Fujitsu Client Computing WL0033 LifeBook P Series w/WM3B2915ABG 11ABG WLAN User Manual P Series
Fujitsu Limited LifeBook P Series w/WM3B2915ABG 11ABG WLAN P Series
Contents
- 1. Users Manual
- 2. Revised Users Manual1
- 3. Revised Users Manual2
Revised Users Manual2
63
6
Care and Maintenance
P Series.book Page 63 Wednesday, July 13, 2005 10:43 AM
64
LifeBook P Series Notebook - Section Six
P Series.book Page 64 Wednesday, July 13, 2005 10:43 AM
65
Care and Maintenance
Care and Maintenance
If you use your LifeBook P Series notebook carefully,
you will increase its life and reliability. This section
provides some tips for looking after the notebook and its
devices.
LIFEBOOK P SERIES NOTEBOOK
Caring for your LifeBook
■Your notebook is a durable but sensitive electronic
device. Treat it with care.
■Make a habit of transporting it in a suitable carrying
case.
■To protect your notebook from damage and to opti-
mize system performance, be sure to keep all air all
vents unobstructed, clean, and clear of debris. This
may require periodic cleaning, depending upon the
environment in which the system is used.
■Do not operate the notebook in areas where the air
vents can be obstructed, such as in tight enclosures or
on soft surfaces like a bed or cushion.
■Do not attempt to service the computer yourself. Any
unauthorized service performed on the computer will
void the warranty.
■ Always follow installation instructions closely.
■Keep it away from food and beverages.
■If you accidentally spill liquid on your notebook:
1. Turn it off.
2. Position it so that the liquid can run out.
3. Let it dry out for 24 hours, or longer if needed.
4. If your notebook will not boot after it has dried
out, call your support representative.
■Do not use your notebook in a wet environment (near
a bathtub, swimming pool).
■Always use the AC adapter and batteries that are
approved for your notebook.
■Avoid exposure to sand, dust and other environmental
hazards.
■Do not expose your notebook to direct sunlight for
long periods of time as temperatures above 140° F
(60° C) may damage your notebook.
■Keep the covers closed on the connectors and slots
when they are not in use.
■Do not put heavy or sharp objects on the computer.
■If you are carrying your notebook in a briefcase, or
any other carrying case, make sure that there are no
objects in the case pressing on the lid.
■Do not drop your notebook.
■Do not touch the screen with any sharp objects.
Cleaning your LifeBook
■Always disconnect the power plug. (Pull the plug, not
the cord.)
■Clean your notebook with a damp, lint-free cloth. Do
not use abrasives or solvents.
■Use a soft cloth to remove dust from the screen. Never
use glass cleaners.
Storing your LifeBook
■If storing your notebook for a month or longer, turn
the notebook off, fully charge the battery, then remove
and store all Lithium ion batteries.
■Store your notebook and batteries separately. If you
store your notebook with a battery installed, the bat-
tery will discharge, and battery life will be reduced. In
addition, a faulty battery might damage the notebook.
■Store your notebook in a cool, dry location.
Temperatures should remain between 13º F (-25º C)
and 140º F (60º C).
Traveling with your LifeBook
■Do not transport your notebook while it is turned on.
■Do not check your notebook as baggage. Carry it with
you.
■When traveling with the hard drive removed, wrap the
drive in a non-conducting materials (cloth or paper).
If you have the drive checked by hand, be ready to
install the drive if needed. Never put your hard drive
through a metal detector. Have your hard drive hand-
inspected by security personnel. You can however, put
your hard drive through a properly tuned X-ray
machine.
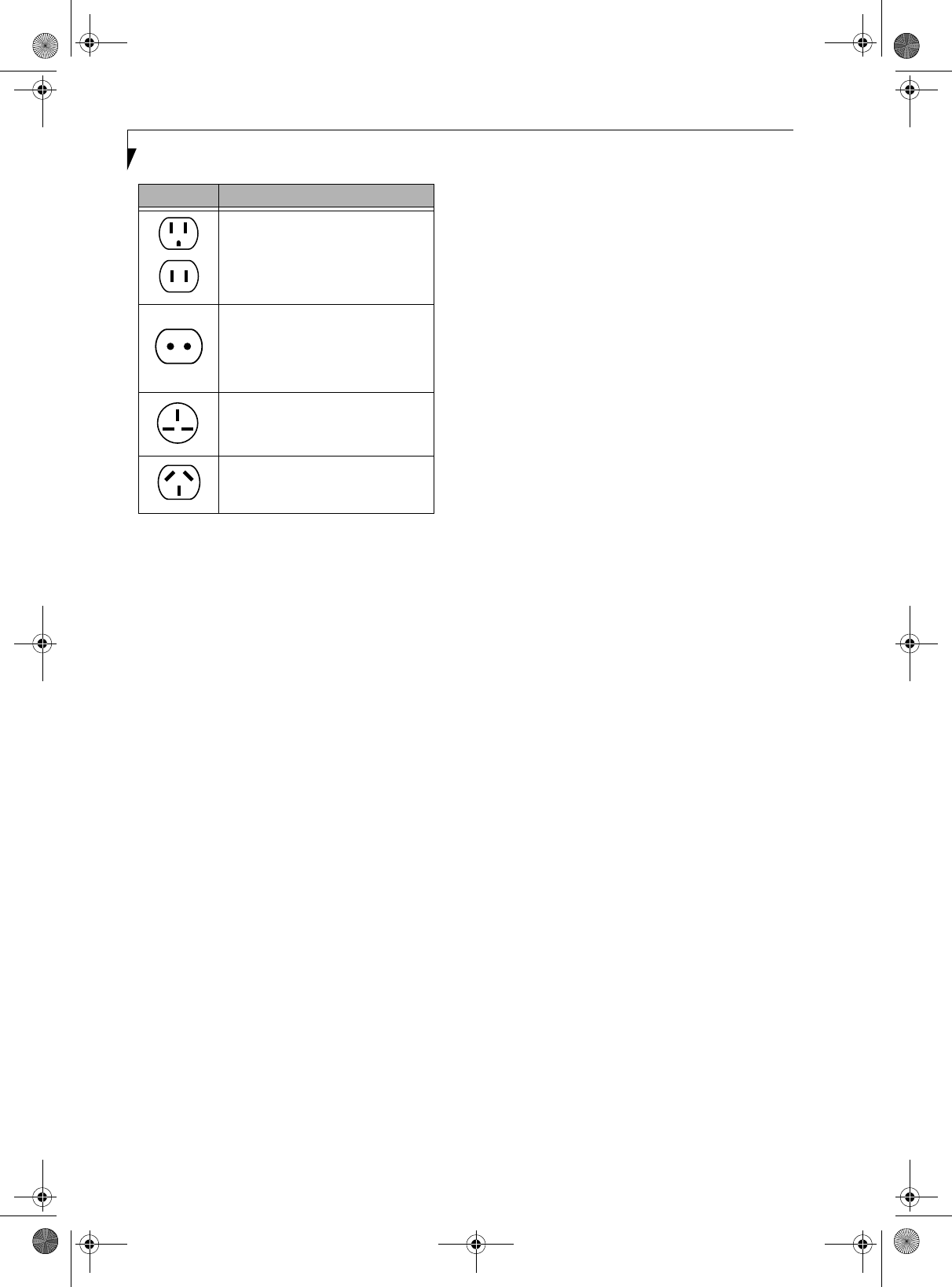
■Take the necessary plug adapters if you're traveling
overseas. Check the following diagram to determine
which adapter you'll need or ask your travel agent.
Electrical equipment may be hazardous if
misused. Operations of this product or
similar products, must always be supervised
by an adult. Do not allow children access to
the interior of any electrical products and
do not permit them to handle any cables.
Do not use excessive force when tapping
or writing on the screen with the stylus or
your finger. Use of excessive force could
result in damage to the LCD and/or Touch
Screen.
P Series.book Page 65 Wednesday, July 13, 2005 10:43 AM
66
LifeBook P Series Notebook - Section Six
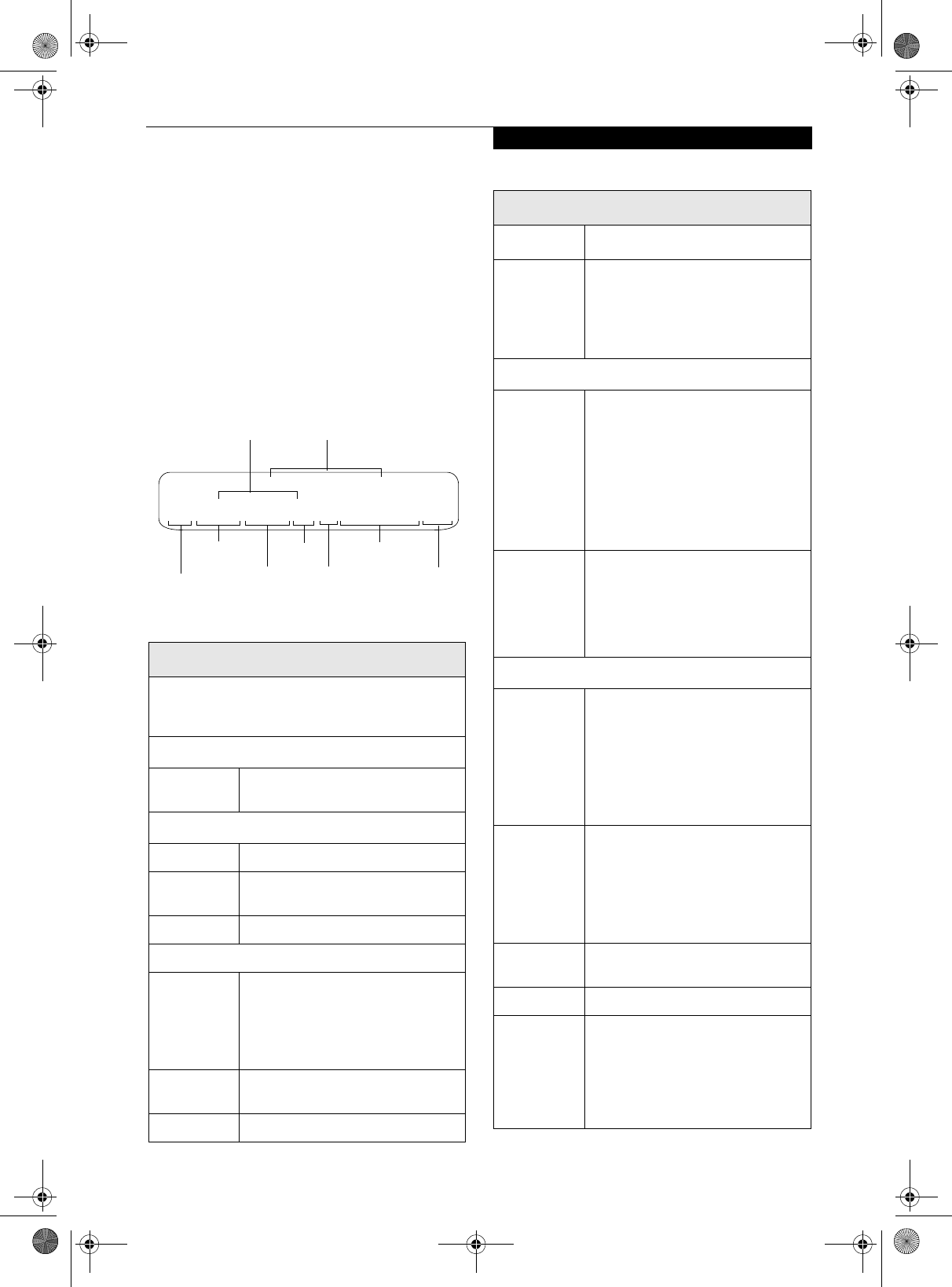
Figure 6-1. Outlet types
KEYBOARD
Caring for your Keyboard
The keyboard of your computer is a very sensitive
instrument. It is made up of many switches that are
activated when you press on the keys. The keyboard is a
major component of the heat dissipation system in a
notebook. Due to heat and size considerations the
keyboard is not sealed. Because the keys are so close
together, it is not easy for the user to see when liquids
have fallen onto the circuitry below the keys.
Attempting to clean the keyboard with a spray on
cleaner or rag soaked with cleaner the liquid can drip
onto the circuitry sight unseen. Once the liquid seeps
between the layers of circuitry, it can cause corrosion or
other damage to the circuits. This can result in keys
which no longer operate, or which, when pressed, record
the wrong characters and other similar failures.
There is no repair for this problem other than replace-
ment. The solution is to become aware of the issue and
take appropriate steps to protect your keyboard.
To clean the keyboard, use a rag dampened slightly with
cleaning solution. Use extreme care to prevent liquid
from dripping between the keys. Spraying directly on the
keys should be avoided. The spray should be applied first
to the cloth, and then the cloth wiped over the keys.
BATTERIES
Caring for your Batteries
■Always handle batteries carefully.
■Do not short-circuit the battery terminals (that is, do
not touch both terminals with a metal object). Do not
carry lose batteries in a pocket or purse where they
may mix with coins, keys, or other metal objects.
Doing so may cause an explosion or fire.
■Do not drop, puncture, disassemble, mutilate or incin-
erate the battery.
■Recharge batteries only as described in this manual
and only in ventilated areas.
■Do not leave batteries in hot locations for more than a
day or two. Intense heat can shorten battery life.
■Do not leave a battery in storage for longer than six
months without recharging it.
Increasing Battery Life
■Keep brightness to the lowest comfortable level.
■Set the power management for maximum battery life.
■Put your notebook in Standby mode when it is turned
on and you are not actually using it.
■Disable the Windows CD auto insert function.
■Always use fully charged batteries.
OPTIONAL FLOPPY DISK DRIVE
AND FLOPPY DISKS
Caring for your Floppy Disks
■Avoid using floppy disks in damp and dusty locations.
■Never store a floppy disk near a magnet or magnetic
field.
■Do not use a pencil or an eraser on a disk or disk label.
■Avoid storing the floppy disks in extremely hot or cold
locations, or in locations subject to severe temperature
changes. Store at temperatures between 50º F (10º C)
and 125º F (52º C).
■Do not touch the exposed part of the disk behind the
metal shutter.
Caring for your Optional Floppy Disk Drive
■To clean, wipe the floppy disk drive clean with a dry
soft cloth, or with a soft cloth dampened with water or
a solution of neutral detergent. Never use benzene,
paint thinner or other volatile material.
■Avoid storing the floppy disk drive in extremely hot or
cold locations, or in locations subject to severe
temperature changes. Store at temperatures between
50º F (10º C) and 125º F (52º C).
■Keep the floppy disk drive out of direct sunlight and
away from heating equipment.
■Avoid storing the floppy disk drive in locations subject
to shock and vibration.
■Never use the floppy disk drive with any liquid, metal,
or other foreign matter inside the drive or disk.
■Never disassemble or dismantle your floppy disk drive.
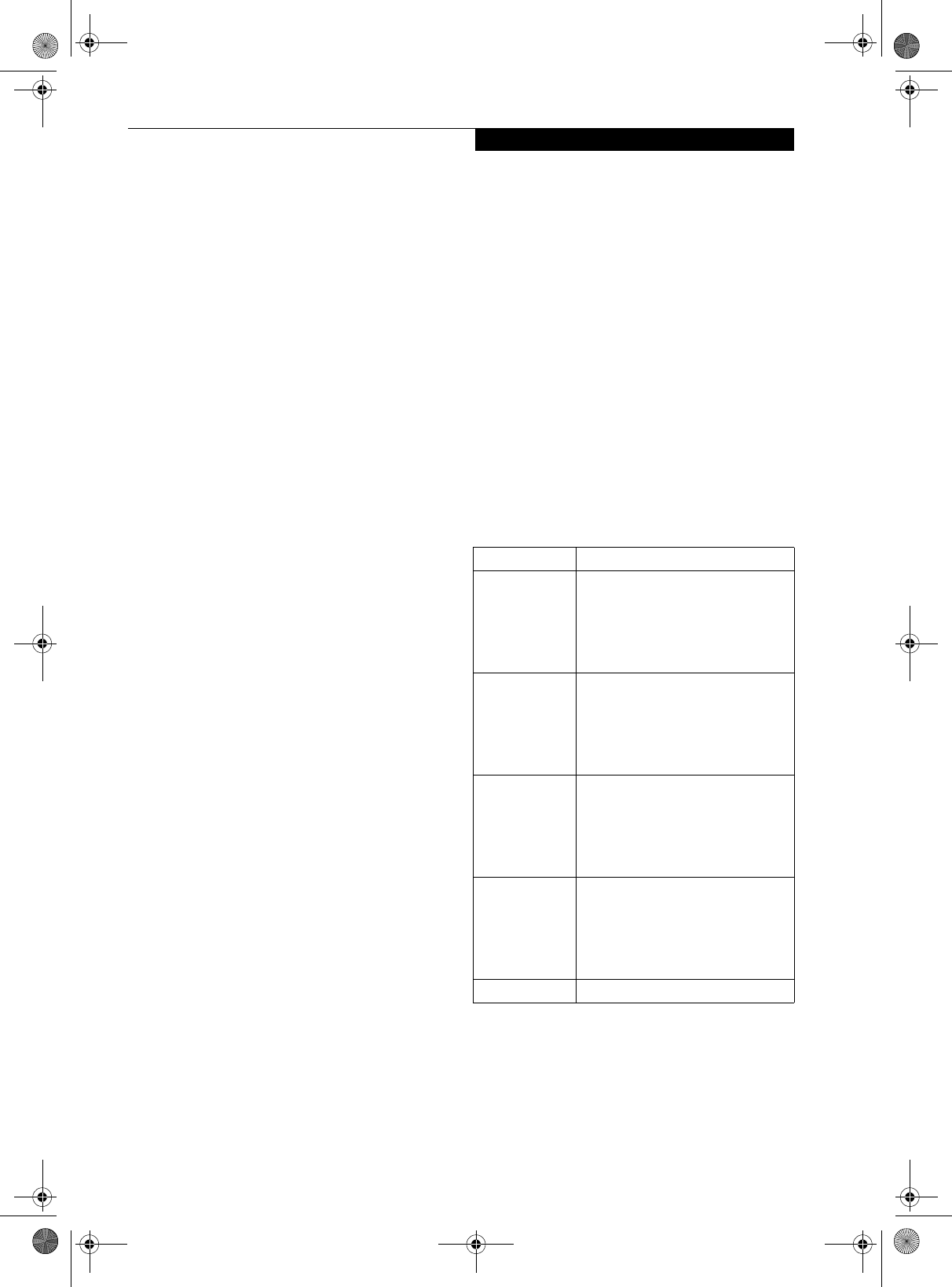
Outlet Type Location
United States, Canada, Mexico, parts
of Latin America, Japan, Korea, the
Philippines, Taiwan
Russia and the Commonwealth of
Independent States (CIS), most of
Europe, parts of Latin America, the
Middle East, parts of Africa, Hong
Kong, India, most of South Asia
United Kingdom, Ireland, Malaysia,
Singapore, parts of Africa
China, Australia, New Zealand
P Series.book Page 66 Wednesday, July 13, 2005 10:43 AM
67
Care and Maintenance
OPTIONAL OPTICAL DRIVE AND DISCS
Caring for your discs
CDs and DVD discs are precision devices and will func-
tion reliably if given reasonable care.
