ZyXEL Communications NWA1100 Access Point User Manual NWA1100 UG v 1 00 Ed 1 July 2008
ZyXEL Communications Corporation Access Point NWA1100 UG v 1 00 Ed 1 July 2008
Contents
- 1. Installation guide I
- 2. Installation guide II
- 3. Installation guide III
Installation guide III
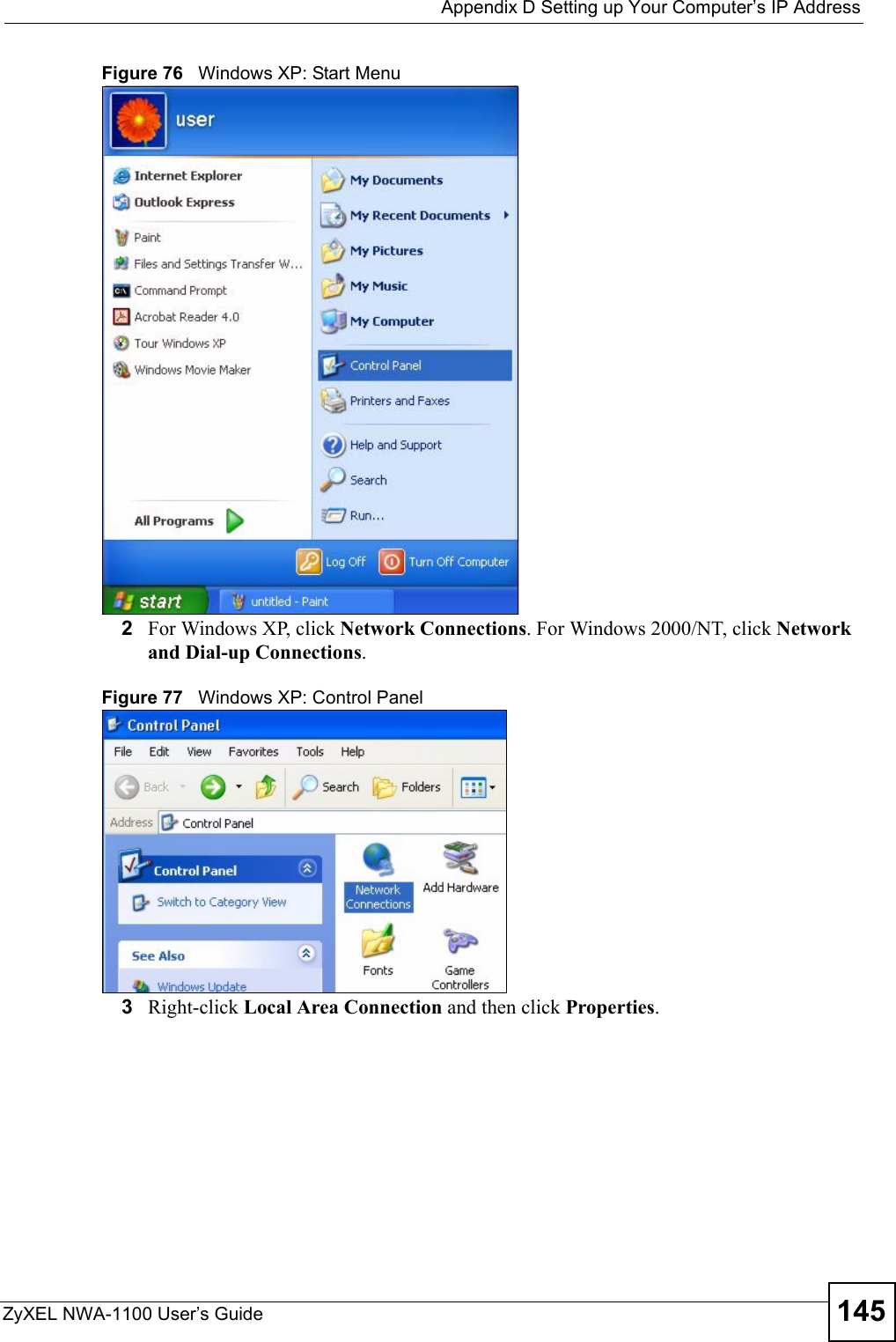
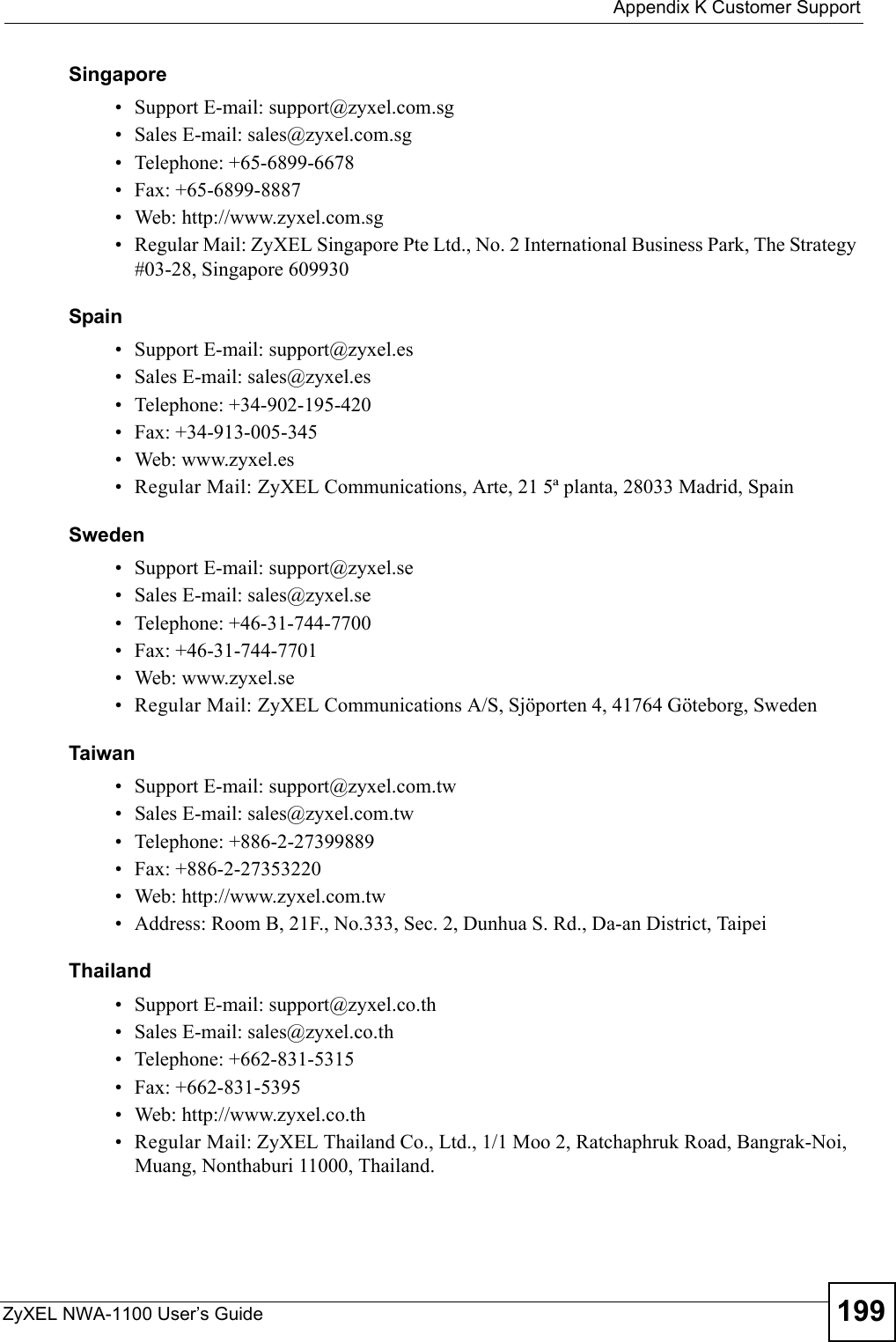
![Appendix D Setting up Your Computer’s IP AddressZyXEL NWA-1100 User’s Guide148Figure 81 Windows XP: Internet Protocol (TCP/IP) Properties8Click OK to close the Internet Protocol (TCP/IP) Properties window.9Click OK to close the Local Area Connection Properties window.10 Turn on your ZyXEL Device and restart your computer (if prompted).Verifying Settings1Click Start, All Programs, Accessories and then Command Prompt.2In the Command Prompt window, type "ipconfig" and then press [ENTER]. You can also