Cambium Networks XN12 WIRELESS LAN ARRAY User Manual
Xirrus, Inc. WIRELESS LAN ARRAY
Contents
- 1. Users Manual 1of5
- 2. Users Manual 2of5
- 3. Users Manual 3of5
- 4. Users Manual 4of5
- 5. Users Manual 5of5
- 6. A Pages 1 to 125 from ArrayGuide Rel4 SS Dec02 2008
- 7. B Pages 126 to 225 from ArrayGuide Rel 4 SS Dec02 2008
- 8. C Pages 226 to 350 from ArrayGuide Rel4 SS Dec02 2008
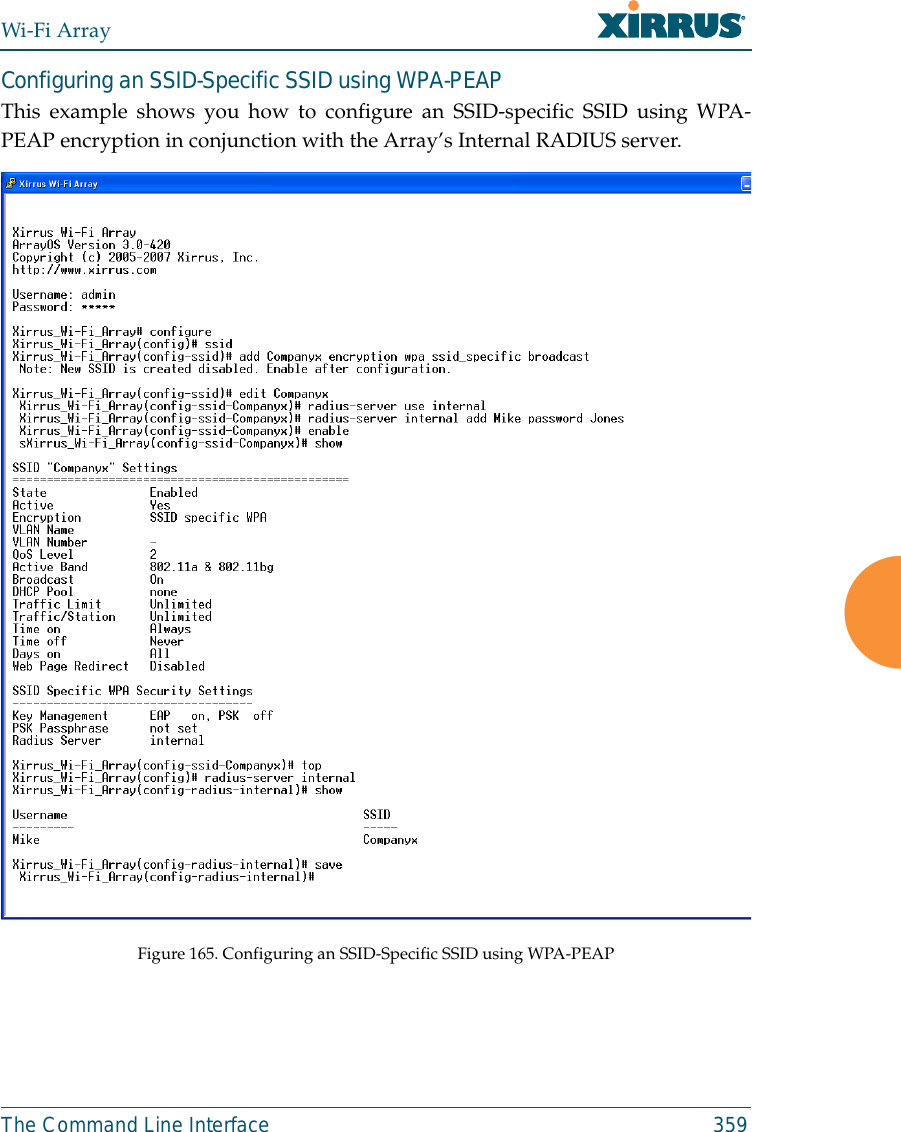
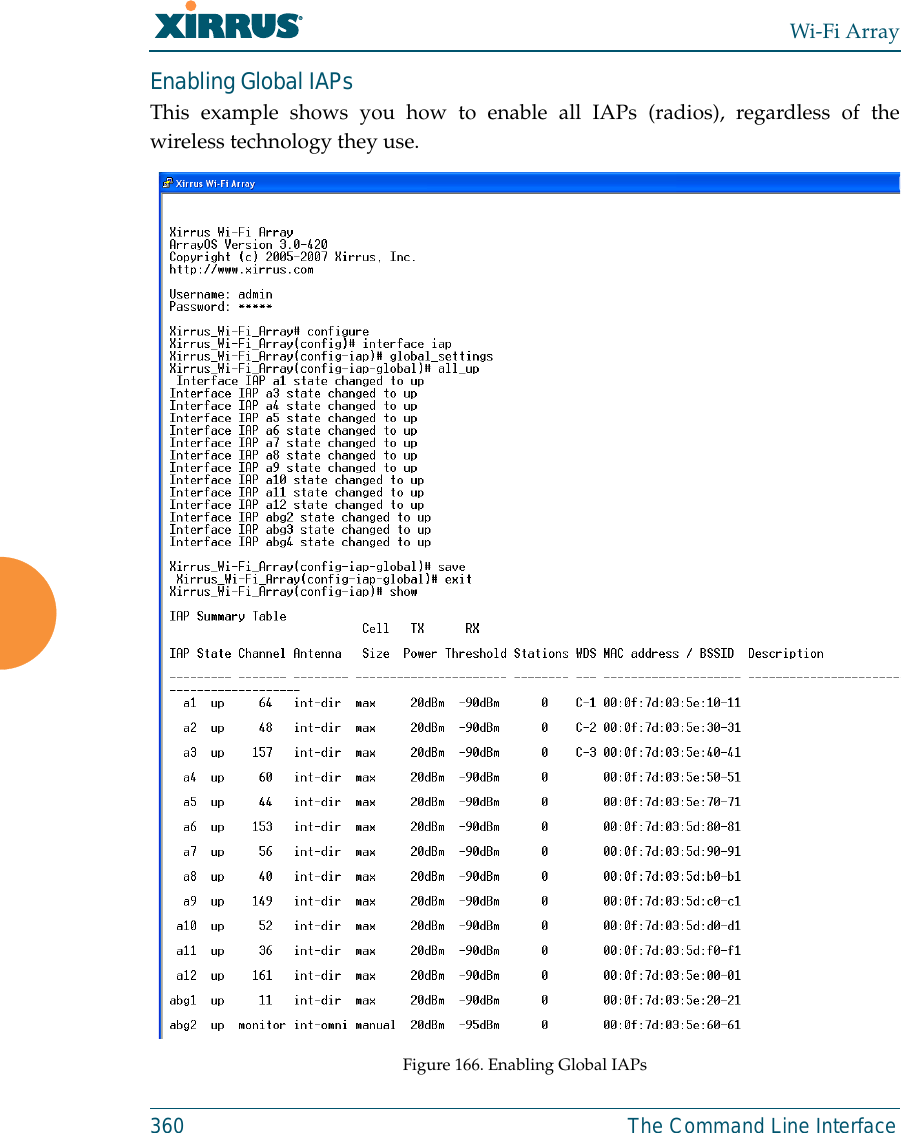
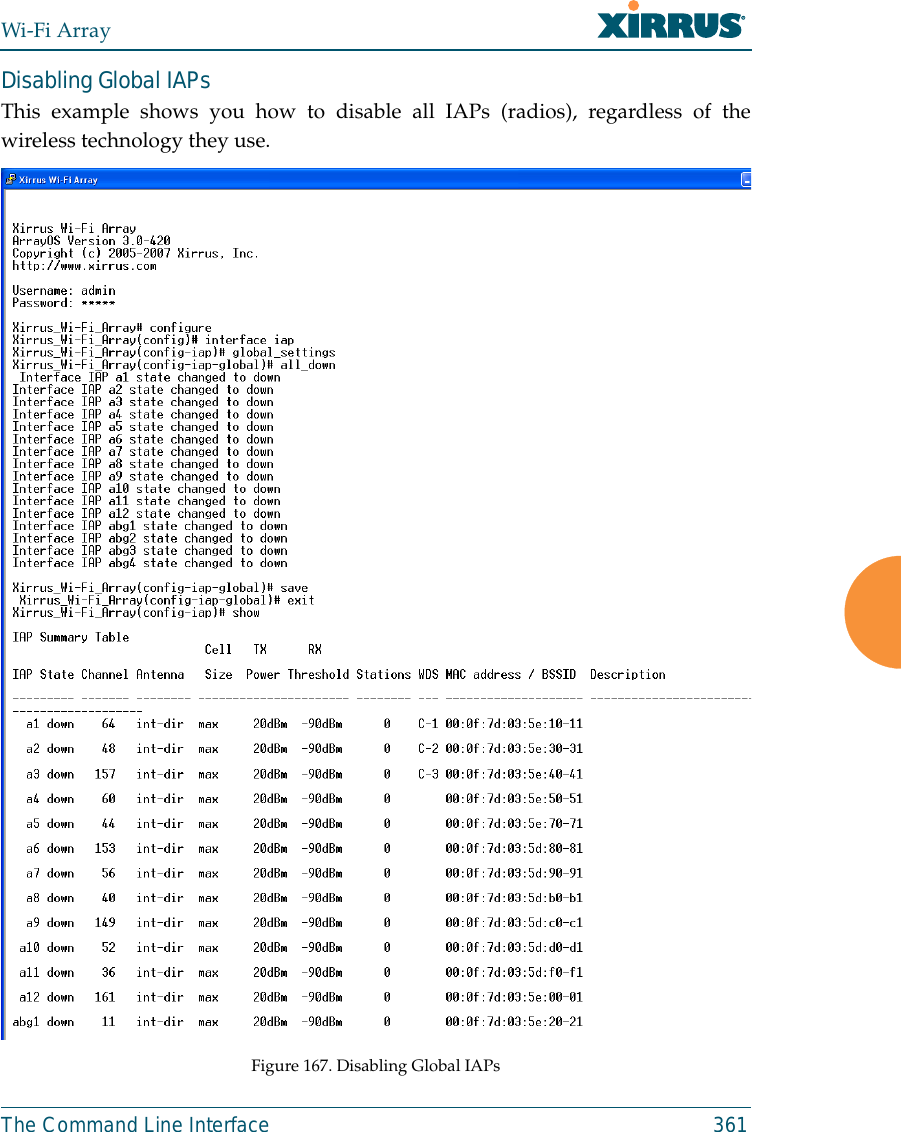
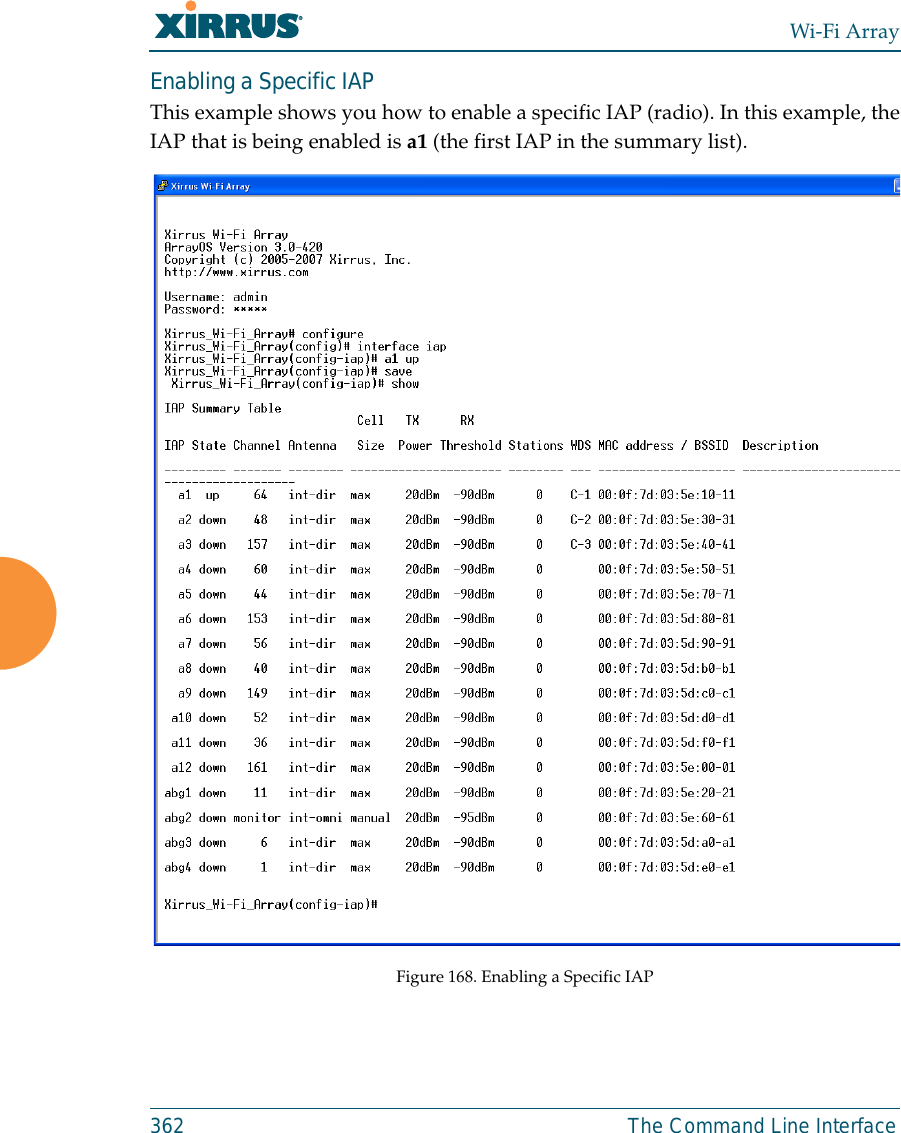
- 9. D Pages 351 to 496 from ArrayGuide Rel4 SS Dec02 2008 Small 5
- 10. XN Guide small 1 of 5 revised
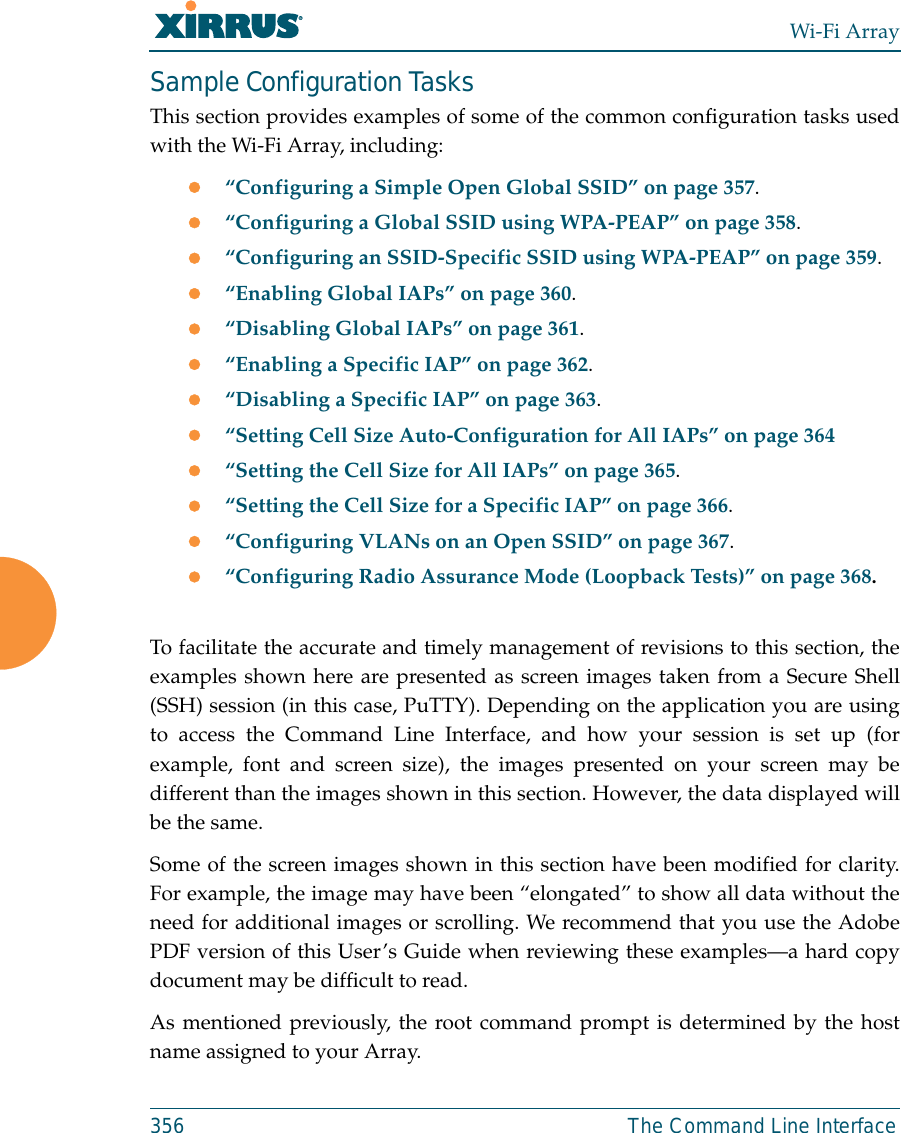
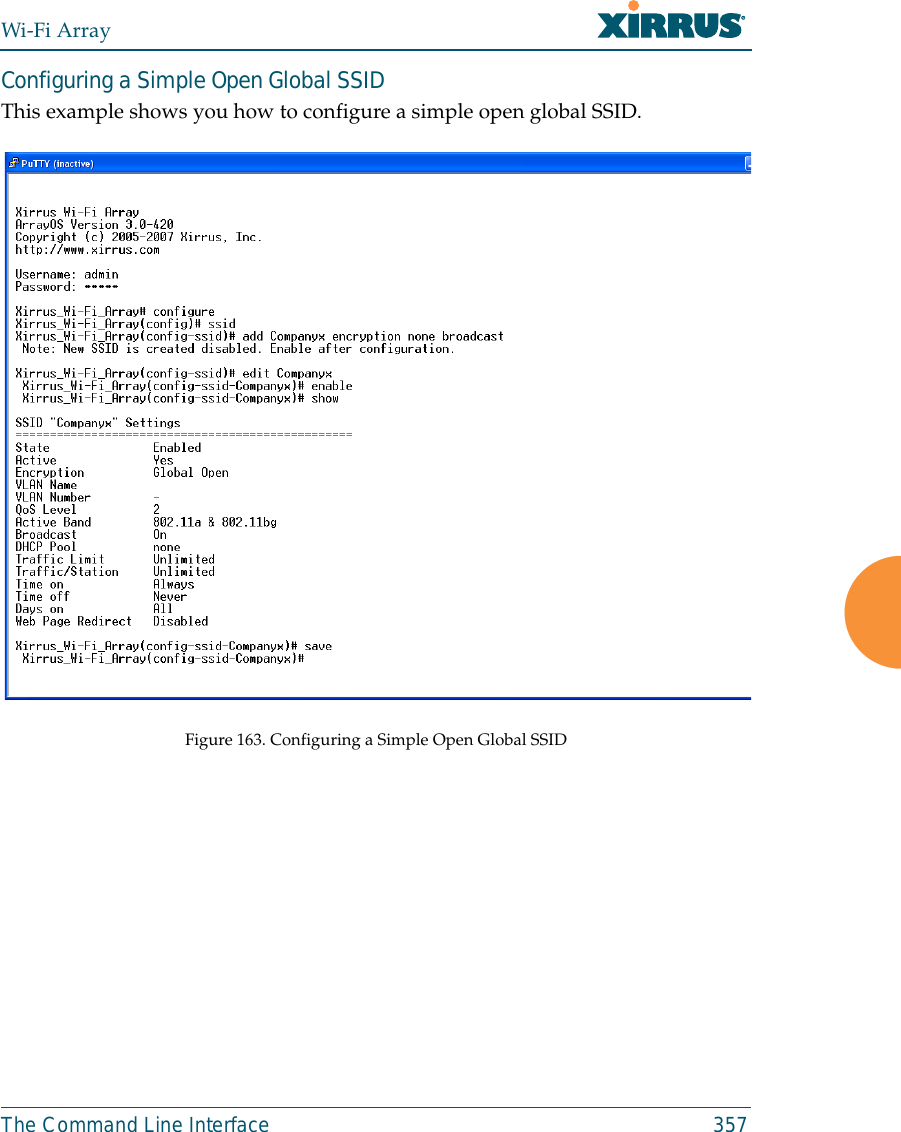
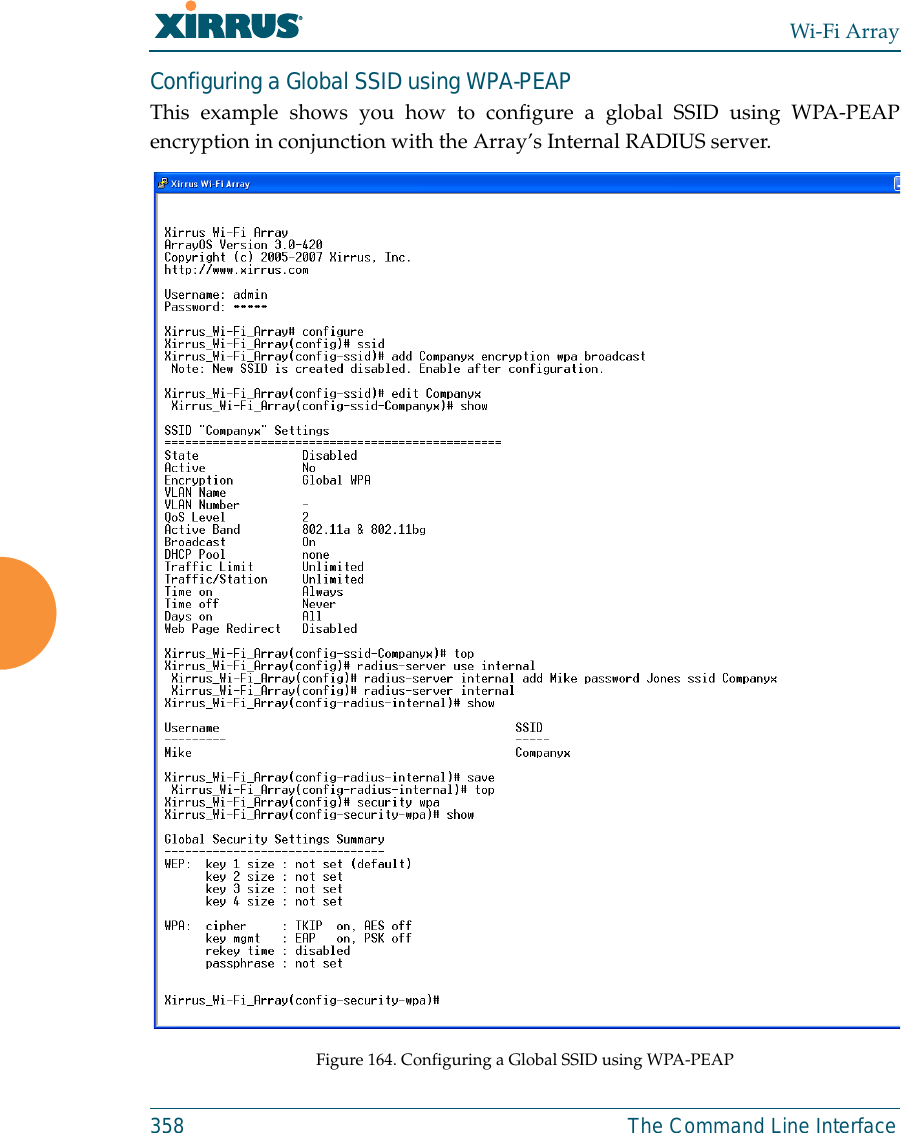
D Pages 351 to 496 from ArrayGuide Rel4 SS Dec02 2008 Small 5
![Wi-Fi ArrayThe Command Line Interface 331filter The filter command [Xirrus_Wi-Fi_Array(config-filter)#] is used to manageprotocol filters and filter lists.Command Descriptionadd Add a filter.FORMAT:filter add [name]add-list Add a filter list.FORMAT:filter add-list [name]del Delete a filter.FORMAT:filter del [name]del-list Delete a filter list.FORMAT:filter del-list [name]edit Edit a filter.FORMAT:filter edit [name type]edit-list Edit a filter listFORMAT:filter edit-list [name type]enable Enable a filter list.FORMAT:filter enable move Change a filter priority.FORMAT:filter move [name priority]](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-1.png)
![Wi-Fi ArrayThe Command Line Interface 333fips The fips command [Xirrus_Wi-Fi_Array(config)# fips] is used to set theparameter values required for FIPS 140-2, Level 2 security. For more information,see Appendix D: Implementing Security Standards. Command Descriptiondisable Reverts FIPS settings to the values they had before performing a fips on command. FORMAT:fips disableenable Set FIPS security on the Array. Remembers the values of parameters prior to setting them.FORMAT:fips enableoff Reverts FIPS settings to the values they had before performing a fips on command. FORMAT:fips offon Set FIPS security on the Array. Remembers the values of parameters prior to setting them.FORMAT:fips on](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-3.png)
![Wi-Fi Array334 The Command Line Interfacegroup The group command [Xirrus_Wi-Fi_Array(config)# group] is used to create andconfigure user groups. User groups allow administrators to assign specificnetwork parameters to users through RADIUS privileges rather than having tomap users to a specific SSID. Groups provide flexible control over user privilegeswithout the need to create large numbers of SSIDs. For more information, see“Groups” on page 245. hostname The hostname command [Xirrus_Wi-Fi_Array(config)# hostname] is used tochange the hostname used by the Array.Command Descriptionadd Create a new user group. FORMAT:group add [group-name]del Delete a user group.FORMAT:group del [group-name]edit Set parameters values for a group. FORMAT:group edit [group-name]reset Reset the group.FORMAT:group resetCommand Descriptionhostname Change the hostname of the Array.FORMAT:hostname [name]](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-4.png)
![Wi-Fi ArrayThe Command Line Interface 335https The https command [Xirrus_Wi-Fi_Array(config)# https] is used to enable ordisable the Web Management Interface (https), which is enabled by default. It alsoallows you to establish a timeout for your Web management session.Command Descriptiondisable Disable the https feature.FORMAT:https disableenable Enable the https feature.FORMAT:https enableoff Disable the https feature.FORMAT:https offon Enable the https feature.FORMAT:https ontimeout Define an elapsed period (in seconds) after which the Web Management Interface will time out.FORMAT:https timeout 5000](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-5.png)
