U MEDIA Communications WST375L 2.4GHz Wireless Bridge User Manual
U-MEDIA Communications, Inc. 2.4GHz Wireless Bridge
User Manual
U-MEDIA Communications, Inc.
Proprietary and Confidential 1
2.4GHz Wireless 802.11n Bridge
Model: WST-375L
User’s Guide
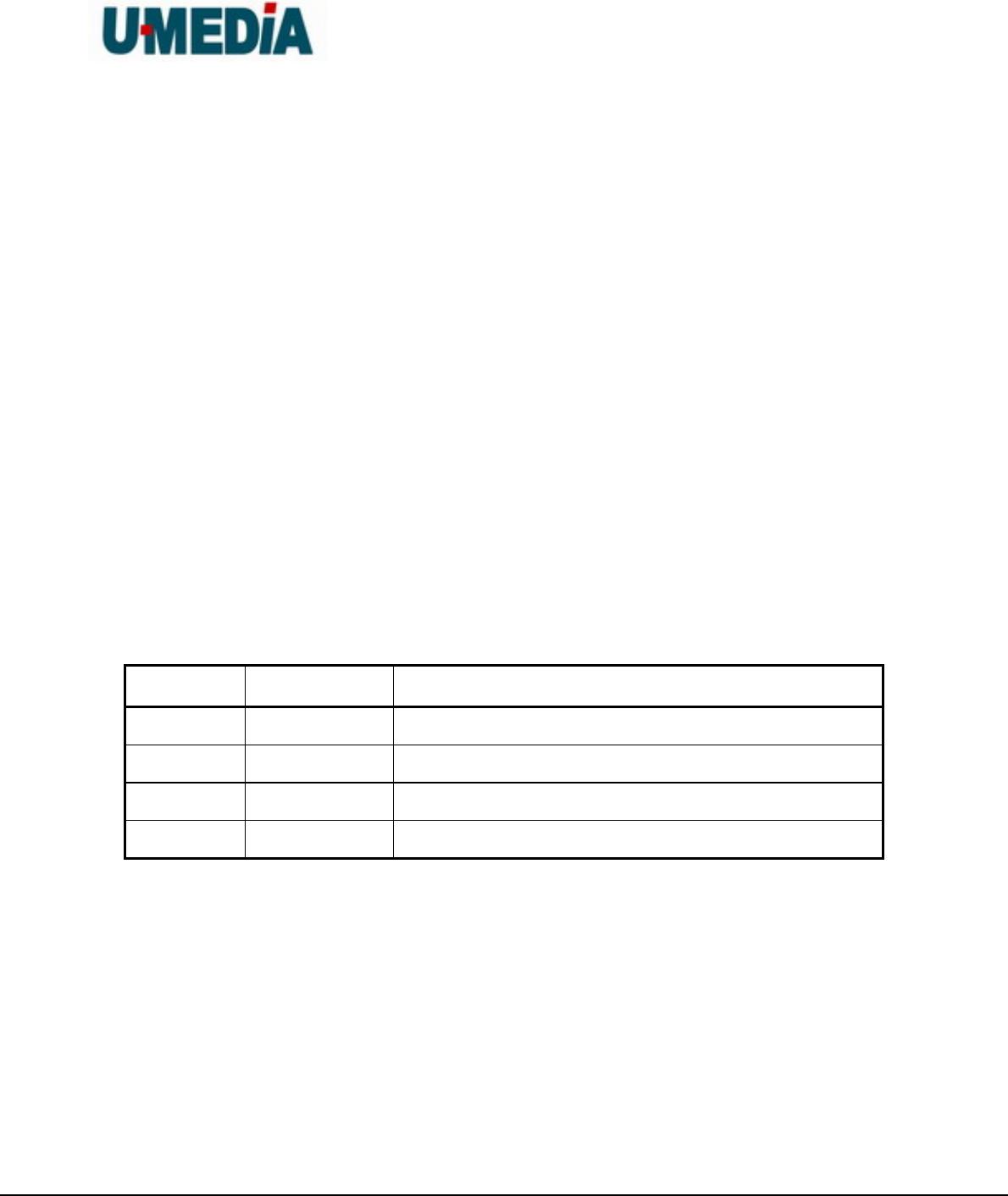
Version Date Description
01 11/07/2008 Draft rev. 01

U-MEDIA Communications, Inc.
Proprietary and Confidential 2
Federal Communication Commission Interference Statement
This equipment has been tested and found to comply with the limits for a Class B digital device,
pursuant to Part 15 of the FCC Rules. These limits are designed to provide reasonable
protection against harmful interference in a residential installation. This equipment generates
uses and can radiate radio frequency energy and, if not installed and used in accordance with
the instructions, may cause harmful interference to radio communications. However, there is
no guarantee that interference will not occur in a particular installation. If this equipment does
cause harmful interference to radio or television reception, which can be determined by turning
the equipment off and on, the user is encouraged to try to correct the interference by one of the
following measures:
Reorient or relocate the receiving antenna.
Increase the separation between the equipment and receiver.
Connect the equipment into an outlet on a circuit different from that to which the receiver is
connected.
Consult the dealer or an experienced radio/TV technician for help.
FCC Caution: Any changes or modifications not expressly approved by the party responsible for
compliance could void the user's authority to operate this equipment.
This device complies with Part 15 of the FCC Rules. Operation is subject to the following two
conditions: (1) This device may not cause harmful interference, and (2) this device must accept
any interference received, including interference that may cause undesired operation.
IMPORTANT NOTE:
FCC Radiation Exposure Statement:
This equipment complies with FCC radiation exposure limits set forth for an uncontrolled
environment. This equipment should be installed and operated with minimum distance
20cm between the radiator & your body.
This transmitter must not be co-located or operating in conjunction with any other antenna or
transmitter.
The availability of some specific channels and/or operational frequency bands are country
dependent and are firmware programmed at the factory to match the intended destination. The

U-MEDIA Communications, Inc.
Proprietary and Confidential 3
firmware setting is not accessible by the end user.
Country Code Statement
For product available in the USA/Canada market, only channel 1~11 can be operated. Selection
of other channels is not possible.
European Union Notice:
Radio products with the CE marking comply with the R&TTE Directive (1999/5/EC), the EMC
Directive (89/336/EEC) and the Low Voltage Directive (73/23/EEC) issued by the Commission
of the European Community.
Compliance with these directives implies conformity to the following European Norms:
EN 60950 Product Safety
EN 300 328 Technical requirement for radio equipment
EN 301 489-1/-17 General EMC requirements for radio equipment
Trademark recognition
All product names used in this manual are the properties of their respective owners and are
acknowledged.