open Network Connections, right-click a network connection, click Status and then click the Support tab.Macintosh OS 8/9 1Click the Apple menu, Control Panel and double-click TCP/IP to open the TCP/IP Control Panel.](https://usermanual.wiki/ZyXEL-Communications/NWA1100.Installation-guide-III/User-Guide-988473-Page-8.png)

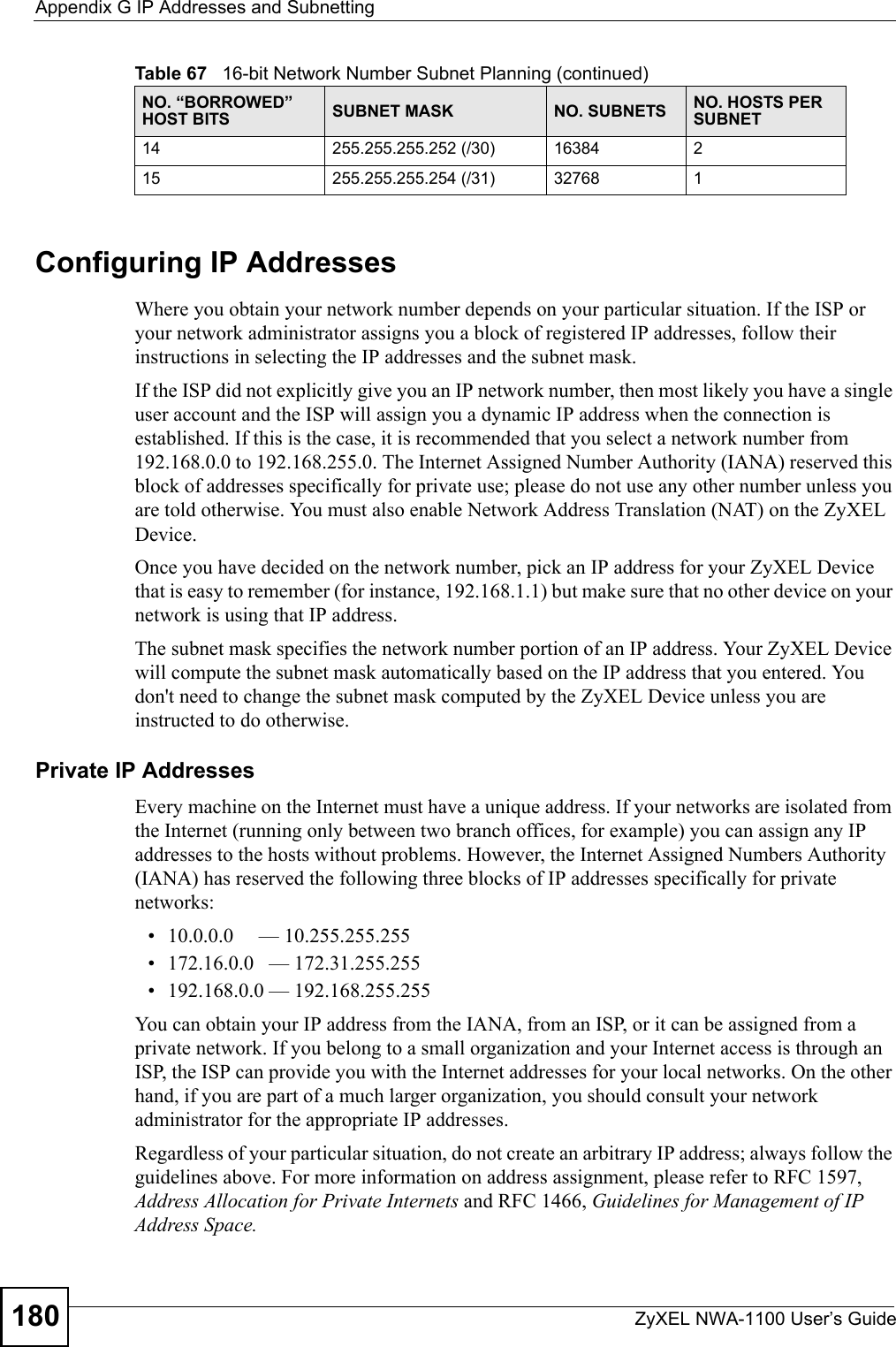
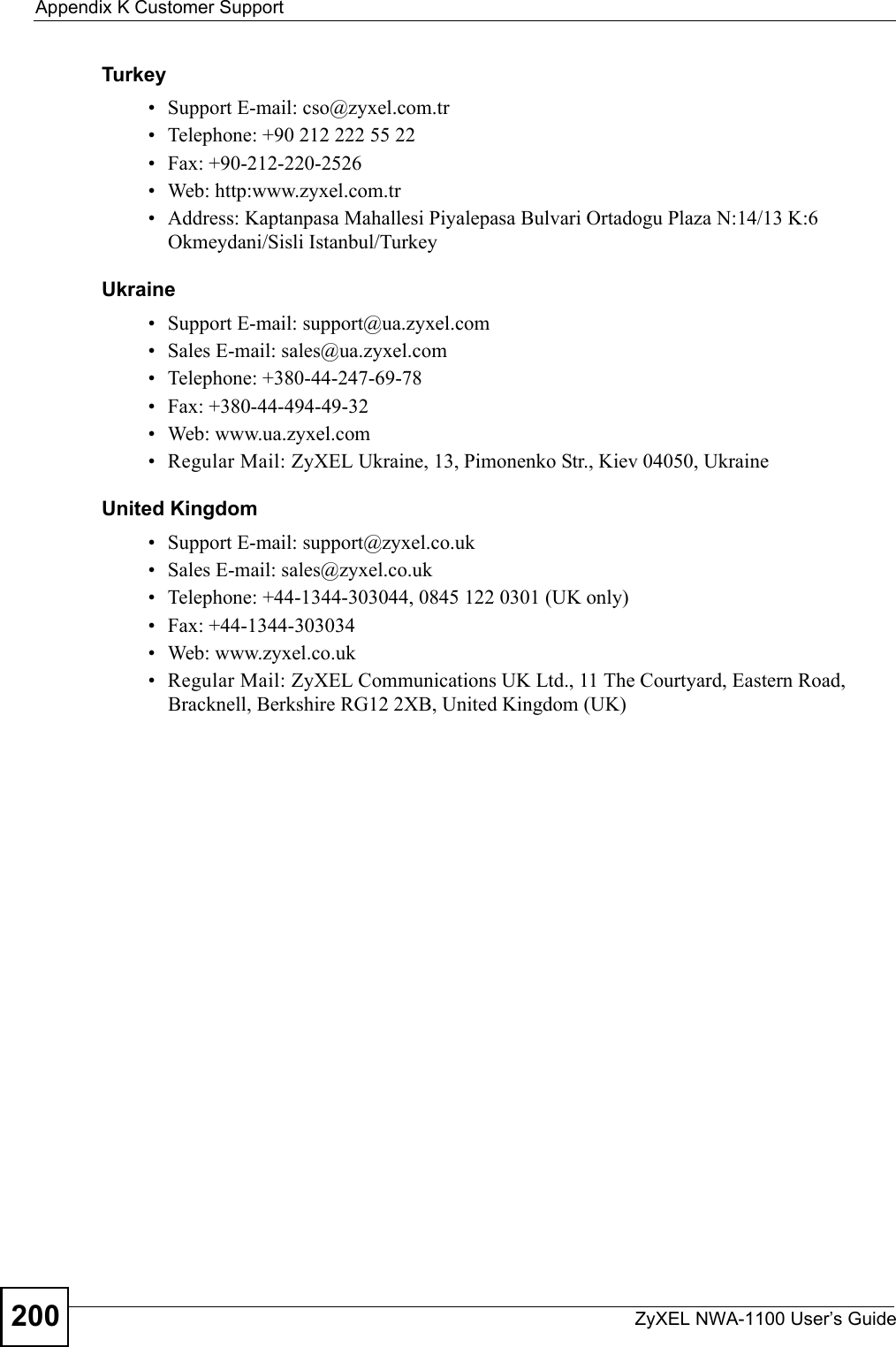
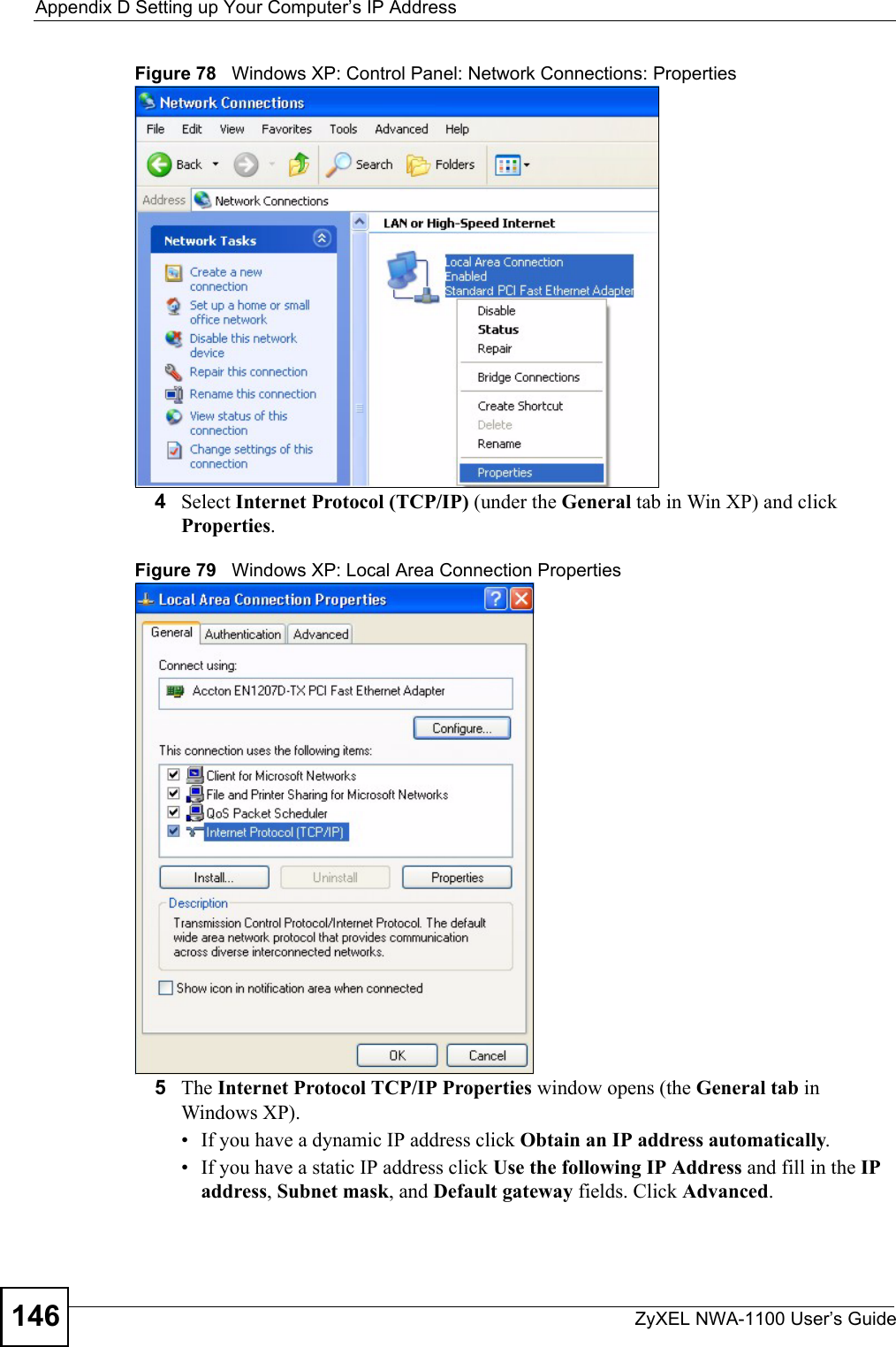
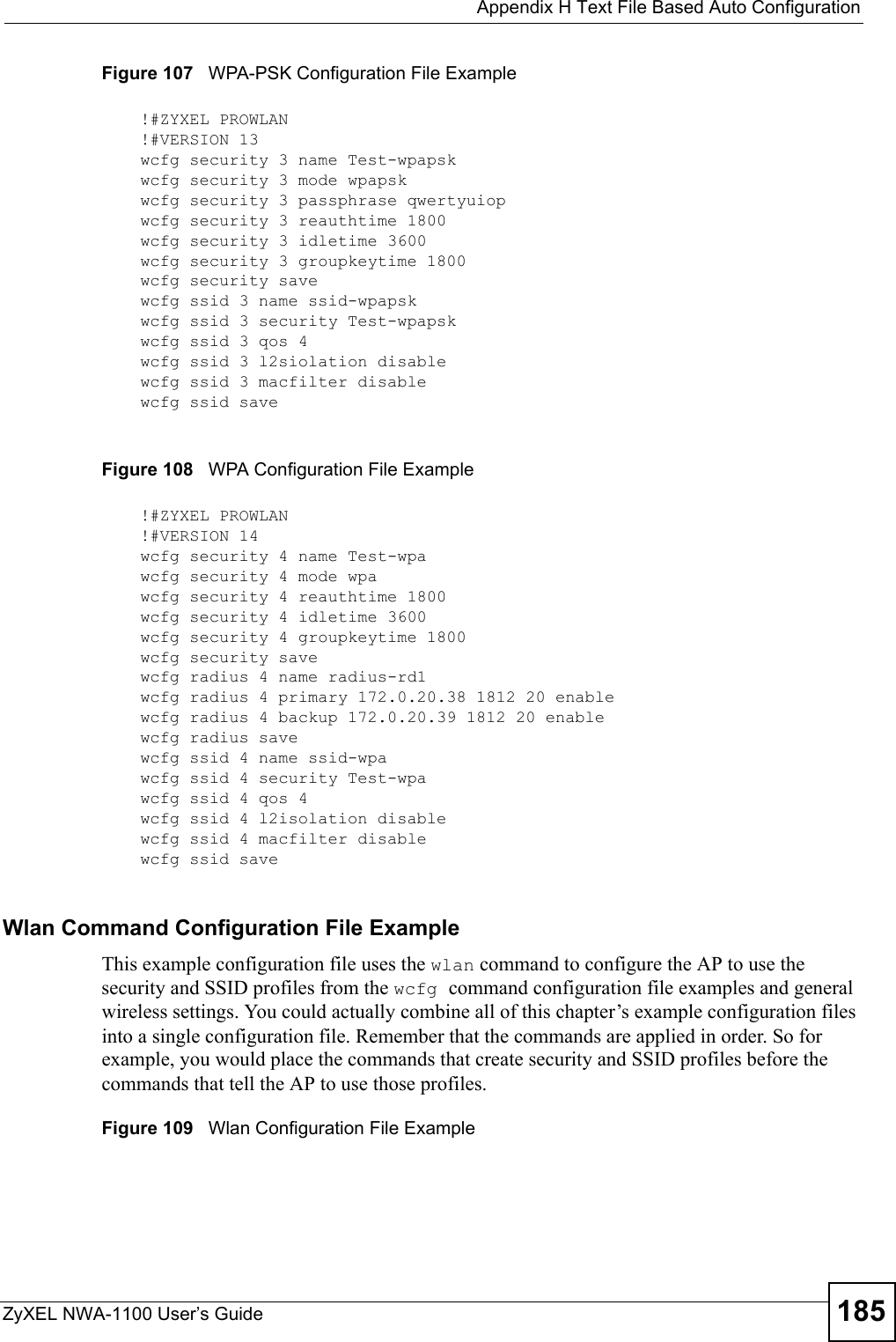
![Appendix H Text File Based Auto ConfigurationZyXEL NWA-1100 User’s Guide182"If adjacent APs use the same configuration file, you should leave out the channel setting since they could interfere with each other’s wireless traffic.Auto Configuration by DHCPA DHCP response can use options 66 and 67 to assign a TFTP server IP address and a filename. If the AP is configured as a