Netgear orporated FWG114P WIRELESS FIREWALL User Manual FullManual
Netgear Incorporated WIRELESS FIREWALL FullManual
Contents
- 1. USERS MANUAL 1
- 2. USERS MANUAL 2
- 3. USERS MANUAL 3
USERS MANUAL 2

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Troubleshooting 9-3
M-10177-01
Troubleshooting the Web Configuration Interface
If you are unable to access the router’s Web Configuration interface from a PC on your local
network, check the following:
• Check the Ethernet connection between the PC and the router as described in the previous
section.
• Make sure your PC’s IP address is on the same subnet as the router. If you are using the
recommended addressing scheme, your PC’s address should be in the range of 192.168.0.2 to
192.168.0.254. Refer to “Verifying TCP/IP Properties” on page 3-5 or “Verifying TCP/IP
Properties (Macintosh)” on page 3-8 to find your PC’s IP address. Follow the instructions in
Chapter 4 to configure your PC.
Note: If your PC’s IP address is shown as 169.254.x.x: Recent versions of Windows and
MacOS will generate and assign an IP address if the computer cannot reach a DHCP server.
These auto-generated addresses are in the range of 169.254.x.x. If your IP address is in this
range, check the connection from the PC to the router and reboot your PC.
• If your router’s IP address has been changed and you don’t know the current IP address, clear
the router’s configuration to factory defaults. This will set the router’s IP address to
192.168.0.1. This procedure is explained in “Restoring the Default Configuration and
Password” on page 7-7.
• Make sure your browser has Java, JavaScript, or ActiveX enabled. If you are using Internet
Explorer, click Refresh to be sure the Java applet is loaded.
• Try quitting the browser and launching it again.
• Make sure you are using the correct login information. The factory default login name is
admin and the password is password. Make sure that CAPS LOCK is off when entering this
information.
If the router does not save changes you have made in the Web Configuration Interface, check the
following:
• When entering configuration settings, be sure to click the APPLY button before moving to
another menu or tab, or your changes are lost.
• Click the Refresh or Reload button in the Web browser. The changes may have occurred, but
the Web browser may be caching the old configuration.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
9-4 Troubleshooting
M-10177-01
Troubleshooting the ISP Connection
If your router is unable to access the Internet, you should first determine whether the router is able
to obtain a WAN IP address from the ISP. Unless you have been assigned a static IP address, your
router must request an IP address from the ISP. You can determine whether the request was
successful using the Web Configuration Manager.
To check the WAN IP address:
1. Launch your browser and select an external site such as www.netgear.com
2. Access the Main Menu of the router’s configuration at http://192.168.0.1
3. Under the Maintenance heading, select Router Status
4. Check that an IP address is shown for the WAN Port
If 0.0.0.0 is shown, your router has not obtained an IP address from your ISP.
If your router is unable to obtain an IP address from the ISP, you may need to force your
broadband modem to recognize your new router by performing the following procedure:
1. Turn off power to the broadband modem.
2. Turn off power to your router.
3. Wait five minutes and reapply power to the broadband modem.
4. When the modem’s LEDs indicate that it has reacquired sync with the ISP, reapply power to
your router.
If your router is still unable to obtain an IP address from the ISP, the problem may be one of the
following:
• Your ISP may require a login program.
Ask your ISP whether they require PPP over Ethernet (PPPoE) or some other type of login.
• If your ISP requires a login, you may have incorrectly set the login name and password.
• Your ISP may check for your PC's host name.
Assign the PC Host Name of your ISP account as the Account Name in the Basic Settings
menu.
• Your ISP only allows one Ethernet MAC address to connect to Internet, and may check for
your PC’s MAC address. In this case:
Inform your ISP that you have bought a new network device, and ask them to use the router’s
MAC address.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Troubleshooting 9-5
M-10177-01
OR
Configure your router to spoof your PC’s MAC address. This can be done in the Basic Settings
menu. Refer to “Manually Configuring Your Internet Connection” on page 3-11.
If your router can obtain an IP address, but your PC is unable to load any web pages from the
Internet:
• Your PC may not recognize any DNS server addresses.
A DNS server is a host on the Internet that translates Internet names (such as www addresses)
to numeric IP addresses. Typically your ISP will provide the addresses of one or two DNS
servers for your use. If you entered a DNS address during the router’s configuration, reboot
your PC and verify the DNS address as described in “Verifying TCP/IP Properties” on
page 3-5. Alternatively, you may configure your PC manually with DNS addresses, as
explained in your operating system documentation.
• Your PC may not have the router configured as its TCP/IP gateway.
If your PC obtains its information from the router by DHCP, reboot the PC and verify the
gateway address as described in “Verifying TCP/IP Properties” on page 3-5.
Troubleshooting a TCP/IP Network Using a Ping Utility
Most TCP/IP terminal devices and routers contain a ping utility that sends an echo request packet
to the designated device. The device then responds with an echo reply. Troubleshooting a TCP/IP
network is made very easy by using the ping utility in your PC or workstation.
Testing the LAN Path to Your Router
You can ping the router from your PC to verify that the LAN path to your router is set up correctly.
To ping the router from a PC running Windows 95 or later:
1. From the Windows toolbar, click on the Start button and select Run.
2. In the field provided, type Ping followed by the IP address of the router, as in this example:
ping 192.168.0.1
3. Click on OK.
You should see a message like this one:
Pinging <IP address> with 32 bytes of data

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
9-6 Troubleshooting
M-10177-01
If the path is working, you see this message:
Reply from < IP address >: bytes=32 time=NN ms TTL=xxx
If the path is not working, you see this message:
Request timed out
If the path is not functioning correctly, you could have one of the following problems:
• Wrong physical connections
— Make sure the LAN port LED is on. If the LED is off, follow the instructions in “LAN
or Internet Port LEDs Not On” on page 9-2.
— Check that the corresponding Link LEDs are on for your network interface card and
for the hub ports (if any) that are connected to your workstation and router.
• Wrong network configuration
— Verify that the Ethernet card driver software and TCP/IP software are both installed
and configured on your PC or workstation.
— Verify that the IP address for your router and your workstation are correct and that the
addresses are on the same subnet.
Testing the Path from Your PC to a Remote Device
After verifying that the LAN path works correctly, test the path from your PC to a remote device.
From the Windows run menu, type:
PING -n 10 <IP address>
where <IP address> is the IP address of a remote device such as your ISP’s DNS server.
If the path is functioning correctly, replies as in the previous section are displayed. If you do not
receive replies:
— Check that your PC has the IP address of your router listed as the default gateway. If the IP
configuration of your PC is assigned by DHCP, this information will not be visible in your
PC’s Network Control Panel. Verify that the IP address of the router is listed as the default
gateway as described in “Verifying TCP/IP Properties” on page 3-5.
— Check to see that the network address of your PC (the portion of the IP address specified
by the netmask) is different from the network address of the remote device.
— Check that your broadband modem is connected and functioning.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Troubleshooting 9-7
M-10177-01
— If your ISP assigned a host name to your PC, enter that host name as the Account Name in
the Basic Settings menu.
— Your ISP could be rejecting the Ethernet MAC addresses of all but one of your PCs. Many
broadband ISPs restrict access by only allowing traffic from the MAC address of your
broadband modem, but some ISPs additionally restrict access to the MAC address of a
single PC connected to that modem. If this is the case, you must configure your router to
“clone” or “spoof” the MAC address from the authorized PC. Refer to “Manually
Configuring Your Internet Connection” on page 3-11.
Restoring the Default Configuration and Password
This section explains how to restore the factory default configuration settings, changing the
router’s administration password to password and the IP address to 192.168.0.1. You can erase the
current configuration and restore factory defaults in two ways:
• Use the Erase function of the router (see “Erasing the Configuration” on page 5-8).
• Use the Default Reset button on the rear panel of the router. Use this method for cases when
the administration password or IP address is not known.
To restore the factory default configuration settings without knowing the administration password
or IP address, you must use the Default Reset button on the rear panel of the router.
1. Press and hold the Default Reset button until the Test LED turns on (about 10 seconds).
2. Release the Default Reset button and wait for the router to reboot.
Problems with Date and Time
The E-Mail menu in the Content Filtering section displays the current date and time of day. The
FWG114P Wireless Firewall/Print Server uses the Network Time Protocol (NTP) to obtain the
current time from one of several Network Time Servers on the Internet. Each entry in the log is
stamped with the date and time of day. Problems with the date and time function can include:
• Date shown is January 1, 2000. Cause: The router has not yet successfully reached a Network
Time Server. Check that your Internet access settings are configured correctly. If you have just
completed configuring the router, wait at least five minutes and check the date and time again.
• Time is off by one hour. Cause: The router does not automatically sense Daylight Savings
Time. In the E-Mail menu, check or uncheck the box marked “Adjust for Daylight Savings
Time”.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
9-8 Troubleshooting
M-10177-01
Technical Specifications A-1
M-10177-01
Appendix A
Technical Specifications
This appendix provides technical specifications for the ProSafe Wireless 802.11g Firewall/Print
Server Model FWG114P.
Network Protocol and Standards Compatibility
Data and Routing Protocols: TCP/IP, RIP-1, RIP-2, DHCP
PPP over Ethernet (PPPoE)
Power Adapter
North America: 120V, 60 Hz, input
United Kingdom, Australia: 240V, 50 Hz, input
Europe: 230V, 50 Hz, input
Japan: 100V, 50/60 Hz, input
All regions (output): 12 V DC @ 1.2 A output, 18W maximum
Physical Specifications
Dimensions: 28 x 175 x 118 mm (1.1 x 6.89 x 4.65 in.)
Weight: 0.3 kg (0.66 lb)
Environmental Specifications
Operating temperature: 0° to 40° C (32º to 104º F)
Operating humidity: 90% maximum relative humidity, noncondensing
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
A-2 Technical Specifications
M-10177-01
Electromagnetic Emissions
Meets requirements of: FCC Part 15 Class B
VCCI Class B
EN 55 022 (CISPR 22), Class B
Interface Specifications
LAN: 10BASE-T or 100BASE-Tx, RJ-45
WAN: 10BASE-T or 100BASE-Tx
Wireless
Data Encoding: Direct Sequence Spread Spectrum (DSSS)
Maximum Computers Per
Wireless Network:
Limited by the amount of wireless network traffic generated
by each node. Typically 30-70 nodes.
802.11b and g
Radio Data Rate
1, 2, 5.5, & 11 Mbps (Auto-rate capable)
802.11b and g
Operating Frequencies
2.412 ~ 2.462 GHz (US) 2.457 ~ 2.462 GHz (Spain)
2.412 ~ 2.484 GHz (Japan) 2.457 ~ 2.472 GHz (France)
2.412 ~ 2.472 GHz (Europe ETSI)
802.11b and g
Operating Range
Outdoor environment Indoor environment
@ 11 Mbps 398 ft (120 m) 198 ft (60 m)
@ 5.5 Mbps 561 ft (170 m) 264 ft (80 m)
@ 2 Mbps 890 ft (270 m) 430 ft (130 m)
@ 1 Mbps 1485 ft (450 m) 660 ft (200 m)
802.11b and g Encryption 40-bits (also called 64-bits), 128-bits WEP data encryption
Networks, Routing, and Firewall Basics B-1
M-10146-01
Appendix B
Networks, Routing, and Firewall Basics
This chapter provides an overview of IP networks, routing, and firewalls.
Related Publications
As you read this document, you may be directed to various RFC documents for further
information. An RFC is a Request For Comment (RFC) published by the Internet Engineering
Task Force (IETF), an open organization that defines the architecture and operation of the Internet.
The RFC documents outline and define the standard protocols and procedures for the Internet. The
documents are listed on the World Wide Web at www.ietf.org and are mirrored and indexed at
many other sites worldwide.
Basic Router Concepts
Large amounts of bandwidth can be provided easily and relatively inexpensively in a local area
network (LAN). However, providing high bandwidth between a local network and the Internet can
be very expensive. Because of this expense, Internet access is usually provided by a slower-speed
wide-area network (WAN) link such as a cable or DSL modem. In order to make the best use of the
slower WAN link, a mechanism must be in place for selecting and transmitting only the data traffic
meant for the Internet. The function of selecting and forwarding this data is performed by a router.
What is a Router?
A router is a device that forwards traffic between networks based on network layer information in
the data and on routing tables maintained by the router. In these routing tables, a router builds up a
logical picture of the overall network by gathering and exchanging information with other routers
in the network. Using this information, the router chooses the best path for forwarding network
traffic.
Routers vary in performance and scale, number of routing protocols supported, and types of
physical WAN connection they support. The FVS318 Broadband ProSafe VPN Firewall is a small
office router that routes the IP protocol over a single-user broadband connection.

Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
B-2 Networks, Routing, and Firewall Basics
M-10146-01
Routing Information Protocol
One of the protocols used by a router to build and maintain a picture of the network is the Routing
Information Protocol (RIP). Using RIP, routers periodically update one another and check for
changes to add to the routing table.
The FVS318 VPN Firewall supports both the older RIP-1 and the newer RIP-2 protocols. Among
other improvements, RIP-2 supports subnet and multicast protocols. RIP is not required for most
home applications.
IP Addresses and the Internet
Because TCP/IP networks are interconnected across the world, every machine on the Internet must
have a unique address to make sure that transmitted data reaches the correct destination. Blocks of
addresses are assigned to organizations by the Internet Assigned Numbers Authority (IANA).
Individual users and small organizations may obtain their addresses either from the IANA or from
an Internet service provider (ISP). You can contact IANA at www.iana.org.
The Internet Protocol (IP) uses a 32-bit address structure. The address is usually written in dot
notation (also called dotted-decimal notation), in which each group of eight bits is written in
decimal form, separated by decimal points.
For example, the following binary address:
11000011 00100010 00001100 00000111
is normally written as:
195.34.12.7
The latter version is easier to remember and easier to enter into your computer.
In addition, the 32 bits of the address are subdivided into two parts. The first part of the address
identifies the network, and the second part identifies the host node or station on the network. The
dividing point may vary depending on the address range and the application.
There are five standard classes of IP addresses. These address classes have different ways of
determining the network and host sections of the address, allowing for different numbers of hosts
on a network. Each address type begins with a unique bit pattern, which is used by the TCP/IP
software to identify the address class. After the address class has been determined, the software
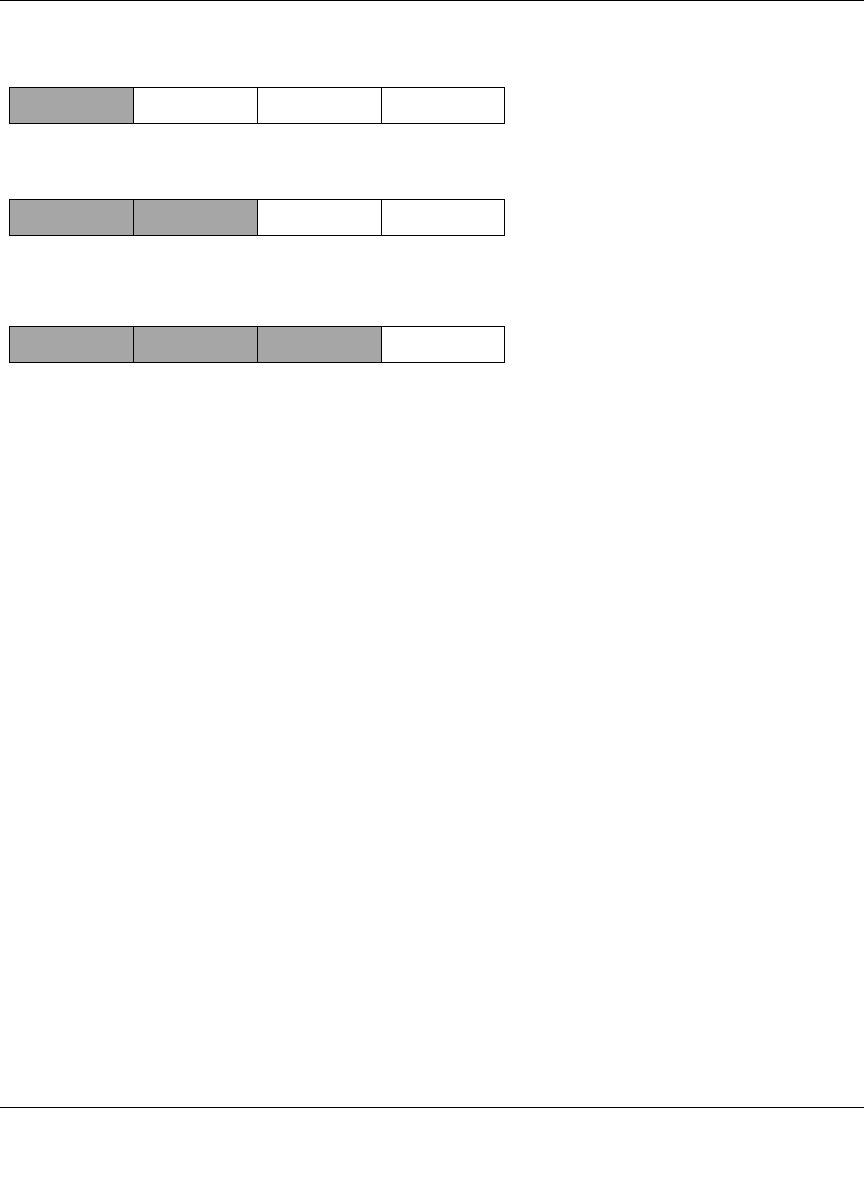
can correctly identify the host section of the address. The follow figure shows the three main
address classes, including network and host sections of the address for each address type.
Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
Networks, Routing, and Firewall Basics B-3
M-10146-01
Figure B-1: Three Main Address Classes
The five address classes are:
• Class A
Class A addresses can have up to 16,777,214 hosts on a single network. They use an eight-bit
network number and a 24-bit node number. Class A addresses are in this range:
1.x.x.x to 126.x.x.x.
• Class B
Class B addresses can have up to 65,354 hosts on a network. A Class B address uses a 16-bit
network number and a 16-bit node number. Class B addresses are in this range:
128.1.x.x to 191.254.x.x.
• Class C
Class C addresses can have 254 hosts on a network. Class C addresses use 24 bits for the
network address and eight bits for the node. They are in this range:
192.0.1.x to 223.255.254.x.
• Class D
Class D addresses are used for multicasts (messages sent to many hosts). Class D addresses are
in this range:
224.0.0.0 to 239.255.255.255.
• Class E
Class E addresses are for experimental use.
7261
C
lass A
N
etwork Node
C
lass B
C
lass C
Network Node
Network Node

Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
B-4 Networks, Routing, and Firewall Basics
M-10146-01
This addressing structure allows IP addresses to uniquely identify each physical network and each
node on each physical network.
For each unique value of the network portion of the address, the base address of the range (host
address of all zeros) is known as the network address and is not usually assigned to a host. Also,
the top address of the range (host address of all ones) is not assigned, but is used as the broadcast
address for simultaneously sending a packet to all hosts with the same network address.
Netmask
In each of the address classes previously described, the size of the two parts (network address and
host address) is implied by the class. This partitioning scheme can also be expressed by a netmask
associated with the IP address. A netmask is a 32-bit quantity that, when logically combined (using
an AND operator) with an IP address, yields the network address. For instance, the netmasks for
Class A, B, and C addresses are 255.0.0.0, 255.255.0.0, and 255.255.255.0, respectively.
For example, the address 192.168.170.237 is a Class C IP address whose network portion is the
upper 24 bits. When combined (using an AND operator) with the Class C netmask, as shown here,
only the network portion of the address remains:
11000000 10101000 10101010 11101101 (192.168.170.237)
combined with:
11111111 11111111 11111111 00000000 (255.255.255.0)
Equals:
11000000 10101000 10101010 00000000 (192.168.170.0)
As a shorter alternative to dotted-decimal notation, the netmask may also be expressed in terms of
the number of ones from the left. This number is appended to the IP address, following a backward
slash (/), as “/n.” In the example, the address could be written as 192.168.170.237/24, indicating
that the netmask is 24 ones followed by 8 zeros.
Subnet Addressing
By looking at the addressing structures, you can see that even with a Class C address, there are a
large number of hosts per network. Such a structure is an inefficient use of addresses if each end of
a routed link requires a different network number. It is unlikely that the smaller office LANs would
have that many devices. You can resolve this problem by using a technique known as subnet
addressing.
Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
Networks, Routing, and Firewall Basics B-5
M-10146-01
Subnet addressing allows us to split one IP network address into smaller multiple physical
networks known as subnetworks. Some of the node numbers are used as a subnet number instead.
A Class B address gives us 16 bits of node numbers translating to 64,000 nodes. Most
organizations do not use 64,000 nodes, so there are free bits that can be reassigned. Subnet
addressing makes use of those bits that are free, as shown below.
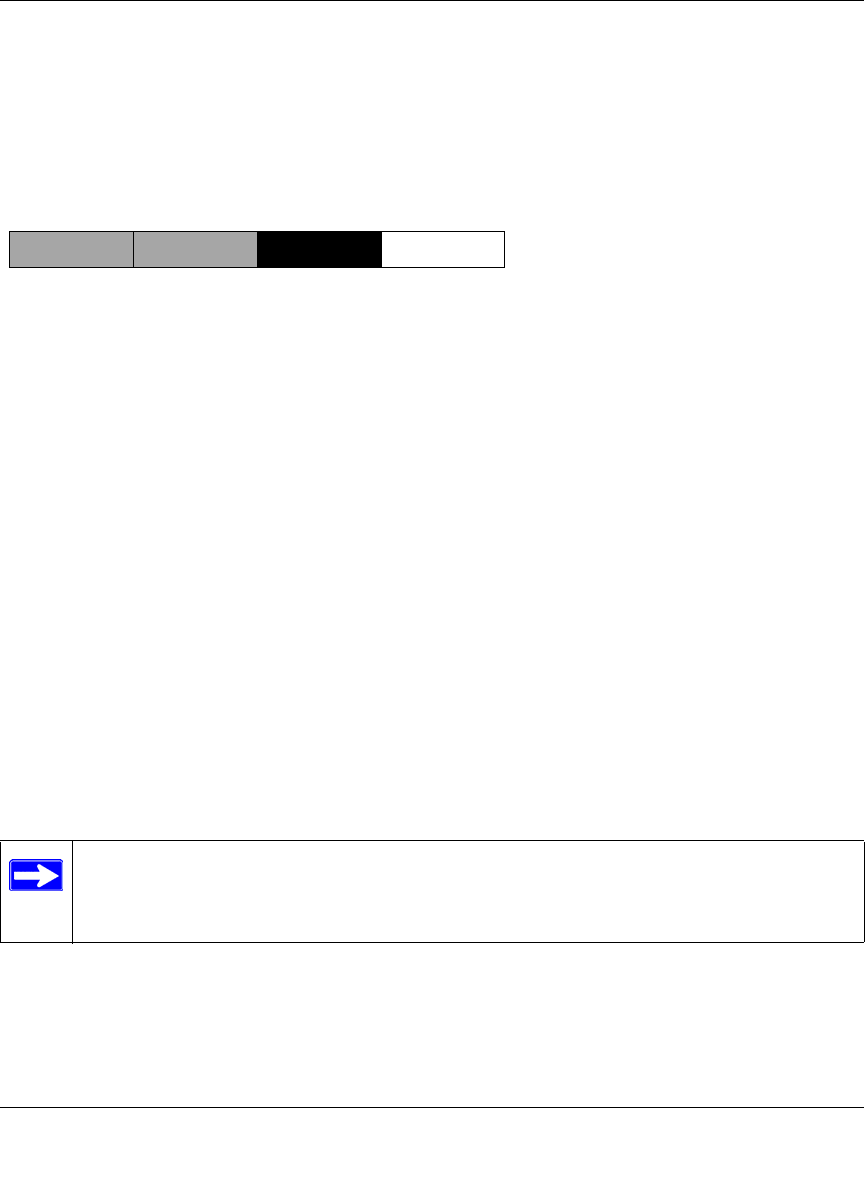
Figure B-2: Example of Subnetting a Class B Address
A Class B address can be effectively translated into multiple Class C addresses. For example, the
IP address of 172.16.0.0 is assigned, but node addresses are limited to 255 maximum, allowing
eight extra bits to use as a subnet address. The IP address of 172.16.97.235 would be interpreted as
IP network address 172.16, subnet number 97, and node number 235. In addition to extending
the number of addresses available, subnet addressing provides other benefits. Subnet addressing
allows a network manager to construct an address scheme for the network by using different
subnets for other geographical locations in the network or for other departments in the
organization.
Although the preceding example uses the entire third octet for a subnet address, note that you are
not restricted to octet boundaries in subnetting. To create more network numbers, you need only
shift some bits from the host address to the network address. For instance, to partition a Class C
network number (192.68.135.0) into two, you shift one bit from the host address to the network
address. The new netmask (or subnet mask) is 255.255.255.128. The first subnet has network
number 192.68.135.0 with hosts 192.68.135.1 to 129.68.135.126, and the second subnet has
network number 192.68.135.128 with hosts 192.68.135.129 to 192.68.135.254.
Note: The number 192.68.135.127 is not assigned because it is the broadcast address
of the first subnet. The number 192.68.135.128 is not assigned because it is the network
address of the second subnet.
7262
C
lass B
Network Subnet Node
Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
B-6 Networks, Routing, and Firewall Basics
M-10146-01
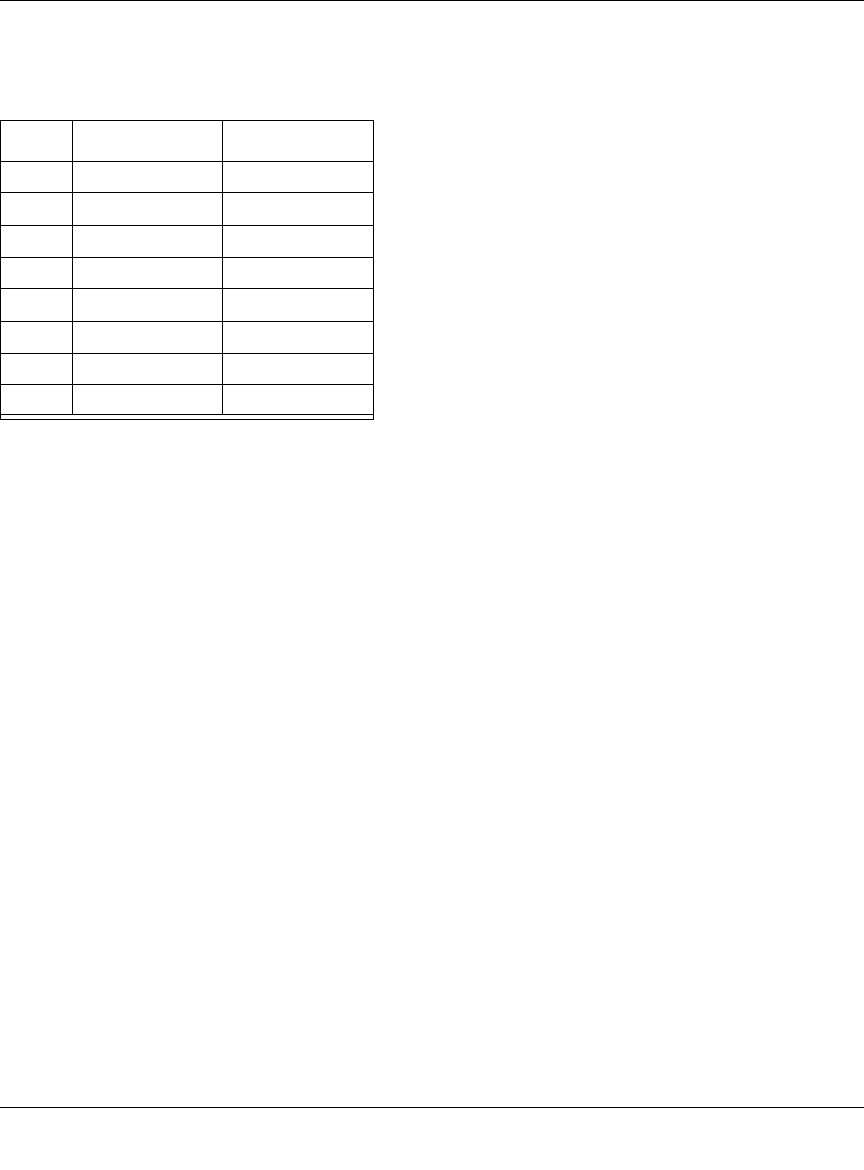
The following table lists the additional subnet mask bits in dotted-decimal notation. To use the
table, write down the original class netmask and replace the 0 value octets with the dotted-decimal
value of the additional subnet bits. For example, to partition your Class C network with subnet
mask 255.255.255.0 into 16 subnets (4 bits), the new subnet mask becomes 255.255.255.240.
The following table displays several common netmask values in both the dotted-decimal and the
mask length formats.
Table B-1. Netmask Notation Translation Table for One Octet
Number of Bits Dotted-Decimal Value
1 128
2 192
3 224
4 240
5 248
6 252
7 254
8 255
Table B-2. Netmask Formats
Dotted-Decimal Masklength
255.0.0.0 /8
255.255.0.0 /16
255.255.255.0 /24
255.255.255.128 /25
255.255.255.192 /26
255.255.255.224 /27
255.255.255.240 /28
255.255.255.248 /29
255.255.255.252 /30

Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
Networks, Routing, and Firewall Basics B-7
M-10146-01
NETGEAR strongly recommends that you configure all hosts on a LAN segment to use the same
netmask for the following reasons:
• So that hosts recognize local IP broadcast packets
When a device broadcasts to its segment neighbors, it uses a destination address of the local
network address with all ones for the host address. In order for this scheme to work, all devices
on the segment must agree on which bits comprise the host address.
• So that a local router or bridge recognizes which addresses are local and which are remote
Private IP Addresses
If your local network is isolated from the Internet (for example, when using NAT), you can assign
any IP addresses to the hosts without problems. However, the IANA has reserved the following
three blocks of IP addresses specifically for private networks:
10.0.0.0 - 10.255.255.255
172.16.0.0 - 172.31.255.255
192.168.0.0 - 192.168.255.255
NETGEAR recommends that you choose your private network number from this range. The
DHCP server of the FVS318 VPN Firewall is preconfigured to automatically assign private
addresses.
Regardless of your particular situation, do not create an arbitrary IP address; always follow the
guidelines explained here. For more information about address assignment, refer to RFC 1597,
Address Allocation for Private Internets, and RFC 1466, Guidelines for Management of IP
Address Space. The Internet Engineering Task Force (IETF) publishes RFCs on its Web site at
www.ietf.org.
255.255.255.254 /31
255.255.255.255 /32
Table B-2. Netmask Formats
Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
B-8 Networks, Routing, and Firewall Basics
M-10146-01
Single IP Address Operation Using NAT
In the past, if multiple PCs on a LAN needed to access the Internet simultaneously, you had to
obtain a range of IP addresses from the ISP. This type of Internet account is more costly than a
single-address account typically used by a single user with a modem, rather than a router. The
FVS318 VPN Firewall employs an address-sharing method called Network Address Translation
(NAT). This method allows several networked PCs to share an Internet account using only a single
IP address, which may be statically or dynamically assigned by your ISP.
The router accomplishes this address sharing by translating the internal LAN IP addresses to a
single address that is globally unique on the Internet. The internal LAN IP addresses can be either
private addresses or registered addresses. For more information about IP address translation, refer
to RFC 1631, The IP Network Address Translator (NAT).
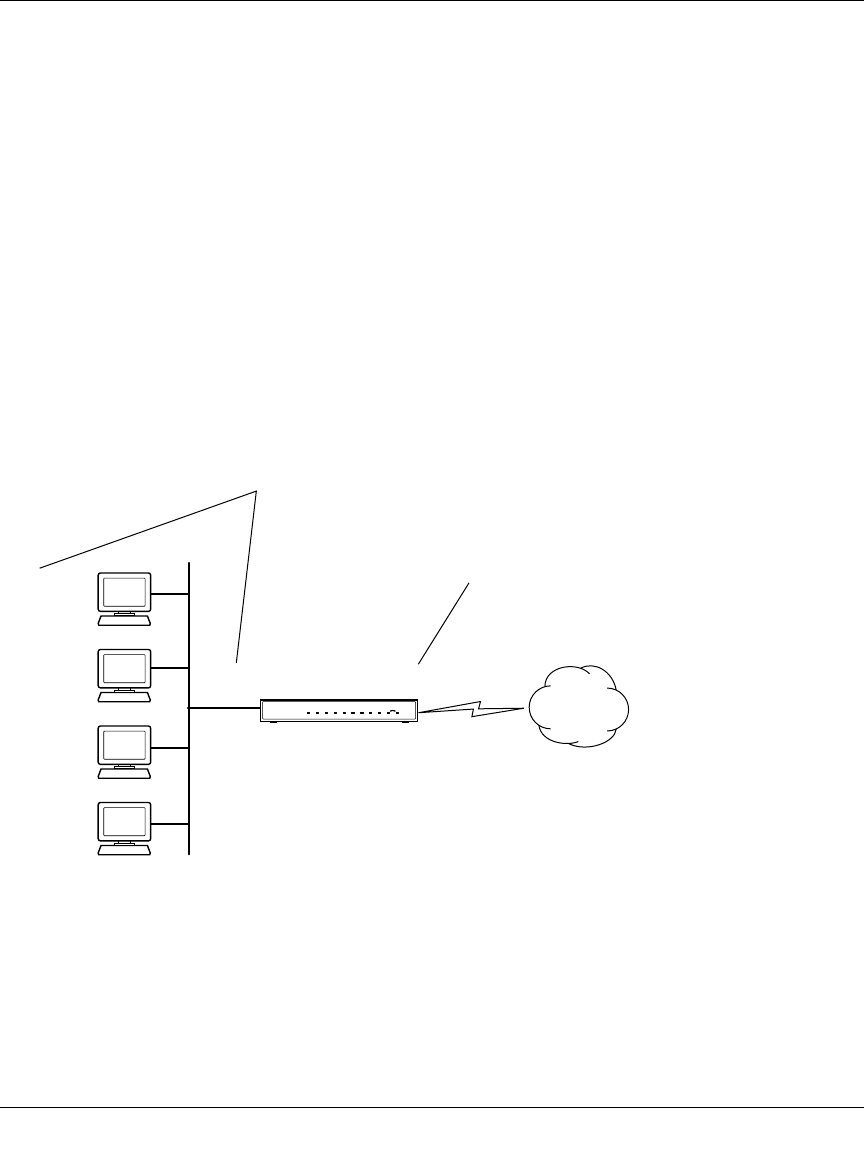
The following figure illustrates a single IP address operation.
Figure B-3: Single IP Address Operation Using NAT
This scheme offers the additional benefit of firewall-like protection because the internal LAN
addresses are not available to the Internet through the translated connection. All incoming
inquiries are filtered out by the router. This filtering can prevent intruders from probing your
system. However, using port forwarding, you can allow one PC (for example, a Web server) on
your local network to be accessible to outside users.
1
92.168.0.2
1
92.168.0.3
1
92.168.0.4
1
92.168.0.5
192.168.0.1 172.21.15.105
Private IP addresses
assigned by user
Internet
IP addresses
assigned by ISP

Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
Networks, Routing, and Firewall Basics B-9
M-10146-01
MAC Addresses and Address Resolution Protocol
An IP address alone cannot be used to deliver data from one LAN device to another. To send data
between LAN devices, you must convert the IP address of the destination device to its media
access control (MAC) address. Each device on an Ethernet network has a unique MAC address,
which is a 48-bit number assigned to each device by the manufacturer. The technique that
associates the IP address with a MAC address is known as address resolution. Internet Protocol
uses the Address Resolution Protocol (ARP) to resolve MAC addresses.
If a device sends data to another station on the network and the destination MAC address is not yet
recorded, ARP is used. An ARP request is broadcast onto the network. All stations on the network
receive and read the request. The destination IP address for the chosen station is included as part of
the message so that only the station with this IP address responds to the ARP request. All other
stations discard the request.
Related Documents
The station with the correct IP address responds with its own MAC address directly to the sending
device. The receiving station provides the transmitting station with the required destination MAC
address. The IP address data and MAC address data for each station are held in an ARP table. The
next time data is sent, the address can be obtained from the address information in the table.
For more information about address assignment, refer to the IETF documents RFC 1597, Address
Allocation for Private Internets, and RFC 1466, Guidelines for Management of IP Address Space.
For more information about IP address translation, refer to RFC 1631, The IP Network Address
Translator (NAT).
Domain Name Server
Many of the resources on the Internet can be addressed by simple descriptive names such as
www.NETGEAR.com. This addressing is very helpful at the application level, but the descriptive
name must be translated to an IP address in order for a user to actually contact the resource. Just as
a telephone directory maps names to phone numbers, or as an ARP table maps IP addresses to
MAC addresses, a domain name system (DNS) server maps descriptive names of network
resources to IP addresses.
Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
B-10 Networks, Routing, and Firewall Basics
M-10146-01
When a PC accesses a resource by its descriptive name, it first contacts a DNS server to obtain the
IP address of the resource. The PC sends the desired message using the IP address. Many large
organizations, such as ISPs, maintain their own DNS servers and allow their customers to use the
servers to look up addresses.
IP Configuration by DHCP
When an IP-based local area network is installed, each PC must be configured with an IP address.
If the PCs need to access the Internet, they should also be configured with a gateway address and
one or more DNS server addresses. As an alternative to manual configuration, there is a method by
which each PC on the network can automatically obtain this configuration information. A device
on the network may act as a Dynamic Host Configuration Protocol (DHCP) server. The DHCP
server stores a list or pool of IP addresses, along with other information (such as gateway and DNS
addresses) that it may assign to the other devices on the network. The FVS318 VPN Firewall has
the capacity to act as a DHCP server.
The FVS318 VPN Firewall also functions as a DHCP client when connecting to the ISP. The
firewall can automatically obtain an IP address, subnet mask, DNS server addresses, and a
gateway address if the ISP provides this information by DHCP.
Internet Security and Firewalls
When your LAN connects to the Internet through a router, an opportunity is created for outsiders
to access or disrupt your network. A NAT router provides some protection because by the very
nature of the Network Address Translation (NAT) process, the network behind the NAT router is
shielded from access by outsiders on the Internet. However, there are methods by which a
determined hacker can possibly obtain information about your network or at the least can disrupt
your Internet access. A greater degree of protection is provided by a firewall router.
Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
Networks, Routing, and Firewall Basics B-11
M-10146-01
What is a Firewall?
A firewall is a device that protects one network from another, while allowing communication
between the two. A firewall incorporates the functions of the NAT router, while adding features for
dealing with a hacker intrusion or attack. Several known types of intrusion or attack can be
recognized when they occur. When an incident is detected, the firewall can log details of the
attempt, and can optionally send email to an administrator notifying them of the incident. Using
information from the log, the administrator can take action with the ISP of the hacker. In some
types of intrusions, the firewall can fend off the hacker by discarding all further packets from the
hacker’s IP address for a period of time.
Stateful Packet Inspection
Unlike simple Internet sharing routers, a firewall uses a process called stateful packet inspection to
ensure secure firewall filtering to protect your network from attacks and intrusions. Since
user-level applications such as FTP and Web browsers can create complex patterns of network
traffic, it is necessary for the firewall to analyze groups of network connection states. Using
Stateful Packet Inspection, an incoming packet is intercepted at the network layer and then
analyzed for state-related information associated with all network connections. A central cache
within the firewall keeps track of the state information associated with all network connections.
All traffic passing through the firewall is analyzed against the state of these connections in order to
determine whether or not it will be allowed to pass through or rejected.
Denial of Service Attack
A hacker may be able to prevent your network from operating or communicating by launching a
Denial of Service (DoS) attack. The method used for such an attack can be as simple as merely
flooding your site with more requests than it can handle. A more sophisticated attack may attempt
to exploit some weakness in the operating system used by your router or gateway. Some operating
systems can be disrupted by simply sending a packet with incorrect length information.
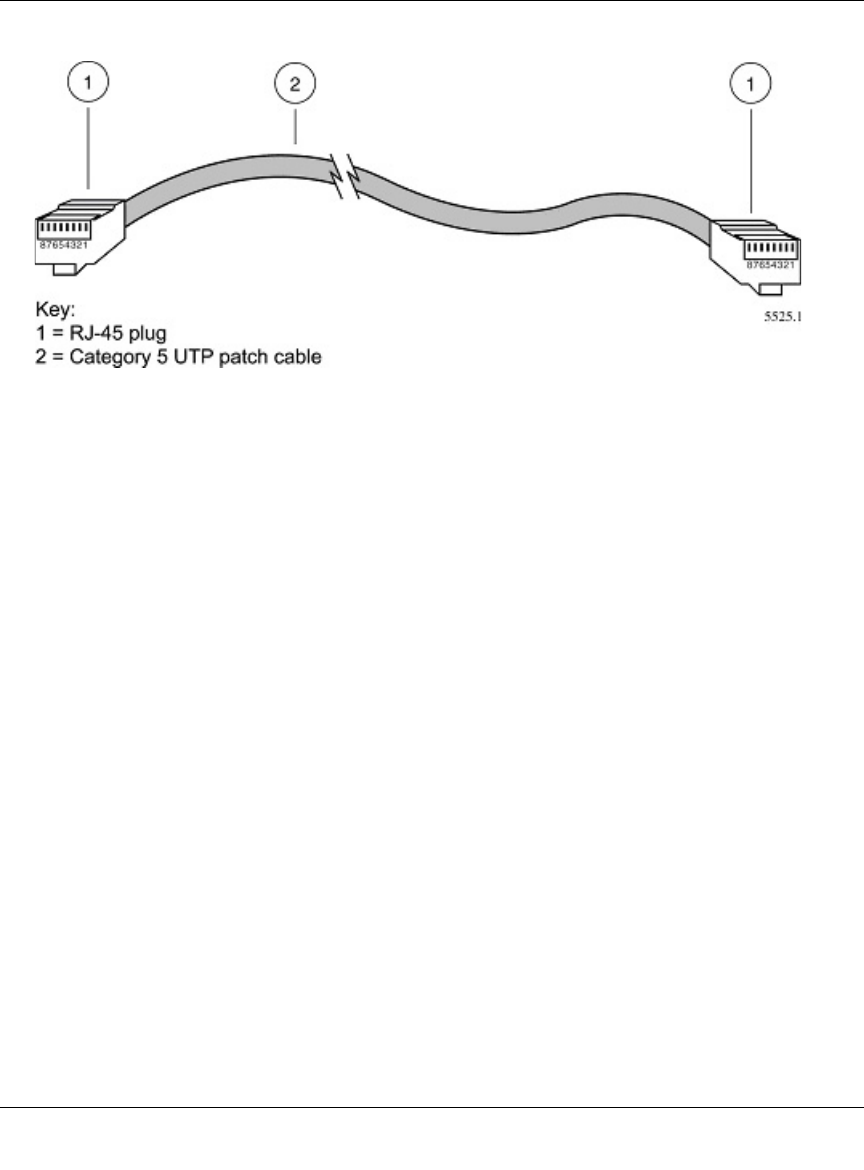
Ethernet Cabling
Although Ethernet networks originally used thick or thin coaxial cable, most installations currently
use unshielded twisted pair (UTP) cabling. The UTP cable contains eight conductors, arranged in
four twisted pairs, and terminated with an RJ45 type connector. A normal straight-through UTP
Ethernet cable follows the EIA568B standard wiring as described below in Table B-1
Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
B-12 Networks, Routing, and Firewall Basics
M-10146-01
.
Category 5 Cable Quality
Category 5 distributed cable that meets ANSI/EIA/TIA-568-A building wiring standards can be a
maximum of 328 feet (ft.) or 100 meters (m) in length, divided as follows:
20 ft. (6 m) between the hub and the patch panel (if used)
295 ft. (90 m) from the wiring closet to the wall outlet
10 ft. (3 m) from the wall outlet to the desktop device
The patch panel and other connecting hardware must meet the requirements for 100 Mbps
operation (Category 5). Only 0.5 inch (1.5 cm) of untwist in the wire pair is allowed at any
termination point.
A twisted pair Ethernet network operating at 10 Mbits/second (10BASE-T) will often tolerate low
quality cables, but at 100 Mbits/second (10BASE-Tx) the cable must be rated as Category 5, or
Cat 5, by the Electronic Industry Association (EIA). This rating will be printed on the cable jacket.
A Category 5 cable will meet specified requirements regarding loss and crosstalk. In addition,
there are restrictions on maximum cable length for both 10 and 100 Mbits/second networks.
Table B-1. UTP Ethernet cable wiring, straight-through
Pin Wire color Signal
1 Orange/White Transmit (Tx) +
2 Orange Transmit (Tx) -
3 Green/White Receive (Rx) +
4Blue
5 Blue/White
6 Green Receive (Rx) -
7 Brown/White
8Brown
Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
Networks, Routing, and Firewall Basics B-13
M-10146-01
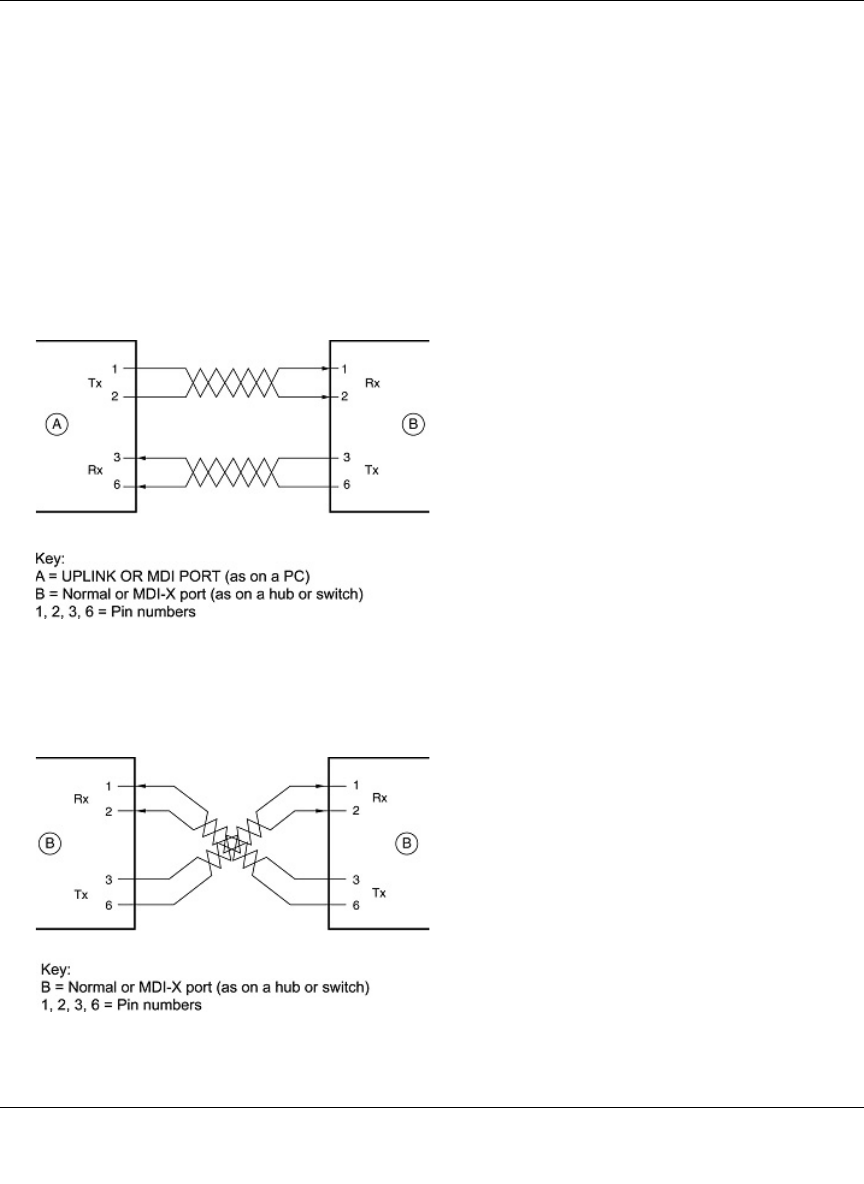
Inside Twisted Pair Cables
For two devices to communicate, the transmitter of each device must be connected to the receiver
of the other device. The crossover function is usually implemented internally as part of the
circuitry in the device. Computers and workstation adapter cards are usually media-dependent
interface ports, called MDI or uplink ports. Most repeaters and switch ports are configured as
media-dependent interfaces with built-in crossover ports, called MDI-X or normal ports. Auto
Uplink technology automatically senses which connection, MDI or MDI-X, is needed and makes
the right connection.
Figure B-4 illustrates straight-through twisted pair cable.
Figure B-4: Straight-Through Twisted-Pair Cable
Figure B-5 illustrates crossover twisted pair cable.
Figure B-5: Crossover Twisted-Pair Cable
Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
B-14 Networks, Routing, and Firewall Basics
M-10146-01
Figure B-6: Category 5 UTP Cable with Male RJ-45 Plug at Each End
Note: Flat “silver satin” telephone cable may have the same RJ-45 plug. However, using telephone
cable results in excessive collisions, causing the attached port to be partitioned or disconnected
from the network.
Uplink Switches, Crossover Cables, and MDI/MDIX Switching
In the wiring table above, the concept of transmit and receive are from the perspective of the PC,
which is wired as Media Dependant Interface (MDI). In this wiring, the PC transmits on pins 1 and
2. At the hub, the perspective is reversed, and the hub receives on pins 1 and 2. This wiring is
referred to as Media Dependant Interface - Crossover (MDI-X).
When connecting a PC to a PC, or a hub port to another hub port, the transmit pair must be
exchanged with the receive pair. This exchange is done by one of two mechanisms. Most hubs
provide an Uplink switch which will exchange the pairs on one port, allowing that port to be
connected to another hub using a normal Ethernet cable. The second method is to use a crossover
cable, which is a special cable in which the transmit and receive pairs are exchanged at one of the
two cable connectors. Crossover cables are often unmarked as such, and must be identified by
comparing the two connectors. Since the cable connectors are clear plastic, it is easy to place them
side by side and view the order of the wire colors on each. On a straight-through cable, the color
order will be the same on both connectors. On a crossover cable, the orange and blue pairs will be
exchanged from one connector to the other.

Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
Networks, Routing, and Firewall Basics B-15
M-10146-01
The FVS318 VPN Firewall incorporates Auto UplinkTM technology (also called MDI/MDIX).
Each LOCAL Ethernet port will automatically sense whether the Ethernet cable plugged into the
port should have a normal connection (e.g. connecting to a PC) or an uplink connection (e.g.
connecting to a router, switch, or hub). That port will then configure itself to the correct
configuration. This feature also eliminates the need to worry about crossover cables, as Auto
UplinkTM will accommodate either type of cable to make the right connection.