■Always store your discs in their case when not in use.
■Always handle discs by the edges and avoid touching
the surface.
■Avoid storing any discs in extreme temperatures.
■Do not bend discs or set heavy objects on them.
■Do not spill liquids on discs.
■Do not scratch discs.
■Do not put a label on discs.
■Do not get dust on discs.
■Never write on the label surface with a ballpoint pen
or pencil. Always use a felt pen.
■If a disc is subjected to a sudden change in tempera-
ture, cold to warm condensation may form on the sur-
face. Wipe the moisture off with a clean, soft, lint free
cloth and let it dry at room temperature. DO NOT use
a hair dryer or heater to dry discs.
■If a disc is dirty, use only a disc cleaner or wipe it with
a clean, soft, lint free cloth starting from the inner
edge and wiping to the outer edge.
Caring for your Optional Optical Drive
Your optical drive is durable but you must treat it with
care. Please pay attention to the following points:
■The drive rotates the compact disk at a very high
speed. Do not carry it around or subject it to shock or
vibration with the power on.
■Avoid using or storing the drive where it will be
exposed to extreme temperatures.
■Avoid using or storing the drive where it is damp or
dusty.
■Use of a commercially-available lens cleaner kit is
recommended to maintain the drive lens.
■Avoid using or storing the drive near magnets or
devices that generate strong magnetic fields.
■Avoid using or storing the drive where it will be
subjected to shock or vibration.
■Do not disassemble or dismantle the optical drive.
CF CARDS
Caring for your CF Cards
CF Cards are durable, but you must treat them with
care. The documentation supplied with your CF Cards
provides specific information for caring for the cards.
When you don’t have a CF Card installed in your system,
you should be sure to install the CF Card slot inserts that
came with your system. These will help to keep dust and
dirt out of your system.
P Series.book Page 67 Wednesday, July 13, 2005 10:43 AM
68
LifeBook P Series Notebook - Section Six
P Series.book Page 68 Wednesday, July 13, 2005 10:43 AM
69
7
Specifications
P Series.book Page 69 Wednesday, July 13, 2005 10:43 AM
70
LifeBook P Series Notebook - Section Seven
P Series.book Page 70 Wednesday, July 13, 2005 10:43 AM
71
Specifications
Specifications
This section provides the hardware and environmental
specifications for your LifeBook P Series notebook.
Specifications of particular configurations will vary.
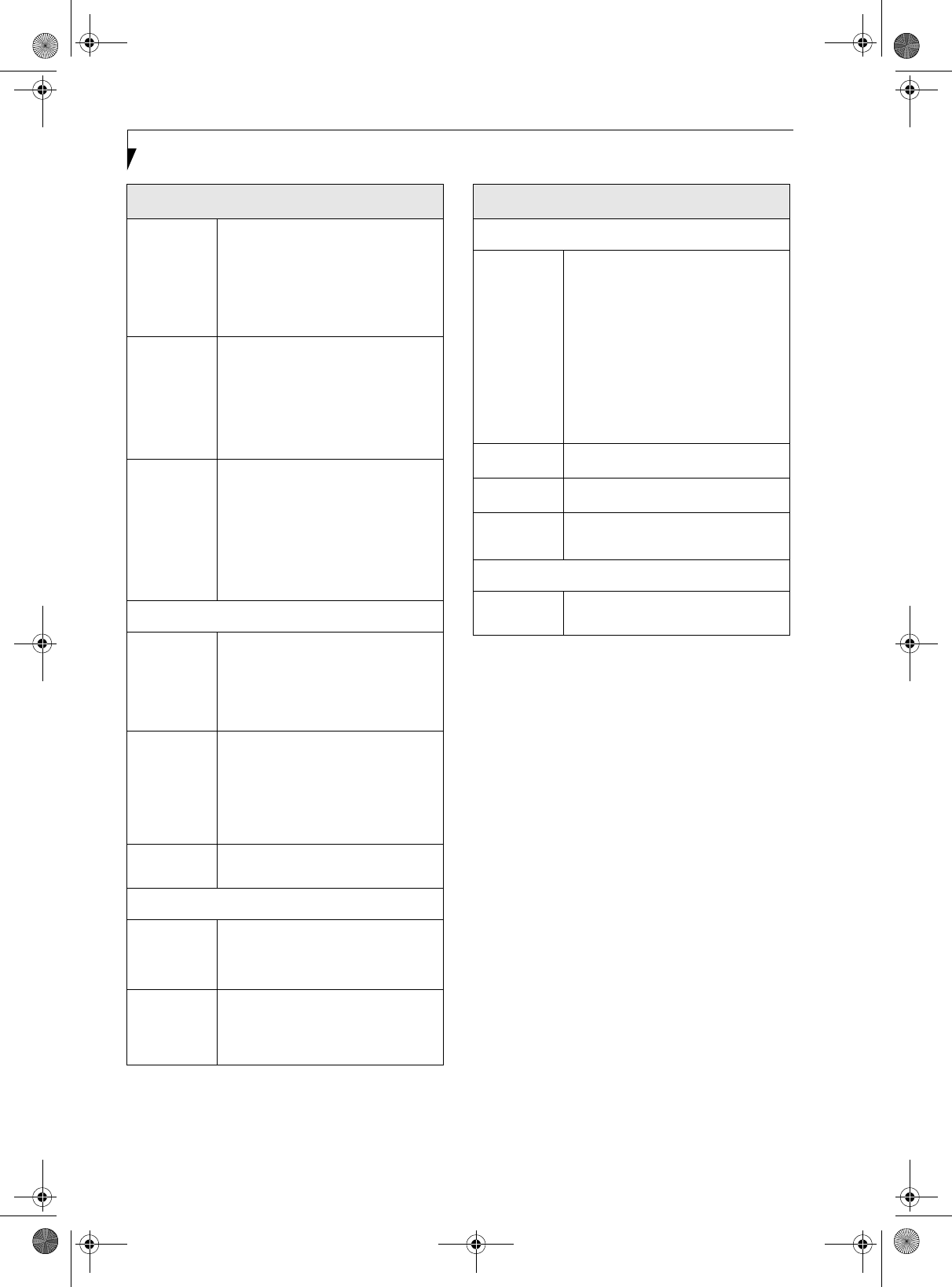
CONFIGURATION LABEL
Your LifeBook P Series notebook has a configuration
label located on the bottom. (See figure 2-8 on page 13
for location). This label contains specific information
regarding the options you’ve chosen for your notebook.
Following is an example label and information on how
to read your own configuration label.
Figure 7-1. Configuration Label
LifeBook P Series notebook Specifications
The specifications for your particular model may vary.
To determine the specifications for your system, please
visit our Web site at: us.fujitsu.com/computers.
Physical Specifications
Dimensions 9.13” w x 6.57” d x 1.36" / 1.46"
(232 mm x 167 mm x 34.5/37 mm)
Processing Specifications
CPU/Speed Intel Pentium M ULV 753
Front Side
Bus (FSB)
400 MHz
Chip set 915GMS
Memory/Storage Specifications
Main RAM • 256 MB SDRAM (DDR2 400 MHz)
• 172-pin Micro DIMM slot
256 MB, 512 MB, and 1.0 GB
modules available, with a system
maximum of 1.0 GB.
L1 cache
(CPU)
64 KB on-die
L2 cache 2 MB on-die
P1500, PM ULV 753, 8.9 WSVGA, 256M, 60G, MODEM/LAN/WLAN, WIN XP
Configuration P/N: APZXXXXXXXXXXXXX
FPC P/N: FPCMXXXXXX
Model
Processor
Screen
Size
Operating
System
Hard Drive
Part Number
Configuration ID
Memory Communications
BIOS ROM 1 MB (Boot Block Type Flash ROM)
Hard disk
drive
• 1.8” HDD
• 30 GB or 60 GB IDE (4200 rpm)
ATA 100
• Shock-mounted
• SMART Support
Display Specifications
Display 8.9" TFT WSVGA (1024 x600),
16M colors:
• Color LCD
• Active Digitizer
• 32-bit color
• External monitor support: SXGA
(1280x1024 maximum)
• Dot pitch: 0.240 x 0.240 mm
VRAM Up to 128 MB of shared memory
using Unified Memory Architecture
(UMA). Dynamically responds to
application requirements and allocates
the proper amount of memory for
optimal graphics and performance.
Interface Specifications
Integrated
Interfaces
• Modem (RJ-11)
• LAN (RJ-45)
• USB 2.0 x 2
•DC-In
• Analog RGB, Mini D-SUB 15-pin
connector for external VGA monitor
• Docking connector
Interfaces
on Optional
Port
Replicator
• DC Power
• LAN (RJ-45)
• 15-pin D-SUB connector for
external VGA monitor
• USB 2.0 x 2
• Docking Port
CF Card Slot Dedicated slot for Compact Flash
Card, Type II
SD Slot Dedicated slot for SD Card
User
Interface
support
• Keyboard
Pitch: 19 mm, Stroke: 3 mm
• Quick Point pointing device with
scroll button
• Passive digitizer with pen input
• On-screen keyboard
LifeBook P Series notebook Specifications (Continued)
P Series.book Page 71 Wednesday, July 13, 2005 10:43 AM
72
LifeBook P Series Notebook - Section Seven
Audio • Realtek ALC203
• Internal mono microphone
• Mono speaker
• Mono microphone and stereo
headphone jacks
• 26 adjustable audio levels
User
Controls
• Programmable Application Buttons,
each with primary and secondary
functions (default applications:
Calculator and WordPad)
• Trusted Platform Module (TPM)
support (on some models)
• Suspend/Resume button
Status
Indicators
(LCDs)
•Power
• Battery charging
• Battery level
• Hard disk drive
• Caps Lock
•Num Lock
• Scroll Lock
Power Specifications
Main Battery • 3-cell
• Removable, Lithium ion
• 10.8 V @2600 mAh, max. 28 WHr
•Recharge Time:
Approximately 2.5 hours
Optional
Battery
•6-cell
• Removable, Lithium ion
• 10.8V @ 5200 mAh,
max. 56.0 WHr
•Recharge Time:
Approximately 4.5 hours
AC Adapter Autosensing 100 - 240V, supplying 16
VDC, with a current of 2.5 A
Environmental Specifications
Temperature Operating: 41o to 95o F (5o to 35o C)
Non-operating: 5o to 140o F
(-15o to 60o C)
Humidity Operating:
20 to 85% non-condensing
Non-operating:
8 to 85% non-condensing
LifeBook P Series notebook Specifications (Continued)
Agency Approval Specifications
Emissions
• EN55022 (CISPR22) Class B
• FCC 15, Class B
• FCC 15C, 15.247
• ICES-003
• Canada RSS-210
• ETSI EN 300 328-1 V1.3.1 : 2001
• ETSI EN 300 328-2 V1.2.1 :
2001_12
• ETSI EN 301 498-17 V1.2.1 : 2002
• ETSI EN 301 498-1 V1.4.1 : 2002
Immunity • EN55024 (1998)
Safety • UL and cUL Listed, UL 60950
Telecom • FCC Part 68
• IC CS-03
Additional Specifications
Operating
System • Microsoft® Windows® XP Pro
LifeBook P Series notebook Specifications (Continued)
P Series.book Page 72 Wednesday, July 13, 2005 10:43 AM
73
Regulatory Information
Regulatory Information
FCC NOTICES
Notice to Users of Radios and Television
These limits are designed to provide reasonable protec-
tion against harmful interference in a residential installa-
tion. This equipment generates, uses, and can radiate
radio frequency energy and, if not installed and used in
accordance with the instructions, may cause harmful
interference to radio communications. However, there is
no guarantee that interference will not occur in a partic-
ular installation. If this equipment does cause harmful
interference to radio or television reception, which can
be determined by turning the equipment off and on, the
user is encouraged to try to correct the interference by
one or more of the following measures:
• Reorient or relocate the receiving antenna.
• Increase the separation between the equipment and
receiver.
• Connect the equipment into an outlet that is on a
different circuit than the receiver.
• Consult the dealer or an experienced radio/TV
technician for help.
Shielded interconnect cables must be employed with this
equipment to ensure compliance with the pertinent RF
emission limits governing this device.
Notice to Users of the US Telephone Network
This equipment contains an internal modem that
complies with Part 68 of the FCC rules. On the bottom
of this equipment is a label that contains, among other
information, the FCC registration number and ringer
equivalence number (REN) for this equipment. If
requested, this information must be provided to the tele-
phone company.
This equipment is designed to be connected to the tele-
phone network or premises wiring using a standard jack
type USOC RJ11C. A plug and jack used to connect this
equipment to the premises wiring and telephone
network must comply with the applicable FCC Part 68
rules and requirements adopted by the ACTA. A
compliant telephone cord and modular plug is provided
with this product. It is designed to be connected to a
compatible modular jack that is also compliant.
The ringer equivalent number (REN) of this equipment
is 0.1B as shown on the label. The REN is used to deter-
mine the number of devices that may be connected to a
telephone line. Excessive RENs on a telephone may
result in the devices not ringing in response to an
incoming call. In most but not all areas, the sum of
RENs should not exceed five (5.0). To be certain of the
number of devices that may be connected to a line, as
determined by the total RENs, contact the local tele-
phone company.
If this equipment causes harm to the telephone network,
the telephone company will notify you in advance that
temporary discontinuance of service may be required.
But if advance notice isn’t practical, the telephone
company will notify the customer as soon as possible.
Also, you will be advised of your right to file a complaint
with the FCC if you believe it is necessary.
The telephone company may make changes in its facili-
ties, equipment, operations or procedures that could
effect the operation of the equipment. If this happens
the telephone company will provide advance notice in
order for you to make necessary modifications to main-
tain uninterrupted service.
If trouble is experienced with this equipment, for repair
or warranty information, please refer to the manual or
contact Fujitsu Computer Systems Corporation,
Customer Service. If the equipment is causing harm to
the telephone network, the telephone company may
request that you disconnect the equipment until the
problem is resolved.
The equipment cannot be used on public coin service
provided by the telephone company. Connection to
party line service is subject to state tariffs. (Contact the
state public utility commission, public service commis-
sion or corporation commission for information).
If your home has specially wired alarm equipment
connected to the telephone line, ensure the installation
of this computer does not disable your alarm equip-
ment. If you have any questions about what will disable
alarm equipment, consult your telephone company or a
qualified installer.
The Telephone Consumer Protection Act of 1991 makes
it unlawful for any person to use a computer or other
electronic device to send any message via a telephone fax
machine unless such message clearly contains in a
margin at the top or bottom of each transmitted page or
on the first page of the transmission, the date an time it
is sent and an identification of the business or other
entity, or other individual sending the message and the
telephone number of the sending machine or such busi-
ness, other entity, or individual.
Changes or modifications not expressly
approved by Fujitsu could void this user’s
authority to operate the equipment
P Series.book Page 73 Wednesday, July 13, 2005 10:43 AM
74
LifeBook P Series Notebook - Section Seven
DOC (INDUSTRY CANADA) NOTICES
Notice to Users of Radios and Television
This Class B digital apparatus meets all requirements of
Canadian Interference-Causing Equipment Regulations.
CET appareil numérique de la class B respecte toutes les
exigence du Réglement sur le matérial brouilleur du
Canada.
Notice to Users of the Canadian Telephone Network
NOTICE: This equipment meets the applicable Industry
Canada Terminal Equipment Technical Specifications.
This is confirmed by the registration number. The
abbreviation, IC, before the registration number
(4061A-8687) signifies that registration was performed
based on a Declaration of Conformity indicating that
Industry Canada technical specifications were met. It
does not imply that Industry Canada approved the
equipment.
Before connecting this equipment to a telephone line the
user should ensure that it is permissible to connect this
equipment to the local telecommunication facilities. The
user should be aware that compliance with the certifica-
tion standards does not prevent service degradation in
some situations.
Repairs to telecommunication equipment should be
made by a Canadian authorized maintenance facility.
Any repairs or alterations not expressly approved by
Fujitsu or any equipment failures may give the telecom-
munication company cause to request the user to
disconnect the equipment from the telephone line.
NOTICE: The Ringer Equivalence Number (REN) for
this terminal equipment is 0.1B. The REN assigned to
each terminal equipment provides an indication of the
maximum number of terminals allowed to be connected
to a telephone interface. The termination on an interface
may consist of any combination of devices subject only
to the requirement that the sum of the Ringer Equiva-
lence Numbers of all the devices does not exceed five.
Avis Aux Utilisateurs Du Réseau
Téléphonique Canadien
AVIS: Le présent matériel est conforme aux spécifica-
tions techniques d’Industrie Canada applicables au
matériel terminal. Cette conformité est confirmée par le
numéro d’enregistrement. Le sigle IC, placé devant le
numéro d’enregistrement (4061A-8687), signifie que
l’enregistrement s’est effectué conformément à une
déclaration de conformité et indique que les spécifica-
tions techniques d’Industrie Canada ont été respectées.
Il n’implique pas qu’Industrie Canada a approuvé le
matériel.
Avant de connecter cet équipement à une ligne télépho-
nique, l’utilisateur doit vérifier s’il est permis de
connecter cet équipement aux installations de télécom-
munications locales. L’utilisateur est averti que même la
conformité aux normes de certification ne peut dans
certains cas empêcher la dégradation du service.
Les réparations de l’équipement de télécommunications
doivent être eVectuées par un service de maintenance
agréé au Canada. Toute réparation ou modification, qui
n’est pas expressément approuvée par Fujitsu, ou toute
défaillance de l’équipement peut entraîner la compagnie
de télécommunications à exiger que l’utilisateur décon-
necte l’équipement de la ligne téléphonique.
AVIS: L’indice d’équivalence de la sonnerie (IES) du
présent matériel est de 0.1B. L’IES assigné à chaque
dispositif terminal indique le nombre maximal de
terminaux qui peuvent être raccordés à une interface
téléphonique. La terminaison d’une interface peut
consister en une combinaison quelconque de dispositifs,
à la seule condition que la somme d’indices d’équiva-
lence de la sonnerie de tous les dispositifs n’excède pas 5.
For safety, users should ensure that the
electrical ground of the power utility, the
telephone lines and the metallic water
pipes are connected together. Users should
NOT attempt to make such connections
themselves but should contact the appro-
priate electric inspection authority or elec-
trician. This may be particularly important
in rural areas.
Pour assurer la sécurité, les utilisateurs
doivent vérifier que la prise de terre du ser-
vice d’électricité, les lignes télphoniques et
les conduites d’eau métalliques sont con-
nectées ensemble. Les utilisateurs NE
doivent PAS tenter d’établir ces connex-
ions eux-mêmes, mais doivent contacter
les services d’inspection d’installations
électriques appropriés ou un électricien.
Ceci peut être particulièrement important
en régions rurales.