DHCP client, these settings can be used to perform auto configuration. If this feature is enabled and the DHCP response provides a TFTP server IP address and a filename, the AP will try to download the file from the specified TFTP server. The AP then uses the file to configure wireless LAN settings."Not all DHCP servers allow you to specify options 66 and 67. Configuration Via SNMPYou can configure and trigger the auto configuration remotely via SNMP.Use the following procedure to have the AP download the configuration file.Verifying Your Configuration File Upload Via SNMPYou can use SNMP management software to display the configuration file version currently on the device by using the following MIB.Table 68 Auto Configuration by DHCPCOMMAND DESCRIPTIONwcfg autocfg dhcp [enable | disable]Turn configuration of TFTP server IP address and filename through DHCP on or off.Table 69 Configuration via SNMPSTEPS MIB VARIABLE VALUEStep 1 pwTftpServer Set the IP address of the TFTP server.Step 2 pwTftpFileName Set the file name, for example, g3000hcfg.txt.Step 3 pwTftpFileType Set to 3 (text configuration file).Step 4 pwTftpOpCommand Set to 2 (download).Table 70 Displaying the File VersionITEM OBJECT ID DESCRIPTIONpwCfgVersion 1.3.6.1.4.1.890.1.9.1.2 This displays the current configuration file version.](https://usermanual.wiki/ZyXEL-Communications/NWA1100.Installation-guide-III/User-Guide-988473-Page-42.png)
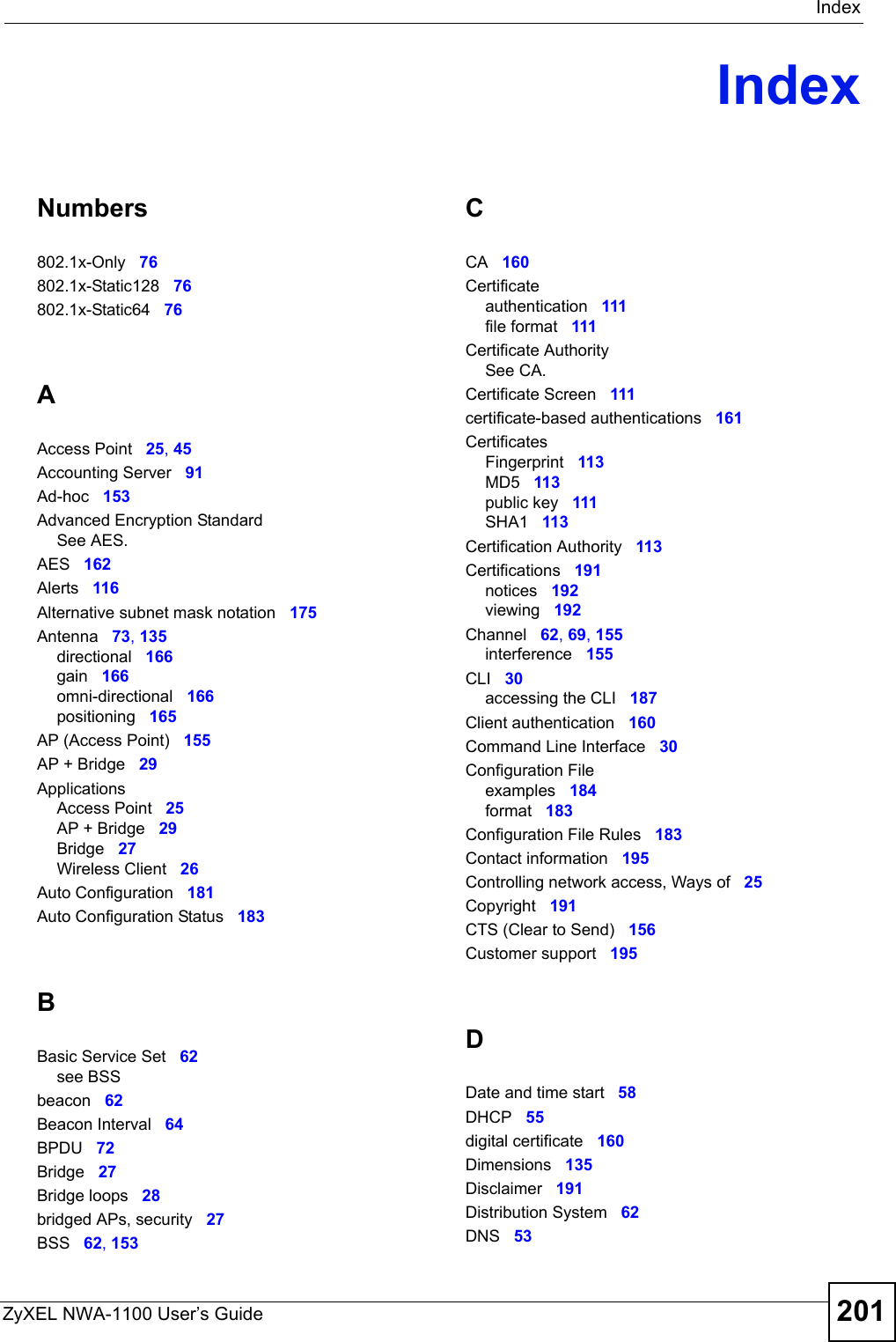
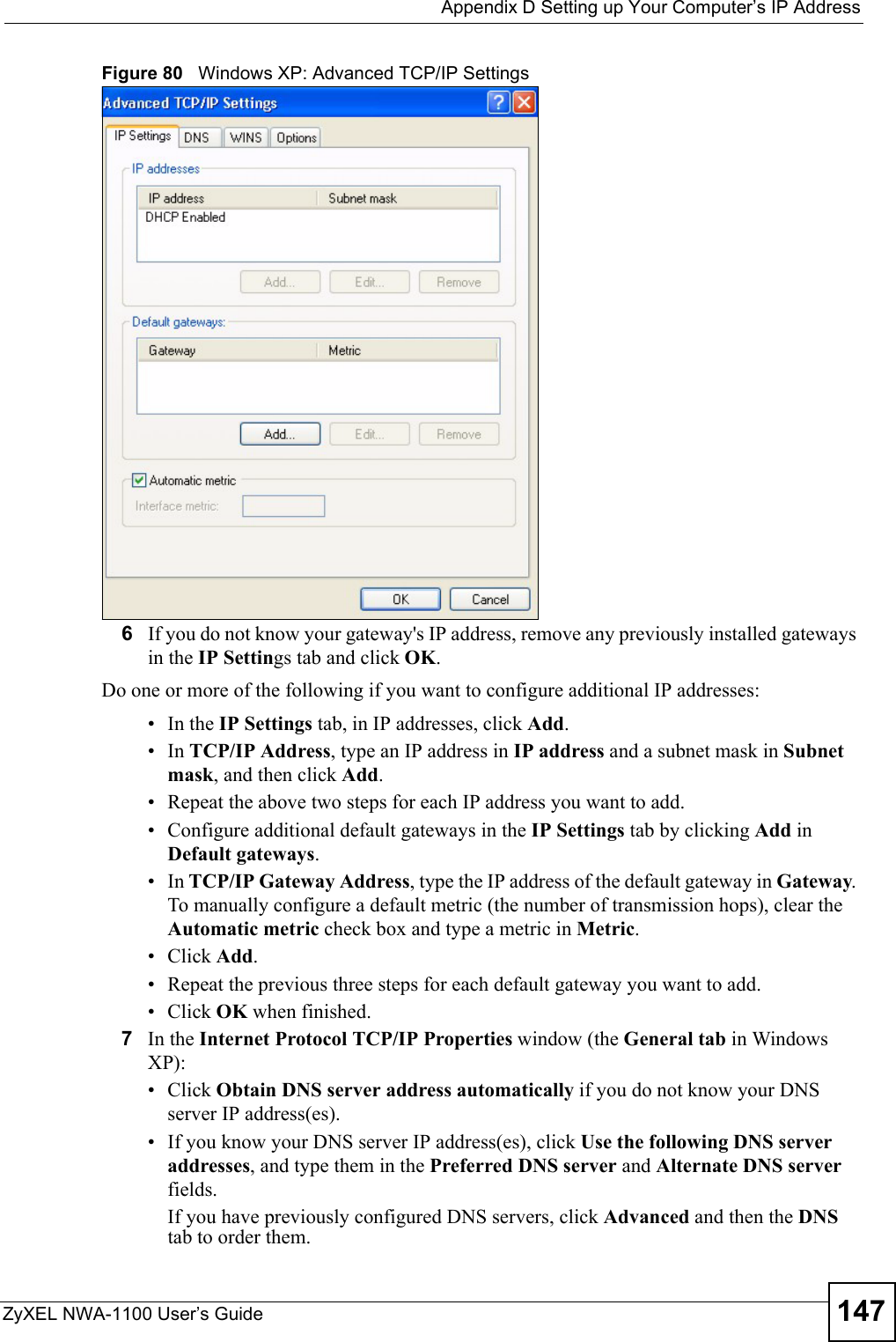
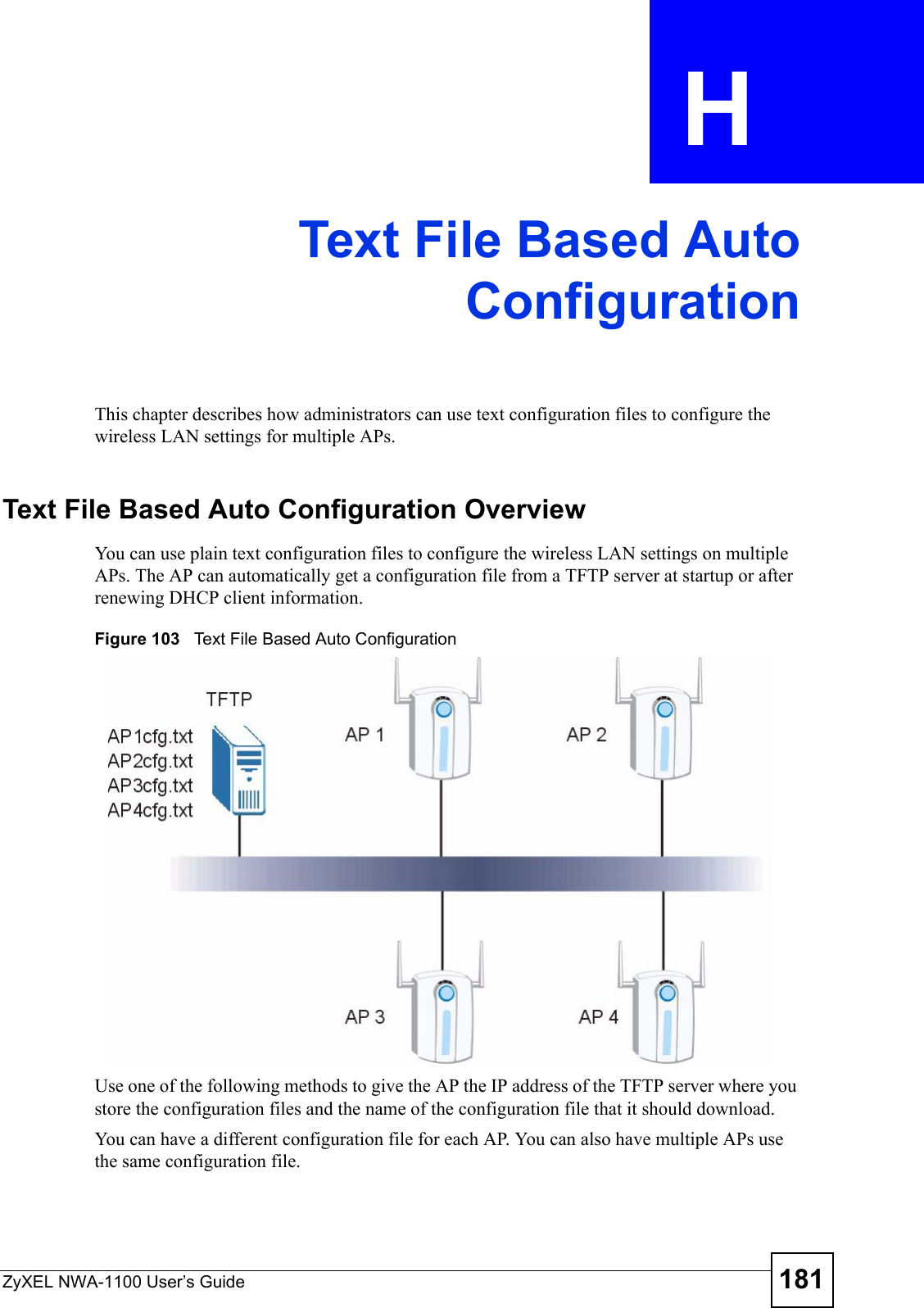
![Appendix I How to Access and Use the CLIZyXEL NWA-1100 User’s Guide188Command ConventionsCommand descriptions follow these conventions:• Commands are in courier new font.