![Wi-Fi Array336 The Command Line Interfaceinterface The interface command [Xirrus_Wi-Fi_Array(config)# interface] is used to selectthe interface that you want to configure. To see a listing of the commands that areavailable for each interface, use the ? command at the selected interface prompt.For example, using the ? command at the Xirrus_Wi-Fi_Array(config-gig1}#prompt displays a listing of all commands for the gig1 interface.Command Descriptionconsole Select the console interface. The console interface is used for management purposes only.FORMAT:interface consoleeth0 Select the Fast Ethernet interface. The Fast Ethernet interface is used for management purposes only.FORMAT:interface eth0Note: To configure a static route for management traffic, next enter:static-route addr [ip-addr]static-route mask [subnet-mask]gig1 Select the Gigabit 1 interface.FORMAT:interface gig1gig2 Select the Gigabit 2 interface.FORMAT:interface gig2iap Select an IAP.FORMAT:interface iap](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-6.png)
![Wi-Fi ArrayThe Command Line Interface 337load The load command [Xirrus_Wi-Fi_Array(config)# load] loads a configurationfile.location The location command [Xirrus_Wi-Fi_Array(config)# location] is used to set thelocation for the Array.Command Descriptionfactory.conf Load the factory settings configuration file. FORMAT:load [factory.conf]lastboot.conf Load the configuration file from the last boot-up. FORMAT:load [lastboot.conf][myfile].conf If you have saved a configuration, enter its name to load it. FORMAT:load [myfile.conf]saved.conf Load the configuration file with the last saved settings. FORMAT:load [saved.conf]Command Description<cr> Set the location for the Array.FORMAT:location [newlocation]When you enter the location, simply hit the Enter key <cr> to input the new location.](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-7.png)
![Wi-Fi Array338 The Command Line Interfacemanagement The management command [Xirrus_Wi-Fi_Array(config)# management] entersmanagement mode, where you may configure console management parameters.more The more command [Xirrus_Wi-Fi_Array(config)# more] is used to turn terminalpagination ON or OFF.Command Description<cr> Enter management mode.FORMAT:management <cr>Command Descriptionoff Turn OFF terminal pagination.FORMAT:more offon Turn ON terminal pagination.FORMAT:more on](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-8.png)
![Wi-Fi ArrayThe Command Line Interface 339netflowThe netflow command [Xirrus_Wi-Fi_Array(config-netflow)#] is used to enableor disable, or configure sending IP flow information (traffic statistics) to thecollector you specify.Command Descriptiondisable Disable netflow.FORMAT:netflow disableenable Enable netflow.FORMAT:netflow enableoff Disable netflow.FORMAT:netflow offon Enable netflow.FORMAT:netflow oncollector Set the netflow collector IP address or fully qualified domain name (host.domain). Only one collector may be set. If port is not specified, the default is 2055. FORMAT:netflow collector host {<ip-addr> | <domain>} [port <port#>]](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-9.png)
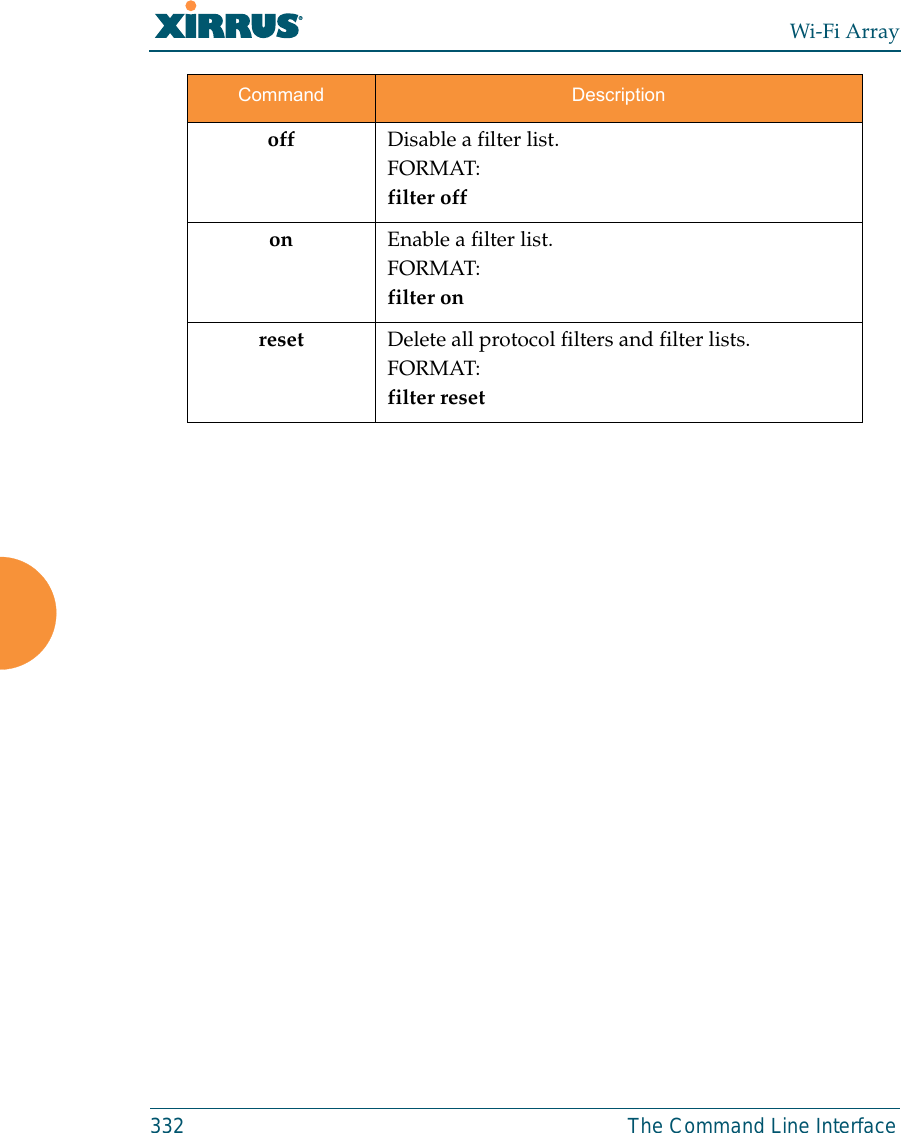
