D Link DIR628A2 RangeBooster N Dual Band Router User Manual 4
D Link Corporation RangeBooster N Dual Band Router 4
D Link >
Contents
User manual 4
47D-Link DIR-628 User Manual
Section 3 - Configuration
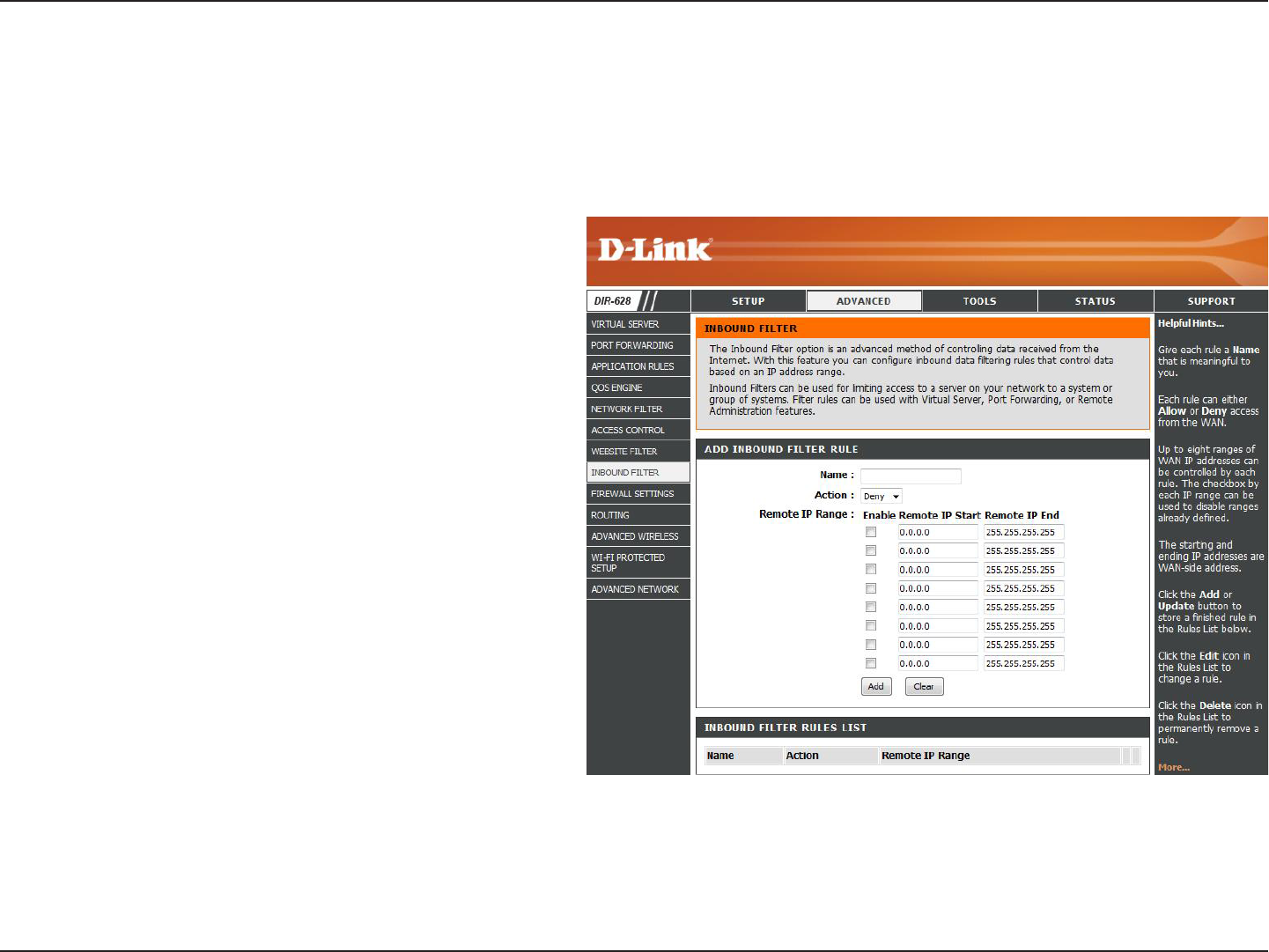
Enter a name for the inbound filter rule.
Select Allow or Deny.
Check to enable rule.
Enter the starting IP address. Enter 0.0.0.0 if
you do not want to specify an IP range.
Enter the ending IP address. Enter
255.255.255.255 if you do not want to specify
and IP range.
Click the Add button to apply your settings.
You must click Save. Settings at the top to
save the settings.
This section will list any rules that are created.
You may click the Edit icon to change the
settings or enable/disable the rule, or click the
Delete icon to remove the rule.
Name:
Action:
Enable:
Remote IP Start:
Remote IP End:
Add:
Inbound Filter
Rules List:
The Inbound Filter option is an advanced method of controlling data received from the Internet. With this feature you
can configure inbound data filtering rules that control data based on an IP address range. Inbound Filters can be used
with Virtual Server, Port Forwarding, or Remote Administration features.
