ZyXEL Communications NWA1123AC 802.11 a/b/g/n/ac Dual-Radio Ceiling Mount PoE Access Point User Manual Book
ZyXEL Communications Corporation 802.11 a/b/g/n/ac Dual-Radio Ceiling Mount PoE Access Point Book
Contents
- 1. User Manual Part 1.pdf
- 2. User Manual Part 2.pdf
User Manual Part 2.pdf
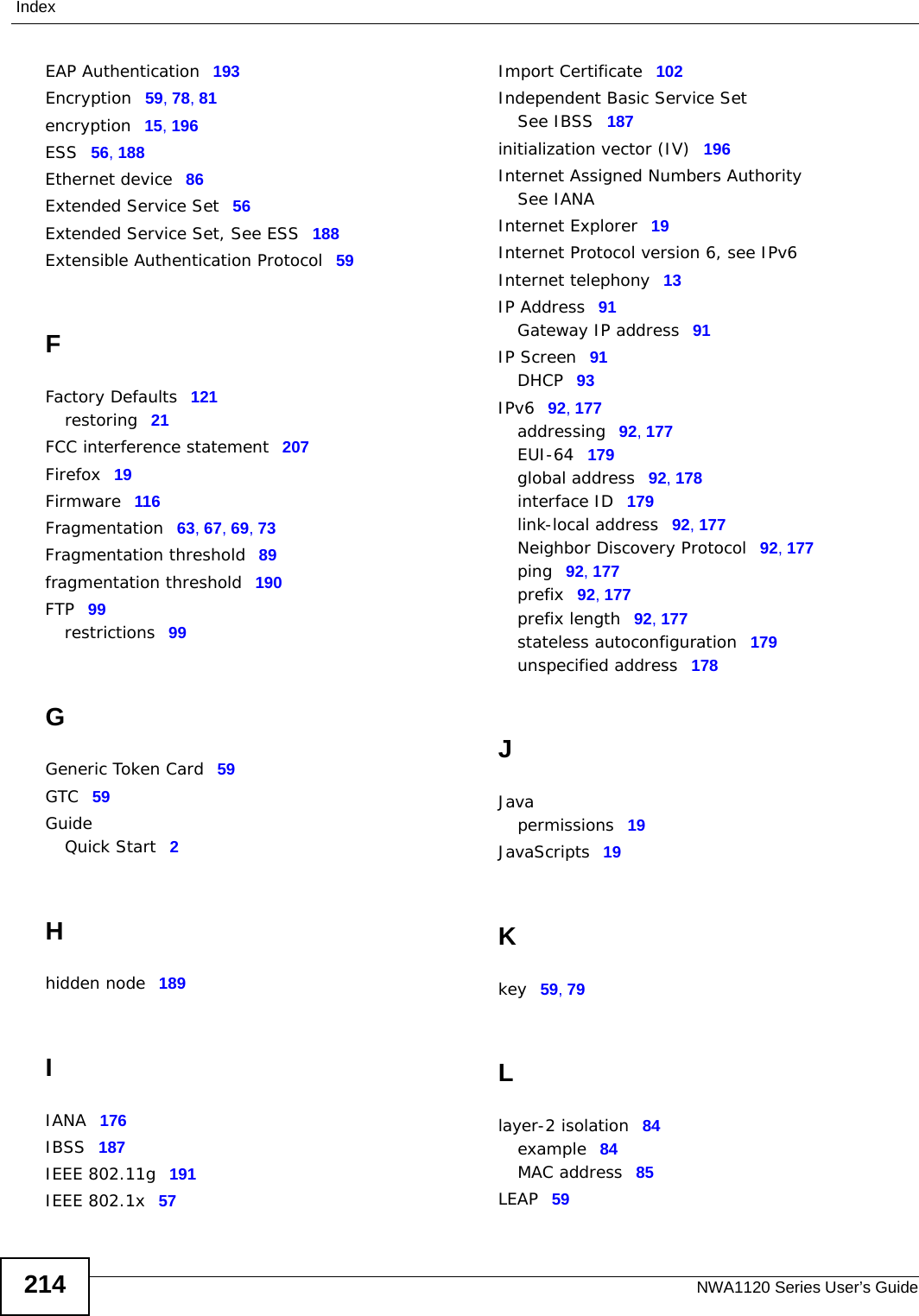
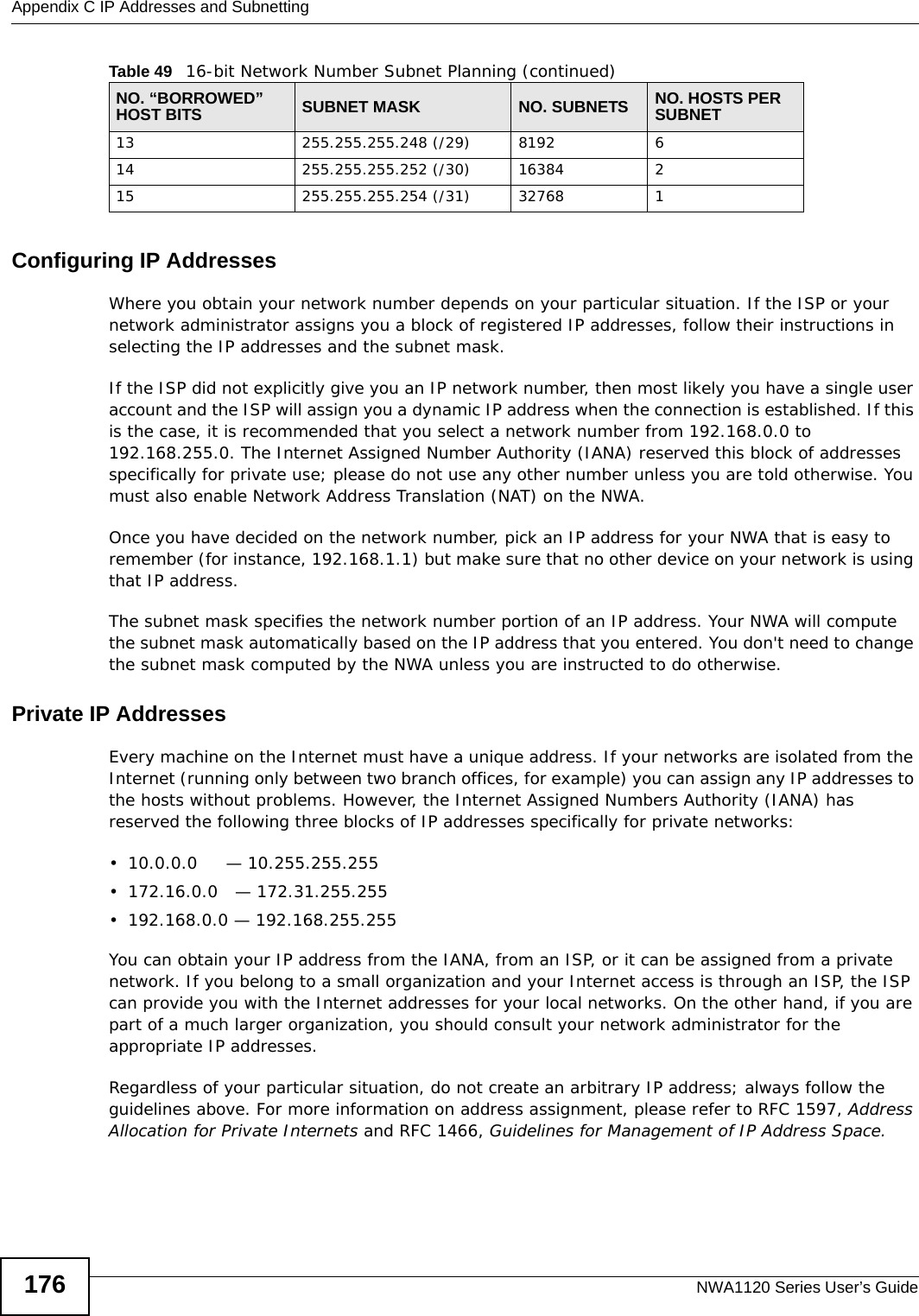
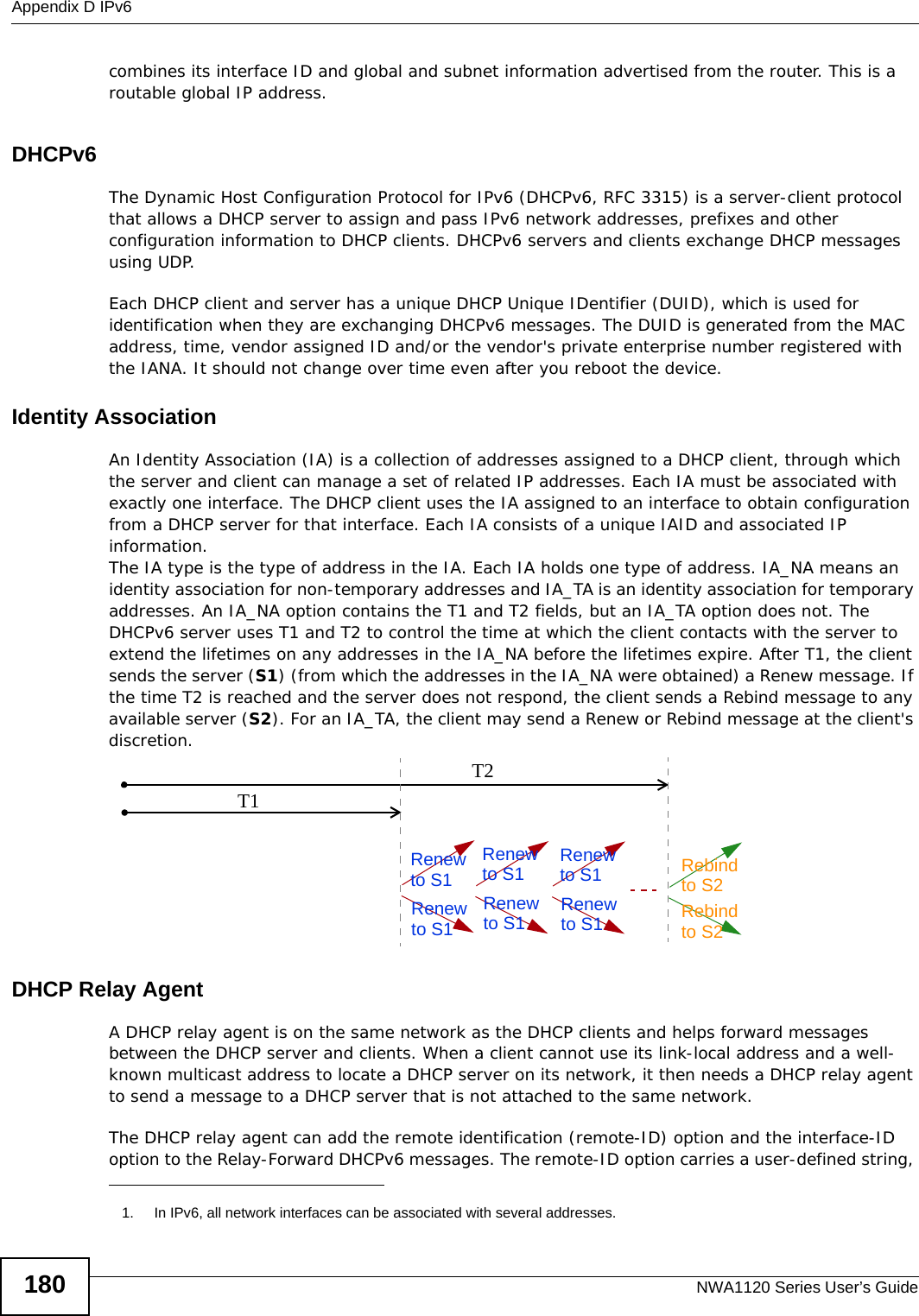
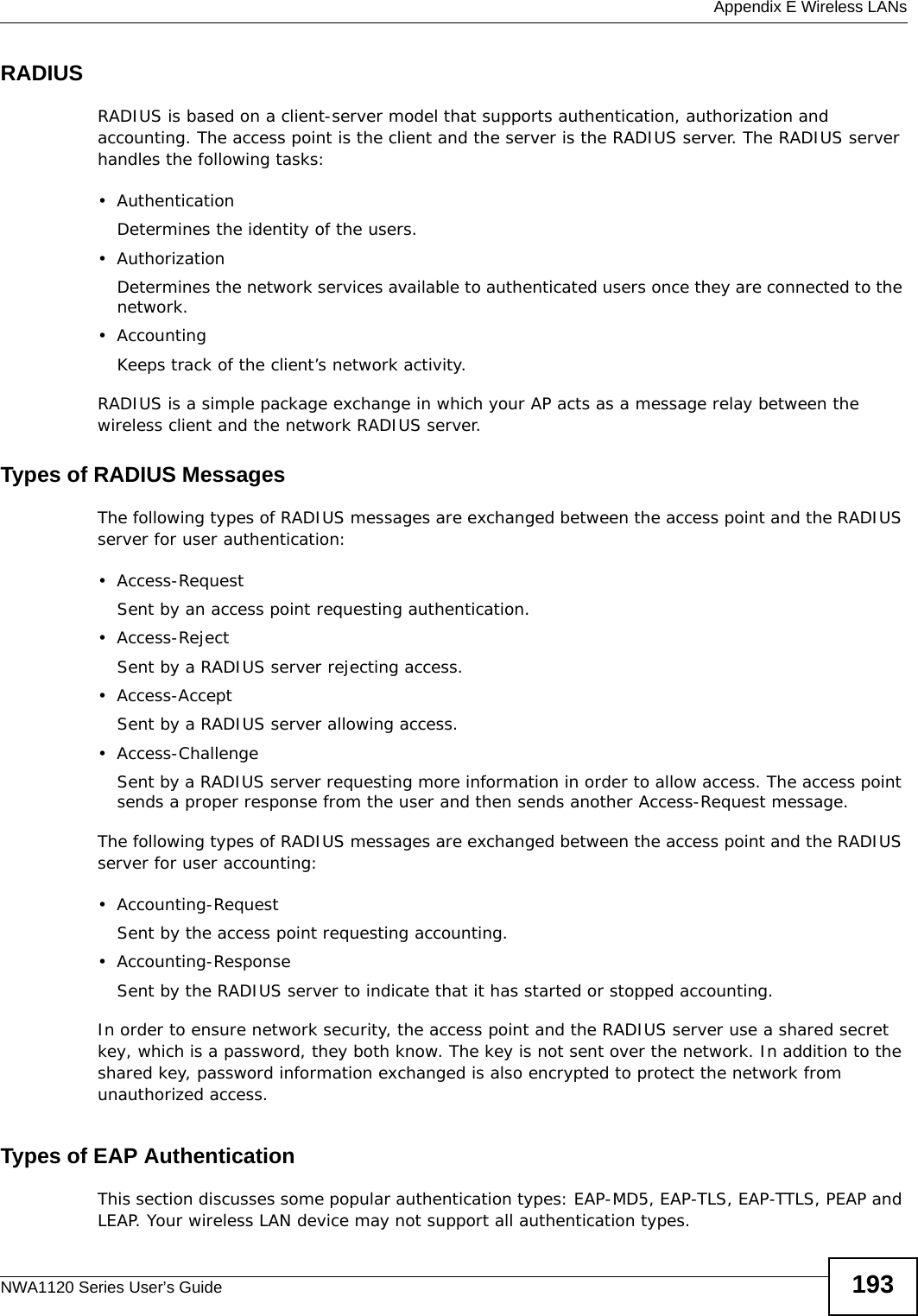
![Appendix A Setting Up Your Computer’s IP AddressNWA1120 Series User’s Guide1325The Internet Protocol TCP/IP Properties window opens.6Select Obtain an IP address automatically if your network administrator or ISP assigns your IP address dynamically.Select Use the following IP Address and fill in the IP address, Subnet mask, and Default gateway fields if you have a static IP address that was assigned to you by your network administrator or ISP. You may also have to enter a Preferred DNS server and an Alternate DNS server, if that information was provided.7Click OK to close the Internet Protocol (TCP/IP) Properties window.8Click OK to close the Local Area Connection