P Series.book Page 74 Wednesday, July 13, 2005 10:43 AM
75
8
Glossary
P Series.book Page 75 Wednesday, July 13, 2005 10:43 AM
76
LifeBook P Series Notebook - Section Eight
P Series.book Page 76 Wednesday, July 13, 2005 10:43 AM
77
Glossary
Glossary
AC Adapter
A device which converts the AC voltage from a wall
outlet to the DC voltage needed to power your note-
book.
ACPI
Advanced Configuration and Power Interface
Active-Matrix Display
A type of technology for making flat-panel displays
which has a transistor or similar device for every pixel
on the screen.
AdHoc
A designation for wireless LAN network configuration.
It indicates a form of communication limited to those
personal computers which have wireless LAN function.
For details, refer to “Ad hoc mode” on page 86.
ADSL
Asymmetric Digital Subscriber Line
Technology for transporting high bit-rate services over
ordinary phone lines.
Auto/Airline Adapter
A device which converts the DC voltage from an auto-
mobile cigarette lighter or aircraft DC power outlet to
the DC voltage needed to power your notebook.
BIOS
Basic Input-Output System. A program and set of
default parameters stored in ROM which tests and
operates your notebook when you turn it on until it
loads your installed operating system from disk. Infor-
mation from the BIOS is transferred to the installed
operating system to provide it with information on the
configuration and status of the hardware.
Bit
An abbreviation for binary digit. A single piece of
information which is either a one (1) or a zero (0).
bps
An abbreviation for bits per second. Used to describe
data transfer rates.
Boot
To start-up a computer and load its operating system
from disk, ROM or other storage media into RAM.
Bus
An electrical circuit which passes data between the CPU
and the sub-assemblies inside your notebook.
Byte
8 bits of parallel binary information.
Cache Memory
A block of memory built into the micro-processor
which is much faster to access than your system RAM
and used in specially structured ways to make your
overall data handling time faster.
CardBus
A faster, 32-bit version of the PC Card interface which
offers performance similar to the 32-bit PCI
architecture.
CD-ROM
Compact disk read only memory. This is a form of
digital data storage which is read optically with a laser
rather than a magnetic head. A typical CD-ROM can
contain about 600MB of data and is not subject to heads
crashing into the surface and destroying the data when
there is a failure nor to wear from reading.
Channel
The frequency band of wireless LAN to be used in
communications over wireless LAN or at the access
point.
CMOS RAM
Complementary metal oxide semiconductor random
access memory. This is a technology for manufacturing
random access memory which requires very low levels of
power to operate.
Command
An instruction which you give your operating system.
Example: run a particular application or format a floppy
disk.
Configuration
The combination of hardware and software that makes
up your system and how it is allocated for use.
CRT
Cathode Ray Tube. A display device which uses a beam
of electronic particles striking a luminescent screen. It
produces a visual image by varying the position and
intensity of the beam.
Data
The information a system stores and processes.
DC
Direct current. A voltage or current that does not
fluctuate periodically with time.
Default Value
A pre programmed value to be used if you fail to set
your own.
P Series.book Page 77 Wednesday, July 13, 2005 10:43 AM
78
LifeBook P Series Notebook - Section Eight
DHCP
Dynamic Host Configuration Protocol
A protocol used for automatically fetching communica-
tion parameters such as IP addresses. The side which
assigns IP address is called DHCP server and the side
that is assigned it is called DHCP client.
DIMM
Dual-in-line memory module.
Disk
A spinning platter of magnetic data storage media. If the
platter is very stiff it is a hard drive, if it is highly flexible
it is a floppy disk, if it is a floppy disk in a hard housing
with a shutter it is commonly called a diskette.
Disk Drive
The hardware which spins the disk and has the heads
and control circuitry for reading and writing the data
on the disk.
Diskette
A floppy disk in a hard housing with a shutter.
DMA
Direct Memory Access
Special circuitry for memory to memory transfers of
data which do not require CPU action.
DMI
Desktop Management Interface
A standard that provides PC management applications
with a common method of locally or remotely querying
and configuring PC computer systems, hardware and
software components, and peripherals.
DNS
Domain Name System
A function that controls the correspondence of IP
addresses assigned to a computer with the name. Even
for those computers whose IP addresses are unknown, if
their names are known, it is possible to communicate
with them.
DOS
Disk Operating System (MS-DOS is a Microsoft Disk
Operating System).
Driver
A computer program which converts application and
operating system commands to external devices into the
exact form required by a specific brand and model of
device in order to produce the desired results from that
particular equipment.
ECP
Extended Capability Port. A set of standards for high
speed data communication and interconnection
between electronic devices.
Encryption Key (Network Key)
Key information used to encode data for data transfer.
This device uses the same encryption key to encode and
decode the data, and the identical encryption key is
required between the sender and receiver.
ESD
Electro-Static Discharge. The sudden discharge of elec-
tricity from a static charge which has built-up slowly.
Example: the shock you get from a doorknob on a dry
day or the sparks you get from brushing hair on a dry
day.
Extended Memory
All memory more than the 640KB recognized by
MS-DOS as system memory.
FCC
Federal Communication Commission.
Floppy Disk
A spinning platter of magnetic data storage media which
is highly flexible.
GB
Gigabyte.
Hard drive
A spinning platter of magnetic data storage media where
the platter is very stiff.
I/O
Input/Output. Data entering and leaving your notebook
in electronic form.
I/O Port
The connector and associated control circuits for data
entering and leaving your notebook in electronic form.
IDE
Intelligent Drive Electronics. A type of control interface
for a hard drive which is inside the hard drive unit.
IEEE 1394
Industry standard that allows you to connect between
your notebook and a peripheral device such as a digital
camera. Also known as “Firewire” or “iLINK”.
P Series.book Page 78 Wednesday, July 13, 2005 10:43 AM
79
Glossary
IEEE802.11a
One of the wireless LAN standards prescribed by the 802
committee in charge of establishing standards of LAN
technology in IEEE (Institute of Electrical and Elec-
tronic Engineers). This standard allows communica-
tions at the maximum speed of 54 Mbps by using a 5
GHz band which can freely be used without radio
communication license.
IEEE802.11b
One of the wireless LAN standards prescribed by 802
committee in charge of establishing standards of LAN
technology in IEEE (Institute of Electrical and Elec-
tronic Engineers). It allows communications at the
maximum speed of 11 Mbps by a band of 2.4 GHz (ISM
band) which can freely be used without radio communi-
cation license.
IEEE802.11g
One of the wireless LAN standards prescribed by 802
committee in charge of establishing standards of LAN
technology in IEEE (Institute of Electrical and Elec-
tronic Engineers). It allows communications at the
maximum speed of 54 Mbps by a band of 2.4 GHz (ISM
band) which can freely be used without radio communi-
cation license.
Infrared
Light just beyond the red portion of the visible light
spectrum which is invisible to humans.
Infrastructure
A designation of Wireless LAN network configurations.
It indicates a form of communication using an Access
Point. For details, refer to “Infrastructure connection”
on page 86.
IP Address
An address used for computers to communicate in the
TCP/IP environment.
Current IPv4 (version 4) uses four values in the range
between 1 and 255. (Example: 192.168.100.123).
There are two types of IP address: global address and
private address.
The global address is an only address in the world. It is
controlled by JPNIC (Japan Network Information
Center). A private address is an only address in the
closed network.
IR
An abbreviation for infrared.
IrDA
Infrared Data Association. An organization which
produces standards for communication using infrared
as the carrier.
IRQ
Interrupt Request
An acronym for the hardware signal to the CPU that an
external event has occurred which needs to be
processed.
KB
Kilobyte.
LAN
Local Area Network
An interconnection of computers and peripherals
within a single limited geographic location which can
pass programs and data amongst themselves.
LCD
Liquid Crystal Display
A type of display which makes images by controlling the
orientation of crystals in a crystalline liquid.
Lithium ion Battery
A type of rechargeable battery which has a high power-
time life for its size and is not subject to the memory
effect as Nickel Cadmium batteries.
LPT Port
Line Printer Port. A way of referring to parallel interface
ports because historically line printers were the first and
latter the most common device connected to parallel
ports.
MAC Address
Media Access Control Address
A unique physical address of a network card. For
Ethernet, the first three bytes are used as the vendor
code, controlled and assigned by IEEE. The remaining
three bytes are controlled by each vendor (preventing
overlap), therefore, every Ethernet card is given a unique
physical address in the world, being assigned with a
different address from other cards. For Ethernet, frames
are sent and received based on this address.
MB
Megabyte.
Megahertz
1,000,000 cycles per second.
Memory
A repository for data and applications which is readily
accessible to your notebook’s CPU.
MHz
Megahertz.
P Series.book Page 79 Wednesday, July 13, 2005 10:43 AM
80
LifeBook P Series Notebook - Section Eight
MIDI
Musical Instrument Digital Interface. A standard
communication protocol for exchange of information
between computers and sound producers such as
synthesizers.
Modem
A contraction for MOdulator-DEModulator. The
equipment which connects a computer or other data
terminal to a communication line.
Monaural
A system using one channel to process sound from all
sources.
MPU-401
A standard for MIDI interfaces and connectors.
MTU
Maximum Transmission Unit
The maximum data size that can be transferred at a time
through the Internet or other networks. You can set a
smaller MTU size to obtain successful communication,
if you have difficulty transferring data due to the fact
that the maximum size is too large.
Network authentication
The method of authentication performed by wireless
LAN clients to connect with the access point. There are
two types: open system authentication and shared key
authentication. The type of authentication must be set
to each client and also coincide with the setting of access
point with which to communicate. Network authentica-
tion is sometimes called authentication mode.
Network key
Data that is used for encrypting data in data communi-
cation. The personal computer uses the same network
key both for data encryption and decryption, therefore,
it is necessary to set the same network key as the other
side of communication.
Network name (SSID: Security Set Identifier)
When a wireless LAN network is configured, grouping is
performed to avoid interference or data theft. This
grouping is performed with “Network name (SSID)”. In
order to improve security, the network key is set
allowing no communication unless “Network name
(SSID)” coincides with the network key.
NTSC
National TV Standards Commission. The standard for
TV broadcast and reception for the USA.
Open system authentication
One of network authentication types for wireless LAN.
Since there is no check of network key upon authentica-
tion, clients can connect to the access point without
submitting correct network keys. However, in case of
actual communications, the same network key must be
set. Open system authentication is sometimes called
Open key authentication.
Operating System
A group of control programs that convert application
commands, including driver programs, into the exact
form required by a specific brand and model of micro-
processor in order to produce the desired results from
that particular equipment.
Partition
A block of space on a hard drive which is set aside and
made to appear to the operating system as if it were a
separate disk, and addressed by the operating system
accordingly.
PCMCIA
PCMCIA is a trademark of the Personal Computer
Memory Card International Association. The Personal
Computer Memory Card International Association is an
organization that sets standards for add-in cards for
personal computers.
Peripheral Device
A piece of equipment which performs a specific function
associated with but not integral to a computer.
Examples: a printer, a modem, a CD-ROM.
Pitch (keyboard)
The distance between the centers of the letter keys of a
keyboard.
Pixel
The smallest element of a display, a dot of color on your
display screen. The more pixels per area the clearer your
image will appear.
POST
Power On Self Test. A program which is part of the BIOS
which checks the configuration and operating condition
of your hardware whenever power is applied to your
notebook. Status and error messages may be displayed
before the operating system is loaded. If the self test
detects failures that are so serious that operation can not
continue, the operating system will not be loaded.
PPPoE
Point to Point Protocol over Ethernet.
A protocol for Ethernet, using a Point-to-Point Protocol
(PPP), which is used for connection on the phone line.
Program
An integrated set of coded commands to your
computers telling your hardware what to do and how
and when to do it.
P Series.book Page 80 Wednesday, July 13, 2005 10:43 AM
81
Glossary
Protocol
Procedures and rules use to send and receive data
between computers.
- Method of sending and receiving data
- Process used to handle communication errors
Conditions required for communication are organized
in procedures for correct transfer of information.
RAM
Random Access Memory. A hardware component of
your notebook that holds binary information (both
program and data) as long as it has the proper power
applied to it.
RAM Module
A printed circuit card with memory and associated
circuitry which allows the user to add additional
memory to the computer without special tools.
Reset
The act of reloading the operating system. A reset erases
all information stored in RAM.
Restart
See Reset.
Resume
To proceed after interruption. In your notebook this
refers to returning to active operation after having been
in one of the suspension states.
ROM
Read Only Memory. A form of memory in which infor-
mation is stored by physically altering the material. Data
stored in this way can not be changed by your notebook
and does not require power to maintain it.
SDRAM
Synchronous Dynamic Random Access Memory.
Serial Port
A connection to another device through which data is
transferred one bit at a time on a single wire with any
other wires only for control of the device not for transfer
of data.
Shared key authentication
One of the network authentication types for wireless
LAN. Upon authentication, the access point checks
whether the same network key is set to the client. If the
client uses a wrong network key or the network key itself
is not set, authentication is unsuccessful, allowing no
communications with the access point.
SMART
Self-Monitoring, Analysis and Reporting Technology
(SMART) is an emerging technology that provides near-
term failure predictions for hard drives. When SMART
is enabled the hard drive monitors pre-determined drive
attributes that are susceptible to degradation over time.
If a failure is likely to occur, SMART makes a status
report available so that the notebook can prompt the
user to back up the data on the drive. Naturally not all
failures are predictable. SMART predictability is limited
to those attributes which the drive can self-monitor. In
those cases where SMART can give advance warning, a
considerable amount of precious data can be saved.
SRAM
Static random access memory. A specific technology of
making RAM which does not require periodic data
refreshing.
SSID
Service Set Identifier
Specifies which network you are joining. Some systems
allow you to specify any SSID as an option so you can
join any network.
Standby
To make inoperative for a period of time. Your notebook
uses various suspension states to reduce power
consumption and prolong the charge of your battery.
Status Indicator
A display which reports the condition of some portion
of your hardware. On your notebook this is an LCD
screen just above the keyboard.
Stereo (audio)
A system using two channels to process sound from two
different sources.
Subnet mask
TCP-IP network is controlled by being divided into
multiple smaller networks (subnets). IP address consists
of the subnet address and the address of each computer.
Subnet mask defines how many bits of IP address
comprise the subnet address. The same value shall be set
among computers communicating with each other.
SVGA
Super VGA.
S-Video
Super Video. A component video system for driving a
TV or computer monitor.
System Clock
An oscillator of fixed precise frequency which synchro-
nizes the operation of the system and is counted to
provide time of day and date.
TCP/IP
Transmission Control Protocol/Internet Protocol.
A standard Internet protocol that is most widely used.
P Series.book Page 81 Wednesday, July 13, 2005 10:43 AM
82
LifeBook P Series Notebook - Section Eight
TFT
Thin Film Transistor – A technology for flat display
panels which uses a thin film matrix of transistors to
control each pixel of the display screen individually.
UL
Underwriters Laboratories – An independent organiza-
tion that tests and certifies the electrical safety of devices.
USB
Universal Serial Bus.
Standard that allows you to simultaneously connect up
to 127 USB devices such as game pads, pointing devices,
printers, and keyboards to your computer.
VGA
Video Graphics Array. A video display standard
originally introduced by IBM with the PS/2 series of
personal computers.
VRAM
Video Random Access Memory. A memory dedicated to
video display data and control.
Wi-Fi Compatible
Wi-Fi (Wireless Fidelity) Identifies that the product has
passed the interoperability test, supplied by the WECA
(Wireless Ethernet Compatibility Alliance), which guar-
antees the interoperability of wireless IEEE 802.11 LAN
products. For more information on the Wi-Fi standard,
go to the WECA website at: www.wirelessethernet.com.
WLAN
Wireless Local Area Network. A wireless interconnection
of computers and peripherals within a single limited
geographic location which can pass programs and data
amongst themselves.
Write Protect
Prevent alteration of the binary state of all bits in a
storage media. Example: all information on a device
such as a floppy diskette; a block of space in a storage
media such as a partition of a hard drive; a file or direc-
tory of floppy diskette or hard drive.
XGA
Extended VGA.
P Series.book Page 82 Wednesday, July 13, 2005 10:43 AM
83
Appendix A
Integrated Wireless
LAN* User’s Guide
*Optional Device
P Series.book Page 83 Wednesday, July 13, 2005 10:43 AM
84
LifeBook P Series Notebook - Appendix A
P Series.book Page 84 Wednesday, July 13, 2005 10:43 AM
85
Wireless LAN User’s Guide
FCC REGULATORY INFORMATION
Please note the following regulatory information related to
the optional wireless LAN device.
Regulatory Notes and Statements
Wireless LAN, Health and Authorization for use
Radio frequency electromagnetic energy is emitted from
Wireless LAN devices. The energy levels of these emissions,
however, are far much less than the electromagnetic energy
emissions from wireless devices such as mobile phones.
Wireless LAN devices are safe for use by consumers because
they operate within the guidelines found in radio frequency
safety standards and recommendations. The use of Wireless
LAN devices may be restricted in some situations or envi-
ronments, such as:
On board an airplane, or
In an explosive environment, or
In situations where the interference risk to other devices
or services is perceived or identified as harmful.
In cases in which the policy regarding use of Wireless LAN
devices in specific environments is not clear (e.g., airports,
hospitals, chemical/oil/gas industrial plants, private build-
ings), obtain authorization to use these devices prior to
operating the equipment.
Regulatory Information/Disclaimers
Installation and use of this Wireless LAN device must be in
strict accordance with the instructions included in the user
documentation provided with the product. Any changes or
modifications made to this device that are not expressly
approved by the manufacturer may void the user’s authority
to operate the equipment. The manufacturer is not respon-
sible for any radio or television interference caused by
unauthorized modification of this device, or the substitu-
tion or attachment of connecting cables and equipment
other than those specified by the manufacturer. It is the
responsibility of the user to correct any interference caused
by such unauthorized modification, substitution or attach-
ment. The manufacturer and its authorized resellers or
distributors will assume no liability for any damage or
violation of government regulations arising from failure to
comply with these guidelines.
This device must not be co-located or operating in conjunc-
tion with any other antenna or transmitter.
For operation within 5.15~5.25 GHz frequency range, it is
restricted to indoor environments, and the antenna of the
device must be integral.
Federal Communications Commission statement
This device complies with Part 15 of FCC Rules.
Operation is subject to the following two conditions: (1)
This device may not cause interference, and, (2) This device
must accept any interference, including interference that
may cause undesired operation of this device.
FCC Interference Statement
This equipment has been tested and found to comply with
the limits for a Class B digital device, pursuant to Part 15 of
able protection against harmful interference in a residential
installation. This equipment generates, uses, and can radiate
radio frequency energy. If not installed and used in accordance
with the instructions, it may cause harmful interference to
radio communications. However, there is no guarantee that
interference will not occur in a particular installation.
If this equipment does cause harmful interference to radio or
television reception, which can be determined by turning the
equipment off and on, the user is encouraged to try and correct
the interference by one or more of the following measures:
1. Reorient or relocate the receiving antenna.
2. Increase the distance between the equipment and the receiver.
3. Connect the equipment to an outlet on a circuit
different from the one the receiver is connected to.