Reference Manual for the Model FVS318 Broadband ProSafe VPN Firewall
B-16 Networks, Routing, and Firewall Basics
M-10146-01
Preparing Your Network C-1
M-10177-01
Appendix C
Preparing Your Network
This appendix describes how to prepare your network to connect to the Internet through the
ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P and how to verify the readiness
of broadband Internet service from an Internet service provider (ISP).
Preparing Your Computers for TCP/IP Networking
Computers access the Internet using a protocol called TCP/IP (Transmission Control Protocol/
Internet Protocol). Each computer on your network must have TCP/IP installed and selected as its
networking protocol. If a Network Interface Card (NIC) is already installed in your PC, then TCP/
IP is probably already installed as well.
Most operating systems include the software components you need for networking with TCP/IP:
•Windows
® 95 or later includes the software components for establishing a TCP/IP network.
• Windows 3.1 does not include a TCP/IP component. You need to purchase a third-party TCP/
IP application package such as NetManage Chameleon.
• Macintosh Operating System 7 or later includes the software components for establishing a
TCP/IP network.
• All versions of UNIX or Linux include TCP/IP components. Follow the instructions provided
with your operating system or networking software to install TCP/IP on your computer.
Note: If an ISP technician configured your computer during the installation of a
broadband modem, or if you configured it using instructions provided by your ISP, you
may need to copy the current configuration information for use in the configuration of
your firewall. Write down this information before reconfiguring your computers. Refer
to “Obtaining ISP Configuration Information for Windows Computers” on page C-19 or
“Obtaining ISP Configuration Information for Macintosh Computers” on page C-20 for
further information.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
C-2 Preparing Your Network
M-10177-01
In your IP network, each PC and the firewall must be assigned a unique IP addresses. Each PC
must also have certain other IP configuration information such as a subnet mask (netmask), a
domain name server (DNS) address, and a default gateway address. In most cases, you should
install TCP/IP so that the PC obtains its specific network configuration information automatically
from a DHCP server during bootup. For a detailed explanation of the meaning and purpose of
these configuration items, refer to “Appendix B, “Network, Routing, Firewall, and Basics.”
The FWG114P Wireless Firewall/Print Server is shipped preconfigured as a DHCP server. The
firewall assigns the following TCP/IP configuration information automatically when the PCs are
rebooted:
• PC or workstation IP addresses—192.168.0.2 through 192.168.0.254
• Subnet mask—255.255.255.0
• Gateway address (the firewall)—192.168.0.1
These addresses are part of the IETF-designated private address range for use in private networks.
Configuring Windows 95, 98, and Me for TCP/IP Networking
As part of the PC preparation process, you need to manually install and configure TCP/IP on each
networked PC. Before starting, locate your Windows CD; you may need to insert it during the
TCP/IP installation process.
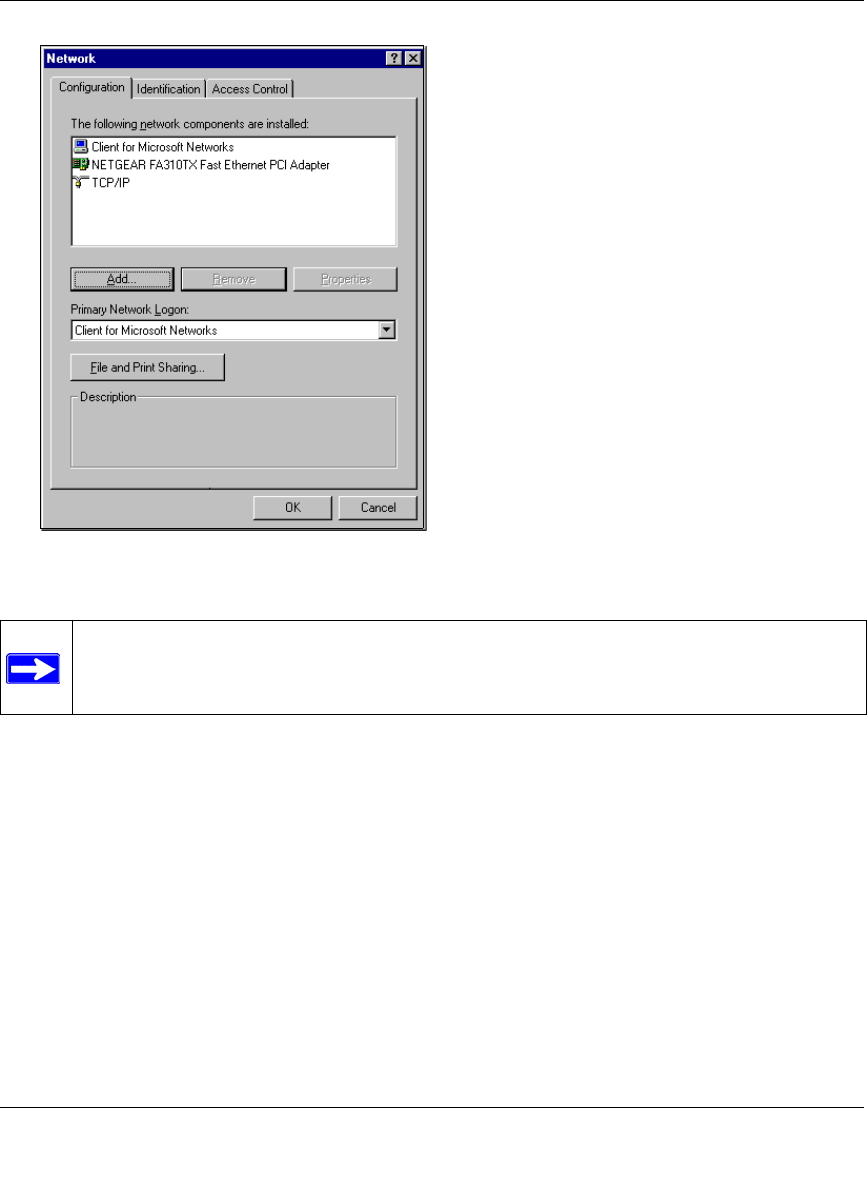
Install or Verify Windows Networking Components
To install or verify the necessary components for IP networking:
1. On the Windows taskbar, click the Start button, point to Settings, and then click Control Panel.
2. Double-click the Network icon.
The Network window opens, which displays a list of installed components:
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Preparing Your Network C-3
M-10177-01
You must have an Ethernet adapter, the TCP/IP protocol, and Client for Microsoft Networks.
If you need to install a new adapter, follow these steps:
a. Click the Add button.
b. Select Adapter, and then click Add.
c. Select the manufacturer and model of your Ethernet adapter, and then click OK.
If you need TCP/IP:
a. Click the Add button.
b. Select Protocol, and then click Add.
c. Select Microsoft.
d. Select TCP/IP, and then click OK.
Note: It is not necessary to remove any other network components shown in the
Network window in order to install the adapter, TCP/IP, or Client for Microsoft
Networks.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
C-4 Preparing Your Network
M-10177-01
If you need Client for Microsoft Networks:
a. Click the Add button.
b. Select Client, and then click Add.
c. Select Microsoft.
d. Select Client for Microsoft Networks, and then click OK.
3. Restart your PC for the changes to take effect.
Enabling DHCP to Automatically Configure TCP/IP Settings
After the TCP/IP protocol components are installed, each PC must be assigned specific
information about itself and resources that are available on its network. The simplest way to
configure this information is to allow the PC to obtain the information from a DHCP server in the
network.
You will find there are many similarities in the procedures for different Windows systems
when using DHCP to configure TCP/IP.
The following steps will walk you through the configuration process for each of these
versions of Windows.
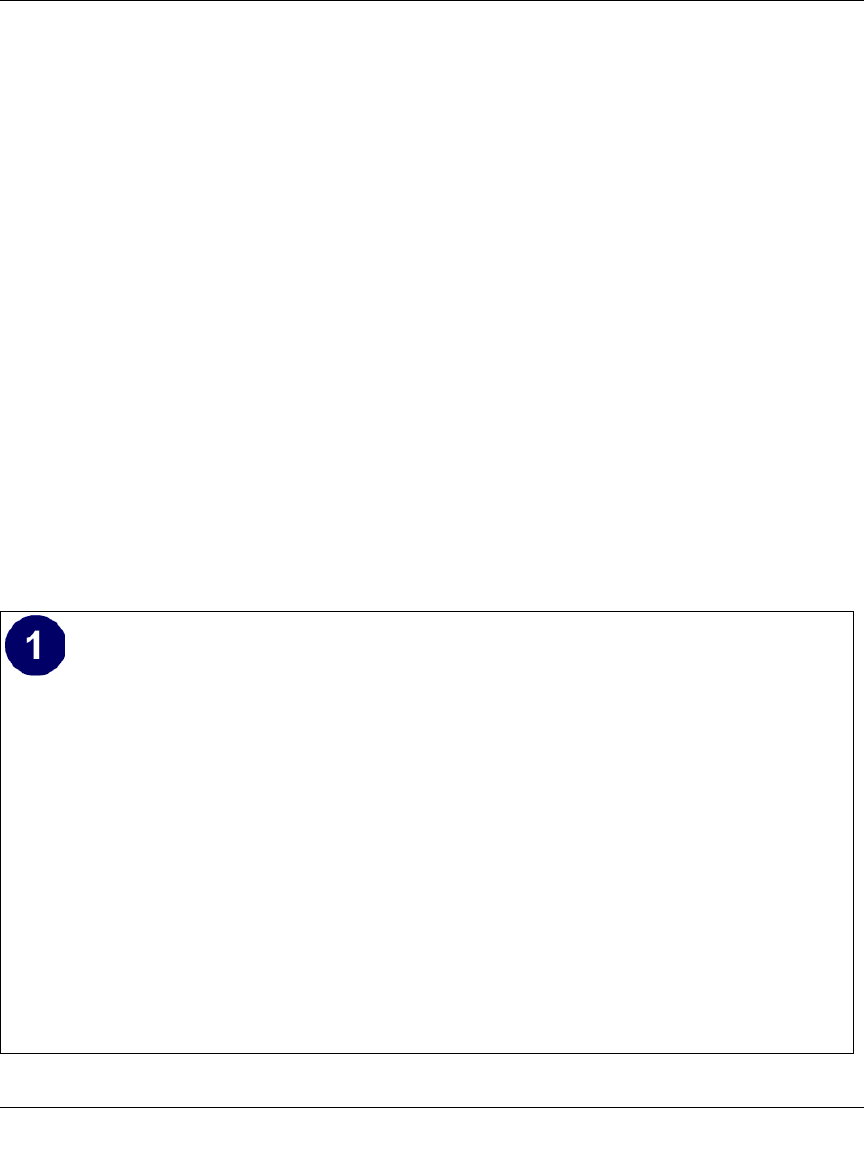
Locate your Network Neighborhood icon.
• If the Network Neighborhood icon is on the Windows desktop, position your mouse
pointer over it and right-click your mouse button.
• If the icon is not on the desktop,
• Click Start on the task bar located at the bottom left of the window.
• Choose Settings, and then Control Panel.
• Locate the Network Neighborhood icon and click on it. This will open the Network
panel as shown below.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Preparing Your Network C-5
M-10177-01
Verify the following settings as shown:
• Client for Microsoft Network exists
• Ethernet adapter is present
• TCP/IP is present
•Primary Network Logon is set to
Windows logon
Click on the Properties button. The
following TCP/IP Properties window will
display.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
C-6 Preparing Your Network
M-10177-01
Selecting Windows’ Internet Access Method
1. On the Windows taskbar, click the Start button, point to Settings, and then click Control Panel.
2. Double-click the Internet Options icon.
3. Select “I want to set up my Internet connection manually” or “I want to connect through a
Local Area Network” and click Next.
4. Select “I want to connect through a Local Area Network” and click Next.
5. Uncheck all boxes in the LAN Internet Configuration screen and click Next.
6. Proceed to the end of the Wizard.
Verifying TCP/IP Properties
After your PC is configured and has rebooted, you can check the TCP/IP configuration using the
utility winipcfg.exe:
1. On the Windows taskbar, click the Start button, and then click Run.
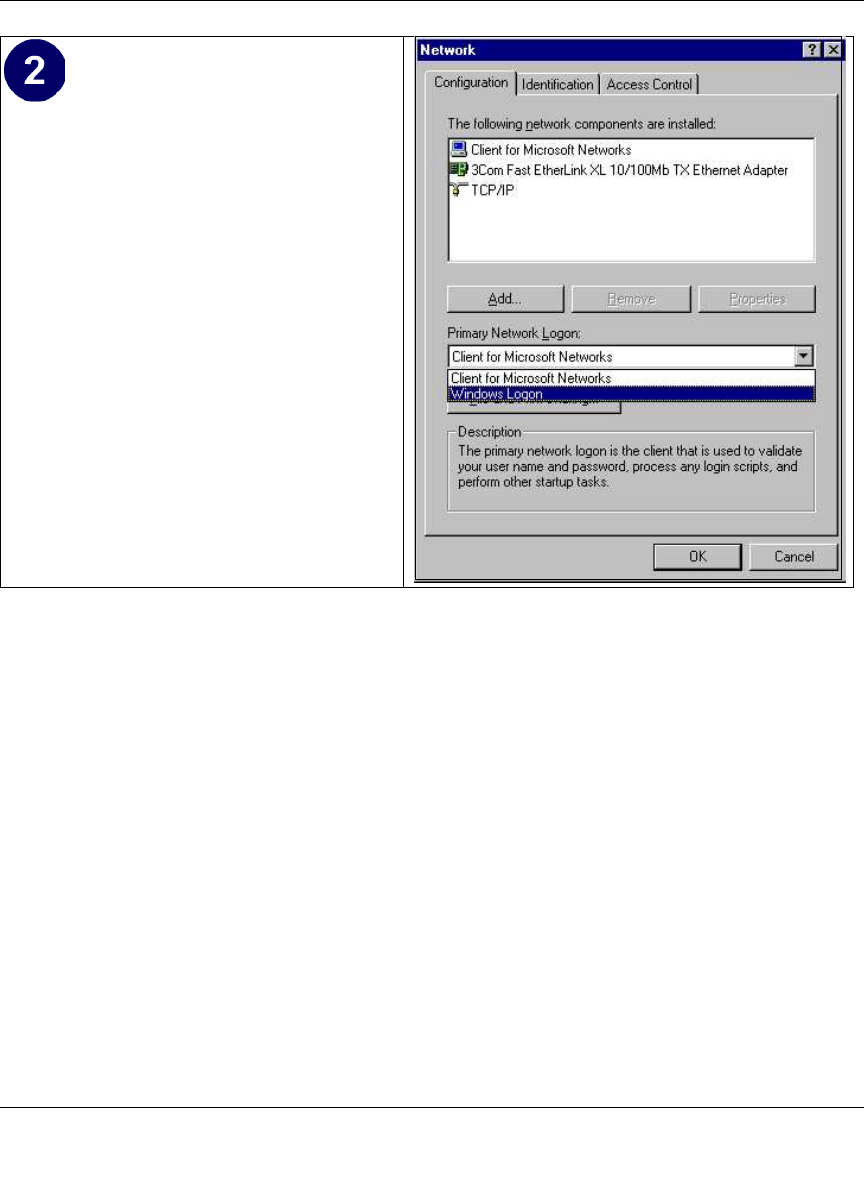
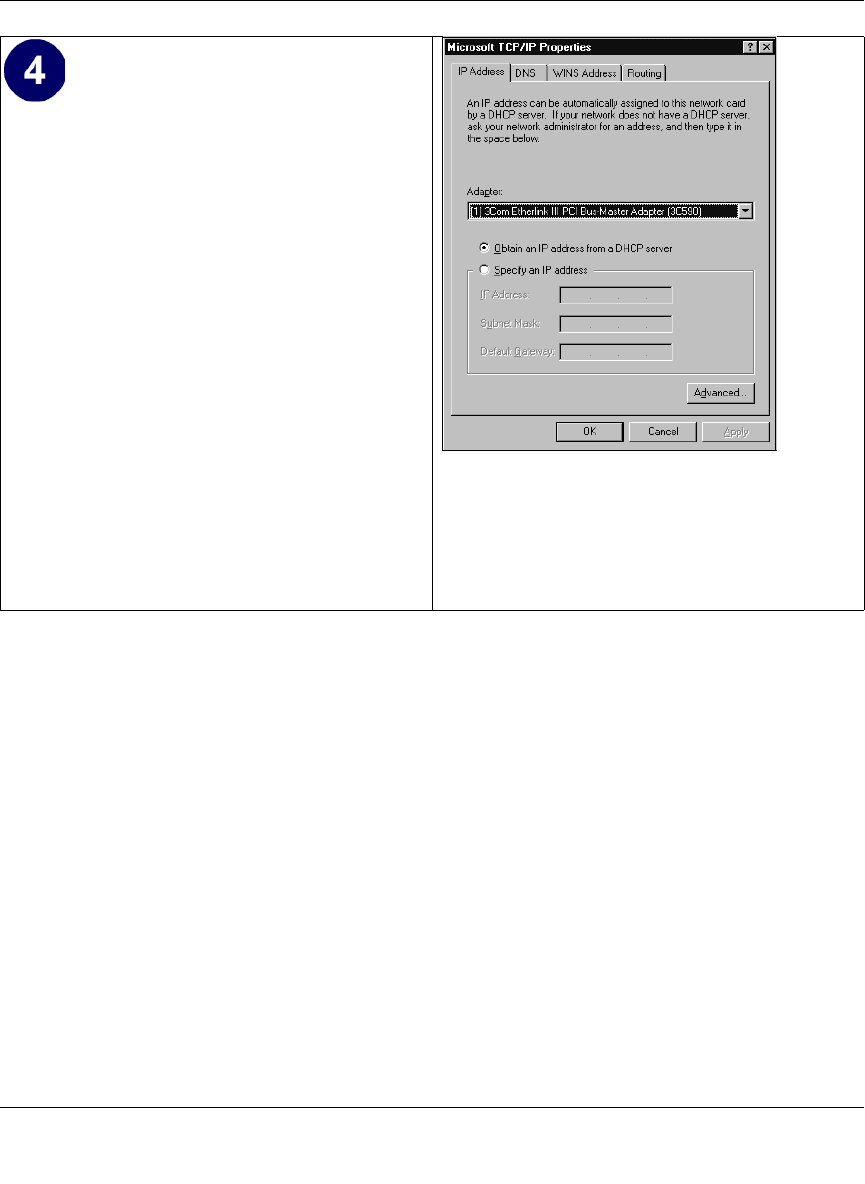
• By default, the IP Address tab is open on
this window.
• Verify the following:
Obtain an IP address automatically is
selected. If not selected, click in the radio
button to the left of it to select it. This
setting is required to enable the DHCP server
to automatically assign an IP address.
• Click OK to continue.
Restart the PC.
Repeat these steps for each PC with this
version of Windows on your network.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Preparing Your Network C-7
M-10177-01
2. Type winipcfg, and then click OK.
The IP Configuration window opens, which lists (among other things), your IP address, subnet
mask, and default gateway.
3. From the drop-down box, select your Ethernet adapter.
The window is updated to show your settings, which should match the values below if you are
using the default TCP/IP settings that NETGEAR recommends for connecting through a
router or gateway:
• The IP address is between 192.168.0.2 and 192.168.0.254
• The subnet mask is 255.255.255.0
• The default gateway is 192.168.0.1
Configuring Windows NT4, 2000 or XP for IP Networking
As part of the PC preparation process, you may need to install and configure
TCP/IP on each networked PC. Before starting, locate your Windows CD; you may need to insert
it during the TCP/IP installation process.
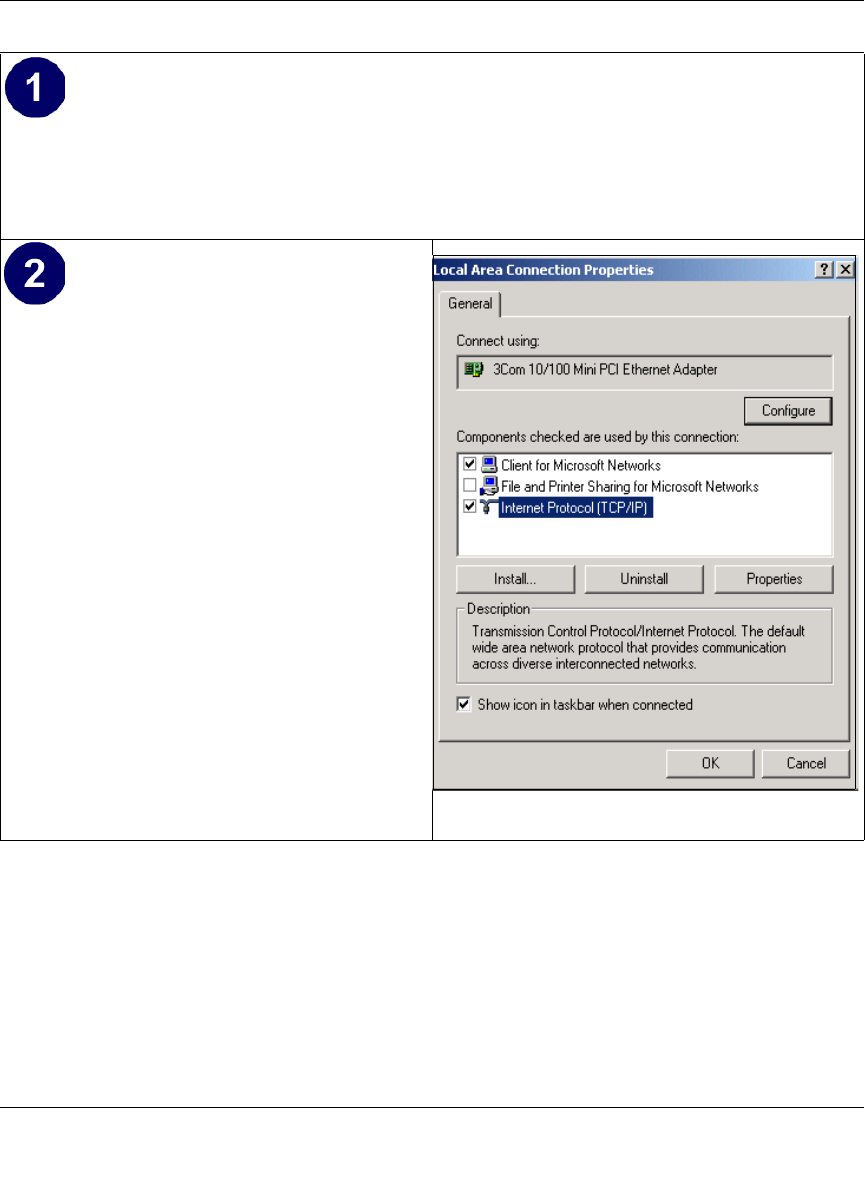
Install or Verify Windows Networking Components
To install or verify the necessary components for IP networking:
1. On the Windows taskbar, click the Start button, point to Settings, and then click Control Panel.
2. Double-click the Network and Dialup Connections icon.
3. If an Ethernet adapter is present in your PC, you should see an entry for Local Area
Connection. Double-click that entry.
4. Select Properties.
5. Verify that ‘Client for Microsoft Networks’ and ‘Internet Protocol (TCP/IP)’ are present. If
not, select Install and add them.
6. Select ‘Internet Protocol (TCP/IP)’, click Properties, and verify that “Obtain an IP address
automatically is selected.
7. Click OK and close all Network and Dialup Connections windows.
8. Then, restart your PC.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
C-8 Preparing Your Network
M-10177-01
Enabling DHCP to Automatically Configure TCP/IP Settings
