Wistron NeWeb DCUA WLAN 802.11 a/b/g USB2.0 Adapter User Manual DCUA 81 G Manual Eng V2 0 20050721 Jessy3805
Wistron NeWeb Corporation WLAN 802.11 a/b/g USB2.0 Adapter DCUA 81 G Manual Eng V2 0 20050721 Jessy3805
Contents
- 1. User manual 1
- 2. User manual 2
User manual 2
31
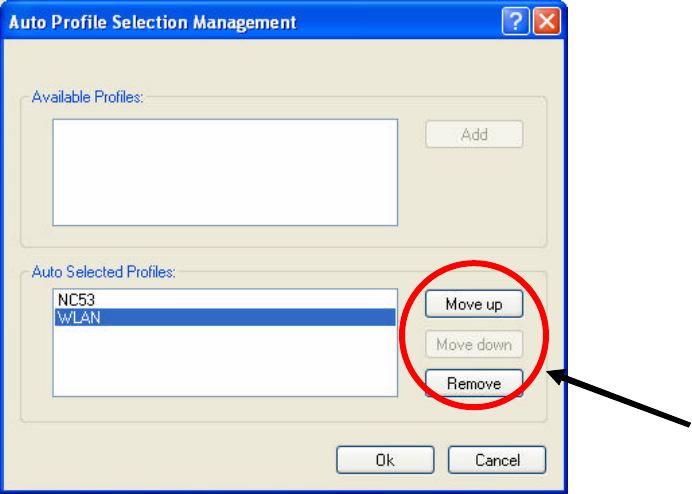
2. Select the profile to remove from the list of configuration profiles.
3. Click Remove.
4.3.3 Profile Auto Selection
n Including a profile in the auto selection feature allows the wireless adapter to
automatically select that profile from the list of profiles and use it to connect to
the network.
n Including a profile in auto profile selection:
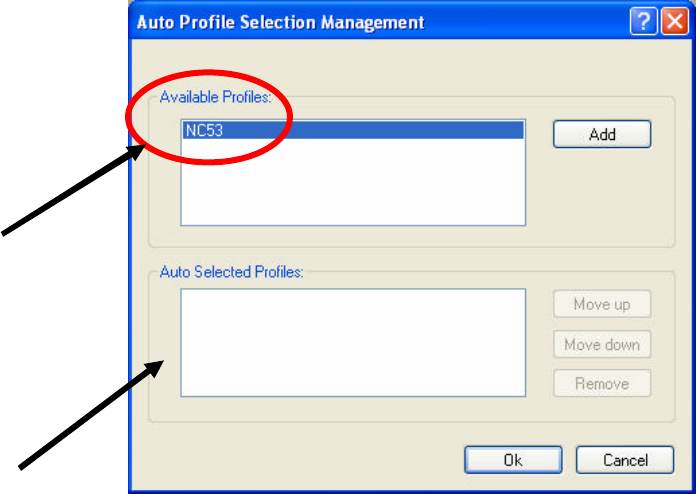
1. On the Profile Management tab, click Order Profiles.
2. The Auto Profile Selection Management window pops up, with a list of all
created profiles in the Available Profile box.
3. Highlight the profiles to add to Auto Profile selection, and then click Add. The
profiles appear in the Auto Selected Profiles box.
32
n Ordering the auto selected profiles:
1. On the Profile Management tab, click Order Profiles.
2. Highlight a profile in the Auto Selected Profiles box.
3. Click Move up or Move down as appropriate.
4. Click OK.
5. Check the Auto Selected Profiles box.
6. Save the modified configuration file.
7. With Auto Profile Selection enabled, the wireless adapter scans for available
networks. The highest priority profile with the same SSID as a found network is
used to connect to the network. On a failed connection, the client adapter tries
with the next highest priority profile.
NOTE! When Auto Profile Selection is enabled by checking Auto Select Profiles
on the Profile Management tab, the client adapter scans for an available
network. The profile with the highest priority and the same SSID as one of
the found networks is the one that is used to connect to the network. If the
connection fails, the client adapter tries the next highest priority profile that
matches the SSID, and so on.
4.3.4 Switching Profiles
1. To switch to a different profile, go to the Profile Management tab.
2. Click on the Profile Name in the Profile List.
3. Click Activate.
4. The Profile List provides icons that specify the Operational State for that profile.
33
The list also provides icons that specify the Signal Strength for that profile.
4.4 Security
You may select WPA, WPA Passphrase, 802.1x, Pre-Shared Key or None.
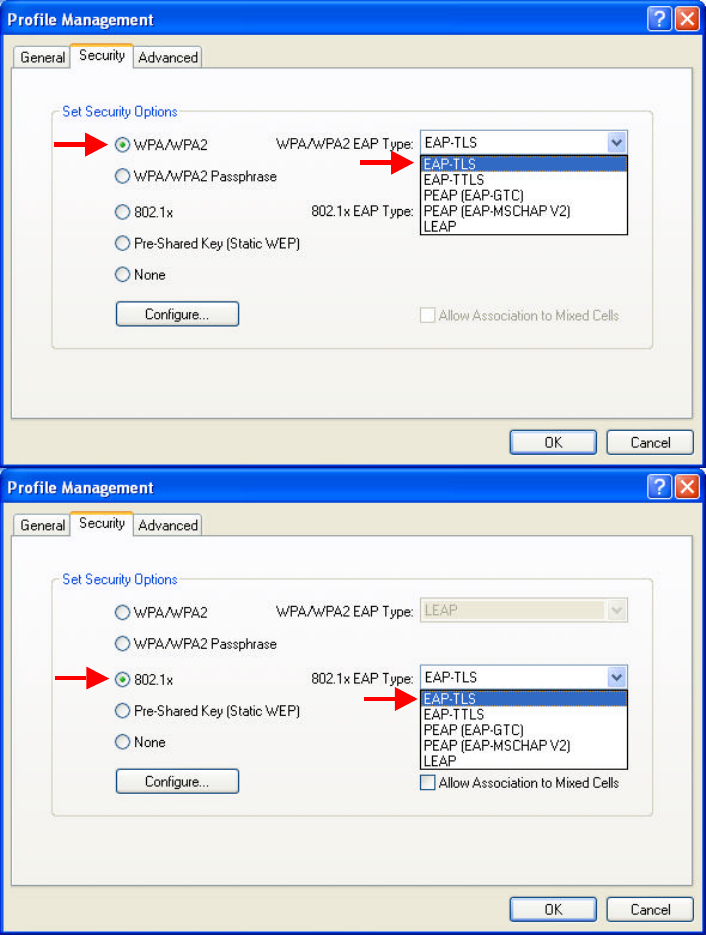
4.4.1 Using EAP-TLS Security
To use EAP-TLS security in the Utility, access the Security tab in the Profile
Management window.