4. Consult the dealer or an experienced radio/TV
technician for help.
FCC Radio Frequency Exposure statement
The available scientific evidence does not show that any health
problems are associated with using low power wireless devices.
There is no proof, however, that these low power wilreless devices
are absolutely safe. Low power Wireless devices emit low levels of
radio frequency energy (RF) in the microwave range while being used.
Whereas high level of RF can produce health effects (by heating
tissue), exposure to low-level RF that does not produce heating
effects causes no known adverse health effects. Many studies of low-
level RF exposure have not found any biological effects, Some
studies have suggested that some biological effects might occur, but
Export restrictions
This product or software contains encryption code which
may not be exported or transferred from the US or Canada
without an approved US Department of Commerce export
license. This device complies with Part 15 of FCC Rules., as
well as ICES 003 B / NMB 003 B. Operation is subject to the
following two conditions: (1) this device may not cause
harmful interference, and (2) this device must accept any
interference received, including interference that may cause
undesirable operation. Modifications not expressly autho-
rized by Fujitsu Computer Systems Corporation may invali-
date the user's right to operate this equipment.
Canadian Notice
To prevent radio interference to the licensed service, this
device is intended to be operated indoors and away from
windows to provide maximum shielding. Equipment (or its
transmit antenna) that is installed outdoors is subject to
licensing.
High power radars are allocated as primary users of 5250-
5350 MHz and 5650-5850 MHz and these radars could
cause interference and/or damage to LELAN (license-
exempt LAN) devices operating in these bands.
P Series.book Page 85 Wednesday, July 13, 2005 10:43 AM
such findings have not been confirmed by additional research. The
wireless LAN radio device has been tested and found to comply with
FCC radiation exposure limits set forth for an uncontrolled equip-
ment and meets the FCC radio frequency (RF) Exposure Guidelines
in Supplement C to OET65.
the FCC Rules. These limits are designed to provide reason-
The maximum SAR value measured from the devices are:
• 2.4GHz - band: 0.182 W/kg
• 5.25GHz - band: 1.35 W/kg
• 5.8GHz - band: 0.794 W/kg at Body
86
LifeBook P Series Notebook - Appendix A
Before Using the Wireless LAN
This manual describes the procedures required to prop-
erly setup and configure the optional integrated Wireless
LAN Mini-PCI device (referred to as "WLAN device" in
the rest of the manual). Before using the WLAN device,
read this manual carefully to ensure it's correct opera-
tion. Keep this manual in a safe place for future refer-
ence.
Wireless LAN Devices Covered by this Document
This document is applicable to systems containing an
Atheros AR5006XS (WLL4070) Mini-PCI wireless
network card
Characteristics of the WLAN Device
■The WLAN device is a Mini-PCI card attached to the
main board of the mobile computer.
■It is a dual-band radio that operates in two license-free
RF bands, therefore eliminating the need to procure an
FCC license to operate. It operates in the 2.4GHz
Industrial, Scientific, and Medical (ISM) RF band.
Additionally, the Atheros device operates in the lower,
middle, and upper bands of the 5GHz Unlicensed
National Information Infrastructure (UNII) bands.
■The Atheros Super AG WLAN is capable of three oper-
ating modes, IEEE802.11a, IEEE802.11b and
IEEE802.11g, wireless LAN standards governed by the
IEEE (Institute of Electronics and Electrical Engi-
neers).
■Encoding of data is modulated using Direct Sequence
Spread Spectrum (DSSS) and Complementary Code
Keying (CCK) when the WLAN device is operating in
IEEE 802.11b mode and Orthogonal Frequency Divi-
sion Multiplexing (OFDM) when operating in
IEEE802.11a or IEEE802.11g mode.
■The WLAN device is Wi-Fi certified and operates at
the maximum data transfer rate of 54 Mbps in
IEEE802.11a or IEEE802.11g mode and 11 Mbps in
IEEE802.11b mode.
■The maximum communication range indoors is
approximately 80 feet (25 meters). However, that
range will increase or decrease depending on factors
such as number of walls, reflective material, or inter-
ference from external RF sources.
■The WLAN device supports the following encryption
methods - WEP, TKIP, CKIP, and AES encryption.
WIRELESS LAN MODES USING THIS DEVICE
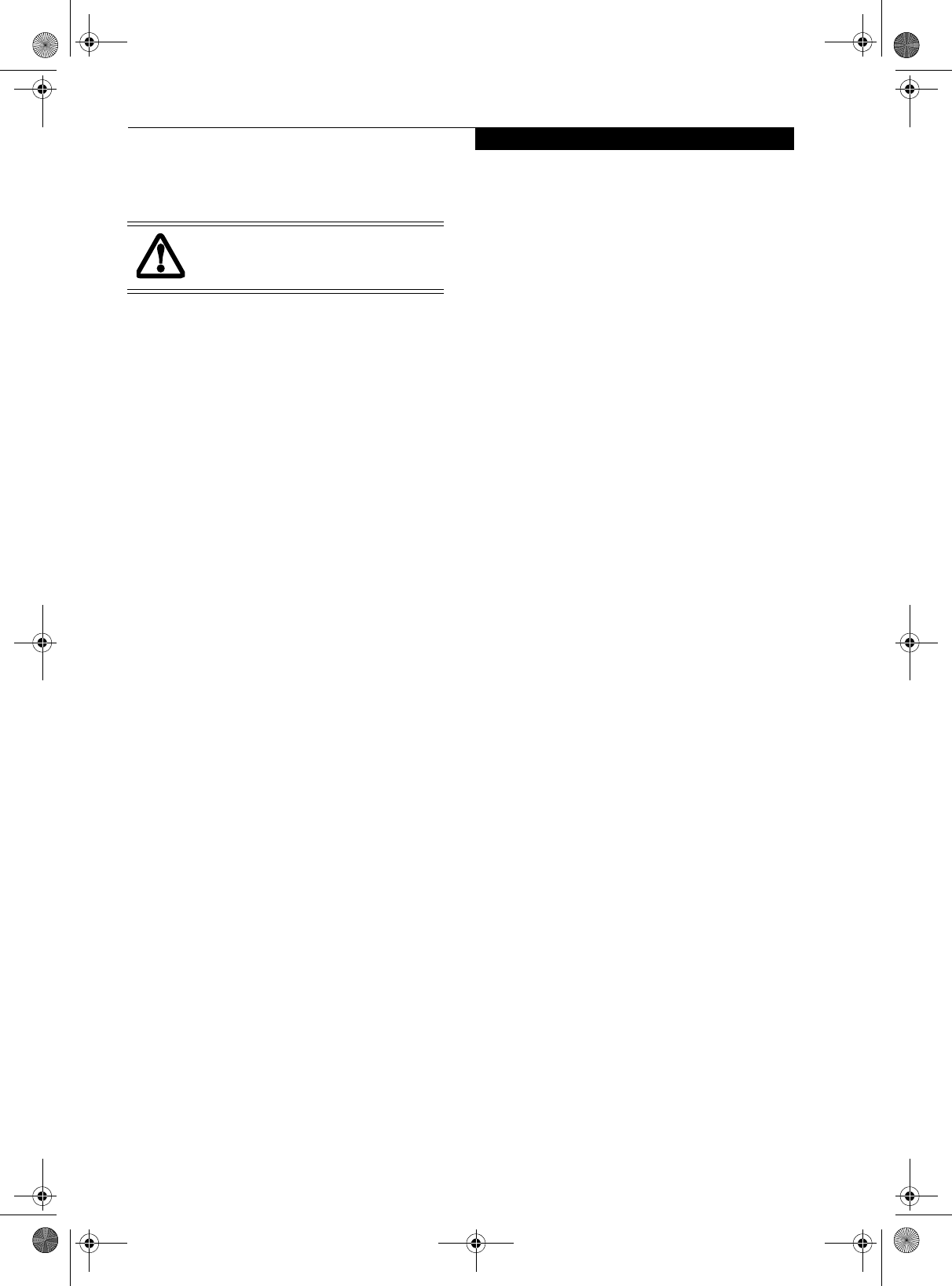
Ad Hoc Mode
(See Figure A-1)
"Ad Hoc Mode" refers to a wireless network architecture
where wireless network connectivity between multiple
computers is established without a central wireless
network device, typically known as Access Point(s).
Connectivity is accomplished using only client devices in
a peer-to-peer fashion. That is why Ad Hoc networks are
also known as peer-to-peer networks. Ad Hoc networks
are an easy and inexpensive method for establishing
network connectivity between multiple computers.
Ad Hoc mode requires that the SSID (service set identi-
fier), network authentication, and encryption key
settings are identically configured on all computers in
the Ad Hoc network.
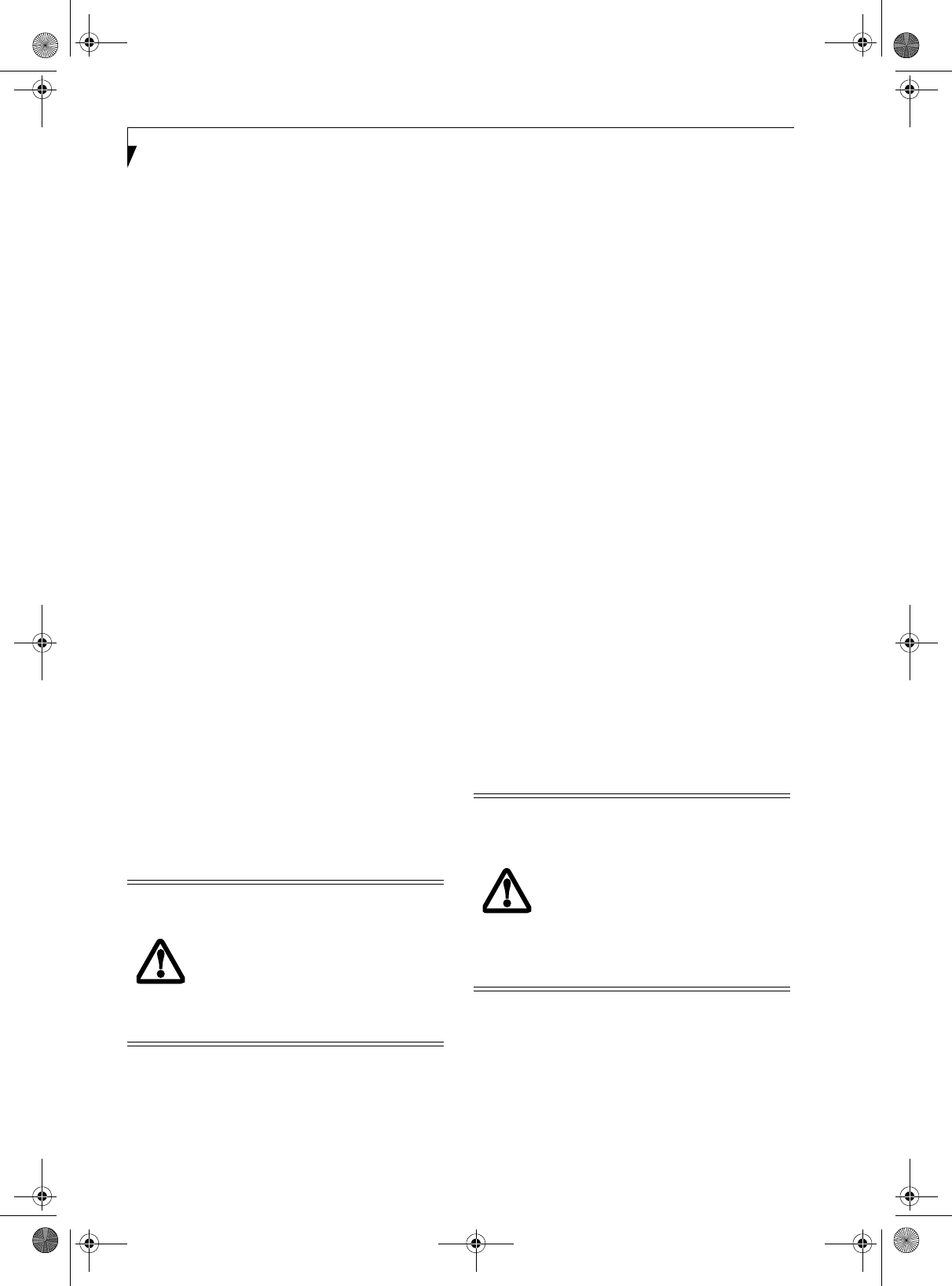
Access Point (Infrastructure) Mode
(See Figure A-2)
Infrastructure mode refers to a wireless network archi-
tecture in which devices communicate with wireless or
wired network devices by communicating through an
Access Point. In infrastructure mode, wireless devices
can communicate with each other or with a wired
network. Corporate wireless networks operate in infra-
structure mode because they require access to the wired
LAN in order to access computers, devices, and services
such as file servers, printers, and databases.
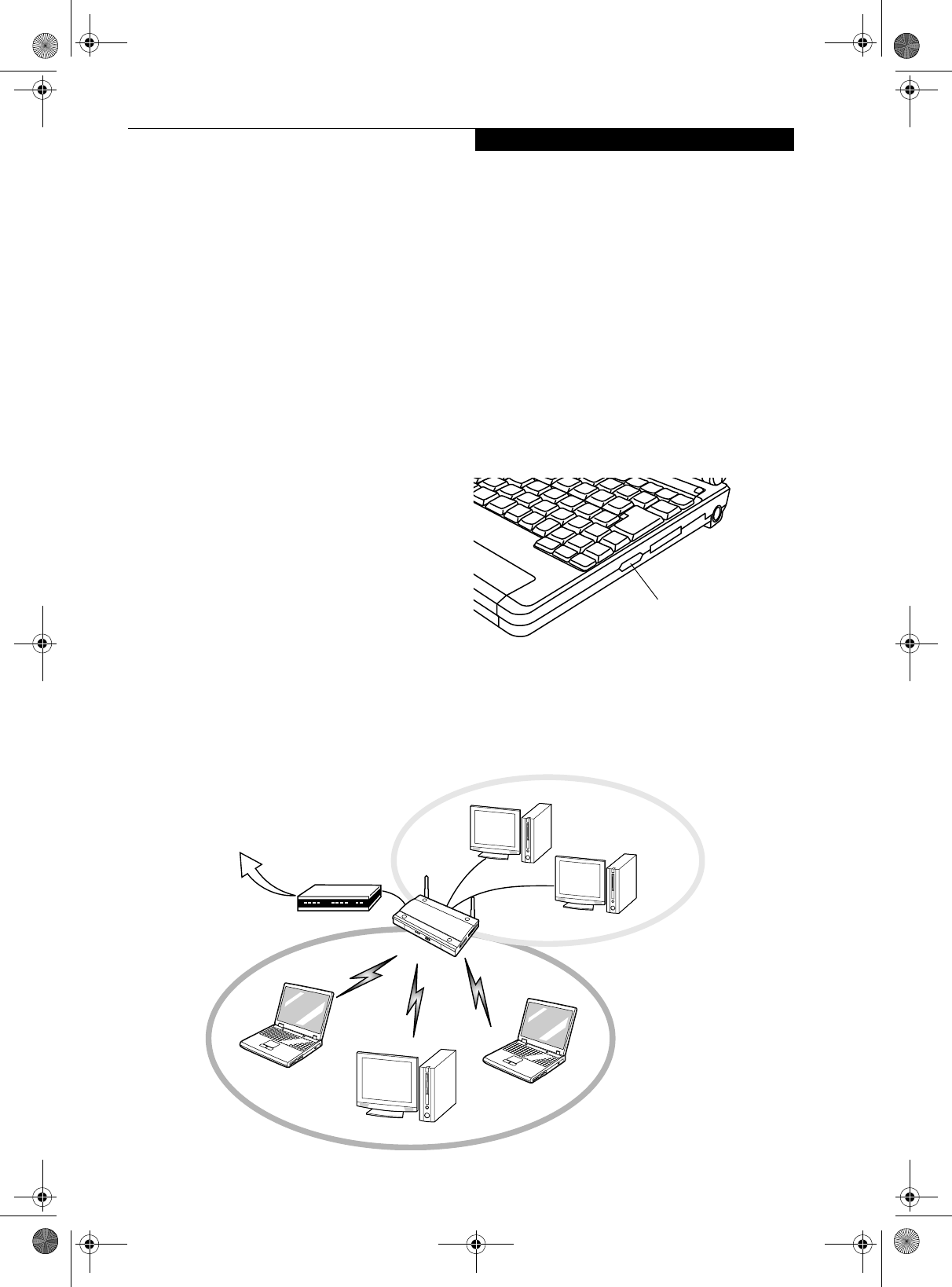
Figure A-1. Ad Hoc Mode Network
P Series.book Page 86 Wednesday, July 13, 2005 10:43 AM
87
Wireless LAN User’s Guide
How to Handle This Device
The WLAN device comes pre-installed in your mobile
computer. Under normal circumstances, it should not be
necessary for you to remove or re-install it. The Oper-
ating System that your mobile computer comes with has
been pre-configured to support the WLAN device.
WIRELESS NETWORK CONSIDERATIONS
■The Atheros WLAN device supports IEEE802.11a/b/g
and operates in the 2.4GHz ISM band and the 5 GHz
UNII bands.
■The maximum range of the WLAN device indoors is
typically 80 feet (25 meters). Please note that the max-
imum range you achieve may be shorter or longer than
80 feet, depending on factors such as access point
transmit power, number and density of obstructions,
or external RF interference.
■Microwave ovens will interfere with the operation of
WLAN device as microwave ovens operate in the same
2.4GHz frequency range that IEEE802.11b/g devices
operate in. Interference by microwaves does not occur
with IEEE802.11a radio which operates in the 5 GHz
RF band.
■Wireless devices that transmit in the 2.4GHz fre-
quency range may interfere with the operation of
WLAN devices in IEEE802.11b/g modes. Symptoms of
interference include reduced throughput, intermittent
disconnects, and large amounts of frame errors. It is
HIGHLY recommended that these interfering devices
be powered off to ensure the proper operation of the
WLAN device.
DEACTIVATING THE WLAN DEVICE
Deactivation of the WLAN device may be desired in
certain circumstances (to extend battery life) or where
certain environments require it (i.e. hospitals, clinics,
airplanes, etc.). Fujitsu mobile computers employ two
methods with which to deactivate the WLAN device:
■Using the Wireless On/Off Switch, or,
■In Windows, using the Atheros Client Utility software.