![Wi-Fi Array340 The Command Line Interfaceno The no command [Xirrus_Wi-Fi_Array(config)# no] is used to disable a selectedelement or set the element to its default value.Command Descriptionacl Disable the Access Control List.FORMAT:no acldot11a Disable all 802.11a(n) IAPs (radios).FORMAT:no dot11adot11bg Disable all 802.11bg(n) IAPs (radios).FORMAT:no dot11bghttps Disable https access.FORMAT:no httpsintrude-detect Disable intrusion detection.FORMAT:no intrude-detectmanagement Disable management on all Ethernet interfaces.FORMAT:no managementmore Disable terminal pagination.FORMAT:no morentp Disable the NTP server.FORMAT:no ntp](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-10.png)
![Wi-Fi Array342 The Command Line Interfacepci-audit The pci-audit command [Xirrus_Wi-Fi_Array(config)# pci-audit] checks theconfiguration of the Array for conformance with PCI DSS standards. When youenter the pci-audit command, it lists any settings that violate PCI DSSrequirements. In addition, if pci-audit is on (enabled), the Array will warn you ifyou change any parameters in a way that violates PCI DSS requirements. Forexample, if you enable pci-audit and then set encryption to none on an SSID (inthe CLI or the WMI), a warning will be displayed and a Syslog message will beissued. For more information, see Appendix D: Implementing Security Standards. Command Descriptiondisable The Array will not check configuration changes for PCI DSS violations. FORMAT:pci-audit disableenable The Array reports any current settings that violate PCI DSS, and will warn you and issue a Syslog message if you make configuration changes that that violate PCI DSS. FORMAT:pci-audit enableoff The Array will not check configuration changes for PCI DSS violations. FORMAT:pci-audit offon The Array reports any current settings that violate PCI DSS, and will warn you and issue a Syslog message if you make configuration changes that that violate PCI DSS. FORMAT:pci-audit on](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-12.png)
![Wi-Fi ArrayThe Command Line Interface 343quit The quit command [Xirrus_Wi-Fi_Array(config)# quit] is used to exit theCommand Line Interface.radius-server The radius-server command [Xirrus_Wi-Fi_Array(config-radius-server)#] isused to configure the external and internal RADIUS server parameters.Command Description<cr> Exit the Command Line Interface.FORMAT:quitIf you have made any configuration changes and your changes have not been saved, you are prompted to save your changes to Flash.At the prompt, answer Yes to save your changes, or answer No to discard your changes.Command Descriptionexternal Configure an external RADIUS server.FORMAT:radius-server externalTo configure a RADIUS server (primary, secondary, or accounting server, by IP address or host name), and the reporting interval use:radius-server external accountinginternal Configure the external RADIUS server.FORMAT:radius-server internaluse Choose the active RADIUS server (either external or internal).FORMAT:use external (or internal)](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-13.png)
![Wi-Fi Array344 The Command Line Interfacereboot The reboot command [Xirrus_Wi-Fi_Array(config)# reboot] is used to reboot theArray. If you have unsaved changes, the command will notify you and give you achance to cancel the reboot. reset The reset command [Xirrus_Wi-Fi_Array(config)# reset] is used to reset allsettings to their default values then reboot the Array.Command Description<cr> Reboot the Array.FORMAT:rebootdelay Reboot the Array after a delay of 1 to 60 seconds.FORMAT:reboot delay [n]Command Description<cr> Reset all configuration parameters to their factory default values.FORMAT:resetThe Array is rebooted automatically.preserve-ip-settings Preserve all ethernet and VLAN settings and reset all other configuration parameters to their factory default values.FORMAT:reset preserve-ip-settingsThe Array is rebooted automatically.](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-14.png)