1. On the Security tab, click WPA/WPA2 or 802.1x.
2. Select EAP-TLS from the drop-down menu.
34
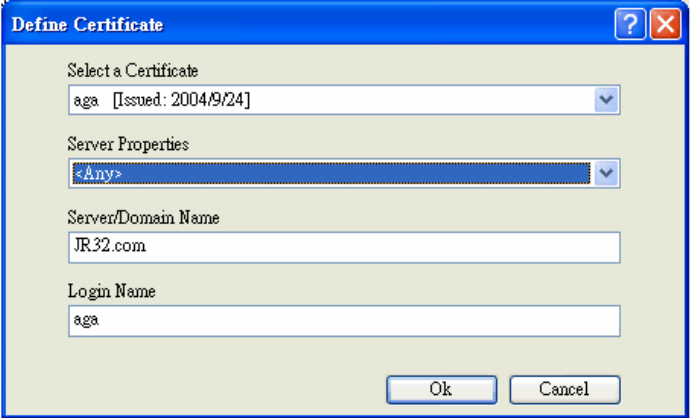
4.4.2 Enabling EAP-TLS Security
To use EAP-TLS security, the machine must already have the EAP-TLS certificates
downloaded onto it. Check with the IT manager.
1. Click Configure.
2. Select the appropriate certificate authority. Select Server Properties. The
Server/Domain Name and the Login Name are filled in automatically from the
certificate information.
3. Click OK again.
4. Activate the profile.
35
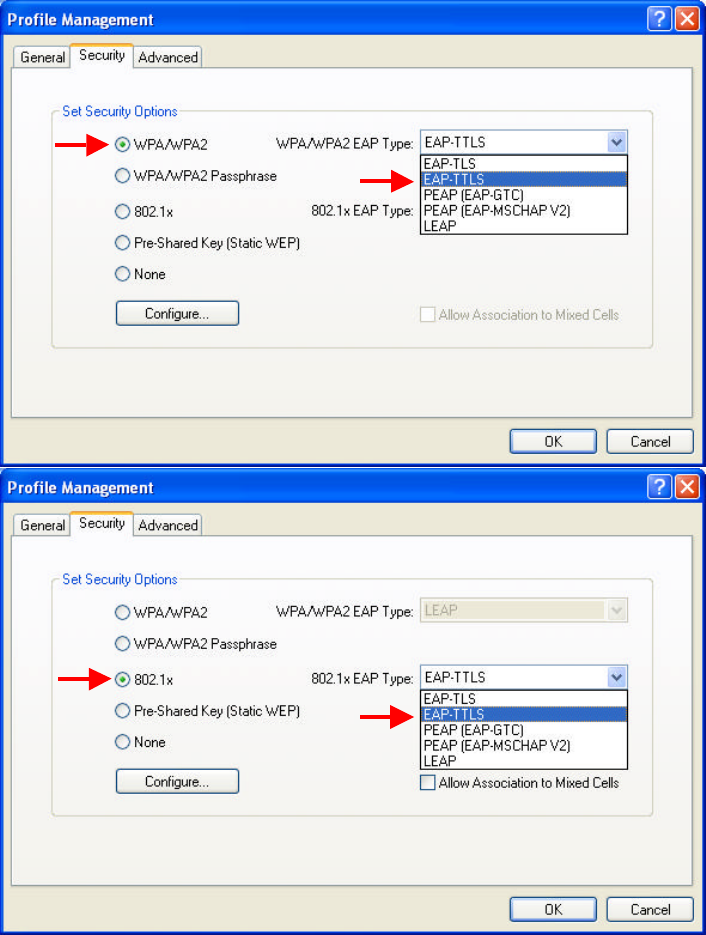
4.4.3 Using EAP-TTLS Security
To use EAP-TTLS security in the WLAN 802.11a/b/g Utility, access the Security tab
in the Profile Management window.
1. On the Security tab, click WPA/WPA2 or 802.1x.
2. Select EAP-TTLS from the drop-down menu.
36
4.4.4 Enabling EAP-TTLS Security
To use EAP-TTLS security, the machine must already have the EAP-TTLS
certificates downloaded onto it. Check with the IT manager.
1. Click Configure.
2. Select the appropriate certificate from the drop-down list and click OK.
3. Specify a user name for EAP authentication:
ü Enter an EAP user name in the User Name field to use a separate user name
and password and start the EAP authentication process.
4. Click Advanced and:
ü Enter the Specific Server or Domain name of the server from which the client
will accept a certificate.
ü Change the login name if needed.