Inbound Filters
48D-Link DIR-628 User Manual
Section 3 - Configuration
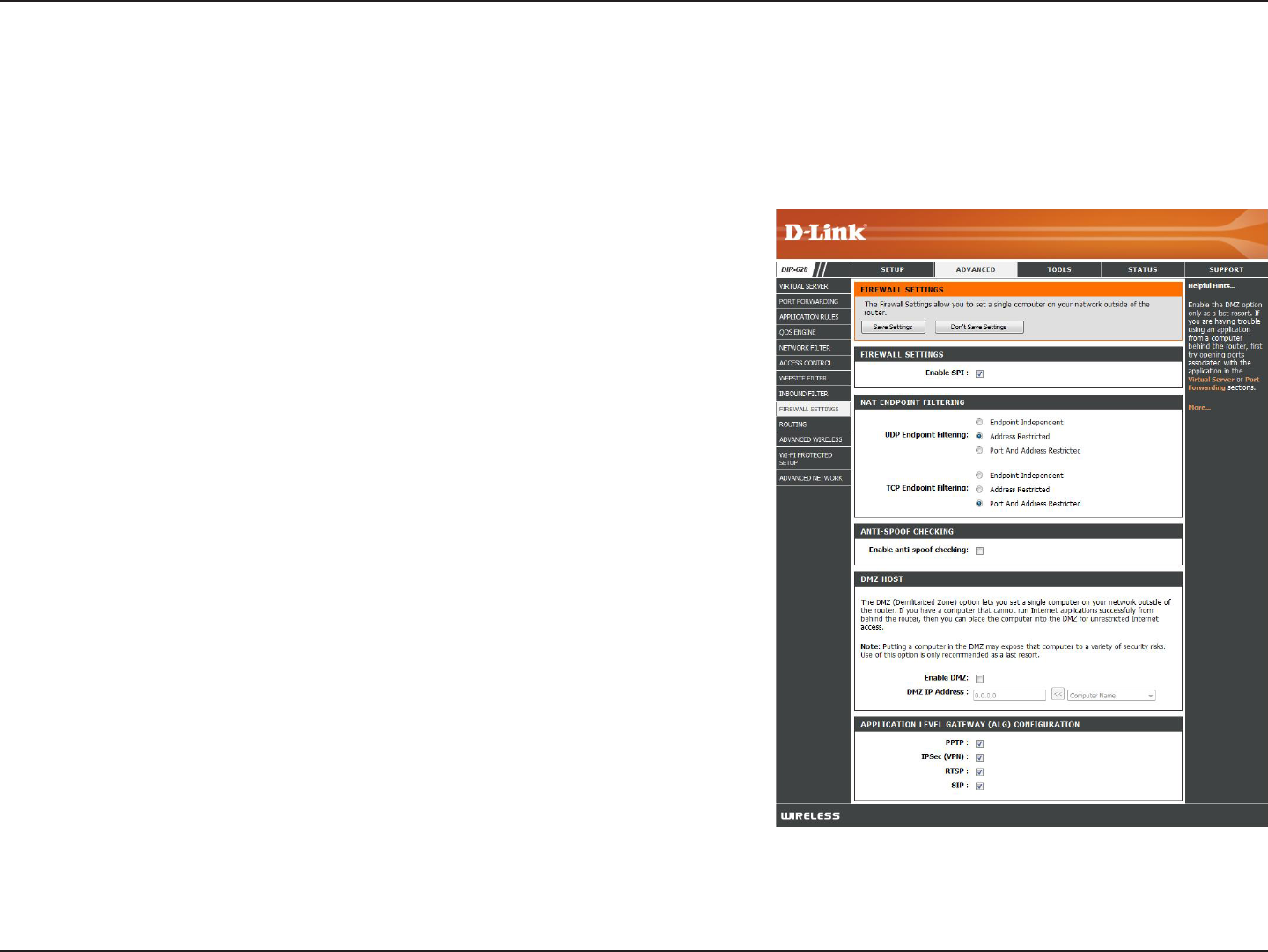
Firewall Settings
A firewall protects your network from the outside world. The D-Link DIR-628 offers a firewall type functionality. The SPI
feature helps prevent cyber attacks. Sometimes you may want a computer exposed to the outside world for certain
types of applications. If you choose to expose a computer, you cam enable DMZ. DMZ is short for Demilitarized Zone.
This option will expose the chosen computer completely to the outside world.
SPI (Stateful Packet Inspection, also known as dynamic packet
filtering) helps to prevent cyber attacks by tracking more state per
session. It validates that the traffic passing through the session
conforms to the protocol.
Select one of the following for TCP and UDP ports:
Endpoint.Independent.- Any incoming traffic sent to an open port
will be forwarded to the application that opened the port. The port will
close if idle for 5 minutes.
Address.Restricted - Incoming traffic must match the IP address of
the outgoing connection.
Address.+.Port. Restriction - Incoming traffic must match the IP
address and port of the outgoing connection.
Enable this feature to protect your network from certain kinds of
“spoofing” attacks.
If an application has trouble working from behind the router, you can
expose one computer to the Internet and run the application on that
computer.
Note: Placing a computer in the DMZ may expose that computer to
a variety of security risks. Use of this option is only recommended
as a last resort.
Specify the IP address of the computer on the LAN that you want to have unrestricted Internet communication. If this computer
obtains it’s IP address automatically using DHCP, be sure to make a static reservation on the Basic > DHCP page so that
the IP address of the DMZ machine does not change.
Enable SPI:
NAT Endpoint
Filtering:
Anti-Spoof Check:
Enable DMZ:
DMZ IP Address:

49D-Link DIR-628 User Manual
Section 3 - Configuration
Application Level Gateway Configuration
Here you can enable or disable ALG’s. Some protocols and applications require special handling of the IP payload to
make them work with network address translation (NAT). Each ALG provides special handling for a specific protocol
or application. A number of ALGs for common applications are enabled by default.
Allows multiple machines on the LAN to connect to their corporate network using PPTP protocol.
Allows multiple VPN clients to connect to their corporate network using IPSec. Some VPN clients support traversal of IPSec
through NAT. This ALG may interfere with the operation of such VPN clients. If you are having trouble connecting with your
corporate network, try turning this ALG off. Please check with the system adminstrator of your corporate network whether
your VPN client supports NAT traversal.
Allows applications that use Real Time Streaming Protocol to receive streaming media from the internet. QuickTime and
Real Player are some of the common applications using this protocol.
Allows devices and applications using VoIP (Voice over IP) to communicate across NAT. Some VoIP applications and devices
have the ability to discover NAT devices and work around them. This ALG may interfere with the operation of such devices.
