National Datacomm 3050S01 802.11g+ MiniPCI Module User Manual NWH1050 User s Guide
National Datacomm Corporation 802.11g+ MiniPCI Module NWH1050 User s Guide
User Manual
NWH3050
802.11g+ MiniPCI Module
User’s Guide
October 9, 2003
TRADEMARKS
All names mentioned in this document are trademarks or registered trademarks of their respective
owners.
DISCLAIMER
This document is provided “as is,” without warranty of any kind, either expressed or implied,
including, but not limited to, warranties of merchantability or fitness for a particular purpose. The
manufacturer may release improved or modified versions of this manual or any product or
program described in this manual at any time. This document could include technical inaccuracies
or typographical errors.
FCC WARNING
This equipment has been tested and found to comply with the limits for a Class B Digital device
pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection
against harmful interference in a residential installation. This equipment generates, uses, and can
radiate radio-frequency energy and, if not installed and used in accordance with the instructions,
may cause harmful interference to radio communications. However, there is no guarantee that
interference will not occur in a particular installation. If this equipment does cause harmful
interference to radio or television reception, which can be determined by turning the equipment
off and on, the user is encouraged to try to correct the interference by one or more of the
following measures:
• Reorient or relocate the receiving antenna.
• Increase the separation between the equipment and the receiver.
• Connect the equipment to an outlet on a circuit different from that to which the receiver is
connected.
• Consult the dealer or an experienced radio/TV technician for help.
You are cautioned that changes or modifications not expressly approved by the party responsible
for compliance could void your authority to operate the equipment.
This device complies with part 15 of the FCC Rules. Operation is subject to the following two
conditions:
• This device may not cause harmful interference, and
• This device must accept any interference received, including interference that may cause
undesired operation.
FCC RF Radiation Exposure Statement
This equipment complies with FCC RF radiation exposure limits set forth for an uncontrolled
environment. This equipment should be installed and operated with a minimum distance of 20
centimeters between the radiator and your body.
Packing List
Your NWH3050 802.11g+ MiniPCI Module package should contain the following items:
• One NWH3050 802.11g+ MiniPCI Module
Contents
Introduction 1
1 System Requirements 2
1.1 Hardware Requirements 2
1.2 Software Requirements 2
2 Terminology Used in this Guide 3
3 Familiarization and Installation 5
3.1 The Parts of the Adapter 5
3.2 Adapter Installation 5
4 Driver Installation and Operation 9
4.1 Installation Preview 錯誤! 尚未定義書籤。
4.2 Installation Details 錯誤! 尚未定義書籤。
4.3 Driver Operation and Adapter Removal 錯誤! 尚
未定義書籤。
4.4 Uninstalling the Driver 12
5 Utility Installation, Startup, and Shutdown 13
5.1 Installing the Utility 13
5.2 Controlling the Utility 13
6 Operation 15
6.1 Understanding Connection Profiles 15
6.2 Understanding the Utility’s Panels 15
6.3 Connecting for the First Time 16
7 Utility Reference 19
7.1 The Information Panel 19
7.2 The Configuration Panel 21
7.3 The Security Panel 24
7.4 The Site Survey Panel 26
7.5 The Profiles Panel 28
7.6 The About Panel 30
Appendixes
A Troubleshooting 31
B Technical Support 31
C Limited Warranty 32
D Specifications 34
E Channels and Regulations 35
18. The Profiles panel 28
19. The About panel 30
Introduction
Congratulations on choosing an outstanding wireless networking product, and thank you for
taking the time to read this user’s guide.
About the NWH3050
Your NWH3050 802.11g+ MiniPCI Module has standards-based and enhanced features.
Standards-based features: The adapter conforms fully to Institute of Electrical and Electronics
Engineers (IEEE) standards 802.11b and 802.11g. IEEE 802.11b-compliant products form the
heart of wireless local-area networks (WLANs) all over the world, including “hotspots” in many
public areas. Using your adapter, you can connect wirelessly wherever you have the permission
of the network operator to do so. It does not matter what brand or brands of wireless networking
equipment the network is built on. IEEE 802.11b and 802.11g are worldwide standards.
IEEE 802.11b allows communication speeds up to 11 megabits per second (Mbps), transmission
ranges (depending on electromagnetic conditions) up to tens of meters (yards) indoors and
hundreds of meters outdoors (or more, at lower communication speeds), and, for security, Wired
Equivalent Privacy (WEP) encryption using a digital “key” 64 or 128 bits long. IEEE 802.11g
allows communication speeds up to 54 Mpbs.
Enhanced features: Your adapter has several capabilities not present in IEEE 802.11b-only or
802.11g-only devices:
• 4X mode. This allows the packets exchanged between devices to be longer, reducing
overhead and increasing throughput.
• 256-bit WEP encryption. This greatly increases network security, as a longer key is
many times harder to “crack.”
These capabilities can be used on wireless links to products in the same family as your adapter.
The adapter can automatically detect when 4X mode can be used; you can also control its use
through the software included with the adapter.
About this Guide
This guide contains detailed instructions on installing and using your adapter and the software
included with it. Basic terms and concepts of wireless networking are also introduced. Follow the
instructions in this guide carefully to ensure that your adapter will give you many years of
trouble-free, high-performance operation.
1
1 System Requirements
Before installing the adapter and related software, make sure the computer system meets the
minimum requirements described below.
1. Open the task bar’s Start menu, go to Settings, and click Control Panel.
2. Double-click the
System icon.
The System Properties window will appear.
3. Find and click the Device Manager tab or button.
If there is no Device Manager tab in the System Properties window, click the Hardware tab.
The Device Manager button will be in the middle of the panel that appears.
4. Expand the MiniPCI Module entry.
1.2 Software Requirements
The drivers included with the adapter allow the adapter to be used in Microsoft® Windows 98,
ME, 2000, and XP. Third-party drivers may allow the adapter to be used, with reduced
functionality, in these and other operating systems.
2
2 Terminology Used in this Guide
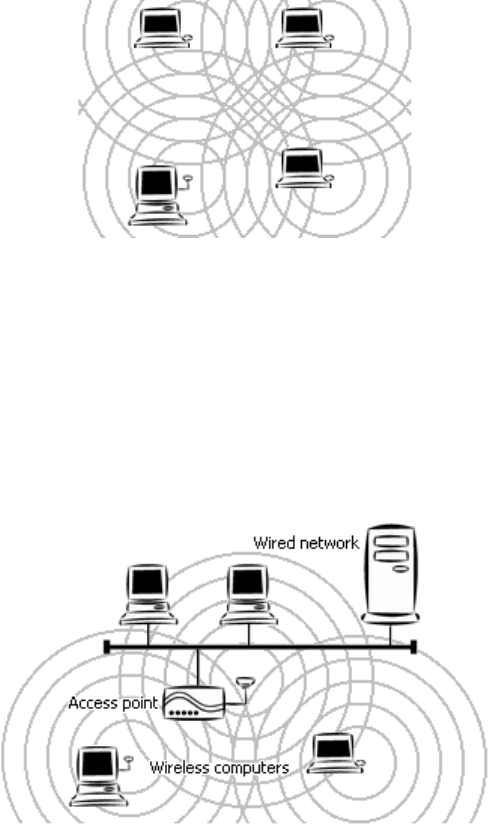
Ad-hoc Network
An ad-hoc network is a wireless local-area network (WLAN) made up of stations
communicating directly with each other through their wireless interfaces. There is no central
relay point, and normally no connection to a wired network. Ad-hoc mode is sometimes
referred to as peer-to-peer, computer-to-computer, or Independent Basic Service Set (IBSS)
mode. Figure 1 shows a typical ad-hoc network.
Figure 1. Ad-hoc network
Infrastructure Network
An infrastructure network is a WLAN made up of wireless stations and at least one wireless
relay point, known as a base station or access point (AP). The AP usually has a connection
to a wired network, allowing wireless stations to use resources on that network. The AP also
relays all communications between wireless stations in its coverage area; these stations
never communicate directly with each other. Infrastructure mode is sometimes referred to as
managed or Basic Service Set (BSS) mode. Figure 2 shows a typical infrastructure network.
Figure 2. Infrastructure network
BSSID/MAC Address
A Basic Service Set (BSS) is two or more wireless devices that are in communication with
each other. Like every wired Ethernet device, every wireless device has a fixed, unique
“medium access control” (MAC) address. When wireless devices establish communication,
3
they automatically select the MAC address of one BSS member as an identifier for the group;
this is the BSSID.
It has become customary to refer to a wireless device’s MAC address as its BSSID even
when the address is not being used to identify an active BSS.
A BSS that includes an access point is often referred to as a cell.
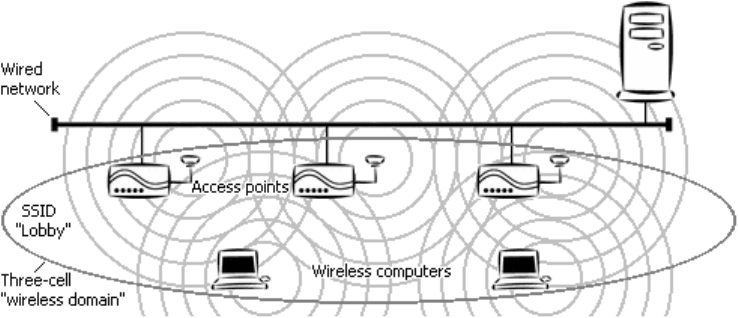
SSID/Domain Identifier
A Service Set Identifier (SSID) is a shared name, usually assigned by a network
administrator, that identifies wireless devices that are allowed to communicate with each
other. This is one way of providing basic security on a wireless network. An SSID can be up
to 32 characters long, is case-sensitive, and can include letters, symbols, and numbers.
Giving multiple access points the same SSID and encryption settings allows mobile stations
that also share those settings to “roam” from one AP to another. When at least one AP is
among the devices sharing an SSID, the name may be referred to as an Extended Service Set
Identifier (ESSID).
An SSID is sometimes called a “domain name,” but it is unrelated to the domain names used
to identify machines and networks on the Internet. Other terms for SSID are domain ID, net
ID, network name, extended network ID, and wireless network name. The set of devices that
an SSID identifies is sometimes called a communication domain or wireless domain.