5. Click OK.
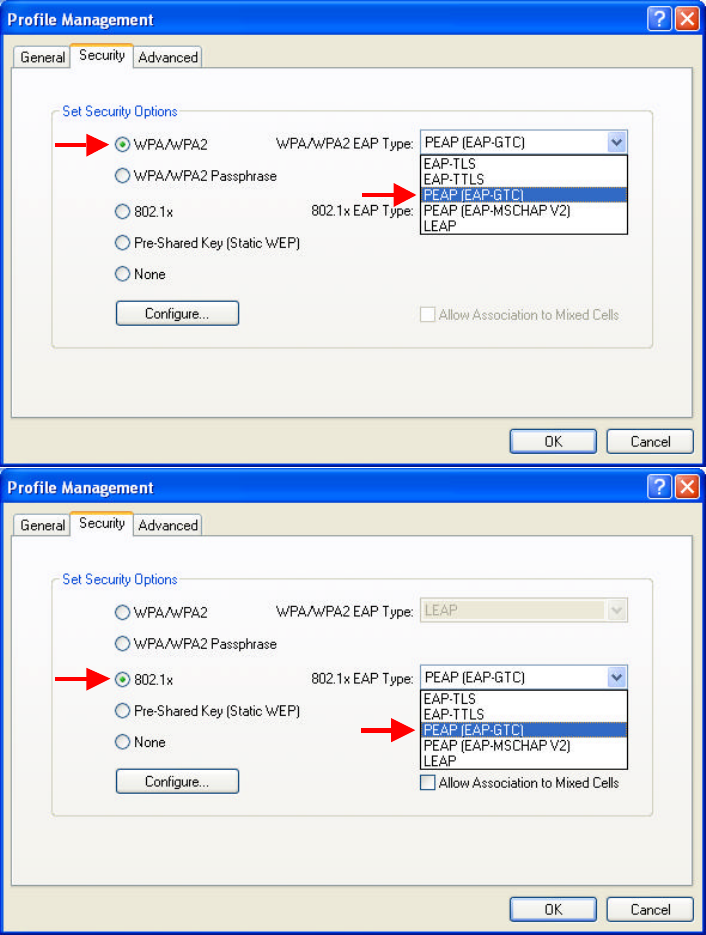
37
6. Enable the profile.
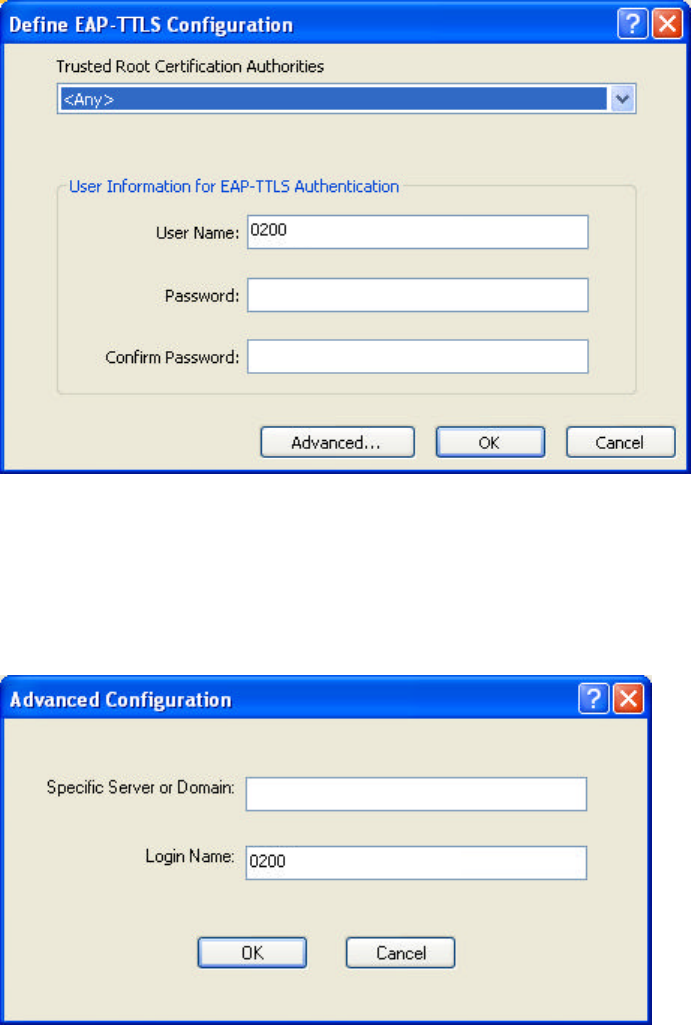
4.4.5 Using PEAP(EAP-GTC) Security
To use PEAP-GTC security in the WLAN 802.11a/b/g Utility, access the Security
tab in the Profile Management window.
1. On the Security tab, click WPA/WPA2 or 802.1x.
2. Select PEAP(EAP-GTC) from the drop-down menu.
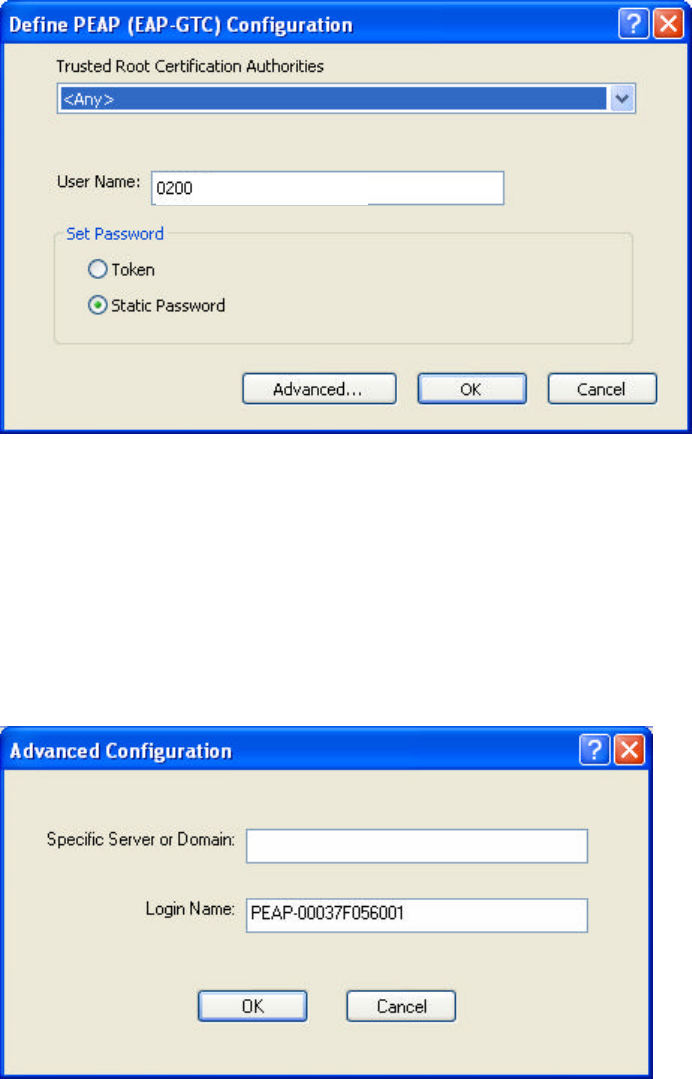
38
4.4.6 Enabling PEAP(EAP-GTC) Security
To use PEAP-GTC security, the server must have the PEAP-GTC certificates, and the
server properties must already be set. Check with the IT manager.