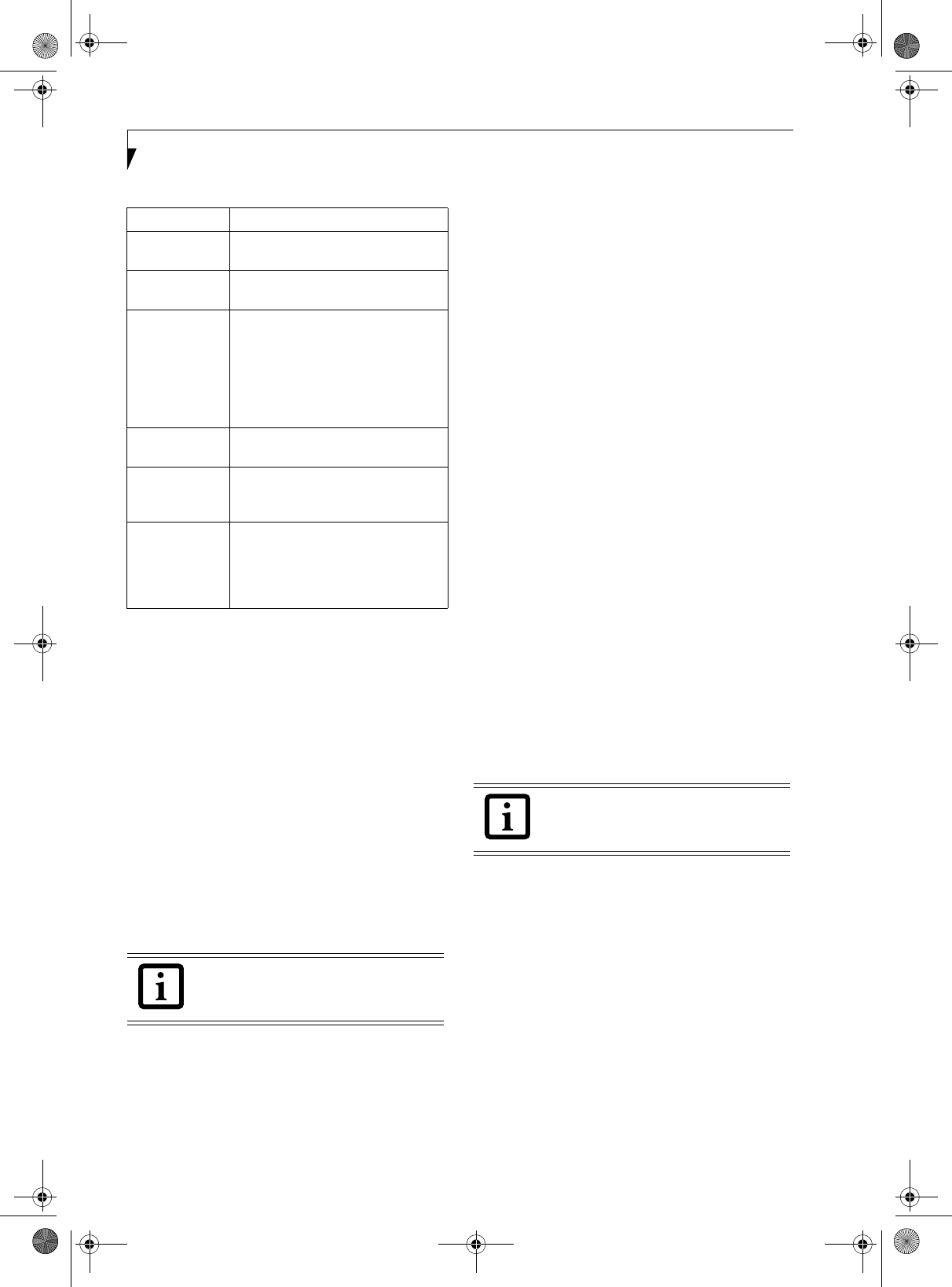
Deactivation using the Wireless On/Off Switch
The WLAN device can be deactivated quickly and effi-
ciently by toggling the Wireless On/Off Switch to the Off
position. (Figure A-3)
The wireless On/Off switch has no effect on non-Wire-
less LAN models
.
Figure A-3. Wireless LAN On/Off Switch Location
Wireless LAN Switch
Figure A-2. Access Point (Infrastructure) Mode Network
ADSL modem,
cable modem,
or similar
Internet
Wired LAN
Access Point*
Wireless LAN
*An optional hub for a wired
LAN may be required depending
upon the type of access point used.
P Series.book Page 87 Wednesday, July 13, 2005 10:43 AM
88
LifeBook P Series Notebook - Appendix A
Deactivation using Atheros Client Utility software
1. Click [Start] -> [Program Files] -> [Atheros] ->
Atheros Client Utility.
2. Choose Action and click Disable Radio.
ACTIVATING THE WLAN DEVICE
Activation of the WLAN device can be accomplished
using the same methods as the deactivation process
■Using the Wireless On/Off Switch
■In Windows using the Atheros software See “Configu-
ration Using Atheros Client Utility Software” on
page 89.
P Series.book Page 88 Wednesday, July 13, 2005 10:43 AM
89
Wireless LAN User’s Guide
Configuration of the WLAN Device
The optional WLAN device can be configured to estab-
lish wireless network connectivity using the Atheros
Client Utility software. The Atheros Client Utility soft-
ware allows for multiple profile setups and supports
automatic profile switching. Support for most industry
standard security solutions, as well as Cisco Compatible
Extensions (CCX), is contained in this software.
FLOW OF OPERATIONS
1. Activate the WLAN Device (See Activating the
WLAN Device on page 88 for more information).
2. Configure the Wireless Network Key parameters
(See “Configuration Using Atheros Client Utility
Software” on page 89 for more information).
■Enter the network name (SSID)
■Choose the appropriate WLAN architecture (Ad
Hoc or Infrastructure)
■Choose Authentication method: Open, Shared,
WPA, or WPA-PSK
■If using static WEP keys, enter static WEP key and
choose key index.
3. Configure network settings
■TCP/IP settings
■Workgroup or Domain settings.
CONFIGURATION USING
ATHEROS CLIENT UTILITY SOFTWARE
This section explains the procedure to properly
configure the WLAN device using the Atheros Client
Utility. Pre-defined parameters will be required for this
procedure. Please consult with your network adminis-
trator for these parameters:
Network Name: Also known as the SSID
Network Key (WEP): Required if using static WEP keys.
Authentication Type: Open, Shared, WPA, or WPA-PSK
Procedure
1. Activate the WLAN device using either the Wireless
On/Off Switch or the Atheros Client Utility
2. Click [Start] -> Programs -> Atheros -> Atheros
Client Utility.
3. Click the Profile Management tab.
4. If this is your first time using this utility, highlight
the profile [Default] and Click the [Modify] button,
otherwise Click the [New] button. The Profile
Management dialog displays.
5. From the General tab, enter a profile name in the
Profile Name field.
6. Enter the network SSID, in the SSID1 field. If you
wish to create a profile that can connect to up to 3
different wireless networks, SSID's can be entered
in the SSID2 and SSID3 fields as well.
7. Click the Security tab.
8. The Security tab allows for the configuration of the
Security modes listed in the table below. Please
select the radio button of the desired security
mode. If these settings are not known to you,
please consult with your network administrator for
the correct settings.
9. Click [OK].
10. Click the Advanced tab.
11. The Advanced tab allows for the configuration of
the options detailed in the table below.
Field Name Description
WPA/WPA2 Enables the use of Wi-Fi Protected
Access. Choosing WPA opens the
WPA EAP drop-down menu. If these
settings are not known to you,
please consult with your network
administrator for the correct settings.
WPA/WPA2
Passphrase
Enables WPA-Pre-Shared Key. Click
on the Configure button to enter the
WPA Passphrase. If these settings
are not known to you, please consult
with your network administrator for
the correct settings.
802.1x Enables 802.1x security. If these
settings are not known to you,
please consult with your network
administrator for the correct settings.
Choosing this option opens the
802.1x EAP type drop-down menu.
Pre-Shared Key Enables the use of pre-shared keys
that are defined on both the access
point and the station. This is where
static WEP keys are entered. Click
the Configure button to fill in the
Define Pre-Shared Keys window.
None No security
P Series.book Page 89 Wednesday, July 13, 2005 10:43 AM
90
LifeBook P Series Notebook - Appendix A
12. Click [OK].
13. If the profile you just created does not activate
immediately, click the Profile Management tab,
highlight the desired Profile, and click Activate.
14. Click [OK] to close the Atheros Client Utility.
CONNECTION TO THE NETWORK
This section explains connection to the network.
If there is an administrator of the network, contact the
network administrator for data settings.
Setting the network
Perform the “Setting TCP/IP” and “Confirming the
computer and work group names” operations required for
network connection.
Setting TCP/IP
1. Click the [Start] button first and then [Control
Panel].
2. If the Control Panel is in Category view, switch to
Classic view by clicking “Switch to Classic View”
under Control Panel the left frame. (If you are
already in Classic view, “Switch to Category View”
will be displayed.)
3. Double-click [Network Connections]. A list of cur-
rently installed networks will be displayed.
4. Right-click [Wireless Network Connection] in the
list, and then click [Properties] in the menu dis-
played. The [Wireless Network Connection Proper-
ties] window will be displayed.
5. Click the [General] tab if it is not already selected.
6. Click [Internet Protocol (TCP/IP] and then click
[Properties]. The [Internet Protocol (TCP/IP)
Properties] window will be displayed.
7. Set the IP address as follows:
■For ad hoc connection: Select [Use the following
IP address:] and then enter data for [IP address]
and [Subnet mask]. See page 96 for IP address
setting.
■For access point (infrastructure) connection: If
your network uses DHCP, select [Obtain an IP
address automatically] and [Obtain DNS server
address automatically]. If your network uses static
IP addresses, consult with your network adminis-
trator for the correct IP address settings.
8. Click the [OK] button. Processing will return to the
[Wireless Network Connection Properties] window.
9. Click the [OK] button.
10. Close the [Network Connection] window.
Following this operation, confirm the names of the
computer and the workgroup as follows.
Confirming the computer and work group names
1. Click the [Start] button, then [Control Panel].
2. If the Control Panel is in Category view, switch to
Classic view by clicking “Switch to Classic View”
under Control Panel the left frame. (If you are
already in Classic view, “Switch to Category View”
will be displayed.)
3. Double-click the [System] icon. The [System Prop-
erties] window will be displayed.
4. Click the [Computer Name] tab.
5. Confirm the settings of [Full computer name:] and
[Workgroup:].
a. The setting of [Full computer name:] denotes the
name for identifying the computer. Any name
can be assigned for each personal computer.
Field Name Description
Power Save
Mode
Options are Maximum, Normal, or
Off
Network Type Options are AP (Infrastructure) or Ad
Hoc
802.11b
Preamble
Specifies the preamble setting in
802.11b. The default setting is Short
and Long (Access Point mode),
which allows both short and long
headers in the 802.11b frames. Set
to Long Only to override allowing
short frames.
Transmit Power
Level
Select the desired transmit power
level from the dropdown list.
Wireless Mode Specifies 5 GHz 54 Mbps, 2.4 GHz
11 Mbps, or 2.4 GHz 54 Mbps oper-
ation in an access point network.
Wireless Mode
when Starting
Ad Hoc
Network
Specifies 5GHz 54 Mbps, 5 GHz 108
Mbps, or 2.4 GHz 11 Mbps to start
an Ad Hoc network if no matching
network name is found after scan-
ning all available modes.
To change the setting of the IP address,
you need to be logged in from Windows
as an administrator.
To modify the computer name and/or the
work group name, you need to be logged
in from Windows as an administrator.
P Series.book Page 90 Wednesday, July 13, 2005 10:43 AM
91
Wireless LAN User’s Guide
Enter the desired name in less than 15 ASCII
character code format. Identifiability can be
enhanced by entering the model number, the
user name, and other factors.
b. [Workgroup name] is the group name of the
network. Enter the desired name in less than 15
ASCII character code format.
For ad hoc connection: Assign the same network
name to all personal computers existing on the
network.
For access point (infrastructure) connection:
Assign the name of the work group to be
accessed.
6. Click the [OK] button. If a message is displayed
that requests you to restart the personal computer,
click [Yes] to restart the computer.
Setting the sharing function
Set the sharing function to make file and/or printer sharing
with other network-connected personal computers valid.
This operation is not required unless the sharing func-
tion is to be used.
The folder and printer for which the sharing function
has been set will be usable from any personal computer
present on the network.
Setting the Microsoft network-sharing service
1. Click the [Start] button first and then [Control
Panel].
2. If the Control Panel is in Category view, switch to
Classic view by clicking “Switch to Classic View”
under Control Panel the left frame. (If you are
already in Classic view, “Switch to Category View”
will be displayed.)
3. Double-click [Network Connections]. A list of cur-
rently installed networks will be displayed.
4. Right-click [Wireless Network Connection] in the
list, and then click [Properties] in the menu dis-
played. The [Wireless Network Connection Proper-
ties] window will be displayed.
5. If [File and Printer Sharing for Microsoft Net-
works] is displayed, proceed to step 6. If [File and
Printer Sharing for Microsoft Networks] is not dis-
played, skip to step 7.
6. Make sure that the [File and Printer Sharing for
Microsoft Networks] check box is checked, and
then click the [OK] button. Skip to “Setting file-
sharing function”.
7. Click [Install]. The [Select Network Component
Type] window will be displayed.
8. Click [Service], then click the [Add] button. The
[Select Network Service] window will be displayed.
9. Click [File and Printer Sharing for Microsoft Net-
works] and then click the [OK] button. Processing
will return to the [Wireless Network Connection
Properties] window, and [File and Printer Sharing
for Microsoft Networks] will be added to the list.
10. Click the [Close] button.
Setting the file-sharing function
The procedure for setting the file-sharing function
follows, with the “work” folder in drive C: as an
example.
1. Double-click [My Computer] on the desktop.
2. Double-click [Local disk (C:)].
3. Right-click the “work” folder (or whichever folder
you want to share), and then click [Sharing and
Security...] in the menu displayed. The [Folder
Name Properties] window will be displayed.
4. Click [Sharing] if it isn’t already selected.
5. Click the link stating “If you understand the secu-
rity risks, but want to share files without running
the wizard, click here”.
6. Click “Just enable file sharing” and click [OK].
7. Check the [Share this folder on the network] check
box.
To change the name, click [Change] and
then proceed in accordance with the
instruction messages displayed on the
screen.
To share a file and/or the connected
printer, you need to be logged in as an
administrator.
Setting the file-sharing function for the file
which has been used to execute Network
Setup Wizard is suggested on the screen.
For the wireless LAN, however, since
security is guaranteed by entry of the
network name (SSID) and the network
key, the steps to be taken to set the file-
sharing function easily without using
Network Setup Wizard are given below.
P Series.book Page 91 Wednesday, July 13, 2005 10:43 AM
92
LifeBook P Series Notebook - Appendix A
8. Click the [OK] button. The folder will be set as a
sharable folder, and the display of the icon for the
“work” folder will change.
Setting the printer-sharing function
1. Click [Start] -> Settings and then [Printers and
Faxes]. A list of connected printers will be dis-
played.
2. Right-click the printer for which the sharing func-
tion is to be set, and then click [Sharing] in the
menu displayed. The property window correspond-
ing to the selected printer will be displayed.
3. Click the [Sharing] tab.
4. Click [Share this printer].
5. Enter the sharing printer name in [Share name].
6. Click the [OK] button.
Confirming connection
After you have finished the network setup operations,
access the folder whose sharing has been set for other
personal computers. Also, confirm the status of the radio
waves in case of trouble such as a network connection
failure.
Connecting your personal computer to another
personal computer
1. Click [Start] first and then [My Computer]. The
[My Computer] window will be displayed in the left
frame.
2. Click [My Network Places] in the “Other Places”
list. The window [My Network Places] will be dis-
played.
3. Click [View workgroup computers] under Network
Tasks in the left frame.
4. Double-click the personal computer to which your
personal computer is to be connected. The folder
that was specified in “Setting the file-sharing func-
tion” on page 91 will be displayed.
5. Double-click the folder to be accessed.
Confirming the status of the radio
1. Right-click the Atheros icon in the lower right cor-
ner of the screen.
2. Click [Open Atheros Client Utility]. The Atheros
Client Utility window opens.
3. Contained within the Current Status and Profile
Management tabs, you will find the current operat-
ing status of the radio. (When the radio is turned
off or the computer is not yet connected, some of
the conditions will not be displayed.)
Among the information displayed are the follow-
ing:
■Network Name (SSID)
Displays the Network Name (SSID) currently
used by the radio.
■Profile Name
The current configuration profile is displayed.
■Mode
Displays the current operating mode. [Infra-
structure (AP)] or [Ad Hoc] will be displayed.
■Data Encryption
Displays the current security status of the profile
being used:
None: No encryption used.
WEP: WEP encryption algorithm used.
CKIP: WEP encryption algorithm used.
TKIP: WEP encryption algorithm used.
■Signal Strength
Displays the current strength of the signal being
received by the radio.
■Current Channel
Displays the current transmit and receive
channel being used.
■Radio Status
Displays the current status of the radio.
To specify the corresponding folder as a
read-only folder, select the [Read only]
checkbox under the General tab.
Setting the printer-sharing function when
Network Setup Wizard has been executed
is suggested on the screen. For the wireless
LAN, however, since security is guaranteed
by entry of the network name (SSID) and
the network key, the steps to be taken to
set the printer-sharing function without
using Network Setup Wizard are laid down
below.
In the case of access point (infrastructure)
connection, enter the necessary data for
the access point before confirming
connection. Refer to the manual of the
access point for the access point setup
procedure.