Figure 3 shows a common wireless network setup. If the APs share SSID and encryption
settings, mobile devices that also share those settings can roam among them.
Figure 3. Roamable multi-AP infrastructure network
Roaming
When APs covering adjacent areas have the same SSID and encryption settings, a mobile
device that also shares those settings can communicate through the APs continuously while
moving from one coverage area to another. This is known as roaming. When one AP’s
signal begins to weaken, the mobile device automatically searches for another AP that it is
authorized to “associate with” (that is, connect to); when the second AP’s signal quality is
better than that of the first, the station automatically switches over.
4
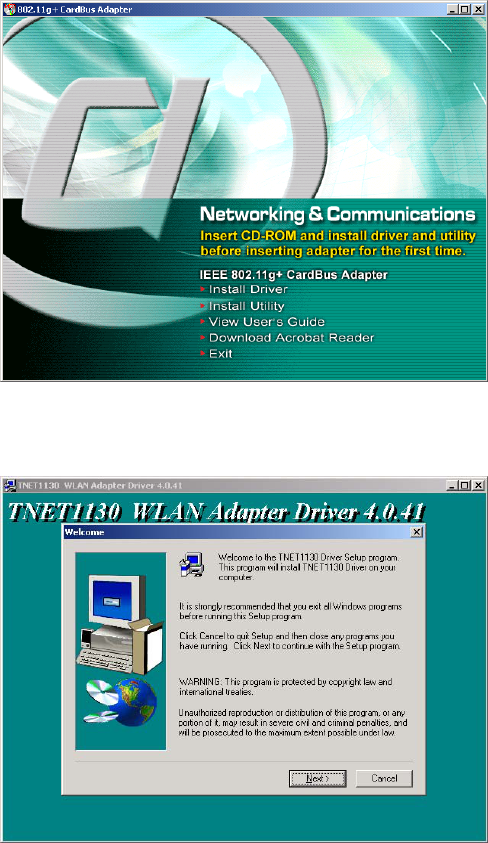
4 Software Installation
You must install the driver and utility from the adapter CD-ROM before inserting the adapter in
the computer for the first time.
To install the driver and utility, insert the CD-ROM and wait for the window shown below to
appear. This may take 20 to 30 seconds on a laptop or notebook computer.
Click Install Driver, and then click Next in each window that appears. In the final window, click
Finish. This process is illustrated below.
5
6
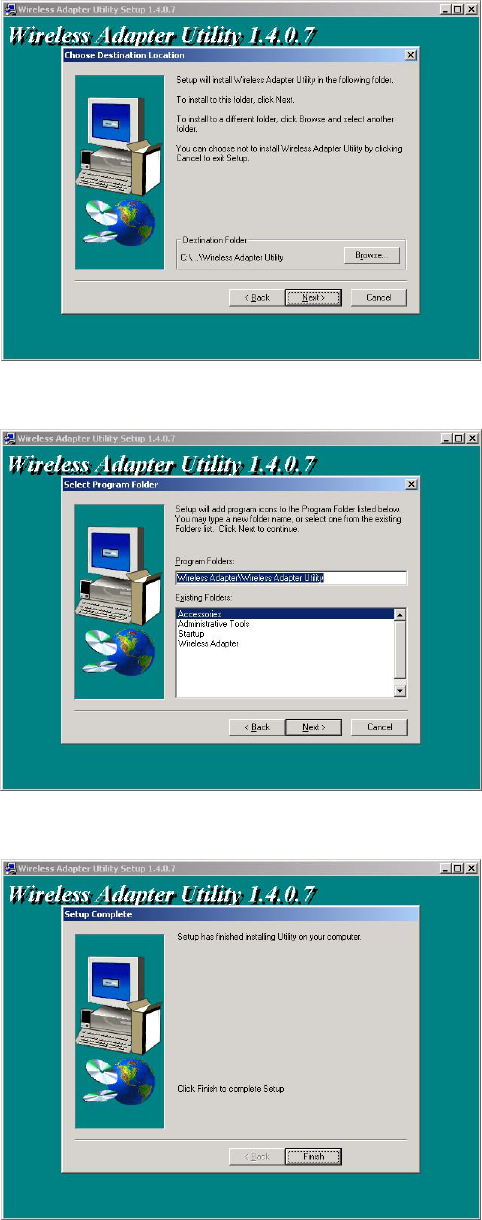
The original window will reappear. Click Install Utility. Then, as before, click Next in each
window that appears, and at the end click Finish. This process is illustrated below.
7
The original window will reappear. Click Exit and remove the CD-ROM.
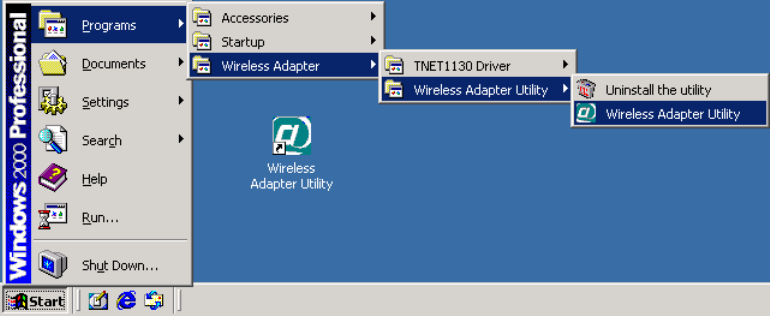
Commands for starting the utility, and for uninstalling the utility and the driver, will be added to
the Start menu, and a shortcut icon for starting the utility will be added to your desktop display,
as shown below.
8
5 Adapter Installation
Before inserting the adapter in the computer for the first time, be sure to install the driver and
utility as described above. Also take note of the following tips and cautions:
• If the adapter is inserted or removed while the computer is running, the operating system
may beep very loudly even if the sound control has been set to Mute or Muted.
• If the adapter will be connected to an extender card installed in a desktop computer, make
sure the extender card is firmly bolted to the computer’s housing before inserting or
removing the adapter. Shifting or rocking of a loose extender card can result in
momentary loss of contact, which can permanently damage sensitive electronic
components.
• Microsoft® Windows lets you “stop” (deactivate) the adapter before removing it. It is
strongly recommended that you use this function and avoid removing the adapter while it
is operating.
The location of the MiniPCI slot depends on the make and model of the computer. There may be
a button next to it for physically ejecting an adapter from the slot. See your computer manual for
details. Remember that the adapter should be “stopped” (deactivated) through the operating
system before being ejected while the computer is on.
When inserting the adapter, make sure it goes in straight, so there is no resistance until its metal
body is almost all the way in. When the adapter is fully inserted, its metal body will be
completely inside the slot, and most of its plastic outer end will extend outside the computer.
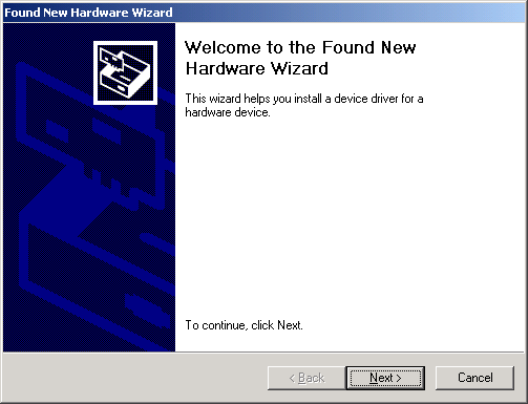
The first time you insert the adapter, Windows will start up a program for installing a driver.
Although the driver has already been placed on the system, Windows needs to confirm its
location. The window that appears in Windows 2000 is shown below.
In Windows ME, click Next in each window that appears, and then click Finish.
9
In Windows XP, click Next until a message about “Windows logo testing” appears. Indicate that
you wish to continue with installation. Click the Finish button when it appears.
In Windows 98, click Next until you are prompted to insert your Windows CD-ROM. Follow the
on-screen instructions. Click the Finish button when it appears. You will be prompted to restart
the computer. Allow the system to restart.
In Windows 2000, you must make sure a certain option is unchecked. The full procedure is
illustrated and explained below.
After you click Next in the window shown above, the following window will appear.
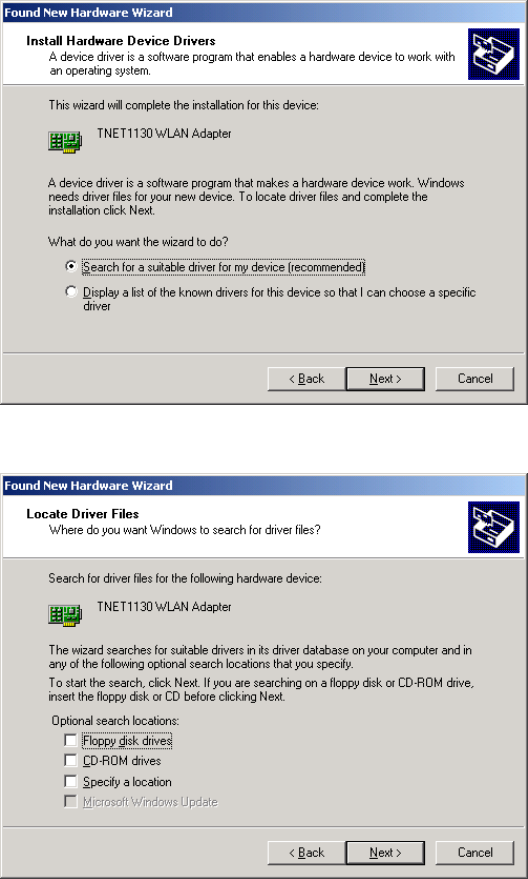
Click Next. The window shown below will appear.
If the check box next to Specify a location is checked, click it to clear it. Then click Next. The
window shown below will appear. Windows will indicate that it found the driver.
