 802.11b bands.
The Configuration Service features:
• The Configuration Service is launched when you log on to your computer.
• No active profile switching will be performed. Once the adapter is associated with the
access point, if a higher priority profile becomes available, no switching will occur.
• The Configuration Service is only be available if the Intel(R) PROSet is installed.
• If a connection to an access point cannot be made using any of the profiles in the
Profile List, a dialog will display the available networks.
• If there are multiple profiles listed for an available network, a dialog box will list the
profiles for you to choose from.
• If an available network is detected with WEP encryption and authentication, a dialog for
setting up WEP encryption displays before the connection is made.
The Configuration Service can be used in two ways:
1. Connect to available network using profiles only: In this mode the Configuration Service
attempts to connect to a network access point using profiles from the Profile List only. If
no matching profile is found, a dialog appears that lists the available networks. You can
also close this dialog without connecting by clicking the Cancel button. The adapter will
remain unassociated, and the list of available networks will NOT be displayed again
unless another available network is detected. This mode is set in the Advanced Setting
options.
2. Connect to any available network if no matching profile found: In this mode the
Configuration Service attempts to connect to a network access point first using profiles
from the Profile List. If no matching profile is found, the Configuration Service
automatically connects to any available network. This mode is set in the Advanced
Setting options.
Enabling Automatic Connection
The Configuration Service also monitors for the "resume status" after a laptop computer
suspend event. When this occurs, the Configuration Service will re-enable the automatic
connection service.
These features can be enabled again after rebooting your computer or after a suspend and
resume cycle.
Enable profile management features: Check this setting in the Advanced Settings options to
manually re-enable the Configuration Service profile management features after being disabled
from the notification dialog when another profile management application is detected. This
option can only be used to re-enable the Configuration Service features, it cannot be used to
manually disable the Configuration Service features. Refer to Profile Switching for more
information.
Profile Management Options
The following Profile Management options can be found in Advanced Settings.
Display available networks when not associated: If no networks are available that match any
profiles in the Profile List, the Configuration Service dialog is displayed, listing the available
networks. By checking "Don’t show this again" option, the dialog listing the available networks
will not be displayed again, if the adapter becomes unassociated. The Configuration Service will
continue to function and attempt to connect, using a profile from the Profile List, or to an
available network depending on the selection mode. This mean that if Connect Using Preferred
Profiles Only is selected and no matching profile is found, then the adapter will remain
unassociated. You can still use the Connect button from the Networks tab to connect to an
available network. The Configuration Service dialog can be re-enabled from the Advanced
Settings options.
Notify when disabling profile management features: Check this box to display the service
disabling notification dialog when another Profile Management service is detected such as
Windows XP Zero Configuration or AAA clients. The notification dialog is displayed, indicating
that another service has been detected and that some of the Intel(R) PROSet management
features will be disabled. From this dialog, you can also choose "Don’t show this again," in
which case the Intel(R) PROSet features will automatically be disabled without notification. This
dialog can be re-enabled from the Advanced Settings options.
Features affected when another profile management application is detected
For AAA Client:
Select OK, and the AAA Client application will manage the adapter. The current connection will
continue with the affected Intel(R) PROSet features show below. To avoid conflicts, the Intel(R)
PROSet profile management features have been temporarily disabled. To re-enable these
features, first disable the other LAN utility and then either:
1. Re-enable from Intel(R) PROSet's Advanced Settings.
2. Resume after a computer suspend.
3. Reboot the computer.
For Windows XP Zero Configuration:
• Select Yes, to disable Windows XP Zero Configuration. Intel(R) PROSet will continue to
manage the
adapter.
• Select No, Windows XP will manage the adapter. The current connection will continue
with the affected Intel(R) PROSet features show below. You can also prevent the dialog
from being displayed again, in which case Windows XP Zero Configuration will
automatically manage the wireless adapter. The notification dialog can be re-enabled
from the Advanced Settings options.
Affected Intel(R) PROSet features:
• The Connect button on the Profile page is non-functioning.
• The Scan button can be used to scan for available networks, however, the Connect
button is non-functioning when used to connect to an available network.
• Ad hoc mode is disabled. The Connect button in the ad hoc connect dialog is non-
functioning.
• Task tray icon menu: Launching an ad hoc profile and applying a profile from the task
tray menu is not available.
NOTE: If the buttons described above are used, the following message displays:
"Another wireless LAN utility is communicating with the Intel(R) PRO/Wireless LAN
adapter. To avoid conflicts, Intel(R) PROSet has temporarily disabled its Profile
Management features."
Scanning for Available Networks
A fast way to connect to a network is to use the Scan button to search for a network access
point in range of your wireless adapter. When a network is found, you can instantly connect
without a profile or create a new profile.
NOTE: Profiles with the Enable Auto-Import feature enabled will also be displayed in the
profile list of available networks. Refer to Automatic Profile Distribution for more
information.
To scan for available networks:
1. From the General page, select the wireless adapter on the left side pane.
2. Select the
Networks tab.
3. Click the
Scan button.
4. The Available Networks dialog displays the names of the available networks.
5. Select the network from the list, and click the Connect button. Click the Refresh button
to refresh the list of available networks.
6. To connect without creating a profile, click No, connect me directly without creating
a profile.

7. To create a new profile using the Profile Wizard, click Yes, create a profile for this
network now.
8. Click
OK to connect to a network.
Connecting to a Network Using an Access Point
An infrastructure network consists of one or more access points and one or more computers
with wireless adapters installed. Each access point must have a wired connection to the Local
Area Network (LAN).
The following describes how to create a new profile using the Profile Wizard and connect to an
access point using the Connect button. You can also connect to a network, by using the Scan
button.
1. From the General page, select the wireless adapter on the left side pane.
2. Click the
Networks tab.
3. Click the
Add button.
4. Enter the profile name in the text box.
5. Enter a network name (SSID) in the text box.
6. Select Infrastructure for the operating mode.
7. Use this option to connect to a specific access point. Click the Mandatory AP button,
enter the Ethernet address for the access point. Click OK to save the setting and return
to the General Settings page.
8. Click the Configure TCP/IP and VPN settings check box and click the Next button to
access the TCP/IP and VPN settings. If these settings are not required, leave the box
unchecked and proceed to step 11.
9. Click the Next button to select the WEP security settings.
10. Click the
Password protect this profile checkbox and click Next button to access the
Password Protection settings. Click Finish after the password information has been
entered. If this option is not required, leave the box unchecked and proceed to step 11.
11. Click OK to save the profile settings and return to the Networks page.
12. After creating the new profile, click the profile in the Profile List. Profiles using
infrastructure mode are indicated by a computer icon next to the profile name.