P Series.book Page 92 Wednesday, July 13, 2005 10:43 AM
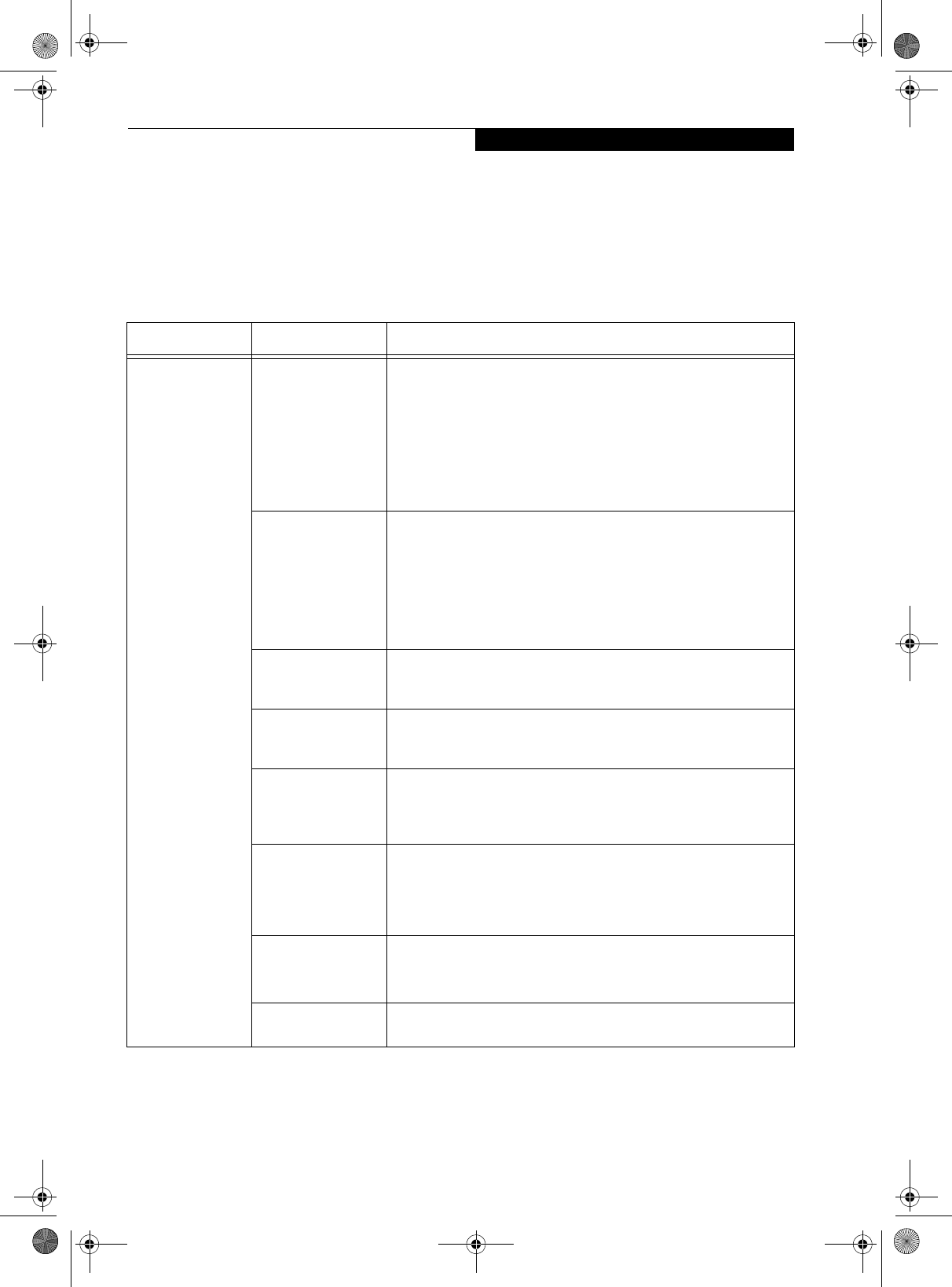
93
Wireless LAN User’s Guide
Troubleshooting the WLAN
TROUBLESHOOTING TABLE
Causes and countermeasures for troubles you may encounter while using your wireless LAN are described in the
following table.
Problem Possible Cause Possible Solution
Unavailable
network
connection
Incorrect network
name (SSID) or
network key
Ad hoc connection: verify that the network names (SSID’s) and network
keys (WEP) of all computers to be connected have been configured
correctly. SSID’s and WEP key values must be identical on each machine.
Access Point (Infrastructure) connection: set the network name (SSID)
and network key to the same values as those of the access point.
Set the Network Authentication value identically to that of the Access
Point. Please consult your network administrator for this value, if
necessary.
Weak received signal
strength and/or link
quality
Ad hoc connection: Retry connection after shortening the distance to
the destination computer or removing any obstacles for better sight.
Access Point (Infrastructure) connection: Retry connection after short-
ening the distance to the access point or removing any obstacles for
better sight.
To check the wave condition, refer to the following page:· “Confirming
the status of the radio” on page 92.
The WLAN device
has been deactivated
or disabled
Check if the wireless switch is turned ON. Also verify “Disable Radio” is
not checked in “Network setting” window.
The computer to be
connected is turned
off
Check if the computer to be connected is turned ON.
RF interference from
Access Points or
other wireless
networks
The use of identical or overlapping RF channels can cause interference
with the operation of the WLAN device. Change the channel of your
Access Point to a channel that does not overlap with the interfering
device.
Wireless network
authentication has
failed
Re-check your Network Authentication, Encryption, and Security
settings. Incorrectly configured security settings such as an incorrectly
typed WEP key, a misconfigured LEAP username, or an incorrectly
chosen authentication method will cause the LAN device to associate
but not authenticate to the wireless network.
Incorrectly
configured network
settings
Recheck the configuration of your network settings.
For the method of checking, refer to the following page:·“Connection to
the Network” on page 90.
Incorrect IP address
configuration
This only applies to networks using static IP addresses. Please contact
your network administrator for the correct settings.
P Series.book Page 93 Wednesday, July 13, 2005 10:43 AM
94
LifeBook P Series Notebook - Appendix A
Wireless LAN Glossary
GLOSSARY
Ad Hoc Mode
Ad Hoc Mode refers to a wireless network architecture
where wireless network connectivity between multiple
computers is established without a central wireless
network device, typically known as Access Points.
Connectivity is accomplished using only client devices in
a peer-to-peer fashion. For details, refer to “Ad hoc
connection” on page 86.
Channel
Range of narrow-band frequencies used by the WLAN
device to transmit data. IEEE802.11b/g - 11 channels, 22
MHz wide channels.
DHCP (Dynamic Host Configuration Protocol)
A protocol that provides a means to dynamically allocate
IP addresses to computers on a local area network.
DNS (Domain Name System)
A data query service that provides a mechanism with
which to translate host names into Internet addresses.
IEEE802.11a
Wireless LAN standard that supports a maximum data
rate of 54 Mbps. 802.11a devices operate in the 5 GHz
lower and middle UNII bands.
IEEE802.11b
Wireless LAN standard that supports a maximum data
rate of 11 Mbps. 802.11b devices operate in the 2.4 GHz
ISM band.
Access point
Wireless network device used to bridge wireless and
wired network traffic.
IP address
The logical 32-bit host address defined by the Internet
Protocol that uniquely identifies a computer on a
network. The IP address is usually expressed in dotted
decimal notation.
LAN (Local Area Network)
A LAN or Local Area Network is a computer network (or
data communications network) which is confined to a
limited geographical area.
MAC address (Media Access Control Address)
A MAC address (also called an Ethernet address or IEEE
MAC address) is the 48-bit address (typically written as
twelve hexadecimal digits, 0 through 9 and A through F,
or as six hexadecimal numbers separated by periods or
colons, e.g., 0080002012ef, 0:80:0:2:20:ef) which
uniquely identifies a computer that has an Ethernet
interface.
MTU (Maximum Transmission Unit)
The maximum size of data which can be transmitted at
one time in networks including the Internet. In an envi-
ronment whose maximum size of data is too large to
correctly receive data, normal communications can be
restored by setting the size of MTU to a smaller value.
Network key
Data that is used for encrypting data in data communi-
cation. The personal computer uses the same network
key both for data encryption and decryption, therefore,
it is necessary to set the same network key as the other
side of communication.
Network name (SSID: Service Set Identifier)
When a wireless LAN network is configured, grouping is
performed to avoid interference or data theft. This
grouping is performed with “Network name (SSID)”. In
order to improve security, the network key is set
allowing no communication unless “Network name
(SSID)” coincides with the network key.
Open system authentication
Null authentication method specified in the 802.11 stan-
dard that performs no authentication checks on a wire-
less client before allowing it to associate.
PPPoE (Point to Point Protocol over Ethernet)
A method of allowing the authentication protocol
adopted in telephone line connection (PPP) to be used
over an Ethernet.
Protocol
A procedure or rule of delivering data among
computers. Ordered data communication is allowed by
making all conditions required for communication
including the method of data transmission/reception
and actions upon communication errors into proce-
dures.
P Series.book Page 94 Wednesday, July 13, 2005 10:43 AM
95
Wireless LAN User’s Guide
Shared key authentication
802.11 network authentication method in which the AP
sends the client device a challenge text packet that the
client must then encrypt with the correct WEP key and
return to the AP. If the client has the wrong key or no
key, authentication will fail and the client will not be
allowed to associate with the AP. Shared key authentica-
tion is not considered secure, because a hacker who
detects both the clear-text challenge and the same chal-
lenge encrypted with a WEP key can decipher the WEP
key.
SSID (Service Set Identifier)
Service Set Identifier, a 32-character unique identifier
attached to the header of packets sent over a WLAN that
acts as a password when a mobile device tries to connect
to the BSS. The SSID differentiates one WLAN from
another, so all access points and all devices attempting to
connect to a specific WLAN must use the same SSID. A
device will not be permitted to join the BSS unless it can
provide the unique SSID. Because the SSID is broadcast
in plain text, it does not supply any security to the
network.
Subnet mask
TCP-IP network is controlled by being divided into
multiple smaller networks (subnets). IP address consists
of the subnet address and the address of each computer.
Subnet mask defines how many bits of IP address
comprise the subnet address. The same value shall be set
among computers communicating with each other.
TCP/IP (Transmission Control Protocol/Internet
Protocol)
A standard protocol of the Internet.
Wi-Fi
Wi-Fi, or Wireless Fidelity, is a set of standards for wire-
less local area networks (WLAN) based on the IEEE
802.11 specifications. Certified products can use the
official Wi-Fi logo, which indicates that the product is
interoperable with any other product also showing that
logo.
P Series.book Page 95 Wednesday, July 13, 2005 10:43 AM
96
LifeBook P Series Notebook - Appendix A
IP address information
ABOUT IP ADDRESSES
If IP address is unknown, set IP address as follows,
or,
If you have an access point (DHCP server) on the
network, set the IP address as follows:
[Obtain an IP address automatically]
If the IP address is already assigned to the computer in
the network, ask the network administrator to check the
IP address to be set for the computer.
If no access point is found in the network:
An IP address is expressed with four values in the range
between 1 and 255.
Set the each computer as follows: The value in paren-
theses is a subnet mask.
<Example>
Computer A: 192.168.100.2 (255.255.255.0)
Computer B: 192.168.100.3 (255.255.255.0)
Computer C: 192.168.100.4 (255.255.255.0)
:
:
Computer X: 192.168.100.254 (255.255.255.0)
IP addressing is much more complicated
than can be briefly explained in this
document. You are advised to consult with
your network administrator for additional
information.
A DHCP server is a server that
automatically assigns IP addresses to
computers or other devices in the network.
There is no DHCP server for the AdHoc
network.
P Series.book Page 96 Wednesday, July 13, 2005 10:43 AM
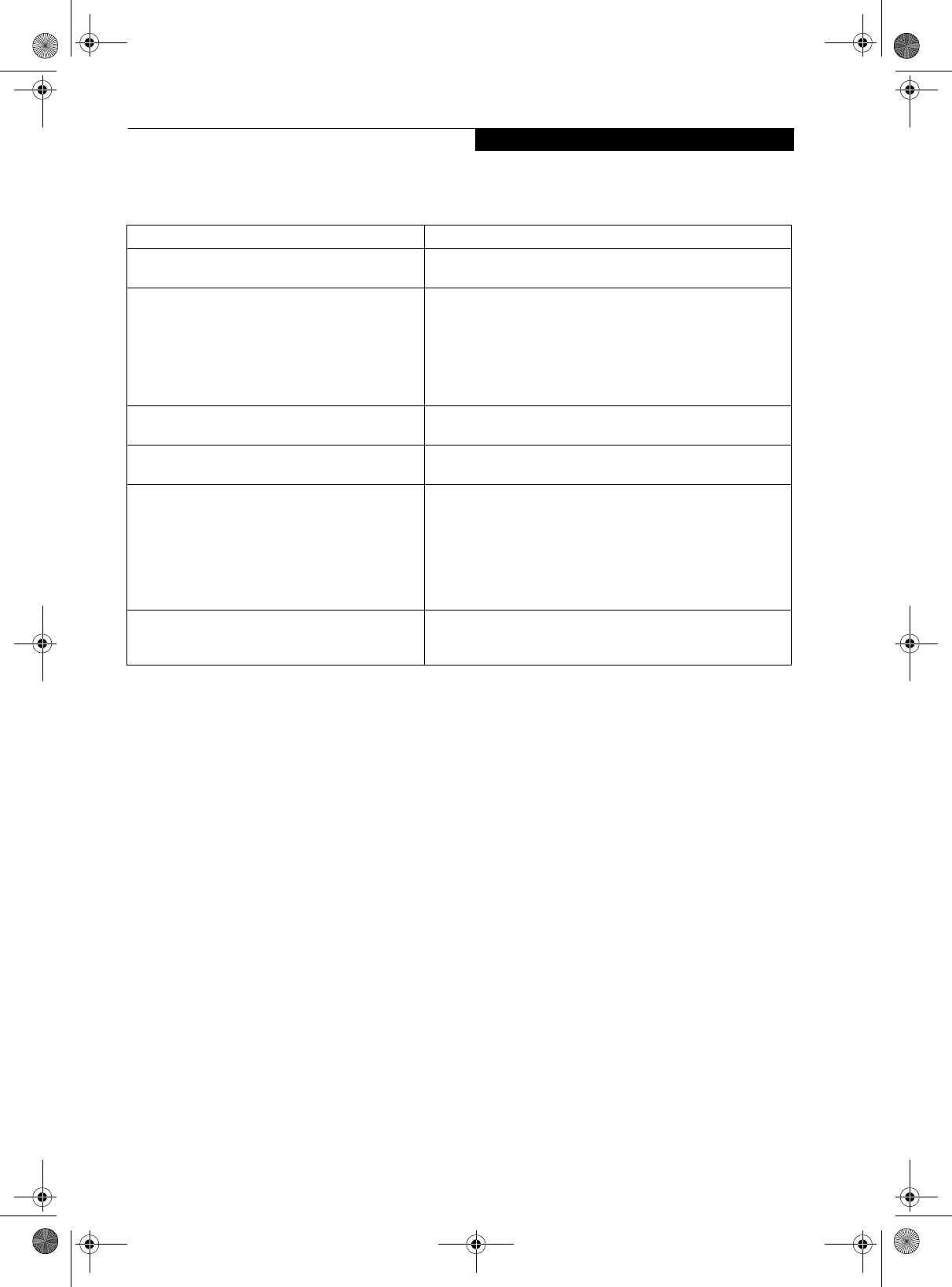
97
Wireless LAN User’s Guide
Specifications
* “Wi-Fi based” indicates that the interconnectivity test of the organization which guarantees the interconnectivity of
wireless LAN (Wi-Fi Alliance) has been passed.
** Encryption with network key (WEP) is performed using the above number of bits, however, users can set 40 bits/
104 bits after subtracting the fixed length of 24 bits.
*** Depending on practical environments, the allowable number of computers to be connected may be decreased.
Item Specification
Type of network Atheros Super AG (802.11a+b/g) WLAN device conforms to
IEEE 802.11a and 802.11b/g (Wi-Fi based)*
Transfer rate (Automatic switching)
IEEE 802.11a/g: 54 Mbps maximum data rate (108 Mbps
maximum data rate with compatible access points)
The access point must be set to channel 6 only, and must have
Atheros chip set to support this mode.
IEEE 802.11b: 11 Mbps maximum data rate
Active frequency 802.11b/g: 2400~2473 MHz
802.11a: 5050 ~ 5850 MHz
Number of channels 802.11a: 8 independent channels
802.11b/g: 11 channels, 3 non-overlapping channels
Security Encryption Types - WEP, TKIP, AES**
WPA 1.0 compliant
Encryption Key lengths Supported: 64 bits, 128 bits, and 152 bits
(Atheros module using AES encryption only)
802.1x/EAP
CCX 2.0 compliant
Maximum recommended number of computers to
be connected over wireless LAN (during ad hoc
connection)
10 units or less ***
P Series.book Page 97 Wednesday, July 13, 2005 10:43 AM
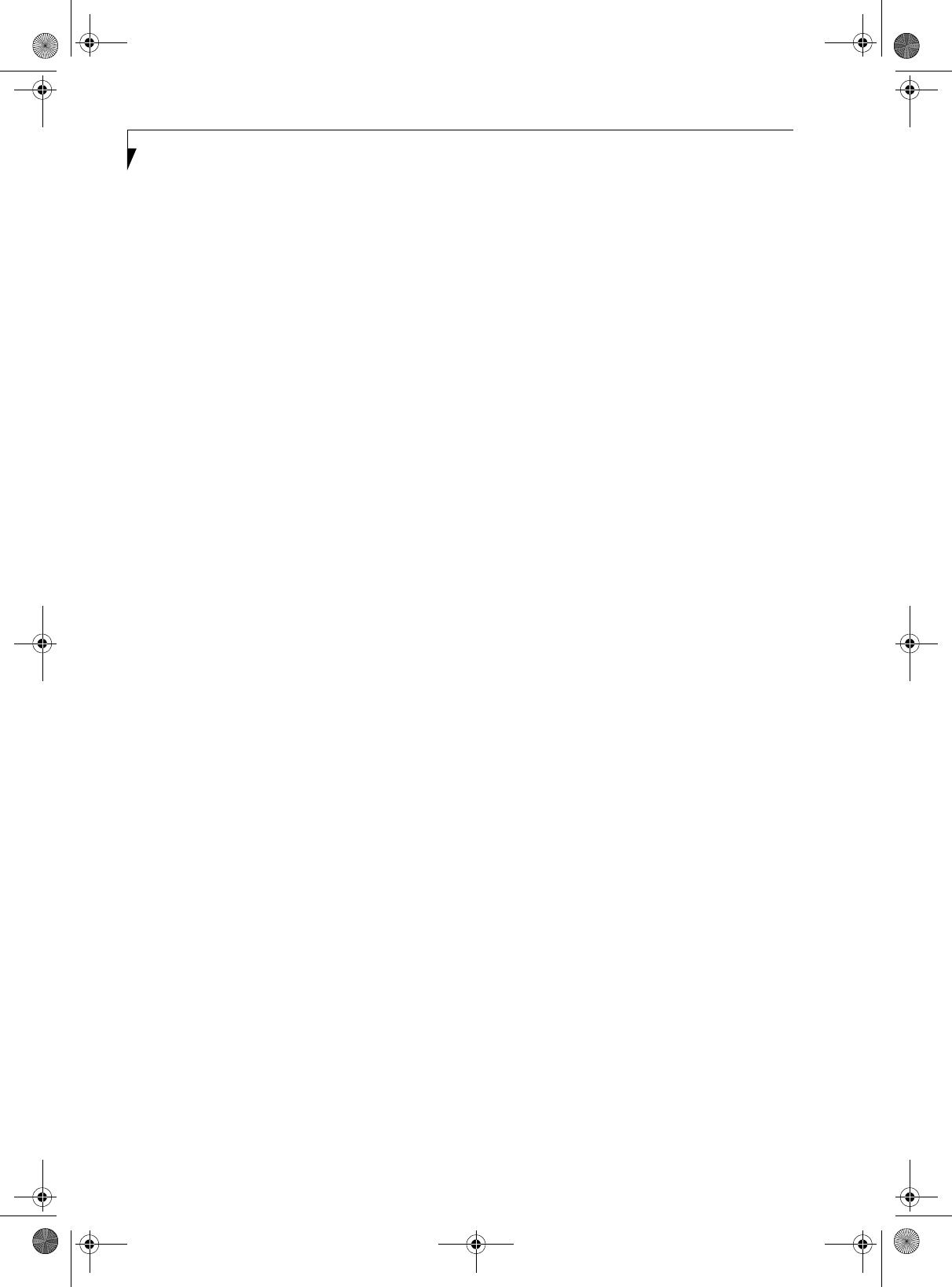
98
LifeBook P Series Notebook - Appendix A
P Series.book Page 98 Wednesday, July 13, 2005 10:43 AM
99
Appendix B
Using the
Fingerprint
Swipe Sensor
P Series.book Page 99 Wednesday, July 13, 2005 10:43 AM
100
LifeBook T Series Tablet PC - Appendix B
P Series.book Page 100 Wednesday, July 13, 2005 10:43 AM
101
FIngerprint Sensor User’s Guide
Fingerprint Sensor Device
INTRODUCING THE
FINGERPRINT SENSOR DEVICE
Your system has a fingerprint sensor device in the loca-
tion shown in the figure below.