![Wi-Fi ArrayThe Command Line Interface 345run-tests The run-tests command [Xirrus_Wi-Fi_Array(run-tests)#] is used to enter run-tests mode, which allows you to perform a range of tests on the Array.Command Description<cr> Enter run-tests mode.FORMAT:run-tests iperf Execute iperf utility.FORMAT:run-tests iperfkill-beacons Turn off beacons for selected single IAP.FORMAT:run-tests kill-beacons [off | iap-name] kill-probe-responses Turn off probe responses for selected single IAP.FORMAT:run-tests kill-probe-responses [off | iap-name] led LED test.FORMAT:run-tests led [flash | rotate] memtest Execute memory tests.FORMAT:run-tests memtestping Execute ping utility.FORMAT:run-tests ping [host-name | ip-addr]](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-15.png)
![Wi-Fi Array346 The Command Line Interfaceradius-ping Special ping utility to test the connection to a RADIUS server.FORMAT:run-tests radius-ping [external | ssid <ssidnum>] [primary | secondary] user <raduser> password <radpasswd> auth-type [CHAP | PAP]run-tests radius-ping [internal | server <radserver> port <radport> secret <radsecret> ] user <raduser> password <radpasswd> auth-type [CHAP | PAP]You may select a RADIUS server that you have already configured (ssid or external or internal) or specify another server (server). rlb Run manufacturing radio loopback test.FORMAT:run-tests rlb {optional command line switches}self-test Execute self-test.FORMAT:run-tests self-test {logfile-name (optional)]site-survey Enable or disable site survey mode.FORMAT:run-tests site-survey [on | off | enable | disable] ssh Execute ssh utility.FORMAT:run-tests ssh [hostname | ip-addr] [command-line-switches (optional)] tcpdump Execute tcpdump utility to dump traffic for selected interface or VLAN. FORMAT:run-tests tcpdumpCommand Description](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-16.png)
![Wi-Fi ArrayThe Command Line Interface 347security The security command [Xirrus_Wi-Fi_Array(config-security)#] is used toestablish the security parameters for the Array.telnet Execute telnet utility.FORMAT:run-tests telnet [hostname | ip-addr] [command-line-switches (optional)] traceroute Execute traceroute utility.FORMAT:run-tests traceroute [host-name | ip-addr]Command Descriptionwep Set the WEP encryption parameters.FORMAT:security wepwpa Set the WEP encryption parameters.FORMAT:security wpaCommand Description](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-17.png)
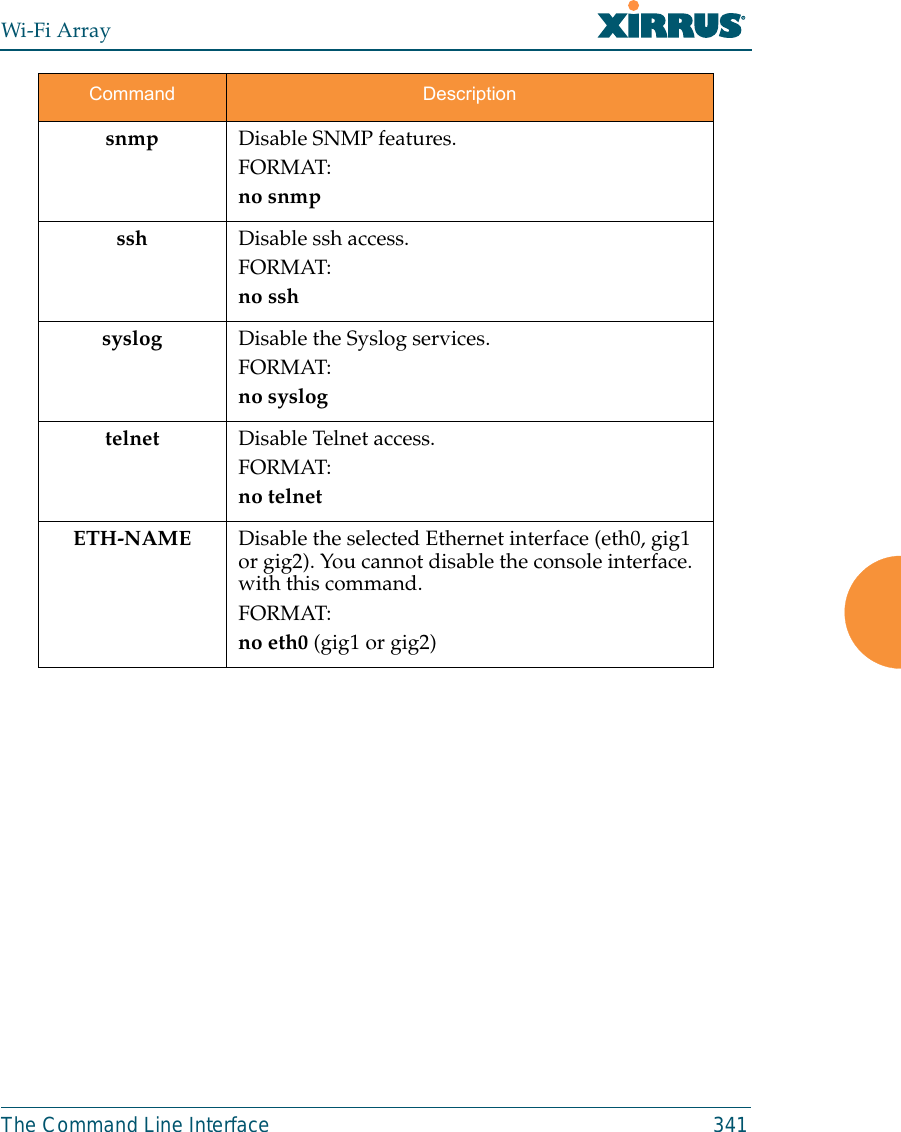
![Wi-Fi Array348 The Command Line Interfacesnmp The snmp command [Xirrus_Wi-Fi_Array(config-snmp)#] is used to enable,disable, or configure SNMP.ssh The ssh command [Xirrus_Wi-Fi_Array(config)# ssh] is used to enable or disablethe SSH feature. The Array only allows SSH-2 connections, so be sure that yourSSH client is configured to use SSH-2. Command Descriptionv2 Enable SNMP v2.FORMAT:snmp v2v3 Enable SNMP v3.FORMAT:snmp v3trap Configure traps for SNMP. Up to four trap destinations may be configured, and you may specify whether to send traps for authentication failure. FORMAT:snmp trap Command Descriptiondisable Disable SSH.FORMAT:ssh disableenable Enable SSH.FORMAT:ssh enable](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-18.png)