13. Click the Connect button to connect to the ad hoc network.
Connecting to a Peer-to-Peer (Ad Hoc) Network
In peer-to-peer (ad hoc) mode, you can send and receive information to other computers
without using an access point. Each computer in a peer-to-peer network is called a peer.
To create or join an ad hoc network, enter a personal password. Network related settings
(SSID), operating mode, WEP 128-bit encryption, and IP addresses are automatically created.
Once a network connection is established, after permission rights are given by other computers
in the ad hoc network, you can freely share files. All wireless clients in the ad hoc network must
use the same network name (SSID) and channel number. For a list of allowed 802.11b ad hoc
channels, refer to the Adapter Settings for more information.
NOTE: While scanning with an ad hoc profile set to a specific transmit channel, if an ad
hoc network is found on another channel, you will be connected using the new channel.
The new channel number is displayed in the Adapter Settings.
Connect or Start an Ad Hoc Network
NOTE: For information about connecting to an ad hoc using a profile, refer to Create an
Ad Hoc Profile using the Profile Wizard.
1. Connect using an ad hoc profile. Refer to Creating a New Profile for details. Select an
ad hoc profile from the Profile List and click the Connect button. This method uses a
pre-defined ad hoc profile created by the Profile Wizard. The ad hoc profile is displayed
in the Profile List. When joining an ad hoc network, the transmit channel established by
the first computer is used. This channel may be different than the one selected when
the ad hoc profile was created by the Profile Wizard.
2. Join a one-time ad hoc session without a profile. Refer to Starting an Ad Hoc (peer-to-
peer) Connection below for details. This method does not use a pre-defined profile. To
connect to any ad hoc network, use the Scan button to scan for any ad hoc networks,
enter the password (SSID), then click the Connect button to connect. To end the
session, click the Close button to end the session.
Start an Ad Hoc Network
Refer to Starting an Ad Hoc (peer-to-peer) Connection below for details.
• This method uses your computer's SSID to establish the ad hoc network for other users
to connect to.
• When you are the originator of an ad hoc network, all other users must use the channel
and SSID.
Ending an Ad Hoc Session
To end an ad hoc session, click the Close button. After the session is ended, an attempt is
made to re-connect to the last profile used from the Profile List.
Creating an Ad Hoc Profile Using the Profile Wizard
The following describes how to create a new ad hoc profile using the Profile Wizard and
connect to an ad hoc network. You can also connect to a network, by using the Scan button.
1. From the General page, select the wireless adapter on the left side pane.
2. Click the Networks tab.
3. Click the Add button.
4. Enter the profile name in the text box.
5. Enter a network name (SSID) in the text box.
6. Select
Ad Hoc for the operating mode.
7. Click the Configure TCP/IP and VPN settings check box and click the Next button to
access the TCP/IP and VPN settings. If these settings are not required, leave the box
unchecked and proceed to step 11.
8. Click the Next button to select the WEP security settings.
9. Click the Password protect this profile checkbox and click Next button to access the
Password Protection settings. Click Finish after the password information has been
entered. If this option is not required, leave the box unchecked and proceed to step 11.
10. Click OK to save the profile settings and return to the Networks page.
11. Set the Transmit channel from the Adapter tab: Channel 7 is the default transmit
channel. Unless the other computers in the ad hoc network use a different channel,
there is no need to change the default channel. Click the Adapter tab, and click the
Configure button under Ad Hoc Channel Selection. Choose the operating band select a
channel. Click OK to save the setting.
12. Select the Networks tab
13. After creating the new profile, click the profile in the Profile List. Profiles using
infrastructure mode are indicated by a computer icon next to the profile name.
14. Click the
Connect button to connect to the ad hoc network.
Starting an Ad Hoc (peer-to-peer) Connection
To communicate properly, all computers/peers on an ad hoc network must have Intel wireless
adapters installed. To connect to an ad hoc network for a one-time session:
1. From the General page, select the wireless adapter on the left side pane.
2. Click the Networks tab.
3. Click the Start button.
4. Enter the password (SSID) for your computer in the text box. If you establish the ad hoc
network, then this SSID and assigned transmit channel must be used by other users to
connect to the ad hoc network. The entered SSID can also be the same as the other
users in the established ad hoc network, in this case your computer will join the ad hoc
network.
5. To join the ad hoc network, select the peer name from the displayed list of computers in
the ad hoc network and click the Connect button
6. To establish an ad hoc network, after your computer's SSID is entered, click the
Connect button to scan for other users in the ad hoc network
7. Under Send Files, files can be sent to another computer in the ad hoc network. To
send a file, click the Send File button. Locate the file you want to sent, and click Send.
8. Click the
Close button to end the ad hoc session.
Disconnecting from a Network
To disconnect from a network, turn the radio to OFF from the General page in Intel(R) PROSet.
Switching the Adapter Off and On
The wireless adapter can be switched off and on from the optional hardware radio switch on
your laptop computer, Intel(R) PROSet application, and the Windows operating system.
Note: When your laptop is switched on, the radio is constantly transmitting signals. In certain
situations, such as in a plane, signals from the radio may cause interference. Use the following
methods if you need to disable the radio and use your laptop without emitting radio signals.
Using the optional hardware radio on/off switch
If your laptop computer has an optional external hardware switch installed, it can be used to
switch the radio on or off. Refer to the laptop manufacturer for more information about this
switch. If you have Intel(R) PROSet installed, the current state of the radio is displayed on the
General page.
Using Intel(R) PROSet to switch the radio on/off
From Intel(R) PROSet, the radio can be switched on or off from the General page. The current
state of the radio is displayed, which also includes the state of the optional hardware radio
switch.
Hardware radio switch On/Off
Depending on the current state of the external optional hardware switch, displays on or off on
the General page.
Switching the radio On/Off
Note: When your laptop is switched on, the radio is constantly transmitting signals. In certain
situations, such as in a plane, signals from the radio may cause interference.
To switch the radio OFF: From the General page, click the Off button. next to Switch Radio
On/Off.
• The wireless adapter is not associated with the network when the radio is off.
• Intel(R) PROSet can be used to edit or add profile contents when the radio is off.
To switch the radio ON: From the General page, click the On button, next to Switch Radio
On/Off.
When the radio is on, an attempt will be made to associate with the network access point using
the last profile. If the adapter cannot connect to the access point, the Configuration Service will
attempt to find an available network. Refer to Configuration Service for more information.
Switching the radio on or off from the Task Tray Icon
Right-click on the Intel(R) PROSet task tray icon and click Switch radio Off.
Using the Windows operating system to switch the radio on/off
The radio can be switched on or off via the Windows operating system from the Device
Properties dialog.