Properties window.Verifying Settings1Click Start > All Programs > Accessories > Command Prompt.2In the Command Prompt window, type "ipconfig" and then press [ENTER]. You can also go to Start > Control Panel > Network Connections, right-click a network connection, click Status and then click the Support tab to view your IP address and connection information.](https://usermanual.wiki/ZyXEL-Communications/NWA1123AC.User-Manual-Part-2-pdf/User-Guide-2123423-Page-4.png)
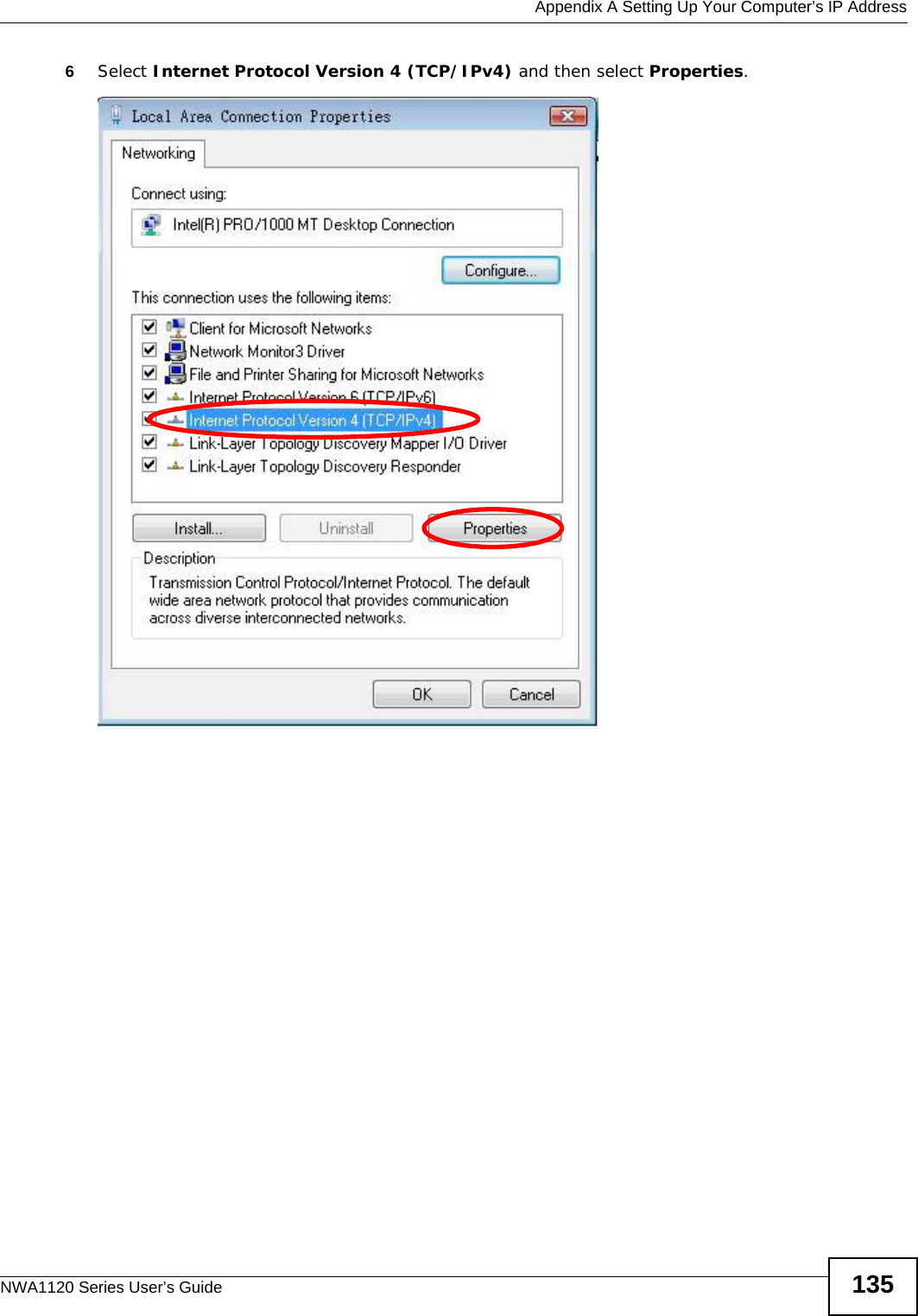
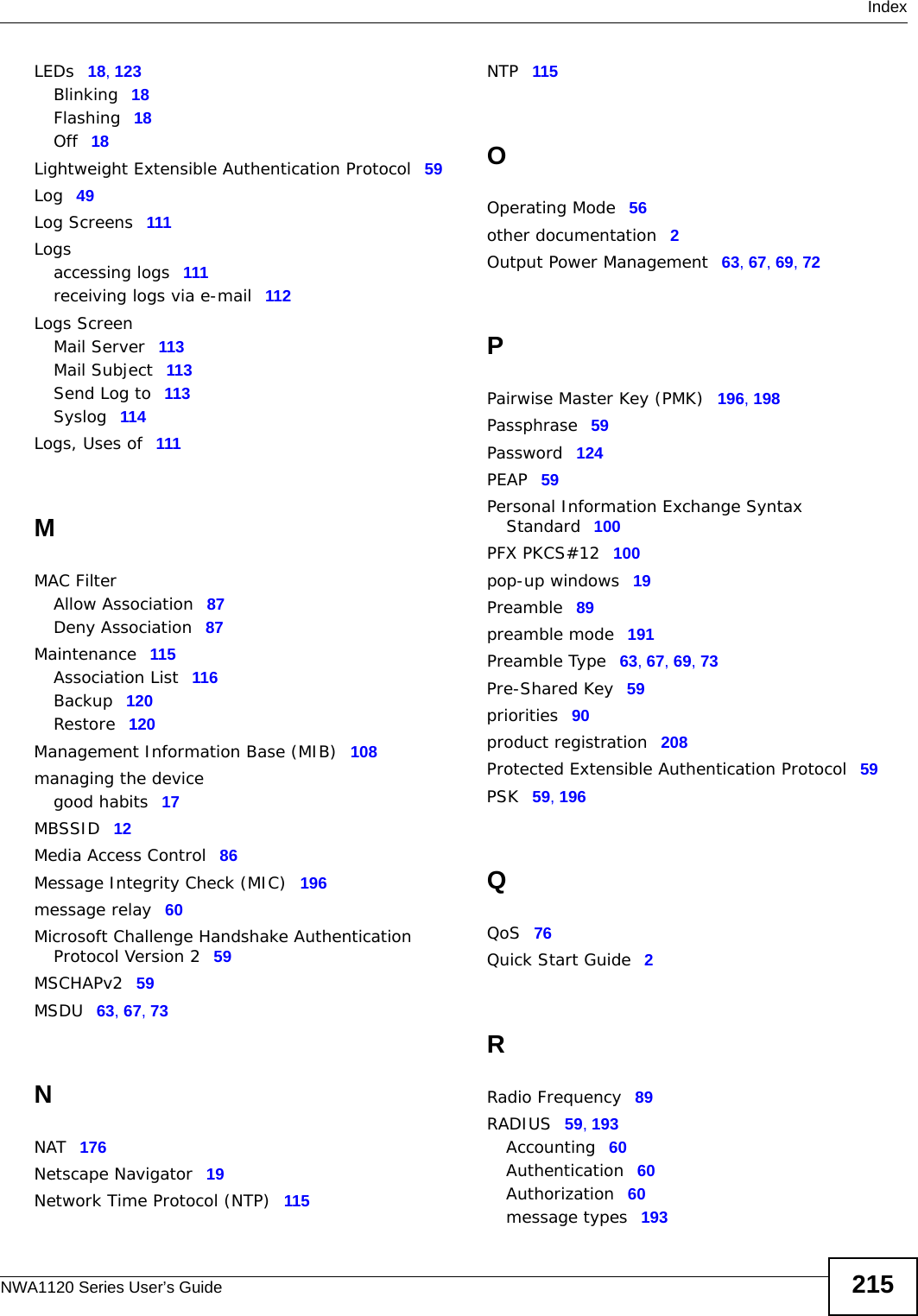
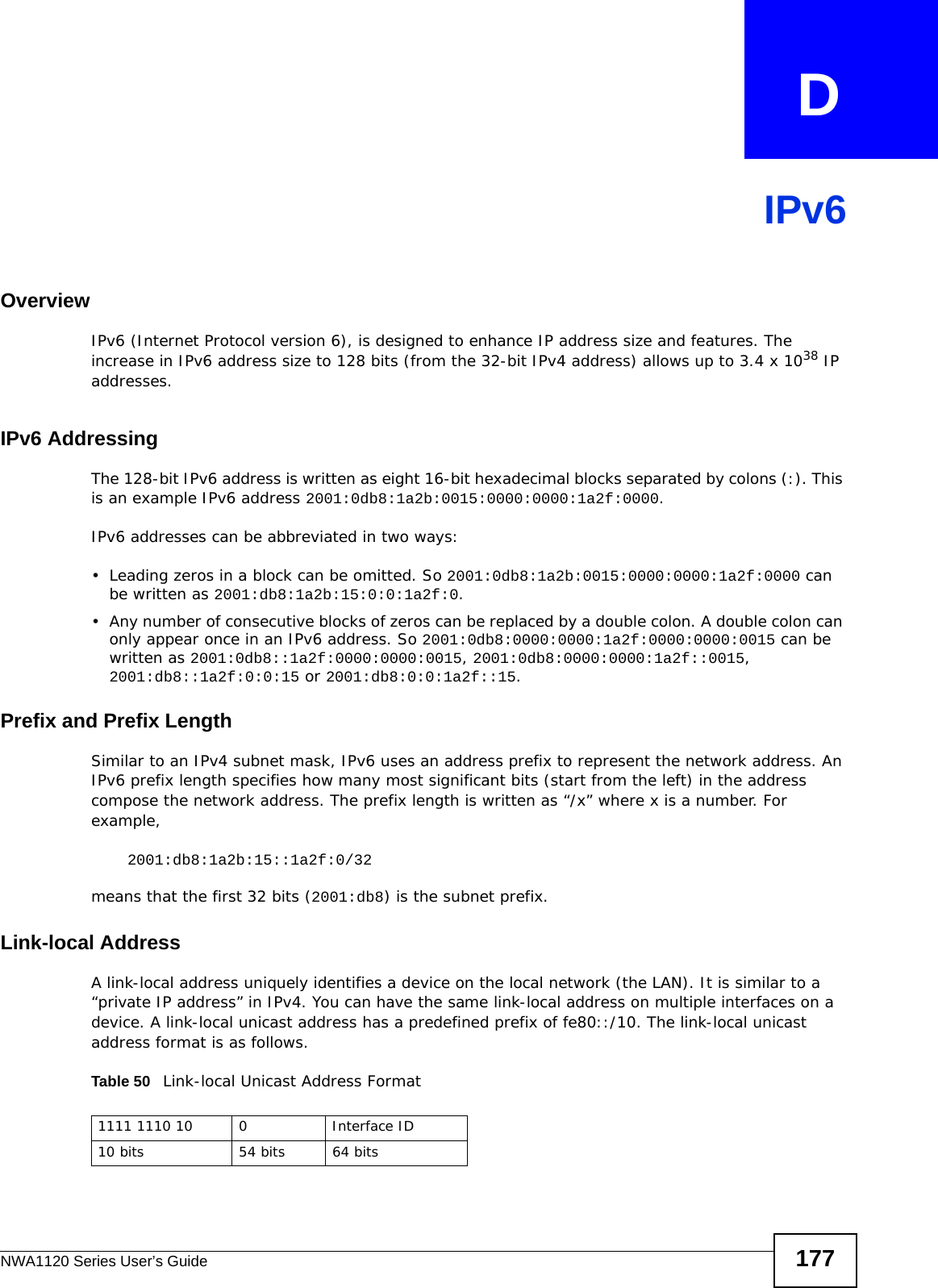
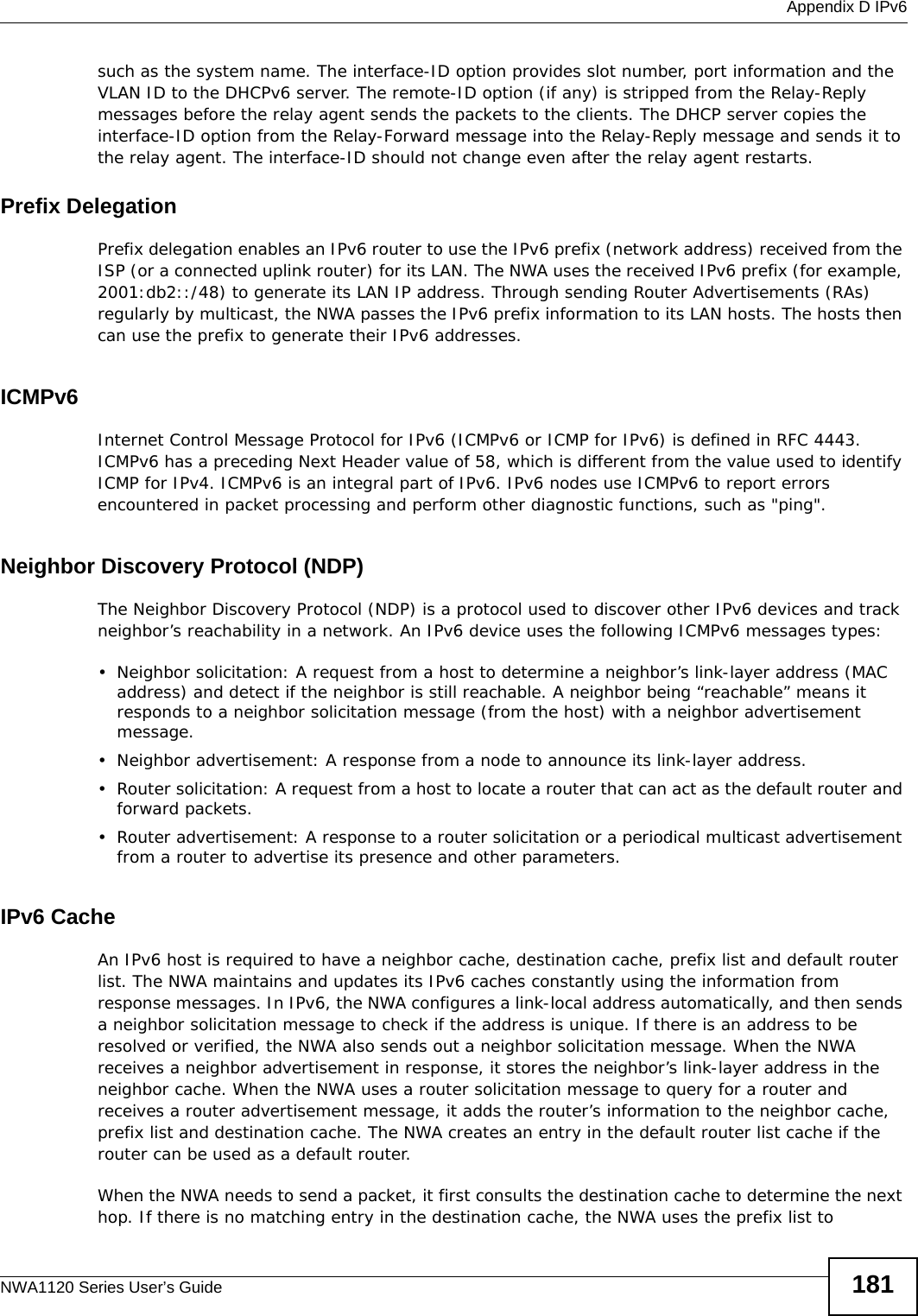
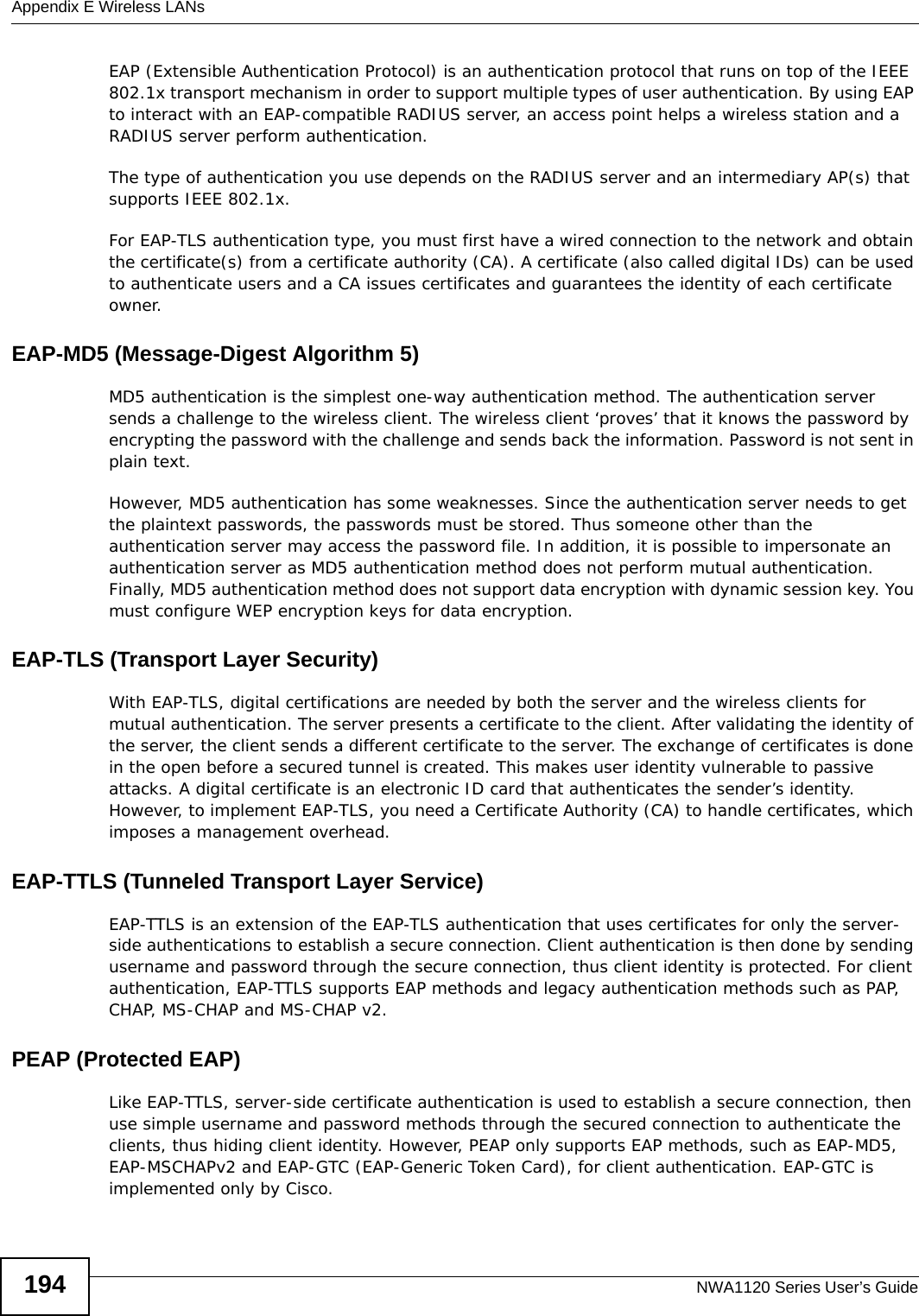
![Appendix A Setting Up Your Computer’s IP AddressNWA1120 Series User’s Guide1367The Internet Protocol Version 4 (TCP/IPv4) Properties window opens.8Select Obtain an IP address automatically if your network administrator or ISP assigns your IP address dynamically.Select Use the following IP Address and fill in the IP address, Subnet mask, and Default gateway fields if you have a static IP address that was assigned to you by your network administrator