If you are having trouble making VoIP calls, try turning this ALG off.
PPTP:
IPSEC (VPN):
RTSP:
SIP:
50D-Link DIR-628 User Manual
Section 3 - Configuration
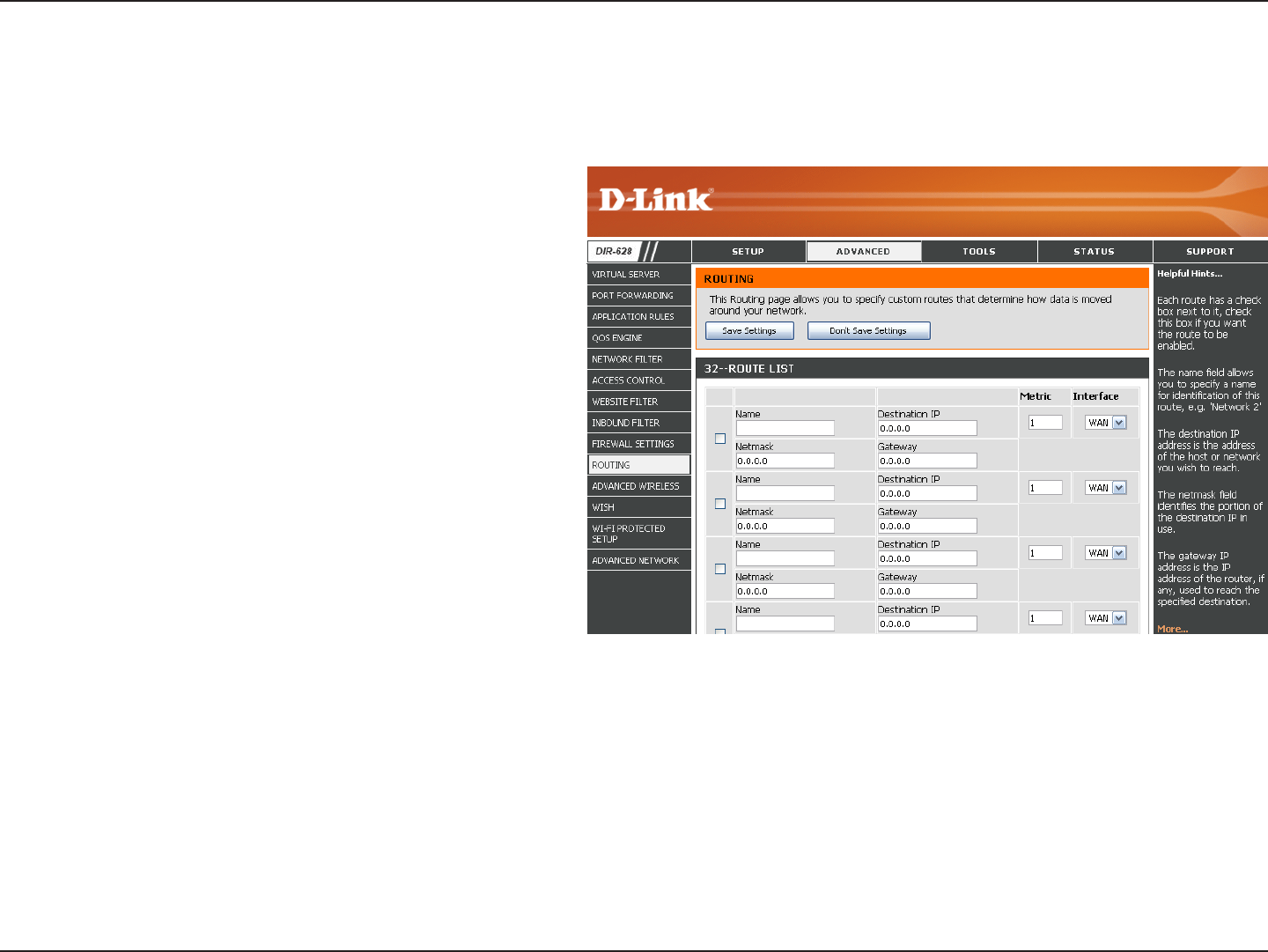
Enter the IP address of packets that will take
this route.
Enter the netmask of the route, please note
that the octets must match your destination
IP address.
Enter your next hop gateway to be taken if this
route is used.
The route metric is a value from 1 to 16 that
indicates the cost of using this route. A value 1
is the lowest cost and 15 is the highest cost.
Select the interface that the IP packet must
use to transit out of the router when this route
is used.
Destination IP:
Netmask:
Gateway:
Metric:
Interface:
Routing
The Routing option is an advanced method of customizing specific routes of data through your network.
