ZyXEL Communications NBG334SH1 Wireless Router User Manual SMG 700 User s Guide V1 00 Nov 2004
ZyXEL Communications Corporation Wireless Router SMG 700 User s Guide V1 00 Nov 2004
Contents
- 1. users manual pt1
- 2. users manual pt2
- 3. users manual pt3
- 4. users manual pt4
users manual pt4


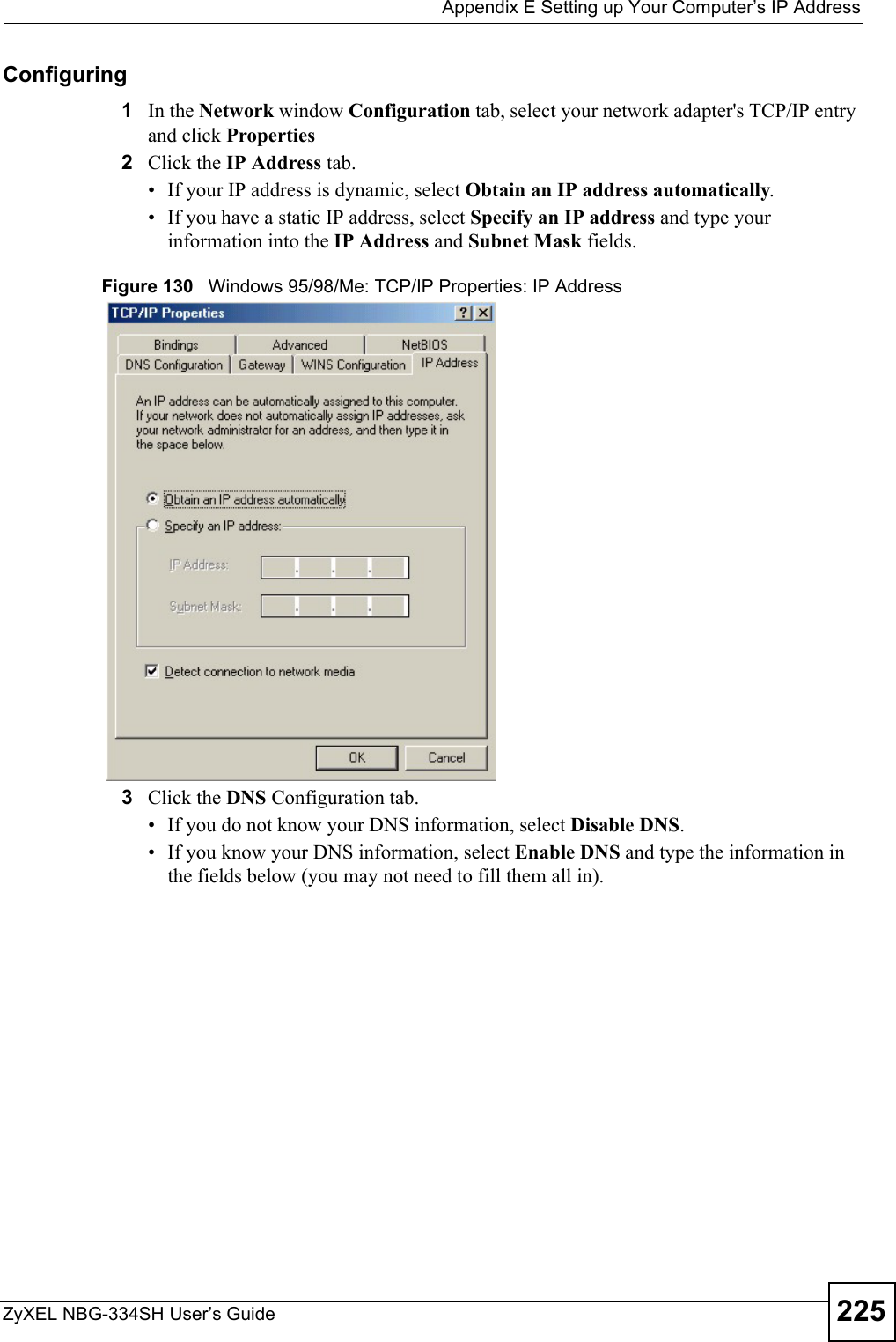
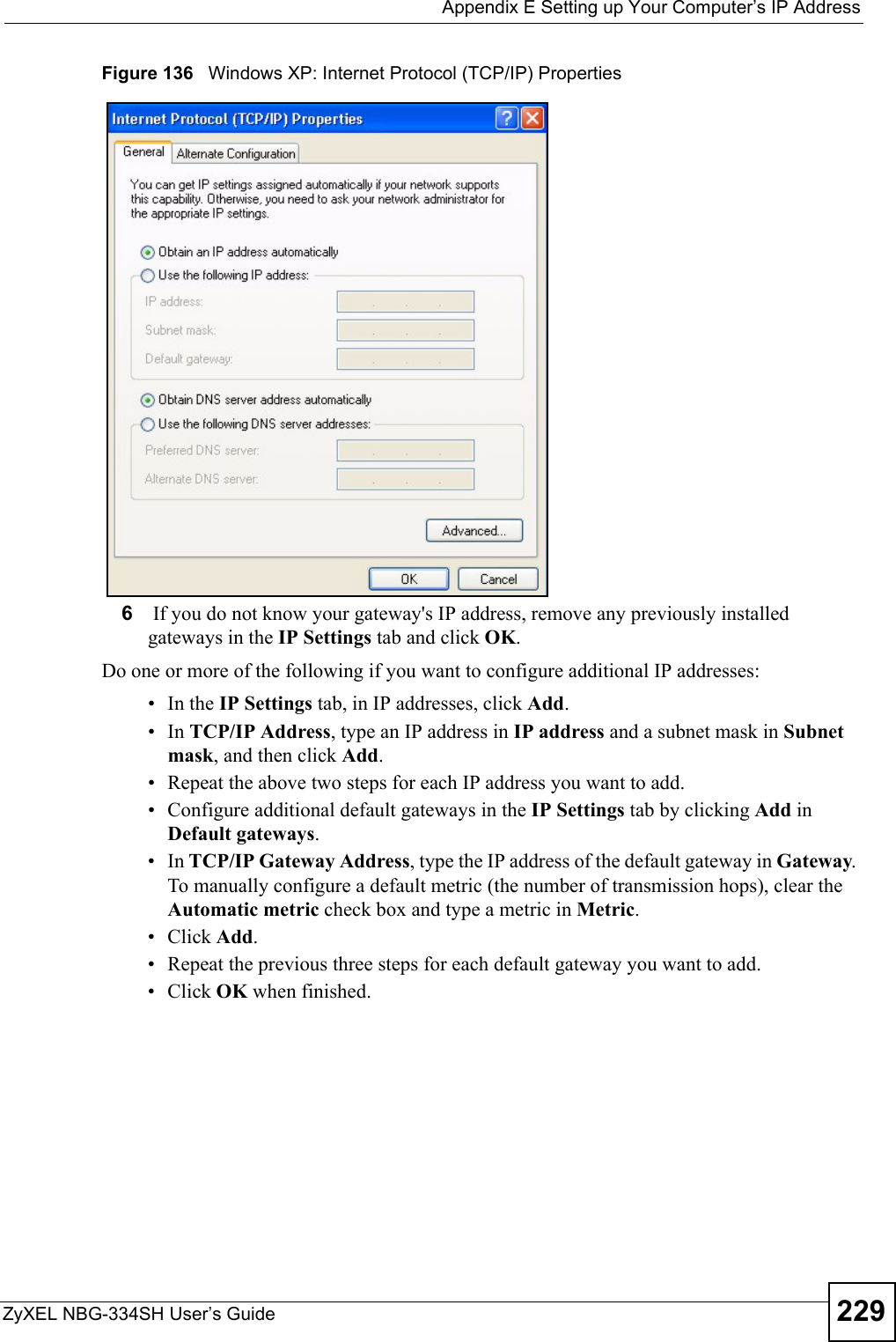
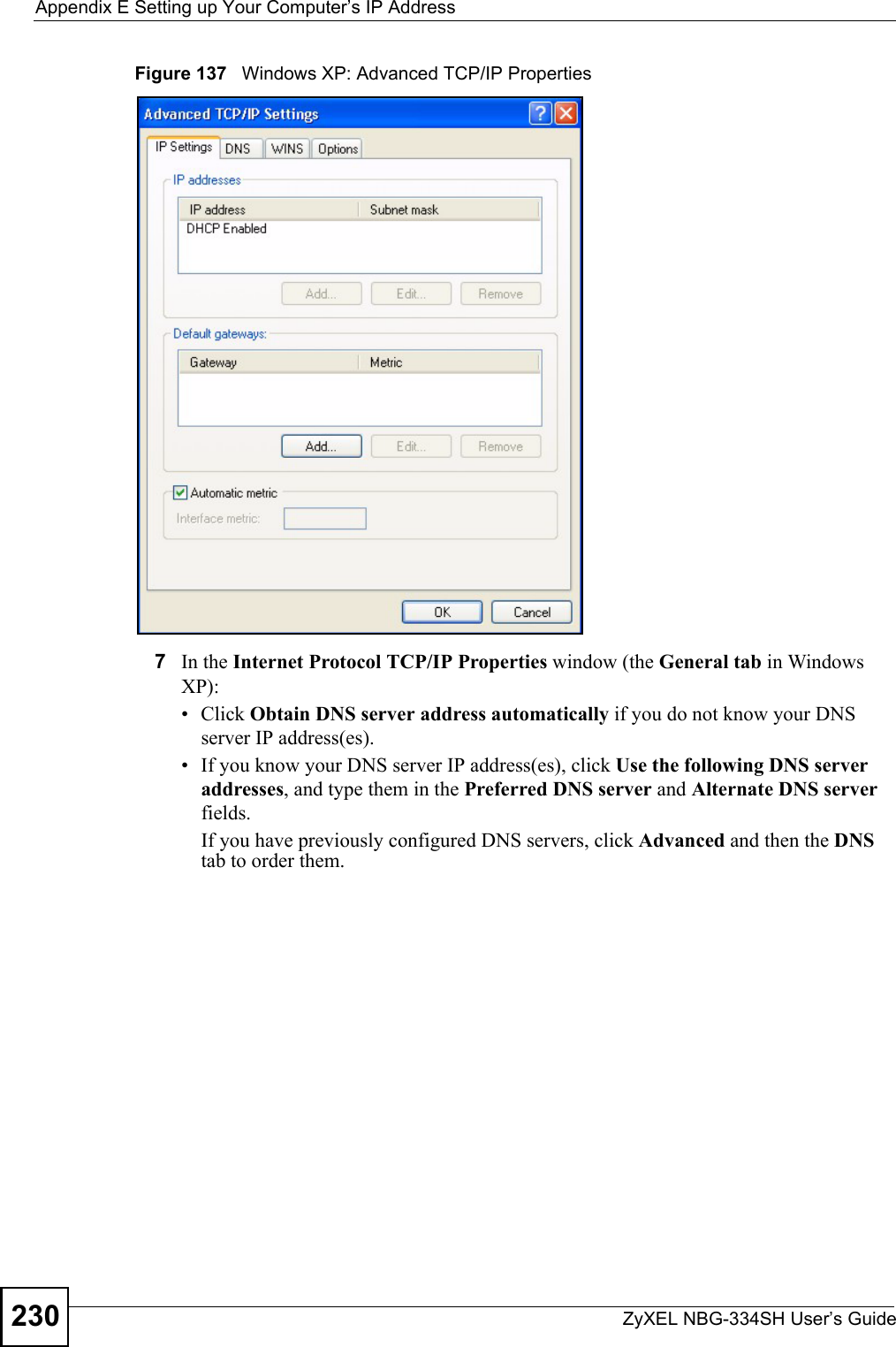
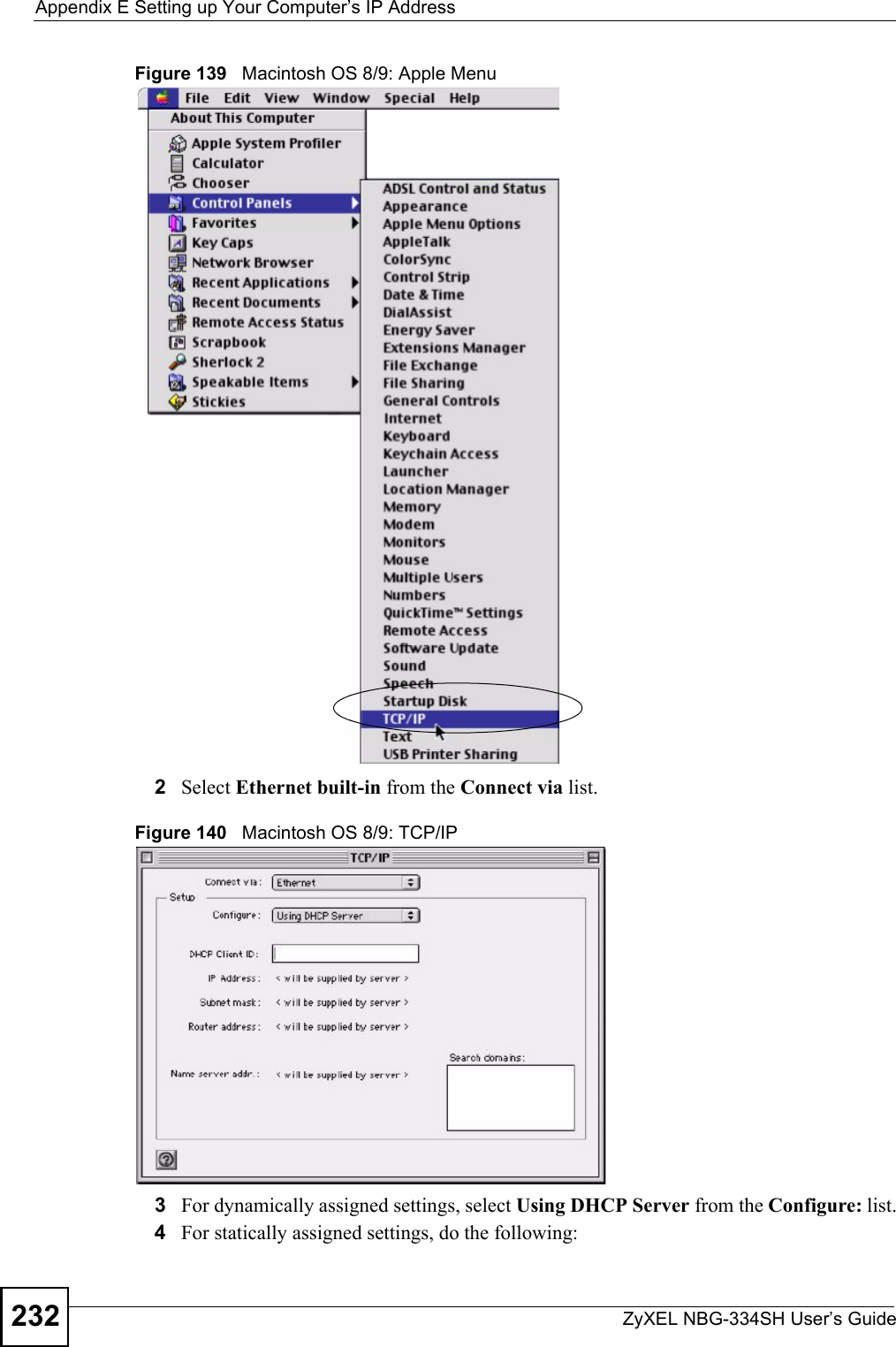
![Appendix E Setting up Your Computer’s IP AddressZyXEL NBG-334SH User’s Guide 231Figure 138 Windows XP: Internet Protocol (TCP/IP) Properties8Click OK to close the Internet Protocol (TCP/IP) Properties window.9Click Close (OK in Windows 2000/NT) to close the Local Area Connection Properties window.10 Close the Network Connections window (Network and Dial-up Connections in Windows 2000/NT).11 Turn on your Prestige and restart your computer (if prompted).Verifying Settings1Click