D Link DWLG132B1 AirPlus Xtreme G DWL-G132 Wireless USB Adapter User Manual dwl120v F manual 102103
D Link Corporation AirPlus Xtreme G DWL-G132 Wireless USB Adapter dwl120v F manual 102103
D Link >
Contents
- 1. Users Manual 1
- 2. Users Manual 2
Users Manual 1

Manual
Building Networks for People
802.11g (2.4GHz)
Wireless G USB 2.0 Adapter
DWL-G132
D-Link
AirPlus X
TREME
G
TM
2
Contents
Package Contents ................................................................................3
Introduction............................................................................................4
Features and Benefits ...........................................................................6
Wireless Basics ....................................................................................7
Installation Considerations ....................................................................7
Getting Started ......................................................................................9
Using the Configuration Utility ..............................................................12
Networking Basics ..............................................................................26
Troubleshooting...................................................................................39
Technical Specifications ......................................................................42
Contacting Technical Support ..............................................................44
Warranty and Registration ...................................................................45

3
D-Link AirPlus Xtreme GTM DWL-G132
2.4 GHz Wireless G USB 2.0 Adapter
At least 64MB of memory and a 500MHz processor
Properly installed and working USB Controller
Windows XP/2000
A computer or laptop with an available USB 2.0 port
Manual on CD-ROM
Quick Installation Guide
Cradle
Contents of Package:
Package Contents
If any of the above items are missing, please contact your reseller.
System Requirements:
4
Introduction
The D-Link AirPlus Xtreme G DWL-G132 Wireless G USB Adapter is an
802.11b/802.11g high-performance,convenient Plug & Play USB 2.0 solution that
brings wireless networking to your laptop or desktop PC.
With a maximum wireless signal rate of up to 54Mbps (108Mbps* in Turbo
mode) you can connect to a wireless network at home, at the office or at any
wireless hotspot. Now you can stay connected wherever you are and wherever
you go.
The DWL-G132 is Wi-Fi compliant, meaning that it can connect and interoperate
with other 802.11b or 802.11g Wi-Fi-compliant wireless routers, access points
and adapters. The DWL-G132 connects to any available USB port on a laptop
or desktop Windows -based computer and also includes a USB cradle. With
the optional USB cradle, the DWL-G132 can be positioned virtually anywhere
at a workstation to achieve the best available wireless signal reception - whether
that workstation is in your office, on your deck or patio, by the pool, at the local
coffee shop, or in an airport terminal while waiting to board your next flight.
The adapter works with Microsoft Windows XP and Windows 2000 operating
systems to ensure that you’ll be up and running on a wireless network in just a
matter of seconds.
Using its default settings, the DWL-G132 automatically connects to other
D-Link AirPlus Xtreme GTM wireless products as soon as it’s active.
TM
*Maximum wireless signal rate derived from IEEE Standard 802.11g specifications. Actual data
throughput will vary. Network conditions and evironmental factors lower actual data throughput rate.
The DWL-G132 has the newest, strongest and most advanced security features
available today. When used with other 802.11 WPA (Wi-Fi Protected Access)
and 802.1x compatible products in a network with a RADIUS server, the security
features include:
WPA: Wi-Fi Protected Access which authorizes and identifies users based
on a secret key that changes automatically at regular intervals. WPA
uses TKIP (Temporal Key Integrity Protocol) to change the temporal
key every 10,000 packets (a packet is a kind of message transmitted
over a network.) This ensures much greater security than the standard
WEP security. (By contrast, the previous WEP encryption
implementations required the keys to be changed manually.)

5
For home users that will not incorporate a RADIUS server in their network, the
security for the DWL-G132, used in conjunction with other WPA-compatible
802.11 products, will still be much stronger than ever before. Utilizing the
Pre-Shared Key mode of WPA, the DWL-G132 will obtain a new security key
every time it connects to the 802.11 network. You only need to input your
encryption information once in the configuration menu. No longer will you have
to manually input a new WEP key frequently to ensure security. With the
DWL-G132, you will automatically receive a new key every time you connect,
vastly increasing the safety of your communication.
Introduction (continued)
802.1x: Authentication which is a first line of defense against intrusion. In the
authentication process, the Authentication Server verifies the identity of
the client attempting to connect to the network. Unfamiliar clients would
be denied access.
6
Features and Benefits
**
3Environmental factors may adversely affect range.
User-friendly configuration and diagnostic utilities.
Supports Infrastructure networks via an access point and
Peer-to-Peer communication in Ad-Hoc mode.
Connects at up to 328 feet indoors3.
1 year warranty.
2Using a USB 1.1 port will adversely affect throughput.
1Maximum wireless signal rate derived from IEEE Standard 802.11g specifications. Actual data
throughput will vary. Network conditions and environmental factors lower actual data throughput rate.
Compact size for placement anywhere.
Convenience of Plug & Play installation.
Fully 802.11b/802.11g compatible.
Powered by the USB port; no external power source is required.
USB 2.0 standard2.
Better Security with 802.1x and WPA - In addition to 64-,128-bit WEP
encryption, you can also securely connect to a wireless network using
802.1x for wireless authentication, as well as WPA (Wi-Fi Protected
Access) providing you a much higher level of security for your data and
communication than has previously been available.
Provides maximum wireless signal rate of up to 54Mbps
(108Mbps1 in Turbo mode).
Optimal wireless reception using its cradle (included). Position the
DWL-G132 almost anywhere in your workspace to achieve the best
reception possible.
7
Wireless Basics
Wireless users can use the same applications they use on a wired network.
Wireless adapter cards used on laptop and desktop systems support the same
protocols as Ethernet adapter cards.
D-Link wireless products are based on industry standards to provide
easy-to-use and compatible high-speed wireless connectivity within your home,
business or public access wireless networks. D-Link wireless products will
allow you access to the data you want, when and where you want it. You will be
able to enjoy the freedom that wireless networking brings.
A wireless local area network (WLAN) is a computer network that transmits
and receives data with radio signals instead of wires. WLANs are used
increasingly in both home and office environments, and public areas such as
airports, coffee shops and universities. Innovative ways to utilize WLAN
technology are helping people to work and communicate more efficiently.
Increased mobility and the absence of cabling and other fixed infrastructure
have proven to be beneficial to many users.
People use WLAN technology for many different purposes:
Mobility - Productivity increases when people have access to data in any
location within the operating range of the WLAN. Management decisions based
on real-time information can significantly improve worker efficiency.
Low Implementation Costs - WLANs are easy to set up, manage, change
and relocate. Networks that frequently change can benefit from WLANs ease
of implementation. WLANs can operate in locations where installation of wiring
may be impractical.
Installation and Network Expansion - Installing a WLAN system can be fast
and easy and can eliminate the need to pull cable through walls and ceilings.
Wireless technology allows the network to go where wires cannot go - even
outside the home or office.