Switching Between Wired and Wireless Adapters
Adapter switching enables your computer to automatically switch between wired and the
wireless adapter, so your laptop computer can maintain the best possible connection to the
network while moving from one location to another. When Adapter Switching is enabled, DHCP
is disabled on all other wired adapters except for the adapter currently being used. However,
connection is possible using another wired adapter using an auto IP address setting.
Adapter switching switches between wired and wireless adapters for the following Intel PRO
adapters:
• Wired LAN adapters. This type of adapter connects to a network through an Ethernet
network cable. Adapter Switching supports adapters in the PRO/100 family, including
the PRO/100 Mobile Adapters.
• Intel PRO/Wireless LAN 7100 3B Mini PCI adapter and the Intel PRO/Wireless LAN
2100 3B Mini PCI adapter. These adapter send data to and from the network through
the adapter's antenna.
By default, adapter switching uses the wired Ethernet adapter when both wired and wireless
adapters are present and working. If you detach the wired adapter, adapter switching
automatically switches to the wireless adapter. When you attach an Ethernet cable again,
adapter switching automatically switches back to the wired Ethernet connection.
You can change your wireless preferences from the Advanced Settings dialog and prioritize
your wireless and wired adapters from the Adapter Switching dialog.
You can also install multiple wired adapters, or install two wireless adapters if the network
supports both 802.11a and 802.11b wireless standards. Then when you detach the wired
adapter, your computer uses the wireless adapter that gives the best data rate.
Wireless Preferences
One or more wired adapter and one or two wireless adapter can be installed in the same
computer. Using the adapter switching feature, you can select your priority for a specific type of
adapter, wired or wireless.
If adapter switching is enabled, the installed adapters are selected from a preference list. To
access the network preferences:
1. From the General page, select the wireless adapter on the left side pane.
2. Click the Networks tab.
3. Click the Advanced button.
4. Select your preferences from the options shown.
5. Click OK to save the settings and return to the Profiles dialog.
Adapter Switching Considerations
Consider the following issues when switching adapters:
• Adapter switching requires the use of DHCP. It cannot be used with fixed IP addressing.
• Only Intel wired and wireless adapters are supported when using the Start button to
connect to an ad hoc network.
• Adapter switching cannot be used on a Virtual Private Network (VPN).
• Adapter switching should not be applied while an active data transfer is in progress.
• Intel(R) PROSet determines how many wireless adapters are present in the computer.
• Intel(R) PROSet supports simultaneous wireless adapter operation for the following:
o 2.4 GHz and 5 GHz installed adapters: Supports simultaneous operation in
either ad hoc or infrastructure mode.
o 2.4 GHz and 2.4 GHz installed adapters: Supports simultaneous operation
where one adapter is in ad hoc mode and the other adapter is in infrastructure
mode. Simultaneous operation with both adapters in infrastructure or ad hoc
mode is not be supported.
o The second adapter added is not supported.
o 5 GHz and 5 GHz installed adapters: Supports simultaneous operation where
one adapter is in ad hoc mode and the other adapter is in infrastructure mode.
Simultaneous operation with both adapters in infrastructure mode or ad hoc is
not supported.
o The second adapter added is not supported.
o Maximum of four adapters is supported.
Switching Between 2.4 and 5 GHz Bands
Intel(R) PROSet supports switching between 802.11a (5 GHz) and 802.11b (2.4 GHz) bands.
Using the Advanced Settings options, you can define band priorities.
Changing the Settings for Adapter Switching
If you have two adapters installed, you can define the adapter to be used first. Adapter priorities
can be set in the Adapter Switching dialog.
To change the adapter switching settings:
1. From the General page, select the wireless adapter on the left side pane.
2. Click the
Adapter Switching icon on the left side pane.
3. Click the Adapter Switching checkbox under the Settings heading.
4. Prioritize adapters in the lower adapter display list.
Select an adapter in the Adapter Type list and use the up/down arrows on the left side
of the dialog to arrange the adapters in priority. The adapter in the highest position is
used first.
5. Click the adapter name that you want to use in the upper display list. The current
adapter link status displays next to the adapter name.
NOTE: One wireless adapter can be used for each band operating at a time.
6. After you have switched to the desired adapter, click OK to close the Adapter Switching
dialog and return to the General tab.
5.Security Overview
Wireless Security
Since wireless networking devices transmit information through radio waves, it is imperative that
you protect your information by configuring your security settings. There are three main
components that, when used together, can protect your wireless network:
• Service Set Identifier (SSID) — The name of a device on a network, the SSID is the first
level of security, but it is not fool-proof because the access points broadcast the SSIDs
across a wireless network. This level of security is okay if you are on a peer-to-peer
network without any access points, but for larger networks, more complex security
measures should be put in place.
• Wired Equivalent Privacy (WEP) — Supported by the IEEE 802.11 standard, WEP uses
64- or 128-bit encryption keys to encrypt data as it is sent or received by each client on
a wireless network. The way these keys are authenticated determines the level of
security on your wireless network. Using the default keys, however, makes your
wireless network vulnerable and you should not use them.
• Authentication Server — An authentication server works with each client to authenticate
access with a session-specific WEP key. This type of server protects sensitive user and
password information from intruders.
Security Guidelines
The following can help to achieve maximum security for your wireless network:
1. Enable WEP on your wireless network and change the WEP key daily or weekly.
2. Protect your drives and folders with passwords.
3. Change the default SSID.
4. Change the WEP key with each session, if possible.
5. Enable MAC address filtering, if possible.
6. Implement a Virtual Private Network (VPN) system to increase security. A VPN client is
included in most operating systems.
Protecting Your Network
Authentication Types
The IEEE 802.1x standard provides a general authentication framework for 802 LANs and
specifies an extensible authentication protocol (EAP) to enable LAN transport for many different
types of authentication protocols.
Encryption Keys
To protect client traffic, the 802.11 standard defines Wireless Encryption Privacy (WEP) with
fixed encryption keys (and three optional key lengths). The use of fixed keys has made it easy
to mount several types of attack against WEP.
WEP Encryption
You can prevent unauthorized reception of your wireless data using the IEEE 802.11 Wired
Equivalent Privacy (WEP). The standard includes two levels of security, using a 64-bit key
(sometimes referred to as 40-bit) or a 128-bit key. For better security, use a 128-bit key. If you
use encryption, all wireless devices on your WLAN must use the same encryption settings.
Refer to Setting up WEP Encryption for more information.
802.1x
A WAN client initiates an authorization request to the access point, which authenticates the
client to an Extensible Authentication Protocol (EAP) compliant RADIUS server. This RADIUS
server may authenticate either the user (via passwords) or the machine (by MAC address).
IPSEC
Software based IPSEC transport security.