![Wi-Fi Array350 The Command Line Interfacessid The ssid command [Xirrus_Wi-Fi_Array(config-ssid)#] is used to establish yourSSID parameters.standby The standby command [Xirrus_Wi-Fi_Array(config-ssid)#] sets this Array tofunction as a standby unit for another Array.Command Descriptionadd Add an SSID.FORMAT:ssid add [newssid]del Delete an SSID.FORMAT:ssid del [oldssid]edit Edit an existing SSID.FORMAT:ssid edit [existingssid]reset Delete all SSIDs and restore the default SSID.FORMAT:ssid resetCommand Descriptionmode Enable or disable standby mode on this Array.FORMAT:standby mode [disable|enable|off|on]target Specify the MAC address of the target Array to be monitored for failure.FORMAT:standby target [AA:BB:CC:DD:EE:FF]](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-20.png)
![Wi-Fi ArrayThe Command Line Interface 351syslog The syslog command [Xirrus_Wi-Fi_Array(config-syslog)#] is used to enable,disable, or configure the Syslog server.Command Descriptionconsole Enable or disable the display of Syslog messages on the console, and set the level to be displayed. All messages at this level and lower (i.e., more severe) will be displayed.FORMAT:syslog console [on/off] level [0-7]disable Disable the Syslog server.FORMAT:syslog disableemail Disable the Syslog server.FORMAT:syslog email from [email-from-address] level [0-7]password [email-acct-password]server [email-server-IPaddr] test [test-msg-text]to-list [recipient-email-addresses]user [email-acct-username]enable Enable the Syslog server.FORMAT:syslog enablelocal-file Set the size and/or severity level (all messages at this level and lower will be logged).FORMAT:syslog local-file size [1-500] level [0-7]no Disable the selected feature.FORMAT:syslog no [feature]](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-21.png)
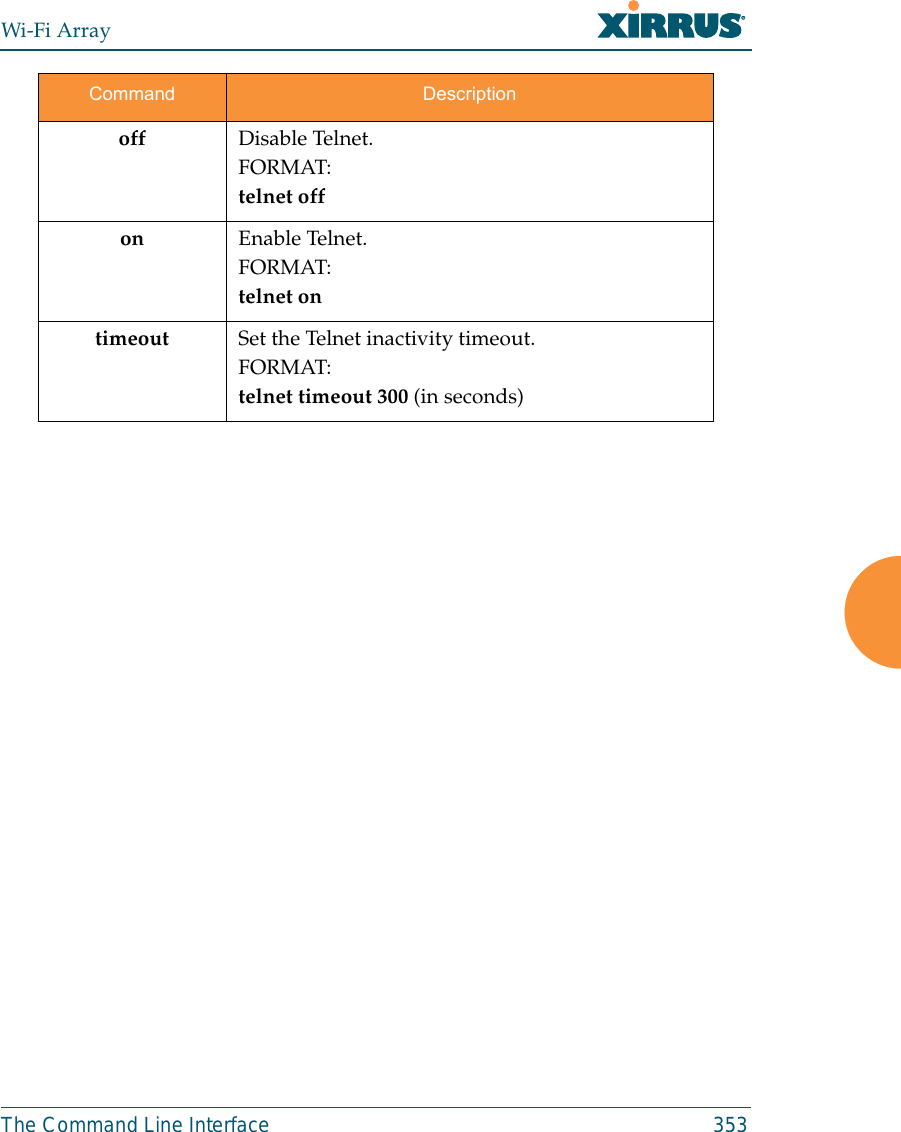
![Wi-Fi Array352 The Command Line Interfacetelnet The telnet command [Xirrus_Wi-Fi_Array(config)# telnet] is used to enable ordisable Telnet.off Disable the Syslog server.FORMAT:syslog offon Enable the Syslog server.FORMAT:syslog onprimary Set the IP address of the primary Syslog server and/or the severity level of messages to be logged.FORMAT:syslog primary [1.2.3.4] level [0-7]secondary Set the IP address of the secondary (backup) Syslog server and/or the severity level of messages to be logged.FORMAT:syslog primary [1.2.3.4] level [0-7]Command Descriptiondisable Disable Telnet.FORMAT:telnet disableenable Enable Telnet.FORMAT:telnet enableCommand Description](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-22.png)
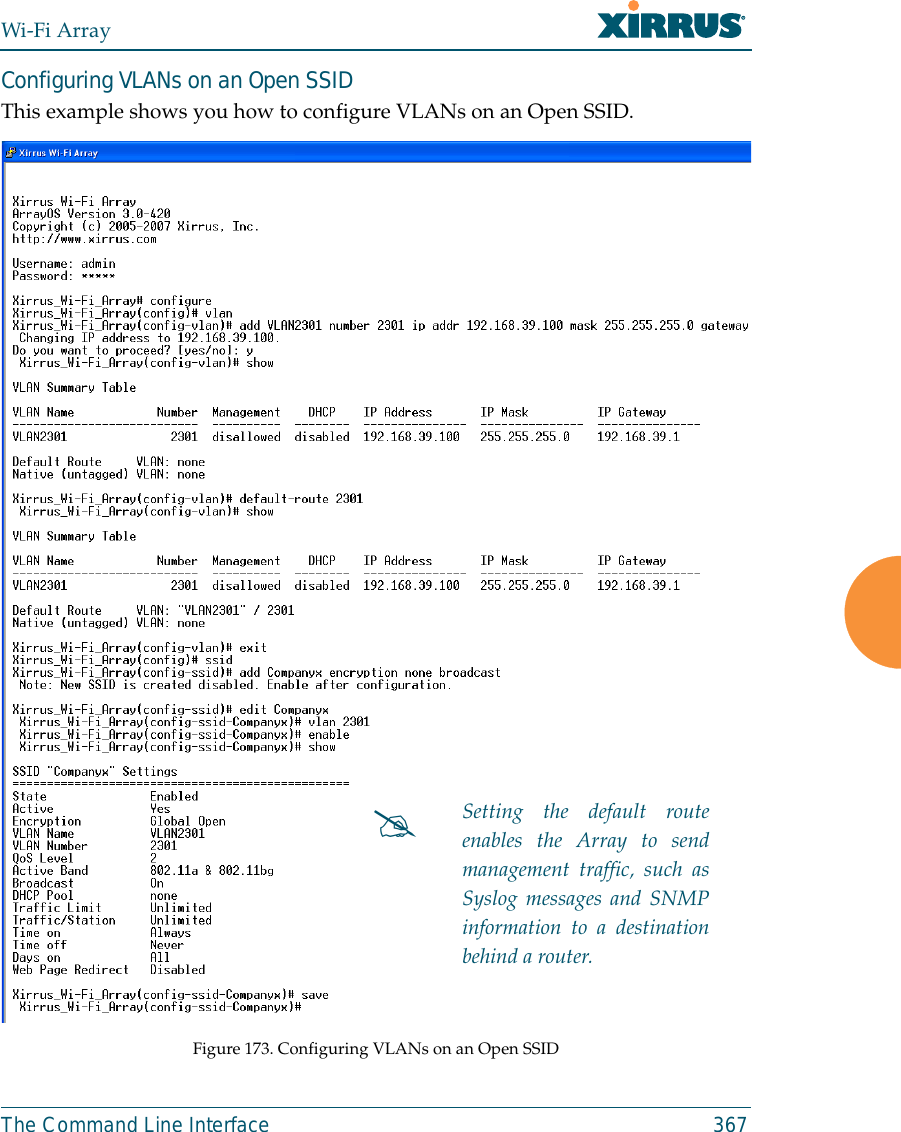
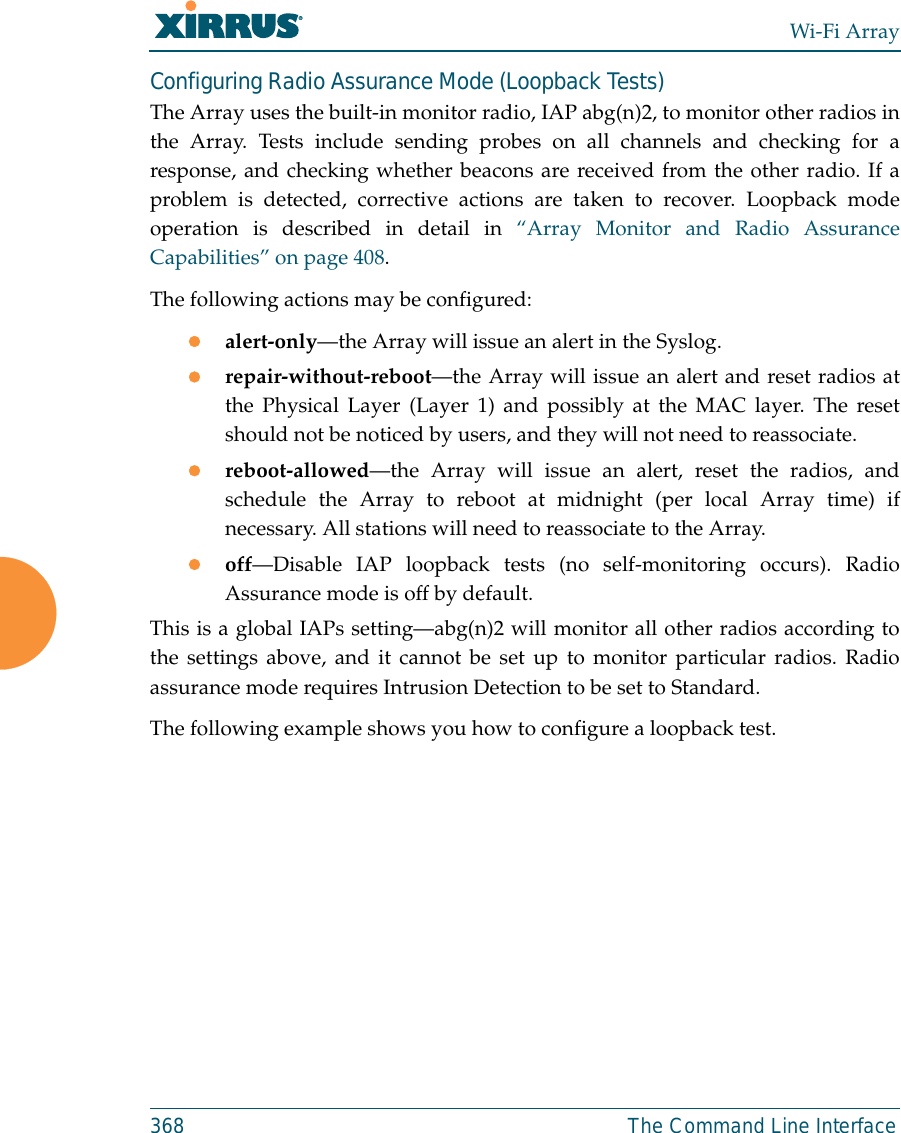
![Wi-Fi Array354 The Command Line Interfaceuptime The uptime command [Xirrus_Wi-Fi_Array(config)# uptime] is used to displaythe elapsed time since you last rebooted the Array. vlan The vlan command [Xirrus_Wi-Fi_Array(config-vlan)#] is used to establish yourVLAN parameters.Command Description<cr> Display time since last reboot.FORMAT:uptimeCommand Descriptionadd Add a VLAN.FORMAT:vlan add [newvlan]default-route Assign a VLAN for the default route (for outbound management traffic).FORMAT:vlan default-route [defaultroute]delete Delete a VLAN.FORMAT:vlan delete [oldvlan]edit Modify an existing VLAN.FORMAT:vlan edit [existingvlan]native-vlan Assign a native VLAN (traffic is untagged).FORMAT:vlan native-vlan [nativevlan]](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-24.png)
![Wi-Fi ArrayThe Command Line Interface 355no Disable the selected feature.FORMAT:vlan no [feature]reset Delete all existing VLANs.FORMAT:vlan resetCommand Description](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-25.png)