You will find there are many similarities in the procedures for different Windows systems when
using DHCP to configure TCP/IP.
The following steps will walk you through the configuration process for each of these versions of
Windows.
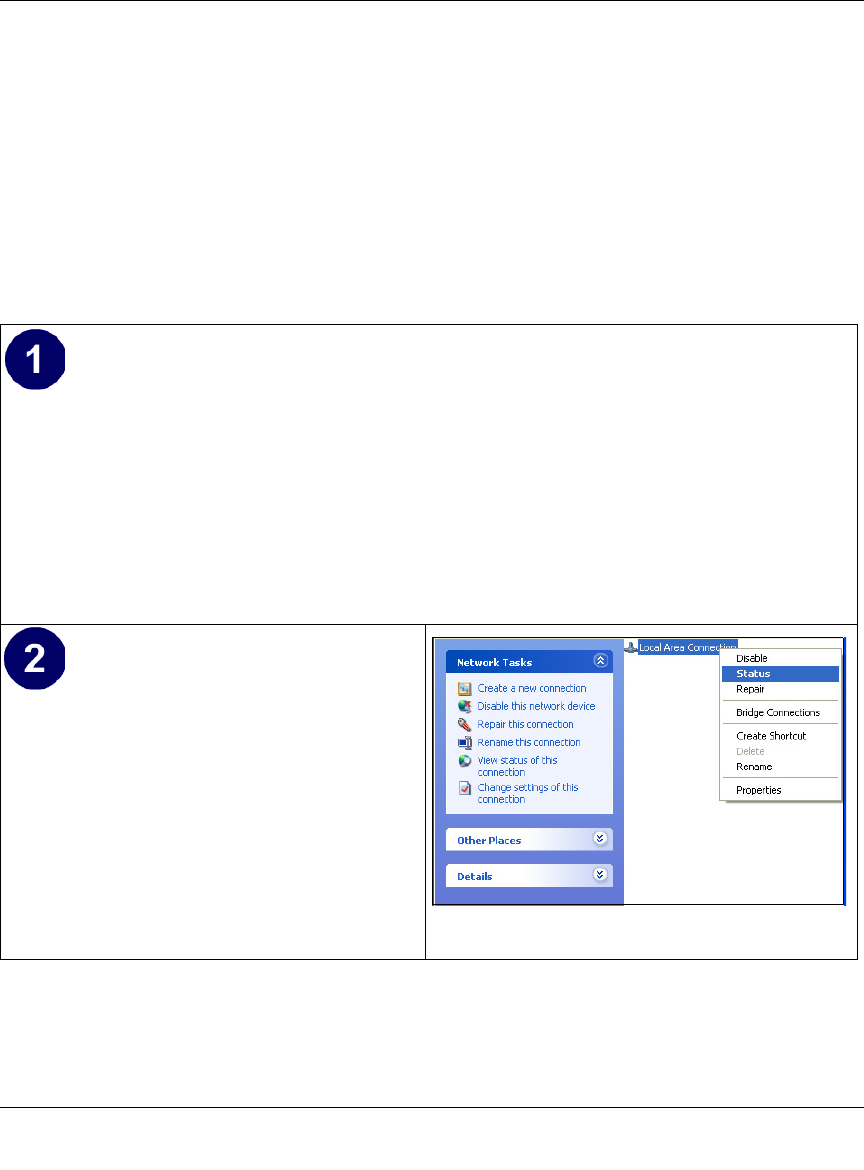
DHCP Configuration of TCP/IP in Windows XP
Locate your Network Neighborhood icon.
• Select Control Panel from the Windows XP new Start Menu.
• Select the Network Connections icon on the Control Panel. This will take you to the next
step.
• Now the Network Connection window
displays.
The Connections List that shows all the
network connections set up on the PC,
located to the right of the window.
• Right-click on the Connection you will
use and choose Status.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Preparing Your Network C-9
M-10177-01
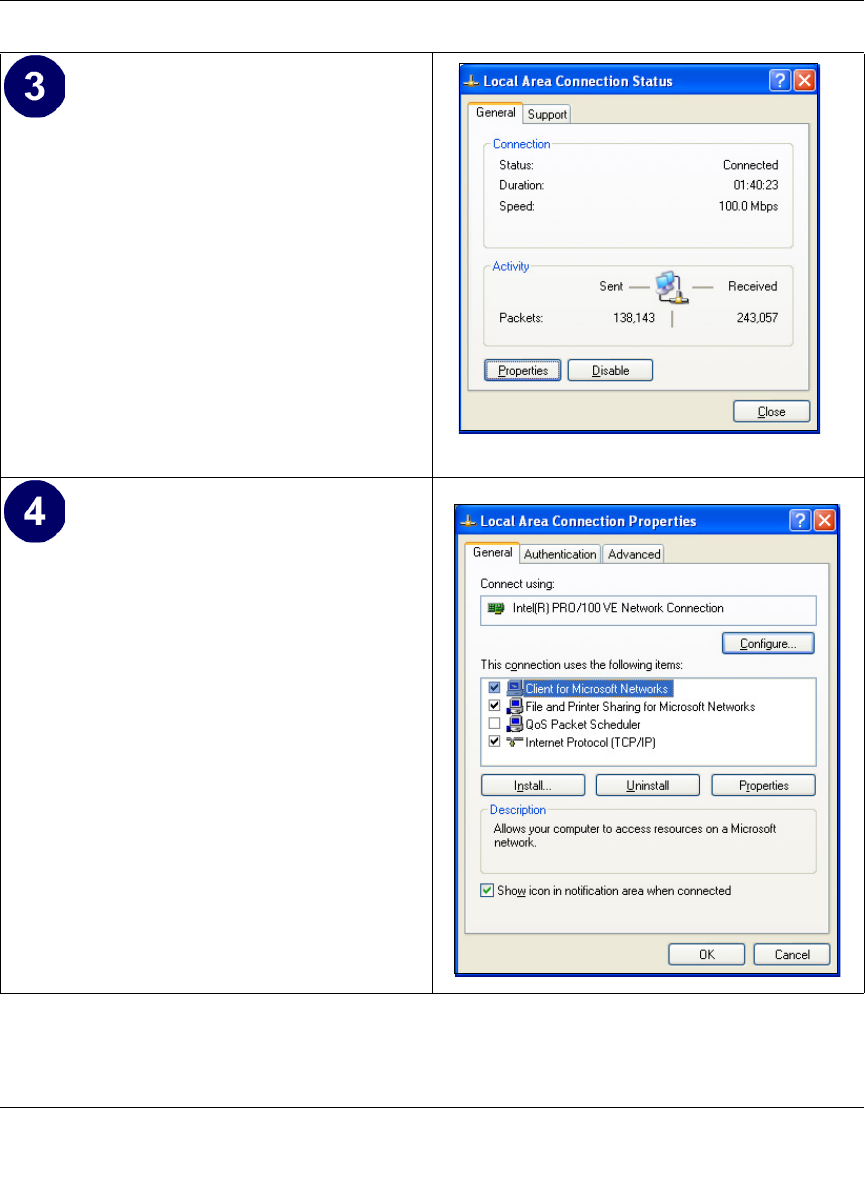
• Now you should be at the Local Area
Network Connection Status window. This
box displays the connection status, duration,
speed, and activity statistics.
• Administrator logon access rights are needed
to use this window.
• Click the Properties button to view details
about the connection.
• The TCP/IP details are presented on the
Support tab page.
• Select Internet Protocol, and click
Properties to view the configuration
information.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
C-10 Preparing Your Network
M-10177-01
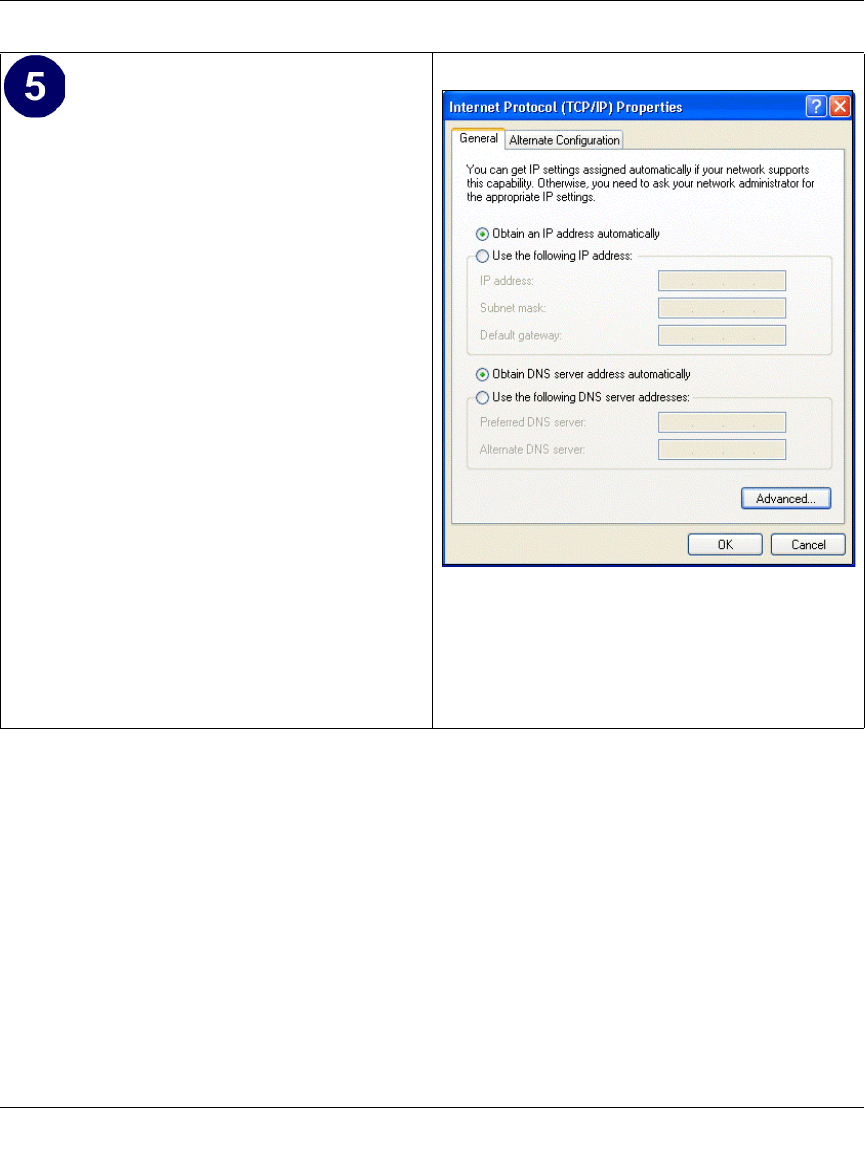
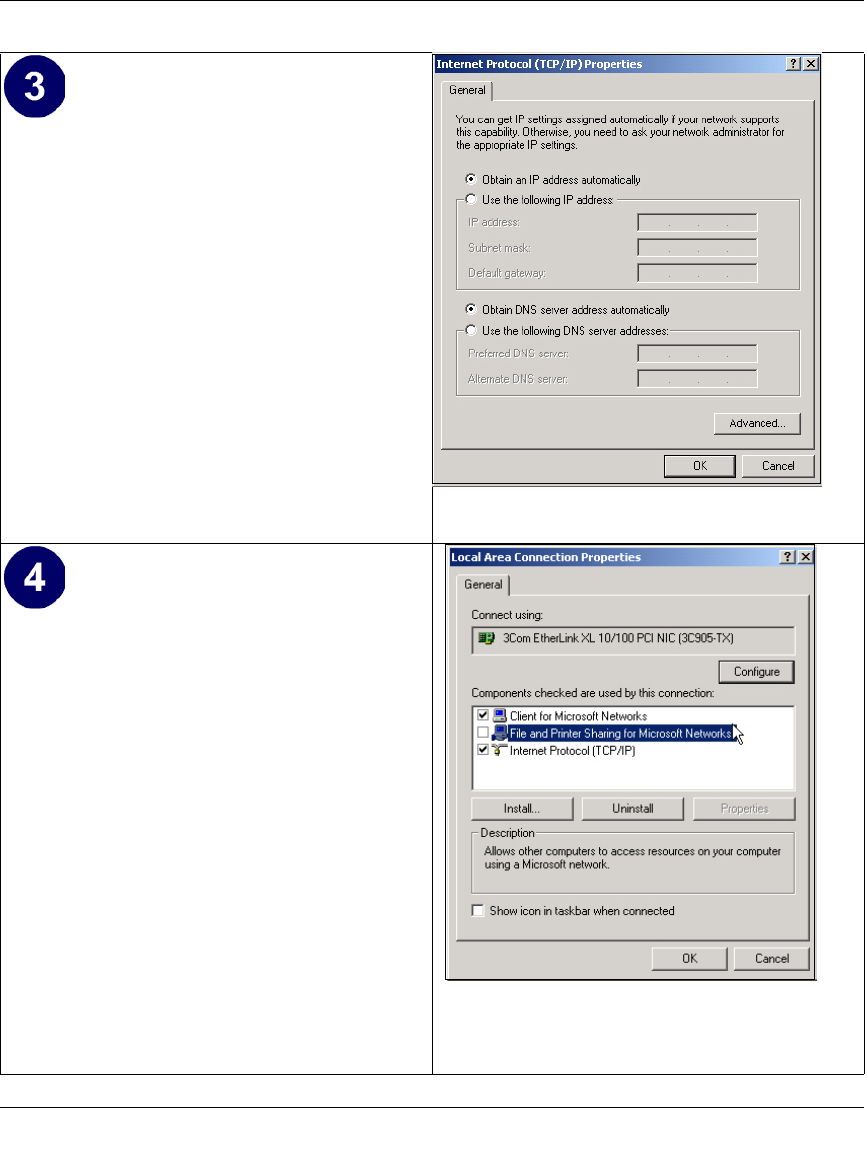
DHCP Configuration of TCP/IP in Windows 2000
Once again, after you have installed the network card, TCP/IP for Windows 2000 is configured.
TCP/IP should be added by default and set to DHCP without your having to configure it.
However, if there are problems, follow these steps to configure TCP/IP with DHCP for Windows
2000.
• Verify that the Obtain an IP address
automatically radio button is selected.
• Verify that Obtain DNS server address
automatically radio button is selected.
• Click the OK button.
This completes the DHCP configuration of TCP/
IP in Windows XP.
Repeat these steps for each PC with this version
of Windows on your network.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Preparing Your Network C-11
M-10177-01
• Click on the My Network Places icon on the Windows desktop. This will bring up a window
called Network and Dial-up Connections.
• Right click on Local Area Connection and select Properties.
•The Local Area Connection Properties
dialog box appears.
• Verify that you have the correct Ethernet
card selected in the Connect using: box.
• Verify that at least the following two items
are displayed and selected in the box of
“Components checked are used by this
connection:”
• Client for Microsoft Networks and
• Internet Protocol (TCP/IP)
• Click OK.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
C-12 Preparing Your Network
M-10177-01
• With Internet Protocol (TCP/IP) selected,
click on Properties to open the Internet
Protocol (TCP/IP) Properties dialogue box.
• Verify that
•Obtain an IP address automatically is
selected.
•Obtain DNS server address
automatically is selected.
• Click OK to return to Local Area
Connection Properties.
• Click OK again to complete the
configuration process for Windows 2000.
Restart the PC.
Repeat these steps for each PC with this version
of Windows on your network.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Preparing Your Network C-13
M-10177-01
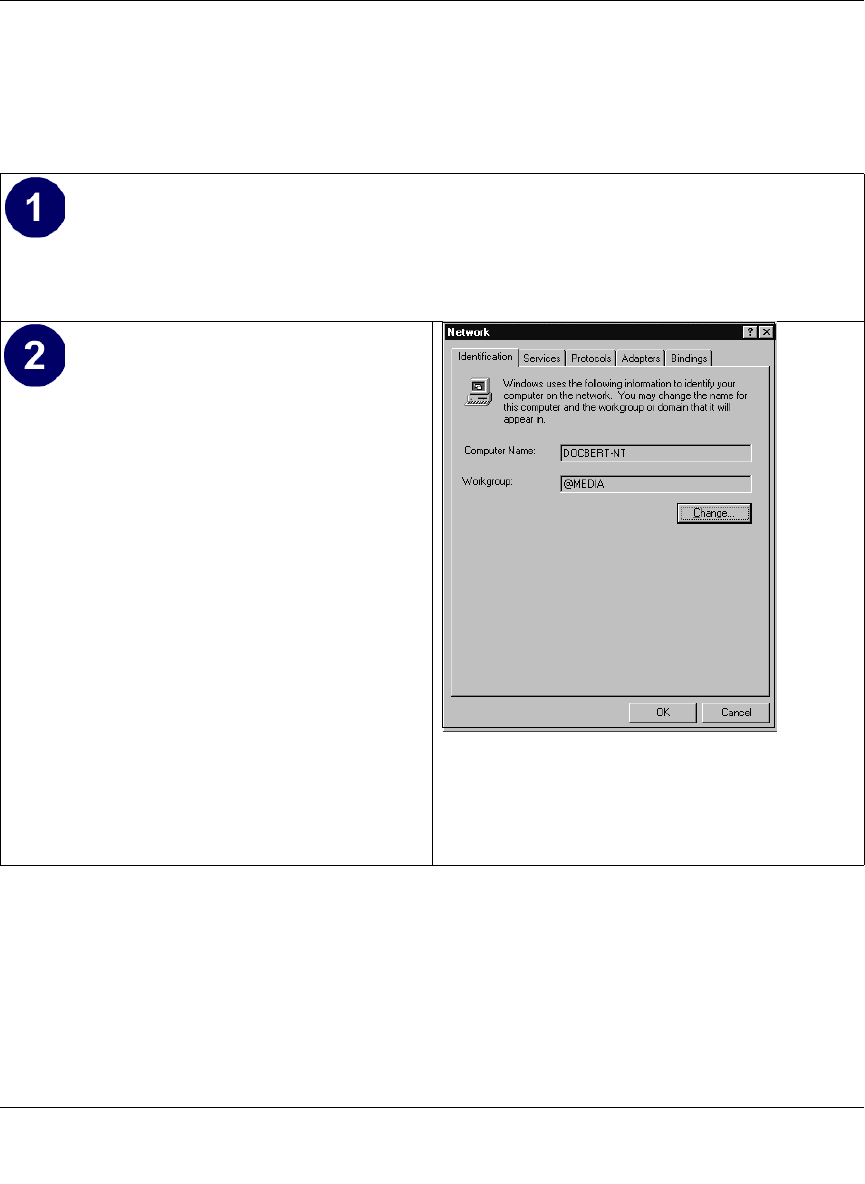
DHCP Configuration of TCP/IP in Windows NT4
Once you have installed the network card, you need to configure the TCP/IP environment for
Windows NT 4.0. Follow this procedure to configure TCP/IP with DHCP in Windows NT 4.0.
• Choose Settings from the Start Menu, and then select Control Panel.
This will display Control Panel window.
• Double-click the Network icon in the
Control Panel window.
The Network panel will display.
• Select the Protocols tab to continue.
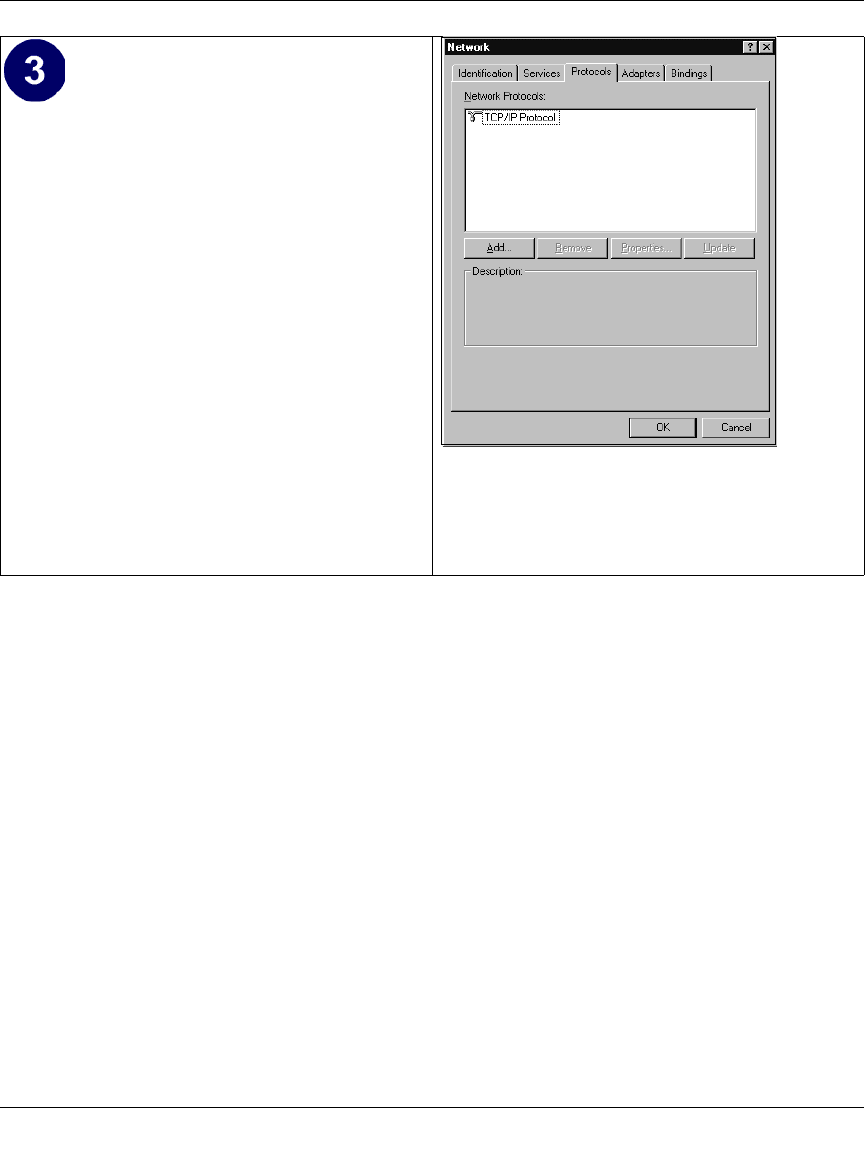
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
C-14 Preparing Your Network
M-10177-01
• Highlight the TCP/IP Protocol in the
Network Protocols box, and click on the
Properties button.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Preparing Your Network C-15
M-10177-01
Verifying TCP/IP Properties for Windows XP, 2000, and NT4
To check your PC’s TCP/IP configuration:
1. On the Windows taskbar, click the Start button, and then click Run.
The Run window opens.
2. Type cmd and then click OK.
A command window opens
3. Type ipconfig /all
Your IP Configuration information will be listed, and should match the values below if you are
using the default TCP/IP settings that NETGEAR recommends for connecting through a
router or gateway:
• The IP address is between 192.168.0.2 and 192.168.0.254
• The subnet mask is 255.255.255.0
•The TCP/IP Properties dialog box now
displays.
• Click the IP Address tab.
• Select the radio button marked Obtain an IP
address from a DHCP server.
• Click OK. This completes the configuration
of TCP/IP in Windows NT.
Restart the PC.
Repeat these steps for each PC with this version
of Windows on your network.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
C-16 Preparing Your Network
M-10177-01
• The default gateway is 192.168.0.1
4. Type exit
Configuring the Macintosh for TCP/IP Networking
Beginning with Macintosh Operating System 7, TCP/IP is already installed on the Macintosh. On
each networked Macintosh, you will need to configure TCP/IP to use DHCP.
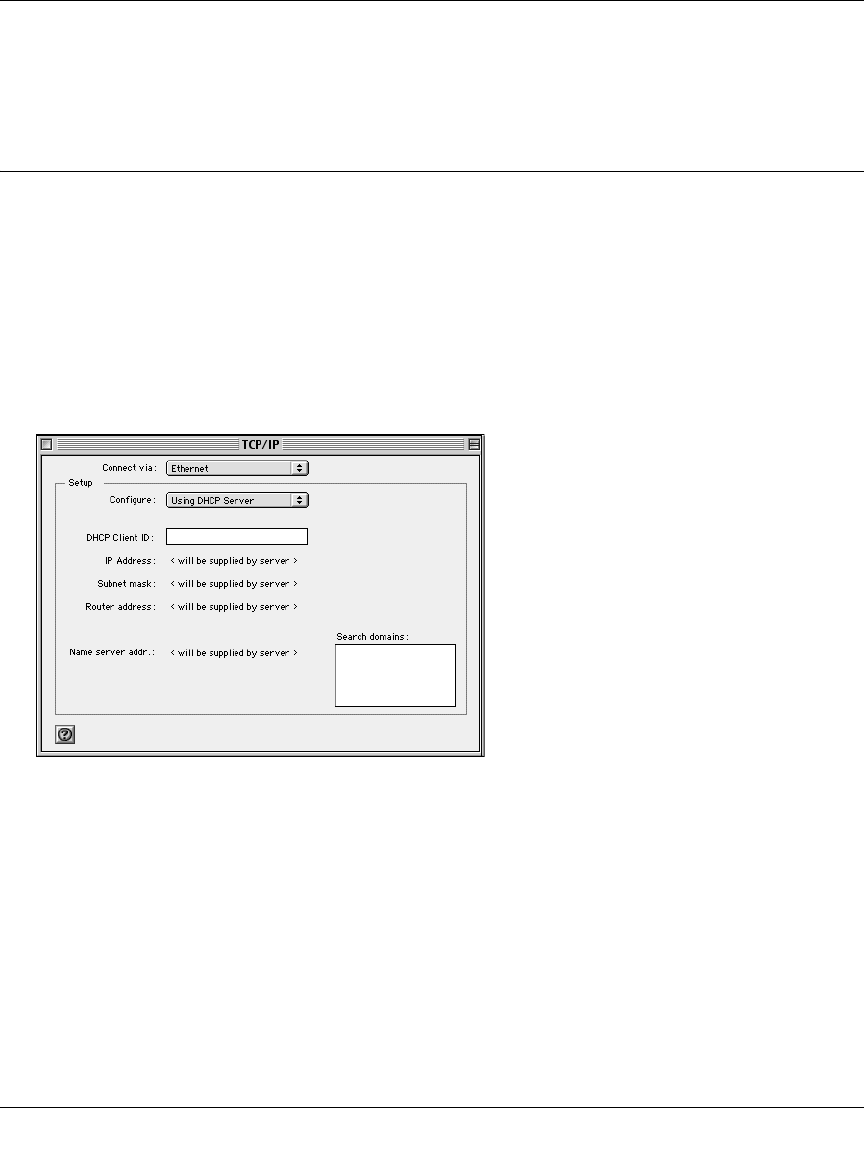
MacOS 8.6 or 9.x
1. From the Apple menu, select Control Panels, then TCP/IP.
The TCP/IP Control Panel opens:
2. From the “Connect via” box, select your Macintosh’s Ethernet interface.
3. From the “Configure” box, select Using DHCP Server.
You can leave the DHCP Client ID box empty.
4. Close the TCP/IP Control Panel.
5. Repeat this for each Macintosh on your network.
MacOS X
1. From the Apple menu, choose System Preferences, then Network.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Preparing Your Network C-17
M-10177-01
2. If not already selected, select Built-in Ethernet in the Configure list.
3. If not already selected, Select Using DHCP in the TCP/IP tab.
4. Click Save.
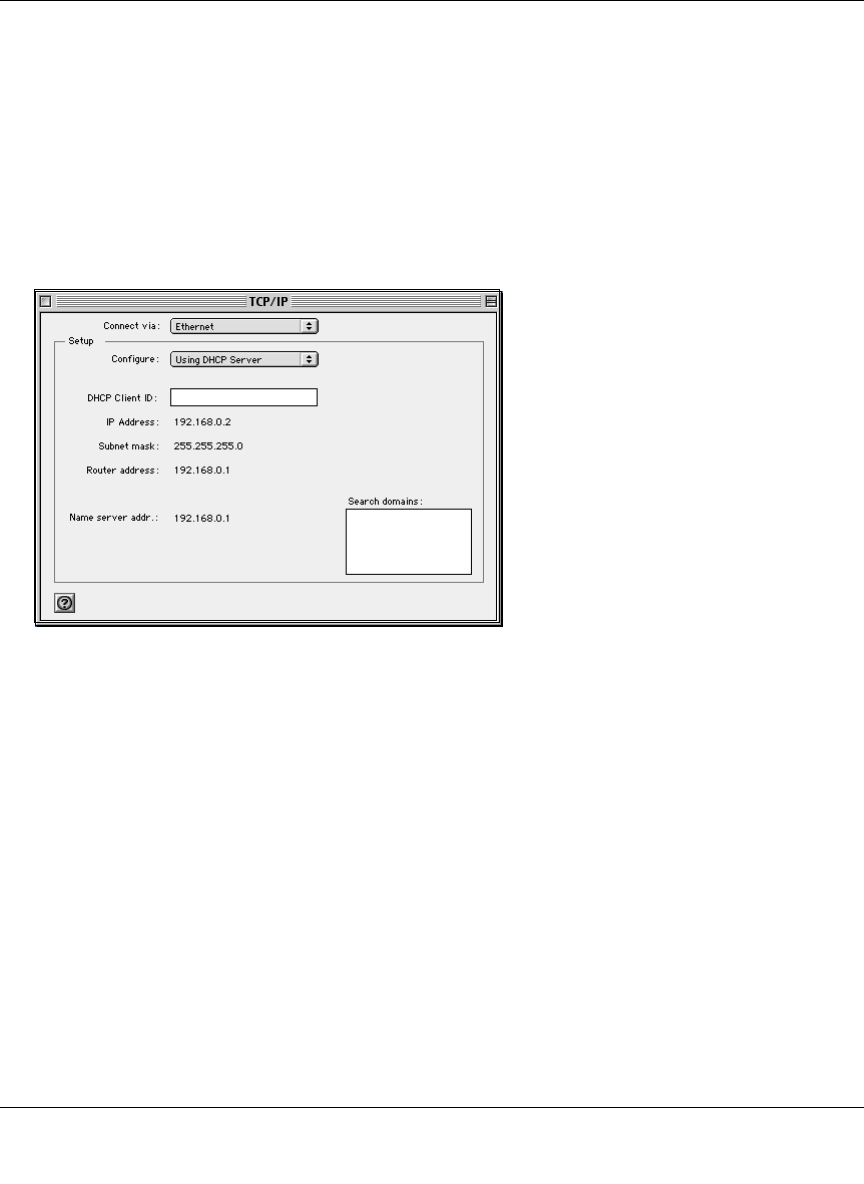
Verifying TCP/IP Properties for Macintosh Computers
After your Macintosh is configured and has rebooted, you can check the TCP/IP configuration by
returning to the TCP/IP Control Panel. From the Apple menu, select Control Panels, then TCP/IP.
The panel is updated to show your settings, which should match the values below if you are using
the default TCP/IP settings that NETGEAR recommends:
• The IP Address is between 192.168.0.2 and 192.168.0.254
• The Subnet mask is 255.255.255.0
• The Router address is 192.168.0.1
If you do not see these values, you may need to restart your Macintosh or you may need to switch
the “Configure” setting to a different option, then back again to “Using DHCP Server”.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
C-18 Preparing Your Network
M-10177-01
Verifying the Readiness of Your Internet Account
For broadband access to the Internet, you need to contract with an Internet service provider (ISP)
for a single-user Internet access account using a cable modem or DSL modem. This modem must
be a separate physical box (not a card) and must provide an Ethernet port intended for connection
to a Network Interface Card (NIC) in a computer. Your firewall does not support a USB-connected
broadband modem.
For a single-user Internet account, your ISP supplies TCP/IP configuration information for one
computer. With a typical account, much of the configuration information is dynamically assigned
when your PC is first booted up while connected to the ISP, and you will not need to know that
dynamic information.
In order to share the Internet connection among several computers, your firewall takes the place of
the single PC, and you need to configure it with the TCP/IP information that the single PC would
normally use. When the firewall’s Internet port is connected to the broadband modem, the firewall
appears to be a single PC to the ISP. The firewall then allows the PCs on the local network to
masquerade as the single PC to access the Internet through the broadband modem. The method
used by the firewall to accomplish this is called Network Address Translation (NAT) or IP
masquerading.
Are Login Protocols Used?
Some ISPs require a special login protocol, in which you must enter a login name and password in
order to access the Internet. If you normally log in to your Internet account by running a program
such as WinPOET or EnterNet, then your account uses PPP over Ethernet (PPPoE).
When you configure your router, you will need to enter your login name and password in the
router’s configuration menus. After your network and firewall are configured, the firewall will
perform the login task when needed, and you will no longer need to run the login program from
your PC. It is not necessary to uninstall the login program.
What Is Your Configuration Information?
More and more, ISPs are dynamically assigning configuration information. However, if your ISP
does not dynamically assign configuration information but instead used fixed configurations, your
ISP should have given you the following basic information for your account:

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Preparing Your Network C-19
M-10177-01
• An IP address and subnet mask
• A gateway IP address, which is the address of the ISP’s router
• One or more domain name server (DNS) IP addresses
• Host name and domain suffix
For example, your account’s full server names may look like this:
mail.xxx.yyy.com
In this example, the domain suffix is xxx.yyy.com.
If any of these items are dynamically supplied by the ISP, your firewall automatically acquires
them.
If an ISP technician configured your PC during the installation of the broadband modem, or if you
configured it using instructions provided by your ISP, you need to copy the configuration
information from your PC’s Network TCP/IP Properties window or Macintosh TCP/IP Control
Panel before reconfiguring your PC for use with the firewall. These procedures are described next.
Obtaining ISP Configuration Information for Windows Computers
As mentioned above, you may need to collect configuration information from your PC so that you
can use this information when you configure the FWG114P Wireless Firewall/Print Server.
Following this procedure is only necessary when your ISP does not dynamically supply the
account information.
To get the information you need to configure the firewall for Internet access:
1. On the Windows taskbar, click the Start button, point to Settings, and then click Control Panel.
2. Double-click the Network icon.
The Network window opens, which displays a list of installed components.
3. Select TCP/IP, and then click Properties.
The TCP/IP Properties dialog box opens.
4. Select the IP Address tab.
If an IP address and subnet mask are shown, write down the information. If an address is
present, your account uses a fixed (static) IP address. If no address is present, your account
uses a dynamically-assigned IP address. Click “Obtain an IP address automatically”.
5. Select the Gateway tab.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
C-20 Preparing Your Network
M-10177-01
If an IP address appears under Installed Gateways, write down the address. This is the ISP’s
gateway address. Select the address and then click Remove to remove the gateway address.
6. Select the DNS Configuration tab.
If any DNS server addresses are shown, write down the addresses. If any information appears
in the Host or Domain information box, write it down. Click Disable DNS.
7. Click OK to save your changes and close the TCP/IP Properties dialog box.
You are returned to the Network window.
8. Click OK.
9. Reboot your PC at the prompt. You may also be prompted to insert your Windows CD.
Obtaining ISP Configuration Information for Macintosh
Computers
As mentioned above, you may need to collect configuration information from your Macintosh so
that you can use this information when you configure the FWG114P Wireless Firewall/Print
Server. Following this procedure is only necessary when your ISP does not dynamically supply the
account information.
To get the information you need to configure the firewall for Internet access:
1. From the Apple menu, select Control Panels, then TCP/IP.
The TCP/IP Control Panel opens, which displays a list of configuration settings. If the
“Configure” setting is “Using DHCP Server”, your account uses a dynamically-assigned IP
address. In this case, close the Control Panel and skip the rest of this section.
2. If an IP address and subnet mask are shown, write down the information.
3. If an IP address appears under Router address, write down the address. This is the ISP’s
gateway address.
4. If any Name Server addresses are shown, write down the addresses. These are your ISP’s DNS
addresses.
5. If any information appears in the Search domains information box, write it down.
6. Change the “Configure” setting to “Using DHCP Server”.
7. Close the TCP/IP Control Panel.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Preparing Your Network C-21
M-10177-01
Restarting the Network
Once you’ve set up your computers to work with the firewall, you must reset the network for the
devices to be able to communicate correctly. Restart any computer that is connected to the
FWG114P Wireless Firewall/Print Server.
After configuring all of your computers for TCP/IP networking and restarting them, and
connecting them to the local network of your FWG114P Wireless Firewall/Print Server, you are
ready to access and configure the firewall.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
C-22 Preparing Your Network
M-10177-01
Wireless Networking Basics D-1
M-10177-01
Appendix D
Wireless Networking Basics
This chapter provides an overview of Wireless networking.
Wireless Networking Overview
The FWG114P Wireless Firewall/Print Server conforms to the Institute of Electrical and
Electronics Engineers (IEEE) 802.11b and 802.11g standards for wireless LANs (WLANs). On an
802.11b or g wireless link, data is encoded using direct-sequence spread-spectrum (DSSS)
technology and is transmitted in the unlicensed radio spectrum at 2.5GHz. The maximum data rate
for the 802.11b wireless link is 11 Mbps, but it will automatically back down from 11 Mbps to 5.5,
2, and 1 Mbps when the radio signal is weak or when interference is detected. The 802.11g auto
rate sensing rates are 1, 2, 5.5, 6, 9, 12, 18, 24, 36, 48, and 54 Mbps.
The 802.11 standard is also called Wireless Ethernet or Wi-Fi by the Wireless Ethernet
Compatibility Alliance (WECA, see http://www.wi-fi.net), an industry standard group promoting
interoperability among 802.11 devices. The 802.11 standard offers two methods for configuring a
wireless network - ad hoc and infrastructure.
Infrastructure Mode
With a wireless Access Point, you can operate the wireless LAN in the infrastructure mode. This
mode provides wireless connectivity to multiple wireless network devices within a fixed range or
area of coverage, interacting with wireless nodes via an antenna.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
D-2 Wireless Networking Basics
M-10177-01
In the infrastructure mode, the wireless access point converts airwave data into wired Ethernet
data, acting as a bridge between the wired LAN and wireless clients. Connecting multiple Access
Points via a wired Ethernet backbone can further extend the wireless network coverage. As a
mobile computing device moves out of the range of one access point, it moves into the range of
another. As a result, wireless clients can freely roam from one Access Point domain to another and
still maintain seamless network connection.
Ad Hoc Mode (Peer-to-Peer Workgroup)
In an ad hoc network, computers are brought together as needed; thus, there is no structure or fixed
points to the network - each node can generally communicate with any other node. There is no
Access Point involved in this configuration. This mode enables you to quickly set up a small
wireless workgroup and allows workgroup members to exchange data or share printers as
supported by Microsoft networking in the various Windows operating systems. Some vendors also
refer to ad hoc networking as peer-to-peer group networking.
In this configuration, network packets are directly sent and received by the intended transmitting
and receiving stations. As long as the stations are within range of one another, this is the easiest
and least expensive way to set up a wireless network.
Network Name: Extended Service Set Identification (ESSID)
The Extended Service Set Identification (ESSID) is one of two types of Service Set Identification
(SSID). In an ad hoc wireless network with no access points, the Basic Service Set Identification
(BSSID) is used. In an infrastructure wireless network that includes an access point, the ESSID is
used, but may still be referred to as SSID.
An SSID is a thirty-two character (maximum) alphanumeric key identifying the name of the
wireless local area network. Some vendors refer to the SSID as network name. For the wireless
devices in a network to communicate with each other, all devices must be configured with the
same SSID.
The ESSID is usually broadcast in the air from an access point. The wireless station sometimes can
be configured with the ESSID ANY. This means the wireless station will try to associate with
whichever access point has the stronger radio frequency (RF) signal, providing that both the access
point and wireless station use Open System authentication.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Wireless Networking Basics D-3
M-10177-01
Authentication and WEP Data Encryption
The absence of a physical connection between nodes makes the wireless links vulnerable to
eavesdropping and information theft. To provide a certain level of security, the IEEE 802.11
standard has defined these two types of authentication methods:
•Open System. With Open System authentication, a wireless PC can join any network and
receive any messages that are not encrypted.
•Shared Key. With Shared Key authentication, only those PCs that possess the correct
authentication key can join the network. By default, IEEE 802.11 wireless devices operate in
an Open System network.
Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are configured
to operate in Shared Key authentication mode.
802.11 Authentication
The 802.11 standard defines several services that govern how two 802.11 devices communicate.
The following events must occur before an 802.11 Station can communicate with an Ethernet
network through an access point such as the one built in to the FWG114P:
1. Turn on the wireless station.
2. The station listens for messages from any access points that are in range.
3. The station finds a message from an access point that has a matching SSID.
4. The station sends an authentication request to the access point.
5. The access point authenticates the station.
6. The station sends an association request to the access point.
7. The access point associates with the station.
8. The station can now communicate with the Ethernet network through the access point.
An access point must authenticate a station before the station can associate with the access point or
communicate with the network. The IEEE 802.11 standard defines two types of authentication:
Open System and Shared Key.
• Open System Authentication allows any device to join the network, assuming that the device
SSID matches the access point SSID. Alternatively, the device can use the “ANY” SSID
option to associate with any available Access Point within range, regardless of its SSID.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
D-4 Wireless Networking Basics
M-10177-01
• Shared Key Authentication requires that the station and the access point have the same WEP
Key to authenticate. These two authentication procedures are described below.
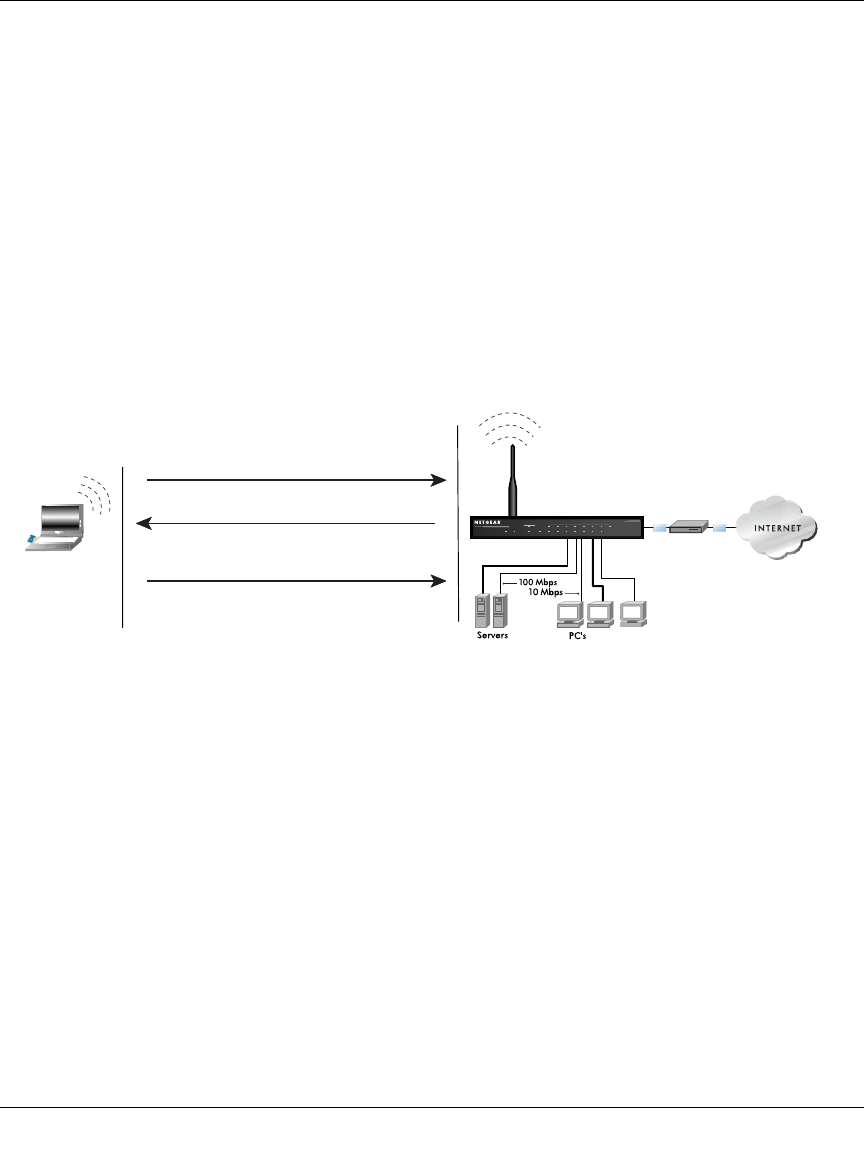
Open System Authentication
The following steps occur when two devices use Open System Authentication:
1. The station sends an authentication request to the access point.
2. The access point authenticates the station.
3. The station associates with the access point and joins the network.
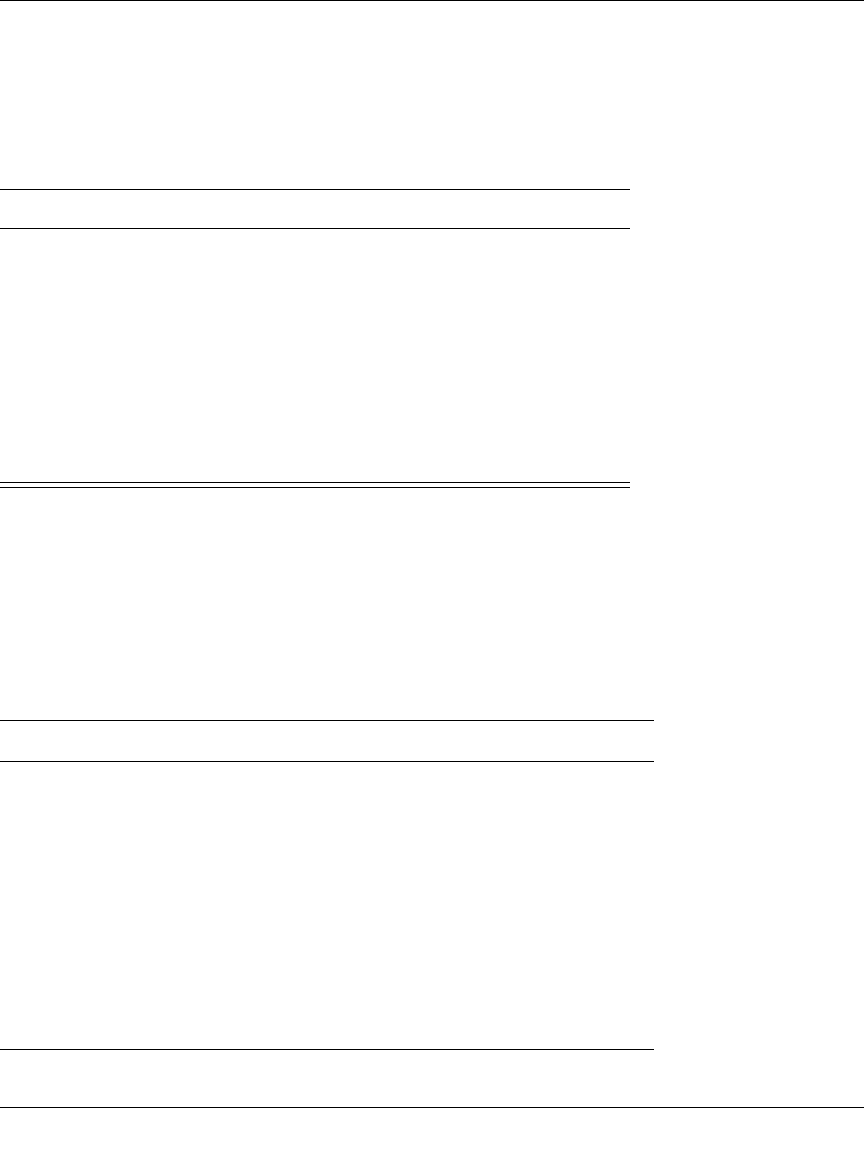
This process is illustrated in below.
Figure 9-1: Open system authentication
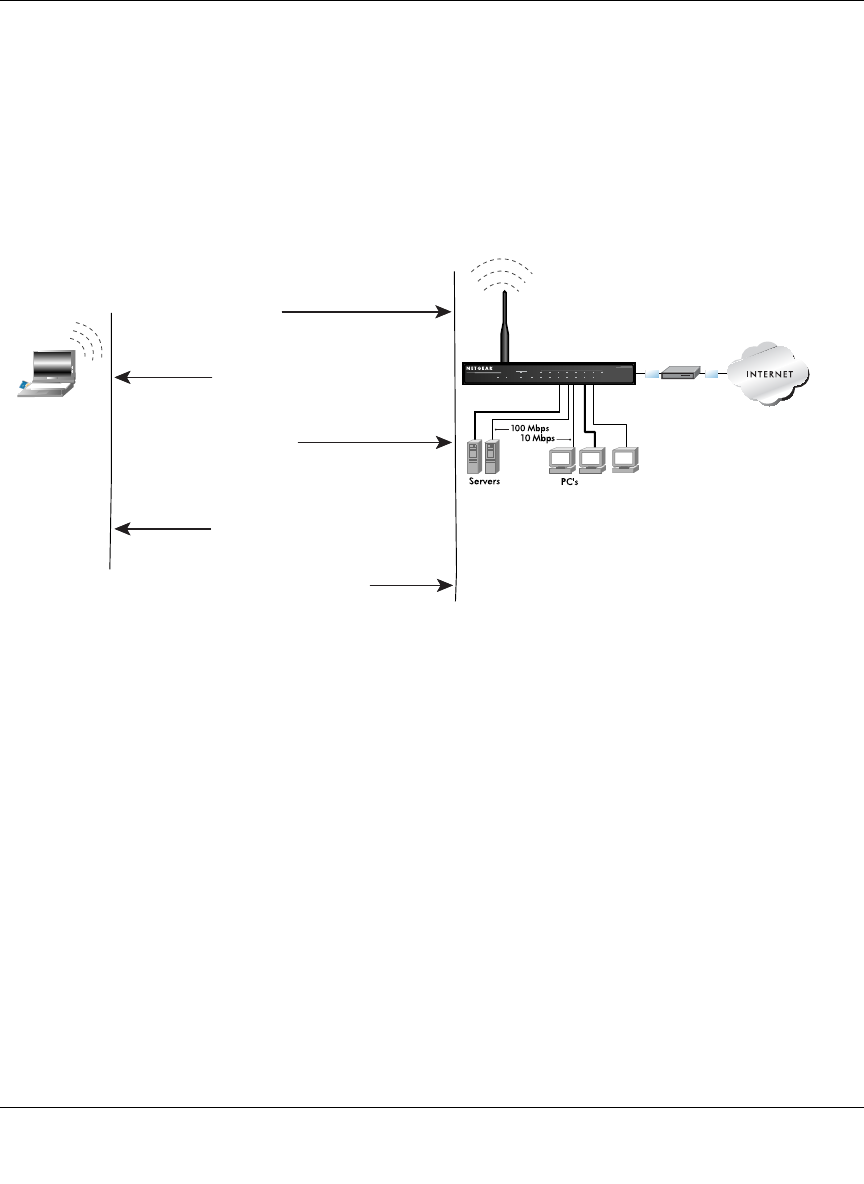
Shared Key Authentication
The following steps occur when two devices use Shared Key Authentication:
1. The station sends an authentication request to the access point.
2. The access point sends challenge text to the station.
3. The station uses its configured 64-bit or 128-bit default key to encrypt the challenge text, and
sends the encrypted text to the access point.
4. The access point decrypts the encrypted text using its configured WEP Key that corresponds
to the station’s default key. The access point compares the decrypted text with the original
challenge text. If the decrypted text matches the original challenge text, then the access point
and the station share the same WEP Key and the access point authenticates the station.
INTERNET LOCAL
ACT
12345678
LNK
LNK/ACT
100
Cable/DSL ProSafeWirelessVPN Security Firewall
MODEL FVM318
PWR TEST
WLAN
Enable
Access Point (AP)
1) Authentication request sent to AP
2) AP authenticates
3) Client connects to network
Open System
Authentication Steps
Cable or
DLS modem
Client
attempting
to connect
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Wireless Networking Basics D-5
M-10177-01
5. The station connects to the network.
If the decrypted text does not match the original challenge text (i.e., the access point and station do
not share the same WEP Key), then the access point will refuse to authenticate the station and the
station will be unable to communicate with either the 802.11 network or Ethernet network.
This process is illustrated in below.
Figure 9-2: Shared key authentication
Overview of WEP Parameters
Before enabling WEP on an 802.11 network, you must first consider what type of encryption you
require and the key size you want to use. Typically, there are three WEP Encryption options
available for 802.11 products:
1. Do Not Use WEP: The 802.11 network does not encrypt data. For authentication purposes, the
network uses Open System Authentication.
2. Use WEP for Encryption: A transmitting 802.11 device encrypts the data portion of every
packet it sends using a configured WEP Key. The receiving device decrypts the data using the
same WEP Key. For authentication purposes, the network uses Open System Authentication.
INTERNET LOCAL
ACT
12345678
LNK
LNK/ACT
100
Cable/DSL ProSafeWirelessVPN Security Firewall
MODEL FVM318
PWR TEST
WLAN
Enable
Access Point1) Authentication
request sent to AP
2) AP sends challenge text
3) Client encrypts
challenge text and
sends it back to AP
4) AP decrypts, and if correct,
authenticates client
5) Client connects to network
Shared Key
Authentication Steps
Cable or
DLS modem
Client
attempting
to connect