Inexpensive Solution - Wireless network devices are as competitively priced
as conventional Ethernet network devices.
Scalability - WLANs can be configured in a variety of ways to meet the needs
of specific applications and installations. Configurations are easily changed
and range from Peer-to-Peer networks suitable for a small number of users to
larger Infrastructure networks to accommodate hundreds or thousands of
users, depending on the number of wireless devices deployed.
8
Installation Considerations
The DWL-G132 lets you access your network using a wireless connection
from virtually anywhere within its operating range. Keep in mind, however, that
the number, thickness and location of walls, ceilings, or other objects that the
wireless signals must pass through, may limit the range. Typical ranges vary
depending on the types of materials and background RF (radio frequency) noise
in your home or business. The key to maximizing wireless range is to follow
these basic guidelines:
Keep your product away (at least 3-6 feet or 1-2 meters) from electrical
devices or appliances that generate RF noise.
4
Keep the number of walls and ceilings between the DWL-G132 and
other network devices to a minimum - each wall or ceiling can reduce
your DWL-G132’s range from 3-90 feet (1-30 meters.) Position your
devices so that the number of walls or ceilings is minimized.
1
Be aware of the direct line between network devices. A wall that is 1.5
feet thick (.5 meters), at a 45-degree angle appears to be almost 3 feet
(1 meter) thick. At a 2-degree angle it looks over 42 feet (14 meters)
thick! Position devices so that the signal will travel straight through a
wall or ceiling (instead of at an angle) for better reception.
2
Building materials can impede the wireless signal - a solid metal door
or aluminum studs may have a negative effect on range. Try to position
wireless devices and computers with wireless adapters so that the
signal passes through drywall or open doorways and not other materials.
3
Wireless Basics (continued)
9
A wireless router - D-Link AirPlus Xtreme GTM DI-624
A laptop computer with a D-Link AirPlus Xtreme GTM DWL-G132
A desktop computer with a D-Link AirPlus Xtreme GTM DWL-G132
A cable modem - D-Link DCM-201
With its default settings, the DWL-G132 will connect with other
D-Link AirPlus Xtreme GTM products, right out of the box.
Getting Started
There are basically two modes of networking:
Infrastructure – using an access point or router, such as the DI-624.
Ad-Hoc – directly connecting to another computer, for Peer-to-Peer
communication, using wireless network adapters on each computer,
such as two or more DWL-G132 Wireless Network USB adapters.
On the following pages we will show you an example of an Infrastructure
Network and an Ad-Hoc Network.
An Infrastructure network contains an access point or router. The
Infrastructure network example shown on the following page contains the
following D-Link network devices (your existing network may be comprised of
other devices):
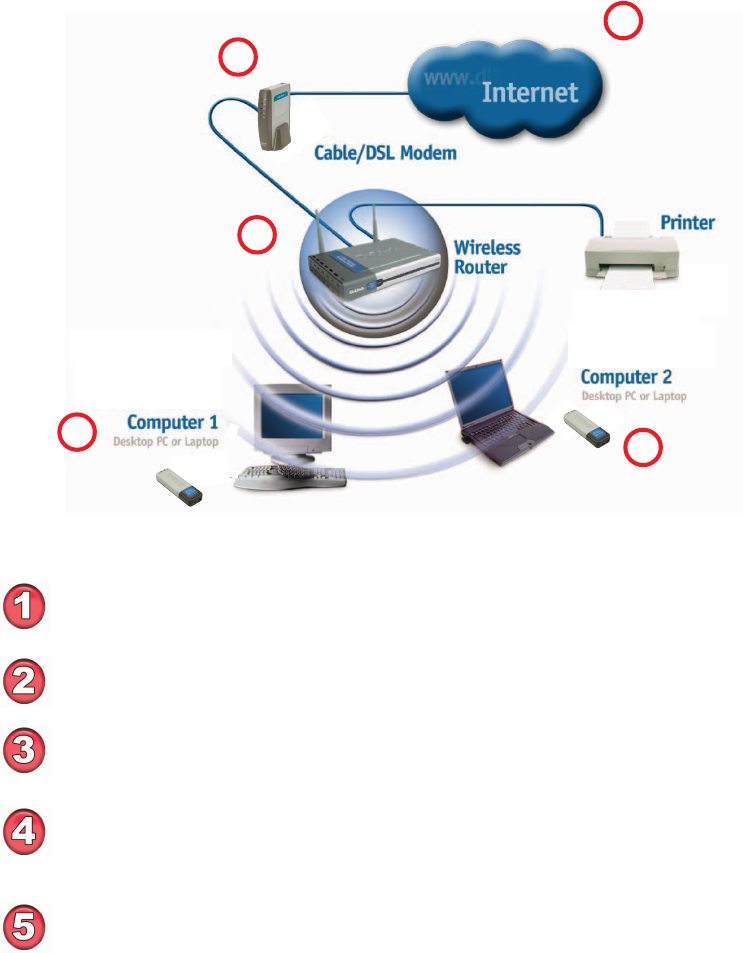
10
You will need broadband Internet access (a cable or DSL-subscriber
line into your home or office).
Consult with your cable or DSL provider for proper installation of the
modem.
Connect the cable or DSL modem to your broadband router.
(See the Quick Installation Guide included with your router.)
Install the D-Link AirPlus Xtreme G DWL-G132 Wireless USB 2.0
adapter into an available USB port on your desktop computer.
(See the Quick Installation Guide included with the DWL-G132.)
Getting Started (continued)
For a typical wireless setup at home (as shown above), please do the following:
55
55
5
Setting up a Wireless Infrastructure Network
11
11
1
22
22
2
33
33
3
Install the D-Link AirPlus Xtreme G DWL-G132 wireless USB 2.0
adapter into an available USB port on your laptop computer.
(See the Quick Installation Guide included with the DWL-G132.)