51D-Link DIR-628 User Manual
Section 3 - Configuration
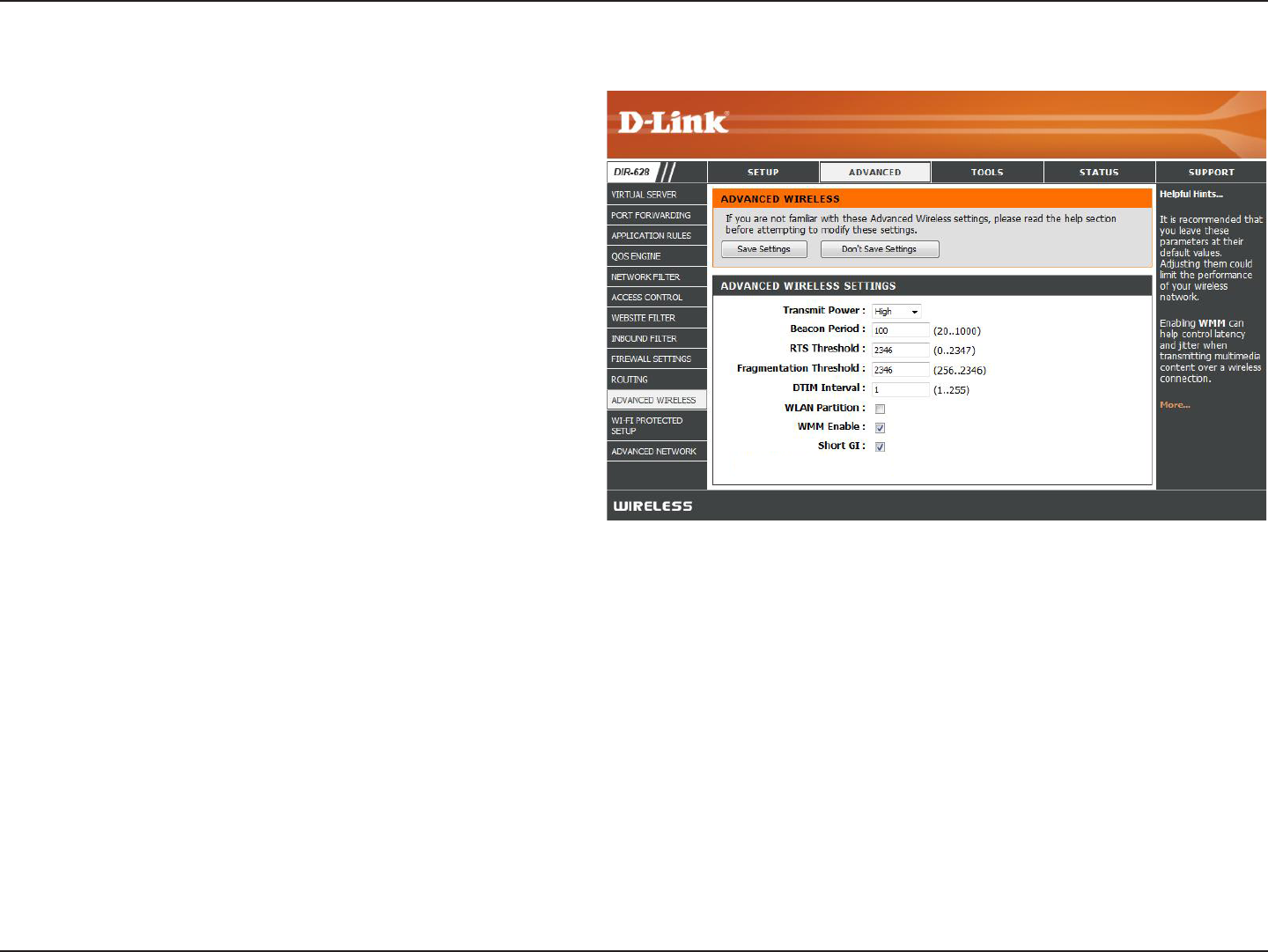
Set the transmit power of the antennas.
Beacons are packets sent by an Access Point to
synchronize a wireless network. Specify a value.
100 is the default setting and is recommended.
This value should remain at its default setting of
2432. If inconsistent data flow is a problem, only a
minor modification should be made.
The fragmentation threshold, which is specified
in bytes, determines whether packets will be
fragmented. Packets exceeding the 2346 byte
setting will be fragmented before transmission. 2346
is the default setting.
(Delivery Traffic Indication Message) 3 is the default
setting. A DTIM is a countdown informing clients
of the next window for listening to broadcast and
multicast messages.
WMM is QoS for your wireless network. This will improve the quality of video and voice applications for your wireless
clients.
Check this box to reduce the guard interval time therefore increasing the data capacity. However, it’s less reliable and may
create higher data loss.
Transmit Power:
Beacon Period:
RTS Threshold:
Fragmentation
Threshold:
DTIM Interval:
WMM Function:
Short GI:
Advanced Wireless Settings
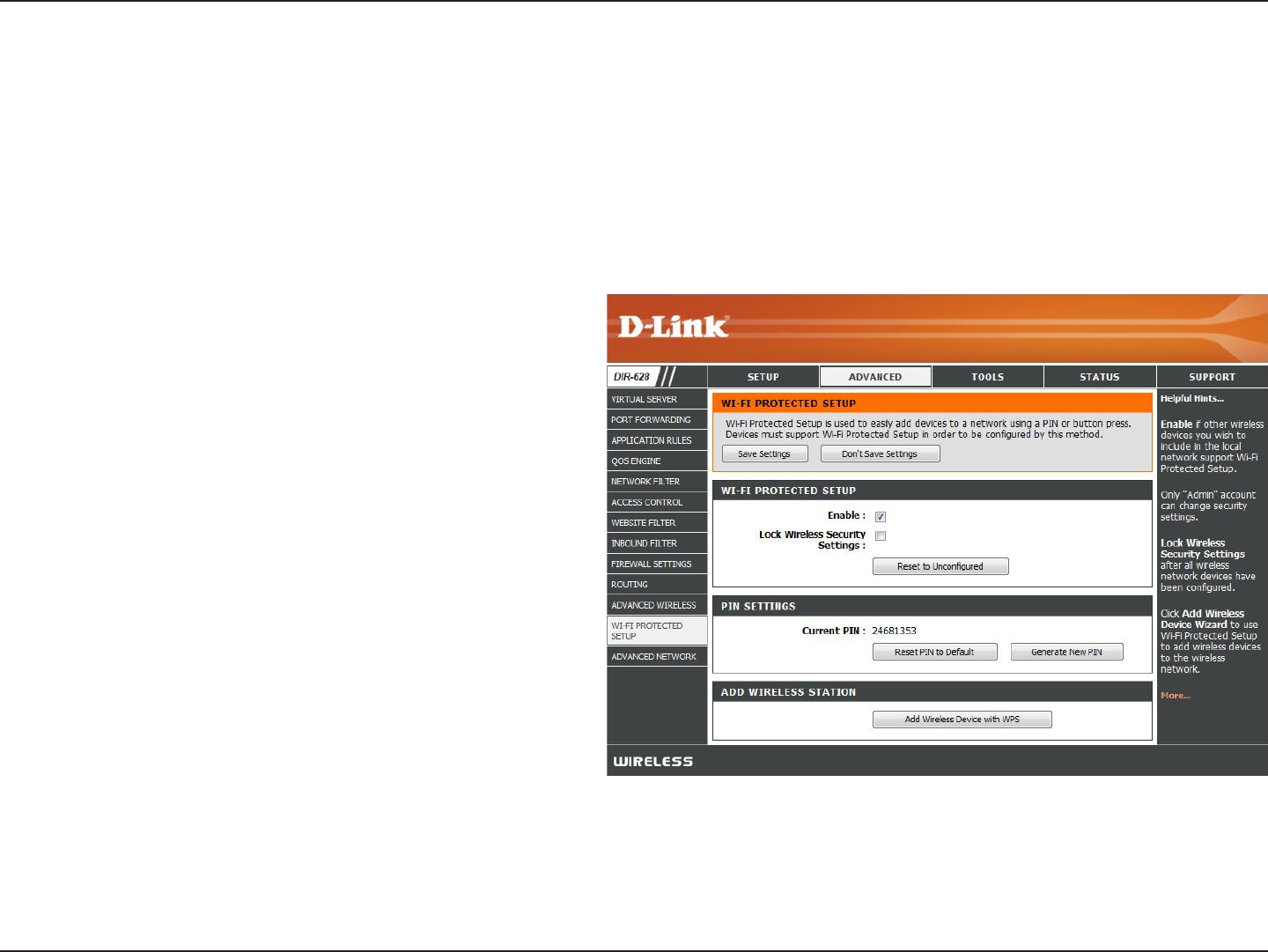
52D-Link DIR-628 User Manual
Section 3 - Configuration
Enable the Wi-Fi Protected Setup feature.
Locking the wireless security settings prevents the
settings from being changed by the Wi-Fi Protected
Setup feature of the router. Devices can still be
added to the network using Wi-Fi Protected Setup.
However, the settings of the network will not change
once this option is checked.
A PIN is a unique number that can be used to add