10
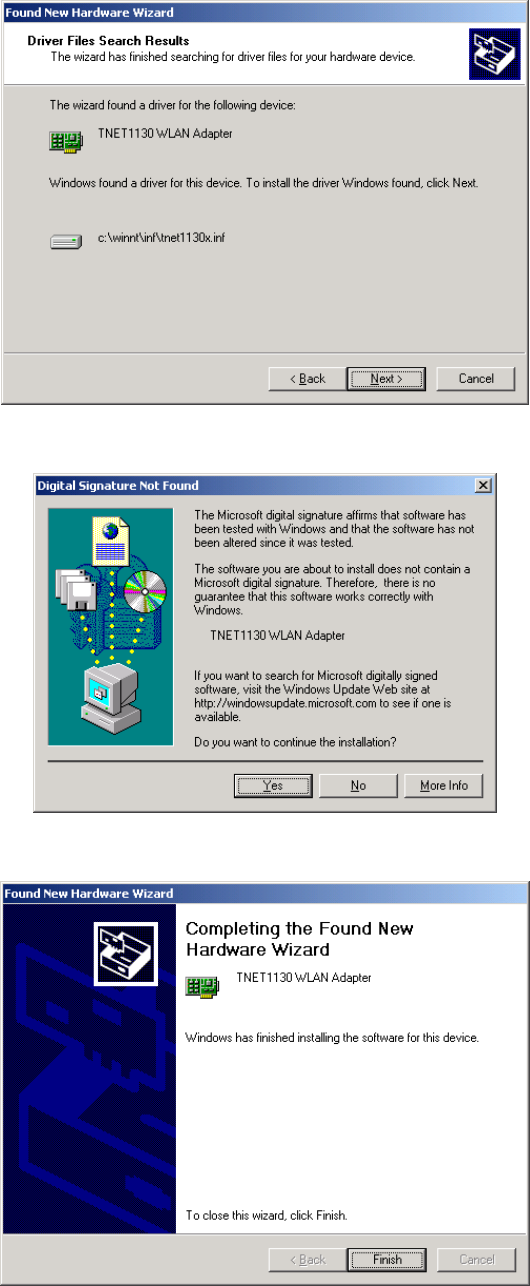
Click Next. A message about a “digital signature” will appear.
Click Yes, and then click Finish in the window shown below.
11
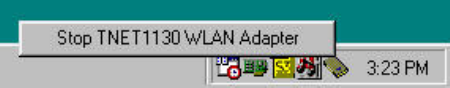
6 Driver Operation and Adapter Removal
The driver is automatically loaded into the computer’s memory whenever the system detects the
adapter. When the adapter is not present, the driver is not loaded. The “removable device” icon in
the system tray (also known as the “PC Card” or “Unplug/Eject” icon) lets you unload the driver
and deactivate the adapter for safe removal.
• To unload the driver and deactivate the adapter: Click the “removable device” icon
using the mouse’s main button (usually the button on the left), move the pointer onto the
menu that appears, and choose the command to “stop” (or, in Windows XP, “safely
remove”) the TNET1130 WLAN adapter.
Figure 7. Tray icon menus (1): main button
This will unload the driver and deactivate the adapter. The adapter’s activity LED will go
dark. (The power LED will continue to shine. This is normal, and not a cause for worry.)
A message indicating that you can safely remove the adapter will appear. Choose OK to
continue.
You should then remove the adapter from the slot. The driver will automatically be
reloaded when the adapter is re-inserted.
• To hide the tray icon without unloading the driver: In Windows ME and 2000, click
the “removable device” icon with the mouse’s secondary button (usually the button on
the right) and choose Unplug or eject hardware from the menu that appears. Select the
adapter from the list of hardware devices and uncheck the option Show Unplug/Eject
icon on the taskbar.
In some versions of Windows you can, instead, open the Start menu, go to Settings,
choose Control Panel, open the PC Card (PCMCIA) icon, select the adapter, uncheck the
Show control on taskbar box, and choose OK.
In Windows 98, click the tray icon using the mouse’s secondary button (usually the
button on the right) and choose Disable PC Card Tray Icon.
Whenever you wish to remove the adapter while the computer is running, it is strongly
recommended that you choose Stop (or Safely Remove) TNET1130 WLAN Adapter or Unplug
or eject hardware and deactivate the adapter before physically removing it.
Uninstalling the Driver: “Uninstalling” the driver means removing the driver files from your
hard disk. You should uninstall the driver before installing a newer version. To do this, open the
Start menu, go to Wireless Adapter and then to TNET1130 Driver, and click Uninstall the
driver.
12
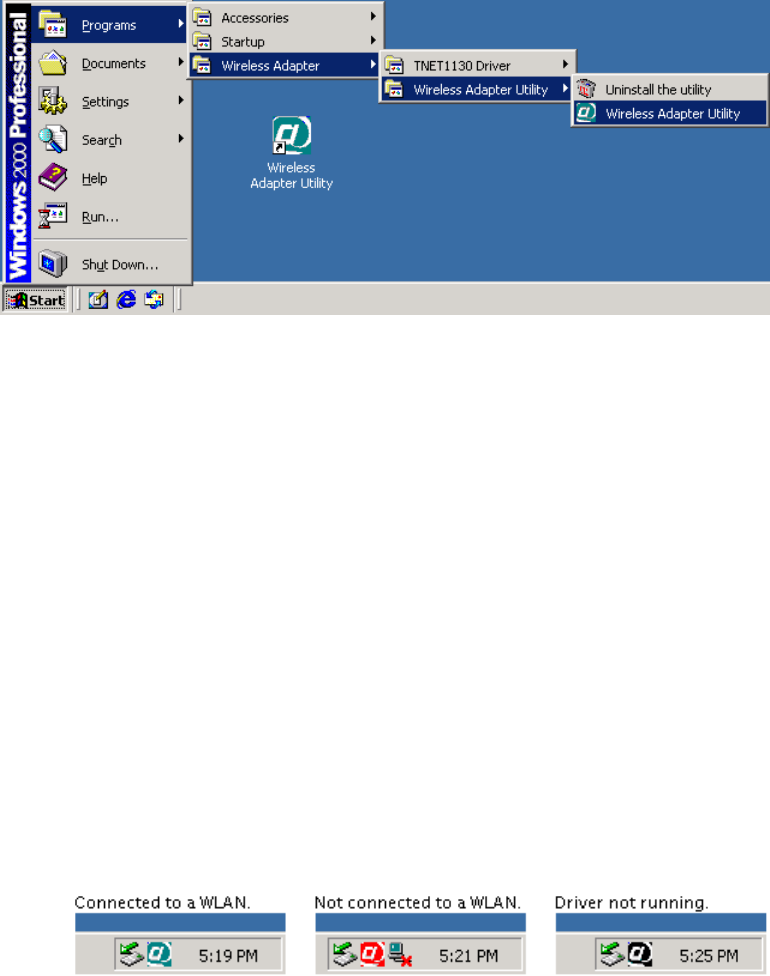
7 Utility Startup and Shutdown
The Wireless Adapter Utility is used to connect to wireless networks and use the adapter’s special
features.
Figure 9. Utility icons in the Start menu and on the desktop
7.1 Controlling the Utility
The Wireless Adapter Utility behaves slightly differently from most programs with icons on the
desktop and in the Start menu. Take note of the following so you will know what to expect when
you start using the utility:
• Startup: You can start the utility up in either of two ways:
o by opening the Start menu, going to Programs, choosing the Wireless Adapter
Utility folder, and choosing the Wireless Adapter Utility command, or
o by choosing the Wireless Adapter Utility icon on the desktop.
• Tray icon: When the utility is running, its icon, a stylized white “at” sign on a colored
background, appears in the system tray (usually located at the right end of the task bar).
This icon has three states: (1) A blue-green background shows that you are connected to
a wireless network. (2) A red background shows that the adapter and driver are working,
but a wireless connection has not been established. (3) A black background shows that
the utility cannot communicate with the driver.
Figure 10. Utility icon in the system tray
• Window controls: It is important to understand the effects of the utility window’s OK
button, Cancel button, and other controls. These are explained below.
13
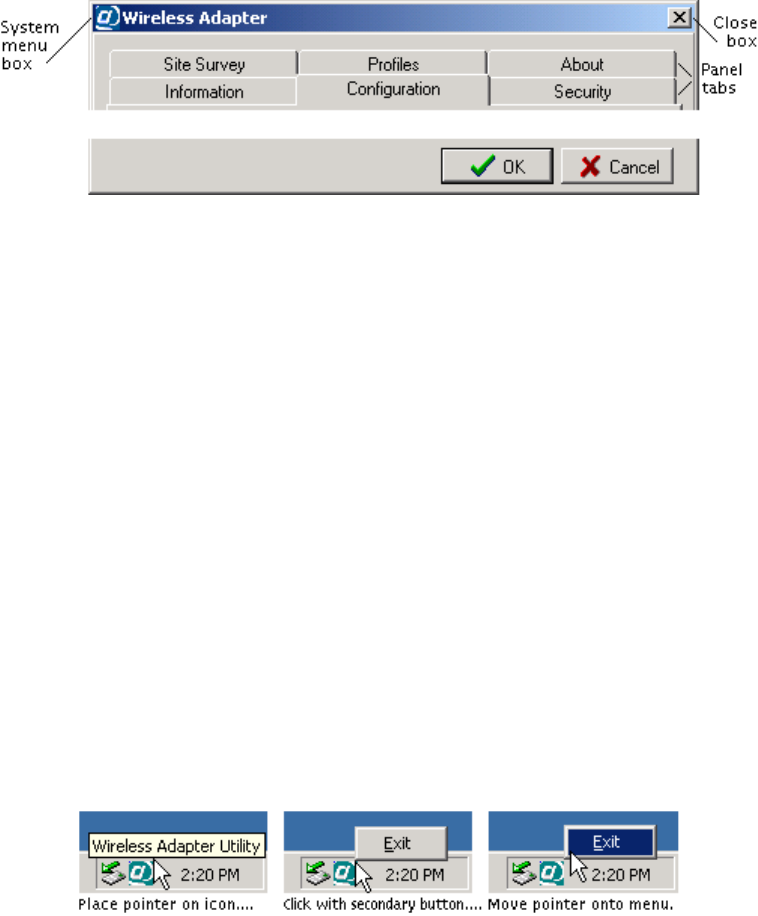
OK button: Clicking OK applies (sends to the adapter) any changes you have made in
the adapter settings shown in the utility window. It also hides the window, whether you
have made changes or not. Pressing the Enter key is the same as clicking OK.
Cancel button: Clicking Cancel discards any unapplied changes you have made in the
adapter settings shown in the utility window. It also hides the window, whether you have
made changes or not. Pressing the Esc key is the same as clicking Cancel.