1. Click Configure.
2. Select the appropriate network certificate authority from the drop-down list.
3. Specify a user name for inner PEAP tunnel authentication:
ü Enter a PEAP user name in the User Name field to use a separate user name
and start the PEAP authentication process.
4. Select Token or Static Password, depending on the user database.
NOTE! Token uses a hardware token device or the Secure Computing SofToken
program (version 1.3 or later) to obtain and enter a one-time password during
authentication.
5. Click Advanced and:
ü Enter the Specific Server or Domain name of the server from which the client
will accept a certificate.
39
ü The login name used for PEAP tunnel authentication, fills in automatically as
PEAP-XXXXXXXXXX, where XXXXXXXXXX is the computer’s MAC
address. Change the login name if needed.
6. Click OK.
7. Enable the profile.
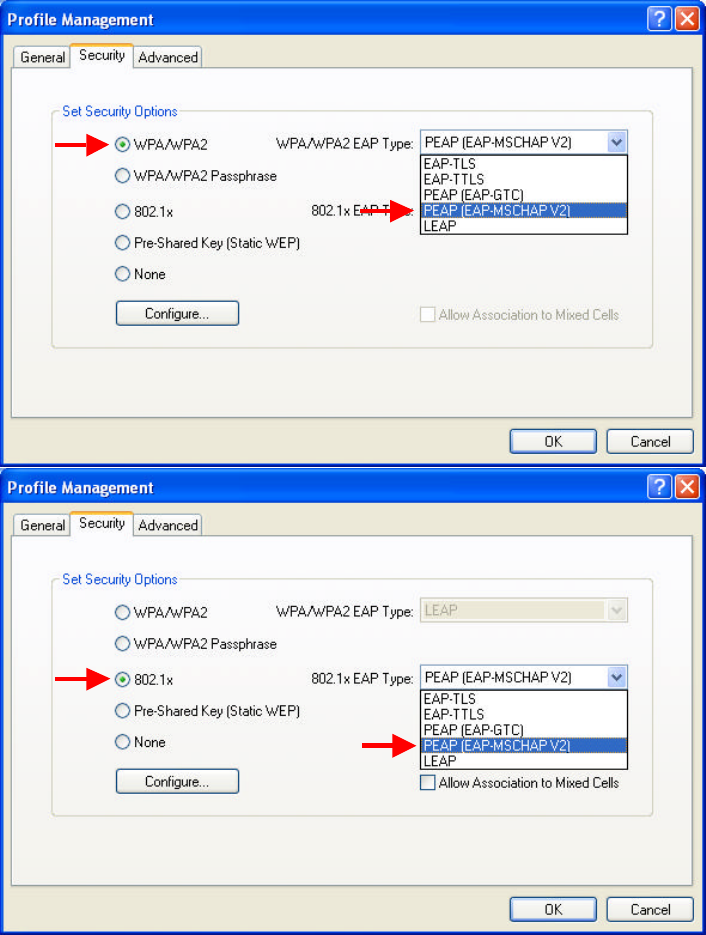
4.4.7 Using PEAP-MSCHAP V2 Security
To use PEAP-MSCHAP V2 security in the WLAN 802.11a/b/g Utility, access the
Security tab in the Profile Management window.
1. On the Security tab, click WPA/WPA2 or 802.1x.
2. Select PEAP- MSCHAP V2 from the drop-down menu.
40
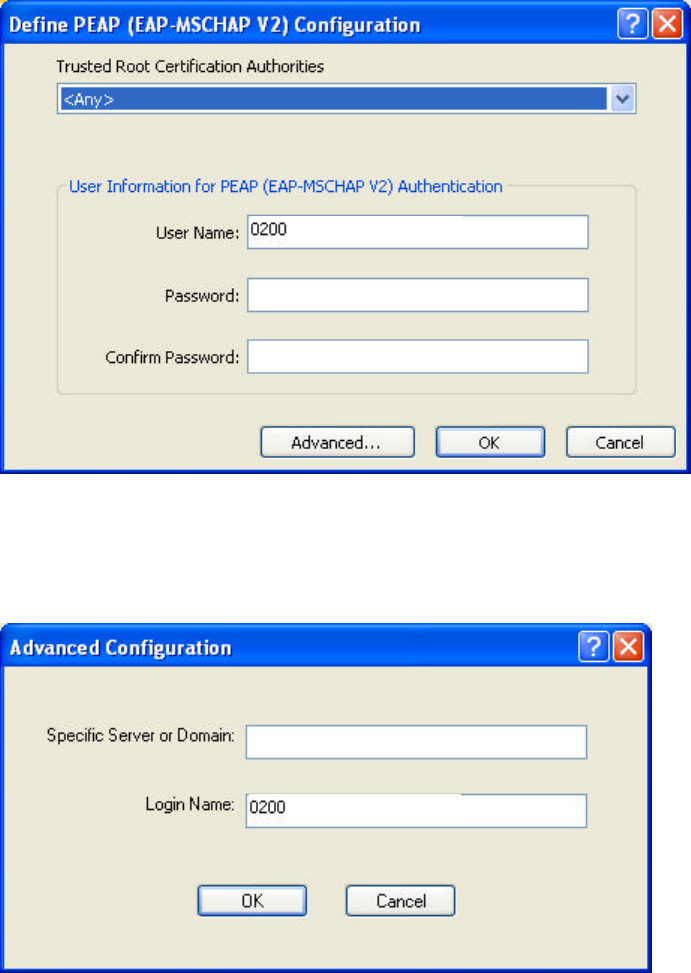
4.4.8 Enabling PEAP- MSCHAP V2 Security
To use PEAP-MSCHAP V2 security, the server must have the PEAP-MSCHAP V2
certificates, and the server properties must already be set. Check with the IT manager.
