ZyXEL Communications EMG2881-T20A Dual-Band Wireless AC1300 Gigabit Ethernet Gateway User Manual Part 2
ZyXEL Communications Corporation Dual-Band Wireless AC1300 Gigabit Ethernet Gateway Users Manual Part 2
Contents
- 1. Users Manual Part 1.pdf
- 2. Users Manual Part 2.pdf
Users Manual Part 2.pdf
![Chapter 12 TroubleshootingEMG2881-T20A User’s Guide1085Reset the device to its factory defaults, and try to access the EMG2881-T20A with the default IP address. See Section 1.5.6 on page 14.6If the problem continues, contact the network administrator or vendor, or try one of the advanced suggestions.Advanced Suggestions• Try to access the EMG2881-T20A using another service, such as Telnet. If you can access the EMG2881-T20A, check the remote management settings and firewall rules to find out why the EMG2881-T20A does not respond to HTTP.• If your computer is connected to the WAN port or is connected wirelessly, use a computer that is connected to a LAN/ETHERNET port.I can see the Login screen, but I cannot log in to the EMG2881-T20A.1Make sure you have entered the password correctly. The default password is the factory default (see the device label). This field is case-sensitive, so make sure [Caps Lock] is not on. 2This can happen when you fail to log out properly from your last session. Try logging in again after 10 minutes.3Disconnect and re-connect the power adaptor or cord to the EMG2881-T20A. 4If this does not work, you have to reset the device to its factory defaults. See Section 12.5 on page 