Start, All Programs, Accessories and then Command Prompt.2In the Command Prompt window, type "ipconfig" and then press [ENTER]. You can also open Network Connections, right-click a network connection, click Status and then click the Support tab.Macintosh OS 8/9 1Click the Apple menu, Control Panel and double-click TCP/IP to open the TCP/IP Control Panel.](https://usermanual.wiki/ZyXEL-Communications/NBG334SH1.users-manual-pt4/User-Guide-811559-Page-31.png)
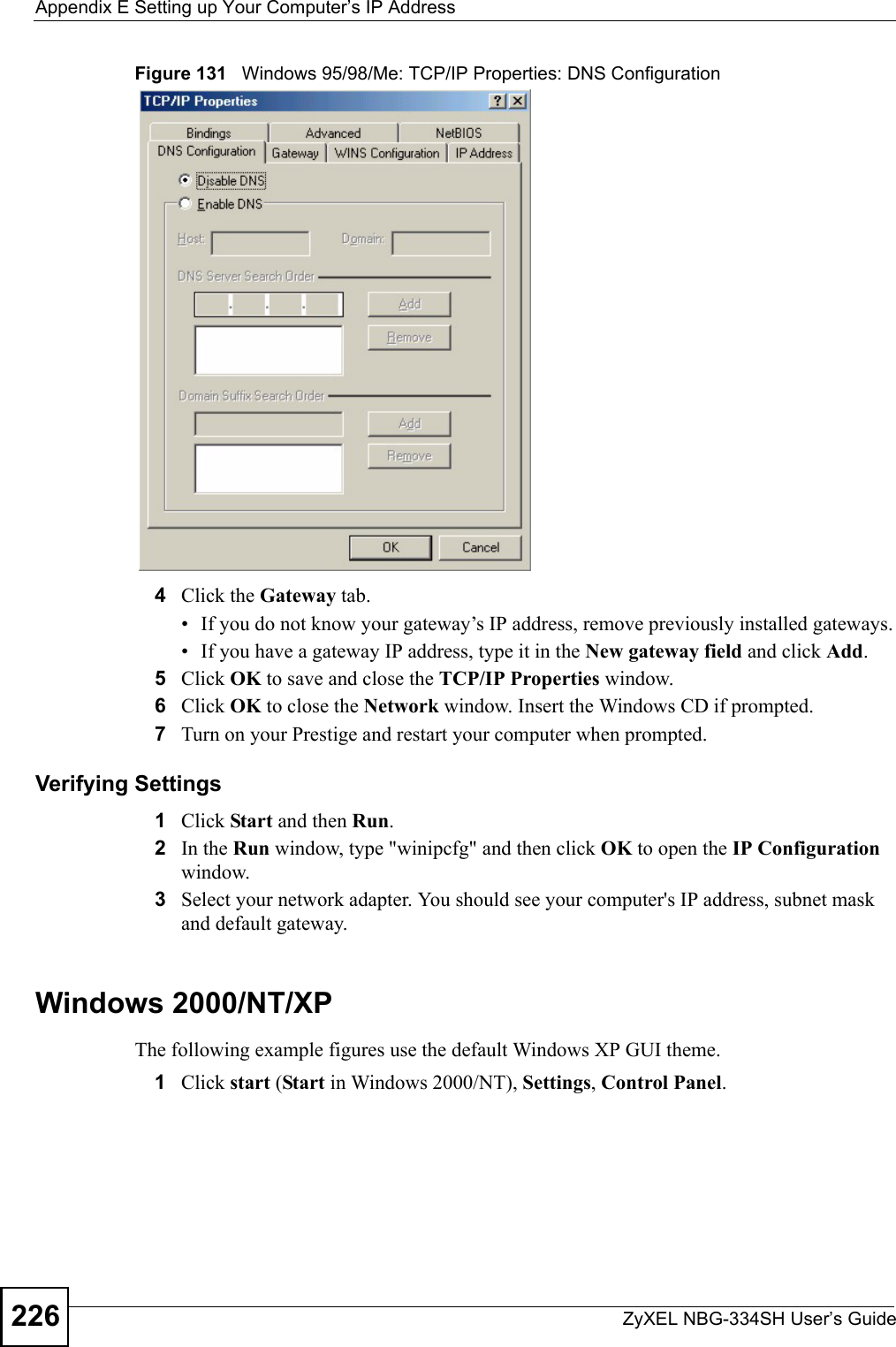
![Appendix E Setting up Your Computer’s IP AddressZyXEL NBG-334SH User’s Guide2382If you know your DNS server IP address(es), enter the DNS server information in the resolv.conf file in the /etc directory. The following figure shows an example where two DNS server IP addresses are specified.Figure 149 Red Hat 9.0: DNS Settings in resolv.conf 3After you edit and save the configuration files, you must restart the network card. Enter ./network restart in the /etc/rc.d/init.d directory. The following figure shows an example.Figure 150 Red Hat 9.0: Restart Ethernet Card 21.5.1 Verifying SettingsEnter ifconfig in a terminal screen to check your TCP/IP properties. Figure 151 Red Hat 9.0: Checking TCP/IP Properties nameserver 172.23.5.1nameserver 172.23.5.2[root@localhost init.d]# network restartShutting down interface eth0: [OK]Shutting down loopback interface: [OK]Setting network parameters: [OK]Bringing up loopback interface: [OK]Bringing up interface eth0: [OK][root@localhost]# ifconfig eth0 Link encap:Ethernet HWaddr 00:50:BA:72:5B:44 inet addr:172.23.19.129 Bcast:172.23.19.255 Mask:255.255.255.0 UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:717 errors:0 dropped:0 overruns:0 frame:0 TX packets:13 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:100 RX bytes:730412 (713.2 Kb) TX bytes:1570 (1.5 Kb) Interrupt:10 Base address:0x1000 [root@localhost]#](https://usermanual.wiki/ZyXEL-Communications/NBG334SH1.users-manual-pt4/User-Guide-811559-Page-38.png)

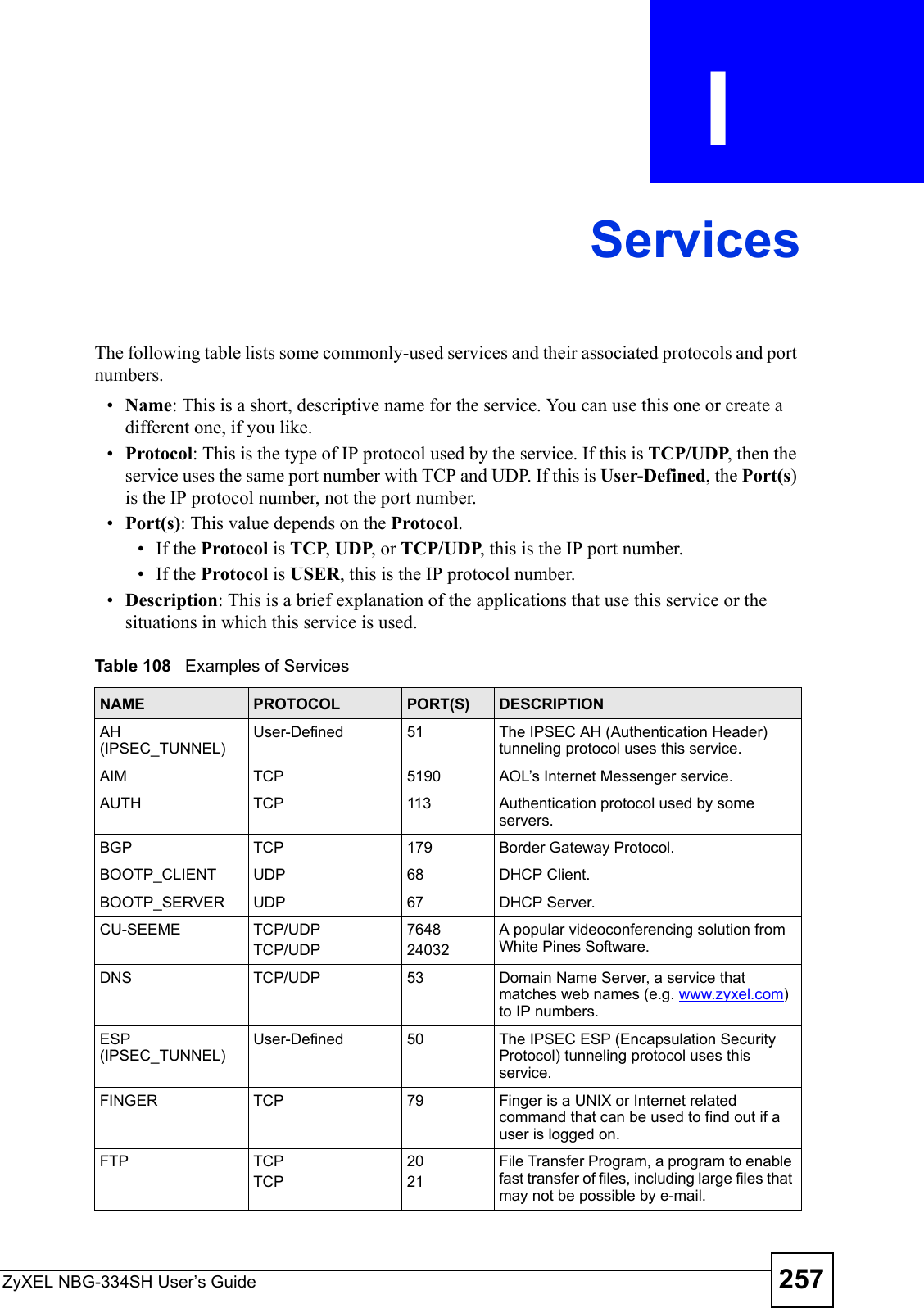
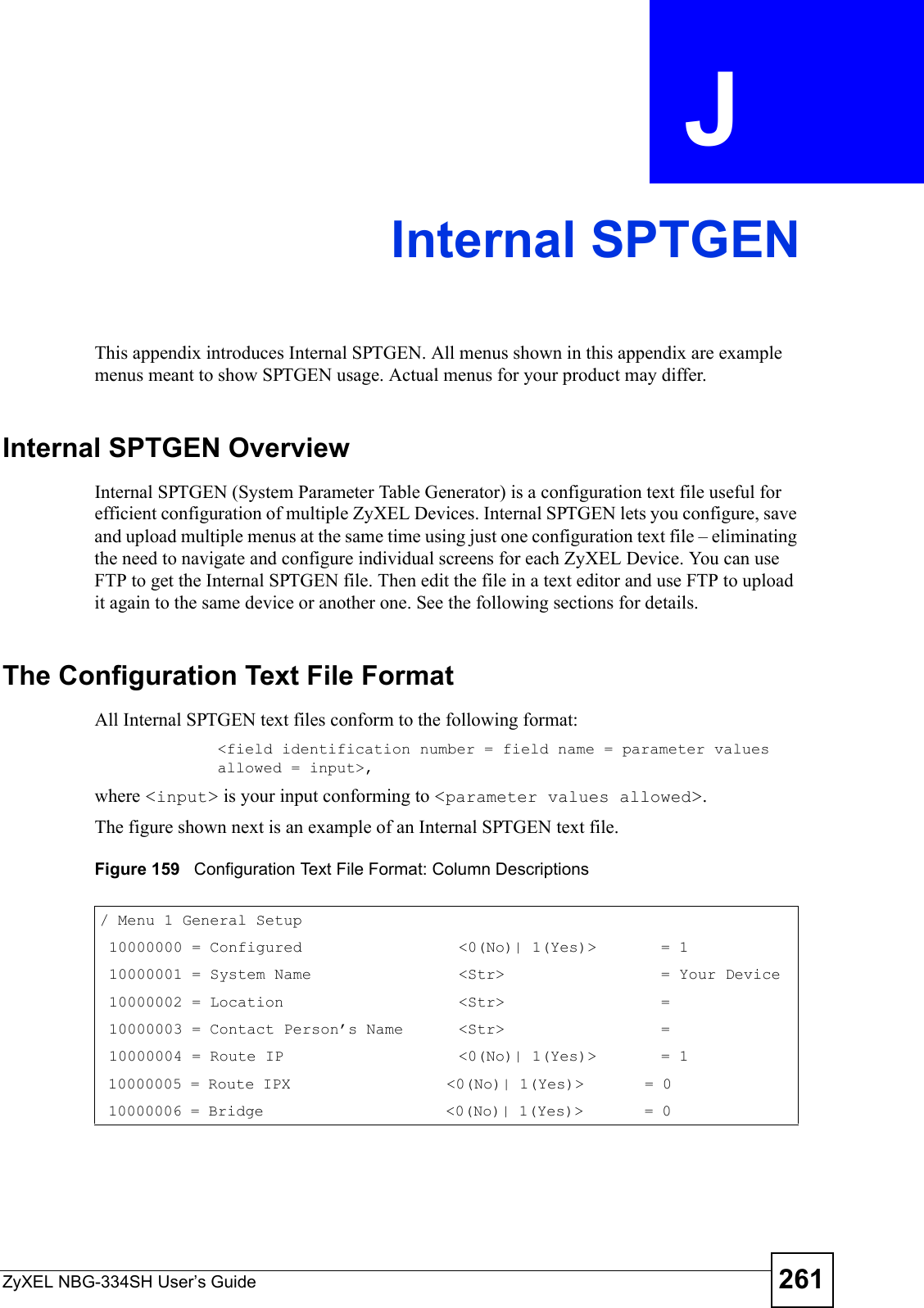
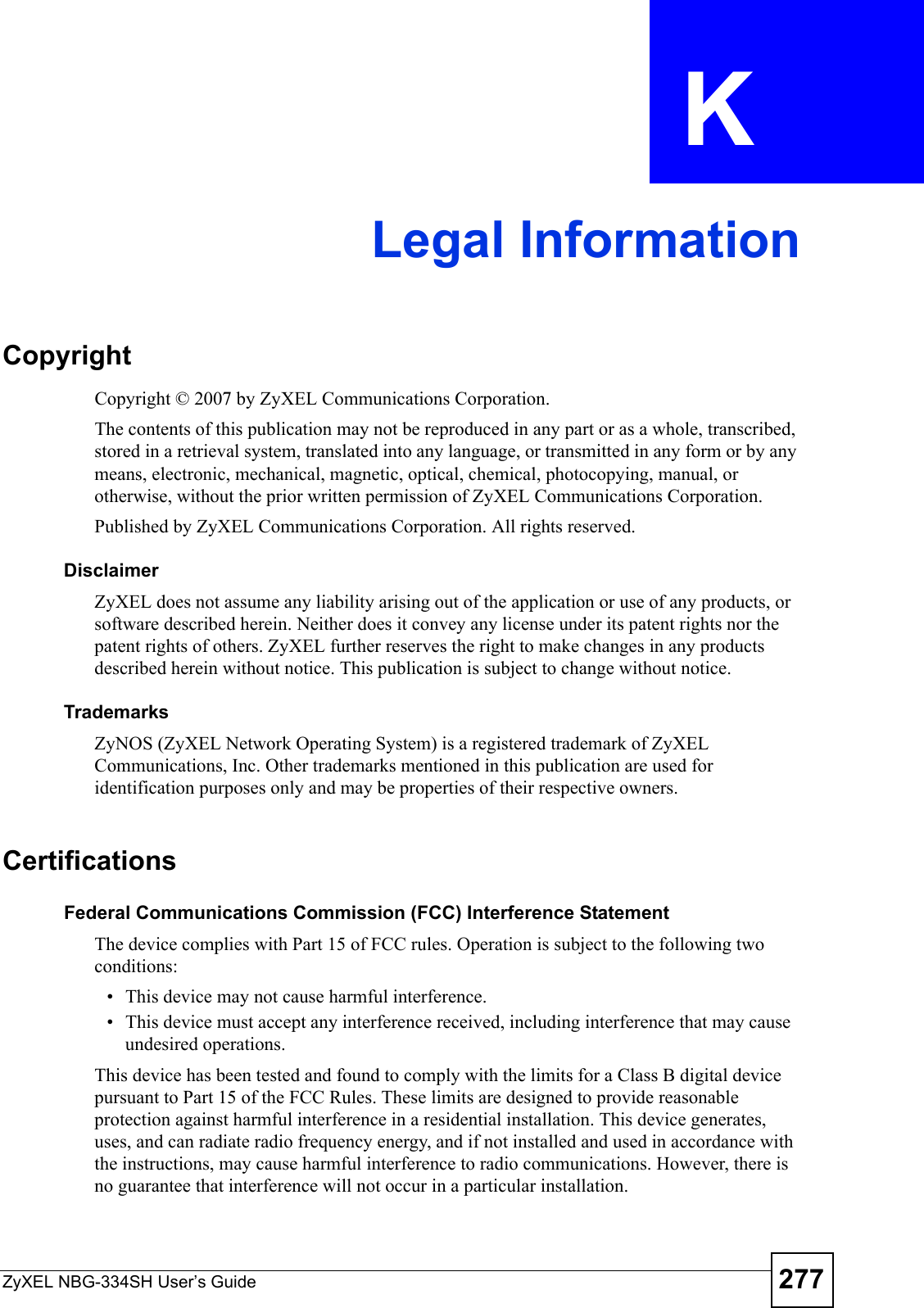
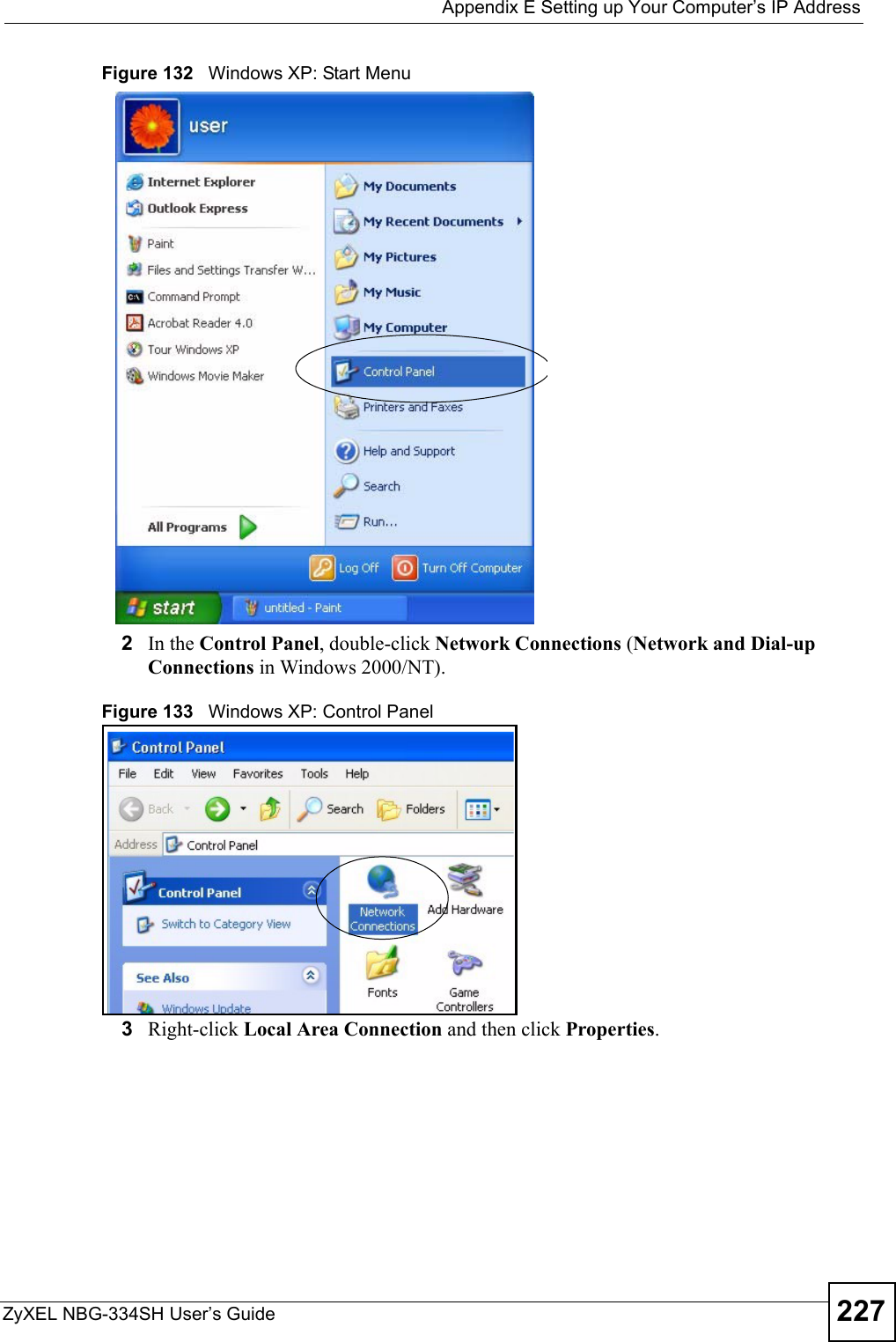
![ZyXEL NBG-334SH User’s Guide 251APPENDIX G Command InterpreterThe following describes how to use the command interpreter. See the included disk or zyxel.com for more detailed information on these commands."Use of undocumented commands or misconfiguration can damage the unit and possibly render it unusable.Accessing the Command InterpreterIf your device has SMT, enter 24 in the main menu to bring up the system maintenance menu. Enter 8 to go to Menu 24.8 - Command Interpreter Mode. If your device does not have SMT, simply Telnet to the ZyXEL Device’s IP address. You will log directly into the command interpreter. Command Syntax• The command keywords are in courier new font.