Figure 11. Utility window controls
To apply or discard changes but keep the window visible, click a tab other than the tab of
the panel currently shown. If there are unapplied changes, you will be asked if you want
to apply them. Click Yes to apply them, No to discard them.
To hide the window without applying or discarding any changes, click the window’s
Close box (in the top right corner), or open the window’s System menu (in the top left
corner) and choose Close. Pressing Alt+F4 is the same as clicking the Close box or
choosing Close.
When you are connected to a wireless network, hiding the utility window has no effect on
the connection. (The connection will be broken, however, if settings unsuitable for the
network are applied.)
• Redisplaying the utility: To redisplay the utility when it is hidden, double-click its icon
in the system tray, or carry out either of the procedures for starting it up (this will not
cause a second copy of it to start up).
• Shutting down the utility: To shut the utility down completely, click its icon in the
system tray with your pointing device’s secondary button (most often the button on the
right), move the pointer onto the menu that pops out, and choose the Exit command.
Figure 12. Shutting down the utility
Shutting down the utility will not break any existing connection to a wireless network.
14
8 Operation
This chapter explains how to establish wireless connections using your adapter and the Wireless
Adapter Utility. It is assumed here that —
• you have completed installation of the driver, utility, and adapter;
• you know how to start the utility, hide and redisplay its window, and shut it down (see
section 5.2, “Controlling the Utility”); and
• you are within range of at least one wireless device that will accept a connection from
you.
Any wireless connection, even a connection to a single device, is treated in this chapter as a
connection to a wireless network. There is, in fact, no difference in the steps required to connect
wirelessly to a single device or a whole network, and a connection to a single device works in all
the same ways as a connection to a network with many devices on it.
6.1 Understanding Connection Profiles
The utility makes connecting to wireless networks simpler by the use of connection profiles. A
connection profile is a group of settings used to join a particular wireless local-area network
(WLAN). Connection profiles are referred to simply as profiles in the rest of this guide.
For a low-security WLAN, you often can create a profile with two clicks, save it with another
click, and apply it (that is, use the settings in it to join the WLAN) with one more click. For some
WLANs, however — especially high-security WLANs — you must input settings supplied by the
WLAN operator to create a profile and join the WLAN for the first time.
A profile is automatically saved for each WLAN that you join. The next time you want to join
that WLAN, you can do so by simply applying the profile. There is no limit to the number of
profiles you can save. You can also save multiple profiles for a single WLAN, if it requires
different settings at different times (this is done on some WLANs for security reasons). You can
create, edit, and delete profiles at any time, whether you are connected to a WLAN or not.
6.2 Understanding the Utility’s Panels
The utility has six tabbed panels. When the program starts up, the Information panel is shown,
and a dotted rectangle on the tab shows that the panel name is selected. For convenience on
laptop computers, you can switch panels with the right, left, and up arrow keys when a panel
name is selected.
Figure 13. The utility’s panel tabs
15
The utility’s panels are explained briefly below. The order of the explanations matches the order
in which the right and left arrow keys take you through the panels.
The Information panel shows if you are connected to a WLAN. When you have a connection,
information about it appears here. This panel can also display important error messages. A
Rescan button, present only when this panel appears, is for attempting to reconnect if the radio
link has gone down.
The Configuration panel shows the adapter’s current settings (except for security settings), and
lets you change them. Changes are applied (that is, sent to the adapter) when you switch panels or
click OK. This lets you test changes to the current profile before editing and resaving the profile
itself.
The Security panel shows the adapter’s current Wired Equivalent Privacy (WEP) settings, and
lets you change them. WEP is a form of encryption that can help prevent snooping. To join a
WLAN that uses WEP, you must obtain WEP settings from the WLAN operator. WEP settings
are part of the current profile, and can be changed and tested like the settings in the
Configuration panel.
The Site Survey panel shows the results of searches for WLANs. A search is carried out at
startup, any time you click the Search button, and whenever necessary to establish or maintain a
connection. You can double-click a WLAN in the search results to display a dialog box for
creating a profile for that WLAN. When you click that dialog box’s OK button, the profile is
saved, and you are asked if you want to join the WLAN.
The Profiles panel lists existing profiles. Click a profile to enable buttons that let you edit, apply,
or remove it. Double-clicking a profile is another way of applying it. The New button is for
creating a profile manually (this may be necessary for joining a WLAN that does not allow
automatic detection). After creating or editing a profile, you are asked if you want to apply it.
The About panel contains a copyright notice and information about the operating system, the
utility, the driver, and the adapter. The final item, “regulatory domain,” is the country or region
whose laws the adapter’s radio transmission characteristics conform to.
6.3 Connecting for the First Time
Connecting to a WLAN is often referred to as joining the network. Another term you might often
see is associate: a station is said to “associate with” (or to) an access point in an infrastructure
WLAN, or with other stations in an ad-hoc WLAN. The term join is used below for brevity.
Joining a WLAN is like connecting a cable to a wired network. Additional steps might be needed
to make full access to network resources possible. Such steps are outside the scope of this guide.
These instructions assume that the adapter is inserted and in operation, that you have successfully
installed the driver and utility, and that you are within radio range of the WLAN you want to join.
If the WLAN is set up for the easiest possible access, you can join as follows: (1) Start the utility.
(2) Go to the Site Survey panel. (3) Double-click the line showing information about the WLAN.
(4) Click OK to save the profile created by the utility. (5) Click Yes to confirm that you want to
connect.
16
This process is described in greater detail below.
1. Start up the Wireless Adapter Utility.
The utility’s Information panel will appear. In most cases, the first time you run the
utility, this panel will show that you have not joined a WLAN.
If the WLAN you want to join allows automatic detection, the utility can create a profile
containing all or most of the settings required for joining. You will need little or no
information from the network operator.
If the WLAN does not allow automatic detection, you will have to obtain configuration
and security information from the operator. Then, to create a profile and join the WLAN,
go to the Profiles panel, click New, input all the information, and click OK.
It is assumed here that the WLAN allows automatic detection. If it does, information
about it will appear on your screen in the next step.
2. Go to the Site Survey panel. Note the information shown in the SSID and WEP
columns.
An SSID (Service Set Identifier) is a name assigned to a WLAN by the operator. If more
than one WLAN is listed, the SSIDs should help you identify the one you want to join.
(The SSID is sometimes called the network [or domain] name [or ID].)
WEP is Wired Equivalent Privacy, a means of encrypting digital radio transmissions to
prevent snooping. Look to see if WEP is disabled or enabled on the WLAN; this affects
what you must do in this step and the next.
• If WEP is disabled, the utility can create a profile containing all the settings required
for joining the WLAN. Go straight to step 3.
• If WEP is enabled, encryption is used for security on the WLAN, and you will need
to know (1) the encryption method (64-, 128-, or 256-bit WEP), (2) the format of
the “key” or keys (“hex” or “ASCII” — that is, numeric or textual), (3) the key or
keys, and in some cases, (4) the “authentication mode” (“open” or “shared”).
The encryption method is sometimes called the “key length,” and 64-bit WEP is
sometimes called “40-bit WEP.” If you have received a key or keys but are not sure
of the method and format, see the additional explanations in step 3.
3. Double-click the WLAN that you want to join.
A window titled New Profile will appear. It will show a suggested name for the profile
and, in a panel titled Configuration, adapter settings that the utility has determined are
suitable for joining the WLAN.
The name and most of the settings should be left unchanged. If you need to conserve
battery power on a laptop computer, you can set the Power Saving Mode control to
Maximum Power Save. This will make the adapter turn its receiver off and on
periodically when you are connected to this WLAN. As a result, the connection might
sometimes seem slower than usual.
17
• If WEP is disabled on the WLAN, go straight to step 4.
• If WEP is enabled on the WLAN, go to the New Profile window’s Security panel.
To enable WEP in this profile, pull down the Method list and select 64-Bit, 128-Bit,
or 256-Bit. Controls for selecting the “key input method” (that is, key format) and
for entering keys will appear.
If you are unsure of how to set the Method and Key Input Method controls, you
can determine the correct settings from the length and contents of the WLAN’s key
or keys. Read the following two paragraphs very carefully.
“Hex” is hexadecimal (base 16) notation. A WEP key in hex format can contain
only hex digits. The hex digits are the numerals 0 through 9 and the letters A
through F (case does not matter: “A” has the same meaning as “a” in hex). The
key must contain an exact number of hex digits: 10 for 64-bit WEP, 26 for 128-
bit WEP, and 58 for 256-bit WEP. (A WEP key in hex format may be written
with spaces or colons between pairs of digits. Be sure to count and type only the
digits.)
ASCII (American Standard Code for Information Interchange) means plain text.
A WEP key in ASCII format can contain any characters you can type on your
keyboard, including spaces. Case matters: “A” and “a” are treated as different
characters. The key must contain an exact number of characters: 5 for 64-bit
WEP, 13 for 128-bit WEP, and 29 for 256-bit WEP.
64-bit WEP allows the use of one to four keys, and the Default Key control must be
set to the key currently in use on the WLAN. If using 128- or 256-bit WEP, type the
key into the Key 1 box. Remember that 256-bit WEP can only be used by devices
from the same product family as your adapter.
The Auth. Mode (authentication mode) control is set by default to Open. In open
authentication, a request to join a WLAN is never encrypted. If the WLAN uses
“shared” authentication (where requests to join must be encrypted), set this control
to Shared. (If Auth. Mode is set to Auto, the adapter will try both methods. Some
WLANs allow this, and some do not.).
4. Click
OK.
The utility will save the profile and ask if you want to connect to the WLAN.
5. Click
Yes.
Connection is usually very quick. If your computer needs to obtain settings (such as an IP
address) from a server on the network, this may take a few seconds. The utility’s
Information panel shows the state of the connection. It also displays your computer's IP
address and other TCP/IP settings (this is for convenience only; these settings are not
directly related to wireless networking).
18
7 Utility Reference
This chapter explains all the indicators and controls in each of the Wireless Adapter Utility’s
panels. The panels are explained in the order in which the right arrow key takes you through them
when the program has just been started up: Information, Configuration, Security, Site Survey,
Profiles, and About.
Note: The Configuration and Security panels in the Profile and New Profile
dialog boxes contain all the same controls as those in the utility’s main window.
For information on these panels, see sections 7.2 and 7.3 in this chapter.