1. Click Configure.
2. Select the appropriate network certificate authority from the drop-down list.
3. Specify a user name for inner PEAP tunnel authentication:
ü Enter a PEAP user name in the User Name field to use a separate user name
and start the PEAP authentication process.
4. Click Advanced and:
ü Enter the Specific Server or Domain name of the server from which the
client will accept a certificate.
ü Change the login name if needed.
5. Click OK.
6. Enable the profile.
41
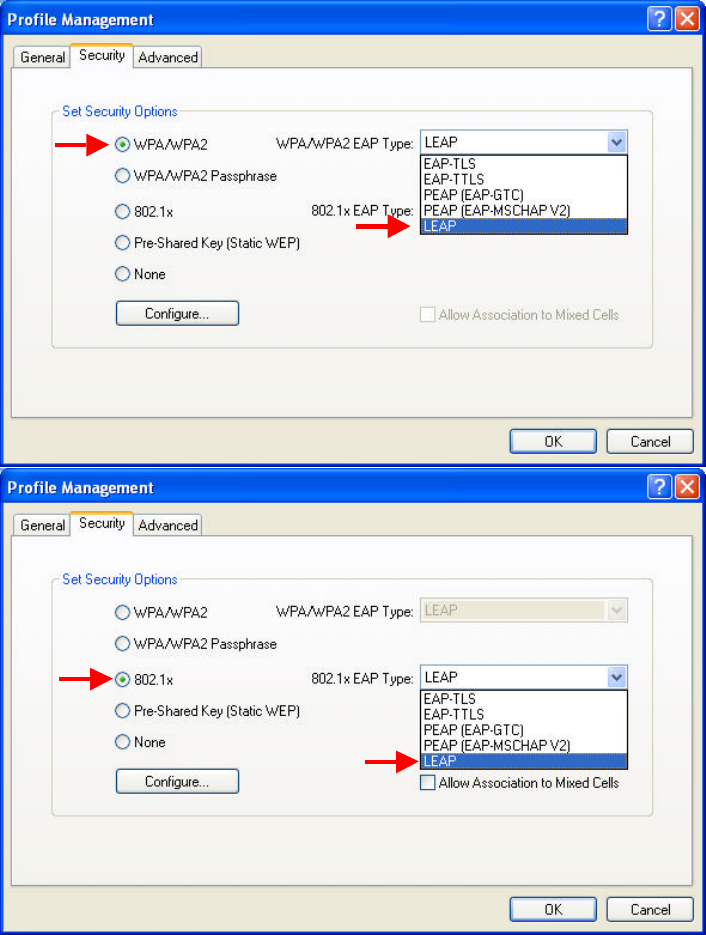
4.4.9 Using LEAP Security
To use LEAP security in the WLAN 802.11a/b/g Utility, access the Security tab in
the Profile Management window.
1. On the Security tab, click WPA/WPA2 or 802.1x.
2. Select LEAP from the drop-down menu.
4.4.10 Configuring LEAP
1. Click Configure.
2. Specify a user name and password:
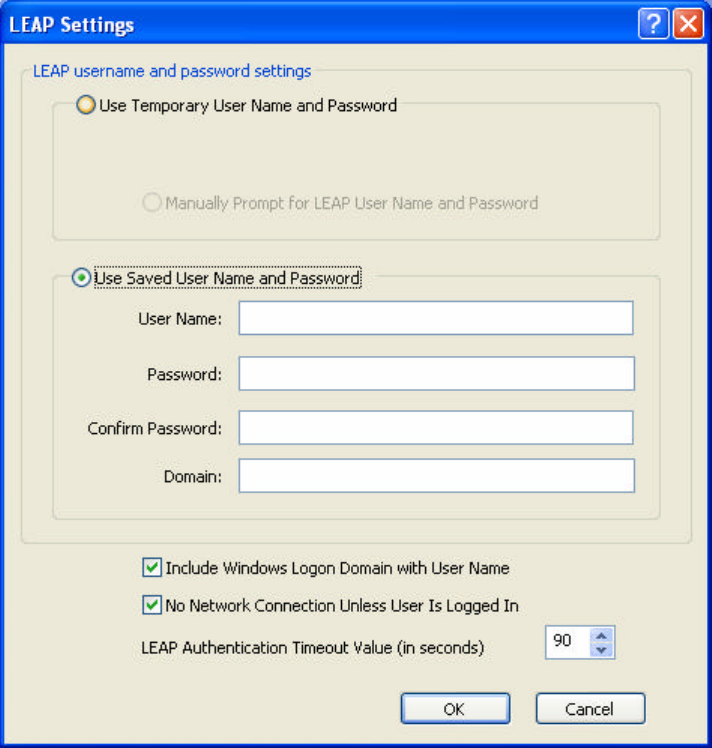
42
Option 1: Select to Use Temporary User Name and Password by choosing the
radio button:
(1) Manually Prompt for Leap User Name and Password is
checked automatically.
Option 2: Select to Use Saved User Name and Password by choosing the radio
button:
(1) Enter the user name and password.
(2) Confirm the password.
(3) Enter a specific domain name.
3. Check the Include Windows Logon Domain with User Name setting to pass the
Windows login domain and user name to the RADIUS server (default).