• Enter the command keywords exactly as shown, do not abbreviate.• The required fields in a command are enclosed in angle brackets <>. • The optional fields in a command are enclosed in square brackets [].•The |symbol means or.For example,sys filter netbios config <type> <on|off>means that you must specify the type of netbios filter and whether to turn it on or off.Command UsageA list of valid commands can be found by typing help or ? at the command prompt. Always type the full command. Type exit when finished.](https://usermanual.wiki/ZyXEL-Communications/NBG334SH1.users-manual-pt4/User-Guide-811559-Page-51.png)
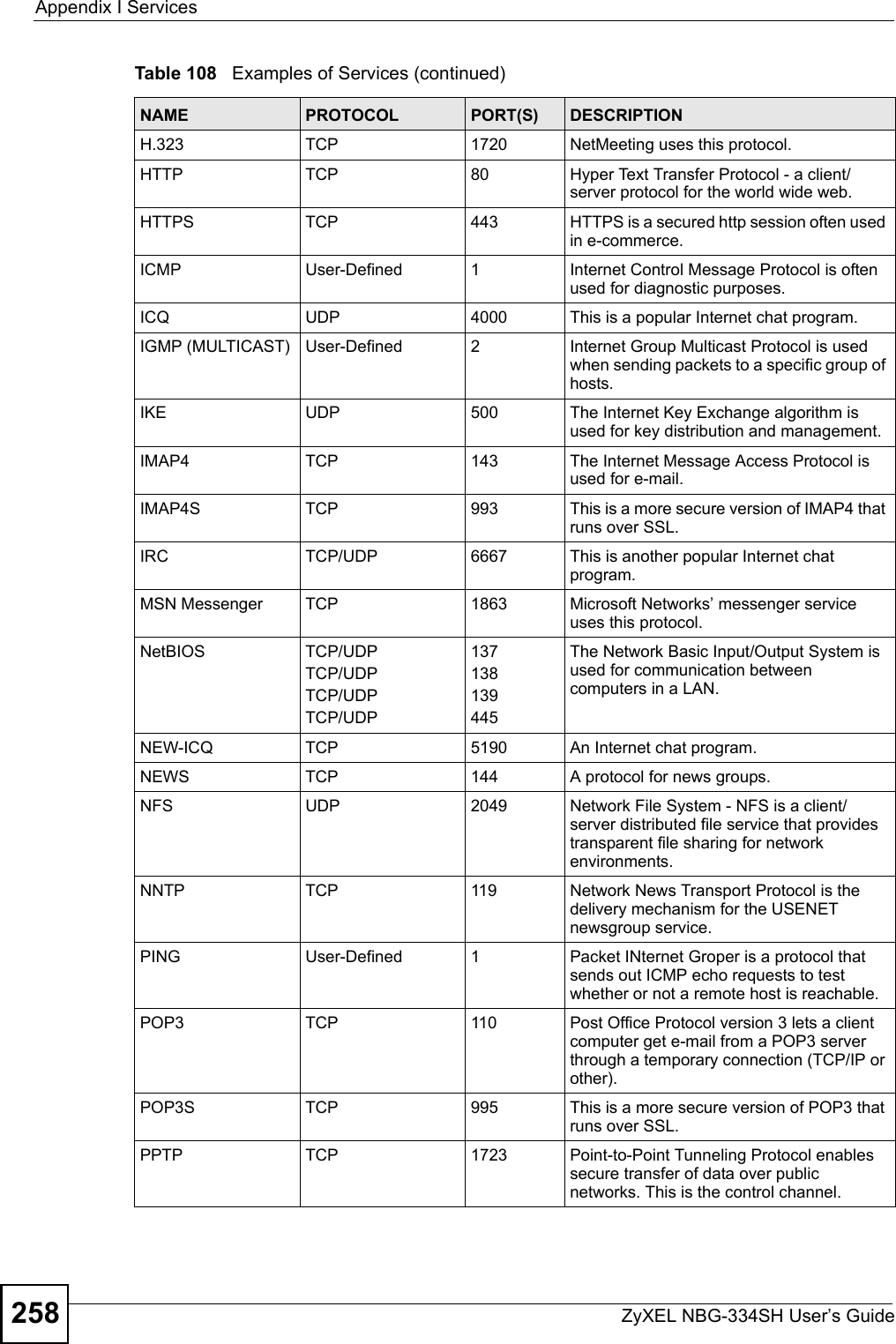
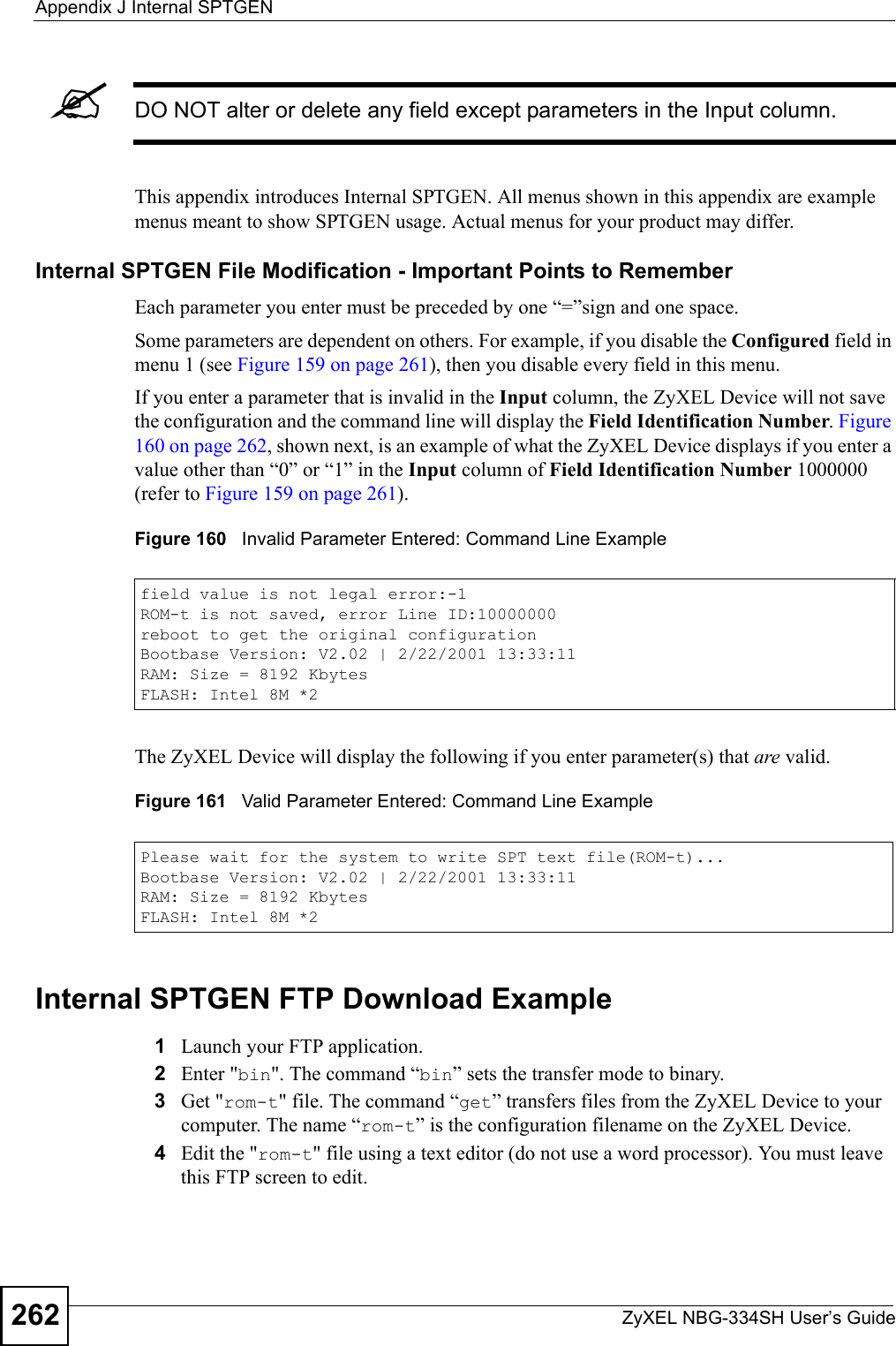
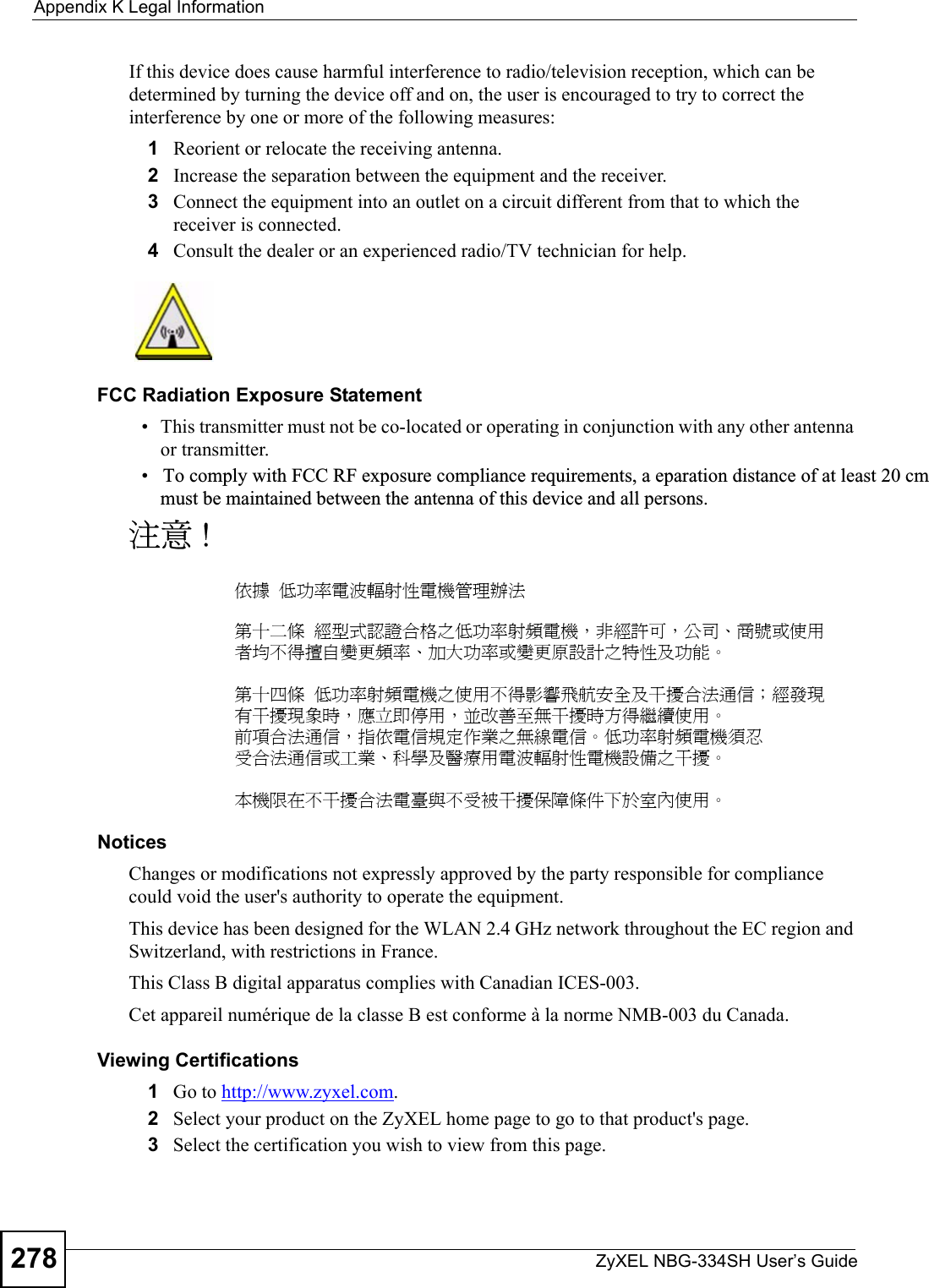
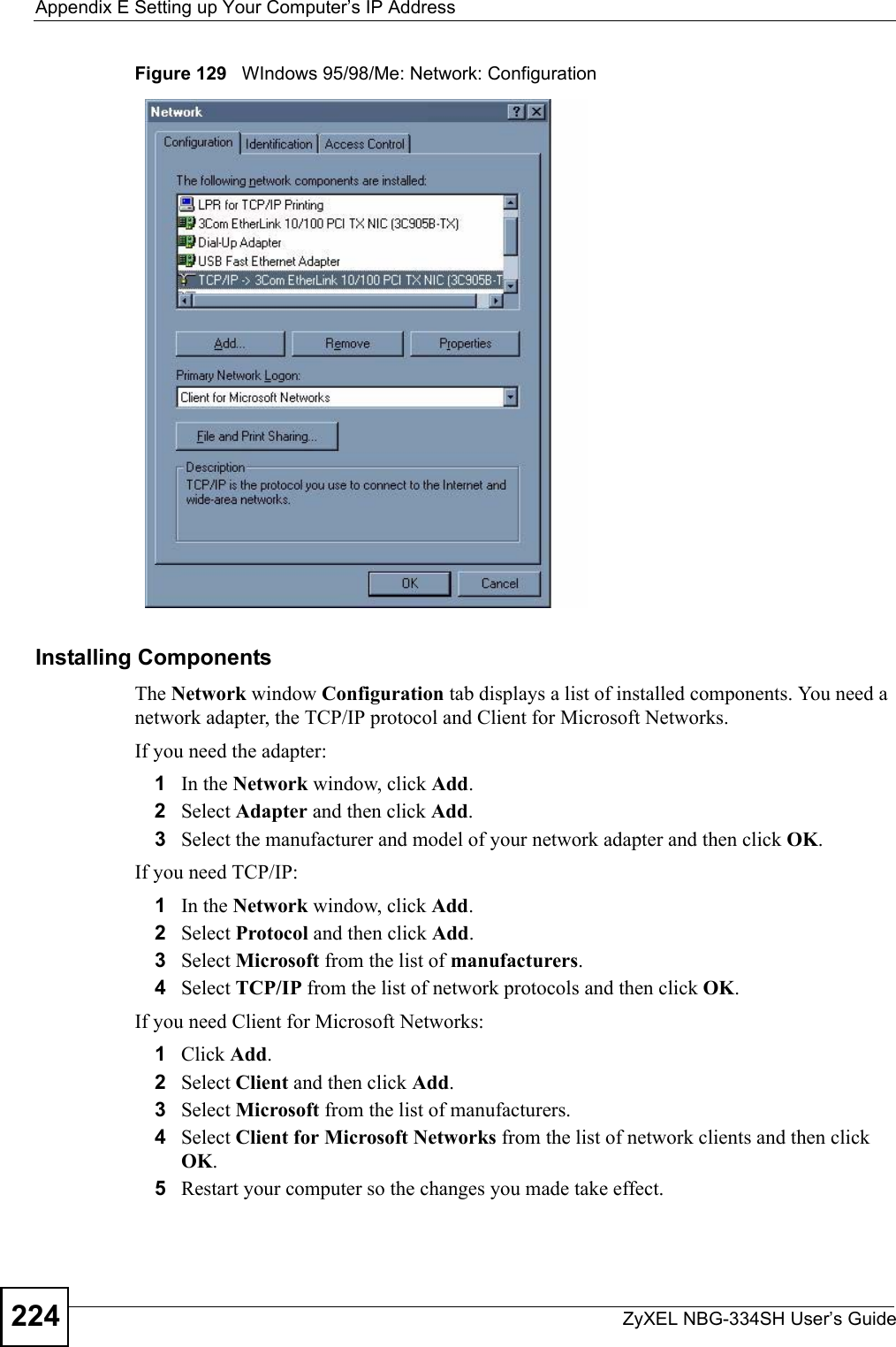
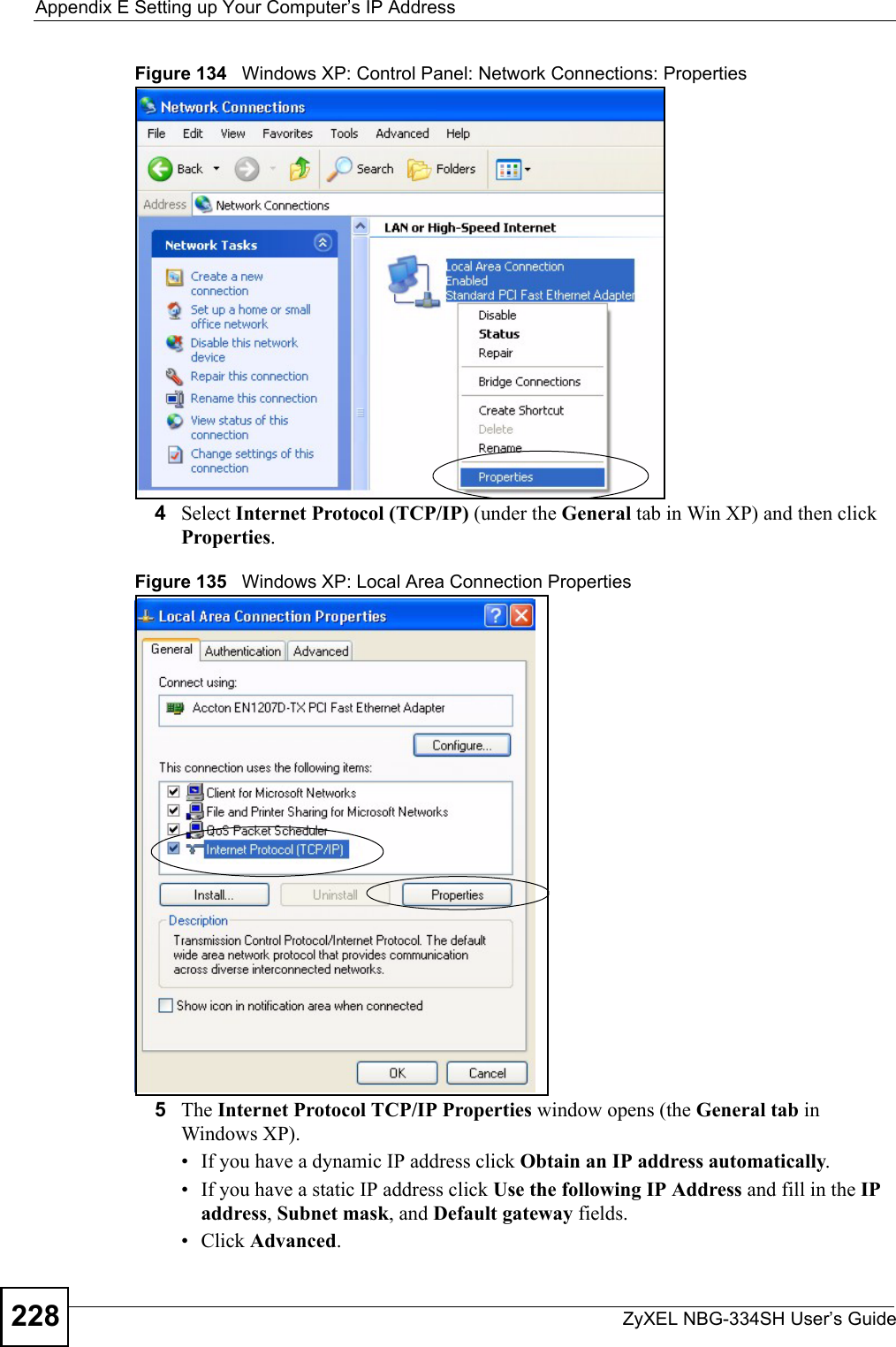
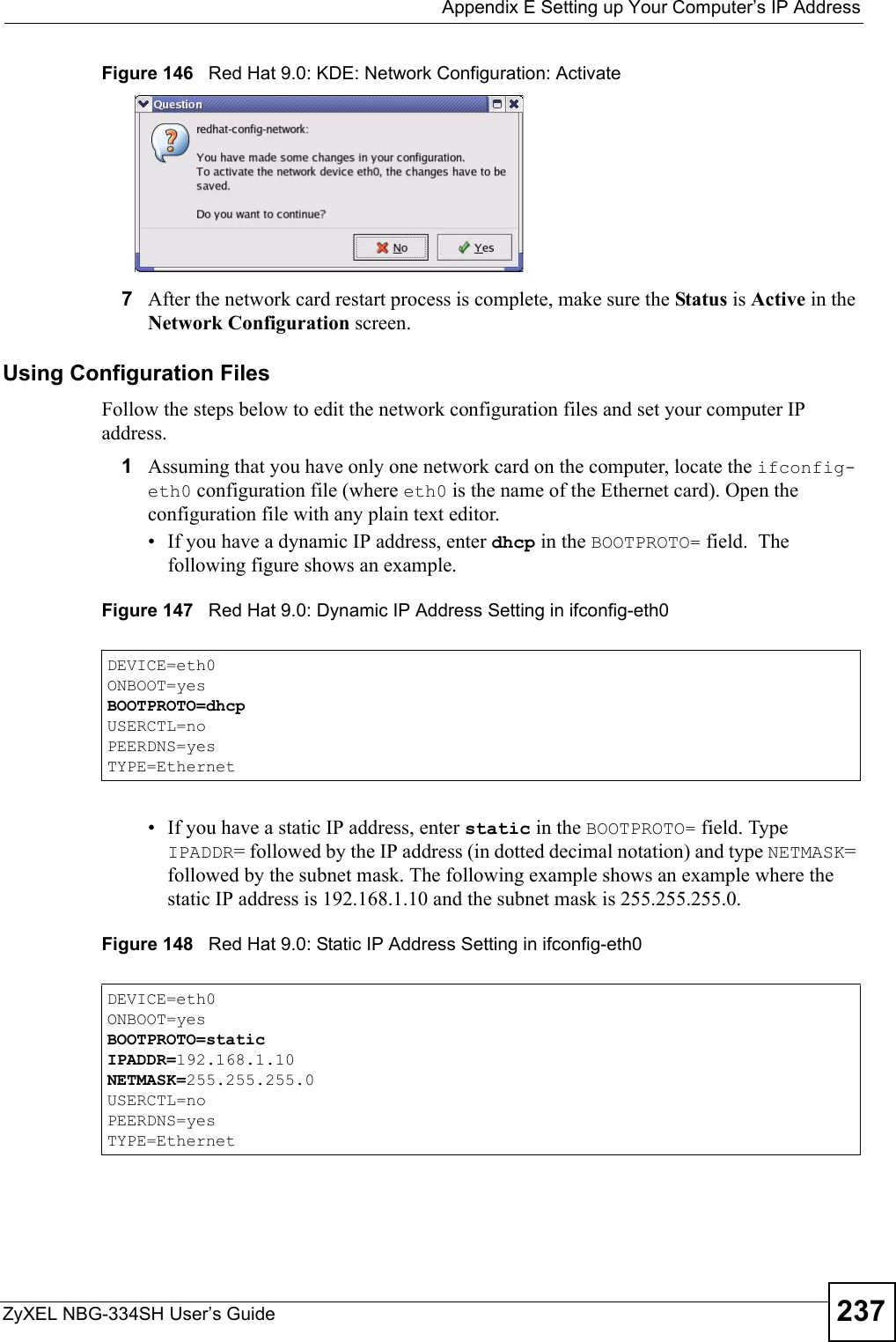