TKIP (Temporal key Integrity Protocol)
Uses an encryption method called fast-packet rekeying, that changes the encryption keys
frequency.
Virtual Private Networks (VPN)
The following VPN client software is supported by PROSet. Refer to Virtual Private Network
(VPN) for more information.
• Netstructure VPN (SST)

• Netstructure VPN (IPsec-IKE)
• Cisco 3000 VPN
• Checkpoint VPN (Non office transparent mode, connect office mode and connect non-
office mode)
• Microsoftt VPN (L2TP over IPsec transport, L2TP for configuration with ESP-in-UDP)
802.11a and 802.11b can be augmented with VPN security to protect TCP/IP based services.
6.Setting Up WEP Encryption and Authentication
Wired Equivalent Privacy (WEP) encryption and shared authentication provides protect for your
data on the network. WEP uses an encryption key to encrypt data before transmitting it. Only
computers using the same encryption key can access the network or decrypt the encrypted data
transmitted by other computers. Authentication provides an additional validation process from
the adapter to the access point.
Supported authentication schemes are Open and Shared-Key authentication:
• Shared-Key authentication is supported using 64-bit and 128-bit WEP encryption keys.
• Open mode does not use an encryption authentication method to associate to a specific
access point.
Encryption Overview
Security in the WLAN can be achieved by enabling data encryption using WEP (Wireless
Encryption Protocol). You can choose a 64 or 128 bit level encryption. Also, the data can then
be encrypted with a key. Another parameter called the key index is provides the option to create
multiple keys for that profile. However, only one key can be used at a time. You can also
choose to password protect the profile to ensure privacy.
The pass phrase is used to generate a WEP key automatically. You have the option of either
using a pass phrase or entering a WEP key manually. Using 64-bit encryption, the pass phrase
is 5 characters long and you can choose to enter any arbitrary and easy to remember phrase
like Acme1 or enter 10 Hexadecimal numbers for the WEP key corresponding to the network
the user wants to connect to. For 128-bit encryption, the pass phrase is 13 characters long or
you can enter a 26 hexadecimal numbers for the WEP key to get connected to the appropriate
network.
Note: You must use the same encryption type, key index number, and WEP key as other
devices on your wireless network. Also, if 802.1x authentication is being used, WEP encryption
must be disabled.
To enable 64-bit (40-bit) or 128-bit encryption with authentication:
1. Select the wireless adapter in the left-side pane.
2. From the General page, click the Networks tab.
3. Select the profile from the Profile List and click the Edit button or click the Add button if
you are using the Profile Wizard.
4. Click the
Security tab. Select Security Settings, the third dialog if using the Profile
Wizard.
5. Select Shared from the Network Authentication drop-down box.

6. Select 64-bit or 128-bit from the Encryption Level drop-down box.
7. Select a key index number 1, 2, 3, or 4 from the Encrypt data with key index drop-down
box to use for encryption. Key selection corresponds to the WEP encryption pass
phrase or WEP key.
8. Select either of the following:
• Pass phrase: Click Use Pass Phrase to enable it. Enter a text phrase,
up to five (using 64-bit) or 13 (using 128-bit) alphanumeric characters
(0-9, a-z or A-Z), in the pass phrase field.
• WEP key: Click Use WEP Keys to enable it. Enter up to ten (using
64-bit) alphanumeric characters, 0-9, A-F, or twenty-six (using 128-
bit) alphanumeric characters, 0-9, A-F in the WEP key field.
9. Click
OK if editing a profile or Finish if in the Profile Wizard to save the settings.
NOTE: You must use the same encryption type, index number, and WEP key as other
devices on your wireless network.
7.Troubleshooting
Using a Profile with an incorrect WEP Encryption Key
When connected to an access point using a profile with an incorrect WEP key encryption, the
task tray icon and the General page will both indicate good signal strength and that you are
associated with the AP. However, when you attempt to send data to the AP using this profile,
because of the incorrect WEP key encryption, authentication cannot be established to acquire
an IP address from the AP to allow data transfer.
Refer to the following WEP encryption and authentication settings.
Open Authentication with an incorrect WEP 64 or 128-bit encryption key:
• A profile with an incorrect WEP encryption key will allow the wireless adapter to
associate with the access point.
• No data transfer
Open Authentication with no WEP encryption:
• Allows association to an access point
• Data transfer is allowed
Shared Authentication:
• Associated to an AP always allows data transfer.
Problems with installation
Windows does not detect the wireless adapter:
1. Remove and re-install the adapter.
2. Uninstall and reinstall the adapter's drivers.
Before calling Customer Support
Make a note of the following answers before calling customer support:
• How many remote units do you have talking to each access point?
• What channels are you using, and how are they dispersed?
• How much coverage overlap is there between access points?
• How high above the floor are the access points mounted?
• What revision of Intel(R) PROSet software or other LAN software are you running?
• What other electronic equipment is operating in the same band?
• What construction materials are used in wall and floors?
Users are dropped from the wireless network
Suggested causes and solutions:
• Find out if a person or workgroup moved or if the building has been rearranged.
• If two or more users are seated too close to each other, performance can suffer. Instruct
your users to space themselves a small distance apart to keep receivers from being
overloaded.
• Delivery trucks with very large metal sides can affect performance by reflecting
destructive signals back into a building. If you have an installation that includes a
shipping dock, check to see if the problem coincides with the arrival of large trucks.
• Personal “systems” can also interfere with your network. Wireless speakers, cordless
earphones, some Bluetooth devices, and similar systems can be the source of an
infrequent but hard to find the problem. Some systems do not conform to wireless
regulations. Shut off suspect devices or remove them from the area.
• If possible, remove and reinstall your new software. Conflicts with other resident
software packages are always a possibility, and they are not always the fault of the
newest addition. Sometimes just starting over fixes the problem.
• Swap units around. Does your problem follow the changed units, or is it unique to a
specific location? If it follows the product, the swapped unit could be damaged, or
improperly configured. If the problem stays with the location, try to find out what is
different about that particular room or area.
Range decreases as data rate increases
This is a normal condition. Range is inversely proportional to data rate: the faster the data, the
shorter the range. This has to do with the modulation technology used. Very fast data rates
require extremely complex signal waveforms, where even minor distortions can result in data
errors. Slower data rates are much more tolerant, and consequently will get through even in the
presence of some amount of noise, interference, distortion and echo.
Signal doesn't pass through a short or thin wall
Range is highly dependent on the physical environment. In a line-of-sight location, with elevated
and calibrated antennas, range predictions are quite accurate. This is not true in a “typical”
office building, where the walls may be simple drywall (which is almost transparent to
microwaves), or could be plaster with metal underneath. Most sites are somewhere between
these two extremes, and consist of a mixture of surfaces. You can’t tell what is inside a wall by
just looking at it, and we can’t tell you exactly what distance you will achieve. Consider
published range information to be typical, average, common or usual. Do not expect it to be
exact.