44
44
4
TM
DWL-G132
DWL-G132
TM
11
Getting Started (continued)
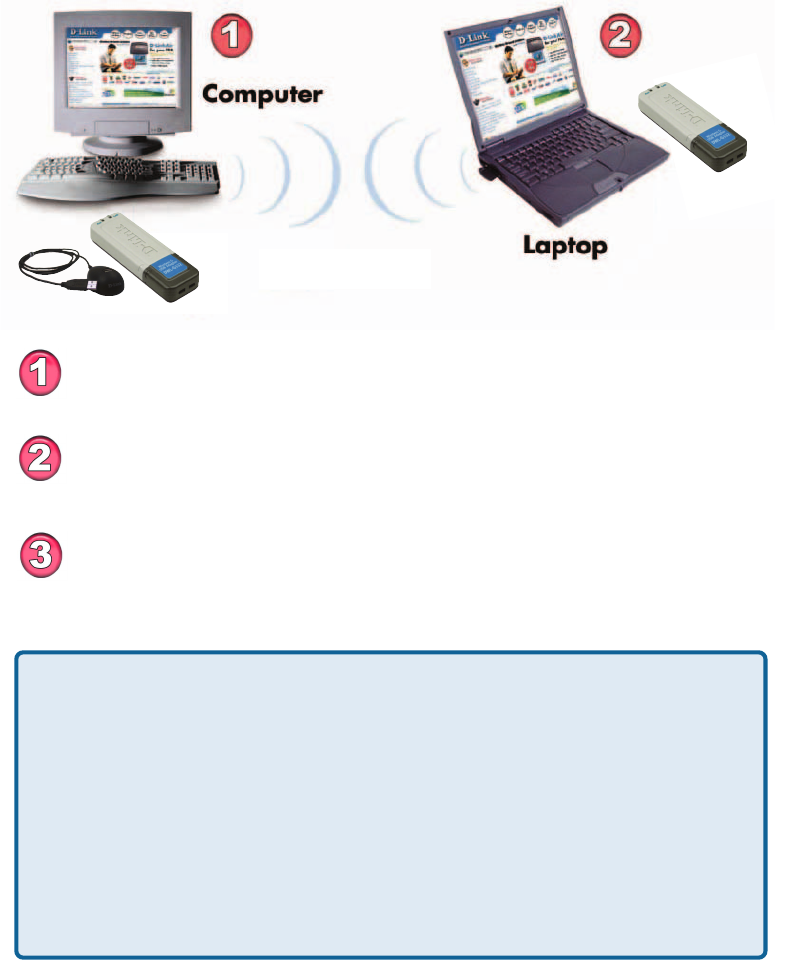
Setting up a Wireless Ad-Hoc Network
When assigning IP addresses to the computers on the network, please
remember that the IP address for each computer must be in the same
IP address range as all the computers in the network, and the subnet
mask must be exactly the same for all the computers in the network.
For example: If the first computer is assigned an IP address of 192.168.0.2
with a subnet mask of 255.255.255.0, then the second computer can be
assigned an IP address of 192.168.0.3 with a subnet mask of 255.255.255.0,
etc.
IMPORTANT: If computers or other devices are assigned the same IP
address, one or more of the devices may not be visible on the network.
IP Address
Install the D-Link AirPlus Xtreme GTM DWL-G132 Wireless USB 2.0
adapter into the desktop computer. (See the Quick Installation Guide
included with the product.)
Set the wireless configuration for the adapters to Ad-Hoc mode, set
the adapters to the same channel, and assign an IP address to each
computer on the Ad-Hoc network.
Install the D-Link AirPlus Xtreme GTM DWL-G132 Wireless USB 2.0
adapter into the laptop computer. (See the Quick Installation Guide
included with the product.)
DWL-G132
Wireless G USB 2.0 Adapter
12
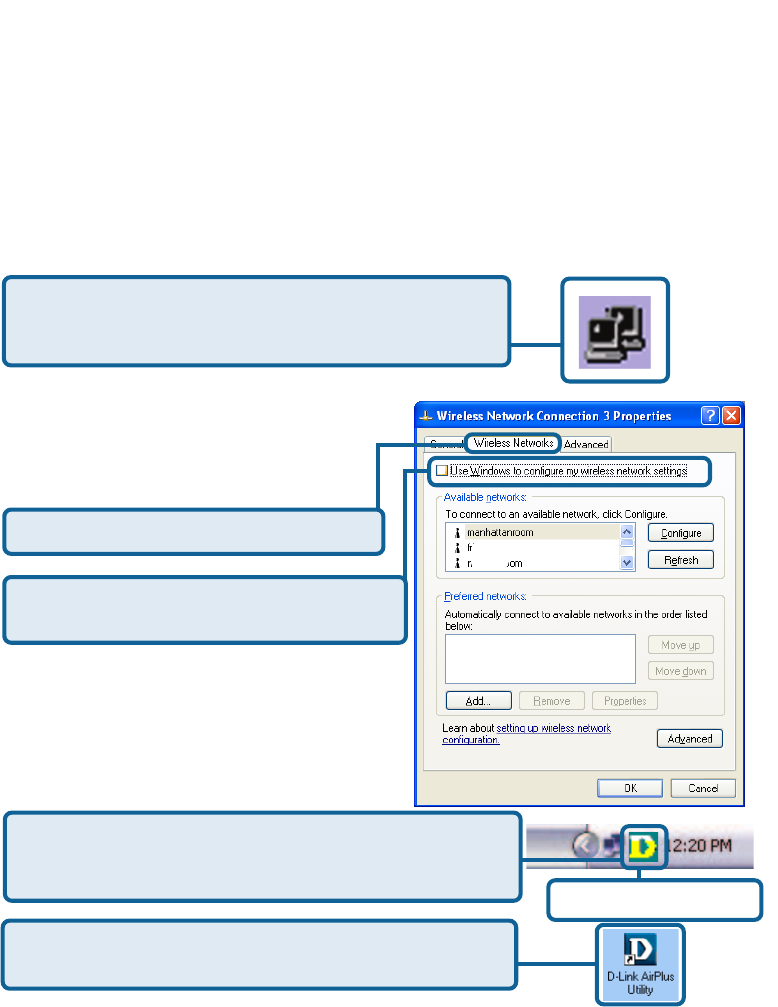
Select the Wireless Networks tab.
Uncheck the box in the properties window
that enables windows configuration.
D-Link AirPlus Xtreme GTM DWL-G132 uses the Configuration Utility as
the management software. The utility provides the user an easy interface to
change any settings related to the wireless adapter. After you have completed
the installation of the DWL-G132 (refer to the Quick Installation Guide that
came with your purchase) whenever you start the computer, the Configuration
Utility starts automatically and the system tray icon is loaded in the toolbar
(see illustration below.*) Clicking on the utility icon will start the Configuration
Utility. Another way to start the Configuration Utility is to click on
Start>Programs>D-Link AirPlus Xtreme G >D-Link AirPlus Xtreme G Utility.
Using the Configuration Utility
If you are using Windows XP, you can use either the Zero Configuration Utility
or the D-Link Configuration Utility.
If the icon does not display in the taskbar, then click on
this icon on your desktop to open.
To use the D-Link Configuration Utility with XP, right-click
on the wireless network icon in the taskbar in the lower
right-hand corner of your computer screen.
In the window that appears, select
View Available Wireless Networks
and click the Advanced button. The
screen at right will appear.