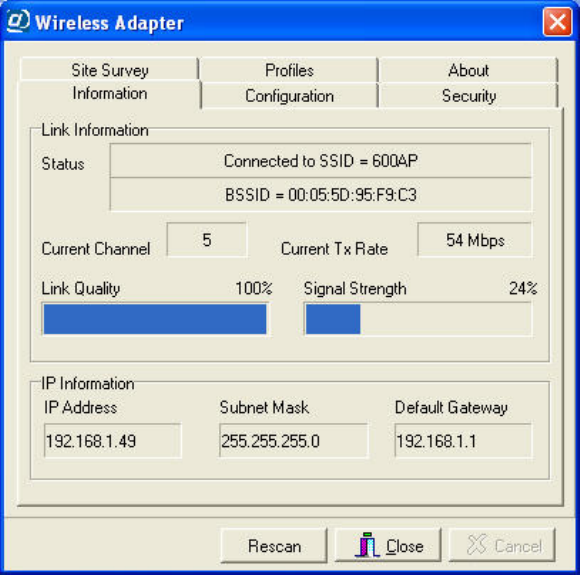
7.1 The Information Panel
The Information panel shows the adapter’s current connection status and the computer’s current
IP (Internet Protocol) address settings. The information shown is “read-only,” that is, this panel
does not let you directly change any settings.
Figure 14. The Information Panel
Status display: When you are connected to a WLAN, the Status display consists of a box
showing the SSID and a box showing the BSSID. At other times, it consists of a single box
showing a status message such as “Not connected to network” or “Couldn’t communicate
with driver.”
19
The SSID, a human-assigned name, defines the WLAN. It is sometimes called the network
(or domain) name (or ID). Groups of devices using different SSIDs in the same area are
considered to make up different WLANs. Your computer must be set to use the same SSID as
all other machines on the WLAN. A “detectable” WLAN is one that broadcasts its SSID.
SSID broadcasts (often called “beacons”) enable the utility to show the WLAN in the Site
Survey listing and automatically fill in the correct SSID when creating a profile.
The BSSID is a numeric, factory-set identifier identical to the medium access control (MAC)
address (also called the MAC ID) of one of the devices on the WLAN. On an infrastructure
WLAN, it is usually the MAC address of the access point; on an ad-hoc WLAN, it is usually
the MAC address of one of the members. BSSIDs are shown in hexadecimal (base 16)
notation.
The BSSID can change as you move between cells of a roamable infrastructure WLAN. On
an ad-hoc WLAN, it may change as different stations take on the role of “coordinator” (this
change is automatic).
Current Channel display: A channel is one of 14 groups of adjacent frequencies in the radio
band used for wireless networking. The channel can change as you move between cells of a
roamable infrastructure WLAN; the adapter automatically detects and uses the channel used
by the access point with the best signal. An ad-hoc WLAN always uses a single, fixed
channel decided on by its users.
Current Tx Rate display: The Tx (transmission) rate is the communication speed in megabits
per second (Mbps). If the Transmission Rate setting in the current profile is Auto, the figure
shown here can vary as the adapter adjusts to changing interference levels, distance, etc.
When the adapter is operating in 4X mode, +4X appears after the transmission rate. 4X mode
uses larger packets to reduce overhead and increase throughput; it does not change the
number of bits transmitted per second.
Link Quality and Signal Strength display: Link quality can be compared to the clarity, and
signal strength to the volume, of audible speech. Radio-frequency interference, reflection, and
obstructions can reduce link quality even when signal strength is high. These figures are often
useful in diagnosing problems on a wireless network.
IP Address, Subnet Mask, and Default Gateway display: This information is obtained from
the operating system, and can be of use to technicians in diagnosing network problems. It can
also help non-technical users determine when they are “on the Internet.”
20
If your computer is set to obtain IP (Internet Protocol) settings automatically, the IP Address
and Subnet Mask boxes will contain 0.0.0.0, and the Default Gateway box will be blank,
before you join a WLAN. After you join a WLAN and receive IP settings from a server on
the network, the settings will appear in these boxes. This is a way of letting you know that
you are “fully connected” and can access e-mail, the World Wide Web, and other Internet-
based resources.
Rescan button: Click Rescan to try to re-establish a link that has gone down. You can also
click Rescan to make the adapter “renegotiate” a link that has become slow; the connection
will be re-established at the highest speed possible.
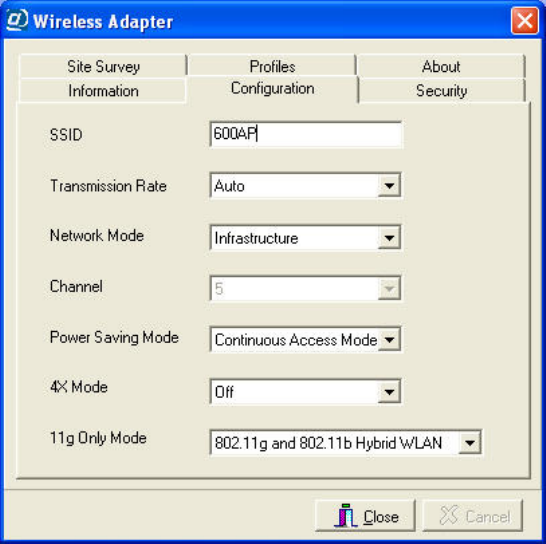
7.2 Configuration Panel
The descriptions in this section apply to the Configuration panels in the main window, the New
Profile dialog box, and the Profile dialog box. These panels all contain the same controls.
Use the main window’s Configuration panel to view the adapter’s current settings and to make
experimental or temporary changes. When you want to save a configuration, access the New
Profile or Profile dialog box, either from the Site Survey panel (by double-clicking a listed
WLAN) or from the Profiles panel (by clicking New, or by selecting a profile and clicking Edit).
Figure 15. The main window’s Configuration panel
Auto-detected configuration settings — those that appear in the New Profile or Profile dialog box
just after you double-click a WLAN in the Site Survey listing — ordinarily should not be changed.
Changing the auto-detected SSID or network mode setting will prevent you from establishing or
maintaining a connection to the WLAN.
21
SSID control: The SSID is a name that a wireless device uses to indicate which WLAN it is on
or wants to join. It is case-sensitive, can be up to 32 characters long, and can contain letters,
numbers, and symbols. All devices on a WLAN must have exactly the same SSID setting.
Other terms often used for SSID are Extended Service Set Identifier (ESSID), domain ID, net
ID, network name, extended network ID, and wireless network (or domain) name. The set of
devices that an SSID identifies is sometimes called a communication domain or wireless
domain.
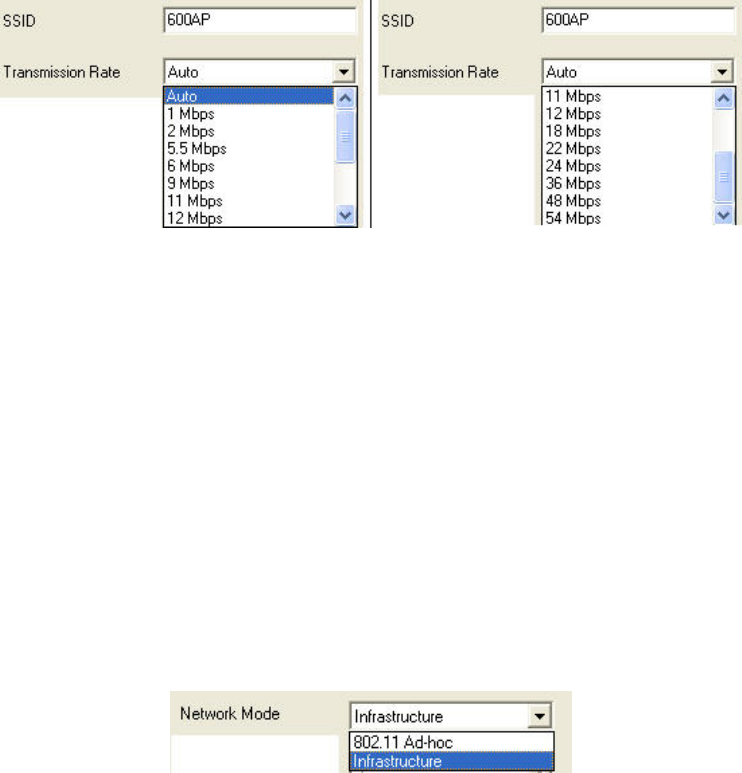
Transmission Rate control: The adapter can transmit at many different bit rates (measured in
megabits per second, or Mbps), and it can automatically adjust its speed according to link
quality, signal strength, and the capabilities of whatever device it is exchanging signals with.
The default setting of the Transmission Rate control is Auto.
There is rarely a need to change the setting of this control. The benefits of a fixed, low speed
(greater range) or a fixed, high speed (smaller range for greater security) can be obtained only
if all the devices on the WLAN are set the same way. A setting of Auto offers the best
combination of throughput, range, and resistance to interference.
A speed of 22 Mbps can be used only on connections to devices from the same product
family as your adapter. Even if the Transmission Rate control is set to 22 Mbps, the adapter
will not use a higher speed than the device at the other end of the link can handle.
Network Mode control: This control can be set to Infrastructure or 802.11 Ad-hoc. The default
setting is Infrastructure. To establish and maintain a wireless connection, the adapter must
be set to the same mode as all the other devices on the WLAN.
A WLAN with a connection to a wired network (such as the Internet) is certain to be working
in infrastructure mode. An ad-hoc WLAN is usually a temporary, “on-the-spot” arrangement
among a group of people who need to connect only with each other and do not need the
resources of a wired network.
Some controls in the Configuration panel are disabled or enabled according to which
network mode is selected. Infrastructure mode requires automatic channel switching. Packet
length standards must be observed in 802.11 ad-hoc mode, ruling out the use of 4X mode.
When you select high-speed ad-hoc mode, it is assumed that you want to use the highest
possible speed.
22

Channel control: This control is enabled only when the network mode (see above) is set to
ad-hoc (either 802.11 or high-speed). An infrastructure WLAN can include many access
points using different channels, and to allow roaming, the adapter must be able to switch
channels automatically. An ad-hoc WLAN uses a single fixed channel, and the adapter must
be set to that channel to join the WLAN. Channel detection is automatic for any WLAN that
appears in the Site Survey listing, so the setting of this control rarely needs to be changed.