the router to an existing network or to create a
new network. The default PIN may be printed on
the bottom of the router. For extra security, a new
PIN can be generated. You can restore the default
PIN at any time. Only the Administrator (“admin”
account) can change or reset the PIN.
Shows the current value of the router’s PIN.
Restore the default PIN of the router.
Create a random number that is a valid PIN. This becomes the router’s PIN. You can then copy this PIN to the user interface
of the registrar.
Enable:
Lock Wireless
Security Settings:
PIN Settings:
Current PIN:
Reset PIN to
Default:
Generate New PIN:
Wi-Fi Protected Setup
Wi-Fi Protected Setup (WPS) System is a simplified method for securing your wireless network during the “Initial setup”
as well as the “Add New Device” processes. The Wi-Fi Alliance (WFA) has certified it across different products as well
as manufactures. The process is just as easy, as depressing a button for the Push-Button Method or correctly entering
the 8-digit code for the Pin-Code Method. The time reduction in setup and ease of use are quite beneficial, while the
highest wireless Security setting of WPA2 is automatically used.
53D-Link DIR-628 User Manual
Section 3 - Configuration
This Wizard helps you add wireless devices to the wireless network.
The wizard will either display the wireless network settings to guide you through manual configuration, prompt you to enter
the PIN for the device, or ask you to press the configuration button on the device. If the device supports Wi-Fi Protected Setup
and has a configuration button, you can add it to the network by pressing the configuration button on the device and then