Signal strength drops when a cell phone is used in the area
Range also depends on the electronic environment. If other equipment that could cause
interference is nearby, the range of your transceiver could vary widely, and could change
suddenly when the other equipment activates. This is particularly true for 802.11b installations,
which share their frequencies with microwave ovens, cordless phones, wireless hi-fi speakers,
electronics toys and similar devices. Try to keep your system away from other transmitters, and
from other sources of electrical noise, such as large motors, spot welders, and similar
“electronically noisy” devices.
Range is shorter than it should be
Repeat some tests late in the evening, or on a weekend, when there may be less interference.
However, some users leave their networks turned all the time so this test is not foolproof. By all
means, try more than one channel. Your range problem may just be a nearby user whose
system uses your present test channel.
Interference from fluorescent lights
If you mount an access point close to fluorescent light fixtures, the lamp glow appears constant,
but inside the lamp tube, ionization appears and disappears 120 times a second. This can
modulate or “chop” an incoming signal and interfere with reception.
When too much range is undesirable
Too much range is not necessarily a good thing. At first it would appear that you would want as
much range as possible, but with the increase in range comes an increase in interference
potential, as your unit hears not only your other units but also manages to hear the systems of
other companies up and down the street. If you have a large installation, you will also wind up
with more than one access point using the same channel. If a remote unit hears two or more
access points, this will slow the network
Prevent access to wireless networks from outside the building
Excess transmit range presents a special reverse problem. For example, putting an access
point adjacent to a second floor bay window invites anyone with the right software on the street
below to pick up and enjoy all network transmissions. We discuss some possible solutions to
this problem further on.
Problems with Network Connectivity
If you cannot connect to the wireless network, try the following:
Check Network Settings
1. Select the wireless adapter in the Intel(R) PROSet left side pane.
2. From the General page, check that the Network Name (SSID) and operating mode are
correct. If the laptop is configured for ad hoc networking, make sure that the channel is
correct.
3. To correct these settings, click the Networks tab.
4. Select the profile being used.
5. Click the
Edit button and make the changes.
Check Security Settings
1. Select the wireless adapter in the Intel(R) PROSet left side pane.
2. From the General page, check that the security settings are correct.
3. To correct the security settings, click the Networks tab.
4. Select the profile being used.
5. Click the Edit button.
6. Click the Security tab. Make sure that the settings for WEP encryption are correct.
Check Adapter Switching
1. Select the wireless adapter in the Intel(R) PROSet left side pane.
2. Select the Adapter Switching icon.
3. Check that the adapter is "Linked" to the network.
Checking Adapter Statistics
Adapter Statistics
If the adapter is communicating with an access point (infrastructure mode) or other
computers in peer-to-peer mode, click the Statistics button in the Troubleshooting tab to
display the current information about how well the adapter is transmitting and receiving
information.
8.Specifications
Intel(R) PRO/Wireless LAN 2100 3B Mini PCI Adapter Model WM3B2100
Physical Characteristics
Form Factor Mini PCI Type 3B (model WM3B2100)
Dimensions (HxWxD) Type 3B card: 2.34 in x 1.75 in x 0.20 in (59.45 mm x
44.45 mm x 5 mm)
Weight 0.6 oz (17 g)
Antenna Interface Connector Hirose U.FL-R-SMT mates with cable connector U.FL-LP-
066
Dual Diversity Antenna On-board dual diversity switching
Connector Interface 124-pin SO-DIMM edge connector
Operating Temperature 0 to +70 degrees Celsius
Humidity 50 to 85% non-condensing
Frequency Modulation 2.4 GHz (802.11b)
Frequency band 2.4 GHz to 2.497 GHz
Modulation CCK, DQPSK, DBPSK
Wireless Medium 2.4 GHz ISM: Direct Sequence Spread Spectrum
(DSSS)
Channels 11 channel support
Data Rates 11, 5.5, 2, 1 Mbps
Indoor Range 100 ft (30 m) @ 11 Mbps / 300 ft (90 m) @ 1 Mbps
Outdoor Range 400 ft (120 m) @ 11 Mbps / 1500 ft (460 m) @ 1 Mbps
Power
Transmit Output Power 16 dBm (typical)
Adapter Power Consumption
Transmit 1.6 W
Receive 1.0 W
Standby 135 mW
Sleep 45 mW
Voltage 3.3 V
Operating Systems Windows* XP, 2000, 98, 98SE, Me, NT 4.0
WECA WiFi certification for 802.11b
WHQL Yes
WLAN Standard IEEE 802.11b
Architecture Infrastructure or ad hoc (peer-to-peer)
Roaming 802.11b compliant for seamless roaming between
respective access points (802.11b)
Security LEAP, TKIP, 802.1x, EAP-TLS, 128-bit and 64-bit WEP
Product Safety UL, C-UL, CB (IEC 60590)
9.Glossary
Numerical
802.11 x: A series of IEEE specifications for LANs: currently 802.11b, 802.11a, and 802.11g.
Using any one of these extensions to the 802.11 standard permits wireless communication
between a client and an access point or between two clients. The various specifications govern
transmission speeds and radio frequencies as well as fall-back rates and other characteristics.
The upcoming standard 802.11i will provide additional security specific to WLANs, and 802.11e
will address quality of service.
A
Access Point: A device that serves as a communications hub for wireless clients and provides
a connection to a wired LAN.
Advanced Encryption Standard (AES): A federal information-processing standard, supporting
128-, 192-, and 256-bit keys.
B
Basic Service Set Identifier (BSSID): A unique identifier for each wireless client on a wireless
network. The BSSID is the Ethernet MAC address of each adapter on the network.
Bit Rate: The total number of bits (ones and zeros) per second that a network connection can
support. Note that this bit rate will vary, under software control, with different signal path
conditions.
Bluetooth: An incompatible, very short-range lower speed communications system (PAN),
developed first in Europe as a “cable replacement” for printers and similar peripheral
connections. Its usage has expanded to include cordless earphones and similar devices. It uses
the 2.4 GHz ISM band, and “co-exists” with 802.11b. Here the term, “co-exist” means that not all
researchers agree on the amount of mutual interference generated when both systems operate
in the same location.
Broadcast SSID: Used to allow an access point to respond to clients on a wireless network by
sending probes.
D
Data Rate (Information Rate): Not all bits carry user information. Each group (packet) of bits
contains headers, trailers, echo control, destination information, and other data required by the
transmission protocol. It is important to understand the difference between bit rate and data rate,
since the overhead information may consume more than 40% of the total transmission. This
difference is common to many such data systems, including Ethernet.