After you have done this, you can then use the D-Link
Configuration Utility with XP by clicking on the D-Link
Configuration Utility icon. *Configuration Utility icon
in the system tray
13
Using the Configuration Utility (continued)
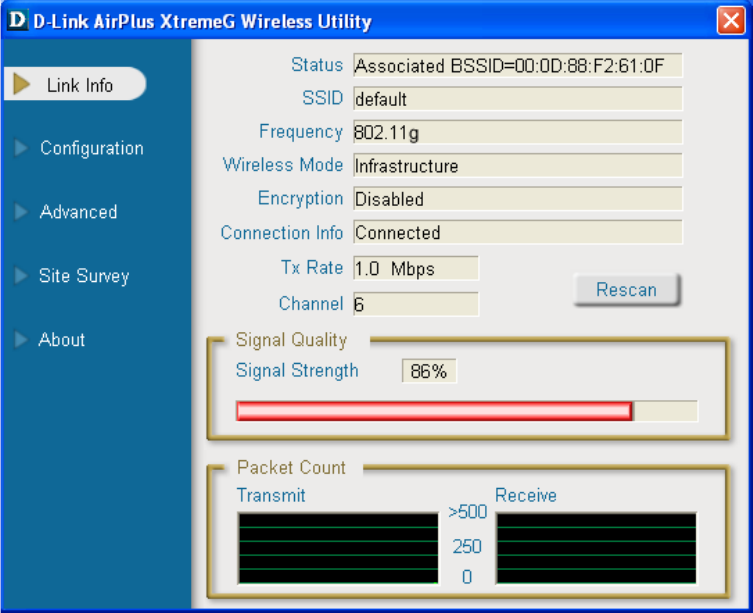
Link Info
SSID:
The Service Set Identifier is the name assigned to the wireless network. The
factory SSID setting is default.
Status:
Displays the MAC address of the access point or router to which the
DWL-G132 is associated.
Frequency:
802.11b indicates that the DWL-G132 is communicating in the 2.4GHz band.
Wireless Mode:
Either Infrastructure or Ad-Hoc will be displayed here. (Please see the Getting
Started section in this manual for an explanation of these two modes.)
14
Using the Configuration Utility (continued)
Tx Rate:
The default setting is Auto; Tx Rate settings are automatically determined for
a maximum wireless signal rate of up to 54Mbps (108Mbps* in Turbo mode).
Channel:
The default setting is Auto. The channel selection is automatically determined
by the DWL-G132.
Signal Quality:
Displays the signal strength and the link quality of the DWL-G132’s wireless
connection to the access point or router.
Packet Count:
Displays the statistics of the data packets that are transmitted and received.
Encryption:
You can see if WEP (Wired Equivalent Privacy) is Enabled or Disabled here.
Rescan Button:
Rescans for the strongest signal with the current SSID and associates with
that access point or router.
Connection Info:
When the DWL-G132 is connected to a wireless network, Connected will be
displayed in this field.
*Maximum wireless signal rate derived from 802.11g specifications. Actual data throughput
will vary. Network conditions and environmental factors lower actual data throughput rate.
15
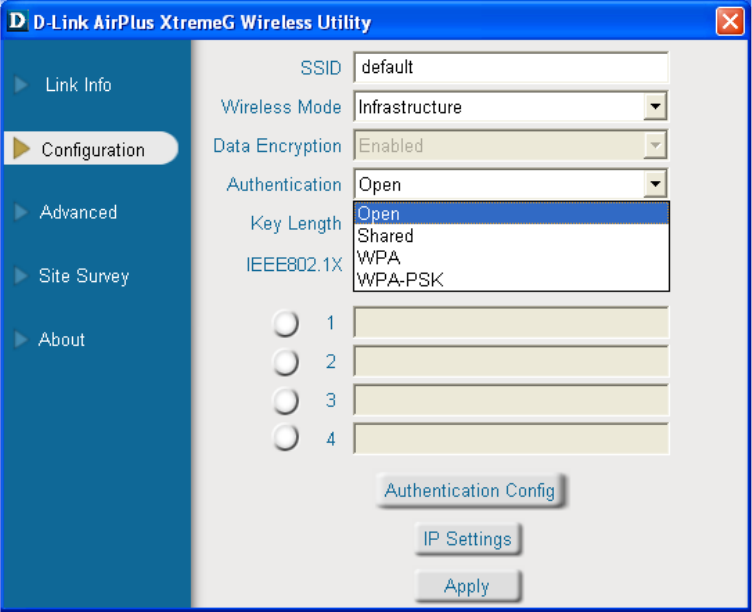
Configuration
Using the Configuration Utility (continued)
Wireless Mode:
SSID:
Data Encryption:
Service Set Identifier is a name that identifies a wireless network. Access points
and wireless devices attempting to connect to a specific WLAN (Wireless Local
Area Network) must use the same SSID. The default setting is default.
Click on the pull-down menu; select from the following options:
Infrastructure - connecting to the WLAN using an access point. (This is
the default setting).
Ad-Hoc – wireless mode used when connecting directly to a computer
equipped with a wireless adapter in a Peer-to-Peer environment.
Select Enabled or Disabled.
16
Using the Configuration Utility (continued)
Authentication:
Keys 1-4:
When you select WEP encryption, you will enter up to four WEP keys in the
fields provided, using either Hexadecimal or ASCII format. From the keys you
have entered, select the default key by clicking on the button next to it.
Choose one of the following modes:
Open Authentication – the DWL-G132
is visible to all devices on the network.
Shared Authentication – allows
communication only with other devices
with identical WEP settings.
WPA – Wi-Fi protected access improves
upon WEP security. In conjunction with
a RADIUS server and EAP (extensible
authentication protocol), WPA ensures
that only authenticated users access the
network.
Click Apply to save changes.
Authentication Config:
When you enable IEEE 802.1X click on Authentication Config.
The Advanced Security Settings screen will appear. See the following pages
for more information.
IP Settings
Hexadecimal digits consist of the numbers 0-9 and the letters A-F.
ASCII (American Standard Code for Information Interchange) is a code for
representing English letters as numbers from 0-127.
IEEE 802.1X:
Select Enabled or Disabled. 802.1x requires that a RADIUS server be included
in your network in order to authenticate users.
Key Length:
Select the key length and either ASCII (e.g., a word) or hexadecimal format.
WPA-PSK – provides user authentication without a RADIUS server in
the network. PSK (Pre-Shared Key) provides authentication through use
of a passphrase that is shared by the devices on the network. This is the
most secure encryption available without a RADIUS server.