• Required input values are in angle brackets <>; for example, ping <ip-address> means that you must specify an IP address for this command.• Optional fields are in square brackets []; for instance in the show logins [name]command, the name field is optional.The following is an example of a required field within an optional field: snmp-server [contact <system contact>], the contact field is optional. However, if you use contact, then you must provide the system contact information. •The | (bar) symbol means “or”.•italic terms represent user-defined input values; for example, in sys datetime date [year month date], year month date can be replaced by the actual year month and date that you want to set, for example, 2007 08 15.• A key stroke is denoted by square brackets and uppercase text, for example, [ENTER] means the “Enter” or “Return” key on your keyboard.•<cr> means press the [ENTER] key.• An arrow (-->) indicates that this line is a continuation of the previous line.A long list of pre-defined values may be replaced by a command input value ‘variable’ so as to avoid a very long command in the description table. Refer to the command input values table if you are unsure of what to enter."Commands are case sensitive! Enter commands exactly as seen in the command interface. Remember to also include underscores if required.Table 75 Common Command Input ValuesLABEL DESCRIPTIONdescription Used when a command has a description field in order to add more detail.ip-address An IP address in dotted decimal notation. For example, 192.168.1.3. mask The subnet mask in dotted decimal notation, for example, 255.255.255.0.mask-bits The number of bits in an address’s subnet mask. For example type /24 for a subnet mask of 255.255.255.0.port