or ISP. You may also have to enter a Preferred DNS server and an Alternate DNS server, if that information was provided.Click Advanced.9Click OK to close the Internet Protocol (TCP/IP) Properties window.10 Click OK to close the Local Area Connection Properties window.Verifying Settings1Click Start > All Programs > Accessories > Command Prompt.2In the Command Prompt window, type "ipconfig" and then press [ENTER]. You can also go to Start > Control Panel > Network Connections, right-click a network connection, click Status and then click the Support tab to view your IP address and connection information.](https://usermanual.wiki/ZyXEL-Communications/NWA1123AC.User-Manual-Part-2-pdf/User-Guide-2123423-Page-8.png)
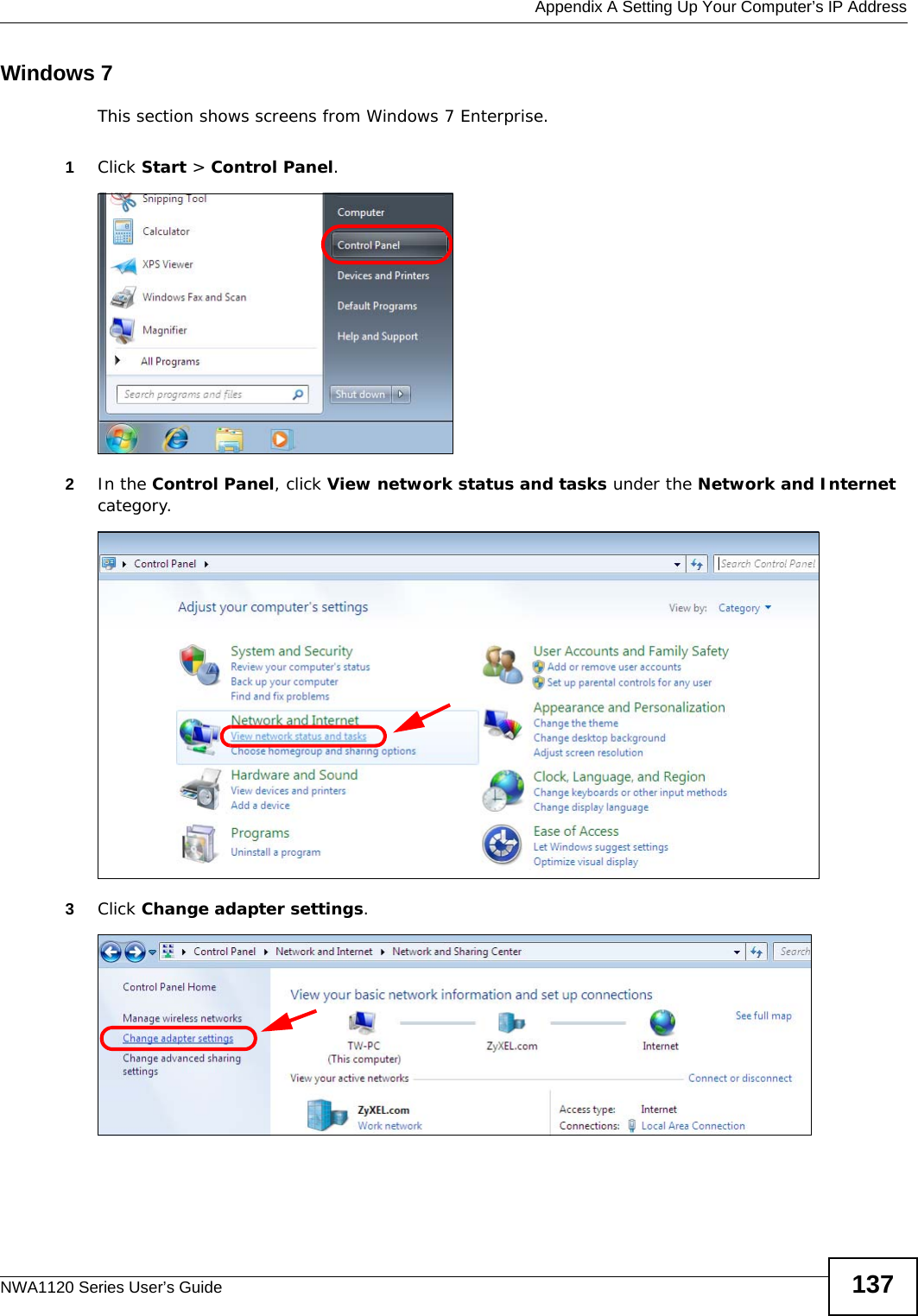
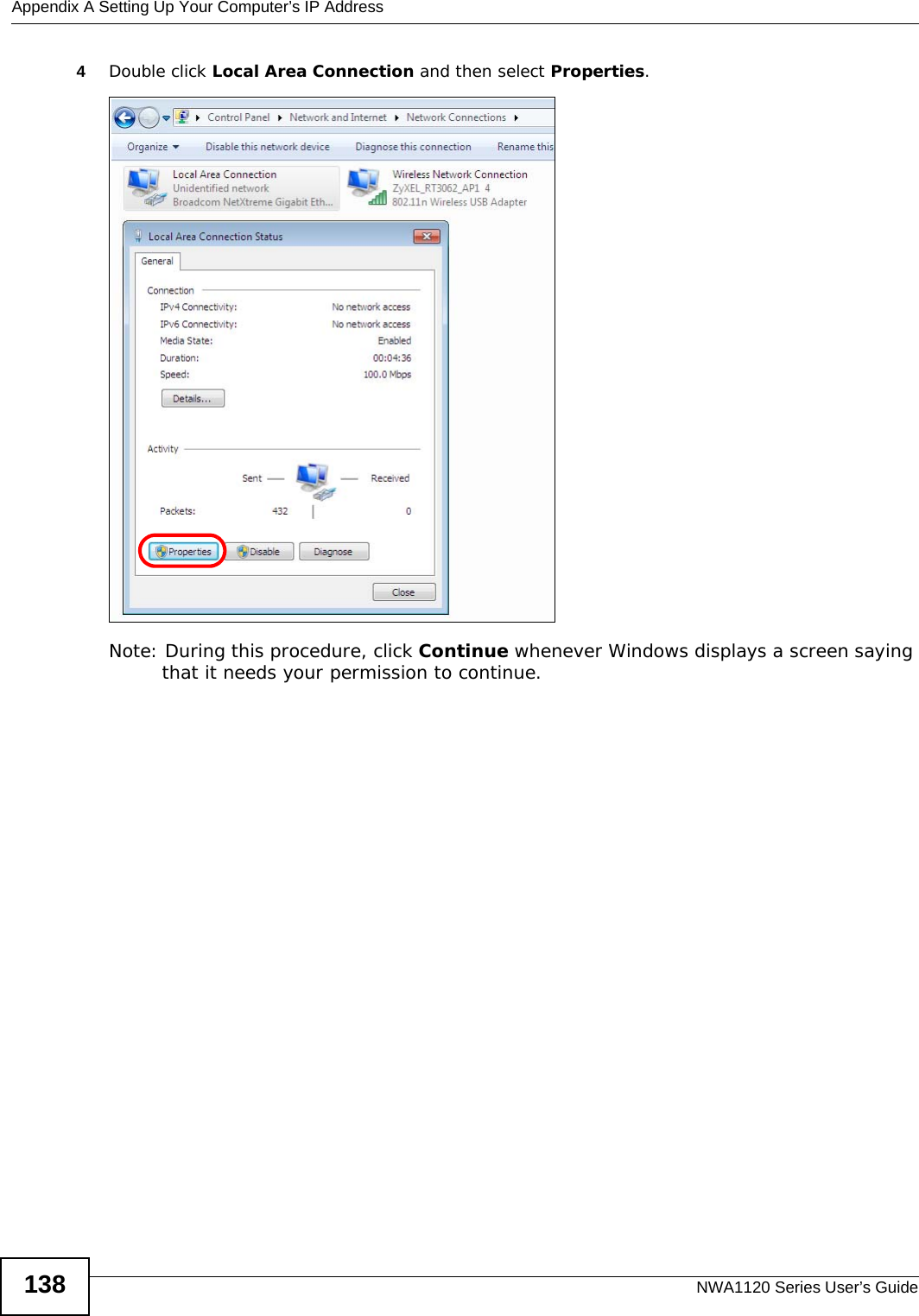
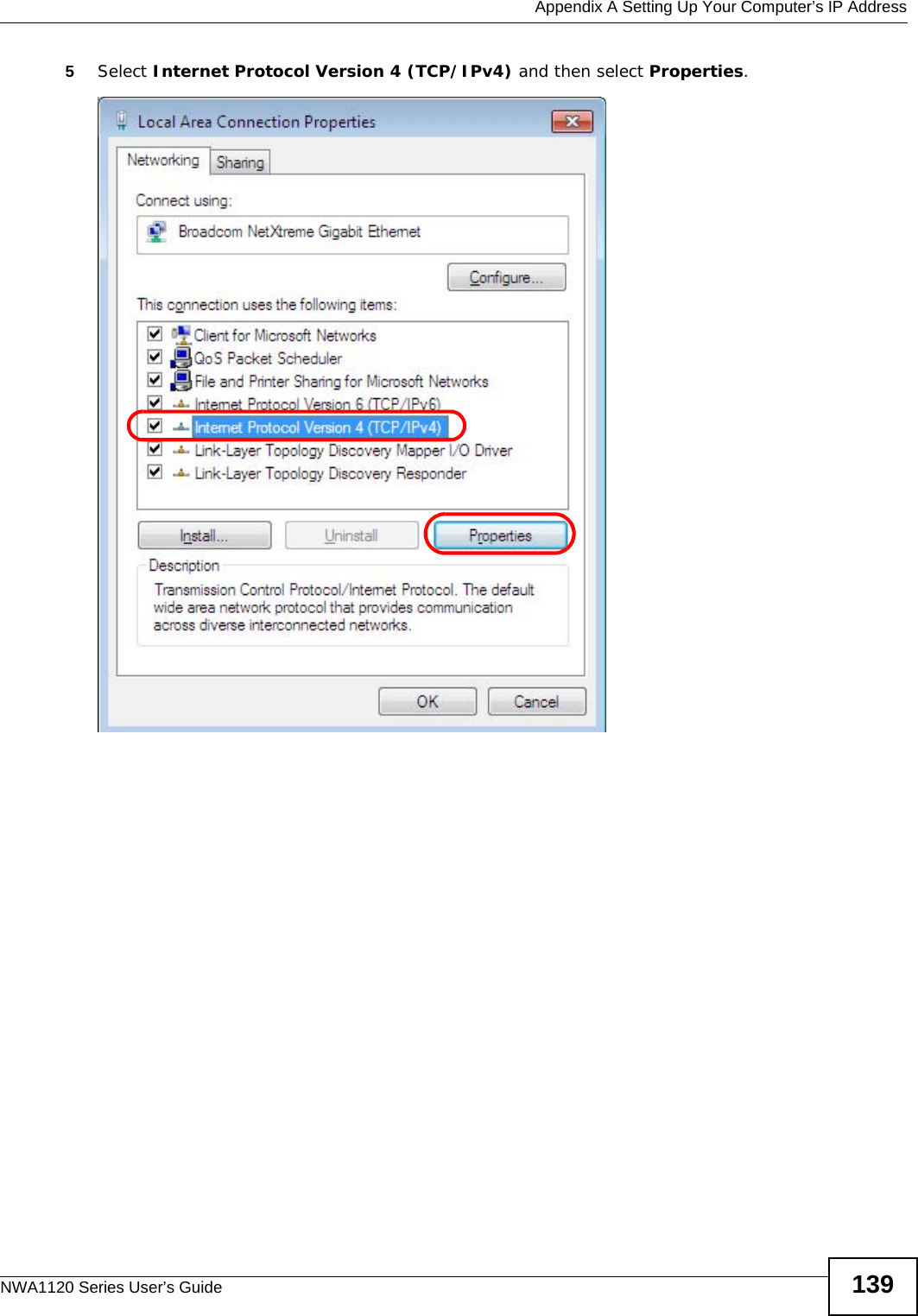
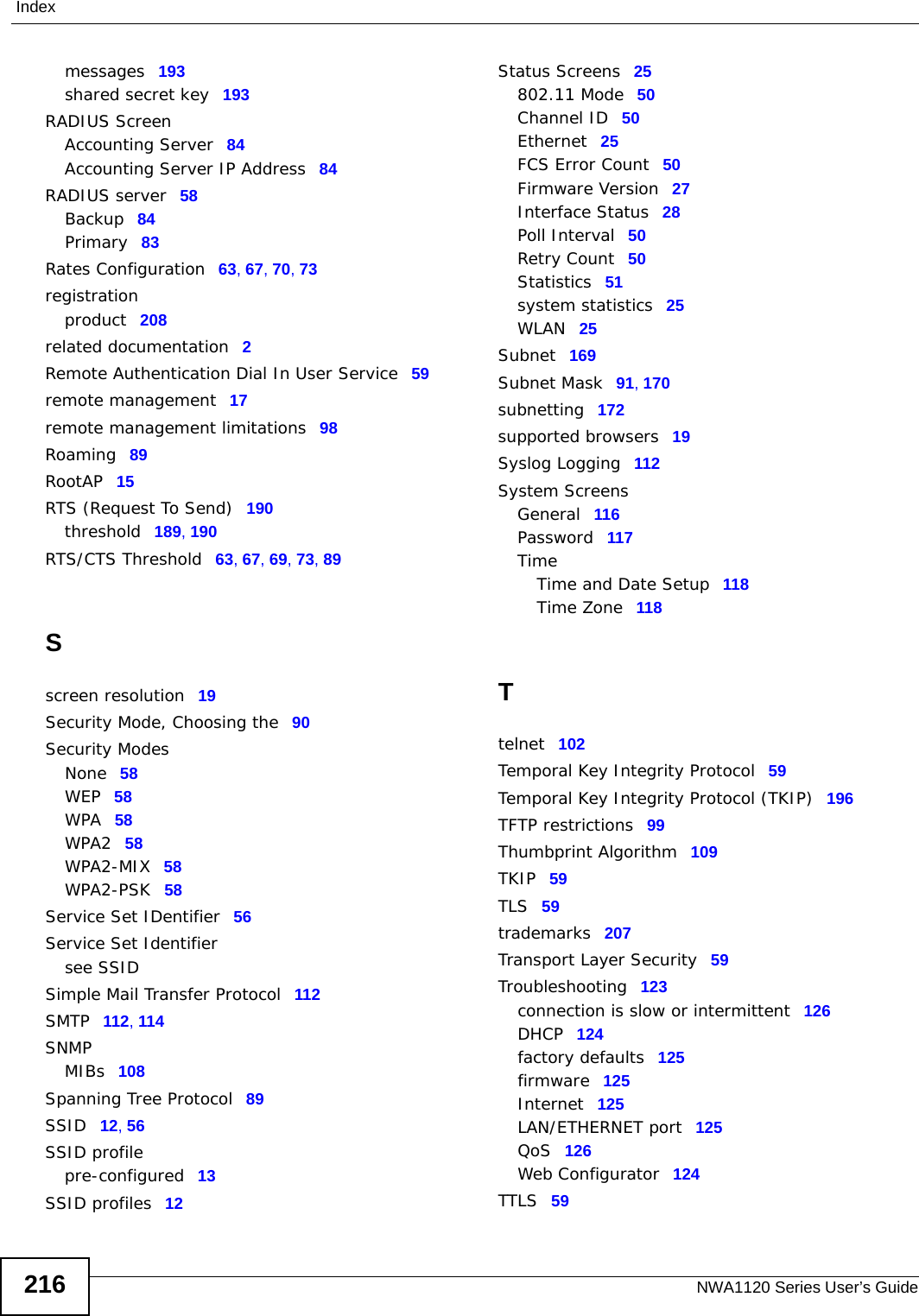
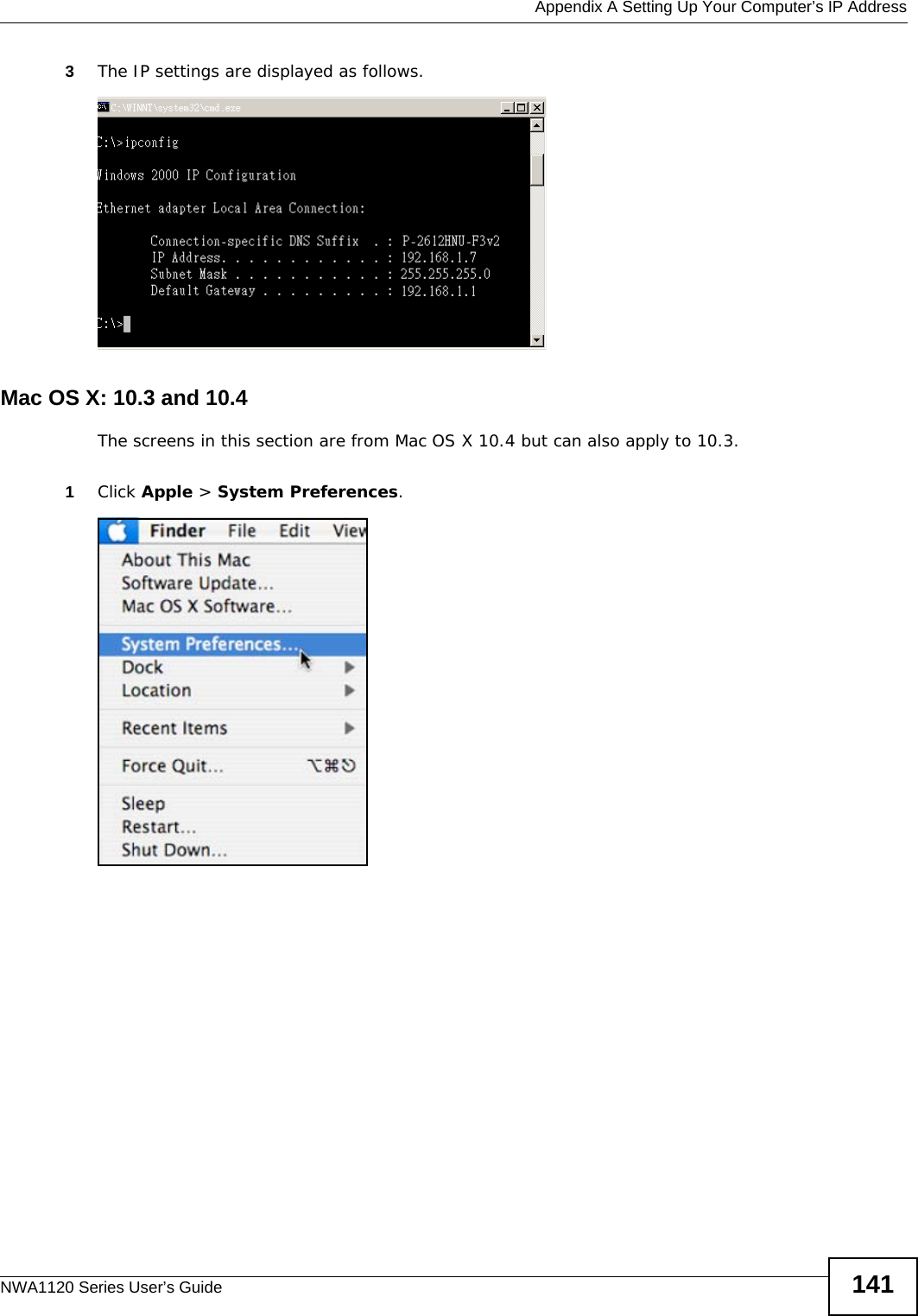
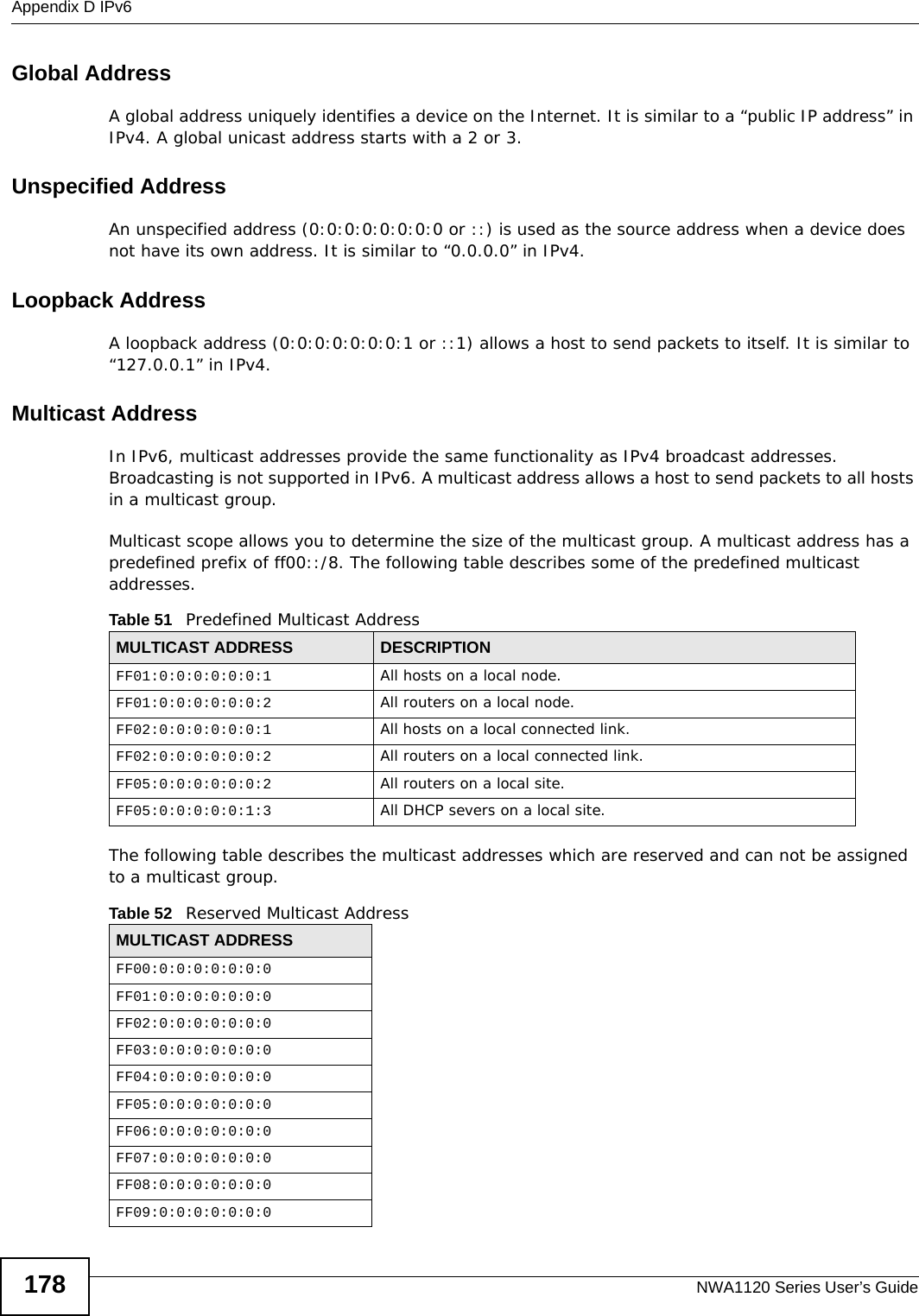
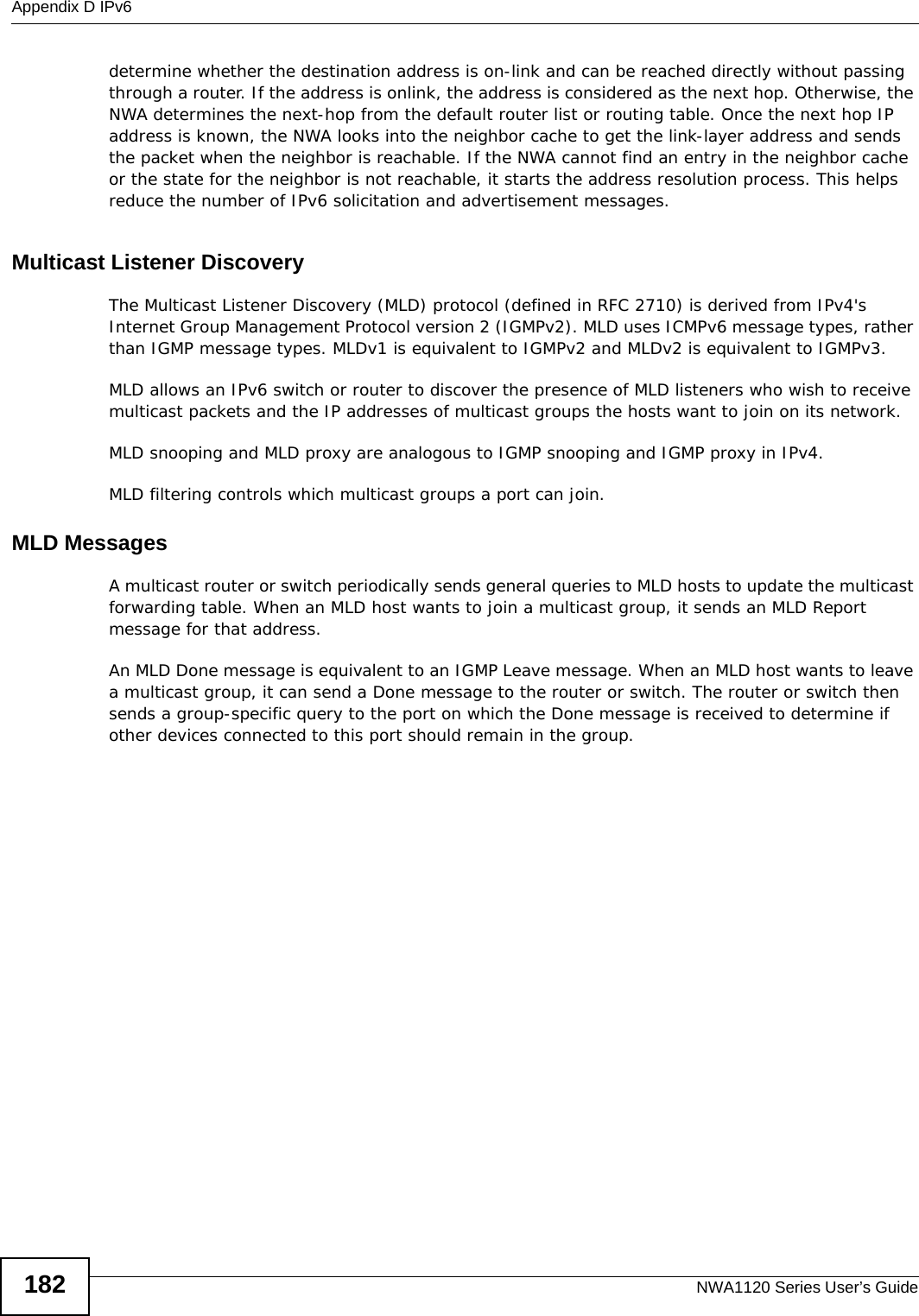
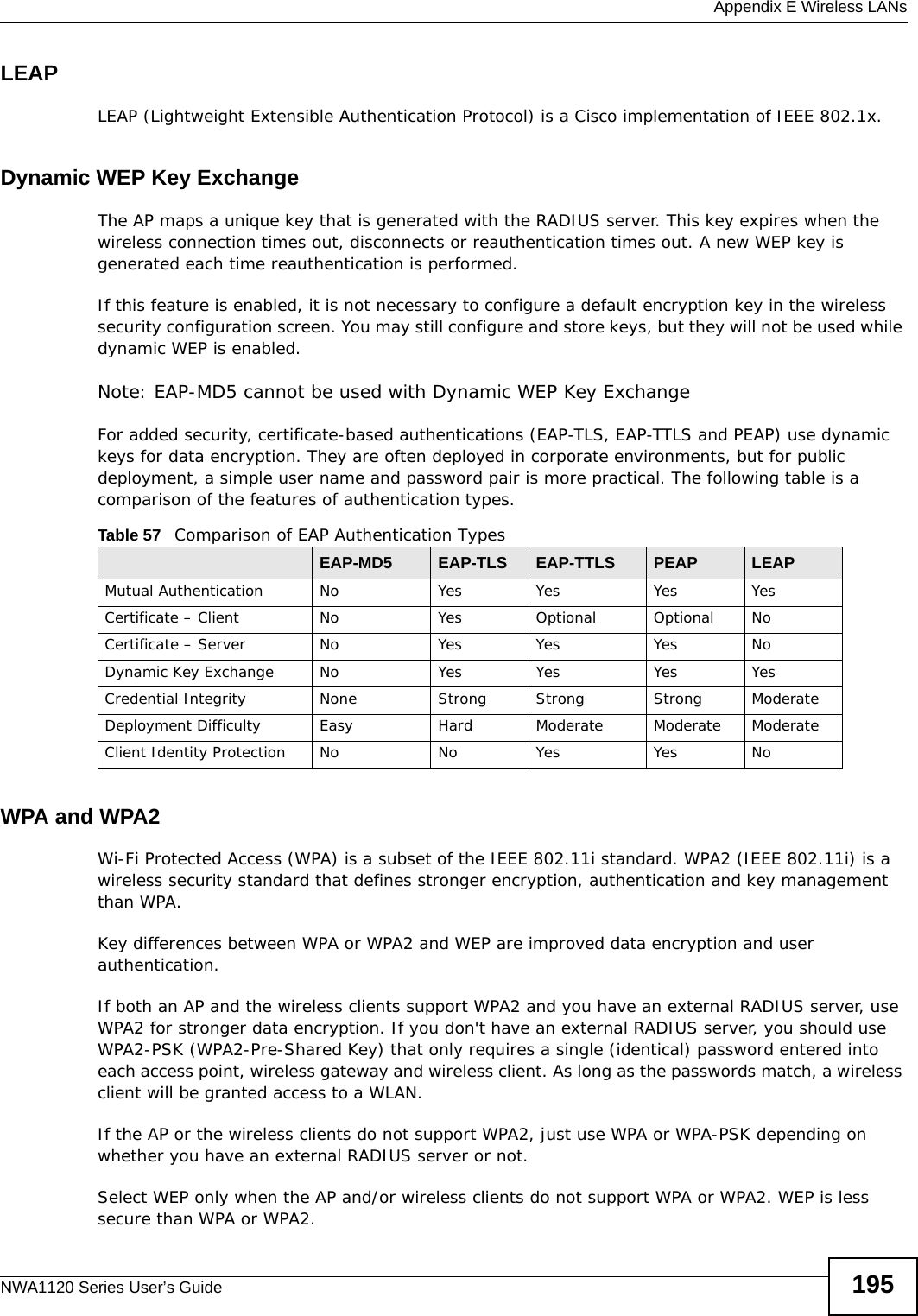