![Appendix G Command InterpreterZyXEL NBG-334SH User’s Guide252Log CommandsThis section provides some general examples of how to use the log commands. The items that display with your device may vary but the basic function should be the same. Go to the command interpreter interface. Configuring What You Want the ZyXEL Device to Log1Use the sys logs load command to load the log setting buffer that allows you to configure which logs the ZyXEL Device is to record. 2Use sys logs category to view a list of the log categories.Figure 157 Displaying Log Categories Example3Use sys logs category followed by a log category to display the parameters that are available for the category.Figure 158 Displaying Log Parameters Example4Use sys logs category followed by a log category and a parameter to decide what to record.Use 0 to not record logs for that category, 1 to record only logs for that category, 2 to record only alerts for that category, and 3 to record both logs and alerts for that category. Not every parameter is available with every category.5Use the sys logs save command to store the settings in the ZyXEL Device (you must do this in order to record logs).Displaying Logs• Use the sys logs display command to show all of the logs in the ZyXEL Device’s log.• Use the sys logs category display command to show the log settings for all of the log categories.Copyright (c) 1994 - 2006 ZyXEL Communications Corp.ras> sys logs category8021x access attack displayerror icmp javablocked mtenpacketfilter ppp cdr remotetcpreset traffic upnp urlblockedurlforward wirelessras>ras> sys logs category accessUsage: [0:none/1:log/2:alert/3:both] [0:don't show debug type/1:show debug type]](https://usermanual.wiki/ZyXEL-Communications/NBG334SH1.users-manual-pt4/User-Guide-811559-Page-52.png)
![Appendix G Command InterpreterZyXEL NBG-334SH User’s Guide 253• Use the sys logs display [log category] command to show the logs in an individual ZyXEL Device log category.• Use the sys logs clear command to erase all of the ZyXEL Device’s logs.Log Command ExampleThis example shows how to set the ZyXEL Device to record the access logs and alerts and then view the results.ras> sys logs loadras> sys logs category access 3ras> sys logs saveras> sys logs display access#.time source destination notes message 0|01/02/2000 04:06:35 |192.168.1.33:2190 |207.69.188.186:135 |ACCESS FORWARD Firewall default policy: TCP (L to W) 1|01/02/2000 04:06:28 |192.168.1.33:2190 |207.69.188.186:135 |ACCESS FORWARD Firewall default policy: TCP (L to W) 3|01/02/2000 04:06:25 |192.168.1.33:2190 |207.69.188.186:135 |ACCESS FORWARD Firewall default policy: UDP (L to W) 4|01/02/2000 04:06:16 |192.168.1.33:2187 |207.69.188.186:80 |ACCESS FORWARD Firewall default policy: TCP (L to W)](https://usermanual.wiki/ZyXEL-Communications/NBG334SH1.users-manual-pt4/User-Guide-811559-Page-53.png)