![Wi-Fi Array412 Appendix C: Technical SupportBoot your Array and watch the progress messages. When Press space barto exit to bootloader: is displayed, press the space bar. The rest of thisprocedure is performed using the bootloader. The following steps assume that you are running DHCP on your localnetwork. 5. Type dhcp and hit return. This instructs the Array to obtain a DHCPaddress and use it during this boot in the bootloader environment. 6. Type dir and hit return to see what's currently in the compact flash. 7. Type del and hit return to delete the contents of the compact flash. 8. Type update server <TFTP-server-ip-addr> xs-3.x-xxxx.bin (the actualXirrus file name will vary depending on Array model number andsoftware version—use the file name from your software update) and hitreturn. The software update will be transferred to the Array's memoryand will be written to the it’s compact flash card. (See output below.)9. Type reset and hit return. Your Array will reboot, running your newversion of software. Sample Output for the Upgrade Procedure:The user actions are highlighted in the output below, for clarity.Username: adminPassword: *****Xirrus-WiFi-Array# configureXirrus-WiFi-Array(config)# rebootAre you sure you want to reboot? [yes/no]: yesArray is being rebooted.Xirrus Boot Loader 1.0.0 (Oct 17 2006 - 13:11:42), Build: 2725Processor | Motorola PowerPC, PVR=80200020 SVR=80300020Board | Xirrus MPC8540 CPU BoardClocks | CPU : 825 MHz DDR : 330 MHz Local Bus: 41 MHz](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-82.png)
![Wi-Fi ArrayAppendix C: Technical Support 413L1 cache | Data: 32 KB Inst: 32 KB Status : EnabledWatchdog | Enabled (5 secs)I2C Bus | 400 KHzDTT | CPU:34C RF0:34C RF1:34C RF2:27C RF3:29CRTC | Wed 2007-Nov-05 6:43:14 GMTSystem DDR | 256 MB, Unbuffered Non-ECC (2T)L2 cache | 256 KB, EnabledFLASH | 4 MB, CRC: OKFPGA | 2 Devices programmedPacket DDR | 256 MB, Unbuffered Non-ECC, EnabledNetwork | Mot FEC Mot TSEC1 [Primary] Mot TSEC2IDE Bus 0 | OKCFCard | 122 MB, Model: Hitachi XXM2.3.0Environment| 4 KB, InitializedIn: serialOut: serialErr: serialPress space bar to exit to bootloader: XBL>dhcp[DHCP ] Device : Mot TSEC1 1000BT Full Duplex[DHCP ] IP Addr : 192.168.39.195XBL>dir[CFCard] Directory of / Date Time Size File or Directory name----------- -------- -------- ---------------------------2007-Nov-05 6:01:56 29 lastboot2007-Apr-05 15:47:46 28210390 xs-3.1-0433.bak2007-Mar-01 16:39:42 storage/2007-Apr-05 15:56:38 28210430 xs-3.1-0440.bin2007-Mar-03 0:56:28 wpr/3 file(s), 2 dir(s)](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-83.png)
![Wi-Fi Array414 Appendix C: Technical SupportXBL>del * [CFCard] Delete : 2 file(s) deletedXBL>update server 192.168.39.102 xs-3.0-0425.bin[TFTP ] Device : Mot TSEC1 1000BT Full Duplex[TFTP ] Client : 192.168.39.195[TFTP ] Server : 192.168.39.102[TFTP ] File : xs-3.0-0425.bin[TFTP ] Address : 0x1000000[TFTP ] Loading : ##################################################[TFTP ] Loading : ##################################################[TFTP ] Loading : ###### done[TFTP ] Complete: 12.9 sec, 2.1 MB/sec[TFTP ] Bytes : 27752465 (1a77811 hex)[CFCard] File : xs-3.0-0425.bin[CFCard] Address : 0x1000000[CFCard] Saving : ############################################### done[CFCard] Complete: 137.4 sec, 197.2 KB/sec[CFCard] Bytes : 27752465 (1a77811 hex)XBL>reset[RESET ]Xirrus Boot Loader 1.0.0 (Oct 17 2006 - 13:11:42), Build: 2725Processor | Motorola PowerPC, PVR=80200020 SVR=80300020Board | Xirrus MPC8540 CPU BoardClocks | CPU : 825 MHz DDR : 330 MHz Local Bus: 41 MHzL1 cache | Data: 32 KB Inst: 32 KB Status : EnabledWatchdog | Enabled (5 secs)I2C Bus | 400 KHzDTT | CPU:33C RF0:32C RF1:31C RF2:26C RF3:27CRTC | Wed 2007-Nov-05 6:48:44 GMTSystem DDR | 256 MB, Unbuffered Non-ECC (2T)](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-84.png)