![Appendix A Setting Up Your Computer’s IP AddressNWA1120 Series User’s Guide1406The Internet Protocol Version 4 (TCP/IPv4) Properties window opens.7Select Obtain an IP address automatically if your network administrator or ISP assigns your IP address dynamically.Select Use the following IP Address and fill in the IP address, Subnet mask, and Default gateway fields if you have a static IP address that was assigned to you by your network administrator or ISP. You may also have to enter a Preferred DNS server and an Alternate DNS server, if that information was provided. Click Advanced if you want to configure advanced settings for IP, DNS and WINS. 8Click OK to close the Internet Protocol (TCP/IP) Properties window.9Click OK to close the Local Area Connection Properties window.Verifying Settings1Click Start > All Programs > Accessories > Command Prompt.2In the Command Prompt window, type "ipconfig" and then press [ENTER].](https://usermanual.wiki/ZyXEL-Communications/NWA1123AC.User-Manual-Part-2-pdf/User-Guide-2123423-Page-12.png)


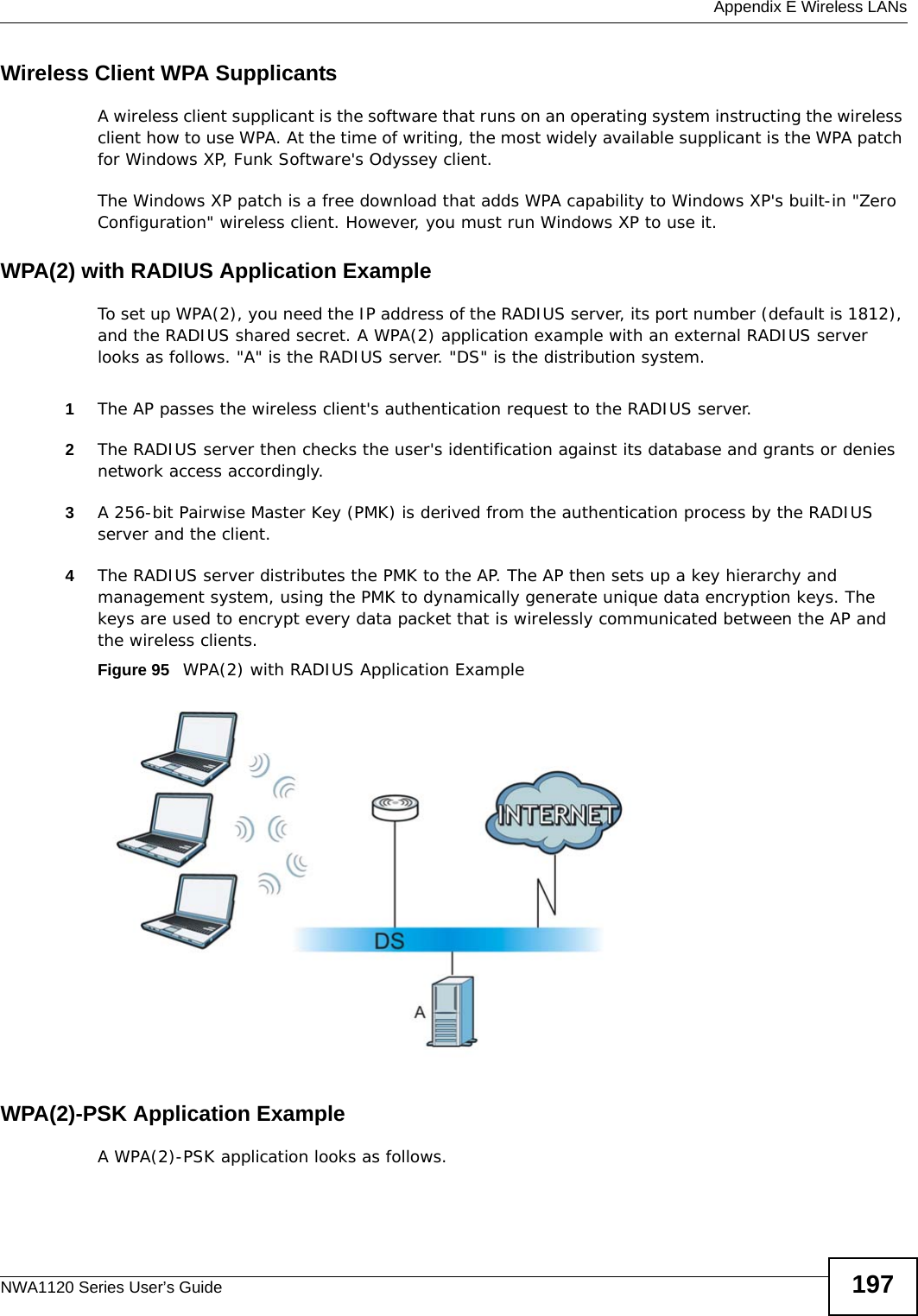
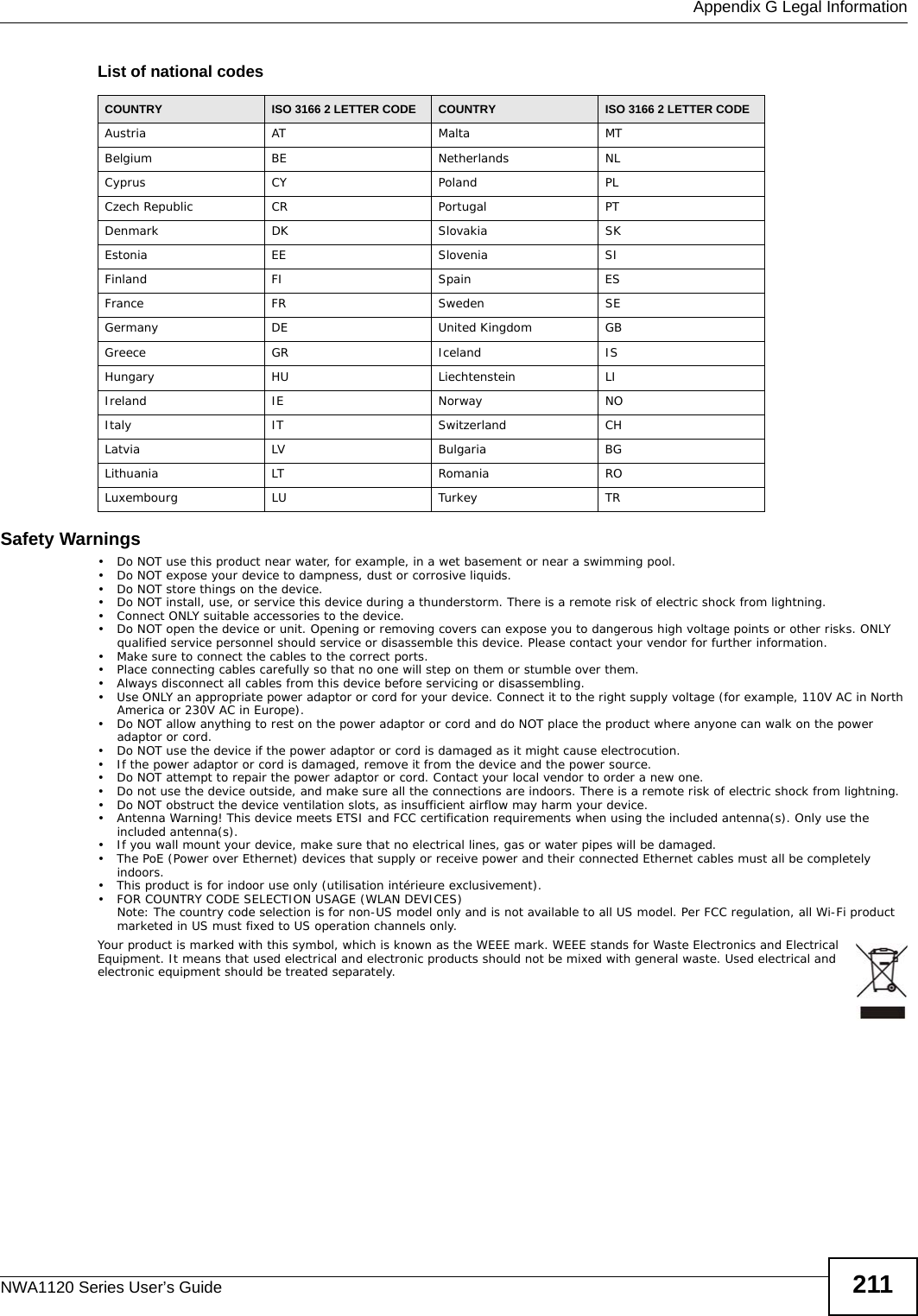
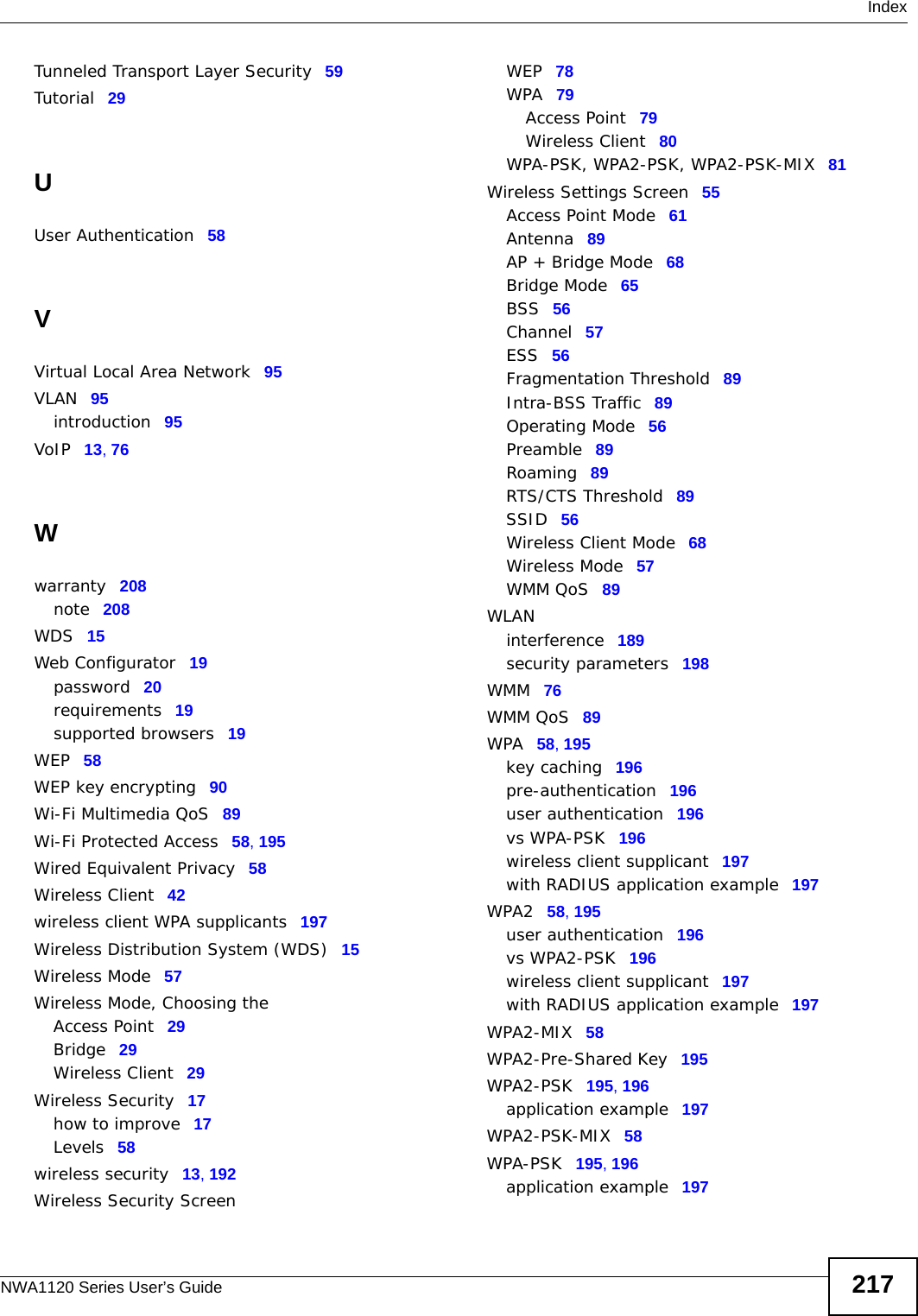