the on the router within 60 seconds. The status LED on the router will flash three times if the device has been successfully
added to the network.
There are several ways to add a wireless device to your network. A “registrar” controls access to the wireless network. A
registrar only allows devices onto the wireless network if you have entered the PIN, or pressed a special Wi-Fi Protected Setup
button on the device. The router acts as a registrar for the network, although other devices may act as a registrar as well.
Start the wizard.
Add Wireless
Station:
Add Wireless
Device Wizard:
54D-Link DIR-628 User Manual
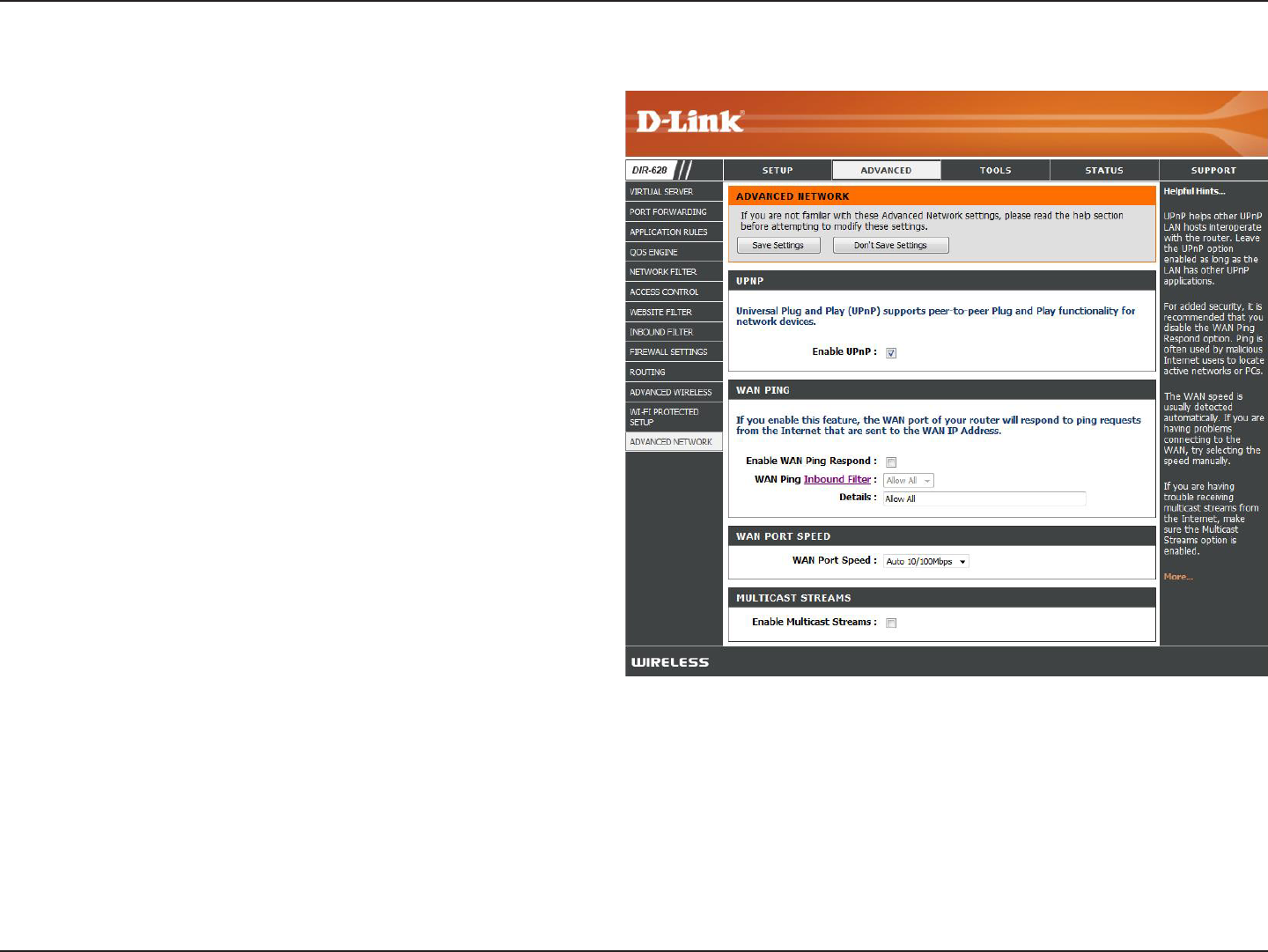
Section 3 - Configuration
To use the Universal Plug and Play (UPnP™)
feature check the Enabled. UPnP box. UPNP
provides compatibility with networking equipment,
software and peripherals.
Unchecking the box will not allow the DIR-628 to
respond to pings. Blocking the Ping may provide
some extra security from hackers. Check the box
to allow the WAN port to be “pinged”.
This section will list any rules that are created. You
may click the Edit icon to change the settings or
enable/disable the rule, or click the Delete icon
to remove the rule.
You may set the port speed of the Internet port
to 10Mbps, 100Mbps, or auto. Some older cable
or DSL modems may require you to set the port
speed to 10Mbps.
Check the box to allow multicast traffic to pass
through the router from the Internet.
UPnP:
WAN Ping:
Inbound Filter:
WAN Port Speed:
Multicast
streams:
Advanced Network Settings
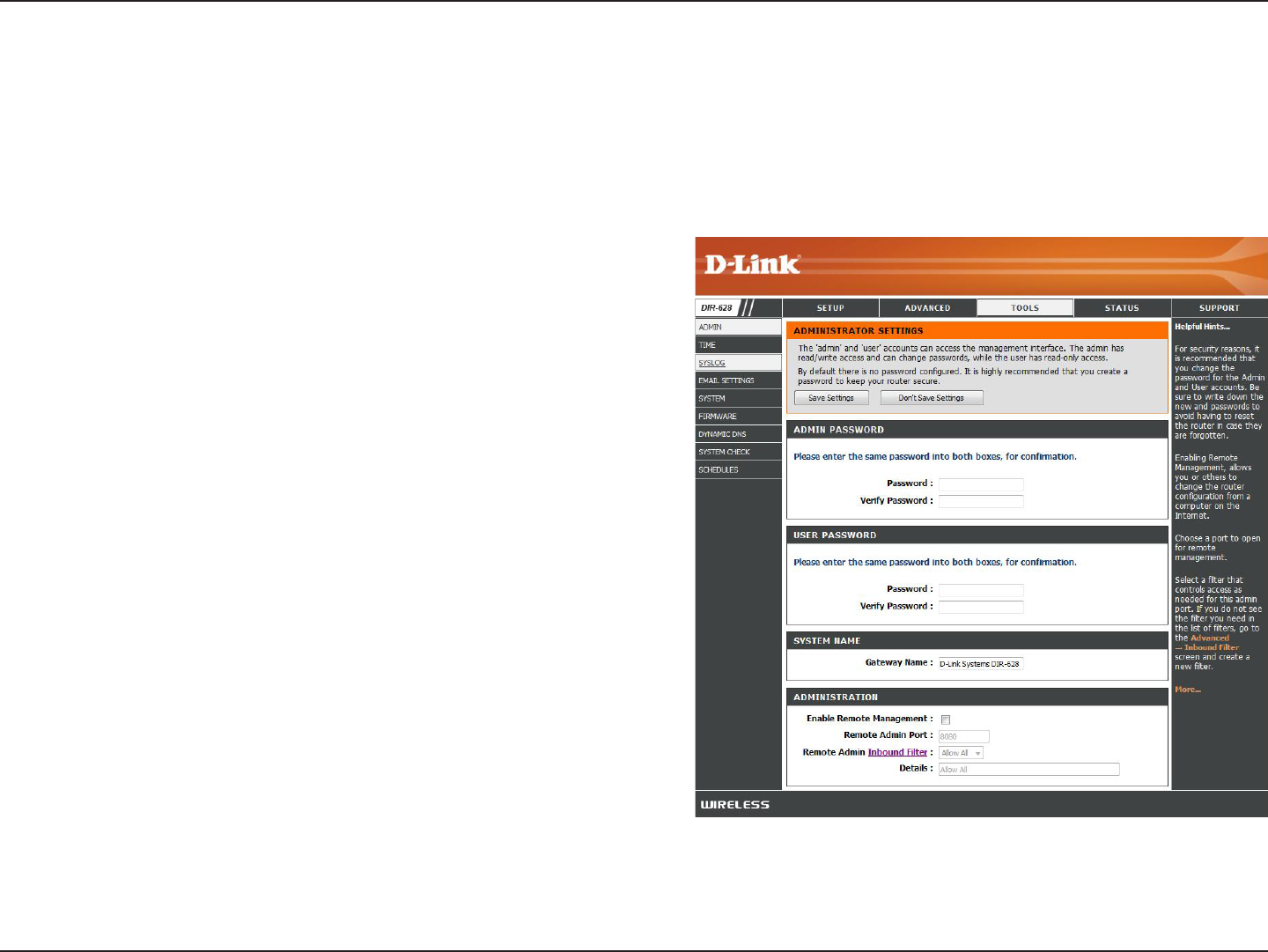
55D-Link DIR-628 User Manual
Section 3 - Configuration
Enter a new password for the Administrator Login Name. The
administrator can make changes to the settings.