4. Check No Network Connection Unless User Is Logged In to force the wireless
adapter to disassociate after logging off (default).
5. Enter the LEAP authentication timeout time (between 30 and 500 seconds) to
specify how long LEAP should wait before declaring authentication failed, and
sending an error message. The default is 90 seconds.
6. Click OK.
43
7. Enable the profile.
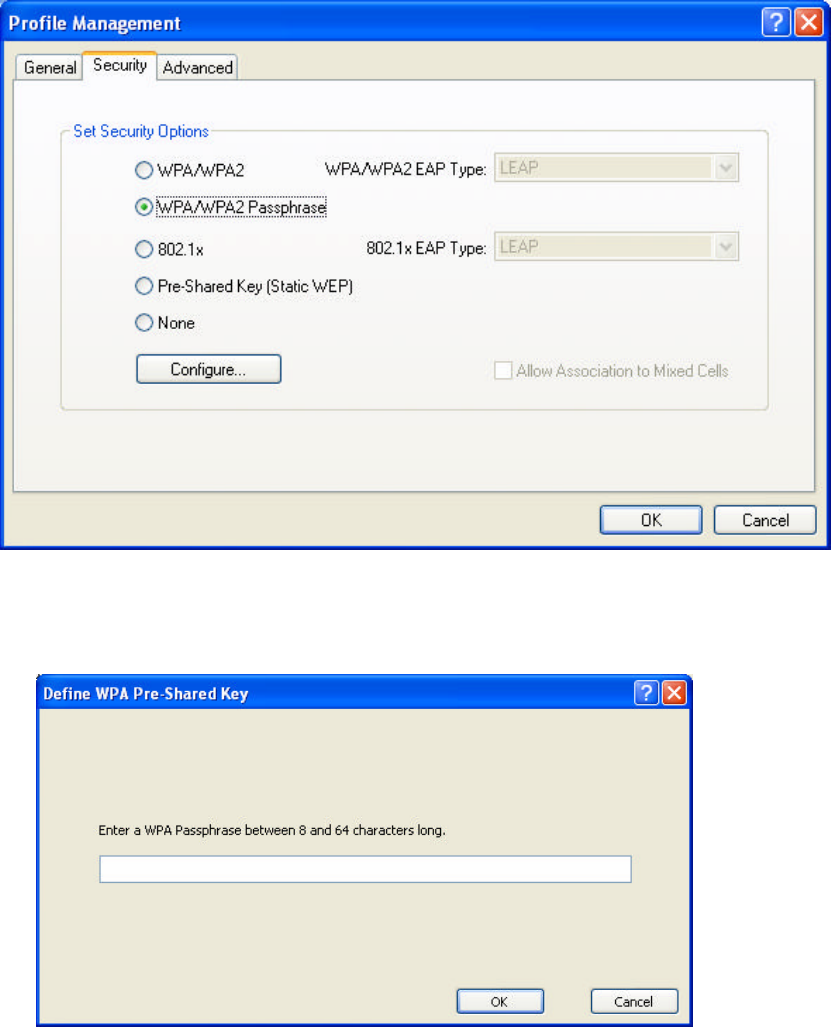
4.4.11 Using WPA Passphrase Security
To use WEAP Passphrase security in the WLAN 802.11a/b/g Utility, access the
Security tab in the Profile Management window.
1. On the Security tab, click WPA/WPA2 Passphrase.
2. Click Configure.
3. Fill in the WPA Passphrase.
4. Click OK.
44
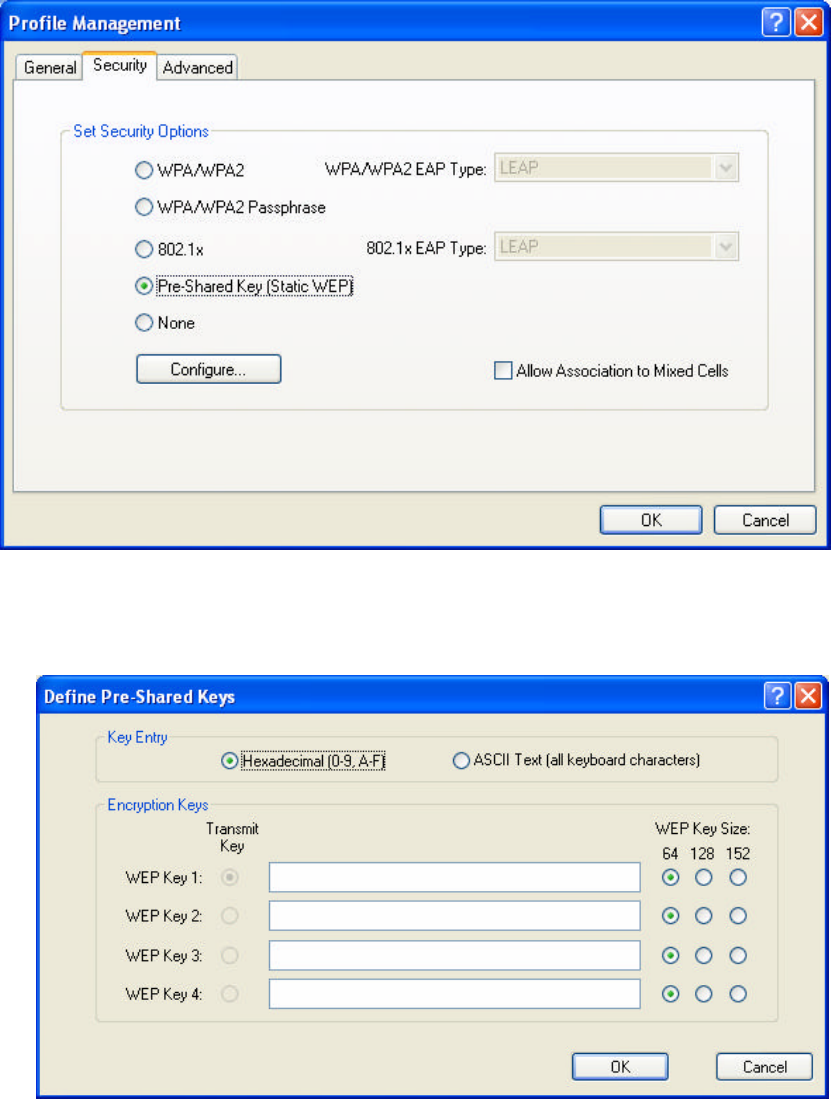
4.4.12 Using Pre-Shared Key (Static WEP) Security
To use Pre-Shared Key (Static Web) security in the WLAN 802.11a/b/g Utility,
access the Security tab in the Profile Management window.