![Appendix G Legal InformationNWA1120 Series User’s Guide 209Open Source LicensesThis product contains in part some free software distributed under GPL license terms and/or GPL like licenses. Open source licenses are provided with the firmware package. You can download the latest firmware at www.zyxel.com. To obtain the source code covered under those Licenses, please contact support@zyxel.com.tw to get it. Regulatory InformationEuropean UnionThe following information applies if you use the product within the European Union. Declaration of Conformity with Regard to EU Directive 1999/5/EC (R&TTE Directive)Compliance Information for 2.4GHz and 5GHz Wireless Products Relevant to the EU and Other Countries Following the EU Directive 1999/5/EC (R&TTE Directive) [Czech] ZyXEL tímto prohlašuje, že tento zařízení je ve shodě se základními požadavky a dalšími příslušnými ustanoveními směrnice 1999/5/EC.[Danish] Undertegnede ZyXEL erklærer herved, at følgende udstyr udstyr overholder de væsentlige krav og øvrige relevante krav i direktiv 1999/5/EF.[German] Hiermit erklärt ZyXEL, dass sich das Gerät Ausstattung in Übereinstimmung mit den grundlegenden Anforderungen und den übrigen einschlägigen Bestimmungen der Richtlinie 1999/5/EU befindet.[Estonian] Käesolevaga kinnitab ZyXEL seadme seadmed vastavust direktiivi 1999/5/EÜ põhinõuetele ja nimetatud direktiivist tulenevatele teistele asjakohastele sätetele.English Hereby, ZyXEL declares that this equipment is in compliance with the essential requirements and other relevant provisions of Directive 1999/5/EC.[Spanish] Por medio de la presente ZyXEL declara que el equipo cumple con los requisitos esenciales y cualesquiera otras disposiciones aplicables o exigibles de la Directiva 1999/5/CE.[Greek] ΜΕ ΤΗΝ ΠΑΡΟΥΣΑ ZyXEL ΔΗΛΩΝΕΙ ΟΤΙ εξοπλισμός ΣΥΜΜΟΡΦΩΝΕΤΑΙ ΠΡΟΣ ΤΙΣ ΟΥΣΙΩΔΕΙΣ ΑΠΑΙΤΗΣΕΙΣ ΚΑΙ ΤΙΣ ΛΟΙΠΕΣ ΣΧΕΤΙΚΕΣ ΔΙΑΤΑΞΕΙΣ ΤΗΣ ΟΔΗΓΙΑΣ 1999/5/ΕC.[French] Par la présente ZyXEL déclare que l'appareil équipements est conforme aux exigences essentielles et aux autres dispositions pertinentes de la directive 1999/5/EC.[Italian] Con la presente ZyXEL dichiara che questo attrezzatura è conforme ai requisiti essenziali ed alle altre disposizioni pertinenti stabilite dalla direttiva 1999/5/CE.