A port number.hostname The hostname can be an IP address or domain name.name Used for the name of a rule, policy, set, group and so on.number Used for a number, for example 10, that you have to enter.](https://usermanual.wiki/ZyXEL-Communications/NWA1100.Installation-guide-III/User-Guide-988473-Page-48.png)
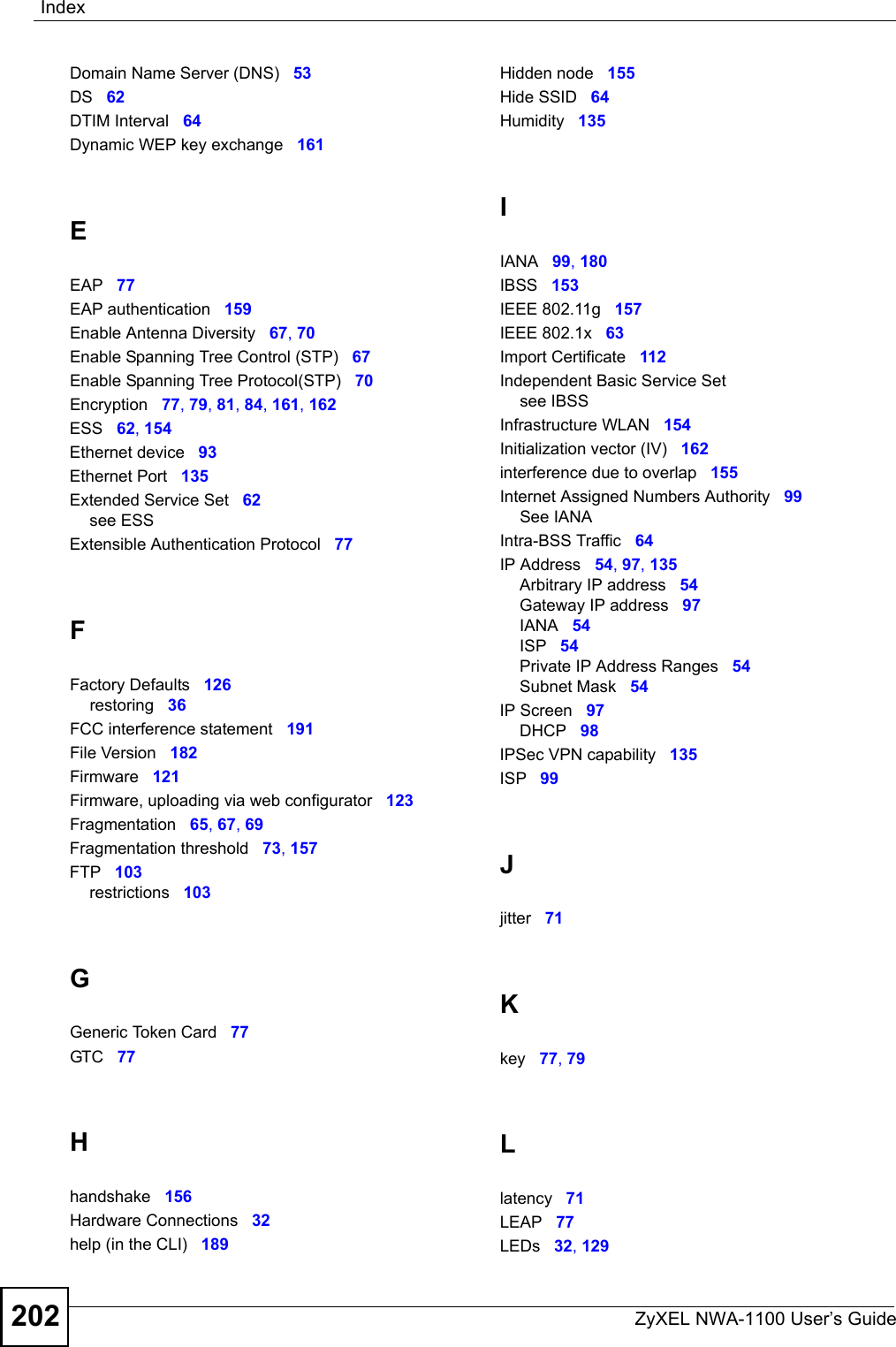
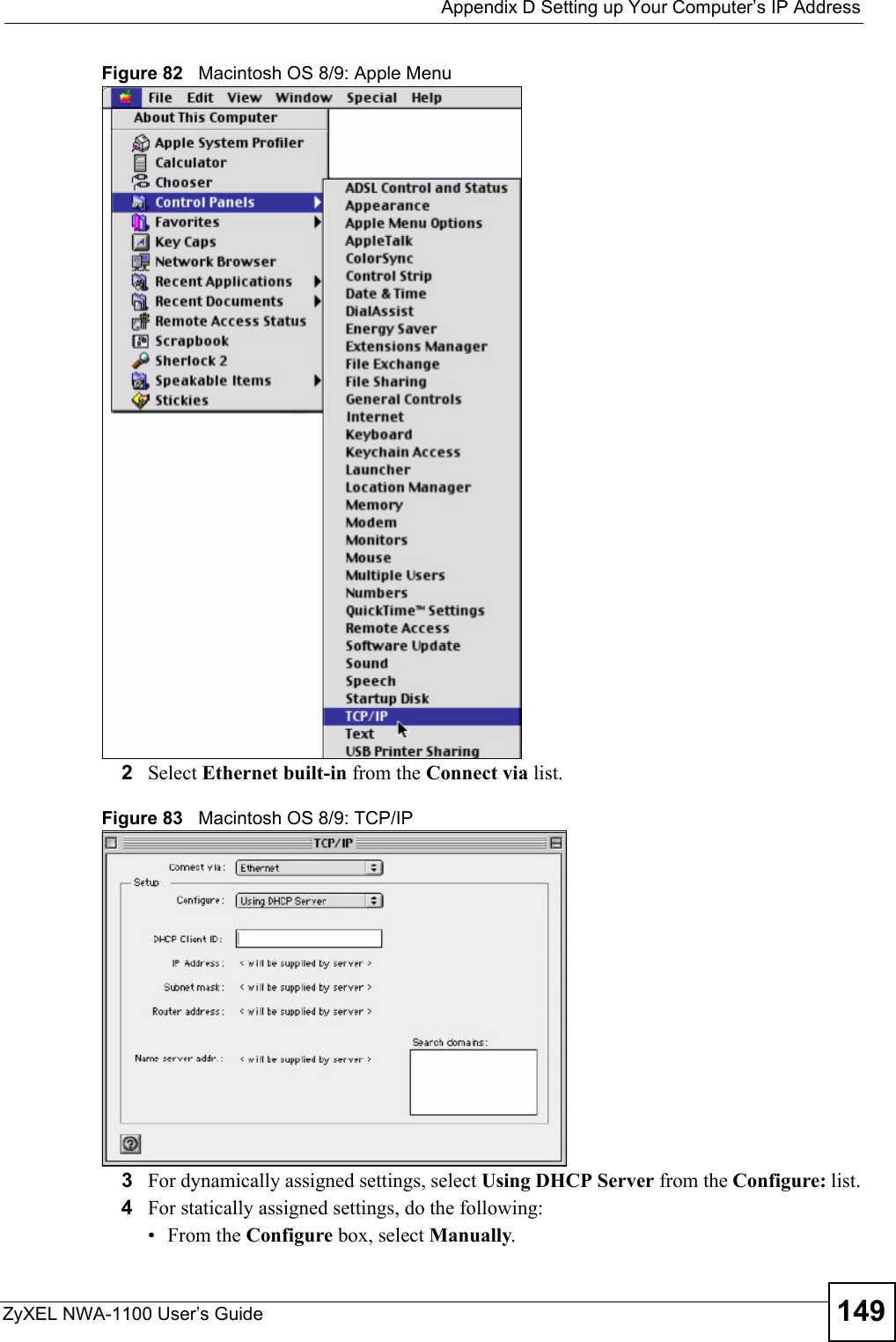
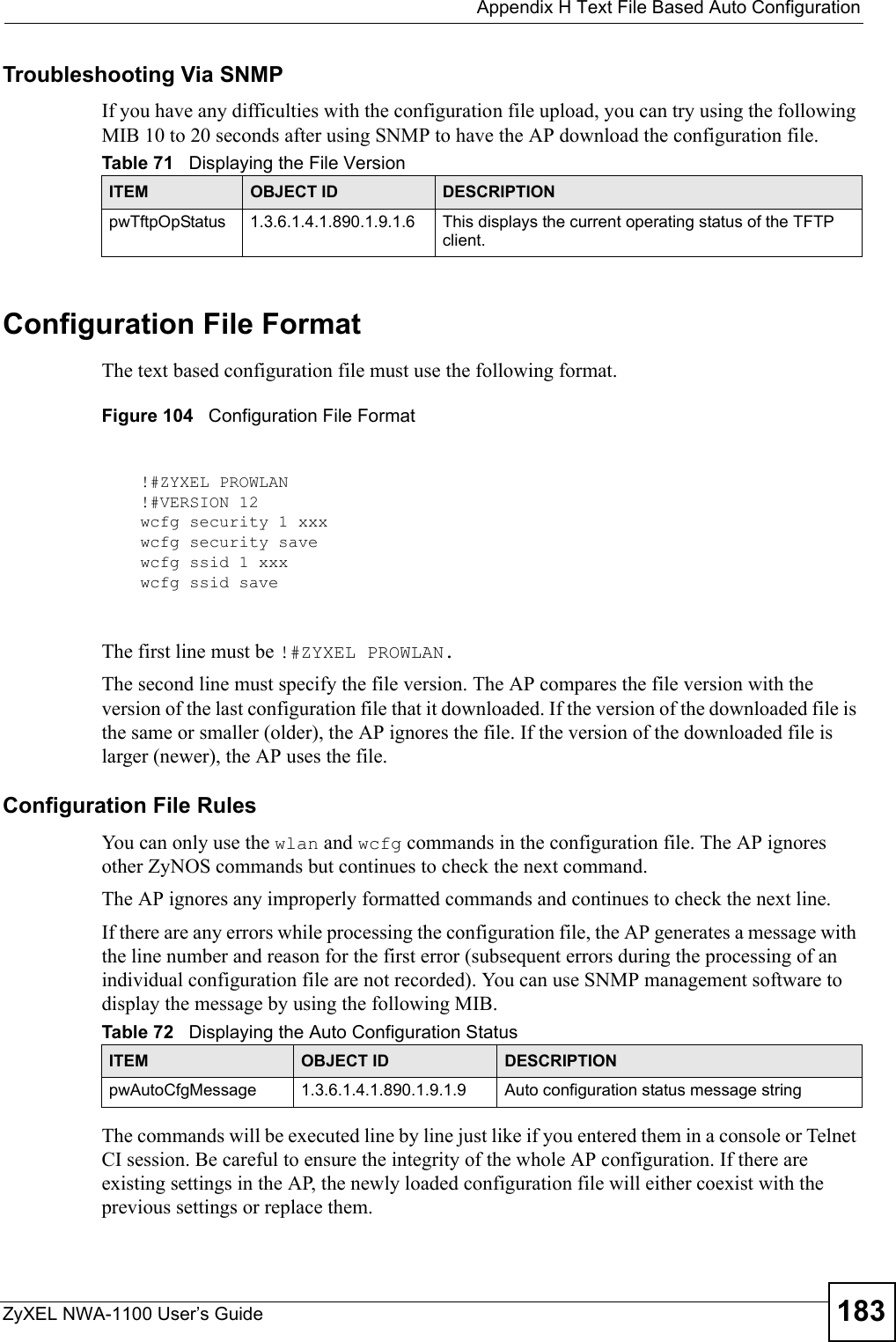
![Appendix I How to Access and Use the CLIZyXEL NWA-1100 User’s Guide 189Copy and Paste CommandsYou can copy and paste commands directly from this document into your terminal emulation console window (such as HyperTerminal). Use right-click (not [CTRL]-[V]) to paste your command into the console window as shown next. Using Shortcuts and Getting HelpThis table identifies some shortcuts in the CLI, as well as how to get help.1Use of undocumented commands or misconfiguration can damage the unit and possibly render it unusable.Use the help command to view the executable commands on the ZyXEL Device. Follow these steps to create a list of supported commands:1Log into the CLI. 2Type help and press [ENTER]. A list comes up which shows all the commands available for this device.Table 76 CLI Shortcuts and HelpCOMMAND / KEY(S) DESCRIPTIONyz (up/down arrow keys) Scrolls through the list of recently-used commands. You can edit any command or press [ENTER] to run it again.?Displays the keywords and/or input values that are allowed in place of the ?.help Displays the (full) commands that are allowed in place of help.ras> helpalarm chsh config exit ip statistics switchsys voipras>](https://usermanual.wiki/ZyXEL-Communications/NWA1100.Installation-guide-III/User-Guide-988473-Page-49.png)