Direct-Sequence Spread Spectrum (DSSS) and Frequency-Hop Spread Spectrum (FHSS):
Two incompatible technologies used in radio transmission.
E
Extensible Authentication Protocol (EAP): An authentication protocol that supports multiple
authentication methods, such as Kerberos, passwords, or smart cards. Cisco's authentication
protocol, LEAP, is based on EAP, an extension to PPP (Point-to-Point Protocol).
Encryption: Scrambling data so that only the authorized recipient can read it. Usually a key is
needed to decrypt the data.
Extended Service Set IDentifier (ESSID): A type of unique identifier applied to both the AP
and the wireless PC Card that is attached to each packet. This allows the AP to recognize each
wireless client and its traffic.
F
Frequencies: Strike a piano key and you generate a tone. Pick up the tone with a microphone
and your tone turns in to a “vibrating” or “cycling” electronic signal. The rate of vibration
depends on the key struck. In electronics we refer to this rate of vibration as the number of
“cycles per second.” The formal term for this value is Hertz. As we move up in rate, such as in
the Broadcast Band, we can use Kilohertz (KHz) to represent 1,000 Hz, or Megahertz (MHz) to
represent 1,000,000 Hz. Continuing much further upward, we finally reach 1,000,000,000 Hz,
which we can fortunately shorten to a Gigahertz (GHz). These frequencies are the home of both
802.11a (5 GHz) and 802.11b (2.4 GHz).
I
Independent Basic Service Set Identifier (IBSSID): Used to identify a wireless network
configured to allow each wireless client to communicate directly with each other without an
access point.
Independent Network: A network that provides (usually temporarily) peer-to-peer connectivity
without relying on a complete network infrastructure.
Infrastructure Mode: A wireless network centered around an access point. In this environment,
the access point not only provides communication with the wired network but also mediates
wireless network traffic in the immediate neighborhood.
Institute of Electrical and Electronics Engineers (IEEE): An organization involved in setting
computing and communications standards.
ISM Bands: A series of frequency bands, set aside by the FCC for Industrial, Scientific and
Medical applications. Users of these bands operate equipment on a shared basis, meaning that
they must expect, and accept interference from other legal users. Products manufactured for
ISM Band use must be approved by the FCC, but the user does not have to be licensed. In
addition to WLAN, ISM bands support cordless phones, microwave ovens, baby monitors, toys,
ham radio transceivers, and other wireless services.
K
Kerberos: An authentication system enabling protected communication over an open network
using a unique key called a ticket.
M
Media Access Control (MAC) Address: A hardwired address applied at the factory. It uniquely
identifies network hardware, such as a wireless PC Card, on a LAN or WAN.
Microcell: A bounded physical space in which a number of wireless devices can communicate.
Because it is possible to have overlapping cells as well as isolated cells, the boundaries of the
cell are established by some rule or convention.
Microwave: Technically, the term describes any frequency above 1.0 GHz. Unfortunately the
advertising industry has contorted this meaning considerably. In our discussion we will stick to
the technical definition.
Multipath: The signal variation caused when radio signals take multiple paths from transmitter
to receiver.
O
Orthogonal Frequency Division Multiplexing (OFDM): A modulation technique for
transmitting large amounts of digital data over radio waves. 802.11a uses OFDM, as will
802.11g.
P
Peer-to-Peer Mode: A wireless network structure that allows wireless clients to communicate
with each other without using an access point.
Personal Area Network (PAN): A personal area network, or PAN, is a networking scheme that
enables computing devices such as PCs, laptop computers, handheld personal computers,
printers and personal digital assistants (PDAs) to communicate with each other over short
distances either with or without wires.
Preamble: A preliminary signal transmitted over a WLAN to control signal detection and clock
synchronization.
R
Radio Frequency (RF) Terms (GHz, MHz, Hz): The international unit for measuring frequency
is Hertz (Hz), which is equivalent to the older unit of cycles per second. One Mega-Hertz (MHz)
is one million Hertz. One Giga-Hertz (GHz) is one billion Hertz. For reference: the standard US
electrical power frequency is 60 Hz, the AM broadcast radio frequency band is 0.55 -1.6 MHz,
the FM broadcast radio frequency band is 88-108 MHz, and microwave ovens typically operate
at 2.45 GHz.
Range: The distance over which a given system can communicate. This subject is discussed in
detail below.
RC4: An encryption algorithm designed at RSA Laboratories; specifically, a stream cipher of
pseudo-random bytes that is used in WEP encryption.
Remote Authentication Dial-In User Service (RAID): An authentication and accounting
system that verifies users' credentials and grants access to requested resources.
Roaming: Movement of a wireless node between two microcells. Roaming usually occurs in
infrastructure networks built around multiple access points.
S
Service Set Identifier (SSID): Used to identify clients on a wireless network.
Shared key An encryption key known only to the receiver and sender of data.
Site Survey: A process where you set up one transceiver in a fixed location, and then use
another unit to plot the field strength of the first unit’s transmitted signal. By moving the
transmitter around, and repeating the plots, you can develop a plan as to the best locations for
access points. You will also identify dead zones and other areas in need of special attention.
This can be a long, slow process, but it beats ripping up an unsatisfactory installation and
starting over. These tests require special software commands. Refer to your manual for specific
instructions. If you have a very large, or unusually complex installation situation, you might want
to consider calling in professionals to do your survey. We are not permitted to suggest installer
names, but you can check your yellow pages or similar sources for likely candidates.
T
Transceiver: A commonly used term that describes a combination transmitter and receiver.
Both 802.11a and 802.11b devices would be properly described as data transceivers.
U
UNII Bands: Unlicensed National Information Infrastructure. In contrast to the ISM bands, these
are a group of frequency bands set aside by the FCC for WLAN type communications only.
Users must accept interference from other legal WLAN users, but the other sources of
interference problems are, or legally should be, missing.
W
WECA: The Wireless Ethernet Compatibility Alliance...
WEP64 and WEP128: Wired Equivalent Privacy, 64 bit and 128 bit (64 bit is sometimes
referred to as 40 bit). This is a low-level encryption technique designed to give the user about
the same amount of privacy that he would expect from a LAN. It is extremely important to
understand that WEP is not some CIA-proof supercode! It performs as intended, giving the user
a simple level of data security and protection from casual electronic eavesdropping. Use of the
128 bit option at all possible times is recommended. Remember that 802.11 devices transmit
(broadcast) in all directions, and that it is possible, with very complex software, to copy and
decode WEP transmissions. The task is not trivial, but it is possible. If your data is extremely
sensitive, you should consider some form of secondary protection, such as strong passwords
and an additional level of encryption. Suitable software packages are available from reputable
suppliers. Although not intended by the original architects, WEP also prevents unauthorized
access to your system by an outsider. Hackers have been known to access systems from
outside a building, and to then to access the Web for a leisurely session, all at the system
owner’s expense.