[Latvian] Ar šo ZyXEL deklarē, ka iekārtas atbilst Direktīvas 1999/5/EK būtiskajām prasībām un citiem ar to saistītajiem noteikumiem.[Lithuanian] Šiuo ZyXEL deklaruoja, kad šis įranga atitinka esminius reikalavimus ir kitas 1999/5/EB Direktyvos nuostatas.[Dutch] Hierbij verklaart ZyXEL dat het toestel uitrusting in overeenstemming is met de essentiële eisen en de andere relevante bepalingen van richtlijn 1999/5/EC.[Maltese] Hawnhekk, ZyXEL, jiddikjara li dan tagħmir jikkonforma mal-ħtiġijiet essenzjali u ma provvedimenti oħrajn relevanti li hemm fid-Dirrettiva 1999/5/EC.[Hungarian] Alulírott, ZyXEL nyilatkozom, hogy a berendezés megfelel a vonatkozó alapvetõ követelményeknek és az 1999/5/EK irányelv egyéb elõírásainak.[Polish] Niniejszym ZyXEL oświadcza, że sprzęt jest zgodny z zasadniczymi wymogami oraz pozostałymi stosownymi postanowieniami Dyrektywy 1999/5/EC.[Portuguese] ZyXEL declara que este equipamento está conforme com os requisitos essenciais e outras disposições da Directiva 1999/5/EC.[Slovenian] ZyXEL izjavlja, da je ta oprema v skladu z bistvenimi zahtevami in ostalimi relevantnimi določili direktive 1999/5/EC.