109.12.4 Internet AccessI cannot access the Internet.1Check the hardware connections, and make sure the LEDs are behaving as expected. See the Quick Start Guide.2Make sure the WAN port is connected to a broadband modem or router with Internet access. Your computer and the EMG2881-T20A should be in the same subnet.3Make sure you entered your ISP account information correctly in the wizard or the WAN screen. These fields are case-sensitive, so make sure [Caps Lock] is not on.4If you are trying to access the Internet wirelessly, make sure the wireless settings in the wireless client are the same as the settings in the AP.5Disconnect all the cables from your device, and follow the directions in the Quick Start Guide again. 6If the problem continues, contact your ISP.](https://usermanual.wiki/ZyXEL-Communications/EMG2881-T20A.Users-Manual-Part-2-pdf/User-Guide-3733667-Page-26.png)
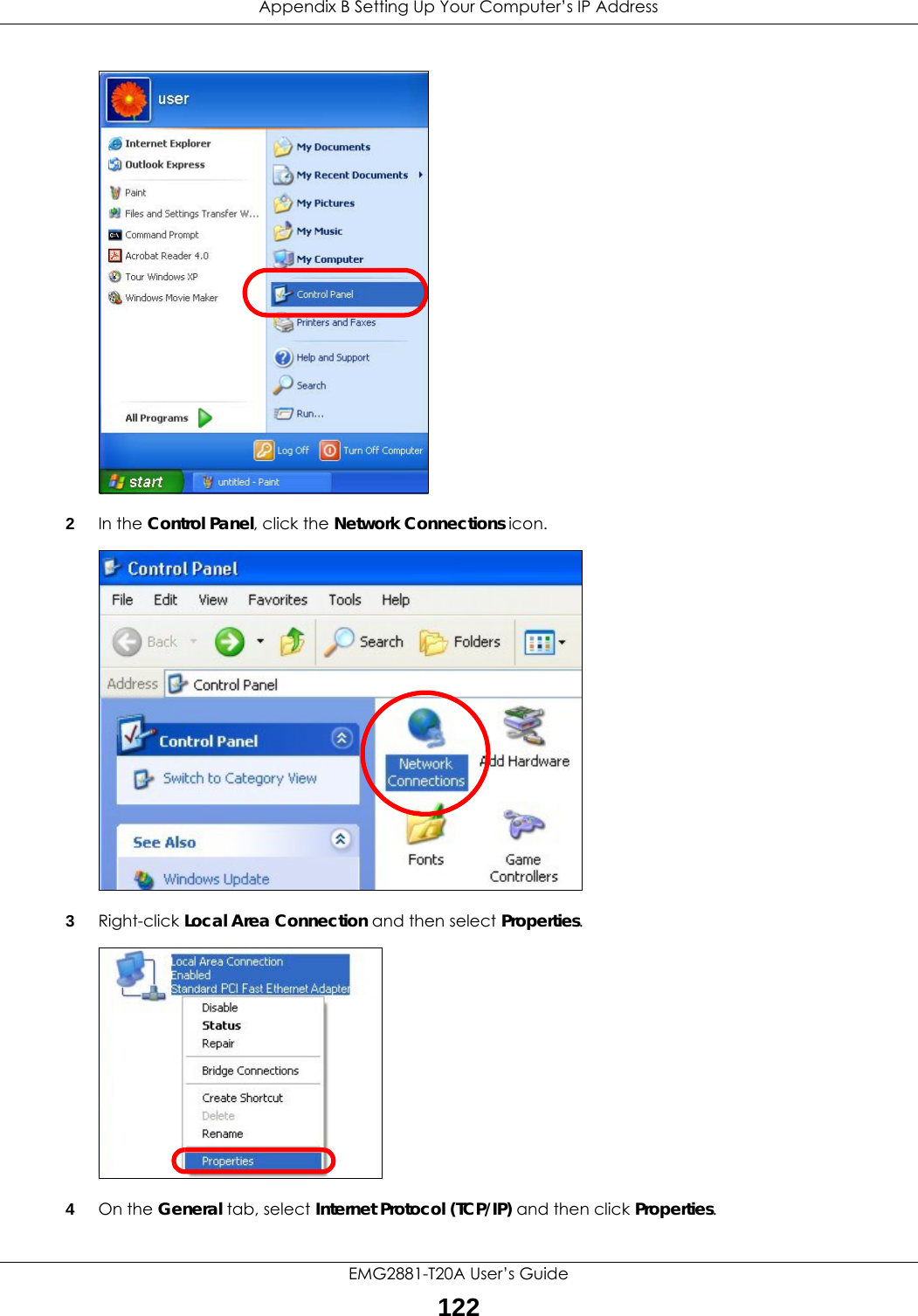
![Appendix B Setting Up Your Computer’s IP AddressEMG2881-T20A User’s Guide1246Select Obtain an IP address automatically if your network administrator or ISP assigns your IP address dynamically.Select Use the following IP Address and fill in the IP address, Subnet mask, and Default gateway fields if you have a static IP address that was assigned to you by your network administrator or ISP. You may also have to enter a Preferred DNS server and an Alternate DNS server, if that information was provided.7Click OK to close the Internet Protocol (TCP/IP) Properties window.8Click OK to close the