The radio band used for wireless networking contains 95 frequencies spaced 1 MHz apart.
These are organized into 14 staggered clusters of 23 adjacent frequencies each. Such a cluster
is called a channel. There is much frequency overlap among channels. When overlapping
channels are used in the same area, this causes interference, which reduces throughput.
Which channels are available can differ from country to country (see appendix E).
On an infrastructure WLAN, access points with overlapping coverage areas should use non-
overlapping channels. Non-overlapping channels are those with numbers that differ by 5 or
more, for example, channels 1, 6, and 11, or channels 3, 8, and 13. An ad-hoc WLAN should
use a channel that has little or no frequency overlap with any other channels being used in the
same area.
Power Saving Mode control: The Power Saving Mode control is a drop-down list that offers
two settings: Continuous Access Mode and Maximum Power Save.
In Continuous Access mode, your adapter’s receiver is always on. This is the default setting.
Maximum Power Save mode is a “doze” mode in which the adapter turns its receiver off but
“wakes up” at fixed intervals to see if any communications are waiting for it. Before entering
this mode, it tells the access point (or, on an ad-hoc network, the current coordinating station)
that it is going to do so. The access point (or coordinating station) will “buffer” (temporarily
store) communications destined for your machine. The adapter stays “awake” only long
enough to check for and receive waiting communications.
4X Mode control: 4X mode is a means of reducing communication overhead and increasing
throughput by allowing packets to be much longer than is normally allowed. This mode can
be used only on connections to devices from the same product family as your adapter.
When the 4X Mode control is set to On, the adapter uses 4X mode whenever possible.
Detection of whether it can be used or not is completely automatic, so interoperation with
devices from other product families is unaffected. When the control is set to Off, 4X mode is
never used. The default setting is On.
23
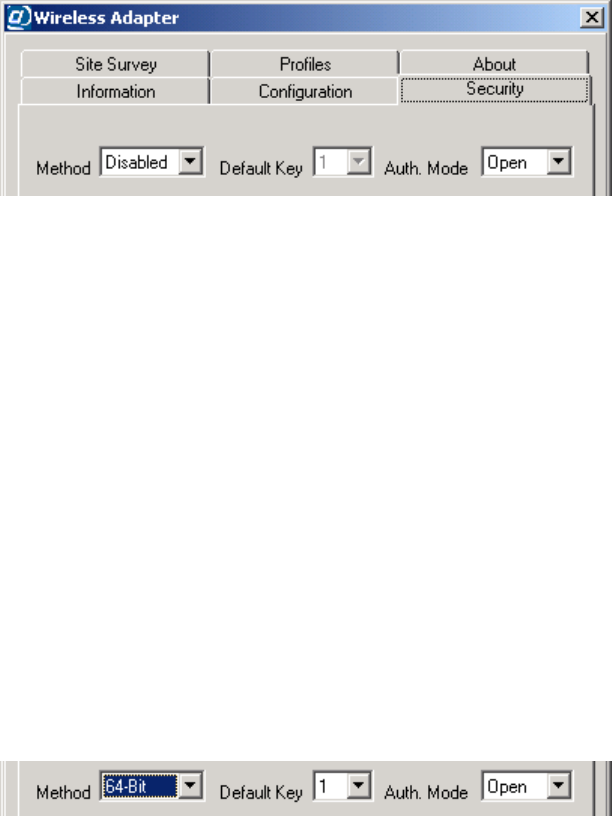
7.3 The Security Panel
The descriptions in this section apply to the Security panels in the main window, the New Profile
dialog box, and the Profile dialog box. These panels all contain the same controls.
Use the main window’s Security panel (shown below, without its initially blank lower part) to
view the adapter’s current security settings, and to make experimental or temporary changes.
Figure 16. The main window’s Security panel
When you want to save security settings, you must (1) access the New Profile or Profile dialog
box, either from the Site Survey panel (by double-clicking a listed WLAN) or from the Profiles
panel (by clicking New, or by selecting a profile and clicking Edit), and then (2) click the New
Profile or Profile dialog box’s Security tab.
When a WLAN is auto-detected, the adapter can detect only whether security (in the form of
Wired Equivalent Privacy [WEP] encryption) is on or off (“enabled” or “disabled”). Where
security is on (that is, WEP is enabled), you must obtain WEP settings from the WLAN operator
and input them in the Security panel to be able to join the WLAN.
Method control: The Method control is a drop-down list for selecting a WEP setting. Four
settings are offered: Disabled, 64-Bit, 128-Bit, and 256-Bit.
(So-called 40-bit WEP encryption is the same as that offered by the 64-Bit setting. On all
wireless networking products, only 40 bits of a 64-bit key, and 104 bits of a 128-bit key, are
input by the user.)
The default setting is Disabled. Selecting any other setting enables the Default Key control
and causes the Key Input Method, Key 1, Key 2, Key 3, and Key 4 controls to appear.
Default Key control: On a WLAN that uses 64-bit WEP, each device can store one to four WEP
keys. The WLAN can then switch among these keys from time to time for better security.
The “default key” is the key currently in use on the WLAN. This control lets you switch
quickly, without having to input the current key each time it is switched. The default setting
is Key 1.
Auth. Mode control: “Authentication” is the process of determining whether a requesting station
should be permitted to join the WLAN. A station authenticates itself by using the correct
SSID in its request to join. If WEP is enabled, the WLAN may require that requests to join be
24
unencrypted (“open” authentication) or that they be encrypted (“shared” authentication), or it
may allow stations to try both methods (“auto” determination of the authentication mode).
The default setting of the Auth. Mode control is Open. If WEP is enabled on the WLAN, the
operator has a responsibility to tell you if you need to set this control to Shared or Auto.
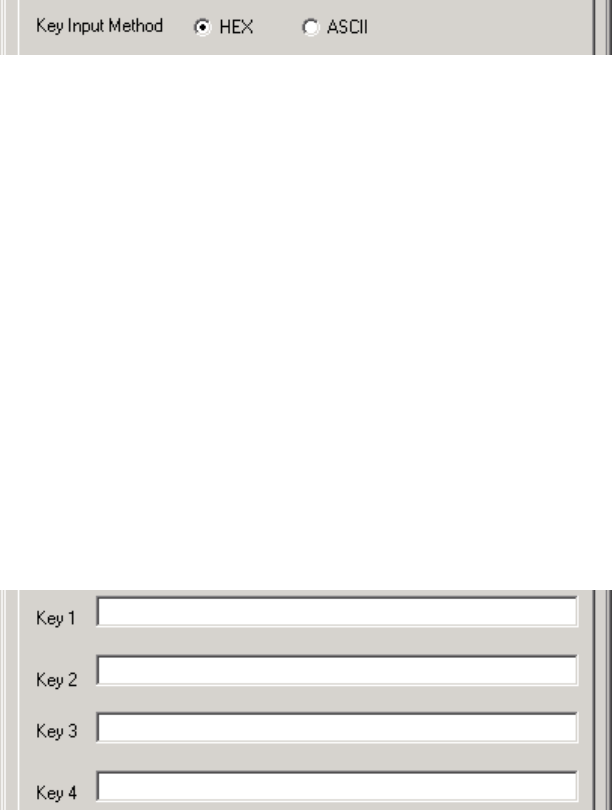
Key Input Method control: This control determines how the utility will interpret the key or keys
you type before it sends the actual bits to the adapter for use and storage. It can treat your
input as “hex” or as “ASCII.”
“Hex” is hexadecimal (base 16) numeric notation. When input in hex, a key can contain only
hex digits, that is, the numerals 0 through 9 and the letters A through F — no spaces, symbols,
punctuation marks, or letters other than A through F. Letters can be uppercase or lowercase;
“A” is interpreted the same way as “a” in hex.
If 64-bit WEP is used and the key input method is hex, each key must contain exactly 10 hex
digits. If 128-bit WEP is used and the key input method is hex, the key must contain exactly
26 hex digits. A 256-bit WEP key in hex format must contain exactly 58 hex digits.
“ASCII” (American Standard Code for Information Interchange) has become a synonym for
plain text, that is, whatever characters you can type on your keyboard, including spaces.
If 64-bit WEP is used and the key input method is ASCII, each key must contain exactly 5
characters. If 128-bit WEP is used and the key input method is ASCII, the key must contain
exactly 13 characters. A 256-bit WEP key in ASCII format must contain exactly 29
characters. Remember that 256-bit WEP can only be used by devices from the same product
family as your adapter.
Key 1, Key 2, Key 3, and Key 4 controls: These boxes are for typing in the key or keys used for
WEP encryption on the WLAN. If there is only one key, type it into the Key 1 box.
To help ensure that your input is correct, the utility enforces the rules for length and
acceptable characters of the key input method currently selected. To help maintain the
security of the WLAN, after security settings are sent to the adapter or stored in a profile,
only asterisks appear in the key input boxes when the settings are viewed again.
25
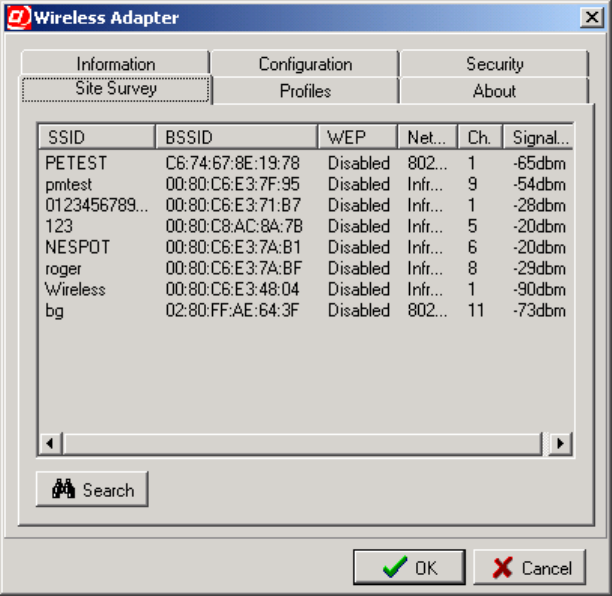
7.4 The Site Survey Panel
The Site Survey panel shows the results of searches for WLANs. A search is carried out
automatically when the utility starts up and whenever necessary to establish or maintain a
connection. You can start a search manually by clicking the Search button.