1. On the Security tab, click Pre-Shared Key (Static WEP).
2. Click Configure.
3. Choose Hexadecimal or ASCII Text and then fill in the value of each WEP Key.
45
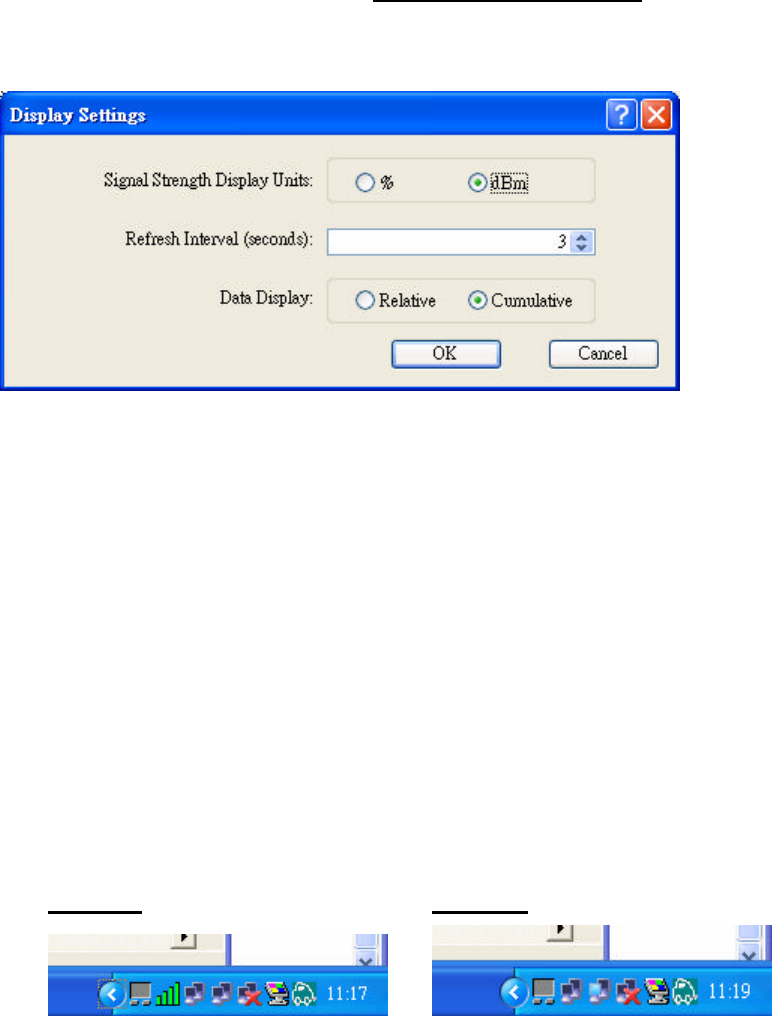
4.5 Display Setting
To change the display settings, choose Options → Display Settings from the menu.
The Display Settings dialog box contains tools to set the Signal Strength Display
Units, Refresh Interval and Data Display.
n Signal Strength Display Units: Sets the units used when displaying signal
strength: percentage (%) or dBm.
n Refresh Interval: Use the up/down arrows to set the display refresh interval in
seconds.
n Data Display: Sets the display to cumulative or relative. Relative displays the
change in statistical data since the last update. Cumulative displays statistical data
collected since opening the profile.
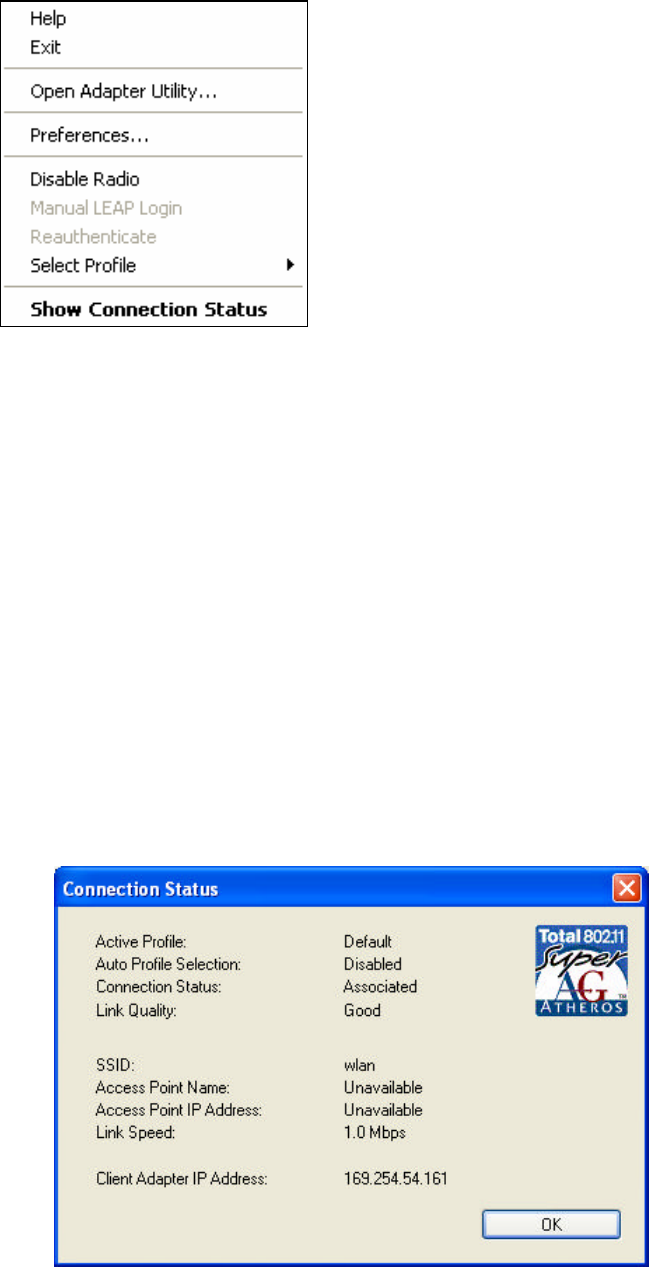
4.6 Actions Tools
Click Action from the menu to access the tools.