Wide Area Network (WAN): A wide area network (WAN) is a voice, data, or video network that
provides connections from one or more computers or networks within a business to one or more
computers or networks that are external to such business.
Wireless: A microwave transceiver system.
Wireless LAN (WLAN): Wireless LAN is a type of local-area network that uses high-frequency
radio waves rather than wires to communicate between nodes. WLAN is a flexible data
communication system used as an alternative to, or an extension of a wired LAN.
Wireless Node: A user computer with a wireless network interface card (adapter).
10.Customer Support
Intel support is available online or by telephone. Available services include the most up-to-date
product information, installation instructions about specific products, and troubleshooting tips.
Online Support
Technical Support: http://support.intel.com
Network Product Support: http://www.intel.com/network
Corporate Web Site: http://www.intel.com
11.Software License Agreement
INTEL SOFTWARE LICENSE AGREEMENT
IMPORTANT - READ BEFORE COPYING, INSTALLING OR USING
Do not use or load this software and any associated materials (collectively, the
"Software") until you have carefully read the following terms and conditions. By loading
or using the Software, you agree to the terms of this Agreement. If you do not agree with
the terms of this Agreement, do not install or use the Software.
LICENSE. You may copy the Software onto a single computer for your personal, non-
commercial use, and you may make one back-up copy of the Software, subject to these
conditions:
1. This Software is licensed for use only in conjunction with Intel® component
products. Use of the Software in conjunction with non-Intel component products
is not licensed hereunder.
2. You may not copy, modify, rent, sell, distribute or transfer any part of the Software
except as provided in this Agreement, and you agree to prevent unauthorized copying
of the Software.
3. You may not reverse engineer, decompile, or disassemble the Software.
4. You may not sublicense or permit simultaneous use of the Software by more than one
user.
5. The Software may contain the software or other property of third party suppliers, some
of which may be identified in, and licensed in accordance with, any enclosed
"license.txt" file or other text or file.
OWNERSHIP OF SOFTWARE AND COPYRIGHTS. Title to all copies of the Software remains
with Intel or its suppliers. The Software is copyrighted and protected by the laws of the United
States and other countries, and international treaty provisions. You may not remove any
copyright notices from the Software. Intel may make changes to the Software, or to items
referenced therein, at any time without notice, but is not obligated to support or update the
Software. Except as otherwise expressly provided, Intel grants no express or implied right under
Intel patents, copyrights, trademarks, or other intellectual property rights. You may transfer the
Software only if the recipient agrees to be fully bound by these terms and if you retain no copies
of the Software.
LIMITED MEDIA WARRANTY. If the Software has been delivered by Intel on physical media,
Intel warrants the media to be free from material physical defects for a period of ninety (90)
days after delivery by Intel. If such a defect is found, return the media to Intel for replacement or
alternate delivery of the Software as Intel may select.
EXCLUSION OF OTHER WARRANTIES. EXCEPT AS PROVIDED ABOVE, THE SOFTWARE
IS PROVIDED "AS IS" WITHOUT ANY EXPRESS OR IMPLIED WARRANTY OF ANY KIND
INCLUDING WARRANTIES OF MERCHANTABILITY, NON-INFRINGEMENT, OR FITNESS
FOR A PARTICULAR PURPOSE. Intel does not warrant or assume responsibility for the
accuracy or completeness of any information, text, graphics, links or other items contained
within the Software.
LIMITATION OF LIABILITY. IN NO EVENT SHALL INTEL OR ITS SUPPLIERS BE LIABLE
FOR ANY DAMAGES WHATSOEVER (INCLUDING, WITHOUT LIMITATION, LOST
PROFITS, BUSINESS INTERRUPTION, OR LOST INFORMATION) ARISING OUT OF THE
USE OF OR INABILITY TO USE THE SOFTWARE, EVEN IF INTEL HAS BEEN ADVISED OF
THE POSSIBILITY OF SUCH DAMAGES. SOME JURISDICTIONS PROHIBIT EXCLUSION
OR LIMITATION OF LIABILITY FOR IMPLIED WARRANTIES OR CONSEQUENTIAL OR
INCIDENTAL DAMAGES, SO THE ABOVE LIMITATION MAY NOT APPLY TO YOU. YOU
MAY ALSO HAVE OTHER LEGAL RIGHTS THAT VARY FROM JURISDICTION TO
JURISDICTION.
TERMINATION OF THIS AGREEMENT. Intel may terminate this Agreement at any time if you
violate its terms. Upon termination, you will immediately destroy the Software or return all copies
of the Software to Intel.
APPLICABLE LAWS. Claims arising under this Agreement shall be governed by the laws of
California, excluding its principles of conflict of laws and the United Nations Convention on
Contracts for the Sale of Goods. You may not export the Software in violation of applicable
export laws and regulations. Intel is not obligated under any other agreements unless they are
in writing and signed by an authorized representative of Intel.
GOVERNMENT RESTRICTED RIGHTS. The Software is provided with "RESTRICTED
RIGHTS." Use, duplication, or disclosure by the Government is subject to restrictions as set
forth in FAR52.227-14 and DFAR252.227-7013 et seq. or their successors. Use of the Software
by the Government constitutes acknowledgment of Intel's proprietary rights therein. Contractor
or Manufacturer is Intel Corporation, 2200 Mission College Blvd., Santa Clara, CA 95052.
12.Safety and Regulatory Notices
This notebook has been tested and certified to FCC part 15 and RSS 210 for
simultaneous operation of the Wireless LAN device and Bluetooth device.
Certification Ids: FCC ID: QK3-WB0001 and Industry Canada ID: IC-337H-WB0001
FCC Part 15 Declaration of Conformity (DoC)
This device is herewith confirmed to comply with the requirements of FCC Part 15 rules. The
operation is subject to the following two conditions:
1. This device may not cause harmful interference, and
2. This device must accept any interference received, including interference that may cause
undesired operation.
FCC Rules and Regulations - Part 15
Warning: This device has been tested and found to comply with the limits for a Class B digital
device pursuant to Part 15 of the Federal Communications Commissions Rules and Regulation.
These limits are designed to provide reasonable protection against harmful interference when
the equipment is operated in a commercial environment. This equipment generates, uses, and
can radiate radio frequency energy and, if not installed and used in accordance with the
instruction manual, may cause harmful interference to radio communications.