[Slovak] ZyXEL týmto vyhlasuje, že zariadenia spĺňa základné požiadavky a všetky príslušné ustanovenia Smernice 1999/5/EC.[Finnish] ZyXEL vakuuttaa täten että laitteet tyyppinen laite on direktiivin 1999/5/EY oleellisten vaatimusten ja sitä koskevien direktiivin muiden ehtojen mukainen.[Swedish] Härmed intygar ZyXEL att denna utrustning står I överensstämmelse med de väsentliga egenskapskrav och övriga relevanta bestämmelser som framgår av direktiv 1999/5/EC.[Bulgarian] С настоящото ZyXEL декларира, че това оборудване е в съответствие със съществените изисквания и другите приложими разпоредбите на Директива 1999/5/ЕC.[Icelandic] Hér með lýsir, ZyXEL því yfir að þessi búnaður er í samræmi við grunnkröfur og önnur viðeigandi ákvæði tilskipunar 1999/5/EC.[Norwegian] Erklærer herved ZyXEL at dette utstyret er I samsvar med de grunnleggende kravene og andre relevante bestemmelser I direktiv 1999/5/EF.[Romanian] Prin prezenta, ZyXEL declară că acest echipament este în conformitate cu cerinţele esenţiale şi alte prevederi relevante ale Directivei 1999/5/EC.](https://usermanual.wiki/ZyXEL-Communications/NWA1123AC.User-Manual-Part-2-pdf/User-Guide-2123423-Page-81.png)