Figure 17. The Site Survey panel
Each WLAN found in a search appears on a line of its own in the Site Survey listing. The
information shown is divided into the following columns:
SSID column: The SSID is a name, usually assigned by the network operator, that is shared by
all members of the WLAN. It is sometimes called the network (or domain) name (or ID).
BSSID column: The BSSID is an automatically assigned numeric identifier. On an infrastructure
WLAN, the BSSID shown is usually the medium access control (MAC) address of the closest
access point; on an ad-hoc network, it is usually the MAC address of one of the members.
BSSIDs are shown in hexadecimal (base 16) notation, with a colon [:] added between each
pair of digits to aid readability.
WEP column: WEP stands for Wired Equivalent Privacy, an encryption method that can
enhance network security. WEP can be enabled or disabled. If it is enabled, you must enable
it with the correct settings on your machine to join the network.
Network Mode column: The network mode can be infrastructure, 802.11 ad-hoc, or high-speed
ad-hoc. In infrastructure mode, all wireless stations communicate through an access point. In
26
ad-hoc mode, wireless stations communicate directly with each other. Only networking
devices from the same product family as your adapter can operate in high-speed ad-hoc mode.
Ch. (Channel) column: A channel is one of 14 groups of adjacent frequencies in the band used
for wireless networking. Not all channels are available in all countries. A station operating in
infrastructure mode automatically finds the channel used by any access point it is within
range of. An ad-hoc WLAN must use a single, fixed channel agreed upon by the members.
Signal Level column: This is the strength of the radio signal as measured at the adapter’s
antenna input. It is shown in dBm, that is, decibels referenced to 1 milliwatt (mW). Decibels
are a logarithmic unit, so -10 dBm equals 0.1 mW, -20 dBm equals 0.01 mW, -30 dBm
equals 0.001 mW, and so on. The closer the figure is to zero, the stronger the signal is (for
example, “-13dbm” represents a stronger signal than “-78dbm”).
The actions you can take in the Site Survey panel are described below.
• To change the order in which site survey results are displayed, click a column heading.
For example, you can click the WEP column heading to have all WLANs where WEP is
disabled listed above all WLANs where WEP is enabled. Click again to reverse the order.
• To see all of an item (for example, an SSID) that exceeds the width of its column, let the
pointer rest on it for at least half a second.
The full name will usually appear in a pop-up description box. In some columns, more
text must be cut off than in others for the full name to pop up. You can also widen a
column by dragging the right edge of the column header to the right.
• To search again for WLANs in your vicinity, choose the Search button.
The utility will “listen” for about five seconds and then display the results.
• To join a listed WLAN (or just to create or edit a profile for it) double-click anywhere on
the line showing information about it.
The utility requires that a profile exist for a WLAN before you can join. A dialog box for
creating or editing a profile will appear.
By default, the utility uses the WLAN’s SSID as the profile name. If no profile with that
name exists, the New Profile dialog box will appear. If you already have a profile with
that name, the Profile dialog box will appear. These dialog boxes both contain a
Configuration panel and a Security panel.
In either case, settings that are required for joining the WLAN and were auto-detected
during the Site Survey search will automatically be filled in for you. You might wish to
change the Power Saving Mode setting, and you might need to input or edit security
settings. See section 7.2, “The Configuration Panel,” and section 7.3, “The Security
Panel,” for details.
When finished checking or editing the profile, click the dialog box’s OK button. The
profile will be saved, and you will be asked if you wish to join the WLAN.
27
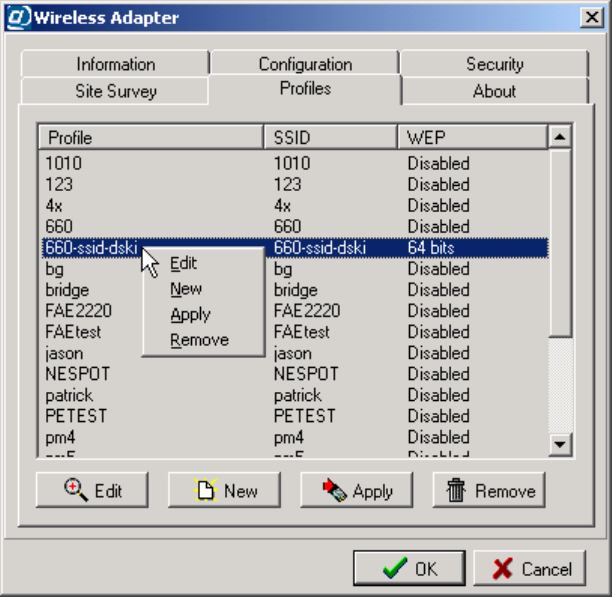
7.5 The Profiles Panel
The Profiles panel lists existing profiles. The list is initially in order of creation, with the oldest
profiles at the top.
After you have created profiles for a number of WLANs, you will probably use this panel more
than any other. When you are within range of a WLAN that you have a profile for, just (1) start
the utility, (2) click the Profiles tab, (3) double-click the profile, and (4) confirm that you want to
apply the profile and join the WLAN. As long as the WLAN’s settings have not changed, you
will be connected, and you can hide or shut down the utility and start using the network.
The Apply function is also available, along with others, when you “left-click” or “right-click” a
profile in the Profiles panel, as shown below.
Figure 18. The Profiles panel
Each profile occupies a single line in the listing. There are three columns of information:
Profile column: The profile name appears here.
SSID column: This column shows the SSID of the WLAN the profile is for.
WEP column: This column shows the status of Wired Equivalent Privacy encryption in the
profile: disabled, or set to 64, 128, or 256 bits.
28
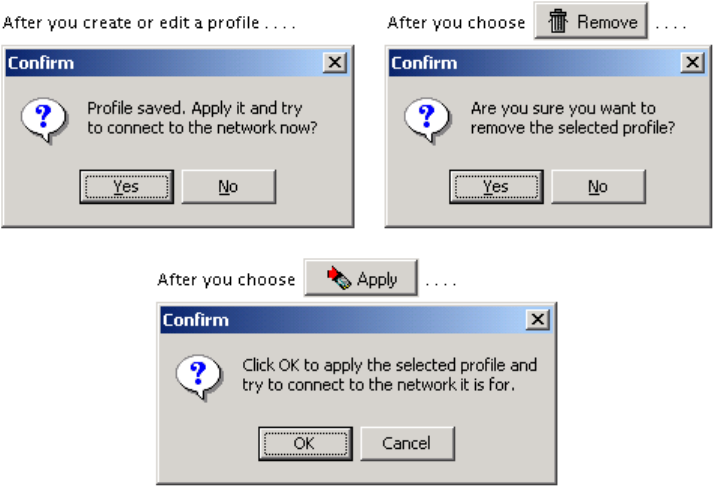
The actions you can take in the Profiles panel are described below.
• To change the order in which profiles are listed, click a column heading.
For example, you can click the SSID column heading to have the list arranged in
alphabetical order of the SSIDs. Click the heading again for reverse alphabetical order.
• To see all of a profile name or SSID that exceeds the width of its column, let the pointer
rest on it for at least half a second.
The full name will usually appear in a pop-up description box. In some columns, more
text must be cut off than in others for the full name to pop up. You can also widen a
column by dragging the right edge of the column header to the right.
• To apply a profile as quickly as possible, double-click anywhere on the line showing
information about it.
To apply a profile is to send the settings in it to the adapter and try to join the WLAN the
profile is for. You will be asked to confirm that this is what you want to do.
• To edit, apply, or remove a profile, click it with the mouse’s main or secondary button
and choose the appropriate button or command.
Clicking a profile with your pointing device’s main button (usually the button on the left)
selects the profile and enables the Edit, Apply, and Remove buttons under the list.
Clicking a profile with the secondary button (usually the button on the right) does all of
this and displays a pop-up menu containing Edit, New, Apply, and Remove commands.
The Edit and New buttons and commands display dialog boxes containing Configuration
and Security panels identical in content and function to the panels of the same names in
the utility’s main window. See section 7.2, “The Configuration Panel,” and section 7.3,
“The Security Panel,” for details. You are asked for confirmation after all major actions.
29
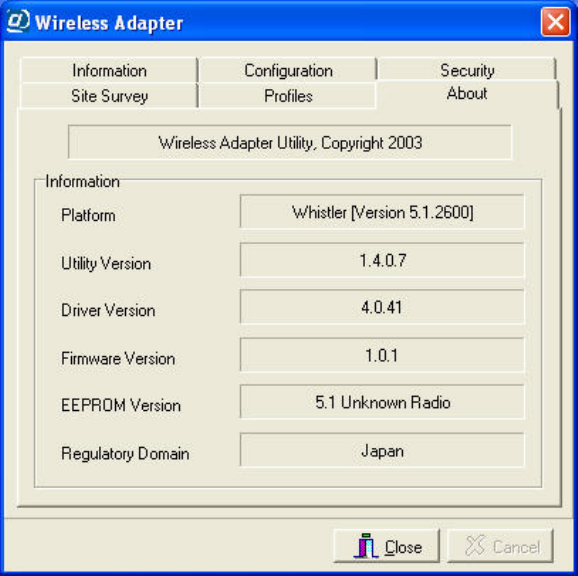
7.6 The About Panel
The About panel contains a copyright statement; gives hardware, software, and firmware version
information; and shows the “regulatory domain” for the which the adapter was made. The
regulatory domain is the country or region whose laws regarding radio transmissions the
adapter’s capabilities conform to.
Figure 19. The About panel
This information can be helpful in the event that you require service or have an opportunity to
upgrade the software. It is a good idea to keep a record of this information for future reference.
30
Appendix A: Technical Support
If you encounter a problem that cannot be solved by following the steps in the troubleshooting
section, call your networking equipment supplier for help. Have the following information ready
before you make the call:
• Full product name and, if possible, firmware version number
• Version numbers of all software products included in the package
• Operating system name and version
• Network type and configuration, and any recent configuration changes
• Actions that led to the situation that prompted the call
• LED status and any on-screen messages seen in connection with the problem
If it appears that a return or exchange will be required, you may be asked to provide the serial
number of the product.