U-MEDIA Communications, Inc.
Proprietary and Confidential 4
Table of Contents
Table of Contents...................................................................................................................................... 4
1. Getting Started with the WST-375L................................................................................................... 6
1.1. Package Contents............................................................................................................ 6
1.2. Minimum System Requirements.................................................................................... 6
2. Introduction........................................................................................................................................... 7
2.1. Features............................................................................................................................. 7
3. Hardware Overview.............................................................................................................................. 8
3.1. LED Indications................................................................................................................. 8
3.2. Rear Panel......................................................................................................................... 9
3.3 Top View ............................................................................................................................ 9
3.4 Bottom View...................................................................................................................... 9
3.3 Installation Considerations............................................................................................ 10
3.4 Getting Start .................................................................................................................... 11
4. Using the Configuration Menu.......................................................................................................... 12
4.1. Network............................................................................................................................ 13
4.1.1 LAN Setting................................................................................................. 13
4.2 Wireless ........................................................................................................................... 14
4.3.1 Profile.......................................................................................................... 14
4.3.2 Site Survey.................................................................................................. 15
4.3.3 Statistics...................................................................................................... 16
4.3.4 Advance...................................................................................................... 17
4.3.5 QoS............................................................................................................. 18
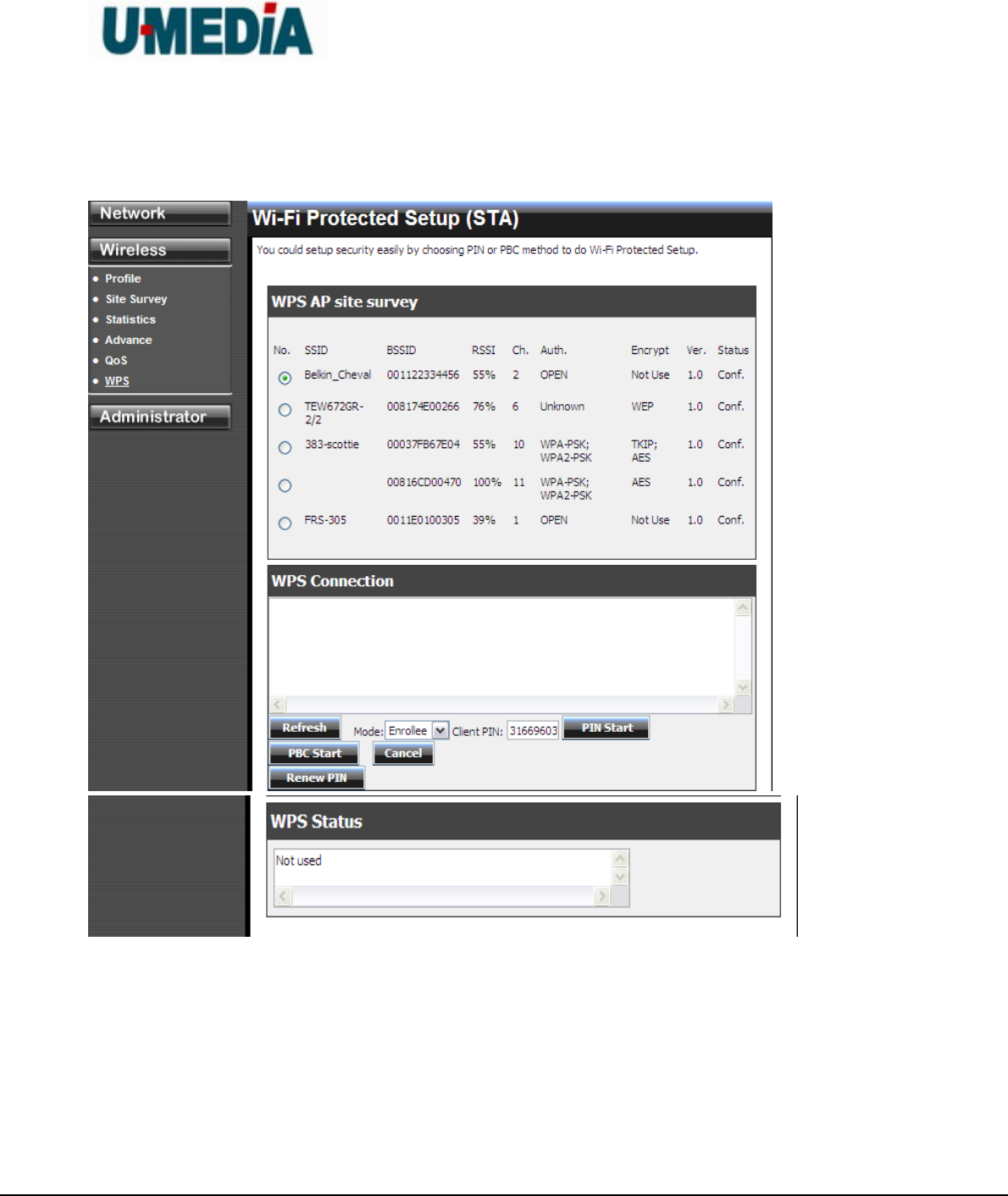
4.3.6 WPS............................................................................................................ 19
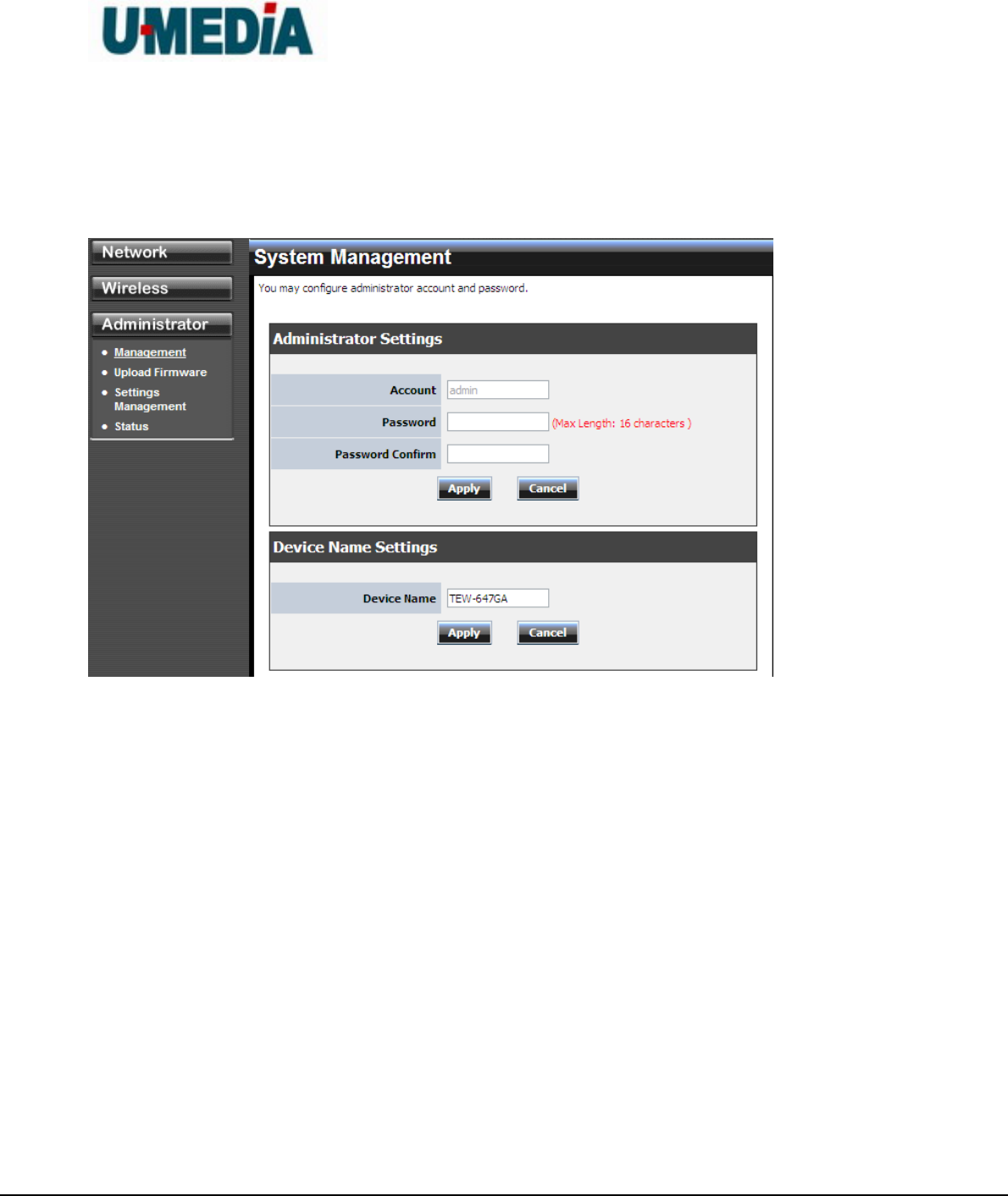
4.3 Administrator................................................................................................................... 20
4.3.1 Management ............................................................................................... 20
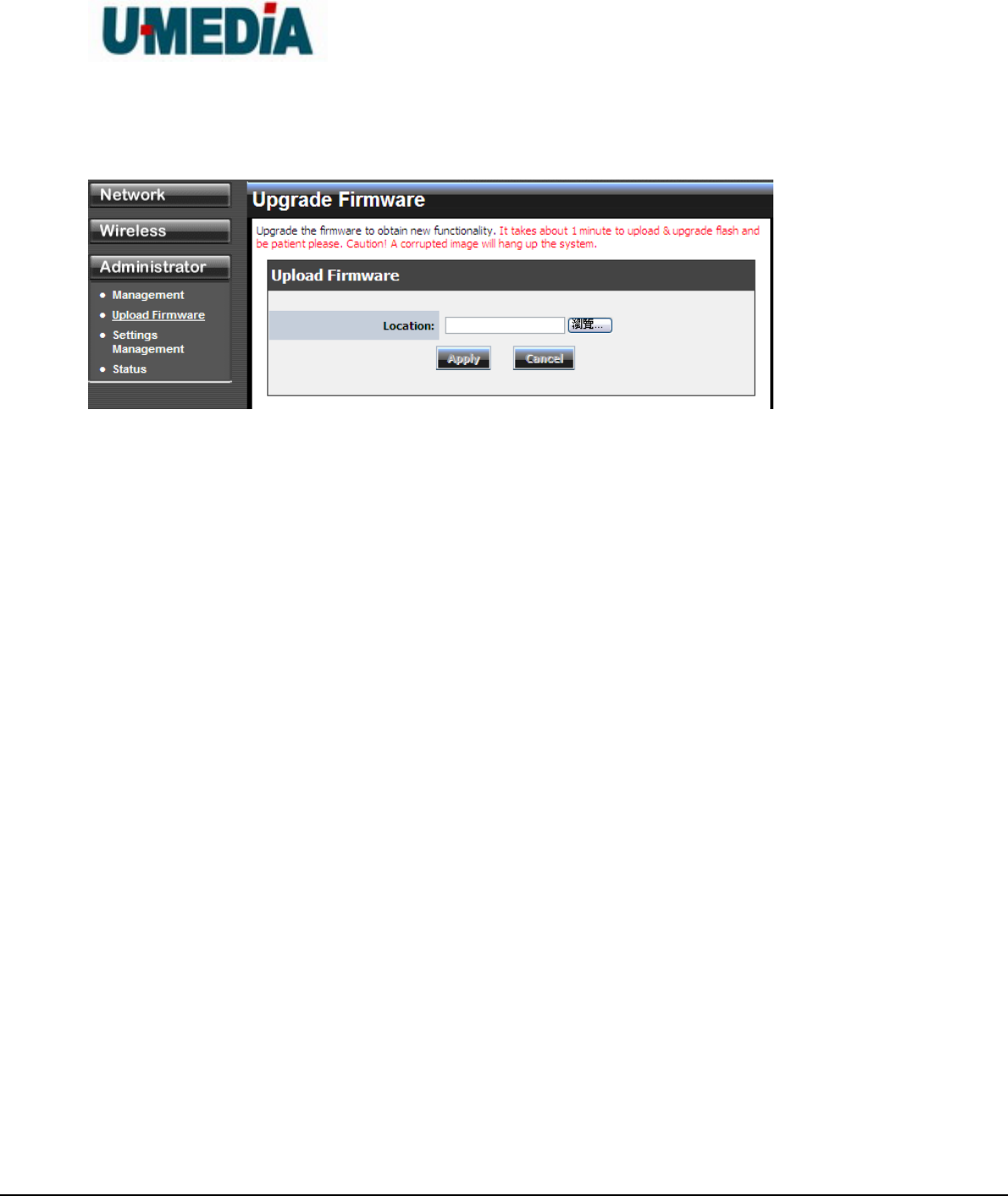
4.3.2 Upload Firmware......................................................................................... 21
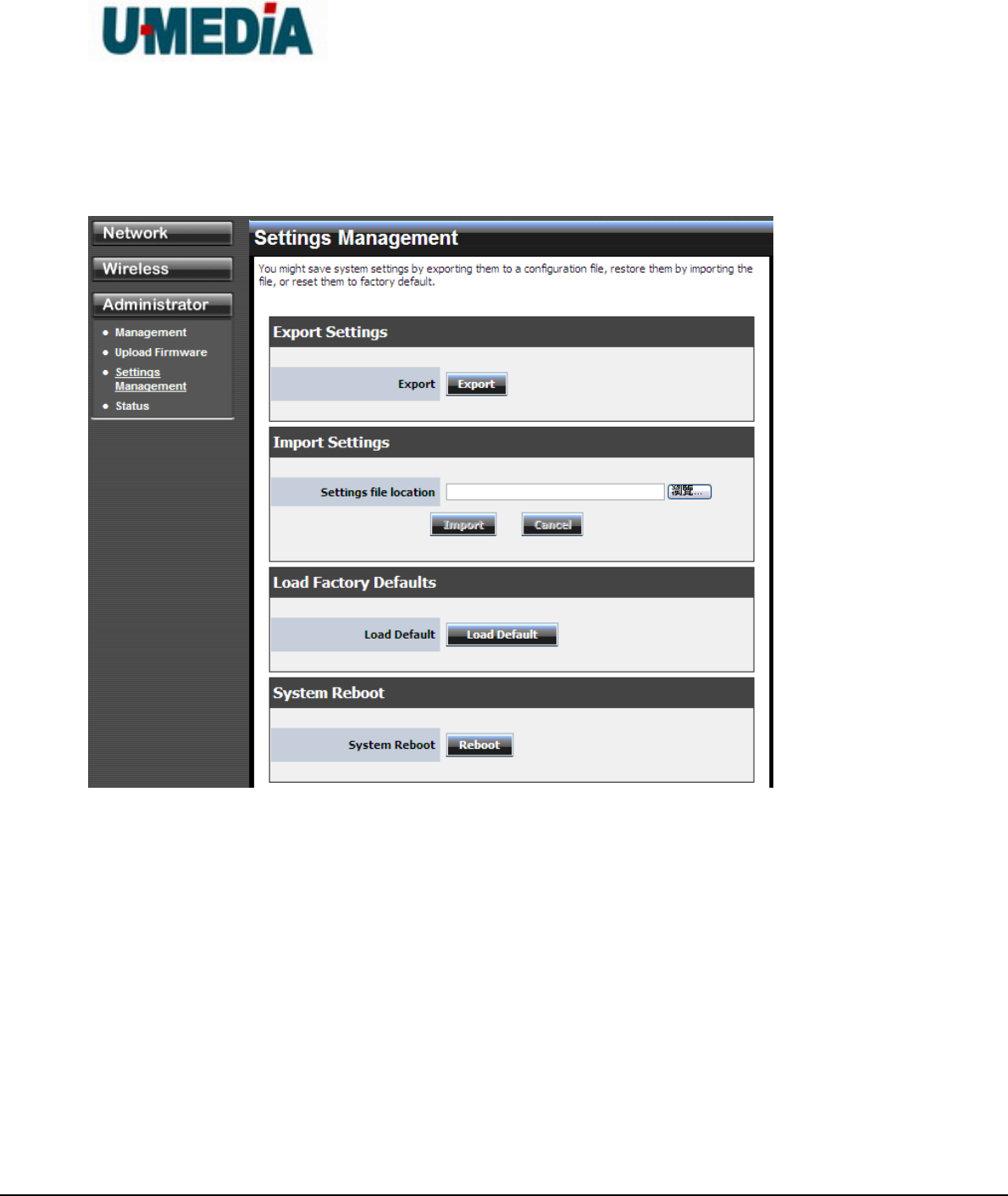
4.3.3 Setting Management................................................................................... 22
4.3.4 Status.......................................................................................................... 24
5. Glossary................................................................................................................................................ 25
A........................................................................................................................................................... 25
B........................................................................................................................................................... 26