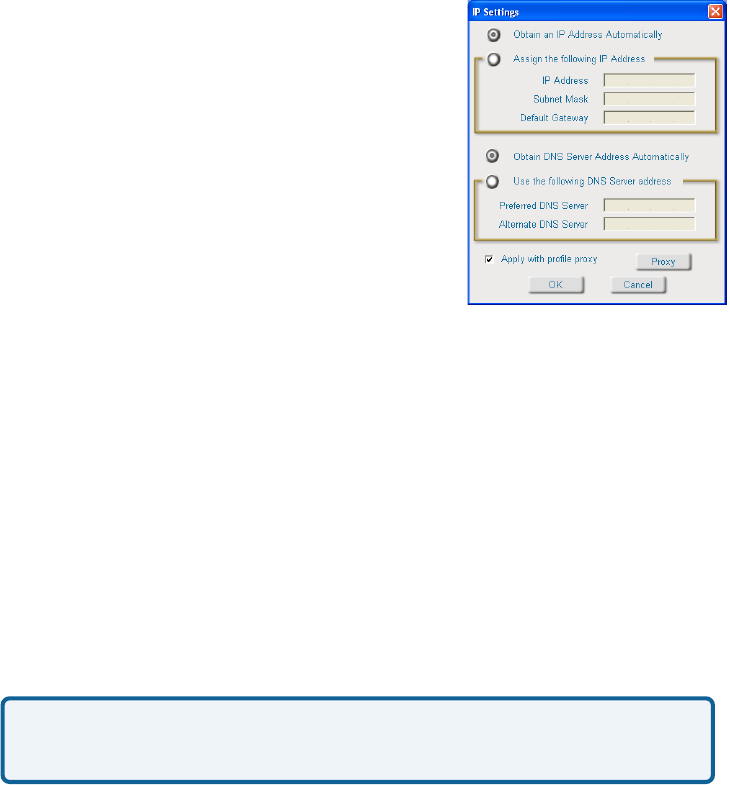
IP Settings:
When you click IP Settings in the Configuration window, the pop-up screen
above will appear. Configure the IP Settings in this window.
17
Using the Configuration Utility (continued)
IP Settings
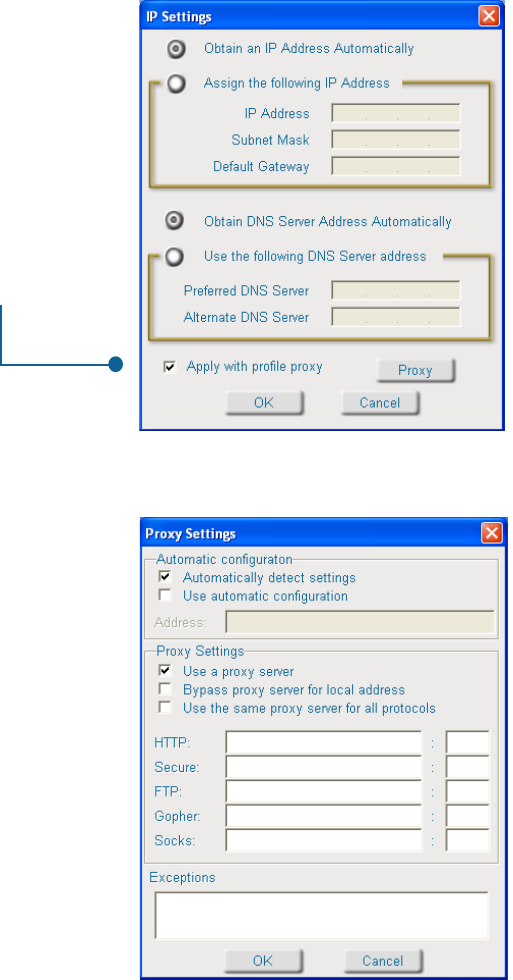
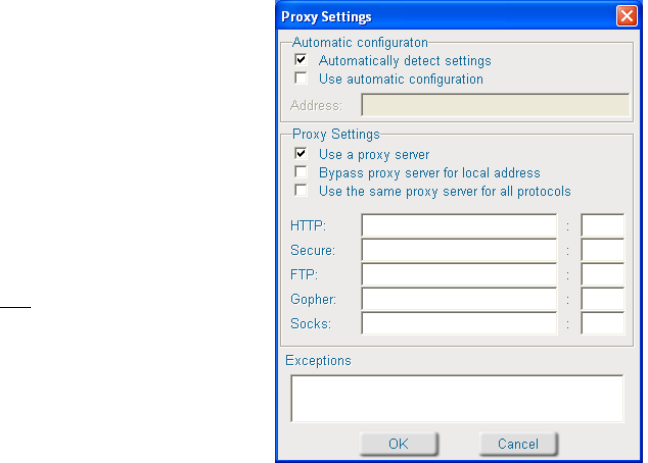
Proxy Settings
Check Apply with a profile proxy to
use a proxy server in your network. A
proxy server increases the speed of
web page retrieval and can also act
as a filter to limit access to specific
Web sites.
Using a Proxy Server
When this option is selected, the proxy
server will automatically adjust to the
settings of the network.
Automatically detect settings:
Select this option and input the IP
address of the proxy server to ensure
that the proxy server will be utilized.
Use automatic configuration:
To use a proxy server, select this
option.
Use a proxy server:
Select this to allow direct access to
local internal addresses without
including the extra step of routing the
request through the proxy server.
Bypass proxy server for local
address:
18
Using the Configuration Utility (continued)
Proxy Settings (continued)
To use the same proxy server for all
protocols, select this option and enter
the IP address for the proxy server in
the HTTP field. Other fields will be
unavailable. Enter the port number for
the proxy server.
Use the same proxy server for
all protocols:
HTTP, Secure, FTP, Gopher,
Socks:
if you are not using the same proxy
server for all protocols, enter the proxy
server address, either in IP address
or domain name format and its
corresponding port, for each of these
protocols.
HTTP: Hyper Text Transfer Protocol
is used to transfer files from a Web server onto a browser for viewing.
FTP: File Transfer Protocol. FTP is most commonly used to upload and
download files on the Internet.
Gopher: Gopher is an early Internet protocol that organizes files in a
structured list for database searching.
Secure: HTTPS protocol is based on SSL (Secure Sockets Layer) technology.
It is a protocol for transmitting private documents over the Internet using a
private key to encrypt data. URLs that begin with HTTPS often use the protocol
to securely obtain confidential information such as credit card numbers.
Socks: Socks is a proxy server that provides a simple firewall. SocksV5 offers
authentication.
Exceptions: To allow specific IP addresses to bypass proxy servers, enter the
IP addresses here. You can also enter “wildcards” to allow a category of website
to bypass the proxy servers. For instance, if you enter www.*.com, the browser
will bypass the proxy servers for most Websites.
19
Using the Configuration Utility (continued)
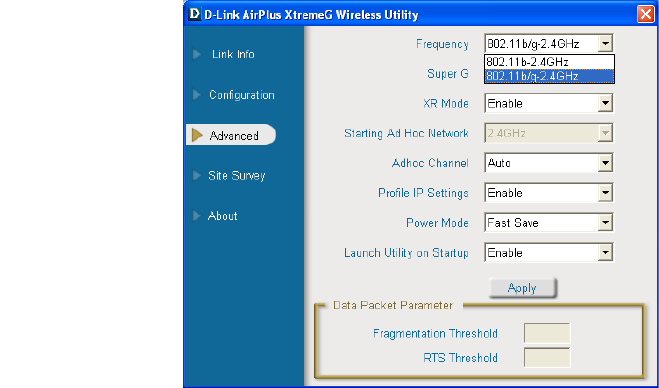
Advanced
Frequency:
Select 802.11b/g for
compatibility with both
802.11b or 802.11g
networks, or select 802.11b
only.