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
D-6 Wireless Networking Basics
M-10177-01
3. Use WEP for Authentication and Encryption: A transmitting 802.11 device encrypts the data
portion of every packet it sends using a configured WEP Key. The receiving device decrypts the
data using the same WEP Key. For authentication purposes, the wireless network uses Shared Key
Authentication.
Note: Some 802.11 access points also support Use WEP for Authentication Only (Shared Key
Authentication without data encryption).
Key Size
The IEEE 802.11 standard supports two types of WEP encryption: 40-bit and 128-bit.
The 64-bit WEP data encryption method, allows for a five-character (40-bit) input. Additionally,
24 factory-set bits are added to the forty-bit input to generate a 64-bit encryption key. (The 24
factory-set bits are not user-configurable). This encryption key will be used to encrypt/decrypt all
data transmitted via the wireless interface. Some vendors refer to the 64-bit WEP data encryption
as 40-bit WEP data encryption since the user-configurable portion of the encryption key is 40 bits
wide.
The 128-bit WEP data encryption method consists of 104 user-configurable bits. Similar to the
forty-bit WEP data encryption method, the remaining 24 bits are factory set and not user
configurable. Some vendors allow passphrases to be entered instead of the cryptic hexadecimal
characters to ease encryption key entry.
128-bit encryption is stronger than 40-bit encryption, but 128-bit encryption may not be available
outside of the United States due to U.S. export regulations.
When configured for 40-bit encryption, 802.11 products typically support up to four WEP Keys.
Each 40-bit WEP Key is expressed as 5 sets of two hexadecimal digits (0-9 and A-F). For
example, “12 34 56 78 90” is a 40-bit WEP Key.
When configured for 128-bit encryption, 802.11 products typically support four WEP Keys but
some manufacturers support only one 128-bit key. The 128-bit WEP Key is expressed as 13 sets of
two hexadecimal digits (0-9 and A-F). For example, “12 34 56 78 90 AB CD EF 12 34 56 78 90”
is a 128-bit WEP Key.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Wireless Networking Basics D-7
M-10177-01
Table D-1: Encryption Key Sizes
Note: Typically, 802.11 access points can store up to four 128-bit WEP Keys but some 802.11
client adapters can only store one. Therefore, make sure that your 802.11 access and client
adapters configurations match.
WEP Configuration Options
The WEP settings must match on all 802.11 devices that are within the same wireless network as
identified by the SSID. In general, if your mobile clients will roam between access points, then all
of the 802.11 access points and all of the 802.11 client adapters on the network must have the same
WEP settings.
Note: Whatever keys you enter for an AP, you must also enter the same keys for the client adapter
in the same order. In other words, WEP key 1 on the AP must match WEP key 1 on the client
adapter, WEP key 2 on the AP must match WEP key 2 on the client adapter, etc.
Note: The AP and the client adapters can have different default WEP Keys as long as the keys are
in the same order. In other words, the AP can use WEP key 2 as its default key to transmit while a
client adapter can use WEP key 3 as its default key to transmit. The two devices will communicate
as long as the AP’s WEP key 2 is the same as the client’s WEP key 2 and the AP’s WEP key 3 is
the same as the client’s WEP key 3.
Wireless Channels
The wireless frequencies used by 802.11b/g networks are discussed below.
IEEE 802.11b/g wireless nodes communicate with each other using radio frequency signals in the
ISM (Industrial, Scientific, and Medical) band between 2.4 GHz and 2.5 GHz. Neighboring
channels are 5 MHz apart. However, due to spread spectrum effect of the signals, a node sending
signals using a particular channel will utilize frequency spectrum 12.5 MHz above and below the
center channel frequency. As a result, two separate wireless networks using neighboring channels
(for example, channel 1 and channel 2) in the same general vicinity will interfere with each other.
Applying two channels that allow the maximum channel separation will decrease the amount of
Encryption Key Size # of Hexadecimal Digits Example of Hexadecimal Key Content
64-bit (24+40) 10 4C72F08AE1
128-bit (24+104) 26 4C72F08AE19D57A3FF6B260037
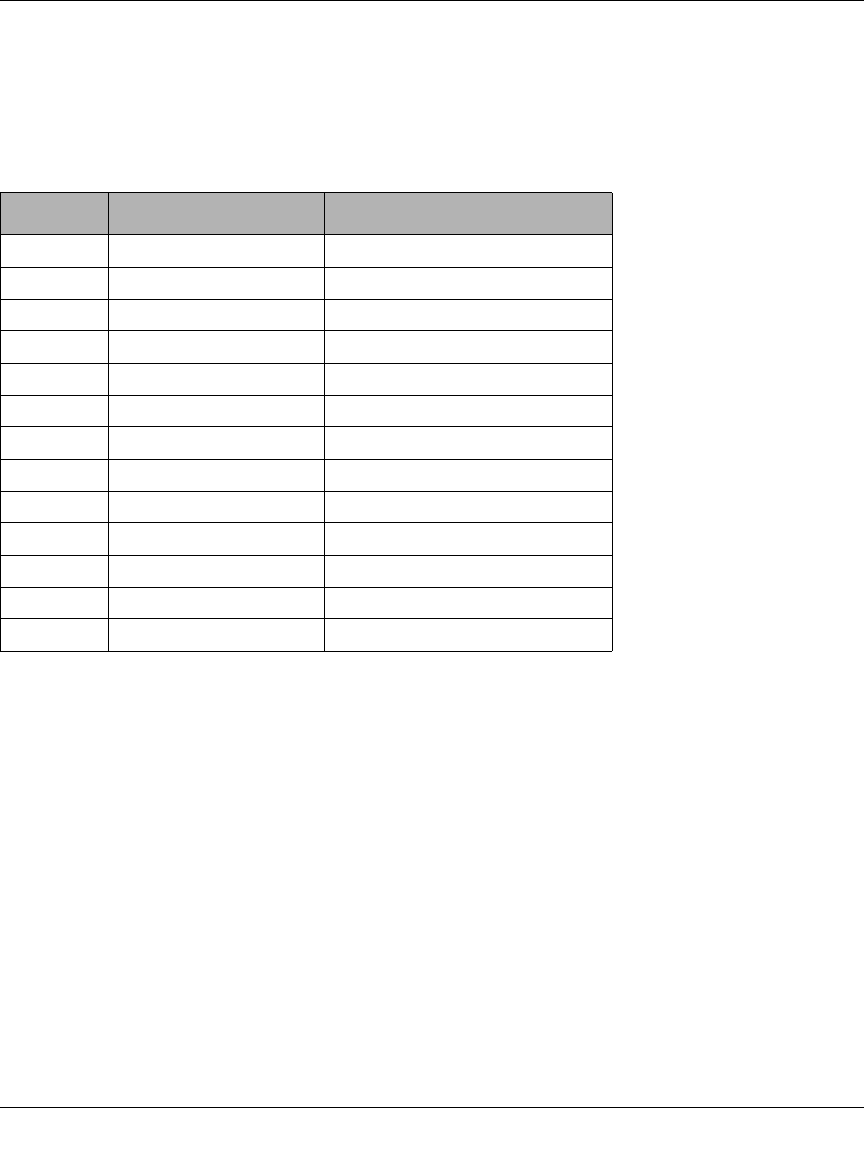
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
D-8 Wireless Networking Basics
M-10177-01
channel cross-talk, and provide a noticeable performance increase over networks with minimal
channel separation.
The radio frequency channels used in 802.11b/g networks are listed in Table D-2:
Note: The available channels supported by the wireless products in various countries are different.
For example, Channels 1 to 11 are supported in the U.S. and Canada, and Channels 1 to 13 are
supported in Europe and Australia.
The preferred channel separation between the channels in neighboring wireless networks is 25
MHz (5 channels). This means that you can apply up to three different channels within your
wireless network. There are only 11 usable wireless channels in the United States. It is
recommended that you start using channel 1 and grow to use channel 6, and 11 when necessary, as
these three channels do not overlap.
Table D-2: 802.11b/g Radio Frequency Channels
Channel Center Frequency Frequency Spread
1 2412 MHz 2399.5 MHz - 2424.5 MHz
2 2417 MHz 2404.5 MHz - 2429.5 MHz
3 2422 MHz 2409.5 MHz - 2434.5 MHz
4 2427 MHz 2414.5 MHz - 2439.5 MHz
5 2432 MHz 2419.5 MHz - 2444.5 MHz
6 2437 MHz 2424.5 MHz - 2449.5 MHz
7 2442 MHz 2429.5 MHz - 2454.5 MHz
8 2447 MHz 2434.5 MHz - 2459.5 MHz
9 2452 MHz 2439.5 MHz - 2464.5 MHz
10 2457 MHz 2444.5 MHz - 2469.5 MHz
11 2462 MHz 2449.5 MHz - 2474.5 MHz
12 2467 MHz 2454.5 MHz - 2479.5 MHz
13 2472 MHz 2459.5 MHz - 2484.5 MHz
M-10177-01
Glossary 1
Glossary
List of Glossary Terms
Use the list below to find definitions for technical terms used in this manual.
10BASE-T
IEEE 802.3 specification for 10 Mbps Ethernet over twisted pair wiring.
100BASE-Tx
IEEE 802.3 specification for 100 Mbps Ethernet over twisted pair wiring.
802.1x
802.1x defines port-based, network access control used to provide authenticated network access and
automated data encryption key management.
The IEEE 802.1x draft standard offers an effective framework for authenticating and controlling user traffic
to a protected network, as well as dynamically varying encryption keys. 802.1x uses a protocol called EAP
(Extensible Authentication Protocol) and supports multiple authentication methods, such as token cards,
Kerberos, one-time passwords, certificates, and public key authentication. For details on EAP specifically,
refer to IETF's RFC 2284.
802.11b
IEEE specification for wireless networking at 11 Mbps using direct-sequence spread-spectrum (DSSS)
technology and operating in the unlicensed radio spectrum at 2.4-2.5GHz.
802.11g
A soon to be ratified IEEE specification for wireless networking at 54 Mbps using direct-sequence
spread-spectrum (DSSS) technology and operating in the unlicensed radio spectrum at 2.4GHz. 802.11g is
backwards compatible with 802.11b.
ADSL
Short for asymmetric digital subscriber line, a technology that allows data to be sent over existing copper
telephone lines at data rates of from 1.5 to 9 Mbps when receiving data (known as the downstream rate) and
from 16 to 640 Kbps when sending data (known as the upstream rate).
ADSL requires a special ADSL modem. ADSL is growing in popularity as more areas around the world
gain access.
Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
2Glossary
M-10177-01
ARP
Address Resolution Protocol, a TCP/IP protocol used to convert an IP address into a physical address (called
a DLC address), such as an Ethernet address.
A host wishing to obtain a physical address broadcasts an ARP request onto the TCP/IP network. The host
on the network that has the IP address in the request then replies with its physical hardware address. There is
also Reverse ARP (RARP) which can be used by a host to discover its IP address. In this case, the host
broadcasts its physical address and a RARP server replies with the host's IP address.
Auto Uplink
Auto UplinkTM technology (also called MDI/MDIX) eliminates the need to worry about crossover vs.
straight-through Ethernet cables. Auto UplinkTM will accommodate either type of cable to make the right
connection.
CA
A Certificate Authority is a trusted third-party organization or company that issues digital certificates used
to create digital signatures and public-private key pairs.
Cat 5
Category 5 unshielded twisted pair (UTP) cabling. An Ethernet network operating at 10 Mbits/second
(10BASE-T) will often tolerate low quality cables, but at 100 Mbits/second (10BASE-Tx) the cable must be
rated as Category 5, or Cat 5 or Cat V, by the Electronic Industry Association (EIA).
This rating will be printed on the cable jacket. Cat 5 cable contains eight conductors, arranged in four
twisted pairs, and terminated with an RJ45 type connector. In addition, there are restrictions on maximum
cable length for both 10 and 100 Mbits/second networks.
Certificate Authority
A Certificate Authority is a trusted third-party organization or company that issues digital certificates used
to create digital signatures and public-private key pairs.
The role of the CA in this process is to guarantee that the individual granted the unique certificate is, in fact,
who he or she claims to be. Usually, this means that the CA has an arrangement with a financial institution,
such as a credit card company, which provides it with information to confirm an individual's claimed
identity. CAs are a critical component in data security and electronic commerce because they guarantee that
the two parties exchanging information are really who they claim to be.
DHCP
An Ethernet protocol specifying how a centralized DHCP server can assign network configuration
information to multiple DHCP clients. The assigned information includes IP addresses, DNS addresses, and
gateway (router) addresses.
DMZ
Specifying a Default DMZ Server allows you to set up a computer or server that is available to anyone on
the Internet for services that you haven't defined. There are security issues with doing this, so only do this if
you'll willing to risk open access.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Glossary 3
M-10177-01
DNS
Short for Domain Name System (or Service), an Internet service that translates domain names into IP
addresses.
Because domain names are alphabetic, they're easier to remember. The Internet however, is really based on
IP addresses. Every time you use a domain name, therefore, a DNS service must translate the name into the
corresponding IP address. For example, the domain name www.example.com might translate to
198.105.232.4. The DNS system is, in fact, its own network. If one DNS server doesn't know how to
translate a particular domain name, it asks another one, and so on, until the correct IP address is returned.
Domain Name
A descriptive name for an address or group of addresses on the Internet. Domain names are of the form of a
registered entity name plus one of a number of predefined top level suffixes such as .com, .edu, .uk, etc. For
example, in the address mail.NETGEAR.com, mail is a server name and NETGEAR.com is the domain.
DSL
Short for digital subscriber line, but is commonly used in reference to the asymmetric version of this
technology (ADSL) that allows data to be sent over existing copper telephone lines at data rates of from 1.5
to 9 Mbps when receiving data (known as the downstream rate) and from 16 to 640 Kbps when sending data
(known as the upstream rate).
ADSL requires a special ADSL modem. ADSL is growing in popularity as more areas around the world
gain access.
Dynamic Host Configuration Protocol
DHCP. An Ethernet protocol specifying how a centralized DHCP server can assign network configuration
information to multiple DHCP clients. The assigned information includes IP addresses, DNS addresses, and
gateway (router) addresses.
EAP
Extensible Authentication Protocol is a general protocol for authentication that supports multiple
authentication methods.
EAP, an extension to PPP, supports such authentication methods as token cards, Kerberos, one-time
passwords, certificates, public key authentication and smart cards. In wireless communications using EAP, a
user requests connection to a WLAN through an AP, which then requests the identity of the user and
transmits that identity to an authentication server such as RADIUS. The server asks the AP for proof of
identity, which the AP gets from the user and then sends back to the server to complete the authentication.
EAP is defined by RFC 2284.
ESSID
The Extended Service Set Identification (ESSID) is a thirty-two character (maximum) alphanumeric key
identifying the wireless local area network.
Gateway
A local device, usually a router, that connects hosts on a local network to other networks.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
4Glossary
M-10177-01
IP
Internet Protocol is the main internetworking protocol used in the Internet. Used in conjunction with the
Transfer Control Protocol (TCP) to form TCP/IP.
IP Address
A four-byte number uniquely defining each host on the Internet, usually written in dotted-decimal notation
with periods separating the bytes (for example, 134.177.244.57).
Ranges of addresses are assigned by Internic, an organization formed for this purpose.
ISP
Internet service provider.
Internet Protocol
The main internetworking protocol used in the Internet. Used in conjunction with the Transfer Control
Protocol (TCP) to form TCP/IP.
LAN
A communications network serving users within a limited area, such as one floor of a building.
local area network
LAN. A communications network serving users within a limited area, such as one floor of a building.
A LAN typically connects multiple personal computers and shared network devices such as storage and
printers. Although many technologies exist to implement a LAN, Ethernet is the most common for
connecting personal computers.
MAC address
The Media Access Control address is a unique 48-bit hardware address assigned to every network interface
card. Usually written in the form 01:23:45:67:89:ab.
Mbps
Megabits per second.
MD5
MD5 creates digital signatures using a one-way hash function, meaning that it takes a message and converts
it into a fixed string of digits, also called a message digest.
When using a one-way hash function, one can compare a calculated message digest against the message
digest that is decrypted with a public key to verify that the message hasn't been tampered with. This
comparison is called a "hashcheck."
MDI/MDIX
In cable wiring, the concept of transmit and receive are from the perspective of the PC, which is wired as a
Media Dependant Interface (MDI). In MDI wiring, a PC transmits on pins 1 and 2. At the hub, switch,
router, or access point, the perspective is reversed, and the hub receives on pins 1 and 2. This wiring is
referred to as Media Dependant Interface - Crossover (MDI-X). See also Auto Uplink.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Glossary 5
M-10177-01
NAT
A technique by which several hosts share a single IP address for access to the Internet.
NetBIOS
Network Basic Input Output System. An application programming interface (API) for sharing services
and information on local-area networks (LANs). Provides for communication between stations of a
network where each station is given a name. These names are alphanumeric names, 16 characters in length.
netmask
Combined with the IP address, the IP Subnet Mask allows a device to know which other addresses are local
to it, and which must be reached through a gateway or router.
A number that explains which part of an IP address comprises the network address and which part is the host
address on that network. It can be expressed in dotted-decimal notation or as a number appended to the IP
address. For example, a 28-bit mask starting from the MSB can be shown as 255.255.255.192 or as /28
appended to the IP address.
Network Address Translation
A technique by which several hosts share a single IP address for access to the Internet.
packet
A block of information sent over a network. A packet typically contains a source and destination network
address, some protocol and length information, a block of data, and a checksum.
Point-to-Point Protocol
PPP. A protocol allowing a computer using TCP/IP to connect directly to the Internet.
RADIUS
Short for Remote Authentication Dial-In User Service, RADIUS is an authentication system.
Using RADIUS, you must enter your user name and password before gaining access to a network. This
information is passed to a RADIUS server, which checks that the information is correct, and then authorizes
access. Though not an official standard, the RADIUS specification is maintained by a working group of the
IETF.
RIP
A protocol in which routers periodically exchange information with one another so that they can determine
minimum distance paths between sources and destinations.
router
A device that forwards data between networks. An IP router forwards data based on IP source and
destination addresses.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
6Glossary
M-10177-01
SSID
A Service Set Identification is a thirty-two character (maximum) alphanumeric key identifying a wireless
local area network. For the wireless devices in a network to communicate with each other, all devices must
be configured with the same SSID.
This is typically the configuration parameter for a wireless PC card. It corresponds to the ESSID in the
wireless Access Point and to the wireless network name. See also Wireless Network Name and ESSID.
Subnet Mask
Combined with the IP address, the IP Subnet Mask allows a device to know which other addresses are local
to it, and which must be reached through a gateway or router.
TLS
Short for Transport Layer Security, TLS is a protocol that guarantees privacy and data integrity between
client/server applications communicating over the Internet.
The TLS protocol is made up of two layers. The TLS Record Protocol ensures that a connection is private by
using symmetric data encryption and ensures that the connection is reliable. The second TLS layer is the
TLS Handshake Protocol, which allows authentication between the server and client and the negotiation of
an encryption algorithm and cryptographic keys before data is transmitted or received. Based on Netscape’s
SSL 3.0, TLS supercedes and is an extension of SSL. TLS and SSL are not interoperable.
UTP
Unshielded twisted pair is the cable used by 10BASE-T and 100BASE-Tx Ethernet networks.
WAN
A long distance link used to extend or connect remotely located local area networks. The Internet is a large
WAN.
WEP
Wired Equivalent Privacy is a data encryption protocol for 802.11b wireless networks.
All wireless nodes and access points on the network are configured with a 64-bit or 128-bit Shared Key for
data encryption.
wide area network
WAN. A long distance link used to extend or connect remotely located local area networks. The Internet is a
large WAN.
Wi-Fi
A trade name for the 802.11b wireless networking standard, given by the Wireless Ethernet Compatibility
Alliance (WECA, see http://www.wi-fi.net), an industry standards group promoting interoperability among
802.11b devices.
Windows Internet Naming Service
WINS. Windows Internet Naming Service is a server process for resolving Windows-based computer names
to IP addresses.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
Glossary 7
M-10177-01
If a remote network contains a WINS server, your Windows PCs can gather information from that WINS
server about its local hosts. This allows your PCs to browse that remote network using the Windows
Network Neighborhood feature.
WINS
WINS. Windows Internet Naming Service is a server process for resolving Windows-based computer names
to IP addresses.
Wireless Network Name (SSID)
Wireless Network Name (SSID) is the name assigned to a wireless network. This is the same as the SSID or
ESSID configuration parameter.

Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P
8Glossary
M-10177-01

Index 1
Numerics
802.11b D-1
A
Account Name 3-9, 3-12
Address Resolution Protocol B-9
ad-hoc mode D-2
Auto MDI/MDI-X B-15, G-2
Auto Uplink 2-3, B-15, G-2
B
backup configuration 5-7
Basic Wireless Connectivity 4-7
BSSID D-2
C
Cabling B-11
Cat5 cable 3-1, B-12, G-2
configuration
automatic by DHCP 2-4
backup 5-7
erasing 5-8
restore 5-6
router, initial 3-1
content filtering 2-2, 5-1
crossover cable 2-3, 7-2, B-14, B-15, G-2
D
date and time 7-7
Daylight Savings Time 7-7
daylight savings time 5-12
Default DMZ Server 6-2
Denial of Service (DoS) protection 2-2
denial of service attack B-11
DHCP B-10
DHCP Client ID C-16
DMZ 2-3, 6-2
DMZ Server 6-2
DNS Proxy 2-4
DNS server 3-9, 3-12, C-20
domain C-20
Domain Name 3-9, 3-12
domain name server (DNS) B-9
DoS attack B-11
E
Enable VPN Passthrough (IPSec, PPTP, L2TP) 5-9
EnterNet C-18
erase configuration 5-8
ESSID 4-7, D-2
Ethernet 2-3
Ethernet cable B-11
exposed host 6-2
F
factory settings, restoring 5-8
firewall features 2-2
Flash memory, for firmware upgrade 2-1
front panel 2-6, 2-8
fully qualified domain name (FQDN) 4-4
G
gateway address C-20
Index

2Index
H
host name 3-9, 3-12
I
IANA
contacting B-2
IETF B-1
Web site address B-7
inbound rules 5-5
infrastructure mode D-2
installation 2-4
Internet account
address information C-18
establishing C-18
Internet Service Provider 3-1
IP addresses C-19, C-20
and NAT B-8
and the Internet B-2
assigning B-2, B-9
auto-generated 7-3
private B-7
translating B-9
IP configuration by DHCP B-10
IP networking
for Macintosh C-16
for Windows C-2, C-7
ISP 3-1
L
LAN IP Setup Menu 6-5
LEDs
description 2-7
troubleshooting 7-2
log
sending 5-13
LPD/LPR Printing 6-1
M
MAC address 7-7, B-9
spoofing 3-12, 7-5
Macintosh C-19
configuring for IP networking C-16
DHCP Client ID C-16
network printing 6-8
Obtaining ISP Configuration Information C-20
masquerading C-18
MDI/MDI-X B-15, G-2
MDI/MDI-X wiring B-14, G-4
metric 6-9
Modem 3-15, 3-16
modem 2-4, 2-8, 3-13
N
NAT C-18
NAT. See Network Address Translation
netmask
translation table B-6
Network Address Translation 2-3, B-8, C-18
Network Time Protocol 5-12, 7-7
newsgroup 5-3
NTP 5-12, 7-7
O
Open System authentication D-3
outbound rules 5-7
P
package contents 2-5
Passphrase 4-5, 4-9
passphrase 2-2
password
restoring 7-7
PC, using to configure C-21
ping 6-2
port filtering 5-7
port forwarding 5-5
port forwarding behind NAT B-8
port numbers 5-10

Index 3
PPP over Ethernet 2-4, C-18
PPPoE 2-4, C-18
Primary DNS Server 3-8, 3-9, 3-12
protocols
Address Resolution B-9
DHCP B-10
Routing Information 2-3, B-2
support 2-1
PTP Driver 6-1
publications, related B-1
R
range 4-1
rear panel 2-8
remote management 6-10
requirements
hardware 3-1
reserved IP adresses 6-7
restore configuration 5-6
restore factory settings 5-8
Restrict Wireless Access by MAC Address 4-8
RFC
1466 B-7, B-9
1597 B-7, B-9
1631 B-8, B-9
finding B-7
RIP (Router Information Protocol) 6-6
router concepts B-1
Router Status 5-1
Routing Information Protocol 2-3, B-2
rules
inbound 5-5
outbound 5-7
S
Secondary DNS Server 3-8, 3-9, 3-12
security 2-1, 2-3
Serial 3-14, 3-15
serial 2-1, 2-8
service blocking 5-7
service numbers 5-10
Setup Wizard 3-1
Shared Key authentication D-3
SMTP 5-13
spoof MAC address 7-5
SSID 4-4, 4-7, 4-8, D-2
stateful packet inspection 2-2, 5-1, B-11
subnet addressing B-4
subnet mask B-5, C-19, C-20
syslog 5-17
T
TCP/IP
configuring C-1
network, troubleshooting 7-5
TCP/IP properties
verifying for Macintosh C-17
verifying for Windows C-6, C-15
time of day 7-7
time zone 5-12
time-stamping 5-12
troubleshooting 7-1
Trusted Host 5-3
U
Universal Plug and Play 6-11
Uplink switch B-14
UPnP 6-11
USB C-18
USB 2.0 2-8
W
WEP D-3
Wi-Fi D-1
Windows, configuring for IP routing C-2, C-7
winipcfg utility C-6
WinPOET C-18
Wired Equivalent Privacy. See WEP

4Index
wireless authentication scheme 4-5
Wireless Ethernet D-1
Wireless Security 4-2