Figure A-1 Fingerprint sensor
With a fingerprint sensor, you can avoid having to enter
a username and password every time you want to:
■Log onto Windows
■Recover from suspend mode
■Cancel a password-protected screen saver
■Log into homepages that require a username and pass-
word
After you have “enrolled” - or registered - your finger-
print, you can simply swipe your fingertip over the
sensor for the system recognize you.
The fingerprint sensor uses Softex OmniPass which
provides password management capabilities to
Microsoft Windows operating systems. OmniPass
enables you to use a "master password" for all Windows,
applications, and on-line passwords.
OmniPass requires users to authenticate themselves
using the fingerprint sensor before granting access to the
Windows desktop. This device results in a secure
authentication system for restricting access to your
computer, applications, web sites, and other password-
protected resources.
OmniPass presents a convenient graphical user interface,
through which you can securely manage passwords,
users, and multiple identities for each user.
GETTING STARTED
This section guides you through the preparation of your
system for the OmniPass fingerprint recognition
application. You will be led through the OmniPass
installation process. You will also be led through the
procedure of enrolling your first user into OmniPass.
INSTALLING OMNIPASS
If OmniPass has already been installed on your system,
skip this section and go directly to “User Enrollment” on
page 102. You can determine whether OmniPass has
already been installed by checking to see if the following
are present:
■The presence of the gold key-shaped OmniPass icon in
the system tray at the bottom right of the screen.
■The presence of the Softex program group in the
Programs group of the Start menu
System Requirements
The OmniPass application requires space on your hard
drive; it also requires specific Operating Systems (OS’s).
The minimum requirements are as follows:
■Windows XP Home Edition, Windows XP Profes-
sional or Windows 2000 operating system
■At least 35 MB available hard disk space
Installing the OmniPass Application
If OmniPass is already installed on your system, go to
“User Enrollment” on page 102. Otherwise continue
with this section on software installation.
To install OmniPass on your system you must:
1. Insert the installation media for the OmniPass appli-
cation into the appropriate drive. If you are
installing from CD-ROM or DVD-ROM, you must
find and launch the OmniPass installation program
(setup.exe) from the media.
2. Follow the directions provided in the OmniPass
installation program. Specify a location to which
you would like OmniPass installed. It is recom-
mended that you NOT install OmniPass in the root
directory (e.g. C:\).
3. Once OmniPass has completed installation you will
be prompted to restart you system. Once your
system has rebooted you will be able to use
OmniPass. If you choose not to restart immediately
after installation, OmniPass will not be available for
use until the next reboot.
The installation program automatically places an icon
(Softex OmniPass) in the Windows Control Panel as well
as a golden key shaped icon in the taskbar.
For installation, OmniPass requires that the
user installing OmniPass have
administrative privileges to the system. If
your current user does not have
administrative privileges, log out and then
log in with an administrator user before
proceeding with OmniPass installation.
P Series.book Page 101 Wednesday, July 13, 2005 10:43 AM
102
LifeBook T Series Tablet PC - Appendix B
Verifying Information about OmniPass
After you have completed installing OmniPass and
restarted your system, you may wish to check the version
of OmniPass on your system.
To check the version information of OmniPass:
1. From the Windows Desktop, double-click the key-
shaped OmniPass icon in the taskbar (usually
located in the lower right corner of the screen),
or,
Click the Start button, select Settings, and click
Control Panel (if you are using Windows XP you
will see the Control Panel directly in the Start menu;
click it, then click Switch to Classic View). Double-
click Softex OmniPass in the Control Panel, and the
OmniPass Control Center will appear. If it does not
appear, then the program is not properly installed,
or,
Click the Start button, select Programs, and from
the submenu select the Softex program group, from
that submenu click OmniPass Control Center.
2. Select the About tab at the top of the OmniPass
Control Panel. The About tab window appears with
version information about OmniPass.
Uninstalling OmniPass
To remove the OmniPass application from your system:
1. Click Start on the Windows taskbar. Select Settings,
and then Control Panel.
2. Double-click Add/Remove Programs.
3. Select OmniPass, and then click Change/Remove.
4. Follow the directions to uninstall the OmniPass
application.
5. Once OmniPass has finished uninstalling, reboot
your system when prompted.
USER ENROLLMENT
Before you can use any OmniPass features you must first
enroll a user into OmniPass.
Master Password Concept
Computer resources are often protected with passwords.
Whether you are logging into your computer, accessing
your email, e-banking, paying bills online, or accessing
network resources, you often have to supply credentials
to gain access. This can result in dozens of sets of creden-
tials that you have to remember.
During OmniPass user enrollment a "master password”
is created for the enrolled user. This master password
“replaces” all other passwords for sites you register with
OmniPass.
Example: A user, John, installs OmniPass on his system
(his home computer) and enrolls an OmniPass user with
username “John_01” and password “freq14”. He then
goes to his webmail site to log onto his account. He
inputs his webmail credentials as usual (username
“John_02” and password “tablet”), but instead of
clicking [Submit], he directs OmniPass to Remember
Password. Now whenever he returns to that site,
OmniPass will prompt him to supply access credentials.
John enters his OmniPass user credentials (“John_01”
and “freq14”) in the OmniPass authentication prompt,
and he is allowed into his webmail account. He can do
this with as many web sites or password protected
resources he likes, and he will gain access to all those
sites with his OmniPass user credentials (“John_01” and
“freq14”). This is assuming he is accessing those sites
with the system onto which he enrolled his OmniPass
user. OmniPass does not actually change the credentials
of the password protected resource. If John were to go to
an Internet cafe to access his webmail, he would need to
enter his original webmail credentials (“John_02” and
“tablet”) to gain access. If he attempts his OmniPass user
credentials on a system other than where he enrolled
that OmniPass user, he will not gain access.
Basic Enrollment
The Enrollment Wizard will guide you through the
process of enrolling a user. Unless you specified other-
wise, after OmniPass installation the Enrollment Wizard
will launch on Windows login. If you do not see the
Enrollment Wizard, you can bring it up by clicking Start
on the Windows taskbar; select Programs; select Softex;
click OmniPass Enrollment Wizard.
1. Click Enroll to proceed to username and password
verification. By default, the OmniPass Enrollment
Wizard enters the credentials of the currently logged
in Windows user.
2. Enter the password you use to log in to Windows.
This will become the “master password” for this
OmniPass user. In most cases, the Domain: value
For uninstallation, OmniPass requires that
the user uninstalling OmniPass have
administrative privileges to the system. If
your current user does not have
administrative privileges, log out and then
log in with an administrator user before
proceeding with OmniPass uninstallation.
The basic enrollment procedure assumes
you have no hardware authentication
devices or alternate storage locations that
you wish to integrate with OmniPass. If
you desire such functionality, consult the
appropriate sections after reviewing this
section.
P Series.book Page 102 Wednesday, July 13, 2005 10:43 AM
103
FIngerprint Sensor User’s Guide
will be your Windows computer name. In a corpo-
rate environment, or when accessing corporate
resources, the Domain: may not be your Windows
computer name. Click [Next] to continue.
3. In this step OmniPass captures your fingerprint.
Refer to “Enrolling a Fingerprint” on page 103 for
additional information.
4. Next, choose how OmniPass notifies you of various
events. We recommend you keep Taskbar Tips on
Beginner mode taskbar tips and Audio Tips on at
least Prompt with system beeps only until you get
accustomed to how OmniPass operates. Click [Next]
to proceed with user enrollment. You will then see a
Congratulations screen indicating your completion
of user enrollment.
5. Click [Done] to exit the OmniPass Enrollment
Wizard. You will be asked if you’d like to log in to
OmniPass with your newly enrolled user; click [Yes].
Enrolling a Fingerprint
Enrolling a fingerprint will increase the security of your
system and streamline the authentication procedure.
You enroll fingerprints in the OmniPass Control Center.
With an OmniPass user logged in, double-click the
system tray OmniPass icon. Select the User Settings tab
and click Enrollment under the User Settings area. Click
Enroll Authentication Device and authenticate at the
authentication prompt to start device enrollment.
1. During initial user enrollment, you will be
prompted to select the finger you wish to enroll.
Fingers that have already been enrolled will be
marked by a green check. The finger you select to
enroll at this time will be marked by a red arrow.
OmniPass will allow you re-enroll a finger. If you
choose a finger that has already been enrolled and
continue enrollment, OmniPass will enroll the
fingerprint, overwriting the old fingerprint. Select a
finger to enroll and click [Next].
2. It is now time for OmniPass to capture your selected
fingerprint. It may take a several capture attempts
before OmniPass acquires your fingerprint. Should
OmniPass fail to acquire your fingerprint, or if the
capture screen times out, click [Back] to restart the
fingerprint enrollment process.
Your system has a “swipe” fingerprint sensor. A
swipe sensor is small and resembles a skinny elon-
gated rectangle. To capture a fingerprint, gently
swipe or pull your fingertip over the sensor (starting
at the second knuckle) towards yourself. Swiping too
fast or too slow will result in a failed capture. The
Choose Finger screen has a [Practice] button; click it
to practice capturing your fingerprint. When you are
comfortable with how your fingerprint is captured,
proceed to enroll a finger.
3. Once OmniPass has successfully acquired the finger-
print, the Ver if y F i n g er p r i nt screen will automati-
cally appear. To verify your enrolled fingerprint,
place your fingertip on the sensor and hold it there
as if you were having a fingerprint captured.
Successful fingerprint verification will show a green
fingerprint in the capture window and the text Ver i -
fication Successful under the capture window.
USING OMNIPASS
You are now ready to begin using OmniPass. Used
regularly, OmniPass will streamline your authentication
procedures.
Password Replacement
You will often use the password replacement function.
When you go to a restricted access website (e.g., your
bank, your web-based email, online auction or payment
sites), you are always prompted to enter your login
credentials. OmniPass can detect these prompts and you
can teach OmniPass your login credentials. The next
time you go to that website, you can authenticate with
your fingerprint to gain access.
OmniPass Authentication Toolbar
After installing OmniPass and restarting, you will notice
a dialog you have not seen before at Windows Logon.
This is the OmniPass Authentication Toolbar, and it is
displayed whenever the OmniPass authentication system
is invoked. The OmniPass authentication system may be
invoked frequently: during Windows Logon, during
OmniPass Logon, when unlocking your workstation,
when resuming from standby or hibernate, when
unlocking a password-enabled screensaver, during pass-
word replacement for remembered site or application
logins, and more. When you see this toolbar, OmniPass
is prompting you to authenticate.
The Logon Authentication window indicates what
OmniPass-restricted function you are attempting. The
icons in the lower left (fingerprint and key) show what
authentication methods are available to you. Selected
authentication methods are highlighted while unselected
methods are not. When you click the icon for an unse-
lected authentication method, the authentication
prompt associated with that method is displayed.
When prompted to authenticate, you must supply the
appropriate credentials: an enrolled finger for the finger-
print capture window or your master password for the
master password prompt (the key icon).
Remembering a Password
OmniPass can remember any application, GUI, or pass-
word protected resource that has a password prompt.
Using the following procedure, you can store a set of
credentials into OmniPass. These credentials will then be
linked to your “master password” or fingerprint.
P Series.book Page 103 Wednesday, July 13, 2005 10:43 AM
104
LifeBook T Series Tablet PC - Appendix B
Go to a site that requires a login (username and pass-
word), but do not log in yet. At the site login prompt,
enter your username and password in the prompted
fields, but do not enter the site (do not hit [Enter],
[Submit], [OK], or Login). Right-click the OmniPass
system tray icon and select Remember Password from
the submenu. The Windows arrow cursor will change to
a golden key OmniPass cursor. Click this OmniPass
cursor in the login prompt area, but do not click the
[Login] or [Submit] button.
Associating a Friendly Name
After clicking the OmniPass key cursor near the login
prompt, OmniPass will prompt you to enter a “friendly
name” for this site. You should enter something that
reminds you of the website, the company, or the service
you are logging into. In its secure database, OmniPass
associates this friendly name with this website.
Additional Settings for Remembering a Site
When OmniPass prompts you to enter a “friendly name”
you also have the opportunity to set how OmniPass
authenticates you to this site. There are three effective
settings for how OmniPass handles a remembered site.
The default setting is Automatically click the “OK” or
“Submit” button for this password protected site once
the user is authenticated. With this setting, each time
you navigate to this site OmniPass will prompt you for
your master password or fingerprint authentication
device. Once you have authenticated with OmniPass,
you will automatically be logged into the site.
Less secure is the option to Automatically enter this
password protected site when it is activated. Do not
prompt for authentication. Check the upper box to get
this setting, and each time you navigate to this site
OmniPass will log you into the site without prompting
you to authenticate.
If you uncheck both boxes in Settings for this Password
Site, OmniPass will prompt you for your master pass-
word or fingerprint authentication device. Once you
have authenticated with OmniPass your credentials will
be filled in to the site login prompt, but you will have to
click the website [OK], [Submit], or [Login] button to
gain access to the site.
Click Finish to complete the remember password proce-
dure. The site location, the credentials to access the site,
and the OmniPass authentication settings for the site are
now stored in the OmniPass secure database. The
OmniPass authentication settings (Settings for this Pass-
word Site) can always be changed in Vault Management.
Logging in to a Remembered Site
Whether or not OmniPass prompts you to authenticate
when you return to a remembered site is determined by
Settings for this Password Site and can be changed in
Vault Management.
The following cases are applicable to using OmniPass to
login to: Windows, remembered web sites, and all other
password protected resources.
With Master Password
Once you return to a site you have remembered with
OmniPass, you may be presented with a master pass-
word prompt. Enter your master password and you will
be allowed into the site.
Logging into Windows with a Fingerprint Device
When logging into Windows with a fingerprint device,
the fingerprint capture window will now appear next to
the Windows Login screen. Place your enrolled fingertip
on the sensor to authenticate. You will be simultaneously
logged into Windows and OmniPass. The capture
window will also appear if you have used Ctrl-Alt-Del to
lock a system, and the fingerprint device can be used to
log back in as stated above.
In Windows XP, your login options must be set either for
classic login, or for fast user switching and logon screen
to be enabled to use your fingerprint to log on to
Windows. To change this go to Control Panel, select
User Accounts and then click Change the way users log
on or off. If your Windows screensaver is password
protected, the fingerprint capture window will now
appear next to screensaver password dialog during
resume. You can authenticate to your screensaver pass-
word prompt with your enrolled finger.
Password Management
OmniPass provides an interface that lets you manage
your passwords. To access this GUI, double-click the
OmniPass key in the system tray. Click Vaul t Manag e-
ment; you will be prompted to authenticate. Once you
gain access to Vault Management, click Manage Pass-
words under Vault Settings. You will see the Manage
Passwords interface, with a list of friendly names.
This setting is more convenient in that
whenever you go to a site remembered
with this setting, you will bypass any
authentication procedure and gain instant
access to the site. But should you leave
your system unattended with your
OmniPass user logged in, anyone using
your system can browse to your password
protected sites and gain automatic access.
If a machine is locked and OmniPass
detects a different user logging back in
with a fingerprint, the first user will be
logged out and the second user logged in.
P Series.book Page 104 Wednesday, July 13, 2005 10:43 AM
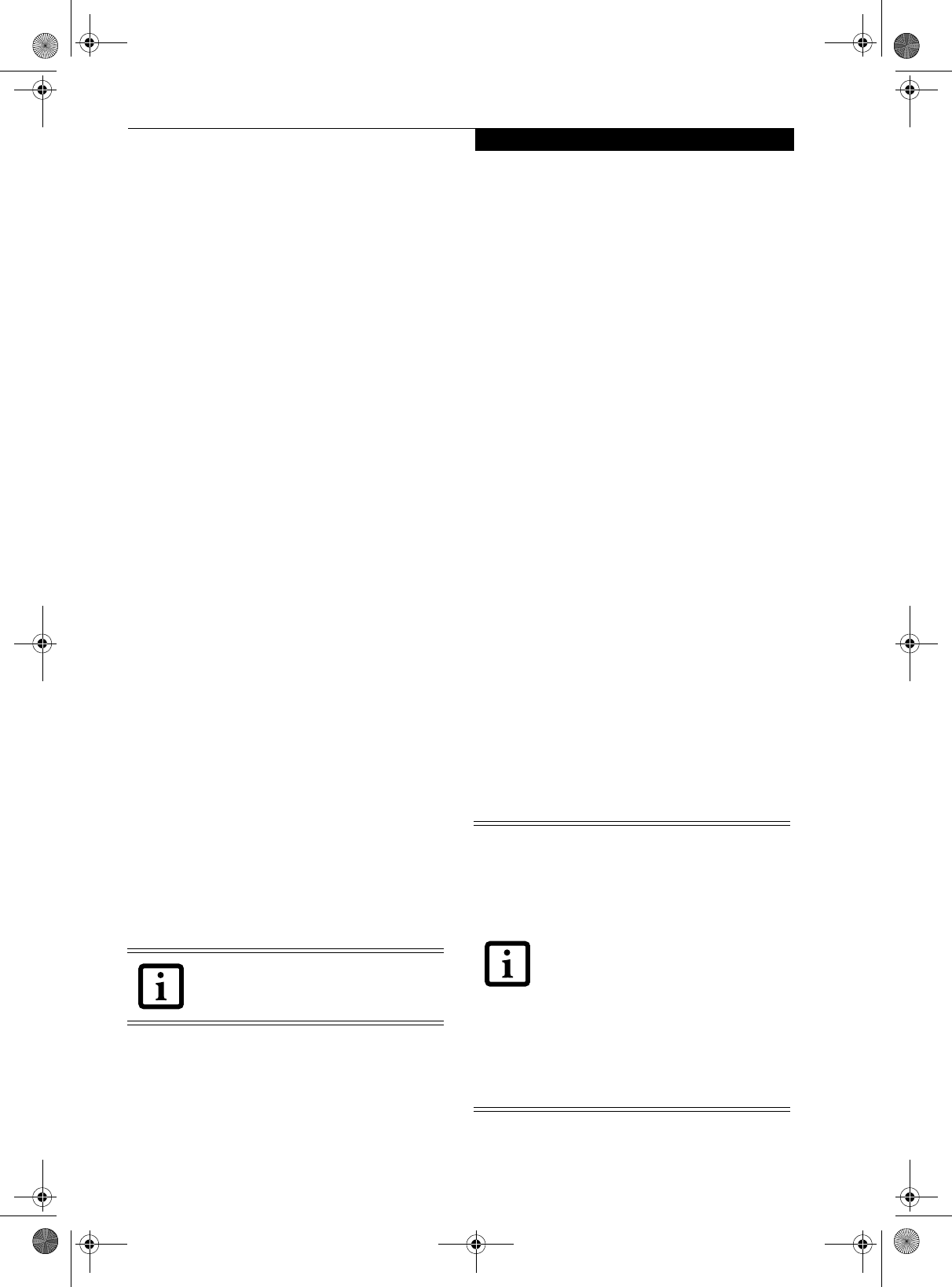
105
FIngerprint Sensor User’s Guide
You can view the credentials stored for any remembered
website by highlighting the desired resource under Pass-
word Protected Dialog and clicking Unmask Values.