Enter the new password for the User login. If you login as
the User, you can only see the settings, but cannot change
them.
Enter a name for the DIR-628 router.
Remote management allows the DIR-628 to be configured
from the Internet by a web browser. A username and
password is still required to access the Web-Management
interface. In general, only a member of your network can
browse the built-in web pages to perform Administrator tasks.
This feature enables you to perform Administrator tasks from
the remote (Internet) host.
The port number used to access the DIR-628.
Example: http://x.x.x.x:8080 where x.x.x.x is the Internet IP
address of the DIR-628 and 8080 is the port used for the
Web Management interface.
This section will list any rules that are created. You may click
the Edit icon to change the settings or enable/disable the
rule, or click the Delete icon to remove the rule.
Admin Password:
User Password:
Gateway Name:
Remote
Management:
Remote Admin
Port:
Inbound Filter:
Administrator Settings
This page will allow you to change the Administrator and User passwords. You can also enable Remote Management.
There are two accounts that can access the management interface through the web browser. The accounts are admin
and user. Admin has read/write access while user has read-only access. User can only view the settings but cannot
make any changes. Only the admin account has the ability to change both admin and user account passwords.
56D-Link DIR-628 User Manual
Section 3 - Configuration
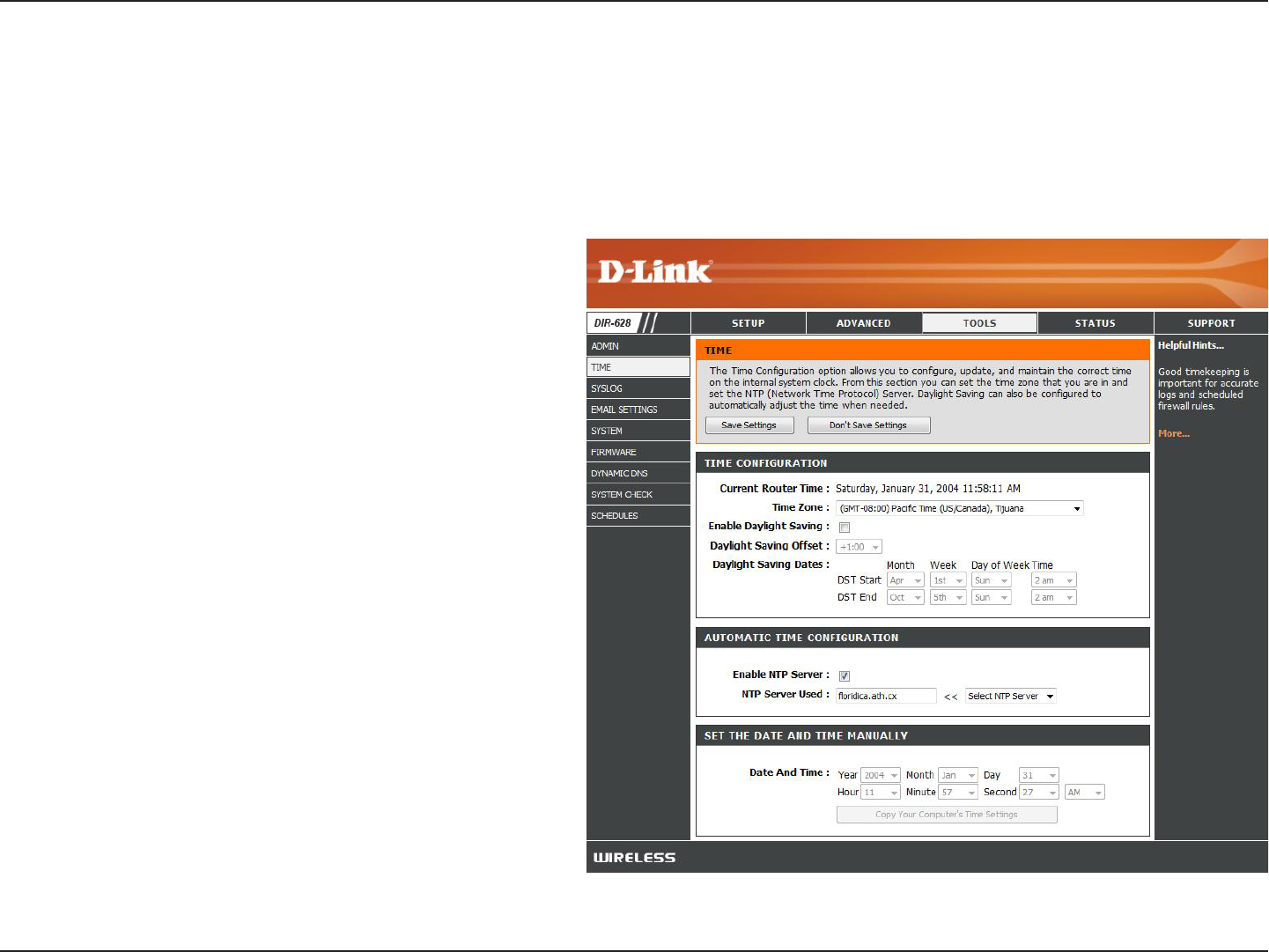
Time Settings
Select the Time Zone from the drop-down
menu.