Local Area Connection Properties window.Verifying Settings1Click Start > All Programs > Accessories > Command Prompt.2In the Command Prompt window, type "ipconfig" and then press [ENTER]. You can also go to Start > Control Panel > Network Connections, right-click a network connection, click Status and then click the Support tab to view your IP address and connection information.Windows VistaThis section shows screens from Windows Vista Professional.](https://usermanual.wiki/ZyXEL-Communications/EMG2881-T20A.Users-Manual-Part-2-pdf/User-Guide-3733667-Page-42.png)
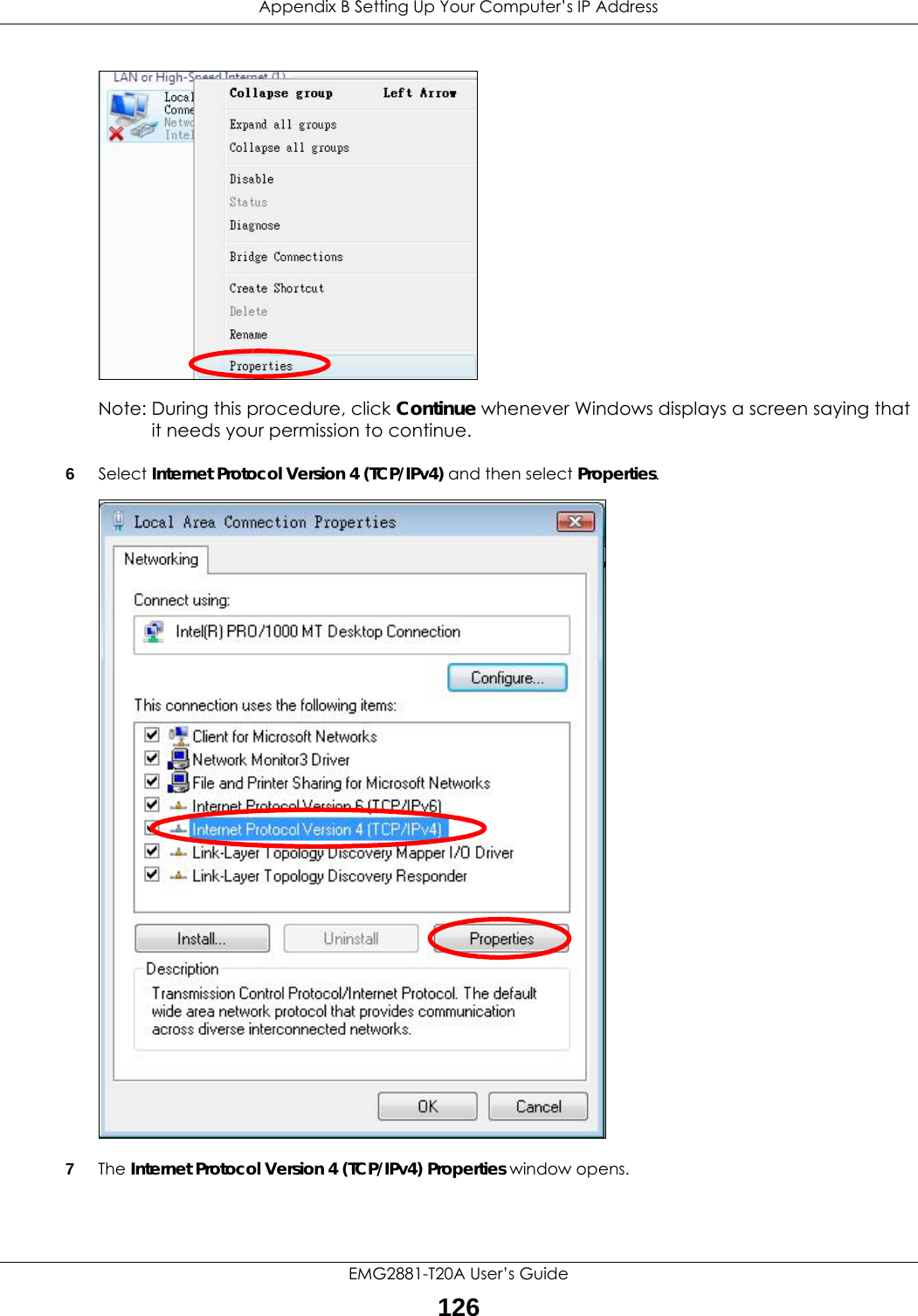
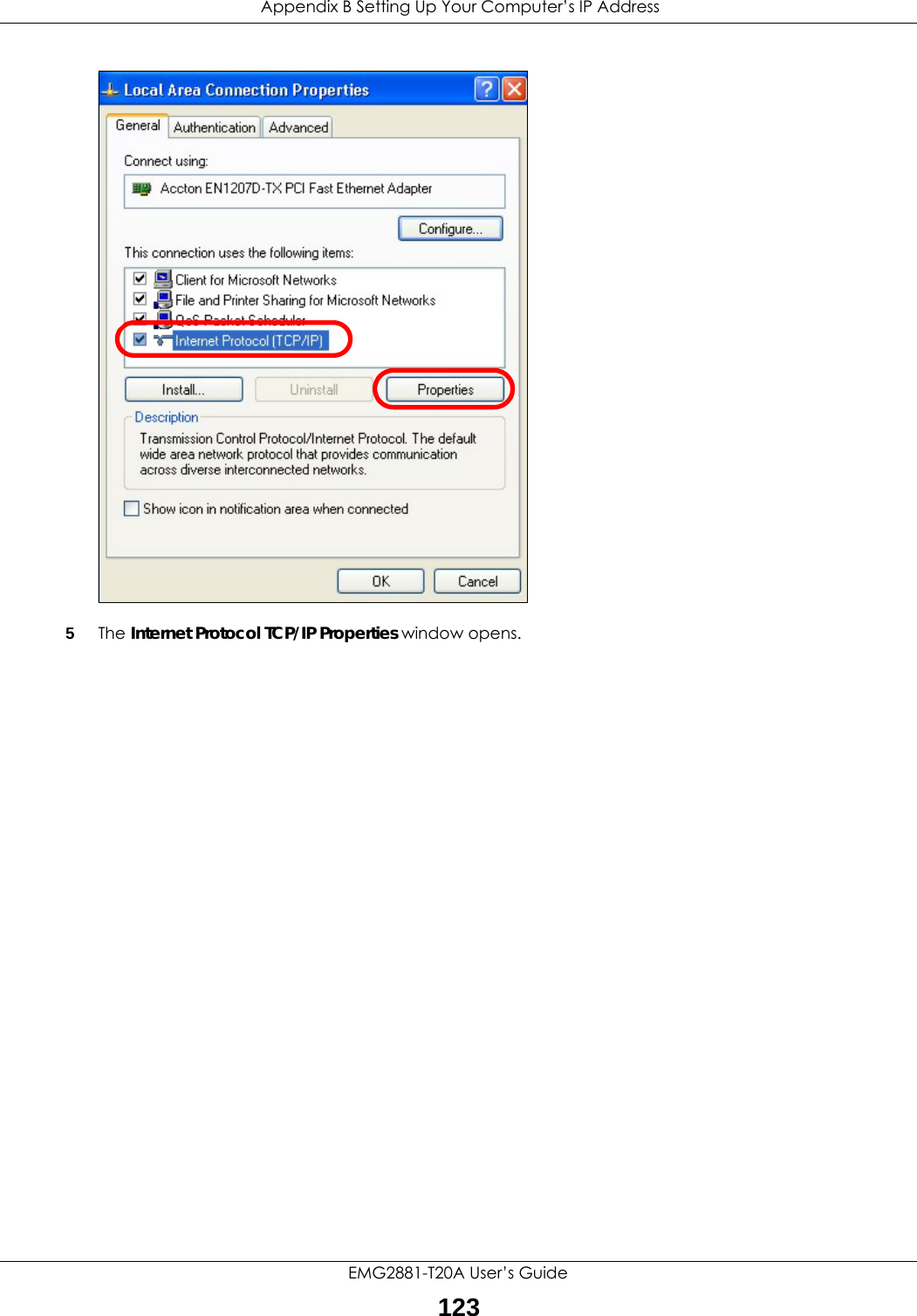
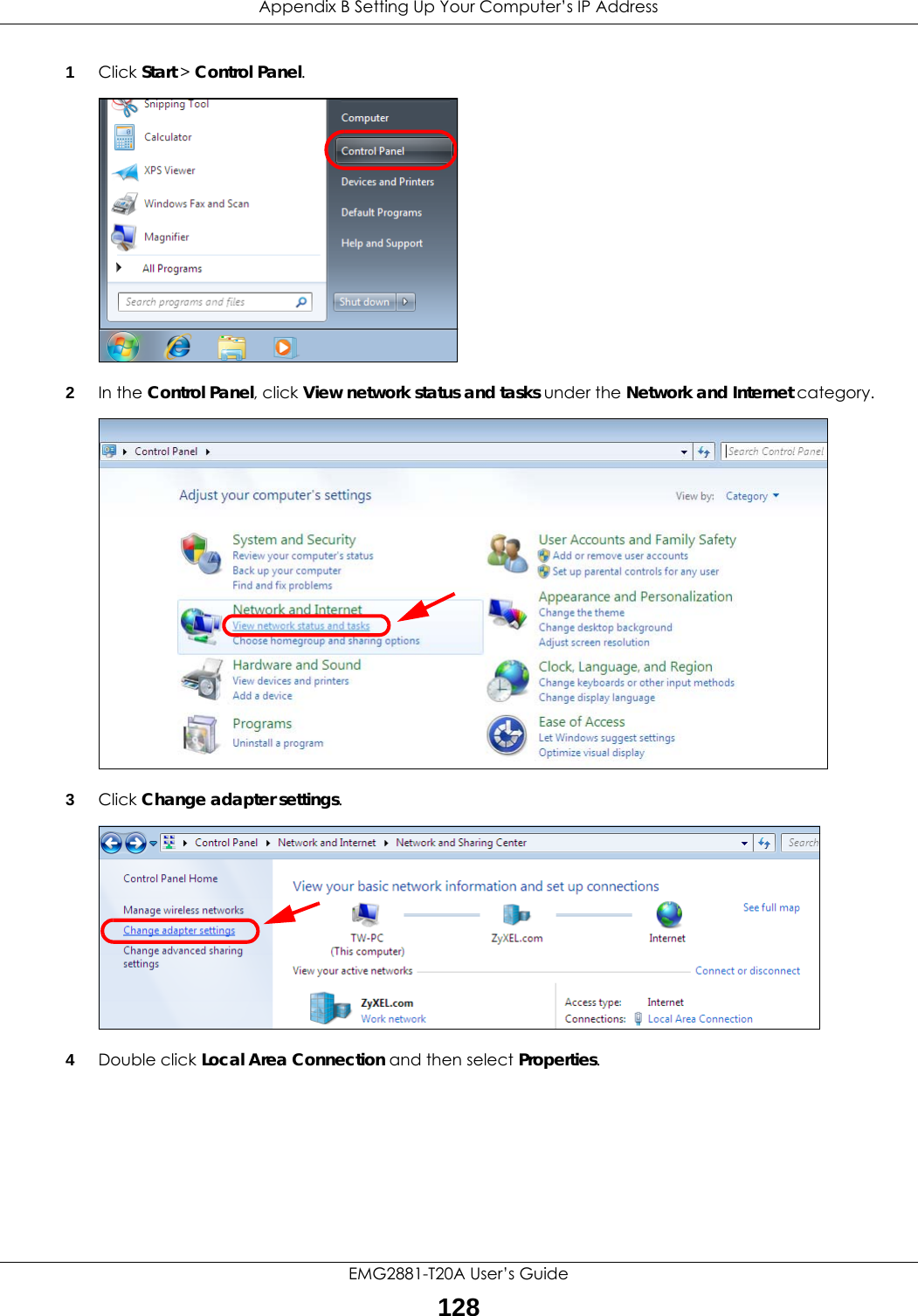
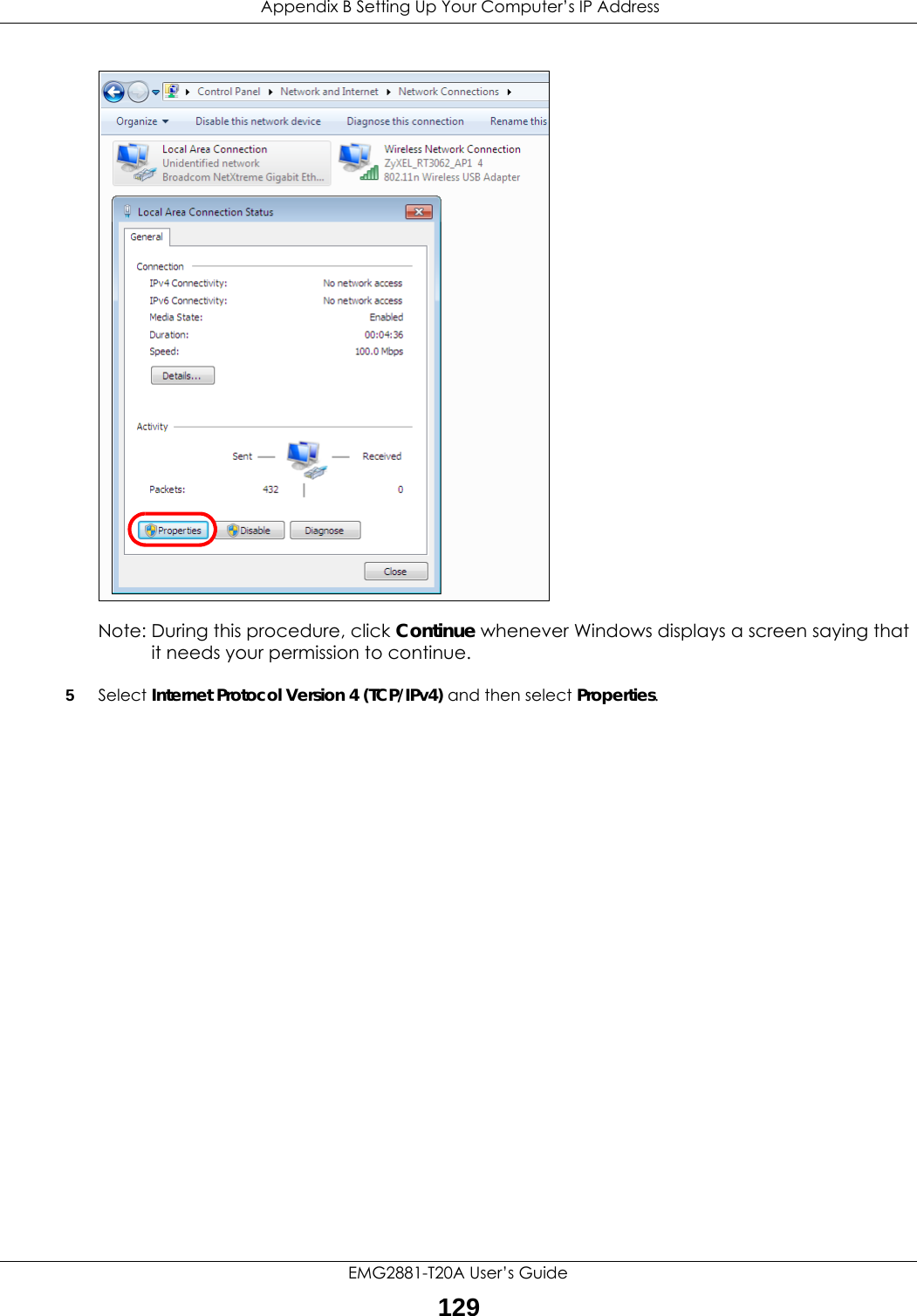