U-MEDIA Communications, Inc.
Proprietary and Confidential 5
C........................................................................................................................................................... 26
D........................................................................................................................................................... 27
E............................................................................................................................................................ 28
F............................................................................................................................................................ 28
G........................................................................................................................................................... 29
H........................................................................................................................................................... 30
I............................................................................................................................................................. 30
J............................................................................................................................................................ 32
K........................................................................................................................................................... 32
L............................................................................................................................................................ 32
M........................................................................................................................................................... 33
N........................................................................................................................................................... 33
O........................................................................................................................................................... 34
P............................................................................................................................................................ 35
Q........................................................................................................................................................... 36
R........................................................................................................................................................... 36
S............................................................................................................................................................ 37
T............................................................................................................................................................ 38
U........................................................................................................................................................... 39
V............................................................................................................................................................ 39
W.......................................................................................................................................................... 40
X............................................................................................................................................................ 41
Y............................................................................................................................................................ 41
Z............................................................................................................................................................ 41
#............................................................................................................................................................ 41
1............................................................................................................................................................ 41
U-MEDIA Communications, Inc.
Proprietary and Confidential 6
1. Getting Started with the WST-375L
Congratulations on purchasing the WST-375L! This manual provides information for setting up
and configuring the WST-375L. This manual is intended for both home users and professionals.
1.1. Package Contents
WST-375L 2.4GHz Wireless 802.11n(DRAFT) Bridge
CD-ROM (User’s Guide)
Multi-Language Quick Installation Guide
CAT-5 Ethernet Cable
Power Adapter (12V, 0.5A)
Using a power supply with a different voltage than the one included with your
product will cause damage and void the warranty for this product.
1.2. Minimum System Requirements
Installation Requirements
Web Browser: Internet Explorer (6 or higher) Mozilla or Safari.
A computer with a network adapter or wireless adapter properly installed.
CD-ROM drive
A router with an available network LAN port.
A RJ-45 network cable.

U-MEDIA Communications, Inc.
Proprietary and Confidential 7
2. Introduction
The WST-375L 2.4GHz Wireless 802.11n(DRAFT) Bridge is an high-performance, supports
high-speed wireless networking at home, at work or in public places.
Unlike most routers, the WST-375L provides data transfers at up to 300Mbps in 11n receiving
mode. This bridge is also back compatible with 802.11g or 11b devices. This means that you do
not need to change your entire network to maintain connectivity. You may sacrifice some of
11n’s speed when you mix 11n and 11b/g devices, but you will not lose the ability to
communicate when you incorporate the 11n standard into your 11b/g network. You may choose
to slowly change your network by gradually replacing the 11b/g devices with 11n devices.
2.1. Features
Compact form factor design
Affordable 11n product for easily migrating current 11b/g network to 11n network with
higher data rate benefit
Supports IEEE 802.11n (draft 2.0) & 11b/g 2.4GHz wireless Local Area Network (WLAN)
application
2.412~2.472GHz frequency band operation
Compliant with IEEE 802.3 & 3u standards
Support OFDM and CCK modulation
Delivers data rate up to 300 Mbps in 11n receiving mode.
Support one LAN port
Support WEP & WPA security
Support two printed antennas