Super G:
Selecting Super G mode
enables a maximum
wireless signal rate of up to
108Mbps.*
*Maximum wireless signal rate derived from IEEE Standard 802.11g specifications. Actual data
throughput will vary. Network conditions and environmental factors lower actual data throughput rate.
XR Mode:
Launch Utility on Startup:
Power Mode:
Disable -This default setting consumes the most power.
Enable - This setting consumes the least power.
Starting Ad Hoc Network:
When using Ad Hoc mode, select the frequency here.
Ad Hoc Channel:
Select the Ad Hoc channel when in Ad Hoc mode. When communicating in
Ad Hoc mode, all devices must share the same channel.
Profile IP Settings:
Select Enable or Disable.
Click Apply if you have made any changes.
Enable or Disable range
extension mode. Enabling
this feature allows you to
increase the range of your communication without adding additional hardware.
You can Enable or Disable the IP Settings portion of your profile here. If you
select Disable you will need to configure the IP address information each time
you connect to a network. If you select Enable you will maintain the same IP
address information each time you connect to a network.
20
Using the Configuration Utility (continued)
Fragmentation Threshold:
This value should remain at its default setting of 2432. If you experience a high
packet error rate, you may slightly increase your Fragmentation Threshold within
the value range of 256 to 2432. Setting the Fragmentation Threshold too low
may result in poor performance.
This value should remain at its default setting of 2432. If inconsistent data flow
is a problem, only a minor modification should be made.
RTS Threshold:
Advanced (continued)
21
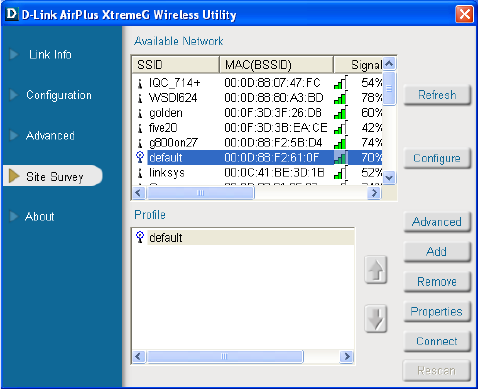
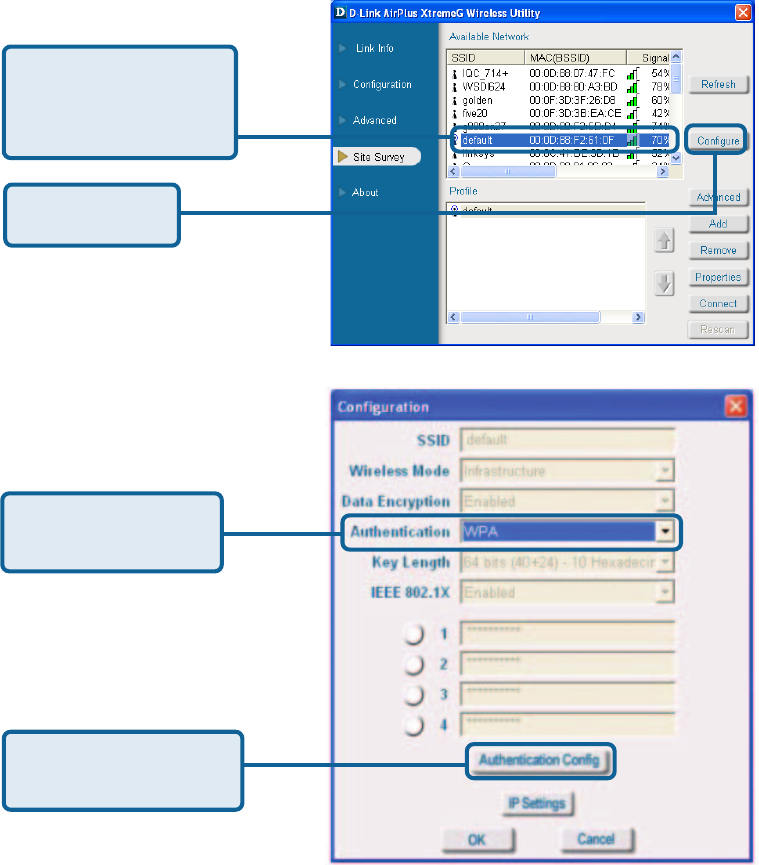
Refresh:
Click on Refresh to get the
most updated list of
available networks.
Using the Configuration Utility (continued)
Site Survey
Available Network:
The top section of the window displays the Available Networks. Scroll up and
down the list and highlight the network to which you wish to connect. Click on
the Connect button.
Profile:
In the lower half of the screen, you can manage the profiles that you have
created for the wireless network at home, at the office and in public places.
Scroll up and down and highlight the profile that you wish to configure. You can
Add or Remove a profile, or configure the Properties of the profile in order to
connect with an available network.
Connect:
Highlight a network profile; click Connect to connect to that network.
Rescan:
Click Rescan to rescan and connect to the strongest signal with the current
SSID.
Configure:
Highlight an existing
network and click
Configure; the
configuration window on the
next page will appear.
Advanced:
Highlight a network; click
Advanced to and the
screen on the next page
will appear.
Add:
Click Add and the screen on the next page will appear.
Remove:
Highlight a network profile; click Remove to remove a network from the profile
list.
Properties:
Highlight a network profile; click Properties and the screen on the next page
will appear.