To select Daylight Saving time manually, select
enabled or disabled, and enter a start date and
an end date for daylight saving time.
NTP is short for Network Time Protocol. NTP
synchronizes computer clock times in a network
of computers. Check this box to use a NTP
server. This will only connect to a server on the
Internet, not a local server.
Enter the NTP server or select one from the
drop-down menu.
To manually input the time, enter the values
in these fields for the Year, Month, Day, Hour,
Minute, and Second and then click Set.Time.
You can also click Copy.Your.Computer’s.Time.
Settings.
Time Zone:
Daylight Saving:
Enable NTP
Server:
NTP Server Used:
Manual:
The Time Configuration option allows you to configure, update, and maintain the correct time on the internal system
clock. From this section you can set the time zone that you are in and set the Time Server. Daylight Saving can also
be configured to automatically adjust the time when needed.
57D-Link DIR-628 User Manual
Section 3 - Configuration
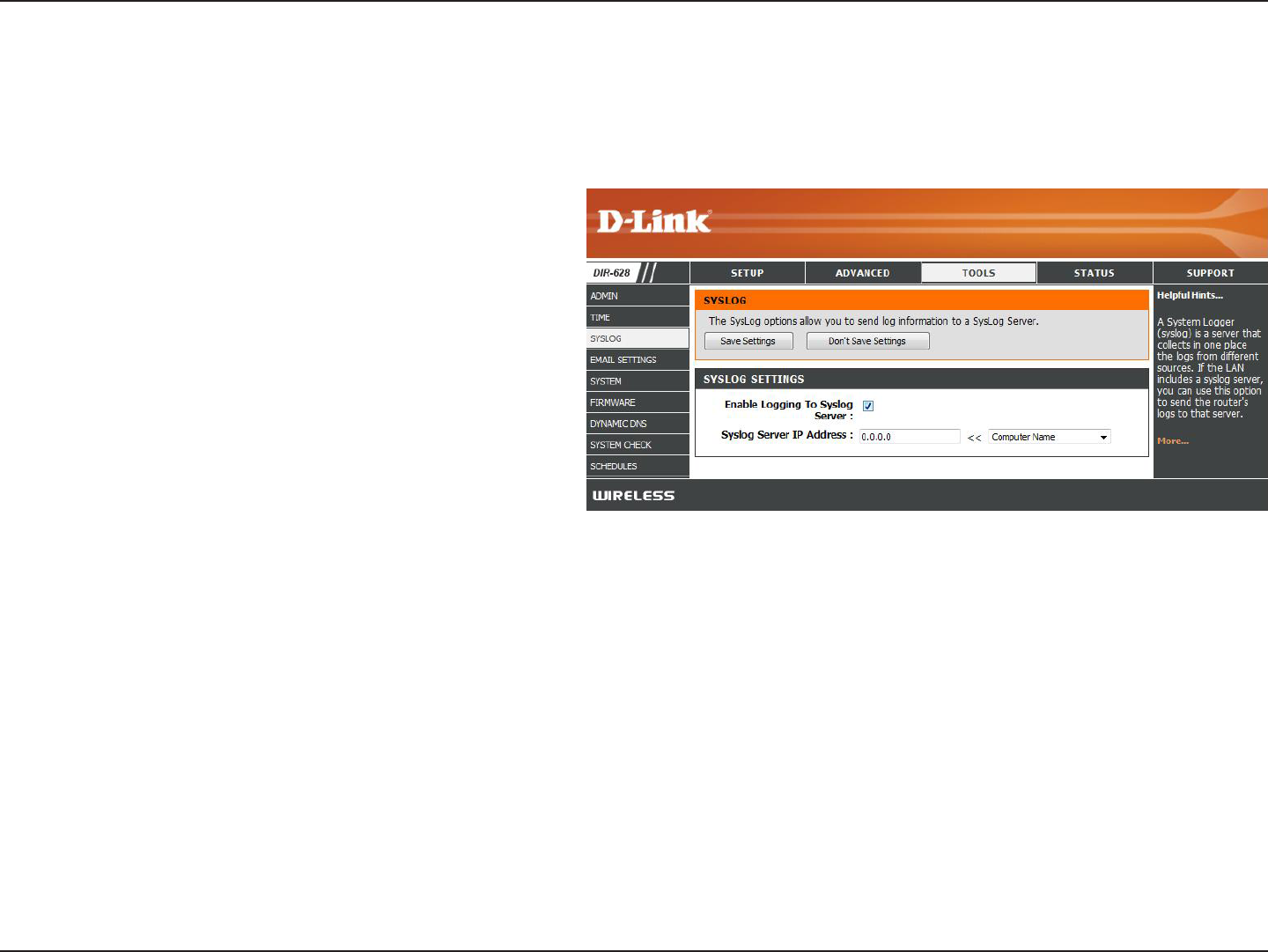
SysLog
The Broadband Router keeps a running log of events and activities occurring on the Router. You may send these logs
to a SysLog server on your network.
Enable Logging to
SysLog Server:
SysLog Server IP
Address:
Check this box to send the router logs to a
SysLog Server.
The address of the SysLog server that will be
used to send the logs. You may also select
your computer from the drop-down menu (only
if receiving an IP address from the router via
DHCP).