U-MEDIA Communications, Inc.
Proprietary and Confidential 8
3. Hardware Overview
3.1. LED Indications
U-MEDIA Communications, Inc.
Proprietary and Confidential 9
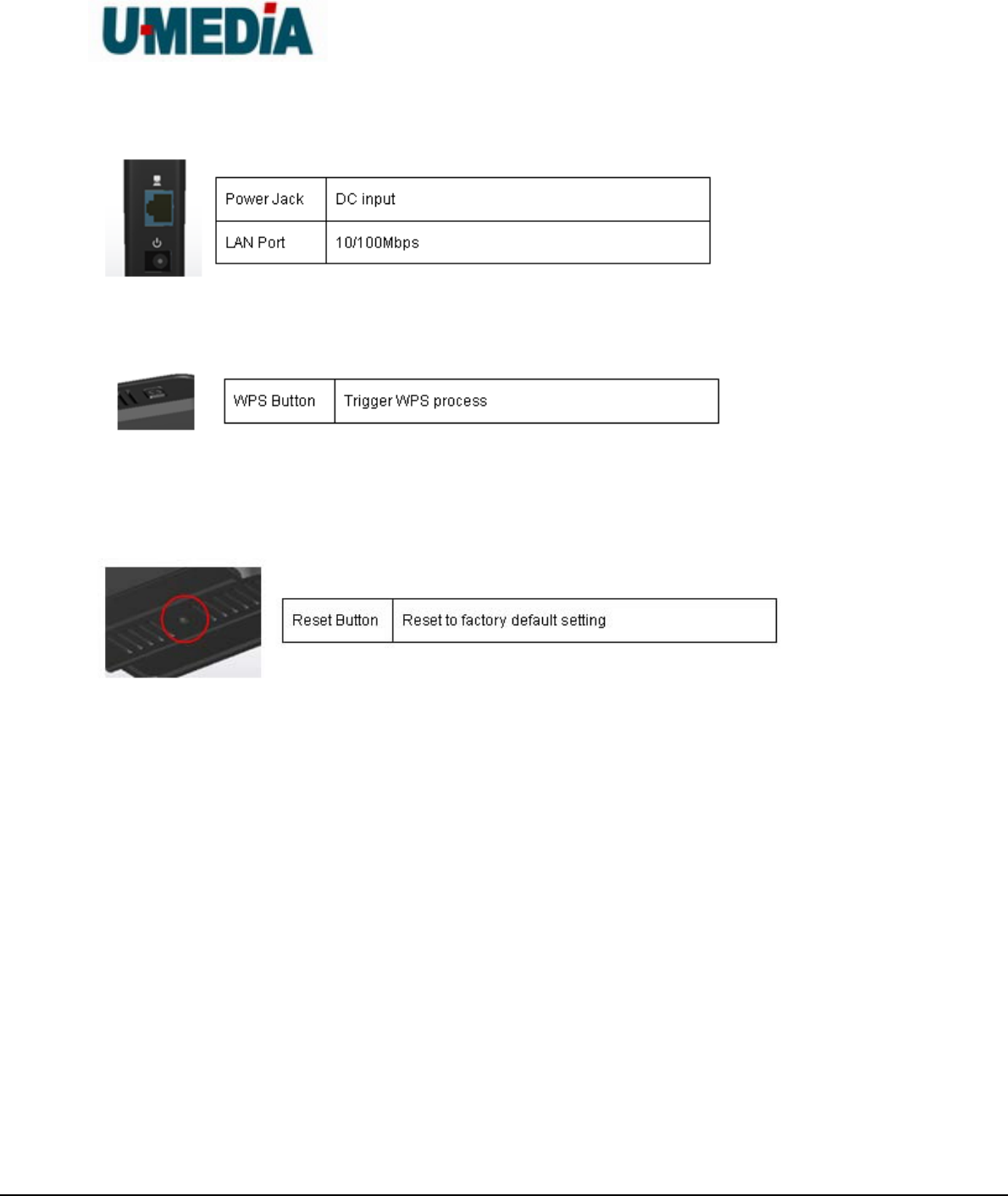
3.2. Rear Panel
3.3 Top View
3.4 Bottom View

U-MEDIA Communications, Inc.
Proprietary and Confidential 10
3.3 Installation Considerations
The TEW-638APB AP lets you access your network, using a wireless connection, from
virtually anywhere within its operating range. Keep in mind, however, that the number,
thickness and location of walls, ceilings, or other objects that the wireless signals must
pass through, may limit the range. Typical ranges vary depending on the types of
materials and background RF (radio frequency) noise in your home or business. The key
to maximizing wireless range is to follow these basic guidelines:
1. Keep the number of walls and ceilings between the WST-375L and other network
devices to a minimum - each wall or ceiling can reduce your wireless product’s range
from 3-90 feet (1-30 meters.) Position your devices so that the number of walls or
ceilings is minimized.
2. Be aware of the direct line between network devices. A wall that is 1.5 feet thick (.5
meters), at a 45-degree angle appears to be almost 3 feet (1 meter) thick. At a
2-degree angle it looks over 42 feet (14 meters) thick! Position devices so that the
signal will travel straight through a wall or ceiling (instead of at an angle) for better
reception.
3. Building Materials can impede the wireless signal - a solid metal door or aluminum
studs may have a negative effect on range. Try to position wireless devices and
computers with wireless adapters so that the signal passes through drywall or open
doorways and not other materials.
4. Keep your product away (at least 3-6 feet or 1-2 meters) from electrical devices or
appliances that generate extreme RF noise.

U-MEDIA Communications, Inc.
Proprietary and Confidential 11
3.4 Getting Start
1 You will need broadband Internet access (a Cable or DSL-subscriber line into your home or
office)
2 Consult with your Cable or DSL provider for proper installation of the modem.
3 Connect the Cable or DSL modem to the WRT-390L Wireless Broadband Router (WAN
port).
4 Ethernet LAN ports of the WRT-390L are Auto MDI/MDIX and will work with both
Straight-Through and Cross-Over cable.
U-MEDIA Communications, Inc.
Proprietary and Confidential 12
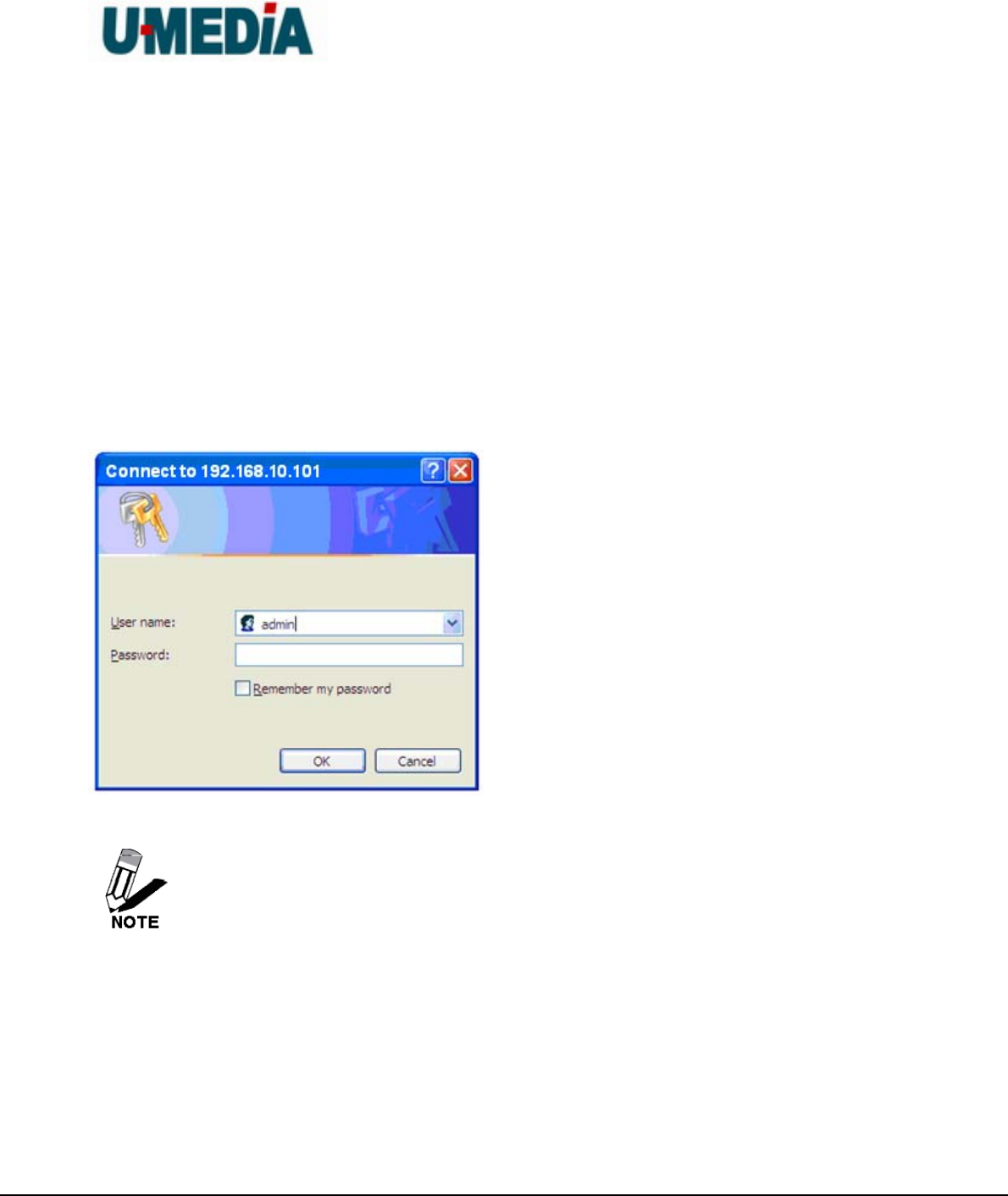
4. Using the Configuration Menu
Whenever you want to configure your WST-375L, you can access the Configuration Menu
through your PC by opening the Web-browser and typing in the IP Address of the WST-375L.
The WST-375L’s default IP Address is http://192.168.10.101
Open the Web browser.
Type in the IP Address of the Bridge (http:// 192.168.10.101)
If you have changed the default IP Address assigned to the WST-375L, make sure
to enter the correct IP Address.
Select admin in the User Name field.
Leave the Password blank.
Click Login In.
U-MEDIA Communications, Inc.
Proprietary and Confidential 13
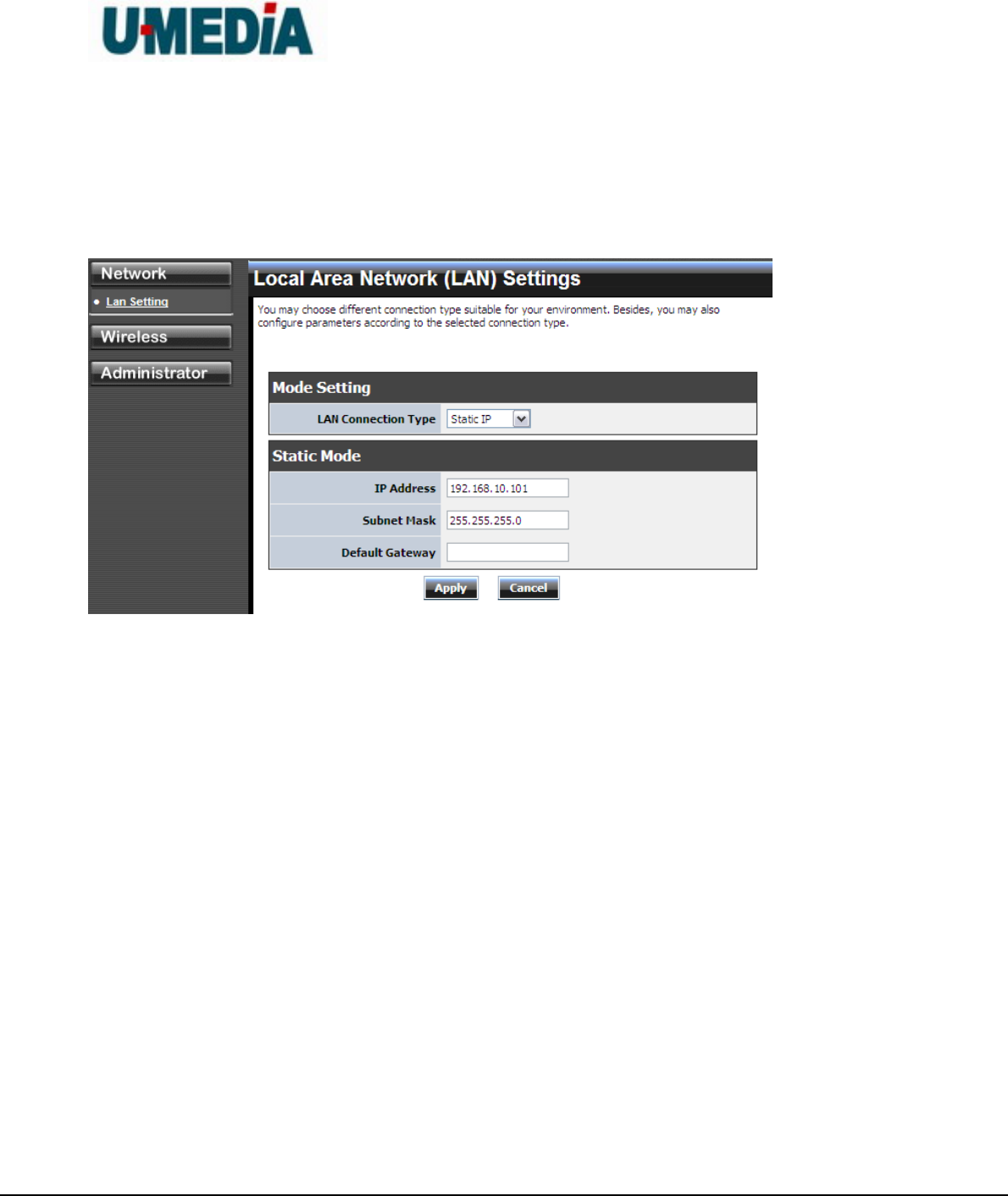
4.1. Network
4.1.1 LAN Setting
LAN Connection Type
Choose "Static IP (fixed IP)" if your router does not support DHCP or if for any other reason
you need to assign a fixed address to the AP. In this case, you must also configure the
following fields.
IP Address
The IP address of the AP on the local area network. Assign any unused IP address in the
range of IP addresses available for the LAN. For example, 192.168.10.100.
Subnet Mask
The subnet mask of the local area network.
Default Gateway
The IP address of the router on the local area network.
Choose “DHCP (Auto Config)” if your router supports DHCP and you want the router to
assign an IP address to the AP.