22
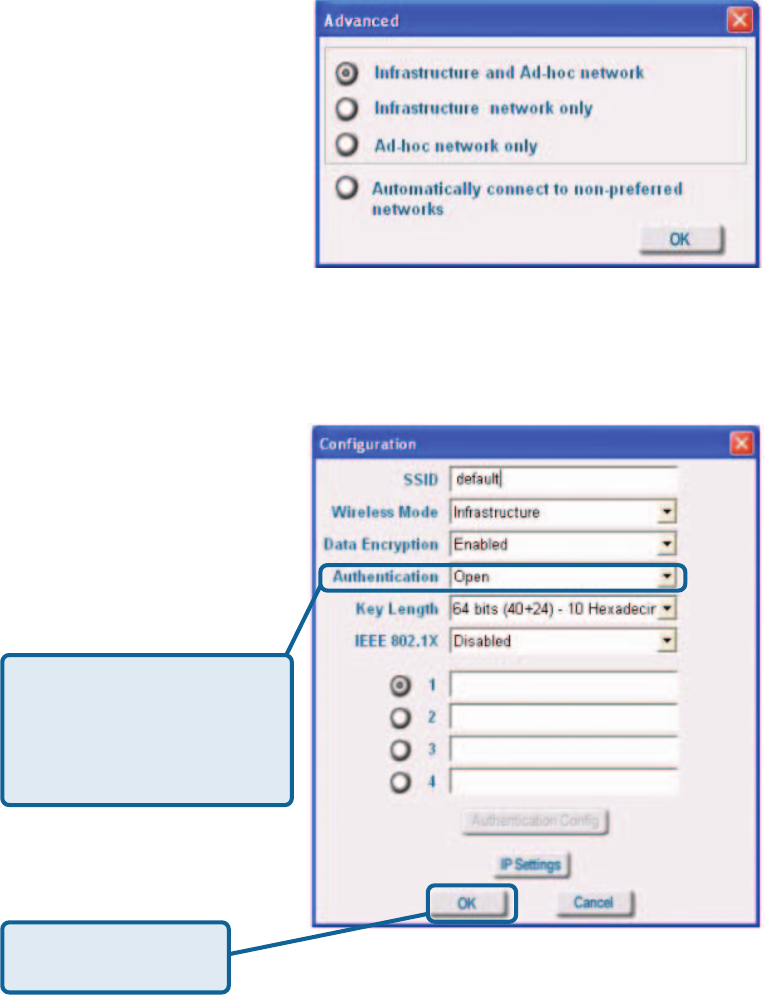
Using the Configuration Utility (continued)
Site Survey > Add
If you clicked on Add, you
can configure, in this
window, all the properties of
a profile that you wish to add
to the network.
In this window you can
select the type of network
connection.
Click OK to save the
changes.
If you clicked on
Configuration or
Properties you can
configure, in this window, all
the properties of a profile that
already exists in the
network.
Click OK to save the
changes.
Advanced
Configuration, Add or Properties
If you select WPA in the
Authentication field, please
see detailed instructions for
configuring WPA on the
following pages.
23
Using the Configuration Utility (continued)
Authentication > WPA
After you click Authentication Config, the Advanced Security Settings screen
will appear. Please see the following page.
Select the available
network to which you
want to connect.
Click
Configure.
Click Authentication
Config.
Select WPA in the
Authentication field.
24
Using the Configuration Utility (continued)
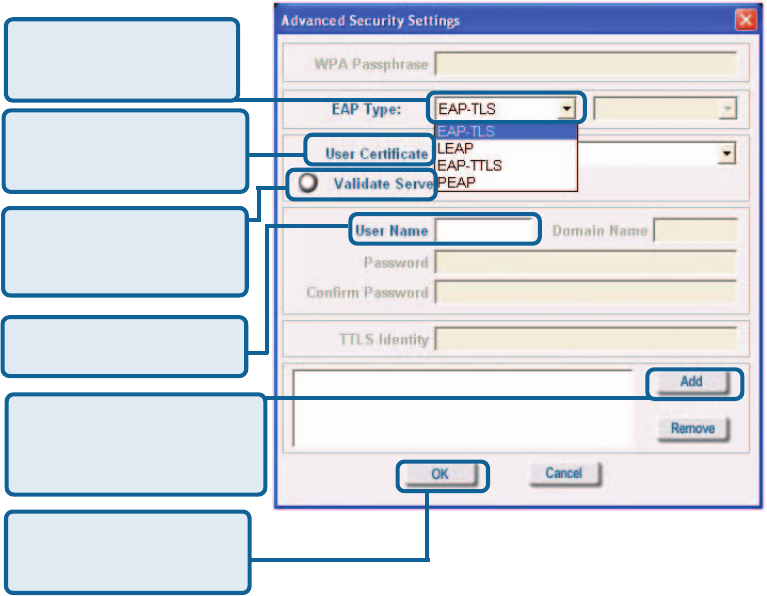
Authentication > WPA > Advanced Security Settings
Select the EAP type
here.
Click Validate Server
if your authentication
server requires it.
Enter the User Name.
Click Add and the
window on the following
page will appear.
Click OK to save the
changes.
Leave the User
Certificate field blank.
EAP Type: Extensible Authentication Protocols (EAP-TLS, LEAP, EAP-TTLS,
PEAP) allow devices on the network to request authentication from the
RADIUS server in the network. All the devices on the network must use the
same EAP type when using a RADIUS server for authentication.
Validate Server: Some RADIUS servers require that the Validate Server
field be selected. Check this field if your RADIUS server requires validation.
User Certificate: A certificate authority (CA) issues User Certificates to
verify that a public key belongs to a specific individual or company. This field
is not required here and is left blank.
User Name: Enter the user name (admin) here.
25
Using the Configuration Utility (continued)
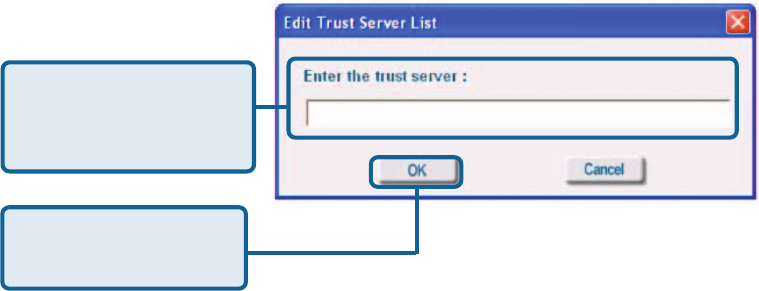
Authentication > WPA > Advanced Security Settings > Add
Enter the IP address of
the RADIUS server in
your network.
Click OK to save the
changes.
After entering the information and clicking OK in the dialog box above,the window
on the previous page will appear. Click OK to complete the WPA configuration.
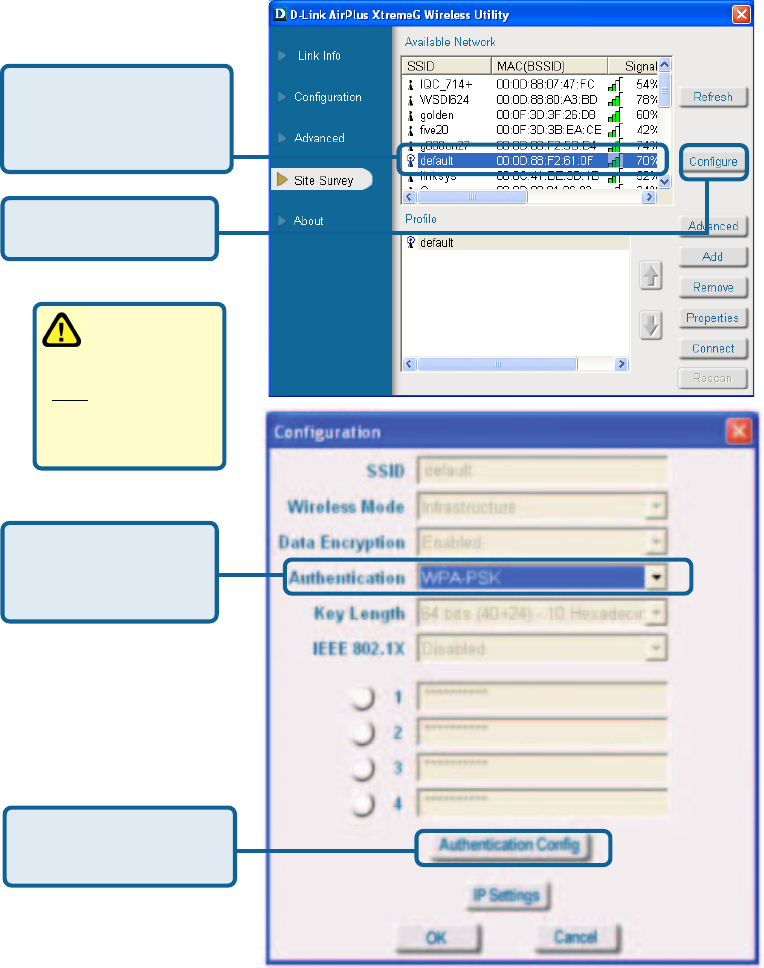
Authentication > WPA -PSK
Suitable for the home user, WPA-PSK (WPA Pre-Shared Key) is a superior
form of security that does not require a RADIUS server in the network.