Support personnel may ask you to try to reproduce the problem. They may also ask you to run
some simple tests using diagnostic tools included with the system. Proper preparation on your
part can greatly reduce the amount of time needed to solve the problem.
31
Appendix B: Limited Warranty
Hardware
The manufacturer warrants its products to be free of defects in workmanship and materials, under
normal use and service, for a period of 12 months from the date of purchase from the
manufacturer or its authorized reseller, and for the period of time specified in the documentation
supplied with each product.
Should a product fail to be in good working order during the applicable warranty period, the
manufacturer will, at its option and expense, repair or replace it, or deliver to the purchaser an
equivalent product or part at no additional charge except as set forth below. Repair parts and
replacement products are furnished on an exchange basis and will be either reconditioned or new.
All replaced products and parts will become the property of the manufacturer. Any replaced or
repaired product or part has a warranty of ninety (90) days or the remainder of the initial warranty
period, whichever is longer.
The manufacturer shall not be liable under this warranty if its testing and examination disclose
that the alleged defect in the product does not exist or was caused by the purchaser’s or any third
party’s misuse, neglect, improper installation or testing, unauthorized attempt at repair or
modification, or any other cause beyond the range of the intended use, or by accident, fire,
lightning, or other hazard.
Software
Software and documentation materials are supplied “as is,” without warranty as to their
performance, merchantability, or fitness for any particular purpose. However, the media
containing the software is covered by a 90-day warranty that protects the purchaser against failure
within that period.
Limited Warranty Service Procedure
Any product (1) received in error, (2) received in a defective or non-functioning condition, or (3)
exhibiting a defect under normal working conditions, can be returned to the manufacturer by
following these steps:
1. Prepare the following in printed or electronic form:
• Dated proof of purchase
• Product model number and quantity
• Product serial number
• Precise reason for return
• Your name, address, email address, phone number, and fax number
2. Inform the distributor or retailer.
3. Ship the product back to the distributor/retailer with freight charges prepaid. The
purchaser must pay the cost of shipping from the distributor/retailer to the manufacturer.
Any package sent C.O.D. (Cash On Delivery) will be refused.
32
Charges: Usually, RMA (Returned Material Authorization) items will be returned to the
purchaser via airmail, prepaid by the manufacturer. If any item is returned by another carrier, the
purchaser will pay the difference. A return freight and handling fee will be charged to the
purchaser if the manufacturer determines that the product is not defective or that the damage was
caused by the user.
Warning
The manufacturer is not responsible for the integrity of any data on storage equipment (hard
drives, tape drives, floppy diskettes, etc.). We strongly recommend that our customers back their
data up before sending such equipment in for diagnosis or repair.
Service After Warranty Period
After the warranty period expires, all products can be repaired for a reasonable service charge.
The shipping charges to and from the manufacturer’s facility will be borne by the purchaser.
Return for Credit
In the case of a DOA item (an item that is “dead on arrival”) or a shipping error, a return for
credit will automatically be applied to the purchaser’s account, unless otherwise requested.
Limitation of Liability
All expressed and implied warranties of a product’s merchantability, or of its fitness for a
particular purpose, are limited in duration to the applicable period as set forth in this limited
warranty, and no warranty will be considered valid after its expiration date.
If this product does not function as warranted, your sole remedy shall be repair or replacement as
provided for above. In no case shall the manufacturer be liable for any incidental, consequential,
special, or indirect damages resulting from loss of data, loss of profits, or loss of use, even if the
manufacturer or its authorized distributor/dealer has been advised of the possibility of such
damages, or for any claim by any other party.
33
Appendix C: Specifications
Standards compliance IEEE 802.11b, IEEE 802.11g, MiniPCI
Regulatory compliance
USA: FCC Part 15 Class B
Frequency band 2400.0 to 2497.0 MHz (Japan)
2400.0 to 2483.5 MHz (North America and Europe)
2445.0 to 2475.0 MHz (Spain)
2446.5 to 2483.5 MHz (France)
Transmitter power 17 dBm (typical)
Receiver sensitivity* 11 Mbps: 8% PER, -82 dBm (typical)
54 Mbps: 10% PER -68 dBm (typical)
* Minimum receiver input power level at which a packet error ratio (PER) of less than the indicated percentage can
be maintained, given a packet length of 1024 bytes and conditions of 20° to 30° C.
Input power DC 3.3V ±5%
Power consumption 550 mA/3.3V (transmitting), 350 mA/3.3V (receiving)
Data rates 1, 2, 5.5, 6, 9, 11, 12, 18, 24, 36, 48 and 54 Mbps with auto
fallback; special user-selectable 22 Mbps option
RF spreading scheme Direct-sequence spread-spectrum (DSSS)
Encoding and modulation
methods
BPSK, QPSK, CCK, OFDM, and PBCC
Security 64- and 128-bit Wired Equivalent Privacy (WEP) encryption
Special user-selectable 256-bit WEP option
Environmental requirements
Operating temperature: 0° to 50° C
Storage temperature: -30° to 70° C
Operating humidity: Tested to RH 85% at 40° C (104° F)
for 48 hours
Accompanying software Drivers for Microsoft® Windows 98/ME (NDIS 5.0), 2000
(NDIS 5.0), and XP (NDIS 5.1); configuration utility with
connection profile management for multiple networks
34
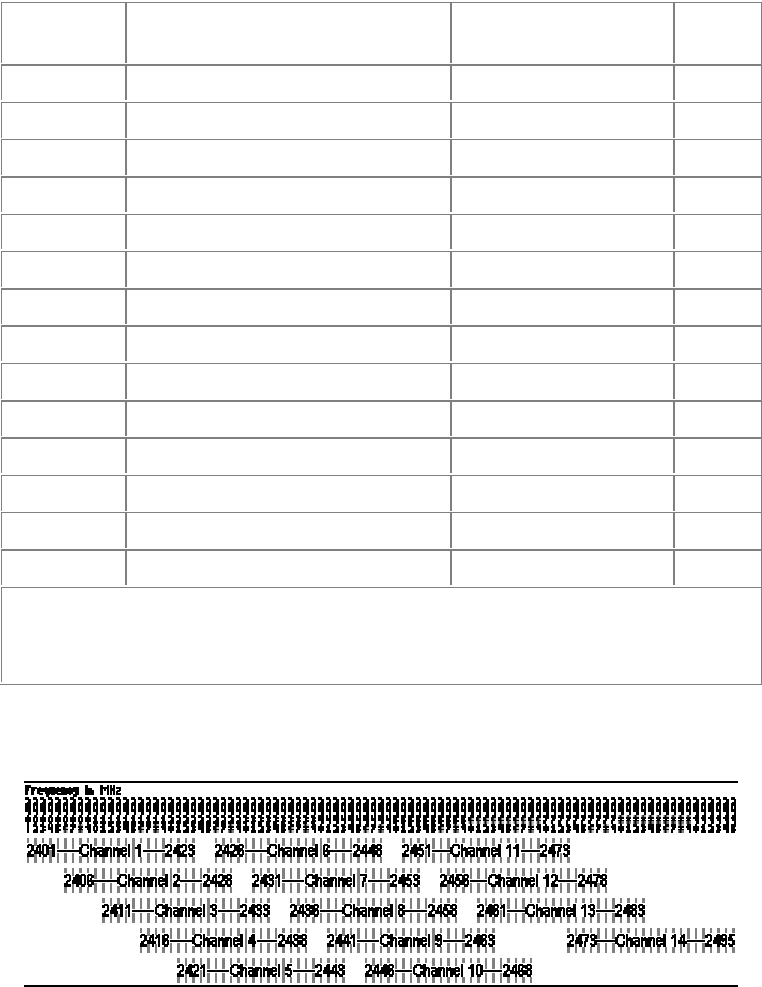
Appendix E: Channels and Regulations
The following table lists the IEEE 802.11b transmission channels and provides important notes
on regulations regarding channel use.
Channel Start, Center, and
End Frequencies (MHz)
Non-overlapped
Channels Notes
1 2401 2412 2423 6-14 1
2 2406 2417 2428 7-14 1
3 2411 2422 2433 8-14 1
4 2416 2427 2438 9-14 1
5 2421 2432 2443 10-14 1
6 2426 2437 2448 1, 11-14 1
7 2431 2442 2453 1, 2, 12-14 1
8 2436 2447 2458 1-3, 13, 14 1
9 2441 2452 2463 1-4, 14 1
10 2446 2457 2468 1-5, 14
11 2451 2462 2473 1-6
12 2456 2467 2478 1-7 2
13 2461 2472 2483 1-8 2
14 2473 2484 2495 1-10 3
1.Notes: Not used where the regulations of Spain or France are in effect.
2. Not used where the regulations of Spain or North America are in effect.
3. Used only where the regulations of Japan are in effect.
An illustration of IEEE 802.11b channel distribution and overlap appears below.
Wireless networking channels in the 2.4-GHz frequency band
35
FCC STATEMEMT:
This device is intended only for OEM integrators under the following conditions:
1) The antenna must be installed such that 20 cm is maintained between the antenna
and users, and
2) The transmitter module may not be co-located with any other transmitter or
antenna.
As long as 2 conditions above are met, further transmitter test will not be required.
However, the OEM integrator is still responsible for testing their end-product for any
additional compliance requirements required with this module installed (for example,
digital device emissions, PC peripheral requirements, etc.).
IMPORTANT NOTE: In the event that these conditions can not be met (for example
certain laptop configurations or co-location with another transmitter), then the FCC
authorization is no longer considered valid and the FCC ID can not be used on the
final product. In these circumstances, the OEM integrator will be responsible for
re-evaluating the end product (including the transmitter) and obtaining a separate FCC
authorization.
End Product Labeling
This transmitter module is authorized only for use in device where the antenna may be
installed such that 20 cm may be maintained between the antenna and users (for
example access points, routers, wireless ADSL modems, and similar equipment). The
final end product must be labeled in a visible area with the following: "Contains TX
FCC ID: IOU3050S01".
Manual Information for End Users
The end user must not have manual instructions to remove or install the device. The
user manual for end users must include the following information in a prominent
location:
"IMPORTANT NOTE: To comply with FCC RF exposure compliance requirements,
the antenna used for this transmitter must be installed to provide a separation distance
of at least 20 cm from all persons and must not be co-located or operating in
conjunction with any other antenna or transmitter."