U-MEDIA Communications, Inc.
Proprietary and Confidential 14
4.2 Wireless
4.3.1 Profile
Create a custom connection to a specific wireless network. Use this option to make custom
profiles and store new profile for later use.
Configure the setting to connect to a wireless network, selection option for network type, SSID,
and wireless security. The profile can be edited, deleted and made active from this option.

U-MEDIA Communications, Inc.
Proprietary and Confidential 15
4.3.2 Site Survey
Use the Site Survey tool to search for wireless networks in the WST-375L area. Click on the
Scan button to search for wireless networks to join. From this window, you can also add your
profile to use with theWST-375L. Click on the Connect button to join a wireless network from
this site survey window.
U-MEDIA Communications, Inc.
Proprietary and Confidential 16
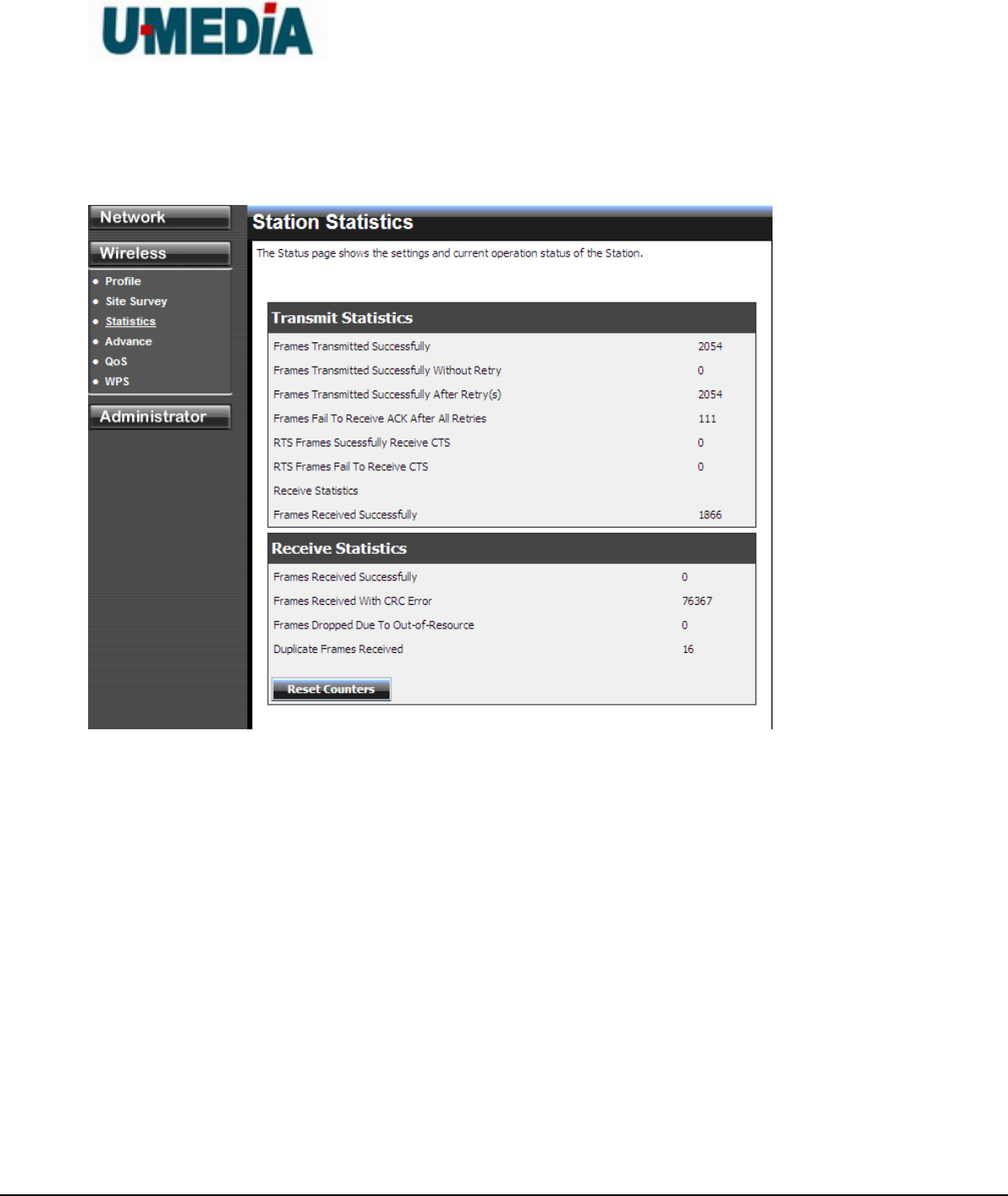
4.3.3 Statistics
View the current operating status of the WST-375L, see the Transmit and Receive data.
U-MEDIA Communications, Inc.
Proprietary and Confidential 17
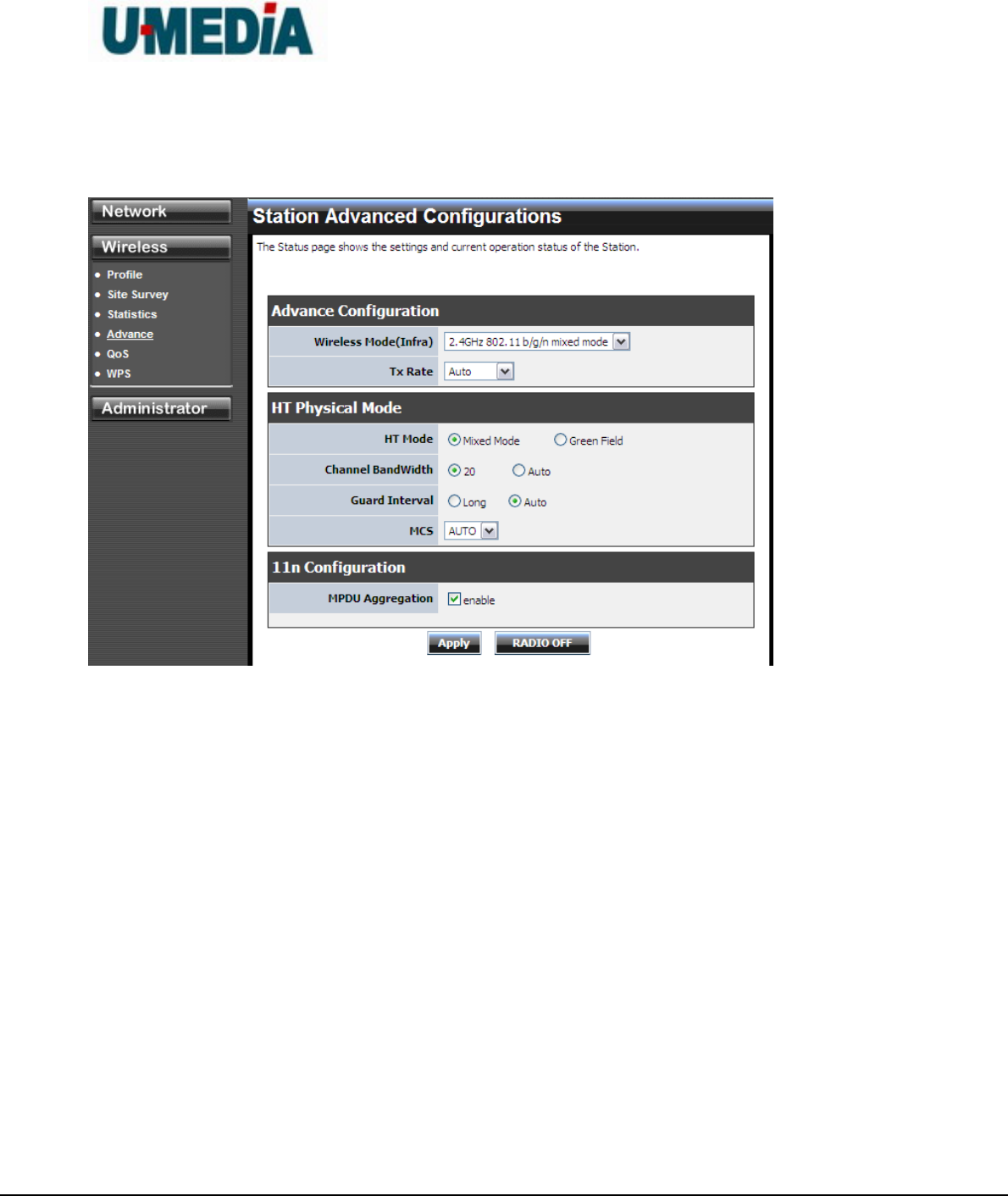
4.3.4 Advance
Use this setting to adjust the wireless environment.
U-MEDIA Communications, Inc.
Proprietary and Confidential 18
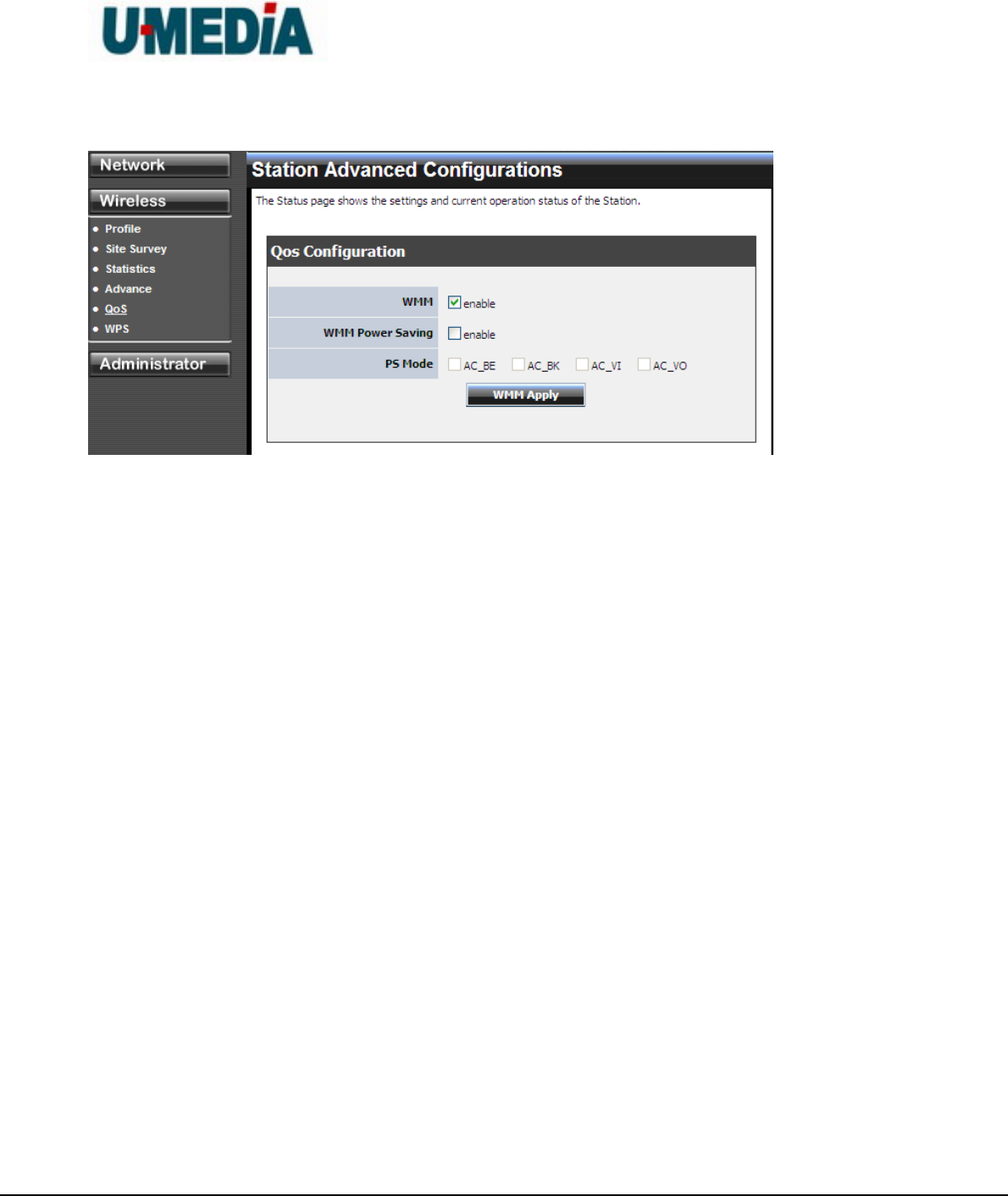
4.3.5 QoS
WMM (Wireless Multi-Media)
use this feature allows wireless devices to take advantage of the wireless environment over
other wireless devices.
WMM Power Saving
An option that allows wireless clients such as notebooks or Laptops to save battery life by
sending less transmission during idle times. Add a check mark to enable this option.
PS Mode
Used for specific application when using WMM Power Saving mode is enabled, use this
feature to help with Quality of Service (QoS) settings; these settings are polled by the priority
given to the option in this section.
AC_BE=Best Effort
AC_BK=Background
AC_VI=Video
AC_VO=Voice
U-MEDIA Communications, Inc.
Proprietary and Confidential 19
4.3.6 WPS
You can setup security easily by choosing PIN or PBC method to do Wi-Fi Protected Setup.
U-MEDIA Communications, Inc.
Proprietary and Confidential 20
4.3 Administrator
4.3.1 Management
At this page, you can configure administrator account and password.
U-MEDIA Communications, Inc.
Proprietary and Confidential 21
4.3.2 Upload Firmware
By assigning firmware location, you can upload firmware at this page.
Once you have a firmware update on your computer, use this option to browse for the file and
then upload the information into the router.
U-MEDIA Communications, Inc.
Proprietary and Confidential 22
4.3.3 Setting Management
You can save system settings by exporting them to a configuration file, restore them by
importing the file, or reset them to factory default.
Export Settings
This option allows you to export and then save the router's configuration to a file on your
computer. Be sure to save the configuration before performing a firmware upgrade.
Import Settings
Use this option to restore previously saved router configuration settings.
Load Factory Defaults
This option restores all configuration settings back to the settings that were in effect at the
time the router was shipped from the factory. Any settings that have not been saved will be