To use WPA-PSK, enter a passphrase that is shared by all the devices on the
network.
By using TKIP (Temporal Key Integrity Protocol), the security keys change at
set intervals, creating a network that is more secure than one that utilizes WEP
encryption alone.
26
Using the Configuration Utility (continued)
Authentication > WPA-PSK
Click
Configure.
Select WPA-PSK in
the Authentication
field.
Select the available
network to which you
want to connect.
WPA-PSK does
not require a
RADIUS Server
in the network.
Click Authentication
Config.
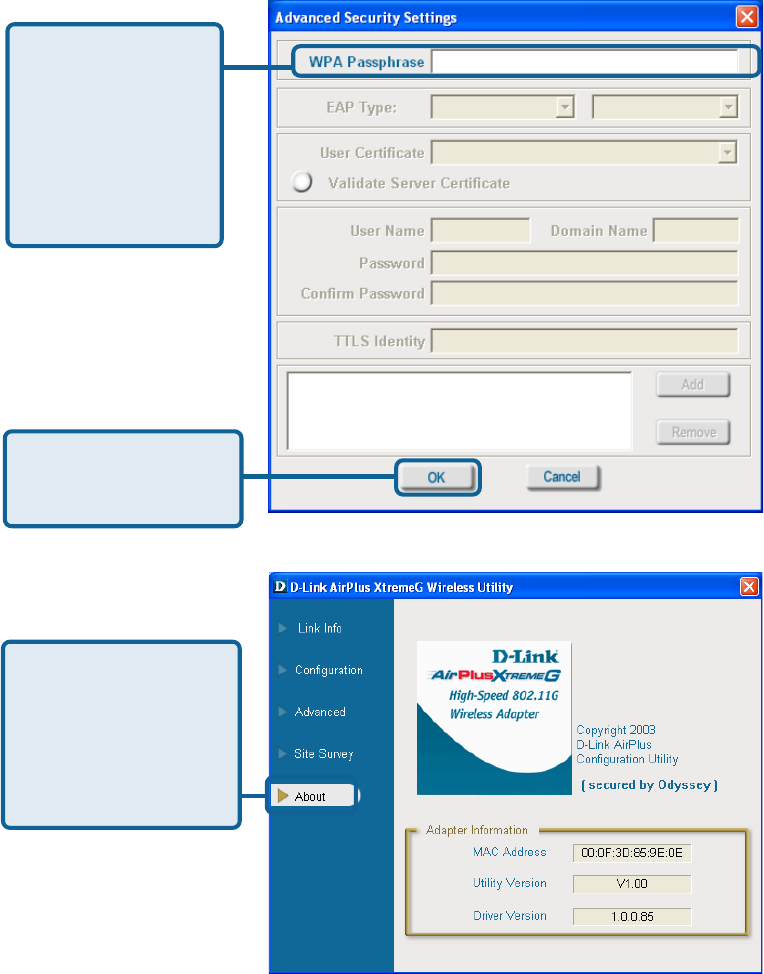
27
Using the Configuration Utility (continued)
Authentication > WPA-PSK (continued)
Enter the WPA
Passphrase. All the
devices on the
network must share
this same
passphrase in order
to communicate on
the network.
About
Advanced Security Settings
The About screen
gives you the MAC
address, Utility
Version and the Driver
Version of the
DWL-G132.
Click OK.
The configuration is
complete.
28
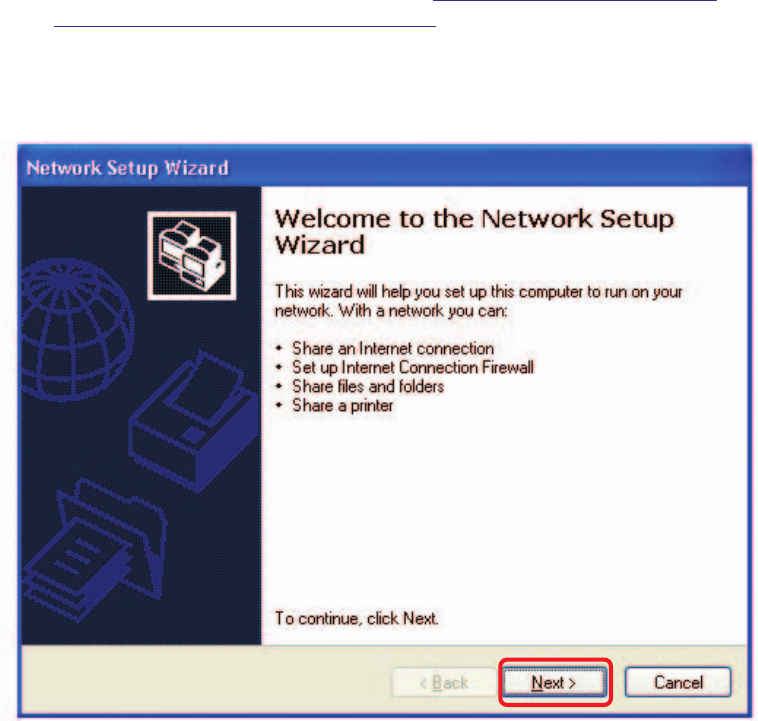
Using the Network Setup Wizard in Windows XP
In this section you will learn how to establish a network at home or work,
using Microsoft Windows XP.
Note: Please refer to websites such as http://www.homenethelp.com
and http://www.microsoft.com/windows2000 for information about networking
computers using Windows 2000/Me/98SE.
Go to Start>Control Panel>Network Connections.
Select Set up a home or small office network.
Networking Basics
When this screen appears, click Next.