![Appendix B Setting Up Your Computer’s IP AddressEMG2881-T20A User’s Guide1278Select Obtain an IP address automatically if your network administrator or ISP assigns your IP address dynamically.Select Use the following IP Address and fill in the IP address, Subnet mask, and Default gateway fields if you have a static IP address that was assigned to you by your network administrator or ISP. You may also have to enter a Preferred DNS server and an Alternate DNS server, if that information was provided.Click Advanced.9Click OK to close the Internet Protocol (TCP/IP) Properties window.10 Click OK to close the Local Area Connection Properties window.Verifying Settings1Click Start > All Programs > Accessories > Command Prompt.2In the Command Prompt window, type "ipconfig" and then press [ENTER]. You can also go to Start > Control Panel > Network Connections, right-click a network connection, click Status and then click the Support tab to view your IP address and connection information.Windows 7This section shows screens from Windows 7 Enterprise.](https://usermanual.wiki/ZyXEL-Communications/EMG2881-T20A.Users-Manual-Part-2-pdf/User-Guide-3733667-Page-45.png)
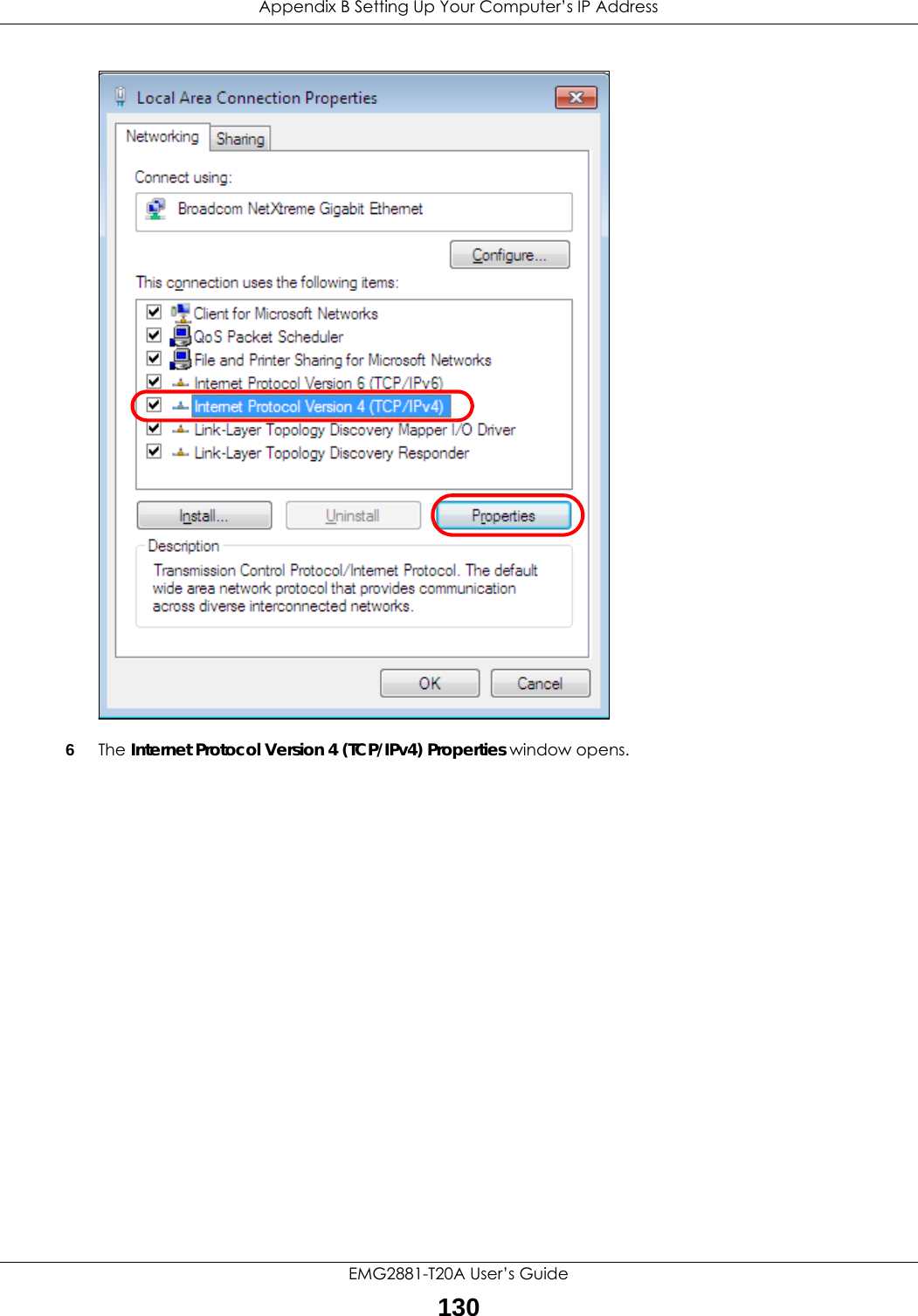
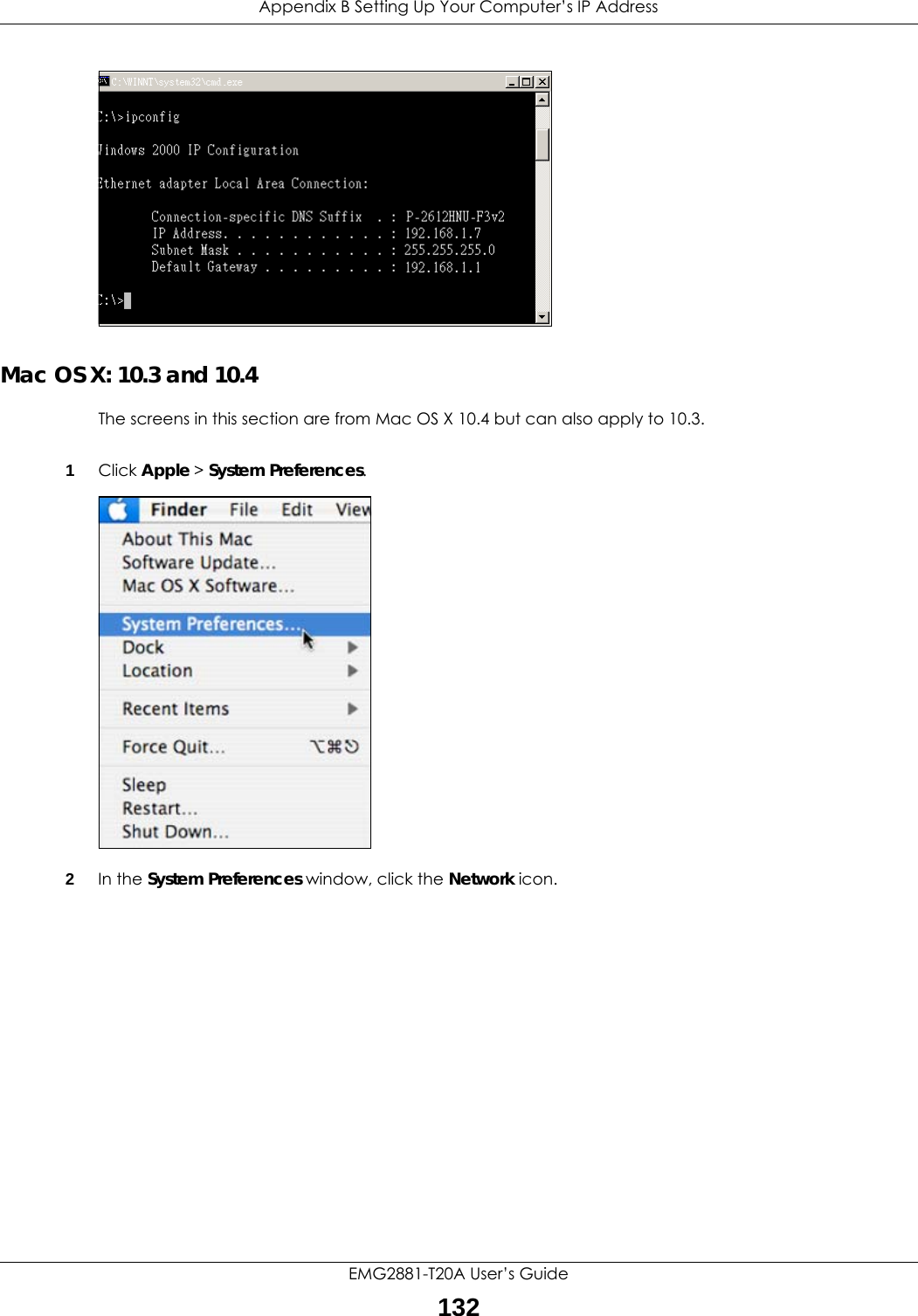
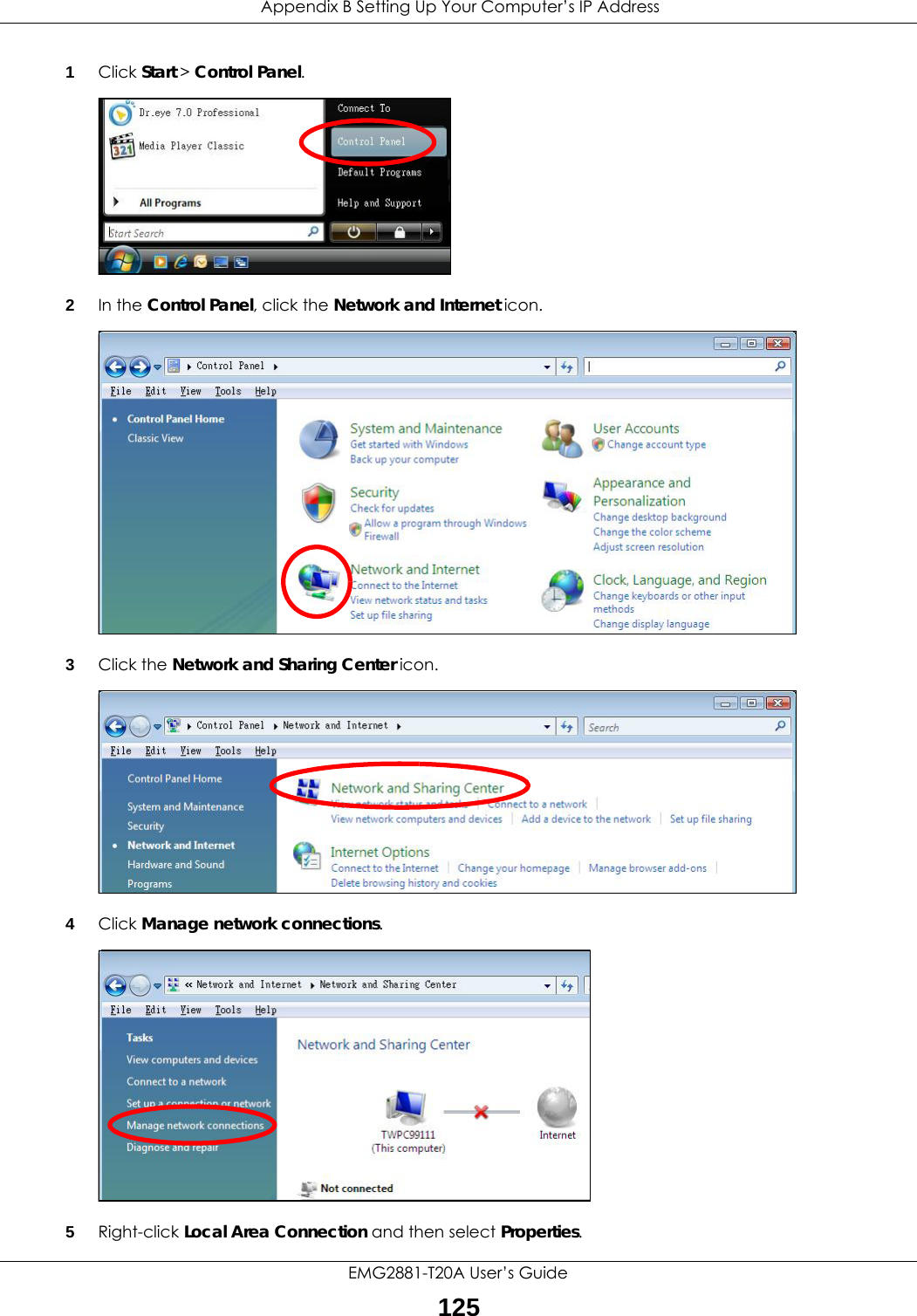
![Appendix B Setting Up Your Computer’s IP AddressEMG2881-T20A User’s Guide1317Select Obtain an IP address automatically if your network administrator or ISP assigns your IP address dynamically.Select Use the following IP Address and fill in the IP address, Subnet mask, and Default gateway fields if you have a static IP address that was assigned to you by your network administrator or ISP. You may also have to enter a Preferred DNS server and an Alternate DNS server, if that information was provided. Click Advanced if you want to configure advanced settings for IP, DNS and WINS. 8Click OK to close the Internet Protocol (TCP/IP) Properties window.9Click OK to close the Local Area Connection Properties window.Verifying Settings1Click Start > All Programs > Accessories > Command Prompt.2In the Command Prompt window, type "ipconfig" and then press [ENTER]. 3The IP settings are displayed as follows.](https://usermanual.wiki/ZyXEL-Communications/EMG2881-T20A.Users-Manual-Part-2-pdf/User-Guide-3733667-Page-49.png)