U-MEDIA Communications, Inc.
Proprietary and Confidential 23
lost. If you want to save your router configuration settings, use the Export Settings option
above.
System Reboot
This restarts the router. It is useful for restarting when you are not near the device.
U-MEDIA Communications, Inc.
Proprietary and Confidential 24
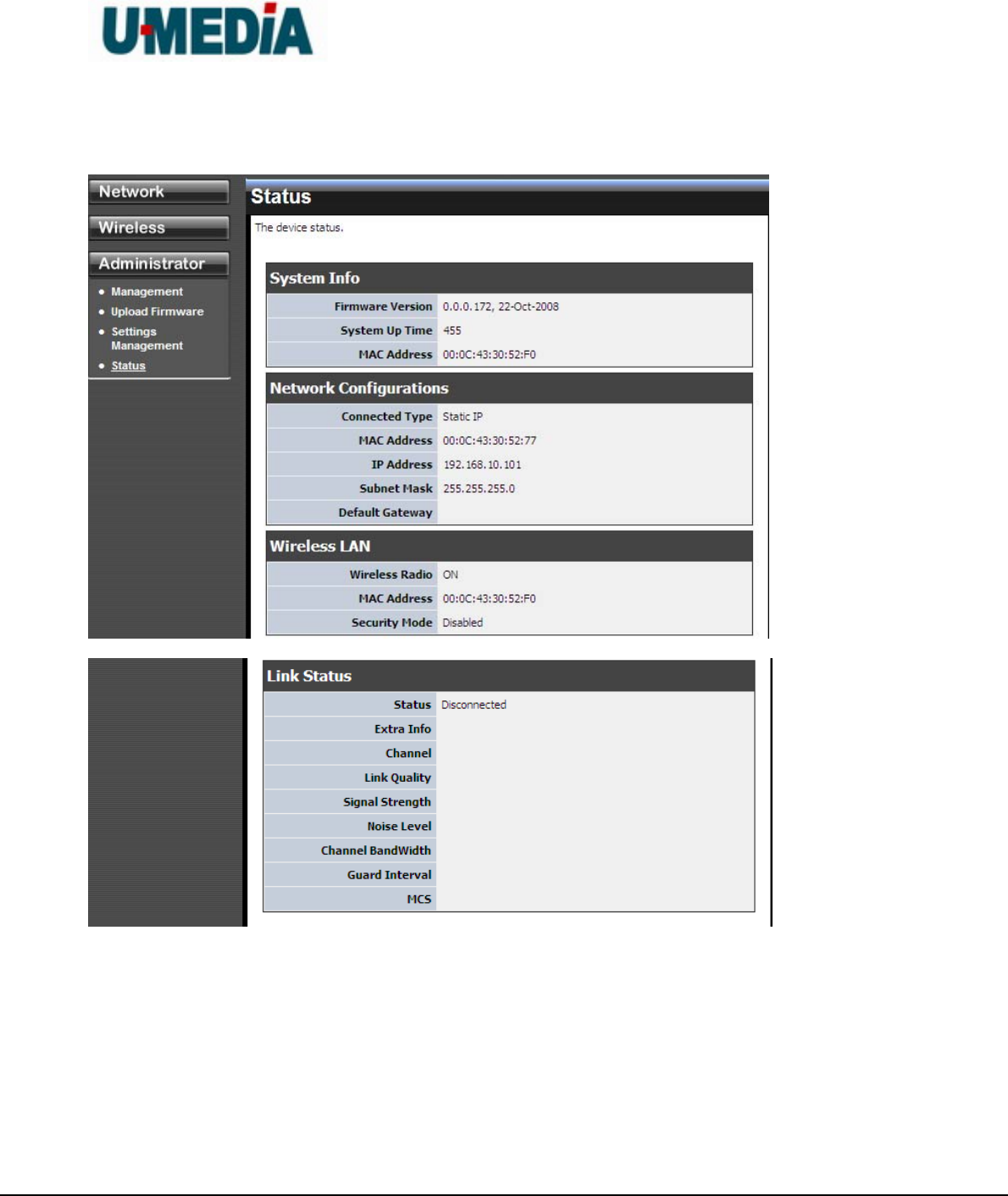
4.3.4 Status
You can check system information and network configurations on this page.
U-MEDIA Communications, Inc.
Proprietary and Confidential 25
5. Glossary
A
Access Control List
ACL. This is a database of network devices that are allowed to access resources on the
network.
Access Point
AP. Device that allows wireless clients to connect to it and access the network
Ad-hoc network
Peer-to-Peer network between wireless clients
Address Resolution Protocol
ARP. Used to map MAC addresses to IP addresses so that conversions can be made in
both directions.
Advanced Encryption Standard
AES. Government encryption standard
Alphanumeric
Characters A-Z and 0-9
Antenna
Used to transmit and receive RF signals.
ASCII
American Standard Code for Information Interchange. This system of characters is most
commonly used for text files
Attenuation
The loss in strength of digital and analog signals. The loss is greater when the signal is
being transmitted over long distances.
Authentication
U-MEDIA Communications, Inc.
Proprietary and Confidential 26
To provide credentials, like a Password, in order to verify that the person or device is
really who they are claiming to be
Automatic Private IP Addressing
APIPA. An IP address that that a Windows computer will assign itself when it is
configured to obtain an IP address automatically but no DHCP server is available on the
network
B
Backward Compatible
The ability for new devices to communicate and interact with older legacy devices to
guarantee interoperability
Bandwidth
The maximum amount of bytes or bits per second that can be transmitted to and from a
network device
Beacon
A data frame by which one of the stations in a Wi-Fi network periodically broadcasts
network control data to other wireless stations.
Bit rate
The amount of bits that pass in given amount of time
Bit/sec
Bits per second
BOOTP
Bootstrap Protocol. Allows for computers to be booted up and given an IP address with
no user intervention
Broadcast
Transmitting data in all directions at once
Browser
A program that allows you to access resources on the web and provides them to you
graphically
C
U-MEDIA Communications, Inc.
Proprietary and Confidential 27
CAT 5
Category 5. Used for 10/100 Mbps or 1Gbps Ethernet connections
Client
A program or user that requests data from a server
Collision
When do two devices on the same Ethernet network try and transmit data at the exact
same time.
Cookie
Information that is stored on the hard drive of your computer that holds your preferences
to the site that gave your computer the cookie
D
Data
Information that has been translated into binary so that it can be processed or moved to
another device
Data-Link layer
The second layer of the OSI model. Controls the movement of data on the physical link
of a network
dBd
Decibels related to dipole antenna
dBi
Decibels relative to isotropic radiator
dBm
Decibels relative to one milliwatt
Decrypt
To unscramble an encrypted message back into plain text
Default
A predetermined value or setting that is used by a program when no user input has been
entered for this value or setting
U-MEDIA Communications, Inc.
Proprietary and Confidential 28
DHCP
Dynamic Host Configuration Protocol: Used to automatically assign IP addresses from a
predefined pool of addresses to computers or devices that request them
Digital certificate:
An electronic method of providing credentials to a server in order to have access to it or a
network
Direct Sequence Spread Spectrum
DSSS: Modulation technique used by 802.11b wireless devices
DNS
Domain Name System: Translates Domain Names to IP addresses
Domain name
A name that is associated with an IP address
Download
To send a request from one computer to another and have the file transmitted back to
the requesting computer
Duplex
Sending and Receiving data transmissions at the sane time
Dynamic IP address
IP address that is assigned by a DHCP server and that may change. Cable Internet
providers usually use this method to assign IP addresses to their customers.
E
EAP
Extensible Authentication Protocol
Encryption
Converting data into cyphertext so that it cannot be easily read
Ethernet
The most widely used technology for Local Area Networks.
F
U-MEDIA Communications, Inc.
Proprietary and Confidential 29
File server
A computer on a network that stores data so that the other computers on the network
can all access it
File sharing
Allowing data from computers on a network to be accessed by other computers on the
network with different levels of access rights
Firewall
A device that protects resources of the Local Area Network from unauthorized users
outside of the local network
Firmware
Programming that is inserted into a hardware device that tells it how to function
Fragmentation
Breaking up data into smaller pieces to make it easier to store
FTP
File Transfer Protocol. Easiest way to transfer files between computers on the Internet
Full-duplex
Sending and Receiving data at the same time
G
Gain
The amount an amplifier boosts the wireless signal
Gateway
A device that connects your network to another, like the internet
Gbps
Gigabits per second
Gigabit Ethernet
Transmission technology that provides a data rate of 1 billion bits per second
GUI
Graphical user interface
U-MEDIA Communications, Inc.
Proprietary and Confidential 30
H
Half-duplex
Data cannot be transmitted and received at the same time
Hashing
Transforming a string of characters into a shorter string with a predefined length
Hexadecimal
Characters 0-9 and A-F
Hop
The action of data packets being transmitted from one AP to another
Host
Computer on a network
HTTP
Hypertext Transfer Protocol is used to transfer files from HTTP servers (web servers) to
HTTP clients (web browsers)
HTTPS
HTTP over SSL is used to encrypt and decrypt HTTP transmissions
Hub
A networking device that connects multiple devices together
I
ICMP
Internet Control Message Protocol
IEEE
Institute of Electrical and Electronics Engineers
IGMP
Internet Group Management Protocol is used to make sure that computers can report
their multicast group membership to adjacent APs
IIS
Internet Information Server is a WEB server and FTP server provided by Microsoft