However, there is no guarantee that interference will not occur in a particular installation. If this
equipment does cause harmful interference to radio or television reception, which can be
determined by turning the equipment off and on, the user is encouraged to try and correct the
interference by one or more of the following measures:
• Relocate your WLAN and Bluetooth equipped laptop computer.
• Increase the separation between the WLAN and Bluetooth equipped laptop computer and
other electronics.
• Connect the WLAN and Bluetooth equipped laptop computer into an outlet on a circuit
different from that of other electronics.
• Consult the dealer or an experienced radio/TV technician for help.
FCC Radiation Exposure Statement
This equipment complies with FCC radiation exposure limits set forth for an uncontrolled
environment. This equipment should be installed and operated with minimum distance of 20cms
between the Wireless LAN and Bluetooth Antenna located on top edge of the LCD screen &
your body.
The transmitters in this device must not be co-located or operated in conjunction with any other
antenna or transmitter
Canadian Notice
To prevent radio interference to the licensed service, this device is intended to be operated
indoors and away from windows to provide maximum shielding. Equipment (or its transmit
antenna) that is installed outdoors is subject to licensing."
13.Limited Warranty
Users are not authorised to modify this product. Any modifications invalidate the
Warranty.
This equipment may not be modified, altered or changed in any way without signed
written permission from Fujitsu. Unauthorised modification will void the equipment
authorisation from the FCC and Industry Canada and the warranty.
Limited Lifetime Hardware Warranty
Intel warrants to the original owner that the adapter product delivered in this package will be
free from defects in material and workmanship. This warranty does not cover the adapter
product if it is damaged in the process of being installed or improperly used.
THE ABOVE WARRANTY IS IN LIEU OF ANY OTHER WARRANTY, WHETHER EXPRESS,
IMPLIED OR STATUTORY, INCLUDING BUT NOT LIMITED TO ANY WARRANTY OF
NONINFRINGEMENT OF INTELLECTUAL PROPERTY, MERCHANTABILITY, FITNESS FOR
A PARTICULAR PURPOSE ARISING OUT OF ANY PROPOSAL, SPECIFICATION, OR
SAMPLE.
This warranty does not cover replacement of adapter products damaged by abuse, accident,
misuse, neglect, alteration, repair, disaster, improper installation, or improper testing. If the
adapter product is found to be defective, Intel, at its option, will replace or repair the hardware
product at no charge except as set forth below, or refund your purchase price provided that you
deliver the adapter product along with a Return Material Authorization (RMA) number (see
below), along with proof of purchase (if not registered), either to the dealer from whom you
purchased it or to Intel with an explanation of any deficiency. If you ship the adapter product,
you must assume the risk of damage or loss in transit. You must use the original container (or
the equivalent) and pay the shipping charge.
Intel may replace or repair the adapter product with either new or reconditioned parts, and any
adapter product, or part thereof replaced by Intel becomes Intel's property. Repaired or replaced
adapter products will be returned to you at the same revision level as received or higher, at
Intel's option. Intel reserves the right to replace discontinued adapter products with an
equivalent current generation adapter product.
Returning a Defective Product

From North America:
Before returning any adapter product, contact Intel Customer Support and obtain a Return
Material Authorization (RMA) number by calling +1 916-377-7000.
If the Customer Support Group verifies that the adapter product is defective, they will have the
RMA department issue you an RMA number to place on the outer package of the adapter
product. Intel cannot accept any product without an RMA number on the package.
All other locations:
Return the adapter product to the place of purchase for a refund or replacement.
Intel Adapter Money-back Guarantee (North America Only)
Intel wants you to be completely satisfied with the Intel adapter product that you have
purchased. Any time within ninety (90) days of purchase, you may return your Intel adapter to
the original place of purchase for a full refund of the purchase price from your dealer. Resellers
and distributors, respectively, accepting returns and refunding money back to their customers
may return Intel adapters to their original place of purchase. Intel guarantees that it will accept
returns under this policy and refund the original purchase price to customers purchasing directly
from Intel.
Limitation of Liability and Remedies
INTEL'S SOLE LIABILITY HEREUNDER SHALL BE LIMITED TO DIRECT, OBJECTIVELY
MEASURABLE DAMAGES. IN NO EVENT SHALL INTEL HAVE ANY LIABILITY FOR ANY
INDIRECT OR SPECULATIVE DAMAGES (INCLUDING, WITHOUT LIMITING THE
FOREGOING, CONSEQUENTIAL, INCIDENTAL, AND SPECIAL DAMAGES) INCLUDING,
BUT NOT LIMITED TO, INFRINGEMENT OF INTELLECTUAL PROPERTY,
REPROCUREMENT COSTS, LOSS OF USE, BUSINESS INTERRUPTIONS, LOSS OF
GOODWILL, AND LOSS OF PROFITS, WHETHER ANY SUCH DAMAGES ARISE OUT OF
CONTRACT NEGLIGENCE, TORT, OR UNDER ANY WARRANTY, IRRESPECTIVE OF
WHETHER INTEL HAS ADVANCE NOTICE OF THE POSSIBILITY OF ANY SUCH DAMAGES.
NOTWITHSTANDING THE FOREGOING, INTEL'S TOTAL LIABILITY FOR ALL CLAIMS
UNDER THIS AGREEMENT SHALL NOT EXCEED THE PRICE PAID FOR THE PRODUCT.
THESE LIMITATIONS ON POTENTIAL LIABILITIES WERE AN ESSENTIAL ELEMENT IN
SETTING THE PRODUCT PRICE. INTEL NEITHER ASSUMES NOR AUTHORIZES ANYONE
TO ASSUME FOR IT ANY OTHER LIABILITIES.
Some states do not allow the exclusion or limitation of incidental or consequential damages, so
the above limitations may not apply to you.
Critical Control Applications: Intel specifically disclaims liability for use of the adapter product in
critical control applications (including, for example only, safety or health care control systems,
nuclear energy control systems, or air or ground traffic control systems) by Licensee or
Sublicensees, and such use is entirely at the user's risk. Licensee agrees to defend, indemnify,
and hold Intel harmless from and against any and all claims arising out of use of the adapter
product in such applications by Licensee or Sublicensees.
Software: Software provided with the adapter product is not covered under the hardware
warranty described above. See the applicable software license agreement which shipped with
the adapter product for details on any software warranty.
14.Legal Notice
Copyright (C) 2001-2003, Intel Corporation. All rights reserved. Intel Corporation, 5200 N.E.
Elam Young Parkway, Hillsboro, OR 97124-6497 USA
Intel Corporation assumes no responsibility for errors or omissions in this document. Nor does
Intel make any commitment to update the information contained herein.
*Other names and brands may be claimed as the property of others.
Intel(R) is a trademark or registered trademark of Intel Corporation or its subsidiaries in the
United States and other countries.