![Wi-Fi ArrayAppendix C: Technical Support 415L2 cache | 256 KB, EnabledFLASH | 4 MB, CRC: OKFPGA | 2 Devices programmedPacket DDR | 256 MB, Unbuffered Non-ECC, EnabledNetwork | Mot FEC Mot TSEC1 [Primary] Mot TSEC2IDE Bus 0 | OKCFCard | 122 MB, Model: Hitachi XXM2.3.0Environment| 4 KB, InitializedIn: serialOut: serialErr: serialPress space bar to exit to bootloader: [CFCard] File : xs*.bin[CFCard] Address : 0x1000000[CFCard] Loading : ############################################### done[CFCard] Complete: 26.9 sec, 1.0 MB/sec[CFCard] Bytes : 27752465 (1a77811 hex)[Boot ] Address : 0x01000000[Boot ] Image : Verifying checksum .... OK[Boot ] Unzip : Multi-File Image .... OK[Boot ] Initrd : Loading RAMDisk Image[Boot ] Initrd : Verifying checksum .... OK[Boot ] Execute : Transferring control to OSInitializing hardware ........................................ OKXirrus Wi-Fi ArrayArrayOS Version 3.0-425Copyright (c) 2005-2007 Xirrus, Inc.http://www.xirrus.comUsername:](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-85.png)


![Wi-Fi Array434 Appendix E: NoticesEU Directive 1999/5/EC Compliance InformationThis section contains compliance information for the Xirrus Wi-Fi Array family ofproducts, which includes the XN16, XN12, XN8, XN4, XS16, XS12, XS8, XS4, XS-3900, XS-3700 and XS-3500. The compliance information contained in this sectionis relevant to the European Union and other countries that have implemented theEU Directive 1999/5/EC.Declaration of ConformityCesky [Czech] Toto zahzeni je v souladu se základnimi požadavky aostatnimi odpovidajcimi ustano veni mi Směrnice1999/5/EC.Dansk [Danish] Dette udstyr er i overensstemmelse med devæsentlige krav og andre relevante bestemmelser iDirektiv 1999/5/EF.Deutsch [German] Dieses Gerat entspricht den grundlegendenAnforderungen und den weiteren entsprechendenVorgaben der Richtinie 1999/5/EU.Eesti [Estonian] See seande vastab direktiivi 1999/5/EU olulistelenöuetele ja teistele as jakohastele sätetele.English This equipment is in compliance with the essentialrequirements and other relevant provisions ofDirective 1999/5/EC.Español [Spain] Este equipo cump le con los requisitos esenciales asicomo con otras disposiciones de la Directiva 1999/5/CE.Ελληνυκη [Greek] Αυτόζ ο εξοπλτσμόζ είναι σε συμμόρφωση με τιζουσιώδειζ απαιτήσειζ και ύλλεζ σχετικέζ διατάξειζ τηζΟδηγιαζ 1999/5/EC.Français [French] Cet appareil est conforme aux exigences essentielleset aux autres dispositions pertinentes de la Directive1999/5/EC.](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-104.png)
![Wi-Fi ArrayAppendix E: Notices 435ĺslenska [Icelandic] Þetta tæki er samkvæmt grunnkröfum og öðrumviðeigandi ákvæðum Tilskipunar 1999/5/EC.Italiano [Italian] Questo apparato é conforme ai requisiti essenziali edagli altri principi sanciti dalla Direttiva 1999/5/CE.Latviski [Latvian] Šī iekārta atbilst Direktīvas 1999/5/EK būtiskajāprasībām un citiem ar to saistītajiem noteikumiem.Lietuvių [Lithuanian] Šis įrenginys tenkina 1995/5/EB Direktyvosesminius reikalavimus ir kitas šios direktyvosnuostatas.Nederlands [Dutch] Dit apparant voldoet aan de essentiele eisen enandere van toepassing zijnde bepalingen van deRichtlijn 1995/5/EC.Malti [Maltese] Dan l-apparant huwa konformi mal-htigiet essenzjaliu l-provedimenti l-ohra rilevanti tad-Direttiva 1999/5/EC.Margyar [Hungarian] Ez a készülék teljesiti az alapvetö követelményeketés más 1999/5/EK irányelvben meghatározottvonatkozó rendelkezéseket.Norsk [Norwegian] Dette utstyret er i samsvar med de grunnleggendekrav og andre relevante bestemmelser i EU-direktiv1999/5/EF.Polski [Polish] Urządzenie jest zgodne z ogólnymi wymaganiamioraz sczególnymi mi warunkami określony miDyrektywą. UE:1999/5/EC.Portuguès [Portuguese] Este equipamento está em conformidade com osrequisitos essenciais e outras provisões relevantes daDirectiva 1999/5/EC.Slovensko [Slovenian] Ta naprava je skladna z bistvenimi zahtevami inostalimi relevantnimi popoji Direktive 1999/5/EC.](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-105.png)