Should a password be reset, or an account expire, you
can remove stored credentials from OmniPass. Highlight
the desired resource under Password Protected Dialog
and click Delete Page. You will be prompted to confirm
the password deletion.
The two check boxes in Manage Passwords govern
whether OmniPass prompts you to authenticate or
directly logs you into the remembered site.
OmniPass will overwrite an old set of credentials for a
website if you attempt to use Remember Password on an
already remembered site.
The exception to the above rule is the resetting of your
Windows password. If your password is reset in
Windows, then the next time you login to Windows,
OmniPass will detect the password change and prompt
you to “Update” or “Reconfirm” your password with
OmniPass. Enter your new Windows password in the
prompt(s) and click OK and your OmniPass "master
password" will still be your Windows password.
OmniPass User Identities
Identities allow OmniPass users to have multiple
accounts to the same site (e.g., bob@biblomail.com and
boballen@biblomail.com). If OmniPass did not provide
you identities, you would be limited to remembering
one account per site.
To create and manage identities, double-click the
OmniPass key in the system tray. Click Vault Mana g e -
ment; OmniPass will prompt you to authenticate. Once
you gain access to Vault Management, click Manage
Identities under Vault Settings. You can only manage
the identities of the currently logged in OmniPass user
To add a new identity, click New Identity or double-click
Click here to add a new identity. Name the new identity
and click [OK], then click [Apply]. You can now switch
to the new identity and start remembering passwords.
To delete an identity, highlight the identity you want to
delete and click [Delete Identity], then click [Apply].
To set the default identity, highlight the identity you
want as default and click [Set as Default]; click [Apply]
to ensure the settings are saved. If you log in to
OmniPass with a fingerprint device, you will automati-
cally be logged in to the default identity for that
OmniPass user. You can choose the identity with which
you are logging in if you login using "master password".
Choosing User Identity during Login
To choose your identity during login, type your user-
name in the User Name: field. Press [Tab] and see that
the Domain: field self-populates. Click the Password:
field to bring the cursor to it, and you will see the pull-
down menu in the Identity: field. Select the identity you
wish to login as and then click OK to login.
Switch User Identity
To switch identities at any time, right-click the
OmniPass system tray icon and click Switch User Iden-
tity from the submenu. The Switch Identity dialog will
appear. Select the desired identity and then click OK.
Identities and Password Management
On the Manage Passwords interface of the Vau l t
Management tab of the OmniPass Control Center, there
is a pull-down selection box labeled, Identity. This field
lets you choose which identity you are managing pass-
words for. When you select an identity here, only those
password protected dialogs that are associated with that
identity are shown. You can perform all the functions
explained in “Password Management” on page 104.
CONFIGURING OMNIPASS
This section gives an overview of both the Export/
Import function and the OmniPass Control Center.
Exporting and Importing Users
Using the OmniPass Control Center, you can export and
import users in and out of OmniPass. The export
process backs up all remembered sites, credentials, and
any enrolled fingerprints for an OmniPass user. All
OmniPass data for a user is backed up to a single
encrypted database file. During the import process, the
Windows login of the exported user is required. If the
proper credentials cannot be supplied, the user profile
will not be imported.
When you delete an identity, all of its
associated remembered sites and password
protected dialogs are lost.
■You should periodically export your user
profile and store it in a safe place. If
anything happens to your system, you
can import your OmniPass profile to a
new system and have all your remem-
bered settings and fingerprints instantly.
■You don't forget the Windows login
credentials when exporting. When you
examine the importation, you are
prompted for authentication. The
credentials that will allow a user profile
to be imported are the Windows login
credentials of the exported user. They
are the credentials that had to be
submitted when the user profile was
exported. You will need User Name,
Password, and Domain.
P Series.book Page 105 Wednesday, July 13, 2005 10:43 AM
106
LifeBook T Series Tablet PC - Appendix B
Exporting an OmniPass User Profile
To export a user, open the OmniPass Control Center,
and click Import/Export User under Manage Users.
Click Exports an OmniPass user profile. OmniPass will
prompt you to authenticate. Upon successfully authenti-
cation, you must name the OmniPass user profile and
decide where to save it. An .opi file is generated, and you
should store a copy of it in a safe place.
This .opi file contains all your user specific OmniPass
data, and it is both encrypted and password protected.
This user profile does NOT contain any of your
encrypted data files.
Importing an OmniPass User Profile
To import an OmniPass user open the OmniPass
Control Center, and click Import/Export User under
Manage Users. Click Imports a new user into OmniPass
and then select OmniPass Import/Export File (*.opi)
and click Next. OmniPass will then prompt you to
browse for the file you had previously exported (.opi
file). When you select the .opi file for importation,
OmniPass will prompt you for authentication. The
credentials that will allow a user profile to be imported
are the Windows login credentials of the exported user.
They are the credentials that had to be submitted when
the user profile was exported. You will need User Name,
Password, and Domain. If you don’t remember the value
for Domain, in a PC or SOHO environment Domain
should be your computer name.
OmniPass will notify you if the user was successfully
imported.
Things to Know Regarding Import/Export
■Assume you export a local Windows User profile from
OmniPass. You want to import that profile to another
machine that has OmniPass. Before you can import
the profile, a Windows user with the same login cre-
dentials must be created on the machine importing the
profile.
Example: I have a Windows user with the username
“Tom” and the password “Sunshine” on my system. I
have enrolled Tom into OmniPass and remembered
passwords. I want to take all my passwords to new sys-
tem. I export Tom’s OmniPass user profile. I go to my
new system and using the Control Panel I create a user
with the username "Tom" and the password "Sun-
shine". I can now successfully import the OmniPass
user data to the new system.
■If you export an OmniPass-only user, you can import
that user to any computer running OmniPass, pro-
vided that a user with that name is not already
enrolled in OmniPass.
■If you attempt to import a user profile who has the
same name as a user already enrolled in OmniPass, the
OmniPass import function will fail.
OMNIPASS CONTROL CENTER
This section will serve to explain functions within the
OmniPass Control Center that weren’t explained earlier.
You can access the OmniPass Control Center any of
three ways:
■Double-click the golden OmniPass key shaped icon in
the Windows taskbar (typically in the lower-right cor-
ner of the desktop)
■Click the Start button; select the Programs group;
select the Softex program group; and click the
OmniPass Control Center selection.
■Open the Windows Control Panel (accessible via Start
button --> Settings --> Control Panel) and double-
click the Softex OmniPass icon.
User Management
The User Management tab has two major interfaces:
Add/Remove User and Import/Export User. Import/
Export User functionality is documented in “Exporting
and Importing Users” on page 105. Add/Remove User
functionality is straightforward.
If you click Adds a new user to OmniPass you will start
the OmniPass Enrollment Wizard. The Enrollment
Wizard is documented in “User Enrollment” on
page 102.
If you click Removes a user from OmniPass, OmniPass
will prompt you to authenticate. Authenticate with the
credentials (or enrolled fingerprint) of the user you wish
to remove. OmniPass will prompt you to confirm user
removal. Click OK to complete user removal.
User Settings
The User Settings tab has four interfaces: Audio Settings,
Task b ar Tips, and Enrollment. User settings allow users
to customize OmniPass to suit individual preferences.
Under User Settings (Audio Settings and Ta s k b ar Tips)
You cannot import a user into OmniPass if
there already is a user with the same name
enrolled in OmniPass.
Removing a user will automatically destroy
all OmniPass data associated with that
user. All identities and credentials
associated with the user will be lost.
If you are sure about removing the user,
we recommend you export the user
profile.
P Series.book Page 106 Wednesday, July 13, 2005 10:43 AM
107
FIngerprint Sensor User’s Guide
you can set how OmniPass notifies the user of OmniPass
events (e.g., successful login, access denied, etc.). The
details of each setting under the Audio Settings and
Task b a r Tips interfaces are self-explanatory.
The Enrollment interface allows you to enroll finger-
prints. For the procedure to enroll and authentication
device refer to Chapter 2.3. To enroll additional finger-
prints, click Enroll Authentication Device, and authen-
ticate with OmniPass. Select the fingerprint recognition
device in the Select Authentication Device screen (it
should already be marked by a green check if you have a
finger enrolled) and click Next.
System Settings
The OmniPass Startup Options interface can be found
in the System Settings tab. With these options you can
specify how your OmniPass Logon is tied to your
Windows Logon.
The first option, Automatically log on to OmniPass as
the current user, will do just as it says; during Windows
login, you will be logged on to OmniPass using your
Windows login credentials. If the user logging into
Windows was never enrolled into OmniPass, upon login
no one will be logged on to OmniPass. This setting is
appropriate for an office setting or any setting where
users must enter a username and password to log into a
computer. This is the default setting.
With the second option, Manually log on to OmniPass
at startup, OmniPass will prompt you to login once you
have logged on to Windows.
With the third option, Do not log on to OmniPass at
startup, OmniPass will not prompt for a user to be
logged on.
You can manually log on to OmniPass by right-clicking
the OmniPass taskbar icon and clicking Log in User
from the right-click menu.
TROUBLESHOOTING
You cannot use OmniPass to create Windows users. You
must first create the Windows user, and you will need
administrative privileges to do that. Once the Windows
user is created, you can add that user to OmniPass using
the same username and password
Cannot add Windows users to OmniPass
If you experience difficulties adding a Windows user
to OmniPass, you may need to adjust your local secu-
rity settings. You can do this by going to Start,
Control Panel, Administrative Tools, and Local
Security Settings. Expand Local Policies, expand
Security Options, and double-click Network Access:
Sharing and Security Model for Local Accounts. The
correct setting should be Classic - Local Users Authen-
ticate as Themselves.
Cannot add a User with a Blank Password to OmniPass
If you experience difficulties adding a user with a
blank password to OmniPass, you may need to adjust
your local security settings. First attempt the proce-
dure explained in the Cannot add Windows user to
OmniPass section. If the difficulties persist, then try
the following procedure.
Click Start, Control Panel, Administrative Tools,
and Local Security Settings. Expand Local Policies,
expand Security Options, and double-click
Accounts: Limit local account use of blank pass-
words to console login only. This setting should be
set to Disabled.
Dialog appears after OmniPass authentication during
Windows Logon
After installing OmniPass on your system, you can
choose to logon to Windows using OmniPass. You
authenticate with OmniPass (via master password, or
an enrolled security device) and OmniPass logs you
into Windows. You may, during this OmniPass
authentication, see a Login Error dialog box.
This dialog box occurs when OmniPass was unable to
log you into Windows with the credentials supplied
(username and password). This could happen for any
of the following reasons:
■Your Windows password has changed
■Your Windows account has been disabled
If you are having difficulties due to the first reason,
you will need to update OmniPass with your changed
Windows account password. Click Update Password
and you will be prompted with a dialog to reconfirm
your password.
Enter the new password to your Windows user
account and click OK. If the error persists, then it is
unlikely the problem is due to your Windows user
account password changing.
P Series.book Page 107 Wednesday, July 13, 2005 10:43 AM
108
LifeBook T Series Tablet PC - Appendix B
P Series.book Page 108 Wednesday, July 13, 2005 10:43 AM
109
Index
Index
A
AC
adapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29
indicator . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14
plug adapters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 65
Anti-theft Lock Slot . . . . . . . . . . . . . . . . . . . . . . . . . . .12
Auto/Airline Adapter . . . . . . . . . . . . . . . . . . . . . . . . . . 29
Automatically Downloading Driver Updates . . . . . . 61
B
Battery . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
alarm . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
care . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 66
cold-swapping . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38
compartment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
conserving power . . . . . . . . . . . . . . . . . . . . . . . . . . . 32
dead . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 54
faulty . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 55
increasing life . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 66
level indicators . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14
lithium ion battery . . . . . . . . . . . . . . . . . . . . . . . . . . 37
low . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
problems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 54, 55
recharging . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
replacing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38
shorted . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38
suspend mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
battery release latch . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8
BIOS
guide . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30
setup utility . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30
Boot Sequence . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30
Built-in Microphone . . . . . . . . . . . . . . . . . . . . . . . . . . 13
Button Icons . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 20
C
CapsLock Indicator . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
CD-ROM
care . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 67
Changing Button Functions . . . . . . . . . . . . . . . . . . . . 21
Click Me! . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 31
Closed Cover Switch . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
Compact Flash Card . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
Configuration Label . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
Conventions used . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3
Cursor Keys . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
D
DC Output Cable . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29
DC Power Jack . . . . . . . . . . . . . . . . . . . . . . . . . .8, 11, 29
Device Ports . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .46
DIMM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
Display Panel . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
brightness . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
opening . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16
problems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .56, 57
Display Panel Latch . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
Display Timeout . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
Docking Port . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
Drivers and Application Restore CD . . . . . . . . . . . . . 60
E
Error Messages . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 58
External Monitor Port . . . . . . . . . . . . . . . . . . . . . . 12, 47
F
FDU . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 61
Floppy Disk
care . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 66
Fujitsu Driver Update utility . . . . . . . . . . . . . . . . . . . . 61
Function Key
F10 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
F3 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
F4 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
F5 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
F6 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
F7 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
F8 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
F9 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
FN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
Fn . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
H
Hard Disk Drive
access indicator . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14
problems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52
Hard Disk Timeout . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
Headphone Jack . . . . . . . . . . . . . . . . . . . . . . . . .8, 10, 46
Hibernate Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
I
Installing a Memory Stick . . . . . . . . . . . . . . . . . . . . . . 41
Internal LAN Jack . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
P Series.book Page 109 Wednesday, July 13, 2005 10:43 AM
110
LifeBook P Series Notebook - Index
K
Keyboard . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9, 18
cursor keys . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
numeric keypad . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
problems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52
windows keys . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
L
LAN (RJ-45) Jack . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12
LifeBook Application Buttons . . . . . . . . . . . . . . . . 9, 20
LifeBook P Series notebook
care . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 65
specifications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 71
storing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 65
traveling . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 65
unpacking . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7
LifeBook P Series notebook specifications
additional . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 72
agency approval . . . . . . . . . . . . . . . . . . . . . . . . . . . . 72
display specifications . . . . . . . . . . . . . . . . . . . . . . . 71
environmental . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 72
physical specifications . . . . . . . . . . . . . . . . . . . . 71, 72
power . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 72
Local Area Network (LAN) . . . . . . . . . . . . . . . . . . . . . 8
M
Memory
capacity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40
compartment . . . . . . . . . . . . . . . . . . . . . . . . . . . 13, 39
installing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
problems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 53
removing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
upgrade module . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
Memory Stick
installing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41
Microphone Jack . . . . . . . . . . . . . . . . . . . . . . . . . . . 8, 46
microprocessor . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 71
modem . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8, 12
Modem (RJ-11) Port . . . . . . . . . . . . . . . . . . . . . . . 12, 46
Modem Result Codes . . . . . . . . . . . . . . . . . . . . . . . . . 59
Mouse
problems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52
See Touchpad
N
Numeric Keypad . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
NumLk Indicator . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
O
optional accessories . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7
P
PC Card
care . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .67
removing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .43
slot . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10
Pen . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .11
Port Replicator . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .44
attaching . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .44
detaching . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .44
problems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .52
Port Replicator Connector . . . . . . . . . . . . . . . . . . . .8, 13
Power
AC adapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .29
Auto/Airline adapter . . . . . . . . . . . . . . . . . . . . . . . .29
failure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .54
indicator . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .14
management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .32
off . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .34
power on . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .30
problems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .55
sources . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .29
Power Management . . . . . . . . . . . . . . . . . . . . . . . .32, 33
Power On Self Test . . . . . . . . . . . . . . . . . . . . . . . . .30, 58
Q
Quick Point
clicking . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .22
control adjustment . . . . . . . . . . . . . . . . . . . . . . . . . .23
double-clicking . . . . . . . . . . . . . . . . . . . . . . . . . . . . .22
dragging . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .22
R
Registration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .31
Re-Installing Individual Drivers and Applications . .60
Removing a Memory Stick . . . . . . . . . . . . . . . . . . . . . .41
Restarting the system . . . . . . . . . . . . . . . . . . . . . . . . . .33
Restoring the Factory Image . . . . . . . . . . . . . . . . . . . .60
Restoring Your Pre-installed Software . . . . . . . . . . . .60
RJ-11 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .46
RJ-45 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8, 46
Rotation Hinge . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9
S
ScrLk Indicator . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .15
SD Card . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .11
removing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .41
SDRAM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .13, 39
Secure Digital Card
removing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .41
P Series.book Page 110 Wednesday, July 13, 2005 10:43 AM
111
Index
Security lock slot . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8
Shut Down . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34
specifications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .71
Standby Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
status indicators . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9, 14
Suspend Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32
Suspend/Resume Button . . . . . . . . . . . . . . . . . . .8, 9, 32
T
Touch Screen . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
calibrating . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
clicking . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
double-clicking . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
dragging . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
Touchpad Pointing Device . . . . . . . . . . . . . . . . . . . 9, 24
Troubleshooting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 51
battery . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .54, 55
built-in Speakers . . . . . . . . . . . . . . . . . . . . . . . . . . . .52
hard drive . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52
memory . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 53
mouse/keyboard . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52
port replicator . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52
ports . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 53
power . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 54
video . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 56
U
Universal Serial Bus Port . . . . . . . . . . . . . . . . . . . . . . .46
USB . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8, 12, 46
problems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 53
Using the system as a Tablet . . . . . . . . . . . . . . . . . . . . 16
V
volume control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25
W
Windows keys . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
Application key . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
Start key . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
Wireless LAN
Before Using the Wireless LAN . . . . . . . . . . . . . . . 86
Using Wireless Zero Configuration Tool . . . . . . . . 89
Infrastructure Mode . . . . . . . . . . . . . . . . . . . . . . . . . 86
IP address information . . . . . . . . . . . . . . . . . . . . . .96
Specifications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 97
Troubleshooting . . . . . . . . . . . . . . . . . . . . . . . . . . . . 93
Wireless LAN Glossary . . . . . . . . . . . . . . . . . . . . . . 94
WLAN On/Off Switch . . . . . . . . . . . . . . . . . . . . . . .8, 11
P Series.book Page 111 Wednesday, July 13, 2005 10:43 AM
112
LifeBook P Series Notebook - Index
P Series.book Page 112 Wednesday, July 13, 2005 10:43 AM
P Series.book Page 113 Wednesday, July 13, 2005 10:43 AM
P Series.book Page 114 Wednesday, July 13, 2005 10:43 AM