LINKSYS WRT54G3GV2 Wireless-G Router for Mobile Broadband User Manual Linksys WRT54G3GV2 ST User Guide
LINKSYS LLC Wireless-G Router for Mobile Broadband Linksys WRT54G3GV2 ST User Guide
LINKSYS >
Contents
- 1. Manual 1
- 2. Manual 2
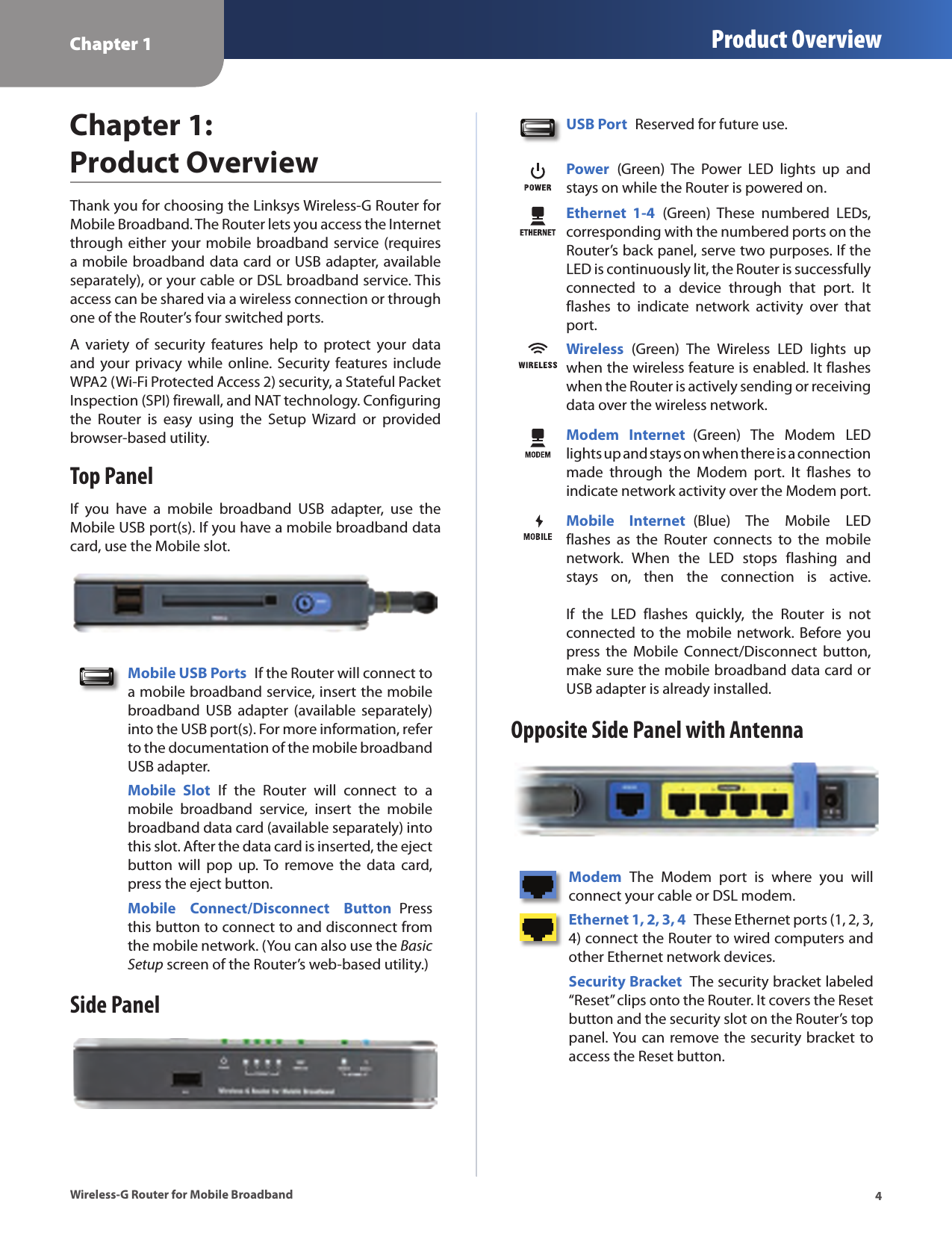
Manual 1