![Wi-Fi Array436 Appendix E: NoticesAssessment CriteriaThe following standards were applied during the assessment of the productagainst the requirements of the Directive 1999/5/EC:zRadio: EN 301 893 and EN 300 328 (if applicable)zEMC: EN 301 489-1 and EN 301 489-17zSafety: EN 50371 to EN 50385 and EN 60601CE MarkingFor the Xirrus Wi-Fi Array (XN16, XN12, XN8, XN4XS16, XS12, XS8, XS4, XS-3900,XS-3700 and XS-3500), the CE mark and Class-2 identifier opposite are affixed tothe equipment and its packaging: Slovensky [Slovak] Toto zariadenie je v zhode so základnýmipožadavkami a inými prislušnými nariadeniamidirektiv: 1999/5/EC.Suomi [Finnish] Tämä laite täyttää direktiivin 1999/5//EY olennaisetvaatimukset ja on siinä asetettujen muiden laitettakoskevien määräysten mukainen.Svenska [Swedish] Denna utrustning är i överensstämmelse med deväsentliga kraven och andra relevanta bestämmelseri Direktiv 1999/5/EC.](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-106.png)
![Wi-Fi Array446 Appendix E: Noticescomputer software or hardware which is designated to defeat any copyprotection or other use limiting device, including any device intended tolimit the number of users or devices accessing the Product. 3. Limited Warranty and Limitation of Liability3.1 Limited Warranty & Exclusions. Licensor warrants that the Software willperform in substantial accordance with the specifications therefor setforth in the Documentation for a period of ninety [90] days afterCustomer's acceptance of the terms of this Agreement with respect to theSoftware (“Warranty Period”). If during the Warranty Period theSoftware does not perform as warranted, Licensor shall, at its option,correct the relevant Software giving rise to such breach of performance orreplace such Software free of charge. THE FOREGOING ARECUSTOMER'S SOLE AND EXCLUSIVE REMEDIES FOR BREACH OFTHE FOREGOING WARRANTY. THE WARRANTY SET FORTHABOVE IS MADE TO AND FOR THE BENEFIT OF CUSTOMER ONLY.The warranty will apply only if (i) the Software has been used at all timesand in accordance with the instructions for use set forth in theDocumentation and this Agreement; (ii) no modification, alteration oraddition has been made to the Software by persons other than Licensor orLicensor's authorized representative; and (iii) the Software or Product onwhich the Software is installed has not been subject to any unusualelectrical charge.3.2 DISCLAIMER. EXCEPT AS EXPRESSLY STATED IN THIS SECTION 3,ALL ADDITIONAL CONDITIONS, REPRESENTATIONS, ANDWARRANTIES, WHETHER IMPLIED, STATUTORY OR OTHERWISE,INCLUDING, WITHOUT LIMITATION, ANY IMPLIED WARRANTIESOR CONDITIONS OF MERCHANTABILITY, FITNESS FOR APARTICULAR PURPOSE, SATISFACTORY QUALITY, ACCURACY,AGAINST INFRINGEMENT OR ARISING FROM A COURSE OFDEALING, USAGE, OR TRADE PRACTICE, ARE HEREBYDISCLAIMED BY LICENSOR AND ITS SUPPLIERS. THIS DISCLAIMERSHALL APPLY EVEN IF ANY EXPRESS WARRANTY AND LIMITEDREMEDY OFFERED BY LICENSOR FAILS OF ITS ESSENTIALPURPOSE. ALL WARRANTIES PROVIDED BY LICENSOR ARESUBJECT TO THE LIMITATIONS OF LIABILITY SET FORTH IN THISAGREEMENT. 3.3 HAZARDOUS APPLICATIONS. THE SOFTWARE IS NOT DESIGNEDOR INTENDED FOR USE IN HAZARDOUS ENVIRONMENTSREQUIRING FAIL SAFE PERFORMANCE, SUCH AS IN THEOPERATION OF A NUCLEAR FACILITY, AIRCRAFT NAVIGATION ORCOMMUNICATIONS SYSTEMS, AIR TRAFFIC CONTROLS OR OTHER](https://usermanual.wiki/Cambium-Networks/XN12.D-Pages-351-to-496-from-ArrayGuide-Rel4-SS-Dec02-2008-Small-5/User-Guide-1071269-Page-116.png)