U-MEDIA Communications, Inc.
Proprietary and Confidential 31
Infrastructure
In terms of a wireless network, this is when wireless clients use an Access Point to gain
access to the network
Internet
A system of worldwide networks which use TCP/IP to allow for resources to be accessed
from computers around the world
Internet Explorer
A World Wide Web browser created and provided by Microsoft
Internet Protocol
The method of transferring data from one computer to another on the Internet
Internet Protocol Security
IPsec provides security at the packet processing layer of network communication
Internet Service Provider
An ISP provides access to the Internet to individuals or companies
Intranet
A private network
Intrusion Detection
A type of security that scans a network to detect attacks coming from inside and outside
of the network
IP
Internet Protocol
IP address
A 32-bit number, when talking about Internet Protocol Version 4, that identifies each
computer that transmits data on the Internet or on an Intranet
IPsec
Internet Protocol Security
IPX
U-MEDIA Communications, Inc.
Proprietary and Confidential 32
Internetwork Packet Exchange is a networking protocol developed by Novel to enable
their Netware clients and servers to communicate
ISP
Internet Service Provider
J
Java
A programming language used to create programs and applets for web pages
K
Kbps
Kilobits per second
Kbyte
Kilobyte
L
LAN
Local Area Network
Latency
The amount of time that it takes a packet to get from the one point to another on a
network. Also referred to as delay
LED
Light Emitting Diode
Legacy
Older devices or technology
Local Area Network
A group of computers in a building that usually access files from a server
LPR/LPD
"Line Printer Requestor"/"Line Printer Daemon". A TCP/IP protocol for transmitting
streams of printer data.
L2TP

U-MEDIA Communications, Inc.
Proprietary and Confidential 33
Layer 2 Tunneling Protocol
M
MAC address
A unique hardware ID assigned to every Ethernet adapter by the manufacturer.
Mbps
Megabits per second
MDI
Medium Dependent Interface is an Ethernet port for a connection to a straight-through
cable
MDIX
Medium Dependent Interface Crossover, is an Ethernet port for a connection to a
crossover cable
MIB
Management Information Base is a set of objects that can be managed by using SNMP
Modem
A device that Modulates digital signals from a computer to an analog signal in order to
transmit the signal over phone lines. It also Demodulates the analog signals coming from
the phone lines to digital signals for your computer
MPPE
Microsoft Point-to-Point Encryption is used to secure data transmissions over PPTP
connections
MTU
Maximum Transmission Unit is the largest packet that can be transmitted on a
packet-based network like the Internet
Multicast
Sending data from one device to many devices on a network
N
NAT
U-MEDIA Communications, Inc.
Proprietary and Confidential 34
Network Address Translation allows many private IP addresses to connect to the
Internet, or another network, through one IP address
NetBEUI
NetBIOS Extended User Interface is a Local Area Network communication protocol. This
is an updated version of NetBIOS
NetBIOS
Network Basic Input/Output System
Netmask
Determines what portion of an IP address designates the Network and which part
designates the Host
Network Interface Card
A card installed in a computer or built onto the motherboard that allows the computer to
connect to a network
Network Layer
The third layer of the OSI model which handles the routing of traffic on a network
Network Time Protocol
Used to synchronize the time of all the computers in a network
NIC
Network Interface Card
NTP
Network Time Protocol
O
OFDM
Orthogonal Frequency-Division Multiplexing is the modulation technique for both
802.11a and 802.wireless g
OSI
Open Systems Interconnection is the reference model for how data should travel
between two devices on a network
U-MEDIA Communications, Inc.
Proprietary and Confidential 35
OSPF
Open Shortest Path First is a routing protocol that is used more than RIP in larger scale
networks because only changes to the routing table are sent to all the other APs in the
network as opposed to sending the entire routing table at a regular interval, which is how
RIP functions
P
Password
A sequence of characters that is used to authenticate requests to resources on a
network
Personal Area Network
The interconnection of networking devices within a range of 10 meters
Physical layer
The first layer of the OSI model. Provides the hardware means of transmitting electrical
signals on a data carrier
Ping
A utility program that verifies that a given Internet address exists and can receive
messages. The utility sends a control packet to the given address and waits for a
response.
PoE
Power over Ethernet is the means of transmitting electricity over the unused pairs in a
category 5 Ethernet cable
Port
A logical channel endpoint in a network. A computer might have only one physical
channel (its Ethernet channel) but can have multiple ports (logical channels) each
identified by a number.
PPP
Point-to-Point Protocol is used for two computers to communicate with each over a serial
interface, like a phone line
PPPoE

U-MEDIA Communications, Inc.
Proprietary and Confidential 36
Point-to-Point Protocol over Ethernet is used to connect multiple computers to a remote
server over Ethernet
PPTP
Point-to-Point Tunneling Protocol is used for creating VPN tunnels over the Internet
between two networks
Preamble
Used to synchronize communication timing between devices on a network
Q
QoS
Quality of Service
R
RADIUS
Remote Authentication Dial-In User Service allows for remote users to dial into a central
server and be authenticated in order to access resources on a network
Reboot
To restart a computer and reload it's operating software or firmware from nonvolatile
storage.
Rendezvous
Apple's version of UPnP, which allows for devices on a network to discover each other
and be connected without the need to configure any settings
Repeater
Retransmits the signal of an Access Point in order to extend it's coverage
RIP
Routing Information Protocol is used to synchronize the routing table of all the APs on a
network
RJ-11
The most commonly used connection method for telephones
RJ-45
U-MEDIA Communications, Inc.
Proprietary and Confidential 37
The most commonly used connection method for Ethernet
RS-232C
The interface for serial communication between computers and other related devices
RSA
Algorithm used for encryption and authentication
S
Server
A computer on a network that provides services and resources to other computers on the
network
Session key
An encryption and decryption key that is generated for every communication session
between two computers
Session layer
The fifth layer of the OSI model which coordinates the connection and communication
between applications on both ends
Simple Mail Transfer Protocol
Used for sending and receiving email
Simple Network Management Protocol
Governs the management and monitoring of network devices
SIP
Session Initiation Protocol. A standard protocol for initiating a user session that involves
multimedia content, such as voice or chat.
SMTP
Simple Mail Transfer Protocol
SNMP
Simple Network Management Protocol
SOHO
Small Office/Home Office
U-MEDIA Communications, Inc.
Proprietary and Confidential 38
SPI
Stateful Packet Inspection
SSH
Secure Shell is a command line interface that allows for secure connections to remote
computers
SSID
Service Set Identifier is a name for a wireless network
Stateful inspection
A feature of a firewall that monitors outgoing and incoming traffic to make sure that only
valid responses to outgoing requests are allowed to pass though the firewall
Subnet mask
Determines what portion of an IP address designates the Network and which part
designates the Host
Syslog
System Logger -- a distributed logging interface for collecting in one place the logs from
different sources. Originally written for UNIX, it is now available for other operating
systems, including Windows.
T
TCP
Transmission Control Protocol
TCP/IP
Transmission Control Protocol/Internet Protocol
TCP Raw
A TCP/IP protocol for transmitting streams of printer data.
TFTP
Trivial File Transfer Protocol is a utility used for transferring files that is simpler to use
than FTP but with less features
Throughput

U-MEDIA Communications, Inc.
Proprietary and Confidential 39
The amount of data that can be transferred in a given time period
Traceroute
A utility displays the routes between you computer and specific destination
U
UDP
User Datagram Protocol
Unicast
Communication between a single sender and receiver
Universal Plug and Play
A standard that allows network devices to discover each other and configure themselves
to be a part of the network
Upgrade
To install a more recent version of a software or firmware product
Upload
To send a request from one computer to another and have a file transmitted from the
requesting computer to the other
UPnP
Universal Plug and Play
URL
Uniform Resource Locator is a unique address for files accessible on the Internet
USB
Universal Serial Bus
UTP
Unshielded Twisted Pair
V
Virtual Private Network
VPN: A secure tunnel over the Internet to connect remote offices or users to their
company's network
U-MEDIA Communications, Inc.
Proprietary and Confidential 40
VLAN
Virtual LAN
Voice over IP
Sending voice information over the Internet as opposed to the PSTN
VoIP
Voice over IP
W
Wake on LAN
Allows you to power up a computer though it's Network Interface Card
WAN
Wide Area Network
WCN
Windows Connect Now. A Microsoft method for configuring and bootstrapping wireless
networking hardware (access points) and wireless clients, including PCs and other
devices.
WDS
Wireless Distribution System. A system that enables the interconnection of access points
wirelessly.
Web browser
A utility that allows you to view content and interact with all of the information on the
World Wide Web
WEP
Wired Equivalent Privacy is security for wireless networks that is supposed to be
comparable to that of a wired network
Wi-Fi
Wireless Fidelity
Wi-Fi Protected Access

U-MEDIA Communications, Inc.
Proprietary and Confidential 41
An updated version of security for wireless networks that provides authentication as well
as encryption
Wide Area Network
The larger network that your LAN is connected to, which may be the Internet itself, or a
regional or corporate network
Wireless ISP
A company that provides a broadband Internet connection over a wireless connection
Wireless LAN
Connecting to a Local Area Network over one of the 802.11 wireless standards
WISP
Wireless Internet Service Provider
WLAN
Wireless Local Area Network
WPA
Wi-Fi Protected Access. A Wi-Fi security enhancement that provides improved data
encryption, relative to WEP.
X
xDSL
A generic term for the family of digital subscriber line (DSL) technologies, such as ADSL,
HDSL, RADSL, and SDSL.
Y
Yagi antenna
A directional antenna used to concentrate wireless signals on a specific location
Z
#
1

U-MEDIA Communications, Inc.
Proprietary and Confidential 42
802.11
A family of specifications for wireless local area networks (WLANs) developed by a
working group of the Institute of Electrical and Electronics Engineers (IEEE).