n Enable/Disable Radio: Enable or disable the RF Signal.
n Enable/Disable Tray Icon: Enable or disable the tray icon.
Enabled: Disabled:
n Manual LEAP Login: Log in to LEAP manually, if LEAP is set to manually
prompt for user name and password on each login. See Chapter 4 Security for
enabling LEAP.
n Reauthenticate: Reauthenticate to a LEAP-configured access point.
n Exit: Exit the Utility application.
46
5. Right clicking the tray icon
Right-click on the tray icon to access the following options:
n Help: Open the online help.
n Exit: Exit the Utility application.
n Open Adapter Utility: Launch the Utility.
n Preferences: Set the startup options and menu options for the Utility. Check
whether the program should start automatically when Windows starts, and check
the menu items that should appear on the popup menu.
n Enable/Disable Radio: Enable or disable the RF Signal.
n Manual LEAP Login: Log in to LEAP manually, if LEAP is set to manually
prompt for user name and password on each login. See Chapter 4 Security for
enabling LEAP.
n Reauthenticate: Reauthenticate to a LEAP-configured access point.
n Select Profile: Click a configuration profile name to switch to it. If no
configuration profile exists for a connection, see Chapter 3 Profile Management
to add a profile first.
n Show Connection Status: Display the Connection Status window.

47
6. Network Application
This section consists of the network applications of 802.11a/b/g USB 2.0 Adapter,
including:
1. To survey the network neighborhood
2. To share your folder with your network member(s)
3. To share your printer with your network member(s)
4. To access the shared folder(s)/file(s) of your network members(s)
5. To use the shared printer(s) of your network member(s)
In fact, the network applications of WLAN 802.11a/b/g USB 2.0 Adapter are the
same as they are in a wired network environment. You may refer to the following 3
examples of Surveying the Network Neighborhood, File Sharing and Using the
Shared Folder.
6.1 Surveying the Network Neighborhood
When multiple base stations are up and running in your wireless network, you can use
the procedure described below to display the other computers:
1. Double-click My Network Places to display all stations in your Microsoft
Windows Network Group.
2. To display other workgroups in the network environment, double-click Entire
Network.
3. If there is a second network operating system running in your network
environment (for example a Novell NetWare network), the “Entire Network”
window will also display available servers running under the second network
operating system. If you click on these servers, you may be asked to enter your
user name and password that applies to the other network operating system. If
you cannot find it, verify whether the other wireless computers are:
n Powered up and logged on to the network.
n Configured to operate with identical Microsoft Network settings
concerning:
ü Networking Protocol.
ü Wireless Network Name.
To enable the sharing of Internet access, you should set your WLAN mode as
“Infrastructure” and connect to the access point.
48
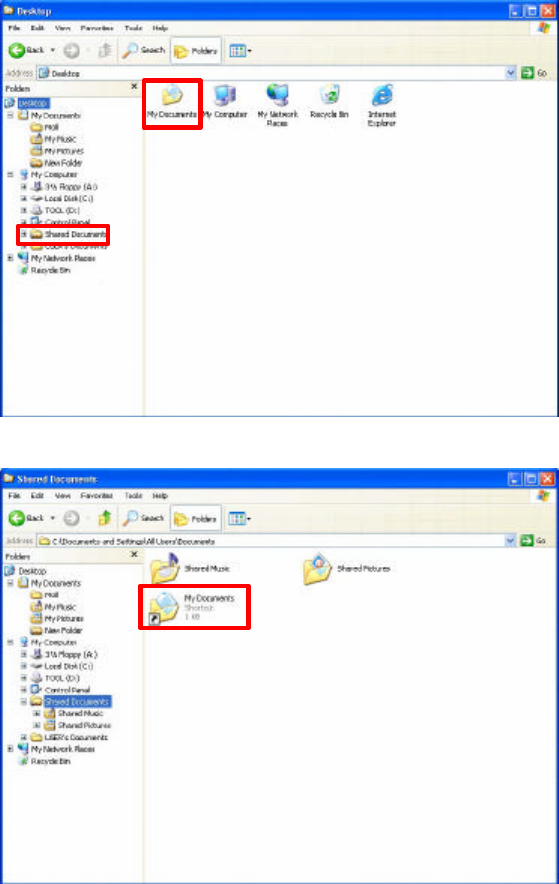
6.2 File Sharing
802.11a/b/g USB 2.0 Adapter allows the sharing of files between computers that are
logged onto the same wireless network. If you want to share your folder “My
Documents” with other computers of the wireless network, please highlight the
folder “My Documents” and drag it to Shared Documents folder.
Sharing files in the IEEE802.11a/b/g wireless network will be like sharing files on a
wired LAN.
49
6.3 Using the Shared Folder
If you would like to access a shared folder stored in other stations of same network,
please follow the process below:
1. Double-click the “My Network Places” icon, and then double-click the computer
where the shared folder is located.
2. Double-click the folder you want to connect to.
3. Now you may open the needed file(s).
NOTE! If a password is required, the Windows will prompt a password column to
you. Then you need to enter the password that had been assigned to this
shared folder.